Task 2 Example Research Question
In the Burp Suite Program that ships with Kali Linux, what mode would you use to manually send a request (often repeating a captured request numerous times)?:
https://brainly.com/question/25315695?cb=1676085236358
 What hash format are modern Windows login passwords stored in?:
What hash format are modern Windows login passwords stored in?:
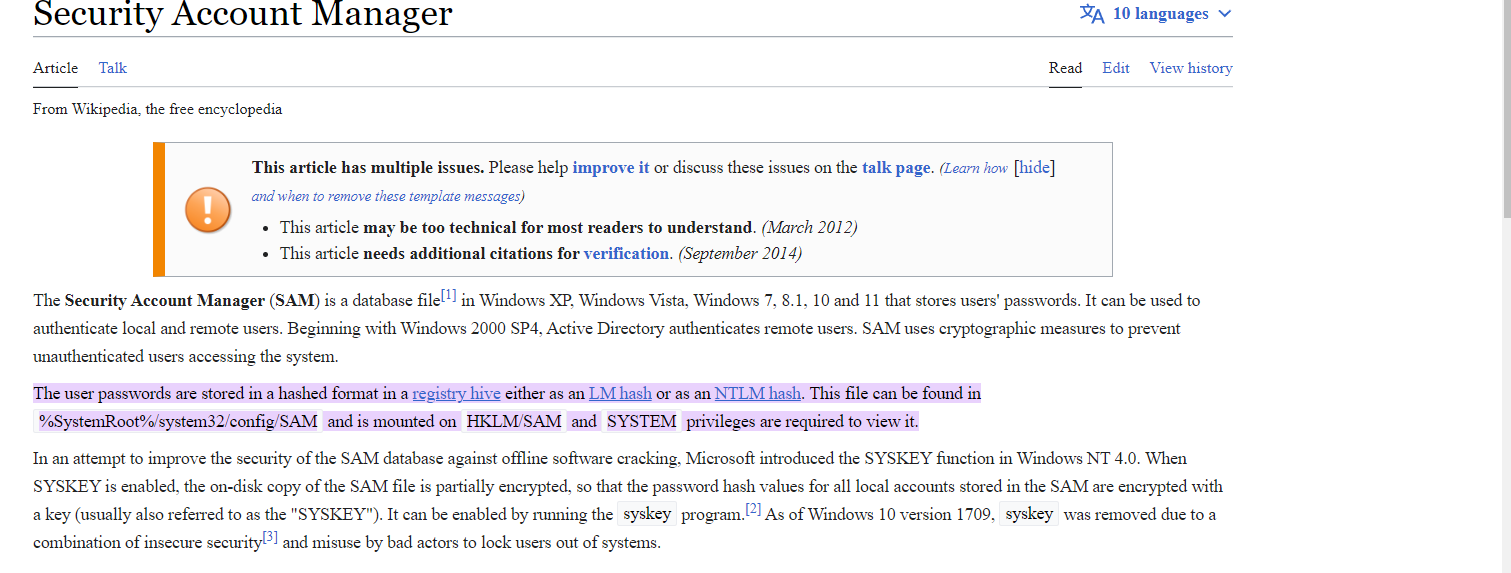
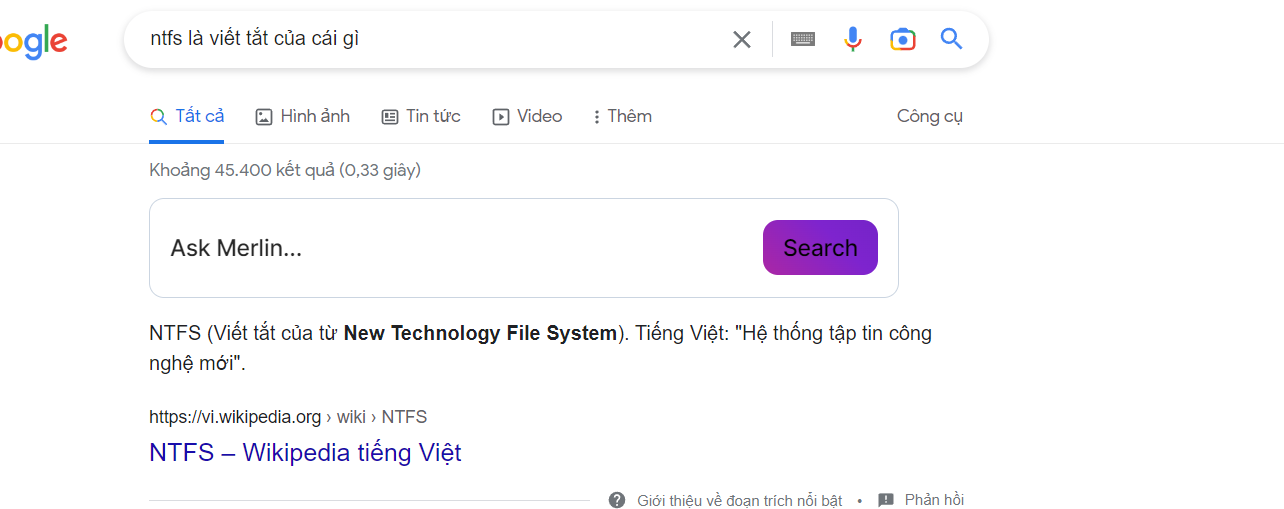
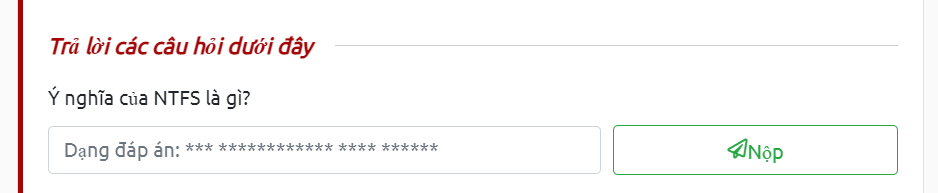
The user passwords are stored in a hashed format in a registry hive either as an LM hash or as an NTLM hash.
các password được mã hóa ở dạng LM hash hoặc NTLM hash nhưng LM hash có tính bảo mật yếu hơn nên thường sẽ dùng NTLM hash. LAN Manager authentication uses a particularly weak method of hashing a user's password known as the LM hash algorithm, stemming from the mid 1980s when viruses transmitted by floppy disks were the major concern.[6] Although it is based on DES, a well-studied block cipher, the LM hash has several weaknesses in its design.[7] This makes such hashes crackable in a matter of seconds using rainbow tables, or in a few minutes using brute force. Starting with Windows NT, it was replaced by NTLM, which is still vulnerable to rainbow tables, and brute force attacks unless long, unpredictable passwords are used, see password cracking. vậy câu trả lời sẽ là NTLM What are automated tasks called in Linux?
cron jobs có tác dụng giúp bạn làm những công việc định kì, tự động hóa trên linux What number base could you use as a shorthand for base 2 (binary)? hệ cơ số hexa 2^4 nên chúng ta có thể nhóm 4 bit của hệ 2 thành 1 số trong hệ cơ số hexa If a password hash starts with $6$, what format is it (Unix variant)?
What is the CVE for the 2020 Cross-Site Scripting (XSS) vulnerability found in WPForms? search CVE mitre: WPForms 2020 thu được:
There was a Local Privilege Escalation vulnerability found in the Debian version of Apache Tomcat, back in 2016. What's the CVE for this vulnerability?
What is the very first CVE found in the VLC media player?
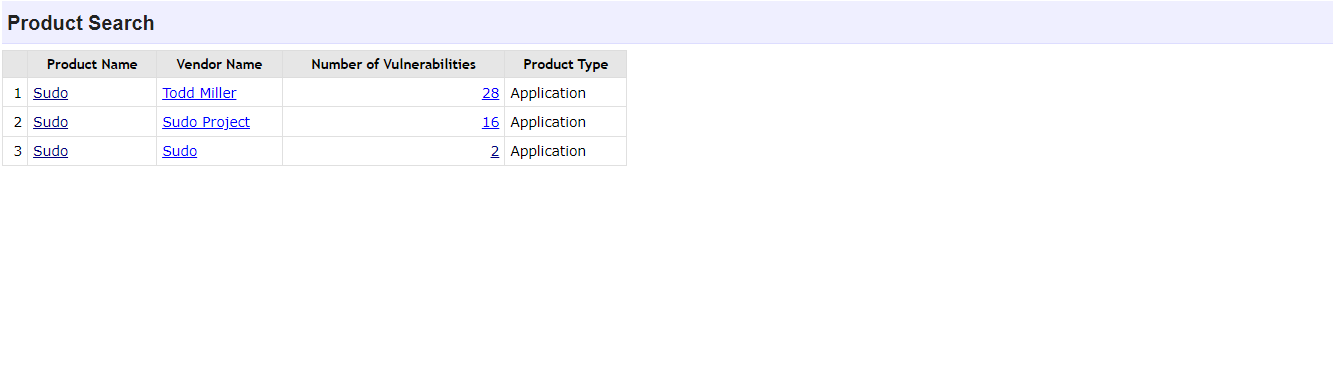
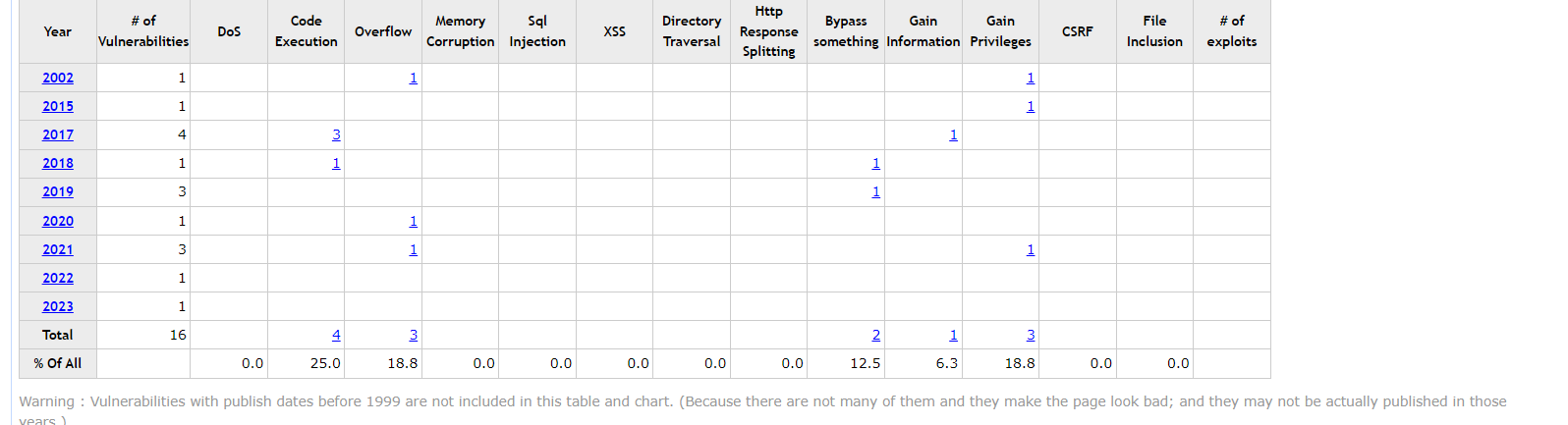
If you wanted to exploit a 2020 buffer overflow in the sudo program, which CVE would you use?
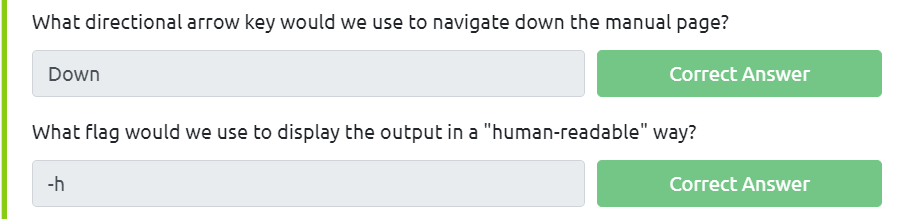
Manual Pages:
fdisk is a command used to view and alter the partitioning scheme used on your hard drive. What switch would you use to list the current partitions?: sử dụng pipe(đường ống) kết hợp cùng grep(tìm 1 chuỗi) để có kết quả
nano is an easy-to-use text editor for Linux. There are arguably better editors (Vim, being the obvious choice); however, nano is a great one to start with. What switch would you use to make a backup when opening a file with nano?
Netcat is a basic tool used to manually send and receive network requests. What command would you use to start netcat in listen mode, using port 12345?
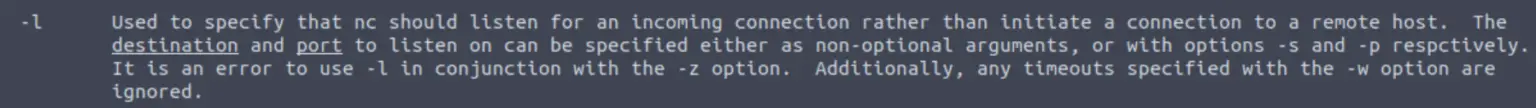
- đáp án nc -p -l 12345
A Bit of Background on Linux
Research: What year was the first release of a Linux operating system?
 Running Your First few Commands
Running Your First few Commands
If we wanted to output the text "TryHackMe", what would our command be?: echo TryHackMe
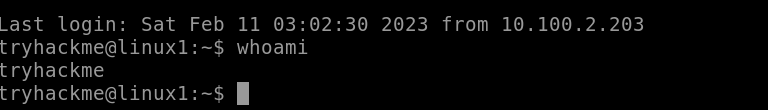
What is the username of who you're logged in as on your deployed Linux machine?
sử dụng câu lệnh whoami để kiểm tra user mình đang sử dụng
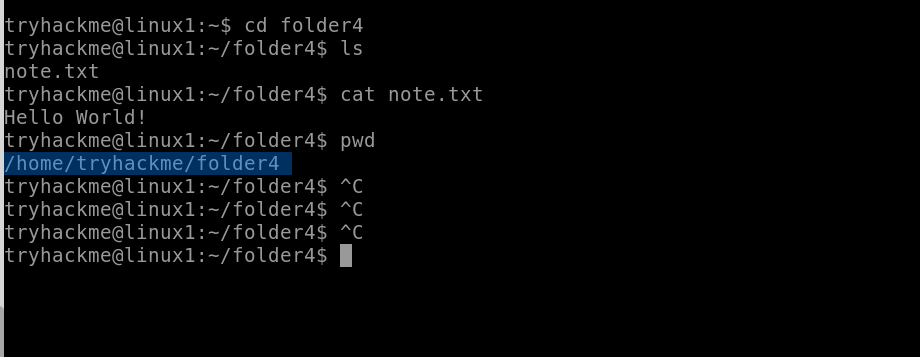
cd: thay đổi thư mục mà chúng ta đang đứng
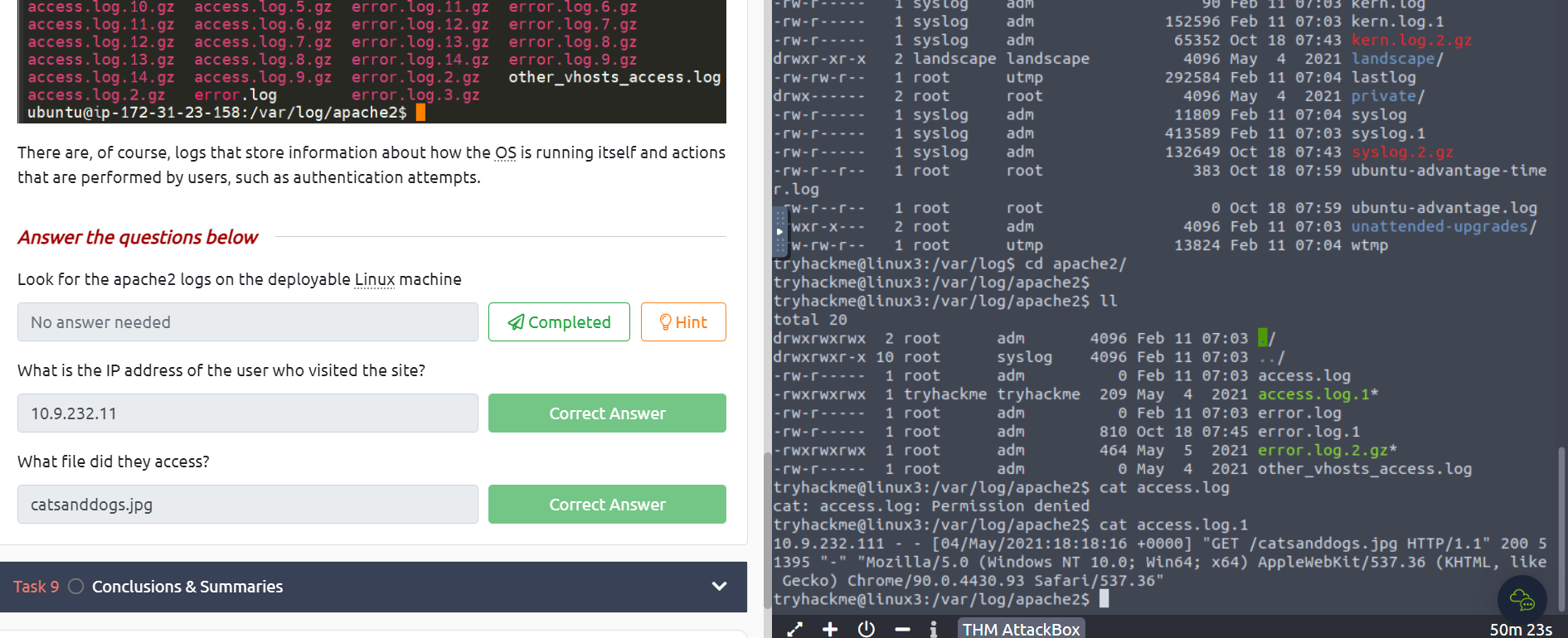
Interacting With the Filesystem! ls: liệt kê các file và folder(không bao gồm các file ẩn) cat: đọc một file hoặc có thể ghép nội dung các file lại với nhau, ghi đè hoặc tạo một file mới pwd: kiểm tra thư mục mà mình đang đứng
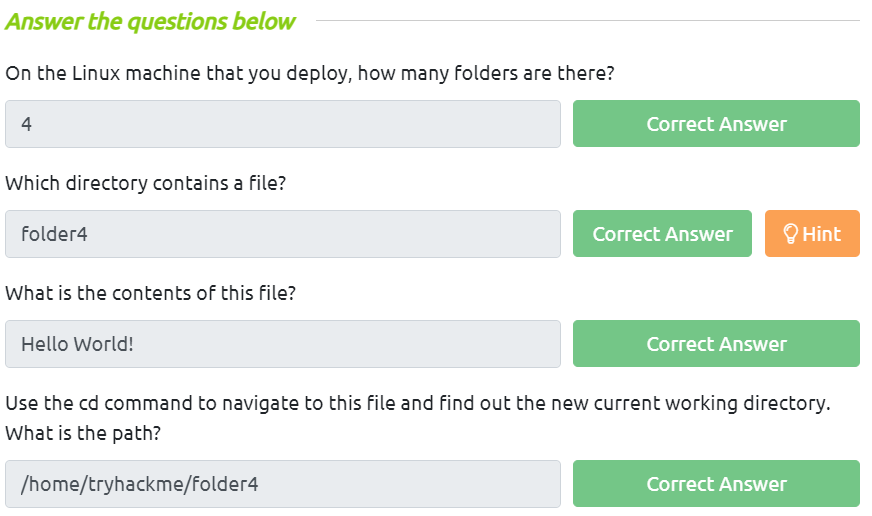
- question 1 dùng lệnh ls để kiểm tra số thư mục đang có
- question 2
thực hiện cd vào từng thư mục để kiểm tra hoặc dùng lệnh ls để kiểm tra với option -R
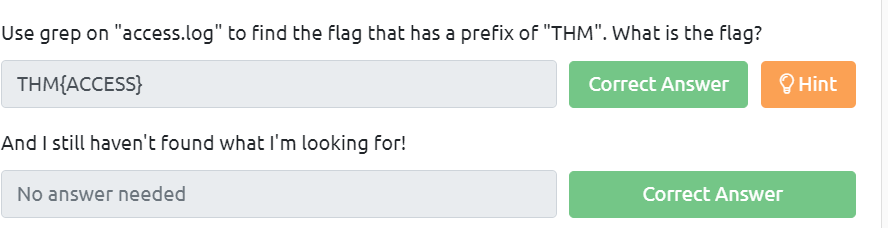
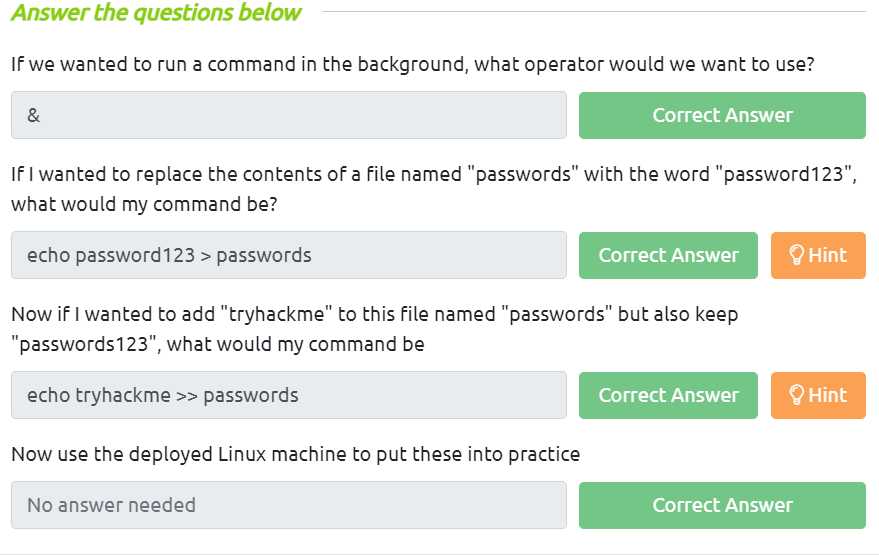
Searching for Files &: thực hiện chạy ngầm task
: ghi đè nội dùng file
Introduction to Flags and Switches
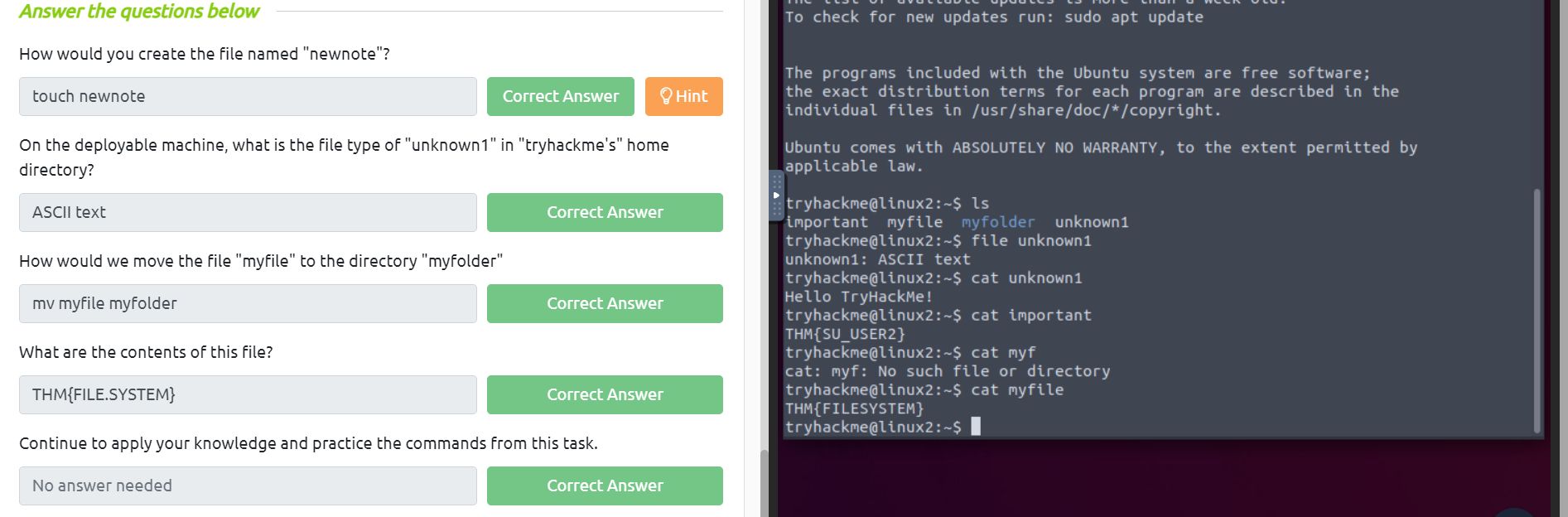
 Filesystem Interaction Continued
touch: tạo 1 file rỗng mới
file: kiểm tra định dạng của file
cat: đọc file
Filesystem Interaction Continued
touch: tạo 1 file rỗng mới
file: kiểm tra định dạng của file
cat: đọc file
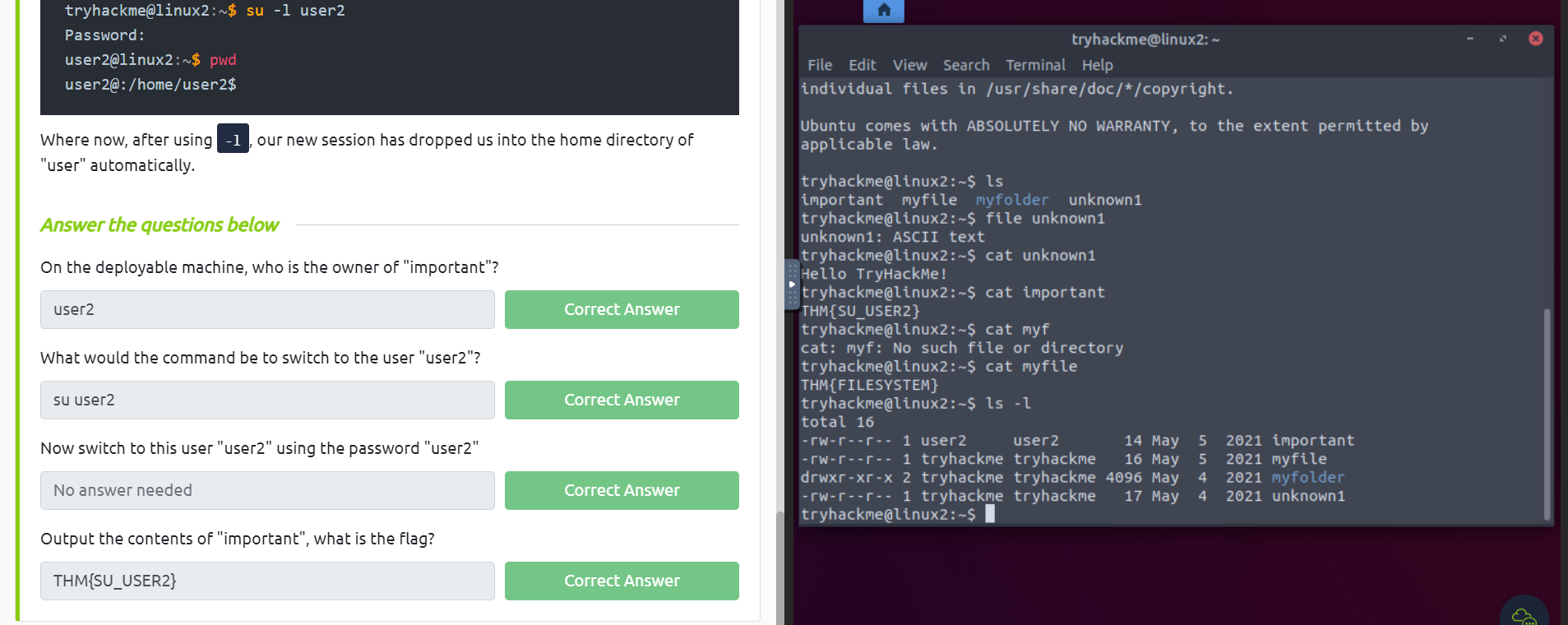
 Permissions 101
Permissions 101
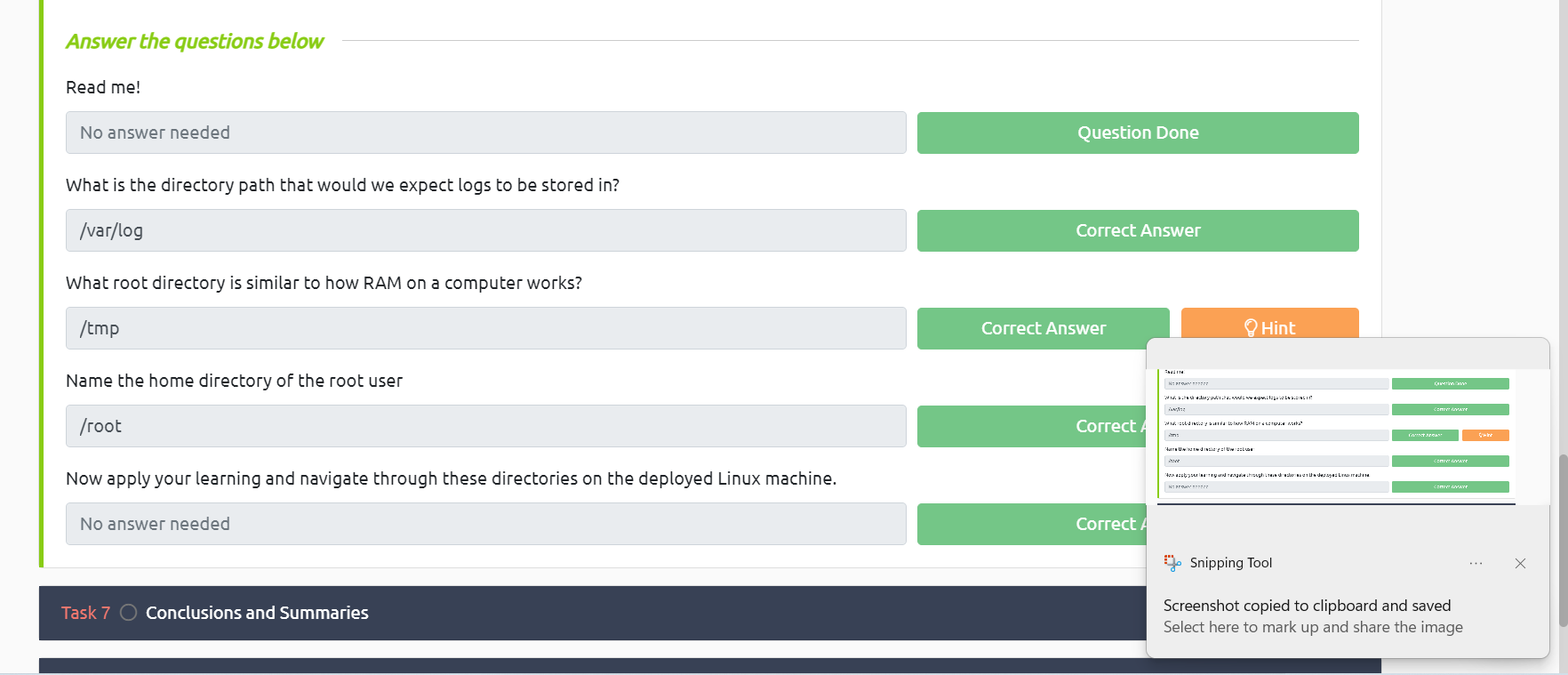
 Common Directories
Common Directories
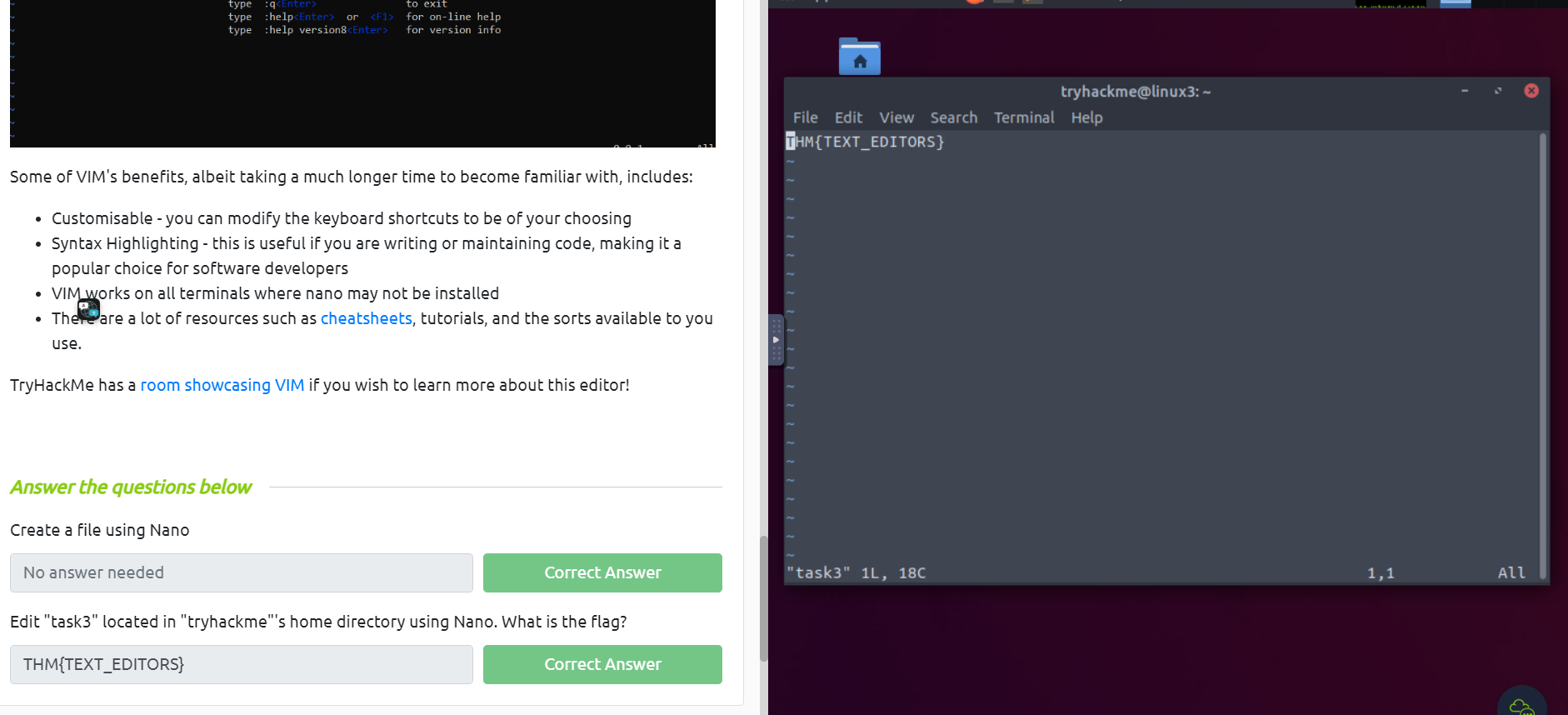
Terminal Text Editors
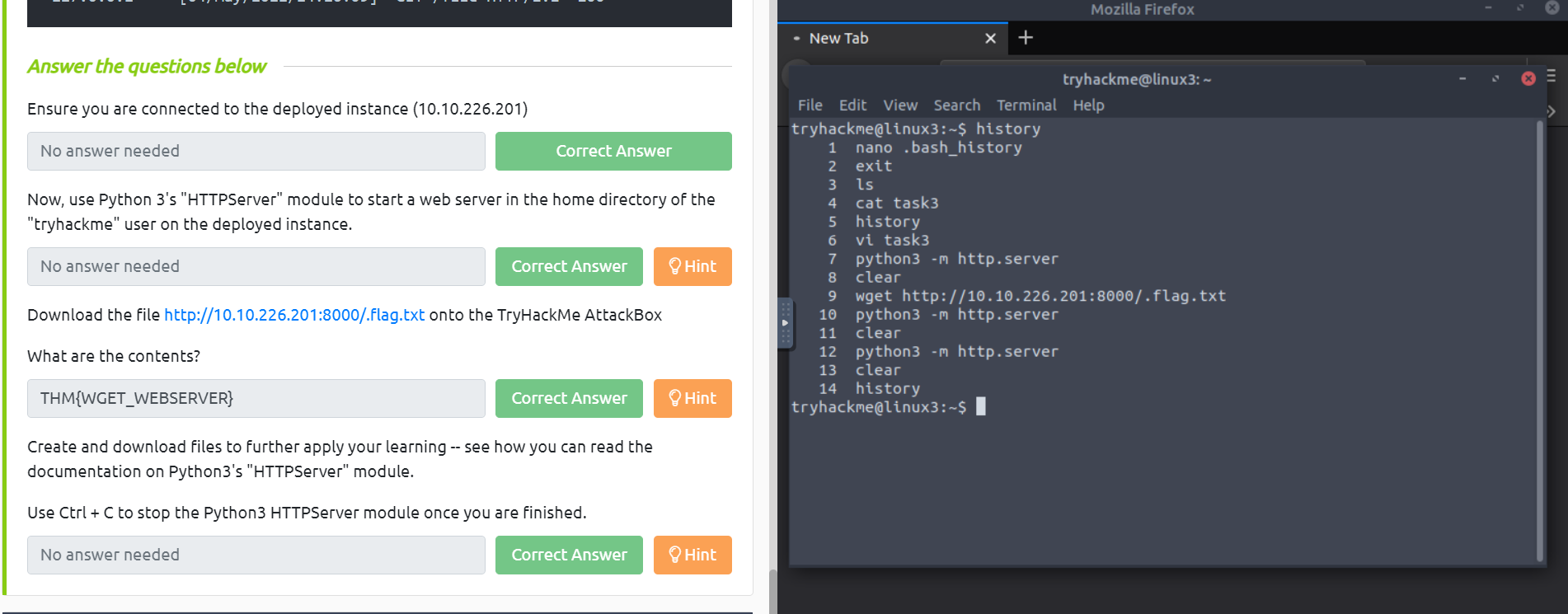
 General/Useful Utilities
General/Useful Utilities
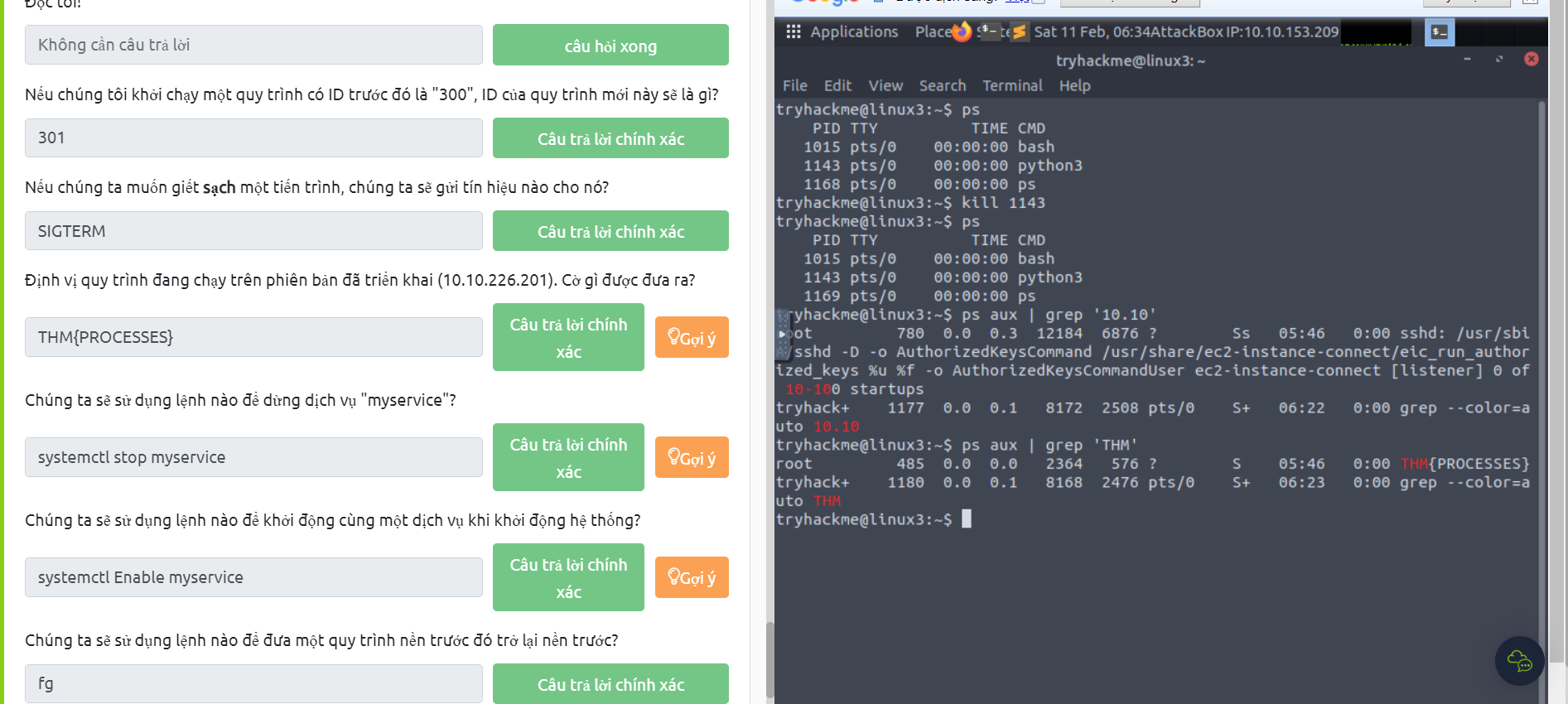
 Processes 101
Processes 101
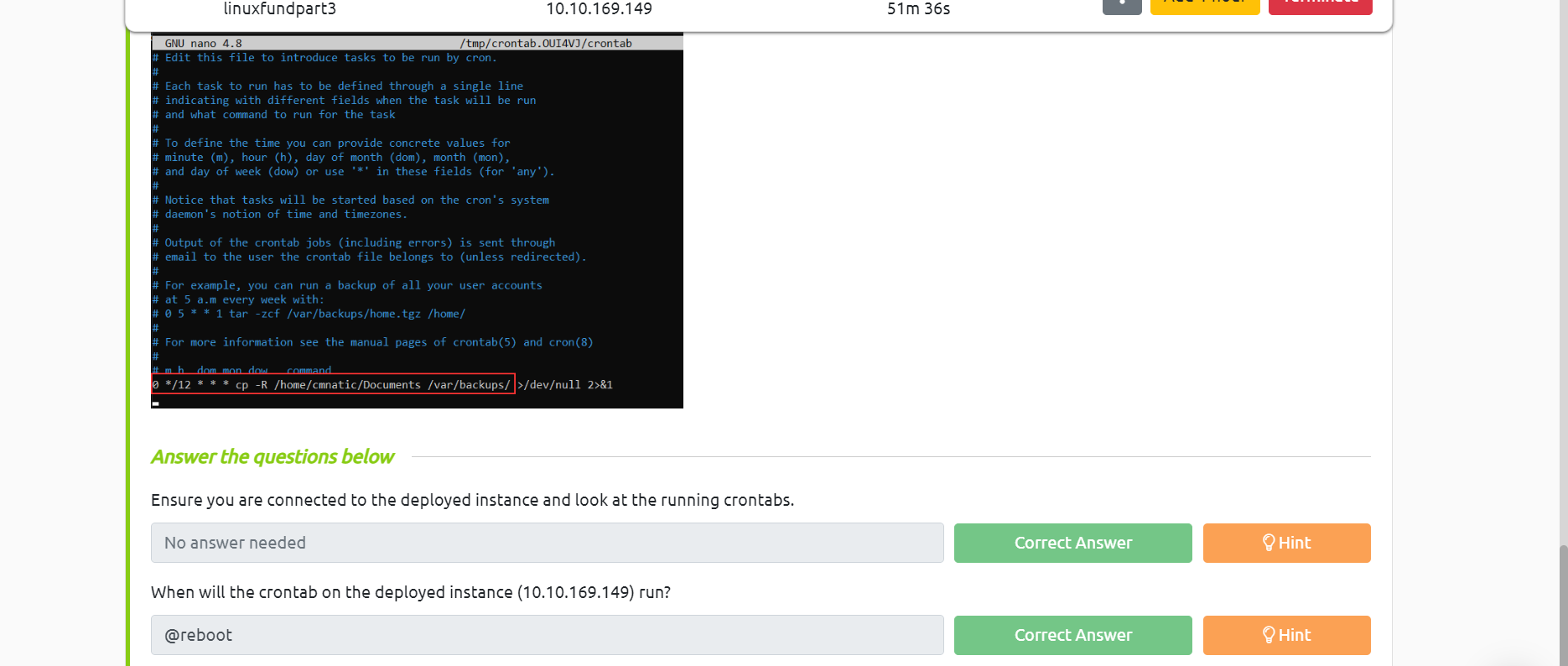
 Maintaining Your System: Automation
Maintaining Your System: Automation
 Maintaining Your System: Package Management
Maintaining Your System: Package Management
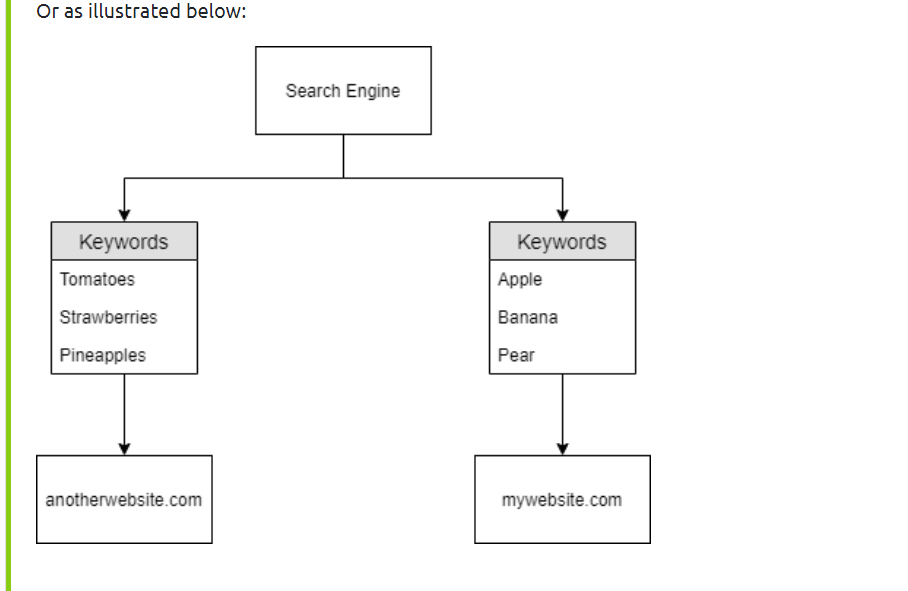
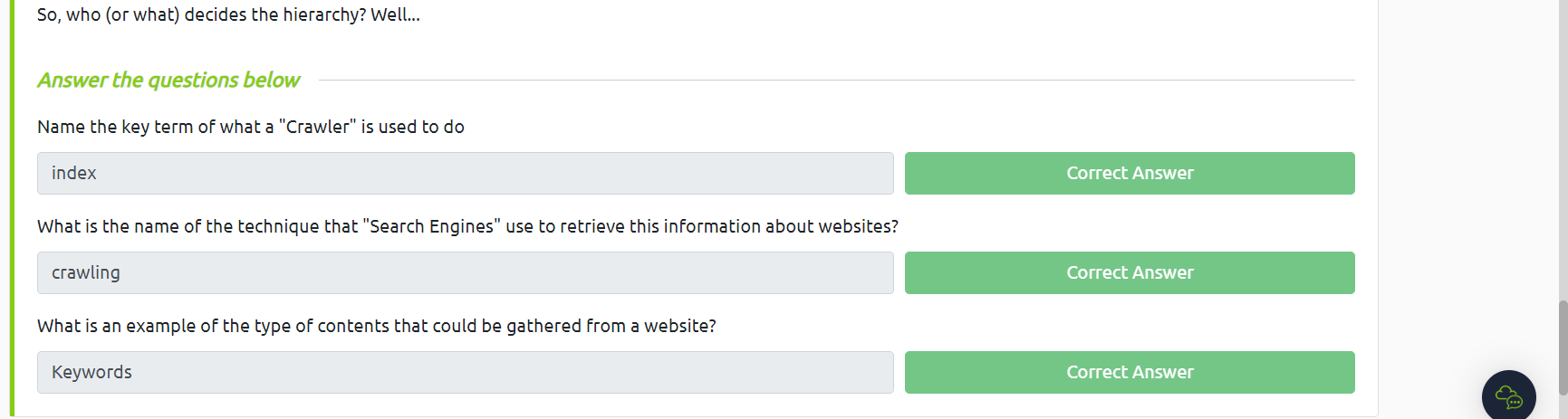
Let's Learn About Crawlers
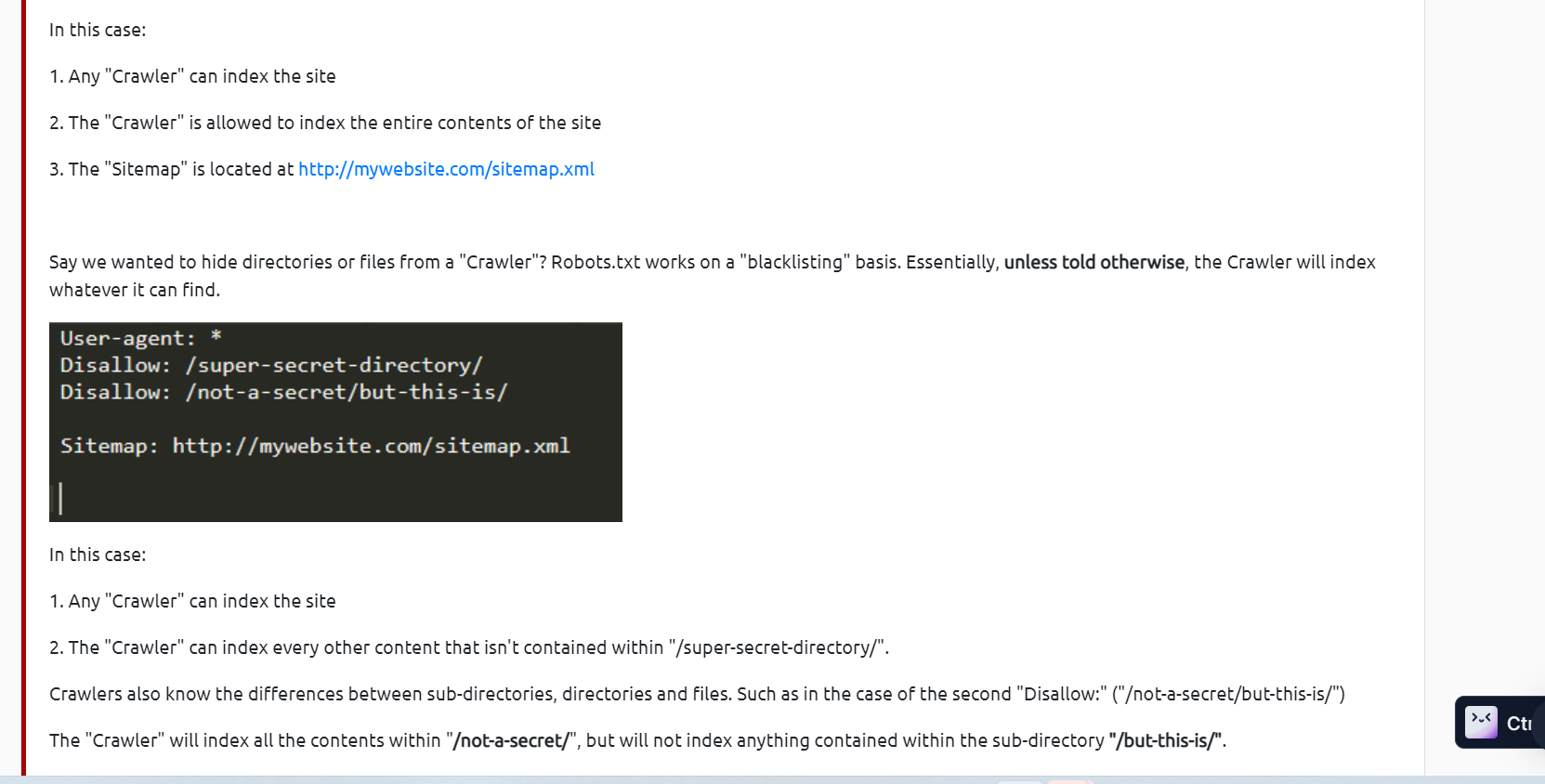
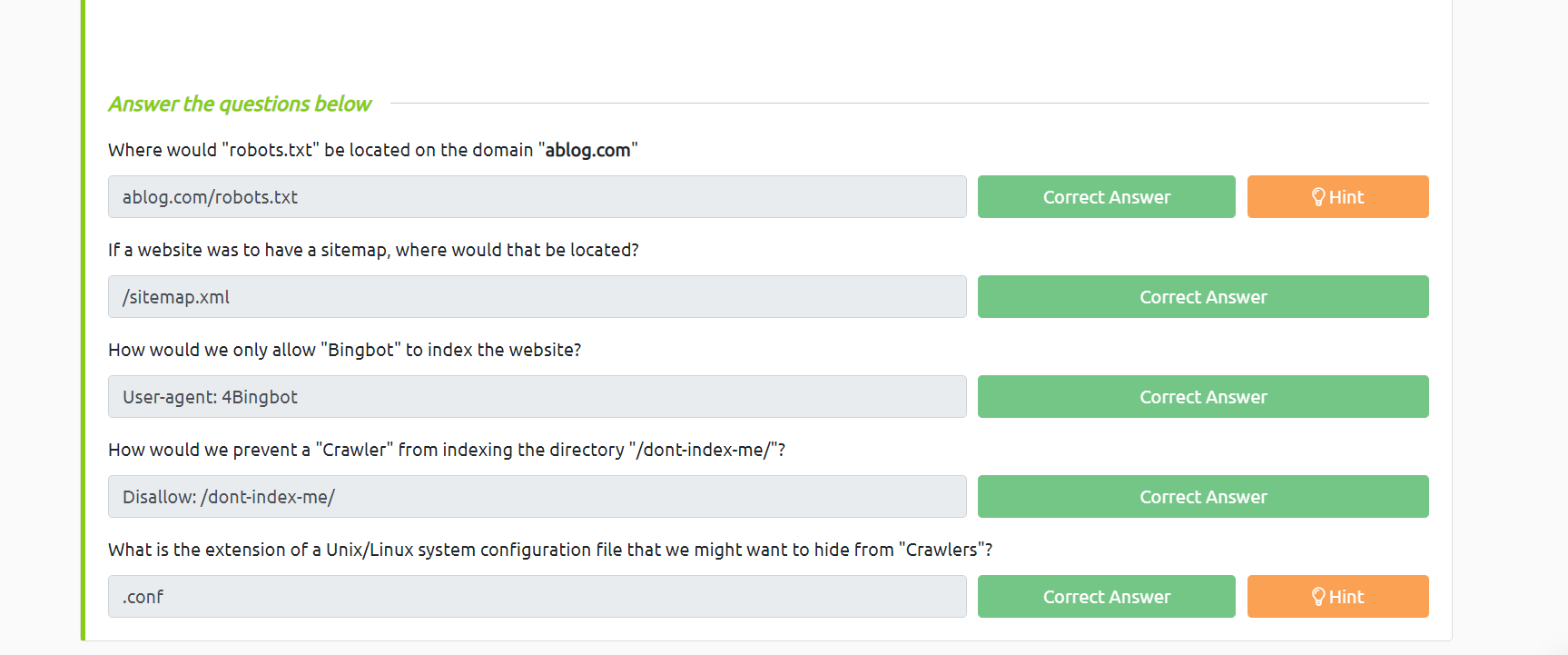
 Beepboop - Robots.txt
phần này thì em đọc và làm giống hướng dẫn thôi
Beepboop - Robots.txt
phần này thì em đọc và làm giống hướng dẫn thôi
 Sitemaps
Sitemaps
 What is Google Dorking?
What is Google Dorking?
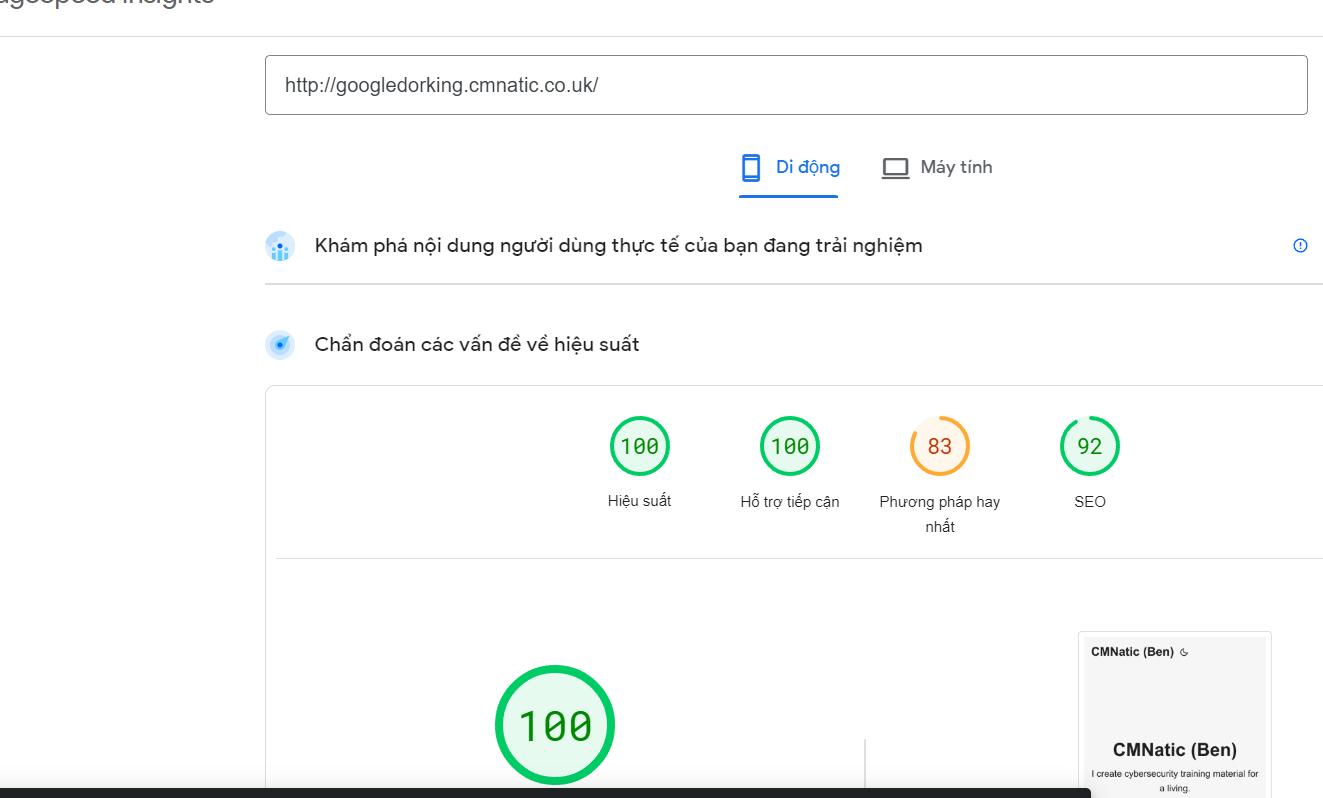
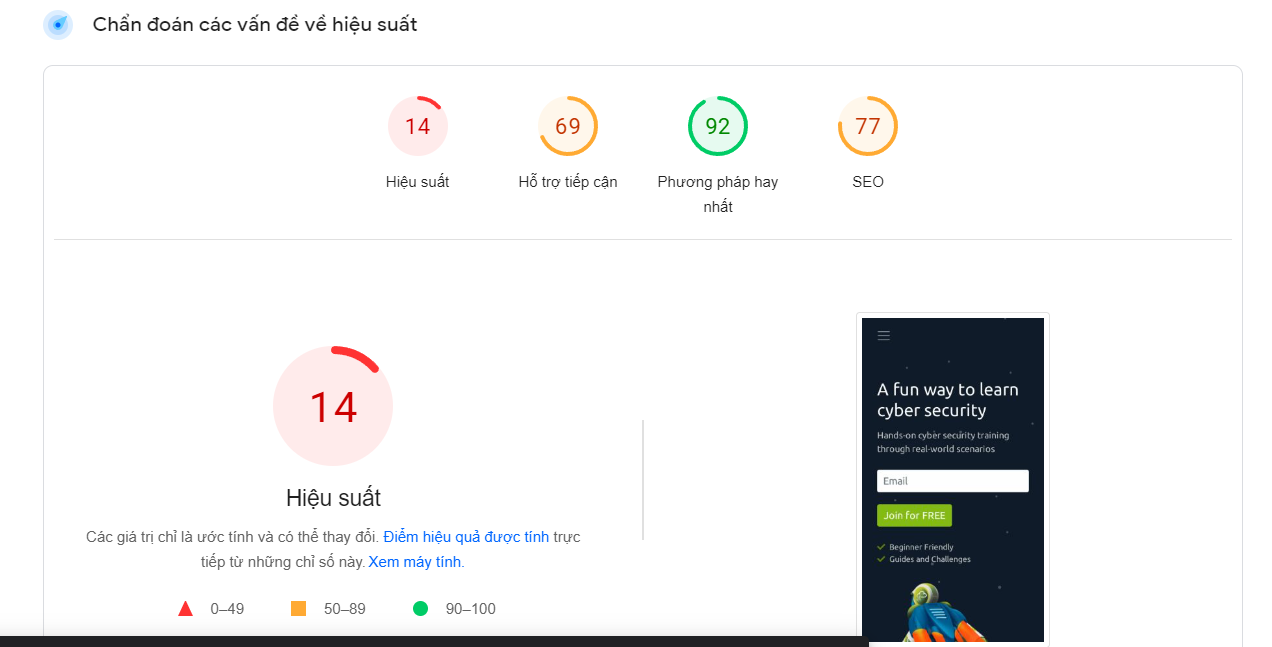
 Enter: Search Engine Optimisation
Enter: Search Engine Optimisation
What is this users avatar of?
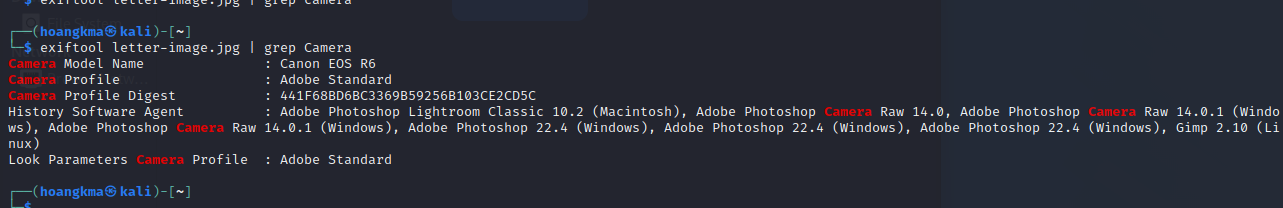
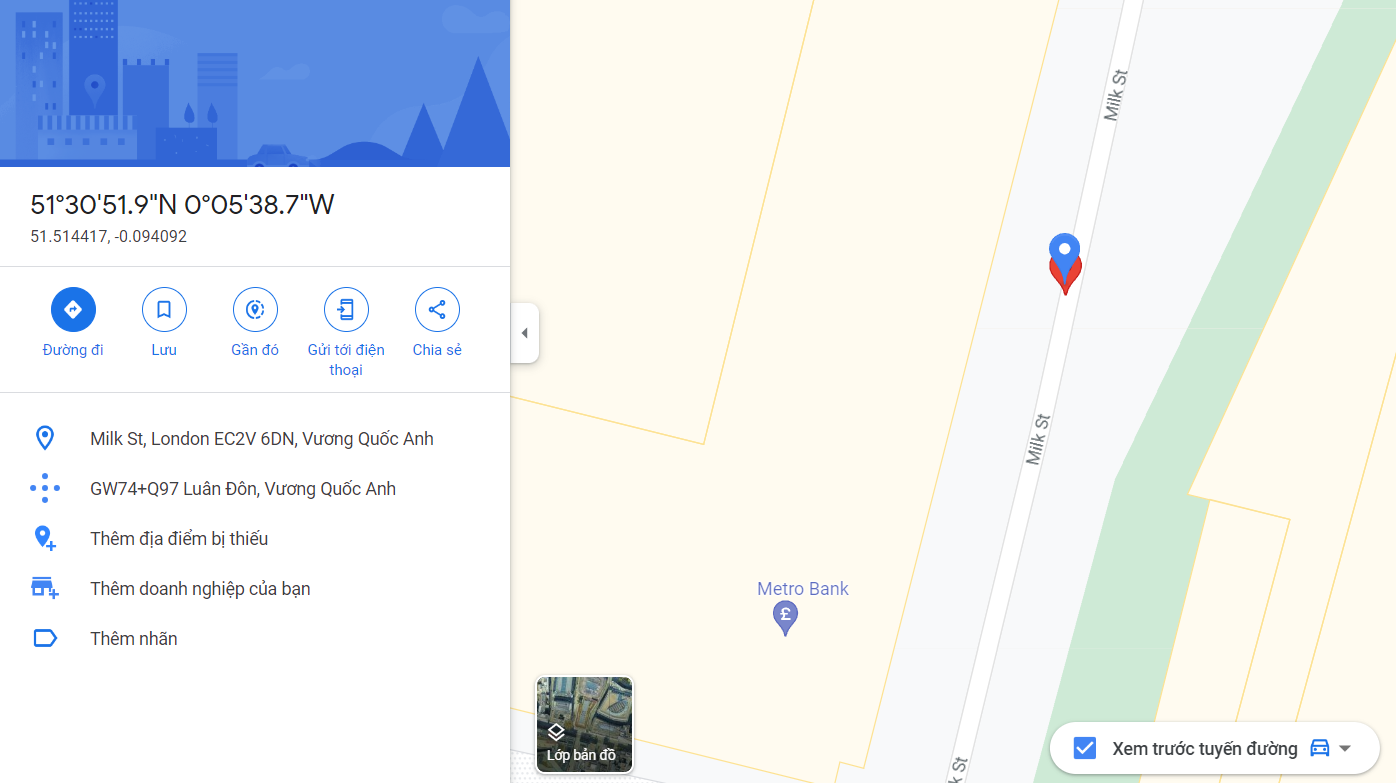
dùng exiftool:
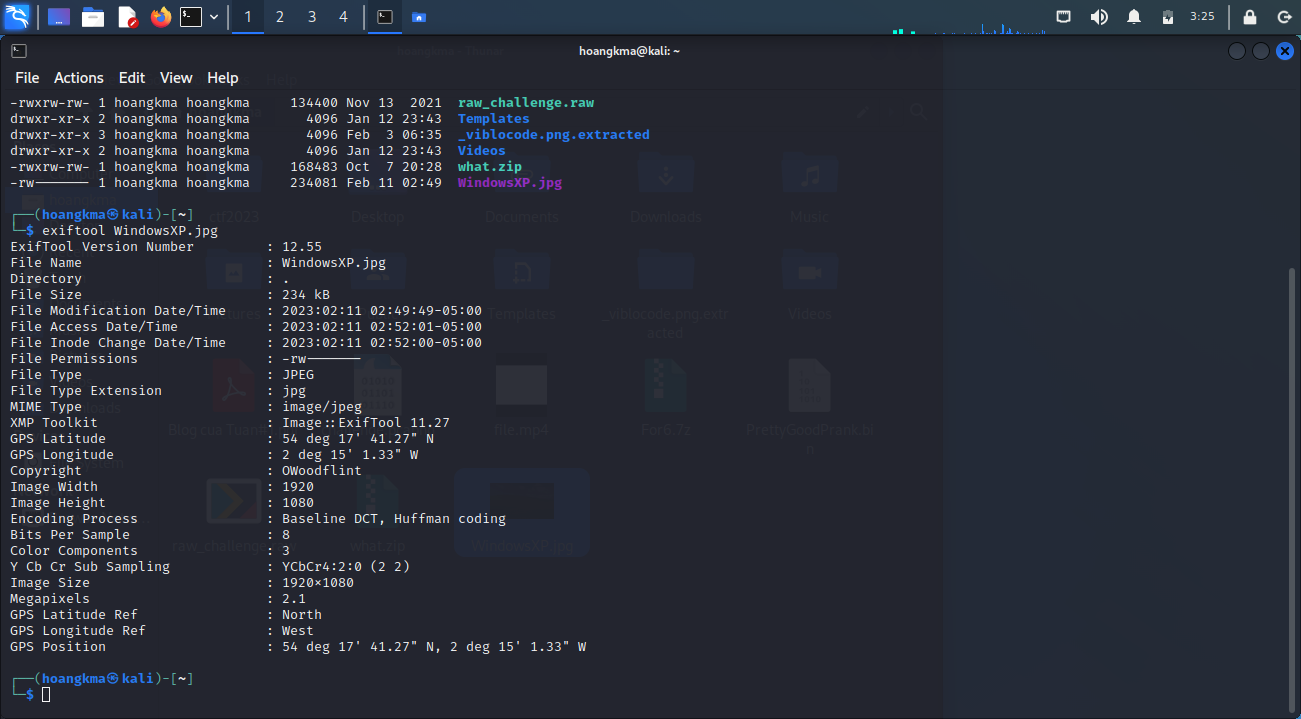 thu được tên người dùng là OWoodflint
tìm được thấy twitter có hình đại diện là một con mèo nên câu trả lời đầu tiên sẽ là cat
What city is this person in?
Whats the SSID of the WAP he connected to?
thu được tên người dùng là OWoodflint
tìm được thấy twitter có hình đại diện là một con mèo nên câu trả lời đầu tiên sẽ là cat
What city is this person in?
Whats the SSID of the WAP he connected to?
dùng chức năng advance search của wigle.net
tìm được câu trả lời cho câu hỏi 2 và 3 lần lượt là LonDon và UnileverWiFi What is his personal email address?
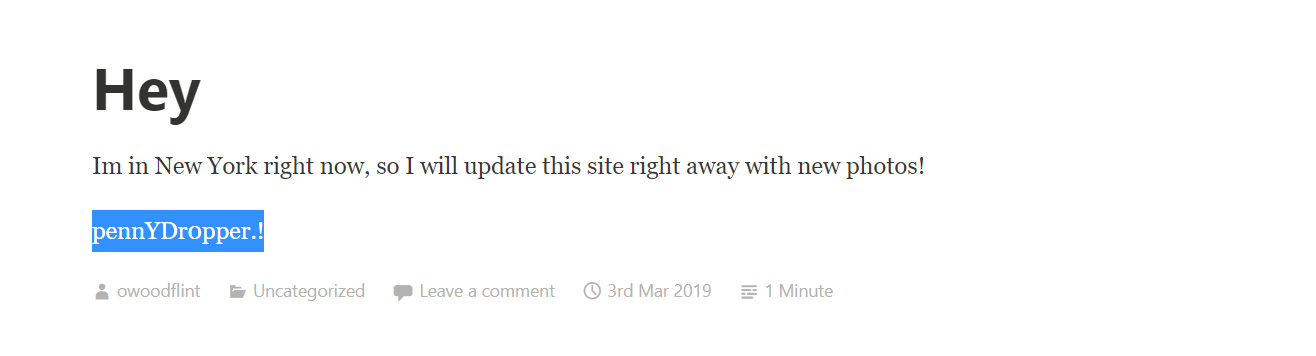
vào github lấy được gmail của chủ sở hữu :OWoodflint@gmail.com What site did you find his email address on?:github Where has he gone on holiday? google tìm thấy một trang wordpress của owoodflint có nội dung
-> New York What is this persons password? do wordpress là trang của người dùng phải tự giấu thông tin nên nó khả nghi nhất trong khi twtitter và github bảo mật về mật khẩu khá tốt em check từng phần trong web thì phần dưới có để màu trắng
Filters
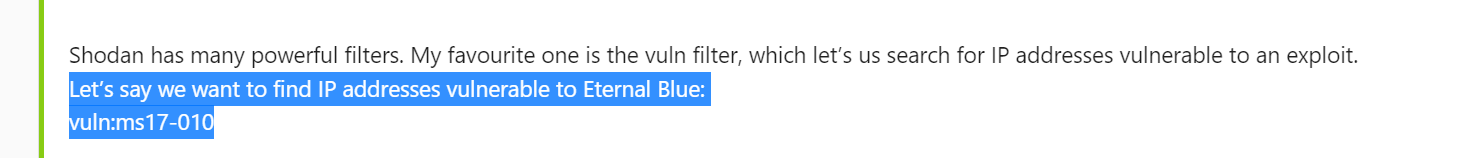 Google & Filtering
What is the 2nd most popular country for MYSQL servers in Google's ASN?
Google & Filtering
What is the 2nd most popular country for MYSQL servers in Google's ASN?
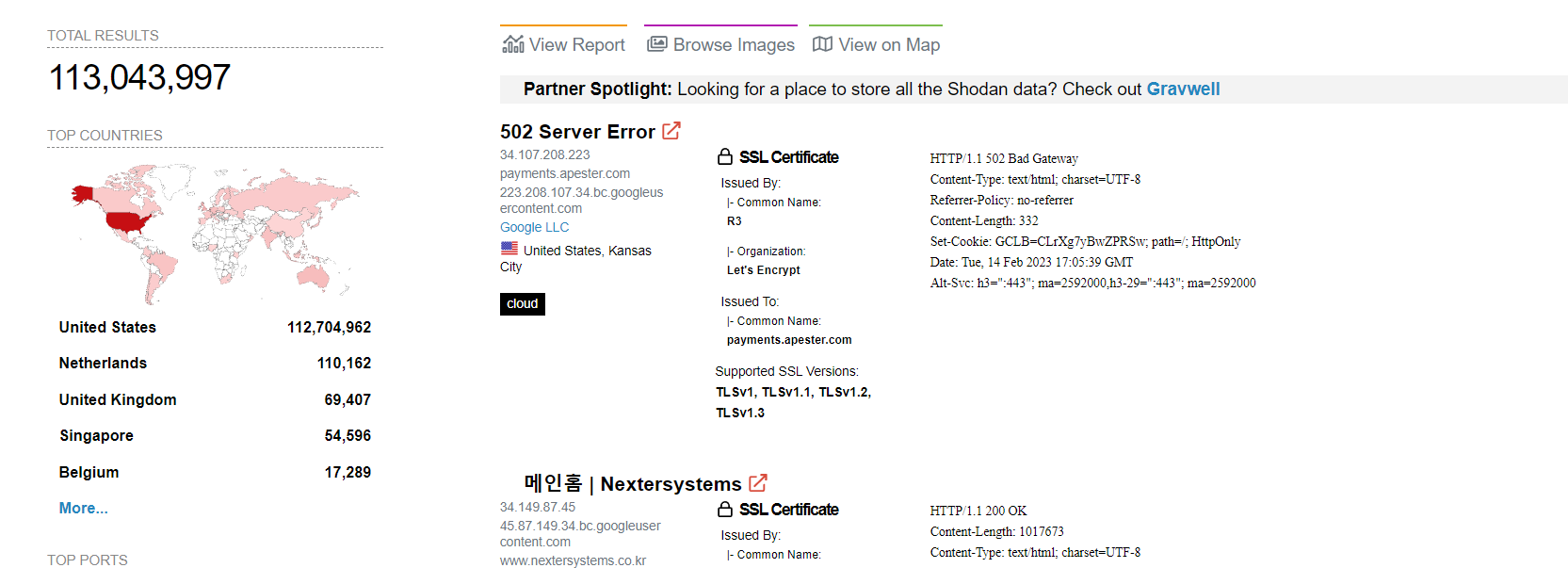 What is the top operating system for MYSQL servers in Google's ASN?
What is the top operating system for MYSQL servers in Google's ASN?
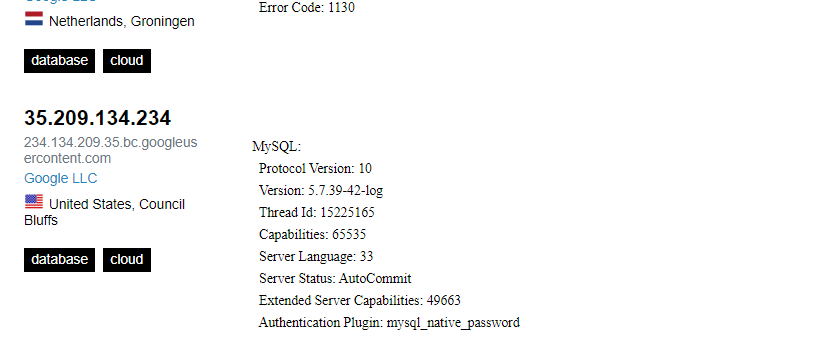
- cái này em dùng kết quả của hint do bài ra từ khoảng năm 2021 nên chắc có thể đã được update
Under Google's ASN, which is more popular for nginx, Hypertext Transfer Protocol or Hypertext Transfer Protocol with SSL?
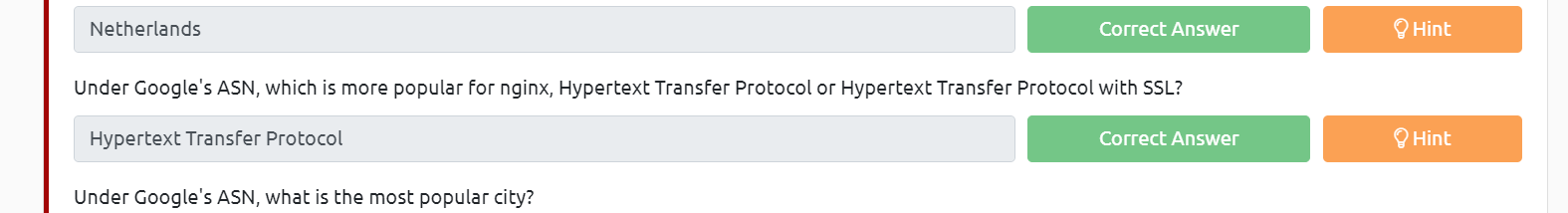
- giao thức này cũng khá là phổ biến nên em nghĩ không cần nói gì thêm
Under Google's ASN, what is the most popular city?
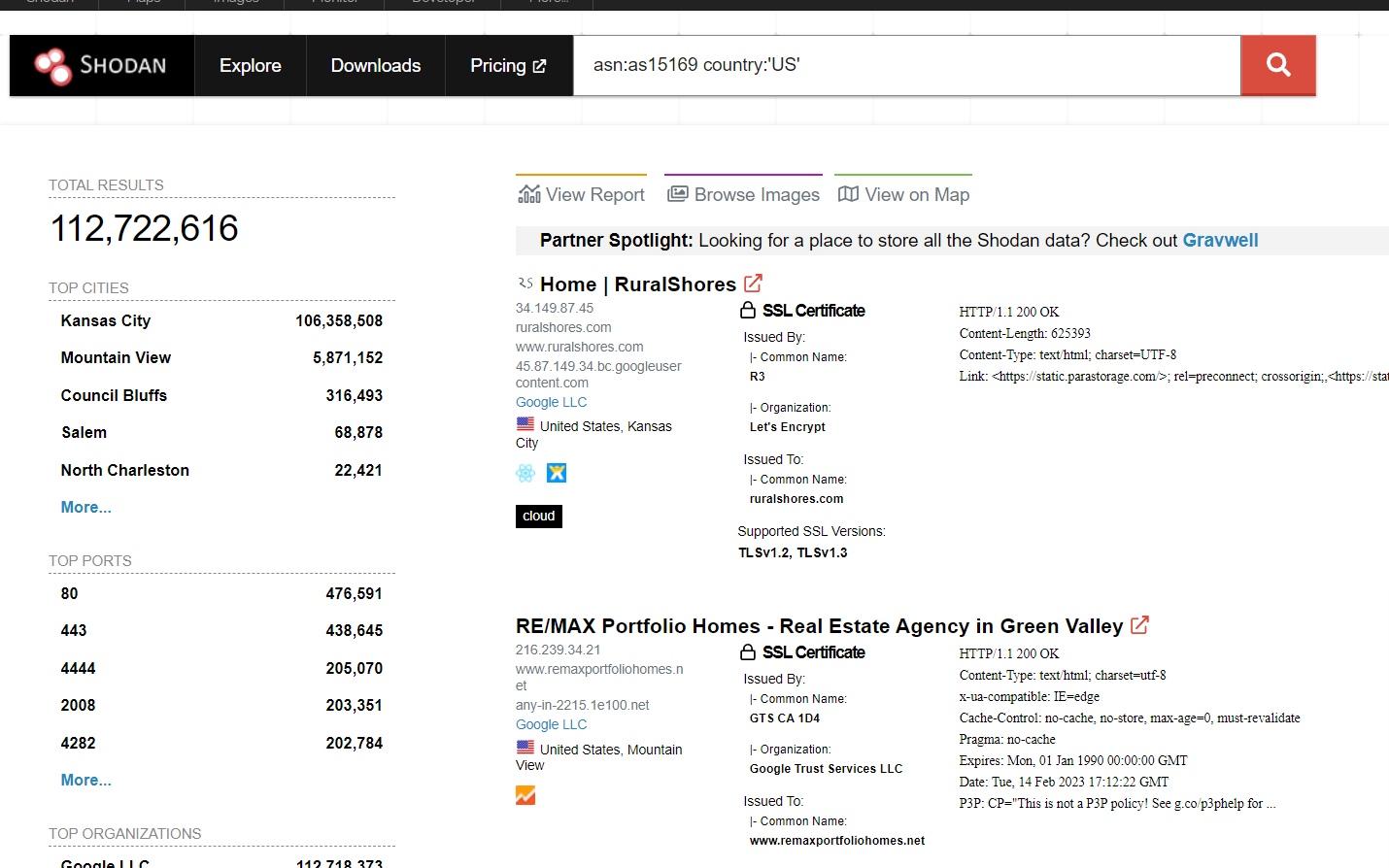
- câu này lại ra kq khác có lẽ tryhackme lâu không update bài này
Under Google's ASN in Los Angeles, what is the top operating system according to Shodan?
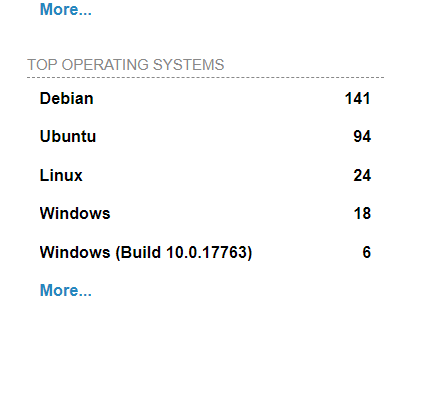
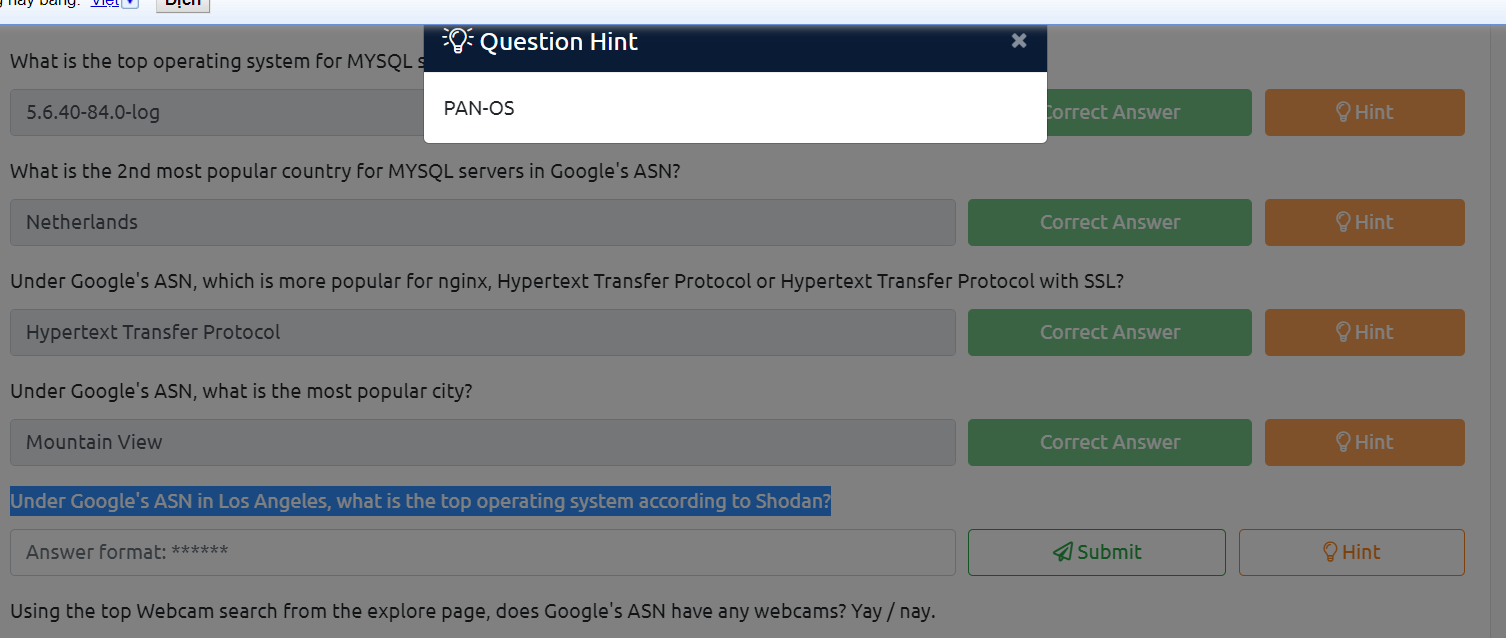
- có lẽ đây vẫn là câu tryhackme chưa cập nhật
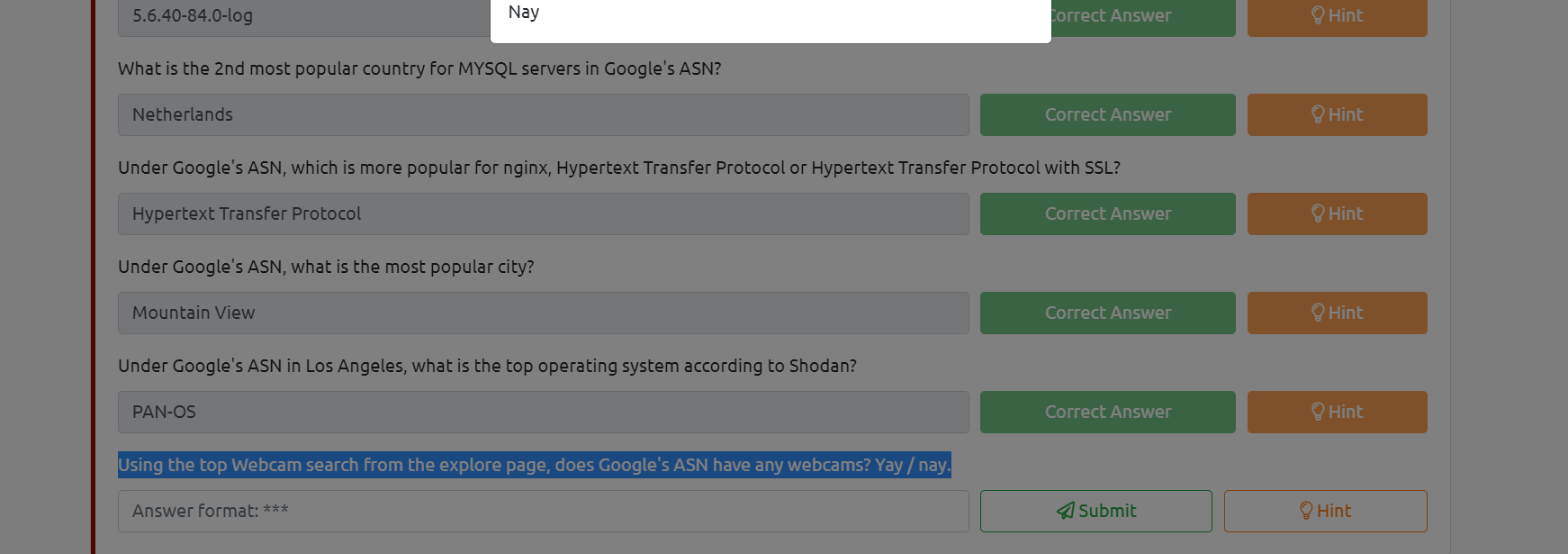
Using the top Webcam search from the explore page, does Google's ASN have any webcams? Yay / nay.
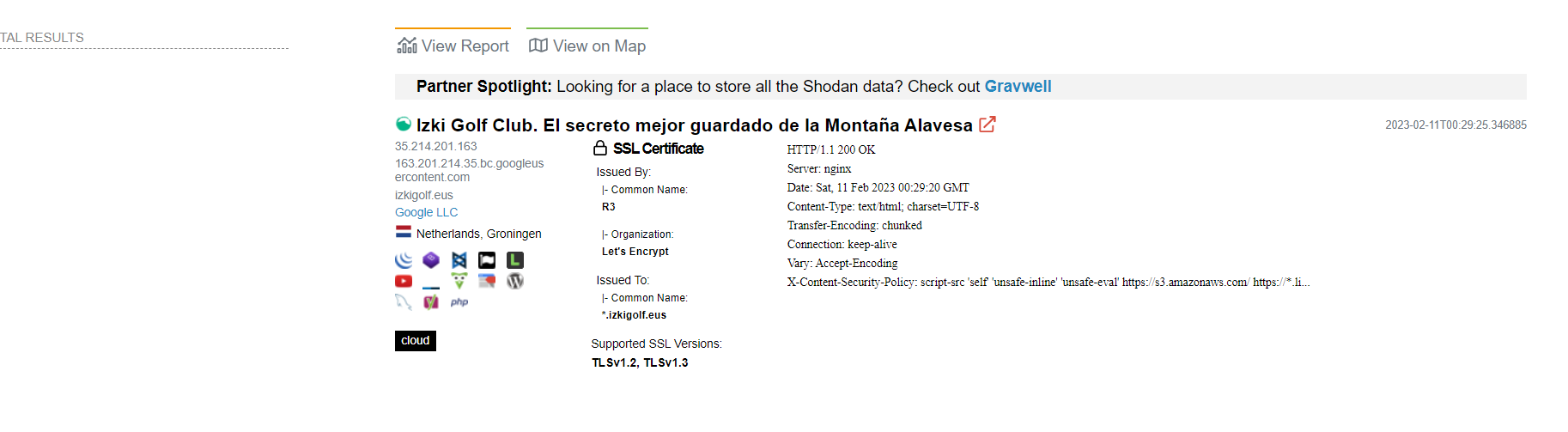
- tiếp tục là 1 câu sai của tryhackme
 Shodan Monitor
Shodan Monitor - câu này chỉ đơn giản là copy đường link phía trên
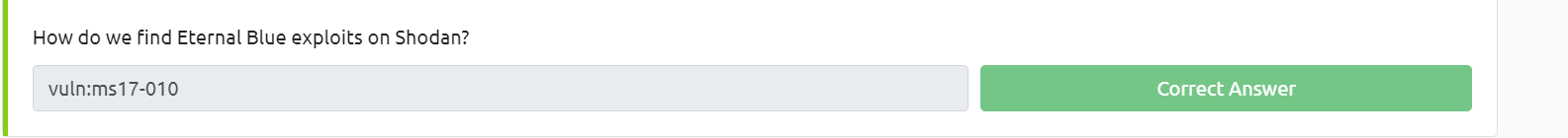
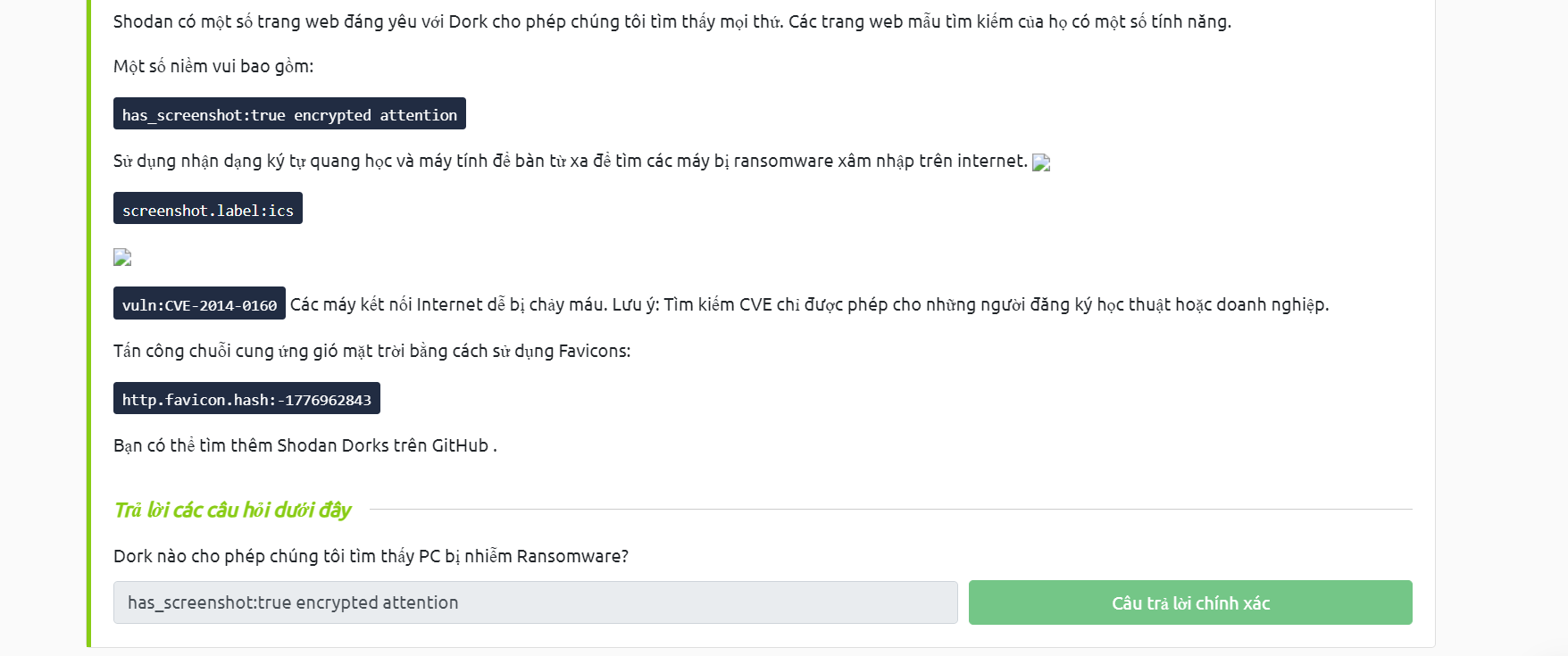
 Shodan Dorking
Shodan Dorking
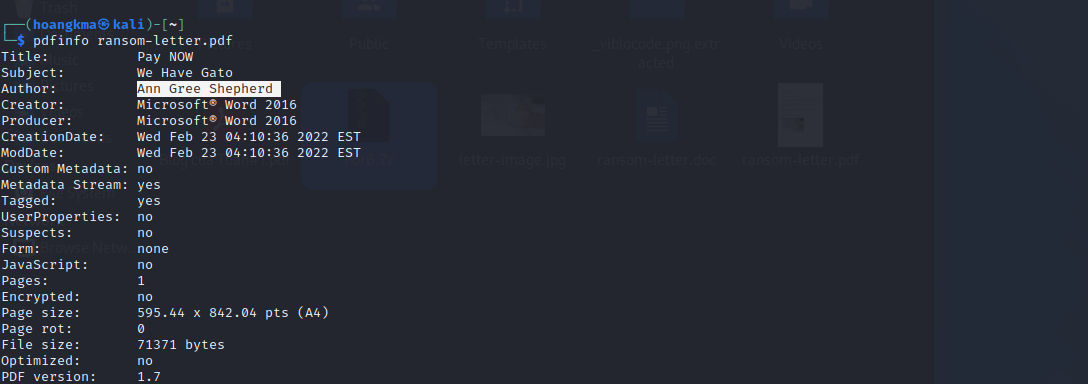
Introduction To Digital Forensics
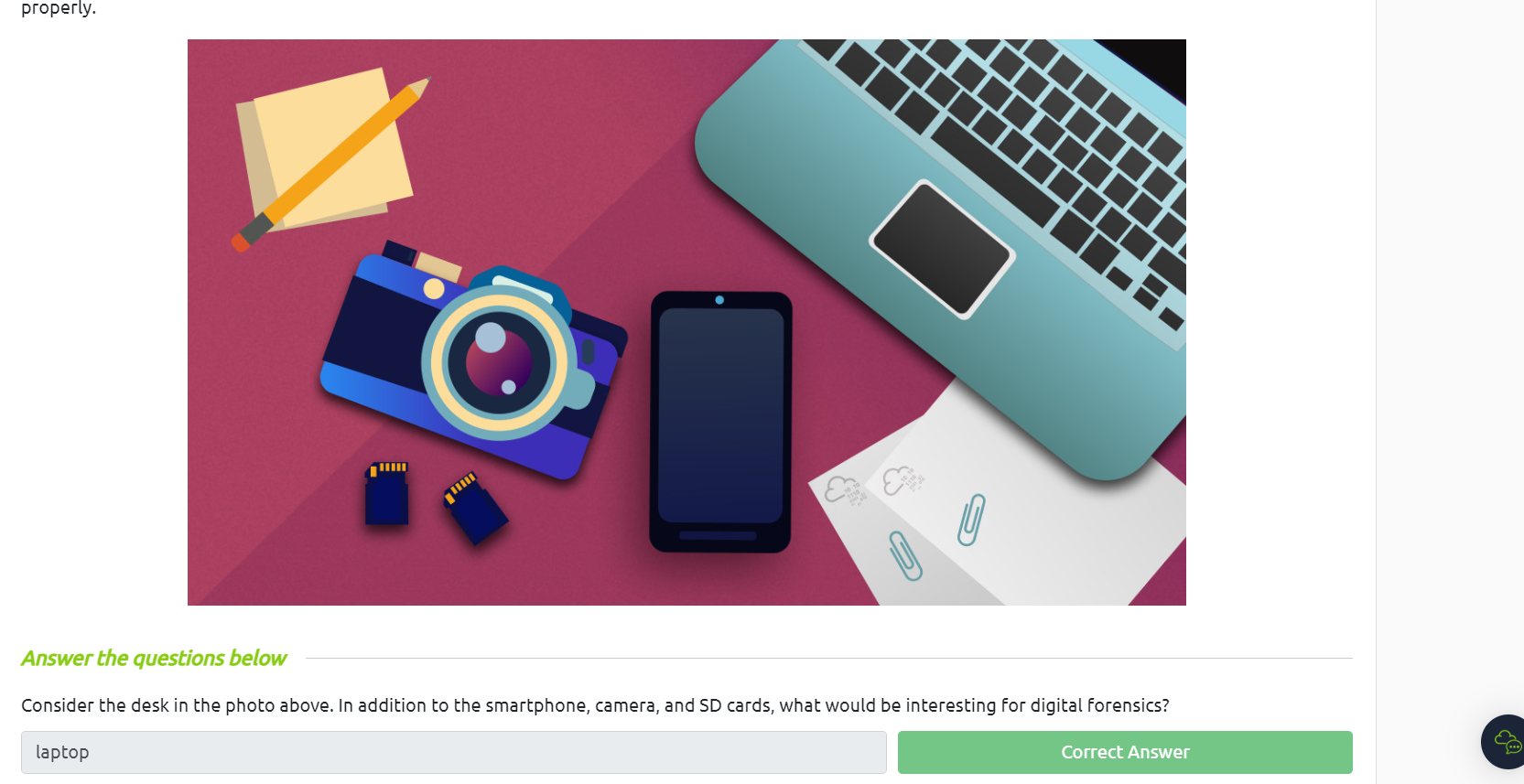 Digital Forensics Process
Digital Forensics Process
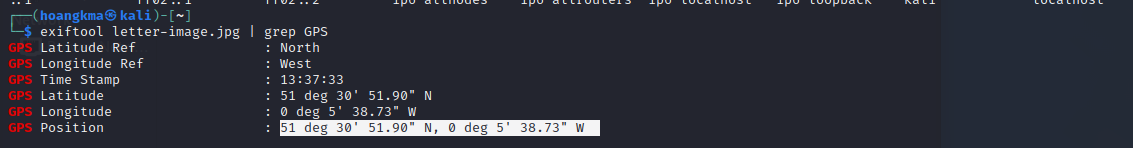
 Practical Example of Digital Forensics
Practical Example of Digital Forensics
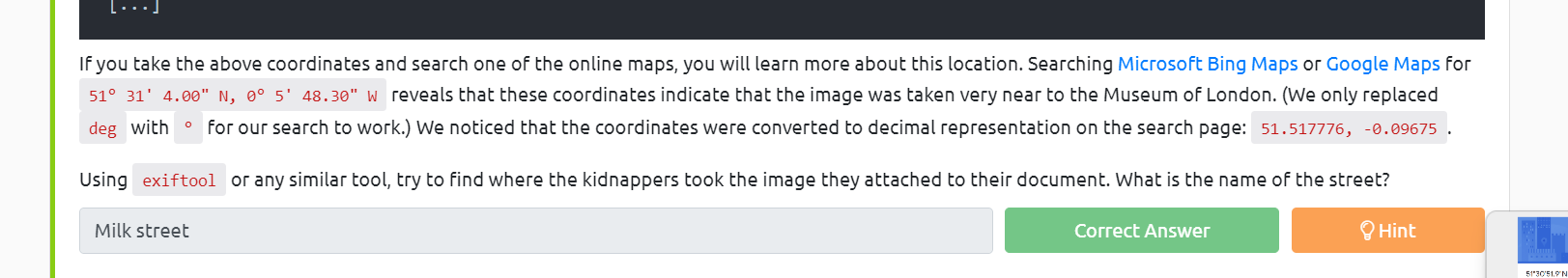
Windows Editions
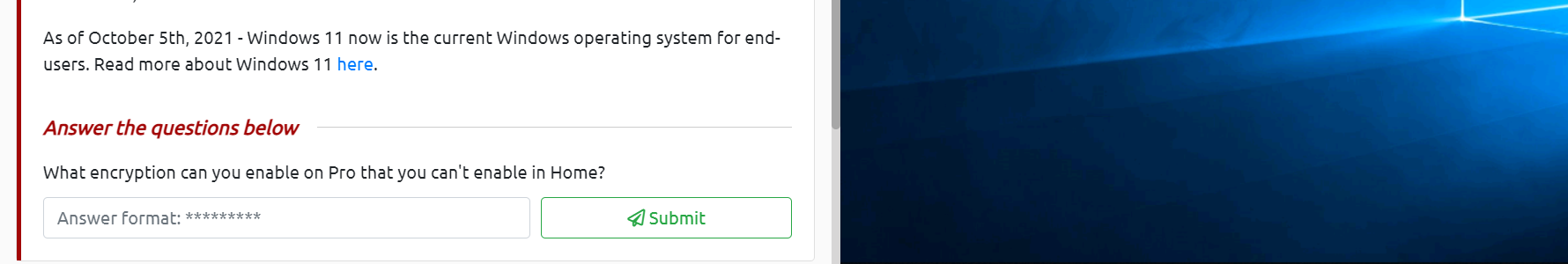
 search google dễ dàng thấy được câu trả lời là bitlocker
The Desktop (GUI)
search google dễ dàng thấy được câu trả lời là bitlocker
The Desktop (GUI)
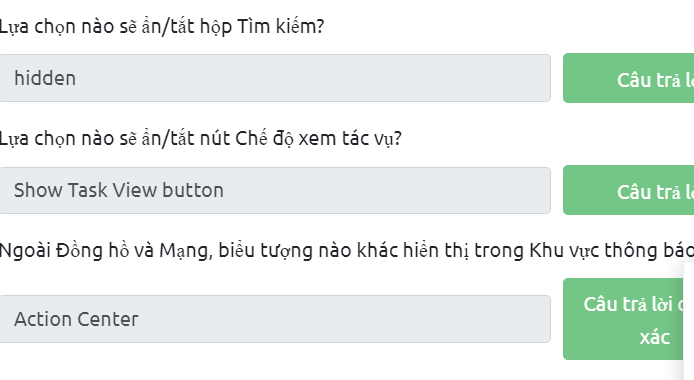 The File System
The File System
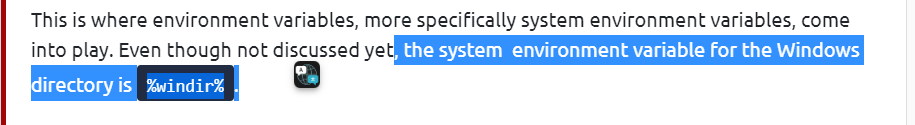
 The Windows\System32 Folders
The Windows\System32 Folders
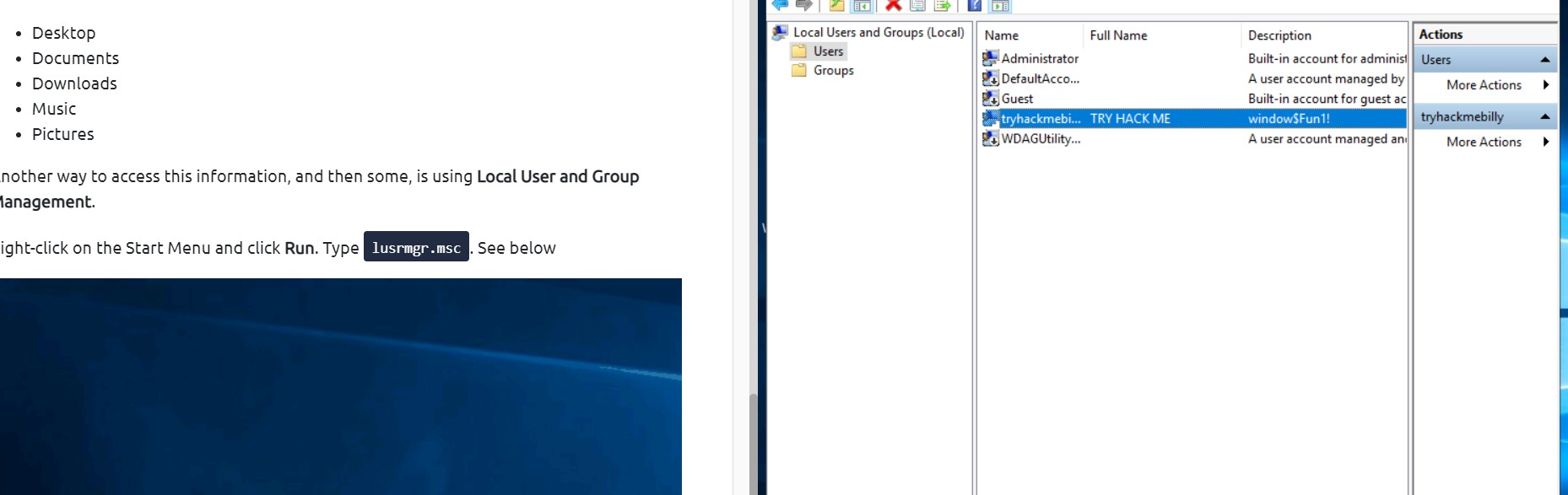
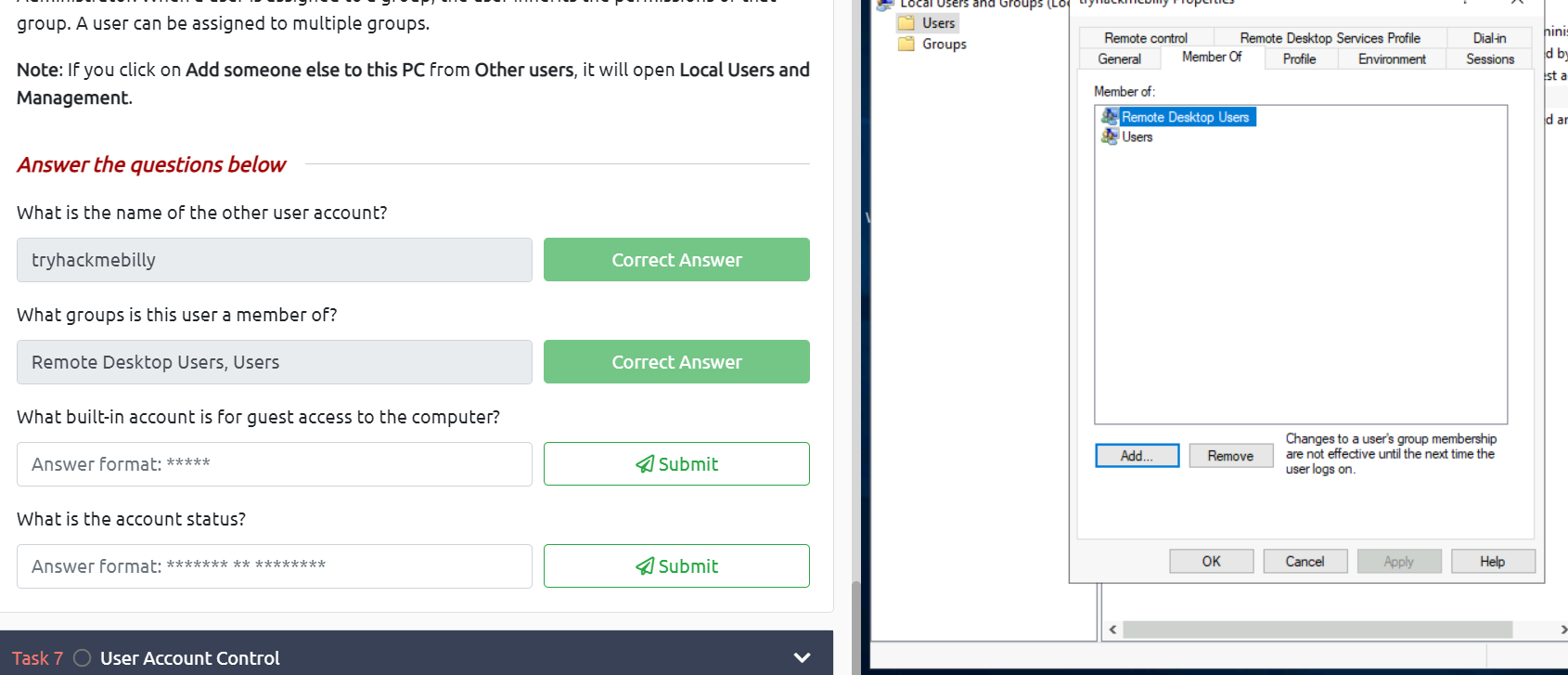
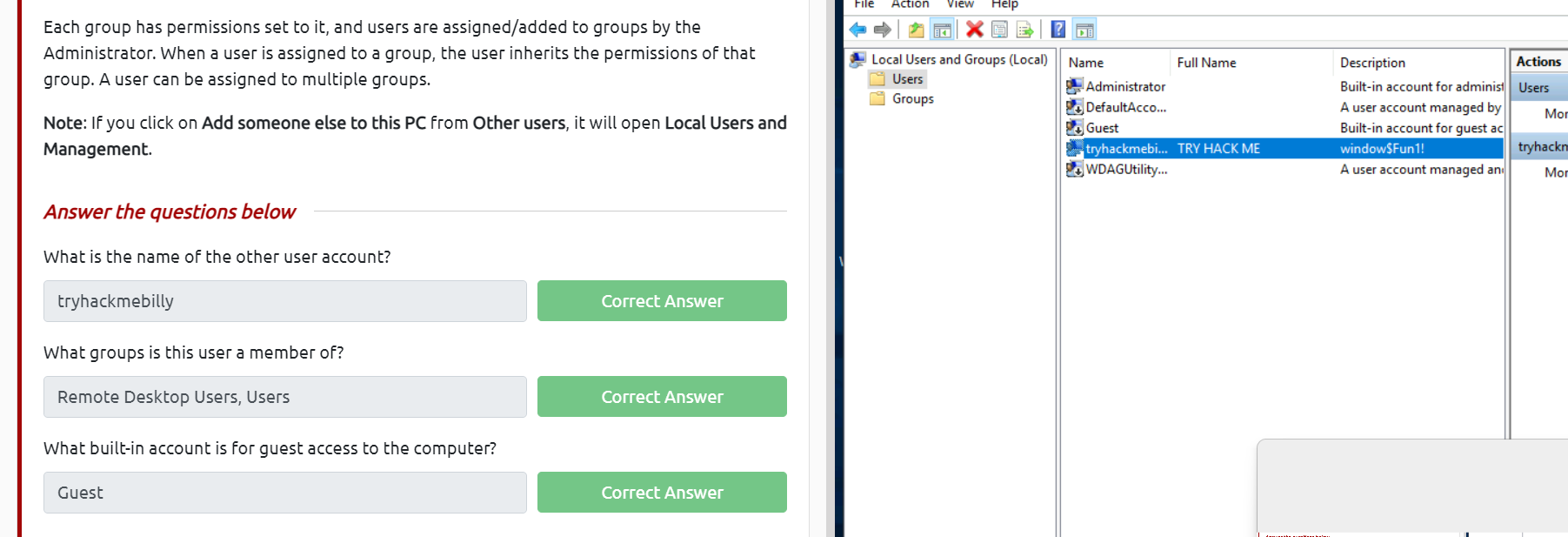
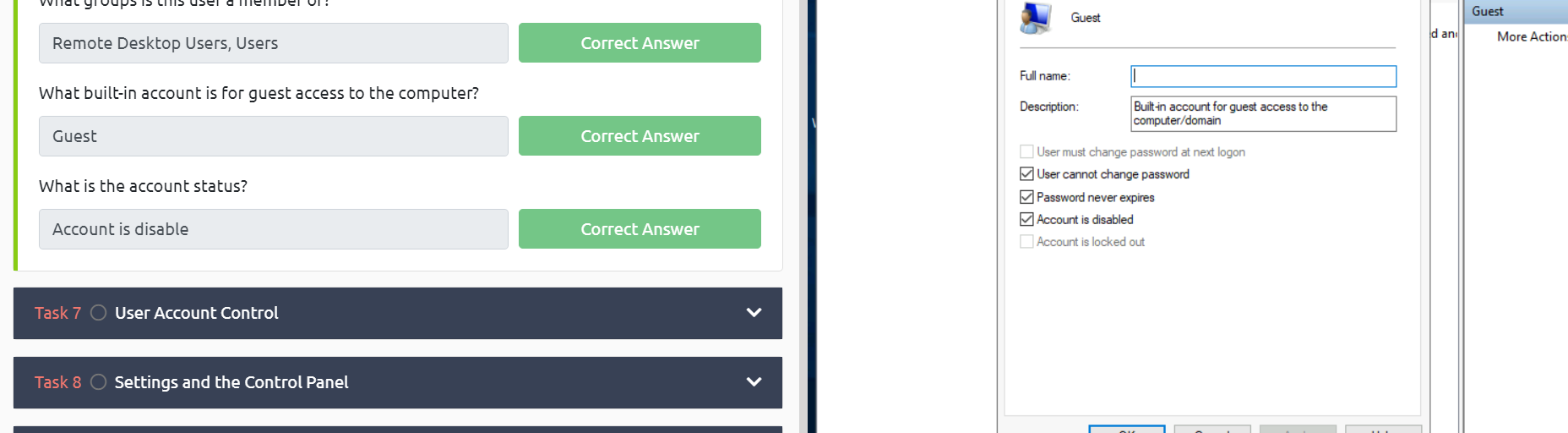
 User Accounts, Profiles, and Permissions
User Accounts, Profiles, and Permissions
 User Account Control
User Account Control
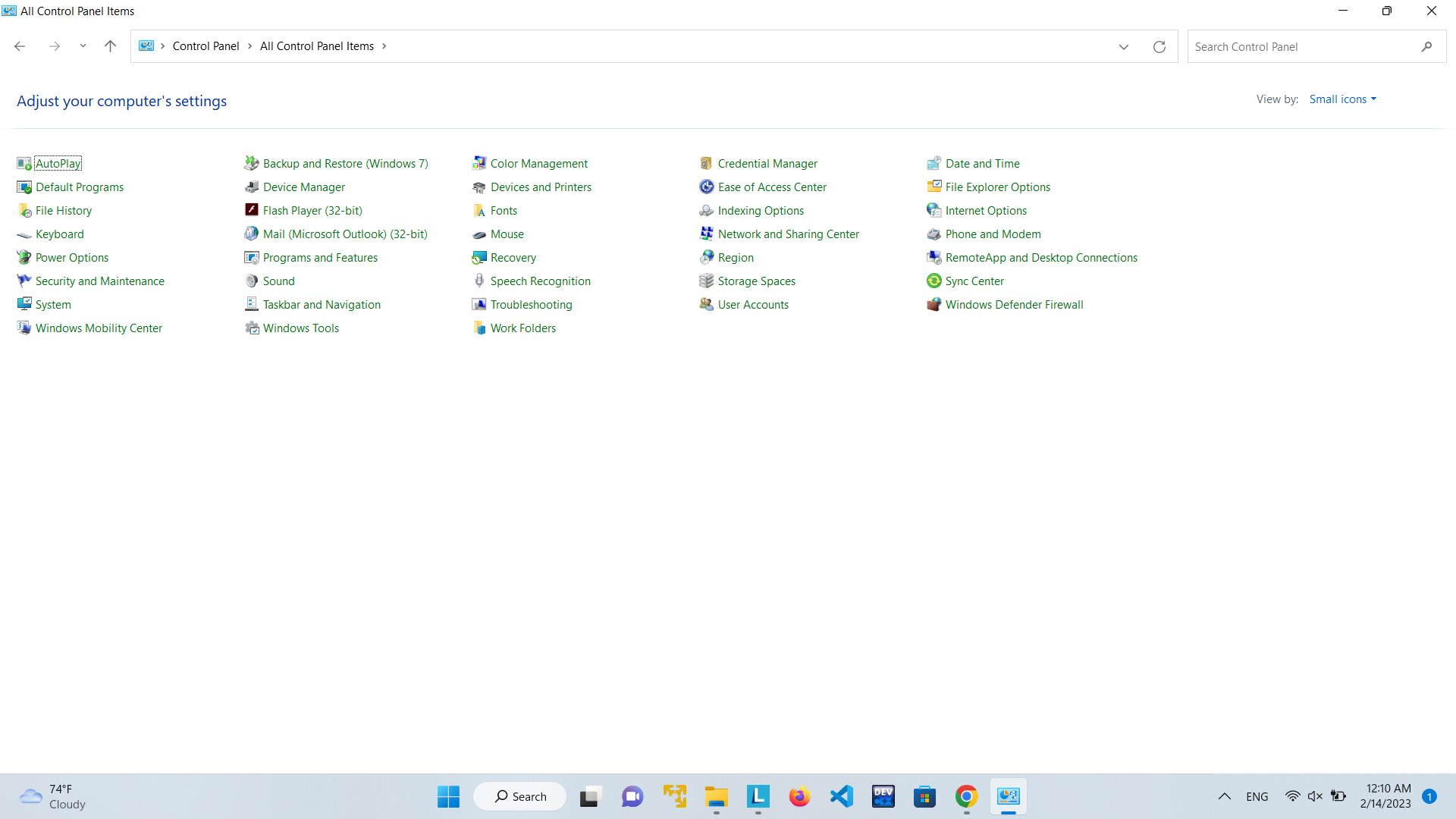
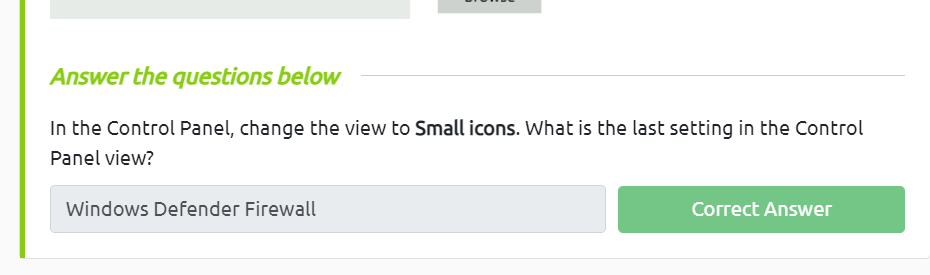
 Settings and the Control Panel
Settings and the Control Panel
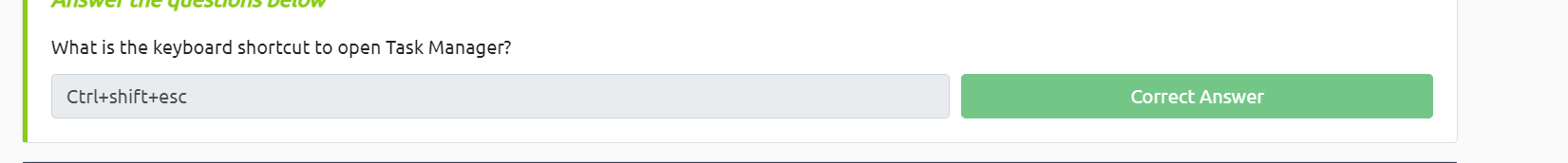
 task manager
task manager
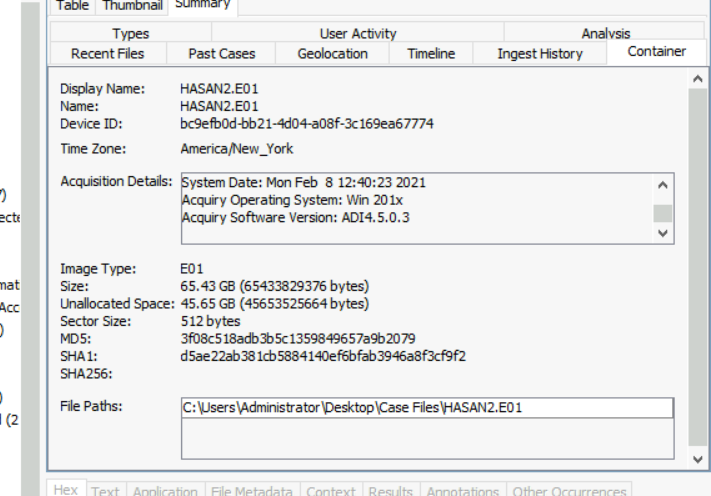
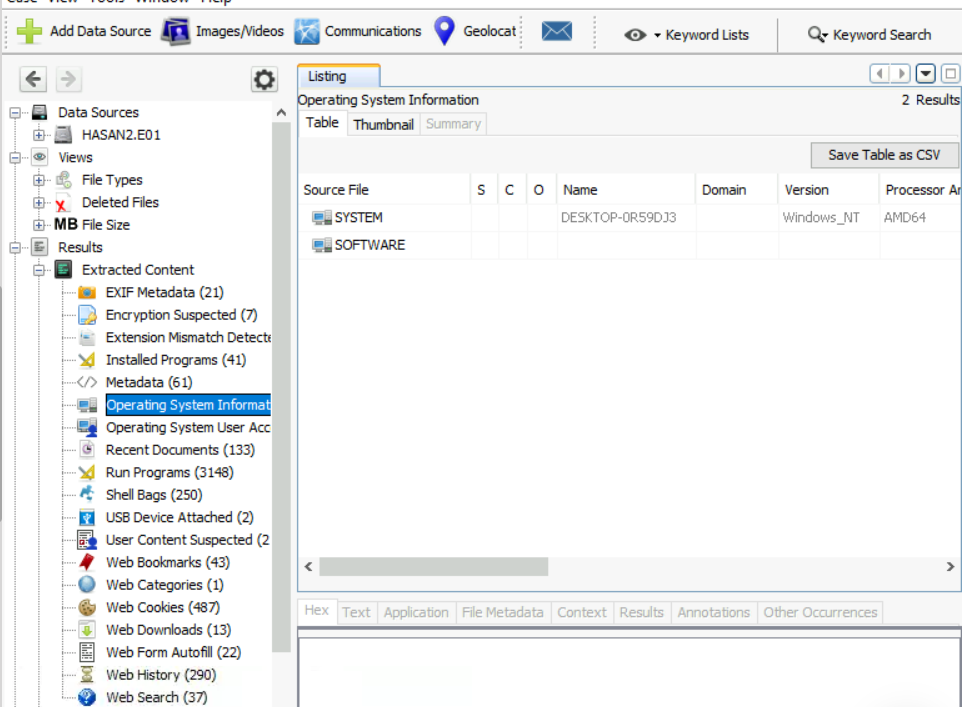
What is the MD5 hash of the E01 image?
mở autospy và dễ dàng tìm được MD5
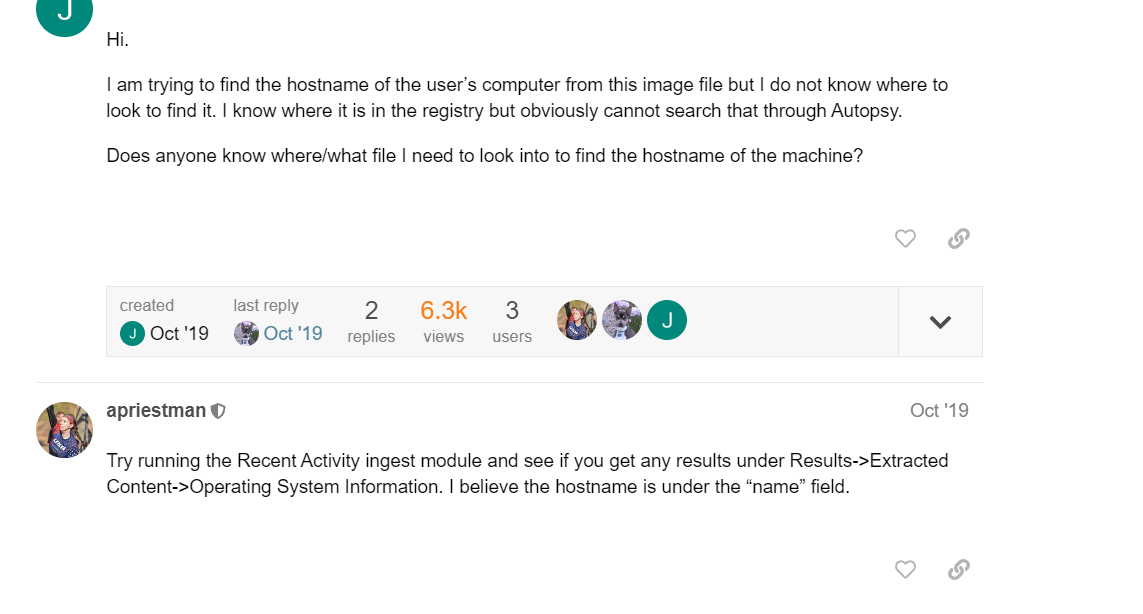
 What is the computer account name?
What is the computer account name?
 List all the user accounts. (alphabetical order)
tương tự câu trên liệt kê ra các user theo thứ tự bảng chữ cái trừ những user mặc định
List all the user accounts. (alphabetical order)
tương tự câu trên liệt kê ra các user theo thứ tự bảng chữ cái trừ những user mặc định
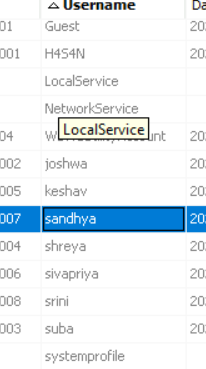 Who was the last user to log into the computer?
filter cột data acess thu được
Who was the last user to log into the computer?
filter cột data acess thu được
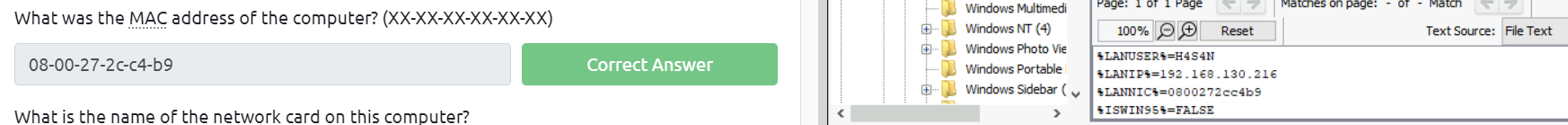
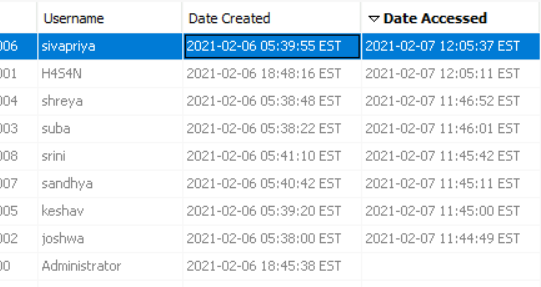 What was the IP address of the computer?
What was the IP address of the computer?
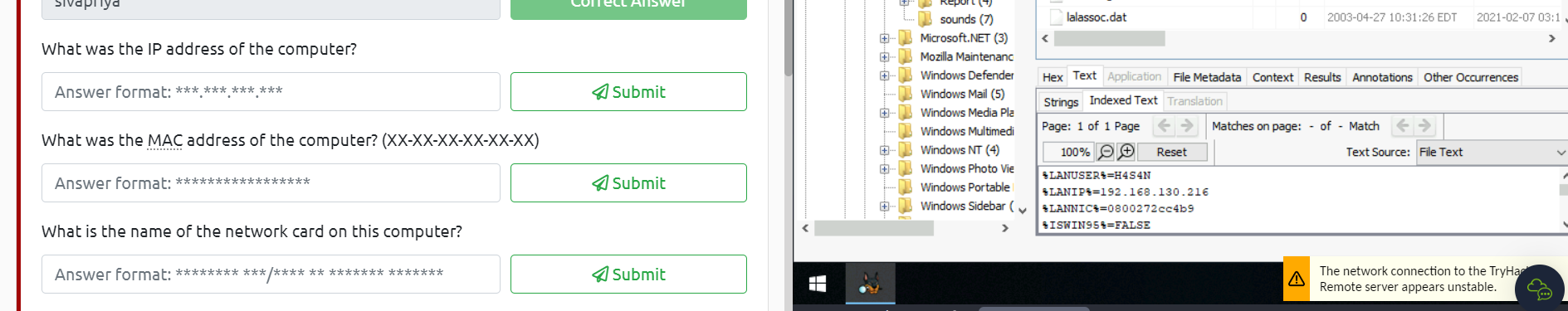 What was the MAC address of the computer? (XX-XX-XX-XX-XX-XX)
What was the MAC address of the computer? (XX-XX-XX-XX-XX-XX)
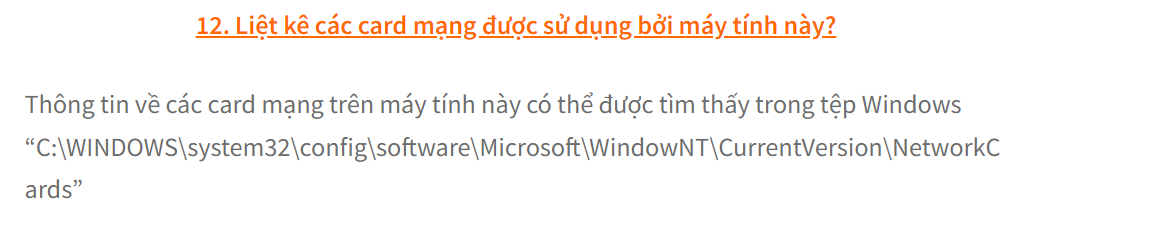
 What is the name of the network card on this computer?
What is the name of the network card on this computer?
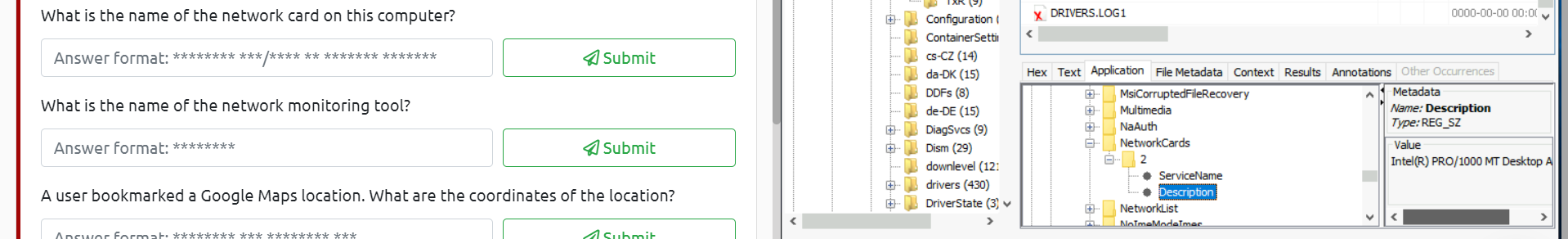
 A user bookmarked a Google Maps location. What are the coordinates of the location?
A user bookmarked a Google Maps location. What are the coordinates of the location?
theo link bookmarked thôi :v
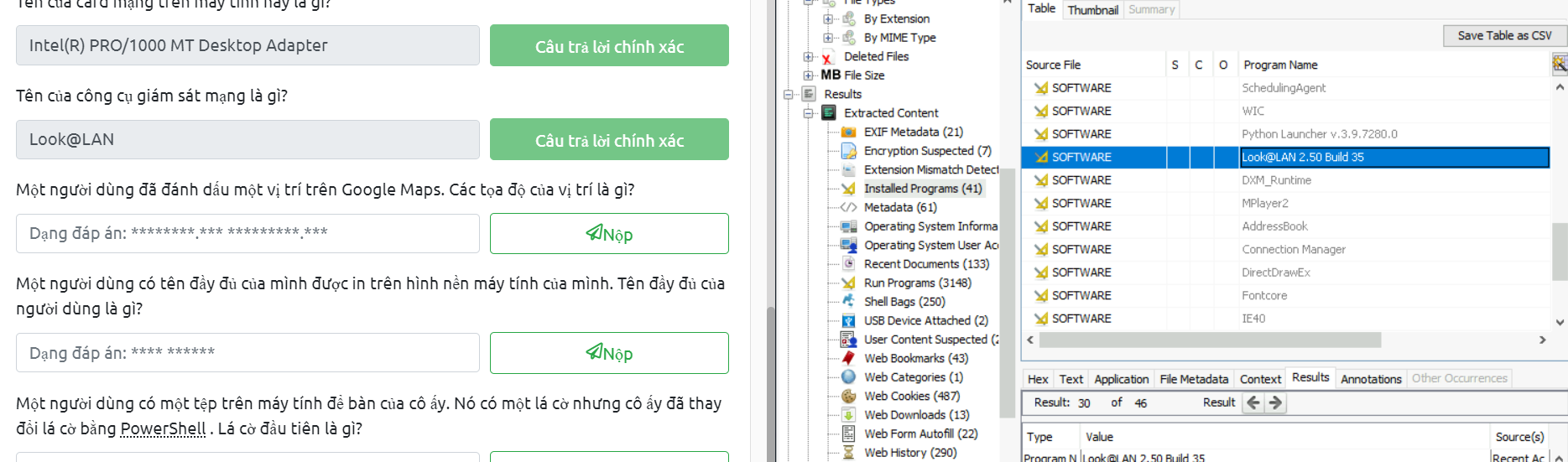
A user has his full name printed on his desktop wallpaper. What is the user's full name?
câu này đơn giản là xuất ảnh và ngồi check thì có thấy joshwa có 1 tấm hình được viết tên ở trên góc mở anh lên và có câu trả lời
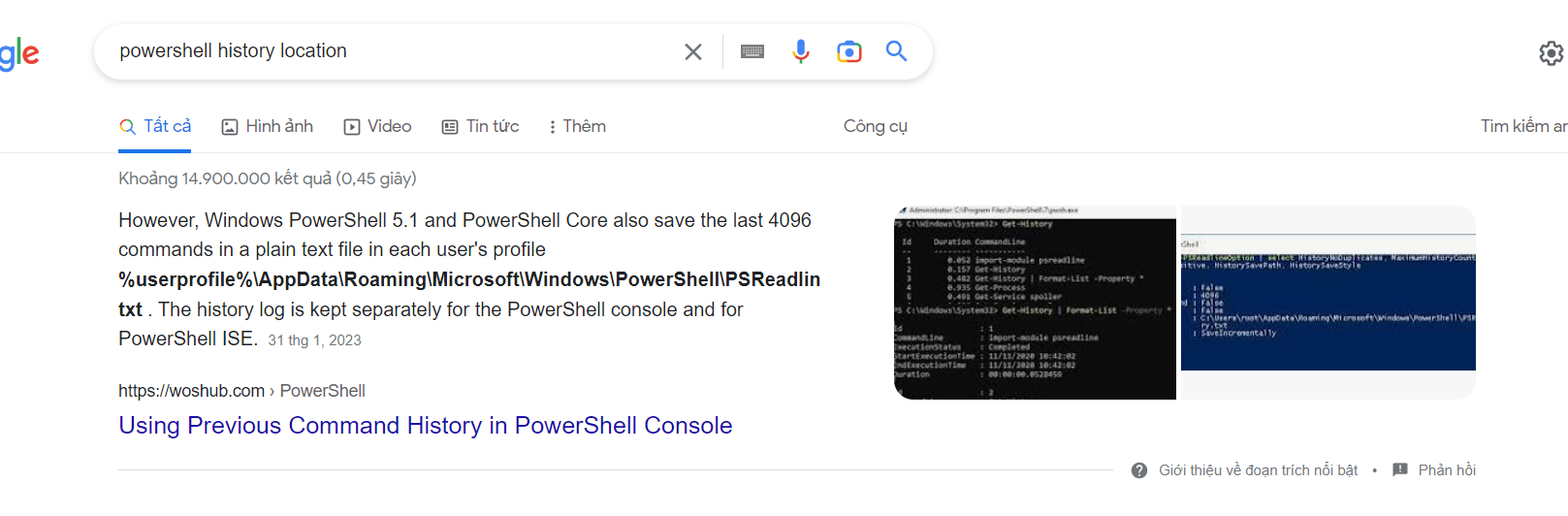
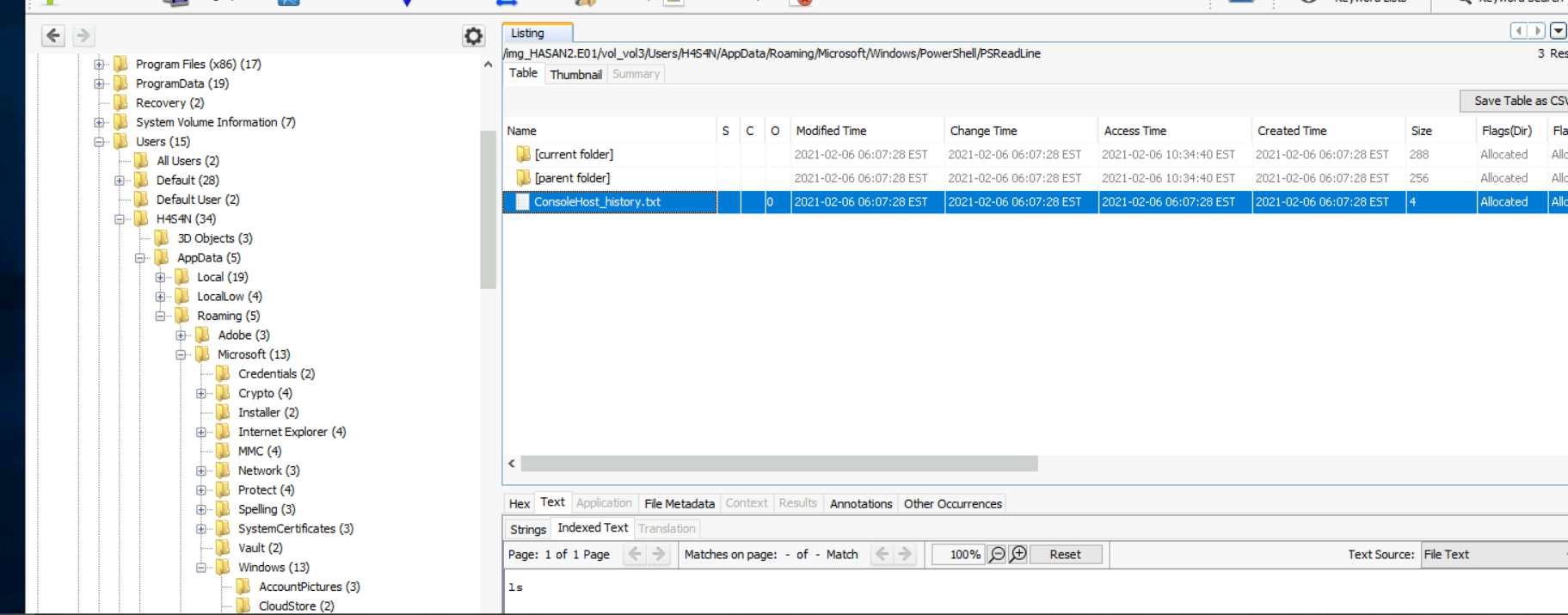
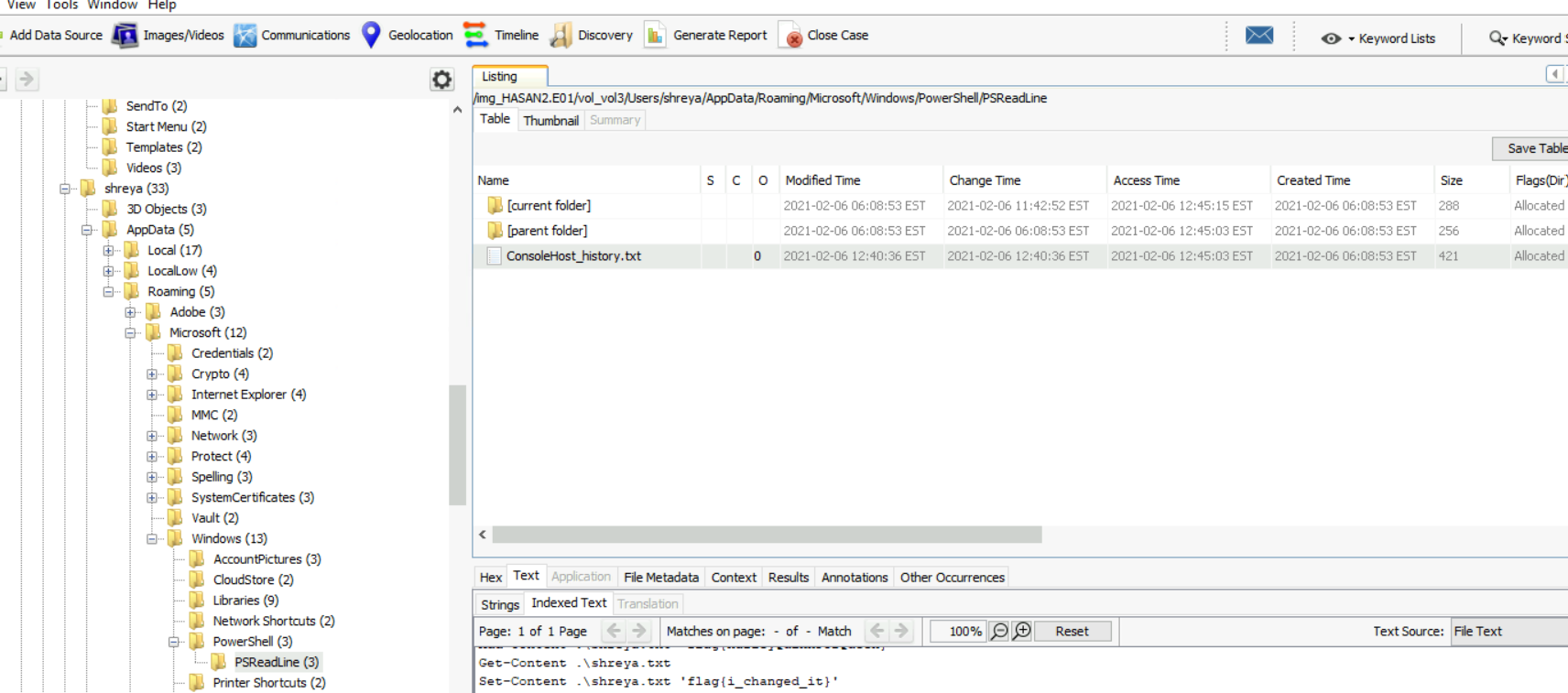
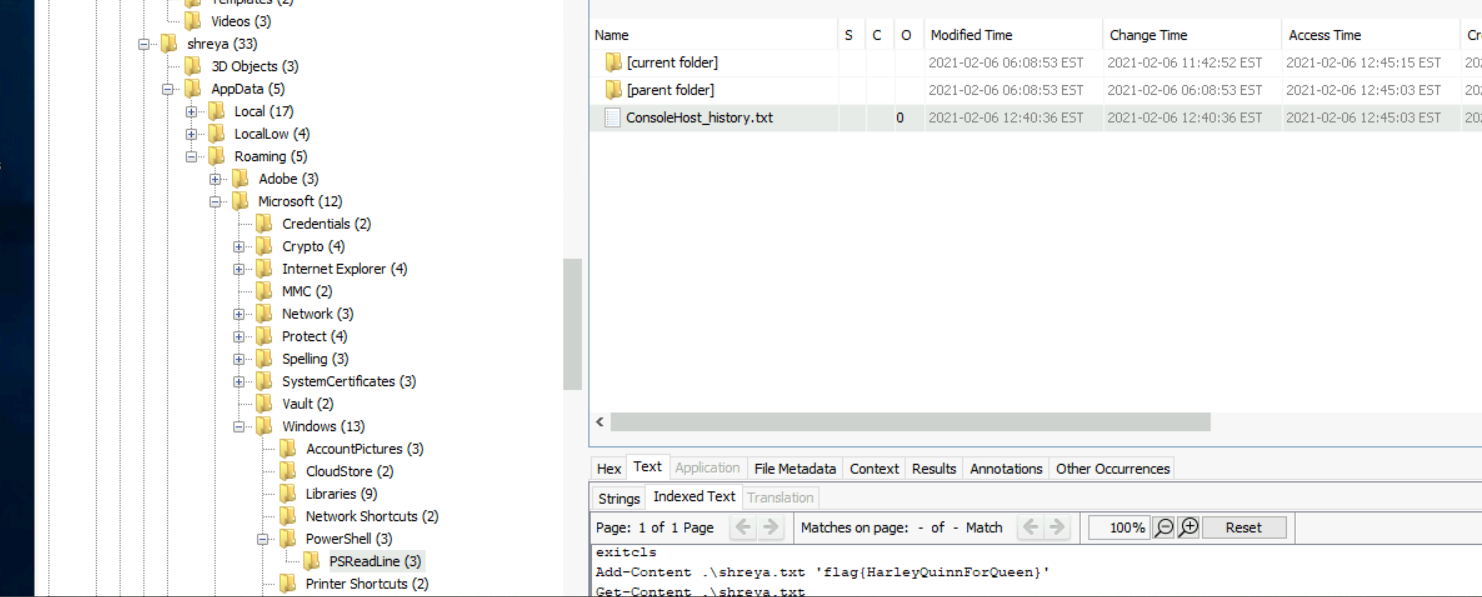
A user had a file on her desktop. It had a flag but she changed the flag using PowerShell. What was the first flag
- cái này thì em ngồi check từng user một thôi
 The same user found an exploit to escalate privileges on the computer. What was the message to the device owner?
The same user found an exploit to escalate privileges on the computer. What was the message to the device owner?
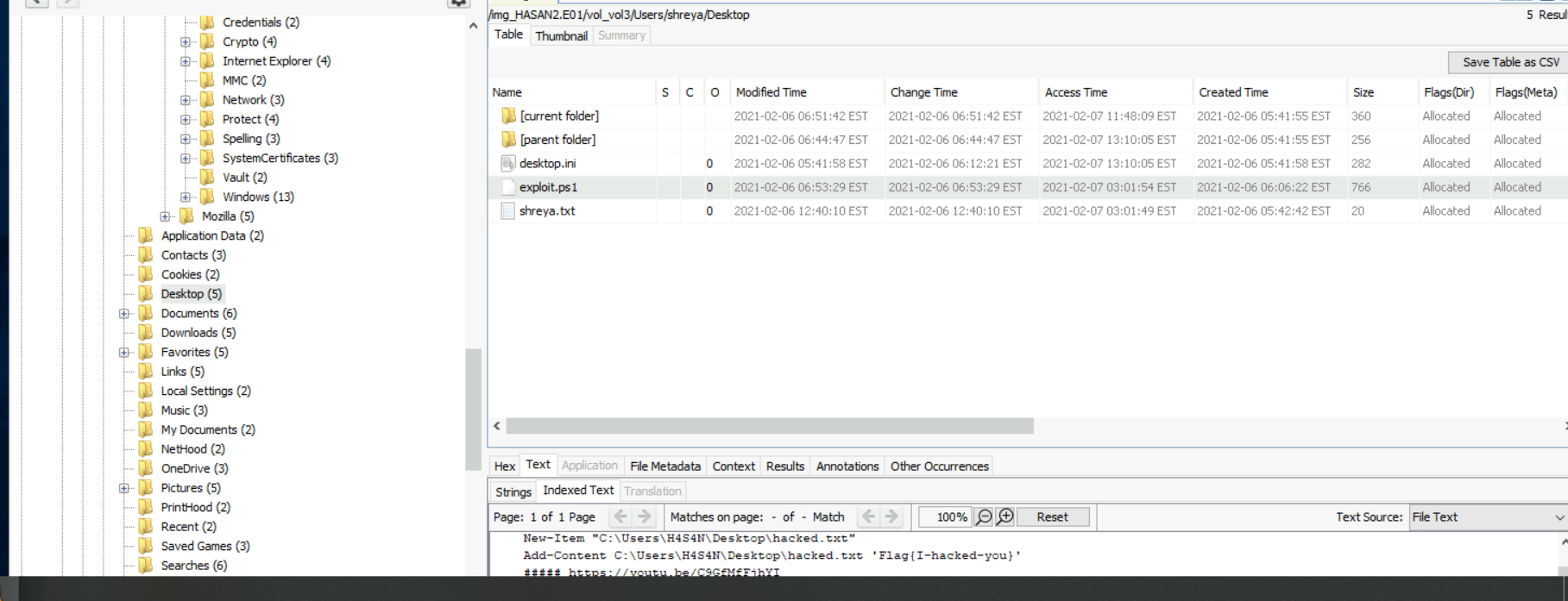
- vẫn thực hiện check đúng trên user đó
The same user found an exploit to escalate privileges on the computer. What was the message to the device owner?
thường các tool sẽ bị windows denfender lưu lại giờ chỉ cần tìm path về lịch sử thôi
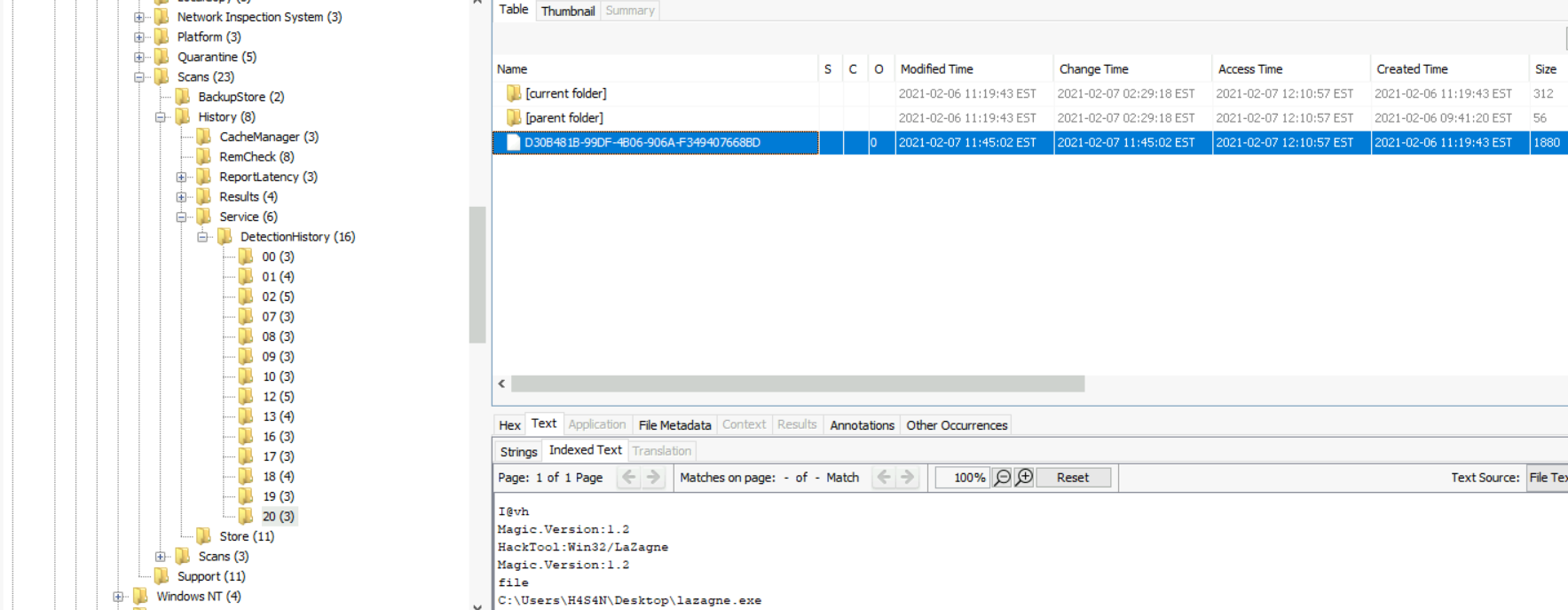 dễ dàng tìm thấy mimikatz và tên 1 tool khác nữa
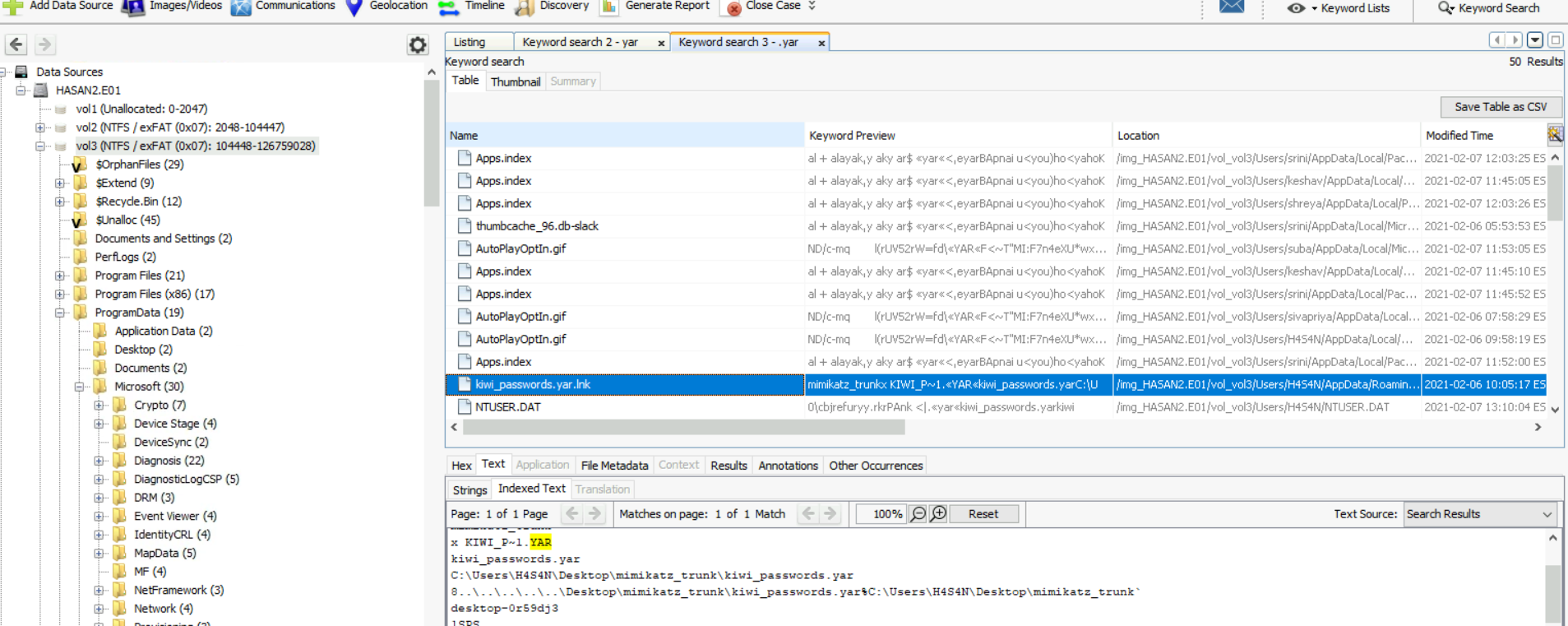
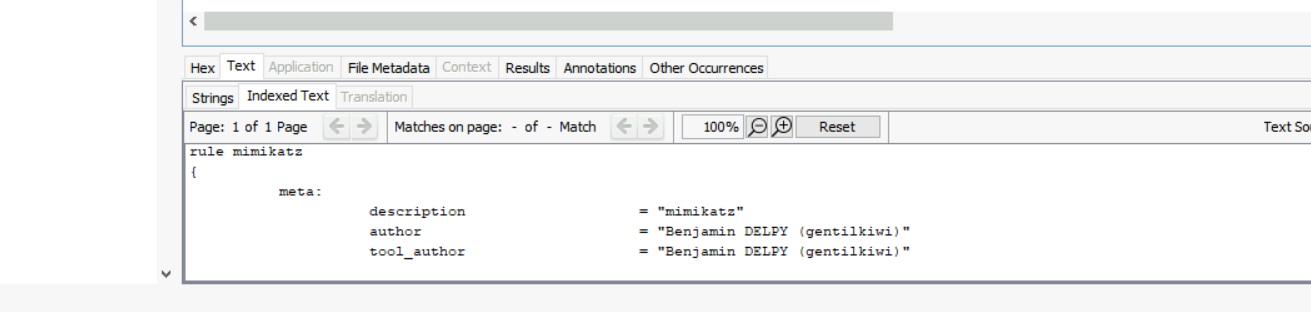
There is a YARA file on the computer. Inspect the file. What is the name of the author?
câu này dùng tính năng keyword search về thu được kết quả path bên dưới
dễ dàng tìm thấy mimikatz và tên 1 tool khác nữa
There is a YARA file on the computer. Inspect the file. What is the name of the author?
câu này dùng tính năng keyword search về thu được kết quả path bên dưới
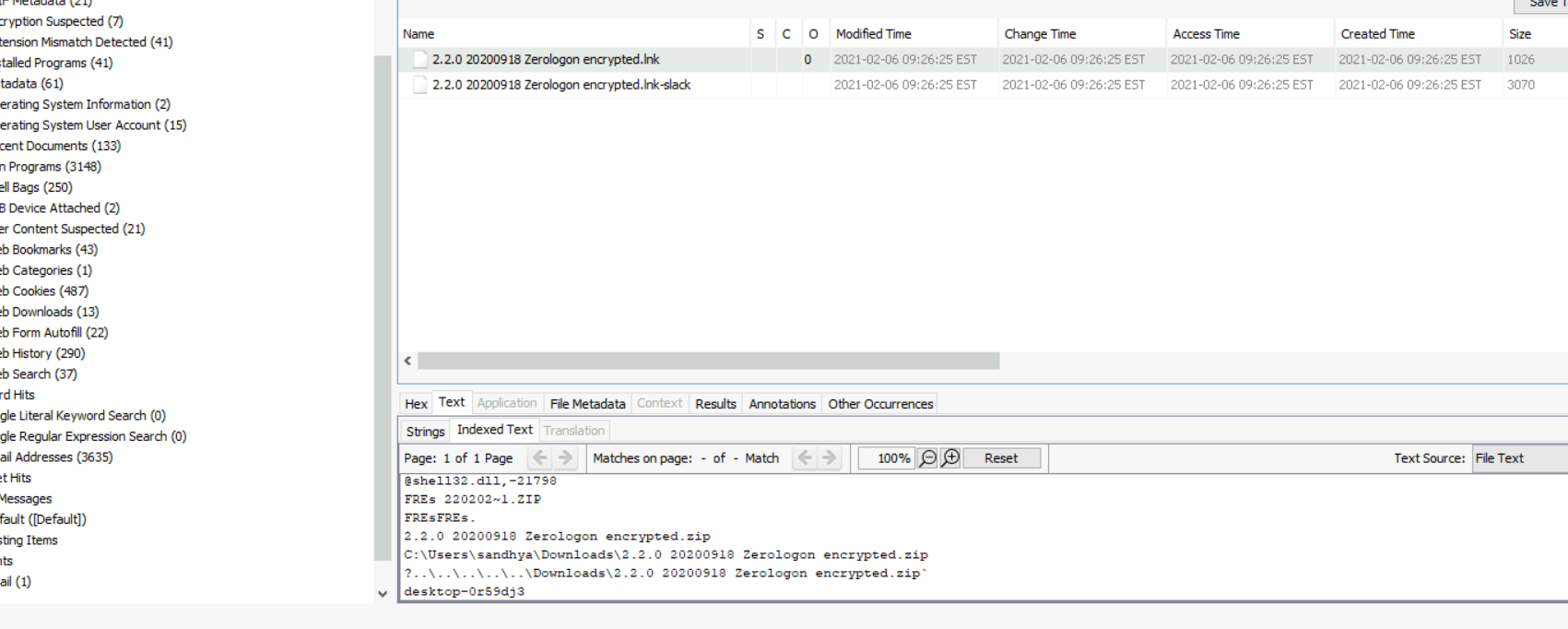
 One of the users wanted to exploit a domain controller with an MS-NRPC based exploit. What is the filename of the archive that you found? (include the spaces in your answer)
search MS-NRPC thì cho kết quả là netlogon sau khi đọc một lúc và có thử search keyword netlogon không ra thì thấy exp;oit này có tên gọi chung là zerologon
dùng tính năng search file name của autospy
One of the users wanted to exploit a domain controller with an MS-NRPC based exploit. What is the filename of the archive that you found? (include the spaces in your answer)
search MS-NRPC thì cho kết quả là netlogon sau khi đọc một lúc và có thử search keyword netlogon không ra thì thấy exp;oit này có tên gọi chung là zerologon
dùng tính năng search file name của autospy
 -> done
-> done
Obtaining Memory Samples
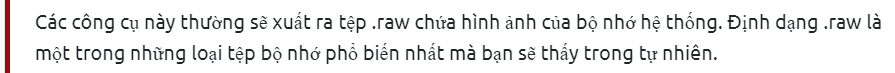
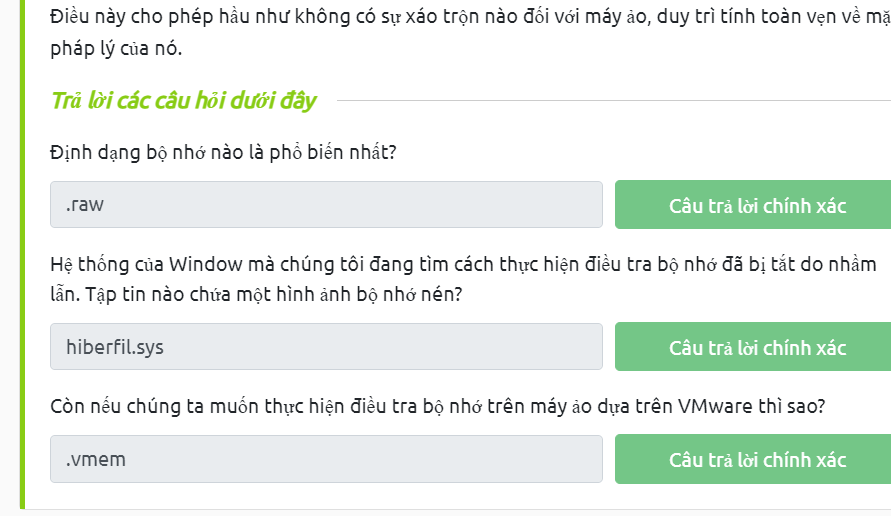
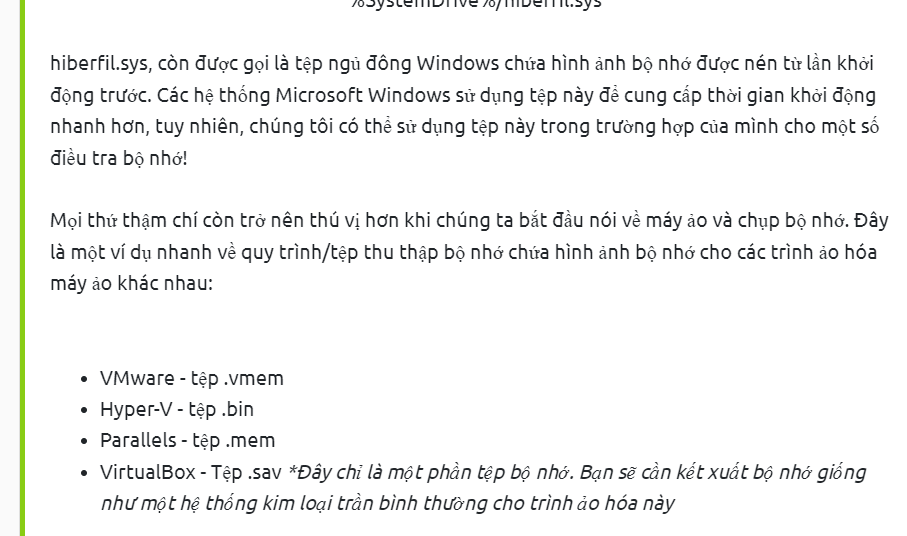 Examining Our Patient
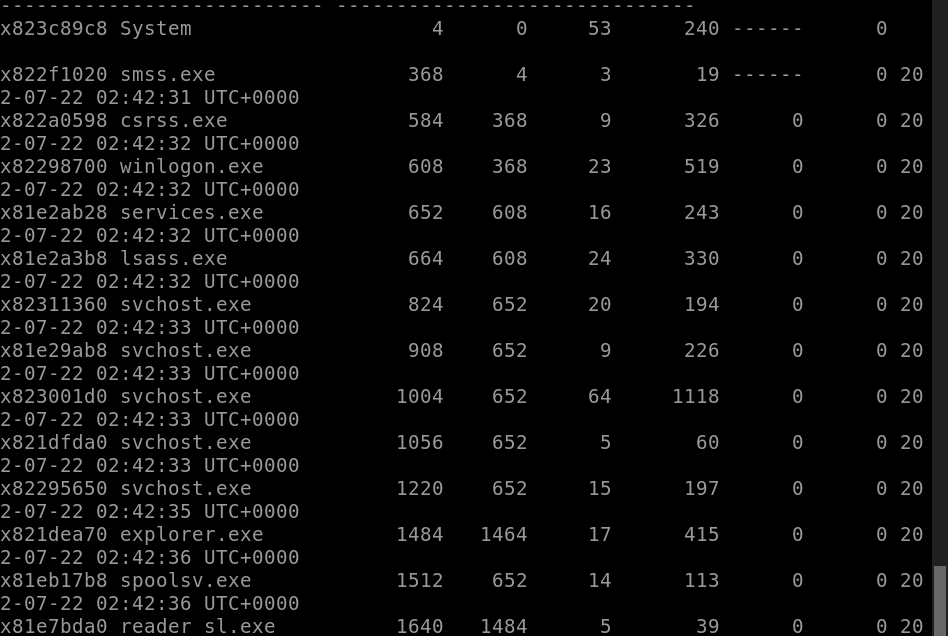
Running the imageinfo command in Volatility will provide us with a number of profiles we can test with, however, only one will be correct. We can test these profiles using the pslist command, validating our profile selection by the sheer number of returned results. Do this now with the command
Examining Our Patient
Running the imageinfo command in Volatility will provide us with a number of profiles we can test with, however, only one will be correct. We can test these profiles using the pslist command, validating our profile selection by the sheer number of returned results. Do this now with the command volatility -f MEMORY_FILE.raw --profile=PROFILE pslist. What profile is correct for this memory image?
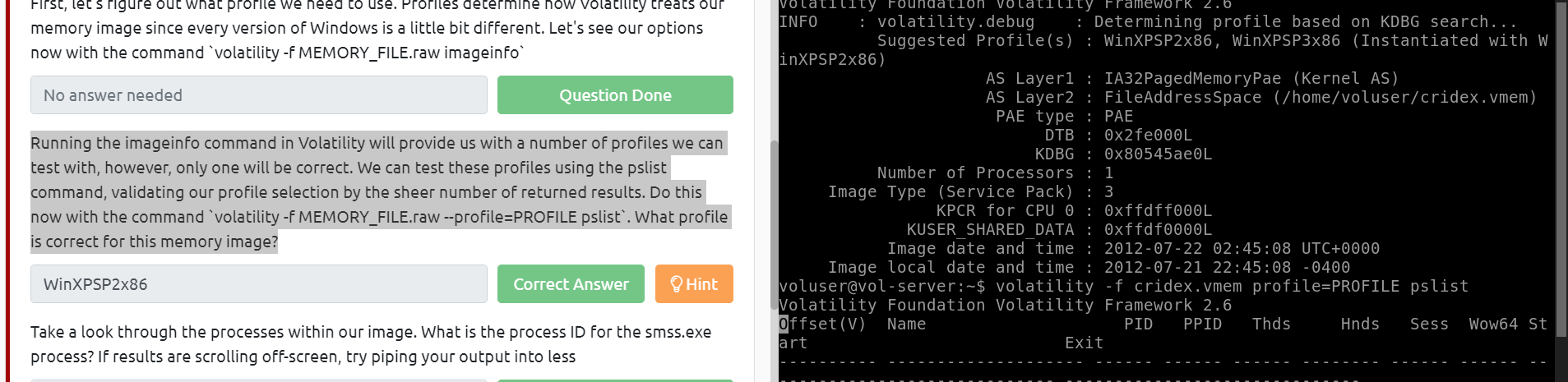 Take a look through the processes within our image. What is the process ID for the smss.exe process? If results are scrolling off-screen, try piping your output into less
Take a look through the processes within our image. What is the process ID for the smss.exe process? If results are scrolling off-screen, try piping your output into less
 It's fairly common for malware to attempt to hide itself and the process associated with it. That being said, we can view intentionally hidden processes via the command
It's fairly common for malware to attempt to hide itself and the process associated with it. That being said, we can view intentionally hidden processes via the command psxview. What process has only one 'False' listed?
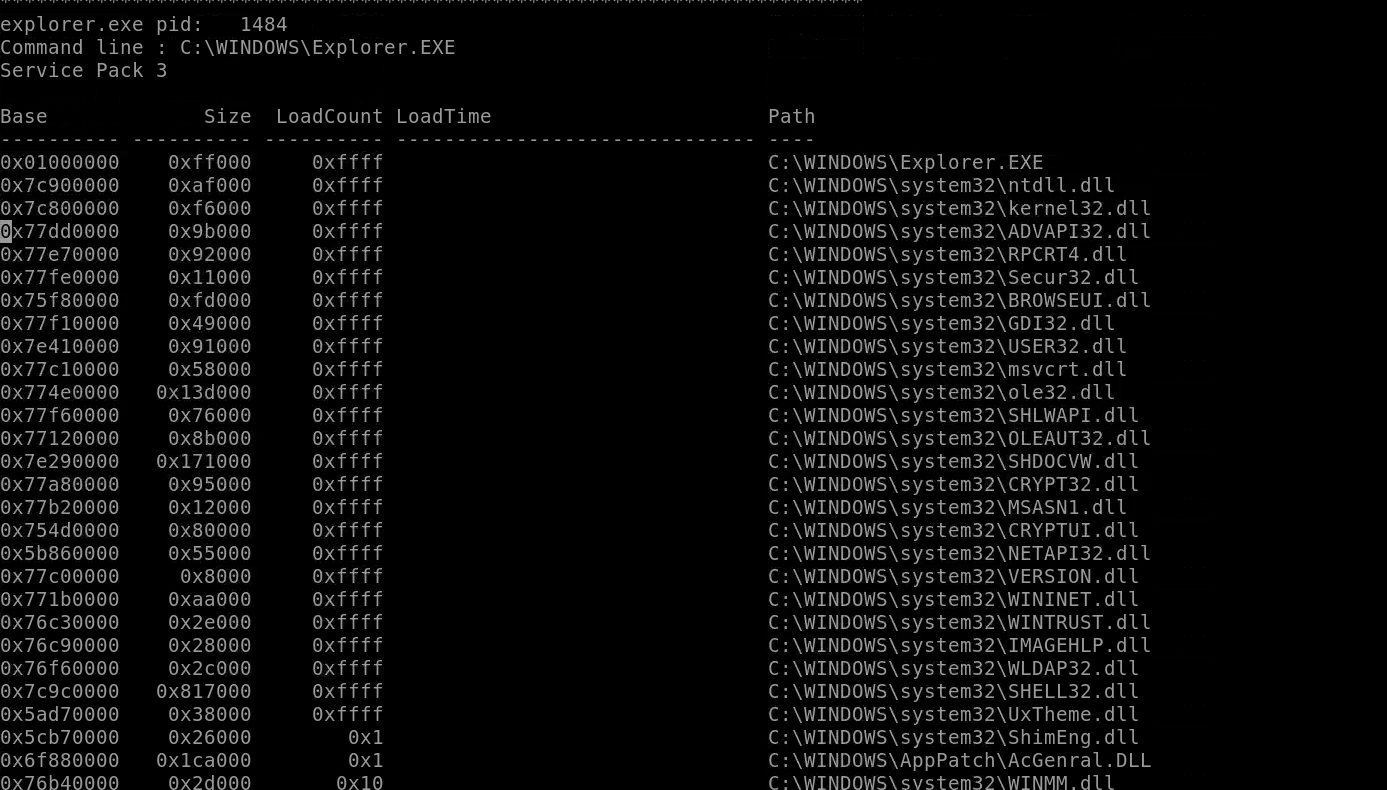
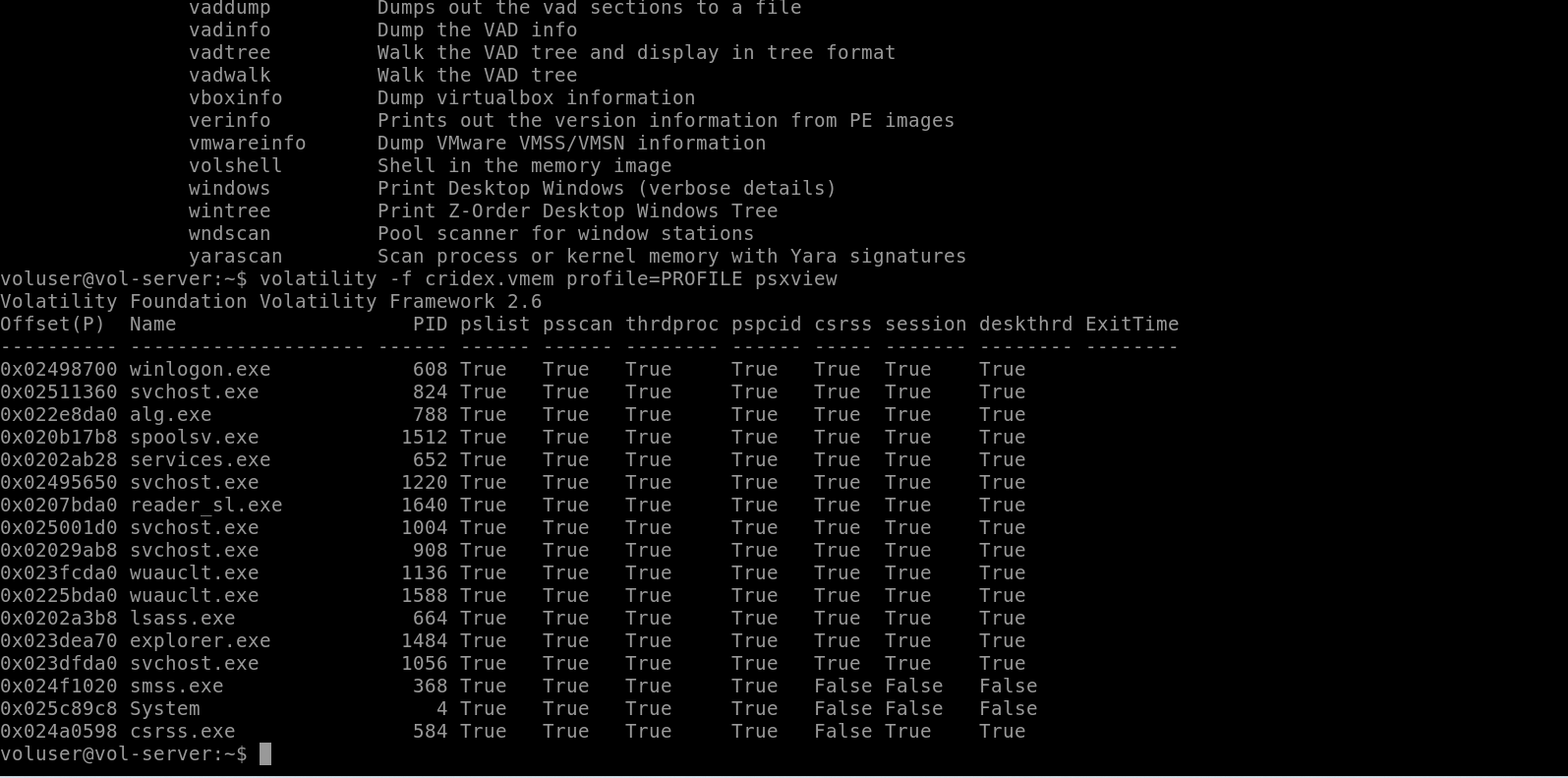 In addition to viewing hidden processes via psxview, we can also check this with a greater focus via the command 'ldrmodules'. Three columns will appear here in the middle, InLoad, InInit, InMem. If any of these are false, that module has likely been injected which is a really bad thing. On a normal system the grep statement above should return no output. Which process has all three columns listed as 'False' (other than System)?
In addition to viewing hidden processes via psxview, we can also check this with a greater focus via the command 'ldrmodules'. Three columns will appear here in the middle, InLoad, InInit, InMem. If any of these are false, that module has likely been injected which is a really bad thing. On a normal system the grep statement above should return no output. Which process has all three columns listed as 'False' (other than System)?
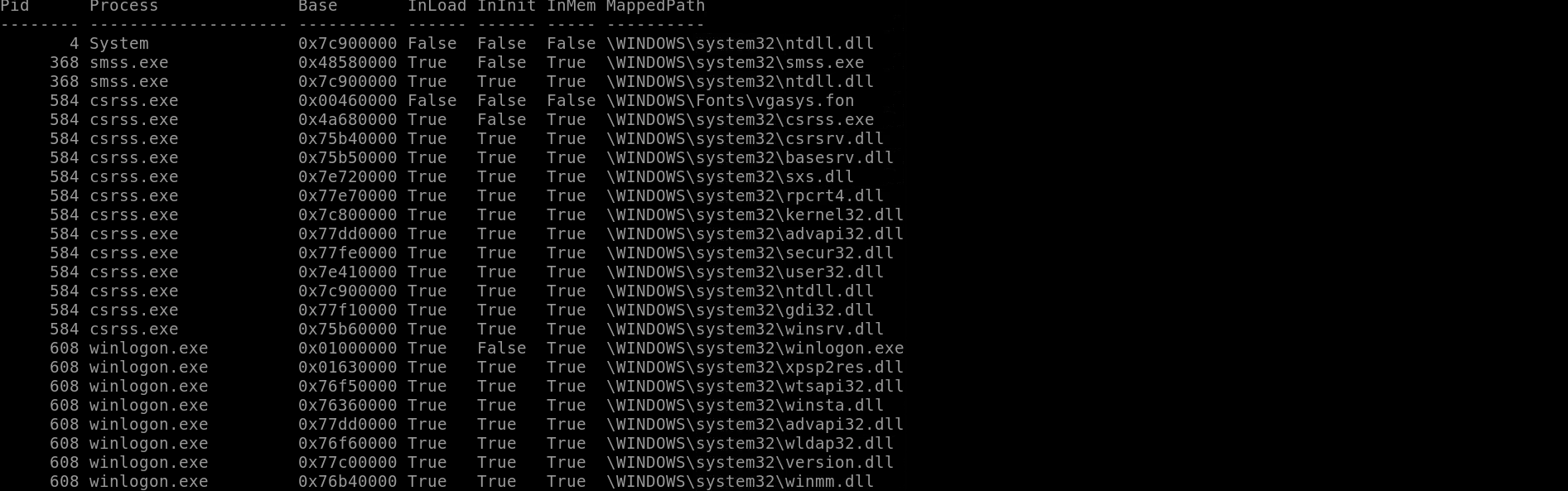
- theo ảnh ở question trên thì đáp án là csrss.exe
Injected code can be a huge issue and is highly indicative of very very bad things. We can check for this with the command
malfind. Using the full commandvolatility -f MEMORY_FILE.raw --profile=PROFILE malfind -D <Destination Directory>we can not only find this code, but also dump it to our specified directory. Let's do this now! We'll use this dump later for more analysis. How many files does this generate?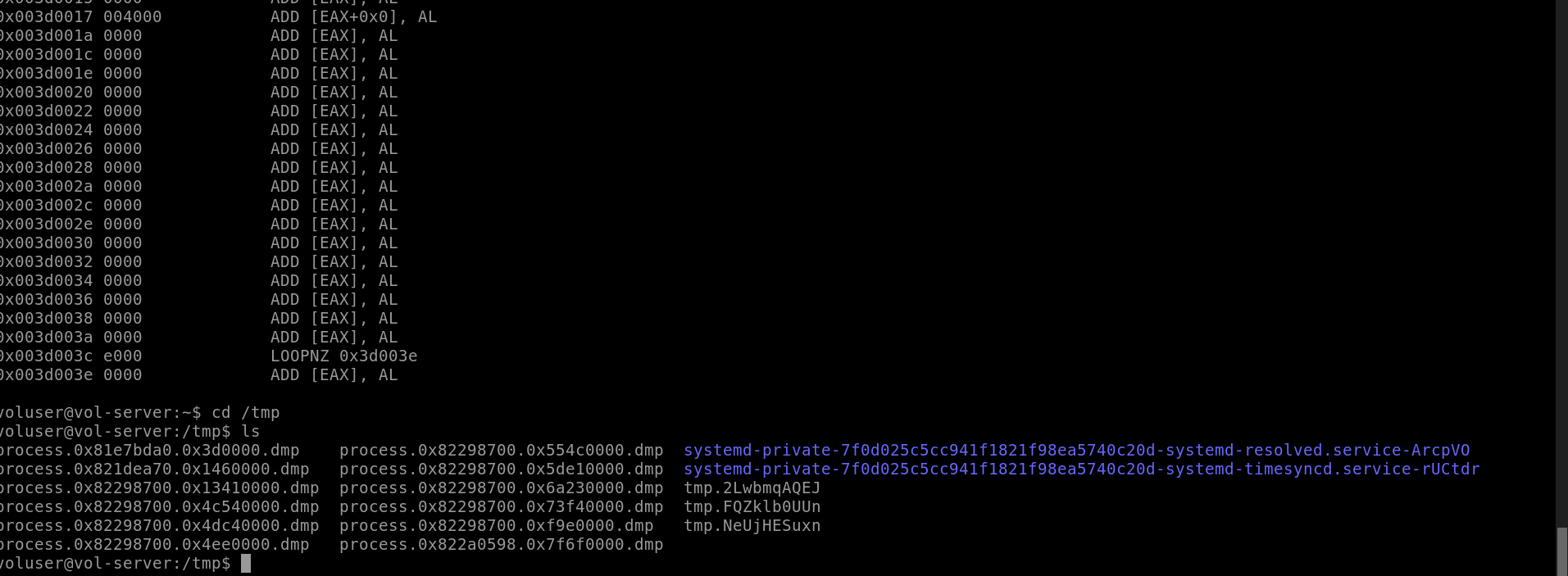
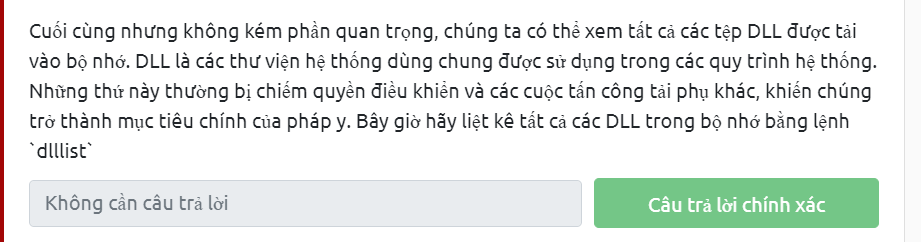
 Now that we've seen all of the DLLs running in memory, let's go a step further and pull them out! Do this now with the command
Now that we've seen all of the DLLs running in memory, let's go a step further and pull them out! Do this now with the command volatility -f MEMORY_FILE.raw --profile=PROFILE --pid=PID dlldump -D <Destination Directory>where the PID is the process ID of the infected process we identified earlier (questions five and six). How many DLLs does this end up pulling? quay lại ảnh của câu hỏi trước dễ thấy PID của csrss.exe là 584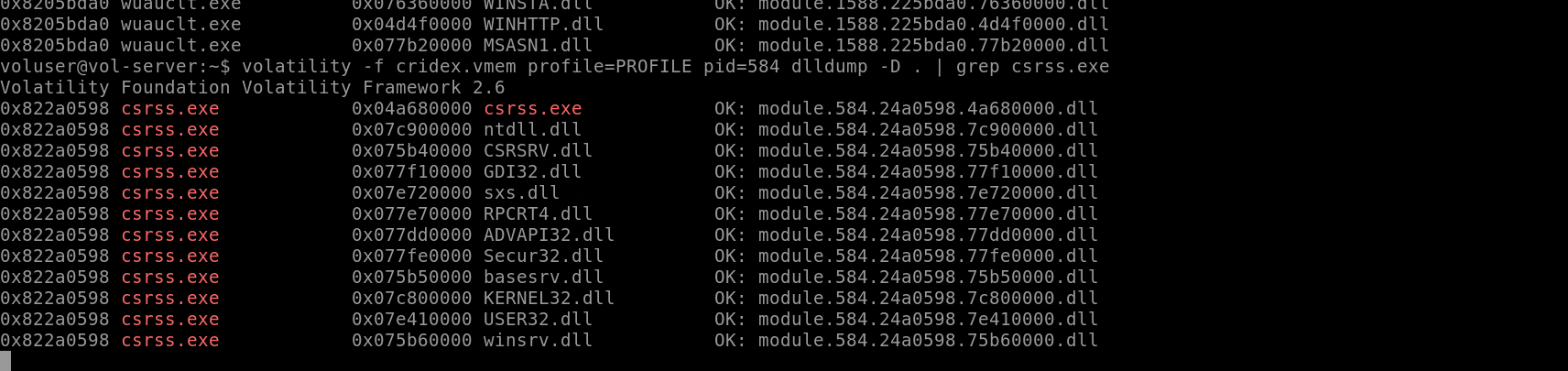 Post Actions
Upload the extracted files to VirusTotal for examination.
Post Actions
Upload the extracted files to VirusTotal for examination.
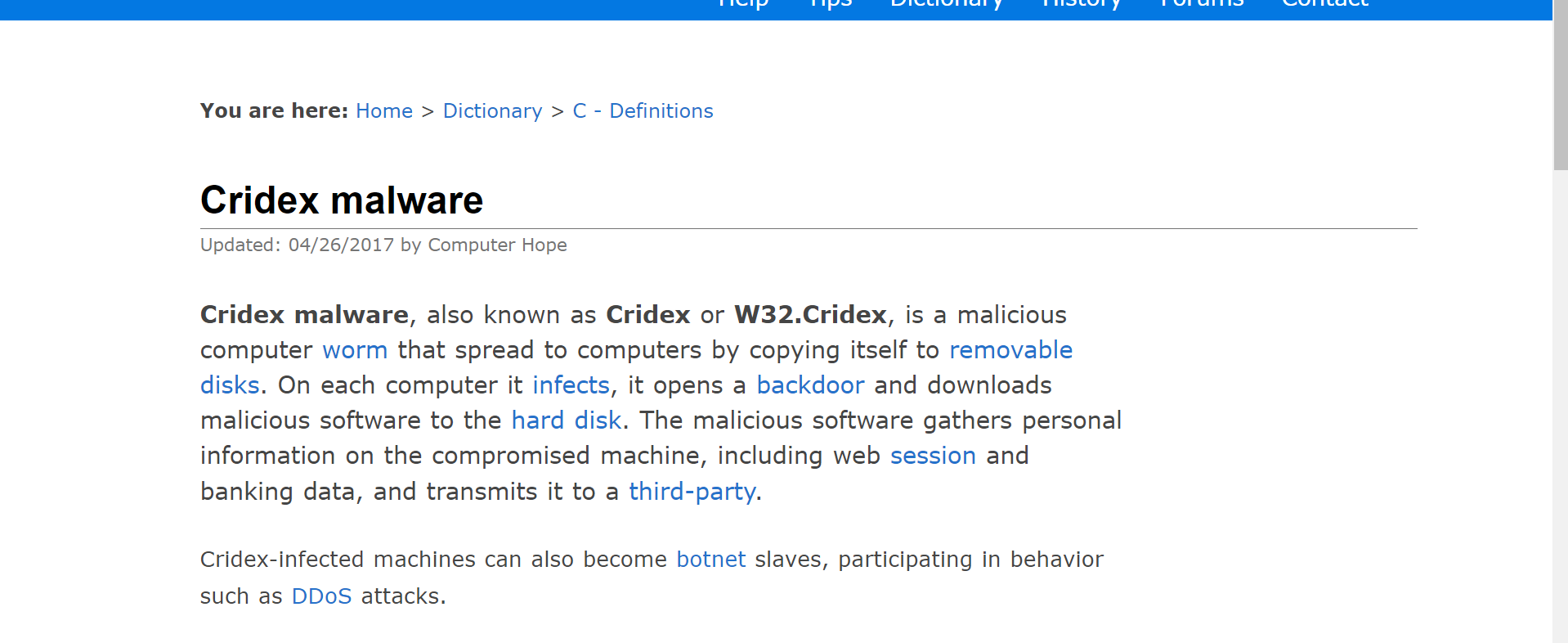
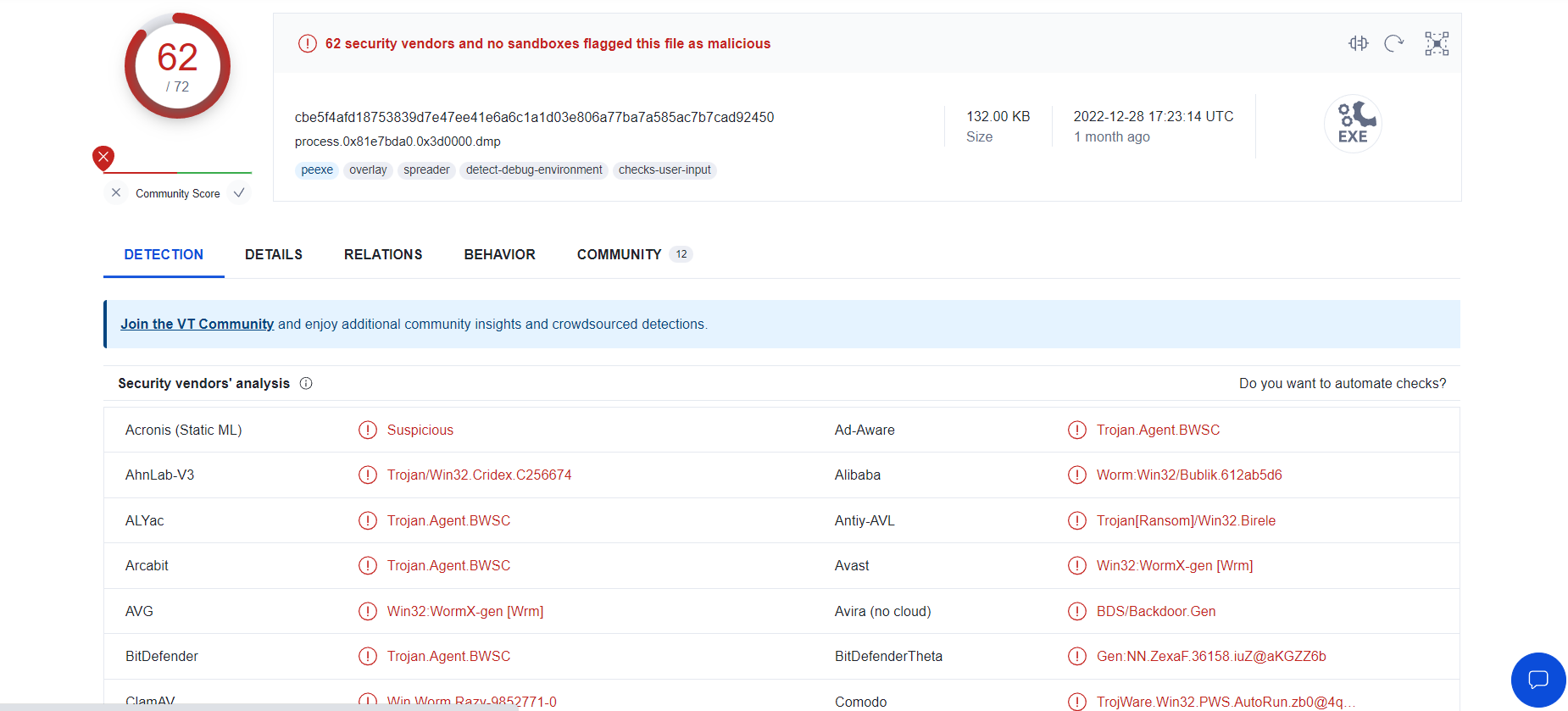 What malware has our sample been infected with? You can find this in the results of VirusTotal and Hybrid Anaylsis.
What malware has our sample been infected with? You can find this in the results of VirusTotal and Hybrid Anaylsis.
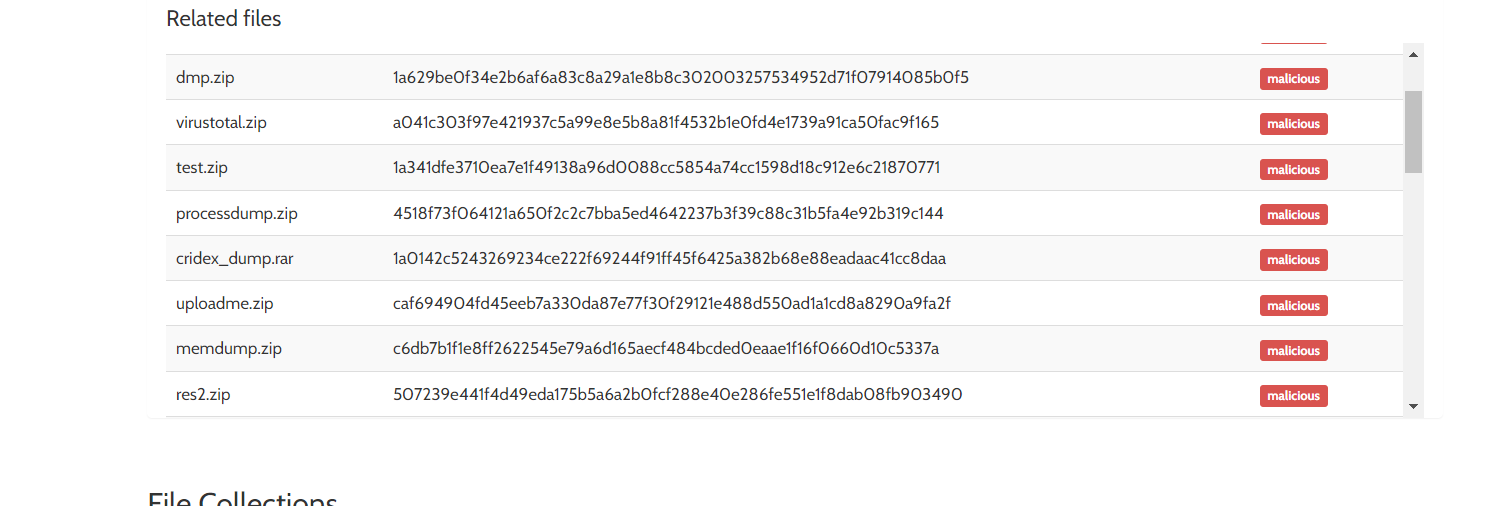 thực hiện search google một lúc thì em có search ra cridex là tên một malware
thực hiện search google một lúc thì em có search ra cridex là tên một malware
Introduction
 Data Collection
What data collection method takes the least amount of time?
You are reading a research paper on a new strain of ransomware. You want to run the data collection on your computer based on the patterns provided, such as domains, hashes, IP addresses, filenames, etc. What method would you choose to run a granular data collection against the known indicators?
Data Collection
What data collection method takes the least amount of time?
You are reading a research paper on a new strain of ransomware. You want to run the data collection on your computer based on the patterns provided, such as domains, hashes, IP addresses, filenames, etc. What method would you choose to run a granular data collection against the known indicators?
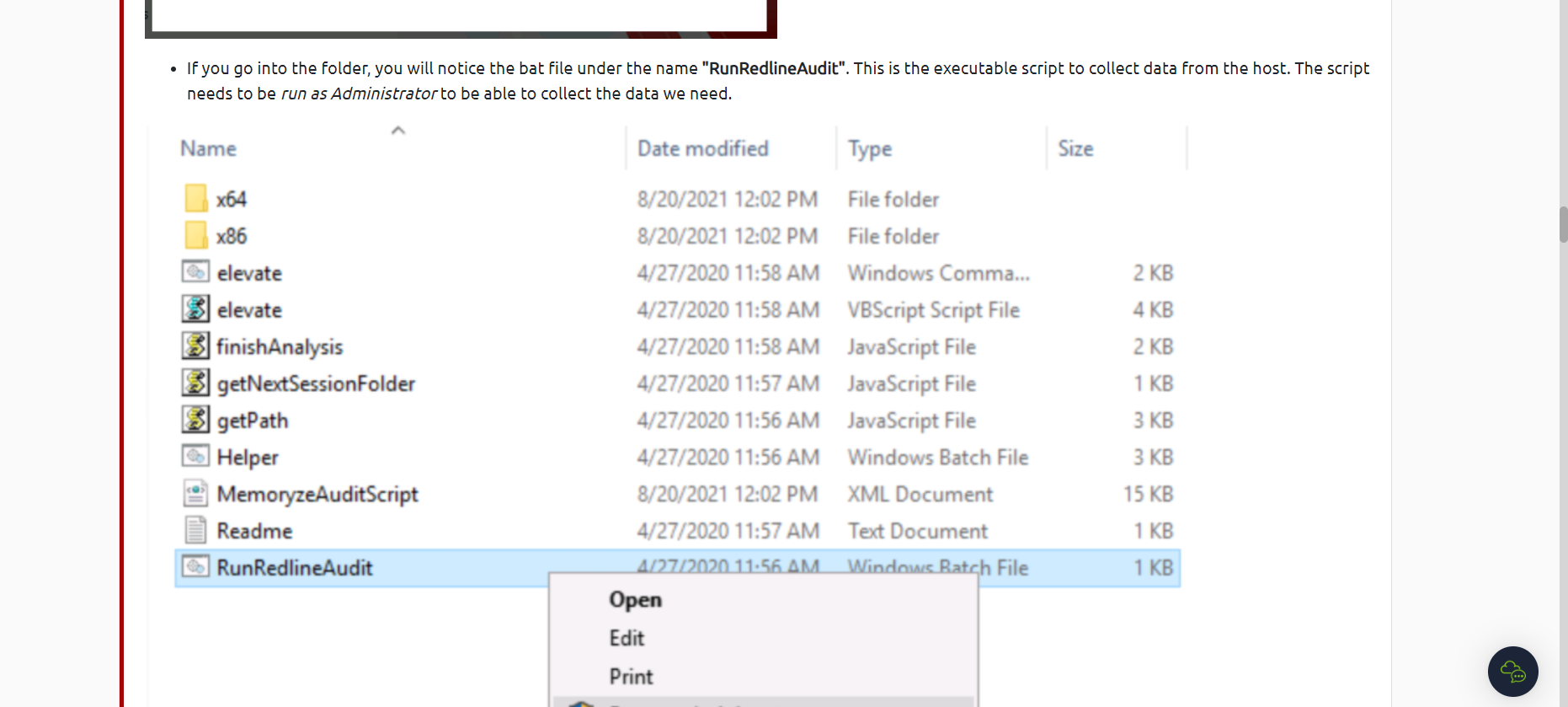
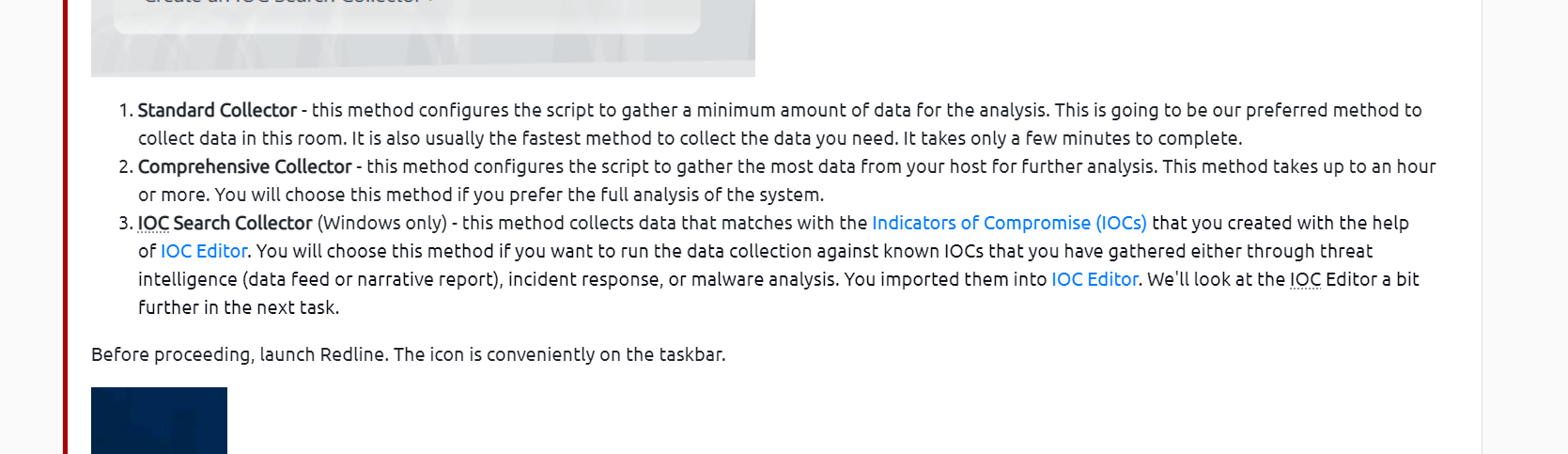 What script would you run to initiate the data collection process? Please include the file extension.
What script would you run to initiate the data collection process? Please include the file extension.
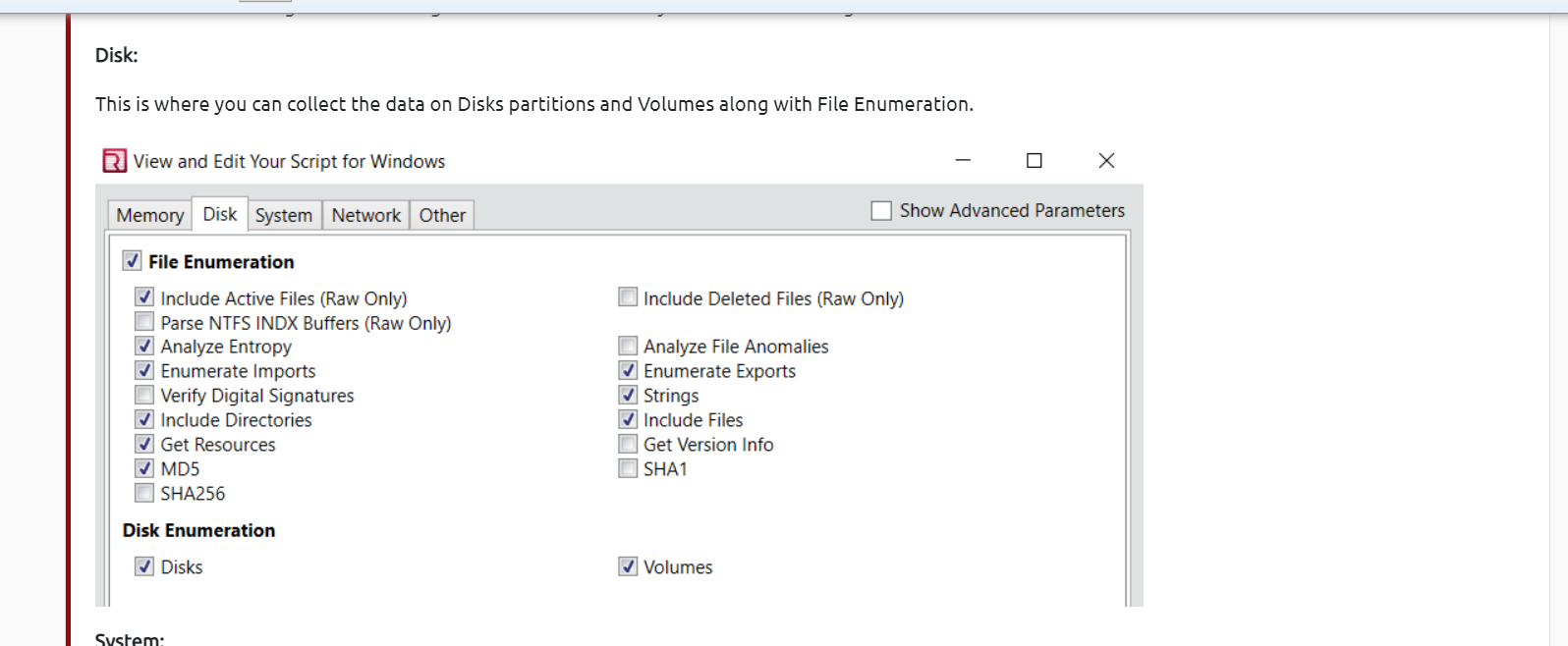
 If you want to collect the data on Disks and Volumes, under which option can you find it?
If you want to collect the data on Disks and Volumes, under which option can you find it?
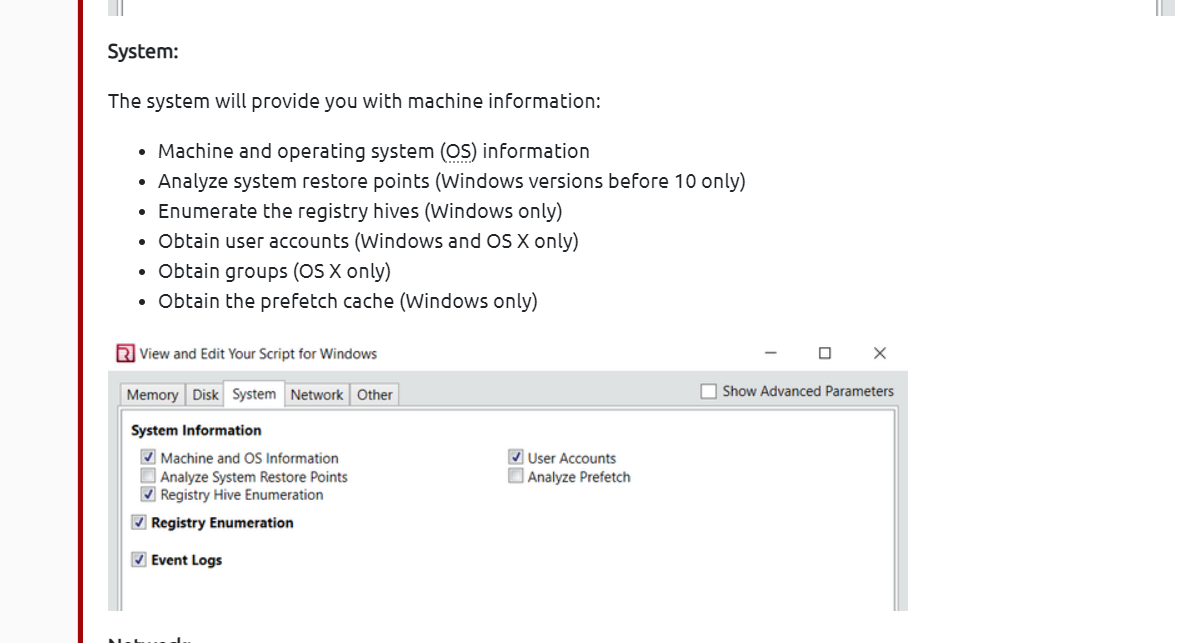
 What cache does Windows use to maintain a preference for recently executed code?
What cache does Windows use to maintain a preference for recently executed code?
 phần này chỉ việc đọc hướng dẫn dùng và trả lời
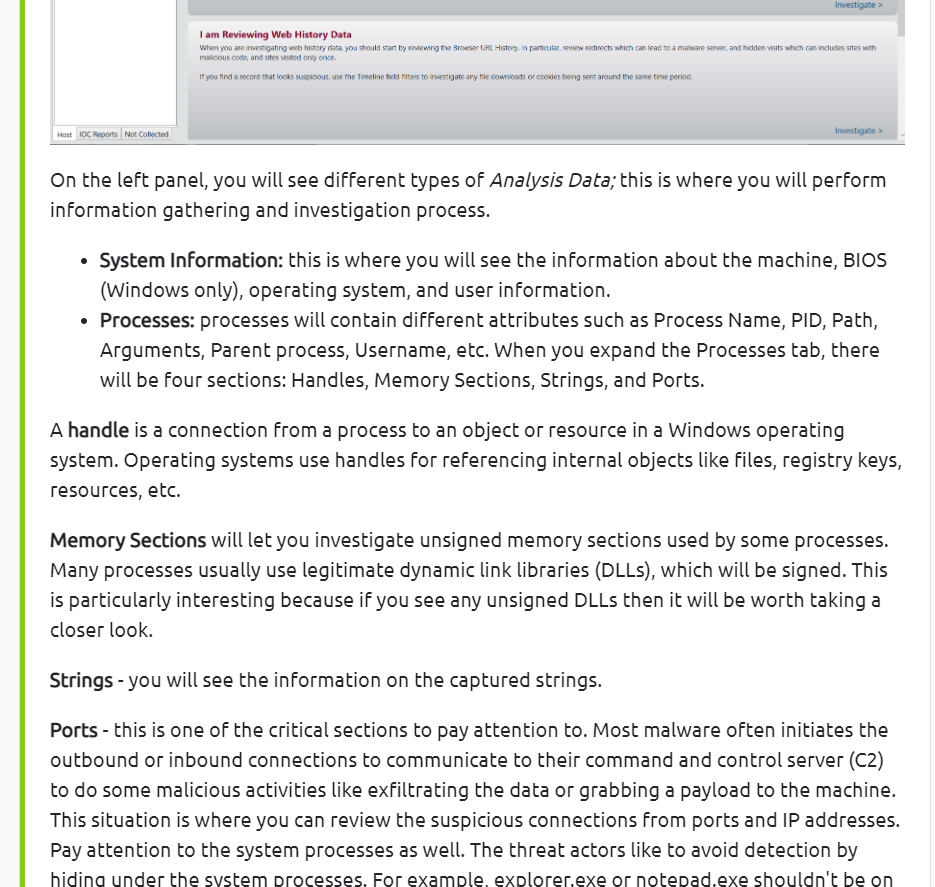
The Redline Interface
Where in the Redline UI can you view information about the Logged in User?
phần này chỉ việc đọc hướng dẫn dùng và trả lời
The Redline Interface
Where in the Redline UI can you view information about the Logged in User?
 Where in the Redline UI can you view information about the Logged in User?
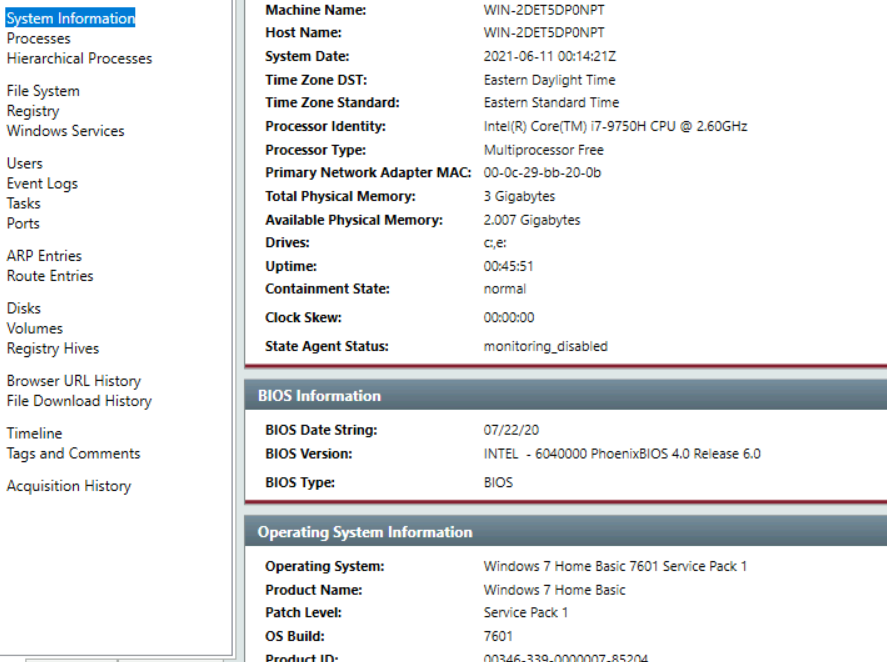
Provide the Operating System detected for the workstation.
Where in the Redline UI can you view information about the Logged in User?
Provide the Operating System detected for the workstation.
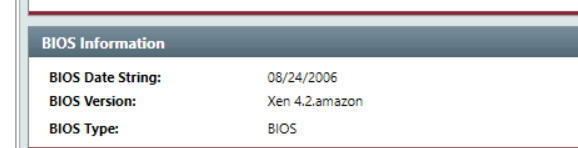
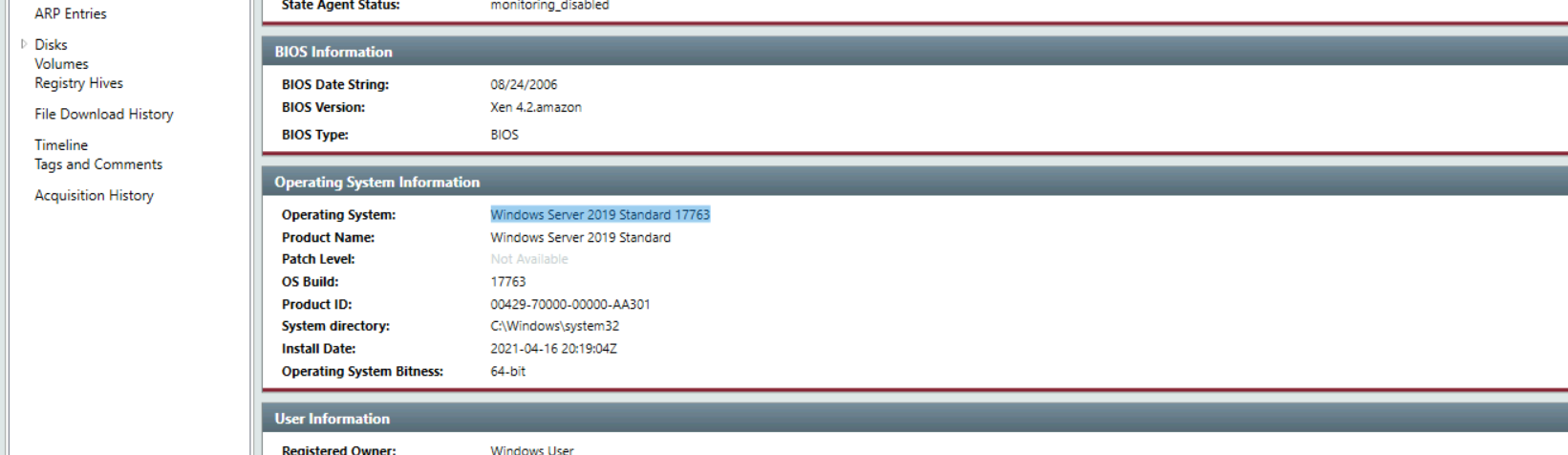 Provide the BIOS Version for the workstation.
Provide the BIOS Version for the workstation.
 What is the suspicious scheduled task that got created on the victim's computer?
What is the suspicious scheduled task that got created on the victim's computer?
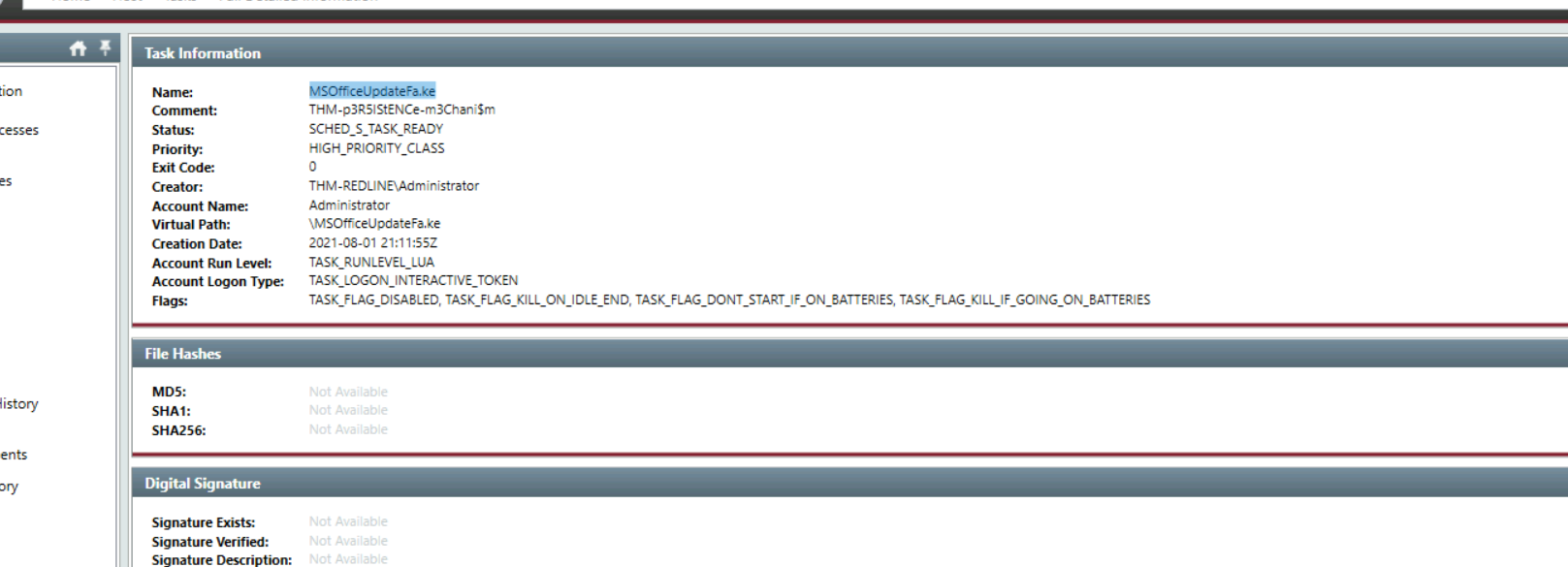
- câu này vào task thì thấy comment hiện khá rõ
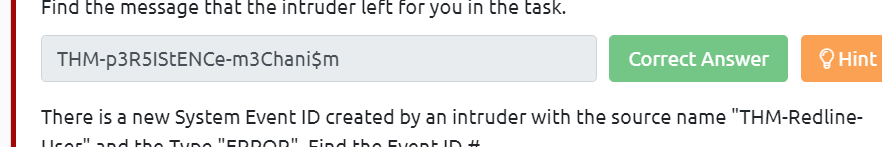
Find the message that the intruder left for you in the task.
 There is a new System Event ID created by an intruder with the source name "THM-Redline-User" and the Type "ERROR". Find the Event ID #.
There is a new System Event ID created by an intruder with the source name "THM-Redline-User" and the Type "ERROR". Find the Event ID #.
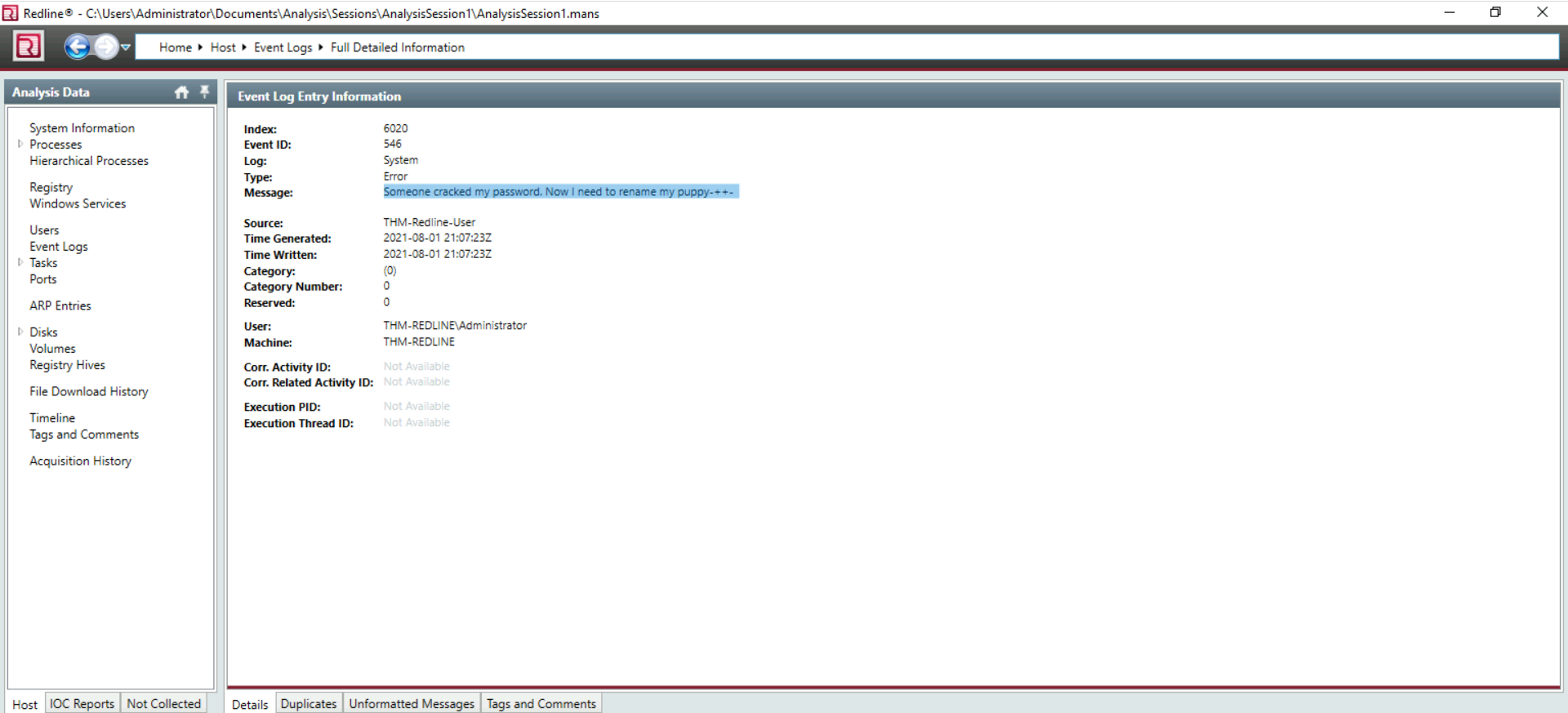
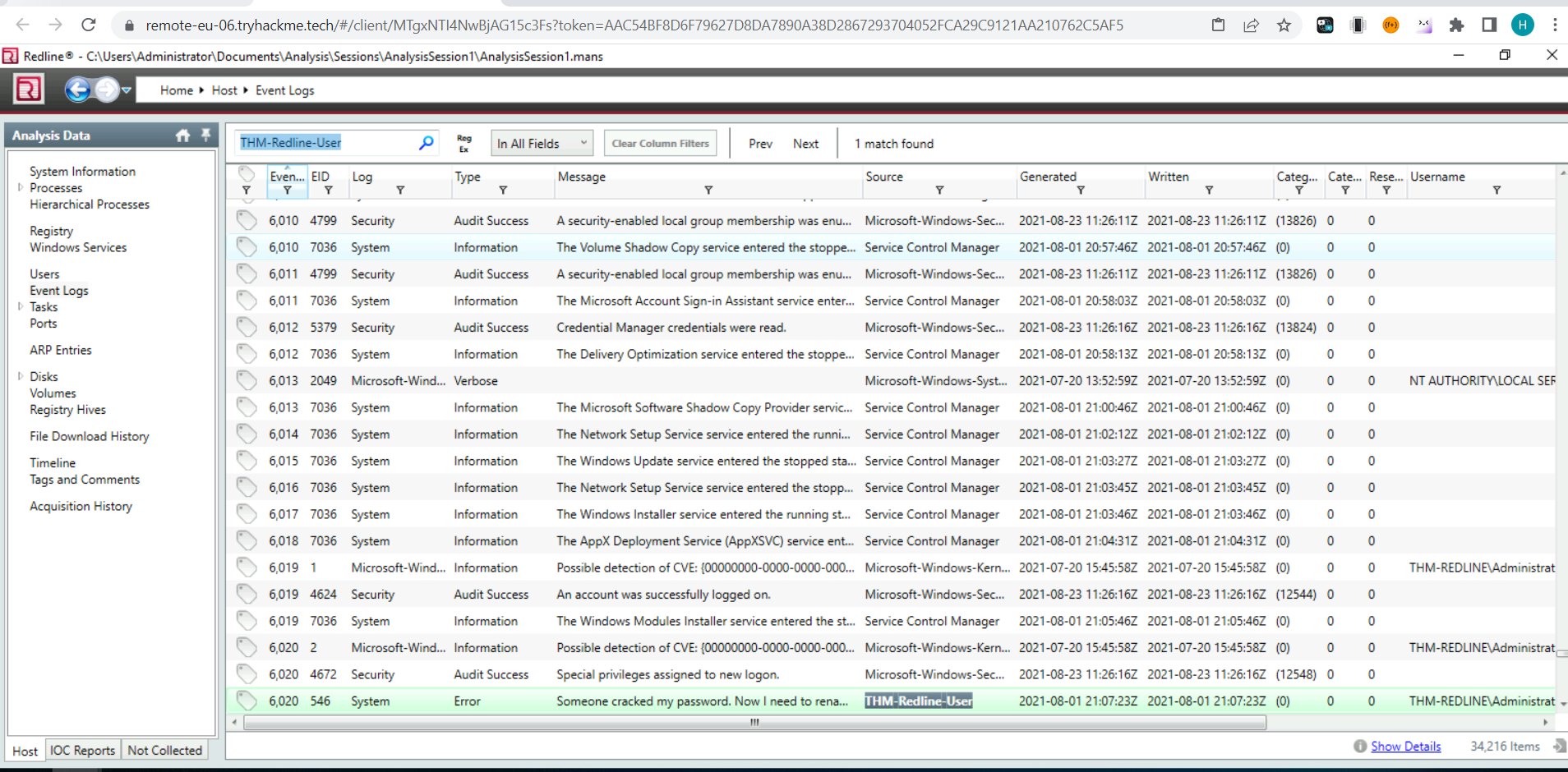 Provide the message for the Event ID.
Provide the message for the Event ID.
 It looks like the intruder downloaded a file containing the flag for Question 8. Provide the full URL of the website.
It looks like the intruder downloaded a file containing the flag for Question 8. Provide the full URL of the website.
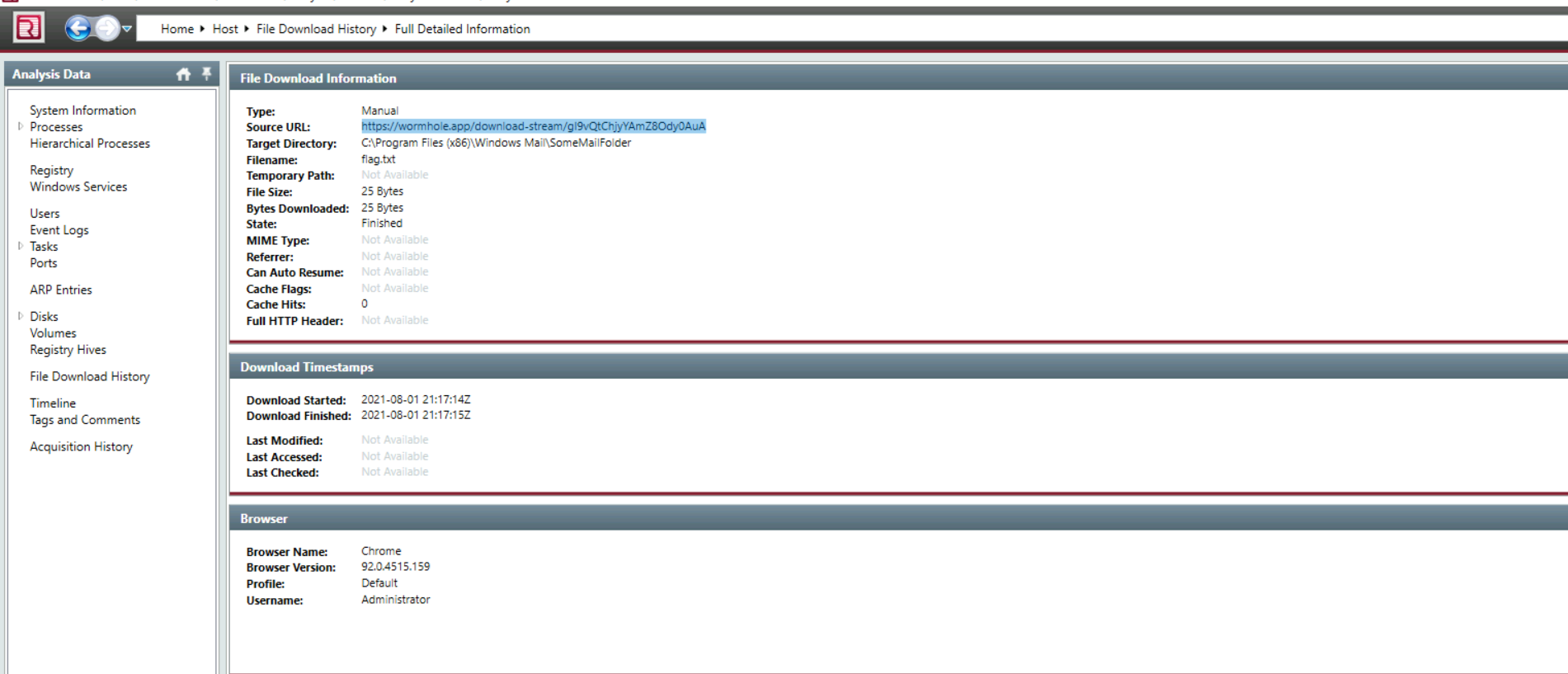 Provide the full path to where the file was downloaded to including the filename.
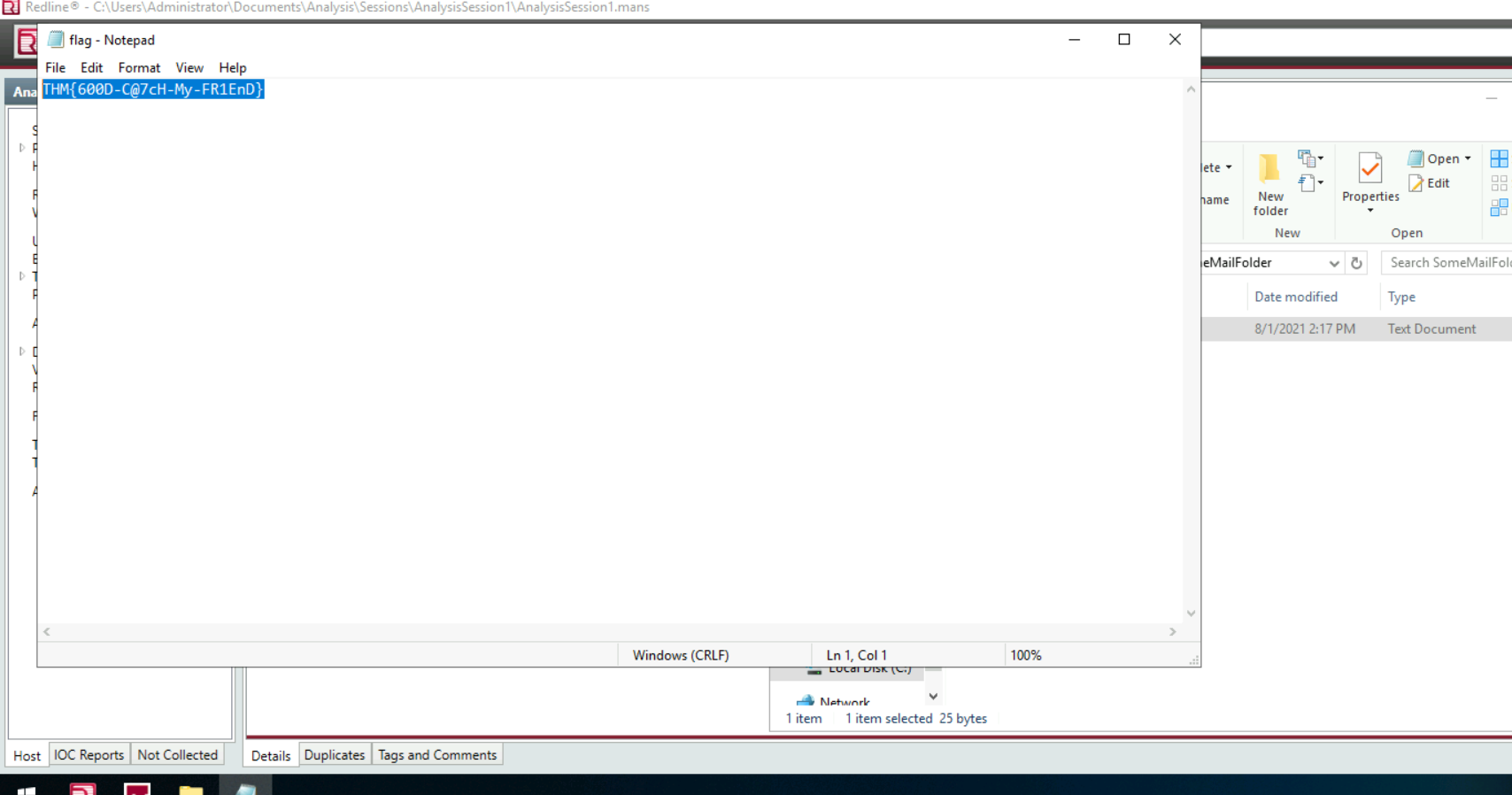
Provide the full path to where the file was downloaded to including the filename. - lấy đường dẫn từ ảnh của question trên Provide the message the intruder left for you in the file.
- THM{600D-C@7cH-My-FR1EnD} đi đến thư mục để download xuống và đọc flag thôi
 IOC Search Collector
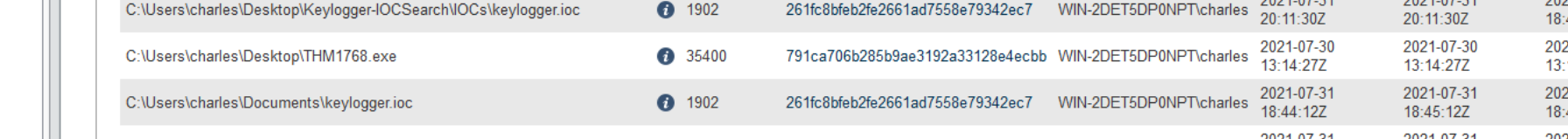
*What is the actual filename of the Keylogger? *
IOC Search Collector
*What is the actual filename of the Keylogger? * - psylog.exe
What filename is the file masquerading as?
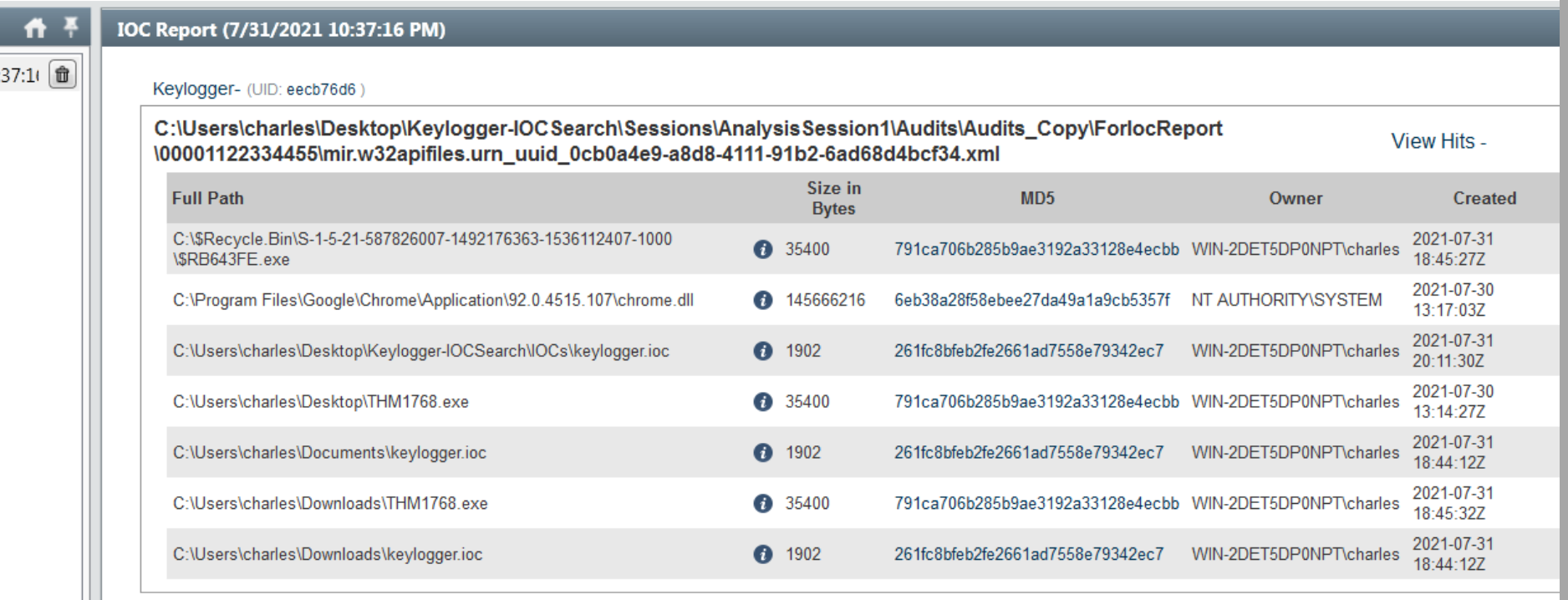
- THM1768.exe
Who is the owner of the file?
- câu này lấy kết quả từ cột owner sang
What is the file size in bytes?
 Provide the full path of where the .ioc file was placed after the Redline analysis, include the .ioc filename as well
Provide the full path of where the .ioc file was placed after the Redline analysis, include the .ioc filename as well
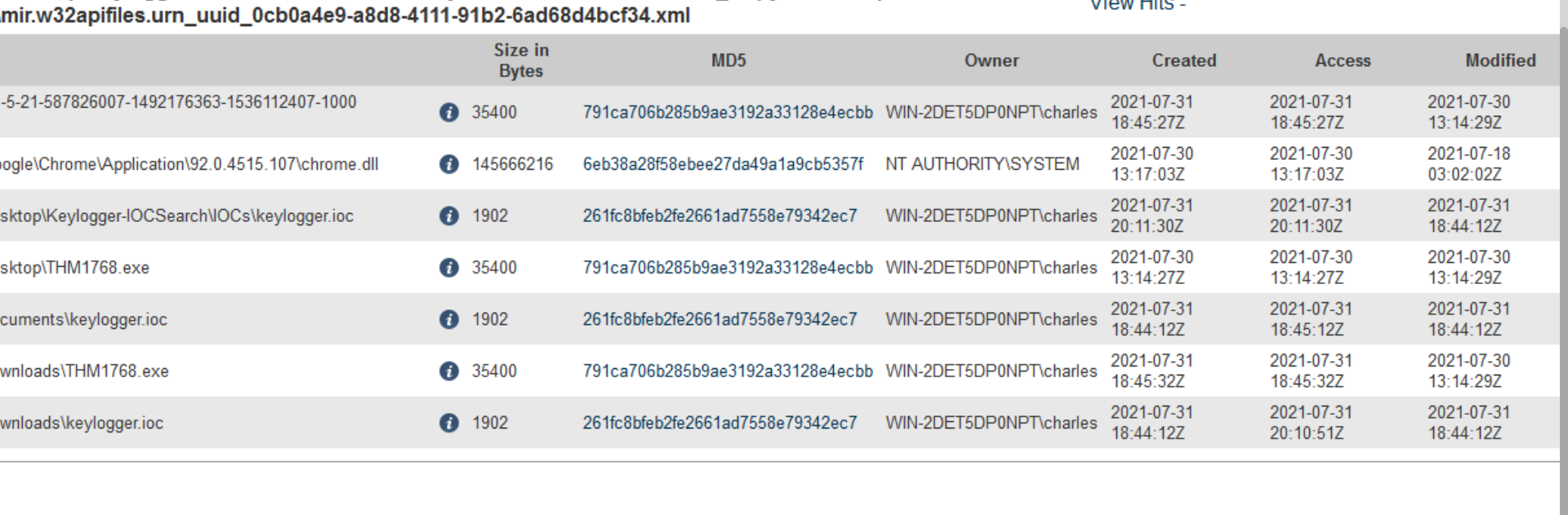
 IOC Search Collector Analysis
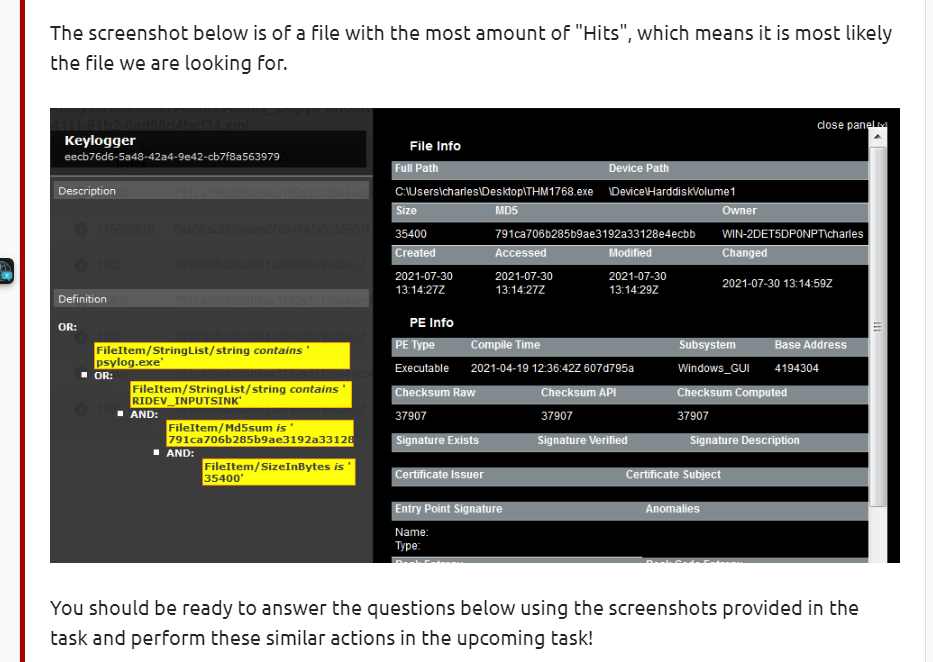
Provide the path of the file that matched all the artifacts along with the filename.
IOC Search Collector Analysis
Provide the path of the file that matched all the artifacts along with the filename.
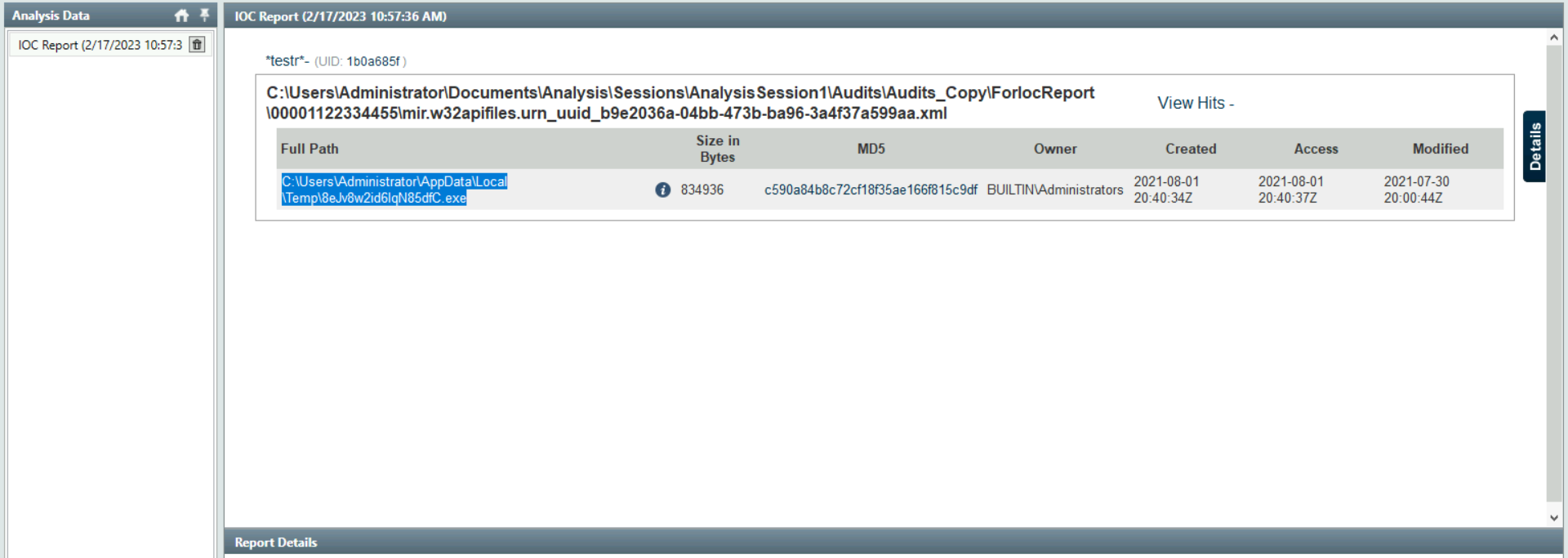 Provide the path where the file is located without including the filename.
Provide the path where the file is located without including the filename.
C:\Users\Administrator\AppData\Local\Temp
Who is the owner of the file? BUILTIN\Administrators(từ ảnh trên) Provide the subsystem for the file.Provide the Device Path where the file is located.
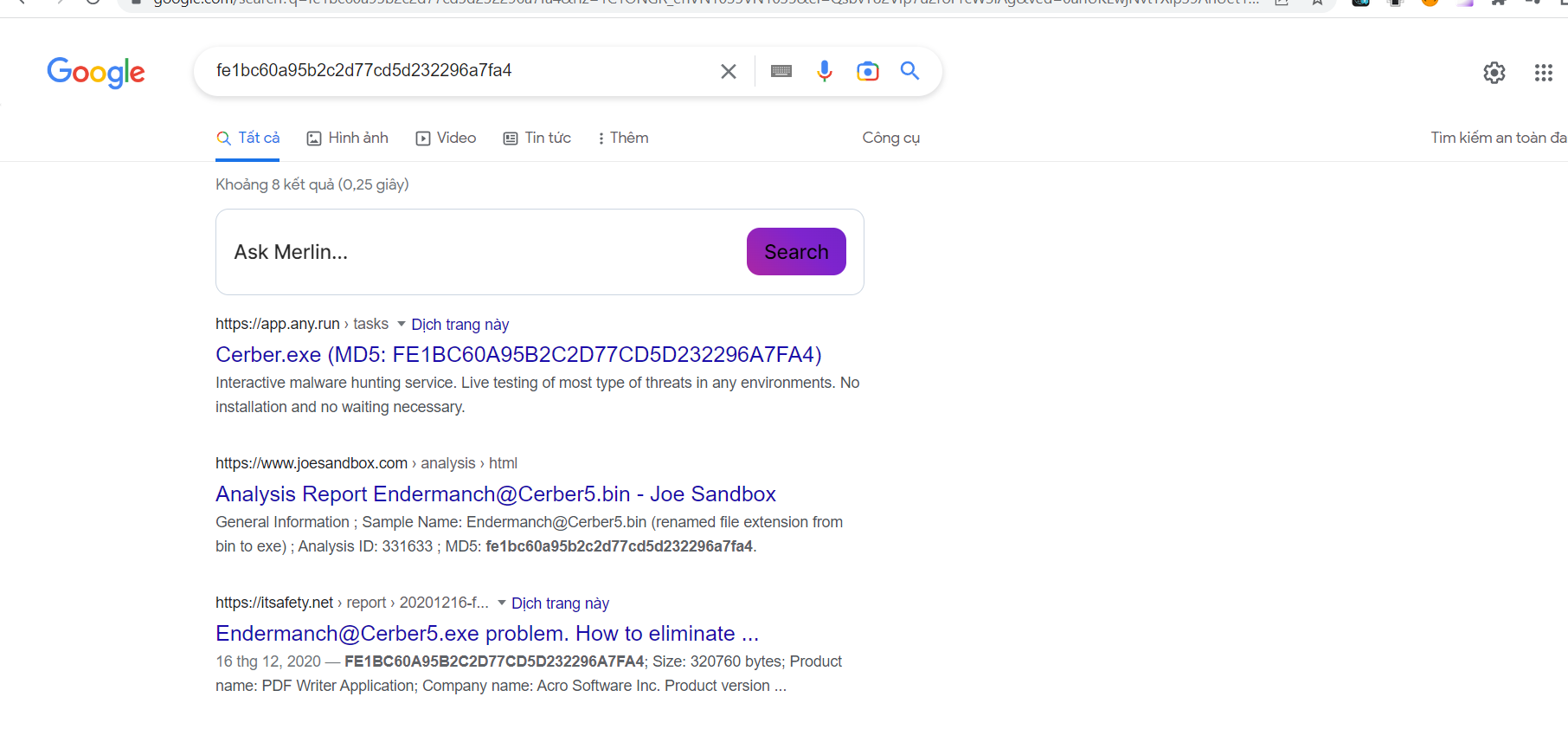
Provide the hash (SHA-256) for the file.
- có md5 của mã độc lên virus total hoặc hybrid analyse check hoặc theo gợi ý dùng câu lệnh get file-hash trong cmd
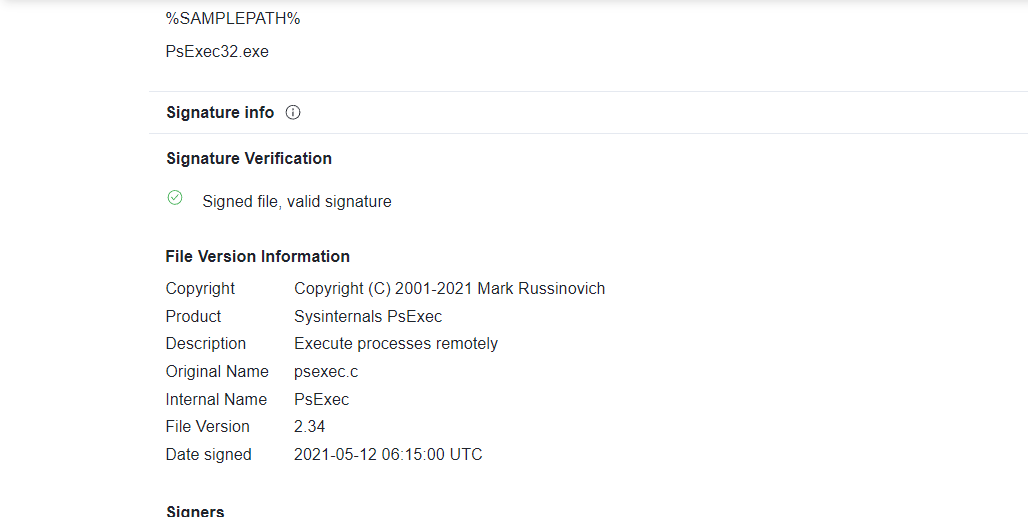
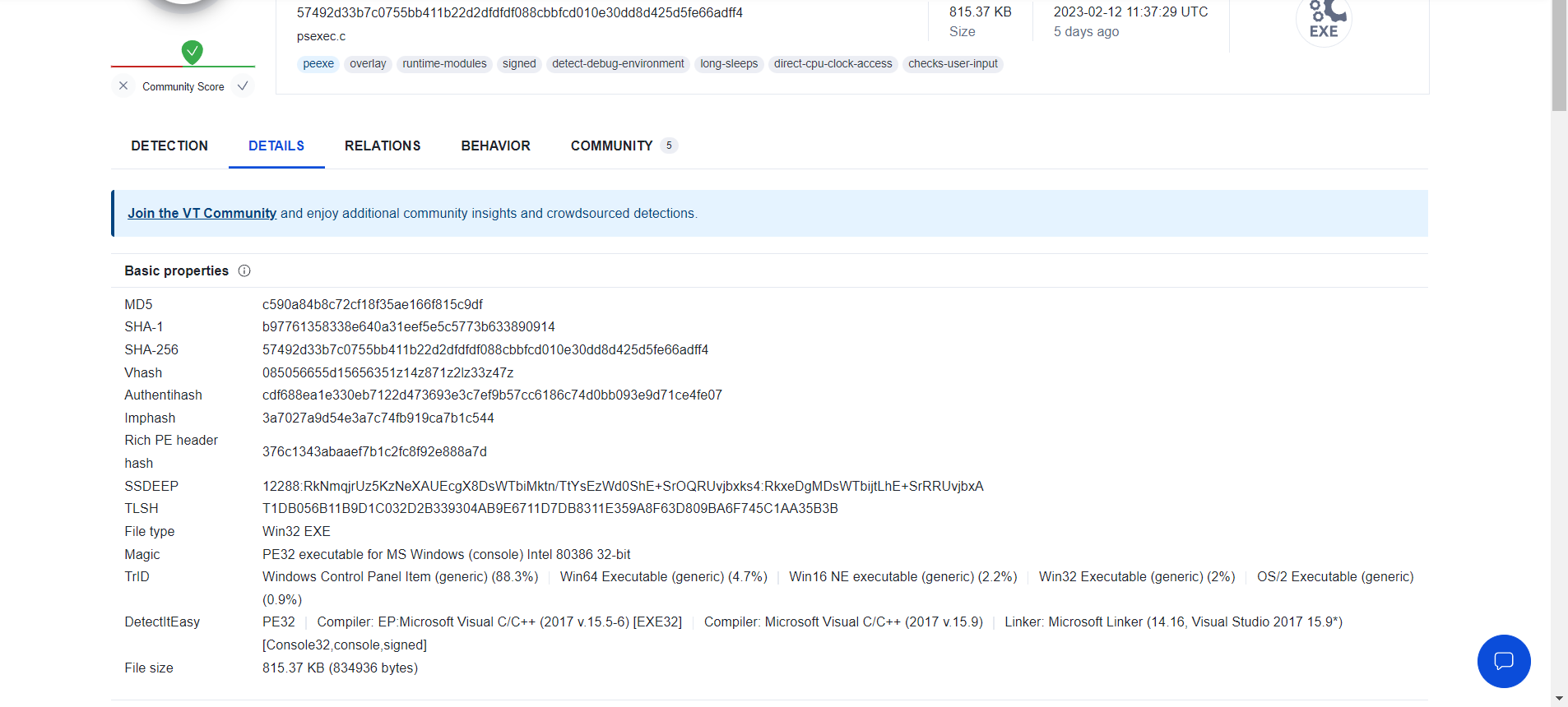 The attacker managed to masquerade the real filename. Can you find it having the hash in your arsenal?
The attacker managed to masquerade the real filename. Can you find it having the hash in your arsenal? - tìm real name thì hint cũng có gợi ý lên virus total :
 Endpoint Investigation
Can you identify the product name of the machine?
Endpoint Investigation
Can you identify the product name of the machine?
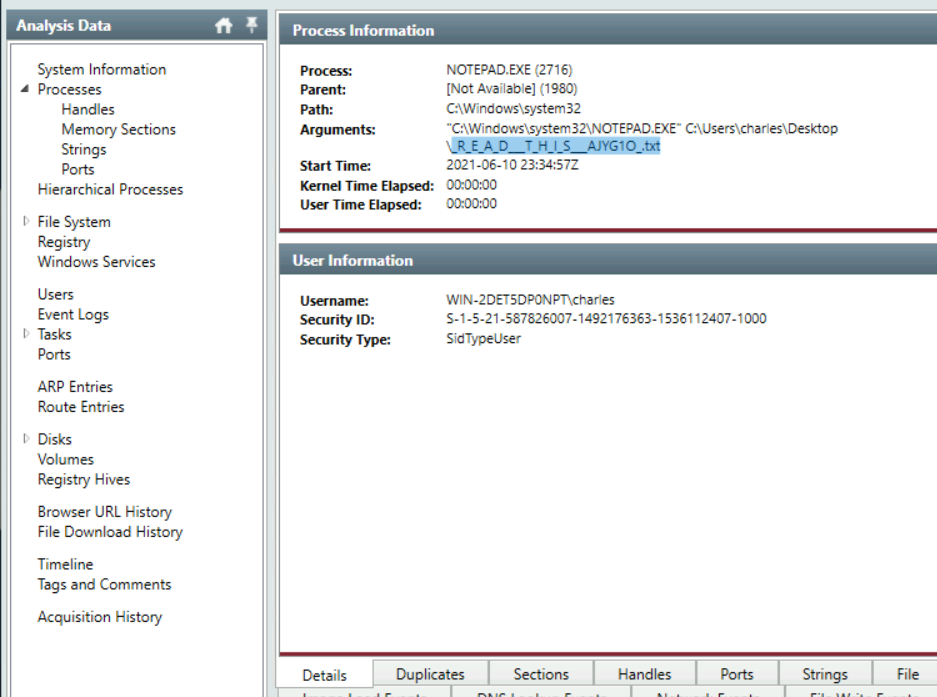
 Can you find the name of the note left on the Desktop for the "Charles"?
Can you find the name of the note left on the Desktop for the "Charles"?
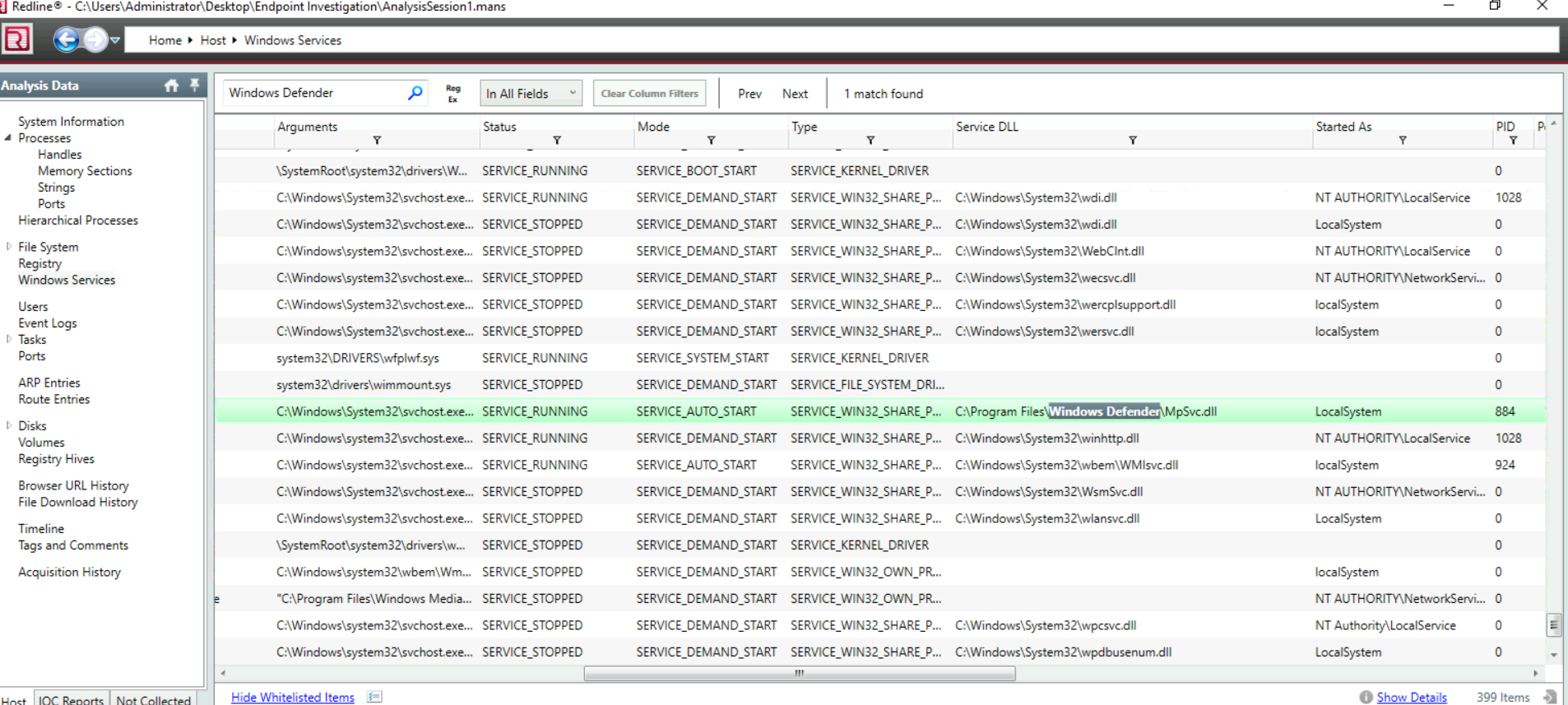
 Find the Windows Defender service; what is the name of its service DLL?
Find the Windows Defender service; what is the name of its service DLL?
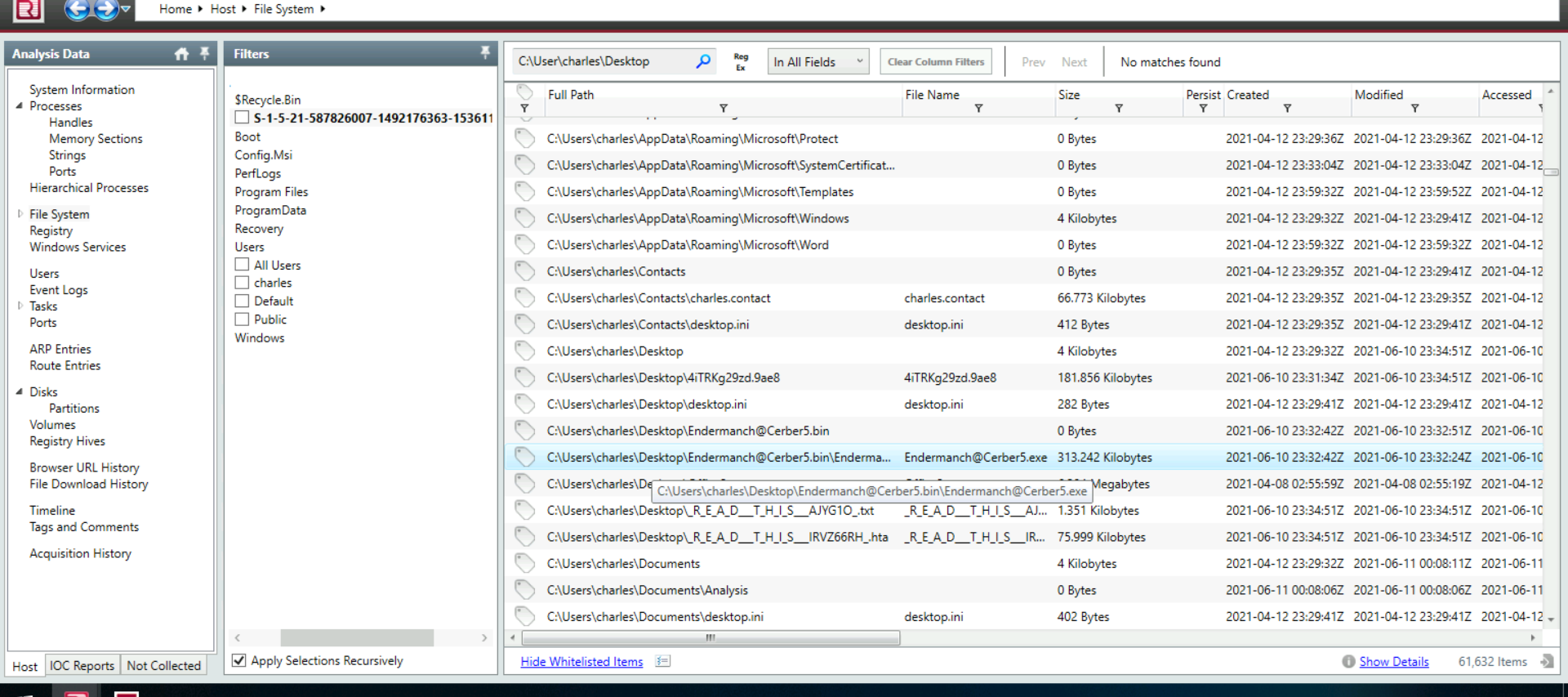
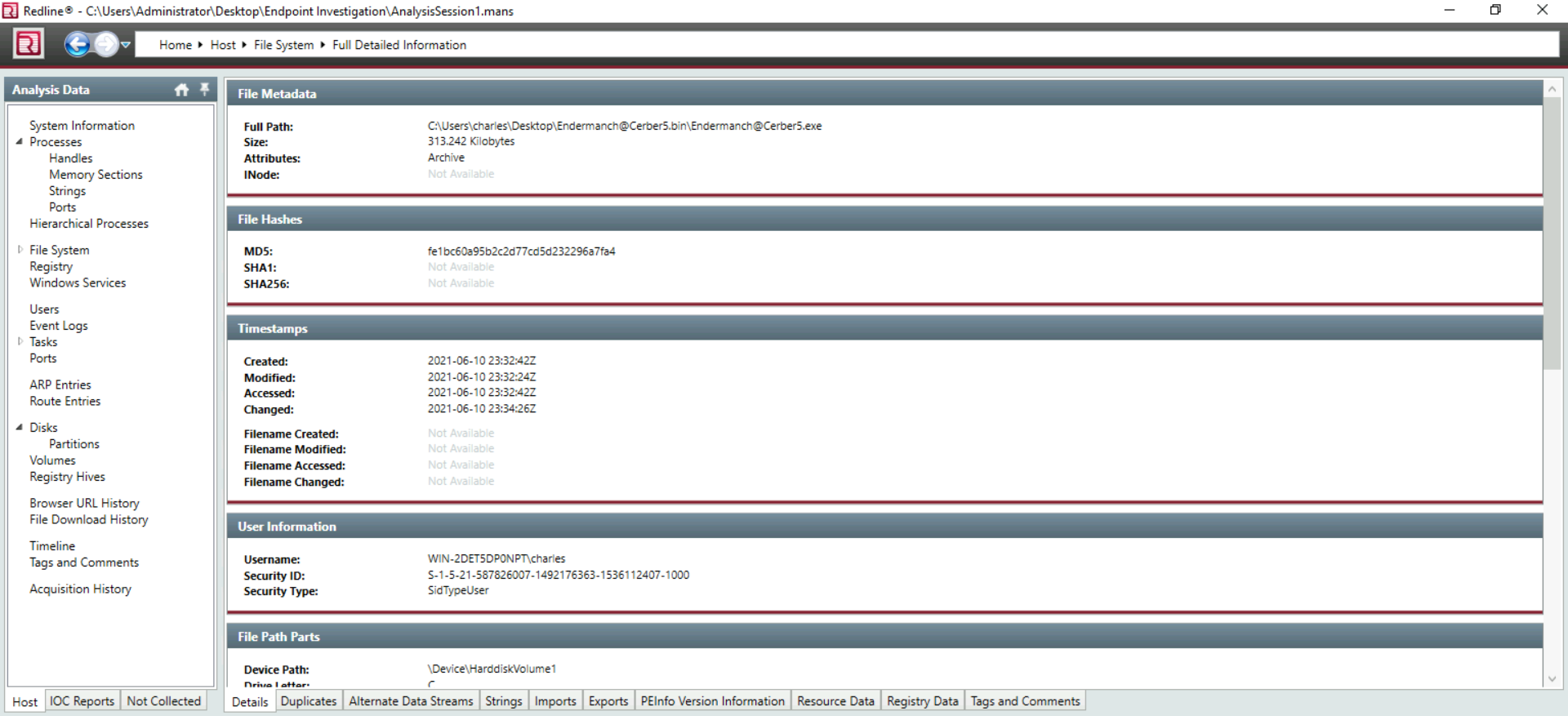
 Provide the filename of the malicious executable that got dropped on the user's Desktop.
Provide the filename of the malicious executable that got dropped on the user's Desktop.
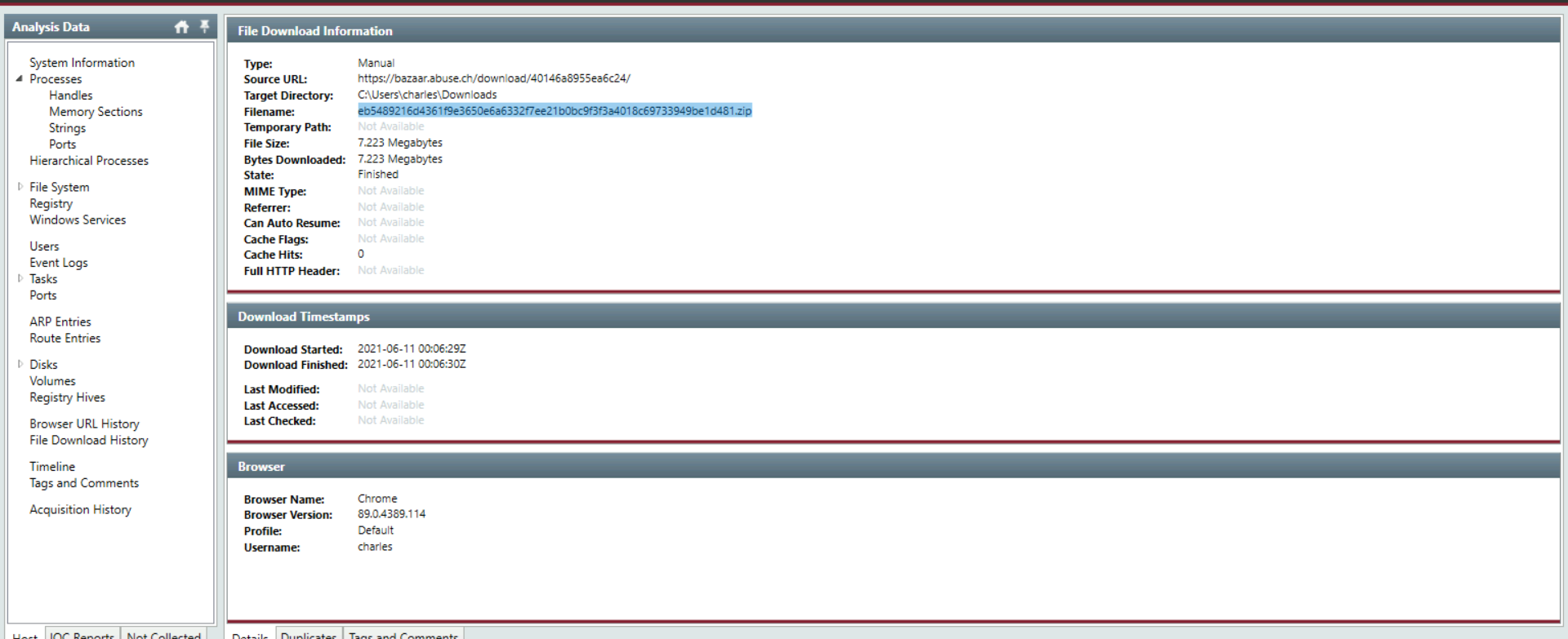
vào file download history search .zip và ra kết quả Provide the filename of the malicious executable that got dropped on the user's Desktop.