[updatecli] Bump tfcmt version to v4.14.15#189
Open
hmcts-dependency-updater[bot] wants to merge 23 commits intomasterfrom
Open
[updatecli] Bump tfcmt version to v4.14.15#189hmcts-dependency-updater[bot] wants to merge 23 commits intomasterfrom
hmcts-dependency-updater[bot] wants to merge 23 commits intomasterfrom
Conversation
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
Made with ❤️️ by updatecli
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
Bump tfcmt version to v4.14.15
Update tfcmt version
Bump tfcmt Version
1 file(s) updated with "TFCMT_VERSION=v4.7.2": * scripts/install-tfcmt.sh
v4.10.0
v4.11.0
v4.12.0
v4.13.0
v4.14.0
Release published on the 2024-10-04 01:31:40 +0000 UTC at the url https://github.com/suzuki-shunsuke/tfcmt/releases/tag/v4.14.0 [Pull Requests](https://github.com/suzuki-shunsuke/tfcmt/pulls?q=is%3Apr+milestone%3Av4.14.0) | [Issues](https://github.com/suzuki-shunsuke/tfcmt/issues?q=is%3Aissue+milestone%3Av4.14.0) | https://github.com/suzuki-shunsuke/tfcmt/compare/v4.13.0...v4.14.0 ## Features #1423 #1425 plan: Add the option `-ignore-warning` We've Added the option `-ignore-warning` to the `tfcmt plan` command. You can also configure this option in your configuration file. ```yaml terraform: plan: ignore_warning: true ``` By default, tfcmt emphasizes the warning of `terraform plan`, and the option `-skip-no-changes` is ignored if `terraform plan` outputs warning.  This is because we think warning should not be ignored. But actually we're aware that some users ignore warning normally and they feel warning is noisy. In this case, it's desirable that `tfcmt plan -skip-no-changes` doesn't post a comment even if warning is outputted. So this pull request introduces a new option `-ignore-warning`. If `terraform plan` outputs warning, this option makes the template variable `.Warning` empty, removing the warning from the default template. If `terraform plan -skip-no-changes` has no change and outputs warning, this option disables to post a comment. #1425 plan: Bind some environment variables to options - TFCMT_PLAN_PATCH - TFCMT_SKIP_NO_CHANGES - TFCMT_IGNORE_WARNING ## Others #1417 Update Go 1.22.6 to 1.23.1 #1409 Create [GitHub Artifact Attestations](https://docs.github.com/en/actions/security-for-github-actions/using-artifact-attestations/using-artifact-attestations-to-establish-provenance-for-builds) https://github.com/suzuki-shunsuke/tfcmt/attestations You can verify downloaded assets from GitHub Releases using GitHub CLI. ```sh # Download assets from GitHub Releases. gh release download -R suzuki-shunsuke/tfcmt v4.14.0 -p tfcmt_darwin_arm64.tar.gz # Verify an asset. gh attestation verify tfcmt_darwin_arm64.tar.gz \ -R suzuki-shunsuke/tfcmt \ --signer-workflow suzuki-shunsuke/go-release-workflow/.github/workflows/release.yaml ```v4.14.1
v4.14.10
v4.14.11
v4.14.12
v4.14.13
v4.14.14
v4.14.15
v4.14.2
v4.14.3
v4.14.4
v4.14.5
v4.14.7
v4.14.9
v4.7.2
v4.7.3
v4.8.0
v4.9.0
Release published on the 2024-02-01 07:30:13 +0000 UTC at the url https://github.com/suzuki-shunsuke/tfcmt/releases/tag/v4.9.0 [Pull Requests](https://github.com/suzuki-shunsuke/tfcmt/pulls?q=is%3Apr+milestone%3Av4.9.0) | [Issues](https://github.com/suzuki-shunsuke/tfcmt/issues?q=is%3Aissue+milestone%3Av4.9.0) | https://github.com/suzuki-shunsuke/tfcmt/compare/v4.8.0...v4.9.0 ## Features [#1083](https://github.com/suzuki-shunsuke/tfcmt/discussions/1083) #1115 Support masking sensitive data You can mask sensitive data in outputs of terraform. This feature prevents the leak of sensitive data. The following outputs are masked. - Standard output of terraform command - Standard error output of terraform command - Pull request comment of `tfcmt plan` and `tfcmt apply` - [local files created by `--output` option](https://suzuki-shunsuke.github.io/tfcmt/output-file) > [!CAUTION] > Even if you maske secrets using this feature, secrets are still stored in Terraform States. > Please see also [Sensitive Data in State](https://developer.hashicorp.com/terraform/language/state/sensitive-data). You can use environment variables `TFCMT_MASKS` and `TFCMT_MASKS_SEPARATOR`. - `TFCMT_MASKS`: A list of masks. Masks are joined by `TFCMT_MASKS_SEPARATOR` - `TFCMT_MASKS_SEPARATOR`: A separator of masks. The default value is `,` The format of each mask is `${type}:${value}`. `${type}` must be either `env` or `regexp`. If `${type}` is `env`, `${value}` is a masked environment variable name. If `${type}` is `regexp`, `${value}` is a masked regular expression. e.g. Mask GitHub access tokens and the environment variable `DATADOG_API_KEY`. ```sh export TFCMT_MASKS='env:GITHUB_TOKEN,env:DATADOG_API_KEY,regexp:ghp_[^ ]+' tfcmt plan -- terraform plan ``` e.g. Change the separator to `/`. ```sh export TFCMT_MASKS_SEPARATOR=/ export TFCMT_MASKS='env:GITHUB_TOKEN/env:DATADOG_API_KEY/regexp:ghp_[^ ]+' ``` All matching strings are replaced with `***`. Replacements are done in order of `TFCMT_MASKS`, so the result depends on the order of `TFCMT_MASKS`. For example, if `TFCMT_MASKS` is `regexp:foo,regexp:foo.*`, `regexp:foo.*` has no meaning because all `foo` are replaced with `***` before replacing `foo.*` with `***` so `foo.*` doesn't match with anything. ### Example This example creates a resource [google_cloudbuild_trigger](https://registry.terraform.io/providers/hashicorp/google/latest/docs/resources/cloudbuild_trigger). This resource has a GitHub Access token as a field `substitutions._GH_TOKEN`. main.tf ```tf resource "google_cloudbuild_trigger" "filename_trigger" { location = "us-central1" trigger_template { branch_name = "main" repo_name = "my-repo" } substitutions = { _GH_TOKEN = var.gh_token # Secret } filename = "cloudbuild.yaml" } variable "gh_token" { type = string description = "GitHub Access token" } terraform { required_providers { google = { source = "hashicorp/google" version = "5.13.0" } } } ``` If you run `terraform plan` without masking, the secret would be leaked. To prevent the leak, let's mask the secret. ```sh export TFCMT_MASKS=env:TF_VAR_gh_token # Mask the environment variable TF_VAR_gh_token ``` Please see `_GH_TOKEN` in the output of `tfcmt plan` and the pull request comment. You can confirm `_GH_TOKEN` is masked as `***` properly. ```console $ tfcmt plan -- terraform plan tfcmt plan -- terraform plan Terraform used the selected providers to generate the following execution plan. Resource actions are indicated with the following symbols: + create Terraform will perform the following actions: # google_cloudbuild_trigger.filename_trigger will be created + resource "google_cloudbuild_trigger" "filename_trigger" { + create_time = (known after apply) + filename = "cloudbuild.yaml" + id = (known after apply) + location = "us-central1" + name = (known after apply) + project = "hello" + substitutions = { + "_GH_TOKEN" = "***" } + trigger_id = (known after apply) + trigger_template { + branch_name = "main" + project_id = (known after apply) + repo_name = "my-repo" } } Plan: 1 to add, 0 to change, 0 to destroy. ───────────────────────────────────────────────────────────────────────────── Note: You didn't use the -out option to save this plan, so Terraform can't guarantee to take exactly these actions if you run "terraform apply" now. ``` 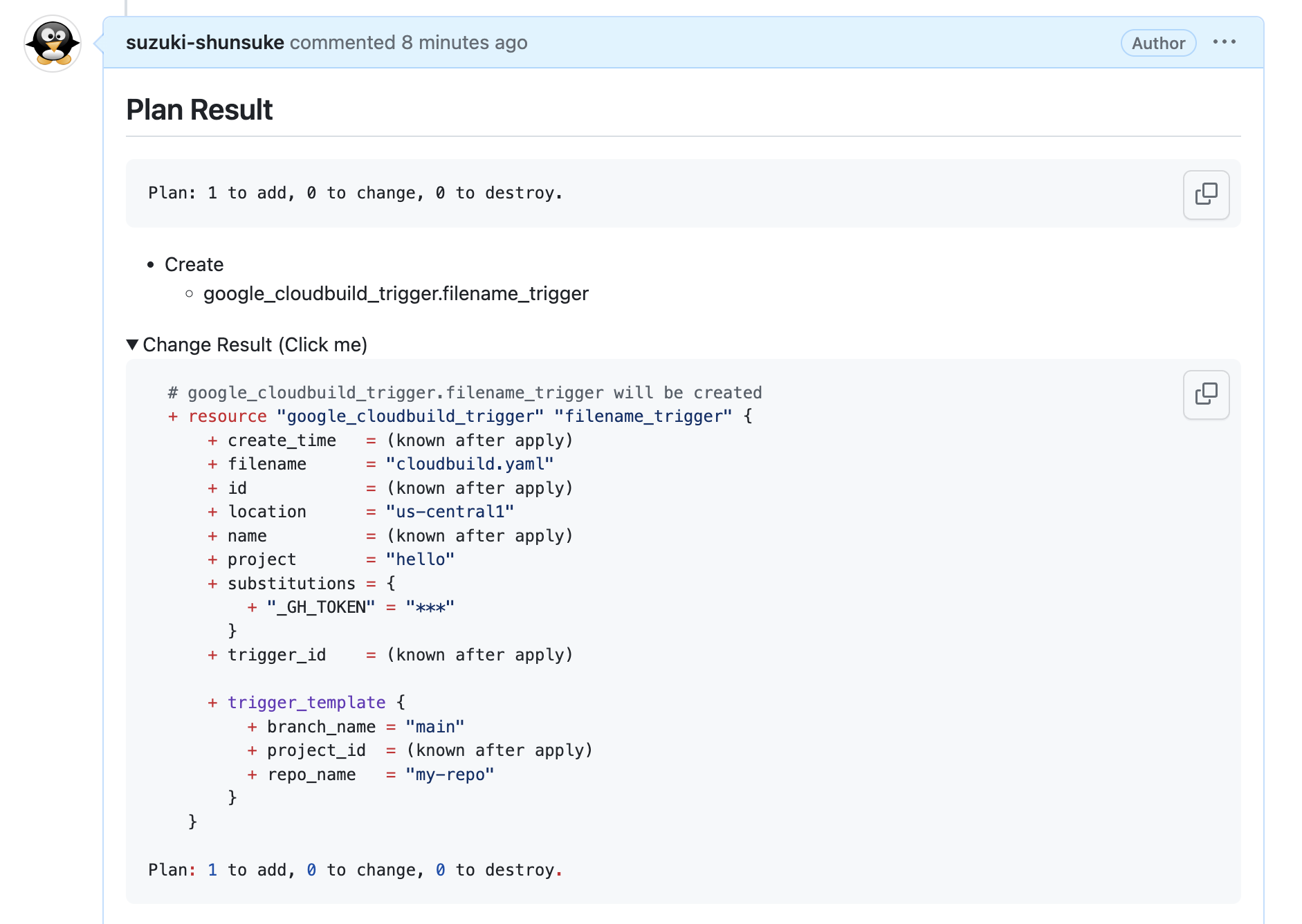 ### Terraform sensitive input variables and outputs and sensitive function Terraform itself has features to prevent sensitive data from being leaked. - https://developer.hashicorp.com/terraform/tutorials/configuration-language/sensitive-variables - https://developer.hashicorp.com/terraform/language/functions/sensitive - https://developer.hashicorp.com/terraform/language/values/outputs#sensitive-suppressing-values-in-cli-output - https://developer.hashicorp.com/terraform/language/values/variables#suppressing-values-in-cli-output - https://www.hashicorp.com/blog/terraform-0-14-adds-the-ability-to-redact-sensitive-values-in-console-output - https://www.hashicorp.com/blog/announcing-hashicorp-terraform-0-15-general-availability So first you should use these features. But even if these features are available, it still makes sense for tfcmt to mask sensitive data. Please imagine the situation that platform engineers manage Terraform workflows and product teams manage Terraform codes in a Monorepo. Then platform engineers need to prevent sensitive data from being leaked, but if product teams forget to protect them with `sensitive` flags, sensitive data would be leaked. By protecting sensitive data using tfcmt, platform engineers can prevent sensitive data from being leaked while delegating the management of Terraform codes to product teams. tfcmt's masking feature works as a guardrail.v4.9.1
Created automatically by Updatecli
Options:
Most of Updatecli configuration is done via its manifest(s).
Feel free to report any issues at github.com/updatecli/updatecli.
If you find this tool useful, do not hesitate to star our GitHub repository as a sign of appreciation, and/or to tell us directly on our chat!