-
Notifications
You must be signed in to change notification settings - Fork 3
Network
Note: These are questions I faced during the interview process!
A subnet mask is a 32-bit number created by setting host bits to all 0s and setting network bits to all 1s. In this way, the subnet mask separates the IP address into the network and host addresses.
The “255” address is always assigned to a broadcast address, and the “0” address is always assigned to a network address. Neither can be assigned to hosts, as they are reserved for these special purposes.
The IP address, subnet mask, and gateway or router comprise an underlying structure—the Internet Protocol—that most networks use to facilitate inter-device communication.
Dynamic Host Configuration Protocol (DHCP) is a network management protocol used in TCP/IP networks to dynamically assign IP addresses and other related configuration information to network devices.
Dynamic Host Configuration Protocol(DHCP) is an application layer protocol which is used to provide:
- Subnet Mask (Option 1 – e.g., 255.255.255.0)
- Router Address (Option 3 – e.g., 192.168.1.1)
- DNS Address (Option 6 – e.g., 8.8.8.8)
- Vendor Class Identifier (Option 43 – e.g., ‘unifi’ = 192.168.1.9 ##where unifi = controller)
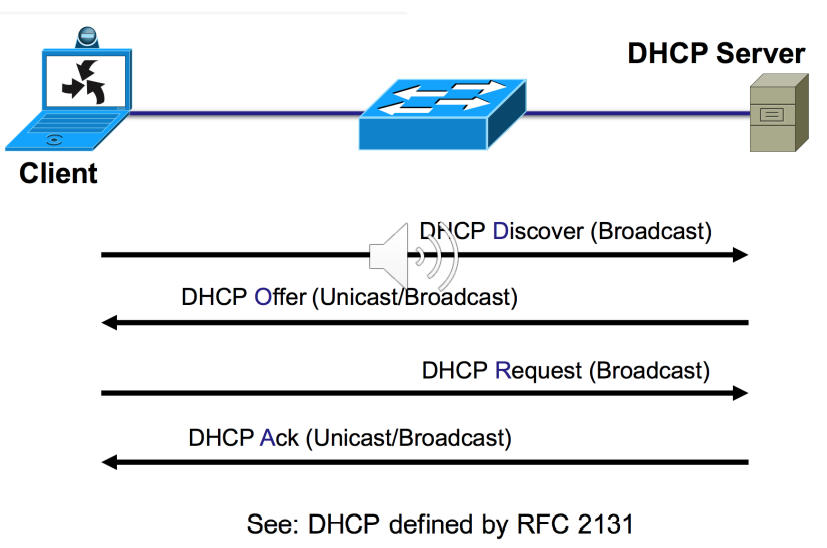
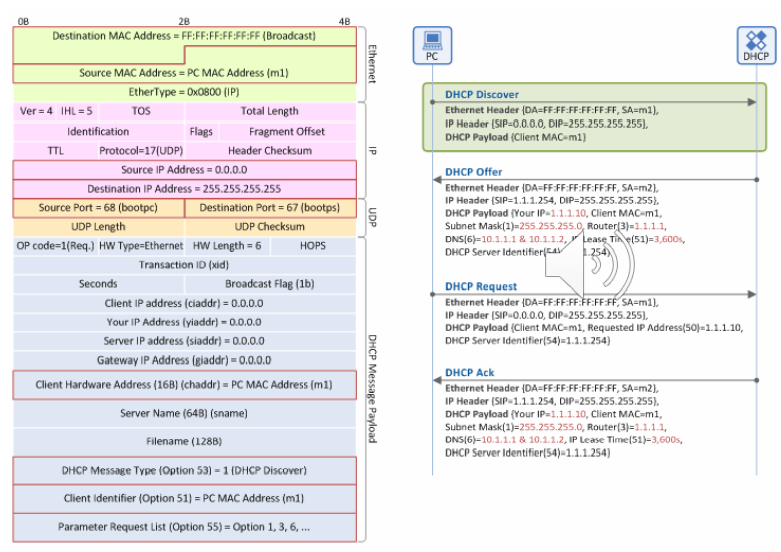
DHCP is based on a client-server model and based on discovery, offer, request, and ACK.
DHCP port number for the server is 67 and for the client is 68. It is a Client-server protocol that uses UDP services. An IP address is assigned from a pool of addresses. In DHCP, the client and the server exchange mainly 4 DHCP messages in order to make a connection, also called the DORA process, but there are 8 DHCP messages in the process.
These messages are given as below:
- DHCP discovers the message
- DHCP offers a message
- DHCP request message
- DHCP acknowledgment message
- DHCP negative acknowledgment message
- DHCP decline
- DHCP release
- DHCP inform
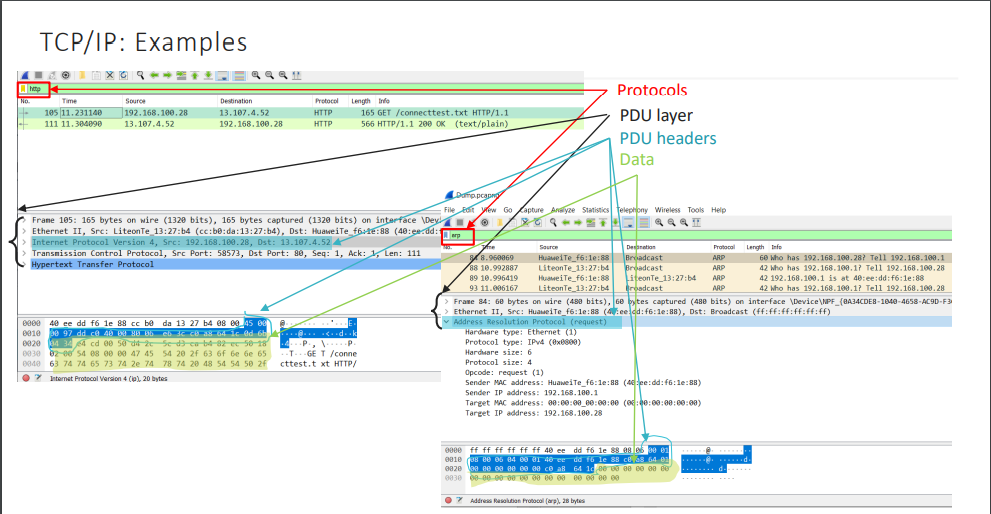
Address Resolution Protocol is one of the most important protocols of the network layer in the OSI model which helps in finding the MAC(Media Access Control) address given the IP address of the system i.e. the main duty of the ARP is to convert the 32-bit IP address(for IPv4) to 48-bit address i.e. the MAC address.
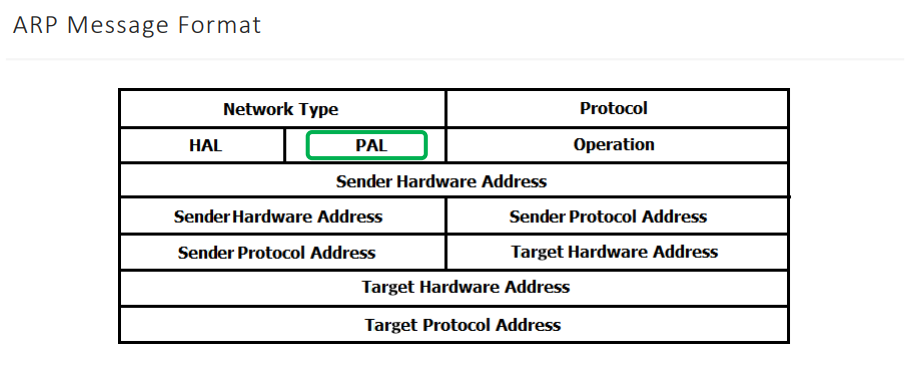
It is useful to:
- detect IP conflicts
- update other machines' ARP tables
- troubleshoot connection issues
ARP:
- The Reverse Address Resolution Protocol - translates Layer 2 addresses to Layer 3 addresses. It is obsolete and replaced by BOOTP, which was later superseded by the Dynamic Host Configuration Protocol (DHCP).
- ARP is vulnerable - it does not authenticate ARP requests and ARP responses. And since the network interfaces on computers support gratuitous requests/responses an ARP spoofing attack is possible.
- In IPv6 Neighbor Discovery Protocol and Secure Neighbor Discovery protocols are used instead of ARP
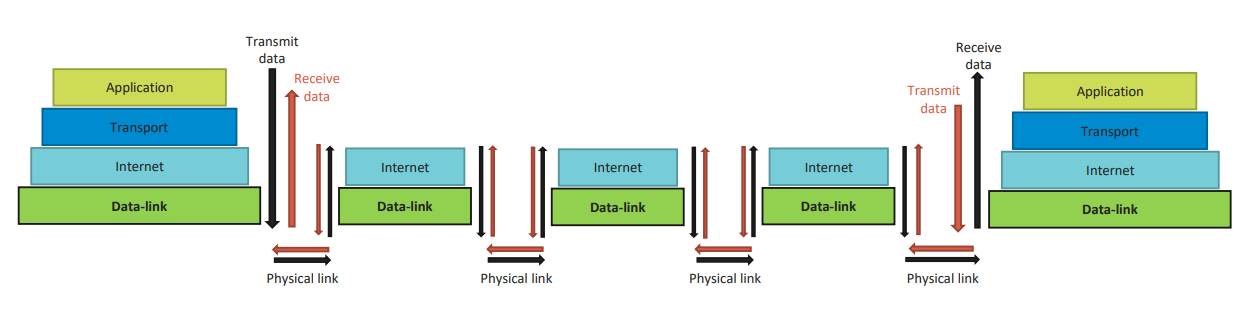
The TCP/IP model is the conceptual model and set of communications protocols used in the Internet and computer networks. The TCP/IP model describes communication between two points using TCP/IP protocols.
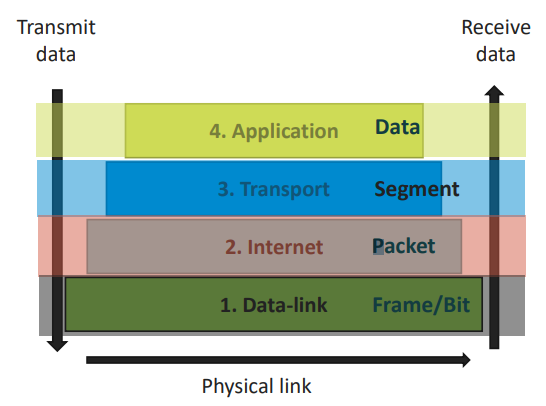
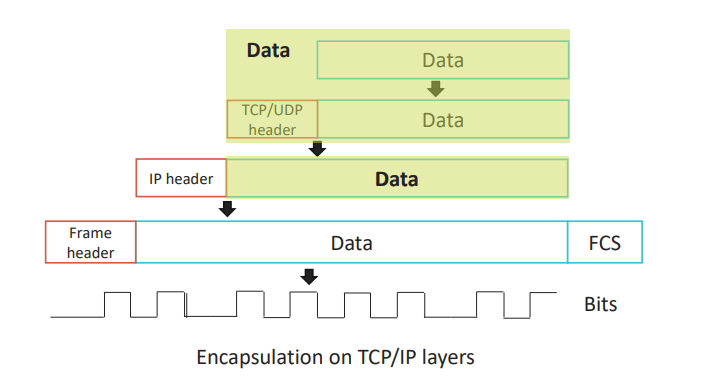
Data Encapsulation is adding a bit of additional information to the user data packet and preparing the information for being delivered in the network. Each layer adds its own information to the data and passes the result to the next layer.
Application Layer
The Application layer includes the protocols used by most applications for providing user services or exchanging application data over the network connections established by the lower-level protocols. The application layer in the TCP/IP model is often compared as equivalent to a combination of the Session, Presentation, and Application layers of the OSI model.
Protocols: HTTP, HTTPS, FTP, DHCP, DNS and etc
Transport Layer
The Transport layer is analogous to the transport layer of the OSI model. It is responsible for end-to-end communication and error-free delivery of data.
Important functions:
- Division into segments and number them to make a sequence.
- Delivery to the correct process on the destination machine.
- Arrival without any error.
Protocols: TCP, UDP
Internet layer
The Internet layer has the responsibility of sending packets across potentially multiple networks. Internetworking requires sending data from the source network to the destination network.
Important functions:
- Host addressing and identification.
- Packet routing.
Protocols: IP, ARP, ICMP, IGMP
Data-link layer
Data-link layer defines how the data should be sent physically through the network. This layer is also called a network access layer.
Important functions:
- Physical addressing
- Framing packets
- Preparing packets for transmission
- Transmit the frames to the physical layer and over a transmission medium
Protocols: Ethernet, Wi-Fi, xDSL
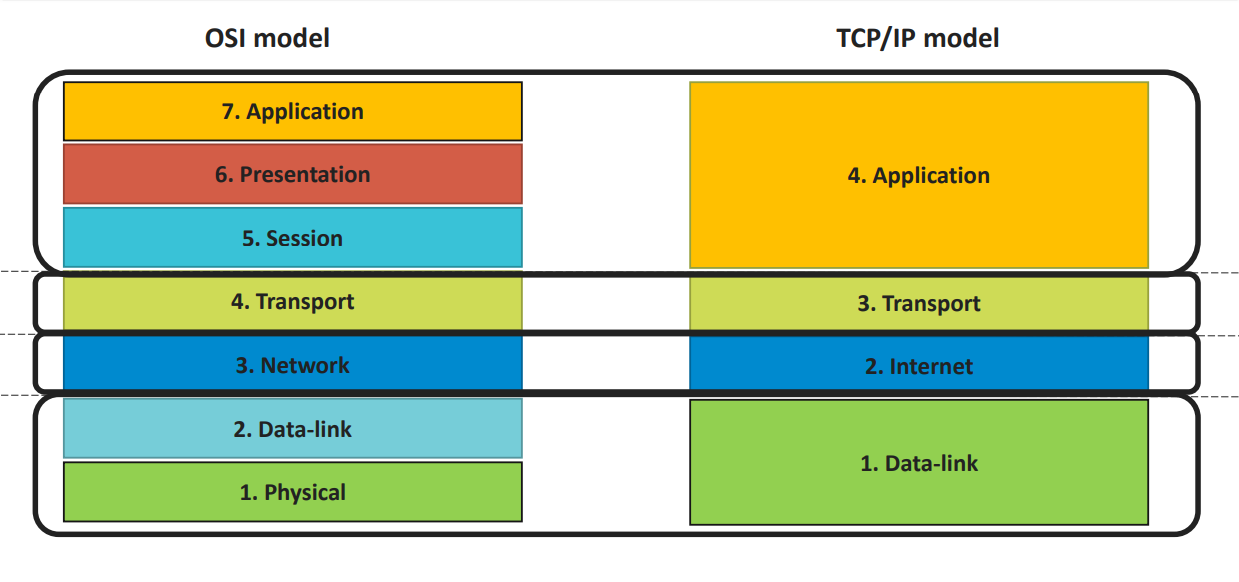
Difference between OSI and TCP/IP models
TCP/IP:
- TCP refers to Transmission Control Protocol.
- TCP/IP has 4 layers.
- TCP/IP follows a horizontal approach.
- TCP/IP uses both session and presentation
- layer in the application layer itself
- TCP/IP developed protocols then model.
OSI:
- OSI refers to Open Systems Interconnection.
- OSI has 7 layers
- OSI follows a vertical approach.
- OSI uses different session and presentation layers
- OSI developed a model and then a protocol.
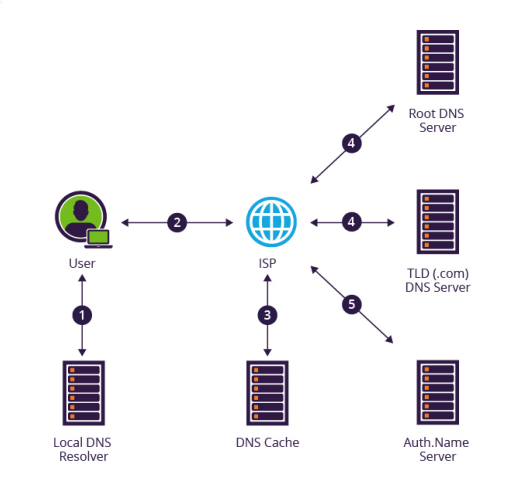
A DNS, short for a domain name system, is used to resolve a particular domain name to its IP equivalent. Domain names (e.g. epam.com) are simply used to be more easily read and remembered by humans, however, all domain names are associated with a particular IP address. This can be compared to a phonebook where a person's name would correspond to the domain name (e.g. yourwebsite.com) and their phone number would correspond to the website's IP (e.g. 159.x.x.x).
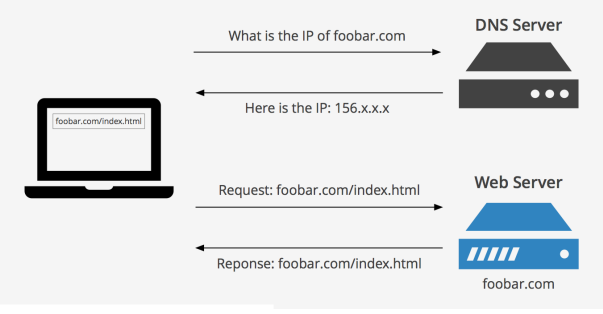
DNS resolving steps
- Website request
- Ask resolver
- Ask the root server
- Ask the TLD server
- Ask authoritative name servers
- Cache the IP and return it to the browser
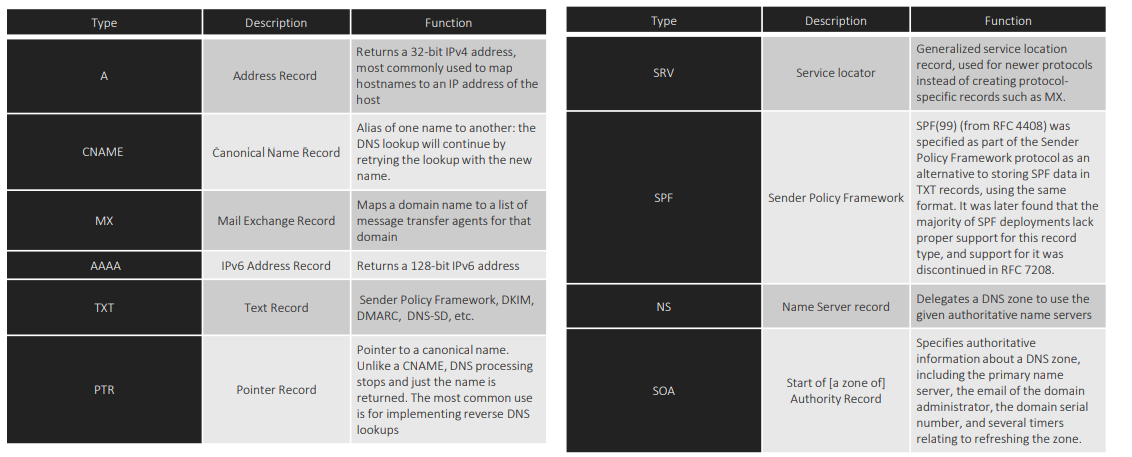
DNS records
- Home
- Programming languages
- Command line
- Networking & security
- Setupping applications
- Infrastructure as code
- Containers
- Container orchestration
- Configuration management
- CI/CD tools
- Monitoring
- Cloud Providers
- DevOps & SRE books
- DevOps Cheat Sheet
- DevOps interview