 +
+ ### Deploy
@@ -320,7 +320,7 @@ Click on the `Deploy & Run Transactions` option in the left sidebar.
1. Choose `Environment` > `JavaScript VM (London)`
2. Now click on `Deploy`
-
### Deploy
@@ -320,7 +320,7 @@ Click on the `Deploy & Run Transactions` option in the left sidebar.
1. Choose `Environment` > `JavaScript VM (London)`
2. Now click on `Deploy`
- +
+ **🎉 Congratulations, your smart contract has been deployed. 🎉**
@@ -335,7 +335,7 @@ Now, under `Deployed Contract` click on `> HOSTEL AT ..... (MEMORY)`
Similar to as follows:
-
**🎉 Congratulations, your smart contract has been deployed. 🎉**
@@ -335,7 +335,7 @@ Now, under `Deployed Contract` click on `> HOSTEL AT ..... (MEMORY)`
Similar to as follows:
- +
+ > **Note:** You're entering your details in `wei` not in `ether` (1 ether = 1000000000000000000 wei)
3. Then click on `transact`
@@ -348,24 +348,24 @@ Similar to as follows:
4. Change the `Account Address` from the dropdown menu. (Choose anyone except the one with 99.99 ether)
-
> **Note:** You're entering your details in `wei` not in `ether` (1 ether = 1000000000000000000 wei)
3. Then click on `transact`
@@ -348,24 +348,24 @@ Similar to as follows:
4. Change the `Account Address` from the dropdown menu. (Choose anyone except the one with 99.99 ether)
- +
+ 5. Add the total amount you have previously chosen as (rent cost + security deposit)
6. And then from the dropdown `wei`, choose `ether`
-
5. Add the total amount you have previously chosen as (rent cost + security deposit)
6. And then from the dropdown `wei`, choose `ether`
- +
+ 7. Scroll down and click on `signAgreement`, enter `1`, and press `signAgreement`
You can check the same by entering `RoomAgreementNo` : `1`
-
7. Scroll down and click on `signAgreement`, enter `1`, and press `signAgreement`
You can check the same by entering `RoomAgreementNo` : `1`
- +
+ **🎉 Congratulations, you've successfully signed your 1st agreement. 🎉**
All your transactions are shown in the `terminal`.
-
**🎉 Congratulations, you've successfully signed your 1st agreement. 🎉**
All your transactions are shown in the `terminal`.
- +
+ Now, you can cross verify this by checking your `ether` account address.
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.png
deleted file mode 100644
index 947063ec9..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.webp
new file mode 100644
index 000000000..e10a79837
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.png
deleted file mode 100644
index 7f5da0728..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.webp
new file mode 100644
index 000000000..eba41e7ec
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.png
deleted file mode 100644
index 2cdb1d572..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.webp
new file mode 100644
index 000000000..6c0a7fc0c
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/index.md b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/index.md
index 455c197ed..31c26f91f 100644
--- a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/index.md
+++ b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/index.md
@@ -2,7 +2,7 @@
title: "How to Build a Progressive Web App (PWA) with React"
date: "2021-10-22"
author: "Abdullah Pathan"
-coverImage: "blog-image.png"
+coverImage: "blog-image.webp"
tags: ["React","PWA","npm"]
description: "Follow this article to understand how to develop a simple React PWA. It explains the step-by-step process to help you easily follow along."
---
@@ -42,9 +42,9 @@ The above command can be broken down as follows:
Hitting 'Enter' after this command should initiate the build of your starter PWA React application. You should see a stream of prompts in your command-line interface. It may take a few minutes, but if you can see this screen after the command, you have created the project.
-
+
-
+
Here, you can see the following folder structure of your application so far. There are a few files that you shall pay attention to when it comes to PWA's:
@@ -119,7 +119,7 @@ npm start
This starts the application at a set `http://localhost` URL. Once the dev server is working and live on the command prompt, go to the URL to view the application. You should see something similar to this:
-
+
Now, it's all good and ready to have the app live and working, but more interested in the PWA aspect.
@@ -146,11 +146,11 @@ serve -s build //if you encounter an error with this command, try 'npx serve -s
Once you use the `serve` command, you should see the following message, having your application deployed to `http://localhost:5000`. It automatically adds the URL to your clipboard as well for quick pasting in your browser.
-
+
If you enter the `http://localhost` URL in your browser, you should see something similar to this:
-
+
## PWA Features
@@ -160,15 +160,15 @@ After registering your service worker from `index.js`, you should be able to see
In the section above, you can see `Manifest` -- opening that should show you the relevant details you listed from your `manifest.json` files.
-
+
With your PWA app running using React, you've successfully built your first PWA React application! From here, you can test many PWA features, such as installation, offline viewing, and Lighthouse audit testing.
-
+
If you hit the '+' symbol on the right side of the URL ba,r you can install your PWA, just as done here.
-
+
Use Workbox Lighthouse for testing the capabilities of your PWA: [Lighthouse](https://developer.chrome.com/docs/lighthouse/overview/)
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.png
deleted file mode 100644
index 95e037309..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.webp
new file mode 100644
index 000000000..6630604ce
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.png
deleted file mode 100644
index c8ee4482c..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.webp
new file mode 100644
index 000000000..6c2614bb3
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.png
deleted file mode 100644
index ec7f8305f..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.webp
new file mode 100644
index 000000000..4edac1e8a
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.png
deleted file mode 100644
index 1e71cb86a..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.webp
new file mode 100644
index 000000000..d420b177a
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.png
deleted file mode 100644
index c04eff9e8..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.webp
new file mode 100644
index 000000000..82965cc4e
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.png
deleted file mode 100644
index f46997347..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.webp
new file mode 100644
index 000000000..d1a79c1a6
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.png
deleted file mode 100644
index 812b369fe..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.webp
new file mode 100644
index 000000000..e4e594470
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.png
deleted file mode 100644
index 81e9bb9f8..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.webp
new file mode 100644
index 000000000..968d73a84
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.png
deleted file mode 100644
index ebbd681dc..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.webp
new file mode 100644
index 000000000..2a4dde078
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.png
deleted file mode 100644
index 5fd46cca7..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.webp
new file mode 100644
index 000000000..0a56984a3
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.png
deleted file mode 100644
index 1d498571e..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.webp
new file mode 100644
index 000000000..7200160a6
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.png
deleted file mode 100644
index d0bba7f7d..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.webp
new file mode 100644
index 000000000..d0185f147
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.png
deleted file mode 100644
index 1d00263be..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.webp
new file mode 100644
index 000000000..b8746ccbd
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.png
deleted file mode 100644
index a7909c16c..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.webp
new file mode 100644
index 000000000..8a808e857
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/index.md b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/index.md
index 1e20ce8b2..5dd43271a 100644
--- a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/index.md
+++ b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/index.md
@@ -1,7 +1,7 @@
---
title: "How to Implement JWT Authentication for CRUD APIs in Deno"
date: "2022-07-28"
-coverImage: "jwt-authentication-with-deno.png"
+coverImage: "jwt-authentication-with-deno.webp"
author: "Ekekenta Odionyenfe Clinton"
tags: ["JWT", "Deno", "Authentication"]
description: "In this hands-on tutorial, you'll learn from scratch how to implement JWT authentication for CRUD APIs in Deno."
@@ -573,21 +573,21 @@ Below is what your final project directory looks like:
Now that your application is ready, you need to test the various routes to ensure they are working. To test the routes, rerun your server with `deno run --allow-net app.ts`.
-
+
Great! The app is running on port:8080. You can now head to the postman to test your routes.
### Signup Route
-
+
-
+
### Sign-in Route
-
+
-
+
Amazing! Now that you have signed up and authenticated a user, the returned token, which shows that the user has been authenticated, can be used to access your todo CRUD APIs.
@@ -597,9 +597,9 @@ First, let's try accessing your todo routes without the token...
#### Create Task Route
-
+
-
+
As you can see, when you tried to create a task, you got a message `You are not authorized to access this route` because a random person did it without a token.
@@ -607,32 +607,32 @@ Now, let's also try accessing the delete by Id route without the token...
#### Delete Task Route
-
+
-
+
Your todo CRUD APIs have been protected, and the only way a user can access them is by getting authenticated. Now let's log in again and use the returned token to access the todo routes.
-
+
So, you have logged a user in and put the returned Bearer's token in the authorization header. You can access our todo APIs now because, with the bearer's token, you are authorized to access the todo APIs.
#### Create Task Route
-
+
-
+
#### Get All Tasks Route
-
+
-
+
#### Get Task By Id Route
-
+
-
+
Feel free to test the other routes to see how things work.
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.png
deleted file mode 100644
index 80044f386..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.webp
new file mode 100644
index 000000000..351e2231b
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.png
deleted file mode 100644
index afdf708b1..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.webp
new file mode 100644
index 000000000..1a79ededc
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.png
deleted file mode 100644
index a7909c16c..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.webp
new file mode 100644
index 000000000..8a808e857
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.png
deleted file mode 100644
index 9b7cc29c5..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.webp
new file mode 100644
index 000000000..a481b527d
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.png
deleted file mode 100644
index 302c0cdef..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.webp
new file mode 100644
index 000000000..d4bad8034
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.png
deleted file mode 100644
index eb3d0e718..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.webp
new file mode 100644
index 000000000..13f59e182
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.png
deleted file mode 100644
index 65be32ac2..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.webp
new file mode 100644
index 000000000..970662793
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.png
deleted file mode 100644
index 684523cb9..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.webp
new file mode 100644
index 000000000..696a50b0c
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.png
deleted file mode 100644
index 812b369fe..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.webp
new file mode 100644
index 000000000..e4e594470
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.png
deleted file mode 100644
index 9a43a7213..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.webp
new file mode 100644
index 000000000..f6121ccda
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.png
deleted file mode 100644
index 120e992a5..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.webp
new file mode 100644
index 000000000..9aff93033
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.png
deleted file mode 100644
index 6b12c1fc8..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.webp
new file mode 100644
index 000000000..8abec3df2
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.webp differ
diff --git a/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.png b/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.png
deleted file mode 100644
index 5bdba6b3b..000000000
Binary files a/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.png and /dev/null differ
diff --git a/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.webp b/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.webp
new file mode 100644
index 000000000..4caf98cb1
Binary files /dev/null and b/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.webp differ
diff --git a/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/index.md b/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/index.md
index e450ab064..7d0490499 100644
--- a/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/index.md
+++ b/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/index.md
@@ -1,7 +1,7 @@
---
title: "Implement HTTP Streaming with Node.js and Fetch API"
date: "2022-04-27"
-coverImage: "http-streaming-with-nodejs-and-fetch-api.png"
+coverImage: "http-streaming-with-nodejs-and-fetch-api.webp"
author: "Nick Van Nieuwenhuyse"
tags: ["Node.js", "Fetch API", "Streaming"]
description: "Do you know that you can stream HTTP data for efficient visualization? Learn more about how you can stream data with HTTP using Node.js and Fetch API."
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.png
deleted file mode 100644
index b8c99edc2..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.webp
new file mode 100644
index 000000000..aa519cb73
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.jpeg b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.jpeg
deleted file mode 100644
index 6e88e8707..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.webp
new file mode 100644
index 000000000..172e5a7c6
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).png
deleted file mode 100644
index 9ac1a1279..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).webp
new file mode 100644
index 000000000..f5cfb7c44
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.png
deleted file mode 100644
index bf9446923..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.webp
new file mode 100644
index 000000000..f6656cbcc
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.png
deleted file mode 100644
index c6ddd650e..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.webp
new file mode 100644
index 000000000..4de9f8f81
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.png
deleted file mode 100644
index ebee3a6a8..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.webp
new file mode 100644
index 000000000..d4a7fabeb
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.png
deleted file mode 100644
index e001db0e8..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.webp
new file mode 100644
index 000000000..20fe83dbe
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.png
deleted file mode 100644
index 2c2d27e00..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.webp
new file mode 100644
index 000000000..6ab1fc65d
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.png
deleted file mode 100644
index 35697397c..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.webp
new file mode 100644
index 000000000..af85159c8
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/index.md b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/index.md
index e061c5d18..89421c358 100644
--- a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/index.md
+++ b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/index.md
@@ -1,7 +1,7 @@
---
title: "How to Implement Registration and Authentication in Django?"
date: "2021-07-30"
-coverImage: "coverImage.png"
+coverImage: "coverImage.webp"
author: "Taminoturoko Briggs"
tags: [Django, Authentication, User Registration]
description: "In this tutorial, you will learn how to implement user registration and authentication in Django using LoginRadius."
@@ -35,13 +35,13 @@ To get started with LoginRadius, you have to first [create a free developer acco
If you already have an account, log into your [LoginRadius dashboard](https://accounts.loginradius.com/auth.aspx?return_url=https://dashboard.loginradius.com/login)
You will see a page like this:
-
+
When you create an account, LoginRadius sets up a free app for you. This is the app you are going to integrate with Django. Here my app name is "tammibriggs".
Click on your app, and you will see a page like this:
-
+
There is one more thing LoginRadius automatically creates for you: an [Auth Page (IDX)](https://www.loginradius.com/developers/).
@@ -62,11 +62,11 @@ This section covers:
Before using any of the APIs that LoginRadius provides, you need to get your **App Name**, **API Key**, and **API Secret**.
On your LoginRadius app, navigate to [Configuration > API Credentials](https://dashboard.loginradius.com/configuration)
-
+
You will find your API key under the **API Key and Secret** subsection.
-
+
**Whitelist your Domain**
@@ -75,7 +75,7 @@ For security reasons, LoginRadius processes the API calls that are received from
Local domains (`http://localhost` and `http://127.0.0.1`) are whitelisted by default. This means you don't have to worry about whitelisting your domain if you are running your application on Django's development server. But in a production environment, you definitely have to whitelist our domain.
To whitelist your domain, in your LoginRadius Dashboard, navigate to [Configuration > Whitelist Your Domain](https://dashboard.loginradius.com/configuration) and add your domain name.
-
+
**Installation of Dependencies**
@@ -374,11 +374,11 @@ Also, in the register and login link, we replaced the {RETURN_URL} parameter wit
Run the development server and open `http://127.0.0.1:8000/`, you will see a page like this:
-
+
Now, when you click the register or login button, you will see a page like this:
-
+
> When LoginRadius successfully authenticates a user, it attaches an access token in the query string as a token parameter to the REDIRECT_URL.
@@ -515,7 +515,7 @@ Here we displayed the Provider, Email and NoOfLogins from the `user_data`. These
Now, if you run your development server, and then register and login a user, you should see a page like this:
-
+
To see the entire data present in the `user_data`, you can do something like this in your `profile.html`, file:
diff --git a/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.png b/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.png
deleted file mode 100644
index 7240e7c0a..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.webp b/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.webp
new file mode 100644
index 000000000..1095edb88
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.png b/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.png
deleted file mode 100644
index 7d41537ab..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.webp b/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.webp
new file mode 100644
index 000000000..90fc5d4eb
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/effects-example.png b/content/engineering/guest-post/introduction-to-solidjs/effects-example.png
deleted file mode 100644
index 63b4a90ca..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/effects-example.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/effects-example.webp b/content/engineering/guest-post/introduction-to-solidjs/effects-example.webp
new file mode 100644
index 000000000..636e48b18
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/effects-example.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.png b/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.png
deleted file mode 100644
index d217a1a78..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.webp b/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.webp
new file mode 100644
index 000000000..79406e013
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/for-example.png b/content/engineering/guest-post/introduction-to-solidjs/for-example.png
deleted file mode 100644
index 9039bb5e0..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/for-example.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/for-example.webp b/content/engineering/guest-post/introduction-to-solidjs/for-example.webp
new file mode 100644
index 000000000..2c2970750
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/for-example.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.png b/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.png
deleted file mode 100644
index 76c5c0549..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.webp b/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.webp
new file mode 100644
index 000000000..4645e4e42
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.png b/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.png
deleted file mode 100644
index b0c05e330..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.webp b/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.webp
new file mode 100644
index 000000000..3d1dbeef7
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/index.md b/content/engineering/guest-post/introduction-to-solidjs/index.md
index a6c4f64f1..133a05795 100644
--- a/content/engineering/guest-post/introduction-to-solidjs/index.md
+++ b/content/engineering/guest-post/introduction-to-solidjs/index.md
@@ -1,7 +1,7 @@
---
title: "Introduction to SolidJS"
date: "2022-06-28"
-coverImage: "introduction-to-solidjs.png"
+coverImage: "introduction-to-solidjs.webp"
author: "Siddhant Varma"
tags: ["SolidJS", "React", "Frontend"]
description: "In this tutorial, you’ll learn what SolidJS is, how it works, and its fundamentals such as reactivity, architecture, events, effects, etc. Then you’ll use this knowledge to build a simple todo app. Finally, you’ll understand how SolidJS compares with React and how it’s better and worse."
@@ -13,7 +13,7 @@ So in this tutorial, I'll give you a complete walkthrough of SolidJS and help yo
## What is SolidJS?
-
+
SolidJS takes the syntax and developer experience of React and combines it with the performance of Svelte to give you the best of both worlds.
@@ -48,7 +48,7 @@ render(() =>
Now, you can cross verify this by checking your `ether` account address.
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.png
deleted file mode 100644
index 947063ec9..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.webp
new file mode 100644
index 000000000..e10a79837
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/blog-image.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.png
deleted file mode 100644
index 7f5da0728..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.webp
new file mode 100644
index 000000000..eba41e7ec
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/counter-base-app.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.png
deleted file mode 100644
index 2cdb1d572..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.webp
new file mode 100644
index 000000000..6c0a7fc0c
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/cra-pwa.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/index.md b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/index.md
index 455c197ed..31c26f91f 100644
--- a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/index.md
+++ b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/index.md
@@ -2,7 +2,7 @@
title: "How to Build a Progressive Web App (PWA) with React"
date: "2021-10-22"
author: "Abdullah Pathan"
-coverImage: "blog-image.png"
+coverImage: "blog-image.webp"
tags: ["React","PWA","npm"]
description: "Follow this article to understand how to develop a simple React PWA. It explains the step-by-step process to help you easily follow along."
---
@@ -42,9 +42,9 @@ The above command can be broken down as follows:
Hitting 'Enter' after this command should initiate the build of your starter PWA React application. You should see a stream of prompts in your command-line interface. It may take a few minutes, but if you can see this screen after the command, you have created the project.
-
+
-
+
Here, you can see the following folder structure of your application so far. There are a few files that you shall pay attention to when it comes to PWA's:
@@ -119,7 +119,7 @@ npm start
This starts the application at a set `http://localhost` URL. Once the dev server is working and live on the command prompt, go to the URL to view the application. You should see something similar to this:
-
+
Now, it's all good and ready to have the app live and working, but more interested in the PWA aspect.
@@ -146,11 +146,11 @@ serve -s build //if you encounter an error with this command, try 'npx serve -s
Once you use the `serve` command, you should see the following message, having your application deployed to `http://localhost:5000`. It automatically adds the URL to your clipboard as well for quick pasting in your browser.
-
+
If you enter the `http://localhost` URL in your browser, you should see something similar to this:
-
+
## PWA Features
@@ -160,15 +160,15 @@ After registering your service worker from `index.js`, you should be able to see
In the section above, you can see `Manifest` -- opening that should show you the relevant details you listed from your `manifest.json` files.
-
+
With your PWA app running using React, you've successfully built your first PWA React application! From here, you can test many PWA features, such as installation, offline viewing, and Lighthouse audit testing.
-
+
If you hit the '+' symbol on the right side of the URL ba,r you can install your PWA, just as done here.
-
+
Use Workbox Lighthouse for testing the capabilities of your PWA: [Lighthouse](https://developer.chrome.com/docs/lighthouse/overview/)
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.png
deleted file mode 100644
index 95e037309..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.webp
new file mode 100644
index 000000000..6630604ce
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-folder-structure.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.png
deleted file mode 100644
index c8ee4482c..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.webp
new file mode 100644
index 000000000..6c2614bb3
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-install.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.png
deleted file mode 100644
index ec7f8305f..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.webp
new file mode 100644
index 000000000..4edac1e8a
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-lighthouse.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.png
deleted file mode 100644
index 1e71cb86a..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.webp
new file mode 100644
index 000000000..d420b177a
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-manifest.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.png
deleted file mode 100644
index c04eff9e8..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.webp
new file mode 100644
index 000000000..82965cc4e
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-serve.webp differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.png b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.png
deleted file mode 100644
index f46997347..000000000
Binary files a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.webp b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.webp
new file mode 100644
index 000000000..d1a79c1a6
Binary files /dev/null and b/content/engineering/guest-post/how-to-build-a-progressive-web-app-with-react/pwa-service-worker.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.png
deleted file mode 100644
index 812b369fe..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.webp
new file mode 100644
index 000000000..e4e594470
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/0bohcxv.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.png
deleted file mode 100644
index 81e9bb9f8..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.webp
new file mode 100644
index 000000000..968d73a84
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/apk23wt.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.png
deleted file mode 100644
index ebbd681dc..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.webp
new file mode 100644
index 000000000..2a4dde078
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/cdkr6ad.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.png
deleted file mode 100644
index 5fd46cca7..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.webp
new file mode 100644
index 000000000..0a56984a3
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/d2orbz0.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.png
deleted file mode 100644
index 1d498571e..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.webp
new file mode 100644
index 000000000..7200160a6
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ehp4zwf.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.png
deleted file mode 100644
index d0bba7f7d..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.webp
new file mode 100644
index 000000000..d0185f147
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/fee5d0s.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.png
deleted file mode 100644
index 1d00263be..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.webp
new file mode 100644
index 000000000..b8746ccbd
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/get-task-by-id.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.png
deleted file mode 100644
index a7909c16c..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.webp
new file mode 100644
index 000000000..8a808e857
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/hph0xmy.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/index.md b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/index.md
index 1e20ce8b2..5dd43271a 100644
--- a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/index.md
+++ b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/index.md
@@ -1,7 +1,7 @@
---
title: "How to Implement JWT Authentication for CRUD APIs in Deno"
date: "2022-07-28"
-coverImage: "jwt-authentication-with-deno.png"
+coverImage: "jwt-authentication-with-deno.webp"
author: "Ekekenta Odionyenfe Clinton"
tags: ["JWT", "Deno", "Authentication"]
description: "In this hands-on tutorial, you'll learn from scratch how to implement JWT authentication for CRUD APIs in Deno."
@@ -573,21 +573,21 @@ Below is what your final project directory looks like:
Now that your application is ready, you need to test the various routes to ensure they are working. To test the routes, rerun your server with `deno run --allow-net app.ts`.
-
+
Great! The app is running on port:8080. You can now head to the postman to test your routes.
### Signup Route
-
+
-
+
### Sign-in Route
-
+
-
+
Amazing! Now that you have signed up and authenticated a user, the returned token, which shows that the user has been authenticated, can be used to access your todo CRUD APIs.
@@ -597,9 +597,9 @@ First, let's try accessing your todo routes without the token...
#### Create Task Route
-
+
-
+
As you can see, when you tried to create a task, you got a message `You are not authorized to access this route` because a random person did it without a token.
@@ -607,32 +607,32 @@ Now, let's also try accessing the delete by Id route without the token...
#### Delete Task Route
-
+
-
+
Your todo CRUD APIs have been protected, and the only way a user can access them is by getting authenticated. Now let's log in again and use the returned token to access the todo routes.
-
+
So, you have logged a user in and put the returned Bearer's token in the authorization header. You can access our todo APIs now because, with the bearer's token, you are authorized to access the todo APIs.
#### Create Task Route
-
+
-
+
#### Get All Tasks Route
-
+
-
+
#### Get Task By Id Route
-
+
-
+
Feel free to test the other routes to see how things work.
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.png
deleted file mode 100644
index 80044f386..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.webp
new file mode 100644
index 000000000..351e2231b
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/jwt-authentication-with-deno.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.png
deleted file mode 100644
index afdf708b1..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.webp
new file mode 100644
index 000000000..1a79ededc
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/nbiaskx.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.png
deleted file mode 100644
index a7909c16c..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.webp
new file mode 100644
index 000000000..8a808e857
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ngozekb.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.png
deleted file mode 100644
index 9b7cc29c5..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.webp
new file mode 100644
index 000000000..a481b527d
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/q6eetmg.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.png
deleted file mode 100644
index 302c0cdef..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.webp
new file mode 100644
index 000000000..d4bad8034
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/sdvkp4h.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.png
deleted file mode 100644
index eb3d0e718..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.webp
new file mode 100644
index 000000000..13f59e182
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/trydtxn.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.png
deleted file mode 100644
index 65be32ac2..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.webp
new file mode 100644
index 000000000..970662793
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/vgvz7bn.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.png
deleted file mode 100644
index 684523cb9..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.webp
new file mode 100644
index 000000000..696a50b0c
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/wncqtya.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.png
deleted file mode 100644
index 812b369fe..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.webp
new file mode 100644
index 000000000..e4e594470
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/y9ilrk9.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.png
deleted file mode 100644
index 9a43a7213..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.webp
new file mode 100644
index 000000000..f6121ccda
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/yrmqo8g.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.png
deleted file mode 100644
index 120e992a5..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.webp
new file mode 100644
index 000000000..9aff93033
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zosrr9u.webp differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.png b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.png
deleted file mode 100644
index 6b12c1fc8..000000000
Binary files a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.png and /dev/null differ
diff --git a/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.webp b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.webp
new file mode 100644
index 000000000..8abec3df2
Binary files /dev/null and b/content/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/zxkgmsm.webp differ
diff --git a/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.png b/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.png
deleted file mode 100644
index 5bdba6b3b..000000000
Binary files a/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.png and /dev/null differ
diff --git a/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.webp b/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.webp
new file mode 100644
index 000000000..4caf98cb1
Binary files /dev/null and b/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/http-streaming-with-nodejs-and-fetch-api.webp differ
diff --git a/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/index.md b/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/index.md
index e450ab064..7d0490499 100644
--- a/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/index.md
+++ b/content/engineering/guest-post/http-streaming-with-nodejs-and-fetch-api/index.md
@@ -1,7 +1,7 @@
---
title: "Implement HTTP Streaming with Node.js and Fetch API"
date: "2022-04-27"
-coverImage: "http-streaming-with-nodejs-and-fetch-api.png"
+coverImage: "http-streaming-with-nodejs-and-fetch-api.webp"
author: "Nick Van Nieuwenhuyse"
tags: ["Node.js", "Fetch API", "Streaming"]
description: "Do you know that you can stream HTTP data for efficient visualization? Learn more about how you can stream data with HTTP using Node.js and Fetch API."
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.png
deleted file mode 100644
index b8c99edc2..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.webp
new file mode 100644
index 000000000..aa519cb73
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API credentials.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.jpeg b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.jpeg
deleted file mode 100644
index 6e88e8707..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.webp
new file mode 100644
index 000000000..172e5a7c6
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/API key and secret.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).png
deleted file mode 100644
index 9ac1a1279..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).webp
new file mode 100644
index 000000000..f5cfb7c44
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Auth page (IDX).webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.png
deleted file mode 100644
index bf9446923..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.webp
new file mode 100644
index 000000000..f6656cbcc
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Dashboard.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.png
deleted file mode 100644
index c6ddd650e..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.webp
new file mode 100644
index 000000000..4de9f8f81
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/LoginRadius app.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.png
deleted file mode 100644
index ebee3a6a8..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.webp
new file mode 100644
index 000000000..d4a7fabeb
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Profile page.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.png
deleted file mode 100644
index e001db0e8..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.webp
new file mode 100644
index 000000000..20fe83dbe
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Register and Login page.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.png
deleted file mode 100644
index 2c2d27e00..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.webp
new file mode 100644
index 000000000..6ab1fc65d
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/Whitelist your domain.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.png b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.png
deleted file mode 100644
index 35697397c..000000000
Binary files a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.png and /dev/null differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.webp b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.webp
new file mode 100644
index 000000000..af85159c8
Binary files /dev/null and b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/coverImage.webp differ
diff --git a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/index.md b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/index.md
index e061c5d18..89421c358 100644
--- a/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/index.md
+++ b/content/engineering/guest-post/implementing-registration-and-authentication-in-django-using-LoginRadius/index.md
@@ -1,7 +1,7 @@
---
title: "How to Implement Registration and Authentication in Django?"
date: "2021-07-30"
-coverImage: "coverImage.png"
+coverImage: "coverImage.webp"
author: "Taminoturoko Briggs"
tags: [Django, Authentication, User Registration]
description: "In this tutorial, you will learn how to implement user registration and authentication in Django using LoginRadius."
@@ -35,13 +35,13 @@ To get started with LoginRadius, you have to first [create a free developer acco
If you already have an account, log into your [LoginRadius dashboard](https://accounts.loginradius.com/auth.aspx?return_url=https://dashboard.loginradius.com/login)
You will see a page like this:
-
+
When you create an account, LoginRadius sets up a free app for you. This is the app you are going to integrate with Django. Here my app name is "tammibriggs".
Click on your app, and you will see a page like this:
-
+
There is one more thing LoginRadius automatically creates for you: an [Auth Page (IDX)](https://www.loginradius.com/developers/).
@@ -62,11 +62,11 @@ This section covers:
Before using any of the APIs that LoginRadius provides, you need to get your **App Name**, **API Key**, and **API Secret**.
On your LoginRadius app, navigate to [Configuration > API Credentials](https://dashboard.loginradius.com/configuration)
-
+
You will find your API key under the **API Key and Secret** subsection.
-
+
**Whitelist your Domain**
@@ -75,7 +75,7 @@ For security reasons, LoginRadius processes the API calls that are received from
Local domains (`http://localhost` and `http://127.0.0.1`) are whitelisted by default. This means you don't have to worry about whitelisting your domain if you are running your application on Django's development server. But in a production environment, you definitely have to whitelist our domain.
To whitelist your domain, in your LoginRadius Dashboard, navigate to [Configuration > Whitelist Your Domain](https://dashboard.loginradius.com/configuration) and add your domain name.
-
+
**Installation of Dependencies**
@@ -374,11 +374,11 @@ Also, in the register and login link, we replaced the {RETURN_URL} parameter wit
Run the development server and open `http://127.0.0.1:8000/`, you will see a page like this:
-
+
Now, when you click the register or login button, you will see a page like this:
-
+
> When LoginRadius successfully authenticates a user, it attaches an access token in the query string as a token parameter to the REDIRECT_URL.
@@ -515,7 +515,7 @@ Here we displayed the Provider, Email and NoOfLogins from the `user_data`. These
Now, if you run your development server, and then register and login a user, you should see a page like this:
-
+
To see the entire data present in the `user_data`, you can do something like this in your `profile.html`, file:
diff --git a/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.png b/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.png
deleted file mode 100644
index 7240e7c0a..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.webp b/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.webp
new file mode 100644
index 000000000..1095edb88
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/add-todo-component.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.png b/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.png
deleted file mode 100644
index 7d41537ab..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.webp b/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.webp
new file mode 100644
index 000000000..90fc5d4eb
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/conditionals-example.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/effects-example.png b/content/engineering/guest-post/introduction-to-solidjs/effects-example.png
deleted file mode 100644
index 63b4a90ca..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/effects-example.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/effects-example.webp b/content/engineering/guest-post/introduction-to-solidjs/effects-example.webp
new file mode 100644
index 000000000..636e48b18
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/effects-example.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.png b/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.png
deleted file mode 100644
index d217a1a78..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.webp b/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.webp
new file mode 100644
index 000000000..79406e013
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/features-of-solidjs.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/for-example.png b/content/engineering/guest-post/introduction-to-solidjs/for-example.png
deleted file mode 100644
index 9039bb5e0..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/for-example.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/for-example.webp b/content/engineering/guest-post/introduction-to-solidjs/for-example.webp
new file mode 100644
index 000000000..2c2970750
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/for-example.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.png b/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.png
deleted file mode 100644
index 76c5c0549..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.webp b/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.webp
new file mode 100644
index 000000000..4645e4e42
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/header-and-hello-world.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.png b/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.png
deleted file mode 100644
index b0c05e330..000000000
Binary files a/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.png and /dev/null differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.webp b/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.webp
new file mode 100644
index 000000000..3d1dbeef7
Binary files /dev/null and b/content/engineering/guest-post/introduction-to-solidjs/hello-world-example.webp differ
diff --git a/content/engineering/guest-post/introduction-to-solidjs/index.md b/content/engineering/guest-post/introduction-to-solidjs/index.md
index a6c4f64f1..133a05795 100644
--- a/content/engineering/guest-post/introduction-to-solidjs/index.md
+++ b/content/engineering/guest-post/introduction-to-solidjs/index.md
@@ -1,7 +1,7 @@
---
title: "Introduction to SolidJS"
date: "2022-06-28"
-coverImage: "introduction-to-solidjs.png"
+coverImage: "introduction-to-solidjs.webp"
author: "Siddhant Varma"
tags: ["SolidJS", "React", "Frontend"]
description: "In this tutorial, you’ll learn what SolidJS is, how it works, and its fundamentals such as reactivity, architecture, events, effects, etc. Then you’ll use this knowledge to build a simple todo app. Finally, you’ll understand how SolidJS compares with React and how it’s better and worse."
@@ -13,7 +13,7 @@ So in this tutorial, I'll give you a complete walkthrough of SolidJS and help yo
## What is SolidJS?
-
+
SolidJS takes the syntax and developer experience of React and combines it with the performance of Svelte to give you the best of both worlds.
@@ -48,7 +48,7 @@ render(() => ` will start showing on the DOM:
-
+
### Loops
@@ -274,7 +274,7 @@ render(() =>
 + src="https://ik.imagekit.io/pibjyepn7p9/Lilac_Navy_Simple_Line_Business_Logo_CGktk8RHK.webp?ik-sdk-version=javascript-1.4.3&updatedAt=1649962071315"/>
+ src="https://ik.imagekit.io/pibjyepn7p9/Lilac_Navy_Simple_Line_Business_Logo_CGktk8RHK.webp?ik-sdk-version=javascript-1.4.3&updatedAt=1649962071315"/>
{heading}
@@ -385,7 +385,7 @@ export default function LoginPage(){
Here's what the login page should now look like:
-
+
Let's now start building the rest of the Login page form.
@@ -521,7 +521,7 @@ export default function LoginPage(){
Now, if you go back to your React app, you should see your Login page input fields appear as follows:
-
+
Excellent, it looks like you're almost there!
@@ -657,7 +657,7 @@ export default function Login(){
And once we do that, we should have a stunning, modern looking login page appear right in front of us:
-
+
## The Signup Page
@@ -751,7 +751,7 @@ export default function SignupPage(){
And that's it! That's all there is to build a great looking signup page that looks as follows:
-
+
Don't worry; if you got stuck somewhere, feel free to [refer to the entire codebase for this tutorial here](https://github.com/LoginRadius/engineering-blog-samples/tree/master/React/react-tailwind-app).
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture-hierarchy.png b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture-hierarchy.png
deleted file mode 100644
index fe1571858..000000000
Binary files a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture-hierarchy.png and /dev/null differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture-hierarchy.webp b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture-hierarchy.webp
new file mode 100644
index 000000000..773ac8ad0
Binary files /dev/null and b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture-hierarchy.webp differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture.png b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture.png
deleted file mode 100644
index 7300cafdd..000000000
Binary files a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture.png and /dev/null differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture.webp b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture.webp
new file mode 100644
index 000000000..c0f1480af
Binary files /dev/null and b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-architecture.webp differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-header.jpeg b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-header.jpeg
deleted file mode 100644
index 2c4e712ab..000000000
Binary files a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-header.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-header.webp b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-header.webp
new file mode 100644
index 000000000..f00179616
Binary files /dev/null and b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-header.webp differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-with-input-fields.jpeg b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-with-input-fields.jpeg
deleted file mode 100644
index 3b1f5635f..000000000
Binary files a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-with-input-fields.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-with-input-fields.webp b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-with-input-fields.webp
new file mode 100644
index 000000000..0304805fd
Binary files /dev/null and b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page-with-input-fields.webp differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page.png b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page.png
deleted file mode 100644
index ac1cfbcd5..000000000
Binary files a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page.png and /dev/null differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page.webp b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page.webp
new file mode 100644
index 000000000..f0eaaff42
Binary files /dev/null and b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/login-page.webp differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/modern-login-and-signup-form-banner.png b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/modern-login-and-signup-form-banner.png
deleted file mode 100644
index 01771bcef..000000000
Binary files a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/modern-login-and-signup-form-banner.png and /dev/null differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/modern-login-and-signup-form-banner.webp b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/modern-login-and-signup-form-banner.webp
new file mode 100644
index 000000000..5724d9296
Binary files /dev/null and b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/modern-login-and-signup-form-banner.webp differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/signup-page.png b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/signup-page.png
deleted file mode 100644
index 520391687..000000000
Binary files a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/signup-page.png and /dev/null differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/signup-page.webp b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/signup-page.webp
new file mode 100644
index 000000000..6bc2f21d4
Binary files /dev/null and b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/signup-page.webp differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-config-files.png b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-config-files.png
deleted file mode 100644
index 543f5ffb9..000000000
Binary files a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-config-files.png and /dev/null differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-config-files.webp b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-config-files.webp
new file mode 100644
index 000000000..6ca9bcc61
Binary files /dev/null and b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-config-files.webp differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-pros.png b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-pros.png
deleted file mode 100644
index 9fcb66e58..000000000
Binary files a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-pros.png and /dev/null differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-pros.webp b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-pros.webp
new file mode 100644
index 000000000..ff8030a54
Binary files /dev/null and b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-pros.webp differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-vs-bootstrap-comparison.png b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-vs-bootstrap-comparison.png
deleted file mode 100644
index d3aaca7d3..000000000
Binary files a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-vs-bootstrap-comparison.png and /dev/null differ
diff --git a/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-vs-bootstrap-comparison.webp b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-vs-bootstrap-comparison.webp
new file mode 100644
index 000000000..4f31595d4
Binary files /dev/null and b/content/engineering/guest-post/modern-login-signup-form-tailwindcss-react/tailwind-css-vs-bootstrap-comparison.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/email-test.jpg b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/email-test.jpg
deleted file mode 100644
index f5a7864da..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/email-test.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/email-test.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/email-test.webp
new file mode 100644
index 000000000..417adb5f9
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/email-test.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/express-and-nodemon-install.jpg b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/express-and-nodemon-install.jpg
deleted file mode 100644
index 1d6101ba7..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/express-and-nodemon-install.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/express-and-nodemon-install.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/express-and-nodemon-install.webp
new file mode 100644
index 000000000..c21019749
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/express-and-nodemon-install.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/folder-structure.png b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/folder-structure.png
deleted file mode 100644
index c2877a701..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/folder-structure.png and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/folder-structure.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/folder-structure.webp
new file mode 100644
index 000000000..9c842afd9
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/folder-structure.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/fredrick-free-db.jpg b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/fredrick-free-db.jpg
deleted file mode 100644
index 87ac908ef..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/fredrick-free-db.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/fredrick-free-db.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/fredrick-free-db.webp
new file mode 100644
index 000000000..90b059f93
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/fredrick-free-db.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/gmail.jpg b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/gmail.jpg
deleted file mode 100644
index c0e6d77db..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/gmail.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/gmail.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/gmail.webp
new file mode 100644
index 000000000..78e3ec4dc
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/gmail.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/index.md b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/index.md
index 701f3aba9..c461a6f65 100644
--- a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/index.md
+++ b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/index.md
@@ -1,7 +1,7 @@
---
title: "Multi-Factor Authentication (MFA) with Redis Cache and OTP"
date: "2022-06-30"
-coverImage: "mfa-with-redis-cache-and-otp.png"
+coverImage: "mfa-with-redis-cache-and-otp.webp"
author: "Fredrick Emmanuel"
tags: ["Node.js", "Redis", "Authentication"]
description: "Want to implement Multi-Factor Authentication (MFA)? Follow this tutorial to implement MFA using Redis Cache and OTP in your applications."
@@ -46,7 +46,7 @@ In this section, you will learn how to start an Express server.
The Express dependency will be used to set up the backend server and nodemon, installed as a devDependency, which will watch the file system and restart the server when a change is made.
- 
+ 
3. Create a new file named `server.js` in the project’s directory. For simplicity, this file will contain all the server code for this application.
@@ -88,7 +88,7 @@ In this section, you will learn how to start an Express server.
6. Start the server in development mode by running `npm run dev` in your terminal.
- 
+ 
## Set Up Nodemailer
@@ -152,7 +152,7 @@ After setting up your Outlook account, the next step is to use your Outlook acco
3. To test the application, use an API testing application like [Postman](https://www.postman.com/) and make a POST request to `http://localhost:5000/auth`, passing `email` and `message` to the body of the request.
- 
+ 
## Generate OTPs
@@ -216,11 +216,11 @@ This tutorial uses the `nanoid` module to generate random numbers.
4. Make a POST request to `http://localhost:5000/auth`, passing only the email address.
- 
+ 
5. Check the email address for which the OTP is sent.
- 
+ 
## Redis
@@ -248,17 +248,17 @@ This tutorial uses [Redis Cloud](https://redis.com/) to set up the Redis databas
1. Create a new Redis Cloud account if you don’t have one.
- 
+ 
2. Click on **Let’s start free** and let Redis create a cloud database.
3. Click on **Configurations** and copy your **Public endpoint.** This endpoint will be used to set up the Redis application.
- 
+ 
4. Still on the **Configurations** tab, copy your **Default user password**.
- 
+ 
5. Run `npm i redis` in your terminal. Import the `redis` dependency into `server.js`, and set up the `redisClient` using the **Redis cloud endpoint**.
@@ -293,7 +293,7 @@ This tutorial uses [Redis Cloud](https://redis.com/) to set up the Redis databas
6. Start up the server in your terminal and view the result.
- 
+ 
## Sessions
@@ -473,7 +473,7 @@ It’s time to put the backend code into actual functionality. This tutorial mak
> When the server is rendering an ejs file, it checks in the views folder for the file. So, this name is not optional.
- 
+ 
> Style these various routes as you like
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/mfa-with-redis-cache-and-otp.png b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/mfa-with-redis-cache-and-otp.png
deleted file mode 100644
index de6afa268..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/mfa-with-redis-cache-and-otp.png and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/mfa-with-redis-cache-and-otp.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/mfa-with-redis-cache-and-otp.webp
new file mode 100644
index 000000000..fdc4add43
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/mfa-with-redis-cache-and-otp.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/npm-run-dev.jpg b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/npm-run-dev.jpg
deleted file mode 100644
index c0632331b..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/npm-run-dev.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/npm-run-dev.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/npm-run-dev.webp
new file mode 100644
index 000000000..4b927b1ca
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/npm-run-dev.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/outlook.jpg b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/outlook.jpg
deleted file mode 100644
index 30de6cad1..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/outlook.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/outlook.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/outlook.webp
new file mode 100644
index 000000000..827eb8f34
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/outlook.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/password.jpg b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/password.jpg
deleted file mode 100644
index b150f7583..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/password.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/password.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/password.webp
new file mode 100644
index 000000000..b68584b51
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/password.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/postman.jpg b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/postman.jpg
deleted file mode 100644
index d9929471a..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/postman.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/postman.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/postman.webp
new file mode 100644
index 000000000..85b4033c5
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/postman.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-cloud-sign-in.jpg b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-cloud-sign-in.jpg
deleted file mode 100644
index 118785506..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-cloud-sign-in.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-cloud-sign-in.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-cloud-sign-in.webp
new file mode 100644
index 000000000..b35d889b8
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-cloud-sign-in.webp differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-test.jpg b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-test.jpg
deleted file mode 100644
index 9d0d7f2dc..000000000
Binary files a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-test.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-test.webp b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-test.webp
new file mode 100644
index 000000000..ee5288ad0
Binary files /dev/null and b/content/engineering/guest-post/multi-factor-authentication-using-redis-cache-and-otp/redis-test.webp differ
diff --git a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/coverimage.png b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/coverimage.png
deleted file mode 100644
index fc6f171e3..000000000
Binary files a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/coverimage.png and /dev/null differ
diff --git a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/coverimage.webp b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/coverimage.webp
new file mode 100644
index 000000000..781b547ba
Binary files /dev/null and b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/coverimage.webp differ
diff --git a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/index.md b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/index.md
index 1e45f42e2..55fd6f2d9 100644
--- a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/index.md
+++ b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/index.md
@@ -1,7 +1,7 @@
---
title: "NestJS User Authentication with LoginRadius API"
date: "2022-03-23"
-coverImage: "coverimage.png"
+coverImage: "coverimage.webp"
author: "Mary Gathoni"
tags: ["NestJS", "Node.js", "Authentication"]
description: "Want to authenticate users on your NestJS app? Follow this tutorial to learn how to authenticate users using a password and perform authorization using access tokens."
@@ -433,7 +433,7 @@ POST http://localhost:3000/auth/signup
You should receive a "Sign up successful" message if the request is successful.
-
+
Next, log in the user by sending the login credentials to the login endpoint of your application.
@@ -443,7 +443,7 @@ POST http://localhost:3000/auth/login
If successful, you should receive the access token.
-
+
Finally, use the access token to access the protected route. Add the token to the authorization header.
@@ -451,7 +451,7 @@ Finally, use the access token to access the protected route. Add the token to th
GET http://localhost:3000/auth/protected
```
-
+
## Conclusion
diff --git a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/login-route.png b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/login-route.png
deleted file mode 100644
index 82e6e7828..000000000
Binary files a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/login-route.png and /dev/null differ
diff --git a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/login-route.webp b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/login-route.webp
new file mode 100644
index 000000000..9efcc0af3
Binary files /dev/null and b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/login-route.webp differ
diff --git a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/protected-route.png b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/protected-route.png
deleted file mode 100644
index 9bfb00041..000000000
Binary files a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/protected-route.png and /dev/null differ
diff --git a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/protected-route.webp b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/protected-route.webp
new file mode 100644
index 000000000..a6714b78e
Binary files /dev/null and b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/protected-route.webp differ
diff --git a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/signup-route.png b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/signup-route.png
deleted file mode 100644
index ed0d772e4..000000000
Binary files a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/signup-route.png and /dev/null differ
diff --git a/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/signup-route.webp b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/signup-route.webp
new file mode 100644
index 000000000..e96e55472
Binary files /dev/null and b/content/engineering/guest-post/nestjs-authentication-with-loginradius-api/signup-route.webp differ
diff --git a/content/engineering/guest-post/nextjs-authentication-guide/index.md b/content/engineering/guest-post/nextjs-authentication-guide/index.md
index dbbdbf497..655836231 100644
--- a/content/engineering/guest-post/nextjs-authentication-guide/index.md
+++ b/content/engineering/guest-post/nextjs-authentication-guide/index.md
@@ -1,7 +1,7 @@
---
title: "Your Ultimate Guide to Next.js Authentication"
date: "2022-01-13"
-coverImage: "next-authentication.png"
+coverImage: "next-authentication.webp"
author: "Emadamerho-Atori Nefe"
tags: ["Authentication", "React", "Next.js", "LoginRadius"]
description: "This tutorial describes Next.js authentication patterns and helps you learn step-by-step how to authenticate a Next.js application."
@@ -418,7 +418,7 @@ Here, the code snippet uses the `withAuthenticationRequired` higher-order compon
The image below shows an authenticated user's profile page.
-
+
## Conclusion
diff --git a/content/engineering/guest-post/nextjs-authentication-guide/next-authentication.png b/content/engineering/guest-post/nextjs-authentication-guide/next-authentication.png
deleted file mode 100644
index 1f1be6f35..000000000
Binary files a/content/engineering/guest-post/nextjs-authentication-guide/next-authentication.png and /dev/null differ
diff --git a/content/engineering/guest-post/nextjs-authentication-guide/next-authentication.webp b/content/engineering/guest-post/nextjs-authentication-guide/next-authentication.webp
new file mode 100644
index 000000000..e27cdbd00
Binary files /dev/null and b/content/engineering/guest-post/nextjs-authentication-guide/next-authentication.webp differ
diff --git a/content/engineering/guest-post/nextjs-authentication-guide/profile-page.png b/content/engineering/guest-post/nextjs-authentication-guide/profile-page.png
deleted file mode 100644
index 241fbc0db..000000000
Binary files a/content/engineering/guest-post/nextjs-authentication-guide/profile-page.png and /dev/null differ
diff --git a/content/engineering/guest-post/nextjs-authentication-guide/profile-page.webp b/content/engineering/guest-post/nextjs-authentication-guide/profile-page.webp
new file mode 100644
index 000000000..08d24acba
Binary files /dev/null and b/content/engineering/guest-post/nextjs-authentication-guide/profile-page.webp differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/Hashedregisterroute.jpeg b/content/engineering/guest-post/nodejs-authentication-guide/Hashedregisterroute.jpeg
deleted file mode 100644
index 328ee2e07..000000000
Binary files a/content/engineering/guest-post/nodejs-authentication-guide/Hashedregisterroute.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/Hashedregisterroute.webp b/content/engineering/guest-post/nodejs-authentication-guide/Hashedregisterroute.webp
new file mode 100644
index 000000000..396280844
Binary files /dev/null and b/content/engineering/guest-post/nodejs-authentication-guide/Hashedregisterroute.webp differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/coverimage.jpeg b/content/engineering/guest-post/nodejs-authentication-guide/coverimage.jpeg
deleted file mode 100644
index 5eab6669b..000000000
Binary files a/content/engineering/guest-post/nodejs-authentication-guide/coverimage.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/coverimage.webp b/content/engineering/guest-post/nodejs-authentication-guide/coverimage.webp
new file mode 100644
index 000000000..660dba1e9
Binary files /dev/null and b/content/engineering/guest-post/nodejs-authentication-guide/coverimage.webp differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/crypto.jpeg b/content/engineering/guest-post/nodejs-authentication-guide/crypto.jpeg
deleted file mode 100644
index 216d87909..000000000
Binary files a/content/engineering/guest-post/nodejs-authentication-guide/crypto.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/crypto.webp b/content/engineering/guest-post/nodejs-authentication-guide/crypto.webp
new file mode 100644
index 000000000..e6edebe9a
Binary files /dev/null and b/content/engineering/guest-post/nodejs-authentication-guide/crypto.webp differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/deleteroute.jpeg b/content/engineering/guest-post/nodejs-authentication-guide/deleteroute.jpeg
deleted file mode 100644
index 7b6ec3d9a..000000000
Binary files a/content/engineering/guest-post/nodejs-authentication-guide/deleteroute.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/deleteroute.webp b/content/engineering/guest-post/nodejs-authentication-guide/deleteroute.webp
new file mode 100644
index 000000000..b1b7e8852
Binary files /dev/null and b/content/engineering/guest-post/nodejs-authentication-guide/deleteroute.webp differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/hashedloginroute.jpeg b/content/engineering/guest-post/nodejs-authentication-guide/hashedloginroute.jpeg
deleted file mode 100644
index 3e48447e2..000000000
Binary files a/content/engineering/guest-post/nodejs-authentication-guide/hashedloginroute.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/hashedloginroute.webp b/content/engineering/guest-post/nodejs-authentication-guide/hashedloginroute.webp
new file mode 100644
index 000000000..4a7fa0084
Binary files /dev/null and b/content/engineering/guest-post/nodejs-authentication-guide/hashedloginroute.webp differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/index.md b/content/engineering/guest-post/nodejs-authentication-guide/index.md
index 3d145c10c..ae0b7408b 100644
--- a/content/engineering/guest-post/nodejs-authentication-guide/index.md
+++ b/content/engineering/guest-post/nodejs-authentication-guide/index.md
@@ -1,7 +1,7 @@
---
title: "Node.js User Authentication Guide"
date: "2022-01-18"
-coverImage: "coverimage.jpeg"
+coverImage: "coverimage.webp"
author: "Uma Victor"
tags: ["JWT", "Authentication", "Node.js"]
description: "Want to authenticate and manage users with specific roles in your Node.js app? This in-depth tutorial explains everything step-by-step to help you implement authentication in your Node.js apps."
@@ -261,7 +261,7 @@ You'll use [Postman](https://www.postman.com/downloads/) to test all the routes.
Open up Postman to send a `POST` request to `http://localhost:5000/api/auth/register` and pass the username and password to the body:
-
+
### Login Function
@@ -327,7 +327,7 @@ module.exports = router;
Make a `POST` request at `http://localhost:5000/api/auth/login` and pass a valid username and password to the body:
-
+
### Update Function
@@ -413,7 +413,7 @@ router.route("/update").put(update);
Send a `put` request to `http://localhost:5000/api/auth/update`:
-
+
### Delete Function
@@ -451,7 +451,7 @@ router.route("/deleteUser").delete(deleteUser);
Send a `delete` request to `http://localhost:5000/api/auth/deleteUser` by passing a valid `id` to the body:
-
+
## Hash User Passwords
@@ -512,7 +512,7 @@ exports.register = async (req, res, next) => {
Send a `POST` request to `http://localhost:5000/api/auth/register` and pass the username and password to the body:
-
+
### Refactor the Login Function
@@ -558,7 +558,7 @@ exports.login = async (req, res, next) => {
Send a `POST` request to `http://localhost:5000/api/auth/login` and pass a valid username and password to the body:
-
+
## Authenticate Users with JSON Web Token (JWT)
@@ -583,7 +583,7 @@ require("crypto").randomBytes(35).toString("hex")
Output:
-
+
Storing this secret string in an environment variable is a safe practice. If this secret string is leaked, unauthenticated users can create fake tokens to access the route.
@@ -818,7 +818,7 @@ password
After you've created the constant `password`, you need to enter `the` `password` in the node terminal to get your hashed password.
-
+
You'll use the hashed password to create your admin:
@@ -1242,11 +1242,11 @@ This section briefly covers how authentication works with LoginRadius.
After signing up for LoginRadius, choose a name for your Node.js app.
-> 
+> 
After completing your LoginRadius signup process, you can get your **App Name**, **API Key**, and **API Secret** from the `configuration` link on the sidebar. With these configurations, you can easily link the server-side of our application to LoginRadius.
-
+
LoginRadius automatically generates a link that will be used to authenticate users. This link contains the name of your LoginRadius application and a `URL` that authenticated users will be redirected to:
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/loginradius.png b/content/engineering/guest-post/nodejs-authentication-guide/loginradius.png
deleted file mode 100644
index 996387ba2..000000000
Binary files a/content/engineering/guest-post/nodejs-authentication-guide/loginradius.png and /dev/null differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/loginradius.webp b/content/engineering/guest-post/nodejs-authentication-guide/loginradius.webp
new file mode 100644
index 000000000..20b9e5e95
Binary files /dev/null and b/content/engineering/guest-post/nodejs-authentication-guide/loginradius.webp differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/loginradius1.png b/content/engineering/guest-post/nodejs-authentication-guide/loginradius1.png
deleted file mode 100644
index bc9b6a627..000000000
Binary files a/content/engineering/guest-post/nodejs-authentication-guide/loginradius1.png and /dev/null differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/loginradius1.webp b/content/engineering/guest-post/nodejs-authentication-guide/loginradius1.webp
new file mode 100644
index 000000000..dd61c128d
Binary files /dev/null and b/content/engineering/guest-post/nodejs-authentication-guide/loginradius1.webp differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/loginroute.jpeg b/content/engineering/guest-post/nodejs-authentication-guide/loginroute.jpeg
deleted file mode 100644
index a282a7385..000000000
Binary files a/content/engineering/guest-post/nodejs-authentication-guide/loginroute.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/loginroute.webp b/content/engineering/guest-post/nodejs-authentication-guide/loginroute.webp
new file mode 100644
index 000000000..23c1c5759
Binary files /dev/null and b/content/engineering/guest-post/nodejs-authentication-guide/loginroute.webp differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/nodebycrypt.jpeg b/content/engineering/guest-post/nodejs-authentication-guide/nodebycrypt.jpeg
deleted file mode 100644
index b2e3db56d..000000000
Binary files a/content/engineering/guest-post/nodejs-authentication-guide/nodebycrypt.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/nodebycrypt.webp b/content/engineering/guest-post/nodejs-authentication-guide/nodebycrypt.webp
new file mode 100644
index 000000000..b4dcd6e9e
Binary files /dev/null and b/content/engineering/guest-post/nodejs-authentication-guide/nodebycrypt.webp differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/registerRoute.jpeg b/content/engineering/guest-post/nodejs-authentication-guide/registerRoute.jpeg
deleted file mode 100644
index 328ee2e07..000000000
Binary files a/content/engineering/guest-post/nodejs-authentication-guide/registerRoute.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/registerRoute.webp b/content/engineering/guest-post/nodejs-authentication-guide/registerRoute.webp
new file mode 100644
index 000000000..396280844
Binary files /dev/null and b/content/engineering/guest-post/nodejs-authentication-guide/registerRoute.webp differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/updateroute.jpeg b/content/engineering/guest-post/nodejs-authentication-guide/updateroute.jpeg
deleted file mode 100644
index ff14b6340..000000000
Binary files a/content/engineering/guest-post/nodejs-authentication-guide/updateroute.jpeg and /dev/null differ
diff --git a/content/engineering/guest-post/nodejs-authentication-guide/updateroute.webp b/content/engineering/guest-post/nodejs-authentication-guide/updateroute.webp
new file mode 100644
index 000000000..b983d89e5
Binary files /dev/null and b/content/engineering/guest-post/nodejs-authentication-guide/updateroute.webp differ
diff --git a/content/engineering/guest-post/opencv-web-app-with-streamlit/coverimage.png b/content/engineering/guest-post/opencv-web-app-with-streamlit/coverimage.png
deleted file mode 100644
index 2414dcbdc..000000000
Binary files a/content/engineering/guest-post/opencv-web-app-with-streamlit/coverimage.png and /dev/null differ
diff --git a/content/engineering/guest-post/opencv-web-app-with-streamlit/coverimage.webp b/content/engineering/guest-post/opencv-web-app-with-streamlit/coverimage.webp
new file mode 100644
index 000000000..773006620
Binary files /dev/null and b/content/engineering/guest-post/opencv-web-app-with-streamlit/coverimage.webp differ
diff --git a/content/engineering/guest-post/opencv-web-app-with-streamlit/index.md b/content/engineering/guest-post/opencv-web-app-with-streamlit/index.md
index 649733046..1e9b278ef 100644
--- a/content/engineering/guest-post/opencv-web-app-with-streamlit/index.md
+++ b/content/engineering/guest-post/opencv-web-app-with-streamlit/index.md
@@ -1,7 +1,7 @@
---
title: "How to Build an OpenCV Web App with Streamlit"
date: "2021-11-10"
-coverImage: "coverimage.png"
+coverImage: "coverimage.webp"
author: "Dingu Sagar"
tags: ["OpenCV", "Streamlit", "Python"]
description: "You can now easily publish your OpenCV apps to the web using Streamlit, a Python library. Follow this tutorial to learn the process step by step."
@@ -42,7 +42,7 @@ def enhance_details(img):
hdr = cv2.detailEnhance(img, sigma_s=12, sigma_r=0.15)
return hdr
-img = cv2.imread(filename='tony_stark.jpg')
+img = cv2.imread(filename='tony_stark.webp')
# do some cool image processing stuff
img = enhance_details(img)
@@ -102,7 +102,7 @@ You should get a similar output as follows.
```
Click on the links in the output to open the Streamlit app in your browser. You'll see something as follows.
-
+
If you see the code, it's very straightforward. It imports streamlit as st. The default is a simple linear layout where you can place components on the webpage in a sequential manner.
@@ -209,7 +209,7 @@ streamlit run demo-app.py
```
Now you can play with the filters. Of course, these are some basic filters, but you can extend it to more interesting filters — like cartoonify filters, etc. — using the rich features of OpenCV.
-
+
## How to Publish Your App?
diff --git a/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-1.png b/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-1.png
deleted file mode 100644
index f29192906..000000000
Binary files a/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-1.png and /dev/null differ
diff --git a/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-1.webp b/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-1.webp
new file mode 100644
index 000000000..e8a2aea17
Binary files /dev/null and b/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-1.webp differ
diff --git a/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-final.png b/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-final.png
deleted file mode 100644
index f5bca59cf..000000000
Binary files a/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-final.png and /dev/null differ
diff --git a/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-final.webp b/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-final.webp
new file mode 100644
index 000000000..7246a7c75
Binary files /dev/null and b/content/engineering/guest-post/opencv-web-app-with-streamlit/streamlit-final.webp differ
diff --git a/content/engineering/guest-post/react-best-coding-practices/Best-Practices.png b/content/engineering/guest-post/react-best-coding-practices/Best-Practices.png
deleted file mode 100644
index 57d66e400..000000000
Binary files a/content/engineering/guest-post/react-best-coding-practices/Best-Practices.png and /dev/null differ
diff --git a/content/engineering/guest-post/react-best-coding-practices/Best-Practices.webp b/content/engineering/guest-post/react-best-coding-practices/Best-Practices.webp
new file mode 100644
index 000000000..586a7d335
Binary files /dev/null and b/content/engineering/guest-post/react-best-coding-practices/Best-Practices.webp differ
diff --git a/content/engineering/guest-post/react-best-coding-practices/index.md b/content/engineering/guest-post/react-best-coding-practices/index.md
index 096325c8a..3a8d61cb1 100644
--- a/content/engineering/guest-post/react-best-coding-practices/index.md
+++ b/content/engineering/guest-post/react-best-coding-practices/index.md
@@ -1,7 +1,7 @@
---
title: "32 React Best Practices That Every Programmer Should Follow"
date: "2021-10-26"
-coverImage: "Best-Practices.png"
+coverImage: "Best-Practices.webp"
author: "Anjali Rohira"
tags: ["React"]
description: "Important React best practices every React developer should follow before, during, & after writing the code. To ensure code maintainability, keep these React coding best practices handy."
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Adding admin role.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Adding admin role.png
deleted file mode 100644
index eb8008e07..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Adding admin role.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Adding admin role.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Adding admin role.webp
new file mode 100644
index 000000000..b6a761c23
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Adding admin role.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/All roles and permissions.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/All roles and permissions.png
deleted file mode 100644
index a3ab8b7fe..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/All roles and permissions.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/All roles and permissions.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/All roles and permissions.webp
new file mode 100644
index 000000000..a29533347
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/All roles and permissions.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Auth page preview.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Auth page preview.png
deleted file mode 100644
index c2b7bd34f..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Auth page preview.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Auth page preview.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Auth page preview.webp
new file mode 100644
index 000000000..0fed0584e
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/Auth page preview.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/User roles.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/User roles.png
deleted file mode 100644
index c31ef04b0..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/User roles.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/User roles.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/User roles.webp
new file mode 100644
index 000000000..70b7950da
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/User roles.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/access-token.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/access-token.png
deleted file mode 100644
index 1d7078fd2..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/access-token.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/access-token.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/access-token.webp
new file mode 100644
index 000000000..75f8a7953
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/access-token.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/application-home.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/application-home.png
deleted file mode 100644
index 8f4369b4d..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/application-home.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/application-home.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/application-home.webp
new file mode 100644
index 000000000..7bf990d8e
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/application-home.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/client role result.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/client role result.png
deleted file mode 100644
index eede4242c..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/client role result.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/client role result.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/client role result.webp
new file mode 100644
index 000000000..47d5b9ae0
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/client role result.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/coverImage.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/coverImage.png
deleted file mode 100644
index bf680d284..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/coverImage.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/coverImage.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/coverImage.webp
new file mode 100644
index 000000000..eeda5ed4a
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/coverImage.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/general role.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/general role.png
deleted file mode 100644
index 246ba2caf..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/general role.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/general role.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/general role.webp
new file mode 100644
index 000000000..611d5edba
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/general role.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/index.md b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/index.md
index 4e7bb5814..4b523f96d 100644
--- a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/index.md
+++ b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/index.md
@@ -1,7 +1,7 @@
---
title: "How to Implement Role-Based Authentication with React Apps"
date: "2021-09-03"
-coverImage: "coverImage.png"
+coverImage: "coverImage.webp"
author: "Victory Tuduo"
tags: ["Authentication", "React", "User Roles"]
description: "This tutorial illustrates how to perform user authentication and assign roles to users in React apps using LoginRadius."
@@ -37,12 +37,12 @@ First, you need to [create a LoginRadius account](https://accounts.loginradius.c
You'll get a page requesting you to create a new application. Click on "create a new application". After which, a page comes up where you should enter the name of your app and the URL to your app. Here, Input any name and URL of your choice.
-
+
### Auth Page (IDX)
LoginRadius allows you to create a custom login page (an auth page that you can customize from the dashboard), which you can then preview. This is a page provided by LoginRadius that you can easily customize to contain different form contents. Features like user log in, signup, email, and password have been pre-implemented on this page. You'll be using this page for registration and authentication with react application. To learn more on how to customize this page to contain more form contents, refer to [customizing Auth Page.](https://www.loginradius.com/developers/)
-
+
To be able to use user roles within your app, you first have to set up these roles and their respective privileges from the dashboard. In this tutorial, you'll set up two roles, namely Admin and Client.
@@ -52,7 +52,7 @@ Click on "manage roles" and click on "add roles". A popup opens in which you add
This tutorial has added a "client" role with a permission called "view" and an "admin" role with permissions: "view, edit, delete". Enable "set as default" for the client role to automatically assign the client role to any user in our app by default.
-
+
## Integrate LoginRadius into React
### Creating a React Application
@@ -287,13 +287,13 @@ npm start
When it successfully starts the server, you would have a similar page as follows:
-
+
This is the landing page you've built in the `Auth` component and is your `/` path in your routes within `App.js`. If you click on the "login/register" button, you'll be redirected to your custom Auth Page (IDX) provided by LoginRadius, where you can create a user account and login. You can manage the users who have accounts from your dashboard in "manage users".
After logging in auth react js, with your user, you'll get redirected to the /login route that then runs the CallAPI component and gives you a result similar to the following:
-
+
This is the current role of the user. Any user would have the role of client assigned since you've set to assign the client role by default to all our users from your dashboard during the creation of roles.
@@ -373,18 +373,18 @@ export default App;
You then need to run the code by starting the server using the `npm start` command. Upon starting the server, when you log in, you'll have your user token displayed on the screen. Your output will be similar to the following:
-
+
Here, you can see the access token and its details. You can then return your code to the previous `CallAPI` component imported from `Return.js`.
### User Data
You can view and manage user accounts from the dashboard. You can find the panel for this under "User management":
-
+
Manage users:
-
+
Here, you can view the account information of your users, search for a particular user details using the email, Uid, or phone number as the query in the search box. Also, the panel provides an option to reset the password of a user, block users, and delete users as the above image shows. You can create new users by clicking on the "add user" button and filling in the details of the new user.
@@ -393,7 +393,7 @@ To view all roles and permissions for your app, change the URL in the fetch requ
Reload your page, and you'll have an output similar as follows:
-
+
## Adding a Role to the Current User
To add the Admin role to the current user, create objects for this by adding the following code within the parenthesis after your fetch URL:
@@ -410,7 +410,7 @@ method: "PUT",
This adds the Admin role to the current logged-in user since it is the `Uid` that is within our URL. `fetch` uses a GET request by default. Since you're making a change to the URL, you're using a PUT method instead. You'll get a result similar to as follows:
-
+
The user has both client and admin roles because you've added client roles by default to all our users.
@@ -495,7 +495,7 @@ In the code above, you've created a const email that returned an array containin
The `async` request block has now been modified to check if the user email being used for logging in is equivalent to a particular email which you've declared. Alternatively, you can have your emails pulled from a database and assign the admin roles to the ones you want. The else block assigns a client role to emails that do not meet the first criteria. When you create a new account with an email similar to what I have in the `if block`, that is admin@example.com; when rerouted to the `/login` path, you'll discover that the role of admin was assigned while any other email will have the client role assigned upon login. The return statement returns the user id of the logged-in user, the email, and then the role in a JSON format. The output would be similar to the following:
-
+
## Conclusion
This tutorial covered:
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/landing page preview.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/landing page preview.png
deleted file mode 100644
index a98d9a9fa..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/landing page preview.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/landing page preview.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/landing page preview.webp
new file mode 100644
index 000000000..015718b83
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/landing page preview.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/manage users.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/manage users.png
deleted file mode 100644
index 287e783db..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/manage users.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/manage users.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/manage users.webp
new file mode 100644
index 000000000..878eea627
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/manage users.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/naming your app.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/naming your app.png
deleted file mode 100644
index 1e57da4fd..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/naming your app.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/naming your app.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/naming your app.webp
new file mode 100644
index 000000000..20b9e5e95
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/naming your app.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/output.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/output.png
deleted file mode 100644
index ea28fdf7f..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/output.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/output.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/output.webp
new file mode 100644
index 000000000..358326085
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/output.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/roles-client-admin.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/roles-client-admin.png
deleted file mode 100644
index 15d88561c..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/roles-client-admin.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/roles-client-admin.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/roles-client-admin.webp
new file mode 100644
index 000000000..bc168bb4b
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/roles-client-admin.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user management.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user management.png
deleted file mode 100644
index 81d292ce1..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user management.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user management.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user management.webp
new file mode 100644
index 000000000..d56e20b49
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user management.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user token.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user token.png
deleted file mode 100644
index f7fb458dc..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user token.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user token.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user token.webp
new file mode 100644
index 000000000..ca53895df
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user token.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles-permissions.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles-permissions.png
deleted file mode 100644
index c408e0064..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles-permissions.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles-permissions.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles-permissions.webp
new file mode 100644
index 000000000..4bc0d5bcd
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles-permissions.webp differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles.png b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles.png
deleted file mode 100644
index 3992f486a..000000000
Binary files a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles.png and /dev/null differ
diff --git a/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles.webp b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles.webp
new file mode 100644
index 000000000..7f4a957fc
Binary files /dev/null and b/content/engineering/guest-post/role-based-user-authentication-with-loginradius-and-reactjs/user-roles.webp differ
diff --git a/content/engineering/guest-post/securing-flask-api-with-jwt/coverImage.png b/content/engineering/guest-post/securing-flask-api-with-jwt/coverImage.png
deleted file mode 100644
index eed4757bb..000000000
Binary files a/content/engineering/guest-post/securing-flask-api-with-jwt/coverImage.png and /dev/null differ
diff --git a/content/engineering/guest-post/securing-flask-api-with-jwt/coverImage.webp b/content/engineering/guest-post/securing-flask-api-with-jwt/coverImage.webp
new file mode 100644
index 000000000..165e5b3a3
Binary files /dev/null and b/content/engineering/guest-post/securing-flask-api-with-jwt/coverImage.webp differ
diff --git a/content/engineering/guest-post/securing-flask-api-with-jwt/index.md b/content/engineering/guest-post/securing-flask-api-with-jwt/index.md
index 2352bad81..1ecf3b35c 100644
--- a/content/engineering/guest-post/securing-flask-api-with-jwt/index.md
+++ b/content/engineering/guest-post/securing-flask-api-with-jwt/index.md
@@ -1,7 +1,7 @@
---
title: "Using JWT Flask JWT Authentication- A Quick Guide"
date: "2021-12-09"
-coverImage: "coverImage.png"
+coverImage: "coverImage.webp"
author: "Babatunde Koiki"
tags: ["Flask", "JWT", "API"]
description: "This tutorial helps you build a simple Flask API and demonstrates how to secure it using JWT. In the end, you can test your API authentication using a sample schema."
diff --git a/content/engineering/guest-post/securing-php-api-with-jwt/index.md b/content/engineering/guest-post/securing-php-api-with-jwt/index.md
index c91cdf218..51d612b71 100644
--- a/content/engineering/guest-post/securing-php-api-with-jwt/index.md
+++ b/content/engineering/guest-post/securing-php-api-with-jwt/index.md
@@ -1,7 +1,7 @@
---
title: "How to Secure a PHP API Using JWT"
date: "2021-12-24"
-coverImage: "jwt.png"
+coverImage: "jwt.webp"
author: "Harikrishna Kundariya"
tags: ["PHP", "JWT", "Authentication"]
description: "This tutorial helps you understand why you should secure your PHP API. Then, it helps you learn how to use JWT with Apache to secure your PHP API."
diff --git a/content/engineering/guest-post/securing-php-api-with-jwt/jwt.png b/content/engineering/guest-post/securing-php-api-with-jwt/jwt.png
deleted file mode 100644
index c819f4457..000000000
Binary files a/content/engineering/guest-post/securing-php-api-with-jwt/jwt.png and /dev/null differ
diff --git a/content/engineering/guest-post/securing-php-api-with-jwt/jwt.webp b/content/engineering/guest-post/securing-php-api-with-jwt/jwt.webp
new file mode 100644
index 000000000..cb729b3ef
Binary files /dev/null and b/content/engineering/guest-post/securing-php-api-with-jwt/jwt.webp differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/Hv_Nxk_A.png b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/Hv_Nxk_A.png
deleted file mode 100644
index 11aae2ece..000000000
Binary files a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/Hv_Nxk_A.png and /dev/null differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/Hv_Nxk_A.webp b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/Hv_Nxk_A.webp
new file mode 100644
index 000000000..ff2ba44d1
Binary files /dev/null and b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/Hv_Nxk_A.webp differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/UZCy1IHQ.png b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/UZCy1IHQ.png
deleted file mode 100644
index 8f9c7c4bd..000000000
Binary files a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/UZCy1IHQ.png and /dev/null differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/UZCy1IHQ.webp b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/UZCy1IHQ.webp
new file mode 100644
index 000000000..3905c07d1
Binary files /dev/null and b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/UZCy1IHQ.webp differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/hDnzpIVA.png b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/hDnzpIVA.png
deleted file mode 100644
index 4bc2085cf..000000000
Binary files a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/hDnzpIVA.png and /dev/null differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/hDnzpIVA.webp b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/hDnzpIVA.webp
new file mode 100644
index 000000000..fe75b4196
Binary files /dev/null and b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/hDnzpIVA.webp differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/index.md b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/index.md
index bc2371a5e..934997d3a 100644
--- a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/index.md
+++ b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/index.md
@@ -1,7 +1,7 @@
---
title: "NestJS: How to Implement Session-Based User Authentication"
date: "2022-04-26"
-coverImage: "session-based-authentication-in-nestjs.png"
+coverImage: "session-based-authentication-in-nestjs.webp"
author: "Ekekenta Odionyenfe Clinton"
tags: ["Authentication", "NestJS", "MongoDB", "Node.js"]
description: "Want to implement user authentication for your NestJS apps? Follow this tutorial to learn how you can implement session-based authentication for your NestJS apps along with MongoDB."
@@ -65,11 +65,11 @@ nest new session-based-auth
The above command creates a Nest application with some boilerplates, then prompts you to choose your preferred package manager to install the required modules to run your application. For demonstration, this tutorial uses **npm**. Hit the enter key to continue with **npm**.
-
+
If everything went well, you should see an output like the one on the screenshot below on your terminal.
-
+
Once the installation is complete, move into your project directory, and run the application with the command below:
@@ -966,23 +966,23 @@ Head over to your Postman. And let’s finally test our application.
### Sign Up As a User
-
+
### Log In As a User
-
+
### Logged-in User’s Cookie ID
-
+
### Request the Protected Route
-
+
### User Logout
-
+
## Alternatively, Implement User Authentication with LoginRadius
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/j38BmlHQ.png b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/j38BmlHQ.png
deleted file mode 100644
index 9b6a9f43b..000000000
Binary files a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/j38BmlHQ.png and /dev/null differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/j38BmlHQ.webp b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/j38BmlHQ.webp
new file mode 100644
index 000000000..f6d23963a
Binary files /dev/null and b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/j38BmlHQ.webp differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/kkX-6pFQ.png b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/kkX-6pFQ.png
deleted file mode 100644
index 175986074..000000000
Binary files a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/kkX-6pFQ.png and /dev/null differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/kkX-6pFQ.webp b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/kkX-6pFQ.webp
new file mode 100644
index 000000000..80b1de317
Binary files /dev/null and b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/kkX-6pFQ.webp differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/mPo9j3Kg.png b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/mPo9j3Kg.png
deleted file mode 100644
index 3573f409b..000000000
Binary files a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/mPo9j3Kg.png and /dev/null differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/mPo9j3Kg.webp b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/mPo9j3Kg.webp
new file mode 100644
index 000000000..472a7c728
Binary files /dev/null and b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/mPo9j3Kg.webp differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/p0GhcMPw.png b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/p0GhcMPw.png
deleted file mode 100644
index 6230a8d54..000000000
Binary files a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/p0GhcMPw.png and /dev/null differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/p0GhcMPw.webp b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/p0GhcMPw.webp
new file mode 100644
index 000000000..dd63c8d6c
Binary files /dev/null and b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/p0GhcMPw.webp differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/session-based-authentication-in-nestjs.png b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/session-based-authentication-in-nestjs.png
deleted file mode 100644
index 93ca3e83b..000000000
Binary files a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/session-based-authentication-in-nestjs.png and /dev/null differ
diff --git a/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/session-based-authentication-in-nestjs.webp b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/session-based-authentication-in-nestjs.webp
new file mode 100644
index 000000000..e9d39e928
Binary files /dev/null and b/content/engineering/guest-post/session-authentication-with-nestjs-and-mongodb/session-based-authentication-in-nestjs.webp differ
diff --git a/content/engineering/guest-post/tips-for-managing-remote-software-engineering-teams/cover.jpg b/content/engineering/guest-post/tips-for-managing-remote-software-engineering-teams/cover.jpg
deleted file mode 100644
index 5f8bae303..000000000
Binary files a/content/engineering/guest-post/tips-for-managing-remote-software-engineering-teams/cover.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/tips-for-managing-remote-software-engineering-teams/cover.webp b/content/engineering/guest-post/tips-for-managing-remote-software-engineering-teams/cover.webp
new file mode 100644
index 000000000..70109c2f8
Binary files /dev/null and b/content/engineering/guest-post/tips-for-managing-remote-software-engineering-teams/cover.webp differ
diff --git a/content/engineering/guest-post/tips-for-managing-remote-software-engineering-teams/index.md b/content/engineering/guest-post/tips-for-managing-remote-software-engineering-teams/index.md
index 9a80ad8a8..07f7cb32a 100644
--- a/content/engineering/guest-post/tips-for-managing-remote-software-engineering-teams/index.md
+++ b/content/engineering/guest-post/tips-for-managing-remote-software-engineering-teams/index.md
@@ -1,7 +1,7 @@
---
title: "11 Tips for Managing Remote Software Engineering Teams"
date: "2021-07-26"
-coverImage: "cover.jpg"
+coverImage: "cover.webp"
author: "Erkki Muuga"
tags: ["Remote Work", "Developer", "Software Engineering"]
description: "This article will give you 11 tips for managing remote software engineering teams, so you can adjust and improve your hiring, communication, and your team's collective output."
diff --git a/content/engineering/guest-post/user-authentication-in-python/1zsvbg3rk013zlbpxx2u.png b/content/engineering/guest-post/user-authentication-in-python/1zsvbg3rk013zlbpxx2u.png
deleted file mode 100644
index c09e7a348..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/1zsvbg3rk013zlbpxx2u.png and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/1zsvbg3rk013zlbpxx2u.webp b/content/engineering/guest-post/user-authentication-in-python/1zsvbg3rk013zlbpxx2u.webp
new file mode 100644
index 000000000..b3e040549
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/1zsvbg3rk013zlbpxx2u.webp differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/5ng50vbosmuhdhfuz-gi.png b/content/engineering/guest-post/user-authentication-in-python/5ng50vbosmuhdhfuz-gi.png
deleted file mode 100644
index e2c098735..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/5ng50vbosmuhdhfuz-gi.png and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/5ng50vbosmuhdhfuz-gi.webp b/content/engineering/guest-post/user-authentication-in-python/5ng50vbosmuhdhfuz-gi.webp
new file mode 100644
index 000000000..cf87d6d88
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/5ng50vbosmuhdhfuz-gi.webp differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/7gs3xz6qhxhas7qgtjma.png b/content/engineering/guest-post/user-authentication-in-python/7gs3xz6qhxhas7qgtjma.png
deleted file mode 100644
index 14427ea22..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/7gs3xz6qhxhas7qgtjma.png and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/7gs3xz6qhxhas7qgtjma.webp b/content/engineering/guest-post/user-authentication-in-python/7gs3xz6qhxhas7qgtjma.webp
new file mode 100644
index 000000000..f8808290b
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/7gs3xz6qhxhas7qgtjma.webp differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/7lev6yc_ebtxcg62wrbe.png b/content/engineering/guest-post/user-authentication-in-python/7lev6yc_ebtxcg62wrbe.png
deleted file mode 100644
index ef5b42ad4..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/7lev6yc_ebtxcg62wrbe.png and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/7lev6yc_ebtxcg62wrbe.webp b/content/engineering/guest-post/user-authentication-in-python/7lev6yc_ebtxcg62wrbe.webp
new file mode 100644
index 000000000..543d09d8c
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/7lev6yc_ebtxcg62wrbe.webp differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/coverImage.jpg b/content/engineering/guest-post/user-authentication-in-python/coverImage.jpg
deleted file mode 100644
index 1593a26e3..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/coverImage.jpg and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/coverImage.webp b/content/engineering/guest-post/user-authentication-in-python/coverImage.webp
new file mode 100644
index 000000000..f33d51660
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/coverImage.webp differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/f2p7ddnwin3yihucx2em.png b/content/engineering/guest-post/user-authentication-in-python/f2p7ddnwin3yihucx2em.png
deleted file mode 100644
index 717476412..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/f2p7ddnwin3yihucx2em.png and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/f2p7ddnwin3yihucx2em.webp b/content/engineering/guest-post/user-authentication-in-python/f2p7ddnwin3yihucx2em.webp
new file mode 100644
index 000000000..3ee5a2c1d
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/f2p7ddnwin3yihucx2em.webp differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/i_alrgdnugpmtschkuuj.png b/content/engineering/guest-post/user-authentication-in-python/i_alrgdnugpmtschkuuj.png
deleted file mode 100644
index f9dc007a0..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/i_alrgdnugpmtschkuuj.png and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/i_alrgdnugpmtschkuuj.webp b/content/engineering/guest-post/user-authentication-in-python/i_alrgdnugpmtschkuuj.webp
new file mode 100644
index 000000000..e7f5aad01
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/i_alrgdnugpmtschkuuj.webp differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/index.md b/content/engineering/guest-post/user-authentication-in-python/index.md
index 1c9a10dc2..6be7a764a 100644
--- a/content/engineering/guest-post/user-authentication-in-python/index.md
+++ b/content/engineering/guest-post/user-authentication-in-python/index.md
@@ -1,7 +1,7 @@
---
title: Implementing User Authentication in a Python Application
date: "2021-07-07"
-coverImage: "coverImage.jpg"
+coverImage: "coverImage.webp"
author: "Solomon Esenyi"
description: "Learn about user authentication, user identity management, and implementing it correctly into a Python application using LoginRadius."
tags: ["Python", "Authentication", "Flask"]
@@ -60,21 +60,21 @@ To proceed with this tutorial, you will need an account with LoginRadius. If you
Login to your [LoginRadius dashboard](https://accounts.loginradius.com/auth.aspx?return_url=https://dashboard.loginradius.com/login), then navigate to the app you want to integrate with Python (LoginRadius will set up a free app for you when you create an account).
-
+
Next, head over to the `Configuration` tab on the LoginRadius sidebar (left side of the screen).
-
+
Your API credentials are located under the `API Key And Secret` section. Once you have retrieved this, copy the `APP Name`, `API Key`, and `API Secret` and store them somewhere secure and easily retrievable.
-
+
### Whitelisting Your Domains
LoginRadius requires you to whitelist domains you will be integrating with your app. To whitelist, a domain, scroll down to the `Whitelist Your Domain` section in the `Configuration` tab of your app dashboard and add it.
-
+
> By default, LoginRadius whitelists your local computer (localhost).
@@ -116,7 +116,7 @@ if __name__ == "__main__":
When you run the `server.py` script and open your browser, you will get a response similar to the image below:
-
+
### Initializing the LoginRadius SDK
@@ -157,7 +157,7 @@ def register():
In the code above, we created a `register` route that redirects users to our LoginRadius registration IDX. We also set our `AUTH_ACTION` to “register” and our `RETURN_URL` to our application home page.
-
+
> NOTE: Don’t forget to replace the placeholder with your LoginRadius app name we saved earlier.
@@ -182,9 +182,9 @@ def login():
In the code above, we redirect users to our LoginRadius login IDX if the `token` parameter is absent (this means LoginRadius did not redirect the user here). We also set our `AUTH_ACTION` to “login” and our `RETURN_URL` to our login page.
-
+
-
+
## Fetching User Profiles From Access Tokens
@@ -220,7 +220,7 @@ def dashboard():
In the code above, we used the `authentication.get_profile_by_access_token` method from the LoginRadius SDK to fetch our user’s details. If the request was successful and the result does not contain an `ErrorCode` parameter, we save the access token in the user’s session and redirect them to the `dashboard` route. But if an error occurs somewhere, e.g., the access token is invalid/expired, we redirect the user back to the `login` route.
-
+
Next, we want to add more functionality to the `dashboard` route. Instead of just displaying a dummy text, let it show the user information we fetched earlier. Update the `dashboard` route with the code below:
@@ -244,7 +244,7 @@ def dashboard():
Here, we fetched the access token stored in the user’s session earlier, used it to get their details, and rendered the result.
-
+
### Invalidating Access Tokens (User Logout)
@@ -266,7 +266,7 @@ def logout():
return "You have successfully logged out!"
```
-
+
## Conclusion
diff --git a/content/engineering/guest-post/user-authentication-in-python/pw6s1mqnn-yrtard7nbx.png b/content/engineering/guest-post/user-authentication-in-python/pw6s1mqnn-yrtard7nbx.png
deleted file mode 100644
index c1877e0fa..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/pw6s1mqnn-yrtard7nbx.png and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/pw6s1mqnn-yrtard7nbx.webp b/content/engineering/guest-post/user-authentication-in-python/pw6s1mqnn-yrtard7nbx.webp
new file mode 100644
index 000000000..2c969eb0f
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/pw6s1mqnn-yrtard7nbx.webp differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/smn-8jr5ahgmhtynezje.png b/content/engineering/guest-post/user-authentication-in-python/smn-8jr5ahgmhtynezje.png
deleted file mode 100644
index e60f2f850..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/smn-8jr5ahgmhtynezje.png and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/smn-8jr5ahgmhtynezje.webp b/content/engineering/guest-post/user-authentication-in-python/smn-8jr5ahgmhtynezje.webp
new file mode 100644
index 000000000..da474e218
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/smn-8jr5ahgmhtynezje.webp differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/vordrrnvz-vekwuickak.png b/content/engineering/guest-post/user-authentication-in-python/vordrrnvz-vekwuickak.png
deleted file mode 100644
index a0f7ae955..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/vordrrnvz-vekwuickak.png and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/vordrrnvz-vekwuickak.webp b/content/engineering/guest-post/user-authentication-in-python/vordrrnvz-vekwuickak.webp
new file mode 100644
index 000000000..4d501d906
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/vordrrnvz-vekwuickak.webp differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/xwzztcogdtmnyfq4j5nc.png b/content/engineering/guest-post/user-authentication-in-python/xwzztcogdtmnyfq4j5nc.png
deleted file mode 100644
index 82f6ae133..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/xwzztcogdtmnyfq4j5nc.png and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/xwzztcogdtmnyfq4j5nc.webp b/content/engineering/guest-post/user-authentication-in-python/xwzztcogdtmnyfq4j5nc.webp
new file mode 100644
index 000000000..b1554ffd1
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/xwzztcogdtmnyfq4j5nc.webp differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/xyvodwpjtxjrjgxoffx5.png b/content/engineering/guest-post/user-authentication-in-python/xyvodwpjtxjrjgxoffx5.png
deleted file mode 100644
index 1afcf39f4..000000000
Binary files a/content/engineering/guest-post/user-authentication-in-python/xyvodwpjtxjrjgxoffx5.png and /dev/null differ
diff --git a/content/engineering/guest-post/user-authentication-in-python/xyvodwpjtxjrjgxoffx5.webp b/content/engineering/guest-post/user-authentication-in-python/xyvodwpjtxjrjgxoffx5.webp
new file mode 100644
index 000000000..58f3d5d82
Binary files /dev/null and b/content/engineering/guest-post/user-authentication-in-python/xyvodwpjtxjrjgxoffx5.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 1.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 1.png
deleted file mode 100644
index cabe01523..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 1.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 1.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 1.webp
new file mode 100644
index 000000000..bd0be3af6
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 1.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 10.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 10.png
deleted file mode 100644
index c8fcd377a..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 10.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 10.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 10.webp
new file mode 100644
index 000000000..24dc2fe92
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 10.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 11.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 11.png
deleted file mode 100644
index 9f4ed520f..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 11.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 11.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 11.webp
new file mode 100644
index 000000000..198035df1
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 11.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 12.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 12.png
deleted file mode 100644
index 83fd67372..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 12.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 12.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 12.webp
new file mode 100644
index 000000000..a9d7695a9
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 12.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 13.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 13.png
deleted file mode 100644
index 28021bd13..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 13.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 13.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 13.webp
new file mode 100644
index 000000000..a776e27e8
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 13.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 2.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 2.png
deleted file mode 100644
index 5bd82ef55..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 2.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 2.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 2.webp
new file mode 100644
index 000000000..ea1172074
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 2.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 3.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 3.png
deleted file mode 100644
index 1f98cfb44..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 3.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 3.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 3.webp
new file mode 100644
index 000000000..a321669a5
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 3.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 4.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 4.png
deleted file mode 100644
index 93bdaec7e..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 4.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 4.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 4.webp
new file mode 100644
index 000000000..c6aa8eb4a
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 4.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 5.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 5.png
deleted file mode 100644
index 0f802cc43..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 5.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 5.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 5.webp
new file mode 100644
index 000000000..c2c719aea
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 5.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 6.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 6.png
deleted file mode 100644
index b773d1e91..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 6.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 6.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 6.webp
new file mode 100644
index 000000000..e2ba25244
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 6.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 7.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 7.png
deleted file mode 100644
index 146257ea5..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 7.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 7.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 7.webp
new file mode 100644
index 000000000..6f5c8b800
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 7.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 8.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 8.png
deleted file mode 100644
index f1fc6abab..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 8.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 8.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 8.webp
new file mode 100644
index 000000000..1e5e9f4e8
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 8.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 9.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 9.png
deleted file mode 100644
index 0ba56b74f..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 9.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 9.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 9.webp
new file mode 100644
index 000000000..ea6bb4232
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/Images/Fig 9.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/image.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/image.png
deleted file mode 100644
index bdf692d2f..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/image.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/image.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/image.webp
new file mode 100644
index 000000000..db1940041
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/image.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/index.md b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/index.md
index 434980d78..6ea8bab5b 100644
--- a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/index.md
+++ b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/index.md
@@ -1,7 +1,7 @@
---
title: "How to Use Azure Key Vault With an Azure Web App in C#"
date: "2021-08-09"
-coverImage: "image.png"
+coverImage: "image.webp"
author: "Joydip Kanjilal"
tags: ["Azure","Key Vault","C#"]
description: "In this tutorial, you'll learn how to work with Azure Key Vault in C#."
@@ -82,13 +82,13 @@ You'll now create an Azure Web App instance with the permissions to access Azure
2. Select "Web App" from the list
- 
+ 
1. Specify the name and a region for your web app
2. Mention the resource group and app service plan for your web app
- 
+ 
3. In the Publish section, there are two choices: "Code" and "Docker Container". Choose "Code"
4. Specify ".NET 5" as the Runtime stack
@@ -109,7 +109,7 @@ To enable the system-assigned managed identity for the Azure Web App we just cre
3. Copy the "Object ID" that would be available after a few seconds
-
+
## Create and Configure Azure Key Vault
@@ -127,11 +127,11 @@ You'll now create an Azure Key Vault in the Azure Portal and then add a secret t
4. Click "Create"
-
+
5. In the "Create key vault" screen provide the name, subscription, resource group name, and location. Leave the other options to their default values.
-
+
6. Click “Review + Create”
@@ -155,7 +155,7 @@ Now that you've created a Key Value instance, you'll add a secret to it and then
7. Click "Create"
-
+
### Authorize the Web App to access Your Key Vault
@@ -176,7 +176,7 @@ To provide access to the secret you created, follow the steps below:
7. Click "Save" to persist the changes and complete the process
-
+
## Create a New ASP.NET 5 Core application
@@ -188,7 +188,7 @@ First of all, you'll create an ASP.NET Core 5 web application. The project type
3. In the "Add a new project" window, choose "ASP.NET Core Web API" from the list of the project templates
-
+
4. Select "C#" as the programming language from the "Language" list
5. Click "Next"
@@ -196,7 +196,7 @@ First of all, you'll create an ASP.NET Core 5 web application. The project type
7. Then, choose "Next"
8. In the "Additional information" window, ensure that .NET 5.0 (current) is selected as the framework version
-
+
1. Since you'll not be using authentication, HTTPS or Docker, or OpenAPI, ensure that all these checkboxes are disabled
@@ -398,15 +398,15 @@ To deploy the application, follow the steps below:
3. Select "Azure" as the target from the "Publish" window as shown below:
-
+
4. Select "Azure App Service (Windows)" as the specific target as shown below:
-
+
5. Specify, or associate, the "App Service instance" with your application
-
+
6. Click "Finish"
@@ -414,7 +414,7 @@ To deploy the application, follow the steps below:
Lastly, you can use Postman to send a `Http Get` request to the endpoint to retrieve the stored secret as shown below:
-
+
## Summary
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/20064fe32ee34d74ab431409b7b3fcf6.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/20064fe32ee34d74ab431409b7b3fcf6.png
deleted file mode 100644
index 0a5665463..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/20064fe32ee34d74ab431409b7b3fcf6.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/20064fe32ee34d74ab431409b7b3fcf6.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/20064fe32ee34d74ab431409b7b3fcf6.webp
new file mode 100644
index 000000000..6f5c8b800
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/20064fe32ee34d74ab431409b7b3fcf6.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/2e9e15c8ac1dfa31c0399b8d95112706.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/2e9e15c8ac1dfa31c0399b8d95112706.png
deleted file mode 100644
index a3c08b275..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/2e9e15c8ac1dfa31c0399b8d95112706.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/2e9e15c8ac1dfa31c0399b8d95112706.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/2e9e15c8ac1dfa31c0399b8d95112706.webp
new file mode 100644
index 000000000..a321669a5
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/2e9e15c8ac1dfa31c0399b8d95112706.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/307b2784a56ac53e9fac3730a568c92d.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/307b2784a56ac53e9fac3730a568c92d.png
deleted file mode 100644
index 510e37af6..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/307b2784a56ac53e9fac3730a568c92d.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/307b2784a56ac53e9fac3730a568c92d.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/307b2784a56ac53e9fac3730a568c92d.webp
new file mode 100644
index 000000000..ea6bb4232
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/307b2784a56ac53e9fac3730a568c92d.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/383d2af1fcf9e2a16f2960de147ca549.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/383d2af1fcf9e2a16f2960de147ca549.png
deleted file mode 100644
index f6f86e6b6..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/383d2af1fcf9e2a16f2960de147ca549.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/383d2af1fcf9e2a16f2960de147ca549.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/383d2af1fcf9e2a16f2960de147ca549.webp
new file mode 100644
index 000000000..a776e27e8
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/383d2af1fcf9e2a16f2960de147ca549.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/5624143e58bd0b77651c034c295db13c.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/5624143e58bd0b77651c034c295db13c.png
deleted file mode 100644
index e33ebf2d0..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/5624143e58bd0b77651c034c295db13c.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/5624143e58bd0b77651c034c295db13c.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/5624143e58bd0b77651c034c295db13c.webp
new file mode 100644
index 000000000..5c36ed7c6
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/5624143e58bd0b77651c034c295db13c.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/68f5590f4a272da6dca010ff6f0bcfde.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/68f5590f4a272da6dca010ff6f0bcfde.png
deleted file mode 100644
index d23d0516c..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/68f5590f4a272da6dca010ff6f0bcfde.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/68f5590f4a272da6dca010ff6f0bcfde.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/68f5590f4a272da6dca010ff6f0bcfde.webp
new file mode 100644
index 000000000..1e5e9f4e8
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/68f5590f4a272da6dca010ff6f0bcfde.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/881710611150de6c542f6656de3b727e.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/881710611150de6c542f6656de3b727e.png
deleted file mode 100644
index e738e0e04..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/881710611150de6c542f6656de3b727e.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/881710611150de6c542f6656de3b727e.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/881710611150de6c542f6656de3b727e.webp
new file mode 100644
index 000000000..bd0be3af6
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/881710611150de6c542f6656de3b727e.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/89177ae5689c32f917b8d609f07f8ecc.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/89177ae5689c32f917b8d609f07f8ecc.png
deleted file mode 100644
index c5152a70a..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/89177ae5689c32f917b8d609f07f8ecc.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/89177ae5689c32f917b8d609f07f8ecc.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/89177ae5689c32f917b8d609f07f8ecc.webp
new file mode 100644
index 000000000..a9d7695a9
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/89177ae5689c32f917b8d609f07f8ecc.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/8e627ca65b5d868ab7fca443032bc43c.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/8e627ca65b5d868ab7fca443032bc43c.png
deleted file mode 100644
index 44f5d93c6..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/8e627ca65b5d868ab7fca443032bc43c.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/8e627ca65b5d868ab7fca443032bc43c.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/8e627ca65b5d868ab7fca443032bc43c.webp
new file mode 100644
index 000000000..ef65350c9
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/8e627ca65b5d868ab7fca443032bc43c.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9216ad5fd03240b518e4facf1d4e7127.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9216ad5fd03240b518e4facf1d4e7127.png
deleted file mode 100644
index adebbdbb5..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9216ad5fd03240b518e4facf1d4e7127.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9216ad5fd03240b518e4facf1d4e7127.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9216ad5fd03240b518e4facf1d4e7127.webp
new file mode 100644
index 000000000..c6aa8eb4a
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9216ad5fd03240b518e4facf1d4e7127.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9af0907aec14ae465c57c97a6c4ec146.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9af0907aec14ae465c57c97a6c4ec146.png
deleted file mode 100644
index 410132e06..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9af0907aec14ae465c57c97a6c4ec146.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9af0907aec14ae465c57c97a6c4ec146.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9af0907aec14ae465c57c97a6c4ec146.webp
new file mode 100644
index 000000000..6afa3a578
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/9af0907aec14ae465c57c97a6c4ec146.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f0c25e31cb9de4940c50cf37bf04e26d.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f0c25e31cb9de4940c50cf37bf04e26d.png
deleted file mode 100644
index eddeeaad9..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f0c25e31cb9de4940c50cf37bf04e26d.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f0c25e31cb9de4940c50cf37bf04e26d.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f0c25e31cb9de4940c50cf37bf04e26d.webp
new file mode 100644
index 000000000..e2ba25244
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f0c25e31cb9de4940c50cf37bf04e26d.webp differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f80e91e7daf51e89558a3e863ce72e2a.png b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f80e91e7daf51e89558a3e863ce72e2a.png
deleted file mode 100644
index 8cc991072..000000000
Binary files a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f80e91e7daf51e89558a3e863ce72e2a.png and /dev/null differ
diff --git a/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f80e91e7daf51e89558a3e863ce72e2a.webp b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f80e91e7daf51e89558a3e863ce72e2a.webp
new file mode 100644
index 000000000..198035df1
Binary files /dev/null and b/content/engineering/guest-post/using-azure-key-vault-with-an-azure-web-app-in-c-sharp/media/f80e91e7daf51e89558a3e863ce72e2a.webp differ
diff --git a/content/engineering/guest-post/vim-level-up/Vim.png b/content/engineering/guest-post/vim-level-up/Vim.png
deleted file mode 100644
index 4748fffc7..000000000
Binary files a/content/engineering/guest-post/vim-level-up/Vim.png and /dev/null differ
diff --git a/content/engineering/guest-post/vim-level-up/Vim.webp b/content/engineering/guest-post/vim-level-up/Vim.webp
new file mode 100644
index 000000000..787acbe91
Binary files /dev/null and b/content/engineering/guest-post/vim-level-up/Vim.webp differ
diff --git a/content/engineering/guest-post/vim-level-up/index.md b/content/engineering/guest-post/vim-level-up/index.md
index 5b3797563..46e1c3b4c 100644
--- a/content/engineering/guest-post/vim-level-up/index.md
+++ b/content/engineering/guest-post/vim-level-up/index.md
@@ -2,7 +2,7 @@
title: "How to Upgrade Your Vim Skills"
date: "2021-09-23"
author: "Shubhankar Khare"
-coverImage: "Vim.png"
+coverImage: "Vim.webp"
tags: ["Vim", "Text Editor", "UNIX"]
description: "Vim is Vi's newest and most common reincarnation, which is supported on every known platform. Go through this tutorial to learn about what Vim is and how to make the most out of it."
---
@@ -88,7 +88,7 @@ Now, to repeat your macro 99 times:
And that's all.
-
+
## Buffers & Splitting
In simple terms, a _buffer_ is a file that has been loaded into memory. Everything you do in Vim is in a buffer. You can list all the buffers by `:buffers`. And then, if you want to check out a particular buffer, use `:b n` -- where n is the buffer number.
diff --git a/content/engineering/guest-post/vim-level-up/vim-macro-demo.png b/content/engineering/guest-post/vim-level-up/vim-macro-demo.png
deleted file mode 100644
index 6899aeb36..000000000
Binary files a/content/engineering/guest-post/vim-level-up/vim-macro-demo.png and /dev/null differ
diff --git a/content/engineering/guest-post/vim-level-up/vim-macro-demo.webp b/content/engineering/guest-post/vim-level-up/vim-macro-demo.webp
new file mode 100644
index 000000000..2aca0c529
Binary files /dev/null and b/content/engineering/guest-post/vim-level-up/vim-macro-demo.webp differ
diff --git a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWE_algo.png b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWE_algo.png
deleted file mode 100644
index 3ddd80560..000000000
Binary files a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWE_algo.png and /dev/null differ
diff --git a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWE_algo.webp b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWE_algo.webp
new file mode 100644
index 000000000..b74b567a8
Binary files /dev/null and b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWE_algo.webp differ
diff --git a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWK_algo.png b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWK_algo.png
deleted file mode 100644
index 7b01b4989..000000000
Binary files a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWK_algo.png and /dev/null differ
diff --git a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWK_algo.webp b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWK_algo.webp
new file mode 100644
index 000000000..43bdb0896
Binary files /dev/null and b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWK_algo.webp differ
diff --git a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWS_algo.png b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWS_algo.png
deleted file mode 100644
index 33f1862d3..000000000
Binary files a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWS_algo.png and /dev/null differ
diff --git a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWS_algo.webp b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWS_algo.webp
new file mode 100644
index 000000000..a08ce5df1
Binary files /dev/null and b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/JWS_algo.webp differ
diff --git a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/coverImage.png b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/coverImage.png
deleted file mode 100644
index 3666a6ff4..000000000
Binary files a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/coverImage.png and /dev/null differ
diff --git a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/coverImage.webp b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/coverImage.webp
new file mode 100644
index 000000000..abacf8323
Binary files /dev/null and b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/coverImage.webp differ
diff --git a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/index.md b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/index.md
index 9763b6887..0892ced3e 100644
--- a/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/index.md
+++ b/content/engineering/guest-post/what-are-jwt-jws-jwe-jwk-jwa/index.md
@@ -1,7 +1,7 @@
---
title: "What are JWT, JWS, JWE, JWK, and JWA?"
date: "2021-11-24"
-coverImage: "coverImage.png"
+coverImage: "coverImage.webp"
author: "Yashesvinee V"
tags: ["JSON", "Encryption"]
description: "Learn about the JOSE framework and its specifications, including JSON Web Token (JWT), JSON Web Signature (JWS), JSON Web Encryption (JWE), JSON Web Key (JWK), and JSON Web Algorithms (JWA). For easier reference, bookmark this article."
@@ -173,21 +173,21 @@ The JWA specification focuses mainly on enumerating the algorithms necessary for
**Algorithms for JWS:** These algorithms are used to sign the contents of the JWS Header and the JWS Payload
-  +
+ 
Source: ietf-jose-json-web-algorithms
**Algorithms for JWE** These algorithms encrypt the Content Encryption Key (CEK) and produce the JWE Encrypted Key
-  +
+ 
Source: ietf-jose-json-web-algorithms
**Algorithms for JWK:** JWA specifies a set of algorithm families to be used for the public keys represented by JWK
-  +
+ 
Source: ietf-jose-json-web-algorithms
diff --git a/content/engineering/guest-post/what-are-refresh-tokens-and-when-to-use-them/coverImage.png b/content/engineering/guest-post/what-are-refresh-tokens-and-when-to-use-them/coverImage.png
deleted file mode 100644
index 442c828e8..000000000
Binary files a/content/engineering/guest-post/what-are-refresh-tokens-and-when-to-use-them/coverImage.png and /dev/null differ
diff --git a/content/engineering/guest-post/what-are-refresh-tokens-and-when-to-use-them/coverImage.webp b/content/engineering/guest-post/what-are-refresh-tokens-and-when-to-use-them/coverImage.webp
new file mode 100644
index 000000000..3a8ace1bf
Binary files /dev/null and b/content/engineering/guest-post/what-are-refresh-tokens-and-when-to-use-them/coverImage.webp differ
diff --git a/content/engineering/guest-post/what-are-refresh-tokens-and-when-to-use-them/index.md b/content/engineering/guest-post/what-are-refresh-tokens-and-when-to-use-them/index.md
index 0c0f06041..8df056d46 100644
--- a/content/engineering/guest-post/what-are-refresh-tokens-and-when-to-use-them/index.md
+++ b/content/engineering/guest-post/what-are-refresh-tokens-and-when-to-use-them/index.md
@@ -1,7 +1,7 @@
---
title: What Are Refresh Tokens? When & How to Use Them
date: "2021-10-05"
-coverImage: "coverImage.png"
+coverImage: "coverImage.webp"
author: "Mcvean Soans"
tags: ["Authentication","Tokens", "UX"]
description: "This is your guide to understanding refresh tokens, and why you may need to use them to enhance the user experience of your applications."
diff --git a/content/engineering/guid-query-mongo-shell/index.md b/content/engineering/guid-query-mongo-shell/index.md
index 925661139..ab93ba600 100644
--- a/content/engineering/guid-query-mongo-shell/index.md
+++ b/content/engineering/guid-query-mongo-shell/index.md
@@ -1,7 +1,7 @@
---
title: "GUID Query Through Mongo Shell"
date: "2015-02-23"
-coverImage: "mongo-db-guid.png"
+coverImage: "mongo-db-guid.webp"
author: "Kundan Singh"
tags: ["Engineering","GUID","Mongo"]
---
diff --git a/content/engineering/guid-query-mongo-shell/mongo-db-guid.png b/content/engineering/guid-query-mongo-shell/mongo-db-guid.png
deleted file mode 100644
index ab03fc979..000000000
Binary files a/content/engineering/guid-query-mongo-shell/mongo-db-guid.png and /dev/null differ
diff --git a/content/engineering/guid-query-mongo-shell/mongo-db-guid.webp b/content/engineering/guid-query-mongo-shell/mongo-db-guid.webp
new file mode 100644
index 000000000..e663d00c5
Binary files /dev/null and b/content/engineering/guid-query-mongo-shell/mongo-db-guid.webp differ
diff --git a/content/engineering/guide-to-jwt/api-economy.webp b/content/engineering/guide-to-jwt/api-economy.webp
new file mode 100644
index 000000000..64fd7f698
Binary files /dev/null and b/content/engineering/guide-to-jwt/api-economy.webp differ
diff --git a/content/engineering/guide-to-jwt/guide-to-jwt.webp b/content/engineering/guide-to-jwt/guide-to-jwt.webp
new file mode 100644
index 000000000..74fe7c960
Binary files /dev/null and b/content/engineering/guide-to-jwt/guide-to-jwt.webp differ
diff --git a/content/engineering/guide-to-jwt/index.md b/content/engineering/guide-to-jwt/index.md
new file mode 100644
index 000000000..ad268053d
--- /dev/null
+++ b/content/engineering/guide-to-jwt/index.md
@@ -0,0 +1,381 @@
+---
+title: "Complete Guide to JSON Web Token (JWT) and How It Works"
+date: "2025-04-07"
+coverImage: "guide-to-jwt.webp"
+author: "Kundan Singh"
+description: "Understand JSON Web Tokens (JWT), their compact and secure structure, and their critical role in authentication and authorization. Learn how JWT enables stateless sessions, improves scalability, and secures APIs. This guide explores JWT's working principles and best practices for robust security implementation."
+metatitle: "Complete Guide to JWT and How It Works"
+metadescription: "Learn how JWT (JSON Web Token) works, its structure, and best practices for secure authentication and stateless session management."
+tags: ["Oauth","Authorization Code Flow","Authorization","Authentication"]
+---
+
+## Introduction
+
+Have you ever logged into a website by clicking “Login with Google” or “Sign in with Facebook,” without entering your password? Or used a web app that keeps you logged in even after closing your browser?
+
+These seamless experiences often rely on JSON Web Tokens (JWTs) — a way to authorize users after they have been authenticated.
+
+In today’s digital landscape, securing user identity and managing access is critical. JWT is a compact and secure method for transmitting claims between parties, typically used after authentication to handle authorization, session management, and secure API access.
+
+But what exactly is a JWT, how does it work, and why is it important? This blog offers a comprehensive explanation.
+
+## What are Tokens and Why Are They Needed?
+
+Tokens are digital artifacts used in authentication systems to represent user identity. Instead of maintaining session state on the server, modern applications issue tokens to clients. These tokens are sent along with each request to authorize access to protected resources.
+
+When a user makes an authenticated request, the token is included in the request header. The server verifies the token’s validity—typically by checking its signature and expiration time. If the token is valid, access is granted. This approach supports stateless and scalable systems, compared to traditional session-based models.
+
+
+
+## What is JWT (JSON Web Token)?
+
+[A JWT (JSON Web Token)](https://www.loginradius.com/blog/engineering/jwt/) is a compact, self-contained token used to securely transmit claims between parties. JWTs are digitally signed using a secret (with HMAC) or a public/private key pair (with RSA or ECDSA).
+
+One of the main advantages of JWT authentication is that it doesn't require storing session data on the server—making it ideal for distributed applications.
+
+## Types of JWT
+
+There are two main types of JWT based on how the payload is protected- JWS and JWE. Let’s learn more about them.
+
+### JWS (JSON Web Signature)
+
+JWS is a type of JWT where the payload (data) is digitally signed, ensuring integrity and authenticity of the token.
+
+* The payload is Base64URL encoded and signed using a secret or private key.
+
+* It is not encrypted, meaning the contents can be read by anyone who has the token.
+
+* Commonly used in authentication and authorization scenarios like OAuth 2.0 access tokens.
+
+**Use Case:** Verifying that the data has not been tampered with.
+
+### JWE (JSON Web Encryption)?
+
+JWE is a type of JWT where the payload is encrypted, ensuring confidentiality in addition to integrity.
+
+* The entire payload is encrypted using a public key or shared secret.
+
+* Only the intended recipient can decrypt and read the token contents.
+
+* Less common than JWS, but ideal for sensitive data transmission.
+
+**Use Case:** Protecting personal or confidential information during transit.
+
+## JWT vs JWS vs JWE – Comparison Table
+
+
+
+ Feature
+
+ JWT (General)
+
+ JWS (Signed JWT)
+
+ JWE (Encrypted JWT)
+
+
+
+ Security Focus
+
+ Token Format
+
+ Integrity, authenticity
+
+ Confidentiality + integrity
+
+
+
+ Payload
+
+ Not specified
+
+ Base64URL encoded (readable)
+
+ Encrypted (not readable)
+
+
+
+ Signature
+
+ Optional
+
+ Required
+
+ Encrypted along with payload
+
+
+
+ Encryption
+
+ Optional
+
+ Not encrypted
+
+ Fully encrypted
+
+
+
+ Use Case
+
+ ID and Access Tokens
+
+ OAuth 2.0, OpenID Connect
+
+ Highly sensitive information
+
+
+
+
+Note: JWT is the umbrella format. JWS and JWE are implementation types. The most commonly used JWTs in web apps are of the JWS type.
+
+## Structure of JWT
+
+A JWT is composed of three parts:
+
+1. **Header**
+2. **Payload**
+3. **Signature**
+
+Each part is Base64URL encoded and separated by a period (.).
+
+**Example:**
+
+php-template
+
+CopyEdit
+
+<Header>.<Payload>.<Signature>
+
+### 1. Header
+
+The header typically includes the token type and the signing algorithm being used.
+
+json
+
+CopyEdit
+
+{
+
+ "alg": "HS256",
+
+ "typ": "JWT"
+
+}
+
+### 2. Payload
+
+The payload contains the **claims**—statements about an entity (usually the user) and additional metadata.
+
+json
+
+CopyEdit
+
+{
+
+ "iss": "https://lrSiteName.hub.loginradius.com/",
+
+ "sub": "{uid}",
+
+ "jti": "unique string",
+
+ "iat": 1573849217,
+
+ "nbf": 1573849217,
+
+ "exp": 1573849817,
+
+ "Key1": "value1",
+
+ "Key2": "value2"
+
+}
+
+#### **Standard JWT Claims**
+
+* **iss (Issuer):** Identifies the token issuer (e.g., your LoginRadius domain).
+
+* **sub (Subject):** Identifies the user or entity to whom the token refers.
+
+* **jti (JWT ID):** Unique identifier for the token, often used to prevent replay attacks.
+
+* **iat (Issued At):** Timestamp of when the token was issued.
+
+* **nbf (Not Before):** Specifies the time before which the token must not be accepted.
+
+* **exp (Expiration):** Sets token expiration—once expired, access is denied.
+
+Note: The payload is not encrypted by default, and can be decoded by anyone. Do not include sensitive information unless using an encrypted JWT (JWE).
+
+### 3. Signature
+
+The signature ensures the token has not been altered. It is created by signing the encoded header and payload using a secret or private key.
+
+text
+
+CopyEdit
+
+HMACSHA256(
+
+ base64UrlEncode(header) + "." +
+
+ base64UrlEncode(payload),
+
+ secret)
+
+This helps validate the token’s integrity and authenticity.
+
+## How Does JWT Work?
+
+JWT-based authentication typically follows this flow:
+
+1. **User Logs In**
+
+The user provides login credentials (e.g., username and password).
+
+2. **Server Verifies Credentials**
+
+The server validates the credentials against its data store.
+
+3. **JWT is Issued**
+
+Upon successful login, the server issues a JWT signed with a secret/private key (post authentication).
+
+4. **Client Stores JWT**
+
+The client stores the token (e.g., in localStorage, sessionStorage, or a secure cookie).
+
+5. **Token Sent on Requests**
+
+The client attaches the token to the Authorization header (Bearer <token>) in future authorization/authentication API requests.
+
+6. **Server Validates JWT**
+
+The server checks the token's signature, expiry, and validity.
+
+7. **Access is Granted**
+
+If valid, the user is granted access to protected resources.
+
+This stateless model makes JWT ideal for scalable web and mobile apps.
+
+## How to Use OAuth 2.0 with JWT
+
+[OAuth 2.0](https://www.loginradius.com/blog/engineering/what-is-oauth2-0/) is an industry-standard protocol for authorization. It enables users to grant third-party apps access to their resources without sharing their credentials.
+
+When integrated with JWT, OAuth 2.0 uses JWTs as access tokens to represent the user's authorization.
+
+JWTs are commonly used as OAuth 2.0 access tokens—but not required by the specification. Some providers use opaque tokens instead.
+
+[](https://www.loginradius.com/resource/whitepaper/secure-api-using-oauth2)
+
+### Why JWTs in OAuth 2.0?
+
+* JWTs are **self-contained**, carrying all claims.
+
+* They are **digitally signed**, allowing recipients to verify them without contacting the issuer.
+
+* They improve performance by **eliminating database lookups** during request processing.
+
+## Implementation of JWT using LoginRadius APIs
+
+To implement JWT with LoginRadius:
+
+### **Step 1: Configure a JWT App**
+
+Set up a JWT app in your [LoginRadius Admin Console](https://accounts.loginradius.com/auth.aspx?return_url=https://console.loginradius.com/login&action=register). Follow the JWT Admin Console Configuration guide.
+
+
+
+### **Step 2: Use APIs to Retrieve JWT**
+
+If you are directly implementing your Login forms or already have an access token or want to generate a JWT based on email/username/Phone number or a password, you can leverage the following APIs:
+
+* [JWT Token](https://www.loginradius.com/docs/api/v2/single-sign-on/federated-sso/jwt-login/jwt-token-by-access-token/): This GET API is used to exchange access tokens with your JWT.
+
+* [JWT Token by Email](https://www.loginradius.com/docs/api/v2/single-sign-on/federated-sso/jwt-login/jwt-token-by-email-and-password/): This API is used to get a JWT by Email and Password.
+
+* [JWT Token by Username](https://www.loginradius.com/docs/api/v2/single-sign-on/federated-sso/jwt-login/jwt-token-by-username-and-password/): This API is used to get JWT by Username and password.
+
+* [JWT Token by Phone](https://www.loginradius.com/docs/api/v2/single-sign-on/federated-sso/jwt-login/jwt-token-by-phone-and-password/): This API is used to get JWT by Phone and password.
+
+**API Response Example:**
+
+json
+
+CopyEdit
+
+{
+
+ "signature": "<JWTresponse>"
+
+}
+
+These tokens can then be used in your client app for authenticated requests.
+
+## Best Practices for Secure JWT Authentication
+
+To implement JWT securely, follow these key practices:
+
+1. **Keep Signing Keys Secure**
+
+Private keys or secrets used to sign JWTs must be stored securely.
+
+2. **Avoid Sensitive Data in Payload**
+
+Payload is only base64 encoded—not encrypted. Do not include passwords, PII, or credentials unless using encrypted JWT (JWE).
+
+3. **Limit Token Claims**
+
+Include only essential claims in the token to reduce size and exposure.
+
+4. **Use HTTPS**
+
+Always transmit JWTs over HTTPS to prevent man-in-the-middle attacks.
+
+5. **Set Short Expiry Times**
+
+Use short exp durations and implement refresh tokens to reduce impact if a token is compromised.
+
+6. **Implement Token Revocation**
+
+Use jti with a blacklist or maintain a revocation strategy for enhanced control.
+
+## Why Are JWTs Important for Authentication and Security?
+
+JWTs offer numerous benefits in authentication systems:
+
+* **Stateless Authentication** – No need to maintain session state on the server.
+
+* **Scalability** – Suitable for microservices and distributed systems.
+
+* **Tamper Resistance** – Digitally signed tokens ensure data integrity.
+
+* **Performance** – Reduces server load and database dependencies.
+
+* **Cross-Platform Support** – Easily used across web, mobile, and API ecosystems.
+
+* **Enhanced Security** – Signed tokens ensure authenticity and tamper-proof data.
+
+* **Developer Convenience** – Simplifies session management.
+
+JWTs are widely adopted in OAuth 2.0, OpenID Connect, and API security implementations.
+
+## Conclusion
+
+JWT authentication is a robust, efficient, and secure method for protecting web and mobile applications. By understanding its structure, use cases, and best practices, you can confidently implement JWTs in modern authentication systems.
+
+Looking to implement JWT in your application? Check out the [developer documentation](https://www.loginradius.com/docs/single-sign-on/federated-sso/jwt-login/overview/?q=jwt+) to get started with seamless JWT integration using LoginRadius.
+
+## **FAQ’s**
+
+### **1.** What is the expiration time of JWT, and what is the measurement of time in JWT?
+
+**A:** By default, the expiry time of a JWT is 600 seconds (10 Minutes). It is shown in the form of seconds in the JWT configuration. The expiry time can be set from 1 second to 2592000 seconds (30 days) as per your use case.
+
+### **2.** What is the difference between OAuth and JWT?
+
+**A:** OAuth is an authorization framework, that allows third-party apps to access user data without exposing their credentials.JWT is used at the end of authentication to securely transmit user info (identity and authorization). Use OAuth for delegated access; use JWT for stateless authentication and API authorization (verifying within your own system).
+
+### **3.** How many types of JWT are there?
+
+**A:** JWTs mainly come in two types, with one being JSON Web Signature (JWS) and JSON Web Encryption (JWE). In JWS, the token’s content is digitally signed to protect it from tampering during transmission between sender and receiver. While the data is secure from modification, its contents (claims) can still be visible to others.
\ No newline at end of file
diff --git a/content/engineering/guide-to-jwt/jwt-configuration.webp b/content/engineering/guide-to-jwt/jwt-configuration.webp
new file mode 100644
index 000000000..e5d2acd45
Binary files /dev/null and b/content/engineering/guide-to-jwt/jwt-configuration.webp differ
diff --git a/content/engineering/guide-to-jwt/token-authentication-method.webp b/content/engineering/guide-to-jwt/token-authentication-method.webp
new file mode 100644
index 000000000..48be9fff7
Binary files /dev/null and b/content/engineering/guide-to-jwt/token-authentication-method.webp differ
diff --git a/content/engineering/hacktoberfest-2021/Hacktoberfest-2021.png b/content/engineering/hacktoberfest-2021/Hacktoberfest-2021.png
deleted file mode 100644
index 27e16965b..000000000
Binary files a/content/engineering/hacktoberfest-2021/Hacktoberfest-2021.png and /dev/null differ
diff --git a/content/engineering/hacktoberfest-2021/Hacktoberfest-2021.webp b/content/engineering/hacktoberfest-2021/Hacktoberfest-2021.webp
new file mode 100644
index 000000000..da9c414ab
Binary files /dev/null and b/content/engineering/hacktoberfest-2021/Hacktoberfest-2021.webp differ
diff --git a/content/engineering/hacktoberfest-2021/index.md b/content/engineering/hacktoberfest-2021/index.md
index f813a3486..a1d2147eb 100644
--- a/content/engineering/hacktoberfest-2021/index.md
+++ b/content/engineering/hacktoberfest-2021/index.md
@@ -1,7 +1,7 @@
---
title: "Hacktoberfest 2021: Contribute and Win Swag from LoginRadius"
date: "2021-09-23"
-coverImage: "Hacktoberfest-2021.png"
+coverImage: "Hacktoberfest-2021.webp"
author: "Raghunath Reddy"
tags: ["Hacktoberfest","Open Source","LoginRadius"]
description: "At LoginRadius, we're excited to celebrate Hacktoberfest 2021. Contribute to our open source projects and win cool LoginRadius branded swag to show off!"
diff --git a/content/engineering/hacktoberfest-participation-as-maintainer/cover.png b/content/engineering/hacktoberfest-participation-as-maintainer/cover.png
deleted file mode 100644
index eb3536557..000000000
Binary files a/content/engineering/hacktoberfest-participation-as-maintainer/cover.png and /dev/null differ
diff --git a/content/engineering/hacktoberfest-participation-as-maintainer/cover.webp b/content/engineering/hacktoberfest-participation-as-maintainer/cover.webp
new file mode 100644
index 000000000..a70e17408
Binary files /dev/null and b/content/engineering/hacktoberfest-participation-as-maintainer/cover.webp differ
diff --git a/content/engineering/hacktoberfest-participation-as-maintainer/index.md b/content/engineering/hacktoberfest-participation-as-maintainer/index.md
index b1ff33a57..6a4852147 100644
--- a/content/engineering/hacktoberfest-participation-as-maintainer/index.md
+++ b/content/engineering/hacktoberfest-participation-as-maintainer/index.md
@@ -3,7 +3,7 @@ title: How to Participate in Hacktoberfest as a Maintainer
date: 2021-09-28
author: Narendra Pareek
tags: ["Hacktoberfest", "Hacktoberfest 2021", "Open Source"]
-coverImage: "cover.png"
+coverImage: "cover.webp"
description: This ultimate guide is the resource you need to open source your project and participate in Hacktoberfest to get valuable contributions from the community.
---
diff --git a/content/engineering/handling-cheapest-fuel-data/a.png b/content/engineering/handling-cheapest-fuel-data/a.png
deleted file mode 100644
index 7c2a8e789..000000000
Binary files a/content/engineering/handling-cheapest-fuel-data/a.png and /dev/null differ
diff --git a/content/engineering/handling-cheapest-fuel-data/a.webp b/content/engineering/handling-cheapest-fuel-data/a.webp
new file mode 100644
index 000000000..dbfc60668
Binary files /dev/null and b/content/engineering/handling-cheapest-fuel-data/a.webp differ
diff --git a/content/engineering/handling-cheapest-fuel-data/b.png b/content/engineering/handling-cheapest-fuel-data/b.png
deleted file mode 100644
index f9a6b224f..000000000
Binary files a/content/engineering/handling-cheapest-fuel-data/b.png and /dev/null differ
diff --git a/content/engineering/handling-cheapest-fuel-data/b.webp b/content/engineering/handling-cheapest-fuel-data/b.webp
new file mode 100644
index 000000000..367b56b31
Binary files /dev/null and b/content/engineering/handling-cheapest-fuel-data/b.webp differ
diff --git a/content/engineering/handling-cheapest-fuel-data/c.png b/content/engineering/handling-cheapest-fuel-data/c.png
deleted file mode 100644
index 9e35777d9..000000000
Binary files a/content/engineering/handling-cheapest-fuel-data/c.png and /dev/null differ
diff --git a/content/engineering/handling-cheapest-fuel-data/c.webp b/content/engineering/handling-cheapest-fuel-data/c.webp
new file mode 100644
index 000000000..220515a04
Binary files /dev/null and b/content/engineering/handling-cheapest-fuel-data/c.webp differ
diff --git a/content/engineering/handling-cheapest-fuel-data/d.png b/content/engineering/handling-cheapest-fuel-data/d.png
deleted file mode 100644
index c5b56c10f..000000000
Binary files a/content/engineering/handling-cheapest-fuel-data/d.png and /dev/null differ
diff --git a/content/engineering/handling-cheapest-fuel-data/d.webp b/content/engineering/handling-cheapest-fuel-data/d.webp
new file mode 100644
index 000000000..107d4c6c0
Binary files /dev/null and b/content/engineering/handling-cheapest-fuel-data/d.webp differ
diff --git a/content/engineering/handling-cheapest-fuel-data/e.png b/content/engineering/handling-cheapest-fuel-data/e.png
deleted file mode 100644
index d1258bd57..000000000
Binary files a/content/engineering/handling-cheapest-fuel-data/e.png and /dev/null differ
diff --git a/content/engineering/handling-cheapest-fuel-data/e.webp b/content/engineering/handling-cheapest-fuel-data/e.webp
new file mode 100644
index 000000000..0d058c69b
Binary files /dev/null and b/content/engineering/handling-cheapest-fuel-data/e.webp differ
diff --git a/content/engineering/handling-cheapest-fuel-data/index.md b/content/engineering/handling-cheapest-fuel-data/index.md
index 537801ce1..678e63038 100644
--- a/content/engineering/handling-cheapest-fuel-data/index.md
+++ b/content/engineering/handling-cheapest-fuel-data/index.md
@@ -2,7 +2,7 @@
title: "Handling the Cheapest Fuel- Data"
date: "2020-10-06"
author: "Samriddhi Mishra"
-coverImage: "a.png"
+coverImage: "a.webp"
tags: ["Data", "BigData", "Hadoop"]
description: "You can have data without information, but you cannot have information without data. Huge data is generated per day. What are the issues in handling it? How big companies manage and analyze it?"
---
@@ -27,7 +27,7 @@ This is the sixth edition of DOMO's report, and according to their research:
** "Over 2.5 quintillion bytes of data are created every single day, and it's only going to grow from there. By 2020, it's estimated that 1.7MB of data will be created every second for every person on earth."**
As 1 Exabyte = 1 quintillion bytes, so 2.5 Exabytes ( 2.5 * 10¹⁸ bytes) of data is generated per day.
-
+
Big companies like Google, Amazon, Netflix, Instagram, Facebook, Twitter, and many more are generating tons of data daily.
Information is taken from [here](https://www.smartdatacollective.com/how-much-big-data-companies-make-on-internet/).
@@ -77,7 +77,7 @@ All these problems combined are called Big Data. Below are some subparts of the
3) Thirdly, **Velocity of data transfer(I/O Operations)**. If we ignore the above limitations, the next problem posed is the time taken by Processing units to process this data. Because of the huge volume of data stored in large-capacity storage devices, data transfer is time-consuming.
-
+
## Solution:-
@@ -86,7 +86,7 @@ One of the concepts that solve the above problem is Distributed Storage.
**Distributed Storage Cluster-**
-
+
Distributed storage is a method that provides huge storage(even exceeding from physical storage) shared by multiple systems. These systems or the servers are connected following horizontal scaling. This multiple commodity server hardware is comparatively cheap than optimized servers with large storage(Hard Disk). Each virtual machine contributes directory to a centralized system and thereby shares its storage. The team of master and slave nodes working together for one purpose called a cluster.
@@ -99,7 +99,7 @@ As the data is split and stored in(and loaded from) other devices/nodes, the I/O
**Hence, distributed storage solves all the problems- Volume, Cost, and Velocity.**
## Apache Hadoop
-
+
Distributed storage is just a concept, and some companies have launched different software or products that work on this concept which solve the problem of Big Data. One such company is **APACHE and the software APACHE HADOOP**.
The Apache Hadoop software is a collection of libraries that provides facility to create clusters/network of systems following the distributed system. It can be used in processing the huge data distributes in thousands of machines, each offering local computation and storage.
diff --git a/content/engineering/hello-developers-and-designers/desdev.png b/content/engineering/hello-developers-and-designers/desdev.png
deleted file mode 100644
index 621e3f218..000000000
Binary files a/content/engineering/hello-developers-and-designers/desdev.png and /dev/null differ
diff --git a/content/engineering/hello-developers-and-designers/desdev.webp b/content/engineering/hello-developers-and-designers/desdev.webp
new file mode 100644
index 000000000..06c99b0ff
Binary files /dev/null and b/content/engineering/hello-developers-and-designers/desdev.webp differ
diff --git a/content/engineering/hello-developers-and-designers/index.md b/content/engineering/hello-developers-and-designers/index.md
index a620c83f2..13ec04c33 100644
--- a/content/engineering/hello-developers-and-designers/index.md
+++ b/content/engineering/hello-developers-and-designers/index.md
@@ -1,7 +1,7 @@
---
title: "Hello developers and designers!"
date: "2014-05-02"
-coverImage: "desdev.png"
+coverImage: "desdev.webp"
author: "Team LoginRadius"
tags: ["Engineering"]
---
diff --git a/content/engineering/hello-world-deno/cmd.png b/content/engineering/hello-world-deno/cmd.png
deleted file mode 100644
index f4c3ea4c3..000000000
Binary files a/content/engineering/hello-world-deno/cmd.png and /dev/null differ
diff --git a/content/engineering/hello-world-deno/cmd.webp b/content/engineering/hello-world-deno/cmd.webp
new file mode 100644
index 000000000..f2399f748
Binary files /dev/null and b/content/engineering/hello-world-deno/cmd.webp differ
diff --git a/content/engineering/hello-world-deno/deno.png b/content/engineering/hello-world-deno/deno.png
deleted file mode 100644
index 1338f14ee..000000000
Binary files a/content/engineering/hello-world-deno/deno.png and /dev/null differ
diff --git a/content/engineering/hello-world-deno/deno.webp b/content/engineering/hello-world-deno/deno.webp
new file mode 100644
index 000000000..c3f5b8a01
Binary files /dev/null and b/content/engineering/hello-world-deno/deno.webp differ
diff --git a/content/engineering/hello-world-deno/index.md b/content/engineering/hello-world-deno/index.md
index 6b1e2468c..02a15fa0c 100644
--- a/content/engineering/hello-world-deno/index.md
+++ b/content/engineering/hello-world-deno/index.md
@@ -1,7 +1,7 @@
---
title: "Hello world with Deno"
date: "2020-06-02"
-coverImage: "deno.png"
+coverImage: "deno.webp"
author: "Ashish Sharma"
tags: ["Deno", "HelloWorld","NodeJs"]
---
@@ -17,7 +17,7 @@ Btw, this is the best damn geeky one-liner code to explain what is Deno. Totally
-
+
### Installation
@@ -87,7 +87,7 @@ deno run index.ts
You can check the result here
-
+
Yupppp it works this is your first Deno program !!
diff --git a/content/engineering/hello-world-deno/twitter.png b/content/engineering/hello-world-deno/twitter.png
deleted file mode 100644
index 3e666a398..000000000
Binary files a/content/engineering/hello-world-deno/twitter.png and /dev/null differ
diff --git a/content/engineering/hello-world-deno/twitter.webp b/content/engineering/hello-world-deno/twitter.webp
new file mode 100644
index 000000000..cc2195cad
Binary files /dev/null and b/content/engineering/hello-world-deno/twitter.webp differ
diff --git a/content/engineering/hosts-file/index.jpg b/content/engineering/hosts-file/index.jpg
deleted file mode 100644
index 94c592061..000000000
Binary files a/content/engineering/hosts-file/index.jpg and /dev/null differ
diff --git a/content/engineering/hosts-file/index.md b/content/engineering/hosts-file/index.md
index f4cc09c59..bd43ff5d0 100644
--- a/content/engineering/hosts-file/index.md
+++ b/content/engineering/hosts-file/index.md
@@ -1,7 +1,7 @@
---
title: "Benefits and usages of Hosts File"
date: "2020-07-20"
-coverImage: "index.jpg"
+coverImage: "index.webp"
author: "Vijay Singh Shekhawat"
tags: ["Computer tricks","Networking", "Hosts File"]
description: "Hosts file maps hostnames to IP addresses, sometimes required to be edited either to block some sites or to test some custom domain.This blog explains how can we edit the hosts in different operating systems."
@@ -31,13 +31,13 @@ Windows operating system we need to open the host file
2. Right-click Notepad and choose Run as administrator
- 
+ 
3. Open the hosts file. Click on File > Open and Copy and Paste the following path`
`c:\Windows\System32\Drivers\etc\hosts`
- 
+ 
You can edit the hosts file
@@ -49,16 +49,16 @@ Suppose you want to block facebook.com on your system and want to add a custom d
0.0.0.0 www.facebook.com
127.0.0.1 www.customdomain.com
```
- 
+ 
After finishing the Editing, **Save your hosts file**
- 
+ 
Open your browser and try to access www.facebook.com and see you can’t access this site
- 
+ 
##### Linux
@@ -68,7 +68,7 @@ Use following instructions for Linux
$ sudo vim /etc/hosts
```
- 
+ 
It will prompt for the password, enter your administrator password.
@@ -77,7 +77,7 @@ Use following instructions for Linux
2. Using the vim or your favorite text editor you can easily edit. The Linux hosts file is similar to the windows hosts file. Now again I am blocking Facebook and adding a custom domain
- 
+ 
3. Save the Changes
@@ -87,7 +87,7 @@ Use following instructions for macOS
1. Find the terminal application on your system
-- We can use Spotlight application to search
- 
+ 
@@ -95,17 +95,17 @@ Use following instructions for macOS
-- It will prompt for the password, enter your administrator password
-- Enter administrator Password
- 
+ 
*Using the vim text editor you can easily edit you. The macOS hosts file is also similar to the windows and Linux hosts file. I am blocking Facebook and adding custom domain here as well*.
- 
+ 
3. Save Changes
Open your browser and try to access www.facebook.com and see you can’t access this site.
- 
+ 
### Conclusion
diff --git a/content/engineering/hosts-file/index.webp b/content/engineering/hosts-file/index.webp
new file mode 100644
index 000000000..456a60923
Binary files /dev/null and b/content/engineering/hosts-file/index.webp differ
diff --git a/content/engineering/hosts-file/linux1.png b/content/engineering/hosts-file/linux1.png
deleted file mode 100644
index 5a7573954..000000000
Binary files a/content/engineering/hosts-file/linux1.png and /dev/null differ
diff --git a/content/engineering/hosts-file/linux1.webp b/content/engineering/hosts-file/linux1.webp
new file mode 100644
index 000000000..8f1d763a2
Binary files /dev/null and b/content/engineering/hosts-file/linux1.webp differ
diff --git a/content/engineering/hosts-file/linux2.png b/content/engineering/hosts-file/linux2.png
deleted file mode 100644
index 39861d776..000000000
Binary files a/content/engineering/hosts-file/linux2.png and /dev/null differ
diff --git a/content/engineering/hosts-file/linux2.webp b/content/engineering/hosts-file/linux2.webp
new file mode 100644
index 000000000..3d67b4aee
Binary files /dev/null and b/content/engineering/hosts-file/linux2.webp differ
diff --git a/content/engineering/hosts-file/mac1.png b/content/engineering/hosts-file/mac1.png
deleted file mode 100644
index 81364b170..000000000
Binary files a/content/engineering/hosts-file/mac1.png and /dev/null differ
diff --git a/content/engineering/hosts-file/mac1.webp b/content/engineering/hosts-file/mac1.webp
new file mode 100644
index 000000000..df15a0179
Binary files /dev/null and b/content/engineering/hosts-file/mac1.webp differ
diff --git a/content/engineering/hosts-file/mac2.png b/content/engineering/hosts-file/mac2.png
deleted file mode 100644
index dafa6204f..000000000
Binary files a/content/engineering/hosts-file/mac2.png and /dev/null differ
diff --git a/content/engineering/hosts-file/mac2.webp b/content/engineering/hosts-file/mac2.webp
new file mode 100644
index 000000000..f295156e5
Binary files /dev/null and b/content/engineering/hosts-file/mac2.webp differ
diff --git a/content/engineering/hosts-file/mac3.png b/content/engineering/hosts-file/mac3.png
deleted file mode 100644
index 2310a7e48..000000000
Binary files a/content/engineering/hosts-file/mac3.png and /dev/null differ
diff --git a/content/engineering/hosts-file/mac3.webp b/content/engineering/hosts-file/mac3.webp
new file mode 100644
index 000000000..941c84893
Binary files /dev/null and b/content/engineering/hosts-file/mac3.webp differ
diff --git a/content/engineering/hosts-file/mac4.png b/content/engineering/hosts-file/mac4.png
deleted file mode 100644
index d5b225761..000000000
Binary files a/content/engineering/hosts-file/mac4.png and /dev/null differ
diff --git a/content/engineering/hosts-file/mac4.webp b/content/engineering/hosts-file/mac4.webp
new file mode 100644
index 000000000..fd281a667
Binary files /dev/null and b/content/engineering/hosts-file/mac4.webp differ
diff --git a/content/engineering/hosts-file/windows1.png b/content/engineering/hosts-file/windows1.png
deleted file mode 100644
index 26684af90..000000000
Binary files a/content/engineering/hosts-file/windows1.png and /dev/null differ
diff --git a/content/engineering/hosts-file/windows1.webp b/content/engineering/hosts-file/windows1.webp
new file mode 100644
index 000000000..e472df31a
Binary files /dev/null and b/content/engineering/hosts-file/windows1.webp differ
diff --git a/content/engineering/hosts-file/windows2.png b/content/engineering/hosts-file/windows2.png
deleted file mode 100644
index e691e42c9..000000000
Binary files a/content/engineering/hosts-file/windows2.png and /dev/null differ
diff --git a/content/engineering/hosts-file/windows2.webp b/content/engineering/hosts-file/windows2.webp
new file mode 100644
index 000000000..a72a0f44b
Binary files /dev/null and b/content/engineering/hosts-file/windows2.webp differ
diff --git a/content/engineering/hosts-file/windows3.png b/content/engineering/hosts-file/windows3.png
deleted file mode 100644
index 82f58fe55..000000000
Binary files a/content/engineering/hosts-file/windows3.png and /dev/null differ
diff --git a/content/engineering/hosts-file/windows3.webp b/content/engineering/hosts-file/windows3.webp
new file mode 100644
index 000000000..0c211d4a5
Binary files /dev/null and b/content/engineering/hosts-file/windows3.webp differ
diff --git a/content/engineering/hosts-file/windows4.png b/content/engineering/hosts-file/windows4.png
deleted file mode 100644
index 579a7f7d1..000000000
Binary files a/content/engineering/hosts-file/windows4.png and /dev/null differ
diff --git a/content/engineering/hosts-file/windows4.webp b/content/engineering/hosts-file/windows4.webp
new file mode 100644
index 000000000..5ac94838c
Binary files /dev/null and b/content/engineering/hosts-file/windows4.webp differ
diff --git a/content/engineering/hosts-file/windows5.png b/content/engineering/hosts-file/windows5.png
deleted file mode 100644
index d5b225761..000000000
Binary files a/content/engineering/hosts-file/windows5.png and /dev/null differ
diff --git a/content/engineering/hosts-file/windows5.webp b/content/engineering/hosts-file/windows5.webp
new file mode 100644
index 000000000..fd281a667
Binary files /dev/null and b/content/engineering/hosts-file/windows5.webp differ
diff --git a/content/engineering/how-does-bitwise-xor-work/index.md b/content/engineering/how-does-bitwise-xor-work/index.md
index dc3b3340f..04eaf2554 100644
--- a/content/engineering/how-does-bitwise-xor-work/index.md
+++ b/content/engineering/how-does-bitwise-xor-work/index.md
@@ -1,7 +1,7 @@
---
title: "How does bitwise ^ (XOR) work?"
date: "2020-11-24"
-coverImage: "xor.png"
+coverImage: "xor.webp"
author: Kheenvraj Lomror
tags: ["bitwise", "XOR"]
description: "Everything you should know about bitwise ^ xor operator."
diff --git a/content/engineering/how-does-bitwise-xor-work/xor.png b/content/engineering/how-does-bitwise-xor-work/xor.png
deleted file mode 100644
index c66e464bf..000000000
Binary files a/content/engineering/how-does-bitwise-xor-work/xor.png and /dev/null differ
diff --git a/content/engineering/how-does-bitwise-xor-work/xor.webp b/content/engineering/how-does-bitwise-xor-work/xor.webp
new file mode 100644
index 000000000..7af92a3bb
Binary files /dev/null and b/content/engineering/how-does-bitwise-xor-work/xor.webp differ
diff --git a/content/engineering/how-enum-tryparse-works-in-csharp/coverimage.png b/content/engineering/how-enum-tryparse-works-in-csharp/coverimage.png
deleted file mode 100644
index e9a43469e..000000000
Binary files a/content/engineering/how-enum-tryparse-works-in-csharp/coverimage.png and /dev/null differ
diff --git a/content/engineering/how-enum-tryparse-works-in-csharp/coverimage.webp b/content/engineering/how-enum-tryparse-works-in-csharp/coverimage.webp
new file mode 100644
index 000000000..96eb190f7
Binary files /dev/null and b/content/engineering/how-enum-tryparse-works-in-csharp/coverimage.webp differ
diff --git a/content/engineering/how-enum-tryparse-works-in-csharp/index.md b/content/engineering/how-enum-tryparse-works-in-csharp/index.md
index 5b7cae4fc..5df594d24 100644
--- a/content/engineering/how-enum-tryparse-works-in-csharp/index.md
+++ b/content/engineering/how-enum-tryparse-works-in-csharp/index.md
@@ -1,7 +1,7 @@
---
title: "How Enum.TryParse() works in C#"
date: "2021-04-28"
-coverImage: "coverimage.png"
+coverImage: "coverimage.webp"
author: "Hemant Manwani"
tags: ["C#","Enum"]
description: "In this article, I will talk about how Enum.TryParse() works in C# and mistake which we can make while using it."
diff --git a/content/engineering/how-git-local-repository-works/10.png b/content/engineering/how-git-local-repository-works/10.png
deleted file mode 100644
index bf21574cf..000000000
Binary files a/content/engineering/how-git-local-repository-works/10.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/10.webp b/content/engineering/how-git-local-repository-works/10.webp
new file mode 100644
index 000000000..4d70f3598
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/10.webp differ
diff --git a/content/engineering/how-git-local-repository-works/11.png b/content/engineering/how-git-local-repository-works/11.png
deleted file mode 100644
index ba9a6687b..000000000
Binary files a/content/engineering/how-git-local-repository-works/11.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/11.webp b/content/engineering/how-git-local-repository-works/11.webp
new file mode 100644
index 000000000..dfbc93a5c
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/11.webp differ
diff --git a/content/engineering/how-git-local-repository-works/12.png b/content/engineering/how-git-local-repository-works/12.png
deleted file mode 100644
index 4d2a872fa..000000000
Binary files a/content/engineering/how-git-local-repository-works/12.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/12.webp b/content/engineering/how-git-local-repository-works/12.webp
new file mode 100644
index 000000000..ed7b5d835
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/12.webp differ
diff --git a/content/engineering/how-git-local-repository-works/13.png b/content/engineering/how-git-local-repository-works/13.png
deleted file mode 100644
index 740e98425..000000000
Binary files a/content/engineering/how-git-local-repository-works/13.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/13.webp b/content/engineering/how-git-local-repository-works/13.webp
new file mode 100644
index 000000000..d05cb62c0
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/13.webp differ
diff --git a/content/engineering/how-git-local-repository-works/14.png b/content/engineering/how-git-local-repository-works/14.png
deleted file mode 100644
index 5e6ad2744..000000000
Binary files a/content/engineering/how-git-local-repository-works/14.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/14.webp b/content/engineering/how-git-local-repository-works/14.webp
new file mode 100644
index 000000000..f456ccbce
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/14.webp differ
diff --git a/content/engineering/how-git-local-repository-works/3.png b/content/engineering/how-git-local-repository-works/3.png
deleted file mode 100644
index 089ed0c98..000000000
Binary files a/content/engineering/how-git-local-repository-works/3.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/3.webp b/content/engineering/how-git-local-repository-works/3.webp
new file mode 100644
index 000000000..80ab37a94
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/3.webp differ
diff --git a/content/engineering/how-git-local-repository-works/4.png b/content/engineering/how-git-local-repository-works/4.png
deleted file mode 100644
index af4b63793..000000000
Binary files a/content/engineering/how-git-local-repository-works/4.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/4.webp b/content/engineering/how-git-local-repository-works/4.webp
new file mode 100644
index 000000000..6870b7a52
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/4.webp differ
diff --git a/content/engineering/how-git-local-repository-works/5.png b/content/engineering/how-git-local-repository-works/5.png
deleted file mode 100644
index 4a813fbdb..000000000
Binary files a/content/engineering/how-git-local-repository-works/5.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/5.webp b/content/engineering/how-git-local-repository-works/5.webp
new file mode 100644
index 000000000..72a37c146
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/5.webp differ
diff --git a/content/engineering/how-git-local-repository-works/6.png b/content/engineering/how-git-local-repository-works/6.png
deleted file mode 100644
index 6a1414e96..000000000
Binary files a/content/engineering/how-git-local-repository-works/6.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/6.webp b/content/engineering/how-git-local-repository-works/6.webp
new file mode 100644
index 000000000..448a7ae3b
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/6.webp differ
diff --git a/content/engineering/how-git-local-repository-works/7.png b/content/engineering/how-git-local-repository-works/7.png
deleted file mode 100644
index 4a63324e1..000000000
Binary files a/content/engineering/how-git-local-repository-works/7.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/7.webp b/content/engineering/how-git-local-repository-works/7.webp
new file mode 100644
index 000000000..65908c104
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/7.webp differ
diff --git a/content/engineering/how-git-local-repository-works/8.png b/content/engineering/how-git-local-repository-works/8.png
deleted file mode 100644
index 401cfe4e2..000000000
Binary files a/content/engineering/how-git-local-repository-works/8.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/8.webp b/content/engineering/how-git-local-repository-works/8.webp
new file mode 100644
index 000000000..47efcb2ac
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/8.webp differ
diff --git a/content/engineering/how-git-local-repository-works/9.png b/content/engineering/how-git-local-repository-works/9.png
deleted file mode 100644
index f3e88adb1..000000000
Binary files a/content/engineering/how-git-local-repository-works/9.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/9.webp b/content/engineering/how-git-local-repository-works/9.webp
new file mode 100644
index 000000000..e31f9fac5
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/9.webp differ
diff --git a/content/engineering/how-git-local-repository-works/git.png b/content/engineering/how-git-local-repository-works/git.png
deleted file mode 100644
index 781a1b5b6..000000000
Binary files a/content/engineering/how-git-local-repository-works/git.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/git.webp b/content/engineering/how-git-local-repository-works/git.webp
new file mode 100644
index 000000000..6880607d4
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/git.webp differ
diff --git a/content/engineering/how-git-local-repository-works/index.md b/content/engineering/how-git-local-repository-works/index.md
index b1b6f08f6..db6eee602 100644
--- a/content/engineering/how-git-local-repository-works/index.md
+++ b/content/engineering/how-git-local-repository-works/index.md
@@ -1,7 +1,7 @@
---
title: How Git Local Repository Works
date: "2021-04-12"
-coverImage: "git.png"
+coverImage: "git.webp"
author: "Abhimanyu Singh Rathore"
description: "In this article, I will talk about how Git Local Repository Works"
tags: ["GIT"]
@@ -14,7 +14,7 @@ Once we initialize or clone any git project that will set up a local project en
that whole environment will look like the below picture
-
+
**Project Folder**: The main folder consists of a workspace and local repository
@@ -27,29 +27,29 @@ that whole environment will look like the below picture
Let's get into it step by step and see how we perform command or action and behind the scene, git do its own activity.
- Step 1. Git clone and project:
- 
+ 
- 
+ 
- Step 2. Explore what we got in repository
- 
+ 
- 
+ 
- Step 3. Do some modification in a files
- 
+ 
- 
+ 
- Step 4. Add this file in to staging (ready for commit)
- 
+ 
- 
+ 
- Step 5. Commit the file
- 
+ 
- 
+ 
- Step 6. Push the changes
- 
+ 
- 
+ 
Hope this makes clear how git handling things at the local repository.
diff --git a/content/engineering/how-git-local-repository-works/localrepository.png b/content/engineering/how-git-local-repository-works/localrepository.png
deleted file mode 100644
index d80845f96..000000000
Binary files a/content/engineering/how-git-local-repository-works/localrepository.png and /dev/null differ
diff --git a/content/engineering/how-git-local-repository-works/localrepository.webp b/content/engineering/how-git-local-repository-works/localrepository.webp
new file mode 100644
index 000000000..4fc5ced17
Binary files /dev/null and b/content/engineering/how-git-local-repository-works/localrepository.webp differ
diff --git a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.02.46-AM-300x177.png b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.02.46-AM-300x177.png
deleted file mode 100644
index 1830f607f..000000000
Binary files a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.02.46-AM-300x177.png and /dev/null differ
diff --git a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.02.46-AM-300x177.webp b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.02.46-AM-300x177.webp
new file mode 100644
index 000000000..6e70b18f9
Binary files /dev/null and b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.02.46-AM-300x177.webp differ
diff --git a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.41.30-AM-300x288.png b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.41.30-AM-300x288.png
deleted file mode 100644
index 76d68357c..000000000
Binary files a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.41.30-AM-300x288.png and /dev/null differ
diff --git a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.41.30-AM-300x288.webp b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.41.30-AM-300x288.webp
new file mode 100644
index 000000000..b3ff85e48
Binary files /dev/null and b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.41.30-AM-300x288.webp differ
diff --git a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.42.03-AM-300x193.png b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.42.03-AM-300x193.png
deleted file mode 100644
index 8aca17f0b..000000000
Binary files a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.42.03-AM-300x193.png and /dev/null differ
diff --git a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.42.03-AM-300x193.webp b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.42.03-AM-300x193.webp
new file mode 100644
index 000000000..49f70d71d
Binary files /dev/null and b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-10.42.03-AM-300x193.webp differ
diff --git a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-9.47.33-AM-300x280.png b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-9.47.33-AM-300x280.png
deleted file mode 100644
index cf7d3aa90..000000000
Binary files a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-9.47.33-AM-300x280.png and /dev/null differ
diff --git a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-9.47.33-AM-300x280.webp b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-9.47.33-AM-300x280.webp
new file mode 100644
index 000000000..f73010eca
Binary files /dev/null and b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/Screen-Shot-2018-05-30-at-9.47.33-AM-300x280.webp differ
diff --git a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/google-home-max-13.jpg b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/google-home-max-13.jpg
deleted file mode 100644
index b42dc6499..000000000
Binary files a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/google-home-max-13.jpg and /dev/null differ
diff --git a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/google-home-max-13.webp b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/google-home-max-13.webp
new file mode 100644
index 000000000..1f47c34a4
Binary files /dev/null and b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/google-home-max-13.webp differ
diff --git a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/index.md b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/index.md
index 663328dcd..b03d1b223 100644
--- a/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/index.md
+++ b/content/engineering/how-to-configure-the-actions-on-google-console-for-google-assistant/index.md
@@ -1,7 +1,7 @@
---
title: "How to configure the 'Actions on Google' console for Google Assistant"
date: "2018-06-18"
-coverImage: "google-home-max-13.jpg"
+coverImage: "google-home-max-13.webp"
author: "Vincent Lin"
tags: ["Engineering","GoogleAssistant"]
---
@@ -18,14 +18,14 @@ This tutorial will go over how to configure the ‘Actions on Google’ console
1. Create an Actions project and a Dialogflow agent [here](https://console.actions.google.com/u/0/).
1. Add/import project.
- 
+ 
2. Click on Skip(in the upper right corner) choosing a category and click Build -> Actions in the left nav to add your first actions.
- 
+ 
2. Configuration for your action intent in the dialogflow console.
1. In the Intent section, enter your training phrases. Start with “talk to”, “speak to”, “ask” and etc, learn more [here.](https://developers.google.com/actions/localization/languages-locales)
- 
+ 
- 2. Enter the default text response. This will be the default response for your action until you link your account with LoginRadius and build your customized response. (This will return errors if you leave this empty, even if you handle the response in your code.)
+ 2. Enter the default text response. This will be the default response for your action until you link your account with LoginRadius and build your customized response. (This will return errors if you leave this empty, even if you handle the response in your code.)
By then, you should have finished the setup for google assistant.
diff --git a/content/engineering/how-to-create-and-use-dictionary-csharp/coverimage.png b/content/engineering/how-to-create-and-use-dictionary-csharp/coverimage.png
deleted file mode 100644
index 43dbaf6c9..000000000
Binary files a/content/engineering/how-to-create-and-use-dictionary-csharp/coverimage.png and /dev/null differ
diff --git a/content/engineering/how-to-create-and-use-dictionary-csharp/coverimage.webp b/content/engineering/how-to-create-and-use-dictionary-csharp/coverimage.webp
new file mode 100644
index 000000000..32bd0914d
Binary files /dev/null and b/content/engineering/how-to-create-and-use-dictionary-csharp/coverimage.webp differ
diff --git a/content/engineering/how-to-create-and-use-dictionary-csharp/index.md b/content/engineering/how-to-create-and-use-dictionary-csharp/index.md
index 28d57383d..57406b1ae 100644
--- a/content/engineering/how-to-create-and-use-dictionary-csharp/index.md
+++ b/content/engineering/how-to-create-and-use-dictionary-csharp/index.md
@@ -1,7 +1,7 @@
---
title: "How to create and use the Dictionary in C#"
date: "2021-05-27"
-coverImage: "coverimage.png"
+coverImage: "coverimage.webp"
author: "Hemant Manwani"
tags: ["C#","Dictionary"]
description: "In this article, we will talk about how to create and use the Dictionary in C#."
diff --git a/content/engineering/how-to-get-email-alerts-for-unhandled-php-exceptions/email-alerts-unhandled-php.png b/content/engineering/how-to-get-email-alerts-for-unhandled-php-exceptions/email-alerts-unhandled-php.png
deleted file mode 100644
index 9501c09a4..000000000
Binary files a/content/engineering/how-to-get-email-alerts-for-unhandled-php-exceptions/email-alerts-unhandled-php.png and /dev/null differ
diff --git a/content/engineering/how-to-get-email-alerts-for-unhandled-php-exceptions/email-alerts-unhandled-php.webp b/content/engineering/how-to-get-email-alerts-for-unhandled-php-exceptions/email-alerts-unhandled-php.webp
new file mode 100644
index 000000000..fe83348d8
Binary files /dev/null and b/content/engineering/how-to-get-email-alerts-for-unhandled-php-exceptions/email-alerts-unhandled-php.webp differ
diff --git a/content/engineering/how-to-get-email-alerts-for-unhandled-php-exceptions/index.md b/content/engineering/how-to-get-email-alerts-for-unhandled-php-exceptions/index.md
index 3d0569233..2ecdd51b0 100644
--- a/content/engineering/how-to-get-email-alerts-for-unhandled-php-exceptions/index.md
+++ b/content/engineering/how-to-get-email-alerts-for-unhandled-php-exceptions/index.md
@@ -1,7 +1,7 @@
---
title: "How to Get Email Alerts for Unhandled PHP Exceptions"
date: "2015-10-26"
-coverImage: "email-alerts-unhandled-php.png"
+coverImage: "email-alerts-unhandled-php.webp"
author: "Team LoginRadius"
tags: ["PHP","Email"]
---
diff --git a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/1.png b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/1.png
deleted file mode 100644
index 9560846aa..000000000
Binary files a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/1.png and /dev/null differ
diff --git a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/1.webp b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/1.webp
new file mode 100644
index 000000000..b5874879c
Binary files /dev/null and b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/1.webp differ
diff --git a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/2.png b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/2.png
deleted file mode 100644
index 58c9726a5..000000000
Binary files a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/2.png and /dev/null differ
diff --git a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/2.webp b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/2.webp
new file mode 100644
index 000000000..f3847ebc6
Binary files /dev/null and b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/2.webp differ
diff --git a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/3.png b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/3.png
deleted file mode 100644
index 004bd78b0..000000000
Binary files a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/3.png and /dev/null differ
diff --git a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/3.webp b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/3.webp
new file mode 100644
index 000000000..3992c516f
Binary files /dev/null and b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/3.webp differ
diff --git a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/index.md b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/index.md
index 522ade290..43d08614c 100644
--- a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/index.md
+++ b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/index.md
@@ -1,7 +1,7 @@
---
title: "Maintain Test Cases in Excel Sheets"
date: "2015-11-03"
-coverImage: "test_cases.png"
+coverImage: "test_cases.webp"
author: "Shefali Yaduvanshi"
tags: ["Excel", "Tes"]
description: "Learn how to maintain test cases in Excel sheets"
@@ -23,7 +23,7 @@ Test cases are the part of testing by which a product can be tested properly acc
**Standard format of Test Cases**
Some common fields that are used in test case writing are:
-
+
1. 1. **Test Case Id:** This field is defined by what type of system we are testing. Below are the standard rules:
- If we are making a test case for any application which doesn’t belong to any specific module then ID would start as TEST\_ID 1.
@@ -74,7 +74,7 @@ Traceability Matrix can be divided into 2 parts:-
1.7 **Test Summary**: This field contains the status of the product: how many test
cases are passed, how many are failed, how many are on hold or how many are Invalid etc.
-
+
2. **Traceability Matrix** :
@@ -90,7 +90,7 @@ Traceability Matrix can be divided into 2 parts:-
As per the image below:
-
+
Requirement ID REQ\_ID 1 covered in Test Case Id TEST\_ID 1 and TEST\_ID 2
Requirement ID REQ\_ID 2 covered in Test Case Id TEST\_ID 3 ,TEST\_ID 4, TEST\_ID 5
diff --git a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/test_cases.png b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/test_cases.png
deleted file mode 100644
index 16c66cd06..000000000
Binary files a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/test_cases.png and /dev/null differ
diff --git a/content/engineering/how-to-maintain-test-cases-in-excel-sheets/test_cases.webp b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/test_cases.webp
new file mode 100644
index 000000000..413fd538f
Binary files /dev/null and b/content/engineering/how-to-maintain-test-cases-in-excel-sheets/test_cases.webp differ
diff --git a/content/engineering/how-to-make-telegram-bot/bot.png b/content/engineering/how-to-make-telegram-bot/bot.png
deleted file mode 100644
index 279e9d8d7..000000000
Binary files a/content/engineering/how-to-make-telegram-bot/bot.png and /dev/null differ
diff --git a/content/engineering/how-to-make-telegram-bot/bot.webp b/content/engineering/how-to-make-telegram-bot/bot.webp
new file mode 100644
index 000000000..05b941d72
Binary files /dev/null and b/content/engineering/how-to-make-telegram-bot/bot.webp differ
diff --git a/content/engineering/how-to-make-telegram-bot/index.md b/content/engineering/how-to-make-telegram-bot/index.md
index fd17c2790..c807e5fb7 100644
--- a/content/engineering/how-to-make-telegram-bot/index.md
+++ b/content/engineering/how-to-make-telegram-bot/index.md
@@ -1,7 +1,7 @@
---
title: How to make a telegram bot
date: "2020-10-20"
-coverImage: "bot.png"
+coverImage: "bot.webp"
author: "Rajan Puri"
tags: ["Telegram Bot", "Python"]
description: "What is a bot and How to make our own Telegram bot."
diff --git a/content/engineering/how-to-mitigate-ddos-attack/How-to-mitigate-DDoS-attack.png b/content/engineering/how-to-mitigate-ddos-attack/How-to-mitigate-DDoS-attack.png
deleted file mode 100644
index c0dc10f97..000000000
Binary files a/content/engineering/how-to-mitigate-ddos-attack/How-to-mitigate-DDoS-attack.png and /dev/null differ
diff --git a/content/engineering/how-to-mitigate-ddos-attack/How-to-mitigate-DDoS-attack.webp b/content/engineering/how-to-mitigate-ddos-attack/How-to-mitigate-DDoS-attack.webp
new file mode 100644
index 000000000..38a89d160
Binary files /dev/null and b/content/engineering/how-to-mitigate-ddos-attack/How-to-mitigate-DDoS-attack.webp differ
diff --git a/content/engineering/how-to-mitigate-ddos-attack/What-is-a-DDoS-attack.png b/content/engineering/how-to-mitigate-ddos-attack/What-is-a-DDoS-attack.png
deleted file mode 100644
index 0df2f7380..000000000
Binary files a/content/engineering/how-to-mitigate-ddos-attack/What-is-a-DDoS-attack.png and /dev/null differ
diff --git a/content/engineering/how-to-mitigate-ddos-attack/What-is-a-DDoS-attack.webp b/content/engineering/how-to-mitigate-ddos-attack/What-is-a-DDoS-attack.webp
new file mode 100644
index 000000000..627e2606c
Binary files /dev/null and b/content/engineering/how-to-mitigate-ddos-attack/What-is-a-DDoS-attack.webp differ
diff --git a/content/engineering/how-to-mitigate-ddos-attack/index.md b/content/engineering/how-to-mitigate-ddos-attack/index.md
index 0ccbda9b8..3bd1d7a83 100644
--- a/content/engineering/how-to-mitigate-ddos-attack/index.md
+++ b/content/engineering/how-to-mitigate-ddos-attack/index.md
@@ -1,7 +1,7 @@
---
title: "What is a DDoS Attack and How to Mitigate it"
date: "2021-02-24"
-coverImage: "What-is-a-DDoS-attack.png"
+coverImage: "What-is-a-DDoS-attack.webp"
author: "Vijay Singh Shekhawat"
description: Learn what a DDoS attack is, including the various classifications of attacks, and how to defend your site from one.
tags: ["DDoS", "DDos mitigate","DDoS Prevention"]
@@ -11,7 +11,7 @@ Did you know that in only a few minutes, a DDoS attack can bring your website do
## What is DDoS Attack?
-
+
A Distributed Denial of Service (DDoS) is a targeted [cyber attack on a website](https://www.loginradius.com/blog/identity/2019/10/cybersecurity-attacks-business/) or device where a malicious attacker's flood of traffic is sent from single or multiple sources. The primary purpose of DDoS is to make a machine or network resource unavailable to its genuine users by temporarily or disrupting the services of a host connected to the Internet. If we do not use appropriate security practices or tools, it makes your application into a non-functional situation.
@@ -49,7 +49,7 @@ Here is the list of [sites or services](https://en.wikipedia.org/wiki/2016_Dyn_c
## Best Practices for Preventing DDoS attacks
-
+
### 1. Traffic Monitoring
Application traffic monitoring is essential. We can identify most of the attacks using the proper monitoring. Commonly DDoS attacks are made with high volume traffic but DDoS attacks could be possible with a single vulnerable HTTP endpoint.
diff --git a/content/engineering/how-to-obtain-ios-application-logs-without-mac/Log.png b/content/engineering/how-to-obtain-ios-application-logs-without-mac/Log.png
deleted file mode 100644
index bb6f5697d..000000000
Binary files a/content/engineering/how-to-obtain-ios-application-logs-without-mac/Log.png and /dev/null differ
diff --git a/content/engineering/how-to-obtain-ios-application-logs-without-mac/Log.webp b/content/engineering/how-to-obtain-ios-application-logs-without-mac/Log.webp
new file mode 100644
index 000000000..437dd1cdd
Binary files /dev/null and b/content/engineering/how-to-obtain-ios-application-logs-without-mac/Log.webp differ
diff --git a/content/engineering/how-to-obtain-ios-application-logs-without-mac/index.md b/content/engineering/how-to-obtain-ios-application-logs-without-mac/index.md
index 408b584aa..7bf3ee9a7 100644
--- a/content/engineering/how-to-obtain-ios-application-logs-without-mac/index.md
+++ b/content/engineering/how-to-obtain-ios-application-logs-without-mac/index.md
@@ -1,7 +1,7 @@
---
title: "How to obtain iOS application logs without Mac"
date: "2020-07-22"
-coverImage: "Log.png"
+coverImage: "Log.webp"
author: "Tanvi Jain"
tags: ["Logs","ios","xcode","iPhone","troubleshoot","Mac"]
---
diff --git a/content/engineering/how-to-promise/index.md b/content/engineering/how-to-promise/index.md
index 26d47c31a..53210969f 100644
--- a/content/engineering/how-to-promise/index.md
+++ b/content/engineering/how-to-promise/index.md
@@ -1,7 +1,7 @@
---
title: "How to Promise"
date: "2016-01-05"
-coverImage: "promise-300x300.png"
+coverImage: "promise-300x300.webp"
author: "Solomon Yu"
tags: ["JavaScript", "Promise"]
---
diff --git a/content/engineering/how-to-promise/promise-300x300.png b/content/engineering/how-to-promise/promise-300x300.png
deleted file mode 100644
index 2eaf231b4..000000000
Binary files a/content/engineering/how-to-promise/promise-300x300.png and /dev/null differ
diff --git a/content/engineering/how-to-promise/promise-300x300.webp b/content/engineering/how-to-promise/promise-300x300.webp
new file mode 100644
index 000000000..2020109e9
Binary files /dev/null and b/content/engineering/how-to-promise/promise-300x300.webp differ
diff --git a/content/engineering/how-to-send-emails-through-csharp-dotnet-using-smtp/coverimage.jpg b/content/engineering/how-to-send-emails-through-csharp-dotnet-using-smtp/coverimage.jpg
deleted file mode 100644
index a5e8b3579..000000000
Binary files a/content/engineering/how-to-send-emails-through-csharp-dotnet-using-smtp/coverimage.jpg and /dev/null differ
diff --git a/content/engineering/how-to-send-emails-through-csharp-dotnet-using-smtp/coverimage.webp b/content/engineering/how-to-send-emails-through-csharp-dotnet-using-smtp/coverimage.webp
new file mode 100644
index 000000000..a319dab71
Binary files /dev/null and b/content/engineering/how-to-send-emails-through-csharp-dotnet-using-smtp/coverimage.webp differ
diff --git a/content/engineering/how-to-send-emails-through-csharp-dotnet-using-smtp/index.md b/content/engineering/how-to-send-emails-through-csharp-dotnet-using-smtp/index.md
index 1f6e72985..065fe05be 100644
--- a/content/engineering/how-to-send-emails-through-csharp-dotnet-using-smtp/index.md
+++ b/content/engineering/how-to-send-emails-through-csharp-dotnet-using-smtp/index.md
@@ -1,7 +1,7 @@
---
title: "How to send emails in C#/.NET using SMTP"
date: "2020-11-19"
-coverImage: "coverimage.jpg"
+coverImage: "coverimage.webp"
author: "Hemant Manwani"
description: " In this article, we will learn how to send emails in .NET/C# using SMTP"
tags: [".NET","C#","SMTP"]
diff --git a/content/engineering/how-to-use-bower-to-install-bootstrap/bower-logo.png b/content/engineering/how-to-use-bower-to-install-bootstrap/bower-logo.png
deleted file mode 100644
index 41d1e7215..000000000
Binary files a/content/engineering/how-to-use-bower-to-install-bootstrap/bower-logo.png and /dev/null differ
diff --git a/content/engineering/how-to-use-bower-to-install-bootstrap/bower-logo.webp b/content/engineering/how-to-use-bower-to-install-bootstrap/bower-logo.webp
new file mode 100644
index 000000000..5be58d8d4
Binary files /dev/null and b/content/engineering/how-to-use-bower-to-install-bootstrap/bower-logo.webp differ
diff --git a/content/engineering/how-to-use-bower-to-install-bootstrap/index.md b/content/engineering/how-to-use-bower-to-install-bootstrap/index.md
index bdbd33f51..63ada84ae 100644
--- a/content/engineering/how-to-use-bower-to-install-bootstrap/index.md
+++ b/content/engineering/how-to-use-bower-to-install-bootstrap/index.md
@@ -1,7 +1,7 @@
---
title: "Install Bootstrap with Bower"
date: "2017-07-05"
-coverImage: "bower-logo.png"
+coverImage: "bower-logo.webp"
author: "Pascal Noel"
tags: ["Bootstrap", "Bower"]
description: "Learn how the Bower package manager helps into quick components deploy and install Bootstrap using Bower"
diff --git a/content/engineering/how-to-use-jcenter-dependencies-in-android-studio/index.md b/content/engineering/how-to-use-jcenter-dependencies-in-android-studio/index.md
index 004184463..206bd8a71 100644
--- a/content/engineering/how-to-use-jcenter-dependencies-in-android-studio/index.md
+++ b/content/engineering/how-to-use-jcenter-dependencies-in-android-studio/index.md
@@ -1,7 +1,7 @@
---
title: "jCenter Dependencies in Android Studio"
date: "2017-07-11"
-coverImage: "jCenter.png"
+coverImage: "jCenter.webp"
author: "Hitesh Pamnani"
tags: ["JCenter", "Android"]
description: "Learn how to make use of jCenter dependencies in Android Studio."
diff --git a/content/engineering/how-to-use-jcenter-dependencies-in-android-studio/jCenter.png b/content/engineering/how-to-use-jcenter-dependencies-in-android-studio/jCenter.png
deleted file mode 100644
index 9e432d554..000000000
Binary files a/content/engineering/how-to-use-jcenter-dependencies-in-android-studio/jCenter.png and /dev/null differ
diff --git a/content/engineering/how-to-use-jcenter-dependencies-in-android-studio/jCenter.webp b/content/engineering/how-to-use-jcenter-dependencies-in-android-studio/jCenter.webp
new file mode 100644
index 000000000..b2d794544
Binary files /dev/null and b/content/engineering/how-to-use-jcenter-dependencies-in-android-studio/jCenter.webp differ
diff --git a/content/engineering/how-to-use-maven-dependency-in-eclipse/index.md b/content/engineering/how-to-use-maven-dependency-in-eclipse/index.md
index d64a34890..cf091bcb8 100644
--- a/content/engineering/how-to-use-maven-dependency-in-eclipse/index.md
+++ b/content/engineering/how-to-use-maven-dependency-in-eclipse/index.md
@@ -1,7 +1,7 @@
---
title: "Maven Dependency in Eclipse"
date: "2017-07-11"
-coverImage: "maven.png"
+coverImage: "maven.webp"
author: "Giriraj Yadav"
tags: ["Java", "Maven", "Eclipse"]
description: "Learn step by step setting up and resolution of maven dependency using eclipse IDE."
diff --git a/content/engineering/how-to-use-maven-dependency-in-eclipse/maven.png b/content/engineering/how-to-use-maven-dependency-in-eclipse/maven.png
deleted file mode 100644
index 4294047cb..000000000
Binary files a/content/engineering/how-to-use-maven-dependency-in-eclipse/maven.png and /dev/null differ
diff --git a/content/engineering/how-to-use-maven-dependency-in-eclipse/maven.webp b/content/engineering/how-to-use-maven-dependency-in-eclipse/maven.webp
new file mode 100644
index 000000000..28c5e0b9f
Binary files /dev/null and b/content/engineering/how-to-use-maven-dependency-in-eclipse/maven.webp differ
diff --git a/content/engineering/html-email-concept/email_picture.png b/content/engineering/html-email-concept/email_picture.png
deleted file mode 100644
index 04322fc1d..000000000
Binary files a/content/engineering/html-email-concept/email_picture.png and /dev/null differ
diff --git a/content/engineering/html-email-concept/email_picture.webp b/content/engineering/html-email-concept/email_picture.webp
new file mode 100644
index 000000000..482d49f69
Binary files /dev/null and b/content/engineering/html-email-concept/email_picture.webp differ
diff --git a/content/engineering/html-email-concept/index.md b/content/engineering/html-email-concept/index.md
index 363ba487b..510e15d9f 100644
--- a/content/engineering/html-email-concept/index.md
+++ b/content/engineering/html-email-concept/index.md
@@ -1,7 +1,7 @@
---
title: HTML Email Concept
date: "2020-10-09"
-coverImage: "email_picture.png"
+coverImage: "email_picture.webp"
author: "Nivedita Singh"
tags: ["Html","Email"]
description: "If you choose to code your HTML email by hand, there are many different things you need to use while creating HTML email."
diff --git a/content/engineering/html5-limitation-in-internet-explorer/index.md b/content/engineering/html5-limitation-in-internet-explorer/index.md
index b9d3781c9..e99c3005a 100644
--- a/content/engineering/html5-limitation-in-internet-explorer/index.md
+++ b/content/engineering/html5-limitation-in-internet-explorer/index.md
@@ -1,7 +1,7 @@
---
title: "HTML5 Limitation in Internet Explorer"
date: "2015-06-30"
-coverImage: "radio-check-buttons-css.png"
+coverImage: "radio-check-buttons-css.webp"
author: "Team LoginRadius"
tags: ["Java", "Maven", "Eclipse"]
---
diff --git a/content/engineering/html5-limitation-in-internet-explorer/radio-check-buttons-css.png b/content/engineering/html5-limitation-in-internet-explorer/radio-check-buttons-css.png
deleted file mode 100644
index 4c805986f..000000000
Binary files a/content/engineering/html5-limitation-in-internet-explorer/radio-check-buttons-css.png and /dev/null differ
diff --git a/content/engineering/html5-limitation-in-internet-explorer/radio-check-buttons-css.webp b/content/engineering/html5-limitation-in-internet-explorer/radio-check-buttons-css.webp
new file mode 100644
index 000000000..5fbf5ff01
Binary files /dev/null and b/content/engineering/html5-limitation-in-internet-explorer/radio-check-buttons-css.webp differ
diff --git a/content/engineering/http-security-headers/http-security-headers.jpg b/content/engineering/http-security-headers/http-security-headers.jpg
deleted file mode 100644
index d3a9a96df..000000000
Binary files a/content/engineering/http-security-headers/http-security-headers.jpg and /dev/null differ
diff --git a/content/engineering/http-security-headers/http-security-headers.webp b/content/engineering/http-security-headers/http-security-headers.webp
new file mode 100644
index 000000000..1b6190a4e
Binary files /dev/null and b/content/engineering/http-security-headers/http-security-headers.webp differ
diff --git a/content/engineering/http-security-headers/index.md b/content/engineering/http-security-headers/index.md
index ba620dda1..a5d88b21e 100644
--- a/content/engineering/http-security-headers/index.md
+++ b/content/engineering/http-security-headers/index.md
@@ -1,7 +1,7 @@
---
title: "HTTP Security Headers"
date: "2020-07-15"
-coverImage: "http-security-headers.jpg"
+coverImage: "http-security-headers.webp"
author: "Vijay Singh Shekhawat"
tags: ["Security","HTTP Headers"]
description: "HTTP security headers are a fundamental part of website security. Upon implementation, they protect you against the types of attacks that your site is most likely to come across. These headers protect against XSS, code injection, clickjacking, etc. This article explains most commonly used HTTP headers in context to application security"
diff --git a/content/engineering/identity-impact-of-google-chrome-thirdparty-cookie-restrictions/index.md b/content/engineering/identity-impact-of-google-chrome-thirdparty-cookie-restrictions/index.md
index ca5627145..c3560b270 100644
--- a/content/engineering/identity-impact-of-google-chrome-thirdparty-cookie-restrictions/index.md
+++ b/content/engineering/identity-impact-of-google-chrome-thirdparty-cookie-restrictions/index.md
@@ -1,7 +1,7 @@
---
title: "How Chrome’s Third-Party Cookie Restrictions Affect User Authentication?"
date: "2024-07-08"
-coverImage: "third-party-cookies-phaseout-chrome.png"
+coverImage: "third-party-cookies-phaseout-chrome.webp"
author: "Raghunath Reddy"
tags: ["Identity", "Cookies", "Chrome"]
description: "Google Chrome has planned to phase out third-party cookies, which will affect different website functionalities depending on third-party cookies. This blog focuses on how this phase-out affects identity and user authentication and discusses alternatives for overcoming challenges."
diff --git a/content/engineering/identity-impact-of-google-chrome-thirdparty-cookie-restrictions/third-party-cookies-phaseout-chrome.png b/content/engineering/identity-impact-of-google-chrome-thirdparty-cookie-restrictions/third-party-cookies-phaseout-chrome.png
deleted file mode 100644
index ca41990f6..000000000
Binary files a/content/engineering/identity-impact-of-google-chrome-thirdparty-cookie-restrictions/third-party-cookies-phaseout-chrome.png and /dev/null differ
diff --git a/content/engineering/identity-impact-of-google-chrome-thirdparty-cookie-restrictions/third-party-cookies-phaseout-chrome.webp b/content/engineering/identity-impact-of-google-chrome-thirdparty-cookie-restrictions/third-party-cookies-phaseout-chrome.webp
new file mode 100644
index 000000000..ee5876816
Binary files /dev/null and b/content/engineering/identity-impact-of-google-chrome-thirdparty-cookie-restrictions/third-party-cookies-phaseout-chrome.webp differ
diff --git a/content/engineering/identity-management-for-b2b-companies/b2b-identity-management.png b/content/engineering/identity-management-for-b2b-companies/b2b-identity-management.png
deleted file mode 100644
index 910b5aea3..000000000
Binary files a/content/engineering/identity-management-for-b2b-companies/b2b-identity-management.png and /dev/null differ
diff --git a/content/engineering/identity-management-for-b2b-companies/b2b-identity-management.webp b/content/engineering/identity-management-for-b2b-companies/b2b-identity-management.webp
new file mode 100644
index 000000000..0713fc53e
Binary files /dev/null and b/content/engineering/identity-management-for-b2b-companies/b2b-identity-management.webp differ
diff --git a/content/engineering/identity-management-for-b2b-companies/index.md b/content/engineering/identity-management-for-b2b-companies/index.md
index 044752570..49068fb70 100644
--- a/content/engineering/identity-management-for-b2b-companies/index.md
+++ b/content/engineering/identity-management-for-b2b-companies/index.md
@@ -1,7 +1,7 @@
---
title: "Why B2B Companies Should Implement Identity Management"
date: "2022-05-31"
-coverImage: "b2b-identity-management.png"
+coverImage: "b2b-identity-management.webp"
author: "Ravi Teja Ganta"
tags: ["Identity", "Access Management", "B2B"]
description: "B2B companies need to manage identity differently to meet customer needs and deliver value efficiently while ensuring secure and seamless access. Read more to learn how your company can implement B2B identity management."
diff --git a/content/engineering/image-colorizer-tool-kolorizer/01.jpg b/content/engineering/image-colorizer-tool-kolorizer/01.jpg
deleted file mode 100644
index 20d827b10..000000000
Binary files a/content/engineering/image-colorizer-tool-kolorizer/01.jpg and /dev/null differ
diff --git a/content/engineering/image-colorizer-tool-kolorizer/01.webp b/content/engineering/image-colorizer-tool-kolorizer/01.webp
new file mode 100644
index 000000000..645ee3906
Binary files /dev/null and b/content/engineering/image-colorizer-tool-kolorizer/01.webp differ
diff --git a/content/engineering/image-colorizer-tool-kolorizer/02.jpg b/content/engineering/image-colorizer-tool-kolorizer/02.jpg
deleted file mode 100644
index 36be83631..000000000
Binary files a/content/engineering/image-colorizer-tool-kolorizer/02.jpg and /dev/null differ
diff --git a/content/engineering/image-colorizer-tool-kolorizer/02.webp b/content/engineering/image-colorizer-tool-kolorizer/02.webp
new file mode 100644
index 000000000..ab5de2cb3
Binary files /dev/null and b/content/engineering/image-colorizer-tool-kolorizer/02.webp differ
diff --git a/content/engineering/image-colorizer-tool-kolorizer/03.png b/content/engineering/image-colorizer-tool-kolorizer/03.png
deleted file mode 100644
index e0351fc49..000000000
Binary files a/content/engineering/image-colorizer-tool-kolorizer/03.png and /dev/null differ
diff --git a/content/engineering/image-colorizer-tool-kolorizer/03.webp b/content/engineering/image-colorizer-tool-kolorizer/03.webp
new file mode 100644
index 000000000..1096413f5
Binary files /dev/null and b/content/engineering/image-colorizer-tool-kolorizer/03.webp differ
diff --git a/content/engineering/image-colorizer-tool-kolorizer/cover.png b/content/engineering/image-colorizer-tool-kolorizer/cover.png
deleted file mode 100644
index 41aa07752..000000000
Binary files a/content/engineering/image-colorizer-tool-kolorizer/cover.png and /dev/null differ
diff --git a/content/engineering/image-colorizer-tool-kolorizer/cover.webp b/content/engineering/image-colorizer-tool-kolorizer/cover.webp
new file mode 100644
index 000000000..7ea1ffb76
Binary files /dev/null and b/content/engineering/image-colorizer-tool-kolorizer/cover.webp differ
diff --git a/content/engineering/image-colorizer-tool-kolorizer/index.md b/content/engineering/image-colorizer-tool-kolorizer/index.md
index 6313f8bd3..a4146da39 100644
--- a/content/engineering/image-colorizer-tool-kolorizer/index.md
+++ b/content/engineering/image-colorizer-tool-kolorizer/index.md
@@ -1,7 +1,7 @@
---
title: "Image Colorizer Tool - Kolorizer"
date: "2021-02-09"
-coverImage: "cover.png"
+coverImage: "cover.webp"
author: "Max Sergeyenko"
tags: ["Design","Photos","Brand"]
description: Kolorizer is a free photo coloring tool to help you align the images on a website with your brand.
@@ -30,7 +30,7 @@ You might be thinking right now: "Sounds like I need an expensive designer to fi
## The solution
-
+
This is where our little tool comes in - Kolorizer. This incredibly simple online tool will have a huge impact on your brand, whether you are kicking it off or simplifying and growing an existing one.
@@ -42,21 +42,21 @@ The task is simple - to make colors in all the imagery on your website match you
In the **"The overlay" method**, the color overlay is simply applied on top of the image. While it is the easiest and quickest way of adding some brand colors to the images, it comes with some downsides. The image becomes darker and some other colors might still peek through, which is not great.
-
+
*Image created using "The overlay" method*
The second, **"The changing of the base color" method**, is less common because it requires a few more steps. First, the image is converted to black and white, making every pixel in the image based on black color. So every single pixel is a percentage of black color. Now we can replace that black color with any of the dark colors you have in your brand, like dark blue or dark orange. And voila! Every pixel in our image is now based on that color, without any overlay that darkens the image and without any other colors peeking through the overlay. This does create a little problem: since we are basing our image on a dark color that is not black, the image is lighter and we have to adjust the brightness of the image a little bit to compensate for this. The amount depends on the image itself - some would be good right after the conversion, some would need to be darkened or lightened.
-
+
*Image created using "The changing of the base color" method*
Kolorizer is built using the second method, and most of the steps are done automatically.
-
+
After you upload the image, it is converted to your selected brand color right away. Adjust the color if you need to. Maybe try a different dark color out of your brand colors. Then adjust the brightness of the image if needed and download the finished colorized image. That is it!
diff --git a/content/engineering/image-colorizer-tool-kolorizer/logo.png b/content/engineering/image-colorizer-tool-kolorizer/logo.png
deleted file mode 100644
index 49f17e727..000000000
Binary files a/content/engineering/image-colorizer-tool-kolorizer/logo.png and /dev/null differ
diff --git a/content/engineering/image-colorizer-tool-kolorizer/logo.webp b/content/engineering/image-colorizer-tool-kolorizer/logo.webp
new file mode 100644
index 000000000..a8cd82bfc
Binary files /dev/null and b/content/engineering/image-colorizer-tool-kolorizer/logo.webp differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_login.png b/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_login.png
deleted file mode 100644
index 72fea13e5..000000000
Binary files a/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_login.png and /dev/null differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_login.webp b/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_login.webp
new file mode 100644
index 000000000..06096b6e8
Binary files /dev/null and b/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_login.webp differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_schema.png b/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_schema.png
deleted file mode 100644
index e0d9e95c6..000000000
Binary files a/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_schema.png and /dev/null differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_schema.webp b/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_schema.webp
new file mode 100644
index 000000000..091aa4eb8
Binary files /dev/null and b/content/engineering/implement-authentication-in-react-using-loginradius-cli/add_schema.webp differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/api_creds.png b/content/engineering/implement-authentication-in-react-using-loginradius-cli/api_creds.png
deleted file mode 100644
index 812246319..000000000
Binary files a/content/engineering/implement-authentication-in-react-using-loginradius-cli/api_creds.png and /dev/null differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/api_creds.webp b/content/engineering/implement-authentication-in-react-using-loginradius-cli/api_creds.webp
new file mode 100644
index 000000000..e7d5f94ee
Binary files /dev/null and b/content/engineering/implement-authentication-in-react-using-loginradius-cli/api_creds.webp differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/cover.jpg b/content/engineering/implement-authentication-in-react-using-loginradius-cli/cover.jpg
deleted file mode 100644
index e7d450f10..000000000
Binary files a/content/engineering/implement-authentication-in-react-using-loginradius-cli/cover.jpg and /dev/null differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/cover.webp b/content/engineering/implement-authentication-in-react-using-loginradius-cli/cover.webp
new file mode 100644
index 000000000..98b57a964
Binary files /dev/null and b/content/engineering/implement-authentication-in-react-using-loginradius-cli/cover.webp differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/domain.png b/content/engineering/implement-authentication-in-react-using-loginradius-cli/domain.png
deleted file mode 100644
index 563418cf2..000000000
Binary files a/content/engineering/implement-authentication-in-react-using-loginradius-cli/domain.png and /dev/null differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/domain.webp b/content/engineering/implement-authentication-in-react-using-loginradius-cli/domain.webp
new file mode 100644
index 000000000..9bab8575c
Binary files /dev/null and b/content/engineering/implement-authentication-in-react-using-loginradius-cli/domain.webp differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/index.md b/content/engineering/implement-authentication-in-react-using-loginradius-cli/index.md
index b4d3d6f5b..0a6f919b0 100644
--- a/content/engineering/implement-authentication-in-react-using-loginradius-cli/index.md
+++ b/content/engineering/implement-authentication-in-react-using-loginradius-cli/index.md
@@ -1,7 +1,7 @@
---
title: "Implement Authentication in React Applications using LoginRadius CLI "
date: "2021-05-12"
-coverImage: "cover.jpg"
+coverImage: "cover.webp"
author: "Akash Patil"
tags: ["Authentication", "React", "CLI", "LoginRadius CLI"]
description: "In this tutorial, we will learn about implementing authentication for React applications using LoginRadius in under 5 mins. We will be using the LoginRadius CLI, through which we can perform basic actions of the LoginRadius Dashboard on the command line in a fast and proficient manner."
@@ -43,7 +43,7 @@ $ lr register
```
This command will open the Portal in the browser, where you can register yourself and create the app.
-
+
If you already have a LoginRadius account, use the command below to directly login :
@@ -70,19 +70,19 @@ $ lr login
Once the **login/register** process has been completed, run the `lr get config` command to fetch your **API Key/Secret** as shown below.
-
+
### Configuring Callback URLs
Here, a callback URL refers to a URL in your application that LoginRadius would redirect a user to after they have been authenticated. These URLs must be added to your Application Configuration. If not set, users will be unable to login into the application and receive an error.
-
+
For security reasons, LoginRadius only processes API calls that are received from the whitelisted domains. To get the list of whitelisted domains, run `lr get domain` command from the CLI. Similarly, to add a domain, use the `lr add domain` command.
> For the purposes of this tutorial, make sure that you set `http://localhost` as a whitelisted domain.
-
+
## Setup React JS application
@@ -281,21 +281,21 @@ This section explains the use of the LoginRadius CLI in enabling users to quickl
We can add social login methods like Google, Facebook, etc., to the LoginRadius Auth Page using the CLI. Use the `lr add social` command to add a Login method and the `lr get social` command to view the current active social login methods. Check the image below for a visual representation.
-
+
After adding the new login method (in this example, it is Facebook), navigate to the LoginRadius Auth Page by using the `lr demo` command.
-
+
### Updating the theme
We can update the **theme** of the LoginRadius Auth Page using the `lr set theme` command. You can use the `lr get theme` command to get a list of all available themes and the currently active theme. See the image below for visual representation.
-
+
After changing the theme, navigate to the LoginRadius Auth Page using `lr demo` command to view the changes.
-
+
### Adding to the Registration schema
@@ -305,11 +305,11 @@ After changing the theme, navigate to the LoginRadius Auth Page using `lr demo`
We can update the Registration Page schema using the `lr add schema` command. Use the `lr get schema` command with `--active` or `--all` flags to get the current Registration fields or view all available fields with their schemas. You can also configure addtional features by choosing the `setup advance configuration` option.
See the image below for a visual representation of the command flow.
-
+
In the below image 2 fields have been added to the registration schema, `Confirm Password` and `Gender`. To view the changes, navigate to the LoginRadius Auth Page using `lr demo`command.
-
+
> Instead of using the `lr demo` command, you can also view the **LoginRadius Auth Page** by visiting locahost:3000 and following the same workflow as explained earlier.
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_schema.png b/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_schema.png
deleted file mode 100644
index 649835941..000000000
Binary files a/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_schema.png and /dev/null differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_schema.webp b/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_schema.webp
new file mode 100644
index 000000000..4d3082979
Binary files /dev/null and b/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_schema.webp differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_social.png b/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_social.png
deleted file mode 100644
index 8cc28ac6a..000000000
Binary files a/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_social.png and /dev/null differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_social.webp b/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_social.webp
new file mode 100644
index 000000000..bdb6fae88
Binary files /dev/null and b/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_social.webp differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_theme.png b/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_theme.png
deleted file mode 100644
index 7b95e3890..000000000
Binary files a/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_theme.png and /dev/null differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_theme.webp b/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_theme.webp
new file mode 100644
index 000000000..2626c404b
Binary files /dev/null and b/content/engineering/implement-authentication-in-react-using-loginradius-cli/lr_theme.webp differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/register_page.png b/content/engineering/implement-authentication-in-react-using-loginradius-cli/register_page.png
deleted file mode 100644
index a9ca655d8..000000000
Binary files a/content/engineering/implement-authentication-in-react-using-loginradius-cli/register_page.png and /dev/null differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/register_page.webp b/content/engineering/implement-authentication-in-react-using-loginradius-cli/register_page.webp
new file mode 100644
index 000000000..4864dddce
Binary files /dev/null and b/content/engineering/implement-authentication-in-react-using-loginradius-cli/register_page.webp differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/set_theme.png b/content/engineering/implement-authentication-in-react-using-loginradius-cli/set_theme.png
deleted file mode 100644
index dd354cab4..000000000
Binary files a/content/engineering/implement-authentication-in-react-using-loginradius-cli/set_theme.png and /dev/null differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/set_theme.webp b/content/engineering/implement-authentication-in-react-using-loginradius-cli/set_theme.webp
new file mode 100644
index 000000000..c62663836
Binary files /dev/null and b/content/engineering/implement-authentication-in-react-using-loginradius-cli/set_theme.webp differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/whitelist_error.png b/content/engineering/implement-authentication-in-react-using-loginradius-cli/whitelist_error.png
deleted file mode 100644
index d034c1980..000000000
Binary files a/content/engineering/implement-authentication-in-react-using-loginradius-cli/whitelist_error.png and /dev/null differ
diff --git a/content/engineering/implement-authentication-in-react-using-loginradius-cli/whitelist_error.webp b/content/engineering/implement-authentication-in-react-using-loginradius-cli/whitelist_error.webp
new file mode 100644
index 000000000..3bf4105a3
Binary files /dev/null and b/content/engineering/implement-authentication-in-react-using-loginradius-cli/whitelist_error.webp differ
diff --git a/content/engineering/implement-facebook-social-login/Zoie-FacebookBlog.png b/content/engineering/implement-facebook-social-login/Zoie-FacebookBlog.png
deleted file mode 100644
index 77de55323..000000000
Binary files a/content/engineering/implement-facebook-social-login/Zoie-FacebookBlog.png and /dev/null differ
diff --git a/content/engineering/implement-facebook-social-login/Zoie-FacebookBlog.webp b/content/engineering/implement-facebook-social-login/Zoie-FacebookBlog.webp
new file mode 100644
index 000000000..b9f201c70
Binary files /dev/null and b/content/engineering/implement-facebook-social-login/Zoie-FacebookBlog.webp differ
diff --git a/content/engineering/implement-facebook-social-login/fb-feat-img.png b/content/engineering/implement-facebook-social-login/fb-feat-img.png
deleted file mode 100644
index a0187c4c6..000000000
Binary files a/content/engineering/implement-facebook-social-login/fb-feat-img.png and /dev/null differ
diff --git a/content/engineering/implement-facebook-social-login/fb-feat-img.webp b/content/engineering/implement-facebook-social-login/fb-feat-img.webp
new file mode 100644
index 000000000..e761841bf
Binary files /dev/null and b/content/engineering/implement-facebook-social-login/fb-feat-img.webp differ
diff --git a/content/engineering/implement-facebook-social-login/index.md b/content/engineering/implement-facebook-social-login/index.md
index 4f35a65f9..94f467f73 100644
--- a/content/engineering/implement-facebook-social-login/index.md
+++ b/content/engineering/implement-facebook-social-login/index.md
@@ -1,7 +1,7 @@
---
title: "How to Implement Facebook Social Login"
date: "2015-02-24"
-coverImage: "fb-feat-img.png"
+coverImage: "fb-feat-img.webp"
author: "Zoie Carnegie"
tags: ["Facebook", "SocialLogin"]
---
@@ -89,7 +89,7 @@ Now if you save this page as index.html and open it in a browser you should see
**Facebook Page example**
-
+
Log In and look at the console output. You’ll now see some basic info including id, email, first\_name, gender, last\_name, link, locale, name, timezone, updated\_time, verified
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/add_login_method.png b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/add_login_method.png
deleted file mode 100644
index aec16f963..000000000
Binary files a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/add_login_method.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/add_login_method.webp b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/add_login_method.webp
new file mode 100644
index 000000000..67e137ff1
Binary files /dev/null and b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/add_login_method.webp differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/angulat_demo_auth.jpg b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/angulat_demo_auth.jpg
deleted file mode 100644
index 7a97cdc6b..000000000
Binary files a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/angulat_demo_auth.jpg and /dev/null differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/angulat_demo_auth.webp b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/angulat_demo_auth.webp
new file mode 100644
index 000000000..505ab5091
Binary files /dev/null and b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/angulat_demo_auth.webp differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/index.md b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/index.md
index 26d28baa5..46409861b 100644
--- a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/index.md
+++ b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/index.md
@@ -1,7 +1,7 @@
---
title: "Implement Authentication in Angular 2+ application using LoginRadius CLI in 5 mins"
date: "2021-04-14"
-coverImage: "angulat_demo_auth.jpg"
+coverImage: "angulat_demo_auth.webp"
author: "Mohammed Modi"
description: "In this tutorial, you will learn about how to implement the authentication for Angular 2+ application in just 5 mins. We will be using LoginRadius for authentication."
tags: ["Authentication", "Angular", "CLI", "LoginRadius CLI"]
@@ -44,7 +44,7 @@ $ lr register
This command will open the Loginradius in the browser to register yourself and create the app.
-
+
Once you successfully register you will be able to see the below message on the browser, you can close the tab and come back to the CLI.
@@ -56,19 +56,19 @@ You are Successfully Authenticated, Kindly Close this browser window and go back
Once you **login/register** using the CLI, You can now run the `lr get config` command to get your API credentials.
-
+
### Configuring Callback URLs
A callback URL is a URL in your application where LoginRadius redirects the user after they have authenticated. The callback URL for your app must be added to your Application Configuration. If this field is not set, users will be unable to log in to the application and get an error.
-
+
To get the list of whitelisted domains, you can run `lr get domain` command from the cmd prompt. And to add a domain in the list using `lr add domain` command.
> If you are following this tutorial, you should set the `http://localhost` as a whitelisted domain. Check the below image for how to add the domain using LoginRadius CLI.
-
+
### Setup Angular application
@@ -298,21 +298,21 @@ Run `ng serve` to start the local server, and you will be able to see the output
You can configure the LoginRadius Auth Page by adding social login methods like Facebook, Google, etc. To add the login method, you can use the command `lr get social` and `lr add social` command. Check the below image on how to add the social configuration.
-
+
After adding, visit the LoginRadius Auth Page either by visiting `locahost:4200` and log out. Or using the command `lr demo`. You will find the new login method added.
-
+
### Customizing theme for LoginRadius Auth Page
LoginRadius Dashboard Support three pre-defined themes for you. You can check out the [Theme Customization](https://dashboard.loginradius.com/auth-page) section in the LoginRadius Dashboard for all the customization options available.
-
+
You can also get/set your current theme using LoginRadius CLI by using the commands like `lr get theme` and `lr set theme`.
-
+
### Adding/Updating Registeration Schema for LoginRadius Auth Page
@@ -320,7 +320,7 @@ LoginRadius Auth Page supports 3 predefined fields for LoginRadius Auth Page i.e
Check out the below commands to add the new registration field in your LoginRadius Application. After adding the new schema field you can always check your LoginRadius Auth Page by running `lr demo` command from the terminal.
-
+
### LoginRadius Site Management
@@ -328,7 +328,7 @@ LoginRadius Dashboard provides a feature where you can create and manage multipl
With the help of LoginRadius CLI you can manage your sites via terminal using commands like `lr get site`, `lr set site`, `lr add site`, `lr delete site`.
-
+
### Contributing to LoginRadius CLI
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_domain.png b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_domain.png
deleted file mode 100644
index 0ceb29665..000000000
Binary files a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_domain.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_domain.webp b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_domain.webp
new file mode 100644
index 000000000..a713033b9
Binary files /dev/null and b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_domain.webp differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_social.png b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_social.png
deleted file mode 100644
index d7be4ff15..000000000
Binary files a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_social.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_social.webp b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_social.webp
new file mode 100644
index 000000000..8d4c00bca
Binary files /dev/null and b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_add_social.webp differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_get_config.png b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_get_config.png
deleted file mode 100644
index 9602857f7..000000000
Binary files a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_get_config.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_get_config.webp b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_get_config.webp
new file mode 100644
index 000000000..d95ee9028
Binary files /dev/null and b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/lr_get_config.webp differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/registration_schema.png b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/registration_schema.png
deleted file mode 100644
index d5bc77ab7..000000000
Binary files a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/registration_schema.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/registration_schema.webp b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/registration_schema.webp
new file mode 100644
index 000000000..1fcb247f7
Binary files /dev/null and b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/registration_schema.webp differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/resgister_page.png b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/resgister_page.png
deleted file mode 100644
index 6718ae9db..000000000
Binary files a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/resgister_page.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/resgister_page.webp b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/resgister_page.webp
new file mode 100644
index 000000000..c32837e4b
Binary files /dev/null and b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/resgister_page.webp differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/site_management.png b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/site_management.png
deleted file mode 100644
index 112fa3eb9..000000000
Binary files a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/site_management.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/site_management.webp b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/site_management.webp
new file mode 100644
index 000000000..009514fdb
Binary files /dev/null and b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/site_management.webp differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_cli.png b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_cli.png
deleted file mode 100644
index 485261c31..000000000
Binary files a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_cli.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_cli.webp b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_cli.webp
new file mode 100644
index 000000000..445e15de0
Binary files /dev/null and b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_cli.webp differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_custom.png b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_custom.png
deleted file mode 100644
index fafcf95cb..000000000
Binary files a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_custom.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_custom.webp b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_custom.webp
new file mode 100644
index 000000000..4fc9038e4
Binary files /dev/null and b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/theme_custom.webp differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/whitelist_domain_error.png b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/whitelist_domain_error.png
deleted file mode 100644
index 6d58c358c..000000000
Binary files a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/whitelist_domain_error.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/whitelist_domain_error.webp b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/whitelist_domain_error.webp
new file mode 100644
index 000000000..7d999284e
Binary files /dev/null and b/content/engineering/implementing-authentication-in-angular-2-plus-with-loginradius-cli/whitelist_domain_error.webp differ
diff --git a/content/engineering/implementing-authentication-on-vuejs-using-jwt/AppWorkflow.png b/content/engineering/implementing-authentication-on-vuejs-using-jwt/AppWorkflow.png
deleted file mode 100644
index ccb5c2c7a..000000000
Binary files a/content/engineering/implementing-authentication-on-vuejs-using-jwt/AppWorkflow.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-on-vuejs-using-jwt/AppWorkflow.webp b/content/engineering/implementing-authentication-on-vuejs-using-jwt/AppWorkflow.webp
new file mode 100644
index 000000000..a957c898f
Binary files /dev/null and b/content/engineering/implementing-authentication-on-vuejs-using-jwt/AppWorkflow.webp differ
diff --git a/content/engineering/implementing-authentication-on-vuejs-using-jwt/coverimage.png b/content/engineering/implementing-authentication-on-vuejs-using-jwt/coverimage.png
deleted file mode 100644
index bbf757aff..000000000
Binary files a/content/engineering/implementing-authentication-on-vuejs-using-jwt/coverimage.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-on-vuejs-using-jwt/coverimage.webp b/content/engineering/implementing-authentication-on-vuejs-using-jwt/coverimage.webp
new file mode 100644
index 000000000..a944cb8ff
Binary files /dev/null and b/content/engineering/implementing-authentication-on-vuejs-using-jwt/coverimage.webp differ
diff --git a/content/engineering/implementing-authentication-on-vuejs-using-jwt/index.md b/content/engineering/implementing-authentication-on-vuejs-using-jwt/index.md
index de0359ac1..977cf50c9 100644
--- a/content/engineering/implementing-authentication-on-vuejs-using-jwt/index.md
+++ b/content/engineering/implementing-authentication-on-vuejs-using-jwt/index.md
@@ -1,7 +1,7 @@
---
title: "Implementing Authentication on Vue.js using JWTtoken"
date: "2021-06-02"
-coverImage: "coverimage.png"
+coverImage: "coverimage.webp"
author: "Uma Victor"
tags: ["Auth","JWT","Vue.js"]
description: "In recent times, when building a modern application, users are required to verify their identity. The process by which we carry out this verification is what we call authentication, and in this tutorial, we would look at how we can carry out this task using JWTauthentication on a Vuejs app."
@@ -13,7 +13,7 @@ In this tutorial, we will be covering some authentication concepts and learn abo
In our app, we have a login form. The user enters a username and password that is then posted to an endpoint. The flow of the app is the user opens the app, then the login page appears, the user submits the login form, which makes a post request to a login endpoint, then we check if the username and password check out, then we return a JWT and store the token in vuex and depending on the token we display a different page.
-
+
## Setting up our Vue app
@@ -127,7 +127,7 @@ export default {
```
-
+
For the login method that runs when you click the button, we would like to perform an HTTP request to our express backend. We want to make a post request to our `/login` route we will create in our server.
@@ -382,7 +382,6 @@ In this tutorial, we looked at how to authenticate a person using the JSON web t
## Resources
- [GIthub souce code](https://github.com/LoginRadius/engineering-blog-samples/tree/master/Vuejs/AuthenticationUsingJWT)
-- [jwt.io](https://jwt.io/)
- [What are json web token](https://www.loginradius.com/blog/engineering/jwt/)
diff --git a/content/engineering/implementing-authentication-on-vuejs-using-jwt/loginForm.png b/content/engineering/implementing-authentication-on-vuejs-using-jwt/loginForm.png
deleted file mode 100644
index 4b22d038d..000000000
Binary files a/content/engineering/implementing-authentication-on-vuejs-using-jwt/loginForm.png and /dev/null differ
diff --git a/content/engineering/implementing-authentication-on-vuejs-using-jwt/loginForm.webp b/content/engineering/implementing-authentication-on-vuejs-using-jwt/loginForm.webp
new file mode 100644
index 000000000..adca0a8e8
Binary files /dev/null and b/content/engineering/implementing-authentication-on-vuejs-using-jwt/loginForm.webp differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Credentials.jpeg b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Credentials.jpeg
deleted file mode 100644
index 0e2e65a7f..000000000
Binary files a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Credentials.jpeg and /dev/null differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Credentials.webp b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Credentials.webp
new file mode 100644
index 000000000..5b1594949
Binary files /dev/null and b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Credentials.webp differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Setup.jpeg b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Setup.jpeg
deleted file mode 100644
index b452c9b85..000000000
Binary files a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Setup.jpeg and /dev/null differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Setup.webp b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Setup.webp
new file mode 100644
index 000000000..e3d4affe7
Binary files /dev/null and b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/App-Setup.webp differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/OIDC-App.jpeg b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/OIDC-App.jpeg
deleted file mode 100644
index 8899ced96..000000000
Binary files a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/OIDC-App.jpeg and /dev/null differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/OIDC-App.webp b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/OIDC-App.webp
new file mode 100644
index 000000000..a8486f03f
Binary files /dev/null and b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/OIDC-App.webp differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/Whitelisting-Domain.jpeg b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/Whitelisting-Domain.jpeg
deleted file mode 100644
index 984c87d38..000000000
Binary files a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/Whitelisting-Domain.jpeg and /dev/null differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/Whitelisting-Domain.webp b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/Whitelisting-Domain.webp
new file mode 100644
index 000000000..3e87379bd
Binary files /dev/null and b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/Whitelisting-Domain.webp differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/coverImage.jpeg b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/coverImage.jpeg
deleted file mode 100644
index 092b5fb63..000000000
Binary files a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/coverImage.jpeg and /dev/null differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/coverImage.webp b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/coverImage.webp
new file mode 100644
index 000000000..ea7110bc9
Binary files /dev/null and b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/coverImage.webp differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/implementing-oidc-sso.png b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/implementing-oidc-sso.png
deleted file mode 100644
index c35df650d..000000000
Binary files a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/implementing-oidc-sso.png and /dev/null differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/implementing-oidc-sso.webp b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/implementing-oidc-sso.webp
new file mode 100644
index 000000000..1922eba47
Binary files /dev/null and b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/implementing-oidc-sso.webp differ
diff --git a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/index.md b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/index.md
index 36b8a40de..189f5ec61 100644
--- a/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/index.md
+++ b/content/engineering/implementing-oidc-sso-loginradius-as-identity-provider/index.md
@@ -1,7 +1,7 @@
---
title: "How to Implement OpenID Connect (OIDC) SSO with LoginRadius?"
date: "2024-05-30"
-coverImage: "implementing-oidc-sso.png"
+coverImage: "implementing-oidc-sso.webp"
author: "Sanjay Velu"
tags: ["SSO", "OIDC", "LoginRadius"]
description: "In this tutorial, you will learn how to implement Single Sign-On (SSO) using OpenID Connect (OIDC) with LoginRadius as your Identity Provider."
@@ -33,18 +33,18 @@ After setting up the OIDC app from the LoginRadius dashboard, you'll use the [`g
Go to [OIDC Application Configuration](https://adminconsole.loginradius.com/platform-configuration/access-configuration/federated-sso/openid-connect) and click on **Add App button**
-
+
Enter the **App name** and click one of the following:
**Native App**, **Single page App** or **Web App** according to your application.
-
+
After clicking the **Create** button, you'll get the OIDC application configuration page. This page contains details like your application's **Client ID** and **Client Secret**, which are necessary for setting up the OIDC provider and configuration when you code in Golang.
-
+
#### Upon reaching the configuration page for your OIDC Application, you'll encounter a variety of fields ripe for customization:
@@ -72,7 +72,7 @@ To ensure seamless redirection of requests and successful callbacks to your endp
1) Click on the __Add New Site__ button.
2) Enter the domain name of the website (example: "`https://localhost:8080`").
-
+
### Whitelisting Domain from OIDC Application Configuration
diff --git a/content/engineering/importance-of-rpa/RPA.jpg b/content/engineering/importance-of-rpa/RPA.jpg
deleted file mode 100644
index 23b3262e9..000000000
Binary files a/content/engineering/importance-of-rpa/RPA.jpg and /dev/null differ
diff --git a/content/engineering/importance-of-rpa/RPA.webp b/content/engineering/importance-of-rpa/RPA.webp
new file mode 100644
index 000000000..f6bdc1a42
Binary files /dev/null and b/content/engineering/importance-of-rpa/RPA.webp differ
diff --git a/content/engineering/importance-of-rpa/index.md b/content/engineering/importance-of-rpa/index.md
index 76e958b2e..6f2b07aa2 100644
--- a/content/engineering/importance-of-rpa/index.md
+++ b/content/engineering/importance-of-rpa/index.md
@@ -1,7 +1,7 @@
---
title: "Why RPA is important for businesses"
date: "2020-10-23"
-coverImage: "RPA.jpg"
+coverImage: "RPA.webp"
author: "Vikram Jain"
description: "It's very important for every business to evolve with technologies, understand their customers needs and and market senitment to sustain and grow.This article will give you some insights that how RPA can help in that with different industries/domain."
tags: ["Engineering","RPA","Automation"]
diff --git a/content/engineering/importance-of-search-functionality-for-websites/index.md b/content/engineering/importance-of-search-functionality-for-websites/index.md
index 0b7438477..df820fc1e 100644
--- a/content/engineering/importance-of-search-functionality-for-websites/index.md
+++ b/content/engineering/importance-of-search-functionality-for-websites/index.md
@@ -1,7 +1,7 @@
---
title: "Why Implement Search Functionality for Your Websites"
date: "2022-02-24"
-coverImage: "search-functionality.png"
+coverImage: "search-functionality.webp"
author: "Neha Vyas"
tags: ["Search"]
description: "Adding a search functionality is important for any website to improve user experience. Read more to understand the benefits of enabling search on your website."
diff --git a/content/engineering/importance-of-search-functionality-for-websites/search-functionality.png b/content/engineering/importance-of-search-functionality-for-websites/search-functionality.png
deleted file mode 100644
index 05c2900e4..000000000
Binary files a/content/engineering/importance-of-search-functionality-for-websites/search-functionality.png and /dev/null differ
diff --git a/content/engineering/importance-of-search-functionality-for-websites/search-functionality.webp b/content/engineering/importance-of-search-functionality-for-websites/search-functionality.webp
new file mode 100644
index 000000000..3dbace030
Binary files /dev/null and b/content/engineering/importance-of-search-functionality-for-websites/search-functionality.webp differ
diff --git a/content/engineering/index-in-mongodb/index.md b/content/engineering/index-in-mongodb/index.md
index 40d956a05..3029be9a4 100644
--- a/content/engineering/index-in-mongodb/index.md
+++ b/content/engineering/index-in-mongodb/index.md
@@ -1,7 +1,7 @@
---
title: "Index in MongoDB"
date: "2015-09-01"
-coverImage: "mongo-db-index1.png"
+coverImage: "mongo-db-index1.webp"
author: "Mark Duan"
tags: ["MongoDB", "Database"]
---
diff --git a/content/engineering/index-in-mongodb/mongo-db-index1.png b/content/engineering/index-in-mongodb/mongo-db-index1.png
deleted file mode 100644
index c83d36bf3..000000000
Binary files a/content/engineering/index-in-mongodb/mongo-db-index1.png and /dev/null differ
diff --git a/content/engineering/index-in-mongodb/mongo-db-index1.webp b/content/engineering/index-in-mongodb/mongo-db-index1.webp
new file mode 100644
index 000000000..d981ddaa4
Binary files /dev/null and b/content/engineering/index-in-mongodb/mongo-db-index1.webp differ
diff --git a/content/engineering/integrate-invisible-captcha-for-bot-protection/configure-invisible-reCAPTCHA.png b/content/engineering/integrate-invisible-captcha-for-bot-protection/configure-invisible-reCAPTCHA.png
deleted file mode 100644
index 9ddf566f7..000000000
Binary files a/content/engineering/integrate-invisible-captcha-for-bot-protection/configure-invisible-reCAPTCHA.png and /dev/null differ
diff --git a/content/engineering/integrate-invisible-captcha-for-bot-protection/configure-invisible-reCAPTCHA.webp b/content/engineering/integrate-invisible-captcha-for-bot-protection/configure-invisible-reCAPTCHA.webp
new file mode 100644
index 000000000..65b590de4
Binary files /dev/null and b/content/engineering/integrate-invisible-captcha-for-bot-protection/configure-invisible-reCAPTCHA.webp differ
diff --git a/content/engineering/integrate-invisible-captcha-for-bot-protection/index.md b/content/engineering/integrate-invisible-captcha-for-bot-protection/index.md
index 6e2e30127..1f9937f10 100644
--- a/content/engineering/integrate-invisible-captcha-for-bot-protection/index.md
+++ b/content/engineering/integrate-invisible-captcha-for-bot-protection/index.md
@@ -1,7 +1,7 @@
---
title: "How to Integrate Invisible reCAPTCHA for Bot Protection"
date: "2022-04-08"
-coverImage: "configure-invisible-reCAPTCHA.png"
+coverImage: "configure-invisible-reCAPTCHA.webp"
author: "Versha Gupta"
tags: ["reCAPTCHA", "LoginRadius"]
description: "If you only want to integrate reCAPTCHA invisibly on specific pages, LoginRadius can help you. This tutorial explains how you can quickly integrate invisible reCAPTCHA."
diff --git a/content/engineering/integrate-linkedin-social-login-website/index.md b/content/engineering/integrate-linkedin-social-login-website/index.md
index 504586870..e0534648f 100644
--- a/content/engineering/integrate-linkedin-social-login-website/index.md
+++ b/content/engineering/integrate-linkedin-social-login-website/index.md
@@ -1,7 +1,7 @@
---
title: "Integrating LinkedIn Social Login on a Website"
date: "2015-02-11"
-coverImage: "linkedin-feat-img.png"
+coverImage: "linkedin-feat-img.webp"
author: "Lucius Yu"
tags: ["LinkedIn", "SocialLogin"]
---
@@ -16,7 +16,7 @@ Creating an app for the social platform is always the first step, no matter whic
After creating the app, you need to set the "JavaScript API domain" field for your app. In that field, fill in your website URL. Here we have used `http://localhost` for this article.
-
+
Implement the script in your html file
@@ -30,7 +30,7 @@ api_key: your_api_key_goes_here
You can find your API key inside your application, the first entry under OAuth Keys "Consumer Key / API Key." This script is used to load the LinkedIn script into your website, and it will not display anything on your page, at least not the frontend.
-
+
Next, you will need to add another script inside your body tag. It is actually used to display the sign-in button.
@@ -42,6 +42,6 @@ Hello, ; .
If everything has been implemented correctly, load your page, and you will see this lovely button appear on your site.
-
+
Want to extend your social systems with additional provider functionality? Check out this post on [Twitter social login](https://www.loginradius.com/blog/engineering/integrating-twitter-social-login/ "Integrating Twitter Social Login").
diff --git a/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.png b/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.png
deleted file mode 100644
index f0bff849b..000000000
Binary files a/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.png and /dev/null differ
diff --git a/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.webp b/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.webp
new file mode 100644
index 000000000..11b23ddc1
Binary files /dev/null and b/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.webp differ
diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.png b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.png
deleted file mode 100644
index ad581eb43..000000000
Binary files a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.png and /dev/null differ
diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.webp b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.webp
new file mode 100644
index 000000000..f877ae1a3
Binary files /dev/null and b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.webp differ
diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.png b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.png
deleted file mode 100644
index 9e02353c7..000000000
Binary files a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.png and /dev/null differ
diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.webp b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.webp
new file mode 100644
index 000000000..04d28a83b
Binary files /dev/null and b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.webp differ
diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.png b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.png
deleted file mode 100644
index a2815f4d5..000000000
Binary files a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.png and /dev/null differ
diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.webp b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.webp
new file mode 100644
index 000000000..1a7923c6e
Binary files /dev/null and b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.webp differ
diff --git a/content/engineering/intro-curl-fsockopen/fsock-and-curl.png b/content/engineering/intro-curl-fsockopen/fsock-and-curl.png
deleted file mode 100644
index 1a83a41a5..000000000
Binary files a/content/engineering/intro-curl-fsockopen/fsock-and-curl.png and /dev/null differ
diff --git a/content/engineering/intro-curl-fsockopen/fsock-and-curl.webp b/content/engineering/intro-curl-fsockopen/fsock-and-curl.webp
new file mode 100644
index 000000000..e1f574844
Binary files /dev/null and b/content/engineering/intro-curl-fsockopen/fsock-and-curl.webp differ
diff --git a/content/engineering/intro-curl-fsockopen/index.md b/content/engineering/intro-curl-fsockopen/index.md
index cc3ad1aab..802a4c55d 100644
--- a/content/engineering/intro-curl-fsockopen/index.md
+++ b/content/engineering/intro-curl-fsockopen/index.md
@@ -1,7 +1,7 @@
---
title: "An Intro to Curl & Fsockopen"
date: "2015-03-09"
-coverImage: "fsock-and-curl.png"
+coverImage: "fsock-and-curl.webp"
author: "Zoie Carnegie"
tags: ["curl", "Fsock"]
---
diff --git a/content/engineering/introducing-loginradius-cli/api-cred.png b/content/engineering/introducing-loginradius-cli/api-cred.png
deleted file mode 100644
index bc88c1ce8..000000000
Binary files a/content/engineering/introducing-loginradius-cli/api-cred.png and /dev/null differ
diff --git a/content/engineering/introducing-loginradius-cli/api-cred.webp b/content/engineering/introducing-loginradius-cli/api-cred.webp
new file mode 100644
index 000000000..55f27194d
Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/api-cred.webp differ
diff --git a/content/engineering/introducing-loginradius-cli/cli.png b/content/engineering/introducing-loginradius-cli/cli.png
deleted file mode 100644
index 949819b0b..000000000
Binary files a/content/engineering/introducing-loginradius-cli/cli.png and /dev/null differ
diff --git a/content/engineering/introducing-loginradius-cli/cli.webp b/content/engineering/introducing-loginradius-cli/cli.webp
new file mode 100644
index 000000000..8123de361
Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/cli.webp differ
diff --git a/content/engineering/introducing-loginradius-cli/domain.png b/content/engineering/introducing-loginradius-cli/domain.png
deleted file mode 100644
index 19ec31333..000000000
Binary files a/content/engineering/introducing-loginradius-cli/domain.png and /dev/null differ
diff --git a/content/engineering/introducing-loginradius-cli/domain.webp b/content/engineering/introducing-loginradius-cli/domain.webp
new file mode 100644
index 000000000..47a823f8a
Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/domain.webp differ
diff --git a/content/engineering/introducing-loginradius-cli/index.md b/content/engineering/introducing-loginradius-cli/index.md
index e29531581..c335e0327 100644
--- a/content/engineering/introducing-loginradius-cli/index.md
+++ b/content/engineering/introducing-loginradius-cli/index.md
@@ -1,7 +1,7 @@
---
title: "Introducing LoginRadius CLI"
date: "2021-07-02"
-coverImage: "cli.png"
+coverImage: "cli.webp"
author: "Mohammed Modi"
description: "LoginRadius CLI helps you to perform basic actions of your LoginRadius Dashboard through the command line. The actions include login, register, logout, email configuration, domain whitelisting, etc."
tags: ["Authentication", "DevTools", "CLI", "LoginRadius CLI"]
@@ -20,25 +20,25 @@ Check out a few examples of how LoginRadius CLI can help manage your [Loginradiu
### Login/Register to your LoginRadius Dashboard
-
+
This command will help you to log in to the CLI. Once you logged in to the CLI, you can configure all your LoginRadius Applications through CLI.
### Manage your App Credentials
-
+
Get your API Credentials in a single command. You can also reset your secret and generate sott using the LoginRadius CLI.
### Domain Whitelisting
-
+
Manage your white-listed domain for your application with simple commands.
### Theme Management
-
+
You can update the LoginRadius IDX Page theme from the predefined themes available through LoginRadius CLI.
@@ -46,7 +46,7 @@ You can update the LoginRadius IDX Page theme from the predefined themes availab
### Add Social Logins
-
+
With the help of LoginRadius CLI, you can add social logins to your LoginRadius IDX Page.
diff --git a/content/engineering/introducing-loginradius-cli/login.png b/content/engineering/introducing-loginradius-cli/login.png
deleted file mode 100644
index d46bab8ff..000000000
Binary files a/content/engineering/introducing-loginradius-cli/login.png and /dev/null differ
diff --git a/content/engineering/introducing-loginradius-cli/login.webp b/content/engineering/introducing-loginradius-cli/login.webp
new file mode 100644
index 000000000..4a8036d38
Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/login.webp differ
diff --git a/content/engineering/introducing-loginradius-cli/social.png b/content/engineering/introducing-loginradius-cli/social.png
deleted file mode 100644
index 5d11c56b2..000000000
Binary files a/content/engineering/introducing-loginradius-cli/social.png and /dev/null differ
diff --git a/content/engineering/introducing-loginradius-cli/social.webp b/content/engineering/introducing-loginradius-cli/social.webp
new file mode 100644
index 000000000..df633364a
Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/social.webp differ
diff --git a/content/engineering/introducing-loginradius-cli/theme.png b/content/engineering/introducing-loginradius-cli/theme.png
deleted file mode 100644
index 4753b2146..000000000
Binary files a/content/engineering/introducing-loginradius-cli/theme.png and /dev/null differ
diff --git a/content/engineering/introducing-loginradius-cli/theme.webp b/content/engineering/introducing-loginradius-cli/theme.webp
new file mode 100644
index 000000000..76424695b
Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/theme.webp differ
diff --git a/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.png b/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.png
deleted file mode 100644
index eb6c08a90..000000000
Binary files a/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.png and /dev/null differ
diff --git a/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.webp b/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.webp
new file mode 100644
index 000000000..ca1c968ab
Binary files /dev/null and b/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.webp differ
diff --git a/content/engineering/introduction-of-Idx-Auto-Tester/index.md b/content/engineering/introduction-of-Idx-Auto-Tester/index.md
index 064e21d55..d20c60a9e 100644
--- a/content/engineering/introduction-of-Idx-Auto-Tester/index.md
+++ b/content/engineering/introduction-of-Idx-Auto-Tester/index.md
@@ -1,7 +1,7 @@
---
title: "Introduction of Idx-Auto-Tester"
date: "2020-06-22"
-coverImage: idx-auto-tester.png
+coverImage: idx-auto-tester.webp
author: Himanshi Sharma
tags: ["Automation", "Idx-Auto-Tester"]
---
diff --git a/content/engineering/introduction-to-android-studio/configure.png b/content/engineering/introduction-to-android-studio/configure.png
deleted file mode 100644
index a3c7b654c..000000000
Binary files a/content/engineering/introduction-to-android-studio/configure.png and /dev/null differ
diff --git a/content/engineering/introduction-to-android-studio/configure.webp b/content/engineering/introduction-to-android-studio/configure.webp
new file mode 100644
index 000000000..fa1b12a87
Binary files /dev/null and b/content/engineering/introduction-to-android-studio/configure.webp differ
diff --git a/content/engineering/introduction-to-android-studio/cover.png b/content/engineering/introduction-to-android-studio/cover.png
deleted file mode 100644
index 6753d4a1d..000000000
Binary files a/content/engineering/introduction-to-android-studio/cover.png and /dev/null differ
diff --git a/content/engineering/introduction-to-android-studio/cover.webp b/content/engineering/introduction-to-android-studio/cover.webp
new file mode 100644
index 000000000..df717daf1
Binary files /dev/null and b/content/engineering/introduction-to-android-studio/cover.webp differ
diff --git a/content/engineering/introduction-to-android-studio/empty.png b/content/engineering/introduction-to-android-studio/empty.png
deleted file mode 100644
index ad4462ebe..000000000
Binary files a/content/engineering/introduction-to-android-studio/empty.png and /dev/null differ
diff --git a/content/engineering/introduction-to-android-studio/empty.webp b/content/engineering/introduction-to-android-studio/empty.webp
new file mode 100644
index 000000000..cf664244f
Binary files /dev/null and b/content/engineering/introduction-to-android-studio/empty.webp differ
diff --git a/content/engineering/introduction-to-android-studio/gradle.png b/content/engineering/introduction-to-android-studio/gradle.png
deleted file mode 100644
index e195933b1..000000000
Binary files a/content/engineering/introduction-to-android-studio/gradle.png and /dev/null differ
diff --git a/content/engineering/introduction-to-android-studio/gradle.webp b/content/engineering/introduction-to-android-studio/gradle.webp
new file mode 100644
index 000000000..ba11e8df0
Binary files /dev/null and b/content/engineering/introduction-to-android-studio/gradle.webp differ
diff --git a/content/engineering/introduction-to-android-studio/index.md b/content/engineering/introduction-to-android-studio/index.md
index 4d6caadf2..e70719c98 100644
--- a/content/engineering/introduction-to-android-studio/index.md
+++ b/content/engineering/introduction-to-android-studio/index.md
@@ -1,7 +1,7 @@
---
title: "Introduction to Android Studio"
date: "2020-10-30"
-coverImage: "cover.png"
+coverImage: "cover.webp"
author: "Prithviraj Biswas"
tags: ["Android Studio", "Android App"]
description: "Getting Started with Android Studio and making your first app."
@@ -29,30 +29,30 @@ To create the application, we will follow these steps through the process in a p
**Step 1. Open your Android Studio after installing, and this following screen appears after starting:**
-
+
**Step 2. Click on "Start a New Android Project" and choose the activity we want the project to be. For me, I'm selecting an empty activity.**
-
+
**Step 3. Configure your project by changing the project's name and the desired language the user wants to code with. Android Studio supports two languages, i.e., Java and Kotlin. The user can also choose their desired API, like which android version they want to run, and then click on finish.**
-
+
**Step 4.Wait until your Gradle build finishes successfully and find your java and .xml file from folders of the app, as shown in the given image.**
-
+
**Step 5. Click onto your .xml file to see the initial layout of the file like the given image. You can drag and drop from the palette's items and change your layout by dragging and dropping.**
-
+
**Step 6. At last, Run your file by the run button on the top right corner in your emulator configured.**
diff --git a/content/engineering/introduction-to-android-studio/welcomepage.png b/content/engineering/introduction-to-android-studio/welcomepage.png
deleted file mode 100644
index ea83e6485..000000000
Binary files a/content/engineering/introduction-to-android-studio/welcomepage.png and /dev/null differ
diff --git a/content/engineering/introduction-to-android-studio/welcomepage.webp b/content/engineering/introduction-to-android-studio/welcomepage.webp
new file mode 100644
index 000000000..d838044bc
Binary files /dev/null and b/content/engineering/introduction-to-android-studio/welcomepage.webp differ
diff --git a/content/engineering/introduction-to-android-studio/xml.png b/content/engineering/introduction-to-android-studio/xml.png
deleted file mode 100644
index b561e8ee9..000000000
Binary files a/content/engineering/introduction-to-android-studio/xml.png and /dev/null differ
diff --git a/content/engineering/introduction-to-android-studio/xml.webp b/content/engineering/introduction-to-android-studio/xml.webp
new file mode 100644
index 000000000..99d5d3e60
Binary files /dev/null and b/content/engineering/introduction-to-android-studio/xml.webp differ
diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.jpg b/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.jpg
deleted file mode 100644
index 5a2b1a7cd..000000000
Binary files a/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.jpg and /dev/null differ
diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.webp b/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.webp
new file mode 100644
index 000000000..504ea65d4
Binary files /dev/null and b/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.webp differ
diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.png b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.png
deleted file mode 100644
index d23f6847e..000000000
Binary files a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.png and /dev/null differ
diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.webp b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.webp
new file mode 100644
index 000000000..c0659f6ae
Binary files /dev/null and b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.webp differ
diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.png b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.png
deleted file mode 100644
index 100dba0ec..000000000
Binary files a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.png and /dev/null differ
diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.webp b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.webp
new file mode 100644
index 000000000..8e22f9acf
Binary files /dev/null and b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.webp differ
diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.png b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.png
deleted file mode 100644
index ae905c6a2..000000000
Binary files a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.png and /dev/null differ
diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.webp b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.webp
new file mode 100644
index 000000000..d333238b1
Binary files /dev/null and b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.webp differ
diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/index.md b/content/engineering/introduction-to-cross-site-request-forgery-csrf/index.md
index 73daaacfa..961be21ef 100644
--- a/content/engineering/introduction-to-cross-site-request-forgery-csrf/index.md
+++ b/content/engineering/introduction-to-cross-site-request-forgery-csrf/index.md
@@ -1,7 +1,7 @@
---
title: "Introduction to Cross-Site Request Forgery (CSRF)"
date: "2019-10-30"
-coverImage: "crosspath.jpg"
+coverImage: "crosspath.webp"
author: "Andy Yeung"
tags: ["CSRF"]
---
@@ -18,7 +18,7 @@ In order to understand CSRF, it is important to know how cookies and authenticat
CSRF takes advantage of the storage of auth tokens in the browser, and constructs http requests to a target server on behalf of the user. Imitating http requests from the legitimate site requires research and preparation from the attacker beforehand, such as finding vulnerable websites and api’s suitable for the attack.
-
+
Here is a high-level example of an CSRF attack. Note that some details are excluded for simplicity, but the key aspects are included.
@@ -35,11 +35,11 @@ Here is a high-level example of an CSRF attack. Note that some details are exclu
A common and effective way of mitigating CSRF is called the double submit cookie. Essentially the client will have two paired and encrypted tokens: one hidden in the page HTML and the other stored as a cookie.
-
+
When a request is made by the client, both tokens are sent to the server, and the server will then ensure the tokens are valid pairs before processing the request as normal.
-
+
Now the attacker will be unable to perform CSRF since they will not have access to the token hidden in the pages HTML, and the target server requires a valid token pair before processing the request.
diff --git a/content/engineering/introduction-to-redux-saga/index.md b/content/engineering/introduction-to-redux-saga/index.md
index 49c378776..0a5ffdf9f 100644
--- a/content/engineering/introduction-to-redux-saga/index.md
+++ b/content/engineering/introduction-to-redux-saga/index.md
@@ -1,7 +1,7 @@
---
title: "Introduction to Redux Saga"
date: "2020-11-23"
-coverImage: "unsplash.png"
+coverImage: "unsplash.webp"
author: "Nick Chim"
tags: ["React", "Redux", "Redux Saga"]
description: "A high level introduction to Redux Saga."
diff --git a/content/engineering/introduction-to-redux-saga/unsplash.png b/content/engineering/introduction-to-redux-saga/unsplash.png
deleted file mode 100644
index d819c8d4d..000000000
Binary files a/content/engineering/introduction-to-redux-saga/unsplash.png and /dev/null differ
diff --git a/content/engineering/introduction-to-redux-saga/unsplash.webp b/content/engineering/introduction-to-redux-saga/unsplash.webp
new file mode 100644
index 000000000..ffd590e92
Binary files /dev/null and b/content/engineering/introduction-to-redux-saga/unsplash.webp differ
diff --git a/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.png b/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.png
deleted file mode 100644
index 56594b24b..000000000
Binary files a/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.png and /dev/null differ
diff --git a/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.webp b/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.webp
new file mode 100644
index 000000000..d5fabdb6b
Binary files /dev/null and b/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.webp differ
diff --git a/content/engineering/introduction-to-web-accessibility-with-semantic-html5/index.md b/content/engineering/introduction-to-web-accessibility-with-semantic-html5/index.md
index dede71e96..3a1a9b2ef 100644
--- a/content/engineering/introduction-to-web-accessibility-with-semantic-html5/index.md
+++ b/content/engineering/introduction-to-web-accessibility-with-semantic-html5/index.md
@@ -1,7 +1,7 @@
---
title: "Introduction to Web Accessibility with Semantic HTML5"
date: "2019-07-24"
-coverImage: "handicapped.png"
+coverImage: "handicapped.webp"
author: "Greg Sakai"
tags: ["HTML5", "HTML", "Web Accessibility", "Semantic HTML5"]
---
diff --git a/content/engineering/invalidating-jwt/index.md b/content/engineering/invalidating-jwt/index.md
index c1fa33052..6b6f280d8 100644
--- a/content/engineering/invalidating-jwt/index.md
+++ b/content/engineering/invalidating-jwt/index.md
@@ -1,7 +1,7 @@
---
title: "Invalidating JSON Web Tokens"
date: "2021-01-18"
-coverImage: "unsplash.png"
+coverImage: "unsplash.webp"
author: "Nick Chim"
tags: ["JSON Web Tokens", "JWT"]
description: "A discussion on invalidating JSON Web Tokens."
diff --git a/content/engineering/invalidating-jwt/unsplash.png b/content/engineering/invalidating-jwt/unsplash.png
deleted file mode 100644
index 2d5233f89..000000000
Binary files a/content/engineering/invalidating-jwt/unsplash.png and /dev/null differ
diff --git a/content/engineering/invalidating-jwt/unsplash.webp b/content/engineering/invalidating-jwt/unsplash.webp
new file mode 100644
index 000000000..8f859b68b
Binary files /dev/null and b/content/engineering/invalidating-jwt/unsplash.webp differ
diff --git a/content/engineering/is-your-database-secured-think-again/database_secure-300x300.png b/content/engineering/is-your-database-secured-think-again/database_secure-300x300.png
deleted file mode 100644
index a6a0de596..000000000
Binary files a/content/engineering/is-your-database-secured-think-again/database_secure-300x300.png and /dev/null differ
diff --git a/content/engineering/is-your-database-secured-think-again/database_secure-300x300.webp b/content/engineering/is-your-database-secured-think-again/database_secure-300x300.webp
new file mode 100644
index 000000000..8cde27bcb
Binary files /dev/null and b/content/engineering/is-your-database-secured-think-again/database_secure-300x300.webp differ
diff --git a/content/engineering/is-your-database-secured-think-again/index.md b/content/engineering/is-your-database-secured-think-again/index.md
index dc7ea38f1..97a7d3686 100644
--- a/content/engineering/is-your-database-secured-think-again/index.md
+++ b/content/engineering/is-your-database-secured-think-again/index.md
@@ -1,7 +1,7 @@
---
title: "Is Your Database Secured? Think Again"
date: "2016-02-23"
-coverImage: "database_secure-300x300.png"
+coverImage: "database_secure-300x300.webp"
author: "Kunal"
tags: ["Database", "Security"]
---
@@ -10,7 +10,7 @@ tags: ["Database", "Security"]
Many known attacks are possible only once physically accessing a machine. For this reason, it is best to have the application server and the database server on different machines. If this is not possible, greater care must be taken, Otherwise, by executing remote commands via an application server, an attacker may be able to harm your database even without permissions. For this reason, any service running on the same machine as the database should be granted the lowest possible permission that still allows the service to operate.
-
+
Do not forget to install the whole security package: Antivirus and Anti-spam, Firewall, and all of the security packages recommended by your operating system's vendor. Also, do not forget to spend 10 minutes thinking of your server's physical location - in the wrong location, your server can be stolen, flooded, harmed by wild animals or vagrants.
**2\. Localhost Security or Disable or restrict remote access**
diff --git a/content/engineering/is-your-database-secured-think-again/server-network-structure.png b/content/engineering/is-your-database-secured-think-again/server-network-structure.png
deleted file mode 100644
index d9126c16a..000000000
Binary files a/content/engineering/is-your-database-secured-think-again/server-network-structure.png and /dev/null differ
diff --git a/content/engineering/is-your-database-secured-think-again/server-network-structure.webp b/content/engineering/is-your-database-secured-think-again/server-network-structure.webp
new file mode 100644
index 000000000..10c0f96f4
Binary files /dev/null and b/content/engineering/is-your-database-secured-think-again/server-network-structure.webp differ
diff --git a/content/engineering/istio-installation-and-service-configuration/Istio.png b/content/engineering/istio-installation-and-service-configuration/Istio.png
deleted file mode 100644
index 84227923d..000000000
Binary files a/content/engineering/istio-installation-and-service-configuration/Istio.png and /dev/null differ
diff --git a/content/engineering/istio-installation-and-service-configuration/Istio.webp b/content/engineering/istio-installation-and-service-configuration/Istio.webp
new file mode 100644
index 000000000..b7f0cf718
Binary files /dev/null and b/content/engineering/istio-installation-and-service-configuration/Istio.webp differ
diff --git a/content/engineering/istio-installation-and-service-configuration/index.md b/content/engineering/istio-installation-and-service-configuration/index.md
index a2ab4b7e9..0e3389ded 100644
--- a/content/engineering/istio-installation-and-service-configuration/index.md
+++ b/content/engineering/istio-installation-and-service-configuration/index.md
@@ -1,7 +1,7 @@
---
title: "How to Install and Configure Istio"
date: "2021-01-22"
-coverImage: "Istio.png"
+coverImage: "Istio.webp"
author: "Piyush Kumar"
tags: ["Istio", "Service Mesh"]
description: "This article will provide a step by step process on how to install and configure services using Istio."
diff --git a/content/engineering/istio-service-mesh/Istio.png b/content/engineering/istio-service-mesh/Istio.png
deleted file mode 100644
index 84227923d..000000000
Binary files a/content/engineering/istio-service-mesh/Istio.png and /dev/null differ
diff --git a/content/engineering/istio-service-mesh/Istio.webp b/content/engineering/istio-service-mesh/Istio.webp
new file mode 100644
index 000000000..b7f0cf718
Binary files /dev/null and b/content/engineering/istio-service-mesh/Istio.webp differ
diff --git a/content/engineering/istio-service-mesh/index.md b/content/engineering/istio-service-mesh/index.md
index 51566e38b..0211dff94 100644
--- a/content/engineering/istio-service-mesh/index.md
+++ b/content/engineering/istio-service-mesh/index.md
@@ -1,7 +1,7 @@
---
title: "Istio Service Mesh: A Beginners Guide"
date: "2020-12-07"
-coverImage: "Istio.png"
+coverImage: "Istio.webp"
author: "Piyush Kumar"
tags: ["Istio", "Service Mesh"]
description: "This post will give a high-level introduction to Istio and its related concepts and terminologies."
@@ -29,7 +29,7 @@ The data plane is composed of Envoy proxy deployed as sidecars. Envoy itself is
The control plane manages and configures the proxies to route traffic.
-
+
## Istio Core Components
diff --git a/content/engineering/jamstack-introduction/image1.png b/content/engineering/jamstack-introduction/image1.png
deleted file mode 100644
index 137994c20..000000000
Binary files a/content/engineering/jamstack-introduction/image1.png and /dev/null differ
diff --git a/content/engineering/jamstack-introduction/image1.webp b/content/engineering/jamstack-introduction/image1.webp
new file mode 100644
index 000000000..c230068d7
Binary files /dev/null and b/content/engineering/jamstack-introduction/image1.webp differ
diff --git a/content/engineering/jamstack-introduction/index.md b/content/engineering/jamstack-introduction/index.md
index 350967a1f..f5a375f14 100644
--- a/content/engineering/jamstack-introduction/index.md
+++ b/content/engineering/jamstack-introduction/index.md
@@ -1,7 +1,7 @@
---
title: "Introduction to JAMstack"
date: "2020-10-29"
-coverImage: "jamstack_cover.png"
+coverImage: "jamstack_cover.webp"
author: "Versha Gupta"
tags: ["Jamstack", "Web"]
description: "You may have heard the term JAMstack before, but you may not have understood what it means. In this article, We will introduce you to JAMstack as to why you need, best practice, and value."
@@ -47,7 +47,7 @@ We can easily understand the JAMstack value when comparing it with a monolithic
In a JAMstack architecture, the page request does not go to the server for Html because it directly fetches Html from CDN, where the Html file has been pre-built, and it's ready to be downloaded; that's why no server is involved here.
## Workflow comparison (JAMstack vs. traditional)
-
+
**Traditional workflow**
diff --git a/content/engineering/jamstack-introduction/jamstack_cover.png b/content/engineering/jamstack-introduction/jamstack_cover.png
deleted file mode 100644
index a387544ea..000000000
Binary files a/content/engineering/jamstack-introduction/jamstack_cover.png and /dev/null differ
diff --git a/content/engineering/jamstack-introduction/jamstack_cover.webp b/content/engineering/jamstack-introduction/jamstack_cover.webp
new file mode 100644
index 000000000..78654d68c
Binary files /dev/null and b/content/engineering/jamstack-introduction/jamstack_cover.webp differ
diff --git a/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.png b/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.png
deleted file mode 100644
index 523441449..000000000
Binary files a/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.png and /dev/null differ
diff --git a/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.webp b/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.webp
new file mode 100644
index 000000000..74c11cdfc
Binary files /dev/null and b/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.webp differ
diff --git a/content/engineering/javascript-events-bubbling-capturing-and-propagation/index.md b/content/engineering/javascript-events-bubbling-capturing-and-propagation/index.md
index acbecf47b..581b7883b 100644
--- a/content/engineering/javascript-events-bubbling-capturing-and-propagation/index.md
+++ b/content/engineering/javascript-events-bubbling-capturing-and-propagation/index.md
@@ -1,7 +1,7 @@
---
title: "JavaScript Events: Bubbling, Capturing, and Propagation"
date: "2019-07-22"
-coverImage: "bubbles.png"
+coverImage: "bubbles.webp"
author: "Greg Sakai"
tags: ["JavaScript", "JavaScript Events"]
---
diff --git a/content/engineering/jwt-authentication-with-deno/deno_jwt.png b/content/engineering/jwt-authentication-with-deno/deno_jwt.png
deleted file mode 100644
index eacd80fd3..000000000
Binary files a/content/engineering/jwt-authentication-with-deno/deno_jwt.png and /dev/null differ
diff --git a/content/engineering/jwt-authentication-with-deno/deno_jwt.webp b/content/engineering/jwt-authentication-with-deno/deno_jwt.webp
new file mode 100644
index 000000000..574400abf
Binary files /dev/null and b/content/engineering/jwt-authentication-with-deno/deno_jwt.webp differ
diff --git a/content/engineering/jwt-authentication-with-deno/index.md b/content/engineering/jwt-authentication-with-deno/index.md
index 22960fd5e..0626c026d 100644
--- a/content/engineering/jwt-authentication-with-deno/index.md
+++ b/content/engineering/jwt-authentication-with-deno/index.md
@@ -1,7 +1,7 @@
---
title: How to create and validate JSON Web Tokens in Deno
date: "2020-07-10"
-coverImage: "deno_jwt.png"
+coverImage: "deno_jwt.webp"
author: "Puneet Singh"
tags: ["Deno","JWT", "JSON Web Token"]
canonical: https://www.loginradius.com/blog/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/
diff --git a/content/engineering/jwt-signing-algorithms/index.md b/content/engineering/jwt-signing-algorithms/index.md
index e7ca4ea74..2e4abb384 100644
--- a/content/engineering/jwt-signing-algorithms/index.md
+++ b/content/engineering/jwt-signing-algorithms/index.md
@@ -1,7 +1,7 @@
---
title: "JWT Signing Algorithms"
date: "2020-09-24"
-coverImage: "unsplash.png"
+coverImage: "unsplash.webp"
author: "Nick Chim"
tags: ["JWT", "JSON Web Tokens"]
description: "Deciding between which signing algorithm to use."
diff --git a/content/engineering/jwt-signing-algorithms/unsplash.png b/content/engineering/jwt-signing-algorithms/unsplash.png
deleted file mode 100644
index 96b7605d6..000000000
Binary files a/content/engineering/jwt-signing-algorithms/unsplash.png and /dev/null differ
diff --git a/content/engineering/jwt-signing-algorithms/unsplash.webp b/content/engineering/jwt-signing-algorithms/unsplash.webp
new file mode 100644
index 000000000..ec6be2234
Binary files /dev/null and b/content/engineering/jwt-signing-algorithms/unsplash.webp differ
diff --git a/content/engineering/jwt/index.md b/content/engineering/jwt/index.md
index c2a8ae40f..08ed6dec7 100644
--- a/content/engineering/jwt/index.md
+++ b/content/engineering/jwt/index.md
@@ -1,7 +1,7 @@
---
title: "What is JSON Web Token"
date: "2018-07-11"
-coverImage: "jwt.png"
+coverImage: "jwt.webp"
author: "Mayank Agarwal"
tags: ["JWT", "JSON Web Token"]
---
diff --git a/content/engineering/jwt/jwt.png b/content/engineering/jwt/jwt.png
deleted file mode 100644
index 466bf7075..000000000
Binary files a/content/engineering/jwt/jwt.png and /dev/null differ
diff --git a/content/engineering/jwt/jwt.webp b/content/engineering/jwt/jwt.webp
new file mode 100644
index 000000000..be661c497
Binary files /dev/null and b/content/engineering/jwt/jwt.webp differ
diff --git a/content/engineering/lazy-loading-in-react/index.md b/content/engineering/lazy-loading-in-react/index.md
index e87c18ac0..a88beadcd 100644
--- a/content/engineering/lazy-loading-in-react/index.md
+++ b/content/engineering/lazy-loading-in-react/index.md
@@ -1,7 +1,7 @@
---
title: "Lazy loading in React"
date: "2020-10-05"
-coverImage: "react.jpg"
+coverImage: "react.webp"
author: "Akshay Avinash"
tags: ["React", "Lazy loading", "React Suspense"]
description: "Learn about lazy loading in React and how/when to use it"
diff --git a/content/engineering/lazy-loading-in-react/react.jpg b/content/engineering/lazy-loading-in-react/react.jpg
deleted file mode 100644
index 533f9505f..000000000
Binary files a/content/engineering/lazy-loading-in-react/react.jpg and /dev/null differ
diff --git a/content/engineering/lazy-loading-in-react/react.webp b/content/engineering/lazy-loading-in-react/react.webp
new file mode 100644
index 000000000..715664070
Binary files /dev/null and b/content/engineering/lazy-loading-in-react/react.webp differ
diff --git a/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.png b/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.png
deleted file mode 100644
index ac3d8fc9a..000000000
Binary files a/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.png and /dev/null differ
diff --git a/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.webp b/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.webp
new file mode 100644
index 000000000..883138998
Binary files /dev/null and b/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.webp differ
diff --git a/content/engineering/learn-to-code-using-10-websites/index.md b/content/engineering/learn-to-code-using-10-websites/index.md
index b32454784..fbb269874 100644
--- a/content/engineering/learn-to-code-using-10-websites/index.md
+++ b/content/engineering/learn-to-code-using-10-websites/index.md
@@ -1,7 +1,7 @@
---
title: "Learn How To Code Using The 10 Cool Websites"
date: "2016-10-21"
-coverImage: "How-to-code-using-the-10-cool-websites-768x564-300x220.png"
+coverImage: "How-to-code-using-the-10-cool-websites-768x564-300x220.webp"
author: "Team LoginRadius"
tags: ["Courses", "Learning Websites"]
---
diff --git a/content/engineering/learning-how-to-code/begin-code-300x300.png b/content/engineering/learning-how-to-code/begin-code-300x300.png
deleted file mode 100644
index 2d1e67868..000000000
Binary files a/content/engineering/learning-how-to-code/begin-code-300x300.png and /dev/null differ
diff --git a/content/engineering/learning-how-to-code/begin-code-300x300.webp b/content/engineering/learning-how-to-code/begin-code-300x300.webp
new file mode 100644
index 000000000..4884327a3
Binary files /dev/null and b/content/engineering/learning-how-to-code/begin-code-300x300.webp differ
diff --git a/content/engineering/learning-how-to-code/index.md b/content/engineering/learning-how-to-code/index.md
index 419d1e53c..74569b4c0 100644
--- a/content/engineering/learning-how-to-code/index.md
+++ b/content/engineering/learning-how-to-code/index.md
@@ -1,7 +1,7 @@
---
title: "Learning How to Code"
date: "2015-12-29"
-coverImage: "begin-code-300x300.png"
+coverImage: "begin-code-300x300.webp"
author: "Carling"
tags: ["Learning", "Coding", "Learning resources"]
---
diff --git a/content/engineering/lets-encrypt-with-ssl-certificates/index.md b/content/engineering/lets-encrypt-with-ssl-certificates/index.md
index f746130c9..2f63bc997 100644
--- a/content/engineering/lets-encrypt-with-ssl-certificates/index.md
+++ b/content/engineering/lets-encrypt-with-ssl-certificates/index.md
@@ -1,7 +1,7 @@
---
title: "Let's Encrypt with SSL Certificates"
date: "2019-01-14"
-coverImage: "ssl.png"
+coverImage: "ssl.webp"
author: "Ruben Gonzalez"
tags: ["SSL", "SSL Certificate", "Security"]
---
diff --git a/content/engineering/lets-encrypt-with-ssl-certificates/ssl.png b/content/engineering/lets-encrypt-with-ssl-certificates/ssl.png
deleted file mode 100644
index 95a298ad1..000000000
Binary files a/content/engineering/lets-encrypt-with-ssl-certificates/ssl.png and /dev/null differ
diff --git a/content/engineering/lets-encrypt-with-ssl-certificates/ssl.webp b/content/engineering/lets-encrypt-with-ssl-certificates/ssl.webp
new file mode 100644
index 000000000..b0b76cc96
Binary files /dev/null and b/content/engineering/lets-encrypt-with-ssl-certificates/ssl.webp differ
diff --git a/content/engineering/lets-take-meme-break/1.png b/content/engineering/lets-take-meme-break/1.png
deleted file mode 100644
index 2b3e3a733..000000000
Binary files a/content/engineering/lets-take-meme-break/1.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/1.webp b/content/engineering/lets-take-meme-break/1.webp
new file mode 100644
index 000000000..9e7efefbb
Binary files /dev/null and b/content/engineering/lets-take-meme-break/1.webp differ
diff --git a/content/engineering/lets-take-meme-break/10.png b/content/engineering/lets-take-meme-break/10.png
deleted file mode 100644
index accb23516..000000000
Binary files a/content/engineering/lets-take-meme-break/10.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/10.webp b/content/engineering/lets-take-meme-break/10.webp
new file mode 100644
index 000000000..04dcdb7bc
Binary files /dev/null and b/content/engineering/lets-take-meme-break/10.webp differ
diff --git a/content/engineering/lets-take-meme-break/11.png b/content/engineering/lets-take-meme-break/11.png
deleted file mode 100644
index 369ef692d..000000000
Binary files a/content/engineering/lets-take-meme-break/11.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/11.webp b/content/engineering/lets-take-meme-break/11.webp
new file mode 100644
index 000000000..aa38c4190
Binary files /dev/null and b/content/engineering/lets-take-meme-break/11.webp differ
diff --git a/content/engineering/lets-take-meme-break/12.png b/content/engineering/lets-take-meme-break/12.png
deleted file mode 100644
index 1d35db1b5..000000000
Binary files a/content/engineering/lets-take-meme-break/12.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/12.webp b/content/engineering/lets-take-meme-break/12.webp
new file mode 100644
index 000000000..3ddb4fbdb
Binary files /dev/null and b/content/engineering/lets-take-meme-break/12.webp differ
diff --git a/content/engineering/lets-take-meme-break/13.png b/content/engineering/lets-take-meme-break/13.png
deleted file mode 100644
index 100d21aef..000000000
Binary files a/content/engineering/lets-take-meme-break/13.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/13.webp b/content/engineering/lets-take-meme-break/13.webp
new file mode 100644
index 000000000..08360cf39
Binary files /dev/null and b/content/engineering/lets-take-meme-break/13.webp differ
diff --git a/content/engineering/lets-take-meme-break/14.png b/content/engineering/lets-take-meme-break/14.png
deleted file mode 100644
index cb1c5cdf4..000000000
Binary files a/content/engineering/lets-take-meme-break/14.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/14.webp b/content/engineering/lets-take-meme-break/14.webp
new file mode 100644
index 000000000..c4258266c
Binary files /dev/null and b/content/engineering/lets-take-meme-break/14.webp differ
diff --git a/content/engineering/lets-take-meme-break/15.png b/content/engineering/lets-take-meme-break/15.png
deleted file mode 100644
index d9dbe333f..000000000
Binary files a/content/engineering/lets-take-meme-break/15.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/15.webp b/content/engineering/lets-take-meme-break/15.webp
new file mode 100644
index 000000000..0a0fe8702
Binary files /dev/null and b/content/engineering/lets-take-meme-break/15.webp differ
diff --git a/content/engineering/lets-take-meme-break/16.png b/content/engineering/lets-take-meme-break/16.png
deleted file mode 100644
index 0eb166953..000000000
Binary files a/content/engineering/lets-take-meme-break/16.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/16.webp b/content/engineering/lets-take-meme-break/16.webp
new file mode 100644
index 000000000..575525a99
Binary files /dev/null and b/content/engineering/lets-take-meme-break/16.webp differ
diff --git a/content/engineering/lets-take-meme-break/17.png b/content/engineering/lets-take-meme-break/17.png
deleted file mode 100644
index 0d2e3d2b6..000000000
Binary files a/content/engineering/lets-take-meme-break/17.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/17.webp b/content/engineering/lets-take-meme-break/17.webp
new file mode 100644
index 000000000..4415498fe
Binary files /dev/null and b/content/engineering/lets-take-meme-break/17.webp differ
diff --git a/content/engineering/lets-take-meme-break/18.png b/content/engineering/lets-take-meme-break/18.png
deleted file mode 100644
index 1c595c52d..000000000
Binary files a/content/engineering/lets-take-meme-break/18.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/18.webp b/content/engineering/lets-take-meme-break/18.webp
new file mode 100644
index 000000000..06e0103f5
Binary files /dev/null and b/content/engineering/lets-take-meme-break/18.webp differ
diff --git a/content/engineering/lets-take-meme-break/19.png b/content/engineering/lets-take-meme-break/19.png
deleted file mode 100644
index 19e38f2ee..000000000
Binary files a/content/engineering/lets-take-meme-break/19.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/19.webp b/content/engineering/lets-take-meme-break/19.webp
new file mode 100644
index 000000000..d0691e9e9
Binary files /dev/null and b/content/engineering/lets-take-meme-break/19.webp differ
diff --git a/content/engineering/lets-take-meme-break/2.png b/content/engineering/lets-take-meme-break/2.png
deleted file mode 100644
index a55e9ce48..000000000
Binary files a/content/engineering/lets-take-meme-break/2.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/2.webp b/content/engineering/lets-take-meme-break/2.webp
new file mode 100644
index 000000000..ca5c0f20c
Binary files /dev/null and b/content/engineering/lets-take-meme-break/2.webp differ
diff --git a/content/engineering/lets-take-meme-break/20.png b/content/engineering/lets-take-meme-break/20.png
deleted file mode 100644
index c7daa6038..000000000
Binary files a/content/engineering/lets-take-meme-break/20.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/20.webp b/content/engineering/lets-take-meme-break/20.webp
new file mode 100644
index 000000000..bb855c6b5
Binary files /dev/null and b/content/engineering/lets-take-meme-break/20.webp differ
diff --git a/content/engineering/lets-take-meme-break/21.png b/content/engineering/lets-take-meme-break/21.png
deleted file mode 100644
index c1204c35a..000000000
Binary files a/content/engineering/lets-take-meme-break/21.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/21.webp b/content/engineering/lets-take-meme-break/21.webp
new file mode 100644
index 000000000..885e3648d
Binary files /dev/null and b/content/engineering/lets-take-meme-break/21.webp differ
diff --git a/content/engineering/lets-take-meme-break/3.png b/content/engineering/lets-take-meme-break/3.png
deleted file mode 100644
index 3ddc63f4d..000000000
Binary files a/content/engineering/lets-take-meme-break/3.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/3.webp b/content/engineering/lets-take-meme-break/3.webp
new file mode 100644
index 000000000..2238e792f
Binary files /dev/null and b/content/engineering/lets-take-meme-break/3.webp differ
diff --git a/content/engineering/lets-take-meme-break/4.png b/content/engineering/lets-take-meme-break/4.png
deleted file mode 100644
index 28e27a3bc..000000000
Binary files a/content/engineering/lets-take-meme-break/4.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/4.webp b/content/engineering/lets-take-meme-break/4.webp
new file mode 100644
index 000000000..01b75c392
Binary files /dev/null and b/content/engineering/lets-take-meme-break/4.webp differ
diff --git a/content/engineering/lets-take-meme-break/5.jpg b/content/engineering/lets-take-meme-break/5.jpg
deleted file mode 100644
index 2ff12a001..000000000
Binary files a/content/engineering/lets-take-meme-break/5.jpg and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/5.webp b/content/engineering/lets-take-meme-break/5.webp
new file mode 100644
index 000000000..2baf5bbc0
Binary files /dev/null and b/content/engineering/lets-take-meme-break/5.webp differ
diff --git a/content/engineering/lets-take-meme-break/6.png b/content/engineering/lets-take-meme-break/6.png
deleted file mode 100644
index 903fbbca8..000000000
Binary files a/content/engineering/lets-take-meme-break/6.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/6.webp b/content/engineering/lets-take-meme-break/6.webp
new file mode 100644
index 000000000..50c56070a
Binary files /dev/null and b/content/engineering/lets-take-meme-break/6.webp differ
diff --git a/content/engineering/lets-take-meme-break/7.png b/content/engineering/lets-take-meme-break/7.png
deleted file mode 100644
index 4e6ffea2f..000000000
Binary files a/content/engineering/lets-take-meme-break/7.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/7.webp b/content/engineering/lets-take-meme-break/7.webp
new file mode 100644
index 000000000..809521fb5
Binary files /dev/null and b/content/engineering/lets-take-meme-break/7.webp differ
diff --git a/content/engineering/lets-take-meme-break/8.png b/content/engineering/lets-take-meme-break/8.png
deleted file mode 100644
index 22618c3cc..000000000
Binary files a/content/engineering/lets-take-meme-break/8.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/8.webp b/content/engineering/lets-take-meme-break/8.webp
new file mode 100644
index 000000000..cfae7c7a1
Binary files /dev/null and b/content/engineering/lets-take-meme-break/8.webp differ
diff --git a/content/engineering/lets-take-meme-break/9.png b/content/engineering/lets-take-meme-break/9.png
deleted file mode 100644
index 333cbd7b9..000000000
Binary files a/content/engineering/lets-take-meme-break/9.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/9.webp b/content/engineering/lets-take-meme-break/9.webp
new file mode 100644
index 000000000..be4d13878
Binary files /dev/null and b/content/engineering/lets-take-meme-break/9.webp differ
diff --git a/content/engineering/lets-take-meme-break/cover.png b/content/engineering/lets-take-meme-break/cover.png
deleted file mode 100644
index 3eebcf6c4..000000000
Binary files a/content/engineering/lets-take-meme-break/cover.png and /dev/null differ
diff --git a/content/engineering/lets-take-meme-break/cover.webp b/content/engineering/lets-take-meme-break/cover.webp
new file mode 100644
index 000000000..367b66219
Binary files /dev/null and b/content/engineering/lets-take-meme-break/cover.webp differ
diff --git a/content/engineering/lets-take-meme-break/index.md b/content/engineering/lets-take-meme-break/index.md
index 8e1eb9c01..83bde73c9 100644
--- a/content/engineering/lets-take-meme-break/index.md
+++ b/content/engineering/lets-take-meme-break/index.md
@@ -1,7 +1,7 @@
---
title: "Let’s Take A MEME Break!!!"
date: "2020-09-04"
-coverImage: "cover.png"
+coverImage: "cover.webp"
author: "Ashish Sharma"
tags: ["MEME","Programming","Humor"]
---
@@ -17,83 +17,83 @@ MEMEs can light the environment for every programmer in the world. On that note,
### 1. Always ready for new!!! - [Kunal](/author/kunal/)
-
+
### 2. Nothing Changes With Time - [Tanvi Jain](/author/tanvi-jain/)
-
+
### 3. Heaviest Object In The Universe - [Nitesh Jain](/author/nitesh-jain/)
-
+
### 4. Perception!! - [Vikram Jain](/author/vikram-jain/)
-
+
### 5. Maths Always A hurdle !! - [Mohammed Modi](/author/mohammed-modi/)
-
+
### 6. I had a problem so I thought to use Java - [Indrasen Kumar](/author/indrasen-kumar/)
-
+
### 7. Avoid Handshakes. - [Piyush Kumar](/author/piyush-kumar/)
-
+
### 8. I’m Really Unsure About My Own Creation - [Kheenvraj Lomror](/author/kheenvraj-lomror/)
-
+
### 9. That Missing Fact - [Priyadarshan Mohanty](/author/priyadarshan-mohanty/)
-
+
### 10. Every IT Administrator. - [Narendra Pareek](/author/narendra-pareek/)
-
+
### 11. Imma Genius! - [Abhimanyu Singh Rathore](/author/abhimanyu-singh-rathore/)
-
+
### 12. My Logical Thinking as Programmer. - [Ankit Singh](/author/ankit-singh/)
-
+
### 13. HTML is a Programming Language - [Hitesh Kumawat](/author/hitesh-kumawat/)
-
+
### 14. Programmers while Sleeping. - [Versha Gupta](/author/versha-gupta/)
-
+
### 15. Programmer Swag!! - [Gaurav Bewal](/author/gaurav-bewal/)
-
+
### 16. QA Life!! - [Rakesh Pareek](/author/rakesh-pareek/)
-
+
### 17. Infinite... - [Hridayesh Sharma](/author/hridayesh-sharma/)
-
+
### 18. Python Lover!! - [Aman Agrawal](/author/aman-agrawal/)
-
+
### 19. What's your address? - [Vijay Singh Shekhawat](/author/vijay-singh-shekhawat/)
-
+
### 20. Gamer and Programmer - [Chinmaya Pati](/author/chinmaya-pati/)
-
+
If you have better ones, reply in the comments below and we’ll include them.
diff --git a/content/engineering/linkedin-login-using-node-passport/app-credentials.png b/content/engineering/linkedin-login-using-node-passport/app-credentials.png
deleted file mode 100644
index 22b8b817b..000000000
Binary files a/content/engineering/linkedin-login-using-node-passport/app-credentials.png and /dev/null differ
diff --git a/content/engineering/linkedin-login-using-node-passport/app-credentials.webp b/content/engineering/linkedin-login-using-node-passport/app-credentials.webp
new file mode 100644
index 000000000..6aa10d0ca
Binary files /dev/null and b/content/engineering/linkedin-login-using-node-passport/app-credentials.webp differ
diff --git a/content/engineering/linkedin-login-using-node-passport/create-app.png b/content/engineering/linkedin-login-using-node-passport/create-app.png
deleted file mode 100644
index afed68c9c..000000000
Binary files a/content/engineering/linkedin-login-using-node-passport/create-app.png and /dev/null differ
diff --git a/content/engineering/linkedin-login-using-node-passport/create-app.webp b/content/engineering/linkedin-login-using-node-passport/create-app.webp
new file mode 100644
index 000000000..4baaf39fb
Binary files /dev/null and b/content/engineering/linkedin-login-using-node-passport/create-app.webp differ
diff --git a/content/engineering/linkedin-login-using-node-passport/index.md b/content/engineering/linkedin-login-using-node-passport/index.md
index 70b4594c9..de25522fc 100644
--- a/content/engineering/linkedin-login-using-node-passport/index.md
+++ b/content/engineering/linkedin-login-using-node-passport/index.md
@@ -1,7 +1,7 @@
---
title: "LinkedIn Login using Node JS and passport"
date: "2020-06-10"
-coverImage: "linkedin_login_node.png"
+coverImage: "linkedin_login_node.webp"
author: "Aman Agrawal"
tags: ["LinkedIn", "Login", "NodeJs", "PassportJS"]
description: "Learn social login benefits and how we can implement LinkedIn Login on our website or mobile app."
@@ -24,7 +24,7 @@ Passport is an authentication middleware for Node, which authenticates requests
- Go to [Developer Linkedin](https://www.linkedin.com/developers/) and login with your Linkedin account.
- Once you have registered, click on the `create app` link and add the required details to create an app
-
+
Provide basic details about your app:
- App name
@@ -35,7 +35,7 @@ Provide basic details about your app:
- After creating apps go to the `auth` tab in the navigation bar as shown below. You can now copy your secret and ID from here
- 
+ 
2. Now enough, let's move to code, First of all, create a directory named `Linkedin-node-authentication`
@@ -320,10 +320,10 @@ npm start
- 
+ 
Click on the sign in button, and you will be asked to login through Linkedin. Once logged in you will be redirected to profile page as below:
- 
+ 
The complete sample code for the above tutorial can be found [here](https://github.com/LoginRadius/engineering-blog-samples/tree/master/NodeJs/LinkedinLoginPassport)
\ No newline at end of file
diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.png b/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.png
deleted file mode 100644
index eac9b8b24..000000000
Binary files a/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.png and /dev/null differ
diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.webp b/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.webp
new file mode 100644
index 000000000..2e97db849
Binary files /dev/null and b/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.webp differ
diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.png b/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.png
deleted file mode 100644
index 3a15d01e0..000000000
Binary files a/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.png and /dev/null differ
diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.webp b/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.webp
new file mode 100644
index 000000000..a1aa0dc5e
Binary files /dev/null and b/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.webp differ
diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.png b/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.png
deleted file mode 100644
index 32da4b032..000000000
Binary files a/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.png and /dev/null differ
diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.webp b/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.webp
new file mode 100644
index 000000000..f443dfbbd
Binary files /dev/null and b/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.webp differ
diff --git a/content/engineering/list-csharp/coverimage.jpg b/content/engineering/list-csharp/coverimage.jpg
deleted file mode 100644
index a0733a7b0..000000000
Binary files a/content/engineering/list-csharp/coverimage.jpg and /dev/null differ
diff --git a/content/engineering/list-csharp/coverimage.webp b/content/engineering/list-csharp/coverimage.webp
new file mode 100644
index 000000000..317728b16
Binary files /dev/null and b/content/engineering/list-csharp/coverimage.webp differ
diff --git a/content/engineering/list-csharp/index.md b/content/engineering/list-csharp/index.md
index 890826a7c..1e8931dac 100644
--- a/content/engineering/list-csharp/index.md
+++ b/content/engineering/list-csharp/index.md
@@ -1,7 +1,7 @@
---
title: "How to Create List in C#"
date: "2021-02-25"
-coverImage: "coverimage.jpg"
+coverImage: "coverimage.webp"
author: "Hemant Manwani"
tags: ["C#", "List"]
description: "In this article, we will learn how to create lists in C# also how to use the C# list class to add, remove, and search items in a collection of objects."
diff --git a/content/engineering/live-data-migration-mongodb/index.md b/content/engineering/live-data-migration-mongodb/index.md
index a14b337a3..369e7cc2a 100644
--- a/content/engineering/live-data-migration-mongodb/index.md
+++ b/content/engineering/live-data-migration-mongodb/index.md
@@ -1,7 +1,7 @@
---
title: "How to Migrate Data In MongoDB"
date: "2020-12-14"
-coverImage: "index.png"
+coverImage: "index.webp"
author: "Chinmaya Pati"
tags: ["MongoDB"]
description: "This article covers the guide to migrate data from offline or live MongoDB instance using oplog replay alongside mitigate connection switch latency with existing utilities."
diff --git a/content/engineering/live-data-migration-mongodb/index.png b/content/engineering/live-data-migration-mongodb/index.png
deleted file mode 100644
index 67caa5d98..000000000
Binary files a/content/engineering/live-data-migration-mongodb/index.png and /dev/null differ
diff --git a/content/engineering/live-data-migration-mongodb/index.webp b/content/engineering/live-data-migration-mongodb/index.webp
new file mode 100644
index 000000000..dfac39605
Binary files /dev/null and b/content/engineering/live-data-migration-mongodb/index.webp differ
diff --git a/content/engineering/login-with-facebook/facebook-login-wow.png b/content/engineering/login-with-facebook/facebook-login-wow.png
deleted file mode 100644
index 6323b95a1..000000000
Binary files a/content/engineering/login-with-facebook/facebook-login-wow.png and /dev/null differ
diff --git a/content/engineering/login-with-facebook/facebook-login-wow.webp b/content/engineering/login-with-facebook/facebook-login-wow.webp
new file mode 100644
index 000000000..dd845f22e
Binary files /dev/null and b/content/engineering/login-with-facebook/facebook-login-wow.webp differ
diff --git a/content/engineering/login-with-facebook/index.md b/content/engineering/login-with-facebook/index.md
index c6fd19d27..88fb90a60 100644
--- a/content/engineering/login-with-facebook/index.md
+++ b/content/engineering/login-with-facebook/index.md
@@ -1,7 +1,7 @@
---
title: "How to implement Facebook Login"
date: "2020-09-16"
-coverImage: "index.png"
+coverImage: "index.webp"
author: "Vijay Singh Shekhawat"
tags: ["Login With Facebook", "Facebook","Facebook Login", "Login", "Oauth"]
description: "This article will explain about social login benefits and how we can implement Sign In using Facebook on our website or mobile app."
@@ -11,7 +11,7 @@ There are more than 1 million websites or apps are using **"SignIn with Facebook
According to multiple surveys, there are more than 3 billion users worldwide are using social media and it is around 50% of the world's population.
-
+
The biggest challenge and most important things are to make user registration and login quick and easy while developing our application. The registration forms required a lot of data that need to be filled by users manually and it causes lost, potential users. Additionally, users need to enter their usernames/emails and passwords in the login forms to authenticate themselves and also need to remember more individual IDs and passwords.
@@ -31,45 +31,45 @@ Go to [Facebook Developer](https://developers.facebook.com) and log in using you
**NOTE**: Please do not log in using a business account as Facebook will not allow you to create an app if you do so.
-
+
#### Step 2
Select the **My Apps** as displayed on the below screen.
-
+
#### Step 3
Click on **Add a New App** as displayed in the below screen.
-
+
#### Step 4
Input display name and contact email. Once you have done so, click on **Create App ID**
-
+
#### Step 5
In the security check, Complete the security steps and click on the **submit** button.
-
+
#### Step 6
Once you land on the App dashboard, Select Facebook Login, and click **Set Up**.
-
+
#### Step 7
Click on Settings in the sidebar under Facebook Login. Turn on Client OAuth Login. Turn on Web OAuth Login. Put the valid redirect URL on **"Valid OAuth redirect URIs"**. Click on the Save button.
-
+
#### Step 8
Click on Basic under settings in the sidebar. Under App, Domains include your website Url. Enter all the required details. Change the status of the app from Development to Live from the top-right corner. Click on the **Save Changes** button.
Now your Facebook app is ready. You can start implementing Facebook login
-
+
### Data Selection
diff --git a/content/engineering/login-with-facebook/index.png b/content/engineering/login-with-facebook/index.png
deleted file mode 100644
index fc28df2c8..000000000
Binary files a/content/engineering/login-with-facebook/index.png and /dev/null differ
diff --git a/content/engineering/login-with-facebook/index.webp b/content/engineering/login-with-facebook/index.webp
new file mode 100644
index 000000000..40a9b4d62
Binary files /dev/null and b/content/engineering/login-with-facebook/index.webp differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img1.png b/content/engineering/login-with-facebook/loginadius-facebook-img1.png
deleted file mode 100644
index 88d0b1497..000000000
Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img1.png and /dev/null differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img1.webp b/content/engineering/login-with-facebook/loginadius-facebook-img1.webp
new file mode 100644
index 000000000..97d9b4599
Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img1.webp differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img2.png b/content/engineering/login-with-facebook/loginadius-facebook-img2.png
deleted file mode 100644
index 9f1435258..000000000
Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img2.png and /dev/null differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img2.webp b/content/engineering/login-with-facebook/loginadius-facebook-img2.webp
new file mode 100644
index 000000000..3fb0e46f1
Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img2.webp differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img3.png b/content/engineering/login-with-facebook/loginadius-facebook-img3.png
deleted file mode 100644
index 53cfcb0ff..000000000
Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img3.png and /dev/null differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img3.webp b/content/engineering/login-with-facebook/loginadius-facebook-img3.webp
new file mode 100644
index 000000000..bbd755003
Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img3.webp differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img4.png b/content/engineering/login-with-facebook/loginadius-facebook-img4.png
deleted file mode 100644
index e77035ece..000000000
Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img4.png and /dev/null differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img4.webp b/content/engineering/login-with-facebook/loginadius-facebook-img4.webp
new file mode 100644
index 000000000..ef6767da4
Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img4.webp differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img5.png b/content/engineering/login-with-facebook/loginadius-facebook-img5.png
deleted file mode 100644
index 5292f038c..000000000
Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img5.png and /dev/null differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img5.webp b/content/engineering/login-with-facebook/loginadius-facebook-img5.webp
new file mode 100644
index 000000000..d97982a0b
Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img5.webp differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img6.png b/content/engineering/login-with-facebook/loginadius-facebook-img6.png
deleted file mode 100644
index caccd16f9..000000000
Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img6.png and /dev/null differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img6.webp b/content/engineering/login-with-facebook/loginadius-facebook-img6.webp
new file mode 100644
index 000000000..3d9ee634f
Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img6.webp differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img7.png b/content/engineering/login-with-facebook/loginadius-facebook-img7.png
deleted file mode 100644
index b57aa0aeb..000000000
Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img7.png and /dev/null differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img7.webp b/content/engineering/login-with-facebook/loginadius-facebook-img7.webp
new file mode 100644
index 000000000..13bebd091
Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img7.webp differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img8.png b/content/engineering/login-with-facebook/loginadius-facebook-img8.png
deleted file mode 100644
index 9a3f45163..000000000
Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img8.png and /dev/null differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img8.webp b/content/engineering/login-with-facebook/loginadius-facebook-img8.webp
new file mode 100644
index 000000000..11419bae3
Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img8.webp differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img9.png b/content/engineering/login-with-facebook/loginadius-facebook-img9.png
deleted file mode 100644
index f6e58a1c6..000000000
Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img9.png and /dev/null differ
diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img9.webp b/content/engineering/login-with-facebook/loginadius-facebook-img9.webp
new file mode 100644
index 000000000..1750b7201
Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img9.webp differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.png
deleted file mode 100644
index 7771f482e..000000000
Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.png and /dev/null differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.webp
new file mode 100644
index 000000000..ef2546be7
Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.webp differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.png
deleted file mode 100644
index 26efe0f88..000000000
Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.png and /dev/null differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.webp
new file mode 100644
index 000000000..d2c1751df
Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.webp differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.png
deleted file mode 100644
index 094ccea5a..000000000
Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.png and /dev/null differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.webp
new file mode 100644
index 000000000..55a33fb6f
Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.webp differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.png
deleted file mode 100644
index 794345aff..000000000
Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.png and /dev/null differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.webp
new file mode 100644
index 000000000..185d19dec
Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.webp differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.png
deleted file mode 100644
index ac8d117e0..000000000
Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.png and /dev/null differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.webp
new file mode 100644
index 000000000..d30eb1f45
Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.webp differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.png
deleted file mode 100644
index 6f77eea8b..000000000
Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.png and /dev/null differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.webp
new file mode 100644
index 000000000..5101e3eff
Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.webp differ
diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/index.md b/content/engineering/loginradius-launches-cli-enterprise-dashboard/index.md
index fb5563d14..c0eeb5f1b 100644
--- a/content/engineering/loginradius-launches-cli-enterprise-dashboard/index.md
+++ b/content/engineering/loginradius-launches-cli-enterprise-dashboard/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Launches a CLI for Enterprise Dashboard"
date: "2023-01-16"
-coverImage: "cli-1.png"
+coverImage: "cli-1.webp"
author: "Kundan Singh"
tags: ["enterprise", "admin console", "developers"]
description: "We are happy to announce that we have launched LoginRadius CLI for enterprise dashboard."
@@ -35,7 +35,7 @@ To add a domain through LoginRadius Admin Console, you need to: \
On the flip side, you can do this by running a single command:
-
+
**Here are some more of LoginRadius CLI Enterprise's commands:**
@@ -43,7 +43,7 @@ On the flip side, you can do this by running a single command:
**1. Login/Logout to your LoginRadius Dashboard**
-
+
This command (_lr login_) will help you to login to your LoginRadius Enterprise Dashboard. Once logged in, you can perform other operations and configure your LoginRadius Application through CLI.
@@ -51,7 +51,7 @@ This command (_lr login_) will help you to login to your LoginRadius Enterprise
**2. Manage Application Credentials**
-
+
You can get our App Credentials, reset Secret key, update account password and generate SOTT through LoginRadius CLI.
@@ -59,7 +59,7 @@ You can get our App Credentials, reset Secret key, update account password and g
**Set Schema for Your LoginRadius Application**
-
+
@@ -68,7 +68,7 @@ This command will help you set the schema for your application. We can get all t
**Theme Management (LoginRadius Page)**
-
+
You can update the LoginRadius IDX Page(Hosted Page) from the available themes through LoginRadius CLI commands.
@@ -87,4 +87,4 @@ We hope you will love trying LoginRadius CLI for Enterprise Dashboard. We will a
We are eager to know your feedback, test cases and also what we can bring up next in our CLI. If you have any suggestions, please create an issue on our [open source github repository](https://github.com/LoginRadius/lr-cli/issues).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-launches-cli-enterprise-dashboard)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-launches-cli-enterprise-dashboard)
diff --git a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.png b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.png
deleted file mode 100644
index 70406afa9..000000000
Binary files a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.png and /dev/null differ
diff --git a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.webp b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.webp
new file mode 100644
index 000000000..a05b6946a
Binary files /dev/null and b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.webp differ
diff --git a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/index.md b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/index.md
index 656b2d096..0ab4f6355 100644
--- a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/index.md
+++ b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Open Source For Hacktoberfest 2020"
date: "2020-09-25"
-coverImage: "hacktober-fest-banner.png"
+coverImage: "hacktober-fest-banner.webp"
author: "Hridayesh Sharma"
description: "Checkout LoginRadius Open Source Repositories where you can contribute for hackotberfest 2020"
tags: ["hacktoberfest", "open-source", "LoginRadius"]
@@ -15,7 +15,7 @@ Just 1 week left in hacktoberfest 2020 and being part of it, we at LoginRadius a
**Here is a list of our open source projects available on Github for hacktoberfest 2020**
-
+
- [LoginRadius Engineering Portal](https://github.com/LoginRadius/engineering-portal)
- Our Engineering Blog where you can contribute by writing a guest blog of fixing any issue you find with any of the available blogs.
diff --git a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.png b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.png
deleted file mode 100644
index 60a409a33..000000000
Binary files a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.png and /dev/null differ
diff --git a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.webp b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.webp
new file mode 100644
index 000000000..e7547b6d0
Binary files /dev/null and b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.webp differ
diff --git a/content/engineering/loginradius-sponsorship-freecodecamp/cover.png b/content/engineering/loginradius-sponsorship-freecodecamp/cover.png
deleted file mode 100644
index 6f8b4663f..000000000
Binary files a/content/engineering/loginradius-sponsorship-freecodecamp/cover.png and /dev/null differ
diff --git a/content/engineering/loginradius-sponsorship-freecodecamp/cover.webp b/content/engineering/loginradius-sponsorship-freecodecamp/cover.webp
new file mode 100644
index 000000000..1c4016f1d
Binary files /dev/null and b/content/engineering/loginradius-sponsorship-freecodecamp/cover.webp differ
diff --git a/content/engineering/loginradius-sponsorship-freecodecamp/index.md b/content/engineering/loginradius-sponsorship-freecodecamp/index.md
index 91f154505..90af4fbd3 100644
--- a/content/engineering/loginradius-sponsorship-freecodecamp/index.md
+++ b/content/engineering/loginradius-sponsorship-freecodecamp/index.md
@@ -1,7 +1,7 @@
---
title: "One Vision, Many Paths: How We’re Supporting freeCodeCamp"
date: "2021-07-16"
-coverImage: "cover.png"
+coverImage: "cover.webp"
author: "Raghunath Reddy"
tags: ["LoginRadius", "sponsorship", "freeCodeCamp"]
description: "LoginRadius now supports the freeCodeCamp community through a sponsorship program. We also offer $200 credits to freeCodeCamp developers to help them rapidly implement world-class customer identity and access management in their applications."
diff --git a/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.png b/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.png
deleted file mode 100644
index 70406afa9..000000000
Binary files a/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.png and /dev/null differ
diff --git a/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.webp b/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.webp
new file mode 100644
index 000000000..a05b6946a
Binary files /dev/null and b/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.webp differ
diff --git a/content/engineering/loginradius-supports-hacktoberfest-2020/index.md b/content/engineering/loginradius-supports-hacktoberfest-2020/index.md
index d4aba5242..197116dc9 100644
--- a/content/engineering/loginradius-supports-hacktoberfest-2020/index.md
+++ b/content/engineering/loginradius-supports-hacktoberfest-2020/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Supports Hacktoberfest 2020"
date: "2020-09-18"
-coverImage: "hacktober-fest-banner.png"
+coverImage: "hacktober-fest-banner.webp"
author: "Hridayesh Sharma"
description: "Open Source is changing the world, One Pull Request at a time. Join LoginRadius this year in supporting hacktoerbest 2020 by contributing to open source and get cool swags from LoginRadius"
tags: ["hacktoberfest", "open-source", "LoginRadius"]
diff --git a/content/engineering/loginscreen-testing-tips/CoverImage.jpg b/content/engineering/loginscreen-testing-tips/CoverImage.jpg
deleted file mode 100644
index 42d7d27a2..000000000
Binary files a/content/engineering/loginscreen-testing-tips/CoverImage.jpg and /dev/null differ
diff --git a/content/engineering/loginscreen-testing-tips/CoverImage.webp b/content/engineering/loginscreen-testing-tips/CoverImage.webp
new file mode 100644
index 000000000..b488b239c
Binary files /dev/null and b/content/engineering/loginscreen-testing-tips/CoverImage.webp differ
diff --git a/content/engineering/loginscreen-testing-tips/Login-Page.png b/content/engineering/loginscreen-testing-tips/Login-Page.png
deleted file mode 100644
index cbc4ba713..000000000
Binary files a/content/engineering/loginscreen-testing-tips/Login-Page.png and /dev/null differ
diff --git a/content/engineering/loginscreen-testing-tips/Login-Page.webp b/content/engineering/loginscreen-testing-tips/Login-Page.webp
new file mode 100644
index 000000000..ef7be3907
Binary files /dev/null and b/content/engineering/loginscreen-testing-tips/Login-Page.webp differ
diff --git a/content/engineering/loginscreen-testing-tips/index.md b/content/engineering/loginscreen-testing-tips/index.md
index 6b59a35ee..ddcfcbbcb 100644
--- a/content/engineering/loginscreen-testing-tips/index.md
+++ b/content/engineering/loginscreen-testing-tips/index.md
@@ -2,7 +2,7 @@
title: "Login Screen - Tips and Ideas for Testing"
date: "2020-10-30"
author: "Sudhey Sharma"
-coverImage: "CoverImage.jpg"
+coverImage: "CoverImage.webp"
tags: ["LoginScreen", "TestingTips"]
description: "Login process is the most important feature for any system/application as it provides access to an entire web-site/application or part of it. This article is providing you with some important tips & ideas about login testing."
---
@@ -10,7 +10,7 @@ description: "Login process is the most important feature for any system/applica
A **login screen** is a web **page** or an entry **page** to a web/mobile application that requires user identification and authentication, regularly performed by entering a username and password combination.
The login process is the most essential feature for any system/application as it provides access to an entire **web-site/application** or part of it. So, testing of the login screen needs complete coverage.
-
+
Mentioned below are few tips that can be referred for testing the login screen of any system/application.
diff --git a/content/engineering/memcach-memory-management/index.md b/content/engineering/memcach-memory-management/index.md
index 753f00618..c73c605b4 100644
--- a/content/engineering/memcach-memory-management/index.md
+++ b/content/engineering/memcach-memory-management/index.md
@@ -1,7 +1,7 @@
---
title: "Memcached Memory Management"
date: "2015-07-07"
-coverImage: "memcached-memory-management.png"
+coverImage: "memcached-memory-management.webp"
author: "Mark Duan"
tags: ["Memory Management"]
---
@@ -10,7 +10,7 @@ The [memcached](https://github.com/memcached) is one of the most popular open
### Chunk and Slab
-
+
```cpp
/* powers-of-N allocation structures */
@@ -37,7 +37,7 @@ This is the struct declaration of slabclass\_t. Each slab class contains the sam
The content value factor is defined when memcached memory is deployed with -f, which can change the size between slab classes. For this loop, the size is multiplied by a specified factor.
-
+
You can get this information by adding -vvv and you can use the command
diff --git a/content/engineering/memcach-memory-management/memcached-1.png b/content/engineering/memcach-memory-management/memcached-1.png
deleted file mode 100644
index f6ba61e2c..000000000
Binary files a/content/engineering/memcach-memory-management/memcached-1.png and /dev/null differ
diff --git a/content/engineering/memcach-memory-management/memcached-1.webp b/content/engineering/memcach-memory-management/memcached-1.webp
new file mode 100644
index 000000000..c20fb6cac
Binary files /dev/null and b/content/engineering/memcach-memory-management/memcached-1.webp differ
diff --git a/content/engineering/memcach-memory-management/memcached-2.png b/content/engineering/memcach-memory-management/memcached-2.png
deleted file mode 100644
index f3ca4a704..000000000
Binary files a/content/engineering/memcach-memory-management/memcached-2.png and /dev/null differ
diff --git a/content/engineering/memcach-memory-management/memcached-2.webp b/content/engineering/memcach-memory-management/memcached-2.webp
new file mode 100644
index 000000000..030973aa5
Binary files /dev/null and b/content/engineering/memcach-memory-management/memcached-2.webp differ
diff --git a/content/engineering/memcach-memory-management/memcached-memory-management.png b/content/engineering/memcach-memory-management/memcached-memory-management.png
deleted file mode 100644
index cdcf46e1d..000000000
Binary files a/content/engineering/memcach-memory-management/memcached-memory-management.png and /dev/null differ
diff --git a/content/engineering/memcach-memory-management/memcached-memory-management.webp b/content/engineering/memcach-memory-management/memcached-memory-management.webp
new file mode 100644
index 000000000..0cf8ad335
Binary files /dev/null and b/content/engineering/memcach-memory-management/memcached-memory-management.webp differ
diff --git a/content/engineering/memcach-memory-management/memcached1.png b/content/engineering/memcach-memory-management/memcached1.png
deleted file mode 100644
index f6ba61e2c..000000000
Binary files a/content/engineering/memcach-memory-management/memcached1.png and /dev/null differ
diff --git a/content/engineering/memcach-memory-management/memcached1.webp b/content/engineering/memcach-memory-management/memcached1.webp
new file mode 100644
index 000000000..c20fb6cac
Binary files /dev/null and b/content/engineering/memcach-memory-management/memcached1.webp differ
diff --git a/content/engineering/mongodb-as-datasource-in-golang/gomongo.png b/content/engineering/mongodb-as-datasource-in-golang/gomongo.png
deleted file mode 100644
index 3a25b8c59..000000000
Binary files a/content/engineering/mongodb-as-datasource-in-golang/gomongo.png and /dev/null differ
diff --git a/content/engineering/mongodb-as-datasource-in-golang/gomongo.webp b/content/engineering/mongodb-as-datasource-in-golang/gomongo.webp
new file mode 100644
index 000000000..a120a6a10
Binary files /dev/null and b/content/engineering/mongodb-as-datasource-in-golang/gomongo.webp differ
diff --git a/content/engineering/mongodb-as-datasource-in-golang/index.md b/content/engineering/mongodb-as-datasource-in-golang/index.md
index a2a5d76c2..25b87fba6 100644
--- a/content/engineering/mongodb-as-datasource-in-golang/index.md
+++ b/content/engineering/mongodb-as-datasource-in-golang/index.md
@@ -1,7 +1,7 @@
---
title: Using MongoDB as Datasource in GoLang
date: "2020-09-21"
-coverImage: "gomongo.png"
+coverImage: "gomongo.webp"
author: "Puneet Singh"
tags: ["Go","MongoDB"]
description: "Learn how to use MongoDB as a data source for your Go application using the mongo-go driver"
diff --git a/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.png b/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.png
deleted file mode 100644
index eb80e51fa..000000000
Binary files a/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.png and /dev/null differ
diff --git a/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.webp b/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.webp
new file mode 100644
index 000000000..e96a60e28
Binary files /dev/null and b/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.webp differ
diff --git a/content/engineering/my-name-is-darryl-this-is-how-work/index.md b/content/engineering/my-name-is-darryl-this-is-how-work/index.md
index 6f91cccd4..85c1d4f1b 100644
--- a/content/engineering/my-name-is-darryl-this-is-how-work/index.md
+++ b/content/engineering/my-name-is-darryl-this-is-how-work/index.md
@@ -1,7 +1,7 @@
---
title: "Hi, My Name is Darryl, and This is How I Work"
date: "2015-09-22"
-coverImage: "darryl-how-i-work-300x300.png"
+coverImage: "darryl-how-i-work-300x300.webp"
author: "Team LoginRadius"
tags: ["Tools", "Engineering"]
---
@@ -39,4 +39,4 @@ As a normal human being — and not an extraterrestrial or alien as you tiny hum
### Getting out of a sticky situation
-Now that my brain is full of design food. How do I put it to work? There's this thing called a notebook. If you don't know what that is. It looks like this.  This is where I start sketching or wireframing all the things I need before moving on to the digital format. And there you have it. A sneak peek on how I work. I hope that this gave you an idea on how to improve your everyday design life. A word of advice. _There are a thousand ways to do 1 thing. If someone told you it can't be done; prove them wrong._
+Now that my brain is full of design food. How do I put it to work? There's this thing called a notebook. If you don't know what that is. It looks like this.  This is where I start sketching or wireframing all the things I need before moving on to the digital format. And there you have it. A sneak peek on how I work. I hope that this gave you an idea on how to improve your everyday design life. A word of advice. _There are a thousand ways to do 1 thing. If someone told you it can't be done; prove them wrong._
diff --git a/content/engineering/my-name-is-darryl-this-is-how-work/notebook.jpg b/content/engineering/my-name-is-darryl-this-is-how-work/notebook.jpg
deleted file mode 100644
index 7f2a41f29..000000000
Binary files a/content/engineering/my-name-is-darryl-this-is-how-work/notebook.jpg and /dev/null differ
diff --git a/content/engineering/my-name-is-darryl-this-is-how-work/notebook.webp b/content/engineering/my-name-is-darryl-this-is-how-work/notebook.webp
new file mode 100644
index 000000000..33ffc6666
Binary files /dev/null and b/content/engineering/my-name-is-darryl-this-is-how-work/notebook.webp differ
diff --git a/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/index.md b/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/index.md
index 03c99602a..da96acc23 100644
--- a/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/index.md
+++ b/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/index.md
@@ -1,7 +1,7 @@
---
title: "Nim Game, Add Digits, Maximum Depth of Binary Tree"
date: "2015-11-24"
-coverImage: "nim-blog-150x150.png"
+coverImage: "nim-blog-150x150.webp"
author: "Lucius Yu"
tags: ["Nim", "JavaScript"]
---
diff --git a/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.png b/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.png
deleted file mode 100644
index fda13ab89..000000000
Binary files a/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.png and /dev/null differ
diff --git a/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.webp b/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.webp
new file mode 100644
index 000000000..f1f389943
Binary files /dev/null and b/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.webp differ
diff --git a/content/engineering/node-http-module-server/coverImage.jpg b/content/engineering/node-http-module-server/coverImage.jpg
deleted file mode 100644
index 811d5d360..000000000
Binary files a/content/engineering/node-http-module-server/coverImage.jpg and /dev/null differ
diff --git a/content/engineering/node-http-module-server/coverImage.webp b/content/engineering/node-http-module-server/coverImage.webp
new file mode 100644
index 000000000..d63acdaaa
Binary files /dev/null and b/content/engineering/node-http-module-server/coverImage.webp differ
diff --git a/content/engineering/node-http-module-server/index.md b/content/engineering/node-http-module-server/index.md
index 6e4b3c0f6..ebfd7014c 100644
--- a/content/engineering/node-http-module-server/index.md
+++ b/content/engineering/node-http-module-server/index.md
@@ -1,7 +1,7 @@
---
title: "NodeJS Server using Core HTTP Module"
date: "2020-11-27"
-coverImage: "coverImage.jpg"
+coverImage: "coverImage.webp"
author: "Hridayesh Sharma"
tags: ["NodeJs", "JavaScript"]
description: "Let us understand the core http module in NodeJS, which is the basic building block of frameworks like ExpressJS etc."
diff --git a/content/engineering/node-package-manager-npm/image1.png b/content/engineering/node-package-manager-npm/image1.png
deleted file mode 100644
index f15704fc4..000000000
Binary files a/content/engineering/node-package-manager-npm/image1.png and /dev/null differ
diff --git a/content/engineering/node-package-manager-npm/image1.webp b/content/engineering/node-package-manager-npm/image1.webp
new file mode 100644
index 000000000..0c9b03b04
Binary files /dev/null and b/content/engineering/node-package-manager-npm/image1.webp differ
diff --git a/content/engineering/node-package-manager-npm/index.md b/content/engineering/node-package-manager-npm/index.md
index e619106dd..f34f129b0 100644
--- a/content/engineering/node-package-manager-npm/index.md
+++ b/content/engineering/node-package-manager-npm/index.md
@@ -1,12 +1,12 @@
---
title: "Node Package Manager (NPM)"
date: "2017-08-04"
-coverImage: "the-guide-to-NPM.png"
+coverImage: "the-guide-to-NPM.webp"
author: "Eric Chan"
tags: ["NodeJs", "NPM"]
---
-##### What is This, and Why Should I Care?
+##### What is This, and Why Should I Care?
NPM is a package manager for javascript. It is used to share and distribute code amongst the coding community. There are over half a million packages for free developed and shared to help your JavaScript development.
@@ -32,7 +32,7 @@ Head over here to search for your package. Once you’ve found it, type in your
Since NPM packages are open-source, be wary that some of the packages may not be built correctly. A good way to tell would be viewing the top of the page for any errors.
-
+
##### How Do I Keep My Packages Up-To-Date?
diff --git a/content/engineering/node-package-manager-npm/the-guide-to-NPM.png b/content/engineering/node-package-manager-npm/the-guide-to-NPM.png
deleted file mode 100644
index 3697a6b32..000000000
Binary files a/content/engineering/node-package-manager-npm/the-guide-to-NPM.png and /dev/null differ
diff --git a/content/engineering/node-package-manager-npm/the-guide-to-NPM.webp b/content/engineering/node-package-manager-npm/the-guide-to-NPM.webp
new file mode 100644
index 000000000..63167a85d
Binary files /dev/null and b/content/engineering/node-package-manager-npm/the-guide-to-NPM.webp differ
diff --git a/content/engineering/nullable-csharp/coverimage.jpg b/content/engineering/nullable-csharp/coverimage.jpg
deleted file mode 100644
index b385d9396..000000000
Binary files a/content/engineering/nullable-csharp/coverimage.jpg and /dev/null differ
diff --git a/content/engineering/nullable-csharp/coverimage.webp b/content/engineering/nullable-csharp/coverimage.webp
new file mode 100644
index 000000000..fd08894e2
Binary files /dev/null and b/content/engineering/nullable-csharp/coverimage.webp differ
diff --git a/content/engineering/nullable-csharp/index.md b/content/engineering/nullable-csharp/index.md
index 2429b7f89..49fed967a 100644
--- a/content/engineering/nullable-csharp/index.md
+++ b/content/engineering/nullable-csharp/index.md
@@ -1,7 +1,7 @@
---
title: "How to Work with Nullable Types in C#"
date: "2021-01-29"
-coverImage: "coverimage.jpg"
+coverImage: "coverimage.webp"
author: "Hemant Manwani"
tags: ["C#","Nullable"]
description: "Nullable is a term in C# that allows an extra value null to be owned by a form. We will learn in this article how to work with Nullable types in C#."
diff --git a/content/engineering/oAuth-implemenation-using-node/git_new_app.jpg b/content/engineering/oAuth-implemenation-using-node/git_new_app.jpg
deleted file mode 100644
index 367d28e06..000000000
Binary files a/content/engineering/oAuth-implemenation-using-node/git_new_app.jpg and /dev/null differ
diff --git a/content/engineering/oAuth-implemenation-using-node/git_new_app.webp b/content/engineering/oAuth-implemenation-using-node/git_new_app.webp
new file mode 100644
index 000000000..658cbd709
Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/git_new_app.webp differ
diff --git a/content/engineering/oAuth-implemenation-using-node/github_auth.jpg b/content/engineering/oAuth-implemenation-using-node/github_auth.jpg
deleted file mode 100644
index 417fd40e7..000000000
Binary files a/content/engineering/oAuth-implemenation-using-node/github_auth.jpg and /dev/null differ
diff --git a/content/engineering/oAuth-implemenation-using-node/github_auth.webp b/content/engineering/oAuth-implemenation-using-node/github_auth.webp
new file mode 100644
index 000000000..c9bca4b3b
Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/github_auth.webp differ
diff --git a/content/engineering/oAuth-implemenation-using-node/github_cred.jpg b/content/engineering/oAuth-implemenation-using-node/github_cred.jpg
deleted file mode 100644
index 1a5e56be6..000000000
Binary files a/content/engineering/oAuth-implemenation-using-node/github_cred.jpg and /dev/null differ
diff --git a/content/engineering/oAuth-implemenation-using-node/github_cred.webp b/content/engineering/oAuth-implemenation-using-node/github_cred.webp
new file mode 100644
index 000000000..d97be192b
Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/github_cred.webp differ
diff --git a/content/engineering/oAuth-implemenation-using-node/github_login.jpg b/content/engineering/oAuth-implemenation-using-node/github_login.jpg
deleted file mode 100644
index 59f6e3ab1..000000000
Binary files a/content/engineering/oAuth-implemenation-using-node/github_login.jpg and /dev/null differ
diff --git a/content/engineering/oAuth-implemenation-using-node/github_login.webp b/content/engineering/oAuth-implemenation-using-node/github_login.webp
new file mode 100644
index 000000000..4d11a0801
Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/github_login.webp differ
diff --git a/content/engineering/oAuth-implemenation-using-node/github_profile.jpg b/content/engineering/oAuth-implemenation-using-node/github_profile.jpg
deleted file mode 100644
index a5014c67e..000000000
Binary files a/content/engineering/oAuth-implemenation-using-node/github_profile.jpg and /dev/null differ
diff --git a/content/engineering/oAuth-implemenation-using-node/github_profile.webp b/content/engineering/oAuth-implemenation-using-node/github_profile.webp
new file mode 100644
index 000000000..5ab785f14
Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/github_profile.webp differ
diff --git a/content/engineering/oAuth-implemenation-using-node/index.md b/content/engineering/oAuth-implemenation-using-node/index.md
index 094f8aece..227409ece 100644
--- a/content/engineering/oAuth-implemenation-using-node/index.md
+++ b/content/engineering/oAuth-implemenation-using-node/index.md
@@ -1,7 +1,7 @@
---
title: "OAuth implementation with Node.js and Github"
date: "2020-03-22"
-coverImage: "oauth.png"
+coverImage: "oauth.webp"
author: "Puneet Singh"
tags: ["Oauth", "NodeJs"]
canonical: https://www.loginradius.com/blog/engineering/google-authentication-with-nodejs-and-passportjs/
@@ -23,14 +23,14 @@ To implement Github Auth we need to register a new application in [Github OAuth
Once you start the process you will get a form like this.
-
+
You need to fill all the required details and put the Authorization callback URL as `http://localhost:2400/github/callback` (This will be the URL on which Github will send the authorization code once authorization is finished)
Once you register the application you will get the App's Client Id and Secret which we will use in our code.
-
+
@@ -200,15 +200,15 @@ node index.js
Once our server is running, we can see our social login page on `http://localhost:2400/`
-
+
We need to click on the **Github Login button**, which will redirect us to google login page.
-
+
After login with our GitHub credentials, it will redirect back to our application and on the success page, we can see the details of users' GitHub profile and can save this detail in a database for future use also.
-
+
You can implement the OAuth in Node.js by the above process, You can found the complete code used in this tutorial on out
diff --git a/content/engineering/oAuth-implemenation-using-node/oauth.png b/content/engineering/oAuth-implemenation-using-node/oauth.png
deleted file mode 100644
index 790e19a37..000000000
Binary files a/content/engineering/oAuth-implemenation-using-node/oauth.png and /dev/null differ
diff --git a/content/engineering/oAuth-implemenation-using-node/oauth.webp b/content/engineering/oAuth-implemenation-using-node/oauth.webp
new file mode 100644
index 000000000..7e9e91ff4
Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/oauth.webp differ
diff --git a/content/engineering/oauth2/image2.png b/content/engineering/oauth2/image2.png
deleted file mode 100644
index d24853faf..000000000
Binary files a/content/engineering/oauth2/image2.png and /dev/null differ
diff --git a/content/engineering/oauth2/image2.webp b/content/engineering/oauth2/image2.webp
new file mode 100644
index 000000000..920c9987c
Binary files /dev/null and b/content/engineering/oauth2/image2.webp differ
diff --git a/content/engineering/oauth2/image3.png b/content/engineering/oauth2/image3.png
deleted file mode 100644
index 8994b0ccb..000000000
Binary files a/content/engineering/oauth2/image3.png and /dev/null differ
diff --git a/content/engineering/oauth2/image3.webp b/content/engineering/oauth2/image3.webp
new file mode 100644
index 000000000..9c40253dc
Binary files /dev/null and b/content/engineering/oauth2/image3.webp differ
diff --git a/content/engineering/oauth2/image4.png b/content/engineering/oauth2/image4.png
deleted file mode 100644
index 163cdd137..000000000
Binary files a/content/engineering/oauth2/image4.png and /dev/null differ
diff --git a/content/engineering/oauth2/image4.webp b/content/engineering/oauth2/image4.webp
new file mode 100644
index 000000000..2b7270832
Binary files /dev/null and b/content/engineering/oauth2/image4.webp differ
diff --git a/content/engineering/oauth2/index.md b/content/engineering/oauth2/index.md
index 6b91e8e28..a43fb9e20 100644
--- a/content/engineering/oauth2/index.md
+++ b/content/engineering/oauth2/index.md
@@ -1,7 +1,7 @@
---
title: Getting Started with OAuth 2.0
date: "2020-08-24"
-coverImage: "oauth2.png"
+coverImage: "oauth2.webp"
author: "Indrasen Kumar"
tags: ["Engineering", "Oauth", "Authentication"]
description: "Using this blog one can easily understand the basic concept of Oauth 2.0"
@@ -41,7 +41,7 @@ In total, there are five different grant type flows defined and described to per
### Authorization Code Grant
The Authorization Code Grant Type is the most commonly used grant type.
-
+
**The Story:** A user tries to log in on abc.com but he can’t remember his password and he discovers an option to sign in with google, by clicking on this, the user will easily get logged using google account.
@@ -72,7 +72,7 @@ In the entire flow, the access token is never exposed to a web browser.
### Implicit Grant
The Implicit flow was a simplified OAuth flow previously recommended for client-side applications like JavaScript apps where the access token was returned immediately without an extra authorization code exchange step.
-
+
The Story: In this flow abc.com directly get access token without an extra authorization code exchange steps and able to access resources on a resource server
@@ -108,7 +108,7 @@ The client then sends a POST request with following body parameters to the autho
Using this flow the client can request an access token using only its client credentials (or other supported means of authentication).
-
+
**The Story:** The client application presents its client credentials (client identifier and client secret) to the authorization server requesting approval to access the protected resource (owned by the client application) on the resource server.
The authorization server authenticates the client credential and issues an access token.
diff --git a/content/engineering/oauth2/oauth2.png b/content/engineering/oauth2/oauth2.png
deleted file mode 100644
index c91932ab6..000000000
Binary files a/content/engineering/oauth2/oauth2.png and /dev/null differ
diff --git a/content/engineering/oauth2/oauth2.webp b/content/engineering/oauth2/oauth2.webp
new file mode 100644
index 000000000..6baa070f2
Binary files /dev/null and b/content/engineering/oauth2/oauth2.webp differ
diff --git a/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.png b/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.png
deleted file mode 100644
index f3774cd10..000000000
Binary files a/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.png and /dev/null differ
diff --git a/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.webp b/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.webp
new file mode 100644
index 000000000..18b7cc390
Binary files /dev/null and b/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.webp differ
diff --git a/content/engineering/okta-and-the-lapsus-breach/index.md b/content/engineering/okta-and-the-lapsus-breach/index.md
index 90173cd80..7da2586fa 100644
--- a/content/engineering/okta-and-the-lapsus-breach/index.md
+++ b/content/engineering/okta-and-the-lapsus-breach/index.md
@@ -1,7 +1,7 @@
---
title: "How Lapsus$ Breached Okta and What Organizations Should Learn"
date: "2022-03-25"
-coverImage: "how-lapsus-breached-okta.png"
+coverImage: "how-lapsus-breached-okta.webp"
author: "Kundan Singh"
tags: ["Breach", "Cybersecurity"]
description: "Businesses have to be extra vigilant in safeguarding customer data. Minor mistakes can cause a massive data breach, violating data privacy regulations and attracting penalties from regulatory authorities."
@@ -87,4 +87,4 @@ In this specific example, the hackers accessed the laptop of one of Okta's custo
However, it offers a valuable learning experience that business entities should not ignore the minutest of details regarding network security. It surfaces the adage that ' A chain is only as strong as its weakest link.'
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=okta-and-the-lapsus-breach)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=okta-and-the-lapsus-breach)
\ No newline at end of file
diff --git a/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.png b/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.png
deleted file mode 100644
index ade48958e..000000000
Binary files a/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.png and /dev/null differ
diff --git a/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.webp b/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.webp
new file mode 100644
index 000000000..5dcf1865c
Binary files /dev/null and b/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.webp differ
diff --git a/content/engineering/open-source-business-email-validator-by-loginradius/index.md b/content/engineering/open-source-business-email-validator-by-loginradius/index.md
index b5437d80b..cad687a08 100644
--- a/content/engineering/open-source-business-email-validator-by-loginradius/index.md
+++ b/content/engineering/open-source-business-email-validator-by-loginradius/index.md
@@ -1,7 +1,7 @@
---
title: "Open Source Business Email Validator By Loginradius"
date: "2017-04-25"
-coverImage: "Open-Source-Business-Validator-By-Loginradius.png"
+coverImage: "Open-Source-Business-Validator-By-Loginradius.webp"
author: "Team LoginRadius"
tags: ["Engineering"]
---
diff --git a/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.png b/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.png
deleted file mode 100644
index 52eff7be5..000000000
Binary files a/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.png and /dev/null differ
diff --git a/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.webp b/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.webp
new file mode 100644
index 000000000..18290289a
Binary files /dev/null and b/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.webp differ
diff --git a/content/engineering/opensource-Automation-for-identity-experience-framework/index.md b/content/engineering/opensource-Automation-for-identity-experience-framework/index.md
index c20529e2d..b19fc66db 100644
--- a/content/engineering/opensource-Automation-for-identity-experience-framework/index.md
+++ b/content/engineering/opensource-Automation-for-identity-experience-framework/index.md
@@ -1,7 +1,7 @@
---
title: "Automation for Identity Experience Framework is now open-source !!!"
date: "2020-06-04"
-coverImage: automation_ief.png
+coverImage: automation_ief.webp
author: Sudhey Sharma
tags: ["OpenSource","Automation"]
canonical: https://www.loginradius.com/blog/identity/loginradius-identity-experience-framework/
diff --git a/content/engineering/optimize-jquery-sizzle-element-selector/index.md b/content/engineering/optimize-jquery-sizzle-element-selector/index.md
index f6e514036..65c256675 100644
--- a/content/engineering/optimize-jquery-sizzle-element-selector/index.md
+++ b/content/engineering/optimize-jquery-sizzle-element-selector/index.md
@@ -1,7 +1,7 @@
---
title: "Optimize jQuery & Sizzle Element Selector"
date: "2015-11-05"
-coverImage: "jquery-sizzle-element-selector-150x150.png"
+coverImage: "jquery-sizzle-element-selector-150x150.webp"
author: "Kundan Singh"
tags: ["Engineering", "JQuery"]
---
diff --git a/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.png b/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.png
deleted file mode 100644
index 335e64012..000000000
Binary files a/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.png and /dev/null differ
diff --git a/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.webp b/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.webp
new file mode 100644
index 000000000..e59793c83
Binary files /dev/null and b/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.webp differ
diff --git a/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.png b/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.png
deleted file mode 100644
index a94d36663..000000000
Binary files a/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.png and /dev/null differ
diff --git a/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.webp b/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.webp
new file mode 100644
index 000000000..1e2555cbe
Binary files /dev/null and b/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.webp differ
diff --git a/content/engineering/part-2-creating-a-custom-login-form/index.md b/content/engineering/part-2-creating-a-custom-login-form/index.md
index d9c3d7eb8..45db03c04 100644
--- a/content/engineering/part-2-creating-a-custom-login-form/index.md
+++ b/content/engineering/part-2-creating-a-custom-login-form/index.md
@@ -1,7 +1,7 @@
---
title: "Part 2 - Creating a Custom Login Form"
date: "2015-12-08"
-coverImage: "cust-login-2-150x150.png"
+coverImage: "cust-login-2-150x150.webp"
author: "Zoie Carnegie"
tags: ["Engineering", "Login"]
---
@@ -10,7 +10,7 @@ In this tutorial I will demonstrate how to build a custom login form scratch. Th
## Building a Custom Login Form
-
+
This is what WordPress gives us out of the box.. Boring, right?
@@ -47,7 +47,7 @@ Remember me
```
-
+
Let's take a look at that custom form
diff --git a/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.png b/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.png
deleted file mode 100644
index 6f299ebdf..000000000
Binary files a/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.png and /dev/null differ
diff --git a/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.webp b/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.webp
new file mode 100644
index 000000000..45a3145aa
Binary files /dev/null and b/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.webp differ
diff --git a/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.png b/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.png
deleted file mode 100644
index 59ae3519c..000000000
Binary files a/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.png and /dev/null differ
diff --git a/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.webp b/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.webp
new file mode 100644
index 000000000..984450396
Binary files /dev/null and b/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.webp differ
diff --git a/content/engineering/password-hashing-with-nodejs/cover.png b/content/engineering/password-hashing-with-nodejs/cover.png
deleted file mode 100644
index 5d38968b6..000000000
Binary files a/content/engineering/password-hashing-with-nodejs/cover.png and /dev/null differ
diff --git a/content/engineering/password-hashing-with-nodejs/cover.webp b/content/engineering/password-hashing-with-nodejs/cover.webp
new file mode 100644
index 000000000..9a7ca0d78
Binary files /dev/null and b/content/engineering/password-hashing-with-nodejs/cover.webp differ
diff --git a/content/engineering/password-hashing-with-nodejs/index.md b/content/engineering/password-hashing-with-nodejs/index.md
index 36d41c9e6..a0bdff893 100644
--- a/content/engineering/password-hashing-with-nodejs/index.md
+++ b/content/engineering/password-hashing-with-nodejs/index.md
@@ -1,7 +1,7 @@
---
title: "Password hashing with NodeJS"
date: "2020-06-25"
-coverImage: "cover.png"
+coverImage: "cover.webp"
author: "Ashish Sharma"
tags: ["Security", "NodeJs"]
---
diff --git a/content/engineering/password-secure/index.md b/content/engineering/password-secure/index.md
index 55d6cd708..cefec144d 100644
--- a/content/engineering/password-secure/index.md
+++ b/content/engineering/password-secure/index.md
@@ -1,7 +1,7 @@
---
title: "Password Security"
date: "2015-05-14"
-coverImage: "password-security.png"
+coverImage: "password-security.webp"
author: "Kundan Singh"
tags: ["Security", "Password"]
---
diff --git a/content/engineering/password-secure/password-security.png b/content/engineering/password-secure/password-security.png
deleted file mode 100644
index 00ed50cdc..000000000
Binary files a/content/engineering/password-secure/password-security.png and /dev/null differ
diff --git a/content/engineering/password-secure/password-security.webp b/content/engineering/password-secure/password-security.webp
new file mode 100644
index 000000000..8c949da5c
Binary files /dev/null and b/content/engineering/password-secure/password-security.webp differ
diff --git a/content/engineering/password-security-best-practices-compliance/index.md b/content/engineering/password-security-best-practices-compliance/index.md
index 603344b09..613d3f394 100644
--- a/content/engineering/password-security-best-practices-compliance/index.md
+++ b/content/engineering/password-security-best-practices-compliance/index.md
@@ -1,7 +1,7 @@
---
title: "Password Security Best Practices & Compliance"
date: "2020-11-12"
-coverImage: "password-security.jpg"
+coverImage: "password-security.webp"
author: "Vijay Singh Shekhawat"
tags: ["Security", "Password","Compliance","Passowrd Policy"]
---
diff --git a/content/engineering/password-security-best-practices-compliance/password-security.jpg b/content/engineering/password-security-best-practices-compliance/password-security.jpg
deleted file mode 100644
index beb0419c4..000000000
Binary files a/content/engineering/password-security-best-practices-compliance/password-security.jpg and /dev/null differ
diff --git a/content/engineering/password-security-best-practices-compliance/password-security.webp b/content/engineering/password-security-best-practices-compliance/password-security.webp
new file mode 100644
index 000000000..31495200f
Binary files /dev/null and b/content/engineering/password-security-best-practices-compliance/password-security.webp differ
diff --git a/content/engineering/personal-branding-for-developers/Apple-logo-248x300.png b/content/engineering/personal-branding-for-developers/Apple-logo-248x300.png
deleted file mode 100644
index 7c58bfb68..000000000
Binary files a/content/engineering/personal-branding-for-developers/Apple-logo-248x300.png and /dev/null differ
diff --git a/content/engineering/personal-branding-for-developers/Apple-logo-248x300.webp b/content/engineering/personal-branding-for-developers/Apple-logo-248x300.webp
new file mode 100644
index 000000000..6fa4c91af
Binary files /dev/null and b/content/engineering/personal-branding-for-developers/Apple-logo-248x300.webp differ
diff --git a/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.jpg b/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.jpg
deleted file mode 100644
index 2f7f49b0e..000000000
Binary files a/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.jpg and /dev/null differ
diff --git a/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.webp b/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.webp
new file mode 100644
index 000000000..4a2b962c9
Binary files /dev/null and b/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.webp differ
diff --git a/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.jpg b/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.jpg
deleted file mode 100644
index 1f93205a2..000000000
Binary files a/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.jpg and /dev/null differ
diff --git a/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.webp b/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.webp
new file mode 100644
index 000000000..fe4565ad9
Binary files /dev/null and b/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.webp differ
diff --git a/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.jpg b/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.jpg
deleted file mode 100644
index d49fd0add..000000000
Binary files a/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.jpg and /dev/null differ
diff --git a/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.webp b/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.webp
new file mode 100644
index 000000000..b0273cdf5
Binary files /dev/null and b/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.webp differ
diff --git a/content/engineering/personal-branding-for-developers/index.md b/content/engineering/personal-branding-for-developers/index.md
index 743364b85..fa75049c3 100644
--- a/content/engineering/personal-branding-for-developers/index.md
+++ b/content/engineering/personal-branding-for-developers/index.md
@@ -1,7 +1,7 @@
---
title: "Personal Branding For Developers: Why and How?"
date: "2016-09-23"
-coverImage: "Personal-Branding-For-Developers-150x150.jpg"
+coverImage: "Personal-Branding-For-Developers-150x150.webp"
author: "Sreekant"
tags: ["Branding"]
---
@@ -12,7 +12,7 @@ In this article I am going to focus on why as a developer you should focus on pe
**What is personal branding?**
-Do you recognize this logo? Well, Of course you do! But have you ever wondered how come you recognized this logo without even a name? Well, you recognized it because the brand is so strong that without even a proper title, you are able to recognize it and that’s what branding do.
+Do you recognize this logo? Well, Of course you do! But have you ever wondered how come you recognized this logo without even a name? Well, you recognized it because the brand is so strong that without even a proper title, you are able to recognize it and that’s what branding do.
The concept of personal branding is quite similar to that of company branding. Personal branding is all about thinking yourself as a brand. It is about showing people who you are and what is your passion. When you think about some specific programming language, your mind goes back to some specific names associated with that language, who are either the father of that language or have done some amazing work in that field, right?
@@ -55,11 +55,11 @@ You might have the best expertise in certain technology, you might have designed
1. **Try your hand at blogging :**
Blogging is an amazing way to tell people who you are. Blog about anything you hold expertize in, whether it is a programming language or it is some kind of technology, let people understand who you actually are. There are many developers out there who have some awesome technical blogs where they share their knowledge and write about their specialities.For inspiration you can have a look at the blog of [John Resig](http://ejohn.org/), the creator and founder of jQuery. Another tech blog champion is Scott Hanselman. Make sure to have a look on his popular blogs [www.hanselman.com](http://www.hanselman.com), [hanselminutes](http://hanselminutes.com/), etc.
- Stick to one topic, you are best at and select the blogging platform that suits you like Wordpress, Tumblr, Blogspot, etc. Post informative content on regular basis and soon you will have a huge audience waiting for your content and engaging with you. Posting two to three informative blog is enough to keep you in demand. Also there are some specific sites like[www.asp.net](http://www.asp.net) where you can submit articles to gain immense popularity.
+ Stick to one topic, you are best at and select the blogging platform that suits you like Wordpress, Tumblr, Blogspot, etc. Post informative content on regular basis and soon you will have a huge audience waiting for your content and engaging with you. Posting two to three informative blog is enough to keep you in demand. Also there are some specific sites like[www.asp.net](http://www.asp.net) where you can submit articles to gain immense popularity.
2. **Embrace Social Media :**
You might have heard that Facebook and Twitter are all about wasting time, but let me tell you this is not at all true. Social media provides you a great opportunity to build networks. It is must to get visibility on various social media networks if you want to be found by people who share same niche as you.
- 
+ 
There are various ways how you can track your brand on social media. My personal favorite is Google Alert which notifies whenever people are talking about me or my projects. While some times they are talking about the work I have done, sometimes they also complaint which helps me understand where I am wrong. There are many others, like on Twitter, you can use [Tweetdeck](https://tweetdeck.twitter.com/) . Apart from that, create a strong persona on Linkedin, Facebook, Google+, etc. Interact with people, reply to their queries and become social media champion.
Some popular developers who are social media champions as well include [Scott Hanselman](https://twitter.com/shanselman), [John Resig](https://www.linkedin.com/in/jeresig), etc
diff --git a/content/engineering/pkce/index.md b/content/engineering/pkce/index.md
index 98fc887d8..02d4ddc41 100644
--- a/content/engineering/pkce/index.md
+++ b/content/engineering/pkce/index.md
@@ -2,7 +2,7 @@
title: "PKCE: What it is and how to use it with OAuth 2.0"
date: "2020-09-03"
author: "Narendra Pareek"
-coverImage: "pkce.png"
+coverImage: "pkce.webp"
tags: ["PKCE", "Oauth", "OIDC"]
description: "If you are working with OAuth and OIDC authorization code flow and want to setup PKCE flow then this article will help you to understand everything about PKCE."
---
diff --git a/content/engineering/pkce/pkce.png b/content/engineering/pkce/pkce.png
deleted file mode 100644
index 32e0aa702..000000000
Binary files a/content/engineering/pkce/pkce.png and /dev/null differ
diff --git a/content/engineering/pkce/pkce.webp b/content/engineering/pkce/pkce.webp
new file mode 100644
index 000000000..44ade1d0e
Binary files /dev/null and b/content/engineering/pkce/pkce.webp differ
diff --git a/content/engineering/production-grade-development-using-docker-compose/UserToSystem.png b/content/engineering/production-grade-development-using-docker-compose/UserToSystem.png
deleted file mode 100644
index 7cb968452..000000000
Binary files a/content/engineering/production-grade-development-using-docker-compose/UserToSystem.png and /dev/null differ
diff --git a/content/engineering/production-grade-development-using-docker-compose/UserToSystem.webp b/content/engineering/production-grade-development-using-docker-compose/UserToSystem.webp
new file mode 100644
index 000000000..612555e27
Binary files /dev/null and b/content/engineering/production-grade-development-using-docker-compose/UserToSystem.webp differ
diff --git a/content/engineering/production-grade-development-using-docker-compose/example-arch.png b/content/engineering/production-grade-development-using-docker-compose/example-arch.png
deleted file mode 100644
index 21551b94a..000000000
Binary files a/content/engineering/production-grade-development-using-docker-compose/example-arch.png and /dev/null differ
diff --git a/content/engineering/production-grade-development-using-docker-compose/example-arch.webp b/content/engineering/production-grade-development-using-docker-compose/example-arch.webp
new file mode 100644
index 000000000..e0a2f80df
Binary files /dev/null and b/content/engineering/production-grade-development-using-docker-compose/example-arch.webp differ
diff --git a/content/engineering/production-grade-development-using-docker-compose/index.md b/content/engineering/production-grade-development-using-docker-compose/index.md
index 251ea79ff..6858a4461 100644
--- a/content/engineering/production-grade-development-using-docker-compose/index.md
+++ b/content/engineering/production-grade-development-using-docker-compose/index.md
@@ -1,7 +1,7 @@
---
title: "Production Grade Development using Docker-Compose"
date: "2020-09-11"
-coverImage: "index.png"
+coverImage: "index.webp"
author: "Anurag Choudhary"
tags: ["Docker", "Docker-compose"]
---
@@ -28,7 +28,7 @@ the developer has two choices, create a script in a scripting language of choice
Here in this *kind of* practical example, we are going to demonstrate a similar situation, where multiple containers talk to each other. We are going to use docker-compose as our primary tool to build and deploy images.
-
+
The picture above depicts the architecture of a hypothetical portal of flash sale.
@@ -54,7 +54,7 @@ You may fork a copy from here.
``` git clone https://github.com/LoginRadius/engineering-blog-samples/tree/master/Docker/docker-compose-dev-sample ```
-
+
### The use of docker-compose and why?
@@ -232,7 +232,7 @@ upstream apiserver{
The Nginx container opens port 80 to an external port 5500. The Nginx container keeps configuration where the user can see just one port 5500 from out of the system, everything else is gray.
-
+
And this is, how it happens in the real world as well!
@@ -254,7 +254,7 @@ To stop
This scratches the surface of using docker-compose for a production-grade development environment.
-
+
Thanks for reading the blog. For detailed information and execution example of this blog, please refer to the video below:
diff --git a/content/engineering/production-grade-development-using-docker-compose/index.png b/content/engineering/production-grade-development-using-docker-compose/index.png
deleted file mode 100644
index a58184170..000000000
Binary files a/content/engineering/production-grade-development-using-docker-compose/index.png and /dev/null differ
diff --git a/content/engineering/production-grade-development-using-docker-compose/index.webp b/content/engineering/production-grade-development-using-docker-compose/index.webp
new file mode 100644
index 000000000..5cd8db50d
Binary files /dev/null and b/content/engineering/production-grade-development-using-docker-compose/index.webp differ
diff --git a/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.png b/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.png
deleted file mode 100644
index b6d4b3c93..000000000
Binary files a/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.png and /dev/null differ
diff --git a/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.webp b/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.webp
new file mode 100644
index 000000000..0baff8079
Binary files /dev/null and b/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.webp differ
diff --git a/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.jpg b/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.jpg
deleted file mode 100644
index c45218a0e..000000000
Binary files a/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.jpg and /dev/null differ
diff --git a/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.webp b/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.webp
new file mode 100644
index 000000000..87d526362
Binary files /dev/null and b/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.webp differ
diff --git a/content/engineering/progressive-app-vs-native-app/index.md b/content/engineering/progressive-app-vs-native-app/index.md
index ccef57acd..388d7f094 100644
--- a/content/engineering/progressive-app-vs-native-app/index.md
+++ b/content/engineering/progressive-app-vs-native-app/index.md
@@ -1,7 +1,7 @@
---
title: "PWA vs Native App: Which one is Better for you?"
date: "2021-02-04"
-coverImage: "index.png"
+coverImage: "index.webp"
author: Nathan Nguyen
tags: ["Progressive App", "PWA", "JavaScript"]
description: "How do Native Apps compare to Progressive Web Apps, and which platform does your company use to communicate with your clients? read on!"
diff --git a/content/engineering/progressive-app-vs-native-app/index.png b/content/engineering/progressive-app-vs-native-app/index.png
deleted file mode 100644
index d969b8662..000000000
Binary files a/content/engineering/progressive-app-vs-native-app/index.png and /dev/null differ
diff --git a/content/engineering/progressive-app-vs-native-app/index.webp b/content/engineering/progressive-app-vs-native-app/index.webp
new file mode 100644
index 000000000..a7cdf1db5
Binary files /dev/null and b/content/engineering/progressive-app-vs-native-app/index.webp differ
diff --git a/content/engineering/python-basics-in-minutes/index.md b/content/engineering/python-basics-in-minutes/index.md
index e05c01279..6c6effa79 100644
--- a/content/engineering/python-basics-in-minutes/index.md
+++ b/content/engineering/python-basics-in-minutes/index.md
@@ -1,7 +1,7 @@
---
title: "Python basics in minutes"
date: "2020-11-06"
-coverImage: "python.png"
+coverImage: "python.webp"
author: "Sara Lins"
description: "Learn the basics of Python programming lanuage (For Beginners)"
tags: ["Python"]
diff --git a/content/engineering/python-basics-in-minutes/python.png b/content/engineering/python-basics-in-minutes/python.png
deleted file mode 100644
index dcc8db1fa..000000000
Binary files a/content/engineering/python-basics-in-minutes/python.png and /dev/null differ
diff --git a/content/engineering/python-basics-in-minutes/python.webp b/content/engineering/python-basics-in-minutes/python.webp
new file mode 100644
index 000000000..376f59b84
Binary files /dev/null and b/content/engineering/python-basics-in-minutes/python.webp differ
diff --git a/content/engineering/python-virtual-environments/activate.png b/content/engineering/python-virtual-environments/activate.png
deleted file mode 100644
index 4c428c881..000000000
Binary files a/content/engineering/python-virtual-environments/activate.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/activate.webp b/content/engineering/python-virtual-environments/activate.webp
new file mode 100644
index 000000000..d56ffea29
Binary files /dev/null and b/content/engineering/python-virtual-environments/activate.webp differ
diff --git a/content/engineering/python-virtual-environments/activated.png b/content/engineering/python-virtual-environments/activated.png
deleted file mode 100644
index 3fd159656..000000000
Binary files a/content/engineering/python-virtual-environments/activated.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/activated.webp b/content/engineering/python-virtual-environments/activated.webp
new file mode 100644
index 000000000..e3daeed68
Binary files /dev/null and b/content/engineering/python-virtual-environments/activated.webp differ
diff --git a/content/engineering/python-virtual-environments/check.png b/content/engineering/python-virtual-environments/check.png
deleted file mode 100644
index 7a0b60611..000000000
Binary files a/content/engineering/python-virtual-environments/check.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/check.webp b/content/engineering/python-virtual-environments/check.webp
new file mode 100644
index 000000000..8f4ab3dc0
Binary files /dev/null and b/content/engineering/python-virtual-environments/check.webp differ
diff --git a/content/engineering/python-virtual-environments/deactivate.png b/content/engineering/python-virtual-environments/deactivate.png
deleted file mode 100644
index fc12d0cd8..000000000
Binary files a/content/engineering/python-virtual-environments/deactivate.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/deactivate.webp b/content/engineering/python-virtual-environments/deactivate.webp
new file mode 100644
index 000000000..7963ce9c8
Binary files /dev/null and b/content/engineering/python-virtual-environments/deactivate.webp differ
diff --git a/content/engineering/python-virtual-environments/index.md b/content/engineering/python-virtual-environments/index.md
index 025a6275f..56baecb19 100644
--- a/content/engineering/python-virtual-environments/index.md
+++ b/content/engineering/python-virtual-environments/index.md
@@ -1,7 +1,7 @@
---
title: "Python Virtual Environment: What is it and how it works?"
date: "2020-10-16"
-coverImage: "python.jpg"
+coverImage: "python.webp"
author: "Ashish Maharjan"
tags: ["Python"]
description: "We'll cover the basics of virtual environments in this guide and how to use them. We will then take a closer look at how virtual environments actually work."
@@ -30,49 +30,49 @@ If project1 uses Django-2.2 and project2 uses Django-3.2, they would be stored i
To create a virtual environment, we need a [module named](https://pypi.org/project/virtualenv/) virtualenv. It creates a folder with all the necessary executables to run Python projects. Make sure **pip** is installed on your computer. If not, then use the following command:
-
+
### Install virtualenv:
Open the terminal and paste the following command to install a virtualenv:
-
+
### Check your version of virtualenv:
If you want to confirm whether it is installed or not, paste the command below in your terminal:
-
+
### Create a virtual environment:
After successful installation of virtualenv, now you can create a virtual environment with your desired name using following command:
-
+
Here, I created `venv` as the name of my virtual environment. You can name it whatever you desire. The folder with the name `venv` is created that contains all the necessary executables to [run the Python project](/speed-up-python-code/). This is the folder where all your python packages will run.
To specify the Python interpreter of your choice, you can do it easily by specifying Python{version-name}.
Eg: To create python2.7 virtual environment, we use following command:
-
+
After successfully creating the virtual environment, you need to activate it to enter into that particular isolated environment. Always remember to activate the required virtual environment before working on the project. To activate it, we move to the location where the name of your desired virtual environment is located and follow the command below:
-
+
**Note:** Instead of `venv`, you write the name of your virtual environment you created.
#### In Windows,
-
+
After activating the virtual environment, you can see your name on the virtual environment on the terminal's left side. It confirms the activation of your virtual environment and is currently active.
-
+
Finally, you successfully created and activated your virtual environment. Now, you can install the dependencies and requirements your project asks for without interfering with other projects.
Once you completed your work, then you can return to the system default environment by just using the **deactivate** command as shown below:
- +
+ diff --git a/content/engineering/python-virtual-environments/install.png b/content/engineering/python-virtual-environments/install.png
deleted file mode 100644
index 3e8133321..000000000
Binary files a/content/engineering/python-virtual-environments/install.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/install.webp b/content/engineering/python-virtual-environments/install.webp
new file mode 100644
index 000000000..a61c396f4
Binary files /dev/null and b/content/engineering/python-virtual-environments/install.webp differ
diff --git a/content/engineering/python-virtual-environments/name.png b/content/engineering/python-virtual-environments/name.png
deleted file mode 100644
index 8543e362d..000000000
Binary files a/content/engineering/python-virtual-environments/name.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/name.webp b/content/engineering/python-virtual-environments/name.webp
new file mode 100644
index 000000000..59e30503d
Binary files /dev/null and b/content/engineering/python-virtual-environments/name.webp differ
diff --git a/content/engineering/python-virtual-environments/pip.png b/content/engineering/python-virtual-environments/pip.png
deleted file mode 100644
index 945ed1afa..000000000
Binary files a/content/engineering/python-virtual-environments/pip.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/pip.webp b/content/engineering/python-virtual-environments/pip.webp
new file mode 100644
index 000000000..b0b2279a1
Binary files /dev/null and b/content/engineering/python-virtual-environments/pip.webp differ
diff --git a/content/engineering/python-virtual-environments/python.jpg b/content/engineering/python-virtual-environments/python.jpg
deleted file mode 100644
index 4acb9db7a..000000000
Binary files a/content/engineering/python-virtual-environments/python.jpg and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/python.webp b/content/engineering/python-virtual-environments/python.webp
new file mode 100644
index 000000000..609ffa433
Binary files /dev/null and b/content/engineering/python-virtual-environments/python.webp differ
diff --git a/content/engineering/python-virtual-environments/version.png b/content/engineering/python-virtual-environments/version.png
deleted file mode 100644
index 30ddd8e47..000000000
Binary files a/content/engineering/python-virtual-environments/version.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/version.webp b/content/engineering/python-virtual-environments/version.webp
new file mode 100644
index 000000000..ce9e88498
Binary files /dev/null and b/content/engineering/python-virtual-environments/version.webp differ
diff --git a/content/engineering/python-virtual-environments/windows.png b/content/engineering/python-virtual-environments/windows.png
deleted file mode 100644
index 82e9d374a..000000000
Binary files a/content/engineering/python-virtual-environments/windows.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/windows.webp b/content/engineering/python-virtual-environments/windows.webp
new file mode 100644
index 000000000..9cb5d066a
Binary files /dev/null and b/content/engineering/python-virtual-environments/windows.webp differ
diff --git a/content/engineering/qa-teams-deliver-quality-software/index.md b/content/engineering/qa-teams-deliver-quality-software/index.md
index 62b160718..356e07852 100644
--- a/content/engineering/qa-teams-deliver-quality-software/index.md
+++ b/content/engineering/qa-teams-deliver-quality-software/index.md
@@ -1,7 +1,7 @@
---
title: "QA Testing Process: How to Deliver Quality Software"
date: "2021-03-01"
-coverImage: "software-testing.png"
+coverImage: "software-testing.webp"
author: "Neha Vyas"
description: "A comprehensive overview of the QA testing process is given. Learn what it takes to get top-notch testing facilities."
tags: ["QA", "Processes", "Testing"]
diff --git a/content/engineering/qa-teams-deliver-quality-software/software-testing.png b/content/engineering/qa-teams-deliver-quality-software/software-testing.png
deleted file mode 100644
index 179f9aa33..000000000
Binary files a/content/engineering/qa-teams-deliver-quality-software/software-testing.png and /dev/null differ
diff --git a/content/engineering/qa-teams-deliver-quality-software/software-testing.webp b/content/engineering/qa-teams-deliver-quality-software/software-testing.webp
new file mode 100644
index 000000000..ab46a211c
Binary files /dev/null and b/content/engineering/qa-teams-deliver-quality-software/software-testing.webp differ
diff --git a/content/engineering/quick-kafka-installation/index.md b/content/engineering/quick-kafka-installation/index.md
index 736f68096..8a35e8466 100644
--- a/content/engineering/quick-kafka-installation/index.md
+++ b/content/engineering/quick-kafka-installation/index.md
@@ -1,7 +1,7 @@
---
title: "Setting Up and Running Apache Kafka on Windows OS"
date: "2020-08-25"
-coverImage: "messagelog.png"
+coverImage: "messagelog.webp"
author: "Ashish Sharma"
tags: ["Kafka", "Windows"]
---
@@ -39,7 +39,7 @@ tar -xvzf kafka_2.12-2.4.1.tgz
**Step 3:** Copy the path of the Kafka folder. Now go to _config_ inside Kafka folder and open _zookeeper.properties_ file. Copy the path against the field _dataDir_ and add _/zookeeper-data_ to the path.
-
+
**Step 4:** we have to modify the config/server.properties file. Below is the change:
diff --git a/content/engineering/quick-kafka-installation/messagelog.png b/content/engineering/quick-kafka-installation/messagelog.png
deleted file mode 100644
index 47f716339..000000000
Binary files a/content/engineering/quick-kafka-installation/messagelog.png and /dev/null differ
diff --git a/content/engineering/quick-kafka-installation/messagelog.webp b/content/engineering/quick-kafka-installation/messagelog.webp
new file mode 100644
index 000000000..9b5f8e93b
Binary files /dev/null and b/content/engineering/quick-kafka-installation/messagelog.webp differ
diff --git a/content/engineering/quick-kafka-installation/zookeeper.png b/content/engineering/quick-kafka-installation/zookeeper.png
deleted file mode 100644
index fe9c5eb93..000000000
Binary files a/content/engineering/quick-kafka-installation/zookeeper.png and /dev/null differ
diff --git a/content/engineering/quick-kafka-installation/zookeeper.webp b/content/engineering/quick-kafka-installation/zookeeper.webp
new file mode 100644
index 000000000..debbd0f99
Binary files /dev/null and b/content/engineering/quick-kafka-installation/zookeeper.webp differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/index.md b/content/engineering/quick-look-at-react-speech-recognition/index.md
index 0544235c6..cd77b78c0 100644
--- a/content/engineering/quick-look-at-react-speech-recognition/index.md
+++ b/content/engineering/quick-look-at-react-speech-recognition/index.md
@@ -1,7 +1,7 @@
---
title: "A Quick Look at the React Speech Recognition Hook"
date: "2020-10-29"
-coverImage: "mic.jpg"
+coverImage: "mic.webp"
author: "Krista Singleton"
tags: ["React", "React Speech Recognition", "React Speech", "React Hook"]
description: "Learning and exploring the react-speech-recognition hook basics."
@@ -31,7 +31,7 @@ Note: This framework uses WebSpeech API. Browser support for this API is current
I will be making a simple voice memo app with basic voice commands that run in the browser. If you would like to follow this tutorial, please be ready to work with the create-react-app boilerplate.
-
+
## Let's Get Started
diff --git a/content/engineering/quick-look-at-react-speech-recognition/mic.jpg b/content/engineering/quick-look-at-react-speech-recognition/mic.jpg
deleted file mode 100644
index 71884632c..000000000
Binary files a/content/engineering/quick-look-at-react-speech-recognition/mic.jpg and /dev/null differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/mic.webp b/content/engineering/quick-look-at-react-speech-recognition/mic.webp
new file mode 100644
index 000000000..816a21698
Binary files /dev/null and b/content/engineering/quick-look-at-react-speech-recognition/mic.webp differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/styledExample.png b/content/engineering/quick-look-at-react-speech-recognition/styledExample.png
deleted file mode 100644
index cc35d7c45..000000000
Binary files a/content/engineering/quick-look-at-react-speech-recognition/styledExample.png and /dev/null differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp b/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp
new file mode 100644
index 000000000..ee46f472f
Binary files /dev/null and b/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp differ
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/index.md b/content/engineering/react-code-splitting-with-lazy-suspense/index.md
index 8db7ef374..c7b776ac0 100644
--- a/content/engineering/react-code-splitting-with-lazy-suspense/index.md
+++ b/content/engineering/react-code-splitting-with-lazy-suspense/index.md
@@ -1,7 +1,7 @@
---
title: Code spliting in React via lazy and suspense
date: "2021-05-13"
-coverImage: "react.png"
+coverImage: "react.webp"
author: "Abhimanyu Singh Rathore"
description: "Load Application faster with code spliting and dynamic loading"
tags: ["React"]
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/react.png b/content/engineering/react-code-splitting-with-lazy-suspense/react.png
deleted file mode 100644
index 5969c4dd3..000000000
Binary files a/content/engineering/react-code-splitting-with-lazy-suspense/react.png and /dev/null differ
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/react.webp b/content/engineering/react-code-splitting-with-lazy-suspense/react.webp
new file mode 100644
index 000000000..4f4f67d78
Binary files /dev/null and b/content/engineering/react-code-splitting-with-lazy-suspense/react.webp differ
diff --git a/content/engineering/react-constructor-get-initial-state/index.md b/content/engineering/react-constructor-get-initial-state/index.md
index a2dc65dd4..ab2ee63b1 100644
--- a/content/engineering/react-constructor-get-initial-state/index.md
+++ b/content/engineering/react-constructor-get-initial-state/index.md
@@ -1,7 +1,7 @@
---
title: "Constructor vs getInitialState in React"
date: "2021-01-05"
-coverImage: "index.png"
+coverImage: "index.webp"
author: Nathan Nguyen
tags: ["JavaScript", "React"]
description: "No ES6? No problem. getInitialState is the ES5 friendly method to define the initial state of a React component."
diff --git a/content/engineering/react-constructor-get-initial-state/index.png b/content/engineering/react-constructor-get-initial-state/index.png
deleted file mode 100644
index fd3825ea4..000000000
Binary files a/content/engineering/react-constructor-get-initial-state/index.png and /dev/null differ
diff --git a/content/engineering/react-constructor-get-initial-state/index.webp b/content/engineering/react-constructor-get-initial-state/index.webp
new file mode 100644
index 000000000..d72d1b5ec
Binary files /dev/null and b/content/engineering/react-constructor-get-initial-state/index.webp differ
diff --git a/content/engineering/react-context-api-guide-with-Example/index.md b/content/engineering/react-context-api-guide-with-Example/index.md
index 69e450eca..48cfe0797 100644
--- a/content/engineering/react-context-api-guide-with-Example/index.md
+++ b/content/engineering/react-context-api-guide-with-Example/index.md
@@ -1,7 +1,7 @@
---
title: "React's Context API Guide with Example"
date: "2021-06-09"
-coverImage: "title-image.png"
+coverImage: "title-image.webp"
author: "Versha Gupta"
tags: ["React", "Redux", "Hooks"]
description: "Deep Dive into React's Context API with example"
diff --git a/content/engineering/react-context-api-guide-with-Example/title-image.png b/content/engineering/react-context-api-guide-with-Example/title-image.png
deleted file mode 100644
index 1feb7118a..000000000
Binary files a/content/engineering/react-context-api-guide-with-Example/title-image.png and /dev/null differ
diff --git a/content/engineering/react-context-api-guide-with-Example/title-image.webp b/content/engineering/react-context-api-guide-with-Example/title-image.webp
new file mode 100644
index 000000000..e884d7a9d
Binary files /dev/null and b/content/engineering/react-context-api-guide-with-Example/title-image.webp differ
diff --git a/content/engineering/react-context-api/index.md b/content/engineering/react-context-api/index.md
index 5ee467147..f133b5272 100644
--- a/content/engineering/react-context-api/index.md
+++ b/content/engineering/react-context-api/index.md
@@ -1,7 +1,7 @@
---
title: "React Context API: What is it and How it works?"
date: "2020-10-07"
-coverImage: "react.jpg"
+coverImage: "react.webp"
author: "Eylon Ronen"
tags: ["React", "Redux", "Hooks"]
description: "Context API is a (kind of) new feature added in version 16.3 of React that allows one to share state across the entire app (or part of it) lightly and with ease. Let's see how to use it."
diff --git a/content/engineering/react-context-api/react.jpg b/content/engineering/react-context-api/react.jpg
deleted file mode 100644
index 2e22923df..000000000
Binary files a/content/engineering/react-context-api/react.jpg and /dev/null differ
diff --git a/content/engineering/react-context-api/react.webp b/content/engineering/react-context-api/react.webp
new file mode 100644
index 000000000..5b729e68d
Binary files /dev/null and b/content/engineering/react-context-api/react.webp differ
diff --git a/content/engineering/react-error-boundaries/error_boundary_cover.png b/content/engineering/react-error-boundaries/error_boundary_cover.png
deleted file mode 100644
index ef42fee87..000000000
Binary files a/content/engineering/react-error-boundaries/error_boundary_cover.png and /dev/null differ
diff --git a/content/engineering/react-error-boundaries/error_boundary_cover.webp b/content/engineering/react-error-boundaries/error_boundary_cover.webp
new file mode 100644
index 000000000..54cab35cc
Binary files /dev/null and b/content/engineering/react-error-boundaries/error_boundary_cover.webp differ
diff --git a/content/engineering/react-error-boundaries/index.md b/content/engineering/react-error-boundaries/index.md
index d5ea641e8..da317942f 100644
--- a/content/engineering/react-error-boundaries/index.md
+++ b/content/engineering/react-error-boundaries/index.md
@@ -1,7 +1,7 @@
---
title: "React Error Boundaries"
date: "2021-05-20"
-coverImage: "error_boundary_cover.png"
+coverImage: "error_boundary_cover.webp"
author: "Versha Gupta"
tags: ["React", "Error Handling", "JavaScript"]
description: "Error Handling in React using React Error Boundaries"
diff --git a/content/engineering/react-hooks-guide/index.md b/content/engineering/react-hooks-guide/index.md
index bc9d0952f..44d8a2683 100644
--- a/content/engineering/react-hooks-guide/index.md
+++ b/content/engineering/react-hooks-guide/index.md
@@ -2,7 +2,7 @@
title: "React Hooks: A Beginners Guide"
date: "2020-08-07"
author: "Mohammed Modi"
-coverImage: "react-hooks.png"
+coverImage: "react-hooks.webp"
tags: ["React", "Hooks"]
description: "A walkthrough guide on React Hooks, what is React Hooks, benefits of Hooks, and how to use Hooks in React and more."
---
diff --git a/content/engineering/react-hooks-guide/react-hooks.png b/content/engineering/react-hooks-guide/react-hooks.png
deleted file mode 100644
index b06e44fa2..000000000
Binary files a/content/engineering/react-hooks-guide/react-hooks.png and /dev/null differ
diff --git a/content/engineering/react-hooks-guide/react-hooks.webp b/content/engineering/react-hooks-guide/react-hooks.webp
new file mode 100644
index 000000000..5f712b755
Binary files /dev/null and b/content/engineering/react-hooks-guide/react-hooks.webp differ
diff --git a/content/engineering/react-renderer/index.md b/content/engineering/react-renderer/index.md
index 92819ae21..aa888f280 100644
--- a/content/engineering/react-renderer/index.md
+++ b/content/engineering/react-renderer/index.md
@@ -1,7 +1,7 @@
---
title: "React renderers, react everywhere?"
date: "2021-06-23"
-coverImage: "react.png"
+coverImage: "react.webp"
author: "Abhimanyu Singh Rathore"
description: "There is an advanced feature of React is that it can write renderers for multiple different env."
tags: ["JavaScript", "React", "Renderer"]
diff --git a/content/engineering/react-renderer/react.png b/content/engineering/react-renderer/react.png
deleted file mode 100644
index dfe1b03e1..000000000
Binary files a/content/engineering/react-renderer/react.png and /dev/null differ
diff --git a/content/engineering/react-renderer/react.webp b/content/engineering/react-renderer/react.webp
new file mode 100644
index 000000000..b53a41959
Binary files /dev/null and b/content/engineering/react-renderer/react.webp differ
diff --git a/content/engineering/react-router-basics/image1.png b/content/engineering/react-router-basics/image1.png
deleted file mode 100644
index 12c01b68e..000000000
Binary files a/content/engineering/react-router-basics/image1.png and /dev/null differ
diff --git a/content/engineering/react-router-basics/image1.webp b/content/engineering/react-router-basics/image1.webp
new file mode 100644
index 000000000..e414a9a97
Binary files /dev/null and b/content/engineering/react-router-basics/image1.webp differ
diff --git a/content/engineering/react-router-basics/index.md b/content/engineering/react-router-basics/index.md
index b31566425..462600279 100644
--- a/content/engineering/react-router-basics/index.md
+++ b/content/engineering/react-router-basics/index.md
@@ -1,7 +1,7 @@
---
title: "React Router Basics: Routing in a Single-page Application"
date: "2020-11-20"
-coverImage: "index.png"
+coverImage: "index.webp"
author: Nathan Nguyen
tags: ["JavaScript", "Node", "React", "React Router"]
description: "Everything essential you need to know about React Router."
@@ -105,7 +105,7 @@ If you are currently looking at the render of this structure from the CodePen, y
-
+
Clicking on the
diff --git a/content/engineering/python-virtual-environments/install.png b/content/engineering/python-virtual-environments/install.png
deleted file mode 100644
index 3e8133321..000000000
Binary files a/content/engineering/python-virtual-environments/install.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/install.webp b/content/engineering/python-virtual-environments/install.webp
new file mode 100644
index 000000000..a61c396f4
Binary files /dev/null and b/content/engineering/python-virtual-environments/install.webp differ
diff --git a/content/engineering/python-virtual-environments/name.png b/content/engineering/python-virtual-environments/name.png
deleted file mode 100644
index 8543e362d..000000000
Binary files a/content/engineering/python-virtual-environments/name.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/name.webp b/content/engineering/python-virtual-environments/name.webp
new file mode 100644
index 000000000..59e30503d
Binary files /dev/null and b/content/engineering/python-virtual-environments/name.webp differ
diff --git a/content/engineering/python-virtual-environments/pip.png b/content/engineering/python-virtual-environments/pip.png
deleted file mode 100644
index 945ed1afa..000000000
Binary files a/content/engineering/python-virtual-environments/pip.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/pip.webp b/content/engineering/python-virtual-environments/pip.webp
new file mode 100644
index 000000000..b0b2279a1
Binary files /dev/null and b/content/engineering/python-virtual-environments/pip.webp differ
diff --git a/content/engineering/python-virtual-environments/python.jpg b/content/engineering/python-virtual-environments/python.jpg
deleted file mode 100644
index 4acb9db7a..000000000
Binary files a/content/engineering/python-virtual-environments/python.jpg and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/python.webp b/content/engineering/python-virtual-environments/python.webp
new file mode 100644
index 000000000..609ffa433
Binary files /dev/null and b/content/engineering/python-virtual-environments/python.webp differ
diff --git a/content/engineering/python-virtual-environments/version.png b/content/engineering/python-virtual-environments/version.png
deleted file mode 100644
index 30ddd8e47..000000000
Binary files a/content/engineering/python-virtual-environments/version.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/version.webp b/content/engineering/python-virtual-environments/version.webp
new file mode 100644
index 000000000..ce9e88498
Binary files /dev/null and b/content/engineering/python-virtual-environments/version.webp differ
diff --git a/content/engineering/python-virtual-environments/windows.png b/content/engineering/python-virtual-environments/windows.png
deleted file mode 100644
index 82e9d374a..000000000
Binary files a/content/engineering/python-virtual-environments/windows.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/windows.webp b/content/engineering/python-virtual-environments/windows.webp
new file mode 100644
index 000000000..9cb5d066a
Binary files /dev/null and b/content/engineering/python-virtual-environments/windows.webp differ
diff --git a/content/engineering/qa-teams-deliver-quality-software/index.md b/content/engineering/qa-teams-deliver-quality-software/index.md
index 62b160718..356e07852 100644
--- a/content/engineering/qa-teams-deliver-quality-software/index.md
+++ b/content/engineering/qa-teams-deliver-quality-software/index.md
@@ -1,7 +1,7 @@
---
title: "QA Testing Process: How to Deliver Quality Software"
date: "2021-03-01"
-coverImage: "software-testing.png"
+coverImage: "software-testing.webp"
author: "Neha Vyas"
description: "A comprehensive overview of the QA testing process is given. Learn what it takes to get top-notch testing facilities."
tags: ["QA", "Processes", "Testing"]
diff --git a/content/engineering/qa-teams-deliver-quality-software/software-testing.png b/content/engineering/qa-teams-deliver-quality-software/software-testing.png
deleted file mode 100644
index 179f9aa33..000000000
Binary files a/content/engineering/qa-teams-deliver-quality-software/software-testing.png and /dev/null differ
diff --git a/content/engineering/qa-teams-deliver-quality-software/software-testing.webp b/content/engineering/qa-teams-deliver-quality-software/software-testing.webp
new file mode 100644
index 000000000..ab46a211c
Binary files /dev/null and b/content/engineering/qa-teams-deliver-quality-software/software-testing.webp differ
diff --git a/content/engineering/quick-kafka-installation/index.md b/content/engineering/quick-kafka-installation/index.md
index 736f68096..8a35e8466 100644
--- a/content/engineering/quick-kafka-installation/index.md
+++ b/content/engineering/quick-kafka-installation/index.md
@@ -1,7 +1,7 @@
---
title: "Setting Up and Running Apache Kafka on Windows OS"
date: "2020-08-25"
-coverImage: "messagelog.png"
+coverImage: "messagelog.webp"
author: "Ashish Sharma"
tags: ["Kafka", "Windows"]
---
@@ -39,7 +39,7 @@ tar -xvzf kafka_2.12-2.4.1.tgz
**Step 3:** Copy the path of the Kafka folder. Now go to _config_ inside Kafka folder and open _zookeeper.properties_ file. Copy the path against the field _dataDir_ and add _/zookeeper-data_ to the path.
-
+
**Step 4:** we have to modify the config/server.properties file. Below is the change:
diff --git a/content/engineering/quick-kafka-installation/messagelog.png b/content/engineering/quick-kafka-installation/messagelog.png
deleted file mode 100644
index 47f716339..000000000
Binary files a/content/engineering/quick-kafka-installation/messagelog.png and /dev/null differ
diff --git a/content/engineering/quick-kafka-installation/messagelog.webp b/content/engineering/quick-kafka-installation/messagelog.webp
new file mode 100644
index 000000000..9b5f8e93b
Binary files /dev/null and b/content/engineering/quick-kafka-installation/messagelog.webp differ
diff --git a/content/engineering/quick-kafka-installation/zookeeper.png b/content/engineering/quick-kafka-installation/zookeeper.png
deleted file mode 100644
index fe9c5eb93..000000000
Binary files a/content/engineering/quick-kafka-installation/zookeeper.png and /dev/null differ
diff --git a/content/engineering/quick-kafka-installation/zookeeper.webp b/content/engineering/quick-kafka-installation/zookeeper.webp
new file mode 100644
index 000000000..debbd0f99
Binary files /dev/null and b/content/engineering/quick-kafka-installation/zookeeper.webp differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/index.md b/content/engineering/quick-look-at-react-speech-recognition/index.md
index 0544235c6..cd77b78c0 100644
--- a/content/engineering/quick-look-at-react-speech-recognition/index.md
+++ b/content/engineering/quick-look-at-react-speech-recognition/index.md
@@ -1,7 +1,7 @@
---
title: "A Quick Look at the React Speech Recognition Hook"
date: "2020-10-29"
-coverImage: "mic.jpg"
+coverImage: "mic.webp"
author: "Krista Singleton"
tags: ["React", "React Speech Recognition", "React Speech", "React Hook"]
description: "Learning and exploring the react-speech-recognition hook basics."
@@ -31,7 +31,7 @@ Note: This framework uses WebSpeech API. Browser support for this API is current
I will be making a simple voice memo app with basic voice commands that run in the browser. If you would like to follow this tutorial, please be ready to work with the create-react-app boilerplate.
-
+
## Let's Get Started
diff --git a/content/engineering/quick-look-at-react-speech-recognition/mic.jpg b/content/engineering/quick-look-at-react-speech-recognition/mic.jpg
deleted file mode 100644
index 71884632c..000000000
Binary files a/content/engineering/quick-look-at-react-speech-recognition/mic.jpg and /dev/null differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/mic.webp b/content/engineering/quick-look-at-react-speech-recognition/mic.webp
new file mode 100644
index 000000000..816a21698
Binary files /dev/null and b/content/engineering/quick-look-at-react-speech-recognition/mic.webp differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/styledExample.png b/content/engineering/quick-look-at-react-speech-recognition/styledExample.png
deleted file mode 100644
index cc35d7c45..000000000
Binary files a/content/engineering/quick-look-at-react-speech-recognition/styledExample.png and /dev/null differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp b/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp
new file mode 100644
index 000000000..ee46f472f
Binary files /dev/null and b/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp differ
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/index.md b/content/engineering/react-code-splitting-with-lazy-suspense/index.md
index 8db7ef374..c7b776ac0 100644
--- a/content/engineering/react-code-splitting-with-lazy-suspense/index.md
+++ b/content/engineering/react-code-splitting-with-lazy-suspense/index.md
@@ -1,7 +1,7 @@
---
title: Code spliting in React via lazy and suspense
date: "2021-05-13"
-coverImage: "react.png"
+coverImage: "react.webp"
author: "Abhimanyu Singh Rathore"
description: "Load Application faster with code spliting and dynamic loading"
tags: ["React"]
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/react.png b/content/engineering/react-code-splitting-with-lazy-suspense/react.png
deleted file mode 100644
index 5969c4dd3..000000000
Binary files a/content/engineering/react-code-splitting-with-lazy-suspense/react.png and /dev/null differ
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/react.webp b/content/engineering/react-code-splitting-with-lazy-suspense/react.webp
new file mode 100644
index 000000000..4f4f67d78
Binary files /dev/null and b/content/engineering/react-code-splitting-with-lazy-suspense/react.webp differ
diff --git a/content/engineering/react-constructor-get-initial-state/index.md b/content/engineering/react-constructor-get-initial-state/index.md
index a2dc65dd4..ab2ee63b1 100644
--- a/content/engineering/react-constructor-get-initial-state/index.md
+++ b/content/engineering/react-constructor-get-initial-state/index.md
@@ -1,7 +1,7 @@
---
title: "Constructor vs getInitialState in React"
date: "2021-01-05"
-coverImage: "index.png"
+coverImage: "index.webp"
author: Nathan Nguyen
tags: ["JavaScript", "React"]
description: "No ES6? No problem. getInitialState is the ES5 friendly method to define the initial state of a React component."
diff --git a/content/engineering/react-constructor-get-initial-state/index.png b/content/engineering/react-constructor-get-initial-state/index.png
deleted file mode 100644
index fd3825ea4..000000000
Binary files a/content/engineering/react-constructor-get-initial-state/index.png and /dev/null differ
diff --git a/content/engineering/react-constructor-get-initial-state/index.webp b/content/engineering/react-constructor-get-initial-state/index.webp
new file mode 100644
index 000000000..d72d1b5ec
Binary files /dev/null and b/content/engineering/react-constructor-get-initial-state/index.webp differ
diff --git a/content/engineering/react-context-api-guide-with-Example/index.md b/content/engineering/react-context-api-guide-with-Example/index.md
index 69e450eca..48cfe0797 100644
--- a/content/engineering/react-context-api-guide-with-Example/index.md
+++ b/content/engineering/react-context-api-guide-with-Example/index.md
@@ -1,7 +1,7 @@
---
title: "React's Context API Guide with Example"
date: "2021-06-09"
-coverImage: "title-image.png"
+coverImage: "title-image.webp"
author: "Versha Gupta"
tags: ["React", "Redux", "Hooks"]
description: "Deep Dive into React's Context API with example"
diff --git a/content/engineering/react-context-api-guide-with-Example/title-image.png b/content/engineering/react-context-api-guide-with-Example/title-image.png
deleted file mode 100644
index 1feb7118a..000000000
Binary files a/content/engineering/react-context-api-guide-with-Example/title-image.png and /dev/null differ
diff --git a/content/engineering/react-context-api-guide-with-Example/title-image.webp b/content/engineering/react-context-api-guide-with-Example/title-image.webp
new file mode 100644
index 000000000..e884d7a9d
Binary files /dev/null and b/content/engineering/react-context-api-guide-with-Example/title-image.webp differ
diff --git a/content/engineering/react-context-api/index.md b/content/engineering/react-context-api/index.md
index 5ee467147..f133b5272 100644
--- a/content/engineering/react-context-api/index.md
+++ b/content/engineering/react-context-api/index.md
@@ -1,7 +1,7 @@
---
title: "React Context API: What is it and How it works?"
date: "2020-10-07"
-coverImage: "react.jpg"
+coverImage: "react.webp"
author: "Eylon Ronen"
tags: ["React", "Redux", "Hooks"]
description: "Context API is a (kind of) new feature added in version 16.3 of React that allows one to share state across the entire app (or part of it) lightly and with ease. Let's see how to use it."
diff --git a/content/engineering/react-context-api/react.jpg b/content/engineering/react-context-api/react.jpg
deleted file mode 100644
index 2e22923df..000000000
Binary files a/content/engineering/react-context-api/react.jpg and /dev/null differ
diff --git a/content/engineering/react-context-api/react.webp b/content/engineering/react-context-api/react.webp
new file mode 100644
index 000000000..5b729e68d
Binary files /dev/null and b/content/engineering/react-context-api/react.webp differ
diff --git a/content/engineering/react-error-boundaries/error_boundary_cover.png b/content/engineering/react-error-boundaries/error_boundary_cover.png
deleted file mode 100644
index ef42fee87..000000000
Binary files a/content/engineering/react-error-boundaries/error_boundary_cover.png and /dev/null differ
diff --git a/content/engineering/react-error-boundaries/error_boundary_cover.webp b/content/engineering/react-error-boundaries/error_boundary_cover.webp
new file mode 100644
index 000000000..54cab35cc
Binary files /dev/null and b/content/engineering/react-error-boundaries/error_boundary_cover.webp differ
diff --git a/content/engineering/react-error-boundaries/index.md b/content/engineering/react-error-boundaries/index.md
index d5ea641e8..da317942f 100644
--- a/content/engineering/react-error-boundaries/index.md
+++ b/content/engineering/react-error-boundaries/index.md
@@ -1,7 +1,7 @@
---
title: "React Error Boundaries"
date: "2021-05-20"
-coverImage: "error_boundary_cover.png"
+coverImage: "error_boundary_cover.webp"
author: "Versha Gupta"
tags: ["React", "Error Handling", "JavaScript"]
description: "Error Handling in React using React Error Boundaries"
diff --git a/content/engineering/react-hooks-guide/index.md b/content/engineering/react-hooks-guide/index.md
index bc9d0952f..44d8a2683 100644
--- a/content/engineering/react-hooks-guide/index.md
+++ b/content/engineering/react-hooks-guide/index.md
@@ -2,7 +2,7 @@
title: "React Hooks: A Beginners Guide"
date: "2020-08-07"
author: "Mohammed Modi"
-coverImage: "react-hooks.png"
+coverImage: "react-hooks.webp"
tags: ["React", "Hooks"]
description: "A walkthrough guide on React Hooks, what is React Hooks, benefits of Hooks, and how to use Hooks in React and more."
---
diff --git a/content/engineering/react-hooks-guide/react-hooks.png b/content/engineering/react-hooks-guide/react-hooks.png
deleted file mode 100644
index b06e44fa2..000000000
Binary files a/content/engineering/react-hooks-guide/react-hooks.png and /dev/null differ
diff --git a/content/engineering/react-hooks-guide/react-hooks.webp b/content/engineering/react-hooks-guide/react-hooks.webp
new file mode 100644
index 000000000..5f712b755
Binary files /dev/null and b/content/engineering/react-hooks-guide/react-hooks.webp differ
diff --git a/content/engineering/react-renderer/index.md b/content/engineering/react-renderer/index.md
index 92819ae21..aa888f280 100644
--- a/content/engineering/react-renderer/index.md
+++ b/content/engineering/react-renderer/index.md
@@ -1,7 +1,7 @@
---
title: "React renderers, react everywhere?"
date: "2021-06-23"
-coverImage: "react.png"
+coverImage: "react.webp"
author: "Abhimanyu Singh Rathore"
description: "There is an advanced feature of React is that it can write renderers for multiple different env."
tags: ["JavaScript", "React", "Renderer"]
diff --git a/content/engineering/react-renderer/react.png b/content/engineering/react-renderer/react.png
deleted file mode 100644
index dfe1b03e1..000000000
Binary files a/content/engineering/react-renderer/react.png and /dev/null differ
diff --git a/content/engineering/react-renderer/react.webp b/content/engineering/react-renderer/react.webp
new file mode 100644
index 000000000..b53a41959
Binary files /dev/null and b/content/engineering/react-renderer/react.webp differ
diff --git a/content/engineering/react-router-basics/image1.png b/content/engineering/react-router-basics/image1.png
deleted file mode 100644
index 12c01b68e..000000000
Binary files a/content/engineering/react-router-basics/image1.png and /dev/null differ
diff --git a/content/engineering/react-router-basics/image1.webp b/content/engineering/react-router-basics/image1.webp
new file mode 100644
index 000000000..e414a9a97
Binary files /dev/null and b/content/engineering/react-router-basics/image1.webp differ
diff --git a/content/engineering/react-router-basics/index.md b/content/engineering/react-router-basics/index.md
index b31566425..462600279 100644
--- a/content/engineering/react-router-basics/index.md
+++ b/content/engineering/react-router-basics/index.md
@@ -1,7 +1,7 @@
---
title: "React Router Basics: Routing in a Single-page Application"
date: "2020-11-20"
-coverImage: "index.png"
+coverImage: "index.webp"
author: Nathan Nguyen
tags: ["JavaScript", "Node", "React", "React Router"]
description: "Everything essential you need to know about React Router."
@@ -105,7 +105,7 @@ If you are currently looking at the render of this structure from the CodePen, y
-
+
Clicking on the <Link>’s in the navigation bar will “navigate” you to the corresponding paths. In effect, what this does is twofold:
diff --git a/content/engineering/react-router-basics/index.png b/content/engineering/react-router-basics/index.png
deleted file mode 100644
index 8e0750cc9..000000000
Binary files a/content/engineering/react-router-basics/index.png and /dev/null differ
diff --git a/content/engineering/react-router-basics/index.webp b/content/engineering/react-router-basics/index.webp
new file mode 100644
index 000000000..24503fe81
Binary files /dev/null and b/content/engineering/react-router-basics/index.webp differ
diff --git a/content/engineering/react-security-vulnerabilities/index.md b/content/engineering/react-security-vulnerabilities/index.md
index 1007dc410..508a2e6fd 100644
--- a/content/engineering/react-security-vulnerabilities/index.md
+++ b/content/engineering/react-security-vulnerabilities/index.md
@@ -1,7 +1,7 @@
---
title: "React Security Vulnerabilities and How to Fix/Prevent Them"
date: "2021-12-24"
-coverImage: "react-security.png"
+coverImage: "react-security.webp"
author: "Gaurav Kumar Roy"
tags: ["React", "Vulnerability"]
description: "React security vulnerabilities are hard to detect. However, this article talks about the top 7 vulnerabilities and how to fix them to enjoy all the benefits React caters to in developing Progressive Web Applications."
diff --git a/content/engineering/react-security-vulnerabilities/react-security.png b/content/engineering/react-security-vulnerabilities/react-security.png
deleted file mode 100644
index 6a4ada3c6..000000000
Binary files a/content/engineering/react-security-vulnerabilities/react-security.png and /dev/null differ
diff --git a/content/engineering/react-security-vulnerabilities/react-security.webp b/content/engineering/react-security-vulnerabilities/react-security.webp
new file mode 100644
index 000000000..d9ad352a9
Binary files /dev/null and b/content/engineering/react-security-vulnerabilities/react-security.webp differ
diff --git a/content/engineering/react-state-management/image1.png b/content/engineering/react-state-management/image1.png
deleted file mode 100644
index 38e7d0c3f..000000000
Binary files a/content/engineering/react-state-management/image1.png and /dev/null differ
diff --git a/content/engineering/react-state-management/image1.webp b/content/engineering/react-state-management/image1.webp
new file mode 100644
index 000000000..285314639
Binary files /dev/null and b/content/engineering/react-state-management/image1.webp differ
diff --git a/content/engineering/react-state-management/index.md b/content/engineering/react-state-management/index.md
index 3b7f0a5d2..31a6cd64a 100644
--- a/content/engineering/react-state-management/index.md
+++ b/content/engineering/react-state-management/index.md
@@ -1,7 +1,7 @@
---
title: "React state management: What is it and why to use it?"
date: "2020-07-17"
-coverImage: "title-image.png"
+coverImage: "title-image.webp"
author: "Versha Gupta"
tags: ["React","Redux","Hooks"]
description: "Learn about React state management and why we need state management and how to use it with React hooks and Redux in the best possible way."
@@ -39,7 +39,7 @@ Let’s discuss how to use react state management using react hooks and redux
Redux was created to resolve this particular issue. it provides a central store that holds all states of your application. Each component can access the stored state without sending it from one component to another. Here is a simple view of how Redux works.
-
+
There are three building parts: actions, store, and reducers. Let’s briefly discuss what each of them does.
diff --git a/content/engineering/react-state-management/title-image.png b/content/engineering/react-state-management/title-image.png
deleted file mode 100644
index 26d6ac7b8..000000000
Binary files a/content/engineering/react-state-management/title-image.png and /dev/null differ
diff --git a/content/engineering/react-state-management/title-image.webp b/content/engineering/react-state-management/title-image.webp
new file mode 100644
index 000000000..952ff5252
Binary files /dev/null and b/content/engineering/react-state-management/title-image.webp differ
diff --git a/content/engineering/react-with-refs/index.md b/content/engineering/react-with-refs/index.md
index 89d8bfb9b..9aad4d02b 100644
--- a/content/engineering/react-with-refs/index.md
+++ b/content/engineering/react-with-refs/index.md
@@ -1,7 +1,7 @@
---
title: "React with Ref"
date: "2021-04-16"
-coverImage: "title-image.png"
+coverImage: "title-image.webp"
author: "Versha Gupta"
tags: ["React","Refs","DOM"]
description: "Learn about manipulation of DOM elements with Ref directly with React"
diff --git a/content/engineering/react-with-refs/title-image.png b/content/engineering/react-with-refs/title-image.png
deleted file mode 100644
index 64bcc8204..000000000
Binary files a/content/engineering/react-with-refs/title-image.png and /dev/null differ
diff --git a/content/engineering/react-with-refs/title-image.webp b/content/engineering/react-with-refs/title-image.webp
new file mode 100644
index 000000000..1bda575f8
Binary files /dev/null and b/content/engineering/react-with-refs/title-image.webp differ
diff --git a/content/engineering/reacts-reconciliation-algorithm/Capture.png b/content/engineering/reacts-reconciliation-algorithm/Capture.png
deleted file mode 100644
index 7fad59a4b..000000000
Binary files a/content/engineering/reacts-reconciliation-algorithm/Capture.png and /dev/null differ
diff --git a/content/engineering/reacts-reconciliation-algorithm/Capture.webp b/content/engineering/reacts-reconciliation-algorithm/Capture.webp
new file mode 100644
index 000000000..063759fb2
Binary files /dev/null and b/content/engineering/reacts-reconciliation-algorithm/Capture.webp differ
diff --git a/content/engineering/reacts-reconciliation-algorithm/index.md b/content/engineering/reacts-reconciliation-algorithm/index.md
index 9c91bac7c..5722e2d60 100644
--- a/content/engineering/reacts-reconciliation-algorithm/index.md
+++ b/content/engineering/reacts-reconciliation-algorithm/index.md
@@ -1,7 +1,7 @@
---
title: "React's Reconciliation Algorithm"
date: "2019-12-03"
-coverImage: "react-fiber.png"
+coverImage: "react-fiber.webp"
author: "Team LoginRadius"
tags: ["React"]
---
diff --git a/content/engineering/reacts-reconciliation-algorithm/react-fiber.png b/content/engineering/reacts-reconciliation-algorithm/react-fiber.png
deleted file mode 100644
index 7052c9d32..000000000
Binary files a/content/engineering/reacts-reconciliation-algorithm/react-fiber.png and /dev/null differ
diff --git a/content/engineering/reacts-reconciliation-algorithm/react-fiber.webp b/content/engineering/reacts-reconciliation-algorithm/react-fiber.webp
new file mode 100644
index 000000000..54252e8c9
Binary files /dev/null and b/content/engineering/reacts-reconciliation-algorithm/react-fiber.webp differ
diff --git a/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.png b/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.png
deleted file mode 100644
index da91f8515..000000000
Binary files a/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.png and /dev/null differ
diff --git a/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.webp b/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.webp
new file mode 100644
index 000000000..f13aa9b56
Binary files /dev/null and b/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.webp differ
diff --git a/content/engineering/read-and-write-in-a-local-file-with-deno/index.md b/content/engineering/read-and-write-in-a-local-file-with-deno/index.md
index 25a982534..3dc9cff97 100644
--- a/content/engineering/read-and-write-in-a-local-file-with-deno/index.md
+++ b/content/engineering/read-and-write-in-a-local-file-with-deno/index.md
@@ -1,7 +1,7 @@
---
title: Read and Write in a local file with Deno
date: "2020-06-09"
-coverImage: "deno_file_system.png"
+coverImage: "deno_file_system.webp"
author: "Puneet Singh"
tags: ["Deno"]
---
diff --git a/content/engineering/recoiling-the-react/index.md b/content/engineering/recoiling-the-react/index.md
index 1dcfd850c..8617f4647 100644
--- a/content/engineering/recoiling-the-react/index.md
+++ b/content/engineering/recoiling-the-react/index.md
@@ -1,7 +1,7 @@
---
title: What is recoil.js and how it is managing in react?
date: "2021-04-30"
-coverImage: "react.png"
+coverImage: "react.webp"
author: "Abhimanyu Singh Rathore"
description: "Recoil is an experimental state management library and It provides several capabilities that are difficult to achieve with React alone.In this article we learn about the recoil.js, and how it is managing state in react."
tags: [JavaScript,React,Recoil]
diff --git a/content/engineering/recoiling-the-react/react.png b/content/engineering/recoiling-the-react/react.png
deleted file mode 100644
index 56a6acf20..000000000
Binary files a/content/engineering/recoiling-the-react/react.png and /dev/null differ
diff --git a/content/engineering/recoiling-the-react/react.webp b/content/engineering/recoiling-the-react/react.webp
new file mode 100644
index 000000000..9255c63cc
Binary files /dev/null and b/content/engineering/recoiling-the-react/react.webp differ
diff --git a/content/engineering/relational-database-management-system-rdbms-vs-nosql/index.md b/content/engineering/relational-database-management-system-rdbms-vs-nosql/index.md
index 2ed7c0fb8..10d15a3b8 100644
--- a/content/engineering/relational-database-management-system-rdbms-vs-nosql/index.md
+++ b/content/engineering/relational-database-management-system-rdbms-vs-nosql/index.md
@@ -1,7 +1,7 @@
---
title: "RDBMS vs NoSQL"
date: "2015-04-28"
-coverImage: "rdbms-vs-nosql.png"
+coverImage: "rdbms-vs-nosql.webp"
author: "Team LoginRadius"
tags: ["Database"]
description: "Learn about RDBMS and NoSQL Database systems, their differences, benefits and limitations"
diff --git a/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.png b/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.png
deleted file mode 100644
index 81bde6ccc..000000000
Binary files a/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.png and /dev/null differ
diff --git a/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.webp b/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.webp
new file mode 100644
index 000000000..1727b2ea2
Binary files /dev/null and b/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.webp differ
diff --git a/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.png b/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.png
deleted file mode 100644
index 711d9912e..000000000
Binary files a/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.png and /dev/null differ
diff --git a/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.webp b/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.webp
new file mode 100644
index 000000000..f6a4e52b1
Binary files /dev/null and b/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.webp differ
diff --git a/content/engineering/rest-api-cucumber-blog/index.md b/content/engineering/rest-api-cucumber-blog/index.md
index b7c013d47..6eb2bcb8e 100644
--- a/content/engineering/rest-api-cucumber-blog/index.md
+++ b/content/engineering/rest-api-cucumber-blog/index.md
@@ -1,7 +1,7 @@
---
title: "Automating Rest API's using Cucumber and Java"
date: "2020-11-05"
-coverImage: "cucumber_rest_assured.png"
+coverImage: "cucumber_rest_assured.webp"
author: "Surendranath Reddy Birudala"
tags: ["Automation", "Cucumber", "Rest API", "Java"]
description: "This article is about basic overview of how to automate Rest API using Cucumber and JAVA."
diff --git a/content/engineering/rest-api-kubernetes/cover.png b/content/engineering/rest-api-kubernetes/cover.png
deleted file mode 100644
index d9133312c..000000000
Binary files a/content/engineering/rest-api-kubernetes/cover.png and /dev/null differ
diff --git a/content/engineering/rest-api-kubernetes/cover.webp b/content/engineering/rest-api-kubernetes/cover.webp
new file mode 100644
index 000000000..5f27cdcf8
Binary files /dev/null and b/content/engineering/rest-api-kubernetes/cover.webp differ
diff --git a/content/engineering/rest-api-kubernetes/index.md b/content/engineering/rest-api-kubernetes/index.md
index 0a8da52bc..8d35ec817 100644
--- a/content/engineering/rest-api-kubernetes/index.md
+++ b/content/engineering/rest-api-kubernetes/index.md
@@ -1,7 +1,7 @@
---
title: "How to Deploy a REST API in Kubernetes"
date: "2021-02-03"
-coverImage: "cover.png"
+coverImage: "cover.webp"
author: "Andy Yeung"
tags: ["Kubernetes"]
description: "Beginner guide on how to create and deploy a REST API in local Kubernetes."
diff --git a/content/engineering/risk-based-authentication/cover.jpg b/content/engineering/risk-based-authentication/cover.jpg
deleted file mode 100644
index 83d253ef9..000000000
Binary files a/content/engineering/risk-based-authentication/cover.jpg and /dev/null differ
diff --git a/content/engineering/risk-based-authentication/cover.webp b/content/engineering/risk-based-authentication/cover.webp
new file mode 100644
index 000000000..3f7dae913
Binary files /dev/null and b/content/engineering/risk-based-authentication/cover.webp differ
diff --git a/content/engineering/risk-based-authentication/incorrect.jpg b/content/engineering/risk-based-authentication/incorrect.jpg
deleted file mode 100644
index 9bb1c2645..000000000
Binary files a/content/engineering/risk-based-authentication/incorrect.jpg and /dev/null differ
diff --git a/content/engineering/risk-based-authentication/incorrect.webp b/content/engineering/risk-based-authentication/incorrect.webp
new file mode 100644
index 000000000..e744164fa
Binary files /dev/null and b/content/engineering/risk-based-authentication/incorrect.webp differ
diff --git a/content/engineering/risk-based-authentication/index.md b/content/engineering/risk-based-authentication/index.md
index 2eca3b1f4..53eab1f4c 100644
--- a/content/engineering/risk-based-authentication/index.md
+++ b/content/engineering/risk-based-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "What is Risk-Based Authentication? And Why Should You Implement It?"
date: "2021-05-25"
-coverImage: "cover.jpg"
+coverImage: "cover.webp"
author: "Raghunath Reddy"
tags: ["RBA","Authentication"]
description: "RBA is a process of assessing the risk of an authentication request in real-time and requesting additional layers of authentication and identification based on the risk profile to validate that a user attempting to authenticate is who they claim to be."
@@ -11,7 +11,7 @@ While most of you — developers and architects — understand the need for stro
For years security researchers have been hollering about the risks of weak, repeated passwords. Still, average Joe seems to be complacent about it and reuses the same or similar passwords across multiple logins, despite the fact that even a strong password is secure only if used for a single login.
-
+
A good password manager can alleviate the problem of remembering tens of passwords, if not hundreds. However, in reality, the average Joe doesn't invest in a password manager and carries on with life.
diff --git a/content/engineering/roadmap-idx-autotester/index.md b/content/engineering/roadmap-idx-autotester/index.md
index 3b9d36039..77d3fe6ff 100644
--- a/content/engineering/roadmap-idx-autotester/index.md
+++ b/content/engineering/roadmap-idx-autotester/index.md
@@ -1,7 +1,7 @@
---
title: "Roadmap of idx-auto-tester"
date: "2020-06-30"
-coverImage: "roadmap_idx_auto_tester.png"
+coverImage: "roadmap_idx_auto_tester.webp"
author: "Rakesh Pareek"
tags: ["Automation", "idx", "roadmap"]
canonical: https://www.loginradius.com/blog/engineering/introduction-of-idx-auto-tester/
diff --git a/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.png b/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.png
deleted file mode 100644
index c1a4e8a89..000000000
Binary files a/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.png and /dev/null differ
diff --git a/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.webp b/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.webp
new file mode 100644
index 000000000..4f067d758
Binary files /dev/null and b/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.webp differ
diff --git a/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.png b/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.png
deleted file mode 100644
index be559cb7a..000000000
Binary files a/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.png and /dev/null differ
diff --git a/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.webp b/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.webp
new file mode 100644
index 000000000..bfc6256cb
Binary files /dev/null and b/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.webp differ
diff --git a/content/engineering/saas-single-tenancy-vs-multi-tenancy/index.md b/content/engineering/saas-single-tenancy-vs-multi-tenancy/index.md
index 12d82c979..66fa37d74 100644
--- a/content/engineering/saas-single-tenancy-vs-multi-tenancy/index.md
+++ b/content/engineering/saas-single-tenancy-vs-multi-tenancy/index.md
@@ -1,7 +1,7 @@
---
title: "Single-Tenant vs. Multi-Tenant: Which SaaS Architecture is better for Your Business? "
date: "2021-12-01"
-coverImage: "coverImage.png"
+coverImage: "coverImage.webp"
author: "Rakesh Soni"
tags: ["saas", "Architecture"]
description: "When choosing a SaaS architecture for your business, the decision between single-tenant and multi-tenant models can significantly impact performance, security, and cost. This blog explores the key differences, advantages, and potential drawbacks of each approach, helping you determine which solution best aligns with your business needs."
diff --git a/content/engineering/sdk-version-10-0-0/SDK.png b/content/engineering/sdk-version-10-0-0/SDK.png
deleted file mode 100644
index 95971dff2..000000000
Binary files a/content/engineering/sdk-version-10-0-0/SDK.png and /dev/null differ
diff --git a/content/engineering/sdk-version-10-0-0/SDK.webp b/content/engineering/sdk-version-10-0-0/SDK.webp
new file mode 100644
index 000000000..7a3830350
Binary files /dev/null and b/content/engineering/sdk-version-10-0-0/SDK.webp differ
diff --git a/content/engineering/sdk-version-10-0-0/index.md b/content/engineering/sdk-version-10-0-0/index.md
index b71911959..75d58e822 100644
--- a/content/engineering/sdk-version-10-0-0/index.md
+++ b/content/engineering/sdk-version-10-0-0/index.md
@@ -1,7 +1,7 @@
---
title: "SDK Version 10.0.0"
date: "2019-10-31"
-coverImage: "SDK.png"
+coverImage: "SDK.webp"
author: "Indrasen Kumar"
tags: ["Engineering", "SDK", "Version"]
---
diff --git a/content/engineering/self-hosted-mongo/atlas.png b/content/engineering/self-hosted-mongo/atlas.png
deleted file mode 100644
index 6cf420feb..000000000
Binary files a/content/engineering/self-hosted-mongo/atlas.png and /dev/null differ
diff --git a/content/engineering/self-hosted-mongo/atlas.webp b/content/engineering/self-hosted-mongo/atlas.webp
new file mode 100644
index 000000000..7643b9f1a
Binary files /dev/null and b/content/engineering/self-hosted-mongo/atlas.webp differ
diff --git a/content/engineering/self-hosted-mongo/aws.png b/content/engineering/self-hosted-mongo/aws.png
deleted file mode 100644
index 9b0980a56..000000000
Binary files a/content/engineering/self-hosted-mongo/aws.png and /dev/null differ
diff --git a/content/engineering/self-hosted-mongo/aws.webp b/content/engineering/self-hosted-mongo/aws.webp
new file mode 100644
index 000000000..6b89a7d19
Binary files /dev/null and b/content/engineering/self-hosted-mongo/aws.webp differ
diff --git a/content/engineering/self-hosted-mongo/blkid.png b/content/engineering/self-hosted-mongo/blkid.png
deleted file mode 100644
index c5f381f95..000000000
Binary files a/content/engineering/self-hosted-mongo/blkid.png and /dev/null differ
diff --git a/content/engineering/self-hosted-mongo/blkid.webp b/content/engineering/self-hosted-mongo/blkid.webp
new file mode 100644
index 000000000..0fced3f21
Binary files /dev/null and b/content/engineering/self-hosted-mongo/blkid.webp differ
diff --git a/content/engineering/self-hosted-mongo/cover.jpeg b/content/engineering/self-hosted-mongo/cover.jpeg
deleted file mode 100644
index 5a3aae58a..000000000
Binary files a/content/engineering/self-hosted-mongo/cover.jpeg and /dev/null differ
diff --git a/content/engineering/self-hosted-mongo/cover.webp b/content/engineering/self-hosted-mongo/cover.webp
new file mode 100644
index 000000000..8f52e5640
Binary files /dev/null and b/content/engineering/self-hosted-mongo/cover.webp differ
diff --git a/content/engineering/self-hosted-mongo/index.md b/content/engineering/self-hosted-mongo/index.md
index 6aa25d7cd..850085074 100644
--- a/content/engineering/self-hosted-mongo/index.md
+++ b/content/engineering/self-hosted-mongo/index.md
@@ -1,7 +1,7 @@
---
title: "Self-Hosted MongoDB"
date: "2020-06-30T12:00:00"
-coverImage: "cover.jpeg"
+coverImage: "cover.webp"
author: "Chinmaya Pati"
tags: ["MongoDB", "Mongo", "AWS", "Atlas"]
description: "Learn how to optimize your DB cost? This article will help you with the complete migration steps from a cloud to a self-hosted environment."
@@ -15,11 +15,11 @@ BTW, how much savings are we talking about? Let’s do a quick comparison betwee
**Atlas (~$166/month)**
-
+
$0.23/hour based on the above-selected requirements (~ [cloud.mongodb.com](https://cloud.mongodb.com))
**AWS (~$36/month)**
-
+
$0.0416/hour for the instance and additional pricing based on the EBS type and storage (~ [calculator.aws](https://calculator.aws/))
@@ -65,7 +65,7 @@ $ sudo lsblk
The additional volumes will be listed right after the root block (refer to the arrows)
-
+
In the image above, you can see that the additional volumes are named
1. **xvdb** (30Gb space to store data)
@@ -93,7 +93,7 @@ Before that let's copy the UUID of the above partitions(*because they are unique
$ sudo blkid
```
-
+
Copy the UUIDs listed for **/dev/xvdb** and **/dev/xvdc**. Refer to the **“LABEL”** for block identification
diff --git a/content/engineering/self-hosted-mongo/lsblk.png b/content/engineering/self-hosted-mongo/lsblk.png
deleted file mode 100644
index 0396ca6eb..000000000
Binary files a/content/engineering/self-hosted-mongo/lsblk.png and /dev/null differ
diff --git a/content/engineering/self-hosted-mongo/lsblk.webp b/content/engineering/self-hosted-mongo/lsblk.webp
new file mode 100644
index 000000000..8fd9ddb88
Binary files /dev/null and b/content/engineering/self-hosted-mongo/lsblk.webp differ
diff --git a/content/engineering/sending-emails-with-golang/email_cover.jpg b/content/engineering/sending-emails-with-golang/email_cover.jpg
deleted file mode 100644
index 25569ede9..000000000
Binary files a/content/engineering/sending-emails-with-golang/email_cover.jpg and /dev/null differ
diff --git a/content/engineering/sending-emails-with-golang/email_cover.webp b/content/engineering/sending-emails-with-golang/email_cover.webp
new file mode 100644
index 000000000..f5b5b10a5
Binary files /dev/null and b/content/engineering/sending-emails-with-golang/email_cover.webp differ
diff --git a/content/engineering/sending-emails-with-golang/index.md b/content/engineering/sending-emails-with-golang/index.md
index 694eb1282..ed16e1841 100644
--- a/content/engineering/sending-emails-with-golang/index.md
+++ b/content/engineering/sending-emails-with-golang/index.md
@@ -1,7 +1,7 @@
---
title: Different ways to send an email with Golang
date: "2020-08-03"
-coverImage: "email_cover.jpg"
+coverImage: "email_cover.webp"
author: "Puneet Singh"
tags: ["Go","Email"]
description: "In this blog, we’ll look at different methods to send an email with Go, First we will explore inbuilt smtp package, then we will move to use a popular package Gomail and finally we will send HTML emails using custom templates."
diff --git a/content/engineering/separate-login-page-for-admin-and-user/drupal.png b/content/engineering/separate-login-page-for-admin-and-user/drupal.png
deleted file mode 100644
index 7ccb47873..000000000
Binary files a/content/engineering/separate-login-page-for-admin-and-user/drupal.png and /dev/null differ
diff --git a/content/engineering/separate-login-page-for-admin-and-user/drupal.webp b/content/engineering/separate-login-page-for-admin-and-user/drupal.webp
new file mode 100644
index 000000000..883abc12b
Binary files /dev/null and b/content/engineering/separate-login-page-for-admin-and-user/drupal.webp differ
diff --git a/content/engineering/separate-login-page-for-admin-and-user/index.md b/content/engineering/separate-login-page-for-admin-and-user/index.md
index eca75a4aa..a4b9b4503 100644
--- a/content/engineering/separate-login-page-for-admin-and-user/index.md
+++ b/content/engineering/separate-login-page-for-admin-and-user/index.md
@@ -1,7 +1,7 @@
---
title: "Separate Drupal Login Page for Admin and User"
date: "2015-10-29"
-coverImage: "drupal.png"
+coverImage: "drupal.webp"
author: Versha Gupta
tags: ["Drupal", "Admin Panel"]
---
diff --git a/content/engineering/serverless-overview/cover.png b/content/engineering/serverless-overview/cover.png
deleted file mode 100644
index e999a7383..000000000
Binary files a/content/engineering/serverless-overview/cover.png and /dev/null differ
diff --git a/content/engineering/serverless-overview/cover.webp b/content/engineering/serverless-overview/cover.webp
new file mode 100644
index 000000000..93b905d4f
Binary files /dev/null and b/content/engineering/serverless-overview/cover.webp differ
diff --git a/content/engineering/serverless-overview/index.md b/content/engineering/serverless-overview/index.md
index 1fefff770..518447eb7 100644
--- a/content/engineering/serverless-overview/index.md
+++ b/content/engineering/serverless-overview/index.md
@@ -1,7 +1,7 @@
---
title: "Top 4 Serverless Computing Platforms in 2021"
date: "2021-03-04"
-coverImage: "cover.png"
+coverImage: "cover.webp"
author: "Andy Yeung"
tags: ["Serverless"]
description: "Traditional software development is being transformed by serverless computing. Check out the best serveless computing platforms that will assist you in getting started."
diff --git a/content/engineering/service-mesh-with-envoy/front-image.jpeg b/content/engineering/service-mesh-with-envoy/front-image.jpeg
deleted file mode 100644
index b9b6eea72..000000000
Binary files a/content/engineering/service-mesh-with-envoy/front-image.jpeg and /dev/null differ
diff --git a/content/engineering/service-mesh-with-envoy/front-image.webp b/content/engineering/service-mesh-with-envoy/front-image.webp
new file mode 100644
index 000000000..596ab1a58
Binary files /dev/null and b/content/engineering/service-mesh-with-envoy/front-image.webp differ
diff --git a/content/engineering/service-mesh-with-envoy/index.md b/content/engineering/service-mesh-with-envoy/index.md
index 9fa2a0fa6..eb291c81f 100644
--- a/content/engineering/service-mesh-with-envoy/index.md
+++ b/content/engineering/service-mesh-with-envoy/index.md
@@ -1,7 +1,7 @@
---
title: "Service Mesh with Envoy"
date: "2020-07-06"
-coverImage: "front-image.jpeg"
+coverImage: "front-image.webp"
author: "Piyush Kumar"
tags: ["Service Mesh", "Envoy", "Microservices"]
---
diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.png b/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.png
deleted file mode 100644
index 08ca7e676..000000000
Binary files a/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.png and /dev/null differ
diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.webp b/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.webp
new file mode 100644
index 000000000..1d290ef07
Binary files /dev/null and b/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.webp differ
diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.png b/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.png
deleted file mode 100644
index 6d5c3b63a..000000000
Binary files a/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.png and /dev/null differ
diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.webp b/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.webp
new file mode 100644
index 000000000..462c36053
Binary files /dev/null and b/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.webp differ
diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/index.md b/content/engineering/setup-blog-in-minutes-with-jekyll/index.md
index eff007cd1..c67540562 100644
--- a/content/engineering/setup-blog-in-minutes-with-jekyll/index.md
+++ b/content/engineering/setup-blog-in-minutes-with-jekyll/index.md
@@ -1,7 +1,7 @@
---
title: "Setup a blog in minutes with Jekyll & Github"
date: "2020-10-26"
-coverImage: "jekyll-github-pages.png"
+coverImage: "jekyll-github-pages.webp"
author: "Malathi T"
tags: ["jekyll", "blogging", "blog", "github-pages"]
description: Getting started with Jekyll & Github pages
@@ -18,7 +18,7 @@ bundle exec jekyll serve
```
That's it. You can navigate to `http://localhost:8080` and see your blog up and running like this
-
+
## Customizing the blog
As you see, the blog is a bare minimum, and the default values mentioned in the config file (`_config.yml`) are used. You can use the `_config.yml` file to add new plugins, provide metadata about the blog, add your social media profiles, modify themes, etc.
@@ -46,11 +46,11 @@ Using your GitHub account, create a new repository. Push the contents of the jek
`https://github.com//my-new-blog/settings`.
In the settings page, under the `Github pages` section, specify the branch to use for the github source. This can be the `main` branch or some other branch in the repository.
-
+
As soon as the github page is enabled on a branch, github automatically creates actions to build the jeyll blog on a new commit to the branch.
-
+
## Advantages of using Jekyll & Github pages
- Open-source
diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/jekyll-github-pages.png b/content/engineering/setup-blog-in-minutes-with-jekyll/jekyll-github-pages.png
deleted file mode 100644
index bdaa1a604..000000000
Binary files a/content/engineering/setup-blog-in-minutes-with-jekyll/jekyll-github-pages.png and /dev/null differ
diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/jekyll-github-pages.webp b/content/engineering/setup-blog-in-minutes-with-jekyll/jekyll-github-pages.webp
new file mode 100644
index 000000000..93431d054
Binary files /dev/null and b/content/engineering/setup-blog-in-minutes-with-jekyll/jekyll-github-pages.webp differ
diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/new-blog.png b/content/engineering/setup-blog-in-minutes-with-jekyll/new-blog.png
deleted file mode 100644
index 0a7d9eb00..000000000
Binary files a/content/engineering/setup-blog-in-minutes-with-jekyll/new-blog.png and /dev/null differ
diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/new-blog.webp b/content/engineering/setup-blog-in-minutes-with-jekyll/new-blog.webp
new file mode 100644
index 000000000..3fa02d741
Binary files /dev/null and b/content/engineering/setup-blog-in-minutes-with-jekyll/new-blog.webp differ
diff --git a/content/engineering/shopify-embedded-app/index.md b/content/engineering/shopify-embedded-app/index.md
index d4595e424..49ffe7e09 100644
--- a/content/engineering/shopify-embedded-app/index.md
+++ b/content/engineering/shopify-embedded-app/index.md
@@ -1,7 +1,7 @@
---
title: "Shopify Embedded App"
date: "2015-06-02"
-coverImage: "shopify.png"
+coverImage: "shopify.webp"
author: Lucius Yu
tags: ["Shopify", "PHP"]
---
diff --git a/content/engineering/shopify-embedded-app/shopify.png b/content/engineering/shopify-embedded-app/shopify.png
deleted file mode 100644
index 77224339d..000000000
Binary files a/content/engineering/shopify-embedded-app/shopify.png and /dev/null differ
diff --git a/content/engineering/shopify-embedded-app/shopify.webp b/content/engineering/shopify-embedded-app/shopify.webp
new file mode 100644
index 000000000..c117271ff
Binary files /dev/null and b/content/engineering/shopify-embedded-app/shopify.webp differ
diff --git a/content/engineering/signup-using-passwordless/index.md b/content/engineering/signup-using-passwordless/index.md
index 673c0e198..60e3922e7 100644
--- a/content/engineering/signup-using-passwordless/index.md
+++ b/content/engineering/signup-using-passwordless/index.md
@@ -1,7 +1,7 @@
---
title: "Optimize Your Sign Up Page By Going Passwordless"
date: "2021-02-10"
-coverImage: "open-source.png"
+coverImage: "open-source.webp"
author: "Ravi Teja Ganta"
tags: ["Passwordless"]
description: "How passwordless can be an excellent approach to reduce user drops on the signup page with better UX practices."
diff --git a/content/engineering/signup-using-passwordless/open-source.png b/content/engineering/signup-using-passwordless/open-source.png
deleted file mode 100644
index d7ef1337d..000000000
Binary files a/content/engineering/signup-using-passwordless/open-source.png and /dev/null differ
diff --git a/content/engineering/signup-using-passwordless/open-source.webp b/content/engineering/signup-using-passwordless/open-source.webp
new file mode 100644
index 000000000..449e5171a
Binary files /dev/null and b/content/engineering/signup-using-passwordless/open-source.webp differ
diff --git a/content/engineering/simple-popup-tutorial/index.md b/content/engineering/simple-popup-tutorial/index.md
index 5563f278f..3bd5d1135 100644
--- a/content/engineering/simple-popup-tutorial/index.md
+++ b/content/engineering/simple-popup-tutorial/index.md
@@ -1,7 +1,7 @@
---
title: "A Simple Popup Tutorial"
date: "2015-01-05"
-coverImage: "simplepop.png"
+coverImage: "simplepop.webp"
author: Zoie Carnegie
tags: ["HTML", "CSS", "UI"]
---
@@ -81,7 +81,7 @@ We’ve created a div with id overlay to cover all the page content when the pop
We’ve now added some CSS for the overlay and the popup. At this point, we can see a white box above our grey overlay. We’ve added an h1 tag inside our popup a page title and some main page content. We should now see something like this:
-
+
Next let's add a control to close this popup. We’ll add a span containing an X that we can click on to close this popup and JavaScript to handle this event.
diff --git a/content/engineering/simple-popup-tutorial/popup-example-01.png b/content/engineering/simple-popup-tutorial/popup-example-01.png
deleted file mode 100644
index 9bad637b1..000000000
Binary files a/content/engineering/simple-popup-tutorial/popup-example-01.png and /dev/null differ
diff --git a/content/engineering/simple-popup-tutorial/popup-example-01.webp b/content/engineering/simple-popup-tutorial/popup-example-01.webp
new file mode 100644
index 000000000..56179e845
Binary files /dev/null and b/content/engineering/simple-popup-tutorial/popup-example-01.webp differ
diff --git a/content/engineering/simple-popup-tutorial/simplepop.png b/content/engineering/simple-popup-tutorial/simplepop.png
deleted file mode 100644
index be6fe3d7d..000000000
Binary files a/content/engineering/simple-popup-tutorial/simplepop.png and /dev/null differ
diff --git a/content/engineering/simple-popup-tutorial/simplepop.webp b/content/engineering/simple-popup-tutorial/simplepop.webp
new file mode 100644
index 000000000..f1813330d
Binary files /dev/null and b/content/engineering/simple-popup-tutorial/simplepop.webp differ
diff --git a/content/engineering/simple-social-media-solutions/index.md b/content/engineering/simple-social-media-solutions/index.md
index 076664236..a757f543c 100644
--- a/content/engineering/simple-social-media-solutions/index.md
+++ b/content/engineering/simple-social-media-solutions/index.md
@@ -1,7 +1,7 @@
---
title: "Social Media Solutions"
date: "2015-10-08"
-coverImage: "social-media.png"
+coverImage: "social-media.webp"
author: Karl Wittig
tags: ["Social Media", "Social Login"]
---
diff --git a/content/engineering/simple-social-media-solutions/social-media.png b/content/engineering/simple-social-media-solutions/social-media.png
deleted file mode 100644
index 3baf42a2b..000000000
Binary files a/content/engineering/simple-social-media-solutions/social-media.png and /dev/null differ
diff --git a/content/engineering/simple-social-media-solutions/social-media.webp b/content/engineering/simple-social-media-solutions/social-media.webp
new file mode 100644
index 000000000..0e7dfbf45
Binary files /dev/null and b/content/engineering/simple-social-media-solutions/social-media.webp differ
diff --git a/content/engineering/smart-cache-redis-cloud-aws-elasticache-for-redis/index.md b/content/engineering/smart-cache-redis-cloud-aws-elasticache-for-redis/index.md
index da86565c6..0d7206bc9 100644
--- a/content/engineering/smart-cache-redis-cloud-aws-elasticache-for-redis/index.md
+++ b/content/engineering/smart-cache-redis-cloud-aws-elasticache-for-redis/index.md
@@ -1,7 +1,7 @@
---
title: "Breaking Down the Decision: Why We Chose AWS ElastiCache Over Redis Cloud"
date: "2023-08-09"
-coverImage: "migrating-to-aws-elasticache-for-redis.jpg"
+coverImage: "migrating-to-aws-elasticache-for-redis.webp"
author: "Kundan Singh"
tags: ["Cache", "AWS", "Redis", "LoginRadius"]
description: "ElastiCache’s capabilities are better suited than Redis Cloud for our technical requirements and use cases, especially better scalability and pricing."
diff --git a/content/engineering/smart-cache-redis-cloud-aws-elasticache-for-redis/migrating-to-aws-elasticache-for-redis.jpg b/content/engineering/smart-cache-redis-cloud-aws-elasticache-for-redis/migrating-to-aws-elasticache-for-redis.jpg
deleted file mode 100644
index 7469e6d32..000000000
Binary files a/content/engineering/smart-cache-redis-cloud-aws-elasticache-for-redis/migrating-to-aws-elasticache-for-redis.jpg and /dev/null differ
diff --git a/content/engineering/smart-cache-redis-cloud-aws-elasticache-for-redis/migrating-to-aws-elasticache-for-redis.webp b/content/engineering/smart-cache-redis-cloud-aws-elasticache-for-redis/migrating-to-aws-elasticache-for-redis.webp
new file mode 100644
index 000000000..123ddb2af
Binary files /dev/null and b/content/engineering/smart-cache-redis-cloud-aws-elasticache-for-redis/migrating-to-aws-elasticache-for-redis.webp differ
diff --git a/content/engineering/snapshot-testing-using-nightwatch-and-mocha/index.md b/content/engineering/snapshot-testing-using-nightwatch-and-mocha/index.md
index 33db90a3d..d555b1802 100644
--- a/content/engineering/snapshot-testing-using-nightwatch-and-mocha/index.md
+++ b/content/engineering/snapshot-testing-using-nightwatch-and-mocha/index.md
@@ -1,7 +1,7 @@
---
title: "Snapshot testing using Nightwatch and mocha"
date: "2020-07-29"
-coverImage: "snapshot_nightwatch.png"
+coverImage: "snapshot_nightwatch.webp"
author: "Nitesh Jain"
tags: ["QA", "Nightwatch","snapshot-testing"]
description: "Snapshot testing is one of many different testing tools, which compares the previous and current snapshot. Unlike TDD, snapshot testing relies on the fact that your component renders correctly already. "
diff --git a/content/engineering/snapshot-testing-using-nightwatch-and-mocha/snapshot_nightwatch.png b/content/engineering/snapshot-testing-using-nightwatch-and-mocha/snapshot_nightwatch.png
deleted file mode 100644
index dbad95c16..000000000
Binary files a/content/engineering/snapshot-testing-using-nightwatch-and-mocha/snapshot_nightwatch.png and /dev/null differ
diff --git a/content/engineering/snapshot-testing-using-nightwatch-and-mocha/snapshot_nightwatch.webp b/content/engineering/snapshot-testing-using-nightwatch-and-mocha/snapshot_nightwatch.webp
new file mode 100644
index 000000000..8ac37338a
Binary files /dev/null and b/content/engineering/snapshot-testing-using-nightwatch-and-mocha/snapshot_nightwatch.webp differ
diff --git a/content/engineering/social-media-colors-hex/darrylblog1-150x150.png b/content/engineering/social-media-colors-hex/darrylblog1-150x150.png
deleted file mode 100644
index ff9eb6c6a..000000000
Binary files a/content/engineering/social-media-colors-hex/darrylblog1-150x150.png and /dev/null differ
diff --git a/content/engineering/social-media-colors-hex/darrylblog1-150x150.webp b/content/engineering/social-media-colors-hex/darrylblog1-150x150.webp
new file mode 100644
index 000000000..bbf6fe26a
Binary files /dev/null and b/content/engineering/social-media-colors-hex/darrylblog1-150x150.webp differ
diff --git a/content/engineering/social-media-colors-hex/index.md b/content/engineering/social-media-colors-hex/index.md
index 82cacf2c5..9755547d7 100644
--- a/content/engineering/social-media-colors-hex/index.md
+++ b/content/engineering/social-media-colors-hex/index.md
@@ -1,7 +1,7 @@
---
title: "Social Media Colors in Hex"
date: "2015-02-06"
-coverImage: "darrylblog1-150x150.png"
+coverImage: "darrylblog1-150x150.webp"
author: "Team LoginRadius"
tags: ["SocialMedia","Facebook","Google","Color"]
---
diff --git a/content/engineering/social-network-branding-guidelines/1.png b/content/engineering/social-network-branding-guidelines/1.png
deleted file mode 100644
index d47cc0d02..000000000
Binary files a/content/engineering/social-network-branding-guidelines/1.png and /dev/null differ
diff --git a/content/engineering/social-network-branding-guidelines/1.webp b/content/engineering/social-network-branding-guidelines/1.webp
new file mode 100644
index 000000000..a188c2ca9
Binary files /dev/null and b/content/engineering/social-network-branding-guidelines/1.webp differ
diff --git a/content/engineering/social-network-branding-guidelines/2.jpg b/content/engineering/social-network-branding-guidelines/2.jpg
deleted file mode 100644
index 3b555e6a6..000000000
Binary files a/content/engineering/social-network-branding-guidelines/2.jpg and /dev/null differ
diff --git a/content/engineering/social-network-branding-guidelines/2.webp b/content/engineering/social-network-branding-guidelines/2.webp
new file mode 100644
index 000000000..0e1a2b085
Binary files /dev/null and b/content/engineering/social-network-branding-guidelines/2.webp differ
diff --git a/content/engineering/social-network-branding-guidelines/3.png b/content/engineering/social-network-branding-guidelines/3.png
deleted file mode 100644
index e74781198..000000000
Binary files a/content/engineering/social-network-branding-guidelines/3.png and /dev/null differ
diff --git a/content/engineering/social-network-branding-guidelines/3.webp b/content/engineering/social-network-branding-guidelines/3.webp
new file mode 100644
index 000000000..186b283ab
Binary files /dev/null and b/content/engineering/social-network-branding-guidelines/3.webp differ
diff --git a/content/engineering/social-network-branding-guidelines/4.png b/content/engineering/social-network-branding-guidelines/4.png
deleted file mode 100644
index d72ec1be7..000000000
Binary files a/content/engineering/social-network-branding-guidelines/4.png and /dev/null differ
diff --git a/content/engineering/social-network-branding-guidelines/4.webp b/content/engineering/social-network-branding-guidelines/4.webp
new file mode 100644
index 000000000..c05712ca8
Binary files /dev/null and b/content/engineering/social-network-branding-guidelines/4.webp differ
diff --git a/content/engineering/social-network-branding-guidelines/5.png b/content/engineering/social-network-branding-guidelines/5.png
deleted file mode 100644
index 8bd4e353b..000000000
Binary files a/content/engineering/social-network-branding-guidelines/5.png and /dev/null differ
diff --git a/content/engineering/social-network-branding-guidelines/5.webp b/content/engineering/social-network-branding-guidelines/5.webp
new file mode 100644
index 000000000..bdae70d8f
Binary files /dev/null and b/content/engineering/social-network-branding-guidelines/5.webp differ
diff --git a/content/engineering/social-network-branding-guidelines/6.png b/content/engineering/social-network-branding-guidelines/6.png
deleted file mode 100644
index 3cd9b7191..000000000
Binary files a/content/engineering/social-network-branding-guidelines/6.png and /dev/null differ
diff --git a/content/engineering/social-network-branding-guidelines/6.webp b/content/engineering/social-network-branding-guidelines/6.webp
new file mode 100644
index 000000000..88255e0f6
Binary files /dev/null and b/content/engineering/social-network-branding-guidelines/6.webp differ
diff --git a/content/engineering/social-network-branding-guidelines/index.md b/content/engineering/social-network-branding-guidelines/index.md
index c1da55cc6..fa0f75acd 100644
--- a/content/engineering/social-network-branding-guidelines/index.md
+++ b/content/engineering/social-network-branding-guidelines/index.md
@@ -1,7 +1,7 @@
---
title: "Social Network Branding Guidelines"
date: "2015-09-08"
-coverImage: "social-network-branding-300x300.png"
+coverImage: "social-network-branding-300x300.webp"
author: "Team LoginRadius"
tags: ["Social","SocialLogin","Branding"]
---
@@ -12,15 +12,15 @@ Hello and welcome to another segment of me telling you things that you need to k
Social Login and Social Sharing are everywhere. Some people even combine it with with their User Registration. There’s no surprise that on every website you go to, you’ll see either well designed social icons or just plain ugliness. We can’t blame them, they want their icons to be unique and eye catching.
-_Beauty!_
+_Beauty!_
But, the universe is full of holes inside an “A” whom sometimes destroy a thing of beauty.
-_Just. Stop!_
+_Just. Stop!_
Then there’s the “I use my own brand color” kind of people.
-
+
_So, what’s happening here? What’s the orange f? Does that stands for forangebook? \*badum tsss\* I’ll see myself out._
@@ -30,7 +30,7 @@ One thing we need to realize is, we don’t own these icons. The companies still
Let’s start with the most used social network, Facebook and their “ f ” logo. They’re pretty straightforward, as long as you don’t modify the “ f ” logo’s design and color, you’re good to go. To simplify this more; don’t make the facebook logo look like it’s been scratched by a chicken and made it bleed too much that it turns red.
-
+
_Quick, somebody call 911!_
@@ -38,7 +38,7 @@ _Quick, somebody call 911!_
-  Nonetheless, it’s simple.
+  Nonetheless, it’s simple.
- Don’t use their old logo (because, let’s face it, it’s ugly).
- Don’t use a speech bubble (because that’s so 1995)
@@ -54,7 +54,7 @@ On Google+ (yes “ + “ not “plus“), they prefer that you don’t change o
If you’re using the icon with the title, You should use “Google” without the plus (word and sign), because… well… that’s redundant.
-LinkedIn is kind of ridiculous with their [branding guidelines](https://brand.linkedin.com/en-us). They still have the same drill with no distorting or changing the color and so forth. But there’s one thing you won’t expect, you cannot change the radius or the box. 
+LinkedIn is kind of ridiculous with their [branding guidelines](https://brand.linkedin.com/en-us). They still have the same drill with no distorting or changing the color and so forth. But there’s one thing you won’t expect, you cannot change the radius or the box. 
diff --git a/content/engineering/social-network-branding-guidelines/social-network-branding-300x300.png b/content/engineering/social-network-branding-guidelines/social-network-branding-300x300.png
deleted file mode 100644
index 6939da03c..000000000
Binary files a/content/engineering/social-network-branding-guidelines/social-network-branding-300x300.png and /dev/null differ
diff --git a/content/engineering/social-network-branding-guidelines/social-network-branding-300x300.webp b/content/engineering/social-network-branding-guidelines/social-network-branding-300x300.webp
new file mode 100644
index 000000000..429876d66
Binary files /dev/null and b/content/engineering/social-network-branding-guidelines/social-network-branding-300x300.webp differ
diff --git a/content/engineering/social-provider-social-sharing-troubleshooting-resources/index.md b/content/engineering/social-provider-social-sharing-troubleshooting-resources/index.md
index c00f92af5..221e611b1 100644
--- a/content/engineering/social-provider-social-sharing-troubleshooting-resources/index.md
+++ b/content/engineering/social-provider-social-sharing-troubleshooting-resources/index.md
@@ -1,7 +1,7 @@
---
title: "Social Provider Social Sharing Troubleshooting Resources"
date: "2015-02-09"
-coverImage: "social.png"
+coverImage: "social.webp"
author: "Karl Wittig"
tags: ["Engineering","SocialSharing","Facebook","Google","LinkedIn"]
---
@@ -12,7 +12,7 @@ Social Sharing is an extremely powerful tool to expand your user base and produc
Setting up custom sharing with Facebook uses Facebook Open Graph meta tags, which are cached on Facebooks end and can lead to some confusion when making updates to your customizations. In order to identify the cached details that are being used for your implementation Facebook provides the [Open Graph Debugger tool](https://developers.facebook.com/tools/debug/). All you need to do is input your sites URL and click on Debug.
-
+
This will then crawl your page and display some useful information on the currently scraped details and warnings and error messages. It also give you the option at this point to refresh this scrapped data with any changes that you have made to our existing cached details.
@@ -27,7 +27,7 @@ Google uses a combination of a few different methods in order to define the cust
The [structured data testing tool](http://www.google.com/webmasters/tools/richsnippets) allows you to view what Google has interpreted from your webpage. Start by entering the URL of the page that you are sharing and click on preview.
-
+
You will be able to view the scrapped data as well as a listing of the meta tags that have been included on the page.
@@ -39,7 +39,7 @@ You can view the details that will be shared by generating out the sharing butto
Insert the URL in the "URL to be shared field" and click on Get Code. This will generate a sample share icon in the preview section.
-
+
To test the share functionality click on the generated icon to display the share interface as determined by the provided URL.
@@ -49,7 +49,7 @@ Twitter also uses multiple systems to determine the content that will be tweeted
To test the tweet you can use Twitters [button generator](https://about.twitter.com/resources/buttons). Select the "Share a link" option under "Choose a button".
-
+
Input your site URL in the "share URL" field, This will cause the Tweet button under "Preview and code" to be updated.
diff --git a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-1_001.png b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-1_001.png
deleted file mode 100644
index 77d4337db..000000000
Binary files a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-1_001.png and /dev/null differ
diff --git a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-1_001.webp b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-1_001.webp
new file mode 100644
index 000000000..a932fe20e
Binary files /dev/null and b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-1_001.webp differ
diff --git a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-2.png b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-2.png
deleted file mode 100644
index 7023011e1..000000000
Binary files a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-2.png and /dev/null differ
diff --git a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-2.webp b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-2.webp
new file mode 100644
index 000000000..a01975b7f
Binary files /dev/null and b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-2.webp differ
diff --git a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-3.png b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-3.png
deleted file mode 100644
index df7b99e94..000000000
Binary files a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-3.png and /dev/null differ
diff --git a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-3.webp b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-3.webp
new file mode 100644
index 000000000..15e1d9b5c
Binary files /dev/null and b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-3.webp differ
diff --git a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-4.png b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-4.png
deleted file mode 100644
index d60eab300..000000000
Binary files a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-4.png and /dev/null differ
diff --git a/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-4.webp b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-4.webp
new file mode 100644
index 000000000..f943011dc
Binary files /dev/null and b/content/engineering/social-provider-social-sharing-troubleshooting-resources/karlblog1-4.webp differ
diff --git a/content/engineering/social-provider-social-sharing-troubleshooting-resources/social.png b/content/engineering/social-provider-social-sharing-troubleshooting-resources/social.png
deleted file mode 100644
index 205c49a3d..000000000
Binary files a/content/engineering/social-provider-social-sharing-troubleshooting-resources/social.png and /dev/null differ
diff --git a/content/engineering/social-provider-social-sharing-troubleshooting-resources/social.webp b/content/engineering/social-provider-social-sharing-troubleshooting-resources/social.webp
new file mode 100644
index 000000000..29513eb53
Binary files /dev/null and b/content/engineering/social-provider-social-sharing-troubleshooting-resources/social.webp differ
diff --git a/content/engineering/software-development-engineer-in-test/cover.png b/content/engineering/software-development-engineer-in-test/cover.png
deleted file mode 100644
index a99360c32..000000000
Binary files a/content/engineering/software-development-engineer-in-test/cover.png and /dev/null differ
diff --git a/content/engineering/software-development-engineer-in-test/cover.webp b/content/engineering/software-development-engineer-in-test/cover.webp
new file mode 100644
index 000000000..c95185810
Binary files /dev/null and b/content/engineering/software-development-engineer-in-test/cover.webp differ
diff --git a/content/engineering/software-development-engineer-in-test/index.md b/content/engineering/software-development-engineer-in-test/index.md
index 23311289e..3e5a92d41 100644
--- a/content/engineering/software-development-engineer-in-test/index.md
+++ b/content/engineering/software-development-engineer-in-test/index.md
@@ -1,7 +1,7 @@
---
title: "The Upcoming Future of Software Testers and SDETs in 2021"
date: "2021-03-12"
-coverImage: "cover.png"
+coverImage: "cover.webp"
author: "Rakesh Pareek"
tags: ["SDET", "SDET vs Automation Engineer"]
description: "A brief overview about the upcoming future of software testers and SDETs and the requirement of SDET role and responsibility in 2021."
@@ -12,7 +12,7 @@ description: "A brief overview about the upcoming future of software testers and
> Presently, several organizations, are demanding such SDET professionals who can develop the software and test the software developed.
-  +
+ 
## What is the Difference Between SDET and Automation Engineer?
diff --git a/content/engineering/software-development-engineer-in-test/sdet_role.png b/content/engineering/software-development-engineer-in-test/sdet_role.png
deleted file mode 100644
index 4ef4cd43f..000000000
Binary files a/content/engineering/software-development-engineer-in-test/sdet_role.png and /dev/null differ
diff --git a/content/engineering/software-development-engineer-in-test/sdet_role.webp b/content/engineering/software-development-engineer-in-test/sdet_role.webp
new file mode 100644
index 000000000..36dc73236
Binary files /dev/null and b/content/engineering/software-development-engineer-in-test/sdet_role.webp differ
diff --git a/content/engineering/sonarqube/index.md b/content/engineering/sonarqube/index.md
index 224096aae..99cab3f63 100644
--- a/content/engineering/sonarqube/index.md
+++ b/content/engineering/sonarqube/index.md
@@ -1,7 +1,7 @@
---
title: "Sonarqube: What it is and why to use it?"
date: "2020-07-11"
-coverImage: "sonarqube.png"
+coverImage: "sonarqube.webp"
author: "Kheenvraj Lomror"
tags: ["Code Quality", "SonarQube"]
description: "SonarQube is a universal tool for static code analysis that has become more or less the industry standard. Keeping code clean, simple, and easy to read is also a lot easier with SonarQube."
diff --git a/content/engineering/sonarqube/sonarqube.png b/content/engineering/sonarqube/sonarqube.png
deleted file mode 100644
index 47ac1a4c9..000000000
Binary files a/content/engineering/sonarqube/sonarqube.png and /dev/null differ
diff --git a/content/engineering/sonarqube/sonarqube.webp b/content/engineering/sonarqube/sonarqube.webp
new file mode 100644
index 000000000..044d45e41
Binary files /dev/null and b/content/engineering/sonarqube/sonarqube.webp differ
diff --git a/content/engineering/speed-up-python-code/index.md b/content/engineering/speed-up-python-code/index.md
index 271c45fd3..654eddbb1 100644
--- a/content/engineering/speed-up-python-code/index.md
+++ b/content/engineering/speed-up-python-code/index.md
@@ -1,7 +1,7 @@
---
title: Speed Up Python Code
date: "2020-10-15"
-coverImage: "speed-up-python-code-1.jpg"
+coverImage: "speed-up-python-code-1.webp"
author: "Md. Tahmid Hossain"
tags: ["Python", "Performance"]
description: "Learn a few ways to speed up your python code."
diff --git a/content/engineering/speed-up-python-code/speed-up-python-code-1.jpg b/content/engineering/speed-up-python-code/speed-up-python-code-1.jpg
deleted file mode 100644
index f70164479..000000000
Binary files a/content/engineering/speed-up-python-code/speed-up-python-code-1.jpg and /dev/null differ
diff --git a/content/engineering/speed-up-python-code/speed-up-python-code-1.webp b/content/engineering/speed-up-python-code/speed-up-python-code-1.webp
new file mode 100644
index 000000000..1530cca41
Binary files /dev/null and b/content/engineering/speed-up-python-code/speed-up-python-code-1.webp differ
diff --git a/content/engineering/speed-up-python-code/speed-up-python-code.jpg b/content/engineering/speed-up-python-code/speed-up-python-code.jpg
deleted file mode 100644
index eaa6acbd5..000000000
Binary files a/content/engineering/speed-up-python-code/speed-up-python-code.jpg and /dev/null differ
diff --git a/content/engineering/speed-up-python-code/speed-up-python-code.webp b/content/engineering/speed-up-python-code/speed-up-python-code.webp
new file mode 100644
index 000000000..8e216f013
Binary files /dev/null and b/content/engineering/speed-up-python-code/speed-up-python-code.webp differ
diff --git a/content/engineering/sso-for-wordpress-site/DS-SSO.png b/content/engineering/sso-for-wordpress-site/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/engineering/sso-for-wordpress-site/DS-SSO.png and /dev/null differ
diff --git a/content/engineering/sso-for-wordpress-site/DS-SSO.webp b/content/engineering/sso-for-wordpress-site/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/engineering/sso-for-wordpress-site/DS-SSO.webp differ
diff --git a/content/engineering/sso-for-wordpress-site/coverImage.jpg b/content/engineering/sso-for-wordpress-site/coverImage.jpg
deleted file mode 100644
index 7e899974a..000000000
Binary files a/content/engineering/sso-for-wordpress-site/coverImage.jpg and /dev/null differ
diff --git a/content/engineering/sso-for-wordpress-site/coverImage.webp b/content/engineering/sso-for-wordpress-site/coverImage.webp
new file mode 100644
index 000000000..b4d841825
Binary files /dev/null and b/content/engineering/sso-for-wordpress-site/coverImage.webp differ
diff --git a/content/engineering/sso-for-wordpress-site/index.md b/content/engineering/sso-for-wordpress-site/index.md
index be70867b1..f93bed23d 100644
--- a/content/engineering/sso-for-wordpress-site/index.md
+++ b/content/engineering/sso-for-wordpress-site/index.md
@@ -1,7 +1,7 @@
---
title: How to add SSO for your WordPress Site!
date: "2021-03-26"
-coverImage: "sso-wp.jpg"
+coverImage: "sso-wp.webp"
author: "Saikiran Babladi"
tags: ["WordPress", "SSO", "Single Sign On"]
description: "Providing a seamless experience for your consumers is non-negotiable, especially when running multiple WordPress sites. Single Sign-On provides that experience to your users. Here's how to provide a frictionless experience to your users."
@@ -35,7 +35,7 @@ We have detailed [documentation](https://www.loginradius.com/developers/).
LoginRadius aims to help developers, web development agencies, and businesses to add SSO in the simplest way possible.
LoginRadius allows you to store your consumer profiles securely and add our customizable login interfaces into your applications in minutes. By enabling our SSO, you can create a frictionless user experience, thus boosting your conversion rate.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
## Benefits
@@ -50,5 +50,5 @@ LoginRadius allows you to store your consumer profiles securely and add our cust
## Your Take?
We always want to hear from our customers. Like many others in the market, we want developers to install it and offer feedback. This feedback will help us enhance the plugin and make it more user-friendly.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-for-wordpress-site)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-for-wordpress-site)
diff --git a/content/engineering/sso-for-wordpress-site/sso-wordpress.jpg b/content/engineering/sso-for-wordpress-site/sso-wordpress.jpg
deleted file mode 100644
index d9704800d..000000000
Binary files a/content/engineering/sso-for-wordpress-site/sso-wordpress.jpg and /dev/null differ
diff --git a/content/engineering/sso-for-wordpress-site/sso-wordpress.webp b/content/engineering/sso-for-wordpress-site/sso-wordpress.webp
new file mode 100644
index 000000000..8150cc96c
Binary files /dev/null and b/content/engineering/sso-for-wordpress-site/sso-wordpress.webp differ
diff --git a/content/engineering/sso-for-wordpress-site/sso-wp.jpg b/content/engineering/sso-for-wordpress-site/sso-wp.jpg
deleted file mode 100644
index 3b4f01fcc..000000000
Binary files a/content/engineering/sso-for-wordpress-site/sso-wp.jpg and /dev/null differ
diff --git a/content/engineering/sso-for-wordpress-site/sso-wp.webp b/content/engineering/sso-for-wordpress-site/sso-wp.webp
new file mode 100644
index 000000000..307243380
Binary files /dev/null and b/content/engineering/sso-for-wordpress-site/sso-wp.webp differ
diff --git a/content/engineering/stackexchange-8-best-resources-every-developer-must-follow/8-stackexchange-resources-dev-follow.png b/content/engineering/stackexchange-8-best-resources-every-developer-must-follow/8-stackexchange-resources-dev-follow.png
deleted file mode 100644
index 993f3ae17..000000000
Binary files a/content/engineering/stackexchange-8-best-resources-every-developer-must-follow/8-stackexchange-resources-dev-follow.png and /dev/null differ
diff --git a/content/engineering/stackexchange-8-best-resources-every-developer-must-follow/8-stackexchange-resources-dev-follow.webp b/content/engineering/stackexchange-8-best-resources-every-developer-must-follow/8-stackexchange-resources-dev-follow.webp
new file mode 100644
index 000000000..abda2d6c9
Binary files /dev/null and b/content/engineering/stackexchange-8-best-resources-every-developer-must-follow/8-stackexchange-resources-dev-follow.webp differ
diff --git a/content/engineering/stackexchange-8-best-resources-every-developer-must-follow/index.md b/content/engineering/stackexchange-8-best-resources-every-developer-must-follow/index.md
index 2bf84d5d5..5914c8007 100644
--- a/content/engineering/stackexchange-8-best-resources-every-developer-must-follow/index.md
+++ b/content/engineering/stackexchange-8-best-resources-every-developer-must-follow/index.md
@@ -1,7 +1,7 @@
---
title: "StackExchange - The 8 best resources every developer must follow"
date: "2020-04-25"
-coverImage: "8-stackexchange-resources-dev-follow.png"
+coverImage: "8-stackexchange-resources-dev-follow.webp"
author: "Kundan Singh"
tags: ["Programmer","Skills"]
---
diff --git a/content/engineering/stream-processing-using-kafka/header.png b/content/engineering/stream-processing-using-kafka/header.png
deleted file mode 100644
index 08d6783ae..000000000
Binary files a/content/engineering/stream-processing-using-kafka/header.png and /dev/null differ
diff --git a/content/engineering/stream-processing-using-kafka/header.webp b/content/engineering/stream-processing-using-kafka/header.webp
new file mode 100644
index 000000000..34f179825
Binary files /dev/null and b/content/engineering/stream-processing-using-kafka/header.webp differ
diff --git a/content/engineering/stream-processing-using-kafka/index.md b/content/engineering/stream-processing-using-kafka/index.md
index 6e9ccb1e8..2e747249e 100644
--- a/content/engineering/stream-processing-using-kafka/index.md
+++ b/content/engineering/stream-processing-using-kafka/index.md
@@ -1,7 +1,7 @@
---
title: "Kafka Streams: A stream processing guide"
date: "2020-07-01"
-coverImage: "header.png"
+coverImage: "header.webp"
author: "Priyadarshan Mohanty"
tags: ["Scala", "Kafka", "Kafka Streams"]
description: "Learn about Kafka Streams, key concepts and highlights with simple streaming or a word count application using Kafka Streams in Scala"
@@ -38,7 +38,7 @@ There are two individual processors in the topology:
- **Sink Processor**: A sink processor is a special type of stream processor that does not have down-stream processors. It sends any received records from its up-stream processors to a specified Kafka topic.
-
+
- **Kstream**: KStream is nothing but that, a Kafka Stream. It’s a never-ending flow of data in a stream. Each piece of data — a record or a fact — is a collection of key-value pairs. Data records in a record stream are always interpreted as an "INSERT".
diff --git a/content/engineering/stream-processing-using-kafka/streams-architecture-topology.jpg b/content/engineering/stream-processing-using-kafka/streams-architecture-topology.jpg
deleted file mode 100644
index f42e8cddf..000000000
Binary files a/content/engineering/stream-processing-using-kafka/streams-architecture-topology.jpg and /dev/null differ
diff --git a/content/engineering/stream-processing-using-kafka/streams-architecture-topology.webp b/content/engineering/stream-processing-using-kafka/streams-architecture-topology.webp
new file mode 100644
index 000000000..69f558b23
Binary files /dev/null and b/content/engineering/stream-processing-using-kafka/streams-architecture-topology.webp differ
diff --git a/content/engineering/styling-radio-and-check-buttons-with-css/checked-check.png b/content/engineering/styling-radio-and-check-buttons-with-css/checked-check.png
deleted file mode 100644
index fbf64d873..000000000
Binary files a/content/engineering/styling-radio-and-check-buttons-with-css/checked-check.png and /dev/null differ
diff --git a/content/engineering/styling-radio-and-check-buttons-with-css/checked-check.webp b/content/engineering/styling-radio-and-check-buttons-with-css/checked-check.webp
new file mode 100644
index 000000000..8a6eb3900
Binary files /dev/null and b/content/engineering/styling-radio-and-check-buttons-with-css/checked-check.webp differ
diff --git a/content/engineering/styling-radio-and-check-buttons-with-css/checked-radio.png b/content/engineering/styling-radio-and-check-buttons-with-css/checked-radio.png
deleted file mode 100644
index 3fb29f30c..000000000
Binary files a/content/engineering/styling-radio-and-check-buttons-with-css/checked-radio.png and /dev/null differ
diff --git a/content/engineering/styling-radio-and-check-buttons-with-css/checked-radio.webp b/content/engineering/styling-radio-and-check-buttons-with-css/checked-radio.webp
new file mode 100644
index 000000000..3d94c7b1b
Binary files /dev/null and b/content/engineering/styling-radio-and-check-buttons-with-css/checked-radio.webp differ
diff --git a/content/engineering/styling-radio-and-check-buttons-with-css/index.md b/content/engineering/styling-radio-and-check-buttons-with-css/index.md
index 28a5db13c..060191eae 100644
--- a/content/engineering/styling-radio-and-check-buttons-with-css/index.md
+++ b/content/engineering/styling-radio-and-check-buttons-with-css/index.md
@@ -1,7 +1,7 @@
---
title: "Styling Radio and Check buttons with CSS"
date: "2015-06-16"
-coverImage: "radio-check-buttons-css-1.png"
+coverImage: "radio-check-buttons-css-1.webp"
author: "Team LoginRadius"
tags: ["CSS"]
---
@@ -64,9 +64,9 @@ label input[type="radio"]:checked ~ span:before {
}
```
-
+
-
+
By now it should like this.
@@ -115,9 +115,9 @@ label.spin input[type="checkbox"]:checked ~ span:before {
Oh yes! Beautiful toggle.
-
+
-
+
**Bonus!**
diff --git a/content/engineering/styling-radio-and-check-buttons-with-css/radio-check-buttons-css-1.png b/content/engineering/styling-radio-and-check-buttons-with-css/radio-check-buttons-css-1.png
deleted file mode 100644
index 4c805986f..000000000
Binary files a/content/engineering/styling-radio-and-check-buttons-with-css/radio-check-buttons-css-1.png and /dev/null differ
diff --git a/content/engineering/styling-radio-and-check-buttons-with-css/radio-check-buttons-css-1.webp b/content/engineering/styling-radio-and-check-buttons-with-css/radio-check-buttons-css-1.webp
new file mode 100644
index 000000000..5fbf5ff01
Binary files /dev/null and b/content/engineering/styling-radio-and-check-buttons-with-css/radio-check-buttons-css-1.webp differ
diff --git a/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-checkbox.png b/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-checkbox.png
deleted file mode 100644
index d22e34bc6..000000000
Binary files a/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-checkbox.png and /dev/null differ
diff --git a/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-checkbox.webp b/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-checkbox.webp
new file mode 100644
index 000000000..bb0836958
Binary files /dev/null and b/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-checkbox.webp differ
diff --git a/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-radio.png b/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-radio.png
deleted file mode 100644
index 60fc598c4..000000000
Binary files a/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-radio.png and /dev/null differ
diff --git a/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-radio.webp b/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-radio.webp
new file mode 100644
index 000000000..bc7b54d90
Binary files /dev/null and b/content/engineering/styling-radio-and-check-buttons-with-css/unchecked-radio.webp differ
diff --git a/content/engineering/the-truth-about-css-preprocessors-and-how-they-can-help-you/desdev-150x150.png b/content/engineering/the-truth-about-css-preprocessors-and-how-they-can-help-you/desdev-150x150.png
deleted file mode 100644
index 9ba252021..000000000
Binary files a/content/engineering/the-truth-about-css-preprocessors-and-how-they-can-help-you/desdev-150x150.png and /dev/null differ
diff --git a/content/engineering/the-truth-about-css-preprocessors-and-how-they-can-help-you/desdev-150x150.webp b/content/engineering/the-truth-about-css-preprocessors-and-how-they-can-help-you/desdev-150x150.webp
new file mode 100644
index 000000000..a6af37699
Binary files /dev/null and b/content/engineering/the-truth-about-css-preprocessors-and-how-they-can-help-you/desdev-150x150.webp differ
diff --git a/content/engineering/the-truth-about-css-preprocessors-and-how-they-can-help-you/index.md b/content/engineering/the-truth-about-css-preprocessors-and-how-they-can-help-you/index.md
index f780d54fc..2f7500aea 100644
--- a/content/engineering/the-truth-about-css-preprocessors-and-how-they-can-help-you/index.md
+++ b/content/engineering/the-truth-about-css-preprocessors-and-how-they-can-help-you/index.md
@@ -1,7 +1,7 @@
---
title: "The truth about CSS preprocessors and how they can help you"
date: "2015-11-17"
-coverImage: "desdev-150x150.png"
+coverImage: "desdev-150x150.webp"
author: Zakary Hughes
tags: ["CSS"]
---
diff --git a/content/engineering/the-ultimate-guide-to-website-pop-ups/Creating-a-simple-pop-up.png b/content/engineering/the-ultimate-guide-to-website-pop-ups/Creating-a-simple-pop-up.png
deleted file mode 100644
index 820220033..000000000
Binary files a/content/engineering/the-ultimate-guide-to-website-pop-ups/Creating-a-simple-pop-up.png and /dev/null differ
diff --git a/content/engineering/the-ultimate-guide-to-website-pop-ups/Creating-a-simple-pop-up.webp b/content/engineering/the-ultimate-guide-to-website-pop-ups/Creating-a-simple-pop-up.webp
new file mode 100644
index 000000000..5c2de1671
Binary files /dev/null and b/content/engineering/the-ultimate-guide-to-website-pop-ups/Creating-a-simple-pop-up.webp differ
diff --git a/content/engineering/the-ultimate-guide-to-website-pop-ups/The-Ultimate-guide-to-website-pop-ups.png b/content/engineering/the-ultimate-guide-to-website-pop-ups/The-Ultimate-guide-to-website-pop-ups.png
deleted file mode 100644
index f4ed3a804..000000000
Binary files a/content/engineering/the-ultimate-guide-to-website-pop-ups/The-Ultimate-guide-to-website-pop-ups.png and /dev/null differ
diff --git a/content/engineering/the-ultimate-guide-to-website-pop-ups/The-Ultimate-guide-to-website-pop-ups.webp b/content/engineering/the-ultimate-guide-to-website-pop-ups/The-Ultimate-guide-to-website-pop-ups.webp
new file mode 100644
index 000000000..9e1622656
Binary files /dev/null and b/content/engineering/the-ultimate-guide-to-website-pop-ups/The-Ultimate-guide-to-website-pop-ups.webp differ
diff --git a/content/engineering/the-ultimate-guide-to-website-pop-ups/index.md b/content/engineering/the-ultimate-guide-to-website-pop-ups/index.md
index 995c506c7..afaf2eebe 100644
--- a/content/engineering/the-ultimate-guide-to-website-pop-ups/index.md
+++ b/content/engineering/the-ultimate-guide-to-website-pop-ups/index.md
@@ -1,7 +1,7 @@
---
title: "Know The Types of Website Popups and How to Create Them"
date: "2017-04-20"
-coverImage: "The-Ultimate-guide-to-website-pop-ups.png"
+coverImage: "The-Ultimate-guide-to-website-pop-ups.webp"
author: "Team LoginRadius"
tags: ["CSS"]
---
@@ -10,7 +10,7 @@ POPUPS! They can annoy you but if used properly, they can be a boon to any marke
### **1\. Creating a basic popup:**
-
+
This section talks about creating a basic popup using simple HTML and CSS. There is a separate section for header, footer and content. I have also added a close button at top right corner of the popup. There are three steps to create this popup.
diff --git a/content/engineering/three-ways-to-do-crud-operations-on-redis/browser.png b/content/engineering/three-ways-to-do-crud-operations-on-redis/browser.png
deleted file mode 100644
index 4fd77d9d1..000000000
Binary files a/content/engineering/three-ways-to-do-crud-operations-on-redis/browser.png and /dev/null differ
diff --git a/content/engineering/three-ways-to-do-crud-operations-on-redis/browser.webp b/content/engineering/three-ways-to-do-crud-operations-on-redis/browser.webp
new file mode 100644
index 000000000..e04a4a59e
Binary files /dev/null and b/content/engineering/three-ways-to-do-crud-operations-on-redis/browser.webp differ
diff --git a/content/engineering/three-ways-to-do-crud-operations-on-redis/connect.png b/content/engineering/three-ways-to-do-crud-operations-on-redis/connect.png
deleted file mode 100644
index e4cf1c9b8..000000000
Binary files a/content/engineering/three-ways-to-do-crud-operations-on-redis/connect.png and /dev/null differ
diff --git a/content/engineering/three-ways-to-do-crud-operations-on-redis/connect.webp b/content/engineering/three-ways-to-do-crud-operations-on-redis/connect.webp
new file mode 100644
index 000000000..78a549029
Binary files /dev/null and b/content/engineering/three-ways-to-do-crud-operations-on-redis/connect.webp differ
diff --git a/content/engineering/three-ways-to-do-crud-operations-on-redis/filter.png b/content/engineering/three-ways-to-do-crud-operations-on-redis/filter.png
deleted file mode 100644
index 7efdd9157..000000000
Binary files a/content/engineering/three-ways-to-do-crud-operations-on-redis/filter.png and /dev/null differ
diff --git a/content/engineering/three-ways-to-do-crud-operations-on-redis/filter.webp b/content/engineering/three-ways-to-do-crud-operations-on-redis/filter.webp
new file mode 100644
index 000000000..ba0e6a1f4
Binary files /dev/null and b/content/engineering/three-ways-to-do-crud-operations-on-redis/filter.webp differ
diff --git a/content/engineering/three-ways-to-do-crud-operations-on-redis/index.md b/content/engineering/three-ways-to-do-crud-operations-on-redis/index.md
index 47fe81cf3..224d92d8a 100644
--- a/content/engineering/three-ways-to-do-crud-operations-on-redis/index.md
+++ b/content/engineering/three-ways-to-do-crud-operations-on-redis/index.md
@@ -1,7 +1,7 @@
---
title: "Three Ways to do CRUD Operations On Redis"
date: "2020-10-21"
-coverImage: "index.png"
+coverImage: "index.webp"
author: "Chris Yee"
tags: ["Redis", "NodeJs", "CLI", "GUI"]
description: "Start working with Redis in three different ways."
@@ -19,17 +19,17 @@ For users that do not like working with command-line interfaces, the first tool
After installing and running the application, you will add the connection information for your Redis instance. If running a local instance of Redis, the connection information in the image will typically suffice. If connecting to a remote instance, you might need to fill in some additional details for TLS, such as connection certificates.
-
+
When connected to your Redis instance, the dashboard UI appears. Clicking the Browser sidebar tab will display all existing keys in your database.
-
+
From here, CRUD operations are relatively straightforward. Key-value pair creation can be done by using the ADD KEY button. This will prompt for the type of key-value pair to be added (Hash, String, JSON, etc.) and the data that will be stored with the key.
If a specific key is required to be queried, fill in the field next to the blue filter icon with search criteria, then click the icon. It will prompt the type of data stored with the key, and the results will be displayed.
-
+
Finally, keys can be deleted by clicking the trash can icon on the right side.
diff --git a/content/engineering/three-ways-to-do-crud-operations-on-redis/index.png b/content/engineering/three-ways-to-do-crud-operations-on-redis/index.png
deleted file mode 100644
index 433c5752f..000000000
Binary files a/content/engineering/three-ways-to-do-crud-operations-on-redis/index.png and /dev/null differ
diff --git a/content/engineering/three-ways-to-do-crud-operations-on-redis/index.webp b/content/engineering/three-ways-to-do-crud-operations-on-redis/index.webp
new file mode 100644
index 000000000..9bc70eb12
Binary files /dev/null and b/content/engineering/three-ways-to-do-crud-operations-on-redis/index.webp differ
diff --git a/content/engineering/top-cyber-threats-in-2022/index.md b/content/engineering/top-cyber-threats-in-2022/index.md
index 348d855e8..b963958cf 100644
--- a/content/engineering/top-cyber-threats-in-2022/index.md
+++ b/content/engineering/top-cyber-threats-in-2022/index.md
@@ -1,7 +1,7 @@
---
title: "Top 10 Cyber Threats in 2022"
date: "2022-05-31"
-coverImage: "top-10-cyber-threats-in-2022.png"
+coverImage: "top-10-cyber-threats-in-2022.webp"
author: "Vijay Singh Shekhawat"
tags: ["Cyber Threats", "Security"]
description: "Cybercriminals are using an increasing number of attacks to exploit web apps and steal valuable data. This article teaches about the ten most common types of cyber threats."
diff --git a/content/engineering/top-cyber-threats-in-2022/top-10-cyber-threats-in-2022.png b/content/engineering/top-cyber-threats-in-2022/top-10-cyber-threats-in-2022.png
deleted file mode 100644
index 5e17823da..000000000
Binary files a/content/engineering/top-cyber-threats-in-2022/top-10-cyber-threats-in-2022.png and /dev/null differ
diff --git a/content/engineering/top-cyber-threats-in-2022/top-10-cyber-threats-in-2022.webp b/content/engineering/top-cyber-threats-in-2022/top-10-cyber-threats-in-2022.webp
new file mode 100644
index 000000000..7ca62bd3e
Binary files /dev/null and b/content/engineering/top-cyber-threats-in-2022/top-10-cyber-threats-in-2022.webp differ
diff --git a/content/engineering/traversing-the-realms-of-quantum-network/Phio-Network-by-Quantum-Xchange-1.jpg b/content/engineering/traversing-the-realms-of-quantum-network/Phio-Network-by-Quantum-Xchange-1.jpg
deleted file mode 100644
index 84bd154a3..000000000
Binary files a/content/engineering/traversing-the-realms-of-quantum-network/Phio-Network-by-Quantum-Xchange-1.jpg and /dev/null differ
diff --git a/content/engineering/traversing-the-realms-of-quantum-network/Phio-Network-by-Quantum-Xchange-1.webp b/content/engineering/traversing-the-realms-of-quantum-network/Phio-Network-by-Quantum-Xchange-1.webp
new file mode 100644
index 000000000..96a59c5a0
Binary files /dev/null and b/content/engineering/traversing-the-realms-of-quantum-network/Phio-Network-by-Quantum-Xchange-1.webp differ
diff --git a/content/engineering/traversing-the-realms-of-quantum-network/index.md b/content/engineering/traversing-the-realms-of-quantum-network/index.md
index e0d9ecfd5..c7cc1d60b 100644
--- a/content/engineering/traversing-the-realms-of-quantum-network/index.md
+++ b/content/engineering/traversing-the-realms-of-quantum-network/index.md
@@ -1,7 +1,7 @@
---
title: "Traversing the realms of Quantum Network"
date: "2020-10-21"
-coverImage: "quantum_comp_FB.png"
+coverImage: "quantum_comp_FB.webp"
author: "Devansh Markan"
tags: ["Engineering","Quantum","Networking"]
description: "Basic structure and knowledge of Quantum Networking and how it can change the field of technology."
@@ -13,7 +13,7 @@ Or, have you ever thought of the amplification of photon particles in a laser be
With huge advancements in this field, the concept of quantum computers and quantum internet has now come to life. Typical computers are based on binary digits, that is, 0 and 1. Quantum computers, on the other hand, are based on qubits. A qubit or quantum bit is the basic unit for quantum information. They are based on particle's physical properties, such as the spin of an electron, and hence differ in various ways. We know that electron spin can either up or down, but things change when it comes to quantum mechanics. It follows the concept of superposition, according to which an electron can exist in a state in which it has a spin in both directions simultaneously. This may sound strange according to what we observe generally, yet this is how Quantum mechanics work.
-
+
The peculiar behaviour that particles display can be useful in various ways. Qubits can store much more information than conventional bits. This can be explained as two bits with one of the four possible values, 00, 01, 10, or 11. Qubits, on the other hand, can be both 0 and 1 at once. This implies they can have all the four values all at once.
Thus, the amount of information you store using qubits increases tremendously.
diff --git a/content/engineering/traversing-the-realms-of-quantum-network/quantum_comp_FB.png b/content/engineering/traversing-the-realms-of-quantum-network/quantum_comp_FB.png
deleted file mode 100644
index c0e3475a4..000000000
Binary files a/content/engineering/traversing-the-realms-of-quantum-network/quantum_comp_FB.png and /dev/null differ
diff --git a/content/engineering/traversing-the-realms-of-quantum-network/quantum_comp_FB.webp b/content/engineering/traversing-the-realms-of-quantum-network/quantum_comp_FB.webp
new file mode 100644
index 000000000..08075ea97
Binary files /dev/null and b/content/engineering/traversing-the-realms-of-quantum-network/quantum_comp_FB.webp differ
diff --git a/content/engineering/tune-the-go-http-client-for-high-performance/index.jpg b/content/engineering/tune-the-go-http-client-for-high-performance/index.jpg
deleted file mode 100644
index 6068562ad..000000000
Binary files a/content/engineering/tune-the-go-http-client-for-high-performance/index.jpg and /dev/null differ
diff --git a/content/engineering/tune-the-go-http-client-for-high-performance/index.md b/content/engineering/tune-the-go-http-client-for-high-performance/index.md
index cbc6a8130..13dc3fa52 100644
--- a/content/engineering/tune-the-go-http-client-for-high-performance/index.md
+++ b/content/engineering/tune-the-go-http-client-for-high-performance/index.md
@@ -1,7 +1,7 @@
---
title: How to Use the HTTP Client in GO To Enhance Performance
date: "2021-01-12"
-coverImage: "index.jpg"
+coverImage: "index.webp"
author: "Mayank Agarwal"
tags: ["Golang", "HTTP", "Performance"]
description: "In this post, we will discuss how to make HTTP requests for higher performance in Go, and also how to tune it."
diff --git a/content/engineering/tune-the-go-http-client-for-high-performance/index.webp b/content/engineering/tune-the-go-http-client-for-high-performance/index.webp
new file mode 100644
index 000000000..fa5494c59
Binary files /dev/null and b/content/engineering/tune-the-go-http-client-for-high-performance/index.webp differ
diff --git a/content/engineering/twitter-authentication-with-golang-and-goth/auth.png b/content/engineering/twitter-authentication-with-golang-and-goth/auth.png
deleted file mode 100644
index 1a35bdcd9..000000000
Binary files a/content/engineering/twitter-authentication-with-golang-and-goth/auth.png and /dev/null differ
diff --git a/content/engineering/twitter-authentication-with-golang-and-goth/auth.webp b/content/engineering/twitter-authentication-with-golang-and-goth/auth.webp
new file mode 100644
index 000000000..16753fa61
Binary files /dev/null and b/content/engineering/twitter-authentication-with-golang-and-goth/auth.webp differ
diff --git a/content/engineering/twitter-authentication-with-golang-and-goth/cover.jpg b/content/engineering/twitter-authentication-with-golang-and-goth/cover.jpg
deleted file mode 100644
index a91361bc3..000000000
Binary files a/content/engineering/twitter-authentication-with-golang-and-goth/cover.jpg and /dev/null differ
diff --git a/content/engineering/twitter-authentication-with-golang-and-goth/cover.webp b/content/engineering/twitter-authentication-with-golang-and-goth/cover.webp
new file mode 100644
index 000000000..0dbf78c06
Binary files /dev/null and b/content/engineering/twitter-authentication-with-golang-and-goth/cover.webp differ
diff --git a/content/engineering/twitter-authentication-with-golang-and-goth/index.md b/content/engineering/twitter-authentication-with-golang-and-goth/index.md
index c984e6742..e6d1a8f8f 100644
--- a/content/engineering/twitter-authentication-with-golang-and-goth/index.md
+++ b/content/engineering/twitter-authentication-with-golang-and-goth/index.md
@@ -1,7 +1,7 @@
---
title: Twitter authentication with Go Language and Goth
date: "2020-06-15"
-coverImage: "cover.jpg"
+coverImage: "cover.webp"
author: "Ashish Sharma"
tags: ["Go","SocialLogin","Oauth"]
---
@@ -215,21 +215,21 @@ Step 8. Visit the browser with the URL `http://127.0.0.1:3000`.
-
+
We need to click on **Authorize button**, which will redirect us to google login page
-
+
After login with our twitter credentials, it will redirect back to our application and on the success page, we can see the details of the logged-in user and can save this detail in the database for future use also.
-
+
As we have seen it is fairly easy to build a twitter social authentication system with Go and Goth, You can found the complete code used in this tutorial on our[ Github Repo](https://github.com/LoginRadius/engineering-blog-samples/tree/master/GoLang/TwitterAuthenticationGoth)
diff --git a/content/engineering/twitter-authentication-with-golang-and-goth/login.png b/content/engineering/twitter-authentication-with-golang-and-goth/login.png
deleted file mode 100644
index 92d7cea4c..000000000
Binary files a/content/engineering/twitter-authentication-with-golang-and-goth/login.png and /dev/null differ
diff --git a/content/engineering/twitter-authentication-with-golang-and-goth/login.webp b/content/engineering/twitter-authentication-with-golang-and-goth/login.webp
new file mode 100644
index 000000000..5fb1e0ebb
Binary files /dev/null and b/content/engineering/twitter-authentication-with-golang-and-goth/login.webp differ
diff --git a/content/engineering/twitter-authentication-with-golang-and-goth/profile.png b/content/engineering/twitter-authentication-with-golang-and-goth/profile.png
deleted file mode 100644
index 827f459b2..000000000
Binary files a/content/engineering/twitter-authentication-with-golang-and-goth/profile.png and /dev/null differ
diff --git a/content/engineering/twitter-authentication-with-golang-and-goth/profile.webp b/content/engineering/twitter-authentication-with-golang-and-goth/profile.webp
new file mode 100644
index 000000000..f3c9c6247
Binary files /dev/null and b/content/engineering/twitter-authentication-with-golang-and-goth/profile.webp differ
diff --git a/content/engineering/understanding-event-loop/call_stack.png b/content/engineering/understanding-event-loop/call_stack.png
deleted file mode 100644
index 7029ba697..000000000
Binary files a/content/engineering/understanding-event-loop/call_stack.png and /dev/null differ
diff --git a/content/engineering/understanding-event-loop/call_stack.webp b/content/engineering/understanding-event-loop/call_stack.webp
new file mode 100644
index 000000000..4717cc364
Binary files /dev/null and b/content/engineering/understanding-event-loop/call_stack.webp differ
diff --git a/content/engineering/understanding-event-loop/event_loop_illustration.png b/content/engineering/understanding-event-loop/event_loop_illustration.png
deleted file mode 100644
index 7c9af2c6e..000000000
Binary files a/content/engineering/understanding-event-loop/event_loop_illustration.png and /dev/null differ
diff --git a/content/engineering/understanding-event-loop/event_loop_illustration.webp b/content/engineering/understanding-event-loop/event_loop_illustration.webp
new file mode 100644
index 000000000..d154d79a5
Binary files /dev/null and b/content/engineering/understanding-event-loop/event_loop_illustration.webp differ
diff --git a/content/engineering/understanding-event-loop/index.md b/content/engineering/understanding-event-loop/index.md
index 13928b26a..2aa91280b 100644
--- a/content/engineering/understanding-event-loop/index.md
+++ b/content/engineering/understanding-event-loop/index.md
@@ -1,7 +1,7 @@
---
title: "Understanding event loop in JavaScript"
date: "2020-09-19"
-coverImage: "index.png"
+coverImage: "index.webp"
author: "Aman Agrawal"
tags: ["JavaScript", "event-loop", "call stack", "event queue", "multi-threaded"]
description: "Learn the basic concepts about the JavaScript Event Loop."
@@ -57,7 +57,7 @@ The above snippet is an example of defining a `cube` function, which is calling
5. Since at this step, we have got the `square` function result, so `cube` function would be executed and popped out of the call stack.
6. At last, the `console.log()` would be executed and this function would be popped out of the stack and the stack would now be empty.
-
+
Now since we have understood that call stacks are possible to execute the function in a step by step manner, there seems to be no possibility of keeping something into parallel. But there is something called **"WEB APIs"** in the browser environment, which is some additional capabilities provided by browsers in addition to JavaScript Engine.
@@ -96,7 +96,7 @@ Now when a setTimeout operation is processed in the call stack. On its execution
Here need to mention that, just placing our function does not necessarily imply that the function will get executed. This function has to be pushed into the call stack for execution and here the event loop comes into the picture. The event loop waits for the function stack to be empty, once the call stack is empty this will push the first function from the event queue to the call stack, and in this way, the desired function will be called.
-
+
Thus event loop works in a cyclic manner, where it continually checks whether or not the call stack is empty. If it is empty, new functions are added from the event queue. If it is not, then the current function call is processed.
diff --git a/content/engineering/understanding-event-loop/index.png b/content/engineering/understanding-event-loop/index.png
deleted file mode 100644
index 47a19a36a..000000000
Binary files a/content/engineering/understanding-event-loop/index.png and /dev/null differ
diff --git a/content/engineering/understanding-event-loop/index.webp b/content/engineering/understanding-event-loop/index.webp
new file mode 100644
index 000000000..21943a4b3
Binary files /dev/null and b/content/engineering/understanding-event-loop/index.webp differ
diff --git a/content/engineering/understanding-jsonp/Screenshot-2018-06-29-12.21.27.png b/content/engineering/understanding-jsonp/Screenshot-2018-06-29-12.21.27.png
deleted file mode 100644
index f871994e0..000000000
Binary files a/content/engineering/understanding-jsonp/Screenshot-2018-06-29-12.21.27.png and /dev/null differ
diff --git a/content/engineering/understanding-jsonp/Screenshot-2018-06-29-12.21.27.webp b/content/engineering/understanding-jsonp/Screenshot-2018-06-29-12.21.27.webp
new file mode 100644
index 000000000..7bde8a222
Binary files /dev/null and b/content/engineering/understanding-jsonp/Screenshot-2018-06-29-12.21.27.webp differ
diff --git a/content/engineering/understanding-jsonp/index.md b/content/engineering/understanding-jsonp/index.md
index 552a08ec6..b6dec8837 100644
--- a/content/engineering/understanding-jsonp/index.md
+++ b/content/engineering/understanding-jsonp/index.md
@@ -1,7 +1,7 @@
---
title: "Understanding JSONP"
date: "2018-06-29"
-coverImage: "Screenshot-2018-06-29-12.21.27.png"
+coverImage: "Screenshot-2018-06-29-12.21.27.webp"
author: "Rakesh Soni"
tags: ["JavaScript","JSONP","API"]
---
diff --git a/content/engineering/understanding-kubernetes/image1.png b/content/engineering/understanding-kubernetes/image1.png
deleted file mode 100644
index b694bcc6a..000000000
Binary files a/content/engineering/understanding-kubernetes/image1.png and /dev/null differ
diff --git a/content/engineering/understanding-kubernetes/image1.webp b/content/engineering/understanding-kubernetes/image1.webp
new file mode 100644
index 000000000..5b33c4582
Binary files /dev/null and b/content/engineering/understanding-kubernetes/image1.webp differ
diff --git a/content/engineering/understanding-kubernetes/image2.png b/content/engineering/understanding-kubernetes/image2.png
deleted file mode 100644
index 935f40dd4..000000000
Binary files a/content/engineering/understanding-kubernetes/image2.png and /dev/null differ
diff --git a/content/engineering/understanding-kubernetes/image2.webp b/content/engineering/understanding-kubernetes/image2.webp
new file mode 100644
index 000000000..fbffa15cb
Binary files /dev/null and b/content/engineering/understanding-kubernetes/image2.webp differ
diff --git a/content/engineering/understanding-kubernetes/image3.png b/content/engineering/understanding-kubernetes/image3.png
deleted file mode 100644
index adf9ff89a..000000000
Binary files a/content/engineering/understanding-kubernetes/image3.png and /dev/null differ
diff --git a/content/engineering/understanding-kubernetes/image3.webp b/content/engineering/understanding-kubernetes/image3.webp
new file mode 100644
index 000000000..8d2550fce
Binary files /dev/null and b/content/engineering/understanding-kubernetes/image3.webp differ
diff --git a/content/engineering/understanding-kubernetes/image4.jpeg b/content/engineering/understanding-kubernetes/image4.jpeg
deleted file mode 100644
index fef674891..000000000
Binary files a/content/engineering/understanding-kubernetes/image4.jpeg and /dev/null differ
diff --git a/content/engineering/understanding-kubernetes/image4.webp b/content/engineering/understanding-kubernetes/image4.webp
new file mode 100644
index 000000000..31cd2a5b2
Binary files /dev/null and b/content/engineering/understanding-kubernetes/image4.webp differ
diff --git a/content/engineering/understanding-kubernetes/index.md b/content/engineering/understanding-kubernetes/index.md
index 92c4ade42..4c0f99c52 100644
--- a/content/engineering/understanding-kubernetes/index.md
+++ b/content/engineering/understanding-kubernetes/index.md
@@ -1,7 +1,7 @@
---
title: "What is Kubernetes? - A Basic Guide"
date: "2020-10-26"
-coverImage: "image3.png"
+coverImage: "image3.webp"
author: Prabhat Kumar
description: "Learn about the Kubernetes. A container Orchestration tool on a basic level, and how it is making the job of Developers simpler."
tags: ["Kubernetes","Deployment","Distributed Systems"]
@@ -57,7 +57,7 @@ To meet evolving business demands, the development team needs to build new produ
That is where Kubernetes comes into the picture. It handles all the above requirements effectively and reduces a lot of burden from the developer's shoulders.
-
+
### Technical Aspect
@@ -70,7 +70,7 @@ A typical computer cluster in Kubernetes consists of:
> The Master is responsible for managing the cluster. The master nodes will coordinate all the activities in your cluster, such as scheduling applications, maintaining their desired state, scaling applications, and rolling new updates. Whereas a Node is a VM or a physical computer that is used as a worker machine in a Kubernetes cluster to actually, run the application
-
+
*A master node contains processes that continuously watch the deployment for any CPU or Memory requirement and smartly allocated it in the form of new pods to auto-scale the application, which handles the vast amount of requests coming to the server.*
@@ -79,7 +79,7 @@ Most of the current cloud services like Amazon Web Service(AWS), Microsoft Azure
A Kubernetes cluster can be deployed on either virtual or physical machines. A software named Minikube can be installed on your local machine that creates a VM on your local machine and deploys a simple cluster containing only one node.
Minikube provides a CLI through which we can execute commands & simulate a small-scale Kubernetes cluster.
-
+
#### Some of the basic Kubernetes CLI commands are:
- **kubectl get nodes** - It gets the total number of working nodes available in the k8s cluster.
diff --git a/content/engineering/understanding-react-rendering/image1.png b/content/engineering/understanding-react-rendering/image1.png
deleted file mode 100644
index 0dad4b7e0..000000000
Binary files a/content/engineering/understanding-react-rendering/image1.png and /dev/null differ
diff --git a/content/engineering/understanding-react-rendering/image1.webp b/content/engineering/understanding-react-rendering/image1.webp
new file mode 100644
index 000000000..518136077
Binary files /dev/null and b/content/engineering/understanding-react-rendering/image1.webp differ
diff --git a/content/engineering/understanding-react-rendering/index.md b/content/engineering/understanding-react-rendering/index.md
index ee5efe19d..d92360fc8 100644
--- a/content/engineering/understanding-react-rendering/index.md
+++ b/content/engineering/understanding-react-rendering/index.md
@@ -1,7 +1,7 @@
---
title: "How to Render React with optimization"
date: "2020-09-23"
-coverImage: "index.png"
+coverImage: "index.webp"
author: Nathan Nguyen
tags: ["Node.js", "React"]
description: "Optimized rendering in the frontend is a crucial procedure. Let's learn how to optimize React rendering process."
@@ -30,7 +30,7 @@ If you have the [Codepen](https://codepen.io/n-nguyen/pen/WNwYrRG) opened at thi
Once the set of alerts is dismissed, a very simple UI will render:
-
+
The dotted border line distinguishes between elements that belong to the Child component of the example (inside the dotted line) versus the Parent component.
diff --git a/content/engineering/understanding-react-rendering/index.png b/content/engineering/understanding-react-rendering/index.png
deleted file mode 100644
index 25ed68c3a..000000000
Binary files a/content/engineering/understanding-react-rendering/index.png and /dev/null differ
diff --git a/content/engineering/understanding-react-rendering/index.webp b/content/engineering/understanding-react-rendering/index.webp
new file mode 100644
index 000000000..5408df45a
Binary files /dev/null and b/content/engineering/understanding-react-rendering/index.webp differ
diff --git a/content/engineering/unit-testing/index.md b/content/engineering/unit-testing/index.md
index 8921215c8..0028ac0a7 100644
--- a/content/engineering/unit-testing/index.md
+++ b/content/engineering/unit-testing/index.md
@@ -1,7 +1,7 @@
---
title: "Unit Testing: What is it and why do you need it?"
date: "2020-09-29"
-coverImage: "unit-testing.jpg"
+coverImage: "unit-testing.webp"
author: Sudhanshu Pandey
tags: ["Unit Testing", "QA", "Testing"]
description: "Unit testing is one of the types of software testing that requires an initial phase of testing. Find out the benefits and why its important for developers."
diff --git a/content/engineering/unit-testing/unit-testing.jpg b/content/engineering/unit-testing/unit-testing.jpg
deleted file mode 100644
index 1fe6ff6a9..000000000
Binary files a/content/engineering/unit-testing/unit-testing.jpg and /dev/null differ
diff --git a/content/engineering/unit-testing/unit-testing.webp b/content/engineering/unit-testing/unit-testing.webp
new file mode 100644
index 000000000..6a3c56a50
Binary files /dev/null and b/content/engineering/unit-testing/unit-testing.webp differ
diff --git a/content/engineering/upload-files-with-node-and-multer/index.md b/content/engineering/upload-files-with-node-and-multer/index.md
index 674832563..3c4c2a164 100644
--- a/content/engineering/upload-files-with-node-and-multer/index.md
+++ b/content/engineering/upload-files-with-node-and-multer/index.md
@@ -1,7 +1,7 @@
---
title: "Upload files using NodeJS + Multer"
date: "2020-10-12"
-coverImage: "node-multer-upload.png"
+coverImage: "node-multer-upload.webp"
author: Gabriel Rabelo
description: "Learn how to upload files in a NodeJS application using Multer, Multer is a middleware for handling multipart/form-data that is used to send files in forms."
tags: ["NodeJs", "Express", "Multer"]
diff --git a/content/engineering/upload-files-with-node-and-multer/node-multer-upload.png b/content/engineering/upload-files-with-node-and-multer/node-multer-upload.png
deleted file mode 100644
index 7a4a626c6..000000000
Binary files a/content/engineering/upload-files-with-node-and-multer/node-multer-upload.png and /dev/null differ
diff --git a/content/engineering/upload-files-with-node-and-multer/node-multer-upload.webp b/content/engineering/upload-files-with-node-and-multer/node-multer-upload.webp
new file mode 100644
index 000000000..2445c97e3
Binary files /dev/null and b/content/engineering/upload-files-with-node-and-multer/node-multer-upload.webp differ
diff --git a/content/engineering/use-php-to-generate-filter-portfolio/folder-structure.png b/content/engineering/use-php-to-generate-filter-portfolio/folder-structure.png
deleted file mode 100644
index d2c680678..000000000
Binary files a/content/engineering/use-php-to-generate-filter-portfolio/folder-structure.png and /dev/null differ
diff --git a/content/engineering/use-php-to-generate-filter-portfolio/folder-structure.webp b/content/engineering/use-php-to-generate-filter-portfolio/folder-structure.webp
new file mode 100644
index 000000000..f521765cc
Binary files /dev/null and b/content/engineering/use-php-to-generate-filter-portfolio/folder-structure.webp differ
diff --git a/content/engineering/use-php-to-generate-filter-portfolio/index.md b/content/engineering/use-php-to-generate-filter-portfolio/index.md
index bd435b33e..fa442a901 100644
--- a/content/engineering/use-php-to-generate-filter-portfolio/index.md
+++ b/content/engineering/use-php-to-generate-filter-portfolio/index.md
@@ -1,7 +1,7 @@
---
title: "Use PHP to generate filter portfolio"
date: "2015-05-19"
-coverImage: "php-filter-portfolio.png"
+coverImage: "php-filter-portfolio.webp"
author: Lucius Yu
tags: ["PHP"]
---
@@ -16,7 +16,7 @@ The logic is like this, first we have a folder to contain all the portfolio imag
"assets->img->logos->businesses"
-
+
And in the "businesses" folder, we have some sub-folders to put all the images in different categories, like this:
diff --git a/content/engineering/use-php-to-generate-filter-portfolio/php-filter-portfolio.png b/content/engineering/use-php-to-generate-filter-portfolio/php-filter-portfolio.png
deleted file mode 100644
index 99c9a1880..000000000
Binary files a/content/engineering/use-php-to-generate-filter-portfolio/php-filter-portfolio.png and /dev/null differ
diff --git a/content/engineering/use-php-to-generate-filter-portfolio/php-filter-portfolio.webp b/content/engineering/use-php-to-generate-filter-portfolio/php-filter-portfolio.webp
new file mode 100644
index 000000000..8e94e8e52
Binary files /dev/null and b/content/engineering/use-php-to-generate-filter-portfolio/php-filter-portfolio.webp differ
diff --git a/content/engineering/user-authentication-react-application/authentication-main.png b/content/engineering/user-authentication-react-application/authentication-main.png
deleted file mode 100644
index a3fe3094d..000000000
Binary files a/content/engineering/user-authentication-react-application/authentication-main.png and /dev/null differ
diff --git a/content/engineering/user-authentication-react-application/authentication-main.webp b/content/engineering/user-authentication-react-application/authentication-main.webp
new file mode 100644
index 000000000..fba36d408
Binary files /dev/null and b/content/engineering/user-authentication-react-application/authentication-main.webp differ
diff --git a/content/engineering/user-authentication-react-application/index.md b/content/engineering/user-authentication-react-application/index.md
index e5270c90a..2216134b2 100644
--- a/content/engineering/user-authentication-react-application/index.md
+++ b/content/engineering/user-authentication-react-application/index.md
@@ -1,7 +1,7 @@
---
title: "A Guide To React User Authentication with LoginRadius"
date: "2020-12-10"
-coverImage: "authentication-main.png"
+coverImage: "authentication-main.webp"
author: "Versha Gupta"
tags: ["Authentication", "LoginRadius", "React"]
description: "This article focuses on helping developers learn how to integrate user authentication in React applications and determine the basic principles of authentication with React."
diff --git a/content/engineering/user-privacy-data-masking-in-nginx-logs/data-masking-in-nginx-logs-for-user-data-privacy-and-compliance.jpg b/content/engineering/user-privacy-data-masking-in-nginx-logs/data-masking-in-nginx-logs-for-user-data-privacy-and-compliance.jpg
deleted file mode 100644
index 9a9bd3c30..000000000
Binary files a/content/engineering/user-privacy-data-masking-in-nginx-logs/data-masking-in-nginx-logs-for-user-data-privacy-and-compliance.jpg and /dev/null differ
diff --git a/content/engineering/user-privacy-data-masking-in-nginx-logs/data-masking-in-nginx-logs-for-user-data-privacy-and-compliance.webp b/content/engineering/user-privacy-data-masking-in-nginx-logs/data-masking-in-nginx-logs-for-user-data-privacy-and-compliance.webp
new file mode 100644
index 000000000..b446c9ad0
Binary files /dev/null and b/content/engineering/user-privacy-data-masking-in-nginx-logs/data-masking-in-nginx-logs-for-user-data-privacy-and-compliance.webp differ
diff --git a/content/engineering/user-privacy-data-masking-in-nginx-logs/index.md b/content/engineering/user-privacy-data-masking-in-nginx-logs/index.md
index 0fff67bbf..a8b0005e2 100644
--- a/content/engineering/user-privacy-data-masking-in-nginx-logs/index.md
+++ b/content/engineering/user-privacy-data-masking-in-nginx-logs/index.md
@@ -1,7 +1,7 @@
---
title: "Data Masking In Nginx Logs For User Data Privacy And Compliance"
date: "2021-05-18"
-coverImage: "data-masking-in-nginx-logs-for-user-data-privacy-and-compliance.jpg"
+coverImage: "data-masking-in-nginx-logs-for-user-data-privacy-and-compliance.webp"
author: "Vijay Singh Shekhawat"
tags: ["Nginx", "Logs", "Data Masking", "Compliance", "Privacy"]
description: "Learn about data masking in nginx logs for user data privacy and compliance."
diff --git a/content/engineering/using-facebook-graph-api-after-login/fb-feat-img-150x150.png b/content/engineering/using-facebook-graph-api-after-login/fb-feat-img-150x150.png
deleted file mode 100644
index 6d66790b8..000000000
Binary files a/content/engineering/using-facebook-graph-api-after-login/fb-feat-img-150x150.png and /dev/null differ
diff --git a/content/engineering/using-facebook-graph-api-after-login/fb-feat-img-150x150.webp b/content/engineering/using-facebook-graph-api-after-login/fb-feat-img-150x150.webp
new file mode 100644
index 000000000..41b44681e
Binary files /dev/null and b/content/engineering/using-facebook-graph-api-after-login/fb-feat-img-150x150.webp differ
diff --git a/content/engineering/using-facebook-graph-api-after-login/index.md b/content/engineering/using-facebook-graph-api-after-login/index.md
index 6921b8fa5..df652cb6f 100644
--- a/content/engineering/using-facebook-graph-api-after-login/index.md
+++ b/content/engineering/using-facebook-graph-api-after-login/index.md
@@ -1,7 +1,7 @@
---
title: "Using Facebook Graph API After Login"
date: "2015-09-29"
-coverImage: "fb-feat-img-150x150.png"
+coverImage: "fb-feat-img-150x150.webp"
author: Karl Wittig
tags: ["Facebook","Graph API"]
---
diff --git a/content/engineering/using-jwt-with-oauth2-when-and-why/index.md b/content/engineering/using-jwt-with-oauth2-when-and-why/index.md
index 7ce7d5326..e599cb220 100644
--- a/content/engineering/using-jwt-with-oauth2-when-and-why/index.md
+++ b/content/engineering/using-jwt-with-oauth2-when-and-why/index.md
@@ -1,7 +1,7 @@
---
title: "How to Use JWT with OAuth"
date: "2019-03-11"
-coverImage: "photo-1454165804606-c3d57bc86b40.jpeg"
+coverImage: "photo-1454165804606-c3d57bc86b40.webp"
author: Ti Zhang
tags: ["JWT","Oauth", "JSON Web Token"]
description: "Learn how to use JWT with OAuth and when & why"
diff --git a/content/engineering/using-jwt-with-oauth2-when-and-why/photo-1454165804606-c3d57bc86b40.jpeg b/content/engineering/using-jwt-with-oauth2-when-and-why/photo-1454165804606-c3d57bc86b40.jpeg
deleted file mode 100644
index c423d8a35..000000000
Binary files a/content/engineering/using-jwt-with-oauth2-when-and-why/photo-1454165804606-c3d57bc86b40.jpeg and /dev/null differ
diff --git a/content/engineering/using-jwt-with-oauth2-when-and-why/photo-1454165804606-c3d57bc86b40.webp b/content/engineering/using-jwt-with-oauth2-when-and-why/photo-1454165804606-c3d57bc86b40.webp
new file mode 100644
index 000000000..357ce74a9
Binary files /dev/null and b/content/engineering/using-jwt-with-oauth2-when-and-why/photo-1454165804606-c3d57bc86b40.webp differ
diff --git a/content/engineering/using-m2m-authorization-for-apis-and-apps/client-credentials-grant-flow.png b/content/engineering/using-m2m-authorization-for-apis-and-apps/client-credentials-grant-flow.png
deleted file mode 100644
index 9e5c0cda6..000000000
Binary files a/content/engineering/using-m2m-authorization-for-apis-and-apps/client-credentials-grant-flow.png and /dev/null differ
diff --git a/content/engineering/using-m2m-authorization-for-apis-and-apps/client-credentials-grant-flow.webp b/content/engineering/using-m2m-authorization-for-apis-and-apps/client-credentials-grant-flow.webp
new file mode 100644
index 000000000..2efdb638d
Binary files /dev/null and b/content/engineering/using-m2m-authorization-for-apis-and-apps/client-credentials-grant-flow.webp differ
diff --git a/content/engineering/using-m2m-authorization-for-apis-and-apps/index.md b/content/engineering/using-m2m-authorization-for-apis-and-apps/index.md
index 26bb7b861..d8b2a6e6f 100644
--- a/content/engineering/using-m2m-authorization-for-apis-and-apps/index.md
+++ b/content/engineering/using-m2m-authorization-for-apis-and-apps/index.md
@@ -1,7 +1,7 @@
---
title: "M2M Authorization: Authenticate Apps, APIs, and Web Services"
date: "2022-04-29"
-coverImage: "m2m-authorization-for-apis-apps-and-web-services.png"
+coverImage: "m2m-authorization-for-apis-apps-and-web-services.webp"
author: "Kundan Singh"
tags: ["M2M", "Authorization", "Authentication"]
description: "How can you ensure APIs, web services, and business systems communicate and access the information securely without human intervention? The answer is machine-to-machine (M2M) authorization."
@@ -44,13 +44,13 @@ The following two scenarios explain how you can use LoginRadius M2M Authenticati
To start using the M2M Authorization for this scenario, you need to create an M2M App and define the desired scope of API(s), as [explained here](https://www.loginradius.com/docs/api/v2/single-sign-on/Machine-to-Machine/overview/#adminconsoleconfigurationformmauthentication3).
-
+
**[Scenario 2](#implement-m2m-authorization-with-business-apis):** To grant desired access to your Business APIs.
To start using the M2M Authorization for this scenario, you need to define your API in LoginRadius with name, identifier, and scope details and then create an M2M App with the desired scope of API(s), as [explained here](https://www.loginradius.com/docs/api/v2/single-sign-on/Machine-to-Machine/overview/#adminconsoleconfigurationformmauthentication3).
-
+
In both scenarios, you get the Client Id and Client Secret for the created app, which you need to share with the partner or service who wants to access your APIs.
@@ -59,7 +59,7 @@ LoginRadius M2M Authorization uses client credentials grant flow from OAuth 2.0.
This grant-type flow occurs strictly between a client app and the authorization server. The user does not participate in this grant-type flow.
-
+
- The client (server) requests with the Client ID, Client Secret, Audience, and Claims to the authorization server.
diff --git a/content/engineering/using-m2m-authorization-for-apis-and-apps/m2m-authorization-for-apis-apps-and-web-services.png b/content/engineering/using-m2m-authorization-for-apis-and-apps/m2m-authorization-for-apis-apps-and-web-services.png
deleted file mode 100644
index 7f9c6adcb..000000000
Binary files a/content/engineering/using-m2m-authorization-for-apis-and-apps/m2m-authorization-for-apis-apps-and-web-services.png and /dev/null differ
diff --git a/content/engineering/using-m2m-authorization-for-apis-and-apps/m2m-authorization-for-apis-apps-and-web-services.webp b/content/engineering/using-m2m-authorization-for-apis-and-apps/m2m-authorization-for-apis-apps-and-web-services.webp
new file mode 100644
index 000000000..1df1f8f93
Binary files /dev/null and b/content/engineering/using-m2m-authorization-for-apis-and-apps/m2m-authorization-for-apis-apps-and-web-services.webp differ
diff --git a/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-authorization-server-apis.png b/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-authorization-server-apis.png
deleted file mode 100644
index 301d93f76..000000000
Binary files a/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-authorization-server-apis.png and /dev/null differ
diff --git a/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-authorization-server-apis.webp b/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-authorization-server-apis.webp
new file mode 100644
index 000000000..98cf26433
Binary files /dev/null and b/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-authorization-server-apis.webp differ
diff --git a/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-machine-to-machine-app.png b/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-machine-to-machine-app.png
deleted file mode 100644
index eeead02d4..000000000
Binary files a/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-machine-to-machine-app.png and /dev/null differ
diff --git a/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-machine-to-machine-app.webp b/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-machine-to-machine-app.webp
new file mode 100644
index 000000000..83f9dfe90
Binary files /dev/null and b/content/engineering/using-m2m-authorization-for-apis-and-apps/manage-machine-to-machine-app.webp differ
diff --git a/content/engineering/using-nuget-to-publish-net-packages/desdev.png b/content/engineering/using-nuget-to-publish-net-packages/desdev.png
deleted file mode 100644
index 621e3f218..000000000
Binary files a/content/engineering/using-nuget-to-publish-net-packages/desdev.png and /dev/null differ
diff --git a/content/engineering/using-nuget-to-publish-net-packages/desdev.webp b/content/engineering/using-nuget-to-publish-net-packages/desdev.webp
new file mode 100644
index 000000000..06c99b0ff
Binary files /dev/null and b/content/engineering/using-nuget-to-publish-net-packages/desdev.webp differ
diff --git a/content/engineering/using-nuget-to-publish-net-packages/index.md b/content/engineering/using-nuget-to-publish-net-packages/index.md
index 2b6b756b3..0328b2959 100644
--- a/content/engineering/using-nuget-to-publish-net-packages/index.md
+++ b/content/engineering/using-nuget-to-publish-net-packages/index.md
@@ -1,7 +1,7 @@
---
title: "Using NuGet to publish .NET packages"
date: "2018-06-28"
-coverImage: "desdev.png"
+coverImage: "desdev.webp"
author: Hitesh Pamnani
tags: ["NuGet",".NET"]
---
diff --git a/content/engineering/using-nuget-to-publish-net-packages/logo-header.svg b/content/engineering/using-nuget-to-publish-net-packages/logo-header.svg
deleted file mode 100644
index 225b9b588..000000000
--- a/content/engineering/using-nuget-to-publish-net-packages/logo-header.svg
+++ /dev/null
@@ -1 +0,0 @@
-
\ No newline at end of file
diff --git a/content/engineering/using-nuget-to-publish-net-packages/logo-header.webp b/content/engineering/using-nuget-to-publish-net-packages/logo-header.webp
new file mode 100644
index 000000000..833af0b4a
Binary files /dev/null and b/content/engineering/using-nuget-to-publish-net-packages/logo-header.webp differ
diff --git a/content/engineering/using-pgp-encryption-with-nodejs/cover.png b/content/engineering/using-pgp-encryption-with-nodejs/cover.png
deleted file mode 100644
index 5fd6983e6..000000000
Binary files a/content/engineering/using-pgp-encryption-with-nodejs/cover.png and /dev/null differ
diff --git a/content/engineering/using-pgp-encryption-with-nodejs/cover.webp b/content/engineering/using-pgp-encryption-with-nodejs/cover.webp
new file mode 100644
index 000000000..89814fab8
Binary files /dev/null and b/content/engineering/using-pgp-encryption-with-nodejs/cover.webp differ
diff --git a/content/engineering/using-pgp-encryption-with-nodejs/index.md b/content/engineering/using-pgp-encryption-with-nodejs/index.md
index 4c6577a77..247f0b345 100644
--- a/content/engineering/using-pgp-encryption-with-nodejs/index.md
+++ b/content/engineering/using-pgp-encryption-with-nodejs/index.md
@@ -1,7 +1,7 @@
---
title: "Using PGP Encryption with Nodejs"
date: "2020-11-10"
-coverImage: "cover.png"
+coverImage: "cover.webp"
author: "Andy Yeung"
tags: ["Security", "NodeJs", "Encryption"]
description: "Starter guide on Pretty Good Privacy(PGP) with Nodejs. PGP, a cryptographic process used to encrypt and decrypt information."
diff --git a/content/engineering/vim-getting-started/BadVim.png b/content/engineering/vim-getting-started/BadVim.png
deleted file mode 100644
index 65163e84f..000000000
Binary files a/content/engineering/vim-getting-started/BadVim.png and /dev/null differ
diff --git a/content/engineering/vim-getting-started/BadVim.webp b/content/engineering/vim-getting-started/BadVim.webp
new file mode 100644
index 000000000..b9d75e40f
Binary files /dev/null and b/content/engineering/vim-getting-started/BadVim.webp differ
diff --git a/content/engineering/vim-getting-started/Vim.png b/content/engineering/vim-getting-started/Vim.png
deleted file mode 100644
index bd18116dc..000000000
Binary files a/content/engineering/vim-getting-started/Vim.png and /dev/null differ
diff --git a/content/engineering/vim-getting-started/Vim.webp b/content/engineering/vim-getting-started/Vim.webp
new file mode 100644
index 000000000..787acbe91
Binary files /dev/null and b/content/engineering/vim-getting-started/Vim.webp differ
diff --git a/content/engineering/vim-getting-started/index.md b/content/engineering/vim-getting-started/index.md
index b60e17408..6cd78017d 100644
--- a/content/engineering/vim-getting-started/index.md
+++ b/content/engineering/vim-getting-started/index.md
@@ -2,7 +2,7 @@
title: "Vim: What is it and Why to use it?"
date: "2020-10-08"
author: "Shubhankar Khare"
-coverImage: "Vim.png"
+coverImage: "Vim.webp"
tags: ["Vim", "Text Editor"]
description: "Vim is Vi's newest and most common reincarnation that is supported on every known platform, check out the article to learn about what is ViM, and why to use it."
---
@@ -70,7 +70,7 @@ So to sum up,
First of all, don't get disheartened when you see VIM for the first time, it's known to make a **horrible first impression.** We'll learn to customize it later in the blog.
- 
+ 
To get started, get your hands dirty on **vimtutor** . It's a 20-30 minute vim tutorial which teaches you all the basics. Just type `vimtutor` in your terminal (in a machine where you have vim installed) to open it.
@@ -148,10 +148,10 @@ VIM makes you write code at the speed of thoughts. Just get started, and the res
If you want to slowly blend in into the world of vim then use some vim plugin for your text editor. All popular text editors have a vim plugin ( [Here's one for VsCode ](https://marketplace.visualstudio.com/items?itemName=vscodevim.vim))
Here you go, best of both worlds! When you're comfortable enough, go for that complete switch.
-
+
Here's how my vim setup looks.
-
+
Now go give it a try. I wish you luck!!
diff --git a/content/engineering/vim-getting-started/vscodevim.png b/content/engineering/vim-getting-started/vscodevim.png
deleted file mode 100644
index 16266a11d..000000000
Binary files a/content/engineering/vim-getting-started/vscodevim.png and /dev/null differ
diff --git a/content/engineering/vim-getting-started/vscodevim.webp b/content/engineering/vim-getting-started/vscodevim.webp
new file mode 100644
index 000000000..359ca0120
Binary files /dev/null and b/content/engineering/vim-getting-started/vscodevim.webp differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/deployment.jpg b/content/engineering/visualizing-data-using-leaflet-and-netlify/deployment.jpg
deleted file mode 100644
index 48f81dc8b..000000000
Binary files a/content/engineering/visualizing-data-using-leaflet-and-netlify/deployment.jpg and /dev/null differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/deployment.webp b/content/engineering/visualizing-data-using-leaflet-and-netlify/deployment.webp
new file mode 100644
index 000000000..87f01b467
Binary files /dev/null and b/content/engineering/visualizing-data-using-leaflet-and-netlify/deployment.webp differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/geojson.jpg b/content/engineering/visualizing-data-using-leaflet-and-netlify/geojson.jpg
deleted file mode 100644
index cdedaf6de..000000000
Binary files a/content/engineering/visualizing-data-using-leaflet-and-netlify/geojson.jpg and /dev/null differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/geojson.webp b/content/engineering/visualizing-data-using-leaflet-and-netlify/geojson.webp
new file mode 100644
index 000000000..443eee354
Binary files /dev/null and b/content/engineering/visualizing-data-using-leaflet-and-netlify/geojson.webp differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/gitRepo.jpg b/content/engineering/visualizing-data-using-leaflet-and-netlify/gitRepo.jpg
deleted file mode 100644
index 796d11aba..000000000
Binary files a/content/engineering/visualizing-data-using-leaflet-and-netlify/gitRepo.jpg and /dev/null differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/gitRepo.webp b/content/engineering/visualizing-data-using-leaflet-and-netlify/gitRepo.webp
new file mode 100644
index 000000000..25aa553c4
Binary files /dev/null and b/content/engineering/visualizing-data-using-leaflet-and-netlify/gitRepo.webp differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/index.md b/content/engineering/visualizing-data-using-leaflet-and-netlify/index.md
index dad46ba8c..de097f817 100644
--- a/content/engineering/visualizing-data-using-leaflet-and-netlify/index.md
+++ b/content/engineering/visualizing-data-using-leaflet-and-netlify/index.md
@@ -1,7 +1,7 @@
---
title: "Visualizing Data using Leaflet and Netlify"
date: "2020-10-14"
-coverImage: "map.jpg"
+coverImage: "map.webp"
author: Sudipto Ghosh
tags: ["GIS", "Serverless", "JavaScript"]
description: "Let's visualize geospatial data on the web using Leaflet and host it on Netlify!"
@@ -23,7 +23,7 @@ The Leaflet is a great library for implementing interactive web maps as it provi
>
> _source: leafletjs.com_
-
+
We can include Leaflet in our application by including the CSS stylesheet and the JS file from the unpkg CDN. Let's start building the application by starting with the following code at the project root. Create a file named `index.html` and put the following markup in it. The map shall be rendered in `div#mapid`.
@@ -171,7 +171,7 @@ fetch(dataUrl)
As the dataset contains `Point` features, markers will be added at the respective coordinates. Our web page will now look like the following:
-
+
We can show tooltips upon clicking on the markers by modifying the code as follows, to include some custom HTML using the properties in the feature, in the popup:
@@ -200,7 +200,7 @@ We can show tooltips upon clicking on the markers by modifying the code as follo
Uupon clicking any marker, we will now see the following popup:
-
+
We can also customize the marker icon using the `pointToLayer` option of the `geoJSON` constructor as follows:
@@ -214,7 +214,7 @@ We can also customize the marker icon using the `pointToLayer` option of the `ge
iconSize: [30, 30],
iconAnchor: [15, 15],
popupAnchor: [1, -24],
- iconUrl: 'https://cdn.iconscout.com/icon/free/png-256/metro-subway-underground-train-railway-engine-emoj-symbol-30744.png'
+ iconUrl: 'https://cdn.iconscout.com/icon/free/png-256/metro-subway-underground-train-railway-engine-emoj-symbol-30744.webp'
})
});
},
@@ -234,7 +234,7 @@ We can also customize the marker icon using the `pointToLayer` option of the `ge
Our updated web page will now look like the following:
-
+
Now, we can move on to deploy this web page on Netlify.
@@ -242,23 +242,23 @@ Now, we can move on to deploy this web page on Netlify.
Netlify is an awesome platform to host your web applications. It also offers many other features such as serverless functions.
-
+
Once you have pushed your web page to a Git repository, hosted either on GitHub, GitLab or BitBucket, navigate to [Netlify](https://app.netlify.com) and click on the **New Site from Git** button.
-
+
Next, select your Git provider and your repository:
-
+
-
+
Go ahead with the defaults, and now your site shall be published on Netlify, and all future pushes should result in a Netlify deployment:
-
+
Nice! Now we have a web map, even though a very basic one, live! Check out the [Leaflet documentation](https://leafletjs.com/reference.html) for more!
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/leaflet.png b/content/engineering/visualizing-data-using-leaflet-and-netlify/leaflet.png
deleted file mode 100644
index 27a0f1057..000000000
Binary files a/content/engineering/visualizing-data-using-leaflet-and-netlify/leaflet.png and /dev/null differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/leaflet.webp b/content/engineering/visualizing-data-using-leaflet-and-netlify/leaflet.webp
new file mode 100644
index 000000000..99e1c1786
Binary files /dev/null and b/content/engineering/visualizing-data-using-leaflet-and-netlify/leaflet.webp differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/map.jpg b/content/engineering/visualizing-data-using-leaflet-and-netlify/map.jpg
deleted file mode 100644
index 8c2251cbf..000000000
Binary files a/content/engineering/visualizing-data-using-leaflet-and-netlify/map.jpg and /dev/null differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/map.webp b/content/engineering/visualizing-data-using-leaflet-and-netlify/map.webp
new file mode 100644
index 000000000..d3a7b4461
Binary files /dev/null and b/content/engineering/visualizing-data-using-leaflet-and-netlify/map.webp differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/mapIcon.jpg b/content/engineering/visualizing-data-using-leaflet-and-netlify/mapIcon.jpg
deleted file mode 100644
index 5116d6d54..000000000
Binary files a/content/engineering/visualizing-data-using-leaflet-and-netlify/mapIcon.jpg and /dev/null differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/mapIcon.webp b/content/engineering/visualizing-data-using-leaflet-and-netlify/mapIcon.webp
new file mode 100644
index 000000000..ec5af45eb
Binary files /dev/null and b/content/engineering/visualizing-data-using-leaflet-and-netlify/mapIcon.webp differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/mapInitial.jpg b/content/engineering/visualizing-data-using-leaflet-and-netlify/mapInitial.jpg
deleted file mode 100644
index 32dede8f2..000000000
Binary files a/content/engineering/visualizing-data-using-leaflet-and-netlify/mapInitial.jpg and /dev/null differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/mapInitial.webp b/content/engineering/visualizing-data-using-leaflet-and-netlify/mapInitial.webp
new file mode 100644
index 000000000..3280a6946
Binary files /dev/null and b/content/engineering/visualizing-data-using-leaflet-and-netlify/mapInitial.webp differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/mapPopup.jpg b/content/engineering/visualizing-data-using-leaflet-and-netlify/mapPopup.jpg
deleted file mode 100644
index 9204de193..000000000
Binary files a/content/engineering/visualizing-data-using-leaflet-and-netlify/mapPopup.jpg and /dev/null differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/mapPopup.webp b/content/engineering/visualizing-data-using-leaflet-and-netlify/mapPopup.webp
new file mode 100644
index 000000000..0678e3510
Binary files /dev/null and b/content/engineering/visualizing-data-using-leaflet-and-netlify/mapPopup.webp differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/netlify.png b/content/engineering/visualizing-data-using-leaflet-and-netlify/netlify.png
deleted file mode 100644
index 0f14f3854..000000000
Binary files a/content/engineering/visualizing-data-using-leaflet-and-netlify/netlify.png and /dev/null differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/netlify.webp b/content/engineering/visualizing-data-using-leaflet-and-netlify/netlify.webp
new file mode 100644
index 000000000..d24f22989
Binary files /dev/null and b/content/engineering/visualizing-data-using-leaflet-and-netlify/netlify.webp differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/netlifySigningUp.jpg b/content/engineering/visualizing-data-using-leaflet-and-netlify/netlifySigningUp.jpg
deleted file mode 100644
index bfba56bf2..000000000
Binary files a/content/engineering/visualizing-data-using-leaflet-and-netlify/netlifySigningUp.jpg and /dev/null differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/netlifySigningUp.webp b/content/engineering/visualizing-data-using-leaflet-and-netlify/netlifySigningUp.webp
new file mode 100644
index 000000000..f43a59a2c
Binary files /dev/null and b/content/engineering/visualizing-data-using-leaflet-and-netlify/netlifySigningUp.webp differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/repoSelection.jpg b/content/engineering/visualizing-data-using-leaflet-and-netlify/repoSelection.jpg
deleted file mode 100644
index 5f9abc137..000000000
Binary files a/content/engineering/visualizing-data-using-leaflet-and-netlify/repoSelection.jpg and /dev/null differ
diff --git a/content/engineering/visualizing-data-using-leaflet-and-netlify/repoSelection.webp b/content/engineering/visualizing-data-using-leaflet-and-netlify/repoSelection.webp
new file mode 100644
index 000000000..9f417f91f
Binary files /dev/null and b/content/engineering/visualizing-data-using-leaflet-and-netlify/repoSelection.webp differ
diff --git a/content/engineering/w3c-validation/index.md b/content/engineering/w3c-validation/index.md
index 554bc9e3b..a06d683e5 100644
--- a/content/engineering/w3c-validation/index.md
+++ b/content/engineering/w3c-validation/index.md
@@ -1,7 +1,7 @@
---
title: "W3C Validation: What is it and why to use it?"
date: "2015-01-26"
-coverImage: "w3c.png"
+coverImage: "w3c.webp"
author: "Team LoginRadius"
tags: ["W3C", "Validation"]
description: "Learn what w3c is and why to use it, and also how to validate your web page for W3C standards, a simple guide on W3C validation."
diff --git a/content/engineering/w3c-validation/w3c.png b/content/engineering/w3c-validation/w3c.png
deleted file mode 100644
index f8545f287..000000000
Binary files a/content/engineering/w3c-validation/w3c.png and /dev/null differ
diff --git a/content/engineering/w3c-validation/w3c.webp b/content/engineering/w3c-validation/w3c.webp
new file mode 100644
index 000000000..82a1084b2
Binary files /dev/null and b/content/engineering/w3c-validation/w3c.webp differ
diff --git a/content/engineering/web-workers/index.md b/content/engineering/web-workers/index.md
index 7d7d670e8..cc2c2d6dd 100644
--- a/content/engineering/web-workers/index.md
+++ b/content/engineering/web-workers/index.md
@@ -1,7 +1,7 @@
---
title: "Web Workers in JS - An Introductory Guide"
date: "2020-12-28"
-coverImage: "unsplash.png"
+coverImage: "unsplash.webp"
author: "Nick Chim"
tags: ["Web Workers"]
description: "Learn how to use JavaScript web workers to create parallel programming and execute multiple operations concurrently rather than interconnecting them."
diff --git a/content/engineering/web-workers/unsplash.png b/content/engineering/web-workers/unsplash.png
deleted file mode 100644
index c27a65fec..000000000
Binary files a/content/engineering/web-workers/unsplash.png and /dev/null differ
diff --git a/content/engineering/web-workers/unsplash.webp b/content/engineering/web-workers/unsplash.webp
new file mode 100644
index 000000000..c45a86d6d
Binary files /dev/null and b/content/engineering/web-workers/unsplash.webp differ
diff --git a/content/engineering/webauthn-authentication-application/authenticators.png b/content/engineering/webauthn-authentication-application/authenticators.png
deleted file mode 100644
index b37d5de58..000000000
Binary files a/content/engineering/webauthn-authentication-application/authenticators.png and /dev/null differ
diff --git a/content/engineering/webauthn-authentication-application/authenticators.webp b/content/engineering/webauthn-authentication-application/authenticators.webp
new file mode 100644
index 000000000..3e127567a
Binary files /dev/null and b/content/engineering/webauthn-authentication-application/authenticators.webp differ
diff --git a/content/engineering/webauthn-authentication-application/index.md b/content/engineering/webauthn-authentication-application/index.md
index 1d5b561ea..4bf657991 100644
--- a/content/engineering/webauthn-authentication-application/index.md
+++ b/content/engineering/webauthn-authentication-application/index.md
@@ -1,7 +1,7 @@
---
title: "WebAuthn: A Guide To Authenticate Your Application"
date: "2020-12-09"
-coverImage: "webauthn-logo.png"
+coverImage: "webauthn-logo.webp"
author: "Chris Yee"
tags: ["WebAuthn", "FIDO", "Authentication"]
description: "Web authentication, or WebAuthn in short. A go-to guide for developers to learn more about WebAuthn API, and how to set it up in their services.."
@@ -17,7 +17,7 @@ The WebAuthn authentication process involves the interaction between three entit
The registration process begins when the client generates some sort of identifying information about themselves. Typically, this would be a user name or an email from the user but could be another identifier sent from the client, such as a randomly generated GUID. Using the Web Authentication APIs with JavaScript, the client can request the relying party to register the authenticator credentials.
-
+
After receiving the request from the client, the relying party generates a challenge based on the options provided by the client. The client receives the response and attempts to get the user to verify the authenticator being used. For example, with Windows Hello as the authenticator, the user can enter their PIN. After verifying the authenticator, it signs the challenge-response back with identifying details and returns it to the relying party, which validates the authenticator and registers the user.
diff --git a/content/engineering/webauthn-authentication-application/webauthn-flow.png b/content/engineering/webauthn-authentication-application/webauthn-flow.png
deleted file mode 100644
index 79efbf9c9..000000000
Binary files a/content/engineering/webauthn-authentication-application/webauthn-flow.png and /dev/null differ
diff --git a/content/engineering/webauthn-authentication-application/webauthn-flow.webp b/content/engineering/webauthn-authentication-application/webauthn-flow.webp
new file mode 100644
index 000000000..72ddc774f
Binary files /dev/null and b/content/engineering/webauthn-authentication-application/webauthn-flow.webp differ
diff --git a/content/engineering/webauthn-authentication-application/webauthn-logo.png b/content/engineering/webauthn-authentication-application/webauthn-logo.png
deleted file mode 100644
index 7acf636b8..000000000
Binary files a/content/engineering/webauthn-authentication-application/webauthn-logo.png and /dev/null differ
diff --git a/content/engineering/webauthn-authentication-application/webauthn-logo.webp b/content/engineering/webauthn-authentication-application/webauthn-logo.webp
new file mode 100644
index 000000000..2b7e970e7
Binary files /dev/null and b/content/engineering/webauthn-authentication-application/webauthn-logo.webp differ
diff --git a/content/engineering/website-authentication-protocols/index.md b/content/engineering/website-authentication-protocols/index.md
index 52ae7d47e..103ec7e56 100644
--- a/content/engineering/website-authentication-protocols/index.md
+++ b/content/engineering/website-authentication-protocols/index.md
@@ -1,7 +1,7 @@
---
title: "Website Authentication Protocols"
date: "2015-12-01"
-coverImage: "server-proc-150x150.png"
+coverImage: "server-proc-150x150.webp"
author: Karl Wittig
tags: ["Authentication","Oauth"]
---
diff --git a/content/engineering/website-authentication-protocols/server-proc-150x150.png b/content/engineering/website-authentication-protocols/server-proc-150x150.png
deleted file mode 100644
index b14fb5266..000000000
Binary files a/content/engineering/website-authentication-protocols/server-proc-150x150.png and /dev/null differ
diff --git a/content/engineering/website-authentication-protocols/server-proc-150x150.webp b/content/engineering/website-authentication-protocols/server-proc-150x150.webp
new file mode 100644
index 000000000..15e28cae4
Binary files /dev/null and b/content/engineering/website-authentication-protocols/server-proc-150x150.webp differ
diff --git a/content/engineering/what-is-an-api/index.md b/content/engineering/what-is-an-api/index.md
index e32e4a171..fbcffddd5 100644
--- a/content/engineering/what-is-an-api/index.md
+++ b/content/engineering/what-is-an-api/index.md
@@ -1,7 +1,7 @@
---
title: "What is an API"
date: "2015-06-23"
-coverImage: "whats-an-api-300x300.png"
+coverImage: "whats-an-api-300x300.webp"
author: Zoie Carnegie
tags: ["API","Postman"]
---
diff --git a/content/engineering/what-is-an-api/whats-an-api-300x300.png b/content/engineering/what-is-an-api/whats-an-api-300x300.png
deleted file mode 100644
index acddd17dd..000000000
Binary files a/content/engineering/what-is-an-api/whats-an-api-300x300.png and /dev/null differ
diff --git a/content/engineering/what-is-an-api/whats-an-api-300x300.webp b/content/engineering/what-is-an-api/whats-an-api-300x300.webp
new file mode 100644
index 000000000..2c2526f9a
Binary files /dev/null and b/content/engineering/what-is-an-api/whats-an-api-300x300.webp differ
diff --git a/content/engineering/what-is-cocoapods-and-installation/cocoapods-orange-on-grey.jpg b/content/engineering/what-is-cocoapods-and-installation/cocoapods-orange-on-grey.jpg
deleted file mode 100644
index 0227ca970..000000000
Binary files a/content/engineering/what-is-cocoapods-and-installation/cocoapods-orange-on-grey.jpg and /dev/null differ
diff --git a/content/engineering/what-is-cocoapods-and-installation/cocoapods-orange-on-grey.webp b/content/engineering/what-is-cocoapods-and-installation/cocoapods-orange-on-grey.webp
new file mode 100644
index 000000000..616aef388
Binary files /dev/null and b/content/engineering/what-is-cocoapods-and-installation/cocoapods-orange-on-grey.webp differ
diff --git a/content/engineering/what-is-cocoapods-and-installation/index.md b/content/engineering/what-is-cocoapods-and-installation/index.md
index 25365ce1a..0080e1526 100644
--- a/content/engineering/what-is-cocoapods-and-installation/index.md
+++ b/content/engineering/what-is-cocoapods-and-installation/index.md
@@ -1,7 +1,7 @@
---
title: "Cocoapods : What It Is And How To Install?"
date: "2017-09-06"
-coverImage: "cocoapods-orange-on-grey.jpg"
+coverImage: "cocoapods-orange-on-grey.webp"
author: Thompson Sanjoto
tags: ["Swift","Objective-C","xcode"]
---
diff --git a/content/engineering/what-is-graphql/graph.png b/content/engineering/what-is-graphql/graph.png
deleted file mode 100644
index 0d89fd835..000000000
Binary files a/content/engineering/what-is-graphql/graph.png and /dev/null differ
diff --git a/content/engineering/what-is-graphql/graph.webp b/content/engineering/what-is-graphql/graph.webp
new file mode 100644
index 000000000..201b70c7d
Binary files /dev/null and b/content/engineering/what-is-graphql/graph.webp differ
diff --git a/content/engineering/what-is-graphql/index.md b/content/engineering/what-is-graphql/index.md
index 5dd471eb6..814f43746 100644
--- a/content/engineering/what-is-graphql/index.md
+++ b/content/engineering/what-is-graphql/index.md
@@ -1,7 +1,7 @@
---
title: "What is GraphQL? - A Basic Guide"
date: "2020-10-01"
-coverImage: "graph.png"
+coverImage: "graph.webp"
author: "Anup Aglawe"
description: "GraphQL is a syntax that specifies how data can be requested and is usually used to load data to a client from a server. Find out why to use it and any other advantages."
tags: ["Engineering", "API", "GraphQL", "Performance"]
@@ -29,7 +29,7 @@ In the current scenario, traditional [REST APIs](/best-practice-guide-for-rest-a
API endpoints generally fetch specific data, hence to load a certain data-rich application, there have to be **multiple requests to the server.** But, applications should fetch relevant data in one round trip to avoid **degrading performance.** The flexibility and richness of the GraphQL, allows us to define all the data to fetch in a single request, avoiding multiple Round trips
-
+
_Wrapping REST API in graphQL - Source - Joey Ng'ethe | TwigaTech_
## Fundamentals of GraphQL
diff --git a/content/engineering/what-is-graphql/wrapper.png b/content/engineering/what-is-graphql/wrapper.png
deleted file mode 100644
index 43f27bdf3..000000000
Binary files a/content/engineering/what-is-graphql/wrapper.png and /dev/null differ
diff --git a/content/engineering/what-is-graphql/wrapper.webp b/content/engineering/what-is-graphql/wrapper.webp
new file mode 100644
index 000000000..effdb8196
Binary files /dev/null and b/content/engineering/what-is-graphql/wrapper.webp differ
diff --git a/content/engineering/what-is-the-difference-between-oauth1-and-oauth2/index.md b/content/engineering/what-is-the-difference-between-oauth1-and-oauth2/index.md
index ed8dd5801..815426c77 100644
--- a/content/engineering/what-is-the-difference-between-oauth1-and-oauth2/index.md
+++ b/content/engineering/what-is-the-difference-between-oauth1-and-oauth2/index.md
@@ -1,7 +1,7 @@
---
title: "OAuth 1.0 VS OAuth 2.0"
date: "2019-05-31"
-coverImage: "pexels-photo-373543.jpeg"
+coverImage: "pexels-photo-373543.webp"
author: Ti Zhang
tags: ["Oauth","Engineering"]
description: "Learn about the differences between OAuth 1.0 and OAuth 2.0 and how OAuth 2.0 is superior to OAuth 1.0"
diff --git a/content/engineering/what-is-the-difference-between-oauth1-and-oauth2/pexels-photo-373543.jpeg b/content/engineering/what-is-the-difference-between-oauth1-and-oauth2/pexels-photo-373543.jpeg
deleted file mode 100644
index b866caefc..000000000
Binary files a/content/engineering/what-is-the-difference-between-oauth1-and-oauth2/pexels-photo-373543.jpeg and /dev/null differ
diff --git a/content/engineering/what-is-the-difference-between-oauth1-and-oauth2/pexels-photo-373543.webp b/content/engineering/what-is-the-difference-between-oauth1-and-oauth2/pexels-photo-373543.webp
new file mode 100644
index 000000000..a75e32828
Binary files /dev/null and b/content/engineering/what-is-the-difference-between-oauth1-and-oauth2/pexels-photo-373543.webp differ
diff --git a/content/engineering/what-is-the-new-go-1-15/index.md b/content/engineering/what-is-the-new-go-1-15/index.md
index e05e6f294..0abb74a5c 100644
--- a/content/engineering/what-is-the-new-go-1-15/index.md
+++ b/content/engineering/what-is-the-new-go-1-15/index.md
@@ -1,7 +1,7 @@
---
title: "What's new in the go 1.15"
date: "2020-09-07"
-coverImage: "index.png"
+coverImage: "index.webp"
author: "Vijay Singh Shekhawat"
tags: ["Go", "Golang","Go 1.15"]
---
@@ -38,9 +38,9 @@ Mobile applications were crashing in some devices due to some invalid lld linker
### Smaller binaries & Performance improvements
Always new Go 1.15 brings many minor/major performance improvements. The first major improvement has reduced the executable's binary size by almost 5% - 10% as compared to Go 1.14. As Brad Fitzpatrick [tweet](https://twitter.com/bradfitz/status/1256348714198654976?lang=en), test program down from 8.2MB in Go 1.14 to 3.9MB in 1.15.
-
+
-
+
Go 1.15 has improved the code build process now unused code is eliminating in the new linker, along with several targeted improvements, such as Clements's CL 230544, which reduces the number of stack and register maps included in the executable.
diff --git a/content/engineering/what-is-the-new-go-1-15/index.png b/content/engineering/what-is-the-new-go-1-15/index.png
deleted file mode 100644
index f27ff601a..000000000
Binary files a/content/engineering/what-is-the-new-go-1-15/index.png and /dev/null differ
diff --git a/content/engineering/what-is-the-new-go-1-15/index.webp b/content/engineering/what-is-the-new-go-1-15/index.webp
new file mode 100644
index 000000000..164d86b3f
Binary files /dev/null and b/content/engineering/what-is-the-new-go-1-15/index.webp differ
diff --git a/content/engineering/what-is-the-new-go-1-15/lr-tweet1.png b/content/engineering/what-is-the-new-go-1-15/lr-tweet1.png
deleted file mode 100644
index d61e7303b..000000000
Binary files a/content/engineering/what-is-the-new-go-1-15/lr-tweet1.png and /dev/null differ
diff --git a/content/engineering/what-is-the-new-go-1-15/lr-tweet1.webp b/content/engineering/what-is-the-new-go-1-15/lr-tweet1.webp
new file mode 100644
index 000000000..9ecbe3023
Binary files /dev/null and b/content/engineering/what-is-the-new-go-1-15/lr-tweet1.webp differ
diff --git a/content/engineering/what-is-the-new-go-1-15/lr-tweet2.png b/content/engineering/what-is-the-new-go-1-15/lr-tweet2.png
deleted file mode 100644
index c0e44caac..000000000
Binary files a/content/engineering/what-is-the-new-go-1-15/lr-tweet2.png and /dev/null differ
diff --git a/content/engineering/what-is-the-new-go-1-15/lr-tweet2.webp b/content/engineering/what-is-the-new-go-1-15/lr-tweet2.webp
new file mode 100644
index 000000000..6980ef9c3
Binary files /dev/null and b/content/engineering/what-is-the-new-go-1-15/lr-tweet2.webp differ
diff --git a/content/engineering/why-mfa-important/index.md b/content/engineering/why-mfa-important/index.md
index a8cb75c60..2a3269cf5 100644
--- a/content/engineering/why-mfa-important/index.md
+++ b/content/engineering/why-mfa-important/index.md
@@ -1,7 +1,7 @@
---
title: "The Importance of Multi-Factor Authentication (MFA)"
date: "2021-02-11"
-coverImage: "multifactor-authentication.jpg"
+coverImage: "multifactor-authentication.webp"
author: "Jitender Agarwal"
tags: ["MFA", "2FA", "PIN Auth", "Push-based Auth"]
description: "Multi-factor authentication verifies the consumer's identity in multiple steps using different methods. Hence, it provides another layer of security on top of the login credentials."
diff --git a/content/engineering/why-mfa-important/multifactor-authentication.jpg b/content/engineering/why-mfa-important/multifactor-authentication.jpg
deleted file mode 100644
index 5c888f7f9..000000000
Binary files a/content/engineering/why-mfa-important/multifactor-authentication.jpg and /dev/null differ
diff --git a/content/engineering/why-mfa-important/multifactor-authentication.webp b/content/engineering/why-mfa-important/multifactor-authentication.webp
new file mode 100644
index 000000000..34fcce060
Binary files /dev/null and b/content/engineering/why-mfa-important/multifactor-authentication.webp differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/basic-architecture.png b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/basic-architecture.png
deleted file mode 100644
index 56ef06ff8..000000000
Binary files a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/basic-architecture.png and /dev/null differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/basic-architecture.webp b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/basic-architecture.webp
new file mode 100644
index 000000000..f848245aa
Binary files /dev/null and b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/basic-architecture.webp differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/high-performance-identity-apis.png b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/high-performance-identity-apis.png
deleted file mode 100644
index 2ad1364ba..000000000
Binary files a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/high-performance-identity-apis.png and /dev/null differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/high-performance-identity-apis.webp b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/high-performance-identity-apis.webp
new file mode 100644
index 000000000..f7435d9a1
Binary files /dev/null and b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/high-performance-identity-apis.webp differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/index.md b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/index.md
index ed70bbed0..0dd017d4b 100644
--- a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/index.md
+++ b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/index.md
@@ -1,7 +1,7 @@
---
title: "Why We Re-engineered LoginRadius APIs with Go?"
date: "2022-06-06"
-coverImage: "high-performance-identity-apis.png"
+coverImage: "high-performance-identity-apis.webp"
author: "Vijay Singh Shekhawat"
tags: ["Go", "API", ".NET", LoginRadius]
description: "At Loginradius, we strive to leverage technology and ingenuity to push the boundaries of what our Identity Platform can deliver. In this engineering article, learn how we improved the performance of our APIs with Go."
@@ -44,11 +44,11 @@ We've been utilizing a multi-cloud and multi-region architecture for years based
This is the basic architecture of the environment in the US:
-
+
Each request is processed as follows:
-
+
The above diagram shows two cloud regions — US East and US West.
@@ -161,17 +161,17 @@ Golang application has performed much better.
#### Existing Application Matrix — .NET Core
-  +
+ 
Graph - 1(a): Requests and Responses per Second (.NET Core)
-  +
+ 
Graph -1(b): API Response Time (.NET Core)
-  +
+ 
Graph - 1(c): Overall Matrix (.NET Core)
@@ -184,17 +184,17 @@ The application can recover after a couple of seconds, and after that, the appli
We did the same stress test with the new Go application. It is easily able to handle this kind of concurrency without any issue.
-  +
+ 
Graph - 2(a): Requests and Responses per Second (Go)
-  +
+ 
Graph -2(b): API Response Time (Go)
-  +
+ 
Graph - 2(c): Overall Matrix (Go)
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-dot-net-core.png b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-dot-net-core.png
deleted file mode 100644
index e35f8a00b..000000000
Binary files a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-dot-net-core.png and /dev/null differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-dot-net-core.webp b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-dot-net-core.webp
new file mode 100644
index 000000000..60d1c98f9
Binary files /dev/null and b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-dot-net-core.webp differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-go-lang.png b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-go-lang.png
deleted file mode 100644
index 4fae362ff..000000000
Binary files a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-go-lang.png and /dev/null differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-go-lang.webp b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-go-lang.webp
new file mode 100644
index 000000000..5226d641b
Binary files /dev/null and b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/overall-matrix-go-lang.webp differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/request-processing-flow.png b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/request-processing-flow.png
deleted file mode 100644
index 3ca321ae8..000000000
Binary files a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/request-processing-flow.png and /dev/null differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/request-processing-flow.webp b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/request-processing-flow.webp
new file mode 100644
index 000000000..d9b5f15cf
Binary files /dev/null and b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/request-processing-flow.webp differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-dot-net-core.png b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-dot-net-core.png
deleted file mode 100644
index 2376d9e4c..000000000
Binary files a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-dot-net-core.png and /dev/null differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-dot-net-core.webp b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-dot-net-core.webp
new file mode 100644
index 000000000..a10018ecb
Binary files /dev/null and b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-dot-net-core.webp differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-go-lang.png b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-go-lang.png
deleted file mode 100644
index ca2935eb1..000000000
Binary files a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-go-lang.png and /dev/null differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-go-lang.webp b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-go-lang.webp
new file mode 100644
index 000000000..68cd91c72
Binary files /dev/null and b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/requests-and-responses-per-second-go-lang.webp differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-dot-net-core.png b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-dot-net-core.png
deleted file mode 100644
index 016f515b8..000000000
Binary files a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-dot-net-core.png and /dev/null differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-dot-net-core.webp b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-dot-net-core.webp
new file mode 100644
index 000000000..88ff0f8e7
Binary files /dev/null and b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-dot-net-core.webp differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-go-lang.png b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-go-lang.png
deleted file mode 100644
index e74e26d1b..000000000
Binary files a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-go-lang.png and /dev/null differ
diff --git a/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-go-lang.webp b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-go-lang.webp
new file mode 100644
index 000000000..7f64a7b17
Binary files /dev/null and b/content/engineering/why-we-rebuilt-loginradius-dot-net-core-apis-with-go/response-time-percentiles-go-lang.webp differ
diff --git a/content/engineering/wordpress-custom-login-form-part-1/custom-login.png b/content/engineering/wordpress-custom-login-form-part-1/custom-login.png
deleted file mode 100644
index 1f1645558..000000000
Binary files a/content/engineering/wordpress-custom-login-form-part-1/custom-login.png and /dev/null differ
diff --git a/content/engineering/wordpress-custom-login-form-part-1/custom-login.webp b/content/engineering/wordpress-custom-login-form-part-1/custom-login.webp
new file mode 100644
index 000000000..85064d431
Binary files /dev/null and b/content/engineering/wordpress-custom-login-form-part-1/custom-login.webp differ
diff --git a/content/engineering/wordpress-custom-login-form-part-1/index.md b/content/engineering/wordpress-custom-login-form-part-1/index.md
index f871d8bf2..6d249f735 100644
--- a/content/engineering/wordpress-custom-login-form-part-1/index.md
+++ b/content/engineering/wordpress-custom-login-form-part-1/index.md
@@ -1,7 +1,7 @@
---
title: "Wordpress Custom Login Form Part 1"
date: "2016-03-01"
-coverImage: "wordpress-icon-150x1501-150x150.png"
+coverImage: "wordpress-icon-150x1501-150x150.webp"
author: Zoie Carnegie
tags: ["WordPress","Learning"]
---
@@ -17,7 +17,7 @@ In this tutorial, I will demonstrate how to build a custom login form using the
This is what WordPress gives us out of the box.
-
+
There are quite a few different options available to make a custom login page. You can build a [shortcode](https://codex.wordpress.org/Shortcode_API) so that you could simply put \[wp-login\] or something you like on any page/post, make a page theme file and use that page to attach to a post/page, a widget could be a good solution too, or maybe you'd like to simply edit the existing form and add some pizzazz to it.
I am going to show you all of this tutorial using the page-theme method because it is probably the easiest to implement for beginners. This will also give you an intro into page themes, if your not familiar with it.
@@ -65,7 +65,7 @@ To quickly show you how to get this login on the page Let's paste the following
Look at what that small piece of code do
-
+
Now we need to set some arguments that we can provide to this form to customize it. Let's take a look at the documentation for [wp_login_form()](https://developer.wordpress.org/reference/functions/wp_login_form/)
diff --git a/content/engineering/wordpress-custom-login-form-part-1/wordpress-icon-150x1501-150x150.png b/content/engineering/wordpress-custom-login-form-part-1/wordpress-icon-150x1501-150x150.png
deleted file mode 100644
index 77784f6f2..000000000
Binary files a/content/engineering/wordpress-custom-login-form-part-1/wordpress-icon-150x1501-150x150.png and /dev/null differ
diff --git a/content/engineering/wordpress-custom-login-form-part-1/wordpress-icon-150x1501-150x150.webp b/content/engineering/wordpress-custom-login-form-part-1/wordpress-icon-150x1501-150x150.webp
new file mode 100644
index 000000000..31340b26f
Binary files /dev/null and b/content/engineering/wordpress-custom-login-form-part-1/wordpress-icon-150x1501-150x150.webp differ
diff --git a/content/engineering/wordpress-custom-login-form-part-1/wp-login.png b/content/engineering/wordpress-custom-login-form-part-1/wp-login.png
deleted file mode 100644
index 64d07d997..000000000
Binary files a/content/engineering/wordpress-custom-login-form-part-1/wp-login.png and /dev/null differ
diff --git a/content/engineering/wordpress-custom-login-form-part-1/wp-login.webp b/content/engineering/wordpress-custom-login-form-part-1/wp-login.webp
new file mode 100644
index 000000000..b6fbe1b8c
Binary files /dev/null and b/content/engineering/wordpress-custom-login-form-part-1/wp-login.webp differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-1.png b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-1.png
deleted file mode 100644
index 6fca7f67a..000000000
Binary files a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-1.png and /dev/null differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-1.webp b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-1.webp
new file mode 100644
index 000000000..1c7ce5ab3
Binary files /dev/null and b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-1.webp differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-2.png b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-2.png
deleted file mode 100644
index 3df455efc..000000000
Binary files a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-2.png and /dev/null differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-2.webp b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-2.webp
new file mode 100644
index 000000000..12b889b2a
Binary files /dev/null and b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-2.webp differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-3-1024x447.png b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-3-1024x447.png
deleted file mode 100644
index 7b974e2b4..000000000
Binary files a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-3-1024x447.png and /dev/null differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-3-1024x447.webp b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-3-1024x447.webp
new file mode 100644
index 000000000..058777cf3
Binary files /dev/null and b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-3-1024x447.webp differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-4.png b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-4.png
deleted file mode 100644
index c9a2f3deb..000000000
Binary files a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-4.png and /dev/null differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-4.webp b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-4.webp
new file mode 100644
index 000000000..923e24430
Binary files /dev/null and b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-4.webp differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-5.png b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-5.png
deleted file mode 100644
index baf5a640e..000000000
Binary files a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-5.png and /dev/null differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-5.webp b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-5.webp
new file mode 100644
index 000000000..b0a52cbb5
Binary files /dev/null and b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-5.webp differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-6.png b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-6.png
deleted file mode 100644
index ebffc5928..000000000
Binary files a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-6.png and /dev/null differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-6.webp b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-6.webp
new file mode 100644
index 000000000..284ad4693
Binary files /dev/null and b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-6.webp differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-7.png b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-7.png
deleted file mode 100644
index cde6a13b2..000000000
Binary files a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-7.png and /dev/null differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-7.webp b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-7.webp
new file mode 100644
index 000000000..403bbd1f8
Binary files /dev/null and b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda-sqs-7.webp differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda.png b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda.png
deleted file mode 100644
index 6fca7f67a..000000000
Binary files a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda.png and /dev/null differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda.webp b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda.webp
new file mode 100644
index 000000000..1c7ce5ab3
Binary files /dev/null and b/content/engineering/working-with-aws-lambda-and-sqs/blog-aws-lambda.webp differ
diff --git a/content/engineering/working-with-aws-lambda-and-sqs/index.md b/content/engineering/working-with-aws-lambda-and-sqs/index.md
index 435a47ac6..cf78beb3a 100644
--- a/content/engineering/working-with-aws-lambda-and-sqs/index.md
+++ b/content/engineering/working-with-aws-lambda-and-sqs/index.md
@@ -1,14 +1,14 @@
---
title: "Working with AWS Lambda and SQS"
date: "2020-02-13"
-coverImage: "blog-aws-lambda.png"
+coverImage: "blog-aws-lambda.webp"
author: "Team LoginRadius"
tags: ["Engineering", "General"]
---
This blog is a short guide on implementing AWS Lambda and SQS together. First we’ll introduce these technologies and explain why they work well together, then walkthrough some configurations and invocation using a simple Nodejs script.
-
+
**What are they?**
AWS Lambda is a popular choice in serverless computing. As an event-driven platform, AWS Lambda requires users to configure event sources in order to run a function. Their built-in support for many AWS services like S3 and SQS as event sources allow for relatively simple configuration. Note that Lambda functions can also be triggered via HTTP(S) by using AWS API Gateway service.
@@ -17,7 +17,7 @@ AWS SQS (Simple Queue Service) is a queue service with 2 types: standard and FIF
As previously mentioned, AWS SQS can be an event source for AWS Lambda. This means that when a message is added to the queue, the configured Lambda function will be invoked with an event containing this message.
-
+
**But why use them together?**
Common reasons include better handling Lambda function invocations and errors. For function invocations, the default concurrency limit is 1000. If a function has reached this limit, any additional invocations will fail with a throttling error. However, with SQS as an event source, events resulting in throttling errors are automatically retried based on set configs. This prevents the loss of events due to unexpected jumps in usage. Additionally, dead-letter queues (DLQ) can be configured as a place where failed events go, to avoid retrying indefinitely. Failed events in DLQ can then be sent somewhere like a DB for analysis.
@@ -31,22 +31,22 @@ Let’s set up a basic “Hello World” application with SQS and Lambda.
2\. Now, add a Lambda function:
-
+
3\. Create a new execution role with the following configs:
a. Trusted Entity: Lambda
b. Permissions: AWSLambdaBasicExecutionRole; AWSLambdaSQSQueueExecutionRole
-
+
4\. Use newly created role in Lambda function. Remember to save (top right).
-
+
5\. Add a trigger:
a. Batch size set to 1, so the Lambda Function will process 1 message at a time.
-
+
6\. Programmatically enqueue a message into SQS with the following code in Nodejs:
@@ -71,4 +71,4 @@ c. Fill in your specific AWS account details. Find AWS\_SQS\_URL by selecting th
d. Run script with \`node app.js\`
e. Navigate to Monitoring tab in your Lambda function, the invocations graph should have a new data point (may take a few minutes to update).
-
+
diff --git a/content/engineering/write-a-highly-efficient-python-web-crawler/index.md b/content/engineering/write-a-highly-efficient-python-web-crawler/index.md
index 0a3c05a75..9140cd9f8 100644
--- a/content/engineering/write-a-highly-efficient-python-web-crawler/index.md
+++ b/content/engineering/write-a-highly-efficient-python-web-crawler/index.md
@@ -1,7 +1,7 @@
---
title: "Write a highly efficient python Web Crawler"
date: "2015-07-14"
-coverImage: "python-web-crawler.png"
+coverImage: "python-web-crawler.webp"
author: Mark Duan
tags: ["Python","Coding"]
---
diff --git a/content/engineering/write-a-highly-efficient-python-web-crawler/python-web-crawler.png b/content/engineering/write-a-highly-efficient-python-web-crawler/python-web-crawler.png
deleted file mode 100644
index b232171a8..000000000
Binary files a/content/engineering/write-a-highly-efficient-python-web-crawler/python-web-crawler.png and /dev/null differ
diff --git a/content/engineering/write-a-highly-efficient-python-web-crawler/python-web-crawler.webp b/content/engineering/write-a-highly-efficient-python-web-crawler/python-web-crawler.webp
new file mode 100644
index 000000000..b0941aaf5
Binary files /dev/null and b/content/engineering/write-a-highly-efficient-python-web-crawler/python-web-crawler.webp differ
diff --git a/content/engineering/write-a-javascript-library-using-webpack-and-babel/cover.png b/content/engineering/write-a-javascript-library-using-webpack-and-babel/cover.png
deleted file mode 100644
index 79e26915a..000000000
Binary files a/content/engineering/write-a-javascript-library-using-webpack-and-babel/cover.png and /dev/null differ
diff --git a/content/engineering/write-a-javascript-library-using-webpack-and-babel/cover.webp b/content/engineering/write-a-javascript-library-using-webpack-and-babel/cover.webp
new file mode 100644
index 000000000..8325e5de9
Binary files /dev/null and b/content/engineering/write-a-javascript-library-using-webpack-and-babel/cover.webp differ
diff --git a/content/engineering/write-a-javascript-library-using-webpack-and-babel/index.md b/content/engineering/write-a-javascript-library-using-webpack-and-babel/index.md
index 2ea4ef59d..3c7ea9203 100644
--- a/content/engineering/write-a-javascript-library-using-webpack-and-babel/index.md
+++ b/content/engineering/write-a-javascript-library-using-webpack-and-babel/index.md
@@ -1,7 +1,7 @@
---
title: "Let's Write a JavaScript Library in ES6 using Webpack and Babel"
date: "2020-08-18"
-coverImage: "cover.png"
+coverImage: "cover.webp"
author: "Hridayesh Sharma"
tags: ["JavaScript", "Webpack", "NodeJs"]
description: "Writing your own webpack configuration for a JavaScript library in ES6 and learn webpack along the way."
diff --git a/content/growth/10-Video-Marketing-Stats-That-Brands-Cant-Ignore-in-2021/index.md b/content/growth/10-Video-Marketing-Stats-That-Brands-Cant-Ignore-in-2021/index.md
index b1ea597b5..5722a756e 100644
--- a/content/growth/10-Video-Marketing-Stats-That-Brands-Cant-Ignore-in-2021/index.md
+++ b/content/growth/10-Video-Marketing-Stats-That-Brands-Cant-Ignore-in-2021/index.md
@@ -1,7 +1,7 @@
---
title: "10 Video Marketing Stats That Brands Can't Ignore in 2021"
date: "2021-04-26"
-coverImage: "video-marketing-loginradius.jpg"
+coverImage: "video-marketing-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Navanita Devi"
@@ -204,4 +204,4 @@ Even the most experienced video content creators use a system to make sure every
If you're looking to draft a campaign, start by defining your goals and then create a video production plan that follows those goals.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=10-video-marketing-stats-that-brands-cant-ignore-in-2021)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=10-video-marketing-stats-that-brands-cant-ignore-in-2021)
diff --git a/content/growth/10-Video-Marketing-Stats-That-Brands-Cant-Ignore-in-2021/video-marketing-loginradius.jpg b/content/growth/10-Video-Marketing-Stats-That-Brands-Cant-Ignore-in-2021/video-marketing-loginradius.jpg
deleted file mode 100644
index e209e79c9..000000000
Binary files a/content/growth/10-Video-Marketing-Stats-That-Brands-Cant-Ignore-in-2021/video-marketing-loginradius.jpg and /dev/null differ
diff --git a/content/growth/10-Video-Marketing-Stats-That-Brands-Cant-Ignore-in-2021/video-marketing-loginradius.webp b/content/growth/10-Video-Marketing-Stats-That-Brands-Cant-Ignore-in-2021/video-marketing-loginradius.webp
new file mode 100644
index 000000000..bdc3caf38
Binary files /dev/null and b/content/growth/10-Video-Marketing-Stats-That-Brands-Cant-Ignore-in-2021/video-marketing-loginradius.webp differ
diff --git a/content/growth/10-smart-tips-to-make-you-more-resilient-at-office/10-Smart-Tips-to-Make-You-More-Resilient-At-Office.png b/content/growth/10-smart-tips-to-make-you-more-resilient-at-office/10-Smart-Tips-to-Make-You-More-Resilient-At-Office.png
deleted file mode 100644
index 3a08325d2..000000000
Binary files a/content/growth/10-smart-tips-to-make-you-more-resilient-at-office/10-Smart-Tips-to-Make-You-More-Resilient-At-Office.png and /dev/null differ
diff --git a/content/growth/10-smart-tips-to-make-you-more-resilient-at-office/10-Smart-Tips-to-Make-You-More-Resilient-At-Office.webp b/content/growth/10-smart-tips-to-make-you-more-resilient-at-office/10-Smart-Tips-to-Make-You-More-Resilient-At-Office.webp
new file mode 100644
index 000000000..097821005
Binary files /dev/null and b/content/growth/10-smart-tips-to-make-you-more-resilient-at-office/10-Smart-Tips-to-Make-You-More-Resilient-At-Office.webp differ
diff --git a/content/growth/10-smart-tips-to-make-you-more-resilient-at-office/index.md b/content/growth/10-smart-tips-to-make-you-more-resilient-at-office/index.md
index 0002b9446..67221fce7 100644
--- a/content/growth/10-smart-tips-to-make-you-more-resilient-at-office/index.md
+++ b/content/growth/10-smart-tips-to-make-you-more-resilient-at-office/index.md
@@ -1,7 +1,7 @@
---
title: "10 Smart Tips to Make You More Resilient At Office"
date: "2017-04-07"
-coverImage: "10-Smart-Tips-to-Make-You-More-Resilient-At-Office.png"
+coverImage: "10-Smart-Tips-to-Make-You-More-Resilient-At-Office.webp"
category: ["All"]
featured: false
author: "Rakesh Soni"
diff --git a/content/growth/10-things-know-about-social-login/index.md b/content/growth/10-things-know-about-social-login/index.md
index c5bbd415b..8db2797ab 100644
--- a/content/growth/10-things-know-about-social-login/index.md
+++ b/content/growth/10-things-know-about-social-login/index.md
@@ -1,7 +1,7 @@
---
title: "10 Things You Need to Know About Allowing Users to Login With Their Social Media Profiles"
date: "2022-09-27"
-coverImage: "social.jpg"
+coverImage: "social.webp"
category: ["social media login","sso","cx"]
author: "Ivana Radevska"
description: "Businesses are still relying on old-school login and authentication mechanisms, including organization-level IAM, which is why their business lags behind their competitors. Let’s discuss why businesses need to replace their traditional IAM with new-age CIAM."
@@ -131,7 +131,7 @@ In addition, asking users to fill out a lengthy registration form with more than
On the other hand, when users sign up via a social account, businesses typically access a larger amount of data points. They have an additional layer of verification of the user's information.
-[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
### 3. Eliminates Mistargeted Marketing
@@ -207,4 +207,4 @@ A social account refers to an individual's profile or account on a social media
Yes, social login is typically free for both businesses and users, although there may be costs associated with implementing and maintaining the integration.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=10-things-know-about-social-login)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=10-things-know-about-social-login)
diff --git a/content/growth/10-things-know-about-social-login/social-login-ds.png b/content/growth/10-things-know-about-social-login/social-login-ds.png
deleted file mode 100644
index 98e481315..000000000
Binary files a/content/growth/10-things-know-about-social-login/social-login-ds.png and /dev/null differ
diff --git a/content/growth/10-things-know-about-social-login/social-login-ds.webp b/content/growth/10-things-know-about-social-login/social-login-ds.webp
new file mode 100644
index 000000000..5e3eaf627
Binary files /dev/null and b/content/growth/10-things-know-about-social-login/social-login-ds.webp differ
diff --git a/content/growth/10-things-know-about-social-login/social.jpg b/content/growth/10-things-know-about-social-login/social.jpg
deleted file mode 100644
index 85d6bd620..000000000
Binary files a/content/growth/10-things-know-about-social-login/social.jpg and /dev/null differ
diff --git a/content/growth/10-things-know-about-social-login/social.webp b/content/growth/10-things-know-about-social-login/social.webp
new file mode 100644
index 000000000..1bac0252d
Binary files /dev/null and b/content/growth/10-things-know-about-social-login/social.webp differ
diff --git a/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/Product-Social-Login.png b/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/Product-Social-Login.png
deleted file mode 100644
index 98e481315..000000000
Binary files a/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/Product-Social-Login.png and /dev/null differ
diff --git a/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/Product-Social-Login.webp b/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/Product-Social-Login.webp
new file mode 100644
index 000000000..5e3eaf627
Binary files /dev/null and b/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/Product-Social-Login.webp differ
diff --git a/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/index.md b/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/index.md
index 719bea5fd..d91bd3f62 100644
--- a/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/index.md
+++ b/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/index.md
@@ -1,7 +1,7 @@
---
title: "20 Content Ideas for Most Engaging B2B LinkedIn Posts"
date: "2021-03-19"
-coverImage: "linkedin-post-loginradius.jpg"
+coverImage: "linkedin-post-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Navanita Devi"
@@ -20,7 +20,7 @@ In recent times, LinkedIn has become home to [94% of B2B marketers](https://busi
The reason for the success of B2B LinkedIn Marketing is its massive network of professionals with [approximately 760 million users](https://kinsta.com/blog/linkedin-statistics/). This gives marketers access to entrepreneurs and professionals from varied social networks and backgrounds looking to invest in an interesting product or service.
-
+
## Top 20 B2B LinkedIn Post Ideas
@@ -62,7 +62,7 @@ According to research, the LinkedIn algorithm does not promote posts that contai
Short videos are all the rage at the moment. In fact, most video sharing platforms and **[social login](https://www.loginradius.com/social-login/)** platforms incorporate the short video format. The beauty of a short video is that the viewer will not mind devoting their attention to the content on the screen for just a few seconds. Therefore, one will be able to relay information easily and start building a large customer base.
-[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
### 8. Go live
@@ -120,4 +120,4 @@ Audiences love to share their opinion, especially if they are a passionate fanba
Content on LinkedIn makes all the difference to the promotion of a brand. It can make or break one's presence on LinkedIn. Therefore, it is essential to figure out the tone of LinkedIn posts, depending on the target demographic. Once the tone is chosen, implementing the rest of the marketing strategy is easy to do.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=20-content-ideas-for-most-engaging-b2b-linkedin-posts)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=20-content-ideas-for-most-engaging-b2b-linkedin-posts)
diff --git a/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-post-loginradius.jpg b/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-post-loginradius.jpg
deleted file mode 100644
index 21314875f..000000000
Binary files a/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-post-loginradius.jpg and /dev/null differ
diff --git a/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-post-loginradius.webp b/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-post-loginradius.webp
new file mode 100644
index 000000000..0894e17da
Binary files /dev/null and b/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-post-loginradius.webp differ
diff --git a/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-sales-post-loginradius.jpg b/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-sales-post-loginradius.jpg
deleted file mode 100644
index 9152a3d9e..000000000
Binary files a/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-sales-post-loginradius.jpg and /dev/null differ
diff --git a/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-sales-post-loginradius.webp b/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-sales-post-loginradius.webp
new file mode 100644
index 000000000..c118e2664
Binary files /dev/null and b/content/growth/20-Content-Ideas-for-Most-Engaging-B2B-LinkedIn-Posts/linkedin-sales-post-loginradius.webp differ
diff --git a/content/growth/360-degree-growth-data-driven/360-degree-growth-with-data-driven.jpg b/content/growth/360-degree-growth-data-driven/360-degree-growth-with-data-driven.jpg
deleted file mode 100644
index e53332db7..000000000
Binary files a/content/growth/360-degree-growth-data-driven/360-degree-growth-with-data-driven.jpg and /dev/null differ
diff --git a/content/growth/360-degree-growth-data-driven/360-degree-growth-with-data-driven.webp b/content/growth/360-degree-growth-data-driven/360-degree-growth-with-data-driven.webp
new file mode 100644
index 000000000..f5713c780
Binary files /dev/null and b/content/growth/360-degree-growth-data-driven/360-degree-growth-with-data-driven.webp differ
diff --git a/content/growth/360-degree-growth-data-driven/consumer-audit-trail.jpg b/content/growth/360-degree-growth-data-driven/consumer-audit-trail.jpg
deleted file mode 100644
index 81d15ecd6..000000000
Binary files a/content/growth/360-degree-growth-data-driven/consumer-audit-trail.jpg and /dev/null differ
diff --git a/content/growth/360-degree-growth-data-driven/consumer-audit-trail.webp b/content/growth/360-degree-growth-data-driven/consumer-audit-trail.webp
new file mode 100644
index 000000000..864059a33
Binary files /dev/null and b/content/growth/360-degree-growth-data-driven/consumer-audit-trail.webp differ
diff --git a/content/growth/360-degree-growth-data-driven/index.md b/content/growth/360-degree-growth-data-driven/index.md
index 4911e807f..52cc78ee7 100644
--- a/content/growth/360-degree-growth-data-driven/index.md
+++ b/content/growth/360-degree-growth-data-driven/index.md
@@ -1,7 +1,7 @@
---
title: "How to Achieve a 360-Degree Growth with Data-Driven Approach"
date: "2021-01-25"
-coverImage: "360-degree-growth-with-data-driven.jpg"
+coverImage: "360-degree-growth-with-data-driven.webp"
category: ["all"]
featured: false
author: "Shachindra Saxena"
@@ -62,7 +62,7 @@ Furthermore, to uncover key predictors of growth in existing customers and who a
Finally, to reduce revenue leakage, you could capture data for pricing strategy or discount strategy. You could also be monitoring industry data, deal sizes, and details to analyze and maximize revenue for each deal.
-[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail)
+[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail)
### **Analyze and capture insights.**
@@ -90,4 +90,4 @@ So, there you go —
"Leverage" data, "analyze," "implement," "measure," and then "repeat success."
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=360-degree-growth-data-driven)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=360-degree-growth-data-driven)
diff --git a/content/growth/4-features-enterprise-software/EB-GD-to-MFA.png b/content/growth/4-features-enterprise-software/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/growth/4-features-enterprise-software/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/growth/4-features-enterprise-software/EB-GD-to-MFA.webp b/content/growth/4-features-enterprise-software/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/growth/4-features-enterprise-software/EB-GD-to-MFA.webp differ
diff --git a/content/growth/4-features-enterprise-software/enteprise-software.jpg b/content/growth/4-features-enterprise-software/enteprise-software.jpg
deleted file mode 100644
index c7c56dbe3..000000000
Binary files a/content/growth/4-features-enterprise-software/enteprise-software.jpg and /dev/null differ
diff --git a/content/growth/4-features-enterprise-software/enteprise-software.webp b/content/growth/4-features-enterprise-software/enteprise-software.webp
new file mode 100644
index 000000000..f411462a8
Binary files /dev/null and b/content/growth/4-features-enterprise-software/enteprise-software.webp differ
diff --git a/content/growth/4-features-enterprise-software/index.md b/content/growth/4-features-enterprise-software/index.md
index 2c92f24c1..98119878b 100644
--- a/content/growth/4-features-enterprise-software/index.md
+++ b/content/growth/4-features-enterprise-software/index.md
@@ -1,7 +1,7 @@
---
title: "4 Main Features of Enterprise Software"
date: "2021-10-27"
-coverImage: "enteprise-software.jpg"
+coverImage: "enteprise-software.webp"
tags: ["enterprise security", "mfa","sso","authentication"]
author: "Shivangini Yadav"
description: "Companies want to stay competitive and so their actions must be cost-efficient, adaptable, and time-saving. Enterprise software ensures the fulfillment of those specific needs by drastically improving the workflow between countless departments that make up corporate systems."
@@ -50,7 +50,7 @@ The global information security market is forecasted to grow to [$170.4 billion
A deeper level of security should require a customization system concerning one’s password. Hashing and security questions aside, there should also be a limited time for the password usage or a number of times one user can use it before applying a new one.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
An additional vital way to make people’s data safe is encryption. Digitalization calls for an interrupted exchange of information and the safest way to make it inaccessible to unwanted eyes and ears is to encode it.
@@ -66,4 +66,4 @@ An updated system can majorly increase the capabilities of an HR manager, making
Enterprise software is an irreplaceable tool that is meant to increase a business's efficiency. Huge companies cannot properly operate without it due to the human factor coming into play. This is the way to go when it comes to scalability, robustness, and automation.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=4-features-enterprise-software)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=4-features-enterprise-software)
diff --git a/content/growth/4-features-enterprise-software/mfa-eb.png b/content/growth/4-features-enterprise-software/mfa-eb.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/growth/4-features-enterprise-software/mfa-eb.png and /dev/null differ
diff --git a/content/growth/4-features-enterprise-software/mfa-eb.webp b/content/growth/4-features-enterprise-software/mfa-eb.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/growth/4-features-enterprise-software/mfa-eb.webp differ
diff --git a/content/growth/4-things-consider-starting-digital-transformation/4-things-consider-starting-digital-transformation.jpg b/content/growth/4-things-consider-starting-digital-transformation/4-things-consider-starting-digital-transformation.jpg
deleted file mode 100644
index 4947956cb..000000000
Binary files a/content/growth/4-things-consider-starting-digital-transformation/4-things-consider-starting-digital-transformation.jpg and /dev/null differ
diff --git a/content/growth/4-things-consider-starting-digital-transformation/4-things-consider-starting-digital-transformation.webp b/content/growth/4-things-consider-starting-digital-transformation/4-things-consider-starting-digital-transformation.webp
new file mode 100644
index 000000000..6a4dd2684
Binary files /dev/null and b/content/growth/4-things-consider-starting-digital-transformation/4-things-consider-starting-digital-transformation.webp differ
diff --git a/content/growth/4-things-consider-starting-digital-transformation/austin-chan-275638-unsplash-1024x683.jpg b/content/growth/4-things-consider-starting-digital-transformation/austin-chan-275638-unsplash-1024x683.jpg
deleted file mode 100644
index b84e2de20..000000000
Binary files a/content/growth/4-things-consider-starting-digital-transformation/austin-chan-275638-unsplash-1024x683.jpg and /dev/null differ
diff --git a/content/growth/4-things-consider-starting-digital-transformation/austin-chan-275638-unsplash-1024x683.webp b/content/growth/4-things-consider-starting-digital-transformation/austin-chan-275638-unsplash-1024x683.webp
new file mode 100644
index 000000000..81be73951
Binary files /dev/null and b/content/growth/4-things-consider-starting-digital-transformation/austin-chan-275638-unsplash-1024x683.webp differ
diff --git a/content/growth/4-things-consider-starting-digital-transformation/index.md b/content/growth/4-things-consider-starting-digital-transformation/index.md
index 0f7791582..700767fb7 100644
--- a/content/growth/4-things-consider-starting-digital-transformation/index.md
+++ b/content/growth/4-things-consider-starting-digital-transformation/index.md
@@ -1,7 +1,7 @@
---
title: "4 Things to Consider When Starting a Digital Transformation"
date: "2018-08-09"
-coverImage: "4-things-consider-starting-digital-transformation.jpg"
+coverImage: "4-things-consider-starting-digital-transformation.webp"
category: ["all", "other"]
featured: false
author: "Rakesh Soni"
@@ -16,7 +16,7 @@ A recent study by Gartner found that 66% of leaders have plans for a digital tra
## 1\. Get Connected and Bring Value to Your Organization
-
+
A good place to start your digital transformation is to build initiatives that focus on changing your operating model. But what does being more connected actually mean? Well, for starters, one of the main ways that companies are getting more connected is by making their data more available and transparent across their entire digital ecosystem. This will actually help you make money in new ways. For example, you can gather and use that data to create new revenue-generating services.
@@ -24,7 +24,7 @@ Being more connected will help your organization cross the threshold of your tra
## 2\. Optimize Your Business Initiatives with Automation Tools
-
+
Automation tends to overlap with all the other starting points, but it will truly help you reinvent the way that value is delivered. For example, with automation tools, data can flow in real-time and be automatically updated across your entire digital ecosystem.
@@ -32,7 +32,7 @@ This not only greatly improves productivity, but can also enable you to understa
## 3\. Empower Your Business Partners and Customers
-
+
While the first two steps are focused on improving your operating model, this one will help you change your business model completely. For example, by utilizing the right tools and technology, you will be able to empower your partners and customers to create value for themselves, which will multiply your business's potential.
@@ -42,7 +42,7 @@ Instead of you proving to your partners and customers the benefits of working wi
## 4\. Programmable Platforms to Bring Value to YOU
-
+
This last step is key, as it will help you focus on changing both your business and operating models. Simply by utilizing others to help create and deliver the value to your business. For example, instead of using your own resources to build tools that would help bring value, you can outsource and have experts do it for you, so you can focus on what you do best.
diff --git a/content/growth/4-things-consider-starting-digital-transformation/jordan-mcqueen-99269-unsplash-1024x683.jpg b/content/growth/4-things-consider-starting-digital-transformation/jordan-mcqueen-99269-unsplash-1024x683.jpg
deleted file mode 100644
index 0768aa6f5..000000000
Binary files a/content/growth/4-things-consider-starting-digital-transformation/jordan-mcqueen-99269-unsplash-1024x683.jpg and /dev/null differ
diff --git a/content/growth/4-things-consider-starting-digital-transformation/jordan-mcqueen-99269-unsplash-1024x683.webp b/content/growth/4-things-consider-starting-digital-transformation/jordan-mcqueen-99269-unsplash-1024x683.webp
new file mode 100644
index 000000000..79b69189e
Binary files /dev/null and b/content/growth/4-things-consider-starting-digital-transformation/jordan-mcqueen-99269-unsplash-1024x683.webp differ
diff --git a/content/growth/4-things-consider-starting-digital-transformation/rawpixel-268378-unsplash-1024x683.jpg b/content/growth/4-things-consider-starting-digital-transformation/rawpixel-268378-unsplash-1024x683.jpg
deleted file mode 100644
index cebb837da..000000000
Binary files a/content/growth/4-things-consider-starting-digital-transformation/rawpixel-268378-unsplash-1024x683.jpg and /dev/null differ
diff --git a/content/growth/4-things-consider-starting-digital-transformation/rawpixel-268378-unsplash-1024x683.webp b/content/growth/4-things-consider-starting-digital-transformation/rawpixel-268378-unsplash-1024x683.webp
new file mode 100644
index 000000000..f3c665ae4
Binary files /dev/null and b/content/growth/4-things-consider-starting-digital-transformation/rawpixel-268378-unsplash-1024x683.webp differ
diff --git a/content/growth/4-things-consider-starting-digital-transformation/riccardo-annandale-140624-unsplash-e1533839787184-1024x714.jpg b/content/growth/4-things-consider-starting-digital-transformation/riccardo-annandale-140624-unsplash-e1533839787184-1024x714.jpg
deleted file mode 100644
index 97e2bafc9..000000000
Binary files a/content/growth/4-things-consider-starting-digital-transformation/riccardo-annandale-140624-unsplash-e1533839787184-1024x714.jpg and /dev/null differ
diff --git a/content/growth/4-things-consider-starting-digital-transformation/riccardo-annandale-140624-unsplash-e1533839787184-1024x714.webp b/content/growth/4-things-consider-starting-digital-transformation/riccardo-annandale-140624-unsplash-e1533839787184-1024x714.webp
new file mode 100644
index 000000000..0f6459065
Binary files /dev/null and b/content/growth/4-things-consider-starting-digital-transformation/riccardo-annandale-140624-unsplash-e1533839787184-1024x714.webp differ
diff --git a/content/growth/4-tips-secure-frictionless-ux/WP-Social-Login-rec.png b/content/growth/4-tips-secure-frictionless-ux/WP-Social-Login-rec.png
deleted file mode 100644
index 4ea16b064..000000000
Binary files a/content/growth/4-tips-secure-frictionless-ux/WP-Social-Login-rec.png and /dev/null differ
diff --git a/content/growth/4-tips-secure-frictionless-ux/WP-Social-Login-rec.webp b/content/growth/4-tips-secure-frictionless-ux/WP-Social-Login-rec.webp
new file mode 100644
index 000000000..7e6ca6673
Binary files /dev/null and b/content/growth/4-tips-secure-frictionless-ux/WP-Social-Login-rec.webp differ
diff --git a/content/growth/4-tips-secure-frictionless-ux/index.md b/content/growth/4-tips-secure-frictionless-ux/index.md
index 0c35b4ea8..2b861f533 100644
--- a/content/growth/4-tips-secure-frictionless-ux/index.md
+++ b/content/growth/4-tips-secure-frictionless-ux/index.md
@@ -1,7 +1,7 @@
---
title: "How to Blend Security with Frictionless User Experience"
date: "2021-11-24"
-coverImage: "ux-cover.jpg"
+coverImage: "ux-cover.webp"
tags: ["data security","social login","cybersecurity","cx"]
author: "Shivangini Yadav"
description: "By striking the right balance between UX and security, you can provide a product that consumers trust and enjoy using. If, on the other hand, you compromise one for the other, customer churn is a more likely scenario."
@@ -59,7 +59,7 @@ The only issue that often arises is password reuse. Many users tend to come up w
All you can do is educate your users about the importance of strong, varied passwords. If you do offer social login, know that you are reaching for the most pleasant UX available.
-[](https://www.loginradius.com/resource/social-login-reconsidered/)
+[](https://www.loginradius.com/resource/social-login-reconsidered/)
### #3. Make use of Single Sign-on
@@ -82,4 +82,4 @@ You can also outsource security testing, as it makes uncovering a potential thre
By striking the right balance between UX and security, you can provide a product that consumers trust and enjoy using. If, on the other hand, you compromise one for the other, customer churn is a more likely scenario.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=4-tips-secure-frictionless-ux)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=4-tips-secure-frictionless-ux)
diff --git a/content/growth/4-tips-secure-frictionless-ux/social-login-wp.png b/content/growth/4-tips-secure-frictionless-ux/social-login-wp.png
deleted file mode 100644
index 412e2195c..000000000
Binary files a/content/growth/4-tips-secure-frictionless-ux/social-login-wp.png and /dev/null differ
diff --git a/content/growth/4-tips-secure-frictionless-ux/social-login-wp.webp b/content/growth/4-tips-secure-frictionless-ux/social-login-wp.webp
new file mode 100644
index 000000000..6e975bd35
Binary files /dev/null and b/content/growth/4-tips-secure-frictionless-ux/social-login-wp.webp differ
diff --git a/content/growth/4-tips-secure-frictionless-ux/ux-cover.jpg b/content/growth/4-tips-secure-frictionless-ux/ux-cover.jpg
deleted file mode 100644
index a6b676c99..000000000
Binary files a/content/growth/4-tips-secure-frictionless-ux/ux-cover.jpg and /dev/null differ
diff --git a/content/growth/4-tips-secure-frictionless-ux/ux-cover.webp b/content/growth/4-tips-secure-frictionless-ux/ux-cover.webp
new file mode 100644
index 000000000..10b1f2168
Binary files /dev/null and b/content/growth/4-tips-secure-frictionless-ux/ux-cover.webp differ
diff --git a/content/growth/5-signs-ciam-over-traditional-iam/EB-GD-to-cons-id.png b/content/growth/5-signs-ciam-over-traditional-iam/EB-GD-to-cons-id.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/growth/5-signs-ciam-over-traditional-iam/EB-GD-to-cons-id.png and /dev/null differ
diff --git a/content/growth/5-signs-ciam-over-traditional-iam/EB-GD-to-cons-id.webp b/content/growth/5-signs-ciam-over-traditional-iam/EB-GD-to-cons-id.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/growth/5-signs-ciam-over-traditional-iam/EB-GD-to-cons-id.webp differ
diff --git a/content/growth/5-signs-ciam-over-traditional-iam/index.md b/content/growth/5-signs-ciam-over-traditional-iam/index.md
index d2a757957..b36c22c77 100644
--- a/content/growth/5-signs-ciam-over-traditional-iam/index.md
+++ b/content/growth/5-signs-ciam-over-traditional-iam/index.md
@@ -1,7 +1,7 @@
---
title: "5 Signs Your Traditional IAM System Needs a CIAM Makeover"
date: "2022-05-10"
-coverImage: "traditional-iam.jpg"
+coverImage: "traditional-iam.webp"
tags: ["ciam solution","login authentication","cx"]
author: "Rakesh Soni"
description: "Businesses are still relying on old-school login and authentication mechanisms, including organization-level IAM, which is why their business lags behind their competitors. Let’s discuss why businesses need to replace their traditional IAM with new-age CIAM."
@@ -53,7 +53,7 @@ Well, a cutting-edge cloud-based CIAM solution like LoginRadius can help you inc
With features like Social Login, Single Sign-On (SSO), and Progressive Profiling, you can stay assured your users aren’t facing any hurdles from the moment they interact with your brand.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
### #2. You need more user data for improving sales & marketing strategy, but you’re clueless about where to get it.
@@ -108,4 +108,4 @@ Also, the traditional IAM cannot meet the surging demands of today’s customers
If you’re facing any of the challenges mentioned above, it’s high time to switch to a reliable CIAM solution.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-signs-ciam-over-traditional-iam)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-signs-ciam-over-traditional-iam)
diff --git a/content/growth/5-signs-ciam-over-traditional-iam/modern-ciam-eb.png b/content/growth/5-signs-ciam-over-traditional-iam/modern-ciam-eb.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/growth/5-signs-ciam-over-traditional-iam/modern-ciam-eb.png and /dev/null differ
diff --git a/content/growth/5-signs-ciam-over-traditional-iam/modern-ciam-eb.webp b/content/growth/5-signs-ciam-over-traditional-iam/modern-ciam-eb.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/growth/5-signs-ciam-over-traditional-iam/modern-ciam-eb.webp differ
diff --git a/content/growth/5-signs-ciam-over-traditional-iam/traditional-iam.jpg b/content/growth/5-signs-ciam-over-traditional-iam/traditional-iam.jpg
deleted file mode 100644
index cf9aabedc..000000000
Binary files a/content/growth/5-signs-ciam-over-traditional-iam/traditional-iam.jpg and /dev/null differ
diff --git a/content/growth/5-signs-ciam-over-traditional-iam/traditional-iam.webp b/content/growth/5-signs-ciam-over-traditional-iam/traditional-iam.webp
new file mode 100644
index 000000000..b08a59157
Binary files /dev/null and b/content/growth/5-signs-ciam-over-traditional-iam/traditional-iam.webp differ
diff --git a/content/growth/5-ways-reduce-cloud-cost-optimization/cloud-cost.jpg b/content/growth/5-ways-reduce-cloud-cost-optimization/cloud-cost.jpg
deleted file mode 100644
index bdad8a1a3..000000000
Binary files a/content/growth/5-ways-reduce-cloud-cost-optimization/cloud-cost.jpg and /dev/null differ
diff --git a/content/growth/5-ways-reduce-cloud-cost-optimization/cloud-cost.webp b/content/growth/5-ways-reduce-cloud-cost-optimization/cloud-cost.webp
new file mode 100644
index 000000000..819d12f6d
Binary files /dev/null and b/content/growth/5-ways-reduce-cloud-cost-optimization/cloud-cost.webp differ
diff --git a/content/growth/5-ways-reduce-cloud-cost-optimization/index.md b/content/growth/5-ways-reduce-cloud-cost-optimization/index.md
index b433167ca..16f111a36 100644
--- a/content/growth/5-ways-reduce-cloud-cost-optimization/index.md
+++ b/content/growth/5-ways-reduce-cloud-cost-optimization/index.md
@@ -1,7 +1,7 @@
---
title: "How to Reduce Your Cloud Bills Without Compromising Security"
date: "2022-09-15"
-coverImage: "cloud-cost.jpg"
+coverImage: "cloud-cost.webp"
category: ["cloud computing", "cloud storage", "single tenant", "multi tenant"]
author: "Rakesh Soni"
description: "Although cloud computing has offered endless opportunities to businesses embarking on a digital transformation journey, the cost associated with the number of unused resources could be a worrying aspect. This blog covers the aspects of cloud cost optimization with tips to reduce your cloud bills."
@@ -76,4 +76,4 @@ With the increasing adoption of the cloud worldwide, most organizations are worr
The above tips could help organizations manage cloud storage and deployments and eventually reduce costs.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-ways-reduce-cloud-cost-optimization)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-ways-reduce-cloud-cost-optimization)
diff --git a/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/Credential-stuffing.png b/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/Credential-stuffing.png
deleted file mode 100644
index 904e3a28e..000000000
Binary files a/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/Credential-stuffing.png and /dev/null differ
diff --git a/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/Credential-stuffing.webp b/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/Credential-stuffing.webp
new file mode 100644
index 000000000..c2d6821c3
Binary files /dev/null and b/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/Credential-stuffing.webp differ
diff --git a/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/book-a-demo-Consultation.png b/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/book-a-demo-Consultation.png
deleted file mode 100644
index e7cfcf9a0..000000000
Binary files a/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/book-a-demo-Consultation.png and /dev/null differ
diff --git a/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/book-a-demo-Consultation.webp b/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/book-a-demo-Consultation.webp
new file mode 100644
index 000000000..735ec1c8d
Binary files /dev/null and b/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/book-a-demo-Consultation.webp differ
diff --git a/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/email-business-Loginradius.jpg b/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/email-business-Loginradius.jpg
deleted file mode 100644
index 87190e619..000000000
Binary files a/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/email-business-Loginradius.jpg and /dev/null differ
diff --git a/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/email-business-Loginradius.webp b/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/email-business-Loginradius.webp
new file mode 100644
index 000000000..e3235d222
Binary files /dev/null and b/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/email-business-Loginradius.webp differ
diff --git a/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/index.md b/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/index.md
index 5508dd3ab..e92792bff 100644
--- a/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/index.md
+++ b/content/growth/7-Best-Marketing-Emails-to-Attract-Consumers-Right-Away/index.md
@@ -1,7 +1,7 @@
---
title: "7 Best Marketing Emails to Attract Consumers Right Away"
date: "2021-03-30"
-coverImage: "email-business-Loginradius.jpg"
+coverImage: "email-business-Loginradius.webp"
category: ["loginradius"]
featured: false
author: "Deependra Singh"
@@ -24,7 +24,7 @@ The right type of marketing emails with an interesting subject line and body can
Having said that, email fatigue is also a real problem – with thousands of promotional emails flooding our inboxes. How can you use email marketing to attract customers without sounding "too salesy" or making it a "hard sell?"
- [](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
+ [](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
Here are the seven best types of promotional emails that should be part of your email marketing strategy:
@@ -167,4 +167,4 @@ Even in this day and age of social media marketing, email marketing remains amon
For any marketing business, protecting their customer identities is also important to prevent any data breaches. LoginRadius provides the **[best identity management tools](https://www.loginradius.com/)** that can protect your customers during the login, registration process, and other customer touchpoints on your website.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-best-marketing-emails-to-attract-consumers-right-away)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-best-marketing-emails-to-attract-consumers-right-away)
diff --git a/content/growth/7-mistakes-companies-make-during-digital-transformation/DS-customer-identity.png b/content/growth/7-mistakes-companies-make-during-digital-transformation/DS-customer-identity.png
deleted file mode 100644
index 6bddf0db4..000000000
Binary files a/content/growth/7-mistakes-companies-make-during-digital-transformation/DS-customer-identity.png and /dev/null differ
diff --git a/content/growth/7-mistakes-companies-make-during-digital-transformation/DS-customer-identity.webp b/content/growth/7-mistakes-companies-make-during-digital-transformation/DS-customer-identity.webp
new file mode 100644
index 000000000..2842c3bcc
Binary files /dev/null and b/content/growth/7-mistakes-companies-make-during-digital-transformation/DS-customer-identity.webp differ
diff --git a/content/growth/7-mistakes-companies-make-during-digital-transformation/customer-id-ds.png b/content/growth/7-mistakes-companies-make-during-digital-transformation/customer-id-ds.png
deleted file mode 100644
index eaa925c92..000000000
Binary files a/content/growth/7-mistakes-companies-make-during-digital-transformation/customer-id-ds.png and /dev/null differ
diff --git a/content/growth/7-mistakes-companies-make-during-digital-transformation/customer-id-ds.webp b/content/growth/7-mistakes-companies-make-during-digital-transformation/customer-id-ds.webp
new file mode 100644
index 000000000..449e28840
Binary files /dev/null and b/content/growth/7-mistakes-companies-make-during-digital-transformation/customer-id-ds.webp differ
diff --git a/content/growth/7-mistakes-companies-make-during-digital-transformation/digitize-mistakes.jpg b/content/growth/7-mistakes-companies-make-during-digital-transformation/digitize-mistakes.jpg
deleted file mode 100644
index 9c1f6220b..000000000
Binary files a/content/growth/7-mistakes-companies-make-during-digital-transformation/digitize-mistakes.jpg and /dev/null differ
diff --git a/content/growth/7-mistakes-companies-make-during-digital-transformation/digitize-mistakes.webp b/content/growth/7-mistakes-companies-make-during-digital-transformation/digitize-mistakes.webp
new file mode 100644
index 000000000..6c8f079e3
Binary files /dev/null and b/content/growth/7-mistakes-companies-make-during-digital-transformation/digitize-mistakes.webp differ
diff --git a/content/growth/7-mistakes-companies-make-during-digital-transformation/index.md b/content/growth/7-mistakes-companies-make-during-digital-transformation/index.md
index 8da70e90f..975ac7d4b 100644
--- a/content/growth/7-mistakes-companies-make-during-digital-transformation/index.md
+++ b/content/growth/7-mistakes-companies-make-during-digital-transformation/index.md
@@ -1,7 +1,7 @@
---
title: "7 Mistakes Companies Make During Digitization And Their Fixes"
date: "2022-03-07"
-coverImage: "digitize-mistakes.jpg"
+coverImage: "digitize-mistakes.webp"
tags: ["digital transformation", "identity management","cx"]
author: "Hazel Raoult"
description: "Today, most companies realize that technology presents an opportunity to transform their business models and products. But, not many have any clue about the mistakes they make while adopting."
@@ -82,7 +82,7 @@ This just proves that digital transformation is never a destination, as most com
The goal here is to become a dynamic enterprise that can respond to changes quickly, keeping digital transformation at the core.
-[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
+[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
Take the example of Disney. After facing the challenges of the worldwide closure of theaters during the COVID-19 pandemic, it started leveraging its streaming platform for releasing its content. It transitioned from a distribution model to a direct-to-consumer model. This helped the company to stabilize its revenues through increased subscriptions and ultimately positioned itself for success.
@@ -107,4 +107,4 @@ Define metrics based on your digital transformation goals and measure the progre
A venture as massive as digital transformation is never going to be an easy path. And there are high chances you will encounter numerous failures too. But you have a choice, to either fall prey to the fears that can lead to succumbing to the intense competition in the market or to wholeheartedly embrace these challenges and collectively look for solutions that can get you on a path to success.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-mistakes-companies-make-during-digital-transformation)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-mistakes-companies-make-during-digital-transformation)
diff --git a/content/growth/7-tips-enjoy-cybersecurity-awareness-month/cybermonth.jpg b/content/growth/7-tips-enjoy-cybersecurity-awareness-month/cybermonth.jpg
deleted file mode 100644
index 70ff183d4..000000000
Binary files a/content/growth/7-tips-enjoy-cybersecurity-awareness-month/cybermonth.jpg and /dev/null differ
diff --git a/content/growth/7-tips-enjoy-cybersecurity-awareness-month/cybermonth.webp b/content/growth/7-tips-enjoy-cybersecurity-awareness-month/cybermonth.webp
new file mode 100644
index 000000000..d9dd5a07a
Binary files /dev/null and b/content/growth/7-tips-enjoy-cybersecurity-awareness-month/cybermonth.webp differ
diff --git a/content/growth/7-tips-enjoy-cybersecurity-awareness-month/index.md b/content/growth/7-tips-enjoy-cybersecurity-awareness-month/index.md
index 7c3840353..80efb79c1 100644
--- a/content/growth/7-tips-enjoy-cybersecurity-awareness-month/index.md
+++ b/content/growth/7-tips-enjoy-cybersecurity-awareness-month/index.md
@@ -1,7 +1,7 @@
---
title: "7 Tips For Your Enterprise To Have A Great Cybersecurity Awareness Month 2022"
date: "2022-10-06"
-coverImage: "cybermonth.jpg"
+coverImage: "cybermonth.webp"
category: ["cybersecurity awareness month", "online security"]
author: "Rakesh Soni"
description: "This October, we're celebrating Cybersecurity Awareness Month by sharing a few ideas you can do with your team at work. The first step to keeping your company safe is knowing what to look for, and these activities will help you raise awareness about the vulnerabilities out there."
@@ -84,4 +84,4 @@ A breach readiness plan is a document that outlines what to do if your company e
You don’t have to be a security expert to celebrate Cybersecurity Awareness Month—you just have to care about keeping your company safe! October is a great opportunity to implement strategies, ideas, and planning that will help you introduce better ways to maintain organizational resilience. Have a good month :)
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-tips-enjoy-cybersecurity-awareness-month)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-tips-enjoy-cybersecurity-awareness-month)
diff --git a/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/How-Public-Sector-Companies-Use-the-LoginRadius-Identity-Platform.png b/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/How-Public-Sector-Companies-Use-the-LoginRadius-Identity-Platform.png
deleted file mode 100644
index dce0d6e37..000000000
Binary files a/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/How-Public-Sector-Companies-Use-the-LoginRadius-Identity-Platform.png and /dev/null differ
diff --git a/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/How-Public-Sector-Companies-Use-the-LoginRadius-Identity-Platform.webp b/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/How-Public-Sector-Companies-Use-the-LoginRadius-Identity-Platform.webp
new file mode 100644
index 000000000..ec9c7ffe4
Binary files /dev/null and b/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/How-Public-Sector-Companies-Use-the-LoginRadius-Identity-Platform.webp differ
diff --git a/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/communication-strategies-Loginradius.jpg b/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/communication-strategies-Loginradius.jpg
deleted file mode 100644
index 91b576e08..000000000
Binary files a/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/communication-strategies-Loginradius.jpg and /dev/null differ
diff --git a/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/communication-strategies-Loginradius.webp b/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/communication-strategies-Loginradius.webp
new file mode 100644
index 000000000..8a6791c90
Binary files /dev/null and b/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/communication-strategies-Loginradius.webp differ
diff --git a/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/index.md b/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/index.md
index 611b0e2d7..041a65dc2 100644
--- a/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/index.md
+++ b/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/index.md
@@ -1,7 +1,7 @@
---
title: "8 Effective Communication Strategies for Internal Alignment and Growth in 2021"
date: "2021-03-24"
-coverImage: "communication-strategies-Loginradius.jpg"
+coverImage: "communication-strategies-Loginradius.webp"
category: ["loginradius"]
featured: false
author: "Yash Rathi"
@@ -82,7 +82,7 @@ Lack of an effective internal communications strategy can lead to confusion, dec
Not having a plan can be disastrous, and that's not exclusive to internal comms alone. Draw up goals and objectives and achieve them to lead your employees in the right direction efficiently.
-[](https://www.loginradius.com/resource/how-public-sector-companies-use-the-loginradius-identity-platform/)
+[](https://www.loginradius.com/resource/how-public-sector-companies-use-the-loginradius-identity-platform/)
## 8 Internal Communications Strategies for B2B Tech Companies
@@ -154,5 +154,5 @@ Internal communications 2021 especially requires comms professionals to remind t
All the above internal communication strategies are tried and tested. See which one works best for your organization, and eventually, you'll be able to come up with your strategies that aid in your business's growth.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=8-effective-communication-strategies-for-internal-alignment-and-growth-in-2021)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=8-effective-communication-strategies-for-internal-alignment-and-growth-in-2021)
diff --git a/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/loginradius-free-Consultation.png b/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/loginradius-free-Consultation.png
deleted file mode 100644
index e7cfcf9a0..000000000
Binary files a/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/loginradius-free-Consultation.png and /dev/null differ
diff --git a/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/loginradius-free-Consultation.webp b/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/loginradius-free-Consultation.webp
new file mode 100644
index 000000000..735ec1c8d
Binary files /dev/null and b/content/growth/8-Effective-Communication-Strategies-for-Internal-Alignment-and-Growth-in-2021/loginradius-free-Consultation.webp differ
diff --git a/content/growth/9-facts-about-social-login-and-cro/Product-Social-Login.png b/content/growth/9-facts-about-social-login-and-cro/Product-Social-Login.png
deleted file mode 100644
index 98e481315..000000000
Binary files a/content/growth/9-facts-about-social-login-and-cro/Product-Social-Login.png and /dev/null differ
diff --git a/content/growth/9-facts-about-social-login-and-cro/Product-Social-Login.webp b/content/growth/9-facts-about-social-login-and-cro/Product-Social-Login.webp
new file mode 100644
index 000000000..5e3eaf627
Binary files /dev/null and b/content/growth/9-facts-about-social-login-and-cro/Product-Social-Login.webp differ
diff --git a/content/growth/9-facts-about-social-login-and-cro/conversion-rate-increase.jpg b/content/growth/9-facts-about-social-login-and-cro/conversion-rate-increase.jpg
deleted file mode 100644
index 54750f471..000000000
Binary files a/content/growth/9-facts-about-social-login-and-cro/conversion-rate-increase.jpg and /dev/null differ
diff --git a/content/growth/9-facts-about-social-login-and-cro/conversion-rate-increase.webp b/content/growth/9-facts-about-social-login-and-cro/conversion-rate-increase.webp
new file mode 100644
index 000000000..2e92b11b9
Binary files /dev/null and b/content/growth/9-facts-about-social-login-and-cro/conversion-rate-increase.webp differ
diff --git a/content/growth/9-facts-about-social-login-and-cro/conversion-rate-optimization.jpg b/content/growth/9-facts-about-social-login-and-cro/conversion-rate-optimization.jpg
deleted file mode 100644
index 90d8735ca..000000000
Binary files a/content/growth/9-facts-about-social-login-and-cro/conversion-rate-optimization.jpg and /dev/null differ
diff --git a/content/growth/9-facts-about-social-login-and-cro/conversion-rate-optimization.webp b/content/growth/9-facts-about-social-login-and-cro/conversion-rate-optimization.webp
new file mode 100644
index 000000000..b44a56b08
Binary files /dev/null and b/content/growth/9-facts-about-social-login-and-cro/conversion-rate-optimization.webp differ
diff --git a/content/growth/9-facts-about-social-login-and-cro/index.md b/content/growth/9-facts-about-social-login-and-cro/index.md
index 7a9fa330d..392b89eb4 100644
--- a/content/growth/9-facts-about-social-login-and-cro/index.md
+++ b/content/growth/9-facts-about-social-login-and-cro/index.md
@@ -1,7 +1,7 @@
---
title: "9 Facts About Social Login & CRO That You Should Know About"
date: "2021-08-12"
-coverImage: "conversion-rate-optimization.jpg"
+coverImage: "conversion-rate-optimization.webp"
category: ["loginradius"]
featured: false
author: "Rashmi Mathur"
@@ -15,7 +15,7 @@ Conversion rate is an all-important metric that every website keeps a close eye
CRO marketing focuses majorly on improving the experience that a user may have, which may result in them making purchases. To ensure that this takes place, businesses that also have websites use login services like [social login](https://www.loginradius.com/social-login/). These services allow them to cater to customers better.
-[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
## Essential Facts To Know Before Implementing Login Identity Solutions
@@ -60,7 +60,7 @@ Consumers are heavily influenced by the recommendations they see online. This fa
Allowing users to register using social logins will mean that businesses can get to know their customers better. They can form a cohesive idea of what users belonging to a particular demographic may like. Therefore, a company can use social logins to create feedback loops to better understand its audience and [improve customer retention](https://www.loginradius.com/blog/fuel/how-customer-retention-can-help-businesses-grow/).
- 
+ 
5. Dislike Towards Account Creation
@@ -107,10 +107,10 @@ Implementing social logins and increasing the number of registrations will furth
-According to a research paper, around [77%](http://www.webhostingbuzz.com/blog/wp-content/uploads/2013/03/Who-s-sharing-what.jpg) of users believe that social logins are a safe and highly effective method to register users. The reason being that in addition to implementing important customer data security measures, it can also [encourage user engagement](https://www.loginradius.com/blog/fuel/consumer-management-to-consumer-engagement/).
+According to a research paper, around [77%](http://www.webhostingbuzz.com/blog/wp-content/uploads/2013/03/Who-s-sharing-what.webp) of users believe that social logins are a safe and highly effective method to register users. The reason being that in addition to implementing important customer data security measures, it can also [encourage user engagement](https://www.loginradius.com/blog/fuel/consumer-management-to-consumer-engagement/).
Considering all these benefits that social login authentication offers, a marketing company can orient their social media marketing and user engagement to be more effective. Finally, a marketing team will surely improve their conversion rates and see a drastic improvement in sales.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=9-facts-about-social-login-and-cro)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=9-facts-about-social-login-and-cro)
diff --git a/content/growth/A-Brief-Guide-to-Online-Reputation-Management/book-a-demo-Consultation.png b/content/growth/A-Brief-Guide-to-Online-Reputation-Management/book-a-demo-Consultation.png
deleted file mode 100644
index e7cfcf9a0..000000000
Binary files a/content/growth/A-Brief-Guide-to-Online-Reputation-Management/book-a-demo-Consultation.png and /dev/null differ
diff --git a/content/growth/A-Brief-Guide-to-Online-Reputation-Management/book-a-demo-Consultation.webp b/content/growth/A-Brief-Guide-to-Online-Reputation-Management/book-a-demo-Consultation.webp
new file mode 100644
index 000000000..735ec1c8d
Binary files /dev/null and b/content/growth/A-Brief-Guide-to-Online-Reputation-Management/book-a-demo-Consultation.webp differ
diff --git a/content/growth/A-Brief-Guide-to-Online-Reputation-Management/index.md b/content/growth/A-Brief-Guide-to-Online-Reputation-Management/index.md
index 4172eb186..9872a0d05 100644
--- a/content/growth/A-Brief-Guide-to-Online-Reputation-Management/index.md
+++ b/content/growth/A-Brief-Guide-to-Online-Reputation-Management/index.md
@@ -1,7 +1,7 @@
---
title: "A Brief Guide to Online Reputation Management (ORM)"
date: "2021-04-30"
-coverImage: "online-reputation-management-loginradius.jpg"
+coverImage: "online-reputation-management-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Vishal Sharma"
@@ -108,4 +108,4 @@ It doesn’t matter how much you focus on the overall quality of the product or
The aforementioned aspects provide the basic introduction to ORM and can be considered by businesses to begin enhancing their online brand reputation.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=a-brief-guide-to-online-reputation-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=a-brief-guide-to-online-reputation-management)
diff --git a/content/growth/A-Brief-Guide-to-Online-Reputation-Management/online-reputation-management-loginradius.jpg b/content/growth/A-Brief-Guide-to-Online-Reputation-Management/online-reputation-management-loginradius.jpg
deleted file mode 100644
index 98f39a159..000000000
Binary files a/content/growth/A-Brief-Guide-to-Online-Reputation-Management/online-reputation-management-loginradius.jpg and /dev/null differ
diff --git a/content/growth/A-Brief-Guide-to-Online-Reputation-Management/online-reputation-management-loginradius.webp b/content/growth/A-Brief-Guide-to-Online-Reputation-Management/online-reputation-management-loginradius.webp
new file mode 100644
index 000000000..efa30c78d
Binary files /dev/null and b/content/growth/A-Brief-Guide-to-Online-Reputation-Management/online-reputation-management-loginradius.webp differ
diff --git a/content/growth/B2B-Lead-Generation-for-2021/B2B-marketing-strategies-loginradius.jpg b/content/growth/B2B-Lead-Generation-for-2021/B2B-marketing-strategies-loginradius.jpg
deleted file mode 100644
index 097963e34..000000000
Binary files a/content/growth/B2B-Lead-Generation-for-2021/B2B-marketing-strategies-loginradius.jpg and /dev/null differ
diff --git a/content/growth/B2B-Lead-Generation-for-2021/B2B-marketing-strategies-loginradius.webp b/content/growth/B2B-Lead-Generation-for-2021/B2B-marketing-strategies-loginradius.webp
new file mode 100644
index 000000000..fbca27c87
Binary files /dev/null and b/content/growth/B2B-Lead-Generation-for-2021/B2B-marketing-strategies-loginradius.webp differ
diff --git a/content/growth/B2B-Lead-Generation-for-2021/Guide-to-Modern-Customer-Identity.png b/content/growth/B2B-Lead-Generation-for-2021/Guide-to-Modern-Customer-Identity.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/growth/B2B-Lead-Generation-for-2021/Guide-to-Modern-Customer-Identity.png and /dev/null differ
diff --git a/content/growth/B2B-Lead-Generation-for-2021/Guide-to-Modern-Customer-Identity.webp b/content/growth/B2B-Lead-Generation-for-2021/Guide-to-Modern-Customer-Identity.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/growth/B2B-Lead-Generation-for-2021/Guide-to-Modern-Customer-Identity.webp differ
diff --git a/content/growth/B2B-Lead-Generation-for-2021/b2b-lead-generation-loginradius.jpg b/content/growth/B2B-Lead-Generation-for-2021/b2b-lead-generation-loginradius.jpg
deleted file mode 100644
index 57a106f8c..000000000
Binary files a/content/growth/B2B-Lead-Generation-for-2021/b2b-lead-generation-loginradius.jpg and /dev/null differ
diff --git a/content/growth/B2B-Lead-Generation-for-2021/b2b-lead-generation-loginradius.webp b/content/growth/B2B-Lead-Generation-for-2021/b2b-lead-generation-loginradius.webp
new file mode 100644
index 000000000..501b489dc
Binary files /dev/null and b/content/growth/B2B-Lead-Generation-for-2021/b2b-lead-generation-loginradius.webp differ
diff --git a/content/growth/B2B-Lead-Generation-for-2021/index.md b/content/growth/B2B-Lead-Generation-for-2021/index.md
index 7fdf2188d..ac59230f5 100644
--- a/content/growth/B2B-Lead-Generation-for-2021/index.md
+++ b/content/growth/B2B-Lead-Generation-for-2021/index.md
@@ -1,7 +1,7 @@
---
title: "B2B Lead Generation for 2021: 11 Proven Strategies"
date: "2021-03-31"
-coverImage: "B2B-marketing-strategies-loginradius.jpg"
+coverImage: "B2B-marketing-strategies-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Navanita Devi"
@@ -96,7 +96,7 @@ Depending upon the level a lead is at, B2B companies can launch nurturing campai
After multiple meetings and discussions with all the stakeholders and a successful sales pitch, a prospect chooses you over others, and the deal is done. After a lead is successfully converted into a sale, they would be transferred to consumer services for onboarding and other processes.
-[](https://www.loginradius.com/b2b-identity/)
+[](https://www.loginradius.com/b2b-identity/)
## Effective Channels for B2B Lead Generation (Online and Offline)
@@ -118,7 +118,7 @@ In order to come up with relevant B2B strategies for your organization, it’s e
7. Print media: Don’t knock it before at least trying it! There is still a segment of potential leads that get their information from newspapers and magazines and other print media forms. Based on your target audience, investing in print for leads might work, depending on your product or service.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
## 12 B2B Lead Generation Strategies for 2021
@@ -200,6 +200,6 @@ Avoid marketing lingo and keep your message simple and straight, and get right t
Our tried and tested list of B2B lead generation tips has helped many generate some quality leads. Make sure you have quality content as well to transform leads into sales successfully.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2b-lead-generation-for-2021)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2b-lead-generation-for-2021)
diff --git a/content/growth/B2B-Lead-Generation-for-2021/loginradius-book-a-demo.png b/content/growth/B2B-Lead-Generation-for-2021/loginradius-book-a-demo.png
deleted file mode 100644
index 7602d120d..000000000
Binary files a/content/growth/B2B-Lead-Generation-for-2021/loginradius-book-a-demo.png and /dev/null differ
diff --git a/content/growth/B2B-Lead-Generation-for-2021/loginradius-book-a-demo.webp b/content/growth/B2B-Lead-Generation-for-2021/loginradius-book-a-demo.webp
new file mode 100644
index 000000000..9a00697f9
Binary files /dev/null and b/content/growth/B2B-Lead-Generation-for-2021/loginradius-book-a-demo.webp differ
diff --git a/content/growth/Benefits-of-Google-Tag-Manager/Benefits-of-Google-Tag-Manager.png b/content/growth/Benefits-of-Google-Tag-Manager/Benefits-of-Google-Tag-Manager.png
deleted file mode 100644
index ad0b15b9c..000000000
Binary files a/content/growth/Benefits-of-Google-Tag-Manager/Benefits-of-Google-Tag-Manager.png and /dev/null differ
diff --git a/content/growth/Benefits-of-Google-Tag-Manager/Benefits-of-Google-Tag-Manager.webp b/content/growth/Benefits-of-Google-Tag-Manager/Benefits-of-Google-Tag-Manager.webp
new file mode 100644
index 000000000..4615e1212
Binary files /dev/null and b/content/growth/Benefits-of-Google-Tag-Manager/Benefits-of-Google-Tag-Manager.webp differ
diff --git a/content/growth/Benefits-of-Google-Tag-Manager/Google-Tag-Manager.jpg b/content/growth/Benefits-of-Google-Tag-Manager/Google-Tag-Manager.jpg
deleted file mode 100644
index 15b0c3fb4..000000000
Binary files a/content/growth/Benefits-of-Google-Tag-Manager/Google-Tag-Manager.jpg and /dev/null differ
diff --git a/content/growth/Benefits-of-Google-Tag-Manager/Google-Tag-Manager.webp b/content/growth/Benefits-of-Google-Tag-Manager/Google-Tag-Manager.webp
new file mode 100644
index 000000000..88416fd25
Binary files /dev/null and b/content/growth/Benefits-of-Google-Tag-Manager/Google-Tag-Manager.webp differ
diff --git a/content/growth/Benefits-of-Google-Tag-Manager/index.md b/content/growth/Benefits-of-Google-Tag-Manager/index.md
index 915dee897..0695c2a3b 100644
--- a/content/growth/Benefits-of-Google-Tag-Manager/index.md
+++ b/content/growth/Benefits-of-Google-Tag-Manager/index.md
@@ -1,7 +1,7 @@
---
title: "Benefits of Google Tag Manager — Easy To Use And Easy To Launch"
date: "2021-05-11"
-coverImage: "Google-Tag-Manager.jpg"
+coverImage: "Google-Tag-Manager.webp"
category: ["loginradius"]
featured: false
author: "Rashmi Mathur"
@@ -37,7 +37,7 @@ A tag manager essentially acts as a platform where marketers can manage several
The best part is, only minimum technical knowledge is required to use the Tag Manager. The working of the Google Tag Manager relies heavily on a data layer that relays information from the website to the Tag Manager.
-
+
This information from the GTM data layer can then be used to deploy or fire desired tags. For example, the Google data layer will integrate the information in the tag to Google Analytics.
@@ -88,4 +88,4 @@ There can be some problems with the various components that are involved in the
## Conclusion
You can utilize Google Tag Assistant to attain better functionality of GTM. This is a free Chrome extension that can be downloaded [here](https://get.google.com/tagassistant/). Now, get a user-friendly website that suits the needs and wants of your consumers with all the required analytics.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=benefits-of-google-tag-manager)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=benefits-of-google-tag-manager)
diff --git a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/Getting-PCI-Right.png b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/Getting-PCI-Right.png
deleted file mode 100644
index 3a89c425d..000000000
Binary files a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/Getting-PCI-Right.png and /dev/null differ
diff --git a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/Getting-PCI-Right.webp b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/Getting-PCI-Right.webp
new file mode 100644
index 000000000..35012da92
Binary files /dev/null and b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/Getting-PCI-Right.webp differ
diff --git a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/WP-PCI.png b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/WP-PCI.png
deleted file mode 100644
index b2b959fea..000000000
Binary files a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/WP-PCI.png and /dev/null differ
diff --git a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/WP-PCI.webp b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/WP-PCI.webp
new file mode 100644
index 000000000..955c2ab34
Binary files /dev/null and b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/WP-PCI.webp differ
diff --git a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-ecommerce.jpg b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-ecommerce.jpg
deleted file mode 100644
index d3b7332d0..000000000
Binary files a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-ecommerce.jpg and /dev/null differ
diff --git a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-ecommerce.webp b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-ecommerce.webp
new file mode 100644
index 000000000..5ba8ea752
Binary files /dev/null and b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-ecommerce.webp differ
diff --git a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-tips-for-ecommerce.jpg b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-tips-for-ecommerce.jpg
deleted file mode 100644
index 6446c7d64..000000000
Binary files a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-tips-for-ecommerce.jpg and /dev/null differ
diff --git a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-tips-for-ecommerce.webp b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-tips-for-ecommerce.webp
new file mode 100644
index 000000000..20346434f
Binary files /dev/null and b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/cybersecurity-tips-for-ecommerce.webp differ
diff --git a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/index.md b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/index.md
index 0ca216fe7..0792719b7 100644
--- a/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/index.md
+++ b/content/growth/Cybersecurity-Tips-for-Ecommerce-Websites/index.md
@@ -1,7 +1,7 @@
---
title: "Cybersecurity Tips for Ecommerce Websites"
date: "2021-05-19"
-coverImage: "cybersecurity-tips-for-ecommerce.jpg"
+coverImage: "cybersecurity-tips-for-ecommerce.webp"
tags: ["data security","cybersecurity","compliance","cx"]
author: "David Smith"
description: "Whether you run a big business or a small niche online store, you should always be on your guard against possible security threats. Here are some of the most important tips to remember about keeping your site secure."
@@ -38,7 +38,7 @@ Therefore, making the right decision is extremely important. Here are some initi
Your SSL certificate will help to make the data transfer more secure, provide [credit card security](http://www.cardzgroup.com/ContactSmartCard.html), and secure login information for your customers. Moreover, SSL certificates are also deployed on social media websites to make web browsing more secure.
-
+
### Comply with PCI DSS Standards
@@ -52,7 +52,7 @@ Remember that [PCI compliance](https://www.comptia.org/blog/5-simple-ways-to-bec
Moreover, the standards need to be installed, the firewall configurations need to be maintained and anti-virus software needs to be updated. Also, remember to change the passwords and other details at the time of the purchase.
-[](https://www.loginradius.com/resource/pci-dss-framework-whitepaper)
+[](https://www.loginradius.com/resource/pci-dss-framework-whitepaper)
### Run Frequent Security Audits
@@ -74,4 +74,4 @@ Moreover, installing the right anti-virus programs is also a great way to track
The more frequently you update software the better chances you have of maintaining the online security of your website.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersecurity-tips-for-ecommerce-websites)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersecurity-tips-for-ecommerce-websites)
diff --git a/content/growth/Digitization-of-Agile-Marketing-Principles/Agile-Marketing.jpg b/content/growth/Digitization-of-Agile-Marketing-Principles/Agile-Marketing.jpg
deleted file mode 100644
index 8bb5c1aa2..000000000
Binary files a/content/growth/Digitization-of-Agile-Marketing-Principles/Agile-Marketing.jpg and /dev/null differ
diff --git a/content/growth/Digitization-of-Agile-Marketing-Principles/Agile-Marketing.webp b/content/growth/Digitization-of-Agile-Marketing-Principles/Agile-Marketing.webp
new file mode 100644
index 000000000..628a9cb81
Binary files /dev/null and b/content/growth/Digitization-of-Agile-Marketing-Principles/Agile-Marketing.webp differ
diff --git a/content/growth/Digitization-of-Agile-Marketing-Principles/index.md b/content/growth/Digitization-of-Agile-Marketing-Principles/index.md
index 7d4922ade..eeee6ec2b 100644
--- a/content/growth/Digitization-of-Agile-Marketing-Principles/index.md
+++ b/content/growth/Digitization-of-Agile-Marketing-Principles/index.md
@@ -1,7 +1,7 @@
---
title: "The Digitization of Agile Marketing Principles - How Has It Changed Over the Years"
date: "2021-05-17"
-coverImage: "Agile-Marketing.jpg"
+coverImage: "Agile-Marketing.webp"
category: ["loginradius"]
featured: false
author: "Navanita Devi"
@@ -179,6 +179,6 @@ The department was then divided into small teams with as many generalists as pos
## Wrapping Up
Incorporating agile into digital marketing can be extremely beneficial to an online campaign. An enterprise can tackle several campaigns at once on different platforms. Thus, they are capable of relating to a large audience on a global scale.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digitization-of-agile-marketing-principles)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digitization-of-agile-marketing-principles)
diff --git a/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/index.md b/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/index.md
index d3c047fe9..cc81748de 100644
--- a/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/index.md
+++ b/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/index.md
@@ -1,7 +1,7 @@
---
title: "Does Your Site’s Imagery Reflect Your Brand Identity"
date: "2021-04-09"
-coverImage: "website-branding-loginradius.jpg"
+coverImage: "website-branding-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Vishal Sharma"
@@ -105,4 +105,4 @@ The perfect intermingling of text and graphics with the right choice of colors i
The aforementioned aspects help businesses in enhancing brand imagery that further improves brand identity in the long run.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=does-your-website-imagery-reflect-your-brand-identity)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=does-your-website-imagery-reflect-your-brand-identity)
diff --git a/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.jpg b/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.jpg
deleted file mode 100644
index 162126172..000000000
Binary files a/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.jpg and /dev/null differ
diff --git a/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.webp b/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.webp
new file mode 100644
index 000000000..45b1388e1
Binary files /dev/null and b/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.webp differ
diff --git a/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.png b/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.png
deleted file mode 100644
index e7cfcf9a0..000000000
Binary files a/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.png and /dev/null differ
diff --git a/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.webp b/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.webp
new file mode 100644
index 000000000..735ec1c8d
Binary files /dev/null and b/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.webp differ
diff --git a/content/growth/Duplicate-Content-and-SEO/content-writing-skills.jpg b/content/growth/Duplicate-Content-and-SEO/content-writing-skills.jpg
deleted file mode 100644
index 427dd1ba7..000000000
Binary files a/content/growth/Duplicate-Content-and-SEO/content-writing-skills.jpg and /dev/null differ
diff --git a/content/growth/Duplicate-Content-and-SEO/content-writing-skills.webp b/content/growth/Duplicate-Content-and-SEO/content-writing-skills.webp
new file mode 100644
index 000000000..95468c223
Binary files /dev/null and b/content/growth/Duplicate-Content-and-SEO/content-writing-skills.webp differ
diff --git a/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.jpg b/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.jpg
deleted file mode 100644
index c7de5d0f9..000000000
Binary files a/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.jpg and /dev/null differ
diff --git a/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.webp b/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.webp
new file mode 100644
index 000000000..b97c19f28
Binary files /dev/null and b/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.webp differ
diff --git a/content/growth/Duplicate-Content-and-SEO/duplicate-content.jpg b/content/growth/Duplicate-Content-and-SEO/duplicate-content.jpg
deleted file mode 100644
index 1f3dd49fb..000000000
Binary files a/content/growth/Duplicate-Content-and-SEO/duplicate-content.jpg and /dev/null differ
diff --git a/content/growth/Duplicate-Content-and-SEO/duplicate-content.webp b/content/growth/Duplicate-Content-and-SEO/duplicate-content.webp
new file mode 100644
index 000000000..65435b478
Binary files /dev/null and b/content/growth/Duplicate-Content-and-SEO/duplicate-content.webp differ
diff --git a/content/growth/Duplicate-Content-and-SEO/index.md b/content/growth/Duplicate-Content-and-SEO/index.md
index 5c078fb7b..372113137 100644
--- a/content/growth/Duplicate-Content-and-SEO/index.md
+++ b/content/growth/Duplicate-Content-and-SEO/index.md
@@ -1,7 +1,7 @@
---
title: "Duplicate Content and SEO: What’s the Big Deal"
date: "2021-05-06"
-coverImage: "duplicate-content-and-seo.jpg"
+coverImage: "duplicate-content-and-seo.webp"
category: ["loginradius"]
featured: false
author: "Deependra Singh"
@@ -25,7 +25,7 @@ Let’s have a quick look at some of the aspects associated with duplicate conte
Every business seeks substantial growth by leveraging best-in-class **[content marketing](https://www.loginradius.com/blog/fuel/2021/03/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/)** and website optimization tactics that also build a brand reputation.
But if the content on a website is duplicated, the owner may face traffic issues and dwindling website rankings.
-
+
Since search engines precisely crawl content on every website and won’t show multiple versions of content that is already published on different websites, there’s a huge chance that the duplicate one wouldn’t be listed in the search results.
@@ -51,7 +51,7 @@ Businesses need to quickly analyze their website and figure out the actual cause
Here are few effective ways to ensure your website contains any duplicate content pages, especially due to some technical glitches.
-
+
### 1. Check your website’s indexed pages.
@@ -87,4 +87,4 @@ Besides the fact that duplicate content leads to traffic and ranking issues, som
It’s advised to consider auditing your website frequently to shun any chance of availability of duplicate content or pages.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=duplicate-content-and-seo)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=duplicate-content-and-seo)
\ No newline at end of file
diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.jpg b/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.jpg
deleted file mode 100644
index 50f8cf210..000000000
Binary files a/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.jpg and /dev/null differ
diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.webp b/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.webp
new file mode 100644
index 000000000..12bdb78d9
Binary files /dev/null and b/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.webp differ
diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/index.md b/content/growth/Future-Of-Social-Media-Video-Marketing/index.md
index 689f9260a..b882590cc 100644
--- a/content/growth/Future-Of-Social-Media-Video-Marketing/index.md
+++ b/content/growth/Future-Of-Social-Media-Video-Marketing/index.md
@@ -1,7 +1,7 @@
---
title: "Social Media Video Marketing: What Is In Store For Future Marketers"
date: "2021-06-02"
-coverImage: "social-videos.jpg"
+coverImage: "social-videos.webp"
category: ["loginradius"]
featured: false
author: "Deependra Singh"
@@ -28,7 +28,7 @@ Fortunately, companies already know the reasons why using social media videos is
Videos are one of the most profitable digital marketing tools. 91% of marketers believe video is crucial for business growth even during the coronavirus pandemic. Yet, if you are still not convinced, here are the reasons why marketers will love to use social media video marketing in 2021 and even in the years to come.
-
+
## Reasons Why the Future of Social Media Video Marketing is Bright
@@ -74,7 +74,7 @@ Even though Facebook, YouTube, and Instagram are the giants in social media vide
Twitter has also started using video with its newest feature, Fleets. With this feature, users can post videos to their timelines and promote their business creatively. Below is an example.
- 
+ 
Image Source: [Twitter](https://twitter.com/charts_k/status/1384136283547594757)
@@ -94,4 +94,4 @@ So, it is not surprising when YouTube reports mobile video consumption rising ev
Today, many brands are posting consumer testimonial videos on their website and hosting Q&A sessions to boost their social content marketing with a dash of digital decoration. Therefore, it will be wiser to start creating videos that matter to you and your audiences and be a part of the golden future of social media video marketing.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-of-social-media-video-marketing)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-of-social-media-video-marketing)
\ No newline at end of file
diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.jpg b/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.jpg
deleted file mode 100644
index 2680c70df..000000000
Binary files a/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.jpg and /dev/null differ
diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.webp b/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.webp
new file mode 100644
index 000000000..cc8f49bac
Binary files /dev/null and b/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.webp differ
diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.png b/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.png
deleted file mode 100644
index 6d2bdaaf7..000000000
Binary files a/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.png and /dev/null differ
diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.webp b/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.webp
new file mode 100644
index 000000000..8b6c9c38c
Binary files /dev/null and b/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.webp differ
diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.jpg b/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.jpg
deleted file mode 100644
index e8e977db2..000000000
Binary files a/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.jpg and /dev/null differ
diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.webp b/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.webp
new file mode 100644
index 000000000..bda056203
Binary files /dev/null and b/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.webp differ
diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.jpg b/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.jpg
deleted file mode 100644
index bf047630c..000000000
Binary files a/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.jpg and /dev/null differ
diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.webp b/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.webp
new file mode 100644
index 000000000..27eb11772
Binary files /dev/null and b/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.webp differ
diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.png b/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.png
deleted file mode 100644
index e7cfcf9a0..000000000
Binary files a/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.png and /dev/null differ
diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.webp b/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.webp
new file mode 100644
index 000000000..735ec1c8d
Binary files /dev/null and b/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.webp differ
diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.jpg b/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.jpg
deleted file mode 100644
index fd49cbafa..000000000
Binary files a/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.jpg and /dev/null differ
diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.webp b/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.webp
new file mode 100644
index 000000000..e878904c5
Binary files /dev/null and b/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.webp differ
diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/index.md b/content/growth/Hotjar-vs-Microsoft-Clarity/index.md
index ab46bbe58..1f0faebd3 100644
--- a/content/growth/Hotjar-vs-Microsoft-Clarity/index.md
+++ b/content/growth/Hotjar-vs-Microsoft-Clarity/index.md
@@ -1,7 +1,7 @@
---
title: "Website Heat Mapping with Hotjar vs. Microsoft Clarity"
date: "2021-05-07"
-coverImage: "hotjar-vs-ms-clarity.jpg"
+coverImage: "hotjar-vs-ms-clarity.webp"
category: ["loginradius"]
featured: false
author: "Deependra Singh"
@@ -89,7 +89,7 @@ Several case studies reveal how heatmap tracking can help you improve your websi
After understanding what heatmaps are and why they are essential, it’s time to compare Hotjar with Microsoft Clarity.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hotjar-vs-microsoft-clarity)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hotjar-vs-microsoft-clarity)
## Hotjar vs. Microsoft Clarity
@@ -230,4 +230,4 @@ But it’s adding plenty of features at a fast pace. Putting all drawbacks aside
## Our Verdict
Ideally, you must go with Hotjar if you are looking to access highly advanced [website tracking and Analytics features](https://www.loginradius.com/integrations/google-analytics/). But if you receive less traffic on your website and are looking for excellent free heat map software, then Clarity is your best bet.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hotjar-vs-microsoft-clarity)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hotjar-vs-microsoft-clarity)
\ No newline at end of file
diff --git a/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.jpg b/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.jpg
deleted file mode 100644
index 81d15ecd6..000000000
Binary files a/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.jpg and /dev/null differ
diff --git a/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.webp b/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.webp
new file mode 100644
index 000000000..864059a33
Binary files /dev/null and b/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.webp differ
diff --git a/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.jpg b/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.jpg
deleted file mode 100644
index 47a56022b..000000000
Binary files a/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.jpg and /dev/null differ
diff --git a/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.webp b/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.webp
new file mode 100644
index 000000000..cc2a2ab33
Binary files /dev/null and b/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.webp differ
diff --git a/content/growth/How-customer-retention-can-help-businesses-grow/index.md b/content/growth/How-customer-retention-can-help-businesses-grow/index.md
index dbfb9e31b..5a701895c 100644
--- a/content/growth/How-customer-retention-can-help-businesses-grow/index.md
+++ b/content/growth/How-customer-retention-can-help-businesses-grow/index.md
@@ -1,7 +1,7 @@
---
title: "How Customer Retention Can Help Businesses Grow"
date: "2021-03-15"
-coverImage: "customer-retention-LoginRadius-colorized.jpg"
+coverImage: "customer-retention-LoginRadius-colorized.webp"
category: ["loginradius"]
featured: false
author: "Yash Rathi"
@@ -51,7 +51,7 @@ Customer retention strategies aim to maintain the existing customer base, which
It is important to note that none of these strategies should be considered enough in isolation. They serve different purposes and goals to collectively increase the customer retention rate if implemented consistently and accurately.
-[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail)
+[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail)
Some of the customer retention strategies are listed below:
@@ -99,4 +99,4 @@ The training and development programs specifically designed to improve customer
Customer acquisition and maintenance should not be seen as two mutually exclusive parts of the broader process of business growth. This is because the former can grow the business, while the latter is necessary for its expansion. Retaining the existing customers makes the business more recognizable as it focuses on creating brand loyalty and emotional bonding by prioritizing how the customers feel. Maintaining these customers becomes easy with customer loyalty programs, feedback, understanding customer churn patterns, and customer-oriented marketing.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-customer-retention-can-help-businesses-grow)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-customer-retention-can-help-businesses-grow)
\ No newline at end of file
diff --git a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.jpg b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.jpg
deleted file mode 100644
index 7cde5f9fa..000000000
Binary files a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.jpg and /dev/null differ
diff --git a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.webp b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.webp
new file mode 100644
index 000000000..ce7c8f3ac
Binary files /dev/null and b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.webp differ
diff --git a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/index.md b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/index.md
index 156d0efff..5310ac62e 100644
--- a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/index.md
+++ b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/index.md
@@ -1,7 +1,7 @@
---
title: "How to Boost Your B2B Marketing Strategy with Hyper-Personalization"
date: "2021-03-31"
-coverImage: "Effective-Communication-Strategies.jpg"
+coverImage: "Effective-Communication-Strategies.webp"
category: ["loginradius"]
featured: false
author: "Vishal Sharma"
@@ -109,4 +109,4 @@ The ones that will leverage hyper-personalization by understanding its impact on
The aforementioned aspects depict the role of artificial intelligence coupled with content strategies that helps in winning consumer trust and getting chosen over competitors.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-boost-your-b2b-marketing-strategy-with-hyper-personalization)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-boost-your-b2b-marketing-strategy-with-hyper-personalization)
\ No newline at end of file
diff --git a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.png b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.png
deleted file mode 100644
index 7602d120d..000000000
Binary files a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.png and /dev/null differ
diff --git a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.webp b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.webp
new file mode 100644
index 000000000..9a00697f9
Binary files /dev/null and b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.webp differ
diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.png b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.png and /dev/null differ
diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.webp b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.webp differ
diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.jpg b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.jpg
deleted file mode 100644
index 9b807448a..000000000
Binary files a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.jpg and /dev/null differ
diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.webp b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.webp
new file mode 100644
index 000000000..fa200ed3a
Binary files /dev/null and b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.webp differ
diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.jpg b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.jpg
deleted file mode 100644
index 0ffe32b3f..000000000
Binary files a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.jpg and /dev/null differ
diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.webp b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.webp
new file mode 100644
index 000000000..e2e0f303d
Binary files /dev/null and b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.webp differ
diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/index.md b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/index.md
index 87d11aaab..dd15a260e 100644
--- a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/index.md
+++ b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/index.md
@@ -1,7 +1,7 @@
---
title: "How to Drive in the Highest Quality Leads in 2021 with Content and SEO"
date: "2021-03-23"
-coverImage: "content-marketing-loginradius.jpg"
+coverImage: "content-marketing-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Deependra Singh"
@@ -42,7 +42,7 @@ As more businesses and consumers shift online for ease, the only way to stay con
SEO helps your content to rank higher on Search Engine Result Pages (SERPs). Thus, driving in more traffic and, in turn, leading to more conversions. The major use of SEO is to generate more leads and conversions by diverting more traffic towards your webpage. [57% B2B marketers](https://blog.hubspot.com/marketing/the-future-of-content-marketing) swear by SEO for generating more leads and prefer the same more than other marketing forms.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
## Important Questions to Ask When Using SEO for Lead Generation
@@ -129,7 +129,7 @@ Content marketing through social media platforms or blog posts provides the user
The basics of content marketing strategies are the same for all. To ensure that your content stands out amongst the thousands of web pages, implementing a winning content strategy is necessary. [69% of B2B marketers](https://www.smartinsights.com/content-management/content-marketing-strategy/essential-content-marketing-statistics/) have a sound content marketing strategy, and you need one, too.
- 
+ 
Here are some strategies you can employ for your business:
@@ -193,4 +193,4 @@ The only constant when working with content marketing strategies is change. As l
SEO lead generation is all about constant change. Understanding the market trends and keeping up with them is necessary. With the proper keywords and SEO strategy, business owners can successfully generate leads and conversions to sell their products and services. SEO leads have a [14.6% close rate](https://cdn2.hubspot.net/hub/212967/file-28030930-pdf/the_2012_state_of_inbound_marketing.pdf), more than any type. Therefore, effective SEO usage is necessary for businesses to stand apart from other competitors in the market.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-drive-in-the-highest-quality-leads-in-2021-with-content-and-seo)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-drive-in-the-highest-quality-leads-in-2021-with-content-and-seo)
diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.png b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.png
deleted file mode 100644
index 2fc6ddac9..000000000
Binary files a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.png and /dev/null differ
diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.webp b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.webp
new file mode 100644
index 000000000..5522d721c
Binary files /dev/null and b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.webp differ
diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png
deleted file mode 100644
index 9dc5bea48..000000000
Binary files a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png and /dev/null differ
diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp
new file mode 100644
index 000000000..7e0c48356
Binary files /dev/null and b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp differ
diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.png b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.png
deleted file mode 100644
index 7602d120d..000000000
Binary files a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.png and /dev/null differ
diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.webp b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.webp
new file mode 100644
index 000000000..9a00697f9
Binary files /dev/null and b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.webp differ
diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.jpg b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.jpg
deleted file mode 100644
index 9282aabce..000000000
Binary files a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.jpg and /dev/null differ
diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.webp b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.webp
new file mode 100644
index 000000000..161bfb0c7
Binary files /dev/null and b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.webp differ
diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.jpg b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.jpg
deleted file mode 100644
index 06c7975dc..000000000
Binary files a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.jpg and /dev/null differ
diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.webp b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.webp
new file mode 100644
index 000000000..5df733218
Binary files /dev/null and b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.webp differ
diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/index.md b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/index.md
index e0010d156..47abcc2fc 100644
--- a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/index.md
+++ b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/index.md
@@ -1,7 +1,7 @@
---
title: "Thinking Beyond the Pandemic: How to Make Marketing Plans After Coronavirus"
date: "2021-03-25"
-coverImage: "business-after-covid-loginradius.jpg"
+coverImage: "business-after-covid-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Rakesh Soni"
@@ -41,7 +41,7 @@ Creative content strategy has now emerged as one of the most reliable B2B market
Let's now explore some of the strategies employed by companies to survive in a post-pandemic world.
-
+
## 9 Successful B2B Marketing Strategies Post COVID
@@ -101,7 +101,7 @@ From search engine optimization to email marketing, digital ad campaigns, and cr
Companies are better served by taking advantage of the digital spectrum and remain omnipresent across various digital marketing platforms.
-[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
+[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
### 6. Employ data-driven storytelling.
@@ -138,4 +138,4 @@ High-value B2B rarely deals closely with a conversation, and companies need thei
While there is no way to tell which B2B marketing trends post COVID continue to remain in favor, consumer-centric offerings will always find relevance in a post-pandemic world. Incorporate any of the above suggestions in your B2B marketing strategies to reap the combined benefits of maximum consumer loyalty, satisfaction, and sustained profitability.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-make-businesses-marketing-plans-after-coronavirus)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-make-businesses-marketing-plans-after-coronavirus)
\ No newline at end of file
diff --git a/content/growth/How-to-add-Twitter-Blue-Checkmark/index.md b/content/growth/How-to-add-Twitter-Blue-Checkmark/index.md
index 47ff8c62e..021ba116a 100644
--- a/content/growth/How-to-add-Twitter-Blue-Checkmark/index.md
+++ b/content/growth/How-to-add-Twitter-Blue-Checkmark/index.md
@@ -1,7 +1,7 @@
---
title: "Why Should You Have A Blue Checkmark In Front of Your Twitter Account"
date: "2021-06-04"
-coverImage: "twitter-verified-account.jpg"
+coverImage: "twitter-verified-account.webp"
category: ["loginradius"]
featured: false
author: "Rashmi Mathur"
@@ -88,7 +88,7 @@ When you go through this process, Twitter will ask if the account name is the on
Ideally, this is what the verification dialog box will look like:
-
+
Once you submit this form, you just need to wait for the verification mark. And you are done.
@@ -98,4 +98,4 @@ Twitter verification badge, commonly known as the blue checkmark, is super impor
So, what are you waiting for? Get your Twitter account verified today!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-add-twitter-blue-checkmark)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-add-twitter-blue-checkmark)
diff --git a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.png b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.png
deleted file mode 100644
index 19f9aab8a..000000000
Binary files a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.png and /dev/null differ
diff --git a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.webp b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.webp
new file mode 100644
index 000000000..4d327df28
Binary files /dev/null and b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.webp differ
diff --git a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.jpg b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.jpg
deleted file mode 100644
index a4bde541e..000000000
Binary files a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.jpg and /dev/null differ
diff --git a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.webp b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.webp
new file mode 100644
index 000000000..0d4e5f19e
Binary files /dev/null and b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.webp differ
diff --git a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.jpg b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.jpg
deleted file mode 100644
index 4856545e2..000000000
Binary files a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.jpg and /dev/null differ
diff --git a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.webp b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.webp
new file mode 100644
index 000000000..4b9b2208f
Binary files /dev/null and b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.webp differ
diff --git a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.png b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.png
deleted file mode 100644
index 98e481315..000000000
Binary files a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.png and /dev/null differ
diff --git a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.webp b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.webp
new file mode 100644
index 000000000..5e3eaf627
Binary files /dev/null and b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.webp differ
diff --git a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/index.md b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/index.md
index 8feead1eb..5d7a64d9c 100644
--- a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/index.md
+++ b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/index.md
@@ -1,7 +1,7 @@
---
title: "Instagram vs Facebook – Which One is Better for Your Business in 2021?"
date: "2021-04-28"
-coverImage: "Facebook-Instagram.jpg"
+coverImage: "Facebook-Instagram.webp"
tags: ["social media","social login","cx"]
author: "Vishal Sharma"
description: "Even the most experienced video content creators use a system to make sure everything goes smoothly so they don't miss deadlines or lose track of what they need to do next. A transparent plan with checklists and milestones will help you adopt a more professional tone in your videos."
@@ -21,7 +21,7 @@ Both of these platforms are powerful and influential with endless opportunities
So, let’s take a quick look at both of these platforms and learn the differences and advantages so that you can understand where to focus attention.
-[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
## Instagram vs. Facebook: Audience Demographics
@@ -77,4 +77,4 @@ When it comes to choosing between Facebook and Instagram, both platforms have th
We can’t say Facebook > Instagram or vice-versa. It’s just the fact that as a marketer, one needs to understand its audience and their behavior. This will help in building a winning social media marketing strategy.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=instagram-vs-facebook-which-one-is-better-for-your-business-in-2021)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=instagram-vs-facebook-which-one-is-better-for-your-business-in-2021)
diff --git a/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.jpg b/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.jpg
deleted file mode 100644
index e6da87f70..000000000
Binary files a/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.jpg and /dev/null differ
diff --git a/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.webp b/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.webp
new file mode 100644
index 000000000..9a5705035
Binary files /dev/null and b/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.webp differ
diff --git a/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/index.md b/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/index.md
index 528409389..2f6707abc 100644
--- a/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/index.md
+++ b/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/index.md
@@ -1,7 +1,7 @@
---
title: "Myth or True - Is AI Really Transforming the Digital Marketing Industry?"
date: "2021-05-18"
-coverImage: "AI-Myth-True.jpg"
+coverImage: "AI-Myth-True.webp"
category: ["loginradius"]
featured: false
author: "Ashley Lipman"
@@ -62,4 +62,4 @@ While all artificially intelligent tools and software aren’t always cheap, the
In conclusion, yes, AI is transforming the digital marketing industry. We hope the information in this [marketing growth blog](https://www.loginradius.com/blog/fuel/) has been able to show you how.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=is-ai-really-transforming-the-digital-marketing-industry)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=is-ai-really-transforming-the-digital-marketing-industry)
diff --git a/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.jpg b/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.jpg
deleted file mode 100644
index 0e2981a86..000000000
Binary files a/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.jpg and /dev/null differ
diff --git a/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.webp b/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.webp
new file mode 100644
index 000000000..b8b9bbd2b
Binary files /dev/null and b/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.webp differ
diff --git a/content/growth/Leverage-Website-for-More-Conversions/index.md b/content/growth/Leverage-Website-for-More-Conversions/index.md
index a84fa986f..2a328d08a 100644
--- a/content/growth/Leverage-Website-for-More-Conversions/index.md
+++ b/content/growth/Leverage-Website-for-More-Conversions/index.md
@@ -1,7 +1,7 @@
---
title: "5 Quick Steps to Leverage your Website for More Conversions"
date: "2021-04-21"
-coverImage: "Leads-conversion-Loginradius.jpg"
+coverImage: "Leads-conversion-Loginradius.webp"
category: ["loginradius"]
featured: false
author: "Vishal Sharma"
@@ -25,7 +25,7 @@ Though driving conversions isn’t a piece of cake, it largely depends on the wa
Here we’ve clubbed some crucial aspects that will help your business enhance conversion rate through correct utilization of your website in this ever-increasing competitive world.
-
+
1. Mobile Optimization
@@ -80,4 +80,4 @@ A business website holds a bunch of opportunities that can be fostered by utiliz
Marketers need to put their best foot forward in understanding their targeted audience and what exactly they’re looking for in a business website.
The aforementioned aspects can be quite fruitful for every business regardless of the industry to [enhance conversion rates](https://www.loginradius.com/blog/fuel/2021/03/how-to-drive-in-the-highest-quality-leads-in-2021-with-content-and-seo/) and improve overall traffic.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=leverage-website-for-more-conversions)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=leverage-website-for-more-conversions)
\ No newline at end of file
diff --git a/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.jpg b/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.jpg
deleted file mode 100644
index 5b4a179d2..000000000
Binary files a/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.jpg and /dev/null differ
diff --git a/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.webp b/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.webp
new file mode 100644
index 000000000..d98e81357
Binary files /dev/null and b/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.webp differ
diff --git a/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.jpg b/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.jpg
deleted file mode 100644
index 2f59dd1a9..000000000
Binary files a/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.jpg and /dev/null differ
diff --git a/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.webp b/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.webp
new file mode 100644
index 000000000..5cbcc24fb
Binary files /dev/null and b/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.webp differ
diff --git a/content/growth/PR-Trends-to-Consider-in-2021/index.md b/content/growth/PR-Trends-to-Consider-in-2021/index.md
index 7c9279b88..94ac6db12 100644
--- a/content/growth/PR-Trends-to-Consider-in-2021/index.md
+++ b/content/growth/PR-Trends-to-Consider-in-2021/index.md
@@ -1,7 +1,7 @@
---
title: "Three Unique PR Trends to Consider in 2021"
date: "2021-04-22"
-coverImage: "pr-trends-2021.jpg"
+coverImage: "pr-trends-2021.webp"
category: ["loginradius"]
featured: false
author: "Yash Rathi"
@@ -27,7 +27,7 @@ Can companies continue to pursue the "traditional" form of PR and risk falling b
Along with the masks and social distancing, here are 3 unique PR trends to consider in 2021 – they are here to stay over the next decade. Let us discuss each one of them in detail.
-
+
## PR Trends to Follow in 2021
@@ -122,4 +122,4 @@ As businesses adopt digital technologies, brand honesty is among the top concern
## Conclusion
The evolving post-pandemic business world brings both challenges and opportunities to PR and communication teams. With more businesses going remote and to online platforms, it will be interesting to see how corporate PR responds to this change and devise their organizational strategy for the next decade.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pr-trends-to-consider-in-2021)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pr-trends-to-consider-in-2021)
diff --git a/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.jpg b/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.jpg
deleted file mode 100644
index ffbfc7311..000000000
Binary files a/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.jpg and /dev/null differ
diff --git a/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.webp b/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.webp
new file mode 100644
index 000000000..2e9dff170
Binary files /dev/null and b/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.webp differ
diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.png b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.png
deleted file mode 100644
index e7cfcf9a0..000000000
Binary files a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.png and /dev/null differ
diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.webp b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.webp
new file mode 100644
index 000000000..735ec1c8d
Binary files /dev/null and b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.webp differ
diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/index.md b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/index.md
index 56228ffad..93b3d845c 100644
--- a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/index.md
+++ b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/index.md
@@ -1,7 +1,7 @@
---
title: "Top 10 Tips to Enhance Your Creativity While Working From Home"
date: "2021-04-14"
-coverImage: "work-from-home-loginradius.jpg"
+coverImage: "work-from-home-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Deependra Singh"
@@ -28,7 +28,7 @@ So, what does the picture look like now?
According to statistics, [25-30% of the workforce will be working from home by the end of 2021.](https://globalworkplaceanalytics.com/work-at-home-after-covid-19-our-forecast)
- 
+ 
Living at home has its pros and cons. You can enjoy quality time with your family, save on travel expenses, and focus more on your kids.
@@ -69,7 +69,7 @@ Deadlines play a significant role in developing a sense of accountability, wheth
Strict timelines generate a sense of urgency in the employee and motivate them to find creative solutions to finish the task in a specified duration. Creativity allows them to judge their capabilities well, increase productivity and submit deliverables on time.
- 
+ 
### 3. Consider multiple perspectives while having meetings
@@ -99,7 +99,7 @@ For example, before you start discussing business issues, lighten your team's mo
Share the recipe of your favorite cuisine or talk about the song your kid sang last night. You can gradually shift the focus towards more essential issues once you see people actively participating in the conversation.
-
+
### 5. Read, read, and read!
@@ -168,4 +168,4 @@ But data alone doesn't lead anywhere. You need to have storytelling skills that
## Conclusion
As the second wave of the coronavirus pandemic has spread across the world, work from home is here to stay, at least for a while. So, this is the best time to identify your strengths, polish your skills, and learn something new. Follow the ten tips given in this article to enhance your creativity while working from home and make the best use of your skills, time, and money during the pandemic.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-10-tips-to-enhance-your-creativity-while-working-from-home)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-10-tips-to-enhance-your-creativity-while-working-from-home)
\ No newline at end of file
diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.jpg b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.jpg
deleted file mode 100644
index 3ece32e0f..000000000
Binary files a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.jpg and /dev/null differ
diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.webp b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.webp
new file mode 100644
index 000000000..067507538
Binary files /dev/null and b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.webp differ
diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.jpg b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.jpg
deleted file mode 100644
index 8c7a6d92d..000000000
Binary files a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.jpg and /dev/null differ
diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.webp b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.webp
new file mode 100644
index 000000000..ce2d97312
Binary files /dev/null and b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.webp differ
diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.jpg b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.jpg
deleted file mode 100644
index a855bf456..000000000
Binary files a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.jpg and /dev/null differ
diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.webp b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.webp
new file mode 100644
index 000000000..995084c21
Binary files /dev/null and b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.webp differ
diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.jpg b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.jpg
deleted file mode 100644
index afd0398c7..000000000
Binary files a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.jpg and /dev/null differ
diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.webp b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.webp
new file mode 100644
index 000000000..77f6895ac
Binary files /dev/null and b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.webp differ
diff --git a/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.jpg b/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.jpg
deleted file mode 100644
index 1140d86f2..000000000
Binary files a/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.jpg and /dev/null differ
diff --git a/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.webp b/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.webp
new file mode 100644
index 000000000..128a5f7b2
Binary files /dev/null and b/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.webp differ
diff --git a/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/index.md b/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/index.md
index 9e3ae0dc0..28a306bae 100644
--- a/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/index.md
+++ b/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/index.md
@@ -1,7 +1,7 @@
---
title: "5 Features of Google My Business You Should Be Using"
date: "2021-05-18"
-coverImage: "Google-Local-Business.jpg"
+coverImage: "Google-Local-Business.webp"
category: ["loginradius"]
featured: false
author: "Deependra Singh"
@@ -61,4 +61,4 @@ When a subjective FAQ list is slowly generated, consumers can find answers to al
There are over tens of Google Business features that you can use to build a targeted marketing campaign. And like the above five, they are created to ensure you get the highest SERP ranking. You can read our article on [Benefits of Google Tag Manager](https://www.loginradius.com/blog/fuel/2021/05/Benefits-of-Google-Tag-Manager/) to learn more marketing techniques. With Google My Business, you have an additional platform to get in touch with your consumers and generate more leads.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-features-of-google-my-business-for-marketers)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-features-of-google-my-business-for-marketers)
diff --git a/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/index.md b/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/index.md
index bcc08af7b..248dac6d6 100644
--- a/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/index.md
+++ b/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/index.md
@@ -1,7 +1,7 @@
---
title: "Top 5 Marketing Strategies to Power-up Your Business"
date: "2021-04-15"
-coverImage: "top-5-marketing-strategy.jpg"
+coverImage: "top-5-marketing-strategy.webp"
category: ["loginradius"]
featured: false
author: "Deependra Singh"
@@ -99,4 +99,4 @@ These three practices can help gain your client’s trust and help build a long-
Marketing strategies are dynamic, and you should never grow comfortable in a single marketing strategy. While this can help create a **[brand identity](https://www.loginradius.com/blog/fuel/2021/04/does-your-website-imagery-reflect-your-brand-identity/)**, consumers can quickly grow bored if they see the same content. This means, while you promise them data security best practices, you should also ensure to change and adapt your marketing strategies as the market grows. Digital Marketing evolves faster than any business can expect. The best way to ensure you’re on par with your competition is to keep track of all the trends, the data, the various data security best practices, and your campaign’s performance.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-marketing-strategies-to-power-up-your-business)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-marketing-strategies-to-power-up-your-business)
diff --git a/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.jpg b/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.jpg
deleted file mode 100644
index cf04664c0..000000000
Binary files a/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.jpg and /dev/null differ
diff --git a/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.webp b/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.webp
new file mode 100644
index 000000000..530082cda
Binary files /dev/null and b/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.webp differ
diff --git a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.png b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.png
deleted file mode 100644
index e7cfcf9a0..000000000
Binary files a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.png and /dev/null differ
diff --git a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.webp b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.webp
new file mode 100644
index 000000000..735ec1c8d
Binary files /dev/null and b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.webp differ
diff --git a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/index.md b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/index.md
index 4de274c1d..24488d84b 100644
--- a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/index.md
+++ b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/index.md
@@ -1,7 +1,7 @@
---
title: "Top 5 tools to Audit Wordpress Website"
date: "2021-05-06"
-coverImage: "top-5-wp-seo-tools.jpg"
+coverImage: "top-5-wp-seo-tools.webp"
category: ["loginradius"]
featured: false
author: "Tanvi Soni"
@@ -157,4 +157,4 @@ SEO tools help rank your website on the first page of Google and other search en
It would be best if you begin by using free SEO tools available on the internet. If you notice any visible improvements on your website, you can purchase the paid version to get maximum benefits.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-seo-tools-for-auditing-wordpress-website)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-seo-tools-for-auditing-wordpress-website)
diff --git a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.jpg b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.jpg
deleted file mode 100644
index 4c92a3ba1..000000000
Binary files a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.jpg and /dev/null differ
diff --git a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.webp b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.webp
new file mode 100644
index 000000000..8f4d559bc
Binary files /dev/null and b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.webp differ
diff --git a/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.jpg b/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.jpg
deleted file mode 100644
index d1d76248a..000000000
Binary files a/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.jpg and /dev/null differ
diff --git a/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.webp b/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.webp
new file mode 100644
index 000000000..5e7c17f38
Binary files /dev/null and b/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.webp differ
diff --git a/content/growth/Top-UI-UX-Design-Tools-2021/index.md b/content/growth/Top-UI-UX-Design-Tools-2021/index.md
index a3ccdcec3..ab49ceb81 100644
--- a/content/growth/Top-UI-UX-Design-Tools-2021/index.md
+++ b/content/growth/Top-UI-UX-Design-Tools-2021/index.md
@@ -1,7 +1,7 @@
---
title: "Top UI/UX Design Tools 2021"
date: "2021-04-19"
-coverImage: "best-ui-ux-design-loginradius.jpg"
+coverImage: "best-ui-ux-design-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Rakesh Soni"
@@ -161,4 +161,4 @@ User behavior and expectations constantly evolve, so designers need to adapt and
You can also work with a web design agency that provides comprehensive web design services to create an excellent user interface and user experience design. This also helps ensure your website retains or improves its current search rankings after the Google page experience update.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-ui-ux-design-tools-2021)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-ui-ux-design-tools-2021)
diff --git a/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.jpg b/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.jpg
deleted file mode 100644
index caf0d77a8..000000000
Binary files a/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.jpg and /dev/null differ
diff --git a/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.webp b/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.webp
new file mode 100644
index 000000000..720a3e0d1
Binary files /dev/null and b/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.webp differ
diff --git a/content/growth/Twitter-for-B2B-Marketing-in-2021/index.md b/content/growth/Twitter-for-B2B-Marketing-in-2021/index.md
index 82316c245..394efc4f7 100644
--- a/content/growth/Twitter-for-B2B-Marketing-in-2021/index.md
+++ b/content/growth/Twitter-for-B2B-Marketing-in-2021/index.md
@@ -1,7 +1,7 @@
---
title: "How to Use Twitter for B2B Marketing in 2021"
date: "2021-05-13"
-coverImage: "Twitter-for-B2B-Marketing-in-2021.jpg"
+coverImage: "Twitter-for-B2B-Marketing-in-2021.webp"
category: ["loginradius"]
featured: false
author: "Navanita Devi"
@@ -14,7 +14,7 @@ Twitter launched way back in 2006 and hasn't undergone any radical changes like
-Research by the Content Marketing Institute tells that [82% of B2B content marketers](https://contentmarketinginstitute.com/wp-content/uploads/2020/09/b2b-2021-research-final.pdf) use Twitter for running marketing campaigns.
+Research by the Content Marketing Institute tells that *82% of B2B content marketers* use Twitter for running marketing campaigns.
@@ -86,7 +86,7 @@ Community building is emerging as an essential B2B online marketing strategy. Ma
-A study found out that [32% of B2B marketers](https://contentmarketinginstitute.com/wp-content/uploads/2020/09/b2b-2021-research-final.pdf) work in organizations with established online communities, and 27% are looking forward to doing the same in the next 12 months.
+A study found out that *32% of B2B marketers* work in organizations with established online communities, and 27% are looking forward to doing the same in the next 12 months.
@@ -111,4 +111,4 @@ Each of the three marketing strategies explained in this article will help you g
Firstly, you should check whether the Twitter B2B marketing strategies are aligned with your social media marketing strategy. Secondly, assess whether you have the resources and expertise to deal with businesses. And then, you are good to go!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=twitter-for-b2b-marketing-in-2021)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=twitter-for-b2b-marketing-in-2021)
diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.jpg b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.jpg
deleted file mode 100644
index 097963e34..000000000
Binary files a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.jpg and /dev/null differ
diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.webp b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.webp
new file mode 100644
index 000000000..fbca27c87
Binary files /dev/null and b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.webp differ
diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.png b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.png
deleted file mode 100644
index e7cfcf9a0..000000000
Binary files a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.png and /dev/null differ
diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.webp b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.webp
new file mode 100644
index 000000000..735ec1c8d
Binary files /dev/null and b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.webp differ
diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.jpg b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.jpg
deleted file mode 100644
index 81d15ecd6..000000000
Binary files a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.jpg and /dev/null differ
diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.webp b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.webp
new file mode 100644
index 000000000..864059a33
Binary files /dev/null and b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.webp differ
diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.jpg b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.jpg
deleted file mode 100644
index 06aefad1f..000000000
Binary files a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.jpg and /dev/null differ
diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.webp b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.webp
new file mode 100644
index 000000000..055a2c748
Binary files /dev/null and b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.webp differ
diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.jpg b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.jpg
deleted file mode 100644
index e6faba40c..000000000
Binary files a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.jpg and /dev/null differ
diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.webp b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.webp
new file mode 100644
index 000000000..bcef1714b
Binary files /dev/null and b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.webp differ
diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/index.md b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/index.md
index 61e0c3c4f..6a0c4bf18 100644
--- a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/index.md
+++ b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/index.md
@@ -1,7 +1,7 @@
---
title: "Growth Hacking: What it is and How SaaS Businesses Can Use it to Optimize Growth"
date: "2021-03-30"
-coverImage: "growth-hacking-2-colorized.jpg"
+coverImage: "growth-hacking-2-colorized.webp"
category: ["loginradius"]
featured: false
author: "Shachindra Saxena"
@@ -116,7 +116,7 @@ Revenue is what remains after the cost that you invested in the acquisition of t
-[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail)
+[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail)
## Beginner's Guide to Start With Growth Hacking
@@ -156,7 +156,7 @@ As you kickstart your business, set specific goals that you aim to achieve. For
Growth hacking is based on analyzing data and implementing tasks based on the results. The data will dictate the prospect of the company. For example, if a SaaS company has a [retention rate of more than 35%](https://mixpanel.com/topics/whats-a-good-retention-rate/) then it is considered faring well.
-
+
@@ -252,7 +252,7 @@ Another one of the case studies of growth hacking is Dropbox. It offered 16 GB
Growth hacking is not a string of strategies that can be taught. It won't be wrong to call it a mindset one gains when their only focus is the business's growth. With affordable techniques suitable even for start-ups and analysis of the data, one can achieve millions of users in the least period.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=understanding-growth-hacking-and-how-saas-businesses-can-use-it-to-optimize-growth)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=understanding-growth-hacking-and-how-saas-businesses-can-use-it-to-optimize-growth)
diff --git a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.jpg b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.jpg
deleted file mode 100644
index 7f0b95783..000000000
Binary files a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.jpg and /dev/null differ
diff --git a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.webp b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.webp
new file mode 100644
index 000000000..a55aa085b
Binary files /dev/null and b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.webp differ
diff --git a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/index.md b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/index.md
index c55ace2cb..593a5918d 100644
--- a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/index.md
+++ b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/index.md
@@ -1,7 +1,7 @@
---
title: "COVID-19 Vaccine Success in USA and Remote Working – What’s The Connection"
date: "2021-05-26"
-coverImage: "COVID-vaccines-for-remote-culture.jpg"
+coverImage: "COVID-vaccines-for-remote-culture.webp"
category: ["loginradius"]
featured: false
author: "Navanita Devi"
@@ -32,7 +32,7 @@ The study took a thorough look into the effectiveness of the mRNA vaccines among
The findings clearly show that the USA has eventually got the better of the issue (or at least gotten very close to eliminating it) and is looking at a tomorrow that is safe and completely free from the pandemic that has claimed the lives of millions.
-
+
## Slowly but Steadily, Work from Home in the USA has Begun to Ease
Even though work from home has by and large been quite productive, there is no substitute for the real-world interaction that professionals have in the office. It not only bolsters collaboration but also enhances the much-needed bonds among colleagues that eventually turn out to be the key aspects for overall growth.
@@ -64,5 +64,5 @@ Considering that it would be apt to remain guarded against COVID-19 so that the
The remarkable [COVID-19 business success](https://www.loginradius.com/blog/fuel/2021/03/how-to-make-businesses-marketing-plans-after-coronavirus/) in the USA is going to pave the way forward for other countries as well, especially the ones that are struggling to find the right answers to get rid of the pandemic. This success is all set to have a huge impact on the work from home culture and help people return to real-world interaction and teamwork, which are essential for long-term growth. The hybrid model will most likely lead the change.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=vaccine-success-can-impact-the-remote-working-culture)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=vaccine-success-can-impact-the-remote-working-culture)
diff --git a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.jpg b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.jpg
deleted file mode 100644
index 509ce9e96..000000000
Binary files a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.jpg and /dev/null differ
diff --git a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.webp b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.webp
new file mode 100644
index 000000000..c22460970
Binary files /dev/null and b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.webp differ
diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/index.md b/content/growth/Which-Marketing-Strategy-is-Best-for-You/index.md
index 064120ef9..415f5d2fe 100644
--- a/content/growth/Which-Marketing-Strategy-is-Best-for-You/index.md
+++ b/content/growth/Which-Marketing-Strategy-is-Best-for-You/index.md
@@ -1,7 +1,7 @@
---
title: "Inbound Vs Outbound: Which Marketing Strategy is Best for You"
date: "2021-03-31"
-coverImage: "marketing-plan.jpg"
+coverImage: "marketing-plan.webp"
category: ["loginradius"]
featured: false
author: "Shachindra Saxena"
@@ -37,7 +37,7 @@ Previously known just as simply ‘marketing,’ outbound marketing is an interr
While once perhaps the only way to get people’s attention, outdoor marketing has steadily fallen out of favor with audiences. These days, audiences ignore these advances and do not feel obliged in the slightest.
-[](https://www.loginradius.com/resource/digital-identity-future-whitepaper)
+[](https://www.loginradius.com/resource/digital-identity-future-whitepaper)
## Inbound Marketing Methodology
@@ -96,4 +96,4 @@ Marketing pixels allow companies to gather information about visitors and send t
Companies would benefit from trying out new strategies while continuing to deploy those that work for them. Combining with regular data analysis to assess profitability will help companies stay on top of the game.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=which-marketing-strategy-is-best-for-you)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=which-marketing-strategy-is-best-for-you)
\ No newline at end of file
diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.png b/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.png
deleted file mode 100644
index 7602d120d..000000000
Binary files a/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.png and /dev/null differ
diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.webp b/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.webp
new file mode 100644
index 000000000..9a00697f9
Binary files /dev/null and b/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.webp differ
diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.jpg b/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.jpg
deleted file mode 100644
index b81dd8903..000000000
Binary files a/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.jpg and /dev/null differ
diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.webp b/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.webp
new file mode 100644
index 000000000..c7ff82441
Binary files /dev/null and b/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.webp differ
diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.png b/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.png
deleted file mode 100644
index 1338927e7..000000000
Binary files a/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.png and /dev/null differ
diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.webp b/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.webp
new file mode 100644
index 000000000..468202b9e
Binary files /dev/null and b/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.webp differ
diff --git a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.png b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.png
deleted file mode 100644
index e7cfcf9a0..000000000
Binary files a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.png and /dev/null differ
diff --git a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.webp b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.webp
new file mode 100644
index 000000000..735ec1c8d
Binary files /dev/null and b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.webp differ
diff --git a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/index.md b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/index.md
index b8c9e744a..7eb13d27e 100644
--- a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/index.md
+++ b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/index.md
@@ -1,7 +1,7 @@
---
title: "Why Video Testimonials Are A Marketing Must"
date: "2021-04-16"
-coverImage: "video-testimonial-client-loginradius.jpg"
+coverImage: "video-testimonial-client-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Navanita Devi"
@@ -107,4 +107,4 @@ By now, it must be clear how important it is to develop video testimonials and t
However, creating impactful video testimonials isn't a cakewalk. It requires a potent mixture of creativity, understanding of user needs, and digital marketing methods. So, start focusing more on video testimonials instead of investing resources for developing text-based marketing collaterals. With time, you will get better at it and create a massive impact on your audience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-video-testimonials-are-a-marketing-must)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-video-testimonials-are-a-marketing-must)
\ No newline at end of file
diff --git a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.jpg b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.jpg
deleted file mode 100644
index cc7e41739..000000000
Binary files a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.jpg and /dev/null differ
diff --git a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.webp b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.webp
new file mode 100644
index 000000000..883ea53dd
Binary files /dev/null and b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.webp differ
diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.jpg b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.jpg
deleted file mode 100644
index dbbc9659f..000000000
Binary files a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.jpg and /dev/null differ
diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.webp b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.webp
new file mode 100644
index 000000000..8f262e4dd
Binary files /dev/null and b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.webp differ
diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.jpg b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.jpg
deleted file mode 100644
index 4d47fc0b1..000000000
Binary files a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.jpg and /dev/null differ
diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.webp b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.webp
new file mode 100644
index 000000000..2e9888530
Binary files /dev/null and b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.webp differ
diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.jpg b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.jpg
deleted file mode 100644
index 30badd2a4..000000000
Binary files a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.jpg and /dev/null differ
diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.webp b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.webp
new file mode 100644
index 000000000..eff3f719c
Binary files /dev/null and b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.webp differ
diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/index.md b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/index.md
index 978bda595..48aa7e86f 100644
--- a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/index.md
+++ b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/index.md
@@ -1,7 +1,7 @@
---
title: "Why is Consumer Onboarding Critical for Startups"
date: "2021-03-18"
-coverImage: "client-onboard-loginradius-fuel-blog.jpg"
+coverImage: "client-onboard-loginradius-fuel-blog.webp"
category: ["loginradius"]
featured: false
author: "Rakesh Soni"
@@ -30,7 +30,7 @@ It is imperative that consumers achieve desired results from your product or ser
Approximately [52% of consumers abandon products](https://www.kickstartall.com/what-is-orchestrated-onboarding/) or services within 90 days due to a flawed onboarding process. 55% of people say they've [returned a product](https://www.wyzowl.com/customer-onboarding-statistics) because they didn't fully understand how to use it.
- 
+ 
A good consumer onboarding process ensures that your consumer is achieving the desired outcome of your product or services and as a result, it will help you reduce the churn rate.
@@ -65,7 +65,7 @@ There is no single method of successful consumer onboarding as it depends on the
This is the first touchpoint of your consumer onboarding. Therefore, the signup process should be simple and secure. Nowadays, consumers are concerned with the lengthy signup process and data security. Instead of building your signup form, you can opt for [**Best CIAM providers**](https://www.loginradius.com/resource/loginradius-ciam-developers-whitepaper) to ensure a good user experience, data security, and compliance.
-
+
### Welcome email
@@ -91,4 +91,4 @@ Don't forget to take feedback from the consumer after onboarding. Ask them if th
There are many free and paid tools available that help you set up a good consumer onboarding process. You can also [**refer to this article**](https://www.loginradius.com/blog/fuel/2021/01/user-onboarding-tools/) for the list of highly recommended consumer onboarding tools for businesses.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-is-consumer-onboarding-critical-for-startups)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-is-consumer-onboarding-critical-for-startups)
diff --git a/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.png b/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.png
deleted file mode 100644
index 4ea16b064..000000000
Binary files a/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.png and /dev/null differ
diff --git a/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.webp b/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.webp
new file mode 100644
index 000000000..7e6ca6673
Binary files /dev/null and b/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.webp differ
diff --git a/content/growth/advantage-social-login-as-marketer/index.md b/content/growth/advantage-social-login-as-marketer/index.md
index ac3c3b4f1..ebaa07c89 100644
--- a/content/growth/advantage-social-login-as-marketer/index.md
+++ b/content/growth/advantage-social-login-as-marketer/index.md
@@ -1,7 +1,7 @@
---
title: "Can Social Login Boost Conversion Rates? 5 Things Marketers Should Know"
date: "2021-11-12"
-coverImage: "social-login-marketer.jpg"
+coverImage: "social-login-marketer.webp"
tags: ["social login","cx","data privacy"]
author: "Navanita Devi"
description: "Using social login to drive sign-ups usually makes sense because it increases user privacy. If users like the site, they're more likely to return, and you're more likely to convert them into paying customers. This blog explains how social login can boost conversion rates."
@@ -28,7 +28,7 @@ The companies pull the user information to create a wholesome experience for the
2. **It enables the usage of social media functionalities.** Social login enables users to like, share, comment, subscribe, play online games, and much more without having to create an account or waste time by typing their login credentials over and over again.
3. **It doesn't force the users to create a new password:** The process utilizes the information of social media accounts of the users. Thus, they have one less password to remember. It is something they might appreciate and hence visit the website more frequently.
-[](https://www.loginradius.com/resource/social-login-reconsidered/)
+[](https://www.loginradius.com/resource/social-login-reconsidered/)
4. **It results in fewer unsuccessful logins:** The users only need to click on the social media account they want to log in with. Thus, they will not have the scope of making mistakes while entering their login credentials.
@@ -58,4 +58,4 @@ Marketers can use personalized emails to [build relationships with customers](ht
Thus, if used properly, **social logins** can boost conversion rates like no other authentication tool.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advantage-social-login-as-marketer)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advantage-social-login-as-marketer)
diff --git a/content/growth/advantage-social-login-as-marketer/social-login-marketer.jpg b/content/growth/advantage-social-login-as-marketer/social-login-marketer.jpg
deleted file mode 100644
index b39b73c77..000000000
Binary files a/content/growth/advantage-social-login-as-marketer/social-login-marketer.jpg and /dev/null differ
diff --git a/content/growth/advantage-social-login-as-marketer/social-login-marketer.webp b/content/growth/advantage-social-login-as-marketer/social-login-marketer.webp
new file mode 100644
index 000000000..208b41776
Binary files /dev/null and b/content/growth/advantage-social-login-as-marketer/social-login-marketer.webp differ
diff --git a/content/growth/advantage-social-login-as-marketer/social-login-wp.png b/content/growth/advantage-social-login-as-marketer/social-login-wp.png
deleted file mode 100644
index 412e2195c..000000000
Binary files a/content/growth/advantage-social-login-as-marketer/social-login-wp.png and /dev/null differ
diff --git a/content/growth/advantage-social-login-as-marketer/social-login-wp.webp b/content/growth/advantage-social-login-as-marketer/social-login-wp.webp
new file mode 100644
index 000000000..6e975bd35
Binary files /dev/null and b/content/growth/advantage-social-login-as-marketer/social-login-wp.webp differ
diff --git a/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.png b/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.png
deleted file mode 100644
index 1116bcde5..000000000
Binary files a/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.png and /dev/null differ
diff --git a/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.webp b/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.webp
new file mode 100644
index 000000000..8efa78c3e
Binary files /dev/null and b/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.webp differ
diff --git a/content/growth/ai-innovations-transforming-compliance/ai-compliance.jpg b/content/growth/ai-innovations-transforming-compliance/ai-compliance.jpg
deleted file mode 100644
index 1990c1172..000000000
Binary files a/content/growth/ai-innovations-transforming-compliance/ai-compliance.jpg and /dev/null differ
diff --git a/content/growth/ai-innovations-transforming-compliance/ai-compliance.webp b/content/growth/ai-innovations-transforming-compliance/ai-compliance.webp
new file mode 100644
index 000000000..24b5ec723
Binary files /dev/null and b/content/growth/ai-innovations-transforming-compliance/ai-compliance.webp differ
diff --git a/content/growth/ai-innovations-transforming-compliance/index.md b/content/growth/ai-innovations-transforming-compliance/index.md
index dcff36a65..4f2b548fd 100644
--- a/content/growth/ai-innovations-transforming-compliance/index.md
+++ b/content/growth/ai-innovations-transforming-compliance/index.md
@@ -1,7 +1,7 @@
---
title: "5 Breakthrough Innovations: How AI is Transforming Compliance"
date: "2024-07-23"
-coverImage: "ai-compliance.jpg"
+coverImage: "ai-compliance.webp"
tags: ["ai","consent management","compliance"]
author: "Rakesh Soni"
description: "Artificial Intelligence is reshaping the landscape of compliance with groundbreaking innovations. Here are five transformative ways AI is revolutionizing compliance, offering enhanced accuracy, efficiency, and risk management."
@@ -50,7 +50,7 @@ AI can analyze patterns and behaviors to detect anomalies indicative of fraudule
* Deploy AI-powered behavioral analytics tools to continuously monitor transactions and activities, flagging any suspicious behavior for further investigation.
-[](https://www.loginradius.com/resource/whitepaper/how-ai-change-iam-initiatives/)
+[](https://www.loginradius.com/resource/whitepaper/how-ai-change-iam-initiatives/)
### 5. Predictive Analytics for Compliance Trends
@@ -68,4 +68,4 @@ As regulatory landscapes continue to evolve, leveraging AI will be crucial for b
Embrace these AI-driven innovations and position your organization at the forefront of compliance efficiency and accuracy.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-innovations-transforming-compliance)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-innovations-transforming-compliance)
\ No newline at end of file
diff --git a/content/growth/attract-consumers-to-your-website/consumer-to-website.jpg b/content/growth/attract-consumers-to-your-website/consumer-to-website.jpg
deleted file mode 100644
index 6de9cd7ec..000000000
Binary files a/content/growth/attract-consumers-to-your-website/consumer-to-website.jpg and /dev/null differ
diff --git a/content/growth/attract-consumers-to-your-website/consumer-to-website.webp b/content/growth/attract-consumers-to-your-website/consumer-to-website.webp
new file mode 100644
index 000000000..67610aa56
Binary files /dev/null and b/content/growth/attract-consumers-to-your-website/consumer-to-website.webp differ
diff --git a/content/growth/attract-consumers-to-your-website/index.md b/content/growth/attract-consumers-to-your-website/index.md
index edd2f9a60..b6726a47b 100644
--- a/content/growth/attract-consumers-to-your-website/index.md
+++ b/content/growth/attract-consumers-to-your-website/index.md
@@ -1,7 +1,7 @@
---
title: "5 Tricks to Attract MORE Consumers to Your Website"
date: "2021-02-23"
-coverImage: "consumer-to-website.jpg"
+coverImage: "consumer-to-website.webp"
category: ["all"]
featured: false
author: "Rakesh Soni"
@@ -79,7 +79,7 @@ By considering these factors, you can get a hold of the social media channels ha
Once you've identified and started concentrating on platforms, build a publishing plan for social media that allows you to keep to a schedule. You will find several resources that will help you plan social media posts in advance, giving you time to interact with your audience and checking out the competitors every day. Being disciplined about this will allow you to get more visitors to your site.
-Many businesses today rely a lot on sharing and advertising their material on social media, with around [83% of marketers](https://contentmarketinginstitute.com/wp-content/uploads/2020/09/b2b-2021-research-final.pdf) using and viewing them as a lucrative marketing channel. They use social media to connect and share their content and that of others, and so should you. Through social media accounts, you can share your blog posts with your audience; doing so can increase traffic to your website.
+Many businesses today rely a lot on sharing and advertising their material on social media, with around *83% of marketers* using and viewing them as a lucrative marketing channel. They use social media to connect and share their content and that of others, and so should you. Through social media accounts, you can share your blog posts with your audience; doing so can increase traffic to your website.
Since not many brands reply to follower comments, if you do it, your audience is more likely to go through the funnel quickly, i.e., they convert into consumers of your products or services._ _
@@ -122,4 +122,4 @@ Don't forget to build growth strategies after creating content to draw users to
By following these five tricks, you can make the most of your strategies to attract online consumers while also maintaining them and ensuring that they get converted into leads.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=attract-consumers-to-your-website)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=attract-consumers-to-your-website)
diff --git a/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.png b/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.png
deleted file mode 100644
index b6c1daad3..000000000
Binary files a/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.png and /dev/null differ
diff --git a/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.webp b/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.webp
new file mode 100644
index 000000000..3e81105a6
Binary files /dev/null and b/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.webp differ
diff --git a/content/growth/authentication-challenges-retail-industry/index.md b/content/growth/authentication-challenges-retail-industry/index.md
index 6abf935cd..21b7ecdcb 100644
--- a/content/growth/authentication-challenges-retail-industry/index.md
+++ b/content/growth/authentication-challenges-retail-industry/index.md
@@ -1,7 +1,7 @@
---
title: "What are the Authentication Challenges in the Retail Industry?"
date: "2021-10-26"
-coverImage: "retail-auth.jpg"
+coverImage: "retail-auth.webp"
tags: ["data security","retail authentication","cx"]
author: "Rashmi Mathur"
description: "Losing business means paying for remediation, business disruption, legal expenses, identity repair, regulatory penalties, and other clean-up costs. Although retail has some distinct differences from other industries regarding identity and authentication, it also faces many challenges."
@@ -39,7 +39,7 @@ Along with providing authentication solutions, it is important to protect the di
Cloud applications have made applications and data accessible from anywhere in the world. However, the local laws require several retailers to be tight over how and from where the employees can access the data. Additionally, various governments might have different regulations. Hence, complying with multiple rules at the same time might prove to be a challenge.
-[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
+[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
## Solving These Challenges
@@ -73,4 +73,4 @@ Typical business-to-employee scenarios, like e-commerce portals, require a much
The ability to authenticate customers in real time using multiple modalities is challenging. Understanding how solutions vary by use case, threat model and authentication technology used is crucial to choosing the right one for your unique requirements. [Contact us](https://www.loginradius.com/contact-sales) for better understanding.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-challenges-retail-industry)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-challenges-retail-industry)
diff --git a/content/growth/authentication-challenges-retail-industry/retail-auth.jpg b/content/growth/authentication-challenges-retail-industry/retail-auth.jpg
deleted file mode 100644
index 89347396a..000000000
Binary files a/content/growth/authentication-challenges-retail-industry/retail-auth.jpg and /dev/null differ
diff --git a/content/growth/authentication-challenges-retail-industry/retail-auth.webp b/content/growth/authentication-challenges-retail-industry/retail-auth.webp
new file mode 100644
index 000000000..4d4ebc759
Binary files /dev/null and b/content/growth/authentication-challenges-retail-industry/retail-auth.webp differ
diff --git a/content/growth/authentication-challenges-retail-industry/retail-ciam.png b/content/growth/authentication-challenges-retail-industry/retail-ciam.png
deleted file mode 100644
index 89245ae36..000000000
Binary files a/content/growth/authentication-challenges-retail-industry/retail-ciam.png and /dev/null differ
diff --git a/content/growth/authentication-challenges-retail-industry/retail-ciam.webp b/content/growth/authentication-challenges-retail-industry/retail-ciam.webp
new file mode 100644
index 000000000..929b7daff
Binary files /dev/null and b/content/growth/authentication-challenges-retail-industry/retail-ciam.webp differ
diff --git a/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.jpg b/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.jpg
deleted file mode 100644
index 35564fe12..000000000
Binary files a/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.jpg and /dev/null differ
diff --git a/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.webp b/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.webp
new file mode 100644
index 000000000..38eaa2f02
Binary files /dev/null and b/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.webp differ
diff --git a/content/growth/authentication-critical-customer-acquistion-tool/index.md b/content/growth/authentication-critical-customer-acquistion-tool/index.md
index a9c0bfb34..1024b1b0d 100644
--- a/content/growth/authentication-critical-customer-acquistion-tool/index.md
+++ b/content/growth/authentication-critical-customer-acquistion-tool/index.md
@@ -1,7 +1,7 @@
---
title: "Authentication Has Gone Mainstream: Are Marketers Ready to Take the Responsibility?"
date: "2022-07-29"
-coverImage: "auth-marketers.jpg"
+coverImage: "auth-marketers.webp"
category: ["authentication", "authorization", "customer verification"]
author: "Navanita Devi"
description: "Authentication is the most important security feature any application can have because it's the gateway through which users interact with your data. This blog explains how marketers can leverage user authentication."
@@ -77,4 +77,4 @@ As the world becomes more connected, users have become increasingly more aware o
Marketers need to strike a balance between user security and experience when it comes to user privacy. That means providing security services that won't frustrate customers who want to get the most out of their devices and applications.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-critical-customer-acquistion-tool)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-critical-customer-acquistion-tool)
\ No newline at end of file
diff --git a/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.png b/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.png
deleted file mode 100644
index 4ea16b064..000000000
Binary files a/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.png and /dev/null differ
diff --git a/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.webp b/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.webp
new file mode 100644
index 000000000..7e6ca6673
Binary files /dev/null and b/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.webp differ
diff --git a/content/growth/authentication-evolution-to-passwordless/evolution-auth.jpg b/content/growth/authentication-evolution-to-passwordless/evolution-auth.jpg
deleted file mode 100644
index e56a4dd78..000000000
Binary files a/content/growth/authentication-evolution-to-passwordless/evolution-auth.jpg and /dev/null differ
diff --git a/content/growth/authentication-evolution-to-passwordless/evolution-auth.webp b/content/growth/authentication-evolution-to-passwordless/evolution-auth.webp
new file mode 100644
index 000000000..8d1366811
Binary files /dev/null and b/content/growth/authentication-evolution-to-passwordless/evolution-auth.webp differ
diff --git a/content/growth/authentication-evolution-to-passwordless/index.md b/content/growth/authentication-evolution-to-passwordless/index.md
index b8bed1807..342cd1d09 100644
--- a/content/growth/authentication-evolution-to-passwordless/index.md
+++ b/content/growth/authentication-evolution-to-passwordless/index.md
@@ -1,7 +1,7 @@
---
title: "The Evolution of Authentication: From Passwords to Passwordless & More"
date: "2022-05-27"
-coverImage: "evolution-auth.jpg"
+coverImage: "evolution-auth.webp"
tags: ["passwordless authentication","new age authentication","cx"]
author: "Navanita Devi"
description: "Over the past years, the evolution of authentication portrays the risks associated with unauthorized access and the growing number of cybersecurity threats that leads to compromised user information and sensitive business data. Here’s an insightful read depicting authentication aspects and how it has evolved over a decade."
@@ -48,7 +48,7 @@ It simplifies the sign-in and registration experiences, providing a convenient a
For consumers, social login is a single-click login method for accessing the website and mobile application—one in which there is no need for excess credentials and allows consumers to skip traditional registration methods.
-[](https://www.loginradius.com/resource/social-login-reconsidered/)
+[](https://www.loginradius.com/resource/social-login-reconsidered/)
### #2. Passwordless Authentication
@@ -86,4 +86,4 @@ And the crux of the matter is that businesses relying on old-school authenticati
Businesses leveraging cutting-edge authentication technologies always stand ahead of their competitors since their customers enjoy a seamless user experience reinforced by robust security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-evolution-to-passwordless)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-evolution-to-passwordless)
\ No newline at end of file
diff --git a/content/growth/authentication-evolution-to-passwordless/social-login-wp.png b/content/growth/authentication-evolution-to-passwordless/social-login-wp.png
deleted file mode 100644
index 412e2195c..000000000
Binary files a/content/growth/authentication-evolution-to-passwordless/social-login-wp.png and /dev/null differ
diff --git a/content/growth/authentication-evolution-to-passwordless/social-login-wp.webp b/content/growth/authentication-evolution-to-passwordless/social-login-wp.webp
new file mode 100644
index 000000000..6e975bd35
Binary files /dev/null and b/content/growth/authentication-evolution-to-passwordless/social-login-wp.webp differ
diff --git a/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.png b/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.png
deleted file mode 100644
index c8e655587..000000000
Binary files a/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.png and /dev/null differ
diff --git a/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.webp b/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.webp
new file mode 100644
index 000000000..1082e7522
Binary files /dev/null and b/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.webp differ
diff --git a/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.jpg b/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.jpg
deleted file mode 100644
index 114bb8c17..000000000
Binary files a/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.jpg and /dev/null differ
diff --git a/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.webp b/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.webp
new file mode 100644
index 000000000..b52380171
Binary files /dev/null and b/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.webp differ
diff --git a/content/growth/authentication-mainstream-marketers-benefit/index.md b/content/growth/authentication-mainstream-marketers-benefit/index.md
index f5e754cc5..68ed19554 100644
--- a/content/growth/authentication-mainstream-marketers-benefit/index.md
+++ b/content/growth/authentication-mainstream-marketers-benefit/index.md
@@ -1,7 +1,7 @@
---
title: "How Authentication Leads The Way in Strategic Customer Acquisitions?"
date: "2022-10-12"
-coverImage: "auth-benefit.jpg"
+coverImage: "auth-benefit.webp"
tags: ["passwordless authentication","digital identity","sso","cx"]
author: "Grigori Monaselidze"
description: "With digital businesses taking over the entire industry, improving customer authentication and email communication with customers has never been more important to maintaining a successful business. This blog explains how authentication can help you increase your customer acquisition."
@@ -41,7 +41,7 @@ KBA, or Knowledge-based Authentication is a common method for securely aiding a
[Single sign-on](https://www.loginradius.com/single-sign-on/) or SSO, is mostly used by services using password as their main authentication method. SSO allows a customer to authenticate themselves once to use various accounts or systems. This provides comfort, as it eliminates the need to remember various passwords for various applications.
-[](https://www.loginradius.com/resource/securing-user-authentication-understanding-the-basics-best-practices/)
+[](https://www.loginradius.com/resource/securing-user-authentication-understanding-the-basics-best-practices/)
All of the three above-mentioned customer authentication methods present a challenge, where a business must determine a common ground between comfort and security.
@@ -96,4 +96,4 @@ Email campaigns certainly can be tricky, a lot of resources are invested in stra
With digital businesses taking over the entire industry, improving customer authentication and email communication with customers has never been more important to maintaining a successful business.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-mainstream-marketers-benefit)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-mainstream-marketers-benefit)
\ No newline at end of file
diff --git a/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.png b/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.png
deleted file mode 100644
index 2af543487..000000000
Binary files a/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.png and /dev/null differ
diff --git a/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.webp b/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.webp
new file mode 100644
index 000000000..2e2a4d5c2
Binary files /dev/null and b/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.webp differ
diff --git a/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.png b/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.png
deleted file mode 100644
index a3580f13e..000000000
Binary files a/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.png and /dev/null differ
diff --git a/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.webp b/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.webp
new file mode 100644
index 000000000..0257eff22
Binary files /dev/null and b/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.webp differ
diff --git a/content/growth/authentication-tools-boost-sales/auth-tools.jpg b/content/growth/authentication-tools-boost-sales/auth-tools.jpg
deleted file mode 100644
index 64d56cb05..000000000
Binary files a/content/growth/authentication-tools-boost-sales/auth-tools.jpg and /dev/null differ
diff --git a/content/growth/authentication-tools-boost-sales/auth-tools.webp b/content/growth/authentication-tools-boost-sales/auth-tools.webp
new file mode 100644
index 000000000..ea6e40cdc
Binary files /dev/null and b/content/growth/authentication-tools-boost-sales/auth-tools.webp differ
diff --git a/content/growth/authentication-tools-boost-sales/bio-auth.png b/content/growth/authentication-tools-boost-sales/bio-auth.png
deleted file mode 100644
index 69293181d..000000000
Binary files a/content/growth/authentication-tools-boost-sales/bio-auth.png and /dev/null differ
diff --git a/content/growth/authentication-tools-boost-sales/bio-auth.webp b/content/growth/authentication-tools-boost-sales/bio-auth.webp
new file mode 100644
index 000000000..b272f8563
Binary files /dev/null and b/content/growth/authentication-tools-boost-sales/bio-auth.webp differ
diff --git a/content/growth/authentication-tools-boost-sales/index.md b/content/growth/authentication-tools-boost-sales/index.md
index a91f0ebc3..c8765c359 100644
--- a/content/growth/authentication-tools-boost-sales/index.md
+++ b/content/growth/authentication-tools-boost-sales/index.md
@@ -1,7 +1,7 @@
---
title: "Can Authentication Convert Sales? 4 Authentication Tools for Every Retailer"
date: "2021-11-08"
-coverImage: "auth-tools.jpg"
+coverImage: "auth-tools.webp"
tags: ["biometric authentication","social login","passwordless authentication"]
author: "Navanita Devi"
description: "Authentication is a serious process that can help you convert sales. In many cases, it determines whether a customer will take the time to complete a purchase. Therefore, it is important for your store to have multiple layers of security throughout the checkout process."
@@ -51,7 +51,7 @@ Additionally, it reduces the need to create digital contracts and also the waiti
As a result of the above advantages, customers are more likely to engage with your brand and be loyal to you. Additionally, with more customers, you are more likely to get more data. Proper analysis of it can lead to a further high conversion rate.
-[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
+[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
### #3. Social Logins
@@ -72,4 +72,4 @@ Moving away from traditional **authentication tools** such as standard authentic
There is no doubt that using an authentication tool can improve your website's conversion rate. This is because you will protect your customers better while keeping out hackers, fraudsters and other malicious individuals. However, you should take the time to look for the best authentication solutions in the market today. [Contact us](https://www.loginradius.com/contact-sales) for more information on how we can help!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-tools-boost-sales)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-tools-boost-sales)
diff --git a/content/growth/b2b-saas-security-management/WP-LR-resiliency.png b/content/growth/b2b-saas-security-management/WP-LR-resiliency.png
deleted file mode 100644
index cbe459800..000000000
Binary files a/content/growth/b2b-saas-security-management/WP-LR-resiliency.png and /dev/null differ
diff --git a/content/growth/b2b-saas-security-management/WP-LR-resiliency.webp b/content/growth/b2b-saas-security-management/WP-LR-resiliency.webp
new file mode 100644
index 000000000..efb695fb3
Binary files /dev/null and b/content/growth/b2b-saas-security-management/WP-LR-resiliency.webp differ
diff --git a/content/growth/b2b-saas-security-management/b2b-saas.jpg b/content/growth/b2b-saas-security-management/b2b-saas.jpg
deleted file mode 100644
index 9747952f1..000000000
Binary files a/content/growth/b2b-saas-security-management/b2b-saas.jpg and /dev/null differ
diff --git a/content/growth/b2b-saas-security-management/b2b-saas.webp b/content/growth/b2b-saas-security-management/b2b-saas.webp
new file mode 100644
index 000000000..92d24630a
Binary files /dev/null and b/content/growth/b2b-saas-security-management/b2b-saas.webp differ
diff --git a/content/growth/b2b-saas-security-management/index.md b/content/growth/b2b-saas-security-management/index.md
index 77b5c246c..569d3dd70 100644
--- a/content/growth/b2b-saas-security-management/index.md
+++ b/content/growth/b2b-saas-security-management/index.md
@@ -1,7 +1,7 @@
---
title: "Securing B2B SaaS: How Identity Management Leads the Charge Against Top 5 Security Challenges"
date: "2024-04-12"
-coverImage: "b2b-saas.jpg"
+coverImage: "b2b-saas.webp"
tags: ["saas","digital identity management","compliance"]
author: "Alok Patidar"
description: "Security is paramount in the dynamic B2B SaaS landscape. Explore how Identity Management addresses the top 5 security challenges, from data breaches to compliance, offering insights to fortify digital defenses. Discover proactive measures to safeguard systems and data, letting Identity Management lead the charge in securing the future of B2B SaaS."
@@ -44,7 +44,7 @@ As B2B SaaS businesses scale, so do their security challenges. Identity Manageme
Single Sign-On (SSO) solutions simplify user access management, ensuring seamless scalability without compromising security.
-[](https://www.loginradius.com/resource/enterprise-scalability-and-performance)
+[](https://www.loginradius.com/resource/enterprise-scalability-and-performance)
### 5. Password Woes
@@ -58,4 +58,4 @@ In the face of evolving security challenges, B2B SaaS companies need proactive m
By implementing robust authentication, access controls, and compliance measures, businesses can confidently navigate the security landscape. As the digital realm expands, let Identity Management lead the charge in securing the future of B2B SaaS.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2b-saas-security-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2b-saas-security-management)
diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.png b/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.png
deleted file mode 100644
index 4afe9c15b..000000000
Binary files a/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.png and /dev/null differ
diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.webp b/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.webp
new file mode 100644
index 000000000..982ab7a25
Binary files /dev/null and b/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.webp differ
diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.jpg b/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.jpg
deleted file mode 100644
index 81d15ecd6..000000000
Binary files a/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.jpg and /dev/null differ
diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.webp b/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.webp
new file mode 100644
index 000000000..864059a33
Binary files /dev/null and b/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.webp differ
diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/index.md b/content/growth/b2c-enterprises-ciam-retail-supply-chain/index.md
index 7a5823652..e07e67d28 100644
--- a/content/growth/b2c-enterprises-ciam-retail-supply-chain/index.md
+++ b/content/growth/b2c-enterprises-ciam-retail-supply-chain/index.md
@@ -1,7 +1,7 @@
---
title: "How B2C Industries are Leveraging CIAM in the Retail Supply Chain Management"
date: "2021-10-25"
-coverImage: "retail-supply-chain-cover.jpg"
+coverImage: "retail-supply-chain-cover.webp"
tags: ["ciam solution","iot authentication","cx"]
author: "Navanita Devi"
description: "Retailers hold access to a comprehensive range of technologies. From today's current options, such as RFID tags, to stimulating creativity, such as self-driving trucks, businesses will largely depend on computers to manage their daily operations. Learn how they are incorporating CIAM in their environment."
@@ -30,7 +30,7 @@ Currently, AI assembles and collects client information and consumer audit trail
Retailers benefit from AI solutions that accumulate and analyze consumer data from social media, their purchasing habits, and other sources to render valuable business insights. Retailers who use this information make educated, data-driven decisions about when and ways to target consumers with the most definite promotion or deal.
-[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail)
+[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail)
@@ -75,4 +75,4 @@ Also, clients are now constantly anticipating deeper social connections supplied
Customers likewise expect some control over how companies collect, store, manage, and share their personal information. With the competition just a click away, your company's misuse of customer data, whether intentional or unintentional, can severely harm brand equity. [Contact us](https://www.loginradius.com/contact-sales) to secure your operations with LoginRadius today!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2c-enterprises-ciam-retail-supply-chain)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2c-enterprises-ciam-retail-supply-chain)
diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.jpg b/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.jpg
deleted file mode 100644
index 3fb6d6fa8..000000000
Binary files a/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.jpg and /dev/null differ
diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.webp b/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.webp
new file mode 100644
index 000000000..e59106c81
Binary files /dev/null and b/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.webp differ
diff --git a/content/growth/balance-between-personalization-data-privacy/index.md b/content/growth/balance-between-personalization-data-privacy/index.md
index b1c26a92c..307595a3e 100644
--- a/content/growth/balance-between-personalization-data-privacy/index.md
+++ b/content/growth/balance-between-personalization-data-privacy/index.md
@@ -1,7 +1,7 @@
---
title: "Finding The Balance Between Personalization and Data Privacy"
date: "2022-01-20"
-coverImage: "personalize-cover.jpg"
+coverImage: "personalize-cover.webp"
category: ["all"]
featured: false
author: "Rashmi Mathur"
@@ -56,4 +56,4 @@ Implementing personalization in an effective manner is challenging. Hence, you n
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=balance-between-personalization-data-privacy)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=balance-between-personalization-data-privacy)
\ No newline at end of file
diff --git a/content/growth/balance-between-personalization-data-privacy/personalize-cover.jpg b/content/growth/balance-between-personalization-data-privacy/personalize-cover.jpg
deleted file mode 100644
index 43f709ffe..000000000
Binary files a/content/growth/balance-between-personalization-data-privacy/personalize-cover.jpg and /dev/null differ
diff --git a/content/growth/balance-between-personalization-data-privacy/personalize-cover.webp b/content/growth/balance-between-personalization-data-privacy/personalize-cover.webp
new file mode 100644
index 000000000..19ba4262e
Binary files /dev/null and b/content/growth/balance-between-personalization-data-privacy/personalize-cover.webp differ
diff --git a/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.jpg b/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.jpg
deleted file mode 100644
index 2b1624009..000000000
Binary files a/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.jpg and /dev/null differ
diff --git a/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.webp b/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.webp
new file mode 100644
index 000000000..166cac22b
Binary files /dev/null and b/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.webp differ
diff --git a/content/growth/best-brainstorming-tools-and-techniques/index.md b/content/growth/best-brainstorming-tools-and-techniques/index.md
index 63ddb2039..ef6e3fec4 100644
--- a/content/growth/best-brainstorming-tools-and-techniques/index.md
+++ b/content/growth/best-brainstorming-tools-and-techniques/index.md
@@ -1,7 +1,7 @@
---
title: "Boost Creativity With The Best Brainstorming Tools And Techniques"
date: "2021-06-09"
-coverImage: "best-brainstorming-tools-and-techniques.jpg"
+coverImage: "best-brainstorming-tools-and-techniques.webp"
category: ["loginradius"]
featured: false
author: "Rashmi Mathur"
@@ -12,20 +12,12 @@ metatitle: "How To Spark Creativity In Virtual Brainstorms With The Best Brainst
Today a large number of professionals are working remotely from different locations due to the pandemic. Are you worried that your marketing team won't be able to generate profitable ideas from isolation? Don't worry! According to a [report by CoSo Cloud](https://www.cosocloud.com/press-releases/connectsolutions-survey-shows-working-remotely-benefits-employers-and-employees), 77% of work from home workers have become more productive during isolation.
-
-
Wondering how?
-
-
-
-Research shows that [80% of remote workers](https://velocityglobal.com/blog/the-complete-guide-how-to-successfully-build-and-manage-a-remote-international-workforce/) say that their productivity has improved with real-time collaborative solutions. Virtual brainstorming tools can help you grow your ideas, rethink your marketing strategies, and collaborate theme for successful outcomes.
-
-
+
+Research shows that *80% of remote workers* say that their productivity has improved with real-time collaborative solutions. Virtual brainstorming tools can help you grow your ideas, rethink your marketing strategies, and collaborate theme for successful outcomes.
A brainstorming tool is strategically designed to help organize and gather ideas. It helps in collaborative brainstorming online, making it easier to harness collective mentality to [create content strategies](https://www.loginradius.com/blog/fuel/20-content-ideas-for-most-engaging-b2b-linkedin-posts/).
-
-
So, let's start your online brainstorming practice tips with the tools first.
## 5 Best Brainstorming Tools
@@ -33,9 +25,7 @@ So, let's start your online brainstorming practice tips with the tools first.
### 1. IdeaBoardz
IdeaBoardz is an easy-to-use collaborative brainstorming tool that can help your team members to combine their ideas in one location online. With the help of this tool, your teammates can post notes on a collaborative board and even export the board as a PDF or excel file.
-
-
-
+
### 2. Google Documents
Google Documents is a popular tool to use for brainstorming as it has all the resources that your team may need during brainstorming. It supports multiple files, including TXT, PDF, DOCX, and HTML. Plus, it lets team members track changes in the docs too.
@@ -43,9 +33,7 @@ Google Documents is a popular tool to use for brainstorming as it has all the re
### 3. Coggle
Coggle is another result-oriented brainstorming tool that allows real-time collaboration. It helps share flow charts, complex algorithms, diagrams, mind maps effortlessly with other team members. Plus, Coggle allows unlimited image uploads, the addition of floating texts, etc.
-
-
-
+
### 4. WiseMapping
WiseMapping is an effective tool for brainstorming and mind mapping. This tool is apt for small groups and individuals. Plus, one can install it on their devices or use it online. Moreover, WiseMapping is a free tool for even business users and allows a teammate to share his/her mind map online with other members. The most attractive features of this tool include customizable font, customizable colors, easy export of maps, etc.
@@ -53,17 +41,11 @@ WiseMapping is an effective tool for brainstorming and mind mapping. This tool i
### 5. MindMup
MindMup is a tremendous tool for collaboration planning and brainstorming with its advanced features. It allows you to convert maps easily to PowerPoint and PDF and lets you share and publish your maps online. Further, MindMup enables you to save your mind maps to Google Drive and allows you to access them later through any device. It has an in-built keyboard shortcuts feature too that lets you and your team members jot down ideas faster.
-
-
So, once you've ensured that you have the people you need and the tools and resources they need, here is what you have to do next.
-
-
-
+
Also Read: [Thinking Beyond the Pandemic: How to Make Marketing Plans After Coronavirus](https://www.loginradius.com/blog/fuel/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/)
-
-
## Virtual Brainstorming Tips/Tricks
Here are some of the effective tips for running brainstorming sessions for your [marketing strategies](https://www.loginradius.com/blog/growth/top-5-marketing-strategies-to-power-up-your-business/).
@@ -87,9 +69,7 @@ Moderators can help focus on the goals, clarify ideas, motivate introverts, and
### 5. Let everyone speak
If only a few people talk in your meeting, you won't get as many business ideas as you need. Some of the introverts of your team may not come forward at all. Therefore, it is crucial to approach the session more supportively and positively. Press the Mute button whenever needed. Giving everyone a chance to speak by encouraging others to set themselves to mute will let others speak up, and everyone will listen and hear each other.
-
-
### 6. Experiment with different techniques and tools
Each brainstorming session doesn't have to be the same. If you are thinking about how to boost creativity? You can use different mind mapping tools and an online brainstorming board to create a plan of opportunities, information, and issues.
@@ -101,10 +81,7 @@ Want to motivate your team to participate in brainstorm sessions in the future?
## Wrapping Up
You can also try the rapid virtual Ideation technique, where you give your participants a limited timescale to come up with ideas. You will be surprised that sometimes even time pressure can bring the best out of people. Finally, use the above tips and tools to spark your team's creativity now and [manage remote teams efficiently.](https://www.loginradius.com/blog/fuel/2021/02/tips-managing-remote-team/)
-
-
Keep the ideas flowing!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-brainstorming-tools-and-techniques)
-
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-brainstorming-tools-and-techniques)
\ No newline at end of file
diff --git a/content/growth/best-practices-verification-emails-effective/discord-example.jpg b/content/growth/best-practices-verification-emails-effective/discord-example.jpg
deleted file mode 100644
index 9ccaa4721..000000000
Binary files a/content/growth/best-practices-verification-emails-effective/discord-example.jpg and /dev/null differ
diff --git a/content/growth/best-practices-verification-emails-effective/discord-example.webp b/content/growth/best-practices-verification-emails-effective/discord-example.webp
new file mode 100644
index 000000000..d9f3d3712
Binary files /dev/null and b/content/growth/best-practices-verification-emails-effective/discord-example.webp differ
diff --git a/content/growth/best-practices-verification-emails-effective/harry-potter-example.jpg b/content/growth/best-practices-verification-emails-effective/harry-potter-example.jpg
deleted file mode 100644
index f288d8953..000000000
Binary files a/content/growth/best-practices-verification-emails-effective/harry-potter-example.jpg and /dev/null differ
diff --git a/content/growth/best-practices-verification-emails-effective/harry-potter-example.webp b/content/growth/best-practices-verification-emails-effective/harry-potter-example.webp
new file mode 100644
index 000000000..6cf38cf0e
Binary files /dev/null and b/content/growth/best-practices-verification-emails-effective/harry-potter-example.webp differ
diff --git a/content/growth/best-practices-verification-emails-effective/index.md b/content/growth/best-practices-verification-emails-effective/index.md
index 165a751c0..bbb7b2d25 100644
--- a/content/growth/best-practices-verification-emails-effective/index.md
+++ b/content/growth/best-practices-verification-emails-effective/index.md
@@ -1,7 +1,7 @@
---
title: "Tips to Make Verification Emails Effective: Best Practices & Examples"
date: "2022-03-21"
-coverImage: "verification-email.jpg"
+coverImage: "verification-email.webp"
category: ["all"]
featured: false
author: "Maxim Grigoryev"
@@ -95,17 +95,17 @@ Besides, the examples of validation emails often have information regarding thei
Here is an example of how Discord used fun facts in their [validation emails](https://reallygoodemails.com/emails/verify-email) in 2019:
-
+
While these examples show the usage of call to action buttons and tone of voice to produce additional value when engaging with customers:
-
+
The first case illustrates how the brand uses colors to create a space and underline non-intrusive elements. The particular template is pretty straightforward and suits its purpose.
-
+
@@ -117,4 +117,4 @@ The second example has more to offer with regard to fonts, colors, and tone of v
The goal of the particular article is to convince you that verification emails should not necessarily be basic and boring. They can add to the marketing strategy and be a starting point for your engagement with the customer.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-practices-verification-emails-effective)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-practices-verification-emails-effective)
diff --git a/content/growth/best-practices-verification-emails-effective/typform-example.jpg b/content/growth/best-practices-verification-emails-effective/typform-example.jpg
deleted file mode 100644
index 07a58632a..000000000
Binary files a/content/growth/best-practices-verification-emails-effective/typform-example.jpg and /dev/null differ
diff --git a/content/growth/best-practices-verification-emails-effective/typform-example.webp b/content/growth/best-practices-verification-emails-effective/typform-example.webp
new file mode 100644
index 000000000..9d3e09885
Binary files /dev/null and b/content/growth/best-practices-verification-emails-effective/typform-example.webp differ
diff --git a/content/growth/best-practices-verification-emails-effective/verification-email.jpg b/content/growth/best-practices-verification-emails-effective/verification-email.jpg
deleted file mode 100644
index 89b635cb7..000000000
Binary files a/content/growth/best-practices-verification-emails-effective/verification-email.jpg and /dev/null differ
diff --git a/content/growth/best-practices-verification-emails-effective/verification-email.webp b/content/growth/best-practices-verification-emails-effective/verification-email.webp
new file mode 100644
index 000000000..b984af087
Binary files /dev/null and b/content/growth/best-practices-verification-emails-effective/verification-email.webp differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.jpg b/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.jpg
deleted file mode 100644
index 926fd6f3b..000000000
Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.jpg and /dev/null differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.webp
new file mode 100644
index 000000000..c7462c375
Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.webp differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.png
deleted file mode 100644
index 97820fd89..000000000
Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.png and /dev/null differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.webp
new file mode 100644
index 000000000..562e594d2
Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.webp differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.png
deleted file mode 100644
index f7ee3a134..000000000
Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.png and /dev/null differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.webp
new file mode 100644
index 000000000..2c53e2c91
Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.webp differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.png
deleted file mode 100644
index 1ea0a696c..000000000
Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.png and /dev/null differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.webp
new file mode 100644
index 000000000..732bb450c
Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.webp differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.png
deleted file mode 100644
index cf9bfff24..000000000
Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.png and /dev/null differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.webp
new file mode 100644
index 000000000..fd3d0aa8d
Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.webp differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.png
deleted file mode 100644
index 430c5985b..000000000
Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.png and /dev/null differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.webp
new file mode 100644
index 000000000..cade42b5e
Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.webp differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/index.md b/content/growth/best-writing-tools-software-for-a-creative-blogger/index.md
index a623b1c77..5103b09e9 100644
--- a/content/growth/best-writing-tools-software-for-a-creative-blogger/index.md
+++ b/content/growth/best-writing-tools-software-for-a-creative-blogger/index.md
@@ -1,7 +1,7 @@
---
title: "16 Best Writing Tools and Software For A Creative Blogger [ Free tools Inside]"
date: "2017-02-17"
-coverImage: "Pro-Tip-2.png"
+coverImage: "Pro-Tip-2.webp"
category: ["content", "marketing", "loginradius"]
featured: false
author: "Rakesh Soni"
@@ -41,19 +41,19 @@ Now, here are some tools according to various categories every writer should use
#### **1\. Hubspot’s blog topic generator**
-
+
This blog title generator from Hubspot is very efficient. You just need to provide it with three keywords (even one keyword can work). The tool helps you to find topics you can write upon. Hence, if you are struggling for ideas, [Hubspot’s blog topic generator](https://www.hubspot.com/blog-topic-generator#/Tools%20for%20Writers) is the right tool for you.
#### **2\. TweakYourBiz Title Generator**
-
+
Just like the above line from the text box says “just enter your topic and go” using this tool is insanely easy. The title generator also breaks your given ideas into various categories such as ‘problems,' ‘motivation’ and ‘how to.' So, [Tweak Your Biz Title Generator](http://tweakyourbiz.com/tools/title-generator/index.php) is worth a try.
#### **3\. Portent’s Content Idea Generator**
-
+
This great tool on my favorite list is very easy to use. You just need to enter your idea and Portent’s Content Idea Generator will provide you with a great title for your post. And if you don’t like the title, refresh your subject, and it will give you a different title instantly.
@@ -61,7 +61,7 @@ This great tool on my favorite list is very easy to use. You just need to enter
#### **1\. Google keyword planner**
-
+
Google keyword planner is a chunk from the Google AdWords program. The tool is completely free and is used to figure out and discuss keywords and develop a pay per click strategy. Type a keyword in the search bar, check the competition for your keywords and other related keyword phrases. Moreover, you can find out things like:-
@@ -88,7 +88,7 @@ It is my most favorite tool for graphics generation. This easy to use tool helps
#### **2\. Infogr.am**
-
+
If you want to present your technical content in a fun way, use [Infogr.am](https://infogr.am/app/#/library). Infographics are a great way to attract more readers to your posts. So, sign in and get your data loaded in your favorite theme. Well, you may not be able to customize much with the tool like Canva, and you don’t get a blank option in Infogr.am but it may be a lifesaver tool when you want to create a detailed infographic.
@@ -116,7 +116,7 @@ This user-friendly tool expertly examines your article for a perfect readability
Readable.io is a free tool when you use it occasionally. To move to advanced features, you can select any of these plans.
-
+
Plans are available for individual and business purpose. Features like Readable.io’s API is only for business plans.
@@ -124,7 +124,7 @@ Plans are available for individual and business purpose. Features like Readable.
#### **1\. Grammarly**
-
+
Grammarly is an effective tool which can improve your language skills. It can find typo errors and grammatically incorrect sentences. Just enter your text in the [Grammarly](https://www.grammarly.com/) web app and the Grammarly editor will proofread your blog post.
@@ -140,19 +140,19 @@ So, if you are more convenient using apps than browsers, here are some goodies f
#### **1\. Hemingway App**
-
+
Hemingway App work wonders when it comes to rectifying your content. It increases clarity in your writing. Thought, it was introduced as a web app, later it evolved as one of the best desktop apps for writers. The app edits your content, comes with distraction free mode feature, exports PDFs and does much more. If you want to buy the latest version which is Hemingway 3.0, it will come with a price tag of $19.99. Well, the web app continues to be free.
#### **2\. Evernote**
-
+
Evernote can be your best friend when you like to store media, information or ideas. Devices can easily integrate with the content stored in Evernote which make materials more accessible. You can share your content on LinkedIn, Facebook, Twitter or just your content’s URL to clipboard.
#### **3\. Tomighty Pomodoro timer**
-
+
It is my personal favorite Pomodoro timer. It is a small desktop app which can help you stay productive during your working hours. The free app uses Pomodoro technique to keep you focused throughout the day while allowing you to relax properly at regular intervals.
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.png
deleted file mode 100644
index fa4fcd5df..000000000
Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.png and /dev/null differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.webp
new file mode 100644
index 000000000..8ba013e0d
Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.webp differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.png
deleted file mode 100644
index e8a420260..000000000
Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.png and /dev/null differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.webp
new file mode 100644
index 000000000..8055df39d
Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.webp differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.png
deleted file mode 100644
index 82a0bc54d..000000000
Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.png and /dev/null differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.webp
new file mode 100644
index 000000000..3bd167776
Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.webp differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.png
deleted file mode 100644
index 838fe11b4..000000000
Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.png and /dev/null differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.webp
new file mode 100644
index 000000000..684afec71
Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.webp differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.png
deleted file mode 100644
index 2103bf7bf..000000000
Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.png and /dev/null differ
diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.webp
new file mode 100644
index 000000000..101491c11
Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.webp differ
diff --git a/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.png b/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.png
deleted file mode 100644
index c8e655587..000000000
Binary files a/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.png and /dev/null differ
diff --git a/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.webp b/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.webp
new file mode 100644
index 000000000..1082e7522
Binary files /dev/null and b/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.webp differ
diff --git a/content/growth/biometric-authentication-security-cx-balance/biometric-auth.jpg b/content/growth/biometric-authentication-security-cx-balance/biometric-auth.jpg
deleted file mode 100644
index cd250ebfc..000000000
Binary files a/content/growth/biometric-authentication-security-cx-balance/biometric-auth.jpg and /dev/null differ
diff --git a/content/growth/biometric-authentication-security-cx-balance/biometric-auth.webp b/content/growth/biometric-authentication-security-cx-balance/biometric-auth.webp
new file mode 100644
index 000000000..38c707e0e
Binary files /dev/null and b/content/growth/biometric-authentication-security-cx-balance/biometric-auth.webp differ
diff --git a/content/growth/biometric-authentication-security-cx-balance/index.md b/content/growth/biometric-authentication-security-cx-balance/index.md
index 33392ec76..965951cc0 100644
--- a/content/growth/biometric-authentication-security-cx-balance/index.md
+++ b/content/growth/biometric-authentication-security-cx-balance/index.md
@@ -1,7 +1,7 @@
---
title: "The Power of Behavioral Biometric Authentication in Enhancing Security and CX Synergy"
date: "2024-04-05"
-coverImage: "biometric-auth.jpg"
+coverImage: "biometric-auth.webp"
tags: ["biometric authentication","data security","cx"]
author: "Vishal Sharma"
description: "Explore the innovative world of behavioral biometric authentication and its role in fortifying security and enhancing customer experience (CX). This cutting-edge method analyzes unique behavioral patterns to verify identities, offering a seamless user experience."
@@ -48,7 +48,7 @@ Imagine a user simply picking up their smartphone and typing a message. Unbeknow
This streamlined authentication process saves time and enhances the overall user experience. Customers feel more at ease knowing their interactions are secure yet effortless, increasing satisfaction and loyalty.
-[](https://www.loginradius.com/resource/whitepaper/user-authentication-security/)
+[](https://www.loginradius.com/resource/whitepaper/user-authentication-security/)
## Implementing Behavioral Biometrics: Best Practices
@@ -70,4 +70,4 @@ Behavioral Biometric Authentication represents a significant step forward in sec
As the digital landscape continues to evolve, embracing innovative solutions like behavioral biometrics is not just a choice but a necessity for staying ahead of the curve and earning customer trust.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=biometric-authentication-security-cx-balance)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=biometric-authentication-security-cx-balance)
diff --git a/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.jpg b/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.jpg
deleted file mode 100644
index 508d6206c..000000000
Binary files a/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.jpg and /dev/null differ
diff --git a/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.webp b/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.webp
new file mode 100644
index 000000000..1b7154259
Binary files /dev/null and b/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.webp differ
diff --git a/content/growth/boost-your-business-sales-with-marketing-business/index.md b/content/growth/boost-your-business-sales-with-marketing-business/index.md
index f8e917a42..2898fae3f 100644
--- a/content/growth/boost-your-business-sales-with-marketing-business/index.md
+++ b/content/growth/boost-your-business-sales-with-marketing-business/index.md
@@ -1,7 +1,7 @@
---
title: "Will Focusing on Relationship Marketing Boost Your Business Sales?"
date: "2021-05-27"
-coverImage: "customer-relationship-for-business.jpg"
+coverImage: "customer-relationship-for-business.webp"
category: ["loginradius"]
featured: false
author: "Deependra Singh"
@@ -102,4 +102,4 @@ Businesses can employ a wide variety of tools to market their relationship. This
Many businesses assume that relationship marketing is a method to retain consumers, and this often leads to huge financial investment. However, the core of relationship marketing is building long-term positive relationships with [clients](https://www.loginradius.com/customers/) and prospective clients to build mutual loyalty rather than changing their opinions for short-term gain.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=boost-your-business-sales-with-marketing-business)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=boost-your-business-sales-with-marketing-business)
\ No newline at end of file
diff --git a/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.jpg b/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.jpg
deleted file mode 100644
index 6878e440d..000000000
Binary files a/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.jpg and /dev/null differ
diff --git a/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.webp b/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.webp
new file mode 100644
index 000000000..06e49b224
Binary files /dev/null and b/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.webp differ
diff --git a/content/growth/boosting-ecommerce-marketing-social-login/index.md b/content/growth/boosting-ecommerce-marketing-social-login/index.md
index fafc26a7c..ee7922608 100644
--- a/content/growth/boosting-ecommerce-marketing-social-login/index.md
+++ b/content/growth/boosting-ecommerce-marketing-social-login/index.md
@@ -1,7 +1,7 @@
---
title: "Why Should Social Login Be a Part of Your E-Commerce Marketing?"
date: "2023-02-28"
-coverImage: "ecommerce-mrktng.jpg"
+coverImage: "ecommerce-mrktng.webp"
tags: ["ecommerce", "social login","cx"]
author: "Vishal Sharma"
description: "Social login is a seamless authentication process that allows users to sign in to an e-commerce site using their existing social media credentials, such as Facebook, Google, Twitter, and LinkedIn. By offering social login options, e-commerce sites can offer customers a more personalized, streamlined, and engaging shopping experience."
@@ -61,4 +61,4 @@ By incorporating social login into e-commerce sites, businesses can improve the
With these benefits in mind, it's easy to see why social login has become a must-have for businesses in the digital age.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=boosting-ecommerce-marketing-social-login)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=boosting-ecommerce-marketing-social-login)
\ No newline at end of file
diff --git a/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.png b/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.png
deleted file mode 100644
index f97184f2f..000000000
Binary files a/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.png and /dev/null differ
diff --git a/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.webp b/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.webp
new file mode 100644
index 000000000..88d19cbb8
Binary files /dev/null and b/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.webp differ
diff --git a/content/growth/build-customer-journeys-data-transparency/customer-journey.jpg b/content/growth/build-customer-journeys-data-transparency/customer-journey.jpg
deleted file mode 100644
index 9dbef816c..000000000
Binary files a/content/growth/build-customer-journeys-data-transparency/customer-journey.jpg and /dev/null differ
diff --git a/content/growth/build-customer-journeys-data-transparency/customer-journey.webp b/content/growth/build-customer-journeys-data-transparency/customer-journey.webp
new file mode 100644
index 000000000..1f04c61e3
Binary files /dev/null and b/content/growth/build-customer-journeys-data-transparency/customer-journey.webp differ
diff --git a/content/growth/build-customer-journeys-data-transparency/index.md b/content/growth/build-customer-journeys-data-transparency/index.md
index 7731ae42f..f4ea49556 100644
--- a/content/growth/build-customer-journeys-data-transparency/index.md
+++ b/content/growth/build-customer-journeys-data-transparency/index.md
@@ -1,7 +1,7 @@
---
title: "Why is Data Transparency Critical To Building Connected Consumer Journeys?"
date: "2022-08-18"
-coverImage: "customer-journey.jpg"
+coverImage: "customer-journey.webp"
tags: ["progressive profiling", "cx", "data transparency"]
author: "Lucy Manole"
description: "Data is your most valuable resource when it comes to enhancing customer transparency. But how exactly can your company sort and apply all the data you collect from different customer touchpoints? This blog shares some actionable ideas."
@@ -72,7 +72,7 @@ The last few years have seen a growth in the use of [progressive profiling](http
This data can also help you come up with innovative ways to engage customers, such as immersive VR experiences that let them ‘try on’ a product or ‘walk through’ a showroom. Plus, the right data helps you be more transparent with your customers at the touchpoints where it’s needed the most.
-[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
+[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
### 3. Efficient decision-making
@@ -100,4 +100,4 @@ In short, data transparency can boost your brand reputation and customer loyalty
Remember, honesty is always the best policy — tell your customers the truth, even if that truth is not always the most pleasant. They will respect your integrity and like you the most for it in the long run. Rely on data transparency to deliver a complete end-to-end experience from the customer’s perspective. All the best!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=build-customer-journeys-data-transparency)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=build-customer-journeys-data-transparency)
diff --git a/content/growth/build-customer-journeys-data-transparency/progressive-profiling.png b/content/growth/build-customer-journeys-data-transparency/progressive-profiling.png
deleted file mode 100644
index c9ad88d9e..000000000
Binary files a/content/growth/build-customer-journeys-data-transparency/progressive-profiling.png and /dev/null differ
diff --git a/content/growth/build-customer-journeys-data-transparency/progressive-profiling.webp b/content/growth/build-customer-journeys-data-transparency/progressive-profiling.webp
new file mode 100644
index 000000000..2b537fe1a
Binary files /dev/null and b/content/growth/build-customer-journeys-data-transparency/progressive-profiling.webp differ
diff --git a/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.png b/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.png
deleted file mode 100644
index cbe459800..000000000
Binary files a/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.png and /dev/null differ
diff --git a/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.webp b/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.webp
new file mode 100644
index 000000000..efb695fb3
Binary files /dev/null and b/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.webp differ
diff --git a/content/growth/business-advantages-cloud-computing/cloud-marketg.jpg b/content/growth/business-advantages-cloud-computing/cloud-marketg.jpg
deleted file mode 100644
index 4d528c09e..000000000
Binary files a/content/growth/business-advantages-cloud-computing/cloud-marketg.jpg and /dev/null differ
diff --git a/content/growth/business-advantages-cloud-computing/cloud-marketg.webp b/content/growth/business-advantages-cloud-computing/cloud-marketg.webp
new file mode 100644
index 000000000..d7190b2bb
Binary files /dev/null and b/content/growth/business-advantages-cloud-computing/cloud-marketg.webp differ
diff --git a/content/growth/business-advantages-cloud-computing/index.md b/content/growth/business-advantages-cloud-computing/index.md
index 903ee2b01..616bb1567 100644
--- a/content/growth/business-advantages-cloud-computing/index.md
+++ b/content/growth/business-advantages-cloud-computing/index.md
@@ -1,7 +1,7 @@
---
title: "Reaping the Benefits of the Cloud Beyond Marketing"
date: "2022-06-21"
-coverImage: "cloud-marketg.jpg"
+coverImage: "cloud-marketg.webp"
category: ["cloud computing", "marketing", "ciam"]
author: "Navanita Devi"
description: "Cloud computing offers more than just helping marketers plan and execute effective marketing campaigns. Let’s look at some advantages of adopting cloud computing and why enterprises should consider relying on cloud computing to thrive overall business success."
@@ -34,7 +34,7 @@ Cloud servers are made to support massive sign-ins and sudden, dramatic surges o
The [LoginRadius Identity Platform](https://www.loginradius.com/) was designed with service provider-class scale in mind. The distributed CIAM network has regularly experienced peak transaction volumes of over 150,000 logins per second and typically handles 10,000 requests per second with less than 500 milliseconds latency.
-[](https://www.loginradius.com/scalability/)
+[](https://www.loginradius.com/scalability/)
### #2. Highly secure
@@ -80,4 +80,4 @@ With the changing digital landscape, businesses relying on on-premise infrastruc
Hence, to ensure they stay ahead of the curve, businesses should put their best efforts into adopting the cloud since it’s secure, scalable, cost-efficient, and maintenance-free.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=business-advantages-cloud-computing)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=business-advantages-cloud-computing)
\ No newline at end of file
diff --git a/content/growth/business-advantages-cloud-computing/wp-resilency.png b/content/growth/business-advantages-cloud-computing/wp-resilency.png
deleted file mode 100644
index 8fb3d9233..000000000
Binary files a/content/growth/business-advantages-cloud-computing/wp-resilency.png and /dev/null differ
diff --git a/content/growth/business-advantages-cloud-computing/wp-resilency.webp b/content/growth/business-advantages-cloud-computing/wp-resilency.webp
new file mode 100644
index 000000000..eebe75dbe
Binary files /dev/null and b/content/growth/business-advantages-cloud-computing/wp-resilency.webp differ
diff --git a/content/growth/business-review-meeting-success/business-review.jpg b/content/growth/business-review-meeting-success/business-review.jpg
deleted file mode 100644
index 272b0c2a7..000000000
Binary files a/content/growth/business-review-meeting-success/business-review.jpg and /dev/null differ
diff --git a/content/growth/business-review-meeting-success/business-review.webp b/content/growth/business-review-meeting-success/business-review.webp
new file mode 100644
index 000000000..def9886b7
Binary files /dev/null and b/content/growth/business-review-meeting-success/business-review.webp differ
diff --git a/content/growth/business-review-meeting-success/index.md b/content/growth/business-review-meeting-success/index.md
index 88f20756a..e594ba90a 100644
--- a/content/growth/business-review-meeting-success/index.md
+++ b/content/growth/business-review-meeting-success/index.md
@@ -1,7 +1,7 @@
---
title: "A Successful Business Review Meeting Paves the Path for Your Business Success"
date: "2022-01-13"
-coverImage: "business-review.jpg"
+coverImage: "business-review.webp"
category: ["all"]
featured: false
author: "Ritika Kapahi"
@@ -103,4 +103,4 @@ Moreover, you can help cement the relationship since you get a lot of feedback f
Enterprises that aren’t yet leveraging the true potential of QBRs must quickly put their best foot forward in conducting the same for ensuring better and lasting relationships with their clients.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=business-review-meeting-success)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=business-review-meeting-success)
\ No newline at end of file
diff --git a/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.png b/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.png
deleted file mode 100644
index fb9e830ba..000000000
Binary files a/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.png and /dev/null differ
diff --git a/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.webp b/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.webp
new file mode 100644
index 000000000..4ea6dbcbf
Binary files /dev/null and b/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.webp differ
diff --git a/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.jpg b/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.jpg
deleted file mode 100644
index 3a5484fd4..000000000
Binary files a/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.jpg and /dev/null differ
diff --git a/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.webp b/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.webp
new file mode 100644
index 000000000..69b8d4d73
Binary files /dev/null and b/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.webp differ
diff --git a/content/growth/cdp-ciam-cookieless-marketing/index.md b/content/growth/cdp-ciam-cookieless-marketing/index.md
index db09a5a30..579c1e16a 100644
--- a/content/growth/cdp-ciam-cookieless-marketing/index.md
+++ b/content/growth/cdp-ciam-cookieless-marketing/index.md
@@ -1,7 +1,7 @@
---
title: "How do CDP and CIAM Help Marketers in Cookieless Marketing?"
date: "2024-02-20"
-coverImage: "customer-data-platform.jpg"
+coverImage: "customer-data-platform.webp"
tags: ["customer data platform","ciam solutions","cx"]
author: "Navanita Devi"
description: "Gone are the days when marketing strategy included collecting and using third-party cookies to target consumers. In today’s era, consumers are calling the shots to control their privacy, leading to a big change in how marketers manage customer data. While the concept evolved into reality, how can marketers move forward? Stay tuned as we explore how CDP and CIAM help marketers thrive in cookieless marketing."
@@ -76,7 +76,7 @@ The identity graphs encompass information about a particular customer. With the
Marketers can also integrate various information, including demographics, purchase data, lifestyle, and more, using CDP and CIAM solutions. The data can create a customer identity that enables targeted marketing campaigns for exclusive customers.
-[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper)
+[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper)
### 4. Remain compliant with regulations
@@ -110,4 +110,4 @@ Complementing each other, CDP and CIAM help brands identify the customer across
Simply put, the ban on third-party cookies will inevitably affect marketers. However, the changes don't have to be too drastic. The blended approach of CDP and CIAM will give you the power to bridge the gaps and boost your marketing strategies in the cookieless world.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cdp-ciam-cookieless-marketing)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cdp-ciam-cookieless-marketing)
diff --git a/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.png b/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.png
deleted file mode 100644
index 6df429ab7..000000000
Binary files a/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.png and /dev/null differ
diff --git a/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.webp b/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.webp
new file mode 100644
index 000000000..9684babf6
Binary files /dev/null and b/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.webp differ
diff --git a/content/growth/change-management-consumer-security-tool/change-managmt.jpg b/content/growth/change-management-consumer-security-tool/change-managmt.jpg
deleted file mode 100644
index ff670f2b3..000000000
Binary files a/content/growth/change-management-consumer-security-tool/change-managmt.jpg and /dev/null differ
diff --git a/content/growth/change-management-consumer-security-tool/change-managmt.webp b/content/growth/change-management-consumer-security-tool/change-managmt.webp
new file mode 100644
index 000000000..40c27b41f
Binary files /dev/null and b/content/growth/change-management-consumer-security-tool/change-managmt.webp differ
diff --git a/content/growth/change-management-consumer-security-tool/ciso-wp.png b/content/growth/change-management-consumer-security-tool/ciso-wp.png
deleted file mode 100644
index d7768e095..000000000
Binary files a/content/growth/change-management-consumer-security-tool/ciso-wp.png and /dev/null differ
diff --git a/content/growth/change-management-consumer-security-tool/ciso-wp.webp b/content/growth/change-management-consumer-security-tool/ciso-wp.webp
new file mode 100644
index 000000000..c3af9b9a1
Binary files /dev/null and b/content/growth/change-management-consumer-security-tool/ciso-wp.webp differ
diff --git a/content/growth/change-management-consumer-security-tool/index.md b/content/growth/change-management-consumer-security-tool/index.md
index df1bfce38..8e76ff35d 100644
--- a/content/growth/change-management-consumer-security-tool/index.md
+++ b/content/growth/change-management-consumer-security-tool/index.md
@@ -1,7 +1,7 @@
---
title: "Unlock the Business Benefits of Change Management in Securing Consumer Identity"
date: "2022-01-19"
-coverImage: "change-managmt.jpg"
+coverImage: "change-managmt.webp"
tags: ["ciam solution","digital identity management","cx"]
author: "Rakesh Soni"
description: "If you are one of the many businesses that have not yet developed an effective change management strategy, this article is for you. With new data privacy regulations coming into effect, organizations face complex compliance issues. Ignoring these rules can turn out to be expensive."
@@ -69,7 +69,7 @@ This plan should take into consideration every possible requirement, outcome, an
Make a great plan, then manage it effectively. Choose the best leader to manage your plan, someone who can oversee the plan effectively. Effective oversight means following the change management procedure, from ensuring quality at each step to adequately resolving issues that arise.
-[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper)
+[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper)
Someone who understands the day-to-day operations of customer identity and access management is essential to a firm's customer security efforts. This person should also be able to visualize the impact of security on the brand, so that they can effectively implement necessary change management strategies.
@@ -93,4 +93,4 @@ Here are some of the tangible benefits of implementing change management strateg
Change management is the need of the hour in this internet driver business market. Enterprises can benefit a lot from focusing on customer identity and access management. A key part of this is ensuring customer security. The implementation of such change management strategies can also be outsourced to firms that specialize in [CIAM solutions](https://www.loginradius.com/), like LoginRadius.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=change-management-consumer-security-tool)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=change-management-consumer-security-tool)
\ No newline at end of file
diff --git a/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.jpg b/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.jpg
deleted file mode 100644
index 5ab02152a..000000000
Binary files a/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.jpg and /dev/null differ
diff --git a/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.webp b/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.webp
new file mode 100644
index 000000000..9f337475f
Binary files /dev/null and b/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.webp differ
diff --git a/content/growth/christmas-spirit-of-giving/index.md b/content/growth/christmas-spirit-of-giving/index.md
index 065c5178e..41d5ef1b5 100644
--- a/content/growth/christmas-spirit-of-giving/index.md
+++ b/content/growth/christmas-spirit-of-giving/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Gets into the Christmas Spirit (of Giving)"
date: "2019-12-17"
-coverImage: "christmas-spirit-of-giving.jpg"
+coverImage: "christmas-spirit-of-giving.webp"
category: ["media-and-publication"]
featured: false
author: "Rakesh Soni"
diff --git a/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.png b/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.png and /dev/null differ
diff --git a/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.webp b/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.webp differ
diff --git a/content/growth/ciam-budget-2023-recession/budget.jpg b/content/growth/ciam-budget-2023-recession/budget.jpg
deleted file mode 100644
index 8923bdf6d..000000000
Binary files a/content/growth/ciam-budget-2023-recession/budget.jpg and /dev/null differ
diff --git a/content/growth/ciam-budget-2023-recession/budget.webp b/content/growth/ciam-budget-2023-recession/budget.webp
new file mode 100644
index 000000000..a99fe2fd3
Binary files /dev/null and b/content/growth/ciam-budget-2023-recession/budget.webp differ
diff --git a/content/growth/ciam-budget-2023-recession/index.md b/content/growth/ciam-budget-2023-recession/index.md
index 7fa5c860d..45ced627f 100644
--- a/content/growth/ciam-budget-2023-recession/index.md
+++ b/content/growth/ciam-budget-2023-recession/index.md
@@ -1,7 +1,7 @@
---
title: "How To Plan Your CIAM Budget In A Recession As We Look Ahead Towards 2023?"
date: "2022-12-21"
-coverImage: "budget.jpg"
+coverImage: "budget.webp"
category: ["ciam", "cybersecurity", "budget"]
author: "Rakesh Soni"
description: "The key to optimizing and protecting your CIAM budget is to be clear and sure about everything that adds value to your organization. Here are some tips that can help you plan your CIAM budget smartly for 2023 on the declining global economy."
@@ -54,7 +54,7 @@ Many organizations understand the importance of investing in cybersecurity tools
* Enable risk-based authentication
* Frequent employee training sessions
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
## Making the Most out of Your Current CIAM Budget
@@ -77,4 +77,4 @@ As you plan your CIAM budget for 2023, consider which challenges pose the most s
An intelligent approach to budget planning can make all the difference for your security team.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-budget-2023-recession)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-budget-2023-recession)
diff --git a/content/growth/ciam-budget-2023-recession/zerotrust-wp.png b/content/growth/ciam-budget-2023-recession/zerotrust-wp.png
deleted file mode 100644
index 3e6b81ee6..000000000
Binary files a/content/growth/ciam-budget-2023-recession/zerotrust-wp.png and /dev/null differ
diff --git a/content/growth/ciam-budget-2023-recession/zerotrust-wp.webp b/content/growth/ciam-budget-2023-recession/zerotrust-wp.webp
new file mode 100644
index 000000000..2f7c01062
Binary files /dev/null and b/content/growth/ciam-budget-2023-recession/zerotrust-wp.webp differ
diff --git a/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.png b/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.png
deleted file mode 100644
index 6bddf0db4..000000000
Binary files a/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.png and /dev/null differ
diff --git a/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.webp b/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.webp
new file mode 100644
index 000000000..2842c3bcc
Binary files /dev/null and b/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.webp differ
diff --git a/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.png b/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.png
deleted file mode 100644
index 8bad2f974..000000000
Binary files a/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.png and /dev/null differ
diff --git a/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.webp b/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.webp
new file mode 100644
index 000000000..903afa91e
Binary files /dev/null and b/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.webp differ
diff --git a/content/growth/ciam-challenges-saas-business-app/index.md b/content/growth/ciam-challenges-saas-business-app/index.md
index f7bc6b0bd..25cfebedf 100644
--- a/content/growth/ciam-challenges-saas-business-app/index.md
+++ b/content/growth/ciam-challenges-saas-business-app/index.md
@@ -1,7 +1,7 @@
---
title: "8 Common Challenges With Your SaaS Business that CIAM Can Solve"
date: "2021-09-10"
-coverImage: "saas-buisness.jpg"
+coverImage: "saas-buisness.webp"
tags: ["saas","customer identity management","ciam solution"]
author: "Rashmi Mathur"
description: "To be successful, your SaaS needs to use the right application performance management software. CIAM is the first step you need to take to avoid common challenges like lack of compliance, and incompetent onboarding."
@@ -13,7 +13,7 @@ Digital communication between clients and a company is now a regular practice ac
The data gathered in databases can be vulnerable to cyber attacks that result in stolen customer and business identities. Hence, businesses look to increase their cybersecurity with the help of SaaS-based CIAM business solutions.
-[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
+[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
## Top Challenges With SaaS Apps and How CIAM Overcomes Them
@@ -61,4 +61,4 @@ One of the surpassing advantages of cloud applications is that admittance is obt
To summarize, we can say that a cloud-based CIAM service should present accurate visibility of user access. Also, providing your customers with the required protection against identity theft is crucial in preserving your company prominence. This is why it is vital to overcome these challenges to better leverage the benefits of CIAM to protect your business and clients.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-challenges-saas-business-app)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-challenges-saas-business-app)
\ No newline at end of file
diff --git a/content/growth/ciam-challenges-saas-business-app/saas-buisness.jpg b/content/growth/ciam-challenges-saas-business-app/saas-buisness.jpg
deleted file mode 100644
index 30fa6b6fb..000000000
Binary files a/content/growth/ciam-challenges-saas-business-app/saas-buisness.jpg and /dev/null differ
diff --git a/content/growth/ciam-challenges-saas-business-app/saas-buisness.webp b/content/growth/ciam-challenges-saas-business-app/saas-buisness.webp
new file mode 100644
index 000000000..1a5ff6795
Binary files /dev/null and b/content/growth/ciam-challenges-saas-business-app/saas-buisness.webp differ
diff --git a/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.jpg b/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.jpg
deleted file mode 100644
index b71009e0f..000000000
Binary files a/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.jpg and /dev/null differ
diff --git a/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.webp b/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.webp
new file mode 100644
index 000000000..f8b508c06
Binary files /dev/null and b/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.webp differ
diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.png b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.png
deleted file mode 100644
index 93302c0ce..000000000
Binary files a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.png and /dev/null differ
diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.webp b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.webp
new file mode 100644
index 000000000..9d62b96b8
Binary files /dev/null and b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.webp differ
diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.png b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.png
deleted file mode 100644
index 6784e19bd..000000000
Binary files a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.png and /dev/null differ
diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.webp b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.webp
new file mode 100644
index 000000000..c27d2fee5
Binary files /dev/null and b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.webp differ
diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.jpg b/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.jpg
deleted file mode 100644
index de44c8838..000000000
Binary files a/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.jpg and /dev/null differ
diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.webp b/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.webp
new file mode 100644
index 000000000..41d5677b8
Binary files /dev/null and b/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.webp differ
diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/index.md b/content/growth/ciam-improves-customer-trust-and-loyalty/index.md
index d4ed162d3..5d8312023 100644
--- a/content/growth/ciam-improves-customer-trust-and-loyalty/index.md
+++ b/content/growth/ciam-improves-customer-trust-and-loyalty/index.md
@@ -1,7 +1,7 @@
---
title: "How Can CIAM Help Businesses Build Trust And Loyalty?"
date: "2023-04-05"
-coverImage: "customer-trust.jpg"
+coverImage: "customer-trust.webp"
tags: ["ciam solution","mfa","compliance","sso","cx"]
author: "Vishal Sharma"
description: "By implementing CIAM solutions, businesses can provide customers with a personalized and secure experience while improving operational efficiency. Let’s figure out how companies can leverage the true potential of a robust CIAM to build trust and loyalty."
@@ -49,7 +49,7 @@ Many industries are subject to strict regulatory requirements around data privac
By demonstrating a commitment to compliance, businesses can build trust and confidence among customers, who will feel reassured that their data is being handled responsibly.
-[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
+[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
### 4. Convenience
Customers expect a seamless and hassle-free experience when interacting with businesses. CIAM solutions can help companies to deliver this by enabling [single sign-on](https://www.loginradius.com/single-sign-on/) (SSO) across multiple channels and applications.
@@ -66,4 +66,4 @@ CIAM is undoubtedly the need of the hour for businesses looking to build trust a
By providing a personalized, secure, compliant, convenient, and transparent experience, businesses can differentiate themselves from their competitors and build long-lasting customer relationships.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-improves-customer-trust-and-loyalty)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-improves-customer-trust-and-loyalty)
diff --git a/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.png b/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.png and /dev/null differ
diff --git a/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.webp b/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.webp differ
diff --git a/content/growth/ciam-minimizes-expenses-access-management/access-managemt.jpg b/content/growth/ciam-minimizes-expenses-access-management/access-managemt.jpg
deleted file mode 100644
index 57a8ff437..000000000
Binary files a/content/growth/ciam-minimizes-expenses-access-management/access-managemt.jpg and /dev/null differ
diff --git a/content/growth/ciam-minimizes-expenses-access-management/access-managemt.webp b/content/growth/ciam-minimizes-expenses-access-management/access-managemt.webp
new file mode 100644
index 000000000..a9fe5ce89
Binary files /dev/null and b/content/growth/ciam-minimizes-expenses-access-management/access-managemt.webp differ
diff --git a/content/growth/ciam-minimizes-expenses-access-management/index.md b/content/growth/ciam-minimizes-expenses-access-management/index.md
index 1c179efa5..9183aa475 100644
--- a/content/growth/ciam-minimizes-expenses-access-management/index.md
+++ b/content/growth/ciam-minimizes-expenses-access-management/index.md
@@ -1,7 +1,7 @@
---
title: "An Exclusive CIAM Benefit: The Role of Access Management in Cost Optimization"
date: "2023-01-13"
-coverImage: "access-managemt.jpg"
+coverImage: "access-managemt.webp"
category: ["ciam", "access managment", "user onboarding"]
author: "Rakesh Soni"
description: "Whether we talk about delivering a seamless authentication experience or reinforcing the overall business and customer identity security, a CIAM solution leaves no stone unturned in scaling business growth. This blog explains the aspects of leveraging the role of a CIAM’s access management in cost optimization."
@@ -58,7 +58,7 @@ CIAM is an integrated digital security platform combining advanced and user beha
And if you're wondering how it all fits together, here's how: CIAM incorporates MFA and risk-based authentication that helps mitigate the risks of identity theft and prevents a breach by gathering data about user behavior patterns for each employee or user account based on their specific role within your organization.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
Risk assessments are performed based on this data to determine whether or not an unauthorized user should have access to sensitive information via an online portal or application portal.
@@ -88,4 +88,4 @@ LoginRadius' extensive experience in the identity and access management market w
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-minimizes-expenses-access-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-minimizes-expenses-access-management)
diff --git a/content/growth/ciam-minimizes-expenses-access-management/rba-gd.png b/content/growth/ciam-minimizes-expenses-access-management/rba-gd.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/growth/ciam-minimizes-expenses-access-management/rba-gd.png and /dev/null differ
diff --git a/content/growth/ciam-minimizes-expenses-access-management/rba-gd.webp b/content/growth/ciam-minimizes-expenses-access-management/rba-gd.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/growth/ciam-minimizes-expenses-access-management/rba-gd.webp differ
diff --git a/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.png b/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.webp b/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.webp differ
diff --git a/content/growth/ciam-opportunity-for-cmos/cmo-ciam.jpg b/content/growth/ciam-opportunity-for-cmos/cmo-ciam.jpg
deleted file mode 100644
index b85bccaec..000000000
Binary files a/content/growth/ciam-opportunity-for-cmos/cmo-ciam.jpg and /dev/null differ
diff --git a/content/growth/ciam-opportunity-for-cmos/cmo-ciam.webp b/content/growth/ciam-opportunity-for-cmos/cmo-ciam.webp
new file mode 100644
index 000000000..e82d5dc8a
Binary files /dev/null and b/content/growth/ciam-opportunity-for-cmos/cmo-ciam.webp differ
diff --git a/content/growth/ciam-opportunity-for-cmos/index.md b/content/growth/ciam-opportunity-for-cmos/index.md
index 2d9c19f64..9d1e611c0 100644
--- a/content/growth/ciam-opportunity-for-cmos/index.md
+++ b/content/growth/ciam-opportunity-for-cmos/index.md
@@ -1,7 +1,7 @@
---
title: "Why CMOs should care about CIAM"
date: "2021-11-22"
-coverImage: "cmo-ciam.jpg"
+coverImage: "cmo-ciam.webp"
tags: ["data security","ciam solution","cx","mfa"]
author: "Rakesh Soni"
description: "CMOs can deliver more efficient, secure, and relevant services and goods if they have a detailed grasp of who their customers are and what they require. Learn how a CIAM solution may be a valuable strategic asset for CMOs to utilize in their department."
@@ -54,7 +54,7 @@ It entails a legitimate registration procedure that can be conducted and finishe
The advancement of 2FA/MFA (multi-factor authentication) with features like biometrics, geolocation, face recognition, and so on has resulted in higher degrees of protection. These characteristics make it simpler to spot abnormalities and strange actions in a less time-consuming manner.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### #4. Privacy and regulatory compliance
@@ -86,4 +86,4 @@ The goal of digital transformation is to [improve the customer experience](https
Consumer behavior and aspirations have never been static. A consumer identity management solution may be a valuable strategic asset for CMOs to utilize in their department.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-opportunity-for-cmos)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-opportunity-for-cmos)
diff --git a/content/growth/ciam-opportunity-for-cmos/mfa-eb.png b/content/growth/ciam-opportunity-for-cmos/mfa-eb.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/growth/ciam-opportunity-for-cmos/mfa-eb.png and /dev/null differ
diff --git a/content/growth/ciam-opportunity-for-cmos/mfa-eb.webp b/content/growth/ciam-opportunity-for-cmos/mfa-eb.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/growth/ciam-opportunity-for-cmos/mfa-eb.webp differ
diff --git a/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.png b/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.png
deleted file mode 100644
index f97184f2f..000000000
Binary files a/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.png and /dev/null differ
diff --git a/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.webp b/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.webp
new file mode 100644
index 000000000..88d19cbb8
Binary files /dev/null and b/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.webp differ
diff --git a/content/growth/ciam-prevents-abandoned-carts/cart-abandon.jpg b/content/growth/ciam-prevents-abandoned-carts/cart-abandon.jpg
deleted file mode 100644
index 81c3dffa4..000000000
Binary files a/content/growth/ciam-prevents-abandoned-carts/cart-abandon.jpg and /dev/null differ
diff --git a/content/growth/ciam-prevents-abandoned-carts/cart-abandon.webp b/content/growth/ciam-prevents-abandoned-carts/cart-abandon.webp
new file mode 100644
index 000000000..fd0900b95
Binary files /dev/null and b/content/growth/ciam-prevents-abandoned-carts/cart-abandon.webp differ
diff --git a/content/growth/ciam-prevents-abandoned-carts/index.md b/content/growth/ciam-prevents-abandoned-carts/index.md
index 6fa049b4f..5672dc082 100644
--- a/content/growth/ciam-prevents-abandoned-carts/index.md
+++ b/content/growth/ciam-prevents-abandoned-carts/index.md
@@ -1,7 +1,7 @@
---
title: "How CIAM can help in Preventing Abandoned Carts"
date: "2021-11-16"
-coverImage: "cart-abandon.jpg"
+coverImage: "cart-abandon.webp"
tags: ["progressive profiling","ciam solution","mfa","cx"]
author: "Rashmi Mathur"
description: "Shoppers leave their carts behind all the time. When this happens, it usually means that they're abandoning their purchase but also that they're possibly losing interest in your brand altogether. This blog takes a deeper look into how CIAM can stop the issue of abandoned carts."
@@ -34,7 +34,7 @@ Customer identity and other credentials are sensitive information that hackers c
Thankfully, CIAM helps you collect data as well as secure it. What makes it even better is that you can collect customers’ data that is beyond just registration! That’s right, through CIAM, you can even collect helpful information such as customers’ shopping patterns, buying choices, etc. And of course, you can use this information to boost your targeted marketing strategies and other ventures.
-[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
+[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
Talking about security, CIAM solutions tokenize customer identities to detach them from sensitive data while it's in storage. Furthermore, these solutions also use robust [data encryption and hashing](https://www.loginradius.com/blog/engineering/encryption-and-hashing/) to ensure the privacy of sensitive information and credentials.
@@ -65,4 +65,4 @@ It helps enable the organizations to have greater control of their information a
Consumers expect simplicity and speed with new-age authentication like the use of biometrics that replace passwords for secure and seamless login. Likewise, CIAM helps streamline the data storage and authentication to secure your customer experience and provide you with a competitive edge. The combination of these factors makes CIAM a powerful platform for any eCommerce enterprise.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-prevents-abandoned-carts)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-prevents-abandoned-carts)
diff --git a/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.png b/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.png
deleted file mode 100644
index c9ad88d9e..000000000
Binary files a/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.png and /dev/null differ
diff --git a/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.webp b/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.webp
new file mode 100644
index 000000000..2b537fe1a
Binary files /dev/null and b/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.webp differ
diff --git a/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.png b/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.png
deleted file mode 100644
index cbe459800..000000000
Binary files a/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.png and /dev/null differ
diff --git a/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.webp b/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.webp
new file mode 100644
index 000000000..efb695fb3
Binary files /dev/null and b/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.webp differ
diff --git a/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.jpg b/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.jpg
deleted file mode 100644
index 35b39f712..000000000
Binary files a/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.jpg and /dev/null differ
diff --git a/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.webp b/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.webp
new file mode 100644
index 000000000..f8d57c575
Binary files /dev/null and b/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.webp differ
diff --git a/content/growth/ciam-solution-digital-native-business/index.md b/content/growth/ciam-solution-digital-native-business/index.md
index 08a4578ba..77f67ff3b 100644
--- a/content/growth/ciam-solution-digital-native-business/index.md
+++ b/content/growth/ciam-solution-digital-native-business/index.md
@@ -1,7 +1,7 @@
---
title: "How is CIAM Solution a Critical Part of DNBs’ Digital Transformation Strategy?"
date: "2024-02-16"
-coverImage: "ciam-dig-transformation.jpg"
+coverImage: "ciam-dig-transformation.webp"
tags: ["digital transformation","ciam solutions","cx"]
author: "Vishal Sharma"
description: "Customer Identity and Access Management is about keeping customer data safe and giving them the proper access to things online. In today's interconnected era, digital native businesses must help them stay nimble and grow with evolving times. Let's explore the indispensable role of CIAM solutions in digital companies more!"
@@ -52,7 +52,7 @@ With CIAM solution, MFA is employed broadly in every business, including financi
A **CIAM solution** can handle millions of users across web and mobile channels to accommodate large volumes of users and spikes in registrations and access requests without affecting the high level of performance.
-[](https://www.loginradius.com/resource/enterprise-scalability-and-performance)
+[](https://www.loginradius.com/resource/enterprise-scalability-and-performance)
### 3. Privacy and Compliance
@@ -98,4 +98,4 @@ Today, CIAM has become more than just an identity gateway for customers. It has
At LoginRadius, we offer constructive CIAM solutions and add the factor of the outcome – a better performing, more scalable, flexible, and secure system that will scale your business to billions of customers. As a trustworthy **CIAM provider,** we help you earn their trust and set you up for long-term success in the digital age.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-solution-digital-native-business)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-solution-digital-native-business)
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.jpg b/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.jpg
deleted file mode 100644
index 6476faf01..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.jpg and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.webp b/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.webp
new file mode 100644
index 000000000..ef0a00d8d
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.png b/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.png
deleted file mode 100644
index 76b1c7bae..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.webp b/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.webp
new file mode 100644
index 000000000..265f4380c
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.png
deleted file mode 100644
index c49cb67a7..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.webp
new file mode 100644
index 000000000..d9f323285
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.png
deleted file mode 100644
index fd32e89f4..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.webp
new file mode 100644
index 000000000..4583e99aa
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.png
deleted file mode 100644
index e7dedd6b6..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.webp
new file mode 100644
index 000000000..244d96f86
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.png
deleted file mode 100644
index 596540f99..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.webp
new file mode 100644
index 000000000..dded6d4ed
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.png
deleted file mode 100644
index e3ba2b701..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.webp
new file mode 100644
index 000000000..6474361cc
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.png
deleted file mode 100644
index 28c7174df..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.webp
new file mode 100644
index 000000000..18df8cb4f
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.jpg b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.jpg
deleted file mode 100644
index 6b02e681e..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.jpg and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.webp
new file mode 100644
index 000000000..ee91429c5
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.jpg b/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.jpg
deleted file mode 100644
index 64aee97a5..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.jpg and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.webp b/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.webp
new file mode 100644
index 000000000..4075a053e
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Departika.png b/content/growth/complete-color-scheme-guide-for-your-website/Departika.png
deleted file mode 100644
index e7489e714..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Departika.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Departika.webp b/content/growth/complete-color-scheme-guide-for-your-website/Departika.webp
new file mode 100644
index 000000000..87a5dddd3
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Departika.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.png b/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.png
deleted file mode 100644
index 904dbdad3..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.webp b/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.webp
new file mode 100644
index 000000000..a820766bd
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Magoz.png b/content/growth/complete-color-scheme-guide-for-your-website/Magoz.png
deleted file mode 100644
index 23884a37d..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Magoz.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Magoz.webp b/content/growth/complete-color-scheme-guide-for-your-website/Magoz.webp
new file mode 100644
index 000000000..74f3451f3
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Magoz.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.png b/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.png
deleted file mode 100644
index e473ad3bb..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.webp b/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.webp
new file mode 100644
index 000000000..5cb722a71
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.png b/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.png
deleted file mode 100644
index f8e8a9c56..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.webp b/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.webp
new file mode 100644
index 000000000..c19026d55
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.png b/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.png
deleted file mode 100644
index 4fec530f2..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.webp b/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.webp
new file mode 100644
index 000000000..c32a2d7f0
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.png b/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.png
deleted file mode 100644
index 5e14abdd5..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.webp b/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.webp
new file mode 100644
index 000000000..918ee89c3
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.png b/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.png
deleted file mode 100644
index 367d9c4b3..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.png and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.webp b/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.webp
new file mode 100644
index 000000000..d5806bca1
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.jpg b/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.jpg
deleted file mode 100644
index d59962368..000000000
Binary files a/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.jpg and /dev/null differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.webp b/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.webp
new file mode 100644
index 000000000..8f1ed86b6
Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.webp differ
diff --git a/content/growth/complete-color-scheme-guide-for-your-website/index.md b/content/growth/complete-color-scheme-guide-for-your-website/index.md
index d10770ec2..ae1924130 100644
--- a/content/growth/complete-color-scheme-guide-for-your-website/index.md
+++ b/content/growth/complete-color-scheme-guide-for-your-website/index.md
@@ -1,7 +1,7 @@
---
title: "A Complete Color Scheme Guide For Your Website"
date: "2017-05-19"
-coverImage: "A-Complete-Color-Scheme-Guide-For-Your-Website.jpg"
+coverImage: "A-Complete-Color-Scheme-Guide-For-Your-Website.webp"
category: ["business", "Marketing", "technology"]
featured: false
author: "Rakesh Soni"
@@ -32,15 +32,15 @@ Whether it is your brand image or your website, colors can work like magic on yo
What are the things that come to your mind when I say the word Coca Cola? Obviously, a bottle of it. Then, the red logo of Coca-Cola. There was a reason why Coca-Cola chose the color “Red”.
-
+
-**[Source](http://1.bp.blogspot.com/-feRUkS6z3uo/VIctsB0pI1I/AAAAAAAAAAo/nbmsMeSl_ls/s1600/india.png?ver=1553881376)**
+**[Source](http://1.bp.blogspot.com/-feRUkS6z3uo/VIctsB0pI1I/AAAAAAAAAAo/nbmsMeSl_ls/s1600/india.webp?ver=1553881376)**
Red shows excitement, passion and boldness and these were the emotions Coca-Cola wanted to convey with its product. Moreover, the color red makes it more visible on the shelves from its competitors. Well, here is an image showing reasons for different brands choosing respective colors in their logos.
-
+
-**[Source](http://blog.dahmundfreunde.de/wp-content/uploads/2014/05/grafik.png?ver=1553881376)**
+**[Source](http://blog.dahmundfreunde.de/wp-content/uploads/2014/05/grafik.webp?ver=1553881376)**
Kissmetrics says that there is an [80% increase in brand recognition](https://blog.kissmetrics.com/color-psychology/) when colors are used.
@@ -52,15 +52,15 @@ Create an awesome color scheme and here’s **how you can create a color scheme*
Your customers will connect their emotions with your brand through your prominent color. Hence, choose a color that convey the emotions about your company (like the red color in Coca-Cola does). Your logo should contain your prominent color as the primary color. However, if you have no clue which color to cast as your prominent color, see this image to decide the color of your choice.
-
+
-**[Source](https://mustafa12abdall.files.wordpress.com/2015/01/colors_customers_2.jpg?ver=1553881376)**
+**[Source](https://mustafa12abdall.files.wordpress.com/2015/01/colors_customers_2.webp?ver=1553881376)**
You can also see for this chart to decide which colors to pick from the slot:-
-
+
-[**Source**](https://s-media-cache-ak0.pinimg.com/originals/25/93/1f/25931fe9980a8a2e06cd66df76a055ee.jpg?ver=1553881376)
+[**Source**](https://s-media-cache-ak0.pinimg.com/originals/25/93/1f/25931fe9980a8a2e06cd66df76a055ee.webp?ver=1553881376)
Other than these psychological facts, you can check whether you are going to serve a youthful and energetic audience or your product is targeting a female audience. Hence, you have to decide the color on the basis of your targeted audience.
@@ -70,13 +70,13 @@ It is found out that most of the color blind patients are red-green color blinde
_Some statistics that show what color do what men and women get attracted to while shopping_
-
+
[**Source**](https://blog.kissmetrics.com/how-colors-affect-conversions/)
Also in another experiment, it was found that men preferred shades and bright colors while women preferred tints and soft colors.
-**[Source](https://blog.kissmetrics.com/gender-and-color/)**
+**[Source](https://blog.kissmetrics.com/gender-and-color/)**
By these data, you can certainly improve your color marketing strategies through color scheme.
@@ -88,7 +88,7 @@ Now, let’s discuss about the areas on your website where we can use the promin
Only use prominent color on areas which you want to highlight to you customers like you logo, menu tabs, call to actions, and any important information. Here’s, how we do it at LoginRadius.
-
+
**[Source](https://loginradius.com/)**
@@ -100,7 +100,7 @@ For example, you can use accent colors on secondary information, current menu ta
Also, do not use more than two accent colors on your webpages. It may confuse your prospects. Here’s a simple example to use accent colors on your website:-
- **[Source](https://loginradius.com/)**
+ **[Source](https://loginradius.com/)**
Now, there are two ways to select your color scheme. Pursue a Phd career in color psychology or use these color matching tools to create a color palette (well, hiring a good designer may cost you more).
@@ -130,7 +130,7 @@ Thus, here I have divided the websites into three types on the basis of their in
You will find that majority of the content driven or e-commerce websites have neutral or white background. The intent of such websites is to promote their products or ideas rather than flashing the background of the website. Hence, the prominent and accent colors provide focus and personality to your website whereas the neutral background keeps your customers focused on your products or content.
-
+
#### **2\. Corporate Websites**
@@ -142,7 +142,7 @@ While you are promoting a brand, use your prominent colors as a part of your bac
In case, you have a bold prominent color, then you can use less intense shades of the prominent colors. Here’s an example of how [Cadbury](https://www.cadbury.co.uk/) does it:-
-
+
You can use the above discussed tools to choose different shades of your prominent colors that will go well with your website’s background.
@@ -150,7 +150,7 @@ You can use the above discussed tools to choose different shades of your promine
Now, when you want your services to be the attention grabbers, use light colors for background as it will automatically highlight the content (product) on the page. Our web designers have done a good job highlighting our services.
-
+
[**Source**](https://loginradius.com/)
@@ -158,9 +158,9 @@ Now, when you want your services to be the attention grabbers, use light colors
When it comes to creative or stylish websites (creative, beauty, restaurant, design and fashion industries), you can use any colors in the background of your website. You can design a black background to provide a luxurious look or you can inspire your visitors with a rainbow background. Don’t lose your content’s visibility for the sake of charm on your website. Here’s a great template you can use for your creative website.
-
+
-[**Source**](https://blog.spoongraphics.co.uk/wp-content/uploads/2008/doodle-websites/24.jpg?ver=1553881376)
+[**Source**](https://blog.spoongraphics.co.uk/wp-content/uploads/2008/doodle-websites/24.webp?ver=1553881376)
In a nutshell, the best background for your website will make your content more visible and will render a good feeling to your visitors while browsing. And still if you are struggling with the background color, use a light color for your background. Don’t expect your website to look inspirational enough, however, your content will be noticed.
@@ -178,37 +178,37 @@ Here are some websites you can take a look for some inspiration.
#### **1.** [**Departika**](http://www.departika.com/)
-
+
Specialty: Minimal yet effective
#### **2\. [Magoz](https://magoz.is/)**
-
+
Specialty: Vibrant
#### **3. [SecretKey](https://www.secretkey.it/)**
-
+
Specialty: Attractive combination of multiple colors
#### **4. [Softwaremill](https://softwaremill.com/)**
-
+
Specialty: Beautiful yet elegant
#### **5. [Spektrum](http://spektrummedia.com/)**
-
+
Specialty: Wise usage of neon colors to give it modern touch
#### **6. [Enterprise England](http://enterpriseengland.org.uk/)**
-
+
Specialty: Beautiful color combination
diff --git a/content/growth/consent-management-business-advantages/DS-consent-mngmnt.png b/content/growth/consent-management-business-advantages/DS-consent-mngmnt.png
deleted file mode 100644
index b2c0a4d84..000000000
Binary files a/content/growth/consent-management-business-advantages/DS-consent-mngmnt.png and /dev/null differ
diff --git a/content/growth/consent-management-business-advantages/DS-consent-mngmnt.webp b/content/growth/consent-management-business-advantages/DS-consent-mngmnt.webp
new file mode 100644
index 000000000..8dcbd7082
Binary files /dev/null and b/content/growth/consent-management-business-advantages/DS-consent-mngmnt.webp differ
diff --git a/content/growth/consent-management-business-advantages/index.md b/content/growth/consent-management-business-advantages/index.md
index d61b8ba27..5274d6a90 100644
--- a/content/growth/consent-management-business-advantages/index.md
+++ b/content/growth/consent-management-business-advantages/index.md
@@ -1,7 +1,7 @@
---
title: "The Power Of Consent Marketing- A Deep Dive Into Its Endless Advantages"
date: "2024-04-16"
-coverImage: "power-consent-mngmnt.jpg"
+coverImage: "power-consent-mngmnt.webp"
tags: ["consent management","data security","compliance"]
author: "Navanita Devi"
description: "Discover the pivotal role of consent marketing in today's digital landscape. Explore how it goes beyond legal compliance to build trust, enhance targeting, ensure legal compliance, and foster long-term customer relationships."
@@ -38,7 +38,7 @@ Consent marketing allows for more targeted campaigns, ensuring that messages are
This targeted approach improves engagement rates and enhances the overall [user experience](https://www.loginradius.com/blog/growth/4-tips-secure-frictionless-ux/). Users receive content that is meaningful to them, leading to higher conversion rates and customer satisfaction.
-[](https://www.loginradius.com/resource/loginradius-consent-management)
+[](https://www.loginradius.com/resource/loginradius-consent-management)
### Legal Compliance
@@ -80,4 +80,4 @@ Consent marketing is not just a legal requirement; it's a strategic approach tha
By respecting user preferences, businesses can create a more trustworthy and engaging brand image while fostering long-lasting customer relationships. With solutions like LoginRadius' consent management, businesses can navigate the complexities of consent marketing with ease, ensuring compliance and building customer trust every step of the way.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consent-management-business-advantages)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consent-management-business-advantages)
diff --git a/content/growth/consent-management-business-advantages/power-consent-mngmnt.jpg b/content/growth/consent-management-business-advantages/power-consent-mngmnt.jpg
deleted file mode 100644
index 751ebda5e..000000000
Binary files a/content/growth/consent-management-business-advantages/power-consent-mngmnt.jpg and /dev/null differ
diff --git a/content/growth/consent-management-business-advantages/power-consent-mngmnt.webp b/content/growth/consent-management-business-advantages/power-consent-mngmnt.webp
new file mode 100644
index 000000000..28b5a65d7
Binary files /dev/null and b/content/growth/consent-management-business-advantages/power-consent-mngmnt.webp differ
diff --git a/content/growth/consent-management-online-retail/DS-ccpa-compliance.png b/content/growth/consent-management-online-retail/DS-ccpa-compliance.png
deleted file mode 100644
index 93302c0ce..000000000
Binary files a/content/growth/consent-management-online-retail/DS-ccpa-compliance.png and /dev/null differ
diff --git a/content/growth/consent-management-online-retail/DS-ccpa-compliance.webp b/content/growth/consent-management-online-retail/DS-ccpa-compliance.webp
new file mode 100644
index 000000000..9d62b96b8
Binary files /dev/null and b/content/growth/consent-management-online-retail/DS-ccpa-compliance.webp differ
diff --git a/content/growth/consent-management-online-retail/index.md b/content/growth/consent-management-online-retail/index.md
index e497a2498..610356ee9 100644
--- a/content/growth/consent-management-online-retail/index.md
+++ b/content/growth/consent-management-online-retail/index.md
@@ -1,7 +1,7 @@
---
title: "Exploring the Vital Role of Consent Management for Your Online Store"
date: "2023-09-08"
-coverImage: "online-store-consent-mngmnt.jpg"
+coverImage: "online-store-consent-mngmnt.webp"
tags: ["consent management","data privacy","compliance","cx"]
author: "Vishal Sharma"
description: "In today’s modern digital world, online success hinges on more than just great products and user-friendly interfaces. It's about respecting privacy, complying with regulations, and fostering trust. Consent management plays a vital role in achieving these goals. By being transparent about data usage, respecting customer privacy, and complying with regulations like GDPR, you not only avoid legal troubles but also gain a competitive edge."
@@ -55,7 +55,7 @@ Customers are often annoyed by relentless marketing emails and ads that seem irr
Proper consent management includes safeguarding customer data. You reduce the risk of data breaches by implementing robust security measures, limiting data access to authorized personnel, and monitoring for suspicious activity. Customers appreciate the peace of mind that their data is protected.
-[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
+[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
### 2. Data Portability
@@ -77,4 +77,4 @@ Consent management is a legal requirement and a strategic business practice. It'
Implementing an effective consent management system should be a top priority for any online business looking to thrive in the digital era. Your commitment to data privacy can set you apart from competitors and create long-lasting customer relationships.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consent-management-online-retail)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consent-management-online-retail)
diff --git a/content/growth/consent-management-online-retail/online-store-consent-mngmnt.jpg b/content/growth/consent-management-online-retail/online-store-consent-mngmnt.jpg
deleted file mode 100644
index 4bc171ef9..000000000
Binary files a/content/growth/consent-management-online-retail/online-store-consent-mngmnt.jpg and /dev/null differ
diff --git a/content/growth/consent-management-online-retail/online-store-consent-mngmnt.webp b/content/growth/consent-management-online-retail/online-store-consent-mngmnt.webp
new file mode 100644
index 000000000..00bc7ce74
Binary files /dev/null and b/content/growth/consent-management-online-retail/online-store-consent-mngmnt.webp differ
diff --git a/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.jpg b/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.jpg
deleted file mode 100644
index f223fce72..000000000
Binary files a/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.jpg and /dev/null differ
diff --git a/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.webp b/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.webp
new file mode 100644
index 000000000..e810c34c2
Binary files /dev/null and b/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.webp differ
diff --git a/content/growth/consumer-experience-and-privacy/index.md b/content/growth/consumer-experience-and-privacy/index.md
index 7f6b7c589..b997ee36c 100644
--- a/content/growth/consumer-experience-and-privacy/index.md
+++ b/content/growth/consumer-experience-and-privacy/index.md
@@ -1,7 +1,7 @@
---
title: "Walking the Fine Line Between Consumer Experience and Privacy"
date: "2021-02-24"
-coverImage: "consumer-experience-privacy.jpg"
+coverImage: "consumer-experience-privacy.webp"
category: ["all"]
featured: false
author: "Rakesh Soni"
@@ -64,4 +64,4 @@ Unfortunately, the current consumer experience and [data security practices](htt
Consent as well as robust security protocols play key roles in walking the fine line between data management and consumer privacy expectations. An organization that handles their consumers’ data ethically stands to gain a considerable edge against competitors through greater access to data, greater consumer trust, and potential to secure more privacy-conscious consumers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-experience-and-privacy)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-experience-and-privacy)
diff --git a/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.jpg b/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.jpg
deleted file mode 100644
index 3425702c2..000000000
Binary files a/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.jpg and /dev/null differ
diff --git a/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.webp b/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.webp
new file mode 100644
index 000000000..6a7acacba
Binary files /dev/null and b/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.webp differ
diff --git a/content/growth/consumer-experience-b2b-saas/index.md b/content/growth/consumer-experience-b2b-saas/index.md
index f49b09d48..287f32efb 100644
--- a/content/growth/consumer-experience-b2b-saas/index.md
+++ b/content/growth/consumer-experience-b2b-saas/index.md
@@ -1,7 +1,7 @@
---
title: "5 Tips to Enhance the Consumer Experience in B2B SaaS"
date: "2021-01-15"
-coverImage: "5-tips-consumer-experience-b2b-saas.jpg"
+coverImage: "5-tips-consumer-experience-b2b-saas.webp"
category: ["all"]
featured: false
author: "Rakesh Soni"
@@ -43,7 +43,7 @@ Speak to them about the business principles they would anticipate from using you
In reality, companies should organize their teams to facilitate and carry out substantive consumer discussions about adding value to their businesses. It includes pre-sales, post-sales, marketing, and consumer/technology support.
-[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience)
+[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience)
## #4. Omnichannel approach for B2B SaaS.
@@ -71,4 +71,4 @@ To bring it all together, the basis of B2B SaaS consumer experience depends on h
It is essential to make sure that anything your client comes across from your business should turn out to be an enjoyable experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-experience-b2b-saas)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-experience-b2b-saas)
\ No newline at end of file
diff --git a/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.jpg b/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.jpg
deleted file mode 100644
index 17940ab41..000000000
Binary files a/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.jpg and /dev/null differ
diff --git a/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.webp b/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.webp
new file mode 100644
index 000000000..39f6da380
Binary files /dev/null and b/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.webp differ
diff --git a/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.jpg b/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.jpg
deleted file mode 100644
index e59da3184..000000000
Binary files a/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.jpg and /dev/null differ
diff --git a/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.webp b/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.webp
new file mode 100644
index 000000000..086a5ed87
Binary files /dev/null and b/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.webp differ
diff --git a/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.png b/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.png
deleted file mode 100644
index 69d26339f..000000000
Binary files a/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.png and /dev/null differ
diff --git a/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.webp b/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.webp
new file mode 100644
index 000000000..96ed92a38
Binary files /dev/null and b/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.webp differ
diff --git a/content/growth/consumer-identity-role-in-the-digital-banking/index.md b/content/growth/consumer-identity-role-in-the-digital-banking/index.md
index 86ecbf29b..0a0757330 100644
--- a/content/growth/consumer-identity-role-in-the-digital-banking/index.md
+++ b/content/growth/consumer-identity-role-in-the-digital-banking/index.md
@@ -1,7 +1,7 @@
---
title: "Role of Consumer Identity Authentication in Digital Banking"
date: "2021-07-19"
-coverImage: "Digital-banking-platform-making-opt.jpg"
+coverImage: "Digital-banking-platform-making-opt.webp"
category: ["loginradius"]
featured: false
author: "Navanita Devi"
@@ -39,7 +39,7 @@ To put that in context, identity solutions for digital marketing and access mana
The instruments that assure the legality of these distant movements are the electronic signature and systems for certified evidence retention. The main problem, however, is identity identification, which ensures the transaction's authenticity and intentionality. It is no longer sufficient to protect a basic user code and password.
-[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
## What To Do To Highlight Consumer Identity
@@ -75,4 +75,4 @@ If identification is the real cash, then digital identity and banking authentica
[LoginRadius](https://www.loginradius.com/) provides seamless, call or SMS-based Multi-Factor Authentication with a visible layer of security protection. You get to choose whether this security system is mandatory or optional for your consumers. The SMS and call systems hold zero lag with global coverage! [Contact the team](https://www.loginradius.com/contact-sales/) today!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-identity-role-in-the-digital-banking)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-identity-role-in-the-digital-banking)
diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.png b/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.png and /dev/null differ
diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.webp b/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.webp differ
diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/index.md b/content/growth/consumer-identity-rule-personalized-marketing-2022/index.md
index a35140c1b..6d77a6035 100644
--- a/content/growth/consumer-identity-rule-personalized-marketing-2022/index.md
+++ b/content/growth/consumer-identity-rule-personalized-marketing-2022/index.md
@@ -1,7 +1,7 @@
---
title: "Do Consumer Identity Programs Really Work for Personalized Marketing?"
date: "2021-12-14"
-coverImage: "personalized-marketing.jpg"
+coverImage: "personalized-marketing.webp"
tags: ["identity management","ciam solution","mfa","cx"]
author: "Navanita Devi"
description: "Consumer identity management is actually a great way to help companies grow. It is through high quality CIAM that a business can create better targeted, safer, more meaningful marketing experiences for their customers."
@@ -49,7 +49,7 @@ When registering for an application the first time, you have to fill out details
After this, the application observes your activities and keeps the interface evolving according to the user activities.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
* **_Multi-factor authentication_**
@@ -73,4 +73,4 @@ Consumer data is precious for your business, and its safety is the number one co
There are many benefits of consumer identity programs for marketing, the two most important benefits being safety and personalization. Both of these can be achieved by proper implementation of CIAM from the business leaders.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-identity-rule-personalized-marketing-2022)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-identity-rule-personalized-marketing-2022)
diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.png b/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.png and /dev/null differ
diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.webp b/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.webp differ
diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.jpg b/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.jpg
deleted file mode 100644
index f0d218a47..000000000
Binary files a/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.jpg and /dev/null differ
diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.webp b/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.webp
new file mode 100644
index 000000000..6fabe031a
Binary files /dev/null and b/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.webp differ
diff --git a/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.jpg b/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.jpg
deleted file mode 100644
index 731b4880c..000000000
Binary files a/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.jpg and /dev/null differ
diff --git a/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.webp b/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.webp
new file mode 100644
index 000000000..8939c20bc
Binary files /dev/null and b/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.webp differ
diff --git a/content/growth/consumer-journey-from-sign-up-to-purchase/index.md b/content/growth/consumer-journey-from-sign-up-to-purchase/index.md
index 7989e801b..ef53f71ac 100644
--- a/content/growth/consumer-journey-from-sign-up-to-purchase/index.md
+++ b/content/growth/consumer-journey-from-sign-up-to-purchase/index.md
@@ -1,7 +1,7 @@
---
title: "From Sign-Up to Purchase – How LoginRadius Offers a Frictionless Consumer Journey"
date: "2021-07-14"
-coverImage: "consumer-signup-to-purchase.jpg"
+coverImage: "consumer-signup-to-purchase.webp"
tags: ["user onboarding","ciam solution","cx"]
author: "Vishal Sharma"
description: " Enterprises, today, must be aware of the fact that the secret to success lies in quickly identifying and eliminating any pain point that occurs when consumers interact with their brand. Here’s an insightful read depicting how LoginRadius helps enterprises navigate their business success through a frictionless consumer journey."
@@ -124,4 +124,4 @@ LoginRadius understands the importance of consumer onboarding and has designed a
Ready to leverage the next level of CIAM solution? Or have any doubts? [Schedule a Quick Personalized Call](https://www.loginradius.com/contact-sales/) and understand how LoginRadius can be a game-changer for your business success.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-journey-from-sign-up-to-purchase)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-journey-from-sign-up-to-purchase)
diff --git a/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.jpg b/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.jpg
deleted file mode 100644
index c1302a657..000000000
Binary files a/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.jpg and /dev/null differ
diff --git a/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.webp b/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.webp
new file mode 100644
index 000000000..32a9bee9d
Binary files /dev/null and b/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.webp differ
diff --git a/content/growth/consumer-management-to-consumer-engagement/index.md b/content/growth/consumer-management-to-consumer-engagement/index.md
index 9c63aa302..b1741ecca 100644
--- a/content/growth/consumer-management-to-consumer-engagement/index.md
+++ b/content/growth/consumer-management-to-consumer-engagement/index.md
@@ -1,7 +1,7 @@
---
title: "How to Shift Focus From Consumer Management to Consumer Engagement"
date: "2021-02-12"
-coverImage: "consumer-engagement.jpg"
+coverImage: "consumer-engagement.webp"
category: ["customer-engagement", "customer-experience"]
author: "Yash Rathi"
description: "Historically, organizations were more focused on managing and facilitating consumers' to be on top of everything. However, in the past couple of years, the paradigm has shifted from working as the facilitator to acting as a consultant and driving consumer engagement."
@@ -72,4 +72,4 @@ Strategies that bring out the 'wow' factor are always the best ones. Be it via s
I hope these consumer engagement strategies will induce you to get into action. Keep in touch for more strategies and possible outcomes. Keep reading :)
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-management-to-consumer-engagement)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-management-to-consumer-engagement)
diff --git a/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.jpg b/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.jpg
deleted file mode 100644
index 007557626..000000000
Binary files a/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.jpg and /dev/null differ
diff --git a/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.webp b/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.webp
new file mode 100644
index 000000000..39a554bb3
Binary files /dev/null and b/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.webp differ
diff --git a/content/growth/consumer-onboarding-strategies-for-saas-businesses/index.md b/content/growth/consumer-onboarding-strategies-for-saas-businesses/index.md
index 26ca18684..1f4038f53 100644
--- a/content/growth/consumer-onboarding-strategies-for-saas-businesses/index.md
+++ b/content/growth/consumer-onboarding-strategies-for-saas-businesses/index.md
@@ -1,7 +1,7 @@
---
title: "Consumer Onboarding Strategies for SaaS Businesses"
date: "2021-06-17"
-coverImage: "customer-onboarding.jpg"
+coverImage: "customer-onboarding.webp"
category: ["loginradius"]
featured: false
author: "Vishal Sharma"
@@ -96,4 +96,4 @@ As an enterprise, you may have a lot of information regarding your potential cli
LoginRadius can be your best onboarding partner that can help increase conversions and also minimize consumer churn.
With a long list of features to enhance your business growth, LoginRadius paves the path for a successful onboarding journey.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-onboarding-strategies-for-saas-businesses)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-onboarding-strategies-for-saas-businesses)
diff --git a/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.png b/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.png and /dev/null differ
diff --git a/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.webp b/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.webp differ
diff --git a/content/growth/consumer-sentiments-on-modern-identity/index.md b/content/growth/consumer-sentiments-on-modern-identity/index.md
index 541667d58..8ad9d65ba 100644
--- a/content/growth/consumer-sentiments-on-modern-identity/index.md
+++ b/content/growth/consumer-sentiments-on-modern-identity/index.md
@@ -1,7 +1,7 @@
---
title: "Uncovering Consumer Sentiments on Modern Identity: A Deep Dive Into Their Behavior"
date: "2023-06-26"
-coverImage: "modern-identity.jpg"
+coverImage: "modern-identity.webp"
tags: ["customer identity","identity management","authentication","cx"]
author: "Rakesh Soni"
description: "Today, consumers' attitudes toward modern identity are evolving rapidly. This blog explains the complexities of consumer sentiments, exploring the impact of social media, privacy concerns, inclusivity, and authenticity. Learn how businesses can effectively engage with their target audiences in this ever-changing landscape."
@@ -46,7 +46,7 @@ Modern identity is closely intertwined with the concepts of inclusivity and dive
Brands that embrace and celebrate diversity resonate more with consumers as they align with their values and aspirations. Fostering inclusivity enhances brand perception and cultivates a sense of belonging and loyalty among consumers.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
### 5. Authenticity and purpose-driven brands
@@ -74,4 +74,4 @@ By recognizing and understanding the complexities of consumer perceptions, busin
Brands that embrace inclusivity prioritize data security, and demonstrate authenticity will stand out in today's competitive landscape. Ultimately, brands can forge meaningful connections and build a loyal customer base by aligning their values with their consumers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-sentiments-on-modern-identity)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-sentiments-on-modern-identity)
\ No newline at end of file
diff --git a/content/growth/consumer-sentiments-on-modern-identity/modern-identity.jpg b/content/growth/consumer-sentiments-on-modern-identity/modern-identity.jpg
deleted file mode 100644
index 20229b861..000000000
Binary files a/content/growth/consumer-sentiments-on-modern-identity/modern-identity.jpg and /dev/null differ
diff --git a/content/growth/consumer-sentiments-on-modern-identity/modern-identity.webp b/content/growth/consumer-sentiments-on-modern-identity/modern-identity.webp
new file mode 100644
index 000000000..949d7bfd5
Binary files /dev/null and b/content/growth/consumer-sentiments-on-modern-identity/modern-identity.webp differ
diff --git a/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.png b/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.png and /dev/null differ
diff --git a/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.webp b/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.webp differ
diff --git a/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.jpg b/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.jpg
deleted file mode 100644
index a6ae8bb89..000000000
Binary files a/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.jpg and /dev/null differ
diff --git a/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.webp b/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.webp
new file mode 100644
index 000000000..6a9069d91
Binary files /dev/null and b/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.webp differ
diff --git a/content/growth/continuous-adaptive-authentication-future-2024/index.md b/content/growth/continuous-adaptive-authentication-future-2024/index.md
index 47eacfbc7..7e0cf22e9 100644
--- a/content/growth/continuous-adaptive-authentication-future-2024/index.md
+++ b/content/growth/continuous-adaptive-authentication-future-2024/index.md
@@ -1,7 +1,7 @@
---
title: "Continuous Adaptive Trust - Adaptive Authentication Future"
date: "2023-11-23"
-coverImage: "continuous-adptive-auth.jpg"
+coverImage: "continuous-adptive-auth.webp"
tags: ["continuous adaptive authentication","compliance","cx"]
author: "Rakesh Soni"
description: "Discover the game-changing evolution of authentication with Continuous Adaptive Trust (CAT) in 2024 & beyond. CAT ensures a secure, seamless digital experience by continuously assessing trust in real time, making it a pivotal shift in cybersecurity."
@@ -32,7 +32,7 @@ This ongoing evaluation ensures that trust levels are dynamically adjusted, resp
CAT enables organizations to assess risk continuously, allowing for immediate response to any suspicious activities. This real-time approach minimizes the window of opportunity for attackers, providing a proactive defense against emerging threats.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
### Enhanced User Experience
@@ -52,4 +52,4 @@ The continuous evaluation in CAT minimizes false positives by understanding the
As we enter 2024, Continuous Adaptive Trust emerges as a beacon of innovation, promising a future where adaptive authentication secures digital interactions and does so with unparalleled precision and adaptability. This paradigm shift heralds a new era in cybersecurity, where trust is not a static state but an ever-evolving, continuous journey.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=continuous-adaptive-authentication-future-2024)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=continuous-adaptive-authentication-future-2024)
diff --git a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.png b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.png
deleted file mode 100644
index 97611c609..000000000
Binary files a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.png and /dev/null differ
diff --git a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.webp b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.webp
new file mode 100644
index 000000000..0db381c53
Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.webp differ
diff --git a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.png b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.png
deleted file mode 100644
index cf28a6f97..000000000
Binary files a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.png and /dev/null differ
diff --git a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.webp b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.webp
new file mode 100644
index 000000000..4cd58ff77
Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.webp differ
diff --git a/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.jpg b/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.jpg
deleted file mode 100644
index a18057b42..000000000
Binary files a/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.jpg and /dev/null differ
diff --git a/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.webp b/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.webp
new file mode 100644
index 000000000..4b00d26d8
Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.webp differ
diff --git a/content/growth/customer-experience-media-entertainment-industry/image4.jpg b/content/growth/customer-experience-media-entertainment-industry/image4.jpg
deleted file mode 100644
index dcde4a14c..000000000
Binary files a/content/growth/customer-experience-media-entertainment-industry/image4.jpg and /dev/null differ
diff --git a/content/growth/customer-experience-media-entertainment-industry/image4.webp b/content/growth/customer-experience-media-entertainment-industry/image4.webp
new file mode 100644
index 000000000..5cf995130
Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/image4.webp differ
diff --git a/content/growth/customer-experience-media-entertainment-industry/image5.png b/content/growth/customer-experience-media-entertainment-industry/image5.png
deleted file mode 100644
index 924fec52b..000000000
Binary files a/content/growth/customer-experience-media-entertainment-industry/image5.png and /dev/null differ
diff --git a/content/growth/customer-experience-media-entertainment-industry/image5.webp b/content/growth/customer-experience-media-entertainment-industry/image5.webp
new file mode 100644
index 000000000..97f0f4080
Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/image5.webp differ
diff --git a/content/growth/customer-experience-media-entertainment-industry/index.md b/content/growth/customer-experience-media-entertainment-industry/index.md
index 5fe67bf91..3661cce63 100644
--- a/content/growth/customer-experience-media-entertainment-industry/index.md
+++ b/content/growth/customer-experience-media-entertainment-industry/index.md
@@ -1,7 +1,7 @@
---
title: "Digital Trends Transforming the Media and Entertainment Industry in 2020"
date: "2020-02-25"
-coverImage: "media-industry.jpg"
+coverImage: "media-industry.webp"
tags: ["digital transformation","ciam solution","cx"]
author: "Rakesh Soni"
description: "The worldwide media and entertainment industry is going through a huge transformation at the moment. 2020 aims to be the year of digital change in the media and entertainment sector with a large-scale roll-out of technology."
@@ -33,7 +33,7 @@ According to an estimation by Strategy Analytics, revenue from OTT video in the
These figures grab attention and are hard to ignore.
-
+
Data source: Strategy analytics OTT video forecast
@@ -55,7 +55,7 @@ Following suit came the [California Consumer Privacy Act (CCPA)](https://www.log
But will it hit the right chords among organizations and individuals? Only time will tell.
-
+
## 5 Technologies That Will Impact User Experience in Media and Entertainment Industry
@@ -91,7 +91,7 @@ Facial Recognition is swiftly turning into one of the most common forms of biome
For instance, it will identify individuals in-store and offer purchasing recommendations based on their demographic.
-
+
## How will CIAM solutions gain momentum in the media and entertainment industry?
@@ -111,7 +111,7 @@ The digitization of media content has also changed the way companies earn revenu
A [CIAM platform like LoginRadius](https://www.loginradius.com/blog/identity/perfect-ciam-platform/) can record the preferences of their audience in unified customer profiles and generate relevant content.
-[](https://www.loginradius.com/resource/how-media-and-publication-companies-use-loginradius-identity-platform/)
+[](https://www.loginradius.com/resource/how-media-and-publication-companies-use-loginradius-identity-platform/)
### **Frictionless customer interaction.**
@@ -125,4 +125,4 @@ With a large scale roll-out of the technology, 2020 promises to be the year of d
Amidst the ever-changing regulatory landscape, there are high chances that new opportunities are waiting to be capitalized. _Now_ is your chance to reap the benefits.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-experience-media-entertainment-industry)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-experience-media-entertainment-industry)
diff --git a/content/growth/customer-experience-media-entertainment-industry/media-industry.jpg b/content/growth/customer-experience-media-entertainment-industry/media-industry.jpg
deleted file mode 100644
index 092e63f46..000000000
Binary files a/content/growth/customer-experience-media-entertainment-industry/media-industry.jpg and /dev/null differ
diff --git a/content/growth/customer-experience-media-entertainment-industry/media-industry.webp b/content/growth/customer-experience-media-entertainment-industry/media-industry.webp
new file mode 100644
index 000000000..6153655ad
Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/media-industry.webp differ
diff --git a/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.png b/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.png and /dev/null differ
diff --git a/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.webp b/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.webp differ
diff --git a/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png b/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png
deleted file mode 100644
index b53535020..000000000
Binary files a/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png and /dev/null differ
diff --git a/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp b/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp
new file mode 100644
index 000000000..02dbccb4e
Binary files /dev/null and b/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp differ
diff --git a/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.jpg b/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.jpg
deleted file mode 100644
index 340570c91..000000000
Binary files a/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.jpg and /dev/null differ
diff --git a/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.webp b/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.webp
new file mode 100644
index 000000000..13131c015
Binary files /dev/null and b/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.webp differ
diff --git a/content/growth/customer-experience-retail-industry/customer-exp-retail.jpg b/content/growth/customer-experience-retail-industry/customer-exp-retail.jpg
deleted file mode 100644
index 2fe697885..000000000
Binary files a/content/growth/customer-experience-retail-industry/customer-exp-retail.jpg and /dev/null differ
diff --git a/content/growth/customer-experience-retail-industry/customer-exp-retail.webp b/content/growth/customer-experience-retail-industry/customer-exp-retail.webp
new file mode 100644
index 000000000..fb8c52ff6
Binary files /dev/null and b/content/growth/customer-experience-retail-industry/customer-exp-retail.webp differ
diff --git a/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.jpg b/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.jpg
deleted file mode 100644
index f29a7d5f9..000000000
Binary files a/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.jpg and /dev/null differ
diff --git a/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.webp b/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.webp
new file mode 100644
index 000000000..2943d9a80
Binary files /dev/null and b/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.webp differ
diff --git a/content/growth/customer-experience-retail-industry/index.md b/content/growth/customer-experience-retail-industry/index.md
index 72829bf89..b7f48b0e3 100644
--- a/content/growth/customer-experience-retail-industry/index.md
+++ b/content/growth/customer-experience-retail-industry/index.md
@@ -1,7 +1,7 @@
---
title: "Enhancing Customer Experience in Retail Industry"
date: "2020-05-05"
-coverImage: "retail-cx.jpg"
+coverImage: "retail-cx.webp"
tags: ["cx", "ciam solution","compliance"]
author: "Rakesh Soni"
description: "Not only does a perfect plan for customer experience rely on the product, store, and customers, but also on how companies smartly coordinate the entities listed. They need to integrate customer service through multiple genres of retail."
@@ -62,7 +62,7 @@ Moving on, let's find out a few ways how [brands can enhance customer experience
## How Retail Companies Can Benefit From Customer Experience
-
+
The retail industry is brutally competitive. It takes more than offering the right product at the right price to deliver amazing customer experiences. As already discussed, brands also need to treat customers with respect and trigger them on an emotional level.
@@ -82,7 +82,7 @@ When it comes to customer experience in the retail industry, compared to [brick-
There is one downside, though - and it is the inability to touch and feel the products before making a decision. Retailers need to break even to rebuild customer loyalty. They need to bring the convenience of online shopping to brick and mortar stores and make in-store experiences as smooth and easy as possible.
-[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
+[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
The good news is that initiatives like smaller format stores, auto-checkout, online ordering (while inside the store), and mobile app offers are in action to lure shoppers back into physical stores.
@@ -104,7 +104,7 @@ Furthermore, it will be easier for brands to consolidate all customer data (purc
## The role of LoginRadius to protect customer data for online retail business
-
+
LoginRadius is a [customer identity and access management](https://www.loginradius.com/blog/2019/06/customer-identity-and-access-management/) tool that offers a seamless and secure way to access customer information - in your case, shoppers' data.
@@ -128,4 +128,4 @@ Rivalry in the retail industry has always been a big deal. Amidst online players
It is only a matter of time that customer experience in the retail industry will win the war, and nothing else will matter.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-experience-retail-industry)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-experience-retail-industry)
diff --git a/content/growth/customer-experience-retail-industry/retail-cx.jpg b/content/growth/customer-experience-retail-industry/retail-cx.jpg
deleted file mode 100644
index 1f4129d0f..000000000
Binary files a/content/growth/customer-experience-retail-industry/retail-cx.jpg and /dev/null differ
diff --git a/content/growth/customer-experience-retail-industry/retail-cx.webp b/content/growth/customer-experience-retail-industry/retail-cx.webp
new file mode 100644
index 000000000..b781f37d9
Binary files /dev/null and b/content/growth/customer-experience-retail-industry/retail-cx.webp differ
diff --git a/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.png b/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.png
deleted file mode 100644
index 9fd09f050..000000000
Binary files a/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.png and /dev/null differ
diff --git a/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.webp b/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.webp
new file mode 100644
index 000000000..e2c41fa9b
Binary files /dev/null and b/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.webp differ
diff --git a/content/growth/customer-identity-drives-business-growth/business-growth.jpg b/content/growth/customer-identity-drives-business-growth/business-growth.jpg
deleted file mode 100644
index 93e291360..000000000
Binary files a/content/growth/customer-identity-drives-business-growth/business-growth.jpg and /dev/null differ
diff --git a/content/growth/customer-identity-drives-business-growth/business-growth.webp b/content/growth/customer-identity-drives-business-growth/business-growth.webp
new file mode 100644
index 000000000..7e111e53b
Binary files /dev/null and b/content/growth/customer-identity-drives-business-growth/business-growth.webp differ
diff --git a/content/growth/customer-identity-drives-business-growth/index.md b/content/growth/customer-identity-drives-business-growth/index.md
index 141da462d..013a6609e 100644
--- a/content/growth/customer-identity-drives-business-growth/index.md
+++ b/content/growth/customer-identity-drives-business-growth/index.md
@@ -1,7 +1,7 @@
---
title: "The Strategic Impact of Customer Identity on Business Growth"
date: "2024-07-03"
-coverImage: "business-growth.jpg"
+coverImage: "business-growth.webp"
tags: ["customer identity management","cx"]
author: "Cooper Matheson"
description: "Understanding and leveraging customer identity is crucial for driving business growth in today's competitive market. By personalizing customer experiences and utilizing data effectively, businesses can meet customer expectations and achieve substantial growth."
@@ -30,7 +30,7 @@ For example, a customer who frequently purchases eco-friendly products would app
Loyal customers are invaluable to any business. They not only make repeat purchases but also act as brand advocates, spreading positive word-of-mouth and attracting new customers. Understanding customer identity helps businesses identify loyal customers and reward them appropriately.
-[](https://www.loginradius.com/resource/datasheet/ciam-loyalty-programs/)
+[](https://www.loginradius.com/resource/datasheet/ciam-loyalty-programs/)
Loyalty programs tailored to individual customers' preferences and behaviors can significantly boost customer retention. Offering exclusive discounts, early access to sales, or personalized rewards based on past purchases can make customers feel valued and appreciated, strengthening their loyalty to the brand.
@@ -66,4 +66,4 @@ Understanding and leveraging customer identity is a powerful strategy for drivin
Embrace the power of customer identity to unlock new opportunities and pave the way for sustained success.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-drives-business-growth)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-drives-business-growth)
diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.png b/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.png and /dev/null differ
diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.webp b/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.webp differ
diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.png b/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.webp b/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.webp differ
diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.jpg b/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.jpg
deleted file mode 100644
index 61fb95aa5..000000000
Binary files a/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.jpg and /dev/null differ
diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.webp b/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.webp
new file mode 100644
index 000000000..9a332ac6b
Binary files /dev/null and b/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.webp differ
diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/index.md b/content/growth/customer-identity-drives-digital-eCommerce-success/index.md
index d8e933bb0..c27d4a4df 100644
--- a/content/growth/customer-identity-drives-digital-eCommerce-success/index.md
+++ b/content/growth/customer-identity-drives-digital-eCommerce-success/index.md
@@ -1,7 +1,7 @@
---
title: "How Customer Identity Solution Drives Digital eCommerce Success"
date: "2021-07-10"
-coverImage: "ecommerce-digital-identity-solutions.jpg"
+coverImage: "ecommerce-digital-identity-solutions.webp"
tags: ["identity management","digital transformation","cx"]
author: "Vishal Sharma"
description: "Learn how a CIAM solution paves the path for an eCommerce business success and why enterprises thinking to step into the eCommerce world should leverage a cutting-edge CIAM solution."
@@ -31,7 +31,7 @@ In a world when data and identity thefts lead to losses worth millions of dollar
Adding more robust authentication layers, including multi-factor authentication (MFA) and [risk-based authentication](https://www.loginradius.com/blog/identity/risk-based-authentication/) (RBA) to log in and sign-up procedures, can help secure consumer data and prevent a breach.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
Also, these secure authentication practices help enterprises to verify the individuals quickly they say they are.
@@ -78,4 +78,4 @@ Here's how this works. For example, you want some details from your customers to
Ecommerce is the new normal in a pandemic era and beyond. Businesses that are swiftly adopting the new age of selling products and services must emphasize delivering a seamless and secure user experience.
A consumer identity and access management solution is undoubtedly the key to win consumer success as enterprises can identify their visitors and [build personalized experiences](https://www.loginradius.com/customer-experience-solutions/) around foremost touchpoints, including research, purchase, discovery, and more.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-drives-digital-ecommerce-success)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-drives-digital-ecommerce-success)
diff --git a/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.png b/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.png
deleted file mode 100644
index 99b5a25ea..000000000
Binary files a/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.png and /dev/null differ
diff --git a/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.webp b/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.webp
new file mode 100644
index 000000000..a8ae17db9
Binary files /dev/null and b/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.webp differ
diff --git a/content/growth/customer-identity-resolution-marketing-success/customer-id-res.jpg b/content/growth/customer-identity-resolution-marketing-success/customer-id-res.jpg
deleted file mode 100644
index 780c59b7f..000000000
Binary files a/content/growth/customer-identity-resolution-marketing-success/customer-id-res.jpg and /dev/null differ
diff --git a/content/growth/customer-identity-resolution-marketing-success/customer-id-res.webp b/content/growth/customer-identity-resolution-marketing-success/customer-id-res.webp
new file mode 100644
index 000000000..5681405ab
Binary files /dev/null and b/content/growth/customer-identity-resolution-marketing-success/customer-id-res.webp differ
diff --git a/content/growth/customer-identity-resolution-marketing-success/index.md b/content/growth/customer-identity-resolution-marketing-success/index.md
index 2d18547f5..738dce7c6 100644
--- a/content/growth/customer-identity-resolution-marketing-success/index.md
+++ b/content/growth/customer-identity-resolution-marketing-success/index.md
@@ -1,7 +1,7 @@
---
title: "How to Leverage Advanced Customer Identity Resolution for Better Marketing Outcomes"
date: "2024-06-27"
-coverImage: "customer-id-res.jpg"
+coverImage: "customer-id-res.webp"
tags: ["identity resolution","compliance","cx"]
author: "Cooper Matheson"
description: "In the digital marketing landscape, understanding your customers is crucial for driving exceptional results. Advanced customer identity resolution unifies disparate data points to create comprehensive customer profiles. This enables personalized experiences, precise targeting, and higher ROI. Explore the power and implementation of this technology to enhance your marketing strategy."
@@ -28,7 +28,7 @@ This involves matching identifiers from different data sources, such as email ad
3. **Increased ROI**: Personalization and precise targeting lead to more efficient marketing spend. By focusing efforts on high-potential customers and reducing wasted ad spend on uninterested audiences, businesses can achieve a higher return on investment (ROI) for their marketing campaigns.
-[](https://www.loginradius.com/resource/guide/ciam-increase-roi-for-enterprise/)
+[](https://www.loginradius.com/resource/guide/ciam-increase-roi-for-enterprise/)
4. **Omnichannel Consistency**: Customers today interact with brands across multiple touchpoints, including social media, websites, mobile apps, and in-store visits. Advanced identity resolution ensures a consistent and seamless experience across all these channels, fostering brand loyalty and trust.
@@ -62,4 +62,4 @@ Advanced customer identity resolution is a powerful tool for driving exceptional
As the digital landscape continues to evolve, investing in advanced identity management solutions will be crucial for staying ahead of the competition and achieving long-term success in your marketing efforts.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-resolution-marketing-success)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-resolution-marketing-success)
diff --git a/content/growth/customer-identity-use-case/EB-gd-mci.png b/content/growth/customer-identity-use-case/EB-gd-mci.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/growth/customer-identity-use-case/EB-gd-mci.png and /dev/null differ
diff --git a/content/growth/customer-identity-use-case/EB-gd-mci.webp b/content/growth/customer-identity-use-case/EB-gd-mci.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/growth/customer-identity-use-case/EB-gd-mci.webp differ
diff --git a/content/growth/customer-identity-use-case/cust-identity.jpg b/content/growth/customer-identity-use-case/cust-identity.jpg
deleted file mode 100644
index 1546ff7f9..000000000
Binary files a/content/growth/customer-identity-use-case/cust-identity.jpg and /dev/null differ
diff --git a/content/growth/customer-identity-use-case/cust-identity.webp b/content/growth/customer-identity-use-case/cust-identity.webp
new file mode 100644
index 000000000..c8a02c1c6
Binary files /dev/null and b/content/growth/customer-identity-use-case/cust-identity.webp differ
diff --git a/content/growth/customer-identity-use-case/index.md b/content/growth/customer-identity-use-case/index.md
index 52fabafc4..01ae2fea4 100644
--- a/content/growth/customer-identity-use-case/index.md
+++ b/content/growth/customer-identity-use-case/index.md
@@ -1,7 +1,7 @@
---
title: "Unveiling the Customer Identity Business Case: Strategies for Success"
date: "2023-10-19"
-coverImage: "cust-identity.jpg"
+coverImage: "cust-identity.webp"
tags: ["customer identity management","ciam solutions","cx"]
author: "Rakesh Soni"
description: "Dive into the world of the customer identity base case – your key to personalized success. Explore strategies for tailored experiences, fraud prevention, and ethical data practices. Stay ahead in the digital era with our expert insights."
@@ -46,7 +46,7 @@ As we move into an era dominated by digital interactions, the importance of the
Emerging technologies like the Internet of Things (IoT) and augmented reality are reshaping customer interactions, providing even more touchpoints for data collection. By embracing these technologies and integrating the insights gained into their customer identity base case, businesses can create seamless, omnichannel experiences that delight customers across various platforms.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
Moreover, the rise of ethical consumerism underscores the significance of transparent data practices. Companies that prioritize customer privacy and utilize data responsibly will not only comply with regulations but also earn the trust and loyalty of their customer base.
@@ -90,4 +90,4 @@ The customer identity base case is the cornerstone of a successful business stra
Embracing these strategies and understanding the value of the customer identity base case will undoubtedly pave the way for long-term success in the digital realm.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-use-case)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-use-case)
\ No newline at end of file
diff --git a/content/growth/customer-relationship-business/customer-relations-management.jpg b/content/growth/customer-relationship-business/customer-relations-management.jpg
deleted file mode 100644
index c321593ba..000000000
Binary files a/content/growth/customer-relationship-business/customer-relations-management.jpg and /dev/null differ
diff --git a/content/growth/customer-relationship-business/customer-relations-management.webp b/content/growth/customer-relationship-business/customer-relations-management.webp
new file mode 100644
index 000000000..f116a5acd
Binary files /dev/null and b/content/growth/customer-relationship-business/customer-relations-management.webp differ
diff --git a/content/growth/customer-relationship-business/index.md b/content/growth/customer-relationship-business/index.md
index d76d6f889..392d1030e 100644
--- a/content/growth/customer-relationship-business/index.md
+++ b/content/growth/customer-relationship-business/index.md
@@ -1,7 +1,7 @@
---
title: "Why Is Customer Relationship Important for Every Business in 2021"
date: "2021-02-26"
-coverImage: "customer-relations-management.jpg"
+coverImage: "customer-relations-management.webp"
tags: ["customer relation management","ciam solution","cx"]
author: "Rakesh Soni"
description: "Positive customer relations help you connect with your customers on a much more personal level. When you connect with the target audience deeply, you are much more likely to understand their requirements, resolve their problems, and create a sense of mutual understanding."
@@ -104,4 +104,4 @@ Some reasons as to why the CRM system(s) are so prevalent:
So, having learned about customer relationship management, you would be able to decide hows of customer relationships approach it, and make the most of it! However, one thing that is sure to happen when you build profound customer relations is that you would witness an increasing customer base. Moreover, when you have a positive relationship with your customers, you are not very far from establishing some favourable B2B customer relationships!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-relationship-business)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-relationship-business)
diff --git a/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.png b/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.png and /dev/null differ
diff --git a/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.webp b/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.webp differ
diff --git a/content/growth/customer-retention-magic-links/customer-retention.jpg b/content/growth/customer-retention-magic-links/customer-retention.jpg
deleted file mode 100644
index 7c5be30e2..000000000
Binary files a/content/growth/customer-retention-magic-links/customer-retention.jpg and /dev/null differ
diff --git a/content/growth/customer-retention-magic-links/customer-retention.webp b/content/growth/customer-retention-magic-links/customer-retention.webp
new file mode 100644
index 000000000..be7b2e517
Binary files /dev/null and b/content/growth/customer-retention-magic-links/customer-retention.webp differ
diff --git a/content/growth/customer-retention-magic-links/index.md b/content/growth/customer-retention-magic-links/index.md
index 00648d69c..4403aa1da 100644
--- a/content/growth/customer-retention-magic-links/index.md
+++ b/content/growth/customer-retention-magic-links/index.md
@@ -1,7 +1,7 @@
---
title: "Enhancing Customer Retention with Magic Links: A User-Friendly Approach to Authentication"
date: "2024-03-28"
-coverImage: "customer-retention.jpg"
+coverImage: "customer-retention.webp"
tags: ["user authentication","customer retention","cx"]
author: "Cooper Matheson"
description: "Discover the magic of Magic Links, a frictionless authentication method that simplifies login. Easily enhance security and boost customer retention. Say goodbye to password woes and 2FA complexity. Learn how to implement Magic Links for a seamless user experience."
@@ -74,7 +74,7 @@ Inform your users about this new feature and highlight its benefits. Clear commu
As with any new feature, monitoring its performance is essential. Gather user feedback and analyze metrics such as login success rates and user satisfaction. Use this data to make improvements and further optimize the Magic Links experience.
-[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
+[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
## How LoginRadius's Passwordless Magic Link Thrives Business Success?
@@ -104,4 +104,4 @@ User authentication for customer retention is not just a technical necessity; it
By adopting innovative approaches like Magic Links, businesses can transform a potentially tedious process into a delightful user experience. Remember, the magic lies in simplicity, security, and the profound impact it can have on customer loyalty.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-retention-magic-links)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-retention-magic-links)
\ No newline at end of file
diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.png b/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.png
deleted file mode 100644
index f5fa0b0f9..000000000
Binary files a/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.png and /dev/null differ
diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.webp b/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.webp
new file mode 100644
index 000000000..b0761321e
Binary files /dev/null and b/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.webp differ
diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.jpg b/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.jpg
deleted file mode 100644
index 5f0d20d7b..000000000
Binary files a/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.jpg and /dev/null differ
diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.webp b/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.webp
new file mode 100644
index 000000000..f7eeecdf4
Binary files /dev/null and b/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.webp differ
diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/index.md b/content/growth/customize-marketing-programs-on-consumer-journey/index.md
index 21ef9fafd..e54452532 100644
--- a/content/growth/customize-marketing-programs-on-consumer-journey/index.md
+++ b/content/growth/customize-marketing-programs-on-consumer-journey/index.md
@@ -1,7 +1,7 @@
---
title: "Why You Should Customize Your Marketing Programs Based on Consumer Journey"
date: "2021-11-10"
-coverImage: "customer-marketing.jpg"
+coverImage: "customer-marketing.webp"
tags: ["ciam solution","cx","mfa"]
author: "Vishal Sharma"
description: "Personalized consumer experience is becoming the need of the hour. Let’s understand how a personalized consumer journey can help businesses stay ahead of the curve and how a CIAM solution like LoginRadius offers valuable insights for creating personalized user experiences."
@@ -38,7 +38,7 @@ Well, consumers are already interacting with established brands, including Apple
As a vendor, if you have the data regarding the buyer’s behavior, you can pitch exactly the same product or service for which they have landed.
-[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
+[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
## How LoginRadius Helps Build Personalized Consumer Journeys?
@@ -70,4 +70,4 @@ Consumer data can help businesses craft personalized consumer journeys that not
With a [consumer identity and access management (CIAM)](https://www.loginradius.com/blog/identity/customer-identity-and-access-management/#:~:text=Customer%20identity%20and%20access%20management%20(CIAM)%20is%20a%20digital%20identity,while%20securely%20managing%20customer%20identities.) solution in place, enterprises can yield better results by creating rich, personalized user experiences that help engage potential clients and increase the chances of conversions.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customize-marketing-programs-on-consumer-journey)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customize-marketing-programs-on-consumer-journey)
diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.png b/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.png
deleted file mode 100644
index 86c15a159..000000000
Binary files a/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.png and /dev/null differ
diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.webp b/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.webp
new file mode 100644
index 000000000..025782e92
Binary files /dev/null and b/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.webp differ
diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.png b/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.webp b/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.webp differ
diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.jpg b/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.jpg
deleted file mode 100644
index 26b5cedbb..000000000
Binary files a/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.jpg and /dev/null differ
diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.webp b/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.webp
new file mode 100644
index 000000000..ed8cc4378
Binary files /dev/null and b/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.webp differ
diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/index.md b/content/growth/cyberinsurance-2023-insurers-adapt-survive/index.md
index 6bd66bf78..ffad7d989 100644
--- a/content/growth/cyberinsurance-2023-insurers-adapt-survive/index.md
+++ b/content/growth/cyberinsurance-2023-insurers-adapt-survive/index.md
@@ -1,7 +1,7 @@
---
title: "Cyber Insurance in 2023: Takeaways For The Future And How To Prepare For It"
date: "2023-01-06"
-coverImage: "cyber-insurance.jpg"
+coverImage: "cyber-insurance.webp"
tags: ["cybersecurity", "cyberinsurance", "risk management"]
author: "Alok Patidar"
description: "As cyber risks continue to evolve and increase, it is no surprise that cyber insurance is becoming one of the fastest-growing insurance products in the market. Learn how it will shape the security space in 2023."
@@ -70,7 +70,7 @@ When it comes to cyber insurance renewals, here are a few things insurers will w
Multi-factor authentication protection on all remote access to your network, including any remote desktop protocol connections, email server, cloud services, and backup data solutions. Ensure that all network administrator accounts and any other user accounts with elevated permissions have multi-factor authentication protection.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### 2. Endpoint security
@@ -103,6 +103,6 @@ As cyber security threats continue to grow and evolve into a full-blown crisis,
In 2023, we will have many more concrete innovations, propelling the insurance industry into a better place than it ever has before. This will put them in a prime position to meet the challenges of tomorrow with agility, not uncertainty.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cyberinsurance-2023-insurers-adapt-survive)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cyberinsurance-2023-insurers-adapt-survive)
diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.png b/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.png and /dev/null differ
diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.webp b/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.webp differ
diff --git a/content/growth/data-privacy-boost-marketing-success/WP-privacy.png b/content/growth/data-privacy-boost-marketing-success/WP-privacy.png
deleted file mode 100644
index fb9e830ba..000000000
Binary files a/content/growth/data-privacy-boost-marketing-success/WP-privacy.png and /dev/null differ
diff --git a/content/growth/data-privacy-boost-marketing-success/WP-privacy.webp b/content/growth/data-privacy-boost-marketing-success/WP-privacy.webp
new file mode 100644
index 000000000..4ea6dbcbf
Binary files /dev/null and b/content/growth/data-privacy-boost-marketing-success/WP-privacy.webp differ
diff --git a/content/growth/data-privacy-boost-marketing-success/index.md b/content/growth/data-privacy-boost-marketing-success/index.md
index 5a472cc23..6f47c62f9 100644
--- a/content/growth/data-privacy-boost-marketing-success/index.md
+++ b/content/growth/data-privacy-boost-marketing-success/index.md
@@ -1,7 +1,7 @@
---
title: "Strategic Insights: Leveraging Data Privacy for Marketers' Success"
date: "2024-03-20"
-coverImage: "marketing-success.jpg"
+coverImage: "marketing-success.webp"
tags: ["data privacy","compliance","cx"]
author: "Rakesh Soni"
description: "Data has become invaluable in digital marketing. However, amidst the quest for personalization, data privacy often takes a back seat. Explore how a strategic approach to data privacy can ensure compliance, build trust, and drive long-term success for marketers. Discover the importance of transparency and ethical data practices and how prioritizing privacy can set brands apart in a crowded marketplace."
@@ -39,7 +39,7 @@ Beyond legal compliance, marketers should prioritize ethical considerations in t
An example of ethical data use is implementing granular consent mechanisms. Instead of blanket opt-ins, give consumers control over what they share. Allow them to choose the types of communication they receive and the data they're comfortable sharing. This not only builds trust but also ensures that the data collected is more accurate and relevant.
-[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper)
+[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper)
## Data Privacy as a Competitive Advantage
@@ -53,4 +53,4 @@ Data privacy is not just a legal requirement for marketers; it's a strategic imp
Brands that prioritize privacy comply with regulations and build lasting relationships with customers. In an era where data is abundant but trust is scarce, cultivating a privacy-first mindset is not just good ethics—it's good business. As marketers navigate the evolving landscape of digital marketing, let data privacy be their guiding star toward success.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-boost-marketing-success)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-boost-marketing-success)
diff --git a/content/growth/data-privacy-boost-marketing-success/marketing-success.jpg b/content/growth/data-privacy-boost-marketing-success/marketing-success.jpg
deleted file mode 100644
index aafcea017..000000000
Binary files a/content/growth/data-privacy-boost-marketing-success/marketing-success.jpg and /dev/null differ
diff --git a/content/growth/data-privacy-boost-marketing-success/marketing-success.webp b/content/growth/data-privacy-boost-marketing-success/marketing-success.webp
new file mode 100644
index 000000000..fdc4a9804
Binary files /dev/null and b/content/growth/data-privacy-boost-marketing-success/marketing-success.webp differ
diff --git a/content/growth/data-privacy-marketers-success/WP-building-privacy.png b/content/growth/data-privacy-marketers-success/WP-building-privacy.png
deleted file mode 100644
index fb9e830ba..000000000
Binary files a/content/growth/data-privacy-marketers-success/WP-building-privacy.png and /dev/null differ
diff --git a/content/growth/data-privacy-marketers-success/WP-building-privacy.webp b/content/growth/data-privacy-marketers-success/WP-building-privacy.webp
new file mode 100644
index 000000000..4ea6dbcbf
Binary files /dev/null and b/content/growth/data-privacy-marketers-success/WP-building-privacy.webp differ
diff --git a/content/growth/data-privacy-marketers-success/data-privacy.jpg b/content/growth/data-privacy-marketers-success/data-privacy.jpg
deleted file mode 100644
index 7f42a68c2..000000000
Binary files a/content/growth/data-privacy-marketers-success/data-privacy.jpg and /dev/null differ
diff --git a/content/growth/data-privacy-marketers-success/data-privacy.webp b/content/growth/data-privacy-marketers-success/data-privacy.webp
new file mode 100644
index 000000000..b1f5ecb66
Binary files /dev/null and b/content/growth/data-privacy-marketers-success/data-privacy.webp differ
diff --git a/content/growth/data-privacy-marketers-success/index.md b/content/growth/data-privacy-marketers-success/index.md
index 969c63715..9a7834d26 100644
--- a/content/growth/data-privacy-marketers-success/index.md
+++ b/content/growth/data-privacy-marketers-success/index.md
@@ -1,7 +1,7 @@
---
title: "Seizing Opportunities: How Can Marketers Leverage Data Privacy for Success"
date: "2024-01-16"
-coverImage: "data-privacy.jpg"
+coverImage: "data-privacy.webp"
tags: ["data privacy","compliance","cx"]
author: "Rakesh Soni"
description: "Data privacy is one of the most essential aspects of data security. With stringent data privacy laws all around the world, marketers are finding it challenging to navigate through this new framework. Let’s discuss how data privacy laws for marketers are actually beneficial."
@@ -44,7 +44,7 @@ In this world with stringent data protection laws, it becomes the responsibility
* Marketers are in a better position to explain what data will be required and where. So, while approaching the [customer for marketing consent](https://www.loginradius.com/consent-preference-management/), ensure to spell out clearly and specifically if an email address is required for daily mail-outs regarding specific product details. You can even give them options to narrow down how the customer wants to move forward with the relationship, like through emails, phones, or texts, SMS.
* Marketers need to ensure data visibility is in accordance with the consent of the authority, like who has access to view and edit it. When it comes to data privacy for marketers, an identity access management tool can help define who can access it and change the data over time.
-[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper)
+[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper)
* Email marketing is a boon, but as a marketer, it is best to clean and verify email lists. Like, perform regular sweeps for addresses that are no longer current. Most data regulations mention that storing obsolete data does not demonstrate a careful approach to the duty of data protection.
* When the data comes from different sources, there is a chance of data disparity. A DRM (Data Relationship Management) can provide a way to keep on top of multiple data inputs and structuring them in a meaningful way.
@@ -53,4 +53,4 @@ In this world with stringent data protection laws, it becomes the responsibility
Data privacy necessitates the requirement to preview the processes that can improve the entire company’s operation, not only the marketing vertical. With the help of the right tools for compliance and privacy regulations, marketers can implement their data-driven marketing strategies while capturing customer trust and providing enhanced user experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-marketers-success)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-marketers-success)
diff --git a/content/growth/data-privacy-marketing-regulations/DS-privacy.png b/content/growth/data-privacy-marketing-regulations/DS-privacy.png
deleted file mode 100644
index 67c1c093f..000000000
Binary files a/content/growth/data-privacy-marketing-regulations/DS-privacy.png and /dev/null differ
diff --git a/content/growth/data-privacy-marketing-regulations/DS-privacy.webp b/content/growth/data-privacy-marketing-regulations/DS-privacy.webp
new file mode 100644
index 000000000..42c0492a7
Binary files /dev/null and b/content/growth/data-privacy-marketing-regulations/DS-privacy.webp differ
diff --git a/content/growth/data-privacy-marketing-regulations/data-privacy.jpg b/content/growth/data-privacy-marketing-regulations/data-privacy.jpg
deleted file mode 100644
index 6b34ed54b..000000000
Binary files a/content/growth/data-privacy-marketing-regulations/data-privacy.jpg and /dev/null differ
diff --git a/content/growth/data-privacy-marketing-regulations/data-privacy.webp b/content/growth/data-privacy-marketing-regulations/data-privacy.webp
new file mode 100644
index 000000000..7f92af196
Binary files /dev/null and b/content/growth/data-privacy-marketing-regulations/data-privacy.webp differ
diff --git a/content/growth/data-privacy-marketing-regulations/index.md b/content/growth/data-privacy-marketing-regulations/index.md
index e96b3b2e5..70de25081 100644
--- a/content/growth/data-privacy-marketing-regulations/index.md
+++ b/content/growth/data-privacy-marketing-regulations/index.md
@@ -1,7 +1,7 @@
---
title: "Navigating the Shifting Landscape of Data Privacy Regulations: Embracing Core Marketing Principles"
date: "2024-04-30"
-coverImage: "data-privacy.jpg"
+coverImage: "data-privacy.webp"
tags: ["data privacy","compliance","cx"]
author: "Cooper Matheson"
description: "In today's digital business landscape, navigating data privacy regulations is paramount. Discover how businesses worldwide are adapting to safeguard user data privacy while embracing transparency and responsible personalization. Explore the importance of empowering users through choice and accountability in the ever-evolving regulatory landscape."
@@ -24,7 +24,7 @@ Users are increasingly aware of the value of their personal information and dema
Central to effective marketing in this era is transparency. Honesty about data collection and usage builds trust and fosters stronger relationships with customers.
-[](https://www.loginradius.com/resource/datasheet/privacy-policy-management/)
+[](https://www.loginradius.com/resource/datasheet/privacy-policy-management/)
It's essential to communicate clearly with users about what data is being collected, how it's being used, and how they can opt-in or opt-out. Transparency should permeate every aspect of marketing, from email campaigns to targeted advertising.
@@ -60,4 +60,4 @@ This might mean providing easy-to-use privacy settings, allowing users to opt ou
By putting users in the driver's seat, businesses not only comply with regulations but also foster a sense of empowerment and respect that can lead to long-term loyalty and advocacy. In the ever-evolving landscape of data privacy regulations, prioritizing user empowerment is not just good ethics—it's good business.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-marketing-regulations)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-marketing-regulations)
\ No newline at end of file
diff --git a/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.png b/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.webp b/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.webp differ
diff --git a/content/growth/digital-identity-key-to-economic-growth/digital-id.jpg b/content/growth/digital-identity-key-to-economic-growth/digital-id.jpg
deleted file mode 100644
index 547c2f197..000000000
Binary files a/content/growth/digital-identity-key-to-economic-growth/digital-id.jpg and /dev/null differ
diff --git a/content/growth/digital-identity-key-to-economic-growth/digital-id.webp b/content/growth/digital-identity-key-to-economic-growth/digital-id.webp
new file mode 100644
index 000000000..f2749e3e5
Binary files /dev/null and b/content/growth/digital-identity-key-to-economic-growth/digital-id.webp differ
diff --git a/content/growth/digital-identity-key-to-economic-growth/index.md b/content/growth/digital-identity-key-to-economic-growth/index.md
index 931d4354d..6fdded9c6 100644
--- a/content/growth/digital-identity-key-to-economic-growth/index.md
+++ b/content/growth/digital-identity-key-to-economic-growth/index.md
@@ -1,7 +1,7 @@
---
title: "How Digital Identification Could Be the Key to Inclusive and Economic Growth?"
date: "2022-11-09"
-coverImage: "digital-id.jpg"
+coverImage: "digital-id.webp"
tags: ["digital identity","mfa","cx","data security"]
author: "Alex Williams"
description: "A digital ID is a digitized representation of legal identity, and unlike traditional paper-based IDs, digital identification allows for remote verification via digital channels. In this article, we’ll look at how digital identification can help with growth on an economic level."
@@ -59,7 +59,7 @@ At face value, these advantages appear to benefit institutions primarily. Howeve
The fact that individuals are becoming savvier to the [benefits of digital ID](https://blog.loginradius.com/identity/pros-cons-reusable-digital-identity/) is seen with most consumers looking for banking accounts that come with essential security features such as Multi-Factor Authentication (MFA), among other digital identification features.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### 4. Financial inclusion
@@ -84,4 +84,4 @@ Besides enabling social and civic empowerment, digital identification is critica
Through sound design principles and policy enforcement, digital protects individual rights from abuse and creates economic benefits for states, institutions, and people.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-identity-key-to-economic-growth)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-identity-key-to-economic-growth)
\ No newline at end of file
diff --git a/content/growth/digital-identity-key-to-economic-growth/mfa-eb.png b/content/growth/digital-identity-key-to-economic-growth/mfa-eb.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/growth/digital-identity-key-to-economic-growth/mfa-eb.png and /dev/null differ
diff --git a/content/growth/digital-identity-key-to-economic-growth/mfa-eb.webp b/content/growth/digital-identity-key-to-economic-growth/mfa-eb.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/growth/digital-identity-key-to-economic-growth/mfa-eb.webp differ
diff --git a/content/growth/digital-trust-business-invest-2022/GD-to-RBA.png b/content/growth/digital-trust-business-invest-2022/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/growth/digital-trust-business-invest-2022/GD-to-RBA.png and /dev/null differ
diff --git a/content/growth/digital-trust-business-invest-2022/GD-to-RBA.webp b/content/growth/digital-trust-business-invest-2022/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/growth/digital-trust-business-invest-2022/GD-to-RBA.webp differ
diff --git a/content/growth/digital-trust-business-invest-2022/digital-trust.jpg b/content/growth/digital-trust-business-invest-2022/digital-trust.jpg
deleted file mode 100644
index 0aeadd833..000000000
Binary files a/content/growth/digital-trust-business-invest-2022/digital-trust.jpg and /dev/null differ
diff --git a/content/growth/digital-trust-business-invest-2022/digital-trust.webp b/content/growth/digital-trust-business-invest-2022/digital-trust.webp
new file mode 100644
index 000000000..9605527ed
Binary files /dev/null and b/content/growth/digital-trust-business-invest-2022/digital-trust.webp differ
diff --git a/content/growth/digital-trust-business-invest-2022/index.md b/content/growth/digital-trust-business-invest-2022/index.md
index bed46178c..22ebbeefb 100644
--- a/content/growth/digital-trust-business-invest-2022/index.md
+++ b/content/growth/digital-trust-business-invest-2022/index.md
@@ -1,7 +1,7 @@
---
title: "Earning Digital Trust in 2022: Where Should Businesses Invest?"
date: "2022-06-28"
-coverImage: "digital-trust.jpg"
+coverImage: "digital-trust.webp"
tags: ["digital transformation", "customer trust", "enterprises"]
author: "Rakesh Soni"
description: "Whether securing access control or rethinking privacy policies, businesses skipping a small step in protecting customer information could lead to losses worth millions of dollars and reputational damages since bad actors are already exploring new ways to exploit customer information. Here’s an insightful post that uncovers the aspects of digital trust and where businesses need to invest to earn digital trust in 2022 and beyond."
@@ -81,7 +81,7 @@ The risk-based implementation allows your application to challenge the consumer
It is a method of applying various levels of stringency to authentication processes based on the likelihood that access to a given system could result in compromise. As the level of risk increases, the authentication process becomes more complicated and restrictive.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
Risk-based authentication is an essential security feature because it works in real-time to prevent cyber frauds like accounts from getting compromised without causing an inconvenience for legitimate consumers. And thus building digital trust.
@@ -96,6 +96,6 @@ Hence, businesses embarking on a digital transformation journey shouldn’t unde
The aspects mentioned above could help businesses build digital trust that further fosters growth in the future.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-trust-business-invest-2022)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-trust-business-invest-2022)
diff --git a/content/growth/digital-trust-business-invest-2022/rba-gd.png b/content/growth/digital-trust-business-invest-2022/rba-gd.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/growth/digital-trust-business-invest-2022/rba-gd.png and /dev/null differ
diff --git a/content/growth/digital-trust-business-invest-2022/rba-gd.webp b/content/growth/digital-trust-business-invest-2022/rba-gd.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/growth/digital-trust-business-invest-2022/rba-gd.webp differ
diff --git a/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.png b/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.png and /dev/null differ
diff --git a/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.webp b/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.webp differ
diff --git a/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.png b/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.webp b/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.webp differ
diff --git a/content/growth/driving-merchant-growth-robust-authentication/index.md b/content/growth/driving-merchant-growth-robust-authentication/index.md
index 85d73e862..c328d184e 100644
--- a/content/growth/driving-merchant-growth-robust-authentication/index.md
+++ b/content/growth/driving-merchant-growth-robust-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "The Crucial Role of Security and CX in Providing Robust Authentication for Merchants"
date: "2023-03-09"
-coverImage: "robust-authntcation.jpg"
+coverImage: "robust-authntcation.webp"
tags: ["online shopping","data security","cx"]
author: "Vishal Sharma"
description: "Customers expect great experiences backed with robust security while interacting with a brand online. Hence, businesses must cater to them with the appropriate services by leveraging a robust authentication mechanism. Let’s have a look at some of the authentication benefits for merchants."
@@ -61,7 +61,7 @@ CIAM helps merchants to better manage risk by identifying potentially fraudulent
Merchants can implement CIAM using two-factor authentication (2FA) or multi-factor authentication (MFA). 2FA requires customers to provide two forms of identification: a password and a code sent to their mobile device.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
MFA requires customers to provide three or more forms of identification, such as a password, a code sent to their mobile device, and a fingerprint scan.
@@ -74,4 +74,4 @@ As e-commerce continues to grow, merchants must take measures to protect themsel
By implementing CIAM, merchants can protect against fraud, comply with regulations, increase customer trust, improve the customer experience, and better manage risk. With the right tools and strategies, merchants can ensure the security of their online transactions and build a successful and profitable e-commerce business.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=driving-merchant-growth-robust-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=driving-merchant-growth-robust-authentication)
diff --git a/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.jpg b/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.jpg
deleted file mode 100644
index 30be39383..000000000
Binary files a/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.jpg and /dev/null differ
diff --git a/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.webp b/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.webp
new file mode 100644
index 000000000..4dc6475e6
Binary files /dev/null and b/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.webp differ
diff --git a/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.png b/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.png
deleted file mode 100644
index cf809b333..000000000
Binary files a/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.png and /dev/null differ
diff --git a/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.webp b/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.webp
new file mode 100644
index 000000000..dd88d73ba
Binary files /dev/null and b/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.webp differ
diff --git a/content/growth/driving-success-through-customer-onboarding/customer-onboarding.jpg b/content/growth/driving-success-through-customer-onboarding/customer-onboarding.jpg
deleted file mode 100644
index 04cafa4d7..000000000
Binary files a/content/growth/driving-success-through-customer-onboarding/customer-onboarding.jpg and /dev/null differ
diff --git a/content/growth/driving-success-through-customer-onboarding/customer-onboarding.webp b/content/growth/driving-success-through-customer-onboarding/customer-onboarding.webp
new file mode 100644
index 000000000..d447d2feb
Binary files /dev/null and b/content/growth/driving-success-through-customer-onboarding/customer-onboarding.webp differ
diff --git a/content/growth/driving-success-through-customer-onboarding/index.md b/content/growth/driving-success-through-customer-onboarding/index.md
index 91708ad13..c179fefbf 100644
--- a/content/growth/driving-success-through-customer-onboarding/index.md
+++ b/content/growth/driving-success-through-customer-onboarding/index.md
@@ -1,7 +1,7 @@
---
title: "Driving Success Through Customer Onboarding: The Role of Marketing Strategies"
date: "2023-05-24"
-coverImage: "customer-onboarding.jpg"
+coverImage: "customer-onboarding.webp"
tags: ["customer onboarding","customer experience"]
author: "Yash Rathi"
description: "Explore the role of marketing in enhancing customer onboarding. Learn practical strategies like personalized communication, clear materials, streamlined experience, and continuous support for successful onboarding."
@@ -41,7 +41,7 @@ Marketing strategies contribute significantly to creating a streamlined user exp
This can involve optimizing the user interface, refining the registration process, and incorporating intuitive navigation elements. A seamless user experience enhances customer satisfaction and reduces the likelihood of customers abandoning the onboarding process prematurely.
-[](https://www.loginradius.com/resource/loginradius-ciam-registration-service/)
+[](https://www.loginradius.com/resource/loginradius-ciam-registration-service/)
### 4. Continuous Support and Education
@@ -75,4 +75,4 @@ By focusing on personalized communication, explicit onboarding materials, stream
Investing in these strategies benefits the individual customer and contributes to business growth, increased customer retention, and a strong brand reputation. Businesses can pave the way for success in today's competitive landscape by optimizing the customer onboarding process.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=driving-success-through-customer-onboarding)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=driving-success-through-customer-onboarding)
\ No newline at end of file
diff --git a/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.png b/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.png
deleted file mode 100644
index 4ea16b064..000000000
Binary files a/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.png and /dev/null differ
diff --git a/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.webp b/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.webp
new file mode 100644
index 000000000..7e6ca6673
Binary files /dev/null and b/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.webp differ
diff --git a/content/growth/ecommerce-social-login-success/ecommerce-social-login.jpg b/content/growth/ecommerce-social-login-success/ecommerce-social-login.jpg
deleted file mode 100644
index db1cd4715..000000000
Binary files a/content/growth/ecommerce-social-login-success/ecommerce-social-login.jpg and /dev/null differ
diff --git a/content/growth/ecommerce-social-login-success/ecommerce-social-login.webp b/content/growth/ecommerce-social-login-success/ecommerce-social-login.webp
new file mode 100644
index 000000000..8ec84aa16
Binary files /dev/null and b/content/growth/ecommerce-social-login-success/ecommerce-social-login.webp differ
diff --git a/content/growth/ecommerce-social-login-success/index.md b/content/growth/ecommerce-social-login-success/index.md
index 5bf64d76b..57d13fef4 100644
--- a/content/growth/ecommerce-social-login-success/index.md
+++ b/content/growth/ecommerce-social-login-success/index.md
@@ -1,7 +1,7 @@
---
title: "8 Essential Insights for Enabling E-Commerce Social Login"
date: "2023-09-20"
-coverImage: "ecommerce-social-login.jpg"
+coverImage: "ecommerce-social-login.webp"
tags: ["ecommerce","social login","data privacy","cx"]
author: "Vishal Sharma"
description: "E-commerce social login is the way forward for businesses looking to simplify user authentication and improve the overall user experience. However, success lies in the details, from offering multiple social login options to prioritizing data privacy and security. Explore these eight essential insights to ensure your e-commerce platform thrives in the age of social login."
@@ -34,7 +34,7 @@ While convenience is paramount, it's crucial to [prioritize data privacy and sec
Your privacy policy and terms of service clearly outline how user data obtained through social login will be utilized. Be transparent about data protection measures and assure users that their information will not be misused or shared without consent. This transparency builds trust and encourages users to embrace social login.
-[](https://www.loginradius.com/resource/whitepaper/social-login-reconsidered/)
+[](https://www.loginradius.com/resource/whitepaper/social-login-reconsidered/)
### #4. Streamline Checkout
@@ -60,4 +60,4 @@ Leverage the user data obtained through social login to provide tailored product
Enabling social media profile login for users can be a game-changer for your e-commerce application/platform, enhancing user convenience and providing valuable data. However, balancing this convenience with robust data privacy and security measures is essential. By implementing these eight aspects, you can create a seamless experience for your customers for your e-commerce store.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ecommerce-social-login-success)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ecommerce-social-login-success)
\ No newline at end of file
diff --git a/content/growth/emotional-intelligence/1.png b/content/growth/emotional-intelligence/1.png
deleted file mode 100644
index 6ffed62c5..000000000
Binary files a/content/growth/emotional-intelligence/1.png and /dev/null differ
diff --git a/content/growth/emotional-intelligence/1.webp b/content/growth/emotional-intelligence/1.webp
new file mode 100644
index 000000000..61279c240
Binary files /dev/null and b/content/growth/emotional-intelligence/1.webp differ
diff --git a/content/growth/emotional-intelligence/2.png b/content/growth/emotional-intelligence/2.png
deleted file mode 100644
index f04b28d4e..000000000
Binary files a/content/growth/emotional-intelligence/2.png and /dev/null differ
diff --git a/content/growth/emotional-intelligence/2.webp b/content/growth/emotional-intelligence/2.webp
new file mode 100644
index 000000000..e6d97b6da
Binary files /dev/null and b/content/growth/emotional-intelligence/2.webp differ
diff --git a/content/growth/emotional-intelligence/emotional-intelligence-loginradius.jpg b/content/growth/emotional-intelligence/emotional-intelligence-loginradius.jpg
deleted file mode 100644
index 67d7f84e2..000000000
Binary files a/content/growth/emotional-intelligence/emotional-intelligence-loginradius.jpg and /dev/null differ
diff --git a/content/growth/emotional-intelligence/emotional-intelligence-loginradius.webp b/content/growth/emotional-intelligence/emotional-intelligence-loginradius.webp
new file mode 100644
index 000000000..47ea009b2
Binary files /dev/null and b/content/growth/emotional-intelligence/emotional-intelligence-loginradius.webp differ
diff --git a/content/growth/emotional-intelligence/index.md b/content/growth/emotional-intelligence/index.md
index 65eadc190..eb611b1a5 100644
--- a/content/growth/emotional-intelligence/index.md
+++ b/content/growth/emotional-intelligence/index.md
@@ -1,7 +1,7 @@
---
title: "Steps to Grow Your Emotional Intelligence for Better Consumer Relations"
date: "2021-03-31"
-coverImage: "emotional-intelligence-loginradius.jpg"
+coverImage: "emotional-intelligence-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Lesley Vos"
@@ -48,7 +48,7 @@ Psychologist and science journalist, Goleman examined EI with application to lea
It appeared that the [top five components of EI](https://www.cognitiveinstitute.org/get-smart-about-emotional-intelligence/) — self-awareness, self-regulation, motivation, empathy, and social skills — result in an influence on business communication.
-
+
In plain English, emotional intelligence is "the ability to perceive, control and evaluate emotions – in oneself and others – and to use that information appropriately." ([Source](https://www.psychologytoday.com/intl/blog/your-mind-your-body/201201/10-ways-enhance-your-emotional-intelligence))
@@ -64,7 +64,7 @@ That's how Goleman explained the growing interest in emotional intelligence in t
He described EI with four domains and [twelve competencies](https://hbr.org/2017/02/emotional-intelligence-has-12-elements-which-do-you-need-to-work-on) a person needed to develop to become emotionally intelligent:
-
+
Today, experts agree on two statements:
@@ -237,4 +237,4 @@ Emotional intelligence is the ability to control emotions and relate well to oth
It takes commitment and time but yields loyalty. Grow the emotional intelligence of your agents, be emotionally intelligent yourself, and implement them across business communication systems for productive consumer relations.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=emotional-intelligence)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=emotional-intelligence)
\ No newline at end of file
diff --git a/content/growth/emotional-intelligence/loginradius-book-a-demo.png b/content/growth/emotional-intelligence/loginradius-book-a-demo.png
deleted file mode 100644
index 7602d120d..000000000
Binary files a/content/growth/emotional-intelligence/loginradius-book-a-demo.png and /dev/null differ
diff --git a/content/growth/emotional-intelligence/loginradius-book-a-demo.webp b/content/growth/emotional-intelligence/loginradius-book-a-demo.webp
new file mode 100644
index 000000000..9a00697f9
Binary files /dev/null and b/content/growth/emotional-intelligence/loginradius-book-a-demo.webp differ
diff --git a/content/growth/engineering-as-marketing/engineering-as-marketing.jpg b/content/growth/engineering-as-marketing/engineering-as-marketing.jpg
deleted file mode 100644
index 25911e0d8..000000000
Binary files a/content/growth/engineering-as-marketing/engineering-as-marketing.jpg and /dev/null differ
diff --git a/content/growth/engineering-as-marketing/engineering-as-marketing.webp b/content/growth/engineering-as-marketing/engineering-as-marketing.webp
new file mode 100644
index 000000000..8767178f6
Binary files /dev/null and b/content/growth/engineering-as-marketing/engineering-as-marketing.webp differ
diff --git a/content/growth/engineering-as-marketing/index.md b/content/growth/engineering-as-marketing/index.md
index 882cb0d76..5b7b26de6 100644
--- a/content/growth/engineering-as-marketing/index.md
+++ b/content/growth/engineering-as-marketing/index.md
@@ -1,7 +1,7 @@
---
title: "Engineering As Marketing: 5 Growth Hack Strategies For Modern Businesses"
date: "2021-01-05"
-coverImage: "engineering-as-marketing.jpg"
+coverImage: "engineering-as-marketing.webp"
category: ["all"]
featured: false
author: "Rakesh Soni"
@@ -73,4 +73,4 @@ If it blends into the overall story with goal and vision, the use of resources t
If you build the lead magnets so that they deliver a quick win and do not give too many possibilities to the consumer, you lay the foundation stone for throwing out a net in which you can attract the long-term attention of prospective customers to yourself.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=engineering-as-marketing)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=engineering-as-marketing)
diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.png b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.png
deleted file mode 100644
index 3fad38dd7..000000000
Binary files a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.png and /dev/null differ
diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.webp b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.webp
new file mode 100644
index 000000000..3e1dc7d36
Binary files /dev/null and b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.webp differ
diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.png b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.png
deleted file mode 100644
index b042ccc74..000000000
Binary files a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.png and /dev/null differ
diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.webp b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.webp
new file mode 100644
index 000000000..ad52fb6e1
Binary files /dev/null and b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.webp differ
diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.jpg b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.jpg
deleted file mode 100644
index c4547121e..000000000
Binary files a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.jpg and /dev/null differ
diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.webp b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.webp
new file mode 100644
index 000000000..591108cec
Binary files /dev/null and b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.webp differ
diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/index.md b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/index.md
index c3acb39dc..57eed3b51 100644
--- a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/index.md
+++ b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/index.md
@@ -1,7 +1,7 @@
---
title: "Enhance Your Consumer Experience in Insurance Companies With CIAM"
date: "2021-08-09"
-coverImage: "couple-meeting-with-insurance-agent.jpg"
+coverImage: "couple-meeting-with-insurance-agent.webp"
tags: ["ciam solution","mfa","passwordless authentication"]
author: "Deependra Singh"
description: "Unaided consumer interactions are a lost opportunity. The main goal of an insurance company should be to reduce the time taken in all their consumer interactions and increase the consumer experience level. This can only happen by implementing excellent systems and processes, which is where a CIAM comes into play."
@@ -21,7 +21,7 @@ A [consumer identity and access management](https://www.loginradius.com/blog/ide
The seamless user onboarding of new consumers, the overall [consumer experience](https://www.loginradius.com/resource/how-customer-identity-drives-digital-transformation-for-insurance-companies-2/), and good authentication services and identification process when individuals use their online apps are some of the primary concerns. Other issues include managing multiple brands within a single organization and managing personal data both within and outside the company.
-[](https://www.loginradius.com/resource/how-customer-identity-drives-digital-transformation-for-insurance-companies-2/)
+[](https://www.loginradius.com/resource/how-customer-identity-drives-digital-transformation-for-insurance-companies-2/)
## What Businesses Use CIAM
@@ -100,4 +100,4 @@ Insurance companies will have to make trade-offs between protection and the clie
Insurance companies often operate in a fast-paced environment, serving both consumers and businesses. They also deal with a complex IT infrastructure resulting from the multiple acquisitions that make up a typical contemporary insurance company.
[Implementing the right CIAM](https://www.loginradius.com/) solution is critical in the digital world of insurance firms in order to achieve their objectives and go above and beyond. This [CIAM digital strategy](https://www.loginradius.com/blog/identity/digital-transformation-consumer-iam/) can assist in the transformation of a conventional life insurance product into a more modern digital banking offering geared at wider consumer segments while still utilizing the traditional agent channel.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enhance-customer-experience-in-insurance-companies-with-ciam)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enhance-customer-experience-in-insurance-companies-with-ciam)
\ No newline at end of file
diff --git a/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.png b/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.png
deleted file mode 100644
index f97184f2f..000000000
Binary files a/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.png and /dev/null differ
diff --git a/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.webp b/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.webp
new file mode 100644
index 000000000..88d19cbb8
Binary files /dev/null and b/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.webp differ
diff --git a/content/growth/enhancing-ciam-customer-experience/customer-experience.jpg b/content/growth/enhancing-ciam-customer-experience/customer-experience.jpg
deleted file mode 100644
index 0700debe1..000000000
Binary files a/content/growth/enhancing-ciam-customer-experience/customer-experience.jpg and /dev/null differ
diff --git a/content/growth/enhancing-ciam-customer-experience/customer-experience.webp b/content/growth/enhancing-ciam-customer-experience/customer-experience.webp
new file mode 100644
index 000000000..4421f9531
Binary files /dev/null and b/content/growth/enhancing-ciam-customer-experience/customer-experience.webp differ
diff --git a/content/growth/enhancing-ciam-customer-experience/index.md b/content/growth/enhancing-ciam-customer-experience/index.md
index 98a8d579a..40ea0fd86 100644
--- a/content/growth/enhancing-ciam-customer-experience/index.md
+++ b/content/growth/enhancing-ciam-customer-experience/index.md
@@ -1,7 +1,7 @@
---
title: "Transforming Customer Experience: Enhancing CX through CIAM and Insights"
date: "2024-04-25"
-coverImage: "customer-experience.jpg"
+coverImage: "customer-experience.webp"
tags: ["ciam solutions","data security","cx"]
author: "Vishal Sharma"
description: "Learn how to elevate your CX strategies with CIAM and data-driven insights. From seamless digital experiences to proactive customer engagement, discover the key to driving growth and loyalty in a competitive market."
@@ -40,7 +40,7 @@ These insights empower CMOs to personalize marketing campaigns, tailor product o
One of the key advantages of CIAM is its integration capabilities with other business systems such as CRM platforms, marketing automation tools, and analytics solutions. By integrating CIAM with these systems, CMOs can gain a comprehensive view of the customer journey, from initial interaction to post-purchase engagement.
-[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
+[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
This holistic understanding enables organizations to identify areas for improvement, optimize touchpoints, and deliver consistent and personalized experiences across all channels.
@@ -66,4 +66,4 @@ By leveraging CIAM to create seamless digital experiences and harnessing data in
As CX continues to evolve, CMOs must embrace innovative solutions like LoginRadius CIAM to stay ahead of the curve and deliver exceptional experiences that drive growth and loyalty.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enhancing-ciam-customer-experience)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enhancing-ciam-customer-experience)
diff --git a/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.png b/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.png
deleted file mode 100644
index a448013ef..000000000
Binary files a/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.png and /dev/null differ
diff --git a/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.webp b/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.webp
new file mode 100644
index 000000000..31886ad27
Binary files /dev/null and b/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.webp differ
diff --git a/content/growth/enterprise-level-security-trends/GD-Incident-RP.png b/content/growth/enterprise-level-security-trends/GD-Incident-RP.png
deleted file mode 100644
index a7dbc3ac7..000000000
Binary files a/content/growth/enterprise-level-security-trends/GD-Incident-RP.png and /dev/null differ
diff --git a/content/growth/enterprise-level-security-trends/GD-Incident-RP.webp b/content/growth/enterprise-level-security-trends/GD-Incident-RP.webp
new file mode 100644
index 000000000..e57053baa
Binary files /dev/null and b/content/growth/enterprise-level-security-trends/GD-Incident-RP.webp differ
diff --git a/content/growth/enterprise-level-security-trends/ceo-enterprise-security.jpg b/content/growth/enterprise-level-security-trends/ceo-enterprise-security.jpg
deleted file mode 100644
index eda598c2c..000000000
Binary files a/content/growth/enterprise-level-security-trends/ceo-enterprise-security.jpg and /dev/null differ
diff --git a/content/growth/enterprise-level-security-trends/ceo-enterprise-security.webp b/content/growth/enterprise-level-security-trends/ceo-enterprise-security.webp
new file mode 100644
index 000000000..cccd3343f
Binary files /dev/null and b/content/growth/enterprise-level-security-trends/ceo-enterprise-security.webp differ
diff --git a/content/growth/enterprise-level-security-trends/index.md b/content/growth/enterprise-level-security-trends/index.md
index 19f225dc2..921d9c5e3 100644
--- a/content/growth/enterprise-level-security-trends/index.md
+++ b/content/growth/enterprise-level-security-trends/index.md
@@ -1,7 +1,7 @@
---
title: "Enterprise-Level Security Trends: 5 Things to Know As a CEO"
date: "2023-05-17"
-coverImage: "ceo-enterprise-security.jpg"
+coverImage: "ceo-enterprise-security.webp"
tags: ["enterprise level security","cybersecurity","cx"]
author: "Lucy Manole"
description: "A gradual transition towards a robust security culture signifies the importance of integrating cybersecurity awareness. As a result, many organizations are now building dedicated board-level cybersecurity committees under the CEO’s wing to better address this growing concern."
@@ -55,7 +55,7 @@ CEOs should consider some key aspects when building a dedicated board-level cybe
* **Top-down approach:** A security culture must be driven from the top down, with the CEO and executive team demonstrating a commitment to security. This helps set a strong example for the rest of the organization.
* **Incident response plan:** A CEO must approve a comprehensive incident response plan that outlines steps to be taken in case of a security breach, including communication, containment, and recovery.
-[](https://www.loginradius.com/resource/survive-a-cyber-apocalypse)
+[](https://www.loginradius.com/resource/survive-a-cyber-apocalypse)
* **Review and evaluation:** The committee periodically reviews and evaluates the organization's cybersecurity posture, including the effectiveness of its risk management strategies, incident response plans, and overall security controls.
@@ -87,4 +87,4 @@ Cybersecurity is no longer just an IT concern but a top strategic priority for e
Remember, a robust security posture prevents potential attacks and demonstrates to customers, investors, and stakeholders that your organization is committed to ensuring the highest levels of trust and confidence.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enterprise-level-security-trends)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enterprise-level-security-trends)
diff --git a/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.png b/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.png
deleted file mode 100644
index b2c0a4d84..000000000
Binary files a/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.png and /dev/null differ
diff --git a/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.webp b/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.webp
new file mode 100644
index 000000000..8dcbd7082
Binary files /dev/null and b/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.webp differ
diff --git a/content/growth/evolution-digital-identity-better-cx/consent-ds.png b/content/growth/evolution-digital-identity-better-cx/consent-ds.png
deleted file mode 100644
index 51524f116..000000000
Binary files a/content/growth/evolution-digital-identity-better-cx/consent-ds.png and /dev/null differ
diff --git a/content/growth/evolution-digital-identity-better-cx/consent-ds.webp b/content/growth/evolution-digital-identity-better-cx/consent-ds.webp
new file mode 100644
index 000000000..ae3c4b53d
Binary files /dev/null and b/content/growth/evolution-digital-identity-better-cx/consent-ds.webp differ
diff --git a/content/growth/evolution-digital-identity-better-cx/digital.jpg b/content/growth/evolution-digital-identity-better-cx/digital.jpg
deleted file mode 100644
index efb304bc4..000000000
Binary files a/content/growth/evolution-digital-identity-better-cx/digital.jpg and /dev/null differ
diff --git a/content/growth/evolution-digital-identity-better-cx/digital.webp b/content/growth/evolution-digital-identity-better-cx/digital.webp
new file mode 100644
index 000000000..3919c6d36
Binary files /dev/null and b/content/growth/evolution-digital-identity-better-cx/digital.webp differ
diff --git a/content/growth/evolution-digital-identity-better-cx/index.md b/content/growth/evolution-digital-identity-better-cx/index.md
index f5194ef06..1b91135c5 100644
--- a/content/growth/evolution-digital-identity-better-cx/index.md
+++ b/content/growth/evolution-digital-identity-better-cx/index.md
@@ -1,7 +1,7 @@
---
title: "Your Digital Identity Is Changing - So, What Does It Mean For Customer Experience?"
date: "2022-12-16"
-coverImage: "digital.jpg"
+coverImage: "digital.webp"
tags: ["digital id", "cx", "customer identity"]
author: "Rakesh Soni"
description: "Now, more than ever, customer experience is baked into every business. That means that as a business owner, you need to deliver great digital experiences and customer interactions every time. This blog covers some of the important aspects of an effective digital strategy."
@@ -65,7 +65,7 @@ When it comes to customer data management, laws are changing fast. New regulatio
While this may seem to be a lot of work, your business must comply with new laws and regulations. While collecting data from your website, you will need to know how to get consent from your visitors and store that information securely.
-[](https://www.loginradius.com/resource/loginradius-consent-management)
+[](https://www.loginradius.com/resource/loginradius-consent-management)
## How To Learn From Customer Behavior And Stay Ahead Of Evolving Needs?
@@ -88,5 +88,5 @@ When you invest in proper training and technology, your team will be empowered t
By looking at customer identity, both online and off, you should be able to create a connection with customers you could not have made before. This improves understanding between your brand and your audience and provides an insightful picture that can help build stronger relationships for more tremendous digital success.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=evolution-digital-identity-better-cx)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=evolution-digital-identity-better-cx)
diff --git a/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.png b/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.png
deleted file mode 100644
index e73f6428b..000000000
Binary files a/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.png and /dev/null differ
diff --git a/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.webp b/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.webp
new file mode 100644
index 000000000..2ceed6beb
Binary files /dev/null and b/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.webp differ
diff --git a/content/growth/fight-mediocrity-at-your-workplace/index.md b/content/growth/fight-mediocrity-at-your-workplace/index.md
index 2db5a850e..ec98f7276 100644
--- a/content/growth/fight-mediocrity-at-your-workplace/index.md
+++ b/content/growth/fight-mediocrity-at-your-workplace/index.md
@@ -1,7 +1,7 @@
---
title: "Fight Mediocrity at Your Workplace, Dare to be Awesome!"
date: "2017-04-07"
-coverImage: "Fight-mediocrity-at-your-workplace-dare-to-be-awesome.png"
+coverImage: "Fight-mediocrity-at-your-workplace-dare-to-be-awesome.webp"
category: ["business","General"]
featured: false
author: "Rakesh Soni"
diff --git a/content/growth/finding-ideal-customer-user-profile-management/index.md b/content/growth/finding-ideal-customer-user-profile-management/index.md
index e60dc17c3..64a8cf8be 100644
--- a/content/growth/finding-ideal-customer-user-profile-management/index.md
+++ b/content/growth/finding-ideal-customer-user-profile-management/index.md
@@ -1,7 +1,7 @@
---
title: "How to Target Your Ideal Customer with User Profile Management?"
date: "2023-02-22"
-coverImage: "profile-mangemnt.jpg"
+coverImage: "profile-mangemnt.webp"
category: ["user experience", "ciam", "user management"]
author: "Rakesh Soni"
description: "Targeting the right audience isn’t a piece of cake. It requires much effort, detailed user insights from user profiles, and research to develop a plan to increase engagement. This blog uncovers the aspects of user profile management with CIAM and how businesses can navigate their success journey by targeting the right audience."
@@ -87,5 +87,5 @@ Targeting your ideal customer is essential for any business looking to grow and
By following these steps, companies can build lasting relationships with their customers and drive long-term success.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=finding-ideal-customer-user-profile-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=finding-ideal-customer-user-profile-management)
diff --git a/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.jpg b/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.jpg
deleted file mode 100644
index 133bb34e1..000000000
Binary files a/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.jpg and /dev/null differ
diff --git a/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.webp b/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.webp
new file mode 100644
index 000000000..b3f9a80b8
Binary files /dev/null and b/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.webp differ
diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/cta.png b/content/growth/flexible-work-culture-game-changer-for-employees/cta.png
deleted file mode 100644
index 600361d60..000000000
Binary files a/content/growth/flexible-work-culture-game-changer-for-employees/cta.png and /dev/null differ
diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/cta.webp b/content/growth/flexible-work-culture-game-changer-for-employees/cta.webp
new file mode 100644
index 000000000..bf117ad57
Binary files /dev/null and b/content/growth/flexible-work-culture-game-changer-for-employees/cta.webp differ
diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.jpg b/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.jpg
deleted file mode 100644
index 9c1430dca..000000000
Binary files a/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.jpg and /dev/null differ
diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.webp b/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.webp
new file mode 100644
index 000000000..8818ee363
Binary files /dev/null and b/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.webp differ
diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/index.md b/content/growth/flexible-work-culture-game-changer-for-employees/index.md
index 007ffecdc..bdb458e49 100644
--- a/content/growth/flexible-work-culture-game-changer-for-employees/index.md
+++ b/content/growth/flexible-work-culture-game-changer-for-employees/index.md
@@ -1,7 +1,7 @@
---
title: "Flexible Work Culture: A Game-Changer for LoginRadius and its Employees"
date: "2023-07-13"
-coverImage: "flexible-work-culture.jpg"
+coverImage: "flexible-work-culture.webp"
tags: ["flexible work culture","work life balance","LoginRadius"]
author: "Azharuddin Mohammad"
description: "At LoginRadius, we believe that good work comes from a healthy work-life balance. That's why we've created a flexible working environment that allows our employees to make the most of their time and energy while they're at work. But what does it mean to have a flexible work culture, anyway? Let's dig in."
@@ -28,7 +28,7 @@ The combination of in-office and remote work at LoginRadius has successfully fos
## Daily Virtual Zumba Sessions: Shake, Sweat, and Smile!
-
+
In addition to providing flexibility and autonomy, LoginRadius has taken employee well-being to another level by organizing daily virtual Zumba sessions. These fitness sessions are a testament to the company's commitment to fostering a healthy and vibrant work environment. The virtual Zumba sessions offer a fun and energetic outlet for us to stay active, destress, and recharge our minds. It's an opportunity to connect with colleagues virtually, share positive energy, and build camaraderie.
@@ -38,7 +38,7 @@ LoginRadius TT League is an interdepartmental table tennis league that brings ou
## Celebrate You: Let's Party!
-
+
LoginRadius understands the importance of celebrating milestones, recognizing achievements, and fostering a sense of community among its employees. To honor our hard work and create memorable experiences, LoginRadius organizes Celebrate You: Month End celebrations. These celebrations encompass a range of activities, including team-building exercises, recognition ceremonies, and engaging games. It's a time to come together as a team, celebrate our collective achievements, and forge deeper connections.
@@ -52,4 +52,4 @@ As an [employee at LoginRadius](https://www.loginradius.com/careers/), I am grat
Together, we are embracing the exciting future of flexible work at LoginRadius, where collaboration, well-being, and celebration go hand in hand.
-[](https://www.loginradius.com/careers/)
\ No newline at end of file
+[](https://www.loginradius.com/careers/)
\ No newline at end of file
diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.jpg b/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.jpg
deleted file mode 100644
index 6b47dff91..000000000
Binary files a/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.jpg and /dev/null differ
diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.webp b/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.webp
new file mode 100644
index 000000000..d6ddbc8e2
Binary files /dev/null and b/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.webp differ
diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.jpg b/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.jpg
deleted file mode 100644
index 1efb1717f..000000000
Binary files a/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.jpg and /dev/null differ
diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.webp b/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.webp
new file mode 100644
index 000000000..bf4fd645c
Binary files /dev/null and b/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.webp differ
diff --git a/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.png b/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.png
deleted file mode 100644
index d036bd814..000000000
Binary files a/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.png and /dev/null differ
diff --git a/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.webp b/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.webp
new file mode 100644
index 000000000..d11016a0f
Binary files /dev/null and b/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.webp differ
diff --git a/content/growth/free-resources-that-you-might-not-have-heard-of/index.md b/content/growth/free-resources-that-you-might-not-have-heard-of/index.md
index 4c8989b02..413e76243 100644
--- a/content/growth/free-resources-that-you-might-not-have-heard-of/index.md
+++ b/content/growth/free-resources-that-you-might-not-have-heard-of/index.md
@@ -1,7 +1,7 @@
---
title: "Free Resources That You Might Not Have Heard Of"
date: "2017-01-23"
-coverImage: "free-resources-150x150.png"
+coverImage: "free-resources-150x150.webp"
tags: ["resources","article","cx"]
author: "Rakesh Soni"
description: "It is said that every good thing comes with a price tag attached. Well, looks like this is not applicable to all good things. The articles lists down some useful free resources you might not have heard of."
@@ -31,4 +31,4 @@ Here are some things which are not that popular but are worth trying at least on
So here are my favorite free resources that make my everyday life easier! Have you tried these? Or do you know about any other free resources that can make my job easier, would love to know in the comments below!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=free-resources-that-you-might-not-have-heard-of)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=free-resources-that-you-might-not-have-heard-of)
\ No newline at end of file
diff --git a/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.png b/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.png
deleted file mode 100644
index a3580f13e..000000000
Binary files a/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.png and /dev/null differ
diff --git a/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.webp b/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.webp
new file mode 100644
index 000000000..0257eff22
Binary files /dev/null and b/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.webp differ
diff --git a/content/growth/future-customer-authentication-market-needs/auth-future.jpg b/content/growth/future-customer-authentication-market-needs/auth-future.jpg
deleted file mode 100644
index c16da3515..000000000
Binary files a/content/growth/future-customer-authentication-market-needs/auth-future.jpg and /dev/null differ
diff --git a/content/growth/future-customer-authentication-market-needs/auth-future.webp b/content/growth/future-customer-authentication-market-needs/auth-future.webp
new file mode 100644
index 000000000..c2cf5208f
Binary files /dev/null and b/content/growth/future-customer-authentication-market-needs/auth-future.webp differ
diff --git a/content/growth/future-customer-authentication-market-needs/bio-auth.png b/content/growth/future-customer-authentication-market-needs/bio-auth.png
deleted file mode 100644
index 69293181d..000000000
Binary files a/content/growth/future-customer-authentication-market-needs/bio-auth.png and /dev/null differ
diff --git a/content/growth/future-customer-authentication-market-needs/bio-auth.webp b/content/growth/future-customer-authentication-market-needs/bio-auth.webp
new file mode 100644
index 000000000..b272f8563
Binary files /dev/null and b/content/growth/future-customer-authentication-market-needs/bio-auth.webp differ
diff --git a/content/growth/future-customer-authentication-market-needs/index.md b/content/growth/future-customer-authentication-market-needs/index.md
index 95fadb4de..6240a260a 100644
--- a/content/growth/future-customer-authentication-market-needs/index.md
+++ b/content/growth/future-customer-authentication-market-needs/index.md
@@ -1,7 +1,7 @@
---
title: "Customer Authentication: Unfolding The Market Needs Of The Future"
date: "2022-01-06"
-coverImage: "auth-future.jpg"
+coverImage: "auth-future.webp"
tags: ["data security","biometric authentication","mfa","cx"]
author: "Navanita Devi"
description: "Consumer authentication is getting more challenging than ever. Learn how the biggest brands in the world are innovating their way through the disruption that's already underway, and get the tactics you need to deliver a seamless experience to your customers."
@@ -47,7 +47,7 @@ Here’s how you can implement biometric authentication into your system:
* **Voice recognition:** The vocal input, analog data are taken in and converted into digital data. The comparator checks the stored patterns with the output of the A/D converter to confirm the authentication.
* **Face recognition:** The captured face image details like alignment, size, and shape of the face are analysed and processed with deep learning techniques.
-[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
+[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
### 3. Behavioural biometrics authentication
@@ -78,5 +78,5 @@ As another customer authentication future trend, cloud-based authentication uses
Organizations need to enlarge and modify their capabilities to take control of security more efficiently in this new environment. Identity platforms like [LoginRadius](https://www.loginradius.com/) provide customer registration, SSO, MFA, directory services, user management, and data access governance to help companies achieve top-notch for their consumers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-customer-authentication-market-needs)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-customer-authentication-market-needs)
diff --git a/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.png b/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.png and /dev/null differ
diff --git a/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.webp b/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.webp differ
diff --git a/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.png b/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.webp b/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.webp differ
diff --git a/content/growth/future-of-authentication-service-market/future-of-authentication-market.jpg b/content/growth/future-of-authentication-service-market/future-of-authentication-market.jpg
deleted file mode 100644
index 22b49f0c6..000000000
Binary files a/content/growth/future-of-authentication-service-market/future-of-authentication-market.jpg and /dev/null differ
diff --git a/content/growth/future-of-authentication-service-market/future-of-authentication-market.webp b/content/growth/future-of-authentication-service-market/future-of-authentication-market.webp
new file mode 100644
index 000000000..1e3600801
Binary files /dev/null and b/content/growth/future-of-authentication-service-market/future-of-authentication-market.webp differ
diff --git a/content/growth/future-of-authentication-service-market/index.md b/content/growth/future-of-authentication-service-market/index.md
index e3fb0c201..b88d61d1e 100644
--- a/content/growth/future-of-authentication-service-market/index.md
+++ b/content/growth/future-of-authentication-service-market/index.md
@@ -1,7 +1,7 @@
---
title: "How Does the Future Look Like for the Authentication Services Market?"
date: "2021-09-02"
-coverImage: "future-of-authentication-market.jpg"
+coverImage: "future-of-authentication-market.webp"
tags: ["data security","authentication","mfa","cybersecurity"]
author: "Rakesh Soni"
description: "Authentication services have a lot to offer every sector possible, from healthcare to even defense. It is essentially the future of login security and will play an important role in reducing ransomware attacks."
@@ -31,7 +31,7 @@ The analysis of the authentication services market takes place after segmenting
- Geography: The analysis of the adoption and growth of the market from a geographical standpoint. For example, what does the market look like on different continents or a specific region? These include regions like North America, Europe, Asia-Pacific, Latin America, Middle East and Africa.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
By analysing the market through different segments, it becomes possible to obtain a better understanding of the digital identity trends.
@@ -74,5 +74,5 @@ According to analysis, from a geographical standpoint, North America will be the
Therefore, authentication services have a lot to offer every sector possible, from healthcare to even defense. It is essentially the future of login security and will play an important role in reducing ransomware attacks.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-of-authentication-service-market)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-of-authentication-service-market)
diff --git a/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.png b/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.png and /dev/null differ
diff --git a/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.webp b/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.webp differ
diff --git a/content/growth/good-transaction-security/EB-GD-to-MFA.png b/content/growth/good-transaction-security/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/growth/good-transaction-security/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/growth/good-transaction-security/EB-GD-to-MFA.webp b/content/growth/good-transaction-security/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/growth/good-transaction-security/EB-GD-to-MFA.webp differ
diff --git a/content/growth/good-transaction-security/index.md b/content/growth/good-transaction-security/index.md
index d99cfcfc0..b138078db 100644
--- a/content/growth/good-transaction-security/index.md
+++ b/content/growth/good-transaction-security/index.md
@@ -1,7 +1,7 @@
---
title: "How Good Transaction Security Ensures Smooth Consumer Visits"
date: "2021-09-07"
-coverImage: "smooth-transaction-security-with-loginradius.jpg"
+coverImage: "smooth-transaction-security-with-loginradius.webp"
tags: ["ciam solution","compliance","data security"]
author: "Vishal Sharma"
description: "The sudden increase in the number of transaction-related security breaches is undeniably pointing towards the need for a robust security mechanism that can build consumer trust. This post uncovers the role of secure transactions and how businesses can ensure smooth consumer visits."
@@ -118,7 +118,7 @@ Data security and privacy are ensured through a built-in web application firewal
RBA goes beyond a static list of rules and adapts to ask consumers for the types of verification that best suit a user session.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
LoginRadius incorporates the following additional factors to its RBA solutions:
@@ -154,4 +154,4 @@ Good transaction security coupled with a great user experience is the key to onl
Businesses can leverage the true potential of a robust CIAM solution like LoginRadius to secure their transactions without hampering user experience to get a competitive advantage in terms of smooth consumer visits.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=good-transaction-security)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=good-transaction-security)
\ No newline at end of file
diff --git a/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.jpg b/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.jpg
deleted file mode 100644
index 9fd09c60a..000000000
Binary files a/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.jpg and /dev/null differ
diff --git a/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.webp b/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.webp
new file mode 100644
index 000000000..9a0aa4878
Binary files /dev/null and b/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.webp differ
diff --git a/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.jpg b/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.jpg
deleted file mode 100644
index 19bedb4de..000000000
Binary files a/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.jpg and /dev/null differ
diff --git a/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.webp b/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.webp
new file mode 100644
index 000000000..ea592302d
Binary files /dev/null and b/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.webp differ
diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.png b/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.png
deleted file mode 100644
index 1b5b130e1..000000000
Binary files a/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.png and /dev/null differ
diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.webp b/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.webp
new file mode 100644
index 000000000..f0f286c26
Binary files /dev/null and b/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.webp differ
diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.png b/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.png
deleted file mode 100644
index c6b0e25f6..000000000
Binary files a/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.png and /dev/null differ
diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.webp b/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.webp
new file mode 100644
index 000000000..f50f330d5
Binary files /dev/null and b/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.webp differ
diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.png b/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.png
deleted file mode 100644
index d9dccd99b..000000000
Binary files a/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.png and /dev/null differ
diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.webp b/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.webp
new file mode 100644
index 000000000..0d5c02ead
Binary files /dev/null and b/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.webp differ
diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.png b/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.png
deleted file mode 100644
index 4cf6bb13d..000000000
Binary files a/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.png and /dev/null differ
diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.webp b/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.webp
new file mode 100644
index 000000000..7b4635aa7
Binary files /dev/null and b/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.webp differ
diff --git a/content/growth/google-keep-tips-for-productivity/index.md b/content/growth/google-keep-tips-for-productivity/index.md
index 08edde2f5..41a9a6ac7 100644
--- a/content/growth/google-keep-tips-for-productivity/index.md
+++ b/content/growth/google-keep-tips-for-productivity/index.md
@@ -1,7 +1,7 @@
---
title: "How To Insert Keep Notes in Doc Plus other Keep Tips For Better Productivity"
date: "2017-03-06"
-coverImage: "How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.jpg"
+coverImage: "How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.webp"
category: ["general", "technology", "loginradius"]
featured: false
author: "Rakesh Soni"
@@ -44,7 +44,7 @@ Using Keep for multiple things like homework or some event? Create Labels and ad
### **4\. Add Keep widget in your phone.**
-
+
Add your desired keep note to the home screen of your Android using the Keep widget. You can choose which note you want to display. Using the widget you can also add a note or an image and view the existing notes. For me, the Keep widget is a great way to remind myself about the important tasks I have.
@@ -56,7 +56,7 @@ Saw an awesome DIY bottle and want to make it too? Just save it to Keep by openi
### **6\. Voice Notes**
-
+
You can also add voice notes if you don’t want to type the notes!
@@ -76,13 +76,13 @@ Just like Google Docs, you can also share your keep notes with your team and fri
### **9\. Make a checklist!**
-
+
Add checkpoints to your tasks and mark them check when you are done. The checked points move down to the list.. \[Though you can change that in settings\]
### **10\. Add a pinned note**
-
+
Want to keep a note always at top? Pin it.
diff --git a/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.png b/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.png and /dev/null differ
diff --git a/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.webp b/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.webp differ
diff --git a/content/growth/grow-business-with-right-identity-strategy/id-strategy.jpg b/content/growth/grow-business-with-right-identity-strategy/id-strategy.jpg
deleted file mode 100644
index a7f6977ec..000000000
Binary files a/content/growth/grow-business-with-right-identity-strategy/id-strategy.jpg and /dev/null differ
diff --git a/content/growth/grow-business-with-right-identity-strategy/id-strategy.webp b/content/growth/grow-business-with-right-identity-strategy/id-strategy.webp
new file mode 100644
index 000000000..51b1b315c
Binary files /dev/null and b/content/growth/grow-business-with-right-identity-strategy/id-strategy.webp differ
diff --git a/content/growth/grow-business-with-right-identity-strategy/index.md b/content/growth/grow-business-with-right-identity-strategy/index.md
index b7a8a953e..b385992e3 100644
--- a/content/growth/grow-business-with-right-identity-strategy/index.md
+++ b/content/growth/grow-business-with-right-identity-strategy/index.md
@@ -1,7 +1,7 @@
---
title: "How Implementing the Right Identity Strategy Can Grow Your Business?"
date: "2022-04-07"
-coverImage: "id-strategy.jpg"
+coverImage: "id-strategy.webp"
tags: ["consumer iam solution","digital identity management","cx"]
author: "Rakesh Soni"
description: "The right identity strategy can help businesses stay up and running even in challenging situations since enterprises can rely on valuable consumer insights, including their preferences, behavior, and purchase trends. Let’s understand the role of identity management and how a good strategy for managing consumer identities can help businesses excel in growth."
@@ -67,7 +67,7 @@ Here’s how LoginRadius manages security and usability:
* **Safeguard sensitive data:** Our modern cloud infrastructure is protected to the highest industry standards. LoginRadius maintains all major security compliances for our application and data storage.
* **Manage consumer consent:** Stay current on regulations for acquiring consumer consent, data collection and use, age verification, and site access. Give consumers transparency into the consent process to demonstrate good faith.
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
Hence, businesses must understand the importance of a modern CIAM solution like LoginRadius and consider incorporating it into their identity strategy.
@@ -79,4 +79,4 @@ By implementing the benefits of the LoginRadius CIAM as a unified solution, you
Need more information about how [LoginRadius CIAM benefits](https://www.loginradius.com/blog/identity/loginradius-private-cloud-ciam-benefits/) your business? Reach us for a free personalized demo.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=grow-business-with-right-identity-strategy)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=grow-business-with-right-identity-strategy)
\ No newline at end of file
diff --git a/content/growth/grow-business-with-right-identity-strategy/zero-trust1.png b/content/growth/grow-business-with-right-identity-strategy/zero-trust1.png
deleted file mode 100644
index 3e6b81ee6..000000000
Binary files a/content/growth/grow-business-with-right-identity-strategy/zero-trust1.png and /dev/null differ
diff --git a/content/growth/grow-business-with-right-identity-strategy/zero-trust1.webp b/content/growth/grow-business-with-right-identity-strategy/zero-trust1.webp
new file mode 100644
index 000000000..2f7c01062
Binary files /dev/null and b/content/growth/grow-business-with-right-identity-strategy/zero-trust1.webp differ
diff --git a/content/growth/happy-12th-birthday-loginradius/WP-ai.png b/content/growth/happy-12th-birthday-loginradius/WP-ai.png
deleted file mode 100644
index 1116bcde5..000000000
Binary files a/content/growth/happy-12th-birthday-loginradius/WP-ai.png and /dev/null differ
diff --git a/content/growth/happy-12th-birthday-loginradius/WP-ai.webp b/content/growth/happy-12th-birthday-loginradius/WP-ai.webp
new file mode 100644
index 000000000..8efa78c3e
Binary files /dev/null and b/content/growth/happy-12th-birthday-loginradius/WP-ai.webp differ
diff --git a/content/growth/happy-12th-birthday-loginradius/bday-cover.jpg b/content/growth/happy-12th-birthday-loginradius/bday-cover.jpg
deleted file mode 100644
index 04224745f..000000000
Binary files a/content/growth/happy-12th-birthday-loginradius/bday-cover.jpg and /dev/null differ
diff --git a/content/growth/happy-12th-birthday-loginradius/bday-cover.webp b/content/growth/happy-12th-birthday-loginradius/bday-cover.webp
new file mode 100644
index 000000000..7dbcb01a6
Binary files /dev/null and b/content/growth/happy-12th-birthday-loginradius/bday-cover.webp differ
diff --git a/content/growth/happy-12th-birthday-loginradius/cta.png b/content/growth/happy-12th-birthday-loginradius/cta.png
deleted file mode 100644
index 600361d60..000000000
Binary files a/content/growth/happy-12th-birthday-loginradius/cta.png and /dev/null differ
diff --git a/content/growth/happy-12th-birthday-loginradius/cta.webp b/content/growth/happy-12th-birthday-loginradius/cta.webp
new file mode 100644
index 000000000..bf117ad57
Binary files /dev/null and b/content/growth/happy-12th-birthday-loginradius/cta.webp differ
diff --git a/content/growth/happy-12th-birthday-loginradius/index.md b/content/growth/happy-12th-birthday-loginradius/index.md
index 51893244a..81b5361dd 100644
--- a/content/growth/happy-12th-birthday-loginradius/index.md
+++ b/content/growth/happy-12th-birthday-loginradius/index.md
@@ -1,7 +1,7 @@
---
title: "Happy Birthday, LoginRadius: One Year Away from the Big Teen Milestone!"
date: "2024-07-20"
-coverImage: "bday-cover.jpg"
+coverImage: "bday-cover.webp"
tags: ["LoginRadius birthday"]
author: "Rakesh Soni"
description: "As LoginRadius celebrates its 12th anniversary, we reflect on a year filled with significant milestones and innovations. From groundbreaking features like Push Notification MFA and Passkeys to impactful CSR initiatives, we continue to set new standards in digital identity and social responsibility. Join us in celebrating our journey, and looking forward to an exciting future."
@@ -76,7 +76,7 @@ We are committed to staying ahead of the curve, leveraging cutting-edge technolo
Our goal is to make digital identities even more secure, user-friendly, and efficient, empowering businesses to thrive in the digital age through the advancement of AI.
-[](https://www.loginradius.com/resource/whitepaper/how-ai-change-iam-initiatives/)
+[](https://www.loginradius.com/resource/whitepaper/how-ai-change-iam-initiatives/)
## Gratitude and Reflection: A Heartfelt Thank You
@@ -108,4 +108,4 @@ As we celebrate our 12th birthday, we not only look back at our achievements but
Here’s to many more years of innovation, growth, and success. Happy Birthday, LoginRadius!
-[](https://www.loginradius.com/careers/)
\ No newline at end of file
+[](https://www.loginradius.com/careers/)
\ No newline at end of file
diff --git a/content/growth/happy-birthday-loginradius/CEO-Rakesh.jpg b/content/growth/happy-birthday-loginradius/CEO-Rakesh.jpg
deleted file mode 100644
index 12288c73e..000000000
Binary files a/content/growth/happy-birthday-loginradius/CEO-Rakesh.jpg and /dev/null differ
diff --git a/content/growth/happy-birthday-loginradius/CEO-Rakesh.webp b/content/growth/happy-birthday-loginradius/CEO-Rakesh.webp
new file mode 100644
index 000000000..b4c92de04
Binary files /dev/null and b/content/growth/happy-birthday-loginradius/CEO-Rakesh.webp differ
diff --git a/content/growth/happy-birthday-loginradius/LR-birthday.jpg b/content/growth/happy-birthday-loginradius/LR-birthday.jpg
deleted file mode 100644
index 704136e4a..000000000
Binary files a/content/growth/happy-birthday-loginradius/LR-birthday.jpg and /dev/null differ
diff --git a/content/growth/happy-birthday-loginradius/LR-birthday.webp b/content/growth/happy-birthday-loginradius/LR-birthday.webp
new file mode 100644
index 000000000..d509d0431
Binary files /dev/null and b/content/growth/happy-birthday-loginradius/LR-birthday.webp differ
diff --git a/content/growth/happy-birthday-loginradius/cta.png b/content/growth/happy-birthday-loginradius/cta.png
deleted file mode 100644
index 600361d60..000000000
Binary files a/content/growth/happy-birthday-loginradius/cta.png and /dev/null differ
diff --git a/content/growth/happy-birthday-loginradius/cta.webp b/content/growth/happy-birthday-loginradius/cta.webp
new file mode 100644
index 000000000..bf117ad57
Binary files /dev/null and b/content/growth/happy-birthday-loginradius/cta.webp differ
diff --git a/content/growth/happy-birthday-loginradius/index.md b/content/growth/happy-birthday-loginradius/index.md
index 200bb2a05..f3f085b04 100644
--- a/content/growth/happy-birthday-loginradius/index.md
+++ b/content/growth/happy-birthday-loginradius/index.md
@@ -1,7 +1,7 @@
---
title: "Happy Birthday, LoginRadius: Two Years Away From Becoming A Teenager"
date: "2023-07-24"
-coverImage: "LR-birthday.jpg"
+coverImage: "LR-birthday.webp"
tags: ["LoginRadius birthday"]
author: "Rakesh Soni"
description: "I still vividly remember the day when I incorporated the company on July 20, 2012. At that time, all we had was an idea—an idea to solve the login problem for billions of internet users. As we approach our 11th birthday, I can't help but feel a little nostalgic."
@@ -12,7 +12,7 @@ metatitle: "LoginRadius Turns 11: 2 Years Away From Becoming A Teenager"
I’m struck by the profound similarity between our journey as founders and the experience of raising a child. Just like parents nurture and care for their baby, we have poured our hearts and souls into building and nurturing LoginRadius.
-
+
Throughout this incredible journey, I have experienced a whirlwind of emotions—pride, joy, worry, and excitement. We have celebrated together during moments of triumph, persevered through challenging times, and shared in the deep sense of pride that comes with witnessing the growth and accomplishments of LoginRadius.
@@ -72,4 +72,4 @@ When all these pieces are tied together, I am filled with excitement about Login
Have a great week!
-[](https://www.loginradius.com/careers/)
+[](https://www.loginradius.com/careers/)
diff --git a/content/growth/high-performing-growth-team/growth-team.jpg b/content/growth/high-performing-growth-team/growth-team.jpg
deleted file mode 100644
index 885e47bc4..000000000
Binary files a/content/growth/high-performing-growth-team/growth-team.jpg and /dev/null differ
diff --git a/content/growth/high-performing-growth-team/growth-team.webp b/content/growth/high-performing-growth-team/growth-team.webp
new file mode 100644
index 000000000..70da87f76
Binary files /dev/null and b/content/growth/high-performing-growth-team/growth-team.webp differ
diff --git a/content/growth/high-performing-growth-team/index.md b/content/growth/high-performing-growth-team/index.md
index 2afc48547..56c12e2b2 100644
--- a/content/growth/high-performing-growth-team/index.md
+++ b/content/growth/high-performing-growth-team/index.md
@@ -1,7 +1,7 @@
---
title: "5 Steps to Build a High Performing Growth Team in 2021"
date: "2021-02-23"
-coverImage: "growth-team.jpg"
+coverImage: "growth-team.webp"
category: ["all"]
featured: false
author: "Rakesh Soni"
@@ -144,4 +144,4 @@ The importance of growth teams is more than the startup founders assume, and the
Whether you are a business firm, one of many portfolio corporations, a startup, or a small enterprise, you need to concentrate on creating a professional growth team if your product has already hit the market.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=high-performing-growth-team)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=high-performing-growth-team)
diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.png b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.png
deleted file mode 100644
index 4926b2aaf..000000000
Binary files a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.png and /dev/null differ
diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.webp b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.webp
new file mode 100644
index 000000000..d4581b1bd
Binary files /dev/null and b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.webp differ
diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.jpg b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.jpg
deleted file mode 100644
index 1d1476ae2..000000000
Binary files a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.jpg and /dev/null differ
diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.webp b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.webp
new file mode 100644
index 000000000..b696f8c3a
Binary files /dev/null and b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.webp differ
diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.png b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.png
deleted file mode 100644
index 904e3a28e..000000000
Binary files a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.png and /dev/null differ
diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.webp b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.webp
new file mode 100644
index 000000000..c2d6821c3
Binary files /dev/null and b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.webp differ
diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/index.md b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/index.md
index 63042621d..ead969a58 100644
--- a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/index.md
+++ b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/index.md
@@ -1,7 +1,7 @@
---
title: "How CISOs Can Improve Collaboration on Security Risks"
date: "2021-09-27"
-coverImage: "ciso-cover-image.jpg"
+coverImage: "ciso-cover-image.webp"
tags: ["data security","cybersecurity","cx"]
author: "Shivangini Yadav"
description: "It no longer makes sense to think of security as a single system, because there are so many different layers, and so many different points of entry. This blog explains how CISOs can respond to these multivalent threats across an organization."
@@ -55,7 +55,7 @@ Effective CISOs are those that encourage their team to share their skills with t
Finally, make sure you are using the technology available to you in order to share information and insight across all the teams in your organization. A comprehensive security incident and event management (SIEM) can greatly improve network visibility, but also allow you to share real-time, actionable insights with teams that may be opening themselves up to attack.
-[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
+[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
And, over time, it’s possible to leverage the power of big data to pull the insights drawn from your SIEM into a holistic picture of cybersecurity across your organization. By tracking the types of threats that you are exposed to, and their relative success, you can begin to plan a cybersecurity strategy that reduces your future vulnerability.
@@ -65,4 +65,4 @@ Ultimately, collaboration is a necessary part of the contemporary business envir
Building collaborative ways of working is not a quick process, but it can be done. And just as we’ve seen the evolutionary development of cyber security over the past few years, now we are witnessing the evolution of the business environment itself.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciso-can-improve-collaboration-on-security-risks)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciso-can-improve-collaboration-on-security-risks)
\ No newline at end of file
diff --git a/content/growth/how-businesses-approach-customer-security/EB-omnichannel.png b/content/growth/how-businesses-approach-customer-security/EB-omnichannel.png
deleted file mode 100644
index f5fa0b0f9..000000000
Binary files a/content/growth/how-businesses-approach-customer-security/EB-omnichannel.png and /dev/null differ
diff --git a/content/growth/how-businesses-approach-customer-security/EB-omnichannel.webp b/content/growth/how-businesses-approach-customer-security/EB-omnichannel.webp
new file mode 100644
index 000000000..b0761321e
Binary files /dev/null and b/content/growth/how-businesses-approach-customer-security/EB-omnichannel.webp differ
diff --git a/content/growth/how-businesses-approach-customer-security/growth-comp.jpg b/content/growth/how-businesses-approach-customer-security/growth-comp.jpg
deleted file mode 100644
index 2f17dd28c..000000000
Binary files a/content/growth/how-businesses-approach-customer-security/growth-comp.jpg and /dev/null differ
diff --git a/content/growth/how-businesses-approach-customer-security/growth-comp.webp b/content/growth/how-businesses-approach-customer-security/growth-comp.webp
new file mode 100644
index 000000000..066bd3880
Binary files /dev/null and b/content/growth/how-businesses-approach-customer-security/growth-comp.webp differ
diff --git a/content/growth/how-businesses-approach-customer-security/index.md b/content/growth/how-businesses-approach-customer-security/index.md
index 062a84968..4dc906b5c 100644
--- a/content/growth/how-businesses-approach-customer-security/index.md
+++ b/content/growth/how-businesses-approach-customer-security/index.md
@@ -1,7 +1,7 @@
---
title: "How Should Growth-Minded Enterprises Approach Customer Security?"
date: "2022-04-22"
-coverImage: "growth-comp.jpg"
+coverImage: "growth-comp.webp"
tags: ["data security", "compliance", "ciam", "customer experience"]
author: "Rakesh Soni"
description: "Customer security is crucial for any business striving to stay ahead of the competition. However, balancing customer security with a rich consumer experience is what it all takes to propel growth. Learn the aspects of a robust CIAM solution and how it helps businesses stay ahead of their competitors."
@@ -54,7 +54,7 @@ An omnichannel consumer experience refers to seamless interaction across multipl
For example, it is omnichannel when marketing, sales, consumer support, and even in-store experiences are synced up so users can seamlessly switch channels and make the purchase.
-[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
+[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
### #2. Single consumer view
@@ -92,4 +92,4 @@ Hence, the critical role of a CIAM solution in enhancing customer security and i
Businesses need to invoke the potential of a reliable CIAM like LoginRadius to ensure they get perfect harmony of user experience and security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-businesses-approach-customer-security)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-businesses-approach-customer-security)
\ No newline at end of file
diff --git a/content/growth/how-businesses-approach-customer-security/omnichannel-eb.png b/content/growth/how-businesses-approach-customer-security/omnichannel-eb.png
deleted file mode 100644
index 86c15a159..000000000
Binary files a/content/growth/how-businesses-approach-customer-security/omnichannel-eb.png and /dev/null differ
diff --git a/content/growth/how-businesses-approach-customer-security/omnichannel-eb.webp b/content/growth/how-businesses-approach-customer-security/omnichannel-eb.webp
new file mode 100644
index 000000000..025782e92
Binary files /dev/null and b/content/growth/how-businesses-approach-customer-security/omnichannel-eb.webp differ
diff --git a/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.png b/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.png
deleted file mode 100644
index fc6f98c05..000000000
Binary files a/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.png and /dev/null differ
diff --git a/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.webp b/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.webp
new file mode 100644
index 000000000..c60f3551f
Binary files /dev/null and b/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.webp differ
diff --git a/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.jpg b/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.jpg
deleted file mode 100644
index 1a4bc9e0f..000000000
Binary files a/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.jpg and /dev/null differ
diff --git a/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.webp b/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.webp
new file mode 100644
index 000000000..a3cfef024
Binary files /dev/null and b/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.webp differ
diff --git a/content/growth/how-ciam-and-crm-integration-optimize-cx/index.md b/content/growth/how-ciam-and-crm-integration-optimize-cx/index.md
index b92d6dfee..0e4ed7c41 100644
--- a/content/growth/how-ciam-and-crm-integration-optimize-cx/index.md
+++ b/content/growth/how-ciam-and-crm-integration-optimize-cx/index.md
@@ -1,7 +1,7 @@
---
title: "Customer-Centric Strategies: How CIAM and CRM Integration Optimize Consumer Experience"
date: "2023-08-28"
-coverImage: "customer-experience.jpg"
+coverImage: "customer-experience.webp"
tags: ["ciam solutions","user management","cx"]
author: "King Conrad Fanoga"
description: "Any successful business knows that an excellent customer experience is essential; thus, a customer's needs and expectations are of utmost priority. Learn how to optimize your consumer experiences and boost customer-centric strategies."
@@ -76,7 +76,7 @@ Facilitate collaborative synergy among IT, marketing, and customer service teams
Utilize customer insights and feedback to adjust and optimize your CIAM and CRM strategies continuously. You should also be mindful of the evolving customer preferences and behaviors and be proactive in keeping your approach relative.
-[](https://www.loginradius.com/resource/loginradius-ciam-user-management/)
+[](https://www.loginradius.com/resource/loginradius-ciam-user-management/)
### 4. Harnessing Emerging Technologies for Elevated Experiences
@@ -100,4 +100,4 @@ In conclusion, customer-centric strategies are essential for your business or an
The future holds exciting potential for CIAM and CRM integration. As digital innovations continue to appear, your company should embrace them or, better else, pioneer them. Consistently deliver excellent value and exceptional customer service.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciam-and-crm-integration-optimize-cx)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciam-and-crm-integration-optimize-cx)
diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.png b/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.png
deleted file mode 100644
index a49793446..000000000
Binary files a/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.png and /dev/null differ
diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.webp b/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.webp
new file mode 100644
index 000000000..f5170c511
Binary files /dev/null and b/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.webp differ
diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/index.md b/content/growth/how-ciam-can-resolve-retail-industry-challenges/index.md
index 5cd82098a..c4ba49808 100644
--- a/content/growth/how-ciam-can-resolve-retail-industry-challenges/index.md
+++ b/content/growth/how-ciam-can-resolve-retail-industry-challenges/index.md
@@ -1,7 +1,7 @@
---
title: "5 Key CIAM Benefits and Challenges in the Retail Industry"
date: "2021-09-17"
-coverImage: "retail-industry.jpg"
+coverImage: "retail-industry.webp"
tags: ["mfa","ciam provider","user experience","cx"]
author: "Navanita Devi"
description: "The modern retail industry has several challenges that can be solved by deploying a CIAM solution. Read this blog to learn how CIAM goes beyond just streamlining a platform to make it more intuitive, and how it boosts the marketing and sales efforts of a business in the retail industry."
@@ -39,7 +39,7 @@ It has been established that an [effective marketing strategy](https://www.login
Another challenging aspect that online platforms face is the problem of personalization. Personalization, if executed properly, can urge the customer to make several purchases at a time and keep them coming back for more. In other words, it can improve the loyalty of the customer. However, this requires the platform to get to know the customer and their wants and needs, which is difficult.
-[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience)
+[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience)
## 5 Benefits of Implementing CIAM for E-commerce Platforms
@@ -119,4 +119,4 @@ The critical issues in retailing are fluid platform experience for seamless cust
Retail marketing faces challenges such as reaching customers across multiple platforms, managing data silos, and the need for personalized strategies to enhance customer loyalty.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciam-can-resolve-retail-industry-challenges)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciam-can-resolve-retail-industry-challenges)
diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.jpg b/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.jpg
deleted file mode 100644
index 17940ab41..000000000
Binary files a/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.jpg and /dev/null differ
diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.webp b/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.webp
new file mode 100644
index 000000000..39f6da380
Binary files /dev/null and b/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.webp differ
diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.jpg b/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.jpg
deleted file mode 100644
index 551d54c39..000000000
Binary files a/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.jpg and /dev/null differ
diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.webp b/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.webp
new file mode 100644
index 000000000..5a140a73c
Binary files /dev/null and b/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.webp differ
diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.jpg b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.jpg
deleted file mode 100644
index 28a77df29..000000000
Binary files a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.jpg and /dev/null differ
diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.webp b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.webp
new file mode 100644
index 000000000..9548b267e
Binary files /dev/null and b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.webp differ
diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.png b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.png
deleted file mode 100644
index 4c933839b..000000000
Binary files a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.png and /dev/null differ
diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.webp b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.webp
new file mode 100644
index 000000000..bce6534de
Binary files /dev/null and b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.webp differ
diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.png b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.png
deleted file mode 100644
index bd559ec47..000000000
Binary files a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.png and /dev/null differ
diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.webp b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.webp
new file mode 100644
index 000000000..b3f1a625f
Binary files /dev/null and b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.webp differ
diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/index.md b/content/growth/how-consumer-identity-influence-brand-recognizability/index.md
index 4d0be0bff..86a97aa1c 100644
--- a/content/growth/how-consumer-identity-influence-brand-recognizability/index.md
+++ b/content/growth/how-consumer-identity-influence-brand-recognizability/index.md
@@ -1,7 +1,7 @@
---
title: "How Consumer Identity Influence Brand Recognizability"
date: "2021-08-31"
-coverImage: "brand-identity.jpg"
+coverImage: "brand-identity.webp"
category: ["loginradius"]
featured: false
author: "Conrad Sturdy"
@@ -17,7 +17,7 @@ Brand recognizability depends on various aspects, and consumer identity is one o
Let’s explore more about how people's self-perception influences brand choice and the types of consumer identities for you to consider.
-
+
Image Source: Live Inspired Mag
@@ -41,7 +41,7 @@ The things we buy help us to better express who we are. Sounds fantastic, isn’
Consumers try to express their internal feelings with external means such as brands. We can conclude that purchase is the form of self-expression, and brand is the symbol of our inner self.
-
+
Image Source: XO
@@ -83,4 +83,4 @@ Emotions mean a lot to many of us, but the emotion-oriented type of consumers fi
Now you understand the concept of [brand recognizability](https://www.loginradius.com/blog/growth/does-your-website-imagery-reflect-your-brand-identity/) and its bounds with customer identity. We explored four types of consumer identities you should pay attention to and defined their main preferences.
Brand recognizability is based on the self-perceptions of potential consumers, and you should target their self-concepts properly. These findings can help you build stronger connections with consumers and increase your brand's success.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-consumer-identity-influence-brand-recognizability)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-consumer-identity-influence-brand-recognizability)
diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.png b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.png
deleted file mode 100644
index 86c15a159..000000000
Binary files a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.png and /dev/null differ
diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.webp b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.webp
new file mode 100644
index 000000000..025782e92
Binary files /dev/null and b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.webp differ
diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.png b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.png
deleted file mode 100644
index f5fa0b0f9..000000000
Binary files a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.png and /dev/null differ
diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.webp b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.webp
new file mode 100644
index 000000000..b0761321e
Binary files /dev/null and b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.webp differ
diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.jpg b/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.jpg
deleted file mode 100644
index 4d94cd8d8..000000000
Binary files a/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.jpg and /dev/null differ
diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.webp b/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.webp
new file mode 100644
index 000000000..d5d6f33b3
Binary files /dev/null and b/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.webp differ
diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/index.md b/content/growth/how-digital-identity-unlock-success-in-retail/index.md
index ac224c18e..d5f2d4cb4 100644
--- a/content/growth/how-digital-identity-unlock-success-in-retail/index.md
+++ b/content/growth/how-digital-identity-unlock-success-in-retail/index.md
@@ -1,7 +1,7 @@
---
title: "Digital Identity: The Future of Successful Retail Operations"
date: "2023-04-19"
-coverImage: "dig-identity-retail.jpg"
+coverImage: "dig-identity-retail.webp"
tags: ["digital identity management","ecommerce","cx"]
author: "Vishal Sharma"
description: "With the rise of e-commerce, mobile shopping, and social media, retailers can use digital identity to personalize the customer experience, optimize marketing efforts, and drive sales. Let’s uncover the aspects of digital identity and how it thrives overall retail success."
@@ -45,7 +45,7 @@ Another key benefit of digital identity is the ability to create a seamless, omn
By leveraging digital identity, retailers can create a unified view of each customer that spans all channels, allowing them to deliver a seamless experience whether browsing on a mobile device or shopping in-store.
-[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
+[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
### Privacy and Security Concerns
@@ -73,4 +73,4 @@ However, retailers must also be mindful of the privacy and security implications
As the retail industry continues evolving and increasingly digitizing, digital identity will become an essential tool for retailers looking to stay competitive.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-digital-identity-unlock-success-in-retail)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-digital-identity-unlock-success-in-retail)
diff --git a/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.png b/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.png
deleted file mode 100644
index f5fa0b0f9..000000000
Binary files a/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.png and /dev/null differ
diff --git a/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.webp b/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.webp
new file mode 100644
index 000000000..b0761321e
Binary files /dev/null and b/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.webp differ
diff --git a/content/growth/how-identity-management-help-mistaken-identity/index.md b/content/growth/how-identity-management-help-mistaken-identity/index.md
index 104448429..8a2646beb 100644
--- a/content/growth/how-identity-management-help-mistaken-identity/index.md
+++ b/content/growth/how-identity-management-help-mistaken-identity/index.md
@@ -1,7 +1,7 @@
---
title: "How Identity Management Can Help You Avoid Targeting The Wrong Customers?"
date: "2022-06-14"
-coverImage: "mistaken-id.jpg"
+coverImage: "mistaken-id.webp"
tags: ["identity security", "ciam", "customer experience"]
author: "Yash Rathi"
description: "Since businesses serve customers across various devices and channels, yielding multiple views of the same customer becomes tricky. And the result is a messed experience that hampers customer experience and expectations, leading to mistaken identity. Let’s dig deeper into the aspects of leveraging a CIAM solution that helps overcome the challenges of mistaken identity."
@@ -56,7 +56,7 @@ An omnichannel customer experience refers to seamless interaction across multipl
For example, it is omnichannel when marketing, sales, consumer support, and even in-store experiences are synced up so users can seamlessly switch channels and make the purchase.
-[](https://www.loginradius.com/resource/cloud-streaming-for-omnichannel-experience)
+[](https://www.loginradius.com/resource/cloud-streaming-for-omnichannel-experience)
### #2. Single consumer view
@@ -87,4 +87,4 @@ CIAM ensures brands have a better understanding of consumers. Hence, they can qu
Add to that the top-of-the-line shield against the prying eyes, and the new-age CIAM seems to be a must for modern enterprises.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-identity-management-help-mistaken-identity)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-identity-management-help-mistaken-identity)
\ No newline at end of file
diff --git a/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.jpg b/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.jpg
deleted file mode 100644
index 30a223367..000000000
Binary files a/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.jpg and /dev/null differ
diff --git a/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.webp b/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.webp
new file mode 100644
index 000000000..d5f9adaa5
Binary files /dev/null and b/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.webp differ
diff --git a/content/growth/how-identity-management-help-mistaken-identity/omni-eb.png b/content/growth/how-identity-management-help-mistaken-identity/omni-eb.png
deleted file mode 100644
index 86c15a159..000000000
Binary files a/content/growth/how-identity-management-help-mistaken-identity/omni-eb.png and /dev/null differ
diff --git a/content/growth/how-identity-management-help-mistaken-identity/omni-eb.webp b/content/growth/how-identity-management-help-mistaken-identity/omni-eb.webp
new file mode 100644
index 000000000..025782e92
Binary files /dev/null and b/content/growth/how-identity-management-help-mistaken-identity/omni-eb.webp differ
diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.png b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.png and /dev/null differ
diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.webp b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.webp differ
diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.png b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.webp b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.webp differ
diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/index.md b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/index.md
index 80315efb0..3fcb17bbe 100644
--- a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/index.md
+++ b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/index.md
@@ -1,7 +1,7 @@
---
title: "How MFA Makes Quick Service Restaurants (QSR) Promotion Fraud-Free"
date: "2021-09-01"
-coverImage: "qsr-payment-ciam-loginradius.jpg"
+coverImage: "qsr-payment-ciam-loginradius.webp"
tags: ["mfa","digital transformation","biometric authentication"]
author: "Navanita Devi"
description: "Quick-Service Restaurants are seeing a boom in engagement, but so are the scammers. Read this blog to find out how to boost your restaurant’s confidence in its capacity to defend itself from hackers."
@@ -41,7 +41,7 @@ The majority of MFA authentication methods rely on one of three sorts of extra d
In an interview with PYMNTS, Vikram Dhawan, vice president and senior product leader at Kount, an Equifax business, warned that QSRs and other merchants must safeguard their promotions and customers' accounts to strengthen their defenses against an assault of faceless, digitally-mounted attackers.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
The news came as PYMNTS research revealed that 44 percent of respondents indicated they were more likely to order from restaurants that offered specials or discounts. According to Dhawan, this circumstance allows for marketing misuse and fraud.
@@ -99,4 +99,4 @@ In an age where, even after the pandemic, [digital transformation](https://www.l
Consumers may now eat these goods in a variety of ways. So it would be fascinating for merchants to react to that change and that dynamic nature.”
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-mfa-makes-qsr-promotions-fraud-free)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-mfa-makes-qsr-promotions-fraud-free)
\ No newline at end of file
diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.jpg b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.jpg
deleted file mode 100644
index cb6ab92f5..000000000
Binary files a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.jpg and /dev/null differ
diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.webp b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.webp
new file mode 100644
index 000000000..ce4f6335e
Binary files /dev/null and b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.webp differ
diff --git a/content/growth/how-retailers-balance-security-ux/index.md b/content/growth/how-retailers-balance-security-ux/index.md
index 184b125e1..914a23f5a 100644
--- a/content/growth/how-retailers-balance-security-ux/index.md
+++ b/content/growth/how-retailers-balance-security-ux/index.md
@@ -1,7 +1,7 @@
---
title: "How Can Retailers Lead The Experience Economy While Securing Consumer Identities?"
date: "2022-02-23"
-coverImage: "retailers-balance.jpg"
+coverImage: "retailers-balance.webp"
category: ["security"]
featured: false
author: "Rakesh Soni"
@@ -49,7 +49,7 @@ When combined, these aspects could do wonders for retailers by improving user ex
These are opportunities ready to be grabbed. But are retailers ready to incorporate identity management into their workflow? If not, it is high time that they should.
-**[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)**
+**[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)**
## How Does a Consumer Identity and Access Management (CIAM) Solution Help Retailers?
@@ -94,4 +94,4 @@ Moreover, to meet the stringent [data regulations and compliances](https://www.l
A consumer identity and access management (CIAM) solution can help retailers meet their security and user experience-related requirements like a breeze without compromising compliances and regulations.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-retailers-balance-security-ux)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-retailers-balance-security-ux)
\ No newline at end of file
diff --git a/content/growth/how-retailers-balance-security-ux/retailers-balance.jpg b/content/growth/how-retailers-balance-security-ux/retailers-balance.jpg
deleted file mode 100644
index 889d1f607..000000000
Binary files a/content/growth/how-retailers-balance-security-ux/retailers-balance.jpg and /dev/null differ
diff --git a/content/growth/how-retailers-balance-security-ux/retailers-balance.webp b/content/growth/how-retailers-balance-security-ux/retailers-balance.webp
new file mode 100644
index 000000000..01a070fd8
Binary files /dev/null and b/content/growth/how-retailers-balance-security-ux/retailers-balance.webp differ
diff --git a/content/growth/how-retailers-balance-security-ux/retailers-ds.png b/content/growth/how-retailers-balance-security-ux/retailers-ds.png
deleted file mode 100644
index 89245ae36..000000000
Binary files a/content/growth/how-retailers-balance-security-ux/retailers-ds.png and /dev/null differ
diff --git a/content/growth/how-retailers-balance-security-ux/retailers-ds.webp b/content/growth/how-retailers-balance-security-ux/retailers-ds.webp
new file mode 100644
index 000000000..929b7daff
Binary files /dev/null and b/content/growth/how-retailers-balance-security-ux/retailers-ds.webp differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.png
deleted file mode 100644
index 7f6fe4f49..000000000
Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.png and /dev/null differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.webp
new file mode 100644
index 000000000..3c8f991c0
Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.webp differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.png
deleted file mode 100644
index 185001af7..000000000
Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.png and /dev/null differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.webp
new file mode 100644
index 000000000..b07edb57d
Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.webp differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.png
deleted file mode 100644
index 0cce4e5e8..000000000
Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.png and /dev/null differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.webp
new file mode 100644
index 000000000..780e44e42
Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.webp differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.png
deleted file mode 100644
index 377aec73d..000000000
Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.png and /dev/null differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.webp
new file mode 100644
index 000000000..d97b061aa
Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.webp differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.png
deleted file mode 100644
index bbb625503..000000000
Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.png and /dev/null differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.webp
new file mode 100644
index 000000000..5f1431e73
Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.webp differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.png
deleted file mode 100644
index 8f2015baf..000000000
Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.png and /dev/null differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.webp
new file mode 100644
index 000000000..c9f65ed5a
Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.webp differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.png
deleted file mode 100644
index b44f651b5..000000000
Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.png and /dev/null differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.webp
new file mode 100644
index 000000000..3e66e54d3
Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.webp differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/index.md b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/index.md
index 9d4ffd1f8..67ed11848 100644
--- a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/index.md
+++ b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/index.md
@@ -1,7 +1,7 @@
---
title: "How To Be A Pro At Slack In 6 Simple Steps"
date: "2017-02-11"
-coverImage: "How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.png"
+coverImage: "How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.webp"
category: ["general", "loginradius"]
featured: false
author: "Rakesh Soni"
@@ -30,9 +30,9 @@ So, for people who are still struggling with Slack at their workplace, this arti
Well, there are two ways to access Slack: via browser and via app. But, everything gets faster and automatic with Slack desktop app.
-
+
-[**Source**](https://www.windowscentral.com/sites/wpcentral.com/files/styles/xlarge/public/field/image/2015/03/slack-windows.png?ver=1553881376?itok=aTD2os-J)
+[**Source**](https://www.windowscentral.com/sites/wpcentral.com/files/styles/xlarge/public/field/image/2015/03/slack-windows.webp?ver=1553881376?itok=aTD2os-J)
Slack app launches itself automatically by default every time you start your system. Thus, no need to open your browsers to use Slack from now.
@@ -62,7 +62,7 @@ Well, now coming to joining/choosing channels, you can join any channel that see
- **Step 1:** Go to your channel’s **_notification preferences_** through settings (gear icon on top right corner).
- **Step 2:** Select “mention of my name or highlights” for getting notifications related to your name or highlighted words.
-
+
**Note:** _You can mute a channel through “mute this channel” option. Moreover, you can clear all unread messages through **SHIFT + ESC.**_
@@ -77,7 +77,7 @@ Slack will notify you whenever your name is included in a message but if you wan
- Click **_notifications_** tab.
- Fill the **_highlight words_** box with your choice of highlighted phrases or words.
-
+
### **Make SlackBot your multi-tasking friend:**
@@ -95,11 +95,11 @@ Neither you nor your team can forget a thing when Slackbot is here. Set reminder
- Type ‘/remind \[#channel, a coworker, or yourself\] + \[the work\] + \[time\]. Press Enter.
-
+
- Slackbot will respond to your message.
-
+
_The response will be exclusively for you. So, your little secret about you ‘forgetting things’ will always remain a secret with Slackbot :D_
@@ -196,11 +196,11 @@ Join #CodeNewbie for hanging out with other coders who are mad about coding. You
- **You can Search anything with Ctrl + F in Slack :** Now, don’t waste time by moving your pointer to find things. Just do Ctrl + F to open search dialogue and search your desired files and messages all over Slack.
- You need to love and learn shortcuts at least when you work on Slack.You don’t need to learn all but even a handful of them can make working on Slack simpler.Check the list for shortcut keys through **Ctrl + /**.
-
+
- Using emoji can be really fun and an art worth mastering. There are two ways to use emoji in Slack. You can type the name of emoji starting with “:”. It will raise a menu
-
+
Or else just click on the smiley face in message box section to select your favorite emoji.
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.png
deleted file mode 100644
index 785ac4ae3..000000000
Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.png and /dev/null differ
diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.webp
new file mode 100644
index 000000000..008b49028
Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.jpg b/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.jpg
deleted file mode 100644
index 323aad074..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.jpg and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.webp
new file mode 100644
index 000000000..1cdf84741
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp.png
deleted file mode 100644
index cced7af22..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp.webp
new file mode 100644
index 000000000..ba49903af
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.png
deleted file mode 100644
index e334dd40a..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.webp
new file mode 100644
index 000000000..7c5302298
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.png
deleted file mode 100644
index f3f7babca..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.webp
new file mode 100644
index 000000000..fe8814e78
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.png
deleted file mode 100644
index 6948a23be..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.webp
new file mode 100644
index 000000000..3502d0fea
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.png
deleted file mode 100644
index 738109c4c..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.webp
new file mode 100644
index 000000000..588976a04
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.png
deleted file mode 100644
index 880f75057..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.webp
new file mode 100644
index 000000000..9d3407cb0
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.png
deleted file mode 100644
index 4250d4c4d..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.webp
new file mode 100644
index 000000000..fc6f18327
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.png
deleted file mode 100644
index 4f75f5622..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.webp
new file mode 100644
index 000000000..14f13078b
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.png
deleted file mode 100644
index 5169e3bec..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.webp
new file mode 100644
index 000000000..59d52edbf
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.png
deleted file mode 100644
index 40a6dc588..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.webp
new file mode 100644
index 000000000..240b4733a
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.png
deleted file mode 100644
index 63c94c3fa..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.webp
new file mode 100644
index 000000000..0cdf62c43
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.png
deleted file mode 100644
index 5613de6b8..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.webp
new file mode 100644
index 000000000..86eb7eeae
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.png
deleted file mode 100644
index 2bbfa4aa3..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.webp
new file mode 100644
index 000000000..14d9a75b2
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.png
deleted file mode 100644
index 3d9901b8a..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.webp
new file mode 100644
index 000000000..27b9191b3
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.png
deleted file mode 100644
index 508b9641d..000000000
Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.png and /dev/null differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.webp
new file mode 100644
index 000000000..93c51526e
Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.webp differ
diff --git a/content/growth/how-to-improve-the-customer-xperience/index.md b/content/growth/how-to-improve-the-customer-xperience/index.md
index b95bf76a6..2c8ddb716 100644
--- a/content/growth/how-to-improve-the-customer-xperience/index.md
+++ b/content/growth/how-to-improve-the-customer-xperience/index.md
@@ -1,7 +1,7 @@
---
title: "7 Expert Tips on How to Improve the Customer Experience"
date: "2021-09-22"
-coverImage: "consumer-exp-cover-page.jpg"
+coverImage: "consumer-exp-cover-page.webp"
category: ["loginradius"]
featured: false
author: "Alyse Falk"
@@ -12,7 +12,7 @@ metatitle: "Lets explore top 7 expert tips on how to improve the consumer experi
Excellent customer experiences motivate people to become regular consumers. The main goal of any company is to put itself in the customer’s shoes. An improved user experience brings more leads that will convert into clients and the opportunity to increase your customer base.
-
+
Note that your perfect customer experience depends on numerous factors. These are positive feedback, brand awareness, a good reputation, the SEO-friendliness of your website, and many more.
@@ -27,7 +27,7 @@ According to a [Business2Community](https://www.business2community.com/customer-
Additionally, your company will be able to generate more revenue via customer acquisition by renewing and upselling to your standing customers.
-
+
## Overview of the CX Evolution (2017-2020)
@@ -66,7 +66,7 @@ If you are interested in the best practices that will come in handy for improvin
If you still have not digitized your business, it is time to do it right now. Start with your website and social media network accounts. Your site should be mobile-friendly because about 70% of global traffic is generated via mobile device screens.
-
+
Besides the technical aspects that affect user experience, seven others are described in the following expert tips. Having implemented these approaches into practice, your CX will become significantly improved according to 2021 trends.
### #1 Understand Who Are Your Customers
@@ -83,7 +83,7 @@ For improved customer loyalty with a guaranteed individual approach, you can spl
- For entrepreneurs.
-
+
This way, first-time visitors are easily navigated to the information and features that best fit their segment. So, while being a single platform with many different SEO services, the company has improved the customer experience by providing their potential clients with a simple way to find the package designed for their needs.
@@ -100,7 +100,7 @@ Omnichannel CX is a way to provide an integrated customer experience through syn
Omnichannel CX implements many approaches simultaneously to convert CX into a seamless process. Many integration strategies bring higher conversion rates and more traffic. Additionally, it benefits customer retention. It is worth noting that omnichannel and multichannel user experiences are not the same.
-
+
The main idea of the multichannel approach is to provide many customer service channels that are not linked to each other. It means that social media networks, websites, online shops, and call centers are not synchronized. But omnichannel CX infers that all these multiple channels are connected.
@@ -119,7 +119,7 @@ To strengthen the omnichannel customer experience, tie in a CX-driven combinatio
A good example of omnichannel CX is the pharmaceutical brand [Walgreens](https://www.walgreens.com/). Brand communication takes place via a mobile-friendly app. The shopping experience is improved with the help of convenient digital features such as refilling prescriptions virtually, setting up reminders and notifications. The app saves customers time because they do not need to visit the pharmacy to get medications.
-
+
Simplified interactions and virtual communication is in high demand today and are highly appreciated by consumers and increases Walgreens’ customer retention.
@@ -141,7 +141,7 @@ The customer journey is a full cycle that takes place from the first interaction
7. Loyalty – An utterly positive experience means that the client will likely repeat the purchase and recommend your product. Encourage loyal customers to submit thankful reviews that will improve your reputation, brand awareness, and search rankings.
-
+
## Tips for Customer Journey Optimization
@@ -223,7 +223,7 @@ The rule of a great CX-driven online community is the desire for your loyal cust
For example, [Inkbox](https://inkbox.com/) consists of a community with millions (2 million) of followers. This company makes it a priority of tattooing and shares all completed work on the Internet. The community was created around the popular Instagram hashtag #tattoosfornow. People throughout the world shared beautiful photos with tattoos and grew the community.
-
+
### #5 Take Advantage of Customer Reviews
@@ -234,7 +234,7 @@ You can use reviews for your customer experience purposes. Additionally, you can
-
+
@@ -242,8 +242,8 @@ You can use reviews for your customer experience purposes. Additionally, you can
2. Use reviews for your search ranking. Add a Sitemap with reviews to engage people to visit your site and help Google consider your website as trusted.
-
-
+
+
3. Use reviews to prove your reputation on other online communication channels (social media platforms, forums, blogs).
@@ -253,13 +253,13 @@ You can use reviews for your customer experience purposes. Additionally, you can
4. Use client testimonials in newsletters and for other email marketing purposes. This way, you will increase the chances that your letter will be read and taken into consideration.
-
+
5. Add reviews to your video marketing materials. You can use screenshots of some eye-catching and detailed testimonials in your advertising videos.
6. Analyze your customer satisfaction rates with the help of the percentages that rank positive, neutral, and negative reviews. For example, you can offer short online surveys to get more reviews after any customer journey stage (especially at the last two) and measure them. Here is a set of survey templates by [NiceReply](https://www.nicereply.com/).
-
+
### #6 Personalize Your Content
@@ -268,13 +268,13 @@ According to [Harvard Business Review](https://hbr.org/2018/01/ads-that-dont-ove
[Spotify](https://www.spotify.com/us/) decided to launch the option “Discover Weekly” for this purpose. A personalized playlist is generated according to the listener’s preferences. Some users like this option, while some Spotify fans dislike it. Nevertheless, this is a way to promote a personalized approach and show each customer your meaningful marketing strategy.
-
+
### #7 Make the Customer Experience Safer
A significant number of Internet users are still afraid of scammers and cyber hacks regarding the user experience on a website. Assure visitors that your ecommerce platform and corporate site are risk-free for them. For example, [LoginRadius](https://www.loginradius.com/customer-security/) provides businesses with adoptive safety tools to make their CX 100% secure.
-
+
Having implemented tech solutions to protect client accounts, your company strengthens its brand awareness, improves reputation and loyalty. Usually, the most challenging aspects for customers are the security of personal data and online payments. Your task in the context of CX improvement is to maintain privacy and guarantee safe transactions.
@@ -282,5 +282,5 @@ Having implemented tech solutions to protect client accounts, your company stren
Your CX strategy should meet customer requirements and your business goals. Customer experience is a proven way to develop high retention, cross-sales, and up-sales. If people decide to come back and recommend your products, this is a good sign for your company. An improved user experience benefits SEO, brand awareness, and generally the online presence of your business. 2021 requires marketers, entrepreneurs, and SEO specialists to demonstrate an omnichannel CX approach with comprehensive security, reviews, and customer journey strategies.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-improve-the-customer-xperience)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-improve-the-customer-xperience)
diff --git a/content/growth/how-to-learn-copywriting/index.md b/content/growth/how-to-learn-copywriting/index.md
index d26f97f2d..51a07f3e0 100644
--- a/content/growth/how-to-learn-copywriting/index.md
+++ b/content/growth/how-to-learn-copywriting/index.md
@@ -1,7 +1,7 @@
---
title: "Want to Learn Copywriting? 3 Tips That Will Keep Readers Glued to Your Content"
date: "2021-05-25"
-coverImage: "learn-copywriting.jpg"
+coverImage: "learn-copywriting.webp"
category: ["loginradius"]
featured: false
author: "Navanita Devi"
@@ -188,4 +188,4 @@ Remember that SEO-optimized content is essential to rank your blogs or website p
To develop a unique [brand identity](https://www.loginradius.com/blog/fuel/2021/04/does-your-website-imagery-reflect-your-brand-identity/), you need to have a team of top-notch copywriters who can keep the readers glued to the content and eventually help increase your business.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-learn-copywriting)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-learn-copywriting)
diff --git a/content/growth/how-to-learn-copywriting/learn-copywriting.jpg b/content/growth/how-to-learn-copywriting/learn-copywriting.jpg
deleted file mode 100644
index 09b5dbad8..000000000
Binary files a/content/growth/how-to-learn-copywriting/learn-copywriting.jpg and /dev/null differ
diff --git a/content/growth/how-to-learn-copywriting/learn-copywriting.webp b/content/growth/how-to-learn-copywriting/learn-copywriting.webp
new file mode 100644
index 000000000..ea850919c
Binary files /dev/null and b/content/growth/how-to-learn-copywriting/learn-copywriting.webp differ
diff --git a/content/growth/how-to-leverage-email-automation-personalization/email-automation.jpg b/content/growth/how-to-leverage-email-automation-personalization/email-automation.jpg
deleted file mode 100644
index 7f11984b2..000000000
Binary files a/content/growth/how-to-leverage-email-automation-personalization/email-automation.jpg and /dev/null differ
diff --git a/content/growth/how-to-leverage-email-automation-personalization/email-automation.webp b/content/growth/how-to-leverage-email-automation-personalization/email-automation.webp
new file mode 100644
index 000000000..37082ab01
Binary files /dev/null and b/content/growth/how-to-leverage-email-automation-personalization/email-automation.webp differ
diff --git a/content/growth/how-to-leverage-email-automation-personalization/image1.png b/content/growth/how-to-leverage-email-automation-personalization/image1.png
deleted file mode 100644
index ccf0c0210..000000000
Binary files a/content/growth/how-to-leverage-email-automation-personalization/image1.png and /dev/null differ
diff --git a/content/growth/how-to-leverage-email-automation-personalization/image1.webp b/content/growth/how-to-leverage-email-automation-personalization/image1.webp
new file mode 100644
index 000000000..f8e453304
Binary files /dev/null and b/content/growth/how-to-leverage-email-automation-personalization/image1.webp differ
diff --git a/content/growth/how-to-leverage-email-automation-personalization/image2.png b/content/growth/how-to-leverage-email-automation-personalization/image2.png
deleted file mode 100644
index d08f0c448..000000000
Binary files a/content/growth/how-to-leverage-email-automation-personalization/image2.png and /dev/null differ
diff --git a/content/growth/how-to-leverage-email-automation-personalization/image2.webp b/content/growth/how-to-leverage-email-automation-personalization/image2.webp
new file mode 100644
index 000000000..4b4bd1699
Binary files /dev/null and b/content/growth/how-to-leverage-email-automation-personalization/image2.webp differ
diff --git a/content/growth/how-to-leverage-email-automation-personalization/index.md b/content/growth/how-to-leverage-email-automation-personalization/index.md
index 8dfb1e07c..94d4dd0a9 100644
--- a/content/growth/how-to-leverage-email-automation-personalization/index.md
+++ b/content/growth/how-to-leverage-email-automation-personalization/index.md
@@ -1,7 +1,7 @@
---
title: "How to Make Your Automated Emails Sound Personal, Relevant, and Effective?"
date: "2021-07-02"
-coverImage: "email-automation.jpg"
+coverImage: "email-automation.webp"
tags: ["email marketing","customer experience","personalization"]
author: "Akshay Deogiri"
description: " The chances are that as a marketer, you’re already segmenting your audience and sending them targeted emails. But is that enough? Making your emails relevant is one thing, and making them interesting and engaging is something completely different. If implemented correctly, personalization is a powerful tool that can help you engage your audience and nurture your leads."
@@ -85,7 +85,7 @@ All email automation solutions support triggers. You can choose a trigger that
Here’s a great example from an automated welcome email from Healthline, a health information provider.
-
+
Image Source: [Healthline](https://www.healthline.com/)
@@ -93,7 +93,7 @@ Setting up triggers is great, but not enough. If you want to truly personalize y
For example, Sephora, a cosmetics and personal care brand, sends an email providing a 20% discount to customers who shop for more than $200.
-
+
Image Source: [Sephora](https://www.sephora.com/)
@@ -158,4 +158,4 @@ Personalizing emails isn’t a choice anymore for brands. Customers expect you t
This can help your brand in two ways. First, it can reduce your costs and increase your marketing efficiency. And second, it can make your marketing more personal, relevant, and effective, resulting in better engagement and more customers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-leverage-email-automation-personalization)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-leverage-email-automation-personalization)
diff --git a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/index.md b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/index.md
index a35562d2b..d87846103 100644
--- a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/index.md
+++ b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/index.md
@@ -1,7 +1,7 @@
---
title: "Personalize Your Marketing With The Help Of A CIAM Platform"
date: "2021-07-30"
-coverImage: "personalized-marketing.jpg"
+coverImage: "personalized-marketing.webp"
tags: ["ciam solution","data security","cx","authentication"]
author: "Navanita Devi"
description: "Personalized marketing is a promotional strategy tailored to the individual at the precise moment they require it, and there's no other communication like it. The question is, how will you fulfill that promise? You may utilize tools to acquire and aggregate information about your clients' preferences. Read on to find out what these tools are and how they benefit your business."
@@ -25,7 +25,7 @@ CIAM solutions also typically offer self-service capabilities for customers, suc
## Grow Your Business with CIAM
-
+
Providing consumers with digital services is a delicate balancing act. You must provide an exceptional client experience while also establishing trust in the security of your services. If you get one of these things incorrect, the consequences can be devastating.
@@ -81,4 +81,4 @@ By using a robust CIAM solution, organizations can build trust and loyalty with
In a nutshell, CIAM enables organizations to deliver an exceptional and secure personalized experience that meets the needs of their customers, ultimately leading to increased customer satisfaction and brand loyalty.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-make-personalized-marketing-effective-with-consumer-identity)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-make-personalized-marketing-effective-with-consumer-identity)
\ No newline at end of file
diff --git a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.png b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.png
deleted file mode 100644
index 83ffe682c..000000000
Binary files a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.png and /dev/null differ
diff --git a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.webp b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.webp
new file mode 100644
index 000000000..5527fbf0b
Binary files /dev/null and b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.webp differ
diff --git a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.jpg b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.jpg
deleted file mode 100644
index 8e1713a97..000000000
Binary files a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.jpg and /dev/null differ
diff --git a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.webp b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.webp
new file mode 100644
index 000000000..b0df12f9e
Binary files /dev/null and b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.webp differ
diff --git a/content/growth/how-to-protect-consumer-social-identity/index.md b/content/growth/how-to-protect-consumer-social-identity/index.md
index 9b6663787..244deabe0 100644
--- a/content/growth/how-to-protect-consumer-social-identity/index.md
+++ b/content/growth/how-to-protect-consumer-social-identity/index.md
@@ -1,7 +1,7 @@
---
title: "Why Consumers’ Social Identities Matter & How You Can Protect It?"
date: "2021-12-07"
-coverImage: "social-id.jpg"
+coverImage: "social-id.webp"
category: ["security"]
featured: false
author: "Navanita Devi"
@@ -82,5 +82,5 @@ Businesses can benefit from greater customer engagement and loyalty by providing
Today, data is king. Sensitive information about the social identity of consumers is used by organisations for many reasons, but it's also organisations' responsibility to maintain privacy. This can only be achieved by investing in the best CIAM.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-protect-consumer-social-identity)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-protect-consumer-social-identity)
diff --git a/content/growth/how-to-protect-consumer-social-identity/social-id.jpg b/content/growth/how-to-protect-consumer-social-identity/social-id.jpg
deleted file mode 100644
index 841a3bab5..000000000
Binary files a/content/growth/how-to-protect-consumer-social-identity/social-id.jpg and /dev/null differ
diff --git a/content/growth/how-to-protect-consumer-social-identity/social-id.webp b/content/growth/how-to-protect-consumer-social-identity/social-id.webp
new file mode 100644
index 000000000..8e295c037
Binary files /dev/null and b/content/growth/how-to-protect-consumer-social-identity/social-id.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.jpg
deleted file mode 100644
index cf5d7f92b..000000000
Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.jpg and /dev/null differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.webp
new file mode 100644
index 000000000..dddde8839
Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.jpg
deleted file mode 100644
index adf6e1415..000000000
Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.jpg and /dev/null differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.webp
new file mode 100644
index 000000000..6640ebaa2
Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.jpg
deleted file mode 100644
index 3f6c926b6..000000000
Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.jpg and /dev/null differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.webp
new file mode 100644
index 000000000..17a881a21
Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.jpg
deleted file mode 100644
index d77141fd3..000000000
Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.jpg and /dev/null differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.webp
new file mode 100644
index 000000000..d91162fd0
Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.jpg
deleted file mode 100644
index c72dfb1a9..000000000
Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.jpg and /dev/null differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.webp
new file mode 100644
index 000000000..4926c866e
Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.jpg
deleted file mode 100644
index fee6d7dc3..000000000
Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.jpg and /dev/null differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.webp
new file mode 100644
index 000000000..7e46c6ae6
Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.jpg
deleted file mode 100644
index c8040898a..000000000
Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.jpg and /dev/null differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.webp
new file mode 100644
index 000000000..1b5292b3b
Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.jpg
deleted file mode 100644
index a39d2d500..000000000
Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.jpg and /dev/null differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.webp
new file mode 100644
index 000000000..f2612bd4e
Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.jpg
deleted file mode 100644
index ebb5fca2a..000000000
Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.jpg and /dev/null differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.webp
new file mode 100644
index 000000000..757cd74b2
Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.png b/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.png
deleted file mode 100644
index c4fa3a11c..000000000
Binary files a/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.png and /dev/null differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.webp b/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.webp
new file mode 100644
index 000000000..b15b42635
Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.jpg b/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.jpg
deleted file mode 100644
index c56bcb0e2..000000000
Binary files a/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.jpg and /dev/null differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.webp b/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.webp
new file mode 100644
index 000000000..267cec516
Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.webp differ
diff --git a/content/growth/how-to-throw-a-tiki-tech-party/index.md b/content/growth/how-to-throw-a-tiki-tech-party/index.md
index 79e1539a5..0aa4522d8 100644
--- a/content/growth/how-to-throw-a-tiki-tech-party/index.md
+++ b/content/growth/how-to-throw-a-tiki-tech-party/index.md
@@ -1,7 +1,7 @@
---
title: "How To Throw A Tiki Tech Party"
date: "2019-09-20"
-coverImage: "how-to-throw-a-tiki-tech-party.jpg"
+coverImage: "how-to-throw-a-tiki-tech-party.webp"
category: ["media-and-publication", "LoginRadius"]
featured: false
author: "Karl Wittig"
@@ -13,7 +13,7 @@ metadescription: "Learn more about how LoginRadius organized its first Tiki Tech
Last week, we had a great time participating in Vancouver Startup Week's Community Crawl.
-
+
The Community Crawl is like a pub crawl except you hop from startup offices to startup offices. It’s an engaging open house event where guests can check out different startups. Over a dozen startups opened their doors, so **thanks to everyone who took the time to check us out!**
@@ -21,7 +21,7 @@ Those who attended immediately noticed our new spacious office space, complete w
To celebrate our move and christen our new space and tiki bar, we hosted a tiki party, replete with festive Hawaiian leis and shirts.
-
+
_LoginRadius founder & CEO, Rakesh Soni, enjoying our new custom-made tiki bar._
@@ -37,11 +37,11 @@ Being a startup with a modest budget, we had to be creative with the DIY decor.
We painted colourful signs on cardboard and made little pineapple lanterns which we strung across the room. Then, to brighten the room, we added flamingo-pink dangling paper tissue balls from the ceiling. Hanging decorations from the ceiling are better than sticking them on walls. It makes a room look full and festive with very little material.
-
+
_We bought yellow lanterns and turned them into pineapples._
-
+
_We placed hand-painted signs, including our drinks menu, all over the room._
@@ -49,7 +49,7 @@ _We placed hand-painted signs, including our drinks menu, all over the room._
Another easy way to add more tiki into a room is by playing music. We found a pre-made tiki playlist on a streaming app and let it loop throughout the night. There wasn’t any official dancing at our party, but we had lots of people bobbing their heads or tapping their feet to the beat.
-
+
_Our team members and guests having fun at our tiki tech party._
@@ -59,7 +59,7 @@ The tiki bar was made by a local carpenter. He came by our office to look at the
What he built was better than what we expected! The frame is made of durable wood and lined with the bamboo-like exterior. On the inside, we have a fridge for the keg and another fridge for other drinks. On the surface of the bar is the tap for the beer. The front was lined with LED lights that changed colours. Everything is covered by a thatched roof, completing the tiki look.
-
+
_To the left is Mark from Torlay, our local carpenter, who designed and built our lovely tiki bar!_
@@ -73,7 +73,7 @@ To ensure a fun relaxing night for everyone, we hired a bartender. His lime marg
The tap beer on the tiki bar was also a celebration on its own. Plus, right before the event, one of our team members whipped up some killer tropical sangria.
-
+
_Our bartender, Sam, making amazing tropical drinks for us all night long._
@@ -84,7 +84,7 @@ Whether you do or don’t have a tiki bar, you can create the vibe around your c
The first impression is everything. Each guest who came through our doors received a flower lei over their heads. It’s a great way to create that instant tiki environment. We went a step further and created little tags for each lei with our company logo and a QR code that took them to our [Careers page](https://www.loginradius.com/careers/) for those who are interested in joining us for more than just a tiki party.
-
+
_Lovely volunteers from Vancouver Startup Week helped us give leis to our guests._
@@ -92,7 +92,7 @@ _Lovely volunteers from Vancouver Startup Week helped us give leis to our guests
On our TV, we displayed a one-minute online survey that can be taken on mobile phones. Since LoginRadius secures digital identities, we asked our guests to check all the different digital identities they used in the past week. This included emails, online banking, various video games, social media, and more.
-
+
_Individuals scanned the QR code on our TV to take our one-minute digital identity survey._
@@ -109,7 +109,7 @@ On a weekend night, what better way to end a party than with an after-party? We
Planning fun parties can be exhausting. Allowing spontaneous after parties can help you feel free and serve as a reminder that an enjoyable event doesn’t always have to be stringently planned.
-
+
_The after-party selfie—no party is complete without it!_
diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.png b/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.png
deleted file mode 100644
index 802253f09..000000000
Binary files a/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.png and /dev/null differ
diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.webp b/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.webp
new file mode 100644
index 000000000..c98143e9e
Binary files /dev/null and b/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.webp differ
diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.png b/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.png
deleted file mode 100644
index a2c9e2a07..000000000
Binary files a/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.png and /dev/null differ
diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.webp b/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.webp
new file mode 100644
index 000000000..1717fdcbb
Binary files /dev/null and b/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.webp differ
diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.jpg b/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.jpg
deleted file mode 100644
index 797463755..000000000
Binary files a/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.jpg and /dev/null differ
diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.webp b/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.webp
new file mode 100644
index 000000000..27095170a
Binary files /dev/null and b/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.webp differ
diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/index.md b/content/growth/how-to-use-identity-marketing-privacy-centric-world/index.md
index 6d8228d34..4ae72ed63 100644
--- a/content/growth/how-to-use-identity-marketing-privacy-centric-world/index.md
+++ b/content/growth/how-to-use-identity-marketing-privacy-centric-world/index.md
@@ -1,7 +1,7 @@
---
title: "The Right Way to Use Identity Marketing in a Privacy-Centric World"
date: "2022-02-15"
-coverImage: "identity-marketing.jpg"
+coverImage: "identity-marketing.webp"
tags: ["identity management","compliance","cx"]
author: "Navanita Devi"
description: "There are numerous ways that you can use identity marketing to strengthen your business reputation. With the right techniques, you can make this an extremely powerful strategy. The points mentioned in this blog will help you to understand how identity marketing has transformed the modern digital age."
@@ -37,7 +37,7 @@ First, there's the issue of data protection. The GDPR requires businesses to giv
Second, businesses need to rethink how they use their systems and communicate with their customers. The good news is that many of the issues can be resolved simply by taking an extra minute to verify if the legislations' conditions are met.
-[](https://www.loginradius.com/resource/)
+[](https://www.loginradius.com/resource/)
## Exploring the Concept of Incrementality
@@ -73,4 +73,4 @@ As mentioned above, there are many things that you might want to do with your co
Another important point is that you need to understand when you are asking questions and gathering information from your consumers as well. All these aspects should be discussed with [privacy policies](https://www.loginradius.com/blog/identity/privacy-policy-management/) so that consumers know what they are doing in regards to your brand identity.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-use-identity-marketing-privacy-centric-world)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-use-identity-marketing-privacy-centric-world)
\ No newline at end of file
diff --git a/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.png b/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.png
deleted file mode 100644
index b18dabb9d..000000000
Binary files a/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.png and /dev/null differ
diff --git a/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.webp b/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.webp
new file mode 100644
index 000000000..86a87bf76
Binary files /dev/null and b/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.webp differ
diff --git a/content/growth/how-to-write-professional-bio-with-examples/index.md b/content/growth/how-to-write-professional-bio-with-examples/index.md
index 64d992d9b..e0c8db9ca 100644
--- a/content/growth/how-to-write-professional-bio-with-examples/index.md
+++ b/content/growth/how-to-write-professional-bio-with-examples/index.md
@@ -1,7 +1,7 @@
---
title: "Don’t Waste Time! Facts to learn to write the Best Professional Bio"
date: "2017-02-27"
-coverImage: "Quick-tips-to-learn-to-write-the-Best-Professional-Bio.png"
+coverImage: "Quick-tips-to-learn-to-write-the-Best-Professional-Bio.webp"
category: ["general", "marketing", "loginradius"]
featured: false
author: "Rakesh Soni"
@@ -113,15 +113,15 @@ Most importantly, do not forget to proofread your bio. Always invite some of you
### **Some real life examples of best professional bios that I found in my research:**
-
+
[**Source**](https://twitter.com/adampopescu)
-
+
[**Source**](https://twitter.com/alisoncrowewine)
-
+
[**Source**](https://twitter.com/WaltHickey)
diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.png b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.png
deleted file mode 100644
index 51122125d..000000000
Binary files a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.png and /dev/null differ
diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.webp b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.webp
new file mode 100644
index 000000000..fb269bab7
Binary files /dev/null and b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.webp differ
diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.png b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.png
deleted file mode 100644
index 953880036..000000000
Binary files a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.png and /dev/null differ
diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.webp b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.webp
new file mode 100644
index 000000000..dc22adac0
Binary files /dev/null and b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.webp differ
diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.png b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.png
deleted file mode 100644
index 558f7d35f..000000000
Binary files a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.png and /dev/null differ
diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.webp b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.webp
new file mode 100644
index 000000000..694249287
Binary files /dev/null and b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.webp differ
diff --git a/content/growth/hybrid-workforce/hybrid-workforce.jpg b/content/growth/hybrid-workforce/hybrid-workforce.jpg
deleted file mode 100644
index c52dc4a21..000000000
Binary files a/content/growth/hybrid-workforce/hybrid-workforce.jpg and /dev/null differ
diff --git a/content/growth/hybrid-workforce/hybrid-workforce.webp b/content/growth/hybrid-workforce/hybrid-workforce.webp
new file mode 100644
index 000000000..2314dbfd9
Binary files /dev/null and b/content/growth/hybrid-workforce/hybrid-workforce.webp differ
diff --git a/content/growth/hybrid-workforce/index.md b/content/growth/hybrid-workforce/index.md
index bc9c356a7..410224b41 100644
--- a/content/growth/hybrid-workforce/index.md
+++ b/content/growth/hybrid-workforce/index.md
@@ -1,7 +1,7 @@
---
title: "Hybrid Workforce: Laying The Foundation of Remote Working"
date: "2021-02-22"
-coverImage: "hybrid-workforce.jpg"
+coverImage: "hybrid-workforce.webp"
category: ["all"]
featured: false
author: "Rakesh Soni"
@@ -113,4 +113,4 @@ Companies also need to provide the [employees working remotely](https://www.logi
A Hybrid workforce can prove to be beneficial both for companies and the employees who would work remotely. This change was forced into action due to the covid-19 pandemic, but it'll be the future of the work. It'll lead to a great many changes. It will not only help businesses build more money, but it'll also help them lessen the workload on the employees. In a nutshell, the hybrid workforce model is a win-win for both employers and employees.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hybrid-workforce)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hybrid-workforce)
diff --git a/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.png b/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.png
deleted file mode 100644
index f5fa0b0f9..000000000
Binary files a/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.png and /dev/null differ
diff --git a/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.webp b/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.webp
new file mode 100644
index 000000000..b0761321e
Binary files /dev/null and b/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.webp differ
diff --git a/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.jpg b/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.jpg
deleted file mode 100644
index ab8c0477b..000000000
Binary files a/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.jpg and /dev/null differ
diff --git a/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.webp b/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.webp
new file mode 100644
index 000000000..abc23d05e
Binary files /dev/null and b/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.webp differ
diff --git a/content/growth/identity-at-centre-of-your-customer-strategy/index.md b/content/growth/identity-at-centre-of-your-customer-strategy/index.md
index 8d84ebb8a..b32aa9e97 100644
--- a/content/growth/identity-at-centre-of-your-customer-strategy/index.md
+++ b/content/growth/identity-at-centre-of-your-customer-strategy/index.md
@@ -1,7 +1,7 @@
---
title: "Why Identity Should Be At The Centre of Your Customer Strategy"
date: "2023-07-20"
-coverImage: "identity-at-centre.jpg"
+coverImage: "identity-at-centre.webp"
tags: ["identity management","data security","cx"]
author: "Vishal Sharma"
description: "Dive into the vital role of identity in your customer strategy. Explore how leveraging identity data can revolutionize personalization, establish trust, ensure seamless experiences across channels, drive data-driven decision-making, and maximize customer lifetime value."
@@ -35,7 +35,7 @@ Transparent privacy policies and clear communication regarding data usage also c
Customers expect consistency and continuity as they interact with a brand across different channels. Integrating identity management across your various touchpoints allows you to provide a seamless omnichannel experience.
-[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
+[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
For example, a customer who starts shopping on your website should be able to continue their journey seamlessly on a mobile app or even in-store without any disruptions.
@@ -63,4 +63,4 @@ Incorporating identity into your customer strategy is a strategic imperative in
By placing identity at the center of your customer strategy, you create a customer-centric approach that drives customer satisfaction, enhances brand reputation, and positions your business as a leader in your industry.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-at-centre-of-your-customer-strategy)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-at-centre-of-your-customer-strategy)
diff --git a/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.png b/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.png
deleted file mode 100644
index fb9e830ba..000000000
Binary files a/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.png and /dev/null differ
diff --git a/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.webp b/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.webp
new file mode 100644
index 000000000..4ea6dbcbf
Binary files /dev/null and b/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.webp differ
diff --git a/content/growth/identity-convergence-market-dominance/identity-convergence.jpg b/content/growth/identity-convergence-market-dominance/identity-convergence.jpg
deleted file mode 100644
index 6b33c773b..000000000
Binary files a/content/growth/identity-convergence-market-dominance/identity-convergence.jpg and /dev/null differ
diff --git a/content/growth/identity-convergence-market-dominance/identity-convergence.webp b/content/growth/identity-convergence-market-dominance/identity-convergence.webp
new file mode 100644
index 000000000..ef3fddf6d
Binary files /dev/null and b/content/growth/identity-convergence-market-dominance/identity-convergence.webp differ
diff --git a/content/growth/identity-convergence-market-dominance/index.md b/content/growth/identity-convergence-market-dominance/index.md
index aecef03ad..1d4de3783 100644
--- a/content/growth/identity-convergence-market-dominance/index.md
+++ b/content/growth/identity-convergence-market-dominance/index.md
@@ -1,7 +1,7 @@
---
title: "Unlocking the Secret to Dominating the Market: How Can Give You a Competitive Edge"
date: "2024-05-23"
-coverImage: "identity-convergence.jpg"
+coverImage: "identity-convergence.webp"
tags: ["identity convergence","data privacy","cx"]
author: "Cooper Matheson"
description: "Identity convergence integrates diverse customer data into unified profiles, enabling unmatched personalization and efficiency. Learn how to leverage this strategy for superior business outcomes and gain a competitive edge in today's market."
@@ -40,7 +40,7 @@ Identity convergence allows for the creation of highly targeted marketing campai
* **Predictive Analytics:** By utilizing predictive analytics, businesses can anticipate customer needs and behaviors, enabling proactive marketing efforts that capture attention at the right moment.
-[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper)
+[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper)
### 3. Improved Product Development
@@ -103,4 +103,4 @@ By creating a unified view of the customer, companies can develop more effective
Identity convergence is more than a buzzword; it's a strategic approach that can transform businesses' interactions with their customers and drive long-term growth. Embrace identity convergence today and watch your competitive edge soar.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-convergence-market-dominance)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-convergence-market-dominance)
diff --git a/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.png b/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.png and /dev/null differ
diff --git a/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.webp b/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.webp differ
diff --git a/content/growth/identity-management-critical-revenue-generation/ciam-eb.png b/content/growth/identity-management-critical-revenue-generation/ciam-eb.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/growth/identity-management-critical-revenue-generation/ciam-eb.png and /dev/null differ
diff --git a/content/growth/identity-management-critical-revenue-generation/ciam-eb.webp b/content/growth/identity-management-critical-revenue-generation/ciam-eb.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/growth/identity-management-critical-revenue-generation/ciam-eb.webp differ
diff --git a/content/growth/identity-management-critical-revenue-generation/index.md b/content/growth/identity-management-critical-revenue-generation/index.md
index be84cf865..8d6ee69c0 100644
--- a/content/growth/identity-management-critical-revenue-generation/index.md
+++ b/content/growth/identity-management-critical-revenue-generation/index.md
@@ -1,7 +1,7 @@
---
title: "Demystifying Identity Management For Revenue Generation - Going Beyond Compliance"
date: "2022-10-17"
-coverImage: "revenue-generation.jpg"
+coverImage: "revenue-generation.webp"
tags: ["digital identity management", "ciam", "compliance"]
author: "Rakesh Soni"
description: "Modern businesses quickly realize that leveraging digital identities as fuel for driving their organizational growth through personalization and robust identity security is becoming the need of the hour. This blog outlines the major depicting how identity management paves the way for organizational growth."
@@ -40,7 +40,7 @@ Your users always expect personalization from the moment they interact with your
With a customer identity and access management (CIAM) solution for identity management, organizations can ensure they remain ahead of their competitors by leveraging the true potential of personalization.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
As a brand, one could utilize customer-related details in a way that helps automatically generate suggestions based on a user’s interest and past behavior on your platform. This means you have a greater chance of lead generation and conversion.
@@ -73,4 +73,4 @@ Identity management is a critical part of the revenue generation process. In tod
A modern CIAM solution can help you manage your customers' information, enhance user experience, and ensures you build better-personalized experiences to convert your targetted audience into customers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-critical-revenue-generation)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-critical-revenue-generation)
diff --git a/content/growth/identity-management-critical-revenue-generation/revenue-generation.jpg b/content/growth/identity-management-critical-revenue-generation/revenue-generation.jpg
deleted file mode 100644
index b104f996c..000000000
Binary files a/content/growth/identity-management-critical-revenue-generation/revenue-generation.jpg and /dev/null differ
diff --git a/content/growth/identity-management-critical-revenue-generation/revenue-generation.webp b/content/growth/identity-management-critical-revenue-generation/revenue-generation.webp
new file mode 100644
index 000000000..45eaea07c
Binary files /dev/null and b/content/growth/identity-management-critical-revenue-generation/revenue-generation.webp differ
diff --git a/content/growth/identity-management-for-better-cx/EB-omnichannel.png b/content/growth/identity-management-for-better-cx/EB-omnichannel.png
deleted file mode 100644
index f5fa0b0f9..000000000
Binary files a/content/growth/identity-management-for-better-cx/EB-omnichannel.png and /dev/null differ
diff --git a/content/growth/identity-management-for-better-cx/EB-omnichannel.webp b/content/growth/identity-management-for-better-cx/EB-omnichannel.webp
new file mode 100644
index 000000000..b0761321e
Binary files /dev/null and b/content/growth/identity-management-for-better-cx/EB-omnichannel.webp differ
diff --git a/content/growth/identity-management-for-better-cx/id-cx.jpg b/content/growth/identity-management-for-better-cx/id-cx.jpg
deleted file mode 100644
index f63f28934..000000000
Binary files a/content/growth/identity-management-for-better-cx/id-cx.jpg and /dev/null differ
diff --git a/content/growth/identity-management-for-better-cx/id-cx.webp b/content/growth/identity-management-for-better-cx/id-cx.webp
new file mode 100644
index 000000000..6896847e6
Binary files /dev/null and b/content/growth/identity-management-for-better-cx/id-cx.webp differ
diff --git a/content/growth/identity-management-for-better-cx/index.md b/content/growth/identity-management-for-better-cx/index.md
index ded3b7ed8..228150f41 100644
--- a/content/growth/identity-management-for-better-cx/index.md
+++ b/content/growth/identity-management-for-better-cx/index.md
@@ -1,7 +1,7 @@
---
title: "How To Use Identity To Make Your Customers Feel Safe And Empowered?"
date: "2022-10-28"
-coverImage: "id-cx.jpg"
+coverImage: "id-cx.webp"
category: ["identity management", "cx", "data security"]
author: "Navanita Devi"
description: "It goes without saying that excellent UX can improve conversion rates, reduce churn and increase adoption rates. In this blog post, we'll help you figure out how to use digital identity to improve your relationships with customers and make them feel more confident in their interactions with you."
@@ -37,7 +37,7 @@ They want to be able to access their information from any device at any time, wh
A CIAM improves the omnichannel experience for its customers by making them feel safe and empowered. All they need to do is provide them with one login that works across all their devices and channels.
-[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
+[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
### 3. Balancing between user experience and security
@@ -75,4 +75,4 @@ In the end, CIAM is all about driving revenue. A good CIAM solution can deliver
But if you don't consider all components of your CIAM, you'll miss out on valuable benefits for both businesses and consumers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-for-better-cx)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-for-better-cx)
diff --git a/content/growth/identity-management-for-better-cx/omni-eb.png b/content/growth/identity-management-for-better-cx/omni-eb.png
deleted file mode 100644
index 86c15a159..000000000
Binary files a/content/growth/identity-management-for-better-cx/omni-eb.png and /dev/null differ
diff --git a/content/growth/identity-management-for-better-cx/omni-eb.webp b/content/growth/identity-management-for-better-cx/omni-eb.webp
new file mode 100644
index 000000000..025782e92
Binary files /dev/null and b/content/growth/identity-management-for-better-cx/omni-eb.webp differ
diff --git a/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.png b/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.png
deleted file mode 100644
index f97184f2f..000000000
Binary files a/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.png and /dev/null differ
diff --git a/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.webp b/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.webp
new file mode 100644
index 000000000..88d19cbb8
Binary files /dev/null and b/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.webp differ
diff --git a/content/growth/identity-management-reduce-cpa-marketers/cpa-market.jpg b/content/growth/identity-management-reduce-cpa-marketers/cpa-market.jpg
deleted file mode 100644
index 0c31a2593..000000000
Binary files a/content/growth/identity-management-reduce-cpa-marketers/cpa-market.jpg and /dev/null differ
diff --git a/content/growth/identity-management-reduce-cpa-marketers/cpa-market.webp b/content/growth/identity-management-reduce-cpa-marketers/cpa-market.webp
new file mode 100644
index 000000000..635df37b8
Binary files /dev/null and b/content/growth/identity-management-reduce-cpa-marketers/cpa-market.webp differ
diff --git a/content/growth/identity-management-reduce-cpa-marketers/index.md b/content/growth/identity-management-reduce-cpa-marketers/index.md
index 0fe9000d7..8b16c2a05 100644
--- a/content/growth/identity-management-reduce-cpa-marketers/index.md
+++ b/content/growth/identity-management-reduce-cpa-marketers/index.md
@@ -1,7 +1,7 @@
---
title: "Planning to Reduce Your CPA By 50%? You Need ID Management"
date: "2022-07-06"
-coverImage: "cpa-market.jpg"
+coverImage: "cpa-market.webp"
category: ["cost per acquisition", "identity management", "marketing"]
author: "Navanita Devi"
description: "An essential marketing requirement is to know your customers first and then learn about their preferences. With a reliable CIAM system, marketers need not worry about collecting valuable customer insights; CIAM does it all without burning a pocket! Let’s understand how."
@@ -59,7 +59,7 @@ Collecting unnecessary data wastes resources and increases the risk of identity
With a reliable CIAM, businesses can leverage the true potential of progressive profiling.
-[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
+[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
Progressive profiling for customer registration allows you to split a potentially complicated registration process into multiple steps. You can capture a customer’s information upfront and then slowly build a holistic view of that customer through subsequent actions.
@@ -75,4 +75,4 @@ Apart from reducing the cost per acquisition, businesses can ensure robust custo
Hence, if a business wishes to succeed with minimum investment, it must leverage the true potential of a CIAM solution.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-reduce-cpa-marketers)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-reduce-cpa-marketers)
diff --git a/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.png b/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.png
deleted file mode 100644
index c9ad88d9e..000000000
Binary files a/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.png and /dev/null differ
diff --git a/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.webp b/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.webp
new file mode 100644
index 000000000..2b537fe1a
Binary files /dev/null and b/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.webp differ
diff --git a/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.png b/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.png
deleted file mode 100644
index ccf2bf5b2..000000000
Binary files a/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.png and /dev/null differ
diff --git a/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.webp b/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.webp
new file mode 100644
index 000000000..1c92d79a3
Binary files /dev/null and b/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.webp differ
diff --git a/content/growth/identity-proofing-orchestration-security/id-proofing.jpg b/content/growth/identity-proofing-orchestration-security/id-proofing.jpg
deleted file mode 100644
index d199f04dd..000000000
Binary files a/content/growth/identity-proofing-orchestration-security/id-proofing.jpg and /dev/null differ
diff --git a/content/growth/identity-proofing-orchestration-security/id-proofing.webp b/content/growth/identity-proofing-orchestration-security/id-proofing.webp
new file mode 100644
index 000000000..a566fc9a8
Binary files /dev/null and b/content/growth/identity-proofing-orchestration-security/id-proofing.webp differ
diff --git a/content/growth/identity-proofing-orchestration-security/index.md b/content/growth/identity-proofing-orchestration-security/index.md
index 52522cb61..2f0e8569e 100644
--- a/content/growth/identity-proofing-orchestration-security/index.md
+++ b/content/growth/identity-proofing-orchestration-security/index.md
@@ -1,7 +1,7 @@
---
title: "Mastering Orchestration: The Business Case for End-to-End Identity Proofing Solutions"
date: "2024-08-12"
-coverImage: "id-proofing.jpg"
+coverImage: "id-proofing.webp"
tags: ["identity orchestration","identity proofing","cx"]
author: "Cooper Matheson"
description: "In the rapidly evolving digital landscape, businesses are turning to comprehensive identity-proofing solutions to bolster security, ensure compliance, and enhance customer experiences. By leveraging orchestration, companies can streamline identity verification processes, reduce fraud, and build trust with their users."
@@ -52,7 +52,7 @@ A streamlined and efficient identity verification process is crucial for providi
With orchestration, businesses can reduce the time and effort required for users to prove their identities, leading to higher satisfaction and loyalty. Automated processes also minimize the risk of false positives, ensuring unnecessary security hurdles do not inconvenience legitimate users.
-[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
+[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
### 4. Cost Efficiency
@@ -70,4 +70,4 @@ In a world where digital interactions are becoming the norm, businesses must pri
By embracing comprehensive identity proofing solutions through orchestration, companies can enhance security, ensure compliance, and deliver a superior customer experience. As cyber threats continue to evolve, the adoption of orchestration will be crucial for businesses looking to stay ahead of the curve.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-proofing-orchestration-security)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-proofing-orchestration-security)
\ No newline at end of file
diff --git a/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.png b/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.png
deleted file mode 100644
index 9ecea83f3..000000000
Binary files a/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.png and /dev/null differ
diff --git a/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.webp b/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.webp
new file mode 100644
index 000000000..ec4419e57
Binary files /dev/null and b/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.webp differ
diff --git a/content/growth/identity-resolution-data-accuracy/identity-resolution.jpg b/content/growth/identity-resolution-data-accuracy/identity-resolution.jpg
deleted file mode 100644
index 6a3543298..000000000
Binary files a/content/growth/identity-resolution-data-accuracy/identity-resolution.jpg and /dev/null differ
diff --git a/content/growth/identity-resolution-data-accuracy/identity-resolution.webp b/content/growth/identity-resolution-data-accuracy/identity-resolution.webp
new file mode 100644
index 000000000..e8329f3c8
Binary files /dev/null and b/content/growth/identity-resolution-data-accuracy/identity-resolution.webp differ
diff --git a/content/growth/identity-resolution-data-accuracy/idntity-resolution.jpg b/content/growth/identity-resolution-data-accuracy/idntity-resolution.jpg
deleted file mode 100644
index e9cddd843..000000000
Binary files a/content/growth/identity-resolution-data-accuracy/idntity-resolution.jpg and /dev/null differ
diff --git a/content/growth/identity-resolution-data-accuracy/idntity-resolution.webp b/content/growth/identity-resolution-data-accuracy/idntity-resolution.webp
new file mode 100644
index 000000000..689bcd98e
Binary files /dev/null and b/content/growth/identity-resolution-data-accuracy/idntity-resolution.webp differ
diff --git a/content/growth/identity-resolution-data-accuracy/index.md b/content/growth/identity-resolution-data-accuracy/index.md
index b84a2bb80..dd8e80ec1 100644
--- a/content/growth/identity-resolution-data-accuracy/index.md
+++ b/content/growth/identity-resolution-data-accuracy/index.md
@@ -1,7 +1,7 @@
---
title: "Elevating Data Precision-Power of Identity Resolution"
date: "2023-10-12"
-coverImage: "identity-resolution.jpg"
+coverImage: "identity-resolution.webp"
tags: ["data governance","e-commerce","identity resolution"]
author: "Vishal Sharma"
description: "Dive into the world of identity resolution and learn how businesses connect data dots, ensuring precision in every interaction. Uncover real-life examples in healthcare and retail and understand the challenges organizations face. Embrace these techniques for unparalleled success in today's competitive landscape."
@@ -38,7 +38,7 @@ Accurate data is the foundation of numerous business operations, and identity re
2. **Retail and Marketing:** In the retail industry, identity resolution can be a game-changer for understanding customer behavior. Let's say a customer shop online, subscribes to a newsletter, and makes in-store purchases. By accurately resolving the identity of this customer across different channels, the retailer can gain insights into their preferences and habits, allowing for targeted marketing campaigns that resonate with the customer's interests.
-[](https://www.loginradius.com/resource/digital-transformation-retail-ecommerce-whitepaper)
+[](https://www.loginradius.com/resource/digital-transformation-retail-ecommerce-whitepaper)
### Considerations in Identity Resolution
@@ -54,4 +54,4 @@ From delivering personalized customer experiences to enhancing risk management,
By embracing these techniques and addressing the associated challenges, organizations can unlock a new level of efficiency and effectiveness in their operations, ultimately leading to tremendous success in today's competitive landscape. As technology evolves, identity resolution will remain a cornerstone of data accuracy and a driving force behind data-driven innovation.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-resolution-data-accuracy)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-resolution-data-accuracy)
diff --git a/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.png b/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.png
deleted file mode 100644
index a7a656cfa..000000000
Binary files a/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.png and /dev/null differ
diff --git a/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.webp b/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.webp
new file mode 100644
index 000000000..44c9529c0
Binary files /dev/null and b/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.webp differ
diff --git a/content/growth/identity-security-digital-trade/identity-security.jpg b/content/growth/identity-security-digital-trade/identity-security.jpg
deleted file mode 100644
index 76c59a1fa..000000000
Binary files a/content/growth/identity-security-digital-trade/identity-security.jpg and /dev/null differ
diff --git a/content/growth/identity-security-digital-trade/identity-security.webp b/content/growth/identity-security-digital-trade/identity-security.webp
new file mode 100644
index 000000000..0b58e590e
Binary files /dev/null and b/content/growth/identity-security-digital-trade/identity-security.webp differ
diff --git a/content/growth/identity-security-digital-trade/index.md b/content/growth/identity-security-digital-trade/index.md
index ccfad5738..96903c3c4 100644
--- a/content/growth/identity-security-digital-trade/index.md
+++ b/content/growth/identity-security-digital-trade/index.md
@@ -1,7 +1,7 @@
---
title: "Can Cybersecurity Be a Unifying Factor in Digital Trade Negotiations?"
date: "2024-06-05"
-coverImage: "identity-security.jpg"
+coverImage: "identity-security.webp"
tags: ["cybersecurity","data security","ciam solutions"]
author: "Karl Wittig"
description: "Cybersecurity is crucial for safeguarding digital trade in the interconnected digital economy. This article explores how identity security, supported by robust Customer Identity Management (CIAM) solutions, can unify global digital trade negotiations by building trust and establishing common security standards."
@@ -46,7 +46,7 @@ A robust Customer Identity Management (CIAM) solution plays a pivotal role in ac
2. **Data Privacy and Compliance**: CIAM systems help businesses comply with [data governance](https://www.loginradius.com/data-governance/) regulations such as GDPR and CCPA. They ensure that customer data is collected, stored, and processed in accordance with legal requirements, thereby fostering trust and reducing the risk of regulatory penalties.
-[](https://www.loginradius.com/resource/ebook/loginradius-gdpr-compliance/)
+[](https://www.loginradius.com/resource/ebook/loginradius-gdpr-compliance/)
3. **User Experience**: A robust CIAM solution balances security with user experience. It provides a frictionless login process, personalized experiences, and consistent access across multiple channels, enhancing customer satisfaction and loyalty.
@@ -60,4 +60,4 @@ A robust Customer Identity Management (CIAM) solution, like LoginRadius, is cri
As digital trade grows, cybersecurity will undoubtedly play a central role in shaping its future, unifying diverse stakeholders in pursuing a safe and reliable digital world.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-security-digital-trade)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-security-digital-trade)
diff --git a/content/growth/identity-verification-in-customer-journey/GD-to-RBA.png b/content/growth/identity-verification-in-customer-journey/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/growth/identity-verification-in-customer-journey/GD-to-RBA.png and /dev/null differ
diff --git a/content/growth/identity-verification-in-customer-journey/GD-to-RBA.webp b/content/growth/identity-verification-in-customer-journey/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/growth/identity-verification-in-customer-journey/GD-to-RBA.webp differ
diff --git a/content/growth/identity-verification-in-customer-journey/identity-verification.jpg b/content/growth/identity-verification-in-customer-journey/identity-verification.jpg
deleted file mode 100644
index 6ee78d5bb..000000000
Binary files a/content/growth/identity-verification-in-customer-journey/identity-verification.jpg and /dev/null differ
diff --git a/content/growth/identity-verification-in-customer-journey/identity-verification.webp b/content/growth/identity-verification-in-customer-journey/identity-verification.webp
new file mode 100644
index 000000000..bbeac7a5a
Binary files /dev/null and b/content/growth/identity-verification-in-customer-journey/identity-verification.webp differ
diff --git a/content/growth/identity-verification-in-customer-journey/index.md b/content/growth/identity-verification-in-customer-journey/index.md
index 1a0768124..1d9c5e683 100644
--- a/content/growth/identity-verification-in-customer-journey/index.md
+++ b/content/growth/identity-verification-in-customer-journey/index.md
@@ -1,7 +1,7 @@
---
title: "Achieving Harmony: Balancing Identity Verification in the Customer Journey"
date: "2023-06-07"
-coverImage: "identity-verification.jpg"
+coverImage: "identity-verification.webp"
tags: ["identity verification","ciam authentication","cx"]
author: "Vishal Sharma"
description: "In today's digital landscape, businesses face the challenge of balancing identity verification throughout the customer journey. This blog dives into the complexities and offers actionable strategies to achieve harmony. Find out how to balance security and user experience, fostering trust and driving long-term success."
@@ -37,7 +37,7 @@ Here’s the list of actionable strategies that businesses can employ to achieve
Adopting a risk-based approach allows businesses to calibrate the verification level according to the perceived risk associated with each interaction. By tailoring verification requirements based on factors such as transaction value, user behavior, and historical data, businesses can strike a balance between security and user experience.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
### Leveraging advanced authentication technologies
@@ -77,4 +77,4 @@ Organizations can foster trust, enhance customer satisfaction, and drive long-te
Through the strategic implementation of technology, adaptive verification processes, and a customer-centric approach, businesses can navigate the complexities of identity verification while ensuring a pleasant customer journey in today's digital landscape.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-verification-in-customer-journey)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-verification-in-customer-journey)
diff --git a/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.png b/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.png
deleted file mode 100644
index dac7c2e34..000000000
Binary files a/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.png and /dev/null differ
diff --git a/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.webp b/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.webp
new file mode 100644
index 000000000..a6fdfd674
Binary files /dev/null and b/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.webp differ
diff --git a/content/growth/identity-verification-retailers-benefits/identity-verification.jpg b/content/growth/identity-verification-retailers-benefits/identity-verification.jpg
deleted file mode 100644
index 2945a024c..000000000
Binary files a/content/growth/identity-verification-retailers-benefits/identity-verification.jpg and /dev/null differ
diff --git a/content/growth/identity-verification-retailers-benefits/identity-verification.webp b/content/growth/identity-verification-retailers-benefits/identity-verification.webp
new file mode 100644
index 000000000..c5a186c30
Binary files /dev/null and b/content/growth/identity-verification-retailers-benefits/identity-verification.webp differ
diff --git a/content/growth/identity-verification-retailers-benefits/index.md b/content/growth/identity-verification-retailers-benefits/index.md
index 705b2d86e..c5facb142 100644
--- a/content/growth/identity-verification-retailers-benefits/index.md
+++ b/content/growth/identity-verification-retailers-benefits/index.md
@@ -1,7 +1,7 @@
---
title: "Unveiling the Benefits of Identity Verification for Online Retailers "
date: "2023-08-31"
-coverImage: "identity-verification.jpg"
+coverImage: "identity-verification.webp"
tags: ["digital identity verification","compliance","cx"]
author: "Vishal Sharma"
description: "In the dynamic realm of online retail, establishing trust while countering cyber threats is paramount. Identity verification emerges as a game-changer, bolstering security, trust, compliance, and even personalization. Dive into the advantages it brings to businesses navigating the digital landscape."
@@ -36,7 +36,7 @@ In an increasingly regulated digital landscape, businesses must adhere to strict
Identity verification aids in complying with various data security and privacy regulations, ensuring that businesses operate within legal boundaries and avoid penalties. These regulations include the EU’s GDPR and California’s CCPA.
-[](https://www.loginradius.com/resource/consumer-identity-in-challenges)
+[](https://www.loginradius.com/resource/consumer-identity-in-challenges)
### 4. Reducing Chargebacks and False Positives
@@ -86,4 +86,4 @@ Identity verification is a critical component of the online retail and financial
Use cases encompass enhanced security, fraud prevention, regulatory compliance, personalized customer experiences, and operational efficiency.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-verification-retailers-benefits)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-verification-retailers-benefits)
\ No newline at end of file
diff --git a/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.png b/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.png
deleted file mode 100644
index 7cc78c915..000000000
Binary files a/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.png and /dev/null differ
diff --git a/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.webp b/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.webp
new file mode 100644
index 000000000..86276b545
Binary files /dev/null and b/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.webp differ
diff --git a/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.png b/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.png
deleted file mode 100644
index 46e301e6d..000000000
Binary files a/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.png and /dev/null differ
diff --git a/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.webp b/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.webp
new file mode 100644
index 000000000..7a77e6d27
Binary files /dev/null and b/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.webp differ
diff --git a/content/growth/implement-continuous-authentication-business-value/cont-auth.jpg b/content/growth/implement-continuous-authentication-business-value/cont-auth.jpg
deleted file mode 100644
index ff2f78591..000000000
Binary files a/content/growth/implement-continuous-authentication-business-value/cont-auth.jpg and /dev/null differ
diff --git a/content/growth/implement-continuous-authentication-business-value/cont-auth.webp b/content/growth/implement-continuous-authentication-business-value/cont-auth.webp
new file mode 100644
index 000000000..eb4f1c026
Binary files /dev/null and b/content/growth/implement-continuous-authentication-business-value/cont-auth.webp differ
diff --git a/content/growth/implement-continuous-authentication-business-value/index.md b/content/growth/implement-continuous-authentication-business-value/index.md
index bf4961f8f..0aafe2e57 100644
--- a/content/growth/implement-continuous-authentication-business-value/index.md
+++ b/content/growth/implement-continuous-authentication-business-value/index.md
@@ -1,7 +1,7 @@
---
title: "Implementing The Power Of Continuous Authentication for Boundless Business Value"
date: "2022-01-04"
-coverImage: "cont-auth.jpg"
+coverImage: "cont-auth.webp"
tags: ["continuous authentication","data security","cx"]
author: "Rakesh Soni"
description: "With advancements in technology and the increasing rate of cybercrimes, continuous authentication for business is gaining popularity in modern times. As a smarter and better authentication method, it can help in reducing the number of these attacks."
@@ -42,7 +42,7 @@ Here's a list of the technologies used to implement continuous authentication:
* **Behavioral biometrics** - Here, you can continuously [track a user's behavioral patterns](https://www.loginradius.com/blog/identity/biometric-authentication-mobile-apps/) like interactive gestures, typing style, finger pressure, how long a user holds a key on the keyboard, or how they swipe through the screen or hold the mouse. Variation from the normal behavioral patterns can then be marked.
* **Voice Authentication** - You can monitor pitch and frequency variations in voice for continuous authentication. Also, deviations from ordinary qualities can be identified by constantly tracking input speech against a reference control conversation.
-[](https://www.loginradius.com/resource/continuous-authentication-whitepaper)
+[](https://www.loginradius.com/resource/continuous-authentication-whitepaper)
## Benefits and Drawbacks
@@ -61,4 +61,4 @@ When executed the right way, it can massively enhance corporate security by decr
After years of discussion and product development by security specialists, the concept of continuous authentication has emerged as a new wave in cybersecurity. And it is just the right time to embrace it!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=implement-continuous-authentication-business-value)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=implement-continuous-authentication-business-value)
\ No newline at end of file
diff --git a/content/growth/importance-customer-health-scoring-saas-businesses/index.md b/content/growth/importance-customer-health-scoring-saas-businesses/index.md
index a35cc14cc..48d891ddb 100644
--- a/content/growth/importance-customer-health-scoring-saas-businesses/index.md
+++ b/content/growth/importance-customer-health-scoring-saas-businesses/index.md
@@ -1,7 +1,7 @@
---
title: "How Important is Customer Health Scoring for SaaS Business?"
date: "2023-01-19"
-coverImage: "saas-score.jpg"
+coverImage: "saas-score.webp"
tags: ["saas", "customer retention", "customer behavior"]
author: "Yash Rathi"
description: "A customer health score is an organization's metric to determine whether customers are healthy or at risk of churn. Based on the score of the individual customer, retention strategies are implemented."
@@ -89,4 +89,4 @@ However, you can't simply add it as another feature and hope it'll work out magi
You must understand that customer health scoring is a long-term investment with high returns.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=importance-customer-health-scoring-saas-businesses)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=importance-customer-health-scoring-saas-businesses)
diff --git a/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.jpg b/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.jpg
deleted file mode 100644
index 242f5950d..000000000
Binary files a/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.jpg and /dev/null differ
diff --git a/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.webp b/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.webp
new file mode 100644
index 000000000..cc1aa2d84
Binary files /dev/null and b/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.webp differ
diff --git a/content/growth/importance-customer-onboarding/customer-onboarding-importance.jpg b/content/growth/importance-customer-onboarding/customer-onboarding-importance.jpg
deleted file mode 100644
index ba2a0f850..000000000
Binary files a/content/growth/importance-customer-onboarding/customer-onboarding-importance.jpg and /dev/null differ
diff --git a/content/growth/importance-customer-onboarding/customer-onboarding-importance.webp b/content/growth/importance-customer-onboarding/customer-onboarding-importance.webp
new file mode 100644
index 000000000..7f95f7302
Binary files /dev/null and b/content/growth/importance-customer-onboarding/customer-onboarding-importance.webp differ
diff --git a/content/growth/importance-customer-onboarding/index.md b/content/growth/importance-customer-onboarding/index.md
index efd525ac0..299ac32c3 100644
--- a/content/growth/importance-customer-onboarding/index.md
+++ b/content/growth/importance-customer-onboarding/index.md
@@ -1,7 +1,7 @@
---
title: "Customer Success: The Importance of Customer Onboarding"
date: "2021-02-26"
-coverImage: "customer-onboarding-importance.jpg"
+coverImage: "customer-onboarding-importance.webp"
tags: ["customer onboarding","authentication","cx"]
author: "Karl Wittig"
description: "Customer onboarding is one of the more delicate components of marketing. This process can make or break a business. In addition to increasing the revenue, it also allows businesses to create relationships with their customers."
@@ -104,4 +104,4 @@ In addition to receiving free marketing, one will also understand their customer
Customer onboarding is one of the more delicate components of marketing. This process can make or break a business. In addition to increasing the revenue, it also allows businesses to create relationships with their customers through surveys or even phone calls. The most significant benefits of customer onboarding are that an individual can have an unprecedented amount of faith in the company and product.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=importance-customer-onboarding)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=importance-customer-onboarding)
diff --git a/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.png b/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.png
deleted file mode 100644
index e794b3769..000000000
Binary files a/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.png and /dev/null differ
diff --git a/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.webp b/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.webp
new file mode 100644
index 000000000..371ef34ea
Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.webp differ
diff --git a/content/growth/improve-customer-experience-ecommerce/customer-experience.jpg b/content/growth/improve-customer-experience-ecommerce/customer-experience.jpg
deleted file mode 100644
index c7c694e0b..000000000
Binary files a/content/growth/improve-customer-experience-ecommerce/customer-experience.jpg and /dev/null differ
diff --git a/content/growth/improve-customer-experience-ecommerce/customer-experience.webp b/content/growth/improve-customer-experience-ecommerce/customer-experience.webp
new file mode 100644
index 000000000..23e7d7d9f
Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/customer-experience.webp differ
diff --git a/content/growth/improve-customer-experience-ecommerce/image-2.jpg b/content/growth/improve-customer-experience-ecommerce/image-2.jpg
deleted file mode 100644
index ad3223120..000000000
Binary files a/content/growth/improve-customer-experience-ecommerce/image-2.jpg and /dev/null differ
diff --git a/content/growth/improve-customer-experience-ecommerce/image-2.webp b/content/growth/improve-customer-experience-ecommerce/image-2.webp
new file mode 100644
index 000000000..9b6043452
Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/image-2.webp differ
diff --git a/content/growth/improve-customer-experience-ecommerce/image-3.jpg b/content/growth/improve-customer-experience-ecommerce/image-3.jpg
deleted file mode 100644
index 2b22e710d..000000000
Binary files a/content/growth/improve-customer-experience-ecommerce/image-3.jpg and /dev/null differ
diff --git a/content/growth/improve-customer-experience-ecommerce/image-3.webp b/content/growth/improve-customer-experience-ecommerce/image-3.webp
new file mode 100644
index 000000000..c0d100f2a
Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/image-3.webp differ
diff --git a/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.jpg b/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.jpg
deleted file mode 100644
index ce22930fc..000000000
Binary files a/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.jpg and /dev/null differ
diff --git a/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.webp b/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.webp
new file mode 100644
index 000000000..7448d2be5
Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.webp differ
diff --git a/content/growth/improve-customer-experience-ecommerce/index.md b/content/growth/improve-customer-experience-ecommerce/index.md
index 636024c9f..d8a32a03b 100644
--- a/content/growth/improve-customer-experience-ecommerce/index.md
+++ b/content/growth/improve-customer-experience-ecommerce/index.md
@@ -1,7 +1,7 @@
---
title: "5 Ways to Enhance Customer Experience in E-commerce"
date: "2019-11-28"
-coverImage: "customer-experience.jpg"
+coverImage: "customer-experience.webp"
tags: ["cx", "ecommerce", "digital identity"]
author: "Rakesh Soni"
description: "A smart e-commerce customer service strategy is as critical as a marketing strategy when it comes to growing your business. You will get 360-degree customer profiling, with 100% customer consent, at all touchpoints, with a customer identity and access management solution."
@@ -41,7 +41,7 @@ When it comes to providing a superior customer experience, "people" and "product
Providing excellent mobile e-commerce (m-commerce) shopping [experience can benefit retailers](https://www.loginradius.com/blog/2020/05/customer-experience-retail-industry/) significantly. By 2021, m-commerce sales are expected to be responsible for 54% of overall e-commerce revenue, [predicts](https://www.bigcommerce.com/blog/mobile-commerce/#why-does-mobile-commerce-matter) Big Commerce.
-
+
This is one of the reasons why your online retail store should be easily accessible on mobile devices, not just desktops and laptops.
@@ -79,7 +79,7 @@ In short, integrating digital and traditional touchpoints using CIAM tools will
**–** [**Rick Kenney**](https://twitter.com/rickkenney)**, Head of Consumer Insights, Salesforce**
-
+
### **3\. Emphasize the employee experience to boost customer retention.**
@@ -113,7 +113,7 @@ No matter what e-commerce shopping experience you offer your customers, data sec
What's worse is that most customers often don’t take the necessary steps to protect themselves. [CreditDonkey](https://www.creditdonkey.com/identity-theft-survey.html) reports that 68% of customers use the same password for multiple websites. That’s a good reason for you to be extra vigilant when building a secure e-commerce customer experience. Here’s how you can get started.
-
+
## Tips to protect e-commerce customer data
@@ -134,4 +134,4 @@ What's worse is that most customers often don’t take the necessary steps to pr
When it comes to growing your business, a smart e-commerce customer experience strategy is as important as a marketing strategy. With a customer identity and access management solution, you can get 360-degree customer profiling, with 100% customer consent, across all touchpoints. This allows you to personalize marketing and loyalty programs that engage your audience. And that’s a win-win for you and your customers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=improve-customer-experience-ecommerce)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=improve-customer-experience-ecommerce)
diff --git a/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.jpg b/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.jpg
deleted file mode 100644
index 9ba0bbabe..000000000
Binary files a/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.jpg and /dev/null differ
diff --git a/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.webp b/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.webp
new file mode 100644
index 000000000..38ac2509a
Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.webp differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/hospitality.jpg b/content/growth/improve-customer-experience-hospitality-industry/hospitality.jpg
deleted file mode 100644
index e35eb8efd..000000000
Binary files a/content/growth/improve-customer-experience-hospitality-industry/hospitality.jpg and /dev/null differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/hospitality.webp b/content/growth/improve-customer-experience-hospitality-industry/hospitality.webp
new file mode 100644
index 000000000..989ec4212
Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/hospitality.webp differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/image2-1.png b/content/growth/improve-customer-experience-hospitality-industry/image2-1.png
deleted file mode 100644
index f17e3d6aa..000000000
Binary files a/content/growth/improve-customer-experience-hospitality-industry/image2-1.png and /dev/null differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/image2-1.webp b/content/growth/improve-customer-experience-hospitality-industry/image2-1.webp
new file mode 100644
index 000000000..c1a39bba2
Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/image2-1.webp differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/image3-1.png b/content/growth/improve-customer-experience-hospitality-industry/image3-1.png
deleted file mode 100644
index 5fd3cb530..000000000
Binary files a/content/growth/improve-customer-experience-hospitality-industry/image3-1.png and /dev/null differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/image3-1.webp b/content/growth/improve-customer-experience-hospitality-industry/image3-1.webp
new file mode 100644
index 000000000..4a7ca7fef
Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/image3-1.webp differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/image4-1.png b/content/growth/improve-customer-experience-hospitality-industry/image4-1.png
deleted file mode 100644
index ca9006b5a..000000000
Binary files a/content/growth/improve-customer-experience-hospitality-industry/image4-1.png and /dev/null differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/image4-1.webp b/content/growth/improve-customer-experience-hospitality-industry/image4-1.webp
new file mode 100644
index 000000000..011dbd014
Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/image4-1.webp differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/image5-1.png b/content/growth/improve-customer-experience-hospitality-industry/image5-1.png
deleted file mode 100644
index 4922420fd..000000000
Binary files a/content/growth/improve-customer-experience-hospitality-industry/image5-1.png and /dev/null differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/image5-1.webp b/content/growth/improve-customer-experience-hospitality-industry/image5-1.webp
new file mode 100644
index 000000000..437fd7a9c
Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/image5-1.webp differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.png b/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.png
deleted file mode 100644
index 155ded62b..000000000
Binary files a/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.png and /dev/null differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.webp b/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.webp
new file mode 100644
index 000000000..9c97d4ed9
Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.webp differ
diff --git a/content/growth/improve-customer-experience-hospitality-industry/index.md b/content/growth/improve-customer-experience-hospitality-industry/index.md
index a745af9e9..745515f9e 100644
--- a/content/growth/improve-customer-experience-hospitality-industry/index.md
+++ b/content/growth/improve-customer-experience-hospitality-industry/index.md
@@ -1,7 +1,7 @@
---
title: "Improving Customer Experience in the Hospitality Industry"
date: "2020-03-13"
-coverImage: "hospitality.jpg"
+coverImage: "hospitality.webp"
tags: ["digital transformation","cx","ciam solution"]
author: "Rakesh Soni"
description: "It has always been about luxury, pleasure, and excellent customer service in the hospitality industry. Modern guests travel for both company and fun. They also want business owners to better connect and understand them well."
@@ -50,7 +50,7 @@ IoT solutions for hotels will add extra oomph to customer experience in 2020.
At the core of the hospitality industry lies the ultimate guest experience. People love to feel special – a reason why the concept of customization went mainstream. Blending hospitality with IoT will do [wonders for hotel operators](https://www.ezeeabsolute.com/blog/iot-in-hospitality-industry/).
-
+
Wondering how? Let’s find out.
@@ -85,7 +85,7 @@ Augmented Reality, on the other hand, simulates real-world surroundings with dig
The hospitality industry can use it to its [advantage in a number of ways](https://www.revfine.com/augmented-reality-hospitality-industry/). Imagine the walls of your room are infused with AR-powered technology. At the tap of a button, it can transform into any surrounding (beach, forest, cloud, city heights) you like and let you enjoy the experience without actually being physically present.
-
+
### 5\. Digital registration forms will replace the use of pen and paper
@@ -105,7 +105,7 @@ Simply put, data security is a crucial metric for hotel owners. Guests should ne
Henceforth, advanced identity management policies, coupled with frictionless verification should make security seem effortless.
-[](https://www.loginradius.com/resource/how-travel-and-leisure-companies-use-loginradius-identity-solution/)
+[](https://www.loginradius.com/resource/how-travel-and-leisure-companies-use-loginradius-identity-solution/)
When your business revolves around accommodating customer preferences, the need for identity verification becomes crucial. LoginRadius is a [customer identity and access management](https://www.loginradius.com/blog/2019/06/customer-identity-and-access-management/) (CIAM) platform that helps hotel owners to roll out strict security policies while offering excellent customer experiences.
@@ -115,7 +115,7 @@ With LoginRadius, here’s what you can offer your customers:
The hospitality industry is a booming market at the moment. With intense competition happening at the backdrop, taking charge of internal processes and increasing security within the hotel staff has become more crucial than ever.
-
+
Looking ahead, LoginRadius’ biometric technology will help you:
@@ -146,4 +146,4 @@ Most businesses in the hospitality sector offer complex ownership structures. He
After all, the hospitality industry is all about customer experiences and keeping up with their changing expectations.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=improve-customer-experience-hospitality-industry)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=improve-customer-experience-hospitality-industry)
diff --git a/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.png b/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.png and /dev/null differ
diff --git a/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.webp b/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.webp differ
diff --git a/content/growth/improve-customer-relation-brand-identity/brand-identity.jpg b/content/growth/improve-customer-relation-brand-identity/brand-identity.jpg
deleted file mode 100644
index 5b4f56318..000000000
Binary files a/content/growth/improve-customer-relation-brand-identity/brand-identity.jpg and /dev/null differ
diff --git a/content/growth/improve-customer-relation-brand-identity/brand-identity.webp b/content/growth/improve-customer-relation-brand-identity/brand-identity.webp
new file mode 100644
index 000000000..d28d93001
Binary files /dev/null and b/content/growth/improve-customer-relation-brand-identity/brand-identity.webp differ
diff --git a/content/growth/improve-customer-relation-brand-identity/index.md b/content/growth/improve-customer-relation-brand-identity/index.md
index f6c7eac44..d2ce14cb4 100644
--- a/content/growth/improve-customer-relation-brand-identity/index.md
+++ b/content/growth/improve-customer-relation-brand-identity/index.md
@@ -1,7 +1,7 @@
---
title: "How to Create Brand Identity to Attract More Customers"
date: "2022-02-04"
-coverImage: "brand-identity.jpg"
+coverImage: "brand-identity.webp"
tags: ["identity management","customer identity","cx"]
author: "Mike Abelson"
description: "Branding is composed of so much more other than just your logo and chosen brand colors. Developing customer identity is also a must when it comes to getting your brand out for consumers. These tips will help you refine your branding to suit the goals of your business."
@@ -39,7 +39,7 @@ Aside from that, don’t forget to develop who your
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=product-marketing-tips-for-b2c)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=product-marketing-tips-for-b2c)
diff --git a/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.png b/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.png
deleted file mode 100644
index f97184f2f..000000000
Binary files a/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.png and /dev/null differ
diff --git a/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.webp b/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.webp
new file mode 100644
index 000000000..88d19cbb8
Binary files /dev/null and b/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.webp differ
diff --git a/content/growth/progressive-profiling-lead-generation-tool/index.md b/content/growth/progressive-profiling-lead-generation-tool/index.md
index 62bcb562d..8d6c0401e 100644
--- a/content/growth/progressive-profiling-lead-generation-tool/index.md
+++ b/content/growth/progressive-profiling-lead-generation-tool/index.md
@@ -1,7 +1,7 @@
---
title: "How Progressive Profiling Reduces Registration Fatigue and Improves Lead Quality?"
date: "2022-07-15"
-coverImage: "lead-gen.jpg"
+coverImage: "lead-gen.webp"
category: ["Progressive profiling", "lead generation", "marketing"]
author: "Vishal Sharma"
description: "Progressive profiling ensures valuable information about a user is gradually collected over time so that it doesn’t create friction while a user lands on a platform, which enhances the overall quality and number of leads. This blog explains the role of progressive profiling in improving overall lead quality and quantity."
@@ -38,7 +38,7 @@ In this way, digital marketing teams obtain several data points about a lead wit
Hence, if a business strives for quality leads, it must incorporate the true potential of progressive profiling that eventually helps generate quality leads.
-[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
+[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
## Why Your Business Needs Progressive Profiling in 2022 and Beyond
@@ -90,4 +90,4 @@ And if customers are bombarded with registration forms when they land on your we
Progressive profiling is undeniably the best way to nurture and improve the quality of leads, which helps businesses enhance their overall growth and revenues.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=progressive-profiling-lead-generation-tool)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=progressive-profiling-lead-generation-tool)
diff --git a/content/growth/progressive-profiling-lead-generation-tool/lead-gen.jpg b/content/growth/progressive-profiling-lead-generation-tool/lead-gen.jpg
deleted file mode 100644
index e41f93a37..000000000
Binary files a/content/growth/progressive-profiling-lead-generation-tool/lead-gen.jpg and /dev/null differ
diff --git a/content/growth/progressive-profiling-lead-generation-tool/lead-gen.webp b/content/growth/progressive-profiling-lead-generation-tool/lead-gen.webp
new file mode 100644
index 000000000..7060dfb70
Binary files /dev/null and b/content/growth/progressive-profiling-lead-generation-tool/lead-gen.webp differ
diff --git a/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.png b/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.png
deleted file mode 100644
index c9ad88d9e..000000000
Binary files a/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.png and /dev/null differ
diff --git a/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.webp b/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.webp
new file mode 100644
index 000000000..2b537fe1a
Binary files /dev/null and b/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.webp differ
diff --git a/content/growth/protect-digital-customer-onboarding-deepfakes/cta.png b/content/growth/protect-digital-customer-onboarding-deepfakes/cta.png
deleted file mode 100644
index c1f47d8bc..000000000
Binary files a/content/growth/protect-digital-customer-onboarding-deepfakes/cta.png and /dev/null differ
diff --git a/content/growth/protect-digital-customer-onboarding-deepfakes/cta.webp b/content/growth/protect-digital-customer-onboarding-deepfakes/cta.webp
new file mode 100644
index 000000000..89e798f06
Binary files /dev/null and b/content/growth/protect-digital-customer-onboarding-deepfakes/cta.webp differ
diff --git a/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.jpg b/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.jpg
deleted file mode 100644
index 35a771ea3..000000000
Binary files a/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.jpg and /dev/null differ
diff --git a/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.webp b/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.webp
new file mode 100644
index 000000000..4008d695e
Binary files /dev/null and b/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.webp differ
diff --git a/content/growth/protect-digital-customer-onboarding-deepfakes/index.md b/content/growth/protect-digital-customer-onboarding-deepfakes/index.md
index 8f34f544b..f2b7ed986 100644
--- a/content/growth/protect-digital-customer-onboarding-deepfakes/index.md
+++ b/content/growth/protect-digital-customer-onboarding-deepfakes/index.md
@@ -1,7 +1,7 @@
---
title: "Strengthening Digital Customer Onboarding to Combat Deep Fakes"
date: "2024-07-15"
-coverImage: "deepfake.jpg"
+coverImage: "deepfake.webp"
tags: ["customer onboarding", "cx", "deepfake", "authentication"]
author: "Kundan Singh"
description: "As deepfake technology advances, the risk of fraudulent activities in digital customer onboarding increases. This article explores how to safeguard your onboarding processes against deepfakes, ensuring a secure and trustworthy experience for your customers."
@@ -82,7 +82,7 @@ In digital onboarding, deepfakes can be used to impersonate individuals, potenti
- Allocate resources to acquire and integrate advanced identity verification and deepfake detection technologies.
-[](https://www.loginradius.com/resource/whitepaper/identity-management-data-governance/)
+[](https://www.loginradius.com/resource/whitepaper/identity-management-data-governance/)
- Prioritize systems that offer scalability and adaptability to future advancements in deepfake techniques.
diff --git a/content/growth/publishers-start-using-single-sign-on/DS-SSO.png b/content/growth/publishers-start-using-single-sign-on/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/growth/publishers-start-using-single-sign-on/DS-SSO.png and /dev/null differ
diff --git a/content/growth/publishers-start-using-single-sign-on/DS-SSO.webp b/content/growth/publishers-start-using-single-sign-on/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/growth/publishers-start-using-single-sign-on/DS-SSO.webp differ
diff --git a/content/growth/publishers-start-using-single-sign-on/SSO-LR.png b/content/growth/publishers-start-using-single-sign-on/SSO-LR.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/growth/publishers-start-using-single-sign-on/SSO-LR.png and /dev/null differ
diff --git a/content/growth/publishers-start-using-single-sign-on/SSO-LR.webp b/content/growth/publishers-start-using-single-sign-on/SSO-LR.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/growth/publishers-start-using-single-sign-on/SSO-LR.webp differ
diff --git a/content/growth/publishers-start-using-single-sign-on/index.md b/content/growth/publishers-start-using-single-sign-on/index.md
index d79500e47..a188f08d4 100644
--- a/content/growth/publishers-start-using-single-sign-on/index.md
+++ b/content/growth/publishers-start-using-single-sign-on/index.md
@@ -1,7 +1,7 @@
---
title: "5 Reasons Why Publishers Should (Seriously) Consider Using SSO"
date: "2022-09-20"
-coverImage: "sso-publish.jpg"
+coverImage: "sso-publish.webp"
tags: ["sso","data privacy","cx"]
author: "Navanita Devi"
description: "Single sign-on allows publishers to seamlessly integrate their existing subscription services into one platform so they can collect first party data without having to worry about anything else."
@@ -46,7 +46,7 @@ With single sign-on, there’s no need for third parties by design; everything h
The ability to track user behavior across multiple platforms allows publishers to offer customized content and advertising that is relevant to each individual reader's interests. This helps publishers retain loyal readers who value having access to personalized content and ads.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
### 5. Combine seamless digitization with data privacy for reader trust
@@ -58,4 +58,4 @@ Publishers can benefit from SSO technology by ensuring data protection and provi
So, there you have it. SSO is a great way to improve the user experience and boost conversions on your site. If you're looking to implement a solution that will benefit your users, improve your bottom line, and make life easier for your team—all while being easy to manage—SSO is definitely worth considering.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=publishers-start-using-single-sign-on)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=publishers-start-using-single-sign-on)
diff --git a/content/growth/publishers-start-using-single-sign-on/sso-publish.jpg b/content/growth/publishers-start-using-single-sign-on/sso-publish.jpg
deleted file mode 100644
index 90420fd3e..000000000
Binary files a/content/growth/publishers-start-using-single-sign-on/sso-publish.jpg and /dev/null differ
diff --git a/content/growth/publishers-start-using-single-sign-on/sso-publish.webp b/content/growth/publishers-start-using-single-sign-on/sso-publish.webp
new file mode 100644
index 000000000..53ee253b6
Binary files /dev/null and b/content/growth/publishers-start-using-single-sign-on/sso-publish.webp differ
diff --git a/content/growth/qr-code-in-marketing/index.md b/content/growth/qr-code-in-marketing/index.md
index 12bfd4464..dd9cececf 100644
--- a/content/growth/qr-code-in-marketing/index.md
+++ b/content/growth/qr-code-in-marketing/index.md
@@ -1,7 +1,7 @@
---
title: "How QR Codes are Shaping the Future of Marketing"
date: "2021-06-28"
-coverImage: "qr-codes-digital-contactless-payments.jpg"
+coverImage: "qr-codes-digital-contactless-payments.webp"
tags: ["brand identity","smart authentication","cx"]
author: "Vishal Sharma"
description: "From redirecting customers to social media pages to asking them to leave feedback and review, enterprises can do a lot through a QR Code. This insightful read covers all the aspects that depict the role of QR codes in enhancing marketing for enterprises during uncertain times."
@@ -82,4 +82,4 @@ There’s no second thought to the fact that the market for QR Codes is helping
With correct marketing strategies, including adequate content placement and website responsiveness, marketers must quickly understand that just adding a QR Code won’t speed up sales.
Also, adequate analysis strategies must be in place to trace the user behavior that can be further utilized to build personalized experiences for enhanced business growth during the uncertain times of COVID-19.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=qr-code-in-marketing)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=qr-code-in-marketing)
diff --git a/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.jpg b/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.jpg
deleted file mode 100644
index 0e2e83118..000000000
Binary files a/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.jpg and /dev/null differ
diff --git a/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.webp b/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.webp
new file mode 100644
index 000000000..8263b92e3
Binary files /dev/null and b/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.webp differ
diff --git a/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.jpg b/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.jpg
deleted file mode 100644
index 3304adc84..000000000
Binary files a/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.jpg and /dev/null differ
diff --git a/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.webp b/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.webp
new file mode 100644
index 000000000..274e5c9d6
Binary files /dev/null and b/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.webp differ
diff --git a/content/growth/questions-to-ask-your-identity-provider-2022/index.md b/content/growth/questions-to-ask-your-identity-provider-2022/index.md
index 96a687b36..004d05374 100644
--- a/content/growth/questions-to-ask-your-identity-provider-2022/index.md
+++ b/content/growth/questions-to-ask-your-identity-provider-2022/index.md
@@ -1,7 +1,7 @@
---
title: "What Should You Ask Your Identity Provider in 2022"
date: "2021-12-21"
-coverImage: "id-provider.jpg"
+coverImage: "id-provider.webp"
category: ["all"]
featured: false
author: "Yash Rathi"
@@ -144,4 +144,4 @@ However, LoginRadius offers endless possibilities and provides all the features,
You can choose LoginRadius as your CIAM to witness substantial business growth. Reach us for a free personalized demo today.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=questions-to-ask-your-identity-provider-2022)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=questions-to-ask-your-identity-provider-2022)
diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.png b/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.png and /dev/null differ
diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.webp b/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.webp differ
diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.png b/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.png and /dev/null differ
diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.webp b/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.webp differ
diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.jpg b/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.jpg
deleted file mode 100644
index 0b6edf8fa..000000000
Binary files a/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.jpg and /dev/null differ
diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.webp b/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.webp
new file mode 100644
index 000000000..774e707e5
Binary files /dev/null and b/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.webp differ
diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.jpg b/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.jpg
deleted file mode 100644
index b3384ebe4..000000000
Binary files a/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.jpg and /dev/null differ
diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.webp b/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.webp
new file mode 100644
index 000000000..4b7191c98
Binary files /dev/null and b/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.webp differ
diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/index.md b/content/growth/reasons-business-needs-customer-identity-strategy/index.md
index abf8ad4ab..ca4f2e0f7 100644
--- a/content/growth/reasons-business-needs-customer-identity-strategy/index.md
+++ b/content/growth/reasons-business-needs-customer-identity-strategy/index.md
@@ -1,7 +1,7 @@
---
title: "5 Reasons Why a Strong Customer Identity Strategy Can Benefit Your Business"
date: "2023-03-22"
-coverImage: "customer-idntity.jpg"
+coverImage: "customer-idntity.webp"
tags: ["customer identity management","data security","cx"]
author: "Yash Rathi"
description: "Whether deep consumer insights or delivering seamless and secure customer experiences, an identity management solution could help businesses stay ahead of the curve. Let’s uncover some of the top reasons your business needs an identity strategy."
@@ -39,7 +39,7 @@ In today's digital age, cybersecurity threats are a constant concern for busines
Whether multi-factor or risk-based, an identity management solution can reinforce authentication security even in the highest-risk environments.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
Adding multiple layers of authentication not only protects customers' personal information and helps build trust and credibility with customers, which can lead to increased loyalty and referrals.
@@ -61,4 +61,4 @@ A customer identity strategy is critical for businesses that want to grow and su
By personalizing experiences, gaining better customer insights, enhancing security, improving marketing ROI, and increasing customer loyalty, businesses can create a strong foundation for growth and long-term success. If you haven't already implemented a customer identity strategy, now is the time to start.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=reasons-business-needs-customer-identity-strategy)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=reasons-business-needs-customer-identity-strategy)
\ No newline at end of file
diff --git a/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.png b/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.png
deleted file mode 100644
index 1f39a27f3..000000000
Binary files a/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.png and /dev/null differ
diff --git a/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.webp b/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.webp
new file mode 100644
index 000000000..8a8067f56
Binary files /dev/null and b/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.webp differ
diff --git a/content/growth/risk-based-authentication-gaming-industry/index.md b/content/growth/risk-based-authentication-gaming-industry/index.md
index 3ab84330e..f36fc7d2d 100644
--- a/content/growth/risk-based-authentication-gaming-industry/index.md
+++ b/content/growth/risk-based-authentication-gaming-industry/index.md
@@ -1,7 +1,7 @@
---
title: "Embracing Risk-Based Authentication in the Gaming Industry"
date: "2021-10-18"
-coverImage: "rba-gaming-cover.jpg"
+coverImage: "rba-gaming-cover.webp"
category: ["security"]
featured: false
author: "Navanita Devi"
@@ -40,7 +40,7 @@ If the system detects any risk, then it follows either of the following measures
* The system blocks the user if any risk is observed.
* The system uses [multi-factor authentication](https://www.loginradius.com/blog/identity/multi-factor-authentication-a-beginners-guide/) to authenticate the user identity, i.e., using SMS or Google authenticator.
-[](https://www.loginradius.com/resource/fixing-broken-authentication-with-adaptive-mfa/)
+[](https://www.loginradius.com/resource/fixing-broken-authentication-with-adaptive-mfa/)
## How to Use RBA in the Gaming Industry
@@ -86,4 +86,4 @@ An effective RBA can make a huge difference between a safe and unsafe gaming exp
The focus is to confide the users' personal information, and with LoginRadius, you will find more than just one solution to your digital predicaments. [Contact us](https://www.loginradius.com/contact-sales) to know more.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=risk-based-authentication-gaming-industry)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=risk-based-authentication-gaming-industry)
\ No newline at end of file
diff --git a/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.jpg b/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.jpg
deleted file mode 100644
index 92bbcae18..000000000
Binary files a/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.jpg and /dev/null differ
diff --git a/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.webp b/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.webp
new file mode 100644
index 000000000..279886fd7
Binary files /dev/null and b/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.webp differ
diff --git a/content/growth/role-cookieless-authentication-marketers/cookieless-auth.jpg b/content/growth/role-cookieless-authentication-marketers/cookieless-auth.jpg
deleted file mode 100644
index a992f8755..000000000
Binary files a/content/growth/role-cookieless-authentication-marketers/cookieless-auth.jpg and /dev/null differ
diff --git a/content/growth/role-cookieless-authentication-marketers/cookieless-auth.webp b/content/growth/role-cookieless-authentication-marketers/cookieless-auth.webp
new file mode 100644
index 000000000..5ad759cba
Binary files /dev/null and b/content/growth/role-cookieless-authentication-marketers/cookieless-auth.webp differ
diff --git a/content/growth/role-cookieless-authentication-marketers/index.md b/content/growth/role-cookieless-authentication-marketers/index.md
index cf3c861f5..3a92a2160 100644
--- a/content/growth/role-cookieless-authentication-marketers/index.md
+++ b/content/growth/role-cookieless-authentication-marketers/index.md
@@ -1,7 +1,7 @@
---
title: "The Peerless Role of Cookieless Identity Solution for Marketers"
date: "2022-06-09"
-coverImage: "cookieless-auth.jpg"
+coverImage: "cookieless-auth.webp"
category: ["marketing", "authentication", "ciam"]
author: "Vishal Sharma"
description: "With cookieless authentication, enterprises can leverage the true potential of a CIAM solution in marketing their products and services without compromising user experience. This post explains why businesses quickly need to put their best foot forward in adopting a cookieless authentication platform."
@@ -80,4 +80,4 @@ Businesses can choose [a reliable CIAM platform](https://www.loginradius.com/blo
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-cookieless-authentication-marketers)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-cookieless-authentication-marketers)
\ No newline at end of file
diff --git a/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.png b/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.png
deleted file mode 100644
index f97184f2f..000000000
Binary files a/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.png and /dev/null differ
diff --git a/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.webp b/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.webp
new file mode 100644
index 000000000..88d19cbb8
Binary files /dev/null and b/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.webp differ
diff --git a/content/growth/role-it-marketing-customer-identity-management/index.md b/content/growth/role-it-marketing-customer-identity-management/index.md
index be6f6ffc5..93e3b9ca2 100644
--- a/content/growth/role-it-marketing-customer-identity-management/index.md
+++ b/content/growth/role-it-marketing-customer-identity-management/index.md
@@ -1,7 +1,7 @@
---
title: "How IT and Marketing Go Hand-in-Hand in the Business of Customer Identity Management?"
date: "2022-05-31"
-coverImage: "it-marketing.jpg"
+coverImage: "it-marketing.webp"
tags: ["marketing", "ciam", "IT"]
author: "Rakesh Soni"
description: "Promoting your brand and delivering out-of-the-box services reinforced with robust security is paramount for business success. However, delivering rich experiences remains the most underrated catalyst that can pave the path for exponential growth!"
@@ -48,7 +48,7 @@ A [customer identity and access management](https://www.loginradius.com/blog/ide
Through progressive profiling, users aren’t bombarded with big registration forms; instead, they are asked to share their details when they interact with the platform gradually. This ensures a seamless and rich user experience.
-[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
+[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
## What About Security? Should it be a Part of Preference Management and Digital Experience Strategy?
@@ -105,4 +105,4 @@ Customer identity management is crucial for businesses striving for growth in a
With a new-age CIAM like LoginRadius, businesses can ensure they deliver a rich consumer experience backed with robust security that can offer endless marketing opportunities.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-it-marketing-customer-identity-management)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-it-marketing-customer-identity-management)
\ No newline at end of file
diff --git a/content/growth/role-it-marketing-customer-identity-management/it-marketing.jpg b/content/growth/role-it-marketing-customer-identity-management/it-marketing.jpg
deleted file mode 100644
index 64287bdd9..000000000
Binary files a/content/growth/role-it-marketing-customer-identity-management/it-marketing.jpg and /dev/null differ
diff --git a/content/growth/role-it-marketing-customer-identity-management/it-marketing.webp b/content/growth/role-it-marketing-customer-identity-management/it-marketing.webp
new file mode 100644
index 000000000..e59a0763d
Binary files /dev/null and b/content/growth/role-it-marketing-customer-identity-management/it-marketing.webp differ
diff --git a/content/growth/role-it-marketing-customer-identity-management/visitor-eb.png b/content/growth/role-it-marketing-customer-identity-management/visitor-eb.png
deleted file mode 100644
index c9ad88d9e..000000000
Binary files a/content/growth/role-it-marketing-customer-identity-management/visitor-eb.png and /dev/null differ
diff --git a/content/growth/role-it-marketing-customer-identity-management/visitor-eb.webp b/content/growth/role-it-marketing-customer-identity-management/visitor-eb.webp
new file mode 100644
index 000000000..2b537fe1a
Binary files /dev/null and b/content/growth/role-it-marketing-customer-identity-management/visitor-eb.webp differ
diff --git a/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.png b/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.png
deleted file mode 100644
index f5fa0b0f9..000000000
Binary files a/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.png and /dev/null differ
diff --git a/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.webp b/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.webp
new file mode 100644
index 000000000..b0761321e
Binary files /dev/null and b/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.webp differ
diff --git a/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.jpg b/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.jpg
deleted file mode 100644
index 169a8f3c0..000000000
Binary files a/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.jpg and /dev/null differ
diff --git a/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.webp b/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.webp
new file mode 100644
index 000000000..db3327067
Binary files /dev/null and b/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.webp differ
diff --git a/content/growth/role-of-frictionless-payments-for-businesses/index.md b/content/growth/role-of-frictionless-payments-for-businesses/index.md
index 4b6603565..fc5561df8 100644
--- a/content/growth/role-of-frictionless-payments-for-businesses/index.md
+++ b/content/growth/role-of-frictionless-payments-for-businesses/index.md
@@ -1,7 +1,7 @@
---
title: "5 Reasons Why Frictionless Payments Matter To Marketers And Business Owners"
date: "2022-03-11"
-coverImage: "frictionless-paymt.jpg"
+coverImage: "frictionless-paymt.webp"
tags: ["omnichannel cx","authentication","user experience","ciam solution"]
author: "Vishal Sharma"
description: "When it comes to frictionless payments, most brands ignore that a bit of hustle in the overall payment process could encourage their users to switch. Let’s understand why frictionless payments matter today more than ever before, especially for business owners and marketers."
@@ -52,7 +52,7 @@ Admit it; a great user experience is paramount for online business success in to
Users need not enter their card details or provide pins every time they shop from the same platform. Instead, they can use different authentication methods, including a fingerprint that completes payment in a fraction of seconds.
-[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
+[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
### #3. Better payment security
@@ -91,4 +91,4 @@ Adding frictionless payment methods to their branding strategy is the need of th
Businesses can quickly adopt frictionless payments by leveraging [seamless authentication methods](https://www.loginradius.com/blog/identity/authentication-option-for-your-product/) that offer a great experience and eventually reinforce payment security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-of-frictionless-payments-for-businesses)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-of-frictionless-payments-for-businesses)
\ No newline at end of file
diff --git a/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.png b/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.png
deleted file mode 100644
index 86c15a159..000000000
Binary files a/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.png and /dev/null differ
diff --git a/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.webp b/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.webp
new file mode 100644
index 000000000..025782e92
Binary files /dev/null and b/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.webp differ
diff --git a/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.png b/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.png
deleted file mode 100644
index 1e4c62adb..000000000
Binary files a/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.png and /dev/null differ
diff --git a/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.webp b/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.webp
new file mode 100644
index 000000000..53e9a5b34
Binary files /dev/null and b/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.webp differ
diff --git a/content/growth/role-sso-in-digital-marketing/index.md b/content/growth/role-sso-in-digital-marketing/index.md
index 2290b0223..ccdc739f6 100644
--- a/content/growth/role-sso-in-digital-marketing/index.md
+++ b/content/growth/role-sso-in-digital-marketing/index.md
@@ -1,7 +1,7 @@
---
title: "The Critical Role of SSO in Reshaping Digital Marketing Landscape"
date: "2023-02-10"
-coverImage: "sso.jpg"
+coverImage: "sso.webp"
tags: ["sso","ciam platform","customer retention"]
author: "Vishal Sharma"
description: "With SSO, enterprises can understand their target audience's needs, preferences, and behavior when they land on their platform for the first time. And this helps them in creating winning digital marketing campaigns to foster growth."
@@ -61,7 +61,7 @@ Another thing SSO does is reduce barriers for users. By leveraging single sign-o
That means one login, one set of credentials, and one consistent experience—and we all know how important consistency is when converting new users.
-[](https://www.loginradius.com/resource/authentication-sso-native-mobile-apps-datasheet)
+[](https://www.loginradius.com/resource/authentication-sso-native-mobile-apps-datasheet)
### 4. Helps Craft Personalized Experiences
@@ -77,4 +77,4 @@ While SSO offers a convenient, secure, and efficient way for users to access mul
Brands that are thinking about accelerating their digital marketing efforts shouldn’t wait, and just put their best foot forward in implementing SSO into their website/mobile applications.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-sso-in-digital-marketing)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-sso-in-digital-marketing)
\ No newline at end of file
diff --git a/content/growth/role-sso-in-digital-marketing/native-ds.png b/content/growth/role-sso-in-digital-marketing/native-ds.png
deleted file mode 100644
index 9368b122c..000000000
Binary files a/content/growth/role-sso-in-digital-marketing/native-ds.png and /dev/null differ
diff --git a/content/growth/role-sso-in-digital-marketing/native-ds.webp b/content/growth/role-sso-in-digital-marketing/native-ds.webp
new file mode 100644
index 000000000..44fba692f
Binary files /dev/null and b/content/growth/role-sso-in-digital-marketing/native-ds.webp differ
diff --git a/content/growth/role-sso-in-digital-marketing/sso-role.jpg b/content/growth/role-sso-in-digital-marketing/sso-role.jpg
deleted file mode 100644
index 4d0169064..000000000
Binary files a/content/growth/role-sso-in-digital-marketing/sso-role.jpg and /dev/null differ
diff --git a/content/growth/role-sso-in-digital-marketing/sso-role.webp b/content/growth/role-sso-in-digital-marketing/sso-role.webp
new file mode 100644
index 000000000..41941f421
Binary files /dev/null and b/content/growth/role-sso-in-digital-marketing/sso-role.webp differ
diff --git a/content/growth/role-sso-in-digital-marketing/sso.jpg b/content/growth/role-sso-in-digital-marketing/sso.jpg
deleted file mode 100644
index 329a2a2fa..000000000
Binary files a/content/growth/role-sso-in-digital-marketing/sso.jpg and /dev/null differ
diff --git a/content/growth/role-sso-in-digital-marketing/sso.webp b/content/growth/role-sso-in-digital-marketing/sso.webp
new file mode 100644
index 000000000..0d4ee682a
Binary files /dev/null and b/content/growth/role-sso-in-digital-marketing/sso.webp differ
diff --git a/content/growth/saas-consumer-support/index.md b/content/growth/saas-consumer-support/index.md
index eb58f0027..20d99f9b4 100644
--- a/content/growth/saas-consumer-support/index.md
+++ b/content/growth/saas-consumer-support/index.md
@@ -1,7 +1,7 @@
---
title: "How to Deliver the Perfect Consumer Support System for SaaS Companies"
date: "2021-02-12"
-coverImage: "saas-consumer-support.jpg"
+coverImage: "saas-consumer-support.webp"
category: ["all"]
featured: false
author: "Rakesh Soni"
@@ -232,4 +232,4 @@ They can help to define your organization and drive your organization's reputati
Hopefully, the above insights into the LoginRadius support team and some of the things that have helped us to support our consumers enable you to drive efficiencies within your organization.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=saas-consumer-support)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=saas-consumer-support)
diff --git a/content/growth/saas-consumer-support/saas-consumer-support.jpg b/content/growth/saas-consumer-support/saas-consumer-support.jpg
deleted file mode 100644
index 0da446195..000000000
Binary files a/content/growth/saas-consumer-support/saas-consumer-support.jpg and /dev/null differ
diff --git a/content/growth/saas-consumer-support/saas-consumer-support.webp b/content/growth/saas-consumer-support/saas-consumer-support.webp
new file mode 100644
index 000000000..c77bc95aa
Binary files /dev/null and b/content/growth/saas-consumer-support/saas-consumer-support.webp differ
diff --git a/content/growth/sanitary-pad-donation-drive/LR-donation-drive.jpg b/content/growth/sanitary-pad-donation-drive/LR-donation-drive.jpg
deleted file mode 100644
index 522d95f9e..000000000
Binary files a/content/growth/sanitary-pad-donation-drive/LR-donation-drive.jpg and /dev/null differ
diff --git a/content/growth/sanitary-pad-donation-drive/LR-donation-drive.webp b/content/growth/sanitary-pad-donation-drive/LR-donation-drive.webp
new file mode 100644
index 000000000..612cfc4d0
Binary files /dev/null and b/content/growth/sanitary-pad-donation-drive/LR-donation-drive.webp differ
diff --git a/content/growth/sanitary-pad-donation-drive/cta-careers.png b/content/growth/sanitary-pad-donation-drive/cta-careers.png
deleted file mode 100644
index 600361d60..000000000
Binary files a/content/growth/sanitary-pad-donation-drive/cta-careers.png and /dev/null differ
diff --git a/content/growth/sanitary-pad-donation-drive/cta-careers.webp b/content/growth/sanitary-pad-donation-drive/cta-careers.webp
new file mode 100644
index 000000000..bf117ad57
Binary files /dev/null and b/content/growth/sanitary-pad-donation-drive/cta-careers.webp differ
diff --git a/content/growth/sanitary-pad-donation-drive/hope-basket.jpg b/content/growth/sanitary-pad-donation-drive/hope-basket.jpg
deleted file mode 100644
index cd931234a..000000000
Binary files a/content/growth/sanitary-pad-donation-drive/hope-basket.jpg and /dev/null differ
diff --git a/content/growth/sanitary-pad-donation-drive/hope-basket.webp b/content/growth/sanitary-pad-donation-drive/hope-basket.webp
new file mode 100644
index 000000000..8e52dcd99
Binary files /dev/null and b/content/growth/sanitary-pad-donation-drive/hope-basket.webp differ
diff --git a/content/growth/sanitary-pad-donation-drive/index.md b/content/growth/sanitary-pad-donation-drive/index.md
index d9cc0765d..5d35f790a 100644
--- a/content/growth/sanitary-pad-donation-drive/index.md
+++ b/content/growth/sanitary-pad-donation-drive/index.md
@@ -1,7 +1,7 @@
---
title: "Making a Difference: LoginRadius' Sanitary Pad Donation Drive"
date: "2023-09-27"
-coverImage: "social-cause.jpg"
+coverImage: "social-cause.webp"
tags: ["LoginRadius donation drive","women empowerment","hope basket foundation"]
author: "Azharuddin Mohammad"
description: "Join LoginRadius in our mission to create a positive change in our community. Learn how we're providing sanitary pads, educating women, and making a difference in the lives of underprivileged girls. Together, we can ensure dignity, comfort, and safety for all during their menstrual cycles."
@@ -24,7 +24,7 @@ Many women still prefer using clothes during their menstrual cycles due to conce
The market prices of sanitary pads are often beyond the reach of underprivileged women and girls. The high cost of these essential hygiene products forces them to compromise their health and well-being.
-
+
### 3. Stigma and Shyness
@@ -40,7 +40,7 @@ Our donation drive is being carried out in phases, targeting different underpriv
None of this would have been possible without the dedication and commitment of our operations team and volunteers who stepped up to make a difference. We thank Naveen, Vikas, Shreya, Soniya, Sudhey, and Pankaj for their invaluable contributions to this noble cause.
-
+
## Conclusion:
@@ -50,4 +50,4 @@ Join us in our mission to create a positive change in our community. We can empo
Stay tuned for updates on our Sanitary Pad Donation Drive and the impact we're creating in the lives of underprivileged girls. Together, we can make a difference.
-[](https://www.loginradius.com/careers/)
\ No newline at end of file
+[](https://www.loginradius.com/careers/)
\ No newline at end of file
diff --git a/content/growth/sanitary-pad-donation-drive/social-cause.jpg b/content/growth/sanitary-pad-donation-drive/social-cause.jpg
deleted file mode 100644
index 81adcb03d..000000000
Binary files a/content/growth/sanitary-pad-donation-drive/social-cause.jpg and /dev/null differ
diff --git a/content/growth/sanitary-pad-donation-drive/social-cause.webp b/content/growth/sanitary-pad-donation-drive/social-cause.webp
new file mode 100644
index 000000000..876d04f1f
Binary files /dev/null and b/content/growth/sanitary-pad-donation-drive/social-cause.webp differ
diff --git a/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.jpg b/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.jpg
deleted file mode 100644
index 3c4d54db0..000000000
Binary files a/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.jpg and /dev/null differ
diff --git a/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.webp b/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.webp
new file mode 100644
index 000000000..33ef68a75
Binary files /dev/null and b/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.webp differ
diff --git a/content/growth/scale-business-with-loginradius-customer-segmentation/index.md b/content/growth/scale-business-with-loginradius-customer-segmentation/index.md
index d888315d9..f2817ae76 100644
--- a/content/growth/scale-business-with-loginradius-customer-segmentation/index.md
+++ b/content/growth/scale-business-with-loginradius-customer-segmentation/index.md
@@ -1,7 +1,7 @@
---
title: "Driving Revenue Using LoginRadius' Customer Segmentation Insights"
date: "2022-03-15"
-coverImage: "customer-segmt.jpg"
+coverImage: "customer-segmt.webp"
category: ["business", "Marketing", "technology"]
featured: false
author: "Manish Tiwari"
@@ -81,4 +81,4 @@ Businesses can’t ignore the importance of user insights that can help them und
LoginRadius helps businesses transform the way they approach their marketing by taking the guesswork out of their efforts. One can quickly segment their customers and get specific about their population right from the LoginRadius Admin Console.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=scale-business-with-loginradius-customer-segmentation)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=scale-business-with-loginradius-customer-segmentation)
diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.png b/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.png and /dev/null differ
diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.webp b/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.webp differ
diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.png b/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.png
deleted file mode 100644
index 3e6b81ee6..000000000
Binary files a/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.png and /dev/null differ
diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.webp b/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.webp
new file mode 100644
index 000000000..2f7c01062
Binary files /dev/null and b/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.webp differ
diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/index.md b/content/growth/secure-your-remote-workforce-with-identity-management/index.md
index 5882fc065..0529a8908 100644
--- a/content/growth/secure-your-remote-workforce-with-identity-management/index.md
+++ b/content/growth/secure-your-remote-workforce-with-identity-management/index.md
@@ -1,7 +1,7 @@
---
title: "7 Best Practices for Securing Your Remote Workforce with Identity Management"
date: "2021-08-04"
-coverImage: "remote-workforce.jpg"
+coverImage: "remote-workforce.webp"
tags: ["zero trust security","identity management","cybersecurity","cx"]
author: "Vishal Sharma"
description: "Learn about the best practices to ensure cybersecurity for remote workers using identity management"
@@ -40,7 +40,7 @@ Businesses should be wary of everything on the internet. In fact, even on-premis
Consider adopting this approach into your remote work policies and protocols so your remote employees will be guided accordingly. One great example would be implementing multi-factor authentication for each login. This will add an extra layer of protection and verification for your users.
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
## 3. Perform routine review of accounts
@@ -79,5 +79,5 @@ As your business migrates to a virtual workplace, you must learn how to maintain
Through identity management, you reduce password issues and enhance security for your remote teams. It streamlines the process of logging in, authenticating, and authorizing access to your organization’s data and resources. To find out more about the benefits of identity management, [contact our team](https://www.loginradius.com/contact-sales2/).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-your-remote-workforce-with-identity-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-your-remote-workforce-with-identity-management)
diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.png b/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.png
deleted file mode 100644
index e7cfcf9a0..000000000
Binary files a/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.png and /dev/null differ
diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.webp b/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.webp
new file mode 100644
index 000000000..735ec1c8d
Binary files /dev/null and b/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.webp differ
diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.jpg b/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.jpg
deleted file mode 100644
index b3648a108..000000000
Binary files a/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.jpg and /dev/null differ
diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.webp b/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.webp
new file mode 100644
index 000000000..6b9660902
Binary files /dev/null and b/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.webp differ
diff --git a/content/growth/secure-your-wi-fi-against-hackers/index.md b/content/growth/secure-your-wi-fi-against-hackers/index.md
index 10655abe3..12a297fac 100644
--- a/content/growth/secure-your-wi-fi-against-hackers/index.md
+++ b/content/growth/secure-your-wi-fi-against-hackers/index.md
@@ -1,7 +1,7 @@
---
title: "10 Tips to Ensure Your Wi-Fi is Private and Blocking Hackers"
date: "2021-08-19"
-coverImage: "secure-wi-fi-against-hackers.jpg"
+coverImage: "secure-wi-fi-against-hackers.webp"
category: ["loginradius"]
featured: false
author: "Rashmi Mathur"
@@ -203,4 +203,4 @@ To maintain the system with firewalls and anti-malware software. Always keep the
Many hackers are using different methods like [ransomware](https://www.loginradius.com/resource/with-ransomware-on-the-rise-how-safe-is-your-business/) and identity theft. To avoid all these issues, you can make some changes by practicing these tips.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-your-wi-fi-against-hackers)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-your-wi-fi-against-hackers)
\ No newline at end of file
diff --git a/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.jpg b/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.jpg
deleted file mode 100644
index b1600c310..000000000
Binary files a/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.jpg and /dev/null differ
diff --git a/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.webp b/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.webp
new file mode 100644
index 000000000..d1432879c
Binary files /dev/null and b/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.webp differ
diff --git a/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.png b/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.png
deleted file mode 100644
index f12e48c23..000000000
Binary files a/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.png and /dev/null differ
diff --git a/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.webp b/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.webp
new file mode 100644
index 000000000..56ca58866
Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.webp differ
diff --git a/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.png b/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.png
deleted file mode 100644
index a166c214e..000000000
Binary files a/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.png and /dev/null differ
diff --git a/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.webp b/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.webp
new file mode 100644
index 000000000..0d5102393
Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.webp differ
diff --git "a/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.jpg" "b/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.jpg"
deleted file mode 100644
index 8adab10af..000000000
Binary files "a/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.jpg" and /dev/null differ
diff --git "a/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.webp" "b/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.webp"
new file mode 100644
index 000000000..ab9d2994c
Binary files /dev/null and "b/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.webp" differ
diff --git a/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.jpg b/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.jpg
deleted file mode 100644
index 0c86a73fc..000000000
Binary files a/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.jpg and /dev/null differ
diff --git a/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.webp b/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.webp
new file mode 100644
index 000000000..cbcff4ce9
Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.webp differ
diff --git a/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.png b/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.png
deleted file mode 100644
index 22caf4e48..000000000
Binary files a/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.png and /dev/null differ
diff --git a/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.webp b/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.webp
new file mode 100644
index 000000000..b4dfdd332
Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.webp differ
diff --git a/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.png b/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.png
deleted file mode 100644
index 817131a60..000000000
Binary files a/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.png and /dev/null differ
diff --git a/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.webp b/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.webp
new file mode 100644
index 000000000..176bb730c
Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.webp differ
diff --git a/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.png b/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.png
deleted file mode 100644
index af997195a..000000000
Binary files a/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.png and /dev/null differ
diff --git a/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.webp b/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.webp
new file mode 100644
index 000000000..4259974c8
Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.webp differ
diff --git a/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.png b/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.png
deleted file mode 100644
index 9e4619738..000000000
Binary files a/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.png and /dev/null differ
diff --git a/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.webp b/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.webp
new file mode 100644
index 000000000..171e1040a
Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.webp differ
diff --git a/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.png b/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.png
deleted file mode 100644
index 98fb88c37..000000000
Binary files a/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.png and /dev/null differ
diff --git a/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.webp b/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.webp
new file mode 100644
index 000000000..6b0ac103f
Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.webp differ
diff --git a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.png b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.png
deleted file mode 100644
index 72e5392e5..000000000
Binary files a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.png and /dev/null differ
diff --git a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.webp b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.webp
new file mode 100644
index 000000000..0010c4149
Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.webp differ
diff --git a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.jpg b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.jpg
deleted file mode 100644
index 344e1896b..000000000
Binary files a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.jpg and /dev/null differ
diff --git a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.webp b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.webp
new file mode 100644
index 000000000..56f44d40c
Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.webp differ
diff --git a/content/growth/sign-up-forms-best-practices/index.md b/content/growth/sign-up-forms-best-practices/index.md
index 823eb696e..be4bf5474 100644
--- a/content/growth/sign-up-forms-best-practices/index.md
+++ b/content/growth/sign-up-forms-best-practices/index.md
@@ -1,7 +1,7 @@
---
title: "The Ultimate Guide to Craft Sign-up Forms That Convert Like Crazy"
date: "2017-04-28"
-coverImage: "The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.png"
+coverImage: "The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.webp"
category: ["technology"]
featured: false
author: "Rakesh Soni"
@@ -32,7 +32,7 @@ _Your goal is to acquire leads!_
Engaged time generally declines till the time the prospect hits below the fold of your page. Hence, make it a practice to introduce them above the fold. Other than forms, you can also introduce CTAs and other important elements on your page. Thus, you can acquire utmost exposure to your business prospects that can help you to convert maximum leads. For example, if you are selling a software, just introduce your product with an eye-catching title, some images and a call -to-action button. This layout should crack a deal for you. Modifying the Unbounce’s page layout and placing plans with a call-to-action button [increased their conversion to 41%](https://econsultancy.com/blog/63139-six-useful-case-studies-on-where-to-place-your-cta-to-maximise-conversions).
-
+
### **Lessen your Number of Fields**
@@ -52,23 +52,23 @@ In the previous image, Semrush does a great job by keeping just two fields in th
There is a golden rule when you want your prospects to perform an email signup- “ ask less but provide as good as you can”. It means that you need to trade your idea of an email signup with a commodity or a service. For example, if your prospect is on your website to download a file, ask them to provide their email address and a couple of data in return. Now, that’s a successful transaction!
-
+
-[Source](https://help.aweber.com/hc/en-us/article_attachments/211926128/227394387_step01.png?ver=1553881376)
+[Source](https://help.aweber.com/hc/en-us/article_attachments/211926128/227394387_step01.webp?ver=1553881376)
### **Have an Effective CTA**
I still wonder why [72% of B2B marketers](http://contentmarketinginstitute.com/2013/09/small-businesses-website-content-calls-to-action/) do not think of placing CTAs on their internal pages. Hence, while you are placing a CTA on your website, ensure to make it eye-catching. This will assist to change your bounce rates into conversion rates. Moreover, replace “Submit” buttons with some buttons that perform an action. For example, use “**Start your Free Trial**” or “**Start Bookmarking**” instead of “Submit”.
-
+
-[Source](https://blog.aweber.com/wp-content/uploads/2016/08/marie-forleo-sign-up-form-cta.png?ver=1553881376)
+[Source](https://blog.aweber.com/wp-content/uploads/2016/08/marie-forleo-sign-up-form-cta.webp?ver=1553881376)
### **Show Your User Base**
Giving a proof for your social acceptance is a good technique to attract more customers. Look at the different companies who have endorsed themselves with this technique. You can also add some client testimonials to support your brand.
-
+
[Source](https://signup.ballparkapp.com/)
@@ -94,7 +94,7 @@ _Perform A/B testing._
Intuition, experience and expertise are certainly required for page positioning, nothing can replace testing. So, decide the appearance of your form with testing.
-
+
### **Try Out Templates like Mad Libs**
@@ -111,9 +111,9 @@ Don’t be so choosy about the characteristics of your fields. For example, if t
Many websites ask for passwords over again just for the sake that other websites have done it earlier. The sole purpose of asking passwords again is to prevent typo errors. Thus, a more user friendly method to do it is giving an option to view the password.
-
+
-[Source](https://i.stack.imgur.com/pO6KD.png?ver=1553881376)
+[Source](https://i.stack.imgur.com/pO6KD.webp?ver=1553881376)
### **Use Auto-fill Fields instead of Drop Down Lists**
@@ -121,15 +121,15 @@ Drop down lists are not a good option when the list of choices are too long, eg:
_Don’t do this_
-
+
-[Source](https://i1.wp.com/conversionxl.com/wp-content/uploads/2011/12/dropdown.jpg?ver=1553881376)
+[Source](https://i1.wp.com/conversionxl.com/wp-content/uploads/2011/12/dropdown.webp?ver=1553881376)
Instead,
-
+
-[Source](https://www.smashingmagazine.com/wp-content/uploads/2011/03/signup4.png?ver=1553881376)
+[Source](https://www.smashingmagazine.com/wp-content/uploads/2011/03/signup4.webp?ver=1553881376)
@@ -137,9 +137,9 @@ Instead,
Small CTA buttons are poor implementations and can look less effective from the users point of view. Hence, it is recommended to equal the width of submit button with the width of the adjacent input field.
-
+
-[Source](https://codropspz-tympanus.netdna-ssl.com/codrops/wp-content/uploads/2012/10/CustomLoginForms_02.jpg?ver=1553881376)
+[Source](https://codropspz-tympanus.netdna-ssl.com/codrops/wp-content/uploads/2012/10/CustomLoginForms_02.webp?ver=1553881376)
### **Please! Don’t use Captchas**
@@ -147,9 +147,9 @@ Adding Captchas are new methods to put someone to eternal torture. I know that w
‘[Honeypot captcha technique](http://haacked.com/archive/2007/09/11/honeypot-captcha.aspx/)’ is an anti-spam technique which helps your website to identify spammers by hiding a field in your form that is only visible to spamming tools. Hence, if that field is checked or filled, you can easily confirm it as spam. Still, if you want captchas to be a part of your form, try out some fun questions that prove the user is a human. For example, ask simple math calculations like ‘2+7=’.
-
+
-[Source](http://carlofontanos.com/wp-content/uploads/2014/04/Math_Captcha-300x202.jpg?ver=1553881376)
+[Source](http://carlofontanos.com/wp-content/uploads/2014/04/Math_Captcha-300x202.webp?ver=1553881376)
### **It’s all about user comfort and trust**
diff --git a/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.png b/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.png
deleted file mode 100644
index 848826bd5..000000000
Binary files a/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.png and /dev/null differ
diff --git a/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.webp b/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.webp
new file mode 100644
index 000000000..b76ff5fdf
Binary files /dev/null and b/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.webp differ
diff --git a/content/growth/sign-up-tips-conversion-rate/index.md b/content/growth/sign-up-tips-conversion-rate/index.md
index 1f82b04e8..6dc49baac 100644
--- a/content/growth/sign-up-tips-conversion-rate/index.md
+++ b/content/growth/sign-up-tips-conversion-rate/index.md
@@ -1,7 +1,7 @@
---
title: "9 Signup Tips To Skyrocket The Conversion Rate"
date: "2021-01-05"
-coverImage: "sign-up-rate.jpg"
+coverImage: "sign-up-rate.webp"
category: ["all"]
featured: false
author: "Rakesh Soni"
@@ -51,7 +51,7 @@ Shorter forms are not only easier to fill out, but the visitor is also less intr
Longer forms need more details. But the visitor to the website may be unwilling to provide you with any information about themselves.
-
+
Source: wingify
@@ -69,7 +69,7 @@ The key here is as much as possible to lower the barrier to entry. You don't wan
To find the best balance between customer experience and protection, the LoginRadius Identity Platform provides a full range of [customer registration and authentication options](https://www.loginradius.com/authentication/).
-
+
Source: moreconversion
@@ -103,7 +103,7 @@ For users, [social login](https://www.loginradius.com/social-login/) is easy to
Nevertheless, with social sign-up, the user's privacy is again in the spotlight. Most of them do not realize that, with this registration form, they agree to the use of their data by businesses. An opportunity that companies take to sell the product that best fits their preferences and desires to each customer, in a much more segmented and customized way.
-[](https://www.loginradius.com/resource/social-login-reconsidered/)
+[](https://www.loginradius.com/resource/social-login-reconsidered/)
Few advantages of using social signups:
@@ -157,4 +157,4 @@ Make sure it has a simple value proposition when writing a copy of your sign-up
Following the tips and examples shown in this article is your next move. If you can get it right, you can build better sign-up forms for conversion and increase the number of quality leads created.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sign-up-tips-conversion-rate)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sign-up-tips-conversion-rate)
\ No newline at end of file
diff --git a/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.png b/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.png
deleted file mode 100644
index 0f48687fa..000000000
Binary files a/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.png and /dev/null differ
diff --git a/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.webp b/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.webp
new file mode 100644
index 000000000..4f4683121
Binary files /dev/null and b/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.webp differ
diff --git a/content/growth/sign-up-tips-conversion-rate/sign-up-rate.jpg b/content/growth/sign-up-tips-conversion-rate/sign-up-rate.jpg
deleted file mode 100644
index e440247c9..000000000
Binary files a/content/growth/sign-up-tips-conversion-rate/sign-up-rate.jpg and /dev/null differ
diff --git a/content/growth/sign-up-tips-conversion-rate/sign-up-rate.webp b/content/growth/sign-up-tips-conversion-rate/sign-up-rate.webp
new file mode 100644
index 000000000..bb06bce51
Binary files /dev/null and b/content/growth/sign-up-tips-conversion-rate/sign-up-rate.webp differ
diff --git a/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.png b/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.png
deleted file mode 100644
index 412e2195c..000000000
Binary files a/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.png and /dev/null differ
diff --git a/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.webp b/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.webp
new file mode 100644
index 000000000..6e975bd35
Binary files /dev/null and b/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.png b/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.png
deleted file mode 100644
index 16ef5993b..000000000
Binary files a/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.png and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.webp b/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.webp
new file mode 100644
index 000000000..4ebbfc00a
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/Asana_logo_new.png b/content/growth/slack-integrations-for-productivity/Asana_logo_new.png
deleted file mode 100644
index 680f8b14f..000000000
Binary files a/content/growth/slack-integrations-for-productivity/Asana_logo_new.png and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/Asana_logo_new.webp b/content/growth/slack-integrations-for-productivity/Asana_logo_new.webp
new file mode 100644
index 000000000..3538dd085
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/Asana_logo_new.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/Hangouts_Icon.png b/content/growth/slack-integrations-for-productivity/Hangouts_Icon.png
deleted file mode 100644
index f3c6f87ee..000000000
Binary files a/content/growth/slack-integrations-for-productivity/Hangouts_Icon.png and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/Hangouts_Icon.webp b/content/growth/slack-integrations-for-productivity/Hangouts_Icon.webp
new file mode 100644
index 000000000..1c65150e2
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/Hangouts_Icon.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/JIRA.png b/content/growth/slack-integrations-for-productivity/JIRA.png
deleted file mode 100644
index 6427eb684..000000000
Binary files a/content/growth/slack-integrations-for-productivity/JIRA.png and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/JIRA.webp b/content/growth/slack-integrations-for-productivity/JIRA.webp
new file mode 100644
index 000000000..f73cefe05
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/JIRA.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.png b/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.png
deleted file mode 100644
index 8e27f2eac..000000000
Binary files a/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.png and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.webp b/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.webp
new file mode 100644
index 000000000..81908d4f6
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/Untitled-design-6.png b/content/growth/slack-integrations-for-productivity/Untitled-design-6.png
deleted file mode 100644
index 3ccc592e9..000000000
Binary files a/content/growth/slack-integrations-for-productivity/Untitled-design-6.png and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/Untitled-design-6.webp b/content/growth/slack-integrations-for-productivity/Untitled-design-6.webp
new file mode 100644
index 000000000..e577f4924
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/Untitled-design-6.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.png b/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.png
deleted file mode 100644
index 2b641562b..000000000
Binary files a/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.png and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.webp b/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.webp
new file mode 100644
index 000000000..1ccb5e3f4
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/github.jpg b/content/growth/slack-integrations-for-productivity/github.jpg
deleted file mode 100644
index bceac6e3a..000000000
Binary files a/content/growth/slack-integrations-for-productivity/github.jpg and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/github.webp b/content/growth/slack-integrations-for-productivity/github.webp
new file mode 100644
index 000000000..b8054ee7e
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/github.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/hubot.png b/content/growth/slack-integrations-for-productivity/hubot.png
deleted file mode 100644
index 2df25bd95..000000000
Binary files a/content/growth/slack-integrations-for-productivity/hubot.png and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/hubot.webp b/content/growth/slack-integrations-for-productivity/hubot.webp
new file mode 100644
index 000000000..9b788738d
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/hubot.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/index.md b/content/growth/slack-integrations-for-productivity/index.md
index 068ca7499..23b27debd 100644
--- a/content/growth/slack-integrations-for-productivity/index.md
+++ b/content/growth/slack-integrations-for-productivity/index.md
@@ -1,7 +1,7 @@
---
title: "11 Slack App Integrations to Boost Productivity at Your Workplace"
date: "2017-02-28"
-coverImage: "Untitled-design-6.png"
+coverImage: "Untitled-design-6.webp"
category: ["business", "technology", "loginradius"]
featured: false
author: "Rakesh Soni"
@@ -21,7 +21,7 @@ Slack is well known for its chatting environment. You can create various channel
#### **Asana**
-
+
As one of the best tools to manage projects in many organizations, [Asana](https://asana.com/customers/) is widely used. So, if your organization is one of them, you can highly benefit in terms of productivity with this app integration.
@@ -33,7 +33,7 @@ As one of the best tools to manage projects in many organizations, [Asana](https
#### **Mailchimp**
-
+
As one of the best online platforms for email marketing, [Mailchimp-Slack integration](https://slack.com/apps/new/A0F82E726-mailchimp) can help you to get updates about the number of subscriptions and you can check a campaign’ sent status. The process includes authentication from your Mailchimp account. Afterwards, you can also select which lists to monitor through Slack.
@@ -45,7 +45,7 @@ In a nutshell, you can [check the following events](https://connect.mailchimp.co
#### **Github**
-
+
With [Github](https://github.com/)\-Slack integration, you can have access to the repository of source codes for your Git projects. This integration provides you with the privilege to cooperate, analyze, and practice codes for your private projects.
@@ -69,19 +69,19 @@ Process to [connect your Slack with Github](https://get.slack.help/hc/en-us/arti
#### **Hubot**
-
+
[Hubot](https://hubot.github.com/) is a popular chatbot which can be used for anything in your team. For example, you can have a poll of what your team is going to have for lunch or you can look for people who want to have a coffee. Well, this bot is fun and this is how you can [integrate](https://slack.com/apps/A0F7XDU93-hubot) it with Slack.
#### **Google Hangouts**
-
+
Integrating [Google Hangouts](https://hangouts.google.com/?hl=en&authuser=0) with Slack will help you to communicate with your team via voice calls and video conferencing. So, you can boost your communication in a certain channel and accelerate conversations through Hangout. People across different niche such as marketers, developers, and other professionals can benefit from [Google Hangouts-Slack](https://slack.com/apps/new/A0F7YS351-google-hangouts) integration.
#### **Google Drive**
-
+
[Google drive](https://drive.google.com/) is used to create, save and **corporate** documents online. Many people can work simultaneously on a document in Google drive.
@@ -89,7 +89,7 @@ Well, it is one of the most popular integrations in Slack. You just simply need
#### **Intercom**
-
+
[Intercom](https://www.intercom.com/) is a great tool to interact with the users of your software. You can send in-app messages and targeted emails to your users through your app during special occurrences.
@@ -102,7 +102,7 @@ Integrating Slack to Intercom will allow you to receive following notifications
#### **WordPress**
-
+
[WordPress](https://wordpress.com/), which is another highly customizable tool which creates and manages your blog or website.
@@ -110,13 +110,13 @@ Integrating Slack to Intercom will allow you to receive following notifications
#### **Stripe**
-
+
[Stripe](https://stripe.com/) is an app for accepting payments online. You will be able to get updates about transfers, subscriptions, invoice payments, charges etc. through integrating [Stripe with Slack](https://slack.com/apps/new/A0F81FNVC-stripe).
#### **Jira**
-
+
[Jira](https://www.atlassian.com/software/jira) is a powerful project management tool which can help to keep track of issues related to a project, assign tasks, and check team’s activity.
@@ -124,7 +124,7 @@ You can receive notifications about your new and existing [JIRA issues on Slack]
#### **Zendesk**
-
+
[Zendesk](https://www.zendesk.com/), which is another tool to support tickets against issues can be [integrated to Slack](https://slack.com/apps/new/A0F81FPJS-zendesk) to get notifications about your tickets. The following events are notified on Slack:- 1\. Open 2\. Pending 3\. Solved 4. Closed
diff --git a/content/growth/slack-integrations-for-productivity/intercom.png b/content/growth/slack-integrations-for-productivity/intercom.png
deleted file mode 100644
index aaf224e19..000000000
Binary files a/content/growth/slack-integrations-for-productivity/intercom.png and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/intercom.webp b/content/growth/slack-integrations-for-productivity/intercom.webp
new file mode 100644
index 000000000..5c8702594
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/intercom.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/mailchimp.jpg b/content/growth/slack-integrations-for-productivity/mailchimp.jpg
deleted file mode 100644
index 408ce08bd..000000000
Binary files a/content/growth/slack-integrations-for-productivity/mailchimp.jpg and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/mailchimp.webp b/content/growth/slack-integrations-for-productivity/mailchimp.webp
new file mode 100644
index 000000000..8c980b071
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/mailchimp.webp differ
diff --git a/content/growth/slack-integrations-for-productivity/zendesk-300x300.jpg b/content/growth/slack-integrations-for-productivity/zendesk-300x300.jpg
deleted file mode 100644
index 6ce047f09..000000000
Binary files a/content/growth/slack-integrations-for-productivity/zendesk-300x300.jpg and /dev/null differ
diff --git a/content/growth/slack-integrations-for-productivity/zendesk-300x300.webp b/content/growth/slack-integrations-for-productivity/zendesk-300x300.webp
new file mode 100644
index 000000000..77cdb2fa4
Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/zendesk-300x300.webp differ
diff --git a/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.png b/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.png
deleted file mode 100644
index f97184f2f..000000000
Binary files a/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.png and /dev/null differ
diff --git a/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.webp b/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.webp
new file mode 100644
index 000000000..88d19cbb8
Binary files /dev/null and b/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.webp differ
diff --git a/content/growth/smooth-onboarding-positive-user-impression/index.md b/content/growth/smooth-onboarding-positive-user-impression/index.md
index d81737576..f5f15d2e5 100644
--- a/content/growth/smooth-onboarding-positive-user-impression/index.md
+++ b/content/growth/smooth-onboarding-positive-user-impression/index.md
@@ -1,7 +1,7 @@
---
title: "How to Make a Strong Impression With Your Onboarding Process?"
date: "2022-02-02"
-coverImage: "onboarding.jpg"
+coverImage: "onboarding.webp"
tags: ["user onboarding","progressive profiling","cx"]
author: "Navanita Devi"
description: "The key to a seamless onboarding experience is to make the process as simple and safe as possible – from the first moment a new customer accesses your site until the moment they are authenticated and logged in. This article explains how."
@@ -67,7 +67,7 @@ How will this app aid them in fulfilling their needs? You can easily demonstrate
In many ways, onboarding can provide the personalization every user is searching for. Progressive onboarding ensures you don't overwhelm the user with too many functions they aren't prepared to work with. Instead, as they gradually glide through the app, they require new information, so their experience isn’t monotonous. The instructions correspond to the unique page the user is on, allowing the user to learn as they get deeper into the app. As a result, the user can only grab what they need out of the app.
-[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
+[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/)
## Conclusion
@@ -76,4 +76,4 @@ While including onboarding into your app strategy helps the overall UX, the onbo
The end goal remains to provision your users with a positive experience from the beginning of the app to the end of the game when they achieve their main goal. Onboarding is just one cog in the wheel that can help you get a more positive experience. While the goal remains to make certain the user is satisfied with the product, your business also benefits from [providing a positive experience](https://www.loginradius.com/customer-experience-solutions/).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=smooth-onboarding-positive-user-impression)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=smooth-onboarding-positive-user-impression)
diff --git a/content/growth/smooth-onboarding-positive-user-impression/onboarding.jpg b/content/growth/smooth-onboarding-positive-user-impression/onboarding.jpg
deleted file mode 100644
index 6ec170de5..000000000
Binary files a/content/growth/smooth-onboarding-positive-user-impression/onboarding.jpg and /dev/null differ
diff --git a/content/growth/smooth-onboarding-positive-user-impression/onboarding.webp b/content/growth/smooth-onboarding-positive-user-impression/onboarding.webp
new file mode 100644
index 000000000..f864fc3d0
Binary files /dev/null and b/content/growth/smooth-onboarding-positive-user-impression/onboarding.webp differ
diff --git a/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.png b/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.png
deleted file mode 100644
index c9ad88d9e..000000000
Binary files a/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.png and /dev/null differ
diff --git a/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.webp b/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.webp
new file mode 100644
index 000000000..2b537fe1a
Binary files /dev/null and b/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.webp differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.png b/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.png
deleted file mode 100644
index ef9040a01..000000000
Binary files a/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.png and /dev/null differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.webp b/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.webp
new file mode 100644
index 000000000..5c6b32599
Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.webp differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.jpg b/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.jpg
deleted file mode 100644
index 9ee8bf8d6..000000000
Binary files a/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.jpg and /dev/null differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.webp b/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.webp
new file mode 100644
index 000000000..177a76a7f
Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.webp differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.jpg b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.jpg
deleted file mode 100644
index 13ba22de9..000000000
Binary files a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.jpg and /dev/null differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.webp b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.webp
new file mode 100644
index 000000000..df6681469
Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.webp differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.png b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.png
deleted file mode 100644
index 9cab71078..000000000
Binary files a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.png and /dev/null differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.webp b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.webp
new file mode 100644
index 000000000..fed0bdd44
Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.webp differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.jpg b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.jpg
deleted file mode 100644
index 0f11557f3..000000000
Binary files a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.jpg and /dev/null differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.webp b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.webp
new file mode 100644
index 000000000..8305a2679
Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.webp differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.jpg b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.jpg
deleted file mode 100644
index ec7a9ea28..000000000
Binary files a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.jpg and /dev/null differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.webp b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.webp
new file mode 100644
index 000000000..1063b395c
Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.webp differ
diff --git a/content/growth/spice-up-your-resume-create-visual-one/index.md b/content/growth/spice-up-your-resume-create-visual-one/index.md
index 8d4053299..8481d9946 100644
--- a/content/growth/spice-up-your-resume-create-visual-one/index.md
+++ b/content/growth/spice-up-your-resume-create-visual-one/index.md
@@ -1,7 +1,7 @@
---
title: "Spice Up Your Resume: Create a Visual One"
date: "2017-05-15"
-coverImage: "Spice-up-your-resume-Create-a-virtual-one.jpg"
+coverImage: "Spice-up-your-resume-Create-a-virtual-one.webp"
category: ["General"]
featured: false
author: "Navanita Devi"
@@ -25,17 +25,17 @@ Visual resumes are welcomed as the next thing in the recruitment world. Still ma
### **Some Examples**
-
+
**[Source](https://www.behance.net/gallery/26611697/Curriculum-Vitae)**
-
+
-**[Source](https://biginterview.com/wp-content/uploads/2013-6-18-infographic-resume-3.jpg?ver=1553881376)**
+**[Source](https://biginterview.com/wp-content/uploads/2013-6-18-infographic-resume-3.webp?ver=1553881376)**
-
+
-**[Source](https://staticblog.virtualvocations.com/2012/12/4_PERSONALITY.jpg?ver=1553881376)**
+**[Source](https://staticblog.virtualvocations.com/2012/12/4_PERSONALITY.webp?ver=1553881376)**
### **How to Make a Visual Resume (using Adobe Photoshop)**
@@ -50,7 +50,7 @@ _Note:- The steps are written according to Adobe Photoshop CS6._
You can also use Canva to create a stunning resume. There are many templates available in Canva which are well suited for visual resumes. Here’s an example which I carved out from my favorite tool Canva:-
-
+
Well, you can also use these FREE tools to have a seamless resume creation experience:-
diff --git a/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.png b/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.png
deleted file mode 100644
index 99b5a25ea..000000000
Binary files a/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.png and /dev/null differ
diff --git a/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.webp b/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.webp
new file mode 100644
index 000000000..a8ae17db9
Binary files /dev/null and b/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.webp differ
diff --git a/content/growth/sso-saas-business-sales/business-sales.jpg b/content/growth/sso-saas-business-sales/business-sales.jpg
deleted file mode 100644
index 0e5647637..000000000
Binary files a/content/growth/sso-saas-business-sales/business-sales.jpg and /dev/null differ
diff --git a/content/growth/sso-saas-business-sales/business-sales.webp b/content/growth/sso-saas-business-sales/business-sales.webp
new file mode 100644
index 000000000..366ef6657
Binary files /dev/null and b/content/growth/sso-saas-business-sales/business-sales.webp differ
diff --git a/content/growth/sso-saas-business-sales/index.md b/content/growth/sso-saas-business-sales/index.md
index ade74ec48..b067e7755 100644
--- a/content/growth/sso-saas-business-sales/index.md
+++ b/content/growth/sso-saas-business-sales/index.md
@@ -1,7 +1,7 @@
---
title: "SSO for SaaS Business: The Key to Boost Sales For Enterprises"
date: "2024-03-07"
-coverImage: "business-sales.jpg"
+coverImage: "business-sales.webp"
tags: ["saas","sso","cx"]
author: "Vishal Sharma"
description: "Explore the impact of Single Sign-On (SSO) on SaaS businesses, from enhancing user experiences to improving sales performance. Discover the benefits of SSO and how LoginRadius stands out as a reliable solution for enterprises seeking a competitive edge."
@@ -51,7 +51,7 @@ The benefits of leveraging a reliable SSO solution for SaaS businesses are manif
* **Cost Efficiency:** SSO reduces the burden on IT support teams, leading to lower operational costs. Additionally, the time saved by users in managing passwords translates into tangible cost savings for enterprises.
-[](https://www.loginradius.com/resource/how-ciam-increases-roi-for-your-enterprise/)
+[](https://www.loginradius.com/resource/how-ciam-increases-roi-for-your-enterprise/)
## How LoginRadius SSO Offers Competitive Advantage to SaaS Enterprises?
@@ -75,4 +75,4 @@ For SaaS businesses looking to gain a competitive advantage and boost sales, inv
In the evolving SaaS landscape, where user experience is the ultimate differentiator, SSO for SaaS businesses is not just a convenience—it's a necessity for success.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-saas-business-sales)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-saas-business-sales)
diff --git a/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.png b/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.png
deleted file mode 100644
index 6df429ab7..000000000
Binary files a/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.png and /dev/null differ
diff --git a/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.webp b/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.webp
new file mode 100644
index 000000000..9684babf6
Binary files /dev/null and b/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.webp differ
diff --git a/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.png b/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.png
deleted file mode 100644
index d7768e095..000000000
Binary files a/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.png and /dev/null differ
diff --git a/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.webp b/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.webp
new file mode 100644
index 000000000..c3af9b9a1
Binary files /dev/null and b/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.webp differ
diff --git a/content/growth/stakeholder-engagement-modernize-ciam/index.md b/content/growth/stakeholder-engagement-modernize-ciam/index.md
index 1c183aeb8..07101e895 100644
--- a/content/growth/stakeholder-engagement-modernize-ciam/index.md
+++ b/content/growth/stakeholder-engagement-modernize-ciam/index.md
@@ -1,7 +1,7 @@
---
title: "How to Bring Stakeholders Together to Modernize CIAM Across Your Organization"
date: "2022-01-18"
-coverImage: "saas-modernize.jpg"
+coverImage: "saas-modernize.webp"
tags: ["ciam solution","compliance","convenience","cx"]
author: "Rakesh Soni"
description: "If you’re ready to modernize your CIAM but aren’t quite sure where to start, then this blog should get you on the right path with your stakeholders."
@@ -49,7 +49,7 @@ The requirements and priorities of each department are different. Your Chief Mar
Each stakeholder has a set of expectations. Stakeholders should be involved from the initial phase of the CIAM modernization process. Doing so will help boost participation and goal alignment, making the overall objectives easier to achieve.
-[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper)
+[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper)
### 4. Manage expectations
Technology can do anything, but if we expect the impossible, we may end up empty-handed. If you listen carefully to each team’s needs and concerns, however, you’re more likely to build a system that works for everyone. It’s important to take many things into account when designing the CIAM solution—for instance, usability, customer experience, convenience, security, and maintainability.
@@ -86,4 +86,4 @@ Cloud-based [CIAM gives better ROI](https://www.loginradius.com/blog/fuel/ciam-o
Even though it may sound like a daunting task, modernizing your CIAM is not impossible if you are willing to put in the work. The key lies in communicating how and why modernization will be beneficial for all stakeholders, and eventually getting everyone onboard with the plan. The tips mentioned in this blog will help you make this process easier since stakeholder engagement will simplify things for you.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=stakeholder-engagement-modernize-ciam)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=stakeholder-engagement-modernize-ciam)
diff --git a/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.jpg b/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.jpg
deleted file mode 100644
index d6a3d2a48..000000000
Binary files a/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.jpg and /dev/null differ
diff --git a/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.webp b/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.webp
new file mode 100644
index 000000000..441750abb
Binary files /dev/null and b/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.webp differ
diff --git a/content/growth/striking-balance-with-identity-orchestration/WP-resilience.png b/content/growth/striking-balance-with-identity-orchestration/WP-resilience.png
deleted file mode 100644
index cbe459800..000000000
Binary files a/content/growth/striking-balance-with-identity-orchestration/WP-resilience.png and /dev/null differ
diff --git a/content/growth/striking-balance-with-identity-orchestration/WP-resilience.webp b/content/growth/striking-balance-with-identity-orchestration/WP-resilience.webp
new file mode 100644
index 000000000..efb695fb3
Binary files /dev/null and b/content/growth/striking-balance-with-identity-orchestration/WP-resilience.webp differ
diff --git a/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.jpg b/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.jpg
deleted file mode 100644
index 02c9126eb..000000000
Binary files a/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.jpg and /dev/null differ
diff --git a/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.webp b/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.webp
new file mode 100644
index 000000000..d2a89dfab
Binary files /dev/null and b/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.webp differ
diff --git a/content/growth/striking-balance-with-identity-orchestration/index.md b/content/growth/striking-balance-with-identity-orchestration/index.md
index 63884f6bf..9d4ca155f 100644
--- a/content/growth/striking-balance-with-identity-orchestration/index.md
+++ b/content/growth/striking-balance-with-identity-orchestration/index.md
@@ -1,7 +1,7 @@
---
title: "Striking the Perfect Balance: Leveraging Identity Orchestration for Cost, Security, & Enhanced UX"
date: "2023-06-20"
-coverImage: "identity-orchestration.jpg"
+coverImage: "identity-orchestration.webp"
tags: ["identity orchestration","compliance","cx"]
author: "Rakesh Soni"
description: "Discover the power of identity orchestration in achieving a balanced approach to cost, security, and user experience. Explore the advantages of centralized user management and streamlined authentication for a seamless digital environment that optimizes resources and enhances security measures."
@@ -58,7 +58,7 @@ As organizations expand their digital footprint or undergo mergers and acquisiti
This scalability enables organizations to efficiently manage user identities and access controls across a dynamic and evolving technology landscape.
-[](https://www.loginradius.com/resource/enterprise-scalability-and-performance)
+[](https://www.loginradius.com/resource/enterprise-scalability-and-performance)
### 7. Seamless integration with existing infrastructure
@@ -78,4 +78,4 @@ Achieving the perfect balance between cost, security, and user experience is a c
By optimizing costs, strengthening security measures, and delivering an enhanced user experience, identity orchestration becomes a crucial component of a modern and successful digital strategy. Embracing this approach enables organizations to unlock the full potential of their digital ecosystems while maintaining a competitive edge in today's dynamic business landscape.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=striking-balance-with-identity-orchestration)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=striking-balance-with-identity-orchestration)
\ No newline at end of file
diff --git a/content/growth/successful-saas-onboarding-process/DS-User-management.png b/content/growth/successful-saas-onboarding-process/DS-User-management.png
deleted file mode 100644
index fc6f98c05..000000000
Binary files a/content/growth/successful-saas-onboarding-process/DS-User-management.png and /dev/null differ
diff --git a/content/growth/successful-saas-onboarding-process/DS-User-management.webp b/content/growth/successful-saas-onboarding-process/DS-User-management.webp
new file mode 100644
index 000000000..c60f3551f
Binary files /dev/null and b/content/growth/successful-saas-onboarding-process/DS-User-management.webp differ
diff --git a/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.png b/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.png
deleted file mode 100644
index 4da86607c..000000000
Binary files a/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.png and /dev/null differ
diff --git a/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.webp b/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.webp
new file mode 100644
index 000000000..32fb1890f
Binary files /dev/null and b/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.webp differ
diff --git a/content/growth/successful-saas-onboarding-process/index.md b/content/growth/successful-saas-onboarding-process/index.md
index 8911e5231..3b24fd776 100644
--- a/content/growth/successful-saas-onboarding-process/index.md
+++ b/content/growth/successful-saas-onboarding-process/index.md
@@ -1,7 +1,7 @@
---
title: "The ABCs of a Successful Saas Onboarding Process"
date: "2021-08-27"
-coverImage: "user-onboarding.jpg"
+coverImage: "user-onboarding.webp"
tags: ["user onboarding","saas","login authentication"]
author: "Navanita Devi"
description: "The onboarding process is the lifeline for your customer, and it's one of the most valuable tools that you as a company can control. Here are a few tips for a stellar SaaS company onboarding process that will greatly improve your customer retention and overall satisfaction."
@@ -25,7 +25,7 @@ Here are a few phases you should know about when it comes to [consumer onboardin
The initial onboarding phase does not occur on your website or blog but typically occurs on social media, in a forum or remark, or on another person's blog. Your onboarding experience begins with a customer's first interaction with your brand.
-
+
### User Onboarding: Phase 2
@@ -55,7 +55,7 @@ The onboarding process should be done properly, it can take your business to new
Now, below we will discuss some elements that you need to keep in mind while onboarding consumers for your SaaS business.
-[](https://www.loginradius.com/resource/loginradius-ciam-user-management/)
+[](https://www.loginradius.com/resource/loginradius-ciam-user-management/)
## 4 Important SaaS Onboarding Elements
@@ -95,4 +95,4 @@ When it comes to [SaaS onboarding](https://www.loginradius.com/blog/fuel/why-is-
Start working on fixing your weak points once you've recognized them. Begin by making one adjustment at a time and seeing how it affects your cohort analysis. Your onboarding strategy won't be built in a day, and it won't be modified in a day, either.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=successful-saas-onboarding-process)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=successful-saas-onboarding-process)
\ No newline at end of file
diff --git a/content/growth/successful-saas-onboarding-process/user-onboarding.jpg b/content/growth/successful-saas-onboarding-process/user-onboarding.jpg
deleted file mode 100644
index a8b6dfa71..000000000
Binary files a/content/growth/successful-saas-onboarding-process/user-onboarding.jpg and /dev/null differ
diff --git a/content/growth/successful-saas-onboarding-process/user-onboarding.webp b/content/growth/successful-saas-onboarding-process/user-onboarding.webp
new file mode 100644
index 000000000..e6b004cdc
Binary files /dev/null and b/content/growth/successful-saas-onboarding-process/user-onboarding.webp differ
diff --git a/content/growth/successful-saas-onboarding-process/user-onboarding2.jpg b/content/growth/successful-saas-onboarding-process/user-onboarding2.jpg
deleted file mode 100644
index 703824043..000000000
Binary files a/content/growth/successful-saas-onboarding-process/user-onboarding2.jpg and /dev/null differ
diff --git a/content/growth/successful-saas-onboarding-process/user-onboarding2.webp b/content/growth/successful-saas-onboarding-process/user-onboarding2.webp
new file mode 100644
index 000000000..ad97df2d4
Binary files /dev/null and b/content/growth/successful-saas-onboarding-process/user-onboarding2.webp differ
diff --git a/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.png b/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.png
deleted file mode 100644
index fb5784fcf..000000000
Binary files a/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.png and /dev/null differ
diff --git a/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.webp b/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.webp
new file mode 100644
index 000000000..987fca8c1
Binary files /dev/null and b/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.webp differ
diff --git a/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/index.md b/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/index.md
index 613d774d2..d2daf98c4 100644
--- a/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/index.md
+++ b/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/index.md
@@ -1,7 +1,7 @@
---
title: "Test Cases For Your E-commerce Payment Gateway Page"
date: "2017-07-21"
-coverImage: "Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.png"
+coverImage: "Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.webp"
tags: ["payment gateway", "technology", "ecommerce"]
author: "Rakesh Soni"
description: "Trying to make test cases to build a flawless payment gateway page for your ecommerce website? Here are some factors you need to take seriously before creating test cases for payment gateway page."
diff --git a/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.png b/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.png
deleted file mode 100644
index 98e481315..000000000
Binary files a/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.png and /dev/null differ
diff --git a/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.webp b/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.webp
new file mode 100644
index 000000000..5e3eaf627
Binary files /dev/null and b/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.webp differ
diff --git a/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.jpg b/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.jpg
deleted file mode 100644
index aaf510e3f..000000000
Binary files a/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.jpg and /dev/null differ
diff --git a/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.webp b/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.webp
new file mode 100644
index 000000000..36d17120a
Binary files /dev/null and b/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.webp differ
diff --git a/content/growth/the-relative-importance-of-customer-identity/index.md b/content/growth/the-relative-importance-of-customer-identity/index.md
index b19084e7d..da59d9c1b 100644
--- a/content/growth/the-relative-importance-of-customer-identity/index.md
+++ b/content/growth/the-relative-importance-of-customer-identity/index.md
@@ -1,7 +1,7 @@
---
title: "Exploring the Relative Importance of Identity in Today’s Digital Landscape"
date: "2023-05-05"
-coverImage: "importance-of-customer-identity.jpg"
+coverImage: "importance-of-customer-identity.webp"
tags: ["digital identity","authentication","identity management","cx"]
author: "Vishal Sharma"
description: "With the rapid growth of online platforms and digital communication, our identities are more important than ever. Let’s examine how our identities have evolved in the digital age and explore their relative role in shaping our online experiences."
@@ -42,7 +42,7 @@ Social media platforms have become a primary way to express our identities and c
Understanding the impact of identity on social media can help us navigate these platforms in a way that aligns with our values and goals. This includes being mindful of the information we share, the people we connect with, and the communities we participate in.
-[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
## Identity and the Development of a Digital Society
@@ -64,4 +64,4 @@ Understanding the significance of identity in the digital world is crucial for n
By taking steps to protect and leverage our identities, we can make the most of the benefits technology offers. As we continue integrating technology into our lives, the importance of identity will only continue to grow.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=the-relative-importance-of-customer-identity)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=the-relative-importance-of-customer-identity)
\ No newline at end of file
diff --git a/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.jpg b/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.jpg
deleted file mode 100644
index 3abbe6d42..000000000
Binary files a/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.jpg and /dev/null differ
diff --git a/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.webp b/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.webp
new file mode 100644
index 000000000..8d5940153
Binary files /dev/null and b/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.webp differ
diff --git a/content/growth/tips-and-tricks-b2b-consultant/index.md b/content/growth/tips-and-tricks-b2b-consultant/index.md
index a30d4d4db..d299ea10e 100644
--- a/content/growth/tips-and-tricks-b2b-consultant/index.md
+++ b/content/growth/tips-and-tricks-b2b-consultant/index.md
@@ -1,7 +1,7 @@
---
title: "7 Tips and Tricks for B2B Consultant: How to Grow Your Client's Business"
date: "2021-02-26"
-coverImage: "b2b-consultant.jpg"
+coverImage: "b2b-consultant.webp"
category: ["all"]
featured: false
author: "Lidia Hovhannisyan"
@@ -104,7 +104,7 @@ If you are speaking with someone resistant to pain, focus on cutting costs, mini
While [FedEx](https://www.fedex.com/en-us/home.html) is currently available to individual customers, it has been approved and rated as one of the best B2B companies in the world. The company is placed as [the 2nd most trusted B2B company](https://smallbiztrends.com/2018/08/most-trusted-b2b-brands-2018.html) by SageFrog and appears in Sacunas’ Top 100 B2B brands list. This company hasn’t made to these lists by mistake, this is because it is mostly committed towards customer service, experience, and open communication. Unlike most of its competitors, FedEx has taken into consideration its customers’ pain points and presented itself as a customer-centric company.
-
+
## Be Your Client's Personal Trainer
@@ -145,4 +145,4 @@ As a B2B consultant, you are selling more than just a product. You are selling s
Don't forget to qualify each prospect to see if they fit with your company. Doing so allows you to optimize your limited resources. When you do your due diligence, it would be so much easier to convert your leads and prospects to actual clients.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-and-tricks-b2b-consultant)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-and-tricks-b2b-consultant)
diff --git a/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.png b/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.png
deleted file mode 100644
index c2022eecb..000000000
Binary files a/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.png and /dev/null differ
diff --git a/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.webp b/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.webp
new file mode 100644
index 000000000..7e3b032b0
Binary files /dev/null and b/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.webp differ
diff --git a/content/growth/tips-managing-remote-team/index.md b/content/growth/tips-managing-remote-team/index.md
index b8671ae55..8a574f497 100644
--- a/content/growth/tips-managing-remote-team/index.md
+++ b/content/growth/tips-managing-remote-team/index.md
@@ -1,7 +1,7 @@
---
title: "13 Tips for Leading and Managing Remote Teams"
date: "2021-02-12"
-coverImage: "tips-managing-remote-team.jpg"
+coverImage: "tips-managing-remote-team.webp"
category: ["all"]
featured: false
author: "Vikas Soni"
@@ -135,4 +135,4 @@ Educating employees about the purpose of remote working can help them understand
Each of the tips mentioned above and advice requires patience, attention, flexibility, and consistency. Working out on these tips can lead to better results and help the management handle the remote teams more easily and comfortably.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-managing-remote-team)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-managing-remote-team)
diff --git a/content/growth/tips-managing-remote-team/tips-managing-remote-team.jpg b/content/growth/tips-managing-remote-team/tips-managing-remote-team.jpg
deleted file mode 100644
index 7301d8e51..000000000
Binary files a/content/growth/tips-managing-remote-team/tips-managing-remote-team.jpg and /dev/null differ
diff --git a/content/growth/tips-managing-remote-team/tips-managing-remote-team.webp b/content/growth/tips-managing-remote-team/tips-managing-remote-team.webp
new file mode 100644
index 000000000..79e1ea525
Binary files /dev/null and b/content/growth/tips-managing-remote-team/tips-managing-remote-team.webp differ
diff --git a/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.png b/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.png
deleted file mode 100644
index 6df429ab7..000000000
Binary files a/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.png and /dev/null differ
diff --git a/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.webp b/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.webp
new file mode 100644
index 000000000..9684babf6
Binary files /dev/null and b/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.webp differ
diff --git a/content/growth/tips-on-how-cisos-convince-board-members/board-members.jpg b/content/growth/tips-on-how-cisos-convince-board-members/board-members.jpg
deleted file mode 100644
index 7deec3ad1..000000000
Binary files a/content/growth/tips-on-how-cisos-convince-board-members/board-members.jpg and /dev/null differ
diff --git a/content/growth/tips-on-how-cisos-convince-board-members/board-members.webp b/content/growth/tips-on-how-cisos-convince-board-members/board-members.webp
new file mode 100644
index 000000000..f25eee832
Binary files /dev/null and b/content/growth/tips-on-how-cisos-convince-board-members/board-members.webp differ
diff --git a/content/growth/tips-on-how-cisos-convince-board-members/index.md b/content/growth/tips-on-how-cisos-convince-board-members/index.md
index 03abe22b0..362e1bd1c 100644
--- a/content/growth/tips-on-how-cisos-convince-board-members/index.md
+++ b/content/growth/tips-on-how-cisos-convince-board-members/index.md
@@ -1,7 +1,7 @@
---
title: "7 Tips on How CISOs Should Present Identity Security to Board Members"
date: "2023-08-04"
-coverImage: "board-members.jpg"
+coverImage: "board-members.webp"
tags: ["customer identity security","compliance","cx"]
author: "Rakesh Soni"
description: "While most CISOs are now concerned about the risks associated with customer identity security and identity thefts, they’re struggling to create a strategy to convince the board members to prepare beforehand. And to help CISOs present a compelling identity security strategy to board members, we’ve compiled a list of some helpful tips."
@@ -46,7 +46,7 @@ Hence, you must avoid using technical jargon and complex terms when presenting y
You could translate technical concepts and terms into business terms that resonate with your C-level executives’ expertise. And it would be great if you could focus on tangible risks, potential financial and reputational implications, and regulatory compliance, as this will facilitate more productive and meaningful conversation.
-[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper)
+[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper)
### 4. Provide Real-World Examples
@@ -84,4 +84,4 @@ While cybercriminals are hunting new ways to exploit consumer identities, CISOs
And with a reliable customer identity and access management (CIAM) solution in place, security heads can ensure their customers’ identities are safe, and their board members don’t need to worry about the consequences of identity thefts.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-on-how-cisos-convince-board-members)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-on-how-cisos-convince-board-members)
\ No newline at end of file
diff --git a/content/growth/top-3-ciam-indicators/ciam-loginradius.jpg b/content/growth/top-3-ciam-indicators/ciam-loginradius.jpg
deleted file mode 100644
index c9d858090..000000000
Binary files a/content/growth/top-3-ciam-indicators/ciam-loginradius.jpg and /dev/null differ
diff --git a/content/growth/top-3-ciam-indicators/ciam-loginradius.webp b/content/growth/top-3-ciam-indicators/ciam-loginradius.webp
new file mode 100644
index 000000000..4e0c409dd
Binary files /dev/null and b/content/growth/top-3-ciam-indicators/ciam-loginradius.webp differ
diff --git a/content/growth/top-3-ciam-indicators/index.md b/content/growth/top-3-ciam-indicators/index.md
index fa3da9add..0d7f1aa09 100644
--- a/content/growth/top-3-ciam-indicators/index.md
+++ b/content/growth/top-3-ciam-indicators/index.md
@@ -1,7 +1,7 @@
---
title: "Top 3 CIAM Indicators That You’ll Get the Consumer Satisfaction You Deserve"
date: "2021-07-06"
-coverImage: "ciam-loginradius.jpg"
+coverImage: "ciam-loginradius.webp"
category: ["loginradius"]
featured: false
author: "Vishal Sharma"
@@ -29,7 +29,7 @@ CIAM offers the luxury of a centralized consumer database that links all other a
Moreover, a cutting-edge CIAM solution like LoginRadius offers a seamless login experience through Social Login, Single-Sign-On (SSO), and [Passwordless Login for customers](https://www.loginradius.com/passwordless-login/).
-[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
## CIAM Indicators that Describe Your Consumers Love Your Platform
@@ -102,4 +102,4 @@ The aspects above depict the role and responsibilities of a robust CIAM that can
If you wish to experience the ease of consumer onboarding that increases consumer satisfaction and boosts your business revenues, it’s time to [experience the LoginRadius CIAM](https://www.loginradius.com/contact-sales/).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-3-ciam-indicators)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-3-ciam-indicators)
diff --git a/content/growth/top-3-ciam-indicators/social-login-loginradius.png b/content/growth/top-3-ciam-indicators/social-login-loginradius.png
deleted file mode 100644
index 98e481315..000000000
Binary files a/content/growth/top-3-ciam-indicators/social-login-loginradius.png and /dev/null differ
diff --git a/content/growth/top-3-ciam-indicators/social-login-loginradius.webp b/content/growth/top-3-ciam-indicators/social-login-loginradius.webp
new file mode 100644
index 000000000..5e3eaf627
Binary files /dev/null and b/content/growth/top-3-ciam-indicators/social-login-loginradius.webp differ
diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.png b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.png
deleted file mode 100644
index 6bddf0db4..000000000
Binary files a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.png and /dev/null differ
diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.webp b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.webp
new file mode 100644
index 000000000..2842c3bcc
Binary files /dev/null and b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.webp differ
diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.png b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.png
deleted file mode 100644
index 8bad2f974..000000000
Binary files a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.png and /dev/null differ
diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.webp b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.webp
new file mode 100644
index 000000000..903afa91e
Binary files /dev/null and b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.webp differ
diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/index.md b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/index.md
index b673bf8fb..303fbd170 100644
--- a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/index.md
+++ b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/index.md
@@ -1,7 +1,7 @@
---
title: "8 Common Challenges With Your SaaS Business that CIAM Can Solve"
date: "2021-09-10"
-coverImage: "saas-business-app.jpg"
+coverImage: "saas-business-app.webp"
tags: ["identity management","customer identity","ciam solution"]
author: "Rashmi Mathur"
description: "To be successful, your SaaS needs to use the right application performance management software. CIAM is the first step you need to take to avoid common challenges like lack of compliance, and incompetent onboarding."
@@ -13,7 +13,7 @@ Digital communication between clients and a company is now a regular practice ac
The data gathered in databases can be vulnerable to cyber attacks that result in stolen customer and business identities. Hence, businesses look to increase their cybersecurity with the help of SaaS-based CIAM business solutions.
-[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
+[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
## Top Challenges With SaaS Apps and How CIAM Overcomes Them
@@ -60,4 +60,4 @@ One of the surpassing advantages of cloud applications is that admittance is obt
## Conclusion
To summarize, we can say that a cloud-based CIAM service should present accurate visibility of user access. Also, providing your customers with the required protection against identity theft is crucial in preserving your company prominence. This is why it is vital to overcome these challenges to better leverage the benefits of CIAM to protect your business and clients.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-8-ciam-challenges-with-your-saas-business-app)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-8-ciam-challenges-with-your-saas-business-app)
\ No newline at end of file
diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.jpg b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.jpg
deleted file mode 100644
index b71009e0f..000000000
Binary files a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.jpg and /dev/null differ
diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.webp b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.webp
new file mode 100644
index 000000000..f8b508c06
Binary files /dev/null and b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.webp differ
diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.jpg b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.jpg
deleted file mode 100644
index 30fa6b6fb..000000000
Binary files a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.jpg and /dev/null differ
diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.webp b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.webp
new file mode 100644
index 000000000..1a5ff6795
Binary files /dev/null and b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.webp differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.png
deleted file mode 100644
index 4021a46fc..000000000
Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.png and /dev/null differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.webp
new file mode 100644
index 000000000..0b5d48b48
Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.webp differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.png
deleted file mode 100644
index 8b2d73783..000000000
Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.png and /dev/null differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.webp
new file mode 100644
index 000000000..4ea14fb99
Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.webp differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.jpg b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.jpg
deleted file mode 100644
index 86b32af12..000000000
Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.jpg and /dev/null differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.webp
new file mode 100644
index 000000000..21275632c
Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.webp differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.png
deleted file mode 100644
index e41b6b375..000000000
Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.png and /dev/null differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.webp
new file mode 100644
index 000000000..e3f53067e
Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.webp differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.png
deleted file mode 100644
index dddc5590e..000000000
Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.png and /dev/null differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.webp
new file mode 100644
index 000000000..3b80a20d4
Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.webp differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.png
deleted file mode 100644
index 08f335433..000000000
Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.png and /dev/null differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.webp
new file mode 100644
index 000000000..4b64b438d
Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.webp differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.png
deleted file mode 100644
index 442778014..000000000
Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.png and /dev/null differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.webp
new file mode 100644
index 000000000..e34e0a3e7
Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.webp differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.png
deleted file mode 100644
index e09f1f376..000000000
Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.png and /dev/null differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.webp
new file mode 100644
index 000000000..69a0baa5d
Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.webp differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.png
deleted file mode 100644
index 0e6596130..000000000
Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.png and /dev/null differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.webp
new file mode 100644
index 000000000..a49ee1cb5
Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.webp differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.png
deleted file mode 100644
index 43fb50be5..000000000
Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.png and /dev/null differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.webp
new file mode 100644
index 000000000..9d4d6f453
Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.webp differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/index.md b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/index.md
index 0cb872c78..1eb757ed2 100644
--- a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/index.md
+++ b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/index.md
@@ -1,7 +1,7 @@
---
title: "The Ultimate Guide To Create Professional Email Signatures With Examples"
date: "2017-01-27"
-coverImage: "The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.png"
+coverImage: "The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.webp"
category: ["general", "loginradius"]
featured: false
author: "Rakesh Soni"
@@ -26,7 +26,7 @@ There are many people out there who in the process of creating a professional em
Now at this stage, many of you might be thinking why can’t we just drop the use of email signature**.** But then my friend, you will lose an excellent opportunity as well. What most of us still don’t know is that a right email signature can make a huge difference to your emails. So guys, please wear your marketing hats and dig into the art of creating a perfect signature.
-
+
The email signature rides along with all the emails you send, whether personal or professional but contrast to the importance of right email signature, here are some facts that will blow up your mind
@@ -43,7 +43,7 @@ This data is enough to prove the unawareness lying around signature and that’s
While there are many who don’t have any email signature at all, there are some others as well who treat their email signature like the mini autobiographies, jamming all possible links, quotes, and tons of information. But what they don’t realize is that by adding excessive information, the signature loses its original charm and will seem bulky for readers to even look at it let alone clicking on the same.
-In general, the basic information needed in email signature is as below :Therefore experts recommend to use only the information that best indicates your professional brand, generally the email signature of four lines is standard format. Once you are done with the basic format, the next step is to personalize it.
+In general, the basic information needed in email signature is as below :Therefore experts recommend to use only the information that best indicates your professional brand, generally the email signature of four lines is standard format. Once you are done with the basic format, the next step is to personalize it.
PS.. To condense email signature in fewer lines, make use of pipeline (|) or colons (::) to separate links.
@@ -60,7 +60,7 @@ You must save this place for something more valuable like your social icons, CTA
Ever seen an overstuffed email signature? Here is what it looks like :
-
+
Imagine how difficult and irritating it will be for the reader especially if he or she uses a mobile device.
@@ -76,13 +76,13 @@ But again, nobody is implying you to add links of all of your social media profi
Check out this email signature example of our head marketing analyst, Prince Kapoor who is active on multiple profiles, so it makes sense that he has made social icons a part of his email signature as the points of contact.
-
+
#### **5\. Add Image :**
It is a widely known fact that people remember visuals more than the plain text. But with that, I don’t mean you can put any kind of image in your email signature. There is always a certain kind of image that can make a difference to your email signature. You are more likely to remember a signature like this, won’t you?
-
+
Reason being as per research says, most memorable photos are those that contain people, also color images are often more memorable than the black and white ones. Here are some tips you need to follow :
@@ -97,7 +97,7 @@ One of the smartest way of leveraging the power of email signature is by adding
For more clear idea, check out this email signature that encourages the reader to visit his blog.
-
+
#### **7\. Make sure the links are trackable :**
@@ -118,7 +118,7 @@ Most of the brands these days are opting for the modern email signature approach
- Large text with flat design (3-D looks are strict no)
- Use small splash of the bold color.
-
+
#### **10\. Test your email signature with more than one email clients to make sure it works fine :**
@@ -148,19 +148,19 @@ Now if you don’t want to make email signature on your own, there are various t
It is an awesome free email signature creator that integrates easily with your email client and benefits you with some beautiful and customized email signatures. Using WiseStamp, it is quite simple to add the picture or your blog RSS feed and much more.
-
+
**2. [htmlSig](https://htmlsig.com/)****:**
If a neat email signature with required information without unnecessary clutter is what defines you, htmlsig is the place you need to land. A free and simple way to create email signature for your email clients that can make a long-lasting impression. It also contains the paid option, if you want more creativity.
-
+
**3. [Newoldstamp](https://newoldstamp.com/)** **:**
World’s simplest email signatures creation tool- as they define it. If creativity and uniqueness are your traits, newoldstamp is the perfect place for you. The tool provides you the chance to choose among the 11 professional email signature templates that come in several design, color and formats.
-
+
Other tools that you can opt for :
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.png
deleted file mode 100644
index d408dce8e..000000000
Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.png and /dev/null differ
diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.webp
new file mode 100644
index 000000000..c6c97b41c
Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.webp differ
diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.png b/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.png and /dev/null differ
diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.webp b/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.webp differ
diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.jpg b/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.jpg
deleted file mode 100644
index e7af6ef4e..000000000
Binary files a/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.jpg and /dev/null differ
diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.webp b/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.webp
new file mode 100644
index 000000000..8fa1d62f2
Binary files /dev/null and b/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.webp differ
diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/index.md b/content/growth/unified-identity-ensures-great-customer-interactions/index.md
index dbd843dec..b92687660 100644
--- a/content/growth/unified-identity-ensures-great-customer-interactions/index.md
+++ b/content/growth/unified-identity-ensures-great-customer-interactions/index.md
@@ -1,7 +1,7 @@
---
title: "How Can Enterprises Deliver Better Customer Experiences with Unified Identity?"
date: "2022-05-18"
-coverImage: "customer-interactions.jpg"
+coverImage: "customer-interactions.webp"
tags: ["customer experience","sso","identity management","mfa"]
author: "Yash Rathi"
description: "Unified identity can do wonders for a brand if a business leverages its true potential. Let’s uncover some aspects of unified identity and how brands leverage the same to engage users and foster business growth."
@@ -76,7 +76,7 @@ Risk-based authentication is a non-static authentication system that considers t
It is a method of applying various levels of stringency to authentication processes based on the likelihood that access to a given system could be compromised. As the level of risk increases, the authentication process becomes more complicated and restrictive.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
Hence, managing security doesn't necessarily mean compromising user experience with MFA and RBA. This further boosts engagement and trust in a brand.
@@ -101,4 +101,4 @@ Enterprises that have incorporated a reliable consumer identity and access manag
Hence, it’s the right time for enterprises to understand the importance of rethinking their identity management strategy around a cutting-edge CIAM solution.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=unified-identity-ensures-great-customer-interactions)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=unified-identity-ensures-great-customer-interactions)
\ No newline at end of file
diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.png b/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.png and /dev/null differ
diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.webp b/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.webp differ
diff --git a/content/growth/user-access-management-business-security/GD-to-RBA.png b/content/growth/user-access-management-business-security/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/growth/user-access-management-business-security/GD-to-RBA.png and /dev/null differ
diff --git a/content/growth/user-access-management-business-security/GD-to-RBA.webp b/content/growth/user-access-management-business-security/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/growth/user-access-management-business-security/GD-to-RBA.webp differ
diff --git a/content/growth/user-access-management-business-security/index.md b/content/growth/user-access-management-business-security/index.md
index f03776b33..dee02bf53 100644
--- a/content/growth/user-access-management-business-security/index.md
+++ b/content/growth/user-access-management-business-security/index.md
@@ -1,7 +1,7 @@
---
title: "Strengthening Your Business Security: 7 Key User Access Management Best Practices"
date: "2024-05-14"
-coverImage: "user-access-mngmnt.jpg"
+coverImage: "user-access-mngmnt.webp"
tags: ["user access management","data security","cx"]
author: "Rakesh Soni"
description: "Strengthen your business security with proven user access management strategies. Discover how role-based access control, regular permission reviews, and strong password policies can safeguard your sensitive data and ensure compliance with regulations."
@@ -42,7 +42,7 @@ Additionally, consider implementing [multi-factor authentication](https://www.lo
With risk-based authentication, businesses can define adaptive authentication policies that tailor authentication requirements based on the assessed risk level.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
For low-risk access attempts, users may only need to provide basic credentials, while high-risk attempts may trigger additional authentication factors, such as biometric verification or one-time passwords.
@@ -70,4 +70,4 @@ Optimizing business security requires a proactive approach to user access manage
Prioritize security and invest in comprehensive user access management strategies to protect your business from evolving cyber threats.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-access-management-business-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-access-management-business-security)
diff --git a/content/growth/user-access-management-business-security/user-access-mngmnt.jpg b/content/growth/user-access-management-business-security/user-access-mngmnt.jpg
deleted file mode 100644
index 104bb1d4c..000000000
Binary files a/content/growth/user-access-management-business-security/user-access-mngmnt.jpg and /dev/null differ
diff --git a/content/growth/user-access-management-business-security/user-access-mngmnt.webp b/content/growth/user-access-management-business-security/user-access-mngmnt.webp
new file mode 100644
index 000000000..962842fb0
Binary files /dev/null and b/content/growth/user-access-management-business-security/user-access-mngmnt.webp differ
diff --git a/content/growth/user-onboarding-tools/amplitude.png b/content/growth/user-onboarding-tools/amplitude.png
deleted file mode 100644
index dd8524cdb..000000000
Binary files a/content/growth/user-onboarding-tools/amplitude.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/amplitude.webp b/content/growth/user-onboarding-tools/amplitude.webp
new file mode 100644
index 000000000..a4f48c388
Binary files /dev/null and b/content/growth/user-onboarding-tools/amplitude.webp differ
diff --git a/content/growth/user-onboarding-tools/appcues.png b/content/growth/user-onboarding-tools/appcues.png
deleted file mode 100644
index 1334d466f..000000000
Binary files a/content/growth/user-onboarding-tools/appcues.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/appcues.webp b/content/growth/user-onboarding-tools/appcues.webp
new file mode 100644
index 000000000..6604334de
Binary files /dev/null and b/content/growth/user-onboarding-tools/appcues.webp differ
diff --git a/content/growth/user-onboarding-tools/customer-io.png b/content/growth/user-onboarding-tools/customer-io.png
deleted file mode 100644
index 09d6086f0..000000000
Binary files a/content/growth/user-onboarding-tools/customer-io.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/customer-io.webp b/content/growth/user-onboarding-tools/customer-io.webp
new file mode 100644
index 000000000..f74cc3e78
Binary files /dev/null and b/content/growth/user-onboarding-tools/customer-io.webp differ
diff --git a/content/growth/user-onboarding-tools/diy-github.png b/content/growth/user-onboarding-tools/diy-github.png
deleted file mode 100644
index c57f9bf5d..000000000
Binary files a/content/growth/user-onboarding-tools/diy-github.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/diy-github.webp b/content/growth/user-onboarding-tools/diy-github.webp
new file mode 100644
index 000000000..4c2c008dc
Binary files /dev/null and b/content/growth/user-onboarding-tools/diy-github.webp differ
diff --git a/content/growth/user-onboarding-tools/drip.png b/content/growth/user-onboarding-tools/drip.png
deleted file mode 100644
index e035499ca..000000000
Binary files a/content/growth/user-onboarding-tools/drip.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/drip.webp b/content/growth/user-onboarding-tools/drip.webp
new file mode 100644
index 000000000..a33f95593
Binary files /dev/null and b/content/growth/user-onboarding-tools/drip.webp differ
diff --git a/content/growth/user-onboarding-tools/feedier.png b/content/growth/user-onboarding-tools/feedier.png
deleted file mode 100644
index 99d280830..000000000
Binary files a/content/growth/user-onboarding-tools/feedier.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/feedier.webp b/content/growth/user-onboarding-tools/feedier.webp
new file mode 100644
index 000000000..89f6d99a9
Binary files /dev/null and b/content/growth/user-onboarding-tools/feedier.webp differ
diff --git a/content/growth/user-onboarding-tools/freshdesk.png b/content/growth/user-onboarding-tools/freshdesk.png
deleted file mode 100644
index 32f7f9ae1..000000000
Binary files a/content/growth/user-onboarding-tools/freshdesk.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/freshdesk.webp b/content/growth/user-onboarding-tools/freshdesk.webp
new file mode 100644
index 000000000..f227c9598
Binary files /dev/null and b/content/growth/user-onboarding-tools/freshdesk.webp differ
diff --git a/content/growth/user-onboarding-tools/fullstory.png b/content/growth/user-onboarding-tools/fullstory.png
deleted file mode 100644
index 2771811e8..000000000
Binary files a/content/growth/user-onboarding-tools/fullstory.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/fullstory.webp b/content/growth/user-onboarding-tools/fullstory.webp
new file mode 100644
index 000000000..e07e36846
Binary files /dev/null and b/content/growth/user-onboarding-tools/fullstory.webp differ
diff --git a/content/growth/user-onboarding-tools/google-optimize.png b/content/growth/user-onboarding-tools/google-optimize.png
deleted file mode 100644
index 67eaccf4b..000000000
Binary files a/content/growth/user-onboarding-tools/google-optimize.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/google-optimize.webp b/content/growth/user-onboarding-tools/google-optimize.webp
new file mode 100644
index 000000000..3ff4b8424
Binary files /dev/null and b/content/growth/user-onboarding-tools/google-optimize.webp differ
diff --git a/content/growth/user-onboarding-tools/helpscout.png b/content/growth/user-onboarding-tools/helpscout.png
deleted file mode 100644
index ec0b0c7e2..000000000
Binary files a/content/growth/user-onboarding-tools/helpscout.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/helpscout.webp b/content/growth/user-onboarding-tools/helpscout.webp
new file mode 100644
index 000000000..c02415c84
Binary files /dev/null and b/content/growth/user-onboarding-tools/helpscout.webp differ
diff --git a/content/growth/user-onboarding-tools/helpshelf.png b/content/growth/user-onboarding-tools/helpshelf.png
deleted file mode 100644
index 5bcd55c43..000000000
Binary files a/content/growth/user-onboarding-tools/helpshelf.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/helpshelf.webp b/content/growth/user-onboarding-tools/helpshelf.webp
new file mode 100644
index 000000000..c1b3e541b
Binary files /dev/null and b/content/growth/user-onboarding-tools/helpshelf.webp differ
diff --git a/content/growth/user-onboarding-tools/hotjar.png b/content/growth/user-onboarding-tools/hotjar.png
deleted file mode 100644
index ad706e662..000000000
Binary files a/content/growth/user-onboarding-tools/hotjar.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/hotjar.webp b/content/growth/user-onboarding-tools/hotjar.webp
new file mode 100644
index 000000000..6c96a1e1c
Binary files /dev/null and b/content/growth/user-onboarding-tools/hotjar.webp differ
diff --git a/content/growth/user-onboarding-tools/index.md b/content/growth/user-onboarding-tools/index.md
index d51e7d09f..5e465c687 100644
--- a/content/growth/user-onboarding-tools/index.md
+++ b/content/growth/user-onboarding-tools/index.md
@@ -1,7 +1,7 @@
---
title: "Top 27 User Onboarding Tools: Highly Recommended for Businesses"
date: "2021-01-20"
-coverImage: "user-onboarding.jpg"
+coverImage: "user-onboarding.webp"
category: ["all"]
featured: false
author: "Navanita Devi"
@@ -84,7 +84,7 @@ Tool #27: Helpshelf
## 1. AppCues
-
+
Without writing a single line of code, create customized user onboarding flows, and increase adoption and retention rates with [appcues](https://www.appcues.com/). Within one dashboard, you can design, publish, and manage your onboarding experience, enabling your users to delve deeper into your platform. Patterns and templates are available, including easy tooltips, full-screen takeovers, slide outs, and in-app alerts.
@@ -93,7 +93,7 @@ Without writing a single line of code, create customized user onboarding flows,
## 2. DIY with JavaScript
-
+
Onboarding helps to familiarise new users with an interface. There are several different styles of this, and there is no perfect way of doing it. But you can pick up ideas for your work if you study [how onboarding sites](https://speckyboy.com/onboarding-ui-css-javascript/) and apps do.
@@ -110,7 +110,7 @@ Just include the CSS and JS files on your page to get started, and you can start
## 3. Seamless Sign-in Experience With Single Sign-On
-
+
[Single sign-on](https://www.loginradius.com/blog/identity/2019/05/what-is-single-sign-on/) (SSO) is an access control property of several related but independent software systems. To gain access to a linked device, a user logs in with a single ID and password with this house.
@@ -132,7 +132,7 @@ LoginRadius supports both programming languages, so it doesn't matter if you hav
## 4. Intercom
-
+
[Intercom](https://www.intercom.com/) tells you who your clients are and what your product is doing. You can also interact with them using in-app and email messages in real-time. Using Intercom implies making educated decisions by asking for input with event-triggered notes at the right time.
@@ -143,7 +143,7 @@ It is simple to embed and convert new users to become active customers, and you
## 5. MailJet
-
+
[Mailjet](https://www.mailjet.com/) is an easy-to-use and all-in-one email-sending network. It's excellent for research and cooperation with A/B.
@@ -154,7 +154,7 @@ It enables you to collaborate, target specific users, and create personalized em
## 6. Drip
-
+
[Drip](https://www.drip.com/) is an onboarding email creation tool. Without going to the promotion channel (if the user uses Gmail), it will send trigger-based emails directly in the inbox.
@@ -165,7 +165,7 @@ Drip helps you to go beyond simple emails and build multiple onboard processes f
## 7. Customer.io (Paid)
-
+
The [Customer.io](https://customer.io/) tool for submitting drip campaigns is a little more costly. It's nice to start onboarding, converting, and keeping your audience for your needs.
@@ -180,7 +180,7 @@ What separates Customer.io from Mailjet and Drip is its ability for every custom
-
+
One of the best-known and most common experimentation platforms for SaaS companies is [Optimizely](https://www.optimizely.com/).
@@ -192,7 +192,7 @@ It enables both product and marketing divisions to experiment with each other. Y
-
+
[Omniconvert](https://www.omniconvert.com/) is a platform for optimizing conversion rates that provides an A/B testing tool and tools for surveying, personalization, overlay, and segmentation. You can run desktop, mobile, and tablet A/B tests using their A/B testing tool. To validate your tests, you can convert winning versions of an A / B test into the control for a future trial and leverage Frequentist or Bayesian statistics.
@@ -202,7 +202,7 @@ It enables both product and marketing divisions to experiment with each other. Y
-
+
[Google Optimize](https://support.google.com/analytics/answer/12979939) can be an excellent way for you to A / B test various things if you're at your company's early stage. It's free, and it will meet all your needs at the start.
@@ -214,7 +214,7 @@ Currently, Google Optimize's most extensive feature is its in-depth integration
-
+
Trusted by over 4,500 enterprise brands, [VWO](https://vwo.com/) is a platform designed specifically for enterprise brands for A/B testing and conversion rate optimization. In their suit, with a drop-and-drop editor, you can create A / B tests, Split URL tests, and multivariate tests.
@@ -227,7 +227,7 @@ Trusted by over 4,500 enterprise brands, [VWO](https://vwo.com/) is a platform d
-
+
With a simple-to-use analytics app and dashboard, [Amplitude](https://amplitude.com/) enables you to monitor your data and metrics. The real-time platform tracks the use of your product and statistics from second to second, letting you know when your app crashes, or checkout flows break down.
@@ -237,7 +237,7 @@ With a simple-to-use analytics app and dashboard, [Amplitude](https://amplitude.
-
+
A behavioral analytics framework such as [Mixpanel](https://mixpanel.com/) can be used to run tests, such as slideouts and tooltips, on the performance of individual UI elements in your user onboarding.
@@ -252,7 +252,7 @@ You can gather accurate information about your product use with Mixpanel, recogn
-
+
[Feedier](https://feedier.com/) is an all-in-one feedback collection platform for your application, product, in-app interactions, or even onboarding processes for a customer.
@@ -266,7 +266,7 @@ Feedier has incorporated incentive management to make the survey enjoyable and s
-
+
[Qualaroo](https://qualaroo.com/) user research and feedback tools promise the capacity to do precisely that. At each point of the onboarding process, you can segment your clients by attribute, plan the timing or action exactly when you want questions to pop up, and get the hot take.
@@ -276,7 +276,7 @@ Feedier has incorporated incentive management to make the survey enjoyable and s
-
+
[Wootric](https://www.wootric.com/) is one of the best onboarding methods for customer loyalty and happiness tracking.
@@ -290,7 +290,7 @@ You can monitor the satisfaction of your customers in real time and even generat
-
+
Use a simple form development tool like [Typeform](https://www.typeform.com/) if you're strapped for cash but still need to get the answers you need. Its conversational, collaborative survey style is one benefit of Typeform. The simplicity of producing a survey is another advantage; it is similar to typing in a notepad, with no coding necessary.
@@ -303,7 +303,7 @@ Use a simple form development tool like [Typeform](https://www.typeform.com/) if
-
+
Through heatmaps, session recordings, and conversion funnels, [Hotjar](https://www.hotjar.com/) offers invaluable insights into the behavior of your users.
@@ -317,7 +317,7 @@ Knowing what your customers already do on your website will help you build smoot
-
+
Another tool for analyzing heat maps and digital experiences is [FullStory](https://www.fullstory.com/).
@@ -334,7 +334,7 @@ Almost every session made on your website or application can be looked at. Your
-
+
Live chat is an excellent platform for onboarding your new users and gathering feedback for your product.
@@ -350,7 +350,7 @@ It has a fantastic dashboard that supports all of your tickets on multiple platf
-
+
A simple way to frustrate them and create unnecessary pressure is to disturb the users and sign in as they go through onboarding or complete vital tasks. With a live chat tool like Olark, you can do this. Using a chat box that suits your branding, [Olark](https://www.olark.com/) allows you to live chat with clients that run into an issue.
@@ -360,7 +360,7 @@ A simple way to frustrate them and create unnecessary pressure is to disturb the
-
+
[Helpscout](https://www.helpscout.com/) is another perfect solution to incorporate live chat support in your user onboarding.
@@ -374,7 +374,7 @@ with this tool you can create more personalized ticket emails for every user. To
-
+
Another great software tool for talking to clients and solving their problems in real-time is [LiveChat](https://www.livechat.com/). Use it to speak with your users and address their issues as they happen. LiveChat's rich analytics show you where your users face most roadblocks during their onboarding (or elsewhere in their journey). Using LiveChat to monitor the onboarding process and recognize the moments of friction that your clients encounter.
@@ -384,7 +384,7 @@ Another great software tool for talking to clients and solving their problems in
-
+
Knowledge base tools such as [Zendesk](https://www.zendesk.com/) allow you to build an online support center where customers can access FAQs, fixes for prevalent problems, step-by-step posts, and community-cured solutions. Before it's too late, help the clients help themselves.
@@ -397,7 +397,7 @@ Knowledge base tools such as [Zendesk](https://www.zendesk.com/) allow you to bu
-
+
One of the helpful onboarding video tools for customers is [Loom](https://www.loom.com/). Video user onboarding is the next best thing to offer you a competitive advantage if you do not have the time or the workers to hold in-person training or training seminars.
@@ -411,7 +411,7 @@ By encouraging your future clients to watch a short video rather than read an en
-
+
The [Inline Manual](https://inlinemanual.com/) is an advanced method for onboarding users, inline documentation, and quicker adoption of greater conversions applications. To engage and help your customers, you can quickly produce walkthroughs, onboarding guides, videos, and product documentation by presenting a new layer on top of your website or application that enables your customers to learn on the go.
@@ -421,7 +421,7 @@ The [Inline Manual](https://inlinemanual.com/) is an advanced method for onboard
-
+
[Helpshelf](https://helpshelf.co/) is a fantastic user-onboarding knowledge base application.
@@ -438,4 +438,4 @@ Luckily, the market gives us an overwhelming range of different resources. We ha
Customer Onboarding is a critical step that forms the entire lifecycle of the user. The best onboarding experiences help users quickly achieve their magic moment; they also set up new users for long-term success.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-onboarding-tools)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-onboarding-tools)
diff --git a/content/growth/user-onboarding-tools/inline-manual.png b/content/growth/user-onboarding-tools/inline-manual.png
deleted file mode 100644
index f2550553b..000000000
Binary files a/content/growth/user-onboarding-tools/inline-manual.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/inline-manual.webp b/content/growth/user-onboarding-tools/inline-manual.webp
new file mode 100644
index 000000000..8193d5136
Binary files /dev/null and b/content/growth/user-onboarding-tools/inline-manual.webp differ
diff --git a/content/growth/user-onboarding-tools/intercom.png b/content/growth/user-onboarding-tools/intercom.png
deleted file mode 100644
index bb61a30f4..000000000
Binary files a/content/growth/user-onboarding-tools/intercom.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/intercom.webp b/content/growth/user-onboarding-tools/intercom.webp
new file mode 100644
index 000000000..c4d46d106
Binary files /dev/null and b/content/growth/user-onboarding-tools/intercom.webp differ
diff --git a/content/growth/user-onboarding-tools/livechat.png b/content/growth/user-onboarding-tools/livechat.png
deleted file mode 100644
index 598981f49..000000000
Binary files a/content/growth/user-onboarding-tools/livechat.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/livechat.webp b/content/growth/user-onboarding-tools/livechat.webp
new file mode 100644
index 000000000..4a148e67f
Binary files /dev/null and b/content/growth/user-onboarding-tools/livechat.webp differ
diff --git a/content/growth/user-onboarding-tools/loginradius-sso.png b/content/growth/user-onboarding-tools/loginradius-sso.png
deleted file mode 100644
index d7ed9afa6..000000000
Binary files a/content/growth/user-onboarding-tools/loginradius-sso.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/loginradius-sso.webp b/content/growth/user-onboarding-tools/loginradius-sso.webp
new file mode 100644
index 000000000..c9ad26bb8
Binary files /dev/null and b/content/growth/user-onboarding-tools/loginradius-sso.webp differ
diff --git a/content/growth/user-onboarding-tools/loom.png b/content/growth/user-onboarding-tools/loom.png
deleted file mode 100644
index c19d5d42d..000000000
Binary files a/content/growth/user-onboarding-tools/loom.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/loom.webp b/content/growth/user-onboarding-tools/loom.webp
new file mode 100644
index 000000000..ac8ee5f35
Binary files /dev/null and b/content/growth/user-onboarding-tools/loom.webp differ
diff --git a/content/growth/user-onboarding-tools/mailjet.png b/content/growth/user-onboarding-tools/mailjet.png
deleted file mode 100644
index b8834113d..000000000
Binary files a/content/growth/user-onboarding-tools/mailjet.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/mailjet.webp b/content/growth/user-onboarding-tools/mailjet.webp
new file mode 100644
index 000000000..dc096fe2b
Binary files /dev/null and b/content/growth/user-onboarding-tools/mailjet.webp differ
diff --git a/content/growth/user-onboarding-tools/mixpanel.png b/content/growth/user-onboarding-tools/mixpanel.png
deleted file mode 100644
index f542d99d8..000000000
Binary files a/content/growth/user-onboarding-tools/mixpanel.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/mixpanel.webp b/content/growth/user-onboarding-tools/mixpanel.webp
new file mode 100644
index 000000000..52d403b96
Binary files /dev/null and b/content/growth/user-onboarding-tools/mixpanel.webp differ
diff --git a/content/growth/user-onboarding-tools/olark.png b/content/growth/user-onboarding-tools/olark.png
deleted file mode 100644
index 4ead3ffc5..000000000
Binary files a/content/growth/user-onboarding-tools/olark.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/olark.webp b/content/growth/user-onboarding-tools/olark.webp
new file mode 100644
index 000000000..76b121d75
Binary files /dev/null and b/content/growth/user-onboarding-tools/olark.webp differ
diff --git a/content/growth/user-onboarding-tools/omniconvert.png b/content/growth/user-onboarding-tools/omniconvert.png
deleted file mode 100644
index caa99bfb2..000000000
Binary files a/content/growth/user-onboarding-tools/omniconvert.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/omniconvert.webp b/content/growth/user-onboarding-tools/omniconvert.webp
new file mode 100644
index 000000000..1792d365e
Binary files /dev/null and b/content/growth/user-onboarding-tools/omniconvert.webp differ
diff --git a/content/growth/user-onboarding-tools/optimizely.png b/content/growth/user-onboarding-tools/optimizely.png
deleted file mode 100644
index 3b258f16c..000000000
Binary files a/content/growth/user-onboarding-tools/optimizely.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/optimizely.webp b/content/growth/user-onboarding-tools/optimizely.webp
new file mode 100644
index 000000000..57766c978
Binary files /dev/null and b/content/growth/user-onboarding-tools/optimizely.webp differ
diff --git a/content/growth/user-onboarding-tools/qualaroo.png b/content/growth/user-onboarding-tools/qualaroo.png
deleted file mode 100644
index a8d83b917..000000000
Binary files a/content/growth/user-onboarding-tools/qualaroo.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/qualaroo.webp b/content/growth/user-onboarding-tools/qualaroo.webp
new file mode 100644
index 000000000..95143c03b
Binary files /dev/null and b/content/growth/user-onboarding-tools/qualaroo.webp differ
diff --git a/content/growth/user-onboarding-tools/typeform.png b/content/growth/user-onboarding-tools/typeform.png
deleted file mode 100644
index a028058d8..000000000
Binary files a/content/growth/user-onboarding-tools/typeform.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/typeform.webp b/content/growth/user-onboarding-tools/typeform.webp
new file mode 100644
index 000000000..8c9c2012e
Binary files /dev/null and b/content/growth/user-onboarding-tools/typeform.webp differ
diff --git a/content/growth/user-onboarding-tools/user-onboarding.jpg b/content/growth/user-onboarding-tools/user-onboarding.jpg
deleted file mode 100644
index 8609842c7..000000000
Binary files a/content/growth/user-onboarding-tools/user-onboarding.jpg and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/user-onboarding.webp b/content/growth/user-onboarding-tools/user-onboarding.webp
new file mode 100644
index 000000000..5a765e211
Binary files /dev/null and b/content/growth/user-onboarding-tools/user-onboarding.webp differ
diff --git a/content/growth/user-onboarding-tools/vwo.png b/content/growth/user-onboarding-tools/vwo.png
deleted file mode 100644
index 9f8d3631c..000000000
Binary files a/content/growth/user-onboarding-tools/vwo.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/vwo.webp b/content/growth/user-onboarding-tools/vwo.webp
new file mode 100644
index 000000000..f9672ed94
Binary files /dev/null and b/content/growth/user-onboarding-tools/vwo.webp differ
diff --git a/content/growth/user-onboarding-tools/wootric.png b/content/growth/user-onboarding-tools/wootric.png
deleted file mode 100644
index 057f82072..000000000
Binary files a/content/growth/user-onboarding-tools/wootric.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/wootric.webp b/content/growth/user-onboarding-tools/wootric.webp
new file mode 100644
index 000000000..b73174728
Binary files /dev/null and b/content/growth/user-onboarding-tools/wootric.webp differ
diff --git a/content/growth/user-onboarding-tools/zendesk.png b/content/growth/user-onboarding-tools/zendesk.png
deleted file mode 100644
index 6d97d2aea..000000000
Binary files a/content/growth/user-onboarding-tools/zendesk.png and /dev/null differ
diff --git a/content/growth/user-onboarding-tools/zendesk.webp b/content/growth/user-onboarding-tools/zendesk.webp
new file mode 100644
index 000000000..77e017050
Binary files /dev/null and b/content/growth/user-onboarding-tools/zendesk.webp differ
diff --git a/content/growth/what-advanced-identity-means-for-cx/cx-identity.jpg b/content/growth/what-advanced-identity-means-for-cx/cx-identity.jpg
deleted file mode 100644
index 27d4d7e8b..000000000
Binary files a/content/growth/what-advanced-identity-means-for-cx/cx-identity.jpg and /dev/null differ
diff --git a/content/growth/what-advanced-identity-means-for-cx/cx-identity.webp b/content/growth/what-advanced-identity-means-for-cx/cx-identity.webp
new file mode 100644
index 000000000..bda4892ca
Binary files /dev/null and b/content/growth/what-advanced-identity-means-for-cx/cx-identity.webp differ
diff --git a/content/growth/what-advanced-identity-means-for-cx/index.md b/content/growth/what-advanced-identity-means-for-cx/index.md
index cdedc8fdf..9d298251c 100644
--- a/content/growth/what-advanced-identity-means-for-cx/index.md
+++ b/content/growth/what-advanced-identity-means-for-cx/index.md
@@ -1,7 +1,7 @@
---
title: "The Future of Customer Experience is All About Advanced Identity"
date: "2022-09-08"
-coverImage: "cx-identity.jpg"
+coverImage: "cx-identity.webp"
category: ["customer experience", "identity management", "compliance"]
author: "Vishal Sharma"
description: "Since customer journeys are becoming increasingly complex, brands should focus more on improving their identity management infrastructure. This blog explains the aspects of identity management and how to deliver a rich and secure CX across multiple touchpoints."
@@ -42,7 +42,7 @@ A rich customer experience begins when users interact with their platform for th
Besides, global data privacy and security compliances, including the GDPR and CCPA, are more stringent than ever. Hence, to comply with these regulations, brands should adopt a robust identity management solution to continue delivering services to their customers.
-[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
+[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
## Your Customers Know What to Share What Not
@@ -71,4 +71,4 @@ The power of identity management is helping brands navigate their digital transf
With a reliable customer identity and access management solution, brands can ensure they stand ahead of the curve by delivering rich customer experiences backed with robust security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-advanced-identity-means-for-cx)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-advanced-identity-means-for-cx)
\ No newline at end of file
diff --git a/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.png b/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.png
deleted file mode 100644
index 6784e19bd..000000000
Binary files a/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.png and /dev/null differ
diff --git a/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.webp b/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.webp
new file mode 100644
index 000000000..c27d2fee5
Binary files /dev/null and b/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.webp differ
diff --git a/content/growth/what-is-digital-privacy/WP-compliance-retailers.png b/content/growth/what-is-digital-privacy/WP-compliance-retailers.png
deleted file mode 100644
index 802253f09..000000000
Binary files a/content/growth/what-is-digital-privacy/WP-compliance-retailers.png and /dev/null differ
diff --git a/content/growth/what-is-digital-privacy/WP-compliance-retailers.webp b/content/growth/what-is-digital-privacy/WP-compliance-retailers.webp
new file mode 100644
index 000000000..c98143e9e
Binary files /dev/null and b/content/growth/what-is-digital-privacy/WP-compliance-retailers.webp differ
diff --git a/content/growth/what-is-digital-privacy/compliance-wp.png b/content/growth/what-is-digital-privacy/compliance-wp.png
deleted file mode 100644
index a2c9e2a07..000000000
Binary files a/content/growth/what-is-digital-privacy/compliance-wp.png and /dev/null differ
diff --git a/content/growth/what-is-digital-privacy/compliance-wp.webp b/content/growth/what-is-digital-privacy/compliance-wp.webp
new file mode 100644
index 000000000..1717fdcbb
Binary files /dev/null and b/content/growth/what-is-digital-privacy/compliance-wp.webp differ
diff --git a/content/growth/what-is-digital-privacy/digi-privacy.jpg b/content/growth/what-is-digital-privacy/digi-privacy.jpg
deleted file mode 100644
index a42c7c0f8..000000000
Binary files a/content/growth/what-is-digital-privacy/digi-privacy.jpg and /dev/null differ
diff --git a/content/growth/what-is-digital-privacy/digi-privacy.webp b/content/growth/what-is-digital-privacy/digi-privacy.webp
new file mode 100644
index 000000000..c23ff4abe
Binary files /dev/null and b/content/growth/what-is-digital-privacy/digi-privacy.webp differ
diff --git a/content/growth/what-is-digital-privacy/index.md b/content/growth/what-is-digital-privacy/index.md
index d1c53bcac..b92a02815 100644
--- a/content/growth/what-is-digital-privacy/index.md
+++ b/content/growth/what-is-digital-privacy/index.md
@@ -1,7 +1,7 @@
---
title: "Decoding the Business Advantage of Digital Privacy for Customers"
date: "2022-11-03"
-coverImage: "digi-privacy.jpg"
+coverImage: "digi-privacy.webp"
category: ["digital privacy","compliance","passwordless authentication"]
author: "Alok Patidar"
description: "Investing in privacy isn’t just a matter of mitigating risks pertaining to data breaches; it’s also about navigating business success by building trust and offering value to customers through enhanced security and protections. Let’s understand how businesses can invoke the true potential of digital privacy."
@@ -57,7 +57,7 @@ Businesses operating in different parts of the world couldn’t deny that meetin
However, digital privacy has more to offer besides the security and privacy advantages; it navigates overall business success.
-[](https://www.loginradius.com/resource/role-of-data-and-privacy-compliance-in-retail)
+[](https://www.loginradius.com/resource/role-of-data-and-privacy-compliance-in-retail)
According to a consumer data protection and privacy survey conducted by [McKinsey](https://www.mckinsey.com/business-functions/risk-and-resilience/our-insights/the-consumer-data-opportunity-and-the-privacy-imperative), half of the respondents agreed that they are most likely to trust a business/organization that asks for only information relevant to its products/services.
@@ -83,4 +83,4 @@ In conclusion, we’ve found that building a foundation of strong digital privac
Brands can’t afford to lose a single customer because of non-compliance issues. Hence, it won’t be a good decision for businesses to miss out on the chance to stay ahead of the competition.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-digital-privacy)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-digital-privacy)
\ No newline at end of file
diff --git a/content/growth/what-is-identity-resolution/DS-user-mngmnt.png b/content/growth/what-is-identity-resolution/DS-user-mngmnt.png
deleted file mode 100644
index fc6f98c05..000000000
Binary files a/content/growth/what-is-identity-resolution/DS-user-mngmnt.png and /dev/null differ
diff --git a/content/growth/what-is-identity-resolution/DS-user-mngmnt.webp b/content/growth/what-is-identity-resolution/DS-user-mngmnt.webp
new file mode 100644
index 000000000..c60f3551f
Binary files /dev/null and b/content/growth/what-is-identity-resolution/DS-user-mngmnt.webp differ
diff --git a/content/growth/what-is-identity-resolution/identity-resolution.jpg b/content/growth/what-is-identity-resolution/identity-resolution.jpg
deleted file mode 100644
index 5bb891709..000000000
Binary files a/content/growth/what-is-identity-resolution/identity-resolution.jpg and /dev/null differ
diff --git a/content/growth/what-is-identity-resolution/identity-resolution.webp b/content/growth/what-is-identity-resolution/identity-resolution.webp
new file mode 100644
index 000000000..c408d7c32
Binary files /dev/null and b/content/growth/what-is-identity-resolution/identity-resolution.webp differ
diff --git a/content/growth/what-is-identity-resolution/index.md b/content/growth/what-is-identity-resolution/index.md
index 01ee6a365..ba7b92c6b 100644
--- a/content/growth/what-is-identity-resolution/index.md
+++ b/content/growth/what-is-identity-resolution/index.md
@@ -1,7 +1,7 @@
---
title: "What Is Identity Resolution And How Can It Benefit Your Business?"
date: "2023-08-09"
-coverImage: "identity-resolution.jpg"
+coverImage: "identity-resolution.webp"
tags: ["identity resolution","user management","compliance","cx"]
author: "Vishal Sharma"
description: "Uncover the power of identity resolution to boost your business. Enhance customer experiences, optimize marketing efforts, and mitigate fraud risks with accurate, unified customer data."
@@ -38,7 +38,7 @@ Identity resolution empowers marketers to segment and target their audience with
These segmented profiles enable marketers to tailor their messages, promotions, and advertisements to specific customer segments, maximizing relevance and driving higher conversion rates. With identity resolution, businesses can optimize their marketing strategies and allocate resources more effectively.
-[](https://www.loginradius.com/resource/loginradius-ciam-user-management/)
+[](https://www.loginradius.com/resource/loginradius-ciam-user-management/)
### 3. Fraud Detection and Risk Mitigation
@@ -76,4 +76,4 @@ By leveraging the power of identity resolution, businesses can unlock a wealth o
Investing in identity resolution enables organizations to optimize their operations, deepen customer relationships, and stay ahead in a rapidly evolving marketplace. Embrace identity resolution as a core component of your business strategy and unlock its transformative potential.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-resolution)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-resolution)
\ No newline at end of file
diff --git a/content/growth/what-is-omnichannel-cx/Omnichannel-CX.jpg b/content/growth/what-is-omnichannel-cx/Omnichannel-CX.jpg
deleted file mode 100644
index 0039316f8..000000000
Binary files a/content/growth/what-is-omnichannel-cx/Omnichannel-CX.jpg and /dev/null differ
diff --git a/content/growth/what-is-omnichannel-cx/Omnichannel-CX.webp b/content/growth/what-is-omnichannel-cx/Omnichannel-CX.webp
new file mode 100644
index 000000000..5cd87f332
Binary files /dev/null and b/content/growth/what-is-omnichannel-cx/Omnichannel-CX.webp differ
diff --git a/content/growth/what-is-omnichannel-cx/index.md b/content/growth/what-is-omnichannel-cx/index.md
index 47b1ed6b9..d39bf116f 100644
--- a/content/growth/what-is-omnichannel-cx/index.md
+++ b/content/growth/what-is-omnichannel-cx/index.md
@@ -1,7 +1,7 @@
---
title: "Omnichannel CX : Your Key to Consumer Experience Success"
date: "2021-06-30"
-coverImage: "Omnichannel-CX.jpg"
+coverImage: "Omnichannel-CX.webp"
category: ["loginradius"]
featured: false
author: "Tanvi Soni"
@@ -109,4 +109,4 @@ For seamless humanized omnichannel journeys and consumer experience, [consumer
Continue the conversation effortlessly if consumers switch from one channel to another. Start with chat, move on to voice, and then interact through video seamlessly. [Contact LoginRadius](https://www.loginradius.com/contact-us/) to know more.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-omnichannel-cx)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-omnichannel-cx)
\ No newline at end of file
diff --git a/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.png b/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.png
deleted file mode 100644
index bdd52a34c..000000000
Binary files a/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.png and /dev/null differ
diff --git a/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.webp b/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.webp
new file mode 100644
index 000000000..19580a6f8
Binary files /dev/null and b/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.webp differ
diff --git a/content/growth/when-to-switch-your-security-vendor/index.md b/content/growth/when-to-switch-your-security-vendor/index.md
index 8822f0ed1..1b0f454a4 100644
--- a/content/growth/when-to-switch-your-security-vendor/index.md
+++ b/content/growth/when-to-switch-your-security-vendor/index.md
@@ -1,7 +1,7 @@
---
title: "Renewing Your Security Vendor Contract? Know When It’s the Time to Switch"
date: "2022-08-31"
-coverImage: "sec-vendor.jpg"
+coverImage: "sec-vendor.webp"
tags: ["cybersecurity", "mfa", "digital identity","cloud security"]
author: "Rakesh Soni"
description: "Since cybercriminals are constantly exploring new ways to exploit sensitive business and customer information, companies must upgrade their security infrastructure to ensure they remain in a safe zone. Here are some aspects of upgrading your security practices and when businesses must rethink their cybersecurity posture."
@@ -40,7 +40,7 @@ But besides endless security mechanisms working simultaneously to prevent a brea
Hence, when organizations face violations, they must consider switching their security vendor or renewing the same with added security features.
-[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
+[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
## Signs You Need to Switch/Renew Your Security Vendor Contract
@@ -86,4 +86,4 @@ Technology has provided endless opportunities to enterprises. However, adopting
Companies need to understand that they may need to change their cybersecurity policies or rely on third-party vendors to ensure the highest level of security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=when-to-switch-your-security-vendor)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=when-to-switch-your-security-vendor)
diff --git a/content/growth/when-to-switch-your-security-vendor/sec-vendor.jpg b/content/growth/when-to-switch-your-security-vendor/sec-vendor.jpg
deleted file mode 100644
index 101c52a66..000000000
Binary files a/content/growth/when-to-switch-your-security-vendor/sec-vendor.jpg and /dev/null differ
diff --git a/content/growth/when-to-switch-your-security-vendor/sec-vendor.webp b/content/growth/when-to-switch-your-security-vendor/sec-vendor.webp
new file mode 100644
index 000000000..510894fbe
Binary files /dev/null and b/content/growth/when-to-switch-your-security-vendor/sec-vendor.webp differ
diff --git a/content/growth/when-to-switch-your-security-vendor/security-wp.png b/content/growth/when-to-switch-your-security-vendor/security-wp.png
deleted file mode 100644
index 9b885caa8..000000000
Binary files a/content/growth/when-to-switch-your-security-vendor/security-wp.png and /dev/null differ
diff --git a/content/growth/when-to-switch-your-security-vendor/security-wp.webp b/content/growth/when-to-switch-your-security-vendor/security-wp.webp
new file mode 100644
index 000000000..62f54b93f
Binary files /dev/null and b/content/growth/when-to-switch-your-security-vendor/security-wp.webp differ
diff --git a/content/growth/why-brand-authenticity-is-important/brand-engagement.jpg b/content/growth/why-brand-authenticity-is-important/brand-engagement.jpg
deleted file mode 100644
index dada5592c..000000000
Binary files a/content/growth/why-brand-authenticity-is-important/brand-engagement.jpg and /dev/null differ
diff --git a/content/growth/why-brand-authenticity-is-important/brand-engagement.webp b/content/growth/why-brand-authenticity-is-important/brand-engagement.webp
new file mode 100644
index 000000000..8b8362c51
Binary files /dev/null and b/content/growth/why-brand-authenticity-is-important/brand-engagement.webp differ
diff --git a/content/growth/why-brand-authenticity-is-important/index.md b/content/growth/why-brand-authenticity-is-important/index.md
index c1448a6c1..5c8095f6a 100644
--- a/content/growth/why-brand-authenticity-is-important/index.md
+++ b/content/growth/why-brand-authenticity-is-important/index.md
@@ -1,7 +1,7 @@
---
title: "Why Brand Authenticity is Important & How to Build it"
date: "2021-06-24"
-coverImage: "brand-engagement.jpg"
+coverImage: "brand-engagement.webp"
category: ["loginradius"]
featured: false
author: "Navanita Devi"
@@ -126,4 +126,4 @@ The final step towards achieving brand authenticity is to showcase your [brand r
Brand authenticity is not a one-time activity, but a constant process of discovering what your brand means for your consumers. No matter which industry you are in, brand identity is critical for business success in today’s times. As outlined in this article, an authentic brand can connect with consumers and establish a brand value that goes way beyond profits and revenues.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-brand-authenticity-is-important)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-brand-authenticity-is-important)
diff --git a/content/growth/why-should-implement-social-login-authentication/Social-Login.png b/content/growth/why-should-implement-social-login-authentication/Social-Login.png
deleted file mode 100644
index 98e481315..000000000
Binary files a/content/growth/why-should-implement-social-login-authentication/Social-Login.png and /dev/null differ
diff --git a/content/growth/why-should-implement-social-login-authentication/Social-Login.webp b/content/growth/why-should-implement-social-login-authentication/Social-Login.webp
new file mode 100644
index 000000000..5e3eaf627
Binary files /dev/null and b/content/growth/why-should-implement-social-login-authentication/Social-Login.webp differ
diff --git a/content/growth/why-should-implement-social-login-authentication/index.md b/content/growth/why-should-implement-social-login-authentication/index.md
index 3aecae763..085f8cbe9 100644
--- a/content/growth/why-should-implement-social-login-authentication/index.md
+++ b/content/growth/why-should-implement-social-login-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Why Should You Implement Social Login Authentication?"
date: "2021-08-16"
-coverImage: "social-login-1.jpg"
+coverImage: "social-login-1.webp"
tags: ["social login authentication","data security","cx"]
author: "Navanita Devi"
description: "If you're building a startup today, social login should be the default, not an afterthought. It will give you a huge competitive advantage, because your users won't have to register or even create an email address to use your site."
@@ -28,7 +28,7 @@ Social logins is usually manifested using the following steps:
4. Finally, the social media provider will confirm the identity of the user, who will then obtain access to the application or site.
-[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
Depending on the social network provider and their respective CIAM management practices, the process of social login authentication differs slightly. This is because each platform collects different user information and implements distinct consumer data security strategies.
@@ -129,4 +129,4 @@ Organizations can implement social login by using a robust CIAM solution like Lo
Single Sign-On (SSO) allows users to access multiple applications with one set of credentials. At the same time, social login is an authentication mechanism that specifically uses social media credentials for user authentication.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-should-implement-social-login-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-should-implement-social-login-authentication)
\ No newline at end of file
diff --git a/content/growth/why-should-implement-social-login-authentication/social-login-1.jpg b/content/growth/why-should-implement-social-login-authentication/social-login-1.jpg
deleted file mode 100644
index 0e38b9458..000000000
Binary files a/content/growth/why-should-implement-social-login-authentication/social-login-1.jpg and /dev/null differ
diff --git a/content/growth/why-should-implement-social-login-authentication/social-login-1.webp b/content/growth/why-should-implement-social-login-authentication/social-login-1.webp
new file mode 100644
index 000000000..0d0559b38
Binary files /dev/null and b/content/growth/why-should-implement-social-login-authentication/social-login-1.webp differ
diff --git a/content/growth/zero-party-data/DS-Progressive-Profiling.png b/content/growth/zero-party-data/DS-Progressive-Profiling.png
deleted file mode 100644
index c98c144d4..000000000
Binary files a/content/growth/zero-party-data/DS-Progressive-Profiling.png and /dev/null differ
diff --git a/content/growth/zero-party-data/DS-Progressive-Profiling.webp b/content/growth/zero-party-data/DS-Progressive-Profiling.webp
new file mode 100644
index 000000000..b34c41174
Binary files /dev/null and b/content/growth/zero-party-data/DS-Progressive-Profiling.webp differ
diff --git a/content/growth/zero-party-data/index.md b/content/growth/zero-party-data/index.md
index 27a020955..efe5a32ce 100644
--- a/content/growth/zero-party-data/index.md
+++ b/content/growth/zero-party-data/index.md
@@ -1,7 +1,7 @@
---
title: "Unlocking Success: Marketing in a Cookieless World with Zero-Party Data"
date: "2023-11-07"
-coverImage: "zero-party-data.jpg"
+coverImage: "zero-party-data.webp"
tags: ["zero-party","progressive profiling","compliance","cx"]
author: "Yash Rathi"
description: "Discover the power of zero-party data in the cookieless era. Explore innovative strategies for personalized marketing and trust-building. Embrace ethical practices and human connection to unlock unprecedented success in the digital world."
@@ -35,7 +35,7 @@ Zero-party data enables businesses to tailor their marketing messages to individ
Progressive profiling helps businesses collect useful customer details gradually over time. When customers willingly share their data, it fosters a sense of trust and transparency between the brand and the consumer. By respecting user privacy and preferences, businesses can create lasting relationships with their audience.
-[](https://www.loginradius.com/resource/progressive-profiling-by-loginradius-2/)
+[](https://www.loginradius.com/resource/progressive-profiling-by-loginradius-2/)
### 3. Improved Customer Engagement
@@ -85,4 +85,4 @@ By adopting innovative strategies to collect and utilize zero-party data effecti
Embracing this paradigm shift not only meets the demands of the evolving digital ecosystem but also establishes a foundation for ethical and customer-centric marketing practices, leading to long-term brand loyalty and business growth.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=zero-party-data)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=zero-party-data)
diff --git a/content/growth/zero-party-data/zero-party-data.jpg b/content/growth/zero-party-data/zero-party-data.jpg
deleted file mode 100644
index 18dcedd24..000000000
Binary files a/content/growth/zero-party-data/zero-party-data.jpg and /dev/null differ
diff --git a/content/growth/zero-party-data/zero-party-data.webp b/content/growth/zero-party-data/zero-party-data.webp
new file mode 100644
index 000000000..f70a6321e
Binary files /dev/null and b/content/growth/zero-party-data/zero-party-data.webp differ
diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.png b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.png and /dev/null differ
diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.webp b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.webp differ
diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.jpg b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.jpg
deleted file mode 100644
index 3df9b3b8b..000000000
Binary files a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.jpg and /dev/null differ
diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.webp b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.webp
new file mode 100644
index 000000000..8b9a2bb63
Binary files /dev/null and b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.webp differ
diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/index.md b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/index.md
index 25b847a6c..b57745410 100644
--- a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/index.md
+++ b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/index.md
@@ -1,7 +1,7 @@
---
title: "10 Ways To Keep Your Business Safe On Black Friday and Cyber Monday"
date: "2022-11-23"
-coverImage: "cyber-monday.jpg"
+coverImage: "cyber-monday.webp"
tags: ["online shopping", "online security", "cx"]
author: "Navanita Devi"
description: "Black Friday and Cyber Monday mean big deals, but they also mean big risks. Take control of your security and privacy with these tips to keep your business safe for cyber attacks."
@@ -61,7 +61,7 @@ As a retailer, your organization will likely experience a significant increase i
To avoid this, retailers need to shift to a more pragmatic and strategic security approach to ensure the organization can recover quickly from a cybersecurity event and get back to business with zero data loss.
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
### 6. Think of uptime as an opportunity to maximize efficiency.
@@ -105,4 +105,4 @@ When you take some time to craft a post-purchase journey tailored to your custom
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=10-black-friday-cyber-monday-tips-for-businesses)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=10-black-friday-cyber-monday-tips-for-businesses)
diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.png b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.png
deleted file mode 100644
index 3e6b81ee6..000000000
Binary files a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.png and /dev/null differ
diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.webp b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.webp
new file mode 100644
index 000000000..2f7c01062
Binary files /dev/null and b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.webp differ
diff --git a/content/identity/1fa-vs-2fa-vs-mfa/index.md b/content/identity/1fa-vs-2fa-vs-mfa/index.md
index 0db283527..1bdd3b80b 100644
--- a/content/identity/1fa-vs-2fa-vs-mfa/index.md
+++ b/content/identity/1fa-vs-2fa-vs-mfa/index.md
@@ -282,4 +282,4 @@ Yes, MFA is highly secure as it requires multiple factors, reducing the chances
Yes, 2FA codes typically expire within 30–60 seconds, ensuring they can’t be reused by attackers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=1fa-vs-2fa-vs-mfa)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=1fa-vs-2fa-vs-mfa)
\ No newline at end of file
diff --git a/content/identity/2fa-mfa-key-differences/2fa-vs-mfa.webp b/content/identity/2fa-mfa-key-differences/2fa-vs-mfa.webp
new file mode 100644
index 000000000..4db479189
Binary files /dev/null and b/content/identity/2fa-mfa-key-differences/2fa-vs-mfa.webp differ
diff --git a/content/identity/2fa-mfa-key-differences/EB-GD-to-MFA.webp b/content/identity/2fa-mfa-key-differences/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/2fa-mfa-key-differences/EB-GD-to-MFA.webp differ
diff --git a/content/identity/2fa-mfa-key-differences/index.md b/content/identity/2fa-mfa-key-differences/index.md
index e816a8206..2b2c02382 100644
--- a/content/identity/2fa-mfa-key-differences/index.md
+++ b/content/identity/2fa-mfa-key-differences/index.md
@@ -259,4 +259,4 @@ To incorporate MFA or advanced adaptive MFA from LoginRadius, you can [reach us
**A:** Absolutely. Two-factor authentication significantly enhances security compared to just using passwords, effectively reducing common cyber threats.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=2fa-mfa-key-differences)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=2fa-mfa-key-differences)
\ No newline at end of file
diff --git a/content/identity/2fa-security-measures/2fa-security.jpg b/content/identity/2fa-security-measures/2fa-security.jpg
deleted file mode 100644
index a01ce75fc..000000000
Binary files a/content/identity/2fa-security-measures/2fa-security.jpg and /dev/null differ
diff --git a/content/identity/2fa-security-measures/2fa-security.webp b/content/identity/2fa-security-measures/2fa-security.webp
new file mode 100644
index 000000000..d594388ac
Binary files /dev/null and b/content/identity/2fa-security-measures/2fa-security.webp differ
diff --git a/content/identity/2fa-security-measures/GD-to-RBA.png b/content/identity/2fa-security-measures/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/2fa-security-measures/GD-to-RBA.png and /dev/null differ
diff --git a/content/identity/2fa-security-measures/GD-to-RBA.webp b/content/identity/2fa-security-measures/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/2fa-security-measures/GD-to-RBA.webp differ
diff --git a/content/identity/2fa-security-measures/index.md b/content/identity/2fa-security-measures/index.md
index 3ead8f8f5..2c00868c4 100644
--- a/content/identity/2fa-security-measures/index.md
+++ b/content/identity/2fa-security-measures/index.md
@@ -1,7 +1,7 @@
---
title: "Strengthening Security Measures: The Role of Two-Factor Authentication (2FA)"
date: "2023-11-17"
-coverImage: "2fa-security.jpg"
+coverImage: "2fa-security.webp"
tags: ["data security","2FA","MFA","cx"]
author: "Rakesh Soni"
description: "Dive into the world of Two-Factor Authentication (2FA) and its pivotal role in fortifying security. Discover the dual-layered defense, benefits against cyber threats, and insights on implementing MFA and RBA for a proactive defense strategy."
@@ -46,7 +46,7 @@ Whether combining something you know (like a password) with something you have (
As the digital landscape evolves, so do the strategies employed by cybercriminals. In response to this ever-changing threat landscape, organizations increasingly turn to Risk-Based Authentication (RBA) to fortify their authentication security.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
RBA is a dynamic approach that assesses various risk factors in real-time to determine the level of authentication required for a particular user or transaction. By analyzing contextual data such as device information, location, user behavior, and the sensitivity of the requested action, RBA adapts the authentication process to match the perceived risk level.
@@ -58,4 +58,4 @@ As we stand at the intersection of technological advancement and heightened cybe
By comprehending its significance, embracing its implementation, and adapting to evolving technologies, individuals and organizations can proactively defend against the ever-shifting landscape of cyber threats.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=2fa-security-measures)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=2fa-security-measures)
\ No newline at end of file
diff --git a/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.png b/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.png
deleted file mode 100644
index f5fa0b0f9..000000000
Binary files a/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.png and /dev/null differ
diff --git a/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.webp b/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.webp
new file mode 100644
index 000000000..b0761321e
Binary files /dev/null and b/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.webp differ
diff --git a/content/identity/3-digital-onboarding-trends-2023/digi-onboard.jpg b/content/identity/3-digital-onboarding-trends-2023/digi-onboard.jpg
deleted file mode 100644
index 0150acead..000000000
Binary files a/content/identity/3-digital-onboarding-trends-2023/digi-onboard.jpg and /dev/null differ
diff --git a/content/identity/3-digital-onboarding-trends-2023/digi-onboard.webp b/content/identity/3-digital-onboarding-trends-2023/digi-onboard.webp
new file mode 100644
index 000000000..425dd6115
Binary files /dev/null and b/content/identity/3-digital-onboarding-trends-2023/digi-onboard.webp differ
diff --git a/content/identity/3-digital-onboarding-trends-2023/index.md b/content/identity/3-digital-onboarding-trends-2023/index.md
index b67103a98..b5d7a084b 100644
--- a/content/identity/3-digital-onboarding-trends-2023/index.md
+++ b/content/identity/3-digital-onboarding-trends-2023/index.md
@@ -1,7 +1,7 @@
---
title: "3 Digital Onboarding Trends To Watch In 2023 (And What You Can Do About It Now)"
date: "2023-01-06"
-coverImage: "digi-onboard.jpg"
+coverImage: "digi-onboard.webp"
tags: ["user onboarding", "digital transformation", "omnichannel"]
author: "Rakesh Soni"
description: "Digital onboarding plays a crucial role in enhancing user experience. This blog will help you understand what digital onboarding is, how it impacts conversions, and the trends in digital onboarding that will shape the future of identity verification."
@@ -38,7 +38,7 @@ An omnichannel customer experience is a multifold approach to advertising, selli
A digital omnichannel strategy adopts a multichannel approach for sales, consumer service, and marketing. It focuses on providing a united consumer experience regardless of the channel they contact your company.
-[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
+[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
The key to providing constant omnichannel engagement is to offer a smooth experience across all online and offline platforms. Every contact should be considered a single experience from the consumer's perspective. It implies it shouldn't be segregated or repetitious.
@@ -81,4 +81,4 @@ Learn more about the LoginRadius Identity Platform, starting with a Quick Person
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=3-digital-onboarding-trends-2023)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=3-digital-onboarding-trends-2023)
diff --git a/content/identity/3-digital-onboarding-trends-2023/omni-eb.png b/content/identity/3-digital-onboarding-trends-2023/omni-eb.png
deleted file mode 100644
index 86c15a159..000000000
Binary files a/content/identity/3-digital-onboarding-trends-2023/omni-eb.png and /dev/null differ
diff --git a/content/identity/3-digital-onboarding-trends-2023/omni-eb.webp b/content/identity/3-digital-onboarding-trends-2023/omni-eb.webp
new file mode 100644
index 000000000..025782e92
Binary files /dev/null and b/content/identity/3-digital-onboarding-trends-2023/omni-eb.webp differ
diff --git a/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.png b/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.png
deleted file mode 100644
index 1b6f5ad00..000000000
Binary files a/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.png and /dev/null differ
diff --git a/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.webp b/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.webp
new file mode 100644
index 000000000..2e16ce904
Binary files /dev/null and b/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.webp differ
diff --git a/content/identity/3-stages-gartner-carta-it-security/carta.jpg b/content/identity/3-stages-gartner-carta-it-security/carta.jpg
deleted file mode 100644
index 5e4916d12..000000000
Binary files a/content/identity/3-stages-gartner-carta-it-security/carta.jpg and /dev/null differ
diff --git a/content/identity/3-stages-gartner-carta-it-security/carta.webp b/content/identity/3-stages-gartner-carta-it-security/carta.webp
new file mode 100644
index 000000000..2f9f457f8
Binary files /dev/null and b/content/identity/3-stages-gartner-carta-it-security/carta.webp differ
diff --git a/content/identity/3-stages-gartner-carta-it-security/index.md b/content/identity/3-stages-gartner-carta-it-security/index.md
index a111141db..4f4d94aef 100644
--- a/content/identity/3-stages-gartner-carta-it-security/index.md
+++ b/content/identity/3-stages-gartner-carta-it-security/index.md
@@ -1,7 +1,7 @@
---
title: "3 Best Stages of IT Security for Implementing Gartner's CARTA"
date: "2021-11-10"
-coverImage: "carta.jpg"
+coverImage: "carta.webp"
tags: ["security"]
featured: false
author: "Vishal Sharma"
@@ -72,4 +72,4 @@ CARTA’s risk reduction model is [built on the premise](https://www.loginradius
Hence, businesses striving to implement the best security practices must consider relying on CARTA for enhanced risk management for their organization.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=3-stages-gartner-carta-it-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=3-stages-gartner-carta-it-security)
diff --git a/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.jpg b/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.jpg
deleted file mode 100644
index ebbb1948f..000000000
Binary files a/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.jpg and /dev/null differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.webp b/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.webp
new file mode 100644
index 000000000..f416611c0
Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.webp differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.jpg b/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.jpg
deleted file mode 100644
index 3d2fa2fd1..000000000
Binary files a/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.jpg and /dev/null differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.webp b/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.webp
new file mode 100644
index 000000000..04194cb2c
Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.webp differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.png b/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.png
deleted file mode 100644
index dbb57ace9..000000000
Binary files a/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.png and /dev/null differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.webp b/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.webp
new file mode 100644
index 000000000..98937f902
Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.webp differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/image5.png b/content/identity/4-barriers-building-digital-business-overcome/image5.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/4-barriers-building-digital-business-overcome/image5.png and /dev/null differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/image5.webp b/content/identity/4-barriers-building-digital-business-overcome/image5.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/image5.webp differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/index.md b/content/identity/4-barriers-building-digital-business-overcome/index.md
index 51944615f..c7f22acbd 100644
--- a/content/identity/4-barriers-building-digital-business-overcome/index.md
+++ b/content/identity/4-barriers-building-digital-business-overcome/index.md
@@ -1,7 +1,7 @@
---
title: "4 Barriers to Building a Digital Business and How to Overcome Them"
date: "2018-08-02"
-coverImage: "4-barriers-building-digital-business-overcome.jpg"
+coverImage: "4-barriers-building-digital-business-overcome.webp"
tags: ["customer-experience"]
featured: false
author: "Rakesh Soni"
@@ -13,7 +13,7 @@ metadescription: "Thinking about starting a business online? Here are the most c
The movement towards digitalization is occurring across all business sectors. Even industries that have always been solely focused on growing and expanding their existing business models are joining the movement. However, there are some roadblocks that these companies have to overcome in order to successfully build a digital business. But don't let these roadblocks stunt your digital growth! Here are some tips to help you along:
### 1\. Inability to work as a team
-
+
Many companies across industries are actively working towards transforming their businesses to digital. This includes using technology to improve/optimize the existing business model, in order to pave the way towards building more efficient digital workflows.
@@ -25,7 +25,7 @@ This team, comprised of different representations from within the company, will
### 2\. Lack of corporate vision
-
+
While the majority of your company may have the same goal of moving towards digital, the motives and driving force behind achieving this goal can differ from one person or team to the other. Some may be looking to simply optimize the current workflows to enhance productivity and business outcomes, while others are seeing this as a move towards bigger innovations that will potentially disrupt the entire industry. In this case, there are conflicting ideas of why the company is undergoing a digital reform and how to proceed.
@@ -35,7 +35,7 @@ In order to do this, however, you first need to consider and be certain to commu
### 3\. Gaps in organizational capabilities to deliver digital innovation
-
+
Your goals are set and you've got everyone on board to work towards a common digital outcome.
@@ -49,17 +49,17 @@ More often than not, it's not the team's incapabilities to deliver certain resul
### 4\. Inadequate leadership
-
+
[Digital transformation is exciting](https://www.loginradius.com/blog/identity/what-is-digital-transformation/), but it is also a new concept that companies across industries are only experimenting with in the past few years. Excitement aside, new processes, especially one that affects entire business models and operations, can be daunting.
Transforming existing processes and building new ones are dramatic changes that affect the entire company. Changes such as this can lead to discomfort and conflict. Therefore, strong leadership is essential at all levels to drive beneficial change without increasing risk or creating organizational chaos. Make sure you have the right leadership roles in place as the company moves towards its digital initiatives to ensure its success.
-
+
@@ -85,5 +85,5 @@ Successful digital transformation involves the full breadth of an enterprise –
If you or your company are currently going through digital transformation, see how [LoginRadius can help you speed this up](https://www.loginradius.com/customer-identity-management-b2c-ciam/)!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=4-barriers-building-digital-business-overcome)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=4-barriers-building-digital-business-overcome)
diff --git a/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.jpg b/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.jpg
deleted file mode 100644
index 64b1e0ced..000000000
Binary files a/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.jpg and /dev/null differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.webp b/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.webp
new file mode 100644
index 000000000..996bdb339
Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.webp differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.jpg b/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.jpg
deleted file mode 100644
index 4b759fc7f..000000000
Binary files a/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.jpg and /dev/null differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.webp b/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.webp
new file mode 100644
index 000000000..0fa935c27
Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.webp differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.jpg b/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.jpg
deleted file mode 100644
index 6e6196d67..000000000
Binary files a/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.jpg and /dev/null differ
diff --git a/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.webp b/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.webp
new file mode 100644
index 000000000..41eebfab3
Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.webp differ
diff --git a/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.png b/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.webp b/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.webp differ
diff --git a/content/identity/5-access-management-best-practices-enterprises/access-mangmt.jpg b/content/identity/5-access-management-best-practices-enterprises/access-mangmt.jpg
deleted file mode 100644
index c7fcf8cf8..000000000
Binary files a/content/identity/5-access-management-best-practices-enterprises/access-mangmt.jpg and /dev/null differ
diff --git a/content/identity/5-access-management-best-practices-enterprises/access-mangmt.webp b/content/identity/5-access-management-best-practices-enterprises/access-mangmt.webp
new file mode 100644
index 000000000..147bdbc4e
Binary files /dev/null and b/content/identity/5-access-management-best-practices-enterprises/access-mangmt.webp differ
diff --git a/content/identity/5-access-management-best-practices-enterprises/index.md b/content/identity/5-access-management-best-practices-enterprises/index.md
index 748042e65..605b7c2d6 100644
--- a/content/identity/5-access-management-best-practices-enterprises/index.md
+++ b/content/identity/5-access-management-best-practices-enterprises/index.md
@@ -1,7 +1,7 @@
---
title: " 5 Access Management Best Practices and Benefits For Businesses"
date: "2022-05-10"
-coverImage: "access-mangmt.jpg"
+coverImage: "access-mangmt.webp"
tags: ["zero trust", "mfa", "enterprise security", "access control"]
author: "Vikas Kalwani"
description: "Access management is essential for modern businesses. This blog will walk you through the five access management best practices to help you keep your systems reserved for valid users only."
@@ -61,7 +61,7 @@ One of the best ways to protect your company’s digital assets is to implement
[Zero trust](https://www.loginradius.com/blog/identity/beginners-guide-zero-trust-security/) is exactly what it sounds like. Every member of your organization is forced to authenticate their identities before being able to access any resources. This includes employees who are already active inside a company network.
-
+
([Image Source](https://www.infusedinnovations.com/blog/secure-intelligent-workplace/pros-and-cons-of-the-zero-trust-model))
@@ -86,7 +86,7 @@ That’s why multi-factor authentication has become an essential access manageme
When you use MFA, anyone logging in will be asked to provide an additional method of verification once they enter their password. This could be entering a code sent to their email or via text message. It could also be a biometric scan on a mobile device like a fingerprint or facial recognition.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### 4. Get rid of high-risk systems
@@ -125,4 +125,4 @@ Use these best practices to manage access to your systems and ensure that all da
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-access-management-best-practices-enterprises)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-access-management-best-practices-enterprises)
diff --git a/content/identity/5-access-management-best-practices-enterprises/mfa-eb.png b/content/identity/5-access-management-best-practices-enterprises/mfa-eb.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/5-access-management-best-practices-enterprises/mfa-eb.png and /dev/null differ
diff --git a/content/identity/5-access-management-best-practices-enterprises/mfa-eb.webp b/content/identity/5-access-management-best-practices-enterprises/mfa-eb.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/5-access-management-best-practices-enterprises/mfa-eb.webp differ
diff --git a/content/identity/5-access-management-best-practices-enterprises/zero-trust.png b/content/identity/5-access-management-best-practices-enterprises/zero-trust.png
deleted file mode 100644
index 992596c7f..000000000
Binary files a/content/identity/5-access-management-best-practices-enterprises/zero-trust.png and /dev/null differ
diff --git a/content/identity/5-access-management-best-practices-enterprises/zero-trust.webp b/content/identity/5-access-management-best-practices-enterprises/zero-trust.webp
new file mode 100644
index 000000000..678c59027
Binary files /dev/null and b/content/identity/5-access-management-best-practices-enterprises/zero-trust.webp differ
diff --git a/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.png b/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.png
deleted file mode 100644
index 4926b2aaf..000000000
Binary files a/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.png and /dev/null differ
diff --git a/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.webp b/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.webp
new file mode 100644
index 000000000..d4581b1bd
Binary files /dev/null and b/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.webp differ
diff --git a/content/identity/5-myths-about-phishing-attack/cred-stuffing.png b/content/identity/5-myths-about-phishing-attack/cred-stuffing.png
deleted file mode 100644
index 904e3a28e..000000000
Binary files a/content/identity/5-myths-about-phishing-attack/cred-stuffing.png and /dev/null differ
diff --git a/content/identity/5-myths-about-phishing-attack/cred-stuffing.webp b/content/identity/5-myths-about-phishing-attack/cred-stuffing.webp
new file mode 100644
index 000000000..c2d6821c3
Binary files /dev/null and b/content/identity/5-myths-about-phishing-attack/cred-stuffing.webp differ
diff --git a/content/identity/5-myths-about-phishing-attack/index.md b/content/identity/5-myths-about-phishing-attack/index.md
index d97d70bdd..441fb1f12 100644
--- a/content/identity/5-myths-about-phishing-attack/index.md
+++ b/content/identity/5-myths-about-phishing-attack/index.md
@@ -1,7 +1,7 @@
---
title: "5 Myths About Phishing You Should Know"
date: "2022-03-28"
-coverImage: "phish-email.jpg"
+coverImage: "phish-email.webp"
tags: ["data security","mfa","cx"]
author: "Lucy Manole"
description: "Most of us think we can spot a phishing email, but are we really safe against online fraud? Here are some truths about credential phishing."
@@ -34,7 +34,7 @@ Credential phishing attacks are usually targeted attacks that are backed by exte
The victims' credentials are then used to carry out secondary attacks like fraudulent funds transfer, stealing company data, identity fraud, and other fraudulent activities.
-[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
+[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
## Top 5 Myths About Credential Phishing You Should Know
@@ -75,7 +75,7 @@ copying the same messaging format, logo, and signature. They project urgency in
For example, this is a new email intercepted by MailGuard that seems like an auto-generated notification about password expiry.
-
+
[Source](https://www.mailguard.com.au/blog/phishing-email-employing-cpanel-branding-claims-your-password-has-expired)
@@ -126,4 +126,4 @@ Regardless of [how secure your email systems](https://www.loginradius.com/blog/i
We are sure the information shared in this post will help keep your organization safe from such attacks.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-myths-about-phishing-attack)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-myths-about-phishing-attack)
diff --git a/content/identity/5-myths-about-phishing-attack/phish-email.jpg b/content/identity/5-myths-about-phishing-attack/phish-email.jpg
deleted file mode 100644
index 8e0d77ddf..000000000
Binary files a/content/identity/5-myths-about-phishing-attack/phish-email.jpg and /dev/null differ
diff --git a/content/identity/5-myths-about-phishing-attack/phish-email.webp b/content/identity/5-myths-about-phishing-attack/phish-email.webp
new file mode 100644
index 000000000..6718fd37f
Binary files /dev/null and b/content/identity/5-myths-about-phishing-attack/phish-email.webp differ
diff --git a/content/identity/5-myths-about-phishing-attack/ss-1.jpg b/content/identity/5-myths-about-phishing-attack/ss-1.jpg
deleted file mode 100644
index 1407e55cc..000000000
Binary files a/content/identity/5-myths-about-phishing-attack/ss-1.jpg and /dev/null differ
diff --git a/content/identity/5-myths-about-phishing-attack/ss-1.webp b/content/identity/5-myths-about-phishing-attack/ss-1.webp
new file mode 100644
index 000000000..284f4d877
Binary files /dev/null and b/content/identity/5-myths-about-phishing-attack/ss-1.webp differ
diff --git a/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.jpg b/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.jpg
deleted file mode 100644
index 884181a12..000000000
Binary files a/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.jpg and /dev/null differ
diff --git a/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.webp b/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.webp
new file mode 100644
index 000000000..f34b7c0a6
Binary files /dev/null and b/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.webp differ
diff --git a/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.png b/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.png
deleted file mode 100644
index b32dcb27b..000000000
Binary files a/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.png and /dev/null differ
diff --git a/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.webp b/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.webp
new file mode 100644
index 000000000..6c250a4f7
Binary files /dev/null and b/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.webp differ
diff --git a/content/identity/5-ways-to-handle-a-data-breach/index.md b/content/identity/5-ways-to-handle-a-data-breach/index.md
index c3c502c8d..300e6fe32 100644
--- a/content/identity/5-ways-to-handle-a-data-breach/index.md
+++ b/content/identity/5-ways-to-handle-a-data-breach/index.md
@@ -1,7 +1,7 @@
---
title: "How to Manage Situation After a Data Breach"
date: "2021-07-27"
-coverImage: "5-ways-to-handle-a-data-breach-cover.jpg"
+coverImage: "5-ways-to-handle-a-data-breach-cover.webp"
tags: ["data security","cybersecurity","cx"]
author: "Rakesh Soni"
description: "Data breaches are becoming the new normal and enterprises aren’t aware of the necessary steps that should be taken immediately after a breach. This post offers valuable insights that help organizations to quickly and effectively manage a situation after a data breach is detected."
@@ -74,7 +74,7 @@ But many of you would wonder why we need to mention a breach if it isn’t causi
Organizations must take adequate measures to maintain integrity and reputation since a data breach isn’t something that one can hide for an extended period.
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
### **4. Investigate- How did it Happen?**
@@ -104,4 +104,4 @@ The aspects mentioned above can be quite helpful in managing the overall situati
It’s recommended that enterprises should consider stringent security measures to avoid any chance of sneaking into the company’s network.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-ways-to-handle-a-data-breach)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-ways-to-handle-a-data-breach)
\ No newline at end of file
diff --git a/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.png b/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.webp b/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.webp differ
diff --git a/content/identity/6-reliable-authentication-methods-customers/auth-method.png b/content/identity/6-reliable-authentication-methods-customers/auth-method.png
deleted file mode 100644
index c37e9b0a2..000000000
Binary files a/content/identity/6-reliable-authentication-methods-customers/auth-method.png and /dev/null differ
diff --git a/content/identity/6-reliable-authentication-methods-customers/auth-method.webp b/content/identity/6-reliable-authentication-methods-customers/auth-method.webp
new file mode 100644
index 000000000..bf1da33a0
Binary files /dev/null and b/content/identity/6-reliable-authentication-methods-customers/auth-method.webp differ
diff --git a/content/identity/6-reliable-authentication-methods-customers/index.md b/content/identity/6-reliable-authentication-methods-customers/index.md
index 1019ab91c..e5b1a55ab 100644
--- a/content/identity/6-reliable-authentication-methods-customers/index.md
+++ b/content/identity/6-reliable-authentication-methods-customers/index.md
@@ -1,7 +1,7 @@
---
title: "6 Alternative Authentication Methods For Your Online Customers"
date: "2022-08-26"
-coverImage: "reliable-auth.jpg"
+coverImage: "reliable-auth.webp"
tags: ["authentication", "biometric authentication", "digital trust"]
author: "Andre Oentoro"
description: "Providing alternative authentication methods to your customers will not only make your site more secure but will also give them peace of mind knowing that their information is well-protected. This blog breaks down the popular authentication methods to consider for your customers."
@@ -19,7 +19,7 @@ Providing alternative authentication methods will not only make your site more s
This blog will break down popular authentication methods to consider.
-
+
## Alternative Authentications: Why Do You Need Them?
@@ -67,7 +67,7 @@ MFA essentially adds an extra layer of security by requiring users to provide mo
This could include a password, as well as a code that’s sent to the user’s mobile phone or email address.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### #2. SMS-based authentication
@@ -115,4 +115,4 @@ Ultimately, the decision comes down to what you feel is best for your business.
It’s also important to keep in mind that no single authentication method is perfect. The best way to keep your site secure is to use a combination of methods. This will make it more difficult for hackers to gain access to your site and ensure that your customers’ data is safe.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=6-reliable-authentication-methods-customers)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=6-reliable-authentication-methods-customers)
diff --git a/content/identity/6-reliable-authentication-methods-customers/mfa-eb.png b/content/identity/6-reliable-authentication-methods-customers/mfa-eb.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/6-reliable-authentication-methods-customers/mfa-eb.png and /dev/null differ
diff --git a/content/identity/6-reliable-authentication-methods-customers/mfa-eb.webp b/content/identity/6-reliable-authentication-methods-customers/mfa-eb.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/6-reliable-authentication-methods-customers/mfa-eb.webp differ
diff --git a/content/identity/6-reliable-authentication-methods-customers/reliable-auth.jpg b/content/identity/6-reliable-authentication-methods-customers/reliable-auth.jpg
deleted file mode 100644
index 611a87b0f..000000000
Binary files a/content/identity/6-reliable-authentication-methods-customers/reliable-auth.jpg and /dev/null differ
diff --git a/content/identity/6-reliable-authentication-methods-customers/reliable-auth.webp b/content/identity/6-reliable-authentication-methods-customers/reliable-auth.webp
new file mode 100644
index 000000000..ff281e80f
Binary files /dev/null and b/content/identity/6-reliable-authentication-methods-customers/reliable-auth.webp differ
diff --git a/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.png b/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.png
deleted file mode 100644
index 31b7cc833..000000000
Binary files a/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.png and /dev/null differ
diff --git a/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.webp b/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.webp
new file mode 100644
index 000000000..61229103e
Binary files /dev/null and b/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.webp differ
diff --git a/content/identity/7-uncommon-cyberattacks-2023/index.md b/content/identity/7-uncommon-cyberattacks-2023/index.md
index 7ca59b2be..9a7801bdf 100644
--- a/content/identity/7-uncommon-cyberattacks-2023/index.md
+++ b/content/identity/7-uncommon-cyberattacks-2023/index.md
@@ -1,7 +1,7 @@
---
title: "7 Uncommon Cyber Attacks in 2023: Why Your Organization Needs To Be Ready For The Worst-Case Scenarios"
date: "2023-01-27"
-coverImage: "uncommon.jpg"
+coverImage: "uncommon.webp"
tags: ["cybersecurity", "identity management", "cyberattacks"]
author: "Alok Patidar"
description: "Cybercriminals are resourceful and innovative creatures who constantly develop new ways to exploit businesses and customer information to reap benefits. While every organization is aware of the potential threats, they are equally unaware of the uncommon attacks that could severely impact their overall cybersecurity posture."
@@ -51,7 +51,7 @@ The Internet of Things is a growing industry; several intelligent, interconnecte
IoT networks are mainly vulnerable to spoofing, denial-of-service attacks (DDoS), and phishing. And these kinds of attacks can be avoided by leveraging various network security measures, including encryption, identity management, robust authentication, and authorization.
-[](https://www.loginradius.com/resource/digital-trade-zone-threats-cybersecurity-whitepaper)
+[](https://www.loginradius.com/resource/digital-trade-zone-threats-cybersecurity-whitepaper)
### #5. Deepfake
@@ -88,4 +88,4 @@ Cyberattacks are inevitable. As business teams continue to invest in securing th
While organizations need to be wary of both, they should also gear up for complex commodity watering hole attacks and dark web compromises. These are some of the uncommon cyberattacks that all companies should keep an eye out for, especially in a digital transformation environment.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-uncommon-cyberattacks-2023)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-uncommon-cyberattacks-2023)
diff --git a/content/identity/7-uncommon-cyberattacks-2023/trade-wp.png b/content/identity/7-uncommon-cyberattacks-2023/trade-wp.png
deleted file mode 100644
index 24d5add74..000000000
Binary files a/content/identity/7-uncommon-cyberattacks-2023/trade-wp.png and /dev/null differ
diff --git a/content/identity/7-uncommon-cyberattacks-2023/trade-wp.webp b/content/identity/7-uncommon-cyberattacks-2023/trade-wp.webp
new file mode 100644
index 000000000..cce7d892c
Binary files /dev/null and b/content/identity/7-uncommon-cyberattacks-2023/trade-wp.webp differ
diff --git a/content/identity/7-uncommon-cyberattacks-2023/uncommon.jpg b/content/identity/7-uncommon-cyberattacks-2023/uncommon.jpg
deleted file mode 100644
index bdde8cee6..000000000
Binary files a/content/identity/7-uncommon-cyberattacks-2023/uncommon.jpg and /dev/null differ
diff --git a/content/identity/7-uncommon-cyberattacks-2023/uncommon.webp b/content/identity/7-uncommon-cyberattacks-2023/uncommon.webp
new file mode 100644
index 000000000..56f8fab80
Binary files /dev/null and b/content/identity/7-uncommon-cyberattacks-2023/uncommon.webp differ
diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.jpg b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.jpg
deleted file mode 100644
index 2afea04eb..000000000
Binary files a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.jpg and /dev/null differ
diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.webp b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.webp
new file mode 100644
index 000000000..7df2b6150
Binary files /dev/null and b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.webp differ
diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.png b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.png
deleted file mode 100644
index 3e43eac92..000000000
Binary files a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.png and /dev/null differ
diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.webp b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.webp
new file mode 100644
index 000000000..8f2a0af16
Binary files /dev/null and b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.webp differ
diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.png b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.png
deleted file mode 100644
index 991f7c73b..000000000
Binary files a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.png and /dev/null differ
diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.webp b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.webp
new file mode 100644
index 000000000..d8afed4d0
Binary files /dev/null and b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.webp differ
diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.jpg b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.jpg
deleted file mode 100644
index 3925fedcd..000000000
Binary files a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.jpg and /dev/null differ
diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.webp b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.webp
new file mode 100644
index 000000000..9dd29f119
Binary files /dev/null and b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.webp differ
diff --git a/content/identity/7-web-app-sec-threats/credential-stuffing.png b/content/identity/7-web-app-sec-threats/credential-stuffing.png
deleted file mode 100644
index 904e3a28e..000000000
Binary files a/content/identity/7-web-app-sec-threats/credential-stuffing.png and /dev/null differ
diff --git a/content/identity/7-web-app-sec-threats/credential-stuffing.webp b/content/identity/7-web-app-sec-threats/credential-stuffing.webp
new file mode 100644
index 000000000..c2d6821c3
Binary files /dev/null and b/content/identity/7-web-app-sec-threats/credential-stuffing.webp differ
diff --git a/content/identity/7-web-app-sec-threats/index.md b/content/identity/7-web-app-sec-threats/index.md
index b5042ba58..4c61d28e9 100644
--- a/content/identity/7-web-app-sec-threats/index.md
+++ b/content/identity/7-web-app-sec-threats/index.md
@@ -1,7 +1,7 @@
---
title: "7 Common Web Application Security Threats"
date: "2021-01-29"
-coverImage: "7-Common-Web-Application-Security-Threats-cover.jpg"
+coverImage: "7-Common-Web-Application-Security-Threats-cover.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -10,7 +10,7 @@ metatitle: "7 Common Web Application Security Threats | LoginRadius"
metadescription: "Use this list of the top 7 common web application threats and vulnerabilities to find a sound security base for your web apps. Also, learn how to prevent them."
---
-
+
Malicious actors and security experts are in an endless battle over data. While the former wants to steal it, the latter seeks to protect it.
Each year, attackers develop inventive web application security threats to compromise sensitive data and access their targets' database. Consequently, security experts build on the exploited vulnerabilities and strengthen their systems through their learnings every year.
@@ -21,7 +21,7 @@ To ensure adequate safety against web application security threats, businesses s
## 7 Common Web Application Security Threats
-
+
### 1. Injection Attacks
@@ -94,7 +94,7 @@ According to [OWASP top 10 2017](https://owasp.org/www-project-top-ten/), this i
Given how easy it is to detect and exploit default settings that were initially placed to accommodate a simple [user experience](https://www.loginradius.com/customer-experience-solutions/), the implications of such a vulnerability can be vast once the website is live: from admin privileges to complete database access.
-[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
+[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
**How to prevent:**
@@ -138,7 +138,7 @@ Like, IDOR, access to these functions can be gained through URL manipulation as
## How Loginradius Helps in Securing Web Applications for Businesses While Providing a Seamless Experience
-
+
\
Despite the multitude of solutions available to each vulnerability, it is hardly easy to produce your own code to secure a site against web application security threats. Managing an extensive portfolio can be unscalable.
@@ -164,4 +164,4 @@ Among other features, LoginRadius offers:
We recommend using this list of top 7 web application threats and vulnerabilities to find a sound security base for your web apps. Developers can build on these vulnerabilities and learn from previous exploits of other entities to create a more secure application.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-web-app-sec-threats)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-web-app-sec-threats)
diff --git a/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.png b/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.png and /dev/null differ
diff --git a/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.webp b/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.webp differ
diff --git a/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.jpg b/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.jpg
deleted file mode 100644
index e09cc99c1..000000000
Binary files a/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.jpg and /dev/null differ
diff --git a/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.webp b/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.webp
new file mode 100644
index 000000000..d26bfbce8
Binary files /dev/null and b/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.webp differ
diff --git a/content/identity/Maintaining-Quality-Data-Security-Practices/index.md b/content/identity/Maintaining-Quality-Data-Security-Practices/index.md
index 2c86c4c3b..cc16ea951 100644
--- a/content/identity/Maintaining-Quality-Data-Security-Practices/index.md
+++ b/content/identity/Maintaining-Quality-Data-Security-Practices/index.md
@@ -1,7 +1,7 @@
---
title: "Maintaining Quality Data Security Practices"
date: "2021-04-30"
-coverImage: "data-security-loginradius.jpg"
+coverImage: "data-security-loginradius.webp"
tags: ["data security","mfa","cx"]
author: "Rakesh Soni"
description: "Data security is important for businesses today, more than it ever was. By definition, data security is the practice of protecting digital information from unauthorised access, cyber corruption or theft."
@@ -31,7 +31,7 @@ It's not uncommon for businesses to face security risks due to employee’s weak
It's highly recommended to implement [multi-factor authentication](https://www.loginradius.com/blog/identity/2019/06/what-is-multi-factor-authentication/) because it can reduce the likelihood of being attacked by a cyber-criminal.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
**2. Strict Permissions**
@@ -75,4 +75,4 @@ Therefore, educating and training employees is important as it ensures that ever
To conclude, as technology advances and more activities are being processed in the digital space, it’s becoming more and more important to keep data private and secure. There are several ways organisations can do this; some of which are easy to implement while others may take more time, resources, and focus than others.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=maintaining-quality-data-security-practices)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=maintaining-quality-data-security-practices)
\ No newline at end of file
diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.png b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.webp b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.webp differ
diff --git "a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.png" "b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.png"
deleted file mode 100644
index d63fdd4ac..000000000
Binary files "a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.png" and /dev/null differ
diff --git "a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.webp" "b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.webp"
new file mode 100644
index 000000000..4486d4d7d
Binary files /dev/null and "b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.webp" differ
diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.jpg b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.jpg
deleted file mode 100644
index 93d151248..000000000
Binary files a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.jpg and /dev/null differ
diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.webp b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.webp
new file mode 100644
index 000000000..08abf7133
Binary files /dev/null and b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.webp differ
diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.jpg b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.jpg
deleted file mode 100644
index 59f4bb9db..000000000
Binary files a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.jpg and /dev/null differ
diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.webp b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.webp
new file mode 100644
index 000000000..613155ae1
Binary files /dev/null and b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.webp differ
diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/index.md b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/index.md
index 85120d41a..555059b1c 100644
--- a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/index.md
+++ b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/index.md
@@ -1,7 +1,7 @@
---
title: "Multi-Factor Authentication - A Beginner’s Guide"
date: "2021-03-23"
-coverImage: "MFA-Loginradius.jpg"
+coverImage: "MFA-Loginradius.webp"
tags: ["mfa","password security","compliance"]
author: "Ashish Kumar Yadav"
description: "MFA or multi-factor authentication is a feature widely used by businesses to ensure that the consumers coming on their website are actually who they say they are. There are multiple ways to implement multifactor authentication. We will get to them one by one in this blog."
@@ -38,7 +38,7 @@ It is done by providing at least two pieces of proof or evidence to state their
MFA works in this way because, let’s suppose one of the factors is hacked by the attackers or invalid user, the chances of another factor also getting compromised are pretty low. That is why **[MFA authentication](https://www.loginradius.com/multi-factor-authentication/)** requires multiple factors, and this is how it provides a higher level of API security to consumers’ identity data.
- [](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+ [](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
## Why MFA is So Important
@@ -71,7 +71,7 @@ These are three main reasons which are most relevant to explain how and why **[I
Now that you’ve learned why MFA is critical, you may be keen to know how this feature works and how you can implement it.
-
+
## How Does Multi-Factor Authentication Work
@@ -115,5 +115,5 @@ In this article, we talked about applying a simple approach of using Multi-facto
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=multi-factor-authentication-a-beginners-guide)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=multi-factor-authentication-a-beginners-guide)
diff --git a/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.jpg b/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.jpg
deleted file mode 100644
index ec1570d08..000000000
Binary files a/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.jpg and /dev/null differ
diff --git a/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.webp b/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.webp
new file mode 100644
index 000000000..bd49597f2
Binary files /dev/null and b/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.webp differ
diff --git a/content/identity/OAuth-authentication-vulnerabilities/index.md b/content/identity/OAuth-authentication-vulnerabilities/index.md
index 72ef8604b..24088f89f 100644
--- a/content/identity/OAuth-authentication-vulnerabilities/index.md
+++ b/content/identity/OAuth-authentication-vulnerabilities/index.md
@@ -1,7 +1,7 @@
---
title: "5 Tips to Prevent OAuth Authentication Vulnerabilities"
date: "2021-04-01"
-coverImage: "OAuth-authentication-vulnerabilities-cover.jpg"
+coverImage: "OAuth-authentication-vulnerabilities-cover.webp"
tags: ["security"]
featured: false
author: "Vishal Sharma"
@@ -102,4 +102,4 @@ Avoiding implementation mistakes is the only way to ensure maximum safety for co
The aforementioned methods are proven to minimize security threats and ensure seamless interaction between the end-user and resource owner.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=oauth-authentication-vulnerabilities)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=oauth-authentication-vulnerabilities)
diff --git a/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.jpg b/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.jpg
deleted file mode 100644
index 29ddecb57..000000000
Binary files a/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.jpg and /dev/null differ
diff --git a/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.webp b/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.webp
new file mode 100644
index 000000000..d3ff3ea01
Binary files /dev/null and b/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.webp differ
diff --git a/content/identity/OAuth2-0-guide/index.md b/content/identity/OAuth2-0-guide/index.md
index 8de218d6a..c7f548be1 100644
--- a/content/identity/OAuth2-0-guide/index.md
+++ b/content/identity/OAuth2-0-guide/index.md
@@ -1,7 +1,7 @@
---
title: "Working With Industry Authorization: A Beginner's Guide to OAuth 2.0"
date: "2021-06-08"
-coverImage: "OAuth2.0-guide-cover.jpg"
+coverImage: "OAuth2.0-guide-cover.webp"
tags: ["data security","authorization","cx"]
author: "Vishal Sharma"
description: " OAuth 2.0 is an authorization protocol designed to control access within a web application or a mobile application. Here’s an interesting read showcasing the role of OAuth 2.0 for offering secure access to resources and why enterprises should get it in place."
@@ -94,4 +94,4 @@ Businesses seeking the finest modes of authentication coupled with authorization
The LoginRadius CIAM is designed to empower businesses by offering the finest user experience and maximum security through industry-standard protocols including OAuth 2.0.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=oauth2-0-guide)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=oauth2-0-guide)
diff --git a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.png b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.png and /dev/null differ
diff --git a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.webp b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.webp differ
diff --git a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/index.md b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/index.md
index 3469bdc19..3cfe189e2 100644
--- a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/index.md
+++ b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/index.md
@@ -1,7 +1,7 @@
---
title: "How to Put Yourself In Control of Your Data by Leveraging LoginRadius' SSO"
date: "2021-03-18"
-coverImage: "sso-loginradius.jpg"
+coverImage: "sso-loginradius.webp"
tags: ["customer-experience"]
featured: false
author: "Rakesh Soni"
@@ -38,7 +38,7 @@ With the advent of remote, mobile, and fluid workforces, several of whom may cho
The costs of **[identity and access management](https://www.loginradius.com/blog/identity/2021/01/what-is-iam/)** often entail several components, including the technology platform, IT overheads, and any required physical infrastructure. The initial costs of establishing this system can be relatively high. It is easy to go overboard with it or make expensive choices that are not suitable for the company.
-[](https://www.loginradius.com/single-sign-on/)
+[](https://www.loginradius.com/single-sign-on/)
Smart investment is essential here, and the right tools can have a massive impact on the ROI in terms of minimizing risk, securing identities, and better compliance.
@@ -106,4 +106,4 @@ We have explained the importance of having an SSO strategy that fits the organiz
If you would like to speak to an expert about developing an SSO strategy for your organization, please click to your Book A Demo Link.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=put-yourself-in-control-of-your-data-by-leveraging-loginradius-sso)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=put-yourself-in-control-of-your-data-by-leveraging-loginradius-sso)
diff --git a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.jpg b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.jpg
deleted file mode 100644
index c62ea2bed..000000000
Binary files a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.jpg and /dev/null differ
diff --git a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.webp b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.webp
new file mode 100644
index 000000000..4d13319ea
Binary files /dev/null and b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.webp differ
diff --git a/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.png b/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.png
deleted file mode 100644
index c5d330417..000000000
Binary files a/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.png and /dev/null differ
diff --git a/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.webp b/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.webp
new file mode 100644
index 000000000..82a4caffb
Binary files /dev/null and b/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.webp differ
diff --git a/content/identity/Single-Sign-On-A-Beginners-Guide/index.md b/content/identity/Single-Sign-On-A-Beginners-Guide/index.md
index 13e48c21a..f22713b72 100644
--- a/content/identity/Single-Sign-On-A-Beginners-Guide/index.md
+++ b/content/identity/Single-Sign-On-A-Beginners-Guide/index.md
@@ -1,7 +1,7 @@
---
title: "Single Sign-On- A Beginner’s Guide"
date: "2021-03-23"
-coverImage: "sso-loginradius.jpg"
+coverImage: "sso-loginradius.webp"
tags: ["single sign on","data security","cx"]
author: "Ashish Kumar Yadav"
description: "The beauty of single sign-on lies in its simplicity. The feature authenticates you on a one-on-one designated platform, allowing you to utilize tons of available services without having to login and logout every time. Consumers can think of this as similar to the social sign-in via Google, Facebook, Twitter, etc."
@@ -26,7 +26,7 @@ Today, a single consumer interacts with various apps/websites which require them
Unfortunately, when it comes to the protection of such data, 100% prevention is never possible. However, there are various methods to reduce this breach possibility to a bare minimum. One such way is Single Sign-On.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
## What is Single Sign-On
@@ -72,4 +72,4 @@ In this article, we talked about applying a simple approach of using Single Sign
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=single-sign-on-a-beginners-guide)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=single-sign-on-a-beginners-guide)
\ No newline at end of file
diff --git a/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.jpg b/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.jpg
deleted file mode 100644
index a086d1101..000000000
Binary files a/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.jpg and /dev/null differ
diff --git a/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.webp b/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.webp
new file mode 100644
index 000000000..85d88b1f4
Binary files /dev/null and b/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.webp differ
diff --git a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.png b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.png
deleted file mode 100644
index 9b885caa8..000000000
Binary files a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.png and /dev/null differ
diff --git a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.webp b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.webp
new file mode 100644
index 000000000..62f54b93f
Binary files /dev/null and b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.webp differ
diff --git a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.jpg b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.jpg
deleted file mode 100644
index 6031ea088..000000000
Binary files a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.jpg and /dev/null differ
diff --git a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.webp b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.webp
new file mode 100644
index 000000000..429a0fc59
Binary files /dev/null and b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.webp differ
diff --git a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/index.md b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/index.md
index 50cbc65ae..1bd17c6f9 100644
--- a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/index.md
+++ b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/index.md
@@ -1,7 +1,7 @@
---
title: "Top 10 Cybersecurity Predictions for 2021 That SMBs Must Know"
date: "2021-03-19"
-coverImage: "cybersecurity-loginradius.jpg"
+coverImage: "cybersecurity-loginradius.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -43,7 +43,7 @@ Targeted phishing attacks are one of the leading cybersecurity threats that SMBs
Last year, despite the pandemic, hackers actively targeted **[healthcare](https://www.loginradius.com/industry-healthcare/)** and pharma companies and spread fake news about vaccine development. Data breaches in the healthcare sector peaked in 2020 and are expected to continue in the short-term future.
- [](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
+ [](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
[**McKinsey**](https://www.mckinsey.com/business-functions/risk/our-insights/covid-19-crisis-shifts-cybersecurity-priorities-and-budgets) predicts that the healthcare industry will be among the top four spenders in cybersecurity solutions in the coming decade. Apart from increasing their spending, SME players in the healthcare sector also need to evaluate their security infrastructure to counter these cyber threats.
@@ -107,4 +107,4 @@ Some of the common threats faced by the financial services industry include phis
For SMBs, the global market for cybersecurity solutions is expected to touch [$80 billion](https://www.infosecurity-magazine.com/news/attacks-on-banks-spike-238-during/) in the future. This article has highlighted ten of the biggest cybersecurity predictions for SMBs in the coming decade.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-10-cybersecurity-predictions-for-2021-that-smbs-must-know)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-10-cybersecurity-predictions-for-2021-that-smbs-must-know)
diff --git a/content/identity/What-is-User-Management/DS-user-management.png b/content/identity/What-is-User-Management/DS-user-management.png
deleted file mode 100644
index fc6f98c05..000000000
Binary files a/content/identity/What-is-User-Management/DS-user-management.png and /dev/null differ
diff --git a/content/identity/What-is-User-Management/DS-user-management.webp b/content/identity/What-is-User-Management/DS-user-management.webp
new file mode 100644
index 000000000..c60f3551f
Binary files /dev/null and b/content/identity/What-is-User-Management/DS-user-management.webp differ
diff --git a/content/identity/What-is-User-Management/LoginRadius-User-Management.png b/content/identity/What-is-User-Management/LoginRadius-User-Management.png
deleted file mode 100644
index 4da86607c..000000000
Binary files a/content/identity/What-is-User-Management/LoginRadius-User-Management.png and /dev/null differ
diff --git a/content/identity/What-is-User-Management/LoginRadius-User-Management.webp b/content/identity/What-is-User-Management/LoginRadius-User-Management.webp
new file mode 100644
index 000000000..32fb1890f
Binary files /dev/null and b/content/identity/What-is-User-Management/LoginRadius-User-Management.webp differ
diff --git a/content/identity/What-is-User-Management/index.md b/content/identity/What-is-User-Management/index.md
index 2622ac670..460121c51 100644
--- a/content/identity/What-is-User-Management/index.md
+++ b/content/identity/What-is-User-Management/index.md
@@ -1,7 +1,7 @@
---
title: "What Is User Management?"
date: "2021-03-16"
-coverImage: "user-mngmnt.jpg"
+coverImage: "user-mngmnt.webp"
tags: ["user management","identity access management","cx"]
author: "Rakesh Soni"
description: "Though user management has been around for a long time now, especially within the IAM and ITAM space, it has assumed new importance with introducing cloud-based subscriptions. Recent trends show that there is a sure shift to cloud-based IAM, granting administrators greater access and control over digital assets management."
@@ -124,7 +124,7 @@ The third generation of user management solutions is designed for the cloud-firs
These solutions support a wide range of authentication methods, including [social login](https://www.loginradius.com/social-login/) and multi-factor authentication, and can integrate with existing identity and access management systems. They also provide advanced analytics and monitoring capabilities to detect and prevent security threats.
-[](https://www.loginradius.com/resource/loginradius-user-management-datasheet)
+[](https://www.loginradius.com/resource/loginradius-user-management-datasheet)
## **Why Should Businesses Use LoginRadius’ Effective User Management?**
@@ -160,4 +160,4 @@ Example: Granting specific employees access to financial data while restricting
User access management includes assigning permissions, managing passwords, implementing multi-factor authentication, and monitoring login attempts.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-user-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-user-management)
diff --git a/content/identity/What-is-User-Management/user-mngmnt.jpg b/content/identity/What-is-User-Management/user-mngmnt.jpg
deleted file mode 100644
index 94a03628f..000000000
Binary files a/content/identity/What-is-User-Management/user-mngmnt.jpg and /dev/null differ
diff --git a/content/identity/What-is-User-Management/user-mngmnt.webp b/content/identity/What-is-User-Management/user-mngmnt.webp
new file mode 100644
index 000000000..b07c58595
Binary files /dev/null and b/content/identity/What-is-User-Management/user-mngmnt.webp differ
diff --git a/content/identity/What-is-User-Management/what-is-user-management-loginradius.jpg b/content/identity/What-is-User-Management/what-is-user-management-loginradius.jpg
deleted file mode 100644
index 1379ab046..000000000
Binary files a/content/identity/What-is-User-Management/what-is-user-management-loginradius.jpg and /dev/null differ
diff --git a/content/identity/What-is-User-Management/what-is-user-management-loginradius.webp b/content/identity/What-is-User-Management/what-is-user-management-loginradius.webp
new file mode 100644
index 000000000..c33fbd620
Binary files /dev/null and b/content/identity/What-is-User-Management/what-is-user-management-loginradius.webp differ
diff --git a/content/identity/account-security-consumers/account-security-consumers-cover.jpg b/content/identity/account-security-consumers/account-security-consumers-cover.jpg
deleted file mode 100644
index 7b754a1d2..000000000
Binary files a/content/identity/account-security-consumers/account-security-consumers-cover.jpg and /dev/null differ
diff --git a/content/identity/account-security-consumers/account-security-consumers-cover.webp b/content/identity/account-security-consumers/account-security-consumers-cover.webp
new file mode 100644
index 000000000..ffa70d5eb
Binary files /dev/null and b/content/identity/account-security-consumers/account-security-consumers-cover.webp differ
diff --git a/content/identity/account-security-consumers/index.md b/content/identity/account-security-consumers/index.md
index c55cdc273..994d8fe76 100644
--- a/content/identity/account-security-consumers/index.md
+++ b/content/identity/account-security-consumers/index.md
@@ -1,7 +1,7 @@
---
title: "How Companies can Enable Account security for their Consumers"
date: "2021-04-09"
-coverImage: "account-security-consumers-cover.jpg"
+coverImage: "account-security-consumers-cover.webp"
tags: ["Security"]
featured: false
author: "Navanita Devi"
@@ -68,7 +68,7 @@ Integrating a two-factor authentication process adds an extra layer of security
Multi-factor authentication can easily be done by adding a verification code, personal security question, or biometrics. These can easily be integrated into any business or company to increase overall account security. This reduces the likelihood of fraud and identity theft.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
However, integration of the two-factor or multi-factor authentication process can take time, especially because consumers upgrade their account security at their own pace. In the meanwhile, companies can take other security measures to increase their data security.
@@ -131,4 +131,4 @@ What else makes [LoginRadius' Single Sign-On](https://www.loginradius.com/protoc
With data at more risk than ever, more users are demanding businesses streamline their user onboarding process while protecting the data at the same time. This usually results in compromising the account security in favor of user-friendliness. As technology advances rapidly, businesses should keep track of the emerging cybersecurity trends and upgrade their data security systems accordingly.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=account-security-consumers)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=account-security-consumers)
diff --git a/content/identity/account-security-consumers/mfa.png b/content/identity/account-security-consumers/mfa.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/account-security-consumers/mfa.png and /dev/null differ
diff --git a/content/identity/account-security-consumers/mfa.webp b/content/identity/account-security-consumers/mfa.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/account-security-consumers/mfa.webp differ
diff --git a/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.png b/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.png
deleted file mode 100644
index 1f39a27f3..000000000
Binary files a/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.png and /dev/null differ
diff --git a/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.webp b/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.webp
new file mode 100644
index 000000000..8a8067f56
Binary files /dev/null and b/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.webp differ
diff --git a/content/identity/adaptive-authentication/adaptive-authentication.jpg b/content/identity/adaptive-authentication/adaptive-authentication.jpg
deleted file mode 100644
index 528ea7bb0..000000000
Binary files a/content/identity/adaptive-authentication/adaptive-authentication.jpg and /dev/null differ
diff --git a/content/identity/adaptive-authentication/adaptive-authentication.webp b/content/identity/adaptive-authentication/adaptive-authentication.webp
new file mode 100644
index 000000000..bec684d35
Binary files /dev/null and b/content/identity/adaptive-authentication/adaptive-authentication.webp differ
diff --git a/content/identity/adaptive-authentication/index.md b/content/identity/adaptive-authentication/index.md
index be6136155..ea0b7312c 100644
--- a/content/identity/adaptive-authentication/index.md
+++ b/content/identity/adaptive-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Adaptive Authentication- Is it the Next Breakthrough in Customer Authentication?"
date: "2021-07-15"
-coverImage: "adaptive-authentication.jpg"
+coverImage: "adaptive-authentication.webp"
tags: ["adaptive authentication","mfa","ciam solution"]
author: "Vishal Sharma"
description: "Adaptive authentication is a game-changer for enterprises that require strong fencing to protect consumer and enterprise data. Here’s a quick read depicting the role and need for adaptive authentication instead of just multi-factor authentication."
@@ -65,7 +65,7 @@ Apart from this, adaptive authentication is considered far smarter than multi-fa
This means the mechanism automatically implements robust authentication controls whenever a login seems to be suspicious.
-[](https://www.loginradius.com/resource/fixing-broken-authentication-with-adaptive-mfa/)
+[](https://www.loginradius.com/resource/fixing-broken-authentication-with-adaptive-mfa/)
## Adaptive Authentication and Strong Customer Authentication
@@ -118,4 +118,4 @@ Enterprises seeking the highest level of consumer and organization data security
Need more help? [Reach us](https://www.loginradius.com/contact-sales2/) to know how LoginRadius’ “Adaptive Authentication” can help secure your consumer identities and business information.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=adaptive-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=adaptive-authentication)
diff --git a/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.png b/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.png and /dev/null differ
diff --git a/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.webp b/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.webp differ
diff --git a/content/identity/advanced-identity-security-based-attacks/identity-attacks.jpg b/content/identity/advanced-identity-security-based-attacks/identity-attacks.jpg
deleted file mode 100644
index 6d0396f2f..000000000
Binary files a/content/identity/advanced-identity-security-based-attacks/identity-attacks.jpg and /dev/null differ
diff --git a/content/identity/advanced-identity-security-based-attacks/identity-attacks.webp b/content/identity/advanced-identity-security-based-attacks/identity-attacks.webp
new file mode 100644
index 000000000..0b341036c
Binary files /dev/null and b/content/identity/advanced-identity-security-based-attacks/identity-attacks.webp differ
diff --git a/content/identity/advanced-identity-security-based-attacks/index.md b/content/identity/advanced-identity-security-based-attacks/index.md
index 19094cabc..908d57f78 100644
--- a/content/identity/advanced-identity-security-based-attacks/index.md
+++ b/content/identity/advanced-identity-security-based-attacks/index.md
@@ -1,7 +1,7 @@
---
title: "The Growing Threat of Identity-Based Attacks and the Need for an Advanced Identity Security Approach"
date: "2024-06-05"
-coverImage: "identity-attacks.jpg"
+coverImage: "identity-attacks.webp"
tags: ["identity security","zero trust security","cx"]
author: "Kundan Singh"
description: "Identity-based attacks are escalating, targeting personal data and business secrets with unprecedented sophistication. Traditional security measures fall short; a new approach is essential. Explore advanced identity security strategies like Zero Trust, MFA, CIAM, and behavioral analytics to safeguard against these evolving threats."
@@ -55,7 +55,7 @@ To address the growing threat of identity-based attacks, organizations must adop
1. **Zero Trust Architecture**: Zero Trust assumes that no entity, whether inside or outside the network, should be trusted by default. It requires continuous verification of identities and strict access controls based on the principle of least privilege.
-[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-modern-business/)
+[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-modern-business/)
2. **Multi-Factor Authentication (MFA)**: MFA should be implemented with robust factors beyond SMS-based verification, such as biometrics, hardware tokens, and adaptive authentication that assesses risk based on user behavior and context.
@@ -75,4 +75,4 @@ By adopting an advanced identity security approach that emphasizes Zero Trust, r
As cybercriminals continue to evolve their tactics, staying ahead requires a proactive and comprehensive strategy that prioritizes identity security at every level.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advanced-identity-security-based-attacks)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advanced-identity-security-based-attacks)
\ No newline at end of file
diff --git a/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.png b/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.png and /dev/null differ
diff --git a/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.webp b/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.webp differ
diff --git a/content/identity/advanced-risk-based-authentication-2024/index.md b/content/identity/advanced-risk-based-authentication-2024/index.md
index 1c956dec9..cac00238a 100644
--- a/content/identity/advanced-risk-based-authentication-2024/index.md
+++ b/content/identity/advanced-risk-based-authentication-2024/index.md
@@ -1,7 +1,7 @@
---
title: "Reinforcing Security with Advanced Risk-Based Authentication in 2024 & Beyond"
date: "2024-02-08"
-coverImage: "rba.jpg"
+coverImage: "rba.webp"
tags: ["risk based authentication","mfa","cx"]
author: "Rakesh Soni"
description: "Explore the significance of Risk-Based Authentication (RBA) in today's digital landscape, where robust security measures are essential. Learn how RBA adds an extra layer of defense against sophisticated cyber threats, shields against modern attack vectors, and enhances security in high-risk situations."
@@ -42,7 +42,7 @@ Securing sensitive accounts and data against unauthorized access and fraudulent
The Device Factor in Risk-Based Authentication (RBA) offers a vital layer of defense by validating user authenticity through device characteristics, significantly reducing the risk of unauthorized access and bolstering overall security posture.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
LoginRadius’s Device Factor in RBA precisely considers factors such as device type, operating system, and security patches; RBA systems can make informed decisions about granting access, ensuring that only trusted devices are permitted.
@@ -64,4 +64,4 @@ Advanced Risk-Based Authentication (RBA) is an indispensable component of modern
By leveraging solutions like LoginRadius CIAM, businesses can harness the full potential of RBA to fortify their defenses, safeguard user accounts, and uphold trust in their digital ecosystems, both now and in the years to come.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advanced-risk-based-authentication-2024)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advanced-risk-based-authentication-2024)
\ No newline at end of file
diff --git a/content/identity/advanced-risk-based-authentication-2024/rba.jpg b/content/identity/advanced-risk-based-authentication-2024/rba.jpg
deleted file mode 100644
index 55cdf90ca..000000000
Binary files a/content/identity/advanced-risk-based-authentication-2024/rba.jpg and /dev/null differ
diff --git a/content/identity/advanced-risk-based-authentication-2024/rba.webp b/content/identity/advanced-risk-based-authentication-2024/rba.webp
new file mode 100644
index 000000000..6e6ed1b4d
Binary files /dev/null and b/content/identity/advanced-risk-based-authentication-2024/rba.webp differ
diff --git a/content/identity/ai-cybersecurity-online-security/cta.png b/content/identity/ai-cybersecurity-online-security/cta.png
deleted file mode 100644
index 1116bcde5..000000000
Binary files a/content/identity/ai-cybersecurity-online-security/cta.png and /dev/null differ
diff --git a/content/identity/ai-cybersecurity-online-security/cta.webp b/content/identity/ai-cybersecurity-online-security/cta.webp
new file mode 100644
index 000000000..8efa78c3e
Binary files /dev/null and b/content/identity/ai-cybersecurity-online-security/cta.webp differ
diff --git a/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.jpg b/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.jpg
deleted file mode 100644
index 925ad6dd8..000000000
Binary files a/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.jpg and /dev/null differ
diff --git a/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.webp b/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.webp
new file mode 100644
index 000000000..1e390e7db
Binary files /dev/null and b/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.webp differ
diff --git a/content/identity/ai-cybersecurity-online-security/index.md b/content/identity/ai-cybersecurity-online-security/index.md
index bf0c90e8a..9460a6da7 100644
--- a/content/identity/ai-cybersecurity-online-security/index.md
+++ b/content/identity/ai-cybersecurity-online-security/index.md
@@ -1,7 +1,7 @@
---
title: "How AI-Enabled Cybersecurity Solutions Are Strengthening Our Online Security"
date: "2024-09-30"
-coverImage: "cyber-security-technology-online-data-protection-by-ai-robot.jpg"
+coverImage: "cyber-security-technology-online-data-protection-by-ai-robot.webp"
tags: ["cybersecurity","AI","customer identity"]
author: "Carl Torrence"
description: "CIAM gets a major upgrade with AI, which secures customer identities, streamlines access, and ensures only the right people get in. But we can't just set it and forget it. Discover why AI is a game changer, key applications in the field, and what the future looks like with AI advancements."
@@ -58,7 +58,7 @@ For example, the credit union knowledge base includes large volumes of sensitive
This dual focus on security and efficiency helps credit unions maintain the trust of their members while navigating the complexities of modern digital threats.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### 4. Fraud detection and prevention
diff --git a/content/identity/ai-enterprise-security-threats/cta.png b/content/identity/ai-enterprise-security-threats/cta.png
deleted file mode 100644
index c8e655587..000000000
Binary files a/content/identity/ai-enterprise-security-threats/cta.png and /dev/null differ
diff --git a/content/identity/ai-enterprise-security-threats/cta.webp b/content/identity/ai-enterprise-security-threats/cta.webp
new file mode 100644
index 000000000..1082e7522
Binary files /dev/null and b/content/identity/ai-enterprise-security-threats/cta.webp differ
diff --git a/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.jpg b/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.jpg
deleted file mode 100644
index 0fba23a25..000000000
Binary files a/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.jpg and /dev/null differ
diff --git a/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.webp b/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.webp
new file mode 100644
index 000000000..d2c164f1b
Binary files /dev/null and b/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.webp differ
diff --git a/content/identity/ai-enterprise-security-threats/index.md b/content/identity/ai-enterprise-security-threats/index.md
index cc682b23d..00f88b0dc 100644
--- a/content/identity/ai-enterprise-security-threats/index.md
+++ b/content/identity/ai-enterprise-security-threats/index.md
@@ -1,7 +1,7 @@
---
title: "AI and the Changing Face of Enterprise Security Threats"
date: "2024-07-15"
-coverImage: "future-artificial-intelligence-robot-cyborg.jpg"
+coverImage: "future-artificial-intelligence-robot-cyborg.webp"
tags: ["enterprise security", "ai", "cyberattacks"]
author: "Rakesh Soni"
description: "Explore how AI is revolutionizing enterprise security by improving threat detection, prevention, and response. Learn about the new challenges and opportunities that AI brings to the cybersecurity landscape."
@@ -52,7 +52,7 @@ Cybercriminals are leveraging AI to develop more sophisticated and targeted atta
AI-generated deepfakes pose a significant threat to enterprise security. These realistic fake videos and audio can be used for social engineering attacks, manipulating individuals into divulging sensitive information or performing unauthorized actions.
-[](https://www.loginradius.com/resource/whitepaper/user-authentication-security/)
+[](https://www.loginradius.com/resource/whitepaper/user-authentication-security/)
### 3. Automated Vulnerability Exploitation
diff --git a/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.png b/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.png
deleted file mode 100644
index 7cc78c915..000000000
Binary files a/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.png and /dev/null differ
diff --git a/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.webp b/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.webp
new file mode 100644
index 000000000..86276b545
Binary files /dev/null and b/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.webp differ
diff --git a/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.jpg b/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.jpg
deleted file mode 100644
index 2c42544f5..000000000
Binary files a/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.jpg and /dev/null differ
diff --git a/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.webp b/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.webp
new file mode 100644
index 000000000..49f7df794
Binary files /dev/null and b/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.webp differ
diff --git a/content/identity/ai-revolutionizing-user-authentication/index.md b/content/identity/ai-revolutionizing-user-authentication/index.md
index 0741a53ea..da8c12c7b 100644
--- a/content/identity/ai-revolutionizing-user-authentication/index.md
+++ b/content/identity/ai-revolutionizing-user-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "How AI Is Changing the Game in User Authentication"
date: "2024-05-23"
-coverImage: "artificial-intelligence.jpg"
+coverImage: "artificial-intelligence.webp"
tags: ["user authentication","data security","artificial intelligence"]
author: "Maya Kirianova"
description: "This blog explores how AI can revolutionize authentication, from addressing the limitations of traditional methods to utilizing innovative techniques that use machine learning algorithms."
@@ -20,9 +20,9 @@ This blog explores how AI can revolutionize [authentication](https://www.loginra
## Traditional Methods of User Authentication
-
+
-Source: [safety4sea.com](https://safety4sea.com/wp-content/uploads/2019/01/NCSC-Password-Security-1140x806.png)
+Source: [safety4sea.com](https://safety4sea.com/wp-content/uploads/2019/01/NCSC-Password-Security-1140x806.webp)
[Password-based authentication](https://www.loginradius.com/blog/identity/common-vulnerabilities-password-based-login/) is the oldest and most widely used method. A user is required to enter a username and password and nothing else. However, this way of accessing the account is pretty vulnerable to phishing and brute-force attacks. Hackers can use automated tools to try different password combinations until they find the correct one or just send fraudulent emails or website links to compromise security. If a user utilizes the same password across multiple accounts, the threat of a security breach grows.
@@ -34,7 +34,7 @@ Source: [safety4sea.com](https://safety4sea.com/wp-content/uploads/2019/01/NCSC-
AI-powered authentication involves the use of machine learning algorithms to analyze user behavior, detect anomalies, and verify identities in real-time. It can adapt to dynamic patterns and learn from user interactions. It means that AI provides continuous authentication. Such an approach can detect suspicious activities or authorized access attempts in real-time.
-[](https://www.loginradius.com/resource/whitepaper/continuous-authentication/)
+[](https://www.loginradius.com/resource/whitepaper/continuous-authentication/)
AI algorithms can evaluate the risks related to each authentication attempt. They use device characteristics, location, and behavioral patterns to adjust authentication requirements. Moreover, AI-powered authentication systems can identify unusual or suspicious behavior that may indicate fraud or cyber-attacks. They can flag potential security threats before they escalate.
@@ -94,4 +94,4 @@ The future for AI in user authentication is promising, though more potential cha
Although AI is changing the game in user authentication, everyone must be aware of its potential benefits and drawbacks to protect sensitive information and reduce security risks. In this way, organizations and companies will be able to secure important data and build trust with users.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-revolutionizing-user-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-revolutionizing-user-authentication)
\ No newline at end of file
diff --git a/content/identity/ai-revolutionizing-user-authentication/password-security.png b/content/identity/ai-revolutionizing-user-authentication/password-security.png
deleted file mode 100644
index 71146b196..000000000
Binary files a/content/identity/ai-revolutionizing-user-authentication/password-security.png and /dev/null differ
diff --git a/content/identity/ai-revolutionizing-user-authentication/password-security.webp b/content/identity/ai-revolutionizing-user-authentication/password-security.webp
new file mode 100644
index 000000000..19d2690fd
Binary files /dev/null and b/content/identity/ai-revolutionizing-user-authentication/password-security.webp differ
diff --git a/content/identity/ai-security-risk-management/ai-security.jpg b/content/identity/ai-security-risk-management/ai-security.jpg
deleted file mode 100644
index 7ac37c071..000000000
Binary files a/content/identity/ai-security-risk-management/ai-security.jpg and /dev/null differ
diff --git a/content/identity/ai-security-risk-management/ai-security.webp b/content/identity/ai-security-risk-management/ai-security.webp
new file mode 100644
index 000000000..ed4d586bb
Binary files /dev/null and b/content/identity/ai-security-risk-management/ai-security.webp differ
diff --git a/content/identity/ai-security-risk-management/index.md b/content/identity/ai-security-risk-management/index.md
index 88d102a05..a6c8bc2a9 100644
--- a/content/identity/ai-security-risk-management/index.md
+++ b/content/identity/ai-security-risk-management/index.md
@@ -1,7 +1,7 @@
---
title: "Managing Generative AI Security Risks in the Enterprise- A Quick Guide"
date: "2023-10-25"
-coverImage: "ai-security.jpg"
+coverImage: "ai-security.webp"
tags: ["data security","artificial intelligence","ciam solutions","cx"]
author: "Rakesh Soni"
description: "Navigate generative AI security with our concise guide for enterprises. From data encryption to countering adversarial attacks, discover essential strategies for safeguarding your digital assets. Embrace transparency and empower your team to stay ahead in the rapidly evolving landscape of AI innovation."
@@ -44,7 +44,7 @@ Ethical Implications: AI systems can inadvertently generate biased or inappropri
The field of AI security is ever-evolving, with security threats and defense mechanisms advancing rapidly. Enterprises must adopt a proactive stance by staying updated with the latest AI security research and practice developments.
-[](https://www.loginradius.com/resource/how-ai-is-going-to-change-your-iam-initiatives/)
+[](https://www.loginradius.com/resource/how-ai-is-going-to-change-your-iam-initiatives/)
Regularly reassessing security protocols and investing in cutting-edge technologies can significantly enhance an organization's resilience against emerging threats. Moreover, fostering a culture of innovation within the organization can lead to the development of novel solutions and strategies.
Encouraging research and development in AI security benefits the enterprise and contributes to the broader cybersecurity community.
@@ -65,4 +65,4 @@ By understanding the unique threats, implementing robust security measures, and
Staying informed and prepared is the key to success. As technologies continue advancing, enterprises must remain vigilant, adapt their security strategies, and explore innovative ways to protect their assets and stakeholders in the digital age.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-security-risk-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-security-risk-management)
diff --git a/content/identity/ai-security-risk-management/wp-ai.png b/content/identity/ai-security-risk-management/wp-ai.png
deleted file mode 100644
index 1116bcde5..000000000
Binary files a/content/identity/ai-security-risk-management/wp-ai.png and /dev/null differ
diff --git a/content/identity/ai-security-risk-management/wp-ai.webp b/content/identity/ai-security-risk-management/wp-ai.webp
new file mode 100644
index 000000000..8efa78c3e
Binary files /dev/null and b/content/identity/ai-security-risk-management/wp-ai.webp differ
diff --git a/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.jpg b/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.jpg
deleted file mode 100644
index ffbd5fdd9..000000000
Binary files a/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.jpg and /dev/null differ
diff --git a/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.webp b/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.webp
new file mode 100644
index 000000000..8acaba125
Binary files /dev/null and b/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.webp differ
diff --git a/content/identity/alok-patidar-answers-cybersecurity-questions/index.md b/content/identity/alok-patidar-answers-cybersecurity-questions/index.md
index 7c0090cb7..d073c6840 100644
--- a/content/identity/alok-patidar-answers-cybersecurity-questions/index.md
+++ b/content/identity/alok-patidar-answers-cybersecurity-questions/index.md
@@ -1,7 +1,7 @@
---
title: "InfoSec Director, Alok Patidar Answers Your Most Difficult Questions on Cybersecurity"
date: "2022-10-28"
-coverImage: "cyber.jpg"
+coverImage: "cyber.webp"
tags: ["cybersecurity", "cyberattacks", "compliance"]
author: "Vishal Sharma"
description: "Every organization has unique needs, which means each one has to be protected in its own way. Therefore, we asked Alok Patidar to chip in. As the Director of Information Security at LoginRadius, he’s dedicated his career to helping businesses protect themselves from cyber criminals."
@@ -107,4 +107,4 @@ Hence, the aforementioned questions can help clear their doubts regarding cybers
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=alok-patidar-answers-cybersecurity-questions)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=alok-patidar-answers-cybersecurity-questions)
diff --git a/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.png b/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.png
deleted file mode 100644
index f395fc87a..000000000
Binary files a/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.png and /dev/null differ
diff --git a/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.webp b/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.webp
new file mode 100644
index 000000000..9d7f96b4e
Binary files /dev/null and b/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.webp differ
diff --git a/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.png b/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.png
deleted file mode 100644
index a77a88ecc..000000000
Binary files a/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.png and /dev/null differ
diff --git a/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.webp b/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.webp
new file mode 100644
index 000000000..53eae8e39
Binary files /dev/null and b/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.webp differ
diff --git a/content/identity/announcing-new-look-of-loginradius/index.md b/content/identity/announcing-new-look-of-loginradius/index.md
index faf160996..90c7fd204 100644
--- a/content/identity/announcing-new-look-of-loginradius/index.md
+++ b/content/identity/announcing-new-look-of-loginradius/index.md
@@ -1,7 +1,7 @@
---
title: "Announcing New Look of LoginRadius"
date: "2020-03-25"
-coverImage: "Announcing-New-Look-of-LoginRadius.png"
+coverImage: "Announcing-New-Look-of-LoginRadius.webp"
tags: ["LoginRadius", "industry-news"]
featured: false
author: "Rakesh Soni"
@@ -16,7 +16,7 @@ Yes! We loved the old one, but we decided to upgrade it as part of our ever-evol
So, here’s our new look.
-
+
As a leader in cloud-based Customer Identity and Access Management (CIAM) solution that the following two core principles are reflected in the branding:
@@ -46,7 +46,7 @@ First, we would like to take a moment to highlight the retirement of our current
Fast-forward to the present day, the new logo marks a crucial milestone towards representing our brand-building process.
-
+
- **Brandmark**: It comprises two concentric circles. Most obvious is the negative space showing a keyhole which is also a literal radius from the centre to the outer edge. The keyhole represents robust security foundation of our platform. It can also be seen as a user icon, protected by white arms implied by the negative space and by the light blue circle. This demonstrates our philosophy of putting the user at the centre of everything. Both of these ideas speak to the concept of protecting identity.
@@ -58,7 +58,7 @@ Letting go of our core designing heritage was never our objective. Our color pal
## Logo Color Combinations
-
+
## A Final Word
@@ -66,4 +66,4 @@ The new logo is an attempt at modernizing our brand and helping it connect more
Amidst the huge chunk of workload that rebranding brings along, we are super thrilled to share this news and would like to take a moment to thank our loyal customer base. Do share your comments about the change.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=announcing-new-look-of-loginradius)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=announcing-new-look-of-loginradius)
diff --git a/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.png b/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.png
deleted file mode 100644
index 2f2f14377..000000000
Binary files a/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.png and /dev/null differ
diff --git a/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.webp b/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.webp
new file mode 100644
index 000000000..af62cf468
Binary files /dev/null and b/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.webp differ
diff --git a/content/identity/announcing-new-look-of-loginradius/logo-1024x991.png b/content/identity/announcing-new-look-of-loginradius/logo-1024x991.png
deleted file mode 100644
index 8bc117428..000000000
Binary files a/content/identity/announcing-new-look-of-loginradius/logo-1024x991.png and /dev/null differ
diff --git a/content/identity/announcing-new-look-of-loginradius/logo-1024x991.webp b/content/identity/announcing-new-look-of-loginradius/logo-1024x991.webp
new file mode 100644
index 000000000..05727e6d2
Binary files /dev/null and b/content/identity/announcing-new-look-of-loginradius/logo-1024x991.webp differ
diff --git a/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.png b/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.png
deleted file mode 100644
index faebe4a27..000000000
Binary files a/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.png and /dev/null differ
diff --git a/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.webp b/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.webp
new file mode 100644
index 000000000..db78ea1ea
Binary files /dev/null and b/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.webp differ
diff --git a/content/identity/api-authentication-analytics/api-authentication-analytics-cover.png b/content/identity/api-authentication-analytics/api-authentication-analytics-cover.png
deleted file mode 100644
index dcb92dfe0..000000000
Binary files a/content/identity/api-authentication-analytics/api-authentication-analytics-cover.png and /dev/null differ
diff --git a/content/identity/api-authentication-analytics/api-authentication-analytics-cover.webp b/content/identity/api-authentication-analytics/api-authentication-analytics-cover.webp
new file mode 100644
index 000000000..43f7155a8
Binary files /dev/null and b/content/identity/api-authentication-analytics/api-authentication-analytics-cover.webp differ
diff --git a/content/identity/api-authentication-analytics/index.md b/content/identity/api-authentication-analytics/index.md
index e4dbdeadb..baa35de50 100644
--- a/content/identity/api-authentication-analytics/index.md
+++ b/content/identity/api-authentication-analytics/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - Authentication API Analytics to Evaluate the Performance of LoginRadius APIs for Your Applications"
date: "2021-03-23"
-coverImage: "api-authentication-analytics-cover.png"
+coverImage: "api-authentication-analytics-cover.webp"
tags: ["authentication","ciam solution","cx"]
author: "Kundan Singh"
description: "Recently, LoginRadius launched Authentication API Analytics to provide an analytics report to businesses and their developers for requests made to different LoginRadius APIs. The feature contains useful charts and analytic tools to view and measure an application's overall performance (where using LoginRadius)."
@@ -25,7 +25,7 @@ The feature contains useful charts and analytic tools to view and measure an app
-[](https://www.loginradius.com/resource/authentication-api-analytics/)
+[](https://www.loginradius.com/resource/authentication-api-analytics/)
@@ -44,7 +44,7 @@ The [Authentication API Analytics](https://www.loginradius.com/resource/authenti
-
+
The API analytical and performance data are available in the following three categories:
@@ -57,7 +57,7 @@ The API analytical and performance data are available in the following three cat
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=api-authentication-analytics)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=api-authentication-analytics)
diff --git a/content/identity/api-authentication-analytics/lets-talk.png b/content/identity/api-authentication-analytics/lets-talk.png
deleted file mode 100644
index 2fc6ddac9..000000000
Binary files a/content/identity/api-authentication-analytics/lets-talk.png and /dev/null differ
diff --git a/content/identity/api-authentication-analytics/lets-talk.webp b/content/identity/api-authentication-analytics/lets-talk.webp
new file mode 100644
index 000000000..5522d721c
Binary files /dev/null and b/content/identity/api-authentication-analytics/lets-talk.webp differ
diff --git a/content/identity/api-authentication-analytics/loginradius-api-authentication.png b/content/identity/api-authentication-analytics/loginradius-api-authentication.png
deleted file mode 100644
index c1fdf0aa5..000000000
Binary files a/content/identity/api-authentication-analytics/loginradius-api-authentication.png and /dev/null differ
diff --git a/content/identity/api-authentication-analytics/loginradius-api-authentication.webp b/content/identity/api-authentication-analytics/loginradius-api-authentication.webp
new file mode 100644
index 000000000..af708e831
Binary files /dev/null and b/content/identity/api-authentication-analytics/loginradius-api-authentication.webp differ
diff --git a/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.png b/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.png and /dev/null differ
diff --git a/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.webp b/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.webp differ
diff --git a/content/identity/apple-lockdown-mode-robust-security/apple-inc.jpg b/content/identity/apple-lockdown-mode-robust-security/apple-inc.jpg
deleted file mode 100644
index fcdae6908..000000000
Binary files a/content/identity/apple-lockdown-mode-robust-security/apple-inc.jpg and /dev/null differ
diff --git a/content/identity/apple-lockdown-mode-robust-security/apple-inc.webp b/content/identity/apple-lockdown-mode-robust-security/apple-inc.webp
new file mode 100644
index 000000000..d937689cc
Binary files /dev/null and b/content/identity/apple-lockdown-mode-robust-security/apple-inc.webp differ
diff --git a/content/identity/apple-lockdown-mode-robust-security/index.md b/content/identity/apple-lockdown-mode-robust-security/index.md
index 14457d27f..3555799a3 100644
--- a/content/identity/apple-lockdown-mode-robust-security/index.md
+++ b/content/identity/apple-lockdown-mode-robust-security/index.md
@@ -1,7 +1,7 @@
---
title: "Will Apple’s ‘Lockdown Mode’ Reduce State-Sponsored Attacks?"
date: "2022-07-07"
-coverImage: "apple-inc.jpg"
+coverImage: "apple-inc.webp"
tags: ["cyberattacks", "apple", "zero trust"]
author: "Rakesh Soni"
description: "The ‘lockdown mode’ is considered a giant leap as a part of their information security for protecting operating systems of iPhone, iPad, and Mac against various threats, including spyware. Let’s understand what a state-sponsored attack is and how this new feature in Apple devices would work to protect critical customer information."
@@ -28,7 +28,7 @@ These attacks usually target a specific group of people that can be spied on to
Various states employ hackers through their government authorities or militaries, making it easier to deny any state involvement even if an attack is detected.
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
## How Does Apple’s ‘Lockdown Mode’ Work?
@@ -52,4 +52,4 @@ However, the underlying risks associated with state-sponsored attacks can’t be
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=apple-lockdown-mode-robust-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=apple-lockdown-mode-robust-security)
diff --git a/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.png b/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.png
deleted file mode 100644
index 3e6b81ee6..000000000
Binary files a/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.png and /dev/null differ
diff --git a/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.webp b/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.webp
new file mode 100644
index 000000000..2f7c01062
Binary files /dev/null and b/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.webp differ
diff --git a/content/identity/assess-improve-your-authentication-system/WP-digitization.png b/content/identity/assess-improve-your-authentication-system/WP-digitization.png
deleted file mode 100644
index 526ebf3e8..000000000
Binary files a/content/identity/assess-improve-your-authentication-system/WP-digitization.png and /dev/null differ
diff --git a/content/identity/assess-improve-your-authentication-system/WP-digitization.webp b/content/identity/assess-improve-your-authentication-system/WP-digitization.webp
new file mode 100644
index 000000000..6ed0d46f2
Binary files /dev/null and b/content/identity/assess-improve-your-authentication-system/WP-digitization.webp differ
diff --git a/content/identity/assess-improve-your-authentication-system/api-wp.png b/content/identity/assess-improve-your-authentication-system/api-wp.png
deleted file mode 100644
index a268e3d22..000000000
Binary files a/content/identity/assess-improve-your-authentication-system/api-wp.png and /dev/null differ
diff --git a/content/identity/assess-improve-your-authentication-system/api-wp.webp b/content/identity/assess-improve-your-authentication-system/api-wp.webp
new file mode 100644
index 000000000..234c6abdc
Binary files /dev/null and b/content/identity/assess-improve-your-authentication-system/api-wp.webp differ
diff --git a/content/identity/assess-improve-your-authentication-system/index.md b/content/identity/assess-improve-your-authentication-system/index.md
index 937cfd4f1..167a4488c 100644
--- a/content/identity/assess-improve-your-authentication-system/index.md
+++ b/content/identity/assess-improve-your-authentication-system/index.md
@@ -1,7 +1,7 @@
---
title: "How to Evaluate the Quality of Your User Authentication System"
date: "2021-11-18"
-coverImage: "user-authentication.jpg"
+coverImage: "user-authentication.webp"
tags: ["user authentication","authorization","compliance"]
author: "Arpita Garg"
description: "Whether we talk about data leaks or identity thefts, businesses that become victims of security breaches compromise their brand reputation and lose millions of dollars every year. Hence, robust authentication and authorization mechanisms become a necessity and not just a luxury. Let’s understand how businesses can evaluate the quality of a user authentication system."
@@ -68,7 +68,7 @@ A CIAM solution uses authentication and authorization technologies like JWT, SAM
* **OpenID Authorization:** It verifies user identity based on an authorization server's authentication.
* **OAuth:** It allows the API to authenticate and access the requested system or resource.
-[](https://www.loginradius.com/resource/how-to-secure-api-using-oauth2)
+[](https://www.loginradius.com/resource/how-to-secure-api-using-oauth2)
Since we’ve got a fair understanding of the authentication and authorization system, let’s just quickly jump to the aspects that define the quality of the authentication system.
@@ -141,4 +141,4 @@ The aspects mentioned above could help businesses choose the most exemplary auth
Moreover, businesses can witness the world-class authentication system in action with LoginRadius CIAM that helps establish a secure and user-friendly authentication and authorization system.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=assess-improve-your-authentication-system)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=assess-improve-your-authentication-system)
\ No newline at end of file
diff --git a/content/identity/assess-improve-your-authentication-system/user-authentication.jpg b/content/identity/assess-improve-your-authentication-system/user-authentication.jpg
deleted file mode 100644
index ffb087acd..000000000
Binary files a/content/identity/assess-improve-your-authentication-system/user-authentication.jpg and /dev/null differ
diff --git a/content/identity/assess-improve-your-authentication-system/user-authentication.webp b/content/identity/assess-improve-your-authentication-system/user-authentication.webp
new file mode 100644
index 000000000..5dfa71a09
Binary files /dev/null and b/content/identity/assess-improve-your-authentication-system/user-authentication.webp differ
diff --git a/content/identity/assess-improve-your-authentication-system/verification.jpg b/content/identity/assess-improve-your-authentication-system/verification.jpg
deleted file mode 100644
index cc5c00f79..000000000
Binary files a/content/identity/assess-improve-your-authentication-system/verification.jpg and /dev/null differ
diff --git a/content/identity/assess-improve-your-authentication-system/verification.webp b/content/identity/assess-improve-your-authentication-system/verification.webp
new file mode 100644
index 000000000..ba84d92d3
Binary files /dev/null and b/content/identity/assess-improve-your-authentication-system/verification.webp differ
diff --git a/content/identity/attack-surface-vs-attack-vector/attack-vector.jpg b/content/identity/attack-surface-vs-attack-vector/attack-vector.jpg
deleted file mode 100644
index f9bc74887..000000000
Binary files a/content/identity/attack-surface-vs-attack-vector/attack-vector.jpg and /dev/null differ
diff --git a/content/identity/attack-surface-vs-attack-vector/attack-vector.webp b/content/identity/attack-surface-vs-attack-vector/attack-vector.webp
new file mode 100644
index 000000000..8d7dd7b01
Binary files /dev/null and b/content/identity/attack-surface-vs-attack-vector/attack-vector.webp differ
diff --git a/content/identity/attack-surface-vs-attack-vector/index.md b/content/identity/attack-surface-vs-attack-vector/index.md
index a479b5563..9e110dc68 100644
--- a/content/identity/attack-surface-vs-attack-vector/index.md
+++ b/content/identity/attack-surface-vs-attack-vector/index.md
@@ -1,7 +1,7 @@
---
title: "What’s the Difference Between Attack Surface and Attack Vector?"
date: "2022-11-11"
-coverImage: "attack-vector.jpg"
+coverImage: "attack-vector.webp"
tags: ["surface attack", "attack vector", "login security"]
author: "Vishal Sharma"
description: "Vulnerability management is essential in security, but more is needed. Attack surface and attack vector are two terms that can help you understand where vulnerabilities are most likely to occur, so you can improve your security posture and reduce risk."
@@ -88,4 +88,4 @@ Choosing a robust security mechanism is essential to overall security hygiene wi
Once a business knows potential threat vectors, it can deploy stringent authentication security mechanisms to mitigate the risks.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=attack-surface-vs-attack-vector)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=attack-surface-vs-attack-vector)
diff --git a/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.jpg b/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.jpg
deleted file mode 100644
index 6c14d6e93..000000000
Binary files a/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.jpg and /dev/null differ
diff --git a/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.webp b/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.webp
new file mode 100644
index 000000000..3423afcbf
Binary files /dev/null and b/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.webp differ
diff --git a/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.jpg b/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.jpg
deleted file mode 100644
index 6c14d6e93..000000000
Binary files a/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.jpg and /dev/null differ
diff --git a/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.webp b/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.webp
new file mode 100644
index 000000000..3423afcbf
Binary files /dev/null and b/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.webp differ
diff --git a/content/identity/aurora-wdc-loginradius-customer-success-story/index.md b/content/identity/aurora-wdc-loginradius-customer-success-story/index.md
index 9fa4bf182..bde6686e6 100644
--- a/content/identity/aurora-wdc-loginradius-customer-success-story/index.md
+++ b/content/identity/aurora-wdc-loginradius-customer-success-story/index.md
@@ -1,7 +1,7 @@
---
title: "Aurora WDC, a LoginRadius Customer Success Story"
date: "2017-05-26"
-coverImage: "aurora-wdc-loginradius-customer-success-story.jpg"
+coverImage: "aurora-wdc-loginradius-customer-success-story.webp"
tags: ["media-and-publication"]
featured: false
author: "Karl Wittig"
@@ -12,7 +12,7 @@ metadescription: "Aurora WDC is leading analytics & intelligence firm who, with
---
-
+
Founded in 1995 by Arik Johnson, [Aurora Worldwide Development Corporation (WDC)](https://aurorawdc.com/) is a leading analytics and intelligence firm providing consultative services to corporate clients worldwide. We are grateful to be able to have such a long-standing relationship with Aurora WDC and glad that we have been able to help them in providing a better user experience and a well-rounded solution to better manage their client relationships.
@@ -49,4 +49,4 @@ As Aurora WDC transitioned to Hubspot, we stepped up our game and re-integrated
Aurora WDC - LoginRadius Customer Success Story
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=aurora-wdc-loginradius-customer-success-story)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=aurora-wdc-loginradius-customer-success-story)
diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.png b/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.png
deleted file mode 100644
index 79ef6d6fa..000000000
Binary files a/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.png and /dev/null differ
diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.webp b/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.webp
new file mode 100644
index 000000000..4ad020497
Binary files /dev/null and b/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.webp differ
diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.png b/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.png
deleted file mode 100644
index bfcdef5af..000000000
Binary files a/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.png and /dev/null differ
diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.webp b/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.webp
new file mode 100644
index 000000000..785585d66
Binary files /dev/null and b/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.webp differ
diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/index.md b/content/identity/authenticating-in-the-age-of-no-code-technology/index.md
index f84362b5a..b6ea5536f 100644
--- a/content/identity/authenticating-in-the-age-of-no-code-technology/index.md
+++ b/content/identity/authenticating-in-the-age-of-no-code-technology/index.md
@@ -1,7 +1,7 @@
---
title: "Age of No-Code Technologies: Identification and Authentication"
date: "2022-06-03"
-coverImage: "no-code.jpg"
+coverImage: "no-code.webp"
tags: ["no code", "identification", "authentication"]
author: "Tim Ferguson"
description: "No code is a process of developing applications through a graphical interface that requires zero coding. All you need to know is your requirements and you are ready to go. Let’s take a look at how it has improved the identification and authentication process for businesses."
@@ -86,7 +86,7 @@ No-code development requires fewer engineers. This reduces all the auxiliaries t
Updating processes and systems that were created using no-code technology is also easier. Often, it is taken care of by the platform.
-[](https://www.loginradius.com/resource/ciam-buyers-guide-to-secure-your-roi)
+[](https://www.loginradius.com/resource/ciam-buyers-guide-to-secure-your-roi)
### 4. Increased customer satisfaction.
@@ -107,4 +107,4 @@ Identification and authentication are two major processes that secure customer d
The good news is that no-code technologies are helping businesses secure their services by enabling the developers to create processes faster.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authenticating-in-the-age-of-no-code-technology)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authenticating-in-the-age-of-no-code-technology)
diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.jpg b/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.jpg
deleted file mode 100644
index 0b9c8570c..000000000
Binary files a/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.jpg and /dev/null differ
diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.webp b/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.webp
new file mode 100644
index 000000000..762b432e2
Binary files /dev/null and b/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.webp differ
diff --git a/content/identity/authentication-authorization-encryption/index.md b/content/identity/authentication-authorization-encryption/index.md
index 9e04bcce3..ac0c1a396 100644
--- a/content/identity/authentication-authorization-encryption/index.md
+++ b/content/identity/authentication-authorization-encryption/index.md
@@ -187,4 +187,4 @@ We’ve come a long way from passwords and PINs. In today’s zero-trust, cloud-
### 4. Is SSO authentication or authorization?
**A.** SSO is an authentication method. It lets you log in once and access multiple systems without logging in again. Authorization still controls what you can do once inside.
-[](https://www.loginradius.com/contact-us)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us)
\ No newline at end of file
diff --git a/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.png b/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.png and /dev/null differ
diff --git a/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.webp b/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.webp differ
diff --git a/content/identity/authentication-identity-verification-identification/auth-identity.jpg b/content/identity/authentication-identity-verification-identification/auth-identity.jpg
deleted file mode 100644
index 636e66817..000000000
Binary files a/content/identity/authentication-identity-verification-identification/auth-identity.jpg and /dev/null differ
diff --git a/content/identity/authentication-identity-verification-identification/auth-identity.webp b/content/identity/authentication-identity-verification-identification/auth-identity.webp
new file mode 100644
index 000000000..37909346e
Binary files /dev/null and b/content/identity/authentication-identity-verification-identification/auth-identity.webp differ
diff --git a/content/identity/authentication-identity-verification-identification/ciam-eb.png b/content/identity/authentication-identity-verification-identification/ciam-eb.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/identity/authentication-identity-verification-identification/ciam-eb.png and /dev/null differ
diff --git a/content/identity/authentication-identity-verification-identification/ciam-eb.webp b/content/identity/authentication-identity-verification-identification/ciam-eb.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/identity/authentication-identity-verification-identification/ciam-eb.webp differ
diff --git a/content/identity/authentication-identity-verification-identification/index.md b/content/identity/authentication-identity-verification-identification/index.md
index 391b9fc9a..2c9c464c8 100644
--- a/content/identity/authentication-identity-verification-identification/index.md
+++ b/content/identity/authentication-identity-verification-identification/index.md
@@ -1,7 +1,7 @@
---
title: "Authentication, Identity Verification, and Identification: What's the Difference"
date: "2022-07-06"
-coverImage: "auth-identity.jpg"
+coverImage: "auth-identity.webp"
tags: ["authentication","identity verification","identity security"]
author: "Rakesh Soni"
description: "People usually consider authentication, id verification, and identification the same thing, but they are entirely different when we see stuff through the lens of information security experts. Learn the fundamental differences between the three and the importance of each from an information security perspective."
@@ -55,7 +55,7 @@ Moreover, identity theft is swiftly becoming the new way of exploiting customer
Adding stringent security layers in the form of multi-factor authentication (MFA) and risk-based authentication (RBA) could significantly decrease the chances of identity theft.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
## What is the Purpose of Identity Security?
@@ -95,4 +95,4 @@ What puts LoginRadius ahead of the curve are the three most fundamental aspects:
If you wish to experience the next level of account security and authentication, reach the LoginRadius team to schedule a personalized demo.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-identity-verification-identification)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-identity-verification-identification)
diff --git a/content/identity/authentication-option-for-your-product/DS-magic-link-pass.png b/content/identity/authentication-option-for-your-product/DS-magic-link-pass.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/authentication-option-for-your-product/DS-magic-link-pass.png and /dev/null differ
diff --git a/content/identity/authentication-option-for-your-product/DS-magic-link-pass.webp b/content/identity/authentication-option-for-your-product/DS-magic-link-pass.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/authentication-option-for-your-product/DS-magic-link-pass.webp differ
diff --git a/content/identity/authentication-option-for-your-product/index.md b/content/identity/authentication-option-for-your-product/index.md
index d5298ef3c..20f5bbec1 100644
--- a/content/identity/authentication-option-for-your-product/index.md
+++ b/content/identity/authentication-option-for-your-product/index.md
@@ -2,7 +2,7 @@
title: "How to Choose the Right User Authentication Option for your Product"
date: "2021-11-08"
author: "Rakesh Soni"
-coverImage: "user-authentication.jpg"
+coverImage: "user-authentication.webp"
tags: ["data security","passwordless login","authentication","mfa"]
description: "When choosing the right authentication option for your product, there’s a lot of confusion and misconceptions that may eventually make it difficult to finalize one or even more."
metatitle: "Here’s the Ideal Authentication Option for Your Product"
@@ -80,7 +80,7 @@ Passwordless login eliminates the need to generate passwords altogether. There
Since one needs not type passwords anymore, it leads to a better screen time experience. While for organizations, it will lead to fewer breaches and support costs.
-[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
**#5. Social Authentication**
@@ -128,6 +128,6 @@ LoginRadius understands the importance of frictionless authentication and helps
With LoginRadius’ Passwordless Authentication and Social Authentication, businesses can ensure the highest level of security coupled with a flawless user experience while they prove their identity.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-option-for-your-product)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-option-for-your-product)
diff --git a/content/identity/authentication-option-for-your-product/magiclink-ds.png b/content/identity/authentication-option-for-your-product/magiclink-ds.png
deleted file mode 100644
index f0d635566..000000000
Binary files a/content/identity/authentication-option-for-your-product/magiclink-ds.png and /dev/null differ
diff --git a/content/identity/authentication-option-for-your-product/magiclink-ds.webp b/content/identity/authentication-option-for-your-product/magiclink-ds.webp
new file mode 100644
index 000000000..16c0455b4
Binary files /dev/null and b/content/identity/authentication-option-for-your-product/magiclink-ds.webp differ
diff --git a/content/identity/authentication-option-for-your-product/user-authentication.jpg b/content/identity/authentication-option-for-your-product/user-authentication.jpg
deleted file mode 100644
index 1853272f4..000000000
Binary files a/content/identity/authentication-option-for-your-product/user-authentication.jpg and /dev/null differ
diff --git a/content/identity/authentication-option-for-your-product/user-authentication.webp b/content/identity/authentication-option-for-your-product/user-authentication.webp
new file mode 100644
index 000000000..18ea3400b
Binary files /dev/null and b/content/identity/authentication-option-for-your-product/user-authentication.webp differ
diff --git a/content/identity/authentication-sso-native-mobile-apps/index.md b/content/identity/authentication-sso-native-mobile-apps/index.md
index ccd26812c..ec586e298 100644
--- a/content/identity/authentication-sso-native-mobile-apps/index.md
+++ b/content/identity/authentication-sso-native-mobile-apps/index.md
@@ -2,7 +2,7 @@
title: "Announcement - LoginRadius Announces Authentication and SSO for Native Mobile Apps"
date: "2020-11-25"
author: "Rakesh Soni"
-coverImage: "loginradius-mobile-native-app.png"
+coverImage: "loginradius-mobile-native-app.webp"
tags: ["authentication","SSO","data security","compliance"]
description: "Both companies and their customers benefit from LoginRadius Native Mobile SDKs. It allows companies to build and deploy seamless authentication and SSO functionality, while stable, easy and improved customer experiences are on-the-go for later."
metatitle: "LoginRadius Authentication and SSO for Native Mobile Apps"
@@ -33,7 +33,7 @@ The recently launched LoginRadius Authentication and SSO for Native Mobile Apps
-[](https://www.loginradius.com/resource/authentication-sso-native-mobile-apps-datasheet)
+[](https://www.loginradius.com/resource/authentication-sso-native-mobile-apps-datasheet)
## Key Features Offered by LoginRadius Android and iOS SDKs
@@ -53,6 +53,6 @@ The recently launched LoginRadius Authentication and SSO for Native Mobile Apps
LoginRadius Native Mobile SDKs benefit both businesses and their consumers. It helps in developing and deploying seamless authentication and [SSO features for businesses](https://www.loginradius.com/single-sign-on/), while for the later, secure, simple, and enhanced consumer experiences are on-the-go.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-sso-native-mobile-apps)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-sso-native-mobile-apps)
diff --git a/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.png b/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.png
deleted file mode 100644
index 00d6adb36..000000000
Binary files a/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.png and /dev/null differ
diff --git a/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.webp b/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.webp
new file mode 100644
index 000000000..a2de2b338
Binary files /dev/null and b/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.webp differ
diff --git a/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.png b/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.png
deleted file mode 100644
index 9368b122c..000000000
Binary files a/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.png and /dev/null differ
diff --git a/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.webp b/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.webp
new file mode 100644
index 000000000..44fba692f
Binary files /dev/null and b/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.webp differ
diff --git a/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.png b/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.png
deleted file mode 100644
index f21e58bc7..000000000
Binary files a/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.png and /dev/null differ
diff --git a/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.webp b/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.webp
new file mode 100644
index 000000000..c63b4b200
Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.webp differ
diff --git a/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.png b/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.png
deleted file mode 100644
index 87a04b8f9..000000000
Binary files a/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.png and /dev/null differ
diff --git a/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.webp b/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.webp
new file mode 100644
index 000000000..aa8921d95
Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.webp differ
diff --git a/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.png b/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.png and /dev/null differ
diff --git a/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.webp b/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.webp differ
diff --git a/content/identity/authentication-vs-authorization-infographic/SASE-approach.png b/content/identity/authentication-vs-authorization-infographic/SASE-approach.png
deleted file mode 100644
index 9b885caa8..000000000
Binary files a/content/identity/authentication-vs-authorization-infographic/SASE-approach.png and /dev/null differ
diff --git a/content/identity/authentication-vs-authorization-infographic/SASE-approach.webp b/content/identity/authentication-vs-authorization-infographic/SASE-approach.webp
new file mode 100644
index 000000000..62f54b93f
Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/SASE-approach.webp differ
diff --git a/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.jpg b/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.jpg
deleted file mode 100644
index e5dffc2fb..000000000
Binary files a/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.jpg and /dev/null differ
diff --git a/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.webp b/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.webp
new file mode 100644
index 000000000..1efaf4b64
Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.webp differ
diff --git a/content/identity/authentication-vs-authorization-infographic/index.md b/content/identity/authentication-vs-authorization-infographic/index.md
index 6f7f9f11d..2986b1a06 100644
--- a/content/identity/authentication-vs-authorization-infographic/index.md
+++ b/content/identity/authentication-vs-authorization-infographic/index.md
@@ -1,7 +1,7 @@
---
title: "Authentication and Authorization Defined: What's the Difference? [Infographic]"
date: "2020-06-11"
-coverImage: "authentication-vs-authorization.jpg"
+coverImage: "authentication-vs-authorization.webp"
tags: ["authentication","authorization","ciam solution"]
author: "Rakesh Soni"
description: "As companies progress towards digital maturity in times of robust cloud-based systems and stringent online security, authentication and authorization are used in conjunction with each other."
@@ -163,7 +163,7 @@ Here is the common authentication vs authorization techniques used by CIAM solut
- **Password-based authentication** is a simple [method of authentication](https://www.loginradius.com/blog/2019/06/what-is-multi-factor-authentication/) that requires a password to verify the user's identity.
- **Passwordless authentication** is [where a user is verified](https://www.loginradius.com/blog/2019/10/passwordless-authentication-the-future-of-identity-and-security/) through OTP or a magic link delivered to the registered email or phone number.
-[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
- **2FA/MFA** requires [more than one security level](https://www.loginradius.com/blog/2019/06/what-is-multi-factor-authentication/), like an additional PIN or security question, to identify a user and grant access to a system.
- **Single sign-on** (SSO) allows users to access multiple applications with a single set of credentials.
@@ -179,7 +179,7 @@ Here is the common authentication vs authorization techniques used by CIAM solut
To learn more about the authentication vs authorization - concept, differences, and techniques, check out the infographic created by LoginRadius.
-
+
## Implementing Identity and Access Management with LoginRadius
@@ -217,4 +217,4 @@ Properly implemented authentication and authorization processes can ensure data
The future likely involves more advanced biometrics, continuous authentication, and AI-driven security measures to combat evolving cyber threats and enhance user experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-vs-authorization-infographic)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-vs-authorization-infographic)
diff --git a/content/identity/authentication-vs-authorization-infographic/passwordless-login.png b/content/identity/authentication-vs-authorization-infographic/passwordless-login.png
deleted file mode 100644
index 69d26339f..000000000
Binary files a/content/identity/authentication-vs-authorization-infographic/passwordless-login.png and /dev/null differ
diff --git a/content/identity/authentication-vs-authorization-infographic/passwordless-login.webp b/content/identity/authentication-vs-authorization-infographic/passwordless-login.webp
new file mode 100644
index 000000000..96ed92a38
Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/passwordless-login.webp differ
diff --git a/content/identity/authentication-vs-authorization/authentication-vs-authorization.webp b/content/identity/authentication-vs-authorization/authentication-vs-authorization.webp
new file mode 100644
index 000000000..eefe132c6
Binary files /dev/null and b/content/identity/authentication-vs-authorization/authentication-vs-authorization.webp differ
diff --git a/content/identity/authentication-vs-authorization/index.md b/content/identity/authentication-vs-authorization/index.md
new file mode 100644
index 000000000..3135bb5fa
--- /dev/null
+++ b/content/identity/authentication-vs-authorization/index.md
@@ -0,0 +1,260 @@
+---
+title: "Authentication vs Authorization: What's the Difference?"
+date: "2025-04-08"
+coverImage: "authentication-vs-authorization.webp"
+tags: ["Authentication","Authorization","Data Privacy","Identity Management"]
+author: "Rakesh Soni"
+description: "Authentication and authorization are often confused but play very different roles in cybersecurity. This blog breaks down what each term means, why authentication always comes first, and how both work together to keep systems secure. With relatable examples and real-world scenarios, you'll understand the key differences, best practices, and why mastering both is essential for protecting digital assets."
+metatitle: "Authentication vs Authorization: Key Differences Explained"
+metadescription: "Discover the core difference between authentication vs authorization. Learn how each secures access, their roles in cybersecurity, and real-world use cases."
+---
+
+## Introduction
+
+In a world where cyber threats like data breaches and identity theft are making headlines almost daily, securing digital systems isn’t just important — it’s essential. That’s where two commonly confused terms come in: authentication and authorization. You’ve probably heard them used together (or even interchangeably), but they serve very different purposes.
+
+Whether you're building secure apps, managing access for a team, or simply curious about how systems stay protected, understanding the difference between authentication and authorization is key.
+
+In this blog, we’ll unpack both concepts with relatable examples and clear insights — so you can confidently grasp how each one keeps your data and users safe.
+
+## What is Authentication?
+
+[Authentication ](https://www.loginradius.com/blog/identity/what-is-authentication/)is the process of verifying who a user is. It answers the question: Are you really who you say you are?
+
+For authentication, users typically provide credentials — such as a username and password, biometric data, or a one-time code — to prove their identity. It acts like a digital passport that validates a person before letting them into a system.
+
+Imagine you walk into a secured office building. At the entrance, a security guard checks your ID. If it matches the employee database, you’re allowed in. That’s authentication.
+
+In technical aspects, imagine a user logs into an online banking app with a password and receives a 2FA code on their phone. Only after both credentials are verified is the user granted access. This is a prime example of authentication in cyber security.
+
+
+
+## What is the Purpose of Authentication?
+
+The core goal of authentication is to ensure that only verified users can access a system. It prevents impersonation, data theft, and breaches by validating user identities before granting entry.
+
+In today’s digital landscape, where everything from cloud apps to enterprise databases is remotely accessible, robust authentication methods — like biometrics, OTPs, and social logins — are critical for security.
+
+Authentication lays the foundation. Without it, systems wouldn’t know *who* they are dealing with — making any additional security effort meaningless.
+
+## What is Authorization?
+
+Authorization, on the other hand, determines *what* an authenticated user is allowed to do. It answers: *Do you have permission to access this resource or perform this action?*
+
+If authentication is the security guard verifying your ID, authorization is the list showing what rooms or data you're allowed to access.
+
+In simple terms, authorization in cybersecurity is about assigning privileges and access levels to different users based on their role, location, or behavior.
+
+## Common Types of Authorization
+
+There are various ways to authorize users, depending on the system’s needs. Here are some of the most common:
+
+### 1. Role-Based Access Control (RBAC):
+
+In role-based access control, users are granted permissions based on roles (admin, editor, viewer). For example, in the [LoginRadius console](https://accounts.loginradius.com/auth.aspx?return_url=https://console.loginradius.com/login&action=register) below, the “Admin” has permission to broadcast, download, edit, and read. On the other hand, the “Customer” is only authorized to download and read.
+
+
+
+Explore how [Role-Based Access Control (RBAC)](https://www.loginradius.com/blog/identity/what-is-rbac/) simplifies permissions and strengthens security.
+In a nutshell, RBAC simplifies access management by assigning permissions based on user roles, such as admin, editor, or viewer, rather than handling access at the individual level.
+
+In a B2C context, this often means differentiating capabilities between everyday users and internal staff. For instance, a streaming platform might allow viewers to consume content, while admins manage uploads and settings.
+
+In B2B scenarios, this concept scales to entire organizations. For example, a retail company which collaborates with suppliers, franchisees, and distributors, requires precise control over who can access what across partner ecosystems.
+
+Our Partner IAM feature enables role-based permissions at the organization level, such as Partner Admin or Franchise Manager with access defined down to specific resources or workflows.
+
+Discover how LoginRadius Partner IAM enables precise, organization-level [RBAC tailored for complex B2B environments](https://www.loginradius.com/docs/user-management/roles-and-permissions/).
+
+### 2. Attribute-Based Access Control (ABAC)
+
+Attribute-based access ensures that access is granted based on a combination of user attributes such as department, role, location, time of day, or device type.
+
+For example, an employee from the finance department can access payroll data only during working hours and only when using a company-issued device—ensuring granular and context-aware security controls.
+
+You can read our [RBAC vs ABAC guide](https://www.loginradius.com/blog/identity/rbac-vs-abac/)for a detailed comparison between RBAC and ABAC to ensure you make the right decision that meets your business requirements.
+
+### 3. JSON Web Token (JWT) Authorization
+
+JWT (JSON Web Token) authorization is a widely used method for securely transmitting user data between parties—particularly in modern web applications and services. It's especially popular in systems that use stateless authentication, such as RESTful APIs. For instance, after a user logs in, the server issues a JWT that the client includes in subsequent requests to authenticate without needing to re-enter credentials.
+
+If you’d like to dive deeper into how JWTs work and when to use them, check out our full guide on [JWT authorization best practices](https://www.loginradius.com/blog/engineering/guest-post/jwt-authentication-best-practices-and-when-to-use/).
+
+### 4. OAuth 2.0
+
+OAuth 2.0 is a widely adopted protocol for delegating access without exposing user credentials. For example, when you log into Spotify using your Google account, Google handles the authentication, and Spotify receives limited, authorized access to your basic profile—without ever seeing your Google password. This secure delegation is ideal for third-party integrations and API-based systems.
+
+To understand how OAuth 2.0 works, its core flows, and when to use it, check out our in-depth breakdown on[ OAuth 2.0 and its role in modern identity management.](https://www.loginradius.com/blog/engineering/what-is-oauth2-0/)
+
+The aforementioned types show the depth of authorization in cybersecurity, shaping how users interact with systems securely.
+
+## Authentication vs Authorization
+
+To put it plainly, authentication and authorization are two sides of the same coin — often paired but serving different purposes.
+
+* *Authentication*: Confirms your identity.
+
+* *Authorization*: Grants or denies permissions based on that identity.
+
+Let’s go back to the real world: You check into a hotel (authentication), but your key card only grants you access to your room and the gym — not the penthouse suite (authorization).
+
+### Key Differences Between Authentication and Authorization
+
+
+
+ Feature
+
+ Authentication
+
+ Authorization
+
+
+
+ Definition
+
+ Verifies identity
+
+ Determines access rights
+
+
+
+ Function
+
+ "Who are you?"
+
+ "What are you allowed to do?"
+
+
+
+ Process
+
+ Done before authorization
+
+ Done after authentication
+
+
+
+ Data
+
+ Requires login credentials
+
+ Requires permission policies
+
+
+
+ Visibility to user
+
+ Visible (e.g., login form)
+
+ Often invisible to the user
+
+
+
+ Use case
+
+ Login portals, biometric scans
+
+ Accessing internal dashboards or APIs
+
+
+
+
+This comparison helps answer the question: How is authentication different from authorization? If you need a more detailed comparison, [read this insightful blog](https://www.loginradius.com/blog/identity/authentication-vs-authorization-infographic/).
+
+## Authentication vs Authorization: Factors & Permissions
+
+When we take a closer look at auth vs authorization, it's evident that both processes serve different purposes and rely on separate sets of criteria to function effectively. Understanding these underlying components helps demystify how modern systems maintain security without compromising user experience.
+
+Authentication is all about identity verification — confirming that a user is who they claim to be. This is typically done through one or more of the following factors:
+
+* **Something you know** – such as a password, PIN, or secret answer to a security question.
+
+* **Something you have** – like a hardware token, mobile authenticator app, or a smart card.
+
+* **Something you are** – biometric data such as fingerprints, facial recognition, or iris scans.
+
+These layers form the foundation of secure access. For example, logging into your online banking account may require both your password (*something you know*) and a fingerprint scan (*something you are*), especially when sensitive transactions are involved.
+
+Authorization, on the other hand, determines what that authenticated user is allowed to do once access has been granted. It sets boundaries and defines permissions based on rules, roles, or policies. Common types of access include:
+
+* **Read-only access** – allowing users to view content without making changes, such as viewing reports or dashboards.
+
+* **Edit or write access** – enabling users to create, update, or delete content, like editing a document in a CMS.
+
+* **Administrative access** – providing full control over a system or platform, including managing users, permissions, and settings.
+
+Both authentication and authorization are vital to protecting sensitive data and ensuring users only have access to the resources they genuinely need.
+
+[](https://www.loginradius.com/resource/whitepaper/user-authentication-security/)
+
+## Which Comes First, Authentication or Authorization?
+
+Authentication always comes before authorization. This sequence is non-negotiable in cybersecurity and access control. Why? Because a system must first verify who the user is before it can determine what the user is allowed to do.
+
+Think of it as meeting someone at your front door. You wouldn’t ask them which rooms they’d like to enter before confirming they’re a trusted friend or family member. Similarly, in digital systems, authentication validates identity, and only then can authorization define access levels.
+
+Here’s a breakdown to illustrate this better:
+
+### Step 1 – Authentication:
+
+The system checks the user’s credentials — such as a username and password, fingerprint, or OTP — to confirm their identity. During this step, encryption protocols like TLS are typically used to protect credential data as it travels between the client and server, ensuring it can’t be intercepted or tampered with.
+
+### Step 2 – Authorization:
+
+Once the identity is verified, the system evaluates what resources that identity has permission to access — like read-only access to a report, admin rights on a dashboard, or restricted areas in a company portal.
+
+### Step 3 – Encryption in Action:
+
+While encryption supports both steps, it becomes even more critical once access is granted. Sensitive data that the authorized user accesses—whether in transit or at rest—should be encrypted to maintain confidentiality and integrity throughout the session.
+
+Skipping authentication and jumping straight to authorization would be like giving someone the keys to your office without knowing if they even work there. It's not just risky — it's a security failure waiting to happen.
+
+This foundational flow—authentication first, followed by authorization, and supported by encryption throughout—ensures your digital ecosystem remains secure and logically controlled.
+
+Learn more in our guide on[ Authentication, Authorization, and Encryption](https://www.loginradius.com/blog/identity/authentication-authorization-encryption/).
+
+## Conclusion
+
+In cybersecurity and identity management, knowing the difference between authorization and authentication is foundational. While they’re often mentioned together, they perform distinct — and equally vital — roles in protecting systems.
+
+Whether you’re building a secure app, managing employee access, or integrating APIs, always start with authentication and then apply authorization based on roles, policies, or attributes.
+
+By mastering both, you’ll reduce vulnerabilities, improve user experience, and align with best practices in authentication and authorization.
+
+Need help implementing secure authentication and authorization for your applications? [Contact LoginRadius](https://www.loginradius.com/contact-us) to get expert guidance today.
+
+## FAQs
+
+### 1. Can a person be authenticated and still not authorized?
+
+**A.** Yes. Being authenticated simply proves identity. A user might log in (authenticated) but lack the right permissions (not authorized) to access certain features or data.
+
+### 2. What are the different types of authentication?
+
+**A.** Common types include:
+
+* Password-based authentication
+
+* Biometric (fingerprint, facial recognition)
+
+* Multi-factor authentication (MFA)
+
+* Token-based (e.g., JWT)
+
+* Social login (OAuth)
+
+These are essential for **authentication in cyber security**.
+
+### 3. How is authentication different from authorization?
+
+**A.** Authentication checks identity; authorization checks access rights. It’s the classic **authorize vs authenticate** debate — where both are needed, but for different reasons.
+
+### 4. What is authorization testing?
+
+**A.** Authorization testing ensures users can only access what they are permitted to. It checks for access control vulnerabilities and misconfigurations — key in **authorization in cybersecurity**.
+
+### 5. How does authentication work?
+
+**A.** Authentication works by matching provided credentials against stored user data. If the credentials match, access is granted. Methods include passwords, biometric scans, OTPs, and digital certificates.
+
+[](https://www.loginradius.com/contact-us)
\ No newline at end of file
diff --git a/content/identity/authentication-vs-authorization/roles-and-permissions-settings.webp b/content/identity/authentication-vs-authorization/roles-and-permissions-settings.webp
new file mode 100644
index 000000000..0da98eca2
Binary files /dev/null and b/content/identity/authentication-vs-authorization/roles-and-permissions-settings.webp differ
diff --git a/content/identity/authentication-vs-authorization/securing-user-auth.webp b/content/identity/authentication-vs-authorization/securing-user-auth.webp
new file mode 100644
index 000000000..9db8f6844
Binary files /dev/null and b/content/identity/authentication-vs-authorization/securing-user-auth.webp differ
diff --git a/content/identity/authentication-vs-authorization/user-authentication-flow.webp b/content/identity/authentication-vs-authorization/user-authentication-flow.webp
new file mode 100644
index 000000000..eae34afc9
Binary files /dev/null and b/content/identity/authentication-vs-authorization/user-authentication-flow.webp differ
diff --git a/content/identity/authentication-vulnerabilities-security/GD-salt-hashing.png b/content/identity/authentication-vulnerabilities-security/GD-salt-hashing.png
deleted file mode 100644
index 698c87b68..000000000
Binary files a/content/identity/authentication-vulnerabilities-security/GD-salt-hashing.png and /dev/null differ
diff --git a/content/identity/authentication-vulnerabilities-security/GD-salt-hashing.webp b/content/identity/authentication-vulnerabilities-security/GD-salt-hashing.webp
new file mode 100644
index 000000000..f0938b9a0
Binary files /dev/null and b/content/identity/authentication-vulnerabilities-security/GD-salt-hashing.webp differ
diff --git a/content/identity/authentication-vulnerabilities-security/auth-vulnerabilities.jpg b/content/identity/authentication-vulnerabilities-security/auth-vulnerabilities.jpg
deleted file mode 100644
index f3ec28d84..000000000
Binary files a/content/identity/authentication-vulnerabilities-security/auth-vulnerabilities.jpg and /dev/null differ
diff --git a/content/identity/authentication-vulnerabilities-security/auth-vulnerabilities.webp b/content/identity/authentication-vulnerabilities-security/auth-vulnerabilities.webp
new file mode 100644
index 000000000..e08557568
Binary files /dev/null and b/content/identity/authentication-vulnerabilities-security/auth-vulnerabilities.webp differ
diff --git a/content/identity/authentication-vulnerabilities-security/index.md b/content/identity/authentication-vulnerabilities-security/index.md
index 303ae688a..1313e52da 100644
--- a/content/identity/authentication-vulnerabilities-security/index.md
+++ b/content/identity/authentication-vulnerabilities-security/index.md
@@ -1,7 +1,7 @@
---
title: "7 Common Authentication Vulnerabilities to Steer Clear of"
date: "2023-11-09"
-coverImage: "auth-vulnerabilities.jpg"
+coverImage: "auth-vulnerabilities.webp"
tags: ["data security","authentication","mfa","cx"]
author: "Alok Patidar"
description: "Explore the prevalent authentication vulnerabilities that put your online identity at risk. Learn how LoginRadius MFA enhances security, ensuring a safer online experience."
@@ -43,7 +43,7 @@ Credential stuffing occurs when cybercriminals use stolen usernames and password
One of the most common authentication vulnerabilities is weak passwords. Many users still opt for easily guessable passwords, such as "123456" or "password." Creating strong, unique passwords for each account is essential to mitigate this risk. Hence, businesses must encourage their customers to use strong passwords. Also, companies should consider relying on secure password storage mechanisms to ensure the highest level of security.
-[](https://www.loginradius.com/resource/adding-salt-to-hashing-a-step-by-step-guide-to-store-passwords/)
+[](https://www.loginradius.com/resource/adding-salt-to-hashing-a-step-by-step-guide-to-store-passwords/)
### #4. Insecure Authentication Protocols
@@ -75,4 +75,4 @@ Staying vigilant and proactive in addressing these common authentication vulnera
By adopting secure practices, using strong and unique passwords, and integrating multi-factor authentication solutions like LoginRadius MFA, you can significantly reduce the risk of falling victim to cyber threats and enjoy a safer online experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-vulnerabilities-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-vulnerabilities-security)
diff --git a/content/identity/b2b-saas-security-challenges-iam/DS-LR-CCPA-comp.png b/content/identity/b2b-saas-security-challenges-iam/DS-LR-CCPA-comp.png
deleted file mode 100644
index 93302c0ce..000000000
Binary files a/content/identity/b2b-saas-security-challenges-iam/DS-LR-CCPA-comp.png and /dev/null differ
diff --git a/content/identity/b2b-saas-security-challenges-iam/DS-LR-CCPA-comp.webp b/content/identity/b2b-saas-security-challenges-iam/DS-LR-CCPA-comp.webp
new file mode 100644
index 000000000..9d62b96b8
Binary files /dev/null and b/content/identity/b2b-saas-security-challenges-iam/DS-LR-CCPA-comp.webp differ
diff --git a/content/identity/b2b-saas-security-challenges-iam/b2bsaas.jpg b/content/identity/b2b-saas-security-challenges-iam/b2bsaas.jpg
deleted file mode 100644
index 1f664825a..000000000
Binary files a/content/identity/b2b-saas-security-challenges-iam/b2bsaas.jpg and /dev/null differ
diff --git a/content/identity/b2b-saas-security-challenges-iam/b2bsaas.webp b/content/identity/b2b-saas-security-challenges-iam/b2bsaas.webp
new file mode 100644
index 000000000..37c5108d7
Binary files /dev/null and b/content/identity/b2b-saas-security-challenges-iam/b2bsaas.webp differ
diff --git a/content/identity/b2b-saas-security-challenges-iam/index.md b/content/identity/b2b-saas-security-challenges-iam/index.md
index b3a560f10..b48aa69a6 100644
--- a/content/identity/b2b-saas-security-challenges-iam/index.md
+++ b/content/identity/b2b-saas-security-challenges-iam/index.md
@@ -1,7 +1,7 @@
---
title: "How does identity management address the top 5 security challenges in B2B SaaS?"
date: "2024-02-12"
-coverImage: "b2bsaas.jpg"
+coverImage: "b2bsaas.webp"
tags: ["b2b","saas","identity management"]
author: "Rakesh Soni"
description: "As the usage and adoption of B2B SaaS applications are growing, businesses need to find a robust solution to overcome the associated security concerns. Presenting IAM or Identity Access Management, a world-class solution to create a secure digital experience for your business partners."
@@ -47,7 +47,7 @@ SaaS applications provide APIs for integration with other cloud services and on-
Depending on the industry, companies have to comply with regulations like HIPAA, PCI DSS, GDPR, CCPA, etc. Non-compliance can lead to fines and reputational damage. Weak identity and access controls conflict with compliance mandates around data security, privacy, and user access governance. It leads to increased audit scrutiny and financial risk.
-[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
+[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
## Identity and Access Management - Solution to B2B SaaS Security Challenges
@@ -127,4 +127,4 @@ Robust identity and access management (IAM) solutions provide businesses with th
By investing in [LoginRadius](https://www.loginradius.com/) cloud-native Identity-as-a-Service platform, SaaS companies can future-proof security while also enabling great customer experiences. Schedule a demo and discuss a risk-free pilot project for your **B2B SaaS** identity needs.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2b-saas-security-challenges-iam)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2b-saas-security-challenges-iam)
\ No newline at end of file
diff --git a/content/identity/b2b-saas-sso-login/DS-SSO.png b/content/identity/b2b-saas-sso-login/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/b2b-saas-sso-login/DS-SSO.png and /dev/null differ
diff --git a/content/identity/b2b-saas-sso-login/DS-SSO.webp b/content/identity/b2b-saas-sso-login/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/b2b-saas-sso-login/DS-SSO.webp differ
diff --git a/content/identity/b2b-saas-sso-login/b2b-saas.jpg b/content/identity/b2b-saas-sso-login/b2b-saas.jpg
deleted file mode 100644
index b2c03d664..000000000
Binary files a/content/identity/b2b-saas-sso-login/b2b-saas.jpg and /dev/null differ
diff --git a/content/identity/b2b-saas-sso-login/b2b-saas.webp b/content/identity/b2b-saas-sso-login/b2b-saas.webp
new file mode 100644
index 000000000..f71c63b9d
Binary files /dev/null and b/content/identity/b2b-saas-sso-login/b2b-saas.webp differ
diff --git a/content/identity/b2b-saas-sso-login/index.md b/content/identity/b2b-saas-sso-login/index.md
index f9f642c14..bc5e4a0af 100644
--- a/content/identity/b2b-saas-sso-login/index.md
+++ b/content/identity/b2b-saas-sso-login/index.md
@@ -1,7 +1,7 @@
---
title: "B2B SaaS SSO Login: Exploring Enterprise Considerations in 2024"
date: "2023-12-01"
-coverImage: "b2b-saas.jpg"
+coverImage: "b2b-saas.webp"
tags: ["b2b","sso","saas","cx"]
author: "Rakesh Soni"
description: "Discover the role of SSO login in B2B SaaS. This blog explores challenges, emerging trends, and crucial considerations for enterprises in 2024. From security measures to user-centric design, stay ahead in the dynamic realm of B2B SaaS."
@@ -28,7 +28,7 @@ While the advantages of implementing SSO Login are evident, enterprises are not
From issues related to identity federation to the complexities of maintaining a balance between security and usability, we'll explore how enterprises proactively address these challenges. Moreover, the blog will shed light on innovative solutions and best practices that are emerging in the B2B SaaS sector to overcome these hurdles, offering readers practical insights for a smoother SSO implementation.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
## Emerging Trends in B2B SaaS Single Sign-On for 2024
@@ -70,4 +70,4 @@ As we step into 2024, the landscape of B2B SSO login is marked by innovation, se
Stay tuned for a comprehensive exploration of the considerations shaping the future of Single Sign-On in the enterprise space.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2b-saas-sso-login)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2b-saas-sso-login)
\ No newline at end of file
diff --git a/content/identity/balancing-security-cx/EB-GDPR-comp.png b/content/identity/balancing-security-cx/EB-GDPR-comp.png
deleted file mode 100644
index a7a656cfa..000000000
Binary files a/content/identity/balancing-security-cx/EB-GDPR-comp.png and /dev/null differ
diff --git a/content/identity/balancing-security-cx/EB-GDPR-comp.webp b/content/identity/balancing-security-cx/EB-GDPR-comp.webp
new file mode 100644
index 000000000..44c9529c0
Binary files /dev/null and b/content/identity/balancing-security-cx/EB-GDPR-comp.webp differ
diff --git a/content/identity/balancing-security-cx/LoginRadius-and-GDPR-Compliance.png b/content/identity/balancing-security-cx/LoginRadius-and-GDPR-Compliance.png
deleted file mode 100644
index f7e5453b4..000000000
Binary files a/content/identity/balancing-security-cx/LoginRadius-and-GDPR-Compliance.png and /dev/null differ
diff --git a/content/identity/balancing-security-cx/LoginRadius-and-GDPR-Compliance.webp b/content/identity/balancing-security-cx/LoginRadius-and-GDPR-Compliance.webp
new file mode 100644
index 000000000..a7b013719
Binary files /dev/null and b/content/identity/balancing-security-cx/LoginRadius-and-GDPR-Compliance.webp differ
diff --git a/content/identity/balancing-security-cx/balancing-security-cx-cover.jpg b/content/identity/balancing-security-cx/balancing-security-cx-cover.jpg
deleted file mode 100644
index 50cd3cbb6..000000000
Binary files a/content/identity/balancing-security-cx/balancing-security-cx-cover.jpg and /dev/null differ
diff --git a/content/identity/balancing-security-cx/balancing-security-cx-cover.webp b/content/identity/balancing-security-cx/balancing-security-cx-cover.webp
new file mode 100644
index 000000000..1f183a719
Binary files /dev/null and b/content/identity/balancing-security-cx/balancing-security-cx-cover.webp differ
diff --git a/content/identity/balancing-security-cx/index.md b/content/identity/balancing-security-cx/index.md
index ce4d7da02..e1f7a8380 100644
--- a/content/identity/balancing-security-cx/index.md
+++ b/content/identity/balancing-security-cx/index.md
@@ -1,7 +1,7 @@
---
title: "How to Strike the Right Balance Between Security and Consumer Experience"
date: "2021-07-22"
-coverImage: "balancing-security-cx-cover.jpg"
+coverImage: "balancing-security-cx-cover.webp"
tags: ["data security","compliance","identity management","cx"]
author: "Navanita Devi"
description: "Delivering a perfect harmony of a great user experience along with the highest level of security is crucial today. Let’s learn why a great user experience shouldn’t be compromised for security and how LoginRadius helps enterprises create great personalized user experiences reinforced by strict security."
@@ -103,7 +103,7 @@ Make passwords harder to crack with rigorous password policies and LoginRadius M
Our modern cloud infrastructure is protected to the highest industry standards. LoginRadius maintains all [major security compliances](https://www.loginradius.com/compliances-list/) for our application and data storage.
-[](https://www.loginradius.com/resource/loginradius-and-gdpr-compliance/)
+[](https://www.loginradius.com/resource/loginradius-and-gdpr-compliance/)
* **Maintain Data Privacy**
@@ -124,4 +124,4 @@ You need a delightful yet secure[ consumer experience](https://www.loginradius.c
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=balancing-security-cx)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=balancing-security-cx)
\ No newline at end of file
diff --git a/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-1.png b/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-1.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-1.png and /dev/null differ
diff --git a/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-1.webp b/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-1.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-1.webp differ
diff --git a/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-security.png b/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-security.png
deleted file mode 100644
index 3e6b81ee6..000000000
Binary files a/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-security.png and /dev/null differ
diff --git a/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-security.webp b/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-security.webp
new file mode 100644
index 000000000..2f7c01062
Binary files /dev/null and b/content/identity/beginners-guide-zero-trust-security/WP-zero-trust-security.webp differ
diff --git a/content/identity/beginners-guide-zero-trust-security/beginners-guide-zero-trust-security-cover.jpg b/content/identity/beginners-guide-zero-trust-security/beginners-guide-zero-trust-security-cover.jpg
deleted file mode 100644
index ae9b6d9c4..000000000
Binary files a/content/identity/beginners-guide-zero-trust-security/beginners-guide-zero-trust-security-cover.jpg and /dev/null differ
diff --git a/content/identity/beginners-guide-zero-trust-security/beginners-guide-zero-trust-security-cover.webp b/content/identity/beginners-guide-zero-trust-security/beginners-guide-zero-trust-security-cover.webp
new file mode 100644
index 000000000..37d8a1329
Binary files /dev/null and b/content/identity/beginners-guide-zero-trust-security/beginners-guide-zero-trust-security-cover.webp differ
diff --git a/content/identity/beginners-guide-zero-trust-security/index.md b/content/identity/beginners-guide-zero-trust-security/index.md
index f8c7d8d3e..4065cf9d2 100644
--- a/content/identity/beginners-guide-zero-trust-security/index.md
+++ b/content/identity/beginners-guide-zero-trust-security/index.md
@@ -1,7 +1,7 @@
---
title: "A Beginner's Guide to Zero Trust Security Model"
date: "2021-08-05"
-coverImage: "beginners-guide-zero-trust-security-cover.jpg"
+coverImage: "beginners-guide-zero-trust-security-cover.webp"
tags: ["zero trust security","cybersecurity","mfa"]
author: "Rakesh Soni"
description: "With the rising number of cyberattacks, there’s an immediate need for a robust mechanism that provides a risk-free digital ecosystem. Zero trust helps businesses create the most secure environment that mitigates the risk of any kind of security breach."
@@ -49,7 +49,7 @@ Since the network is too open for all inside the organization, anyone can share
Hence enterprises today need a whole new way of thinking regarding access management within the organization, which helps minimize data compromise by a bad external actor.
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
## Benefits of Getting Zero Trust Security Mechanism
@@ -91,4 +91,4 @@ With the increasing risk of security breaches from within a network, the need fo
Decision-makers and IT department heads of an organization should consider putting their best foot forward in [securing important consumer information](https://www.loginradius.com/blog/identity/maintaining-quality-data-security-practices/) and business data by leveraging robust layers of defense through a zero trust security model.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=beginners-guide-zero-trust-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=beginners-guide-zero-trust-security)
diff --git a/content/identity/benefits-of-mfa/WP-mfa-digital-identity.png b/content/identity/benefits-of-mfa/WP-mfa-digital-identity.png
deleted file mode 100644
index e028d55fb..000000000
Binary files a/content/identity/benefits-of-mfa/WP-mfa-digital-identity.png and /dev/null differ
diff --git a/content/identity/benefits-of-mfa/WP-mfa-digital-identity.webp b/content/identity/benefits-of-mfa/WP-mfa-digital-identity.webp
new file mode 100644
index 000000000..96ac842dc
Binary files /dev/null and b/content/identity/benefits-of-mfa/WP-mfa-digital-identity.webp differ
diff --git a/content/identity/benefits-of-mfa/benefits-of-mfa.png b/content/identity/benefits-of-mfa/benefits-of-mfa.png
deleted file mode 100644
index 68de5ede7..000000000
Binary files a/content/identity/benefits-of-mfa/benefits-of-mfa.png and /dev/null differ
diff --git a/content/identity/benefits-of-mfa/benefits-of-mfa.webp b/content/identity/benefits-of-mfa/benefits-of-mfa.webp
index b4b7ef883..67973daca 100644
Binary files a/content/identity/benefits-of-mfa/benefits-of-mfa.webp and b/content/identity/benefits-of-mfa/benefits-of-mfa.webp differ
diff --git a/content/identity/benefits-of-mfa/buyer-guide-to-multi-factor-authentication-ebook.png b/content/identity/benefits-of-mfa/buyer-guide-to-multi-factor-authentication-ebook.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/benefits-of-mfa/buyer-guide-to-multi-factor-authentication-ebook.png and /dev/null differ
diff --git a/content/identity/benefits-of-mfa/buyer-guide-to-multi-factor-authentication-ebook.webp b/content/identity/benefits-of-mfa/buyer-guide-to-multi-factor-authentication-ebook.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/benefits-of-mfa/buyer-guide-to-multi-factor-authentication-ebook.webp differ
diff --git a/content/identity/benefits-of-mfa/index.md b/content/identity/benefits-of-mfa/index.md
index 9be6618b7..491e7f0f0 100644
--- a/content/identity/benefits-of-mfa/index.md
+++ b/content/identity/benefits-of-mfa/index.md
@@ -64,7 +64,7 @@ Before we learn the benefits of multi-factor authentication, let’s understand
MFA significantly reduces the risk of cyber attacks such as phishing, credential stuffing, and brute-force attacks. It’s particularly valuable for businesses with remote employees, as it ensures that only verified users can access company systems, reducing the risk of a data breach. These are key MFA benefits that improve cybersecurity measures.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
## Benefits of MFA (Multi-Factor Authentication)
diff --git a/content/identity/benefits-of-mfa/loginradius-mfa.png b/content/identity/benefits-of-mfa/loginradius-mfa.png
deleted file mode 100644
index d5c401b9f..000000000
Binary files a/content/identity/benefits-of-mfa/loginradius-mfa.png and /dev/null differ
diff --git a/content/identity/benefits-of-mfa/loginradius-mfa.webp b/content/identity/benefits-of-mfa/loginradius-mfa.webp
new file mode 100644
index 000000000..3090f63fc
Binary files /dev/null and b/content/identity/benefits-of-mfa/loginradius-mfa.webp differ
diff --git a/content/identity/benefits-of-reauthentication/GD-salt-hashing.png b/content/identity/benefits-of-reauthentication/GD-salt-hashing.png
deleted file mode 100644
index 698c87b68..000000000
Binary files a/content/identity/benefits-of-reauthentication/GD-salt-hashing.png and /dev/null differ
diff --git a/content/identity/benefits-of-reauthentication/GD-salt-hashing.webp b/content/identity/benefits-of-reauthentication/GD-salt-hashing.webp
new file mode 100644
index 000000000..f0938b9a0
Binary files /dev/null and b/content/identity/benefits-of-reauthentication/GD-salt-hashing.webp differ
diff --git a/content/identity/benefits-of-reauthentication/benefits-of-reauthentication-cover.jpg b/content/identity/benefits-of-reauthentication/benefits-of-reauthentication-cover.jpg
deleted file mode 100644
index 900da3d78..000000000
Binary files a/content/identity/benefits-of-reauthentication/benefits-of-reauthentication-cover.jpg and /dev/null differ
diff --git a/content/identity/benefits-of-reauthentication/benefits-of-reauthentication-cover.webp b/content/identity/benefits-of-reauthentication/benefits-of-reauthentication-cover.webp
new file mode 100644
index 000000000..31f4cea72
Binary files /dev/null and b/content/identity/benefits-of-reauthentication/benefits-of-reauthentication-cover.webp differ
diff --git a/content/identity/benefits-of-reauthentication/hashing-salt-GD.png b/content/identity/benefits-of-reauthentication/hashing-salt-GD.png
deleted file mode 100644
index 5c89d019a..000000000
Binary files a/content/identity/benefits-of-reauthentication/hashing-salt-GD.png and /dev/null differ
diff --git a/content/identity/benefits-of-reauthentication/hashing-salt-GD.webp b/content/identity/benefits-of-reauthentication/hashing-salt-GD.webp
new file mode 100644
index 000000000..1340466fe
Binary files /dev/null and b/content/identity/benefits-of-reauthentication/hashing-salt-GD.webp differ
diff --git a/content/identity/benefits-of-reauthentication/index.md b/content/identity/benefits-of-reauthentication/index.md
index d35ab402d..10473e182 100644
--- a/content/identity/benefits-of-reauthentication/index.md
+++ b/content/identity/benefits-of-reauthentication/index.md
@@ -1,7 +1,7 @@
---
title: "Discover the Benefits of Re-Authentication for Enhanced Security"
date: "2021-09-16"
-coverImage: "benefits-of-reauthentication-cover.jpg"
+coverImage: "benefits-of-reauthentication-cover.webp"
tags: ["data security","reauthentication","password management"]
author: "Navanita Devi"
description: "Re-authentication ensures that hackers don’t get easy access to a system’s content and leverage no other loopholes to exploit sensitive consumer credentials. Apart from internal combustion, re-authentication can also save you from external intrusion."
@@ -25,7 +25,7 @@ When a user requires to generate and remember more than one password, password f
Thus, a re-authentication is considered ideal for the elimination of password fatigue. The system will undertake the identity test without the need to type the password and ensure a safe environment for the users.
-[](https://www.loginradius.com/resource/adding-salt-to-hashing-a-step-by-step-guide-to-store-passwords/)
+[](https://www.loginradius.com/resource/adding-salt-to-hashing-a-step-by-step-guide-to-store-passwords/)
### 3. It reduces the need for IT support calls.
@@ -59,4 +59,4 @@ Re-authentication ensures that hackers don’t get easy access to a system’s c
All-in-all, you can save a lot of time and password exploitation with re-authentication. Speaking of which, the LoginRadius Re-authentication feature can help businesses securely re-authenticate consumers without taking a toll on user experience. [Contact us](https://www.loginradius.com/contact-sales) today to find out more.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=benefits-of-reauthentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=benefits-of-reauthentication)
diff --git a/content/identity/benefits-single-sign-on/7-benefits-of-sso.png b/content/identity/benefits-single-sign-on/7-benefits-of-sso.png
deleted file mode 100644
index a948a6dd3..000000000
Binary files a/content/identity/benefits-single-sign-on/7-benefits-of-sso.png and /dev/null differ
diff --git a/content/identity/benefits-single-sign-on/7-benefits-of-sso.webp b/content/identity/benefits-single-sign-on/7-benefits-of-sso.webp
new file mode 100644
index 000000000..33e95461d
Binary files /dev/null and b/content/identity/benefits-single-sign-on/7-benefits-of-sso.webp differ
diff --git a/content/identity/benefits-single-sign-on/CART-abandonment-7-Benefits-of-Single-Sign-On-V01.03-08-1024x296.png b/content/identity/benefits-single-sign-on/CART-abandonment-7-Benefits-of-Single-Sign-On-V01.03-08-1024x296.png
deleted file mode 100644
index d44843daa..000000000
Binary files a/content/identity/benefits-single-sign-on/CART-abandonment-7-Benefits-of-Single-Sign-On-V01.03-08-1024x296.png and /dev/null differ
diff --git a/content/identity/benefits-single-sign-on/CART-abandonment-7-Benefits-of-Single-Sign-On-V01.03-08-1024x296.webp b/content/identity/benefits-single-sign-on/CART-abandonment-7-Benefits-of-Single-Sign-On-V01.03-08-1024x296.webp
new file mode 100644
index 000000000..dcdc32360
Binary files /dev/null and b/content/identity/benefits-single-sign-on/CART-abandonment-7-Benefits-of-Single-Sign-On-V01.03-08-1024x296.webp differ
diff --git a/content/identity/benefits-single-sign-on/DS-LoginRadius-Single-Sign-on-1024x310.png b/content/identity/benefits-single-sign-on/DS-LoginRadius-Single-Sign-on-1024x310.png
deleted file mode 100644
index 702d43032..000000000
Binary files a/content/identity/benefits-single-sign-on/DS-LoginRadius-Single-Sign-on-1024x310.png and /dev/null differ
diff --git a/content/identity/benefits-single-sign-on/DS-LoginRadius-Single-Sign-on-1024x310.webp b/content/identity/benefits-single-sign-on/DS-LoginRadius-Single-Sign-on-1024x310.webp
new file mode 100644
index 000000000..5b5ca6d71
Binary files /dev/null and b/content/identity/benefits-single-sign-on/DS-LoginRadius-Single-Sign-on-1024x310.webp differ
diff --git a/content/identity/benefits-single-sign-on/benefits-sso.jpg b/content/identity/benefits-single-sign-on/benefits-sso.jpg
deleted file mode 100644
index ab6deef0a..000000000
Binary files a/content/identity/benefits-single-sign-on/benefits-sso.jpg and /dev/null differ
diff --git a/content/identity/benefits-single-sign-on/benefits-sso.webp b/content/identity/benefits-single-sign-on/benefits-sso.webp
new file mode 100644
index 000000000..ffdd90ce6
Binary files /dev/null and b/content/identity/benefits-single-sign-on/benefits-sso.webp differ
diff --git a/content/identity/benefits-single-sign-on/hacker-blocked-RBA-graphic-7-Benefits-SSO-1024x805.png b/content/identity/benefits-single-sign-on/hacker-blocked-RBA-graphic-7-Benefits-SSO-1024x805.png
deleted file mode 100644
index 0255055d8..000000000
Binary files a/content/identity/benefits-single-sign-on/hacker-blocked-RBA-graphic-7-Benefits-SSO-1024x805.png and /dev/null differ
diff --git a/content/identity/benefits-single-sign-on/hacker-blocked-RBA-graphic-7-Benefits-SSO-1024x805.webp b/content/identity/benefits-single-sign-on/hacker-blocked-RBA-graphic-7-Benefits-SSO-1024x805.webp
new file mode 100644
index 000000000..ac317e704
Binary files /dev/null and b/content/identity/benefits-single-sign-on/hacker-blocked-RBA-graphic-7-Benefits-SSO-1024x805.webp differ
diff --git a/content/identity/benefits-single-sign-on/index.md b/content/identity/benefits-single-sign-on/index.md
index 897cd810d..6d9ec875b 100644
--- a/content/identity/benefits-single-sign-on/index.md
+++ b/content/identity/benefits-single-sign-on/index.md
@@ -1,7 +1,7 @@
---
title: "7 Benefits of Single Sign-On (SSO) and Why Your Business Needs It"
date: "2019-11-12"
-coverImage: "benefits-sso.jpg"
+coverImage: "benefits-sso.webp"
tags: ["single sign on","mfa","cx",]
author: "Rakesh Soni"
description: "Now that more enterprises are moving to the cloud, customers expect seamless access from anywhere, anywhere, and on any computer, to multiple applications. Likewise, as most large corporations have hundreds of touchpoints under different labels, trying to handle them all will strain their IT departments."
@@ -65,7 +65,7 @@ With single sign-on, you can:
As you can see, the ability to increase the productivity of end-users is one of the greatest single sign on benefits.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
### 2. It improves security capabilities.
@@ -77,7 +77,7 @@ Since users only need to remember one password for multiple applications, they
As explained in the next section, a single sign-on strategy can also be combined with [multi-factor authentication (MFA)](https://www.loginradius.com/blog/identity/what-is-multi-factor-authentication/) for extra security.
-
+
### 3. It combines with Risk-Based Authentication (RBA).
@@ -97,7 +97,7 @@ How does password fatigue hurt enterprises? In short, more passwords, more probl
A [recent usability study](https://baymard.com/blog/password-requirements-and-password-reset) by Baymard Institute proves this point. In this study, Baymard tested existing account users at two e-commerce sites (Amazon and ASOS) and found that 18.75% of users abandon their carts due to forgotten passwords or password reset issues.
-
+
The benefit of single sign-on is that it’s only one password for customers to remember, for all of your applications.
@@ -203,4 +203,4 @@ SSO between two applications enables users to log in once and access both applic
Single sign-on (SSO) is an authentication method that allows users to access multiple applications or systems with a single set of credentials, improving convenience and security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=benefits-single-sign-on)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=benefits-single-sign-on)
diff --git a/content/identity/best-idaas-provider-loginradius/Best-IDaaS-provider.png b/content/identity/best-idaas-provider-loginradius/Best-IDaaS-provider.png
deleted file mode 100644
index 5ef06b2ac..000000000
Binary files a/content/identity/best-idaas-provider-loginradius/Best-IDaaS-provider.png and /dev/null differ
diff --git a/content/identity/best-idaas-provider-loginradius/Best-IDaaS-provider.webp b/content/identity/best-idaas-provider-loginradius/Best-IDaaS-provider.webp
new file mode 100644
index 000000000..3bfff267d
Binary files /dev/null and b/content/identity/best-idaas-provider-loginradius/Best-IDaaS-provider.webp differ
diff --git a/content/identity/best-idaas-provider-loginradius/Best-IDaaS-solution-1.png b/content/identity/best-idaas-provider-loginradius/Best-IDaaS-solution-1.png
deleted file mode 100644
index 348c92c83..000000000
Binary files a/content/identity/best-idaas-provider-loginradius/Best-IDaaS-solution-1.png and /dev/null differ
diff --git a/content/identity/best-idaas-provider-loginradius/Best-IDaaS-solution-1.webp b/content/identity/best-idaas-provider-loginradius/Best-IDaaS-solution-1.webp
new file mode 100644
index 000000000..d13ff8c1a
Binary files /dev/null and b/content/identity/best-idaas-provider-loginradius/Best-IDaaS-solution-1.webp differ
diff --git a/content/identity/best-idaas-provider-loginradius/Book-a-free-demo-request.png b/content/identity/best-idaas-provider-loginradius/Book-a-free-demo-request.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/best-idaas-provider-loginradius/Book-a-free-demo-request.png and /dev/null differ
diff --git a/content/identity/best-idaas-provider-loginradius/Book-a-free-demo-request.webp b/content/identity/best-idaas-provider-loginradius/Book-a-free-demo-request.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/best-idaas-provider-loginradius/Book-a-free-demo-request.webp differ
diff --git a/content/identity/best-idaas-provider-loginradius/EB-Guide-to-Modern-Customer-Identity.png b/content/identity/best-idaas-provider-loginradius/EB-Guide-to-Modern-Customer-Identity.png
deleted file mode 100644
index 2f87dc40c..000000000
Binary files a/content/identity/best-idaas-provider-loginradius/EB-Guide-to-Modern-Customer-Identity.png and /dev/null differ
diff --git a/content/identity/best-idaas-provider-loginradius/EB-Guide-to-Modern-Customer-Identity.webp b/content/identity/best-idaas-provider-loginradius/EB-Guide-to-Modern-Customer-Identity.webp
new file mode 100644
index 000000000..4e4ab1a98
Binary files /dev/null and b/content/identity/best-idaas-provider-loginradius/EB-Guide-to-Modern-Customer-Identity.webp differ
diff --git a/content/identity/best-idaas-provider-loginradius/idaas-provider.jpg b/content/identity/best-idaas-provider-loginradius/idaas-provider.jpg
deleted file mode 100644
index 8d952fa41..000000000
Binary files a/content/identity/best-idaas-provider-loginradius/idaas-provider.jpg and /dev/null differ
diff --git a/content/identity/best-idaas-provider-loginradius/idaas-provider.webp b/content/identity/best-idaas-provider-loginradius/idaas-provider.webp
new file mode 100644
index 000000000..c18f08f71
Binary files /dev/null and b/content/identity/best-idaas-provider-loginradius/idaas-provider.webp differ
diff --git a/content/identity/best-idaas-provider-loginradius/index.md b/content/identity/best-idaas-provider-loginradius/index.md
index c8375c409..af6c57d8d 100644
--- a/content/identity/best-idaas-provider-loginradius/index.md
+++ b/content/identity/best-idaas-provider-loginradius/index.md
@@ -1,7 +1,7 @@
---
title: "Best IDaaS Provider - Why Loginradius is Considered as the Best IDaaS Solution"
date: "2020-10-09"
-coverImage: "idaas-provider.jpg"
+coverImage: "idaas-provider.webp"
tags: ["data privacy","idaas provider","cx"]
author: "Rakesh Soni"
description: "Identity-as-a-service or IDaaS refers to cloud-based applications for identity and access management provided on the basis of subscription. At its heart, IDaaS provides consumers’ systems with access, intelligence, and identity governance capabilities."
@@ -27,7 +27,7 @@ The best IDaaS providers are evolving, and new ones are emerging. How do you cho
## 5 Factors to Consider Before Choosing the Best IDaaS Provider
-
+
**1\. It should connect to mixed platform environments.**
@@ -67,7 +67,7 @@ The best IDaaS provider should include MFA with (at least) the following combina
Also, ensure that your IDaaS provider offers custom configurations, whenever necessary for optimal performance. Make sure it is affordable, flexible, and designed to scale (forecasting your rapid growth).
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
## Why LoginRadius Is Considered to Be Your One-Stop Solution for IDaaS for Both Developers and Businesses
@@ -98,4 +98,4 @@ It is incredibly important for IT professionals to safeguard systems and data wh
LoginRadius is the comprehensive ideal solution for enterprises who need to implement identity management into applications quickly and easily.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-idaas-provider-loginradius)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-idaas-provider-loginradius)
diff --git a/content/identity/best-janrain-alternative/CTA-Graphics-for-Blogs-V02.01-15.png b/content/identity/best-janrain-alternative/CTA-Graphics-for-Blogs-V02.01-15.png
deleted file mode 100644
index 934b6a2f3..000000000
Binary files a/content/identity/best-janrain-alternative/CTA-Graphics-for-Blogs-V02.01-15.png and /dev/null differ
diff --git a/content/identity/best-janrain-alternative/CTA-Graphics-for-Blogs-V02.01-15.webp b/content/identity/best-janrain-alternative/CTA-Graphics-for-Blogs-V02.01-15.webp
new file mode 100644
index 000000000..63906573a
Binary files /dev/null and b/content/identity/best-janrain-alternative/CTA-Graphics-for-Blogs-V02.01-15.webp differ
diff --git a/content/identity/best-janrain-alternative/index.md b/content/identity/best-janrain-alternative/index.md
index 09505685c..51cd277a3 100644
--- a/content/identity/best-janrain-alternative/index.md
+++ b/content/identity/best-janrain-alternative/index.md
@@ -1,7 +1,7 @@
---
title: "Why LoginRadius Is the Best Akamai Identity Cloud (Janrain) Alternative"
date: "2019-06-24"
-coverImage: "janrain-feature.png"
+coverImage: "janrain-feature.webp"
tags: ["public-sector"]
featured: false
author: "Rakesh Soni"
@@ -88,4 +88,4 @@ LoginRadius is a CIAM solution that offers seamless migration from your current
Want to hear more about making the switch to LoginRadius? Call a LoginRadius digital identity consultant today at 1-844-625-8889. We’ll be happy to give you a product demo so you can compare LoginRadius with your current provider.
-[](https://www.loginradius.com/book-demo/)
+[](https://www.loginradius.com/book-demo/)
diff --git a/content/identity/best-janrain-alternative/janrain-feature.png b/content/identity/best-janrain-alternative/janrain-feature.png
deleted file mode 100644
index ab2ea4079..000000000
Binary files a/content/identity/best-janrain-alternative/janrain-feature.png and /dev/null differ
diff --git a/content/identity/best-janrain-alternative/janrain-feature.webp b/content/identity/best-janrain-alternative/janrain-feature.webp
new file mode 100644
index 000000000..40ef4c8f8
Binary files /dev/null and b/content/identity/best-janrain-alternative/janrain-feature.webp differ
diff --git a/content/identity/best-practices-business-resilience/business-resilience.jpg b/content/identity/best-practices-business-resilience/business-resilience.jpg
deleted file mode 100644
index 27e62987f..000000000
Binary files a/content/identity/best-practices-business-resilience/business-resilience.jpg and /dev/null differ
diff --git a/content/identity/best-practices-business-resilience/business-resilience.webp b/content/identity/best-practices-business-resilience/business-resilience.webp
new file mode 100644
index 000000000..1d4c22d32
Binary files /dev/null and b/content/identity/best-practices-business-resilience/business-resilience.webp differ
diff --git a/content/identity/best-practices-business-resilience/index.md b/content/identity/best-practices-business-resilience/index.md
index 463a904b2..e08894e8b 100644
--- a/content/identity/best-practices-business-resilience/index.md
+++ b/content/identity/best-practices-business-resilience/index.md
@@ -1,7 +1,7 @@
---
title: "5 Best Practices of Implementing Business Resilience during a Data Breach"
date: "2021-02-18"
-coverImage: "business-resilience.jpg"
+coverImage: "business-resilience.webp"
tags: ["data security","resiliency","cx"]
author: "Rakesh Soni"
description: "Business resilience can be defined as a business’ ability to quickly adapt and respond to impending risks or disruptions. More like a combination of crisis management and business continuity strategies post-disaster."
@@ -11,7 +11,7 @@ metadescription: "What is business resiliency and the best practices of implemen
Today, data breaches have become a significant threat to businesses across the globe. Therefore, considering the long list of resultant consequences to be faced as an aftermath, it is crucial for companies to come out the other side of a breach intact.
-The Annual Cybercrime Report 2019 by [Cybersecurity Ventures](https://www.herjavecgroup.com/the-2019-official-annual-cybercrime-report/#:~:text=Cybersecurity%20Ventures%20has%20reaffirmed%20their,associated%20with%20cybercrime%20are%20vast.) says that these data breaches can cost global businesses around $6 trillion in 2021!
+The Annual Cybercrime Report 2019 by Cybersecurity Ventures says that these data breaches can cost global businesses around $6 trillion in 2021!
According to experts, implementing business resilience best practices can help companies overcome issues that come with a data breach.
@@ -23,7 +23,7 @@ Read on!
During a data breach, companies’ confidential data are accessed by attackers without permission. It is not only about sensitive information going out to the wrong hands. These cyber attackers can also hack your database and conduct malicious activities, costing you both money and reputation.
-As per [Cost of a Data Breach Report 2020](https://www.ibm.com/security/digital-assets/cost-data-breach-report/#/) by IBM, the global average total cost of a data breach in 2020 was $3.86M. If this situation continues, by 2021, a business is expected to fall victim to a [ransomware attack every 11 seconds](https://www.herjavecgroup.com/wp-content/uploads/2018/12/CV-HG-2019-Official-Annual-Cybercrime-Report.pdf).
+As per [Cost of a Data Breach Report 2020](https://www.ibm.com/security/digital-assets/cost-data-breach-report/#/) by IBM, the global average total cost of a data breach in 2020 was $3.86M. If this situation continues, by 2021, a business is expected to fall victim to a ransomware attack every 11 seconds.
Now let’s consider some of the negative impacts of data breaches that make companies susceptible to financial and credibility loss.
@@ -62,7 +62,7 @@ On the other side, business resilience best practices will assure that all your
This can even cultivate a resilient organizational culture. It makes the whole business, including employees, quickly adapt to unforeseen challenges whenever the business operations or processes go awry. Or under threat like a data breach.
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
## 5 Best Practices of Implementing Business Resiliency during a Data Breach
@@ -124,4 +124,4 @@ A standard business resilience plan in the need of the hour. A recent study show
So, it is important to implement fail-proof business resilience practices in your business to survive unexpected data breaches.
-[](https://www.loginradius.com/contact-us)
+[](https://www.loginradius.com/contact-us)
diff --git a/content/identity/best-practices-business-resilience/protecting-pii-against-data-breaches.png b/content/identity/best-practices-business-resilience/protecting-pii-against-data-breaches.png
deleted file mode 100644
index a86e6d940..000000000
Binary files a/content/identity/best-practices-business-resilience/protecting-pii-against-data-breaches.png and /dev/null differ
diff --git a/content/identity/best-practices-business-resilience/protecting-pii-against-data-breaches.webp b/content/identity/best-practices-business-resilience/protecting-pii-against-data-breaches.webp
new file mode 100644
index 000000000..fc95b4d7d
Binary files /dev/null and b/content/identity/best-practices-business-resilience/protecting-pii-against-data-breaches.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/EB-buyers-GD-to-MFA.png b/content/identity/best-practices-choosing-good-security-questions/EB-buyers-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/EB-buyers-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/EB-buyers-GD-to-MFA.webp b/content/identity/best-practices-choosing-good-security-questions/EB-buyers-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/EB-buyers-GD-to-MFA.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-login-options.png b/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-login-options.png
deleted file mode 100644
index 949e5b64b..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-login-options.png and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-login-options.webp b/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-login-options.webp
new file mode 100644
index 000000000..90e385323
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-login-options.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-steps.png b/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-steps.png
deleted file mode 100644
index 60f8770b3..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-steps.png and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-steps.webp b/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-steps.webp
new file mode 100644
index 000000000..c5e9b4412
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/MBNA-2factor-steps.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/adorable-blur-child-573293.jpg b/content/identity/best-practices-choosing-good-security-questions/adorable-blur-child-573293.jpg
deleted file mode 100644
index 49bbe0fca..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/adorable-blur-child-573293.jpg and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/adorable-blur-child-573293.webp b/content/identity/best-practices-choosing-good-security-questions/adorable-blur-child-573293.webp
new file mode 100644
index 000000000..1d101f7b9
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/adorable-blur-child-573293.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/arms-bonding-closeness-1645634.jpg b/content/identity/best-practices-choosing-good-security-questions/arms-bonding-closeness-1645634.jpg
deleted file mode 100644
index 64114f6f0..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/arms-bonding-closeness-1645634.jpg and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/arms-bonding-closeness-1645634.webp b/content/identity/best-practices-choosing-good-security-questions/arms-bonding-closeness-1645634.webp
new file mode 100644
index 000000000..d42eb37e6
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/arms-bonding-closeness-1645634.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/automobile-automotive-car-1386649.jpg b/content/identity/best-practices-choosing-good-security-questions/automobile-automotive-car-1386649.jpg
deleted file mode 100644
index be46a87c1..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/automobile-automotive-car-1386649.jpg and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/automobile-automotive-car-1386649.webp b/content/identity/best-practices-choosing-good-security-questions/automobile-automotive-car-1386649.webp
new file mode 100644
index 000000000..c2ef66bcc
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/automobile-automotive-car-1386649.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/balance-beach-boulder-1051449.jpg b/content/identity/best-practices-choosing-good-security-questions/balance-beach-boulder-1051449.jpg
deleted file mode 100644
index 36b617abe..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/balance-beach-boulder-1051449.jpg and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/balance-beach-boulder-1051449.webp b/content/identity/best-practices-choosing-good-security-questions/balance-beach-boulder-1051449.webp
new file mode 100644
index 000000000..7354f7adb
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/balance-beach-boulder-1051449.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/best-practices-good-security-question.jpg b/content/identity/best-practices-choosing-good-security-questions/best-practices-good-security-question.jpg
deleted file mode 100644
index f6dd0ae08..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/best-practices-good-security-question.jpg and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/best-practices-good-security-question.webp b/content/identity/best-practices-choosing-good-security-questions/best-practices-good-security-question.webp
new file mode 100644
index 000000000..7840f3227
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/best-practices-good-security-question.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/boy-car-child-1266014.jpg b/content/identity/best-practices-choosing-good-security-questions/boy-car-child-1266014.jpg
deleted file mode 100644
index e5878f4ae..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/boy-car-child-1266014.jpg and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/boy-car-child-1266014.webp b/content/identity/best-practices-choosing-good-security-questions/boy-car-child-1266014.webp
new file mode 100644
index 000000000..bb9570dab
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/boy-car-child-1266014.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/buyer-guide-to-multi-factor-authentication-ebook.png b/content/identity/best-practices-choosing-good-security-questions/buyer-guide-to-multi-factor-authentication-ebook.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/buyer-guide-to-multi-factor-authentication-ebook.png and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/buyer-guide-to-multi-factor-authentication-ebook.webp b/content/identity/best-practices-choosing-good-security-questions/buyer-guide-to-multi-factor-authentication-ebook.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/buyer-guide-to-multi-factor-authentication-ebook.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/coverinfo.jpg b/content/identity/best-practices-choosing-good-security-questions/coverinfo.jpg
deleted file mode 100644
index f6dd0ae08..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/coverinfo.jpg and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/coverinfo.webp b/content/identity/best-practices-choosing-good-security-questions/coverinfo.webp
new file mode 100644
index 000000000..7840f3227
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/coverinfo.webp differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/index.md b/content/identity/best-practices-choosing-good-security-questions/index.md
index a1aaf3596..477c6c17b 100644
--- a/content/identity/best-practices-choosing-good-security-questions/index.md
+++ b/content/identity/best-practices-choosing-good-security-questions/index.md
@@ -1,7 +1,7 @@
---
title: "Best Practices for Choosing Good Security Questions"
date: "2019-01-31"
-coverImage: "security-questions.jpg"
+coverImage: "security-questions.webp"
tags: ["data security","password management","cx"]
author: "Rakesh Soni"
description: "Security questions will bring to your authentication process an extra layer of certainty. Security problems are an alternative way to recognise your customers when they have forgotten their password, entered too many times the wrong passwords, or attempted to log in from a location or unknown computer."
@@ -38,7 +38,7 @@ _You can see examples of good security questions from the_ _[University of Virgi
### 1. Safe
-
+
When choosing security question and answers, it’s extremely important that the correct answers cannot be guessed or researched over the internet.
@@ -51,7 +51,7 @@ This question could be considered unsafe because the information can be found on
Aside from these issues, if a hacker was interested in a specific account, it might be easy to brute-force their way past this question since there are only a fixed number of counties in each US state.
### 2. Stable
-
+
A good security question should have a fixed answer, meaning that it won’t change over time.
@@ -74,7 +74,7 @@ Both of these examples make for poor security questions because their answers wi
### 3. Memorable
-
+
A good security question should be easily answered by the account holders but not readily obvious to others or quickly researched.
@@ -88,7 +88,7 @@ _“In what city or town did your mother and father meet?”_
Most consumers know the answer to a question like this, making it fit the criteria of being memorable. It is also more difficult to guess or research this fact. Best of all, it fits the stability criteria as well.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
Some examples of question and answers that are unmemorable include:
@@ -102,7 +102,7 @@ The answer to this question may be quick to recall for someone younger, but for
### 4. Simple
-
+
A simple question has a precise answer that doesn’t create confusion.
@@ -123,7 +123,7 @@ _“When is your anniversary?”_
### 5. Many
-
+
A good security question should have many potential answers. This makes guessing the answer much more difficult and will also slow down automated or brute-force attempts at gaining access to the consumer’s account.
@@ -181,13 +181,13 @@ Passwords and security questions aren’t the only methods for locking down cons
As an example, the [MBNA bank](https://www.mbna.ca/) recently decided that security questions were not doing enough for them and their consumers to keep their accounts safe. To upgrade their security, they decided to go with two-factor authentication instead of security questions in order to verify their consumer’s identities.
-
+
_Source: MBNA website_
In these screenshots, you can see that the transition from security questions to two-factor authentication was fairly seamless for MBNA consumers. They even had the option to choose how often they would be prompted to provide a security code as their second factor.
-
+
_Source: MBNA website_
@@ -203,4 +203,4 @@ By requiring your consumers to follow [strong password rules](https://www.loginr
If you’re interested in learning why passwords are slowly becoming a thing of the past, download our e-book [The Death of Passwords](https://www.loginradius.com/resource/the-death-of-passwords/). There are better authentication methods than passwords and security questions available for your company—and with support from LoginRadius, you can adopt them quickly and easily.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-practices-choosing-good-security-questions)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-practices-choosing-good-security-questions)
diff --git a/content/identity/best-practices-choosing-good-security-questions/security-questions.jpg b/content/identity/best-practices-choosing-good-security-questions/security-questions.jpg
deleted file mode 100644
index 2c31c8cc7..000000000
Binary files a/content/identity/best-practices-choosing-good-security-questions/security-questions.jpg and /dev/null differ
diff --git a/content/identity/best-practices-choosing-good-security-questions/security-questions.webp b/content/identity/best-practices-choosing-good-security-questions/security-questions.webp
new file mode 100644
index 000000000..9c72a3c46
Binary files /dev/null and b/content/identity/best-practices-choosing-good-security-questions/security-questions.webp differ
diff --git a/content/identity/best-practices-username-password-authentication/DS-LoginRadius-SSO.png b/content/identity/best-practices-username-password-authentication/DS-LoginRadius-SSO.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/best-practices-username-password-authentication/DS-LoginRadius-SSO.png and /dev/null differ
diff --git a/content/identity/best-practices-username-password-authentication/DS-LoginRadius-SSO.webp b/content/identity/best-practices-username-password-authentication/DS-LoginRadius-SSO.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/best-practices-username-password-authentication/DS-LoginRadius-SSO.webp differ
diff --git a/content/identity/best-practices-username-password-authentication/DS-SSO.png b/content/identity/best-practices-username-password-authentication/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/best-practices-username-password-authentication/DS-SSO.png and /dev/null differ
diff --git a/content/identity/best-practices-username-password-authentication/DS-SSO.webp b/content/identity/best-practices-username-password-authentication/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/best-practices-username-password-authentication/DS-SSO.webp differ
diff --git a/content/identity/best-practices-username-password-authentication/index.md b/content/identity/best-practices-username-password-authentication/index.md
index 346a87b92..b373898ae 100644
--- a/content/identity/best-practices-username-password-authentication/index.md
+++ b/content/identity/best-practices-username-password-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Best Practices for Username and Password Authentication"
date: "2023-03-09"
-coverImage: "username-pswrd.jpg"
+coverImage: "username-pswrd.webp"
tags: ["passwordless authentication","user management","mfa","cx"]
author: "Rakesh Soni"
description: "While the username and password authentication method is convenient and widely used, it is also vulnerable to attacks and breaches, making it essential for organizations to implement best practices for secure authentication. Let’s discuss the best practices for username and password authentication to ensure the highest level of security."
@@ -99,7 +99,7 @@ There are several password alternatives that organizations can consider, includi
* **Single sign-on (SSO):** Single sign-on allows users to access multiple systems with a single login credential. SSO offers a seamless user experience between multiple interconnected applications and ensures zero friction while users switch from one application to another since they need not re-authenticate themselves while switching.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
## Best Practices for Password Storage and Transmission
@@ -171,4 +171,4 @@ The authentication method that uses usernames and passwords is known as "usernam
The best practice for user authentication includes creating a firm password policy, using salted and hashed passwords, implementing multi-factor authentication (MFA), and using password managers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-practices-username-password-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-practices-username-password-authentication)
diff --git a/content/identity/best-practices-username-password-authentication/password-authntication.jpg b/content/identity/best-practices-username-password-authentication/password-authntication.jpg
deleted file mode 100644
index 5e834baef..000000000
Binary files a/content/identity/best-practices-username-password-authentication/password-authntication.jpg and /dev/null differ
diff --git a/content/identity/best-practices-username-password-authentication/password-authntication.webp b/content/identity/best-practices-username-password-authentication/password-authntication.webp
new file mode 100644
index 000000000..adc6b7531
Binary files /dev/null and b/content/identity/best-practices-username-password-authentication/password-authntication.webp differ
diff --git a/content/identity/best-practices-username-password-authentication/username-pswrd.jpg b/content/identity/best-practices-username-password-authentication/username-pswrd.jpg
deleted file mode 100644
index 80020b923..000000000
Binary files a/content/identity/best-practices-username-password-authentication/username-pswrd.jpg and /dev/null differ
diff --git a/content/identity/best-practices-username-password-authentication/username-pswrd.webp b/content/identity/best-practices-username-password-authentication/username-pswrd.webp
new file mode 100644
index 000000000..6c8ed7ffd
Binary files /dev/null and b/content/identity/best-practices-username-password-authentication/username-pswrd.webp differ
diff --git a/content/identity/best-sso-providers-loginradius/Best-SSO-Provider-4.png b/content/identity/best-sso-providers-loginradius/Best-SSO-Provider-4.png
deleted file mode 100644
index 6703fa2a8..000000000
Binary files a/content/identity/best-sso-providers-loginradius/Best-SSO-Provider-4.png and /dev/null differ
diff --git a/content/identity/best-sso-providers-loginradius/Best-SSO-Provider-4.webp b/content/identity/best-sso-providers-loginradius/Best-SSO-Provider-4.webp
new file mode 100644
index 000000000..8cdb5d45e
Binary files /dev/null and b/content/identity/best-sso-providers-loginradius/Best-SSO-Provider-4.webp differ
diff --git a/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-2.png b/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-2.png
deleted file mode 100644
index a21a9bd31..000000000
Binary files a/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-2.png and /dev/null differ
diff --git a/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-2.webp b/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-2.webp
new file mode 100644
index 000000000..871064800
Binary files /dev/null and b/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-2.webp differ
diff --git a/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-3.png b/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-3.png
deleted file mode 100644
index 86a0ca343..000000000
Binary files a/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-3.png and /dev/null differ
diff --git a/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-3.webp b/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-3.webp
new file mode 100644
index 000000000..f9a0f280c
Binary files /dev/null and b/content/identity/best-sso-providers-loginradius/Best-SSO-Providers-3.webp differ
diff --git a/content/identity/best-sso-providers-loginradius/Best-SSO-Providers.png b/content/identity/best-sso-providers-loginradius/Best-SSO-Providers.png
deleted file mode 100644
index 4d297b76b..000000000
Binary files a/content/identity/best-sso-providers-loginradius/Best-SSO-Providers.png and /dev/null differ
diff --git a/content/identity/best-sso-providers-loginradius/Best-SSO-Providers.webp b/content/identity/best-sso-providers-loginradius/Best-SSO-Providers.webp
new file mode 100644
index 000000000..1d84913fc
Binary files /dev/null and b/content/identity/best-sso-providers-loginradius/Best-SSO-Providers.webp differ
diff --git a/content/identity/best-sso-providers-loginradius/Book-a-free-demo-request-1024x310.png b/content/identity/best-sso-providers-loginradius/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/best-sso-providers-loginradius/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/best-sso-providers-loginradius/Book-a-free-demo-request-1024x310.webp b/content/identity/best-sso-providers-loginradius/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/best-sso-providers-loginradius/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/best-sso-providers-loginradius/DS-LoginRadius-Single-Sign-on.png b/content/identity/best-sso-providers-loginradius/DS-LoginRadius-Single-Sign-on.png
deleted file mode 100644
index 702d43032..000000000
Binary files a/content/identity/best-sso-providers-loginradius/DS-LoginRadius-Single-Sign-on.png and /dev/null differ
diff --git a/content/identity/best-sso-providers-loginradius/DS-LoginRadius-Single-Sign-on.webp b/content/identity/best-sso-providers-loginradius/DS-LoginRadius-Single-Sign-on.webp
new file mode 100644
index 000000000..5b5ca6d71
Binary files /dev/null and b/content/identity/best-sso-providers-loginradius/DS-LoginRadius-Single-Sign-on.webp differ
diff --git a/content/identity/best-sso-providers-loginradius/best-sso-provider.jpg b/content/identity/best-sso-providers-loginradius/best-sso-provider.jpg
deleted file mode 100644
index 991b2b656..000000000
Binary files a/content/identity/best-sso-providers-loginradius/best-sso-provider.jpg and /dev/null differ
diff --git a/content/identity/best-sso-providers-loginradius/best-sso-provider.webp b/content/identity/best-sso-providers-loginradius/best-sso-provider.webp
new file mode 100644
index 000000000..62612a322
Binary files /dev/null and b/content/identity/best-sso-providers-loginradius/best-sso-provider.webp differ
diff --git a/content/identity/best-sso-providers-loginradius/fim.png b/content/identity/best-sso-providers-loginradius/fim.png
deleted file mode 100644
index 01a289614..000000000
Binary files a/content/identity/best-sso-providers-loginradius/fim.png and /dev/null differ
diff --git a/content/identity/best-sso-providers-loginradius/fim.webp b/content/identity/best-sso-providers-loginradius/fim.webp
new file mode 100644
index 000000000..3d4c0a8aa
Binary files /dev/null and b/content/identity/best-sso-providers-loginradius/fim.webp differ
diff --git a/content/identity/best-sso-providers-loginradius/index.md b/content/identity/best-sso-providers-loginradius/index.md
index 9f209829f..2d9e2d54b 100644
--- a/content/identity/best-sso-providers-loginradius/index.md
+++ b/content/identity/best-sso-providers-loginradius/index.md
@@ -1,7 +1,7 @@
---
title: "Best SSO Provider: Why LoginRadius Is Considered As The Best SSO Solution"
date: "2020-09-11"
-coverImage: "best-sso-provider.jpg"
+coverImage: "best-sso-provider.webp"
tags: ["sso provider","compliance","cx"]
author: "Rakesh Soni"
description: "A unique authentication mechanism that allows users to access several programmes with a single set of credentials, such as a username and password, is Single Sign-on (or SSO)."
@@ -53,7 +53,7 @@ This one is interlinked. When there are lesser passwords to remember, there will
## Top 5 Feature of the Best Single Sign-on Solutions Provider
-
+
Looking for factors to consider when selecting an SSO solution. The following are the top five.
@@ -85,7 +85,7 @@ Though not an unconditional necessity, it is a good gesture if the SSO solutions
## Why LoginRadius Is the Best SSO Solution Provider for Developers and Businesses
-
+
LoginRadius goes beyond a single sign-on solution with its broader consumer identity and access management functions, but it is an excellent platform for SSO nonetheless.
@@ -108,7 +108,7 @@ Another good reason for developers to shift to LoginRadius is they can embed SSO
Because developers need not focus on complex authentication anymore, it (kind of) gives the liberty to work on other functions of the application.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
### Single Sign-On for Enterprise
@@ -142,11 +142,11 @@ Here is the step-by-step guide on configuring Web Single Sign-On with LoginRadiu
**Step 1:** Log in to the LoginRadius Admin Console account. Navigate to Deployment and click on Apps.
-
+
**Step 2:** Under the Production Website URL, add the domains you want to implement your Web SSO. There is an Add New Site button at the bottom. Click on it to add the domains.
-
+
## Conclusion
@@ -154,4 +154,4 @@ Single Sign-On clearly improves consumer experience and boosts productivity by a
By implementing the benefits of the LoginRadius SSO as a unified solution, you increase business agility, security, convenient and streamlined experience for your business and consumers alike. And, that's awesome!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-sso-providers-loginradius)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-sso-providers-loginradius)
diff --git a/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps-datasheet.png b/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps-datasheet.png
deleted file mode 100644
index 69293181d..000000000
Binary files a/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps-datasheet.png and /dev/null differ
diff --git a/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps-datasheet.webp b/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps-datasheet.webp
new file mode 100644
index 000000000..b272f8563
Binary files /dev/null and b/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps-datasheet.webp differ
diff --git a/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps.png b/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps.png
deleted file mode 100644
index ac15f1090..000000000
Binary files a/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps.png and /dev/null differ
diff --git a/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps.webp b/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps.webp
new file mode 100644
index 000000000..6ebff8151
Binary files /dev/null and b/content/identity/biometric-authentication-mobile-apps/biometric-authentication-mobile-apps.webp differ
diff --git a/content/identity/biometric-authentication-mobile-apps/index.md b/content/identity/biometric-authentication-mobile-apps/index.md
index 433765d9b..cec163b7a 100644
--- a/content/identity/biometric-authentication-mobile-apps/index.md
+++ b/content/identity/biometric-authentication-mobile-apps/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - LoginRadius Introduces Convenient and Secure Biometric Authentication for Mobile Apps"
date: "2021-02-16"
-coverImage: "biometric-authentication-mobile-apps.png"
+coverImage: "biometric-authentication-mobile-apps.webp"
tags: ["biometric authentication","cx","ciam solution"]
author: "Rakesh Soni"
description: "The LoginRadius Mobile Biometric Authentication feature is dedicated to mobile applications and enables users to use the FaceID and TouchID of their mobile devices for authentication purposes."
@@ -34,7 +34,7 @@ Let's underline some of the major benefits of Mobile Biometric Authentication.
* For biometric authentication, physical proximity is required if hackers want to bypass the login process. Cybercriminals coming into the physical proximity of the actual consumer is rare.
-[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
+[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
## Key Features Offered by LoginRadius
@@ -52,4 +52,4 @@ You can configure both authentication options for your app and later, ask the co
The Mobile Biometric Authentication by LoginRadius is a local authentication concept and consumers' biometric data don't even leave their mobile devices. Hence, as a business, you don't need to worry about storing, processing, and securing your consumer's biometric data.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=biometric-authentication-mobile-apps)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=biometric-authentication-mobile-apps)
diff --git a/content/identity/biometric-multi-factor-authentication/WP-mfa-evolution.png b/content/identity/biometric-multi-factor-authentication/WP-mfa-evolution.png
deleted file mode 100644
index bcada2908..000000000
Binary files a/content/identity/biometric-multi-factor-authentication/WP-mfa-evolution.png and /dev/null differ
diff --git a/content/identity/biometric-multi-factor-authentication/WP-mfa-evolution.webp b/content/identity/biometric-multi-factor-authentication/WP-mfa-evolution.webp
new file mode 100644
index 000000000..c1e17eff4
Binary files /dev/null and b/content/identity/biometric-multi-factor-authentication/WP-mfa-evolution.webp differ
diff --git a/content/identity/biometric-multi-factor-authentication/biometric-auth-mfa.jpg b/content/identity/biometric-multi-factor-authentication/biometric-auth-mfa.jpg
deleted file mode 100644
index 9e14cdb6e..000000000
Binary files a/content/identity/biometric-multi-factor-authentication/biometric-auth-mfa.jpg and /dev/null differ
diff --git a/content/identity/biometric-multi-factor-authentication/biometric-auth-mfa.webp b/content/identity/biometric-multi-factor-authentication/biometric-auth-mfa.webp
new file mode 100644
index 000000000..c3910ce22
Binary files /dev/null and b/content/identity/biometric-multi-factor-authentication/biometric-auth-mfa.webp differ
diff --git a/content/identity/biometric-multi-factor-authentication/index.md b/content/identity/biometric-multi-factor-authentication/index.md
index ae7373c94..d851ce5d5 100644
--- a/content/identity/biometric-multi-factor-authentication/index.md
+++ b/content/identity/biometric-multi-factor-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "7 Reasons to Use Biometric Authentication for Multi-Factor Authentication"
date: "2024-01-30"
-coverImage: "biometric-auth-mfa.jpg"
+coverImage: "biometric-auth-mfa.webp"
tags: ["biometric authentication","mfa","cx"]
author: "Vishal Sharma"
description: "Gone are the days when businesses used to rely on usernames, passwords, and OTPs to provide a secure and seamless user experience. Businesses are shifting to modern and advanced authentication methods, like multi-factor authorization (MFA), which is a crucial part of ensuring security. MFA comprises different authentication factors, but why is biometric authentication one of the secure options? Let’s find out!"
@@ -52,7 +52,7 @@ The key factor differentiating biometrics authentication from other multi-factor
Implementing other authentication methods requires specialized software, and integrating it with other systems can be expensive. The best part of implementing the biometrics authentication method is there is no need to invest in additional capital once the biometric verification system is integrated. It significantly reduces upfront investment costs and prevents the risks of loss due to fraud and illegal entries.
-[](https://www.loginradius.com/resource/mfa-evolution-ebook/)
+[](https://www.loginradius.com/resource/mfa-evolution-ebook/)
### 4. Scalable
@@ -74,4 +74,4 @@ When fraudsters or hackers get their hands on the user’s identity, they can co
Implementing **multi-factor authentication through biometrics** is an emerging trend to create a secure work environment for your end-users. Biometrics verification protects the data and keeps the information secure through encryption, secure storage, data minimization, secure data transmission, and Anonymization and Pseudonymization. [Customer Identity Access and Management solutions](https://www.loginradius.com/), like LoginRadius, can help businesses implement robust MFA authentication methods easily.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=biometric-multi-factor-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=biometric-multi-factor-authentication)
\ No newline at end of file
diff --git a/content/identity/biometric-vs-password-authentication/DS-mob-biometric-auth.png b/content/identity/biometric-vs-password-authentication/DS-mob-biometric-auth.png
deleted file mode 100644
index a3580f13e..000000000
Binary files a/content/identity/biometric-vs-password-authentication/DS-mob-biometric-auth.png and /dev/null differ
diff --git a/content/identity/biometric-vs-password-authentication/DS-mob-biometric-auth.webp b/content/identity/biometric-vs-password-authentication/DS-mob-biometric-auth.webp
new file mode 100644
index 000000000..0257eff22
Binary files /dev/null and b/content/identity/biometric-vs-password-authentication/DS-mob-biometric-auth.webp differ
diff --git a/content/identity/biometric-vs-password-authentication/biometric-vs-password.jpg b/content/identity/biometric-vs-password-authentication/biometric-vs-password.jpg
deleted file mode 100644
index 8214ac65a..000000000
Binary files a/content/identity/biometric-vs-password-authentication/biometric-vs-password.jpg and /dev/null differ
diff --git a/content/identity/biometric-vs-password-authentication/biometric-vs-password.webp b/content/identity/biometric-vs-password-authentication/biometric-vs-password.webp
new file mode 100644
index 000000000..91c03ebf8
Binary files /dev/null and b/content/identity/biometric-vs-password-authentication/biometric-vs-password.webp differ
diff --git a/content/identity/biometric-vs-password-authentication/index.md b/content/identity/biometric-vs-password-authentication/index.md
index f25b8f9cf..53fba7586 100644
--- a/content/identity/biometric-vs-password-authentication/index.md
+++ b/content/identity/biometric-vs-password-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Which is Safer: Biometric or Password?"
date: "2024-01-31"
-coverImage: "biometric-vs-password.jpg"
+coverImage: "biometric-vs-password.webp"
tags: ["biometric authentication","password authentication","data privacy"]
author: "Rakesh Soni"
description: "The ongoing debate over the use of traditional passwords and biometric authentication underscores the evolving digital security landscape. While traditional password-based authentication is less expensive and ensures minimum friction during the consumer journey, biometric password authentication overcomes all the drawbacks of traditional passwords. Let’s understand more about the strategies to find out the optimal solution to biometric authentication vs password debate."
@@ -58,7 +58,7 @@ When it comes to “**Are biometrics safer than passwords**, " yes, they are. [B
Businesses prefer biometrics because they provide the convenience absent in password-based authentication. Users do not have to remember complex passwords, write them in a diary or somewhere, and save the passwords in the system, which third-party applications can steal. All they need to do is give their biometric information, and the system will verify their identity.
-[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
+[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
3. **Improved user experience**
@@ -118,4 +118,4 @@ When it comes to which is safer, **biometric authentication or password**-based
[Multi-factor authentication](https://www.loginradius.com/multi-factor-authentication/) is a powerful security measure that significantly enhances the protection of applications and data by adding two or more layers for identity verification. MFA is a core component of IAM (identity access management) and CIAM (customer identity access management). One of the layers with password-based authentication and a second layer with biometric authentication can strengthen your security infrastructure.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=biometric-vs-password-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=biometric-vs-password-authentication)
\ No newline at end of file
diff --git a/content/identity/bot-attacks/Bot-attacks-Cover.png b/content/identity/bot-attacks/Bot-attacks-Cover.png
deleted file mode 100644
index fa4ba79a9..000000000
Binary files a/content/identity/bot-attacks/Bot-attacks-Cover.png and /dev/null differ
diff --git a/content/identity/bot-attacks/Bot-attacks-Cover.webp b/content/identity/bot-attacks/Bot-attacks-Cover.webp
new file mode 100644
index 000000000..3862f352c
Binary files /dev/null and b/content/identity/bot-attacks/Bot-attacks-Cover.webp differ
diff --git a/content/identity/bot-attacks/LRbotprotection.png b/content/identity/bot-attacks/LRbotprotection.png
deleted file mode 100644
index 5e15479a5..000000000
Binary files a/content/identity/bot-attacks/LRbotprotection.png and /dev/null differ
diff --git a/content/identity/bot-attacks/LRbotprotection.webp b/content/identity/bot-attacks/LRbotprotection.webp
new file mode 100644
index 000000000..adf7ae505
Binary files /dev/null and b/content/identity/bot-attacks/LRbotprotection.webp differ
diff --git a/content/identity/bot-attacks/bot-attacks.jpg b/content/identity/bot-attacks/bot-attacks.jpg
deleted file mode 100644
index 24437ee46..000000000
Binary files a/content/identity/bot-attacks/bot-attacks.jpg and /dev/null differ
diff --git a/content/identity/bot-attacks/bot-attacks.webp b/content/identity/bot-attacks/bot-attacks.webp
new file mode 100644
index 000000000..1715b1920
Binary files /dev/null and b/content/identity/bot-attacks/bot-attacks.webp differ
diff --git a/content/identity/bot-attacks/botintro.png b/content/identity/bot-attacks/botintro.png
deleted file mode 100644
index 37a78745f..000000000
Binary files a/content/identity/bot-attacks/botintro.png and /dev/null differ
diff --git a/content/identity/bot-attacks/botintro.webp b/content/identity/bot-attacks/botintro.webp
new file mode 100644
index 000000000..e118b2fbe
Binary files /dev/null and b/content/identity/bot-attacks/botintro.webp differ
diff --git a/content/identity/bot-attacks/credential-stuffing.png b/content/identity/bot-attacks/credential-stuffing.png
deleted file mode 100644
index 904e3a28e..000000000
Binary files a/content/identity/bot-attacks/credential-stuffing.png and /dev/null differ
diff --git a/content/identity/bot-attacks/credential-stuffing.webp b/content/identity/bot-attacks/credential-stuffing.webp
new file mode 100644
index 000000000..c2d6821c3
Binary files /dev/null and b/content/identity/bot-attacks/credential-stuffing.webp differ
diff --git a/content/identity/bot-attacks/index.md b/content/identity/bot-attacks/index.md
index c19770737..90927c2f7 100644
--- a/content/identity/bot-attacks/index.md
+++ b/content/identity/bot-attacks/index.md
@@ -1,7 +1,7 @@
---
title: "How To Secure Your Contact Form From Bot Attacks"
date: "2020-12-24"
-coverImage: "bot-attacks.jpg"
+coverImage: "bot-attacks.webp"
tags: ["data security","ciam solution","cx"]
author: "Rakesh Soni"
description: "It is no surprise that the contact form attracts a lot of bot attacks. Hackers not only create false traffic, but also result in malicious attacks on websites. The objective of this blog is to help you to secure contact form from random audacious attacks."
@@ -18,7 +18,7 @@ We will explore the various methods that can be used to prevent bots from submit
# What Is a Spambot?
-
+
A spambot is a malicious program or unethical activity specially designed to gather email addresses or information from contact forms. It is usually done by sending spam emails.
As emails have a distinct structure, a bot creation process is easy for hackers. Hence, you need to be extra cautious while using contact forms for your website or important marketing campaigns.
@@ -54,7 +54,7 @@ Honeypots are hidden fields that are added to the user registration form to prev
This is again a great way to identify spammers since humans usually will take some time to fill out all the fields of a form while bots can do it instantly. So, measuring the time taken to fill a form can be helpful when finalizing your contact list.
-[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
+[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
### 6. "Hide target request."
@@ -97,11 +97,11 @@ Another way to prevent contact form spam is to disable the right-click functiona
LoginRadius offers all the options mentioned above to secure contact forms from spam or fake signups. The consumer identity and access provider also offers world-class security for consumers to ensure that their data is safe during login, registration, password setup, and any other data touchpoints.
The [CIAM platform](https://www.loginradius.com/) is a powerhouse of open source SDKs, pre-designed and customizable login interfaces, and robust data security products such as MFA, RBA, and Advanced Password Policies.
-
+
## Final Words
Spambots will not go anywhere so soon. Take your time and learn to implement these strategies to make things easier for you in the long-run. It demands a lot of effort and practice to implement these ideas, but the result is worth it.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=bot-attacks)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=bot-attacks)
diff --git a/content/identity/bot-attacks/spambot.png b/content/identity/bot-attacks/spambot.png
deleted file mode 100644
index 74f526415..000000000
Binary files a/content/identity/bot-attacks/spambot.png and /dev/null differ
diff --git a/content/identity/bot-attacks/spambot.webp b/content/identity/bot-attacks/spambot.webp
new file mode 100644
index 000000000..ede75d961
Binary files /dev/null and b/content/identity/bot-attacks/spambot.webp differ
diff --git a/content/identity/bring-your-own-identity/bring-your-own-identity-cover.jpg b/content/identity/bring-your-own-identity/bring-your-own-identity-cover.jpg
deleted file mode 100644
index a65e92f89..000000000
Binary files a/content/identity/bring-your-own-identity/bring-your-own-identity-cover.jpg and /dev/null differ
diff --git a/content/identity/bring-your-own-identity/bring-your-own-identity-cover.webp b/content/identity/bring-your-own-identity/bring-your-own-identity-cover.webp
new file mode 100644
index 000000000..56649df97
Binary files /dev/null and b/content/identity/bring-your-own-identity/bring-your-own-identity-cover.webp differ
diff --git a/content/identity/bring-your-own-identity/index.md b/content/identity/bring-your-own-identity/index.md
index 0d5829295..426989dae 100644
--- a/content/identity/bring-your-own-identity/index.md
+++ b/content/identity/bring-your-own-identity/index.md
@@ -1,7 +1,7 @@
---
title: "The Rise of BYOI (Bring your own Identity)"
date: "2021-07-09"
-coverImage: "bring-your-own-identity-cover.jpg"
+coverImage: "bring-your-own-identity-cover.webp"
tags: ["security"]
featured: false
author: "Saikiran Babladi"
@@ -50,4 +50,4 @@ The possibilities are endless with the LoginRadius platform in how you can set u
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=bring-your-own-identity)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=bring-your-own-identity)
diff --git a/content/identity/broadcastmed-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.png b/content/identity/broadcastmed-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/broadcastmed-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.png and /dev/null differ
diff --git a/content/identity/broadcastmed-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.webp b/content/identity/broadcastmed-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/broadcastmed-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.webp differ
diff --git a/content/identity/broadcastmed-loginradius-customer-success-story/LR-and-BroadcastMed.jpg b/content/identity/broadcastmed-loginradius-customer-success-story/LR-and-BroadcastMed.jpg
deleted file mode 100644
index fc705a26e..000000000
Binary files a/content/identity/broadcastmed-loginradius-customer-success-story/LR-and-BroadcastMed.jpg and /dev/null differ
diff --git a/content/identity/broadcastmed-loginradius-customer-success-story/LR-and-BroadcastMed.webp b/content/identity/broadcastmed-loginradius-customer-success-story/LR-and-BroadcastMed.webp
new file mode 100644
index 000000000..09999312e
Binary files /dev/null and b/content/identity/broadcastmed-loginradius-customer-success-story/LR-and-BroadcastMed.webp differ
diff --git a/content/identity/broadcastmed-loginradius-customer-success-story/index.md b/content/identity/broadcastmed-loginradius-customer-success-story/index.md
index c72cf14d3..35e4d5fe3 100644
--- a/content/identity/broadcastmed-loginradius-customer-success-story/index.md
+++ b/content/identity/broadcastmed-loginradius-customer-success-story/index.md
@@ -1,7 +1,7 @@
---
title: "BroadcastMed, a LoginRadius Customer Success Story"
date: "2018-07-05"
-coverImage: "LR-and-BroadcastMed.jpg"
+coverImage: "LR-and-BroadcastMed.webp"
tags: ["media-and-publication"]
featured: false
author: "Karl Wittig"
@@ -55,4 +55,4 @@ BroadcastMed had a few concerns that they wanted to address as they evaluated th
BroadcastMed - LoginRadius Customer Success Story
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=broadcastmed-loginradius-customer-success-story)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=broadcastmed-loginradius-customer-success-story)
diff --git a/content/identity/brute-force-lockout/WP-Credential-stuffing.png b/content/identity/brute-force-lockout/WP-Credential-stuffing.png
deleted file mode 100644
index 4926b2aaf..000000000
Binary files a/content/identity/brute-force-lockout/WP-Credential-stuffing.png and /dev/null differ
diff --git a/content/identity/brute-force-lockout/WP-Credential-stuffing.webp b/content/identity/brute-force-lockout/WP-Credential-stuffing.webp
new file mode 100644
index 000000000..d4581b1bd
Binary files /dev/null and b/content/identity/brute-force-lockout/WP-Credential-stuffing.webp differ
diff --git a/content/identity/brute-force-lockout/brute-force-lockout.jpg b/content/identity/brute-force-lockout/brute-force-lockout.jpg
deleted file mode 100644
index 8e98f3efe..000000000
Binary files a/content/identity/brute-force-lockout/brute-force-lockout.jpg and /dev/null differ
diff --git a/content/identity/brute-force-lockout/brute-force-lockout.webp b/content/identity/brute-force-lockout/brute-force-lockout.webp
new file mode 100644
index 000000000..b7f9c6aa0
Binary files /dev/null and b/content/identity/brute-force-lockout/brute-force-lockout.webp differ
diff --git a/content/identity/brute-force-lockout/brute-force.jpg b/content/identity/brute-force-lockout/brute-force.jpg
deleted file mode 100644
index 25dc0dda0..000000000
Binary files a/content/identity/brute-force-lockout/brute-force.jpg and /dev/null differ
diff --git a/content/identity/brute-force-lockout/brute-force.webp b/content/identity/brute-force-lockout/brute-force.webp
new file mode 100644
index 000000000..a3a1f5605
Binary files /dev/null and b/content/identity/brute-force-lockout/brute-force.webp differ
diff --git a/content/identity/brute-force-lockout/credential-stuffing.png b/content/identity/brute-force-lockout/credential-stuffing.png
deleted file mode 100644
index 904e3a28e..000000000
Binary files a/content/identity/brute-force-lockout/credential-stuffing.png and /dev/null differ
diff --git a/content/identity/brute-force-lockout/credential-stuffing.webp b/content/identity/brute-force-lockout/credential-stuffing.webp
new file mode 100644
index 000000000..c2d6821c3
Binary files /dev/null and b/content/identity/brute-force-lockout/credential-stuffing.webp differ
diff --git a/content/identity/brute-force-lockout/how-bruteforce-works.jpg b/content/identity/brute-force-lockout/how-bruteforce-works.jpg
deleted file mode 100644
index 6b8382998..000000000
Binary files a/content/identity/brute-force-lockout/how-bruteforce-works.jpg and /dev/null differ
diff --git a/content/identity/brute-force-lockout/how-bruteforce-works.webp b/content/identity/brute-force-lockout/how-bruteforce-works.webp
new file mode 100644
index 000000000..48da50e84
Binary files /dev/null and b/content/identity/brute-force-lockout/how-bruteforce-works.webp differ
diff --git a/content/identity/brute-force-lockout/index.md b/content/identity/brute-force-lockout/index.md
index 9ab5adb78..96500010d 100644
--- a/content/identity/brute-force-lockout/index.md
+++ b/content/identity/brute-force-lockout/index.md
@@ -1,7 +1,7 @@
---
title: "What is Brute Force Attack"
date: "2021-02-27"
-coverImage: "brute-force-lockout.jpg"
+coverImage: "brute-force-lockout.webp"
tags: ["data security","cybersecurity","mfa","cx"]
author: "Manish Tiwari"
description: "In brute force attacks, you are not exploiting any vulnerability in the web application. Instead, you are trying all the possible combinations and permutations of passwords and usernames of the victim and trying to see if you get any of those right."
@@ -15,7 +15,7 @@ Brute Force is a hacking technique used to find out the user credentials by tryi
So in brute force attacks, you are not exploiting any vulnerability in the web application. Instead, you are trying all the possible combinations and permutations of passwords and usernames of the victim and trying to see if you get any of those right.
-
+
## How Brute Force works
@@ -25,7 +25,7 @@ Thereafter, the tool sends the combinations of these usernames and passwords to
If the login is successful, then the username and password combination is considered as correct. If the login was a failure, then the combination of those credentials was wrong.
-
+
## Types of Brute Force Attacks
@@ -40,7 +40,7 @@ If the login is successful, then the username and password combination is consid
- **Credential Recycling:** Credential recycling refers to the hacking practice of re-using username and password combinations gathered in previous brute-force attacks. A special form of credential recycling is passed the hash, where unsalted hashed credentials are stolen and re-used without first being brute-forced.
-[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
+[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
- **Rainbow Table Attacks:** A rainbow table is a database used to gain authentication by cracking the password. It is a dictionary of plaintext passwords and their corresponding hash values that can be used to find out what plaintext password produces a particular hash.
@@ -63,4 +63,4 @@ Brute force attack takes time. It could take from a few weeks to even months. So
In this blog we have tried to explain the brute force in simple language. Bruteforce is not only used for hacking purposes but many companies use it for testing their security system also. This gives us the knowledge about how we can protect our accounts from hackers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=brute-force-lockout)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=brute-force-lockout)
\ No newline at end of file
diff --git a/content/identity/brute-force-lockout/what-is-bruteforce.jpg b/content/identity/brute-force-lockout/what-is-bruteforce.jpg
deleted file mode 100644
index 5eac33e40..000000000
Binary files a/content/identity/brute-force-lockout/what-is-bruteforce.jpg and /dev/null differ
diff --git a/content/identity/brute-force-lockout/what-is-bruteforce.webp b/content/identity/brute-force-lockout/what-is-bruteforce.webp
new file mode 100644
index 000000000..a7d6df01a
Binary files /dev/null and b/content/identity/brute-force-lockout/what-is-bruteforce.webp differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/Build-vs-Buy-Securing-Customer-Identity.jpg b/content/identity/build-vs-buy-securing-customer-identity/Build-vs-Buy-Securing-Customer-Identity.jpg
deleted file mode 100644
index f2bb84e4f..000000000
Binary files a/content/identity/build-vs-buy-securing-customer-identity/Build-vs-Buy-Securing-Customer-Identity.jpg and /dev/null differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/Build-vs-Buy-Securing-Customer-Identity.webp b/content/identity/build-vs-buy-securing-customer-identity/Build-vs-Buy-Securing-Customer-Identity.webp
new file mode 100644
index 000000000..8fa065a41
Binary files /dev/null and b/content/identity/build-vs-buy-securing-customer-identity/Build-vs-Buy-Securing-Customer-Identity.webp differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/The-Case-for-Buying-over-Building-1.png b/content/identity/build-vs-buy-securing-customer-identity/The-Case-for-Buying-over-Building-1.png
deleted file mode 100644
index c79f206c4..000000000
Binary files a/content/identity/build-vs-buy-securing-customer-identity/The-Case-for-Buying-over-Building-1.png and /dev/null differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/The-Case-for-Buying-over-Building-1.webp b/content/identity/build-vs-buy-securing-customer-identity/The-Case-for-Buying-over-Building-1.webp
new file mode 100644
index 000000000..3af84a503
Binary files /dev/null and b/content/identity/build-vs-buy-securing-customer-identity/The-Case-for-Buying-over-Building-1.webp differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/image2-1-1.jpg b/content/identity/build-vs-buy-securing-customer-identity/image2-1-1.jpg
deleted file mode 100644
index 3c726c524..000000000
Binary files a/content/identity/build-vs-buy-securing-customer-identity/image2-1-1.jpg and /dev/null differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/image2-1-1.webp b/content/identity/build-vs-buy-securing-customer-identity/image2-1-1.webp
new file mode 100644
index 000000000..e2016f7ca
Binary files /dev/null and b/content/identity/build-vs-buy-securing-customer-identity/image2-1-1.webp differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/image3.png b/content/identity/build-vs-buy-securing-customer-identity/image3.png
deleted file mode 100644
index 008efdf48..000000000
Binary files a/content/identity/build-vs-buy-securing-customer-identity/image3.png and /dev/null differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/image3.webp b/content/identity/build-vs-buy-securing-customer-identity/image3.webp
new file mode 100644
index 000000000..fe14dbcbc
Binary files /dev/null and b/content/identity/build-vs-buy-securing-customer-identity/image3.webp differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/image4.png b/content/identity/build-vs-buy-securing-customer-identity/image4.png
deleted file mode 100644
index 16128b02f..000000000
Binary files a/content/identity/build-vs-buy-securing-customer-identity/image4.png and /dev/null differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/image4.webp b/content/identity/build-vs-buy-securing-customer-identity/image4.webp
new file mode 100644
index 000000000..87202aee8
Binary files /dev/null and b/content/identity/build-vs-buy-securing-customer-identity/image4.webp differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/image5.png b/content/identity/build-vs-buy-securing-customer-identity/image5.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/build-vs-buy-securing-customer-identity/image5.png and /dev/null differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/image5.webp b/content/identity/build-vs-buy-securing-customer-identity/image5.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/build-vs-buy-securing-customer-identity/image5.webp differ
diff --git a/content/identity/build-vs-buy-securing-customer-identity/index.md b/content/identity/build-vs-buy-securing-customer-identity/index.md
index dac594d72..7452b5991 100644
--- a/content/identity/build-vs-buy-securing-customer-identity/index.md
+++ b/content/identity/build-vs-buy-securing-customer-identity/index.md
@@ -1,7 +1,7 @@
---
title: "Build vs Buy: Securing Customer Identity with Loginradius"
date: "2020-07-16"
-coverImage: "Build-vs-Buy-Securing-Customer-Identity.jpg"
+coverImage: "Build-vs-Buy-Securing-Customer-Identity.webp"
tags: ["ciam solution","mfa","compliance"]
author: "Rakesh Soni"
description: "The most important assets of any company are customer identification and personal data. In most situations, businesses come across two simple options when designing a platform that collects, handles, and uses consumer data: to create or to purchase."
@@ -51,7 +51,7 @@ Either a company lacks the technical expertise or the resources or both to imple
On the other hand, a managed solution comes with the assurance that your CIAM performance will meet or exceed industry standards.
-[](https://www.loginradius.com/resource/the-case-for-buying-over-building/)
+[](https://www.loginradius.com/resource/the-case-for-buying-over-building/)
## Who should build a Customer IAM solution
@@ -67,7 +67,7 @@ A report by MarketsandMarkets suggests the customer identity management market m
## Is Buying Better Than Building When Choosing a CIAM Solution
-
+
A well-implemented CIAM platform offers a host of benefits—enhanced user experience with self-service registration, password management, sign-sign on, and other premium features like [progressive profiling](https://www.loginradius.com/blog/2019/02/presenting-progressive-profiling-loginradius/), API-focused, transactional security, and data encryption to drive customer engagement and keep businesses compliant.
@@ -119,7 +119,7 @@ They take care of login, authentication, or preference management seamlessly and
## Benefits of an Advance CIAM Solution
-
+
One of the immediate results of buying a CIAM platform is its impact on your in-house team. You won't need to invest in the engineering team and dramatically reduce [your identity management development](https://www.loginradius.com/blog/2019/10/digital-identity-management/) and maintenance hours.
@@ -131,7 +131,7 @@ Because there are no additional in-house parameters involved, your CIAM platform
## Why the LoginRadius CIAM Platform Is the Best Solution for Your Business
-
+
LoginRadius is a privacy-first cloud-based customer IAM platform that enables companies to secure, identify, and authorize their workforces and customers. Let's take a look at how it offers accelerated time-to-market and regulation enforcement at the API level for your digital projects.
@@ -163,4 +163,4 @@ The decision centering around build vs buy needs some serious consideration. How
Use our Build vs Buy [calculator to find out](https://www.loginradius.com/resource/ciam-build-vs-buy/) which option can deliver the most cost-effective solution for your business.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=build-vs-buy-securing-customer-identity)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=build-vs-buy-securing-customer-identity)
diff --git a/content/identity/calcualting-roi-build-vs-buy/The-Case-for-Buying-over-Building-1.png b/content/identity/calcualting-roi-build-vs-buy/The-Case-for-Buying-over-Building-1.png
deleted file mode 100644
index c79f206c4..000000000
Binary files a/content/identity/calcualting-roi-build-vs-buy/The-Case-for-Buying-over-Building-1.png and /dev/null differ
diff --git a/content/identity/calcualting-roi-build-vs-buy/The-Case-for-Buying-over-Building-1.webp b/content/identity/calcualting-roi-build-vs-buy/The-Case-for-Buying-over-Building-1.webp
new file mode 100644
index 000000000..3af84a503
Binary files /dev/null and b/content/identity/calcualting-roi-build-vs-buy/The-Case-for-Buying-over-Building-1.webp differ
diff --git a/content/identity/calcualting-roi-build-vs-buy/calcualting-roi-build-vs-buy-cover.jpg b/content/identity/calcualting-roi-build-vs-buy/calcualting-roi-build-vs-buy-cover.jpg
deleted file mode 100644
index b27112d1f..000000000
Binary files a/content/identity/calcualting-roi-build-vs-buy/calcualting-roi-build-vs-buy-cover.jpg and /dev/null differ
diff --git a/content/identity/calcualting-roi-build-vs-buy/calcualting-roi-build-vs-buy-cover.webp b/content/identity/calcualting-roi-build-vs-buy/calcualting-roi-build-vs-buy-cover.webp
new file mode 100644
index 000000000..be6bbcb8f
Binary files /dev/null and b/content/identity/calcualting-roi-build-vs-buy/calcualting-roi-build-vs-buy-cover.webp differ
diff --git a/content/identity/calcualting-roi-build-vs-buy/index.md b/content/identity/calcualting-roi-build-vs-buy/index.md
index 345b10dc8..48a13b4d6 100644
--- a/content/identity/calcualting-roi-build-vs-buy/index.md
+++ b/content/identity/calcualting-roi-build-vs-buy/index.md
@@ -1,7 +1,7 @@
---
title: "Calculating ROI, Build vs Buy (Part 1)"
date: "2021-03-31"
-coverImage: "calcualting-roi-build-vs-buy-cover.jpg"
+coverImage: "calcualting-roi-build-vs-buy-cover.webp"
tags: ["customer authentication","identity management","cx"]
author: "Cooper Matheson"
description: "Most businesses with legacy systems are stuck between choosing to maintain an existing in-house system, investing in building a new in-house system, or working with a vendor. Making the wrong decision can be expensive. This blog is a multi-part series where we have outlined the value of working with LoginRadius over maintaining and building up your existing systems."
@@ -95,7 +95,7 @@ When businesses embark on a project to improve or update those systems, those co
Customer service efforts make up a huge chunk of the hidden costs associated with legacy authentication systems. These teams see large swaths of their time drained by dealing with end-users trying to reset their passwords, recover their accounts, cancel memberships, revoke access to data, and more.
-[](https://www.loginradius.com/resource/the-case-for-buying-over-building/)
+[](https://www.loginradius.com/resource/the-case-for-buying-over-building/)
## Case Study
@@ -112,4 +112,4 @@ If the business decision is already made, you could easily add a [social login](
**Stayed tuned for Part II of this series, where I will help you calculate lost revenue associated with authentication and system availability.**
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=calcualting-roi-build-vs-buy)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=calcualting-roi-build-vs-buy)
\ No newline at end of file
diff --git a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/05_aftermath-100703535-large.jpg b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/05_aftermath-100703535-large.jpg
deleted file mode 100644
index 331fa0623..000000000
Binary files a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/05_aftermath-100703535-large.jpg and /dev/null differ
diff --git a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/05_aftermath-100703535-large.webp b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/05_aftermath-100703535-large.webp
new file mode 100644
index 000000000..5963d1a70
Binary files /dev/null and b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/05_aftermath-100703535-large.webp differ
diff --git a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/Book-a-free-demo-request-1024x310.png b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/Book-a-free-demo-request-1024x310.webp b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/canada-to-fine-companies.jpg b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/canada-to-fine-companies.jpg
deleted file mode 100644
index 331fa0623..000000000
Binary files a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/canada-to-fine-companies.jpg and /dev/null differ
diff --git a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/canada-to-fine-companies.webp b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/canada-to-fine-companies.webp
new file mode 100644
index 000000000..5963d1a70
Binary files /dev/null and b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/canada-to-fine-companies.webp differ
diff --git a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/ccpa-customer-identity.png b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/ccpa-customer-identity.png
deleted file mode 100644
index 0ed0f3bce..000000000
Binary files a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/ccpa-customer-identity.png and /dev/null differ
diff --git a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/ccpa-customer-identity.webp b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/ccpa-customer-identity.webp
new file mode 100644
index 000000000..6d67557e6
Binary files /dev/null and b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/ccpa-customer-identity.webp differ
diff --git a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/index.md b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/index.md
index f44c0e486..c33a719a5 100644
--- a/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/index.md
+++ b/content/identity/canada-to-fine-companies-for-not-reporting-data-breaches/index.md
@@ -1,7 +1,7 @@
---
title: "Canada To Fine Companies For Not Reporting Data Breaches"
date: "2017-09-07"
-coverImage: "canada-to-fine-companies.jpg"
+coverImage: "canada-to-fine-companies.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -12,11 +12,11 @@ metadescription: "The news of Canada to fine corporations for not reporting data
On Sept. 2, the Canadian Government announced an update to the [Digital Privacy Act (June 2015)](https://laws-lois.justice.gc.ca/eng/annualstatutes/2015_32/page-1.html) that will make it mandatory for all Canadian companies to report if their data has been breached. Currently, Alberta is the only province where companies are required to report breaches by law. This change makes this a requirement across the country.
-Under the new proposed rules, any company that has a data breach will be required to do a risk assessment to determine if the breach poses a “Risk of significant harm”. If so, they’re required to notify all individuals that are affected and also report the breach to the Canadian Privacy Commissioner’s Office.
+Under the new proposed rules, any company that has a data breach will be required to do a risk assessment to determine if the breach poses a “Risk of significant harm”. If so, they’re required to notify all individuals that are affected and also report the breach to the Canadian Privacy Commissioner’s Office.
A 2017 study by the Ponemon Institute found data breaches are most expensive in the United States and Canada. The average per capita cost of a data breach was $225 in the United States and $190 in Canada. However, because breach reporting is not mandatory, it’s difficult to get a full picture of the number of breaches. Still, over the last few years there have been a number of high profile [data breaches](https://www.loginradius.com/blog/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/) where the personal information of Canadians was stolen. It’s hoped that mandatory reporting will create an incentive for organizations to take information security more seriously.
-[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
+[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
The consequences for organizations that decide not to comply with the new rules are two-fold. First of all is the public relations nightmare that occurs when knowledge of the breach eventually becomes public. Typically this comes in the form of loss of confidence in the brand and will result in loss of customers; up to a third of customers will leave after a breach. Second, are the fines for non-compliance under the proposed new rules; up to $10,000 for a summary offence and up to $100,000 for an indictable offence.
diff --git a/content/identity/ccpa-introduction/LoginRadius-and-GDPR.png b/content/identity/ccpa-introduction/LoginRadius-and-GDPR.png
deleted file mode 100644
index 5d6b450bb..000000000
Binary files a/content/identity/ccpa-introduction/LoginRadius-and-GDPR.png and /dev/null differ
diff --git a/content/identity/ccpa-introduction/LoginRadius-and-GDPR.webp b/content/identity/ccpa-introduction/LoginRadius-and-GDPR.webp
new file mode 100644
index 000000000..a6fa87936
Binary files /dev/null and b/content/identity/ccpa-introduction/LoginRadius-and-GDPR.webp differ
diff --git a/content/identity/ccpa-introduction/ccpa-and-customer-identity.png b/content/identity/ccpa-introduction/ccpa-and-customer-identity.png
deleted file mode 100644
index 0ed0f3bce..000000000
Binary files a/content/identity/ccpa-introduction/ccpa-and-customer-identity.png and /dev/null differ
diff --git a/content/identity/ccpa-introduction/ccpa-and-customer-identity.webp b/content/identity/ccpa-introduction/ccpa-and-customer-identity.webp
new file mode 100644
index 000000000..6d67557e6
Binary files /dev/null and b/content/identity/ccpa-introduction/ccpa-and-customer-identity.webp differ
diff --git a/content/identity/ccpa-introduction/ccpa-certification-copy.png b/content/identity/ccpa-introduction/ccpa-certification-copy.png
deleted file mode 100644
index 83567352f..000000000
Binary files a/content/identity/ccpa-introduction/ccpa-certification-copy.png and /dev/null differ
diff --git a/content/identity/ccpa-introduction/ccpa-certification-copy.webp b/content/identity/ccpa-introduction/ccpa-certification-copy.webp
new file mode 100644
index 000000000..350b9c6cb
Binary files /dev/null and b/content/identity/ccpa-introduction/ccpa-certification-copy.webp differ
diff --git a/content/identity/ccpa-introduction/ccpa-intro.jpg b/content/identity/ccpa-introduction/ccpa-intro.jpg
deleted file mode 100644
index da6a72365..000000000
Binary files a/content/identity/ccpa-introduction/ccpa-intro.jpg and /dev/null differ
diff --git a/content/identity/ccpa-introduction/ccpa-intro.webp b/content/identity/ccpa-introduction/ccpa-intro.webp
new file mode 100644
index 000000000..d738dce3c
Binary files /dev/null and b/content/identity/ccpa-introduction/ccpa-intro.webp differ
diff --git a/content/identity/ccpa-introduction/featured-image-CCPA_image-certification-copy.png b/content/identity/ccpa-introduction/featured-image-CCPA_image-certification-copy.png
deleted file mode 100644
index 83567352f..000000000
Binary files a/content/identity/ccpa-introduction/featured-image-CCPA_image-certification-copy.png and /dev/null differ
diff --git a/content/identity/ccpa-introduction/featured-image-CCPA_image-certification-copy.webp b/content/identity/ccpa-introduction/featured-image-CCPA_image-certification-copy.webp
new file mode 100644
index 000000000..350b9c6cb
Binary files /dev/null and b/content/identity/ccpa-introduction/featured-image-CCPA_image-certification-copy.webp differ
diff --git a/content/identity/ccpa-introduction/index.md b/content/identity/ccpa-introduction/index.md
index 3eb2ff149..c803c7be6 100644
--- a/content/identity/ccpa-introduction/index.md
+++ b/content/identity/ccpa-introduction/index.md
@@ -1,7 +1,7 @@
---
title: "California's CCPA 2.0 Passed: Everything You Need to Know About the New CPRA"
date: "2019-05-03"
-coverImage: "ccpa-intro.jpg"
+coverImage: "ccpa-intro.webp"
tags: ["ccpa","data privacy","compliance","customer trust"]
author: "Rakesh Soni"
description: "On November 3, 2020, the voters in California approved the Consumer Privacy Rights Act (on the ballot as Proposition 24) with 56.1% of the vote. This revised version of the CCPA will further strengthen the consumer privacy rights for California citizens."
@@ -55,7 +55,7 @@ A GDPR Privacy Policy will meet CalOPPA/CCPA requirements, but a CalOPPA/CCPA po
It’s also helpful to train your customer-facing employees on how privacy policies and CCPA compliance can [improve customer trust](https://www.loginradius.com/customer-trust/) and increase engagement.
-[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
+[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
## **CCPA 2.0: What You Need to Know About the New CPRA**
@@ -227,4 +227,4 @@ Last but not least, LoginRadius provides [top-notch security](https://www.loginr
Following the old CCPA rules will _not automatically_ lead to CCPA 2.0 compliance; don’t wait to be sued to find out. Let LoginRadius help your business become globally compliant. Not only does our technology meet the new CPRA regulations, but we continuously update it to meet new international privacy laws.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ccpa-introduction)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ccpa-introduction)
\ No newline at end of file
diff --git a/content/identity/ccpa-introduction/lighter-lines-ccpa-image-300x143.png b/content/identity/ccpa-introduction/lighter-lines-ccpa-image-300x143.png
deleted file mode 100644
index 58c26bcf4..000000000
Binary files a/content/identity/ccpa-introduction/lighter-lines-ccpa-image-300x143.png and /dev/null differ
diff --git a/content/identity/ccpa-introduction/lighter-lines-ccpa-image-300x143.webp b/content/identity/ccpa-introduction/lighter-lines-ccpa-image-300x143.webp
new file mode 100644
index 000000000..02d8f419b
Binary files /dev/null and b/content/identity/ccpa-introduction/lighter-lines-ccpa-image-300x143.webp differ
diff --git a/content/identity/ccpa-introduction/the-ccpa-and-customer-identity-charts3.jpg b/content/identity/ccpa-introduction/the-ccpa-and-customer-identity-charts3.jpg
deleted file mode 100644
index 2fd0e025b..000000000
Binary files a/content/identity/ccpa-introduction/the-ccpa-and-customer-identity-charts3.jpg and /dev/null differ
diff --git a/content/identity/ccpa-introduction/the-ccpa-and-customer-identity-charts3.webp b/content/identity/ccpa-introduction/the-ccpa-and-customer-identity-charts3.webp
new file mode 100644
index 000000000..e350752b4
Binary files /dev/null and b/content/identity/ccpa-introduction/the-ccpa-and-customer-identity-charts3.webp differ
diff --git a/content/identity/ccpa-vs-gdpr-the-compliance-war/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance-1024x310.png b/content/identity/ccpa-vs-gdpr-the-compliance-war/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance-1024x310.png
deleted file mode 100644
index c02a1338a..000000000
Binary files a/content/identity/ccpa-vs-gdpr-the-compliance-war/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance-1024x310.png and /dev/null differ
diff --git a/content/identity/ccpa-vs-gdpr-the-compliance-war/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance-1024x310.webp b/content/identity/ccpa-vs-gdpr-the-compliance-war/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance-1024x310.webp
new file mode 100644
index 000000000..1b0055d88
Binary files /dev/null and b/content/identity/ccpa-vs-gdpr-the-compliance-war/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance-1024x310.webp differ
diff --git a/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr-the-compliance-war.jpg b/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr-the-compliance-war.jpg
deleted file mode 100644
index 214a3915d..000000000
Binary files a/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr-the-compliance-war.jpg and /dev/null differ
diff --git a/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr-the-compliance-war.webp b/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr-the-compliance-war.webp
new file mode 100644
index 000000000..347970456
Binary files /dev/null and b/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr-the-compliance-war.webp differ
diff --git a/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr.jpg b/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr.jpg
deleted file mode 100644
index b08dd5073..000000000
Binary files a/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr.jpg and /dev/null differ
diff --git a/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr.webp b/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr.webp
new file mode 100644
index 000000000..f71990277
Binary files /dev/null and b/content/identity/ccpa-vs-gdpr-the-compliance-war/ccpa-vs-gdpr.webp differ
diff --git a/content/identity/ccpa-vs-gdpr-the-compliance-war/index.md b/content/identity/ccpa-vs-gdpr-the-compliance-war/index.md
index a70331c94..31649a128 100644
--- a/content/identity/ccpa-vs-gdpr-the-compliance-war/index.md
+++ b/content/identity/ccpa-vs-gdpr-the-compliance-war/index.md
@@ -1,7 +1,7 @@
---
title: "CCPA vs GDPR: Global Compliance Guide [Infographic]"
date: "2019-09-18"
-coverImage: "ccpa-vs-gdpr.jpg"
+coverImage: "ccpa-vs-gdpr.webp"
tags: ["data privacy","compliance","data security"]
author: "Rakesh Soni"
description: "It's natural that there will be new legislation to protect customer data in a world where data is the most important resource. With more data scandal storeys than ever before reported by media outlets, users are constantly aware of data collection and how it impacts them. With this in mind, enforcement laws foster data protection and consent rights for users."
@@ -26,7 +26,7 @@ To help you understand [how these regulations can affect you](https://www.loginr
- **When is a business responsible?** Anytime they interact with the data of a resident.
- **What rights do customers have over their data?** Both CCPA and GDPR compliance rules allow users the right to access, correct, stop the processing of, and delete their data.
-[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
+[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
**For more info on CCPA compliance, check out our white paper.**
@@ -39,8 +39,8 @@ To help you understand [how these regulations can affect you](https://www.loginr
For more tips on CCPA and GDPR compliance, check out the infographic by LoginRadius.
-
+
Want to get your company compliance-ready and keep it up-to-date, automatically? Contact a LoginRadius expert to learn how.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ccpa-vs-gdpr-the-compliance-war)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ccpa-vs-gdpr-the-compliance-war)
diff --git a/content/identity/ccpa-vs-gdpr-the-compliance-war/new_CCPA-VS-GDPR-V01.06-PNG-01-1-2.png b/content/identity/ccpa-vs-gdpr-the-compliance-war/new_CCPA-VS-GDPR-V01.06-PNG-01-1-2.png
deleted file mode 100644
index da8cca4e7..000000000
Binary files a/content/identity/ccpa-vs-gdpr-the-compliance-war/new_CCPA-VS-GDPR-V01.06-PNG-01-1-2.png and /dev/null differ
diff --git a/content/identity/ccpa-vs-gdpr-the-compliance-war/new_CCPA-VS-GDPR-V01.06-PNG-01-1-2.webp b/content/identity/ccpa-vs-gdpr-the-compliance-war/new_CCPA-VS-GDPR-V01.06-PNG-01-1-2.webp
new file mode 100644
index 000000000..01f98e26f
Binary files /dev/null and b/content/identity/ccpa-vs-gdpr-the-compliance-war/new_CCPA-VS-GDPR-V01.06-PNG-01-1-2.webp differ
diff --git a/content/identity/changing-user-authentication-in-metaverse/EB-GD-to-MFA.png b/content/identity/changing-user-authentication-in-metaverse/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/changing-user-authentication-in-metaverse/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/changing-user-authentication-in-metaverse/EB-GD-to-MFA.webp b/content/identity/changing-user-authentication-in-metaverse/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/changing-user-authentication-in-metaverse/EB-GD-to-MFA.webp differ
diff --git a/content/identity/changing-user-authentication-in-metaverse/index.md b/content/identity/changing-user-authentication-in-metaverse/index.md
index fa8c9712a..9f33b83ad 100644
--- a/content/identity/changing-user-authentication-in-metaverse/index.md
+++ b/content/identity/changing-user-authentication-in-metaverse/index.md
@@ -1,7 +1,7 @@
---
title: "User Authentication in the Metaverse: What’s Changing?"
date: "2022-10-12"
-coverImage: "metaverse.jpg"
+coverImage: "metaverse.webp"
tags: ["user authentication", "mfa","passwordless login","biometric authentication"]
author: "James Durr"
description: "The importance of user authentication is paramount to maintaining the security of the metaverse. This blog looks into a number of widely-used authentication models and, in doing so, explores the future of user authentication in the metaverse."
@@ -50,7 +50,7 @@ While this approach is generally more secure than a basic password, many fraudst
What is more, this method includes an additional friction point, which makes it less user-friendly and potentially frustrating.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### 3. Biometric authentication
@@ -94,4 +94,4 @@ The process works in this way:
From user “behaviour” analysis to asymmetric encryption, we can expect the authentication experience to flow more and more easily as the metaverse develops. All changes to the “login” process are likely to follow this pattern throughout the foreseeable future.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=changing-user-authentication-in-metaverse)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=changing-user-authentication-in-metaverse)
diff --git a/content/identity/changing-user-authentication-in-metaverse/metaverse.jpg b/content/identity/changing-user-authentication-in-metaverse/metaverse.jpg
deleted file mode 100644
index 5c2e34e15..000000000
Binary files a/content/identity/changing-user-authentication-in-metaverse/metaverse.jpg and /dev/null differ
diff --git a/content/identity/changing-user-authentication-in-metaverse/metaverse.webp b/content/identity/changing-user-authentication-in-metaverse/metaverse.webp
new file mode 100644
index 000000000..2d30ce274
Binary files /dev/null and b/content/identity/changing-user-authentication-in-metaverse/metaverse.webp differ
diff --git a/content/identity/changing-user-authentication-in-metaverse/mfa-gd.png b/content/identity/changing-user-authentication-in-metaverse/mfa-gd.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/changing-user-authentication-in-metaverse/mfa-gd.png and /dev/null differ
diff --git a/content/identity/changing-user-authentication-in-metaverse/mfa-gd.webp b/content/identity/changing-user-authentication-in-metaverse/mfa-gd.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/changing-user-authentication-in-metaverse/mfa-gd.webp differ
diff --git a/content/identity/choosing-right-zero-trust-vendor/WP-zero-trust-security.png b/content/identity/choosing-right-zero-trust-vendor/WP-zero-trust-security.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/choosing-right-zero-trust-vendor/WP-zero-trust-security.png and /dev/null differ
diff --git a/content/identity/choosing-right-zero-trust-vendor/WP-zero-trust-security.webp b/content/identity/choosing-right-zero-trust-vendor/WP-zero-trust-security.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/choosing-right-zero-trust-vendor/WP-zero-trust-security.webp differ
diff --git a/content/identity/choosing-right-zero-trust-vendor/index.md b/content/identity/choosing-right-zero-trust-vendor/index.md
index 17e3a3b3a..b884473f4 100644
--- a/content/identity/choosing-right-zero-trust-vendor/index.md
+++ b/content/identity/choosing-right-zero-trust-vendor/index.md
@@ -1,7 +1,7 @@
---
title: "A Quick Guide To Choosing The Right Zero Trust Vendor"
date: "2024-05-07"
-coverImage: "right-zero-trust-vendor.jpg"
+coverImage: "right-zero-trust-vendor.webp"
tags: ["zero trust security","data security","compliance"]
author: "Rakesh Soni"
description: "Zero-trust security is imperative in today's digital age. However, choosing the right platform provider can be daunting. Our guide explores crucial factors like security features, scalability, and compliance, empowering you to make the best decision for your organization's cybersecurity needs."
@@ -48,7 +48,7 @@ Compliance with industry regulations and data protection laws is paramount for o
Ensure that the provider adheres to relevant compliance standards, such as [GDPR](https://www.loginradius.com/gdpr-and-privacy/), HIPAA, or PCI DSS, offers documentation and assurances regarding data sovereignty and privacy protections, and provides regular updates and compliance reports to support audit requirements and regulatory scrutiny.
-[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-modern-business/)
+[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-modern-business/)
## Why is the LoginRadius CIAM the Best Zero Trust Vendor?
@@ -64,4 +64,4 @@ Selecting the best zero-trust platform provider is a critical decision that requ
By prioritizing these considerations and evaluating providers based on their ability to meet your organization's specific needs, you can make an informed choice that strengthens your security posture and mitigates cyber risks. Remember, in the realm of cybersecurity, vigilance, and proactive measures are key to staying ahead of evolving threats.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=choosing-right-zero-trust-vendor)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=choosing-right-zero-trust-vendor)
\ No newline at end of file
diff --git a/content/identity/choosing-right-zero-trust-vendor/right-zero-trust-vendor.jpg b/content/identity/choosing-right-zero-trust-vendor/right-zero-trust-vendor.jpg
deleted file mode 100644
index ba0a12187..000000000
Binary files a/content/identity/choosing-right-zero-trust-vendor/right-zero-trust-vendor.jpg and /dev/null differ
diff --git a/content/identity/choosing-right-zero-trust-vendor/right-zero-trust-vendor.webp b/content/identity/choosing-right-zero-trust-vendor/right-zero-trust-vendor.webp
new file mode 100644
index 000000000..3af0b2651
Binary files /dev/null and b/content/identity/choosing-right-zero-trust-vendor/right-zero-trust-vendor.webp differ
diff --git a/content/identity/ciam-addresses-utility-issues/LoginRadius-Single-Sign-on.png b/content/identity/ciam-addresses-utility-issues/LoginRadius-Single-Sign-on.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/ciam-addresses-utility-issues/LoginRadius-Single-Sign-on.png and /dev/null differ
diff --git a/content/identity/ciam-addresses-utility-issues/LoginRadius-Single-Sign-on.webp b/content/identity/ciam-addresses-utility-issues/LoginRadius-Single-Sign-on.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/ciam-addresses-utility-issues/LoginRadius-Single-Sign-on.webp differ
diff --git a/content/identity/ciam-addresses-utility-issues/ciam-addresses-utility-issues-cover.jpg b/content/identity/ciam-addresses-utility-issues/ciam-addresses-utility-issues-cover.jpg
deleted file mode 100644
index 96694b463..000000000
Binary files a/content/identity/ciam-addresses-utility-issues/ciam-addresses-utility-issues-cover.jpg and /dev/null differ
diff --git a/content/identity/ciam-addresses-utility-issues/ciam-addresses-utility-issues-cover.webp b/content/identity/ciam-addresses-utility-issues/ciam-addresses-utility-issues-cover.webp
new file mode 100644
index 000000000..862b66513
Binary files /dev/null and b/content/identity/ciam-addresses-utility-issues/ciam-addresses-utility-issues-cover.webp differ
diff --git a/content/identity/ciam-addresses-utility-issues/ciam-utility.jpg b/content/identity/ciam-addresses-utility-issues/ciam-utility.jpg
deleted file mode 100644
index eee7d6f86..000000000
Binary files a/content/identity/ciam-addresses-utility-issues/ciam-utility.jpg and /dev/null differ
diff --git a/content/identity/ciam-addresses-utility-issues/ciam-utility.webp b/content/identity/ciam-addresses-utility-issues/ciam-utility.webp
new file mode 100644
index 000000000..854b1d5b6
Binary files /dev/null and b/content/identity/ciam-addresses-utility-issues/ciam-utility.webp differ
diff --git a/content/identity/ciam-addresses-utility-issues/index.md b/content/identity/ciam-addresses-utility-issues/index.md
index 4f60fdb5b..a9b302c26 100644
--- a/content/identity/ciam-addresses-utility-issues/index.md
+++ b/content/identity/ciam-addresses-utility-issues/index.md
@@ -1,7 +1,7 @@
---
title: "How CIAM Will Address The 5 Most Popular Issues In The Utility Industry"
date: "2021-03-09"
-coverImage: "ciam-utility.jpg"
+coverImage: "ciam-utility.webp"
tags: ["ciam solution","compliance","cx","data security"]
author: "Rakesh Soni"
description: "A lot of utility companies require a good customer retention percentage—since the nature of their business is recurring and net revenue is dependent on how many times a consumer has used the service. Therefore, to retain consumers, it is vital to understand their needs."
@@ -51,7 +51,7 @@ A CIAM in utility sector comes with a centralized portal that allows the adminis
A good **CIAM in utility sector** would have protocols and procedures (such as [SSO protocols](https://www.loginradius.com/protocols/) including SAML, OAuth, JWT, OpenID, Delegation, and Multipass) when a user is accessing high-risk networks and databases. It also comes with NGFW, next-generation firewalls, which provide application-level security against cyber attacks.
-[](https://www.loginradius.com/single-sign-on/)
+[](https://www.loginradius.com/single-sign-on/)
## The LoginRadius CIAM In Utility Sector
@@ -94,4 +94,4 @@ With hackers getting smarter every day, companies need to implement stringent pr
If this data is compromised, it would be a massive loss to the company's reputation, eventually leading to financial losses as users might withdraw from using their services. In extreme cases, the company might even go bankrupt! Implementing a CIAM in utility sector solution can prevent this from happening and make the consumer experience better!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-addresses-utility-issues)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-addresses-utility-issues)
diff --git a/content/identity/ciam-business-privacy-users/DS-progressive-profiling.png b/content/identity/ciam-business-privacy-users/DS-progressive-profiling.png
deleted file mode 100644
index c98c144d4..000000000
Binary files a/content/identity/ciam-business-privacy-users/DS-progressive-profiling.png and /dev/null differ
diff --git a/content/identity/ciam-business-privacy-users/DS-progressive-profiling.webp b/content/identity/ciam-business-privacy-users/DS-progressive-profiling.webp
new file mode 100644
index 000000000..b34c41174
Binary files /dev/null and b/content/identity/ciam-business-privacy-users/DS-progressive-profiling.webp differ
diff --git a/content/identity/ciam-business-privacy-users/ciam-privacy.jpg b/content/identity/ciam-business-privacy-users/ciam-privacy.jpg
deleted file mode 100644
index 01899a72f..000000000
Binary files a/content/identity/ciam-business-privacy-users/ciam-privacy.jpg and /dev/null differ
diff --git a/content/identity/ciam-business-privacy-users/ciam-privacy.webp b/content/identity/ciam-business-privacy-users/ciam-privacy.webp
new file mode 100644
index 000000000..db0d60829
Binary files /dev/null and b/content/identity/ciam-business-privacy-users/ciam-privacy.webp differ
diff --git a/content/identity/ciam-business-privacy-users/index.md b/content/identity/ciam-business-privacy-users/index.md
index 47b6d9e31..761c57c2c 100644
--- a/content/identity/ciam-business-privacy-users/index.md
+++ b/content/identity/ciam-business-privacy-users/index.md
@@ -1,7 +1,7 @@
---
title: "Is Your CIAM Adapting to Global Needs? 6 Key Areas to Win Privacy-Concerned Customers"
date: "2024-06-11"
-coverImage: "ciam-privacy.jpg"
+coverImage: "ciam-privacy.webp"
tags: ["ciam solutions","data privacy","compliance"]
author: "Rakesh Soni"
description: "In today's data-driven world, adapting your Customer Identity and Access Management (CIAM) system to meet global privacy needs is essential. Explore six key areas to ensure your CIAM solution remains compliant, secure, and user-friendly, building trust with privacy-conscious customers. From implementing enhanced security measures to offering user-centric privacy controls, learn how to stay ahead in a market where data privacy is paramount."
@@ -32,7 +32,7 @@ Data minimization and purpose limitation are essential for protecting user priva
* **Minimal Data Collection**: Design forms and data collection processes that ask only for necessary information. Regularly audit your data collection practices to ensure they align with the principle of data minimization.
-[](https://www.loginradius.com/resource/datasheet/progressive-profiling-cx/)
+[](https://www.loginradius.com/resource/datasheet/progressive-profiling-cx/)
* **Purpose Specification**: Clearly define and document the specific purposes for which data is collected. Avoid using collected data for purposes beyond what was originally disclosed to users.
@@ -88,4 +88,4 @@ With features like consent management, MFA, RBA, and progressive profiling, Logi
Investing in these key areas will ensure your organization is well-positioned to thrive in a market where data privacy is a critical differentiator. Implementing these strategies will help you maintain a competitive edge while fostering a strong, trust-based relationship with your customers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-business-privacy-users)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-business-privacy-users)
\ No newline at end of file
diff --git a/content/identity/ciam-data-security-user-trust/WP-resilience.png b/content/identity/ciam-data-security-user-trust/WP-resilience.png
deleted file mode 100644
index cbe459800..000000000
Binary files a/content/identity/ciam-data-security-user-trust/WP-resilience.png and /dev/null differ
diff --git a/content/identity/ciam-data-security-user-trust/WP-resilience.webp b/content/identity/ciam-data-security-user-trust/WP-resilience.webp
new file mode 100644
index 000000000..efb695fb3
Binary files /dev/null and b/content/identity/ciam-data-security-user-trust/WP-resilience.webp differ
diff --git a/content/identity/ciam-data-security-user-trust/index.md b/content/identity/ciam-data-security-user-trust/index.md
index 7979be1a2..fc421c646 100644
--- a/content/identity/ciam-data-security-user-trust/index.md
+++ b/content/identity/ciam-data-security-user-trust/index.md
@@ -1,7 +1,7 @@
---
title: "CIAM: Enhancing Security & Building Consumer Trust-All At Once"
date: "2023-09-15"
-coverImage: "user-trust.jpg"
+coverImage: "user-trust.webp"
tags: ["data security","cybersecurity","ciam solutions","cx"]
author: "Alok Patidar"
description: "CIAM (customer identity & access management) emerges as a boon for organizations that constantly seek efficient and capable methods of dealing with customer identity management, increasing user engagement, enhancing data security, and building brand loyalty. By implementing CIAM techniques, an organization can improve its overall operational efficiency."
@@ -42,7 +42,7 @@ Consumers want instant digital options to delete, edit, or download their data.
Users always prefer quick and hassle-free registration requiring minimal details (e.g., registration through linking to social accounts).
-[](https://www.loginradius.com/resource/enterprise-scalability-and-performance)
+[](https://www.loginradius.com/resource/enterprise-scalability-and-performance)
* **Guest browsing**
@@ -76,4 +76,4 @@ These CIAM benefits that allow users to control their data and manage their iden
In conclusion, CIAM techniques are beneficial for both business and their customers. It eases a user's purchase journey, requiring minimum effort and details. And side-by-side, CIAM also enhances data security and access control over sensitive information, which helps an organization maintain data integrity and privacy. Overall, CIAM eradicates the risk of security breaches and identity theft.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-data-security-user-trust)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-data-security-user-trust)
diff --git a/content/identity/ciam-data-security-user-trust/user-trust.jpg b/content/identity/ciam-data-security-user-trust/user-trust.jpg
deleted file mode 100644
index cd26fb78b..000000000
Binary files a/content/identity/ciam-data-security-user-trust/user-trust.jpg and /dev/null differ
diff --git a/content/identity/ciam-data-security-user-trust/user-trust.webp b/content/identity/ciam-data-security-user-trust/user-trust.webp
new file mode 100644
index 000000000..2e0dff577
Binary files /dev/null and b/content/identity/ciam-data-security-user-trust/user-trust.webp differ
diff --git a/content/identity/ciam-deployment-flexibility/DS-pswrdless-login.png b/content/identity/ciam-deployment-flexibility/DS-pswrdless-login.png
deleted file mode 100644
index 69d26339f..000000000
Binary files a/content/identity/ciam-deployment-flexibility/DS-pswrdless-login.png and /dev/null differ
diff --git a/content/identity/ciam-deployment-flexibility/DS-pswrdless-login.webp b/content/identity/ciam-deployment-flexibility/DS-pswrdless-login.webp
new file mode 100644
index 000000000..96ed92a38
Binary files /dev/null and b/content/identity/ciam-deployment-flexibility/DS-pswrdless-login.webp differ
diff --git a/content/identity/ciam-deployment-flexibility/ciam-deployment.jpg b/content/identity/ciam-deployment-flexibility/ciam-deployment.jpg
deleted file mode 100644
index f56ca9cc5..000000000
Binary files a/content/identity/ciam-deployment-flexibility/ciam-deployment.jpg and /dev/null differ
diff --git a/content/identity/ciam-deployment-flexibility/ciam-deployment.webp b/content/identity/ciam-deployment-flexibility/ciam-deployment.webp
new file mode 100644
index 000000000..fbc2566f1
Binary files /dev/null and b/content/identity/ciam-deployment-flexibility/ciam-deployment.webp differ
diff --git a/content/identity/ciam-deployment-flexibility/index.md b/content/identity/ciam-deployment-flexibility/index.md
index 270427db5..b490c7354 100644
--- a/content/identity/ciam-deployment-flexibility/index.md
+++ b/content/identity/ciam-deployment-flexibility/index.md
@@ -1,7 +1,7 @@
---
title: "Comprehensive Guide to Flexible CIAM Deployment Options with LoginRadius"
date: "2023-10-06"
-coverImage: "ciam-deployment.jpg"
+coverImage: "ciam-deployment.webp"
tags: ["single sign-on","social login","passwordless login","ciam solutions"]
author: "Rakesh Soni"
description: "User experience and security are non-negotiable in the modern digital world. Dive into our guide on CIAM deployment options with LoginRadius, a leader in the CIAM landscape. Explore seamless features like social login, Single Sign-On (SSO), passwordless login, and cloud integrations. Elevate user engagement, streamline access control, and fortify online security. Discover the strategic necessity of investing in advanced CIAM solutions, ensuring your users enjoy a secure, hassle-free online experience."
@@ -42,7 +42,7 @@ Passwordless login solutions are increasingly replacing traditional password-bas
LoginRadius offers robust passwordless login options, including biometric authentication and one-time passcodes, ensuring top-notch security while enhancing user satisfaction.
-[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
### #4. Cloud Integrations: Seamlessly Integrating CIAM with Existing Systems
@@ -56,4 +56,4 @@ Incorporating flexible CIAM deployment options from LoginRadius empowers busines
In a world where user experience and security are paramount, investing in a robust CIAM solution like LoginRadius is not just a choice but a strategic necessity. Stay ahead of the curve by implementing these advanced CIAM deployment options and ensure your users enjoy a hassle-free, secure, and engaging online experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-deployment-flexibility)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-deployment-flexibility)
\ No newline at end of file
diff --git a/content/identity/ciam-improve-customer-support/DS-user-management.png b/content/identity/ciam-improve-customer-support/DS-user-management.png
deleted file mode 100644
index 4da86607c..000000000
Binary files a/content/identity/ciam-improve-customer-support/DS-user-management.png and /dev/null differ
diff --git a/content/identity/ciam-improve-customer-support/DS-user-management.webp b/content/identity/ciam-improve-customer-support/DS-user-management.webp
new file mode 100644
index 000000000..32fb1890f
Binary files /dev/null and b/content/identity/ciam-improve-customer-support/DS-user-management.webp differ
diff --git a/content/identity/ciam-improve-customer-support/DS-user-mngmnt.png b/content/identity/ciam-improve-customer-support/DS-user-mngmnt.png
deleted file mode 100644
index fc6f98c05..000000000
Binary files a/content/identity/ciam-improve-customer-support/DS-user-mngmnt.png and /dev/null differ
diff --git a/content/identity/ciam-improve-customer-support/DS-user-mngmnt.webp b/content/identity/ciam-improve-customer-support/DS-user-mngmnt.webp
new file mode 100644
index 000000000..c60f3551f
Binary files /dev/null and b/content/identity/ciam-improve-customer-support/DS-user-mngmnt.webp differ
diff --git a/content/identity/ciam-improve-customer-support/ciam-improve-customer-support-cover.jpg b/content/identity/ciam-improve-customer-support/ciam-improve-customer-support-cover.jpg
deleted file mode 100644
index 73fb8e443..000000000
Binary files a/content/identity/ciam-improve-customer-support/ciam-improve-customer-support-cover.jpg and /dev/null differ
diff --git a/content/identity/ciam-improve-customer-support/ciam-improve-customer-support-cover.webp b/content/identity/ciam-improve-customer-support/ciam-improve-customer-support-cover.webp
new file mode 100644
index 000000000..c83d45be3
Binary files /dev/null and b/content/identity/ciam-improve-customer-support/ciam-improve-customer-support-cover.webp differ
diff --git a/content/identity/ciam-improve-customer-support/index.md b/content/identity/ciam-improve-customer-support/index.md
index 71b194ce8..ed70942bc 100644
--- a/content/identity/ciam-improve-customer-support/index.md
+++ b/content/identity/ciam-improve-customer-support/index.md
@@ -1,7 +1,7 @@
---
title: "Stand Out from the Crowd: Improve Your Customer Support with CIAM"
date: "2021-09-14"
-coverImage: "ciam-improve-customer-support-cover.jpg"
+coverImage: "ciam-improve-customer-support-cover.webp"
tags: ["ciam solution","cx","user management"]
author: "Rajeev Sharma"
description: "Whether it’s intuitive and personalized user onboarding or a unified view of every consumer, CIAM is becoming the need of the hour for diverse industries. Let’s learn about the endless possibilities of a CIAM that delivers the highest level of customer support services."
@@ -72,7 +72,7 @@ LoginRadius User Management includes tools for searching, browsing, and viewing
Administrators can also do manual actions on behalf of users, such as triggering verification and password reset emails, provisioning new accounts, and updating user information.
-[](https://www.loginradius.com/resource/loginradius-ciam-user-management/)
+[](https://www.loginradius.com/resource/loginradius-ciam-user-management/)
### Unified View of Each Customer
@@ -92,4 +92,4 @@ The ones finding ways to enhance support services must consider relying on a CIA
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-improve-customer-support)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-improve-customer-support)
diff --git a/content/identity/ciam-role-enterprise-decision-making/ciam-role-enterprise-decision-making-cover.jpg b/content/identity/ciam-role-enterprise-decision-making/ciam-role-enterprise-decision-making-cover.jpg
deleted file mode 100644
index 8a69d2b8d..000000000
Binary files a/content/identity/ciam-role-enterprise-decision-making/ciam-role-enterprise-decision-making-cover.jpg and /dev/null differ
diff --git a/content/identity/ciam-role-enterprise-decision-making/ciam-role-enterprise-decision-making-cover.webp b/content/identity/ciam-role-enterprise-decision-making/ciam-role-enterprise-decision-making-cover.webp
new file mode 100644
index 000000000..4d8eef13c
Binary files /dev/null and b/content/identity/ciam-role-enterprise-decision-making/ciam-role-enterprise-decision-making-cover.webp differ
diff --git a/content/identity/ciam-role-enterprise-decision-making/index.md b/content/identity/ciam-role-enterprise-decision-making/index.md
index 08b180bdb..a2ad3e178 100644
--- a/content/identity/ciam-role-enterprise-decision-making/index.md
+++ b/content/identity/ciam-role-enterprise-decision-making/index.md
@@ -1,7 +1,7 @@
---
title: "The Changing Role of Identity Management in Enterprise Decision-Making"
date: "2021-05-11"
-coverImage: "ciam-role-enterprise-decision-making-cover.jpg"
+coverImage: "ciam-role-enterprise-decision-making-cover.webp"
tags: ["identity management","data security","cx"]
author: "Vishal Sharma"
description: "The increasingly sophisticated audience now considers digital interactions as the sole mechanism for interacting with brands. Let’s learn how an identity management solution helps these brands to deliver rich user experiences backed by adequate data security."
@@ -48,7 +48,7 @@ This not only helps in building trust over potential clients but eventually lend
So, next time you’re thinking of delivering a rich consumer experience with the highest level of data security, get a CIAM in place.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
## Consumer On-Boarding
@@ -72,4 +72,4 @@ Consumer identity and access management solutions help businesses achieve their
In simple words, a modern CIAM solution is undoubtedly paving the path for a rich consumer experience that leads to more subscriptions and sign-ups.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-role-enterprise-decision-making)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-role-enterprise-decision-making)
\ No newline at end of file
diff --git a/content/identity/ciam-role-enterprise-decision-making/modern-customer-identity.png b/content/identity/ciam-role-enterprise-decision-making/modern-customer-identity.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/identity/ciam-role-enterprise-decision-making/modern-customer-identity.png and /dev/null differ
diff --git a/content/identity/ciam-role-enterprise-decision-making/modern-customer-identity.webp b/content/identity/ciam-role-enterprise-decision-making/modern-customer-identity.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/identity/ciam-role-enterprise-decision-making/modern-customer-identity.webp differ
diff --git a/content/identity/ciam-systems-hidden-pitfalls/GD-ciam.png b/content/identity/ciam-systems-hidden-pitfalls/GD-ciam.png
deleted file mode 100644
index 79ef6d6fa..000000000
Binary files a/content/identity/ciam-systems-hidden-pitfalls/GD-ciam.png and /dev/null differ
diff --git a/content/identity/ciam-systems-hidden-pitfalls/GD-ciam.webp b/content/identity/ciam-systems-hidden-pitfalls/GD-ciam.webp
new file mode 100644
index 000000000..4ad020497
Binary files /dev/null and b/content/identity/ciam-systems-hidden-pitfalls/GD-ciam.webp differ
diff --git a/content/identity/ciam-systems-hidden-pitfalls/hidden-pitfalls.jpg b/content/identity/ciam-systems-hidden-pitfalls/hidden-pitfalls.jpg
deleted file mode 100644
index 67a888b23..000000000
Binary files a/content/identity/ciam-systems-hidden-pitfalls/hidden-pitfalls.jpg and /dev/null differ
diff --git a/content/identity/ciam-systems-hidden-pitfalls/hidden-pitfalls.webp b/content/identity/ciam-systems-hidden-pitfalls/hidden-pitfalls.webp
new file mode 100644
index 000000000..b6cd900e0
Binary files /dev/null and b/content/identity/ciam-systems-hidden-pitfalls/hidden-pitfalls.webp differ
diff --git a/content/identity/ciam-systems-hidden-pitfalls/index.md b/content/identity/ciam-systems-hidden-pitfalls/index.md
index 238adcced..d8a277b84 100644
--- a/content/identity/ciam-systems-hidden-pitfalls/index.md
+++ b/content/identity/ciam-systems-hidden-pitfalls/index.md
@@ -1,7 +1,7 @@
---
title: "The Hidden Pitfalls: Why Most CIAM Systems Fail Under Pressure"
date: "2024-08-06"
-coverImage: "hidden-pitfalls.jpg"
+coverImage: "hidden-pitfalls.webp"
tags: ["data security","ciam resilience","cx"]
author: "Karl Wittig"
description: "In times of crisis, companies often find their Customer Identity and Access Management (CIAM) systems under immense pressure. This article explains the common reasons for CIAM failures during emergencies and offers actionable strategies to fortify these systems, ensuring robust security and seamless user experiences."
@@ -40,7 +40,7 @@ In a crisis, the stakes are higher: cyber threats increase, customer demands shi
* **Inconsistent User Interfaces:** A disjointed user experience across different platforms and devices can confuse customers, leading to abandoned transactions and reduced engagement.
-[](https://www.loginradius.com/resource/guide/ciam-buyers-guide-secure-roi/)
+[](https://www.loginradius.com/resource/guide/ciam-buyers-guide-secure-roi/)
4. **Operational Disruptions:**
@@ -82,4 +82,4 @@ By understanding the common pitfalls and implementing robust, scalable, and secu
Investing in resilient customer identity solutions is not just about crisis management; it is about building a foundation for long-term success and customer loyalty.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-systems-hidden-pitfalls)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-systems-hidden-pitfalls)
\ No newline at end of file
diff --git a/content/identity/ciam-trends-2021/WP-zero-trust-1.png b/content/identity/ciam-trends-2021/WP-zero-trust-1.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/ciam-trends-2021/WP-zero-trust-1.png and /dev/null differ
diff --git a/content/identity/ciam-trends-2021/WP-zero-trust-1.webp b/content/identity/ciam-trends-2021/WP-zero-trust-1.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/ciam-trends-2021/WP-zero-trust-1.webp differ
diff --git a/content/identity/ciam-trends-2021/ciam-trends-2021-cover.jpg b/content/identity/ciam-trends-2021/ciam-trends-2021-cover.jpg
deleted file mode 100644
index 120f968e2..000000000
Binary files a/content/identity/ciam-trends-2021/ciam-trends-2021-cover.jpg and /dev/null differ
diff --git a/content/identity/ciam-trends-2021/ciam-trends-2021-cover.webp b/content/identity/ciam-trends-2021/ciam-trends-2021-cover.webp
new file mode 100644
index 000000000..18ff4ab01
Binary files /dev/null and b/content/identity/ciam-trends-2021/ciam-trends-2021-cover.webp differ
diff --git a/content/identity/ciam-trends-2021/index.md b/content/identity/ciam-trends-2021/index.md
index 7adace7c2..2feeb57df 100644
--- a/content/identity/ciam-trends-2021/index.md
+++ b/content/identity/ciam-trends-2021/index.md
@@ -1,7 +1,7 @@
---
title: "The Top 5 Trends in CIAM We’ve Watched in 2021"
date: "2021-10-12"
-coverImage: "ciam-trends-2021-cover.jpg"
+coverImage: "ciam-trends-2021-cover.webp"
tags: ["zero trust","adaptive mfa","passwordless authentication"]
author: "Rakesh Soni"
description: "The modern CIAM is packed with endless capabilities that ensure robust authentication and eventually help businesses stay ahead of the curve. Here’s the list of CIAM trends that we’ve witnessed in 2021 so far."
@@ -73,7 +73,7 @@ This strategic initiative helps prevent data breaches as the concept of trusting
Security experts now firmly believe that the conventional security approach is good for nothing, especially in a world where most data breaches are caused by bypassing the corporate firewalls and hackers could move inside a private network without enough resistance.
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
## #5. Progressive Disclosure
@@ -101,4 +101,4 @@ If you wish to learn more about the cutting-edge features of LoginRadius through
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-trends-2021)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-trends-2021)
diff --git a/content/identity/ciam-trends-2021/wp-zero-trust.png b/content/identity/ciam-trends-2021/wp-zero-trust.png
deleted file mode 100644
index 3e6b81ee6..000000000
Binary files a/content/identity/ciam-trends-2021/wp-zero-trust.png and /dev/null differ
diff --git a/content/identity/ciam-trends-2021/wp-zero-trust.webp b/content/identity/ciam-trends-2021/wp-zero-trust.webp
new file mode 100644
index 000000000..2f7c01062
Binary files /dev/null and b/content/identity/ciam-trends-2021/wp-zero-trust.webp differ
diff --git a/content/identity/cisos-top-cybersecurity-threats-from-scattered-spider-to-deepfakes/index.md b/content/identity/cisos-top-cybersecurity-threats-from-scattered-spider-to-deepfakes/index.md
index a21919564..77945b345 100644
--- a/content/identity/cisos-top-cybersecurity-threats-from-scattered-spider-to-deepfakes/index.md
+++ b/content/identity/cisos-top-cybersecurity-threats-from-scattered-spider-to-deepfakes/index.md
@@ -1,7 +1,7 @@
---
title: "CISOs’ Top Cybersecurity Threats 2025: Scattered Spider, Deepfakes, and More"
date: "2025-01-06"
-coverImage: "lock-business-background-security-concept-3d-rendering.jpg"
+coverImage: "lock-business-background-security-concept-3d-rendering.webp"
tags: ["Cybersecurity"]
author: "Kundan Singh"
description: "From Scattered Spider ransomware to deepfake identities, 2025 poses critical cybersecurity challenges for CISOs. Discover strategies to protect your organization."
diff --git a/content/identity/cisos-top-cybersecurity-threats-from-scattered-spider-to-deepfakes/lock-business-background-security-concept-3d-rendering.jpg b/content/identity/cisos-top-cybersecurity-threats-from-scattered-spider-to-deepfakes/lock-business-background-security-concept-3d-rendering.jpg
deleted file mode 100644
index 378fe01f7..000000000
Binary files a/content/identity/cisos-top-cybersecurity-threats-from-scattered-spider-to-deepfakes/lock-business-background-security-concept-3d-rendering.jpg and /dev/null differ
diff --git a/content/identity/cisos-top-cybersecurity-threats-from-scattered-spider-to-deepfakes/lock-business-background-security-concept-3d-rendering.webp b/content/identity/cisos-top-cybersecurity-threats-from-scattered-spider-to-deepfakes/lock-business-background-security-concept-3d-rendering.webp
new file mode 100644
index 000000000..1c5ed87e0
Binary files /dev/null and b/content/identity/cisos-top-cybersecurity-threats-from-scattered-spider-to-deepfakes/lock-business-background-security-concept-3d-rendering.webp differ
diff --git a/content/identity/cloud-computing-security-challenges/Cloud-Security-Challenges-Today-V01.01_02-1024x621.jpg b/content/identity/cloud-computing-security-challenges/Cloud-Security-Challenges-Today-V01.01_02-1024x621.jpg
deleted file mode 100644
index c0daf3236..000000000
Binary files a/content/identity/cloud-computing-security-challenges/Cloud-Security-Challenges-Today-V01.01_02-1024x621.jpg and /dev/null differ
diff --git a/content/identity/cloud-computing-security-challenges/Cloud-Security-Challenges-Today-V01.01_02-1024x621.webp b/content/identity/cloud-computing-security-challenges/Cloud-Security-Challenges-Today-V01.01_02-1024x621.webp
new file mode 100644
index 000000000..a14260c67
Binary files /dev/null and b/content/identity/cloud-computing-security-challenges/Cloud-Security-Challenges-Today-V01.01_02-1024x621.webp differ
diff --git a/content/identity/cloud-computing-security-challenges/SASE-approach.png b/content/identity/cloud-computing-security-challenges/SASE-approach.png
deleted file mode 100644
index 9b885caa8..000000000
Binary files a/content/identity/cloud-computing-security-challenges/SASE-approach.png and /dev/null differ
diff --git a/content/identity/cloud-computing-security-challenges/SASE-approach.webp b/content/identity/cloud-computing-security-challenges/SASE-approach.webp
new file mode 100644
index 000000000..62f54b93f
Binary files /dev/null and b/content/identity/cloud-computing-security-challenges/SASE-approach.webp differ
diff --git a/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges-cover.jpg b/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges-cover.jpg
deleted file mode 100644
index ace44ed9f..000000000
Binary files a/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges-cover.jpg and /dev/null differ
diff --git a/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges-cover.webp b/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges-cover.webp
new file mode 100644
index 000000000..18eb12a25
Binary files /dev/null and b/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges-cover.webp differ
diff --git a/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges.jpg b/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges.jpg
deleted file mode 100644
index 4d8f00a23..000000000
Binary files a/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges.jpg and /dev/null differ
diff --git a/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges.webp b/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges.webp
new file mode 100644
index 000000000..c79dc930b
Binary files /dev/null and b/content/identity/cloud-computing-security-challenges/cloud-computing-security-challenges.webp differ
diff --git a/content/identity/cloud-computing-security-challenges/image5.png b/content/identity/cloud-computing-security-challenges/image5.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/cloud-computing-security-challenges/image5.png and /dev/null differ
diff --git a/content/identity/cloud-computing-security-challenges/image5.webp b/content/identity/cloud-computing-security-challenges/image5.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/cloud-computing-security-challenges/image5.webp differ
diff --git a/content/identity/cloud-computing-security-challenges/index.md b/content/identity/cloud-computing-security-challenges/index.md
index c9566a585..661957368 100644
--- a/content/identity/cloud-computing-security-challenges/index.md
+++ b/content/identity/cloud-computing-security-challenges/index.md
@@ -1,7 +1,7 @@
---
title: "Cloud Security Challenges Today: Expert Advice on Keeping your Business Safe"
date: "2019-10-24"
-coverImage: "cloud-computing-security-challenges-cover.jpg"
+coverImage: "cloud-computing-security-challenges-cover.webp"
tags: ["cloud computing","ciam solution","cx"]
author: "Rakesh Soni"
description: "For business owners and IT professionals around the world, security in the cloud is still a pressing concern. There are a lot of things you need to consider when moving your business to a cloud environment; from data protection, getting the right platform for your needs, how to protect data during transit, and more."
@@ -71,7 +71,7 @@ In August, we also achieved the ISO 27001 Information Security Standard Accredit
In addition, we hold a Security Trust Assurance and Risk (STAR) certification issued by the Cloud Security Alliance (CSA). CSA describes the STAR program as the [most powerful cloud security assurance program](https://cloudsecurityalliance.org/wp-uploads/2015/04/CSA_STAR-Brochure_April_2015.pdf/), "encompassing key principles of transparency, rigorous auditing, and harmonization of standards."
-
+
## Why choose cloud computing?
@@ -103,7 +103,7 @@ The European Union's [General Data Protection Regulation (GDPR)](https://www.log
Customer access to their data is a requirement of the [California Consumer Privacy Act (CCPA)](https://www.loginradius.com/blog/identity/ccpa-introduction/), and non-compliance can result in hefty fines. However, data stored on cloud services is instantly available to authorized users. On the cloud, centralized data can be backed up regularly and restored quickly in case [disaster recovery](https://searchdisasterrecovery.techtarget.com/definition/disaster-recovery) is ever necessary.
-[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
+[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
**Better Performance**
@@ -124,5 +124,5 @@ The Cloud Security Alliance is the world's leading organization dedicated to def
LoginRadius is a member, along with other experts in cloud security. Together, CSA members share up-to-date developments about the cloud computing environment. We recognize emerging security risks so that we can improve cloud security for everyone.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cloud-computing-security-challenges)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cloud-computing-security-challenges)
diff --git a/content/identity/cloud-governance-business/Future-proof-your-security.png b/content/identity/cloud-governance-business/Future-proof-your-security.png
deleted file mode 100644
index 9b885caa8..000000000
Binary files a/content/identity/cloud-governance-business/Future-proof-your-security.png and /dev/null differ
diff --git a/content/identity/cloud-governance-business/Future-proof-your-security.webp b/content/identity/cloud-governance-business/Future-proof-your-security.webp
new file mode 100644
index 000000000..62f54b93f
Binary files /dev/null and b/content/identity/cloud-governance-business/Future-proof-your-security.webp differ
diff --git a/content/identity/cloud-governance-business/cloud-governance-business-cover.jpg b/content/identity/cloud-governance-business/cloud-governance-business-cover.jpg
deleted file mode 100644
index d9eac887a..000000000
Binary files a/content/identity/cloud-governance-business/cloud-governance-business-cover.jpg and /dev/null differ
diff --git a/content/identity/cloud-governance-business/cloud-governance-business-cover.webp b/content/identity/cloud-governance-business/cloud-governance-business-cover.webp
new file mode 100644
index 000000000..c99cfc70f
Binary files /dev/null and b/content/identity/cloud-governance-business/cloud-governance-business-cover.webp differ
diff --git a/content/identity/cloud-governance-business/index.md b/content/identity/cloud-governance-business/index.md
index dd84b13cb..e6c08c74c 100644
--- a/content/identity/cloud-governance-business/index.md
+++ b/content/identity/cloud-governance-business/index.md
@@ -1,7 +1,7 @@
---
title: "5 Reasons Why Cloud Governance Matters For Your Business"
date: "2021-05-07"
-coverImage: "cloud-governance-business-cover.jpg"
+coverImage: "cloud-governance-business-cover.webp"
tags: ["cloud governance","compliance","data security"]
author: "Vishal Sharma"
description: "Security management platforms are designated systems that work towards providing network security to an enterprise for the storage of data that they have collected. This process involves security and compliance as well."
@@ -41,7 +41,7 @@ One of the biggest advantages of cloud governance is the delivery of precise acc
A strong governance strategy allows enterprises to organize multiple accounts and provide access as per their requirement and designation. This not only strengthens data security but also lends a hand in organizing and maintaining resource allocation on the cloud.
-[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
+[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
**2. Cloud governance minimizes compliance risk.**
@@ -77,4 +77,4 @@ Cloud governance should be the top-most priority for businesses leveraging [clou
The aforementioned aspects depict the role of cloud governance and how it lays the foundation of security and data access within an organization.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cloud-governance-business)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cloud-governance-business)
\ No newline at end of file
diff --git a/content/identity/cloud-identity-platform/EB-cloud-identity-platform.png b/content/identity/cloud-identity-platform/EB-cloud-identity-platform.png
deleted file mode 100644
index c25a9d725..000000000
Binary files a/content/identity/cloud-identity-platform/EB-cloud-identity-platform.png and /dev/null differ
diff --git a/content/identity/cloud-identity-platform/EB-cloud-identity-platform.webp b/content/identity/cloud-identity-platform/EB-cloud-identity-platform.webp
new file mode 100644
index 000000000..1c3498318
Binary files /dev/null and b/content/identity/cloud-identity-platform/EB-cloud-identity-platform.webp differ
diff --git a/content/identity/cloud-identity-platform/cloud-identity-platform.jpg b/content/identity/cloud-identity-platform/cloud-identity-platform.jpg
deleted file mode 100644
index b446fc452..000000000
Binary files a/content/identity/cloud-identity-platform/cloud-identity-platform.jpg and /dev/null differ
diff --git a/content/identity/cloud-identity-platform/cloud-identity-platform.webp b/content/identity/cloud-identity-platform/cloud-identity-platform.webp
new file mode 100644
index 000000000..5a92f8495
Binary files /dev/null and b/content/identity/cloud-identity-platform/cloud-identity-platform.webp differ
diff --git a/content/identity/cloud-identity-platform/index.md b/content/identity/cloud-identity-platform/index.md
index 9074f6672..f5b6f5a6e 100644
--- a/content/identity/cloud-identity-platform/index.md
+++ b/content/identity/cloud-identity-platform/index.md
@@ -1,7 +1,7 @@
---
title: "Above the Horizon: Exploring the Power of a Strong Cloud Identity Platform"
date: "2024-01-12"
-coverImage: "cloud-identity-platform.jpg"
+coverImage: "cloud-identity-platform.webp"
tags: ["cloud identity","user authentication","compliance"]
author: "Rakesh Soni"
description: "Organizations are investing in scalable cloud platforms; however, safeguarding user identities and information becomes fundamental. As technology becomes advanced, there is a chance to identify the gaps. That’s where the cloud identity platform comes in to secure the platform and bridge the gap that could possibly lead the attacker into the cloud platform."
@@ -44,7 +44,7 @@ With the [identity federation](https://www.loginradius.com/federated-sso/), user
With LoginRadius, it becomes easy to customize the authentication and registration flows to match your business application needs. With the availability of SDKs and APIs, businesses can swiftly integrate authentication services into their web and mobile applications.
-[](https://www.loginradius.com/resource/ebook/loginradius-cloud-identity-partner/)
+[](https://www.loginradius.com/resource/ebook/loginradius-cloud-identity-partner/)
### 5. Security and Compliance
@@ -66,4 +66,4 @@ If managing identity and access isn't a core aspect of your business operations,
Cloud identity platforms can make implementing a secure and reliable identity layer in applications easy. The role also extends beyond conventional security measures. These platforms become instrumental in seamlessly implementing a secure and reliable identity layer within applications, simplifying complex processes, and mitigating potential risks.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cloud-identity-platform)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cloud-identity-platform)
\ No newline at end of file
diff --git a/content/identity/cloud-security-governance-digital-protection/GD-response-plan.png b/content/identity/cloud-security-governance-digital-protection/GD-response-plan.png
deleted file mode 100644
index a7dbc3ac7..000000000
Binary files a/content/identity/cloud-security-governance-digital-protection/GD-response-plan.png and /dev/null differ
diff --git a/content/identity/cloud-security-governance-digital-protection/GD-response-plan.webp b/content/identity/cloud-security-governance-digital-protection/GD-response-plan.webp
new file mode 100644
index 000000000..e57053baa
Binary files /dev/null and b/content/identity/cloud-security-governance-digital-protection/GD-response-plan.webp differ
diff --git a/content/identity/cloud-security-governance-digital-protection/cloud-security.jpg b/content/identity/cloud-security-governance-digital-protection/cloud-security.jpg
deleted file mode 100644
index a706a3601..000000000
Binary files a/content/identity/cloud-security-governance-digital-protection/cloud-security.jpg and /dev/null differ
diff --git a/content/identity/cloud-security-governance-digital-protection/cloud-security.webp b/content/identity/cloud-security-governance-digital-protection/cloud-security.webp
new file mode 100644
index 000000000..44ba02468
Binary files /dev/null and b/content/identity/cloud-security-governance-digital-protection/cloud-security.webp differ
diff --git a/content/identity/cloud-security-governance-digital-protection/index.md b/content/identity/cloud-security-governance-digital-protection/index.md
index c612cdb95..0b86da109 100644
--- a/content/identity/cloud-security-governance-digital-protection/index.md
+++ b/content/identity/cloud-security-governance-digital-protection/index.md
@@ -1,7 +1,7 @@
---
title: "Cloud Security Governance: Protecting Assets in the Digital Frontier"
date: "2024-04-30"
-coverImage: "cloud-security.jpg"
+coverImage: "cloud-security.webp"
tags: ["cloud security","data governance","ciam solution"]
author: "Alok Patidar"
description: "Discover the significance of cloud security governance in safeguarding digital assets as businesses transition to cloud computing. Delve into the best practices and challenges organizations face to ensure data security and compliance in the ever-evolving digital frontier."
@@ -34,7 +34,7 @@ Organizations must implement best practices for cloud security governance to pro
Furthermore, organizations should establish clear incident response plans to address security breaches swiftly and minimize their impact on operations.
-[](https://www.loginradius.com/resource/guide/cyber-incident-response-plan/)
+[](https://www.loginradius.com/resource/guide/cyber-incident-response-plan/)
## The Future of Cloud Security Governance
@@ -62,4 +62,4 @@ In today's digital frontier, protecting assets in the cloud is paramount for org
As technology continues to evolve and threats evolve, organizations must remain vigilant, continuously adapting and enhancing their cloud security governance practices to stay one step ahead of cyber adversaries.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cloud-security-governance-digital-protection)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cloud-security-governance-digital-protection)
\ No newline at end of file
diff --git a/content/identity/cloud-security-management/Future-proof-your-security.png b/content/identity/cloud-security-management/Future-proof-your-security.png
deleted file mode 100644
index 9b885caa8..000000000
Binary files a/content/identity/cloud-security-management/Future-proof-your-security.png and /dev/null differ
diff --git a/content/identity/cloud-security-management/Future-proof-your-security.webp b/content/identity/cloud-security-management/Future-proof-your-security.webp
new file mode 100644
index 000000000..62f54b93f
Binary files /dev/null and b/content/identity/cloud-security-management/Future-proof-your-security.webp differ
diff --git a/content/identity/cloud-security-management/cloud-security-management.jpg b/content/identity/cloud-security-management/cloud-security-management.jpg
deleted file mode 100644
index c894fe95e..000000000
Binary files a/content/identity/cloud-security-management/cloud-security-management.jpg and /dev/null differ
diff --git a/content/identity/cloud-security-management/cloud-security-management.webp b/content/identity/cloud-security-management/cloud-security-management.webp
new file mode 100644
index 000000000..96cfa9f2a
Binary files /dev/null and b/content/identity/cloud-security-management/cloud-security-management.webp differ
diff --git a/content/identity/cloud-security-management/index.md b/content/identity/cloud-security-management/index.md
index 908db930c..bd480b300 100644
--- a/content/identity/cloud-security-management/index.md
+++ b/content/identity/cloud-security-management/index.md
@@ -1,7 +1,7 @@
---
title: "Protecting a Unified Cloud Platform through Cloud Security Management"
date: "2021-03-03"
-coverImage: "cloud-security-management.jpg"
+coverImage: "cloud-security-management.webp"
tags: ["cloud security","identity management","cx"]
author: "Rakesh Soni"
description: "Security management platforms are designated systems that work towards providing network security to an enterprise for the storage of data that they have collected. This process involves security and compliance as well."
@@ -101,7 +101,7 @@ The [LoginRadius Directory for Cloud Storage](https://www.loginradius.com/cloud-
* **Gathering data:** The directory will employ the use of open APIs to gather data from third-party resources.
* **Ownership:** The enterprise that uses the platform will receive full ownership of the customer data. Therefore, they can keep firm control over the operations of the business.
-[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
+[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
**2. Efficiency**
@@ -129,4 +129,4 @@ LoginRadius provides top-notch cybersecurity through its openID connect system.
With most business operations going online in recent years, cloud security has started to receive more importance. This is because cloud storage can get easily convoluted and complicated as the number of information increases. This makes it easy for information to be leaked. A unified cloud platform provides its services to protect information while moving to the cloud.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cloud-security-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cloud-security-management)
diff --git a/content/identity/common-vulnerabilities-password-based-login/GD-to-RBA.png b/content/identity/common-vulnerabilities-password-based-login/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/common-vulnerabilities-password-based-login/GD-to-RBA.png and /dev/null differ
diff --git a/content/identity/common-vulnerabilities-password-based-login/GD-to-RBA.webp b/content/identity/common-vulnerabilities-password-based-login/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/common-vulnerabilities-password-based-login/GD-to-RBA.webp differ
diff --git a/content/identity/common-vulnerabilities-password-based-login/index.md b/content/identity/common-vulnerabilities-password-based-login/index.md
index e28d9c7d0..d3df111fe 100644
--- a/content/identity/common-vulnerabilities-password-based-login/index.md
+++ b/content/identity/common-vulnerabilities-password-based-login/index.md
@@ -1,7 +1,7 @@
---
title: "4 Common Security Issues Found In Password-Based Login"
date: "2022-03-17"
-coverImage: "password-login.jpg"
+coverImage: "password-login.webp"
tags: ["passwordless login","cx","mfa","authentication"]
author: "Navanita Devi"
description: "Password-based login is the most commonly used form of authentication, but it's not always the most secure. This blog covers some of the common security issues found in password-based login systems and how to avoid them."
@@ -76,7 +76,7 @@ The "Digital Shadows Photon Research" states that the number of stolen username
* Use risk-based authentication.
* Use bot management to stop malicious bots from making login attempts without impacting legitimate logins.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
### 4. Dictionary Attack
@@ -99,4 +99,4 @@ The problem is that the current digital environment exposes [authentication syst
The tips discussed in this blog can help you avoid the pitfalls that come with password-based login systems.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=common-vulnerabilities-password-based-login)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=common-vulnerabilities-password-based-login)
diff --git a/content/identity/common-vulnerabilities-password-based-login/password-login.jpg b/content/identity/common-vulnerabilities-password-based-login/password-login.jpg
deleted file mode 100644
index 31e3e530f..000000000
Binary files a/content/identity/common-vulnerabilities-password-based-login/password-login.jpg and /dev/null differ
diff --git a/content/identity/common-vulnerabilities-password-based-login/password-login.webp b/content/identity/common-vulnerabilities-password-based-login/password-login.webp
new file mode 100644
index 000000000..9cc6578cf
Binary files /dev/null and b/content/identity/common-vulnerabilities-password-based-login/password-login.webp differ
diff --git a/content/identity/common-vulnerabilities-password-based-login/risk-auth-gd.png b/content/identity/common-vulnerabilities-password-based-login/risk-auth-gd.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/identity/common-vulnerabilities-password-based-login/risk-auth-gd.png and /dev/null differ
diff --git a/content/identity/common-vulnerabilities-password-based-login/risk-auth-gd.webp b/content/identity/common-vulnerabilities-password-based-login/risk-auth-gd.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/identity/common-vulnerabilities-password-based-login/risk-auth-gd.webp differ
diff --git a/content/identity/consent-management/Consent-Management.png b/content/identity/consent-management/Consent-Management.png
deleted file mode 100644
index 88b841ee2..000000000
Binary files a/content/identity/consent-management/Consent-Management.png and /dev/null differ
diff --git a/content/identity/consent-management/Consent-Management.webp b/content/identity/consent-management/Consent-Management.webp
new file mode 100644
index 000000000..7c0b9f3bf
Binary files /dev/null and b/content/identity/consent-management/Consent-Management.webp differ
diff --git a/content/identity/consent-management/DS-Consent-Management-1024x310.png b/content/identity/consent-management/DS-Consent-Management-1024x310.png
deleted file mode 100644
index b16ff74c8..000000000
Binary files a/content/identity/consent-management/DS-Consent-Management-1024x310.png and /dev/null differ
diff --git a/content/identity/consent-management/DS-Consent-Management-1024x310.webp b/content/identity/consent-management/DS-Consent-Management-1024x310.webp
new file mode 100644
index 000000000..179638a91
Binary files /dev/null and b/content/identity/consent-management/DS-Consent-Management-1024x310.webp differ
diff --git a/content/identity/consent-management/LoginRadius-Dashboard-Consent-Management.jpg b/content/identity/consent-management/LoginRadius-Dashboard-Consent-Management.jpg
deleted file mode 100644
index 6cd6235cf..000000000
Binary files a/content/identity/consent-management/LoginRadius-Dashboard-Consent-Management.jpg and /dev/null differ
diff --git a/content/identity/consent-management/LoginRadius-Dashboard-Consent-Management.webp b/content/identity/consent-management/LoginRadius-Dashboard-Consent-Management.webp
new file mode 100644
index 000000000..30682193c
Binary files /dev/null and b/content/identity/consent-management/LoginRadius-Dashboard-Consent-Management.webp differ
diff --git a/content/identity/consent-management/index.md b/content/identity/consent-management/index.md
index 718ff3fde..8e1ddc83a 100644
--- a/content/identity/consent-management/index.md
+++ b/content/identity/consent-management/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Launches Consent Management to Support the EU's GDPR Compliance"
date: "2020-05-29"
-coverImage: "Consent-Management.png"
+coverImage: "Consent-Management.webp"
tags: ["data privacy","compliance","consent management"]
author: "Rakesh Soni"
description: "When the General Data Protection Regulation (GDPR) was officially laid out, it sparked an increasing need to re-consider their security arrangements for organisations running on Customer Identity & Access Management (CIAM) solutions."
@@ -21,7 +21,7 @@ GDPR exposed the world to a whole lot of data security concerns ranging from how
LoginRadius Consent Management will help companies and their security professionals understand the core mechanism of GDPR requirements and improve customer experience in the process.
-
+
## Key Features of the LoginRadius Consent Management to Meet the EU's GDPR
@@ -38,7 +38,7 @@ LoginRadius Consent Management will help companies and their security profession
- Our consent repository is designed as a secure database and a single source of truth for all data processing based on customers’ consent.
- It supports language localization for better and personalized communication.
-[](https://www.loginradius.com/resource/loginradius-consent-management/)
+[](https://www.loginradius.com/resource/loginradius-consent-management/)
## A Final Word
@@ -46,4 +46,4 @@ LoginRadius Consent Management is an effort from the cloud-based CIAM solution p
In addition to the GDPR, the LoginRadius Platform is also compliant with other international data privacy [standards like the CCPA](https://www.loginradius.com/blog/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/), NIST, and HIPPA.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consent-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consent-management)
diff --git a/content/identity/consumer-data-privacy-security/Book-a-free-demo-request-1024x310.png b/content/identity/consumer-data-privacy-security/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/consumer-data-privacy-security/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/consumer-data-privacy-security/Book-a-free-demo-request-1024x310.webp b/content/identity/consumer-data-privacy-security/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/consumer-data-privacy-security/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/consumer-data-privacy-security/Different-data-privacy-laws-and-acts.png b/content/identity/consumer-data-privacy-security/Different-data-privacy-laws-and-acts.png
deleted file mode 100644
index ab800cee3..000000000
Binary files a/content/identity/consumer-data-privacy-security/Different-data-privacy-laws-and-acts.png and /dev/null differ
diff --git a/content/identity/consumer-data-privacy-security/Different-data-privacy-laws-and-acts.webp b/content/identity/consumer-data-privacy-security/Different-data-privacy-laws-and-acts.webp
new file mode 100644
index 000000000..f9d72645e
Binary files /dev/null and b/content/identity/consumer-data-privacy-security/Different-data-privacy-laws-and-acts.webp differ
diff --git a/content/identity/consumer-data-privacy-security/WP-CCPA-consumer-identity.png b/content/identity/consumer-data-privacy-security/WP-CCPA-consumer-identity.png
deleted file mode 100644
index 6f6e61fd8..000000000
Binary files a/content/identity/consumer-data-privacy-security/WP-CCPA-consumer-identity.png and /dev/null differ
diff --git a/content/identity/consumer-data-privacy-security/WP-CCPA-consumer-identity.webp b/content/identity/consumer-data-privacy-security/WP-CCPA-consumer-identity.webp
new file mode 100644
index 000000000..6c1309e8e
Binary files /dev/null and b/content/identity/consumer-data-privacy-security/WP-CCPA-consumer-identity.webp differ
diff --git a/content/identity/consumer-data-privacy-security/WP-The-CCPA.png b/content/identity/consumer-data-privacy-security/WP-The-CCPA.png
deleted file mode 100644
index c02a1338a..000000000
Binary files a/content/identity/consumer-data-privacy-security/WP-The-CCPA.png and /dev/null differ
diff --git a/content/identity/consumer-data-privacy-security/WP-The-CCPA.webp b/content/identity/consumer-data-privacy-security/WP-The-CCPA.webp
new file mode 100644
index 000000000..1b0055d88
Binary files /dev/null and b/content/identity/consumer-data-privacy-security/WP-The-CCPA.webp differ
diff --git a/content/identity/consumer-data-privacy-security/consumer-data-privacy.jpg b/content/identity/consumer-data-privacy-security/consumer-data-privacy.jpg
deleted file mode 100644
index 2ff1d1191..000000000
Binary files a/content/identity/consumer-data-privacy-security/consumer-data-privacy.jpg and /dev/null differ
diff --git a/content/identity/consumer-data-privacy-security/consumer-data-privacy.webp b/content/identity/consumer-data-privacy-security/consumer-data-privacy.webp
new file mode 100644
index 000000000..64b1b68d0
Binary files /dev/null and b/content/identity/consumer-data-privacy-security/consumer-data-privacy.webp differ
diff --git a/content/identity/consumer-data-privacy-security/customer-data-private-and-secure.png b/content/identity/consumer-data-privacy-security/customer-data-private-and-secure.png
deleted file mode 100644
index d7c61a16a..000000000
Binary files a/content/identity/consumer-data-privacy-security/customer-data-private-and-secure.png and /dev/null differ
diff --git a/content/identity/consumer-data-privacy-security/customer-data-private-and-secure.webp b/content/identity/consumer-data-privacy-security/customer-data-private-and-secure.webp
new file mode 100644
index 000000000..36e4f96c6
Binary files /dev/null and b/content/identity/consumer-data-privacy-security/customer-data-private-and-secure.webp differ
diff --git a/content/identity/consumer-data-privacy-security/customer-data-secure.png b/content/identity/consumer-data-privacy-security/customer-data-secure.png
deleted file mode 100644
index 62c69b4b3..000000000
Binary files a/content/identity/consumer-data-privacy-security/customer-data-secure.png and /dev/null differ
diff --git a/content/identity/consumer-data-privacy-security/customer-data-secure.webp b/content/identity/consumer-data-privacy-security/customer-data-secure.webp
new file mode 100644
index 000000000..059849141
Binary files /dev/null and b/content/identity/consumer-data-privacy-security/customer-data-secure.webp differ
diff --git a/content/identity/consumer-data-privacy-security/index.md b/content/identity/consumer-data-privacy-security/index.md
index 6a34d184b..366dc6b44 100644
--- a/content/identity/consumer-data-privacy-security/index.md
+++ b/content/identity/consumer-data-privacy-security/index.md
@@ -1,7 +1,7 @@
---
title: "How LoginRadius Future-Proofs Consumer Data Privacy and Security"
date: "2020-06-17"
-coverImage: "consumer-data-privacy.jpg"
+coverImage: "consumer-data-privacy.webp"
tags: ["data privacy","cx","compliance"]
author: "Rakesh Soni"
description: "The building blocks that sustain customer loyalty in the long run are authenticity, accountability and excellent customer experience. Organizations need to be clear about how cautious they are when it comes to the privacy and protection of customer data."
@@ -63,7 +63,7 @@ Today, consumers are more mindful of the effect data privacy has on their person
New consumer data privacy regulations have been affecting every aspect of a business. Organizations must manage consumer interactions with privacy demands, develop new organizational positions to manage regulatory interactions, and educate employees on the current regulations.
-[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
+[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
In general, consumer data privacy laws have three different impacts on every organization.
@@ -89,7 +89,7 @@ Consumers have the authority to set a brand apart from its competitors. So, when
## List of Popular Data Privacy Laws and Acts Around the World
-
+
#### **The European Union's Data Privacy Laws**
@@ -146,7 +146,7 @@ Organizations are working to build technology environments that can easily handl
## How LoginRadius Keeps Your Customer Data Private and Secure
-
+
One crucial aspect of an organization is the protection of the confidentiality and integrity of consumer data. LoginRadius provides layered security by limiting and monitoring access to consumer's data. The platform offers seamless security with [features like data management](https://www.loginradius.com/data-governance/) and real-time fraud analysis to improve customer experience and detect fraud attempts at the entrance.
@@ -167,4 +167,4 @@ The LoginRadius is an identity management system that continues to support [glob
Your consumer data privacy and security plan should comply with the rapid development of technology and the increasing cyber-attacks. Consider investing in compliance with the latest regulations to future-proof your consumer data protection plan.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-data-privacy-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-data-privacy-security)
diff --git a/content/identity/consumer-digital-identity-trends-report-2024/CTA-RP.png b/content/identity/consumer-digital-identity-trends-report-2024/CTA-RP.png
deleted file mode 100644
index a57e159ce..000000000
Binary files a/content/identity/consumer-digital-identity-trends-report-2024/CTA-RP.png and /dev/null differ
diff --git a/content/identity/consumer-digital-identity-trends-report-2024/CTA-RP.webp b/content/identity/consumer-digital-identity-trends-report-2024/CTA-RP.webp
new file mode 100644
index 000000000..366a4bdf3
Binary files /dev/null and b/content/identity/consumer-digital-identity-trends-report-2024/CTA-RP.webp differ
diff --git a/content/identity/consumer-digital-identity-trends-report-2024/consumer-report-2024.png b/content/identity/consumer-digital-identity-trends-report-2024/consumer-report-2024.png
deleted file mode 100644
index db6a976e7..000000000
Binary files a/content/identity/consumer-digital-identity-trends-report-2024/consumer-report-2024.png and /dev/null differ
diff --git a/content/identity/consumer-digital-identity-trends-report-2024/consumer-report-2024.webp b/content/identity/consumer-digital-identity-trends-report-2024/consumer-report-2024.webp
new file mode 100644
index 000000000..09f5a9b54
Binary files /dev/null and b/content/identity/consumer-digital-identity-trends-report-2024/consumer-report-2024.webp differ
diff --git a/content/identity/consumer-digital-identity-trends-report-2024/index.md b/content/identity/consumer-digital-identity-trends-report-2024/index.md
index 0f605bd90..ecb1ef2e2 100644
--- a/content/identity/consumer-digital-identity-trends-report-2024/index.md
+++ b/content/identity/consumer-digital-identity-trends-report-2024/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Releases 2024 Consumer Identity Report, Highlights the Shifting Trends in Consumer Preferences"
date: "2024-09-06"
-coverImage: "trends-report-2024.jpg"
+coverImage: "trends-report-2024.webp"
tags: ["industry-news", "consumer-identity", "identity-trends", "digital-identity"]
author: "Rakesh Soni"
description: "LoginRadius analyzed data from its Consumer IAM (CIAM) Platform, utilized by over 500 brands globally. The report offers a unique perspective on global consumer identity trends in 2024, delivering insights into consumer behavior regarding digital identities and providing a comprehensive analysis of their behavior patterns and lifecycle."
@@ -22,7 +22,7 @@ Our research examined consumer comfort with [passwordless login](https://www.log
Our analysis shows a clear preference for email-based passwordless login, which has grown since last year. Additionally, the use of Passkeys for passwordless authentication is also on the rise.
-
+
## Key Highlights of the Consumer Identity Report 2024
@@ -34,7 +34,7 @@ As one of the top providers of Customer Identity and Access Management solutions
* The passwordless login has the highest return rate of 42.43%.
-[](https://www.loginradius.com/resource/2024-consumer-digital-identity-trends-report/)
+[](https://www.loginradius.com/resource/2024-consumer-digital-identity-trends-report/)
## Looking Ahead: Gaining a Competitive Edge Through Strategic Customer Identity Management
@@ -46,4 +46,4 @@ These insights are crucial for those aiming to elevate their customer experience
[Download your free copy](https://www.loginradius.com/resource/2024-consumer-digital-identity-trends-report/) of the report today and stay ahead in the dynamic field of customer identity management.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-digital-identity-trends-report-2024)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-digital-identity-trends-report-2024)
diff --git a/content/identity/consumer-digital-identity-trends-report-2024/trends-report-2024.jpg b/content/identity/consumer-digital-identity-trends-report-2024/trends-report-2024.jpg
deleted file mode 100644
index 1e678f91c..000000000
Binary files a/content/identity/consumer-digital-identity-trends-report-2024/trends-report-2024.jpg and /dev/null differ
diff --git a/content/identity/consumer-digital-identity-trends-report-2024/trends-report-2024.webp b/content/identity/consumer-digital-identity-trends-report-2024/trends-report-2024.webp
new file mode 100644
index 000000000..327b90518
Binary files /dev/null and b/content/identity/consumer-digital-identity-trends-report-2024/trends-report-2024.webp differ
diff --git a/content/identity/consumer-identity-management-cmo-ciso-cio/Cyber-risk-for-CMOs-CIOs-and-CISOs.png b/content/identity/consumer-identity-management-cmo-ciso-cio/Cyber-risk-for-CMOs-CIOs-and-CISOs.png
deleted file mode 100644
index 0747fd642..000000000
Binary files a/content/identity/consumer-identity-management-cmo-ciso-cio/Cyber-risk-for-CMOs-CIOs-and-CISOs.png and /dev/null differ
diff --git a/content/identity/consumer-identity-management-cmo-ciso-cio/Cyber-risk-for-CMOs-CIOs-and-CISOs.webp b/content/identity/consumer-identity-management-cmo-ciso-cio/Cyber-risk-for-CMOs-CIOs-and-CISOs.webp
new file mode 100644
index 000000000..48909fdf1
Binary files /dev/null and b/content/identity/consumer-identity-management-cmo-ciso-cio/Cyber-risk-for-CMOs-CIOs-and-CISOs.webp differ
diff --git "a/content/identity/consumer-identity-management-cmo-ciso-cio/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png" "b/content/identity/consumer-identity-management-cmo-ciso-cio/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png"
deleted file mode 100644
index 6b3ba826e..000000000
Binary files "a/content/identity/consumer-identity-management-cmo-ciso-cio/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png" and /dev/null differ
diff --git "a/content/identity/consumer-identity-management-cmo-ciso-cio/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp" "b/content/identity/consumer-identity-management-cmo-ciso-cio/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp"
new file mode 100644
index 000000000..ba14612ce
Binary files /dev/null and "b/content/identity/consumer-identity-management-cmo-ciso-cio/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp" differ
diff --git a/content/identity/consumer-identity-management-cmo-ciso-cio/LoginRadius-Identity-management-for-CIO-CISO-and-CMO.png b/content/identity/consumer-identity-management-cmo-ciso-cio/LoginRadius-Identity-management-for-CIO-CISO-and-CMO.png
deleted file mode 100644
index 5597f04ce..000000000
Binary files a/content/identity/consumer-identity-management-cmo-ciso-cio/LoginRadius-Identity-management-for-CIO-CISO-and-CMO.png and /dev/null differ
diff --git a/content/identity/consumer-identity-management-cmo-ciso-cio/LoginRadius-Identity-management-for-CIO-CISO-and-CMO.webp b/content/identity/consumer-identity-management-cmo-ciso-cio/LoginRadius-Identity-management-for-CIO-CISO-and-CMO.webp
new file mode 100644
index 000000000..c9eb96c46
Binary files /dev/null and b/content/identity/consumer-identity-management-cmo-ciso-cio/LoginRadius-Identity-management-for-CIO-CISO-and-CMO.webp differ
diff --git a/content/identity/consumer-identity-management-cmo-ciso-cio/image1.jpg b/content/identity/consumer-identity-management-cmo-ciso-cio/image1.jpg
deleted file mode 100644
index ed9267cfe..000000000
Binary files a/content/identity/consumer-identity-management-cmo-ciso-cio/image1.jpg and /dev/null differ
diff --git a/content/identity/consumer-identity-management-cmo-ciso-cio/image1.webp b/content/identity/consumer-identity-management-cmo-ciso-cio/image1.webp
new file mode 100644
index 000000000..c8278f5ae
Binary files /dev/null and b/content/identity/consumer-identity-management-cmo-ciso-cio/image1.webp differ
diff --git a/content/identity/consumer-identity-management-cmo-ciso-cio/index.md b/content/identity/consumer-identity-management-cmo-ciso-cio/index.md
index 60548931d..3cc846ba5 100644
--- a/content/identity/consumer-identity-management-cmo-ciso-cio/index.md
+++ b/content/identity/consumer-identity-management-cmo-ciso-cio/index.md
@@ -1,7 +1,7 @@
---
title: "Consumer Identity Management for the CMO, CISO, and CIO"
date: "2020-09-28"
-coverImage: "image1.jpg"
+coverImage: "image1.webp"
tags: ["customer identity management","compliance","cx"]
author: "Rakesh Soni"
description: "A modern-day consumer identity management (CIAM) platform securely collects and manages consumer identity and profile data, along with securing access to apps, computers, and other resources in the network."
@@ -36,7 +36,7 @@ A few other features they look for include:
## Cyber Risk for CMOs CIOs and CISOs
-
+
In the past, cyber risks were often viewed as highly technical. Earlier leaders used to perceive security threats as an IT issue, but that's not the case today.
@@ -48,7 +48,7 @@ Therefore, cybersecurity is a critical problem for the boardroom, and every orga
It takes equal effort from CIOs, CSOs, and CISOs to mitigate the architectural complexities that cybercriminals prey on. To get a headstart, the security team can develop holistic frameworks that can be later adopted and extended across the board.
-[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
+[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
## How Consumer Identity Management meets CIO, CMO, CISO Goals
@@ -88,7 +88,7 @@ For instance, with a seamless login experience, CIAM encourages consumers to try
## LoginRadius Identity Management for CIO, CISO, and CMO
-
+
LoginRadius is a comprehensive, streamlined consumer identity management solution that helps stakeholders of large enterprises to drive automation, authentication, effective compliance, among other requirements.
@@ -118,4 +118,4 @@ The consumer identity management platform lets CIOs, CISOs, and CMOs to manage i
Consumer behavior has never been static—nor have their expectations. A consumer identity management solution can be a strategic asset for CIOs, CISOs, and CMOs to use it to their advantage in their respective departments. Speaking of possibilities, they are _endless_ here.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-identity-management-cmo-ciso-cio)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-identity-management-cmo-ciso-cio)
diff --git a/content/identity/continuous-authentication/continuous-authentication-1.png b/content/identity/continuous-authentication/continuous-authentication-1.png
deleted file mode 100644
index ad1158521..000000000
Binary files a/content/identity/continuous-authentication/continuous-authentication-1.png and /dev/null differ
diff --git a/content/identity/continuous-authentication/continuous-authentication-1.webp b/content/identity/continuous-authentication/continuous-authentication-1.webp
new file mode 100644
index 000000000..6630fbd7b
Binary files /dev/null and b/content/identity/continuous-authentication/continuous-authentication-1.webp differ
diff --git a/content/identity/continuous-authentication/continuous-authentication-cover.jpg b/content/identity/continuous-authentication/continuous-authentication-cover.jpg
deleted file mode 100644
index 54b23c864..000000000
Binary files a/content/identity/continuous-authentication/continuous-authentication-cover.jpg and /dev/null differ
diff --git a/content/identity/continuous-authentication/continuous-authentication-cover.webp b/content/identity/continuous-authentication/continuous-authentication-cover.webp
new file mode 100644
index 000000000..19852620d
Binary files /dev/null and b/content/identity/continuous-authentication/continuous-authentication-cover.webp differ
diff --git a/content/identity/continuous-authentication/continuous-authentication-whitepaper.png b/content/identity/continuous-authentication/continuous-authentication-whitepaper.png
deleted file mode 100644
index 46e301e6d..000000000
Binary files a/content/identity/continuous-authentication/continuous-authentication-whitepaper.png and /dev/null differ
diff --git a/content/identity/continuous-authentication/continuous-authentication-whitepaper.webp b/content/identity/continuous-authentication/continuous-authentication-whitepaper.webp
new file mode 100644
index 000000000..7a77e6d27
Binary files /dev/null and b/content/identity/continuous-authentication/continuous-authentication-whitepaper.webp differ
diff --git a/content/identity/continuous-authentication/index.md b/content/identity/continuous-authentication/index.md
index 56975e2cc..1e9b9a4f0 100644
--- a/content/identity/continuous-authentication/index.md
+++ b/content/identity/continuous-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "What is Continuous Authentication"
date: "2021-03-03"
-coverImage: "continuous-authentication-cover.jpg"
+coverImage: "continuous-authentication-cover.webp"
tags: ["continuous authentication","biometric authentication","cx"]
author: "Rakesh Soni"
description: "Continuous authentication estimates the likelihood that the discrete network users are the ones who they claim to be throughout an entire session. However, the method of continuous authentication is fairly new and has brought a novel perspective to network protection these days."
@@ -60,7 +60,7 @@ In this kind of continuous authentication, the system can easily track the bodil
An example of this kind of continuous authentication can be large multinational companies that employ this authentication to track the movement of their employees.
-[](https://www.loginradius.com/resource/continuous-authentication-whitepaper)
+[](https://www.loginradius.com/resource/continuous-authentication-whitepaper)
@@ -93,7 +93,7 @@ In this method, the system uses digital certificates to identify its users. A di
The use of certificate-based continuous authentication can be seen in software development companies where there is a more threat to data and its privacy.
-
+
## All About LoginRadius' Continuous Authentication Solution
@@ -134,4 +134,4 @@ Many businesses have progressed ahead of password-based authentication and embra
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=continuous-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=continuous-authentication)
diff --git a/content/identity/converged-identity-platforms/DS-FIM.png b/content/identity/converged-identity-platforms/DS-FIM.png
deleted file mode 100644
index 9e03618f7..000000000
Binary files a/content/identity/converged-identity-platforms/DS-FIM.png and /dev/null differ
diff --git a/content/identity/converged-identity-platforms/DS-FIM.webp b/content/identity/converged-identity-platforms/DS-FIM.webp
new file mode 100644
index 000000000..b8fd0ecbb
Binary files /dev/null and b/content/identity/converged-identity-platforms/DS-FIM.webp differ
diff --git a/content/identity/converged-identity-platforms/identity-platforms.jpg b/content/identity/converged-identity-platforms/identity-platforms.jpg
deleted file mode 100644
index ac0976c35..000000000
Binary files a/content/identity/converged-identity-platforms/identity-platforms.jpg and /dev/null differ
diff --git a/content/identity/converged-identity-platforms/identity-platforms.webp b/content/identity/converged-identity-platforms/identity-platforms.webp
new file mode 100644
index 000000000..ce2d2227a
Binary files /dev/null and b/content/identity/converged-identity-platforms/identity-platforms.webp differ
diff --git a/content/identity/converged-identity-platforms/index.md b/content/identity/converged-identity-platforms/index.md
index a1fe45b9e..6f3e4478f 100644
--- a/content/identity/converged-identity-platforms/index.md
+++ b/content/identity/converged-identity-platforms/index.md
@@ -1,7 +1,7 @@
---
title: "Streamlining Access with Converged Identity Platforms"
date: "2023-09-29"
-coverImage: "streamlined-access.jpg"
+coverImage: "streamlined-access.webp"
tags: ["identity governance","user provisioning","sso","mfa"]
author: "Rakesh Soni"
description: "A Converged Identity Platform (CIP) is a unique solution that unifies the management of identities, access controls, and security policies across an organization. It brings together various components like Single Sign-On (SSO), Multi-Factor Authentication (MFA), User Provisioning, and Identity Governance and Administration (IGA) into a single digital ecosystem. CIP eliminates the need for numerous disjointed systems and offers a centralized process for identity management."
@@ -36,7 +36,7 @@ Mentioned below are approaches that CIP utilizes to streamline access management
5. **Identity Federation**: CIP supports identity federation. This process allows the users to access resources across various domains and organizations using their home organization's credentials. This capability reduces the need for separate user accounts and passwords for each platform, making access management more efficient, easy, and less time-consuming.
-[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
+[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
6. **Role-Based Access Control (RBAC)**: CIP often includes Role-Based Access Control, enabling managers to assign access permissions based on users' tasks or job functions. RBAC facilitates access management by grouping users into predefined roles and giving them appropriate access privileges.
@@ -50,4 +50,4 @@ In this rapidly evolving digital world, where security breaches and cyber attack
By integrating various Identity and Access Management (IAM) functionalities into a single ecosystem, CIPs facilitate identity management, authentication, and authorization complications. It offers a convenient user experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=converged-identity-platforms)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=converged-identity-platforms)
diff --git a/content/identity/converged-identity-platforms/streamlined-access.jpg b/content/identity/converged-identity-platforms/streamlined-access.jpg
deleted file mode 100644
index a019f7cba..000000000
Binary files a/content/identity/converged-identity-platforms/streamlined-access.jpg and /dev/null differ
diff --git a/content/identity/converged-identity-platforms/streamlined-access.webp b/content/identity/converged-identity-platforms/streamlined-access.webp
new file mode 100644
index 000000000..ee73e1dcb
Binary files /dev/null and b/content/identity/converged-identity-platforms/streamlined-access.webp differ
diff --git a/content/identity/cookie-management-gdpr-ccpa/EB-LR-GDPR.png b/content/identity/cookie-management-gdpr-ccpa/EB-LR-GDPR.png
deleted file mode 100644
index a7a656cfa..000000000
Binary files a/content/identity/cookie-management-gdpr-ccpa/EB-LR-GDPR.png and /dev/null differ
diff --git a/content/identity/cookie-management-gdpr-ccpa/EB-LR-GDPR.webp b/content/identity/cookie-management-gdpr-ccpa/EB-LR-GDPR.webp
new file mode 100644
index 000000000..44c9529c0
Binary files /dev/null and b/content/identity/cookie-management-gdpr-ccpa/EB-LR-GDPR.webp differ
diff --git a/content/identity/cookie-management-gdpr-ccpa/cookie-mngmnt.jpg b/content/identity/cookie-management-gdpr-ccpa/cookie-mngmnt.jpg
deleted file mode 100644
index bf1304e02..000000000
Binary files a/content/identity/cookie-management-gdpr-ccpa/cookie-mngmnt.jpg and /dev/null differ
diff --git a/content/identity/cookie-management-gdpr-ccpa/cookie-mngmnt.webp b/content/identity/cookie-management-gdpr-ccpa/cookie-mngmnt.webp
new file mode 100644
index 000000000..0d598c415
Binary files /dev/null and b/content/identity/cookie-management-gdpr-ccpa/cookie-mngmnt.webp differ
diff --git a/content/identity/cookie-management-gdpr-ccpa/index.md b/content/identity/cookie-management-gdpr-ccpa/index.md
index 93c875f8d..939fd2611 100644
--- a/content/identity/cookie-management-gdpr-ccpa/index.md
+++ b/content/identity/cookie-management-gdpr-ccpa/index.md
@@ -1,7 +1,7 @@
---
title: "How Cookie Management Supports GDPR and CCPA Compliance"
date: "2024-07-31"
-coverImage: "cookie-mngmnt.jpg"
+coverImage: "cookie-mngmnt.webp"
tags: ["cookie management","data privacy","compliance"]
author: "Jaqueline Kispert"
description: "Discover the main principles of GDPR and CCPA, the purpose of cookie management, how it supports compliance, the different types of cookie management tools available, and tips for choosing the right tool for your business."
@@ -70,7 +70,7 @@ By ensuring users are aware of the types of data being collected, the purposes f
This level of transparency not only benefits users by respecting their autonomy but also cultivates a positive relationship between companies and consumers.
-[](https://www.loginradius.com/resource/ebook/loginradius-gdpr-compliance/)
+[](https://www.loginradius.com/resource/ebook/loginradius-gdpr-compliance/)
### Ensuring data security
@@ -162,4 +162,4 @@ Yes, all websites that collect personal data, including through the use of cooki
Non-compliance with GDPR and CCPA regulations can result in hefty fines and penalties, as well as damage to a company's reputation. Proper cookie management is essential for protecting user data and avoiding legal consequences.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cookie-management-gdpr-ccpa)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cookie-management-gdpr-ccpa)
\ No newline at end of file
diff --git a/content/identity/corporate-account-takeover-attacks/BD-Plexicon1-1024x310.png b/content/identity/corporate-account-takeover-attacks/BD-Plexicon1-1024x310.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/corporate-account-takeover-attacks/BD-Plexicon1-1024x310.png and /dev/null differ
diff --git a/content/identity/corporate-account-takeover-attacks/BD-Plexicon1-1024x310.webp b/content/identity/corporate-account-takeover-attacks/BD-Plexicon1-1024x310.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/corporate-account-takeover-attacks/BD-Plexicon1-1024x310.webp differ
diff --git a/content/identity/corporate-account-takeover-attacks/Protecting-PII-Against-Data-Breaches-1024x310.png b/content/identity/corporate-account-takeover-attacks/Protecting-PII-Against-Data-Breaches-1024x310.png
deleted file mode 100644
index a86e6d940..000000000
Binary files a/content/identity/corporate-account-takeover-attacks/Protecting-PII-Against-Data-Breaches-1024x310.png and /dev/null differ
diff --git a/content/identity/corporate-account-takeover-attacks/Protecting-PII-Against-Data-Breaches-1024x310.webp b/content/identity/corporate-account-takeover-attacks/Protecting-PII-Against-Data-Breaches-1024x310.webp
new file mode 100644
index 000000000..fc95b4d7d
Binary files /dev/null and b/content/identity/corporate-account-takeover-attacks/Protecting-PII-Against-Data-Breaches-1024x310.webp differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-accnt-takeover.jpg b/content/identity/corporate-account-takeover-attacks/corporate-accnt-takeover.jpg
deleted file mode 100644
index 941ed906b..000000000
Binary files a/content/identity/corporate-account-takeover-attacks/corporate-accnt-takeover.jpg and /dev/null differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-accnt-takeover.webp b/content/identity/corporate-account-takeover-attacks/corporate-accnt-takeover.webp
new file mode 100644
index 000000000..2361795f0
Binary files /dev/null and b/content/identity/corporate-account-takeover-attacks/corporate-accnt-takeover.webp differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-2.jpg b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-2.jpg
deleted file mode 100644
index 0d27f3158..000000000
Binary files a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-2.jpg and /dev/null differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-2.webp b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-2.webp
new file mode 100644
index 000000000..1d5828938
Binary files /dev/null and b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-2.webp differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-3.jpg b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-3.jpg
deleted file mode 100644
index a306070f8..000000000
Binary files a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-3.jpg and /dev/null differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-3.webp b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-3.webp
new file mode 100644
index 000000000..a9c7ce7ee
Binary files /dev/null and b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-3.webp differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-4.jpg b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-4.jpg
deleted file mode 100644
index 94339d763..000000000
Binary files a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-4.jpg and /dev/null differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-4.webp b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-4.webp
new file mode 100644
index 000000000..6cee82985
Binary files /dev/null and b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover-4.webp differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover.jpg b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover.jpg
deleted file mode 100644
index ac029b88f..000000000
Binary files a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover.jpg and /dev/null differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-account-takeover.webp b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover.webp
new file mode 100644
index 000000000..7b3a94ae0
Binary files /dev/null and b/content/identity/corporate-account-takeover-attacks/corporate-account-takeover.webp differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-account.jpg b/content/identity/corporate-account-takeover-attacks/corporate-account.jpg
deleted file mode 100644
index 5f6d16cad..000000000
Binary files a/content/identity/corporate-account-takeover-attacks/corporate-account.jpg and /dev/null differ
diff --git a/content/identity/corporate-account-takeover-attacks/corporate-account.webp b/content/identity/corporate-account-takeover-attacks/corporate-account.webp
new file mode 100644
index 000000000..5bae02807
Binary files /dev/null and b/content/identity/corporate-account-takeover-attacks/corporate-account.webp differ
diff --git a/content/identity/corporate-account-takeover-attacks/index.md b/content/identity/corporate-account-takeover-attacks/index.md
index b1a51fdcf..33f37abe0 100644
--- a/content/identity/corporate-account-takeover-attacks/index.md
+++ b/content/identity/corporate-account-takeover-attacks/index.md
@@ -1,7 +1,7 @@
---
title: "Corporate Account Takeover Attacks: Detecting and Preventing it"
date: "2020-04-16"
-coverImage: "corporate-accnt-takeover.jpg"
+coverImage: "corporate-accnt-takeover.webp"
tags: ["data security","ciam solution","compliance"]
author: "Kundan Singh"
description: "How do you defend your company against a Corporate Account Takeover (CATO) fraud with the COVID-19 pandemic causing workers to stay indoors?"
@@ -77,7 +77,7 @@ The goal is to trick the recipient (over a phone call, email, or text messages)
PII is any data that can be used to identify an individual. For example, name, geographic location, SSN, IP address, passport number, etc.
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
**Tips to detect a phishing attack**
@@ -222,4 +222,4 @@ Corporate account takeover can translate into millions of dollars in losses, dam
Stay informed about evolving threats, understand the warning signs, and practice responses to suspected takeovers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=corporate-account-takeover-attacks)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=corporate-account-takeover-attacks)
\ No newline at end of file
diff --git a/content/identity/cross-device-authentication-enterprises/cross-device.jpg b/content/identity/cross-device-authentication-enterprises/cross-device.jpg
deleted file mode 100644
index 99f4661a5..000000000
Binary files a/content/identity/cross-device-authentication-enterprises/cross-device.jpg and /dev/null differ
diff --git a/content/identity/cross-device-authentication-enterprises/cross-device.webp b/content/identity/cross-device-authentication-enterprises/cross-device.webp
new file mode 100644
index 000000000..9130c3f37
Binary files /dev/null and b/content/identity/cross-device-authentication-enterprises/cross-device.webp differ
diff --git a/content/identity/cross-device-authentication-enterprises/index.md b/content/identity/cross-device-authentication-enterprises/index.md
index 4fc5bbd59..5bb3aa9a6 100644
--- a/content/identity/cross-device-authentication-enterprises/index.md
+++ b/content/identity/cross-device-authentication-enterprises/index.md
@@ -1,7 +1,7 @@
---
title: "Cross-Device Authentication and Tracking: The Opportunities and Underlying Privacy Risks"
date: "2022-06-21"
-coverImage: "cross-device.jpg"
+coverImage: "cross-device.webp"
tags: ["cross device", "authentication", "digital transformation"]
author: "Rakesh Soni"
description: "Cross-device tracking enables quick tracking of users across multiple devices. However, leveraging such technologies across multiple platforms has underlying risks. This post uncovers the aspects of cross-device authentication and what business owners need to understand."
@@ -79,4 +79,4 @@ Choosing a reliable customer identity and access management (CIAM) solution like
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cross-device-authentication-enterprises)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cross-device-authentication-enterprises)
diff --git a/content/identity/customer-experience-driving-digital-transformations/guide-to-modern-cover.png b/content/identity/customer-experience-driving-digital-transformations/guide-to-modern-cover.png
deleted file mode 100644
index dbb57ace9..000000000
Binary files a/content/identity/customer-experience-driving-digital-transformations/guide-to-modern-cover.png and /dev/null differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/guide-to-modern-cover.webp b/content/identity/customer-experience-driving-digital-transformations/guide-to-modern-cover.webp
new file mode 100644
index 000000000..98937f902
Binary files /dev/null and b/content/identity/customer-experience-driving-digital-transformations/guide-to-modern-cover.webp differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/index.md b/content/identity/customer-experience-driving-digital-transformations/index.md
index 8fb9599b2..e85ed854e 100644
--- a/content/identity/customer-experience-driving-digital-transformations/index.md
+++ b/content/identity/customer-experience-driving-digital-transformations/index.md
@@ -1,7 +1,7 @@
---
title: "Customer Experience is Driving Digital Transformation"
date: "2018-05-18"
-coverImage: "linkedin-sales-navigator-402831-unsplash1-1.jpg"
+coverImage: "linkedin-sales-navigator-402831-unsplash1-1.webp"
tags: ["digital transformation","modern customer identity","cx"]
author: "Rakesh Soni"
description: "Customers today demand meaningful content which is based on their preferences and behaviours. Companies have to accept these digital transformations to offer this connected customer experience."
@@ -11,7 +11,7 @@ metadescription: "In the era of digital transformation, customers today demand m
Everywhere you look, companies are adopting digital transformations in the hopes of changing their business models and competing in the reality of the new market.
-
+
What’s interesting in this new trend, is that the change is being driven by the customer.
@@ -23,7 +23,7 @@ Digital technology has transformed [customers expectations](https://www.loginrad
It’s a big statement, but mobile devices, apps, machine learning, automation and more allow customers to get what they want, when they want it.
-These new digital technologies have caused a shift in customer expectations, which has resulted in a new modern consumer - they are constantly connected, app-natives, and are very aware of what they can do with technology.
+These new digital technologies have caused a shift in customer expectations, which has resulted in a new modern consumer - they are constantly connected, app-natives, and are very aware of what they can do with technology.
Because of the opportunities that are available with modern technologies, customers are now judging companies on their digital customer experience first. Businesses are now having to rethink how they interact with their users, and are turning to these digital initiatives to help them transform how they engage their customers.
@@ -33,7 +33,7 @@ With a digital transformation, organizations are able to understand the modern c
#### 1\. A Flexible, Cloud-Based Solution
-
+
Having the right technology to support your digital initiatives it essential. Many companies are recognizing this, and seeing the advantages to having a customer identity solution at the foundation of their digital transformation.
@@ -43,7 +43,7 @@ For example, with a customer identity solution, you can gather [first-party cust
#### 2\. Personalizing your Customers Digital Experience
-
+
Modern customers that use your digital properties are looking for relevant content that is based on their interests and habits. They no longer have patients for ads that are not directly targeted towards them. This is why gathering customer data is so important in today’s market. With it, you can personalize the digital experience and paid advertisement towards the individual user.
@@ -55,7 +55,7 @@ But unfortunately, utilizing your customers data and personalizing the digital e
#### 3\. Providing a Seamless Multi-channel Experience
-
+
Today’s customers are not tied down to a single channel. They browse in-store, shop online, share feedback through mobile apps and ask questions to your support team on social media.
@@ -69,7 +69,7 @@ Tying all these interactions together allows you to create a [single profile](ht
Accomplishing these three steps is a great start at improving your customers digital experience. If you get identity right from the start, you will really be able to enjoy the benefits of a digital transformation in terms of scalability, availability, and flexibility.
-[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
+[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
By utilizing a customer identity solution, you will be able to build a great foundation to your digital transformation.
diff --git a/content/identity/customer-experience-driving-digital-transformations/john-schnobrich-520023-unsplash-1.jpg b/content/identity/customer-experience-driving-digital-transformations/john-schnobrich-520023-unsplash-1.jpg
deleted file mode 100644
index 03a4c8c11..000000000
Binary files a/content/identity/customer-experience-driving-digital-transformations/john-schnobrich-520023-unsplash-1.jpg and /dev/null differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/john-schnobrich-520023-unsplash-1.webp b/content/identity/customer-experience-driving-digital-transformations/john-schnobrich-520023-unsplash-1.webp
new file mode 100644
index 000000000..cd20dfd83
Binary files /dev/null and b/content/identity/customer-experience-driving-digital-transformations/john-schnobrich-520023-unsplash-1.webp differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-1.jpg b/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-1.jpg
deleted file mode 100644
index 32e01da45..000000000
Binary files a/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-1.jpg and /dev/null differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-1.webp b/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-1.webp
new file mode 100644
index 000000000..8833632b6
Binary files /dev/null and b/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-1.webp differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-402831-unsplash1-1.jpg b/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-402831-unsplash1-1.jpg
deleted file mode 100644
index d0932931b..000000000
Binary files a/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-402831-unsplash1-1.jpg and /dev/null differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-402831-unsplash1-1.webp b/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-402831-unsplash1-1.webp
new file mode 100644
index 000000000..6987a7bc3
Binary files /dev/null and b/content/identity/customer-experience-driving-digital-transformations/linkedin-sales-navigator-402831-unsplash1-1.webp differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/nordwood-themes.jpg b/content/identity/customer-experience-driving-digital-transformations/nordwood-themes.jpg
deleted file mode 100644
index 5bce6b358..000000000
Binary files a/content/identity/customer-experience-driving-digital-transformations/nordwood-themes.jpg and /dev/null differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/nordwood-themes.webp b/content/identity/customer-experience-driving-digital-transformations/nordwood-themes.webp
new file mode 100644
index 000000000..49162c617
Binary files /dev/null and b/content/identity/customer-experience-driving-digital-transformations/nordwood-themes.webp differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/rawpixel-369788-unsplash.jpg b/content/identity/customer-experience-driving-digital-transformations/rawpixel-369788-unsplash.jpg
deleted file mode 100644
index 804dc4b70..000000000
Binary files a/content/identity/customer-experience-driving-digital-transformations/rawpixel-369788-unsplash.jpg and /dev/null differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/rawpixel-369788-unsplash.webp b/content/identity/customer-experience-driving-digital-transformations/rawpixel-369788-unsplash.webp
new file mode 100644
index 000000000..15554210a
Binary files /dev/null and b/content/identity/customer-experience-driving-digital-transformations/rawpixel-369788-unsplash.webp differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/rawpixel-660359-unsplash.jpg b/content/identity/customer-experience-driving-digital-transformations/rawpixel-660359-unsplash.jpg
deleted file mode 100644
index 68a532995..000000000
Binary files a/content/identity/customer-experience-driving-digital-transformations/rawpixel-660359-unsplash.jpg and /dev/null differ
diff --git a/content/identity/customer-experience-driving-digital-transformations/rawpixel-660359-unsplash.webp b/content/identity/customer-experience-driving-digital-transformations/rawpixel-660359-unsplash.webp
new file mode 100644
index 000000000..728337553
Binary files /dev/null and b/content/identity/customer-experience-driving-digital-transformations/rawpixel-660359-unsplash.webp differ
diff --git a/content/identity/customer-identification-challenges-retail/DS-retail.png b/content/identity/customer-identification-challenges-retail/DS-retail.png
deleted file mode 100644
index 89245ae36..000000000
Binary files a/content/identity/customer-identification-challenges-retail/DS-retail.png and /dev/null differ
diff --git a/content/identity/customer-identification-challenges-retail/DS-retail.webp b/content/identity/customer-identification-challenges-retail/DS-retail.webp
new file mode 100644
index 000000000..929b7daff
Binary files /dev/null and b/content/identity/customer-identification-challenges-retail/DS-retail.webp differ
diff --git a/content/identity/customer-identification-challenges-retail/customer-identification-challenges-retail-cover.jpg b/content/identity/customer-identification-challenges-retail/customer-identification-challenges-retail-cover.jpg
deleted file mode 100644
index bfc2b7e84..000000000
Binary files a/content/identity/customer-identification-challenges-retail/customer-identification-challenges-retail-cover.jpg and /dev/null differ
diff --git a/content/identity/customer-identification-challenges-retail/customer-identification-challenges-retail-cover.webp b/content/identity/customer-identification-challenges-retail/customer-identification-challenges-retail-cover.webp
new file mode 100644
index 000000000..d73e64083
Binary files /dev/null and b/content/identity/customer-identification-challenges-retail/customer-identification-challenges-retail-cover.webp differ
diff --git a/content/identity/customer-identification-challenges-retail/index.md b/content/identity/customer-identification-challenges-retail/index.md
index 2bf208344..36065a130 100644
--- a/content/identity/customer-identification-challenges-retail/index.md
+++ b/content/identity/customer-identification-challenges-retail/index.md
@@ -1,7 +1,7 @@
---
title: "The Major Challenges of Customer Identification in the Retail Industry"
date: "2021-10-07"
-coverImage: "customer-identification-challenges-retail-cover.jpg"
+coverImage: "customer-identification-challenges-retail-cover.webp"
tags: ["customer identity management","data security","ecommerce"]
author: "Rakesh Soni"
description: "Meeting the expectation of consumers these days isn’t a piece of cake for retailers as the modern consumer demands digital experiences at every touchpoint before making a purchase. This insightful read covers all the major challenges that retailers and e-commerce vendors face and how they can overcome them."
@@ -87,7 +87,7 @@ Adding stringent layers of security is a must for any retailer seeking substanti
Whether it’s multi-factor authentication (MFA) or risk-based authentication (RBA), enterprises need to quickly put their best foot forward in adopting advanced security measures to safeguard consumer information to prevent financial and reputational losses.
-[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
+[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
### #4. Engagement and Loyalty
@@ -108,4 +108,4 @@ E-commerce and retail giants are leveraging the perfect symphony of user experie
Brands seeking substantial growth in the ever-challenging retail ecosystem need to understand the importance of cutting-edge technology that paves the path for a rich consumer experience that drives sales and ensures customers’ loyalty.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identification-challenges-retail)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identification-challenges-retail)
diff --git a/content/identity/customer-identification-challenges-retail/retail-DS.png b/content/identity/customer-identification-challenges-retail/retail-DS.png
deleted file mode 100644
index b6c1daad3..000000000
Binary files a/content/identity/customer-identification-challenges-retail/retail-DS.png and /dev/null differ
diff --git a/content/identity/customer-identification-challenges-retail/retail-DS.webp b/content/identity/customer-identification-challenges-retail/retail-DS.webp
new file mode 100644
index 000000000..3e81105a6
Binary files /dev/null and b/content/identity/customer-identification-challenges-retail/retail-DS.webp differ
diff --git "a/content/identity/customer-identity-and-access-management/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity-1024x310.png" "b/content/identity/customer-identity-and-access-management/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity-1024x310.png"
deleted file mode 100644
index 6b3ba826e..000000000
Binary files "a/content/identity/customer-identity-and-access-management/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity-1024x310.png" and /dev/null differ
diff --git "a/content/identity/customer-identity-and-access-management/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity-1024x310.webp" "b/content/identity/customer-identity-and-access-management/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity-1024x310.webp"
new file mode 100644
index 000000000..ba14612ce
Binary files /dev/null and "b/content/identity/customer-identity-and-access-management/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity-1024x310.webp" differ
diff --git a/content/identity/customer-identity-and-access-management/Medium-post-02.png b/content/identity/customer-identity-and-access-management/Medium-post-02.png
deleted file mode 100644
index 60f8cc1fe..000000000
Binary files a/content/identity/customer-identity-and-access-management/Medium-post-02.png and /dev/null differ
diff --git a/content/identity/customer-identity-and-access-management/Medium-post-02.webp b/content/identity/customer-identity-and-access-management/Medium-post-02.webp
new file mode 100644
index 000000000..3809ed84d
Binary files /dev/null and b/content/identity/customer-identity-and-access-management/Medium-post-02.webp differ
diff --git a/content/identity/customer-identity-and-access-management/Medium-post-V01.02-03.png b/content/identity/customer-identity-and-access-management/Medium-post-V01.02-03.png
deleted file mode 100644
index 7df823019..000000000
Binary files a/content/identity/customer-identity-and-access-management/Medium-post-V01.02-03.png and /dev/null differ
diff --git a/content/identity/customer-identity-and-access-management/Medium-post-V01.02-03.webp b/content/identity/customer-identity-and-access-management/Medium-post-V01.02-03.webp
new file mode 100644
index 000000000..492f765fb
Binary files /dev/null and b/content/identity/customer-identity-and-access-management/Medium-post-V01.02-03.webp differ
diff --git a/content/identity/customer-identity-and-access-management/Medium-post-V01.02-04.png b/content/identity/customer-identity-and-access-management/Medium-post-V01.02-04.png
deleted file mode 100644
index c3241c4b2..000000000
Binary files a/content/identity/customer-identity-and-access-management/Medium-post-V01.02-04.png and /dev/null differ
diff --git a/content/identity/customer-identity-and-access-management/Medium-post-V01.02-04.webp b/content/identity/customer-identity-and-access-management/Medium-post-V01.02-04.webp
new file mode 100644
index 000000000..996249f98
Binary files /dev/null and b/content/identity/customer-identity-and-access-management/Medium-post-V01.02-04.webp differ
diff --git a/content/identity/customer-identity-and-access-management/ciam-cover.png b/content/identity/customer-identity-and-access-management/ciam-cover.png
deleted file mode 100644
index e31cbab4e..000000000
Binary files a/content/identity/customer-identity-and-access-management/ciam-cover.png and /dev/null differ
diff --git a/content/identity/customer-identity-and-access-management/ciam-cover.webp b/content/identity/customer-identity-and-access-management/ciam-cover.webp
new file mode 100644
index 000000000..ce9ae7a31
Binary files /dev/null and b/content/identity/customer-identity-and-access-management/ciam-cover.webp differ
diff --git a/content/identity/customer-identity-and-access-management/feature-image-2-1.jpg b/content/identity/customer-identity-and-access-management/feature-image-2-1.jpg
deleted file mode 100644
index 7c50caafb..000000000
Binary files a/content/identity/customer-identity-and-access-management/feature-image-2-1.jpg and /dev/null differ
diff --git a/content/identity/customer-identity-and-access-management/feature-image-2-1.webp b/content/identity/customer-identity-and-access-management/feature-image-2-1.webp
new file mode 100644
index 000000000..10d119f37
Binary files /dev/null and b/content/identity/customer-identity-and-access-management/feature-image-2-1.webp differ
diff --git a/content/identity/customer-identity-and-access-management/index.md b/content/identity/customer-identity-and-access-management/index.md
index e8cfd828a..d1692aad7 100644
--- a/content/identity/customer-identity-and-access-management/index.md
+++ b/content/identity/customer-identity-and-access-management/index.md
@@ -1,7 +1,7 @@
---
title: "What is Customer Identity and Access Management(CIAM)?"
date: "2019-06-03"
-coverImage: "ciam-cover.png"
+coverImage: "ciam-cover.webp"
tags: ["ciam solution","compliance","cx"]
author: "Rakesh Soni"
description: "The customer login experience is taken over by customer identity and access management (CIAM). There's more than just registration and authentication at stake. You're losing out on a host of advantages if all you get from your clients when they log in is an email address to send newsletters and passwords. We illustrate in this article how CIAM will help the organisation face the future head-on."
@@ -50,7 +50,7 @@ Every company wants to become a technology enterprise today. With the explosion
CIAM is a fundamental technology that serves increasingly complex consumer needs and enables businesses to deliver stable, seamless digital experiences.
-[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
+[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
### For Businesses:
@@ -72,7 +72,7 @@ By providing a [smooth login experience](https://blog.loginradius.com/identity/s
For example, [implementing a single sign-on](https://www.loginradius.com/single-sign-on/) through a customer identity and access management system means a customer only needs one account for all of your digital touchpoints. Whether your customers are signing in from a browser or a mobile device, they’ll benefit from not having to sign in repeatedly to different services again and again—encouraging repeat use of your apps and services.
-
+
### **2\. Security for Data and Accounts**
@@ -116,7 +116,7 @@ CIAM can also be tailored to meet the regulatory requirements of different regio
**_“A modern CIAM solution enables you to meet all of these privacy requirements and more while simplifying the process and reducing the costs associated.“_**
-
+
### **6\. Advanced Login Options**
@@ -128,7 +128,7 @@ In the world of CIAM, a business can gain an advantage by implementing new and a
**Smart Login** gives users a quick and secure login for the internet of things (IoT) and smart devices, which are increasingly becoming a vital part of today’s digital ecosystem. Smart login delegates the authentication process for smart TVs, gaming consoles, and other IoT devices to other devices that are easier and more secure for entering and managing passwords.
-
+
### **7\. Optimized Data Collection**
@@ -140,7 +140,7 @@ Progressive Profiling is a great way to leverage today’s limited social login
**Social Login** can be a risk as it is a benefit in today’s digital environment when data leaks and account breaches plague major social providers. With the right precautions in place, [social login can still be a great way](https://www.loginradius.com/blog/2018/11/reconsidering-social-login-security-privacy-angle/) for your customers to access your services.
-
+
### **8\. Consent Management**
@@ -182,4 +182,4 @@ Typically, there are [different plans](https://www.loginradius.com/pricing/) for
You can contact the [LoginRadius sales](https://www.loginradius.com/contact-sales/) team to schedule a free personalized demo and learn how the leading cloud-based CIAM works for your business.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-and-access-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-and-access-management)
diff --git a/content/identity/customer-identity-and-access-management/progressive-data-gather.jpg b/content/identity/customer-identity-and-access-management/progressive-data-gather.jpg
deleted file mode 100644
index 592d0d8f6..000000000
Binary files a/content/identity/customer-identity-and-access-management/progressive-data-gather.jpg and /dev/null differ
diff --git a/content/identity/customer-identity-and-access-management/progressive-data-gather.webp b/content/identity/customer-identity-and-access-management/progressive-data-gather.webp
new file mode 100644
index 000000000..4b113add1
Binary files /dev/null and b/content/identity/customer-identity-and-access-management/progressive-data-gather.webp differ
diff --git a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Book-a-free-demo-request.png b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Book-a-free-demo-request.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Book-a-free-demo-request.png and /dev/null differ
diff --git a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Book-a-free-demo-request.webp b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Book-a-free-demo-request.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Book-a-free-demo-request.webp differ
diff --git a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Ocean-Medallion-Pendant-1.jpg b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Ocean-Medallion-Pendant-1.jpg
deleted file mode 100644
index 061dad7ca..000000000
Binary files a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Ocean-Medallion-Pendant-1.jpg and /dev/null differ
diff --git a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Ocean-Medallion-Pendant-1.webp b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Ocean-Medallion-Pendant-1.webp
new file mode 100644
index 000000000..97f6befa7
Binary files /dev/null and b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/Ocean-Medallion-Pendant-1.webp differ
diff --git a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/cruise-brand.png b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/cruise-brand.png
deleted file mode 100644
index 925dec317..000000000
Binary files a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/cruise-brand.png and /dev/null differ
diff --git a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/cruise-brand.webp b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/cruise-brand.webp
new file mode 100644
index 000000000..ba28c8c26
Binary files /dev/null and b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/cruise-brand.webp differ
diff --git a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/index.md b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/index.md
index 2172c9965..bda35a377 100644
--- a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/index.md
+++ b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/index.md
@@ -1,7 +1,7 @@
---
title: "The Customer Identity Infrastructure that Cruise Line Passengers Don’t See"
date: "2018-12-11"
-coverImage: "peter-hansen-455710-unsplash-2.jpg"
+coverImage: "peter-hansen-455710-unsplash-2.webp"
tags: ["travel-and-hospitality"]
featured: false
author: "Rakesh Soni"
@@ -19,13 +19,13 @@ I fantasize about spending a week in one place without having to make any arrang
Cruise lines are well-known for their innovation in creating enormous ships and fun stuff to do on them. Some of the big players are also doing interesting things around [customer experience](https://www.loginradius.com/resource/customer-identity-your-cruise-brands-next-big-innovation/), both digital and onboard.
-
+
MSC Meraviglia and Royal Caribbean are simplifying embarkation so you don’t have to stand in line. Instead, you can upload all your travel documents and download boarding information ahead of time with online check-in ([Telegraph](https://www.telegraph.co.uk/travel/cruises/articles/cruise-ship-technology-innovation/)).
Onboard, cruise brands are using technology to provide better service than you would get from humans alone. The Ocean Medallion from Carnival carries your guest ID, which connects to your encrypted customer profile in the cloud. You can wear it as a pendant or bracelet—Bluetooth Low Energy and NFC mean no swiping required. The Ocean Medallion automatically unlocks your cabin door as you approach, pays for drinks and merch, and locates your travel companions. Fifteen fewer things to worry about? Sign me up!
-
+
The Ocean Medallion also connects with the Ocean Compass, which acts like a digital concierge delivered on devices all over the ship. So the interactive screens and even the staff people learn your favourite drink and whether you prefer Broadway shows or dance lessons ([Wired](https://www.wired.com/2017/01/carnival-ocean-medallion-wearable/)).
@@ -33,9 +33,9 @@ Innovations like these are certainly attention-getting. But what travelers like
**Online check-in, smart wearables, and interactive screens all depend on a secure and centralized location for [customer profile data](https://www.loginradius.com/customer-profiling/).**
-[](https://www.loginradius.com/resource/customer-identity-your-cruise-brands-next-big-innovation/)
+[](https://www.loginradius.com/resource/customer-identity-your-cruise-brands-next-big-innovation/)
And finally, we explain how a customer identity and access management (CIAM) platform meets those challenges and makes customer experience innovations possible.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-infrastructure-cruise-line-passengers-dont-see)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-infrastructure-cruise-line-passengers-dont-see)
diff --git a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/leonardo-yip-551140-unsplash-1024x683.jpg b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/leonardo-yip-551140-unsplash-1024x683.jpg
deleted file mode 100644
index f65855d68..000000000
Binary files a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/leonardo-yip-551140-unsplash-1024x683.jpg and /dev/null differ
diff --git a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/leonardo-yip-551140-unsplash-1024x683.webp b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/leonardo-yip-551140-unsplash-1024x683.webp
new file mode 100644
index 000000000..d746322fc
Binary files /dev/null and b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/leonardo-yip-551140-unsplash-1024x683.webp differ
diff --git a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/peter-hansen-455710-unsplash-2.jpg b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/peter-hansen-455710-unsplash-2.jpg
deleted file mode 100644
index 25794c195..000000000
Binary files a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/peter-hansen-455710-unsplash-2.jpg and /dev/null differ
diff --git a/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/peter-hansen-455710-unsplash-2.webp b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/peter-hansen-455710-unsplash-2.webp
new file mode 100644
index 000000000..8c551deda
Binary files /dev/null and b/content/identity/customer-identity-infrastructure-cruise-line-passengers-dont-see/peter-hansen-455710-unsplash-2.webp differ
diff --git a/content/identity/customer-identity-preference-trends-q1-2016/2016-Q1-Social-Login_Preference-Users.png b/content/identity/customer-identity-preference-trends-q1-2016/2016-Q1-Social-Login_Preference-Users.png
deleted file mode 100644
index 6f7ec0cba..000000000
Binary files a/content/identity/customer-identity-preference-trends-q1-2016/2016-Q1-Social-Login_Preference-Users.png and /dev/null differ
diff --git a/content/identity/customer-identity-preference-trends-q1-2016/2016-Q1-Social-Login_Preference-Users.webp b/content/identity/customer-identity-preference-trends-q1-2016/2016-Q1-Social-Login_Preference-Users.webp
new file mode 100644
index 000000000..0572d3e98
Binary files /dev/null and b/content/identity/customer-identity-preference-trends-q1-2016/2016-Q1-Social-Login_Preference-Users.webp differ
diff --git a/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Login_Preference-Age.png b/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Login_Preference-Age.png
deleted file mode 100644
index 3c1d590e9..000000000
Binary files a/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Login_Preference-Age.png and /dev/null differ
diff --git a/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Login_Preference-Age.webp b/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Login_Preference-Age.webp
new file mode 100644
index 000000000..6069de281
Binary files /dev/null and b/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Login_Preference-Age.webp differ
diff --git a/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Sharing-Global-Popularity.png b/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Sharing-Global-Popularity.png
deleted file mode 100644
index 87f412e6f..000000000
Binary files a/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Sharing-Global-Popularity.png and /dev/null differ
diff --git a/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Sharing-Global-Popularity.webp b/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Sharing-Global-Popularity.webp
new file mode 100644
index 000000000..08b3209c0
Binary files /dev/null and b/content/identity/customer-identity-preference-trends-q1-2016/2016_Q1_Social-Sharing-Global-Popularity.webp differ
diff --git a/content/identity/customer-identity-preference-trends-q1-2016/Q1_2016_featured.png b/content/identity/customer-identity-preference-trends-q1-2016/Q1_2016_featured.png
deleted file mode 100644
index a2805e663..000000000
Binary files a/content/identity/customer-identity-preference-trends-q1-2016/Q1_2016_featured.png and /dev/null differ
diff --git a/content/identity/customer-identity-preference-trends-q1-2016/Q1_2016_featured.webp b/content/identity/customer-identity-preference-trends-q1-2016/Q1_2016_featured.webp
new file mode 100644
index 000000000..3d81ad39e
Binary files /dev/null and b/content/identity/customer-identity-preference-trends-q1-2016/Q1_2016_featured.webp differ
diff --git a/content/identity/customer-identity-preference-trends-q1-2016/customer-identity-preference-trends-q1-2016.png b/content/identity/customer-identity-preference-trends-q1-2016/customer-identity-preference-trends-q1-2016.png
deleted file mode 100644
index a2805e663..000000000
Binary files a/content/identity/customer-identity-preference-trends-q1-2016/customer-identity-preference-trends-q1-2016.png and /dev/null differ
diff --git a/content/identity/customer-identity-preference-trends-q1-2016/customer-identity-preference-trends-q1-2016.webp b/content/identity/customer-identity-preference-trends-q1-2016/customer-identity-preference-trends-q1-2016.webp
new file mode 100644
index 000000000..3d81ad39e
Binary files /dev/null and b/content/identity/customer-identity-preference-trends-q1-2016/customer-identity-preference-trends-q1-2016.webp differ
diff --git a/content/identity/customer-identity-preference-trends-q1-2016/index.md b/content/identity/customer-identity-preference-trends-q1-2016/index.md
index 33bf4cf7a..db7822550 100644
--- a/content/identity/customer-identity-preference-trends-q1-2016/index.md
+++ b/content/identity/customer-identity-preference-trends-q1-2016/index.md
@@ -1,7 +1,7 @@
---
title: "Customer Identity Preference Trends Q1 2016"
date: "2016-04-15"
-coverImage: "customer-identity-preference-trends-q1-2016.png"
+coverImage: "customer-identity-preference-trends-q1-2016.webp"
tags: ["customer identity management","ciam platform","cx"]
author: "Rakesh Soni"
description: "From the beginning to the end of the customer-business relationship, customer engagement is the central aspect of individual user interactions."
@@ -11,7 +11,7 @@ metadescription: "LoginRadius Customer Identity Preference Trends Report for Q1
In an expansive [article for Harvard Business Review](https://hbr.org/2013/09/the-truth-about-customer-experience), McKinsey and Company analysts have described Customer Experience as “cumulative experiences across multiple touch points and in multiple channels over time.” But if somebody asks for a mathematical definition of something as psychological as Customer Experience, one could blurt out: “Customer Experience is the integral from the beginning to the end of the customer-business relationship of the integral of individual user experiences across all touch points.” Why someone would ask for a mathematical definition is a discussion for another day.
-You can choose the definition you like (we bet you will go with the McKinsey guys) but the point here is about what customers want and what satisfies them. Often the seemingly simpler things matter the most, particularly when these things figure quite a number of times. For instance, let’s say you provide the means for your customers to sign in using their social identities. Owing to obvious constraints, you can only provide for direct links to login with two or three social identities. If your customers choice of identity doesn’t figure in your top two or three list, they are forced to go to another page to look for their choice of identity. It’s a simple thing made difficult because of the lack of knowledge of what your customers preferences are.
+You can choose the definition you like (we bet you will go with the McKinsey guys) but the point here is about what customers want and what satisfies them. Often the seemingly simpler things matter the most, particularly when these things figure quite a number of times. For instance, let’s say you provide the means for your customers to sign in using their social identities. Owing to obvious constraints, you can only provide for direct links to login with two or three social identities. If your customers choice of identity doesn’t figure in your top two or three list, they are forced to go to another page to look for their choice of identity. It’s a simple thing made difficult because of the lack of knowledge of what your customers preferences are.
To know what your customers like and prefer only makes things simpler and clearer. Customer preferences don’t just alter minor things but can also influence long term strategy. Analysis of customer preferences is critical to businesses.
@@ -21,15 +21,15 @@ The LoginRadius Analytics team analyzed customer behavior data from over 160,000
Once again, Facebook held its forte and emerged as the most preferred social identity for logging into websites. Google+ followed in second place but with a much smaller share in the social identity space. About 94% customers use their Facebook or Google+ identities to sign into websites which is mammoth number telling you these two networks should be the top on your list.
-
+
But if your target audience is above 35 years, you will have to think again because only a third of all the customers who used their [social identity to sign into websites](https://www.loginradius.com/social-login/) were aged above 35 years. If that is not all, Social Login from desktop computers (both Windows and Mac) ran up to a mammoth 80% of all which should tell you that if you are targeting mobile, it should be the mobile app.
-
+
Facebook did lose some ground to Google+ in Q1 2016 but not by an amount that would worry the social giant. Nevertheless, Google+ will be heartened by its performance. Sharing, however, is a different story and not one that the search giant would be really happy about. More than half of the social content on the Web is hosted on Facebook while, like in Q4 2015, Twitter comes in second with 16%. Email is not be discounted again as it has notched up the third place and is expected to go strong in the coming quarters too.
-
+
Some more critical insights provided by the analysis are:
@@ -39,4 +39,4 @@ Some more critical insights provided by the analysis are:
- About 92% websites still prefer providing Facebook as one of the options for Social Login leading the favourites list since 2013.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-preference-trends-q1-2016)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-preference-trends-q1-2016)
\ No newline at end of file
diff --git a/content/identity/customer-identity-preference-trends-q2-2016/CIPT-Q2-2016-Report-popout-600x900.png b/content/identity/customer-identity-preference-trends-q2-2016/CIPT-Q2-2016-Report-popout-600x900.png
deleted file mode 100644
index 677a71723..000000000
Binary files a/content/identity/customer-identity-preference-trends-q2-2016/CIPT-Q2-2016-Report-popout-600x900.png and /dev/null differ
diff --git a/content/identity/customer-identity-preference-trends-q2-2016/CIPT-Q2-2016-Report-popout-600x900.webp b/content/identity/customer-identity-preference-trends-q2-2016/CIPT-Q2-2016-Report-popout-600x900.webp
new file mode 100644
index 000000000..3f29fc2bc
Binary files /dev/null and b/content/identity/customer-identity-preference-trends-q2-2016/CIPT-Q2-2016-Report-popout-600x900.webp differ
diff --git a/content/identity/customer-identity-preference-trends-q2-2016/Preferred-identity-of-customers-on-websites.jpg b/content/identity/customer-identity-preference-trends-q2-2016/Preferred-identity-of-customers-on-websites.jpg
deleted file mode 100644
index c01e63ad8..000000000
Binary files a/content/identity/customer-identity-preference-trends-q2-2016/Preferred-identity-of-customers-on-websites.jpg and /dev/null differ
diff --git a/content/identity/customer-identity-preference-trends-q2-2016/Preferred-identity-of-customers-on-websites.webp b/content/identity/customer-identity-preference-trends-q2-2016/Preferred-identity-of-customers-on-websites.webp
new file mode 100644
index 000000000..ccda4a991
Binary files /dev/null and b/content/identity/customer-identity-preference-trends-q2-2016/Preferred-identity-of-customers-on-websites.webp differ
diff --git a/content/identity/customer-identity-preference-trends-q2-2016/Social-sharing-patterns-on-major-social-networks.jpg b/content/identity/customer-identity-preference-trends-q2-2016/Social-sharing-patterns-on-major-social-networks.jpg
deleted file mode 100644
index bc06546a4..000000000
Binary files a/content/identity/customer-identity-preference-trends-q2-2016/Social-sharing-patterns-on-major-social-networks.jpg and /dev/null differ
diff --git a/content/identity/customer-identity-preference-trends-q2-2016/Social-sharing-patterns-on-major-social-networks.webp b/content/identity/customer-identity-preference-trends-q2-2016/Social-sharing-patterns-on-major-social-networks.webp
new file mode 100644
index 000000000..b6f0f86c0
Binary files /dev/null and b/content/identity/customer-identity-preference-trends-q2-2016/Social-sharing-patterns-on-major-social-networks.webp differ
diff --git a/content/identity/customer-identity-preference-trends-q2-2016/customer-identity-preference-trends-q2-2016.png b/content/identity/customer-identity-preference-trends-q2-2016/customer-identity-preference-trends-q2-2016.png
deleted file mode 100644
index 677a71723..000000000
Binary files a/content/identity/customer-identity-preference-trends-q2-2016/customer-identity-preference-trends-q2-2016.png and /dev/null differ
diff --git a/content/identity/customer-identity-preference-trends-q2-2016/customer-identity-preference-trends-q2-2016.webp b/content/identity/customer-identity-preference-trends-q2-2016/customer-identity-preference-trends-q2-2016.webp
new file mode 100644
index 000000000..3f29fc2bc
Binary files /dev/null and b/content/identity/customer-identity-preference-trends-q2-2016/customer-identity-preference-trends-q2-2016.webp differ
diff --git a/content/identity/customer-identity-preference-trends-q2-2016/index.md b/content/identity/customer-identity-preference-trends-q2-2016/index.md
index e5aa6d7ce..e1aa07791 100644
--- a/content/identity/customer-identity-preference-trends-q2-2016/index.md
+++ b/content/identity/customer-identity-preference-trends-q2-2016/index.md
@@ -1,7 +1,7 @@
---
title: "Customer Identity Preference Trends Q2 2016"
date: "2016-08-16"
-coverImage: "customer-identity-preference-trends-q2-2016.png"
+coverImage: "customer-identity-preference-trends-q2-2016.webp"
tags: ["customer identity management","social login","cx"]
author: "Rakesh Soni"
description: "Now's the time when you measure expectations for consumer identity and understand what's right for you."
@@ -11,7 +11,7 @@ metadescription: "LoginRadius 2016 Q2 consumer identity preference trends report
It’s that time of the quarter again when we get to some number crunching and put out our data for the world to analyze, think and act. It’s that time when you can think whether social login is still working and how many consumers actually use [social login against traditional email registration](https://www.loginradius.com/social-login/). It’s that time when you evaluate customer identity preferences to understand what’s best for you.
-Why should you even worry about customer preferences? Because digital marketing starts with customer identity and ends with a great customer experience. Identity is how you connect to your customers and customer experience is how your customers feel about that connection over a period of time. Let’s think of some real world situations to elucidate this. If you have a prospective customer who is really fond of Twitter and wants to login to your website using his or her Twitter identity, but you don’t allow your end users to bring their Twitter identities, the customer is bound to be disappointed. A bad experience on the Web mostly ends in consumers bouncing off. That’s not exactly what you would want, right?
+Why should you even worry about customer preferences? Because digital marketing starts with customer identity and ends with a great customer experience. Identity is how you connect to your customers and customer experience is how your customers feel about that connection over a period of time. Let’s think of some real world situations to elucidate this. If you have a prospective customer who is really fond of Twitter and wants to login to your website using his or her Twitter identity, but you don’t allow your end users to bring their Twitter identities, the customer is bound to be disappointed. A bad experience on the Web mostly ends in consumers bouncing off. That’s not exactly what you would want, right?
But why should you care if you have world beating products and services? Well, the problem is that businesses are increasingly being transacted on the Web and the competition is too heavy. Heavy competition does exist in the real world too but consumers can easily switch companies on the Web, which is not the case in offline stores. That’s exactly why world beating products and service are not enough on the Web. Businesses need more than that. Businesses need Connected Customer Experience. Every tiny thing needs to be optimized to the tastes of your customers. Every tiny bump needs to be roadrolled for a seamless experience on your web and mobile applications.
@@ -21,17 +21,17 @@ Well, let’s get to the business end now. Like every quarter since about 13 qua
If you are expecting majority of website customers to be bringing their own social identities, you are spot on. In Q2 2016, almost 93% consumers preferred social login over traditional email registration on websites.
-
+
If you are expecting Facebook to be the default choice of social identity for majority of the customers, you are right. But where you could be wrong is that majority is not very much. Only 53% customers logged in with their Facebook identities. So, who ate their share? Google, obviously. More and more people are preferring to use their Google identities to sign into websites for reasons that could be varied. The most apt, as per our understanding, is the ease of using Google identities and the fact that consumers don’t really have to worry much about their privacy while using Google identities to login on other websites. This is because most people don’t have a lot of [Personally Identifiable Information (PII)](https://en.wikipedia.org/wiki/Personally_identifiable_information) stored on their Google accounts, unlike Facebook. But, technically, this is still the minority view, though the difference between majority and minority is as thin as a straight line. Both of them together account for 98% social logins so the question of which network to provide for social login on your web or mobile applications is a no-brainer.
-
+
Social networks are not the only things that matter. People’s devices, too, play a role important enough not to be ignored. Once again in Q2 2016, majority of web browser based social login was from websites leading to the same inference as earlier that if you are targeting consumers on their mobile phones, get a mobile app for your business instead of optimizing your website for mobile.
As far as social sharing is concerned, it seems Facebook is scoring where it needs to. Though its usage as a social identity reduced in Q2 2016, content sharing on Facebook increased giving credence to the theory proposed here.
-
+
Some more critical insights you can obtain from the report are:
@@ -41,4 +41,4 @@ Some more critical insights you can obtain from the report are:
Read more detailed analysis and insights in LoginRadius’ Customer Identity Preference Trends report for Q2 2016. Go ahead, [download it now](https://www.loginradius.com/resource/customer-identity-preference-trends-2016/).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-preference-trends-q2-2016)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-preference-trends-q2-2016)
\ No newline at end of file
diff --git a/content/identity/customer-identity-preference-trends-q2-2016/social-identity-preferences.jpg b/content/identity/customer-identity-preference-trends-q2-2016/social-identity-preferences.jpg
deleted file mode 100644
index 498625c0a..000000000
Binary files a/content/identity/customer-identity-preference-trends-q2-2016/social-identity-preferences.jpg and /dev/null differ
diff --git a/content/identity/customer-identity-preference-trends-q2-2016/social-identity-preferences.webp b/content/identity/customer-identity-preference-trends-q2-2016/social-identity-preferences.webp
new file mode 100644
index 000000000..a4746c574
Binary files /dev/null and b/content/identity/customer-identity-preference-trends-q2-2016/social-identity-preferences.webp differ
diff --git a/content/identity/customer-identity-verification-best-practices/WP-consumer-id-theft.png b/content/identity/customer-identity-verification-best-practices/WP-consumer-id-theft.png
deleted file mode 100644
index 25b3b0075..000000000
Binary files a/content/identity/customer-identity-verification-best-practices/WP-consumer-id-theft.png and /dev/null differ
diff --git a/content/identity/customer-identity-verification-best-practices/WP-consumer-id-theft.webp b/content/identity/customer-identity-verification-best-practices/WP-consumer-id-theft.webp
new file mode 100644
index 000000000..3d62deb02
Binary files /dev/null and b/content/identity/customer-identity-verification-best-practices/WP-consumer-id-theft.webp differ
diff --git a/content/identity/customer-identity-verification-best-practices/customer-id-verification.jpg b/content/identity/customer-identity-verification-best-practices/customer-id-verification.jpg
deleted file mode 100644
index e14bc9533..000000000
Binary files a/content/identity/customer-identity-verification-best-practices/customer-id-verification.jpg and /dev/null differ
diff --git a/content/identity/customer-identity-verification-best-practices/customer-id-verification.webp b/content/identity/customer-identity-verification-best-practices/customer-id-verification.webp
new file mode 100644
index 000000000..add98b6ea
Binary files /dev/null and b/content/identity/customer-identity-verification-best-practices/customer-id-verification.webp differ
diff --git a/content/identity/customer-identity-verification-best-practices/index.md b/content/identity/customer-identity-verification-best-practices/index.md
index 2c1cab362..7a88f5945 100644
--- a/content/identity/customer-identity-verification-best-practices/index.md
+++ b/content/identity/customer-identity-verification-best-practices/index.md
@@ -1,7 +1,7 @@
---
title: "Maintaining Trust: Customer Identity Verification Challenges & Best Practices"
date: "2023-09-13"
-coverImage: "customer-id-verification.jpg"
+coverImage: "customer-id-verification.webp"
tags: ["identity verification","customer trust","ciam solution","cx"]
author: "Rakesh Soni"
description: "Trust is paramount for successful customer relationships in our digital age. However, customer identity verification faces evolving challenges, from identity theft to balancing security with a seamless user experience. Explore how adopting multi-layered verification, leveraging AI, complying with regulations, and educating users can help businesses maintain trust in the ever-changing landscape of online interactions."
@@ -75,7 +75,7 @@ As we progress toward technological advancements, cyber attackers become more qu
One of the foremost challenges is the prevalence of identity theft and fraud. Cybercriminals constantly seek ways to impersonate legitimate customers, gaining unauthorized access to accounts and sensitive data. This not only harms the business but erodes customer trust.
-[](https://www.loginradius.com/resource/ciam-role-in-customer-trust/)
+[](https://www.loginradius.com/resource/ciam-role-in-customer-trust/)
3. **Verification of documents:**
@@ -139,4 +139,4 @@ The purpose of customer verification is to enhance security, prevent identity th
Customer verification typically requires valid identification documents, biometric data, knowledge-based information, or a combination of these authentication factors to confirm identity accurately.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-verification-best-practices)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-verification-best-practices)
diff --git a/content/identity/customer-spotlight-hydro-ottawa/HydroOttawa_Logo_RGB-2016-1024x176.jpg b/content/identity/customer-spotlight-hydro-ottawa/HydroOttawa_Logo_RGB-2016-1024x176.jpg
deleted file mode 100644
index 35c8fd87e..000000000
Binary files a/content/identity/customer-spotlight-hydro-ottawa/HydroOttawa_Logo_RGB-2016-1024x176.jpg and /dev/null differ
diff --git a/content/identity/customer-spotlight-hydro-ottawa/HydroOttawa_Logo_RGB-2016-1024x176.webp b/content/identity/customer-spotlight-hydro-ottawa/HydroOttawa_Logo_RGB-2016-1024x176.webp
new file mode 100644
index 000000000..27cc3c540
Binary files /dev/null and b/content/identity/customer-spotlight-hydro-ottawa/HydroOttawa_Logo_RGB-2016-1024x176.webp differ
diff --git a/content/identity/customer-spotlight-hydro-ottawa/customer-spotlight-hydro-ottawa.jpg b/content/identity/customer-spotlight-hydro-ottawa/customer-spotlight-hydro-ottawa.jpg
deleted file mode 100644
index 065bff490..000000000
Binary files a/content/identity/customer-spotlight-hydro-ottawa/customer-spotlight-hydro-ottawa.jpg and /dev/null differ
diff --git a/content/identity/customer-spotlight-hydro-ottawa/customer-spotlight-hydro-ottawa.webp b/content/identity/customer-spotlight-hydro-ottawa/customer-spotlight-hydro-ottawa.webp
new file mode 100644
index 000000000..57e83ab63
Binary files /dev/null and b/content/identity/customer-spotlight-hydro-ottawa/customer-spotlight-hydro-ottawa.webp differ
diff --git a/content/identity/customer-spotlight-hydro-ottawa/index.md b/content/identity/customer-spotlight-hydro-ottawa/index.md
index ddb0fef10..8e294b259 100644
--- a/content/identity/customer-spotlight-hydro-ottawa/index.md
+++ b/content/identity/customer-spotlight-hydro-ottawa/index.md
@@ -1,7 +1,7 @@
---
title: "Customer Spotlight - Hydro Ottawa"
date: "2018-10-16"
-coverImage: "customer-spotlight-hydro-ottawa.jpg"
+coverImage: "customer-spotlight-hydro-ottawa.webp"
tags: ["media-and-publication"]
featured: false
author: "Karl Wittig"
@@ -12,19 +12,19 @@ metadescription: "Hydro Ottawa has totally disrupted the Canadian utility indust
[Hydro Ottawa](https://hydroottawa.com/), the largest local electricity distribution company in eastern Ontario, is also a pioneer in the Canadian utility industry. It is the first utility company in Canada to offer a voice assistant skill through both Amazon Alexa and Google Home. By focusing on their customers’ needs, Hydro Ottawa has fully disrupted the Canadian utility industry for the better.
-
+
We're extremely excited to be able to play a part in this journey with Hydro Ottawa, and we’re thrilled that they were able to leverage the LoginRadius platform and OAuth capabilities to make this happen.
## Identity is Key
-
+
Hydro Ottawa has fully integrated the LoginRadius authentication tools with their internal system and platform. This connection provides a [seamless registration and login process](https://www.loginradius.com/standard-login/) for Hydro Ottawa customers. In doing so, Hydro Ottawa has been able to centralize their customer identity data to make sure that all systems are working off of the same data as they grow and expand their services.
## Disrupting the Utility Industry
-
+
By addressing the need for a unified customer database, Hydro Ottawa is able to leverage their identity architecture and the [OAuth 2.0](https://www.loginradius.com/federation/) capabilities from LoginRadius to build something that no other utility company and very few corporate companies have been able to accomplish—fully interactive home assistant skills for Amazon Alexa and Google Home.
diff --git a/content/identity/customer-spotlight-hydro-ottawa/thomas-kolnowski-723299-unsplash-1024x635.jpg b/content/identity/customer-spotlight-hydro-ottawa/thomas-kolnowski-723299-unsplash-1024x635.jpg
deleted file mode 100644
index 6886a71ac..000000000
Binary files a/content/identity/customer-spotlight-hydro-ottawa/thomas-kolnowski-723299-unsplash-1024x635.jpg and /dev/null differ
diff --git a/content/identity/customer-spotlight-hydro-ottawa/thomas-kolnowski-723299-unsplash-1024x635.webp b/content/identity/customer-spotlight-hydro-ottawa/thomas-kolnowski-723299-unsplash-1024x635.webp
new file mode 100644
index 000000000..ae9790b34
Binary files /dev/null and b/content/identity/customer-spotlight-hydro-ottawa/thomas-kolnowski-723299-unsplash-1024x635.webp differ
diff --git a/content/identity/customer-spotlight-hydro-ottawa/vectorstock_18254714-1024x930.jpg b/content/identity/customer-spotlight-hydro-ottawa/vectorstock_18254714-1024x930.jpg
deleted file mode 100644
index b47921fe8..000000000
Binary files a/content/identity/customer-spotlight-hydro-ottawa/vectorstock_18254714-1024x930.jpg and /dev/null differ
diff --git a/content/identity/customer-spotlight-hydro-ottawa/vectorstock_18254714-1024x930.webp b/content/identity/customer-spotlight-hydro-ottawa/vectorstock_18254714-1024x930.webp
new file mode 100644
index 000000000..3e5c901a8
Binary files /dev/null and b/content/identity/customer-spotlight-hydro-ottawa/vectorstock_18254714-1024x930.webp differ
diff --git a/content/identity/customer-success-story-iom-x/BD-Plexicon1-1024x310-1.png b/content/identity/customer-success-story-iom-x/BD-Plexicon1-1024x310-1.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/customer-success-story-iom-x/BD-Plexicon1-1024x310-1.png and /dev/null differ
diff --git a/content/identity/customer-success-story-iom-x/BD-Plexicon1-1024x310-1.webp b/content/identity/customer-success-story-iom-x/BD-Plexicon1-1024x310-1.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/customer-success-story-iom-x/BD-Plexicon1-1024x310-1.webp differ
diff --git a/content/identity/customer-success-story-iom-x/customer-success-story-iom-x.png b/content/identity/customer-success-story-iom-x/customer-success-story-iom-x.png
deleted file mode 100644
index cbe16b736..000000000
Binary files a/content/identity/customer-success-story-iom-x/customer-success-story-iom-x.png and /dev/null differ
diff --git a/content/identity/customer-success-story-iom-x/customer-success-story-iom-x.webp b/content/identity/customer-success-story-iom-x/customer-success-story-iom-x.webp
new file mode 100644
index 000000000..478f7a2c6
Binary files /dev/null and b/content/identity/customer-success-story-iom-x/customer-success-story-iom-x.webp differ
diff --git a/content/identity/customer-success-story-iom-x/index.md b/content/identity/customer-success-story-iom-x/index.md
index 303bb7d74..f7900c08c 100644
--- a/content/identity/customer-success-story-iom-x/index.md
+++ b/content/identity/customer-success-story-iom-x/index.md
@@ -1,7 +1,7 @@
---
title: "IOM X, a LoginRadius Customer Success Story"
date: "2017-03-01"
-coverImage: "customer-success-story-iom-x.png"
+coverImage: "customer-success-story-iom-x.webp"
tags: ["media-and-publication"]
featured: false
author: "Karl Wittig"
@@ -29,4 +29,4 @@ By centralizing all of their user identities, IOM X was able to gain valuable in
IOMX - LoginRadius Customer Success Story
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-success-story-iom-x)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-success-story-iom-x)
diff --git a/content/identity/cyber-insurance-guide-2022/DS-CCPA-comp.png b/content/identity/cyber-insurance-guide-2022/DS-CCPA-comp.png
deleted file mode 100644
index 93302c0ce..000000000
Binary files a/content/identity/cyber-insurance-guide-2022/DS-CCPA-comp.png and /dev/null differ
diff --git a/content/identity/cyber-insurance-guide-2022/DS-CCPA-comp.webp b/content/identity/cyber-insurance-guide-2022/DS-CCPA-comp.webp
new file mode 100644
index 000000000..9d62b96b8
Binary files /dev/null and b/content/identity/cyber-insurance-guide-2022/DS-CCPA-comp.webp differ
diff --git a/content/identity/cyber-insurance-guide-2022/LR-CCPA.png b/content/identity/cyber-insurance-guide-2022/LR-CCPA.png
deleted file mode 100644
index 6784e19bd..000000000
Binary files a/content/identity/cyber-insurance-guide-2022/LR-CCPA.png and /dev/null differ
diff --git a/content/identity/cyber-insurance-guide-2022/LR-CCPA.webp b/content/identity/cyber-insurance-guide-2022/LR-CCPA.webp
new file mode 100644
index 000000000..c27d2fee5
Binary files /dev/null and b/content/identity/cyber-insurance-guide-2022/LR-CCPA.webp differ
diff --git a/content/identity/cyber-insurance-guide-2022/cyber-insurance.jpg b/content/identity/cyber-insurance-guide-2022/cyber-insurance.jpg
deleted file mode 100644
index 41df39f93..000000000
Binary files a/content/identity/cyber-insurance-guide-2022/cyber-insurance.jpg and /dev/null differ
diff --git a/content/identity/cyber-insurance-guide-2022/cyber-insurance.webp b/content/identity/cyber-insurance-guide-2022/cyber-insurance.webp
new file mode 100644
index 000000000..fdbeb8910
Binary files /dev/null and b/content/identity/cyber-insurance-guide-2022/cyber-insurance.webp differ
diff --git a/content/identity/cyber-insurance-guide-2022/index.md b/content/identity/cyber-insurance-guide-2022/index.md
index aa2218f0b..fef37805c 100644
--- a/content/identity/cyber-insurance-guide-2022/index.md
+++ b/content/identity/cyber-insurance-guide-2022/index.md
@@ -1,7 +1,7 @@
---
title: "Everything You Need to Know Before Buying Cyber Insurance in 2022"
date: "2022-01-11"
-coverImage: "cyber-insurance.jpg"
+coverImage: "cyber-insurance.webp"
tags: ["cybersecurity","compliance","cx"]
author: "Rajeev Sharma"
description: "Before you buy cyber insurance in 2022, make sure you know everything there is to know about it. Learn the ins and outs of what to expect, how much wealth you can save, and more."
@@ -69,7 +69,7 @@ After a data breach or cyberattack, there is a very high chance that the company
Regulatory bodies, both international and national, may require the company to pay a certain amount as a fine for being unable to implement the right security measures.
-**Also Learn**[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
+**Also Learn**[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
### 3. Public relations costs
@@ -92,4 +92,4 @@ Another requirement after a cyberattack is the need for a company to send out no
Cyber insurance can be a source of hope in the dire circumstances of a cyber attack. Companies will no longer have to be financially handicapped and deprived of important resources during this time. Although cyber insurance can be an expensive investment option, in the beginning, it has valuable payoffs, especially for a company that is prone to cyberattacks.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cyber-insurance-guide-2022)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cyber-insurance-guide-2022)
diff --git a/content/identity/cyber-threats-business-risk-covid-19/Best-Practices-for-Companies-to-Deal-With-Cyber-Threats.jpg b/content/identity/cyber-threats-business-risk-covid-19/Best-Practices-for-Companies-to-Deal-With-Cyber-Threats.jpg
deleted file mode 100644
index 35ec36793..000000000
Binary files a/content/identity/cyber-threats-business-risk-covid-19/Best-Practices-for-Companies-to-Deal-With-Cyber-Threats.jpg and /dev/null differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/Best-Practices-for-Companies-to-Deal-With-Cyber-Threats.webp b/content/identity/cyber-threats-business-risk-covid-19/Best-Practices-for-Companies-to-Deal-With-Cyber-Threats.webp
new file mode 100644
index 000000000..c1f766b4b
Binary files /dev/null and b/content/identity/cyber-threats-business-risk-covid-19/Best-Practices-for-Companies-to-Deal-With-Cyber-Threats.webp differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/Book-a-free-demo-request-1024x310.png b/content/identity/cyber-threats-business-risk-covid-19/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/cyber-threats-business-risk-covid-19/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/Book-a-free-demo-request-1024x310.webp b/content/identity/cyber-threats-business-risk-covid-19/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/cyber-threats-business-risk-covid-19/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/Cyber-Threats-Risk-During-COVID-19.jpg b/content/identity/cyber-threats-business-risk-covid-19/Cyber-Threats-Risk-During-COVID-19.jpg
deleted file mode 100644
index d63980adc..000000000
Binary files a/content/identity/cyber-threats-business-risk-covid-19/Cyber-Threats-Risk-During-COVID-19.jpg and /dev/null differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/Cyber-Threats-Risk-During-COVID-19.webp b/content/identity/cyber-threats-business-risk-covid-19/Cyber-Threats-Risk-During-COVID-19.webp
new file mode 100644
index 000000000..bb6f82572
Binary files /dev/null and b/content/identity/cyber-threats-business-risk-covid-19/Cyber-Threats-Risk-During-COVID-19.webp differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png b/content/identity/cyber-threats-business-risk-covid-19/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png
deleted file mode 100644
index b53535020..000000000
Binary files a/content/identity/cyber-threats-business-risk-covid-19/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png and /dev/null differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp b/content/identity/cyber-threats-business-risk-covid-19/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp
new file mode 100644
index 000000000..02dbccb4e
Binary files /dev/null and b/content/identity/cyber-threats-business-risk-covid-19/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/Industries-at-Risk-During-COVID-19.jpg b/content/identity/cyber-threats-business-risk-covid-19/Industries-at-Risk-During-COVID-19.jpg
deleted file mode 100644
index c125692da..000000000
Binary files a/content/identity/cyber-threats-business-risk-covid-19/Industries-at-Risk-During-COVID-19.jpg and /dev/null differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/Industries-at-Risk-During-COVID-19.webp b/content/identity/cyber-threats-business-risk-covid-19/Industries-at-Risk-During-COVID-19.webp
new file mode 100644
index 000000000..6c4c3e4cb
Binary files /dev/null and b/content/identity/cyber-threats-business-risk-covid-19/Industries-at-Risk-During-COVID-19.webp differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/cyber-threats.jpg b/content/identity/cyber-threats-business-risk-covid-19/cyber-threats.jpg
deleted file mode 100644
index f0953eb45..000000000
Binary files a/content/identity/cyber-threats-business-risk-covid-19/cyber-threats.jpg and /dev/null differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/cyber-threats.webp b/content/identity/cyber-threats-business-risk-covid-19/cyber-threats.webp
new file mode 100644
index 000000000..d7029ec93
Binary files /dev/null and b/content/identity/cyber-threats-business-risk-covid-19/cyber-threats.webp differ
diff --git a/content/identity/cyber-threats-business-risk-covid-19/index.md b/content/identity/cyber-threats-business-risk-covid-19/index.md
index e80b2998b..95a1a89c4 100644
--- a/content/identity/cyber-threats-business-risk-covid-19/index.md
+++ b/content/identity/cyber-threats-business-risk-covid-19/index.md
@@ -1,7 +1,7 @@
---
title: "Protecting Organization From Cyber-Threats: Business at Risk During COVID-19"
date: "2020-05-18"
-coverImage: "cyber-threats.jpg"
+coverImage: "cyber-threats.webp"
tags: ["cybersecurity","data security","ciam solution"]
author: "Rakesh Soni"
description: "Cyber risks have always been a big deal for corporations. With the self-quarantined world population at home and the stock market succumbing to the ill-fated Covid-19."
@@ -65,7 +65,7 @@ The [retail industry](https://www.loginradius.com/blog/2020/05/customer-experien
No doubt, attackers have become more opportunist and automated with time. In response to the increasing impersonation attack campaigns and cyber threat for businesses, organizations need to review their cybersecurity strategies and add multiple layers of security as their first line of defense.
-[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
+[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
### **Gaming Industry**
@@ -87,7 +87,7 @@ The breach exposed details of 22 million users and listed 21,909,707 records for
## Best Practices for Companies to Deal With Cyber Threats During COVID-19
-
+
As companies across the globe are adapting to new working environments to remain socially distant, it seems like cybercriminals are competing within themselves to come up with innovative ways to devise new cyber threat for businesses and exploit new vulnerabilities.
@@ -130,7 +130,7 @@ Because employees are working in their network environments, it has become imper
## How LoginRadius Mitigates the Risk for Organizations
-
+
The coronavirus outbreak has pushed more people to go digital. A [customer identity and access management](https://www.loginradius.com/blog/2019/06/customer-identity-and-access-management/) (CIAM) solution like the cloud-based LoginRadius can help businesses deal with scalability and offer a secure environment to sustain the newfound digital identities.
@@ -146,4 +146,4 @@ Few of the advantages for business and its customers include:
The digital space is all about identity, where cyber threat for businesses is at an all-time high. With the world on a standstill due to the pandemic, the idea of secure data governance and scalable identity management in the volatile environment should make the cut.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cyber-threats-business-risk-covid-19)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cyber-threats-business-risk-covid-19)
diff --git a/content/identity/cybersec-roundup-june-2021/Dark-Web-Hackers-e1623404162841.jpg b/content/identity/cybersec-roundup-june-2021/Dark-Web-Hackers-e1623404162841.jpg
deleted file mode 100644
index 0ef052605..000000000
Binary files a/content/identity/cybersec-roundup-june-2021/Dark-Web-Hackers-e1623404162841.jpg and /dev/null differ
diff --git a/content/identity/cybersec-roundup-june-2021/Dark-Web-Hackers-e1623404162841.webp b/content/identity/cybersec-roundup-june-2021/Dark-Web-Hackers-e1623404162841.webp
new file mode 100644
index 000000000..43b7fcb26
Binary files /dev/null and b/content/identity/cybersec-roundup-june-2021/Dark-Web-Hackers-e1623404162841.webp differ
diff --git a/content/identity/cybersec-roundup-june-2021/cybersec-roundup-june-2021-cover.jpg b/content/identity/cybersec-roundup-june-2021/cybersec-roundup-june-2021-cover.jpg
deleted file mode 100644
index 402a2383d..000000000
Binary files a/content/identity/cybersec-roundup-june-2021/cybersec-roundup-june-2021-cover.jpg and /dev/null differ
diff --git a/content/identity/cybersec-roundup-june-2021/cybersec-roundup-june-2021-cover.webp b/content/identity/cybersec-roundup-june-2021/cybersec-roundup-june-2021-cover.webp
new file mode 100644
index 000000000..1dc2ae0e7
Binary files /dev/null and b/content/identity/cybersec-roundup-june-2021/cybersec-roundup-june-2021-cover.webp differ
diff --git a/content/identity/cybersec-roundup-june-2021/index.md b/content/identity/cybersec-roundup-june-2021/index.md
index a18bb2405..f339dca41 100644
--- a/content/identity/cybersec-roundup-june-2021/index.md
+++ b/content/identity/cybersec-roundup-june-2021/index.md
@@ -1,7 +1,7 @@
---
title: "Cyber Security Round-Up: What Happened in June 2021"
date: "2021-07-01"
-coverImage: "cybersec-roundup-june-2021-cover.jpg"
+coverImage: "cybersec-roundup-june-2021-cover.webp"
tags: ["other"]
featured: false
author: "Navanita Devi"
@@ -52,7 +52,7 @@ In addition, the hackers claimed to have Microsoft Xbox and Sony SDKs and API ke
-
+
Screenshot: [Bleepingcomputer](https://www.bleepingcomputer.com/news/security/hackers-breach-gaming-giant-electronic-arts-steal-game-source-code/)
@@ -93,7 +93,7 @@ Seeing how cyber attacks can cause damage should be reason enough to take preven
-
+
**Image Source**: [McKinsey ](https://www.mckinsey.com/business-functions/risk/our-insights/covid-19-crisis-shifts-cybersecurity-priorities-and-budgets)
@@ -115,4 +115,4 @@ What other steps can you take to reinforce your organization's cybersecurity fra
Authenticating consumers is difficult and time-consuming. When used in conjunction, [a CIAM solution like LoginRadius](https://www.loginradius.com/contact-sales/) can significantly improve cybersecurity. It uses the approaches mentioned above and all recommended practices to filter permitted access and avoid typical attack situations.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersec-roundup-june-2021)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersec-roundup-june-2021)
diff --git a/content/identity/cybersec-roundup-june-2021/mckinsey.JPG b/content/identity/cybersec-roundup-june-2021/mckinsey.JPG
deleted file mode 100644
index d06b7d299..000000000
Binary files a/content/identity/cybersec-roundup-june-2021/mckinsey.JPG and /dev/null differ
diff --git a/content/identity/cybersec-roundup-june-2021/mckinsey.webp b/content/identity/cybersec-roundup-june-2021/mckinsey.webp
new file mode 100644
index 000000000..5658ad783
Binary files /dev/null and b/content/identity/cybersec-roundup-june-2021/mckinsey.webp differ
diff --git a/content/identity/cybersecurity-attacks-business/2-4.jpg b/content/identity/cybersecurity-attacks-business/2-4.jpg
deleted file mode 100644
index 7507d695f..000000000
Binary files a/content/identity/cybersecurity-attacks-business/2-4.jpg and /dev/null differ
diff --git a/content/identity/cybersecurity-attacks-business/2-4.webp b/content/identity/cybersecurity-attacks-business/2-4.webp
new file mode 100644
index 000000000..8686e8b95
Binary files /dev/null and b/content/identity/cybersecurity-attacks-business/2-4.webp differ
diff --git "a/content/identity/cybersecurity-attacks-business/RP-Data-Breach-Report-\342\200\223-Protecting-PII-Against-Data-Breaches-1024x310.png" "b/content/identity/cybersecurity-attacks-business/RP-Data-Breach-Report-\342\200\223-Protecting-PII-Against-Data-Breaches-1024x310.png"
deleted file mode 100644
index a86e6d940..000000000
Binary files "a/content/identity/cybersecurity-attacks-business/RP-Data-Breach-Report-\342\200\223-Protecting-PII-Against-Data-Breaches-1024x310.png" and /dev/null differ
diff --git "a/content/identity/cybersecurity-attacks-business/RP-Data-Breach-Report-\342\200\223-Protecting-PII-Against-Data-Breaches-1024x310.webp" "b/content/identity/cybersecurity-attacks-business/RP-Data-Breach-Report-\342\200\223-Protecting-PII-Against-Data-Breaches-1024x310.webp"
new file mode 100644
index 000000000..fc95b4d7d
Binary files /dev/null and "b/content/identity/cybersecurity-attacks-business/RP-Data-Breach-Report-\342\200\223-Protecting-PII-Against-Data-Breaches-1024x310.webp" differ
diff --git a/content/identity/cybersecurity-attacks-business/WORST_BREACHES_IN_HISTORY_smaller.png b/content/identity/cybersecurity-attacks-business/WORST_BREACHES_IN_HISTORY_smaller.png
deleted file mode 100644
index 5579ad504..000000000
Binary files a/content/identity/cybersecurity-attacks-business/WORST_BREACHES_IN_HISTORY_smaller.png and /dev/null differ
diff --git a/content/identity/cybersecurity-attacks-business/WORST_BREACHES_IN_HISTORY_smaller.webp b/content/identity/cybersecurity-attacks-business/WORST_BREACHES_IN_HISTORY_smaller.webp
new file mode 100644
index 000000000..25b182504
Binary files /dev/null and b/content/identity/cybersecurity-attacks-business/WORST_BREACHES_IN_HISTORY_smaller.webp differ
diff --git a/content/identity/cybersecurity-attacks-business/WP-credential-attack.png b/content/identity/cybersecurity-attacks-business/WP-credential-attack.png
deleted file mode 100644
index 4926b2aaf..000000000
Binary files a/content/identity/cybersecurity-attacks-business/WP-credential-attack.png and /dev/null differ
diff --git a/content/identity/cybersecurity-attacks-business/WP-credential-attack.webp b/content/identity/cybersecurity-attacks-business/WP-credential-attack.webp
new file mode 100644
index 000000000..d4581b1bd
Binary files /dev/null and b/content/identity/cybersecurity-attacks-business/WP-credential-attack.webp differ
diff --git a/content/identity/cybersecurity-attacks-business/credential-stuffing.png b/content/identity/cybersecurity-attacks-business/credential-stuffing.png
deleted file mode 100644
index 904e3a28e..000000000
Binary files a/content/identity/cybersecurity-attacks-business/credential-stuffing.png and /dev/null differ
diff --git a/content/identity/cybersecurity-attacks-business/credential-stuffing.webp b/content/identity/cybersecurity-attacks-business/credential-stuffing.webp
new file mode 100644
index 000000000..c2d6821c3
Binary files /dev/null and b/content/identity/cybersecurity-attacks-business/credential-stuffing.webp differ
diff --git a/content/identity/cybersecurity-attacks-business/cybersecurity-attacks-business.jpg b/content/identity/cybersecurity-attacks-business/cybersecurity-attacks-business.jpg
deleted file mode 100644
index 551511c26..000000000
Binary files a/content/identity/cybersecurity-attacks-business/cybersecurity-attacks-business.jpg and /dev/null differ
diff --git a/content/identity/cybersecurity-attacks-business/cybersecurity-attacks-business.webp b/content/identity/cybersecurity-attacks-business/cybersecurity-attacks-business.webp
new file mode 100644
index 000000000..13fd02cac
Binary files /dev/null and b/content/identity/cybersecurity-attacks-business/cybersecurity-attacks-business.webp differ
diff --git a/content/identity/cybersecurity-attacks-business/cybersecurity-attacks.jpg b/content/identity/cybersecurity-attacks-business/cybersecurity-attacks.jpg
deleted file mode 100644
index 6610e2d29..000000000
Binary files a/content/identity/cybersecurity-attacks-business/cybersecurity-attacks.jpg and /dev/null differ
diff --git a/content/identity/cybersecurity-attacks-business/cybersecurity-attacks.webp b/content/identity/cybersecurity-attacks-business/cybersecurity-attacks.webp
new file mode 100644
index 000000000..adcdfa01e
Binary files /dev/null and b/content/identity/cybersecurity-attacks-business/cybersecurity-attacks.webp differ
diff --git a/content/identity/cybersecurity-attacks-business/index.md b/content/identity/cybersecurity-attacks-business/index.md
index 273b6968f..3aaccfe61 100644
--- a/content/identity/cybersecurity-attacks-business/index.md
+++ b/content/identity/cybersecurity-attacks-business/index.md
@@ -1,7 +1,7 @@
---
title: "Cybersecurity Awareness Month: Predicting the Deadliest Cyber Attacks in 2022"
date: "2021-10-05"
-coverImage: "cybersecurity-attacks.jpg"
+coverImage: "cybersecurity-attacks.webp"
tags: ["data security","cybersecurity","compliance","cx"]
author: "Rakesh Soni"
description: "Cybersecurity incidents take place by various means every day. From virtual banking breaches to semi-open attacks, 2021 has been rough on IT security. But, how did we get to this point of compromise and uncertainty?"
@@ -189,7 +189,7 @@ Cybercriminals may use it to distribute malware that could lead to malicious att
* Always download applications from official websites and app developers.
* Avoid clicking ads when possible, even in legitimate software.
-
+
## A Cyberattack’s Impact on Business
@@ -230,7 +230,7 @@ Here’s what you can do if your customer data is ever compromised:
This, of course, is all about the aftermath of a breach.
-[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
+[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
So, how can organizations prevent cybersecurity attacks from happening in the first place?
@@ -251,7 +251,7 @@ No matter what state your security program is in now, these steps will help you
## How Can LoginRadius Protect Enterprises From Cyberattacks
-
+
When it comes to bringing your business online, there are a lot of factors to consider. For instance, securing records and managing customer profiles require a lot of attention. That’s why having a strong [consumer identity and access management (CIAM) solution](https://www.loginradius.com/blog/2019/06/customer-identity-and-access-management/) in place is half the battle won.
@@ -263,4 +263,4 @@ All of these features work together to help you mitigate cybersecurity attacks o
While it seems like a scary world out there, you can protect your [enterprise from cyberattacks](https://www.loginradius.com/blog/identity/cyber-threats-business-risk-covid-19/) with the right tools. A CIAM software provides these tools via centralized monitoring and advanced security features, so you can get back to growing your business. Let’s [join hands](https://www.loginradius.com/contact-sales) for a better 2022!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersecurity-attacks-business)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersecurity-attacks-business)
\ No newline at end of file
diff --git a/content/identity/cybersecurity-attacks-business/security_compliance_cred_loginradius.png b/content/identity/cybersecurity-attacks-business/security_compliance_cred_loginradius.png
deleted file mode 100644
index cc699c38a..000000000
Binary files a/content/identity/cybersecurity-attacks-business/security_compliance_cred_loginradius.png and /dev/null differ
diff --git a/content/identity/cybersecurity-attacks-business/security_compliance_cred_loginradius.webp b/content/identity/cybersecurity-attacks-business/security_compliance_cred_loginradius.webp
new file mode 100644
index 000000000..3e15954ce
Binary files /dev/null and b/content/identity/cybersecurity-attacks-business/security_compliance_cred_loginradius.webp differ
diff --git a/content/identity/cybersecurity-awareness-month-2023/WP-zero-trust-security.png b/content/identity/cybersecurity-awareness-month-2023/WP-zero-trust-security.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/cybersecurity-awareness-month-2023/WP-zero-trust-security.png and /dev/null differ
diff --git a/content/identity/cybersecurity-awareness-month-2023/WP-zero-trust-security.webp b/content/identity/cybersecurity-awareness-month-2023/WP-zero-trust-security.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/cybersecurity-awareness-month-2023/WP-zero-trust-security.webp differ
diff --git a/content/identity/cybersecurity-awareness-month-2023/cybersecurity-awareness-2023.jpg b/content/identity/cybersecurity-awareness-month-2023/cybersecurity-awareness-2023.jpg
deleted file mode 100644
index 17211e45f..000000000
Binary files a/content/identity/cybersecurity-awareness-month-2023/cybersecurity-awareness-2023.jpg and /dev/null differ
diff --git a/content/identity/cybersecurity-awareness-month-2023/cybersecurity-awareness-2023.webp b/content/identity/cybersecurity-awareness-month-2023/cybersecurity-awareness-2023.webp
new file mode 100644
index 000000000..6eb7ec948
Binary files /dev/null and b/content/identity/cybersecurity-awareness-month-2023/cybersecurity-awareness-2023.webp differ
diff --git a/content/identity/cybersecurity-awareness-month-2023/cybersecurity.jpg b/content/identity/cybersecurity-awareness-month-2023/cybersecurity.jpg
deleted file mode 100644
index aa23fb973..000000000
Binary files a/content/identity/cybersecurity-awareness-month-2023/cybersecurity.jpg and /dev/null differ
diff --git a/content/identity/cybersecurity-awareness-month-2023/cybersecurity.webp b/content/identity/cybersecurity-awareness-month-2023/cybersecurity.webp
new file mode 100644
index 000000000..3a0b0660c
Binary files /dev/null and b/content/identity/cybersecurity-awareness-month-2023/cybersecurity.webp differ
diff --git a/content/identity/cybersecurity-awareness-month-2023/index.md b/content/identity/cybersecurity-awareness-month-2023/index.md
index ab595e80b..b61bbf044 100644
--- a/content/identity/cybersecurity-awareness-month-2023/index.md
+++ b/content/identity/cybersecurity-awareness-month-2023/index.md
@@ -1,7 +1,7 @@
---
title: "Small Steps, Big Shields: Navigating Cybersecurity Awareness Month 2023 Safely"
date: "2023-10-03"
-coverImage: "cybersecurity-awareness-2023.jpg"
+coverImage: "cybersecurity-awareness-2023.webp"
tags: ["cybersecurity","passwordless authentication","multi-factor authentication"]
author: "Alok Patidar"
description: "Cybersecurity Awareness Month 2023 is a crucial reminder in the digital age where every click matters. Join us at LoginRadius as we spread the word about the importance of user endpoint security, employee training, strong passwords, multi-factor authentication, and phishing prevention. Discover how these small steps can create impenetrable shields, safeguarding your organization amid evolving cyber threats. Stay safe, stay vigilant, and empower your team with knowledge during Cybersecurity Awareness Month 2023!"
@@ -37,7 +37,7 @@ Ensure every device accessing your network adheres to strict security policies,
Additionally, incorporating the true potential of the zero-trust mechanism can help reinforce overall authentication security.
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
## 2. Train Your Employees: Knowledge is Power
@@ -73,4 +73,4 @@ Remember, in cybersecurity, every small step you take today can fortify your org
Stay tuned for more insights and tips on bolstering your organization's cybersecurity defenses amid Cybersecurity Awareness Month 2023!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersecurity-awareness-month-2023)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersecurity-awareness-month-2023)
diff --git a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices-for-enterprises.png b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices-for-enterprises.png
deleted file mode 100644
index f320a1e9f..000000000
Binary files a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices-for-enterprises.png and /dev/null differ
diff --git a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices-for-enterprises.webp b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices-for-enterprises.webp
new file mode 100644
index 000000000..074489eda
Binary files /dev/null and b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices-for-enterprises.webp differ
diff --git a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices.jpg b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices.jpg
deleted file mode 100644
index 63bab4f71..000000000
Binary files a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices.jpg and /dev/null differ
diff --git a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices.webp b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices.webp
new file mode 100644
index 000000000..71694a62b
Binary files /dev/null and b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-best-practices.webp differ
diff --git a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic.png b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic.png
deleted file mode 100644
index 624423895..000000000
Binary files a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic.png and /dev/null differ
diff --git a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic.webp b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic.webp
new file mode 100644
index 000000000..905e8cb9f
Binary files /dev/null and b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic.webp differ
diff --git a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic2023.png b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic2023.png
deleted file mode 100644
index 38c1a69e8..000000000
Binary files a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic2023.png and /dev/null differ
diff --git a/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic2023.webp b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic2023.webp
new file mode 100644
index 000000000..c0a0a10dd
Binary files /dev/null and b/content/identity/cybersecurity-best-practices-for-enterprises/cybersecurity-infographic2023.webp differ
diff --git a/content/identity/cybersecurity-best-practices-for-enterprises/index.md b/content/identity/cybersecurity-best-practices-for-enterprises/index.md
index e31791483..1b5e66753 100644
--- a/content/identity/cybersecurity-best-practices-for-enterprises/index.md
+++ b/content/identity/cybersecurity-best-practices-for-enterprises/index.md
@@ -1,7 +1,7 @@
---
title: "Cybersecurity Best Practices for Businesses in 2023 & Beyond [Infographic]"
date: "2021-10-21"
-coverImage: "cybersecurity-best-practices.jpg"
+coverImage: "cybersecurity-best-practices.webp"
tags: ["cybersecurity","data security","cx","password management"]
author: "Rakesh Soni"
description: "Today cybercriminals are increasingly able to cover their tracks, hide in the cloud, manipulate the infrastructure of the web, and exploit complex vulnerabilities. This infographic summarizes the key takeaway into the cybersecurity best practices that businesses should adopt in 2023."
@@ -74,8 +74,8 @@ Aside from login security tips, this infographic will also highlight:
To learn more about the cybersecurity best practices for your business in 2023 and beyond, check out the infographic created by LoginRadius.
-
+
Get the best cybersecurity solutions for your enterprise with LoginRadius.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersecurity-best-practices-for-enterprises)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersecurity-best-practices-for-enterprises)
diff --git a/content/identity/cybersecurity-trends-2024/WP-zero-trust-security.png b/content/identity/cybersecurity-trends-2024/WP-zero-trust-security.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/cybersecurity-trends-2024/WP-zero-trust-security.png and /dev/null differ
diff --git a/content/identity/cybersecurity-trends-2024/WP-zero-trust-security.webp b/content/identity/cybersecurity-trends-2024/WP-zero-trust-security.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/cybersecurity-trends-2024/WP-zero-trust-security.webp differ
diff --git a/content/identity/cybersecurity-trends-2024/cybersecurity-trends.jpg b/content/identity/cybersecurity-trends-2024/cybersecurity-trends.jpg
deleted file mode 100644
index 9a5c2a1cb..000000000
Binary files a/content/identity/cybersecurity-trends-2024/cybersecurity-trends.jpg and /dev/null differ
diff --git a/content/identity/cybersecurity-trends-2024/cybersecurity-trends.webp b/content/identity/cybersecurity-trends-2024/cybersecurity-trends.webp
new file mode 100644
index 000000000..f22d53440
Binary files /dev/null and b/content/identity/cybersecurity-trends-2024/cybersecurity-trends.webp differ
diff --git a/content/identity/cybersecurity-trends-2024/index.md b/content/identity/cybersecurity-trends-2024/index.md
index b66a8ee0c..8d1b97a69 100644
--- a/content/identity/cybersecurity-trends-2024/index.md
+++ b/content/identity/cybersecurity-trends-2024/index.md
@@ -1,7 +1,7 @@
---
title: "Now and Beyond- Staying Ahead with the 10 Key Cybersecurity Trends of 2024"
date: "2023-12-07"
-coverImage: "cybersecurity-trends.jpg"
+coverImage: "cybersecurity-trends.webp"
tags: ["data security","cybersecurity","MFA","cx"]
author: "Navanita Devi"
description: "Dive into the future of cybersecurity with the top 10 trends for 2024. From Gen AI Attacks to Quantum Computing Threats, fortify your defense and stay ahead in the digital landscape."
@@ -42,7 +42,7 @@ Phishing attacks have evolved from generic email scams to highly targeted and so
As traditional perimeter-based security models prove insufficient, the industry is witnessing a rapid adoption of Zero Trust frameworks. This approach assumes no inherent trust, requiring verification from everyone, regardless of their location or device. Implementing Zero Trust principles helps organizations fortify their defenses against both internal and external threats.
-[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-modern-business/)
+[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-modern-business/)
### 5. Cyber Resilience:
@@ -72,4 +72,4 @@ The interconnected nature of modern business ecosystems makes supply chains susc
As we stand on the brink of 2024, organizations must proactively address these cybersecurity trends 2024 to stay ahead of malicious actors. A holistic and adaptive cybersecurity strategy, coupled with ongoing education and compliance efforts, will be instrumental in safeguarding digital assets in the dynamic landscape of now and beyond.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersecurity-trends-2024)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cybersecurity-trends-2024)
\ No newline at end of file
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/1.png b/content/identity/d2c-brands-utilize-ciam-for-growth/1.png
deleted file mode 100644
index 4b4966b66..000000000
Binary files a/content/identity/d2c-brands-utilize-ciam-for-growth/1.png and /dev/null differ
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/1.webp b/content/identity/d2c-brands-utilize-ciam-for-growth/1.webp
new file mode 100644
index 000000000..378b27850
Binary files /dev/null and b/content/identity/d2c-brands-utilize-ciam-for-growth/1.webp differ
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/2.png b/content/identity/d2c-brands-utilize-ciam-for-growth/2.png
deleted file mode 100644
index 62e241970..000000000
Binary files a/content/identity/d2c-brands-utilize-ciam-for-growth/2.png and /dev/null differ
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/2.webp b/content/identity/d2c-brands-utilize-ciam-for-growth/2.webp
new file mode 100644
index 000000000..6dd70affa
Binary files /dev/null and b/content/identity/d2c-brands-utilize-ciam-for-growth/2.webp differ
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/3(1).png b/content/identity/d2c-brands-utilize-ciam-for-growth/3(1).png
deleted file mode 100644
index abc71741c..000000000
Binary files a/content/identity/d2c-brands-utilize-ciam-for-growth/3(1).png and /dev/null differ
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/3(1).webp b/content/identity/d2c-brands-utilize-ciam-for-growth/3(1).webp
new file mode 100644
index 000000000..35e32d992
Binary files /dev/null and b/content/identity/d2c-brands-utilize-ciam-for-growth/3(1).webp differ
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/EB-Omnichannel-world.png b/content/identity/d2c-brands-utilize-ciam-for-growth/EB-Omnichannel-world.png
deleted file mode 100644
index f5fa0b0f9..000000000
Binary files a/content/identity/d2c-brands-utilize-ciam-for-growth/EB-Omnichannel-world.png and /dev/null differ
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/EB-Omnichannel-world.webp b/content/identity/d2c-brands-utilize-ciam-for-growth/EB-Omnichannel-world.webp
new file mode 100644
index 000000000..b0761321e
Binary files /dev/null and b/content/identity/d2c-brands-utilize-ciam-for-growth/EB-Omnichannel-world.webp differ
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/d2c.jpg b/content/identity/d2c-brands-utilize-ciam-for-growth/d2c.jpg
deleted file mode 100644
index cef79ac11..000000000
Binary files a/content/identity/d2c-brands-utilize-ciam-for-growth/d2c.jpg and /dev/null differ
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/d2c.webp b/content/identity/d2c-brands-utilize-ciam-for-growth/d2c.webp
new file mode 100644
index 000000000..0ec05f88e
Binary files /dev/null and b/content/identity/d2c-brands-utilize-ciam-for-growth/d2c.webp differ
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/index.md b/content/identity/d2c-brands-utilize-ciam-for-growth/index.md
index 3c3fcd605..005db7db7 100644
--- a/content/identity/d2c-brands-utilize-ciam-for-growth/index.md
+++ b/content/identity/d2c-brands-utilize-ciam-for-growth/index.md
@@ -1,7 +1,7 @@
---
title: "Why Direct-to-Consumer (D2C) Businesses Must Take A Strategic Approach To CIAM?"
date: "2023-02-10"
-coverImage: "d2c.jpg"
+coverImage: "d2c.webp"
tags: ["direct to consumer", "authentication", "ciam"]
author: "Nicholas Woodward"
description: "The greatest value for direct-to-consumer companies comes from creating a valuable, seamless experience. In this blog we will discuss how CIAM allows D2C companies to improve the customer journey directly."
@@ -45,7 +45,7 @@ Along with being secure, CIAM can also be adaptive. You can assign different cri
A few D2C brands also have brick-and-mortar retail outlets. With CIAM, the store can access details about the customers to provide a better experience. The customer can also use their digital identity to purchase at the store. This will add their in-store purchase to the online order history.
-[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
+[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
A CIAM system will ensure that all the information concerning a customer remains associated with one user identity. On the user’s end, it ensures a consistent brand experience across all channels. The customers can also begin the purchase journey on one device and complete it on another.
@@ -68,7 +68,7 @@ CIAM helps you understand the behavior and preferences of the customer. Based on
You can find such opportunities for personalization in marketing and sales. You can use data to suggest products according to the customer’s preferences. You can identify upselling and cross-selling opportunities. These insights can also help you design offers or packages for different customers.
-
+
**_Image: Major benefits of personalizing customer experiences (Evergage)_**
@@ -81,7 +81,7 @@ For instance, if a person has bought a skirt from your D2C store. You can sugges
Online customers do not like complex sign-in or check-out processes. It is one of the biggest reasons for eCommerce cart abandonment and high bounce rates. An eCommerce platform with too many security measures usually creates a complex check-in process. On the other hand, customers also do not trust platforms without security measures either.
-.png)
+.webp)
**_Image: Reasons for abandonment during check out (Baymard Institute)_**
@@ -99,4 +99,4 @@ A CIAM system works well for the customers as well as the sellers. It grants con
Additionally, the CIAM also helps D2C brands control each interaction with their customers. It helps create an easy, secure, and personalized customer experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=d2c-brands-utilize-ciam-for-growth)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=d2c-brands-utilize-ciam-for-growth)
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/omnichannel-eb.png b/content/identity/d2c-brands-utilize-ciam-for-growth/omnichannel-eb.png
deleted file mode 100644
index 86c15a159..000000000
Binary files a/content/identity/d2c-brands-utilize-ciam-for-growth/omnichannel-eb.png and /dev/null differ
diff --git a/content/identity/d2c-brands-utilize-ciam-for-growth/omnichannel-eb.webp b/content/identity/d2c-brands-utilize-ciam-for-growth/omnichannel-eb.webp
new file mode 100644
index 000000000..025782e92
Binary files /dev/null and b/content/identity/d2c-brands-utilize-ciam-for-growth/omnichannel-eb.webp differ
diff --git a/content/identity/data-breaches-common-mistakes/RP-data-breach-report.png b/content/identity/data-breaches-common-mistakes/RP-data-breach-report.png
deleted file mode 100644
index b32dcb27b..000000000
Binary files a/content/identity/data-breaches-common-mistakes/RP-data-breach-report.png and /dev/null differ
diff --git a/content/identity/data-breaches-common-mistakes/RP-data-breach-report.webp b/content/identity/data-breaches-common-mistakes/RP-data-breach-report.webp
new file mode 100644
index 000000000..6c250a4f7
Binary files /dev/null and b/content/identity/data-breaches-common-mistakes/RP-data-breach-report.webp differ
diff --git a/content/identity/data-breaches-common-mistakes/data-breaches-common-mistakes-cover.jpg b/content/identity/data-breaches-common-mistakes/data-breaches-common-mistakes-cover.jpg
deleted file mode 100644
index 4cacd6927..000000000
Binary files a/content/identity/data-breaches-common-mistakes/data-breaches-common-mistakes-cover.jpg and /dev/null differ
diff --git a/content/identity/data-breaches-common-mistakes/data-breaches-common-mistakes-cover.webp b/content/identity/data-breaches-common-mistakes/data-breaches-common-mistakes-cover.webp
new file mode 100644
index 000000000..5bfceaa2c
Binary files /dev/null and b/content/identity/data-breaches-common-mistakes/data-breaches-common-mistakes-cover.webp differ
diff --git a/content/identity/data-breaches-common-mistakes/index.md b/content/identity/data-breaches-common-mistakes/index.md
index d5ac18d1e..fec56ccd9 100644
--- a/content/identity/data-breaches-common-mistakes/index.md
+++ b/content/identity/data-breaches-common-mistakes/index.md
@@ -1,7 +1,7 @@
---
title: "Avoid these Common Mistakes When Dealing with Data Breaches"
date: "2021-10-01"
-coverImage: "data-breaches-common-mistakes-cover.jpg"
+coverImage: "data-breaches-common-mistakes-cover.webp"
tags: ["data security","mfa","cx"]
author: "Deependra Singh"
description: "With hacking events on the rise, it would be wise to take a step back and consider where things went wrong. You can prevent data breach occurrences in your organization by learning to recognize the common mistakes that are committed."
@@ -45,7 +45,7 @@ As mentioned before, the roles that each person and every team plays in handling
This leader will receive reports from every team involved in mitigating the attack and will, therefore, have to coordinate with every party involved. This person will have to be the voice of reason during this trying time and do everything in their power to ensure that the response plan is being implemented properly.
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
### 5. No third-party agencies.
@@ -65,4 +65,4 @@ According to several reports, a data breach typically costs an organization anyw
However, learning from the above mistakes, an organization can remain defenseless in the face of a data breach.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-breaches-common-mistakes)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-breaches-common-mistakes)
diff --git a/content/identity/data-governance-best-practices/BD-Plexicon1-1024x310-1.png b/content/identity/data-governance-best-practices/BD-Plexicon1-1024x310-1.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/data-governance-best-practices/BD-Plexicon1-1024x310-1.png and /dev/null differ
diff --git a/content/identity/data-governance-best-practices/BD-Plexicon1-1024x310-1.webp b/content/identity/data-governance-best-practices/BD-Plexicon1-1024x310-1.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/data-governance-best-practices/BD-Plexicon1-1024x310-1.webp differ
diff --git a/content/identity/data-governance-best-practices/Data-Governance-Best-Practices-for-Enterprises-1.jpg b/content/identity/data-governance-best-practices/Data-Governance-Best-Practices-for-Enterprises-1.jpg
deleted file mode 100644
index b3962a997..000000000
Binary files a/content/identity/data-governance-best-practices/Data-Governance-Best-Practices-for-Enterprises-1.jpg and /dev/null differ
diff --git a/content/identity/data-governance-best-practices/Data-Governance-Best-Practices-for-Enterprises-1.webp b/content/identity/data-governance-best-practices/Data-Governance-Best-Practices-for-Enterprises-1.webp
new file mode 100644
index 000000000..0b6b912bc
Binary files /dev/null and b/content/identity/data-governance-best-practices/Data-Governance-Best-Practices-for-Enterprises-1.webp differ
diff --git a/content/identity/data-governance-best-practices/Data-Governance-Best-Practices.jpg b/content/identity/data-governance-best-practices/Data-Governance-Best-Practices.jpg
deleted file mode 100644
index 44f9b6615..000000000
Binary files a/content/identity/data-governance-best-practices/Data-Governance-Best-Practices.jpg and /dev/null differ
diff --git a/content/identity/data-governance-best-practices/Data-Governance-Best-Practices.webp b/content/identity/data-governance-best-practices/Data-Governance-Best-Practices.webp
new file mode 100644
index 000000000..e0f25949d
Binary files /dev/null and b/content/identity/data-governance-best-practices/Data-Governance-Best-Practices.webp differ
diff --git a/content/identity/data-governance-best-practices/ccpa-customer-identity.png b/content/identity/data-governance-best-practices/ccpa-customer-identity.png
deleted file mode 100644
index 0ed0f3bce..000000000
Binary files a/content/identity/data-governance-best-practices/ccpa-customer-identity.png and /dev/null differ
diff --git a/content/identity/data-governance-best-practices/ccpa-customer-identity.webp b/content/identity/data-governance-best-practices/ccpa-customer-identity.webp
new file mode 100644
index 000000000..6d67557e6
Binary files /dev/null and b/content/identity/data-governance-best-practices/ccpa-customer-identity.webp differ
diff --git a/content/identity/data-governance-best-practices/image3-1.png b/content/identity/data-governance-best-practices/image3-1.png
deleted file mode 100644
index 185ba23d6..000000000
Binary files a/content/identity/data-governance-best-practices/image3-1.png and /dev/null differ
diff --git a/content/identity/data-governance-best-practices/image3-1.webp b/content/identity/data-governance-best-practices/image3-1.webp
new file mode 100644
index 000000000..f543765a0
Binary files /dev/null and b/content/identity/data-governance-best-practices/image3-1.webp differ
diff --git a/content/identity/data-governance-best-practices/index.md b/content/identity/data-governance-best-practices/index.md
index 834822411..335b3cbd4 100644
--- a/content/identity/data-governance-best-practices/index.md
+++ b/content/identity/data-governance-best-practices/index.md
@@ -1,7 +1,7 @@
---
title: "Data Governance Best Practices for Enterprises"
date: "2020-07-22"
-coverImage: "Data-Governance-Best-Practices.jpg"
+coverImage: "Data-Governance-Best-Practices.webp"
tags: ["data governance","compliance","cx"]
author: "Rakesh Soni"
description: "The world has undergone a massive transformation in governing the data and is establishing methods to standardize, integrate, and protect such information. The EU's General Data Protection Regulation implemented in 2018 was a masterstroke to the data governance arrangement."
@@ -63,7 +63,7 @@ Data governance will be at the center of customer and business relationships. To
Needless to say, data governance will emerge as a competitive differentiator when delivering the best customer experiences.
-[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
+[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
## Data Governance Best Practices Enterprises Should Follow
@@ -113,7 +113,7 @@ Following suit, other countries like India, South Korea, Brazil, and Thailand ar
## How Does a Robust Data Governance Framework Impact Your Digital Business
-
+
Digital transformation is actively on the radar of data security professionals. A well-thought and proactively managed data governance framework can drive business transformation throughout organizational levels in the following ways:
@@ -127,7 +127,7 @@ Digital transformation is actively on the radar of data security professionals.
## Choosing the LoginRadius CIAM Platform to Help Enterprises
-
+
Data governance isn’t a one-time project, rather a recurring one. To maintain and sustain such programs require a lot of work. LoginRadius is a customer identity and access management (CIAM) platform that prepares organizations to fuel data-driven decision-making and create better business opportunities.
@@ -150,4 +150,4 @@ As already mentioned, data governance revolves around people, processes, and tec
Maximize benefits and optimize your use of data protection strategies in the new decade. Start with implementing the data governance best practices laid out in this article.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-governance-best-practices)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-governance-best-practices)
diff --git a/content/identity/data-privacy-compliance-future/ccpa-ds.png b/content/identity/data-privacy-compliance-future/ccpa-ds.png
deleted file mode 100644
index 6784e19bd..000000000
Binary files a/content/identity/data-privacy-compliance-future/ccpa-ds.png and /dev/null differ
diff --git a/content/identity/data-privacy-compliance-future/ccpa-ds.webp b/content/identity/data-privacy-compliance-future/ccpa-ds.webp
new file mode 100644
index 000000000..c27d2fee5
Binary files /dev/null and b/content/identity/data-privacy-compliance-future/ccpa-ds.webp differ
diff --git a/content/identity/data-privacy-compliance-future/compliance.jpg b/content/identity/data-privacy-compliance-future/compliance.jpg
deleted file mode 100644
index fc6ad9f74..000000000
Binary files a/content/identity/data-privacy-compliance-future/compliance.jpg and /dev/null differ
diff --git a/content/identity/data-privacy-compliance-future/compliance.webp b/content/identity/data-privacy-compliance-future/compliance.webp
new file mode 100644
index 000000000..790a15821
Binary files /dev/null and b/content/identity/data-privacy-compliance-future/compliance.webp differ
diff --git a/content/identity/data-privacy-compliance-future/index.md b/content/identity/data-privacy-compliance-future/index.md
index 1339412dd..b4f5f1e99 100644
--- a/content/identity/data-privacy-compliance-future/index.md
+++ b/content/identity/data-privacy-compliance-future/index.md
@@ -1,7 +1,7 @@
---
title: "What Brands Need to Know for Building the Future of Data Compliance?"
date: "2022-08-31"
-coverImage: "compliance.jpg"
+coverImage: "compliance.webp"
tags: ["data privacy", "enterprises", "compliance"]
author: "Rakesh Soni"
description: "Unlike the conventional times when brands used to collect heaps of customer data without their consent, organizations must first build trust in clients before expecting even a bit of detail. Let’s look at some aspects that can help organizations stay ahead of the curve by leveraging digital privacy for compliance management."
@@ -47,7 +47,7 @@ Due to increased regulations, including the EU’s GDPR and the United States’
Also, the increased number of cybersecurity threats pertaining to customers’ crucial information has impacted businesses; businesses must incorporate a robust security mechanism for better protection.
-[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
+[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
@@ -76,4 +76,4 @@ And with LoginRadius CIAM, businesses need not worry about getting compliant wit
Need help in getting compliance-ready? [Reach us](https://www.loginradius.com/contact-sales/) for a free consultation today.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-compliance-future)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-compliance-future)
diff --git a/content/identity/data-privacy-immediate-enterprise-priority/dg-privacy.jpg b/content/identity/data-privacy-immediate-enterprise-priority/dg-privacy.jpg
deleted file mode 100644
index cb346237b..000000000
Binary files a/content/identity/data-privacy-immediate-enterprise-priority/dg-privacy.jpg and /dev/null differ
diff --git a/content/identity/data-privacy-immediate-enterprise-priority/dg-privacy.webp b/content/identity/data-privacy-immediate-enterprise-priority/dg-privacy.webp
new file mode 100644
index 000000000..be7aa25ed
Binary files /dev/null and b/content/identity/data-privacy-immediate-enterprise-priority/dg-privacy.webp differ
diff --git a/content/identity/data-privacy-immediate-enterprise-priority/index.md b/content/identity/data-privacy-immediate-enterprise-priority/index.md
index 6c0a7b16a..4b4733776 100644
--- a/content/identity/data-privacy-immediate-enterprise-priority/index.md
+++ b/content/identity/data-privacy-immediate-enterprise-priority/index.md
@@ -1,7 +1,7 @@
---
title: "Why is Data Privacy an Immediate Enterprise Priority?"
date: "2022-07-27"
-coverImage: "dg-privacy.jpg"
+coverImage: "dg-privacy.webp"
tags: ["data privacy", "enterprises", "regulations"]
author: "Rakesh Soni"
description: "In the past ten years, the rise of privacy-conscious consumers and emerging data regulations have compelled enterprises to prioritize their data management programs. Read more to learn how data privacy has become an enterprise priority."
@@ -50,4 +50,4 @@ The chapters are as follows:
In detail, I have organized the eBook into chapters mentioned above in addition to an Executive Summary intended for senior executives for a brief overview.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-immediate-enterprise-priority)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-immediate-enterprise-priority)
diff --git a/content/identity/data-security-best-practices/9-data-security-best-practices-for-2021.jpg b/content/identity/data-security-best-practices/9-data-security-best-practices-for-2021.jpg
deleted file mode 100644
index c2dbcdd1e..000000000
Binary files a/content/identity/data-security-best-practices/9-data-security-best-practices-for-2021.jpg and /dev/null differ
diff --git a/content/identity/data-security-best-practices/9-data-security-best-practices-for-2021.webp b/content/identity/data-security-best-practices/9-data-security-best-practices-for-2021.webp
new file mode 100644
index 000000000..9e83c46fc
Binary files /dev/null and b/content/identity/data-security-best-practices/9-data-security-best-practices-for-2021.webp differ
diff --git a/content/identity/data-security-best-practices/9-data-security-best-practices.png b/content/identity/data-security-best-practices/9-data-security-best-practices.png
deleted file mode 100644
index 2d7d5f515..000000000
Binary files a/content/identity/data-security-best-practices/9-data-security-best-practices.png and /dev/null differ
diff --git a/content/identity/data-security-best-practices/9-data-security-best-practices.webp b/content/identity/data-security-best-practices/9-data-security-best-practices.webp
new file mode 100644
index 000000000..bf387f1fa
Binary files /dev/null and b/content/identity/data-security-best-practices/9-data-security-best-practices.webp differ
diff --git a/content/identity/data-security-best-practices/index.md b/content/identity/data-security-best-practices/index.md
index 3841767fa..b0a2c3ef9 100644
--- a/content/identity/data-security-best-practices/index.md
+++ b/content/identity/data-security-best-practices/index.md
@@ -1,7 +1,7 @@
---
title: "9 Data Security Best Practices For your Business"
date: "2020-12-09"
-coverImage: "9-data-security-best-practices-for-2021.jpg"
+coverImage: "9-data-security-best-practices-for-2021.webp"
tags: ["data security","cybersecurity","cx"]
author: "Rakesh Soni"
description: "Confining data security best practices to the organization's size never helped in the past, nor will it work in the future. What cybercriminals gain is what consumers lose, and those losses add up."
@@ -98,7 +98,7 @@ Your network's endpoints are constantly under threat. Therefore, it is important
* **Firewalls**: Firewalls provide a barrier between your data and cybercriminals, which is why it is one of the highly recommended data security best practices by most experts. You can also install internal firewalls to provide additional protection.
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
### 6. Document your cybersecurity policies.
@@ -146,4 +146,4 @@ Secure data by encrypting sensitive information, using access controls, implemen
Data security in an enterprise involves protecting sensitive information through various measures such as encryption, access controls, and monitoring.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-security-best-practices)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-security-best-practices)
diff --git a/content/identity/data-security-best-practices/protecting-PII-against-data-breaches-report.png b/content/identity/data-security-best-practices/protecting-PII-against-data-breaches-report.png
deleted file mode 100644
index b32dcb27b..000000000
Binary files a/content/identity/data-security-best-practices/protecting-PII-against-data-breaches-report.png and /dev/null differ
diff --git a/content/identity/data-security-best-practices/protecting-PII-against-data-breaches-report.webp b/content/identity/data-security-best-practices/protecting-PII-against-data-breaches-report.webp
new file mode 100644
index 000000000..6c250a4f7
Binary files /dev/null and b/content/identity/data-security-best-practices/protecting-PII-against-data-breaches-report.webp differ
diff --git a/content/identity/data-security-hospitality-industry/data-security-hospitality-industry-cover.jpg b/content/identity/data-security-hospitality-industry/data-security-hospitality-industry-cover.jpg
deleted file mode 100644
index f12cd1ecd..000000000
Binary files a/content/identity/data-security-hospitality-industry/data-security-hospitality-industry-cover.jpg and /dev/null differ
diff --git a/content/identity/data-security-hospitality-industry/data-security-hospitality-industry-cover.webp b/content/identity/data-security-hospitality-industry/data-security-hospitality-industry-cover.webp
new file mode 100644
index 000000000..a6420014b
Binary files /dev/null and b/content/identity/data-security-hospitality-industry/data-security-hospitality-industry-cover.webp differ
diff --git a/content/identity/data-security-hospitality-industry/index.md b/content/identity/data-security-hospitality-industry/index.md
index fe6fe609f..006d14de3 100644
--- a/content/identity/data-security-hospitality-industry/index.md
+++ b/content/identity/data-security-hospitality-industry/index.md
@@ -1,7 +1,7 @@
---
title: "Data Security in Hospitality: Best Practices for Operating In a Post-COVID Era"
date: "2021-04-23"
-coverImage: "data-security-hospitality-industry-cover.jpg"
+coverImage: "data-security-hospitality-industry-cover.webp"
tags: ["security"]
featured: false
author: "Navanita Devi"
@@ -57,7 +57,7 @@ As per the multiple threats that have been uncovered above, it is essential to u
* **Testing computer systems**: The testing process applies to the cyber-security provider. That is to say, businesses are required to carry out several tests to determine if the provider can detect the threat or malware.
* **Track data**: Databases that are stored on various systems require a tracker. Through this tracker, one is capable of determining where the data is present or moving towards.
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
## How Can LoginRadius Mitigate Data Security Concerns for the Hospitality Industry
@@ -80,4 +80,4 @@ According to the AARP, around [1.4 million](https://www.aarp.org/money/scams-fra
To mitigate this, governments across the world have implemented the privacy act. This privacy act hopes to decrease the number of identity theft cases by regulating the information that is collected by businesses. Therefore, investing in proper data security in hospitality can work to protect not only the consumer but also the business from losing large sums of profit.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-security-hospitality-industry)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-security-hospitality-industry)
diff --git a/content/identity/data-security-hospitality-industry/protecting-PII-against-data-breaches-report.png b/content/identity/data-security-hospitality-industry/protecting-PII-against-data-breaches-report.png
deleted file mode 100644
index b32dcb27b..000000000
Binary files a/content/identity/data-security-hospitality-industry/protecting-PII-against-data-breaches-report.png and /dev/null differ
diff --git a/content/identity/data-security-hospitality-industry/protecting-PII-against-data-breaches-report.webp b/content/identity/data-security-hospitality-industry/protecting-PII-against-data-breaches-report.webp
new file mode 100644
index 000000000..6c250a4f7
Binary files /dev/null and b/content/identity/data-security-hospitality-industry/protecting-PII-against-data-breaches-report.webp differ
diff --git a/content/identity/decentralized-authentication-future-of-authentication/WP-decentralized-auth.png b/content/identity/decentralized-authentication-future-of-authentication/WP-decentralized-auth.png
deleted file mode 100644
index cc73eedfd..000000000
Binary files a/content/identity/decentralized-authentication-future-of-authentication/WP-decentralized-auth.png and /dev/null differ
diff --git a/content/identity/decentralized-authentication-future-of-authentication/WP-decentralized-auth.webp b/content/identity/decentralized-authentication-future-of-authentication/WP-decentralized-auth.webp
new file mode 100644
index 000000000..b4ed82617
Binary files /dev/null and b/content/identity/decentralized-authentication-future-of-authentication/WP-decentralized-auth.webp differ
diff --git a/content/identity/decentralized-authentication-future-of-authentication/dec-auth.jpg b/content/identity/decentralized-authentication-future-of-authentication/dec-auth.jpg
deleted file mode 100644
index 275cdd754..000000000
Binary files a/content/identity/decentralized-authentication-future-of-authentication/dec-auth.jpg and /dev/null differ
diff --git a/content/identity/decentralized-authentication-future-of-authentication/dec-auth.webp b/content/identity/decentralized-authentication-future-of-authentication/dec-auth.webp
new file mode 100644
index 000000000..abed744f1
Binary files /dev/null and b/content/identity/decentralized-authentication-future-of-authentication/dec-auth.webp differ
diff --git a/content/identity/decentralized-authentication-future-of-authentication/decentralized-auth.png b/content/identity/decentralized-authentication-future-of-authentication/decentralized-auth.png
deleted file mode 100644
index 3850fd131..000000000
Binary files a/content/identity/decentralized-authentication-future-of-authentication/decentralized-auth.png and /dev/null differ
diff --git a/content/identity/decentralized-authentication-future-of-authentication/decentralized-auth.webp b/content/identity/decentralized-authentication-future-of-authentication/decentralized-auth.webp
new file mode 100644
index 000000000..0452ed92d
Binary files /dev/null and b/content/identity/decentralized-authentication-future-of-authentication/decentralized-auth.webp differ
diff --git a/content/identity/decentralized-authentication-future-of-authentication/index.md b/content/identity/decentralized-authentication-future-of-authentication/index.md
index e43e99f01..747c81e02 100644
--- a/content/identity/decentralized-authentication-future-of-authentication/index.md
+++ b/content/identity/decentralized-authentication-future-of-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Will Decentralized Auth Change the Perception of Consumer Identities in 2022?"
date: "2022-01-18"
-coverImage: "dec-auth.jpg"
+coverImage: "dec-auth.webp"
tags: ["authentication","identity verification","cx"]
author: "Rakesh Soni"
description: "Whether we talk about inappropriate data collection or a loophole in managing consumer identities, anything could lead to compromised sensitive information. Here’s where the concept of decentralized authentication in identity management comes into play."
@@ -43,7 +43,7 @@ If the person desires to get admission to a carrier, it's sufficient to give its
If they match, admission is granted. In greater ideal scenarios, the person can derive separate key pairs from a non-public key to generate different identifiers for one-of-a-kind relationships to allow privacy-pleasant protocols.
-[](https://www.loginradius.com/resource/decentralized-authentication/)
+[](https://www.loginradius.com/resource/decentralized-authentication/)
## Benefits of Decentralized Authentication
@@ -73,4 +73,4 @@ The modern technological ecosystem has offered endless possibilities to build a
Decentralized authentication can be the game-changer in mitigating the risks of [identity theft](https://www.loginradius.com/blog/identity/identity-theft-frauds/) in both the government and private sectors. Organizations thinking of enhancing consumer information security should strictly put their best foot forward to incorporate decentralized authentication for a secure experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=decentralized-authentication-future-of-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=decentralized-authentication-future-of-authentication)
diff --git a/content/identity/decoding-ethics-identity-first-security/EB-GD-to-mod-cust-id.png b/content/identity/decoding-ethics-identity-first-security/EB-GD-to-mod-cust-id.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/identity/decoding-ethics-identity-first-security/EB-GD-to-mod-cust-id.png and /dev/null differ
diff --git a/content/identity/decoding-ethics-identity-first-security/EB-GD-to-mod-cust-id.webp b/content/identity/decoding-ethics-identity-first-security/EB-GD-to-mod-cust-id.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/identity/decoding-ethics-identity-first-security/EB-GD-to-mod-cust-id.webp differ
diff --git a/content/identity/decoding-ethics-identity-first-security/ciam-eb.png b/content/identity/decoding-ethics-identity-first-security/ciam-eb.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/identity/decoding-ethics-identity-first-security/ciam-eb.png and /dev/null differ
diff --git a/content/identity/decoding-ethics-identity-first-security/ciam-eb.webp b/content/identity/decoding-ethics-identity-first-security/ciam-eb.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/identity/decoding-ethics-identity-first-security/ciam-eb.webp differ
diff --git a/content/identity/decoding-ethics-identity-first-security/id-first.jpg b/content/identity/decoding-ethics-identity-first-security/id-first.jpg
deleted file mode 100644
index 04d5c0b8f..000000000
Binary files a/content/identity/decoding-ethics-identity-first-security/id-first.jpg and /dev/null differ
diff --git a/content/identity/decoding-ethics-identity-first-security/id-first.webp b/content/identity/decoding-ethics-identity-first-security/id-first.webp
new file mode 100644
index 000000000..a6e282567
Binary files /dev/null and b/content/identity/decoding-ethics-identity-first-security/id-first.webp differ
diff --git a/content/identity/decoding-ethics-identity-first-security/index.md b/content/identity/decoding-ethics-identity-first-security/index.md
index 1a9306696..8f87b60c0 100644
--- a/content/identity/decoding-ethics-identity-first-security/index.md
+++ b/content/identity/decoding-ethics-identity-first-security/index.md
@@ -1,7 +1,7 @@
---
title: "What Brands Need to Know for Building the Future of Data Compliance?"
date: "2022-09-19"
-coverImage: "id-first.jpg"
+coverImage: "id-first.webp"
tags: ["identity management", "mfa", "ciam","cx"]
author: "Rakesh Soni"
description: "Identity management is undoubtedly the new leadership model for data protection and business growth. And an identity-first security mechanism is swiftly becoming the need of the hour. This blog highlights the aspects of incorporating identity-first security and how businesses can navigate their digital success."
@@ -49,7 +49,7 @@ With an identity-first security approach, businesses can:
* Ensure access is granted to the right person at the right time via automated processes without compromising security.
* Offer stringent layers of security through [multi-factor authentication](https://www.loginradius.com/multi-factor-authentication/) (MFA) and risk-based authentication (RBA)
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
## The Crucial Role of An Identity Management Platform
@@ -70,4 +70,4 @@ If you wish to experience how LoginRadius works for your business, reach us toda
Our product experts will show you the power of the LoginRadius Identity Platform, discuss your use cases, and explain how our cloud-based identity management solution ensures robust security for your business.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=decoding-ethics-identity-first-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=decoding-ethics-identity-first-security)
diff --git a/content/identity/difference-between-authentication-login/auth-login.jpg b/content/identity/difference-between-authentication-login/auth-login.jpg
deleted file mode 100644
index 10dcd5881..000000000
Binary files a/content/identity/difference-between-authentication-login/auth-login.jpg and /dev/null differ
diff --git a/content/identity/difference-between-authentication-login/auth-login.webp b/content/identity/difference-between-authentication-login/auth-login.webp
new file mode 100644
index 000000000..2798979eb
Binary files /dev/null and b/content/identity/difference-between-authentication-login/auth-login.webp differ
diff --git a/content/identity/difference-between-authentication-login/index.md b/content/identity/difference-between-authentication-login/index.md
index 3682ee18d..241d9ee5d 100644
--- a/content/identity/difference-between-authentication-login/index.md
+++ b/content/identity/difference-between-authentication-login/index.md
@@ -1,7 +1,7 @@
---
title: "Authentication vs Login - What’s the Difference?"
date: "2022-05-18"
-coverImage: "auth-login.jpg"
+coverImage: "auth-login.webp"
tags: ["data security","authentication","login"]
author: "Vishal Sharma"
description: "Most cybercriminals attack users and exploit businesses by targeting weak authentication and login mechanisms. Businesses first need to understand the fundamental difference between authentication and login. Once they know the aspects of authentication vs. login, the next step is to ensure a stringent layer of security for their users."
@@ -89,4 +89,4 @@ LoginRadius CIAM platform is designed to help businesses reach their targeted go
If you wish to experience how LoginRadius works for your business, reach us today to schedule a free personalized demo.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=difference-between-authentication-login)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=difference-between-authentication-login)
\ No newline at end of file
diff --git a/content/identity/difference-between-identity-fabrics-zero-trust/WP-Zero-Trust-Security-1.png b/content/identity/difference-between-identity-fabrics-zero-trust/WP-Zero-Trust-Security-1.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/difference-between-identity-fabrics-zero-trust/WP-Zero-Trust-Security-1.png and /dev/null differ
diff --git a/content/identity/difference-between-identity-fabrics-zero-trust/WP-Zero-Trust-Security-1.webp b/content/identity/difference-between-identity-fabrics-zero-trust/WP-Zero-Trust-Security-1.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/difference-between-identity-fabrics-zero-trust/WP-Zero-Trust-Security-1.webp differ
diff --git a/content/identity/difference-between-identity-fabrics-zero-trust/id-fabrics.jpg b/content/identity/difference-between-identity-fabrics-zero-trust/id-fabrics.jpg
deleted file mode 100644
index 8af1c93d1..000000000
Binary files a/content/identity/difference-between-identity-fabrics-zero-trust/id-fabrics.jpg and /dev/null differ
diff --git a/content/identity/difference-between-identity-fabrics-zero-trust/id-fabrics.webp b/content/identity/difference-between-identity-fabrics-zero-trust/id-fabrics.webp
new file mode 100644
index 000000000..ba33d2c4d
Binary files /dev/null and b/content/identity/difference-between-identity-fabrics-zero-trust/id-fabrics.webp differ
diff --git a/content/identity/difference-between-identity-fabrics-zero-trust/index.md b/content/identity/difference-between-identity-fabrics-zero-trust/index.md
index 90072711e..0ea8440d9 100644
--- a/content/identity/difference-between-identity-fabrics-zero-trust/index.md
+++ b/content/identity/difference-between-identity-fabrics-zero-trust/index.md
@@ -1,7 +1,7 @@
---
title: "Identity Fabric vs. Zero Trust: Is One a Better Alternative Than The Other?"
date: "2022-10-27"
-coverImage: "id-fabrics.jpg"
+coverImage: "id-fabrics.webp"
tags: ["identity fabric", "zero trust", "identity management"]
author: "Rakesh Soni"
description: "Identity fabric and zero trust are two different ways of managing business resources, one focusing on identity and the other on data. This blog will help you understand the difference between the two approaches and their benefits for your organization's security strategy."
@@ -102,7 +102,7 @@ By using the Zero Trust strategy, you:
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
## Identity Fabric vs Zero Trust: Which is Better?
@@ -119,4 +119,4 @@ Therefore, both identity fabric and zero trust are two different ways of managin
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=difference-between-identity-fabrics-zero-trust)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=difference-between-identity-fabrics-zero-trust)
diff --git a/content/identity/difference-between-identity-fabrics-zero-trust/zero-trust-wp.png b/content/identity/difference-between-identity-fabrics-zero-trust/zero-trust-wp.png
deleted file mode 100644
index 3e6b81ee6..000000000
Binary files a/content/identity/difference-between-identity-fabrics-zero-trust/zero-trust-wp.png and /dev/null differ
diff --git a/content/identity/difference-between-identity-fabrics-zero-trust/zero-trust-wp.webp b/content/identity/difference-between-identity-fabrics-zero-trust/zero-trust-wp.webp
new file mode 100644
index 000000000..2f7c01062
Binary files /dev/null and b/content/identity/difference-between-identity-fabrics-zero-trust/zero-trust-wp.webp differ
diff --git a/content/identity/difference-between-incident-response-disaster-recovery/WP-enterprise-security.png b/content/identity/difference-between-incident-response-disaster-recovery/WP-enterprise-security.png
deleted file mode 100644
index 0078dc82e..000000000
Binary files a/content/identity/difference-between-incident-response-disaster-recovery/WP-enterprise-security.png and /dev/null differ
diff --git a/content/identity/difference-between-incident-response-disaster-recovery/WP-enterprise-security.webp b/content/identity/difference-between-incident-response-disaster-recovery/WP-enterprise-security.webp
new file mode 100644
index 000000000..91396fdeb
Binary files /dev/null and b/content/identity/difference-between-incident-response-disaster-recovery/WP-enterprise-security.webp differ
diff --git a/content/identity/difference-between-incident-response-disaster-recovery/disaster-recovery.jpg b/content/identity/difference-between-incident-response-disaster-recovery/disaster-recovery.jpg
deleted file mode 100644
index 0a6806f37..000000000
Binary files a/content/identity/difference-between-incident-response-disaster-recovery/disaster-recovery.jpg and /dev/null differ
diff --git a/content/identity/difference-between-incident-response-disaster-recovery/disaster-recovery.webp b/content/identity/difference-between-incident-response-disaster-recovery/disaster-recovery.webp
new file mode 100644
index 000000000..8af1ef6c2
Binary files /dev/null and b/content/identity/difference-between-incident-response-disaster-recovery/disaster-recovery.webp differ
diff --git a/content/identity/difference-between-incident-response-disaster-recovery/enterprise-security.png b/content/identity/difference-between-incident-response-disaster-recovery/enterprise-security.png
deleted file mode 100644
index 54fa85b27..000000000
Binary files a/content/identity/difference-between-incident-response-disaster-recovery/enterprise-security.png and /dev/null differ
diff --git a/content/identity/difference-between-incident-response-disaster-recovery/enterprise-security.webp b/content/identity/difference-between-incident-response-disaster-recovery/enterprise-security.webp
new file mode 100644
index 000000000..f6e811bc7
Binary files /dev/null and b/content/identity/difference-between-incident-response-disaster-recovery/enterprise-security.webp differ
diff --git a/content/identity/difference-between-incident-response-disaster-recovery/index.md b/content/identity/difference-between-incident-response-disaster-recovery/index.md
index c50668912..f46c0da10 100644
--- a/content/identity/difference-between-incident-response-disaster-recovery/index.md
+++ b/content/identity/difference-between-incident-response-disaster-recovery/index.md
@@ -1,7 +1,7 @@
---
title: "Incident Response Vs. Disaster Recovery: What’s The Difference and Which Do You Need?"
date: "2022-11-25"
-coverImage: "disaster-recovery.jpg"
+coverImage: "disaster-recovery.webp"
tags: ["incident response", "disaster recovery", "enterprise security"]
author: "Alok Patidar"
description: "When a business has a disaster, its recovery falls into two categories: incident response and disaster recovery. This blog offers an overview of the most important aspects of each, as well as the reasons you might choose one over the other."
@@ -38,7 +38,7 @@ Disaster recovery plans focus on [business continuity](https://blog.loginradius.
There's a lot of confusion around the difference between incident response vs. disaster recovery plans. It's understandable, as they both address similar types of events and can seem like they're interchangeable. But the truth is that they are very different, and you need to know which one you need before you start planning your company's security strategy.
-[](https://www.loginradius.com/resource/principles-of-enterprise-security/)
+[](https://www.loginradius.com/resource/principles-of-enterprise-security/)
Incident response plans are important to any organization's cyber security strategy. It's a set of policies and procedures that outline what steps need to be taken in case of a cyberattack and how the organization plan to respond to an attack if its networks become compromised. The goal of an incident response plan is to ensure that your business can respond quickly and efficiently when there’s been a breach or loss of data. It also helps you identify what went wrong and how you can prevent it from happening again.
@@ -53,4 +53,4 @@ If you have a disaster recovery plan but no incident response plan, you may ulti
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=difference-between-incident-response-disaster-recovery)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=difference-between-incident-response-disaster-recovery)
\ No newline at end of file
diff --git a/content/identity/difference-between-personal-info-pii/DS-consent-mngmnt.png b/content/identity/difference-between-personal-info-pii/DS-consent-mngmnt.png
deleted file mode 100644
index b2c0a4d84..000000000
Binary files a/content/identity/difference-between-personal-info-pii/DS-consent-mngmnt.png and /dev/null differ
diff --git a/content/identity/difference-between-personal-info-pii/DS-consent-mngmnt.webp b/content/identity/difference-between-personal-info-pii/DS-consent-mngmnt.webp
new file mode 100644
index 000000000..8dcbd7082
Binary files /dev/null and b/content/identity/difference-between-personal-info-pii/DS-consent-mngmnt.webp differ
diff --git a/content/identity/difference-between-personal-info-pii/consent-managmt-ds.png b/content/identity/difference-between-personal-info-pii/consent-managmt-ds.png
deleted file mode 100644
index 51524f116..000000000
Binary files a/content/identity/difference-between-personal-info-pii/consent-managmt-ds.png and /dev/null differ
diff --git a/content/identity/difference-between-personal-info-pii/consent-managmt-ds.webp b/content/identity/difference-between-personal-info-pii/consent-managmt-ds.webp
new file mode 100644
index 000000000..ae3c4b53d
Binary files /dev/null and b/content/identity/difference-between-personal-info-pii/consent-managmt-ds.webp differ
diff --git a/content/identity/difference-between-personal-info-pii/index.md b/content/identity/difference-between-personal-info-pii/index.md
index e8d9fb6d3..3c998c93f 100644
--- a/content/identity/difference-between-personal-info-pii/index.md
+++ b/content/identity/difference-between-personal-info-pii/index.md
@@ -1,7 +1,7 @@
---
title: "Personal Information and PII - What’s the Difference?"
date: "2022-03-10"
-coverImage: "pii.jpg"
+coverImage: "pii.webp"
tags: ["data security","identity management","cx"]
author: "Vishal Sharma"
description: "Before organizations gear up to offer stringent security measures to their clients, it’s crucial to understand the fundamental difference between personal data and personally identifiable information (PII)."
@@ -49,7 +49,7 @@ In addition, the regulatory guidelines also stipulate that if the data is no lon
Moreover, supervision and protection of personally identifiable information may become a significant issue for individuals, companies, and governments in the coming years.
-[](https://www.loginradius.com/resource/loginradius-consent-management)
+[](https://www.loginradius.com/resource/loginradius-consent-management)
## Why Should Businesses Immediately Work on Protecting their Clients’ PII?
@@ -89,4 +89,4 @@ Hence, the consumer data privacy and security plan should comply with the rapid
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=difference-between-personal-info-pii)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=difference-between-personal-info-pii)
diff --git a/content/identity/difference-between-personal-info-pii/pii.jpg b/content/identity/difference-between-personal-info-pii/pii.jpg
deleted file mode 100644
index 39276f99c..000000000
Binary files a/content/identity/difference-between-personal-info-pii/pii.jpg and /dev/null differ
diff --git a/content/identity/difference-between-personal-info-pii/pii.webp b/content/identity/difference-between-personal-info-pii/pii.webp
new file mode 100644
index 000000000..71e81f399
Binary files /dev/null and b/content/identity/difference-between-personal-info-pii/pii.webp differ
diff --git a/content/identity/difference-sso-social-login/index.md b/content/identity/difference-sso-social-login/index.md
index e2373c392..fa0a8a013 100644
--- a/content/identity/difference-sso-social-login/index.md
+++ b/content/identity/difference-sso-social-login/index.md
@@ -1,7 +1,7 @@
---
title: "SSO vs. Social Login: What’s the Difference? [Infographic]"
date: "2022-05-31"
-coverImage: "sso-social-login.jpg"
+coverImage: "sso-social-login.webp"
tags: ["sso","social login","cx"]
author: "Rakesh Soni"
description: "The era of unified login has offered numerous ways through which users can authenticate themselves securely and seamlessly. Let’s understand the fundamental differences between SSO and Social Login that helps you choose the right authentication solution for your business requirements."
@@ -45,7 +45,7 @@ While both authentication mechanisms are widely used for securely and seamlessly
To learn more about the Social Login vs. SSO - concept, differences, and techniques, check out the infographic created by LoginRadius.
-
+
## Implementing Social Login and SSO with LoginRadius CIAM
@@ -55,4 +55,4 @@ With [LoginRadius’ social login](https://www.loginradius.com/social-login/) an
If you wish to witness the future of CIAM and how it works for your business, schedule a free personalized demo today!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=difference-sso-social-login)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=difference-sso-social-login)
\ No newline at end of file
diff --git a/content/identity/difference-sso-social-login/social-login-sso.png b/content/identity/difference-sso-social-login/social-login-sso.png
deleted file mode 100644
index 7eb295498..000000000
Binary files a/content/identity/difference-sso-social-login/social-login-sso.png and /dev/null differ
diff --git a/content/identity/difference-sso-social-login/social-login-sso.webp b/content/identity/difference-sso-social-login/social-login-sso.webp
new file mode 100644
index 000000000..31e3da011
Binary files /dev/null and b/content/identity/difference-sso-social-login/social-login-sso.webp differ
diff --git a/content/identity/difference-sso-social-login/sso-social-login.jpg b/content/identity/difference-sso-social-login/sso-social-login.jpg
deleted file mode 100644
index d016dccc2..000000000
Binary files a/content/identity/difference-sso-social-login/sso-social-login.jpg and /dev/null differ
diff --git a/content/identity/difference-sso-social-login/sso-social-login.webp b/content/identity/difference-sso-social-login/sso-social-login.webp
new file mode 100644
index 000000000..e23489052
Binary files /dev/null and b/content/identity/difference-sso-social-login/sso-social-login.webp differ
diff --git a/content/identity/digital-agility/digital-agility.jpg b/content/identity/digital-agility/digital-agility.jpg
deleted file mode 100644
index de023b67f..000000000
Binary files a/content/identity/digital-agility/digital-agility.jpg and /dev/null differ
diff --git a/content/identity/digital-agility/digital-agility.webp b/content/identity/digital-agility/digital-agility.webp
new file mode 100644
index 000000000..6248b1a34
Binary files /dev/null and b/content/identity/digital-agility/digital-agility.webp differ
diff --git a/content/identity/digital-agility/enterprise-buyer-guide-to-consumer-identity.png b/content/identity/digital-agility/enterprise-buyer-guide-to-consumer-identity.png
deleted file mode 100644
index 6b3ba826e..000000000
Binary files a/content/identity/digital-agility/enterprise-buyer-guide-to-consumer-identity.png and /dev/null differ
diff --git a/content/identity/digital-agility/enterprise-buyer-guide-to-consumer-identity.webp b/content/identity/digital-agility/enterprise-buyer-guide-to-consumer-identity.webp
new file mode 100644
index 000000000..ba14612ce
Binary files /dev/null and b/content/identity/digital-agility/enterprise-buyer-guide-to-consumer-identity.webp differ
diff --git a/content/identity/digital-agility/index.md b/content/identity/digital-agility/index.md
index c0edf08e2..c4ca616d4 100644
--- a/content/identity/digital-agility/index.md
+++ b/content/identity/digital-agility/index.md
@@ -1,7 +1,7 @@
---
title: "Why Organizations Must Use API-Driven CIAM for Digital Agility"
date: "2021-02-24"
-coverImage: "digital-agility.jpg"
+coverImage: "digital-agility.webp"
tags: ["ciam solution","digital transformation","cx"]
author: "Rakesh Soni"
description: "Digital agility is the ease with which any organization can adapt to changing business needs – by enabling or changing their business processes. For a successful digital transformation, organizations need to invest in resilient business operations, consumer experience initiatives, and technology."
@@ -46,7 +46,7 @@ Business leaders must plan on having a flexible IAM solution in their working en
For effective [digital transformation](https://www.loginradius.com/blog/identity/2021/01/what-is-digital-transformation/), technology-enabled companies must move from a fixed and rigid IT infrastructure – to a more flexible and component-based API architecture, which can easily be reconstructed or reused. Next, we shall see how an API-based [consumer Identity and Access Management (or CIAM)](https://www.loginradius.com/blog/identity/2019/06/customer-identity-and-access-management/) can be the foundation of digital agility and transformation.
-[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
+[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
## Importance and Benefits of API-driven CIAM
@@ -76,4 +76,4 @@ Organizations need to maximize their digital footprint – to stay relevant in t
Built using extensive API functionalities and open-source SDKs, LoginRadius CIAM provides the best of customization and security – that can work for your business needs.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-agility)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-agility)
diff --git a/content/identity/digital-identity-management/01-dashboard-1024x865.png b/content/identity/digital-identity-management/01-dashboard-1024x865.png
deleted file mode 100644
index 3b069cc45..000000000
Binary files a/content/identity/digital-identity-management/01-dashboard-1024x865.png and /dev/null differ
diff --git a/content/identity/digital-identity-management/01-dashboard-1024x865.webp b/content/identity/digital-identity-management/01-dashboard-1024x865.webp
new file mode 100644
index 000000000..9eac22c2a
Binary files /dev/null and b/content/identity/digital-identity-management/01-dashboard-1024x865.webp differ
diff --git a/content/identity/digital-identity-management/5-Ways-to-Win.png b/content/identity/digital-identity-management/5-Ways-to-Win.png
deleted file mode 100644
index cbbe2c249..000000000
Binary files a/content/identity/digital-identity-management/5-Ways-to-Win.png and /dev/null differ
diff --git a/content/identity/digital-identity-management/5-Ways-to-Win.webp b/content/identity/digital-identity-management/5-Ways-to-Win.webp
new file mode 100644
index 000000000..05973efc7
Binary files /dev/null and b/content/identity/digital-identity-management/5-Ways-to-Win.webp differ
diff --git a/content/identity/digital-identity-management/Digital-Identity-Management-5-Ways-to-Win-V01.02-02-1024x576.png b/content/identity/digital-identity-management/Digital-Identity-Management-5-Ways-to-Win-V01.02-02-1024x576.png
deleted file mode 100644
index 71349cd15..000000000
Binary files a/content/identity/digital-identity-management/Digital-Identity-Management-5-Ways-to-Win-V01.02-02-1024x576.png and /dev/null differ
diff --git a/content/identity/digital-identity-management/Digital-Identity-Management-5-Ways-to-Win-V01.02-02-1024x576.webp b/content/identity/digital-identity-management/Digital-Identity-Management-5-Ways-to-Win-V01.02-02-1024x576.webp
new file mode 100644
index 000000000..7ca4f8d1a
Binary files /dev/null and b/content/identity/digital-identity-management/Digital-Identity-Management-5-Ways-to-Win-V01.02-02-1024x576.webp differ
diff --git a/content/identity/digital-identity-management/LoginRadius-Consumer-Identity-Trend-Report-1-1024x310.png b/content/identity/digital-identity-management/LoginRadius-Consumer-Identity-Trend-Report-1-1024x310.png
deleted file mode 100644
index 365a0ed8d..000000000
Binary files a/content/identity/digital-identity-management/LoginRadius-Consumer-Identity-Trend-Report-1-1024x310.png and /dev/null differ
diff --git a/content/identity/digital-identity-management/LoginRadius-Consumer-Identity-Trend-Report-1-1024x310.webp b/content/identity/digital-identity-management/LoginRadius-Consumer-Identity-Trend-Report-1-1024x310.webp
new file mode 100644
index 000000000..5c6a31469
Binary files /dev/null and b/content/identity/digital-identity-management/LoginRadius-Consumer-Identity-Trend-Report-1-1024x310.webp differ
diff --git a/content/identity/digital-identity-management/digital-identity-mngmnt.jpg b/content/identity/digital-identity-management/digital-identity-mngmnt.jpg
deleted file mode 100644
index cce6487a9..000000000
Binary files a/content/identity/digital-identity-management/digital-identity-mngmnt.jpg and /dev/null differ
diff --git a/content/identity/digital-identity-management/digital-identity-mngmnt.webp b/content/identity/digital-identity-management/digital-identity-mngmnt.webp
new file mode 100644
index 000000000..893948245
Binary files /dev/null and b/content/identity/digital-identity-management/digital-identity-mngmnt.webp differ
diff --git a/content/identity/digital-identity-management/digital-identity-trends-2019.png b/content/identity/digital-identity-management/digital-identity-trends-2019.png
deleted file mode 100644
index 3ce291f26..000000000
Binary files a/content/identity/digital-identity-management/digital-identity-trends-2019.png and /dev/null differ
diff --git a/content/identity/digital-identity-management/digital-identity-trends-2019.webp b/content/identity/digital-identity-management/digital-identity-trends-2019.webp
new file mode 100644
index 000000000..80fb05df0
Binary files /dev/null and b/content/identity/digital-identity-management/digital-identity-trends-2019.webp differ
diff --git a/content/identity/digital-identity-management/index.md b/content/identity/digital-identity-management/index.md
index 54a45af1d..f32c425a6 100644
--- a/content/identity/digital-identity-management/index.md
+++ b/content/identity/digital-identity-management/index.md
@@ -1,7 +1,7 @@
---
title: "Digital Identity Management: 5 Ways to Win Customer Trust"
date: "2019-10-01"
-coverImage: "digital-identity-mngmnt.jpg"
+coverImage: "digital-identity-mngmnt.webp"
tags: ["digital identity management","ciam solution","cx"]
author: "Rakesh Soni"
description: "In industry , digital identity management relates specifically to how the personal information of a customer is obtained, processed, and accessed safely."
@@ -13,7 +13,7 @@ In business, [digital identity management](https://www.loginradius.com/blog/grow
While this may appear simple, many businesses fall prey to misconceptions about building or managing a customer’s digital identity. To help you leverage customer identity data, let’s discuss the top three misconceptions that trip businesses up.
-
+
## 3 Common misconceptions around digital identity
@@ -33,7 +33,7 @@ With [customer identity and access management](https://www.loginradius.com/blog/
Due to marketing’s reliance on user experience mapping, session analytics, and content engagements, this myth is rampant. As a result, many businesses mistakenly think “behavioral” data is all they need for digital identity management. Not true. In the next section, we’ll explain why.
-- 
+- 
## Why is digital identity management important?
@@ -44,7 +44,7 @@ We live in an era where data is the most valuable commodity in the world. Howeve
Malicious software, hackers, online fraud, and user errors all pose a danger to the digital identification data that you collect or store.
-[](https://www.loginradius.com/resource/digital-identity-trends-2019/)
+[](https://www.loginradius.com/resource/digital-identity-trends-2019/)
For businesses that collect or store customer data, security is vital to winning and maintaining customer trust. If you’re uncertain how, here are 5 methods that can help.
@@ -92,4 +92,4 @@ Did you know that requesting consent can also strengthen your brand reputation a
Yes—with CIAM software. LoginRadius CIAM offers a variety of highly-secure customer identity management features. For added peace of mind, LoginRadius keeps its platforms ahead of emerging data regulations and consistently performs rigorous updates.
-[](https://www.loginradius.com/resource/digital-identity-trends-2020/)
+[](https://www.loginradius.com/resource/digital-identity-trends-2020/)
diff --git a/content/identity/digital-identity-verification/WP-mfa.png b/content/identity/digital-identity-verification/WP-mfa.png
deleted file mode 100644
index e028d55fb..000000000
Binary files a/content/identity/digital-identity-verification/WP-mfa.png and /dev/null differ
diff --git a/content/identity/digital-identity-verification/WP-mfa.webp b/content/identity/digital-identity-verification/WP-mfa.webp
new file mode 100644
index 000000000..96ac842dc
Binary files /dev/null and b/content/identity/digital-identity-verification/WP-mfa.webp differ
diff --git a/content/identity/digital-identity-verification/dig-identity-verification.jpg b/content/identity/digital-identity-verification/dig-identity-verification.jpg
deleted file mode 100644
index 14623b4e0..000000000
Binary files a/content/identity/digital-identity-verification/dig-identity-verification.jpg and /dev/null differ
diff --git a/content/identity/digital-identity-verification/dig-identity-verification.webp b/content/identity/digital-identity-verification/dig-identity-verification.webp
new file mode 100644
index 000000000..dc6bd1377
Binary files /dev/null and b/content/identity/digital-identity-verification/dig-identity-verification.webp differ
diff --git a/content/identity/digital-identity-verification/index.md b/content/identity/digital-identity-verification/index.md
index 6eeed489c..a630b6c01 100644
--- a/content/identity/digital-identity-verification/index.md
+++ b/content/identity/digital-identity-verification/index.md
@@ -1,7 +1,7 @@
---
title: "Exploring Digital Identity Verification with Effective Crucial Data Checks"
date: "2024-01-30"
-coverImage: "dig-identity-verification.jpg"
+coverImage: "dig-identity-verification.webp"
tags: ["identity verification","digital identity management","cx"]
author: "Rakesh Soni"
description: "Ensuring the integrity of digital identities has become businesses' topmost concern in this rapidly evolving world. With every business, especially banking and finance, providing digital services for the customer’s convenience, how do they ensure they have the right person? Well, this blog delves into the intricacies of digital identity verification and how it can benefit businesses struggling with the same situation."
@@ -39,7 +39,7 @@ When a customer visits a new financial app or service, the company takes the use
Multi-factor authentication adds a layer of protection beyond just a username and password. It is one of the **digital identity verification solutions** where users provide multiple forms of identification, like OTPs, email-based authentication, fingerprint scans, and others, which makes it more difficult for the unauthorized person to access the information.
-[](https://www.loginradius.com/resource/whitepaper/mfa-digital-identity-security/)
+[](https://www.loginradius.com/resource/whitepaper/mfa-digital-identity-security/)
### 3. ID Document Verification
@@ -78,4 +78,4 @@ Investing in robust **digital identity verification solutions** is essential bec
Fraudsters can easily identify and exploit improper verification methods; that’s why businesses require robust multi-layered identity and access management solutions, like [LoginRadius’s CIAM](https://www.loginradius.com/authentication/) and risk-based analytics. The robust CIAM solution makes the **digital identity verification** process easy as it works on the three main components of verification: identification, verification, and authentication.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-identity-verification)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-identity-verification)
\ No newline at end of file
diff --git a/content/identity/digital-privacy-best-practices/Book-a-free-demo-request-1024x310.png b/content/identity/digital-privacy-best-practices/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/digital-privacy-best-practices/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/digital-privacy-best-practices/Book-a-free-demo-request-1024x310.webp b/content/identity/digital-privacy-best-practices/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/digital-privacy-best-practices/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/digital-privacy-best-practices/CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.png b/content/identity/digital-privacy-best-practices/CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.png
deleted file mode 100644
index c02a1338a..000000000
Binary files a/content/identity/digital-privacy-best-practices/CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.png and /dev/null differ
diff --git a/content/identity/digital-privacy-best-practices/CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.webp b/content/identity/digital-privacy-best-practices/CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.webp
new file mode 100644
index 000000000..1b0055d88
Binary files /dev/null and b/content/identity/digital-privacy-best-practices/CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.webp differ
diff --git a/content/identity/digital-privacy-best-practices/digital-privacy-best-practices.jpg b/content/identity/digital-privacy-best-practices/digital-privacy-best-practices.jpg
deleted file mode 100644
index 913b219b3..000000000
Binary files a/content/identity/digital-privacy-best-practices/digital-privacy-best-practices.jpg and /dev/null differ
diff --git a/content/identity/digital-privacy-best-practices/digital-privacy-best-practices.webp b/content/identity/digital-privacy-best-practices/digital-privacy-best-practices.webp
new file mode 100644
index 000000000..02ccd440a
Binary files /dev/null and b/content/identity/digital-privacy-best-practices/digital-privacy-best-practices.webp differ
diff --git a/content/identity/digital-privacy-best-practices/digital-privacy.jpg b/content/identity/digital-privacy-best-practices/digital-privacy.jpg
deleted file mode 100644
index b82850dcb..000000000
Binary files a/content/identity/digital-privacy-best-practices/digital-privacy.jpg and /dev/null differ
diff --git a/content/identity/digital-privacy-best-practices/digital-privacy.webp b/content/identity/digital-privacy-best-practices/digital-privacy.webp
new file mode 100644
index 000000000..10944a95b
Binary files /dev/null and b/content/identity/digital-privacy-best-practices/digital-privacy.webp differ
diff --git a/content/identity/digital-privacy-best-practices/image2-3.jpg b/content/identity/digital-privacy-best-practices/image2-3.jpg
deleted file mode 100644
index 8521d2c68..000000000
Binary files a/content/identity/digital-privacy-best-practices/image2-3.jpg and /dev/null differ
diff --git a/content/identity/digital-privacy-best-practices/image2-3.webp b/content/identity/digital-privacy-best-practices/image2-3.webp
new file mode 100644
index 000000000..b53c4cc25
Binary files /dev/null and b/content/identity/digital-privacy-best-practices/image2-3.webp differ
diff --git a/content/identity/digital-privacy-best-practices/index.md b/content/identity/digital-privacy-best-practices/index.md
index a5abaa314..5e6c13416 100644
--- a/content/identity/digital-privacy-best-practices/index.md
+++ b/content/identity/digital-privacy-best-practices/index.md
@@ -1,7 +1,7 @@
---
title: "Digital Privacy: Securing Consumer Privacy with LoginRadius"
date: "2019-12-12"
-coverImage: "digital-privacy.jpg"
+coverImage: "digital-privacy.webp"
tags: ["data privacy","compliance","ciam solution"]
author: "Rakesh Soni"
description: "Concerns over digital data security have always been at the forefront of a CIO 's mind. But it generated fresh concern when the 2017 Equifax hack struck. Here's how executives work to protect the digital privacy of consumer data across business verticals."
@@ -42,7 +42,7 @@ Simply put, data or digital privacy is a basic human right. The concept in busin
After the European Union enacted the [General Data Protection Regulation (GDPR)](https://www.loginradius.com/gdpr-and-privacy/), many companies have begun exploring the role of privacy as a human right. It’s been giving a new direction to companies to develop the necessary tools and processes to collect consumer data and not exploit it.
-[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
+[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
## 5 Major Threats to Data Privacy in the Digital Age
@@ -110,7 +110,7 @@ Don’t wait to draft incident policies for your customers after a data breach.
The ability to demonstrate Return on Mitigation (ROM) is also a critical metric to CEOs. To do this, calculate [potential risks and assess](https://www.loginradius.com/loginradius-business-continuity-covid-19-outbreak/) how much can be saved through on-time mitigation.
-
+
## How LoginRadius Helps Businesses Protect Consumer Data
@@ -140,4 +140,4 @@ LoginRadius complies with major regulatory laws and privacy requirements. It hel
Getting your enterprise onboard with these best practices is the first step to attaining better digital privacy for your consumers. Start by setting up a data maintenance process—operational efficiencies will follow through.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-privacy-best-practices)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-privacy-best-practices)
diff --git "a/content/identity/digital-transformation-consumer-iam/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.png" "b/content/identity/digital-transformation-consumer-iam/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.png"
deleted file mode 100644
index d63fdd4ac..000000000
Binary files "a/content/identity/digital-transformation-consumer-iam/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.png" and /dev/null differ
diff --git "a/content/identity/digital-transformation-consumer-iam/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.webp" "b/content/identity/digital-transformation-consumer-iam/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.webp"
new file mode 100644
index 000000000..4486d4d7d
Binary files /dev/null and "b/content/identity/digital-transformation-consumer-iam/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.webp" differ
diff --git a/content/identity/digital-transformation-consumer-iam/EB-GD-to-MFA.png b/content/identity/digital-transformation-consumer-iam/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/digital-transformation-consumer-iam/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/digital-transformation-consumer-iam/EB-GD-to-MFA.webp b/content/identity/digital-transformation-consumer-iam/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/digital-transformation-consumer-iam/EB-GD-to-MFA.webp differ
diff --git a/content/identity/digital-transformation-consumer-iam/digital-transformation-consumer-iam-cover.jpg b/content/identity/digital-transformation-consumer-iam/digital-transformation-consumer-iam-cover.jpg
deleted file mode 100644
index 24b8c2d94..000000000
Binary files a/content/identity/digital-transformation-consumer-iam/digital-transformation-consumer-iam-cover.jpg and /dev/null differ
diff --git a/content/identity/digital-transformation-consumer-iam/digital-transformation-consumer-iam-cover.webp b/content/identity/digital-transformation-consumer-iam/digital-transformation-consumer-iam-cover.webp
new file mode 100644
index 000000000..6a6c13aa0
Binary files /dev/null and b/content/identity/digital-transformation-consumer-iam/digital-transformation-consumer-iam-cover.webp differ
diff --git a/content/identity/digital-transformation-consumer-iam/index.md b/content/identity/digital-transformation-consumer-iam/index.md
index 06be18df4..e7a0f9439 100644
--- a/content/identity/digital-transformation-consumer-iam/index.md
+++ b/content/identity/digital-transformation-consumer-iam/index.md
@@ -1,7 +1,7 @@
---
title: "How Businesses are Experiencing Digital Transformation with Consumer IAM"
date: "2021-06-25"
-coverImage: "digital-transformation-consumer-iam-cover.jpg"
+coverImage: "digital-transformation-consumer-iam-cover.webp"
tags: ["digital transformation","ciam solution","mfa","cx"]
author: "Navanita Devi"
description: "Digital transformation empowers businesses to change the way they operate. It’s not just a buzzword or marketing gimmick, it’s a real and tangible way to revamp how you do business and improve your company. Let’s understand it through the lens of consumer IAM."
@@ -44,7 +44,7 @@ The experience starts with a compelling registration process that can be complet
Social login via platforms like Google or Facebook might alleviate registration fatigue, but it can also pose security problems which may necessitate the use of [multi-factor authentication](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/). With highly low-friction authentication, the consumer enjoys compelling and consistent interaction across channels.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### 2. **Single consumer view**
@@ -78,4 +78,4 @@ Consumer IAM has swiftly established itself as a critical component of a positiv
If you’re interested in learning more about how the LoginRadius platform works, [schedule a demo](https://www.loginradius.com/schedule-demo/) today.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-transformation-consumer-iam)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-transformation-consumer-iam)
diff --git a/content/identity/digital-transformation-safeguarding-customer-experience/core-of-digital-transformation.png b/content/identity/digital-transformation-safeguarding-customer-experience/core-of-digital-transformation.png
deleted file mode 100644
index eaa925c92..000000000
Binary files a/content/identity/digital-transformation-safeguarding-customer-experience/core-of-digital-transformation.png and /dev/null differ
diff --git a/content/identity/digital-transformation-safeguarding-customer-experience/core-of-digital-transformation.webp b/content/identity/digital-transformation-safeguarding-customer-experience/core-of-digital-transformation.webp
new file mode 100644
index 000000000..449e28840
Binary files /dev/null and b/content/identity/digital-transformation-safeguarding-customer-experience/core-of-digital-transformation.webp differ
diff --git a/content/identity/digital-transformation-safeguarding-customer-experience/digital-transformation-safeguarding.jpg b/content/identity/digital-transformation-safeguarding-customer-experience/digital-transformation-safeguarding.jpg
deleted file mode 100644
index da97c5100..000000000
Binary files a/content/identity/digital-transformation-safeguarding-customer-experience/digital-transformation-safeguarding.jpg and /dev/null differ
diff --git a/content/identity/digital-transformation-safeguarding-customer-experience/digital-transformation-safeguarding.webp b/content/identity/digital-transformation-safeguarding-customer-experience/digital-transformation-safeguarding.webp
new file mode 100644
index 000000000..f8efeedba
Binary files /dev/null and b/content/identity/digital-transformation-safeguarding-customer-experience/digital-transformation-safeguarding.webp differ
diff --git a/content/identity/digital-transformation-safeguarding-customer-experience/index.md b/content/identity/digital-transformation-safeguarding-customer-experience/index.md
index 14e9b9c3b..f3e8b2031 100644
--- a/content/identity/digital-transformation-safeguarding-customer-experience/index.md
+++ b/content/identity/digital-transformation-safeguarding-customer-experience/index.md
@@ -1,7 +1,7 @@
---
title: "Digital Transformation: Safeguarding the Customer Experience"
date: "2018-10-03"
-coverImage: "digital-transformation-safeguarding.jpg"
+coverImage: "digital-transformation-safeguarding.webp"
tags: ["digital transformation","customer identity management","cx"]
author: "Rakesh Soni"
description: "Superior customer service is one of the key factors for company success in today's digitally linked world. Personalization, which harnesses the power of digital transformation in order to create curated interactions that can fuel customer engagement and market differentiation, is at the core of the experience."
@@ -39,7 +39,7 @@ The LoginRadius CIAM platform has hosting and data security approval for all of
Many of these certifications involve rigorous third-party assessment of either our cloud service or our data management and security practices. They also help us achieve compliance with the EU GDPR: the most significant privacy legislation to impact how organizations deal with their customers’ information.
-[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
+[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
In order to [comply with the GDPR](https://www.loginradius.com/resource/loginradius-and-gdpr-compliance/), LoginRadius has worked hard to ensure that our products and capabilities are leveraged to guarantee data privacy and compliance for every one of our 3,000+ customers. Some of these features include gaining [customer consent](https://www.loginradius.com/blog/identity/consent-management/) for access to their personal data, allowing customers to view, export, and edit their personal data at any time, and providing customers with a _right to be forgotten_ by deleting their accounts entirely.
diff --git a/content/identity/dns-cache-poisoning/buyer-guide-to-multi-factor-authentication-ebook.png b/content/identity/dns-cache-poisoning/buyer-guide-to-multi-factor-authentication-ebook.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/dns-cache-poisoning/buyer-guide-to-multi-factor-authentication-ebook.png and /dev/null differ
diff --git a/content/identity/dns-cache-poisoning/buyer-guide-to-multi-factor-authentication-ebook.webp b/content/identity/dns-cache-poisoning/buyer-guide-to-multi-factor-authentication-ebook.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/dns-cache-poisoning/buyer-guide-to-multi-factor-authentication-ebook.webp differ
diff --git a/content/identity/dns-cache-poisoning/dns-cache-poisoning-is-dangerous-for-your-business.jpg b/content/identity/dns-cache-poisoning/dns-cache-poisoning-is-dangerous-for-your-business.jpg
deleted file mode 100644
index 25019a5d5..000000000
Binary files a/content/identity/dns-cache-poisoning/dns-cache-poisoning-is-dangerous-for-your-business.jpg and /dev/null differ
diff --git a/content/identity/dns-cache-poisoning/dns-cache-poisoning-is-dangerous-for-your-business.webp b/content/identity/dns-cache-poisoning/dns-cache-poisoning-is-dangerous-for-your-business.webp
new file mode 100644
index 000000000..68bd8995a
Binary files /dev/null and b/content/identity/dns-cache-poisoning/dns-cache-poisoning-is-dangerous-for-your-business.webp differ
diff --git a/content/identity/dns-cache-poisoning/index.md b/content/identity/dns-cache-poisoning/index.md
index 72f4f24d4..2fddeb250 100644
--- a/content/identity/dns-cache-poisoning/index.md
+++ b/content/identity/dns-cache-poisoning/index.md
@@ -1,7 +1,7 @@
---
title: "DNS Cache Poisoning: Why Is It Dangerous for Your Business"
date: "2021-01-13"
-coverImage: "dns-cache-poisoning-is-dangerous-for-your-business.jpg"
+coverImage: "dns-cache-poisoning-is-dangerous-for-your-business.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -36,7 +36,7 @@ When the computer is poisoned, it will divert you to a fake IP address that look
## What Are the Different Stages of Attack of DNS Cache Poisoning
-
+
* First Stage
@@ -98,7 +98,7 @@ Some of the resources we have specified will help you in this regard.
* Using DNSSEC (Domain Name System Security Extensions) helps to keep DNS lookup fool-proof and authentic.
* You can use end-to-end encryption to send DNS requests and replies. Hackers will not be able to duplicate the unique security certificate that is present on the legitimate website.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### For endpoint users
@@ -120,4 +120,4 @@ This new IP address might be from a malicious phishing website, where the users
Hence, understanding what is DNS cache poisoning, how to detect it, and ways to prevent it is crucial so you can [protect your business](https://www.loginradius.com/blog/identity/2020/06/consumer-data-privacy-security/) against it.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=dns-cache-poisoning)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=dns-cache-poisoning)
\ No newline at end of file
diff --git a/content/identity/dns-cache-poisoning/stages-of-attack-of-DNS-cache-poisoning.png b/content/identity/dns-cache-poisoning/stages-of-attack-of-DNS-cache-poisoning.png
deleted file mode 100644
index 13026a6c9..000000000
Binary files a/content/identity/dns-cache-poisoning/stages-of-attack-of-DNS-cache-poisoning.png and /dev/null differ
diff --git a/content/identity/dns-cache-poisoning/stages-of-attack-of-DNS-cache-poisoning.webp b/content/identity/dns-cache-poisoning/stages-of-attack-of-DNS-cache-poisoning.webp
new file mode 100644
index 000000000..b20a1c654
Binary files /dev/null and b/content/identity/dns-cache-poisoning/stages-of-attack-of-DNS-cache-poisoning.webp differ
diff --git a/content/identity/ecommerce-security/DS-How-Retail-Consumer-Goods-Companies.png b/content/identity/ecommerce-security/DS-How-Retail-Consumer-Goods-Companies.png
deleted file mode 100644
index b53535020..000000000
Binary files a/content/identity/ecommerce-security/DS-How-Retail-Consumer-Goods-Companies.png and /dev/null differ
diff --git a/content/identity/ecommerce-security/DS-How-Retail-Consumer-Goods-Companies.webp b/content/identity/ecommerce-security/DS-How-Retail-Consumer-Goods-Companies.webp
new file mode 100644
index 000000000..02dbccb4e
Binary files /dev/null and b/content/identity/ecommerce-security/DS-How-Retail-Consumer-Goods-Companies.webp differ
diff --git a/content/identity/ecommerce-security/Ecommerce-security-1.png b/content/identity/ecommerce-security/Ecommerce-security-1.png
deleted file mode 100644
index 48691d7a5..000000000
Binary files a/content/identity/ecommerce-security/Ecommerce-security-1.png and /dev/null differ
diff --git a/content/identity/ecommerce-security/Ecommerce-security-1.webp b/content/identity/ecommerce-security/Ecommerce-security-1.webp
new file mode 100644
index 000000000..9138d0b4e
Binary files /dev/null and b/content/identity/ecommerce-security/Ecommerce-security-1.webp differ
diff --git a/content/identity/ecommerce-security/Ecommerce-security-2.png b/content/identity/ecommerce-security/Ecommerce-security-2.png
deleted file mode 100644
index 543e4fc59..000000000
Binary files a/content/identity/ecommerce-security/Ecommerce-security-2.png and /dev/null differ
diff --git a/content/identity/ecommerce-security/Ecommerce-security-2.webp b/content/identity/ecommerce-security/Ecommerce-security-2.webp
new file mode 100644
index 000000000..6d5270ca8
Binary files /dev/null and b/content/identity/ecommerce-security/Ecommerce-security-2.webp differ
diff --git a/content/identity/ecommerce-security/ecommerce-security.jpg b/content/identity/ecommerce-security/ecommerce-security.jpg
deleted file mode 100644
index 4e70bfdfe..000000000
Binary files a/content/identity/ecommerce-security/ecommerce-security.jpg and /dev/null differ
diff --git a/content/identity/ecommerce-security/ecommerce-security.webp b/content/identity/ecommerce-security/ecommerce-security.webp
new file mode 100644
index 000000000..b6af23b7a
Binary files /dev/null and b/content/identity/ecommerce-security/ecommerce-security.webp differ
diff --git a/content/identity/ecommerce-security/index.md b/content/identity/ecommerce-security/index.md
index 8c37b448c..6b1bef6c6 100644
--- a/content/identity/ecommerce-security/index.md
+++ b/content/identity/ecommerce-security/index.md
@@ -1,7 +1,7 @@
---
title: "E-commerce Security: 5 Ways to Enhance Data Protection During the Shopping Season"
date: "2020-11-06"
-coverImage: "ecommerce-security.jpg"
+coverImage: "ecommerce-security.webp"
tags: ["ecommerce security","data security","cx"]
author: "Karl Wittig"
description: "Security for e-commerce is a series of protocols that guarantee protected internet transactions. Major data violations have significantly eroded trust in digital security. Via common networks, consumers are comfortable making purchases. However, when it comes to sharing their credit card details with new businesses, they need a little more convincing."
@@ -62,7 +62,7 @@ WooCommerce is a free, open-source WordPress shopping cart plugin owned and deve
## Security Threats That E-Commerce Stores Face
-
+
Ecommerce security for e-commerce is a must-have and consumers need to be constantly reassured about the safety measures that have been taken to mitigate a security threat. Features which an e-commerce security needs to adapt are:
@@ -100,7 +100,7 @@ Credit card fraud is the unauthorized use of a credit or debit card to make
Bad bots are designed to perform a variety of malicious jobs. They are capable of stealing content from the website, such as product reviews, product pricing, catalogs and so on which they publish on some other site. This affects the search engine ranking of the retailers' website. Bad bots are able to make multiple page visits within a very short span of time thus straining Web servers, which makes the site slow for genuine users.
-[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
+[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
## 5 Ways E-Commerce Can Keep Their Online Stores Safe Using Identity Management
@@ -128,7 +128,7 @@ By implementing [multi-factor authentication (MFA)](https://www.loginradius.com/
## How LoginRadius Enhances E-Commerce Security With Its Advance CIAM Solution
-
+
LoginRadius is a customer identity and access management tool that offers a seamless and secure way to access customer information – in your case, shoppers’ data.
@@ -146,4 +146,4 @@ With LoginRadius, you can get 360-degree customer profiling, with 100% customer
Consumers want to shop with [e-commerce retailers](https://www.loginradius.com/blog/identity/loginradius-ciam-retail-ecommerce-business/) whom they can trust. When they enter their personal information, like credit card numbers or other banking details, they expect it to be well protected. By implementing proper e-commerce security safeguards, you can protect your business and consumers from online threats.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ecommerce-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ecommerce-security)
diff --git a/content/identity/effortless-migration-login-hassles/DS-id-orchestration.png b/content/identity/effortless-migration-login-hassles/DS-id-orchestration.png
deleted file mode 100644
index ccf2bf5b2..000000000
Binary files a/content/identity/effortless-migration-login-hassles/DS-id-orchestration.png and /dev/null differ
diff --git a/content/identity/effortless-migration-login-hassles/DS-id-orchestration.webp b/content/identity/effortless-migration-login-hassles/DS-id-orchestration.webp
new file mode 100644
index 000000000..1c92d79a3
Binary files /dev/null and b/content/identity/effortless-migration-login-hassles/DS-id-orchestration.webp differ
diff --git a/content/identity/effortless-migration-login-hassles/effortless-migration.jpg b/content/identity/effortless-migration-login-hassles/effortless-migration.jpg
deleted file mode 100644
index 29453b7eb..000000000
Binary files a/content/identity/effortless-migration-login-hassles/effortless-migration.jpg and /dev/null differ
diff --git a/content/identity/effortless-migration-login-hassles/effortless-migration.webp b/content/identity/effortless-migration-login-hassles/effortless-migration.webp
new file mode 100644
index 000000000..bb2d35328
Binary files /dev/null and b/content/identity/effortless-migration-login-hassles/effortless-migration.webp differ
diff --git a/content/identity/effortless-migration-login-hassles/index.md b/content/identity/effortless-migration-login-hassles/index.md
index 91ddb6e6f..bc8df16f8 100644
--- a/content/identity/effortless-migration-login-hassles/index.md
+++ b/content/identity/effortless-migration-login-hassles/index.md
@@ -1,7 +1,7 @@
---
title: "No More Login Hassles: Effortless Migration to LoginRadius Awaits"
date: "2024-08-01"
-coverImage: "effortless-migration.jpg"
+coverImage: "effortless-migration.webp"
tags: ["ciam authentication","passwordless login","cx"]
author: "Kundan Singh"
description: "Tired of login woes? Discover how an effortless migration to LoginRadius can revolutionize your user identity management, providing a seamless, secure, and efficient experience for both your business and users."
@@ -38,7 +38,7 @@ LoginRadius stands out for several reasons:
5. **Identity Orchestration**: LoginRadius provides granular flexibility in designing and deploying identity flows without the need for coding, enabling anyone with identity expertise to build production-ready identity workflows within minutes.
-[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
+[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
## Planning Your Migration
@@ -100,4 +100,4 @@ Migrating to LoginRadius is an investment in your business's future. By eliminat
With a strategic approach and thorough preparation, the transition to LoginRadius can be effortless and highly rewarding. Don't let outdated login systems hold you back—embrace the future of user identity management with LoginRadius.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=effortless-migration-login-hassles)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=effortless-migration-login-hassles)
\ No newline at end of file
diff --git a/content/identity/eidas-2-0-digital-revolution-transformation/WP-EU-GDPR.png b/content/identity/eidas-2-0-digital-revolution-transformation/WP-EU-GDPR.png
deleted file mode 100644
index b1155cb67..000000000
Binary files a/content/identity/eidas-2-0-digital-revolution-transformation/WP-EU-GDPR.png and /dev/null differ
diff --git a/content/identity/eidas-2-0-digital-revolution-transformation/WP-EU-GDPR.webp b/content/identity/eidas-2-0-digital-revolution-transformation/WP-EU-GDPR.webp
new file mode 100644
index 000000000..3f5856a3d
Binary files /dev/null and b/content/identity/eidas-2-0-digital-revolution-transformation/WP-EU-GDPR.webp differ
diff --git a/content/identity/eidas-2-0-digital-revolution-transformation/digital-transformation.jpg b/content/identity/eidas-2-0-digital-revolution-transformation/digital-transformation.jpg
deleted file mode 100644
index 8a46888c4..000000000
Binary files a/content/identity/eidas-2-0-digital-revolution-transformation/digital-transformation.jpg and /dev/null differ
diff --git a/content/identity/eidas-2-0-digital-revolution-transformation/digital-transformation.webp b/content/identity/eidas-2-0-digital-revolution-transformation/digital-transformation.webp
new file mode 100644
index 000000000..0456e146d
Binary files /dev/null and b/content/identity/eidas-2-0-digital-revolution-transformation/digital-transformation.webp differ
diff --git a/content/identity/eidas-2-0-digital-revolution-transformation/index.md b/content/identity/eidas-2-0-digital-revolution-transformation/index.md
index 0770c7626..35341c6c0 100644
--- a/content/identity/eidas-2-0-digital-revolution-transformation/index.md
+++ b/content/identity/eidas-2-0-digital-revolution-transformation/index.md
@@ -1,7 +1,7 @@
---
title: "eIDAS 2.0: The Digital Revolution Is Here – Is Your Business Ready to Comply?"
date: "2024-05-21"
-coverImage: "digital-transformation.jpg"
+coverImage: "digital-transformation.webp"
tags: ["digital revolution","consent management","compliance"]
author: "Rakesh Soni"
description: "Explore the impact of eIDAS 2.0 on business operations within the EU. Learn how to leverage this regulatory update to enhance security, streamline cross-border access, and expand service accessibility for a successful digital transformation."
@@ -42,7 +42,7 @@ eIDAS 2.0 represents a pivotal advancement in digital identity management within
This regulation not only enhances the safety and flexibility of digital identities but also ensures their seamless use across various contexts, driving forward the digital transformation of Europe.
-[](https://www.loginradius.com/resource/eu-gdpr-and-ciam/)
+[](https://www.loginradius.com/resource/eu-gdpr-and-ciam/)
Hence, businesses have to ensure they meet the compliance requirements if they wish to serve the customers in the EU since failing to this could lead to hefty fines and reputational losses.
@@ -72,4 +72,4 @@ The digital revolution demands robust security and seamless user experiences, an
Embracing eIDAS 2.0 enhances data protection, streamlines cross-border access, and expands service accessibility, positioning businesses to thrive in the digital era. Leverage the full potential of eIDAS 2.0 to ensure your business is ready to survive and excel.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=eidas-2-0-digital-revolution-transformation)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=eidas-2-0-digital-revolution-transformation)
\ No newline at end of file
diff --git a/content/identity/enterprise-application-security/EB-LR-GDPR-comp.png b/content/identity/enterprise-application-security/EB-LR-GDPR-comp.png
deleted file mode 100644
index a7a656cfa..000000000
Binary files a/content/identity/enterprise-application-security/EB-LR-GDPR-comp.png and /dev/null differ
diff --git a/content/identity/enterprise-application-security/EB-LR-GDPR-comp.webp b/content/identity/enterprise-application-security/EB-LR-GDPR-comp.webp
new file mode 100644
index 000000000..44c9529c0
Binary files /dev/null and b/content/identity/enterprise-application-security/EB-LR-GDPR-comp.webp differ
diff --git a/content/identity/enterprise-application-security/application-security.jpg b/content/identity/enterprise-application-security/application-security.jpg
deleted file mode 100644
index 9ba50f94b..000000000
Binary files a/content/identity/enterprise-application-security/application-security.jpg and /dev/null differ
diff --git a/content/identity/enterprise-application-security/application-security.webp b/content/identity/enterprise-application-security/application-security.webp
new file mode 100644
index 000000000..bcb9cf105
Binary files /dev/null and b/content/identity/enterprise-application-security/application-security.webp differ
diff --git a/content/identity/enterprise-application-security/index.md b/content/identity/enterprise-application-security/index.md
index 8fc1b9ab3..54b2e9e66 100644
--- a/content/identity/enterprise-application-security/index.md
+++ b/content/identity/enterprise-application-security/index.md
@@ -1,7 +1,7 @@
---
title: "Securing Corporate Applications: A Comprehensive Guide to Enterprise Application Security"
date: "2023-11-22"
-coverImage: "application-security.jpg"
+coverImage: "application-security.webp"
tags: ["data security","compliance","cx"]
author: "Rakesh Soni"
description: "In the tech-driven business world, safeguarding corporate applications is crucial. This blog guides you through evolving threats, proactive measures, and key components to ensure the security of critical applications."
@@ -35,7 +35,7 @@ In the realm of enterprise application security, compliance with regulations is
Adhering to these standards not only helps avoid legal consequences but also fosters a culture of ethical responsibility. Beyond compliance, ethical considerations involve transparency in data handling, respect for user privacy, and responsible disclosure of security incidents.
-[](https://www.loginradius.com/resource/loginradius-and-gdpr-compliance/)
+[](https://www.loginradius.com/resource/loginradius-and-gdpr-compliance/)
By aligning security practices with ethical principles, organizations not only safeguard their reputation but also contribute to the broader goal of creating a secure and trustworthy digital environment for all stakeholders.
@@ -82,4 +82,4 @@ In the face of evolving cyber threats, organizations must stay proactive and agi
Remember, in the ever-changing landscape of cybersecurity, staying one step ahead is the key to safeguarding the digital assets that drive the modern enterprise.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enterprise-application-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enterprise-application-security)
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/4-key-entry-points-to-digital-transformation-1024x310.png b/content/identity/enterprise-needs-digital-business-transformation-strategy/4-key-entry-points-to-digital-transformation-1024x310.png
deleted file mode 100644
index 9f376e69d..000000000
Binary files a/content/identity/enterprise-needs-digital-business-transformation-strategy/4-key-entry-points-to-digital-transformation-1024x310.png and /dev/null differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/4-key-entry-points-to-digital-transformation-1024x310.webp b/content/identity/enterprise-needs-digital-business-transformation-strategy/4-key-entry-points-to-digital-transformation-1024x310.webp
new file mode 100644
index 000000000..28479265f
Binary files /dev/null and b/content/identity/enterprise-needs-digital-business-transformation-strategy/4-key-entry-points-to-digital-transformation-1024x310.webp differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/bence-boros-573486-unsplash.jpg b/content/identity/enterprise-needs-digital-business-transformation-strategy/bence-boros-573486-unsplash.jpg
deleted file mode 100644
index 437bb0b9c..000000000
Binary files a/content/identity/enterprise-needs-digital-business-transformation-strategy/bence-boros-573486-unsplash.jpg and /dev/null differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/bence-boros-573486-unsplash.webp b/content/identity/enterprise-needs-digital-business-transformation-strategy/bence-boros-573486-unsplash.webp
new file mode 100644
index 000000000..136ac03c5
Binary files /dev/null and b/content/identity/enterprise-needs-digital-business-transformation-strategy/bence-boros-573486-unsplash.webp differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/damian-zaleski-843-unsplash.jpg b/content/identity/enterprise-needs-digital-business-transformation-strategy/damian-zaleski-843-unsplash.jpg
deleted file mode 100644
index 038cb0ce5..000000000
Binary files a/content/identity/enterprise-needs-digital-business-transformation-strategy/damian-zaleski-843-unsplash.jpg and /dev/null differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/damian-zaleski-843-unsplash.webp b/content/identity/enterprise-needs-digital-business-transformation-strategy/damian-zaleski-843-unsplash.webp
new file mode 100644
index 000000000..ce524ab49
Binary files /dev/null and b/content/identity/enterprise-needs-digital-business-transformation-strategy/damian-zaleski-843-unsplash.webp differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/daniel-gzz-105307-unsplash.jpg b/content/identity/enterprise-needs-digital-business-transformation-strategy/daniel-gzz-105307-unsplash.jpg
deleted file mode 100644
index 4271b8c66..000000000
Binary files a/content/identity/enterprise-needs-digital-business-transformation-strategy/daniel-gzz-105307-unsplash.jpg and /dev/null differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/daniel-gzz-105307-unsplash.webp b/content/identity/enterprise-needs-digital-business-transformation-strategy/daniel-gzz-105307-unsplash.webp
new file mode 100644
index 000000000..6bf83c626
Binary files /dev/null and b/content/identity/enterprise-needs-digital-business-transformation-strategy/daniel-gzz-105307-unsplash.webp differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/heidi-sandstrom-173946-unsplash.jpg b/content/identity/enterprise-needs-digital-business-transformation-strategy/heidi-sandstrom-173946-unsplash.jpg
deleted file mode 100644
index 06205dfe1..000000000
Binary files a/content/identity/enterprise-needs-digital-business-transformation-strategy/heidi-sandstrom-173946-unsplash.jpg and /dev/null differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/heidi-sandstrom-173946-unsplash.webp b/content/identity/enterprise-needs-digital-business-transformation-strategy/heidi-sandstrom-173946-unsplash.webp
new file mode 100644
index 000000000..3ac9aa40d
Binary files /dev/null and b/content/identity/enterprise-needs-digital-business-transformation-strategy/heidi-sandstrom-173946-unsplash.webp differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/index.md b/content/identity/enterprise-needs-digital-business-transformation-strategy/index.md
index 15d4375c6..05a8d05b1 100644
--- a/content/identity/enterprise-needs-digital-business-transformation-strategy/index.md
+++ b/content/identity/enterprise-needs-digital-business-transformation-strategy/index.md
@@ -1,7 +1,7 @@
---
title: "Why Your Enterprise Needs a Digital Business Transformation Strategy"
date: "2018-11-26"
-coverImage: "rawpixel-579231-unsplash-1.jpg"
+coverImage: "rawpixel-579231-unsplash-1.webp"
tags: ["public-sector"]
featured: false
author: "Rakesh Soni"
@@ -23,7 +23,7 @@ By 2020, businesses will have to develop new digital experiences and unique onli
#### Digital capabilities are lagging
-
+
Additional Gartner data highlights the challenges that come with this changing landscape. Over half of all enterprises surveyed have less than expert-level capabilities for implementing or updating critical digital platforms, such as managing data systems for analytics and modernizing technology ecosystems to better serve users.
@@ -37,7 +37,7 @@ Imagine an online portal and an accompanying mobile app where customers have to
## Customer Identity Management to Drive Revenue Growth
-
+
So how can you make sure that your organization stays ahead of the curve with a business digital transformation when faced with resource challenges and competitor pressure?
@@ -65,7 +65,7 @@ But what does this kind of digital identity strategy look like?
#### Identity convergence: responding to the new, diverse customer
-
+
In today’s globalized world, your customers are no longer _merely_ customers when they access your digital services. Instead, they converge from multiple persona types:
@@ -87,7 +87,7 @@ A central, cloud-based solution to handle all of your customer identity needs ca
#### “Device identity”: growing when the internet is everywhere
-
+
With the emergence of the internet of things and myriad mobile devices on the market, taking advantage of identity-based opportunities around all of the devices and electronic items can make the difference in leading the pack among your competitors or constantly having to play catch-up.
@@ -99,7 +99,7 @@ Whatever the device and the customer’s need, your organization has to prepare
## Customer Identity and Access Management (CIAM)
-
+
Planning for Gartner’s 2020 threshold for digital transformation need not be a daunting task after all. A [B2C CIAM solution](https://www.loginradius.com/customer-identity-management-b2c-ciam/) for your company is an example of a cloud-based, holistic solution to store, manage, and secure all of your customer data and identities.
@@ -111,4 +111,4 @@ With the right CIAM platform, for example, you can track your customer’s entir
If you’re interested in learning how a cloud-based CIAM solution can help your enterprise transform your digital infrastructure, download [4 Key Entry Points to a Digital Transformation](https://www.loginradius.com/resource/4-key-entry-points-to-a-digital-transformation/). This e-book features case studies for each specific entry point to help you understand how a best-of-breed identity platform could provide value to you.
-[](https://www.loginradius.com/resource/4-key-entry-points-to-a-digital-transformation/)
+[](https://www.loginradius.com/resource/4-key-entry-points-to-a-digital-transformation/)
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-570911-unsplash-e1543257473342.jpg b/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-570911-unsplash-e1543257473342.jpg
deleted file mode 100644
index e33af6f80..000000000
Binary files a/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-570911-unsplash-e1543257473342.jpg and /dev/null differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-570911-unsplash-e1543257473342.webp b/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-570911-unsplash-e1543257473342.webp
new file mode 100644
index 000000000..84209dc25
Binary files /dev/null and b/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-570911-unsplash-e1543257473342.webp differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-579231-unsplash-1.jpg b/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-579231-unsplash-1.jpg
deleted file mode 100644
index 006cb00bf..000000000
Binary files a/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-579231-unsplash-1.jpg and /dev/null differ
diff --git a/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-579231-unsplash-1.webp b/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-579231-unsplash-1.webp
new file mode 100644
index 000000000..7dedfa1ae
Binary files /dev/null and b/content/identity/enterprise-needs-digital-business-transformation-strategy/rawpixel-579231-unsplash-1.webp differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/CTA-Graphics-for-Blogs-12.png b/content/identity/enterprise-single-sign-on-authentication/CTA-Graphics-for-Blogs-12.png
deleted file mode 100644
index 6e44ae769..000000000
Binary files a/content/identity/enterprise-single-sign-on-authentication/CTA-Graphics-for-Blogs-12.png and /dev/null differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/CTA-Graphics-for-Blogs-12.webp b/content/identity/enterprise-single-sign-on-authentication/CTA-Graphics-for-Blogs-12.webp
new file mode 100644
index 000000000..b4d2fc941
Binary files /dev/null and b/content/identity/enterprise-single-sign-on-authentication/CTA-Graphics-for-Blogs-12.webp differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-02.png b/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-02.png
deleted file mode 100644
index c8dd637ff..000000000
Binary files a/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-02.png and /dev/null differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-02.webp b/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-02.webp
new file mode 100644
index 000000000..d65aec64a
Binary files /dev/null and b/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-02.webp differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-03.png b/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-03.png
deleted file mode 100644
index 38e3ae3ca..000000000
Binary files a/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-03.png and /dev/null differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-03.webp b/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-03.webp
new file mode 100644
index 000000000..60dd57d2c
Binary files /dev/null and b/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-03.webp differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-Cover.png b/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-Cover.png
deleted file mode 100644
index 8dbafa2ba..000000000
Binary files a/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-Cover.png and /dev/null differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-Cover.webp b/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-Cover.webp
new file mode 100644
index 000000000..206eab5ca
Binary files /dev/null and b/content/identity/enterprise-single-sign-on-authentication/SSO-Blog-Cover.webp differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/index.md b/content/identity/enterprise-single-sign-on-authentication/index.md
index 53daa6217..4415643eb 100644
--- a/content/identity/enterprise-single-sign-on-authentication/index.md
+++ b/content/identity/enterprise-single-sign-on-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "5 Reasons To Know Why B2C Enterprises Should Use Single Sign-On"
date: "2019-06-18"
-coverImage: "sso-authentication.jpg"
+coverImage: "sso-authentication.webp"
tags: ["sso authentication","data security","cx"]
author: "Rakesh Soni"
description: "Today, consumers want to log into one place and access all of their favorite sites and services using their preferred login credentials. Single sign-on is a great way to show your consumers that you care about their security and convenience."
@@ -44,7 +44,7 @@ Today’s customers expect SSO. They might not be able to articulate this expect
If you have more than one website or service that requires logging in, you _need_ [single sign-on](https://www.loginradius.com/single-sign-on/) if you don’t want to annoy your customers and appear behind the times. With single sign-on, you can eliminate several common roadblocks that can hurt your business.
-
+
For example, we heard from a consumer in the UK that there's a customer experience disconnect between different divisions at Virgin. People getting cable TV and home broadband services from Virgin Media are encouraged to sign up for Virgin Mobile with several competitively priced offers. However, even though the sites look similar, consumers need to have two separate logins for the two Virgin services. They even have different rules for password strength.
@@ -54,7 +54,7 @@ Don’t be one of these companies. You probably won’t end up with frustrated c
### 2. SSO Makes Companies Smarter
-
+
A unified customer profile is the first step to a smarter company. With [CIAM](https://www.loginradius.com/blog/identity/customer-identity-and-access-management/), you’ll have a single location for everything about individual customers (including their login and service usage data).
@@ -91,7 +91,7 @@ Without any need for passwords, SSO enables your users to come back to your app
Single sign-on directly benefits your organization by gathering a wealth of customer data and credentials securely in one spot for your services, teams, and applications to use. Failing to use SSO will make your consumers notice you in a bad light as they try to navigate your apps and services. By contrast, leaders who bring an SSO solution to their organization will stand out because of the multitude of benefits that single sign-on provides.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
## In Conclusion
@@ -101,4 +101,4 @@ Additionally, it saves time and effort for both customers and IT teams. With the
Therefore, it's a valuable solution that every B2C enterprise should consider. In summary, the benefits of SSO for B2C enterprises are significant, and implementing it can be a game-changer in today's digital age.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enterprise-single-sign-on-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enterprise-single-sign-on-authentication)
diff --git a/content/identity/enterprise-single-sign-on-authentication/sso-authentication.jpg b/content/identity/enterprise-single-sign-on-authentication/sso-authentication.jpg
deleted file mode 100644
index 128294077..000000000
Binary files a/content/identity/enterprise-single-sign-on-authentication/sso-authentication.jpg and /dev/null differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/sso-authentication.webp b/content/identity/enterprise-single-sign-on-authentication/sso-authentication.webp
new file mode 100644
index 000000000..8c969ddd8
Binary files /dev/null and b/content/identity/enterprise-single-sign-on-authentication/sso-authentication.webp differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/sso.png b/content/identity/enterprise-single-sign-on-authentication/sso.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/enterprise-single-sign-on-authentication/sso.png and /dev/null differ
diff --git a/content/identity/enterprise-single-sign-on-authentication/sso.webp b/content/identity/enterprise-single-sign-on-authentication/sso.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/enterprise-single-sign-on-authentication/sso.webp differ
diff --git a/content/identity/etc-loginradius-customer-success-story/DS-SSO.png b/content/identity/etc-loginradius-customer-success-story/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/etc-loginradius-customer-success-story/DS-SSO.png and /dev/null differ
diff --git a/content/identity/etc-loginradius-customer-success-story/DS-SSO.webp b/content/identity/etc-loginradius-customer-success-story/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/etc-loginradius-customer-success-story/DS-SSO.webp differ
diff --git a/content/identity/etc-loginradius-customer-success-story/etc-connect.jpg b/content/identity/etc-loginradius-customer-success-story/etc-connect.jpg
deleted file mode 100644
index 283c9224f..000000000
Binary files a/content/identity/etc-loginradius-customer-success-story/etc-connect.jpg and /dev/null differ
diff --git a/content/identity/etc-loginradius-customer-success-story/etc-connect.webp b/content/identity/etc-loginradius-customer-success-story/etc-connect.webp
new file mode 100644
index 000000000..30fb6b042
Binary files /dev/null and b/content/identity/etc-loginradius-customer-success-story/etc-connect.webp differ
diff --git a/content/identity/etc-loginradius-customer-success-story/index.md b/content/identity/etc-loginradius-customer-success-story/index.md
index 0fce12acc..4700d5ad3 100644
--- a/content/identity/etc-loginradius-customer-success-story/index.md
+++ b/content/identity/etc-loginradius-customer-success-story/index.md
@@ -1,7 +1,7 @@
---
title: "Electronic Theatre Controls: A LoginRadius Customer Success Story"
date: "2022-12-08"
-coverImage: "etc-connect.jpg"
+coverImage: "etc-connect.webp"
tags: ["customer success", "identity management", "cx"]
author: "Saikiran Babladi"
description: "ETC now manages user identity centrally with LoginRadius CIAM. This allows the team to create and manage unified consumer profiles that can be used throughout the business’ entire digital ecosystem."
@@ -54,7 +54,7 @@ With support from LoginRadius, ETC successfully unified its multiple products wi
The centralized login system enables users to seamlessly navigate third-party sites without needing to log back whenever they return.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
## Identifying actionable behavioral insights
@@ -74,4 +74,4 @@ To guarantee ETC's success at every level, LoginRadius introduced dedicated acco
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=etc-loginradius-customer-success-story)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=etc-loginradius-customer-success-story)
\ No newline at end of file
diff --git a/content/identity/etc-loginradius-customer-success-story/sso-ds.png b/content/identity/etc-loginradius-customer-success-story/sso-ds.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/etc-loginradius-customer-success-story/sso-ds.png and /dev/null differ
diff --git a/content/identity/etc-loginradius-customer-success-story/sso-ds.webp b/content/identity/etc-loginradius-customer-success-story/sso-ds.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/etc-loginradius-customer-success-story/sso-ds.webp differ
diff --git a/content/identity/federated-identity-management-vs-sso/DS-fim.png b/content/identity/federated-identity-management-vs-sso/DS-fim.png
deleted file mode 100644
index 9e03618f7..000000000
Binary files a/content/identity/federated-identity-management-vs-sso/DS-fim.png and /dev/null differ
diff --git a/content/identity/federated-identity-management-vs-sso/DS-fim.webp b/content/identity/federated-identity-management-vs-sso/DS-fim.webp
new file mode 100644
index 000000000..b8fd0ecbb
Binary files /dev/null and b/content/identity/federated-identity-management-vs-sso/DS-fim.webp differ
diff --git a/content/identity/federated-identity-management-vs-sso/fim-ds.png b/content/identity/federated-identity-management-vs-sso/fim-ds.png
deleted file mode 100644
index 01a289614..000000000
Binary files a/content/identity/federated-identity-management-vs-sso/fim-ds.png and /dev/null differ
diff --git a/content/identity/federated-identity-management-vs-sso/fim-ds.webp b/content/identity/federated-identity-management-vs-sso/fim-ds.webp
new file mode 100644
index 000000000..3d4c0a8aa
Binary files /dev/null and b/content/identity/federated-identity-management-vs-sso/fim-ds.webp differ
diff --git a/content/identity/federated-identity-management-vs-sso/fim-vs-sso.jpg b/content/identity/federated-identity-management-vs-sso/fim-vs-sso.jpg
deleted file mode 100644
index 0dd9ea612..000000000
Binary files a/content/identity/federated-identity-management-vs-sso/fim-vs-sso.jpg and /dev/null differ
diff --git a/content/identity/federated-identity-management-vs-sso/fim-vs-sso.webp b/content/identity/federated-identity-management-vs-sso/fim-vs-sso.webp
new file mode 100644
index 000000000..40955f84d
Binary files /dev/null and b/content/identity/federated-identity-management-vs-sso/fim-vs-sso.webp differ
diff --git a/content/identity/federated-identity-management-vs-sso/index.md b/content/identity/federated-identity-management-vs-sso/index.md
index 2655520de..493f37eba 100644
--- a/content/identity/federated-identity-management-vs-sso/index.md
+++ b/content/identity/federated-identity-management-vs-sso/index.md
@@ -1,7 +1,7 @@
---
title: "Federated Identity Management vs. SSO: What's The Difference?"
date: "2021-11-22"
-coverImage: "sso-vs-fim.jpg"
+coverImage: "sso-vs-fim.webp"
tags: ["federated identity management","sso","data security"]
author: "Kundan Singh"
description: "Enterprises need to use methods to maximize the use of digital identities for multiple users. Although SSO and FIM are used together, they do not mean the same thing. The main difference between Identity Federation and SSO lies in the range of access."
@@ -87,7 +87,7 @@ The service provider then sends a request to the user's identity provider, which
This process is known as identity federation and allows users to access resources from multiple organizations without the need for separate login credentials for each organization. The FIM system uses industry-standard protocols like [SAML](https://www.loginradius.com/glossary/saml/), OAuth, and OpenID Connect to establish trust and securely exchange identity information between the identity provider and service provider.
-[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
+[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
## Benefits of Federated Identity Management
@@ -157,4 +157,4 @@ Federation identity management is a system allowing users from different organiz
Identity federation in AWS enables users to access AWS resources securely using their existing identity credentials from external identity providers, such as Active Directory or SAML-based systems.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=federated-identity-management-vs-sso)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=federated-identity-management-vs-sso)
\ No newline at end of file
diff --git a/content/identity/federated-identity-management-vs-sso/sso-vs-fim.jpg b/content/identity/federated-identity-management-vs-sso/sso-vs-fim.jpg
deleted file mode 100644
index 049c7b35f..000000000
Binary files a/content/identity/federated-identity-management-vs-sso/sso-vs-fim.jpg and /dev/null differ
diff --git a/content/identity/federated-identity-management-vs-sso/sso-vs-fim.webp b/content/identity/federated-identity-management-vs-sso/sso-vs-fim.webp
new file mode 100644
index 000000000..eecf1bebd
Binary files /dev/null and b/content/identity/federated-identity-management-vs-sso/sso-vs-fim.webp differ
diff --git a/content/identity/federated-identity-providers/federated-identity-providers.png b/content/identity/federated-identity-providers/federated-identity-providers.png
deleted file mode 100644
index d26b64274..000000000
Binary files a/content/identity/federated-identity-providers/federated-identity-providers.png and /dev/null differ
diff --git a/content/identity/federated-identity-providers/federated-identity-providers.webp b/content/identity/federated-identity-providers/federated-identity-providers.webp
new file mode 100644
index 000000000..9edbc25af
Binary files /dev/null and b/content/identity/federated-identity-providers/federated-identity-providers.webp differ
diff --git a/content/identity/federated-identity-providers/index.md b/content/identity/federated-identity-providers/index.md
index e627c8947..3296ed973 100644
--- a/content/identity/federated-identity-providers/index.md
+++ b/content/identity/federated-identity-providers/index.md
@@ -1,7 +1,7 @@
---
title: "What are Federated Identity Providers?"
date: "2021-03-26"
-coverImage: "federated-identity-providers.png"
+coverImage: "federated-identity-providers.webp"
tags: ["federated identity management","saml","cx"]
author: "Rajeev Sharma"
description: "Federated identity management is a configuration that can be made between two or more trusted domains to allow consumers of those domains to access applications and services using the same digital identity. Such identity is known as federated identity, and the use of such a solution pattern is known as identity federation."
@@ -97,4 +97,4 @@ Federated Identity and Access Management (IAM) is a system that enables users to
In cyber security, "federated" refers to a system where different organizations or domains trust each other to authenticate and authorize users, allowing seamless access to resources across these domains.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=federated-identity-providers)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=federated-identity-providers)
\ No newline at end of file
diff --git a/content/identity/financial-grade-api-open-banking/BD-Plexicon1-1024x310.png b/content/identity/financial-grade-api-open-banking/BD-Plexicon1-1024x310.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/financial-grade-api-open-banking/BD-Plexicon1-1024x310.png and /dev/null differ
diff --git a/content/identity/financial-grade-api-open-banking/BD-Plexicon1-1024x310.webp b/content/identity/financial-grade-api-open-banking/BD-Plexicon1-1024x310.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/financial-grade-api-open-banking/BD-Plexicon1-1024x310.webp differ
diff --git a/content/identity/financial-grade-api-open-banking/WP-digitization.png b/content/identity/financial-grade-api-open-banking/WP-digitization.png
deleted file mode 100644
index 526ebf3e8..000000000
Binary files a/content/identity/financial-grade-api-open-banking/WP-digitization.png and /dev/null differ
diff --git a/content/identity/financial-grade-api-open-banking/WP-digitization.webp b/content/identity/financial-grade-api-open-banking/WP-digitization.webp
new file mode 100644
index 000000000..6ed0d46f2
Binary files /dev/null and b/content/identity/financial-grade-api-open-banking/WP-digitization.webp differ
diff --git a/content/identity/financial-grade-api-open-banking/api-oauth.png b/content/identity/financial-grade-api-open-banking/api-oauth.png
deleted file mode 100644
index a268e3d22..000000000
Binary files a/content/identity/financial-grade-api-open-banking/api-oauth.png and /dev/null differ
diff --git a/content/identity/financial-grade-api-open-banking/api-oauth.webp b/content/identity/financial-grade-api-open-banking/api-oauth.webp
new file mode 100644
index 000000000..234c6abdc
Binary files /dev/null and b/content/identity/financial-grade-api-open-banking/api-oauth.webp differ
diff --git a/content/identity/financial-grade-api-open-banking/fapi-cover.jpg b/content/identity/financial-grade-api-open-banking/fapi-cover.jpg
deleted file mode 100644
index 14e505bf7..000000000
Binary files a/content/identity/financial-grade-api-open-banking/fapi-cover.jpg and /dev/null differ
diff --git a/content/identity/financial-grade-api-open-banking/fapi-cover.webp b/content/identity/financial-grade-api-open-banking/fapi-cover.webp
new file mode 100644
index 000000000..385532dda
Binary files /dev/null and b/content/identity/financial-grade-api-open-banking/fapi-cover.webp differ
diff --git a/content/identity/financial-grade-api-open-banking/index.md b/content/identity/financial-grade-api-open-banking/index.md
index aab80c080..76c43e78f 100644
--- a/content/identity/financial-grade-api-open-banking/index.md
+++ b/content/identity/financial-grade-api-open-banking/index.md
@@ -1,7 +1,7 @@
---
title: "An Introduction to Financial-Grade API (FAPI) for Open Banking"
date: "2021-10-27"
-coverImage: "fapi-cover.jpg"
+coverImage: "fapi-cover.webp"
tags: ["data security","oauth","mfa"]
author: "Rakesh Soni"
description: "With open banking, consumers can leverage bank accounts and data networking across diverse institutions through APIs (application programming interfaces), which has reshaped the entire banking industry. However, when it comes to the overall security mechanism of open banking, FAPI becomes the need of the hour."
@@ -44,7 +44,7 @@ It is an OpenID Foundation (OIDF) standard that leverage OAuth 2.0 process flow
By implementing OpenID Connect, leveraging OAuth 2.0 fabricates a unified framework that promises mobile native applications, secure APIs, and browser applications in a single, cohesive architecture.
-[](https://www.loginradius.com/resource/how-to-secure-api-using-oauth2)
+[](https://www.loginradius.com/resource/how-to-secure-api-using-oauth2)
## Risks Associated with Open Banking
@@ -81,4 +81,4 @@ Open banking is paving the way for the next generation of digital experiences, e
However, the risks associated with open banking require organizations to put their best foot forward in adopting FAPI through a reliable service provider that helps enhance API integration security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=financial-grade-api-open-banking)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=financial-grade-api-open-banking)
diff --git a/content/identity/financial-industry-identity-management/BD-Plexicon1-1024x310.png b/content/identity/financial-industry-identity-management/BD-Plexicon1-1024x310.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/financial-industry-identity-management/BD-Plexicon1-1024x310.png and /dev/null differ
diff --git a/content/identity/financial-industry-identity-management/BD-Plexicon1-1024x310.webp b/content/identity/financial-industry-identity-management/BD-Plexicon1-1024x310.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/financial-industry-identity-management/BD-Plexicon1-1024x310.webp differ
diff --git a/content/identity/financial-industry-identity-management/CS-Juhll-Online-Marketing-and-Banks-1024x310.png b/content/identity/financial-industry-identity-management/CS-Juhll-Online-Marketing-and-Banks-1024x310.png
deleted file mode 100644
index 6cf1807c4..000000000
Binary files a/content/identity/financial-industry-identity-management/CS-Juhll-Online-Marketing-and-Banks-1024x310.png and /dev/null differ
diff --git a/content/identity/financial-industry-identity-management/CS-Juhll-Online-Marketing-and-Banks-1024x310.webp b/content/identity/financial-industry-identity-management/CS-Juhll-Online-Marketing-and-Banks-1024x310.webp
new file mode 100644
index 000000000..c7cc7bd42
Binary files /dev/null and b/content/identity/financial-industry-identity-management/CS-Juhll-Online-Marketing-and-Banks-1024x310.webp differ
diff --git a/content/identity/financial-industry-identity-management/Identity-management-in-online-finance-sector.png b/content/identity/financial-industry-identity-management/Identity-management-in-online-finance-sector.png
deleted file mode 100644
index 27b036389..000000000
Binary files a/content/identity/financial-industry-identity-management/Identity-management-in-online-finance-sector.png and /dev/null differ
diff --git a/content/identity/financial-industry-identity-management/Identity-management-in-online-finance-sector.webp b/content/identity/financial-industry-identity-management/Identity-management-in-online-finance-sector.webp
new file mode 100644
index 000000000..f4bab2710
Binary files /dev/null and b/content/identity/financial-industry-identity-management/Identity-management-in-online-finance-sector.webp differ
diff --git a/content/identity/financial-industry-identity-management/customer-insights-data-loginraidus.png b/content/identity/financial-industry-identity-management/customer-insights-data-loginraidus.png
deleted file mode 100644
index 5b067a0be..000000000
Binary files a/content/identity/financial-industry-identity-management/customer-insights-data-loginraidus.png and /dev/null differ
diff --git a/content/identity/financial-industry-identity-management/customer-insights-data-loginraidus.webp b/content/identity/financial-industry-identity-management/customer-insights-data-loginraidus.webp
new file mode 100644
index 000000000..4f212df9d
Binary files /dev/null and b/content/identity/financial-industry-identity-management/customer-insights-data-loginraidus.webp differ
diff --git a/content/identity/financial-industry-identity-management/finance-industry-Identity-management.png b/content/identity/financial-industry-identity-management/finance-industry-Identity-management.png
deleted file mode 100644
index 39c1c38e5..000000000
Binary files a/content/identity/financial-industry-identity-management/finance-industry-Identity-management.png and /dev/null differ
diff --git a/content/identity/financial-industry-identity-management/finance-industry-Identity-management.webp b/content/identity/financial-industry-identity-management/finance-industry-Identity-management.webp
new file mode 100644
index 000000000..a97b3602c
Binary files /dev/null and b/content/identity/financial-industry-identity-management/finance-industry-Identity-management.webp differ
diff --git a/content/identity/financial-industry-identity-management/financial-industry.jpg b/content/identity/financial-industry-identity-management/financial-industry.jpg
deleted file mode 100644
index 0178cf50b..000000000
Binary files a/content/identity/financial-industry-identity-management/financial-industry.jpg and /dev/null differ
diff --git a/content/identity/financial-industry-identity-management/financial-industry.webp b/content/identity/financial-industry-identity-management/financial-industry.webp
new file mode 100644
index 000000000..092aa51b6
Binary files /dev/null and b/content/identity/financial-industry-identity-management/financial-industry.webp differ
diff --git a/content/identity/financial-industry-identity-management/index.md b/content/identity/financial-industry-identity-management/index.md
index 006d341de..1f0cb4b8b 100644
--- a/content/identity/financial-industry-identity-management/index.md
+++ b/content/identity/financial-industry-identity-management/index.md
@@ -1,7 +1,7 @@
---
title: "Why Financial Industry Needs an Identity Management System Now More Than Ever"
date: "2020-04-30"
-coverImage: "financial-industry.jpg"
+coverImage: "financial-industry.webp"
tags: ["compliance","authentication","identity management"]
author: "Rakesh Soni"
description: "A robust identity management system helps financial organizations remain compliant and conduct business in a secure environment."
@@ -69,7 +69,7 @@ To counter, get your financial institute advanced endpoint protections and stren
An identity management system can improve the security and productivity of a financial institute. It offers numerous benefits to keep customers' sensitive data safe and unharmed from attackers.
-
+
Integrating a [reliable CIAM platform](https://www.loginradius.com/blog/2019/06/perfect-ciam-platform/) into your institution can build cyber defenses against criminals that are both comprehensive and resilient. Furthermore, it is equipped with unique advantages where you can:
@@ -94,7 +94,7 @@ To [enhance customer experience](https://www.loginradius.com/customer-experience
They can leverage [single sign-on capabilities](https://www.loginradius.com/blog/2019/05/what-is-single-sign-on/) to login to multiple domains using a single set of credentials. LoginRadius also supports federated SSO for third-party domains.
-
+
Furthermore, companies can improve security, usability, and user experiences with consumer identity data and new-age reporting tools. There is provision for data segmentation too.
@@ -125,7 +125,7 @@ In the fight against high-profile data breaches, the identity management system
One of the best examples of meeting international regulations comes from Juhll. This growth-driven digital marketing service acquired Banks.com to provide financial institutions with a trusted source for financial assistance. LoginRadius has helped Juhll to comply with new regulations in terms of where and how customer data is stored.
-[](https://www.loginradius.com/resource/juhll-case-study)
+[](https://www.loginradius.com/resource/juhll-case-study)
**Juhll Case Study**
@@ -133,4 +133,4 @@ One of the best examples of meeting international regulations comes from Juhll.
LoginRadius adheres to the best practices relating to authentication and access control. With features like multi-factor authentication and role-based data management, the identity management system reduces the risk of financial data theft. The end goal is to keep up with the changing trends and improve customer experience in the financial industry.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=financial-industry-identity-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=financial-industry-identity-management)
diff --git a/content/identity/financial-industry-identity-management/protecting-pii-against-data-breaches.png b/content/identity/financial-industry-identity-management/protecting-pii-against-data-breaches.png
deleted file mode 100644
index b32dcb27b..000000000
Binary files a/content/identity/financial-industry-identity-management/protecting-pii-against-data-breaches.png and /dev/null differ
diff --git a/content/identity/financial-industry-identity-management/protecting-pii-against-data-breaches.webp b/content/identity/financial-industry-identity-management/protecting-pii-against-data-breaches.webp
new file mode 100644
index 000000000..6c250a4f7
Binary files /dev/null and b/content/identity/financial-industry-identity-management/protecting-pii-against-data-breaches.webp differ
diff --git a/content/identity/fix-identity-to-fix-citizens-security/cities-ds.png b/content/identity/fix-identity-to-fix-citizens-security/cities-ds.png
deleted file mode 100644
index 455ac1c9d..000000000
Binary files a/content/identity/fix-identity-to-fix-citizens-security/cities-ds.png and /dev/null differ
diff --git a/content/identity/fix-identity-to-fix-citizens-security/cities-ds.webp b/content/identity/fix-identity-to-fix-citizens-security/cities-ds.webp
new file mode 100644
index 000000000..f1c42b6c0
Binary files /dev/null and b/content/identity/fix-identity-to-fix-citizens-security/cities-ds.webp differ
diff --git a/content/identity/fix-identity-to-fix-citizens-security/citizen-sec.jpg b/content/identity/fix-identity-to-fix-citizens-security/citizen-sec.jpg
deleted file mode 100644
index 03d8602f7..000000000
Binary files a/content/identity/fix-identity-to-fix-citizens-security/citizen-sec.jpg and /dev/null differ
diff --git a/content/identity/fix-identity-to-fix-citizens-security/citizen-sec.webp b/content/identity/fix-identity-to-fix-citizens-security/citizen-sec.webp
new file mode 100644
index 000000000..d225d5096
Binary files /dev/null and b/content/identity/fix-identity-to-fix-citizens-security/citizen-sec.webp differ
diff --git a/content/identity/fix-identity-to-fix-citizens-security/index.md b/content/identity/fix-identity-to-fix-citizens-security/index.md
index a7d05b971..8370fbb92 100644
--- a/content/identity/fix-identity-to-fix-citizens-security/index.md
+++ b/content/identity/fix-identity-to-fix-citizens-security/index.md
@@ -1,7 +1,7 @@
---
title: "The Role of Identity Management in Securing Your Citizen’s Data"
date: "2022-07-29"
-coverImage: "citizen-sec.jpg"
+coverImage: "citizen-sec.webp"
tags: ["digital identity", "smart cities", "authentication"]
author: "Yash Rathi"
description: " Identity management has been a game-changer for enterprises for decades as it helps businesses succeed by ensuring the highest level of security and great user experience.
@@ -41,7 +41,7 @@ A smart CIAM (consumer identity and access management) solution like LoginRadius
Let’s learn how a CIAM solution like LoginRadius can deliver a flawless digital experience to civilians that pushes overall development reinforced by adequate security.
-[](https://www.loginradius.com/resource/how-cities-use-loginradius-identity-platform/-)
+[](https://www.loginradius.com/resource/how-cities-use-loginradius-identity-platform/-)
## How Identity Management Reinforces Security for Citizens?
@@ -88,4 +88,4 @@ And the public sector and government organizations shouldn’t delay a bit in ad
Identity management in the government sector can also help resolve issues related to bad user experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=fix-identity-to-fix-citizens-security)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=fix-identity-to-fix-citizens-security)
\ No newline at end of file
diff --git a/content/identity/free-developer-plan-for-authentication/index.md b/content/identity/free-developer-plan-for-authentication/index.md
index eacdace56..631535382 100644
--- a/content/identity/free-developer-plan-for-authentication/index.md
+++ b/content/identity/free-developer-plan-for-authentication/index.md
@@ -197,4 +197,4 @@ We’d love to hear your feedback and answer any questions.
Have an active CIAM project? Sign up for a free plan or talk to our experts and see how LoginRadius can help.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=free-developer-plan-for-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=free-developer-plan-for-authentication)
\ No newline at end of file
diff --git a/content/identity/google-one-tap-login/google-onetap.jpg b/content/identity/google-one-tap-login/google-onetap.jpg
deleted file mode 100644
index f69a2fa10..000000000
Binary files a/content/identity/google-one-tap-login/google-onetap.jpg and /dev/null differ
diff --git a/content/identity/google-one-tap-login/google-onetap.webp b/content/identity/google-one-tap-login/google-onetap.webp
new file mode 100644
index 000000000..0776f7697
Binary files /dev/null and b/content/identity/google-one-tap-login/google-onetap.webp differ
diff --git a/content/identity/google-one-tap-login/google-onetaplogin-cover.jpg b/content/identity/google-one-tap-login/google-onetaplogin-cover.jpg
deleted file mode 100644
index 8e440e91f..000000000
Binary files a/content/identity/google-one-tap-login/google-onetaplogin-cover.jpg and /dev/null differ
diff --git a/content/identity/google-one-tap-login/google-onetaplogin-cover.webp b/content/identity/google-one-tap-login/google-onetaplogin-cover.webp
new file mode 100644
index 000000000..56936cac9
Binary files /dev/null and b/content/identity/google-one-tap-login/google-onetaplogin-cover.webp differ
diff --git a/content/identity/google-one-tap-login/index.md b/content/identity/google-one-tap-login/index.md
index 60a22a843..590656873 100644
--- a/content/identity/google-one-tap-login/index.md
+++ b/content/identity/google-one-tap-login/index.md
@@ -1,7 +1,7 @@
---
title: "All About Google One Tap Login—Explained!"
date: "2021-06-11"
-coverImage: "google-onetaplogin-cover.jpg"
+coverImage: "google-onetaplogin-cover.webp"
tags: ["social login"]
author: "Manish Tiwari"
description: "Consumers prefer basic login experiences over complicated signup procedures. The Google One-Tap Login feature, available on Android phones, allows users to quickly sign up for apps or web services with their Google credentials without creating an account."
@@ -24,7 +24,7 @@ The login widget appears as a popup, and it will prompt the users to sign in or
* You are logged in to your Gmail account,
* You've signed in to your Chrome browser.
-
+
At first glance, it seems like a convenient feature: you click the web widget and sign in to a site with your existing Google account. There is no need to create a new user, no need to remember the email and password you used to log in before. Just click on a button, and you are good to go.
@@ -68,4 +68,4 @@ In this blog, we have learned how the Google one-tap login can be helpful for co
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=google-one-tap-login)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=google-one-tap-login)
\ No newline at end of file
diff --git a/content/identity/govt-access-control-challenges-2022/govt-access.jpg b/content/identity/govt-access-control-challenges-2022/govt-access.jpg
deleted file mode 100644
index fb29d7451..000000000
Binary files a/content/identity/govt-access-control-challenges-2022/govt-access.jpg and /dev/null differ
diff --git a/content/identity/govt-access-control-challenges-2022/govt-access.webp b/content/identity/govt-access-control-challenges-2022/govt-access.webp
new file mode 100644
index 000000000..f44be4845
Binary files /dev/null and b/content/identity/govt-access-control-challenges-2022/govt-access.webp differ
diff --git a/content/identity/govt-access-control-challenges-2022/govt-agency-guide.png b/content/identity/govt-access-control-challenges-2022/govt-agency-guide.png
deleted file mode 100644
index ae7f7374b..000000000
Binary files a/content/identity/govt-access-control-challenges-2022/govt-agency-guide.png and /dev/null differ
diff --git a/content/identity/govt-access-control-challenges-2022/govt-agency-guide.webp b/content/identity/govt-access-control-challenges-2022/govt-agency-guide.webp
new file mode 100644
index 000000000..4934a3302
Binary files /dev/null and b/content/identity/govt-access-control-challenges-2022/govt-agency-guide.webp differ
diff --git a/content/identity/govt-access-control-challenges-2022/index.md b/content/identity/govt-access-control-challenges-2022/index.md
index 9947022f2..3f9c1d560 100644
--- a/content/identity/govt-access-control-challenges-2022/index.md
+++ b/content/identity/govt-access-control-challenges-2022/index.md
@@ -1,7 +1,7 @@
---
title: "5 Challenges for Government Adoption of Citizens’ Access Control"
date: "2022-01-06"
-coverImage: "govt-access.jpg"
+coverImage: "govt-access.webp"
tags: ["security"]
featured: false
author: "Yash Rathi"
@@ -90,4 +90,4 @@ When it comes to adopting citizen access control, government agencies should inc
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=govt-access-control-challenges-2022)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=govt-access-control-challenges-2022)
diff --git a/content/identity/govtech-shaping-future-gov-services/govtech.jpg b/content/identity/govtech-shaping-future-gov-services/govtech.jpg
deleted file mode 100644
index 2844e7f9b..000000000
Binary files a/content/identity/govtech-shaping-future-gov-services/govtech.jpg and /dev/null differ
diff --git a/content/identity/govtech-shaping-future-gov-services/govtech.webp b/content/identity/govtech-shaping-future-gov-services/govtech.webp
new file mode 100644
index 000000000..36cafc404
Binary files /dev/null and b/content/identity/govtech-shaping-future-gov-services/govtech.webp differ
diff --git a/content/identity/govtech-shaping-future-gov-services/index.md b/content/identity/govtech-shaping-future-gov-services/index.md
index 958d0590f..9ea152927 100644
--- a/content/identity/govtech-shaping-future-gov-services/index.md
+++ b/content/identity/govtech-shaping-future-gov-services/index.md
@@ -1,7 +1,7 @@
---
title: "GovTech is On The Rise: How Can This Technology Improve Government Services?"
date: "2022-05-13"
-coverImage: "govtech.jpg"
+coverImage: "govtech.webp"
tags: ["govtech", "digital-transformation", "consumer-experience"]
author: "Rakesh Soni"
description: "GovTech refers to the efforts to digitally transform public administrations and various government and public sector organizations through innovative technological solutions. This post will help you understand the aspects of GovTech and how it’s offering endless opportunities for the sake of citizens’ benefits."
@@ -55,7 +55,7 @@ What good is a centralized portal if citizens have to create multiple identities
\
Without a seamless user experience, engagement rates drop. But with GovTech incorporating [Single Sign-On](https://www.loginradius.com/single-sign-on/) (SSO), cities and companies can allow customers to access all applications within their platform with a single set of unified credentials rather than register and log in to each service separately.
-[](https://www.loginradius.com/resource/how-public-sector-companies-use-the-loginradius-identity-platform/)
+[](https://www.loginradius.com/resource/how-public-sector-companies-use-the-loginradius-identity-platform/)
### 3. Integrating with third-party applications.
@@ -88,4 +88,4 @@ Whether it’s authentication or delivering a consistent omnichannel experience,
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=govtech-shaping-future-gov-services)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=govtech-shaping-future-gov-services)
diff --git a/content/identity/govtech-shaping-future-gov-services/public-sector-ds.png b/content/identity/govtech-shaping-future-gov-services/public-sector-ds.png
deleted file mode 100644
index dce0d6e37..000000000
Binary files a/content/identity/govtech-shaping-future-gov-services/public-sector-ds.png and /dev/null differ
diff --git a/content/identity/govtech-shaping-future-gov-services/public-sector-ds.webp b/content/identity/govtech-shaping-future-gov-services/public-sector-ds.webp
new file mode 100644
index 000000000..ec9c7ffe4
Binary files /dev/null and b/content/identity/govtech-shaping-future-gov-services/public-sector-ds.webp differ
diff --git a/content/identity/guide-choosing-right-ciam-solution/EB-build-buy.png b/content/identity/guide-choosing-right-ciam-solution/EB-build-buy.png
deleted file mode 100644
index 12aee97b9..000000000
Binary files a/content/identity/guide-choosing-right-ciam-solution/EB-build-buy.png and /dev/null differ
diff --git a/content/identity/guide-choosing-right-ciam-solution/EB-build-buy.webp b/content/identity/guide-choosing-right-ciam-solution/EB-build-buy.webp
new file mode 100644
index 000000000..37f1cc72f
Binary files /dev/null and b/content/identity/guide-choosing-right-ciam-solution/EB-build-buy.webp differ
diff --git a/content/identity/guide-choosing-right-ciam-solution/EB-buy-over-build.png b/content/identity/guide-choosing-right-ciam-solution/EB-buy-over-build.png
deleted file mode 100644
index 9ba2600e9..000000000
Binary files a/content/identity/guide-choosing-right-ciam-solution/EB-buy-over-build.png and /dev/null differ
diff --git a/content/identity/guide-choosing-right-ciam-solution/EB-buy-over-build.webp b/content/identity/guide-choosing-right-ciam-solution/EB-buy-over-build.webp
new file mode 100644
index 000000000..f5dd81ad8
Binary files /dev/null and b/content/identity/guide-choosing-right-ciam-solution/EB-buy-over-build.webp differ
diff --git a/content/identity/guide-choosing-right-ciam-solution/build-vs-buy-eb.png b/content/identity/guide-choosing-right-ciam-solution/build-vs-buy-eb.png
deleted file mode 100644
index b58e0950a..000000000
Binary files a/content/identity/guide-choosing-right-ciam-solution/build-vs-buy-eb.png and /dev/null differ
diff --git a/content/identity/guide-choosing-right-ciam-solution/build-vs-buy-eb.webp b/content/identity/guide-choosing-right-ciam-solution/build-vs-buy-eb.webp
new file mode 100644
index 000000000..23f70e01d
Binary files /dev/null and b/content/identity/guide-choosing-right-ciam-solution/build-vs-buy-eb.webp differ
diff --git a/content/identity/guide-choosing-right-ciam-solution/ciam-solution.jpg b/content/identity/guide-choosing-right-ciam-solution/ciam-solution.jpg
deleted file mode 100644
index 65154f33c..000000000
Binary files a/content/identity/guide-choosing-right-ciam-solution/ciam-solution.jpg and /dev/null differ
diff --git a/content/identity/guide-choosing-right-ciam-solution/ciam-solution.webp b/content/identity/guide-choosing-right-ciam-solution/ciam-solution.webp
new file mode 100644
index 000000000..d260fabcd
Binary files /dev/null and b/content/identity/guide-choosing-right-ciam-solution/ciam-solution.webp differ
diff --git a/content/identity/guide-choosing-right-ciam-solution/index.md b/content/identity/guide-choosing-right-ciam-solution/index.md
index cac8c2637..560ddf644 100644
--- a/content/identity/guide-choosing-right-ciam-solution/index.md
+++ b/content/identity/guide-choosing-right-ciam-solution/index.md
@@ -1,7 +1,7 @@
---
title: "The Ultimate Guide to Choosing the Right CIAM Solution"
date: "2023-03-06"
-coverImage: "right-ciam-sol.jpg"
+coverImage: "right-ciam-sol.webp"
tags: ["compliance","ciam solution","data privacy"]
author: "Rakesh Soni"
description: "With the market for CIAM solutions rapidly evolving, choosing the right one for your organization's unique needs can take time. Hence, you must analyze the entire CIAM landscape, and your business needs to decide wisely."
@@ -220,7 +220,7 @@ CIAM solutions enable businesses to manage customer data, streamline login proce
Here’s the list of benefits of buying a CIAM solution rather than building one from scratch:
-[](https://www.loginradius.com/resource/the-case-for-buying-over-building/)
+[](https://www.loginradius.com/resource/the-case-for-buying-over-building/)
### 1. Time and Cost Savings
@@ -271,4 +271,4 @@ A: Identity and Access Management (IAM) is a framework of policies and technolog
IAM plays a crucial role in managing internal users' access to systems and applications, enforcing security policies, and maintaining compliance within an organization's network.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=guide-choosing-right-ciam-solution)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=guide-choosing-right-ciam-solution)
diff --git a/content/identity/guide-choosing-right-ciam-solution/right-ciam-sol.jpg b/content/identity/guide-choosing-right-ciam-solution/right-ciam-sol.jpg
deleted file mode 100644
index faff5ff43..000000000
Binary files a/content/identity/guide-choosing-right-ciam-solution/right-ciam-sol.jpg and /dev/null differ
diff --git a/content/identity/guide-choosing-right-ciam-solution/right-ciam-sol.webp b/content/identity/guide-choosing-right-ciam-solution/right-ciam-sol.webp
new file mode 100644
index 000000000..487598de4
Binary files /dev/null and b/content/identity/guide-choosing-right-ciam-solution/right-ciam-sol.webp differ
diff --git a/content/identity/guide-consent-management/ccpa-customer-identity.png b/content/identity/guide-consent-management/ccpa-customer-identity.png
deleted file mode 100644
index 0ed0f3bce..000000000
Binary files a/content/identity/guide-consent-management/ccpa-customer-identity.png and /dev/null differ
diff --git a/content/identity/guide-consent-management/ccpa-customer-identity.webp b/content/identity/guide-consent-management/ccpa-customer-identity.webp
new file mode 100644
index 000000000..6d67557e6
Binary files /dev/null and b/content/identity/guide-consent-management/ccpa-customer-identity.webp differ
diff --git a/content/identity/guide-consent-management/guide-consent-management-cover.jpg b/content/identity/guide-consent-management/guide-consent-management-cover.jpg
deleted file mode 100644
index 122fa535b..000000000
Binary files a/content/identity/guide-consent-management/guide-consent-management-cover.jpg and /dev/null differ
diff --git a/content/identity/guide-consent-management/guide-consent-management-cover.webp b/content/identity/guide-consent-management/guide-consent-management-cover.webp
new file mode 100644
index 000000000..3058bc8f3
Binary files /dev/null and b/content/identity/guide-consent-management/guide-consent-management-cover.webp differ
diff --git a/content/identity/guide-consent-management/index.md b/content/identity/guide-consent-management/index.md
index 78ecba9bd..b2923ad57 100644
--- a/content/identity/guide-consent-management/index.md
+++ b/content/identity/guide-consent-management/index.md
@@ -1,7 +1,7 @@
---
title: "A Detail Guide to Consent Management and Processing Data"
date: "2021-04-14"
-coverImage: "guide-consent-management-cover.jpg"
+coverImage: "guide-consent-management-cover.webp"
tags: ["consent management","compliance","cx"]
author: "Abhilash Menon"
description: "The importance of consent management cannot be understated. Whether you are a small business that is starting out or a multinational brand, consent management is going to be a crucial piece of your organization's ability to grow sustainably while building trust within your consumer base. Learn how the GDPR and CCPA define conditions that allow user data to be processed without consent or unconditionally."
@@ -41,7 +41,7 @@ Both the GDPR and CCPA define specific conditions that allow user data to be pro
8. **Business-to-Business Relationships**: Contact information collected as part of a business-to-business (B2B) relationship may also be exempt from CCPA compliance to qualify for this exemption, the product or service taking place between the businesses must have already been CCPA exempt.
9. **Warranty and Recall Information**: Specific to new car dealers and buyers this exemption rules that vehicle ownership information may be kept and shared between dealers and manufacturers without the need to provide an opt-out option.
-[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
+[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
## Advantages of Having a Good Consent Management System
@@ -63,4 +63,4 @@ Whether you are a small business that is starting out or a Multinational brand,
There are a couple of ways you can have these implemented depending on your use case. While some companies will require only basic consent management pieces that can be written by developers fairly easily, others that use consumer data for analytics and personalization of services might find it more suitable to use a Consent Management platform from a third-party vendor.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=guide-consent-management)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=guide-consent-management)
\ No newline at end of file
diff --git a/content/identity/guide-to-five-a-of-cloud-identity-management/DS-consumer-audit-trail.png b/content/identity/guide-to-five-a-of-cloud-identity-management/DS-consumer-audit-trail.png
deleted file mode 100644
index 4afe9c15b..000000000
Binary files a/content/identity/guide-to-five-a-of-cloud-identity-management/DS-consumer-audit-trail.png and /dev/null differ
diff --git a/content/identity/guide-to-five-a-of-cloud-identity-management/DS-consumer-audit-trail.webp b/content/identity/guide-to-five-a-of-cloud-identity-management/DS-consumer-audit-trail.webp
new file mode 100644
index 000000000..982ab7a25
Binary files /dev/null and b/content/identity/guide-to-five-a-of-cloud-identity-management/DS-consumer-audit-trail.webp differ
diff --git a/content/identity/guide-to-five-a-of-cloud-identity-management/cloud-identity-mngmnt.jpg b/content/identity/guide-to-five-a-of-cloud-identity-management/cloud-identity-mngmnt.jpg
deleted file mode 100644
index 70bd61ff7..000000000
Binary files a/content/identity/guide-to-five-a-of-cloud-identity-management/cloud-identity-mngmnt.jpg and /dev/null differ
diff --git a/content/identity/guide-to-five-a-of-cloud-identity-management/cloud-identity-mngmnt.webp b/content/identity/guide-to-five-a-of-cloud-identity-management/cloud-identity-mngmnt.webp
new file mode 100644
index 000000000..b6091502f
Binary files /dev/null and b/content/identity/guide-to-five-a-of-cloud-identity-management/cloud-identity-mngmnt.webp differ
diff --git a/content/identity/guide-to-five-a-of-cloud-identity-management/index.md b/content/identity/guide-to-five-a-of-cloud-identity-management/index.md
index e9c232f77..e0f26b50c 100644
--- a/content/identity/guide-to-five-a-of-cloud-identity-management/index.md
+++ b/content/identity/guide-to-five-a-of-cloud-identity-management/index.md
@@ -1,7 +1,7 @@
---
title: "A Comprehensive Guide to the Five A's of Cloud Identity Management"
date: "2023-08-03"
-coverImage: "cloud-identity-mngmnt.jpg"
+coverImage: "cloud-identity-mngmnt.webp"
tags: ["cloud identity","identity management","biometric authentication"]
author: "Rakesh Soni"
description: "Discover the vital elements contributing to a secure and efficient cloud identity framework, from strong authentication methods to centralized account management and comprehensive audit logging."
@@ -48,7 +48,7 @@ These logs provide an audit trail for compliance purposes, incident investigatio
Regularly monitoring and analyzing these logs enable timely detection and response to security incidents.
-[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail)
+[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail)
### 5. Accountability: Establishing Responsibility and Oversight
@@ -64,4 +64,4 @@ This comprehensive guide to cloud identity management reveals the significance o
By embracing these principles and remaining adaptable to emerging security challenges, organizations can confidently navigate the complex cloud security landscape and maintain a strong security posture in the cloud.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=guide-to-five-a-of-cloud-identity-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=guide-to-five-a-of-cloud-identity-management)
diff --git a/content/identity/hackproof-smartphone-security/DS-Mob-biometric-auth.png b/content/identity/hackproof-smartphone-security/DS-Mob-biometric-auth.png
deleted file mode 100644
index a3580f13e..000000000
Binary files a/content/identity/hackproof-smartphone-security/DS-Mob-biometric-auth.png and /dev/null differ
diff --git a/content/identity/hackproof-smartphone-security/DS-Mob-biometric-auth.webp b/content/identity/hackproof-smartphone-security/DS-Mob-biometric-auth.webp
new file mode 100644
index 000000000..0257eff22
Binary files /dev/null and b/content/identity/hackproof-smartphone-security/DS-Mob-biometric-auth.webp differ
diff --git a/content/identity/hackproof-smartphone-security/hackproof-smartphone.jpg b/content/identity/hackproof-smartphone-security/hackproof-smartphone.jpg
deleted file mode 100644
index 125af347b..000000000
Binary files a/content/identity/hackproof-smartphone-security/hackproof-smartphone.jpg and /dev/null differ
diff --git a/content/identity/hackproof-smartphone-security/hackproof-smartphone.webp b/content/identity/hackproof-smartphone-security/hackproof-smartphone.webp
new file mode 100644
index 000000000..7c52d7531
Binary files /dev/null and b/content/identity/hackproof-smartphone-security/hackproof-smartphone.webp differ
diff --git a/content/identity/hackproof-smartphone-security/index.md b/content/identity/hackproof-smartphone-security/index.md
index 8783e17d8..69221d1c5 100644
--- a/content/identity/hackproof-smartphone-security/index.md
+++ b/content/identity/hackproof-smartphone-security/index.md
@@ -1,7 +1,7 @@
---
title: "Unlocking Smartphone Security: How to Hackproof Your Smartphone"
date: "2023-09-06"
-coverImage: "hackproof-smartphone.jpg"
+coverImage: "hackproof-smartphone.webp"
tags: ["data protection","cybersecurity","biometric authentication","cx"]
author: "Alok Patidar"
description: "In today's digital age, where smartphones are integral to our daily lives, securing them is paramount. But is it possible to truly hackproof your smartphone in an ever-expanding cyber threat landscape? Let’s dive into the types of hacks and attacks you need to be aware of and provide seven practical tips to bolster your smartphone's security."
@@ -60,7 +60,7 @@ Secure your smartphone with a strong, alphanumeric password or passphrase. Avoid
Biometric authentication ensures robust authentication security since the biometric identity of every individual is unique and can’t be compromised easily. Hence, taking advantage of fingerprint or facial recognition features for an extra layer of security is a great option.
-[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
+[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
### #3. Regularly Update Your Operating System and Apps
@@ -92,4 +92,4 @@ In a world where our smartphones have become extensions of ourselves, safeguardi
While achieving absolute hack-proof status might be an unattainable goal, the steps outlined in this blog can significantly enhance your smartphone's security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hackproof-smartphone-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hackproof-smartphone-security)
diff --git a/content/identity/handling-scalability-security-loginradius/handling-scalability-security-loginradius-cover.jpg b/content/identity/handling-scalability-security-loginradius/handling-scalability-security-loginradius-cover.jpg
deleted file mode 100644
index cd9a4b835..000000000
Binary files a/content/identity/handling-scalability-security-loginradius/handling-scalability-security-loginradius-cover.jpg and /dev/null differ
diff --git a/content/identity/handling-scalability-security-loginradius/handling-scalability-security-loginradius-cover.webp b/content/identity/handling-scalability-security-loginradius/handling-scalability-security-loginradius-cover.webp
new file mode 100644
index 000000000..68bbb881a
Binary files /dev/null and b/content/identity/handling-scalability-security-loginradius/handling-scalability-security-loginradius-cover.webp differ
diff --git a/content/identity/handling-scalability-security-loginradius/index.md b/content/identity/handling-scalability-security-loginradius/index.md
index 80e37fc16..309b40f01 100644
--- a/content/identity/handling-scalability-security-loginradius/index.md
+++ b/content/identity/handling-scalability-security-loginradius/index.md
@@ -1,7 +1,7 @@
---
title: "Handling Scalability and Enhancing Security with LoginRadius"
date: "2021-04-30"
-coverImage: "handling-scalability-security-loginradius-cover.jpg"
+coverImage: "handling-scalability-security-loginradius-cover.webp"
tags: ["data security","ciam platform","cx"]
author: "Vishal Sharma"
description: "Without a highly scalable infrastructure, it is not possible to handle increasing account creations and logins. Even peak loads can dramatically impede performance and degrade the consumer experience for any business. Learn how LoginRadius empowers businesses to deliver a secure and delightful user experience to their consumers."
@@ -21,7 +21,7 @@ For this, you need to ensure you have a robust identity solution that grows at t
Here’s LoginRadius for you. A leading CIAM solution provider that empowers businesses to deliver a secure and delightful user experience to their clients through its comprehensive and scalable consumer identity and access management platform.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
Let’s understand how LoginRadius handles scalability with the ability to cater to 5-10x more users with the highest level of security.
@@ -74,4 +74,4 @@ The solution must ensure adequate security for both the clients and enterprise d
LoginRadius is the leading CIAM solution provider that not only empowers businesses to deliver a rich user experience but eventually offers a robust and highly secure infrastructure that ensures the utmost level of [data and privacy security](https://www.loginradius.com/blog/identity/2021/03/privacy-compliance/).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=handling-scalability-security-loginradius)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=handling-scalability-security-loginradius)
\ No newline at end of file
diff --git a/content/identity/handling-scalability-security-loginradius/modern-ciam.png b/content/identity/handling-scalability-security-loginradius/modern-ciam.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/identity/handling-scalability-security-loginradius/modern-ciam.png and /dev/null differ
diff --git a/content/identity/handling-scalability-security-loginradius/modern-ciam.webp b/content/identity/handling-scalability-security-loginradius/modern-ciam.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/identity/handling-scalability-security-loginradius/modern-ciam.webp differ
diff --git a/content/identity/history-human-identity-part-3/454px-MaoriChief1784.jpg b/content/identity/history-human-identity-part-3/454px-MaoriChief1784.jpg
deleted file mode 100644
index df5728c00..000000000
Binary files a/content/identity/history-human-identity-part-3/454px-MaoriChief1784.jpg and /dev/null differ
diff --git a/content/identity/history-human-identity-part-3/454px-MaoriChief1784.webp b/content/identity/history-human-identity-part-3/454px-MaoriChief1784.webp
new file mode 100644
index 000000000..f7b85ed18
Binary files /dev/null and b/content/identity/history-human-identity-part-3/454px-MaoriChief1784.webp differ
diff --git a/content/identity/history-human-identity-part-3/history-human-identity-part-3.jpg b/content/identity/history-human-identity-part-3/history-human-identity-part-3.jpg
deleted file mode 100644
index b90fa2cf8..000000000
Binary files a/content/identity/history-human-identity-part-3/history-human-identity-part-3.jpg and /dev/null differ
diff --git a/content/identity/history-human-identity-part-3/history-human-identity-part-3.webp b/content/identity/history-human-identity-part-3/history-human-identity-part-3.webp
new file mode 100644
index 000000000..c4a70acf6
Binary files /dev/null and b/content/identity/history-human-identity-part-3/history-human-identity-part-3.webp differ
diff --git a/content/identity/history-human-identity-part-3/image-2.jpeg b/content/identity/history-human-identity-part-3/image-2.jpeg
deleted file mode 100644
index f5e0514c0..000000000
Binary files a/content/identity/history-human-identity-part-3/image-2.jpeg and /dev/null differ
diff --git a/content/identity/history-human-identity-part-3/image-2.webp b/content/identity/history-human-identity-part-3/image-2.webp
new file mode 100644
index 000000000..e0a3af0e2
Binary files /dev/null and b/content/identity/history-human-identity-part-3/image-2.webp differ
diff --git a/content/identity/history-human-identity-part-3/image-3.jpg b/content/identity/history-human-identity-part-3/image-3.jpg
deleted file mode 100644
index fa00ef62b..000000000
Binary files a/content/identity/history-human-identity-part-3/image-3.jpg and /dev/null differ
diff --git a/content/identity/history-human-identity-part-3/image-3.webp b/content/identity/history-human-identity-part-3/image-3.webp
new file mode 100644
index 000000000..bdac5dbe8
Binary files /dev/null and b/content/identity/history-human-identity-part-3/image-3.webp differ
diff --git a/content/identity/history-human-identity-part-3/image-4.png b/content/identity/history-human-identity-part-3/image-4.png
deleted file mode 100644
index ba2a47890..000000000
Binary files a/content/identity/history-human-identity-part-3/image-4.png and /dev/null differ
diff --git a/content/identity/history-human-identity-part-3/image-4.webp b/content/identity/history-human-identity-part-3/image-4.webp
new file mode 100644
index 000000000..f8a7f4617
Binary files /dev/null and b/content/identity/history-human-identity-part-3/image-4.webp differ
diff --git a/content/identity/history-human-identity-part-3/image-5.jpg b/content/identity/history-human-identity-part-3/image-5.jpg
deleted file mode 100644
index 7c56daa2c..000000000
Binary files a/content/identity/history-human-identity-part-3/image-5.jpg and /dev/null differ
diff --git a/content/identity/history-human-identity-part-3/image-5.webp b/content/identity/history-human-identity-part-3/image-5.webp
new file mode 100644
index 000000000..cc3c844f9
Binary files /dev/null and b/content/identity/history-human-identity-part-3/image-5.webp differ
diff --git a/content/identity/history-human-identity-part-3/index.md b/content/identity/history-human-identity-part-3/index.md
index df1bf672e..14f20b9c0 100644
--- a/content/identity/history-human-identity-part-3/index.md
+++ b/content/identity/history-human-identity-part-3/index.md
@@ -1,7 +1,7 @@
---
title: "A History of Human Identity in Pictures Part 3"
date: "2019-09-04"
-coverImage: "history-human-identity-part-3.jpg"
+coverImage: "history-human-identity-part-3.webp"
tags: ["public-sector"]
featured: false
author: "Rakesh Soni"
@@ -10,9 +10,9 @@ metatitle: "A History of Human Identity in Pictures Part 3 | LoginRadius"
metadescription: "In Part II of the History of Human Identity, we showed examples of identity verification such as names and unique markings. This blog is the final instalment of our 3-part series. In it, we'll focus on cultural identifiers—their use and their abuse."
---
- Sketch of a Māori chief by [Sydney Parkinson](https://en.wikipedia.org/wiki/Sydney_Parkinson) (1784)
+ Sketch of a Māori chief by [Sydney Parkinson](https://en.wikipedia.org/wiki/Sydney_Parkinson) (1784)
-Source - [MaoriChief1784](https://commons.wikimedia.org/wiki/File:MaoriChief1784.jpg)
+Source - [MaoriChief1784](https://commons.wikimedia.org/wiki/File:MaoriChief1784.webp)
In Part II of the History of Human Identity, we showed examples of identity verification such as names and unique markings. This blog is the final instalment of our 3-part series. In it, we'll focus on cultural identifiers—their use _and_ their abuse.
@@ -28,7 +28,7 @@ In 1540, the granting of “[travelling papers](https://www.theguardian.com/trav
**Charles de Saint-Mémin’s United States passport, June 30, 1810**
- Charles de Saint-Mémin’s United States passport, June 30, 1810
+ Charles de Saint-Mémin’s United States passport, June 30, 1810
Source - [metmuseum](https://www.metmuseum.org/art/collection/search/656327)
@@ -38,17 +38,17 @@ Around 100 countries now have compulsory [national identity cards](https://en.w
[**West German**](https://en.wikipedia.org/wiki/West_Germany) **identity card issued between 1 January 1951 and 31 March 1987**
- [West German](https://en.wikipedia.org/wiki/West_Germany) identity card issued between 1 January 1951 and 31 March 1987
+ [West German](https://en.wikipedia.org/wiki/West_Germany) identity card issued between 1 January 1951 and 31 March 1987
-Source - [West German Identity Card](https://commons.wikimedia.org/wiki/File:1979_identity_card_of_West_Germany_original_size.jpg)
+Source - [West German Identity Card](https://commons.wikimedia.org/wiki/File:1979_identity_card_of_West_Germany_original_size.webp)
A Social Security number (SSN) is another unique identifier. The US government assigned this for taxation and benefits. Issued by the US Social Security Administration in November 1935, SSN numbers were part of the New Deal Social Security program. Today, US citizens still use SSNs to access benefits, pay taxes, receive wages, and show one’s identity.
**A Social Security card issued by the** [**Railroad Retirement Board**](https://en.wikipedia.org/wiki/Railroad_Retirement_Board) **in 1943 to a now-deceased person.**
- A Social Security card issued by the [Railroad Retirement Board](https://en.wikipedia.org/wiki/Railroad_Retirement_Board) in 1943 to a now deceased person.
+ A Social Security card issued by the [Railroad Retirement Board](https://en.wikipedia.org/wiki/Railroad_Retirement_Board) in 1943 to a now deceased person.
-Source - [Social Security Card](https://commons.wikimedia.org/wiki/File:PD_social_security_card.png)
+Source - [Social Security Card](https://commons.wikimedia.org/wiki/File:PD_social_security_card.webp)
A Social Insurance Number (SIN) is a 9-digit form of identification that every individual residing and/or working in Canada must have in order to access government benefits, file income taxes, and legally receive payment. [SIN cards were first issued in 1964](https://blog.wagepoint.com/all-content/the-complete-history-of-the-social-insurance-number) but have not been printed as cards since 2014 due to the risk of theft. Today, Canadian citizens do not carry SIN cards on their person.
@@ -77,9 +77,9 @@ It took roughly 10 years for the Canadian government to approve and implement a
**Public domain photo: Inupiat family, 1929**
- Public domain photo: Inupiat family, 1929
+ Public domain photo: Inupiat family, 1929
-Source - [Inupiat Family](https://commons.wikimedia.org/wiki/File:Inupiat_Family_from_Noatak,_Alaska,_1929,_Edward_S._Curtis_(restored).jpg)
+Source - [Inupiat Family](https://commons.wikimedia.org/wiki/File:Inupiat_Family_from_Noatak,_Alaska,_1929,_Edward_S._Curtis_(restored).webp)
## Project Surname
@@ -93,4 +93,4 @@ Before the arrival of Europeans, the [Inuit](https://www.thecanadianencyclopedi
As cofounder and CTO of LoginRadius, a customer identity and access management solution, I enjoy researching and writing about cultural identifiers. Likewise, I hope that you enjoyed this History of Human Identity series and will return to read our next series.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=history-human-identity-part-3)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=history-human-identity-part-3)
diff --git a/content/identity/history-identity-part-1/history-identity-part-1.jpg b/content/identity/history-identity-part-1/history-identity-part-1.jpg
deleted file mode 100644
index 1f78290fb..000000000
Binary files a/content/identity/history-identity-part-1/history-identity-part-1.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-1/history-identity-part-1.webp b/content/identity/history-identity-part-1/history-identity-part-1.webp
new file mode 100644
index 000000000..046d84150
Binary files /dev/null and b/content/identity/history-identity-part-1/history-identity-part-1.webp differ
diff --git a/content/identity/history-identity-part-1/image-1.jpeg b/content/identity/history-identity-part-1/image-1.jpeg
deleted file mode 100644
index 9fd6a45ee..000000000
Binary files a/content/identity/history-identity-part-1/image-1.jpeg and /dev/null differ
diff --git a/content/identity/history-identity-part-1/image-1.webp b/content/identity/history-identity-part-1/image-1.webp
new file mode 100644
index 000000000..306463090
Binary files /dev/null and b/content/identity/history-identity-part-1/image-1.webp differ
diff --git a/content/identity/history-identity-part-1/image-2.jpg b/content/identity/history-identity-part-1/image-2.jpg
deleted file mode 100644
index 405b53945..000000000
Binary files a/content/identity/history-identity-part-1/image-2.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-1/image-2.webp b/content/identity/history-identity-part-1/image-2.webp
new file mode 100644
index 000000000..3e9f17eae
Binary files /dev/null and b/content/identity/history-identity-part-1/image-2.webp differ
diff --git a/content/identity/history-identity-part-1/image-3.jpg b/content/identity/history-identity-part-1/image-3.jpg
deleted file mode 100644
index 96e8cf20f..000000000
Binary files a/content/identity/history-identity-part-1/image-3.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-1/image-3.webp b/content/identity/history-identity-part-1/image-3.webp
new file mode 100644
index 000000000..87eb8e5f7
Binary files /dev/null and b/content/identity/history-identity-part-1/image-3.webp differ
diff --git a/content/identity/history-identity-part-1/image-4.jpg b/content/identity/history-identity-part-1/image-4.jpg
deleted file mode 100644
index 268d51614..000000000
Binary files a/content/identity/history-identity-part-1/image-4.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-1/image-4.webp b/content/identity/history-identity-part-1/image-4.webp
new file mode 100644
index 000000000..e45579a1a
Binary files /dev/null and b/content/identity/history-identity-part-1/image-4.webp differ
diff --git a/content/identity/history-identity-part-1/image-5.jpg b/content/identity/history-identity-part-1/image-5.jpg
deleted file mode 100644
index f164257fa..000000000
Binary files a/content/identity/history-identity-part-1/image-5.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-1/image-5.webp b/content/identity/history-identity-part-1/image-5.webp
new file mode 100644
index 000000000..a19a8f491
Binary files /dev/null and b/content/identity/history-identity-part-1/image-5.webp differ
diff --git a/content/identity/history-identity-part-1/image-6.jpg b/content/identity/history-identity-part-1/image-6.jpg
deleted file mode 100644
index 9e4cf22ff..000000000
Binary files a/content/identity/history-identity-part-1/image-6.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-1/image-6.webp b/content/identity/history-identity-part-1/image-6.webp
new file mode 100644
index 000000000..057170f04
Binary files /dev/null and b/content/identity/history-identity-part-1/image-6.webp differ
diff --git a/content/identity/history-identity-part-1/image-7.jpg b/content/identity/history-identity-part-1/image-7.jpg
deleted file mode 100644
index 144f317ab..000000000
Binary files a/content/identity/history-identity-part-1/image-7.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-1/image-7.webp b/content/identity/history-identity-part-1/image-7.webp
new file mode 100644
index 000000000..9d58d6bf5
Binary files /dev/null and b/content/identity/history-identity-part-1/image-7.webp differ
diff --git a/content/identity/history-identity-part-1/image-8.jpg b/content/identity/history-identity-part-1/image-8.jpg
deleted file mode 100644
index 14e0ccf71..000000000
Binary files a/content/identity/history-identity-part-1/image-8.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-1/image-8.webp b/content/identity/history-identity-part-1/image-8.webp
new file mode 100644
index 000000000..14bedce16
Binary files /dev/null and b/content/identity/history-identity-part-1/image-8.webp differ
diff --git a/content/identity/history-identity-part-1/image-9.jpg b/content/identity/history-identity-part-1/image-9.jpg
deleted file mode 100644
index c0f81c9f3..000000000
Binary files a/content/identity/history-identity-part-1/image-9.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-1/image-9.webp b/content/identity/history-identity-part-1/image-9.webp
new file mode 100644
index 000000000..952354319
Binary files /dev/null and b/content/identity/history-identity-part-1/image-9.webp differ
diff --git a/content/identity/history-identity-part-1/index.md b/content/identity/history-identity-part-1/index.md
index dbc9e0b5b..bd7896634 100644
--- a/content/identity/history-identity-part-1/index.md
+++ b/content/identity/history-identity-part-1/index.md
@@ -1,7 +1,7 @@
---
title: "A History of Human Identity in Pictures - Part 1"
date: "2019-08-07"
-coverImage: "history-identity-part-1.jpg"
+coverImage: "history-identity-part-1.webp"
tags: ["public-sector"]
featured: false
author: "Rakesh Soni"
@@ -11,7 +11,7 @@ metadescription: "The concept of human identity stretches back thousands of year
---
- Portrait of Thakur Utham Ram, ca. 1760
+ Portrait of Thakur Utham Ram, ca. 1760
Source - [metmuseum](https://www.metmuseum.org/art/collection/search/37876)
@@ -27,23 +27,23 @@ It’s impossible to know when humans first recognized that they had individual
We assume that early hominins knew each other by sight, sound, smell, and touch, as animals do.
- High school students in Binghamton NY, USA, holding replicas of hominin skulls. Photo by Carolyn WIlczynski
+ High school students in Binghamton NY, USA, holding replicas of hominin skulls. Photo by Carolyn WIlczynski
-[Students explore hominid evolution](https://commons.wikimedia.org/wiki/File:Students_explore_hominid_evolution.jpg)
+[Students explore hominid evolution](https://commons.wikimedia.org/wiki/File:Students_explore_hominid_evolution.webp)
Presumably they could tell one Neanderthal from another by their faces, the noises they made, and the way they moved.
There is even [research](https://www.nature.com/articles/ncomms5800) showing that human faces evolved in ways that made it easier for humans to recognize each other. The fact that facial recognition was supported by natural selection implies that it’s very important for social interaction and the success of the species.
- Hands, ca. 7300 BC, at the Cuevas de las Manos upon Río Pinturas, Argentina. Photo by Mariano Cecowski
+ Hands, ca. 7300 BC, at the Cuevas de las Manos upon Río Pinturas, Argentina. Photo by Mariano Cecowski
-[SantaCruz-CuevaManos-P2210651b](https://commons.wikimedia.org/wiki/File:SantaCruz-CuevaManos-P2210651b.jpg)
+[SantaCruz-CuevaManos-P2210651b](https://commons.wikimedia.org/wiki/File:SantaCruz-CuevaManos-P2210651b.webp)
For an example of written identity in prehistory, we can look at cave markings showing stencilled handprints. Archeologists disagree on the meaning behind cave handprints—they could be warning messages or part of shamanic practice—but to our modern eyes they look like signatures or graffiti tags, a way of saying, “I was here.”
- Forensic reconstruction of Oase 2 skull dating to 35,000 BC
+ Forensic reconstruction of Oase 2 skull dating to 35,000 BC
-[Homo sapiens sapiens, Oase, Rumänien (Daniela Hitzemann)](https://commons.wikimedia.org/wiki/File:Neanderthaler,_Oase,_Rum%C3%A4nien_(Daniela_Hitzemann).jpg)
+[Homo sapiens sapiens, Oase, Rumänien (Daniela Hitzemann)](https://commons.wikimedia.org/wiki/File:Neanderthaler,_Oase,_Rum%C3%A4nien_(Daniela_Hitzemann).webp)
Spoken language emerged 100,000 years ago. In fact, the structure of the brain and the size of the spinal cord of Cro-Magnon people suggests that they would have been capable of producing the [same sounds that we use in speech today](https://australianmuseum.net.au/learn/science/human-evolution/how-do-we-know-if-they-could-speak/).
@@ -57,37 +57,37 @@ The oldest artifacts with written names have more everyday origins.
There are several candidates for the distinction of first recorded name.
- A photo of the Kushim Tablet. © [The Schøyen Collection, Oslo and London](https://www.schoyencollection.com/24-smaller-collections/wine-beer/ms-1717-beer-inanna-uruk)
+ A photo of the Kushim Tablet. © [The Schøyen Collection, Oslo and London](https://www.schoyencollection.com/24-smaller-collections/wine-beer/ms-1717-beer-inanna-uruk)
[Leaving A Mark in History: The Oldest Known Named Person](https://www.ancient-origins.net/artifacts-ancient-writings/leaving-mark-history-oldest-known-named-person-007882)
One is a Mesopotamian clay tablet, ca. 3100 BC, found in Iran that appears to document a business transaction. The receipt for barley delivery to the brewery at Inanna Temple is presumably signed with the name of Kushim, an accountant or record keeper.
-\[caption id="attachment\_5348" align="aligncenter" width="1684"\]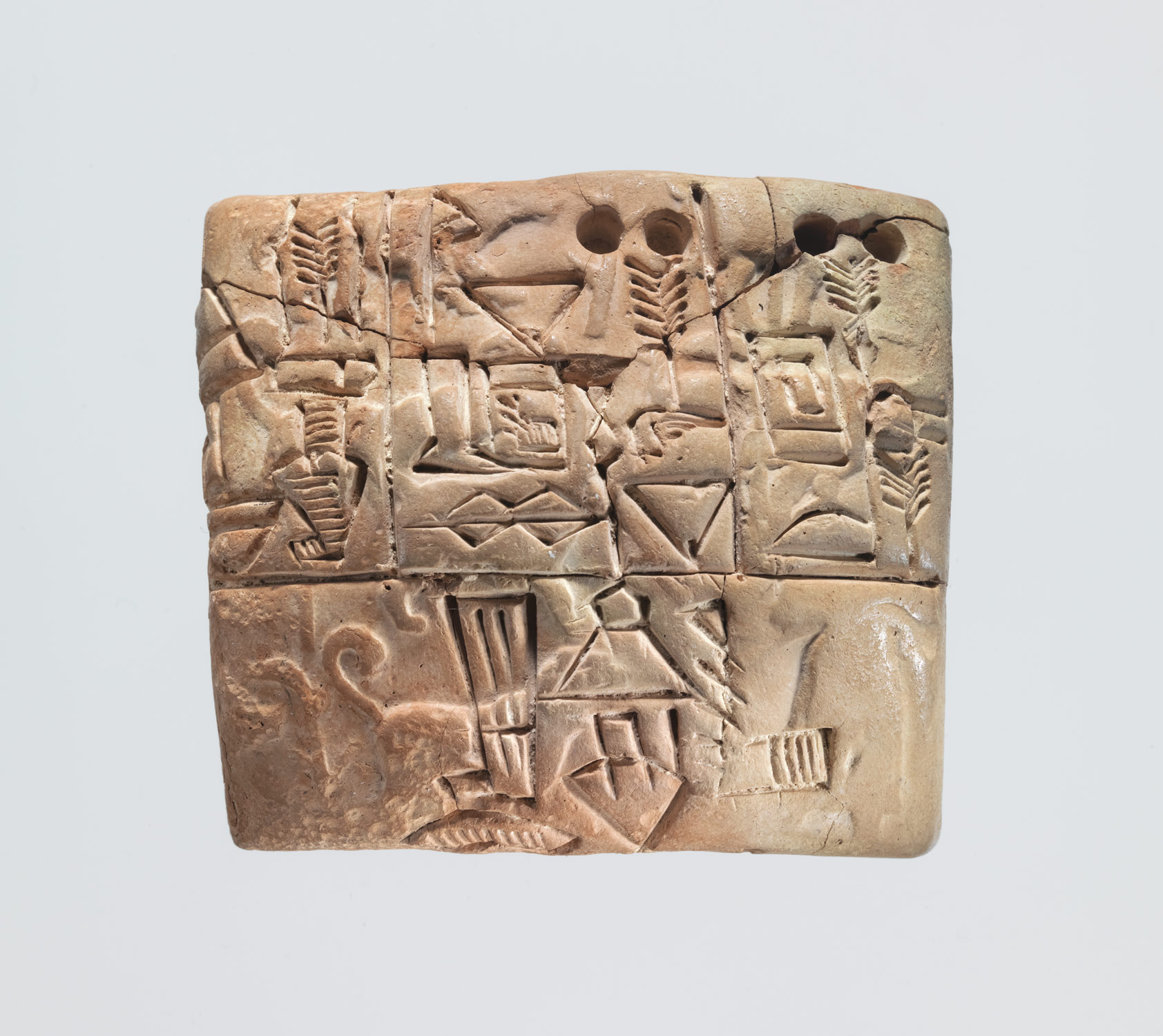 Jamdat Nasr administrative tablet, ca. 3100-2900 BC. Image copyright © The Metropolitan Museum of Art [metmuseum](https://www.metmuseum.org/toah/works-of-art/1988.433.1/)
+\[caption id="attachment\_5348" align="aligncenter" width="1684"\] Jamdat Nasr administrative tablet, ca. 3100-2900 BC. Image copyright © The Metropolitan Museum of Art [metmuseum](https://www.metmuseum.org/toah/works-of-art/1988.433.1/)
The second is another Mesopotamian tablet from the same era that bears the name of a slaveholder, Gal-Sal, and two slaves, En-pap X and Sukkalgir.
## The origins of personal names
- A Machiguenga woman dressed in traditional garb [Machiguenga woman](https://commons.wikimedia.org/wiki/File:Machiguenga_woman.jpg)
+ A Machiguenga woman dressed in traditional garb [Machiguenga woman](https://commons.wikimedia.org/wiki/File:Machiguenga_woman.webp)
Almost every known society refers to individuals by a fixed personal name, but there are some exceptions. One is the Machiguenga of the Amazon, a small tribe that refers to others by their kin relationship, such as “sister.”
Ancient cultures generally used single names, what we might now consider a first name or given name. Single names are also called _mononyms_.
- Dead Sea Scroll, part of Isaiah Scroll (Isa 57:17 - 59:9), ca. 100 BC [Dead Sea Scroll](https://commons.wikimedia.org/wiki/File:1QIsa_b.jpg)
+ Dead Sea Scroll, part of Isaiah Scroll (Isa 57:17 - 59:9), ca. 100 BC [Dead Sea Scroll](https://commons.wikimedia.org/wiki/File:1QIsa_b.webp)
Most Biblical names are mononyms, for example. This fragment of the Hebrew Bible contains the name יַעֲקֹב (Jacob).
Both the Hebrew and Christian scriptures give great significance to names within the narrative. The meanings of names are often described in the text: The man called his wife Eve \[which probably means “living”\] because she would be the mother of all the living.” People sometimes take or receive new names to indicate a change in their identity, such as when God renames Abram and Sarai to Abraham and Sarah as part of a promise to make them a great nation.
- Zeno of Citium. Bust in the Farnese collection, Naples. Photo by Paolo Monti, 1969 [Paolo Monti](https://commons.wikimedia.org/wiki/File:Paolo_Monti_-_Servizio_fotografico_(Napoli,_1969)_-_BEIC_6353768.jpg)
+ Zeno of Citium. Bust in the Farnese collection, Naples. Photo by Paolo Monti, 1969 [Paolo Monti](https://commons.wikimedia.org/wiki/File:Paolo_Monti_-_Servizio_fotografico_(Napoli,_1969)_-_BEIC_6353768.webp)
The ancient Greeks used mononyms as well, although historians added qualifiers called _epithets_ when they needed to distinguish between two people with the same name. Epithets might be descriptive of the person or refer to their home or ancestry, but they are not considered part of their official name. For example, we have Zeno the Stoic (also known as Zeno of Citium) and Zeno of Elea.
For a history of identity in the modern world, read Part II of this series next week.
- A newborn’s hospital name tag
+ A newborn’s hospital name tag
[Pixabay](https://pixabay.com/photos/baby-medicine-child-foot-care-3169975/)
@@ -95,4 +95,4 @@ For a history of identity in the modern world, read Part II of this series next
Learn how to create a unified digital identity for all of your customers. [Book a demo](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=history-identity-part-1) today with LoginRadius.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=history-identity-part-1)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=history-identity-part-1)
diff --git a/content/identity/history-identity-part-2/223px-Signature_of_El_Cid.svg_.png b/content/identity/history-identity-part-2/223px-Signature_of_El_Cid.svg_.png
deleted file mode 100644
index 25f03dec7..000000000
Binary files a/content/identity/history-identity-part-2/223px-Signature_of_El_Cid.svg_.png and /dev/null differ
diff --git a/content/identity/history-identity-part-2/223px-Signature_of_El_Cid.svg_.webp b/content/identity/history-identity-part-2/223px-Signature_of_El_Cid.svg_.webp
new file mode 100644
index 000000000..03916cc89
Binary files /dev/null and b/content/identity/history-identity-part-2/223px-Signature_of_El_Cid.svg_.webp differ
diff --git a/content/identity/history-identity-part-2/Chinese_seal_Han_Dynasty.png b/content/identity/history-identity-part-2/Chinese_seal_Han_Dynasty.png
deleted file mode 100644
index 70b4c5f6a..000000000
Binary files a/content/identity/history-identity-part-2/Chinese_seal_Han_Dynasty.png and /dev/null differ
diff --git a/content/identity/history-identity-part-2/Chinese_seal_Han_Dynasty.webp b/content/identity/history-identity-part-2/Chinese_seal_Han_Dynasty.webp
new file mode 100644
index 000000000..61990c81f
Binary files /dev/null and b/content/identity/history-identity-part-2/Chinese_seal_Han_Dynasty.webp differ
diff --git a/content/identity/history-identity-part-2/history-identity-part-2.jpg b/content/identity/history-identity-part-2/history-identity-part-2.jpg
deleted file mode 100644
index b3b43419d..000000000
Binary files a/content/identity/history-identity-part-2/history-identity-part-2.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-2/history-identity-part-2.webp b/content/identity/history-identity-part-2/history-identity-part-2.webp
new file mode 100644
index 000000000..9dd25500d
Binary files /dev/null and b/content/identity/history-identity-part-2/history-identity-part-2.webp differ
diff --git a/content/identity/history-identity-part-2/image-1.jpg b/content/identity/history-identity-part-2/image-1.jpg
deleted file mode 100644
index c3db1e588..000000000
Binary files a/content/identity/history-identity-part-2/image-1.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-2/image-1.webp b/content/identity/history-identity-part-2/image-1.webp
new file mode 100644
index 000000000..47f92a576
Binary files /dev/null and b/content/identity/history-identity-part-2/image-1.webp differ
diff --git a/content/identity/history-identity-part-2/image-2.jpeg b/content/identity/history-identity-part-2/image-2.jpeg
deleted file mode 100644
index 2a3f90bde..000000000
Binary files a/content/identity/history-identity-part-2/image-2.jpeg and /dev/null differ
diff --git a/content/identity/history-identity-part-2/image-2.webp b/content/identity/history-identity-part-2/image-2.webp
new file mode 100644
index 000000000..727a27e2c
Binary files /dev/null and b/content/identity/history-identity-part-2/image-2.webp differ
diff --git a/content/identity/history-identity-part-2/image-3.jpg b/content/identity/history-identity-part-2/image-3.jpg
deleted file mode 100644
index 57868d491..000000000
Binary files a/content/identity/history-identity-part-2/image-3.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-2/image-3.webp b/content/identity/history-identity-part-2/image-3.webp
new file mode 100644
index 000000000..a4eea9cb7
Binary files /dev/null and b/content/identity/history-identity-part-2/image-3.webp differ
diff --git a/content/identity/history-identity-part-2/image-4.jpg b/content/identity/history-identity-part-2/image-4.jpg
deleted file mode 100644
index e9b164f69..000000000
Binary files a/content/identity/history-identity-part-2/image-4.jpg and /dev/null differ
diff --git a/content/identity/history-identity-part-2/image-4.webp b/content/identity/history-identity-part-2/image-4.webp
new file mode 100644
index 000000000..dc248a4b4
Binary files /dev/null and b/content/identity/history-identity-part-2/image-4.webp differ
diff --git a/content/identity/history-identity-part-2/image-5.jpeg b/content/identity/history-identity-part-2/image-5.jpeg
deleted file mode 100644
index 7382edc27..000000000
Binary files a/content/identity/history-identity-part-2/image-5.jpeg and /dev/null differ
diff --git a/content/identity/history-identity-part-2/image-5.webp b/content/identity/history-identity-part-2/image-5.webp
new file mode 100644
index 000000000..9e534e012
Binary files /dev/null and b/content/identity/history-identity-part-2/image-5.webp differ
diff --git a/content/identity/history-identity-part-2/image-6.jpeg b/content/identity/history-identity-part-2/image-6.jpeg
deleted file mode 100644
index a7fbcfaaa..000000000
Binary files a/content/identity/history-identity-part-2/image-6.jpeg and /dev/null differ
diff --git a/content/identity/history-identity-part-2/image-6.webp b/content/identity/history-identity-part-2/image-6.webp
new file mode 100644
index 000000000..08e5e12ce
Binary files /dev/null and b/content/identity/history-identity-part-2/image-6.webp differ
diff --git a/content/identity/history-identity-part-2/image-7.jpeg b/content/identity/history-identity-part-2/image-7.jpeg
deleted file mode 100644
index bd0522dfd..000000000
Binary files a/content/identity/history-identity-part-2/image-7.jpeg and /dev/null differ
diff --git a/content/identity/history-identity-part-2/image-7.webp b/content/identity/history-identity-part-2/image-7.webp
new file mode 100644
index 000000000..1098d989c
Binary files /dev/null and b/content/identity/history-identity-part-2/image-7.webp differ
diff --git a/content/identity/history-identity-part-2/index.md b/content/identity/history-identity-part-2/index.md
index 86b3cfb76..28aa0c594 100644
--- a/content/identity/history-identity-part-2/index.md
+++ b/content/identity/history-identity-part-2/index.md
@@ -1,7 +1,7 @@
---
title: "A History of Human Identity in Pictures Part 2"
date: "2019-08-20"
-coverImage: "history-identity-part-2.jpg"
+coverImage: "history-identity-part-2.webp"
tags: ["public-sector"]
featured: false
author: "Rakesh Soni"
@@ -18,7 +18,7 @@ The United Nations Convention on the Rights of the Child declares that every chi
Clan names that seem to indicate matrilineal heritage, called _xìng_ (姓), emerged in China around 4000–3000 BC. Many of these names include the character for woman (女), and the character for _xìng_ reads as “born of a woman.” People with the same _xìng_ were not allowed to marry each other.
-[](https://commons.wikimedia.org/wiki/File:Lacquer_painting_from_Ch%27u_State.jpg)
+[](https://commons.wikimedia.org/wiki/File:Lacquer_painting_from_Ch%27u_State.webp)
**Lacquer painting from State of Ch'u (704–223 BC)**
@@ -29,7 +29,7 @@ A person’s _shì_ name might be derived from their state or fiefdom, their pos
Chinese surnames were standardized in 221 BC under the first emperor of the Qin dynasty. The _xìng_ and _shì_ names, which people had been using interchangeably, were merged into the single concept of a family name.
-[](https://www.metmuseum.org/art/collection/search/248783)
+[](https://www.metmuseum.org/art/collection/search/248783)
**Marble portrait of the co-emperor Lucius Verus (130 - 169 AD).** **His name at birth was Lucius Ceionius Commodus, changed to Lucius Aelius Aurelius Commodus when he was adopted.**
@@ -41,7 +41,7 @@ Family names first evolved in the Western world during the time of the Roman Emp
The Roman three-name system started with the aristocracy and spread to the general citizenry as the population grew and people needed more names to distinguish among themselves.
-[](https://commons.wikimedia.org/wiki/File:Jon_Ogmundsson_Icelandic_bishop.jpg)
+[](https://commons.wikimedia.org/wiki/File:Jon_Ogmundsson_Icelandic_bishop.webp)
**Bishop** [**Jón Ögmundsson**](https://commons.wikimedia.org/w/index.php?title=J%C3%B3n_%C3%96gmundsson&action=edit&redlink=1) **of Hólar, from the 19th century Icelandic manuscript JS 629 4to, now in the care of the Icelandic National Library**
@@ -51,13 +51,13 @@ Surnames developed in the rest of Europe starting in the 11th century. Norman ba
Iceland developed a system where children receive a new surname based on their father’s name (or occasionally mother’s name). For example, Iceland's current prime minister is Jóhanna Sigurðardóttir. Her father’s name is Sigurður, so her surname becomes Sigurðardóttir, meaning “daughter of Sigurður.”
-[](https://www.english-heritage.org.uk/learn/story-of-england/early-medieval/architecture/)
+[](https://www.english-heritage.org.uk/learn/story-of-england/early-medieval/architecture/)
**Part of Offa’s Dyke, an 8th-century earthwork boundary in Britain.**
**Location**: Many Anglophone names come from the names of towns or regions (Hamilton, Murray), local topology (Landon means “long hill”), or features (Dyke, Wood, Fields).
-[](https://hausbuecher.nuernberg.de/75-Amb-2-279-81-v/data)
+[](https://hausbuecher.nuernberg.de/75-Amb-2-279-81-v/data)
**A German tailor pictured in die Nürnberger Hausbücher, 1612.**
@@ -69,7 +69,7 @@ Iceland developed a system where children receive a new surname based on their f
Aristocrats considered long names a show of their high place in society. Spanish and Arabic families would give their children paternal or maternal names from previous generations. This practice allowed them to keep track of the child’s family tree.
-[](https://www.metmuseum.org/art/collection/search/451286?&searchField=All&sortBy=Relevance&when=A.D.+1600-1800&ft=royal+name&offset=0&rpp=20&pos=1)
+[](https://www.metmuseum.org/art/collection/search/451286?&searchField=All&sortBy=Relevance&when=A.D.+1600-1800&ft=royal+name&offset=0&rpp=20&pos=1)
**"Rosette Bearing the Names and Titles of Shah Jahan," ca. 1645. The central inscription reads, “His Majesty Shihab al-Din Muhammad Shah Jahan, the king, the vanquisher, may God perpetuate his dominion and sovereignty.”**
@@ -95,7 +95,7 @@ The need to confirm someone’s identity also goes back to ancient times. As soc
Some civilizations developed stamps and seals that represented a person’s identity.
-[](https://www.metmuseum.org/art/collection/search/321391?&searchField=All&sortBy=Relevance&ft=cylinder+seal&offset=0&rpp=20&pos=14)
+[](https://www.metmuseum.org/art/collection/search/321391?&searchField=All&sortBy=Relevance&ft=cylinder+seal&offset=0&rpp=20&pos=14)
**Modern impression of a Cypriot cylinder seal: female figure, ibex, lion, ca. 14th–13th century B.C.**
@@ -103,7 +103,7 @@ Cylinder seals go back to the fourth millennium BC in Mesopotamia. These [carved
The earliest seals in China originated during the Shang Dynasty, 1600 to 1046 BC. Chinese seals known as [chops](https://www.thoughtco.com/chinese-chops-seals-2278409) were carved from jade, stone, or ivory and dipped in red paste to stamp a unique symbol on documents, letters, and artwork.
-[](https://nl.wikipedia.org/wiki/Bestand:Chinese_seal_(Han_Dynasty).png#/media/Bestand:Chinese_seal_(Han_Dynasty).png)
+[](https://nl.wikipedia.org/wiki/Bestand:Chinese_seal_(Han_Dynasty).webp#/media/Bestand:Chinese_seal_(Han_Dynasty).webp)
**Chinese seal with Han and Manchu characters**
@@ -111,7 +111,7 @@ Other types of signature seals can also be found across East Asia. In Japan, sig
In the 5th century BC, the Romans started to write sentences and names at the bottom of documents, in addition to creating wax seals with [signet rings](https://www.thehistorypress.co.uk/articles/a-brief-history-of-signet-rings/). The earliest surviving signature from a famous historical figure is that of Rodrigo Díaz de Vivar, a medieval Spanish nobleman known as El Cid, dated to 1098.
-[](https://commons.wikimedia.org/wiki/File:Signature_of_El_Cid.svg)
+[](https://commons.wikimedia.org/wiki/File:Signature_of_El_Cid.webp)
**Autograph signature of Rodrigo Díaz, \[also\] called El Cid, Archive of the Cathedral of Salamanca.** **It reads in Latin: ego ruderico, "I, Rodrigo".**
@@ -119,4 +119,4 @@ To see how modern society uses and abuses identity, be sure to read Part III of
Learn how to create a unified digital identity for all of your customers. [Book a demo](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=history-identity-part-2) today with LoginRadius.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=history-identity-part-2)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=history-identity-part-2)
\ No newline at end of file
diff --git a/content/identity/how-ciam-helps-ott-platforms-scale-million-viewers/ciam-ott.jpg b/content/identity/how-ciam-helps-ott-platforms-scale-million-viewers/ciam-ott.jpg
deleted file mode 100644
index 54d225bbf..000000000
Binary files a/content/identity/how-ciam-helps-ott-platforms-scale-million-viewers/ciam-ott.jpg and /dev/null differ
diff --git a/content/identity/how-ciam-helps-ott-platforms-scale-million-viewers/ciam-ott.webp b/content/identity/how-ciam-helps-ott-platforms-scale-million-viewers/ciam-ott.webp
new file mode 100644
index 000000000..30f951173
Binary files /dev/null and b/content/identity/how-ciam-helps-ott-platforms-scale-million-viewers/ciam-ott.webp differ
diff --git a/content/identity/how-ciam-helps-ott-platforms-scale-million-viewers/index.md b/content/identity/how-ciam-helps-ott-platforms-scale-million-viewers/index.md
index ce283e97a..be5b86e8d 100644
--- a/content/identity/how-ciam-helps-ott-platforms-scale-million-viewers/index.md
+++ b/content/identity/how-ciam-helps-ott-platforms-scale-million-viewers/index.md
@@ -1,7 +1,7 @@
---
title: "OTT Platforms and CIAM: How Identity Management Ensures Millions of Viewers to Scale with Ease"
date: "2022-03-07"
-coverImage: "ciam-ott.jpg"
+coverImage: "ciam-ott.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -77,4 +77,4 @@ The LoginRadius CIAM offers robust security and a rich user experience to OTT pl
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciam-helps-ott-platforms-scale-million-viewers)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciam-helps-ott-platforms-scale-million-viewers)
\ No newline at end of file
diff --git a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/BD-Plexicon1-1024x310-1.png b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/BD-Plexicon1-1024x310-1.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/BD-Plexicon1-1024x310-1.png and /dev/null differ
diff --git a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/BD-Plexicon1-1024x310-1.webp b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/BD-Plexicon1-1024x310-1.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/BD-Plexicon1-1024x310-1.webp differ
diff --git a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/RP-Data-Breach-Report.png b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/RP-Data-Breach-Report.png
deleted file mode 100644
index a86e6d940..000000000
Binary files a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/RP-Data-Breach-Report.png and /dev/null differ
diff --git a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/RP-Data-Breach-Report.webp b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/RP-Data-Breach-Report.webp
new file mode 100644
index 000000000..fc95b4d7d
Binary files /dev/null and b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/RP-Data-Breach-Report.webp differ
diff --git a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/cover-1.jpg b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/cover-1.jpg
deleted file mode 100644
index dc280f38f..000000000
Binary files a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/cover-1.jpg and /dev/null differ
diff --git a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/cover-1.webp b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/cover-1.webp
new file mode 100644
index 000000000..b9956b58c
Binary files /dev/null and b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/cover-1.webp differ
diff --git a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/email-breach.jpg b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/email-breach.jpg
deleted file mode 100644
index aa12a81ca..000000000
Binary files a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/email-breach.jpg and /dev/null differ
diff --git a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/email-breach.webp b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/email-breach.webp
new file mode 100644
index 000000000..8aeee05fd
Binary files /dev/null and b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/email-breach.webp differ
diff --git a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/image-2.jpg b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/image-2.jpg
deleted file mode 100644
index 56e5525ce..000000000
Binary files a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/image-2.jpg and /dev/null differ
diff --git a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/image-2.webp b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/image-2.webp
new file mode 100644
index 000000000..9d84b3e29
Binary files /dev/null and b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/image-2.webp differ
diff --git a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/index.md b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/index.md
index c17899c0a..0d8cdd5e2 100644
--- a/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/index.md
+++ b/content/identity/how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach/index.md
@@ -1,7 +1,7 @@
---
title: "How Do I Know If My Email Has Been Leaked in a Data Breach?"
date: "2019-01-10"
-coverImage: "email-breach.jpg"
+coverImage: "email-breach.webp"
tags: ["data security","password management","cx"]
author: "Rakesh Soni"
description: "To log into their online accounts, many individuals use their email addresses and a short collection of passwords (or even only one password). Sadly, this means that every hacker already has half your login information with your email address. Add in multiple login violations from big-name digital service providers and you have a catastrophe recipe."
@@ -31,7 +31,7 @@ Check a few of your emails on the site, and chances are that at least one of the
There's also a handy [password checker](https://haveibeenpwned.com/Passwords) to find out if a certain password has made its way into the public domain. (Don’t worry, the site uses hashing to keep your password anonymous and doesn’t store it.)
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
Out of curiosity I checked the statistics for using "password" as a password—it turned out to have been pwned 3,533,661 times, a stark reminder that common sense doesn't always triumph when humans are left to their own devices [regarding password strength](https://www.loginradius.com/blog/2019/12/worst-passwords-list-2019/).
@@ -39,7 +39,7 @@ Subscribing to Have I Been Pwned is free and doing so will alert you to future l
### What Should I Do if I Find My Address in an Email Leak?
-
+
#### 1\. Change Your Passwords
@@ -65,4 +65,4 @@ If you're responsible for your company’s data security or digital platforms, t
LoginRadius has a vested interest in maintaining the highest levels of data protection.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-do-i-know-if-my-email-has-been-leaked-in-a-data-breach)
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/Book-a-free-demo-request-1024x310.png b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/Book-a-free-demo-request-1024x310.webp b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.png b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.png
deleted file mode 100644
index c02a1338a..000000000
Binary files a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.png and /dev/null differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.webp b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.webp
new file mode 100644
index 000000000..1b0055d88
Binary files /dev/null and b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.webp differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/ccpa-compliant.jpg b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/ccpa-compliant.jpg
deleted file mode 100644
index 80fa67113..000000000
Binary files a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/ccpa-compliant.jpg and /dev/null differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/ccpa-compliant.webp b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/ccpa-compliant.webp
new file mode 100644
index 000000000..6273c895c
Binary files /dev/null and b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/ccpa-compliant.webp differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/how-loginradius-helps-enterprises-stay-ccpa-compliant.png b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/how-loginradius-helps-enterprises-stay-ccpa-compliant.png
deleted file mode 100644
index 5937ad269..000000000
Binary files a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/how-loginradius-helps-enterprises-stay-ccpa-compliant.png and /dev/null differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/how-loginradius-helps-enterprises-stay-ccpa-compliant.webp b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/how-loginradius-helps-enterprises-stay-ccpa-compliant.webp
new file mode 100644
index 000000000..a36a7d10a
Binary files /dev/null and b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/how-loginradius-helps-enterprises-stay-ccpa-compliant.webp differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image2.png b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image2.png
deleted file mode 100644
index 5be672c11..000000000
Binary files a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image2.png and /dev/null differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image2.webp b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image2.webp
new file mode 100644
index 000000000..62595e007
Binary files /dev/null and b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image2.webp differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image3.png b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image3.png
deleted file mode 100644
index 91ead503e..000000000
Binary files a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image3.png and /dev/null differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image3.webp b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image3.webp
new file mode 100644
index 000000000..5920edbe3
Binary files /dev/null and b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image3.webp differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image4.png b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image4.png
deleted file mode 100644
index 71b01d8a1..000000000
Binary files a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image4.png and /dev/null differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image4.webp b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image4.webp
new file mode 100644
index 000000000..981d34992
Binary files /dev/null and b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/image4.webp differ
diff --git a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/index.md b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/index.md
index 57322d0b5..b47b9876a 100644
--- a/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/index.md
+++ b/content/identity/how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020/index.md
@@ -1,7 +1,7 @@
---
title: "How LoginRadius Helps Enterprises Stay CCPA Compliant in 2020"
date: "2020-03-06"
-coverImage: "ccpa-compliant.jpg"
+coverImage: "ccpa-compliant.webp"
tags: ["data privacy","compliance","ciam solution"]
author: "Rakesh Soni"
description: "As the risk of data misuse is rising, more and more enterprises are trying to comply with current data protection and regulatory enforcement."
@@ -49,7 +49,7 @@ The California Consumer Privacy Act is a relatively new consumer privacy right e
### What rights do consumers enjoy under CCPA?
-
+
### What data is considered personal under the CCPA?
@@ -89,7 +89,7 @@ When it comes to CCPA, the Californian data privacy law provides some excellent
Wondering how? Let’s find out.
-
+
**1\. CCPA ensures improved data security.**
@@ -107,7 +107,7 @@ Consumers should have the freedom to view or upgrade their consent approval. If
As such, CCPA requires enterprises to display easy-to-understand consent requests, so consumers know what they are getting into.
-[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
+[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity)
**3\. CCPA allows frictionless identity management.**
@@ -121,7 +121,7 @@ LoginRadius is a [customer identity and access management](https://www.loginradi
It helps companies meet CCPA regulatory requirements without compromising the user experience. Its one-of-a-kind data protection features include client registration, sign-in, authentication, single sign-on, data governance, and consent management, among others.
-
+
The following capabilities further help enterprises meet privacy compliance regulations.
@@ -157,4 +157,4 @@ Consumers expect the privacy and security of their personal data, and it is the
With an identity solution like LoginRadius, you can eliminate lengthy processes that ruin the user experience, and still maintain international governance over data privacy.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-loginradius-helps-enterprises-stay-ccpa-compliant-in-2020)
diff --git a/content/identity/how-secure-2fa/DS-SSO.png b/content/identity/how-secure-2fa/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/how-secure-2fa/DS-SSO.png and /dev/null differ
diff --git a/content/identity/how-secure-2fa/DS-SSO.webp b/content/identity/how-secure-2fa/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/how-secure-2fa/DS-SSO.webp differ
diff --git a/content/identity/how-secure-2fa/LR-SSO-DS.png b/content/identity/how-secure-2fa/LR-SSO-DS.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/how-secure-2fa/LR-SSO-DS.png and /dev/null differ
diff --git a/content/identity/how-secure-2fa/LR-SSO-DS.webp b/content/identity/how-secure-2fa/LR-SSO-DS.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/how-secure-2fa/LR-SSO-DS.webp differ
diff --git a/content/identity/how-secure-2fa/how-secure-2fa-cover.jpg b/content/identity/how-secure-2fa/how-secure-2fa-cover.jpg
deleted file mode 100644
index 754b398aa..000000000
Binary files a/content/identity/how-secure-2fa/how-secure-2fa-cover.jpg and /dev/null differ
diff --git a/content/identity/how-secure-2fa/how-secure-2fa-cover.webp b/content/identity/how-secure-2fa/how-secure-2fa-cover.webp
new file mode 100644
index 000000000..2899e9ead
Binary files /dev/null and b/content/identity/how-secure-2fa/how-secure-2fa-cover.webp differ
diff --git a/content/identity/how-secure-2fa/index.md b/content/identity/how-secure-2fa/index.md
index 2587c5e47..0cbc044c9 100644
--- a/content/identity/how-secure-2fa/index.md
+++ b/content/identity/how-secure-2fa/index.md
@@ -1,7 +1,7 @@
---
title: "How Secure is Two-Factor Authentication (2FA)?"
date: "2021-05-13"
-coverImage: "how-secure-2fa-cover.jpg"
+coverImage: "how-secure-2fa-cover.webp"
tags: ["data security","2fa","mfa","cx"]
author: "Navanita Devi"
description: "While we know that it may seem childish to use a password and a username combination, unfortunately, many people don’t learn the risks associated with this type of authentication until they have been victimized by cybercrime. And when that happens, two-factor authentication is one the best ways to protect your consumers’ sensitive data from theft."
@@ -54,7 +54,7 @@ By offering 2FA, businesses demonstrate their commitment to protecting user data
The working process of 2FA differs depending on what kind of information is requested from the user. The login process can involve a combination of two variations given below:
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
* Data is already known to the individual, like login credentials. There are even apps to keep track of this information. For example, the Google Password Manager.
* Data about one’s physical aspect like biometric data.
@@ -140,4 +140,4 @@ The most common 2FA methods include SMS codes and authenticator apps like Google
Authenticator apps like Google Authenticator are generally considered more secure than SMS codes, as SMS can be vulnerable to SIM swapping attacks. However, both methods offer an additional layer of security compared to passwords alone.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-secure-2fa)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-secure-2fa)
\ No newline at end of file
diff --git a/content/identity/how-to-choose-a-secure-password/EB-buyers-GD-to-MFA.png b/content/identity/how-to-choose-a-secure-password/EB-buyers-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/how-to-choose-a-secure-password/EB-buyers-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/how-to-choose-a-secure-password/EB-buyers-GD-to-MFA.webp b/content/identity/how-to-choose-a-secure-password/EB-buyers-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/how-to-choose-a-secure-password/EB-buyers-GD-to-MFA.webp differ
diff --git a/content/identity/how-to-choose-a-secure-password/buyer-guide-to-multi-factor-authentication-ebook.png b/content/identity/how-to-choose-a-secure-password/buyer-guide-to-multi-factor-authentication-ebook.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/how-to-choose-a-secure-password/buyer-guide-to-multi-factor-authentication-ebook.png and /dev/null differ
diff --git a/content/identity/how-to-choose-a-secure-password/buyer-guide-to-multi-factor-authentication-ebook.webp b/content/identity/how-to-choose-a-secure-password/buyer-guide-to-multi-factor-authentication-ebook.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/how-to-choose-a-secure-password/buyer-guide-to-multi-factor-authentication-ebook.webp differ
diff --git a/content/identity/how-to-choose-a-secure-password/do's-and-don't-to-choose-a-strong-password.png b/content/identity/how-to-choose-a-secure-password/do's-and-don't-to-choose-a-strong-password.png
deleted file mode 100644
index e3e3413be..000000000
Binary files a/content/identity/how-to-choose-a-secure-password/do's-and-don't-to-choose-a-strong-password.png and /dev/null differ
diff --git a/content/identity/how-to-choose-a-secure-password/do's-and-don't-to-choose-a-strong-password.webp b/content/identity/how-to-choose-a-secure-password/do's-and-don't-to-choose-a-strong-password.webp
new file mode 100644
index 000000000..aa852c214
Binary files /dev/null and b/content/identity/how-to-choose-a-secure-password/do's-and-don't-to-choose-a-strong-password.webp differ
diff --git a/content/identity/how-to-choose-a-secure-password/how-to-choose-a-secure-password-in-2021.jpg b/content/identity/how-to-choose-a-secure-password/how-to-choose-a-secure-password-in-2021.jpg
deleted file mode 100644
index bd6ae6bf0..000000000
Binary files a/content/identity/how-to-choose-a-secure-password/how-to-choose-a-secure-password-in-2021.jpg and /dev/null differ
diff --git a/content/identity/how-to-choose-a-secure-password/how-to-choose-a-secure-password-in-2021.webp b/content/identity/how-to-choose-a-secure-password/how-to-choose-a-secure-password-in-2021.webp
new file mode 100644
index 000000000..864baeb6f
Binary files /dev/null and b/content/identity/how-to-choose-a-secure-password/how-to-choose-a-secure-password-in-2021.webp differ
diff --git a/content/identity/how-to-choose-a-secure-password/how-to-choose-a-strong-password.png b/content/identity/how-to-choose-a-secure-password/how-to-choose-a-strong-password.png
deleted file mode 100644
index 9cdf7fd06..000000000
Binary files a/content/identity/how-to-choose-a-secure-password/how-to-choose-a-strong-password.png and /dev/null differ
diff --git a/content/identity/how-to-choose-a-secure-password/how-to-choose-a-strong-password.webp b/content/identity/how-to-choose-a-secure-password/how-to-choose-a-strong-password.webp
new file mode 100644
index 000000000..f0b35f81c
Binary files /dev/null and b/content/identity/how-to-choose-a-secure-password/how-to-choose-a-strong-password.webp differ
diff --git a/content/identity/how-to-choose-a-secure-password/index.md b/content/identity/how-to-choose-a-secure-password/index.md
index 304581a83..f21be2aab 100644
--- a/content/identity/how-to-choose-a-secure-password/index.md
+++ b/content/identity/how-to-choose-a-secure-password/index.md
@@ -1,7 +1,7 @@
---
title: "The Do's and Don'ts of Choosing a Secure Password"
date: "2021-01-06"
-coverImage: "how-to-choose-a-secure-password-in-2021.jpg"
+coverImage: "how-to-choose-a-secure-password-in-2021.webp"
tags: ["data security","password management","ciam solution","cx"]
author: "Rakesh Soni"
description: "Passwords are the digital keys to our daily lives. They are the gateway to our professional services, and our network of friends. So, what does a secure password look like? Here is a collection of the do's and don't on how to choose a strong password to avoid being a victim of cyberattack."
@@ -83,7 +83,7 @@ SaaS businesses, e-commerce sites, and users of financial services majorly fall
## The Do's and Don't on How to Choose a Strong Password
-
+
What does a secure password look like? It is usually the one that cannot be guessed easily or cracked using software tools.
@@ -131,7 +131,7 @@ The following are a few types of layers that businesses choose to provide:
**Change your passwords regularly**: Also, do not reuse the same password for a long time. The more sensitive your data is, the more frequently you should change your password.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
**Always remember to log out** of websites and devices once you are done using them.
@@ -421,7 +421,7 @@ Disclaimer: Stay away from these passwords.
## 5 Tips on How to Choose a Strong Password Manager
-
+
A password manager helps you auto-generate strong passwords and stores them in encrypted, centralized locations on your behalf. You can access all your passwords with a master password.
@@ -462,4 +462,4 @@ By now, you know how to choose a strong password. However, hackers will still tr
Follow the steps listed above to make your passwords as strong and unique as possible. Remember, if your password is too easy to remember, it is probably not secure at all.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-choose-a-secure-password)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-choose-a-secure-password)
\ No newline at end of file
diff --git a/content/identity/how-to-choose-authentication/Push-notification-authentication.webp b/content/identity/how-to-choose-authentication/Push-notification-authentication.webp
new file mode 100644
index 000000000..772e3822a
Binary files /dev/null and b/content/identity/how-to-choose-authentication/Push-notification-authentication.webp differ
diff --git a/content/identity/how-to-choose-authentication/access-decisions-based-on-time.webp b/content/identity/how-to-choose-authentication/access-decisions-based-on-time.webp
new file mode 100644
index 000000000..a9fb59465
Binary files /dev/null and b/content/identity/how-to-choose-authentication/access-decisions-based-on-time.webp differ
diff --git a/content/identity/how-to-choose-authentication/facial-recognition.webp b/content/identity/how-to-choose-authentication/facial-recognition.webp
new file mode 100644
index 000000000..9dbb1404f
Binary files /dev/null and b/content/identity/how-to-choose-authentication/facial-recognition.webp differ
diff --git a/content/identity/how-to-choose-authentication/how-to-choose-authentication.webp b/content/identity/how-to-choose-authentication/how-to-choose-authentication.webp
new file mode 100644
index 000000000..6fc5f6e87
Binary files /dev/null and b/content/identity/how-to-choose-authentication/how-to-choose-authentication.webp differ
diff --git a/content/identity/how-to-choose-authentication/index.md b/content/identity/how-to-choose-authentication/index.md
new file mode 100644
index 000000000..f6a4336fa
--- /dev/null
+++ b/content/identity/how-to-choose-authentication/index.md
@@ -0,0 +1,203 @@
+---
+title: "Guide to Authentication Methods & Choosing the Right One"
+date: "2025-04-07"
+coverImage: "how-to-choose-authentication.webp"
+tags: ["Identity","Authentication","Data Security","Data Privacy"]
+author: "Kundan Singh"
+description: "Choosing the right authentication method can impact security, compliance, and user experience. This blog breaks down various authentication types and factors to consider in 2025 and also portrays how LoginRadius makes secure, scalable implementation easy."
+metatitle: "Guide to Authentication Methods & Choosing the Right One"
+metadescription: "Learn about authentication methods, types, and how to choose the right one to secure access and enhance user trust."
+---
+
+## Introduction
+
+In today's digital world, ensuring secure access to systems and data is more than a technical requirement—it's a business necessity.
+
+Whether you're managing user access for a mobile app, an enterprise platform, or a customer-facing portal, choosing the right authentication methods plays a critical role in safeguarding sensitive information and delivering seamless user experiences.
+
+This guide breaks down the core authentication types, why they matter, and how to choose the right fit for your needs. It also explains how modern user authentication methods and authentication protocols work together to secure digital ecosystems.
+
+## What Is User Authentication?
+
+[User authentication](https://www.loginradius.com/blog/identity/what-is-authentication/) is the process of verifying that a user is who they claim to be. It's the first line of defense in any digital environment, determining whether someone can access a system, app, or resource.
+
+At its core, user authentication compares credentials entered by the user (like a password or fingerprint) with the stored data to verify identity. If the information matches, access is granted.
+
+Modern user authentication techniques go far beyond just passwords. Today, businesses use a wide range of authentication mechanisms, including one-time passwords (OTPs), biometrics, smart cards, and more. These methods provide varying levels of security and user convenience.
+
+Authentication also plays a foundational role in digital transformation. As businesses shift to cloud environments and remote work, secure authentication methods help ensure users access the right systems at the right time—without compromising security.
+
+
+
+## Why Is User Authentication Important?
+
+Cyber threats are evolving every day, and attackers constantly look for weak points in your digital systems. Without proper user authentication methods, sensitive data, intellectual property, and customer information are at risk.
+
+Here are a few reasons why user authentication is so crucial:
+
+* **Security**: Strong security authentication methods reduce the risk of unauthorized access and data breaches.
+
+* **Compliance**: Regulations like [GDPR](https://www.loginradius.com/compliance-list/gdpr-compliant/), [HIPAA](https://trust.loginradius.com/), and [CCPA ](https://www.loginradius.com/compliance-list/ccpa/)often require robust authentication protocols to ensure data protection.
+
+* **User Trust**: Customers feel more secure using platforms that implement secure authentication methods.
+
+* **Business Continuity**: Preventing unauthorized access reduces downtime and reputational damage.
+
+* **Scalable Protection**: As businesses grow, the use of adaptive and advanced authentication methods becomes key to mitigating dynamic risks.
+
+Without effective methods for authentication, even the most robust infrastructure can become vulnerable. Authentication supports everything from user onboarding to transaction security.
+
+## Common Authentication Types
+
+There are several authentication types used today, ranging from basic to advanced. Each comes with strengths and trade-offs. Here's a breakdown of the most widely used authentication methods:
+
+### 1. Password-Based Authentication
+
+Still the most common method, password authentication involves users entering a secret password. While simple to implement, it's also the least secure if not paired with additional factors.
+
+Best practices include enforcing password complexity, expiration policies, and using hashing algorithms for storage. However, as threats like credential stuffing rise, relying solely on passwords is no longer advisable—something we’ve covered in detail in our guide on[ username and password authentication best practices](https://www.loginradius.com/blog/identity/best-practices-username-password-authentication/).
+
+### 2. Multi-Factor Authentication (MFA)
+
+[Multi factor authentication](https://www.loginradius.com/blog/identity/what-is-multi-factor-authentication/) requires users to provide two or more credentials from different categories:
+
+* Something you know (password or PIN)
+* Something you have (smartphone or hardware token)
+* Something you are (biometrics like fingerprint or face scan)
+
+Secure authentication methods like MFA greatly reduce the likelihood of a breach. Organizations often deploy MFA for admin logins, financial transactions, and high-risk user activities.
+
+### 3. Risk-Based / Adaptive MFA
+
+[Risk-based or adaptive MFA](https://www.loginradius.com/blog/identity/risk-based-authentication/) analyzes the context of each login attempt and adjusts authentication requirements accordingly. It considers factors like user location, device type, IP reputation, and time of access to assess risk in real time.
+
+For example, if a user logs in from an unfamiliar location or device, the system may prompt for additional verification (like a biometric scan or OTP). In contrast, if the login is from a known device in a trusted environment, the user may face fewer authentication steps.
+
+
+
+This is one of the most intelligent and advanced authentication methods, as it improves both security and user experience by minimizing unnecessary friction while responding dynamically to threats.
+
+### 4. Biometric Authentication
+
+Uses physical characteristics like fingerprints, facial recognition, or retina scans. These user authentication techniques are harder to spoof and offer a seamless experience.
+
+As a form of advanced authentication methods, biometrics are increasingly used in smartphones, airports, banking apps, and secure corporate systems.
+
+### 5. Token-Based Authentication
+
+Users receive a unique token (often time-sensitive) that must be entered to access the system. Common in banking and high-security environments.
+
+[Token-based authentication ](https://www.loginradius.com/blog/identity/what-is-token-authentication/)systems, such as JSON Web Tokens (JWT), are widely used in APIs and microservices architecture. They support stateless authentication and secure session management.
+
+### 6. Certificate-Based Authentication
+
+This method uses digital certificates issued by a trusted authority to verify identity. It's common in corporate and government environments, particularly in environments requiring [machine-to-machine ](https://www.loginradius.com/blog/engineering/using-m2m-authorization-for-apis-and-apps/)trust.
+
+### 7. Single Sign-On (SSO)
+
+With [SSO](https://www.loginradius.com/blog/identity/what-is-single-sign-on/), users log in once to access multiple services. It's one of the most user-friendly methods for authentication, often paired with MFA for added security.
+
+SSO helps reduce password fatigue, streamlines access across enterprise systems, and enhances productivity.
+
+These are just some of the different types of authentication. Choosing the right one depends on several factors we’ll explore next.
+
+### 8. Push Notification-Based MFA
+
+[Push-notification MFA](https://www.loginradius.com/blog/identity/push-notification-authentication/) sends an approval request to a user’s registered mobile device during login. Instead of manually typing a code, the user simply taps “Approve” or “Deny” in an authentication app (such as LoginRadius Authenticator or other TOTP apps with push support).
+
+
+
+This method is highly user-friendly and significantly reduces the risk of phishing compared to traditional SMS or email codes. It’s widely used for its speed, convenience, and strong security, making it a popular option among secure authentication methods for both enterprises and consumer-facing platforms.
+
+### 9. Social Login
+
+[Social login](https://www.loginradius.com/blog/identity/what-is-social-login/) allows users to authenticate using their existing accounts from third-party platforms like Google, Facebook, Apple, or LinkedIn. This method simplifies registration and login by eliminating the need to create new credentials.
+
+Here’s how to quickly set up social login in the[ LoginRadius console](https://accounts.loginradius.com/auth.aspx?return_url=https://console.loginradius.com/login&action=register):
+
+
+
+From a user experience perspective, social login reduces friction and improves conversion rates. From a security standpoint, it delegates authentication to trusted identity providers that follow strong authentication protocols.
+
+It’s an ideal choice for consumer apps, ecommerce platforms, and services aiming to provide quick access while leveraging existing user authentication methods.
+
+## Factors to Consider When Choosing an Authentication Method
+
+Every organization has different security needs, user bases, and compliance requirements. When evaluating authentication methods, here are key considerations:
+
+### 1. Security Level Required
+
+Does your platform deal with highly sensitive data or personal information? If so, consider advanced authentication methods like MFA or biometrics. High-risk sectors like healthcare and finance often mandate these protocols.
+
+### 2. User Experience
+
+Security shouldn’t come at the cost of usability. Opt for authentication mechanisms that are easy to use and don’t create friction for end users. For instance, biometrics offer both security and convenience.
+
+A poor authentication experience can lead to user frustration and churn. Always [balance security with user-centric design.](https://www.loginradius.com/blog/identity/security-ux-can-coexist/)
+
+### 3. Scalability
+
+Will your authentication protocols support a growing user base and adapt to future needs? Ensure the solution is scalable and can integrate with new technologies.
+
+Organizations expanding to new markets or deploying cross-channel platforms should ensure their user authentication methods can scale accordingly.
+
+### 4. Compliance and Industry Standards
+
+Different sectors have different compliance needs. Financial institutions, for example, may need specific security authentication methods to meet regulatory standards like PCI-DSS.
+
+Check for support for industry standards like OAuth 2.0, OpenID Connect, and SAML in your authentication provider.
+
+[](https://www.loginradius.com/resource/datasheet/consent-management/)
+
+### 5. Integration Capabilities
+
+Your chosen method should work seamlessly with existing infrastructure, third-party services, and CIAM platforms like [LoginRadius](https://www.loginradius.com/).
+
+Modern businesses rely on multiple SaaS tools and backend systems. Interoperability is essential for effective authentication mechanisms.
+
+### 6. Risk Profile of the User Base
+
+For higher-risk users (like admins or those accessing financial systems), apply stricter authentication mechanisms. Use contextual authentication to adapt based on location, device, or behavior.
+
+Understanding your organization’s needs and matching them with the appropriate user authentication methods ensures both protection and performance.
+
+## To Conclude
+
+Selecting the right authentication methods is no longer optional—it’s fundamental to digital trust, user satisfaction, and organizational resilience. Whether you’re looking at advanced authentication methods like biometrics or standard authentication protocols like passwords and tokens, the goal is to find the right balance of security, usability, and compliance.
+
+As threats become more sophisticated, your choice of authentication mechanisms can make or break your security posture. Make informed decisions that serve both your users and your business.
+
+When done right, authentication becomes invisible yet secure, empowering users to interact with your brand confidently and securely.
+
+Need help implementing secure and scalable authentication? [Contact LoginRadius](https://www.loginradius.com/contact-us) to speak with an expert.
+
+## FAQs
+
+### **1.** Which methods can be used to implement multifactor authentication?
+
+**A.** Common methods include:
+
+* Password + OTP via SMS or authenticator app
+* Password + biometric scan
+* Smart card + PIN These combinations offer a blend of secure authentication methods for added protection. MFA implementations vary based on risk profiles and user roles.
+
+
+### **2.** What are examples of biometric authentication methods?**
+
+**A.** Biometric user authentication techniques include:
+
+* Fingerprint scanning
+* Facial recognition
+* Voice recognition
+* Retina or iris scans These authentication types are commonly used in mobile apps, banking, and secure facilities. They fall under advanced authentication methods due to their high accuracy and low risk of impersonation.
+
+### **3.** What are the common methods of authentication for network security?
+
+**A.** In network environments, popular security authentication methods include:
+
+* Password-based logins
+* Digital certificates
+* Two-factor authentication (2FA)
+* Token-based systems These methods for authentication ensure only authorized users access your network. They are foundational for VPNs, remote desktop access, and zero trust architectures.
+
+[](https://www.loginradius.com/contact-us)
\ No newline at end of file
diff --git a/content/identity/how-to-choose-authentication/lr-consent-management-datasheet.webp b/content/identity/how-to-choose-authentication/lr-consent-management-datasheet.webp
new file mode 100644
index 000000000..11bc1385d
Binary files /dev/null and b/content/identity/how-to-choose-authentication/lr-consent-management-datasheet.webp differ
diff --git a/content/identity/how-to-choose-authentication/social-login-configuration.webp b/content/identity/how-to-choose-authentication/social-login-configuration.webp
new file mode 100644
index 000000000..63e1337d5
Binary files /dev/null and b/content/identity/how-to-choose-authentication/social-login-configuration.webp differ
diff --git a/content/identity/how-to-handle-data-breaches/EB-GD-to-mod-cust-ID.png b/content/identity/how-to-handle-data-breaches/EB-GD-to-mod-cust-ID.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/identity/how-to-handle-data-breaches/EB-GD-to-mod-cust-ID.png and /dev/null differ
diff --git a/content/identity/how-to-handle-data-breaches/EB-GD-to-mod-cust-ID.webp b/content/identity/how-to-handle-data-breaches/EB-GD-to-mod-cust-ID.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/identity/how-to-handle-data-breaches/EB-GD-to-mod-cust-ID.webp differ
diff --git a/content/identity/how-to-handle-data-breaches/eb-modern-customer-identity.png b/content/identity/how-to-handle-data-breaches/eb-modern-customer-identity.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/identity/how-to-handle-data-breaches/eb-modern-customer-identity.png and /dev/null differ
diff --git a/content/identity/how-to-handle-data-breaches/eb-modern-customer-identity.webp b/content/identity/how-to-handle-data-breaches/eb-modern-customer-identity.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/identity/how-to-handle-data-breaches/eb-modern-customer-identity.webp differ
diff --git a/content/identity/how-to-handle-data-breaches/how-to-handle-data-breaches-cover.jpg b/content/identity/how-to-handle-data-breaches/how-to-handle-data-breaches-cover.jpg
deleted file mode 100644
index b48d48391..000000000
Binary files a/content/identity/how-to-handle-data-breaches/how-to-handle-data-breaches-cover.jpg and /dev/null differ
diff --git a/content/identity/how-to-handle-data-breaches/how-to-handle-data-breaches-cover.webp b/content/identity/how-to-handle-data-breaches/how-to-handle-data-breaches-cover.webp
new file mode 100644
index 000000000..9bc50a61b
Binary files /dev/null and b/content/identity/how-to-handle-data-breaches/how-to-handle-data-breaches-cover.webp differ
diff --git a/content/identity/how-to-handle-data-breaches/index.md b/content/identity/how-to-handle-data-breaches/index.md
index af36ae0b7..5d85d8df6 100644
--- a/content/identity/how-to-handle-data-breaches/index.md
+++ b/content/identity/how-to-handle-data-breaches/index.md
@@ -1,7 +1,7 @@
---
title: "Consumer Data Protection: How to Handle Data Breaches in Your Business"
date: "2021-05-20"
-coverImage: "how-to-handle-data-breaches-cover.jpg"
+coverImage: "how-to-handle-data-breaches-cover.webp"
tags: ["data security","mfa","compliance"]
author: "Vishal Sharma"
description: "With the increasing number of data breaches across the globe, securely managing consumer data is becoming more crucial than ever before. Here are some efficient ways for consumer data protection that every online business must emphasize to ensure a secure line of defense against cyber-attacks."
@@ -56,7 +56,7 @@ A CIAM solution could be the biggest weapon in protecting your consumers’ iden
Many enterprises are leveraging a [CIAM solution](https://www.loginradius.com/customer-security/) that offers high-end data encryption while the data is managed, stored, and retrieved. This increases the overall defense line against any kind of unauthorized attacks by cybercriminals.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
Moreover, a cloud-based CIAM solution can easily handle millions of identities, and that too without hampering the user experience.
@@ -88,4 +88,4 @@ As discussed earlier, a compliance-ready CIAM solution with security features li
Moreover, companies that aren’t focussing on employee training must immediately put their best foot forward to organize cyber awareness training programs to minimize the risk of human error.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-handle-data-breaches)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-handle-data-breaches)
\ No newline at end of file
diff --git a/content/identity/how-to-identity-mitigate-deepfake-attacks/WP-digital-trade.png b/content/identity/how-to-identity-mitigate-deepfake-attacks/WP-digital-trade.png
deleted file mode 100644
index 31b7cc833..000000000
Binary files a/content/identity/how-to-identity-mitigate-deepfake-attacks/WP-digital-trade.png and /dev/null differ
diff --git a/content/identity/how-to-identity-mitigate-deepfake-attacks/WP-digital-trade.webp b/content/identity/how-to-identity-mitigate-deepfake-attacks/WP-digital-trade.webp
new file mode 100644
index 000000000..61229103e
Binary files /dev/null and b/content/identity/how-to-identity-mitigate-deepfake-attacks/WP-digital-trade.webp differ
diff --git a/content/identity/how-to-identity-mitigate-deepfake-attacks/deepfake.jpg b/content/identity/how-to-identity-mitigate-deepfake-attacks/deepfake.jpg
deleted file mode 100644
index 05d939f96..000000000
Binary files a/content/identity/how-to-identity-mitigate-deepfake-attacks/deepfake.jpg and /dev/null differ
diff --git a/content/identity/how-to-identity-mitigate-deepfake-attacks/deepfake.webp b/content/identity/how-to-identity-mitigate-deepfake-attacks/deepfake.webp
new file mode 100644
index 000000000..42c0a4a58
Binary files /dev/null and b/content/identity/how-to-identity-mitigate-deepfake-attacks/deepfake.webp differ
diff --git a/content/identity/how-to-identity-mitigate-deepfake-attacks/digital-trade-wp.png b/content/identity/how-to-identity-mitigate-deepfake-attacks/digital-trade-wp.png
deleted file mode 100644
index 24d5add74..000000000
Binary files a/content/identity/how-to-identity-mitigate-deepfake-attacks/digital-trade-wp.png and /dev/null differ
diff --git a/content/identity/how-to-identity-mitigate-deepfake-attacks/digital-trade-wp.webp b/content/identity/how-to-identity-mitigate-deepfake-attacks/digital-trade-wp.webp
new file mode 100644
index 000000000..cce7d892c
Binary files /dev/null and b/content/identity/how-to-identity-mitigate-deepfake-attacks/digital-trade-wp.webp differ
diff --git a/content/identity/how-to-identity-mitigate-deepfake-attacks/index.md b/content/identity/how-to-identity-mitigate-deepfake-attacks/index.md
index 97ccc4f09..f951901f8 100644
--- a/content/identity/how-to-identity-mitigate-deepfake-attacks/index.md
+++ b/content/identity/how-to-identity-mitigate-deepfake-attacks/index.md
@@ -1,7 +1,7 @@
---
title: "Emerging Threat of Deepfakes: How To Identify And Prepare Against It"
date: "2022-01-13"
-coverImage: "deepfake.jpg"
+coverImage: "deepfake.webp"
tags: ["digital transformation","identity management","cx"]
author: "Vishal Sharma"
description: "The emergence of deepfakes has led to many questions about how to identify and protect against them. This blog will provide an overview towards providing that understanding."
@@ -67,7 +67,7 @@ Algorithms are also emerging to assist video creators in authenticating their vi
Similarly, security practices can help to deter fraudsters. Deepfake attacks, as an emerging threat, thrive on the degree of technology available to fraudsters, particularly machine learning and advanced analytics. Businesses can fight fire with fire by employing the same capabilities.
-**Also Download**: [](https://www.loginradius.com/resource/digital-trade-zone-threats-cybersecurity-whitepaper)
+**Also Download**: [](https://www.loginradius.com/resource/digital-trade-zone-threats-cybersecurity-whitepaper)
## How to Prevent Deepfake Attacks
@@ -98,4 +98,4 @@ However, these methods are not the only measures to address the issue of deepfak
Additionally, technological companies and governments should consider enacting legislation that criminalizes the usage of deepfakes with the goal of damaging individuals' reputations. In this way, we can stop this rising threat.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-identity-mitigate-deepfake-attacks)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-identity-mitigate-deepfake-attacks)
\ No newline at end of file
diff --git a/content/identity/how-to-improve-customer-verification-process/DS-Mob-Biometric.png b/content/identity/how-to-improve-customer-verification-process/DS-Mob-Biometric.png
deleted file mode 100644
index a3580f13e..000000000
Binary files a/content/identity/how-to-improve-customer-verification-process/DS-Mob-Biometric.png and /dev/null differ
diff --git a/content/identity/how-to-improve-customer-verification-process/DS-Mob-Biometric.webp b/content/identity/how-to-improve-customer-verification-process/DS-Mob-Biometric.webp
new file mode 100644
index 000000000..0257eff22
Binary files /dev/null and b/content/identity/how-to-improve-customer-verification-process/DS-Mob-Biometric.webp differ
diff --git a/content/identity/how-to-improve-customer-verification-process/customer-verifcn.jpg b/content/identity/how-to-improve-customer-verification-process/customer-verifcn.jpg
deleted file mode 100644
index 4c0f8dc0e..000000000
Binary files a/content/identity/how-to-improve-customer-verification-process/customer-verifcn.jpg and /dev/null differ
diff --git a/content/identity/how-to-improve-customer-verification-process/customer-verifcn.webp b/content/identity/how-to-improve-customer-verification-process/customer-verifcn.webp
new file mode 100644
index 000000000..4159a3203
Binary files /dev/null and b/content/identity/how-to-improve-customer-verification-process/customer-verifcn.webp differ
diff --git a/content/identity/how-to-improve-customer-verification-process/index.md b/content/identity/how-to-improve-customer-verification-process/index.md
index 3a41b6809..ac6a88af2 100644
--- a/content/identity/how-to-improve-customer-verification-process/index.md
+++ b/content/identity/how-to-improve-customer-verification-process/index.md
@@ -1,7 +1,7 @@
---
title: "5 Ways to Improve Your Customer Verification Process"
date: "2022-04-04"
-coverImage: "customer-verifcn.jpg"
+coverImage: "customer-verifcn.webp"
tags: ["identity verification","customer identity management","cx"]
author: "Gaurav Belani"
description: "In the wake of recent data breaches, many companies are realizing that they need to improve their customer verification process. Learn how to improve the process and make it easy and secure for your customers."
@@ -41,7 +41,7 @@ Now, check out these top ways to improve and streamline your customer verificati
For instance, if you are doing email validation integration for Shopify with ZeroBounce, after a few initial steps, you will be asked to click the verification link to begin the verification process.
-
+
[Source](https://www.zerobounce.net/docs/api-integrations/shopify)
@@ -65,7 +65,7 @@ For instance, you can use behavioral biometrics.
Biometrics is one of the most effective methods of customer verification because physical traits like fingerprints and retina scans cannot be faked. Behavioral biometrics go one step further by considering how a person types or handles their mouse or mobile device as well as their physical characteristics.
-[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
+[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
### 3. Speed things up with SSO.
@@ -105,4 +105,4 @@ In summary, there are many ways eCommerce retailers can improve the customer ver
Whether you choose to [develop your own system](https://www.loginradius.com/blog/identity/build-vs-buy-securing-customer-identity/) or purchase a verification solution from a third-party vendor, ensuring this process is seamless for customers, and free of errors will go a long way towards ensuring that both merchants and buyers have a trusted and satisfying shopping experience every time.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-improve-customer-verification-process)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-improve-customer-verification-process)
\ No newline at end of file
diff --git a/content/identity/how-to-improve-customer-verification-process/mob-bio.png b/content/identity/how-to-improve-customer-verification-process/mob-bio.png
deleted file mode 100644
index 69293181d..000000000
Binary files a/content/identity/how-to-improve-customer-verification-process/mob-bio.png and /dev/null differ
diff --git a/content/identity/how-to-improve-customer-verification-process/mob-bio.webp b/content/identity/how-to-improve-customer-verification-process/mob-bio.webp
new file mode 100644
index 000000000..b272f8563
Binary files /dev/null and b/content/identity/how-to-improve-customer-verification-process/mob-bio.webp differ
diff --git a/content/identity/how-to-improve-customer-verification-process/ss-1.png b/content/identity/how-to-improve-customer-verification-process/ss-1.png
deleted file mode 100644
index 003e7d9b0..000000000
Binary files a/content/identity/how-to-improve-customer-verification-process/ss-1.png and /dev/null differ
diff --git a/content/identity/how-to-improve-customer-verification-process/ss-1.webp b/content/identity/how-to-improve-customer-verification-process/ss-1.webp
new file mode 100644
index 000000000..7d6564937
Binary files /dev/null and b/content/identity/how-to-improve-customer-verification-process/ss-1.webp differ
diff --git a/content/identity/how-to-protect-business-BGP-hijacking/WP-cybersecurty-training.png b/content/identity/how-to-protect-business-BGP-hijacking/WP-cybersecurty-training.png
deleted file mode 100644
index 68c8a6568..000000000
Binary files a/content/identity/how-to-protect-business-BGP-hijacking/WP-cybersecurty-training.png and /dev/null differ
diff --git a/content/identity/how-to-protect-business-BGP-hijacking/WP-cybersecurty-training.webp b/content/identity/how-to-protect-business-BGP-hijacking/WP-cybersecurty-training.webp
new file mode 100644
index 000000000..e10ca30b8
Binary files /dev/null and b/content/identity/how-to-protect-business-BGP-hijacking/WP-cybersecurty-training.webp differ
diff --git a/content/identity/how-to-protect-business-BGP-hijacking/bgp-attacks.jpg b/content/identity/how-to-protect-business-BGP-hijacking/bgp-attacks.jpg
deleted file mode 100644
index aecf538b4..000000000
Binary files a/content/identity/how-to-protect-business-BGP-hijacking/bgp-attacks.jpg and /dev/null differ
diff --git a/content/identity/how-to-protect-business-BGP-hijacking/bgp-attacks.webp b/content/identity/how-to-protect-business-BGP-hijacking/bgp-attacks.webp
new file mode 100644
index 000000000..e8bc6b30a
Binary files /dev/null and b/content/identity/how-to-protect-business-BGP-hijacking/bgp-attacks.webp differ
diff --git a/content/identity/how-to-protect-business-BGP-hijacking/enduser-cyber-wp.png b/content/identity/how-to-protect-business-BGP-hijacking/enduser-cyber-wp.png
deleted file mode 100644
index cc5feb3f3..000000000
Binary files a/content/identity/how-to-protect-business-BGP-hijacking/enduser-cyber-wp.png and /dev/null differ
diff --git a/content/identity/how-to-protect-business-BGP-hijacking/enduser-cyber-wp.webp b/content/identity/how-to-protect-business-BGP-hijacking/enduser-cyber-wp.webp
new file mode 100644
index 000000000..37dfe478a
Binary files /dev/null and b/content/identity/how-to-protect-business-BGP-hijacking/enduser-cyber-wp.webp differ
diff --git a/content/identity/how-to-protect-business-BGP-hijacking/index.md b/content/identity/how-to-protect-business-BGP-hijacking/index.md
index 3c86f6809..a0eabb494 100644
--- a/content/identity/how-to-protect-business-BGP-hijacking/index.md
+++ b/content/identity/how-to-protect-business-BGP-hijacking/index.md
@@ -1,7 +1,7 @@
---
title: "How to Mitigate BGP Attacks and Secure Your User's Data"
date: "2021-11-12"
-coverImage: "bgp-attacks.jpg"
+coverImage: "bgp-attacks.webp"
tags: ["enterprise security","cybersecurity"]
author: "Rakesh Soni"
description: "The reliance on BGP can be a double-edged sword as, on the one hand, it can be extremely convenient, while on the other, it can have major security lapses. However, enterprises can drastically reduce the risk by adopting the practices mentioned in the blog."
@@ -63,7 +63,7 @@ Network operators from around the world will have to release their data so that
This is a technique that is used to identify and drop information that has false IP addresses. The anti-spoofing filters which are used can deny service to spoofed IP addresses which try to gain access to a network. In most cases, if a packet coming from an external network contains an internal IP address, it gets blocked.
-[](https://www.loginradius.com/resource/why-is-end-user-cyber-security-training-mandatory/)
+[](https://www.loginradius.com/resource/why-is-end-user-cyber-security-training-mandatory/)
### #2. RPKI adoption
@@ -79,4 +79,4 @@ However, the only downside of RPKI adoption is that it can be significantly expe
The reliance on BGP can be a double-edged sword as, on the one hand, it can be extremely convenient, while on the other, it can have major security lapses. However, enterprises and ISPs can drastically reduce the risk of BGP hijacking by adopting the aforementioned safe practices.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-protect-business-bgp-hijacking)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-protect-business-bgp-hijacking)
\ No newline at end of file
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/buyer-guide-to-multi-factor-authentication-ebook.png b/content/identity/how-to-setup-2fa-in-online-accounts/buyer-guide-to-multi-factor-authentication-ebook.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/how-to-setup-2fa-in-online-accounts/buyer-guide-to-multi-factor-authentication-ebook.png and /dev/null differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/buyer-guide-to-multi-factor-authentication-ebook.webp b/content/identity/how-to-setup-2fa-in-online-accounts/buyer-guide-to-multi-factor-authentication-ebook.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/how-to-setup-2fa-in-online-accounts/buyer-guide-to-multi-factor-authentication-ebook.webp differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-facebook.png b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-facebook.png
deleted file mode 100644
index 24bf2d11b..000000000
Binary files a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-facebook.png and /dev/null differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-facebook.webp b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-facebook.webp
new file mode 100644
index 000000000..5ebd6d2da
Binary files /dev/null and b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-facebook.webp differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-instagram.jpg b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-instagram.jpg
deleted file mode 100644
index d6a5addbc..000000000
Binary files a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-instagram.jpg and /dev/null differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-instagram.webp b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-instagram.webp
new file mode 100644
index 000000000..a3cf17780
Binary files /dev/null and b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-instagram.webp differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-twitter.jpg b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-twitter.jpg
deleted file mode 100644
index 08dc9bc51..000000000
Binary files a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-twitter.jpg and /dev/null differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-twitter.webp b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-twitter.webp
new file mode 100644
index 000000000..1a8779b31
Binary files /dev/null and b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-twitter.webp differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-whatsapp.jpg b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-whatsapp.jpg
deleted file mode 100644
index 4c78b79ca..000000000
Binary files a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-whatsapp.jpg and /dev/null differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-whatsapp.webp b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-whatsapp.webp
new file mode 100644
index 000000000..2dd51e476
Binary files /dev/null and b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-in-whatsapp.webp differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-on-your-social-media-accounts.png b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-on-your-social-media-accounts.png
deleted file mode 100644
index fb51ca519..000000000
Binary files a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-on-your-social-media-accounts.png and /dev/null differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-on-your-social-media-accounts.webp b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-on-your-social-media-accounts.webp
new file mode 100644
index 000000000..fc1a99e4a
Binary files /dev/null and b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-set-up-2fa-on-your-social-media-accounts.webp differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-in-google.png b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-in-google.png
deleted file mode 100644
index de764367f..000000000
Binary files a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-in-google.png and /dev/null differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-in-google.webp b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-in-google.webp
new file mode 100644
index 000000000..0a68cdde1
Binary files /dev/null and b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-in-google.webp differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-online-accounts.jpg b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-online-accounts.jpg
deleted file mode 100644
index 0ccda07be..000000000
Binary files a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-online-accounts.jpg and /dev/null differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-online-accounts.webp b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-online-accounts.webp
new file mode 100644
index 000000000..760549729
Binary files /dev/null and b/content/identity/how-to-setup-2fa-in-online-accounts/how-to-setup-2fa-online-accounts.webp differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/index.md b/content/identity/how-to-setup-2fa-in-online-accounts/index.md
index 138afc019..cb5166154 100644
--- a/content/identity/how-to-setup-2fa-in-online-accounts/index.md
+++ b/content/identity/how-to-setup-2fa-in-online-accounts/index.md
@@ -1,7 +1,7 @@
---
title: "How to Set Up Two-factor Authentication on All Your Online Accounts?"
date: "2021-01-12"
-coverImage: "how-to-setup-2fa-online-accounts.jpg"
+coverImage: "how-to-setup-2fa-online-accounts.webp"
tags: ["2fa","mfa","cx"]
author: "Rakesh Soni"
description: "2FA is one of the best security methods that use two layers to verify a consumer’s identity. This means, rather than simply entering the password to log into an account, two-factor authentication requires a code to be sent via text message to a consumer's phone number or generated through an app"
@@ -46,7 +46,7 @@ The next time you sign in to your app or service, it will ask for a numerical co
## **How to Set up 2FA on Your Social Media Accounts?**
-
+
A lot of applications offer 2FA currently, especially if you are storing important and sensitive data, financial information, emails, social media, files, contact details, etc.
@@ -64,7 +64,7 @@ If you want to set up an authenticator on the Google account, first you need to
You can add the two-**step verification** process here.
-
+
Source: Google
@@ -87,7 +87,7 @@ To set up 2FA on your WhatsApp account, you will need to:
* Go to Look under Account > Two-step verification > Allow.
* You will be prompted to end a six-digit PIN to verify your account. If you forget your PIN, you can optionally add an email address.
-
+
Source: lifewire
@@ -114,7 +114,7 @@ To set up 2FA on your Facebook account, you will need to:
You can also use the Facebook mobile app for approving sign-ins on the web or set up a third-party authentication app for generating codes.
-
+
Source: Facebook
@@ -128,7 +128,7 @@ To set up 2FA on your Twitter account, you will need to:
* Verify your mobile number and then click Set up a code generator app.
* Scan the QR code with the third-party authenticator app.
-
+
### 7. Apple iCloud
@@ -157,7 +157,7 @@ In 2017, two-factor authentication was added by Instagram to the mobile app, whi
With Instagram, you also get to choose between SMS-based verification and a code sent to the authentication app.
-
+
Source: Kaspersky
@@ -193,7 +193,7 @@ Users can consider these factors when choosing the most suitable authenticator a
## **Setting Up 2FA Login with LoginRadius Adaptive 2FA/ MFA solution**
-
+
LoginRadius provides multi-factor authentication via SMS, email, automated phone calls, account [security questions](https://www.loginradius.com/blog/identity/2019/01/best-practices-choosing-good-security-questions/), and authenticator apps to allow you a customized user experience.
@@ -207,7 +207,7 @@ You can enable 2FA [SMS verification](https://www.loginradius.com/docs/api/v2/cu
As the first step, you'll need to apply a first verification factor, like standard email and password login, username and password, automated phone call, or access token. The second factor can be a one-time password or code sent via SMS.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### Google Authenticator Workflow
@@ -239,4 +239,4 @@ Choose your method (SMS or authenticator app) during setup, then link the code t
Yes, 2FA is user-friendly. It involves entering a code or approving a notification on your phone during logins.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-setup-2fa-in-online-accounts)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-setup-2fa-in-online-accounts)
\ No newline at end of file
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/setting-up-2fa-with-loginradius.png b/content/identity/how-to-setup-2fa-in-online-accounts/setting-up-2fa-with-loginradius.png
deleted file mode 100644
index bf281abe7..000000000
Binary files a/content/identity/how-to-setup-2fa-in-online-accounts/setting-up-2fa-with-loginradius.png and /dev/null differ
diff --git a/content/identity/how-to-setup-2fa-in-online-accounts/setting-up-2fa-with-loginradius.webp b/content/identity/how-to-setup-2fa-in-online-accounts/setting-up-2fa-with-loginradius.webp
new file mode 100644
index 000000000..01a15be9b
Binary files /dev/null and b/content/identity/how-to-setup-2fa-in-online-accounts/setting-up-2fa-with-loginradius.webp differ
diff --git a/content/identity/how-to-stop-phone-hacking/6-signs-that-confirm-your-smartphone-has-already-been-hacked.png b/content/identity/how-to-stop-phone-hacking/6-signs-that-confirm-your-smartphone-has-already-been-hacked.png
deleted file mode 100644
index 9ebc1a58c..000000000
Binary files a/content/identity/how-to-stop-phone-hacking/6-signs-that-confirm-your-smartphone-has-already-been-hacked.png and /dev/null differ
diff --git a/content/identity/how-to-stop-phone-hacking/6-signs-that-confirm-your-smartphone-has-already-been-hacked.webp b/content/identity/how-to-stop-phone-hacking/6-signs-that-confirm-your-smartphone-has-already-been-hacked.webp
new file mode 100644
index 000000000..dfd22a0a3
Binary files /dev/null and b/content/identity/how-to-stop-phone-hacking/6-signs-that-confirm-your-smartphone-has-already-been-hacked.webp differ
diff --git a/content/identity/how-to-stop-phone-hacking/8-ways-to-stop-someone-from-hacking-your-phone-again.png b/content/identity/how-to-stop-phone-hacking/8-ways-to-stop-someone-from-hacking-your-phone-again.png
deleted file mode 100644
index 706334312..000000000
Binary files a/content/identity/how-to-stop-phone-hacking/8-ways-to-stop-someone-from-hacking-your-phone-again.png and /dev/null differ
diff --git a/content/identity/how-to-stop-phone-hacking/8-ways-to-stop-someone-from-hacking-your-phone-again.webp b/content/identity/how-to-stop-phone-hacking/8-ways-to-stop-someone-from-hacking-your-phone-again.webp
new file mode 100644
index 000000000..ac58f8127
Binary files /dev/null and b/content/identity/how-to-stop-phone-hacking/8-ways-to-stop-someone-from-hacking-your-phone-again.webp differ
diff --git a/content/identity/how-to-stop-phone-hacking/buyer-guide-to-multi-factor-authentication-ebook.png b/content/identity/how-to-stop-phone-hacking/buyer-guide-to-multi-factor-authentication-ebook.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/how-to-stop-phone-hacking/buyer-guide-to-multi-factor-authentication-ebook.png and /dev/null differ
diff --git a/content/identity/how-to-stop-phone-hacking/buyer-guide-to-multi-factor-authentication-ebook.webp b/content/identity/how-to-stop-phone-hacking/buyer-guide-to-multi-factor-authentication-ebook.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/how-to-stop-phone-hacking/buyer-guide-to-multi-factor-authentication-ebook.webp differ
diff --git a/content/identity/how-to-stop-phone-hacking/how-to-make-sure-your-phone-isn't-hacked.png b/content/identity/how-to-stop-phone-hacking/how-to-make-sure-your-phone-isn't-hacked.png
deleted file mode 100644
index be43f7106..000000000
Binary files a/content/identity/how-to-stop-phone-hacking/how-to-make-sure-your-phone-isn't-hacked.png and /dev/null differ
diff --git a/content/identity/how-to-stop-phone-hacking/how-to-make-sure-your-phone-isn't-hacked.webp b/content/identity/how-to-stop-phone-hacking/how-to-make-sure-your-phone-isn't-hacked.webp
new file mode 100644
index 000000000..ab1eeb161
Binary files /dev/null and b/content/identity/how-to-stop-phone-hacking/how-to-make-sure-your-phone-isn't-hacked.webp differ
diff --git a/content/identity/how-to-stop-phone-hacking/index.md b/content/identity/how-to-stop-phone-hacking/index.md
index a48c9a617..8a1a67325 100644
--- a/content/identity/how-to-stop-phone-hacking/index.md
+++ b/content/identity/how-to-stop-phone-hacking/index.md
@@ -1,7 +1,7 @@
---
title: "How To Make Sure Your Phone Isn’t Hacked"
date: "2020-12-09"
-coverImage: "stop-phone-hacking.jpg"
+coverImage: "stop-phone-hacking.webp"
tags: ["data security","cybersecurity","authentication"]
author: "Rakesh Soni"
description: "Hacking your smartphone may feel like someone has stolen your home. Go through this checklist to protect your phone from being hacked."
@@ -21,7 +21,7 @@ Hackers do not even have to steal the victim's phone to download malware. They j
If your smartphone is displaying one or more of the following unusual behavior, there is a possibility that your device has already been hacked.
-
+
### 1. Noticeable decrease in battery life
@@ -73,7 +73,7 @@ Many smartphone users believe that their mobile service providers should deploy
Here are a few safety tips to ensure that you do not become a victim of phone hacking:
-
+
### 1. Keep up to date – and don’t dig in holes yourself.
@@ -100,7 +100,7 @@ Users should ensure that they keep their phone locked when not in use and also s
Services like ‘find my device’ are provided by smartphone manufacturers to help users locate their stolen phone on a map and remotely erase their data. All users need to do is set their phone to automatically erase itself after a certain number of incorrect access attempts. It is also possible to make a phone ring even if it is kept on silent. It is helpful in tracking down phone that was just stolen.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
@@ -126,4 +126,4 @@ Locking your phone is important but as a secondary security measure, lock indivi
Smartphones have become an essential part of our daily lives. Once you know about how your phone can be hacked, you can take various safety precautions to protect it from data theft. Furthermore, it will also keep your data secure from opportunist thieves or state-sponsored spies!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-stop-phone-hacking)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-stop-phone-hacking)
diff --git a/content/identity/how-to-stop-phone-hacking/stop-phone-hacking.jpg b/content/identity/how-to-stop-phone-hacking/stop-phone-hacking.jpg
deleted file mode 100644
index 9200d2ddf..000000000
Binary files a/content/identity/how-to-stop-phone-hacking/stop-phone-hacking.jpg and /dev/null differ
diff --git a/content/identity/how-to-stop-phone-hacking/stop-phone-hacking.webp b/content/identity/how-to-stop-phone-hacking/stop-phone-hacking.webp
new file mode 100644
index 000000000..f4feda159
Binary files /dev/null and b/content/identity/how-to-stop-phone-hacking/stop-phone-hacking.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-1.png b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-1.png
deleted file mode 100644
index ad2f80386..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-1.png and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-1.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-1.webp
new file mode 100644
index 000000000..8073111af
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-1.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-2.png b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-2.png
deleted file mode 100644
index 39b33558d..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-2.png and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-2.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-2.webp
new file mode 100644
index 000000000..e18973393
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-2.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-3.png b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-3.png
deleted file mode 100644
index b9430a98b..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-3.png and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-3.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-3.webp
new file mode 100644
index 000000000..27711c238
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-3.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-4.png b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-4.png
deleted file mode 100644
index afbe7f199..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-4.png and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-4.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-4.webp
new file mode 100644
index 000000000..f6579e6f2
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-4.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-5.png b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-5.png
deleted file mode 100644
index 9156d5ca7..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-5.png and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-5.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-5.webp
new file mode 100644
index 000000000..88266018d
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-5.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-canva.jpg b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-canva.jpg
deleted file mode 100644
index 16d5a0945..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-canva.jpg and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-canva.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-canva.webp
new file mode 100644
index 000000000..2e65b556b
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-canva.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-cover.jpg b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-cover.jpg
deleted file mode 100644
index 1d2aef827..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-cover.jpg and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-cover.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-cover.webp
new file mode 100644
index 000000000..ee91f1467
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-cover.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-gnc.jpg b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-gnc.jpg
deleted file mode 100644
index 5fdf2ecc1..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-gnc.jpg and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-gnc.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-gnc.webp
new file mode 100644
index 000000000..59010c9d6
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-gnc.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-landcf.jpg b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-landcf.jpg
deleted file mode 100644
index cde592359..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-landcf.jpg and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-landcf.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-landcf.webp
new file mode 100644
index 000000000..f12eff9d0
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-landcf.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-lr.jpg b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-lr.jpg
deleted file mode 100644
index ca6cc78e5..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-lr.jpg and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-lr.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-lr.webp
new file mode 100644
index 000000000..94acc3adf
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-lr.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-mmt.jpg b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-mmt.jpg
deleted file mode 100644
index 02a97ad32..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-mmt.jpg and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-mmt.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-mmt.webp
new file mode 100644
index 000000000..3f5f09aff
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-mmt.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-pinterest1.jpg b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-pinterest1.jpg
deleted file mode 100644
index d023e2d08..000000000
Binary files a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-pinterest1.jpg and /dev/null differ
diff --git a/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-pinterest1.webp b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-pinterest1.webp
new file mode 100644
index 000000000..97ff2231b
Binary files /dev/null and b/content/identity/how-ui-ux-affects-registration/how-ui-ux-affects-registration-pinterest1.webp differ
diff --git a/content/identity/how-ui-ux-affects-registration/index.md b/content/identity/how-ui-ux-affects-registration/index.md
index b3ec2e822..73a275a7b 100644
--- a/content/identity/how-ui-ux-affects-registration/index.md
+++ b/content/identity/how-ui-ux-affects-registration/index.md
@@ -1,7 +1,7 @@
---
title: "A Detailed Guide on How UX/UI Affects Registration"
date: "2021-04-16"
-coverImage: "how-ui-ux-affects-registration-cover.jpg"
+coverImage: "how-ui-ux-affects-registration-cover.webp"
tags: ["other"]
featured: false
author: "Rakesh Soni"
@@ -77,7 +77,7 @@ And last, perform A/B testing on your signup forms. You will surely get some spa
-
+
Image source: [Pinterest](https://www.pinterest.com/)
@@ -94,7 +94,7 @@ Image source: [Pinterest](https://www.pinterest.com/)
-
+
Image Source: [Lane Crawford](https://secure.lanecrawford.com/account/accountCreation.jsp)
@@ -111,7 +111,7 @@ Image Source: [Lane Crawford](https://secure.lanecrawford.com/account/accountCre
-
+
Image source: [GNC](https://www.gnc.com/checkout/index.jsp)
@@ -128,7 +128,7 @@ Image source: [GNC](https://www.gnc.com/checkout/index.jsp)
-
+
Image source: [Canva](https://www.canva.com/login)
@@ -145,7 +145,7 @@ Image source: [Canva](https://www.canva.com/login)
### 5. Make My Trip
-
+
@@ -171,7 +171,7 @@ In fact, according to [Consumer Digital Identity Trend Report 2020](https://www.
Well, no surprise there!
-
+
@@ -220,36 +220,36 @@ Many companies overlook the crucial factors to consider when integrating social
-
+
2. **38.69%** of females prefer social login compared to 48.55% males.
-
+
3. In **North America**, Facebook and Google are the most popular social networks preferred by 40.23% and 38.04% of consumers, respectively.
-
+
4. In **Europe**, a similar trend is witnessed. Facebook is preferred by 36.12% of consumers, and Google is preferred by 34.89%.
-
+
5. **Facebook** is still preferred by 51.72% of consumers in the APAC region, and Google is preferred by 26.033%.
-
+
So, get cracking! Obviously, you do not want to lose out on your potential customers. Enjoy the endless benefits of Social Login with the [LoginRadius unified social API](https://www.loginradius.com/social-login/).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ui-ux-affects-registration)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ui-ux-affects-registration)
\ No newline at end of file
diff --git a/content/identity/iam-or-ciam-right-call-business-growth/DS-Priv-Pol-Mgnmnt.png b/content/identity/iam-or-ciam-right-call-business-growth/DS-Priv-Pol-Mgnmnt.png
deleted file mode 100644
index 67c1c093f..000000000
Binary files a/content/identity/iam-or-ciam-right-call-business-growth/DS-Priv-Pol-Mgnmnt.png and /dev/null differ
diff --git a/content/identity/iam-or-ciam-right-call-business-growth/DS-Priv-Pol-Mgnmnt.webp b/content/identity/iam-or-ciam-right-call-business-growth/DS-Priv-Pol-Mgnmnt.webp
new file mode 100644
index 000000000..42c0492a7
Binary files /dev/null and b/content/identity/iam-or-ciam-right-call-business-growth/DS-Priv-Pol-Mgnmnt.webp differ
diff --git a/content/identity/iam-or-ciam-right-call-business-growth/iam-ciam.jpg b/content/identity/iam-or-ciam-right-call-business-growth/iam-ciam.jpg
deleted file mode 100644
index 596b05d43..000000000
Binary files a/content/identity/iam-or-ciam-right-call-business-growth/iam-ciam.jpg and /dev/null differ
diff --git a/content/identity/iam-or-ciam-right-call-business-growth/iam-ciam.webp b/content/identity/iam-or-ciam-right-call-business-growth/iam-ciam.webp
new file mode 100644
index 000000000..797bb8aa4
Binary files /dev/null and b/content/identity/iam-or-ciam-right-call-business-growth/iam-ciam.webp differ
diff --git a/content/identity/iam-or-ciam-right-call-business-growth/index.md b/content/identity/iam-or-ciam-right-call-business-growth/index.md
index 3bcb6cacb..f4d0cae04 100644
--- a/content/identity/iam-or-ciam-right-call-business-growth/index.md
+++ b/content/identity/iam-or-ciam-right-call-business-growth/index.md
@@ -1,7 +1,7 @@
---
title: "IAM vs. Customer IAM: Understanding the Role of CIAM in Accelerating Business Growth"
date: "2022-11-03"
-coverImage: "iam-ciam.jpg"
+coverImage: "iam-ciam.webp"
tags: ["iam", "ciam", "data security","compliance"]
author: "Rakesh Soni"
description: "A CIAM can be scaled in real-time depending on the load and number of users accessing the services from a single platform. On the other hand, the traditional IAM can’t deliver results for large-scale deployments. Let’s understand why organizations should switch to customer IAM and how it’s helping businesses stay ahead of the curve."
@@ -58,7 +58,7 @@ These aren’t the only potential costs you can save—legal fees can run high w
Presenting customers with easily self-managed privacy choices and a solid privacy policy also shows them that their data is safe and shows your company is competent and professional in handling these issues. This reputation will encourage customer loyalty in the long run.
-[](https://www.loginradius.com/resource/privacy-policy-management-datasheet)
+[](https://www.loginradius.com/resource/privacy-policy-management-datasheet)
### #3. Scalability and uptime
@@ -83,4 +83,4 @@ The conventional IAM isn’t the right choice for handling many customers, espec
The aspects mentioned above of leveraging a CIAM shouldn’t be ignored by businesses thinking to accelerate overall growth.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=iam-or-ciam-right-call-business-growth)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=iam-or-ciam-right-call-business-growth)
diff --git a/content/identity/iam-or-ciam-right-call-business-growth/privacy-ds.png b/content/identity/iam-or-ciam-right-call-business-growth/privacy-ds.png
deleted file mode 100644
index e738ae27a..000000000
Binary files a/content/identity/iam-or-ciam-right-call-business-growth/privacy-ds.png and /dev/null differ
diff --git a/content/identity/iam-or-ciam-right-call-business-growth/privacy-ds.webp b/content/identity/iam-or-ciam-right-call-business-growth/privacy-ds.webp
new file mode 100644
index 000000000..eb8ed83dc
Binary files /dev/null and b/content/identity/iam-or-ciam-right-call-business-growth/privacy-ds.webp differ
diff --git a/content/identity/iam-vs-ciam/IAM-vs-CIAM-V01.01-01-1.png b/content/identity/iam-vs-ciam/IAM-vs-CIAM-V01.01-01-1.png
deleted file mode 100644
index a73b2539a..000000000
Binary files a/content/identity/iam-vs-ciam/IAM-vs-CIAM-V01.01-01-1.png and /dev/null differ
diff --git a/content/identity/iam-vs-ciam/IAM-vs-CIAM-V01.01-01-1.webp b/content/identity/iam-vs-ciam/IAM-vs-CIAM-V01.01-01-1.webp
new file mode 100644
index 000000000..026dc48da
Binary files /dev/null and b/content/identity/iam-vs-ciam/IAM-vs-CIAM-V01.01-01-1.webp differ
diff --git a/content/identity/iam-vs-ciam/IAM-vs.-CIAM-V03.01.jpg b/content/identity/iam-vs-ciam/IAM-vs.-CIAM-V03.01.jpg
deleted file mode 100644
index 31fc56b4e..000000000
Binary files a/content/identity/iam-vs-ciam/IAM-vs.-CIAM-V03.01.jpg and /dev/null differ
diff --git a/content/identity/iam-vs-ciam/IAM-vs.-CIAM-V03.01.webp b/content/identity/iam-vs-ciam/IAM-vs.-CIAM-V03.01.webp
new file mode 100644
index 000000000..708d8068c
Binary files /dev/null and b/content/identity/iam-vs-ciam/IAM-vs.-CIAM-V03.01.webp differ
diff --git a/content/identity/iam-vs-ciam/employee-iam-vs-ciam.png b/content/identity/iam-vs-ciam/employee-iam-vs-ciam.png
deleted file mode 100644
index 47311a715..000000000
Binary files a/content/identity/iam-vs-ciam/employee-iam-vs-ciam.png and /dev/null differ
diff --git a/content/identity/iam-vs-ciam/employee-iam-vs-ciam.webp b/content/identity/iam-vs-ciam/employee-iam-vs-ciam.webp
new file mode 100644
index 000000000..2632369d4
Binary files /dev/null and b/content/identity/iam-vs-ciam/employee-iam-vs-ciam.webp differ
diff --git a/content/identity/iam-vs-ciam/index.md b/content/identity/iam-vs-ciam/index.md
index a3a2393ae..49d474cc2 100644
--- a/content/identity/iam-vs-ciam/index.md
+++ b/content/identity/iam-vs-ciam/index.md
@@ -1,7 +1,7 @@
---
title: "IAM vs. CIAM: Which Solution is Right For You?"
date: "2019-03-21"
-coverImage: "IAM-vs-CIAM-V01.01-01-1.png"
+coverImage: "IAM-vs-CIAM-V01.01-01-1.webp"
tags: ["iam","ciam","identity management"]
author: "Rakesh Soni"
description: "In order to serve customers, conventional identity management is no longer enough. This truly ought to go without saying. After all, internal management systems were initially designed to handle employee identities, and consumer preferences are not generally matched with their preferences of a successful user experience."
@@ -43,4 +43,4 @@ In this infographic, we compare the following features of both an IAM and CIAM s
* Real-Life Examples
-
+
diff --git a/content/identity/identification-and-authorization/identification-and-authorization.webp b/content/identity/identification-and-authorization/identification-and-authorization.webp
new file mode 100644
index 000000000..764f60631
Binary files /dev/null and b/content/identity/identification-and-authorization/identification-and-authorization.webp differ
diff --git a/content/identity/identification-and-authorization/index.md b/content/identity/identification-and-authorization/index.md
new file mode 100644
index 000000000..70e3fdc1a
--- /dev/null
+++ b/content/identity/identification-and-authorization/index.md
@@ -0,0 +1,215 @@
+---
+title: "Identification and Authentication: A Quick Comparison"
+date: "2025-04-02"
+coverImage: "identification-and-authorization.webp"
+tags: ["Identity management","Authentication","Authorization","Security"]
+author: "Kundan Singh"
+description: "In digital security, identification introduces who you are, authentication verifies your identity, and authorization defines your access. Clearly understanding these distinct roles is essential to protecting sensitive data and ensuring robust access control. Let's explore their differences in detail."
+metadescription: "Learn the difference between identification and authentication. Discover how these access protocols work with authorization to secure digital identity and access."
+metatitle: "Identification & Authentication: Key Differences Explained"
+---
+## Introduction
+
+In the ever-evolving digital ecosystem, maintaining robust access control is more than a security best practice—it's an organizational imperative. At the core of this protection lie three fundamental concepts: identification, authentication, and authorization.
+
+While often used interchangeably, they each serve a distinct role in enabling security identification and safeguarding sensitive information. If misunderstood, organizations risk authentication vulnerabilities, access loopholes, and regulatory non-compliance.
+
+Let’s break down these concepts, explore their differences, and learn how they work together in real-world applications.
+
+## What is Identification?
+
+User identification is the process of stating or declaring who you are to a system. It’s the first checkpoint in [access control](https://www.loginradius.com/products/roles-and-permissions)—providing a unique identifier like a username, email address, or user ID.
+
+In terms of identification in cybersecurity, it's about defining an identity for every human, device, or software system that interacts with an organization’s digital ecosystem. Whether you’re an employee logging into an internal HR system or a customer signing into a mobile app, access identification starts the session.
+
+For instance, imagine a hospital using badge-based RFID systems. A nurse taps their badge on a reader—this act is identification. The system recognizes the badge as belonging to a specific user.
+
+
+
+## What is Authentication?
+
+[Authentication ](https://www.loginradius.com/blog/identity/what-is-authentication/)confirms the identity that was presented. Once you've said, “I’m John Doe,” the system demands proof—your password, a biometric scan, or a token from your phone. This is what identity and authentication boil down to: establishing and proving trust.
+
+Modern authentication also involves layered verification. This includes [multi-factor authentication (MFA)](https://www.loginradius.com/blog/identity/what-is-multi-factor-authentication/) or behavioral biometrics to counter emerging threats like authentication vulnerabilities.
+
+Real-life example: You access your cloud storage by entering your password (knowledge factor) and approving a notification on your phone (possession factor). The system now trusts you are indeed who you say you are.
+
+## What is Authorization?
+
+Once a user is both identified and authenticated, authorization comes into play. It determines what the user can do within a system—like viewing data, making edits, or initiating transactions.
+
+In enterprise environments, authorization often maps to roles:
+
+* A regular employee may view internal documents
+
+* A manager may also approve budgets
+
+* An IT admin may configure entire networks
+
+Without proper authorization, even authenticated users can pose risks. For example, a software developer shouldn’t have access to payroll data. This is where [Role-Based Access Control (RBAC) ](https://www.loginradius.com/blog/identity/what-is-rbac/)becomes essential.
+
+RBAC assigns permissions based on a user’s role within the organization—ensuring that access is granted strictly according to job responsibilities. This minimizes exposure to sensitive information and enforces the principle of least privilege.
+
+Such role-driven access strategies not only reduce authentication vulnerabilities but also strengthen security identification and ensure robust governance in user access.
+
+## Identification vs Authentication vs Authorization
+
+To build a secure and user-friendly system, it’s critical to understand the roles of these three layers of access control.
+
+
+
+ Feature
+
+ Identification
+
+ Authentication
+
+ Authorization
+
+
+
+ Definition
+
+ Claiming an identity
+
+ Proving that identity
+
+ Granting access to resources
+
+
+
+ Example
+
+ Entering your username or email
+
+ Typing your password or scanning fingerprint
+
+ Accessing files based on user role
+
+
+
+ When it Occurs
+
+ First step of login
+
+ Second step—verification
+
+ After successful authentication
+
+
+
+ Used In
+
+ Login forms, registration, device pairing
+
+ MFA systems, biometrics, 2FA
+
+ Role-based access, permissions frameworks
+
+
+
+ Failure Risk
+
+ Misidentification
+
+ Credential theft, phishing
+
+ Privilege escalation
+
+
+
+
+By clearly separating these, businesses can build systems that are secure, user-friendly, and compliant with identification security protocols.
+
+## Real-World Applications of Identification, Authentication, and Authorization
+
+To truly appreciate the difference between identification and authentication, it’s helpful to see where each protocol fits in the real world. These mechanisms don’t exist in isolation—they operate sequentially to protect systems at every stage of a user’s interaction.
+
+Let’s break it down:
+
+### 1. Identification – “Who are you?”
+
+This step is the user’s digital introduction. It typically takes place on login screens or at the beginning of a session. Users enter a unique identifier such as a username, email, or phone number. In more advanced systems, device identifiers or API client IDs may be used to identify machines (through [M2M authorization](https://www.loginradius.com/blog/engineering/using-m2m-authorization-for-apis-and-apps/)) or services instead of humans.
+
+**Used in:**
+
+* Login forms
+
+* Device pairing
+
+* API calls (e.g., passing client ID for system access)
+
+This is the first gate in access identification, helping the system associate incoming actions with a known identity.
+
+### 2. Authentication – “Prove it.”
+
+Once a user claims an identity, the system demands evidence. This could be a password, biometric data, a smart token, or a combination in a multi-factor authentication setup. The aim is to eliminate impostors and ensure the system is engaging with a verified individual.
+
+**Used in:**
+
+* Password logins
+
+* OTP verifications
+
+* Biometric scans (fingerprint, facial recognition)
+
+* Hardware tokens or authenticator apps
+
+Strong authentication mechanisms protect against common authentication vulnerabilities, such as phishing, credential stuffing, or session hijacking.
+
+[](https://www.loginradius.com/resource/ebook/strong-authentication-business-success)
+
+### 3. Authorization – “What can you access?”
+
+After successfully identifying and authenticating the user, the system moves to authorization—defining what that verified user can do. This stage enforces access rules based on roles, privileges, or policies.
+
+**Used in:**
+
+* Access to admin tools or dashboards
+
+* Viewing vs. editing data
+
+* API permission scopes
+
+* Role-based access to internal apps
+
+This step ties directly into identification security and ensures compliance with internal and regulatory access policies.
+
+## To Conclude
+
+The trio of identification, authentication, and authorization is essential to securing digital interactions.
+
+* **Identification** introduces the user.
+
+* **Authentication** proves the user is genuine.
+
+* **Authorization** ensures users can access only what they're allowed.
+
+Each layer supports the others, and missing even one—identification, authentication, or authorization—can leave systems vulnerable to exploitation, ranging from data breaches to account compromise.
+
+To stay ahead of evolving threats, organizations must implement strong identification and authentication workflows, mitigate authentication vulnerabilities using [multifactor authentication](https://www.loginradius.com/platforms/multi-factor-authentication) and behavior-based detection, and ensure airtight identification security with audit trails and device-level recognition.
+
+Whether managing a mobile app, enterprise platform, or IoT network, adopting intelligent identity and authentication strategies is no longer just a technical upgrade—it’s a critical business decision that protects trust, compliance, and long-term resilience.
+
+## **FAQs**
+
+### Q1. What is an identification vs authentication example?
+**A.** Identification: A user enters their email address to log in.
+ Authentication: They then enter their password or fingerprint to verify that identity.
+
+### Q2. Why is verification needed in addition to authentication?
+**A.** Verification adds a secondary check to ensure the person authenticating is genuine. For instance, a phishing attacker may steal a password—but device fingerprinting or behavior-based verification can still detect an anomaly.
+
+### Q3. What is the difference between identifier and authenticator?
+**A.** An identifier is what the system uses to recognize a user (username, email). An authenticator is what the user provides to prove their identity (password, token, biometric scan).
+
+### Q4. How to prevent identification and authentication failures?
+**A.** Here’s what you can do to prevent identification and authentication failure:
+
+* Use adaptive authentication based on risk levels
+* Rotate and encrypt credentials
+* Educate users about phishing and spoofing
+* Implement access identification controls and logging
+* Leverage platforms like LoginRadius for seamless and secure identity and authentication
+
+[](https://www.loginradius.com/contact-us)
\ No newline at end of file
diff --git a/content/identity/identification-and-authorization/passwords-and-facial-recognition.webp b/content/identity/identification-and-authorization/passwords-and-facial-recognition.webp
new file mode 100644
index 000000000..a976ca2d1
Binary files /dev/null and b/content/identity/identification-and-authorization/passwords-and-facial-recognition.webp differ
diff --git a/content/identity/identification-and-authorization/strong-authentication.webp b/content/identity/identification-and-authorization/strong-authentication.webp
new file mode 100644
index 000000000..c9dc1f2fa
Binary files /dev/null and b/content/identity/identification-and-authorization/strong-authentication.webp differ
diff --git a/content/identity/identity-access-management-best-practices/Book-a-demo-banner.png b/content/identity/identity-access-management-best-practices/Book-a-demo-banner.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/identity-access-management-best-practices/Book-a-demo-banner.png and /dev/null differ
diff --git a/content/identity/identity-access-management-best-practices/Book-a-demo-banner.webp b/content/identity/identity-access-management-best-practices/Book-a-demo-banner.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/identity-access-management-best-practices/Book-a-demo-banner.webp differ
diff --git "a/content/identity/identity-access-management-best-practices/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png" "b/content/identity/identity-access-management-best-practices/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png"
deleted file mode 100644
index 6b3ba826e..000000000
Binary files "a/content/identity/identity-access-management-best-practices/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png" and /dev/null differ
diff --git "a/content/identity/identity-access-management-best-practices/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp" "b/content/identity/identity-access-management-best-practices/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp"
new file mode 100644
index 000000000..ba14612ce
Binary files /dev/null and "b/content/identity/identity-access-management-best-practices/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp" differ
diff --git a/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-Best-Practices.jpg b/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-Best-Practices.jpg
deleted file mode 100644
index a0d90303a..000000000
Binary files a/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-Best-Practices.jpg and /dev/null differ
diff --git a/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-Best-Practices.webp b/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-Best-Practices.webp
new file mode 100644
index 000000000..6f6dfb377
Binary files /dev/null and b/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-Best-Practices.webp differ
diff --git a/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-img2.png b/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-img2.png
deleted file mode 100644
index 681e8b10b..000000000
Binary files a/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-img2.png and /dev/null differ
diff --git a/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-img2.webp b/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-img2.webp
new file mode 100644
index 000000000..a5d26eea0
Binary files /dev/null and b/content/identity/identity-access-management-best-practices/Identity-and-Access-Management-img2.webp differ
diff --git a/content/identity/identity-access-management-best-practices/index.md b/content/identity/identity-access-management-best-practices/index.md
index b5570d63c..a6a6d25aa 100644
--- a/content/identity/identity-access-management-best-practices/index.md
+++ b/content/identity/identity-access-management-best-practices/index.md
@@ -1,7 +1,7 @@
---
title: "9 Identity and Access Management Best Practices for 2021"
date: "2020-11-11"
-coverImage: "Identity-and-Access-Management-Best-Practices.jpg"
+coverImage: "Identity-and-Access-Management-Best-Practices.webp"
tags: ["identity management","ciam solution","cx"]
author: "Rakesh Soni"
description: "Enforcing best practices for identity and access management allows you to know who can access the confidential data and under what conditions they can access it. You will need a detailed overview of the IT infrastructure of your company so that you can track all of your components for future and current threats."
@@ -25,7 +25,7 @@ The dust is still settling. With compromised credentials remaining a key compone
- **BYOD-related challenges**: Bring Your Own Device or BYOD turns out to be carrying its own set of advantages and [cybersecurity challenges](https://www.loginradius.com/blog/2019/10/cybersecurity-attacks-business/) for enterprises. On the one hand, businesses enjoy a great deal of cost-cutting by letting employees work on their own devices. But on the other, it has been increasing the strain on security systems. Numerous data leaks and malware infections are already detected. It has turned out to be much harder to track and manage different types of devices.
- **Internet Of Things (IoT)**: With the adoption of IoT, companies are becoming more dependent on interconnected technology. As a result, attackers are exploiting the vulnerabilities in the IoT infrastructure. Security threats like DDoS and ransomware are becoming a common occurrence.
-
+
## What Is Identity and Access Management
@@ -57,7 +57,7 @@ The former could be a key or a security pass. While the later means biometrics,
MFA ensures that even if one layer is compromised, the hacker still has to break in another layer of security to access your system.
-[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
+[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
### 3\. Avoid privileged accounts
@@ -122,4 +122,4 @@ Enforcing identity and access management best practices require that you underst
You also need a comprehensive overview of your organization’s IT infrastructure so you can monitor all your elements for potential and existing threats. Staying updated on the latest industry trends will help you improve your current IAM environment.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-access-management-best-practices)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-access-management-best-practices)
diff --git a/content/identity/identity-as-a-service-for-business/Book-a-free-demo-request-1024x310.png b/content/identity/identity-as-a-service-for-business/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/identity-as-a-service-for-business/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/identity-as-a-service-for-business/Book-a-free-demo-request-1024x310.webp b/content/identity/identity-as-a-service-for-business/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/identity-as-a-service-for-business/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/identity-as-a-service-for-business/EB-Guide-to-Modern-Customer-Identity-1024x310.png b/content/identity/identity-as-a-service-for-business/EB-Guide-to-Modern-Customer-Identity-1024x310.png
deleted file mode 100644
index 2f87dc40c..000000000
Binary files a/content/identity/identity-as-a-service-for-business/EB-Guide-to-Modern-Customer-Identity-1024x310.png and /dev/null differ
diff --git a/content/identity/identity-as-a-service-for-business/EB-Guide-to-Modern-Customer-Identity-1024x310.webp b/content/identity/identity-as-a-service-for-business/EB-Guide-to-Modern-Customer-Identity-1024x310.webp
new file mode 100644
index 000000000..4e4ab1a98
Binary files /dev/null and b/content/identity/identity-as-a-service-for-business/EB-Guide-to-Modern-Customer-Identity-1024x310.webp differ
diff --git a/content/identity/identity-as-a-service-for-business/Leveraging-IDaaS-for-Business-Success.jpg b/content/identity/identity-as-a-service-for-business/Leveraging-IDaaS-for-Business-Success.jpg
deleted file mode 100644
index 22b01d862..000000000
Binary files a/content/identity/identity-as-a-service-for-business/Leveraging-IDaaS-for-Business-Success.jpg and /dev/null differ
diff --git a/content/identity/identity-as-a-service-for-business/Leveraging-IDaaS-for-Business-Success.webp b/content/identity/identity-as-a-service-for-business/Leveraging-IDaaS-for-Business-Success.webp
new file mode 100644
index 000000000..af29af563
Binary files /dev/null and b/content/identity/identity-as-a-service-for-business/Leveraging-IDaaS-for-Business-Success.webp differ
diff --git a/content/identity/identity-as-a-service-for-business/idaas-business.jpg b/content/identity/identity-as-a-service-for-business/idaas-business.jpg
deleted file mode 100644
index b500adb81..000000000
Binary files a/content/identity/identity-as-a-service-for-business/idaas-business.jpg and /dev/null differ
diff --git a/content/identity/identity-as-a-service-for-business/idaas-business.webp b/content/identity/identity-as-a-service-for-business/idaas-business.webp
new file mode 100644
index 000000000..3bf3f0ea4
Binary files /dev/null and b/content/identity/identity-as-a-service-for-business/idaas-business.webp differ
diff --git a/content/identity/identity-as-a-service-for-business/image-3-1-1024x621.jpg b/content/identity/identity-as-a-service-for-business/image-3-1-1024x621.jpg
deleted file mode 100644
index 65f4f3670..000000000
Binary files a/content/identity/identity-as-a-service-for-business/image-3-1-1024x621.jpg and /dev/null differ
diff --git a/content/identity/identity-as-a-service-for-business/image-3-1-1024x621.webp b/content/identity/identity-as-a-service-for-business/image-3-1-1024x621.webp
new file mode 100644
index 000000000..568b8b54c
Binary files /dev/null and b/content/identity/identity-as-a-service-for-business/image-3-1-1024x621.webp differ
diff --git a/content/identity/identity-as-a-service-for-business/imgae2-1024x621.jpg b/content/identity/identity-as-a-service-for-business/imgae2-1024x621.jpg
deleted file mode 100644
index f6ef9806b..000000000
Binary files a/content/identity/identity-as-a-service-for-business/imgae2-1024x621.jpg and /dev/null differ
diff --git a/content/identity/identity-as-a-service-for-business/imgae2-1024x621.webp b/content/identity/identity-as-a-service-for-business/imgae2-1024x621.webp
new file mode 100644
index 000000000..0a000d93f
Binary files /dev/null and b/content/identity/identity-as-a-service-for-business/imgae2-1024x621.webp differ
diff --git a/content/identity/identity-as-a-service-for-business/index.md b/content/identity/identity-as-a-service-for-business/index.md
index 8360cbb90..34b5fe78b 100644
--- a/content/identity/identity-as-a-service-for-business/index.md
+++ b/content/identity/identity-as-a-service-for-business/index.md
@@ -1,7 +1,7 @@
---
title: "Identity as a Service (IDAAS): Managing Digital Identities (Updated)"
date: "2019-12-25"
-coverImage: "idaas-business.jpg"
+coverImage: "idaas-business.webp"
tags: ["idaas","digital identity management","ciam solution"]
author: "Rakesh Soni"
description: "Identity as a service (IDaaS) refers to services provided via the cloud or through SaaS (software-as-a-service) systems for identity and access management. It provides cloud-based authentication provided and managed on a subscription basis by third-party providers."
@@ -53,7 +53,7 @@ With developers constantly bugged to build revenue-generating apps in shorter de
Furthermore, IDaaS has the potential to deliver a secure, streamlined on-demand identity expertise. Such strategies can also do a great deal to reduce internal tension and eventually bridge the gap between developers and the security workforce.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
## 3 Benefits of Identity as a Service (IDaaS) for Businesses
@@ -73,7 +73,7 @@ A modern IDaaS solution secures identities and protects your IT environment. Wit
## 7 Core Components of IDaaS in an Enterprise Environment
-
+
The features and functionalities of an Identity as a Service solution vary across all market segments but generally include digital identity access and management. Here are some of the most common components.
@@ -120,7 +120,7 @@ Using analytics and intelligence capabilities in IDaaS lets enterprises report m
Enterprises can leverage the intelligence capabilities of an Identity as a Service platform to manage [governance and compliance](https://www.loginradius.com/blog/2020/07/data-governance-best-practices/)\-related workflows. Real-world authentication processes can be aligned with governance policies to mitigate security risk.
-
+
## Some new regulations that are protecting identities include:
@@ -174,4 +174,4 @@ CIAM experts are an asset to any company when it comes to implementing IDaaS and
There is a lot of anticipation about Identity as a Service in solving real-world business problems. It is important, and no, you cannot mess it up. Because then, you will be out of business. No wonder, IDaaS has already entered the mainstream and will continue growing from here.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-as-a-service-for-business)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-as-a-service-for-business)
diff --git a/content/identity/identity-fraud-hits-time-high-2017/identity-fraud-hits-time-high-2017.jpg b/content/identity/identity-fraud-hits-time-high-2017/identity-fraud-hits-time-high-2017.jpg
deleted file mode 100644
index 3ddc7801a..000000000
Binary files a/content/identity/identity-fraud-hits-time-high-2017/identity-fraud-hits-time-high-2017.jpg and /dev/null differ
diff --git a/content/identity/identity-fraud-hits-time-high-2017/identity-fraud-hits-time-high-2017.webp b/content/identity/identity-fraud-hits-time-high-2017/identity-fraud-hits-time-high-2017.webp
new file mode 100644
index 000000000..45c8dc24e
Binary files /dev/null and b/content/identity/identity-fraud-hits-time-high-2017/identity-fraud-hits-time-high-2017.webp differ
diff --git a/content/identity/identity-fraud-hits-time-high-2017/index.md b/content/identity/identity-fraud-hits-time-high-2017/index.md
index 9e64e7e60..68e62e67e 100644
--- a/content/identity/identity-fraud-hits-time-high-2017/index.md
+++ b/content/identity/identity-fraud-hits-time-high-2017/index.md
@@ -1,7 +1,7 @@
---
title: "Identity Fraud Hits All-Time High in 2017"
date: "2018-02-20"
-coverImage: "identity-fraud-hits-time-high-2017.jpg"
+coverImage: "identity-fraud-hits-time-high-2017.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -16,6 +16,6 @@ According to Javelin Strategy & Research's annual [Identity Fraud Study](https
### Key Highlights from the Study
-
+
[Learn more](https://www.loginradius.com/customer-identity/) about how LoginRadius can help secure your customers data.
diff --git a/content/identity/identity-fraud-hits-time-high-2017/infographic-Final.jpg b/content/identity/identity-fraud-hits-time-high-2017/infographic-Final.jpg
deleted file mode 100644
index c00f1302e..000000000
Binary files a/content/identity/identity-fraud-hits-time-high-2017/infographic-Final.jpg and /dev/null differ
diff --git a/content/identity/identity-fraud-hits-time-high-2017/infographic-Final.webp b/content/identity/identity-fraud-hits-time-high-2017/infographic-Final.webp
new file mode 100644
index 000000000..bfde3b040
Binary files /dev/null and b/content/identity/identity-fraud-hits-time-high-2017/infographic-Final.webp differ
diff --git a/content/identity/identity-governance-cloud-security-compliance/DS-ccpa-compliance.png b/content/identity/identity-governance-cloud-security-compliance/DS-ccpa-compliance.png
deleted file mode 100644
index 93302c0ce..000000000
Binary files a/content/identity/identity-governance-cloud-security-compliance/DS-ccpa-compliance.png and /dev/null differ
diff --git a/content/identity/identity-governance-cloud-security-compliance/DS-ccpa-compliance.webp b/content/identity/identity-governance-cloud-security-compliance/DS-ccpa-compliance.webp
new file mode 100644
index 000000000..9d62b96b8
Binary files /dev/null and b/content/identity/identity-governance-cloud-security-compliance/DS-ccpa-compliance.webp differ
diff --git a/content/identity/identity-governance-cloud-security-compliance/index.md b/content/identity/identity-governance-cloud-security-compliance/index.md
index 4967ab6f5..97aedb6a8 100644
--- a/content/identity/identity-governance-cloud-security-compliance/index.md
+++ b/content/identity/identity-governance-cloud-security-compliance/index.md
@@ -1,7 +1,7 @@
---
title: "Strengthening Security and Compliance: The Role of Identity Governance"
date: "2023-10-30"
-coverImage: "strength-security.jpg"
+coverImage: "strength-security.webp"
tags: ["identity governance","cloud security","compliance","cx"]
author: "Rakesh Soni"
description: "Discover the challenges posed by cyber threats and regulatory demands, and delve into the integral role of identity governance solutions. From stringent access controls to real-time compliance monitoring, automation, and risk management, these tools provide a comprehensive approach to fortifying cloud security. Stay ahead of evolving threats and industry standards with cutting-edge identity governance strategies, ensuring unparalleled security and compliance for your business."
@@ -20,7 +20,7 @@ Admit it; cybercriminals are becoming more advanced in finding loopholes to expl
**2. Regulatory Compliance:** Various industries are subject to stringent regulations governing the storage and handling of data. Ensuring compliance with these regulations is not only a legal requirement but also essential for maintaining trust among clients and partners.
-[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
+[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
**3. Identity Management:** One of the fundamental aspects of cloud security is efficient identity management. With the growing complexity of cloud infrastructures, managing user identities, access permissions, and data privileges has become a challenging task.
@@ -52,4 +52,4 @@ Identity governance emerges as a vital component in this endeavor, offering comp
By investing in cutting-edge identity governance tools and strategies, businesses can not only safeguard their cloud-stored data but also build a reputation for reliability and trustworthiness. As the cloud landscape evolves, staying ahead of the curve with effective identity governance will remain a cornerstone in the pursuit of unparalleled security and compliance in the digital realm.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-governance-cloud-security-compliance)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-governance-cloud-security-compliance)
\ No newline at end of file
diff --git a/content/identity/identity-governance-cloud-security-compliance/strength-security.jpg b/content/identity/identity-governance-cloud-security-compliance/strength-security.jpg
deleted file mode 100644
index 115f5da08..000000000
Binary files a/content/identity/identity-governance-cloud-security-compliance/strength-security.jpg and /dev/null differ
diff --git a/content/identity/identity-governance-cloud-security-compliance/strength-security.webp b/content/identity/identity-governance-cloud-security-compliance/strength-security.webp
new file mode 100644
index 000000000..7eeb006ae
Binary files /dev/null and b/content/identity/identity-governance-cloud-security-compliance/strength-security.webp differ
diff --git a/content/identity/identity-governance-unlocks-digital-transformation/EB-GDPR-Comp.png b/content/identity/identity-governance-unlocks-digital-transformation/EB-GDPR-Comp.png
deleted file mode 100644
index a7a656cfa..000000000
Binary files a/content/identity/identity-governance-unlocks-digital-transformation/EB-GDPR-Comp.png and /dev/null differ
diff --git a/content/identity/identity-governance-unlocks-digital-transformation/EB-GDPR-Comp.webp b/content/identity/identity-governance-unlocks-digital-transformation/EB-GDPR-Comp.webp
new file mode 100644
index 000000000..44c9529c0
Binary files /dev/null and b/content/identity/identity-governance-unlocks-digital-transformation/EB-GDPR-Comp.webp differ
diff --git a/content/identity/identity-governance-unlocks-digital-transformation/LR-GDPR-EB.png b/content/identity/identity-governance-unlocks-digital-transformation/LR-GDPR-EB.png
deleted file mode 100644
index f7e5453b4..000000000
Binary files a/content/identity/identity-governance-unlocks-digital-transformation/LR-GDPR-EB.png and /dev/null differ
diff --git a/content/identity/identity-governance-unlocks-digital-transformation/LR-GDPR-EB.webp b/content/identity/identity-governance-unlocks-digital-transformation/LR-GDPR-EB.webp
new file mode 100644
index 000000000..a7b013719
Binary files /dev/null and b/content/identity/identity-governance-unlocks-digital-transformation/LR-GDPR-EB.webp differ
diff --git a/content/identity/identity-governance-unlocks-digital-transformation/digital-transformation.jpg b/content/identity/identity-governance-unlocks-digital-transformation/digital-transformation.jpg
deleted file mode 100644
index 091276f1d..000000000
Binary files a/content/identity/identity-governance-unlocks-digital-transformation/digital-transformation.jpg and /dev/null differ
diff --git a/content/identity/identity-governance-unlocks-digital-transformation/digital-transformation.webp b/content/identity/identity-governance-unlocks-digital-transformation/digital-transformation.webp
new file mode 100644
index 000000000..b6675e53f
Binary files /dev/null and b/content/identity/identity-governance-unlocks-digital-transformation/digital-transformation.webp differ
diff --git a/content/identity/identity-governance-unlocks-digital-transformation/index.md b/content/identity/identity-governance-unlocks-digital-transformation/index.md
index cf8a3e770..4d27595ef 100644
--- a/content/identity/identity-governance-unlocks-digital-transformation/index.md
+++ b/content/identity/identity-governance-unlocks-digital-transformation/index.md
@@ -1,7 +1,7 @@
---
title: "How a Culture of Identity Governance Empowers Digital Transformation?"
date: "2023-04-11"
-coverImage: "digital-transformation.jpg"
+coverImage: "digital-transformation.webp"
tags: ["digital transformation","identity governance","ciam solution"]
author: "Yash Rathi"
description: "By prioritizing identity governance as a critical aspect of their digital transformation strategy, organizations can ensure that they are effectively managing user identities and access, both of which are critical to the success of any digital initiative. Here’s a deeper look at the aspects of leveraging identity governance."
@@ -44,7 +44,7 @@ Identity governance helps organizations to streamline access management processe
Identity governance ensures that organizations comply with regulatory requirements around data privacy and security. For instance, the GDPR and the CCPA data privacy and security regulations require businesses to implement identity governance.
-[](https://www.loginradius.com/resource/loginradius-and-gdpr-compliance/)
+[](https://www.loginradius.com/resource/loginradius-and-gdpr-compliance/)
## How a Cutting-Edge CIAM Fulfills the Identity Governance Criteria?
@@ -84,4 +84,4 @@ A culture of identity governance and cutting-edge CIAM solutions are critical to
By prioritizing identity governance and leveraging a robust CIAM solution, organizations can enhance security, improve user experience, increase efficiency, and ensure compliance with regulatory requirements.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-governance-unlocks-digital-transformation)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-governance-unlocks-digital-transformation)
diff --git a/content/identity/identity-governance-vs-identity-management/WP-critical-role-id-mngmnt.png b/content/identity/identity-governance-vs-identity-management/WP-critical-role-id-mngmnt.png
deleted file mode 100644
index c1f47d8bc..000000000
Binary files a/content/identity/identity-governance-vs-identity-management/WP-critical-role-id-mngmnt.png and /dev/null differ
diff --git a/content/identity/identity-governance-vs-identity-management/WP-critical-role-id-mngmnt.webp b/content/identity/identity-governance-vs-identity-management/WP-critical-role-id-mngmnt.webp
new file mode 100644
index 000000000..89e798f06
Binary files /dev/null and b/content/identity/identity-governance-vs-identity-management/WP-critical-role-id-mngmnt.webp differ
diff --git a/content/identity/identity-governance-vs-identity-management/id-governance-vs-id-mngmnt.jpg b/content/identity/identity-governance-vs-identity-management/id-governance-vs-id-mngmnt.jpg
deleted file mode 100644
index 53891fbab..000000000
Binary files a/content/identity/identity-governance-vs-identity-management/id-governance-vs-id-mngmnt.jpg and /dev/null differ
diff --git a/content/identity/identity-governance-vs-identity-management/id-governance-vs-id-mngmnt.webp b/content/identity/identity-governance-vs-identity-management/id-governance-vs-id-mngmnt.webp
new file mode 100644
index 000000000..b091f20a7
Binary files /dev/null and b/content/identity/identity-governance-vs-identity-management/id-governance-vs-id-mngmnt.webp differ
diff --git a/content/identity/identity-governance-vs-identity-management/index.md b/content/identity/identity-governance-vs-identity-management/index.md
index 33387f681..830e307e8 100644
--- a/content/identity/identity-governance-vs-identity-management/index.md
+++ b/content/identity/identity-governance-vs-identity-management/index.md
@@ -1,7 +1,7 @@
---
title: "Identity Governance vs. Identity Management: Navigating the Differences"
date: "2023-08-21"
-coverImage: "id-governance-vs-id-mngmnt.jpg"
+coverImage: "id-governance-vs-id-mngmnt.webp"
tags: ["identity governance","identity management","compliance","cx"]
author: "Rakesh Soni"
description: "Explore the differences between Identity Governance and Identity Management in the dynamic world of digital identities. Discover why businesses must balance these concepts to achieve security, compliance, and operational efficiency in the modern landscape."
@@ -50,7 +50,7 @@ IG examines access controls from a comprehensive viewpoint, connecting the dots
Think of Identity Governance as the strategist who defines access policies and ensures they align with the organization's mission. On the other hand, Identity Management is the executor, ensuring that the defined strategies translate into effective access management.
-[](https://www.loginradius.com/resource/the-critical-role-of-identity-management-in-data-governance/)
+[](https://www.loginradius.com/resource/the-critical-role-of-identity-management-in-data-governance/)
## Why Businesses Need a Perfect Blend of Identity Management and Identity Governance in 2023 & Beyond?
@@ -87,4 +87,4 @@ Think of Identity Management as the gatekeeper, ensuring the right people can ac
By blending these two approaches through a reliable CIAM solution, businesses can work smoothly and keep their sensitive information safe from prying eyes and cyber threats.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-governance-vs-identity-management)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-governance-vs-identity-management)
\ No newline at end of file
diff --git a/content/identity/identity-governance/benefits-identity-governance.png b/content/identity/identity-governance/benefits-identity-governance.png
deleted file mode 100644
index 3766f687f..000000000
Binary files a/content/identity/identity-governance/benefits-identity-governance.png and /dev/null differ
diff --git a/content/identity/identity-governance/benefits-identity-governance.webp b/content/identity/identity-governance/benefits-identity-governance.webp
new file mode 100644
index 000000000..f32cfadd5
Binary files /dev/null and b/content/identity/identity-governance/benefits-identity-governance.webp differ
diff --git a/content/identity/identity-governance/enterprise-buyer-guide-to-consumer-identity.png b/content/identity/identity-governance/enterprise-buyer-guide-to-consumer-identity.png
deleted file mode 100644
index b718f7f4b..000000000
Binary files a/content/identity/identity-governance/enterprise-buyer-guide-to-consumer-identity.png and /dev/null differ
diff --git a/content/identity/identity-governance/enterprise-buyer-guide-to-consumer-identity.webp b/content/identity/identity-governance/enterprise-buyer-guide-to-consumer-identity.webp
new file mode 100644
index 000000000..a57ab4fba
Binary files /dev/null and b/content/identity/identity-governance/enterprise-buyer-guide-to-consumer-identity.webp differ
diff --git a/content/identity/identity-governance/identity-governanc.jpg b/content/identity/identity-governance/identity-governanc.jpg
deleted file mode 100644
index 3c6fbf105..000000000
Binary files a/content/identity/identity-governance/identity-governanc.jpg and /dev/null differ
diff --git a/content/identity/identity-governance/identity-governanc.webp b/content/identity/identity-governance/identity-governanc.webp
new file mode 100644
index 000000000..be079f251
Binary files /dev/null and b/content/identity/identity-governance/identity-governanc.webp differ
diff --git a/content/identity/identity-governance/identity-governance.jpg b/content/identity/identity-governance/identity-governance.jpg
deleted file mode 100644
index d30d39a08..000000000
Binary files a/content/identity/identity-governance/identity-governance.jpg and /dev/null differ
diff --git a/content/identity/identity-governance/identity-governance.webp b/content/identity/identity-governance/identity-governance.webp
new file mode 100644
index 000000000..093e1211e
Binary files /dev/null and b/content/identity/identity-governance/identity-governance.webp differ
diff --git a/content/identity/identity-governance/index.md b/content/identity/identity-governance/index.md
index 71eb59e79..4f1c69aa7 100644
--- a/content/identity/identity-governance/index.md
+++ b/content/identity/identity-governance/index.md
@@ -1,7 +1,7 @@
---
title: "What is Identity Governance & Administration?"
date: "2020-12-16"
-coverImage: "identity-governanc.jpg"
+coverImage: "identity-governanc.webp"
tags: ["data security","identity governance","compliance"]
author: "Rakesh Soni"
description: "Needless to mention, the question of relevant certification of access to specified stakeholders also applies. In an increasingly agility-intensive and virtual work environment, identity governance seems immensely relevant with the automation of policy management and auditing, adding to its benefit."
@@ -57,7 +57,7 @@ IGA adds more functionality to the mainstream Identity Management systems. IGA e
## 5 Benefits of Identity Governance
-
+
### 1. Consumers can get timely access to the data they want.
@@ -78,7 +78,7 @@ The ongoing pandemic has made the importance of flexibility clear. Always workin
This restates the importance of IGA, through which the firm can allow remote access, albeit limited for security, on employees’ personal devices for the operations to keep running.
-[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
+[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
### 4. Helpful in meeting regulations.
@@ -94,7 +94,7 @@ Applications, devices, data, and stakeholders are all linked through the IGA sol
## Empower Your Business Using LoginRadius Identity Governance Solution
-
+
The fundamental factor underpinning IGA is [data governance](https://www.loginradius.com/blog/identity/2020/07/data-governance-best-practices/). LoginRadius offers world-class data governance, which, consequently, bolsters your organization’s cybersecurity and the virtual security of your consumers.
@@ -118,4 +118,4 @@ The demand for IGA is growing year on year. The increased agility granted by int
Needless to say, so does the issue of relevant access certification to designated stakeholders. With the automation of policy management and auditing, adding to its favor, identity governance seems immensely important in an increasingly agility-demanding and virtual work environment.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-governance)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-governance)
diff --git a/content/identity/identity-governance/loginradius-identity-governance-solution.png b/content/identity/identity-governance/loginradius-identity-governance-solution.png
deleted file mode 100644
index c22544f59..000000000
Binary files a/content/identity/identity-governance/loginradius-identity-governance-solution.png and /dev/null differ
diff --git a/content/identity/identity-governance/loginradius-identity-governance-solution.webp b/content/identity/identity-governance/loginradius-identity-governance-solution.webp
new file mode 100644
index 000000000..179cee44f
Binary files /dev/null and b/content/identity/identity-governance/loginradius-identity-governance-solution.webp differ
diff --git a/content/identity/identity-lifecycle-management/DS-ccpa-compliance.png b/content/identity/identity-lifecycle-management/DS-ccpa-compliance.png
deleted file mode 100644
index 93302c0ce..000000000
Binary files a/content/identity/identity-lifecycle-management/DS-ccpa-compliance.png and /dev/null differ
diff --git a/content/identity/identity-lifecycle-management/DS-ccpa-compliance.webp b/content/identity/identity-lifecycle-management/DS-ccpa-compliance.webp
new file mode 100644
index 000000000..9d62b96b8
Binary files /dev/null and b/content/identity/identity-lifecycle-management/DS-ccpa-compliance.webp differ
diff --git a/content/identity/identity-lifecycle-management/index.md b/content/identity/identity-lifecycle-management/index.md
index aeefe6113..d7db6d66b 100644
--- a/content/identity/identity-lifecycle-management/index.md
+++ b/content/identity/identity-lifecycle-management/index.md
@@ -1,7 +1,7 @@
---
title: "What is Identity Lifecycle Management?"
date: "2023-11-02"
-coverImage: "lifecycle-management.jpg"
+coverImage: "lifecycle-management.webp"
tags: ["identity management","user management","compliance","cx"]
author: "Rakesh Soni"
description: "In a digital age filled with online services and remote work, securing sensitive data is paramount. Our blog delves into Identity Lifecycle Management (ILM), an essential business solution. Discover the components of ILM, its role in cybersecurity, and how it ensures authorized access while addressing security concerns and compliance. Stay ahead in the digital landscape by embracing the power of Identity Lifecycle Management."
@@ -43,7 +43,7 @@ Lifecycle governance involves managing identities throughout their entire lifecy
Compliance management ensures the organization's identity management practices align with industry regulations and internal policies. It involves regular audits, monitoring, and reporting to guarantee adherence to legal requirements and data protection standards.
-[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
+[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance)
## The Role of ILM in Modern Cybersecurity
@@ -69,4 +69,4 @@ Identity Lifecycle Management is the cornerstone of modern cybersecurity strateg
As businesses continue to embrace digital transformation, embracing Identity Lifecycle Management is not just a choice but a necessity in safeguarding sensitive data and maintaining a competitive edge in the market.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-lifecycle-management)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-lifecycle-management)
\ No newline at end of file
diff --git a/content/identity/identity-lifecycle-management/lifecycle-management.jpg b/content/identity/identity-lifecycle-management/lifecycle-management.jpg
deleted file mode 100644
index bb3763355..000000000
Binary files a/content/identity/identity-lifecycle-management/lifecycle-management.jpg and /dev/null differ
diff --git a/content/identity/identity-lifecycle-management/lifecycle-management.webp b/content/identity/identity-lifecycle-management/lifecycle-management.webp
new file mode 100644
index 000000000..048ecfd48
Binary files /dev/null and b/content/identity/identity-lifecycle-management/lifecycle-management.webp differ
diff --git a/content/identity/identity-management-developers/Book-a-demo-banner.png b/content/identity/identity-management-developers/Book-a-demo-banner.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/identity-management-developers/Book-a-demo-banner.png and /dev/null differ
diff --git a/content/identity/identity-management-developers/Book-a-demo-banner.webp b/content/identity/identity-management-developers/Book-a-demo-banner.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/identity-management-developers/Book-a-demo-banner.webp differ
diff --git a/content/identity/identity-management-developers/Identity-Management-for-Developers-3.png b/content/identity/identity-management-developers/Identity-Management-for-Developers-3.png
deleted file mode 100644
index c35f3654f..000000000
Binary files a/content/identity/identity-management-developers/Identity-Management-for-Developers-3.png and /dev/null differ
diff --git a/content/identity/identity-management-developers/Identity-Management-for-Developers-3.webp b/content/identity/identity-management-developers/Identity-Management-for-Developers-3.webp
new file mode 100644
index 000000000..5434606ae
Binary files /dev/null and b/content/identity/identity-management-developers/Identity-Management-for-Developers-3.webp differ
diff --git a/content/identity/identity-management-developers/Identity-Management-for-Developers-4.png b/content/identity/identity-management-developers/Identity-Management-for-Developers-4.png
deleted file mode 100644
index 39d23bd01..000000000
Binary files a/content/identity/identity-management-developers/Identity-Management-for-Developers-4.png and /dev/null differ
diff --git a/content/identity/identity-management-developers/Identity-Management-for-Developers-4.webp b/content/identity/identity-management-developers/Identity-Management-for-Developers-4.webp
new file mode 100644
index 000000000..c41ecb09e
Binary files /dev/null and b/content/identity/identity-management-developers/Identity-Management-for-Developers-4.webp differ
diff --git a/content/identity/identity-management-developers/Identity-Management-for-Developers.jpg b/content/identity/identity-management-developers/Identity-Management-for-Developers.jpg
deleted file mode 100644
index c911ff9fe..000000000
Binary files a/content/identity/identity-management-developers/Identity-Management-for-Developers.jpg and /dev/null differ
diff --git a/content/identity/identity-management-developers/Identity-Management-for-Developers.webp b/content/identity/identity-management-developers/Identity-Management-for-Developers.webp
new file mode 100644
index 000000000..a49d55299
Binary files /dev/null and b/content/identity/identity-management-developers/Identity-Management-for-Developers.webp differ
diff --git a/content/identity/identity-management-developers/Identity-Management-for-Developers2.png b/content/identity/identity-management-developers/Identity-Management-for-Developers2.png
deleted file mode 100644
index 82dbc7cfa..000000000
Binary files a/content/identity/identity-management-developers/Identity-Management-for-Developers2.png and /dev/null differ
diff --git a/content/identity/identity-management-developers/Identity-Management-for-Developers2.webp b/content/identity/identity-management-developers/Identity-Management-for-Developers2.webp
new file mode 100644
index 000000000..a857b2c78
Binary files /dev/null and b/content/identity/identity-management-developers/Identity-Management-for-Developers2.webp differ
diff --git a/content/identity/identity-management-developers/index.md b/content/identity/identity-management-developers/index.md
index 1d8bf30f1..72eebb988 100644
--- a/content/identity/identity-management-developers/index.md
+++ b/content/identity/identity-management-developers/index.md
@@ -1,7 +1,7 @@
---
title: "Identity Management for Developers: Why it's required more than ever"
date: "2020-10-29"
-coverImage: "Identity-Management-for-Developers.jpg"
+coverImage: "Identity-Management-for-Developers.webp"
tags: ["customer-experience"]
featured: false
author: "Rakesh Soni"
@@ -60,7 +60,7 @@ One of the best ways to fight security misconfiguration is through increased vis
## Developers are on the front foot
-
+
What can prevent someone from breaking into an application or online software system and stealing information or [accessing sensitive credentials](https://www.loginradius.com/blog/2019/09/prevent-credential-stuffing-attacks/)? Both the challenges and the solutions rely on software, and the situation is well known to many developers. After all, they are the first line of defense.
@@ -78,13 +78,13 @@ To help developers prepare better, we come up with a list of the best applicatio
## Integrating Security in DevOps
-
+
The business IT infrastructure of today is more varied, diverse, and complex than ever before. Environments there were earlier confined to on-premises and are not hosted on multiple clouds and IoT devices.
However, this modern open perimeter has been posing fundamental challenges for cybersecurity. It requires a [zero-trust environment](https://www.loginradius.com/blog/2019/10/cloud-computing-security-challenges/) to thrive in the development and operations (DevOps) life cycle. It takes not only the right tools and technology to bring this approach into effect, but a shift in philosophy focused on the holistic integration of security within the DevOps lifecycle.
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
The safety mechanisms embedded in DevOps offers the following benefits (but not confined to):
@@ -97,7 +97,7 @@ The safety mechanisms embedded in DevOps offers the following benefits (but not
## How LoginRadius Provides Ideal Identity Management for Developers
-
+
Identity is the cornerstone of the modern consumer experience. A good, scalable [CIAM solution](https://www.loginradius.com/blog/2019/06/perfect-ciam-platform/) allows you to manage consumer identity and access securely.
@@ -117,4 +117,4 @@ Identity management for developers is required more than ever. It should be seam
No wonder meeting the demands of both businesses and consumers is an uphill ride. The right CIAM solution comes with improved data security and identity management features that meet the developers' need for top-notch experiences.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-developers)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-developers)
diff --git a/content/identity/identity-management-developers/protecting-pii-against-data-breaches.png b/content/identity/identity-management-developers/protecting-pii-against-data-breaches.png
deleted file mode 100644
index b32dcb27b..000000000
Binary files a/content/identity/identity-management-developers/protecting-pii-against-data-breaches.png and /dev/null differ
diff --git a/content/identity/identity-management-developers/protecting-pii-against-data-breaches.webp b/content/identity/identity-management-developers/protecting-pii-against-data-breaches.webp
new file mode 100644
index 000000000..6c250a4f7
Binary files /dev/null and b/content/identity/identity-management-developers/protecting-pii-against-data-breaches.webp differ
diff --git a/content/identity/identity-management-for-education/BD-Plexicon1-1024x310.png b/content/identity/identity-management-for-education/BD-Plexicon1-1024x310.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/identity-management-for-education/BD-Plexicon1-1024x310.png and /dev/null differ
diff --git a/content/identity/identity-management-for-education/BD-Plexicon1-1024x310.webp b/content/identity/identity-management-for-education/BD-Plexicon1-1024x310.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/identity-management-for-education/BD-Plexicon1-1024x310.webp differ
diff --git "a/content/identity/identity-management-for-education/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png" "b/content/identity/identity-management-for-education/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png"
deleted file mode 100644
index 6b3ba826e..000000000
Binary files "a/content/identity/identity-management-for-education/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png" and /dev/null differ
diff --git "a/content/identity/identity-management-for-education/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp" "b/content/identity/identity-management-for-education/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp"
new file mode 100644
index 000000000..ba14612ce
Binary files /dev/null and "b/content/identity/identity-management-for-education/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp" differ
diff --git a/content/identity/identity-management-for-education/Identity-Management-for-Education-1.jpg b/content/identity/identity-management-for-education/Identity-Management-for-Education-1.jpg
deleted file mode 100644
index 46559610e..000000000
Binary files a/content/identity/identity-management-for-education/Identity-Management-for-Education-1.jpg and /dev/null differ
diff --git a/content/identity/identity-management-for-education/Identity-Management-for-Education-1.webp b/content/identity/identity-management-for-education/Identity-Management-for-Education-1.webp
new file mode 100644
index 000000000..6f2dacb00
Binary files /dev/null and b/content/identity/identity-management-for-education/Identity-Management-for-Education-1.webp differ
diff --git a/content/identity/identity-management-for-education/Identity-Management-for-Education.jpg b/content/identity/identity-management-for-education/Identity-Management-for-Education.jpg
deleted file mode 100644
index 3a2e754a2..000000000
Binary files a/content/identity/identity-management-for-education/Identity-Management-for-Education.jpg and /dev/null differ
diff --git a/content/identity/identity-management-for-education/Identity-Management-for-Education.webp b/content/identity/identity-management-for-education/Identity-Management-for-Education.webp
new file mode 100644
index 000000000..6a461e730
Binary files /dev/null and b/content/identity/identity-management-for-education/Identity-Management-for-Education.webp differ
diff --git a/content/identity/identity-management-for-education/index.md b/content/identity/identity-management-for-education/index.md
index 4553f268a..14dece331 100644
--- a/content/identity/identity-management-for-education/index.md
+++ b/content/identity/identity-management-for-education/index.md
@@ -1,7 +1,7 @@
---
title: "Why Identity Management for Education Sector has Become Crucial"
date: "2020-07-08"
-coverImage: "Identity-Management-for-Education.jpg"
+coverImage: "Identity-Management-for-Education.webp"
tags: ["public-sector"]
featured: false
author: "Rakesh Soni"
@@ -46,7 +46,7 @@ Institutes allow students to store data on their own devices, tablets, or laptop
Most students don't invest in paid antivirus software or anti-malware versions. Also, they download free, pirated apps. So, every time they plug their infected USB into the institute's network, the whole system gets affected.
-[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
+[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
### Potential open network vulnerabilities
@@ -104,7 +104,7 @@ The hacker may, in this case, plant requests that seem to come from a legitimate
## Data Risk and Vulnerabilities in Online Education Apps and Websites
-
+
Software applications – apps – are common on campuses nowadays. From in-class polling devices to driving university-wide learning management systems, educational institutions are swiftly adapting to the new trend.
@@ -184,4 +184,4 @@ Given this rapid upgrade in the classroom environment, experts are curious wheth
If it does (which sure, will), LoginRadius will certainly complement the complex, and unique CIAM needs for schools, colleges, and universities across the globe.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-for-education)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-for-education)
diff --git a/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-1.png b/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-1.png
deleted file mode 100644
index bbf761806..000000000
Binary files a/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-1.png and /dev/null differ
diff --git a/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-1.webp b/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-1.webp
new file mode 100644
index 000000000..fe09eb579
Binary files /dev/null and b/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-1.webp differ
diff --git a/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-2.png b/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-2.png
deleted file mode 100644
index 546e2f924..000000000
Binary files a/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-2.png and /dev/null differ
diff --git a/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-2.webp b/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-2.webp
new file mode 100644
index 000000000..eec207a1d
Binary files /dev/null and b/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare-2.webp differ
diff --git a/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare.jpg b/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare.jpg
deleted file mode 100644
index 85b4957b1..000000000
Binary files a/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare.jpg and /dev/null differ
diff --git a/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare.webp b/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare.webp
new file mode 100644
index 000000000..1044beb8e
Binary files /dev/null and b/content/identity/identity-management-healthcare/Identity-Management-in-Healthcare.webp differ
diff --git a/content/identity/identity-management-healthcare/index.md b/content/identity/identity-management-healthcare/index.md
index ad862ea19..a93d5d473 100644
--- a/content/identity/identity-management-healthcare/index.md
+++ b/content/identity/identity-management-healthcare/index.md
@@ -1,7 +1,7 @@
---
title: "Identity Management in Healthcare: Analyzing the Industry Needs"
date: "2020-11-03"
-coverImage: "Identity-Management-in-Healthcare.jpg"
+coverImage: "Identity-Management-in-Healthcare.webp"
tags: ["customer-experience"]
featured: false
author: "Rakesh Soni"
@@ -25,7 +25,7 @@ First, though, we need to discuss what makes the control of healthcare identitie
## Current Security Challenges in the Healthcare Sector
-
+
Simply put, the more data compromised, the more it leads to regulatory penalties, loss of patient trust, and bad publicity.
@@ -76,7 +76,7 @@ Protected health information (PHI) takes ten times the price of the dark web's f
Modern identity management in healthcare is designed with an essential security strategy for hospitals embedded just right in. IAM prevents unauthorized people from accessing PHI and the right people from leaking it by accident. When obtaining access to sensitive information and facilities, a sound IAM approach would also minimize costs, decrease help desk calls, and improve the overall patient experience.
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
Below are a few things that identity management in healthcare businesses actually do as a cybersecurity and convenience gatekeeper.
@@ -126,7 +126,7 @@ Security departments can produce reliable system audits and documentation effect
## How Can LoginRadius Help the Healthcare Industry Stay Secure and Compliant
-
+
LoginRadius is a powerful player that checks all the major boxes in securing patient identities and authentication throughout the healthcare infrastructure.
@@ -160,4 +160,4 @@ Times are changing—IAM is no longer an administrator-driven set of capabilitie
Moving forward, identity management in healthcare organizations is about to take a giant leap. LoginRadius can help you with that!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-healthcare)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-healthcare)
diff --git a/content/identity/identity-management-healthcare/protecting-pii-against-data-breaches.png b/content/identity/identity-management-healthcare/protecting-pii-against-data-breaches.png
deleted file mode 100644
index b32dcb27b..000000000
Binary files a/content/identity/identity-management-healthcare/protecting-pii-against-data-breaches.png and /dev/null differ
diff --git a/content/identity/identity-management-healthcare/protecting-pii-against-data-breaches.webp b/content/identity/identity-management-healthcare/protecting-pii-against-data-breaches.webp
new file mode 100644
index 000000000..6c250a4f7
Binary files /dev/null and b/content/identity/identity-management-healthcare/protecting-pii-against-data-breaches.webp differ
diff --git a/content/identity/identity-management-in-cloud-computing/Future-proof-your-security.png b/content/identity/identity-management-in-cloud-computing/Future-proof-your-security.png
deleted file mode 100644
index 9b885caa8..000000000
Binary files a/content/identity/identity-management-in-cloud-computing/Future-proof-your-security.png and /dev/null differ
diff --git a/content/identity/identity-management-in-cloud-computing/Future-proof-your-security.webp b/content/identity/identity-management-in-cloud-computing/Future-proof-your-security.webp
new file mode 100644
index 000000000..62f54b93f
Binary files /dev/null and b/content/identity/identity-management-in-cloud-computing/Future-proof-your-security.webp differ
diff --git a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-1.jpg b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-1.jpg
deleted file mode 100644
index e7642bc2a..000000000
Binary files a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-1.jpg and /dev/null differ
diff --git a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-1.webp b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-1.webp
new file mode 100644
index 000000000..f217ab2f6
Binary files /dev/null and b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-1.webp differ
diff --git a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-2.jpg b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-2.jpg
deleted file mode 100644
index d5cb38631..000000000
Binary files a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-2.jpg and /dev/null differ
diff --git a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-2.webp b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-2.webp
new file mode 100644
index 000000000..7c06d52ec
Binary files /dev/null and b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-2.webp differ
diff --git a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-3.png b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-3.png
deleted file mode 100644
index cee693282..000000000
Binary files a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-3.png and /dev/null differ
diff --git a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-3.webp b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-3.webp
new file mode 100644
index 000000000..4ab86448c
Binary files /dev/null and b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-3.webp differ
diff --git a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-cover.jpg b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-cover.jpg
deleted file mode 100644
index c4d7fe8e1..000000000
Binary files a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-cover.jpg and /dev/null differ
diff --git a/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-cover.webp b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-cover.webp
new file mode 100644
index 000000000..35e665b98
Binary files /dev/null and b/content/identity/identity-management-in-cloud-computing/identity-management-in-cloud-computing-cover.webp differ
diff --git a/content/identity/identity-management-in-cloud-computing/index.md b/content/identity/identity-management-in-cloud-computing/index.md
index b19637fce..4dfc005d0 100644
--- a/content/identity/identity-management-in-cloud-computing/index.md
+++ b/content/identity/identity-management-in-cloud-computing/index.md
@@ -1,7 +1,7 @@
---
title: "Identity Management in Cloud Computing"
date: "2021-01-29"
-coverImage: "identity-management-in-cloud-computing-cover.jpg"
+coverImage: "identity-management-in-cloud-computing-cover.webp"
tags: ["cloud computing","digital identity management","cx"]
author: "Rakesh Soni"
description: "Identity management in cloud computing is the subsequent step of identity and access management (IAM) solutions. However, it is a lot more than merely a straightforward web app single sign-on (SSO) solution. This next generation of IAM solution is a holistic move of the identity provider right to the cloud. "
@@ -17,7 +17,7 @@ The primary goal of identity management in cloud computing is dealing with perso
## What is Cloud Identity Management
-
+
@@ -61,7 +61,7 @@ A modern cloud Identity and Access Management (IAM) solution helps to:
These abilities help build a platform that connects users to virtually all IT resources through any provider, protocol, platform, or location.
-[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
+[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
IT admins know that legacy identity management systems (in most cases) struggle when they are matched to cloud services and the likes of AWS.
@@ -70,7 +70,7 @@ So, the newest approach to identity management in cloud computing extends your c
## Introducing Loginradius Cloud IAM - Implemented Across Markets by Industry Leaders
-
+
LoginRadius enables businesses to provide an enhanced consumer experience and protects the managed identities. Utilizing the [CIAM platform](https://www.loginradius.com/), organizations can offer a streamlined login process, registration, password setup, along with safeguarding consumer accounts and complying with precise data privacy regulations.
@@ -93,5 +93,5 @@ However, IAM solutions have to be supple across identity management and access c
If you are locked into some conventional platforms or service providers because of your active directory ad service, explore a vendor-neutral cloud identity management solution.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-in-cloud-computing)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-in-cloud-computing)
diff --git a/content/identity/identity-management-in-media-industry/federated-identity-management.png b/content/identity/identity-management-in-media-industry/federated-identity-management.png
deleted file mode 100644
index 01a289614..000000000
Binary files a/content/identity/identity-management-in-media-industry/federated-identity-management.png and /dev/null differ
diff --git a/content/identity/identity-management-in-media-industry/federated-identity-management.webp b/content/identity/identity-management-in-media-industry/federated-identity-management.webp
new file mode 100644
index 000000000..3d4c0a8aa
Binary files /dev/null and b/content/identity/identity-management-in-media-industry/federated-identity-management.webp differ
diff --git a/content/identity/identity-management-in-media-industry/identity-management-in-media-industry-cover.jpg b/content/identity/identity-management-in-media-industry/identity-management-in-media-industry-cover.jpg
deleted file mode 100644
index 0a9cd3580..000000000
Binary files a/content/identity/identity-management-in-media-industry/identity-management-in-media-industry-cover.jpg and /dev/null differ
diff --git a/content/identity/identity-management-in-media-industry/identity-management-in-media-industry-cover.webp b/content/identity/identity-management-in-media-industry/identity-management-in-media-industry-cover.webp
new file mode 100644
index 000000000..5ab318283
Binary files /dev/null and b/content/identity/identity-management-in-media-industry/identity-management-in-media-industry-cover.webp differ
diff --git a/content/identity/identity-management-in-media-industry/index.md b/content/identity/identity-management-in-media-industry/index.md
index 3714ccecd..6731d76a3 100644
--- a/content/identity/identity-management-in-media-industry/index.md
+++ b/content/identity/identity-management-in-media-industry/index.md
@@ -1,7 +1,7 @@
---
title: "The Role of Identity management in the media industry"
date: "2021-04-21"
-coverImage: "identity-management-in-media-industry-cover.jpg"
+coverImage: "identity-management-in-media-industry-cover.webp"
tags: ["identity management","digital transformation","ciam solution"]
author: "Vishal Sharma"
description: "Media industry has witnessed a tremendous digital transformation journey. But besides the rapid technological enhancement of the media industry, several security challenges linger on businesses serving in this vertical. Here’s an insightful read depicting the role of identity management in the media industry."
@@ -38,7 +38,7 @@ Honestly, nobody likes to remember long credentials, especially if they can util
While [SSO](https://www.loginradius.com/blog/identity/2019/05/what-is-single-sign-on/) is on the verge of becoming an industry standard for authentication, the media industry needs to quickly gear up for enhancing the user experience through SSO and Federated SSO.
-[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
+[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
Since the market is flooded with plenty of OTT platforms and publication websites, the ones offering a seamless experience to the users would get more signups and subscriptions.
@@ -84,4 +84,4 @@ Delivering the best user experience along with the assurance of secured privacy
Just like every other industry, the media industry can leverage a CIAM solution that helps in scaling business growth by meeting the industry-standard compliances and, at the same time, win consumer trust through flawless user experiences.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-in-media-industry)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-in-media-industry)
diff --git a/content/identity/identity-modernization-business-success-2022/WP-Zerotrust-1.png b/content/identity/identity-modernization-business-success-2022/WP-Zerotrust-1.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/identity-modernization-business-success-2022/WP-Zerotrust-1.png and /dev/null differ
diff --git a/content/identity/identity-modernization-business-success-2022/WP-Zerotrust-1.webp b/content/identity/identity-modernization-business-success-2022/WP-Zerotrust-1.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/identity-modernization-business-success-2022/WP-Zerotrust-1.webp differ
diff --git a/content/identity/identity-modernization-business-success-2022/id-modern.jpg b/content/identity/identity-modernization-business-success-2022/id-modern.jpg
deleted file mode 100644
index c5ecec6c2..000000000
Binary files a/content/identity/identity-modernization-business-success-2022/id-modern.jpg and /dev/null differ
diff --git a/content/identity/identity-modernization-business-success-2022/id-modern.webp b/content/identity/identity-modernization-business-success-2022/id-modern.webp
new file mode 100644
index 000000000..c9fc87378
Binary files /dev/null and b/content/identity/identity-modernization-business-success-2022/id-modern.webp differ
diff --git a/content/identity/identity-modernization-business-success-2022/index.md b/content/identity/identity-modernization-business-success-2022/index.md
index be1d88d12..70454ffff 100644
--- a/content/identity/identity-modernization-business-success-2022/index.md
+++ b/content/identity/identity-modernization-business-success-2022/index.md
@@ -1,7 +1,7 @@
---
title: "How Identity Modernization Will Thrive Business Success in 2022 and Beyond"
date: "2022-06-17"
-coverImage: "id-modern.jpg"
+coverImage: "id-modern.webp"
tags: ["identity modernization", "ciam", "zero trust", "ciam"]
author: "Rakesh Soni"
description: "When done correctly, password resets can be easy and relatively painless for both the customer and the enterprise. By following tips mentioned in this blog, enterprises can ensure that the customers have a positive experience when resetting their passwords."
@@ -49,7 +49,7 @@ Zero trust is the security concept based on a belief that enterprises shouldn’
In a nutshell, zero trust relies on the principle of “don’t trust anyone.” This architecture cuts all the access points until proper verification is done and trust is established.
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
No access is provided until the system verifies the individual or device demanding n access to the IP address, device, or storage.
@@ -95,4 +95,4 @@ Incorporating a modern cloud-based identity management system could help busines
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-modernization-business-success-2022)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-modernization-business-success-2022)
diff --git a/content/identity/identity-modernization-business-success-2022/zero-trust-wp.png b/content/identity/identity-modernization-business-success-2022/zero-trust-wp.png
deleted file mode 100644
index 3e6b81ee6..000000000
Binary files a/content/identity/identity-modernization-business-success-2022/zero-trust-wp.png and /dev/null differ
diff --git a/content/identity/identity-modernization-business-success-2022/zero-trust-wp.webp b/content/identity/identity-modernization-business-success-2022/zero-trust-wp.webp
new file mode 100644
index 000000000..2f7c01062
Binary files /dev/null and b/content/identity/identity-modernization-business-success-2022/zero-trust-wp.webp differ
diff --git a/content/identity/identity-proofing/enterprise-buyer-guide-to-consumer-identity.png b/content/identity/identity-proofing/enterprise-buyer-guide-to-consumer-identity.png
deleted file mode 100644
index b718f7f4b..000000000
Binary files a/content/identity/identity-proofing/enterprise-buyer-guide-to-consumer-identity.png and /dev/null differ
diff --git a/content/identity/identity-proofing/enterprise-buyer-guide-to-consumer-identity.webp b/content/identity/identity-proofing/enterprise-buyer-guide-to-consumer-identity.webp
new file mode 100644
index 000000000..a57ab4fba
Binary files /dev/null and b/content/identity/identity-proofing/enterprise-buyer-guide-to-consumer-identity.webp differ
diff --git a/content/identity/identity-proofing/identity-proofing-loginradius.png b/content/identity/identity-proofing/identity-proofing-loginradius.png
deleted file mode 100644
index a44ae223c..000000000
Binary files a/content/identity/identity-proofing/identity-proofing-loginradius.png and /dev/null differ
diff --git a/content/identity/identity-proofing/identity-proofing-loginradius.webp b/content/identity/identity-proofing/identity-proofing-loginradius.webp
new file mode 100644
index 000000000..2c669e78d
Binary files /dev/null and b/content/identity/identity-proofing/identity-proofing-loginradius.webp differ
diff --git a/content/identity/identity-proofing/identity-proofing.jpg b/content/identity/identity-proofing/identity-proofing.jpg
deleted file mode 100644
index f973f5d53..000000000
Binary files a/content/identity/identity-proofing/identity-proofing.jpg and /dev/null differ
diff --git a/content/identity/identity-proofing/identity-proofing.webp b/content/identity/identity-proofing/identity-proofing.webp
new file mode 100644
index 000000000..7a3810520
Binary files /dev/null and b/content/identity/identity-proofing/identity-proofing.webp differ
diff --git a/content/identity/identity-proofing/importance-identity-proofing.png b/content/identity/identity-proofing/importance-identity-proofing.png
deleted file mode 100644
index 5aab0835e..000000000
Binary files a/content/identity/identity-proofing/importance-identity-proofing.png and /dev/null differ
diff --git a/content/identity/identity-proofing/importance-identity-proofing.webp b/content/identity/identity-proofing/importance-identity-proofing.webp
new file mode 100644
index 000000000..a07574164
Binary files /dev/null and b/content/identity/identity-proofing/importance-identity-proofing.webp differ
diff --git a/content/identity/identity-proofing/index.md b/content/identity/identity-proofing/index.md
index e361c5b2e..8b624959f 100644
--- a/content/identity/identity-proofing/index.md
+++ b/content/identity/identity-proofing/index.md
@@ -1,7 +1,7 @@
---
title: "What is Identity Proofing and Why is it Important?"
date: "2020-12-18"
-coverImage: "identity-proofing.jpg"
+coverImage: "identity-proofing.webp"
tags: ["data security","identity proofing","ciam solution"]
author: "Rakesh Soni"
description: "Identity proofing is the process of verifying that the claimed identity of a person matches their actual identity. You’ve probably undergone this process a bunch of times yourself at hotels, financial institutions, and for retailers."
@@ -34,7 +34,7 @@ Therefore, effective identity solutions should be one of the top priorities for
## How to Implement Effective Identity Proofing
-
+
As stated above, identity proofing can be done manually through documentation and interactive checks. This process, as already pointed out, is taxing and poorly affects the user experience. Manual identity solutions are also unscalable for large organizations dealing with hundreds of thousands of consumers every day.
@@ -53,7 +53,7 @@ An adequate identity proofing system should be able to perform most of these tas
## Protect Your Business Identity With LoginRadius CIAM Solutions
-
+
@@ -87,7 +87,7 @@ LoginRadius identity and access management solutions offer password management t
* Multi-factor authentication: Optional to enable Google Authenticator or Phone SMS as the second authentication factor.
-[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
+[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
### Built-in layers of protection
@@ -109,4 +109,4 @@ With the growing reliance on technology and cloud-based ecosystems, there is a h
By improving privacy, the identity proofing process helps build a trustable image in the consumers’ minds towards your brand.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-proofing)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-proofing)
diff --git a/content/identity/identity-proofing/what-is-identity-proofing.png b/content/identity/identity-proofing/what-is-identity-proofing.png
deleted file mode 100644
index bea232442..000000000
Binary files a/content/identity/identity-proofing/what-is-identity-proofing.png and /dev/null differ
diff --git a/content/identity/identity-proofing/what-is-identity-proofing.webp b/content/identity/identity-proofing/what-is-identity-proofing.webp
new file mode 100644
index 000000000..0de38d53e
Binary files /dev/null and b/content/identity/identity-proofing/what-is-identity-proofing.webp differ
diff --git a/content/identity/identity-security-device-trust-2024/DS-M2M-auth.png b/content/identity/identity-security-device-trust-2024/DS-M2M-auth.png
deleted file mode 100644
index c31629290..000000000
Binary files a/content/identity/identity-security-device-trust-2024/DS-M2M-auth.png and /dev/null differ
diff --git a/content/identity/identity-security-device-trust-2024/DS-M2M-auth.webp b/content/identity/identity-security-device-trust-2024/DS-M2M-auth.webp
new file mode 100644
index 000000000..91dd1af2c
Binary files /dev/null and b/content/identity/identity-security-device-trust-2024/DS-M2M-auth.webp differ
diff --git a/content/identity/identity-security-device-trust-2024/identity-security.jpg b/content/identity/identity-security-device-trust-2024/identity-security.jpg
deleted file mode 100644
index 8febef5c8..000000000
Binary files a/content/identity/identity-security-device-trust-2024/identity-security.jpg and /dev/null differ
diff --git a/content/identity/identity-security-device-trust-2024/identity-security.webp b/content/identity/identity-security-device-trust-2024/identity-security.webp
new file mode 100644
index 000000000..d0eef9852
Binary files /dev/null and b/content/identity/identity-security-device-trust-2024/identity-security.webp differ
diff --git a/content/identity/identity-security-device-trust-2024/index.md b/content/identity/identity-security-device-trust-2024/index.md
index f0709fa40..13a93d18c 100644
--- a/content/identity/identity-security-device-trust-2024/index.md
+++ b/content/identity/identity-security-device-trust-2024/index.md
@@ -1,7 +1,7 @@
---
title: "Identity Security for Device Trust: Navigating 2024 & Beyond"
date: "2024-04-18"
-coverImage: "identity-security.jpg"
+coverImage: "identity-security.webp"
tags: ["data security","cybersecurity","cx"]
author: "Alok Patidar"
description: "In the rapidly evolving technology landscape, where our devices have become indispensable extensions of ourselves, ensuring their trustworthiness is paramount. Enter identity security for device trust, a concept that gained unprecedented significance in 2024 and is set to shape the future of cybersecurity. Let’s uncover the intricacies of this crucial topic, exploring its importance, challenges, and the path forward as we navigate the digital landscape of 2024 and beyond."
@@ -23,7 +23,7 @@ This assurance is achieved through robust identity security measures, such as es
These identity security measures are designed to create a fortress around our digital lives, ensuring that only authorized users and trusted software can access sensitive information and critical resources. Whether it's personal photos, financial details, or confidential work documents, the sanctity of this data relies on the strength of our device trust.
-[](https://www.loginradius.com/resource/datasheet/m-2-m-authorization)
+[](https://www.loginradius.com/resource/datasheet/m-2-m-authorization)
In a nutshell, identity security forms the bedrock upon which device trust stands tall. It's the invisible shield that guards against unauthorized access, cyber intrusions, and data breaches.
@@ -69,4 +69,4 @@ As we navigate the digital landscape of 2024 and beyond, one thing is clear: ide
Remember, in the realm of device trust, identity security is the key that unlocks a world of possibilities while safeguarding what matters most—our digital identities.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-security-device-trust-2024)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-security-device-trust-2024)
\ No newline at end of file
diff --git a/content/identity/identity-system-customization/eb-iam-checklist.png b/content/identity/identity-system-customization/eb-iam-checklist.png
deleted file mode 100644
index fe4314152..000000000
Binary files a/content/identity/identity-system-customization/eb-iam-checklist.png and /dev/null differ
diff --git a/content/identity/identity-system-customization/eb-iam-checklist.webp b/content/identity/identity-system-customization/eb-iam-checklist.webp
new file mode 100644
index 000000000..5f870a454
Binary files /dev/null and b/content/identity/identity-system-customization/eb-iam-checklist.webp differ
diff --git a/content/identity/identity-system-customization/identity-system-customization-cover.jpg b/content/identity/identity-system-customization/identity-system-customization-cover.jpg
deleted file mode 100644
index 72a36a110..000000000
Binary files a/content/identity/identity-system-customization/identity-system-customization-cover.jpg and /dev/null differ
diff --git a/content/identity/identity-system-customization/identity-system-customization-cover.webp b/content/identity/identity-system-customization/identity-system-customization-cover.webp
new file mode 100644
index 000000000..634becec5
Binary files /dev/null and b/content/identity/identity-system-customization/identity-system-customization-cover.webp differ
diff --git a/content/identity/identity-system-customization/index.md b/content/identity/identity-system-customization/index.md
index 24d21dd5b..334a01c02 100644
--- a/content/identity/identity-system-customization/index.md
+++ b/content/identity/identity-system-customization/index.md
@@ -1,7 +1,7 @@
---
title: "Why Should You be Customizing Your Identity System to Your Needs"
date: "2021-09-07"
-coverImage: "identity-system-customization-cover.jpg"
+coverImage: "identity-system-customization-cover.webp"
tags: ["security"]
featured: false
author: "Manish Tiwari"
@@ -33,7 +33,7 @@ Moreover, an identity system or a [consumer identity and access management](http
A CIAM solution also offers valuable insights into a consumer’s behavior, which further allows businesses to tailor their marketing and onboarding strategies.
-[](https://www.loginradius.com/resource/an-identity-checklist-to-strategize-ciam-in-the-cloud/)
+[](https://www.loginradius.com/resource/an-identity-checklist-to-strategize-ciam-in-the-cloud/)
## Role of Identity System Customization
@@ -88,4 +88,4 @@ Brands that wish to invoke the true potential of personalization must consider r
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-system-customization)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-system-customization)
diff --git a/content/identity/identity-theft-frauds/identity-theft-fraud-cover.jpg b/content/identity/identity-theft-frauds/identity-theft-fraud-cover.jpg
deleted file mode 100644
index 9530d7bf2..000000000
Binary files a/content/identity/identity-theft-frauds/identity-theft-fraud-cover.jpg and /dev/null differ
diff --git a/content/identity/identity-theft-frauds/identity-theft-fraud-cover.webp b/content/identity/identity-theft-frauds/identity-theft-fraud-cover.webp
new file mode 100644
index 000000000..b0f1d74fe
Binary files /dev/null and b/content/identity/identity-theft-frauds/identity-theft-fraud-cover.webp differ
diff --git a/content/identity/identity-theft-frauds/index.md b/content/identity/identity-theft-frauds/index.md
index 7e4119b02..94a20df25 100644
--- a/content/identity/identity-theft-frauds/index.md
+++ b/content/identity/identity-theft-frauds/index.md
@@ -1,7 +1,7 @@
---
title: "Identity Theft Frauds- Staying Ahead in 2021"
date: "2021-03-31"
-coverImage: "identity-theft-fraud-cover.jpg"
+coverImage: "identity-theft-fraud-cover.webp"
tags: ["data security","mfa","cx"]
author: "Vishal Sharma"
description: "With so many businesses adopting diverse working environments, fraudsters are quickly finding new ways to breach security and gain access to confidential information. Businesses must anticipate potential frauds to minimize the risk for their employees’ and clients’ identities in 2021."
@@ -98,4 +98,4 @@ The aforementioned aspects also require adequate consideration when it comes to
Implementation of identity and access management solutions could be the game-changer for businesses that are striving to [protect consumer identities](https://www.loginradius.com/blog/identity/2019/12/digital-privacy-best-practices/).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-theft-frauds)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-theft-frauds)
\ No newline at end of file
diff --git a/content/identity/identity-theft-impact-on-businesses-in-2023/WP-identity-theft.png b/content/identity/identity-theft-impact-on-businesses-in-2023/WP-identity-theft.png
deleted file mode 100644
index 25b3b0075..000000000
Binary files a/content/identity/identity-theft-impact-on-businesses-in-2023/WP-identity-theft.png and /dev/null differ
diff --git a/content/identity/identity-theft-impact-on-businesses-in-2023/WP-identity-theft.webp b/content/identity/identity-theft-impact-on-businesses-in-2023/WP-identity-theft.webp
new file mode 100644
index 000000000..3d62deb02
Binary files /dev/null and b/content/identity/identity-theft-impact-on-businesses-in-2023/WP-identity-theft.webp differ
diff --git a/content/identity/identity-theft-impact-on-businesses-in-2023/identity-theft.jpg b/content/identity/identity-theft-impact-on-businesses-in-2023/identity-theft.jpg
deleted file mode 100644
index 585d3e917..000000000
Binary files a/content/identity/identity-theft-impact-on-businesses-in-2023/identity-theft.jpg and /dev/null differ
diff --git a/content/identity/identity-theft-impact-on-businesses-in-2023/identity-theft.webp b/content/identity/identity-theft-impact-on-businesses-in-2023/identity-theft.webp
new file mode 100644
index 000000000..337154f84
Binary files /dev/null and b/content/identity/identity-theft-impact-on-businesses-in-2023/identity-theft.webp differ
diff --git a/content/identity/identity-theft-impact-on-businesses-in-2023/index.md b/content/identity/identity-theft-impact-on-businesses-in-2023/index.md
index 8b1eb988d..7adb11726 100644
--- a/content/identity/identity-theft-impact-on-businesses-in-2023/index.md
+++ b/content/identity/identity-theft-impact-on-businesses-in-2023/index.md
@@ -1,7 +1,7 @@
---
title: "Learn the Impact of Identity Theft on Businesses in 2023"
date: "2023-07-26"
-coverImage: "identity-theft.jpg"
+coverImage: "identity-theft.webp"
tags: ["digital identity management","cybersecurity","cx"]
author: "Alok Patidar"
description: "In 2023, identity theft has become a pressing concern for businesses, posing significant risks and consequences. This blog explores the implications of identity theft, including financial loss, reputational damage, and legal consequences. Discover the importance of proactive measures and cybersecurity practices to mitigate the risks."
@@ -64,7 +64,7 @@ Customers rely on businesses to protect their personal information. If a company
Recovering from an identity theft incident can disrupt a business's operations. Remediation efforts, including investigating the breach, implementing security measures, and restoring affected systems. This can consume valuable resources and time, affecting productivity and profitability.
-[](https://www.loginradius.com/resource/ciam-role-in-customer-trust/)
+[](https://www.loginradius.com/resource/ciam-role-in-customer-trust/)
## Preventing and Mitigating Identity Theft
@@ -116,4 +116,4 @@ To mitigate the risks, businesses must prioritize cybersecurity, implement robus
Remember, prevention and preparedness are key in the fight against identity theft. Stay vigilant, stay informed, and stay secure.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-theft-impact-on-businesses-in-2023)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-theft-impact-on-businesses-in-2023)
diff --git a/content/identity/identity-verification-challenges-and-solutions/GD-ciam.png b/content/identity/identity-verification-challenges-and-solutions/GD-ciam.png
deleted file mode 100644
index 79ef6d6fa..000000000
Binary files a/content/identity/identity-verification-challenges-and-solutions/GD-ciam.png and /dev/null differ
diff --git a/content/identity/identity-verification-challenges-and-solutions/GD-ciam.webp b/content/identity/identity-verification-challenges-and-solutions/GD-ciam.webp
new file mode 100644
index 000000000..4ad020497
Binary files /dev/null and b/content/identity/identity-verification-challenges-and-solutions/GD-ciam.webp differ
diff --git a/content/identity/identity-verification-challenges-and-solutions/idntity-verification.jpg b/content/identity/identity-verification-challenges-and-solutions/idntity-verification.jpg
deleted file mode 100644
index 93f762954..000000000
Binary files a/content/identity/identity-verification-challenges-and-solutions/idntity-verification.jpg and /dev/null differ
diff --git a/content/identity/identity-verification-challenges-and-solutions/idntity-verification.webp b/content/identity/identity-verification-challenges-and-solutions/idntity-verification.webp
new file mode 100644
index 000000000..4a314bb64
Binary files /dev/null and b/content/identity/identity-verification-challenges-and-solutions/idntity-verification.webp differ
diff --git a/content/identity/identity-verification-challenges-and-solutions/index.md b/content/identity/identity-verification-challenges-and-solutions/index.md
index 1e79232c1..a910ca0f9 100644
--- a/content/identity/identity-verification-challenges-and-solutions/index.md
+++ b/content/identity/identity-verification-challenges-and-solutions/index.md
@@ -1,7 +1,7 @@
---
title: "Navigating Identity Verification Challenges in Regulated Industries: 7 Effective Solutions"
date: "2023-08-14"
-coverImage: "idntity-verification.jpg"
+coverImage: "idntity-verification.webp"
tags: ["identity verification","compliance","biometric authentication","cx"]
author: "Rakesh Soni"
description: "Explore solutions to identity verification challenges faced by regulated industries. From fraud prevention and compliance management to user experience enhancement, learn how the LoginRadius CIAM platform leverages cutting-edge technologies to navigate the intricate terrain of identity verification while ensuring security and trust."
@@ -52,7 +52,7 @@ Implementing robust data encryption protocols and cybersecurity measures through
Moreover, most businesses may need help transferring data and storing sensitive information over the cloud. With a robust CIAM, they can overcome the issues related to data management, storage, and transmission.
-[](loginradius.com/resource/ciam-buyers-guide-to-secure-your-roi)
+[](loginradius.com/resource/ciam-buyers-guide-to-secure-your-roi)
### 3. Compliance Management
@@ -84,4 +84,4 @@ Businesses can use intelligent authentication mechanisms like fingerprint or fac
Here’s where regulated industries must partner with LoginRadius CIAM to make things easier! With LoginRadius, businesses can stick to the rules without complicating things for users.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-verification-challenges-and-solutions)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-verification-challenges-and-solutions)
\ No newline at end of file
diff --git a/content/identity/ifma-loginradius-customer-success-story/IFMAlogo.jpg b/content/identity/ifma-loginradius-customer-success-story/IFMAlogo.jpg
deleted file mode 100644
index 831a84ed6..000000000
Binary files a/content/identity/ifma-loginradius-customer-success-story/IFMAlogo.jpg and /dev/null differ
diff --git a/content/identity/ifma-loginradius-customer-success-story/IFMAlogo.webp b/content/identity/ifma-loginradius-customer-success-story/IFMAlogo.webp
new file mode 100644
index 000000000..b75c4331b
Binary files /dev/null and b/content/identity/ifma-loginradius-customer-success-story/IFMAlogo.webp differ
diff --git a/content/identity/ifma-loginradius-customer-success-story/ifma-loginradius-customer-success-story.png b/content/identity/ifma-loginradius-customer-success-story/ifma-loginradius-customer-success-story.png
deleted file mode 100644
index e054c8479..000000000
Binary files a/content/identity/ifma-loginradius-customer-success-story/ifma-loginradius-customer-success-story.png and /dev/null differ
diff --git a/content/identity/ifma-loginradius-customer-success-story/ifma-loginradius-customer-success-story.webp b/content/identity/ifma-loginradius-customer-success-story/ifma-loginradius-customer-success-story.webp
new file mode 100644
index 000000000..dee3e9f7d
Binary files /dev/null and b/content/identity/ifma-loginradius-customer-success-story/ifma-loginradius-customer-success-story.webp differ
diff --git a/content/identity/ifma-loginradius-customer-success-story/index.md b/content/identity/ifma-loginradius-customer-success-story/index.md
index 3981b9d2c..aee66f580 100644
--- a/content/identity/ifma-loginradius-customer-success-story/index.md
+++ b/content/identity/ifma-loginradius-customer-success-story/index.md
@@ -1,7 +1,7 @@
---
title: "IFMA, a LoginRadius Customer Success Story"
date: "2018-01-15"
-coverImage: "ifma-loginradius-customer-success-story.png"
+coverImage: "ifma-loginradius-customer-success-story.webp"
tags: ["other"]
featured: false
author: "Karl Wittig"
@@ -11,7 +11,7 @@ metadescription: "IFMA provides credentialing, education programs, and guidance
"
---
-
+
The [International Facility Management Association (IFMA)](https://www.ifma.org/) is the world’s largest international association and guidance body for facility management professionals. Founded in 1980, IFMA provides credentialing, education programs, and guidance to facility management professionals. Headquartered in Houston (USA), IFMA is a not-for-profit organization supporting professionals in 104 countries.
@@ -50,4 +50,4 @@ LoginRadius’ cIAM solution ensured that while an individual member can be asso
IFMA - LoginRadius Customer Success Story
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ifma-loginradius-customer-success-story)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ifma-loginradius-customer-success-story)
diff --git a/content/identity/improving-customer-experience-public-sector/customer-experience.jpg b/content/identity/improving-customer-experience-public-sector/customer-experience.jpg
deleted file mode 100644
index cb12ed38d..000000000
Binary files a/content/identity/improving-customer-experience-public-sector/customer-experience.jpg and /dev/null differ
diff --git a/content/identity/improving-customer-experience-public-sector/customer-experience.webp b/content/identity/improving-customer-experience-public-sector/customer-experience.webp
new file mode 100644
index 000000000..2d88f1fef
Binary files /dev/null and b/content/identity/improving-customer-experience-public-sector/customer-experience.webp differ
diff --git a/content/identity/improving-customer-experience-public-sector/image-2.jpeg b/content/identity/improving-customer-experience-public-sector/image-2.jpeg
deleted file mode 100644
index 019a74619..000000000
Binary files a/content/identity/improving-customer-experience-public-sector/image-2.jpeg and /dev/null differ
diff --git a/content/identity/improving-customer-experience-public-sector/image-2.webp b/content/identity/improving-customer-experience-public-sector/image-2.webp
new file mode 100644
index 000000000..f036091ed
Binary files /dev/null and b/content/identity/improving-customer-experience-public-sector/image-2.webp differ
diff --git a/content/identity/improving-customer-experience-public-sector/image-3.jpg b/content/identity/improving-customer-experience-public-sector/image-3.jpg
deleted file mode 100644
index fe10d413a..000000000
Binary files a/content/identity/improving-customer-experience-public-sector/image-3.jpg and /dev/null differ
diff --git a/content/identity/improving-customer-experience-public-sector/image-3.webp b/content/identity/improving-customer-experience-public-sector/image-3.webp
new file mode 100644
index 000000000..2bd12c8ba
Binary files /dev/null and b/content/identity/improving-customer-experience-public-sector/image-3.webp differ
diff --git a/content/identity/improving-customer-experience-public-sector/imgae-1.jpeg b/content/identity/improving-customer-experience-public-sector/imgae-1.jpeg
deleted file mode 100644
index efcdac476..000000000
Binary files a/content/identity/improving-customer-experience-public-sector/imgae-1.jpeg and /dev/null differ
diff --git a/content/identity/improving-customer-experience-public-sector/imgae-1.webp b/content/identity/improving-customer-experience-public-sector/imgae-1.webp
new file mode 100644
index 000000000..4436b998f
Binary files /dev/null and b/content/identity/improving-customer-experience-public-sector/imgae-1.webp differ
diff --git a/content/identity/improving-customer-experience-public-sector/improving-customer-experience-public-sector.jpg b/content/identity/improving-customer-experience-public-sector/improving-customer-experience-public-sector.jpg
deleted file mode 100644
index e739b8830..000000000
Binary files a/content/identity/improving-customer-experience-public-sector/improving-customer-experience-public-sector.jpg and /dev/null differ
diff --git a/content/identity/improving-customer-experience-public-sector/improving-customer-experience-public-sector.webp b/content/identity/improving-customer-experience-public-sector/improving-customer-experience-public-sector.webp
new file mode 100644
index 000000000..49755dfcb
Binary files /dev/null and b/content/identity/improving-customer-experience-public-sector/improving-customer-experience-public-sector.webp differ
diff --git a/content/identity/improving-customer-experience-public-sector/index.md b/content/identity/improving-customer-experience-public-sector/index.md
index fc9e5dad0..b58e31496 100644
--- a/content/identity/improving-customer-experience-public-sector/index.md
+++ b/content/identity/improving-customer-experience-public-sector/index.md
@@ -1,7 +1,7 @@
---
title: "Improving Customer Experience in the Public Sector"
date: "2018-10-26"
-coverImage: "customer-experience.jpg"
+coverImage: "customer-experience.webp"
tags: ["data security","ciam solutions","cx"]
author: "Rakesh Soni"
description: "When people think of the experience of online users, they will not consider it relevant in the public sector. LoginRadius is currently helping a variety of public sector organisations enhance their customer service in various ways."
@@ -15,7 +15,7 @@ Implementing a [customer identity and access management](https://www.loginradius
## Cities: Centralizing Municipal Services
-
+
In an effort to increase citizen engagement, [more and more cities are moving citizen services to their online platforms](https://www.loginradius.com/resource/how-cities-use-loginradius-identity-platform/). Paying taxes, obtaining a business license, getting election information, and more can all be done online through a centralized portal. Simplifying access to these services by creating a one-stop resource for all online applications increases not only citizen engagement, but also satisfaction with government and municipal services in general.
@@ -23,19 +23,19 @@ The [City of Surrey](https://my.surrey.ca/), British Columbia has implemented th
## Non-Profits & NGOs: Informing Centralized Groups
-
+
Much like cities, many NGOs and non-profit groups depend on interacting with citizens in order to inform them about various initiatives. Without the ability to reach and inform large groups of citizens, these organizations are rendered ineffective. With this communication need in mind, a positive customer experience with their digital properties is extremely important, as it can help in extending the reach of these initiatives, as well as turning online visitors into known users. From there, these groups can individually target the various groups of people they need to interact with.
For example, [Zero Waste Scotland](https://www.youtube.com/watch?v=_11VIYMZh2g&list=PL3PS687CKFEFv2nlnk6NKrmbg4_zwBImw&index=3) is a government non-profit organization that promotes the government’s policy on waste and resources. With a range of users and stakeholders to reach, they needed a CIAM solution that could easily allow these various identities to interact with their multiple digital touchpoints. LoginRadius was able to build centralized profiles for each user in order to gain a complete view of how people are using their services. Leveraging our User Profiling capabilities has helped Zero Waste Scotland and other organizations understand their users and build informed campaign strategies.
-[](https://www.loginradius.com/resource/how-public-sector-companies-use-the-loginradius-identity-platform/)
+[](https://www.loginradius.com/resource/how-public-sector-companies-use-the-loginradius-identity-platform/)
Lastly, when it comes to government agencies like Zero Waste Scotland, data security is one of the main priorities, especially with cloud storage. LoginRadius complies with all major security regulations in the industry, including [GDPR](https://www.loginradius.com/resource/loginradius-and-gdpr-compliance/). We also allow customers to choose which of our 29 global data centers they want personal data to be stored in, to comply with company policies.
## Utilities: Bringing Better Information to the Customer
-
+
For most people, a utility provider represents just another bill to pay at the end of the month. Customers are often limited in the ways that they can interact with utility companies, making customer experience an afterthought. With a CIAM solution, [utility companies can transform their customer experience](https://www.loginradius.com/resource/how-utility-companies-use-loginradius-identity-solution/) by integrating with third-party applications. These integrations help them better understand their customers, offer more useful information, and deliver that information more directly.
@@ -43,4 +43,4 @@ One of the best examples of customer experience innovation for utilities comes f
If you’re ready to see how the LoginRadius CIAM platform can help your company, [schedule your demo now](https://www.loginradius.com/schedule-demo/).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=improving-customer-experience-public-sector)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=improving-customer-experience-public-sector)
\ No newline at end of file
diff --git a/content/identity/improving-customer-experience-public-sector/public-sector.png b/content/identity/improving-customer-experience-public-sector/public-sector.png
deleted file mode 100644
index dce0d6e37..000000000
Binary files a/content/identity/improving-customer-experience-public-sector/public-sector.png and /dev/null differ
diff --git a/content/identity/improving-customer-experience-public-sector/public-sector.webp b/content/identity/improving-customer-experience-public-sector/public-sector.webp
new file mode 100644
index 000000000..ec9c7ffe4
Binary files /dev/null and b/content/identity/improving-customer-experience-public-sector/public-sector.webp differ
diff --git a/content/identity/infographic-the-death-of-passwords/Book-a-demo-1024x310.png b/content/identity/infographic-the-death-of-passwords/Book-a-demo-1024x310.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/infographic-the-death-of-passwords/Book-a-demo-1024x310.png and /dev/null differ
diff --git a/content/identity/infographic-the-death-of-passwords/Book-a-demo-1024x310.webp b/content/identity/infographic-the-death-of-passwords/Book-a-demo-1024x310.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/infographic-the-death-of-passwords/Book-a-demo-1024x310.webp differ
diff --git a/content/identity/infographic-the-death-of-passwords/Infographic-The-Death-of-Passwords-Social-Graphics-V01.01-1.jpg b/content/identity/infographic-the-death-of-passwords/Infographic-The-Death-of-Passwords-Social-Graphics-V01.01-1.jpg
deleted file mode 100644
index 46a9ca5cd..000000000
Binary files a/content/identity/infographic-the-death-of-passwords/Infographic-The-Death-of-Passwords-Social-Graphics-V01.01-1.jpg and /dev/null differ
diff --git a/content/identity/infographic-the-death-of-passwords/Infographic-The-Death-of-Passwords-Social-Graphics-V01.01-1.webp b/content/identity/infographic-the-death-of-passwords/Infographic-The-Death-of-Passwords-Social-Graphics-V01.01-1.webp
new file mode 100644
index 000000000..5c343e8ef
Binary files /dev/null and b/content/identity/infographic-the-death-of-passwords/Infographic-The-Death-of-Passwords-Social-Graphics-V01.01-1.webp differ
diff --git a/content/identity/infographic-the-death-of-passwords/The-Death-of-Passwords-1.jpg b/content/identity/infographic-the-death-of-passwords/The-Death-of-Passwords-1.jpg
deleted file mode 100644
index fa29b5c96..000000000
Binary files a/content/identity/infographic-the-death-of-passwords/The-Death-of-Passwords-1.jpg and /dev/null differ
diff --git a/content/identity/infographic-the-death-of-passwords/The-Death-of-Passwords-1.webp b/content/identity/infographic-the-death-of-passwords/The-Death-of-Passwords-1.webp
new file mode 100644
index 000000000..52571f2e0
Binary files /dev/null and b/content/identity/infographic-the-death-of-passwords/The-Death-of-Passwords-1.webp differ
diff --git a/content/identity/infographic-the-death-of-passwords/WP-Passwords-are-Dead-1024x310.png b/content/identity/infographic-the-death-of-passwords/WP-Passwords-are-Dead-1024x310.png
deleted file mode 100644
index 4ab71a655..000000000
Binary files a/content/identity/infographic-the-death-of-passwords/WP-Passwords-are-Dead-1024x310.png and /dev/null differ
diff --git a/content/identity/infographic-the-death-of-passwords/WP-Passwords-are-Dead-1024x310.webp b/content/identity/infographic-the-death-of-passwords/WP-Passwords-are-Dead-1024x310.webp
new file mode 100644
index 000000000..8f08524fe
Binary files /dev/null and b/content/identity/infographic-the-death-of-passwords/WP-Passwords-are-Dead-1024x310.webp differ
diff --git a/content/identity/infographic-the-death-of-passwords/death-of-passwords.png b/content/identity/infographic-the-death-of-passwords/death-of-passwords.png
deleted file mode 100644
index 7e78b225b..000000000
Binary files a/content/identity/infographic-the-death-of-passwords/death-of-passwords.png and /dev/null differ
diff --git a/content/identity/infographic-the-death-of-passwords/death-of-passwords.webp b/content/identity/infographic-the-death-of-passwords/death-of-passwords.webp
new file mode 100644
index 000000000..559b7285e
Binary files /dev/null and b/content/identity/infographic-the-death-of-passwords/death-of-passwords.webp differ
diff --git a/content/identity/infographic-the-death-of-passwords/index.md b/content/identity/infographic-the-death-of-passwords/index.md
index 2709ecbdf..5b787a941 100644
--- a/content/identity/infographic-the-death-of-passwords/index.md
+++ b/content/identity/infographic-the-death-of-passwords/index.md
@@ -1,7 +1,7 @@
---
title: "The Death of Passwords [Infographic]"
date: "2018-12-19"
-coverImage: "death-of-passwords.png"
+coverImage: "death-of-passwords.webp"
tags: ["passwordless authentication","ciam solutions","mfa","cx"]
author: "Rakesh Soni"
description: "Are usernames and passwords really the best way to protect your customers? Check out this infographic and learn about the new technologies and authentication methods that are replacing passwords."
@@ -15,7 +15,7 @@ Maybe you haven’t visited the website in ages. Or you just changed the passwor
Passwords are there to make it safe for customers to use their accounts. But often passwords aren’t enough. And when passwords get in the way of customers using their accounts at all, something’s wrong.
-[](https://www.loginradius.com/resource/passwords-are-dead/)
+[](https://www.loginradius.com/resource/passwords-are-dead/)
Forward-thinking companies are hurrying along the death of passwords by adopting login features that are more secure than passwords and easier to use. LoginRadius a [customer identity and access management](https://www.loginradius.com/blog/2019/06/customer-identity-and-access-management/) (CIAM) platform provides a secure login solution:
@@ -25,10 +25,10 @@ Forward-thinking companies are hurrying along the death of passwords by adopting
We’ve put together a few alarming and entertaining facts on the current state of passwords. Customers aren’t going to get any better about using passwords safely, so it’s up to businesses to make those pesky strings of characters obsolete once and for all.
-
+
Curious about learning more about these alternative authentication methods?
We further dig into the problems businesses face with existing username/password authentication methods. We will then review the new authentication methods that are becoming popular in the marketplace and how in the near future they might very well replace passwords.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=infographic-the-death-of-passwords)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=infographic-the-death-of-passwords)
diff --git a/content/identity/iot-authentication-airlines/index.md b/content/identity/iot-authentication-airlines/index.md
index 34e594807..4a915262f 100644
--- a/content/identity/iot-authentication-airlines/index.md
+++ b/content/identity/iot-authentication-airlines/index.md
@@ -1,7 +1,7 @@
---
title: "IoT authentication in the airline industry"
date: "2021-03-24"
-coverImage: "iot-authentication-airlines-cover.jpg"
+coverImage: "iot-authentication-airlines-cover.webp"
tags: ["customer-experience"]
featured: false
author: "Rakesh Soni"
@@ -118,4 +118,4 @@ Airports, being large, can be overwhelming for first-time flyers. With IoT cellu
The best aspect of IoT authentication in the airline industry or the general use of IoT is the convenience that it brings. It can ease the anxiety of a passenger as they receive reassurance that their data will not see the light of day. Tracking of luggage and decreased wait times will make the passenger experience a breeze. Therefore, IoT authentication in airlines lay the path towards the future of stress-free traveling.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=iot-authentication-airlines)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=iot-authentication-airlines)
diff --git a/content/identity/iot-authentication-airlines/iot-authentication-airlines-cover.jpg b/content/identity/iot-authentication-airlines/iot-authentication-airlines-cover.jpg
deleted file mode 100644
index ff3002f58..000000000
Binary files a/content/identity/iot-authentication-airlines/iot-authentication-airlines-cover.jpg and /dev/null differ
diff --git a/content/identity/iot-authentication-airlines/iot-authentication-airlines-cover.webp b/content/identity/iot-authentication-airlines/iot-authentication-airlines-cover.webp
new file mode 100644
index 000000000..82816ed5f
Binary files /dev/null and b/content/identity/iot-authentication-airlines/iot-authentication-airlines-cover.webp differ
diff --git a/content/identity/iot-authentication-airlines/iot-smart-authentication-datasheet.png b/content/identity/iot-authentication-airlines/iot-smart-authentication-datasheet.png
deleted file mode 100644
index 7e8cb44e5..000000000
Binary files a/content/identity/iot-authentication-airlines/iot-smart-authentication-datasheet.png and /dev/null differ
diff --git a/content/identity/iot-authentication-airlines/iot-smart-authentication-datasheet.webp b/content/identity/iot-authentication-airlines/iot-smart-authentication-datasheet.webp
new file mode 100644
index 000000000..4b62e787b
Binary files /dev/null and b/content/identity/iot-authentication-airlines/iot-smart-authentication-datasheet.webp differ
diff --git a/content/identity/iot-botnet-attacks-enterprises/WP-Remote-Learning.png b/content/identity/iot-botnet-attacks-enterprises/WP-Remote-Learning.png
deleted file mode 100644
index 355123548..000000000
Binary files a/content/identity/iot-botnet-attacks-enterprises/WP-Remote-Learning.png and /dev/null differ
diff --git a/content/identity/iot-botnet-attacks-enterprises/WP-Remote-Learning.webp b/content/identity/iot-botnet-attacks-enterprises/WP-Remote-Learning.webp
new file mode 100644
index 000000000..f265dfed3
Binary files /dev/null and b/content/identity/iot-botnet-attacks-enterprises/WP-Remote-Learning.webp differ
diff --git a/content/identity/iot-botnet-attacks-enterprises/index.md b/content/identity/iot-botnet-attacks-enterprises/index.md
index 69223d966..2c519448a 100644
--- a/content/identity/iot-botnet-attacks-enterprises/index.md
+++ b/content/identity/iot-botnet-attacks-enterprises/index.md
@@ -1,7 +1,7 @@
---
title: "IoT Botnet Attacks: Are They the Next Big Threat to Enterprises?"
date: "2022-06-28"
-coverImage: "iot-botnet.jpg"
+coverImage: "iot-botnet.webp"
tags: ["iot", "botnet", "cybersecurity", "ux"]
author: "Manish Tiwari"
description: "Enterprises developing IoT devices, smart applications, or other systems in the IoT landscape shouldn’t ignore the risks associated with botnet attacks. Read this insightful post to understand what an IoT botnet attack means and how IoT developers and vendors can mitigate the risk."
@@ -61,7 +61,7 @@ IoT botnet attacks can be prevented, and sensitive business and user information
Good cybersecurity hygiene is key to preventing botnet attacks since attackers must surpass various lines of defense before exploiting crucial business or user information.
-[](https://www.loginradius.com/resource/shifting-safely-to-remote-learning-with-the-best-cyber-security-hygiene/)
+[](https://www.loginradius.com/resource/shifting-safely-to-remote-learning-with-the-best-cyber-security-hygiene/)
Adding multiple layers of authentication in the IoT network and devices through multi-factor authentication (MFA) and [risk-based authentication](https://www.loginradius.com/blog/identity/risk-based-authentication/#:~:text=Risk%2Dbased%20authentication%20is%20a,profile%20associated%20with%20that%20action.) (RBA) could mitigate many risks associated with identity theft and account takeovers.
@@ -91,4 +91,4 @@ On the other hand, businesses relying on poor security mechanisms on the device
Hence, incorporating a robust security policy, as mentioned above, could be the best thing to ensure businesses, vendors, developers, and users in the IoT landscape remain secure.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=iot-botnet-attacks-enterprises)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=iot-botnet-attacks-enterprises)
diff --git a/content/identity/iot-botnet-attacks-enterprises/iot-botnet.jpg b/content/identity/iot-botnet-attacks-enterprises/iot-botnet.jpg
deleted file mode 100644
index 419664dca..000000000
Binary files a/content/identity/iot-botnet-attacks-enterprises/iot-botnet.jpg and /dev/null differ
diff --git a/content/identity/iot-botnet-attacks-enterprises/iot-botnet.webp b/content/identity/iot-botnet-attacks-enterprises/iot-botnet.webp
new file mode 100644
index 000000000..a76e5e0cd
Binary files /dev/null and b/content/identity/iot-botnet-attacks-enterprises/iot-botnet.webp differ
diff --git a/content/identity/iot-botnet-attacks-enterprises/remote-wp.png b/content/identity/iot-botnet-attacks-enterprises/remote-wp.png
deleted file mode 100644
index 5bf580704..000000000
Binary files a/content/identity/iot-botnet-attacks-enterprises/remote-wp.png and /dev/null differ
diff --git a/content/identity/iot-botnet-attacks-enterprises/remote-wp.webp b/content/identity/iot-botnet-attacks-enterprises/remote-wp.webp
new file mode 100644
index 000000000..325fdcb43
Binary files /dev/null and b/content/identity/iot-botnet-attacks-enterprises/remote-wp.webp differ
diff --git a/content/identity/iot-smart-authentication/index.md b/content/identity/iot-smart-authentication/index.md
index a09115e71..2db50d0a2 100644
--- a/content/identity/iot-smart-authentication/index.md
+++ b/content/identity/iot-smart-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - LoginRadius Smart and IoT Authentication to Offer Hassle-Free Login for Input-Constrained Devices"
date: "2020-12-02"
-coverImage: "loginradius-iot-smart-authentication.png"
+coverImage: "loginradius-iot-smart-authentication.webp"
tags: ["authentication","data security","cx"]
author: "Rakesh Soni"
description: "Smart and IoT Authentication from LoginRadius is a realistic solution to ensure customers are securely logged in. It removes the password entry burden and as a result, eliminates data protection threats related to password attacks."
@@ -54,7 +54,7 @@ LoginRadius offers in-built, multilingual email templates for businesses to add
LoginRadius allows businesses to set the login request limits for consumers and also manage the token expiry by restricting the validity of login links to ensure security.
-[](https://www.loginradius.com/resource/smart-iot-authentication-datasheet)
+[](https://www.loginradius.com/resource/smart-iot-authentication-datasheet)
## Implementation and Deployment
@@ -68,4 +68,4 @@ In an increasingly connected world where we see an explosion of networked device
Given the fact that authentication is generally the first step for consumers when experiencing a product, the LoginRadius Smart and IoT Authentication is geared to set your consumer up for hassle-free and user-friendly methods to login.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=iot-smart-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=iot-smart-authentication)
diff --git a/content/identity/iot-smart-authentication/iot-smart-authentication-datasheet.png b/content/identity/iot-smart-authentication/iot-smart-authentication-datasheet.png
deleted file mode 100644
index 7e8cb44e5..000000000
Binary files a/content/identity/iot-smart-authentication/iot-smart-authentication-datasheet.png and /dev/null differ
diff --git a/content/identity/iot-smart-authentication/iot-smart-authentication-datasheet.webp b/content/identity/iot-smart-authentication/iot-smart-authentication-datasheet.webp
new file mode 100644
index 000000000..4b62e787b
Binary files /dev/null and b/content/identity/iot-smart-authentication/iot-smart-authentication-datasheet.webp differ
diff --git a/content/identity/iot-smart-authentication/loginradius-iot-smart-authentication.png b/content/identity/iot-smart-authentication/loginradius-iot-smart-authentication.png
deleted file mode 100644
index 14b6b0be9..000000000
Binary files a/content/identity/iot-smart-authentication/loginradius-iot-smart-authentication.png and /dev/null differ
diff --git a/content/identity/iot-smart-authentication/loginradius-iot-smart-authentication.webp b/content/identity/iot-smart-authentication/loginradius-iot-smart-authentication.webp
new file mode 100644
index 000000000..dc5e8c853
Binary files /dev/null and b/content/identity/iot-smart-authentication/loginradius-iot-smart-authentication.webp differ
diff --git a/content/identity/is-password-reset-ruining-cx/GD-salt-to-hash.png b/content/identity/is-password-reset-ruining-cx/GD-salt-to-hash.png
deleted file mode 100644
index 698c87b68..000000000
Binary files a/content/identity/is-password-reset-ruining-cx/GD-salt-to-hash.png and /dev/null differ
diff --git a/content/identity/is-password-reset-ruining-cx/GD-salt-to-hash.webp b/content/identity/is-password-reset-ruining-cx/GD-salt-to-hash.webp
new file mode 100644
index 000000000..f0938b9a0
Binary files /dev/null and b/content/identity/is-password-reset-ruining-cx/GD-salt-to-hash.webp differ
diff --git a/content/identity/is-password-reset-ruining-cx/index.md b/content/identity/is-password-reset-ruining-cx/index.md
index a2ca50d36..1a01db79a 100644
--- a/content/identity/is-password-reset-ruining-cx/index.md
+++ b/content/identity/is-password-reset-ruining-cx/index.md
@@ -1,7 +1,7 @@
---
title: "How a Simple Password Reset Can Ruin Your Customer's Experience"
date: "2022-05-17"
-coverImage: "paswd-reset.jpg"
+coverImage: "paswd-reset.webp"
tags: ["data security", "consumer-experience", "authentication", "identity-verification"]
author: "Chris Starkhagen"
description: "When done correctly, password resets can be easy and relatively painless for both the customer and the enterprise. By following tips mentioned in this blog, enterprises can ensure that the customers have a positive experience when resetting their passwords."
@@ -28,7 +28,7 @@ And with the average web user having multiple online accounts, with accounts dou
With information and account overload, user behavior such as using the same password for multiple accounts invites security breaches, making authentication a top priority for enterprises.
-[](https://www.loginradius.com/resource/adding-salt-to-hashing-a-step-by-step-guide-to-store-passwords/)
+[](https://www.loginradius.com/resource/adding-salt-to-hashing-a-step-by-step-guide-to-store-passwords/)
## How Can a Password Reset Negatively Affect the Customer Experience?
@@ -109,4 +109,4 @@ No company wants a disgruntled customer, but all too often password resets – a
When done correctly, though, password resets can be easy and relatively painless for both the customer and the enterprise. By following these tips that we went through, enterprises can ensure that the customers have a positive experience when resetting their passwords.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=is-password-reset-ruining-cx)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=is-password-reset-ruining-cx)
diff --git a/content/identity/is-password-reset-ruining-cx/paswd-reset.jpg b/content/identity/is-password-reset-ruining-cx/paswd-reset.jpg
deleted file mode 100644
index 0825b4923..000000000
Binary files a/content/identity/is-password-reset-ruining-cx/paswd-reset.jpg and /dev/null differ
diff --git a/content/identity/is-password-reset-ruining-cx/paswd-reset.webp b/content/identity/is-password-reset-ruining-cx/paswd-reset.webp
new file mode 100644
index 000000000..e3638db09
Binary files /dev/null and b/content/identity/is-password-reset-ruining-cx/paswd-reset.webp differ
diff --git a/content/identity/is-password-reset-ruining-cx/salt-gd.png b/content/identity/is-password-reset-ruining-cx/salt-gd.png
deleted file mode 100644
index 5c89d019a..000000000
Binary files a/content/identity/is-password-reset-ruining-cx/salt-gd.png and /dev/null differ
diff --git a/content/identity/is-password-reset-ruining-cx/salt-gd.webp b/content/identity/is-password-reset-ruining-cx/salt-gd.webp
new file mode 100644
index 000000000..1340466fe
Binary files /dev/null and b/content/identity/is-password-reset-ruining-cx/salt-gd.webp differ
diff --git a/content/identity/json-web-token-stolen/EB-GD-to-mod-cust-id.png b/content/identity/json-web-token-stolen/EB-GD-to-mod-cust-id.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/identity/json-web-token-stolen/EB-GD-to-mod-cust-id.png and /dev/null differ
diff --git a/content/identity/json-web-token-stolen/EB-GD-to-mod-cust-id.webp b/content/identity/json-web-token-stolen/EB-GD-to-mod-cust-id.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/identity/json-web-token-stolen/EB-GD-to-mod-cust-id.webp differ
diff --git a/content/identity/json-web-token-stolen/index.md b/content/identity/json-web-token-stolen/index.md
index 6f54407c8..32288ded6 100644
--- a/content/identity/json-web-token-stolen/index.md
+++ b/content/identity/json-web-token-stolen/index.md
@@ -1,7 +1,7 @@
---
title: "What to Do if Someone Steals Your JSON Web Token?"
date: "2021-06-10"
-coverImage: "json-web-token-stolen-cover.jpg"
+coverImage: "json-web-token-stolen-cover.webp"
tags: ["data security","authentication"]
author: "Vishal Sharma"
description: "JWT tokens provide secure access to an authenticated user, and attackers are always looking for ways to steal these tokens and quickly gain access by impersonating a consumer. Here we’ve clubbed efficient ways for enterprises to ensure maximum security and steps that can help in a situation where a client’s JSON web token is stolen."
@@ -63,7 +63,7 @@ If you suspect any token being used by an unauthorized professional, it is best
Once the token is revoked, ask the client to reset their password and ensure they choose a strong password and must utilize [multi-factor authentication](https://www.loginradius.com/multi-factor-authentication/) in place as offered by LoginRadius CIAM.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
### 3. Look for a Security Breach Within your Network
@@ -89,4 +89,4 @@ The aforementioned aspects could help mitigate the risk and ensure minimum loss
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=json-web-token-stolen)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=json-web-token-stolen)
diff --git a/content/identity/json-web-token-stolen/json-web-token-stolen-cover.jpg b/content/identity/json-web-token-stolen/json-web-token-stolen-cover.jpg
deleted file mode 100644
index 98c2d0f54..000000000
Binary files a/content/identity/json-web-token-stolen/json-web-token-stolen-cover.jpg and /dev/null differ
diff --git a/content/identity/json-web-token-stolen/json-web-token-stolen-cover.webp b/content/identity/json-web-token-stolen/json-web-token-stolen-cover.webp
new file mode 100644
index 000000000..4ba703348
Binary files /dev/null and b/content/identity/json-web-token-stolen/json-web-token-stolen-cover.webp differ
diff --git a/content/identity/json-web-token-stolen/modern-customer-identity-eb.png b/content/identity/json-web-token-stolen/modern-customer-identity-eb.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/identity/json-web-token-stolen/modern-customer-identity-eb.png and /dev/null differ
diff --git a/content/identity/json-web-token-stolen/modern-customer-identity-eb.webp b/content/identity/json-web-token-stolen/modern-customer-identity-eb.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/identity/json-web-token-stolen/modern-customer-identity-eb.webp differ
diff --git a/content/identity/just-in-time-migrations-ciam-transitions/ciam-intime.jpg b/content/identity/just-in-time-migrations-ciam-transitions/ciam-intime.jpg
deleted file mode 100644
index e497f37e9..000000000
Binary files a/content/identity/just-in-time-migrations-ciam-transitions/ciam-intime.jpg and /dev/null differ
diff --git a/content/identity/just-in-time-migrations-ciam-transitions/ciam-intime.webp b/content/identity/just-in-time-migrations-ciam-transitions/ciam-intime.webp
new file mode 100644
index 000000000..be46c5630
Binary files /dev/null and b/content/identity/just-in-time-migrations-ciam-transitions/ciam-intime.webp differ
diff --git a/content/identity/just-in-time-migrations-ciam-transitions/etl-ds.png b/content/identity/just-in-time-migrations-ciam-transitions/etl-ds.png
deleted file mode 100644
index 2ed977c37..000000000
Binary files a/content/identity/just-in-time-migrations-ciam-transitions/etl-ds.png and /dev/null differ
diff --git a/content/identity/just-in-time-migrations-ciam-transitions/etl-ds.webp b/content/identity/just-in-time-migrations-ciam-transitions/etl-ds.webp
new file mode 100644
index 000000000..1794ca313
Binary files /dev/null and b/content/identity/just-in-time-migrations-ciam-transitions/etl-ds.webp differ
diff --git a/content/identity/just-in-time-migrations-ciam-transitions/index.md b/content/identity/just-in-time-migrations-ciam-transitions/index.md
index dac6711a2..d83902761 100644
--- a/content/identity/just-in-time-migrations-ciam-transitions/index.md
+++ b/content/identity/just-in-time-migrations-ciam-transitions/index.md
@@ -1,7 +1,7 @@
---
title: "Business On The Move: How Just-in-Time Migrations Are Making Smooth CIAM Transitions"
date: "2023-01-11"
-coverImage: "ciam-intime.jpg"
+coverImage: "ciam-intime.webp"
tags: ["ciam", "data migration", "identity import manager"]
author: "Yash Rathi"
description: "Just-in-time migrations are the latest buzz in the customer identity and access management (CIAM) industry. While most organizations still use bulk migrations, a growing segment of cloud services is implementing just-in-time (JIT)."
@@ -44,7 +44,7 @@ This process allows organizations to impose strict controls on sensitive informa
The LoginRadius Identity Import Manager is a flexible tool that allows companies to import and manage multiple customer profile data from any different application, service, or database into the LoginRadius database via CSV files.
-[](https://www.loginradius.com/resource/loginradius-identity-import-manager)
+[](https://www.loginradius.com/resource/loginradius-identity-import-manager)
With the new feature, companies can be confident about the consistency and accuracy of the imported data. Here are the LoginRadius’ identity import manager’s capabilities:
@@ -72,4 +72,4 @@ This dramatically reduces the number of systems and platforms involved in a migr
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=just-in-time-migrations-ciam-transitions)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=just-in-time-migrations-ciam-transitions)
diff --git a/content/identity/kuppingercole-ciw-presentation/index.md b/content/identity/kuppingercole-ciw-presentation/index.md
index 15f91d934..fd8fda748 100644
--- a/content/identity/kuppingercole-ciw-presentation/index.md
+++ b/content/identity/kuppingercole-ciw-presentation/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius presents at KuppingerCole Consumer Identity World"
date: "2019-10-04"
-coverImage: "kuppingercole-ciw-presentation.jpg"
+coverImage: "kuppingercole-ciw-presentation.webp"
tags: ["media-and-publication"]
featured: false
author: "Rakesh Soni"
@@ -77,7 +77,7 @@ Make it clear that they both have the same goal:
Both teams want to provide a frictionless online experience for customers.
-[](https://www.loginradius.com/resource/kuppingercole-2019-consumer-authentication-report)
+[](https://www.loginradius.com/resource/kuppingercole-2019-consumer-authentication-report)
Next, highlight each team’s strengths and how the other team contributes to the overall goal. Management should ensure their teams feel empowered and excited to work with each other.
diff --git a/content/identity/kuppingercole-ciw-presentation/kuppingercole-ciw-presentation.jpg b/content/identity/kuppingercole-ciw-presentation/kuppingercole-ciw-presentation.jpg
deleted file mode 100644
index 4400add1c..000000000
Binary files a/content/identity/kuppingercole-ciw-presentation/kuppingercole-ciw-presentation.jpg and /dev/null differ
diff --git a/content/identity/kuppingercole-ciw-presentation/kuppingercole-ciw-presentation.webp b/content/identity/kuppingercole-ciw-presentation/kuppingercole-ciw-presentation.webp
new file mode 100644
index 000000000..f56952900
Binary files /dev/null and b/content/identity/kuppingercole-ciw-presentation/kuppingercole-ciw-presentation.webp differ
diff --git a/content/identity/kuppingercole-ciw-presentation/kuppingercole.png b/content/identity/kuppingercole-ciw-presentation/kuppingercole.png
deleted file mode 100644
index 17f54150b..000000000
Binary files a/content/identity/kuppingercole-ciw-presentation/kuppingercole.png and /dev/null differ
diff --git a/content/identity/kuppingercole-ciw-presentation/kuppingercole.webp b/content/identity/kuppingercole-ciw-presentation/kuppingercole.webp
new file mode 100644
index 000000000..cb59f02c6
Binary files /dev/null and b/content/identity/kuppingercole-ciw-presentation/kuppingercole.webp differ
diff --git a/content/identity/kuppingercole-names-lr-ciam-leader-2024/index.md b/content/identity/kuppingercole-names-lr-ciam-leader-2024/index.md
index a7a229c83..b64d5c745 100644
--- a/content/identity/kuppingercole-names-lr-ciam-leader-2024/index.md
+++ b/content/identity/kuppingercole-names-lr-ciam-leader-2024/index.md
@@ -1,7 +1,7 @@
---
title: "Leading the Charge in Customer IAM: LoginRadius Recognized as an Overall Leader by KuppingerCole"
date: "2024-07-10"
-coverImage: "kc-lr-ciam.jpg"
+coverImage: "kc-lr-ciam.webp"
tags: ["ciam solutions","coverage","b2b"]
author: "Rakesh Soni"
description: "KuppingerCole's 2024 Leadership Compass reports recognize LoginRadius as an overall leader in customer identity and access management (CIAM). LoginRadius excels in innovative workflow management, extensive integration capabilities, comprehensive B2B features, and top-tier security standards. "
@@ -36,7 +36,7 @@ With a wide array of security certifications, including ISO 27001/27017/27018 an
Built on a cloud-first approach with an auto-scalable architecture, LoginRadius provides a resilient foundation for organizations looking to future-proof their CIAM infrastructure.
-[](https://www.loginradius.com/resource/analyst-report/kuppingercole-names-loginradius-top-ciam-platform-2024/)
+[](https://www.loginradius.com/resource/analyst-report/kuppingercole-names-loginradius-top-ciam-platform-2024/)
## Your Customers Desire a Seamless User Experience with Security at Its Heart
@@ -72,4 +72,4 @@ Embrace the future of digital identity management and position your brand at the
Ready to transform your customer identity management? Book a personalized demo today to learn how LoginRadius CIAM transforms your business.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=kuppingercole-names-lr-ciam-leader-2024)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=kuppingercole-names-lr-ciam-leader-2024)
diff --git a/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-cta.png b/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-cta.png
deleted file mode 100644
index 0ba4f9d0e..000000000
Binary files a/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-cta.png and /dev/null differ
diff --git a/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-cta.webp b/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-cta.webp
new file mode 100644
index 000000000..16543affb
Binary files /dev/null and b/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-cta.webp differ
diff --git a/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-lr-ciam.jpg b/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-lr-ciam.jpg
deleted file mode 100644
index 6d4ab91bd..000000000
Binary files a/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-lr-ciam.jpg and /dev/null differ
diff --git a/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-lr-ciam.webp b/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-lr-ciam.webp
new file mode 100644
index 000000000..ffdd68347
Binary files /dev/null and b/content/identity/kuppingercole-names-lr-ciam-leader-2024/kc-lr-ciam.webp differ
diff --git a/content/identity/leadership-updates-lr/cta-careers.png b/content/identity/leadership-updates-lr/cta-careers.png
deleted file mode 100644
index 600361d60..000000000
Binary files a/content/identity/leadership-updates-lr/cta-careers.png and /dev/null differ
diff --git a/content/identity/leadership-updates-lr/cta-careers.webp b/content/identity/leadership-updates-lr/cta-careers.webp
new file mode 100644
index 000000000..bf117ad57
Binary files /dev/null and b/content/identity/leadership-updates-lr/cta-careers.webp differ
diff --git a/content/identity/leadership-updates-lr/index.md b/content/identity/leadership-updates-lr/index.md
index aa1f67673..e5a47d6c5 100644
--- a/content/identity/leadership-updates-lr/index.md
+++ b/content/identity/leadership-updates-lr/index.md
@@ -1,7 +1,7 @@
---
title: "Exciting Leadership Updates Amid Strategic Growth at LoginRadius"
date: "2024-04-02"
-coverImage: "lr-updates.jpg"
+coverImage: "lr-updates.webp"
tags: ["leadership updates","new beginnings"]
author: "Ajoy Anand"
description: "Embarking on this transformative journey goes beyond leadership shifts—it's a renewal of our commitment to excellence, innovation, and the unwavering pursuit of success. We are excited about the opportunities that lie ahead."
@@ -36,4 +36,4 @@ This moment signifies more than just leadership changes; it's a renewal of our c
Thank you for being a part of our journey. Together, let's shape a future that's brighter than ever.
-[](https://www.loginradius.com/careers/)
\ No newline at end of file
+[](https://www.loginradius.com/careers/)
\ No newline at end of file
diff --git a/content/identity/leadership-updates-lr/lr-updates.jpg b/content/identity/leadership-updates-lr/lr-updates.jpg
deleted file mode 100644
index e627338ae..000000000
Binary files a/content/identity/leadership-updates-lr/lr-updates.jpg and /dev/null differ
diff --git a/content/identity/leadership-updates-lr/lr-updates.webp b/content/identity/leadership-updates-lr/lr-updates.webp
new file mode 100644
index 000000000..c66da3514
Binary files /dev/null and b/content/identity/leadership-updates-lr/lr-updates.webp differ
diff --git a/content/identity/legal-implications-of-sso/DS-consent-mngmnt.png b/content/identity/legal-implications-of-sso/DS-consent-mngmnt.png
deleted file mode 100644
index b2c0a4d84..000000000
Binary files a/content/identity/legal-implications-of-sso/DS-consent-mngmnt.png and /dev/null differ
diff --git a/content/identity/legal-implications-of-sso/DS-consent-mngmnt.webp b/content/identity/legal-implications-of-sso/DS-consent-mngmnt.webp
new file mode 100644
index 000000000..8dcbd7082
Binary files /dev/null and b/content/identity/legal-implications-of-sso/DS-consent-mngmnt.webp differ
diff --git a/content/identity/legal-implications-of-sso/index.md b/content/identity/legal-implications-of-sso/index.md
index e92a0957e..bf9854d93 100644
--- a/content/identity/legal-implications-of-sso/index.md
+++ b/content/identity/legal-implications-of-sso/index.md
@@ -1,7 +1,7 @@
---
title: "The Legal Implications of SSO: Privacy, Security, and Compliance"
date: "2023-06-06"
-coverImage: "sso-legal.jpg"
+coverImage: "sso-legal.webp"
tags: ["single sign on", "compliance", "data privacy","identity management"]
author: "Rakesh Soni"
description: "Learn about SSO's privacy concerns, the importance of robust data protection measures, and the need to align SSO implementations with various regulations. Discover how user consent and control play a pivotal role and the significance of implementing strong security measures."
@@ -47,7 +47,7 @@ Users should be able to manage their preferences regarding data usage and make i
Transparent consent mechanisms, user-friendly privacy settings, and easy-to-understand privacy policies are vital in ensuring user trust and compliance with privacy regulations.
-[](https://www.loginradius.com/resource/loginradius-consent-management)
+[](https://www.loginradius.com/resource/loginradius-consent-management)
### 5. Security Measures
@@ -79,4 +79,4 @@ By prioritizing user privacy, implementing robust security measures, ensuring co
And for this, nothing can replace the true potential of a reliable CIAM like LoginRadius that helps businesses seamlessly integrate SSO without any legal setbacks.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=legal-implications-of-sso)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=legal-implications-of-sso)
diff --git a/content/identity/legal-implications-of-sso/sso-legal.jpg b/content/identity/legal-implications-of-sso/sso-legal.jpg
deleted file mode 100644
index c98158a8a..000000000
Binary files a/content/identity/legal-implications-of-sso/sso-legal.jpg and /dev/null differ
diff --git a/content/identity/legal-implications-of-sso/sso-legal.webp b/content/identity/legal-implications-of-sso/sso-legal.webp
new file mode 100644
index 000000000..a9bd336bb
Binary files /dev/null and b/content/identity/legal-implications-of-sso/sso-legal.webp differ
diff --git a/content/identity/login-security/enterprise-buyer-guide-to-consumer-identity.png b/content/identity/login-security/enterprise-buyer-guide-to-consumer-identity.png
deleted file mode 100644
index b718f7f4b..000000000
Binary files a/content/identity/login-security/enterprise-buyer-guide-to-consumer-identity.png and /dev/null differ
diff --git a/content/identity/login-security/enterprise-buyer-guide-to-consumer-identity.webp b/content/identity/login-security/enterprise-buyer-guide-to-consumer-identity.webp
new file mode 100644
index 000000000..a57ab4fba
Binary files /dev/null and b/content/identity/login-security/enterprise-buyer-guide-to-consumer-identity.webp differ
diff --git a/content/identity/login-security/index.md b/content/identity/login-security/index.md
index 9ee5d541f..f79dfe1fc 100644
--- a/content/identity/login-security/index.md
+++ b/content/identity/login-security/index.md
@@ -1,7 +1,7 @@
---
title: "Login Security: 7 Best Practice to Keep Your Online Accounts Secure"
date: "2020-12-11"
-coverImage: "login-security.jpg"
+coverImage: "login-security.webp"
tags: ["data security","login security","mfa","ciam solution"]
author: "Rakesh Soni"
description: "In reality, there are so many mistakes that can make your account vulnerable to cyber attacks. Hackers can read your email, steal money out of your bank account, or sell your data in the dark web. Therefore you need to eliminate as many vulnerabilities as possible to keep your login safe."
@@ -43,7 +43,7 @@ It happens when hackers psychologically manipulate consumers into giving up thei
## 7 Best Login Security Practices That Enterprises Should Follow
-
+
Each risk has individual implications. Therefore, to keep your consumer's login secure, you need to prevent as many vulnerabilities as possible. Here are a few best login security practices that every organization should follow.
@@ -65,7 +65,7 @@ The greatest advantage of biometrics is that in order to gather the information
However, note that each security layer should be guarded by a different tags: something your consumers know, something they have, or something they are. For example, if your consumer has associated their phone number as the second layer of authentication, a one-time passcode (OTP) will be sent to the phone. So, if hackers do not have the phone, they cannot get the code, meaning they cannot log in.
-[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
+[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
### 4. Password hygiene is a necessity.
@@ -157,4 +157,4 @@ Protect your login information by using secure passwords, avoiding public Wi-Fi
Login security focuses on protecting the access to an account through authentication methods like passwords and biometrics. Rights security involves managing permissions and access levels within an account and determining what actions a user can perform once logged in.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=login-security)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=login-security)
\ No newline at end of file
diff --git a/content/identity/login-security/login-security-vulnerabilities.png b/content/identity/login-security/login-security-vulnerabilities.png
deleted file mode 100644
index 472a46820..000000000
Binary files a/content/identity/login-security/login-security-vulnerabilities.png and /dev/null differ
diff --git a/content/identity/login-security/login-security-vulnerabilities.webp b/content/identity/login-security/login-security-vulnerabilities.webp
new file mode 100644
index 000000000..3250de731
Binary files /dev/null and b/content/identity/login-security/login-security-vulnerabilities.webp differ
diff --git a/content/identity/login-security/login-security.jpg b/content/identity/login-security/login-security.jpg
deleted file mode 100644
index ba7b6cb14..000000000
Binary files a/content/identity/login-security/login-security.jpg and /dev/null differ
diff --git a/content/identity/login-security/login-security.png b/content/identity/login-security/login-security.png
deleted file mode 100644
index 820b55b84..000000000
Binary files a/content/identity/login-security/login-security.png and /dev/null differ
diff --git a/content/identity/login-security/login-security.webp b/content/identity/login-security/login-security.webp
new file mode 100644
index 000000000..fb6281d72
Binary files /dev/null and b/content/identity/login-security/login-security.webp differ
diff --git a/content/identity/login-using-microsoft-account/index.md b/content/identity/login-using-microsoft-account/index.md
index 1f581ed4c..bfcb448dc 100644
--- a/content/identity/login-using-microsoft-account/index.md
+++ b/content/identity/login-using-microsoft-account/index.md
@@ -1,7 +1,7 @@
---
title: "Login Using Microsoft Account"
date: "2021-04-15"
-coverImage: "login-using-microsoft-account.png"
+coverImage: "login-using-microsoft-account.webp"
tags: ["authentication"]
featured: false
author: "Vaibhav Jain"
@@ -65,4 +65,4 @@ In this article, we talked about applying [Social login](https://www.loginradius
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=login-using-microsoft-account)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=login-using-microsoft-account)
\ No newline at end of file
diff --git a/content/identity/login-using-microsoft-account/login-using-microsoft-account.png b/content/identity/login-using-microsoft-account/login-using-microsoft-account.png
deleted file mode 100644
index 9072a2465..000000000
Binary files a/content/identity/login-using-microsoft-account/login-using-microsoft-account.png and /dev/null differ
diff --git a/content/identity/login-using-microsoft-account/login-using-microsoft-account.webp b/content/identity/login-using-microsoft-account/login-using-microsoft-account.webp
new file mode 100644
index 000000000..a8dde18a9
Binary files /dev/null and b/content/identity/login-using-microsoft-account/login-using-microsoft-account.webp differ
diff --git a/content/identity/login-with-google-apps/google-apps-cover-pic.jpg b/content/identity/login-with-google-apps/google-apps-cover-pic.jpg
deleted file mode 100644
index 5512ac8fb..000000000
Binary files a/content/identity/login-with-google-apps/google-apps-cover-pic.jpg and /dev/null differ
diff --git a/content/identity/login-with-google-apps/google-apps-cover-pic.webp b/content/identity/login-with-google-apps/google-apps-cover-pic.webp
new file mode 100644
index 000000000..ed1c194df
Binary files /dev/null and b/content/identity/login-with-google-apps/google-apps-cover-pic.webp differ
diff --git a/content/identity/login-with-google-apps/index.md b/content/identity/login-with-google-apps/index.md
index 6ac4352a2..54f6e0cc6 100644
--- a/content/identity/login-with-google-apps/index.md
+++ b/content/identity/login-with-google-apps/index.md
@@ -1,7 +1,7 @@
---
title: "Login with Google Apps"
date: "2021-03-26"
-coverImage: "google-apps-cover-pic.jpg"
+coverImage: "google-apps-cover-pic.webp"
tags: ["authentication"]
featured: false
author: "Keshav Kumar"
@@ -116,4 +116,4 @@ Apart from the [privacy issues](https://www.loginradius.com/customer-security/),
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=login-with-google-apps)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=login-with-google-apps)
\ No newline at end of file
diff --git a/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/funding-img.png b/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/funding-img.png
deleted file mode 100644
index db212f84a..000000000
Binary files a/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/funding-img.png and /dev/null differ
diff --git a/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/funding-img.webp b/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/funding-img.webp
new file mode 100644
index 000000000..01086d884
Binary files /dev/null and b/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/funding-img.webp differ
diff --git a/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/index.md b/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/index.md
index 79679b430..edb2cebe9 100644
--- a/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/index.md
+++ b/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Announces $17M Series A Funding from ForgePoint and Microsoft"
date: "2018-07-24"
-coverImage: "loginradius-announces-17m-series-funding.jpg"
+coverImage: "loginradius-announces-17m-series-funding.webp"
tags: ["industry-news", "other"]
featured: false
author: "Rakesh Soni"
@@ -11,7 +11,7 @@ metadescription: "LoginRadius, led by ForgePoint Capital and Microsoft's venture
---
-[](https://www.loginradius.com/press/loginradius-announces-series-a-funding-from-forgepoint-and-microsoft-venture/)
+[](https://www.loginradius.com/press/loginradius-announces-series-a-funding-from-forgepoint-and-microsoft-venture/)
Today, I’m very excited to announce that [LoginRadius](https://www.loginradius.com/) has raised $17 million Series A funding, led by ForgePoint Capital and Microsoft’s venture fund, M12. In connection with the funding, both companies will also be joining our board to further our partnership, product and innovation cycles.
diff --git a/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/loginradius-announces-17m-series-funding.jpg b/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/loginradius-announces-17m-series-funding.jpg
deleted file mode 100644
index 812c1af1e..000000000
Binary files a/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/loginradius-announces-17m-series-funding.jpg and /dev/null differ
diff --git a/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/loginradius-announces-17m-series-funding.webp b/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/loginradius-announces-17m-series-funding.webp
new file mode 100644
index 000000000..9b4d94e1e
Binary files /dev/null and b/content/identity/loginradius-announces-17m-series-funding-forgepoint-microsoft/loginradius-announces-17m-series-funding.webp differ
diff --git a/content/identity/loginradius-announces-user-management/DS-LoginRadius-User-Management.png b/content/identity/loginradius-announces-user-management/DS-LoginRadius-User-Management.png
deleted file mode 100644
index def2f68e3..000000000
Binary files a/content/identity/loginradius-announces-user-management/DS-LoginRadius-User-Management.png and /dev/null differ
diff --git a/content/identity/loginradius-announces-user-management/DS-LoginRadius-User-Management.webp b/content/identity/loginradius-announces-user-management/DS-LoginRadius-User-Management.webp
new file mode 100644
index 000000000..7fce8ce75
Binary files /dev/null and b/content/identity/loginradius-announces-user-management/DS-LoginRadius-User-Management.webp differ
diff --git a/content/identity/loginradius-announces-user-management/image1.png b/content/identity/loginradius-announces-user-management/image1.png
deleted file mode 100644
index c1a64b8ff..000000000
Binary files a/content/identity/loginradius-announces-user-management/image1.png and /dev/null differ
diff --git a/content/identity/loginradius-announces-user-management/image1.webp b/content/identity/loginradius-announces-user-management/image1.webp
new file mode 100644
index 000000000..3e7515cdd
Binary files /dev/null and b/content/identity/loginradius-announces-user-management/image1.webp differ
diff --git a/content/identity/loginradius-announces-user-management/index.md b/content/identity/loginradius-announces-user-management/index.md
index 6b13eaee9..b91e50563 100644
--- a/content/identity/loginradius-announces-user-management/index.md
+++ b/content/identity/loginradius-announces-user-management/index.md
@@ -2,7 +2,7 @@
title: "Announcement – LoginRadius Announces the Availability of User Management"
date: "2020-09-30"
author: "Kundan Singh"
-coverImage: "image1.png"
+coverImage: "image1.webp"
tags: ["user management","identity management","password management"]
description: "Businesses will enjoy simplified access control and flexible rights for their customers with the newly added User Management functionality of LoginRadius."
metatitle: "Announcement - LoginRadius User Management | LoginRadius"
@@ -25,7 +25,7 @@ It also has been designed to help your business in the following ways:
- It reduces your team effort to maintain and manage consumer data.
- It helps you to migrate the existing consumer data from multiple sources.
-[](https://www.loginradius.com/resource/loginradius-ciam-user-management/)
+[](https://www.loginradius.com/resource/loginradius-ciam-user-management/)
## Key Capabilities of LoginRadius User Management
@@ -48,4 +48,4 @@ It also has been designed to help your business in the following ways:
The User Management feature by LoginRadius is unique in that it monitors and manages the entire consumer journey through automated access permissions, data migration, API support, and other consumer-centric solutions. Now, blend it with creating [meaningful relationships with your consumers](https://www.loginradius.com/customer-experience-solutions/)—that’s what we offer.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-announces-user-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-announces-user-management)
diff --git a/content/identity/loginradius-bans-zoom/Book-a-demo-1024x310.png b/content/identity/loginradius-bans-zoom/Book-a-demo-1024x310.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/loginradius-bans-zoom/Book-a-demo-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-bans-zoom/Book-a-demo-1024x310.webp b/content/identity/loginradius-bans-zoom/Book-a-demo-1024x310.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/loginradius-bans-zoom/Book-a-demo-1024x310.webp differ
diff --git a/content/identity/loginradius-bans-zoom/LoginRadius-Bans-Zoom.jpg b/content/identity/loginradius-bans-zoom/LoginRadius-Bans-Zoom.jpg
deleted file mode 100644
index 1a46c292d..000000000
Binary files a/content/identity/loginradius-bans-zoom/LoginRadius-Bans-Zoom.jpg and /dev/null differ
diff --git a/content/identity/loginradius-bans-zoom/LoginRadius-Bans-Zoom.webp b/content/identity/loginradius-bans-zoom/LoginRadius-Bans-Zoom.webp
new file mode 100644
index 000000000..05b9b625d
Binary files /dev/null and b/content/identity/loginradius-bans-zoom/LoginRadius-Bans-Zoom.webp differ
diff --git a/content/identity/loginradius-bans-zoom/index.md b/content/identity/loginradius-bans-zoom/index.md
index 93bcfcfed..c6d048722 100644
--- a/content/identity/loginradius-bans-zoom/index.md
+++ b/content/identity/loginradius-bans-zoom/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Bans Video Conferencing App ‘Zoom’ Over Security Concerns"
date: "2020-04-23"
-coverImage: "LoginRadius-Bans-Zoom.jpg"
+coverImage: "LoginRadius-Bans-Zoom.webp"
tags: ["industry-news"]
featured: false
author: "Rakesh Soni"
@@ -38,4 +38,4 @@ There is virtually no alternative to securing customer data than adopting string
We are always on the lookout to counter any disruption rising from potential threats that may affect our customers. We assure that personal assets remain protected, and we respond quickly in the event of a disaster.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-bans-zoom)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-bans-zoom)
diff --git a/content/identity/loginradius-business-continuity-covid-19-outbreak/CTA-Graphics-for-Blogs-V03.01-05-3-1024x310.png b/content/identity/loginradius-business-continuity-covid-19-outbreak/CTA-Graphics-for-Blogs-V03.01-05-3-1024x310.png
deleted file mode 100644
index a77a88ecc..000000000
Binary files a/content/identity/loginradius-business-continuity-covid-19-outbreak/CTA-Graphics-for-Blogs-V03.01-05-3-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-business-continuity-covid-19-outbreak/CTA-Graphics-for-Blogs-V03.01-05-3-1024x310.webp b/content/identity/loginradius-business-continuity-covid-19-outbreak/CTA-Graphics-for-Blogs-V03.01-05-3-1024x310.webp
new file mode 100644
index 000000000..53eae8e39
Binary files /dev/null and b/content/identity/loginradius-business-continuity-covid-19-outbreak/CTA-Graphics-for-Blogs-V03.01-05-3-1024x310.webp differ
diff --git a/content/identity/loginradius-business-continuity-covid-19-outbreak/index.md b/content/identity/loginradius-business-continuity-covid-19-outbreak/index.md
index bfad315ff..99e20fef0 100644
--- a/content/identity/loginradius-business-continuity-covid-19-outbreak/index.md
+++ b/content/identity/loginradius-business-continuity-covid-19-outbreak/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Announces Its Business Continuity Plan to Fight COVID-19 Outbreak"
date: "2020-03-17"
-coverImage: "loginradius-business-continuity.png"
+coverImage: "loginradius-business-continuity.webp"
tags: ["LoginRadius" , "industry-news"]
featured: false
author: "Rakesh Soni"
@@ -58,4 +58,4 @@ We place the highest value on the partnerships that we've established with our c
In the end, we wish our customers health, security, and good fortune.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-business-continuity-covid-19-outbreak)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-business-continuity-covid-19-outbreak)
diff --git a/content/identity/loginradius-business-continuity-covid-19-outbreak/loginradius-business-continuity.png b/content/identity/loginradius-business-continuity-covid-19-outbreak/loginradius-business-continuity.png
deleted file mode 100644
index 25861421b..000000000
Binary files a/content/identity/loginradius-business-continuity-covid-19-outbreak/loginradius-business-continuity.png and /dev/null differ
diff --git a/content/identity/loginradius-business-continuity-covid-19-outbreak/loginradius-business-continuity.webp b/content/identity/loginradius-business-continuity-covid-19-outbreak/loginradius-business-continuity.webp
new file mode 100644
index 000000000..07ec4ac8b
Binary files /dev/null and b/content/identity/loginradius-business-continuity-covid-19-outbreak/loginradius-business-continuity.webp differ
diff --git a/content/identity/loginradius-ceo-shifting-data-strategies/index.md b/content/identity/loginradius-ceo-shifting-data-strategies/index.md
index a5e8ce57a..985a169b5 100644
--- a/content/identity/loginradius-ceo-shifting-data-strategies/index.md
+++ b/content/identity/loginradius-ceo-shifting-data-strategies/index.md
@@ -1,7 +1,7 @@
---
title: "Privacy-Centric Enhancements: CEO Rakesh Soni Shares His Thoughts on Shifting Data Strategies"
date: "2022-08-02"
-coverImage: "privacy-centric.jpg"
+coverImage: "privacy-centric.webp"
tags: ["data privacy", "cloud computing", "progressive profiling"]
author: "Rakesh Soni"
description: "With more and more businesses taking place online and grappling with the new privacy and data security complexities, there’s an immediate need to reinvent data management strategies. Let’s understand the role of privacy and data management and how businesses can take the competitive edge."
@@ -82,4 +82,4 @@ The modern digital business landscape has offered endless opportunities for ente
Whether it’s the incorporation of a reliable CIAM or other privacy management solutions, brands have to put their best efforts into ensuring robust privacy management.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-ceo-shifting-data-strategies)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-ceo-shifting-data-strategies)
diff --git a/content/identity/loginradius-ceo-shifting-data-strategies/privacy-centric.jpg b/content/identity/loginradius-ceo-shifting-data-strategies/privacy-centric.jpg
deleted file mode 100644
index 124bd5a3e..000000000
Binary files a/content/identity/loginradius-ceo-shifting-data-strategies/privacy-centric.jpg and /dev/null differ
diff --git a/content/identity/loginradius-ceo-shifting-data-strategies/privacy-centric.webp b/content/identity/loginradius-ceo-shifting-data-strategies/privacy-centric.webp
new file mode 100644
index 000000000..e2e14ef7c
Binary files /dev/null and b/content/identity/loginradius-ceo-shifting-data-strategies/privacy-centric.webp differ
diff --git a/content/identity/loginradius-ciam-china-business/BD-Developers2-1024x310.png b/content/identity/loginradius-ciam-china-business/BD-Developers2-1024x310.png
deleted file mode 100644
index e794b3769..000000000
Binary files a/content/identity/loginradius-ciam-china-business/BD-Developers2-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-ciam-china-business/BD-Developers2-1024x310.webp b/content/identity/loginradius-ciam-china-business/BD-Developers2-1024x310.webp
new file mode 100644
index 000000000..371ef34ea
Binary files /dev/null and b/content/identity/loginradius-ciam-china-business/BD-Developers2-1024x310.webp differ
diff --git a/content/identity/loginradius-ciam-china-business/DS-Product-Chinese-CIAM-1024x310.png b/content/identity/loginradius-ciam-china-business/DS-Product-Chinese-CIAM-1024x310.png
deleted file mode 100644
index 2bf50470e..000000000
Binary files a/content/identity/loginradius-ciam-china-business/DS-Product-Chinese-CIAM-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-ciam-china-business/DS-Product-Chinese-CIAM-1024x310.webp b/content/identity/loginradius-ciam-china-business/DS-Product-Chinese-CIAM-1024x310.webp
new file mode 100644
index 000000000..f507fb3f4
Binary files /dev/null and b/content/identity/loginradius-ciam-china-business/DS-Product-Chinese-CIAM-1024x310.webp differ
diff --git a/content/identity/loginradius-ciam-china-business/LoginRadius-China-CIAM.jpg b/content/identity/loginradius-ciam-china-business/LoginRadius-China-CIAM.jpg
deleted file mode 100644
index 7ecd7b844..000000000
Binary files a/content/identity/loginradius-ciam-china-business/LoginRadius-China-CIAM.jpg and /dev/null differ
diff --git a/content/identity/loginradius-ciam-china-business/LoginRadius-China-CIAM.webp b/content/identity/loginradius-ciam-china-business/LoginRadius-China-CIAM.webp
new file mode 100644
index 000000000..0a7c03e65
Binary files /dev/null and b/content/identity/loginradius-ciam-china-business/LoginRadius-China-CIAM.webp differ
diff --git a/content/identity/loginradius-ciam-china-business/index.md b/content/identity/loginradius-ciam-china-business/index.md
index 4978a12bd..1a9739fb7 100644
--- a/content/identity/loginradius-ciam-china-business/index.md
+++ b/content/identity/loginradius-ciam-china-business/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - LoginRadius China CIAM for Businesses to Benefit From Its Lucrative Market"
date: "2020-05-14"
-coverImage: "LoginRadius-China-CIAM.jpg"
+coverImage: "LoginRadius-China-CIAM.webp"
tags: ["industry-news"]
featured: false
author: "Rakesh Soni"
@@ -30,7 +30,7 @@ We ensure that our LoginRadius China [customer identity and access management](h
**Multilingual Support**: The LoginRadius China CIAM solution provides local language support through simplified and traditional Chinese. Businesses can easily configure language settings too.
-[](https://www.loginradius.com/resource/loginradius-china-ciam)
+[](https://www.loginradius.com/resource/loginradius-china-ciam)
## A Final Word
@@ -38,4 +38,4 @@ Privacy and security rule everything in China. With the LoginRadius China custom
From social integration, [strong authentication](https://www.loginradius.com/multi-factor-authentication/), local language support to meeting the standard regional regulatory compliances, they are the key areas no clients should worry about.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-ciam-china-business)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-ciam-china-business)
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/Book-a-free-demo-request-1024x310.png b/content/identity/loginradius-ciam-retail-ecommerce-business/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/loginradius-ciam-retail-ecommerce-business/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/Book-a-free-demo-request-1024x310.webp b/content/identity/loginradius-ciam-retail-ecommerce-business/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/loginradius-ciam-retail-ecommerce-business/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius-Identity-Platform-1024x310.png b/content/identity/loginradius-ciam-retail-ecommerce-business/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius-Identity-Platform-1024x310.png
deleted file mode 100644
index b53535020..000000000
Binary files a/content/identity/loginradius-ciam-retail-ecommerce-business/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius-Identity-Platform-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius-Identity-Platform-1024x310.webp b/content/identity/loginradius-ciam-retail-ecommerce-business/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius-Identity-Platform-1024x310.webp
new file mode 100644
index 000000000..02dbccb4e
Binary files /dev/null and b/content/identity/loginradius-ciam-retail-ecommerce-business/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius-Identity-Platform-1024x310.webp differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/index.md b/content/identity/loginradius-ciam-retail-ecommerce-business/index.md
index 69984a527..24bd2dfdf 100644
--- a/content/identity/loginradius-ciam-retail-ecommerce-business/index.md
+++ b/content/identity/loginradius-ciam-retail-ecommerce-business/index.md
@@ -1,7 +1,7 @@
---
title: "How LoginRadius Help Retail and E-commerce Industry to Manage Customer Identities"
date: "2020-04-08"
-coverImage: "retail-ecommerce.jpg"
+coverImage: "retail-ecommerce.webp"
tags: ["ciam solution","compliance","cx"]
author: "Rakesh Soni"
description: "As the retail and e-commerce industry enters the modern digitalization age, a giant leap forward has been made by consumer experience when engaging with a brand. In reality, it has moved goods and services into the overall shopping experience as a secondary entity. For customers, they are no longer the motivating impetus to approach a store."
@@ -63,7 +63,7 @@ Among its solutions include the real-time ability for visitors to self-register
Retailers can manage customer profiles and provide a [personalized omnichannel experience](https://www.loginradius.com/blog/2020/04/omnichannel-customer-experience/) with consent and other preferences.
-
+
### Improving Registration and Login Options
@@ -85,7 +85,7 @@ The concept of progressive profiling is getting a lot of attention these days. S
Here's how this works. For example, you want some details from your customers to customize the end-user experience, or you want their consent to use some of your services, but you are afraid of losing them by asking to fill a long registration form.
-[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
+[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
Progressive profiling will do wonders here. For instance, when the customer has placed the first three orders, you can ask them to fill in a small questionnaire. They will more likely answer about their preferences at this stage rather than during the registration.
@@ -103,7 +103,7 @@ LoginRadius simplifies the shopper registration process with social sign-in and
**Single Sign-On:** It means a customer can access multiple accounts with a [single set of credentials](https://www.loginradius.com/blog/2019/05/what-is-single-sign-on/). It offers ease of authentication and reduces the risk of minimizing poor password habits.
-
+
### Providing Customer Security
@@ -127,7 +127,7 @@ The LoginRadius identity platform protects customers and retailers from attacks
For any retailer, account management, verification, and password management is a huge deal. But when it comes to relying on an identity management provider platform, account management seems tricky and often falls short of expectations.
-
+
LoginRadius offers the following security benefits in the e-commerce spectrum.
@@ -142,4 +142,4 @@ Security and seamless customer experience in the retail and e-commerce industry
But, there is no magic formula for mastering security. So, if you are not careful, you can lose your customers' trust. Plan and give your shoppers a hassle-free experience with your brand, every time.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-ciam-retail-ecommerce-business)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-ciam-retail-ecommerce-business)
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-3-1024x560.jpg b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-3-1024x560.jpg
deleted file mode 100644
index 89690a1c7..000000000
Binary files a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-3-1024x560.jpg and /dev/null differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-3-1024x560.webp b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-3-1024x560.webp
new file mode 100644
index 000000000..b2be955fe
Binary files /dev/null and b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-3-1024x560.webp differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-4-1024x620.jpg b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-4-1024x620.jpg
deleted file mode 100644
index 92345ed27..000000000
Binary files a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-4-1024x620.jpg and /dev/null differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-4-1024x620.webp b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-4-1024x620.webp
new file mode 100644
index 000000000..f976ad515
Binary files /dev/null and b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-4-1024x620.webp differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business-1.jpg b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business-1.jpg
deleted file mode 100644
index 2d01939df..000000000
Binary files a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business-1.jpg and /dev/null differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business-1.webp b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business-1.webp
new file mode 100644
index 000000000..662e54489
Binary files /dev/null and b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business-1.webp differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business.jpg b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business.jpg
deleted file mode 100644
index cd93a74e4..000000000
Binary files a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business.jpg and /dev/null differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business.webp b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business.webp
new file mode 100644
index 000000000..27cffd5c0
Binary files /dev/null and b/content/identity/loginradius-ciam-retail-ecommerce-business/loginradius-ciam-retail-ecommerce-business.webp differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/retail-ecommerce.jpg b/content/identity/loginradius-ciam-retail-ecommerce-business/retail-ecommerce.jpg
deleted file mode 100644
index 7d7e15a77..000000000
Binary files a/content/identity/loginradius-ciam-retail-ecommerce-business/retail-ecommerce.jpg and /dev/null differ
diff --git a/content/identity/loginradius-ciam-retail-ecommerce-business/retail-ecommerce.webp b/content/identity/loginradius-ciam-retail-ecommerce-business/retail-ecommerce.webp
new file mode 100644
index 000000000..ec6e7c0ec
Binary files /dev/null and b/content/identity/loginradius-ciam-retail-ecommerce-business/retail-ecommerce.webp differ
diff --git a/content/identity/loginradius-consumer-audit-trail-data-analysis/Book-a-free-demo-request-1024x310.png b/content/identity/loginradius-consumer-audit-trail-data-analysis/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/loginradius-consumer-audit-trail-data-analysis/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-audit-trail-data-analysis/Book-a-free-demo-request-1024x310.webp b/content/identity/loginradius-consumer-audit-trail-data-analysis/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/loginradius-consumer-audit-trail-data-analysis/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/loginradius-consumer-audit-trail-data-analysis/Consumer-Audit-Trail.jpg b/content/identity/loginradius-consumer-audit-trail-data-analysis/Consumer-Audit-Trail.jpg
deleted file mode 100644
index 71f392ad7..000000000
Binary files a/content/identity/loginradius-consumer-audit-trail-data-analysis/Consumer-Audit-Trail.jpg and /dev/null differ
diff --git a/content/identity/loginradius-consumer-audit-trail-data-analysis/Consumer-Audit-Trail.webp b/content/identity/loginradius-consumer-audit-trail-data-analysis/Consumer-Audit-Trail.webp
new file mode 100644
index 000000000..4247b4aaf
Binary files /dev/null and b/content/identity/loginradius-consumer-audit-trail-data-analysis/Consumer-Audit-Trail.webp differ
diff --git a/content/identity/loginradius-consumer-audit-trail-data-analysis/Core-Capabilities-of-LoginRadius-Consumer-Audit-Trail.jpg b/content/identity/loginradius-consumer-audit-trail-data-analysis/Core-Capabilities-of-LoginRadius-Consumer-Audit-Trail.jpg
deleted file mode 100644
index 22796a459..000000000
Binary files a/content/identity/loginradius-consumer-audit-trail-data-analysis/Core-Capabilities-of-LoginRadius-Consumer-Audit-Trail.jpg and /dev/null differ
diff --git a/content/identity/loginradius-consumer-audit-trail-data-analysis/Core-Capabilities-of-LoginRadius-Consumer-Audit-Trail.webp b/content/identity/loginradius-consumer-audit-trail-data-analysis/Core-Capabilities-of-LoginRadius-Consumer-Audit-Trail.webp
new file mode 100644
index 000000000..e0b72ed07
Binary files /dev/null and b/content/identity/loginradius-consumer-audit-trail-data-analysis/Core-Capabilities-of-LoginRadius-Consumer-Audit-Trail.webp differ
diff --git a/content/identity/loginradius-consumer-audit-trail-data-analysis/DS-Cosumer-Audit-Trail-1024x310.jpg b/content/identity/loginradius-consumer-audit-trail-data-analysis/DS-Cosumer-Audit-Trail-1024x310.jpg
deleted file mode 100644
index 6813da59e..000000000
Binary files a/content/identity/loginradius-consumer-audit-trail-data-analysis/DS-Cosumer-Audit-Trail-1024x310.jpg and /dev/null differ
diff --git a/content/identity/loginradius-consumer-audit-trail-data-analysis/DS-Cosumer-Audit-Trail-1024x310.webp b/content/identity/loginradius-consumer-audit-trail-data-analysis/DS-Cosumer-Audit-Trail-1024x310.webp
new file mode 100644
index 000000000..98ab6a778
Binary files /dev/null and b/content/identity/loginradius-consumer-audit-trail-data-analysis/DS-Cosumer-Audit-Trail-1024x310.webp differ
diff --git a/content/identity/loginradius-consumer-audit-trail-data-analysis/index.md b/content/identity/loginradius-consumer-audit-trail-data-analysis/index.md
index af9120142..f1f406b0c 100644
--- a/content/identity/loginradius-consumer-audit-trail-data-analysis/index.md
+++ b/content/identity/loginradius-consumer-audit-trail-data-analysis/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Approves Consumer Audit Trail for In-Depth Data Analysis and Risk Assessment"
date: "2020-07-02"
-coverImage: "Consumer-Audit-Trail.jpg"
+coverImage: "Consumer-Audit-Trail.webp"
tags: ["industry-news"]
featured: false
author: "Rakesh Soni"
@@ -26,7 +26,7 @@ In addition, audit logs can be used to gain deeper insights into an identity clo
## Core Capabilities of LoginRadius Consumer Audit Trail
-
+
- **Data Collection**: The LoginRadius Data Management Platform gathers data from various sources, APIs, and even from migrated data to enrich the user profile data.
- **Secure Data Management**: It offers end-to-end encryption at rest and in transit and ensures [data collection within the compliance](https://www.loginradius.com/data-governance/) boundaries of social networks and website privacy policy terms.
@@ -38,7 +38,7 @@ In addition, audit logs can be used to gain deeper insights into an identity clo
- **Incident Response**: It provides case management, collaboration, and knowledge sharing around security incidents.
- **SIEM Complete Solution Analytics**: LoginRadius offers its SIEM solution via integration to showcase the analytical details for business decisions. It supports integrations with most-used tools like Splunk, logstash, sumo logic, etc.
-[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail/)
+[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail/)
## A Final Word
@@ -46,4 +46,4 @@ The world that we live in today falls under several regulatory laws - be it [the
The LoginRadius' Consumer AuditTrail feature plays a vital role in the maintenance, security, availability, and integrity of the records so businesses can understand the [bigger picture in the cybersecurity threat](https://www.loginradius.com/blog/identity/cyber-threats-business-risk-covid-19/) landscape.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-consumer-audit-trail-data-analysis)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-consumer-audit-trail-data-analysis)
diff --git a/content/identity/loginradius-consumer-digital-identity-report-2023/Infographic-IR-2023.png b/content/identity/loginradius-consumer-digital-identity-report-2023/Infographic-IR-2023.png
deleted file mode 100644
index 01cbf3503..000000000
Binary files a/content/identity/loginradius-consumer-digital-identity-report-2023/Infographic-IR-2023.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-digital-identity-report-2023/Infographic-IR-2023.webp b/content/identity/loginradius-consumer-digital-identity-report-2023/Infographic-IR-2023.webp
new file mode 100644
index 000000000..41bf576c7
Binary files /dev/null and b/content/identity/loginradius-consumer-digital-identity-report-2023/Infographic-IR-2023.webp differ
diff --git a/content/identity/loginradius-consumer-digital-identity-report-2023/RP-Industry-Report-2023.png b/content/identity/loginradius-consumer-digital-identity-report-2023/RP-Industry-Report-2023.png
deleted file mode 100644
index bf131da86..000000000
Binary files a/content/identity/loginradius-consumer-digital-identity-report-2023/RP-Industry-Report-2023.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-digital-identity-report-2023/RP-Industry-Report-2023.webp b/content/identity/loginradius-consumer-digital-identity-report-2023/RP-Industry-Report-2023.webp
new file mode 100644
index 000000000..a34c8a9cc
Binary files /dev/null and b/content/identity/loginradius-consumer-digital-identity-report-2023/RP-Industry-Report-2023.webp differ
diff --git a/content/identity/loginradius-consumer-digital-identity-report-2023/consumer-identity-trends-report-2023.png b/content/identity/loginradius-consumer-digital-identity-report-2023/consumer-identity-trends-report-2023.png
deleted file mode 100644
index 2ed7bfbaa..000000000
Binary files a/content/identity/loginradius-consumer-digital-identity-report-2023/consumer-identity-trends-report-2023.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-digital-identity-report-2023/consumer-identity-trends-report-2023.webp b/content/identity/loginradius-consumer-digital-identity-report-2023/consumer-identity-trends-report-2023.webp
new file mode 100644
index 000000000..215a8a695
Binary files /dev/null and b/content/identity/loginradius-consumer-digital-identity-report-2023/consumer-identity-trends-report-2023.webp differ
diff --git a/content/identity/loginradius-consumer-digital-identity-report-2023/index.md b/content/identity/loginradius-consumer-digital-identity-report-2023/index.md
index 6f5abf191..b497d1a02 100644
--- a/content/identity/loginradius-consumer-digital-identity-report-2023/index.md
+++ b/content/identity/loginradius-consumer-digital-identity-report-2023/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Releases Consumer Identity Trend Report 2023, Highlights The Future of Customer Identity"
date: "2023-05-04"
-coverImage: "consumer-identity-trends-report-2023.png"
+coverImage: "consumer-identity-trends-report-2023.webp"
tags: ["industry-news", "consumer-identity", "identity-trends", "digital-identity"]
author: "Rakesh Soni"
description: "LoginRadius has conducted a comprehensive analysis of its global customer base over the past year. The result is an annual report on Consumer Identity Trends for 2023, which showcases over 40 unique insights and observations."
@@ -29,7 +29,7 @@ The report shows that businesses that offer passwordless login or multi-factor a
Additionally, implementing these authentication methods can help businesses mitigate the risk of identity theft and fraud. By providing a frictionless authentication experience, businesses can enhance the customer journey, increase customer loyalty, and ultimately drive business growth.
-[](https://www.loginradius.com/resource/consumer-digital-identity-trend-report-2023)
+[](https://www.loginradius.com/resource/consumer-digital-identity-trend-report-2023)
## Key Highlights of the Consumer Identity Report 2023
@@ -42,7 +42,7 @@ As a leading provider of [Customer Identity and Access Management](https://www.l
Some more findings of the report have been outlined in the infographic below.
-
+
Overall, the CIAM trend report highlights the following:
@@ -60,4 +60,4 @@ The findings of this report are essential for those seeking to enhance their cus
**Download your complimentary copy** of the report today and stay ahead of the curve in the ever-evolving future of digital identity management.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-consumer-digital-identity-report-2023)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-consumer-digital-identity-report-2023)
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/LoginRadius-Consumer-Identity-Trend-Report.png b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/LoginRadius-Consumer-Identity-Trend-Report.png
deleted file mode 100644
index 365a0ed8d..000000000
Binary files a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/LoginRadius-Consumer-Identity-Trend-Report.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/LoginRadius-Consumer-Identity-Trend-Report.webp b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/LoginRadius-Consumer-Identity-Trend-Report.webp
new file mode 100644
index 000000000..5c6a31469
Binary files /dev/null and b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/LoginRadius-Consumer-Identity-Trend-Report.webp differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Login-Preferences-by-age.png b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Login-Preferences-by-age.png
deleted file mode 100644
index 2713eb901..000000000
Binary files a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Login-Preferences-by-age.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Login-Preferences-by-age.webp b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Login-Preferences-by-age.webp
new file mode 100644
index 000000000..e3a9e4fe5
Binary files /dev/null and b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Login-Preferences-by-age.webp differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Social-Login-Preference-by-End-Users.png b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Social-Login-Preference-by-End-Users.png
deleted file mode 100644
index 23dcd151f..000000000
Binary files a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Social-Login-Preference-by-End-Users.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Social-Login-Preference-by-End-Users.webp b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Social-Login-Preference-by-End-Users.webp
new file mode 100644
index 000000000..18b5ca7b8
Binary files /dev/null and b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Social-Login-Preference-by-End-Users.webp differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Standard-Login-Trends-Registration-Forms.png b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Standard-Login-Trends-Registration-Forms.png
deleted file mode 100644
index dcfc700a1..000000000
Binary files a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Standard-Login-Trends-Registration-Forms.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Standard-Login-Trends-Registration-Forms.webp b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Standard-Login-Trends-Registration-Forms.webp
new file mode 100644
index 000000000..38e55000a
Binary files /dev/null and b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-Standard-Login-Trends-Registration-Forms.webp differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-consumer-identity-report-2020-Login-Preference-by-Businesses.png b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-consumer-identity-report-2020-Login-Preference-by-Businesses.png
deleted file mode 100644
index 426cfae8f..000000000
Binary files a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-consumer-identity-report-2020-Login-Preference-by-Businesses.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-consumer-identity-report-2020-Login-Preference-by-Businesses.webp b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-consumer-identity-report-2020-Login-Preference-by-Businesses.webp
new file mode 100644
index 000000000..5e79eace7
Binary files /dev/null and b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/Loginradius-consumer-identity-report-2020-Login-Preference-by-Businesses.webp differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-report-loginradius.png b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-report-loginradius.png
deleted file mode 100644
index 1ad3861a7..000000000
Binary files a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-report-loginradius.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-report-loginradius.webp b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-report-loginradius.webp
new file mode 100644
index 000000000..a22d7a86a
Binary files /dev/null and b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-report-loginradius.webp differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-trends-2020.png b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-trends-2020.png
deleted file mode 100644
index 4c09a7da4..000000000
Binary files a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-trends-2020.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-trends-2020.webp b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-trends-2020.webp
new file mode 100644
index 000000000..0048acd38
Binary files /dev/null and b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/consumer-identity-trends-2020.webp differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/digital.png b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/digital.png
deleted file mode 100644
index 6c22a1aa5..000000000
Binary files a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/digital.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/digital.webp b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/digital.webp
new file mode 100644
index 000000000..a22d7a86a
Binary files /dev/null and b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/digital.webp differ
diff --git a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/index.md b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/index.md
index 36f0a1d57..d3afd00f3 100644
--- a/content/identity/loginradius-consumer-digital-identity-trend-report-2020/index.md
+++ b/content/identity/loginradius-consumer-digital-identity-trend-report-2020/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Releases Consumer Digital Identity Trend Report 2020"
date: "2020-09-02"
-coverImage: "consumer-identity-report-loginradius.png"
+coverImage: "consumer-identity-report-loginradius.webp"
tags: ["industry news","consumer identity","digital identity"]
author: "Rakesh Soni"
description: "LoginRadius, a pioneer in cloud-based customer identity and access management (CIAM) solution, has released an industry report titled 'Consumer Identity Trend 2020' for C-suite professionals and B2C business product managers concerned with customer identity."
@@ -35,9 +35,9 @@ The key findings of the report have been outlined in the infographic below. It w
The report is available for download. [Request your copy here](https://www.loginradius.com/resource/digital-identity-trends-2020/).
-
+
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-consumer-digital-identity-trend-report-2020)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-consumer-digital-identity-trend-report-2020)
diff --git a/content/identity/loginradius-consumer-identity-trend-report-2022/RP-2022.png b/content/identity/loginradius-consumer-identity-trend-report-2022/RP-2022.png
deleted file mode 100644
index 76a494caf..000000000
Binary files a/content/identity/loginradius-consumer-identity-trend-report-2022/RP-2022.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-identity-trend-report-2022/RP-2022.webp b/content/identity/loginradius-consumer-identity-trend-report-2022/RP-2022.webp
new file mode 100644
index 000000000..0d19ff68b
Binary files /dev/null and b/content/identity/loginradius-consumer-identity-trend-report-2022/RP-2022.webp differ
diff --git a/content/identity/loginradius-consumer-identity-trend-report-2022/index.md b/content/identity/loginradius-consumer-identity-trend-report-2022/index.md
index 10f3609b6..8d7aa8006 100644
--- a/content/identity/loginradius-consumer-identity-trend-report-2022/index.md
+++ b/content/identity/loginradius-consumer-identity-trend-report-2022/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Releases Consumer Identity Trend Report 2022, Key Login Methods Highlighted"
date: "2022-04-27"
-coverImage: "report-cover.jpg"
+coverImage: "report-cover.webp"
tags: ["industry-news", "consumer-identity", "identity-trends", "digital-identity"]
author: "Rakesh Soni"
description: "As a company strongly focused on CIAM, LoginRadius analyzed its global customers over the past year and compiled over 40 unique trends in its annual Consumer Identity Trend report 2022."
@@ -24,7 +24,7 @@ The report findings highlight that if your business wants to stand out in a high
Businesses can achieve this by tailoring authentication and login methods to their customers' preferences, such as passwordless login or multi-factor authentication via email or SMS, or social sign-on.
-[](https://www.loginradius.com/resource/consumer-digital-identity-trend-report-2022)
+[](https://www.loginradius.com/resource/consumer-digital-identity-trend-report-2022)
## Key Highlights of the Consumer Identity Report 2022
@@ -40,7 +40,7 @@ As a company strongly focused on CIAM, we analyzed our global customers over the
Some more findings of the report have been outlined in the infographic below.
-
+
Overall, the CIAM trend report highlights:
@@ -61,4 +61,4 @@ If you are trying to improve your customer experience, the finding of this repor
Download a complimentary copy of the LoginRadius [Consumer Identity Trend Report](https://www.loginradius.com/resource/consumer-digital-identity-trend-report-2022) here.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-consumer-identity-trend-report-2022)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-consumer-identity-trend-report-2022)
diff --git a/content/identity/loginradius-consumer-identity-trend-report-2022/infographic-report-22.png b/content/identity/loginradius-consumer-identity-trend-report-2022/infographic-report-22.png
deleted file mode 100644
index aebecb049..000000000
Binary files a/content/identity/loginradius-consumer-identity-trend-report-2022/infographic-report-22.png and /dev/null differ
diff --git a/content/identity/loginradius-consumer-identity-trend-report-2022/infographic-report-22.webp b/content/identity/loginradius-consumer-identity-trend-report-2022/infographic-report-22.webp
new file mode 100644
index 000000000..c5c0b8b63
Binary files /dev/null and b/content/identity/loginradius-consumer-identity-trend-report-2022/infographic-report-22.webp differ
diff --git a/content/identity/loginradius-consumer-identity-trend-report-2022/report-cover.jpg b/content/identity/loginradius-consumer-identity-trend-report-2022/report-cover.jpg
deleted file mode 100644
index a76670d85..000000000
Binary files a/content/identity/loginradius-consumer-identity-trend-report-2022/report-cover.jpg and /dev/null differ
diff --git a/content/identity/loginradius-consumer-identity-trend-report-2022/report-cover.webp b/content/identity/loginradius-consumer-identity-trend-report-2022/report-cover.webp
new file mode 100644
index 000000000..d746c9763
Binary files /dev/null and b/content/identity/loginradius-consumer-identity-trend-report-2022/report-cover.webp differ
diff --git a/content/identity/loginradius-creates-trusted-digital-experience/digital-exp.jpg b/content/identity/loginradius-creates-trusted-digital-experience/digital-exp.jpg
deleted file mode 100644
index 4b7127ece..000000000
Binary files a/content/identity/loginradius-creates-trusted-digital-experience/digital-exp.jpg and /dev/null differ
diff --git a/content/identity/loginradius-creates-trusted-digital-experience/digital-exp.webp b/content/identity/loginradius-creates-trusted-digital-experience/digital-exp.webp
new file mode 100644
index 000000000..da7f01806
Binary files /dev/null and b/content/identity/loginradius-creates-trusted-digital-experience/digital-exp.webp differ
diff --git a/content/identity/loginradius-creates-trusted-digital-experience/index.md b/content/identity/loginradius-creates-trusted-digital-experience/index.md
index d55d70f0d..e3b93a03d 100644
--- a/content/identity/loginradius-creates-trusted-digital-experience/index.md
+++ b/content/identity/loginradius-creates-trusted-digital-experience/index.md
@@ -1,7 +1,7 @@
---
title: "How LoginRadius Creates a Perfect Harmony of UX and Security"
date: "2022-02-04"
-coverImage: "digital-exp.jpg"
+coverImage: "digital-exp.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -98,4 +98,4 @@ Learn more about the LoginRadius Identity Platform, starting with a [Quick Perso
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-creates-trusted-digital-experience)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-creates-trusted-digital-experience)
\ No newline at end of file
diff --git a/content/identity/loginradius-federated-identity-management/DS-Product-Federated-Identity-Management-1.png b/content/identity/loginradius-federated-identity-management/DS-Product-Federated-Identity-Management-1.png
deleted file mode 100644
index 40f7ca68d..000000000
Binary files a/content/identity/loginradius-federated-identity-management/DS-Product-Federated-Identity-Management-1.png and /dev/null differ
diff --git a/content/identity/loginradius-federated-identity-management/DS-Product-Federated-Identity-Management-1.webp b/content/identity/loginradius-federated-identity-management/DS-Product-Federated-Identity-Management-1.webp
new file mode 100644
index 000000000..2440c699e
Binary files /dev/null and b/content/identity/loginradius-federated-identity-management/DS-Product-Federated-Identity-Management-1.webp differ
diff --git a/content/identity/loginradius-federated-identity-management/fim-image.jpg b/content/identity/loginradius-federated-identity-management/fim-image.jpg
deleted file mode 100644
index 767d01903..000000000
Binary files a/content/identity/loginradius-federated-identity-management/fim-image.jpg and /dev/null differ
diff --git a/content/identity/loginradius-federated-identity-management/fim-image.webp b/content/identity/loginradius-federated-identity-management/fim-image.webp
new file mode 100644
index 000000000..487427bb9
Binary files /dev/null and b/content/identity/loginradius-federated-identity-management/fim-image.webp differ
diff --git a/content/identity/loginradius-federated-identity-management/image-2.png b/content/identity/loginradius-federated-identity-management/image-2.png
deleted file mode 100644
index eb2343833..000000000
Binary files a/content/identity/loginradius-federated-identity-management/image-2.png and /dev/null differ
diff --git a/content/identity/loginradius-federated-identity-management/image-2.webp b/content/identity/loginradius-federated-identity-management/image-2.webp
new file mode 100644
index 000000000..75835828e
Binary files /dev/null and b/content/identity/loginradius-federated-identity-management/image-2.webp differ
diff --git a/content/identity/loginradius-federated-identity-management/index.md b/content/identity/loginradius-federated-identity-management/index.md
index d83b08b10..4bd21ff00 100644
--- a/content/identity/loginradius-federated-identity-management/index.md
+++ b/content/identity/loginradius-federated-identity-management/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - LoginRadius Simplifies the Implementation of Federated SSO With Federated Identity Management"
date: "2020-10-15"
-coverImage: "fim-image.jpg"
+coverImage: "fim-image.webp"
tags: ["industry-news"]
featured: false
author: "Kundan Singh"
@@ -19,7 +19,7 @@ The recently launched Federated Identity Management by LoginRadius is an arrange
Federated Identity Management by LoginRadius helps businesses and applications use a single set of identity data. Consumers need not create multiple accounts for multiple organizations to access their web applications. These applications do not communicate with each other directly and standard SSO protocols like JWT, SAML, OAuth 2.0, OIDC etc are used to establish the communication.
-[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
+[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
[Federated Identity Management](https://www.loginradius.com/federated-sso/) is designed by LoginRadius to help your business in the following ways:
@@ -33,7 +33,7 @@ Federated Identity Management by LoginRadius helps businesses and applications u
**Key Capabilities of Federated Identity Management by LoginRadius**
-
+
1\. **Support for industry-standard SSO protocols**: LoginRadius supports the following standard SSO protocols:
@@ -53,4 +53,4 @@ Federated Identity Management by LoginRadius helps businesses and applications u
Federated Identity Management by LoginRadius is a way to connect multiple web applications and services using the same identity data. It’s a many to one mapping to help your consumers access your business and partners with a single credential set.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-federated-identity-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-federated-identity-management)
diff --git a/content/identity/loginradius-identity-brokering/identity-brokering.png b/content/identity/loginradius-identity-brokering/identity-brokering.png
deleted file mode 100644
index 1ddd4d0da..000000000
Binary files a/content/identity/loginradius-identity-brokering/identity-brokering.png and /dev/null differ
diff --git a/content/identity/loginradius-identity-brokering/identity-brokering.webp b/content/identity/loginradius-identity-brokering/identity-brokering.webp
new file mode 100644
index 000000000..fa06c2016
Binary files /dev/null and b/content/identity/loginradius-identity-brokering/identity-brokering.webp differ
diff --git a/content/identity/loginradius-identity-brokering/index.md b/content/identity/loginradius-identity-brokering/index.md
index f99ed5059..fb2d96380 100644
--- a/content/identity/loginradius-identity-brokering/index.md
+++ b/content/identity/loginradius-identity-brokering/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - LoginRadius Announces Identity Brokering To Establish Trust Between Identity and Service Providers"
date: "2021-01-27"
-coverImage: "loginradius-identity-brokering.png"
+coverImage: "loginradius-identity-brokering.webp"
tags: ["identity management","authentication","sso","cx"]
author: "Rakesh Soni"
description: "Using Identity Brokering, businesses do not require consumers to provide their credentials to authenticate. Instead, LoginRadius acts as an identity broker service between the Identity and Service Providers and enables the authentication process between the two."
@@ -27,7 +27,7 @@ With LoginRadius Identity Brokering service, businesses can enjoy a seamless aut
* **Verified digital identity**: Businesses need not worry about verifying the consumers who authenticate themselves using configured IdPs. Such identities are already verified with respective IdPs.
-[](https://www.loginradius.com/resource/identity-brokering-datasheet)
+[](https://www.loginradius.com/resource/identity-brokering-datasheet)
## Key Features Offered by LoginRadius
@@ -46,4 +46,4 @@ With Identity Brokering, businesses can skip the use of complex protocols and en
Moreover, businesses acquire flexibility and verified digital identities, whereas consumers gain a [seamless authentication experience](https://www.loginradius.com/authentication/). A win-win for both parties!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-identity-brokering)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-identity-brokering)
\ No newline at end of file
diff --git a/content/identity/loginradius-identity-brokering/loginradius-identity-brokering.png b/content/identity/loginradius-identity-brokering/loginradius-identity-brokering.png
deleted file mode 100644
index 0bbaa9f83..000000000
Binary files a/content/identity/loginradius-identity-brokering/loginradius-identity-brokering.png and /dev/null differ
diff --git a/content/identity/loginradius-identity-brokering/loginradius-identity-brokering.webp b/content/identity/loginradius-identity-brokering/loginradius-identity-brokering.webp
new file mode 100644
index 000000000..549449dde
Binary files /dev/null and b/content/identity/loginradius-identity-brokering/loginradius-identity-brokering.webp differ
diff --git a/content/identity/loginradius-identity-experience-framework/Book-a-free-demo-request.png b/content/identity/loginradius-identity-experience-framework/Book-a-free-demo-request.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/loginradius-identity-experience-framework/Book-a-free-demo-request.png and /dev/null differ
diff --git a/content/identity/loginradius-identity-experience-framework/Book-a-free-demo-request.webp b/content/identity/loginradius-identity-experience-framework/Book-a-free-demo-request.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/loginradius-identity-experience-framework/Book-a-free-demo-request.webp differ
diff --git a/content/identity/loginradius-identity-experience-framework/IDX-Product.png b/content/identity/loginradius-identity-experience-framework/IDX-Product.png
deleted file mode 100644
index faac3097d..000000000
Binary files a/content/identity/loginradius-identity-experience-framework/IDX-Product.png and /dev/null differ
diff --git a/content/identity/loginradius-identity-experience-framework/IDX-Product.webp b/content/identity/loginradius-identity-experience-framework/IDX-Product.webp
new file mode 100644
index 000000000..b22bfa7b0
Binary files /dev/null and b/content/identity/loginradius-identity-experience-framework/IDX-Product.webp differ
diff --git a/content/identity/loginradius-identity-experience-framework/IDx.png b/content/identity/loginradius-identity-experience-framework/IDx.png
deleted file mode 100644
index a252d6bf3..000000000
Binary files a/content/identity/loginradius-identity-experience-framework/IDx.png and /dev/null differ
diff --git a/content/identity/loginradius-identity-experience-framework/IDx.webp b/content/identity/loginradius-identity-experience-framework/IDx.webp
new file mode 100644
index 000000000..116fd0183
Binary files /dev/null and b/content/identity/loginradius-identity-experience-framework/IDx.webp differ
diff --git a/content/identity/loginradius-identity-experience-framework/index.md b/content/identity/loginradius-identity-experience-framework/index.md
index bb404f2c5..bc656909d 100644
--- a/content/identity/loginradius-identity-experience-framework/index.md
+++ b/content/identity/loginradius-identity-experience-framework/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - LoginRadius Delivers Exceptional Authentication With The Launch Of Identity Experience Framework"
date: "2020-09-18"
-coverImage: "IDx.png"
+coverImage: "IDx.webp"
tags: ["authentication","identity management","cx"]
author: "Karl Wittig"
description: "Overall, companies need to keep their customers loyal to their goods, services , and brands — which is why the need for the hour is an effective user interface. It can have customer interactions that are most conducive to any company's success."
@@ -28,7 +28,7 @@ Hence, our LoginRadius Identity Experience Framework benefits businesses in th
## Key Capabilities of LoginRadius Identity Experience Framework
-[](https://www.loginradius.com/resource/loginradius-identity-experience-framework-datasheet)
+[](https://www.loginradius.com/resource/loginradius-identity-experience-framework-datasheet)
**Predefined themes**: It offers predefined themes designed to fit all business requirements as per industry standards.
@@ -44,4 +44,4 @@ Hence, our LoginRadius Identity Experience Framework benefits businesses in th
With the LoginRadius Identity Experience Framework, businesses can enjoy a complete set of customizable solutions and provide consumers with seamless experiences. Be it, tweaking the authentication flow or changing the interface designs—this feature can do them all.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-identity-experience-framework)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-identity-experience-framework)
diff --git a/content/identity/loginradius-identity-import-manager-data-migration/Book-a-free-demo-request.png b/content/identity/loginradius-identity-import-manager-data-migration/Book-a-free-demo-request.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/loginradius-identity-import-manager-data-migration/Book-a-free-demo-request.png and /dev/null differ
diff --git a/content/identity/loginradius-identity-import-manager-data-migration/Book-a-free-demo-request.webp b/content/identity/loginradius-identity-import-manager-data-migration/Book-a-free-demo-request.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/loginradius-identity-import-manager-data-migration/Book-a-free-demo-request.webp differ
diff --git a/content/identity/loginradius-identity-import-manager-data-migration/DS-ETL-Services-1.png b/content/identity/loginradius-identity-import-manager-data-migration/DS-ETL-Services-1.png
deleted file mode 100644
index 87997641d..000000000
Binary files a/content/identity/loginradius-identity-import-manager-data-migration/DS-ETL-Services-1.png and /dev/null differ
diff --git a/content/identity/loginradius-identity-import-manager-data-migration/DS-ETL-Services-1.webp b/content/identity/loginradius-identity-import-manager-data-migration/DS-ETL-Services-1.webp
new file mode 100644
index 000000000..c5040586b
Binary files /dev/null and b/content/identity/loginradius-identity-import-manager-data-migration/DS-ETL-Services-1.webp differ
diff --git a/content/identity/loginradius-identity-import-manager-data-migration/LoginRadius-Identity-Import.jpg b/content/identity/loginradius-identity-import-manager-data-migration/LoginRadius-Identity-Import.jpg
deleted file mode 100644
index 3539effe0..000000000
Binary files a/content/identity/loginradius-identity-import-manager-data-migration/LoginRadius-Identity-Import.jpg and /dev/null differ
diff --git a/content/identity/loginradius-identity-import-manager-data-migration/LoginRadius-Identity-Import.webp b/content/identity/loginradius-identity-import-manager-data-migration/LoginRadius-Identity-Import.webp
new file mode 100644
index 000000000..3cac1f6cb
Binary files /dev/null and b/content/identity/loginradius-identity-import-manager-data-migration/LoginRadius-Identity-Import.webp differ
diff --git a/content/identity/loginradius-identity-import-manager-data-migration/index.md b/content/identity/loginradius-identity-import-manager-data-migration/index.md
index de7bd9720..36ce228fa 100644
--- a/content/identity/loginradius-identity-import-manager-data-migration/index.md
+++ b/content/identity/loginradius-identity-import-manager-data-migration/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Identity Import Manager, An Automated Feature for Seamless Data Migration"
date: "2020-07-15"
-coverImage: "LoginRadius-Identity-Import.jpg"
+coverImage: "LoginRadius-Identity-Import.webp"
tags: ["customer-experience"]
featured: false
author: "Rakesh Soni"
@@ -28,7 +28,7 @@ Other benefits of the LoginRadius Identity Import Manager include:
- It improves data professionals' productivity as it codifies and reuses processes that move data without any technical intervention.
- It offers a robust built-in-error handling functionality that empowers companies to build well-instrumented data warehousing systems.
-[](https://loginradius.com/resource/loginradius-identity-import-manager)
+[](https://loginradius.com/resource/loginradius-identity-import-manager)
## Core Capabilities of LoginRadius Identity Import Manager
@@ -47,4 +47,4 @@ Companies produce a wide range of data in a variety of forms that may not be ful
The Identity Import Manager is a built-in feature of the LoginRadius [customer identity and access management](https://www.loginradius.com/blog/identity/customer-identity-and-access-management/) platform that offers frictionless access and integration of data for effective and accurate data processing.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-identity-import-manager-data-migration)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-identity-import-manager-data-migration)
diff --git a/content/identity/loginradius-integrates-search-navigation-better-cx/1.png b/content/identity/loginradius-integrates-search-navigation-better-cx/1.png
deleted file mode 100644
index 41032f471..000000000
Binary files a/content/identity/loginradius-integrates-search-navigation-better-cx/1.png and /dev/null differ
diff --git a/content/identity/loginradius-integrates-search-navigation-better-cx/1.webp b/content/identity/loginradius-integrates-search-navigation-better-cx/1.webp
new file mode 100644
index 000000000..e6b2da06b
Binary files /dev/null and b/content/identity/loginradius-integrates-search-navigation-better-cx/1.webp differ
diff --git a/content/identity/loginradius-integrates-search-navigation-better-cx/2.png b/content/identity/loginradius-integrates-search-navigation-better-cx/2.png
deleted file mode 100644
index 7c5076672..000000000
Binary files a/content/identity/loginradius-integrates-search-navigation-better-cx/2.png and /dev/null differ
diff --git a/content/identity/loginradius-integrates-search-navigation-better-cx/2.webp b/content/identity/loginradius-integrates-search-navigation-better-cx/2.webp
new file mode 100644
index 000000000..e9c953893
Binary files /dev/null and b/content/identity/loginradius-integrates-search-navigation-better-cx/2.webp differ
diff --git a/content/identity/loginradius-integrates-search-navigation-better-cx/3.png b/content/identity/loginradius-integrates-search-navigation-better-cx/3.png
deleted file mode 100644
index a56a041a0..000000000
Binary files a/content/identity/loginradius-integrates-search-navigation-better-cx/3.png and /dev/null differ
diff --git a/content/identity/loginradius-integrates-search-navigation-better-cx/3.webp b/content/identity/loginradius-integrates-search-navigation-better-cx/3.webp
new file mode 100644
index 000000000..07a6ef336
Binary files /dev/null and b/content/identity/loginradius-integrates-search-navigation-better-cx/3.webp differ
diff --git a/content/identity/loginradius-integrates-search-navigation-better-cx/4.png b/content/identity/loginradius-integrates-search-navigation-better-cx/4.png
deleted file mode 100644
index 3bac5bfb1..000000000
Binary files a/content/identity/loginradius-integrates-search-navigation-better-cx/4.png and /dev/null differ
diff --git a/content/identity/loginradius-integrates-search-navigation-better-cx/4.webp b/content/identity/loginradius-integrates-search-navigation-better-cx/4.webp
new file mode 100644
index 000000000..8aa68b85d
Binary files /dev/null and b/content/identity/loginradius-integrates-search-navigation-better-cx/4.webp differ
diff --git a/content/identity/loginradius-integrates-search-navigation-better-cx/LR-search-navigation.jpg b/content/identity/loginradius-integrates-search-navigation-better-cx/LR-search-navigation.jpg
deleted file mode 100644
index 1922cd667..000000000
Binary files a/content/identity/loginradius-integrates-search-navigation-better-cx/LR-search-navigation.jpg and /dev/null differ
diff --git a/content/identity/loginradius-integrates-search-navigation-better-cx/LR-search-navigation.webp b/content/identity/loginradius-integrates-search-navigation-better-cx/LR-search-navigation.webp
new file mode 100644
index 000000000..ef25e719f
Binary files /dev/null and b/content/identity/loginradius-integrates-search-navigation-better-cx/LR-search-navigation.webp differ
diff --git a/content/identity/loginradius-integrates-search-navigation-better-cx/index.md b/content/identity/loginradius-integrates-search-navigation-better-cx/index.md
index 1dd99b275..c245501dc 100644
--- a/content/identity/loginradius-integrates-search-navigation-better-cx/index.md
+++ b/content/identity/loginradius-integrates-search-navigation-better-cx/index.md
@@ -3,7 +3,7 @@ title: "LoginRadius Integrates Search in Navigation for Better Customer Experien
date: "2022-02-15"
featured: false
author: "Archna Yadav"
-coverImage: "LR-search-navigation.jpg"
+coverImage: "LR-search-navigation.webp"
tags: ["industry-news"]
description: "Being a CIAM solution, LoginRadius understands the importance of customer experience. From time to time, we take a look back in the Admin Console and keep improvising it. This time we worked on the Search in navigation."
metatitle: "LoginRadius Introduces Search in Navigation for Better CX"
@@ -33,14 +33,14 @@ Let’s have a look at the new search option.
-
+
Click on the search section and type a keyword or phrase to view results. The following is an example of a feature search for the “Password” keyword:
-
+
You can click the desired result, and it will land you on the respective feature page in the Admin Console. So, no more scrolling through the navigation menu to find out what you are looking for in the console.
@@ -58,7 +58,7 @@ You can quickly locate a customer by using the search filter options such as dom
-
+
Similarly, you can search and manage the blocked customers too.
@@ -72,7 +72,7 @@ The following is an example of search options available in the Identity Analytic
-
+
@@ -81,4 +81,4 @@ The following is an example of search options available in the Identity Analytic
The purpose of all the above searches is to let our customers quickly locate the information or sections they want to access. If you value customer experience as much as we do, [reach out to us](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-integrates-search-navigation-better-cx), and we will help you improve the consumer experience of your application.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-integrates-search-navigation-better-cx)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-integrates-search-navigation-better-cx)
diff --git a/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/Book-a-demo-1024x310-1-1.png b/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/Book-a-demo-1024x310-1-1.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/Book-a-demo-1024x310-1-1.png and /dev/null differ
diff --git a/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/Book-a-demo-1024x310-1-1.webp b/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/Book-a-demo-1024x310-1-1.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/Book-a-demo-1024x310-1-1.webp differ
diff --git a/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Login-with-Magic-Link-or-OTP.png b/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Login-with-Magic-Link-or-OTP.png
deleted file mode 100644
index 1daf042e7..000000000
Binary files a/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Login-with-Magic-Link-or-OTP.png and /dev/null differ
diff --git a/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Login-with-Magic-Link-or-OTP.webp b/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Login-with-Magic-Link-or-OTP.webp
new file mode 100644
index 000000000..f250ed4e4
Binary files /dev/null and b/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Login-with-Magic-Link-or-OTP.webp differ
diff --git a/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Passwordless-Login-with-Magic-Link-or-OTP-1.png b/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Passwordless-Login-with-Magic-Link-or-OTP-1.png
deleted file mode 100644
index e4b4e318c..000000000
Binary files a/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Passwordless-Login-with-Magic-Link-or-OTP-1.png and /dev/null differ
diff --git a/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Passwordless-Login-with-Magic-Link-or-OTP-1.webp b/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Passwordless-Login-with-Magic-Link-or-OTP-1.webp
new file mode 100644
index 000000000..0a08323fb
Binary files /dev/null and b/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/DS-Passwordless-Login-with-Magic-Link-or-OTP-1.webp differ
diff --git a/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/index.md b/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/index.md
index cf4bab563..647ece127 100644
--- a/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/index.md
+++ b/content/identity/loginradius-launches-passwordless-login-with-magic-link-or-otp/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - LoginRadius Launches Passwordless Login with Magic Link or OTP, Keeps Barriers Low During Registration and Login"
date: "2020-10-29"
-coverImage: "DS-Login-with-Magic-Link-or-OTP.png"
+coverImage: "DS-Login-with-Magic-Link-or-OTP.webp"
tags: ["passwordless login","data security","cx"]
author: "Karl Wittig"
description: "The problem with passwords is that they can be guessed, hacked, or coerced out of consumers through social engineering attacks. So, why not eliminate the main source of insecurity by going passwordless?"
@@ -16,7 +16,7 @@ The recently launched Passwordless Login with Magic Link or OTP feature by Login
Passwordless Login with Magic Link or OTP reduces friction during the registration and login processes. Once the customer enters the Email Address or Phone Number, they receive a magic link via email or OTP on the phone number. As the consumer clicks the magic link or enters the OTP, LoginRadius creates an account (provided it doesn’t already exist), and the consumer automatically logs into the account.
-[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
+[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
[Passwordless Login](https://www.loginradius.com/passwordless-login/) with Magic Link or OTP is designed by LoginRadius to help your business in the following ways:
@@ -42,4 +42,4 @@ LoginRadius also supports various **implementation and deployment methods** that
Times are changing. The majority of consumers do not look forward to creating and entering passwords anymore. Passwordless Login with Magic Link or OTP by LoginRadius is the one-click solution for consumers’ fast-paced authentication needs. It helps businesses improve their security posture while providing a better consumer experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-launches-passwordless-login-with-magic-link-or-otp)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-launches-passwordless-login-with-magic-link-or-otp)
diff --git a/content/identity/loginradius-launches-voice-otp-authentication/GD-to-RBA.png b/content/identity/loginradius-launches-voice-otp-authentication/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/loginradius-launches-voice-otp-authentication/GD-to-RBA.png and /dev/null differ
diff --git a/content/identity/loginradius-launches-voice-otp-authentication/GD-to-RBA.webp b/content/identity/loginradius-launches-voice-otp-authentication/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/loginradius-launches-voice-otp-authentication/GD-to-RBA.webp differ
diff --git a/content/identity/loginradius-launches-voice-otp-authentication/index.md b/content/identity/loginradius-launches-voice-otp-authentication/index.md
index 4246ede3f..a97d1a313 100644
--- a/content/identity/loginradius-launches-voice-otp-authentication/index.md
+++ b/content/identity/loginradius-launches-voice-otp-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Voice OTP by LoginRadius: Revolutionizing Secure and Seamless User Authentication"
date: "2024-02-01"
-coverImage: "voiceotp.jpg"
+coverImage: "voiceotp.webp"
tags: ["data security","user authentication","cx"]
author: "Rakesh Soni"
description: "Discover Voice OTP – LoginRadius' innovative solution for secure and seamless user authentication. Explore how Voice OTP is reshaping the digital authentication landscape from strategic integration to inclusivity and global reach."
@@ -32,7 +32,7 @@ One of the key highlights of Voice OTP is its commitment to ensuring the highest
This feature becomes particularly valuable when SMS delivery may encounter difficulties, guaranteeing uninterrupted account access and providing a smooth and dependable user experience.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
## Inclusivity as a Core Value
@@ -60,4 +60,4 @@ As businesses navigate the complexities of the digital landscape, solutions like
Check out the Voice OTP datasheet to learn more about this innovative release.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-launches-voice-otp-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-launches-voice-otp-authentication)
\ No newline at end of file
diff --git a/content/identity/loginradius-launches-voice-otp-authentication/voiceotp.jpg b/content/identity/loginradius-launches-voice-otp-authentication/voiceotp.jpg
deleted file mode 100644
index 46689dafb..000000000
Binary files a/content/identity/loginradius-launches-voice-otp-authentication/voiceotp.jpg and /dev/null differ
diff --git a/content/identity/loginradius-launches-voice-otp-authentication/voiceotp.webp b/content/identity/loginradius-launches-voice-otp-authentication/voiceotp.webp
new file mode 100644
index 000000000..4a4f35b6f
Binary files /dev/null and b/content/identity/loginradius-launches-voice-otp-authentication/voiceotp.webp differ
diff --git a/content/identity/loginradius-m2m-authorization-data-access/BD-Developers2-1024x310.png b/content/identity/loginradius-m2m-authorization-data-access/BD-Developers2-1024x310.png
deleted file mode 100644
index e794b3769..000000000
Binary files a/content/identity/loginradius-m2m-authorization-data-access/BD-Developers2-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-m2m-authorization-data-access/BD-Developers2-1024x310.webp b/content/identity/loginradius-m2m-authorization-data-access/BD-Developers2-1024x310.webp
new file mode 100644
index 000000000..371ef34ea
Binary files /dev/null and b/content/identity/loginradius-m2m-authorization-data-access/BD-Developers2-1024x310.webp differ
diff --git a/content/identity/loginradius-m2m-authorization-data-access/DS-M2M.png b/content/identity/loginradius-m2m-authorization-data-access/DS-M2M.png
deleted file mode 100644
index c31629290..000000000
Binary files a/content/identity/loginradius-m2m-authorization-data-access/DS-M2M.png and /dev/null differ
diff --git a/content/identity/loginradius-m2m-authorization-data-access/DS-M2M.webp b/content/identity/loginradius-m2m-authorization-data-access/DS-M2M.webp
new file mode 100644
index 000000000..91dd1af2c
Binary files /dev/null and b/content/identity/loginradius-m2m-authorization-data-access/DS-M2M.webp differ
diff --git a/content/identity/loginradius-m2m-authorization-data-access/index.md b/content/identity/loginradius-m2m-authorization-data-access/index.md
index 87a3b6460..946afb9ab 100644
--- a/content/identity/loginradius-m2m-authorization-data-access/index.md
+++ b/content/identity/loginradius-m2m-authorization-data-access/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Launches M2M Authorization for Seamless Business Operations"
date: "2021-12-15"
-coverImage: "m2m-cover.jpg"
+coverImage: "m2m-cover.webp"
tags: ["industry-news","authorization","authentication"]
author: "Rakesh Soni"
description: "Machine to Machine (M2M) authorization ensures that business systems communicate autonomously without human intervention and access the needed information securely and reliably."
@@ -40,7 +40,7 @@ Services require authorization while saving and reading the data to and from the
For each M2M application, LoginRadius issues secure credentials, and services automatically get the authorization token from LoginRadius using these [secure credentials](https://www.loginradius.com/blog/identity/login-security/) to perform read or write operations.
-[](https://www.loginradius.com/resource/m-to-m-authorization-)
+[](https://www.loginradius.com/resource/m-to-m-authorization-)
In a nutshell, LoginRadius acts as an authorization server.
@@ -61,4 +61,4 @@ With LoginRadius M2M authorization, businesses can ensure a secure and reliable
LoginRadius M2M helps businesses to provide flexible machine-to-machine communication while ensuring granular access, authorization, and security requirements are enforced.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-m2m-authorization-data-access)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-m2m-authorization-data-access)
diff --git a/content/identity/loginradius-m2m-authorization-data-access/m2m-cover.jpg b/content/identity/loginradius-m2m-authorization-data-access/m2m-cover.jpg
deleted file mode 100644
index 0047269a0..000000000
Binary files a/content/identity/loginradius-m2m-authorization-data-access/m2m-cover.jpg and /dev/null differ
diff --git a/content/identity/loginradius-m2m-authorization-data-access/m2m-cover.webp b/content/identity/loginradius-m2m-authorization-data-access/m2m-cover.webp
new file mode 100644
index 000000000..0fd5a09b4
Binary files /dev/null and b/content/identity/loginradius-m2m-authorization-data-access/m2m-cover.webp differ
diff --git a/content/identity/loginradius-m2m-authorization-data-access/m2m.png b/content/identity/loginradius-m2m-authorization-data-access/m2m.png
deleted file mode 100644
index 030d51b9c..000000000
Binary files a/content/identity/loginradius-m2m-authorization-data-access/m2m.png and /dev/null differ
diff --git a/content/identity/loginradius-m2m-authorization-data-access/m2m.webp b/content/identity/loginradius-m2m-authorization-data-access/m2m.webp
new file mode 100644
index 000000000..d32d95bda
Binary files /dev/null and b/content/identity/loginradius-m2m-authorization-data-access/m2m.webp differ
diff --git a/content/identity/loginradius-named-ciam-leader-owi/BD-Plexicon1-1024x310-1.png b/content/identity/loginradius-named-ciam-leader-owi/BD-Plexicon1-1024x310-1.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/loginradius-named-ciam-leader-owi/BD-Plexicon1-1024x310-1.png and /dev/null differ
diff --git a/content/identity/loginradius-named-ciam-leader-owi/BD-Plexicon1-1024x310-1.webp b/content/identity/loginradius-named-ciam-leader-owi/BD-Plexicon1-1024x310-1.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/loginradius-named-ciam-leader-owi/BD-Plexicon1-1024x310-1.webp differ
diff --git a/content/identity/loginradius-named-ciam-leader-owi/blog-graphic-one-world-identity.png b/content/identity/loginradius-named-ciam-leader-owi/blog-graphic-one-world-identity.png
deleted file mode 100644
index da8b633af..000000000
Binary files a/content/identity/loginradius-named-ciam-leader-owi/blog-graphic-one-world-identity.png and /dev/null differ
diff --git a/content/identity/loginradius-named-ciam-leader-owi/blog-graphic-one-world-identity.webp b/content/identity/loginradius-named-ciam-leader-owi/blog-graphic-one-world-identity.webp
new file mode 100644
index 000000000..8dc66796e
Binary files /dev/null and b/content/identity/loginradius-named-ciam-leader-owi/blog-graphic-one-world-identity.webp differ
diff --git a/content/identity/loginradius-named-ciam-leader-owi/index.md b/content/identity/loginradius-named-ciam-leader-owi/index.md
index 2c621bc96..8bb2f0de8 100644
--- a/content/identity/loginradius-named-ciam-leader-owi/index.md
+++ b/content/identity/loginradius-named-ciam-leader-owi/index.md
@@ -1,7 +1,7 @@
---
title: "One World Identity Report Names LoginRadius a Customer Identity and Access Management (CIAM) Industry Leader"
date: "2019-12-02"
-coverImage: "blog-graphic-one-world-identity.png"
+coverImage: "blog-graphic-one-world-identity.webp"
tags: ["media-and-publication", "LoginRadius"]
featured: false
author: "Rakesh Soni"
@@ -24,7 +24,7 @@ The OWI team interacts with identity companies every day, from startups to enter
“LoginRadius is honoured to be one of the 415 identity companies selected from a pool of over 2,000 companies in the industry,”. “We are committed to empowering businesses to safely secure their customers’ identities while complying with existing and future regulations and delivering a unified digital experience
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
The OWI Identity Landscape is a tool to help companies keep track of market growth and trends and understand the strategic importance of digital identity moving into 2020 and beyond. OWI will be releasing a more detailed research report delving into the details of each market segment and how companies within the industry overlap and intersect in upcoming months.
@@ -40,4 +40,4 @@ LoginRadius is a leading cloud-based [customer identity and access management](h
The LoginRadius Identity Platform empowers business and government organizations to manage customer identities securely, deliver a unified digital experience, and comply with all major privacy regulations such as the EU’s General Data Protection Regulation (GDPR).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-named-ciam-leader-owi)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-named-ciam-leader-owi)
diff --git a/content/identity/loginradius-named-ciam-leader-owi/modern-ciam.png b/content/identity/loginradius-named-ciam-leader-owi/modern-ciam.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/identity/loginradius-named-ciam-leader-owi/modern-ciam.png and /dev/null differ
diff --git a/content/identity/loginradius-named-ciam-leader-owi/modern-ciam.webp b/content/identity/loginradius-named-ciam-leader-owi/modern-ciam.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/identity/loginradius-named-ciam-leader-owi/modern-ciam.webp differ
diff --git a/content/identity/loginradius-password-policy-business-consumer/index.md b/content/identity/loginradius-password-policy-business-consumer/index.md
index a050965ac..36ebd323d 100644
--- a/content/identity/loginradius-password-policy-business-consumer/index.md
+++ b/content/identity/loginradius-password-policy-business-consumer/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - LoginRadius Introduces Password Policy to Ensure Best Practices for Businesses and Consumers"
date: "2021-02-11"
-coverImage: "loginradius-password-policy.png"
+coverImage: "loginradius-password-policy.webp"
tags: ["password management","data security","cx"]
author: "Rakesh Soni"
description: "In securing company and customer data, the LoginRadius Password Policy provides the first line of protection. The newly released function offers a plethora of robust password management opportunities, from setting difficulty criteria to stopping users from choosing previously used passwords."
@@ -28,7 +28,7 @@ Using the Password Policy feature by LoginRadius, businesses can collectively ma
* Businesses can enforce auto-expiry of passwords and then restrict consumers from reusing a previous password.
-[](https://www.loginradius.com/resource/password-policy-datasheet)
+[](https://www.loginradius.com/resource/password-policy-datasheet)
## Key Features Offered by LoginRadius
@@ -67,4 +67,4 @@ The Password Policy feature also offers the following consumer-centric features:
We can’t emphasize enough the importance of using a strong password. Implementing our comprehensive Password Policy can secure both your organization's and consumers' assets. With LoginRadius, you will always be a step ahead and mitigate the risks associated with passwords.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-password-policy-business-consumer)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-password-policy-business-consumer)
\ No newline at end of file
diff --git a/content/identity/loginradius-password-policy-business-consumer/loginradius-password-policy.png b/content/identity/loginradius-password-policy-business-consumer/loginradius-password-policy.png
deleted file mode 100644
index 757092751..000000000
Binary files a/content/identity/loginradius-password-policy-business-consumer/loginradius-password-policy.png and /dev/null differ
diff --git a/content/identity/loginradius-password-policy-business-consumer/loginradius-password-policy.webp b/content/identity/loginradius-password-policy-business-consumer/loginradius-password-policy.webp
new file mode 100644
index 000000000..e6824abb4
Binary files /dev/null and b/content/identity/loginradius-password-policy-business-consumer/loginradius-password-policy.webp differ
diff --git a/content/identity/loginradius-password-policy-business-consumer/password-policy-datasheet.png b/content/identity/loginradius-password-policy-business-consumer/password-policy-datasheet.png
deleted file mode 100644
index 619981a62..000000000
Binary files a/content/identity/loginradius-password-policy-business-consumer/password-policy-datasheet.png and /dev/null differ
diff --git a/content/identity/loginradius-password-policy-business-consumer/password-policy-datasheet.webp b/content/identity/loginradius-password-policy-business-consumer/password-policy-datasheet.webp
new file mode 100644
index 000000000..a5d1adfc4
Binary files /dev/null and b/content/identity/loginradius-password-policy-business-consumer/password-policy-datasheet.webp differ
diff --git a/content/identity/loginradius-perfectmind-integration-sso-ux/BD-Developers2-1024x310.png b/content/identity/loginradius-perfectmind-integration-sso-ux/BD-Developers2-1024x310.png
deleted file mode 100644
index e794b3769..000000000
Binary files a/content/identity/loginradius-perfectmind-integration-sso-ux/BD-Developers2-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-perfectmind-integration-sso-ux/BD-Developers2-1024x310.webp b/content/identity/loginradius-perfectmind-integration-sso-ux/BD-Developers2-1024x310.webp
new file mode 100644
index 000000000..371ef34ea
Binary files /dev/null and b/content/identity/loginradius-perfectmind-integration-sso-ux/BD-Developers2-1024x310.webp differ
diff --git a/content/identity/loginradius-perfectmind-integration-sso-ux/DS-perfectmind-int.png b/content/identity/loginradius-perfectmind-integration-sso-ux/DS-perfectmind-int.png
deleted file mode 100644
index 4bc159969..000000000
Binary files a/content/identity/loginradius-perfectmind-integration-sso-ux/DS-perfectmind-int.png and /dev/null differ
diff --git a/content/identity/loginradius-perfectmind-integration-sso-ux/DS-perfectmind-int.webp b/content/identity/loginradius-perfectmind-integration-sso-ux/DS-perfectmind-int.webp
new file mode 100644
index 000000000..d20e4daea
Binary files /dev/null and b/content/identity/loginradius-perfectmind-integration-sso-ux/DS-perfectmind-int.webp differ
diff --git a/content/identity/loginradius-perfectmind-integration-sso-ux/PerfectMind-Integration.png b/content/identity/loginradius-perfectmind-integration-sso-ux/PerfectMind-Integration.png
deleted file mode 100644
index af884b34f..000000000
Binary files a/content/identity/loginradius-perfectmind-integration-sso-ux/PerfectMind-Integration.png and /dev/null differ
diff --git a/content/identity/loginradius-perfectmind-integration-sso-ux/PerfectMind-Integration.webp b/content/identity/loginradius-perfectmind-integration-sso-ux/PerfectMind-Integration.webp
new file mode 100644
index 000000000..866d72fa9
Binary files /dev/null and b/content/identity/loginradius-perfectmind-integration-sso-ux/PerfectMind-Integration.webp differ
diff --git a/content/identity/loginradius-perfectmind-integration-sso-ux/index.md b/content/identity/loginradius-perfectmind-integration-sso-ux/index.md
index 161454aa3..679843e47 100644
--- a/content/identity/loginradius-perfectmind-integration-sso-ux/index.md
+++ b/content/identity/loginradius-perfectmind-integration-sso-ux/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Offers PerfectMind Integration for a Seamless UX"
date: "2021-12-14"
-coverImage: "perfectmind-cover.jpg"
+coverImage: "perfectmind-cover.webp"
tags: ["authentication","federated sso","passwordless login"]
author: "Jitender Agarwal"
description: "LoginRadius’ cutting-edge single sign-on helps overcome all the challenges related to consumer experience and data integration. Let’s understand how LoginRadius paves the path for a robust user experience by integrating PerfectMind."
@@ -30,7 +30,7 @@ Canadian municipal and community organizations were looking for a way to connect
Since, PerfectMind does not support industry-standard [federated Single Sign-On](https://www.loginradius.com/blog/identity/loginradius-federated-identity-management/) methods like SAML, OAuth/OIDC, or JWT, LoginRadius offered its out-of-the-box SSO Connector solutions to create a Single Sign-on user experience between LoginRadius and the PerfectMind applications by leveraging APIs.
-[](https://www.loginradius.com/resource/perfectmind-integration)
+[](https://www.loginradius.com/resource/perfectmind-integration)
Through LoginRadius PerfectMind integration, the PerfectMind consumers are leveraging all the powerful capabilities of the cutting-edge CIAM platform, including social login, [passwordless login](https://www.loginradius.com/blog/identity/passwordless-authentication-the-future-of-identity-and-security/), single sign-on, reinforced by robust security.
@@ -39,4 +39,4 @@ Through LoginRadius PerfectMind integration, the PerfectMind consumers are lever
With the LoginRadius PerfectMind SSO, businesses can establish a flawless user experience by overcoming the barriers of frictionless authentication and authorization across multiple platforms/ servers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-perfectmind-integration-sso-ux)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-perfectmind-integration-sso-ux)
diff --git a/content/identity/loginradius-perfectmind-integration-sso-ux/perfectmind-cover.jpg b/content/identity/loginradius-perfectmind-integration-sso-ux/perfectmind-cover.jpg
deleted file mode 100644
index 70ab31969..000000000
Binary files a/content/identity/loginradius-perfectmind-integration-sso-ux/perfectmind-cover.jpg and /dev/null differ
diff --git a/content/identity/loginradius-perfectmind-integration-sso-ux/perfectmind-cover.webp b/content/identity/loginradius-perfectmind-integration-sso-ux/perfectmind-cover.webp
new file mode 100644
index 000000000..406e24e25
Binary files /dev/null and b/content/identity/loginradius-perfectmind-integration-sso-ux/perfectmind-cover.webp differ
diff --git a/content/identity/loginradius-pin-based-authentication/Book-a-free-demo-request-1024x310.png b/content/identity/loginradius-pin-based-authentication/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/loginradius-pin-based-authentication/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-pin-based-authentication/Book-a-free-demo-request-1024x310.webp b/content/identity/loginradius-pin-based-authentication/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/loginradius-pin-based-authentication/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/loginradius-pin-based-authentication/DS-PIN-Login-1024x310.png b/content/identity/loginradius-pin-based-authentication/DS-PIN-Login-1024x310.png
deleted file mode 100644
index 4668d1575..000000000
Binary files a/content/identity/loginradius-pin-based-authentication/DS-PIN-Login-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-pin-based-authentication/DS-PIN-Login-1024x310.webp b/content/identity/loginradius-pin-based-authentication/DS-PIN-Login-1024x310.webp
new file mode 100644
index 000000000..408f65401
Binary files /dev/null and b/content/identity/loginradius-pin-based-authentication/DS-PIN-Login-1024x310.webp differ
diff --git a/content/identity/loginradius-pin-based-authentication/LoginRadius-Pin-Authentication.png b/content/identity/loginradius-pin-based-authentication/LoginRadius-Pin-Authentication.png
deleted file mode 100644
index f1f499967..000000000
Binary files a/content/identity/loginradius-pin-based-authentication/LoginRadius-Pin-Authentication.png and /dev/null differ
diff --git a/content/identity/loginradius-pin-based-authentication/LoginRadius-Pin-Authentication.webp b/content/identity/loginradius-pin-based-authentication/LoginRadius-Pin-Authentication.webp
new file mode 100644
index 000000000..5160be63a
Binary files /dev/null and b/content/identity/loginradius-pin-based-authentication/LoginRadius-Pin-Authentication.webp differ
diff --git a/content/identity/loginradius-pin-based-authentication/index.md b/content/identity/loginradius-pin-based-authentication/index.md
index 750f515bc..b159e335f 100644
--- a/content/identity/loginradius-pin-based-authentication/index.md
+++ b/content/identity/loginradius-pin-based-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - LoginRadius Now Supports PIN Login with Enhanced Features"
date: "2020-04-28"
-coverImage: "LoginRadius-Pin-Authentication.png"
+coverImage: "LoginRadius-Pin-Authentication.webp"
tags: ["pin authentication","ciam solution","identity management"]
author: "Kundan Singh"
description: "LoginRadius is a rapidly-expanding identity management platform. And this time, for its current and new clients, the cloud-based client identity and access management solution has introduced a PIN Login authentication environment."
@@ -44,7 +44,7 @@ We have followed strict authentication protocols to make this launch a success.
**Forced account lockouts**: The account will be locked automatically upon hitting the configured number of failed PIN attempts. The PIN will act as the protection layer against vulnerabilities like brute force attacks.
-[](https://www.loginradius.com/resource/loginradius-and-pin-auth)
+[](https://www.loginradius.com/resource/loginradius-and-pin-auth)
**Pin Login Data Sheet**
@@ -60,4 +60,4 @@ PIN login is a successful attempt at not just embracing an alternative two fact
All-in-all, we aim to ensure that logins are secure, simple, seamless, and frictionless. And if it can turn customers into loyal advocates, that will serve our purpose even better.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-pin-based-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-pin-based-authentication)
diff --git a/content/identity/loginradius-pin-based-authentication/pin-authentication.jpg b/content/identity/loginradius-pin-based-authentication/pin-authentication.jpg
deleted file mode 100644
index 01a197c70..000000000
Binary files a/content/identity/loginradius-pin-based-authentication/pin-authentication.jpg and /dev/null differ
diff --git a/content/identity/loginradius-pin-based-authentication/pin-authentication.webp b/content/identity/loginradius-pin-based-authentication/pin-authentication.webp
new file mode 100644
index 000000000..09b44374a
Binary files /dev/null and b/content/identity/loginradius-pin-based-authentication/pin-authentication.webp differ
diff --git a/content/identity/loginradius-private-cloud-ciam-benefits/index.md b/content/identity/loginradius-private-cloud-ciam-benefits/index.md
index 809ac4792..c83eebeeb 100644
--- a/content/identity/loginradius-private-cloud-ciam-benefits/index.md
+++ b/content/identity/loginradius-private-cloud-ciam-benefits/index.md
@@ -1,7 +1,7 @@
---
title: "Take Control of Your CIAM Environment with LoginRadius' Private Cloud"
date: "2021-12-07"
-coverImage: "lr-private-cloud.jpg"
+coverImage: "lr-private-cloud.webp"
tags: ["cloud computing","ciam solutions","cx"]
author: "Manish Tiwari"
description: "Businesses relying on conventional consumer IAMs aren’t aware that they’re not just putting their consumer information at risk but are also missing endless business opportunities. This blog explains how LoginRadius’ CIAM solution offers a private cloud that helps businesses take total control over every aspect of their business."
@@ -53,4 +53,4 @@ LoginRadius’ private cloud helps enterprises deliver a flawless user experienc
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-private-cloud-ciam-benefits)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-private-cloud-ciam-benefits)
\ No newline at end of file
diff --git a/content/identity/loginradius-private-cloud-ciam-benefits/lr-private-cloud.jpg b/content/identity/loginradius-private-cloud-ciam-benefits/lr-private-cloud.jpg
deleted file mode 100644
index c358a08cc..000000000
Binary files a/content/identity/loginradius-private-cloud-ciam-benefits/lr-private-cloud.jpg and /dev/null differ
diff --git a/content/identity/loginradius-private-cloud-ciam-benefits/lr-private-cloud.webp b/content/identity/loginradius-private-cloud-ciam-benefits/lr-private-cloud.webp
new file mode 100644
index 000000000..682a9702f
Binary files /dev/null and b/content/identity/loginradius-private-cloud-ciam-benefits/lr-private-cloud.webp differ
diff --git a/content/identity/loginradius-progressive-profiling/DS-Progressive-Profiling.png b/content/identity/loginradius-progressive-profiling/DS-Progressive-Profiling.png
deleted file mode 100644
index 69a936b7f..000000000
Binary files a/content/identity/loginradius-progressive-profiling/DS-Progressive-Profiling.png and /dev/null differ
diff --git a/content/identity/loginradius-progressive-profiling/DS-Progressive-Profiling.webp b/content/identity/loginradius-progressive-profiling/DS-Progressive-Profiling.webp
new file mode 100644
index 000000000..a709e3b2d
Binary files /dev/null and b/content/identity/loginradius-progressive-profiling/DS-Progressive-Profiling.webp differ
diff --git a/content/identity/loginradius-progressive-profiling/Progressive-Profiling-DS.png b/content/identity/loginradius-progressive-profiling/Progressive-Profiling-DS.png
deleted file mode 100644
index c98c144d4..000000000
Binary files a/content/identity/loginradius-progressive-profiling/Progressive-Profiling-DS.png and /dev/null differ
diff --git a/content/identity/loginradius-progressive-profiling/Progressive-Profiling-DS.webp b/content/identity/loginradius-progressive-profiling/Progressive-Profiling-DS.webp
new file mode 100644
index 000000000..b34c41174
Binary files /dev/null and b/content/identity/loginradius-progressive-profiling/Progressive-Profiling-DS.webp differ
diff --git a/content/identity/loginradius-progressive-profiling/index.md b/content/identity/loginradius-progressive-profiling/index.md
index 77d0cd088..742138e12 100644
--- a/content/identity/loginradius-progressive-profiling/index.md
+++ b/content/identity/loginradius-progressive-profiling/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Delivers a Seamless User Experience that Increases Conversions through Enhanced Progressive Profiling"
date: "2021-10-05"
-coverImage: "loginradius-progressive-profiling-cover.jpg"
+coverImage: "loginradius-progressive-profiling-cover.webp"
tags: ["progressive profiling","user experience","ciam solution"]
author: "Rakesh Soni"
description: "Progressive Profiling helps businesses to split a potentially complicated registration process into multiple steps. you can capture business-critical information upfront and then slowly build out a holistic view of your consumers through subsequent actions."
@@ -25,7 +25,7 @@ Progressive Profiling helps businesses to split a potentially complicated regist
Let’s understand how it works and helps to scale business growth by increasing conversion rates.
-[](https://www.loginradius.com/resource/progressive-profiling-by-loginradius-2/)
+[](https://www.loginradius.com/resource/progressive-profiling-by-loginradius-2/)
## Intent Behind Launch
@@ -51,4 +51,4 @@ Based on consumers’ interaction with the application, Progressive Profiling au
Implementing progressive profiling on an online platform offers a competitive edge to businesses seeking innovative ways to navigate their digital transformation for enhanced business growth.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-progressive-profiling)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-progressive-profiling)
\ No newline at end of file
diff --git a/content/identity/loginradius-progressive-profiling/loginradius-progressive-profiling-cover.jpg b/content/identity/loginradius-progressive-profiling/loginradius-progressive-profiling-cover.jpg
deleted file mode 100644
index a3a21d299..000000000
Binary files a/content/identity/loginradius-progressive-profiling/loginradius-progressive-profiling-cover.jpg and /dev/null differ
diff --git a/content/identity/loginradius-progressive-profiling/loginradius-progressive-profiling-cover.webp b/content/identity/loginradius-progressive-profiling/loginradius-progressive-profiling-cover.webp
new file mode 100644
index 000000000..59eba4062
Binary files /dev/null and b/content/identity/loginradius-progressive-profiling/loginradius-progressive-profiling-cover.webp differ
diff --git a/content/identity/loginradius-roi-enterprises-infographic/EB-buy-build.png b/content/identity/loginradius-roi-enterprises-infographic/EB-buy-build.png
deleted file mode 100644
index 12aee97b9..000000000
Binary files a/content/identity/loginradius-roi-enterprises-infographic/EB-buy-build.png and /dev/null differ
diff --git a/content/identity/loginradius-roi-enterprises-infographic/EB-buy-build.webp b/content/identity/loginradius-roi-enterprises-infographic/EB-buy-build.webp
new file mode 100644
index 000000000..37f1cc72f
Binary files /dev/null and b/content/identity/loginradius-roi-enterprises-infographic/EB-buy-build.webp differ
diff --git a/content/identity/loginradius-roi-enterprises-infographic/ROI.png b/content/identity/loginradius-roi-enterprises-infographic/ROI.png
deleted file mode 100644
index 9c0ac1485..000000000
Binary files a/content/identity/loginradius-roi-enterprises-infographic/ROI.png and /dev/null differ
diff --git a/content/identity/loginradius-roi-enterprises-infographic/ROI.webp b/content/identity/loginradius-roi-enterprises-infographic/ROI.webp
new file mode 100644
index 000000000..633cc18f3
Binary files /dev/null and b/content/identity/loginradius-roi-enterprises-infographic/ROI.webp differ
diff --git a/content/identity/loginradius-roi-enterprises-infographic/build-buy-eb.png b/content/identity/loginradius-roi-enterprises-infographic/build-buy-eb.png
deleted file mode 100644
index b58e0950a..000000000
Binary files a/content/identity/loginradius-roi-enterprises-infographic/build-buy-eb.png and /dev/null differ
diff --git a/content/identity/loginradius-roi-enterprises-infographic/build-buy-eb.webp b/content/identity/loginradius-roi-enterprises-infographic/build-buy-eb.webp
new file mode 100644
index 000000000..23f70e01d
Binary files /dev/null and b/content/identity/loginradius-roi-enterprises-infographic/build-buy-eb.webp differ
diff --git a/content/identity/loginradius-roi-enterprises-infographic/index.md b/content/identity/loginradius-roi-enterprises-infographic/index.md
index bcc231544..d285c0872 100644
--- a/content/identity/loginradius-roi-enterprises-infographic/index.md
+++ b/content/identity/loginradius-roi-enterprises-infographic/index.md
@@ -1,7 +1,7 @@
---
title: "How LoginRadius Offers Customer-Centric Capabilities that Drive ROI"
date: "2021-11-16"
-coverImage: "roi-cover.jpg"
+coverImage: "roi-cover.webp"
tags: ["data management","digital transformation","cx"]
author: "Rakesh Soni"
description: "For businesses to grow and increase their profitability, there is a need to implement robust infrastructure to aid in productivity and increase efficiency. LoginRadius helps organizations scale up security, operability, data integration, and effective data management, among others. Check out our infographic for more ROI-centric details."
@@ -24,7 +24,7 @@ To address the potential of applications growing over time, our platform is desi
LoginRadius offers matchless security with password protection, account verification, auto re-authentication, [risk-based authentication](https://www.loginradius.com/blog/identity/risk-based-authentication/), multi-factor authentication, and in-built fraud email blocks. All these elements come together to form the most formidable and intelligent security system with protocols that enable access to users after thorough verification and authentication, restrict access to unauthorized elements, protect users from external threats and keep sensitive data secure.
-[](https://www.loginradius.com/resource/the-case-for-buying-over-building/)
+[](https://www.loginradius.com/resource/the-case-for-buying-over-building/)
### #3. Seamless integration
@@ -40,7 +40,7 @@ LoginRadius also provides two-way sync, allowing users to synchronize data irres
To learn more on how LoginRadius empowers businesses and delivers the utmost ROI, check out the infographic below.
-
+
## Implementing Customer-Obsessed Capabilities for Your Business
@@ -48,4 +48,4 @@ For businesses to grow and increase their profitability, there is a need to impl
LoginRadius has 35 data centers worldwide and helps companies manage the needs of 1.17 billion user identities with its efficient 24/7 support for its valued customers.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-roi-enterprises-infographic)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-roi-enterprises-infographic)
diff --git a/content/identity/loginradius-roi-enterprises-infographic/roi-cover.jpg b/content/identity/loginradius-roi-enterprises-infographic/roi-cover.jpg
deleted file mode 100644
index ad8f69fa0..000000000
Binary files a/content/identity/loginradius-roi-enterprises-infographic/roi-cover.jpg and /dev/null differ
diff --git a/content/identity/loginradius-roi-enterprises-infographic/roi-cover.webp b/content/identity/loginradius-roi-enterprises-infographic/roi-cover.webp
new file mode 100644
index 000000000..374d661db
Binary files /dev/null and b/content/identity/loginradius-roi-enterprises-infographic/roi-cover.webp differ
diff --git a/content/identity/loginradius-secures-identity-management-bc-municpality/DS-perfectmindint.png b/content/identity/loginradius-secures-identity-management-bc-municpality/DS-perfectmindint.png
deleted file mode 100644
index 4bc159969..000000000
Binary files a/content/identity/loginradius-secures-identity-management-bc-municpality/DS-perfectmindint.png and /dev/null differ
diff --git a/content/identity/loginradius-secures-identity-management-bc-municpality/DS-perfectmindint.webp b/content/identity/loginradius-secures-identity-management-bc-municpality/DS-perfectmindint.webp
new file mode 100644
index 000000000..d20e4daea
Binary files /dev/null and b/content/identity/loginradius-secures-identity-management-bc-municpality/DS-perfectmindint.webp differ
diff --git a/content/identity/loginradius-secures-identity-management-bc-municpality/bc-municipal.jpg b/content/identity/loginradius-secures-identity-management-bc-municpality/bc-municipal.jpg
deleted file mode 100644
index e265a13d0..000000000
Binary files a/content/identity/loginradius-secures-identity-management-bc-municpality/bc-municipal.jpg and /dev/null differ
diff --git a/content/identity/loginradius-secures-identity-management-bc-municpality/bc-municipal.webp b/content/identity/loginradius-secures-identity-management-bc-municpality/bc-municipal.webp
new file mode 100644
index 000000000..69eaa4b52
Binary files /dev/null and b/content/identity/loginradius-secures-identity-management-bc-municpality/bc-municipal.webp differ
diff --git a/content/identity/loginradius-secures-identity-management-bc-municpality/ds-perfectmind.png b/content/identity/loginradius-secures-identity-management-bc-municpality/ds-perfectmind.png
deleted file mode 100644
index af884b34f..000000000
Binary files a/content/identity/loginradius-secures-identity-management-bc-municpality/ds-perfectmind.png and /dev/null differ
diff --git a/content/identity/loginradius-secures-identity-management-bc-municpality/ds-perfectmind.webp b/content/identity/loginradius-secures-identity-management-bc-municpality/ds-perfectmind.webp
new file mode 100644
index 000000000..866d72fa9
Binary files /dev/null and b/content/identity/loginradius-secures-identity-management-bc-municpality/ds-perfectmind.webp differ
diff --git a/content/identity/loginradius-secures-identity-management-bc-municpality/index.md b/content/identity/loginradius-secures-identity-management-bc-municpality/index.md
index fff1f6233..9bdd03e01 100644
--- a/content/identity/loginradius-secures-identity-management-bc-municpality/index.md
+++ b/content/identity/loginradius-secures-identity-management-bc-municpality/index.md
@@ -1,7 +1,7 @@
---
title: "BC Municipality Digitizes its Citizen Services. LoginRadius Brings Identity to the Table."
date: "2022-09-06"
-coverImage: "bc-municipal.jpg"
+coverImage: "bc-municipal.webp"
tags: ["digital identity", "authentication", "cx"]
author: "Saikiran Babladi"
description: "A city in BC was looking for a CIAM solution that would secure the identities and streamline the authentication process for its citizens. Here's why they decided to try LoginRadius and the decision worked in their favor."
@@ -44,10 +44,10 @@ Whenever any citizen logs into the City’s website, they will be automatically
With this integration, citizens are able to access recreational services to search and register for programs with a single account giving them the best experience while surfing the City’s website.
-[](https://www.loginradius.com/resource/perfectmind-integration)
+[](https://www.loginradius.com/resource/perfectmind-integration)
## Support
Right from the [customer onboarding](https://www.loginradius.com/blog/identity/loginradius-streamlines-user-onboarding-harry-rosen/), the City had access to a customer success manager and multiple support channels to ensure the success of the project every step of the way. The LoginRadius team continues to work closely with the city to ensure project success.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-secures-identity-management-bc-municpality)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-secures-identity-management-bc-municpality)
diff --git a/content/identity/loginradius-self-serve-no-code-ciam-console/index.md b/content/identity/loginradius-self-serve-no-code-ciam-console/index.md
index ac36645fb..25cc6b75f 100644
--- a/content/identity/loginradius-self-serve-no-code-ciam-console/index.md
+++ b/content/identity/loginradius-self-serve-no-code-ciam-console/index.md
@@ -63,4 +63,4 @@ Now it’s your turn to experience it firsthand. Log in today and explore the ne
We’d love to hear your thoughts. Your feedback drives our innovation—let’s shape the future of identity together!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-self-serve-no-code-ciam-console)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-self-serve-no-code-ciam-console)
diff --git a/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/Book-a-free-demo-request-1024x310.png b/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/Book-a-free-demo-request-1024x310.webp b/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/harry-rosen.jpg b/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/harry-rosen.jpg
deleted file mode 100644
index e35be9c0e..000000000
Binary files a/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/harry-rosen.jpg and /dev/null differ
diff --git a/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/harry-rosen.webp b/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/harry-rosen.webp
new file mode 100644
index 000000000..be21e797a
Binary files /dev/null and b/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/harry-rosen.webp differ
diff --git a/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/index.md b/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/index.md
index 80c4386b6..54ef77168 100644
--- a/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/index.md
+++ b/content/identity/loginradius-streamlines-user-onboarding-harry-rosen/index.md
@@ -1,7 +1,7 @@
---
title: "Harry Rosen, a LoginRadius Customer Success Story"
date: "2022-01-21"
-coverImage: "harry-rosen.jpg"
+coverImage: "harry-rosen.webp"
tags: ["retail"]
featured: false
author: "Yash Rathi"
@@ -82,4 +82,4 @@ With our cutting-edge consumer identity and access management (CIAM) solution, o
Using the LoginRadius platform, the client is now poised to expand its capabilities with features such as Social Login, Phone Login, and MFA.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-streamlines-user-onboarding-harry-rosen)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-streamlines-user-onboarding-harry-rosen)
diff --git a/content/identity/loginradius-to-spread-cybersecurity-awareness/cybersec-id.jpg b/content/identity/loginradius-to-spread-cybersecurity-awareness/cybersec-id.jpg
deleted file mode 100644
index a4e9e0ee2..000000000
Binary files a/content/identity/loginradius-to-spread-cybersecurity-awareness/cybersec-id.jpg and /dev/null differ
diff --git a/content/identity/loginradius-to-spread-cybersecurity-awareness/cybersec-id.webp b/content/identity/loginradius-to-spread-cybersecurity-awareness/cybersec-id.webp
new file mode 100644
index 000000000..72cb89dc7
Binary files /dev/null and b/content/identity/loginradius-to-spread-cybersecurity-awareness/cybersec-id.webp differ
diff --git a/content/identity/loginradius-to-spread-cybersecurity-awareness/index.md b/content/identity/loginradius-to-spread-cybersecurity-awareness/index.md
index b2fab8096..65aad90ee 100644
--- a/content/identity/loginradius-to-spread-cybersecurity-awareness/index.md
+++ b/content/identity/loginradius-to-spread-cybersecurity-awareness/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Celebrates National Cybersecurity Month 2022 - Here’s Everything You Should Know"
date: "2022-10-06"
-coverImage: "cybersec-id.jpg"
+coverImage: "cybersec-id.webp"
tags: ["cybersecurity awareness", "cybersecurity campaign", "customer identity"]
author: "Vishal Sharma"
description: "The global cybersecurity threat vector has increased exponentially, and governments across the globe are encouraging people to take accountability to improve their digital privacy. LoginRadius pledges to spread awareness about National Cybersecurity Awareness Month (NCSAM) 2022 through awareness campaigns and help individuals stay safe online."
@@ -131,4 +131,4 @@ Our developer-friendly Identity Platform provides a comprehensive set of APIs to
We also offer open source SDKs, integrations with over 150 third-party applications, pre-designed and customizable login interfaces, and best-in-class data security products. LoginRadius is already loved by over 500 brands with a reach of 1.17 billion consumers worldwide.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-to-spread-cybersecurity-awareness)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-to-spread-cybersecurity-awareness)
diff --git a/content/identity/loginradius-top-performing-blogs-2021/index.md b/content/identity/loginradius-top-performing-blogs-2021/index.md
index c5bc3b3bd..b793432c8 100644
--- a/content/identity/loginradius-top-performing-blogs-2021/index.md
+++ b/content/identity/loginradius-top-performing-blogs-2021/index.md
@@ -1,7 +1,7 @@
---
title: "Top 10 Performing Identity Blogs in 2021"
date: "2021-12-29"
-coverImage: "performing-blogs.jpg"
+coverImage: "performing-blogs.webp"
tags: ["LoginRadius"]
featured: false
author: "Navanita Devi"
@@ -125,4 +125,4 @@ Reach us to know more about LoginRadius CIAM and how it can help scale your busi
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-top-performing-blogs-2021)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-top-performing-blogs-2021)
diff --git a/content/identity/loginradius-top-performing-blogs-2021/performing-blogs.jpg b/content/identity/loginradius-top-performing-blogs-2021/performing-blogs.jpg
deleted file mode 100644
index 694d1f5bd..000000000
Binary files a/content/identity/loginradius-top-performing-blogs-2021/performing-blogs.jpg and /dev/null differ
diff --git a/content/identity/loginradius-top-performing-blogs-2021/performing-blogs.webp b/content/identity/loginradius-top-performing-blogs-2021/performing-blogs.webp
new file mode 100644
index 000000000..f374465ef
Binary files /dev/null and b/content/identity/loginradius-top-performing-blogs-2021/performing-blogs.webp differ
diff --git a/content/identity/loginradius-trust-center/index.md b/content/identity/loginradius-trust-center/index.md
index eeeddc473..fca18ec23 100644
--- a/content/identity/loginradius-trust-center/index.md
+++ b/content/identity/loginradius-trust-center/index.md
@@ -91,4 +91,4 @@ Visit the [LoginRadius Trust Center](https://trust.loginradius.com).
And if you have feedback or ideas—we’re all ears!
-[](https://www.loginradius.com/contact-us)
+[](https://www.loginradius.com/contact-us)
diff --git a/content/identity/loginradius-webhook-datasync-realtime/Book-a-free-demo-request-1024x310.png b/content/identity/loginradius-webhook-datasync-realtime/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/loginradius-webhook-datasync-realtime/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/loginradius-webhook-datasync-realtime/Book-a-free-demo-request-1024x310.webp b/content/identity/loginradius-webhook-datasync-realtime/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/loginradius-webhook-datasync-realtime/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/loginradius-webhook-datasync-realtime/DS-webhook.png b/content/identity/loginradius-webhook-datasync-realtime/DS-webhook.png
deleted file mode 100644
index 25427331b..000000000
Binary files a/content/identity/loginradius-webhook-datasync-realtime/DS-webhook.png and /dev/null differ
diff --git a/content/identity/loginradius-webhook-datasync-realtime/DS-webhook.webp b/content/identity/loginradius-webhook-datasync-realtime/DS-webhook.webp
new file mode 100644
index 000000000..15cdf9e6b
Binary files /dev/null and b/content/identity/loginradius-webhook-datasync-realtime/DS-webhook.webp differ
diff --git a/content/identity/loginradius-webhook-datasync-realtime/index.md b/content/identity/loginradius-webhook-datasync-realtime/index.md
index 002ae9811..93077aeeb 100644
--- a/content/identity/loginradius-webhook-datasync-realtime/index.md
+++ b/content/identity/loginradius-webhook-datasync-realtime/index.md
@@ -1,7 +1,7 @@
---
title: "How LoginRadius Webhook Allows You to Sync Your Data in Real-Time"
date: "2021-11-24"
-coverImage: "webhook-cover.jpg"
+coverImage: "webhook-cover.webp"
tags: ["webhook","data security","ciam platform","cx"]
author: "Vishal Sharma"
description: "Businesses can leverage the true potential of Webhook that allows them to build or set up integrations that subscribe to certain events on LoginRadius CIAM. Let’s understand how LoginRadius improves business performance through third-party integrations and helps sync your crucial business data in real-time through Webhook."
@@ -40,7 +40,7 @@ Enterprises shouldn’t worry about the overall security of consumer data since
* Implementing and [maintaining security policies](https://www.loginradius.com/security-policy) and procedures to meet the ISO 27001, ISO 27017, ISO 27018, NIST CSF requirements, and any other compliance that LoginRadius follows.
* Implementing an Information Security Management System and ensuring that it is continually improved and supported with the necessary resources required to achieve the commitments written in this policy statement.
-[](https://www.loginradius.com/resource/webhook-integration-datasheet)
+[](https://www.loginradius.com/resource/webhook-integration-datasheet)
## Benefits of Webhook LoginRadius Integration
@@ -70,4 +70,4 @@ LoginRadius can easily connect customer data to your existing API-driven tools,
If you wish to see the future of CIAM in action, [reach us](https://www.loginradius.com/contact-sales) for a personalized session.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-webhook-datasync-realtime)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-webhook-datasync-realtime)
diff --git a/content/identity/loginradius-webhook-datasync-realtime/webhook-cover.jpg b/content/identity/loginradius-webhook-datasync-realtime/webhook-cover.jpg
deleted file mode 100644
index 8b78c3d5b..000000000
Binary files a/content/identity/loginradius-webhook-datasync-realtime/webhook-cover.jpg and /dev/null differ
diff --git a/content/identity/loginradius-webhook-datasync-realtime/webhook-cover.webp b/content/identity/loginradius-webhook-datasync-realtime/webhook-cover.webp
new file mode 100644
index 000000000..cf0658030
Binary files /dev/null and b/content/identity/loginradius-webhook-datasync-realtime/webhook-cover.webp differ
diff --git a/content/identity/loginradius-webhook-datasync-realtime/webhook-ds.png b/content/identity/loginradius-webhook-datasync-realtime/webhook-ds.png
deleted file mode 100644
index 10e06f68a..000000000
Binary files a/content/identity/loginradius-webhook-datasync-realtime/webhook-ds.png and /dev/null differ
diff --git a/content/identity/loginradius-webhook-datasync-realtime/webhook-ds.webp b/content/identity/loginradius-webhook-datasync-realtime/webhook-ds.webp
new file mode 100644
index 000000000..467b1ccf4
Binary files /dev/null and b/content/identity/loginradius-webhook-datasync-realtime/webhook-ds.webp differ
diff --git a/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/CTA-Graphics-for-Blogs-V02.01-14-1024x310.png b/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/CTA-Graphics-for-Blogs-V02.01-14-1024x310.png
deleted file mode 100644
index e4fb634c2..000000000
Binary files a/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/CTA-Graphics-for-Blogs-V02.01-14-1024x310.png and /dev/null differ
diff --git a/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/CTA-Graphics-for-Blogs-V02.01-14-1024x310.webp b/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/CTA-Graphics-for-Blogs-V02.01-14-1024x310.webp
new file mode 100644
index 000000000..f431ae35a
Binary files /dev/null and b/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/CTA-Graphics-for-Blogs-V02.01-14-1024x310.webp differ
diff --git a/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/STUPID-WPPPPPPP-1.jpg b/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/STUPID-WPPPPPPP-1.jpg
deleted file mode 100644
index ff42866e9..000000000
Binary files a/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/STUPID-WPPPPPPP-1.jpg and /dev/null differ
diff --git a/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/STUPID-WPPPPPPP-1.webp b/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/STUPID-WPPPPPPP-1.webp
new file mode 100644
index 000000000..4ee8abbf3
Binary files /dev/null and b/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/STUPID-WPPPPPPP-1.webp differ
diff --git a/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/index.md b/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/index.md
index 7e4f8bf0a..26db2afab 100644
--- a/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/index.md
+++ b/content/identity/looking-gigya-alternative-try-loginradius-superior-modern-identity-platform/index.md
@@ -1,7 +1,7 @@
---
title: "Looking for a Gigya Alternative? Try LoginRadius, a Superior and Modern Identity Platform"
date: "2019-02-20"
-coverImage: "STUPID-WPPPPPPP-1.jpg"
+coverImage: "STUPID-WPPPPPPP-1.webp"
tags: ["public-sector"]
featured: false
author: "Rakesh Soni"
@@ -100,4 +100,4 @@ We have automated software for a seamless migration and quick go-to-market, and
If you’d like to hear more about customers making the switch to LoginRadius, contact us at 1-844-625-8889. We can also [give you a demo](https://www.loginradius.com/schedule-demo/) so you can see how our features compare.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=looking-gigya-alternative-try-loginradius-superior-modern-identity-platform)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=looking-gigya-alternative-try-loginradius-superior-modern-identity-platform)
diff --git a/content/identity/low-code-ciam-user-experience/WP-ciam-dev.png b/content/identity/low-code-ciam-user-experience/WP-ciam-dev.png
deleted file mode 100644
index e61d04f85..000000000
Binary files a/content/identity/low-code-ciam-user-experience/WP-ciam-dev.png and /dev/null differ
diff --git a/content/identity/low-code-ciam-user-experience/WP-ciam-dev.webp b/content/identity/low-code-ciam-user-experience/WP-ciam-dev.webp
new file mode 100644
index 000000000..5d47dfbbd
Binary files /dev/null and b/content/identity/low-code-ciam-user-experience/WP-ciam-dev.webp differ
diff --git a/content/identity/low-code-ciam-user-experience/index.md b/content/identity/low-code-ciam-user-experience/index.md
index a39fca485..7892030f7 100644
--- a/content/identity/low-code-ciam-user-experience/index.md
+++ b/content/identity/low-code-ciam-user-experience/index.md
@@ -1,7 +1,7 @@
---
title: "How No/Low Code CIAM Balances Security and User Engagement?"
date: "2024-03-07"
-coverImage: "no-code-ciam.jpg"
+coverImage: "no-code-ciam.webp"
tags: ["ciam solutions","data security","cx"]
author: "Navanita Devi"
description: "Discover the revolutionary No/Low Code CIAM world, where robust security meets seamless user engagement. Learn why developers are turning to this solution, explore real-world use cases, and see how LoginRadius is leading the way in transforming digital identity management."
@@ -73,7 +73,7 @@ LoginRadius is a prime example of a No/Low Code CIAM platform that offers a rang
* **Time and Cost Savings:** Reduce development time and costs significantly by leveraging pre-built components and automation.
-[](https://www.loginradius.com/resource/loginradius-ciam-developers-whitepaper)
+[](https://www.loginradius.com/resource/loginradius-ciam-developers-whitepaper)
## The Future of No/Low Code CIAM
@@ -91,4 +91,4 @@ Looking ahead, the future of No/Low Code CIAM is promising. As technology advanc
In conclusion, a no- or low-code [CIAM solution like LoginRadius](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=low-code-ciam-user-experience) is revolutionizing how businesses approach identity and access management. By combining robust security measures with streamlined development processes, these platforms empower developers to create secure, user-friendly experiences without requiring extensive manual coding.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=low-code-ciam-user-experience)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=low-code-ciam-user-experience)
\ No newline at end of file
diff --git a/content/identity/low-code-ciam-user-experience/no-code-ciam.jpg b/content/identity/low-code-ciam-user-experience/no-code-ciam.jpg
deleted file mode 100644
index a6feec2f5..000000000
Binary files a/content/identity/low-code-ciam-user-experience/no-code-ciam.jpg and /dev/null differ
diff --git a/content/identity/low-code-ciam-user-experience/no-code-ciam.webp b/content/identity/low-code-ciam-user-experience/no-code-ciam.webp
new file mode 100644
index 000000000..60b990aea
Binary files /dev/null and b/content/identity/low-code-ciam-user-experience/no-code-ciam.webp differ
diff --git a/content/identity/lr-launches-autolookup-idp/WP-omnichannel-retail.png b/content/identity/lr-launches-autolookup-idp/WP-omnichannel-retail.png
deleted file mode 100644
index a49793446..000000000
Binary files a/content/identity/lr-launches-autolookup-idp/WP-omnichannel-retail.png and /dev/null differ
diff --git a/content/identity/lr-launches-autolookup-idp/WP-omnichannel-retail.webp b/content/identity/lr-launches-autolookup-idp/WP-omnichannel-retail.webp
new file mode 100644
index 000000000..f5170c511
Binary files /dev/null and b/content/identity/lr-launches-autolookup-idp/WP-omnichannel-retail.webp differ
diff --git a/content/identity/lr-launches-autolookup-idp/autolookup-idp.jpg b/content/identity/lr-launches-autolookup-idp/autolookup-idp.jpg
deleted file mode 100644
index 8603e12da..000000000
Binary files a/content/identity/lr-launches-autolookup-idp/autolookup-idp.jpg and /dev/null differ
diff --git a/content/identity/lr-launches-autolookup-idp/autolookup-idp.webp b/content/identity/lr-launches-autolookup-idp/autolookup-idp.webp
new file mode 100644
index 000000000..9344091d1
Binary files /dev/null and b/content/identity/lr-launches-autolookup-idp/autolookup-idp.webp differ
diff --git a/content/identity/lr-launches-autolookup-idp/index.md b/content/identity/lr-launches-autolookup-idp/index.md
index fa26200f2..e281e9a6a 100644
--- a/content/identity/lr-launches-autolookup-idp/index.md
+++ b/content/identity/lr-launches-autolookup-idp/index.md
@@ -1,7 +1,7 @@
---
title: "Streamlining Authentication: Elevate User Experience with LoginRadius AutoLookup"
date: "2023-12-21"
-coverImage: "autolookup-idp.jpg"
+coverImage: "autolookup-idp.webp"
tags: ["identity provider","user authentication","cx"]
author: "Rakesh Soni"
description: "LoginRadius introduces AutoLookup IDP, a game-changer in the CIAM landscape. Simplify authentication, save time, and elevate user satisfaction. Explore the benefits of this innovative solution and step into the future of secure and efficient login experiences."
@@ -26,7 +26,7 @@ The primary goal of Auto Lookup IDP is to provide users with a [significantly im
Users can now enjoy a smoother and more seamless login journey by simplifying the redirection process to the Identity Provider. This enhancement fosters user satisfaction and positions LoginRadius as a platform that prioritizes user-centric design.
-[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience)
+[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience)
### Time-Saving for Customers
@@ -66,4 +66,4 @@ With a focus on improved user experience, streamlined login processes, and cost-
As the digital landscape continues to evolve, LoginRadius stands at the forefront, empowering organizations to deliver secure, efficient, and user-friendly authentication experiences.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=lr-launches-autolookup-idp)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=lr-launches-autolookup-idp)
\ No newline at end of file
diff --git a/content/identity/lr-launches-identity-orchestration/DS-id-orchestration.png b/content/identity/lr-launches-identity-orchestration/DS-id-orchestration.png
deleted file mode 100644
index ccf2bf5b2..000000000
Binary files a/content/identity/lr-launches-identity-orchestration/DS-id-orchestration.png and /dev/null differ
diff --git a/content/identity/lr-launches-identity-orchestration/DS-id-orchestration.webp b/content/identity/lr-launches-identity-orchestration/DS-id-orchestration.webp
new file mode 100644
index 000000000..1c92d79a3
Binary files /dev/null and b/content/identity/lr-launches-identity-orchestration/DS-id-orchestration.webp differ
diff --git a/content/identity/lr-launches-identity-orchestration/identity-orchestration.jpg b/content/identity/lr-launches-identity-orchestration/identity-orchestration.jpg
deleted file mode 100644
index e86ec48a2..000000000
Binary files a/content/identity/lr-launches-identity-orchestration/identity-orchestration.jpg and /dev/null differ
diff --git a/content/identity/lr-launches-identity-orchestration/identity-orchestration.webp b/content/identity/lr-launches-identity-orchestration/identity-orchestration.webp
new file mode 100644
index 000000000..e7852c4c4
Binary files /dev/null and b/content/identity/lr-launches-identity-orchestration/identity-orchestration.webp differ
diff --git a/content/identity/lr-launches-identity-orchestration/index.md b/content/identity/lr-launches-identity-orchestration/index.md
index 1cc3f3d7d..1ac870bda 100644
--- a/content/identity/lr-launches-identity-orchestration/index.md
+++ b/content/identity/lr-launches-identity-orchestration/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Launches Identity Orchestration for Seamless Identity Workflows"
date: "2024-07-24"
-coverImage: "identity-orchestration.jpg"
+coverImage: "identity-orchestration.webp"
tags: ["identity orchestration","identity management","cx"]
author: "Rakesh Soni"
description: "Managing identity in today's digital world requires innovative solutions. LoginRadius launches Identity Orchestration, a no-code/low-code solution to streamline identity workflows and enhance user experiences. This feature empowers enterprises to easily dynamically build, test, deploy, and manage identity use cases."
@@ -44,7 +44,7 @@ LoginRadius Identity Orchestration offers a plethora of business benefits design
Apart from this, the latest update offers a plethora of benefits for overall business growth.
-[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
+[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
## Use Cases
@@ -60,4 +60,4 @@ LoginRadius Identity Orchestration marks a significant advancement in identity
Offering a flexible, no-code/low-code approach, identity orchestration by LoginRadius enables organizations to swiftly create, test, and deploy customized identity workflows, thereby improving user experiences and ensuring robust security. This innovative solution is poised to revolutionize how enterprises handle identity management, making it easier and more efficient than ever before.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=lr-launches-identity-orchestration)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=lr-launches-identity-orchestration)
\ No newline at end of file
diff --git a/content/identity/lr-leads-ciam-landscape-2024-beyond/DS-pswrdless-login-magic-links-otp.png b/content/identity/lr-leads-ciam-landscape-2024-beyond/DS-pswrdless-login-magic-links-otp.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/lr-leads-ciam-landscape-2024-beyond/DS-pswrdless-login-magic-links-otp.png and /dev/null differ
diff --git a/content/identity/lr-leads-ciam-landscape-2024-beyond/DS-pswrdless-login-magic-links-otp.webp b/content/identity/lr-leads-ciam-landscape-2024-beyond/DS-pswrdless-login-magic-links-otp.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/lr-leads-ciam-landscape-2024-beyond/DS-pswrdless-login-magic-links-otp.webp differ
diff --git a/content/identity/lr-leads-ciam-landscape-2024-beyond/ciam-lead-2024.jpg b/content/identity/lr-leads-ciam-landscape-2024-beyond/ciam-lead-2024.jpg
deleted file mode 100644
index f33b962d1..000000000
Binary files a/content/identity/lr-leads-ciam-landscape-2024-beyond/ciam-lead-2024.jpg and /dev/null differ
diff --git a/content/identity/lr-leads-ciam-landscape-2024-beyond/ciam-lead-2024.webp b/content/identity/lr-leads-ciam-landscape-2024-beyond/ciam-lead-2024.webp
new file mode 100644
index 000000000..403d2a34a
Binary files /dev/null and b/content/identity/lr-leads-ciam-landscape-2024-beyond/ciam-lead-2024.webp differ
diff --git a/content/identity/lr-leads-ciam-landscape-2024-beyond/index.md b/content/identity/lr-leads-ciam-landscape-2024-beyond/index.md
index 331a67605..76bc0efa6 100644
--- a/content/identity/lr-leads-ciam-landscape-2024-beyond/index.md
+++ b/content/identity/lr-leads-ciam-landscape-2024-beyond/index.md
@@ -1,7 +1,7 @@
---
title: "5 Reasons Why LoginRadius Leads the Way in the CIAM Landscape in 2024 & Beyond"
date: "2024-01-24"
-coverImage: "ciam-lead-2024.jpg"
+coverImage: "ciam-lead-2024.webp"
tags: ["ciam solution","data security","cx"]
author: "Rakesh Soni"
description: "Discover how LoginRadius’ cutting-edge CIAM solution seamlessly integrates state-of-the-art technology for robust security and unparalleled user experiences, making it the go-to choice for businesses navigating the digital terrain."
@@ -64,7 +64,7 @@ This authentication trend is gaining popularity among users for its simplicity a
LoginRadius's passwordless magic link aligns consumer expectations with advanced security measures, offering a seamless and protected authentication solution.
-[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
+[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
### 4. Autolookup IDP for Next Level of User Experience
@@ -84,4 +84,4 @@ LoginRadius stands out as the definitive leader in the CIAM landscape for 2024 a
By prioritizing innovation and adaptability, LoginRadius goes beyond industry norms, providing businesses with a comprehensive solution that not only meets but exceeds the dynamic demands of the digital age.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=lr-leads-ciam-landscape-2024-beyond)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=lr-leads-ciam-landscape-2024-beyond)
\ No newline at end of file
diff --git a/content/identity/lr-push-notification-mfa/DS-push-notification.png b/content/identity/lr-push-notification-mfa/DS-push-notification.png
deleted file mode 100644
index 346b76a78..000000000
Binary files a/content/identity/lr-push-notification-mfa/DS-push-notification.png and /dev/null differ
diff --git a/content/identity/lr-push-notification-mfa/DS-push-notification.webp b/content/identity/lr-push-notification-mfa/DS-push-notification.webp
new file mode 100644
index 000000000..e940feeff
Binary files /dev/null and b/content/identity/lr-push-notification-mfa/DS-push-notification.webp differ
diff --git a/content/identity/lr-push-notification-mfa/Push-Notification-MFA.png b/content/identity/lr-push-notification-mfa/Push-Notification-MFA.png
deleted file mode 100644
index d52fe2f91..000000000
Binary files a/content/identity/lr-push-notification-mfa/Push-Notification-MFA.png and /dev/null differ
diff --git a/content/identity/lr-push-notification-mfa/Push-Notification-MFA.webp b/content/identity/lr-push-notification-mfa/Push-Notification-MFA.webp
new file mode 100644
index 000000000..e710970d4
Binary files /dev/null and b/content/identity/lr-push-notification-mfa/Push-Notification-MFA.webp differ
diff --git a/content/identity/lr-push-notification-mfa/index.md b/content/identity/lr-push-notification-mfa/index.md
index be96f81df..bede8f28f 100644
--- a/content/identity/lr-push-notification-mfa/index.md
+++ b/content/identity/lr-push-notification-mfa/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - LoginRadius Unveils the Future of Authentication with Push Notification MFA"
date: "2024-06-19"
-coverImage: "Push-Notification-MFA.png"
+coverImage: "Push-Notification-MFA.webp"
tags: ["industry news","MFA","digital security"]
author: "Rakesh Soni"
description: "LoginRadius introduces Push Notification Multi-Factor Authentication (MFA) to enhance digital security and provide a seamless customer authentication experience. This new feature addresses traditional password vulnerabilities intuitively and is user-friendly, ensuring robust security without compromising convenience."
@@ -34,7 +34,7 @@ Our new Push Notification Multi-Factor Authentication (MFA) feature is designed
5. **Detailed Activity Logs**: Gain insights into customer activity and authentication attempts with comprehensive logging capabilities. This feature allows for better monitoring and analysis of security events.
-[](https://www.loginradius.com/resource/datasheet/push-notification-mfa)
+[](https://www.loginradius.com/resource/datasheet/push-notification-mfa)
## Seamless Integration and Deployment
@@ -44,4 +44,4 @@ Push Notification MFA is designed to introduce minimal friction in the customer
Embrace the future of secure digital interactions with Push Notification MFA from LoginRadius and provide your customers with the seamless, secure experience they deserve. You can now enhance your security measures, reduce password-related risks, and maintain an exceptional user experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=lr-push-notification-mfa)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=lr-push-notification-mfa)
diff --git a/content/identity/lr-reshapes-authentication-healthcare-company/healthcare.jpg b/content/identity/lr-reshapes-authentication-healthcare-company/healthcare.jpg
deleted file mode 100644
index cfc8d6a6e..000000000
Binary files a/content/identity/lr-reshapes-authentication-healthcare-company/healthcare.jpg and /dev/null differ
diff --git a/content/identity/lr-reshapes-authentication-healthcare-company/healthcare.webp b/content/identity/lr-reshapes-authentication-healthcare-company/healthcare.webp
new file mode 100644
index 000000000..9bda9c31e
Binary files /dev/null and b/content/identity/lr-reshapes-authentication-healthcare-company/healthcare.webp differ
diff --git a/content/identity/lr-reshapes-authentication-healthcare-company/index.md b/content/identity/lr-reshapes-authentication-healthcare-company/index.md
index 7533acedd..04ba8865d 100644
--- a/content/identity/lr-reshapes-authentication-healthcare-company/index.md
+++ b/content/identity/lr-reshapes-authentication-healthcare-company/index.md
@@ -1,7 +1,7 @@
---
title: "Celebrating 8th Year Milestone: How Our Collaboration with a Leading Healthcare Company Transformed Millions of Lives"
date: "2024-08-28"
-coverImage: "healthcare.jpg"
+coverImage: "healthcare.webp"
tags: ["healthcare","digital transformation","cx"]
author: "Ritika Kapahi"
description: "Discover how LoginRadius transformed authentication for a global healthcare leader, enhancing patient identity management and boosting user accounts by 20.18%. Explore our 8-year journey of digital innovation, seamless integration, and exceptional service."
@@ -46,4 +46,4 @@ Our partnership's impact extends beyond mere operational enhancements; it has en
As we celebrate these accomplishments, we remain excited about the future. Thanks for an amazing eight years!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=lr-reshapes-authentication-healthcare-company)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=lr-reshapes-authentication-healthcare-company)
\ No newline at end of file
diff --git a/content/identity/mapegy-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.png b/content/identity/mapegy-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/mapegy-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/mapegy-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.webp b/content/identity/mapegy-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/mapegy-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/mapegy-loginradius-customer-success-story/Mapegy_LR.jpg b/content/identity/mapegy-loginradius-customer-success-story/Mapegy_LR.jpg
deleted file mode 100644
index d8bd0d7e1..000000000
Binary files a/content/identity/mapegy-loginradius-customer-success-story/Mapegy_LR.jpg and /dev/null differ
diff --git a/content/identity/mapegy-loginradius-customer-success-story/Mapegy_LR.webp b/content/identity/mapegy-loginradius-customer-success-story/Mapegy_LR.webp
new file mode 100644
index 000000000..f94ab2278
Binary files /dev/null and b/content/identity/mapegy-loginradius-customer-success-story/Mapegy_LR.webp differ
diff --git a/content/identity/mapegy-loginradius-customer-success-story/index.md b/content/identity/mapegy-loginradius-customer-success-story/index.md
index 3a73ab2a6..01abc5b24 100644
--- a/content/identity/mapegy-loginradius-customer-success-story/index.md
+++ b/content/identity/mapegy-loginradius-customer-success-story/index.md
@@ -1,7 +1,7 @@
---
title: "Mapegy, a LoginRadius Customer Success Story"
date: "2017-06-15"
-coverImage: "Mapegy_LR.jpg"
+coverImage: "Mapegy_LR.webp"
tags: ["media-and-publication"]
featured: false
author: "Karl Wittig"
@@ -40,4 +40,4 @@ Throughout their implementation process, our support team has always been readil
Mapegy - LoginRadius Customer Success Story
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=mapegy-loginradius-customer-success-story)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=mapegy-loginradius-customer-success-story)
diff --git a/content/identity/marriott-data-breach-2020/BD-Developers2-1024x310.png b/content/identity/marriott-data-breach-2020/BD-Developers2-1024x310.png
deleted file mode 100644
index e794b3769..000000000
Binary files a/content/identity/marriott-data-breach-2020/BD-Developers2-1024x310.png and /dev/null differ
diff --git a/content/identity/marriott-data-breach-2020/BD-Developers2-1024x310.webp b/content/identity/marriott-data-breach-2020/BD-Developers2-1024x310.webp
new file mode 100644
index 000000000..371ef34ea
Binary files /dev/null and b/content/identity/marriott-data-breach-2020/BD-Developers2-1024x310.webp differ
diff --git a/content/identity/marriott-data-breach-2020/Protecting-PII-Against-Data-Breaches.png b/content/identity/marriott-data-breach-2020/Protecting-PII-Against-Data-Breaches.png
deleted file mode 100644
index a86e6d940..000000000
Binary files a/content/identity/marriott-data-breach-2020/Protecting-PII-Against-Data-Breaches.png and /dev/null differ
diff --git a/content/identity/marriott-data-breach-2020/Protecting-PII-Against-Data-Breaches.webp b/content/identity/marriott-data-breach-2020/Protecting-PII-Against-Data-Breaches.webp
new file mode 100644
index 000000000..fc95b4d7d
Binary files /dev/null and b/content/identity/marriott-data-breach-2020/Protecting-PII-Against-Data-Breaches.webp differ
diff --git a/content/identity/marriott-data-breach-2020/index.md b/content/identity/marriott-data-breach-2020/index.md
index 6be8df6a2..3f49c3fe4 100644
--- a/content/identity/marriott-data-breach-2020/index.md
+++ b/content/identity/marriott-data-breach-2020/index.md
@@ -1,7 +1,7 @@
---
title: "Marriott Data Breach 2020: 5.2 Million Guest Records Were Stolen"
date: "2020-04-13"
-coverImage: "marriott-data-breach.jpg"
+coverImage: "marriott-data-breach.webp"
tags: ["other"]
featured: false
author: "Rakesh Soni"
@@ -30,7 +30,7 @@ The hotel giant announced another [data breach in late 2018](https://news.marrio
It could be considered an honest mistake to suffer one data breach but to suffer two in less than two years looks like carelessness. There are some promising signs that the company has learned some valuable information security lessons in spite of how it may look to an outsider. From this experience, the [entire hospitality industry](https://www.loginradius.com/blog/2020/03/improve-customer-experience-hospitality-industry/) should now know better.
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
## What does the Hotel Industry do to avoid data breaches like Marriott’s?
@@ -48,4 +48,4 @@ Companies need to understand that customer data security is part of the revenue
Let’s hope that Marriott and its peers in the travel industry have learned that, while the security of customer accounts may not be their core business, it still needs to be priority number one.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=marriott-data-breach-2020)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=marriott-data-breach-2020)
diff --git a/content/identity/marriott-data-breach-2020/marriott-data-breach.jpg b/content/identity/marriott-data-breach-2020/marriott-data-breach.jpg
deleted file mode 100644
index 2610d5ad0..000000000
Binary files a/content/identity/marriott-data-breach-2020/marriott-data-breach.jpg and /dev/null differ
diff --git a/content/identity/marriott-data-breach-2020/marriott-data-breach.webp b/content/identity/marriott-data-breach-2020/marriott-data-breach.webp
new file mode 100644
index 000000000..2e423d085
Binary files /dev/null and b/content/identity/marriott-data-breach-2020/marriott-data-breach.webp differ
diff --git a/content/identity/media-entertainment-use-loginradius-platform/Book-a-free-demo-request-1024x310.png b/content/identity/media-entertainment-use-loginradius-platform/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/media-entertainment-use-loginradius-platform/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/media-entertainment-use-loginradius-platform/Book-a-free-demo-request-1024x310.webp b/content/identity/media-entertainment-use-loginradius-platform/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/media-entertainment-use-loginradius-platform/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/media-entertainment-use-loginradius-platform/DS-Fed-IM.png b/content/identity/media-entertainment-use-loginradius-platform/DS-Fed-IM.png
deleted file mode 100644
index 9e03618f7..000000000
Binary files a/content/identity/media-entertainment-use-loginradius-platform/DS-Fed-IM.png and /dev/null differ
diff --git a/content/identity/media-entertainment-use-loginradius-platform/DS-Fed-IM.webp b/content/identity/media-entertainment-use-loginradius-platform/DS-Fed-IM.webp
new file mode 100644
index 000000000..b8fd0ecbb
Binary files /dev/null and b/content/identity/media-entertainment-use-loginradius-platform/DS-Fed-IM.webp differ
diff --git a/content/identity/media-entertainment-use-loginradius-platform/FIM-DS.png b/content/identity/media-entertainment-use-loginradius-platform/FIM-DS.png
deleted file mode 100644
index 01a289614..000000000
Binary files a/content/identity/media-entertainment-use-loginradius-platform/FIM-DS.png and /dev/null differ
diff --git a/content/identity/media-entertainment-use-loginradius-platform/FIM-DS.webp b/content/identity/media-entertainment-use-loginradius-platform/FIM-DS.webp
new file mode 100644
index 000000000..3d4c0a8aa
Binary files /dev/null and b/content/identity/media-entertainment-use-loginradius-platform/FIM-DS.webp differ
diff --git a/content/identity/media-entertainment-use-loginradius-platform/index.md b/content/identity/media-entertainment-use-loginradius-platform/index.md
index bd3692e14..6898e901c 100644
--- a/content/identity/media-entertainment-use-loginradius-platform/index.md
+++ b/content/identity/media-entertainment-use-loginradius-platform/index.md
@@ -1,7 +1,7 @@
---
title: "How Entertainment Companies Use the LoginRadius CIAM platform"
date: "2021-05-25"
-coverImage: "media-entertainment-use-loginradius-platform-cover.jpg"
+coverImage: "media-entertainment-use-loginradius-platform-cover.webp"
tags: ["LoginRadius"]
author: "Navanita Devi"
description: "Every industry takes a different approach to identity management. When it comes to media and entertainment, viewers love to move around a lot. As a result, before embarking on the journey, organizations must first understand a few things. For example, what goal they hope to achieve, how does a CIAM platform fits into the picture, and how do they find the best solution."
@@ -38,7 +38,7 @@ A single sign-on provides users with a convenient way to log in to multiple appl
* **Mobile SSO** operates through many mobile applications. If a consumer authenticates on one mobile app and then opens another operated by the same business, the CIAM platform recognizes the consumer. It grants access without requiring you to sign up or authenticate.
* **[Federated SSO](https://www.loginradius.com/federated-sso/)** is a set of rules that can be implemented between two or more trusted domains to allow users to use the same digital identity to access applications and services.
-[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
+[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
LoginRadius supports industry-standard SSO protocols like SAML, JWT, OAuth 2.0, OpenID Connect, and Web Services Federation.
@@ -90,5 +90,5 @@ Every industry has a different set of identity challenges and a unique approach
For example, what goal they hope to achieve, how does [a CIAM platform fits into the picture](https://www.loginradius.com/resource/how-media-and-publication-companies-use-loginradius-identity-platform/), and identify the right solution to get the job done. LoginRadius allows you to equip and support your viewers well so you can adapt to the new way of entertainment.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=media-entertainment-use-loginradius-platform)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=media-entertainment-use-loginradius-platform)
diff --git a/content/identity/media-entertainment-use-loginradius-platform/media-entertainment-use-loginradius-platform-cover.jpg b/content/identity/media-entertainment-use-loginradius-platform/media-entertainment-use-loginradius-platform-cover.jpg
deleted file mode 100644
index 2c464bfe6..000000000
Binary files a/content/identity/media-entertainment-use-loginradius-platform/media-entertainment-use-loginradius-platform-cover.jpg and /dev/null differ
diff --git a/content/identity/media-entertainment-use-loginradius-platform/media-entertainment-use-loginradius-platform-cover.webp b/content/identity/media-entertainment-use-loginradius-platform/media-entertainment-use-loginradius-platform-cover.webp
new file mode 100644
index 000000000..6ed8de23f
Binary files /dev/null and b/content/identity/media-entertainment-use-loginradius-platform/media-entertainment-use-loginradius-platform-cover.webp differ
diff --git a/content/identity/mfa-fatigue-attacks-cybersec-menace/GD-to-RBA.png b/content/identity/mfa-fatigue-attacks-cybersec-menace/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/mfa-fatigue-attacks-cybersec-menace/GD-to-RBA.png and /dev/null differ
diff --git a/content/identity/mfa-fatigue-attacks-cybersec-menace/GD-to-RBA.webp b/content/identity/mfa-fatigue-attacks-cybersec-menace/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/mfa-fatigue-attacks-cybersec-menace/GD-to-RBA.webp differ
diff --git a/content/identity/mfa-fatigue-attacks-cybersec-menace/index.md b/content/identity/mfa-fatigue-attacks-cybersec-menace/index.md
index eb1714d7b..75dab3753 100644
--- a/content/identity/mfa-fatigue-attacks-cybersec-menace/index.md
+++ b/content/identity/mfa-fatigue-attacks-cybersec-menace/index.md
@@ -1,7 +1,7 @@
---
title: "Why MFA Fatigue Attacks May Soon Be Your Worst Nightmare?"
date: "2022-10-31"
-coverImage: "mfa-fatigue.jpg"
+coverImage: "mfa-fatigue.webp"
tags: ["mfa fatigue", "risk-based authentication", "authentication process"]
author: "Rakesh Soni"
description: "MFA fatigue attacks bypass MFA by bombarding a user with multiple login attempts. The account owner accepts the MFA prompt out of desperation or annoyance, leading to an account takeover. Let’s learn how organizations can gear themselves to shield against these attacks."
@@ -49,7 +49,7 @@ It is a method of applying various levels of stringency to [authentication proce
Risk-based authentication is an essential security feature because it works in real-time to prevent cyber frauds like accounts getting compromised without causing an inconvenience for legitimate consumers.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
Risk-based authentication helps businesses in achieving the following goals:
@@ -78,5 +78,5 @@ MFA fatigue attacks are on the rise, and businesses can’t afford to take the r
Adding a more robust authentication mechanism in the form of risk-based authentication can help minimize the chances of MFA fatigue attack and help secure crucial information.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=mfa-fatigue-attacks-cybersec-menace)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=mfa-fatigue-attacks-cybersec-menace)
diff --git a/content/identity/mfa-fatigue-attacks-cybersec-menace/mfa-fatigue.jpg b/content/identity/mfa-fatigue-attacks-cybersec-menace/mfa-fatigue.jpg
deleted file mode 100644
index 3691f3266..000000000
Binary files a/content/identity/mfa-fatigue-attacks-cybersec-menace/mfa-fatigue.jpg and /dev/null differ
diff --git a/content/identity/mfa-fatigue-attacks-cybersec-menace/mfa-fatigue.webp b/content/identity/mfa-fatigue-attacks-cybersec-menace/mfa-fatigue.webp
new file mode 100644
index 000000000..197f406ef
Binary files /dev/null and b/content/identity/mfa-fatigue-attacks-cybersec-menace/mfa-fatigue.webp differ
diff --git a/content/identity/mfa-fatigue-attacks-cybersec-menace/rba-gd.png b/content/identity/mfa-fatigue-attacks-cybersec-menace/rba-gd.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/identity/mfa-fatigue-attacks-cybersec-menace/rba-gd.png and /dev/null differ
diff --git a/content/identity/mfa-fatigue-attacks-cybersec-menace/rba-gd.webp b/content/identity/mfa-fatigue-attacks-cybersec-menace/rba-gd.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/identity/mfa-fatigue-attacks-cybersec-menace/rba-gd.webp differ
diff --git a/content/identity/mfa-prompt-bombing-businesses/GD-to-RBA.png b/content/identity/mfa-prompt-bombing-businesses/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/mfa-prompt-bombing-businesses/GD-to-RBA.png and /dev/null differ
diff --git a/content/identity/mfa-prompt-bombing-businesses/GD-to-RBA.webp b/content/identity/mfa-prompt-bombing-businesses/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/mfa-prompt-bombing-businesses/GD-to-RBA.webp differ
diff --git a/content/identity/mfa-prompt-bombing-businesses/index.md b/content/identity/mfa-prompt-bombing-businesses/index.md
index a8725b84e..0db78f4dc 100644
--- a/content/identity/mfa-prompt-bombing-businesses/index.md
+++ b/content/identity/mfa-prompt-bombing-businesses/index.md
@@ -1,7 +1,7 @@
---
title: "MFA Prompt Bombing: Is it a New Threat Vector to Worry About?"
date: "2022-08-08"
-coverImage: "mfa-prompt.jpg"
+coverImage: "mfa-prompt.webp"
tags: ["MFA", "risk-based authentication", "user access"]
author: "Alok Patidar"
description: "The MFA prompt attacks typically leverage MFA fatigue, where users get annoyed and unknowingly or unwillingly accept authentication attempts initiated by cyber attackers. This post uncovers the aspects associated with MFA prompt bombing attacks and how businesses can reinforce their overall security infrastructure."
@@ -45,7 +45,7 @@ RBA allows users to log in using a username and password without presenting any
Risk-based authentication is a great security mechanism that helps overcome the challenges associated with MFA prompt bombing since it automatically detects the risks and unusual behavior from a particular account and restricts access.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
## How Risk-Based Authentication Works for Protecting Against MFA Prompt Bombing?
@@ -69,5 +69,5 @@ Businesses need to understand the risks associated with account takeovers throug
Organizations can invoke the true potential of risk-based authentication (RBA) to overcome the challenges pertaining to MFA prompt bombing.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=mfa-prompt-bombing-businesses)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=mfa-prompt-bombing-businesses)
diff --git a/content/identity/mfa-prompt-bombing-businesses/mfa-prompt.jpg b/content/identity/mfa-prompt-bombing-businesses/mfa-prompt.jpg
deleted file mode 100644
index 6cc56f61d..000000000
Binary files a/content/identity/mfa-prompt-bombing-businesses/mfa-prompt.jpg and /dev/null differ
diff --git a/content/identity/mfa-prompt-bombing-businesses/mfa-prompt.webp b/content/identity/mfa-prompt-bombing-businesses/mfa-prompt.webp
new file mode 100644
index 000000000..9be032eb4
Binary files /dev/null and b/content/identity/mfa-prompt-bombing-businesses/mfa-prompt.webp differ
diff --git a/content/identity/mfa-prompt-bombing-businesses/rba-gd.png b/content/identity/mfa-prompt-bombing-businesses/rba-gd.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/identity/mfa-prompt-bombing-businesses/rba-gd.png and /dev/null differ
diff --git a/content/identity/mfa-prompt-bombing-businesses/rba-gd.webp b/content/identity/mfa-prompt-bombing-businesses/rba-gd.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/identity/mfa-prompt-bombing-businesses/rba-gd.webp differ
diff --git a/content/identity/mfa-vs-rba/an-enterprises-guide-to-risk-based-authentication.png b/content/identity/mfa-vs-rba/an-enterprises-guide-to-risk-based-authentication.png
deleted file mode 100644
index d0bab20da..000000000
Binary files a/content/identity/mfa-vs-rba/an-enterprises-guide-to-risk-based-authentication.png and /dev/null differ
diff --git a/content/identity/mfa-vs-rba/an-enterprises-guide-to-risk-based-authentication.webp b/content/identity/mfa-vs-rba/an-enterprises-guide-to-risk-based-authentication.webp
new file mode 100644
index 000000000..4f2ffa5fb
Binary files /dev/null and b/content/identity/mfa-vs-rba/an-enterprises-guide-to-risk-based-authentication.webp differ
diff --git a/content/identity/mfa-vs-rba/index.md b/content/identity/mfa-vs-rba/index.md
index c8efb1699..9fd26d89b 100644
--- a/content/identity/mfa-vs-rba/index.md
+++ b/content/identity/mfa-vs-rba/index.md
@@ -98,7 +98,7 @@ With cyber threats constantly evolving, risk-based MFA ensures security policies
Want a detailed guide on risk-based authentication? Download this insightful guide:
-[](https://www.loginradius.com/resource/guide/enterprise-risk-based-authentication/)
+[](https://www.loginradius.com/resource/guide/enterprise-risk-based-authentication/)
## Risk-based vs Traditional MFA
diff --git a/content/identity/mfa-vs-sso/DS-SSO.png b/content/identity/mfa-vs-sso/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/mfa-vs-sso/DS-SSO.png and /dev/null differ
diff --git a/content/identity/mfa-vs-sso/DS-SSO.webp b/content/identity/mfa-vs-sso/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/mfa-vs-sso/DS-SSO.webp differ
diff --git a/content/identity/mfa-vs-sso/index.md b/content/identity/mfa-vs-sso/index.md
index 75f9df487..da9c79ba3 100644
--- a/content/identity/mfa-vs-sso/index.md
+++ b/content/identity/mfa-vs-sso/index.md
@@ -1,7 +1,7 @@
---
title: "What is the Difference Between MFA vs. SSO?"
date: "2022-04-12"
-coverImage: "sso-vs-mfa.jpg"
+coverImage: "sso-vs-mfa.webp"
tags: ["authentication", "mfa", "sso", "ciam"]
author: "Navanita Devi"
description: "Security and user experience are all that a modern online platform demands. And businesses need to create a perfect harmony between security and usability to witness growth. Let’s understand the aspects of MFA vs. SSO in detail and learn how businesses can leverage MFA and SSO to scale growth, ensure security, and maintain a rich consumer experience."
@@ -93,7 +93,7 @@ Single Sign-On clearly minimizes the risk of poor password habits. Also, removin
* **Unifies customer profiles:** Creating a single instance of the customer data provides a [centralized view of the customer](https://www.loginradius.com/profile-management/) across all channels.
* **Reduces IT costs:** Due to fewer help desk calls about passwords, IT can spend less time helping users remember or reset their passwords for hundreds of applications.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
## Best Practices for Implementing MFA and SSO:
@@ -155,4 +155,4 @@ MFA adds layers of verification, making unauthorized access harder, while SSO re
By evaluating security requirements, assessing complexities and usability, and also by considering specific organizational needs.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=mfa-vs-sso)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=mfa-vs-sso)
\ No newline at end of file
diff --git a/content/identity/mfa-vs-sso/mfa-vs-sso.jpg b/content/identity/mfa-vs-sso/mfa-vs-sso.jpg
deleted file mode 100644
index 3583870a2..000000000
Binary files a/content/identity/mfa-vs-sso/mfa-vs-sso.jpg and /dev/null differ
diff --git a/content/identity/mfa-vs-sso/mfa-vs-sso.webp b/content/identity/mfa-vs-sso/mfa-vs-sso.webp
new file mode 100644
index 000000000..38429b13b
Binary files /dev/null and b/content/identity/mfa-vs-sso/mfa-vs-sso.webp differ
diff --git a/content/identity/mfa-vs-sso/sso-vs-mfa.jpg b/content/identity/mfa-vs-sso/sso-vs-mfa.jpg
deleted file mode 100644
index 9f8507a9f..000000000
Binary files a/content/identity/mfa-vs-sso/sso-vs-mfa.jpg and /dev/null differ
diff --git a/content/identity/mfa-vs-sso/sso-vs-mfa.webp b/content/identity/mfa-vs-sso/sso-vs-mfa.webp
new file mode 100644
index 000000000..b1f4cb66d
Binary files /dev/null and b/content/identity/mfa-vs-sso/sso-vs-mfa.webp differ
diff --git a/content/identity/mobile-authentication/index.md b/content/identity/mobile-authentication/index.md
index 9d4768970..c3fe35767 100644
--- a/content/identity/mobile-authentication/index.md
+++ b/content/identity/mobile-authentication/index.md
@@ -134,4 +134,4 @@ A: SMS 2FA is vulnerable to SIM swaps and interception—use authenticator apps,
A: It includes biometrics, adaptive authentication, AI-driven threat detection, and encryption to protect mobile data from cyber threats.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=mobile-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=mobile-authentication)
\ No newline at end of file
diff --git a/content/identity/multi-cloud-environment-optmization-challenges/cloud-multi.jpg b/content/identity/multi-cloud-environment-optmization-challenges/cloud-multi.jpg
deleted file mode 100644
index a2b283ae2..000000000
Binary files a/content/identity/multi-cloud-environment-optmization-challenges/cloud-multi.jpg and /dev/null differ
diff --git a/content/identity/multi-cloud-environment-optmization-challenges/cloud-multi.webp b/content/identity/multi-cloud-environment-optmization-challenges/cloud-multi.webp
new file mode 100644
index 000000000..c8f991839
Binary files /dev/null and b/content/identity/multi-cloud-environment-optmization-challenges/cloud-multi.webp differ
diff --git a/content/identity/multi-cloud-environment-optmization-challenges/index.md b/content/identity/multi-cloud-environment-optmization-challenges/index.md
index ef5403c18..a17e7a621 100644
--- a/content/identity/multi-cloud-environment-optmization-challenges/index.md
+++ b/content/identity/multi-cloud-environment-optmization-challenges/index.md
@@ -1,7 +1,7 @@
---
title: "A Lot Can Happen In The Cloud: Multi-Cloud Environment and its Optimization Challenges"
date: "2023-01-13"
-coverImage: "cloud-multi.jpg"
+coverImage: "cloud-multi.webp"
tags: ["multi cloud", cloud cost optimization", "on prem"]
author: "Rakesh Soni"
description: "Although some features of the cloud are pretty attractive, there exist some that aren’t so attractive but are add-on features that make it highly complex to manage the cloud regularly. Let’s uncover some optimization aspects of multi-cloud environments and the challenges that can help businesses plan their cloud adoption smartly."
@@ -67,7 +67,7 @@ When choosing a reliable cloud architecture, most businesses aren’t sure wheth
For startups and budding entrepreneurs, multi-tenant cloud deployment is the best as they need not spend much money on the services they don’t require. Instead, they just need to pay for the resources they need on shared cloud space.
-[](https://www.loginradius.com/resource/overcome-the-nightmare-of-on-prem-deployment-move-to-cloud/)
+[](https://www.loginradius.com/resource/overcome-the-nightmare-of-on-prem-deployment-move-to-cloud/)
### #2. Analyze Unused Resources
@@ -97,5 +97,5 @@ The multi-cloud challenge is difficult to solve without proper planning, and the
Businesses should carefully consider a number of points before moving forward: which cloud services best meet the needs of their applications? What is the solution's total cost of ownership? And will users be satisfied with that solution?
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=multi-cloud-environment-optmization-challenges)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=multi-cloud-environment-optmization-challenges)
diff --git a/content/identity/multi-cloud-environment-optmization-challenges/nightmare-wp.png b/content/identity/multi-cloud-environment-optmization-challenges/nightmare-wp.png
deleted file mode 100644
index e1de2961b..000000000
Binary files a/content/identity/multi-cloud-environment-optmization-challenges/nightmare-wp.png and /dev/null differ
diff --git a/content/identity/multi-cloud-environment-optmization-challenges/nightmare-wp.webp b/content/identity/multi-cloud-environment-optmization-challenges/nightmare-wp.webp
new file mode 100644
index 000000000..fedbbdabc
Binary files /dev/null and b/content/identity/multi-cloud-environment-optmization-challenges/nightmare-wp.webp differ
diff --git a/content/identity/multi-cloud-environment-optmization-challenges/wp-nightmare.png b/content/identity/multi-cloud-environment-optmization-challenges/wp-nightmare.png
deleted file mode 100644
index 6d7ae87ab..000000000
Binary files a/content/identity/multi-cloud-environment-optmization-challenges/wp-nightmare.png and /dev/null differ
diff --git a/content/identity/multi-cloud-environment-optmization-challenges/wp-nightmare.webp b/content/identity/multi-cloud-environment-optmization-challenges/wp-nightmare.webp
new file mode 100644
index 000000000..c13a51d3a
Binary files /dev/null and b/content/identity/multi-cloud-environment-optmization-challenges/wp-nightmare.webp differ
diff --git a/content/identity/multi-tenancy-ciam-security/WP-identity-mngmnt.png b/content/identity/multi-tenancy-ciam-security/WP-identity-mngmnt.png
deleted file mode 100644
index c1f47d8bc..000000000
Binary files a/content/identity/multi-tenancy-ciam-security/WP-identity-mngmnt.png and /dev/null differ
diff --git a/content/identity/multi-tenancy-ciam-security/WP-identity-mngmnt.webp b/content/identity/multi-tenancy-ciam-security/WP-identity-mngmnt.webp
new file mode 100644
index 000000000..89e798f06
Binary files /dev/null and b/content/identity/multi-tenancy-ciam-security/WP-identity-mngmnt.webp differ
diff --git a/content/identity/multi-tenancy-ciam-security/ciam-security.jpg b/content/identity/multi-tenancy-ciam-security/ciam-security.jpg
deleted file mode 100644
index 087ee4361..000000000
Binary files a/content/identity/multi-tenancy-ciam-security/ciam-security.jpg and /dev/null differ
diff --git a/content/identity/multi-tenancy-ciam-security/ciam-security.webp b/content/identity/multi-tenancy-ciam-security/ciam-security.webp
new file mode 100644
index 000000000..689795444
Binary files /dev/null and b/content/identity/multi-tenancy-ciam-security/ciam-security.webp differ
diff --git a/content/identity/multi-tenancy-ciam-security/index.md b/content/identity/multi-tenancy-ciam-security/index.md
index f719c12ad..94652bbaf 100644
--- a/content/identity/multi-tenancy-ciam-security/index.md
+++ b/content/identity/multi-tenancy-ciam-security/index.md
@@ -1,7 +1,7 @@
---
title: "How Does Multi-Tenancy in Customer IAM Solutions Boost Security?"
date: "2024-03-14"
-coverImage: "ciam-security.jpg"
+coverImage: "ciam-security.webp"
tags: ["ciam solutions","identity management","cx"]
author: "Rakesh Soni"
description: "Multi-tenancy in Customer IAM architecture introduces a significant shift in how organizations manage and protect their users' identities in a shared environment. Let's discover how multi-tenancy enables multiple tenants or customers to co-exist securely within a single CIAM infrastructure."
@@ -68,7 +68,7 @@ The logical separation of tenants contains damage. If a user account on Tenant A
Multi-tenant solutions make it easy to define and implement identity governance policies uniformly. Secure password policies, access reviews and certification, role lifecycle management, and de-provisioning workflows can be standardized across customers.
-[](https://www.loginradius.com/resource/the-critical-role-of-identity-management-in-data-governance/)
+[](https://www.loginradius.com/resource/the-critical-role-of-identity-management-in-data-governance/)
### Consolidated Audit Trail
@@ -118,4 +118,4 @@ Architectural isolation mechanisms naturally provide tenant segmentation and res
Whether you need to onboard business partners, merge acquired companies, or manage a contractor ecosystem, the LoginRadius CIAM platform has proven capabilities trusted by leading enterprises. Schedule a discussion to see the power of multi-tenancy in action!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=multi-tenancy-ciam-security)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=multi-tenancy-ciam-security)
\ No newline at end of file
diff --git a/content/identity/municipals-investing-citizen-engagement/Ebook-thumb.png b/content/identity/municipals-investing-citizen-engagement/Ebook-thumb.png
deleted file mode 100644
index 57e509cfc..000000000
Binary files a/content/identity/municipals-investing-citizen-engagement/Ebook-thumb.png and /dev/null differ
diff --git a/content/identity/municipals-investing-citizen-engagement/Ebook-thumb.webp b/content/identity/municipals-investing-citizen-engagement/Ebook-thumb.webp
new file mode 100644
index 000000000..365c92a0a
Binary files /dev/null and b/content/identity/municipals-investing-citizen-engagement/Ebook-thumb.webp differ
diff --git a/content/identity/municipals-investing-citizen-engagement/advice-advise-advisor-4.jpg b/content/identity/municipals-investing-citizen-engagement/advice-advise-advisor-4.jpg
deleted file mode 100644
index 89135f6b4..000000000
Binary files a/content/identity/municipals-investing-citizen-engagement/advice-advise-advisor-4.jpg and /dev/null differ
diff --git a/content/identity/municipals-investing-citizen-engagement/advice-advise-advisor-4.webp b/content/identity/municipals-investing-citizen-engagement/advice-advise-advisor-4.webp
new file mode 100644
index 000000000..4b9881831
Binary files /dev/null and b/content/identity/municipals-investing-citizen-engagement/advice-advise-advisor-4.webp differ
diff --git a/content/identity/municipals-investing-citizen-engagement/berlin-building-business-3.jpg b/content/identity/municipals-investing-citizen-engagement/berlin-building-business-3.jpg
deleted file mode 100644
index 956fdc648..000000000
Binary files a/content/identity/municipals-investing-citizen-engagement/berlin-building-business-3.jpg and /dev/null differ
diff --git a/content/identity/municipals-investing-citizen-engagement/berlin-building-business-3.webp b/content/identity/municipals-investing-citizen-engagement/berlin-building-business-3.webp
new file mode 100644
index 000000000..b3d70faab
Binary files /dev/null and b/content/identity/municipals-investing-citizen-engagement/berlin-building-business-3.webp differ
diff --git a/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-2.jpg b/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-2.jpg
deleted file mode 100644
index b1d0a22b7..000000000
Binary files a/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-2.jpg and /dev/null differ
diff --git a/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-2.webp b/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-2.webp
new file mode 100644
index 000000000..ecad5e1f5
Binary files /dev/null and b/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-2.webp differ
diff --git a/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-398532-1.jpg b/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-398532-1.jpg
deleted file mode 100644
index 601e09a3d..000000000
Binary files a/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-398532-1.jpg and /dev/null differ
diff --git a/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-398532-1.webp b/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-398532-1.webp
new file mode 100644
index 000000000..a4aa48219
Binary files /dev/null and b/content/identity/municipals-investing-citizen-engagement/collaboration-colleagues-community-398532-1.webp differ
diff --git a/content/identity/municipals-investing-citizen-engagement/index.md b/content/identity/municipals-investing-citizen-engagement/index.md
index 0546237a4..15c3f9262 100644
--- a/content/identity/municipals-investing-citizen-engagement/index.md
+++ b/content/identity/municipals-investing-citizen-engagement/index.md
@@ -1,7 +1,7 @@
---
title: "Why Municipalities Are Investing in Citizen Engagement"
date: "2018-06-18"
-coverImage: "collaboration-colleagues-community-398532-1.jpg"
+coverImage: "collaboration-colleagues-community-398532-1.webp"
tags: ["public-sector"]
featured: false
author: "Rakesh Soni"
@@ -18,7 +18,7 @@ By investing in a well-designed and implemented citizen-centric solution, munici
### 1\. Increase citizen satisfaction with government performance
-
+
Citizens want to engage with their local government. They want to be able to share their views and access channels to participate in the decisions of government, connect with representatives, and be assured that their input has meaning and relevance.
@@ -26,7 +26,7 @@ Citizens have been very vocal about these methods of engagement, so it should co
### 2\. Enhance citizen trust in civic institutions
-
+
The public has been demanding more transparency and accountability from government for years. These demands are prompting municipalities to change how they engage with the public.
@@ -36,7 +36,7 @@ Municipalities need to have a direct line of engagement between themselves and t
### 3\. Get the most out of your digital solutions, which saves an enormous amount of time and money
-
+
Engaging the community to keep them better informed about what is going on will only help in the long run. For example, instead of spending too much time and resources on projects that are only going to get protested, why not get community input from the beginning? If citizens are more involved in the process, municipalities can reduce lengthy and expensive legal appeals as well.
@@ -46,4 +46,4 @@ Many municipalities are now undergoing [digital transformations](https://www.log
Undergoing a digital transformation, however, is just one of the much-needed steps. In order to truly engage your citizens, you need to know who they are. To learn who they are, you have to incorporate digital identity into your transformation.
-How does digital identity help with engagement? In our new e-book, we have listed the top 5 ways to improve your citizen engagement, which include creating a seamless digital service by unifying citizen services and identity, as well as improving your privacy and security efforts. You can check out the new e-book [here](https://www.loginradius.com/resource/top-5-ways-to-improve-citizen-engagement-2/). 
+How does digital identity help with engagement? In our new e-book, we have listed the top 5 ways to improve your citizen engagement, which include creating a seamless digital service by unifying citizen services and identity, as well as improving your privacy and security efforts. You can check out the new e-book [here](https://www.loginradius.com/resource/top-5-ways-to-improve-citizen-engagement-2/). 
diff --git a/content/identity/new-age-ciam/a-new-age-CIAM.jpg b/content/identity/new-age-ciam/a-new-age-CIAM.jpg
deleted file mode 100644
index cc60020db..000000000
Binary files a/content/identity/new-age-ciam/a-new-age-CIAM.jpg and /dev/null differ
diff --git a/content/identity/new-age-ciam/a-new-age-CIAM.webp b/content/identity/new-age-ciam/a-new-age-CIAM.webp
new file mode 100644
index 000000000..ad6d360fd
Binary files /dev/null and b/content/identity/new-age-ciam/a-new-age-CIAM.webp differ
diff --git a/content/identity/new-age-ciam/guide-to-modern-customer-identity.png b/content/identity/new-age-ciam/guide-to-modern-customer-identity.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/identity/new-age-ciam/guide-to-modern-customer-identity.png and /dev/null differ
diff --git a/content/identity/new-age-ciam/guide-to-modern-customer-identity.webp b/content/identity/new-age-ciam/guide-to-modern-customer-identity.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/identity/new-age-ciam/guide-to-modern-customer-identity.webp differ
diff --git a/content/identity/new-age-ciam/index.md b/content/identity/new-age-ciam/index.md
index 4befd0d78..9961fd5bf 100644
--- a/content/identity/new-age-ciam/index.md
+++ b/content/identity/new-age-ciam/index.md
@@ -1,7 +1,7 @@
---
title: "How Is New Age Ciam Revolutionizing Consumer Experience?"
date: "2021-02-11"
-coverImage: "a-new-age-CIAM.jpg"
+coverImage: "a-new-age-CIAM.webp"
tags: ["ciam solution","data security","cx"]
author: "Rakesh Soni"
description: "How New-Age CIAM is Revolutionizing Consumer Experience Consumer Identity and Access Management (CIAM) is on the fast-track to going mainstream. What has put CIAM on the forefront is the proficiency to excel in the three most crucial aspects: profiling consumer data, managing consumer identity, and controlling consumer access to applications."
@@ -117,7 +117,7 @@ In an age where sensational hacking and malicious attacks have become the order
By adding multiple layers of shields, new-age CIAM brings into effect strengthened security. Thus, the entire cluster of data remains protected from the prying eyes or, for that matter falling prey to data trackers.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
New-age CIAM takes advantage of [multi-factor authentication](https://www.loginradius.com/blog/identity/2019/06/what-is-multi-factor-authentication/#:~:text=Team%20LoginRadius&text=10%20min%20read-,Multi%2Dfactor%20authentication%20(or%20MFA)%20is%20a%20multi%2D,user%20account%20will%20remain%20secure.) to guard against unauthorized access. Each layer is designed with the utmost security in mind to prevent hackers from breaking into the account.
@@ -135,7 +135,7 @@ Whether it's adhering to international data protection laws like the GDPR and th
## An Introduction to The LoginRadius Modern CIAM Solution
-
+
LoginRadius' modern CIAM solution is designed to be more flexible, intuitive. It addresses every subtle component that can improve consumers' experience while also providing an unmatched safeguard for the private data.
@@ -153,4 +153,4 @@ CIAM ensures brands have a better understanding of consumers. Hence, they can qu
Add to that the top-of-the-line shield against the prying eyes and the new-age CIAM seems to be a must for modern enterprises.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=new-age-ciam)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=new-age-ciam)
diff --git a/content/identity/new-age-ciam/new-age-ciam-cx.jpg b/content/identity/new-age-ciam/new-age-ciam-cx.jpg
deleted file mode 100644
index 4af337cbb..000000000
Binary files a/content/identity/new-age-ciam/new-age-ciam-cx.jpg and /dev/null differ
diff --git a/content/identity/new-age-ciam/new-age-ciam-cx.webp b/content/identity/new-age-ciam/new-age-ciam-cx.webp
new file mode 100644
index 000000000..9b59285d2
Binary files /dev/null and b/content/identity/new-age-ciam/new-age-ciam-cx.webp differ
diff --git a/content/identity/new-age-ciam/new-age-ciam.png b/content/identity/new-age-ciam/new-age-ciam.png
deleted file mode 100644
index f8d0970a2..000000000
Binary files a/content/identity/new-age-ciam/new-age-ciam.png and /dev/null differ
diff --git a/content/identity/new-age-ciam/new-age-ciam.webp b/content/identity/new-age-ciam/new-age-ciam.webp
new file mode 100644
index 000000000..409efc005
Binary files /dev/null and b/content/identity/new-age-ciam/new-age-ciam.webp differ
diff --git a/content/identity/nist-password-guidelines-2021/DS-passwordless-login.png b/content/identity/nist-password-guidelines-2021/DS-passwordless-login.png
deleted file mode 100644
index 69d26339f..000000000
Binary files a/content/identity/nist-password-guidelines-2021/DS-passwordless-login.png and /dev/null differ
diff --git a/content/identity/nist-password-guidelines-2021/DS-passwordless-login.webp b/content/identity/nist-password-guidelines-2021/DS-passwordless-login.webp
new file mode 100644
index 000000000..96ed92a38
Binary files /dev/null and b/content/identity/nist-password-guidelines-2021/DS-passwordless-login.webp differ
diff --git a/content/identity/nist-password-guidelines-2021/index.md b/content/identity/nist-password-guidelines-2021/index.md
index 381568fea..3267293c6 100644
--- a/content/identity/nist-password-guidelines-2021/index.md
+++ b/content/identity/nist-password-guidelines-2021/index.md
@@ -1,7 +1,7 @@
---
title: "How NIST is Changing Password Creation in 2021"
date: "2021-07-22"
-coverImage: "nist-password-guidelines-2021-cover.jpg"
+coverImage: "nist-password-guidelines-2021-cover.webp"
tags: ["security"]
featured: false
author: "Deependra Singh"
@@ -93,7 +93,7 @@ The NIST Cybersecurity Framework is worth adopting solely for its stated goal of
The NIST Cybersecurity Framework is NOT just for “government applications.” It represents a state-of-the-art approach to security and compliance.
-[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
Here’s what enterprises get with the LoginRadius consumer identity and access management (CIAM) solution:
@@ -119,4 +119,4 @@ LoginRadius is self-attested to the NIST Cybersecurity Framework as part of its
Need help with NIST? [Reach us](https://www.loginradius.com/contact-sales/) for quick guidance today.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=nist-password-guidelines-2021)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=nist-password-guidelines-2021)
diff --git a/content/identity/nist-password-guidelines-2021/nist-password-guidelines-2021-cover.jpg b/content/identity/nist-password-guidelines-2021/nist-password-guidelines-2021-cover.jpg
deleted file mode 100644
index 2b73e2108..000000000
Binary files a/content/identity/nist-password-guidelines-2021/nist-password-guidelines-2021-cover.jpg and /dev/null differ
diff --git a/content/identity/nist-password-guidelines-2021/nist-password-guidelines-2021-cover.webp b/content/identity/nist-password-guidelines-2021/nist-password-guidelines-2021-cover.webp
new file mode 100644
index 000000000..c59da46da
Binary files /dev/null and b/content/identity/nist-password-guidelines-2021/nist-password-guidelines-2021-cover.webp differ
diff --git a/content/identity/no-code-ciam-churn-reduction/index.md b/content/identity/no-code-ciam-churn-reduction/index.md
index 859c836c0..f3edc36cf 100644
--- a/content/identity/no-code-ciam-churn-reduction/index.md
+++ b/content/identity/no-code-ciam-churn-reduction/index.md
@@ -1,7 +1,7 @@
---
title: "The Power of No-code Customer IAM in Reducing Churn"
date: "2023-09-22"
-coverImage: "no-code-ciam-churn.jpg"
+coverImage: "no-code-ciam-churn.webp"
tags: ["ciam solutions","identity management","cx"]
author: "Chirag Bhavsar"
description: "In today's ever-expanding competitive business landscape, combating customer churn is a top priority. This article delves into the game-changing potential of No-code CIAM, exploring its impact on customer onboarding, engagement, security, and data-driven decision-making. Discover how businesses can harness No-code CIAM to foster lasting customer relationships and drive long-term success."
@@ -118,4 +118,4 @@ Reducing churn is paramount for the long-term success of any business, and No-co
Implementing best practices, understanding customer journeys, and ensuring compliance are essential steps in harnessing the full potential of No-code CIAM. As technology advances, No-code CIAM is set to become an even more critical tool in reducing churn and fostering lasting customer relationships.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=no-code-ciam-churn-reduction)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=no-code-ciam-churn-reduction)
\ No newline at end of file
diff --git a/content/identity/no-code-ciam-churn-reduction/no-code-ciam-churn.jpg b/content/identity/no-code-ciam-churn-reduction/no-code-ciam-churn.jpg
deleted file mode 100644
index 5b90f15f3..000000000
Binary files a/content/identity/no-code-ciam-churn-reduction/no-code-ciam-churn.jpg and /dev/null differ
diff --git a/content/identity/no-code-ciam-churn-reduction/no-code-ciam-churn.webp b/content/identity/no-code-ciam-churn-reduction/no-code-ciam-churn.webp
new file mode 100644
index 000000000..aad902e55
Binary files /dev/null and b/content/identity/no-code-ciam-churn-reduction/no-code-ciam-churn.webp differ
diff --git a/content/identity/no-code-identity-orchestration-cx/WP-resiliency.png b/content/identity/no-code-identity-orchestration-cx/WP-resiliency.png
deleted file mode 100644
index cbe459800..000000000
Binary files a/content/identity/no-code-identity-orchestration-cx/WP-resiliency.png and /dev/null differ
diff --git a/content/identity/no-code-identity-orchestration-cx/WP-resiliency.webp b/content/identity/no-code-identity-orchestration-cx/WP-resiliency.webp
new file mode 100644
index 000000000..efb695fb3
Binary files /dev/null and b/content/identity/no-code-identity-orchestration-cx/WP-resiliency.webp differ
diff --git a/content/identity/no-code-identity-orchestration-cx/index.md b/content/identity/no-code-identity-orchestration-cx/index.md
index c6688eedf..a51b3fabc 100644
--- a/content/identity/no-code-identity-orchestration-cx/index.md
+++ b/content/identity/no-code-identity-orchestration-cx/index.md
@@ -1,7 +1,7 @@
---
title: "Gearing Up for Better Customer Experiences? Choose No-Code Identity Orchestration"
date: "2024-07-01"
-coverImage: "no-code-id-orchestration.jpg"
+coverImage: "no-code-id-orchestration.webp"
tags: ["identity orchestration","login authentication","cx"]
author: "Cooper Matheson"
description: "In today’s digital landscape, enhancing customer experience is crucial for business success. No-code identity orchestration offers a powerful solution to streamline user authentication, improve security, and personalize interactions without extensive coding. Discover how this technology can transform your CX strategy, offering speed, cost-efficiency, and innovation. Read on to explore its benefits and implementation tips."
@@ -38,7 +38,7 @@ Ensuring the security of user data is paramount. No-code identity orchestration
As businesses grow, their identity management needs evolve. No-code platforms offer scalability, allowing organizations to easily adapt to increasing user demands and integrate new services without overhauling their existing systems.
-[](https://www.loginradius.com/resource/whitepaper/handling-resiliency-scale/)
+[](https://www.loginradius.com/resource/whitepaper/handling-resiliency-scale/)
## Benefits of No-Code Identity Orchestration
@@ -82,4 +82,4 @@ No-code identity orchestration is a game-changer for businesses looking to eleva
By simplifying the development process, enhancing security, and enabling personalized interactions, the no-code identity orchestration empowers organizations to meet and exceed customer expectations. As digital experiences continue to evolve, investing in no-code identity orchestration will be key to staying competitive and achieving long-term success.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=no-code-identity-orchestration-cx)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=no-code-identity-orchestration-cx)
\ No newline at end of file
diff --git a/content/identity/no-code-identity-orchestration-cx/no-code-id-orchestration.jpg b/content/identity/no-code-identity-orchestration-cx/no-code-id-orchestration.jpg
deleted file mode 100644
index e295d26d3..000000000
Binary files a/content/identity/no-code-identity-orchestration-cx/no-code-id-orchestration.jpg and /dev/null differ
diff --git a/content/identity/no-code-identity-orchestration-cx/no-code-id-orchestration.webp b/content/identity/no-code-identity-orchestration-cx/no-code-id-orchestration.webp
new file mode 100644
index 000000000..ef132672b
Binary files /dev/null and b/content/identity/no-code-identity-orchestration-cx/no-code-id-orchestration.webp differ
diff --git a/content/identity/okta-acquires-auth0/index.md b/content/identity/okta-acquires-auth0/index.md
index b87caeca8..7f144c02e 100644
--- a/content/identity/okta-acquires-auth0/index.md
+++ b/content/identity/okta-acquires-auth0/index.md
@@ -1,7 +1,7 @@
---
title: "CIAM Continues to Draw Attention as Okta acquires Auth0"
date: "2021-03-04"
-coverImage: "loginradius-blog.jpg"
+coverImage: "loginradius-blog.webp"
tags: ["LoginRadius"]
featured: false
author: "Rakesh Soni"
@@ -92,4 +92,4 @@ I’m excited for all the CIAM players.
Together, let's build a world which is more secure, where privacy is protected and where consumers have delighted digital experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=okta-acquires-auth0)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=okta-acquires-auth0)
diff --git a/content/identity/okta-acquires-auth0/loginradius-blog.jpg b/content/identity/okta-acquires-auth0/loginradius-blog.jpg
deleted file mode 100644
index 2b5532cc5..000000000
Binary files a/content/identity/okta-acquires-auth0/loginradius-blog.jpg and /dev/null differ
diff --git a/content/identity/okta-acquires-auth0/loginradius-blog.webp b/content/identity/okta-acquires-auth0/loginradius-blog.webp
new file mode 100644
index 000000000..d9ffc2b9e
Binary files /dev/null and b/content/identity/okta-acquires-auth0/loginradius-blog.webp differ
diff --git a/content/identity/okta-hack-breach-lessons/WP-end-user-cybersecurity.png b/content/identity/okta-hack-breach-lessons/WP-end-user-cybersecurity.png
deleted file mode 100644
index 68c8a6568..000000000
Binary files a/content/identity/okta-hack-breach-lessons/WP-end-user-cybersecurity.png and /dev/null differ
diff --git a/content/identity/okta-hack-breach-lessons/WP-end-user-cybersecurity.webp b/content/identity/okta-hack-breach-lessons/WP-end-user-cybersecurity.webp
new file mode 100644
index 000000000..e10ca30b8
Binary files /dev/null and b/content/identity/okta-hack-breach-lessons/WP-end-user-cybersecurity.webp differ
diff --git a/content/identity/okta-hack-breach-lessons/data-breach.jpg b/content/identity/okta-hack-breach-lessons/data-breach.jpg
deleted file mode 100644
index 8feca9064..000000000
Binary files a/content/identity/okta-hack-breach-lessons/data-breach.jpg and /dev/null differ
diff --git a/content/identity/okta-hack-breach-lessons/data-breach.webp b/content/identity/okta-hack-breach-lessons/data-breach.webp
new file mode 100644
index 000000000..6c68febdf
Binary files /dev/null and b/content/identity/okta-hack-breach-lessons/data-breach.webp differ
diff --git a/content/identity/okta-hack-breach-lessons/index.md b/content/identity/okta-hack-breach-lessons/index.md
index 083ad5240..1ec11bfbd 100644
--- a/content/identity/okta-hack-breach-lessons/index.md
+++ b/content/identity/okta-hack-breach-lessons/index.md
@@ -1,7 +1,7 @@
---
title: "Understanding the Okta Hack: Breach in Customer Support and Lessons for Organizations"
date: "2023-10-27"
-coverImage: "data-breach.jpg"
+coverImage: "data-breach.webp"
tags: ["data security","cybersecurity","compliance","cx"]
author: "Alok Patidar"
description: "Learn about the recent Okta data breach, highlighting the risks businesses face from social engineering attacks. Discover the impact on Okta's customer support unit and understand the importance of stringent security measures for organizations. Learn from the breach and enhance your cybersecurity protocols to safeguard customer data effectively."
@@ -48,7 +48,7 @@ Requesting SOC reports from vendors and contractors aids in understanding how th
The human element is an organization's most valuable asset but can also pose a significant cybersecurity risk. Thus, organizations need to consistently assess training processes and educate employees, vendor-contractors, customers, and users about basic cyber hygiene practices.
-[](https://www.loginradius.com/resource/why-is-end-user-cyber-security-training-mandatory/)
+[](https://www.loginradius.com/resource/why-is-end-user-cyber-security-training-mandatory/)
### 4. Stay Alert
@@ -64,4 +64,4 @@ The Okta breach demonstrates the vulnerability of all businesses to cyber-attack
This incident emphasizes the critical need for businesses to prioritize cybersecurity, update protocols, and educate employees. Staying vigilant and proactive is essential in the face of evolving cyber threats.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=okta-hack-breach-lessons)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=okta-hack-breach-lessons)
\ No newline at end of file
diff --git a/content/identity/okta-token-theft-cloudflare-security/WP-zero-trust-security.png b/content/identity/okta-token-theft-cloudflare-security/WP-zero-trust-security.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/okta-token-theft-cloudflare-security/WP-zero-trust-security.png and /dev/null differ
diff --git a/content/identity/okta-token-theft-cloudflare-security/WP-zero-trust-security.webp b/content/identity/okta-token-theft-cloudflare-security/WP-zero-trust-security.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/okta-token-theft-cloudflare-security/WP-zero-trust-security.webp differ
diff --git a/content/identity/okta-token-theft-cloudflare-security/data-breach.jpg b/content/identity/okta-token-theft-cloudflare-security/data-breach.jpg
deleted file mode 100644
index 34263bbe4..000000000
Binary files a/content/identity/okta-token-theft-cloudflare-security/data-breach.jpg and /dev/null differ
diff --git a/content/identity/okta-token-theft-cloudflare-security/data-breach.webp b/content/identity/okta-token-theft-cloudflare-security/data-breach.webp
new file mode 100644
index 000000000..050832f15
Binary files /dev/null and b/content/identity/okta-token-theft-cloudflare-security/data-breach.webp differ
diff --git a/content/identity/okta-token-theft-cloudflare-security/index.md b/content/identity/okta-token-theft-cloudflare-security/index.md
index 6c34e6599..951e8f8a1 100644
--- a/content/identity/okta-token-theft-cloudflare-security/index.md
+++ b/content/identity/okta-token-theft-cloudflare-security/index.md
@@ -1,7 +1,7 @@
---
title: "Okta Token Theft Implicated in Cloudflare's Security Breach"
date: "2024-02-06"
-coverImage: "data-breach.jpg"
+coverImage: "data-breach.webp"
tags: ["data security","cybersecurity","cx"]
author: "Navanita Devi"
description: "Uncover the connection between the recent Cloudflare breach and stolen Okta authentication tokens. Discover Cloudflare's immediate actions and ongoing efforts to strengthen security measures."
@@ -26,7 +26,7 @@ Cloudflare suspects the attack aimed to gather insights into its network archite
Cloudflare remains committed to fortifying its defenses, exemplified by its thwarted phishing attack in August 2022, demonstrating the efficacy of robust security measures like FIDO2-compliant security keys.
-[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-modern-business/)
+[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-modern-business/)
## What Every Business Needs to Learn from Cloudflare's Recent Breach
@@ -40,4 +40,4 @@ The recent breach at Cloudflare, stemming from stolen Okta authentication tokens
However, this incident serves as a reminder of the importance of continuous vigilance and proactive measures in the face of evolving cybersecurity threats. As Cloudflare continues to fortify its defenses and enhance security protocols, the broader tech community must remain diligent in combating cyber threats to ensure the integrity and safety of digital infrastructure worldwide.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=okta-token-theft-cloudflare-security)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=okta-token-theft-cloudflare-security)
\ No newline at end of file
diff --git a/content/identity/oktapus-phishing-targets-okta-identity-credentials/index.md b/content/identity/oktapus-phishing-targets-okta-identity-credentials/index.md
index ff596c32e..1c8d6d663 100644
--- a/content/identity/oktapus-phishing-targets-okta-identity-credentials/index.md
+++ b/content/identity/oktapus-phishing-targets-okta-identity-credentials/index.md
@@ -1,7 +1,7 @@
---
title: "Okta Identity Credentials on the Radar of Oktapus Phishing Campaign"
date: "2022-09-08"
-coverImage: "oktapus.jpg"
+coverImage: "oktapus.webp"
tags: ["Phishing", "Oktapus", "Okta"]
author: "Alok Patidar"
description: "The phishing campaign, Oktapus, targeted Okta who recently became victim of its phishing attempts. 169 unique domains were identified that fraudsters used to create fake websites."
@@ -38,4 +38,4 @@ The right combination of cybersecurity best practices and employee/customer awar
Looking for an [Okta alternative](https://www.loginradius.com/)? Learn more about the highest rated, most secure CIAM technology in the world.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=oktapus-phishing-targets-okta-identity-credentials)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=oktapus-phishing-targets-okta-identity-credentials)
diff --git a/content/identity/oktapus-phishing-targets-okta-identity-credentials/oktapus.jpg b/content/identity/oktapus-phishing-targets-okta-identity-credentials/oktapus.jpg
deleted file mode 100644
index ad5ca1d32..000000000
Binary files a/content/identity/oktapus-phishing-targets-okta-identity-credentials/oktapus.jpg and /dev/null differ
diff --git a/content/identity/oktapus-phishing-targets-okta-identity-credentials/oktapus.webp b/content/identity/oktapus-phishing-targets-okta-identity-credentials/oktapus.webp
new file mode 100644
index 000000000..a067e45c9
Binary files /dev/null and b/content/identity/oktapus-phishing-targets-okta-identity-credentials/oktapus.webp differ
diff --git a/content/identity/one-time-passwords-security-benefits/DS-passwordless-magic-link.png b/content/identity/one-time-passwords-security-benefits/DS-passwordless-magic-link.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/one-time-passwords-security-benefits/DS-passwordless-magic-link.png and /dev/null differ
diff --git a/content/identity/one-time-passwords-security-benefits/DS-passwordless-magic-link.webp b/content/identity/one-time-passwords-security-benefits/DS-passwordless-magic-link.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/one-time-passwords-security-benefits/DS-passwordless-magic-link.webp differ
diff --git a/content/identity/one-time-passwords-security-benefits/index.md b/content/identity/one-time-passwords-security-benefits/index.md
index 43d0fa6bb..05be7fca8 100644
--- a/content/identity/one-time-passwords-security-benefits/index.md
+++ b/content/identity/one-time-passwords-security-benefits/index.md
@@ -1,7 +1,7 @@
---
title: "Empowering Your Security: Exploring the Advantages of Time-Based One-Time Passwords (TOTP)"
date: "2023-10-17"
-coverImage: "one-time-passwords.jpg"
+coverImage: "one-time-passwords.webp"
tags: ["data security","OTP","passwordless login","cx"]
author: "Rakesh Soni"
description: "From thwarting replay attacks to seamless integration across devices, TOTP ensures robust protection while providing a user-friendly experience. Embrace TOTP as more than a choice—it's a strategic investment in your digital security, promising a safer online journey for individuals and organizations alike."
@@ -40,7 +40,7 @@ Despite its advanced security features, TOTP offers a user-friendly experience.
Every time a user logs in using TOTP, a new, unique password is generated. This uniqueness ensures that even if a password is somehow compromised, it cannot be reused for subsequent logins. The constantly changing nature of TOTP adds an extra layer of complexity, making it exponentially more challenging for attackers to crack the authentication process.
-[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
+[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
### Seamless Integration with Multiple Devices
@@ -66,4 +66,4 @@ Time-Based One-Time Passwords (TOTP) stand at the forefront of this technologica
Incorporating TOTP into your authentication processes isn't just a choice; it's a strategic investment in the future of digital security. Stay ahead of the curve, empower your security, and embrace the transformative advantages of Time-Based One-Time Passwords (TOTP). Your digital fortress awaits.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=one-time-passwords-security-benefits)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=one-time-passwords-security-benefits)
diff --git a/content/identity/one-time-passwords-security-benefits/one-time-passwords.jpg b/content/identity/one-time-passwords-security-benefits/one-time-passwords.jpg
deleted file mode 100644
index 6a7e476ea..000000000
Binary files a/content/identity/one-time-passwords-security-benefits/one-time-passwords.jpg and /dev/null differ
diff --git a/content/identity/one-time-passwords-security-benefits/one-time-passwords.webp b/content/identity/one-time-passwords-security-benefits/one-time-passwords.webp
new file mode 100644
index 000000000..0ba7d4deb
Binary files /dev/null and b/content/identity/one-time-passwords-security-benefits/one-time-passwords.webp differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/How-LoginRadius-Can-Enhance-the-Experience-of-Online-Gaming.png b/content/identity/online-casino-and-gambling-cyber-threat/How-LoginRadius-Can-Enhance-the-Experience-of-Online-Gaming.png
deleted file mode 100644
index 317c4f504..000000000
Binary files a/content/identity/online-casino-and-gambling-cyber-threat/How-LoginRadius-Can-Enhance-the-Experience-of-Online-Gaming.png and /dev/null differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/How-LoginRadius-Can-Enhance-the-Experience-of-Online-Gaming.webp b/content/identity/online-casino-and-gambling-cyber-threat/How-LoginRadius-Can-Enhance-the-Experience-of-Online-Gaming.webp
new file mode 100644
index 000000000..faf233644
Binary files /dev/null and b/content/identity/online-casino-and-gambling-cyber-threat/How-LoginRadius-Can-Enhance-the-Experience-of-Online-Gaming.webp differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/Online-Casino-and-Gambling-Industry.jpg b/content/identity/online-casino-and-gambling-cyber-threat/Online-Casino-and-Gambling-Industry.jpg
deleted file mode 100644
index af014f49e..000000000
Binary files a/content/identity/online-casino-and-gambling-cyber-threat/Online-Casino-and-Gambling-Industry.jpg and /dev/null differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/Online-Casino-and-Gambling-Industry.webp b/content/identity/online-casino-and-gambling-cyber-threat/Online-Casino-and-Gambling-Industry.webp
new file mode 100644
index 000000000..d537d4a0f
Binary files /dev/null and b/content/identity/online-casino-and-gambling-cyber-threat/Online-Casino-and-Gambling-Industry.webp differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/adaptive-mfa.png b/content/identity/online-casino-and-gambling-cyber-threat/adaptive-mfa.png
deleted file mode 100644
index 1f39a27f3..000000000
Binary files a/content/identity/online-casino-and-gambling-cyber-threat/adaptive-mfa.png and /dev/null differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/adaptive-mfa.webp b/content/identity/online-casino-and-gambling-cyber-threat/adaptive-mfa.webp
new file mode 100644
index 000000000..8a8067f56
Binary files /dev/null and b/content/identity/online-casino-and-gambling-cyber-threat/adaptive-mfa.webp differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/europe-online-gambling-market-share.png b/content/identity/online-casino-and-gambling-cyber-threat/europe-online-gambling-market-share.png
deleted file mode 100644
index cf6a8cfa5..000000000
Binary files a/content/identity/online-casino-and-gambling-cyber-threat/europe-online-gambling-market-share.png and /dev/null differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/europe-online-gambling-market-share.webp b/content/identity/online-casino-and-gambling-cyber-threat/europe-online-gambling-market-share.webp
new file mode 100644
index 000000000..f9bc3062d
Binary files /dev/null and b/content/identity/online-casino-and-gambling-cyber-threat/europe-online-gambling-market-share.webp differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/index.md b/content/identity/online-casino-and-gambling-cyber-threat/index.md
index 4b24438b1..edaebb8de 100644
--- a/content/identity/online-casino-and-gambling-cyber-threat/index.md
+++ b/content/identity/online-casino-and-gambling-cyber-threat/index.md
@@ -1,7 +1,7 @@
---
title: "Online Casino and Gambling Industry Is Gaining Momentum, So Is the Cyber Threat"
date: "2020-06-25"
-coverImage: "Online-Casino-and-Gambling-Industry.jpg"
+coverImage: "Online-Casino-and-Gambling-Industry.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -28,7 +28,7 @@ The online gambling industry has undergone various changes over the past decades
For example, the online gambling market is expected to grow at a compound annual growth rate (CAGR) of 11.5% from 2020 to 2027. That's huge!
-
+
Source: www.grandviewresearch.com
@@ -62,7 +62,7 @@ It is no brainer that the customer's habit evolves with time. Social gambling an
[Mobile technology](https://www.casino.org/features/gambling-statistics/) has been a massive influence on people with a huge percentage of the world's population owning a smartphone. Casinos are more than ever investing in gaming applications and creating mobile-friendly games. It seems like mobile games will soon take over their desktop competition.
-
+
_Source: www.grandviewresearch.com_
@@ -84,7 +84,7 @@ In 2020, reducing the effects of cyber attacks and online fraud is crucial to su
Besides, Statista.com estimates that the global online gambling market will be valued at more than [$94 billion USD in 2024](https://www.statista.com/statistics/270728/market-volume-of-online-gaming-worldwide/) - meaning more the figure, more the risk of cybercrime.
-
+
Source: statista
@@ -102,7 +102,7 @@ Here are a few instances of recent breaches that will help you understand its se
## Types of Attacks on Online Casino, Betting and Gambling Sites
-
+
Online gambling and casino sites face security threats from several sources. For starters, some external hackers launch attacks to commit fraud from the comfort of their home or anywhere (for that matter). Next, some insiders hold administrative positions inside the business itself and [steal customer details](https://www.loginradius.com/blog/2019/09/prevent-credential-stuffing-attacks/).
@@ -140,7 +140,7 @@ By breaking into application security measures, hackers can easily pass through
## How LoginRadius Can Enhance the Experience of Online Gaming With Advance Security
-
+
LoginRadius is a powerful [customer identity and access management (CIAM)](https://www.loginradius.com/blog/2019/06/customer-identity-and-access-management/) platform that protects online gamblers' identity and prevents even the most sophisticated bots from infecting the gaming provider. It detects and blocks automated threats, including expediting, scraping, account takeover, DDoS, and more.
@@ -148,7 +148,7 @@ Here's how the LoginRadius platform protects the gaming industry from malicious
- **Multi-Factor Authentication**: The platform adds additional layers of protection by enabling two-factor or [multifactor authentication](https://www.loginradius.com/blog/2019/06/what-is-multi-factor-authentication/) on both player and admin accounts. It also offers real-time fraud analysis and data management features.
-[](https://www.loginradius.com/resource/fixing-broken-authentication-with-adaptive-mfa/)
+[](https://www.loginradius.com/resource/fixing-broken-authentication-with-adaptive-mfa/)
- **Passwordless Login**: Eliminating the [use of passwords](https://www.loginradius.com/blog/2019/10/passwordless-authentication-the-future-of-identity-and-security/) altogether can surprisingly improve gamblers' retention and loyalty because there will be no passwords to hack in the first place. Also, there is a one-touch login feature where customers login with a magic link or OTP.
@@ -162,4 +162,4 @@ Adhering to the COVID situation and keeping social distancing in mind, more and
With the ongoing pandemic situation, gambling providers should primarily focus on ensuring that gambling is fair, crime-free, and protects minors. A [CIAM platform](https://www.loginradius.com/blog/identity/perfect-ciam-platform/) can help you tap all these touchpoints.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=online-casino-and-gambling-cyber-threat)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=online-casino-and-gambling-cyber-threat)
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-casino-and-betting-sectors.png b/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-casino-and-betting-sectors.png
deleted file mode 100644
index 1a6b3cd4a..000000000
Binary files a/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-casino-and-betting-sectors.png and /dev/null differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-casino-and-betting-sectors.webp b/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-casino-and-betting-sectors.webp
new file mode 100644
index 000000000..8c3b1cc31
Binary files /dev/null and b/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-casino-and-betting-sectors.webp differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-market-2017-2024-1-1024x763.png b/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-market-2017-2024-1-1024x763.png
deleted file mode 100644
index e06ee8c17..000000000
Binary files a/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-market-2017-2024-1-1024x763.png and /dev/null differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-market-2017-2024-1-1024x763.webp b/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-market-2017-2024-1-1024x763.webp
new file mode 100644
index 000000000..dcb472fd2
Binary files /dev/null and b/content/identity/online-casino-and-gambling-cyber-threat/online-gambling-market-2017-2024-1-1024x763.webp differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/usa-online-gambling-market-size.png b/content/identity/online-casino-and-gambling-cyber-threat/usa-online-gambling-market-size.png
deleted file mode 100644
index 81685379d..000000000
Binary files a/content/identity/online-casino-and-gambling-cyber-threat/usa-online-gambling-market-size.png and /dev/null differ
diff --git a/content/identity/online-casino-and-gambling-cyber-threat/usa-online-gambling-market-size.webp b/content/identity/online-casino-and-gambling-cyber-threat/usa-online-gambling-market-size.webp
new file mode 100644
index 000000000..1dc2929b2
Binary files /dev/null and b/content/identity/online-casino-and-gambling-cyber-threat/usa-online-gambling-market-size.webp differ
diff --git a/content/identity/online-security-passkeys/DS-pswrdless-login-magic-link.png b/content/identity/online-security-passkeys/DS-pswrdless-login-magic-link.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/online-security-passkeys/DS-pswrdless-login-magic-link.png and /dev/null differ
diff --git a/content/identity/online-security-passkeys/DS-pswrdless-login-magic-link.webp b/content/identity/online-security-passkeys/DS-pswrdless-login-magic-link.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/online-security-passkeys/DS-pswrdless-login-magic-link.webp differ
diff --git a/content/identity/online-security-passkeys/index.md b/content/identity/online-security-passkeys/index.md
index ae74e1453..5aadb7c2c 100644
--- a/content/identity/online-security-passkeys/index.md
+++ b/content/identity/online-security-passkeys/index.md
@@ -1,7 +1,7 @@
---
title: "Say Goodbye to Passwords: How Passkeys Are Reinventing Online Security"
date: "2024-06-20"
-coverImage: "passkey.jpg"
+coverImage: "passkey.webp"
tags: ["online security","passwordless login","compliance"]
author: "Kundan Singh"
description: "Explore how passkeys are revolutionizing online security, replacing passwords with advanced cryptographic keys, and strengthening Multi-Factor Authentication (MFA). Say goodbye to passwords and embrace a secure digital future."
@@ -83,7 +83,7 @@ Regulatory bodies worldwide are enforcing stricter data protection laws. Complia
In addition to enhanced security, passkeys offer greater convenience for users. The need to remember and manage multiple passwords is eliminated, leading to a smoother and more user-friendly authentication experience. This ease of use encourages adoption and helps maintain high-security standards without compromising user experience.
-[](https://www.loginradius.com/resource/datasheet/passwordless-login-magic-link-otp/)
+[](https://www.loginradius.com/resource/datasheet/passwordless-login-magic-link-otp/)
## How MFA with Passkeys Helps Lay the Foundation of a Robust Security Infrastructure
@@ -139,4 +139,4 @@ Passkeys eliminate common password vulnerabilities, such as reuse and phishing,
Yes, passkeys can be part of Multi-Factor Authentication (MFA) when combined with another factor, such as biometrics or a security token, for added security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=online-security-passkeys)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=online-security-passkeys)
\ No newline at end of file
diff --git a/content/identity/online-security-passkeys/passkey.jpg b/content/identity/online-security-passkeys/passkey.jpg
deleted file mode 100644
index 458f821c5..000000000
Binary files a/content/identity/online-security-passkeys/passkey.jpg and /dev/null differ
diff --git a/content/identity/online-security-passkeys/passkey.webp b/content/identity/online-security-passkeys/passkey.webp
new file mode 100644
index 000000000..a666a383a
Binary files /dev/null and b/content/identity/online-security-passkeys/passkey.webp differ
diff --git a/content/identity/online-shopping-tips/17-online-shopping-tips-for-consumer.jpg b/content/identity/online-shopping-tips/17-online-shopping-tips-for-consumer.jpg
deleted file mode 100644
index 7c3e820ce..000000000
Binary files a/content/identity/online-shopping-tips/17-online-shopping-tips-for-consumer.jpg and /dev/null differ
diff --git a/content/identity/online-shopping-tips/17-online-shopping-tips-for-consumer.webp b/content/identity/online-shopping-tips/17-online-shopping-tips-for-consumer.webp
new file mode 100644
index 000000000..0f018e7bf
Binary files /dev/null and b/content/identity/online-shopping-tips/17-online-shopping-tips-for-consumer.webp differ
diff --git a/content/identity/online-shopping-tips/WP-omnichannel-ret.png b/content/identity/online-shopping-tips/WP-omnichannel-ret.png
deleted file mode 100644
index a49793446..000000000
Binary files a/content/identity/online-shopping-tips/WP-omnichannel-ret.png and /dev/null differ
diff --git a/content/identity/online-shopping-tips/WP-omnichannel-ret.webp b/content/identity/online-shopping-tips/WP-omnichannel-ret.webp
new file mode 100644
index 000000000..f5170c511
Binary files /dev/null and b/content/identity/online-shopping-tips/WP-omnichannel-ret.webp differ
diff --git a/content/identity/online-shopping-tips/index.md b/content/identity/online-shopping-tips/index.md
index ad01cb15f..536cc2687 100644
--- a/content/identity/online-shopping-tips/index.md
+++ b/content/identity/online-shopping-tips/index.md
@@ -1,7 +1,7 @@
---
title: "17 Tips to Avoid Shopping Scams on Black Friday & Cyber Monday"
date: "2021-11-24"
-coverImage: "17-online-shopping-tips-for-consumer.jpg"
+coverImage: "17-online-shopping-tips-for-consumer.webp"
tags: ["data protection","cybersecurity","ciam solution","mfa"]
author: "Rakesh Soni"
description: "Many people prefer shopping online these days rather than going to a conventional store. Therefore, securing the data of your customers online is an integral part of protecting the organisation as a whole. Your job is to let them shop with some of the best online shopping tips with confidence."
@@ -57,7 +57,7 @@ Consumer journey hijacking is a cyberattack where hackers inject unauthorized ad
## 17 Online Shopping Tips for Consumers To Follow While Shopping During This Holiday Season
-
+
Do not let the stress of untangling a case of identity theft or financial fraud ruin your consumers' Black Friday and Cyber Monday shopping. Stay ahead of cybercriminals with the best online tips. Here are the best places to start.
@@ -103,7 +103,7 @@ We mean [phishing](https://www.loginradius.com/blog/phishing-for-identity/) scam
It is crucial that your consumers download applications only from trusted platforms like the App Store, the Google Play Store, Amazon App Store, etc. Most of the applications out there ask consumers for various permissions during installation. Encourage your consumers to read those carefully and only check boxes that make sense to them. They can also read reviews and ratings from existing consumers before making any decision.
-[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience)
+[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience)
### 9. Read return policies.
@@ -194,4 +194,4 @@ Q5. How can businesses enhance data security during these events?
A: Solutions like LoginRadius offer secure registration, 360-degree consumer views, and multi-factor authentication.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=online-shopping-tips)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=online-shopping-tips)
diff --git a/content/identity/online-shopping-tips/omnichannel-retailer-whitpaper.jpg b/content/identity/online-shopping-tips/omnichannel-retailer-whitpaper.jpg
deleted file mode 100644
index 17940ab41..000000000
Binary files a/content/identity/online-shopping-tips/omnichannel-retailer-whitpaper.jpg and /dev/null differ
diff --git a/content/identity/online-shopping-tips/omnichannel-retailer-whitpaper.webp b/content/identity/online-shopping-tips/omnichannel-retailer-whitpaper.webp
new file mode 100644
index 000000000..39f6da380
Binary files /dev/null and b/content/identity/online-shopping-tips/omnichannel-retailer-whitpaper.webp differ
diff --git a/content/identity/online-shopping-tips/online-shopping-tips-for-consumers-to-follow-while-shopping.png b/content/identity/online-shopping-tips/online-shopping-tips-for-consumers-to-follow-while-shopping.png
deleted file mode 100644
index 9ae11894d..000000000
Binary files a/content/identity/online-shopping-tips/online-shopping-tips-for-consumers-to-follow-while-shopping.png and /dev/null differ
diff --git a/content/identity/online-shopping-tips/online-shopping-tips-for-consumers-to-follow-while-shopping.webp b/content/identity/online-shopping-tips/online-shopping-tips-for-consumers-to-follow-while-shopping.webp
new file mode 100644
index 000000000..e96d9e84c
Binary files /dev/null and b/content/identity/online-shopping-tips/online-shopping-tips-for-consumers-to-follow-while-shopping.webp differ
diff --git a/content/identity/ott-simplify-authentication/GD-Website-Authentication.png b/content/identity/ott-simplify-authentication/GD-Website-Authentication.png
deleted file mode 100644
index 00ca5a293..000000000
Binary files a/content/identity/ott-simplify-authentication/GD-Website-Authentication.png and /dev/null differ
diff --git a/content/identity/ott-simplify-authentication/GD-Website-Authentication.webp b/content/identity/ott-simplify-authentication/GD-Website-Authentication.webp
new file mode 100644
index 000000000..4d42e6be5
Binary files /dev/null and b/content/identity/ott-simplify-authentication/GD-Website-Authentication.webp differ
diff --git a/content/identity/ott-simplify-authentication/GD-to-web-auth.png b/content/identity/ott-simplify-authentication/GD-to-web-auth.png
deleted file mode 100644
index 47e9359a7..000000000
Binary files a/content/identity/ott-simplify-authentication/GD-to-web-auth.png and /dev/null differ
diff --git a/content/identity/ott-simplify-authentication/GD-to-web-auth.webp b/content/identity/ott-simplify-authentication/GD-to-web-auth.webp
new file mode 100644
index 000000000..fd05c2021
Binary files /dev/null and b/content/identity/ott-simplify-authentication/GD-to-web-auth.webp differ
diff --git a/content/identity/ott-simplify-authentication/index.md b/content/identity/ott-simplify-authentication/index.md
index dbcb3528d..c582752a2 100644
--- a/content/identity/ott-simplify-authentication/index.md
+++ b/content/identity/ott-simplify-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "How OTT Services can Simplify Authentication on Various Devices"
date: "2021-08-10"
-coverImage: "ott-simplify-authentication-cover.jpg"
+coverImage: "ott-simplify-authentication-cover.webp"
tags: ["ciam solution","mfa","progressive profiling"]
author: "Manish Tiwari"
description: "In this post, we’ll understand the importance of secure authentication through a consumer identity and access management (CIAM) solution and how it paves the path for safeguarding consumer identities on different devices for OTT platforms."
@@ -88,7 +88,7 @@ Admit it; nobody wants to share heaps of personal details in a single go, especi
LoginRadius enables you to gather consumer data through various stages of the consumer's journey to share their information as they interact with your business.
-[](https://www.loginradius.com/resource/a-complete-guide-to-website-authentication/)
+[](https://www.loginradius.com/resource/a-complete-guide-to-website-authentication/)
### Multi-Factor Authentication - For Enhanced Layers of Security
@@ -109,4 +109,4 @@ Whether it’s delivering a seamless omnichannel experience across multiple devi
Enterprises can [leverage LoginRadius CIAM](https://www.loginradius.com/contact-sales/) that helps to scale business growth through a state-of-the-art omnichannel experience reinforced by stringent security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ott-simplify-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ott-simplify-authentication)
diff --git a/content/identity/ott-simplify-authentication/ott-simplify-authentication-cover.jpg b/content/identity/ott-simplify-authentication/ott-simplify-authentication-cover.jpg
deleted file mode 100644
index 8b01348fe..000000000
Binary files a/content/identity/ott-simplify-authentication/ott-simplify-authentication-cover.jpg and /dev/null differ
diff --git a/content/identity/ott-simplify-authentication/ott-simplify-authentication-cover.webp b/content/identity/ott-simplify-authentication/ott-simplify-authentication-cover.webp
new file mode 100644
index 000000000..f88d7f8be
Binary files /dev/null and b/content/identity/ott-simplify-authentication/ott-simplify-authentication-cover.webp differ
diff --git a/content/identity/pam-best-practices/GD-authn-autho-encr.png b/content/identity/pam-best-practices/GD-authn-autho-encr.png
deleted file mode 100644
index bcc2c06d6..000000000
Binary files a/content/identity/pam-best-practices/GD-authn-autho-encr.png and /dev/null differ
diff --git a/content/identity/pam-best-practices/GD-authn-autho-encr.webp b/content/identity/pam-best-practices/GD-authn-autho-encr.webp
new file mode 100644
index 000000000..b8563a100
Binary files /dev/null and b/content/identity/pam-best-practices/GD-authn-autho-encr.webp differ
diff --git a/content/identity/pam-best-practices/index.md b/content/identity/pam-best-practices/index.md
index d8a02e4fa..ba4bdf119 100644
--- a/content/identity/pam-best-practices/index.md
+++ b/content/identity/pam-best-practices/index.md
@@ -1,7 +1,7 @@
---
title: "Securing the Throne: Privileged Access Management (PAM) Best Practices Unveiled"
date: "2023-11-14"
-coverImage: "pam.jpg"
+coverImage: "pam.webp"
tags: ["identity access management","compliance","cx"]
author: "Rakesh Soni"
description: "Unveil the secrets of Privileged Access Management (PAM) and fortify your digital castle. Discover key practices like least privilege, secure shared accounts, and robust authentication. PAM is your sovereign shield against cyber threats in the ever-evolving cybersecurity landscape."
@@ -37,7 +37,7 @@ Privileged Access Management is the linchpin in cybersecurity, focusing on secur
In the ever-evolving cybersecurity landscape, the threats we face are dynamic and sophisticated. PAM, too, must evolve to stay ahead. Regularly updating and adapting PAM strategies is akin to reinforcing the castle walls in response to new siege tactics.
-[](https://www.loginradius.com/resource/a-quick-guide-to-authentication-authorization-and-encryption/)
+[](https://www.loginradius.com/resource/a-quick-guide-to-authentication-authorization-and-encryption/)
Stay informed about emerging threats, update software, and conduct regular security assessments to ensure that PAM remains a stalwart defender against the shifting landscape of cyber risks.
@@ -63,4 +63,4 @@ As we navigate the treacherous waters of cybersecurity, Privileged Access Manage
In digital security, PAM isn't just a choice; it's the sovereign shield protecting our most valuable assets from the shadows that seek to exploit vulnerability. As we unveil the best practices of PAM, let us fortify our defenses and ensure that only the worthy wield the keys to the kingdom.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pam-best-practices)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pam-best-practices)
\ No newline at end of file
diff --git a/content/identity/pam-best-practices/pam.jpg b/content/identity/pam-best-practices/pam.jpg
deleted file mode 100644
index 744c55f11..000000000
Binary files a/content/identity/pam-best-practices/pam.jpg and /dev/null differ
diff --git a/content/identity/pam-best-practices/pam.webp b/content/identity/pam-best-practices/pam.webp
new file mode 100644
index 000000000..d684536cd
Binary files /dev/null and b/content/identity/pam-best-practices/pam.webp differ
diff --git a/content/identity/passive-authentication-cx-future/WP-user-authentication.png b/content/identity/passive-authentication-cx-future/WP-user-authentication.png
deleted file mode 100644
index c8e655587..000000000
Binary files a/content/identity/passive-authentication-cx-future/WP-user-authentication.png and /dev/null differ
diff --git a/content/identity/passive-authentication-cx-future/WP-user-authentication.webp b/content/identity/passive-authentication-cx-future/WP-user-authentication.webp
new file mode 100644
index 000000000..1082e7522
Binary files /dev/null and b/content/identity/passive-authentication-cx-future/WP-user-authentication.webp differ
diff --git a/content/identity/passive-authentication-cx-future/index.md b/content/identity/passive-authentication-cx-future/index.md
index 80bb07e83..b2508fc2c 100644
--- a/content/identity/passive-authentication-cx-future/index.md
+++ b/content/identity/passive-authentication-cx-future/index.md
@@ -1,7 +1,7 @@
---
title: "The Customer Experience is About to Get Even Better With Passive Authentication"
date: "2022-11-17"
-coverImage: "passive-auth.jpg"
+coverImage: "passive-auth.webp"
tags: ["customer experience", "passive authentication", "online shopping"]
author: "Rakesh Soni"
description: "Passive authentication lets companies respond to the need for speed and convenience by making authentication seamless and automatic, thus avoiding security risks. Making the shift from active to passive can be a delicate process. But when it's done right, the benefits are immense."
@@ -30,7 +30,7 @@ Passive authentication is the newest wave of customer experience, and it's set t
Passive authentication is frictionless; it lets users get on with their day without taking extra steps or making different decisions that might slow them down or cause frustration.
-[](https://www.loginradius.com/resource/securing-user-authentication-understanding-the-basics-best-practices/)
+[](https://www.loginradius.com/resource/securing-user-authentication-understanding-the-basics-best-practices/)
## Active Authentication vs. Passive Authentication: What's The Difference?
@@ -57,4 +57,4 @@ In the end, it can be seen that passive authentication has spread over the years
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passive-authentication-cx-future)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passive-authentication-cx-future)
diff --git a/content/identity/passive-authentication-cx-future/passive-auth.jpg b/content/identity/passive-authentication-cx-future/passive-auth.jpg
deleted file mode 100644
index 5fc4f3020..000000000
Binary files a/content/identity/passive-authentication-cx-future/passive-auth.jpg and /dev/null differ
diff --git a/content/identity/passive-authentication-cx-future/passive-auth.webp b/content/identity/passive-authentication-cx-future/passive-auth.webp
new file mode 100644
index 000000000..dab8ad74b
Binary files /dev/null and b/content/identity/passive-authentication-cx-future/passive-auth.webp differ
diff --git a/content/identity/passive-authentication-cx-future/secure-auth-wp.png b/content/identity/passive-authentication-cx-future/secure-auth-wp.png
deleted file mode 100644
index 2af543487..000000000
Binary files a/content/identity/passive-authentication-cx-future/secure-auth-wp.png and /dev/null differ
diff --git a/content/identity/passive-authentication-cx-future/secure-auth-wp.webp b/content/identity/passive-authentication-cx-future/secure-auth-wp.webp
new file mode 100644
index 000000000..2e2a4d5c2
Binary files /dev/null and b/content/identity/passive-authentication-cx-future/secure-auth-wp.webp differ
diff --git a/content/identity/passkeys-online-authentication-experience/DS-passkeys.png b/content/identity/passkeys-online-authentication-experience/DS-passkeys.png
deleted file mode 100644
index c9c0196aa..000000000
Binary files a/content/identity/passkeys-online-authentication-experience/DS-passkeys.png and /dev/null differ
diff --git a/content/identity/passkeys-online-authentication-experience/DS-passkeys.webp b/content/identity/passkeys-online-authentication-experience/DS-passkeys.webp
new file mode 100644
index 000000000..fc39d6b8c
Binary files /dev/null and b/content/identity/passkeys-online-authentication-experience/DS-passkeys.webp differ
diff --git a/content/identity/passkeys-online-authentication-experience/index.md b/content/identity/passkeys-online-authentication-experience/index.md
index 46c9c3b75..6bacec8ff 100644
--- a/content/identity/passkeys-online-authentication-experience/index.md
+++ b/content/identity/passkeys-online-authentication-experience/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement - LoginRadius Launches PassKeys to Redefine Authentication Security and User Experience"
date: "2024-06-26"
-coverImage: "passkeys.png"
+coverImage: "passkeys.webp"
tags: ["industry news","passkeys","passwordless login"]
author: "Rakesh Soni"
description: "Passwords pose significant security risks and inconvenience for users. Passkeys by LoginRadius is a revolutionary authentication mechanism offering a secure, passwordless process that enhances security and simplifies the user experience. Learn how Passkeys revolutionize customer authentication with easy integration and robust features."
@@ -24,7 +24,7 @@ LoginRadius is introducing Passkeys to revolutionize the authentication landscap
Passkeys by LoginRadius addresses various security challenges in conventional password-based authentication without hampering the overall user experience.
-[](https://www.loginradius.com/resource/datasheet/passkeys-passwordless-authentication)
+[](https://www.loginradius.com/resource/datasheet/passkeys-passwordless-authentication)
## Key Functions of Passkeys by LoginRadius
@@ -46,4 +46,4 @@ Passkeys by LoginRadius revolutionize your customers' authentication experience
Passkeys are the future of secure and user-friendly authentication. They are quick to implement, reliable in performance, and scalable to meet enterprise demands. LoginRadius is setting a new standard in customer identity and access management by eliminating the need for passwords.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passkeys-online-authentication-experience)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passkeys-online-authentication-experience)
\ No newline at end of file
diff --git a/content/identity/passkeys-online-authentication-experience/passkeys.png b/content/identity/passkeys-online-authentication-experience/passkeys.png
deleted file mode 100644
index ba201a54f..000000000
Binary files a/content/identity/passkeys-online-authentication-experience/passkeys.png and /dev/null differ
diff --git a/content/identity/passkeys-online-authentication-experience/passkeys.webp b/content/identity/passkeys-online-authentication-experience/passkeys.webp
new file mode 100644
index 000000000..605bfb9c1
Binary files /dev/null and b/content/identity/passkeys-online-authentication-experience/passkeys.webp differ
diff --git a/content/identity/passkeys-online-shopping-experience/DS-passkeys.png b/content/identity/passkeys-online-shopping-experience/DS-passkeys.png
deleted file mode 100644
index c9c0196aa..000000000
Binary files a/content/identity/passkeys-online-shopping-experience/DS-passkeys.png and /dev/null differ
diff --git a/content/identity/passkeys-online-shopping-experience/DS-passkeys.webp b/content/identity/passkeys-online-shopping-experience/DS-passkeys.webp
new file mode 100644
index 000000000..fc39d6b8c
Binary files /dev/null and b/content/identity/passkeys-online-shopping-experience/DS-passkeys.webp differ
diff --git a/content/identity/passkeys-online-shopping-experience/index.md b/content/identity/passkeys-online-shopping-experience/index.md
index 391963479..a8344d2b5 100644
--- a/content/identity/passkeys-online-shopping-experience/index.md
+++ b/content/identity/passkeys-online-shopping-experience/index.md
@@ -1,7 +1,7 @@
---
title: "Passkeys: Unlocking Benefits for a Better Online Shopping Experience"
date: "2024-07-23"
-coverImage: "online-shopping.jpg"
+coverImage: "online-shopping.webp"
tags: ["passkeys","data security","cx"]
author: "Cooper Matheson"
description: "Passkeys are revolutionizing how we shop online, providing a seamless, secure, and convenient experience. This blog explores the major benefits of using passkeys and how they can transform your online shopping journey."
@@ -38,7 +38,7 @@ One of the most frustrating aspects of online shopping can be the cumbersome aut
* **Universal Access:** Passkeys work across different devices and platforms, providing a consistent and smooth experience whether you're shopping on your smartphone, tablet, or desktop.
-[](https://www.loginradius.com/resource/datasheet/passkeys-passwordless-authentication)
+[](https://www.loginradius.com/resource/datasheet/passkeys-passwordless-authentication)
### 3. Greater Convenience
@@ -84,4 +84,4 @@ By embracing this innovative authentication method, both shoppers and retailers
Adopting this technology now can provide immediate benefits and prepare you for a password-free future. Embrace the change and unlock the full potential of your online shopping experience today.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passkeys-online-shopping-experience)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passkeys-online-shopping-experience)
diff --git a/content/identity/passkeys-online-shopping-experience/online-shopping.jpg b/content/identity/passkeys-online-shopping-experience/online-shopping.jpg
deleted file mode 100644
index 24e266738..000000000
Binary files a/content/identity/passkeys-online-shopping-experience/online-shopping.jpg and /dev/null differ
diff --git a/content/identity/passkeys-online-shopping-experience/online-shopping.webp b/content/identity/passkeys-online-shopping-experience/online-shopping.webp
new file mode 100644
index 000000000..beedba440
Binary files /dev/null and b/content/identity/passkeys-online-shopping-experience/online-shopping.webp differ
diff --git a/content/identity/password-history-expiration-complexity/Passwordhistory_cover_pic.jpg b/content/identity/password-history-expiration-complexity/Passwordhistory_cover_pic.jpg
deleted file mode 100644
index adabc98d0..000000000
Binary files a/content/identity/password-history-expiration-complexity/Passwordhistory_cover_pic.jpg and /dev/null differ
diff --git a/content/identity/password-history-expiration-complexity/Passwordhistory_cover_pic.webp b/content/identity/password-history-expiration-complexity/Passwordhistory_cover_pic.webp
new file mode 100644
index 000000000..e2a1f973a
Binary files /dev/null and b/content/identity/password-history-expiration-complexity/Passwordhistory_cover_pic.webp differ
diff --git a/content/identity/password-history-expiration-complexity/index.md b/content/identity/password-history-expiration-complexity/index.md
index 355fc44b7..d57979e49 100644
--- a/content/identity/password-history-expiration-complexity/index.md
+++ b/content/identity/password-history-expiration-complexity/index.md
@@ -1,7 +1,7 @@
---
title: "Password History, Expiration, and Complexity: Explained!"
date: "2021-06-08"
-coverImage: "Passwordhistory_cover_pic.jpg"
+coverImage: "Passwordhistory_cover_pic.webp"
tags: ["authentication"]
featured: false
author: "Ashish Kumar Yadav"
@@ -20,7 +20,7 @@ The internet knows about you more than you. Imagine what an individual can do if
We all are conscious about our privacy and data security, and a perfect real-life example can explain this. Most of us know when and where we have to switch to our internal privacy mode according to the situation.
-
+
Passwords are the only measures that help us immensely to protect our data. So don't you think our protector should be more robust? Yes, it should be strong enough to withstand multiple attacks trying to steal your data.
@@ -32,7 +32,7 @@ A password can be used in multiple scenarios, but the motive to use them is simi
Most of the passwords contain letters, numbers, special characters, and symbols, and they can vary in length. Before setting a password, you should ensure that the combination should be easy to remember but hard to crack, which means it should not be that easy that everyone can guess it, and it should not be much hard that you forget it after some time.
-
+
### What are Weak Passwords?
@@ -64,7 +64,7 @@ Password reuse is now an important headache for organizations as users tend to u
The password history feature can have a limit up to which you can not use any such password which you have configured. For example, if you set the limit to 5, then you will be unable to use the last five previous passwords.
-
+
In this way, consumers will be forced not to reuse their old passwords again and again. Setting a new password creates challenges for an attacker, and the account remains safe.
@@ -106,4 +106,4 @@ If you really want to survive in this digital world where everything is digital,
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=password-history-expiration-complexity)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=password-history-expiration-complexity)
\ No newline at end of file
diff --git a/content/identity/password-history-expiration-complexity/password-2781614_960_720--colorized.jpg b/content/identity/password-history-expiration-complexity/password-2781614_960_720--colorized.jpg
deleted file mode 100644
index cb8829ed4..000000000
Binary files a/content/identity/password-history-expiration-complexity/password-2781614_960_720--colorized.jpg and /dev/null differ
diff --git a/content/identity/password-history-expiration-complexity/password-2781614_960_720--colorized.webp b/content/identity/password-history-expiration-complexity/password-2781614_960_720--colorized.webp
new file mode 100644
index 000000000..59b3b4c42
Binary files /dev/null and b/content/identity/password-history-expiration-complexity/password-2781614_960_720--colorized.webp differ
diff --git a/content/identity/password-history-expiration-complexity/phishing-3390518_960_720--colorized.jpg b/content/identity/password-history-expiration-complexity/phishing-3390518_960_720--colorized.jpg
deleted file mode 100644
index cd197a298..000000000
Binary files a/content/identity/password-history-expiration-complexity/phishing-3390518_960_720--colorized.jpg and /dev/null differ
diff --git a/content/identity/password-history-expiration-complexity/phishing-3390518_960_720--colorized.webp b/content/identity/password-history-expiration-complexity/phishing-3390518_960_720--colorized.webp
new file mode 100644
index 000000000..7092eff6b
Binary files /dev/null and b/content/identity/password-history-expiration-complexity/phishing-3390518_960_720--colorized.webp differ
diff --git a/content/identity/password-history-expiration-complexity/photo-1584433144859-1fc3ab64a957--colorized.jpg b/content/identity/password-history-expiration-complexity/photo-1584433144859-1fc3ab64a957--colorized.jpg
deleted file mode 100644
index 373818d36..000000000
Binary files a/content/identity/password-history-expiration-complexity/photo-1584433144859-1fc3ab64a957--colorized.jpg and /dev/null differ
diff --git a/content/identity/password-history-expiration-complexity/photo-1584433144859-1fc3ab64a957--colorized.webp b/content/identity/password-history-expiration-complexity/photo-1584433144859-1fc3ab64a957--colorized.webp
new file mode 100644
index 000000000..61e9f2349
Binary files /dev/null and b/content/identity/password-history-expiration-complexity/photo-1584433144859-1fc3ab64a957--colorized.webp differ
diff --git a/content/identity/password-spraying/index.md b/content/identity/password-spraying/index.md
index 6502d772d..51e35f680 100644
--- a/content/identity/password-spraying/index.md
+++ b/content/identity/password-spraying/index.md
@@ -1,7 +1,7 @@
---
title: "Password Spraying: What Is It And How To Prevent It?"
date: "2021-04-07"
-coverImage: "password-spraying.jpg"
+coverImage: "password-spraying.webp"
tags: ["data security", "mfa", "password management"]
author: "Navanita Devi"
description: "Password spraying is not a targeted attack, it is just one malicious actor acquiring a list of email accounts or gaining access to an active directory and attempting to sign in to all the accounts using a list of the most likely, popular, or common passwords until they get a hit. In this article, we detail what is password spraying, how to not be vulnerable to password spraying."
@@ -87,7 +87,7 @@ As we mentioned earlier, password spraying attacks cannot be prevented but defin
LoginRadius introduces seamless registration and authentication for your valued users with passwordless login. LoginRadius Identity Platform is a unique CIAM platform that is fully customizable to fit your company's needs.
-[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
The Consumer Identity and Access Management (CIAM) platform has also proved valuable to the retail and e-commerce industry, offering seamless and scalable identity management solutions that identify and protect consumer data.
@@ -132,4 +132,4 @@ Password spraying attacks can be detected by monitoring login attempts and looki
Preventing password spraying attacks can be done by implementing multi-factor authentication, strong password policies, and monitoring for suspicious activity on the network.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=password-spraying)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=password-spraying)
diff --git a/content/identity/password-spraying/password-spraying-cover.jpg b/content/identity/password-spraying/password-spraying-cover.jpg
deleted file mode 100644
index 46ea2e093..000000000
Binary files a/content/identity/password-spraying/password-spraying-cover.jpg and /dev/null differ
diff --git a/content/identity/password-spraying/password-spraying-cover.webp b/content/identity/password-spraying/password-spraying-cover.webp
new file mode 100644
index 000000000..611472138
Binary files /dev/null and b/content/identity/password-spraying/password-spraying-cover.webp differ
diff --git a/content/identity/password-spraying/password-spraying.jpg b/content/identity/password-spraying/password-spraying.jpg
deleted file mode 100644
index 9f2624df3..000000000
Binary files a/content/identity/password-spraying/password-spraying.jpg and /dev/null differ
diff --git a/content/identity/password-spraying/password-spraying.webp b/content/identity/password-spraying/password-spraying.webp
new file mode 100644
index 000000000..f476d99be
Binary files /dev/null and b/content/identity/password-spraying/password-spraying.webp differ
diff --git a/content/identity/password-spraying/passwordless-login.png b/content/identity/password-spraying/passwordless-login.png
deleted file mode 100644
index 69d26339f..000000000
Binary files a/content/identity/password-spraying/passwordless-login.png and /dev/null differ
diff --git a/content/identity/password-spraying/passwordless-login.webp b/content/identity/password-spraying/passwordless-login.webp
new file mode 100644
index 000000000..96ed92a38
Binary files /dev/null and b/content/identity/password-spraying/passwordless-login.webp differ
diff --git a/content/identity/passwordless-authentication-automation/DS-passwordless-otp.png b/content/identity/passwordless-authentication-automation/DS-passwordless-otp.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/passwordless-authentication-automation/DS-passwordless-otp.png and /dev/null differ
diff --git a/content/identity/passwordless-authentication-automation/DS-passwordless-otp.webp b/content/identity/passwordless-authentication-automation/DS-passwordless-otp.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/passwordless-authentication-automation/DS-passwordless-otp.webp differ
diff --git a/content/identity/passwordless-authentication-automation/index.md b/content/identity/passwordless-authentication-automation/index.md
index 34d6aa967..ba60e8faf 100644
--- a/content/identity/passwordless-authentication-automation/index.md
+++ b/content/identity/passwordless-authentication-automation/index.md
@@ -1,7 +1,7 @@
---
title: "Unlock Your Digital Freedom: How Automating Passwordless Authentication Can Transform Your Security"
date: "2024-08-27"
-coverImage: "password-auth.jpg"
+coverImage: "password-auth.webp"
tags: ["passwordless authentication","data security","cx"]
author: "Rakesh Soni"
description: "In a world where cybersecurity threats are ever-evolving, automating passwordless authentication emerges as a game-changer. Learn how this innovative approach can not only bolster your security but also streamline the user experience and pave the way for a more secure digital future."
@@ -81,7 +81,7 @@ By leveraging cutting-edge technologies such as biometric authentication, hardwa
With automated workflows and real-time monitoring, LoginRadius ensures consistent security protocols and swift responses to potential threats.
-[](https://www.loginradius.com/resource/datasheet/ciam-passwordless-login/)
+[](https://www.loginradius.com/resource/datasheet/ciam-passwordless-login/)
Moreover, LoginRadius offers a customizable user experience, allowing businesses to tailor authentication methods to fit specific needs and preferences. This adaptability ensures a smooth implementation across various platforms and applications, minimizing disruptions while maximizing security.
@@ -91,4 +91,4 @@ Automating passwordless authentication is a transformative step towards unlockin
By eliminating the vulnerabilities associated with traditional passwords and streamlining the authentication process, you can achieve a higher level of security and user satisfaction. Embrace this innovative approach to stay ahead in the ever-evolving landscape of cybersecurity.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passwordless-authentication-automation)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passwordless-authentication-automation)
\ No newline at end of file
diff --git a/content/identity/passwordless-authentication-automation/password-auth.jpg b/content/identity/passwordless-authentication-automation/password-auth.jpg
deleted file mode 100644
index 15931fdba..000000000
Binary files a/content/identity/passwordless-authentication-automation/password-auth.jpg and /dev/null differ
diff --git a/content/identity/passwordless-authentication-automation/password-auth.webp b/content/identity/passwordless-authentication-automation/password-auth.webp
new file mode 100644
index 000000000..768f11bd4
Binary files /dev/null and b/content/identity/passwordless-authentication-automation/password-auth.webp differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Book-a-free-demo-request-1024x310.png b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Book-a-free-demo-request-1024x310.webp b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/DS-Product-Passwordless-Login-1024x310.png b/content/identity/passwordless-authentication-the-future-of-identity-and-security/DS-Product-Passwordless-Login-1024x310.png
deleted file mode 100644
index 39938606a..000000000
Binary files a/content/identity/passwordless-authentication-the-future-of-identity-and-security/DS-Product-Passwordless-Login-1024x310.png and /dev/null differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/DS-Product-Passwordless-Login-1024x310.webp b/content/identity/passwordless-authentication-the-future-of-identity-and-security/DS-Product-Passwordless-Login-1024x310.webp
new file mode 100644
index 000000000..8affefe0d
Binary files /dev/null and b/content/identity/passwordless-authentication-the-future-of-identity-and-security/DS-Product-Passwordless-Login-1024x310.webp differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-featured-image.png b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-featured-image.png
deleted file mode 100644
index 868fa626f..000000000
Binary files a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-featured-image.png and /dev/null differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-featured-image.webp b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-featured-image.webp
new file mode 100644
index 000000000..0c7169bdc
Binary files /dev/null and b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-featured-image.webp differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-shield-image-1024x576.png b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-shield-image-1024x576.png
deleted file mode 100644
index 41df697d0..000000000
Binary files a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-shield-image-1024x576.png and /dev/null differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-shield-image-1024x576.webp b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-shield-image-1024x576.webp
new file mode 100644
index 000000000..a8576c48d
Binary files /dev/null and b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Authentication-shield-image-1024x576.webp differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Login-Flowchart-1024x549.png b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Login-Flowchart-1024x549.png
deleted file mode 100644
index f016d149d..000000000
Binary files a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Login-Flowchart-1024x549.png and /dev/null differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Login-Flowchart-1024x549.webp b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Login-Flowchart-1024x549.webp
new file mode 100644
index 000000000..0a1ae5a31
Binary files /dev/null and b/content/identity/passwordless-authentication-the-future-of-identity-and-security/Passwordless-Login-Flowchart-1024x549.webp differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/activating-passwordless-login-in-loginradius-1024x504.png b/content/identity/passwordless-authentication-the-future-of-identity-and-security/activating-passwordless-login-in-loginradius-1024x504.png
deleted file mode 100644
index b83c4f540..000000000
Binary files a/content/identity/passwordless-authentication-the-future-of-identity-and-security/activating-passwordless-login-in-loginradius-1024x504.png and /dev/null differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/activating-passwordless-login-in-loginradius-1024x504.webp b/content/identity/passwordless-authentication-the-future-of-identity-and-security/activating-passwordless-login-in-loginradius-1024x504.webp
new file mode 100644
index 000000000..ef70fb67a
Binary files /dev/null and b/content/identity/passwordless-authentication-the-future-of-identity-and-security/activating-passwordless-login-in-loginradius-1024x504.webp differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/index.md b/content/identity/passwordless-authentication-the-future-of-identity-and-security/index.md
index 861cb20a9..94111377c 100644
--- a/content/identity/passwordless-authentication-the-future-of-identity-and-security/index.md
+++ b/content/identity/passwordless-authentication-the-future-of-identity-and-security/index.md
@@ -1,7 +1,7 @@
---
title: "The Role of Passwordless Authentication in Securing Digital Identity"
date: "2019-10-11"
-coverImage: "passwordless-auth.png"
+coverImage: "passwordless-auth.webp"
tags: ["passwordless authentication","digital identity management","cx"]
author: "Rakesh Soni"
description: "The war cry among experts lately when it comes to online safety is: The future is passwordless! So, why does passwordless authentication matter so much?"
@@ -119,7 +119,7 @@ With passwords out of the picture, the following are a few attacks that business
5. **Shoulder Surfing**: It is a type of data theft where the intruder steals login credentials by peeking over the target's shoulder.
-[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
## How Safe Is Passwordless Authentication as Compared to Other Login Methods
@@ -154,7 +154,7 @@ Here’s a convenient, easy-to-implement way to onboard a user. SMS-based login
Biometric authentication services focus on growing technologies like fingerprint, face, or iris scans. The technology works on smartphones where users press their thumbs on their smartphone scanners to authorize their identities and gain access to their accounts. Both Android and Apple offer biometric login options that are popular for their convenience.
-
+
## How Does Passwordless Authentication Work
@@ -169,7 +169,7 @@ This means that whenever a user wishes to create a secure account, a public-priv
Today’s passwordless authentication follows the [FIDO2 standard](https://en.wikipedia.org/wiki/FIDO2_Project). It includes WebAuthn and CTAP that help organizations keep their passwords secure.
-
+
Wondering how it works?
@@ -205,7 +205,7 @@ The LoginRadius Identity Platform is an out-of-the-box way for you to do this ea
Here’s how the platform works.
-
+
### Passwordless authentication with LoginRadius is a three-fold process.
@@ -241,4 +241,4 @@ Q: What is 2FA or passwordless?
A: 2FA (Two-Factor Authentication) requires two forms of verification for access. Passwordless authentication, on the other hand, allows users to log in without using a traditional password, using methods like biometrics or email links.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passwordless-authentication-the-future-of-identity-and-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passwordless-authentication-the-future-of-identity-and-security)
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/passwordless-auth.png b/content/identity/passwordless-authentication-the-future-of-identity-and-security/passwordless-auth.png
deleted file mode 100644
index 5f7466f4b..000000000
Binary files a/content/identity/passwordless-authentication-the-future-of-identity-and-security/passwordless-auth.png and /dev/null differ
diff --git a/content/identity/passwordless-authentication-the-future-of-identity-and-security/passwordless-auth.webp b/content/identity/passwordless-authentication-the-future-of-identity-and-security/passwordless-auth.webp
new file mode 100644
index 000000000..70b235405
Binary files /dev/null and b/content/identity/passwordless-authentication-the-future-of-identity-and-security/passwordless-auth.webp differ
diff --git a/content/identity/passwordless-going-navigate-business-success/ds-passwordless.png b/content/identity/passwordless-going-navigate-business-success/ds-passwordless.png
deleted file mode 100644
index 69d26339f..000000000
Binary files a/content/identity/passwordless-going-navigate-business-success/ds-passwordless.png and /dev/null differ
diff --git a/content/identity/passwordless-going-navigate-business-success/ds-passwordless.webp b/content/identity/passwordless-going-navigate-business-success/ds-passwordless.webp
new file mode 100644
index 000000000..96ed92a38
Binary files /dev/null and b/content/identity/passwordless-going-navigate-business-success/ds-passwordless.webp differ
diff --git a/content/identity/passwordless-going-navigate-business-success/index.md b/content/identity/passwordless-going-navigate-business-success/index.md
index de28aa370..4f79d0b43 100644
--- a/content/identity/passwordless-going-navigate-business-success/index.md
+++ b/content/identity/passwordless-going-navigate-business-success/index.md
@@ -1,7 +1,7 @@
---
title: "Why Your Business Needs A Simple Passwordless Experience (Minus the User Friction)"
date: "2022-07-13"
-coverImage: "passwordless-business.jpg"
+coverImage: "passwordless-business.webp"
tags: ["passwordless", "login security", "progressive profiling"]
author: "Vishal Sharma"
description: "Whether it’s a little friction in login authentication or user fatigue in filling massive registration forms, everything counts when it comes to a bad user experience. Let’s uncover the importance of going passwordless for enterprises."
@@ -34,7 +34,7 @@ Users find it easier to authenticate themselves without remembering passwords fo
Apart from the user experience perspective, passwordless authentication is swiftly becoming the preferred authentication method among businesses seeking ways to protect consumer identities and sensitive business information. Let’s understand how.
-[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
## How Passwordless Experience Thrives Business Growth?
@@ -74,4 +74,4 @@ Hence, businesses need to understand the importance of passwordless authenticati
Businesses leveraging cutting-edge authentication technologies always stand ahead of their competitors since their customers enjoy a seamless user experience reinforced by robust security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passwordless-going-navigate-business-success)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passwordless-going-navigate-business-success)
diff --git a/content/identity/passwordless-going-navigate-business-success/passwordless-business.jpg b/content/identity/passwordless-going-navigate-business-success/passwordless-business.jpg
deleted file mode 100644
index 4a5898a2c..000000000
Binary files a/content/identity/passwordless-going-navigate-business-success/passwordless-business.jpg and /dev/null differ
diff --git a/content/identity/passwordless-going-navigate-business-success/passwordless-business.webp b/content/identity/passwordless-going-navigate-business-success/passwordless-business.webp
new file mode 100644
index 000000000..eb565fe85
Binary files /dev/null and b/content/identity/passwordless-going-navigate-business-success/passwordless-business.webp differ
diff --git a/content/identity/passwordless-login-future-authentication/DS-passwordless-magic-link.png b/content/identity/passwordless-login-future-authentication/DS-passwordless-magic-link.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/passwordless-login-future-authentication/DS-passwordless-magic-link.png and /dev/null differ
diff --git a/content/identity/passwordless-login-future-authentication/DS-passwordless-magic-link.webp b/content/identity/passwordless-login-future-authentication/DS-passwordless-magic-link.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/passwordless-login-future-authentication/DS-passwordless-magic-link.webp differ
diff --git a/content/identity/passwordless-login-future-authentication/index.md b/content/identity/passwordless-login-future-authentication/index.md
index 55c1d1d62..5e17148d8 100644
--- a/content/identity/passwordless-login-future-authentication/index.md
+++ b/content/identity/passwordless-login-future-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Beyond Passwords: Navigating Tomorrow's Authentication Landscape"
date: "2024-02-15"
-coverImage: "passswordless-login.jpg"
+coverImage: "passswordless-login.webp"
tags: ["passwordless login","compliance","cx"]
author: "Rakesh Soni"
description: "Dive into the future of authentication with our insightful exploration of passwordless technology. Learn why users are abandoning passwords, how passwordless authentication ensures compliance, and why LoginRadius is the top choice for a secure and frictionless authentication experience."
@@ -42,7 +42,7 @@ At the forefront of this passwordless revolution is LoginRadius – a leading pr
LoginRadius has recently introduced a game-changing feature: registration without passwords. This innovation enables passwordless authentication, enhancing user convenience while fortifying security measures.
-[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
+[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
With streamlined registration, users can swiftly access their accounts without the hassle of managing passwords. Simultaneously, businesses can ensure compliance with data protection regulations and accommodate diverse registration scenarios, fostering flexibility and trust.
@@ -58,4 +58,4 @@ By partnering with LoginRadius, organizations can unlock many benefits, includin
The era of passwords is ending, paving the way for a new era of passwordless authentication. By embracing passwordless technologies, organizations can enhance security, improve user experience, and ensure compliance with regulatory requirements. And with LoginRadius leading the charge, the future of authentication has never looked brighter.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passwordless-login-future-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passwordless-login-future-authentication)
\ No newline at end of file
diff --git a/content/identity/passwordless-login-future-authentication/passswordless-login.jpg b/content/identity/passwordless-login-future-authentication/passswordless-login.jpg
deleted file mode 100644
index 04dbab450..000000000
Binary files a/content/identity/passwordless-login-future-authentication/passswordless-login.jpg and /dev/null differ
diff --git a/content/identity/passwordless-login-future-authentication/passswordless-login.webp b/content/identity/passwordless-login-future-authentication/passswordless-login.webp
new file mode 100644
index 000000000..0fce51fad
Binary files /dev/null and b/content/identity/passwordless-login-future-authentication/passswordless-login.webp differ
diff --git a/content/identity/passwordless-magic-links/Book-a-free-demo-request-1024x310.png b/content/identity/passwordless-magic-links/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/passwordless-magic-links/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/passwordless-magic-links/Book-a-free-demo-request-1024x310.webp b/content/identity/passwordless-magic-links/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/passwordless-magic-links/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/passwordless-magic-links/DS-Product-Passwordless-Login-1024x310.png b/content/identity/passwordless-magic-links/DS-Product-Passwordless-Login-1024x310.png
deleted file mode 100644
index 39938606a..000000000
Binary files a/content/identity/passwordless-magic-links/DS-Product-Passwordless-Login-1024x310.png and /dev/null differ
diff --git a/content/identity/passwordless-magic-links/DS-Product-Passwordless-Login-1024x310.webp b/content/identity/passwordless-magic-links/DS-Product-Passwordless-Login-1024x310.webp
new file mode 100644
index 000000000..8affefe0d
Binary files /dev/null and b/content/identity/passwordless-magic-links/DS-Product-Passwordless-Login-1024x310.webp differ
diff --git a/content/identity/passwordless-magic-links/index.md b/content/identity/passwordless-magic-links/index.md
index facae3cbc..01fc72a48 100644
--- a/content/identity/passwordless-magic-links/index.md
+++ b/content/identity/passwordless-magic-links/index.md
@@ -1,7 +1,7 @@
---
title: "The Future of Authentication is Passwordless With Magic links"
date: "2021-05-05"
-coverImage: "passwordless-magic-links-cover.jpg"
+coverImage: "passwordless-magic-links-cover.webp"
tags: ["passwordless login","authentication","cx"]
author: "Navanita Devi"
description: "By opting to add the magic link feature to your mobile apps or email accounts, you are likely trying to make your mobile app or site user-friendly, contributing to a strong security strategy. Here are some reasons for which you can opt passwordless magic links."
@@ -82,7 +82,7 @@ Though there are numerous benefits of using a passwordless magic link, there are
Another challenge you might face with magic link apps is that the admins have no control over link sharing. Regardless of the user, admins are unable to keep track of the confidential or sensitive information shared with others. Apart from these challenges the major one is the increased cyber-attacks with nearly [7K global data breaches ](https://thepaypers.com/thought-leader-insights/goodbye-passwords-passwordless-authentication-is-here-to-stay--1245019)in 2019 that risked about 15 billion user records.
-[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/)
## Examples of When Magic Links Are Used
@@ -138,4 +138,4 @@ Yes, magic links enhance security by mitigating password-related risks like brea
Developers program the system to generate a one-time-use magic link upon user request, ensuring secure authentication without passwords.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passwordless-magic-links)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=passwordless-magic-links)
diff --git a/content/identity/passwordless-magic-links/passwordless-magic-links-cover.jpg b/content/identity/passwordless-magic-links/passwordless-magic-links-cover.jpg
deleted file mode 100644
index 2b53b0137..000000000
Binary files a/content/identity/passwordless-magic-links/passwordless-magic-links-cover.jpg and /dev/null differ
diff --git a/content/identity/passwordless-magic-links/passwordless-magic-links-cover.webp b/content/identity/passwordless-magic-links/passwordless-magic-links-cover.webp
new file mode 100644
index 000000000..8c1afaacc
Binary files /dev/null and b/content/identity/passwordless-magic-links/passwordless-magic-links-cover.webp differ
diff --git a/content/identity/perfect-ciam-platform/CTA-Graphics-for-Blogs-13.png b/content/identity/perfect-ciam-platform/CTA-Graphics-for-Blogs-13.png
deleted file mode 100644
index 3b036bea7..000000000
Binary files a/content/identity/perfect-ciam-platform/CTA-Graphics-for-Blogs-13.png and /dev/null differ
diff --git a/content/identity/perfect-ciam-platform/CTA-Graphics-for-Blogs-13.webp b/content/identity/perfect-ciam-platform/CTA-Graphics-for-Blogs-13.webp
new file mode 100644
index 000000000..5d3b68618
Binary files /dev/null and b/content/identity/perfect-ciam-platform/CTA-Graphics-for-Blogs-13.webp differ
diff --git a/content/identity/perfect-ciam-platform/buy-vs-build.png b/content/identity/perfect-ciam-platform/buy-vs-build.png
deleted file mode 100644
index b58e0950a..000000000
Binary files a/content/identity/perfect-ciam-platform/buy-vs-build.png and /dev/null differ
diff --git a/content/identity/perfect-ciam-platform/buy-vs-build.webp b/content/identity/perfect-ciam-platform/buy-vs-build.webp
new file mode 100644
index 000000000..23f70e01d
Binary files /dev/null and b/content/identity/perfect-ciam-platform/buy-vs-build.webp differ
diff --git a/content/identity/perfect-ciam-platform/fetaure-image-1.png b/content/identity/perfect-ciam-platform/fetaure-image-1.png
deleted file mode 100644
index 1ea5d560e..000000000
Binary files a/content/identity/perfect-ciam-platform/fetaure-image-1.png and /dev/null differ
diff --git a/content/identity/perfect-ciam-platform/fetaure-image-1.webp b/content/identity/perfect-ciam-platform/fetaure-image-1.webp
new file mode 100644
index 000000000..153a1923c
Binary files /dev/null and b/content/identity/perfect-ciam-platform/fetaure-image-1.webp differ
diff --git a/content/identity/perfect-ciam-platform/global-compliance-graphic.png b/content/identity/perfect-ciam-platform/global-compliance-graphic.png
deleted file mode 100644
index 2a97ef499..000000000
Binary files a/content/identity/perfect-ciam-platform/global-compliance-graphic.png and /dev/null differ
diff --git a/content/identity/perfect-ciam-platform/global-compliance-graphic.webp b/content/identity/perfect-ciam-platform/global-compliance-graphic.webp
new file mode 100644
index 000000000..add82f2c7
Binary files /dev/null and b/content/identity/perfect-ciam-platform/global-compliance-graphic.webp differ
diff --git a/content/identity/perfect-ciam-platform/index.md b/content/identity/perfect-ciam-platform/index.md
index fff99333c..12ff735c4 100644
--- a/content/identity/perfect-ciam-platform/index.md
+++ b/content/identity/perfect-ciam-platform/index.md
@@ -1,7 +1,7 @@
---
title: "8 Key Components of a Perfect CIAM Platform"
date: "2019-06-10"
-coverImage: "fetaure-image-1.png"
+coverImage: "fetaure-image-1.webp"
tags: ["ciam platform","compliance","cx"]
author: "Rakesh Soni"
description: "More than just individuals, a perfect CIAM platform needs to be able to incorporate. There are plenty of business processes and activities loaded with identity, and the number of these is only set to increase in the future. Both native and third-party applications that manage customer data are linked by a well-designed customer identity solution."
@@ -39,7 +39,7 @@ This reputation will encourage customer loyalty in the long run.
### 3\. Integration with APIs
-
+
A perfect CIAM platform needs to be able to integrate more than just people. There are lots of identity-filled business processes and practices, and in the future the number of these is only set to grow.
@@ -63,7 +63,7 @@ All of these things need to be manageable across future system updates without f
### 5\. Security Compliance
-
+
Your CIAM platform must [meet compliance requirements on a global scale](https://secureprivacy.ai/complete-guide-to-international-data-privacy-laws/), even though many of these requirements are constantly changing and evolving. Currently, here’s what your CIAM platform needs to do:
@@ -86,7 +86,7 @@ One of the best things about an advanced CIAM solution is the ability to tie in
CIAM can be used to both extract and store many different data points, feeding them back to your other systems for use.
-[](https://www.loginradius.com/resource/the-case-for-buying-over-building/)
+[](https://www.loginradius.com/resource/the-case-for-buying-over-building/)
### 7\. Scalability During High Demand
@@ -104,4 +104,4 @@ The main thing to remember is that customer IAM is all about customer experience
Today that means you need to offer self-service data management and make use of the additional customer data that CIAM platform can give you. Only then can you improve what you offer customers at virtually every point in their journey.
-[](https://www.loginradius.com/book-demo/)
+[](https://www.loginradius.com/book-demo/)
diff --git a/content/identity/perfect-ciam-platform/integration-graphic.png b/content/identity/perfect-ciam-platform/integration-graphic.png
deleted file mode 100644
index 1cd3dbdb4..000000000
Binary files a/content/identity/perfect-ciam-platform/integration-graphic.png and /dev/null differ
diff --git a/content/identity/perfect-ciam-platform/integration-graphic.webp b/content/identity/perfect-ciam-platform/integration-graphic.webp
new file mode 100644
index 000000000..63b28db71
Binary files /dev/null and b/content/identity/perfect-ciam-platform/integration-graphic.webp differ
diff --git a/content/identity/phishing-for-identity/index.md b/content/identity/phishing-for-identity/index.md
index d4e5df943..22fefbc6b 100644
--- a/content/identity/phishing-for-identity/index.md
+++ b/content/identity/phishing-for-identity/index.md
@@ -1,7 +1,7 @@
---
title: "Phishing Attacks: How to Identify & Avoid Phishing Scams"
date: "2018-02-13"
-coverImage: "phishing-for-identity.jpg"
+coverImage: "phishing-for-identity.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -51,7 +51,7 @@ A few examples of phishing attacks include:
## 7 Ways to Detect a Phishing Email - Here's How
-
+
### 1. The email is sent from a public domain.
@@ -85,7 +85,7 @@ You should be alarmed if you receive an email containing an attachment from a co
It's good practice always to scan it using antivirus software first, even if you believe the attachment is real.
-[](https://www.loginradius.com/resource/passwords-are-dead/)
+[](https://www.loginradius.com/resource/passwords-are-dead/)
### 5. The message has made you panic.
@@ -119,7 +119,7 @@ We have hashed out the different types of phishing attacks.
## What Are the Common Types of Phishing Attacks and How To Prevent Them
-
+
* Spear Phishing
@@ -195,4 +195,4 @@ Using the tips mentioned above, businesses will be able to identify some of the
With that in mind, you need to be on top of the game every single day. Keep on conducting [security awareness training](https://www.loginradius.com/blog/identity/2019/10/cybersecurity-best-practices-for-enterprises/) so that your employees and executives never fall prey.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=phishing-for-identity)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=phishing-for-identity)
diff --git a/content/identity/phishing-for-identity/passwords-are-dead-whitepaper.png b/content/identity/phishing-for-identity/passwords-are-dead-whitepaper.png
deleted file mode 100644
index 2a8161074..000000000
Binary files a/content/identity/phishing-for-identity/passwords-are-dead-whitepaper.png and /dev/null differ
diff --git a/content/identity/phishing-for-identity/passwords-are-dead-whitepaper.webp b/content/identity/phishing-for-identity/passwords-are-dead-whitepaper.webp
new file mode 100644
index 000000000..11c27d066
Binary files /dev/null and b/content/identity/phishing-for-identity/passwords-are-dead-whitepaper.webp differ
diff --git a/content/identity/phishing-for-identity/phishing-for-identity.jpg b/content/identity/phishing-for-identity/phishing-for-identity.jpg
deleted file mode 100644
index 2fb383d5f..000000000
Binary files a/content/identity/phishing-for-identity/phishing-for-identity.jpg and /dev/null differ
diff --git a/content/identity/phishing-for-identity/phishing-for-identity.webp b/content/identity/phishing-for-identity/phishing-for-identity.webp
new file mode 100644
index 000000000..2b0b25743
Binary files /dev/null and b/content/identity/phishing-for-identity/phishing-for-identity.webp differ
diff --git a/content/identity/phishing-for-identity/types-of-phishing-attacks.png b/content/identity/phishing-for-identity/types-of-phishing-attacks.png
deleted file mode 100644
index 0f935a4d1..000000000
Binary files a/content/identity/phishing-for-identity/types-of-phishing-attacks.png and /dev/null differ
diff --git a/content/identity/phishing-for-identity/types-of-phishing-attacks.webp b/content/identity/phishing-for-identity/types-of-phishing-attacks.webp
new file mode 100644
index 000000000..b50b5957a
Binary files /dev/null and b/content/identity/phishing-for-identity/types-of-phishing-attacks.webp differ
diff --git a/content/identity/phishing-for-identity/ways-detect-phishing-email.jpeg b/content/identity/phishing-for-identity/ways-detect-phishing-email.jpeg
deleted file mode 100644
index 4b3bca323..000000000
Binary files a/content/identity/phishing-for-identity/ways-detect-phishing-email.jpeg and /dev/null differ
diff --git a/content/identity/phishing-for-identity/ways-detect-phishing-email.webp b/content/identity/phishing-for-identity/ways-detect-phishing-email.webp
new file mode 100644
index 000000000..f7eebe3a1
Binary files /dev/null and b/content/identity/phishing-for-identity/ways-detect-phishing-email.webp differ
diff --git a/content/identity/phishing-resistant-mfa-login-mobile-apps/DS-passwordless-login-magic-links.png b/content/identity/phishing-resistant-mfa-login-mobile-apps/DS-passwordless-login-magic-links.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/phishing-resistant-mfa-login-mobile-apps/DS-passwordless-login-magic-links.png and /dev/null differ
diff --git a/content/identity/phishing-resistant-mfa-login-mobile-apps/DS-passwordless-login-magic-links.webp b/content/identity/phishing-resistant-mfa-login-mobile-apps/DS-passwordless-login-magic-links.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/phishing-resistant-mfa-login-mobile-apps/DS-passwordless-login-magic-links.webp differ
diff --git a/content/identity/phishing-resistant-mfa-login-mobile-apps/index.md b/content/identity/phishing-resistant-mfa-login-mobile-apps/index.md
index 626ee3494..4dad5e37a 100644
--- a/content/identity/phishing-resistant-mfa-login-mobile-apps/index.md
+++ b/content/identity/phishing-resistant-mfa-login-mobile-apps/index.md
@@ -2,7 +2,7 @@
title: "Phishing-Resistant MFA Login for Mobile Applications:
Strategies and Challenges"
date: "2023-09-04"
-coverImage: "phishing-resistant.jpg"
+coverImage: "phishing-resistant.webp"
tags: ["data security","mfa login","cybersecurity","cx"]
author: "Alok Patidar"
description: "Phishing-resistant multi-factor Authentication (MFA) login is a unique approach to information security that aims to strengthen the defenses against phishing attacks. Know all about the strategies and challenges involved."
@@ -54,7 +54,7 @@ Below, we have curated a list of the top 6 phishing-resistant strategies for mob
3. **One-Time Password via Mobile App:** Rather than sending OTPs through SMS, try delivering them through the mobile application. OTPs generated via the app are more secure as they avoid the vulnerabilities associated with SMS-based OTPs, which attackers can manipulate.
-[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
+[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
4. **Hardware Tokens:** Incorporate hardware tokens or security keys that connect directly to mobile devices. These tokens generate time-based OTPs or cryptographically signed authentication codes, providing a phishing-resistant alternative to traditional OTP methods.
@@ -71,4 +71,4 @@ In short, phishing-resistant MFA login technique for mobile applications is a di
Applying the MFA login method to mobile applications will increase data security and reliability. Hence, being an impactful communication tool, mobile devices and applications can now resist cyber-attacks.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=phishing-resistant-mfa-login-mobile-apps)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=phishing-resistant-mfa-login-mobile-apps)
\ No newline at end of file
diff --git a/content/identity/phishing-resistant-mfa-login-mobile-apps/phishing-resistant.jpg b/content/identity/phishing-resistant-mfa-login-mobile-apps/phishing-resistant.jpg
deleted file mode 100644
index f6d715daa..000000000
Binary files a/content/identity/phishing-resistant-mfa-login-mobile-apps/phishing-resistant.jpg and /dev/null differ
diff --git a/content/identity/phishing-resistant-mfa-login-mobile-apps/phishing-resistant.webp b/content/identity/phishing-resistant-mfa-login-mobile-apps/phishing-resistant.webp
new file mode 100644
index 000000000..113744539
Binary files /dev/null and b/content/identity/phishing-resistant-mfa-login-mobile-apps/phishing-resistant.webp differ
diff --git a/content/identity/pii-compliance-enterprise/RP-Protecting-PII-Against-Data-Breaches.png b/content/identity/pii-compliance-enterprise/RP-Protecting-PII-Against-Data-Breaches.png
deleted file mode 100644
index b32dcb27b..000000000
Binary files a/content/identity/pii-compliance-enterprise/RP-Protecting-PII-Against-Data-Breaches.png and /dev/null differ
diff --git a/content/identity/pii-compliance-enterprise/RP-Protecting-PII-Against-Data-Breaches.webp b/content/identity/pii-compliance-enterprise/RP-Protecting-PII-Against-Data-Breaches.webp
new file mode 100644
index 000000000..6c250a4f7
Binary files /dev/null and b/content/identity/pii-compliance-enterprise/RP-Protecting-PII-Against-Data-Breaches.webp differ
diff --git a/content/identity/pii-compliance-enterprise/index.md b/content/identity/pii-compliance-enterprise/index.md
index 438caa662..faa35a21b 100644
--- a/content/identity/pii-compliance-enterprise/index.md
+++ b/content/identity/pii-compliance-enterprise/index.md
@@ -1,7 +1,7 @@
---
title: "Understanding PII Compliance: A Key to Enterprise Data Security"
date: "2021-07-07"
-coverImage: "pii-compliance-enterprise-cover.jpg"
+coverImage: "pii-compliance-enterprise-cover.webp"
tags: ["data security","enterprise security","compliance"]
author: "Rakesh Soni"
description: "The security of personal identity and other details is at increasing risk today, with hackers finding new ways to hack into websites. Therefore, enterprises of all sizes must maintain PII compliance to protect the information of the company and its users."
@@ -28,7 +28,7 @@ Data that helps identify a specific individual is called personally identifiable
PII has a principal role in network security, especially when it comes to data breaches and identity theft. For example, if a company that manages personal information encounters a data breach, its customers will likely suffer personal identity theft because the company-managed data will be stolen.
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
The information related to this is stored with online marketers and brokers who trade your data to various companies that "want to show you appropriate ads" and provide you with an "improved user experience."
@@ -72,4 +72,4 @@ The security of personal identity and other details is at increasing risk today,
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pii-compliance-enterprise)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pii-compliance-enterprise)
diff --git a/content/identity/pii-compliance-enterprise/pii-compliance-enterprise-cover.jpg b/content/identity/pii-compliance-enterprise/pii-compliance-enterprise-cover.jpg
deleted file mode 100644
index 7cdcefa0b..000000000
Binary files a/content/identity/pii-compliance-enterprise/pii-compliance-enterprise-cover.jpg and /dev/null differ
diff --git a/content/identity/pii-compliance-enterprise/pii-compliance-enterprise-cover.webp b/content/identity/pii-compliance-enterprise/pii-compliance-enterprise-cover.webp
new file mode 100644
index 000000000..df2483843
Binary files /dev/null and b/content/identity/pii-compliance-enterprise/pii-compliance-enterprise-cover.webp differ
diff --git a/content/identity/pki-future-secure-communications/DS-SSO.png b/content/identity/pki-future-secure-communications/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/pki-future-secure-communications/DS-SSO.png and /dev/null differ
diff --git a/content/identity/pki-future-secure-communications/DS-SSO.webp b/content/identity/pki-future-secure-communications/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/pki-future-secure-communications/DS-SSO.webp differ
diff --git a/content/identity/pki-future-secure-communications/LR-SSO.png b/content/identity/pki-future-secure-communications/LR-SSO.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/pki-future-secure-communications/LR-SSO.png and /dev/null differ
diff --git a/content/identity/pki-future-secure-communications/LR-SSO.webp b/content/identity/pki-future-secure-communications/LR-SSO.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/pki-future-secure-communications/LR-SSO.webp differ
diff --git a/content/identity/pki-future-secure-communications/index.md b/content/identity/pki-future-secure-communications/index.md
index 1f41ee7f5..4ff08102c 100644
--- a/content/identity/pki-future-secure-communications/index.md
+++ b/content/identity/pki-future-secure-communications/index.md
@@ -1,7 +1,7 @@
---
title: "Why is PKI The Future of Secure Communications"
date: "2021-10-26"
-coverImage: "pki-cover.jpg"
+coverImage: "pki-cover.webp"
tags: ["single sign-on","sso","authentication"]
author: "Vishal Sharma"
description: "With PKI, one can ensure that data is adequately encrypted during transit, ensuring only the authorized user can access the data. Let’s understand what PKI is and how it paves the path for secure encryption for businesses."
@@ -83,7 +83,7 @@ Robust authentication mechanisms like PKI ensure that the devices and users are
Businesses can leverage the true potential of PKI through Single Sign-On. Though PKI isn’t an SSO service through specific alterations, enterprises can also benefit from Single Sign-On through PKI.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
### 4. Highly scalable
@@ -109,4 +109,4 @@ PKI is a game-changer when it comes to managing secure access between devices an
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pki-future-secure-communications)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pki-future-secure-communications)
diff --git a/content/identity/pki-future-secure-communications/pki-cover.jpg b/content/identity/pki-future-secure-communications/pki-cover.jpg
deleted file mode 100644
index 830939e94..000000000
Binary files a/content/identity/pki-future-secure-communications/pki-cover.jpg and /dev/null differ
diff --git a/content/identity/pki-future-secure-communications/pki-cover.webp b/content/identity/pki-future-secure-communications/pki-cover.webp
new file mode 100644
index 000000000..f5508dfd0
Binary files /dev/null and b/content/identity/pki-future-secure-communications/pki-cover.webp differ
diff --git a/content/identity/poor-login-concurrency-impact-ott-platforms/Book-a-free-demo-request-1024x310.png b/content/identity/poor-login-concurrency-impact-ott-platforms/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/poor-login-concurrency-impact-ott-platforms/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/poor-login-concurrency-impact-ott-platforms/Book-a-free-demo-request-1024x310.webp b/content/identity/poor-login-concurrency-impact-ott-platforms/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/poor-login-concurrency-impact-ott-platforms/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/poor-login-concurrency-impact-ott-platforms/DS - CIAM 101.png b/content/identity/poor-login-concurrency-impact-ott-platforms/DS - CIAM 101.png
deleted file mode 100644
index 4aef14d2f..000000000
Binary files a/content/identity/poor-login-concurrency-impact-ott-platforms/DS - CIAM 101.png and /dev/null differ
diff --git a/content/identity/poor-login-concurrency-impact-ott-platforms/DS - CIAM 101.webp b/content/identity/poor-login-concurrency-impact-ott-platforms/DS - CIAM 101.webp
new file mode 100644
index 000000000..ff3ecd662
Binary files /dev/null and b/content/identity/poor-login-concurrency-impact-ott-platforms/DS - CIAM 101.webp differ
diff --git a/content/identity/poor-login-concurrency-impact-ott-platforms/DS-CIAM101.png b/content/identity/poor-login-concurrency-impact-ott-platforms/DS-CIAM101.png
deleted file mode 100644
index 181c84344..000000000
Binary files a/content/identity/poor-login-concurrency-impact-ott-platforms/DS-CIAM101.png and /dev/null differ
diff --git a/content/identity/poor-login-concurrency-impact-ott-platforms/DS-CIAM101.webp b/content/identity/poor-login-concurrency-impact-ott-platforms/DS-CIAM101.webp
new file mode 100644
index 000000000..e2cac289d
Binary files /dev/null and b/content/identity/poor-login-concurrency-impact-ott-platforms/DS-CIAM101.webp differ
diff --git a/content/identity/poor-login-concurrency-impact-ott-platforms/index.md b/content/identity/poor-login-concurrency-impact-ott-platforms/index.md
index d228af1f4..2f959a0c4 100644
--- a/content/identity/poor-login-concurrency-impact-ott-platforms/index.md
+++ b/content/identity/poor-login-concurrency-impact-ott-platforms/index.md
@@ -1,7 +1,7 @@
---
title: "How Poor Login Concurrency can Impact OTT Platforms' Business"
date: "2021-08-31"
-coverImage: "poor-login-concurrency-impact-ott-platforms-cover.jpg"
+coverImage: "poor-login-concurrency-impact-ott-platforms-cover.webp"
tags: ["data security","ciam solution","broken authentication"]
author: "Rakesh Soni"
description: "With the increase in subscriptions and the number of audiences online, several underlying threats have severely impacted the OTT businesses. One such issue is poor login concurrency. Learn how login concurrency is affecting OTT platforms and how they can overcome this dilemma."
@@ -47,7 +47,7 @@ Thus, to overcome the situation where concurrent login is exploited in OTT servi
Here’s where the role of a [robust CIAM](https://www.loginradius.com/) (Consumer Identity and Access Management) comes into play.
-[](https://www.loginradius.com/resource/ciam-101/)
+[](https://www.loginradius.com/resource/ciam-101/)
Let’s dig deeper into this.
@@ -104,4 +104,4 @@ With increasing OTT subscriptions and user expectations, OTT platforms need to g
Adding stringent layers of security through a robust CIAM solution becomes the immediate need of the hour for OTT platforms facing concurrent login issues that affect their brand reputation and overall business revenues.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=poor-login-concurrency-impact-ott-platforms)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=poor-login-concurrency-impact-ott-platforms)
diff --git a/content/identity/poor-login-concurrency-impact-ott-platforms/poor-login-concurrency-impact-ott-platforms-cover.jpg b/content/identity/poor-login-concurrency-impact-ott-platforms/poor-login-concurrency-impact-ott-platforms-cover.jpg
deleted file mode 100644
index 77b8bc28e..000000000
Binary files a/content/identity/poor-login-concurrency-impact-ott-platforms/poor-login-concurrency-impact-ott-platforms-cover.jpg and /dev/null differ
diff --git a/content/identity/poor-login-concurrency-impact-ott-platforms/poor-login-concurrency-impact-ott-platforms-cover.webp b/content/identity/poor-login-concurrency-impact-ott-platforms/poor-login-concurrency-impact-ott-platforms-cover.webp
new file mode 100644
index 000000000..060128563
Binary files /dev/null and b/content/identity/poor-login-concurrency-impact-ott-platforms/poor-login-concurrency-impact-ott-platforms-cover.webp differ
diff --git a/content/identity/presenting-progressive-profiling-loginradius/Book-a-free-demo-request-1024x310.png b/content/identity/presenting-progressive-profiling-loginradius/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/presenting-progressive-profiling-loginradius/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/presenting-progressive-profiling-loginradius/Book-a-free-demo-request-1024x310.webp b/content/identity/presenting-progressive-profiling-loginradius/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/presenting-progressive-profiling-loginradius/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/presenting-progressive-profiling-loginradius/Presenting-Progressive-Profiling-from-LoginRadius-V01.01_cover.jpg b/content/identity/presenting-progressive-profiling-loginradius/Presenting-Progressive-Profiling-from-LoginRadius-V01.01_cover.jpg
deleted file mode 100644
index cf8c2a7de..000000000
Binary files a/content/identity/presenting-progressive-profiling-loginradius/Presenting-Progressive-Profiling-from-LoginRadius-V01.01_cover.jpg and /dev/null differ
diff --git a/content/identity/presenting-progressive-profiling-loginradius/Presenting-Progressive-Profiling-from-LoginRadius-V01.01_cover.webp b/content/identity/presenting-progressive-profiling-loginradius/Presenting-Progressive-Profiling-from-LoginRadius-V01.01_cover.webp
new file mode 100644
index 000000000..e5dc72894
Binary files /dev/null and b/content/identity/presenting-progressive-profiling-loginradius/Presenting-Progressive-Profiling-from-LoginRadius-V01.01_cover.webp differ
diff --git a/content/identity/presenting-progressive-profiling-loginradius/final-feb-8.jpeg b/content/identity/presenting-progressive-profiling-loginradius/final-feb-8.jpeg
deleted file mode 100644
index 927e7d82f..000000000
Binary files a/content/identity/presenting-progressive-profiling-loginradius/final-feb-8.jpeg and /dev/null differ
diff --git a/content/identity/presenting-progressive-profiling-loginradius/final-feb-8.webp b/content/identity/presenting-progressive-profiling-loginradius/final-feb-8.webp
new file mode 100644
index 000000000..3770a8f4d
Binary files /dev/null and b/content/identity/presenting-progressive-profiling-loginradius/final-feb-8.webp differ
diff --git a/content/identity/presenting-progressive-profiling-loginradius/index.md b/content/identity/presenting-progressive-profiling-loginradius/index.md
index 145de6ce0..f5364f308 100644
--- a/content/identity/presenting-progressive-profiling-loginradius/index.md
+++ b/content/identity/presenting-progressive-profiling-loginradius/index.md
@@ -1,7 +1,7 @@
---
title: "Presenting: Progressive Profiling from LoginRadius"
date: "2019-02-07"
-coverImage: "progrssive-profiling.jpg"
+coverImage: "progrssive-profiling.webp"
tags: ["progressive profiling","cx","ciam solution"]
author: "Rakesh Soni"
description: "A new feature of the LoginRadius Identity Platform is progressive profiling, which gradually collects data from customers in an automated way."
@@ -35,7 +35,7 @@ There are two types of progressive profiling: multi-step registration and social
Progressive profiling for customer registration allows you to split a potentially complicated registration process into multiple steps. You can capture a customer’s information upfront and then slowly build out a holistic view of that customer through subsequent actions.
- **As customer trust increases, businesses can request more data**.
+ **As customer trust increases, businesses can request more data**.
The subsequent actions often take the place of secondary registration forms or event-driven calls to action for your customer to supply additional profile metadata. For example, you could request more detailed data only after a customer has logged in a certain number of times or navigated to a certain digital property.
@@ -43,10 +43,10 @@ The subsequent actions often take the place of secondary registration forms or e
Progressive profiling with social accounts is the process of progressively requesting additional OAuth Access permissions from your customers. This process allows you to minimize the access permissions requested and get business-critical access from your customers based on their social providers.
- **An example of progressive profiling with social accounts**
+ **An example of progressive profiling with social accounts**
Once the customer interacts more with your platform, you can begin requesting additional permissions from the social provider they are authenticating with. For example, you can ask for basic information, such as name and email, during registration, and then ask for birthdate, likes, and interests from the same customer at a later point.
**To learn more about how LoginRadius can improve customer experience and data collection using Progressive Profiling or other features, Book a demo today.**
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=presenting-progressive-profiling-loginradius)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=presenting-progressive-profiling-loginradius)
diff --git a/content/identity/presenting-progressive-profiling-loginradius/progressive-data-gather.jpg b/content/identity/presenting-progressive-profiling-loginradius/progressive-data-gather.jpg
deleted file mode 100644
index 592d0d8f6..000000000
Binary files a/content/identity/presenting-progressive-profiling-loginradius/progressive-data-gather.jpg and /dev/null differ
diff --git a/content/identity/presenting-progressive-profiling-loginradius/progressive-data-gather.webp b/content/identity/presenting-progressive-profiling-loginradius/progressive-data-gather.webp
new file mode 100644
index 000000000..4b113add1
Binary files /dev/null and b/content/identity/presenting-progressive-profiling-loginradius/progressive-data-gather.webp differ
diff --git a/content/identity/presenting-progressive-profiling-loginradius/progrssive-profiling.jpg b/content/identity/presenting-progressive-profiling-loginradius/progrssive-profiling.jpg
deleted file mode 100644
index 8fa9dfdbb..000000000
Binary files a/content/identity/presenting-progressive-profiling-loginradius/progrssive-profiling.jpg and /dev/null differ
diff --git a/content/identity/presenting-progressive-profiling-loginradius/progrssive-profiling.webp b/content/identity/presenting-progressive-profiling-loginradius/progrssive-profiling.webp
new file mode 100644
index 000000000..a578e427d
Binary files /dev/null and b/content/identity/presenting-progressive-profiling-loginradius/progrssive-profiling.webp differ
diff --git a/content/identity/prevent-accidental-data-exposure-company/data-exposure.jpg b/content/identity/prevent-accidental-data-exposure-company/data-exposure.jpg
deleted file mode 100644
index 5e15afa4a..000000000
Binary files a/content/identity/prevent-accidental-data-exposure-company/data-exposure.jpg and /dev/null differ
diff --git a/content/identity/prevent-accidental-data-exposure-company/data-exposure.webp b/content/identity/prevent-accidental-data-exposure-company/data-exposure.webp
new file mode 100644
index 000000000..85da92585
Binary files /dev/null and b/content/identity/prevent-accidental-data-exposure-company/data-exposure.webp differ
diff --git a/content/identity/prevent-accidental-data-exposure-company/databreach-rp.png b/content/identity/prevent-accidental-data-exposure-company/databreach-rp.png
deleted file mode 100644
index b32dcb27b..000000000
Binary files a/content/identity/prevent-accidental-data-exposure-company/databreach-rp.png and /dev/null differ
diff --git a/content/identity/prevent-accidental-data-exposure-company/databreach-rp.webp b/content/identity/prevent-accidental-data-exposure-company/databreach-rp.webp
new file mode 100644
index 000000000..6c250a4f7
Binary files /dev/null and b/content/identity/prevent-accidental-data-exposure-company/databreach-rp.webp differ
diff --git a/content/identity/prevent-accidental-data-exposure-company/index.md b/content/identity/prevent-accidental-data-exposure-company/index.md
index dcb6c77a8..d59d4e625 100644
--- a/content/identity/prevent-accidental-data-exposure-company/index.md
+++ b/content/identity/prevent-accidental-data-exposure-company/index.md
@@ -1,7 +1,7 @@
---
title: "6 Tips to Prevent Accidental Data Exposure Within Your Company"
date: "2022-12-21"
-coverImage: "data-exposure.jpg"
+coverImage: "data-exposure.webp"
tags: ["data leak", "customer data", "data security"]
author: "Rakesh Soni"
description: "The threat of data exposure is real. With the amount of sensitive personal information that companies are collecting and storing, accidental data exposure can be devastating to a company's reputation. Here are some ways to keep your organization's critical data safe."
@@ -49,7 +49,7 @@ Some of the biggest data breaches involved leaks of personally identifiable info
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
### 2. Company information
@@ -118,4 +118,4 @@ By using the recommendations we have outlined above, you can help prevent any ac
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=prevent-accidental-data-exposure-company)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=prevent-accidental-data-exposure-company)
diff --git a/content/identity/prevent-credential-stuffing-attacks/DS-Product-Passwordless-Login-1024x310.png b/content/identity/prevent-credential-stuffing-attacks/DS-Product-Passwordless-Login-1024x310.png
deleted file mode 100644
index 39938606a..000000000
Binary files a/content/identity/prevent-credential-stuffing-attacks/DS-Product-Passwordless-Login-1024x310.png and /dev/null differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/DS-Product-Passwordless-Login-1024x310.webp b/content/identity/prevent-credential-stuffing-attacks/DS-Product-Passwordless-Login-1024x310.webp
new file mode 100644
index 000000000..8affefe0d
Binary files /dev/null and b/content/identity/prevent-credential-stuffing-attacks/DS-Product-Passwordless-Login-1024x310.webp differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-02-1024x576.png b/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-02-1024x576.png
deleted file mode 100644
index 13c3f5e42..000000000
Binary files a/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-02-1024x576.png and /dev/null differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-02-1024x576.webp b/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-02-1024x576.webp
new file mode 100644
index 000000000..6b64a9f84
Binary files /dev/null and b/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-02-1024x576.webp differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-08-1024x577.png b/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-08-1024x577.png
deleted file mode 100644
index baec769ba..000000000
Binary files a/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-08-1024x577.png and /dev/null differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-08-1024x577.webp b/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-08-1024x577.webp
new file mode 100644
index 000000000..effc7d061
Binary files /dev/null and b/content/identity/prevent-credential-stuffing-attacks/How-Credential-Stuffing-Threatens-Your-Company-V01.01-08-1024x577.webp differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/credential-stuffing-attacks.jpg b/content/identity/prevent-credential-stuffing-attacks/credential-stuffing-attacks.jpg
deleted file mode 100644
index 5351e324e..000000000
Binary files a/content/identity/prevent-credential-stuffing-attacks/credential-stuffing-attacks.jpg and /dev/null differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/credential-stuffing-attacks.webp b/content/identity/prevent-credential-stuffing-attacks/credential-stuffing-attacks.webp
new file mode 100644
index 000000000..47c82a4c1
Binary files /dev/null and b/content/identity/prevent-credential-stuffing-attacks/credential-stuffing-attacks.webp differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/credential-stuffing.png b/content/identity/prevent-credential-stuffing-attacks/credential-stuffing.png
deleted file mode 100644
index 904e3a28e..000000000
Binary files a/content/identity/prevent-credential-stuffing-attacks/credential-stuffing.png and /dev/null differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/credential-stuffing.webp b/content/identity/prevent-credential-stuffing-attacks/credential-stuffing.webp
new file mode 100644
index 000000000..c2d6821c3
Binary files /dev/null and b/content/identity/prevent-credential-stuffing-attacks/credential-stuffing.webp differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/icons_security.png b/content/identity/prevent-credential-stuffing-attacks/icons_security.png
deleted file mode 100644
index f3335bbe2..000000000
Binary files a/content/identity/prevent-credential-stuffing-attacks/icons_security.png and /dev/null differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/icons_security.webp b/content/identity/prevent-credential-stuffing-attacks/icons_security.webp
new file mode 100644
index 000000000..bc16ee50f
Binary files /dev/null and b/content/identity/prevent-credential-stuffing-attacks/icons_security.webp differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/index.md b/content/identity/prevent-credential-stuffing-attacks/index.md
index d02995eb8..15c35011c 100644
--- a/content/identity/prevent-credential-stuffing-attacks/index.md
+++ b/content/identity/prevent-credential-stuffing-attacks/index.md
@@ -1,7 +1,7 @@
---
title: "Credential Stuffing: How To Detect And Prevent It"
date: "2019-09-12"
-coverImage: "credential-stuffing-attacks.jpg"
+coverImage: "credential-stuffing-attacks.webp"
tags: ["data security","mfa","ciam solution"]
author: "Rakesh Soni"
description: "Credential stuffing is a cybersecurity vulnerability in which hackers target web infrastructures and take over user accounts using stolen credentials. When hackers use organisational credentials to login and hijack user accounts, the threat gets further elevated. Not only does the business experience loss of sales and brand harm, the blow is also felt by customers."
@@ -54,7 +54,7 @@ As you can see, when a business suffers from stolen credentials, it can cost the
- The cleanup costs can cripple businesses to the core.
- Customers do not trust businesses that cannot protect their data leading to customers discontinuing their loyalty.
-
+
## How to Detect Credential Stuffing Attacks
@@ -72,7 +72,7 @@ It's built to monitor the telltale signs of bot activity such as the number of a
Luckily, you'll find bot detection in robust [customer identity and access management solutions](https://www.loginradius.com/blog/2019/06/customer-identity-and-access-management/). A CIAM platform will also provide device authentication and customer data protection.
-
+
## A Hacker’s Toolbox
@@ -98,7 +98,7 @@ Match found. What's next? When a match is found, they can easily view a victim's
Because hackers use genuine user credentials, they gain undetected access. What follows is a full-fledged [account takeover](https://www.loginradius.com/blog/2020/04/corporate-account-takeover-attacks/). Next, the attacker can drain the account in seconds or resell access to other cybercriminals.
-
+
## How to Prevent Credential Stuffing Attacks
@@ -130,7 +130,7 @@ Risk-based authentication (RBA) calculates a risk score based on a predefined se
Hackers can also deny access to customers' own resources once they break-in. Having passwords as a factor of authentication can leave corporate and business accounts vulnerable to credential stuffing. So, why not remove them altogether? Use [passwordless authentication](https://www.loginradius.com/blog/2019/10/passwordless-authentication-the-future-of-identity-and-security/) as a safer way to authenticate users for more confined access into their accounts.
-[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
+[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
## Preventing Credential Stuffing With LoginRadius Identity Management
@@ -150,4 +150,4 @@ Credential stuffing is easy to perform, so its popularity with criminals will in
If you're looking for a solution to help prevent credential stuffing, LoginRadius is easy to deploy. It provides robust security with bot detection and multi-factor authentication, among other safeguards.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=prevent-credential-stuffing-attacks)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=prevent-credential-stuffing-attacks)
diff --git a/content/identity/prevent-credential-stuffing-attacks/prevent-credential-stuffing-attacks.jpg b/content/identity/prevent-credential-stuffing-attacks/prevent-credential-stuffing-attacks.jpg
deleted file mode 100644
index 856ec4c8a..000000000
Binary files a/content/identity/prevent-credential-stuffing-attacks/prevent-credential-stuffing-attacks.jpg and /dev/null differ
diff --git a/content/identity/prevent-credential-stuffing-attacks/prevent-credential-stuffing-attacks.webp b/content/identity/prevent-credential-stuffing-attacks/prevent-credential-stuffing-attacks.webp
new file mode 100644
index 000000000..f4ac69d65
Binary files /dev/null and b/content/identity/prevent-credential-stuffing-attacks/prevent-credential-stuffing-attacks.webp differ
diff --git a/content/identity/privacy-compliance/index.md b/content/identity/privacy-compliance/index.md
index 6b18ac2e2..330a3d614 100644
--- a/content/identity/privacy-compliance/index.md
+++ b/content/identity/privacy-compliance/index.md
@@ -1,7 +1,7 @@
---
title: "What is privacy compliance and why is it so important?"
date: "2021-03-31"
-coverImage: "privacy-compliance-cover.jpg"
+coverImage: "privacy-compliance-cover.webp"
tags: ["data privacy","compliance","cx"]
author: "Vishal Sharma"
description: "Privacy compliance is the line between the legal and the illegal. Such regulations help protect consumers in different countries by ensuring data is handled appropriately. Another reason why organizations must comply is to avoid heavy fines."
@@ -15,7 +15,7 @@ For those who don't know what privacy compliance is—it's an important data sec
Here are the stats showcasing total data breaches and exposed records in the US alone from 2005-2020.
-
+
Source: [Statista](https://www.statista.com/statistics/273550/data-breaches-recorded-in-the-united-states-by-number-of-breaches-and-records-exposed/)
@@ -68,7 +68,7 @@ DSAR (Data Subject Access Requests) is a request by an employee or a consumer to
The below-mentioned stats depict the submission of Data Subject Access Requests in the UK in 2020.
-
+
Source: [Statista](https://www.statista.com/statistics/1177143/submitters-of-data-subject-access-requests-uk/)
@@ -122,7 +122,7 @@ Our platform ensures you remain compliant with GDPR and stay ahead of your compe
Need help in getting compliance-ready? [Reach us](https://www.loginradius.com/contact-sales/) for a Free Consultation.
-[](https://www.loginradius.com/resource/privacy-policy-management-datasheet)
+[](https://www.loginradius.com/resource/privacy-policy-management-datasheet)
## Conclusion
@@ -134,4 +134,4 @@ Any security breach leading to personal data theft of consumers could negatively
As discussed earlier, businesses must seek professional help to ensure compliance to stay ahead of the curve.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=privacy-compliance)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=privacy-compliance)
diff --git a/content/identity/privacy-compliance/privacy-compliance-1.png b/content/identity/privacy-compliance/privacy-compliance-1.png
deleted file mode 100644
index f93c03a7a..000000000
Binary files a/content/identity/privacy-compliance/privacy-compliance-1.png and /dev/null differ
diff --git a/content/identity/privacy-compliance/privacy-compliance-1.webp b/content/identity/privacy-compliance/privacy-compliance-1.webp
new file mode 100644
index 000000000..b03e986dc
Binary files /dev/null and b/content/identity/privacy-compliance/privacy-compliance-1.webp differ
diff --git a/content/identity/privacy-compliance/privacy-compliance-2.png b/content/identity/privacy-compliance/privacy-compliance-2.png
deleted file mode 100644
index 51c8b2806..000000000
Binary files a/content/identity/privacy-compliance/privacy-compliance-2.png and /dev/null differ
diff --git a/content/identity/privacy-compliance/privacy-compliance-2.webp b/content/identity/privacy-compliance/privacy-compliance-2.webp
new file mode 100644
index 000000000..ee167aaee
Binary files /dev/null and b/content/identity/privacy-compliance/privacy-compliance-2.webp differ
diff --git a/content/identity/privacy-compliance/privacy-compliance-cover.jpg b/content/identity/privacy-compliance/privacy-compliance-cover.jpg
deleted file mode 100644
index 5a86ebd1a..000000000
Binary files a/content/identity/privacy-compliance/privacy-compliance-cover.jpg and /dev/null differ
diff --git a/content/identity/privacy-compliance/privacy-compliance-cover.webp b/content/identity/privacy-compliance/privacy-compliance-cover.webp
new file mode 100644
index 000000000..0c0a72acd
Binary files /dev/null and b/content/identity/privacy-compliance/privacy-compliance-cover.webp differ
diff --git a/content/identity/privacy-compliance/privacy-policy-management-datasheet.png b/content/identity/privacy-compliance/privacy-policy-management-datasheet.png
deleted file mode 100644
index e738ae27a..000000000
Binary files a/content/identity/privacy-compliance/privacy-policy-management-datasheet.png and /dev/null differ
diff --git a/content/identity/privacy-compliance/privacy-policy-management-datasheet.webp b/content/identity/privacy-compliance/privacy-policy-management-datasheet.webp
new file mode 100644
index 000000000..eb8ed83dc
Binary files /dev/null and b/content/identity/privacy-compliance/privacy-policy-management-datasheet.webp differ
diff --git a/content/identity/privacy-data-security-retail/DS-retail-and-ecommerce.png b/content/identity/privacy-data-security-retail/DS-retail-and-ecommerce.png
deleted file mode 100644
index b6c1daad3..000000000
Binary files a/content/identity/privacy-data-security-retail/DS-retail-and-ecommerce.png and /dev/null differ
diff --git a/content/identity/privacy-data-security-retail/DS-retail-and-ecommerce.webp b/content/identity/privacy-data-security-retail/DS-retail-and-ecommerce.webp
new file mode 100644
index 000000000..3e81105a6
Binary files /dev/null and b/content/identity/privacy-data-security-retail/DS-retail-and-ecommerce.webp differ
diff --git a/content/identity/privacy-data-security-retail/index.md b/content/identity/privacy-data-security-retail/index.md
index 33bc118a6..2fe62bdb3 100644
--- a/content/identity/privacy-data-security-retail/index.md
+++ b/content/identity/privacy-data-security-retail/index.md
@@ -1,7 +1,7 @@
---
title: "How Retailers Can Balance Privacy While Foiling Thieves"
date: "2023-09-27"
-coverImage: "privacy-balancing.jpg"
+coverImage: "privacy-balancing.webp"
tags: ["data privacy","compliance","data security","ciam solutions","cx"]
author: "Jackson Maven"
description: "In the world of retail, finding the balance between privacy and security is paramount. This delicate equilibrium ensures compliance with evolving regulations and builds trust and loyalty among customers. By embracing modern technologies like passwordless authentication and robust data governance, retailers can safeguard privacy while enhancing the customer experience."
@@ -30,7 +30,7 @@ Policymakers must adjust their strategy to cater to their business model and vul
Meanwhile, an ecommerce site would revoke employee ID access to reduce phantom accounts opening vulnerabilities to hackers.
-[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
+[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)
## Why Is Privacy Important to Retailers?
@@ -76,4 +76,4 @@ Modern measures such as passwordless authentication, cloud-based security, and f
In some ways, they enhance it–improving access to personal accounts and the ability to maintain control over their shopping experience. Similarly, these measures help retailers comply with state and national laws, preventing financial loss through fines or breaches.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=privacy-data-security-retail)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=privacy-data-security-retail)
diff --git a/content/identity/privacy-data-security-retail/privacy-balancing.jpg b/content/identity/privacy-data-security-retail/privacy-balancing.jpg
deleted file mode 100644
index 3b5ba8952..000000000
Binary files a/content/identity/privacy-data-security-retail/privacy-balancing.jpg and /dev/null differ
diff --git a/content/identity/privacy-data-security-retail/privacy-balancing.webp b/content/identity/privacy-data-security-retail/privacy-balancing.webp
new file mode 100644
index 000000000..4a9aa45fc
Binary files /dev/null and b/content/identity/privacy-data-security-retail/privacy-balancing.webp differ
diff --git a/content/identity/privacy-policy-management/index.md b/content/identity/privacy-policy-management/index.md
index 1c1b83470..a35803c17 100644
--- a/content/identity/privacy-policy-management/index.md
+++ b/content/identity/privacy-policy-management/index.md
@@ -1,7 +1,7 @@
---
title: "Announcement: LoginRadius Embraces Privacy Policy Management Amid Heightened Regulatory Updates"
date: "2020-12-16"
-coverImage: "privacy-policy-management.png"
+coverImage: "privacy-policy-management.webp"
tags: ["compliance","data privacy","data security","cx"]
author: "Kundan Singh"
description: "Our newly introduced Privacy Policy Management acts as the central place where companies retain versions of their privacy policy, inform customers when it changes, or get new versions adopted by them."
@@ -39,7 +39,7 @@ As the global compliance and data protection landscape continue to evolve, Login
* **Timestamps **- Businesses can set and manage the date and time from when a privacy policy version will be effective. They can set the schedule in advance, and the consumers are notified about the new version with a message of their choice to ensure personalization.
* **Flow Type **- Businesses can choose whether notifying the consumers about the privacy policy change is enough or [consumers should provide acceptance](https://www.loginradius.com/blog/identity/2020/06/consumer-data-privacy-security/) on the same. LoginRadius handles the notification or the acceptance process on their behalf.
-[](https://www.loginradius.com/resource/privacy-policy-management-datasheet)
+[](https://www.loginradius.com/resource/privacy-policy-management-datasheet)
## Implementation and Deployment
@@ -56,4 +56,4 @@ LoginRadius supports the following implementation and deployment methods for Pri
Businesses cannot escape from maintaining privacy policy versions and workflows for their consumers. Looking forward, LoginRadius' Privacy Policy Management will effortlessly ensure a holistic insight into privacy policies where consumers are notified about new updates, everytime.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=privacy-policy-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=privacy-policy-management)
diff --git a/content/identity/privacy-policy-management/privacy-policy-management-datasheet.png b/content/identity/privacy-policy-management/privacy-policy-management-datasheet.png
deleted file mode 100644
index e738ae27a..000000000
Binary files a/content/identity/privacy-policy-management/privacy-policy-management-datasheet.png and /dev/null differ
diff --git a/content/identity/privacy-policy-management/privacy-policy-management-datasheet.webp b/content/identity/privacy-policy-management/privacy-policy-management-datasheet.webp
new file mode 100644
index 000000000..eb8ed83dc
Binary files /dev/null and b/content/identity/privacy-policy-management/privacy-policy-management-datasheet.webp differ
diff --git a/content/identity/privacy-policy-management/privacy-policy-management.png b/content/identity/privacy-policy-management/privacy-policy-management.png
deleted file mode 100644
index ac33c3d6c..000000000
Binary files a/content/identity/privacy-policy-management/privacy-policy-management.png and /dev/null differ
diff --git a/content/identity/privacy-policy-management/privacy-policy-management.webp b/content/identity/privacy-policy-management/privacy-policy-management.webp
new file mode 100644
index 000000000..649616e7c
Binary files /dev/null and b/content/identity/privacy-policy-management/privacy-policy-management.webp differ
diff --git a/content/identity/progressive-disclosure-user-onboarding/index.md b/content/identity/progressive-disclosure-user-onboarding/index.md
index d2f0902b2..13f6bb675 100644
--- a/content/identity/progressive-disclosure-user-onboarding/index.md
+++ b/content/identity/progressive-disclosure-user-onboarding/index.md
@@ -1,7 +1,7 @@
---
title: "How Progressive Disclosure Makes Your User's Onboarding Easy"
date: "2021-08-18"
-coverImage: "progressive-disclosure-user-onboarding-cover.jpg"
+coverImage: "progressive-disclosure-user-onboarding-cover.webp"
tags: ["user onboarding","data security","progressive profiling"]
author: "Vishal Sharma"
description: "Progressive disclosure helps businesses portray essential information initially and then gradually uncover the rest of the features that ensure users aren’t overburdened and that their purpose is solved. This post helps businesses understand the importance of progressive disclosure and progressive profiling that work harmoniously to enhance conversions."
@@ -94,4 +94,4 @@ LoginRadius’ Progressive profiling is helping thousands of businesses to strea
If you wish to see the future of progressive profiling and progressive disclosure in action, [contact us](https://www.loginradius.com/contact-sales/) now.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=progressive-disclosure-user-onboarding)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=progressive-disclosure-user-onboarding)
\ No newline at end of file
diff --git a/content/identity/progressive-disclosure-user-onboarding/progressive-disclosure-user-onboarding-cover.jpg b/content/identity/progressive-disclosure-user-onboarding/progressive-disclosure-user-onboarding-cover.jpg
deleted file mode 100644
index e12746b70..000000000
Binary files a/content/identity/progressive-disclosure-user-onboarding/progressive-disclosure-user-onboarding-cover.jpg and /dev/null differ
diff --git a/content/identity/progressive-disclosure-user-onboarding/progressive-disclosure-user-onboarding-cover.webp b/content/identity/progressive-disclosure-user-onboarding/progressive-disclosure-user-onboarding-cover.webp
new file mode 100644
index 000000000..9dd585539
Binary files /dev/null and b/content/identity/progressive-disclosure-user-onboarding/progressive-disclosure-user-onboarding-cover.webp differ
diff --git a/content/identity/progressive-profiling/index.md b/content/identity/progressive-profiling/index.md
index 2c05114a2..fccd85cdc 100644
--- a/content/identity/progressive-profiling/index.md
+++ b/content/identity/progressive-profiling/index.md
@@ -1,7 +1,7 @@
---
title: "What is Progressive Profiling and How it Works?"
date: "2021-04-08"
-coverImage: "progressive-profiling-cover.jpg"
+coverImage: "progressive-profiling-cover.webp"
tags: ["progressive profiling","ciam platform","cx"]
author: "Shachindra Saxena"
description: "Progressive profiling is emerging as an effective way of cementing the trust gap between the company and its consumers. It is a systematic approach to collecting critical information through smart forms that ask questions intended to guide prospective consumers across the sales funnel. This article details how progressive profiling works and its benefits for your enterprise."
@@ -113,4 +113,4 @@ Progressive profiling allows companies to collect critical consumer information
As we saw, there are numerous ways of collecting data, including questionnaires, social media profiles, and tracking the consumer's digital footprints. Progressive profiling is emerging as an effective way of cementing the trust gap between the company and its consumers and [forming robust and evergreen client relationships](https://www.loginradius.com/blog/fuel/2021/02/customer-relationship-business/).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=progressive-profiling)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=progressive-profiling)
diff --git a/content/identity/progressive-profiling/progressive-profiling-cover.jpg b/content/identity/progressive-profiling/progressive-profiling-cover.jpg
deleted file mode 100644
index 4f5d99cd0..000000000
Binary files a/content/identity/progressive-profiling/progressive-profiling-cover.jpg and /dev/null differ
diff --git a/content/identity/progressive-profiling/progressive-profiling-cover.webp b/content/identity/progressive-profiling/progressive-profiling-cover.webp
new file mode 100644
index 000000000..4f191df26
Binary files /dev/null and b/content/identity/progressive-profiling/progressive-profiling-cover.webp differ
diff --git a/content/identity/pros-cons-open-source-project/index.md b/content/identity/pros-cons-open-source-project/index.md
index 945ca1fb3..582928325 100644
--- a/content/identity/pros-cons-open-source-project/index.md
+++ b/content/identity/pros-cons-open-source-project/index.md
@@ -1,7 +1,7 @@
---
title: "Why You Should Use Open Source Project For Your Business"
date: "2021-11-26"
-coverImage: "open-source.jpg"
+coverImage: "open-source.webp"
tags: ["security"]
featured: false
author: "Jitender Agarwal"
@@ -115,4 +115,4 @@ Experts recommend not to leverage the open-source project in the places where:
Enterprises should carefully analyze and assess their suitability while adopting open source and be cautious when implementing the project.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pros-cons-open-source-project)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pros-cons-open-source-project)
diff --git a/content/identity/pros-cons-open-source-project/open-source.jpg b/content/identity/pros-cons-open-source-project/open-source.jpg
deleted file mode 100644
index b4799cb3d..000000000
Binary files a/content/identity/pros-cons-open-source-project/open-source.jpg and /dev/null differ
diff --git a/content/identity/pros-cons-open-source-project/open-source.webp b/content/identity/pros-cons-open-source-project/open-source.webp
new file mode 100644
index 000000000..daf17c1d2
Binary files /dev/null and b/content/identity/pros-cons-open-source-project/open-source.webp differ
diff --git a/content/identity/pros-cons-reusable-digital-identity/WP-reimagining.png b/content/identity/pros-cons-reusable-digital-identity/WP-reimagining.png
deleted file mode 100644
index 8c6630f20..000000000
Binary files a/content/identity/pros-cons-reusable-digital-identity/WP-reimagining.png and /dev/null differ
diff --git a/content/identity/pros-cons-reusable-digital-identity/WP-reimagining.webp b/content/identity/pros-cons-reusable-digital-identity/WP-reimagining.webp
new file mode 100644
index 000000000..bdcd988fe
Binary files /dev/null and b/content/identity/pros-cons-reusable-digital-identity/WP-reimagining.webp differ
diff --git a/content/identity/pros-cons-reusable-digital-identity/digital-id-wp.png b/content/identity/pros-cons-reusable-digital-identity/digital-id-wp.png
deleted file mode 100644
index 1338927e7..000000000
Binary files a/content/identity/pros-cons-reusable-digital-identity/digital-id-wp.png and /dev/null differ
diff --git a/content/identity/pros-cons-reusable-digital-identity/digital-id-wp.webp b/content/identity/pros-cons-reusable-digital-identity/digital-id-wp.webp
new file mode 100644
index 000000000..468202b9e
Binary files /dev/null and b/content/identity/pros-cons-reusable-digital-identity/digital-id-wp.webp differ
diff --git a/content/identity/pros-cons-reusable-digital-identity/index.md b/content/identity/pros-cons-reusable-digital-identity/index.md
index b0bb5facd..e4f0900b5 100644
--- a/content/identity/pros-cons-reusable-digital-identity/index.md
+++ b/content/identity/pros-cons-reusable-digital-identity/index.md
@@ -1,7 +1,7 @@
---
title: "The Pros & Cons of Reusable Digital Identity: What You Need To Know"
date: "2022-06-14"
-coverImage: "reusable-id.jpg"
+coverImage: "reusable-id.webp"
tags: ["digital identity management","compliance","cx"]
author: "Alex Williams"
description: "Keeping track of multiple digital identities is cumbersome and may lead users to adopt risky practices (like duplicating passwords) just so they can remember them. A better way to deal with it is reusable digital identities. And as the technology matures, the upsides will only increase."
@@ -63,7 +63,7 @@ Making reusable digital IDs generally accessible poses quite a challenge. Many p
But technology is only one side of the issue. Verifying IDs also remains problematic, as the UK experienced when launching its ID verification platform. The UK government projected a 90% verification success rate but managed only about half that after four years. Organizations must apply reasonable verification standards to drive adoption.
-[](https://www.loginradius.com/resource/digital-identity-future-whitepaper)
+[](https://www.loginradius.com/resource/digital-identity-future-whitepaper)
* Security concerns
@@ -80,4 +80,4 @@ Over the years, consumers have grown skeptical about effective interoperability
Consumers, businesses, and governments alike need an easier way to deal with ID verification. Reusable digital identities are the next stage in the [evolution of authentication](https://www.loginradius.com/blog/growth/authentication-evolution-to-passwordless/), providing a better customer experience and simplifying business compliance efforts as well as overall ID administration needs. Their use will grow substantially in the coming years to everyone’s benefit.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pros-cons-reusable-digital-identity)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pros-cons-reusable-digital-identity)
diff --git a/content/identity/pros-cons-reusable-digital-identity/reusable-id.jpg b/content/identity/pros-cons-reusable-digital-identity/reusable-id.jpg
deleted file mode 100644
index 6b8350e38..000000000
Binary files a/content/identity/pros-cons-reusable-digital-identity/reusable-id.jpg and /dev/null differ
diff --git a/content/identity/pros-cons-reusable-digital-identity/reusable-id.webp b/content/identity/pros-cons-reusable-digital-identity/reusable-id.webp
new file mode 100644
index 000000000..8771b1727
Binary files /dev/null and b/content/identity/pros-cons-reusable-digital-identity/reusable-id.webp differ
diff --git a/content/identity/pros-cons-token-authentication/index.md b/content/identity/pros-cons-token-authentication/index.md
index 905223a9c..a17a53474 100644
--- a/content/identity/pros-cons-token-authentication/index.md
+++ b/content/identity/pros-cons-token-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "What is a Token? What are its Pros and Cons?"
date: "2021-07-29"
-coverImage: "pros-cons-token-authentication-cover.jpg"
+coverImage: "pros-cons-token-authentication-cover.webp"
tags: ["token authentication","authorization","cx"]
author: "Rakesh Soni"
description: "Tokens are widely used to provide authorization and authentication to users when they access a website or a mobile application. This post covers detailed information about the use of tokens along with its advantages and disadvantages."
@@ -114,4 +114,4 @@ Although JWT can be the right option in most scenarios if implemented correctly
However, one should consider the above-mentioned aspects before relying on a token for [authentication and authorization](https://www.loginradius.com/blog/identity/authentication-vs-authorization-infographic/).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pros-cons-token-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pros-cons-token-authentication)
diff --git a/content/identity/pros-cons-token-authentication/pros-cons-token-authentication-cover.jpg b/content/identity/pros-cons-token-authentication/pros-cons-token-authentication-cover.jpg
deleted file mode 100644
index 6f065d291..000000000
Binary files a/content/identity/pros-cons-token-authentication/pros-cons-token-authentication-cover.jpg and /dev/null differ
diff --git a/content/identity/pros-cons-token-authentication/pros-cons-token-authentication-cover.webp b/content/identity/pros-cons-token-authentication/pros-cons-token-authentication-cover.webp
new file mode 100644
index 000000000..a0d78abf3
Binary files /dev/null and b/content/identity/pros-cons-token-authentication/pros-cons-token-authentication-cover.webp differ
diff --git a/content/identity/public-cloud-risks-organization-ready/WP-sero-trust-1.png b/content/identity/public-cloud-risks-organization-ready/WP-sero-trust-1.png
deleted file mode 100644
index 404532996..000000000
Binary files a/content/identity/public-cloud-risks-organization-ready/WP-sero-trust-1.png and /dev/null differ
diff --git a/content/identity/public-cloud-risks-organization-ready/WP-sero-trust-1.webp b/content/identity/public-cloud-risks-organization-ready/WP-sero-trust-1.webp
new file mode 100644
index 000000000..832cb0156
Binary files /dev/null and b/content/identity/public-cloud-risks-organization-ready/WP-sero-trust-1.webp differ
diff --git a/content/identity/public-cloud-risks-organization-ready/index.md b/content/identity/public-cloud-risks-organization-ready/index.md
index 7654cd498..3fe1a490a 100644
--- a/content/identity/public-cloud-risks-organization-ready/index.md
+++ b/content/identity/public-cloud-risks-organization-ready/index.md
@@ -1,7 +1,7 @@
---
title: "Public Cloud Risks - Is Your Organization Prepared for Cloud Threats?"
date: "2022-09-22"
-coverImage: "public-cloud-risks.jpg"
+coverImage: "public-cloud-risks.webp"
tags: ["cloud security","data privacy","mfa","zero trust"]
author: "Rakesh Soni"
description: "The rapid adoption of the public and hybrid cloud doesn’t necessarily mean that sensitive information stored on remote servers or shared clouds is secure. This blog highlights the risks associated with the public cloud and how businesses can take timely action to avoid the risks."
@@ -51,7 +51,7 @@ So, how should an organization protect the privacy and security of its consumer
The zero trust model believes no user can be trusted, and verification is no longer an option. It supports the theory that all users must be authenticated, authorized, and regularly verified to ensure they can be trusted with the data in any business hierarchy.
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
### #3. Availability risks.
@@ -73,4 +73,4 @@ Businesses considering leveraging the private cloud shouldn’t overlook the sec
Enterprises thinking about accelerating business growth through cloud adoption shouldn't miss the aspects above.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=public-cloud-risks-organization-ready)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=public-cloud-risks-organization-ready)
diff --git a/content/identity/public-cloud-risks-organization-ready/public-cloud-risks.jpg b/content/identity/public-cloud-risks-organization-ready/public-cloud-risks.jpg
deleted file mode 100644
index ba421687b..000000000
Binary files a/content/identity/public-cloud-risks-organization-ready/public-cloud-risks.jpg and /dev/null differ
diff --git a/content/identity/public-cloud-risks-organization-ready/public-cloud-risks.webp b/content/identity/public-cloud-risks-organization-ready/public-cloud-risks.webp
new file mode 100644
index 000000000..d62210d4a
Binary files /dev/null and b/content/identity/public-cloud-risks-organization-ready/public-cloud-risks.webp differ
diff --git a/content/identity/public-cloud-risks-organization-ready/zero-trsut.png b/content/identity/public-cloud-risks-organization-ready/zero-trsut.png
deleted file mode 100644
index 3e6b81ee6..000000000
Binary files a/content/identity/public-cloud-risks-organization-ready/zero-trsut.png and /dev/null differ
diff --git a/content/identity/public-cloud-risks-organization-ready/zero-trsut.webp b/content/identity/public-cloud-risks-organization-ready/zero-trsut.webp
new file mode 100644
index 000000000..2f7c01062
Binary files /dev/null and b/content/identity/public-cloud-risks-organization-ready/zero-trsut.webp differ
diff --git a/content/identity/push-notification-authentication/index.md b/content/identity/push-notification-authentication/index.md
index f33bb81fd..313f413c0 100644
--- a/content/identity/push-notification-authentication/index.md
+++ b/content/identity/push-notification-authentication/index.md
@@ -45,7 +45,7 @@ Push authentication follows a straightforward and user-friendly process:
* **Phishing Resistance:** Unlike traditional authentication methods, push authentication minimizes the risk of phishing attacks by eliminating the need to enter credentials.
* **Cost-Effective:** Reduces reliance on SMS-based OTPs, lowering operational costs and improving authentication efficiency.
-[](https://www.loginradius.com/resource/datasheet/push-notification-mfa)
+[](https://www.loginradius.com/resource/datasheet/push-notification-mfa)
### Challenges of Push Notification Authentication
@@ -171,4 +171,4 @@ Yes, push notifications are more secure and user-friendly than OTPs, as they eli
To enable push notifications, Navigate to [“Security” settings](https://accounts.loginradius.com/auth.aspx?return_url=https://console.loginradius.com/login&action=register) in your LoginRadius console and choose and enable multi-factor authentication. Choose Push Notification as an MFA Factor: Select “Push Notifications” as an MFA factor to integrate push authentication into your application.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=push-notification-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=push-notification-authentication)
\ No newline at end of file
diff --git a/content/identity/push-notification-authentication/push-notification-mfa-free-download.png b/content/identity/push-notification-authentication/push-notification-mfa-free-download.png
deleted file mode 100644
index 346b76a78..000000000
Binary files a/content/identity/push-notification-authentication/push-notification-mfa-free-download.png and /dev/null differ
diff --git a/content/identity/push-notification-authentication/push-notification-mfa-free-download.webp b/content/identity/push-notification-authentication/push-notification-mfa-free-download.webp
new file mode 100644
index 000000000..e940feeff
Binary files /dev/null and b/content/identity/push-notification-authentication/push-notification-mfa-free-download.webp differ
diff --git a/content/identity/rbac-vs-abac/index.md b/content/identity/rbac-vs-abac/index.md
index 063a66ea9..1c92fb53e 100644
--- a/content/identity/rbac-vs-abac/index.md
+++ b/content/identity/rbac-vs-abac/index.md
@@ -1,7 +1,7 @@
---
title: "RBAC vs ABAC: A Developer’s Guide to Choosing the Right Fit"
date: "2025-01-13"
-coverImage: "lock-business-background-security-concept-3d-rendering.jpg"
+coverImage: "lock-business-background-security-concept-3d-rendering.webp"
tags: ["RBAC","ABAC"]
author: "Kundan Singh"
description: "RBAC vs ABAC: A detailed guide for developers to understand role-based and attribute-based access control, their differences, and the right fit for your projects."
diff --git a/content/identity/rbac-vs-abac/lock-business-background-security-concept-3d-rendering.jpg b/content/identity/rbac-vs-abac/lock-business-background-security-concept-3d-rendering.jpg
deleted file mode 100644
index dbd6259b3..000000000
Binary files a/content/identity/rbac-vs-abac/lock-business-background-security-concept-3d-rendering.jpg and /dev/null differ
diff --git a/content/identity/rbac-vs-abac/lock-business-background-security-concept-3d-rendering.webp b/content/identity/rbac-vs-abac/lock-business-background-security-concept-3d-rendering.webp
new file mode 100644
index 000000000..a21eda3cb
Binary files /dev/null and b/content/identity/rbac-vs-abac/lock-business-background-security-concept-3d-rendering.webp differ
diff --git a/content/identity/real-time-techniques-detect-phishing-attacks/WP-bot-attacks.png b/content/identity/real-time-techniques-detect-phishing-attacks/WP-bot-attacks.png
deleted file mode 100644
index fa1f0af30..000000000
Binary files a/content/identity/real-time-techniques-detect-phishing-attacks/WP-bot-attacks.png and /dev/null differ
diff --git a/content/identity/real-time-techniques-detect-phishing-attacks/WP-bot-attacks.webp b/content/identity/real-time-techniques-detect-phishing-attacks/WP-bot-attacks.webp
new file mode 100644
index 000000000..094822f16
Binary files /dev/null and b/content/identity/real-time-techniques-detect-phishing-attacks/WP-bot-attacks.webp differ
diff --git a/content/identity/real-time-techniques-detect-phishing-attacks/index.md b/content/identity/real-time-techniques-detect-phishing-attacks/index.md
index d530eb60a..1db9484ba 100644
--- a/content/identity/real-time-techniques-detect-phishing-attacks/index.md
+++ b/content/identity/real-time-techniques-detect-phishing-attacks/index.md
@@ -1,7 +1,7 @@
---
title: "Enhancing Security: Leveraging 5 Real-Time Techniques to Detect Phishing Attacks"
date: "2023-08-07"
-coverImage: "phishing-attacks.jpg"
+coverImage: "phishing-attacks.webp"
tags: ["phishing attacks", "data security","cx"]
author: "Alok Patidar"
description: "Enhance your security with real-time techniques for detecting and preventing phishing attacks. Discover how behavior analysis, machine learning, URL reputation assessment, and collaboration empower proactive defense against real-time phishing threats."
@@ -48,7 +48,7 @@ Real-time detection systems employ URL and domain reputation analysis to identif
Additionally, real-time systems can employ machine learning models to analyze the structure of URLs, looking for telltale signs of phishing attempts, such as slight misspellings or extra characters in domain names. By scrutinizing URLs in real time, security systems can thwart phishing attacks before users unknowingly interact with dangerous websites.
-[](https://www.loginradius.com/resource/prevent-bot-attacks-with-loginradius/)
+[](https://www.loginradius.com/resource/prevent-bot-attacks-with-loginradius/)
### 4. Email and Content Analysis
@@ -72,4 +72,4 @@ As real-time phishing attacks continue to pose a significant threat, adopting pr
Prioritizing real-time detection empowers individuals and organizations to stay one step ahead of cybercriminals, safeguarding their valuable information and maintaining a robust defense against real-time phishing attacks.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=real-time-techniques-detect-phishing-attacks)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=real-time-techniques-detect-phishing-attacks)
\ No newline at end of file
diff --git a/content/identity/real-time-techniques-detect-phishing-attacks/phishing-attacks.jpg b/content/identity/real-time-techniques-detect-phishing-attacks/phishing-attacks.jpg
deleted file mode 100644
index f449fb8f8..000000000
Binary files a/content/identity/real-time-techniques-detect-phishing-attacks/phishing-attacks.jpg and /dev/null differ
diff --git a/content/identity/real-time-techniques-detect-phishing-attacks/phishing-attacks.webp b/content/identity/real-time-techniques-detect-phishing-attacks/phishing-attacks.webp
new file mode 100644
index 000000000..f928fd0d8
Binary files /dev/null and b/content/identity/real-time-techniques-detect-phishing-attacks/phishing-attacks.webp differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/1-Content-Asset-social-API.png b/content/identity/reconsidering-social-login-security-privacy-angle/1-Content-Asset-social-API.png
deleted file mode 100644
index d2fe5ecea..000000000
Binary files a/content/identity/reconsidering-social-login-security-privacy-angle/1-Content-Asset-social-API.png and /dev/null differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/1-Content-Asset-social-API.webp b/content/identity/reconsidering-social-login-security-privacy-angle/1-Content-Asset-social-API.webp
new file mode 100644
index 000000000..fafc3f0ff
Binary files /dev/null and b/content/identity/reconsidering-social-login-security-privacy-angle/1-Content-Asset-social-API.webp differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/CTA-Graphics-for-Blogs-V02.01-14-1024x310.png b/content/identity/reconsidering-social-login-security-privacy-angle/CTA-Graphics-for-Blogs-V02.01-14-1024x310.png
deleted file mode 100644
index e4fb634c2..000000000
Binary files a/content/identity/reconsidering-social-login-security-privacy-angle/CTA-Graphics-for-Blogs-V02.01-14-1024x310.png and /dev/null differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/CTA-Graphics-for-Blogs-V02.01-14-1024x310.webp b/content/identity/reconsidering-social-login-security-privacy-angle/CTA-Graphics-for-Blogs-V02.01-14-1024x310.webp
new file mode 100644
index 000000000..f431ae35a
Binary files /dev/null and b/content/identity/reconsidering-social-login-security-privacy-angle/CTA-Graphics-for-Blogs-V02.01-14-1024x310.webp differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/airbnb_social_login_2012.png b/content/identity/reconsidering-social-login-security-privacy-angle/airbnb_social_login_2012.png
deleted file mode 100644
index 47e947496..000000000
Binary files a/content/identity/reconsidering-social-login-security-privacy-angle/airbnb_social_login_2012.png and /dev/null differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/airbnb_social_login_2012.webp b/content/identity/reconsidering-social-login-security-privacy-angle/airbnb_social_login_2012.webp
new file mode 100644
index 000000000..1f622149d
Binary files /dev/null and b/content/identity/reconsidering-social-login-security-privacy-angle/airbnb_social_login_2012.webp differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/index.md b/content/identity/reconsidering-social-login-security-privacy-angle/index.md
index 75c9e77ee..0358ca86b 100644
--- a/content/identity/reconsidering-social-login-security-privacy-angle/index.md
+++ b/content/identity/reconsidering-social-login-security-privacy-angle/index.md
@@ -1,7 +1,7 @@
---
title: "Reconsidering Social Login from a Security and Privacy Angle"
date: "2018-11-20"
-coverImage: "reconsidering-social-login.jpg"
+coverImage: "reconsidering-social-login.webp"
tags: ["social login","data security","cx"]
author: "Rakesh Soni"
description: "Login strategies can come and go, but the identity of the customer is here to stay. In the wake of two major exposures of data on Facebook and Google+ exacerbated by social login, the repercussions for B2C companies can be addressed. Are social login privacy and security threats still worth the convenience? And what steps do businesses take to safeguard consumer data and preserve public confidence? Let 's begin with a bit of history."
@@ -21,13 +21,13 @@ Let’s start with some history.
Facebook came out with its first identity service, Facebook Connect, in 2008. Users started logging in with Twitter in 2009 and with LinkedIn in 2010. Google+ launched in 2011 and added its social login to the mix.
-
+
**Throwback to the Airbnb login page in March 2012**
LoginRadius got its start in 2012 by giving businesses a simple way to implement one or more social login methods on their digital properties. We saw a significant increase in sign-up rates for B2C websites with low-risk accounts that used our social login tools. Small, medium, and mid-market businesses were quick to adopt the LoginRadius solution.
-
+
**LoginRadius supports 40+ social login providers**
@@ -47,7 +47,7 @@ LoginRadius saw this shift coming. That’s why our company isn’t called Socia
### We knew that social login would never be sufficient for the identity needs of B2C enterprises.
-
+
**From the beginning, LoginRadius had a complete identity product roadmap that started with social login and progressed to a full customer identity platform.**
@@ -65,7 +65,7 @@ Most of our current customers offer social login for ease of customer experience
### LoginRadius can make social login more secure for businesses.
-
+
Until now, the market has mainly talked about the advantages of social login but hasn’t been as vocal about the risks. LoginRadius is taking a leadership role in advocating for social login practices that protect businesses and their customers better. Our experience facilitating social login for thousands of companies and hundreds of millions of customers over six years has given us expert insight on this login method.
@@ -73,7 +73,7 @@ Until now, the market has mainly talked about the advantages of social login but
Our white paper, [Social Login Reconsidered](https://www.loginradius.com/resource/social-login-reconsidered/), puts forward four use cases for social login. These use cases cut the risks of illegitimate access and exposure while maintaining the ease of customer experience.
-[](https://www.loginradius.com/resource/social-login-reconsidered/)
+[](https://www.loginradius.com/resource/social-login-reconsidered/)
The right use case for your business depends on the business model, the target audience, and the level of risk for customer accounts.
@@ -84,4 +84,4 @@ Our mission is to empower businesses to provide secure, delightful experiences f
And we will continue to develop and revisit our entire solution, as we have done for social login, to make sure we are fulfilling that mission.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=reconsidering-social-login-security-privacy-angle)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=reconsidering-social-login-security-privacy-angle)
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/rawpixel-1062883-unsplash.jpg b/content/identity/reconsidering-social-login-security-privacy-angle/rawpixel-1062883-unsplash.jpg
deleted file mode 100644
index c41ff0729..000000000
Binary files a/content/identity/reconsidering-social-login-security-privacy-angle/rawpixel-1062883-unsplash.jpg and /dev/null differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/rawpixel-1062883-unsplash.webp b/content/identity/reconsidering-social-login-security-privacy-angle/rawpixel-1062883-unsplash.webp
new file mode 100644
index 000000000..60c612b3d
Binary files /dev/null and b/content/identity/reconsidering-social-login-security-privacy-angle/rawpixel-1062883-unsplash.webp differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/reconsidering-social-login.jpg b/content/identity/reconsidering-social-login-security-privacy-angle/reconsidering-social-login.jpg
deleted file mode 100644
index e171d6123..000000000
Binary files a/content/identity/reconsidering-social-login-security-privacy-angle/reconsidering-social-login.jpg and /dev/null differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/reconsidering-social-login.webp b/content/identity/reconsidering-social-login-security-privacy-angle/reconsidering-social-login.webp
new file mode 100644
index 000000000..4c8f25400
Binary files /dev/null and b/content/identity/reconsidering-social-login-security-privacy-angle/reconsidering-social-login.webp differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/social-login-reconsidered.png b/content/identity/reconsidering-social-login-security-privacy-angle/social-login-reconsidered.png
deleted file mode 100644
index 412e2195c..000000000
Binary files a/content/identity/reconsidering-social-login-security-privacy-angle/social-login-reconsidered.png and /dev/null differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/social-login-reconsidered.webp b/content/identity/reconsidering-social-login-security-privacy-angle/social-login-reconsidered.webp
new file mode 100644
index 000000000..6e975bd35
Binary files /dev/null and b/content/identity/reconsidering-social-login-security-privacy-angle/social-login-reconsidered.webp differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/stephen-petrey-613428-unsplash.jpg b/content/identity/reconsidering-social-login-security-privacy-angle/stephen-petrey-613428-unsplash.jpg
deleted file mode 100644
index fc4b8e93a..000000000
Binary files a/content/identity/reconsidering-social-login-security-privacy-angle/stephen-petrey-613428-unsplash.jpg and /dev/null differ
diff --git a/content/identity/reconsidering-social-login-security-privacy-angle/stephen-petrey-613428-unsplash.webp b/content/identity/reconsidering-social-login-security-privacy-angle/stephen-petrey-613428-unsplash.webp
new file mode 100644
index 000000000..435c95b5d
Binary files /dev/null and b/content/identity/reconsidering-social-login-security-privacy-angle/stephen-petrey-613428-unsplash.webp differ
diff --git a/content/identity/rede-gazeta-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.png b/content/identity/rede-gazeta-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/rede-gazeta-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/rede-gazeta-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.webp b/content/identity/rede-gazeta-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/rede-gazeta-loginradius-customer-success-story/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/rede-gazeta-loginradius-customer-success-story/index.md b/content/identity/rede-gazeta-loginradius-customer-success-story/index.md
index a3bd72bcc..719738876 100644
--- a/content/identity/rede-gazeta-loginradius-customer-success-story/index.md
+++ b/content/identity/rede-gazeta-loginradius-customer-success-story/index.md
@@ -1,7 +1,7 @@
---
title: "Rede Gazeta, a LoginRadius Customer Success Story"
date: "2018-09-06"
-coverImage: "lr-and-rede-gazeta.jpg"
+coverImage: "lr-and-rede-gazeta.webp"
tags: ["media-and-publication"]
featured: false
author: "Karl Wittig"
@@ -10,7 +10,7 @@ metatitle: "Rede Gazeta | Customer Success Story | LoginRadius"
metadescription: "By implementing LoginRadius, Rede Gazeta now have an even better understanding of what their readers are interested in."
---
-
+
Founded in 1928, [Rede Gazeta](https://en.wikipedia.org/wiki/TV_Gazeta) started with one newspaper, A Gazeta. Throughout the years, it has grown into the largest communication network in the Espírito Santo region of Brazil. It has a network of 19 businesses that touches various forms of media outlets, including print newspapers, online media, editorial photography, radio stations, and broadcasting.
@@ -46,4 +46,4 @@ As one of the most important media corporations in Brazil, Rede Gazeta needs to
Rede Gazeta - LoginRadius Customer Success Story
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=rede-gazeta-loginradius-customer-success-story)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=rede-gazeta-loginradius-customer-success-story)
diff --git a/content/identity/rede-gazeta-loginradius-customer-success-story/logo_redegazeta-300x212.png b/content/identity/rede-gazeta-loginradius-customer-success-story/logo_redegazeta-300x212.png
deleted file mode 100644
index 39fa341df..000000000
Binary files a/content/identity/rede-gazeta-loginradius-customer-success-story/logo_redegazeta-300x212.png and /dev/null differ
diff --git a/content/identity/rede-gazeta-loginradius-customer-success-story/logo_redegazeta-300x212.webp b/content/identity/rede-gazeta-loginradius-customer-success-story/logo_redegazeta-300x212.webp
new file mode 100644
index 000000000..e33b75ba5
Binary files /dev/null and b/content/identity/rede-gazeta-loginradius-customer-success-story/logo_redegazeta-300x212.webp differ
diff --git a/content/identity/rede-gazeta-loginradius-customer-success-story/lr-and-rede-gazeta.jpg b/content/identity/rede-gazeta-loginradius-customer-success-story/lr-and-rede-gazeta.jpg
deleted file mode 100644
index 4b4d085fa..000000000
Binary files a/content/identity/rede-gazeta-loginradius-customer-success-story/lr-and-rede-gazeta.jpg and /dev/null differ
diff --git a/content/identity/rede-gazeta-loginradius-customer-success-story/lr-and-rede-gazeta.webp b/content/identity/rede-gazeta-loginradius-customer-success-story/lr-and-rede-gazeta.webp
new file mode 100644
index 000000000..ddc7fe6e3
Binary files /dev/null and b/content/identity/rede-gazeta-loginradius-customer-success-story/lr-and-rede-gazeta.webp differ
diff --git a/content/identity/reduce-attack-surface-online-business/WP-dig-trade-zone.png b/content/identity/reduce-attack-surface-online-business/WP-dig-trade-zone.png
deleted file mode 100644
index 31b7cc833..000000000
Binary files a/content/identity/reduce-attack-surface-online-business/WP-dig-trade-zone.png and /dev/null differ
diff --git a/content/identity/reduce-attack-surface-online-business/WP-dig-trade-zone.webp b/content/identity/reduce-attack-surface-online-business/WP-dig-trade-zone.webp
new file mode 100644
index 000000000..61229103e
Binary files /dev/null and b/content/identity/reduce-attack-surface-online-business/WP-dig-trade-zone.webp differ
diff --git a/content/identity/reduce-attack-surface-online-business/attack-surface.jpg b/content/identity/reduce-attack-surface-online-business/attack-surface.jpg
deleted file mode 100644
index 978f93826..000000000
Binary files a/content/identity/reduce-attack-surface-online-business/attack-surface.jpg and /dev/null differ
diff --git a/content/identity/reduce-attack-surface-online-business/attack-surface.webp b/content/identity/reduce-attack-surface-online-business/attack-surface.webp
new file mode 100644
index 000000000..470ba588c
Binary files /dev/null and b/content/identity/reduce-attack-surface-online-business/attack-surface.webp differ
diff --git a/content/identity/reduce-attack-surface-online-business/digital-trade-wp.png b/content/identity/reduce-attack-surface-online-business/digital-trade-wp.png
deleted file mode 100644
index 24d5add74..000000000
Binary files a/content/identity/reduce-attack-surface-online-business/digital-trade-wp.png and /dev/null differ
diff --git a/content/identity/reduce-attack-surface-online-business/digital-trade-wp.webp b/content/identity/reduce-attack-surface-online-business/digital-trade-wp.webp
new file mode 100644
index 000000000..cce7d892c
Binary files /dev/null and b/content/identity/reduce-attack-surface-online-business/digital-trade-wp.webp differ
diff --git a/content/identity/reduce-attack-surface-online-business/index.md b/content/identity/reduce-attack-surface-online-business/index.md
index 80fc90cd7..cc9669cff 100644
--- a/content/identity/reduce-attack-surface-online-business/index.md
+++ b/content/identity/reduce-attack-surface-online-business/index.md
@@ -1,7 +1,7 @@
---
title: "10 Tips From CIAM Experts to Reduce the Attack Surface of User Authentication"
date: "2021-11-30"
-coverImage: "attack-surface.jpg"
+coverImage: "attack-surface.webp"
tags: ["cybersecurity","user authentication","cx"]
author: "Navanita Devi"
description: "Companies are predominantly facing the challenge of securing their infrastructures from cyber threats. By analyzing and implementing the security measures mentioned in this blog, you can safeguard your company from cyber threats and help it leverage the benefit of a dispersed workforce."
@@ -51,7 +51,7 @@ The larger your attack surface, the more vulnerable you are to attacks. The firs
* Entry points
* Database users and permissions
-[](https://www.loginradius.com/resource/digital-trade-zone-threats-cybersecurity-whitepaper)
+[](https://www.loginradius.com/resource/digital-trade-zone-threats-cybersecurity-whitepaper)
## How to Reduce the Attack Surface of User Authentication
@@ -74,4 +74,4 @@ Today's digital world leaves no room for error. Companies across the globe look
By analyzing and implementing the security measures mentioned in this blog, you can safeguard your company from cyber threats and help it leverage the benefit of a dispersed workforce.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=reduce-attack-surface-online-business)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=reduce-attack-surface-online-business)
\ No newline at end of file
diff --git a/content/identity/refresh-tokens-jwt-interaction/index.md b/content/identity/refresh-tokens-jwt-interaction/index.md
index 3e4b6fb9c..dbf1ce2a5 100644
--- a/content/identity/refresh-tokens-jwt-interaction/index.md
+++ b/content/identity/refresh-tokens-jwt-interaction/index.md
@@ -1,7 +1,7 @@
---
title: "Refresh Tokens: When to Use Them and How They Interact with JWTs"
date: "2021-08-24"
-coverImage: "refresh-tokens-jwt-interaction-cover.jpg"
+coverImage: "refresh-tokens-jwt-interaction-cover.webp"
tags: ["security"]
featured: false
author: "Saikiran Babladi"
@@ -108,4 +108,4 @@ Businesses can leverage LoginRadius’ authentication and authorization services
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=refresh-tokens-jwt-interaction)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=refresh-tokens-jwt-interaction)
\ No newline at end of file
diff --git a/content/identity/refresh-tokens-jwt-interaction/refresh-tokens-jwt-interaction-cover.jpg b/content/identity/refresh-tokens-jwt-interaction/refresh-tokens-jwt-interaction-cover.jpg
deleted file mode 100644
index aa4e45e85..000000000
Binary files a/content/identity/refresh-tokens-jwt-interaction/refresh-tokens-jwt-interaction-cover.jpg and /dev/null differ
diff --git a/content/identity/refresh-tokens-jwt-interaction/refresh-tokens-jwt-interaction-cover.webp b/content/identity/refresh-tokens-jwt-interaction/refresh-tokens-jwt-interaction-cover.webp
new file mode 100644
index 000000000..75ee5f97e
Binary files /dev/null and b/content/identity/refresh-tokens-jwt-interaction/refresh-tokens-jwt-interaction-cover.webp differ
diff --git a/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs-ai.png b/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs-ai.png
deleted file mode 100644
index 953e67500..000000000
Binary files a/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs-ai.png and /dev/null differ
diff --git a/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs-ai.webp b/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs-ai.webp
new file mode 100644
index 000000000..78c2425a4
Binary files /dev/null and b/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs-ai.webp differ
diff --git a/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs.png b/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs.png
deleted file mode 100644
index d1ab33c80..000000000
Binary files a/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs.png and /dev/null differ
diff --git a/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs.webp b/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs.webp
new file mode 100644
index 000000000..288285496
Binary files /dev/null and b/content/identity/revamped-loginradius-docs-with-developer-first-experience/docs.webp differ
diff --git a/content/identity/revamped-loginradius-docs-with-developer-first-experience/hero-section.png b/content/identity/revamped-loginradius-docs-with-developer-first-experience/hero-section.png
deleted file mode 100644
index 2bc7b0313..000000000
Binary files a/content/identity/revamped-loginradius-docs-with-developer-first-experience/hero-section.png and /dev/null differ
diff --git a/content/identity/revamped-loginradius-docs-with-developer-first-experience/hero-section.webp b/content/identity/revamped-loginradius-docs-with-developer-first-experience/hero-section.webp
new file mode 100644
index 000000000..94abab126
Binary files /dev/null and b/content/identity/revamped-loginradius-docs-with-developer-first-experience/hero-section.webp differ
diff --git a/content/identity/revamped-loginradius-docs-with-developer-first-experience/index.md b/content/identity/revamped-loginradius-docs-with-developer-first-experience/index.md
index a9dd4dd4d..22a02a811 100644
--- a/content/identity/revamped-loginradius-docs-with-developer-first-experience/index.md
+++ b/content/identity/revamped-loginradius-docs-with-developer-first-experience/index.md
@@ -1,7 +1,7 @@
---
title: "Code Less, Build More: Unveiling LoginRadius' AI-Powered Developer Documentation"
date: "2025-03-05"
-coverImage: "hero-section.png"
+coverImage: "hero-section.webp"
tags: []
author: "Rakesh Soni"
description: "We rebuilt our docs from the ground up with a developer-first mindset. Now, navigation feels seamless, content follows a logical step-by-step approach, and jumping between topics feels effortless. Let’s start by exploring the new documentation structure and how it improves your workflow."
diff --git a/content/identity/rise-of-machine-identity-m2m-authorization-role/DS-m2m-auth.png b/content/identity/rise-of-machine-identity-m2m-authorization-role/DS-m2m-auth.png
deleted file mode 100644
index c31629290..000000000
Binary files a/content/identity/rise-of-machine-identity-m2m-authorization-role/DS-m2m-auth.png and /dev/null differ
diff --git a/content/identity/rise-of-machine-identity-m2m-authorization-role/DS-m2m-auth.webp b/content/identity/rise-of-machine-identity-m2m-authorization-role/DS-m2m-auth.webp
new file mode 100644
index 000000000..91dd1af2c
Binary files /dev/null and b/content/identity/rise-of-machine-identity-m2m-authorization-role/DS-m2m-auth.webp differ
diff --git a/content/identity/rise-of-machine-identity-m2m-authorization-role/index.md b/content/identity/rise-of-machine-identity-m2m-authorization-role/index.md
index 543a7f5fc..f071863f6 100644
--- a/content/identity/rise-of-machine-identity-m2m-authorization-role/index.md
+++ b/content/identity/rise-of-machine-identity-m2m-authorization-role/index.md
@@ -1,7 +1,7 @@
---
title: "Is the Rise of Machine Identity Posing a Threat to Enterprise Security?"
date: "2022-02-24"
-coverImage: "machine-id.jpg"
+coverImage: "machine-id.webp"
tags: ["data security","authorization","ciam solution"]
author: "Rakesh Soni"
description: "Cybercriminals are always on the hunt to exploit a loophole in the overall security mechanism in the digital world where machine-to-machine communication is the new normal. It’s no longer enough to assume services/devices accessing sensitive data can be trusted."
@@ -47,7 +47,7 @@ M2M Authorization is exclusively used for scenarios in which a business system a
M2M Authorization provides remote systems with secure access to information. Using M2M Authorization, business systems can communicate autonomously and execute business functions based on predefined authorization.
-[](https://www.loginradius.com/resource/m-to-m-authorization-)
+[](https://www.loginradius.com/resource/m-to-m-authorization-)
## Why Do Businesses Need M2M Authorization?
@@ -87,4 +87,4 @@ Organizations need to understand the complexity of the situation and put their b
[LoginRadius’](https://www.loginradius.com/) cutting-edge CIAM offers the best-in-class M2M authorization that helps businesses grow without compromising overall security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=rise-of-machine-identity-m2m-authorization-role)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=rise-of-machine-identity-m2m-authorization-role)
\ No newline at end of file
diff --git a/content/identity/rise-of-machine-identity-m2m-authorization-role/m2m-ds.png b/content/identity/rise-of-machine-identity-m2m-authorization-role/m2m-ds.png
deleted file mode 100644
index 030d51b9c..000000000
Binary files a/content/identity/rise-of-machine-identity-m2m-authorization-role/m2m-ds.png and /dev/null differ
diff --git a/content/identity/rise-of-machine-identity-m2m-authorization-role/m2m-ds.webp b/content/identity/rise-of-machine-identity-m2m-authorization-role/m2m-ds.webp
new file mode 100644
index 000000000..d32d95bda
Binary files /dev/null and b/content/identity/rise-of-machine-identity-m2m-authorization-role/m2m-ds.webp differ
diff --git a/content/identity/rise-of-machine-identity-m2m-authorization-role/machine-id.jpg b/content/identity/rise-of-machine-identity-m2m-authorization-role/machine-id.jpg
deleted file mode 100644
index 180a12961..000000000
Binary files a/content/identity/rise-of-machine-identity-m2m-authorization-role/machine-id.jpg and /dev/null differ
diff --git a/content/identity/rise-of-machine-identity-m2m-authorization-role/machine-id.webp b/content/identity/rise-of-machine-identity-m2m-authorization-role/machine-id.webp
new file mode 100644
index 000000000..2f4bed4af
Binary files /dev/null and b/content/identity/rise-of-machine-identity-m2m-authorization-role/machine-id.webp differ
diff --git a/content/identity/risk-based-authentication/index.md b/content/identity/risk-based-authentication/index.md
index abcdcfc01..294035edf 100644
--- a/content/identity/risk-based-authentication/index.md
+++ b/content/identity/risk-based-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "What is Risk-Based Authentication"
date: "2021-02-26"
-coverImage: "risk-based-authentication.png"
+coverImage: "risk-based-authentication.webp"
tags: ["data security","risk based authentication","cx"]
author: "Rajeev Sharma"
description: "RBA is a method of applying various levels of stringency to authentication processes based on the likelihood that the access to a given system could result in it being compromised. As the level of risk increases, authentication becomes more restrictive."
@@ -27,7 +27,7 @@ Whenever a system identifies any risk with a login activity, there can be multip
In addition to prompting the consumer with challenge and response, there are options to either send an email to the consumer about the suspicious activity or let the Site Administrator know that the account has been compromised. It will alert the consumer as well as the Site Administrator.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
## Why Should Businesses Use RBA
Risk-based authentication is an essential security feature because it works in real-time to prevent cyber frauds like accounts getting compromised without causing an inconvenience for legitimate consumers.
@@ -61,4 +61,4 @@ To learn more about this feature, please visit our [Risk-Based Authentication do
In this article, we talked about making the accounts secured using Risk Based Authentication and learnt how it will enhance the consumer security. This feature helps define the risk areas and take actions if any risk is detected with respect to the defined constraints.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=risk-based-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=risk-based-authentication)
\ No newline at end of file
diff --git a/content/identity/risk-based-authentication/mfa.png b/content/identity/risk-based-authentication/mfa.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/risk-based-authentication/mfa.png and /dev/null differ
diff --git a/content/identity/risk-based-authentication/mfa.webp b/content/identity/risk-based-authentication/mfa.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/risk-based-authentication/mfa.webp differ
diff --git a/content/identity/risk-based-authentication/risk-based-authentication.png b/content/identity/risk-based-authentication/risk-based-authentication.png
deleted file mode 100644
index c9f55a8ac..000000000
Binary files a/content/identity/risk-based-authentication/risk-based-authentication.png and /dev/null differ
diff --git a/content/identity/risk-based-authentication/risk-based-authentication.webp b/content/identity/risk-based-authentication/risk-based-authentication.webp
new file mode 100644
index 000000000..c9e280311
Binary files /dev/null and b/content/identity/risk-based-authentication/risk-based-authentication.webp differ
diff --git a/content/identity/risk-management-essentials-enterprise/EB-GD-to-MFA.png b/content/identity/risk-management-essentials-enterprise/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/risk-management-essentials-enterprise/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/risk-management-essentials-enterprise/EB-GD-to-MFA.webp b/content/identity/risk-management-essentials-enterprise/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/risk-management-essentials-enterprise/EB-GD-to-MFA.webp differ
diff --git a/content/identity/risk-management-essentials-enterprise/index.md b/content/identity/risk-management-essentials-enterprise/index.md
index 59a17f96e..bd95f734b 100644
--- a/content/identity/risk-management-essentials-enterprise/index.md
+++ b/content/identity/risk-management-essentials-enterprise/index.md
@@ -1,7 +1,7 @@
---
title: "COVID-19 and Beyond: 5 Risk Management Essentials for Your Enterprise"
date: "2021-07-20"
-coverImage: "risk-management-essentials-enterprise-cover.jpg"
+coverImage: "risk-management-essentials-enterprise-cover.webp"
tags: ["risk management","cybersecurity","ciam solution","password management"]
author: "Vishal Sharma"
description: "Cybercriminals continuously exploit consumer data and have accelerated outbreaks by taking advantage of the chaotic time, and the weaker first line of defense as businesses adopt new working ecosystems. This post covers all the aspects that require immediate consideration to minimize the risk of identity theft or a security breach."
@@ -52,7 +52,7 @@ For the most secure user sign-ins, you should combine elements like biometrics,
LoginRadius’ CIAM (consumer identity and access management) solution provides multiple layers of security to ensure consumer data and enterprise information remain highly secure.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### 3. Cyber Awareness Training to Avoid Human Error
@@ -91,4 +91,4 @@ With the rising number of identity thefts and security breaches amid the global
[LoginRadius](https://www.loginradius.com/contact-sales/) can be the most acceptable alternative for both the enterprises and startups that are collecting customer data and need to ensure a secure ecosystem without hampering the overall user experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=risk-management-essentials-enterprise)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=risk-management-essentials-enterprise)
\ No newline at end of file
diff --git a/content/identity/risk-management-essentials-enterprise/mfa.png b/content/identity/risk-management-essentials-enterprise/mfa.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/risk-management-essentials-enterprise/mfa.png and /dev/null differ
diff --git a/content/identity/risk-management-essentials-enterprise/mfa.webp b/content/identity/risk-management-essentials-enterprise/mfa.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/risk-management-essentials-enterprise/mfa.webp differ
diff --git a/content/identity/risk-management-essentials-enterprise/risk-management-essentials-enterprise-cover.jpg b/content/identity/risk-management-essentials-enterprise/risk-management-essentials-enterprise-cover.jpg
deleted file mode 100644
index 82d1c8e41..000000000
Binary files a/content/identity/risk-management-essentials-enterprise/risk-management-essentials-enterprise-cover.jpg and /dev/null differ
diff --git a/content/identity/risk-management-essentials-enterprise/risk-management-essentials-enterprise-cover.webp b/content/identity/risk-management-essentials-enterprise/risk-management-essentials-enterprise-cover.webp
new file mode 100644
index 000000000..020dfea40
Binary files /dev/null and b/content/identity/risk-management-essentials-enterprise/risk-management-essentials-enterprise-cover.webp differ
diff --git a/content/identity/risk-management-with-holistic-apis/EB-GD-to-mod-cust-id.png b/content/identity/risk-management-with-holistic-apis/EB-GD-to-mod-cust-id.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/identity/risk-management-with-holistic-apis/EB-GD-to-mod-cust-id.png and /dev/null differ
diff --git a/content/identity/risk-management-with-holistic-apis/EB-GD-to-mod-cust-id.webp b/content/identity/risk-management-with-holistic-apis/EB-GD-to-mod-cust-id.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/identity/risk-management-with-holistic-apis/EB-GD-to-mod-cust-id.webp differ
diff --git a/content/identity/risk-management-with-holistic-apis/index.md b/content/identity/risk-management-with-holistic-apis/index.md
index 37204a18f..b6b6cca86 100644
--- a/content/identity/risk-management-with-holistic-apis/index.md
+++ b/content/identity/risk-management-with-holistic-apis/index.md
@@ -1,7 +1,7 @@
---
title: "Move beyond Traditional Risk Management with Holistic APIs"
date: "2021-06-01"
-coverImage: "risk-management-with-holistic apis-cover.jpg"
+coverImage: "risk-management-with-holistic apis-cover.webp"
tags: ["oauth","identity management","data privacy","cx"]
author: "Vishal Sharma"
description: "Organizations are now struggling more than ever before to face new risks, vulnerabilities, and privacy issues since they adopted a paradigm shift to remote working. This valuable read focuses on the importance of the adequate deployment of APIs that further reduces vulnerabilities and helps maintain a unified user experience."
@@ -57,7 +57,7 @@ LoginRadius offers better insights into data from both a security and marketing
The API capabilities are endless as it covers all areas of threat intelligence that not only helps in predicting vulnerabilities but eventually provides a more insightful structure for overall business growth.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
## Integration with Third-Party Analytics Solution
@@ -100,4 +100,4 @@ In an era where things are going uncertain amid the global pandemic, there’s a
As far as the risks involved in deploying APIs are concerned, LoginRadius CIAM helps businesses swiftly navigate the implementation processes with utmost security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=risk-management-with-holistic-apis)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=risk-management-with-holistic-apis)
diff --git a/content/identity/risk-management-with-holistic-apis/modern-customer-identity.png b/content/identity/risk-management-with-holistic-apis/modern-customer-identity.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/identity/risk-management-with-holistic-apis/modern-customer-identity.png and /dev/null differ
diff --git a/content/identity/risk-management-with-holistic-apis/modern-customer-identity.webp b/content/identity/risk-management-with-holistic-apis/modern-customer-identity.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/identity/risk-management-with-holistic-apis/modern-customer-identity.webp differ
diff --git a/content/identity/risk-management-with-holistic-apis/risk-management-with-holistic apis-cover.jpg b/content/identity/risk-management-with-holistic-apis/risk-management-with-holistic apis-cover.jpg
deleted file mode 100644
index fb98572f8..000000000
Binary files a/content/identity/risk-management-with-holistic-apis/risk-management-with-holistic apis-cover.jpg and /dev/null differ
diff --git a/content/identity/risk-management-with-holistic-apis/risk-management-with-holistic apis-cover.webp b/content/identity/risk-management-with-holistic-apis/risk-management-with-holistic apis-cover.webp
new file mode 100644
index 000000000..e0b054aa7
Binary files /dev/null and b/content/identity/risk-management-with-holistic-apis/risk-management-with-holistic apis-cover.webp differ
diff --git a/content/identity/role-of-ciam-in-iot-security/ciam-paradox-wp.png b/content/identity/role-of-ciam-in-iot-security/ciam-paradox-wp.png
deleted file mode 100644
index 278456c0c..000000000
Binary files a/content/identity/role-of-ciam-in-iot-security/ciam-paradox-wp.png and /dev/null differ
diff --git a/content/identity/role-of-ciam-in-iot-security/ciam-paradox-wp.webp b/content/identity/role-of-ciam-in-iot-security/ciam-paradox-wp.webp
new file mode 100644
index 000000000..755a1ac8c
Binary files /dev/null and b/content/identity/role-of-ciam-in-iot-security/ciam-paradox-wp.webp differ
diff --git a/content/identity/role-of-ciam-in-iot-security/index.md b/content/identity/role-of-ciam-in-iot-security/index.md
index e47bde906..121a2e1fa 100644
--- a/content/identity/role-of-ciam-in-iot-security/index.md
+++ b/content/identity/role-of-ciam-in-iot-security/index.md
@@ -1,7 +1,7 @@
---
title: "The Role of Customer Identity Management in IoT Security: How It's a Must!"
date: "2022-10-27"
-coverImage: "iot-ciam.jpg"
+coverImage: "iot-ciam.webp"
tags: ["ciam", "iot security", "compliance"]
author: "Rakesh Soni"
description: "Just like agility is the way to move quickly and easily; digital agility is now the means to adopt digital transformation quickly through the right tools and processes. This blog explains the aspects of digital agility and how businesses can ensure they’re on the right path to achieving it through the right customer authentication tools and technologies."
@@ -37,7 +37,7 @@ There are huge security risks well documented in the cyber world that affect var
And what’s worrisome is the fact that the [machine-to-machine communication](https://www.loginradius.com/blog/identity/rise-of-machine-identity-m2m-authorization-role/) and authentication in the IoT landscape isn’t secure and can be easily compromised by cybercriminals. Hence, a more robust authentication is required, and brands can’t rely on conventional methods.
-[](https://www.loginradius.com/resource/ciam-in-iot-security-whitepaper)
+[](https://www.loginradius.com/resource/ciam-in-iot-security-whitepaper)
Here’s where the critical role of a reliable CIAM comes into play. Let’s understand how CIAM paves the way for a secure IoT environment.
@@ -73,4 +73,4 @@ Businesses need to understand that IoT environments are always on the radar of c
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-of-ciam-in-iot-security)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-of-ciam-in-iot-security)
\ No newline at end of file
diff --git a/content/identity/role-of-ciam-in-iot-security/iot-ciam.jpg b/content/identity/role-of-ciam-in-iot-security/iot-ciam.jpg
deleted file mode 100644
index 54997dc99..000000000
Binary files a/content/identity/role-of-ciam-in-iot-security/iot-ciam.jpg and /dev/null differ
diff --git a/content/identity/role-of-ciam-in-iot-security/iot-ciam.webp b/content/identity/role-of-ciam-in-iot-security/iot-ciam.webp
new file mode 100644
index 000000000..130695d39
Binary files /dev/null and b/content/identity/role-of-ciam-in-iot-security/iot-ciam.webp differ
diff --git a/content/identity/role-of-customer-authentication-digital-first-cx/ciam-ds.png b/content/identity/role-of-customer-authentication-digital-first-cx/ciam-ds.png
deleted file mode 100644
index eaa925c92..000000000
Binary files a/content/identity/role-of-customer-authentication-digital-first-cx/ciam-ds.png and /dev/null differ
diff --git a/content/identity/role-of-customer-authentication-digital-first-cx/ciam-ds.webp b/content/identity/role-of-customer-authentication-digital-first-cx/ciam-ds.webp
new file mode 100644
index 000000000..449e28840
Binary files /dev/null and b/content/identity/role-of-customer-authentication-digital-first-cx/ciam-ds.webp differ
diff --git a/content/identity/role-of-customer-authentication-digital-first-cx/digital-cx.jpg b/content/identity/role-of-customer-authentication-digital-first-cx/digital-cx.jpg
deleted file mode 100644
index c9f8c0b30..000000000
Binary files a/content/identity/role-of-customer-authentication-digital-first-cx/digital-cx.jpg and /dev/null differ
diff --git a/content/identity/role-of-customer-authentication-digital-first-cx/digital-cx.webp b/content/identity/role-of-customer-authentication-digital-first-cx/digital-cx.webp
new file mode 100644
index 000000000..2eb5ef9cd
Binary files /dev/null and b/content/identity/role-of-customer-authentication-digital-first-cx/digital-cx.webp differ
diff --git a/content/identity/role-of-customer-authentication-digital-first-cx/index.md b/content/identity/role-of-customer-authentication-digital-first-cx/index.md
index 359e549d7..1e04a9961 100644
--- a/content/identity/role-of-customer-authentication-digital-first-cx/index.md
+++ b/content/identity/role-of-customer-authentication-digital-first-cx/index.md
@@ -1,7 +1,7 @@
---
title: "The Role of Customer Authentication in Paving the Way for Digital Agility"
date: "2022-09-06"
-coverImage: "digital-cx.jpg"
+coverImage: "digital-cx.webp"
tags: ["customer authentication", "digital transformation", "ciam"]
author: "Yash Rathi"
description: "Just like agility is the way to move quickly and easily; digital agility is now the means to adopt digital transformation quickly through the right tools and processes. This blog explains the aspects of digital agility and how businesses can ensure they’re on the right path to achieving it through the right customer authentication tools and technologies."
@@ -54,7 +54,7 @@ A robust CIAM solution helps businesses stay ahead of the competition by offerin
This information helps businesses quickly understand user demands and can eventually prepare strategies for future requirements.
-[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
+[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
## How the LoginRadius CIAM Solution Can Help in Your Digital Agility
@@ -77,4 +77,4 @@ Businesses can leverage the true potential of digital agility by incorporating a
Reach us if you wish to see the future of digital agility through a robust cloud-based CIAM solution.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-of-customer-authentication-digital-first-cx)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-of-customer-authentication-digital-first-cx)
\ No newline at end of file
diff --git a/content/identity/saas-security-iam-effective-governance/EB-Adaptive-auth.png b/content/identity/saas-security-iam-effective-governance/EB-Adaptive-auth.png
deleted file mode 100644
index 67f9460b5..000000000
Binary files a/content/identity/saas-security-iam-effective-governance/EB-Adaptive-auth.png and /dev/null differ
diff --git a/content/identity/saas-security-iam-effective-governance/EB-Adaptive-auth.webp b/content/identity/saas-security-iam-effective-governance/EB-Adaptive-auth.webp
new file mode 100644
index 000000000..0ba102653
Binary files /dev/null and b/content/identity/saas-security-iam-effective-governance/EB-Adaptive-auth.webp differ
diff --git a/content/identity/saas-security-iam-effective-governance/adaptive-mfa.png b/content/identity/saas-security-iam-effective-governance/adaptive-mfa.png
deleted file mode 100644
index 1f39a27f3..000000000
Binary files a/content/identity/saas-security-iam-effective-governance/adaptive-mfa.png and /dev/null differ
diff --git a/content/identity/saas-security-iam-effective-governance/adaptive-mfa.webp b/content/identity/saas-security-iam-effective-governance/adaptive-mfa.webp
new file mode 100644
index 000000000..8a8067f56
Binary files /dev/null and b/content/identity/saas-security-iam-effective-governance/adaptive-mfa.webp differ
diff --git a/content/identity/saas-security-iam-effective-governance/index.md b/content/identity/saas-security-iam-effective-governance/index.md
index 94d8a7650..be3e19953 100644
--- a/content/identity/saas-security-iam-effective-governance/index.md
+++ b/content/identity/saas-security-iam-effective-governance/index.md
@@ -1,7 +1,7 @@
---
title: "Protecting Your Cloud Data: The Power of SaaS Security and IAM Governance"
date: "2023-02-16"
-coverImage: "saas-secure.jpg"
+coverImage: "saas-secure.webp"
tags: ["saas", "identity-governance", "authentication"]
author: "Rakesh Soni"
description: "Since organizations today have thousands and even millions of users logging simultaneously into their accounts, ensuring security at every end-point becomes an uphill battle. Hence, a robust identity and access management system becomes more crucial than ever. Let’s glance at some aspects of securing SaaS environments by incorporating a robust identity and access management solution."
@@ -46,7 +46,7 @@ But what makes an IAM solution genuinely effective?
For starters, it should allow you to authenticate users securely through multi-factor and adaptive authentication. Your customers and employees will never have to worry about having their credentials stolen or compromised.
-[](https://www.loginradius.com/resource/adaptive-authentication-in-the-age-of-digital-apocalypse/)
+[](https://www.loginradius.com/resource/adaptive-authentication-in-the-age-of-digital-apocalypse/)
Also, the cutting-edge CIAM system like [LoginRadius](https://www.loginradius.com/) helps meet all the necessary global compliances like CCPA and GDPR to ensure businesses need not worry about hefty fines and regulations while serving their customers in parts of the world.
@@ -90,4 +90,4 @@ As a solution provider of IAM solutions for SaaS companies, LoginRadius’s team
We are keenly aware of the needs of SaaS enterprises, and we will continue to provide advanced identity management solutions that deliver the performance needed for any business to grow in this market.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=saas-security-iam-effective-governance)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=saas-security-iam-effective-governance)
\ No newline at end of file
diff --git a/content/identity/saas-security-iam-effective-governance/saas-secure.jpg b/content/identity/saas-security-iam-effective-governance/saas-secure.jpg
deleted file mode 100644
index af76a9dfc..000000000
Binary files a/content/identity/saas-security-iam-effective-governance/saas-secure.jpg and /dev/null differ
diff --git a/content/identity/saas-security-iam-effective-governance/saas-secure.webp b/content/identity/saas-security-iam-effective-governance/saas-secure.webp
new file mode 100644
index 000000000..a53995232
Binary files /dev/null and b/content/identity/saas-security-iam-effective-governance/saas-secure.webp differ
diff --git a/content/identity/safe-data-act/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.png b/content/identity/safe-data-act/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.png
deleted file mode 100644
index 0ed0f3bce..000000000
Binary files a/content/identity/safe-data-act/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.png and /dev/null differ
diff --git a/content/identity/safe-data-act/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.webp b/content/identity/safe-data-act/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.webp
new file mode 100644
index 000000000..6d67557e6
Binary files /dev/null and b/content/identity/safe-data-act/WP-The-CCPA-and-Customer-Identity-Reaping-the-Benefits-of-Compliance.webp differ
diff --git a/content/identity/safe-data-act/index.md b/content/identity/safe-data-act/index.md
index 055ed657c..c1775f64e 100644
--- a/content/identity/safe-data-act/index.md
+++ b/content/identity/safe-data-act/index.md
@@ -1,7 +1,7 @@
---
title: "Safe Data Act: A New Privacy Law in the Town"
date: "2020-12-03"
-coverImage: "safe-data-act-privacy-law.jpg"
+coverImage: "safe-data-act-privacy-law.webp"
tags: ["privacy-and-compliance"]
featured: false
author: "Rakesh Soni"
@@ -29,7 +29,7 @@ The Safe Data Act combines three previously introduced privacy protection bills
Americans would have a greater choice of control over their data. In particular, the law would create rights to transparency, access, deletion, correction, and portability for consumers. Additionally, businesses would require to make a baseline level of data security, including opt-in consent for the process and transfer of sensitive data.
-
+
Image source: [iapp]
@@ -58,7 +58,7 @@ Moving on, when a new legislation is about to come into force, the first step ev
Here's how you can adopt the best risk management practices to ensure that your business is ready for compliance.
-
+
## 4 Ways to Strengthen Your Compliance and Risk Management Practices
@@ -71,7 +71,7 @@ Here's how you can adopt the best risk management practices to ensure that your
4. **Approach an already compliant identity provider**: Another way to look at this is to get the job done by onboarding providers who are already big names in the industry for their compliance-adherence standards, like LoginRadius. It takes [consumer data privacy](https://www.loginradius.com/blog/2020/06/consumer-data-privacy-security/) very seriously and is compliant with major regulations like the CCPA and the GDPR.
-[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity/)
+[](https://www.loginradius.com/resource/the-ccpa-and-customer-identity/)
## Protect Your Consumer Privacy With the LoginRadius Identity Platform
@@ -91,4 +91,4 @@ In a bid to ensure businesses the highest level of protection, the LoginRadius c
It is in your businesses' best interest to comply with privacy regulations, like the Safe Data Act. Not only does it help you dodge off data breaches and [cyber attacks](https://www.loginradius.com/blog/identity/cybersecurity-attacks-business/), but it also confirms businesses that they can trust you with their confidential consumer data—and that's priceless!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=safe-data-act)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=safe-data-act)
diff --git a/content/identity/safe-data-act/protect-your-consumer-privacy-with-loginradius.png b/content/identity/safe-data-act/protect-your-consumer-privacy-with-loginradius.png
deleted file mode 100644
index e21fb75ad..000000000
Binary files a/content/identity/safe-data-act/protect-your-consumer-privacy-with-loginradius.png and /dev/null differ
diff --git a/content/identity/safe-data-act/protect-your-consumer-privacy-with-loginradius.webp b/content/identity/safe-data-act/protect-your-consumer-privacy-with-loginradius.webp
new file mode 100644
index 000000000..eba65b12a
Binary files /dev/null and b/content/identity/safe-data-act/protect-your-consumer-privacy-with-loginradius.webp differ
diff --git a/content/identity/safe-data-act/safe-data-act-privacy-law.jpg b/content/identity/safe-data-act/safe-data-act-privacy-law.jpg
deleted file mode 100644
index da797ee3c..000000000
Binary files a/content/identity/safe-data-act/safe-data-act-privacy-law.jpg and /dev/null differ
diff --git a/content/identity/safe-data-act/safe-data-act-privacy-law.webp b/content/identity/safe-data-act/safe-data-act-privacy-law.webp
new file mode 100644
index 000000000..985b3b6ae
Binary files /dev/null and b/content/identity/safe-data-act/safe-data-act-privacy-law.webp differ
diff --git a/content/identity/safe-data-act/safe-data-act.png b/content/identity/safe-data-act/safe-data-act.png
deleted file mode 100644
index f3d2f8cf7..000000000
Binary files a/content/identity/safe-data-act/safe-data-act.png and /dev/null differ
diff --git a/content/identity/safe-data-act/safe-data-act.webp b/content/identity/safe-data-act/safe-data-act.webp
new file mode 100644
index 000000000..47fd05d68
Binary files /dev/null and b/content/identity/safe-data-act/safe-data-act.webp differ
diff --git a/content/identity/saml-or-oidc-for-business/DS-SSO.png b/content/identity/saml-or-oidc-for-business/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/saml-or-oidc-for-business/DS-SSO.png and /dev/null differ
diff --git a/content/identity/saml-or-oidc-for-business/DS-SSO.webp b/content/identity/saml-or-oidc-for-business/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/saml-or-oidc-for-business/DS-SSO.webp differ
diff --git a/content/identity/saml-or-oidc-for-business/index.md b/content/identity/saml-or-oidc-for-business/index.md
index ba56bcd3c..0293c5984 100644
--- a/content/identity/saml-or-oidc-for-business/index.md
+++ b/content/identity/saml-or-oidc-for-business/index.md
@@ -1,7 +1,7 @@
---
title: "SAML or OIDC: Which is Better For Your Business?"
date: "2021-06-08"
-coverImage: "saml-or-oidc-for-business-cover.jpg"
+coverImage: "saml-or-oidc-for-business-cover.webp"
tags: ["saml","sso","data security","authentication","cx"]
author: "Rakesh Soni"
description: "For any company concerned about securing its users' data, getting a grip on SSO can be a daunting task. But determining whether SAML or OIDC is right for your enterprise requires weighing a few characteristics against your business goals."
@@ -31,7 +31,7 @@ Before we look at the differences between these protocols, let us understand the
* This selection is then passed onto the browser or app using the IdP.
* The app verifies the user's identity before granting access to the information the end-user is looking for.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
## What are the Differences Between OIDC and SAML?
@@ -107,4 +107,4 @@ LoginRadius also supports federated [SSO protocols](https://www.loginradius.com/
Whether you opt for a SAML or an OIDC verification method, the identity provider you choose can define your app's features and user-friendliness. Partnering with the right platform will help you provide the best security possible and ensure you don't fall victim to any cybercrimes.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=saml-or-oidc-for-business)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=saml-or-oidc-for-business)
diff --git a/content/identity/saml-or-oidc-for-business/saml-or-oidc-for-business-cover.jpg b/content/identity/saml-or-oidc-for-business/saml-or-oidc-for-business-cover.jpg
deleted file mode 100644
index 1da2c4490..000000000
Binary files a/content/identity/saml-or-oidc-for-business/saml-or-oidc-for-business-cover.jpg and /dev/null differ
diff --git a/content/identity/saml-or-oidc-for-business/saml-or-oidc-for-business-cover.webp b/content/identity/saml-or-oidc-for-business/saml-or-oidc-for-business-cover.webp
new file mode 100644
index 000000000..7216f87ca
Binary files /dev/null and b/content/identity/saml-or-oidc-for-business/saml-or-oidc-for-business-cover.webp differ
diff --git a/content/identity/saml-or-oidc-for-business/sso-ds.png b/content/identity/saml-or-oidc-for-business/sso-ds.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/saml-or-oidc-for-business/sso-ds.png and /dev/null differ
diff --git a/content/identity/saml-or-oidc-for-business/sso-ds.webp b/content/identity/saml-or-oidc-for-business/sso-ds.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/saml-or-oidc-for-business/sso-ds.webp differ
diff --git a/content/identity/saml-sso/DS-LR-SSO.png b/content/identity/saml-sso/DS-LR-SSO.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/saml-sso/DS-LR-SSO.png and /dev/null differ
diff --git a/content/identity/saml-sso/DS-LR-SSO.webp b/content/identity/saml-sso/DS-LR-SSO.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/saml-sso/DS-LR-SSO.webp differ
diff --git a/content/identity/saml-sso/DS-SSO.png b/content/identity/saml-sso/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/saml-sso/DS-SSO.png and /dev/null differ
diff --git a/content/identity/saml-sso/DS-SSO.webp b/content/identity/saml-sso/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/saml-sso/DS-SSO.webp differ
diff --git a/content/identity/saml-sso/index.md b/content/identity/saml-sso/index.md
index 3d9a7bc99..bdafcc584 100644
--- a/content/identity/saml-sso/index.md
+++ b/content/identity/saml-sso/index.md
@@ -1,7 +1,7 @@
---
title: "What is SAML SSO?"
date: "2021-06-18"
-coverImage: "saml-sso.jpg"
+coverImage: "saml-sso.webp"
tags: ["saml","sso","user authentication"]
author: "Rajeev Sharma"
description: "SAML SSO is an authentication standard for single sign-on (SSO) based on XML. Learn more about how it works, advantages and its components."
@@ -72,7 +72,7 @@ One can use SAML to 'reuse' a single act of authentication (like logging in with
In SAML, the responsibility for the proper management of identities lies with the identity provider. It is more manageable and desirable rather than handling multiple service provider systems.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
## SAML Components
@@ -113,7 +113,7 @@ Here, following process occurs:
The below diagram illustrates the single sign-on flow for SAML SSO, i.e., when an application triggers SSO.
-
+
If you want to learn more on how LoginRadius can help implement IDP-initiated SSO and SP initiated SAML SSO, refer to the LoginRadius SAML overview documentation.
@@ -121,4 +121,4 @@ If you want to learn more on how LoginRadius can help implement IDP-initiated SS
In this article, we talked about the basics of SAML SSO and its key components. However, before implementing any functionality on your website, it is recommended to analyze and consider the pros and cons from every possible angle.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=saml-sso)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=saml-sso)
diff --git a/content/identity/saml-sso/saml-sso.jpg b/content/identity/saml-sso/saml-sso.jpg
deleted file mode 100644
index d28b0dfef..000000000
Binary files a/content/identity/saml-sso/saml-sso.jpg and /dev/null differ
diff --git a/content/identity/saml-sso/saml-sso.webp b/content/identity/saml-sso/saml-sso.webp
new file mode 100644
index 000000000..6888f350c
Binary files /dev/null and b/content/identity/saml-sso/saml-sso.webp differ
diff --git a/content/identity/sase-zero-trust/index.md b/content/identity/sase-zero-trust/index.md
index 4fbd25c48..b6462d4c0 100644
--- a/content/identity/sase-zero-trust/index.md
+++ b/content/identity/sase-zero-trust/index.md
@@ -1,7 +1,7 @@
---
title: "10 Reasons For Businesses to Implement SASE with a Zero Trust Strategy"
date: "2021-06-04"
-coverImage: "sase-zero-trust-cover.jpg"
+coverImage: "sase-zero-trust-cover.webp"
tags: ["zero trust security","sase","cybersecurity"]
author: "Navanita Devi"
description: "The perimeter-based reactive methods that were the core of old and traditional security systems have become obsolete. The zero trust security model is the future of cybersecurity. But, it is valuable only when implemented across the company's entire network infrastructure. This is where SASE takes the lead."
@@ -110,4 +110,4 @@ Proactive governments and businesses must adopt it to ensure a cyber-secure futu
If you too want to implement a zero trust security model in your organization, [book a demo](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sase-zero-trust) with LoginRadius today!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sase-zero-trust)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sase-zero-trust)
diff --git a/content/identity/sase-zero-trust/sase-zero-trust-cover.jpg b/content/identity/sase-zero-trust/sase-zero-trust-cover.jpg
deleted file mode 100644
index cd9a4b835..000000000
Binary files a/content/identity/sase-zero-trust/sase-zero-trust-cover.jpg and /dev/null differ
diff --git a/content/identity/sase-zero-trust/sase-zero-trust-cover.webp b/content/identity/sase-zero-trust/sase-zero-trust-cover.webp
new file mode 100644
index 000000000..68bbb881a
Binary files /dev/null and b/content/identity/sase-zero-trust/sase-zero-trust-cover.webp differ
diff --git a/content/identity/scale-business-with-identity-management/EB-GD-to-mod-cust-id.png b/content/identity/scale-business-with-identity-management/EB-GD-to-mod-cust-id.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/identity/scale-business-with-identity-management/EB-GD-to-mod-cust-id.png and /dev/null differ
diff --git a/content/identity/scale-business-with-identity-management/EB-GD-to-mod-cust-id.webp b/content/identity/scale-business-with-identity-management/EB-GD-to-mod-cust-id.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/identity/scale-business-with-identity-management/EB-GD-to-mod-cust-id.webp differ
diff --git a/content/identity/scale-business-with-identity-management/eb-customer-identity.png b/content/identity/scale-business-with-identity-management/eb-customer-identity.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/identity/scale-business-with-identity-management/eb-customer-identity.png and /dev/null differ
diff --git a/content/identity/scale-business-with-identity-management/eb-customer-identity.webp b/content/identity/scale-business-with-identity-management/eb-customer-identity.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/identity/scale-business-with-identity-management/eb-customer-identity.webp differ
diff --git a/content/identity/scale-business-with-identity-management/index.md b/content/identity/scale-business-with-identity-management/index.md
index 27ee744fb..0cf724874 100644
--- a/content/identity/scale-business-with-identity-management/index.md
+++ b/content/identity/scale-business-with-identity-management/index.md
@@ -1,7 +1,7 @@
---
title: "How to Scale Your Business Quickly with Identity Management"
date: "2021-07-29"
-coverImage: "scale-business-with-identity-management-cover.jpg"
+coverImage: "scale-business-with-identity-management-cover.webp"
tags: ["identity management","ciam solution","customer identity","cx"]
author: "Rakesh Soni"
description: "Identity management is much more than just a security mechanism for securing consumer data and sensitive business information; it helps businesses accelerate growth. Learn how a CIAM solution can help businesses securely manage consumer identities and build trust that fosters growth."
@@ -50,7 +50,7 @@ Using the LoginRadius[ Consumer Identity APIs](https://www.loginradius.com/ident
With its preconfigured integration with third-party tools and applications, you can pull your latest consumer data – thus eliminating data silos and generating valuable insights.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
## Scalability- The Backbone for Any Enterprise for Digital Transformation
@@ -85,4 +85,4 @@ Businesses embarking on their digital transformation journey must consider relyi
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=scale-business-with-identity-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=scale-business-with-identity-management)
diff --git a/content/identity/scale-business-with-identity-management/scale-business-with-identity-management-cover.jpg b/content/identity/scale-business-with-identity-management/scale-business-with-identity-management-cover.jpg
deleted file mode 100644
index def8a4a31..000000000
Binary files a/content/identity/scale-business-with-identity-management/scale-business-with-identity-management-cover.jpg and /dev/null differ
diff --git a/content/identity/scale-business-with-identity-management/scale-business-with-identity-management-cover.webp b/content/identity/scale-business-with-identity-management/scale-business-with-identity-management-cover.webp
new file mode 100644
index 000000000..f9f586882
Binary files /dev/null and b/content/identity/scale-business-with-identity-management/scale-business-with-identity-management-cover.webp differ
diff --git a/content/identity/seamless-customer-journey-identity-management/DS-PL-magic-link.png b/content/identity/seamless-customer-journey-identity-management/DS-PL-magic-link.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/seamless-customer-journey-identity-management/DS-PL-magic-link.png and /dev/null differ
diff --git a/content/identity/seamless-customer-journey-identity-management/DS-PL-magic-link.webp b/content/identity/seamless-customer-journey-identity-management/DS-PL-magic-link.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/seamless-customer-journey-identity-management/DS-PL-magic-link.webp differ
diff --git a/content/identity/seamless-customer-journey-identity-management/identity-mngmnt.jpg b/content/identity/seamless-customer-journey-identity-management/identity-mngmnt.jpg
deleted file mode 100644
index 14fa21611..000000000
Binary files a/content/identity/seamless-customer-journey-identity-management/identity-mngmnt.jpg and /dev/null differ
diff --git a/content/identity/seamless-customer-journey-identity-management/identity-mngmnt.webp b/content/identity/seamless-customer-journey-identity-management/identity-mngmnt.webp
new file mode 100644
index 000000000..33f98d2b5
Binary files /dev/null and b/content/identity/seamless-customer-journey-identity-management/identity-mngmnt.webp differ
diff --git a/content/identity/seamless-customer-journey-identity-management/index.md b/content/identity/seamless-customer-journey-identity-management/index.md
index 87d9ce4d5..6479f9eda 100644
--- a/content/identity/seamless-customer-journey-identity-management/index.md
+++ b/content/identity/seamless-customer-journey-identity-management/index.md
@@ -1,7 +1,7 @@
---
title: "How to Use Identity Management at Every Stage of the Customer Journey?"
date: "2023-02-28"
-coverImage: "identity-mngmnt.jpg"
+coverImage: "identity-mngmnt.webp"
tags: ["identity management", "progressive profiling", "passwordless login"]
author: "Yash Rathi"
description: "While leveraging personalization at every stage of the customer journey can enhance customer experience and unwind great opportunities, it also ensures returning customers and more referrals. This blog highlights the role of identity management throughout the customer journey and how it helps businesses streamline user experience backed with security."
@@ -55,7 +55,7 @@ CIAM for customers can provide a passwordless experience and an adaptive access
Passwordless authentication provides a streamlined login experience using the customer’s device (something you have) and a biometric, typically via facial recognition or a smartphone’s fingerprint reader (something you are).
-[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
+[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
The customer does not need to remember overly complex passwords or tap into a clunky password manager for help.
@@ -97,4 +97,4 @@ Customer experience is vital to many aspects of your business and the success of
Customer experience and customer journey have been codified in our industry, but changes are still happening in this brave new world under which many struggles to adapt. To build personalized and engaging customer journeys, you must consider using a cutting-edge CIAM solution.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=seamless-customer-journey-identity-management)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=seamless-customer-journey-identity-management)
diff --git a/content/identity/seamless-customer-journey-identity-management/passwordless-login.png b/content/identity/seamless-customer-journey-identity-management/passwordless-login.png
deleted file mode 100644
index f0d635566..000000000
Binary files a/content/identity/seamless-customer-journey-identity-management/passwordless-login.png and /dev/null differ
diff --git a/content/identity/seamless-customer-journey-identity-management/passwordless-login.webp b/content/identity/seamless-customer-journey-identity-management/passwordless-login.webp
new file mode 100644
index 000000000..16c0455b4
Binary files /dev/null and b/content/identity/seamless-customer-journey-identity-management/passwordless-login.webp differ
diff --git a/content/identity/secure-centralized-access-management-without-compromising-cx/SSO-DS.png b/content/identity/secure-centralized-access-management-without-compromising-cx/SSO-DS.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/secure-centralized-access-management-without-compromising-cx/SSO-DS.png and /dev/null differ
diff --git a/content/identity/secure-centralized-access-management-without-compromising-cx/SSO-DS.webp b/content/identity/secure-centralized-access-management-without-compromising-cx/SSO-DS.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/secure-centralized-access-management-without-compromising-cx/SSO-DS.webp differ
diff --git a/content/identity/secure-centralized-access-management-without-compromising-cx/centralized-access.jpg b/content/identity/secure-centralized-access-management-without-compromising-cx/centralized-access.jpg
deleted file mode 100644
index 68c57c42b..000000000
Binary files a/content/identity/secure-centralized-access-management-without-compromising-cx/centralized-access.jpg and /dev/null differ
diff --git a/content/identity/secure-centralized-access-management-without-compromising-cx/centralized-access.webp b/content/identity/secure-centralized-access-management-without-compromising-cx/centralized-access.webp
new file mode 100644
index 000000000..5ea98f064
Binary files /dev/null and b/content/identity/secure-centralized-access-management-without-compromising-cx/centralized-access.webp differ
diff --git a/content/identity/secure-centralized-access-management-without-compromising-cx/ds-sso.png b/content/identity/secure-centralized-access-management-without-compromising-cx/ds-sso.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/secure-centralized-access-management-without-compromising-cx/ds-sso.png and /dev/null differ
diff --git a/content/identity/secure-centralized-access-management-without-compromising-cx/ds-sso.webp b/content/identity/secure-centralized-access-management-without-compromising-cx/ds-sso.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/secure-centralized-access-management-without-compromising-cx/ds-sso.webp differ
diff --git a/content/identity/secure-centralized-access-management-without-compromising-cx/index.md b/content/identity/secure-centralized-access-management-without-compromising-cx/index.md
index 0d09e526b..8ab115f6d 100644
--- a/content/identity/secure-centralized-access-management-without-compromising-cx/index.md
+++ b/content/identity/secure-centralized-access-management-without-compromising-cx/index.md
@@ -1,7 +1,7 @@
---
title: "Securing Centralized Access Without Compromising User Experience"
date: "2022-10-17"
-coverImage: "centralized-access.jpg"
+coverImage: "centralized-access.webp"
tags: ["centralized access management", "sso", "passwordless"]
author: "Rakesh Soni"
description: "While most platforms offer stringent security measures across their devices or applications, many businesses cannot provide a seamless user experience and security when a user switches from one app to another or device to another. Let’s understand how to enhance customer experience without compromising security."
@@ -34,7 +34,7 @@ SSO is an essential feature of an Identity and Access Management (IAM) platform
Enhanced user experience is one of the most valuable benefits of SSO. As repeated logins are no longer required, customers can enjoy a modern digital experience. The benefits for enterprises include increased customer loyalty and higher conversion rates.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
Hence, SSO is undeniably the perfect solution to improve centralized access between devices or applications without compromising security and user experience since users can jump from one app to another without friction.
@@ -78,4 +78,4 @@ With secure centralized access through single sign-on and passwordless login, bu
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-centralized-access-management-without-compromising-cx)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-centralized-access-management-without-compromising-cx)
diff --git a/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/DS-mob-bio-auth.png b/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/DS-mob-bio-auth.png
deleted file mode 100644
index a3580f13e..000000000
Binary files a/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/DS-mob-bio-auth.png and /dev/null differ
diff --git a/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/DS-mob-bio-auth.webp b/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/DS-mob-bio-auth.webp
new file mode 100644
index 000000000..0257eff22
Binary files /dev/null and b/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/DS-mob-bio-auth.webp differ
diff --git a/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/id-crisis.jpg b/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/id-crisis.jpg
deleted file mode 100644
index 132380da3..000000000
Binary files a/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/id-crisis.jpg and /dev/null differ
diff --git a/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/id-crisis.webp b/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/id-crisis.webp
new file mode 100644
index 000000000..416a4d92b
Binary files /dev/null and b/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/id-crisis.webp differ
diff --git a/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/index.md b/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/index.md
index 687bbe52b..699c87069 100644
--- a/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/index.md
+++ b/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/index.md
@@ -1,7 +1,7 @@
---
title: "How Identity-Based Access Ensures Robust Infrastructure Security Amidst the Growing Identity Crisis?"
date: "2022-11-09"
-coverImage: "id-crisis.jpg"
+coverImage: "id-crisis.webp"
tags: ["identity management","robust security","mfa","cx"]
author: "Rakesh Soni"
description: "The conventional identity-management tools aren’t potent enough to shield modern threat vectors. There’s a need for a robust identity management solution that combines existing authentication strategies such as two-factor authentication, biometrics, one-time passwords etc. to help secure an organization's infrastructure."
@@ -50,7 +50,7 @@ Every individual has a unique biometric identity, so using it for authentication
Hence, adding biometric authentication in the multi-factor authentication could help organizations secure their sensitive business information since the chances of data breaches or account takeover decrease significantly.
-[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
+[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet)
## Why is Multi-factor authentication an Essential Component of Infrastructure Security?
@@ -81,4 +81,4 @@ And adding robust layers of multi-factor authentication through biometric authen
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-data-amidst-identity-crisis-via-identity-based-access)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-data-amidst-identity-crisis-via-identity-based-access)
diff --git a/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/mob-bio-ds.png b/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/mob-bio-ds.png
deleted file mode 100644
index 69293181d..000000000
Binary files a/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/mob-bio-ds.png and /dev/null differ
diff --git a/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/mob-bio-ds.webp b/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/mob-bio-ds.webp
new file mode 100644
index 000000000..b272f8563
Binary files /dev/null and b/content/identity/secure-data-amidst-identity-crisis-via-identity-based-access/mob-bio-ds.webp differ
diff --git a/content/identity/secure-email-address-website/buyer-guide-to-multi-factor-authentication-ebook.png b/content/identity/secure-email-address-website/buyer-guide-to-multi-factor-authentication-ebook.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/secure-email-address-website/buyer-guide-to-multi-factor-authentication-ebook.png and /dev/null differ
diff --git a/content/identity/secure-email-address-website/buyer-guide-to-multi-factor-authentication-ebook.webp b/content/identity/secure-email-address-website/buyer-guide-to-multi-factor-authentication-ebook.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/secure-email-address-website/buyer-guide-to-multi-factor-authentication-ebook.webp differ
diff --git a/content/identity/secure-email-address-website/index.md b/content/identity/secure-email-address-website/index.md
index db67d0e3b..5699b073e 100644
--- a/content/identity/secure-email-address-website/index.md
+++ b/content/identity/secure-email-address-website/index.md
@@ -1,7 +1,7 @@
---
title: "How to secure an email address on your website"
date: "2021-01-22"
-coverImage: "secure-email-address-website.jpg"
+coverImage: "secure-email-address-website.webp"
tags: ["all, Security"]
featured: false
author: "Rakesh Soni"
@@ -63,7 +63,7 @@ Hackers use [credential stuffing](https://www.loginradius.com/blog/identity/2019
This is possible because a huge proportion of online users still use the same username and passwords across multiple accounts.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
### 4. Use two-factor authentication or MFA, wherever possible.
@@ -98,4 +98,4 @@ The following techniques can be used to prevent email harvesting:
Although it may take a while to get the hang of them, the results are worth spending time on.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-email-address-website)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-email-address-website)
\ No newline at end of file
diff --git a/content/identity/secure-email-address-website/secure-email-address-website.jpg b/content/identity/secure-email-address-website/secure-email-address-website.jpg
deleted file mode 100644
index b943de0ac..000000000
Binary files a/content/identity/secure-email-address-website/secure-email-address-website.jpg and /dev/null differ
diff --git a/content/identity/secure-email-address-website/secure-email-address-website.webp b/content/identity/secure-email-address-website/secure-email-address-website.webp
new file mode 100644
index 000000000..30735e51f
Binary files /dev/null and b/content/identity/secure-email-address-website/secure-email-address-website.webp differ
diff --git a/content/identity/securing-digital-frontier-using-ai/GD-EG-to-RBA.png b/content/identity/securing-digital-frontier-using-ai/GD-EG-to-RBA.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/identity/securing-digital-frontier-using-ai/GD-EG-to-RBA.png and /dev/null differ
diff --git a/content/identity/securing-digital-frontier-using-ai/GD-EG-to-RBA.webp b/content/identity/securing-digital-frontier-using-ai/GD-EG-to-RBA.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/identity/securing-digital-frontier-using-ai/GD-EG-to-RBA.webp differ
diff --git a/content/identity/securing-digital-frontier-using-ai/GD-to-RBA.png b/content/identity/securing-digital-frontier-using-ai/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/securing-digital-frontier-using-ai/GD-to-RBA.png and /dev/null differ
diff --git a/content/identity/securing-digital-frontier-using-ai/GD-to-RBA.webp b/content/identity/securing-digital-frontier-using-ai/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/securing-digital-frontier-using-ai/GD-to-RBA.webp differ
diff --git a/content/identity/securing-digital-frontier-using-ai/index.md b/content/identity/securing-digital-frontier-using-ai/index.md
index 7ee840182..8a09b1507 100644
--- a/content/identity/securing-digital-frontier-using-ai/index.md
+++ b/content/identity/securing-digital-frontier-using-ai/index.md
@@ -1,7 +1,7 @@
---
title: "Securing the Digital Frontier: The Power of AI in Next-Gen CIAM"
date: "2023-03-17"
-coverImage: "power-of-ai.jpg"
+coverImage: "power-of-ai.webp"
tags: ["artificial intelligence","compliance","ciam"]
author: "Zach Norton"
description: "CIAM platforms are utilizing the power of artificial intelligence to give customers a personalized experience. This blog gives a walkthrough of some of the key roles of AI in CIAM, including personalization, security and advanced analytics."
@@ -43,7 +43,7 @@ We’ve mentioned a few use cases of AI in security, but how can you take advant
You can start by following the behavioral analytics for risk-based authentication. This will help you find fraudulent or suspicious activities to ensure you never miss a fraud attempt, even if it’s unsuccessful.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
### 2. Biometric Authentication
@@ -105,4 +105,4 @@ In the meantime, your customers will receive quick responses from the chatbots a
The use of AI in CIAM will continue to evolve, providing limitless capabilities to keep businesses safe and thriving in the future.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=securing-digital-frontier-using-ai)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=securing-digital-frontier-using-ai)
\ No newline at end of file
diff --git a/content/identity/securing-digital-frontier-using-ai/power-of-ai.jpg b/content/identity/securing-digital-frontier-using-ai/power-of-ai.jpg
deleted file mode 100644
index 0f920dace..000000000
Binary files a/content/identity/securing-digital-frontier-using-ai/power-of-ai.jpg and /dev/null differ
diff --git a/content/identity/securing-digital-frontier-using-ai/power-of-ai.webp b/content/identity/securing-digital-frontier-using-ai/power-of-ai.webp
new file mode 100644
index 000000000..c5adaadb7
Binary files /dev/null and b/content/identity/securing-digital-frontier-using-ai/power-of-ai.webp differ
diff --git a/content/identity/securing-enterprise-mobile-apps/3-1024x621.jpg b/content/identity/securing-enterprise-mobile-apps/3-1024x621.jpg
deleted file mode 100644
index 6593dcdc3..000000000
Binary files a/content/identity/securing-enterprise-mobile-apps/3-1024x621.jpg and /dev/null differ
diff --git a/content/identity/securing-enterprise-mobile-apps/3-1024x621.webp b/content/identity/securing-enterprise-mobile-apps/3-1024x621.webp
new file mode 100644
index 000000000..0b2391533
Binary files /dev/null and b/content/identity/securing-enterprise-mobile-apps/3-1024x621.webp differ
diff --git a/content/identity/securing-enterprise-mobile-apps/Book-a-demo-1024x310.png b/content/identity/securing-enterprise-mobile-apps/Book-a-demo-1024x310.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/securing-enterprise-mobile-apps/Book-a-demo-1024x310.png and /dev/null differ
diff --git a/content/identity/securing-enterprise-mobile-apps/Book-a-demo-1024x310.webp b/content/identity/securing-enterprise-mobile-apps/Book-a-demo-1024x310.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/securing-enterprise-mobile-apps/Book-a-demo-1024x310.webp differ
diff --git "a/content/identity/securing-enterprise-mobile-apps/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png" "b/content/identity/securing-enterprise-mobile-apps/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png"
deleted file mode 100644
index 6b3ba826e..000000000
Binary files "a/content/identity/securing-enterprise-mobile-apps/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.png" and /dev/null differ
diff --git "a/content/identity/securing-enterprise-mobile-apps/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp" "b/content/identity/securing-enterprise-mobile-apps/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp"
new file mode 100644
index 000000000..ba14612ce
Binary files /dev/null and "b/content/identity/securing-enterprise-mobile-apps/EB-The-Enterprise-Buyer\342\200\231s-Guide-to-Consumer-Identity.webp" differ
diff --git a/content/identity/securing-enterprise-mobile-apps/Secure-Enterprise-Mobile-App.jpg b/content/identity/securing-enterprise-mobile-apps/Secure-Enterprise-Mobile-App.jpg
deleted file mode 100644
index 31c5e634c..000000000
Binary files a/content/identity/securing-enterprise-mobile-apps/Secure-Enterprise-Mobile-App.jpg and /dev/null differ
diff --git a/content/identity/securing-enterprise-mobile-apps/Secure-Enterprise-Mobile-App.webp b/content/identity/securing-enterprise-mobile-apps/Secure-Enterprise-Mobile-App.webp
new file mode 100644
index 000000000..54f29be6d
Binary files /dev/null and b/content/identity/securing-enterprise-mobile-apps/Secure-Enterprise-Mobile-App.webp differ
diff --git a/content/identity/securing-enterprise-mobile-apps/image2-1.png b/content/identity/securing-enterprise-mobile-apps/image2-1.png
deleted file mode 100644
index 9b2c3270b..000000000
Binary files a/content/identity/securing-enterprise-mobile-apps/image2-1.png and /dev/null differ
diff --git a/content/identity/securing-enterprise-mobile-apps/image2-1.webp b/content/identity/securing-enterprise-mobile-apps/image2-1.webp
new file mode 100644
index 000000000..a7e8ede77
Binary files /dev/null and b/content/identity/securing-enterprise-mobile-apps/image2-1.webp differ
diff --git a/content/identity/securing-enterprise-mobile-apps/index.md b/content/identity/securing-enterprise-mobile-apps/index.md
index dd736cc03..a0b6bc655 100644
--- a/content/identity/securing-enterprise-mobile-apps/index.md
+++ b/content/identity/securing-enterprise-mobile-apps/index.md
@@ -1,7 +1,7 @@
---
title: "Securing Enterprise Mobile Apps with LoginRadius"
date: "2020-08-07"
-coverImage: "Secure-Enterprise-Mobile-App.jpg"
+coverImage: "Secure-Enterprise-Mobile-App.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -45,7 +45,7 @@ Following are the major threats security teams need to deal with:
**Insecure data storage**: There are many vulnerable places in an application where data can be stored: binary data stores, SQL databases, and cookie stores are a few. Majority of these vulnerabilities are triggered by the OS, frameworks, and compilers involved. Often, the poor storage of data results from inadequate processes to manage device gallery and data cache.
-[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
+[](https://www.loginradius.com/resource/the-enterprise-buyers-guide-to-consumer-identity/)
**Improper encryption**: Encryption is the method of translating data into an unreadable code that is only usable with the secret key after it has been re-translated. Therefore, it is important to evaluate how easy or difficult it might be to crack your application's secret code. This is a common vulnerability that hackers exploit with code and intellectual property theft, leading to [privacy violations](https://www.loginradius.com/blog/2019/12/digital-privacy-best-practices/), and damage to reputation.
@@ -57,11 +57,11 @@ Following are the major threats security teams need to deal with:
A holistic approach to security for mobile devices is regarded as an essential part of a security ecosystem. Keeping data storage and application management at the center, here's what the entire ecosystem looks like.
-
+
## Securing Mobile Apps Using LoginRadius' Secured Platform
-
+
LoginRadius, a [consumer identity and access management](https://www.loginradius.com/blog/2019/06/customer-identity-and-access-management/) (CIAM) solution, offers a comprehensive approach to protecting enterprise mobile applications. While human error is unavoidable, the platform is an all-in-one solution for all mobile security needs. Some of the features include:
@@ -92,4 +92,4 @@ Sadly, very few companies have a well-secured management policy, while still a l
Enterprise mobile app security is the need of the hour. Businesses must consider the changing state of cybersecurity and mobility when implementing the above-mentioned [protection tips](https://www.loginradius.com/resource/infographic/cybersecurity-best-practices-for-enterprise/) to secure their devices.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=securing-enterprise-mobile-apps)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=securing-enterprise-mobile-apps)
diff --git a/content/identity/securing-gen-ai-rbac-implementation/WP-dig-id.png b/content/identity/securing-gen-ai-rbac-implementation/WP-dig-id.png
deleted file mode 100644
index e028d55fb..000000000
Binary files a/content/identity/securing-gen-ai-rbac-implementation/WP-dig-id.png and /dev/null differ
diff --git a/content/identity/securing-gen-ai-rbac-implementation/WP-dig-id.webp b/content/identity/securing-gen-ai-rbac-implementation/WP-dig-id.webp
new file mode 100644
index 000000000..96ac842dc
Binary files /dev/null and b/content/identity/securing-gen-ai-rbac-implementation/WP-dig-id.webp differ
diff --git a/content/identity/securing-gen-ai-rbac-implementation/gen-ai-rbac.jpg b/content/identity/securing-gen-ai-rbac-implementation/gen-ai-rbac.jpg
deleted file mode 100644
index a92252042..000000000
Binary files a/content/identity/securing-gen-ai-rbac-implementation/gen-ai-rbac.jpg and /dev/null differ
diff --git a/content/identity/securing-gen-ai-rbac-implementation/gen-ai-rbac.webp b/content/identity/securing-gen-ai-rbac-implementation/gen-ai-rbac.webp
new file mode 100644
index 000000000..89df833c5
Binary files /dev/null and b/content/identity/securing-gen-ai-rbac-implementation/gen-ai-rbac.webp differ
diff --git a/content/identity/securing-gen-ai-rbac-implementation/index.md b/content/identity/securing-gen-ai-rbac-implementation/index.md
index ef4098b15..b45e67e90 100644
--- a/content/identity/securing-gen-ai-rbac-implementation/index.md
+++ b/content/identity/securing-gen-ai-rbac-implementation/index.md
@@ -1,7 +1,7 @@
---
title: "How To Secure GenAI by Implementing RBAC In The Enterprise"
date: "2024-08-12"
-coverImage: "gen-ai-rbac.jpg"
+coverImage: "gen-ai-rbac.webp"
tags: ["ai","data privacy","cx"]
author: "Kundan Singh"
description: "Generative AI (GenAI) is revolutionizing enterprises, but security challenges loom large. Implementing Role-Based Access Control (RBAC) offers a robust solution. This article explores how defining roles, mapping permissions, and enforcing access controls can protect your GenAI systems, ensuring secure and innovative AI-driven solutions."
@@ -70,7 +70,7 @@ With roles and permissions defined, the next step is to implement access control
* **Authentication:** Ensure all users are authenticated before accessing the system. Use multi-factor authentication (MFA) for added security.
-[](https://www.loginradius.com/resource/whitepaper/mfa-digital-identity-security/)
+[](https://www.loginradius.com/resource/whitepaper/mfa-digital-identity-security/)
* **Authorization:** Implement authorization mechanisms to enforce RBAC policies. Use customer identity and access management (CIAM) tools to manage user roles and permissions.
@@ -100,4 +100,4 @@ By defining roles and responsibilities, mapping permissions, implementing access
By embracing RBAC, organizations not only protect their valuable data but also build a foundation of trust and accountability, paving the way for innovative and secure AI-driven solutions.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=securing-gen-ai-rbac-implementation)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=securing-gen-ai-rbac-implementation)
\ No newline at end of file
diff --git a/content/identity/security-ux-can-coexist/index.md b/content/identity/security-ux-can-coexist/index.md
index ca05652af..9ac91728b 100644
--- a/content/identity/security-ux-can-coexist/index.md
+++ b/content/identity/security-ux-can-coexist/index.md
@@ -1,7 +1,7 @@
---
title: "Can Security and User Experience Co-Exist in the Authenticating and Authorizing Space?"
date: "2023-01-12"
-coverImage: "ux-security.jpg"
+coverImage: "ux-security.webp"
tags: ["security", "user experience", "customer identity"]
author: "Rakesh Soni"
description: "Businesses have leveraged a robust customer identity and access management (CIAM) solution for years to secure customer identities and eventually deliver a seamless user experience across multiple touchpoints. Let’s figure out how a CIAM does wonders for a business while creating a perfect user experience and security harmony."
@@ -75,4 +75,4 @@ With a new-age CIAM solution like LoginRadius CIAM, balancing security with user
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=security-ux-can-coexist)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=security-ux-can-coexist)
diff --git a/content/identity/security-ux-can-coexist/ux-security.jpg b/content/identity/security-ux-can-coexist/ux-security.jpg
deleted file mode 100644
index f8c0a1b13..000000000
Binary files a/content/identity/security-ux-can-coexist/ux-security.jpg and /dev/null differ
diff --git a/content/identity/security-ux-can-coexist/ux-security.webp b/content/identity/security-ux-can-coexist/ux-security.webp
new file mode 100644
index 000000000..c166832a2
Binary files /dev/null and b/content/identity/security-ux-can-coexist/ux-security.webp differ
diff --git a/content/identity/self-managed-vs-service-based-sso-solutions/WP-resilience.png b/content/identity/self-managed-vs-service-based-sso-solutions/WP-resilience.png
deleted file mode 100644
index cbe459800..000000000
Binary files a/content/identity/self-managed-vs-service-based-sso-solutions/WP-resilience.png and /dev/null differ
diff --git a/content/identity/self-managed-vs-service-based-sso-solutions/WP-resilience.webp b/content/identity/self-managed-vs-service-based-sso-solutions/WP-resilience.webp
new file mode 100644
index 000000000..efb695fb3
Binary files /dev/null and b/content/identity/self-managed-vs-service-based-sso-solutions/WP-resilience.webp differ
diff --git a/content/identity/self-managed-vs-service-based-sso-solutions/index.md b/content/identity/self-managed-vs-service-based-sso-solutions/index.md
index d11f57b42..d7b8725a0 100644
--- a/content/identity/self-managed-vs-service-based-sso-solutions/index.md
+++ b/content/identity/self-managed-vs-service-based-sso-solutions/index.md
@@ -1,7 +1,7 @@
---
title: "Choosing Between Self-Managed and Service-Based SSO Solutions: A Comprehensive Comparison"
date: "2023-07-03"
-coverImage: "self-managed-vs-service-based.jpg"
+coverImage: "self-managed-vs-service-based.webp"
tags: ["single sign-on","compliance","authentication","cx"]
author: "Rakesh Soni"
description: "Here’s a comprehensive comparison between self-managed and service-based SSO solutions, exploring factors such as control, customization, maintenance, scalability, security, and cost. This blog will help you make an informed decision that aligns with your organization's needs and goals."
@@ -46,7 +46,7 @@ Service-based solutions excel in terms of scalability and flexibility. They are
As organizations grow or introduce new software, service-based solutions can quickly scale up or down to meet evolving requirements. In contrast, self-managed solutions may require additional resources, expertise, and time to scale effectively, which can challenge organizations with rapidly changing needs.
-[](https://www.loginradius.com/resource/enterprise-scalability-and-performance)
+[](https://www.loginradius.com/resource/enterprise-scalability-and-performance)
### 4. Security and Compliance
@@ -72,4 +72,4 @@ Choosing between self-managed and service-based SSO solutions requires carefully
When deciding, it is crucial to consider factors such as control, maintenance, scalability, security, and cost. Choosing between self-managed and service-based SSO solutions should align with your organization's unique requirements and priorities.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=self-managed-vs-service-based-sso-solutions)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=self-managed-vs-service-based-sso-solutions)
diff --git a/content/identity/self-managed-vs-service-based-sso-solutions/self-managed-vs-service-based.jpg b/content/identity/self-managed-vs-service-based-sso-solutions/self-managed-vs-service-based.jpg
deleted file mode 100644
index d67774aa3..000000000
Binary files a/content/identity/self-managed-vs-service-based-sso-solutions/self-managed-vs-service-based.jpg and /dev/null differ
diff --git a/content/identity/self-managed-vs-service-based-sso-solutions/self-managed-vs-service-based.webp b/content/identity/self-managed-vs-service-based-sso-solutions/self-managed-vs-service-based.webp
new file mode 100644
index 000000000..3c9ece775
Binary files /dev/null and b/content/identity/self-managed-vs-service-based-sso-solutions/self-managed-vs-service-based.webp differ
diff --git a/content/identity/silver-saml-digital-identity-protection/WP-mfa-digital-identity.png b/content/identity/silver-saml-digital-identity-protection/WP-mfa-digital-identity.png
deleted file mode 100644
index e028d55fb..000000000
Binary files a/content/identity/silver-saml-digital-identity-protection/WP-mfa-digital-identity.png and /dev/null differ
diff --git a/content/identity/silver-saml-digital-identity-protection/WP-mfa-digital-identity.webp b/content/identity/silver-saml-digital-identity-protection/WP-mfa-digital-identity.webp
new file mode 100644
index 000000000..96ac842dc
Binary files /dev/null and b/content/identity/silver-saml-digital-identity-protection/WP-mfa-digital-identity.webp differ
diff --git a/content/identity/silver-saml-digital-identity-protection/index.md b/content/identity/silver-saml-digital-identity-protection/index.md
index d93309e9b..f2b5e6c49 100644
--- a/content/identity/silver-saml-digital-identity-protection/index.md
+++ b/content/identity/silver-saml-digital-identity-protection/index.md
@@ -1,7 +1,7 @@
---
title: "What is Silver SAML Vulnerability and How Can We Protect Our Digital Identities?"
date: "2024-04-29"
-coverImage: "silver-saml.jpg"
+coverImage: "silver-saml.webp"
tags: ["saml","digital identity management","data security"]
author: "Alok Patidar"
description: "This blog explores the Silver SAML vulnerability and its significance in protecting digital identities. From SAML basics to mitigation tactics, it provides essential insights for safeguarding against cyber threats."
@@ -56,7 +56,7 @@ Organizations must establish effective patch management protocols to mitigate th
Implementing [multi-factor authentication](https://www.loginradius.com/multi-factor-authentication/) (MFA) strengthens user authentication processes, reducing the likelihood of successful Silver SAML attacks.
-[](https://www.loginradius.com/resource/whitepaper/mfa-digital-identity-security/)
+[](https://www.loginradius.com/resource/whitepaper/mfa-digital-identity-security/)
By incorporating additional layers of verification, such as biometric data or one-time passcodes, organizations can enhance security posture and safeguard against unauthorized access.
@@ -86,4 +86,4 @@ As digital transformation accelerates and reliance on federated identity systems
By understanding the nuances of this vulnerability, implementing proactive security measures, and fostering a culture of vigilance, organizations can navigate the complexities of the modern cybersecurity landscape with resilience and confidence. Together, let us forge a path towards a safer, more secure digital future.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=silver-saml-digital-identity-protection)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=silver-saml-digital-identity-protection)
\ No newline at end of file
diff --git a/content/identity/silver-saml-digital-identity-protection/silver-saml.jpg b/content/identity/silver-saml-digital-identity-protection/silver-saml.jpg
deleted file mode 100644
index 274cdbba8..000000000
Binary files a/content/identity/silver-saml-digital-identity-protection/silver-saml.jpg and /dev/null differ
diff --git a/content/identity/silver-saml-digital-identity-protection/silver-saml.webp b/content/identity/silver-saml-digital-identity-protection/silver-saml.webp
new file mode 100644
index 000000000..c5a4570f6
Binary files /dev/null and b/content/identity/silver-saml-digital-identity-protection/silver-saml.webp differ
diff --git a/content/identity/single-page-applications/Book-a-free-demo-request-1024x310.png b/content/identity/single-page-applications/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/single-page-applications/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/single-page-applications/Book-a-free-demo-request-1024x310.webp b/content/identity/single-page-applications/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/single-page-applications/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/single-page-applications/LoginRadius-Standard-Login-Datasheet.png b/content/identity/single-page-applications/LoginRadius-Standard-Login-Datasheet.png
deleted file mode 100644
index d08410088..000000000
Binary files a/content/identity/single-page-applications/LoginRadius-Standard-Login-Datasheet.png and /dev/null differ
diff --git a/content/identity/single-page-applications/LoginRadius-Standard-Login-Datasheet.webp b/content/identity/single-page-applications/LoginRadius-Standard-Login-Datasheet.webp
new file mode 100644
index 000000000..e6fc24344
Binary files /dev/null and b/content/identity/single-page-applications/LoginRadius-Standard-Login-Datasheet.webp differ
diff --git a/content/identity/single-page-applications/index.md b/content/identity/single-page-applications/index.md
index f17f2d0b0..1fc0beb5c 100644
--- a/content/identity/single-page-applications/index.md
+++ b/content/identity/single-page-applications/index.md
@@ -1,7 +1,7 @@
---
title: "Single-Page Applications: Building A Secure Login Pathway with LoginRadius"
date: "2020-09-03"
-coverImage: "single-page-applications.jpg"
+coverImage: "single-page-applications.webp"
tags: ["cx","authentication","ciam solution"]
author: "Rakesh Soni"
description: "Single-page apps, or SPAs, are web applications that load and update a single HTML page by dynamically rendering details from the browser as (and when) a user interacts with the programme."
@@ -58,7 +58,7 @@ These applications offer continuous user experiences, meaning they are easy to e
Single-page applications can be the best bet for mobile users too. Users spend most of the time scrolling feeds on Facebook and Instagram. They can sit back, relax, and enjoy the show.
-[](https://www.loginradius.com/resource/loginradius-ciam-standard-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-standard-login/)
## Security Challenges With Single-Page Applications
@@ -90,7 +90,7 @@ Here's an instance of how a CSRF can take place:
## Securing Single-Page Applications with LoginRadius
-
+
Now the questions arise, how do you safely [authorize and authenticate](https://www.loginradius.com/blog/2020/06/authentication-vs-authorization-infographic/#:~:text=Though%20both%20the%20terms%20sound,to%20perform%20a%20specific%20function.) your Single Page (SPA) users? Here, we are being particular about JavaScript web applications that run on the same domain as the API.
@@ -123,4 +123,4 @@ Cybersecurity issues aren't unique to Single-Page Applications. The users make r
Unlike the traditional non-SPAs where you had to secure individual pages on the server, all you need is to secure the data endpoints in single-page applications. Going by the options above, [dodging cybercriminals](https://www.loginradius.com/blog/identity/digital-privacy-best-practices/) should not be a big deal.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=single-page-applications)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=single-page-applications)
diff --git a/content/identity/single-page-applications/single-page-app-2.png b/content/identity/single-page-applications/single-page-app-2.png
deleted file mode 100644
index 49db26e6e..000000000
Binary files a/content/identity/single-page-applications/single-page-app-2.png and /dev/null differ
diff --git a/content/identity/single-page-applications/single-page-app-2.webp b/content/identity/single-page-applications/single-page-app-2.webp
new file mode 100644
index 000000000..c8a0d71e4
Binary files /dev/null and b/content/identity/single-page-applications/single-page-app-2.webp differ
diff --git a/content/identity/single-page-applications/single-page-application.png b/content/identity/single-page-applications/single-page-application.png
deleted file mode 100644
index ab2b89c5e..000000000
Binary files a/content/identity/single-page-applications/single-page-application.png and /dev/null differ
diff --git a/content/identity/single-page-applications/single-page-application.webp b/content/identity/single-page-applications/single-page-application.webp
new file mode 100644
index 000000000..70bac5267
Binary files /dev/null and b/content/identity/single-page-applications/single-page-application.webp differ
diff --git a/content/identity/single-page-applications/single-page-applications.jpg b/content/identity/single-page-applications/single-page-applications.jpg
deleted file mode 100644
index 263363ab7..000000000
Binary files a/content/identity/single-page-applications/single-page-applications.jpg and /dev/null differ
diff --git a/content/identity/single-page-applications/single-page-applications.webp b/content/identity/single-page-applications/single-page-applications.webp
new file mode 100644
index 000000000..e22dd84bd
Binary files /dev/null and b/content/identity/single-page-applications/single-page-applications.webp differ
diff --git a/content/identity/single-tenant-vs-multi-tenant/Future-proof-your-security.png b/content/identity/single-tenant-vs-multi-tenant/Future-proof-your-security.png
deleted file mode 100644
index 9b885caa8..000000000
Binary files a/content/identity/single-tenant-vs-multi-tenant/Future-proof-your-security.png and /dev/null differ
diff --git a/content/identity/single-tenant-vs-multi-tenant/Future-proof-your-security.webp b/content/identity/single-tenant-vs-multi-tenant/Future-proof-your-security.webp
new file mode 100644
index 000000000..62f54b93f
Binary files /dev/null and b/content/identity/single-tenant-vs-multi-tenant/Future-proof-your-security.webp differ
diff --git a/content/identity/single-tenant-vs-multi-tenant/index.md b/content/identity/single-tenant-vs-multi-tenant/index.md
index bc34b65b0..c79427d67 100644
--- a/content/identity/single-tenant-vs-multi-tenant/index.md
+++ b/content/identity/single-tenant-vs-multi-tenant/index.md
@@ -1,7 +1,7 @@
---
title: "Understanding the Difference Between Single-Tenant and Multi-Tenant Cloud [Infographic]"
date: "2021-02-26"
-coverImage: "single-tenant-vs-multi-tenant-cover.jpg"
+coverImage: "single-tenant-vs-multi-tenant-cover.webp"
tags: ["cloud computing","single tenant","multi tenant"]
author: "Rakesh Soni"
description: "A single-tenant cloud runs on dedicated infrastructure, while a multi-tenant cloud is a single cloud infrastructure built to serve multiple businesses. Check out the infographic by LoginRadius to understand the difference between the two and find out which is the right solution for your business."
@@ -55,7 +55,7 @@ Cloud providers offer multi-tenancy as a gateway to share the same application w
* **Flexible**: A multi-tenant cloud can allocate a pool of resources to the users who need it, as their needs scale up and down.
* **Efficient**: Multitenancy reduces the need to manage infrastructure and handle updates.
-[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
+[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
@@ -72,8 +72,8 @@ To learn more about Single-Tenant vs Multi-Tenant Cloud, check out the infograph
-
+
Contact us for your personalized deployment requirements.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=single-tenant-vs-multi-tenant)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=single-tenant-vs-multi-tenant)
diff --git a/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-cover.jpg b/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-cover.jpg
deleted file mode 100644
index 63ef26331..000000000
Binary files a/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-cover.jpg and /dev/null differ
diff --git a/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-cover.webp b/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-cover.webp
new file mode 100644
index 000000000..f51758163
Binary files /dev/null and b/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-cover.webp differ
diff --git a/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-infographic.png b/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-infographic.png
deleted file mode 100644
index 312e162bf..000000000
Binary files a/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-infographic.png and /dev/null differ
diff --git a/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-infographic.webp b/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-infographic.webp
new file mode 100644
index 000000000..47ea1d262
Binary files /dev/null and b/content/identity/single-tenant-vs-multi-tenant/single-tenant-vs-multi-tenant-infographic.webp differ
diff --git a/content/identity/skiperformance-loginradius-customer-success-story/Skiperformance-featured-image.jpeg b/content/identity/skiperformance-loginradius-customer-success-story/Skiperformance-featured-image.jpeg
deleted file mode 100644
index 62ff71399..000000000
Binary files a/content/identity/skiperformance-loginradius-customer-success-story/Skiperformance-featured-image.jpeg and /dev/null differ
diff --git a/content/identity/skiperformance-loginradius-customer-success-story/Skiperformance-featured-image.webp b/content/identity/skiperformance-loginradius-customer-success-story/Skiperformance-featured-image.webp
new file mode 100644
index 000000000..aa25aadd0
Binary files /dev/null and b/content/identity/skiperformance-loginradius-customer-success-story/Skiperformance-featured-image.webp differ
diff --git a/content/identity/skiperformance-loginradius-customer-success-story/index.md b/content/identity/skiperformance-loginradius-customer-success-story/index.md
index 3fb73e96e..45dbf5c5c 100644
--- a/content/identity/skiperformance-loginradius-customer-success-story/index.md
+++ b/content/identity/skiperformance-loginradius-customer-success-story/index.md
@@ -1,7 +1,7 @@
---
title: "Skiperformance - a LoginRadius Customer Success Story"
date: "2022-06-23"
-coverImage: "Skiperformance-featured-image.jpeg"
+coverImage: "Skiperformance-featured-image.webp"
tags: ["ecommerce", "customer success"]
author: "Ritika Kapahi"
description: "A greatly transformed user experience that welcomed over 600,000 new customers for Skiperformance."
@@ -91,4 +91,4 @@ Skiperformance has achieved impressive results since that decision, including:
* Better customer experience
* The e-platform meets the demands of resort customers, as well as complying with industry standards for social behavior, legal and privacy issues.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=skiperformance-loginradius-customer-success-story)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=skiperformance-loginradius-customer-success-story)
diff --git a/content/identity/smart-cities-improve-unified-identity/index.md b/content/identity/smart-cities-improve-unified-identity/index.md
index 280d20d78..49244e440 100644
--- a/content/identity/smart-cities-improve-unified-identity/index.md
+++ b/content/identity/smart-cities-improve-unified-identity/index.md
@@ -1,7 +1,7 @@
---
title: "How Cities Can Improve Civilians’ Digital Experience with Unified Identity"
date: "2021-08-25"
-coverImage: "smart-cities-improve-unified-identity-cover.jpg"
+coverImage: "smart-cities-improve-unified-identity-cover.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -72,7 +72,7 @@ Hydro Ottawa is a regulated electricity local distribution company in eastern On
As the third-largest municipally-owned electric utility in Ontario, Hydro Ottawa maintains one of the safest, most reliable, and most cost-effective electricity distribution systems in the province. They serve about 332,000 residential and commercial customers across 1,116 square kilometers.
-[](https://www.loginradius.com/resource/case-study-page-hydro-ottawa/)
+[](https://www.loginradius.com/resource/case-study-page-hydro-ottawa/)
### Client Requirements
@@ -99,4 +99,4 @@ Digital identity is paving the path for a rich unified experience for citizens t
Robust consumer identity and access management solutions like [LoginRadius](https://www.loginradius.com/contact-sales/) can help public sectors deliver great experiences tacked by adequate security to their civilians, reinforcing different smart city projects.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=smart-cities-improve-unified-identity)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=smart-cities-improve-unified-identity)
diff --git a/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-Hydro-Ottawa.png b/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-Hydro-Ottawa.png
deleted file mode 100644
index cfb10b4f4..000000000
Binary files a/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-Hydro-Ottawa.png and /dev/null differ
diff --git a/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-Hydro-Ottawa.webp b/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-Hydro-Ottawa.webp
new file mode 100644
index 000000000..ed2760670
Binary files /dev/null and b/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-Hydro-Ottawa.webp differ
diff --git a/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-cover.jpg b/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-cover.jpg
deleted file mode 100644
index 5edaf5f41..000000000
Binary files a/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-cover.jpg and /dev/null differ
diff --git a/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-cover.webp b/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-cover.webp
new file mode 100644
index 000000000..f2c13f8f6
Binary files /dev/null and b/content/identity/smart-cities-improve-unified-identity/smart-cities-improve-unified-identity-cover.webp differ
diff --git a/content/identity/smart-citiy-cybersecurity-trends-2022/index.md b/content/identity/smart-citiy-cybersecurity-trends-2022/index.md
index 5244956f2..a1b4d44b5 100644
--- a/content/identity/smart-citiy-cybersecurity-trends-2022/index.md
+++ b/content/identity/smart-citiy-cybersecurity-trends-2022/index.md
@@ -1,7 +1,7 @@
---
title: "Smart Cities and Cyber Security Trends to Watch Out in 2022"
date: "2022-02-02"
-coverImage: "smart-cities.jpg"
+coverImage: "smart-cities.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -86,4 +86,4 @@ The threats mentioned above would continue to rise in the new year. Everyone mus
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=smart-citiy-cybersecurity-trends-2022)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=smart-citiy-cybersecurity-trends-2022)
diff --git a/content/identity/smart-citiy-cybersecurity-trends-2022/smart-cities.jpg b/content/identity/smart-citiy-cybersecurity-trends-2022/smart-cities.jpg
deleted file mode 100644
index 3ec18f62c..000000000
Binary files a/content/identity/smart-citiy-cybersecurity-trends-2022/smart-cities.jpg and /dev/null differ
diff --git a/content/identity/smart-citiy-cybersecurity-trends-2022/smart-cities.webp b/content/identity/smart-citiy-cybersecurity-trends-2022/smart-cities.webp
new file mode 100644
index 000000000..4d22d8339
Binary files /dev/null and b/content/identity/smart-citiy-cybersecurity-trends-2022/smart-cities.webp differ
diff --git a/content/identity/smart-credentials-raising-bar-physical-ids/DS-smart-iot-auth.png b/content/identity/smart-credentials-raising-bar-physical-ids/DS-smart-iot-auth.png
deleted file mode 100644
index 280233e92..000000000
Binary files a/content/identity/smart-credentials-raising-bar-physical-ids/DS-smart-iot-auth.png and /dev/null differ
diff --git a/content/identity/smart-credentials-raising-bar-physical-ids/DS-smart-iot-auth.webp b/content/identity/smart-credentials-raising-bar-physical-ids/DS-smart-iot-auth.webp
new file mode 100644
index 000000000..b8bf26c18
Binary files /dev/null and b/content/identity/smart-credentials-raising-bar-physical-ids/DS-smart-iot-auth.webp differ
diff --git a/content/identity/smart-credentials-raising-bar-physical-ids/index.md b/content/identity/smart-credentials-raising-bar-physical-ids/index.md
index 50071a97b..7f10079cb 100644
--- a/content/identity/smart-credentials-raising-bar-physical-ids/index.md
+++ b/content/identity/smart-credentials-raising-bar-physical-ids/index.md
@@ -1,7 +1,7 @@
---
title: "How The Age Of Smart Credentials Is Rewriting The Rules For Physical Verification?"
date: "2022-11-30"
-coverImage: "smart-credentials.jpg"
+coverImage: "smart-credentials.webp"
tags: ["digital identity","smart credentials", "iot", "identity verification"]
author: "Rakesh Soni"
description: "As technology advances, the need for national standards and interoperable applications raises the stakes for physical verification of identity. Smart credentials may offer better solutions to today's problems, but only if proper safeguarding is in place."
@@ -31,7 +31,7 @@ We are getting closer and closer to a world where everything is connected and ca
Smart credentials are already being used by some companies around the world—for everything from employee badges to medical records—and they could change the way we do things forever!
-[](https://www.loginradius.com/resource/smart-iot-authentication-datasheet)
+[](https://www.loginradius.com/resource/smart-iot-authentication-datasheet)
## How Portable Smart Credentials Can Prevent Identity Theft?
@@ -58,4 +58,4 @@ The reason we should all have an interest in smart credentials is simple. [Digit
We will only be dependent on a physical card that might never be accepted where we want it to be. We will increasingly have greater control over protecting our identities by ensuring that sensitive personal information is not disseminated unnecessarily.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=smart-credentials-raising-bar-physical-ids)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=smart-credentials-raising-bar-physical-ids)
diff --git a/content/identity/smart-credentials-raising-bar-physical-ids/smart-credentials.jpg b/content/identity/smart-credentials-raising-bar-physical-ids/smart-credentials.jpg
deleted file mode 100644
index c0b09f09f..000000000
Binary files a/content/identity/smart-credentials-raising-bar-physical-ids/smart-credentials.jpg and /dev/null differ
diff --git a/content/identity/smart-credentials-raising-bar-physical-ids/smart-credentials.webp b/content/identity/smart-credentials-raising-bar-physical-ids/smart-credentials.webp
new file mode 100644
index 000000000..978096eb9
Binary files /dev/null and b/content/identity/smart-credentials-raising-bar-physical-ids/smart-credentials.webp differ
diff --git a/content/identity/smart-credentials-raising-bar-physical-ids/smart-login-ds.png b/content/identity/smart-credentials-raising-bar-physical-ids/smart-login-ds.png
deleted file mode 100644
index 7e8cb44e5..000000000
Binary files a/content/identity/smart-credentials-raising-bar-physical-ids/smart-login-ds.png and /dev/null differ
diff --git a/content/identity/smart-credentials-raising-bar-physical-ids/smart-login-ds.webp b/content/identity/smart-credentials-raising-bar-physical-ids/smart-login-ds.webp
new file mode 100644
index 000000000..4b62e787b
Binary files /dev/null and b/content/identity/smart-credentials-raising-bar-physical-ids/smart-login-ds.webp differ
diff --git a/content/identity/sms-authentication-protect-business/index.md b/content/identity/sms-authentication-protect-business/index.md
index 5c575739a..0c392463b 100644
--- a/content/identity/sms-authentication-protect-business/index.md
+++ b/content/identity/sms-authentication-protect-business/index.md
@@ -1,7 +1,7 @@
---
title: "SMS Authentication — Can it Really Protect Your Business?"
date: "2021-09-02"
-coverImage: "sms-authentication-protect-business-cover.jpg"
+coverImage: "sms-authentication-protect-business-cover.webp"
tags: ["security"]
featured: false
author: "Ashish Kumar Yadav"
@@ -52,7 +52,7 @@ Even after being so convenient and easy to operate, there are some demerits also
3. **Social Engineering Attacks:** Compared to earlier days, more devices are now connected to the internet today. Today, [a simple phishing link](https://www.loginradius.com/blog/identity/phishing-for-identity/) via a text msg or any advertisement will do the job. If a consumer clicks on the link by mistake or falls into any such trap, all his data will be gained by hackers, including SMS.
-[](https://www.loginradius.com/resource/loginradius-ciam-phone-authentication/)
+[](https://www.loginradius.com/resource/loginradius-ciam-phone-authentication/)
## Should Businesses Use SMS Authentication?
@@ -76,4 +76,4 @@ But businesses need to find an alternative for this as SMS authentication cannot
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sms-authentication-protect-business)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sms-authentication-protect-business)
diff --git a/content/identity/sms-authentication-protect-business/phone-auth-DS.png b/content/identity/sms-authentication-protect-business/phone-auth-DS.png
deleted file mode 100644
index c160e816a..000000000
Binary files a/content/identity/sms-authentication-protect-business/phone-auth-DS.png and /dev/null differ
diff --git a/content/identity/sms-authentication-protect-business/phone-auth-DS.webp b/content/identity/sms-authentication-protect-business/phone-auth-DS.webp
new file mode 100644
index 000000000..6121a4a47
Binary files /dev/null and b/content/identity/sms-authentication-protect-business/phone-auth-DS.webp differ
diff --git a/content/identity/sms-authentication-protect-business/sms-authentication-protect-business-cover.jpg b/content/identity/sms-authentication-protect-business/sms-authentication-protect-business-cover.jpg
deleted file mode 100644
index 2f7423eb0..000000000
Binary files a/content/identity/sms-authentication-protect-business/sms-authentication-protect-business-cover.jpg and /dev/null differ
diff --git a/content/identity/sms-authentication-protect-business/sms-authentication-protect-business-cover.webp b/content/identity/sms-authentication-protect-business/sms-authentication-protect-business-cover.webp
new file mode 100644
index 000000000..8377cbcca
Binary files /dev/null and b/content/identity/sms-authentication-protect-business/sms-authentication-protect-business-cover.webp differ
diff --git a/content/identity/social-authentication/index.md b/content/identity/social-authentication/index.md
index 1c1959e96..5c230d650 100644
--- a/content/identity/social-authentication/index.md
+++ b/content/identity/social-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Implementing Effective Social Authentication Solution with LoginRadius"
date: "2021-05-07"
-coverImage: "social-authentication-cover.jpg"
+coverImage: "social-authentication-cover.webp"
tags: ["social authentication","social login","cx"]
author: "Vishal Sharma"
description: "Social login enables users to use existing login credentials from a social networking platform including Facebook, Google, Twitter, and more enabling simplified logins and registrations. Let’s learn how LoginRadius simplifies social authentication and improves the overall user experience."
@@ -41,7 +41,7 @@ LoginRadius is the leading [consumer identity and access management (CIAM) ](htt
Our social authentication solution is helping diverse businesses securely manage millions of identities along and offering quick sign-ups without hampering user experience.
-[](https://www.loginradius.com/resource/social-login-reconsidered/)
+[](https://www.loginradius.com/resource/social-login-reconsidered/)
Let’s learn why LoginRadius is the one-stop-solution for your online platform:
@@ -99,4 +99,4 @@ While social login inches towards the verge of becoming an industry standard for
LoginRadius’ social authentication, driven by cutting-edge technology and backed by the highest level of security ensures clients get a seamless user experience that further improves conversion rate.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=social-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=social-authentication)
\ No newline at end of file
diff --git a/content/identity/social-authentication/social-authentication-cover.jpg b/content/identity/social-authentication/social-authentication-cover.jpg
deleted file mode 100644
index 940e57898..000000000
Binary files a/content/identity/social-authentication/social-authentication-cover.jpg and /dev/null differ
diff --git a/content/identity/social-authentication/social-authentication-cover.webp b/content/identity/social-authentication/social-authentication-cover.webp
new file mode 100644
index 000000000..8e0d5346f
Binary files /dev/null and b/content/identity/social-authentication/social-authentication-cover.webp differ
diff --git a/content/identity/social-authentication/social-login-wp.png b/content/identity/social-authentication/social-login-wp.png
deleted file mode 100644
index 412e2195c..000000000
Binary files a/content/identity/social-authentication/social-login-wp.png and /dev/null differ
diff --git a/content/identity/social-authentication/social-login-wp.webp b/content/identity/social-authentication/social-login-wp.webp
new file mode 100644
index 000000000..6e975bd35
Binary files /dev/null and b/content/identity/social-authentication/social-login-wp.webp differ
diff --git a/content/identity/social-engineering-attacks/BD-Plexicon1-1024x310-1.png b/content/identity/social-engineering-attacks/BD-Plexicon1-1024x310-1.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/social-engineering-attacks/BD-Plexicon1-1024x310-1.png and /dev/null differ
diff --git a/content/identity/social-engineering-attacks/BD-Plexicon1-1024x310-1.webp b/content/identity/social-engineering-attacks/BD-Plexicon1-1024x310-1.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/social-engineering-attacks/BD-Plexicon1-1024x310-1.webp differ
diff --git a/content/identity/social-engineering-attacks/SET-1.png b/content/identity/social-engineering-attacks/SET-1.png
deleted file mode 100644
index 4ab71a655..000000000
Binary files a/content/identity/social-engineering-attacks/SET-1.png and /dev/null differ
diff --git a/content/identity/social-engineering-attacks/SET-1.webp b/content/identity/social-engineering-attacks/SET-1.webp
new file mode 100644
index 000000000..8f08524fe
Binary files /dev/null and b/content/identity/social-engineering-attacks/SET-1.webp differ
diff --git a/content/identity/social-engineering-attacks/Social-Engineering-Attacks-2.png b/content/identity/social-engineering-attacks/Social-Engineering-Attacks-2.png
deleted file mode 100644
index 62fb61170..000000000
Binary files a/content/identity/social-engineering-attacks/Social-Engineering-Attacks-2.png and /dev/null differ
diff --git a/content/identity/social-engineering-attacks/Social-Engineering-Attacks-2.webp b/content/identity/social-engineering-attacks/Social-Engineering-Attacks-2.webp
new file mode 100644
index 000000000..5527c7c1b
Binary files /dev/null and b/content/identity/social-engineering-attacks/Social-Engineering-Attacks-2.webp differ
diff --git a/content/identity/social-engineering-attacks/index.md b/content/identity/social-engineering-attacks/index.md
index 2d38bd429..7dc4dba7b 100644
--- a/content/identity/social-engineering-attacks/index.md
+++ b/content/identity/social-engineering-attacks/index.md
@@ -1,7 +1,7 @@
---
title: "Social Engineering Attacks: Prevention and Best Practices [Infographic]"
date: "2020-10-06"
-coverImage: "social-engineering-attacks.jpg"
+coverImage: "social-engineering-attacks.webp"
tags: ["data security","authentication","mfa"]
author: "Rakesh Soni"
description: "Over the years, social engineering attacks have been a regular phenomenon against companies. It has actually become more and more sophisticated. It is high time for businesses to perform careful research and use the right instruments to remain ahead of fraudsters."
@@ -38,7 +38,7 @@ Here is a quick overview of the most common social engineering scams used agains
For example, the fraudster might pretend to represent a bank, a government organization, or a major corporation trusted by the naive victim. The source can be an email asking the email recipients to click on a link to log in to their accounts. They are then redirected to a fake website appearing to be legitimate, and that's where the attack takes place.
-[](https://www.loginradius.com/resource/passwords-are-dead/)
+[](https://www.loginradius.com/resource/passwords-are-dead/)
### Spear Phishing
@@ -88,6 +88,6 @@ Be careful of what you share. And no, you don't need to be paranoid about these
To learn more about Social Engineering Attacks – preventions and best practices, check out the infographic created by LoginRadius.
-
+
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=social-engineering-attacks)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=social-engineering-attacks)
diff --git a/content/identity/social-engineering-attacks/social-engineering-attack.png b/content/identity/social-engineering-attacks/social-engineering-attack.png
deleted file mode 100644
index a3b85751d..000000000
Binary files a/content/identity/social-engineering-attacks/social-engineering-attack.png and /dev/null differ
diff --git a/content/identity/social-engineering-attacks/social-engineering-attack.webp b/content/identity/social-engineering-attacks/social-engineering-attack.webp
new file mode 100644
index 000000000..e10919bf7
Binary files /dev/null and b/content/identity/social-engineering-attacks/social-engineering-attack.webp differ
diff --git a/content/identity/social-engineering-attacks/social-engineering-attacks.jpg b/content/identity/social-engineering-attacks/social-engineering-attacks.jpg
deleted file mode 100644
index 19aeeabf2..000000000
Binary files a/content/identity/social-engineering-attacks/social-engineering-attacks.jpg and /dev/null differ
diff --git a/content/identity/social-engineering-attacks/social-engineering-attacks.webp b/content/identity/social-engineering-attacks/social-engineering-attacks.webp
new file mode 100644
index 000000000..4f403a2ab
Binary files /dev/null and b/content/identity/social-engineering-attacks/social-engineering-attacks.webp differ
diff --git a/content/identity/social-login-infographic/index.md b/content/identity/social-login-infographic/index.md
index 0119aa097..db2ee36b2 100644
--- a/content/identity/social-login-infographic/index.md
+++ b/content/identity/social-login-infographic/index.md
@@ -1,7 +1,7 @@
---
title: "Why Do Consumers Prefer Social Login [Infographic]"
date: "2021-02-24"
-coverImage: "social-login.jpg"
+coverImage: "social-login.webp"
tags: ["ciam","social login","cx"]
author: "Rakesh Soni"
description: "Social login simplifies registration and login for consumers. For this primary reason, social login is gaining popularity among ecommerce brands and retailers looking to turn visitors into buying customers."
@@ -29,7 +29,7 @@ You don't need to do a lot for work to implement social login. Here's how it wor
**Step 3**: The consumer gets access to the app once the social provider confirms the identity.
-[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
+[](https://www.loginradius.com/resource/loginradius-ciam-social-login/)
## Benefits of Social Login
@@ -47,6 +47,6 @@ You don't need to do a lot for work to implement social login. Here's how it wor
To learn more about Social login – how it works and advantages, check out the infographic created by LoginRadius.
-
+
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=social-login-infographic)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=social-login-infographic)
diff --git a/content/identity/social-login-infographic/social-login-datasheet.png b/content/identity/social-login-infographic/social-login-datasheet.png
deleted file mode 100644
index 98e481315..000000000
Binary files a/content/identity/social-login-infographic/social-login-datasheet.png and /dev/null differ
diff --git a/content/identity/social-login-infographic/social-login-datasheet.webp b/content/identity/social-login-infographic/social-login-datasheet.webp
new file mode 100644
index 000000000..5e3eaf627
Binary files /dev/null and b/content/identity/social-login-infographic/social-login-datasheet.webp differ
diff --git a/content/identity/social-login-infographic/social-login-infographic.png b/content/identity/social-login-infographic/social-login-infographic.png
deleted file mode 100644
index 232b57e3b..000000000
Binary files a/content/identity/social-login-infographic/social-login-infographic.png and /dev/null differ
diff --git a/content/identity/social-login-infographic/social-login-infographic.webp b/content/identity/social-login-infographic/social-login-infographic.webp
new file mode 100644
index 000000000..2cdea0f9a
Binary files /dev/null and b/content/identity/social-login-infographic/social-login-infographic.webp differ
diff --git a/content/identity/social-login-infographic/social-login.jpg b/content/identity/social-login-infographic/social-login.jpg
deleted file mode 100644
index 531e223e9..000000000
Binary files a/content/identity/social-login-infographic/social-login.jpg and /dev/null differ
diff --git a/content/identity/social-login-infographic/social-login.webp b/content/identity/social-login-infographic/social-login.webp
new file mode 100644
index 000000000..f77ed27d4
Binary files /dev/null and b/content/identity/social-login-infographic/social-login.webp differ
diff --git a/content/identity/social-media-privacy-threats-2022/WP-social-login-rec.png b/content/identity/social-media-privacy-threats-2022/WP-social-login-rec.png
deleted file mode 100644
index 4ea16b064..000000000
Binary files a/content/identity/social-media-privacy-threats-2022/WP-social-login-rec.png and /dev/null differ
diff --git a/content/identity/social-media-privacy-threats-2022/WP-social-login-rec.webp b/content/identity/social-media-privacy-threats-2022/WP-social-login-rec.webp
new file mode 100644
index 000000000..7e6ca6673
Binary files /dev/null and b/content/identity/social-media-privacy-threats-2022/WP-social-login-rec.webp differ
diff --git a/content/identity/social-media-privacy-threats-2022/index.md b/content/identity/social-media-privacy-threats-2022/index.md
index 6e76f952f..215395cbf 100644
--- a/content/identity/social-media-privacy-threats-2022/index.md
+++ b/content/identity/social-media-privacy-threats-2022/index.md
@@ -1,7 +1,7 @@
---
title: "5 Privacy Threats in Social Media You Should Know in 2022"
date: "2022-02-11"
-coverImage: "social-privacy.jpg"
+coverImage: "social-privacy.webp"
tags: ["social login","data security","cx"]
author: "Nikola Sekulic"
description: "With the rise in a number of highly publicized cybersecurity breaches, businesses and consumers must remain vigilant to protect sensitive information on social media. There is no doubt that cyber threats will continue to rise over the next few years, so being prepared is key."
@@ -28,7 +28,7 @@ This doesn’t mean that you shouldn’t invest in social media ads, but you nee
Yes, it is important to target the right people, but you don’t want your ads to turn your followers against you - after all, people don’t like ads that seem to “know” too much.
-[](https://www.loginradius.com/resource/social-login-reconsidered/)
+[](https://www.loginradius.com/resource/social-login-reconsidered/)
### Identity theft and impersonation
@@ -79,4 +79,4 @@ Make sure to:
Securing your sensitive data on social media and minimizing cybersecurity risks should be a top priority for companies and consumers in 2022. Make sure to keep these privacy threats in mind and use these tips to keep your business, your employees, and your customers safe in an increasingly dangerous online world.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=social-media-privacy-threats-2022)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=social-media-privacy-threats-2022)
diff --git a/content/identity/social-media-privacy-threats-2022/social-login-wp.png b/content/identity/social-media-privacy-threats-2022/social-login-wp.png
deleted file mode 100644
index 412e2195c..000000000
Binary files a/content/identity/social-media-privacy-threats-2022/social-login-wp.png and /dev/null differ
diff --git a/content/identity/social-media-privacy-threats-2022/social-login-wp.webp b/content/identity/social-media-privacy-threats-2022/social-login-wp.webp
new file mode 100644
index 000000000..6e975bd35
Binary files /dev/null and b/content/identity/social-media-privacy-threats-2022/social-login-wp.webp differ
diff --git a/content/identity/social-media-privacy-threats-2022/social-privacy.jpg b/content/identity/social-media-privacy-threats-2022/social-privacy.jpg
deleted file mode 100644
index f7a7bbc1c..000000000
Binary files a/content/identity/social-media-privacy-threats-2022/social-privacy.jpg and /dev/null differ
diff --git a/content/identity/social-media-privacy-threats-2022/social-privacy.webp b/content/identity/social-media-privacy-threats-2022/social-privacy.webp
new file mode 100644
index 000000000..29810990b
Binary files /dev/null and b/content/identity/social-media-privacy-threats-2022/social-privacy.webp differ
diff --git a/content/identity/sso-business-strategy/index.md b/content/identity/sso-business-strategy/index.md
index 598357eb8..0e7b09ef6 100644
--- a/content/identity/sso-business-strategy/index.md
+++ b/content/identity/sso-business-strategy/index.md
@@ -1,7 +1,7 @@
---
title: "How to Find the Right SSO Strategy that Fits Your Business"
date: "2021-10-25"
-coverImage: "sso-business-strategy.jpg"
+coverImage: "sso-business-strategy.webp"
tags: ["sso provider","data security","cx"]
author: "Manish Tiwari"
description: "In a competitive business environment, SSO (Single Sign-On) establishes a flawless user experience while providing the highest level of security and efficiency. Enterprises need to put their best foot forward in defining the right SSO strategy that fits right for their organization and helps pave the way for overall success."
@@ -77,7 +77,7 @@ Apart from delivering the industry's best consumer, the following are a few ways
* **Globally compliant:** The LoginRadius platform also complies with major global compliances like the GDPR, CCPA, etc. You can keep track of your consumers, manage preferences, and customize the kind of consent consumers want.
* **Security Certifications:** LoginRadius is compliant with international regulatory bodies like AICPA SOC 2, ISAE 3000, Cloud Security Alliance, Privacy Shield, and more.
-[](https://www.loginradius.com/resource/authentication-sso-native-mobile-apps-datasheet)
+[](https://www.loginradius.com/resource/authentication-sso-native-mobile-apps-datasheet)
## Are You Ready to Experience a Future-Ready SSO?
@@ -87,4 +87,4 @@ By implementing the benefits of the LoginRadius SSO as a unified solution, you i
Need more information about how SSO benefits your business? [Contact us](https://www.loginradius.com/contact-sales) for a free personalized demo.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-business-strategy)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-business-strategy)
\ No newline at end of file
diff --git a/content/identity/sso-business-strategy/native-mobile.png b/content/identity/sso-business-strategy/native-mobile.png
deleted file mode 100644
index 9368b122c..000000000
Binary files a/content/identity/sso-business-strategy/native-mobile.png and /dev/null differ
diff --git a/content/identity/sso-business-strategy/native-mobile.webp b/content/identity/sso-business-strategy/native-mobile.webp
new file mode 100644
index 000000000..44fba692f
Binary files /dev/null and b/content/identity/sso-business-strategy/native-mobile.webp differ
diff --git a/content/identity/sso-business-strategy/sso-business-strategy.jpg b/content/identity/sso-business-strategy/sso-business-strategy.jpg
deleted file mode 100644
index 5728232d4..000000000
Binary files a/content/identity/sso-business-strategy/sso-business-strategy.jpg and /dev/null differ
diff --git a/content/identity/sso-business-strategy/sso-business-strategy.webp b/content/identity/sso-business-strategy/sso-business-strategy.webp
new file mode 100644
index 000000000..272c23370
Binary files /dev/null and b/content/identity/sso-business-strategy/sso-business-strategy.webp differ
diff --git a/content/identity/sso-integration-secure-cx/RP-KuppingerCole.png b/content/identity/sso-integration-secure-cx/RP-KuppingerCole.png
deleted file mode 100644
index 0aa16452c..000000000
Binary files a/content/identity/sso-integration-secure-cx/RP-KuppingerCole.png and /dev/null differ
diff --git a/content/identity/sso-integration-secure-cx/RP-KuppingerCole.webp b/content/identity/sso-integration-secure-cx/RP-KuppingerCole.webp
new file mode 100644
index 000000000..e5bf32f97
Binary files /dev/null and b/content/identity/sso-integration-secure-cx/RP-KuppingerCole.webp differ
diff --git a/content/identity/sso-integration-secure-cx/index.md b/content/identity/sso-integration-secure-cx/index.md
index 7429d7a1d..0f78cb126 100644
--- a/content/identity/sso-integration-secure-cx/index.md
+++ b/content/identity/sso-integration-secure-cx/index.md
@@ -1,7 +1,7 @@
---
title: "SSO Integration: How to Secure the Customer Experience on Loyalty Platforms"
date: "2021-10-18"
-coverImage: "sso-integration-secure-cx-cover.jpg"
+coverImage: "sso-integration-secure-cx-cover.webp"
tags: ["sso","identity management","compliance"]
author: "Rakesh Soni"
description: "Today, consumers are enjoying flawless experiences on every platform but can’t indulge in a seamless experience when they connect with a loyalty platform for potential benefits. This post helps you understand the biggest challenge for loyalty platforms and how Single Sign-On (SSO) integration for consumer loyalty platforms solves the purpose."
@@ -109,7 +109,7 @@ The LoginRadius Identity Platform offers SSO in the following ways:
* **Federated SSO:** Login also helps you implement SSO with third-party applications. It is done through [federated SSO](https://www.loginradius.com/federated-sso/). LoginRadius Identity Platform supports all major industry single sign-on protocols like SAML, JWT, OAuth, and OpenID SSO protocols for interaction with various third-party web applications.
* **Custom IDPs:** Consider this as Social Login. Custom IDPs are used to configure a Social Login provider that is not available in the default list of providers by LoginRadius. You can use any external database to authenticate your application users.
-[](https://www.loginradius.com/resource/kuppingercole-industry-report-2020)
+[](https://www.loginradius.com/resource/kuppingercole-industry-report-2020)
## Other Good Reasons to Rely on LoginRadius
@@ -129,4 +129,4 @@ Single Sign-On improves consumer experience and boosts productivity by a conside
By implementing the benefits of the LoginRadius SSO as a unified solution, you increase business agility, security, convenient and streamlined experience for your business and consumers alike. [Contact us](https://www.loginradius.com/contact-sales) today.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-integration-secure-cx)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-integration-secure-cx)
diff --git a/content/identity/sso-integration-secure-cx/sso-integration-secure-cx-cover.jpg b/content/identity/sso-integration-secure-cx/sso-integration-secure-cx-cover.jpg
deleted file mode 100644
index f6ce1fe23..000000000
Binary files a/content/identity/sso-integration-secure-cx/sso-integration-secure-cx-cover.jpg and /dev/null differ
diff --git a/content/identity/sso-integration-secure-cx/sso-integration-secure-cx-cover.webp b/content/identity/sso-integration-secure-cx/sso-integration-secure-cx-cover.webp
new file mode 100644
index 000000000..3729933bd
Binary files /dev/null and b/content/identity/sso-integration-secure-cx/sso-integration-secure-cx-cover.webp differ
diff --git a/content/identity/sso-integrations-must-for-online-businesses/DS-SSO.png b/content/identity/sso-integrations-must-for-online-businesses/DS-SSO.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/sso-integrations-must-for-online-businesses/DS-SSO.png and /dev/null differ
diff --git a/content/identity/sso-integrations-must-for-online-businesses/DS-SSO.webp b/content/identity/sso-integrations-must-for-online-businesses/DS-SSO.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/sso-integrations-must-for-online-businesses/DS-SSO.webp differ
diff --git a/content/identity/sso-integrations-must-for-online-businesses/DS-ciam-SSO.png b/content/identity/sso-integrations-must-for-online-businesses/DS-ciam-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/sso-integrations-must-for-online-businesses/DS-ciam-SSO.png and /dev/null differ
diff --git a/content/identity/sso-integrations-must-for-online-businesses/DS-ciam-SSO.webp b/content/identity/sso-integrations-must-for-online-businesses/DS-ciam-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/sso-integrations-must-for-online-businesses/DS-ciam-SSO.webp differ
diff --git a/content/identity/sso-integrations-must-for-online-businesses/index.md b/content/identity/sso-integrations-must-for-online-businesses/index.md
index 67e412cf3..09eae7503 100644
--- a/content/identity/sso-integrations-must-for-online-businesses/index.md
+++ b/content/identity/sso-integrations-must-for-online-businesses/index.md
@@ -1,7 +1,7 @@
---
title: "4 Reasons Why SSO Integrations Are a Must-Have For Online Businesses"
date: "2023-05-15"
-coverImage: "sso-integration.jpg"
+coverImage: "sso-integration.webp"
tags: ["single sign on","identity and access management","data security","cx"]
author: "Linda Gagaine"
description: "The primary goal of single sign-on is to enable users to access many applications with just one set of credentials. This is convenient for the user since they won't have to sign in as often, and it's safer for the company because there will be fewer instances of forgotten passwords."
@@ -61,7 +61,7 @@ Verizon’s Data Breach Investigations Report 2022 revealed 81% of all hacking e
Users are less likely to experience password fatigue, and hence fewer password resets are required when they are only required to remember one master password as opposed to several app-specific ones. In addition, you reduce the likelihood of users using the same password for several unsecured apps by having them log in just once each day.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
### 3. Fewer Costs
@@ -107,4 +107,4 @@ Bridge the divide between the current system and what is needed. [Existing IAM p
Every day, the world of technology gives us new tools to incorporate into our lives. It's difficult and maybe dangerous to remember different, complicated passwords for every single one of the apps related to your business. However, with single sign-on integration, you can provide your users with streamlined, streamlined, and more secure access to all of your apps and services.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-integrations-must-for-online-businesses)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-integrations-must-for-online-businesses)
diff --git a/content/identity/sso-integrations-must-for-online-businesses/sso-integration.jpg b/content/identity/sso-integrations-must-for-online-businesses/sso-integration.jpg
deleted file mode 100644
index 838763ceb..000000000
Binary files a/content/identity/sso-integrations-must-for-online-businesses/sso-integration.jpg and /dev/null differ
diff --git a/content/identity/sso-integrations-must-for-online-businesses/sso-integration.webp b/content/identity/sso-integrations-must-for-online-businesses/sso-integration.webp
new file mode 100644
index 000000000..bf1bfea5e
Binary files /dev/null and b/content/identity/sso-integrations-must-for-online-businesses/sso-integration.webp differ
diff --git a/content/identity/sso-leverage-for-data-collection/DS-SSO.png b/content/identity/sso-leverage-for-data-collection/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/sso-leverage-for-data-collection/DS-SSO.png and /dev/null differ
diff --git a/content/identity/sso-leverage-for-data-collection/DS-SSO.webp b/content/identity/sso-leverage-for-data-collection/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/sso-leverage-for-data-collection/DS-SSO.webp differ
diff --git a/content/identity/sso-leverage-for-data-collection/SSO-ds.png b/content/identity/sso-leverage-for-data-collection/SSO-ds.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/sso-leverage-for-data-collection/SSO-ds.png and /dev/null differ
diff --git a/content/identity/sso-leverage-for-data-collection/SSO-ds.webp b/content/identity/sso-leverage-for-data-collection/SSO-ds.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/sso-leverage-for-data-collection/SSO-ds.webp differ
diff --git a/content/identity/sso-leverage-for-data-collection/index.md b/content/identity/sso-leverage-for-data-collection/index.md
index c63273d95..9b0bc426d 100644
--- a/content/identity/sso-leverage-for-data-collection/index.md
+++ b/content/identity/sso-leverage-for-data-collection/index.md
@@ -1,7 +1,7 @@
---
title: "How Can Enterprises Use SSO to Boost Data Collection?"
date: "2022-07-19"
-coverImage: "sso-leverage.jpg"
+coverImage: "sso-leverage.webp"
tags: ["sso", "mfa", "data collection", "ux"]
author: "Hanson Cheng"
description: "SSO is a great way to collect data while providing a better user experience and increasing security. This blog will help you get the most out of SSO for data collection, ensuring that your data is collected effectively and efficiently."
@@ -35,7 +35,7 @@ There are two types of SSO:
In general, SSO can also provide a[ more secure and frictionless user experience](https://www.loginradius.com/blog/growth/4-tips-secure-frictionless-ux/). If you have different applications, it can be difficult for users to set and remember passwords for all of them. With SSO, users would only have to remember one set of credentials. This would make it easier for them to access the applications they need and reduce the chance of forgetting their password.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
## The Importance of SSO Tokens
@@ -83,7 +83,7 @@ Let's say customers need to log in to access a sample invoice template and other
If we assume the template is in a PDF format and is behind a paywall, the customer must input their account details to access the content.
-
+
Without an SSO system, the customer would have to remember their username and password for your site. If they can't recall their login credentials, they'll have to go through the process of resetting their password.
@@ -121,4 +121,4 @@ Overall, using SSO for data collection can offer many benefits for businesses. I
If you're looking for a more efficient and secure way to collect data, consider implementing an SSO system in your business.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-leverage-for-data-collection)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-leverage-for-data-collection)
diff --git a/content/identity/sso-leverage-for-data-collection/sample-invoice.png b/content/identity/sso-leverage-for-data-collection/sample-invoice.png
deleted file mode 100644
index 7e68f2168..000000000
Binary files a/content/identity/sso-leverage-for-data-collection/sample-invoice.png and /dev/null differ
diff --git a/content/identity/sso-leverage-for-data-collection/sample-invoice.webp b/content/identity/sso-leverage-for-data-collection/sample-invoice.webp
new file mode 100644
index 000000000..dec5b0089
Binary files /dev/null and b/content/identity/sso-leverage-for-data-collection/sample-invoice.webp differ
diff --git a/content/identity/sso-leverage-for-data-collection/sso-leverage.jpg b/content/identity/sso-leverage-for-data-collection/sso-leverage.jpg
deleted file mode 100644
index 4ca11e817..000000000
Binary files a/content/identity/sso-leverage-for-data-collection/sso-leverage.jpg and /dev/null differ
diff --git a/content/identity/sso-leverage-for-data-collection/sso-leverage.webp b/content/identity/sso-leverage-for-data-collection/sso-leverage.webp
new file mode 100644
index 000000000..f111768a4
Binary files /dev/null and b/content/identity/sso-leverage-for-data-collection/sso-leverage.webp differ
diff --git a/content/identity/stay-compliant-with-data-privacy-laws-2023/EB-GDPR-Comp.png b/content/identity/stay-compliant-with-data-privacy-laws-2023/EB-GDPR-Comp.png
deleted file mode 100644
index a7a656cfa..000000000
Binary files a/content/identity/stay-compliant-with-data-privacy-laws-2023/EB-GDPR-Comp.png and /dev/null differ
diff --git a/content/identity/stay-compliant-with-data-privacy-laws-2023/EB-GDPR-Comp.webp b/content/identity/stay-compliant-with-data-privacy-laws-2023/EB-GDPR-Comp.webp
new file mode 100644
index 000000000..44c9529c0
Binary files /dev/null and b/content/identity/stay-compliant-with-data-privacy-laws-2023/EB-GDPR-Comp.webp differ
diff --git a/content/identity/stay-compliant-with-data-privacy-laws-2023/data-privacy-laws.jpg b/content/identity/stay-compliant-with-data-privacy-laws-2023/data-privacy-laws.jpg
deleted file mode 100644
index 035fc3ead..000000000
Binary files a/content/identity/stay-compliant-with-data-privacy-laws-2023/data-privacy-laws.jpg and /dev/null differ
diff --git a/content/identity/stay-compliant-with-data-privacy-laws-2023/data-privacy-laws.webp b/content/identity/stay-compliant-with-data-privacy-laws-2023/data-privacy-laws.webp
new file mode 100644
index 000000000..f35fb1b81
Binary files /dev/null and b/content/identity/stay-compliant-with-data-privacy-laws-2023/data-privacy-laws.webp differ
diff --git a/content/identity/stay-compliant-with-data-privacy-laws-2023/index.md b/content/identity/stay-compliant-with-data-privacy-laws-2023/index.md
index 336af5453..091d07950 100644
--- a/content/identity/stay-compliant-with-data-privacy-laws-2023/index.md
+++ b/content/identity/stay-compliant-with-data-privacy-laws-2023/index.md
@@ -1,7 +1,7 @@
---
title: "Data Privacy Laws for 2023: A Closer Look at 9 Key Regulations"
date: "2023-06-01"
-coverImage: "data-privacy-laws.jpg"
+coverImage: "data-privacy-laws.webp"
tags: ["data privacy", "cx", "compliance"]
author: "Alok Patidar"
description: "In this digital-first era, data privacy is of paramount importance. Discover the essential data privacy laws for 2023, including GDPR, CCPA, HIPAA, and more. Stay informed, protect sensitive data, and honor individuals' privacy rights with our comprehensive guide."
@@ -29,7 +29,7 @@ The GDPR, implemented by the European Union (EU), remains one of the most influe
The GDPR mandates several vital principles, including lawful and transparent data processing, purpose limitation, data minimization, accuracy, storage limitation, and accountability. It also grants individuals rights such as the right to access their data, the right to be forgotten, and the right to data portability. Non-compliance with the GDPR can result in substantial fines, making it essential for organizations to implement robust data privacy practices and mechanisms.
-[](https://www.loginradius.com/resource/loginradius-and-gdpr-compliance/)
+[](https://www.loginradius.com/resource/loginradius-and-gdpr-compliance/)
### 2. California Consumer Privacy Act (CCPA)
@@ -103,4 +103,4 @@ Staying compliant with these data privacy laws is crucial for organizations to m
By understanding the requirements of each law and implementing appropriate data privacy practices, businesses can navigate the complex landscape of data protection and prioritize the security and privacy of personal information.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=stay-compliant-with-data-privacy-laws-2023)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=stay-compliant-with-data-privacy-laws-2023)
diff --git a/content/identity/step-up-authentication-loginradius/index.md b/content/identity/step-up-authentication-loginradius/index.md
index b93c89ac8..d4b587c01 100644
--- a/content/identity/step-up-authentication-loginradius/index.md
+++ b/content/identity/step-up-authentication-loginradius/index.md
@@ -1,7 +1,7 @@
---
title: "LoginRadius Offers Additional Security Layer through Newly-Enhanced Step-up Authentication Feature"
date: "2021-06-17"
-coverImage: "step-up-authentication-loginradius-cover.jpg"
+coverImage: "step-up-authentication-loginradius-cover.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -51,4 +51,4 @@ Step-up authentication is a revolutionary feature when it comes to authenticatin
Implementing step-up authentication on an online platform offers a competitive edge to businesses seeking innovative ways to enhance authentication and security for their website or application.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=step-up-authentication-loginradius)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=step-up-authentication-loginradius)
diff --git a/content/identity/step-up-authentication-loginradius/step-up-authentication-loginradius-cover.jpg b/content/identity/step-up-authentication-loginradius/step-up-authentication-loginradius-cover.jpg
deleted file mode 100644
index 6437da2af..000000000
Binary files a/content/identity/step-up-authentication-loginradius/step-up-authentication-loginradius-cover.jpg and /dev/null differ
diff --git a/content/identity/step-up-authentication-loginradius/step-up-authentication-loginradius-cover.webp b/content/identity/step-up-authentication-loginradius/step-up-authentication-loginradius-cover.webp
new file mode 100644
index 000000000..d59b1d988
Binary files /dev/null and b/content/identity/step-up-authentication-loginradius/step-up-authentication-loginradius-cover.webp differ
diff --git a/content/identity/stop-scammers-getting-email-address/WP-bot-attacks.png b/content/identity/stop-scammers-getting-email-address/WP-bot-attacks.png
deleted file mode 100644
index fa1f0af30..000000000
Binary files a/content/identity/stop-scammers-getting-email-address/WP-bot-attacks.png and /dev/null differ
diff --git a/content/identity/stop-scammers-getting-email-address/WP-bot-attacks.webp b/content/identity/stop-scammers-getting-email-address/WP-bot-attacks.webp
new file mode 100644
index 000000000..094822f16
Binary files /dev/null and b/content/identity/stop-scammers-getting-email-address/WP-bot-attacks.webp differ
diff --git a/content/identity/stop-scammers-getting-email-address/bot-wp.png b/content/identity/stop-scammers-getting-email-address/bot-wp.png
deleted file mode 100644
index 9dfe42465..000000000
Binary files a/content/identity/stop-scammers-getting-email-address/bot-wp.png and /dev/null differ
diff --git a/content/identity/stop-scammers-getting-email-address/bot-wp.webp b/content/identity/stop-scammers-getting-email-address/bot-wp.webp
new file mode 100644
index 000000000..5228f080c
Binary files /dev/null and b/content/identity/stop-scammers-getting-email-address/bot-wp.webp differ
diff --git a/content/identity/stop-scammers-getting-email-address/index.md b/content/identity/stop-scammers-getting-email-address/index.md
index b989e9b7a..edbd5bf21 100644
--- a/content/identity/stop-scammers-getting-email-address/index.md
+++ b/content/identity/stop-scammers-getting-email-address/index.md
@@ -1,7 +1,7 @@
---
title: "This Is How Scammers Get Your Email Address & How to Stop Them"
date: "2022-01-19"
-coverImage: "scammers.jpg"
+coverImage: "scammers.webp"
tags: ["data security","2fa","mfa","cx"]
author: "Navanita Devi"
description: "When you type your email address into a website, be careful. You might have just given your email address to a scammer. Sadly, this happens all too often and is one of the main ways scammers harvest email addresses. This blog offers solutions on how to stop it from happening."
@@ -54,7 +54,7 @@ Scammers use [brute force attacks](https://www.loginradius.com/blog/identity/bru
Phishing email scams can often result when anyone uses carbon copy (CC) while addressing an email to a group of people. This results in forwarding the same email repetitively, thereby exposing the email addresses of all the people concerned.
-[](https://www.loginradius.com/resource/how-loginradius-prevents-bot-attacks/)
+[](https://www.loginradius.com/resource/how-loginradius-prevents-bot-attacks/)
## How to Prevent Phishing Email Scams
@@ -103,4 +103,4 @@ As email addresses have become ubiquitous and the messaging process more interac
By taking simple precautions, including checking the source of the message and even flagging suspicious emails as spam, you can keep the scammers away, and remain in control of your inbox.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=stop-scammers-getting-email-address)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=stop-scammers-getting-email-address)
diff --git a/content/identity/stop-scammers-getting-email-address/scammers.jpg b/content/identity/stop-scammers-getting-email-address/scammers.jpg
deleted file mode 100644
index cf3aa9af1..000000000
Binary files a/content/identity/stop-scammers-getting-email-address/scammers.jpg and /dev/null differ
diff --git a/content/identity/stop-scammers-getting-email-address/scammers.webp b/content/identity/stop-scammers-getting-email-address/scammers.webp
new file mode 100644
index 000000000..32b2b88b8
Binary files /dev/null and b/content/identity/stop-scammers-getting-email-address/scammers.webp differ
diff --git a/content/identity/strategies-secure-cloud-operations/Future-proof-your-security.png b/content/identity/strategies-secure-cloud-operations/Future-proof-your-security.png
deleted file mode 100644
index 9b885caa8..000000000
Binary files a/content/identity/strategies-secure-cloud-operations/Future-proof-your-security.png and /dev/null differ
diff --git a/content/identity/strategies-secure-cloud-operations/Future-proof-your-security.webp b/content/identity/strategies-secure-cloud-operations/Future-proof-your-security.webp
new file mode 100644
index 000000000..62f54b93f
Binary files /dev/null and b/content/identity/strategies-secure-cloud-operations/Future-proof-your-security.webp differ
diff --git a/content/identity/strategies-secure-cloud-operations/how-to-secure-cloud-operations.png b/content/identity/strategies-secure-cloud-operations/how-to-secure-cloud-operations.png
deleted file mode 100644
index 54d4ab75c..000000000
Binary files a/content/identity/strategies-secure-cloud-operations/how-to-secure-cloud-operations.png and /dev/null differ
diff --git a/content/identity/strategies-secure-cloud-operations/how-to-secure-cloud-operations.webp b/content/identity/strategies-secure-cloud-operations/how-to-secure-cloud-operations.webp
new file mode 100644
index 000000000..8a956930d
Binary files /dev/null and b/content/identity/strategies-secure-cloud-operations/how-to-secure-cloud-operations.webp differ
diff --git a/content/identity/strategies-secure-cloud-operations/index.md b/content/identity/strategies-secure-cloud-operations/index.md
index c95de4001..28def68bb 100644
--- a/content/identity/strategies-secure-cloud-operations/index.md
+++ b/content/identity/strategies-secure-cloud-operations/index.md
@@ -1,7 +1,7 @@
---
title: "6 Strategies to Secure Your Cloud Operations Against Today's Cyber Threats"
date: "2021-02-12"
-coverImage: "secure-cloud.jpg"
+coverImage: "secure-cloud.webp"
tags: ["cloud security","cybersecurity","cx"]
author: "Rakesh Soni"
description: "One of the most important steps for successful cloud operations is to keep your cloud environment safe and secure. Generally, businesses are eager to adopt cloud solutions, but the primary factor that keeps enterprises on their toes is their security issues. In this article, we'll discuss a few strategies needed to secure your cloud operations from cyber threats."
@@ -75,7 +75,7 @@ Accidental deletions, stolen login credentials, dissatisfied employees, unsecure
Mass adoption of cloud technology with ever-increasing sophistication and volume can pave the way for cyber threats that drive the need to implement cybersecurity.
-[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
+[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper)
Here a few tips about how you can improvise on the security of data on the cloud –
@@ -138,7 +138,7 @@ By protecting your cloud users with multi-factor authentication, only authorized
## Why Should Businesses Rely Completely on the LoginRadius Cloud IAM Solution
-
+
If you intend to build a Cloud IAM solution either in-house or through a third-party service on your servers, then you should be aware of its limitations too. There is a time-consuming factor in hardware, software, security, and privacy.
@@ -152,4 +152,4 @@ There is no doubt that cloud computing is the future. And it would be best if yo
You need to think more carefully regarding the cloud security controls to ensure total security. Using the best industry practices and managing your cloud services will help you secure your cloud operations, thereby protecting sensitive data.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=strategies-secure-cloud-operations)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=strategies-secure-cloud-operations)
\ No newline at end of file
diff --git a/content/identity/strategies-secure-cloud-operations/secure-cloud.jpg b/content/identity/strategies-secure-cloud-operations/secure-cloud.jpg
deleted file mode 100644
index 0316c6a73..000000000
Binary files a/content/identity/strategies-secure-cloud-operations/secure-cloud.jpg and /dev/null differ
diff --git a/content/identity/strategies-secure-cloud-operations/secure-cloud.webp b/content/identity/strategies-secure-cloud-operations/secure-cloud.webp
new file mode 100644
index 000000000..7dff4418c
Binary files /dev/null and b/content/identity/strategies-secure-cloud-operations/secure-cloud.webp differ
diff --git a/content/identity/streaming-applications-secure-customer-data/Book-a-free-demo-request-1024x310.png b/content/identity/streaming-applications-secure-customer-data/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/streaming-applications-secure-customer-data/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/streaming-applications-secure-customer-data/Book-a-free-demo-request-1024x310.webp b/content/identity/streaming-applications-secure-customer-data/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/streaming-applications-secure-customer-data/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/streaming-applications-secure-customer-data/CS-BroadcstMed-1024x310.png b/content/identity/streaming-applications-secure-customer-data/CS-BroadcstMed-1024x310.png
deleted file mode 100644
index f90e66923..000000000
Binary files a/content/identity/streaming-applications-secure-customer-data/CS-BroadcstMed-1024x310.png and /dev/null differ
diff --git a/content/identity/streaming-applications-secure-customer-data/CS-BroadcstMed-1024x310.webp b/content/identity/streaming-applications-secure-customer-data/CS-BroadcstMed-1024x310.webp
new file mode 100644
index 000000000..6837fe2ea
Binary files /dev/null and b/content/identity/streaming-applications-secure-customer-data/CS-BroadcstMed-1024x310.webp differ
diff --git a/content/identity/streaming-applications-secure-customer-data/OTT-Over-The-Top-Streaming-Services-and-Apps-1024x703.png b/content/identity/streaming-applications-secure-customer-data/OTT-Over-The-Top-Streaming-Services-and-Apps-1024x703.png
deleted file mode 100644
index 415a2d196..000000000
Binary files a/content/identity/streaming-applications-secure-customer-data/OTT-Over-The-Top-Streaming-Services-and-Apps-1024x703.png and /dev/null differ
diff --git a/content/identity/streaming-applications-secure-customer-data/OTT-Over-The-Top-Streaming-Services-and-Apps-1024x703.webp b/content/identity/streaming-applications-secure-customer-data/OTT-Over-The-Top-Streaming-Services-and-Apps-1024x703.webp
new file mode 100644
index 000000000..afc816d43
Binary files /dev/null and b/content/identity/streaming-applications-secure-customer-data/OTT-Over-The-Top-Streaming-Services-and-Apps-1024x703.webp differ
diff --git a/content/identity/streaming-applications-secure-customer-data/Video-and-Audio-Streaming-Industry-1024x703.png b/content/identity/streaming-applications-secure-customer-data/Video-and-Audio-Streaming-Industry-1024x703.png
deleted file mode 100644
index ef6938525..000000000
Binary files a/content/identity/streaming-applications-secure-customer-data/Video-and-Audio-Streaming-Industry-1024x703.png and /dev/null differ
diff --git a/content/identity/streaming-applications-secure-customer-data/Video-and-Audio-Streaming-Industry-1024x703.webp b/content/identity/streaming-applications-secure-customer-data/Video-and-Audio-Streaming-Industry-1024x703.webp
new file mode 100644
index 000000000..db1d1b525
Binary files /dev/null and b/content/identity/streaming-applications-secure-customer-data/Video-and-Audio-Streaming-Industry-1024x703.webp differ
diff --git a/content/identity/streaming-applications-secure-customer-data/index.md b/content/identity/streaming-applications-secure-customer-data/index.md
index ea6dbe9c8..e24a680be 100644
--- a/content/identity/streaming-applications-secure-customer-data/index.md
+++ b/content/identity/streaming-applications-secure-customer-data/index.md
@@ -1,7 +1,7 @@
---
title: "Streaming Applications: How to Secure Your Customer Data"
date: "2020-05-21"
-coverImage: "secure-customer-data.jpg"
+coverImage: "secure-customer-data.webp"
tags: ["data security","authentication","cx"]
author: "Rakesh Soni"
description: "OTT streaming apps should know how to mitigate data theft. Using a robust identity management solution in online streaming services helps secure digital identities."
@@ -82,7 +82,7 @@ Detecting MitM attacks is difficult, but they can be prevented through cybersecu
## OTT (Over-The-Top) Streaming Services and Apps
-
+
Streaming entertainment giants are completely [aware of the cyber threats](https://www.loginradius.com/blog/2020/05/cyber-threats-business-risk-covid-19/) - a reason why the media landscape is rapidly evolving to accommodate the growing security concerns.
@@ -200,7 +200,7 @@ Now, think of it this way. If nearly all of the population is attached to at lea
## 5 Things Video and Audio Streaming Industry Can Do to Secure the User Experience
-
+
Identity is the most important entity in the digital ecosystem. Streaming applications should know how to associate the required restrictions with the right users and secure customer experiences. Here are five other ways to enhance customer security.
@@ -256,7 +256,7 @@ Wondering how? Let's find out.
Video broadcasting company BroadcastMed's successful implementation of SSO by LoginRadius is a good example.
-[](https://www.loginradius.com/resource/broadcastmed-case-study)
+[](https://www.loginradius.com/resource/broadcastmed-case-study)
The identity provider offered a centralized login system where users can seamlessly navigate to third-party sites and other syndication partners without the need to log in and out every time.
@@ -276,4 +276,4 @@ Frictionless user experience and optimal security drive the transformation of th
Even then data security remains a crucial aspect. You need to balance both the worlds. An identity management platform can help you achieve that.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=streaming-applications-secure-customer-data)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=streaming-applications-secure-customer-data)
diff --git a/content/identity/streaming-applications-secure-customer-data/secure-customer-data.jpg b/content/identity/streaming-applications-secure-customer-data/secure-customer-data.jpg
deleted file mode 100644
index 9cca699d9..000000000
Binary files a/content/identity/streaming-applications-secure-customer-data/secure-customer-data.jpg and /dev/null differ
diff --git a/content/identity/streaming-applications-secure-customer-data/secure-customer-data.webp b/content/identity/streaming-applications-secure-customer-data/secure-customer-data.webp
new file mode 100644
index 000000000..e86602cd0
Binary files /dev/null and b/content/identity/streaming-applications-secure-customer-data/secure-customer-data.webp differ
diff --git a/content/identity/streaming-applications-secure-customer-data/streaming-apps.png b/content/identity/streaming-applications-secure-customer-data/streaming-apps.png
deleted file mode 100644
index f6788ec76..000000000
Binary files a/content/identity/streaming-applications-secure-customer-data/streaming-apps.png and /dev/null differ
diff --git a/content/identity/streaming-applications-secure-customer-data/streaming-apps.webp b/content/identity/streaming-applications-secure-customer-data/streaming-apps.webp
new file mode 100644
index 000000000..ce6681aa2
Binary files /dev/null and b/content/identity/streaming-applications-secure-customer-data/streaming-apps.webp differ
diff --git a/content/identity/the-dual-nature-of-digital-identity/EB-GD-to-CI.png b/content/identity/the-dual-nature-of-digital-identity/EB-GD-to-CI.png
deleted file mode 100644
index 74eef3e01..000000000
Binary files a/content/identity/the-dual-nature-of-digital-identity/EB-GD-to-CI.png and /dev/null differ
diff --git a/content/identity/the-dual-nature-of-digital-identity/EB-GD-to-CI.webp b/content/identity/the-dual-nature-of-digital-identity/EB-GD-to-CI.webp
new file mode 100644
index 000000000..cae55baf0
Binary files /dev/null and b/content/identity/the-dual-nature-of-digital-identity/EB-GD-to-CI.webp differ
diff --git a/content/identity/the-dual-nature-of-digital-identity/GD-Mod-Cus-Identity.png b/content/identity/the-dual-nature-of-digital-identity/GD-Mod-Cus-Identity.png
deleted file mode 100644
index bc0c2b3f3..000000000
Binary files a/content/identity/the-dual-nature-of-digital-identity/GD-Mod-Cus-Identity.png and /dev/null differ
diff --git a/content/identity/the-dual-nature-of-digital-identity/GD-Mod-Cus-Identity.webp b/content/identity/the-dual-nature-of-digital-identity/GD-Mod-Cus-Identity.webp
new file mode 100644
index 000000000..b0f1ac055
Binary files /dev/null and b/content/identity/the-dual-nature-of-digital-identity/GD-Mod-Cus-Identity.webp differ
diff --git a/content/identity/the-dual-nature-of-digital-identity/dual-nature-dig-identity.jpg b/content/identity/the-dual-nature-of-digital-identity/dual-nature-dig-identity.jpg
deleted file mode 100644
index eebf772a8..000000000
Binary files a/content/identity/the-dual-nature-of-digital-identity/dual-nature-dig-identity.jpg and /dev/null differ
diff --git a/content/identity/the-dual-nature-of-digital-identity/dual-nature-dig-identity.webp b/content/identity/the-dual-nature-of-digital-identity/dual-nature-dig-identity.webp
new file mode 100644
index 000000000..225cc1d86
Binary files /dev/null and b/content/identity/the-dual-nature-of-digital-identity/dual-nature-dig-identity.webp differ
diff --git a/content/identity/the-dual-nature-of-digital-identity/index.md b/content/identity/the-dual-nature-of-digital-identity/index.md
index 08cb83edd..680566f98 100644
--- a/content/identity/the-dual-nature-of-digital-identity/index.md
+++ b/content/identity/the-dual-nature-of-digital-identity/index.md
@@ -1,7 +1,7 @@
---
title: "Consumer vs. Enterprise: Navigating the Dual Nature of Digital Identity"
date: "2023-05-11"
-coverImage: "dual-nature-dig-identity.jpg"
+coverImage: "dual-nature-dig-identity.webp"
tags: ["digital identity", "consumer identity", "mfa","cx"]
author: "Rakesh Soni"
description: "The digital era has given rise to the concept of digital identity, the digital representation of our identity online. Consumer and enterprise identities are commonly used in today's digital landscape. In this blog, we dive into the world of digital identity, uncover the importance of securing it, and explore the differences and similarities between consumer and enterprise identity."
@@ -45,7 +45,7 @@ The security of digital identity is paramount in today's digital landscape, give
One effective way to secure digital identity is by implementing a modern customer identity and access management (CIAM) solution. CIAM provides a secure and centralized platform to manage customer identity data, authentication, and authorization.
-[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
+[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/)
CIAM helps to prevent data breaches by securing personal data, managing customer identities, and implementing adequate access controls. With CIAM, businesses can ensure that their customers' personal information is secure and that only authorized users can access it.
@@ -59,4 +59,4 @@ Consumers often create digital identities through self-registration, while enter
Consumer identity is more prone to security risks, while enterprise identity is more prone to insider threats. However, both types of digital identity must be secured through access control, two-factor authentication, and encryption to mitigate security risks. As technology advances, the importance of digital identity will only continue to grow, and we must take the necessary steps to ensure its security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=the-dual-nature-of-digital-identity)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=the-dual-nature-of-digital-identity)
\ No newline at end of file
diff --git a/content/identity/things-customer-iam-leaders-prioritize-2023/EB-omnichannel.png b/content/identity/things-customer-iam-leaders-prioritize-2023/EB-omnichannel.png
deleted file mode 100644
index f5fa0b0f9..000000000
Binary files a/content/identity/things-customer-iam-leaders-prioritize-2023/EB-omnichannel.png and /dev/null differ
diff --git a/content/identity/things-customer-iam-leaders-prioritize-2023/EB-omnichannel.webp b/content/identity/things-customer-iam-leaders-prioritize-2023/EB-omnichannel.webp
new file mode 100644
index 000000000..b0761321e
Binary files /dev/null and b/content/identity/things-customer-iam-leaders-prioritize-2023/EB-omnichannel.webp differ
diff --git a/content/identity/things-customer-iam-leaders-prioritize-2023/ciam-leaders.jpg b/content/identity/things-customer-iam-leaders-prioritize-2023/ciam-leaders.jpg
deleted file mode 100644
index 253bdc23a..000000000
Binary files a/content/identity/things-customer-iam-leaders-prioritize-2023/ciam-leaders.jpg and /dev/null differ
diff --git a/content/identity/things-customer-iam-leaders-prioritize-2023/ciam-leaders.webp b/content/identity/things-customer-iam-leaders-prioritize-2023/ciam-leaders.webp
new file mode 100644
index 000000000..fad6efe71
Binary files /dev/null and b/content/identity/things-customer-iam-leaders-prioritize-2023/ciam-leaders.webp differ
diff --git a/content/identity/things-customer-iam-leaders-prioritize-2023/index.md b/content/identity/things-customer-iam-leaders-prioritize-2023/index.md
index e7504b68a..148550af9 100644
--- a/content/identity/things-customer-iam-leaders-prioritize-2023/index.md
+++ b/content/identity/things-customer-iam-leaders-prioritize-2023/index.md
@@ -1,7 +1,7 @@
---
title: "Top Priorities for Customer IAM Leaders in 2023 and How to Prepare"
date: "2022-12-16"
-coverImage: "ciam-leaders.jpg"
+coverImage: "ciam-leaders.webp"
tags: ["ciam", "authentication", "data security","cx"]
author: "Rakesh Soni"
description: "As we approach the next decade, it is worth looking at what technology will bring to the table and how it can impact the realm of intelligent authentication. Let’s look at some of the top priorities of CIAM leaders in 2023."
@@ -39,7 +39,7 @@ New-age companies are looking to create solutions that deliver a delightful cust
The need for CIAM to lead the company in providing such an experience has never been more pertinent than today when customer expectations have reached an all-time high.
-[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
+[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/)
### 3. Retaining Customers and New Customer Acquisition
@@ -60,4 +60,4 @@ Aside from increasing efforts to secure identity, it is anticipated that custome
While leaders will be able to continue streamlining the security and fraud prevention techniques; however, if they cannot apply the same level of efficiency and innovation to deliver a positive user experience, they risk alienating consumers and ultimately losing their loyalty.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=things-customer-iam-leaders-prioritize-2023)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=things-customer-iam-leaders-prioritize-2023)
diff --git a/content/identity/things-customer-iam-leaders-prioritize-2023/omni-eb.png b/content/identity/things-customer-iam-leaders-prioritize-2023/omni-eb.png
deleted file mode 100644
index 86c15a159..000000000
Binary files a/content/identity/things-customer-iam-leaders-prioritize-2023/omni-eb.png and /dev/null differ
diff --git a/content/identity/things-customer-iam-leaders-prioritize-2023/omni-eb.webp b/content/identity/things-customer-iam-leaders-prioritize-2023/omni-eb.webp
new file mode 100644
index 000000000..025782e92
Binary files /dev/null and b/content/identity/things-customer-iam-leaders-prioritize-2023/omni-eb.webp differ
diff --git a/content/identity/things-to-know-before-creating-ciam-strategy/EB-checklist-ciam-in-cloud.png b/content/identity/things-to-know-before-creating-ciam-strategy/EB-checklist-ciam-in-cloud.png
deleted file mode 100644
index 77bedb0ac..000000000
Binary files a/content/identity/things-to-know-before-creating-ciam-strategy/EB-checklist-ciam-in-cloud.png and /dev/null differ
diff --git a/content/identity/things-to-know-before-creating-ciam-strategy/EB-checklist-ciam-in-cloud.webp b/content/identity/things-to-know-before-creating-ciam-strategy/EB-checklist-ciam-in-cloud.webp
new file mode 100644
index 000000000..a9da23270
Binary files /dev/null and b/content/identity/things-to-know-before-creating-ciam-strategy/EB-checklist-ciam-in-cloud.webp differ
diff --git a/content/identity/things-to-know-before-creating-ciam-strategy/ciam-strategy.jpg b/content/identity/things-to-know-before-creating-ciam-strategy/ciam-strategy.jpg
deleted file mode 100644
index bf04b3fad..000000000
Binary files a/content/identity/things-to-know-before-creating-ciam-strategy/ciam-strategy.jpg and /dev/null differ
diff --git a/content/identity/things-to-know-before-creating-ciam-strategy/ciam-strategy.webp b/content/identity/things-to-know-before-creating-ciam-strategy/ciam-strategy.webp
new file mode 100644
index 000000000..e6b6f199a
Binary files /dev/null and b/content/identity/things-to-know-before-creating-ciam-strategy/ciam-strategy.webp differ
diff --git a/content/identity/things-to-know-before-creating-ciam-strategy/index.md b/content/identity/things-to-know-before-creating-ciam-strategy/index.md
index 95f92ac2c..a7d00f799 100644
--- a/content/identity/things-to-know-before-creating-ciam-strategy/index.md
+++ b/content/identity/things-to-know-before-creating-ciam-strategy/index.md
@@ -1,7 +1,7 @@
---
title: "7 Things Your Security Team Need To Know Before Creating A CIAM Strategy"
date: "2023-07-13"
-coverImage: "ciam-strategy.jpg"
+coverImage: "ciam-strategy.webp"
tags: ["ciam solutions","compliance","mfa","cx"]
author: "Alok Patidar"
description: "The challenges of developing a CIAM strategy can be daunting. We have put together a comprehensive guide on how to create an effective CIAM strategy that will keep your customers happy and your business secure."
@@ -40,7 +40,7 @@ The first step is to conduct a comprehensive evaluation of your organization's e
Defining your organization's goals and objectives is fundamental to developing an effective CIAM strategy. Determine the specific outcomes you wish to achieve, such as enhancing user authentication, securing personal data, or streamlining access management processes. These defined goals will serve as guiding principles throughout the strategy development process.
-[](https://www.loginradius.com/resource/an-identity-checklist-to-strategize-ciam-in-the-cloud/)
+[](https://www.loginradius.com/resource/an-identity-checklist-to-strategize-ciam-in-the-cloud/)
### 3. Understand user profiles and behavior
@@ -80,4 +80,4 @@ With LoginRadius CIAM, organizations can confidently navigate the complexities o
Creatig a CIAM strategy requires careful planning and execution. Following these seven essential actions, your security team can lay a strong foundation for a robust CIAM strategy that prioritizes data security, user experience, and regulatory compliance.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=things-to-know-before-creating-ciam-strategy)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=things-to-know-before-creating-ciam-strategy)
\ No newline at end of file
diff --git a/content/identity/tips-from-loginradius-security-expert-2022/GD-to-RBA.png b/content/identity/tips-from-loginradius-security-expert-2022/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/tips-from-loginradius-security-expert-2022/GD-to-RBA.png and /dev/null differ
diff --git a/content/identity/tips-from-loginradius-security-expert-2022/GD-to-RBA.webp b/content/identity/tips-from-loginradius-security-expert-2022/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/tips-from-loginradius-security-expert-2022/GD-to-RBA.webp differ
diff --git a/content/identity/tips-from-loginradius-security-expert-2022/index.md b/content/identity/tips-from-loginradius-security-expert-2022/index.md
index 5a3de8cbe..7028998e9 100644
--- a/content/identity/tips-from-loginradius-security-expert-2022/index.md
+++ b/content/identity/tips-from-loginradius-security-expert-2022/index.md
@@ -1,7 +1,7 @@
---
title: "Top 7 Security Tips from LoginRadius’ Cybersecurity Expert to Follow in 2023"
date: "2022-01-20"
-coverImage: "security-exp.jpg"
+coverImage: "security-exp.webp"
tags: ["cybersecurity", "security tips","information security"]
author: "Alok Patidar"
description: "Alok Patidar, Information Security Manager at LoginRadius, shares his valuable insights for businesses to secure their sensitive information in 2023 and beyond. Read on to ensure the highest level of security across your organization."
@@ -85,7 +85,7 @@ Risk-based authentication only triggers an elevated-risk situation while keeping
You can configure actions based on the severity of the risk factors like if the consumer logs normally into your system from Vancouver and makes an authentication request to access the application from Cancun, this is an elevated-risk situation, and you might want to block the account instead of sending the notification to the consumer.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
### #5. Create data backups
@@ -131,4 +131,4 @@ Using the best industry practices and strictly following the tips mentioned earl
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-from-loginradius-security-expert-2022)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-from-loginradius-security-expert-2022)
diff --git a/content/identity/tips-from-loginradius-security-expert-2022/risk-auth-gd.png b/content/identity/tips-from-loginradius-security-expert-2022/risk-auth-gd.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/identity/tips-from-loginradius-security-expert-2022/risk-auth-gd.png and /dev/null differ
diff --git a/content/identity/tips-from-loginradius-security-expert-2022/risk-auth-gd.webp b/content/identity/tips-from-loginradius-security-expert-2022/risk-auth-gd.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/identity/tips-from-loginradius-security-expert-2022/risk-auth-gd.webp differ
diff --git a/content/identity/tips-from-loginradius-security-expert-2022/security-exp.jpg b/content/identity/tips-from-loginradius-security-expert-2022/security-exp.jpg
deleted file mode 100644
index 33a4db537..000000000
Binary files a/content/identity/tips-from-loginradius-security-expert-2022/security-exp.jpg and /dev/null differ
diff --git a/content/identity/tips-from-loginradius-security-expert-2022/security-exp.webp b/content/identity/tips-from-loginradius-security-expert-2022/security-exp.webp
new file mode 100644
index 000000000..9275a17b4
Binary files /dev/null and b/content/identity/tips-from-loginradius-security-expert-2022/security-exp.webp differ
diff --git a/content/identity/tips-from-loginradius-security-expert-2023/GD-to-RBA.png b/content/identity/tips-from-loginradius-security-expert-2023/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/tips-from-loginradius-security-expert-2023/GD-to-RBA.png and /dev/null differ
diff --git a/content/identity/tips-from-loginradius-security-expert-2023/GD-to-RBA.webp b/content/identity/tips-from-loginradius-security-expert-2023/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/tips-from-loginradius-security-expert-2023/GD-to-RBA.webp differ
diff --git a/content/identity/tips-from-loginradius-security-expert-2023/index.md b/content/identity/tips-from-loginradius-security-expert-2023/index.md
index 165968785..fcae28387 100644
--- a/content/identity/tips-from-loginradius-security-expert-2023/index.md
+++ b/content/identity/tips-from-loginradius-security-expert-2023/index.md
@@ -1,7 +1,7 @@
---
title: "Top 7 Security Tips from LoginRadius’ Cybersecurity Expert to Follow in 2023"
date: "2022-01-20"
-coverImage: "security-expert.jpg"
+coverImage: "security-expert.webp"
tags: ["cybersecurity tips","data privacy","digital transformation"]
author: "Alok Patidar"
description: "Alok Patidar, Information Security Manager at LoginRadius, shares his valuable insights for businesses to secure their sensitive information in 2023 and beyond. Read on to ensure the highest level of security across your organization."
@@ -77,7 +77,7 @@ Risk-based authentication only triggers an elevated-risk situation while keeping
You can configure actions based on the severity of the risk factors like if the consumer logs normally into your system from Vancouver and makes an authentication request to access the application from Cancun, this is an elevated-risk situation, and you might want to block the account instead of sending the notification to the consumer.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
### #5. Create data backups
@@ -117,4 +117,4 @@ Every business needs to think more carefully regarding the overall security mech
Using the best industry practices and strictly following the tips mentioned earlier will help [enterprises secure their operations](https://www.loginradius.com/blog/identity/risk-management-essentials-enterprise/), protecting sensitive data.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-from-loginradius-security-expert-2023)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-from-loginradius-security-expert-2023)
diff --git a/content/identity/tips-from-loginradius-security-expert-2023/risk-auth-gd.png b/content/identity/tips-from-loginradius-security-expert-2023/risk-auth-gd.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/identity/tips-from-loginradius-security-expert-2023/risk-auth-gd.png and /dev/null differ
diff --git a/content/identity/tips-from-loginradius-security-expert-2023/risk-auth-gd.webp b/content/identity/tips-from-loginradius-security-expert-2023/risk-auth-gd.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/identity/tips-from-loginradius-security-expert-2023/risk-auth-gd.webp differ
diff --git a/content/identity/tips-from-loginradius-security-expert-2023/security-expert.jpg b/content/identity/tips-from-loginradius-security-expert-2023/security-expert.jpg
deleted file mode 100644
index 33a4db537..000000000
Binary files a/content/identity/tips-from-loginradius-security-expert-2023/security-expert.jpg and /dev/null differ
diff --git a/content/identity/tips-from-loginradius-security-expert-2023/security-expert.webp b/content/identity/tips-from-loginradius-security-expert-2023/security-expert.webp
new file mode 100644
index 000000000..9275a17b4
Binary files /dev/null and b/content/identity/tips-from-loginradius-security-expert-2023/security-expert.webp differ
diff --git a/content/identity/tiroler-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.png b/content/identity/tiroler-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/tiroler-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.png and /dev/null differ
diff --git a/content/identity/tiroler-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.webp b/content/identity/tiroler-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/tiroler-loginradius-customer-success-story/BD-Plexicon1-1024x310-1.webp differ
diff --git a/content/identity/tiroler-loginradius-customer-success-story/index.md b/content/identity/tiroler-loginradius-customer-success-story/index.md
index 32f3f1908..8f70526af 100644
--- a/content/identity/tiroler-loginradius-customer-success-story/index.md
+++ b/content/identity/tiroler-loginradius-customer-success-story/index.md
@@ -1,7 +1,7 @@
---
title: "Tiroler Tageszeitung (TT), a LoginRadius Customer Success Story"
date: "2021-09-28"
-coverImage: "tiroler-loginradius-customer-success-story-cover.jpg"
+coverImage: "tiroler-loginradius-customer-success-story-cover.webp"
tags: ["media-and-publication"]
featured: false
author: "Yash Rathi"
@@ -73,4 +73,4 @@ One of the most critical differentiators for TT was LoginRadius’s ability to p
With our state-of-the-art technology, we were able to help the company increase its user base through great user experience coupled with security and convenience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tiroler-loginradius-customer-success-story)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tiroler-loginradius-customer-success-story)
diff --git a/content/identity/tiroler-loginradius-customer-success-story/tiroler-loginradius-customer-success-story-cover.jpg b/content/identity/tiroler-loginradius-customer-success-story/tiroler-loginradius-customer-success-story-cover.jpg
deleted file mode 100644
index c609252e6..000000000
Binary files a/content/identity/tiroler-loginradius-customer-success-story/tiroler-loginradius-customer-success-story-cover.jpg and /dev/null differ
diff --git a/content/identity/tiroler-loginradius-customer-success-story/tiroler-loginradius-customer-success-story-cover.webp b/content/identity/tiroler-loginradius-customer-success-story/tiroler-loginradius-customer-success-story-cover.webp
new file mode 100644
index 000000000..071e99e8c
Binary files /dev/null and b/content/identity/tiroler-loginradius-customer-success-story/tiroler-loginradius-customer-success-story-cover.webp differ
diff --git a/content/identity/token-management-api-product-jwt/DS-pass-magic-link.png b/content/identity/token-management-api-product-jwt/DS-pass-magic-link.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/token-management-api-product-jwt/DS-pass-magic-link.png and /dev/null differ
diff --git a/content/identity/token-management-api-product-jwt/DS-pass-magic-link.webp b/content/identity/token-management-api-product-jwt/DS-pass-magic-link.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/token-management-api-product-jwt/DS-pass-magic-link.webp differ
diff --git a/content/identity/token-management-api-product-jwt/index.md b/content/identity/token-management-api-product-jwt/index.md
index d922c2974..6403e9780 100644
--- a/content/identity/token-management-api-product-jwt/index.md
+++ b/content/identity/token-management-api-product-jwt/index.md
@@ -1,7 +1,7 @@
---
title: "Are You Thinking of Token Management for Your API Product? Think about JWT!"
date: "2022-01-04"
-coverImage: "token-managmt.jpg"
+coverImage: "token-managmt.webp"
tags: ["security"]
author: "Rakesh Soni"
description: "A token plays a crucial role in enhancing the overall security mechanism of an organization. This post will help you better understand what a token is, what is a JWT, and its pros that will help you decide why you need to invoke the potential of JWT for your API product."
@@ -34,7 +34,7 @@ Users can easily access the website or network for which the token is issued and
Tokens are widely used for regular online transactions for enhancing overall security and accuracy.
-[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
+[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
## What is JWT? What is OAuth 2.0?
@@ -83,4 +83,4 @@ The precise use of secure token management through a robust [consumer identity a
JWT can be the right option in most scenarios if implemented correctly and securely by following the proper security measures.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=token-management-api-product-jwt)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=token-management-api-product-jwt)
diff --git a/content/identity/token-management-api-product-jwt/magic-link-otp.png b/content/identity/token-management-api-product-jwt/magic-link-otp.png
deleted file mode 100644
index f0d635566..000000000
Binary files a/content/identity/token-management-api-product-jwt/magic-link-otp.png and /dev/null differ
diff --git a/content/identity/token-management-api-product-jwt/magic-link-otp.webp b/content/identity/token-management-api-product-jwt/magic-link-otp.webp
new file mode 100644
index 000000000..16c0455b4
Binary files /dev/null and b/content/identity/token-management-api-product-jwt/magic-link-otp.webp differ
diff --git a/content/identity/token-management-api-product-jwt/token-managmt.jpg b/content/identity/token-management-api-product-jwt/token-managmt.jpg
deleted file mode 100644
index b725796a8..000000000
Binary files a/content/identity/token-management-api-product-jwt/token-managmt.jpg and /dev/null differ
diff --git a/content/identity/token-management-api-product-jwt/token-managmt.webp b/content/identity/token-management-api-product-jwt/token-managmt.webp
new file mode 100644
index 000000000..2c6ad4fb6
Binary files /dev/null and b/content/identity/token-management-api-product-jwt/token-managmt.webp differ
diff --git a/content/identity/top-10-blogs-2023/index.md b/content/identity/top-10-blogs-2023/index.md
index 9ef3be7e8..b10107eee 100644
--- a/content/identity/top-10-blogs-2023/index.md
+++ b/content/identity/top-10-blogs-2023/index.md
@@ -1,7 +1,7 @@
---
title: "A Journey Through Our Top 10 Blogs from 2023"
date: "2023-12-20"
-coverImage: "top-blog.jpg"
+coverImage: "top-blog.webp"
tags: ["identity blogs","growth blogs","ciam solutions"]
author: "Vishal Sharma"
description: "Embark on a journey through our top 10 blogs from 2023, where we unravel the complexities of CIAM, explore security measures, and delve into growth strategies. Learn about the importance of multi-factor authentication, cloud tenancy nuances, and user management. These blogs provide indispensable insights to secure your business and drive substantial growth."
@@ -108,4 +108,4 @@ The aforementioned blogs offer valuable insights into the CIAM landscape, provid
Feel free to contact us to delve deeper into [LoginRadius CIAM ](https://www.loginradius.com/)and discover how it can effectively propel your business growth, even in unpredictable circumstances.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-10-blogs-2023)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-10-blogs-2023)
\ No newline at end of file
diff --git a/content/identity/top-10-blogs-2023/top-blog.jpg b/content/identity/top-10-blogs-2023/top-blog.jpg
deleted file mode 100644
index 40d442fe0..000000000
Binary files a/content/identity/top-10-blogs-2023/top-blog.jpg and /dev/null differ
diff --git a/content/identity/top-10-blogs-2023/top-blog.webp b/content/identity/top-10-blogs-2023/top-blog.webp
new file mode 100644
index 000000000..4808553a9
Binary files /dev/null and b/content/identity/top-10-blogs-2023/top-blog.webp differ
diff --git a/content/identity/top-authentication-methods/index.md b/content/identity/top-authentication-methods/index.md
index 914a84d88..5f3568c5d 100644
--- a/content/identity/top-authentication-methods/index.md
+++ b/content/identity/top-authentication-methods/index.md
@@ -179,4 +179,4 @@ Need expert help implementing modern authentication mechanisms? [Contact LoginRa
**A.** The process that authenticates clients to a network typically involves validating credentials using protocols like RADIUS or EAP. This ensures that only authorized users can connect securely.
-[](https://www.loginradius.com/contact-us)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us)
\ No newline at end of file
diff --git a/content/identity/top-readers-blogs-2022/index.md b/content/identity/top-readers-blogs-2022/index.md
index 7689bbefa..b74c171dc 100644
--- a/content/identity/top-readers-blogs-2022/index.md
+++ b/content/identity/top-readers-blogs-2022/index.md
@@ -1,7 +1,7 @@
---
title: "A Look Back At Our 20 Top Performing Blogs in 2022"
date: "2022-12-22"
-coverImage: "top-blog.jpg"
+coverImage: "top-blog.webp"
tags: ["identity management","cx"]
author: "Vishal Sharma"
description: "In 2022, we continued to share valuable posts that uphold our mission to help companies manage and secure customer identities. We’re wrapping up the year by compiling a list of our top-performing blogs of 2022."
@@ -194,4 +194,4 @@ The blogs mentioned above can help you understand the CIAM landscape and ensure
Reach us to learn more about the LoginRadius CIAM and how it can help scale your business growth even in the most unpredictable times.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-readers-blogs-2022)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-readers-blogs-2022)
\ No newline at end of file
diff --git a/content/identity/top-readers-blogs-2022/top-blog.jpg b/content/identity/top-readers-blogs-2022/top-blog.jpg
deleted file mode 100644
index cf949ca99..000000000
Binary files a/content/identity/top-readers-blogs-2022/top-blog.jpg and /dev/null differ
diff --git a/content/identity/top-readers-blogs-2022/top-blog.webp b/content/identity/top-readers-blogs-2022/top-blog.webp
new file mode 100644
index 000000000..aae608cce
Binary files /dev/null and b/content/identity/top-readers-blogs-2022/top-blog.webp differ
diff --git a/content/identity/transform-business-with-loginradius-ciam/WP-decoding-resiliance.png b/content/identity/transform-business-with-loginradius-ciam/WP-decoding-resiliance.png
deleted file mode 100644
index cbe459800..000000000
Binary files a/content/identity/transform-business-with-loginradius-ciam/WP-decoding-resiliance.png and /dev/null differ
diff --git a/content/identity/transform-business-with-loginradius-ciam/WP-decoding-resiliance.webp b/content/identity/transform-business-with-loginradius-ciam/WP-decoding-resiliance.webp
new file mode 100644
index 000000000..efb695fb3
Binary files /dev/null and b/content/identity/transform-business-with-loginradius-ciam/WP-decoding-resiliance.webp differ
diff --git a/content/identity/transform-business-with-loginradius-ciam/business-ciam.jpg b/content/identity/transform-business-with-loginradius-ciam/business-ciam.jpg
deleted file mode 100644
index fdfd112b8..000000000
Binary files a/content/identity/transform-business-with-loginradius-ciam/business-ciam.jpg and /dev/null differ
diff --git a/content/identity/transform-business-with-loginradius-ciam/business-ciam.webp b/content/identity/transform-business-with-loginradius-ciam/business-ciam.webp
new file mode 100644
index 000000000..23e87df20
Binary files /dev/null and b/content/identity/transform-business-with-loginradius-ciam/business-ciam.webp differ
diff --git a/content/identity/transform-business-with-loginradius-ciam/decode-LR-WP.png b/content/identity/transform-business-with-loginradius-ciam/decode-LR-WP.png
deleted file mode 100644
index 8fb3d9233..000000000
Binary files a/content/identity/transform-business-with-loginradius-ciam/decode-LR-WP.png and /dev/null differ
diff --git a/content/identity/transform-business-with-loginradius-ciam/decode-LR-WP.webp b/content/identity/transform-business-with-loginradius-ciam/decode-LR-WP.webp
new file mode 100644
index 000000000..eebe75dbe
Binary files /dev/null and b/content/identity/transform-business-with-loginradius-ciam/decode-LR-WP.webp differ
diff --git a/content/identity/transform-business-with-loginradius-ciam/index.md b/content/identity/transform-business-with-loginradius-ciam/index.md
index a33035db8..2f2aa9f57 100644
--- a/content/identity/transform-business-with-loginradius-ciam/index.md
+++ b/content/identity/transform-business-with-loginradius-ciam/index.md
@@ -1,7 +1,7 @@
---
title: "Planning a Digital Makeover For Your Business? LoginRadius CIAM Can Help!"
date: "2022-05-27"
-coverImage: "business-ciam.jpg"
+coverImage: "business-ciam.webp"
tags: ["ciam", "user experience", "sso", "compliance"]
author: "Rakesh Soni"
description: "Incorporating a CIAM solution could be the best way to overcome security and challenges related to customer experience. Learn how LoginRadius can help businesses navigate their digital transformation journey and scale growth."
@@ -75,7 +75,7 @@ Our modern cloud infrastructure is protected to the highest industry standards.
In a technologically-driven interconnected world where every second counts, LoginRadius CIAM guarantees unparalleled uptime of 99.99% every month. The cloud-based identity provider manages 180K logins per second, 20 times more than its major competitors offering similar services.
-[](https://www.loginradius.com/scalability/)
+[](https://www.loginradius.com/scalability/)
Apart from delivering the industry's best consumer experience, the following are a few ways the platform excels compared to its global competitors.
@@ -97,4 +97,4 @@ When choosing the industry leader in the CIAM landscape, LoginRadius CIAM delive
Whether it’s the overall performance or the peak load capacity, LoginRadius is helping global enterprises, including Fortune 500 companies, revamp their consumer journeys.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=transform-business-with-loginradius-ciam)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=transform-business-with-loginradius-ciam)
diff --git a/content/identity/true-passwordless-authentication-cyberattacks/DS-passwordless-login-magic-link.png b/content/identity/true-passwordless-authentication-cyberattacks/DS-passwordless-login-magic-link.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/true-passwordless-authentication-cyberattacks/DS-passwordless-login-magic-link.png and /dev/null differ
diff --git a/content/identity/true-passwordless-authentication-cyberattacks/DS-passwordless-login-magic-link.webp b/content/identity/true-passwordless-authentication-cyberattacks/DS-passwordless-login-magic-link.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/true-passwordless-authentication-cyberattacks/DS-passwordless-login-magic-link.webp differ
diff --git a/content/identity/true-passwordless-authentication-cyberattacks/index.md b/content/identity/true-passwordless-authentication-cyberattacks/index.md
index de6eeadcb..fbb9d9710 100644
--- a/content/identity/true-passwordless-authentication-cyberattacks/index.md
+++ b/content/identity/true-passwordless-authentication-cyberattacks/index.md
@@ -1,7 +1,7 @@
---
title: "True Passwordless Authentication: Stronger Defense Against Cyberattacks"
date: "2023-08-29"
-coverImage: "true-passwordless-auth.jpg"
+coverImage: "true-passwordless-auth.webp"
tags: ["passwordless authentication","cybersecurity","ciam solution","cx"]
author: "Rakesh Soni"
description: "True passwordless authentication has broadened the horizons for businesses seeking secure yet user-friendly authentication mechanisms. This authentication mechanism helps enterprises to safeguard sensitive information and further gain the trust of their customers with a safe digital environment."
@@ -51,7 +51,7 @@ True passwordless authentication depends on asymmetric encryption. This means us
### Signature Verification Process:
The server receives the signed challenge and verifies it with the user's public key. If the signature is accurate, it confirms that the user has the private key associated with the account. These methods enhance identity confirmation processes and help organizations create a safer digital environment for their customers, partners, and employees.
-[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
+[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
## Advantages of True Passwordless Authentication
@@ -97,4 +97,4 @@ True passwordless authentication has revolutionized how businesses secure custom
With a reliable CIAM offering true passwordless authentication, like LoginRadius, businesses can create a perfect harmony of great user experience and security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=true-passwordless-authentication-cyberattacks)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=true-passwordless-authentication-cyberattacks)
\ No newline at end of file
diff --git a/content/identity/true-passwordless-authentication-cyberattacks/true-passwordless-auth.jpg b/content/identity/true-passwordless-authentication-cyberattacks/true-passwordless-auth.jpg
deleted file mode 100644
index f61605ff6..000000000
Binary files a/content/identity/true-passwordless-authentication-cyberattacks/true-passwordless-auth.jpg and /dev/null differ
diff --git a/content/identity/true-passwordless-authentication-cyberattacks/true-passwordless-auth.webp b/content/identity/true-passwordless-authentication-cyberattacks/true-passwordless-auth.webp
new file mode 100644
index 000000000..f877fe04e
Binary files /dev/null and b/content/identity/true-passwordless-authentication-cyberattacks/true-passwordless-auth.webp differ
diff --git a/content/identity/types-of-mfa/authenticateyour-customers-digital-assets-with-mfa.png b/content/identity/types-of-mfa/authenticateyour-customers-digital-assets-with-mfa.png
deleted file mode 100644
index d05f66193..000000000
Binary files a/content/identity/types-of-mfa/authenticateyour-customers-digital-assets-with-mfa.png and /dev/null differ
diff --git a/content/identity/types-of-mfa/authenticateyour-customers-digital-assets-with-mfa.webp b/content/identity/types-of-mfa/authenticateyour-customers-digital-assets-with-mfa.webp
new file mode 100644
index 000000000..010998ce2
Binary files /dev/null and b/content/identity/types-of-mfa/authenticateyour-customers-digital-assets-with-mfa.webp differ
diff --git a/content/identity/types-of-mfa/index.md b/content/identity/types-of-mfa/index.md
index d6f666ef8..3447a98d4 100644
--- a/content/identity/types-of-mfa/index.md
+++ b/content/identity/types-of-mfa/index.md
@@ -1,7 +1,7 @@
---
title: "Types of Multi Factor Authentication & How to Pick the Best"
date: "2025-02-28"
-coverImage: "types-of-mfa.jpg"
+coverImage: "types-of-mfa.webp"
tags: ["Identity Management","User Authentication","CIAM Security"]
author: "Kundan Singh"
description: "Cyber threats are evolving, and passwords alone aren't enough. Multi-Factor Authentication (MFA) adds extra layers of security by requiring multiple verification methods. Explore different MFA types—from biometrics to passkeys—and find the best authentication strategy for your needs."
@@ -163,7 +163,7 @@ Selecting the appropriate MFA authentication method for your business needs depe
If you want a detailed guide on MFA best practices, download this insightful guide:
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
diff --git a/content/identity/types-of-mfa/types-of-mfa.jpg b/content/identity/types-of-mfa/types-of-mfa.jpg
deleted file mode 100644
index 6f6d4e5a9..000000000
Binary files a/content/identity/types-of-mfa/types-of-mfa.jpg and /dev/null differ
diff --git a/content/identity/types-of-mfa/types-of-mfa.webp b/content/identity/types-of-mfa/types-of-mfa.webp
new file mode 100644
index 000000000..6206f6383
Binary files /dev/null and b/content/identity/types-of-mfa/types-of-mfa.webp differ
diff --git a/content/identity/understanding-on-premise-vs-cloud-iam-difference/WP-cloud.png b/content/identity/understanding-on-premise-vs-cloud-iam-difference/WP-cloud.png
deleted file mode 100644
index 6d7ae87ab..000000000
Binary files a/content/identity/understanding-on-premise-vs-cloud-iam-difference/WP-cloud.png and /dev/null differ
diff --git a/content/identity/understanding-on-premise-vs-cloud-iam-difference/WP-cloud.webp b/content/identity/understanding-on-premise-vs-cloud-iam-difference/WP-cloud.webp
new file mode 100644
index 000000000..c13a51d3a
Binary files /dev/null and b/content/identity/understanding-on-premise-vs-cloud-iam-difference/WP-cloud.webp differ
diff --git a/content/identity/understanding-on-premise-vs-cloud-iam-difference/index.md b/content/identity/understanding-on-premise-vs-cloud-iam-difference/index.md
index 71f5a6287..12eb5a7a8 100644
--- a/content/identity/understanding-on-premise-vs-cloud-iam-difference/index.md
+++ b/content/identity/understanding-on-premise-vs-cloud-iam-difference/index.md
@@ -1,7 +1,7 @@
---
title: "Understanding the Difference Between Identity Access Management On-Premise and Cloud"
date: "2023-07-31"
-coverImage: "on-premise-vs-cloud-iam.jpg"
+coverImage: "on-premise-vs-cloud-iam.webp"
tags: ["identity management", "cloud identity", "compliance", "cx"]
author: "Rakesh Soni"
description: "Dive into comparing on-premise and cloud IAM solutions, understanding their unique features and factors to consider. Make the right choice to strengthen your organization's security and access management."
@@ -56,7 +56,7 @@ Cloud-based IAM solutions offer unlimited scalability, allowing organizations to
Cloud-based IAM solutions eliminate the need for upfront infrastructure investments, reducing hardware and maintenance costs. Organizations can pay for the resources and services they use, optimizing cost-efficiency.
-[](https://www.loginradius.com/resource/overcome-the-nightmare-of-on-prem-deployment-move-to-cloud/)
+[](https://www.loginradius.com/resource/overcome-the-nightmare-of-on-prem-deployment-move-to-cloud/)
#### Rapid Deployment
@@ -85,4 +85,4 @@ Identity Access Management is critical to an organization's overall security str
Understanding the differences and evaluating factors such as control, scalability, cost, compliance, and legacy systems will help you make an informed decision to protect your valuable data and resources effectively.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=understanding-on-premise-vs-cloud-iam-difference)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=understanding-on-premise-vs-cloud-iam-difference)
\ No newline at end of file
diff --git a/content/identity/understanding-on-premise-vs-cloud-iam-difference/on-premise-vs-cloud-iam.jpg b/content/identity/understanding-on-premise-vs-cloud-iam-difference/on-premise-vs-cloud-iam.jpg
deleted file mode 100644
index 9cb19bfa2..000000000
Binary files a/content/identity/understanding-on-premise-vs-cloud-iam-difference/on-premise-vs-cloud-iam.jpg and /dev/null differ
diff --git a/content/identity/understanding-on-premise-vs-cloud-iam-difference/on-premise-vs-cloud-iam.webp b/content/identity/understanding-on-premise-vs-cloud-iam-difference/on-premise-vs-cloud-iam.webp
new file mode 100644
index 000000000..a77ddd624
Binary files /dev/null and b/content/identity/understanding-on-premise-vs-cloud-iam-difference/on-premise-vs-cloud-iam.webp differ
diff --git a/content/identity/unified-cx-retail/index.md b/content/identity/unified-cx-retail/index.md
index 639a92b26..7c57f6c23 100644
--- a/content/identity/unified-cx-retail/index.md
+++ b/content/identity/unified-cx-retail/index.md
@@ -1,7 +1,7 @@
---
title: "Why Big Merchants Need to Deliver a Unified Consumer Experience?"
date: "2021-06-15"
-coverImage: "unified-cx-retail-cover.jpg"
+coverImage: "unified-cx-retail-cover.webp"
tags: ["security"]
featured: false
author: "Navanita Devi"
@@ -89,4 +89,4 @@ Surveys indicate that[ 88%](https://searchengineland.com/88-consumers-trust-onli
Every stage of achieving a unified experience is essential, from initial consideration to functional evaluation, time of purchase, and even the post-purchase experience. Each stage is an opportunity to improve the consumer experience in retail**,** and each phase is an opportunity to obtain more information that can give feedback into the marketing processes and take advantage of the next time.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=unified-cx-retail)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=unified-cx-retail)
\ No newline at end of file
diff --git a/content/identity/unified-cx-retail/unified-cx-retail-cover.jpg b/content/identity/unified-cx-retail/unified-cx-retail-cover.jpg
deleted file mode 100644
index 7e89ed96e..000000000
Binary files a/content/identity/unified-cx-retail/unified-cx-retail-cover.jpg and /dev/null differ
diff --git a/content/identity/unified-cx-retail/unified-cx-retail-cover.webp b/content/identity/unified-cx-retail/unified-cx-retail-cover.webp
new file mode 100644
index 000000000..0d662ebc4
Binary files /dev/null and b/content/identity/unified-cx-retail/unified-cx-retail-cover.webp differ
diff --git a/content/identity/unlock-the-future-of-smart-cities/Book-a-demo-1024x310.png b/content/identity/unlock-the-future-of-smart-cities/Book-a-demo-1024x310.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/unlock-the-future-of-smart-cities/Book-a-demo-1024x310.png and /dev/null differ
diff --git a/content/identity/unlock-the-future-of-smart-cities/Book-a-demo-1024x310.webp b/content/identity/unlock-the-future-of-smart-cities/Book-a-demo-1024x310.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/unlock-the-future-of-smart-cities/Book-a-demo-1024x310.webp differ
diff --git a/content/identity/unlock-the-future-of-smart-cities/CS-My-City-MySurrey-1024x310.png b/content/identity/unlock-the-future-of-smart-cities/CS-My-City-MySurrey-1024x310.png
deleted file mode 100644
index 9a45b33c2..000000000
Binary files a/content/identity/unlock-the-future-of-smart-cities/CS-My-City-MySurrey-1024x310.png and /dev/null differ
diff --git a/content/identity/unlock-the-future-of-smart-cities/CS-My-City-MySurrey-1024x310.webp b/content/identity/unlock-the-future-of-smart-cities/CS-My-City-MySurrey-1024x310.webp
new file mode 100644
index 000000000..9390027e8
Binary files /dev/null and b/content/identity/unlock-the-future-of-smart-cities/CS-My-City-MySurrey-1024x310.webp differ
diff --git a/content/identity/unlock-the-future-of-smart-cities/future-of-smart-cities.jpg b/content/identity/unlock-the-future-of-smart-cities/future-of-smart-cities.jpg
deleted file mode 100644
index 36bda1c70..000000000
Binary files a/content/identity/unlock-the-future-of-smart-cities/future-of-smart-cities.jpg and /dev/null differ
diff --git a/content/identity/unlock-the-future-of-smart-cities/future-of-smart-cities.webp b/content/identity/unlock-the-future-of-smart-cities/future-of-smart-cities.webp
new file mode 100644
index 000000000..4e3a4ac01
Binary files /dev/null and b/content/identity/unlock-the-future-of-smart-cities/future-of-smart-cities.webp differ
diff --git a/content/identity/unlock-the-future-of-smart-cities/index.md b/content/identity/unlock-the-future-of-smart-cities/index.md
index 24bb6e7c2..db6ebaca0 100644
--- a/content/identity/unlock-the-future-of-smart-cities/index.md
+++ b/content/identity/unlock-the-future-of-smart-cities/index.md
@@ -1,7 +1,7 @@
---
title: "Unlock the Future of Smart Cities"
date: "2020-03-13"
-coverImage: "future-of-smart-cities.jpg"
+coverImage: "future-of-smart-cities.webp"
tags: ["digital transformation","digital identity","sso"]
author: "Rakesh Soni"
description: "With population growth and the expansion of public services, cities need to be innovative about how to provide services to all people without compromising service quality. There is a need for a single platform where all facilities are centralised and customer experience is considered. Below, for municipalities to follow, we'll look at some examples and best practises."
@@ -29,10 +29,10 @@ Residents are accustomed to 24/7, anywhere access to consumer products and servi
This enables organizations to use that customer data to better understand their customers, offer more useful information and deliver that information more directly.
-[](https://www.loginradius.com/resource/surrey-case-study)
+[](https://www.loginradius.com/resource/surrey-case-study)
The City of Surrey offers a great real-world example of what our Identity Platform can do. This bustling city in Metro Vancouver, British Columbia welcomes approximately 1,500 new residents per month – all in need of municipal services. The City was not able to expand its physical offices or add staff, so the solution was to move all services online.
We’ve created a case study to show you how the LoginRadius Identity Platform helped the City of Surrey transform its online services and unlock its future as a smart city.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=unlock-the-future-of-smart-cities)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=unlock-the-future-of-smart-cities)
diff --git a/content/identity/unlock-the-future-of-smart-cities/unlock-the-future-of-smart-cities.png b/content/identity/unlock-the-future-of-smart-cities/unlock-the-future-of-smart-cities.png
deleted file mode 100644
index 9a7f09946..000000000
Binary files a/content/identity/unlock-the-future-of-smart-cities/unlock-the-future-of-smart-cities.png and /dev/null differ
diff --git a/content/identity/unlock-the-future-of-smart-cities/unlock-the-future-of-smart-cities.webp b/content/identity/unlock-the-future-of-smart-cities/unlock-the-future-of-smart-cities.webp
new file mode 100644
index 000000000..74658bc0d
Binary files /dev/null and b/content/identity/unlock-the-future-of-smart-cities/unlock-the-future-of-smart-cities.webp differ
diff --git "a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication-1024x310.png" "b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication-1024x310.png"
deleted file mode 100644
index d63fdd4ac..000000000
Binary files "a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication-1024x310.png" and /dev/null differ
diff --git "a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication-1024x310.webp" "b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication-1024x310.webp"
new file mode 100644
index 000000000..4486d4d7d
Binary files /dev/null and "b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication-1024x310.webp" differ
diff --git a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/chad-madden-445638-unsplash-1024x683.jpg b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/chad-madden-445638-unsplash-1024x683.jpg
deleted file mode 100644
index 9c81a5334..000000000
Binary files a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/chad-madden-445638-unsplash-1024x683.jpg and /dev/null differ
diff --git a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/chad-madden-445638-unsplash-1024x683.webp b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/chad-madden-445638-unsplash-1024x683.webp
new file mode 100644
index 000000000..848f751d7
Binary files /dev/null and b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/chad-madden-445638-unsplash-1024x683.webp differ
diff --git a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/cover2.jpg b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/cover2.jpg
deleted file mode 100644
index 895b6525b..000000000
Binary files a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/cover2.jpg and /dev/null differ
diff --git a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/cover2.webp b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/cover2.webp
new file mode 100644
index 000000000..4f531e13a
Binary files /dev/null and b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/cover2.webp differ
diff --git a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/image-1.jpg b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/image-1.jpg
deleted file mode 100644
index 960df8501..000000000
Binary files a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/image-1.jpg and /dev/null differ
diff --git a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/image-1.webp b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/image-1.webp
new file mode 100644
index 000000000..a8d0aa63a
Binary files /dev/null and b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/image-1.webp differ
diff --git a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/index.md b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/index.md
index f9827d6b2..9dca57c3b 100644
--- a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/index.md
+++ b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/index.md
@@ -1,7 +1,7 @@
---
title: "How to Use Multi-Factor Authentication When You Don’t Have Cell Phone Access"
date: "2018-12-19"
-coverImage: "use-mfa.jpg"
+coverImage: "use-mfa.webp"
tags: ["mfa","data security","cx"]
author: "Rakesh Soni"
description: "To verify the identity of clients, many security-minded organisations use multi-factor authentication. The most popular approach is to send a code via SMS text message to customers, which the customer then enters on the website or app. But what if you drive and have no mobile phone service? For authenticating yourself, you have a few other choices. Before you fly, just make sure to set them up!"
@@ -26,7 +26,7 @@ These days a simple password isn’t always enough to make sure that someone is
## The Problem with MFA When Traveling
-
+
MFA typically uses a code sent via SMS text message as the second verification factor.
@@ -48,7 +48,7 @@ Both Google and Microsoft offer Android and iOS authenticator apps as part of th
LoginRadius offers a white-labeled version of Google Authenticator for [multi-factor authentication](https://www.loginradius.com/multi-factor-authentication/) to companies that use our customer identity platform.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
#### Setting up Google Authenticator
@@ -108,7 +108,7 @@ There are also a number of third-party authenticator apps out there, from compan
## Balancing Security and Convenience with MFA
-
+
B2C companies that offer MFA for an extra level of security still have their eye on providing a convenient customer experience.
@@ -116,4 +116,4 @@ Travel can make [SMS-based MFA solutions](https://www.loginradius.com/integratio
Providing travelers with easy-to-use MFA solutions doesn’t just keep your data and their data secure. It improves their digital experience and encourages them not to side-step essential security measures when traveling in potentially risky situations.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=use-multi-factor-authentication-dont-cell-phone-access)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=use-multi-factor-authentication-dont-cell-phone-access)
diff --git a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/use-mfa.jpg b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/use-mfa.jpg
deleted file mode 100644
index b59ea2010..000000000
Binary files a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/use-mfa.jpg and /dev/null differ
diff --git a/content/identity/use-multi-factor-authentication-dont-cell-phone-access/use-mfa.webp b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/use-mfa.webp
new file mode 100644
index 000000000..fe0fee11c
Binary files /dev/null and b/content/identity/use-multi-factor-authentication-dont-cell-phone-access/use-mfa.webp differ
diff --git a/content/identity/user-authentication-evolution-challenges/DS-passwordless-magic-link-OTP.png b/content/identity/user-authentication-evolution-challenges/DS-passwordless-magic-link-OTP.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/user-authentication-evolution-challenges/DS-passwordless-magic-link-OTP.png and /dev/null differ
diff --git a/content/identity/user-authentication-evolution-challenges/DS-passwordless-magic-link-OTP.webp b/content/identity/user-authentication-evolution-challenges/DS-passwordless-magic-link-OTP.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/user-authentication-evolution-challenges/DS-passwordless-magic-link-OTP.webp differ
diff --git a/content/identity/user-authentication-evolution-challenges/index.md b/content/identity/user-authentication-evolution-challenges/index.md
index e10139f30..d2f1b5b4c 100644
--- a/content/identity/user-authentication-evolution-challenges/index.md
+++ b/content/identity/user-authentication-evolution-challenges/index.md
@@ -1,7 +1,7 @@
---
title: "From Past to Present: User Authentication's Evolution and Challenges"
date: "2024-03-27"
-coverImage: "user-authentication.jpg"
+coverImage: "user-authentication.webp"
tags: ["user authentication","data security","ciam solutions"]
author: "Rakesh Soni"
description: "From the humble beginnings of legacy authentication mechanisms to today's sophisticated technologies, the journey of user authentication has been a captivating evolution marked by relentless innovation."
@@ -54,7 +54,7 @@ The evolution of user authentication has brought forth a range of emerging techn
Passwordless authentication, for example, eliminates the need for traditional passwords, relying instead on methods such as cryptographic keys, biometrics, and behavioral analytics. This not only enhances security but also simplifies the user experience.
-[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
+[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
## How CIAM Helps Overcome the Authentication Challenges
@@ -78,4 +78,4 @@ The evolution of user authentication from legacy mechanisms to emerging technolo
By embracing these innovations and prioritizing security and user experience, organizations can successfully navigate the complexities of user authentication evolution challenges in the digital age.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-authentication-evolution-challenges)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-authentication-evolution-challenges)
\ No newline at end of file
diff --git a/content/identity/user-authentication-evolution-challenges/user-authentication.jpg b/content/identity/user-authentication-evolution-challenges/user-authentication.jpg
deleted file mode 100644
index bc9a11bbe..000000000
Binary files a/content/identity/user-authentication-evolution-challenges/user-authentication.jpg and /dev/null differ
diff --git a/content/identity/user-authentication-evolution-challenges/user-authentication.webp b/content/identity/user-authentication-evolution-challenges/user-authentication.webp
new file mode 100644
index 000000000..0e242b943
Binary files /dev/null and b/content/identity/user-authentication-evolution-challenges/user-authentication.webp differ
diff --git a/content/identity/user-onboarding-revamp-application/ciam-101.png b/content/identity/user-onboarding-revamp-application/ciam-101.png
deleted file mode 100644
index 181c84344..000000000
Binary files a/content/identity/user-onboarding-revamp-application/ciam-101.png and /dev/null differ
diff --git a/content/identity/user-onboarding-revamp-application/ciam-101.webp b/content/identity/user-onboarding-revamp-application/ciam-101.webp
new file mode 100644
index 000000000..e2cac289d
Binary files /dev/null and b/content/identity/user-onboarding-revamp-application/ciam-101.webp differ
diff --git a/content/identity/user-onboarding-revamp-application/ideal-user-onboarding-process.png b/content/identity/user-onboarding-revamp-application/ideal-user-onboarding-process.png
deleted file mode 100644
index 826904025..000000000
Binary files a/content/identity/user-onboarding-revamp-application/ideal-user-onboarding-process.png and /dev/null differ
diff --git a/content/identity/user-onboarding-revamp-application/ideal-user-onboarding-process.webp b/content/identity/user-onboarding-revamp-application/ideal-user-onboarding-process.webp
new file mode 100644
index 000000000..6bf94f6c3
Binary files /dev/null and b/content/identity/user-onboarding-revamp-application/ideal-user-onboarding-process.webp differ
diff --git a/content/identity/user-onboarding-revamp-application/index.md b/content/identity/user-onboarding-revamp-application/index.md
index 5c64d4356..9ee71d2fb 100644
--- a/content/identity/user-onboarding-revamp-application/index.md
+++ b/content/identity/user-onboarding-revamp-application/index.md
@@ -1,7 +1,7 @@
---
title: "5 Ways User Onboarding Software Can Revamp Your Application"
date: "2021-01-27"
-coverImage: "user-onboarding-application.jpg"
+coverImage: "user-onboarding-application.webp"
tags: ["customer-experience"]
featured: false
author: "Rakesh Soni"
@@ -33,7 +33,7 @@ When the user launches your app for the first time, the onboarding process reinf
## What Are the Primary Elements of an Ideal User Onboarding Process
-
+
The onboarding process should be a mix of inspiration, education, timely and actionable insights. Each product is unique, and how you are going to handle the onboarding will help you to know about your users, their needs, and how your product is going to stay with them.
@@ -84,7 +84,7 @@ This happens when your customer truly appreciates the value of your software. Co
The main goal of onboarding is to show new users the key features and guide users towards the ‘Aha Moment,’ which is called the moment of delight, where the value of the product becomes instantly clear.
-[](https://www.loginradius.com/resource/ciam-101/)
+[](https://www.loginradius.com/resource/ciam-101/)
@@ -137,4 +137,4 @@ You know by now how user onboarding software can revamp your application. But, o
It takes time to build an onboarding process and a lot of work to update it. You cannot change everything immediately, but you can make small changes over a period of time to smoothen the onboarding process.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-onboarding-revamp-application)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-onboarding-revamp-application)
\ No newline at end of file
diff --git a/content/identity/user-onboarding-revamp-application/user-onboarding-application.jpg b/content/identity/user-onboarding-revamp-application/user-onboarding-application.jpg
deleted file mode 100644
index 069cd106f..000000000
Binary files a/content/identity/user-onboarding-revamp-application/user-onboarding-application.jpg and /dev/null differ
diff --git a/content/identity/user-onboarding-revamp-application/user-onboarding-application.webp b/content/identity/user-onboarding-revamp-application/user-onboarding-application.webp
new file mode 100644
index 000000000..f003e9d57
Binary files /dev/null and b/content/identity/user-onboarding-revamp-application/user-onboarding-application.webp differ
diff --git a/content/identity/user-provisioning-mistakes/EB-GD-to-MFA.png b/content/identity/user-provisioning-mistakes/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/user-provisioning-mistakes/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/user-provisioning-mistakes/EB-GD-to-MFA.webp b/content/identity/user-provisioning-mistakes/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/user-provisioning-mistakes/EB-GD-to-MFA.webp differ
diff --git a/content/identity/user-provisioning-mistakes/Image-Stat.PNG b/content/identity/user-provisioning-mistakes/Image-Stat.PNG
deleted file mode 100644
index ecf4cfb10..000000000
Binary files a/content/identity/user-provisioning-mistakes/Image-Stat.PNG and /dev/null differ
diff --git a/content/identity/user-provisioning-mistakes/Image-Stat.webp b/content/identity/user-provisioning-mistakes/Image-Stat.webp
new file mode 100644
index 000000000..f1374ccc9
Binary files /dev/null and b/content/identity/user-provisioning-mistakes/Image-Stat.webp differ
diff --git a/content/identity/user-provisioning-mistakes/index.md b/content/identity/user-provisioning-mistakes/index.md
index 86ea61e47..977fb702d 100644
--- a/content/identity/user-provisioning-mistakes/index.md
+++ b/content/identity/user-provisioning-mistakes/index.md
@@ -1,7 +1,7 @@
---
title: "Top 5 User Provisioning Mistakes Enterprises Should Avoid in 2021"
date: "2021-05-20"
-coverImage: "user-provisioning-mistakes-cover.jpg"
+coverImage: "user-provisioning-mistakes-cover.webp"
tags: ["user provisioning","rba","access management","cx"]
author: "Vishal Sharma"
description: " It’s crucial for online businesses that are collecting user information and storing the same over the cloud to ensure data safety best practices are in place to safeguard clients’ identity and privacy. This insightful read lists some of the common mistakes that enterprises must avoid in 2021 and beyond."
@@ -17,7 +17,7 @@ Above all, the global pandemic also contributed to the sudden upsurge in the num
Here are the stats depicting the global increase in identity theft risk since the coronavirus outbreak in 2020.
-
+
**Image Source**: [Statista](https://www.statista.com/statistics/1175657/increase-identity-theft-coronavirus-outbreak/)
@@ -44,7 +44,7 @@ While unauthorized professionals are exploring new ways to gain access to user p
Since cyber attackers can quickly bypass a single layer of security, MFA is undoubtedly the need of the hour for businesses that need to secure user identities in the ever-expanding digital world.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
**#3 Mistake: Missing SSL (Secure Sockets Layer) Certificate**
@@ -85,4 +85,4 @@ In a world where competitors are just a click away, online businesses collecting
Correct user provisioning is the key to customer success and when brands learn its importance, it provides them a competitive edge.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-provisioning-mistakes)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-provisioning-mistakes)
diff --git a/content/identity/user-provisioning-mistakes/mfa-guide.png b/content/identity/user-provisioning-mistakes/mfa-guide.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/user-provisioning-mistakes/mfa-guide.png and /dev/null differ
diff --git a/content/identity/user-provisioning-mistakes/mfa-guide.webp b/content/identity/user-provisioning-mistakes/mfa-guide.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/user-provisioning-mistakes/mfa-guide.webp differ
diff --git a/content/identity/user-provisioning-mistakes/user-provisioning-mistakes-cover.jpg b/content/identity/user-provisioning-mistakes/user-provisioning-mistakes-cover.jpg
deleted file mode 100644
index 27f021407..000000000
Binary files a/content/identity/user-provisioning-mistakes/user-provisioning-mistakes-cover.jpg and /dev/null differ
diff --git a/content/identity/user-provisioning-mistakes/user-provisioning-mistakes-cover.webp b/content/identity/user-provisioning-mistakes/user-provisioning-mistakes-cover.webp
new file mode 100644
index 000000000..75fe45a6c
Binary files /dev/null and b/content/identity/user-provisioning-mistakes/user-provisioning-mistakes-cover.webp differ
diff --git a/content/identity/user-session-management/coding_user_session.jpg b/content/identity/user-session-management/coding_user_session.jpg
deleted file mode 100644
index 583e41bcb..000000000
Binary files a/content/identity/user-session-management/coding_user_session.jpg and /dev/null differ
diff --git a/content/identity/user-session-management/coding_user_session.webp b/content/identity/user-session-management/coding_user_session.webp
new file mode 100644
index 000000000..db83ac3a9
Binary files /dev/null and b/content/identity/user-session-management/coding_user_session.webp differ
diff --git a/content/identity/user-session-management/index.md b/content/identity/user-session-management/index.md
index a6fd7e8df..a169267cb 100644
--- a/content/identity/user-session-management/index.md
+++ b/content/identity/user-session-management/index.md
@@ -1,7 +1,7 @@
---
title: "What is User Session Management?"
date: "2021-05-31"
-coverImage: "session_cover_pic.jpg"
+coverImage: "session_cover_pic.webp"
tags: ["user management","token authentication","cx"]
author: "Keshav Kumar"
description: "Implementing proper session management usually increases the strength and security of the session token. And if you have not implemented it, then many vulnerabilities can be introduced with insecure session cookies that attackers can leverage to benefit an authenticated user session."
@@ -19,7 +19,7 @@ Generally, if a consumer leaves a website or closes the browser, their session e
Sessions will end when a consumer logs out or when the session lifetime limit is completed. In addition, “**Force Logout**” can also cause sessions to expire.
-
+
## Session Lifetime
@@ -39,7 +39,7 @@ After Password Reset or Password Change, it will expire all active sessions of t
Implementing proper session management usually increases the strength and security of the session token. And if you have not implemented it, then many vulnerabilities can be introduced with [insecure session cookies that attackers can leverage](https://www.loginradius.com/blog/identity/2021/01/7-web-app-sec-threats/) to benefit an authenticated user session.
-
+
Attackers can take measures against Brute Force. They can predict and expose session tokens which ultimately can lead to session hijacking, where the malicious consumer can impersonate the victim and complete transactions from their account.
So to avoid such instances, we use session management so we can adequately secure the session, which helps to provide robust protection against session hijacking.
@@ -130,4 +130,4 @@ User sessions should change when there is a change in authentication status (log
The two types of sessions are: Client-Side Sessions: Stored on the user's browser, usually as cookies. Server-Side Sessions: Stored on the server, often in databases or server memory.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-session-management)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-session-management)
\ No newline at end of file
diff --git a/content/identity/user-session-management/session_cover_pic.jpg b/content/identity/user-session-management/session_cover_pic.jpg
deleted file mode 100644
index 7ce1de7cd..000000000
Binary files a/content/identity/user-session-management/session_cover_pic.jpg and /dev/null differ
diff --git a/content/identity/user-session-management/session_cover_pic.webp b/content/identity/user-session-management/session_cover_pic.webp
new file mode 100644
index 000000000..52f277f3c
Binary files /dev/null and b/content/identity/user-session-management/session_cover_pic.webp differ
diff --git a/content/identity/webauth-secures-user-login/EB-GD-to-MFA.png b/content/identity/webauth-secures-user-login/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/webauth-secures-user-login/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/webauth-secures-user-login/EB-GD-to-MFA.webp b/content/identity/webauth-secures-user-login/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/webauth-secures-user-login/EB-GD-to-MFA.webp differ
diff --git a/content/identity/webauth-secures-user-login/index.md b/content/identity/webauth-secures-user-login/index.md
index 66de803d4..63eda3e83 100644
--- a/content/identity/webauth-secures-user-login/index.md
+++ b/content/identity/webauth-secures-user-login/index.md
@@ -1,7 +1,7 @@
---
title: "How WebAuth Secures Your Users’ Login"
date: "2021-07-20"
-coverImage: "webauth-secures-user-login-cover.jpg"
+coverImage: "webauth-secures-user-login-cover.webp"
tags: ["passwordless authentication","mfa","cx"]
author: "Vishal Sharma"
description: "WebAuthn is a new standard for authentication, which is published by the World Wide Web Consortium and is supported by the FIDO alliance.
@@ -55,7 +55,7 @@ Whenever a user needs to prove their identity, the smart biometric can be utiliz
Let’s understand this with a real-life example where we can use WebAuthn for handling authentication after an individual has registered with a web application.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
Suppose the user is registered from their phone and navigates to the web application to log in. In that case, they are prompted to enter their password or biometric, which is associated with that particular account. The user can simply use their biometric to log in without the need to enter lengthy passwords.
@@ -91,4 +91,4 @@ If you wish to deliver the next level of login experience to your consumers that
[Reach us](https://www.loginradius.com/contact-sales/) for a personalized demo and know-how LoginRadius works for your business.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=webauth-secures-user-login)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=webauth-secures-user-login)
\ No newline at end of file
diff --git a/content/identity/webauth-secures-user-login/mfa.png b/content/identity/webauth-secures-user-login/mfa.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/webauth-secures-user-login/mfa.png and /dev/null differ
diff --git a/content/identity/webauth-secures-user-login/mfa.webp b/content/identity/webauth-secures-user-login/mfa.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/webauth-secures-user-login/mfa.webp differ
diff --git a/content/identity/webauth-secures-user-login/webauth-secures-user-login-cover.jpg b/content/identity/webauth-secures-user-login/webauth-secures-user-login-cover.jpg
deleted file mode 100644
index 75ede5eca..000000000
Binary files a/content/identity/webauth-secures-user-login/webauth-secures-user-login-cover.jpg and /dev/null differ
diff --git a/content/identity/webauth-secures-user-login/webauth-secures-user-login-cover.webp b/content/identity/webauth-secures-user-login/webauth-secures-user-login-cover.webp
new file mode 100644
index 000000000..fcce0406d
Binary files /dev/null and b/content/identity/webauth-secures-user-login/webauth-secures-user-login-cover.webp differ
diff --git a/content/identity/what-are-security-keys/GD-auth-encryp.png b/content/identity/what-are-security-keys/GD-auth-encryp.png
deleted file mode 100644
index 5882b296e..000000000
Binary files a/content/identity/what-are-security-keys/GD-auth-encryp.png and /dev/null differ
diff --git a/content/identity/what-are-security-keys/GD-auth-encryp.webp b/content/identity/what-are-security-keys/GD-auth-encryp.webp
new file mode 100644
index 000000000..eab51f2cf
Binary files /dev/null and b/content/identity/what-are-security-keys/GD-auth-encryp.webp differ
diff --git a/content/identity/what-are-security-keys/GD-to-auth.png b/content/identity/what-are-security-keys/GD-to-auth.png
deleted file mode 100644
index bcc2c06d6..000000000
Binary files a/content/identity/what-are-security-keys/GD-to-auth.png and /dev/null differ
diff --git a/content/identity/what-are-security-keys/GD-to-auth.webp b/content/identity/what-are-security-keys/GD-to-auth.webp
new file mode 100644
index 000000000..b8563a100
Binary files /dev/null and b/content/identity/what-are-security-keys/GD-to-auth.webp differ
diff --git a/content/identity/what-are-security-keys/index.md b/content/identity/what-are-security-keys/index.md
index 7388d7418..8c0833af9 100644
--- a/content/identity/what-are-security-keys/index.md
+++ b/content/identity/what-are-security-keys/index.md
@@ -1,7 +1,7 @@
---
title: "What are Security Keys? What are its Advantages?"
date: "2021-09-23"
-coverImage: "what-are-security-keys-cover.jpg"
+coverImage: "what-are-security-keys-cover.webp"
tags: ["security keys","mfa","authentication","authorization"]
author: "Vishal Sharma"
description: "When it comes to robust security for a seamless authentication and authorization experience, security keys are considered one of the best ways to prove one’s identity. These security practices add an extra security layer other than passwords and ensure that the right person has access to the right information."
@@ -59,7 +59,7 @@ Many organizations utilize security keys and eventually encourage their employee
Besides the endless advantages of security keys regarding [authentication and authorization](https://www.loginradius.com/blog/identity/authentication-vs-authorization-infographic/), the major drawback is that these keys are costly.
-[](https://www.loginradius.com/resource/a-quick-guide-to-authentication-authorization-and-encryption/)
+[](https://www.loginradius.com/resource/a-quick-guide-to-authentication-authorization-and-encryption/)
Organizations and individuals find it more expensive to purchase and maintain a physical key than other software alternatives.
@@ -71,4 +71,4 @@ Security keys are shaping the future of security and are pretty helpful in certa
However, those that require excellent user experience coupled with robust security must consider relying on risk-based authentication (RBA) solutions designed to deliver exceptional user experience with stringent security mechanisms.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-are-security-keys)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-are-security-keys)
diff --git a/content/identity/what-are-security-keys/what-are-security-keys-cover.jpg b/content/identity/what-are-security-keys/what-are-security-keys-cover.jpg
deleted file mode 100644
index 14b5bbdaf..000000000
Binary files a/content/identity/what-are-security-keys/what-are-security-keys-cover.jpg and /dev/null differ
diff --git a/content/identity/what-are-security-keys/what-are-security-keys-cover.webp b/content/identity/what-are-security-keys/what-are-security-keys-cover.webp
new file mode 100644
index 000000000..12a4f256b
Binary files /dev/null and b/content/identity/what-are-security-keys/what-are-security-keys-cover.webp differ
diff --git a/content/identity/what-are-self-sovereign-identities/index.md b/content/identity/what-are-self-sovereign-identities/index.md
index 3cb3f401d..5caee154f 100644
--- a/content/identity/what-are-self-sovereign-identities/index.md
+++ b/content/identity/what-are-self-sovereign-identities/index.md
@@ -1,7 +1,7 @@
---
title: "What are Self-Sovereign Identities?"
date: "2023-02-03"
-coverImage: "sovereign-ids.jpg"
+coverImage: "sovereign-ids.webp"
tags: ["digital identity", "self sovereign id", "customer data security"]
author: "Rakesh Soni"
description: "Today, we take a look at what self-sovereign identity is. And although it's easy to get confused with all the buzzwords floating around, incredibly, when many of them are hyped in the media, self-sovereign identity is an essential concept in the evolving landscape of digital identities."
@@ -69,4 +69,4 @@ The Internet Identity Ecosystem is disrupting the highly centralized paradigm of
Self-sovereign identities are changing the way we interact online. Businesses are taking advantage of the security and transparency offered by this new paradigm to streamline their operations, reduce fraud, and rebuild customer trust.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-are-self-sovereign-identities)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-are-self-sovereign-identities)
\ No newline at end of file
diff --git a/content/identity/what-are-self-sovereign-identities/sovereign-ids.jpg b/content/identity/what-are-self-sovereign-identities/sovereign-ids.jpg
deleted file mode 100644
index 5d1356df8..000000000
Binary files a/content/identity/what-are-self-sovereign-identities/sovereign-ids.jpg and /dev/null differ
diff --git a/content/identity/what-are-self-sovereign-identities/sovereign-ids.webp b/content/identity/what-are-self-sovereign-identities/sovereign-ids.webp
new file mode 100644
index 000000000..adcba9654
Binary files /dev/null and b/content/identity/what-are-self-sovereign-identities/sovereign-ids.webp differ
diff --git a/content/identity/what-is-OTP-authentication/index.md b/content/identity/what-is-OTP-authentication/index.md
index 5bd03b669..add3bc996 100644
--- a/content/identity/what-is-OTP-authentication/index.md
+++ b/content/identity/what-is-OTP-authentication/index.md
@@ -184,4 +184,4 @@ Ready to enhance your authentication strategy with LoginRadius? [Book a free tri
**A.** The secret key is a shared value between client and server, used in algorithms like TOTP or HOTP to generate OTP codes securely.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-otp-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-otp-authentication)
diff --git a/content/identity/what-is-Phone-Login/Benifits_of_phoneLogin_in_business.jpg b/content/identity/what-is-Phone-Login/Benifits_of_phoneLogin_in_business.jpg
deleted file mode 100644
index 23366413f..000000000
Binary files a/content/identity/what-is-Phone-Login/Benifits_of_phoneLogin_in_business.jpg and /dev/null differ
diff --git a/content/identity/what-is-Phone-Login/Benifits_of_phoneLogin_in_business.webp b/content/identity/what-is-Phone-Login/Benifits_of_phoneLogin_in_business.webp
new file mode 100644
index 000000000..29b554d01
Binary files /dev/null and b/content/identity/what-is-Phone-Login/Benifits_of_phoneLogin_in_business.webp differ
diff --git a/content/identity/what-is-Phone-Login/PhoneLogin.jpg b/content/identity/what-is-Phone-Login/PhoneLogin.jpg
deleted file mode 100644
index 72c55ae91..000000000
Binary files a/content/identity/what-is-Phone-Login/PhoneLogin.jpg and /dev/null differ
diff --git a/content/identity/what-is-Phone-Login/PhoneLogin.webp b/content/identity/what-is-Phone-Login/PhoneLogin.webp
new file mode 100644
index 000000000..6ea971ac4
Binary files /dev/null and b/content/identity/what-is-Phone-Login/PhoneLogin.webp differ
diff --git a/content/identity/what-is-Phone-Login/PhoneLogin_cover_pic.jpg b/content/identity/what-is-Phone-Login/PhoneLogin_cover_pic.jpg
deleted file mode 100644
index c943b5153..000000000
Binary files a/content/identity/what-is-Phone-Login/PhoneLogin_cover_pic.jpg and /dev/null differ
diff --git a/content/identity/what-is-Phone-Login/PhoneLogin_cover_pic.webp b/content/identity/what-is-Phone-Login/PhoneLogin_cover_pic.webp
new file mode 100644
index 000000000..e80803dff
Binary files /dev/null and b/content/identity/what-is-Phone-Login/PhoneLogin_cover_pic.webp differ
diff --git a/content/identity/what-is-Phone-Login/PhoneLogin_overview.jpg b/content/identity/what-is-Phone-Login/PhoneLogin_overview.jpg
deleted file mode 100644
index cde01a3b0..000000000
Binary files a/content/identity/what-is-Phone-Login/PhoneLogin_overview.jpg and /dev/null differ
diff --git a/content/identity/what-is-Phone-Login/PhoneLogin_overview.webp b/content/identity/what-is-Phone-Login/PhoneLogin_overview.webp
new file mode 100644
index 000000000..15490f8ba
Binary files /dev/null and b/content/identity/what-is-Phone-Login/PhoneLogin_overview.webp differ
diff --git a/content/identity/what-is-Phone-Login/index.md b/content/identity/what-is-Phone-Login/index.md
index 9b57cb86c..01049bcb7 100644
--- a/content/identity/what-is-Phone-Login/index.md
+++ b/content/identity/what-is-Phone-Login/index.md
@@ -1,7 +1,7 @@
---
title: "What is Phone Login"
date: "2021-02-26"
-coverImage: "PhoneLogin_cover_pic.jpg"
+coverImage: "PhoneLogin_cover_pic.webp"
tags: ["phone login","authentication","cx"]
author: "Ashish Kumar Yadav"
description: "Phone Login is a compelling and handy feature designed to enhance consumer experience and ease the process of login and registration. It eliminates the hassle of filling lengthy registration forms and creating new passwords and usernames, thereby allowing consumers to quickly login or register just by using their mobile phones."
@@ -19,7 +19,7 @@ Today, a single consumer interacts with various apps/websites, which require the
In this type of process, consumers may become frustrated and completely give up the sign-up process as it asks for a lot of information. Ultimately, businesses end up with lower consumer growth rates.
-
+
But if the sign-up and login process is done right, it can trigger the retention of lots of new consumers. If done in an improper method, it may backfire and can have the exact opposite effect.
@@ -69,7 +69,7 @@ It is the process of registering or accessing a user's account by using a phone
It eliminates the hassle of filling lengthy registration forms and creating new passwords and usernames, thereby allowing users to quickly login or register just by using their mobile phones.
-
+
## Why Should Businesses Use Phone Login
@@ -105,7 +105,7 @@ And it should not be tough to understand that consumers will always tend to move
- Merchants shall reach consumers with their promotions and offers quickly through phone number
-
+
Looking at the above benefits, business owners can easily enhance their business strategies and ultimately increase their consumer growth. You've got everything you need to communicate with your end-users in the most concrete and straightforward method.
@@ -115,7 +115,7 @@ Now that you have read all the advantages of using a phone login and you are pla
Don't worry, we've got you covered.
-[](https://www.loginradius.com/resource/loginradius-ciam-phone-authentication/)
+[](https://www.loginradius.com/resource/loginradius-ciam-phone-authentication/)
This whole implementation is divided into two parts.
The user submits the phone number to the website's backend via GUI and obtains a token.
@@ -150,4 +150,4 @@ In this article, we talked about applying a simple approach of using Phone Login
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-phone-login)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-phone-login)
\ No newline at end of file
diff --git a/content/identity/what-is-Phone-Login/phone-authentication.png b/content/identity/what-is-Phone-Login/phone-authentication.png
deleted file mode 100644
index c160e816a..000000000
Binary files a/content/identity/what-is-Phone-Login/phone-authentication.png and /dev/null differ
diff --git a/content/identity/what-is-Phone-Login/phone-authentication.webp b/content/identity/what-is-Phone-Login/phone-authentication.webp
new file mode 100644
index 000000000..6121a4a47
Binary files /dev/null and b/content/identity/what-is-Phone-Login/phone-authentication.webp differ
diff --git a/content/identity/what-is-a-2fa-bypass-attack/2fa-bypass.jpg b/content/identity/what-is-a-2fa-bypass-attack/2fa-bypass.jpg
deleted file mode 100644
index 751983e22..000000000
Binary files a/content/identity/what-is-a-2fa-bypass-attack/2fa-bypass.jpg and /dev/null differ
diff --git a/content/identity/what-is-a-2fa-bypass-attack/2fa-bypass.webp b/content/identity/what-is-a-2fa-bypass-attack/2fa-bypass.webp
new file mode 100644
index 000000000..fec80a105
Binary files /dev/null and b/content/identity/what-is-a-2fa-bypass-attack/2fa-bypass.webp differ
diff --git a/content/identity/what-is-a-2fa-bypass-attack/GD-to-RBA.png b/content/identity/what-is-a-2fa-bypass-attack/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/what-is-a-2fa-bypass-attack/GD-to-RBA.png and /dev/null differ
diff --git a/content/identity/what-is-a-2fa-bypass-attack/GD-to-RBA.webp b/content/identity/what-is-a-2fa-bypass-attack/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/what-is-a-2fa-bypass-attack/GD-to-RBA.webp differ
diff --git a/content/identity/what-is-a-2fa-bypass-attack/index.md b/content/identity/what-is-a-2fa-bypass-attack/index.md
index 0b2578b14..615734771 100644
--- a/content/identity/what-is-a-2fa-bypass-attack/index.md
+++ b/content/identity/what-is-a-2fa-bypass-attack/index.md
@@ -1,7 +1,7 @@
---
title: "2FA Bypass Attacks- Everything You Should Know"
date: "2022-11-04"
-coverImage: "2fa-bypass.jpg"
+coverImage: "2fa-bypass.webp"
tags: ["2fa bypass", "cyberattacks", "risk based authentication"]
author: "Rakesh Soni"
description: "2FA bypass attacks are cyberattacks intended for account takeover when hackers have already accessed the credentials of a particular account, and they bypass the second layer of authentication in several ways. This post covers how businesses can shield themselves from the growing number of such threats."
@@ -69,7 +69,7 @@ These kinds of attacks may affect the privacy of a user/employee and may result
Risk-based authentication (RBA), also called adaptive authentication, monitors consumers’ identity and access using stringent rules. The objective is to authenticate a user profile before allowing access to ensure it is not a threat. These restrictions become more stringent with increasing risks.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
Risk-based authentication works on a model that requires permission and response. A user asks for permission to access a file or software. In response, the file or software responds by presenting options to log in using an ID and password or sending mail or OTP to a registered contact number.
@@ -83,4 +83,4 @@ Also, with robust security mechanisms, including risk-based authentication, busi
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-a-2fa-bypass-attack)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-a-2fa-bypass-attack)
\ No newline at end of file
diff --git a/content/identity/what-is-a-2fa-bypass-attack/rba-gd.png b/content/identity/what-is-a-2fa-bypass-attack/rba-gd.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/identity/what-is-a-2fa-bypass-attack/rba-gd.png and /dev/null differ
diff --git a/content/identity/what-is-a-2fa-bypass-attack/rba-gd.webp b/content/identity/what-is-a-2fa-bypass-attack/rba-gd.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/identity/what-is-a-2fa-bypass-attack/rba-gd.webp differ
diff --git a/content/identity/what-is-account-creation-fraud/GD-to-RBA.png b/content/identity/what-is-account-creation-fraud/GD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/what-is-account-creation-fraud/GD-to-RBA.png and /dev/null differ
diff --git a/content/identity/what-is-account-creation-fraud/GD-to-RBA.webp b/content/identity/what-is-account-creation-fraud/GD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/what-is-account-creation-fraud/GD-to-RBA.webp differ
diff --git a/content/identity/what-is-account-creation-fraud/account-fraud.jpg b/content/identity/what-is-account-creation-fraud/account-fraud.jpg
deleted file mode 100644
index 9086c1d1b..000000000
Binary files a/content/identity/what-is-account-creation-fraud/account-fraud.jpg and /dev/null differ
diff --git a/content/identity/what-is-account-creation-fraud/account-fraud.webp b/content/identity/what-is-account-creation-fraud/account-fraud.webp
new file mode 100644
index 000000000..996fbde44
Binary files /dev/null and b/content/identity/what-is-account-creation-fraud/account-fraud.webp differ
diff --git a/content/identity/what-is-account-creation-fraud/index.md b/content/identity/what-is-account-creation-fraud/index.md
index f8d4fd7f0..5514c403a 100644
--- a/content/identity/what-is-account-creation-fraud/index.md
+++ b/content/identity/what-is-account-creation-fraud/index.md
@@ -1,7 +1,7 @@
---
title: "The Rise of Account Creation Fraud: What You Need to Know"
date: "2023-02-15"
-coverImage: "account-fraud.jpg"
+coverImage: "account-fraud.webp"
tags: ["account fraud", "passwordless authentication", "risk based authentication"]
author: "Alok Patidar"
description: "Account creation fraud, sometimes called new account fraud, is a fraud where cybercriminals create fake accounts of users and exploit their details. And these frauds are often carried out by exploiting the stolen identity of users or through a loophole in a platform's entire identity management system."
@@ -61,7 +61,7 @@ RBA is a process of assessing the risk of an authentication request in real-time
The risk is usually assessed based on various parameters and the environment from which the user is trying to authenticate. Some standard parameters used for risk profiling include geographical location, IP address, device, etc.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
With LoginRadius' risk-based authentication system (RBA), businesses can use risk profiling as another layer of security on top of the traditional methods of identity verification already being used by most online companies today: username and password.
@@ -75,4 +75,4 @@ Account creation frauds are quickly rising, and businesses must ensure robust se
To maintain the trust of your customers, you need to help them spend less time worrying about their security and more time enjoying their experience with your brand. And that's a promise that only a passwordless CIAM platform can fulfill!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-account-creation-fraud)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-account-creation-fraud)
\ No newline at end of file
diff --git a/content/identity/what-is-account-creation-fraud/rba-guide.png b/content/identity/what-is-account-creation-fraud/rba-guide.png
deleted file mode 100644
index c820cfc17..000000000
Binary files a/content/identity/what-is-account-creation-fraud/rba-guide.png and /dev/null differ
diff --git a/content/identity/what-is-account-creation-fraud/rba-guide.webp b/content/identity/what-is-account-creation-fraud/rba-guide.webp
new file mode 100644
index 000000000..9cfe7e407
Binary files /dev/null and b/content/identity/what-is-account-creation-fraud/rba-guide.webp differ
diff --git a/content/identity/what-is-authentication/authentication.webp b/content/identity/what-is-authentication/authentication.webp
new file mode 100644
index 000000000..36b9670b2
Binary files /dev/null and b/content/identity/what-is-authentication/authentication.webp differ
diff --git a/content/identity/what-is-authentication/cover-auth.webp b/content/identity/what-is-authentication/cover-auth.webp
new file mode 100644
index 000000000..a3e3bc86c
Binary files /dev/null and b/content/identity/what-is-authentication/cover-auth.webp differ
diff --git a/content/identity/what-is-authentication/index.md b/content/identity/what-is-authentication/index.md
index 2791f2aad..7e5f63036 100644
--- a/content/identity/what-is-authentication/index.md
+++ b/content/identity/what-is-authentication/index.md
@@ -136,7 +136,7 @@ Need a quick comparison between single-factor authentication, two factor authent
### OTP Authentication
-[One-time passwords (OTPs)](https://www.loginradius.com/blog/identity/what-is-OTP-authentication) are temporary codes sent to users via SMS, email, or an app. They’re valid for a short period and can’t be reused. OTPs are common in 2FA setups and are great for preventing password reuse or simple phishing attacks.
+[One-time passwords (OTPs)](https://www.loginradius.com/blog/identity/what-is-otp-authentication/) are temporary codes sent to users via SMS, email, or an app. They’re valid for a short period and can’t be reused. OTPs are common in 2FA setups and are great for preventing password reuse or simple phishing attacks.
### Multi-Factor Authentication (MFA)
@@ -341,4 +341,4 @@ Ready to upgrade your authentication strategy?
**A:** They remove weak password dependencies and block phishing or credential theft.
-[](https://www.loginradius.com/contact-us)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us)
\ No newline at end of file
diff --git a/content/identity/what-is-broken-authentication/broken-auth.jpg b/content/identity/what-is-broken-authentication/broken-auth.jpg
deleted file mode 100644
index d4ceb81e5..000000000
Binary files a/content/identity/what-is-broken-authentication/broken-auth.jpg and /dev/null differ
diff --git a/content/identity/what-is-broken-authentication/broken-auth.webp b/content/identity/what-is-broken-authentication/broken-auth.webp
new file mode 100644
index 000000000..f005587a4
Binary files /dev/null and b/content/identity/what-is-broken-authentication/broken-auth.webp differ
diff --git a/content/identity/what-is-broken-authentication/buyer-guide-to-multi-factor-authentication-ebook.png b/content/identity/what-is-broken-authentication/buyer-guide-to-multi-factor-authentication-ebook.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/what-is-broken-authentication/buyer-guide-to-multi-factor-authentication-ebook.png and /dev/null differ
diff --git a/content/identity/what-is-broken-authentication/buyer-guide-to-multi-factor-authentication-ebook.webp b/content/identity/what-is-broken-authentication/buyer-guide-to-multi-factor-authentication-ebook.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/what-is-broken-authentication/buyer-guide-to-multi-factor-authentication-ebook.webp differ
diff --git a/content/identity/what-is-broken-authentication/index.md b/content/identity/what-is-broken-authentication/index.md
index 2fe96feb3..92a92e20d 100644
--- a/content/identity/what-is-broken-authentication/index.md
+++ b/content/identity/what-is-broken-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "What is Broken Authentication Vulnerability and How to Prevent It?"
date: "2021-02-17"
-coverImage: "broken-auth.jpg"
+coverImage: "broken-auth.webp"
tags: ["broken authentication","mfa","data security"]
author: "Rakesh Soni"
description: "If a hacker successfully logs with stolen credentials, they can misuse your privileges and impact your company's sustainability. Authentication protects a consumer's identity by allowing only a verified user to enter into the system. But there are numerous ways through which a hacker can impersonate consumers and enter inside the system."
@@ -176,7 +176,7 @@ Sometime later, the hacker opens your Gmail account and gains access to your cru
Thus, if the application session timeouts aren't set properly, hackers can execute a broken authentication attack.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
#### Example 3: Passwords are not properly hashed and salted.
@@ -274,4 +274,4 @@ Risks include unauthorized access to sensitive data, manipulation or deletion of
Effects include data breaches, privacy violations, fraudulent activities on compromised accounts, tarnished reputation for individuals or organizations, financial losses, and potential legal ramifications.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-broken-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-broken-authentication)
\ No newline at end of file
diff --git a/content/identity/what-is-broken-authentication/what-is-broken-authentication.jpg b/content/identity/what-is-broken-authentication/what-is-broken-authentication.jpg
deleted file mode 100644
index 36789c070..000000000
Binary files a/content/identity/what-is-broken-authentication/what-is-broken-authentication.jpg and /dev/null differ
diff --git a/content/identity/what-is-broken-authentication/what-is-broken-authentication.webp b/content/identity/what-is-broken-authentication/what-is-broken-authentication.webp
new file mode 100644
index 000000000..14a4067f6
Binary files /dev/null and b/content/identity/what-is-broken-authentication/what-is-broken-authentication.webp differ
diff --git a/content/identity/what-is-browser-in-browser-attack/DS-SSO.png b/content/identity/what-is-browser-in-browser-attack/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/what-is-browser-in-browser-attack/DS-SSO.png and /dev/null differ
diff --git a/content/identity/what-is-browser-in-browser-attack/DS-SSO.webp b/content/identity/what-is-browser-in-browser-attack/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/what-is-browser-in-browser-attack/DS-SSO.webp differ
diff --git a/content/identity/what-is-browser-in-browser-attack/LR-SSO.png b/content/identity/what-is-browser-in-browser-attack/LR-SSO.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/what-is-browser-in-browser-attack/LR-SSO.png and /dev/null differ
diff --git a/content/identity/what-is-browser-in-browser-attack/LR-SSO.webp b/content/identity/what-is-browser-in-browser-attack/LR-SSO.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/what-is-browser-in-browser-attack/LR-SSO.webp differ
diff --git a/content/identity/what-is-browser-in-browser-attack/bib-attacks.jpg b/content/identity/what-is-browser-in-browser-attack/bib-attacks.jpg
deleted file mode 100644
index fa8d9335f..000000000
Binary files a/content/identity/what-is-browser-in-browser-attack/bib-attacks.jpg and /dev/null differ
diff --git a/content/identity/what-is-browser-in-browser-attack/bib-attacks.webp b/content/identity/what-is-browser-in-browser-attack/bib-attacks.webp
new file mode 100644
index 000000000..8cd8d84c1
Binary files /dev/null and b/content/identity/what-is-browser-in-browser-attack/bib-attacks.webp differ
diff --git a/content/identity/what-is-browser-in-browser-attack/index.md b/content/identity/what-is-browser-in-browser-attack/index.md
index 8d324afd2..1878e2df8 100644
--- a/content/identity/what-is-browser-in-browser-attack/index.md
+++ b/content/identity/what-is-browser-in-browser-attack/index.md
@@ -1,7 +1,7 @@
---
title: "BITB Attacks: The New Destructive Phishing Technique"
date: "2022-04-22"
-coverImage: "bib-attacks.jpg"
+coverImage: "bib-attacks.webp"
tags: ["phishing", "sso", "identity-theft", "mfa"]
author: "Gurjyot Singh"
description: "The browser in the browser attack (BITB) is the latest form of phishing scam that simulates a browser window within a web browser and steals sensitive user information. Let’s understand the aspects of Browser in-browser attacks and how businesses can ensure stringent security for their consumers and employees to protect against these attacks."
@@ -43,7 +43,7 @@ Since SSO has provided endless opportunities to businesses and consumers, avoidi
Adding multiple layers of security while implementing single sign-on (SSO) could help businesses prevent browser in the browser attacks and help mitigate other associated risks.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
Let’s understand how businesses can reinforce security against BITB attacks.
@@ -92,4 +92,4 @@ If you wish to see the future of CIAM in action and understand how it works for
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-browser-in-browser-attack)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-browser-in-browser-attack)
diff --git a/content/identity/what-is-cloud-computing/EB-cloud-computing.png b/content/identity/what-is-cloud-computing/EB-cloud-computing.png
deleted file mode 100644
index c25a9d725..000000000
Binary files a/content/identity/what-is-cloud-computing/EB-cloud-computing.png and /dev/null differ
diff --git a/content/identity/what-is-cloud-computing/EB-cloud-computing.webp b/content/identity/what-is-cloud-computing/EB-cloud-computing.webp
new file mode 100644
index 000000000..1c3498318
Binary files /dev/null and b/content/identity/what-is-cloud-computing/EB-cloud-computing.webp differ
diff --git a/content/identity/what-is-cloud-computing/LR-Cloud-EB.png b/content/identity/what-is-cloud-computing/LR-Cloud-EB.png
deleted file mode 100644
index eec09c1fd..000000000
Binary files a/content/identity/what-is-cloud-computing/LR-Cloud-EB.png and /dev/null differ
diff --git a/content/identity/what-is-cloud-computing/LR-Cloud-EB.webp b/content/identity/what-is-cloud-computing/LR-Cloud-EB.webp
new file mode 100644
index 000000000..6843d161c
Binary files /dev/null and b/content/identity/what-is-cloud-computing/LR-Cloud-EB.webp differ
diff --git a/content/identity/what-is-cloud-computing/cloud-computing.jpg b/content/identity/what-is-cloud-computing/cloud-computing.jpg
deleted file mode 100644
index a83b260a9..000000000
Binary files a/content/identity/what-is-cloud-computing/cloud-computing.jpg and /dev/null differ
diff --git a/content/identity/what-is-cloud-computing/cloud-computing.webp b/content/identity/what-is-cloud-computing/cloud-computing.webp
new file mode 100644
index 000000000..71b9249ce
Binary files /dev/null and b/content/identity/what-is-cloud-computing/cloud-computing.webp differ
diff --git a/content/identity/what-is-cloud-computing/index.md b/content/identity/what-is-cloud-computing/index.md
index cea972923..12c0646f8 100644
--- a/content/identity/what-is-cloud-computing/index.md
+++ b/content/identity/what-is-cloud-computing/index.md
@@ -1,7 +1,7 @@
---
title: "What is Cloud Computing?"
date: "2022-05-24"
-coverImage: "cloud-computing.jpg"
+coverImage: "cloud-computing.webp"
tags: ["cloud computing", "cloud security", "cx"]
author: "Manish Tiwari"
description: "The concept of cloud computing has offered endless possibilities to businesses since enterprises can avoid several upfront costs and can quickly rent access to any application or storage from a cloud provider. This post uncovers the role of cloud computing in shaping the future of a digitally-advanced modern world."
@@ -101,7 +101,7 @@ Edge computing brings processing power closer to data sources, enabling real-tim
Artificial intelligence (AI) and machine learning (ML) will play a pivotal role in the future of cloud computing, with cloud platforms offering scalable and accessible AI and ML capabilities. As technology progresses, cloud computing will remain at the forefront, revolutionizing industries and driving digital transformation.
-[](https://www.loginradius.com/resource/why-is-loginradius-your-best-cloud-identity-partner/)
+[](https://www.loginradius.com/resource/why-is-loginradius-your-best-cloud-identity-partner/)
## What is Single Tenant Cloud Architecture?
@@ -159,4 +159,4 @@ Public cloud is shared infrastructure accessible to the public, while private cl
By implementing robust security measures, encryption, and compliance with relevant regulations.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-cloud-computing)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-cloud-computing)
\ No newline at end of file
diff --git a/content/identity/what-is-cloud-identity-and-its-benefits/EB-BG-to-MFA.png b/content/identity/what-is-cloud-identity-and-its-benefits/EB-BG-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/what-is-cloud-identity-and-its-benefits/EB-BG-to-MFA.png and /dev/null differ
diff --git a/content/identity/what-is-cloud-identity-and-its-benefits/EB-BG-to-MFA.webp b/content/identity/what-is-cloud-identity-and-its-benefits/EB-BG-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/what-is-cloud-identity-and-its-benefits/EB-BG-to-MFA.webp differ
diff --git a/content/identity/what-is-cloud-identity-and-its-benefits/cloud-identity.jpg b/content/identity/what-is-cloud-identity-and-its-benefits/cloud-identity.jpg
deleted file mode 100644
index e00f4f6dc..000000000
Binary files a/content/identity/what-is-cloud-identity-and-its-benefits/cloud-identity.jpg and /dev/null differ
diff --git a/content/identity/what-is-cloud-identity-and-its-benefits/cloud-identity.webp b/content/identity/what-is-cloud-identity-and-its-benefits/cloud-identity.webp
new file mode 100644
index 000000000..b0fae9922
Binary files /dev/null and b/content/identity/what-is-cloud-identity-and-its-benefits/cloud-identity.webp differ
diff --git a/content/identity/what-is-cloud-identity-and-its-benefits/index.md b/content/identity/what-is-cloud-identity-and-its-benefits/index.md
index 2fcca3989..01f9a15f3 100644
--- a/content/identity/what-is-cloud-identity-and-its-benefits/index.md
+++ b/content/identity/what-is-cloud-identity-and-its-benefits/index.md
@@ -1,7 +1,7 @@
---
title: "What is Cloud Identity and its Benefits?"
date: "2023-06-13"
-coverImage: "cloud-identity.jpg"
+coverImage: "cloud-identity.webp"
tags: ["cloud identity", "identity management", "cx"]
author: "Rakesh Soni"
description: "Cloud Identity has emerged as a game-changer in a digitally connected world. Learn how cloud identity simplifies user experiences, enhances security, and enables seamless integration with cloud services. Discover the advantages of centralized identity management and built-in compliance features for organizations of all sizes."
@@ -40,7 +40,7 @@ This simplifies [user provisioning](https://www.loginradius.com/blog/identity/us
Security is a critical concern in the digital realm, and cloud identity offers robust security measures to safeguard user identities and data. It enables organizations to implement multi-factor authentication (MFA), which adds an extra layer of security by requiring users to provide additional credentials, such as a one-time password or a biometric scan, in addition to their username and password.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
Cloud Identity solutions also often enforce strong password policies, such as password complexity requirements and expiration, to mitigate the risk of weak or compromised passwords. Moreover, advanced security protocols like OAuth and SAML are commonly used for secure identity federation, ensuring secure authentication and authorization across different cloud services and applications.
@@ -76,4 +76,4 @@ By leveraging these advantages, organizations can enhance their security posture
As businesses continue to embrace cloud-based solutions, adopting a robust cloud-based consumer identity and access management framework becomes indispensable in harnessing the full potential of the cloud while maintaining control and security over user identities and access controls.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-cloud-identity-and-its-benefits)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-cloud-identity-and-its-benefits)
diff --git a/content/identity/what-is-cloud-security/WP-identity-management.png b/content/identity/what-is-cloud-security/WP-identity-management.png
deleted file mode 100644
index c1f47d8bc..000000000
Binary files a/content/identity/what-is-cloud-security/WP-identity-management.png and /dev/null differ
diff --git a/content/identity/what-is-cloud-security/WP-identity-management.webp b/content/identity/what-is-cloud-security/WP-identity-management.webp
new file mode 100644
index 000000000..89e798f06
Binary files /dev/null and b/content/identity/what-is-cloud-security/WP-identity-management.webp differ
diff --git a/content/identity/what-is-cloud-security/cloud-sec.jpg b/content/identity/what-is-cloud-security/cloud-sec.jpg
deleted file mode 100644
index 96bc0f649..000000000
Binary files a/content/identity/what-is-cloud-security/cloud-sec.jpg and /dev/null differ
diff --git a/content/identity/what-is-cloud-security/cloud-sec.webp b/content/identity/what-is-cloud-security/cloud-sec.webp
new file mode 100644
index 000000000..e822576d8
Binary files /dev/null and b/content/identity/what-is-cloud-security/cloud-sec.webp differ
diff --git a/content/identity/what-is-cloud-security/cloud-security.jpg b/content/identity/what-is-cloud-security/cloud-security.jpg
deleted file mode 100644
index 1cc750394..000000000
Binary files a/content/identity/what-is-cloud-security/cloud-security.jpg and /dev/null differ
diff --git a/content/identity/what-is-cloud-security/cloud-security.webp b/content/identity/what-is-cloud-security/cloud-security.webp
new file mode 100644
index 000000000..249c7b7d3
Binary files /dev/null and b/content/identity/what-is-cloud-security/cloud-security.webp differ
diff --git a/content/identity/what-is-cloud-security/identity-managemt-wp.png b/content/identity/what-is-cloud-security/identity-managemt-wp.png
deleted file mode 100644
index 1571e7a30..000000000
Binary files a/content/identity/what-is-cloud-security/identity-managemt-wp.png and /dev/null differ
diff --git a/content/identity/what-is-cloud-security/identity-managemt-wp.webp b/content/identity/what-is-cloud-security/identity-managemt-wp.webp
new file mode 100644
index 000000000..62bfb9d9c
Binary files /dev/null and b/content/identity/what-is-cloud-security/identity-managemt-wp.webp differ
diff --git a/content/identity/what-is-cloud-security/index.md b/content/identity/what-is-cloud-security/index.md
index 5ed5ace22..c64e09302 100644
--- a/content/identity/what-is-cloud-security/index.md
+++ b/content/identity/what-is-cloud-security/index.md
@@ -1,7 +1,7 @@
---
title: "What is Cloud Security and How it Works?"
date: "2022-06-09"
-coverImage: "cloud-security.jpg"
+coverImage: "cloud-security.webp"
tags: ["cloud security","cloud identity management","data security"]
author: "Navanita Devi"
description: "Cloud security is a growing concern for businesses that rely on cloud-based services. The use of these services has become widespread over the past decade or so, but many companies still don't fully understand how to protect themselves from cyber threats. Read this blog to know what exactly is cloud security and how it works."
@@ -61,7 +61,7 @@ The accessibility capabilities granted to user accounts are managed by [customer
The emphasis of governance is on threat prevention, detection, and mitigation strategies. Threat intelligence may assist SMBs and organizations in identifying and prioritizing threats in order to keep critical systems safe. These are particularly applicable in corporate settings, although standards for safe usage and threat response can be beneficial to any user.
-[](https://www.loginradius.com/resource/the-critical-role-of-identity-management-in-data-governance/)
+[](https://www.loginradius.com/resource/the-critical-role-of-identity-management-in-data-governance/)
* **Data Retention (DR) And Business Continuity (BC)**
@@ -109,4 +109,4 @@ The cloud is critical to the capacity of many firms to do business. They utilize
In summary, cloud security is more about people and processes than technology. The cloud infrastructure must be designed to support secure operations, but ultimately the responsibility for security lies with the individual end user.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-cloud-security)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-cloud-security)
\ No newline at end of file
diff --git a/content/identity/what-is-decentralized-authentication/index.md b/content/identity/what-is-decentralized-authentication/index.md
index 94ae1f242..bdd8f5489 100644
--- a/content/identity/what-is-decentralized-authentication/index.md
+++ b/content/identity/what-is-decentralized-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Decentralized Authentication: What Is It And How It Is Changing the Industry"
date: "2021-09-21"
-coverImage: "what-is-decentralized-authentication-cover.jpg"
+coverImage: "what-is-decentralized-authentication-cover.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -63,4 +63,4 @@ This main area will come from having a holistic approach to identification contr
We know that **Decentralized Authentication** is the key to advancing in the future, and now it depends on how we try to implement it. Some problems may arise, but we never move ahead in the game/life if we are not up for a challenge.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-decentralized-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-decentralized-authentication)
diff --git a/content/identity/what-is-decentralized-authentication/what-is-decentralized-authentication-cover.jpg b/content/identity/what-is-decentralized-authentication/what-is-decentralized-authentication-cover.jpg
deleted file mode 100644
index d2d2c966b..000000000
Binary files a/content/identity/what-is-decentralized-authentication/what-is-decentralized-authentication-cover.jpg and /dev/null differ
diff --git a/content/identity/what-is-decentralized-authentication/what-is-decentralized-authentication-cover.webp b/content/identity/what-is-decentralized-authentication/what-is-decentralized-authentication-cover.webp
new file mode 100644
index 000000000..8f6842d2d
Binary files /dev/null and b/content/identity/what-is-decentralized-authentication/what-is-decentralized-authentication-cover.webp differ
diff --git a/content/identity/what-is-digital-transformation/covid-19-stats-digital-transformation.PNG b/content/identity/what-is-digital-transformation/covid-19-stats-digital-transformation.PNG
deleted file mode 100644
index 2fc155667..000000000
Binary files a/content/identity/what-is-digital-transformation/covid-19-stats-digital-transformation.PNG and /dev/null differ
diff --git a/content/identity/what-is-digital-transformation/covid-19-stats-digital-transformation.webp b/content/identity/what-is-digital-transformation/covid-19-stats-digital-transformation.webp
new file mode 100644
index 000000000..7674bbe16
Binary files /dev/null and b/content/identity/what-is-digital-transformation/covid-19-stats-digital-transformation.webp differ
diff --git a/content/identity/what-is-digital-transformation/customer-identity-the-core-of-digital-transformation.png b/content/identity/what-is-digital-transformation/customer-identity-the-core-of-digital-transformation.png
deleted file mode 100644
index eaa925c92..000000000
Binary files a/content/identity/what-is-digital-transformation/customer-identity-the-core-of-digital-transformation.png and /dev/null differ
diff --git a/content/identity/what-is-digital-transformation/customer-identity-the-core-of-digital-transformation.webp b/content/identity/what-is-digital-transformation/customer-identity-the-core-of-digital-transformation.webp
new file mode 100644
index 000000000..449e28840
Binary files /dev/null and b/content/identity/what-is-digital-transformation/customer-identity-the-core-of-digital-transformation.webp differ
diff --git a/content/identity/what-is-digital-transformation/digital-transformation-changed-with-covid-19-pandemic.png b/content/identity/what-is-digital-transformation/digital-transformation-changed-with-covid-19-pandemic.png
deleted file mode 100644
index d55dea99b..000000000
Binary files a/content/identity/what-is-digital-transformation/digital-transformation-changed-with-covid-19-pandemic.png and /dev/null differ
diff --git a/content/identity/what-is-digital-transformation/digital-transformation-changed-with-covid-19-pandemic.webp b/content/identity/what-is-digital-transformation/digital-transformation-changed-with-covid-19-pandemic.webp
new file mode 100644
index 000000000..be9ecf5f6
Binary files /dev/null and b/content/identity/what-is-digital-transformation/digital-transformation-changed-with-covid-19-pandemic.webp differ
diff --git a/content/identity/what-is-digital-transformation/digital-transformation-trends-to-watch-out-in-2021.png b/content/identity/what-is-digital-transformation/digital-transformation-trends-to-watch-out-in-2021.png
deleted file mode 100644
index f3a1ba476..000000000
Binary files a/content/identity/what-is-digital-transformation/digital-transformation-trends-to-watch-out-in-2021.png and /dev/null differ
diff --git a/content/identity/what-is-digital-transformation/digital-transformation-trends-to-watch-out-in-2021.webp b/content/identity/what-is-digital-transformation/digital-transformation-trends-to-watch-out-in-2021.webp
new file mode 100644
index 000000000..f3583b666
Binary files /dev/null and b/content/identity/what-is-digital-transformation/digital-transformation-trends-to-watch-out-in-2021.webp differ
diff --git a/content/identity/what-is-digital-transformation/index.md b/content/identity/what-is-digital-transformation/index.md
index ab420693d..465e6033c 100644
--- a/content/identity/what-is-digital-transformation/index.md
+++ b/content/identity/what-is-digital-transformation/index.md
@@ -1,7 +1,7 @@
---
title: "What is Digital Transformation"
date: "2021-01-11"
-coverImage: "what-is-digital-transformation.jpg"
+coverImage: "what-is-digital-transformation.webp"
tags: ["digital transformation","cybersecurity","cx"]
author: "Rakesh Soni"
description: "Digital transformation is the process of leveraging digital technology to develop new business processes and consumer experiences to meet the changing market dynamics or to alter the existing ones. So, has the dynamics changed with the COVID-19 pandemic? You are about to find out."
@@ -75,7 +75,7 @@ Wherever you are... START!
## Has Digital Transformation Changed With the COVID-19 Pandemic
-
+
The answer is _yes_. The COVID-19 pandemic has pushed businesses over the "technology" edge forever.
@@ -84,7 +84,7 @@ According to [McKinsey Global Survey](https://www.mckinsey.com/business-function
The survey also shows that the rates of digital adoption are three times likelier now than before the crisis.
-
+
Source: Mckinsey
@@ -113,7 +113,7 @@ Lately, new, emerging technologies are being responsible for a huge part of any
However, in these trying times, it is also crucial that countries invest in digital products and services that aid in national security and the economy at large. We should anticipate strengthened regulatory structures and increased scrutiny on activities related to merger and acquisition (M&A).
-[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
+[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/)
### Futuristic workspaces will rule.
@@ -161,7 +161,7 @@ Digital transformation will be a powerful lever in the response of companies to
## What Drives Digital Transformation
-
+
As we speak of digital transformation or digital conversion, we are often focused on technology. With technology evolving so rapidly, it is tempting to believe it's the main force that has been driving digital transformation all along the way.
@@ -241,7 +241,7 @@ Perform a digital maturity assessment to find how much you have fared in leverag
## Digital Transformation Trends to Watch Out in 2021
-
+
2020 witnessed a massive undertaking of digital transformation across industries. Simultaneously, digital transformation fatigue became a regular appearance.
@@ -314,7 +314,7 @@ Despite the attacks, 2021 may witness an accelerated workload migration to the c
## The Role of Culture in Digital Transformation
-
+
Culture in digital transformation has no mysterious or unseen presence. Digital is about embedding culture into business operations to succeed, and not just update technology, redesign products, and improve client relationships.
@@ -380,4 +380,4 @@ Right now, businesses are rapidly including the creative use of data, be it via
Only the adapters will survive!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-digital-transformation)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-digital-transformation)
\ No newline at end of file
diff --git a/content/identity/what-is-digital-transformation/the-role-of-culture-in-digital-transformation.png b/content/identity/what-is-digital-transformation/the-role-of-culture-in-digital-transformation.png
deleted file mode 100644
index 4a860f018..000000000
Binary files a/content/identity/what-is-digital-transformation/the-role-of-culture-in-digital-transformation.png and /dev/null differ
diff --git a/content/identity/what-is-digital-transformation/the-role-of-culture-in-digital-transformation.webp b/content/identity/what-is-digital-transformation/the-role-of-culture-in-digital-transformation.webp
new file mode 100644
index 000000000..753a657aa
Binary files /dev/null and b/content/identity/what-is-digital-transformation/the-role-of-culture-in-digital-transformation.webp differ
diff --git a/content/identity/what-is-digital-transformation/what-drives-digital-transformation.png b/content/identity/what-is-digital-transformation/what-drives-digital-transformation.png
deleted file mode 100644
index b1e0412f9..000000000
Binary files a/content/identity/what-is-digital-transformation/what-drives-digital-transformation.png and /dev/null differ
diff --git a/content/identity/what-is-digital-transformation/what-drives-digital-transformation.webp b/content/identity/what-is-digital-transformation/what-drives-digital-transformation.webp
new file mode 100644
index 000000000..1c87a625a
Binary files /dev/null and b/content/identity/what-is-digital-transformation/what-drives-digital-transformation.webp differ
diff --git a/content/identity/what-is-digital-transformation/what-is-digital-transformation.jpg b/content/identity/what-is-digital-transformation/what-is-digital-transformation.jpg
deleted file mode 100644
index caffea1cc..000000000
Binary files a/content/identity/what-is-digital-transformation/what-is-digital-transformation.jpg and /dev/null differ
diff --git a/content/identity/what-is-digital-transformation/what-is-digital-transformation.webp b/content/identity/what-is-digital-transformation/what-is-digital-transformation.webp
new file mode 100644
index 000000000..b2a4a1fa8
Binary files /dev/null and b/content/identity/what-is-digital-transformation/what-is-digital-transformation.webp differ
diff --git a/content/identity/what-is-distributed-multi-cloud-identity-management/identity-ds.png b/content/identity/what-is-distributed-multi-cloud-identity-management/identity-ds.png
deleted file mode 100644
index 2ed977c37..000000000
Binary files a/content/identity/what-is-distributed-multi-cloud-identity-management/identity-ds.png and /dev/null differ
diff --git a/content/identity/what-is-distributed-multi-cloud-identity-management/identity-ds.webp b/content/identity/what-is-distributed-multi-cloud-identity-management/identity-ds.webp
new file mode 100644
index 000000000..1794ca313
Binary files /dev/null and b/content/identity/what-is-distributed-multi-cloud-identity-management/identity-ds.webp differ
diff --git a/content/identity/what-is-distributed-multi-cloud-identity-management/index.md b/content/identity/what-is-distributed-multi-cloud-identity-management/index.md
index 98bcc9012..f160a18cf 100644
--- a/content/identity/what-is-distributed-multi-cloud-identity-management/index.md
+++ b/content/identity/what-is-distributed-multi-cloud-identity-management/index.md
@@ -1,7 +1,7 @@
---
title: "Distributed Multi-Cloud Identity Management and Its Endless Business Benefits"
date: "2022-12-06"
-coverImage: "multi-id.jpg"
+coverImage: "multi-id.webp"
tags: ["multi cloud", "identity management", "cloud security"]
author: "Rakesh Soni"
description: "Distributed identity management is a portal for combining cloud resources, services, and digital business applications. You can give your customers a robust customer experience by leveraging a distributed multi-cloud identity to ensure robust security and excellent customer experience."
@@ -32,7 +32,7 @@ And while these systems utilize a specific integrated identity management system
This results in complex migration from the legacy system to the newly-adopted cloud systems as the organization has to manage a challenging transition to ensure the sustainability of the existing infrastructure without any hassle.
-[](https://www.loginradius.com/resource/loginradius-identity-import-manager)
+[](https://www.loginradius.com/resource/loginradius-identity-import-manager)
Apart from this, the overall investments in legacy systems don’t necessarily mean a seamless and secure transition to a multi-cloud environment.
@@ -82,4 +82,4 @@ Distributed multi-cloud identity management is helping businesses in handling mu
If you wish to experience the future of distributed cloud identity management, reach us to schedule a quick demo of LoginRadius’cloud-based customer identity and access management platform.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-distributed-multi-cloud-identity-management)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-distributed-multi-cloud-identity-management)
\ No newline at end of file
diff --git a/content/identity/what-is-distributed-multi-cloud-identity-management/multi-id.jpg b/content/identity/what-is-distributed-multi-cloud-identity-management/multi-id.jpg
deleted file mode 100644
index 1dcadfe4f..000000000
Binary files a/content/identity/what-is-distributed-multi-cloud-identity-management/multi-id.jpg and /dev/null differ
diff --git a/content/identity/what-is-distributed-multi-cloud-identity-management/multi-id.webp b/content/identity/what-is-distributed-multi-cloud-identity-management/multi-id.webp
new file mode 100644
index 000000000..4092daea6
Binary files /dev/null and b/content/identity/what-is-distributed-multi-cloud-identity-management/multi-id.webp differ
diff --git a/content/identity/what-is-dynamic-authorization/WP-compliance-retailers.png b/content/identity/what-is-dynamic-authorization/WP-compliance-retailers.png
deleted file mode 100644
index 802253f09..000000000
Binary files a/content/identity/what-is-dynamic-authorization/WP-compliance-retailers.png and /dev/null differ
diff --git a/content/identity/what-is-dynamic-authorization/WP-compliance-retailers.webp b/content/identity/what-is-dynamic-authorization/WP-compliance-retailers.webp
new file mode 100644
index 000000000..c98143e9e
Binary files /dev/null and b/content/identity/what-is-dynamic-authorization/WP-compliance-retailers.webp differ
diff --git a/content/identity/what-is-dynamic-authorization/compliance-wp.png b/content/identity/what-is-dynamic-authorization/compliance-wp.png
deleted file mode 100644
index a2c9e2a07..000000000
Binary files a/content/identity/what-is-dynamic-authorization/compliance-wp.png and /dev/null differ
diff --git a/content/identity/what-is-dynamic-authorization/compliance-wp.webp b/content/identity/what-is-dynamic-authorization/compliance-wp.webp
new file mode 100644
index 000000000..1717fdcbb
Binary files /dev/null and b/content/identity/what-is-dynamic-authorization/compliance-wp.webp differ
diff --git a/content/identity/what-is-dynamic-authorization/dynamic-authorization.jpg b/content/identity/what-is-dynamic-authorization/dynamic-authorization.jpg
deleted file mode 100644
index 64927bd76..000000000
Binary files a/content/identity/what-is-dynamic-authorization/dynamic-authorization.jpg and /dev/null differ
diff --git a/content/identity/what-is-dynamic-authorization/dynamic-authorization.webp b/content/identity/what-is-dynamic-authorization/dynamic-authorization.webp
new file mode 100644
index 000000000..ece71b902
Binary files /dev/null and b/content/identity/what-is-dynamic-authorization/dynamic-authorization.webp differ
diff --git a/content/identity/what-is-dynamic-authorization/index.md b/content/identity/what-is-dynamic-authorization/index.md
index 0effba93f..ffc96ff14 100644
--- a/content/identity/what-is-dynamic-authorization/index.md
+++ b/content/identity/what-is-dynamic-authorization/index.md
@@ -1,7 +1,7 @@
---
title: "What is Dynamic Authorization & Why Does it Matter?"
date: "2022-11-17"
-coverImage: "dynamic-authorization.jpg"
+coverImage: "dynamic-authorization.webp"
tags: ["dynamic authorization","compliance","cx"]
author: "Rakesh Soni"
description: "Dynamic authorization rewards customers with the security they need and effectively improves their experience with your brand. It helps to meet your customer’s needs and, at the same time, gives you much more control over how users access your services."
@@ -60,7 +60,7 @@ Dynamic authorization helps you stay ahead of regulations and protect your organ
In other words, it ensures that if someone tries to access something they aren't supposed to, they won't be able to do it.
-[](https://www.loginradius.com/resource/role-of-data-and-privacy-compliance-in-retail)
+[](https://www.loginradius.com/resource/role-of-data-and-privacy-compliance-in-retail)
## How Can Dynamic Authorization Improve Customer Experience?
@@ -89,4 +89,4 @@ Dynamic authorization can adapt quickly to changing business requirements now an
With solutions that enable dynamic policy changes, you can easily adapt to changes in your business environment, control access to sensitive data, and minimize loss of control over that data. This allows you to confidently navigate business processes, knowing that you are fully prepared for any data security or compliance challenges.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-dynamic-authorization)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-dynamic-authorization)
diff --git a/content/identity/what-is-federated-identity-management/1.jpg b/content/identity/what-is-federated-identity-management/1.jpg
deleted file mode 100644
index 1b912aa55..000000000
Binary files a/content/identity/what-is-federated-identity-management/1.jpg and /dev/null differ
diff --git a/content/identity/what-is-federated-identity-management/1.webp b/content/identity/what-is-federated-identity-management/1.webp
new file mode 100644
index 000000000..546b58ecf
Binary files /dev/null and b/content/identity/what-is-federated-identity-management/1.webp differ
diff --git a/content/identity/what-is-federated-identity-management/federated-identity-image.jpg b/content/identity/what-is-federated-identity-management/federated-identity-image.jpg
deleted file mode 100644
index 43fa51c91..000000000
Binary files a/content/identity/what-is-federated-identity-management/federated-identity-image.jpg and /dev/null differ
diff --git a/content/identity/what-is-federated-identity-management/federated-identity-image.webp b/content/identity/what-is-federated-identity-management/federated-identity-image.webp
new file mode 100644
index 000000000..1c8392c2e
Binary files /dev/null and b/content/identity/what-is-federated-identity-management/federated-identity-image.webp differ
diff --git a/content/identity/what-is-federated-identity-management/federated-identity-management.png b/content/identity/what-is-federated-identity-management/federated-identity-management.png
deleted file mode 100644
index 01a289614..000000000
Binary files a/content/identity/what-is-federated-identity-management/federated-identity-management.png and /dev/null differ
diff --git a/content/identity/what-is-federated-identity-management/federated-identity-management.webp b/content/identity/what-is-federated-identity-management/federated-identity-management.webp
new file mode 100644
index 000000000..3d4c0a8aa
Binary files /dev/null and b/content/identity/what-is-federated-identity-management/federated-identity-management.webp differ
diff --git a/content/identity/what-is-federated-identity-management/federated-identity2.png b/content/identity/what-is-federated-identity-management/federated-identity2.png
deleted file mode 100644
index 8322177d7..000000000
Binary files a/content/identity/what-is-federated-identity-management/federated-identity2.png and /dev/null differ
diff --git a/content/identity/what-is-federated-identity-management/federated-identity2.webp b/content/identity/what-is-federated-identity-management/federated-identity2.webp
new file mode 100644
index 000000000..0eacb57e6
Binary files /dev/null and b/content/identity/what-is-federated-identity-management/federated-identity2.webp differ
diff --git a/content/identity/what-is-federated-identity-management/federated-identity3.png b/content/identity/what-is-federated-identity-management/federated-identity3.png
deleted file mode 100644
index e66640657..000000000
Binary files a/content/identity/what-is-federated-identity-management/federated-identity3.png and /dev/null differ
diff --git a/content/identity/what-is-federated-identity-management/federated-identity3.webp b/content/identity/what-is-federated-identity-management/federated-identity3.webp
new file mode 100644
index 000000000..895ee89fd
Binary files /dev/null and b/content/identity/what-is-federated-identity-management/federated-identity3.webp differ
diff --git a/content/identity/what-is-federated-identity-management/index.md b/content/identity/what-is-federated-identity-management/index.md
index 55700cf85..91564dd90 100644
--- a/content/identity/what-is-federated-identity-management/index.md
+++ b/content/identity/what-is-federated-identity-management/index.md
@@ -1,7 +1,7 @@
---
title: "What is Federated Identity Management"
date: "2021-02-04"
-coverImage: "what-is-fim.jpg"
+coverImage: "what-is-fim.webp"
tags: ["federated identity management","identity provider","cx"]
author: "Rakesh Soni"
description: " Let's face it upfront. Password management is a painful exercise, which no one wants to deal with. Though guessable passwords make them easy to remember, it exposes consumers to hackers. Fortunately, federated ID management ensures both seamless and secure access that goes a long way in enhancing the overall user-experience."
@@ -55,7 +55,7 @@ As soon as they are granted access, they would be redirected to the partner comp
So, the next time they log in to your company page, the consumer will also get access to the partner page over a quick authentication request.
-
+
## Advantages of Using Federated Identity Management
@@ -69,7 +69,7 @@ Though FIM has several advantages, we are going to highlight the most pivotal on
* **Increases organizational productivity**: Due to the lack of multiple logins, there will be lesser helpdesk calls for password resets. This saves a lot of time and efficiency, which leads to a potential increase in administrative overhead.
-[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
+[](https://www.loginradius.com/resource/federated-identity-management-datasheet)
## Risk Management in Federated Identity Management
@@ -123,7 +123,7 @@ Addressing these challenges requires careful planning, robust infrastructure, an
## Introduction to LoginRadius' Federated Identity Management
-
+
Equipped with custom technologies, LoginRadius' FIM takes federated identity management experience to an altogether new level.
@@ -165,4 +165,4 @@ The three most important components are the Identity Provider (IdP), the Service
A federated identity enables seamless and secure access to multiple applications and services without the need for separate login credentials.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-federated-identity-management)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-federated-identity-management)
\ No newline at end of file
diff --git a/content/identity/what-is-federated-identity-management/what-is-fim.jpg b/content/identity/what-is-federated-identity-management/what-is-fim.jpg
deleted file mode 100644
index 9551ad930..000000000
Binary files a/content/identity/what-is-federated-identity-management/what-is-fim.jpg and /dev/null differ
diff --git a/content/identity/what-is-federated-identity-management/what-is-fim.webp b/content/identity/what-is-federated-identity-management/what-is-fim.webp
new file mode 100644
index 000000000..3a337869a
Binary files /dev/null and b/content/identity/what-is-federated-identity-management/what-is-fim.webp differ
diff --git a/content/identity/what-is-federated-sso/fed-sso.jpg b/content/identity/what-is-federated-sso/fed-sso.jpg
deleted file mode 100644
index 8f1f629ad..000000000
Binary files a/content/identity/what-is-federated-sso/fed-sso.jpg and /dev/null differ
diff --git a/content/identity/what-is-federated-sso/fed-sso.webp b/content/identity/what-is-federated-sso/fed-sso.webp
new file mode 100644
index 000000000..4df2e630b
Binary files /dev/null and b/content/identity/what-is-federated-sso/fed-sso.webp differ
diff --git a/content/identity/what-is-federated-sso/federated-sso.jpg b/content/identity/what-is-federated-sso/federated-sso.jpg
deleted file mode 100644
index f92f4417c..000000000
Binary files a/content/identity/what-is-federated-sso/federated-sso.jpg and /dev/null differ
diff --git a/content/identity/what-is-federated-sso/federated-sso.webp b/content/identity/what-is-federated-sso/federated-sso.webp
new file mode 100644
index 000000000..8142498f3
Binary files /dev/null and b/content/identity/what-is-federated-sso/federated-sso.webp differ
diff --git a/content/identity/what-is-federated-sso/index.md b/content/identity/what-is-federated-sso/index.md
index b601aa165..d0d723507 100644
--- a/content/identity/what-is-federated-sso/index.md
+++ b/content/identity/what-is-federated-sso/index.md
@@ -1,7 +1,7 @@
---
title: "What is Federated SSO (Single Sign-On)?"
date: "2022-08-17"
-coverImage: "federated-sso.jpg"
+coverImage: "federated-sso.webp"
tags: ["single sign-on", "federated sso", "authentication"]
author: "Rakesh Soni"
description: "With fed SSO, businesses can bridge the authentication gap between multiple platforms and enable users to access services without needing a separate login at the partner platform. This blog explains fed SSO and how businesses should leverage it."
@@ -175,4 +175,4 @@ SAML (Security Assertion Markup Language) is favored for SSO due to its standard
The main components are the Identity Provider (IdP) for authentication, the Service Provider (SP) for access, and the Digital Token that verifies a user's identity.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-federated-sso)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-federated-sso)
\ No newline at end of file
diff --git a/content/identity/what-is-formjacking/index.md b/content/identity/what-is-formjacking/index.md
index 4a454abd1..fe82ca503 100644
--- a/content/identity/what-is-formjacking/index.md
+++ b/content/identity/what-is-formjacking/index.md
@@ -1,7 +1,7 @@
---
title: "What is Formjacking"
date: "2021-01-15"
-coverImage: "what-is-formjacking.jpg"
+coverImage: "what-is-formjacking.webp"
tags: ["all, Security"]
featured: false
author: "Rakesh Soni"
@@ -41,7 +41,7 @@ The group injects web-based card skimmers onto eCommerce sites to [steal payment
Magecart group started hacking into Magneto online stores; however, they have now altered their strategies and are increasingly using formjacking attacks to steal payment card details.
-
+
## How Big Is This Formjacking Campaign
@@ -79,7 +79,7 @@ Use credit cards instead of debit cards while shopping online to reduce [financi
If someone uses your credit card information deceptively or indulges in card fraud, they will be exhausting the funds of the credit card companies. In the case of debit cards, the funds are directly tied to your checking account balance.
-[](https://www.loginradius.com/resource/pii-data-breach-report/)
+[](https://www.loginradius.com/resource/pii-data-breach-report/)
## How to Prevent Formjacking Attacks
@@ -99,4 +99,4 @@ Victims don't realize that they have fallen prey to formjacking attacks easily a
Even with all preventive measures in place, it can still be exceedingly difficult to spot formjacking attacks. However, as an online business, you must have all the protocols in place to quickly alert consumers in the case of such attacks.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-formjacking)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-formjacking)
\ No newline at end of file
diff --git a/content/identity/what-is-formjacking/protecting-pii-against-data-breaches.png b/content/identity/what-is-formjacking/protecting-pii-against-data-breaches.png
deleted file mode 100644
index b32dcb27b..000000000
Binary files a/content/identity/what-is-formjacking/protecting-pii-against-data-breaches.png and /dev/null differ
diff --git a/content/identity/what-is-formjacking/protecting-pii-against-data-breaches.webp b/content/identity/what-is-formjacking/protecting-pii-against-data-breaches.webp
new file mode 100644
index 000000000..6c250a4f7
Binary files /dev/null and b/content/identity/what-is-formjacking/protecting-pii-against-data-breaches.webp differ
diff --git a/content/identity/what-is-formjacking/what-is-formjacking.jpg b/content/identity/what-is-formjacking/what-is-formjacking.jpg
deleted file mode 100644
index 579a49c6a..000000000
Binary files a/content/identity/what-is-formjacking/what-is-formjacking.jpg and /dev/null differ
diff --git a/content/identity/what-is-formjacking/what-is-formjacking.webp b/content/identity/what-is-formjacking/what-is-formjacking.webp
new file mode 100644
index 000000000..066805f93
Binary files /dev/null and b/content/identity/what-is-formjacking/what-is-formjacking.webp differ
diff --git a/content/identity/what-is-formjacking/who-is-behind-formjacking-attacks.png b/content/identity/what-is-formjacking/who-is-behind-formjacking-attacks.png
deleted file mode 100644
index f859ed21f..000000000
Binary files a/content/identity/what-is-formjacking/who-is-behind-formjacking-attacks.png and /dev/null differ
diff --git a/content/identity/what-is-formjacking/who-is-behind-formjacking-attacks.webp b/content/identity/what-is-formjacking/who-is-behind-formjacking-attacks.webp
new file mode 100644
index 000000000..49aa840b0
Binary files /dev/null and b/content/identity/what-is-formjacking/who-is-behind-formjacking-attacks.webp differ
diff --git a/content/identity/what-is-iam/What-is-IAM-1.jpg b/content/identity/what-is-iam/What-is-IAM-1.jpg
deleted file mode 100644
index 2381eebd1..000000000
Binary files a/content/identity/what-is-iam/What-is-IAM-1.jpg and /dev/null differ
diff --git a/content/identity/what-is-iam/What-is-IAM-1.webp b/content/identity/what-is-iam/What-is-IAM-1.webp
new file mode 100644
index 000000000..a0500439c
Binary files /dev/null and b/content/identity/what-is-iam/What-is-IAM-1.webp differ
diff --git a/content/identity/what-is-iam/What-is-IAM-3.png b/content/identity/what-is-iam/What-is-IAM-3.png
deleted file mode 100644
index 42a829300..000000000
Binary files a/content/identity/what-is-iam/What-is-IAM-3.png and /dev/null differ
diff --git a/content/identity/what-is-iam/What-is-IAM-3.webp b/content/identity/what-is-iam/What-is-IAM-3.webp
new file mode 100644
index 000000000..8a986be4c
Binary files /dev/null and b/content/identity/what-is-iam/What-is-IAM-3.webp differ
diff --git a/content/identity/what-is-iam/What-is-IAM-4.png b/content/identity/what-is-iam/What-is-IAM-4.png
deleted file mode 100644
index adbe6ca25..000000000
Binary files a/content/identity/what-is-iam/What-is-IAM-4.png and /dev/null differ
diff --git a/content/identity/what-is-iam/What-is-IAM-4.webp b/content/identity/what-is-iam/What-is-IAM-4.webp
new file mode 100644
index 000000000..9d0382574
Binary files /dev/null and b/content/identity/what-is-iam/What-is-IAM-4.webp differ
diff --git a/content/identity/what-is-iam/What-is-IAM-Cover.jpg b/content/identity/what-is-iam/What-is-IAM-Cover.jpg
deleted file mode 100644
index ba791c240..000000000
Binary files a/content/identity/what-is-iam/What-is-IAM-Cover.jpg and /dev/null differ
diff --git a/content/identity/what-is-iam/What-is-IAM-Cover.webp b/content/identity/what-is-iam/What-is-IAM-Cover.webp
new file mode 100644
index 000000000..ba701090e
Binary files /dev/null and b/content/identity/what-is-iam/What-is-IAM-Cover.webp differ
diff --git a/content/identity/what-is-iam/future-of-digital-identity.png b/content/identity/what-is-iam/future-of-digital-identity.png
deleted file mode 100644
index 1338927e7..000000000
Binary files a/content/identity/what-is-iam/future-of-digital-identity.png and /dev/null differ
diff --git a/content/identity/what-is-iam/future-of-digital-identity.webp b/content/identity/what-is-iam/future-of-digital-identity.webp
new file mode 100644
index 000000000..468202b9e
Binary files /dev/null and b/content/identity/what-is-iam/future-of-digital-identity.webp differ
diff --git a/content/identity/what-is-iam/index.md b/content/identity/what-is-iam/index.md
index 90e2135e9..4a697bc3b 100644
--- a/content/identity/what-is-iam/index.md
+++ b/content/identity/what-is-iam/index.md
@@ -1,7 +1,7 @@
---
title: "What is Identity and Access Management (IAM)?"
date: "2021-01-29"
-coverImage: "What-is-IAM-Cover.jpg"
+coverImage: "What-is-IAM-Cover.webp"
tags: ["customer-experience"]
featured: false
author: "Rakesh Soni"
@@ -13,7 +13,7 @@ metadescription: "Learn about identity and access management in cybersecurity, i
# What is IAM
-
+
Identity and Access Management (IAM) is a core discipline for any enterprise IT, as it is inseparably linked to the security and sustainability of companies.
@@ -71,7 +71,7 @@ Here are some of the key terminologies that you will encounter while processing
## How IAM Works
-
+
Identity and access management systems perform three main tasks viz. identification, authentication, and authorization. In other words, IAM functions to provide the right people access to devices, hardware, software applications, or any IT tool to perform a specific task.
@@ -247,7 +247,7 @@ We live in the age of ever-growing cybersecurity threats. Organizations cannot a
Although 2020 has been a year-long roller coaster with the pandemic hitting hard, there's one thing that happened for sure. Digital transformation has progressed at an unparalleled pace, and identity and access management (IAM) is a major part of that evolution.
-[](https://www.loginradius.com/resource/digital-identity-future-whitepaper)
+[](https://www.loginradius.com/resource/digital-identity-future-whitepaper)
Let's look at some of the most changing developments in the IAM market anticipated in 2021.
@@ -277,7 +277,7 @@ And when that happens, it will be easier for enterprises to capture and analyze
## How LoginRadius IAM Solution Can Accommodate Your Enterprise Requirements
-
+
With the [right IAM provider](https://www.loginradius.com/), organizations can enjoy enormous time-saving, efficiency-building, and security-boosting benefits, irrespective of where they operate.
@@ -318,4 +318,4 @@ Powerful identity and access management solutions offer the right tools to ensur
There is a huge demand to invest in new digital methods of communication. And prioritizing [digital security](https://www.loginradius.com/blog/identity/2020/06/consumer-data-privacy-security/) will go a long way.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-iam)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-iam)
diff --git a/content/identity/what-is-identity-modernization/cloud-wp.png b/content/identity/what-is-identity-modernization/cloud-wp.png
deleted file mode 100644
index e1de2961b..000000000
Binary files a/content/identity/what-is-identity-modernization/cloud-wp.png and /dev/null differ
diff --git a/content/identity/what-is-identity-modernization/cloud-wp.webp b/content/identity/what-is-identity-modernization/cloud-wp.webp
new file mode 100644
index 000000000..fedbbdabc
Binary files /dev/null and b/content/identity/what-is-identity-modernization/cloud-wp.webp differ
diff --git a/content/identity/what-is-identity-modernization/id-mod.jpg b/content/identity/what-is-identity-modernization/id-mod.jpg
deleted file mode 100644
index ac61ce4f2..000000000
Binary files a/content/identity/what-is-identity-modernization/id-mod.jpg and /dev/null differ
diff --git a/content/identity/what-is-identity-modernization/id-mod.webp b/content/identity/what-is-identity-modernization/id-mod.webp
new file mode 100644
index 000000000..2373a8693
Binary files /dev/null and b/content/identity/what-is-identity-modernization/id-mod.webp differ
diff --git a/content/identity/what-is-identity-modernization/index.md b/content/identity/what-is-identity-modernization/index.md
index 64709f43e..32eec2ab2 100644
--- a/content/identity/what-is-identity-modernization/index.md
+++ b/content/identity/what-is-identity-modernization/index.md
@@ -1,7 +1,7 @@
---
title: "Identity Modernization: What Is It & Why Should You Care?"
date: "2023-01-19"
-coverImage: "id-mod.jpg"
+coverImage: "id-mod.webp"
tags: ["Identity management", "identity modernization", "identity security"]
author: "Rakesh Soni"
description: "Identity modernization could be defined as shifting from managing identities through on-premises identity providers to a cloud-based identity management solution. Moreover, it could also be a shift from one cloud to multiple clouds. Read this insightful post to understand more about identity modernization benefits for modern businesses."
@@ -37,7 +37,7 @@ Hence, the need for identity modernization becomes more crucial.
Identity modernization is the process of shifting from conventional on-premise identity systems to a cloud-based identity management system that helps reinforce overall identity security against modern threat vectors.
-[](https://www.loginradius.com/resource/overcome-the-nightmare-of-on-prem-deployment-move-to-cloud/)
+[](https://www.loginradius.com/resource/overcome-the-nightmare-of-on-prem-deployment-move-to-cloud/)
While most businesses have already put their best foot forward in adopting robust cloud-based identity management solutions, many are just wondering and waiting for a breach to change their decision.
@@ -81,4 +81,4 @@ Identity modernization can help bring about a new era of security and transparen
Choosing a robust identity management solution like LoginRadius CIAM helps you put identity modernization to work for you today, and reap the rewards of increased security, increased customer confidence, and a future-proofed business that stands ahead of the curve when it comes to compliant data security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-modernization)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-modernization)
\ No newline at end of file
diff --git a/content/identity/what-is-identity-modernization/wp-nightmare.png b/content/identity/what-is-identity-modernization/wp-nightmare.png
deleted file mode 100644
index 6d7ae87ab..000000000
Binary files a/content/identity/what-is-identity-modernization/wp-nightmare.png and /dev/null differ
diff --git a/content/identity/what-is-identity-modernization/wp-nightmare.webp b/content/identity/what-is-identity-modernization/wp-nightmare.webp
new file mode 100644
index 000000000..c13a51d3a
Binary files /dev/null and b/content/identity/what-is-identity-modernization/wp-nightmare.webp differ
diff --git a/content/identity/what-is-identity-orchestration/DS-identity-orchestration.png b/content/identity/what-is-identity-orchestration/DS-identity-orchestration.png
deleted file mode 100644
index ccf2bf5b2..000000000
Binary files a/content/identity/what-is-identity-orchestration/DS-identity-orchestration.png and /dev/null differ
diff --git a/content/identity/what-is-identity-orchestration/DS-identity-orchestration.webp b/content/identity/what-is-identity-orchestration/DS-identity-orchestration.webp
new file mode 100644
index 000000000..1c92d79a3
Binary files /dev/null and b/content/identity/what-is-identity-orchestration/DS-identity-orchestration.webp differ
diff --git a/content/identity/what-is-identity-orchestration/identity-orchestration-hero.jpg b/content/identity/what-is-identity-orchestration/identity-orchestration-hero.jpg
deleted file mode 100644
index e95411d90..000000000
Binary files a/content/identity/what-is-identity-orchestration/identity-orchestration-hero.jpg and /dev/null differ
diff --git a/content/identity/what-is-identity-orchestration/identity-orchestration-hero.webp b/content/identity/what-is-identity-orchestration/identity-orchestration-hero.webp
new file mode 100644
index 000000000..13f641ea7
Binary files /dev/null and b/content/identity/what-is-identity-orchestration/identity-orchestration-hero.webp differ
diff --git a/content/identity/what-is-identity-orchestration/identity-orchestration.png b/content/identity/what-is-identity-orchestration/identity-orchestration.png
deleted file mode 100644
index 50a4ef7ab..000000000
Binary files a/content/identity/what-is-identity-orchestration/identity-orchestration.png and /dev/null differ
diff --git a/content/identity/what-is-identity-orchestration/identity-orchestration.webp b/content/identity/what-is-identity-orchestration/identity-orchestration.webp
new file mode 100644
index 000000000..1a0024933
Binary files /dev/null and b/content/identity/what-is-identity-orchestration/identity-orchestration.webp differ
diff --git a/content/identity/what-is-identity-orchestration/index.md b/content/identity/what-is-identity-orchestration/index.md
index 6f181fd87..f4a932276 100644
--- a/content/identity/what-is-identity-orchestration/index.md
+++ b/content/identity/what-is-identity-orchestration/index.md
@@ -1,7 +1,7 @@
---
title: "What is Identity Orchestration"
date: "2024-09-23"
-coverImage: "identity-orchestration-hero.jpg"
+coverImage: "identity-orchestration-hero.webp"
tags: ["authentication", "identity management", "cloud environment", "ux"]
author: "Rakesh Soni"
description: "Identity orchestration is revolutionizing the way businesses handle digital identities, offering a seamless and secure user experience. In this article, we explain the fundamental concepts of identity orchestration, explore its benefits, and discuss how it can transform identity management for organizations."
@@ -100,7 +100,7 @@ By centralizing policy enforcement through an integrated identity fabric, identi
Transitioning from legacy identity systems to cloud-based solutions often involves migrating multiple applications from old to new infrastructure, typically requiring extensive re-coding for each individual application. This process can be overwhelming when dealing with a large number of applications. Identity orchestration provides a no-code approach to modernizing apps and facilitating the retirement of outdated identity infrastructure. By leveraging orchestration, organizations can achieve cost savings, streamline the migration process, and accelerate app modernization within minutes, rather than months.
-[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
+[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
## Increased developer productivity
@@ -118,7 +118,7 @@ Identity orchestration offers a scalable solution by seamlessly integrating with
LoginRadius Identity Orchestration makes it easy for developers to create and customize identity workflows using a simple drag-and-drop interface. This feature allows teams with limited technical knowledge to quickly manage authentication processes, helping them adapt to changing customer needs and regulations.
-
+
With LoginRadius Identity Orchestration, you can seamlessly integrate with your existing CIAM systems. Whether you use single sign-on, multi-factor authentication, or passwordless login, LoginRadius ensures these elements work together smoothly. This integration doesn't just streamline identity management; it also boosts security and compliance.
diff --git a/content/identity/what-is-identity-provider/DS-SSO.png b/content/identity/what-is-identity-provider/DS-SSO.png
deleted file mode 100644
index 8c6f3fcdd..000000000
Binary files a/content/identity/what-is-identity-provider/DS-SSO.png and /dev/null differ
diff --git a/content/identity/what-is-identity-provider/DS-SSO.webp b/content/identity/what-is-identity-provider/DS-SSO.webp
new file mode 100644
index 000000000..465df5f3d
Binary files /dev/null and b/content/identity/what-is-identity-provider/DS-SSO.webp differ
diff --git a/content/identity/what-is-identity-provider/identity-provider.jpg b/content/identity/what-is-identity-provider/identity-provider.jpg
deleted file mode 100644
index e9fcf6c06..000000000
Binary files a/content/identity/what-is-identity-provider/identity-provider.jpg and /dev/null differ
diff --git a/content/identity/what-is-identity-provider/identity-provider.webp b/content/identity/what-is-identity-provider/identity-provider.webp
new file mode 100644
index 000000000..4869dc02d
Binary files /dev/null and b/content/identity/what-is-identity-provider/identity-provider.webp differ
diff --git a/content/identity/what-is-identity-provider/index.md b/content/identity/what-is-identity-provider/index.md
index 359e46d3a..978ba1136 100644
--- a/content/identity/what-is-identity-provider/index.md
+++ b/content/identity/what-is-identity-provider/index.md
@@ -1,7 +1,7 @@
---
title: "Identity Provider: What Is It And Why Should You Invest In One?"
date: "2021-06-01"
-coverImage: "identity-provider.jpg"
+coverImage: "identity-provider.webp"
tags: ["identity management","ciam solution","cx","mfa"]
author: "Rakesh Soni"
description: "Identity management integration is an essential process in today’s consumer-driven world. Identity providers are a great way to offer your consumers an easy sign-in method. So, when they are connecting to your website or online store, it can allow them to login once with their unique details and not have to remember multiple logins."
@@ -95,7 +95,7 @@ Presenting [multi-factor authentication](https://www.loginradius.com/blog/identi
Many businesses choose to include a Single Sign-on (SSO) feature instead of MFA; there can be various advantages. It allows end-users to use your services without logging in again and again.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
## How To Integrate An Identity Provider With A CIAM Solution?
@@ -222,4 +222,4 @@ IdPs and SPs work together by establishing trust relationships between them, ena
MFA adds an extra layer of security to the authentication process by requiring users to provide two or more authentication factors, such as a password and a security token.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-provider)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-provider)
diff --git a/content/identity/what-is-identity-provider/sso.png b/content/identity/what-is-identity-provider/sso.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/what-is-identity-provider/sso.png and /dev/null differ
diff --git a/content/identity/what-is-identity-provider/sso.webp b/content/identity/what-is-identity-provider/sso.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/what-is-identity-provider/sso.webp differ
diff --git a/content/identity/what-is-identity-provider/what-is-identity-provider-cover.jpg b/content/identity/what-is-identity-provider/what-is-identity-provider-cover.jpg
deleted file mode 100644
index 0bc24f9f6..000000000
Binary files a/content/identity/what-is-identity-provider/what-is-identity-provider-cover.jpg and /dev/null differ
diff --git a/content/identity/what-is-identity-provider/what-is-identity-provider-cover.webp b/content/identity/what-is-identity-provider/what-is-identity-provider-cover.webp
new file mode 100644
index 000000000..e18920c25
Binary files /dev/null and b/content/identity/what-is-identity-provider/what-is-identity-provider-cover.webp differ
diff --git a/content/identity/what-is-identity-security/WP-future-dig-id.png b/content/identity/what-is-identity-security/WP-future-dig-id.png
deleted file mode 100644
index 8c6630f20..000000000
Binary files a/content/identity/what-is-identity-security/WP-future-dig-id.png and /dev/null differ
diff --git a/content/identity/what-is-identity-security/WP-future-dig-id.webp b/content/identity/what-is-identity-security/WP-future-dig-id.webp
new file mode 100644
index 000000000..bdcd988fe
Binary files /dev/null and b/content/identity/what-is-identity-security/WP-future-dig-id.webp differ
diff --git a/content/identity/what-is-identity-security/digital-id-wp.png b/content/identity/what-is-identity-security/digital-id-wp.png
deleted file mode 100644
index 1338927e7..000000000
Binary files a/content/identity/what-is-identity-security/digital-id-wp.png and /dev/null differ
diff --git a/content/identity/what-is-identity-security/digital-id-wp.webp b/content/identity/what-is-identity-security/digital-id-wp.webp
new file mode 100644
index 000000000..468202b9e
Binary files /dev/null and b/content/identity/what-is-identity-security/digital-id-wp.webp differ
diff --git a/content/identity/what-is-identity-security/index.md b/content/identity/what-is-identity-security/index.md
index 4c7ffbb81..5bd5d2bf9 100644
--- a/content/identity/what-is-identity-security/index.md
+++ b/content/identity/what-is-identity-security/index.md
@@ -1,7 +1,7 @@
---
title: "What is Identity Security?"
date: "2021-08-03"
-coverImage: "purpose-identity-security-2021-cover.jpg"
+coverImage: "purpose-identity-security-2021-cover.webp"
tags: ["digital identity management","ciam solution","data security"]
author: "Rakesh Soni"
description: "Thousands of individuals compromise their identities every day because of weak defense and poor authentication at the service providers’ end. Businesses need a robust identity management solution to navigate their digital transformation journey without compromising user identities and sensitive business information."
@@ -48,7 +48,7 @@ Apart from this, the sudden paradigm shift towards online platforms has also inc
Also, specific privacy and data security compliances like the GDPR and CCPA requires organizations storing consumer information to adhere to their regulations to ensure maximum safety to consumers while their data is being collected, stored, and managed.
-[](https://www.loginradius.com/resource/digital-identity-future-whitepaper)
+[](https://www.loginradius.com/resource/digital-identity-future-whitepaper)
Hence there’s an immediate need to deploy a reliable [consumer identity and access management solution](https://www.loginradius.com/blog/identity/customer-identity-and-access-management/) (CIAM) that can offer identity security without hampering user experience.
@@ -90,4 +90,4 @@ However, creating a perfect harmony between identity security and delivering a f
A robust cloud-based CIAM solution like [LoginRadius](https://www.loginradius.com/contact-sales2/) can be a game-changer, especially in a world where data breaches are pretty frequent, leading to losses worth millions of dollars.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-security)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-security)
diff --git a/content/identity/what-is-identity-security/purpose-identity-security-2021-cover.jpg b/content/identity/what-is-identity-security/purpose-identity-security-2021-cover.jpg
deleted file mode 100644
index 3a2d33ec0..000000000
Binary files a/content/identity/what-is-identity-security/purpose-identity-security-2021-cover.jpg and /dev/null differ
diff --git a/content/identity/what-is-identity-security/purpose-identity-security-2021-cover.webp b/content/identity/what-is-identity-security/purpose-identity-security-2021-cover.webp
new file mode 100644
index 000000000..d73a125d7
Binary files /dev/null and b/content/identity/what-is-identity-security/purpose-identity-security-2021-cover.webp differ
diff --git a/content/identity/what-is-identity-verification/EB-Bridging-Trust-Gap.png b/content/identity/what-is-identity-verification/EB-Bridging-Trust-Gap.png
deleted file mode 100644
index 8fc735f07..000000000
Binary files a/content/identity/what-is-identity-verification/EB-Bridging-Trust-Gap.png and /dev/null differ
diff --git a/content/identity/what-is-identity-verification/EB-Bridging-Trust-Gap.webp b/content/identity/what-is-identity-verification/EB-Bridging-Trust-Gap.webp
new file mode 100644
index 000000000..1ad08602c
Binary files /dev/null and b/content/identity/what-is-identity-verification/EB-Bridging-Trust-Gap.webp differ
diff --git a/content/identity/what-is-identity-verification/index.md b/content/identity/what-is-identity-verification/index.md
index 8c7371678..1af075a59 100644
--- a/content/identity/what-is-identity-verification/index.md
+++ b/content/identity/what-is-identity-verification/index.md
@@ -1,7 +1,7 @@
---
title: "What is Digital Identity Verification and Why is it Necessary?"
date: "2021-08-13"
-coverImage: "what-is-identity-verification-cover.jpg"
+coverImage: "what-is-identity-verification-cover.webp"
tags: ["identity verification","digital identity management","cx"]
author: "Rajeev Sharma"
description: "Identity verification is a necessary process that ensures an individual’s identity matches the one that is supposed to be. This post helps better understand what digital identity verification is, how it works, and the types of digital identity verification systems."
@@ -128,7 +128,7 @@ The identity verification process through the identity and access management sys
In other words, a CIAM solution functions to provide the right people access to devices, hardware, software applications, or any IT tool to perform a specific task.
-[](https://www.loginradius.com/resource/digital-consumer-landscape-ebook/)
+[](https://www.loginradius.com/resource/digital-consumer-landscape-ebook/)
The CIAM includes the following core components:
@@ -198,4 +198,4 @@ Digital identity verification is used in various industries like finance and hea
Virtual identity verification is the process of verifying an individual's identity through digital channels without physical presence, often using methods like video calls or AI analysis of facial features or voice patterns.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-verification)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-verification)
diff --git a/content/identity/what-is-identity-verification/what-is-identity-verification-cover.jpg b/content/identity/what-is-identity-verification/what-is-identity-verification-cover.jpg
deleted file mode 100644
index 54c14ce2c..000000000
Binary files a/content/identity/what-is-identity-verification/what-is-identity-verification-cover.jpg and /dev/null differ
diff --git a/content/identity/what-is-identity-verification/what-is-identity-verification-cover.webp b/content/identity/what-is-identity-verification/what-is-identity-verification-cover.webp
new file mode 100644
index 000000000..3729f73ba
Binary files /dev/null and b/content/identity/what-is-identity-verification/what-is-identity-verification-cover.webp differ
diff --git a/content/identity/what-is-ldap-authentication-and-how-it-works/GD-enterpriseGD-to-RBA.png b/content/identity/what-is-ldap-authentication-and-how-it-works/GD-enterpriseGD-to-RBA.png
deleted file mode 100644
index 0d7046172..000000000
Binary files a/content/identity/what-is-ldap-authentication-and-how-it-works/GD-enterpriseGD-to-RBA.png and /dev/null differ
diff --git a/content/identity/what-is-ldap-authentication-and-how-it-works/GD-enterpriseGD-to-RBA.webp b/content/identity/what-is-ldap-authentication-and-how-it-works/GD-enterpriseGD-to-RBA.webp
new file mode 100644
index 000000000..ea0737a8b
Binary files /dev/null and b/content/identity/what-is-ldap-authentication-and-how-it-works/GD-enterpriseGD-to-RBA.webp differ
diff --git a/content/identity/what-is-ldap-authentication-and-how-it-works/index.md b/content/identity/what-is-ldap-authentication-and-how-it-works/index.md
index eca278997..b255b400e 100644
--- a/content/identity/what-is-ldap-authentication-and-how-it-works/index.md
+++ b/content/identity/what-is-ldap-authentication-and-how-it-works/index.md
@@ -1,7 +1,7 @@
---
title: "LDAP Authentication: Meaning and How it Works?"
date: "2023-07-20"
-coverImage: "ldap-authentication.jpg"
+coverImage: "ldap-authentication.webp"
tags: ["user authentication", "identity management", "cx"]
author: "Rakesh Soni"
description: "Explore the world of LDAP authentication, its meaning, and how it works. Discover its applications, including integration with Active Directory. Learn about the client-server authentication process and the challenges involved."
@@ -46,7 +46,7 @@ LDAP and Active Directory are closely related but not the same. LDAP is a protoc
It extends LDAP functionality by incorporating additional security, replication, and domain management features. Active Directory provides a centralized and hierarchical structure for managing resources, including user accounts, computers, and printers.
-[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
+[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/)
## Common Challenges of LDAP Authentication
@@ -66,4 +66,4 @@ By understanding the fundamentals of LDAP authentication and the challenges asso
With ongoing technological advancements, LDAP authentication plays a vital role in ensuring secure user access across diverse platforms and applications.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-ldap-authentication-and-how-it-works)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-ldap-authentication-and-how-it-works)
\ No newline at end of file
diff --git a/content/identity/what-is-ldap-authentication-and-how-it-works/ldap-authentication.jpg b/content/identity/what-is-ldap-authentication-and-how-it-works/ldap-authentication.jpg
deleted file mode 100644
index 3ecbde188..000000000
Binary files a/content/identity/what-is-ldap-authentication-and-how-it-works/ldap-authentication.jpg and /dev/null differ
diff --git a/content/identity/what-is-ldap-authentication-and-how-it-works/ldap-authentication.webp b/content/identity/what-is-ldap-authentication-and-how-it-works/ldap-authentication.webp
new file mode 100644
index 000000000..5b735cbef
Binary files /dev/null and b/content/identity/what-is-ldap-authentication-and-how-it-works/ldap-authentication.webp differ
diff --git a/content/identity/what-is-login-authentication/DS-passwordless-magic.png b/content/identity/what-is-login-authentication/DS-passwordless-magic.png
deleted file mode 100644
index f81b79a36..000000000
Binary files a/content/identity/what-is-login-authentication/DS-passwordless-magic.png and /dev/null differ
diff --git a/content/identity/what-is-login-authentication/DS-passwordless-magic.webp b/content/identity/what-is-login-authentication/DS-passwordless-magic.webp
new file mode 100644
index 000000000..33ac3b3da
Binary files /dev/null and b/content/identity/what-is-login-authentication/DS-passwordless-magic.webp differ
diff --git a/content/identity/what-is-login-authentication/index.md b/content/identity/what-is-login-authentication/index.md
index e718d2056..995a11e5b 100644
--- a/content/identity/what-is-login-authentication/index.md
+++ b/content/identity/what-is-login-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "What is Login Authentication?"
date: "2022-04-07"
-coverImage: "login-authentication.jpg"
+coverImage: "login-authentication.webp"
tags: ["login authentication","identity management","cx"]
author: "Vishal Sharma"
description: "Login authentication is the most common scenario where we’re asked to authenticate ourselves. Let’s look at some aspects and challenges of implementing a seamless authentication mechanism and learn how businesses can deliver a seamless user experience through a CIAM."
@@ -157,7 +157,7 @@ Let your users register and authenticate in seconds with LoginRadius’ social l
With LoginRadius’ Passwordless Login, you can create a completely frictionless registration and authentication process for your customers, freeing them from the hassle of remembering yet another password.
-[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
+[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet)
### Phone authentication and registration
@@ -217,4 +217,4 @@ Yes, a password is a common form of authentication credential.
The best authentication method depends on the security needs of the system. Multi-factor authentication (MFA) is often considered one of the most secure methods.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-login-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-login-authentication)
diff --git a/content/identity/what-is-login-authentication/login-auth.jpg b/content/identity/what-is-login-authentication/login-auth.jpg
deleted file mode 100644
index 412cde856..000000000
Binary files a/content/identity/what-is-login-authentication/login-auth.jpg and /dev/null differ
diff --git a/content/identity/what-is-login-authentication/login-auth.webp b/content/identity/what-is-login-authentication/login-auth.webp
new file mode 100644
index 000000000..1b5707312
Binary files /dev/null and b/content/identity/what-is-login-authentication/login-auth.webp differ
diff --git a/content/identity/what-is-login-authentication/login-authentication.jpg b/content/identity/what-is-login-authentication/login-authentication.jpg
deleted file mode 100644
index dd4e40cd1..000000000
Binary files a/content/identity/what-is-login-authentication/login-authentication.jpg and /dev/null differ
diff --git a/content/identity/what-is-login-authentication/login-authentication.webp b/content/identity/what-is-login-authentication/login-authentication.webp
new file mode 100644
index 000000000..b9ec632bc
Binary files /dev/null and b/content/identity/what-is-login-authentication/login-authentication.webp differ
diff --git a/content/identity/what-is-login-authentication/passwordless-otp.png b/content/identity/what-is-login-authentication/passwordless-otp.png
deleted file mode 100644
index f0d635566..000000000
Binary files a/content/identity/what-is-login-authentication/passwordless-otp.png and /dev/null differ
diff --git a/content/identity/what-is-login-authentication/passwordless-otp.webp b/content/identity/what-is-login-authentication/passwordless-otp.webp
new file mode 100644
index 000000000..16c0455b4
Binary files /dev/null and b/content/identity/what-is-login-authentication/passwordless-otp.webp differ
diff --git a/content/identity/what-is-mitre-att-ck-framework/WP-Dig-Trade-Zone.png b/content/identity/what-is-mitre-att-ck-framework/WP-Dig-Trade-Zone.png
deleted file mode 100644
index 31b7cc833..000000000
Binary files a/content/identity/what-is-mitre-att-ck-framework/WP-Dig-Trade-Zone.png and /dev/null differ
diff --git a/content/identity/what-is-mitre-att-ck-framework/WP-Dig-Trade-Zone.webp b/content/identity/what-is-mitre-att-ck-framework/WP-Dig-Trade-Zone.webp
new file mode 100644
index 000000000..61229103e
Binary files /dev/null and b/content/identity/what-is-mitre-att-ck-framework/WP-Dig-Trade-Zone.webp differ
diff --git a/content/identity/what-is-mitre-att-ck-framework/index.md b/content/identity/what-is-mitre-att-ck-framework/index.md
index 407e78896..32971ed09 100644
--- a/content/identity/what-is-mitre-att-ck-framework/index.md
+++ b/content/identity/what-is-mitre-att-ck-framework/index.md
@@ -1,7 +1,7 @@
---
title: "Understanding MITRE ATT&CK Framework?"
date: "2022-10-28"
-coverImage: "mitre.jpg"
+coverImage: "mitre.webp"
tags: ["mitre attack", "cyberattack", "cybersecurity"]
author: "Alok Patidar"
description: "Introduced in 2013 by MITRE, the ATT&CK (Adversarial Tactics, Techniques & Common Knowledge) is a way to describe adversarial behaviors expressed in matrices. The matrices contain different techniques and tactics associated with the usual behavior of attackers before they try to sneak into a network."
@@ -37,7 +37,7 @@ ATT&CK is a helpful way to map security controls to threat actor behaviors, but
Many of the ATT&CK techniques are performed in multiple ways, so trying to apply a single method of detection may not necessarily prevent all variations of the technique.
-[](https://www.loginradius.com/resource/digital-trade-zone-threats-cybersecurity-whitepaper)
+[](https://www.loginradius.com/resource/digital-trade-zone-threats-cybersecurity-whitepaper)
## Using ATT&CK With Cyber Threat Intelligence
@@ -54,4 +54,4 @@ Organizations that are concerned about their cybersecurity hygiene shouldn’t i
Globally, brands are using this framework to analyze cybersecurity vulnerabilities and to create adequate action plans for robust security.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-mitre-att-ck-framework)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-mitre-att-ck-framework)
\ No newline at end of file
diff --git a/content/identity/what-is-mitre-att-ck-framework/mitre.jpg b/content/identity/what-is-mitre-att-ck-framework/mitre.jpg
deleted file mode 100644
index 84fc0155b..000000000
Binary files a/content/identity/what-is-mitre-att-ck-framework/mitre.jpg and /dev/null differ
diff --git a/content/identity/what-is-mitre-att-ck-framework/mitre.webp b/content/identity/what-is-mitre-att-ck-framework/mitre.webp
new file mode 100644
index 000000000..cb6c94984
Binary files /dev/null and b/content/identity/what-is-mitre-att-ck-framework/mitre.webp differ
diff --git a/content/identity/what-is-mitre-att-ck-framework/trade-wp.png b/content/identity/what-is-mitre-att-ck-framework/trade-wp.png
deleted file mode 100644
index 24d5add74..000000000
Binary files a/content/identity/what-is-mitre-att-ck-framework/trade-wp.png and /dev/null differ
diff --git a/content/identity/what-is-mitre-att-ck-framework/trade-wp.webp b/content/identity/what-is-mitre-att-ck-framework/trade-wp.webp
new file mode 100644
index 000000000..cce7d892c
Binary files /dev/null and b/content/identity/what-is-mitre-att-ck-framework/trade-wp.webp differ
diff --git a/content/identity/what-is-mob-biometric-authentication/Multi-Factor-Authentication.png b/content/identity/what-is-mob-biometric-authentication/Multi-Factor-Authentication.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/what-is-mob-biometric-authentication/Multi-Factor-Authentication.png and /dev/null differ
diff --git a/content/identity/what-is-mob-biometric-authentication/Multi-Factor-Authentication.webp b/content/identity/what-is-mob-biometric-authentication/Multi-Factor-Authentication.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/what-is-mob-biometric-authentication/Multi-Factor-Authentication.webp differ
diff --git a/content/identity/what-is-mob-biometric-authentication/index.md b/content/identity/what-is-mob-biometric-authentication/index.md
index ae28b2833..975b979fa 100644
--- a/content/identity/what-is-mob-biometric-authentication/index.md
+++ b/content/identity/what-is-mob-biometric-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "Introduction to Mobile Biometric Authentication"
date: "2021-04-28"
-coverImage: "what-is-mob-biometric-authentication-cover.jpg"
+coverImage: "what-is-mob-biometric-authentication-cover.webp"
tags: ["mobile biometric authentication","mfa","cx"]
author: "Rajeev Sharma"
description: "In an increasingly digitized world, password-based authentication is no longer sufficient to secure applications and software tools. Can biometrics replace traditional passwords in user authentication? Biometrics does offer a safe and easy mode of authenticating users – without compromising their online experience."
@@ -29,7 +29,7 @@ Why is mobile biometric authentication gaining widespread popularity? Here are s
* Biometrics can also be used as part of the [multi-factor authentication](https://www.loginradius.com/multi-factor-authentication/) (MFA) process – especially when signing into sensitive or confidential accounts.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
Next, let us look at a few use cases of biometric authentication in mobile phones.
@@ -256,4 +256,4 @@ Go to settings on your device, select security or biometrics, and follow prompts
A biometric system verifies individuals based on their unique physical characteristics for secure authentication.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-mob-biometric-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-mob-biometric-authentication)
diff --git a/content/identity/what-is-mob-biometric-authentication/what-is-mob-biometric-authentication-cover.jpg b/content/identity/what-is-mob-biometric-authentication/what-is-mob-biometric-authentication-cover.jpg
deleted file mode 100644
index 60fdd963a..000000000
Binary files a/content/identity/what-is-mob-biometric-authentication/what-is-mob-biometric-authentication-cover.jpg and /dev/null differ
diff --git a/content/identity/what-is-mob-biometric-authentication/what-is-mob-biometric-authentication-cover.webp b/content/identity/what-is-mob-biometric-authentication/what-is-mob-biometric-authentication-cover.webp
new file mode 100644
index 000000000..3034a21cd
Binary files /dev/null and b/content/identity/what-is-mob-biometric-authentication/what-is-mob-biometric-authentication-cover.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/Benefits-of-mfa-1024x869.png b/content/identity/what-is-multi-factor-authentication/Benefits-of-mfa-1024x869.png
deleted file mode 100644
index 9d333b85e..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/Benefits-of-mfa-1024x869.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/Benefits-of-mfa-1024x869.webp b/content/identity/what-is-multi-factor-authentication/Benefits-of-mfa-1024x869.webp
new file mode 100644
index 000000000..b357acebb
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/Benefits-of-mfa-1024x869.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/Book-a-free-demo-request-1024x310.png b/content/identity/what-is-multi-factor-authentication/Book-a-free-demo-request-1024x310.png
deleted file mode 100644
index 0059aade7..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/Book-a-free-demo-request-1024x310.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/Book-a-free-demo-request-1024x310.webp b/content/identity/what-is-multi-factor-authentication/Book-a-free-demo-request-1024x310.webp
new file mode 100644
index 000000000..3b5872929
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/Book-a-free-demo-request-1024x310.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/Multi-Factor-Authentication-secure-1024x747.png b/content/identity/what-is-multi-factor-authentication/Multi-Factor-Authentication-secure-1024x747.png
deleted file mode 100644
index 9cb64cc8d..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/Multi-Factor-Authentication-secure-1024x747.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/Multi-Factor-Authentication-secure-1024x747.webp b/content/identity/what-is-multi-factor-authentication/Multi-Factor-Authentication-secure-1024x747.webp
new file mode 100644
index 000000000..d81f073eb
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/Multi-Factor-Authentication-secure-1024x747.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-google-authenticator-1022x1024.png b/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-google-authenticator-1022x1024.png
deleted file mode 100644
index df4671480..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-google-authenticator-1022x1024.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-google-authenticator-1022x1024.webp b/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-google-authenticator-1022x1024.webp
new file mode 100644
index 000000000..f68739454
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-google-authenticator-1022x1024.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-sms-passcode-1024x438.png b/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-sms-passcode-1024x438.png
deleted file mode 100644
index 76b13db5e..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-sms-passcode-1024x438.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-sms-passcode-1024x438.webp b/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-sms-passcode-1024x438.webp
new file mode 100644
index 000000000..1b352e91c
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/Multi-Factor-authentication-loginradius-sms-passcode-1024x438.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/Multi-factor-authentication.png b/content/identity/what-is-multi-factor-authentication/Multi-factor-authentication.png
deleted file mode 100644
index 12ec7b5f2..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/Multi-factor-authentication.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/Multi-factor-authentication.webp b/content/identity/what-is-multi-factor-authentication/Multi-factor-authentication.webp
new file mode 100644
index 000000000..d43589b7e
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/Multi-factor-authentication.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/Type-of-mfa-1024x747.png b/content/identity/what-is-multi-factor-authentication/Type-of-mfa-1024x747.png
deleted file mode 100644
index 0b1a5344f..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/Type-of-mfa-1024x747.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/Type-of-mfa-1024x747.webp b/content/identity/what-is-multi-factor-authentication/Type-of-mfa-1024x747.webp
new file mode 100644
index 000000000..824e209ae
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/Type-of-mfa-1024x747.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/eb-buyers-guide-to-multi-factor-authentication.png b/content/identity/what-is-multi-factor-authentication/eb-buyers-guide-to-multi-factor-authentication.png
deleted file mode 100644
index d63fdd4ac..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/eb-buyers-guide-to-multi-factor-authentication.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/eb-buyers-guide-to-multi-factor-authentication.webp b/content/identity/what-is-multi-factor-authentication/eb-buyers-guide-to-multi-factor-authentication.webp
new file mode 100644
index 000000000..4486d4d7d
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/eb-buyers-guide-to-multi-factor-authentication.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/how-does-mfa-work.png b/content/identity/what-is-multi-factor-authentication/how-does-mfa-work.png
deleted file mode 100644
index 98fa284ce..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/how-does-mfa-work.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/how-does-mfa-work.webp b/content/identity/what-is-multi-factor-authentication/how-does-mfa-work.webp
new file mode 100644
index 000000000..ce326be99
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/how-does-mfa-work.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/index.md b/content/identity/what-is-multi-factor-authentication/index.md
index 8a2738eed..4914e6049 100644
--- a/content/identity/what-is-multi-factor-authentication/index.md
+++ b/content/identity/what-is-multi-factor-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "What is Multi Factor Authentication (MFA) and How does it Work?"
date: "2019-06-28"
-coverImage: "mfa-cover.png"
+coverImage: "mfa-cover.webp"
tags: ["mfa","authentication","ciam solution","cx"]
author: "Rakesh Soni"
description: "In today’s digital landscape, cybersecurity threats are evolving rapidly. Businesses and individuals alike need stronger security measures to protect sensitive data. A highly effective method to improve security is through Multi-Factor Authentication (MFA). But what is multi factor authentication, and how does it work? Let’s dive into the details."
@@ -81,7 +81,7 @@ This method uses inherent factors like fingerprint scans, facial recognition, or
Biometric authentication is gaining popularity because of its ease of use and strong security. Many modern devices, including smartphones and laptops, integrate biometric authentication as an additional layer of security.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
## What are the Different Types of Authentication Factors?
diff --git a/content/identity/what-is-multi-factor-authentication/mfa-authentication-steps-1024x576.png b/content/identity/what-is-multi-factor-authentication/mfa-authentication-steps-1024x576.png
deleted file mode 100644
index 65b3cfeef..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/mfa-authentication-steps-1024x576.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/mfa-authentication-steps-1024x576.webp b/content/identity/what-is-multi-factor-authentication/mfa-authentication-steps-1024x576.webp
new file mode 100644
index 000000000..4df2e6b1d
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/mfa-authentication-steps-1024x576.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/mfa-cover.png b/content/identity/what-is-multi-factor-authentication/mfa-cover.png
deleted file mode 100644
index 5ffdb14d3..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/mfa-cover.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/mfa-cover.webp b/content/identity/what-is-multi-factor-authentication/mfa-cover.webp
new file mode 100644
index 000000000..25f4d417b
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/mfa-cover.webp differ
diff --git a/content/identity/what-is-multi-factor-authentication/setting-up-mfa-with-loginradius-1024x333.png b/content/identity/what-is-multi-factor-authentication/setting-up-mfa-with-loginradius-1024x333.png
deleted file mode 100644
index c73e1f95c..000000000
Binary files a/content/identity/what-is-multi-factor-authentication/setting-up-mfa-with-loginradius-1024x333.png and /dev/null differ
diff --git a/content/identity/what-is-multi-factor-authentication/setting-up-mfa-with-loginradius-1024x333.webp b/content/identity/what-is-multi-factor-authentication/setting-up-mfa-with-loginradius-1024x333.webp
new file mode 100644
index 000000000..1bab8ef32
Binary files /dev/null and b/content/identity/what-is-multi-factor-authentication/setting-up-mfa-with-loginradius-1024x333.webp differ
diff --git a/content/identity/what-is-oauth/index.md b/content/identity/what-is-oauth/index.md
index 2ee11cbe4..5583c1eb0 100644
--- a/content/identity/what-is-oauth/index.md
+++ b/content/identity/what-is-oauth/index.md
@@ -1,7 +1,7 @@
---
title: "Everything You Need to Know About OAuth and How it Works"
date: "2021-09-23"
-coverImage: "what-is-oauth-cover.jpg"
+coverImage: "what-is-oauth-cover.webp"
tags: ["security"]
featured: false
author: "Vaibhav Jain"
@@ -22,7 +22,7 @@ To understand this, let's take the example of Facebook. When an app on Facebook
-
+
The following explains the working of the above sequence diagram of Oauth 2.0 implementation:
@@ -80,4 +80,4 @@ This article talked about OAuth 2.0 as an authorization framework for delegated
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-oauth)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-oauth)
\ No newline at end of file
diff --git a/content/identity/what-is-oauth/what-is-oauth-1.png b/content/identity/what-is-oauth/what-is-oauth-1.png
deleted file mode 100644
index a2425cc7a..000000000
Binary files a/content/identity/what-is-oauth/what-is-oauth-1.png and /dev/null differ
diff --git a/content/identity/what-is-oauth/what-is-oauth-1.webp b/content/identity/what-is-oauth/what-is-oauth-1.webp
new file mode 100644
index 000000000..c1fc29a61
Binary files /dev/null and b/content/identity/what-is-oauth/what-is-oauth-1.webp differ
diff --git a/content/identity/what-is-oauth/what-is-oauth-cover.jpg b/content/identity/what-is-oauth/what-is-oauth-cover.jpg
deleted file mode 100644
index e551a3c3c..000000000
Binary files a/content/identity/what-is-oauth/what-is-oauth-cover.jpg and /dev/null differ
diff --git a/content/identity/what-is-oauth/what-is-oauth-cover.webp b/content/identity/what-is-oauth/what-is-oauth-cover.webp
new file mode 100644
index 000000000..0c8189989
Binary files /dev/null and b/content/identity/what-is-oauth/what-is-oauth-cover.webp differ
diff --git a/content/identity/what-is-openid-connect/index.md b/content/identity/what-is-openid-connect/index.md
index 6538d93f1..d0795753c 100644
--- a/content/identity/what-is-openid-connect/index.md
+++ b/content/identity/what-is-openid-connect/index.md
@@ -1,7 +1,7 @@
---
title: "Getting Started with OpenID Connect"
date: "2021-09-21"
-coverImage: "what-is-openid-connect-cover.jpg"
+coverImage: "what-is-openid-connect-cover.webp"
tags: ["security"]
featured: false
author: "Gurjyot Singh"
@@ -57,14 +57,14 @@ The OpenID Connect specification has a defined set of standard claims. The set o
-
+
For instance, let us say you want to use OpenID Connect to authenticate the user for your own application using Google’s OAuth URL.
-
+
**Step 1:** On clicking the sign-in button, you are required to pass a few parameters like **scope, **which is a space-delimited list of scopes, **response_type** having the value code, **client_id** having the client identifier, **redirect_uri** having the client redirect URI, and **state** having a random string.
@@ -95,4 +95,4 @@ OpenID Connect, its predecessors, and other [public-key-encryption-based authent
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-openid-connect)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-openid-connect)
\ No newline at end of file
diff --git a/content/identity/what-is-openid-connect/what-is-openid-connect-1.png b/content/identity/what-is-openid-connect/what-is-openid-connect-1.png
deleted file mode 100644
index 4ae7324fa..000000000
Binary files a/content/identity/what-is-openid-connect/what-is-openid-connect-1.png and /dev/null differ
diff --git a/content/identity/what-is-openid-connect/what-is-openid-connect-1.webp b/content/identity/what-is-openid-connect/what-is-openid-connect-1.webp
new file mode 100644
index 000000000..f492d4c13
Binary files /dev/null and b/content/identity/what-is-openid-connect/what-is-openid-connect-1.webp differ
diff --git a/content/identity/what-is-openid-connect/what-is-openid-connect-2.png b/content/identity/what-is-openid-connect/what-is-openid-connect-2.png
deleted file mode 100644
index bb397def9..000000000
Binary files a/content/identity/what-is-openid-connect/what-is-openid-connect-2.png and /dev/null differ
diff --git a/content/identity/what-is-openid-connect/what-is-openid-connect-2.webp b/content/identity/what-is-openid-connect/what-is-openid-connect-2.webp
new file mode 100644
index 000000000..316273f59
Binary files /dev/null and b/content/identity/what-is-openid-connect/what-is-openid-connect-2.webp differ
diff --git a/content/identity/what-is-openid-connect/what-is-openid-connect-cover.jpg b/content/identity/what-is-openid-connect/what-is-openid-connect-cover.jpg
deleted file mode 100644
index 863c26572..000000000
Binary files a/content/identity/what-is-openid-connect/what-is-openid-connect-cover.jpg and /dev/null differ
diff --git a/content/identity/what-is-openid-connect/what-is-openid-connect-cover.webp b/content/identity/what-is-openid-connect/what-is-openid-connect-cover.webp
new file mode 100644
index 000000000..636aac72a
Binary files /dev/null and b/content/identity/what-is-openid-connect/what-is-openid-connect-cover.webp differ
diff --git a/content/identity/what-is-out-of-band-authentication/WP-MFA.png b/content/identity/what-is-out-of-band-authentication/WP-MFA.png
deleted file mode 100644
index bcada2908..000000000
Binary files a/content/identity/what-is-out-of-band-authentication/WP-MFA.png and /dev/null differ
diff --git a/content/identity/what-is-out-of-band-authentication/WP-MFA.webp b/content/identity/what-is-out-of-band-authentication/WP-MFA.webp
new file mode 100644
index 000000000..c1e17eff4
Binary files /dev/null and b/content/identity/what-is-out-of-band-authentication/WP-MFA.webp differ
diff --git a/content/identity/what-is-out-of-band-authentication/index.md b/content/identity/what-is-out-of-band-authentication/index.md
index b986862b4..663a2eb67 100644
--- a/content/identity/what-is-out-of-band-authentication/index.md
+++ b/content/identity/what-is-out-of-band-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "What is Out-of-Band Authentication?"
date: "2022-07-22"
-coverImage: "oob-auth.jpg"
+coverImage: "oob-auth.webp"
tags: ["authentication", "MFA", "customer data security"]
author: "Rakesh Soni"
description: "Securing customer information is becoming more challenging, especially in a remote-first working environment with a poor line of defense. OOB authentication is used as a part of multi-factor authentication (MFA) or 2FA that verifies the identity of a user from two different communications channels, ensuring robust security."
@@ -41,7 +41,7 @@ Whether we talk about loopholes in access management or frail lines of defense,
Hence, a robust authentication mechanism is what every business organization needs. And OOB authentication fulfills their security requirements since it works on a dual means of verifying identity through different communication mechanisms.
-[](https://www.loginradius.com/resource/mfa-evolution-ebook/)
+[](https://www.loginradius.com/resource/mfa-evolution-ebook/)
## How Does OOB Authentication Work?
@@ -150,4 +150,4 @@ Yes, out-of-band authentication is secure due to the added layer of protection u
Out-of-band authentication enhances security and protects against attacks by leveraging a secondary channel for verification.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-out-of-band-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-out-of-band-authentication)
\ No newline at end of file
diff --git a/content/identity/what-is-out-of-band-authentication/mfa-wp.png b/content/identity/what-is-out-of-band-authentication/mfa-wp.png
deleted file mode 100644
index 1703ad51e..000000000
Binary files a/content/identity/what-is-out-of-band-authentication/mfa-wp.png and /dev/null differ
diff --git a/content/identity/what-is-out-of-band-authentication/mfa-wp.webp b/content/identity/what-is-out-of-band-authentication/mfa-wp.webp
new file mode 100644
index 000000000..cf96c255a
Binary files /dev/null and b/content/identity/what-is-out-of-band-authentication/mfa-wp.webp differ
diff --git a/content/identity/what-is-out-of-band-authentication/oob-auth.jpg b/content/identity/what-is-out-of-band-authentication/oob-auth.jpg
deleted file mode 100644
index 283a27278..000000000
Binary files a/content/identity/what-is-out-of-band-authentication/oob-auth.jpg and /dev/null differ
diff --git a/content/identity/what-is-out-of-band-authentication/oob-auth.webp b/content/identity/what-is-out-of-band-authentication/oob-auth.webp
new file mode 100644
index 000000000..e66e724e1
Binary files /dev/null and b/content/identity/what-is-out-of-band-authentication/oob-auth.webp differ
diff --git a/content/identity/what-is-passkey-authentication/cta.png b/content/identity/what-is-passkey-authentication/cta.png
deleted file mode 100644
index c31629290..000000000
Binary files a/content/identity/what-is-passkey-authentication/cta.png and /dev/null differ
diff --git a/content/identity/what-is-passkey-authentication/cta.webp b/content/identity/what-is-passkey-authentication/cta.webp
new file mode 100644
index 000000000..91dd1af2c
Binary files /dev/null and b/content/identity/what-is-passkey-authentication/cta.webp differ
diff --git a/content/identity/what-is-passkey-authentication/hacker.png b/content/identity/what-is-passkey-authentication/hacker.png
deleted file mode 100644
index a6e81d7a6..000000000
Binary files a/content/identity/what-is-passkey-authentication/hacker.png and /dev/null differ
diff --git a/content/identity/what-is-passkey-authentication/hacker.webp b/content/identity/what-is-passkey-authentication/hacker.webp
new file mode 100644
index 000000000..352c3bdb8
Binary files /dev/null and b/content/identity/what-is-passkey-authentication/hacker.webp differ
diff --git a/content/identity/what-is-passkey-authentication/index.md b/content/identity/what-is-passkey-authentication/index.md
index 188f15614..3d4d165d9 100644
--- a/content/identity/what-is-passkey-authentication/index.md
+++ b/content/identity/what-is-passkey-authentication/index.md
@@ -2,7 +2,7 @@
title: "What is Passkey Authentication - A Complete Guide"
description: "Learn about passkey authentication, its role in passwordless authentication, how it ensures secure logins, and its usability across multiple devices and users."
date: "2024-12-30"
-coverImage: "hacker.png"
+coverImage: "hacker.webp"
author: "Kundan Singh"
tags: ["Engineering"]
metatitle: "What is Passkey Authentication - A Complete Guide"
@@ -40,7 +40,7 @@ Passkeys are designed to function seamlessly across devices through cloud servic
For shared devices, passkeys protect each user’s private keys using biometrics or PINs. By adhering to FIDO2 and WebAuthn standards, passkeys ensure cross-platform compatibility, making them a versatile choice for diverse ecosystems. Developers can effortlessly implement these features to cater to multi-user and multi-device scenarios.
-[](https://www.loginradius.com/resource/datasheet/passkeys-passwordless-authentication)
+[](https://www.loginradius.com/resource/datasheet/passkeys-passwordless-authentication)
## Passkey vs Password: Why are Passkeys a Better Choice?
@@ -67,7 +67,7 @@ Moreover, passkeys can complement existing [multi-factor authentication](https:/
## Why Choose LoginRadius for Passkey Authentication?
-
+
Image: A screenshot of LoginRadius Passkeys
diff --git a/content/identity/what-is-passkey-authentication/passkey.png b/content/identity/what-is-passkey-authentication/passkey.png
deleted file mode 100644
index c80edffe8..000000000
Binary files a/content/identity/what-is-passkey-authentication/passkey.png and /dev/null differ
diff --git a/content/identity/what-is-passkey-authentication/passkey.webp b/content/identity/what-is-passkey-authentication/passkey.webp
new file mode 100644
index 000000000..6e83e752c
Binary files /dev/null and b/content/identity/what-is-passkey-authentication/passkey.webp differ
diff --git a/content/identity/what-is-password-vault-how-does-it-work/EB-GD-to-MFA.png b/content/identity/what-is-password-vault-how-does-it-work/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/what-is-password-vault-how-does-it-work/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/what-is-password-vault-how-does-it-work/EB-GD-to-MFA.webp b/content/identity/what-is-password-vault-how-does-it-work/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/what-is-password-vault-how-does-it-work/EB-GD-to-MFA.webp differ
diff --git a/content/identity/what-is-password-vault-how-does-it-work/GD-to-MFA.png b/content/identity/what-is-password-vault-how-does-it-work/GD-to-MFA.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/what-is-password-vault-how-does-it-work/GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/what-is-password-vault-how-does-it-work/GD-to-MFA.webp b/content/identity/what-is-password-vault-how-does-it-work/GD-to-MFA.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/what-is-password-vault-how-does-it-work/GD-to-MFA.webp differ
diff --git a/content/identity/what-is-password-vault-how-does-it-work/index.md b/content/identity/what-is-password-vault-how-does-it-work/index.md
index cf660a3de..c77475852 100644
--- a/content/identity/what-is-password-vault-how-does-it-work/index.md
+++ b/content/identity/what-is-password-vault-how-does-it-work/index.md
@@ -1,7 +1,7 @@
---
title: "What is a Password Vault and How Does it Work?"
date: "2023-04-19"
-coverImage: "password-vault.jpg"
+coverImage: "password-vault.webp"
tags: ["robust security","password management","data privacy"]
author: "Rajeev Sharma"
description: "One of the most significant security concerns is using weak passwords or the same password across multiple accounts, making it easy for hackers to gain unauthorized access to sensitive information. To address these issues, password vaults have become a popular digital identity solution for securely storing passwords."
@@ -148,7 +148,7 @@ There are several pros and cons to using a password vault:
4. **Cost:** Some password vaults require a subscription fee, which can disadvantage users who want to avoid paying for the service.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
## How to Implement Password Vaulting
@@ -200,4 +200,4 @@ Simply create a master password, add your passwords to the vault, and use the ma
A vault stores and manages passwords, providing convenience and enhanced security for digital identity management.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-password-vault-how-does-it-work)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-password-vault-how-does-it-work)
\ No newline at end of file
diff --git a/content/identity/what-is-password-vault-how-does-it-work/password-vault.jpg b/content/identity/what-is-password-vault-how-does-it-work/password-vault.jpg
deleted file mode 100644
index 123b9ef9a..000000000
Binary files a/content/identity/what-is-password-vault-how-does-it-work/password-vault.jpg and /dev/null differ
diff --git a/content/identity/what-is-password-vault-how-does-it-work/password-vault.webp b/content/identity/what-is-password-vault-how-does-it-work/password-vault.webp
new file mode 100644
index 000000000..70a4c1d08
Binary files /dev/null and b/content/identity/what-is-password-vault-how-does-it-work/password-vault.webp differ
diff --git a/content/identity/what-is-passwordless-login/Index.md b/content/identity/what-is-passwordless-login/Index.md
index 97bc72e88..652647b95 100644
--- a/content/identity/what-is-passwordless-login/Index.md
+++ b/content/identity/what-is-passwordless-login/Index.md
@@ -1,7 +1,7 @@
---
title: "What is Passwordless Login?"
date: "2021-03-26"
-coverImage: "what-is-passwordless-login.jpg"
+coverImage: "what-is-passwordless-login.webp"
tags: ["passwordless login","authentication","compliance","cx"]
author: "Keshav Kumar"
description: "Can you exactly recall which accounts what passwords belong to? How frequently do you reuse the same password because you can't have a unique, strong, and easily-remembered password for each of your accounts? Passwordless Login takes the frustration out of the equation to create a better consumer experience."
@@ -178,4 +178,4 @@ Passwordless login simplifies the process, reduces friction, and enhances overal
Passwordless login's future is promising, with advancements in biometrics, multifactor authentication, and hardware tokens driving wider adoption.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-passwordless-login)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-passwordless-login)
\ No newline at end of file
diff --git a/content/identity/what-is-passwordless-login/passwordless-login.jpg b/content/identity/what-is-passwordless-login/passwordless-login.jpg
deleted file mode 100644
index 52fd6cff9..000000000
Binary files a/content/identity/what-is-passwordless-login/passwordless-login.jpg and /dev/null differ
diff --git a/content/identity/what-is-passwordless-login/passwordless-login.webp b/content/identity/what-is-passwordless-login/passwordless-login.webp
new file mode 100644
index 000000000..87f7730ba
Binary files /dev/null and b/content/identity/what-is-passwordless-login/passwordless-login.webp differ
diff --git a/content/identity/what-is-passwordless-login/what-is-passwordless-login.jpg b/content/identity/what-is-passwordless-login/what-is-passwordless-login.jpg
deleted file mode 100644
index edd182372..000000000
Binary files a/content/identity/what-is-passwordless-login/what-is-passwordless-login.jpg and /dev/null differ
diff --git a/content/identity/what-is-passwordless-login/what-is-passwordless-login.webp b/content/identity/what-is-passwordless-login/what-is-passwordless-login.webp
new file mode 100644
index 000000000..3a879d785
Binary files /dev/null and b/content/identity/what-is-passwordless-login/what-is-passwordless-login.webp differ
diff --git a/content/identity/what-is-pin-authentication/index.md b/content/identity/what-is-pin-authentication/index.md
index bc5277892..d690e164e 100644
--- a/content/identity/what-is-pin-authentication/index.md
+++ b/content/identity/what-is-pin-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "What is PIN Authentication"
date: "2021-02-27"
-coverImage: "pin-authenticaton.jpg"
+coverImage: "pin-authenticaton.webp"
tags: ["pin authentication","data security","ciam solution"]
author: "Abhishek Singh"
description: "Logging in through PIN is in popular culture nowadays. This feature allows the consumer to set a PIN in addition to the password during registration or login. Later, during the subsequent logins, the application requests the same PIN to authenticate."
@@ -30,7 +30,7 @@ Some other aspects which prove PIN authentication a robust and a secured model:
3. It can also be used as a Re-Authentication model.
-
+
## What is 3D Secure Authentication PIN
@@ -89,7 +89,7 @@ To further enhance the security of PIN authentication, businesses can implement
By implementing these security measures, businesses can strengthen the integrity of PIN authentication and mitigate the risk of unauthorized access and data breaches.
-[](https://www.loginradius.com/resource/loginradius-and-pin-auth)
+[](https://www.loginradius.com/resource/loginradius-and-pin-auth)
## **How to Implement PIN Authentication?**
@@ -123,4 +123,4 @@ Authentication methods include single-factor (e.g., passwords), two-factor (e.g.
PIN verification data refers to information associated with a user's PIN, including its validity period, device-specificity, and dynamic nature, enhancing security and access control measures.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-pin-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-pin-authentication)
\ No newline at end of file
diff --git a/content/identity/what-is-pin-authentication/pin-authentication.jpg b/content/identity/what-is-pin-authentication/pin-authentication.jpg
deleted file mode 100644
index f99bdfb82..000000000
Binary files a/content/identity/what-is-pin-authentication/pin-authentication.jpg and /dev/null differ
diff --git a/content/identity/what-is-pin-authentication/pin-authentication.webp b/content/identity/what-is-pin-authentication/pin-authentication.webp
new file mode 100644
index 000000000..c7ef75e42
Binary files /dev/null and b/content/identity/what-is-pin-authentication/pin-authentication.webp differ
diff --git a/content/identity/what-is-pin-authentication/pin-authenticaton.jpg b/content/identity/what-is-pin-authentication/pin-authenticaton.jpg
deleted file mode 100644
index 2271230bc..000000000
Binary files a/content/identity/what-is-pin-authentication/pin-authenticaton.jpg and /dev/null differ
diff --git a/content/identity/what-is-pin-authentication/pin-authenticaton.webp b/content/identity/what-is-pin-authentication/pin-authenticaton.webp
new file mode 100644
index 000000000..e494f5ab9
Binary files /dev/null and b/content/identity/what-is-pin-authentication/pin-authenticaton.webp differ
diff --git a/content/identity/what-is-pin-authentication/pin-login.png b/content/identity/what-is-pin-authentication/pin-login.png
deleted file mode 100644
index 8be510ab8..000000000
Binary files a/content/identity/what-is-pin-authentication/pin-login.png and /dev/null differ
diff --git a/content/identity/what-is-pin-authentication/pin-login.webp b/content/identity/what-is-pin-authentication/pin-login.webp
new file mode 100644
index 000000000..7f9ae5df5
Binary files /dev/null and b/content/identity/what-is-pin-authentication/pin-login.webp differ
diff --git a/content/identity/what-is-privileged-access-management/EB-GD-to-MFA.png b/content/identity/what-is-privileged-access-management/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/what-is-privileged-access-management/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/what-is-privileged-access-management/EB-GD-to-MFA.webp b/content/identity/what-is-privileged-access-management/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/what-is-privileged-access-management/EB-GD-to-MFA.webp differ
diff --git a/content/identity/what-is-privileged-access-management/eb-mfa.png b/content/identity/what-is-privileged-access-management/eb-mfa.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/what-is-privileged-access-management/eb-mfa.png and /dev/null differ
diff --git a/content/identity/what-is-privileged-access-management/eb-mfa.webp b/content/identity/what-is-privileged-access-management/eb-mfa.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/what-is-privileged-access-management/eb-mfa.webp differ
diff --git a/content/identity/what-is-privileged-access-management/index.md b/content/identity/what-is-privileged-access-management/index.md
index ac75a5ed7..e0d233c88 100644
--- a/content/identity/what-is-privileged-access-management/index.md
+++ b/content/identity/what-is-privileged-access-management/index.md
@@ -1,7 +1,7 @@
---
title: "A Comprehensive Guide to Privileged Access Management (PAM)"
date: "2021-08-26"
-coverImage: "what-is-privileged-access-management-cover.jpg"
+coverImage: "what-is-privileged-access-management-cover.webp"
tags: ["data security","Privileged Access Management","cx"]
author: "Bhavya Tugnawat"
description: "Privileged access management—finding the right balance between security and convenience. This blog explains why PAM matters, highlights its key features and strategies that the organization should use to ensure the proper implementation of PAM."
@@ -59,7 +59,7 @@ Now, let's discuss the features that the PAM software provides:
* It also provides the facility of dynamic authorization, which means access to individual users for a particular period.
* It also has automatic provisioning and deprovisioning, which helps reduce insider threats, and the Audit logs feature that allows the organization to meet the compliance requirements.
-[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
## Common Strategies that the Organization Should Use to Ensure the Proper Implementation of PAM
@@ -91,4 +91,4 @@ In this article, we have learnt about Privileged Access Management, which helps
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-privileged-access-management)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-privileged-access-management)
\ No newline at end of file
diff --git a/content/identity/what-is-privileged-access-management/what-is-privileged-access-management-cover.jpg b/content/identity/what-is-privileged-access-management/what-is-privileged-access-management-cover.jpg
deleted file mode 100644
index b3887cf58..000000000
Binary files a/content/identity/what-is-privileged-access-management/what-is-privileged-access-management-cover.jpg and /dev/null differ
diff --git a/content/identity/what-is-privileged-access-management/what-is-privileged-access-management-cover.webp b/content/identity/what-is-privileged-access-management/what-is-privileged-access-management-cover.webp
new file mode 100644
index 000000000..df0402d81
Binary files /dev/null and b/content/identity/what-is-privileged-access-management/what-is-privileged-access-management-cover.webp differ
diff --git a/content/identity/what-is-rbac/index.md b/content/identity/what-is-rbac/index.md
index ea5aa4a12..7ed0c27a4 100644
--- a/content/identity/what-is-rbac/index.md
+++ b/content/identity/what-is-rbac/index.md
@@ -211,4 +211,4 @@ Leveraging platforms like LoginRadius further simplifies the implementation and
**A:** RBAC manages access based solely on user roles, whereas IAM (Identity and Access Management) comprehensively manages users' identities, roles, policies, and access privileges.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-rbac)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-rbac)
\ No newline at end of file
diff --git a/content/identity/what-is-replatforming/GD-DIY-CIAM.png b/content/identity/what-is-replatforming/GD-DIY-CIAM.png
deleted file mode 100644
index 75b8a78c5..000000000
Binary files a/content/identity/what-is-replatforming/GD-DIY-CIAM.png and /dev/null differ
diff --git a/content/identity/what-is-replatforming/GD-DIY-CIAM.webp b/content/identity/what-is-replatforming/GD-DIY-CIAM.webp
new file mode 100644
index 000000000..d9d8b7098
Binary files /dev/null and b/content/identity/what-is-replatforming/GD-DIY-CIAM.webp differ
diff --git a/content/identity/what-is-replatforming/GD-DIY-to-CIAM.png b/content/identity/what-is-replatforming/GD-DIY-to-CIAM.png
deleted file mode 100644
index eaaad8184..000000000
Binary files a/content/identity/what-is-replatforming/GD-DIY-to-CIAM.png and /dev/null differ
diff --git a/content/identity/what-is-replatforming/GD-DIY-to-CIAM.webp b/content/identity/what-is-replatforming/GD-DIY-to-CIAM.webp
new file mode 100644
index 000000000..7a309220e
Binary files /dev/null and b/content/identity/what-is-replatforming/GD-DIY-to-CIAM.webp differ
diff --git a/content/identity/what-is-replatforming/digital-transformtion.jpg b/content/identity/what-is-replatforming/digital-transformtion.jpg
deleted file mode 100644
index c591a6242..000000000
Binary files a/content/identity/what-is-replatforming/digital-transformtion.jpg and /dev/null differ
diff --git a/content/identity/what-is-replatforming/digital-transformtion.webp b/content/identity/what-is-replatforming/digital-transformtion.webp
new file mode 100644
index 000000000..37010acd2
Binary files /dev/null and b/content/identity/what-is-replatforming/digital-transformtion.webp differ
diff --git a/content/identity/what-is-replatforming/index.md b/content/identity/what-is-replatforming/index.md
index 5bb394362..8af56f6c2 100644
--- a/content/identity/what-is-replatforming/index.md
+++ b/content/identity/what-is-replatforming/index.md
@@ -1,7 +1,7 @@
---
title: "Replatforming 101: Everything You Need to Know"
date: "2023-03-15"
-coverImage: "replatforming.jpg"
+coverImage: "replatforming.webp"
tags: ["digital transformation","cloud migration","ciam solution"]
author: "Rakesh Soni"
description: "In today's rapidly evolving digital landscape, businesses must keep pace with the latest technology to remain competitive. One way to do this is through re-platforming or migrating from an outdated platform to a newer one, often in the cloud. Let’s have a look at the aspects associated with re-platforming."
@@ -76,7 +76,7 @@ Replatforming IAM solutions to cloud-based platforms can provide numerous benefi
Hence, it’s always a great idea to switch to a robust customer IAM like LoginRadius that can help scale your business growth, enhance security, and meet all the compliances.
-[](https://www.loginradius.com/resource/move-to-a-consumer-iam-solution/)
+[](https://www.loginradius.com/resource/move-to-a-consumer-iam-solution/)
## Customization and Integration of Cloud Replatform
@@ -116,4 +116,4 @@ Cloud re-platforming can provide numerous benefits, including enhanced scalabili
By leveraging LoginRadius CIAM, businesses can stay ahead of the curve and thrive in the fast-paced digital landscape while planning to re-platform.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-replatforming)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-replatforming)
\ No newline at end of file
diff --git a/content/identity/what-is-replatforming/replatforming.jpg b/content/identity/what-is-replatforming/replatforming.jpg
deleted file mode 100644
index fb1c77f31..000000000
Binary files a/content/identity/what-is-replatforming/replatforming.jpg and /dev/null differ
diff --git a/content/identity/what-is-replatforming/replatforming.webp b/content/identity/what-is-replatforming/replatforming.webp
new file mode 100644
index 000000000..886c9f9d0
Binary files /dev/null and b/content/identity/what-is-replatforming/replatforming.webp differ
diff --git a/content/identity/what-is-salt/index.md b/content/identity/what-is-salt/index.md
index 466507923..9a5ce1746 100644
--- a/content/identity/what-is-salt/index.md
+++ b/content/identity/what-is-salt/index.md
@@ -1,7 +1,7 @@
---
title: "What Is a Salt and How Does It Boost Security?"
date: "2021-04-16"
-coverImage: "what-is-salt-cover.jpg"
+coverImage: "what-is-salt-cover.webp"
tags: ["security"]
featured: false
author: "Navanita Devi"
@@ -98,7 +98,7 @@ Most businesses are not well-versed in the language of password salts and hashes
LoginRadius has also launched a unique password policy that provides additional features such as password complexity, profile password prevention, password expiration, and password history.
-[](https://www.loginradius.com/resource/password-policy-datasheet)
+[](https://www.loginradius.com/resource/password-policy-datasheet)
This policy makes LoginRadius an excellent choice for password protection among businesses and consumers alike.
@@ -108,4 +108,4 @@ This policy makes LoginRadius an excellent choice for password protection among
Protecting your data, whether you represent a company or simply for your personal accounts, is essential. Hashing and salting of passwords and cryptographic hash functions are the foolproof methods for this purpose. With salts, you can rest assured that your passwords and data are in good hands.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-salt)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-salt)
\ No newline at end of file
diff --git a/content/identity/what-is-salt/password-policy.png b/content/identity/what-is-salt/password-policy.png
deleted file mode 100644
index 619981a62..000000000
Binary files a/content/identity/what-is-salt/password-policy.png and /dev/null differ
diff --git a/content/identity/what-is-salt/password-policy.webp b/content/identity/what-is-salt/password-policy.webp
new file mode 100644
index 000000000..a5d1adfc4
Binary files /dev/null and b/content/identity/what-is-salt/password-policy.webp differ
diff --git a/content/identity/what-is-salt/what-is-salt-cover.jpg b/content/identity/what-is-salt/what-is-salt-cover.jpg
deleted file mode 100644
index 4f1d6d75f..000000000
Binary files a/content/identity/what-is-salt/what-is-salt-cover.jpg and /dev/null differ
diff --git a/content/identity/what-is-salt/what-is-salt-cover.webp b/content/identity/what-is-salt/what-is-salt-cover.webp
new file mode 100644
index 000000000..e96a8f4c6
Binary files /dev/null and b/content/identity/what-is-salt/what-is-salt-cover.webp differ
diff --git a/content/identity/what-is-scim/cta.png b/content/identity/what-is-scim/cta.png
deleted file mode 100644
index 82c2e3fce..000000000
Binary files a/content/identity/what-is-scim/cta.png and /dev/null differ
diff --git a/content/identity/what-is-scim/cta.webp b/content/identity/what-is-scim/cta.webp
new file mode 100644
index 000000000..1133846fc
Binary files /dev/null and b/content/identity/what-is-scim/cta.webp differ
diff --git a/content/identity/what-is-scim/index.md b/content/identity/what-is-scim/index.md
index 307b09767..2518b5304 100644
--- a/content/identity/what-is-scim/index.md
+++ b/content/identity/what-is-scim/index.md
@@ -1,7 +1,7 @@
---
title: "What is SCIM? A Developer's Guide to Understanding and Using SCIM"
date: "2025-01-17"
-coverImage: "scim.png"
+coverImage: "scim.webp"
tags: ["SCIM"]
author: "Kundan Singh"
description: "Learn how SCIM streamlines cross-domain identity management, automates user provisioning, and ensures secure integration for modern applications."
@@ -58,7 +58,7 @@ Here are the steps to integrate SCIM into your application:
By understanding what is SCIM and leveraging it effectively, developers can focus on enhancing application functionality while relying on the protocol to handle complex identity management workflows.
-[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
+[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
By leveraging the system for cross-domain identity management, organizations can ensure a more consistent and streamlined approach to handling identity data across multiple platforms.
diff --git a/content/identity/what-is-scim/scim.png b/content/identity/what-is-scim/scim.png
deleted file mode 100644
index c6d346e4c..000000000
Binary files a/content/identity/what-is-scim/scim.png and /dev/null differ
diff --git a/content/identity/what-is-scim/scim.webp b/content/identity/what-is-scim/scim.webp
new file mode 100644
index 000000000..73d0358ef
Binary files /dev/null and b/content/identity/what-is-scim/scim.webp differ
diff --git a/content/identity/what-is-single-sign-on/BD-Plexicon1-1024x310-1.png b/content/identity/what-is-single-sign-on/BD-Plexicon1-1024x310-1.png
deleted file mode 100644
index 6bbda92e9..000000000
Binary files a/content/identity/what-is-single-sign-on/BD-Plexicon1-1024x310-1.png and /dev/null differ
diff --git a/content/identity/what-is-single-sign-on/BD-Plexicon1-1024x310-1.webp b/content/identity/what-is-single-sign-on/BD-Plexicon1-1024x310-1.webp
new file mode 100644
index 000000000..0aeacb9f7
Binary files /dev/null and b/content/identity/what-is-single-sign-on/BD-Plexicon1-1024x310-1.webp differ
diff --git a/content/identity/what-is-single-sign-on/DS-LoginRadius-Single-Sign-on-1-1024x310.png b/content/identity/what-is-single-sign-on/DS-LoginRadius-Single-Sign-on-1-1024x310.png
deleted file mode 100644
index 702d43032..000000000
Binary files a/content/identity/what-is-single-sign-on/DS-LoginRadius-Single-Sign-on-1-1024x310.png and /dev/null differ
diff --git a/content/identity/what-is-single-sign-on/DS-LoginRadius-Single-Sign-on-1-1024x310.webp b/content/identity/what-is-single-sign-on/DS-LoginRadius-Single-Sign-on-1-1024x310.webp
new file mode 100644
index 000000000..5b5ca6d71
Binary files /dev/null and b/content/identity/what-is-single-sign-on/DS-LoginRadius-Single-Sign-on-1-1024x310.webp differ
diff --git a/content/identity/what-is-single-sign-on/LoginRadius-as-an-Identity-Provider-1024x974.png b/content/identity/what-is-single-sign-on/LoginRadius-as-an-Identity-Provider-1024x974.png
deleted file mode 100644
index 210e5f588..000000000
Binary files a/content/identity/what-is-single-sign-on/LoginRadius-as-an-Identity-Provider-1024x974.png and /dev/null differ
diff --git a/content/identity/what-is-single-sign-on/LoginRadius-as-an-Identity-Provider-1024x974.webp b/content/identity/what-is-single-sign-on/LoginRadius-as-an-Identity-Provider-1024x974.webp
new file mode 100644
index 000000000..3d0df68b4
Binary files /dev/null and b/content/identity/what-is-single-sign-on/LoginRadius-as-an-Identity-Provider-1024x974.webp differ
diff --git a/content/identity/what-is-single-sign-on/Loginradius-OAuth-1024x452.png b/content/identity/what-is-single-sign-on/Loginradius-OAuth-1024x452.png
deleted file mode 100644
index 61d7b10d4..000000000
Binary files a/content/identity/what-is-single-sign-on/Loginradius-OAuth-1024x452.png and /dev/null differ
diff --git a/content/identity/what-is-single-sign-on/Loginradius-OAuth-1024x452.webp b/content/identity/what-is-single-sign-on/Loginradius-OAuth-1024x452.webp
new file mode 100644
index 000000000..d1cfc74a8
Binary files /dev/null and b/content/identity/what-is-single-sign-on/Loginradius-OAuth-1024x452.webp differ
diff --git a/content/identity/what-is-single-sign-on/Loginradius-secure-sso-solution.jpg b/content/identity/what-is-single-sign-on/Loginradius-secure-sso-solution.jpg
deleted file mode 100644
index dc43799ff..000000000
Binary files a/content/identity/what-is-single-sign-on/Loginradius-secure-sso-solution.jpg and /dev/null differ
diff --git a/content/identity/what-is-single-sign-on/Loginradius-secure-sso-solution.webp b/content/identity/what-is-single-sign-on/Loginradius-secure-sso-solution.webp
new file mode 100644
index 000000000..d54a49afd
Binary files /dev/null and b/content/identity/what-is-single-sign-on/Loginradius-secure-sso-solution.webp differ
diff --git a/content/identity/what-is-single-sign-on/SAML-1024x418.png b/content/identity/what-is-single-sign-on/SAML-1024x418.png
deleted file mode 100644
index 6cf34a777..000000000
Binary files a/content/identity/what-is-single-sign-on/SAML-1024x418.png and /dev/null differ
diff --git a/content/identity/what-is-single-sign-on/SAML-1024x418.webp b/content/identity/what-is-single-sign-on/SAML-1024x418.webp
new file mode 100644
index 000000000..0a9bc15ed
Binary files /dev/null and b/content/identity/what-is-single-sign-on/SAML-1024x418.webp differ
diff --git a/content/identity/what-is-single-sign-on/What-is-single-sign-on-feature-image.jpg b/content/identity/what-is-single-sign-on/What-is-single-sign-on-feature-image.jpg
deleted file mode 100644
index c1cdd4dfe..000000000
Binary files a/content/identity/what-is-single-sign-on/What-is-single-sign-on-feature-image.jpg and /dev/null differ
diff --git a/content/identity/what-is-single-sign-on/What-is-single-sign-on-feature-image.webp b/content/identity/what-is-single-sign-on/What-is-single-sign-on-feature-image.webp
new file mode 100644
index 000000000..4c58d6495
Binary files /dev/null and b/content/identity/what-is-single-sign-on/What-is-single-sign-on-feature-image.webp differ
diff --git a/content/identity/what-is-single-sign-on/index.md b/content/identity/what-is-single-sign-on/index.md
index 3ee627a88..8ac27ec7b 100644
--- a/content/identity/what-is-single-sign-on/index.md
+++ b/content/identity/what-is-single-sign-on/index.md
@@ -1,7 +1,7 @@
---
title: "What is Single Sign-On (SSO) and How it Works?"
date: "2019-05-30"
-coverImage: "what-is-sso.jpg"
+coverImage: "what-is-sso.webp"
tags: ["sso","identity management","cx"]
author: "Rakesh Soni"
description: "SSO is an essential feature of an Identity and Access Management (IAM) access control platform. User identity authentication is important when it comes to understanding which permissions a user will have. One example of controlling access that integrates user identity management solutions with SSO solutions is the LoginRadius Identity platform."
@@ -102,7 +102,7 @@ Because users only need to use one password, SSO makes generating, remembering,
The time spent on re-entering passwords for the same identity. Users will spend less time logging into various apps to do their work. Ultimately it enhances the productivity of businesses.
-[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.loginradius.com/resource/loginradius-single-sign-on/)
### Benefits for Business
@@ -144,7 +144,7 @@ The identity provider must also be configured to authenticate users and provide
Your SSO solution must meet the basic needs to support IT needs. That means a stable solution and a highly functional one. Today, digital transformation relies on a platform for [Customer Identity and Access Management](https://www.loginradius.com/blog/identity/customer-identity-and-access-management/) (CIAM), which includes SSO and other tools. So, here what you need to keep in mind while narrowing down your SSO solution.
-
+
## 7 Key Points to Consider While Choosing a Secure Single Sign-On Solution
@@ -186,7 +186,7 @@ Web single sign-on enables your customers to access any of your connected web pr
[Web Single Sign-On](https://www.loginradius.com/docs/single-sign-on/web-and-mobile-sso/loginradius-web-sso/) also is known as LoginRadius Single Sign-On, is a browser-based session management system that uses browser storage mechanisms (sessionStorage, localStorage, Cookies) to hold the user session across your assets.
-
+
This storage is stored on a centralized domain managed by LoginRadius and can be accessed via our JavaScript Single Sign-On APIs, or directly through a JSONP call. This session is integrated seamlessly into our standard Customer Identity and Access Management scripts.
@@ -194,7 +194,7 @@ This storage is stored on a centralized domain managed by LoginRadius and can be
Mobile single sign-on is like web SSO, except that customers can use a single identity to access connected mobile apps.
-
+
[Mobile SSO enables](https://www.loginradius.com/docs/single-sign-on/web-and-mobile-sso/loginradius-mobile-sso/) you to unify a user session across multiple apps that are serviced by a single account LoginRadius. It works by storing the LoginRadius access token in a shared session, either shared Android preferences or iOS keychain, which allows you to recognize a currently active session and access current user data sessions to configure your user account with each linked program.
@@ -204,7 +204,7 @@ Federated single sign-on [works a little differently](https://datafloq.com/read/
LoginRadius also acts as an IdP that stores and authenticates the identities used by end-users to log in to customer systems, applications, file servers, and more depending on their configuration.
-
+
LoginRadius serves as a software provider providing end-user services. LoginRadius does not authenticate users but instead requests third-party Identity Provider authentication. LoginRadius relies on the identity provider to verify a user's identity and, if necessary, to verify other user attributes that the identity provider manages.
@@ -214,7 +214,7 @@ Security Assertion Markup Language (SAML) is an open standard enabling identity
[LoginRadius supports both SAML 1.1 and SAML 2.0](https://www.loginradius.com/docs/single-sign-on/federated-sso/saml/overview/) flows to support LoginRadius either as an IDP or as a Service Provider (SP). LoginRadius supports SAML flows, both initiated by IDP and initiated by SP.
-
+
The LoginRadius Admin Console allows the SAML settings to be entirely self-service, allowing you to configure statements, keys, and endpoints to suit any SAML provider.
#### JWT
@@ -229,7 +229,7 @@ OAuth is an open-standard authorization protocol or framework that describes how
LoginRadius may either function as an OAuth 2.0 Identity Provider or as a Service Provider delegating the authentication process to an IDP supporting the OAuth Project. The specifications for OAuth 2.0 are protected in RFC 6749.
-
+
Such specs cover the various specifications and [structured processes OAuth embraces](https://www.loginradius.com/docs/single-sign-on/federated-sso/oauth-2-0/oauth-2-0-overview/). From the authorization of the service provider requesting authentication to the request for authorization from the end-user to the generation of the access token used to request the scoped data from the IDP after authentication.
@@ -284,4 +284,4 @@ Same Sign-On is not a standard term; Single Sign-On (SSO) allows users to log in
Simplify authentication for users and enhance security by allowing access to multiple applications with one login.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-single-sign-on)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-single-sign-on)
diff --git a/content/identity/what-is-single-sign-on/mobile-sso-1-1024x247.png b/content/identity/what-is-single-sign-on/mobile-sso-1-1024x247.png
deleted file mode 100644
index 4a7ec60dc..000000000
Binary files a/content/identity/what-is-single-sign-on/mobile-sso-1-1024x247.png and /dev/null differ
diff --git a/content/identity/what-is-single-sign-on/mobile-sso-1-1024x247.webp b/content/identity/what-is-single-sign-on/mobile-sso-1-1024x247.webp
new file mode 100644
index 000000000..bd98e6adf
Binary files /dev/null and b/content/identity/what-is-single-sign-on/mobile-sso-1-1024x247.webp differ
diff --git a/content/identity/what-is-single-sign-on/web-sso-1-1024x294.png b/content/identity/what-is-single-sign-on/web-sso-1-1024x294.png
deleted file mode 100644
index bcc076980..000000000
Binary files a/content/identity/what-is-single-sign-on/web-sso-1-1024x294.png and /dev/null differ
diff --git a/content/identity/what-is-single-sign-on/web-sso-1-1024x294.webp b/content/identity/what-is-single-sign-on/web-sso-1-1024x294.webp
new file mode 100644
index 000000000..85be6adb2
Binary files /dev/null and b/content/identity/what-is-single-sign-on/web-sso-1-1024x294.webp differ
diff --git a/content/identity/what-is-single-sign-on/what-is-sso.jpg b/content/identity/what-is-single-sign-on/what-is-sso.jpg
deleted file mode 100644
index f604ced47..000000000
Binary files a/content/identity/what-is-single-sign-on/what-is-sso.jpg and /dev/null differ
diff --git a/content/identity/what-is-single-sign-on/what-is-sso.webp b/content/identity/what-is-single-sign-on/what-is-sso.webp
new file mode 100644
index 000000000..ada3e1eb5
Binary files /dev/null and b/content/identity/what-is-single-sign-on/what-is-sso.webp differ
diff --git a/content/identity/what-is-social-login/index.md b/content/identity/what-is-social-login/index.md
index 649aeb70d..e5480e1ba 100644
--- a/content/identity/what-is-social-login/index.md
+++ b/content/identity/what-is-social-login/index.md
@@ -1,7 +1,7 @@
---
title: "What is Social Login?"
date: "2020-02-28"
-coverImage: "social-login.jpg"
+coverImage: "social-login.webp"
tags: ["social login","identity verification","cx"]
author: "Vaibhav Jain"
description: "Social login is an attractive feature for developers and businesses that can help streamline consumer verification while also providing more reliable data access for personalization."
@@ -43,7 +43,7 @@ Social login and registration provide benefits in various ways:
- Social login reduces the effort to remember passwords, which means people don’t need to create and keep track of more credentials, lessening password fatigue and login failure.
-[](https://www.google.com/url?q=https://www.loginradius.com/resource/loginradius-single-sign-on/)
+[](https://www.google.com/url?q=https://www.loginradius.com/resource/loginradius-single-sign-on/)
- Consumers feel more comfortable sharing the data via the social platform on which they already have trust compared to unknown sites. Social login provides a recognizable, uniform method of account logging.
@@ -127,4 +127,4 @@ Users can perform social login by clicking on the respective social media button
Facebook login can be integrated with your website or mobile application for seamless login by using the [LoginRadius CIAM](https://www.loginradius.com/social-login/).
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-social-login)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-social-login)
\ No newline at end of file
diff --git a/content/identity/what-is-social-login/social-login.jpg b/content/identity/what-is-social-login/social-login.jpg
deleted file mode 100644
index 151da0d71..000000000
Binary files a/content/identity/what-is-social-login/social-login.jpg and /dev/null differ
diff --git a/content/identity/what-is-social-login/social-login.webp b/content/identity/what-is-social-login/social-login.webp
new file mode 100644
index 000000000..ee47478f3
Binary files /dev/null and b/content/identity/what-is-social-login/social-login.webp differ
diff --git a/content/identity/what-is-social-login/sso.png b/content/identity/what-is-social-login/sso.png
deleted file mode 100644
index 25ea42026..000000000
Binary files a/content/identity/what-is-social-login/sso.png and /dev/null differ
diff --git a/content/identity/what-is-social-login/sso.webp b/content/identity/what-is-social-login/sso.webp
new file mode 100644
index 000000000..015f518c5
Binary files /dev/null and b/content/identity/what-is-social-login/sso.webp differ
diff --git a/content/identity/what-is-social-login/what-is-social-login.jpg b/content/identity/what-is-social-login/what-is-social-login.jpg
deleted file mode 100644
index ffad52132..000000000
Binary files a/content/identity/what-is-social-login/what-is-social-login.jpg and /dev/null differ
diff --git a/content/identity/what-is-social-login/what-is-social-login.webp b/content/identity/what-is-social-login/what-is-social-login.webp
new file mode 100644
index 000000000..6419b9482
Binary files /dev/null and b/content/identity/what-is-social-login/what-is-social-login.webp differ
diff --git a/content/identity/what-is-standard-login/index.md b/content/identity/what-is-standard-login/index.md
index 1cd13984b..41c71ccf5 100644
--- a/content/identity/what-is-standard-login/index.md
+++ b/content/identity/what-is-standard-login/index.md
@@ -1,7 +1,7 @@
---
title: "What is Standard Login"
date: "2021-03-26"
-coverImage: "standard_login_cover_pic.jpg"
+coverImage: "standard_login_cover_pic.webp"
tags: ["login","user authentication","cx"]
author: "Keshav Kumar"
description: "Standard Login is an essential aspect of website authentication. With a better security perspective, your organization can look into more robust registration and login processes that move beyond the traditional offerings. That's why we've created this guide."
@@ -122,4 +122,4 @@ Also, login is incredibly important for enterprises. Consumers want to have ever
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-standard-login)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-standard-login)
\ No newline at end of file
diff --git a/content/identity/what-is-standard-login/standard_login_cover_pic.jpg b/content/identity/what-is-standard-login/standard_login_cover_pic.jpg
deleted file mode 100644
index 36cdd1812..000000000
Binary files a/content/identity/what-is-standard-login/standard_login_cover_pic.jpg and /dev/null differ
diff --git a/content/identity/what-is-standard-login/standard_login_cover_pic.webp b/content/identity/what-is-standard-login/standard_login_cover_pic.webp
new file mode 100644
index 000000000..1352e756d
Binary files /dev/null and b/content/identity/what-is-standard-login/standard_login_cover_pic.webp differ
diff --git a/content/identity/what-is-token-authentication/index.md b/content/identity/what-is-token-authentication/index.md
index a7143de08..107f42c3c 100644
--- a/content/identity/what-is-token-authentication/index.md
+++ b/content/identity/what-is-token-authentication/index.md
@@ -196,4 +196,4 @@ Ready to implement token-based authentication with a powerful CIAM solution?[ Bo
**A.** JWT is a specific type of token used in token-based authentication. While all JWTs are tokens, not all tokens are JWTs. JWTs contain payloads, are signed, and often used in OAuth2 systems.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-token-authentication)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-token-authentication)
\ No newline at end of file
diff --git a/content/identity/what-is-web-sso/index.md b/content/identity/what-is-web-sso/index.md
index 4169565bd..ef4e33d29 100644
--- a/content/identity/what-is-web-sso/index.md
+++ b/content/identity/what-is-web-sso/index.md
@@ -1,7 +1,7 @@
---
title: "What is Web SSO"
date: "2021-06-10"
-coverImage: "web-sso.jpg"
+coverImage: "web-sso.webp"
tags: ["web sso","mfa","data security"]
author: "Vaibhav Jain"
description: " Web SSO is a part of Single Sign-On that brings everything together. Each consumer has one account and one set of credentials that they can use anywhere to interact with your brand. Failing to use SSO will make your consumers notice you in a bad light as they try to navigate your apps and services."
@@ -150,4 +150,4 @@ However, before implementing any functionality on your website, analyze and cons
Cheers!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-web-sso)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-web-sso)
\ No newline at end of file
diff --git a/content/identity/what-is-web-sso/web-sso.jpg b/content/identity/what-is-web-sso/web-sso.jpg
deleted file mode 100644
index 166794f8c..000000000
Binary files a/content/identity/what-is-web-sso/web-sso.jpg and /dev/null differ
diff --git a/content/identity/what-is-web-sso/web-sso.webp b/content/identity/what-is-web-sso/web-sso.webp
new file mode 100644
index 000000000..cd0a8f389
Binary files /dev/null and b/content/identity/what-is-web-sso/web-sso.webp differ
diff --git a/content/identity/what-is-web-sso/what-is-web-sso.png b/content/identity/what-is-web-sso/what-is-web-sso.png
deleted file mode 100644
index 3182d19a5..000000000
Binary files a/content/identity/what-is-web-sso/what-is-web-sso.png and /dev/null differ
diff --git a/content/identity/what-is-web-sso/what-is-web-sso.webp b/content/identity/what-is-web-sso/what-is-web-sso.webp
new file mode 100644
index 000000000..6ede931ee
Binary files /dev/null and b/content/identity/what-is-web-sso/what-is-web-sso.webp differ
diff --git a/content/identity/what-is-workflow-automation/index.md b/content/identity/what-is-workflow-automation/index.md
index 2427921e1..3ad06ef22 100644
--- a/content/identity/what-is-workflow-automation/index.md
+++ b/content/identity/what-is-workflow-automation/index.md
@@ -1,7 +1,7 @@
---
title: "Workflow Automation- What is it and Why Do You Need It?"
date: "2021-04-14"
-coverImage: "what-is-workflow-automation-cover.jpg"
+coverImage: "what-is-workflow-automation-cover.webp"
tags: ["workflow automation","scalability","cx"]
author: "Navanita Devi"
description: "Workflow automation refers to the process of automating a set of manual processes or tasks based on a set of pre-defined rules or conditions. It helps you reduce the use of resources and time, more importantly, the chances of human-made errors. As a result, it improves a business’s overall efficiency, audibility, and accountability."
@@ -106,4 +106,4 @@ Even though you can fully control the logical flows, it requires large resources
Small and medium enterprises around the globe are expected to adopt business workflow automation on a large scale, creating a market of opportunity of US$ 1,600 million between 2017 and 2026. With its excellent built-in automation tools and solutions, multipurpose workflow software such as LoginRadius can help you meet your business goals by increasing efficiency, productivity, and other success factors.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-workflow-automation)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-workflow-automation)
diff --git a/content/identity/what-is-workflow-automation/what-is-workflow-automation-cover.jpg b/content/identity/what-is-workflow-automation/what-is-workflow-automation-cover.jpg
deleted file mode 100644
index a3d9af508..000000000
Binary files a/content/identity/what-is-workflow-automation/what-is-workflow-automation-cover.jpg and /dev/null differ
diff --git a/content/identity/what-is-workflow-automation/what-is-workflow-automation-cover.webp b/content/identity/what-is-workflow-automation/what-is-workflow-automation-cover.webp
new file mode 100644
index 000000000..5ed23dfe9
Binary files /dev/null and b/content/identity/what-is-workflow-automation/what-is-workflow-automation-cover.webp differ
diff --git a/content/identity/what-to-do-when-email-hacked/Multi-Factor-Authentication.png b/content/identity/what-to-do-when-email-hacked/Multi-Factor-Authentication.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/what-to-do-when-email-hacked/Multi-Factor-Authentication.png and /dev/null differ
diff --git a/content/identity/what-to-do-when-email-hacked/Multi-Factor-Authentication.webp b/content/identity/what-to-do-when-email-hacked/Multi-Factor-Authentication.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/what-to-do-when-email-hacked/Multi-Factor-Authentication.webp differ
diff --git a/content/identity/what-to-do-when-email-hacked/index.md b/content/identity/what-to-do-when-email-hacked/index.md
index 745d02996..a5f27062e 100644
--- a/content/identity/what-to-do-when-email-hacked/index.md
+++ b/content/identity/what-to-do-when-email-hacked/index.md
@@ -1,7 +1,7 @@
---
title: "Email is Hacked!: 7 Immediate Steps To Follow"
date: "2020-12-03"
-coverImage: "what-to-do-when-email-is-hacked.jpg"
+coverImage: "what-to-do-when-email-is-hacked.webp"
tags: ["security"]
featured: false
author: "Rakesh Soni"
@@ -70,7 +70,7 @@ You are more likely to open it and click on links inside it when an email comes
Let the people in your contact list know that your email has been compromised and that any suspicious emails should not be opened or connected to any emails you have recently got.
-[](
+[](
https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
@@ -98,4 +98,4 @@ In addition to your password, set your email account to require a [second form o
As an additional security measure, several email providers provide two-factor authentication (2FA). To access an account, this approach requires both a password and some other form of identification.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-to-do-when-email-hacked)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-to-do-when-email-hacked)
diff --git a/content/identity/what-to-do-when-email-hacked/what-to-do-when-email-is-hacked.jpg b/content/identity/what-to-do-when-email-hacked/what-to-do-when-email-is-hacked.jpg
deleted file mode 100644
index bf3f2ea2b..000000000
Binary files a/content/identity/what-to-do-when-email-hacked/what-to-do-when-email-is-hacked.jpg and /dev/null differ
diff --git a/content/identity/what-to-do-when-email-hacked/what-to-do-when-email-is-hacked.webp b/content/identity/what-to-do-when-email-hacked/what-to-do-when-email-is-hacked.webp
new file mode 100644
index 000000000..39473b0fb
Binary files /dev/null and b/content/identity/what-to-do-when-email-hacked/what-to-do-when-email-is-hacked.webp differ
diff --git a/content/identity/why-business-needs-robust-identity-authentication/DS-privacy.png b/content/identity/why-business-needs-robust-identity-authentication/DS-privacy.png
deleted file mode 100644
index 67c1c093f..000000000
Binary files a/content/identity/why-business-needs-robust-identity-authentication/DS-privacy.png and /dev/null differ
diff --git a/content/identity/why-business-needs-robust-identity-authentication/DS-privacy.webp b/content/identity/why-business-needs-robust-identity-authentication/DS-privacy.webp
new file mode 100644
index 000000000..42c0492a7
Binary files /dev/null and b/content/identity/why-business-needs-robust-identity-authentication/DS-privacy.webp differ
diff --git a/content/identity/why-business-needs-robust-identity-authentication/id-auth.jpg b/content/identity/why-business-needs-robust-identity-authentication/id-auth.jpg
deleted file mode 100644
index 20a5a45d4..000000000
Binary files a/content/identity/why-business-needs-robust-identity-authentication/id-auth.jpg and /dev/null differ
diff --git a/content/identity/why-business-needs-robust-identity-authentication/id-auth.webp b/content/identity/why-business-needs-robust-identity-authentication/id-auth.webp
new file mode 100644
index 000000000..9273063e2
Binary files /dev/null and b/content/identity/why-business-needs-robust-identity-authentication/id-auth.webp differ
diff --git a/content/identity/why-business-needs-robust-identity-authentication/identity-authentication.jpg b/content/identity/why-business-needs-robust-identity-authentication/identity-authentication.jpg
deleted file mode 100644
index 72b52afb2..000000000
Binary files a/content/identity/why-business-needs-robust-identity-authentication/identity-authentication.jpg and /dev/null differ
diff --git a/content/identity/why-business-needs-robust-identity-authentication/identity-authentication.webp b/content/identity/why-business-needs-robust-identity-authentication/identity-authentication.webp
new file mode 100644
index 000000000..e60497d86
Binary files /dev/null and b/content/identity/why-business-needs-robust-identity-authentication/identity-authentication.webp differ
diff --git a/content/identity/why-business-needs-robust-identity-authentication/index.md b/content/identity/why-business-needs-robust-identity-authentication/index.md
index 8df3301b1..e6ae15bf0 100644
--- a/content/identity/why-business-needs-robust-identity-authentication/index.md
+++ b/content/identity/why-business-needs-robust-identity-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "5 Reasons Why You Need to Strengthen Your Identity Authentication"
date: "2022-04-20"
-coverImage: "identity-authentication.jpg"
+coverImage: "identity-authentication.webp"
tags: ["identity authentication","compliance","cx"]
author: "Rakesh Soni"
description: "A weak line of defense and poor authentication mechanism at the service providers’ could tarnish a brand's reputation in the global markets and eventually entitle the organization to pay hefty fines. Read on to know more about identity authentication and how it paves the path for businesses embarking on a digital transformation journey."
@@ -42,7 +42,7 @@ Since it protects consumers’ privacy and eventually improves brand value, and
Businesses that don’t implement the privacy regulations could be fined up to millions of dollars and face penalties for years.
-[](https://www.loginradius.com/resource/privacy-policy-management-datasheet)
+[](https://www.loginradius.com/resource/privacy-policy-management-datasheet)
### 3. Developers face identity authentication-related issues while collecting user information
@@ -81,4 +81,4 @@ Through a robust CIAM solution, identity management has endless business advanta
Therefore, enterprises shouldn’t delay their identity management decisions and put their best efforts into incorporating a reliable CIAM to strengthen their identity authentication.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-business-needs-robust-identity-authentication)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-business-needs-robust-identity-authentication)
diff --git a/content/identity/why-business-needs-robust-identity-authentication/privacy-versioning.png b/content/identity/why-business-needs-robust-identity-authentication/privacy-versioning.png
deleted file mode 100644
index e738ae27a..000000000
Binary files a/content/identity/why-business-needs-robust-identity-authentication/privacy-versioning.png and /dev/null differ
diff --git a/content/identity/why-business-needs-robust-identity-authentication/privacy-versioning.webp b/content/identity/why-business-needs-robust-identity-authentication/privacy-versioning.webp
new file mode 100644
index 000000000..eb8ed83dc
Binary files /dev/null and b/content/identity/why-business-needs-robust-identity-authentication/privacy-versioning.webp differ
diff --git a/content/identity/why-multi-factor-authentication-imp-sso/EB-GD-to-MFA.png b/content/identity/why-multi-factor-authentication-imp-sso/EB-GD-to-MFA.png
deleted file mode 100644
index 61deb3295..000000000
Binary files a/content/identity/why-multi-factor-authentication-imp-sso/EB-GD-to-MFA.png and /dev/null differ
diff --git a/content/identity/why-multi-factor-authentication-imp-sso/EB-GD-to-MFA.webp b/content/identity/why-multi-factor-authentication-imp-sso/EB-GD-to-MFA.webp
new file mode 100644
index 000000000..00c5933a4
Binary files /dev/null and b/content/identity/why-multi-factor-authentication-imp-sso/EB-GD-to-MFA.webp differ
diff --git a/content/identity/why-multi-factor-authentication-imp-sso/index.md b/content/identity/why-multi-factor-authentication-imp-sso/index.md
index 552cdb818..cb5a15119 100644
--- a/content/identity/why-multi-factor-authentication-imp-sso/index.md
+++ b/content/identity/why-multi-factor-authentication-imp-sso/index.md
@@ -1,7 +1,7 @@
---
title: "Importance of Multi-factor Authentication for SSO"
date: "2022-02-08"
-coverImage: "mfa-sso.jpg"
+coverImage: "mfa-sso.webp"
tags: ["data security","mfa","sso","authentication","cx"]
author: "Conrad Sturdy"
description: "Multi-factor authentication (MFA) is an essential layer of security that’s becoming standard in enterprise SSO deployments. While it’s not a silver bullet, it’s likely the last line of defense in most situations, so its importance shouldn’t be overlooked. Here’s an insightful read depicting the aspects of SSO authentication and MFA."
@@ -27,7 +27,7 @@ The strengths and weaknesses of multi-factor authentication are generally known.
Password protection is popular but not ideal, so businesses have to use additional tools. SSO is a powerful and effective tool for simplifying employee access to personal websites and applications.
-**Also download**: [](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
+**Also download**: [](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/)
## What is the Authentication Process and Single Sign-On (SSO)?
@@ -145,4 +145,4 @@ Multi-Factor Authentication (MFA) is broader and requires two or more factors fo
Two-Factor Authentication (2FA) adds an extra layer of security to logins, requiring users to provide two types of credentials for verification.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-multi-factor-authentication-imp-sso)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-multi-factor-authentication-imp-sso)
\ No newline at end of file
diff --git a/content/identity/why-multi-factor-authentication-imp-sso/mfa-guide.png b/content/identity/why-multi-factor-authentication-imp-sso/mfa-guide.png
deleted file mode 100644
index 9de9444df..000000000
Binary files a/content/identity/why-multi-factor-authentication-imp-sso/mfa-guide.png and /dev/null differ
diff --git a/content/identity/why-multi-factor-authentication-imp-sso/mfa-guide.webp b/content/identity/why-multi-factor-authentication-imp-sso/mfa-guide.webp
new file mode 100644
index 000000000..3f25bb5dc
Binary files /dev/null and b/content/identity/why-multi-factor-authentication-imp-sso/mfa-guide.webp differ
diff --git a/content/identity/why-multi-factor-authentication-imp-sso/mfa-sso.jpg b/content/identity/why-multi-factor-authentication-imp-sso/mfa-sso.jpg
deleted file mode 100644
index aeae55194..000000000
Binary files a/content/identity/why-multi-factor-authentication-imp-sso/mfa-sso.jpg and /dev/null differ
diff --git a/content/identity/why-multi-factor-authentication-imp-sso/mfa-sso.webp b/content/identity/why-multi-factor-authentication-imp-sso/mfa-sso.webp
new file mode 100644
index 000000000..878c48958
Binary files /dev/null and b/content/identity/why-multi-factor-authentication-imp-sso/mfa-sso.webp differ
diff --git a/content/identity/worst-passwords-list-2019/CTA-book-demo-password-1024x310.png b/content/identity/worst-passwords-list-2019/CTA-book-demo-password-1024x310.png
deleted file mode 100644
index e93d16b6f..000000000
Binary files a/content/identity/worst-passwords-list-2019/CTA-book-demo-password-1024x310.png and /dev/null differ
diff --git a/content/identity/worst-passwords-list-2019/CTA-book-demo-password-1024x310.webp b/content/identity/worst-passwords-list-2019/CTA-book-demo-password-1024x310.webp
new file mode 100644
index 000000000..fddd55c38
Binary files /dev/null and b/content/identity/worst-passwords-list-2019/CTA-book-demo-password-1024x310.webp differ
diff --git a/content/identity/worst-passwords-list-2019/credential-stuffing.png b/content/identity/worst-passwords-list-2019/credential-stuffing.png
deleted file mode 100644
index 904e3a28e..000000000
Binary files a/content/identity/worst-passwords-list-2019/credential-stuffing.png and /dev/null differ
diff --git a/content/identity/worst-passwords-list-2019/credential-stuffing.webp b/content/identity/worst-passwords-list-2019/credential-stuffing.webp
new file mode 100644
index 000000000..c2d6821c3
Binary files /dev/null and b/content/identity/worst-passwords-list-2019/credential-stuffing.webp differ
diff --git a/content/identity/worst-passwords-list-2019/image2.jpg b/content/identity/worst-passwords-list-2019/image2.jpg
deleted file mode 100644
index 8741e691e..000000000
Binary files a/content/identity/worst-passwords-list-2019/image2.jpg and /dev/null differ
diff --git a/content/identity/worst-passwords-list-2019/image2.webp b/content/identity/worst-passwords-list-2019/image2.webp
new file mode 100644
index 000000000..d373b3967
Binary files /dev/null and b/content/identity/worst-passwords-list-2019/image2.webp differ
diff --git a/content/identity/worst-passwords-list-2019/index.md b/content/identity/worst-passwords-list-2019/index.md
index 63f00bca7..d6381c3f4 100644
--- a/content/identity/worst-passwords-list-2019/index.md
+++ b/content/identity/worst-passwords-list-2019/index.md
@@ -1,7 +1,7 @@
---
title: "The Worst Passwords of 2019"
date: "2019-12-23"
-coverImage: "worst-psswrd-list.jpg"
+coverImage: "worst-psswrd-list.webp"
tags: ["passwordless login","password management","data security"]
author: "Rakesh Soni"
description: "Overall, a major challenge for corporations is poor passwords combined with smart hackers. You need cybersecurity that prevents access to your confidential data to protect your business from expensive hacks and breaches. Choose a globally-certified CIAM solution like LoginRadius for state-of-the-art safety and increased customer experience."
@@ -27,7 +27,7 @@ For example, passwords like zinch and g\_czechout may seem harder to crack, yet
You’ll also see popular female names like Jasmine or Jennifer. Another tactic is using a string of letters that forms a pattern or a line on the keyboard. Popular examples include asdfghjkl and 1qaz2wsx.
-[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
+[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper)
Here they all are in top ranking order.
@@ -95,7 +95,7 @@ Unfortunately, many don't. The biggest reason is that remembering multiple passw
Another flawed approach is that people may think their information is insignificant, so they assume that no hacker would care about them. However, a ransomware attack can lock users out of their accounts and become quite costly.
-
+
## How can you improve password security?
@@ -111,4 +111,4 @@ A CIAM solution also saves resources. Your support and development teams can dev
Overall, bad passwords coupled with smart hackers are a big problem for businesses. To protect your company from costly hacks and breaches, you need cybersecurity that prevents access to your sensitive data. For state-of-the-art cybersecurity and enhanced customer experience, choose a globally-certified CIAM solution like LoginRadius.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=worst-passwords-list-2019)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=worst-passwords-list-2019)
diff --git a/content/identity/worst-passwords-list-2019/worst-passwords-list-2019.jpg b/content/identity/worst-passwords-list-2019/worst-passwords-list-2019.jpg
deleted file mode 100644
index 3890a2ed5..000000000
Binary files a/content/identity/worst-passwords-list-2019/worst-passwords-list-2019.jpg and /dev/null differ
diff --git a/content/identity/worst-passwords-list-2019/worst-passwords-list-2019.webp b/content/identity/worst-passwords-list-2019/worst-passwords-list-2019.webp
new file mode 100644
index 000000000..756d5ae22
Binary files /dev/null and b/content/identity/worst-passwords-list-2019/worst-passwords-list-2019.webp differ
diff --git a/content/identity/worst-passwords-list-2019/worst-psswrd-list.jpg b/content/identity/worst-passwords-list-2019/worst-psswrd-list.jpg
deleted file mode 100644
index 21e8b0dee..000000000
Binary files a/content/identity/worst-passwords-list-2019/worst-psswrd-list.jpg and /dev/null differ
diff --git a/content/identity/worst-passwords-list-2019/worst-psswrd-list.webp b/content/identity/worst-passwords-list-2019/worst-psswrd-list.webp
new file mode 100644
index 000000000..ecca06b65
Binary files /dev/null and b/content/identity/worst-passwords-list-2019/worst-psswrd-list.webp differ
diff --git a/content/identity/year-of-ciam-innovations-with-loginradius/background-red-3d-podium-with-mobile-screen-mockup-megaphone.jpg b/content/identity/year-of-ciam-innovations-with-loginradius/background-red-3d-podium-with-mobile-screen-mockup-megaphone.jpg
deleted file mode 100644
index 1cf9c584d..000000000
Binary files a/content/identity/year-of-ciam-innovations-with-loginradius/background-red-3d-podium-with-mobile-screen-mockup-megaphone.jpg and /dev/null differ
diff --git a/content/identity/year-of-ciam-innovations-with-loginradius/background-red-3d-podium-with-mobile-screen-mockup-megaphone.webp b/content/identity/year-of-ciam-innovations-with-loginradius/background-red-3d-podium-with-mobile-screen-mockup-megaphone.webp
new file mode 100644
index 000000000..cf29fef2e
Binary files /dev/null and b/content/identity/year-of-ciam-innovations-with-loginradius/background-red-3d-podium-with-mobile-screen-mockup-megaphone.webp differ
diff --git a/content/identity/year-of-ciam-innovations-with-loginradius/cta.png b/content/identity/year-of-ciam-innovations-with-loginradius/cta.png
deleted file mode 100644
index 787b952b6..000000000
Binary files a/content/identity/year-of-ciam-innovations-with-loginradius/cta.png and /dev/null differ
diff --git a/content/identity/year-of-ciam-innovations-with-loginradius/cta.webp b/content/identity/year-of-ciam-innovations-with-loginradius/cta.webp
new file mode 100644
index 000000000..89f7a725f
Binary files /dev/null and b/content/identity/year-of-ciam-innovations-with-loginradius/cta.webp differ
diff --git a/content/identity/year-of-ciam-innovations-with-loginradius/index.md b/content/identity/year-of-ciam-innovations-with-loginradius/index.md
index 317acbdd3..493375602 100644
--- a/content/identity/year-of-ciam-innovations-with-loginradius/index.md
+++ b/content/identity/year-of-ciam-innovations-with-loginradius/index.md
@@ -2,7 +2,7 @@
title: "LoginRadius 2024: A Year of CIAM Innovations"
description: "LoginRadius wraps up 2024 with transformative CIAM innovations for developers. From Identity Orchestration and Multi-Brand Configuration to Passkeys and a new Admin Console, explore tools designed to simplify workflows and enhance security."
date: "2024-12-31"
-coverImage: "background-red-3d-podium-with-mobile-screen-mockup-megaphone.jpg"
+coverImage: "background-red-3d-podium-with-mobile-screen-mockup-megaphone.webp"
author: "Rakesh Soni"
tags: ["CIAM Innovation","digital identity transformation", "ciam management", "ciam security", "ciam technology", "ciam integration"]
metatitle: "LoginRadius 2024: A Year of CIAM Innovations"
@@ -32,7 +32,7 @@ Key Highlights:
- Advanced Analytics: Gain actionable insights into journey performance and optimize based on real-time data.
-[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
+[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/)
### 2. Multi-Brand Configuration: Tailored Experiences for Every Brand
diff --git a/content/identity/zero-party-data-experience/WP-consumer-identity-theft.png b/content/identity/zero-party-data-experience/WP-consumer-identity-theft.png
deleted file mode 100644
index 25b3b0075..000000000
Binary files a/content/identity/zero-party-data-experience/WP-consumer-identity-theft.png and /dev/null differ
diff --git a/content/identity/zero-party-data-experience/WP-consumer-identity-theft.webp b/content/identity/zero-party-data-experience/WP-consumer-identity-theft.webp
new file mode 100644
index 000000000..3d62deb02
Binary files /dev/null and b/content/identity/zero-party-data-experience/WP-consumer-identity-theft.webp differ
diff --git a/content/identity/zero-party-data-experience/future-of-personalization.jpg b/content/identity/zero-party-data-experience/future-of-personalization.jpg
deleted file mode 100644
index 8c6f43495..000000000
Binary files a/content/identity/zero-party-data-experience/future-of-personalization.jpg and /dev/null differ
diff --git a/content/identity/zero-party-data-experience/future-of-personalization.webp b/content/identity/zero-party-data-experience/future-of-personalization.webp
new file mode 100644
index 000000000..bf3f8234e
Binary files /dev/null and b/content/identity/zero-party-data-experience/future-of-personalization.webp differ
diff --git a/content/identity/zero-party-data-experience/index.md b/content/identity/zero-party-data-experience/index.md
index 6f24fa0ac..766370fbd 100644
--- a/content/identity/zero-party-data-experience/index.md
+++ b/content/identity/zero-party-data-experience/index.md
@@ -1,7 +1,7 @@
---
title: "The Future of Personalization: Embracing Zero-Party Data"
date: "2023-10-10"
-coverImage: "future-of-personalization.jpg"
+coverImage: "future-of-personalization.webp"
tags: ["zero-trust security","cybersecurity","ciam solution","cx"]
author: "Rakesh Soni"
description: "Unlock the secrets behind seamless online personalization with Zero-Party Data! This blog explores how your willingly shared preferences revolutionize digital experiences. From tailored shopping to personalized content, discover the magic of Zero-Party Data and embrace a future where your online adventures are truly yours."
@@ -44,7 +44,7 @@ Zero-Party Data isn't limited to product recommendations; it's transforming how
One of the most remarkable aspects of Zero-Party Data is the trust it builds between businesses and consumers. When companies respect your data privacy and use the information you provide responsibly, it fosters a sense of loyalty.
-[](https://www.loginradius.com/resource/ciam-role-in-customer-trust/)
+[](https://www.loginradius.com/resource/ciam-role-in-customer-trust/)
Imagine receiving a survey from your favorite streaming service asking about your favorite genres. You willingly share your preferences; in return, they recommend movies and shows tailored to your taste. It's a win-win situation that leaves everyone smiling.
@@ -58,4 +58,4 @@ As we venture into the digital age, embracing Zero-Party Data is the way forward
In a nutshell, Zero-Party Data is revolutionizing personalization, making your online adventures more enjoyable and meaningful. So, go ahead, share your preferences, and get ready to be amazed by the tailored experiences that await you.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=zero-party-data-experience)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=zero-party-data-experience)
\ No newline at end of file
diff --git a/content/identity/zero-trust-bulletproof-security-policy/WP-zero-trust-2.png b/content/identity/zero-trust-bulletproof-security-policy/WP-zero-trust-2.png
deleted file mode 100644
index 469a5bd53..000000000
Binary files a/content/identity/zero-trust-bulletproof-security-policy/WP-zero-trust-2.png and /dev/null differ
diff --git a/content/identity/zero-trust-bulletproof-security-policy/WP-zero-trust-2.webp b/content/identity/zero-trust-bulletproof-security-policy/WP-zero-trust-2.webp
new file mode 100644
index 000000000..ab094444e
Binary files /dev/null and b/content/identity/zero-trust-bulletproof-security-policy/WP-zero-trust-2.webp differ
diff --git a/content/identity/zero-trust-bulletproof-security-policy/index.md b/content/identity/zero-trust-bulletproof-security-policy/index.md
index fceda2168..1519cece5 100644
--- a/content/identity/zero-trust-bulletproof-security-policy/index.md
+++ b/content/identity/zero-trust-bulletproof-security-policy/index.md
@@ -1,7 +1,7 @@
---
title: "Implementing Zero Trust? Make Sure You're Doing It Correctly"
date: "2022-08-23"
-coverImage: "zt-1.jpg"
+coverImage: "zt-1.webp"
tags: ["zero trust", "MFA", "ciam solution", "cx"]
author: "Rakesh Soni"
description: "Though zero trust architecture may be potent for reinforcing overall security, chances of sneaking and security breaches aren’t always zero. If not implemented correctly, zero trust could lead to various security and user experience issues and hampers overall business growth."
@@ -30,7 +30,7 @@ Implementing a zero-trust architecture in today’s era is crucial since cybercr
Hence, it’s crucial for organizations to think outside the box and not just rely on conventional security mechanisms, including [multi-factor authentication](https://www.loginradius.com/multi-factor-authentication/). Zero trust architecture has become the new normal.
-[](https://www.loginradius.com/resource/zero-trust-security/)
+[](https://www.loginradius.com/resource/zero-trust-security/)
## Consequences of Poor Implementation of Zero Trust Architecture
@@ -64,4 +64,4 @@ Zero trust architecture is undeniably helping brands reinforce their overall sec
A reliable customer identity and access management (CIAM) could help businesses integrate zero trust architecture across their platform seamlessly. It offers complete transparency reinforced with stringent security and a great user experience.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=zero-trust-bulletproof-security-policy)
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=zero-trust-bulletproof-security-policy)
diff --git a/content/identity/zero-trust-bulletproof-security-policy/zt-1.jpg b/content/identity/zero-trust-bulletproof-security-policy/zt-1.jpg
deleted file mode 100644
index f549c534f..000000000
Binary files a/content/identity/zero-trust-bulletproof-security-policy/zt-1.jpg and /dev/null differ
diff --git a/content/identity/zero-trust-bulletproof-security-policy/zt-1.webp b/content/identity/zero-trust-bulletproof-security-policy/zt-1.webp
new file mode 100644
index 000000000..3f181e198
Binary files /dev/null and b/content/identity/zero-trust-bulletproof-security-policy/zt-1.webp differ
diff --git a/content/identity/zero-trust-bulletproof-security-policy/zt-part2.png b/content/identity/zero-trust-bulletproof-security-policy/zt-part2.png
deleted file mode 100644
index 634e632fb..000000000
Binary files a/content/identity/zero-trust-bulletproof-security-policy/zt-part2.png and /dev/null differ
diff --git a/content/identity/zero-trust-bulletproof-security-policy/zt-part2.webp b/content/identity/zero-trust-bulletproof-security-policy/zt-part2.webp
new file mode 100644
index 000000000..2cd0217f3
Binary files /dev/null and b/content/identity/zero-trust-bulletproof-security-policy/zt-part2.webp differ
diff --git a/content/identity/zero-trust-cybersecurity-government-sector/WP-zero-trust-security-2.png b/content/identity/zero-trust-cybersecurity-government-sector/WP-zero-trust-security-2.png
deleted file mode 100644
index 469a5bd53..000000000
Binary files a/content/identity/zero-trust-cybersecurity-government-sector/WP-zero-trust-security-2.png and /dev/null differ
diff --git a/content/identity/zero-trust-cybersecurity-government-sector/WP-zero-trust-security-2.webp b/content/identity/zero-trust-cybersecurity-government-sector/WP-zero-trust-security-2.webp
new file mode 100644
index 000000000..ab094444e
Binary files /dev/null and b/content/identity/zero-trust-cybersecurity-government-sector/WP-zero-trust-security-2.webp differ
diff --git a/content/identity/zero-trust-cybersecurity-government-sector/govt-sector.jpg b/content/identity/zero-trust-cybersecurity-government-sector/govt-sector.jpg
deleted file mode 100644
index 6dc1c9a4f..000000000
Binary files a/content/identity/zero-trust-cybersecurity-government-sector/govt-sector.jpg and /dev/null differ
diff --git a/content/identity/zero-trust-cybersecurity-government-sector/govt-sector.webp b/content/identity/zero-trust-cybersecurity-government-sector/govt-sector.webp
new file mode 100644
index 000000000..e5b229512
Binary files /dev/null and b/content/identity/zero-trust-cybersecurity-government-sector/govt-sector.webp differ
diff --git a/content/identity/zero-trust-cybersecurity-government-sector/index.md b/content/identity/zero-trust-cybersecurity-government-sector/index.md
index a7fdf434d..60e339b10 100644
--- a/content/identity/zero-trust-cybersecurity-government-sector/index.md
+++ b/content/identity/zero-trust-cybersecurity-government-sector/index.md
@@ -1,7 +1,7 @@
---
title: "Decoding the Rise of Zero-Trust Adoption in Government Sector"
date: "2024-06-24"
-coverImage: "govt-sector.jpg"
+coverImage: "govt-sector.webp"
tags: ["zero-trust security","cybersecurity","data security"]
author: "Kundan Singh"
description: "As cyber threats become increasingly sophisticated, government sectors turn to Zero-Trust architecture to revolutionize their cybersecurity measures. This strategy is crucial for safeguarding sensitive information and maintaining national security."
@@ -56,7 +56,7 @@ Implementing Zero-Trust architecture in government sectors offers numerous benef
* **Improved Visibility**: Zero-Trust provides comprehensive visibility into network traffic, user activity, and device behavior, enabling faster detection and response to threats.
-[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-business-2/)
+[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-business-2/)
* **Reduced Attack Surface**: Micro-segmentation and least privilege access reduce the potential impact of a breach by limiting the reach of attackers within the network.
@@ -90,4 +90,4 @@ By embracing Zero-Trust, government agencies can better protect sensitive data,
Zero trust is not just a trend but a necessary evolution in the ongoing battle against cyber threats. The journey towards full Zero-Trust implementation may be challenging, but the benefits far outweigh the obstacles, paving the way for a more secure and resilient government infrastructure.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=zero-trust-cybersecurity-government-sector)
\ No newline at end of file
+[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=zero-trust-cybersecurity-government-sector)
\ No newline at end of file
diff --git a/gatsby-config.js b/gatsby-config.js
index 358a8eb4c..7616e962b 100644
--- a/gatsby-config.js
+++ b/gatsby-config.js
@@ -5,7 +5,7 @@ module.exports = {
description: "Company Updates, Technology Articles from LoginRadius",
siteUrl: "https://www.loginradius.com",
feedUrl: "https://www.loginradius.com/blog",
- image: "/async.svg",
+ image: "/async.webp",
owner: "LoginRadius",
footerLinks: [
{
@@ -129,7 +129,7 @@ module.exports = {
background_color: `#ffffff`,
theme_color: `#663399`,
display: `minimal-ui`,
- icon: `content/assets/lr-icon.png`,
+ icon: `content/assets/lr-icon.webp`,
},
},
`gatsby-plugin-react-helmet`,
diff --git a/src/components/card.js b/src/components/card.js
index 2032ebd56..8343de477 100644
--- a/src/components/card.js
+++ b/src/components/card.js
@@ -2,7 +2,7 @@ import React from "react"
import styles from "./cardlist.module.scss"
import { Link } from "gatsby"
import Bio from "./bio"
-import defaultImg from "../../content/assets/default-blog.jpg"
+import defaultImg from "../../content/assets/default-blog.webp"
// Utilities
import kebabCase from "lodash/kebabCase"
diff --git a/src/components/cardList.js b/src/components/cardList.js
index b47f362d0..d8e2195c7 100644
--- a/src/components/cardList.js
+++ b/src/components/cardList.js
@@ -3,7 +3,7 @@ import styles from "./cardlist.module.scss"
import Card from "./card"
import Subscribe from "./subscribe"
import headStyles from "./cardlist.module.scss"
-//import Docs from "../../static/consumer-digital-identity-trends-2023.jpg"
+//import Docs from "../../static/consumer-digital-identity-trends-2023.webp"
import AsyncTagMenu from "./tagmenu/async"
import IdentityTagMenu from "./tagmenu/identity"
import { Link, withPrefix } from "gatsby"
@@ -112,7 +112,7 @@ export default function CardList({ posts, currentPage, type }) {
>
Write for us
@@ -163,7 +163,7 @@ export default function CardList({ posts, currentPage, type }) {
>
LoginRadius Open Source
diff --git a/src/components/footer.js b/src/components/footer.js
index a66dedfdc..2d45a17f8 100644
--- a/src/components/footer.js
+++ b/src/components/footer.js
@@ -2,7 +2,7 @@ import React from "react"
import styles from "./footer.module.scss"
-import LogoLr from "../../static/logo.svg"
+import LogoLr from "../../static/logo.webp"
import Modal from "./modal"
const Footer = ({ menuLinks, socialLinks, postPage }) => {
return (
@@ -302,7 +302,7 @@ const Footer = ({ menuLinks, socialLinks, postPage }) => {
rel="noopener noreferrer"
>
}) {
{
 +
+ 
 +
+ 
 +
+ 
| Feature + | +JWT (General) + | +JWS (Signed JWT) + | +JWE (Encrypted JWT) + | +
| Security Focus + | +Token Format + | +Integrity, authenticity + | +Confidentiality + integrity + | +
| Payload + | +Not specified + | +Base64URL encoded (readable) + | +Encrypted (not readable) + | +
| Signature + | +Optional + | +Required + | +Encrypted along with payload + | +
| Encryption + | +Optional + | +Not encrypted + | +Fully encrypted + | +
| Use Case + | +ID and Access Tokens + | +OAuth 2.0, OpenID Connect + | +Highly sensitive information + | +
Implement the script in your html file
@@ -30,7 +30,7 @@ api_key: your_api_key_goes_here You can find your API key inside your application, the first entry under OAuth Keys "Consumer Key / API Key." This script is used to load the LinkedIn script into your website, and it will not display anything on your page, at least not the frontend. - + Next, you will need to add another script inside your body tag. It is actually used to display the sign-in button. @@ -42,6 +42,6 @@ Hello, ; . If everything has been implemented correctly, load your page, and you will see this lovely button appear on your site. - + Want to extend your social systems with additional provider functionality? Check out this post on [Twitter social login](https://www.loginradius.com/blog/engineering/integrating-twitter-social-login/ "Integrating Twitter Social Login"). diff --git a/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.png b/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.png deleted file mode 100644 index f0bff849b..000000000 Binary files a/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.png and /dev/null differ diff --git a/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.webp b/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.webp new file mode 100644 index 000000000..11b23ddc1 Binary files /dev/null and b/content/engineering/integrate-linkedin-social-login-website/linkedin-feat-img.webp differ diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.png b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.png deleted file mode 100644 index ad581eb43..000000000 Binary files a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.png and /dev/null differ diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.webp b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.webp new file mode 100644 index 000000000..f877ae1a3 Binary files /dev/null and b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-1.webp differ diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.png b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.png deleted file mode 100644 index 9e02353c7..000000000 Binary files a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.png and /dev/null differ diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.webp b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.webp new file mode 100644 index 000000000..04d28a83b Binary files /dev/null and b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-2.webp differ diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.png b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.png deleted file mode 100644 index a2815f4d5..000000000 Binary files a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.png and /dev/null differ diff --git a/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.webp b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.webp new file mode 100644 index 000000000..1a7923c6e Binary files /dev/null and b/content/engineering/integrate-linkedin-social-login-website/luciusblog2-3.webp differ diff --git a/content/engineering/intro-curl-fsockopen/fsock-and-curl.png b/content/engineering/intro-curl-fsockopen/fsock-and-curl.png deleted file mode 100644 index 1a83a41a5..000000000 Binary files a/content/engineering/intro-curl-fsockopen/fsock-and-curl.png and /dev/null differ diff --git a/content/engineering/intro-curl-fsockopen/fsock-and-curl.webp b/content/engineering/intro-curl-fsockopen/fsock-and-curl.webp new file mode 100644 index 000000000..e1f574844 Binary files /dev/null and b/content/engineering/intro-curl-fsockopen/fsock-and-curl.webp differ diff --git a/content/engineering/intro-curl-fsockopen/index.md b/content/engineering/intro-curl-fsockopen/index.md index cc3ad1aab..802a4c55d 100644 --- a/content/engineering/intro-curl-fsockopen/index.md +++ b/content/engineering/intro-curl-fsockopen/index.md @@ -1,7 +1,7 @@ --- title: "An Intro to Curl & Fsockopen" date: "2015-03-09" -coverImage: "fsock-and-curl.png" +coverImage: "fsock-and-curl.webp" author: "Zoie Carnegie" tags: ["curl", "Fsock"] --- diff --git a/content/engineering/introducing-loginradius-cli/api-cred.png b/content/engineering/introducing-loginradius-cli/api-cred.png deleted file mode 100644 index bc88c1ce8..000000000 Binary files a/content/engineering/introducing-loginradius-cli/api-cred.png and /dev/null differ diff --git a/content/engineering/introducing-loginradius-cli/api-cred.webp b/content/engineering/introducing-loginradius-cli/api-cred.webp new file mode 100644 index 000000000..55f27194d Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/api-cred.webp differ diff --git a/content/engineering/introducing-loginradius-cli/cli.png b/content/engineering/introducing-loginradius-cli/cli.png deleted file mode 100644 index 949819b0b..000000000 Binary files a/content/engineering/introducing-loginradius-cli/cli.png and /dev/null differ diff --git a/content/engineering/introducing-loginradius-cli/cli.webp b/content/engineering/introducing-loginradius-cli/cli.webp new file mode 100644 index 000000000..8123de361 Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/cli.webp differ diff --git a/content/engineering/introducing-loginradius-cli/domain.png b/content/engineering/introducing-loginradius-cli/domain.png deleted file mode 100644 index 19ec31333..000000000 Binary files a/content/engineering/introducing-loginradius-cli/domain.png and /dev/null differ diff --git a/content/engineering/introducing-loginradius-cli/domain.webp b/content/engineering/introducing-loginradius-cli/domain.webp new file mode 100644 index 000000000..47a823f8a Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/domain.webp differ diff --git a/content/engineering/introducing-loginradius-cli/index.md b/content/engineering/introducing-loginradius-cli/index.md index e29531581..c335e0327 100644 --- a/content/engineering/introducing-loginradius-cli/index.md +++ b/content/engineering/introducing-loginradius-cli/index.md @@ -1,7 +1,7 @@ --- title: "Introducing LoginRadius CLI" date: "2021-07-02" -coverImage: "cli.png" +coverImage: "cli.webp" author: "Mohammed Modi" description: "LoginRadius CLI helps you to perform basic actions of your LoginRadius Dashboard through the command line. The actions include login, register, logout, email configuration, domain whitelisting, etc." tags: ["Authentication", "DevTools", "CLI", "LoginRadius CLI"] @@ -20,25 +20,25 @@ Check out a few examples of how LoginRadius CLI can help manage your [Loginradiu ### Login/Register to your LoginRadius Dashboard - + This command will help you to log in to the CLI. Once you logged in to the CLI, you can configure all your LoginRadius Applications through CLI. ### Manage your App Credentials - + Get your API Credentials in a single command. You can also reset your secret and generate sott using the LoginRadius CLI. ### Domain Whitelisting - + Manage your white-listed domain for your application with simple commands. ### Theme Management - + You can update the LoginRadius IDX Page theme from the predefined themes available through LoginRadius CLI. @@ -46,7 +46,7 @@ You can update the LoginRadius IDX Page theme from the predefined themes availab ### Add Social Logins - + With the help of LoginRadius CLI, you can add social logins to your LoginRadius IDX Page. diff --git a/content/engineering/introducing-loginradius-cli/login.png b/content/engineering/introducing-loginradius-cli/login.png deleted file mode 100644 index d46bab8ff..000000000 Binary files a/content/engineering/introducing-loginradius-cli/login.png and /dev/null differ diff --git a/content/engineering/introducing-loginradius-cli/login.webp b/content/engineering/introducing-loginradius-cli/login.webp new file mode 100644 index 000000000..4a8036d38 Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/login.webp differ diff --git a/content/engineering/introducing-loginradius-cli/social.png b/content/engineering/introducing-loginradius-cli/social.png deleted file mode 100644 index 5d11c56b2..000000000 Binary files a/content/engineering/introducing-loginradius-cli/social.png and /dev/null differ diff --git a/content/engineering/introducing-loginradius-cli/social.webp b/content/engineering/introducing-loginradius-cli/social.webp new file mode 100644 index 000000000..df633364a Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/social.webp differ diff --git a/content/engineering/introducing-loginradius-cli/theme.png b/content/engineering/introducing-loginradius-cli/theme.png deleted file mode 100644 index 4753b2146..000000000 Binary files a/content/engineering/introducing-loginradius-cli/theme.png and /dev/null differ diff --git a/content/engineering/introducing-loginradius-cli/theme.webp b/content/engineering/introducing-loginradius-cli/theme.webp new file mode 100644 index 000000000..76424695b Binary files /dev/null and b/content/engineering/introducing-loginradius-cli/theme.webp differ diff --git a/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.png b/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.png deleted file mode 100644 index eb6c08a90..000000000 Binary files a/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.png and /dev/null differ diff --git a/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.webp b/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.webp new file mode 100644 index 000000000..ca1c968ab Binary files /dev/null and b/content/engineering/introduction-of-Idx-Auto-Tester/idx-auto-tester.webp differ diff --git a/content/engineering/introduction-of-Idx-Auto-Tester/index.md b/content/engineering/introduction-of-Idx-Auto-Tester/index.md index 064e21d55..d20c60a9e 100644 --- a/content/engineering/introduction-of-Idx-Auto-Tester/index.md +++ b/content/engineering/introduction-of-Idx-Auto-Tester/index.md @@ -1,7 +1,7 @@ --- title: "Introduction of Idx-Auto-Tester" date: "2020-06-22" -coverImage: idx-auto-tester.png +coverImage: idx-auto-tester.webp author: Himanshi Sharma tags: ["Automation", "Idx-Auto-Tester"] --- diff --git a/content/engineering/introduction-to-android-studio/configure.png b/content/engineering/introduction-to-android-studio/configure.png deleted file mode 100644 index a3c7b654c..000000000 Binary files a/content/engineering/introduction-to-android-studio/configure.png and /dev/null differ diff --git a/content/engineering/introduction-to-android-studio/configure.webp b/content/engineering/introduction-to-android-studio/configure.webp new file mode 100644 index 000000000..fa1b12a87 Binary files /dev/null and b/content/engineering/introduction-to-android-studio/configure.webp differ diff --git a/content/engineering/introduction-to-android-studio/cover.png b/content/engineering/introduction-to-android-studio/cover.png deleted file mode 100644 index 6753d4a1d..000000000 Binary files a/content/engineering/introduction-to-android-studio/cover.png and /dev/null differ diff --git a/content/engineering/introduction-to-android-studio/cover.webp b/content/engineering/introduction-to-android-studio/cover.webp new file mode 100644 index 000000000..df717daf1 Binary files /dev/null and b/content/engineering/introduction-to-android-studio/cover.webp differ diff --git a/content/engineering/introduction-to-android-studio/empty.png b/content/engineering/introduction-to-android-studio/empty.png deleted file mode 100644 index ad4462ebe..000000000 Binary files a/content/engineering/introduction-to-android-studio/empty.png and /dev/null differ diff --git a/content/engineering/introduction-to-android-studio/empty.webp b/content/engineering/introduction-to-android-studio/empty.webp new file mode 100644 index 000000000..cf664244f Binary files /dev/null and b/content/engineering/introduction-to-android-studio/empty.webp differ diff --git a/content/engineering/introduction-to-android-studio/gradle.png b/content/engineering/introduction-to-android-studio/gradle.png deleted file mode 100644 index e195933b1..000000000 Binary files a/content/engineering/introduction-to-android-studio/gradle.png and /dev/null differ diff --git a/content/engineering/introduction-to-android-studio/gradle.webp b/content/engineering/introduction-to-android-studio/gradle.webp new file mode 100644 index 000000000..ba11e8df0 Binary files /dev/null and b/content/engineering/introduction-to-android-studio/gradle.webp differ diff --git a/content/engineering/introduction-to-android-studio/index.md b/content/engineering/introduction-to-android-studio/index.md index 4d6caadf2..e70719c98 100644 --- a/content/engineering/introduction-to-android-studio/index.md +++ b/content/engineering/introduction-to-android-studio/index.md @@ -1,7 +1,7 @@ --- title: "Introduction to Android Studio" date: "2020-10-30" -coverImage: "cover.png" +coverImage: "cover.webp" author: "Prithviraj Biswas" tags: ["Android Studio", "Android App"] description: "Getting Started with Android Studio and making your first app." @@ -29,30 +29,30 @@ To create the application, we will follow these steps through the process in a p **Step 1. Open your Android Studio after installing, and this following screen appears after starting:** - + **Step 2. Click on "Start a New Android Project" and choose the activity we want the project to be. For me, I'm selecting an empty activity.** - + **Step 3. Configure your project by changing the project's name and the desired language the user wants to code with. Android Studio supports two languages, i.e., Java and Kotlin. The user can also choose their desired API, like which android version they want to run, and then click on finish.** - + **Step 4.Wait until your Gradle build finishes successfully and find your java and .xml file from folders of the app, as shown in the given image.** - + **Step 5. Click onto your .xml file to see the initial layout of the file like the given image. You can drag and drop from the palette's items and change your layout by dragging and dropping.** - + **Step 6. At last, Run your file by the run button on the top right corner in your emulator configured.** diff --git a/content/engineering/introduction-to-android-studio/welcomepage.png b/content/engineering/introduction-to-android-studio/welcomepage.png deleted file mode 100644 index ea83e6485..000000000 Binary files a/content/engineering/introduction-to-android-studio/welcomepage.png and /dev/null differ diff --git a/content/engineering/introduction-to-android-studio/welcomepage.webp b/content/engineering/introduction-to-android-studio/welcomepage.webp new file mode 100644 index 000000000..d838044bc Binary files /dev/null and b/content/engineering/introduction-to-android-studio/welcomepage.webp differ diff --git a/content/engineering/introduction-to-android-studio/xml.png b/content/engineering/introduction-to-android-studio/xml.png deleted file mode 100644 index b561e8ee9..000000000 Binary files a/content/engineering/introduction-to-android-studio/xml.png and /dev/null differ diff --git a/content/engineering/introduction-to-android-studio/xml.webp b/content/engineering/introduction-to-android-studio/xml.webp new file mode 100644 index 000000000..99d5d3e60 Binary files /dev/null and b/content/engineering/introduction-to-android-studio/xml.webp differ diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.jpg b/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.jpg deleted file mode 100644 index 5a2b1a7cd..000000000 Binary files a/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.jpg and /dev/null differ diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.webp b/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.webp new file mode 100644 index 000000000..504ea65d4 Binary files /dev/null and b/content/engineering/introduction-to-cross-site-request-forgery-csrf/crosspath.webp differ diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.png b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.png deleted file mode 100644 index d23f6847e..000000000 Binary files a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.png and /dev/null differ diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.webp b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.webp new file mode 100644 index 000000000..c0659f6ae Binary files /dev/null and b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image1.webp differ diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.png b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.png deleted file mode 100644 index 100dba0ec..000000000 Binary files a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.png and /dev/null differ diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.webp b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.webp new file mode 100644 index 000000000..8e22f9acf Binary files /dev/null and b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image2.webp differ diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.png b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.png deleted file mode 100644 index ae905c6a2..000000000 Binary files a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.png and /dev/null differ diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.webp b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.webp new file mode 100644 index 000000000..d333238b1 Binary files /dev/null and b/content/engineering/introduction-to-cross-site-request-forgery-csrf/image3.webp differ diff --git a/content/engineering/introduction-to-cross-site-request-forgery-csrf/index.md b/content/engineering/introduction-to-cross-site-request-forgery-csrf/index.md index 73daaacfa..961be21ef 100644 --- a/content/engineering/introduction-to-cross-site-request-forgery-csrf/index.md +++ b/content/engineering/introduction-to-cross-site-request-forgery-csrf/index.md @@ -1,7 +1,7 @@ --- title: "Introduction to Cross-Site Request Forgery (CSRF)" date: "2019-10-30" -coverImage: "crosspath.jpg" +coverImage: "crosspath.webp" author: "Andy Yeung" tags: ["CSRF"] --- @@ -18,7 +18,7 @@ In order to understand CSRF, it is important to know how cookies and authenticat CSRF takes advantage of the storage of auth tokens in the browser, and constructs http requests to a target server on behalf of the user. Imitating http requests from the legitimate site requires research and preparation from the attacker beforehand, such as finding vulnerable websites and api’s suitable for the attack. - + Here is a high-level example of an CSRF attack. Note that some details are excluded for simplicity, but the key aspects are included. @@ -35,11 +35,11 @@ Here is a high-level example of an CSRF attack. Note that some details are exclu A common and effective way of mitigating CSRF is called the double submit cookie. Essentially the client will have two paired and encrypted tokens: one hidden in the page HTML and the other stored as a cookie. - + When a request is made by the client, both tokens are sent to the server, and the server will then ensure the tokens are valid pairs before processing the request as normal. - + Now the attacker will be unable to perform CSRF since they will not have access to the token hidden in the pages HTML, and the target server requires a valid token pair before processing the request. diff --git a/content/engineering/introduction-to-redux-saga/index.md b/content/engineering/introduction-to-redux-saga/index.md index 49c378776..0a5ffdf9f 100644 --- a/content/engineering/introduction-to-redux-saga/index.md +++ b/content/engineering/introduction-to-redux-saga/index.md @@ -1,7 +1,7 @@ --- title: "Introduction to Redux Saga" date: "2020-11-23" -coverImage: "unsplash.png" +coverImage: "unsplash.webp" author: "Nick Chim" tags: ["React", "Redux", "Redux Saga"] description: "A high level introduction to Redux Saga." diff --git a/content/engineering/introduction-to-redux-saga/unsplash.png b/content/engineering/introduction-to-redux-saga/unsplash.png deleted file mode 100644 index d819c8d4d..000000000 Binary files a/content/engineering/introduction-to-redux-saga/unsplash.png and /dev/null differ diff --git a/content/engineering/introduction-to-redux-saga/unsplash.webp b/content/engineering/introduction-to-redux-saga/unsplash.webp new file mode 100644 index 000000000..ffd590e92 Binary files /dev/null and b/content/engineering/introduction-to-redux-saga/unsplash.webp differ diff --git a/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.png b/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.png deleted file mode 100644 index 56594b24b..000000000 Binary files a/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.png and /dev/null differ diff --git a/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.webp b/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.webp new file mode 100644 index 000000000..d5fabdb6b Binary files /dev/null and b/content/engineering/introduction-to-web-accessibility-with-semantic-html5/handicapped.webp differ diff --git a/content/engineering/introduction-to-web-accessibility-with-semantic-html5/index.md b/content/engineering/introduction-to-web-accessibility-with-semantic-html5/index.md index dede71e96..3a1a9b2ef 100644 --- a/content/engineering/introduction-to-web-accessibility-with-semantic-html5/index.md +++ b/content/engineering/introduction-to-web-accessibility-with-semantic-html5/index.md @@ -1,7 +1,7 @@ --- title: "Introduction to Web Accessibility with Semantic HTML5" date: "2019-07-24" -coverImage: "handicapped.png" +coverImage: "handicapped.webp" author: "Greg Sakai" tags: ["HTML5", "HTML", "Web Accessibility", "Semantic HTML5"] --- diff --git a/content/engineering/invalidating-jwt/index.md b/content/engineering/invalidating-jwt/index.md index c1fa33052..6b6f280d8 100644 --- a/content/engineering/invalidating-jwt/index.md +++ b/content/engineering/invalidating-jwt/index.md @@ -1,7 +1,7 @@ --- title: "Invalidating JSON Web Tokens" date: "2021-01-18" -coverImage: "unsplash.png" +coverImage: "unsplash.webp" author: "Nick Chim" tags: ["JSON Web Tokens", "JWT"] description: "A discussion on invalidating JSON Web Tokens." diff --git a/content/engineering/invalidating-jwt/unsplash.png b/content/engineering/invalidating-jwt/unsplash.png deleted file mode 100644 index 2d5233f89..000000000 Binary files a/content/engineering/invalidating-jwt/unsplash.png and /dev/null differ diff --git a/content/engineering/invalidating-jwt/unsplash.webp b/content/engineering/invalidating-jwt/unsplash.webp new file mode 100644 index 000000000..8f859b68b Binary files /dev/null and b/content/engineering/invalidating-jwt/unsplash.webp differ diff --git a/content/engineering/is-your-database-secured-think-again/database_secure-300x300.png b/content/engineering/is-your-database-secured-think-again/database_secure-300x300.png deleted file mode 100644 index a6a0de596..000000000 Binary files a/content/engineering/is-your-database-secured-think-again/database_secure-300x300.png and /dev/null differ diff --git a/content/engineering/is-your-database-secured-think-again/database_secure-300x300.webp b/content/engineering/is-your-database-secured-think-again/database_secure-300x300.webp new file mode 100644 index 000000000..8cde27bcb Binary files /dev/null and b/content/engineering/is-your-database-secured-think-again/database_secure-300x300.webp differ diff --git a/content/engineering/is-your-database-secured-think-again/index.md b/content/engineering/is-your-database-secured-think-again/index.md index dc7ea38f1..97a7d3686 100644 --- a/content/engineering/is-your-database-secured-think-again/index.md +++ b/content/engineering/is-your-database-secured-think-again/index.md @@ -1,7 +1,7 @@ --- title: "Is Your Database Secured? Think Again" date: "2016-02-23" -coverImage: "database_secure-300x300.png" +coverImage: "database_secure-300x300.webp" author: "Kunal" tags: ["Database", "Security"] --- @@ -10,7 +10,7 @@ tags: ["Database", "Security"] Many known attacks are possible only once physically accessing a machine. For this reason, it is best to have the application server and the database server on different machines. If this is not possible, greater care must be taken, Otherwise, by executing remote commands via an application server, an attacker may be able to harm your database even without permissions. For this reason, any service running on the same machine as the database should be granted the lowest possible permission that still allows the service to operate. - + Do not forget to install the whole security package: Antivirus and Anti-spam, Firewall, and all of the security packages recommended by your operating system's vendor. Also, do not forget to spend 10 minutes thinking of your server's physical location - in the wrong location, your server can be stolen, flooded, harmed by wild animals or vagrants. **2\. Localhost Security or Disable or restrict remote access** diff --git a/content/engineering/is-your-database-secured-think-again/server-network-structure.png b/content/engineering/is-your-database-secured-think-again/server-network-structure.png deleted file mode 100644 index d9126c16a..000000000 Binary files a/content/engineering/is-your-database-secured-think-again/server-network-structure.png and /dev/null differ diff --git a/content/engineering/is-your-database-secured-think-again/server-network-structure.webp b/content/engineering/is-your-database-secured-think-again/server-network-structure.webp new file mode 100644 index 000000000..10c0f96f4 Binary files /dev/null and b/content/engineering/is-your-database-secured-think-again/server-network-structure.webp differ diff --git a/content/engineering/istio-installation-and-service-configuration/Istio.png b/content/engineering/istio-installation-and-service-configuration/Istio.png deleted file mode 100644 index 84227923d..000000000 Binary files a/content/engineering/istio-installation-and-service-configuration/Istio.png and /dev/null differ diff --git a/content/engineering/istio-installation-and-service-configuration/Istio.webp b/content/engineering/istio-installation-and-service-configuration/Istio.webp new file mode 100644 index 000000000..b7f0cf718 Binary files /dev/null and b/content/engineering/istio-installation-and-service-configuration/Istio.webp differ diff --git a/content/engineering/istio-installation-and-service-configuration/index.md b/content/engineering/istio-installation-and-service-configuration/index.md index a2ab4b7e9..0e3389ded 100644 --- a/content/engineering/istio-installation-and-service-configuration/index.md +++ b/content/engineering/istio-installation-and-service-configuration/index.md @@ -1,7 +1,7 @@ --- title: "How to Install and Configure Istio" date: "2021-01-22" -coverImage: "Istio.png" +coverImage: "Istio.webp" author: "Piyush Kumar" tags: ["Istio", "Service Mesh"] description: "This article will provide a step by step process on how to install and configure services using Istio." diff --git a/content/engineering/istio-service-mesh/Istio.png b/content/engineering/istio-service-mesh/Istio.png deleted file mode 100644 index 84227923d..000000000 Binary files a/content/engineering/istio-service-mesh/Istio.png and /dev/null differ diff --git a/content/engineering/istio-service-mesh/Istio.webp b/content/engineering/istio-service-mesh/Istio.webp new file mode 100644 index 000000000..b7f0cf718 Binary files /dev/null and b/content/engineering/istio-service-mesh/Istio.webp differ diff --git a/content/engineering/istio-service-mesh/index.md b/content/engineering/istio-service-mesh/index.md index 51566e38b..0211dff94 100644 --- a/content/engineering/istio-service-mesh/index.md +++ b/content/engineering/istio-service-mesh/index.md @@ -1,7 +1,7 @@ --- title: "Istio Service Mesh: A Beginners Guide" date: "2020-12-07" -coverImage: "Istio.png" +coverImage: "Istio.webp" author: "Piyush Kumar" tags: ["Istio", "Service Mesh"] description: "This post will give a high-level introduction to Istio and its related concepts and terminologies." @@ -29,7 +29,7 @@ The data plane is composed of Envoy proxy deployed as sidecars. Envoy itself is The control plane manages and configures the proxies to route traffic. - + ## Istio Core Components diff --git a/content/engineering/jamstack-introduction/image1.png b/content/engineering/jamstack-introduction/image1.png deleted file mode 100644 index 137994c20..000000000 Binary files a/content/engineering/jamstack-introduction/image1.png and /dev/null differ diff --git a/content/engineering/jamstack-introduction/image1.webp b/content/engineering/jamstack-introduction/image1.webp new file mode 100644 index 000000000..c230068d7 Binary files /dev/null and b/content/engineering/jamstack-introduction/image1.webp differ diff --git a/content/engineering/jamstack-introduction/index.md b/content/engineering/jamstack-introduction/index.md index 350967a1f..f5a375f14 100644 --- a/content/engineering/jamstack-introduction/index.md +++ b/content/engineering/jamstack-introduction/index.md @@ -1,7 +1,7 @@ --- title: "Introduction to JAMstack" date: "2020-10-29" -coverImage: "jamstack_cover.png" +coverImage: "jamstack_cover.webp" author: "Versha Gupta" tags: ["Jamstack", "Web"] description: "You may have heard the term JAMstack before, but you may not have understood what it means. In this article, We will introduce you to JAMstack as to why you need, best practice, and value." @@ -47,7 +47,7 @@ We can easily understand the JAMstack value when comparing it with a monolithic In a JAMstack architecture, the page request does not go to the server for Html because it directly fetches Html from CDN, where the Html file has been pre-built, and it's ready to be downloaded; that's why no server is involved here. ## Workflow comparison (JAMstack vs. traditional) - + **Traditional workflow** diff --git a/content/engineering/jamstack-introduction/jamstack_cover.png b/content/engineering/jamstack-introduction/jamstack_cover.png deleted file mode 100644 index a387544ea..000000000 Binary files a/content/engineering/jamstack-introduction/jamstack_cover.png and /dev/null differ diff --git a/content/engineering/jamstack-introduction/jamstack_cover.webp b/content/engineering/jamstack-introduction/jamstack_cover.webp new file mode 100644 index 000000000..78654d68c Binary files /dev/null and b/content/engineering/jamstack-introduction/jamstack_cover.webp differ diff --git a/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.png b/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.png deleted file mode 100644 index 523441449..000000000 Binary files a/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.png and /dev/null differ diff --git a/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.webp b/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.webp new file mode 100644 index 000000000..74c11cdfc Binary files /dev/null and b/content/engineering/javascript-events-bubbling-capturing-and-propagation/bubbles.webp differ diff --git a/content/engineering/javascript-events-bubbling-capturing-and-propagation/index.md b/content/engineering/javascript-events-bubbling-capturing-and-propagation/index.md index acbecf47b..581b7883b 100644 --- a/content/engineering/javascript-events-bubbling-capturing-and-propagation/index.md +++ b/content/engineering/javascript-events-bubbling-capturing-and-propagation/index.md @@ -1,7 +1,7 @@ --- title: "JavaScript Events: Bubbling, Capturing, and Propagation" date: "2019-07-22" -coverImage: "bubbles.png" +coverImage: "bubbles.webp" author: "Greg Sakai" tags: ["JavaScript", "JavaScript Events"] --- diff --git a/content/engineering/jwt-authentication-with-deno/deno_jwt.png b/content/engineering/jwt-authentication-with-deno/deno_jwt.png deleted file mode 100644 index eacd80fd3..000000000 Binary files a/content/engineering/jwt-authentication-with-deno/deno_jwt.png and /dev/null differ diff --git a/content/engineering/jwt-authentication-with-deno/deno_jwt.webp b/content/engineering/jwt-authentication-with-deno/deno_jwt.webp new file mode 100644 index 000000000..574400abf Binary files /dev/null and b/content/engineering/jwt-authentication-with-deno/deno_jwt.webp differ diff --git a/content/engineering/jwt-authentication-with-deno/index.md b/content/engineering/jwt-authentication-with-deno/index.md index 22960fd5e..0626c026d 100644 --- a/content/engineering/jwt-authentication-with-deno/index.md +++ b/content/engineering/jwt-authentication-with-deno/index.md @@ -1,7 +1,7 @@ --- title: How to create and validate JSON Web Tokens in Deno date: "2020-07-10" -coverImage: "deno_jwt.png" +coverImage: "deno_jwt.webp" author: "Puneet Singh" tags: ["Deno","JWT", "JSON Web Token"] canonical: https://www.loginradius.com/blog/engineering/guest-post/how-to-implement-jwt-authentication-in-deno/ diff --git a/content/engineering/jwt-signing-algorithms/index.md b/content/engineering/jwt-signing-algorithms/index.md index e7ca4ea74..2e4abb384 100644 --- a/content/engineering/jwt-signing-algorithms/index.md +++ b/content/engineering/jwt-signing-algorithms/index.md @@ -1,7 +1,7 @@ --- title: "JWT Signing Algorithms" date: "2020-09-24" -coverImage: "unsplash.png" +coverImage: "unsplash.webp" author: "Nick Chim" tags: ["JWT", "JSON Web Tokens"] description: "Deciding between which signing algorithm to use." diff --git a/content/engineering/jwt-signing-algorithms/unsplash.png b/content/engineering/jwt-signing-algorithms/unsplash.png deleted file mode 100644 index 96b7605d6..000000000 Binary files a/content/engineering/jwt-signing-algorithms/unsplash.png and /dev/null differ diff --git a/content/engineering/jwt-signing-algorithms/unsplash.webp b/content/engineering/jwt-signing-algorithms/unsplash.webp new file mode 100644 index 000000000..ec6be2234 Binary files /dev/null and b/content/engineering/jwt-signing-algorithms/unsplash.webp differ diff --git a/content/engineering/jwt/index.md b/content/engineering/jwt/index.md index c2a8ae40f..08ed6dec7 100644 --- a/content/engineering/jwt/index.md +++ b/content/engineering/jwt/index.md @@ -1,7 +1,7 @@ --- title: "What is JSON Web Token" date: "2018-07-11" -coverImage: "jwt.png" +coverImage: "jwt.webp" author: "Mayank Agarwal" tags: ["JWT", "JSON Web Token"] --- diff --git a/content/engineering/jwt/jwt.png b/content/engineering/jwt/jwt.png deleted file mode 100644 index 466bf7075..000000000 Binary files a/content/engineering/jwt/jwt.png and /dev/null differ diff --git a/content/engineering/jwt/jwt.webp b/content/engineering/jwt/jwt.webp new file mode 100644 index 000000000..be661c497 Binary files /dev/null and b/content/engineering/jwt/jwt.webp differ diff --git a/content/engineering/lazy-loading-in-react/index.md b/content/engineering/lazy-loading-in-react/index.md index e87c18ac0..a88beadcd 100644 --- a/content/engineering/lazy-loading-in-react/index.md +++ b/content/engineering/lazy-loading-in-react/index.md @@ -1,7 +1,7 @@ --- title: "Lazy loading in React" date: "2020-10-05" -coverImage: "react.jpg" +coverImage: "react.webp" author: "Akshay Avinash" tags: ["React", "Lazy loading", "React Suspense"] description: "Learn about lazy loading in React and how/when to use it" diff --git a/content/engineering/lazy-loading-in-react/react.jpg b/content/engineering/lazy-loading-in-react/react.jpg deleted file mode 100644 index 533f9505f..000000000 Binary files a/content/engineering/lazy-loading-in-react/react.jpg and /dev/null differ diff --git a/content/engineering/lazy-loading-in-react/react.webp b/content/engineering/lazy-loading-in-react/react.webp new file mode 100644 index 000000000..715664070 Binary files /dev/null and b/content/engineering/lazy-loading-in-react/react.webp differ diff --git a/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.png b/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.png deleted file mode 100644 index ac3d8fc9a..000000000 Binary files a/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.png and /dev/null differ diff --git a/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.webp b/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.webp new file mode 100644 index 000000000..883138998 Binary files /dev/null and b/content/engineering/learn-to-code-using-10-websites/How-to-code-using-the-10-cool-websites-768x564-300x220.webp differ diff --git a/content/engineering/learn-to-code-using-10-websites/index.md b/content/engineering/learn-to-code-using-10-websites/index.md index b32454784..fbb269874 100644 --- a/content/engineering/learn-to-code-using-10-websites/index.md +++ b/content/engineering/learn-to-code-using-10-websites/index.md @@ -1,7 +1,7 @@ --- title: "Learn How To Code Using The 10 Cool Websites" date: "2016-10-21" -coverImage: "How-to-code-using-the-10-cool-websites-768x564-300x220.png" +coverImage: "How-to-code-using-the-10-cool-websites-768x564-300x220.webp" author: "Team LoginRadius" tags: ["Courses", "Learning Websites"] --- diff --git a/content/engineering/learning-how-to-code/begin-code-300x300.png b/content/engineering/learning-how-to-code/begin-code-300x300.png deleted file mode 100644 index 2d1e67868..000000000 Binary files a/content/engineering/learning-how-to-code/begin-code-300x300.png and /dev/null differ diff --git a/content/engineering/learning-how-to-code/begin-code-300x300.webp b/content/engineering/learning-how-to-code/begin-code-300x300.webp new file mode 100644 index 000000000..4884327a3 Binary files /dev/null and b/content/engineering/learning-how-to-code/begin-code-300x300.webp differ diff --git a/content/engineering/learning-how-to-code/index.md b/content/engineering/learning-how-to-code/index.md index 419d1e53c..74569b4c0 100644 --- a/content/engineering/learning-how-to-code/index.md +++ b/content/engineering/learning-how-to-code/index.md @@ -1,7 +1,7 @@ --- title: "Learning How to Code" date: "2015-12-29" -coverImage: "begin-code-300x300.png" +coverImage: "begin-code-300x300.webp" author: "Carling" tags: ["Learning", "Coding", "Learning resources"] --- diff --git a/content/engineering/lets-encrypt-with-ssl-certificates/index.md b/content/engineering/lets-encrypt-with-ssl-certificates/index.md index f746130c9..2f63bc997 100644 --- a/content/engineering/lets-encrypt-with-ssl-certificates/index.md +++ b/content/engineering/lets-encrypt-with-ssl-certificates/index.md @@ -1,7 +1,7 @@ --- title: "Let's Encrypt with SSL Certificates" date: "2019-01-14" -coverImage: "ssl.png" +coverImage: "ssl.webp" author: "Ruben Gonzalez" tags: ["SSL", "SSL Certificate", "Security"] --- diff --git a/content/engineering/lets-encrypt-with-ssl-certificates/ssl.png b/content/engineering/lets-encrypt-with-ssl-certificates/ssl.png deleted file mode 100644 index 95a298ad1..000000000 Binary files a/content/engineering/lets-encrypt-with-ssl-certificates/ssl.png and /dev/null differ diff --git a/content/engineering/lets-encrypt-with-ssl-certificates/ssl.webp b/content/engineering/lets-encrypt-with-ssl-certificates/ssl.webp new file mode 100644 index 000000000..b0b76cc96 Binary files /dev/null and b/content/engineering/lets-encrypt-with-ssl-certificates/ssl.webp differ diff --git a/content/engineering/lets-take-meme-break/1.png b/content/engineering/lets-take-meme-break/1.png deleted file mode 100644 index 2b3e3a733..000000000 Binary files a/content/engineering/lets-take-meme-break/1.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/1.webp b/content/engineering/lets-take-meme-break/1.webp new file mode 100644 index 000000000..9e7efefbb Binary files /dev/null and b/content/engineering/lets-take-meme-break/1.webp differ diff --git a/content/engineering/lets-take-meme-break/10.png b/content/engineering/lets-take-meme-break/10.png deleted file mode 100644 index accb23516..000000000 Binary files a/content/engineering/lets-take-meme-break/10.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/10.webp b/content/engineering/lets-take-meme-break/10.webp new file mode 100644 index 000000000..04dcdb7bc Binary files /dev/null and b/content/engineering/lets-take-meme-break/10.webp differ diff --git a/content/engineering/lets-take-meme-break/11.png b/content/engineering/lets-take-meme-break/11.png deleted file mode 100644 index 369ef692d..000000000 Binary files a/content/engineering/lets-take-meme-break/11.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/11.webp b/content/engineering/lets-take-meme-break/11.webp new file mode 100644 index 000000000..aa38c4190 Binary files /dev/null and b/content/engineering/lets-take-meme-break/11.webp differ diff --git a/content/engineering/lets-take-meme-break/12.png b/content/engineering/lets-take-meme-break/12.png deleted file mode 100644 index 1d35db1b5..000000000 Binary files a/content/engineering/lets-take-meme-break/12.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/12.webp b/content/engineering/lets-take-meme-break/12.webp new file mode 100644 index 000000000..3ddb4fbdb Binary files /dev/null and b/content/engineering/lets-take-meme-break/12.webp differ diff --git a/content/engineering/lets-take-meme-break/13.png b/content/engineering/lets-take-meme-break/13.png deleted file mode 100644 index 100d21aef..000000000 Binary files a/content/engineering/lets-take-meme-break/13.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/13.webp b/content/engineering/lets-take-meme-break/13.webp new file mode 100644 index 000000000..08360cf39 Binary files /dev/null and b/content/engineering/lets-take-meme-break/13.webp differ diff --git a/content/engineering/lets-take-meme-break/14.png b/content/engineering/lets-take-meme-break/14.png deleted file mode 100644 index cb1c5cdf4..000000000 Binary files a/content/engineering/lets-take-meme-break/14.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/14.webp b/content/engineering/lets-take-meme-break/14.webp new file mode 100644 index 000000000..c4258266c Binary files /dev/null and b/content/engineering/lets-take-meme-break/14.webp differ diff --git a/content/engineering/lets-take-meme-break/15.png b/content/engineering/lets-take-meme-break/15.png deleted file mode 100644 index d9dbe333f..000000000 Binary files a/content/engineering/lets-take-meme-break/15.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/15.webp b/content/engineering/lets-take-meme-break/15.webp new file mode 100644 index 000000000..0a0fe8702 Binary files /dev/null and b/content/engineering/lets-take-meme-break/15.webp differ diff --git a/content/engineering/lets-take-meme-break/16.png b/content/engineering/lets-take-meme-break/16.png deleted file mode 100644 index 0eb166953..000000000 Binary files a/content/engineering/lets-take-meme-break/16.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/16.webp b/content/engineering/lets-take-meme-break/16.webp new file mode 100644 index 000000000..575525a99 Binary files /dev/null and b/content/engineering/lets-take-meme-break/16.webp differ diff --git a/content/engineering/lets-take-meme-break/17.png b/content/engineering/lets-take-meme-break/17.png deleted file mode 100644 index 0d2e3d2b6..000000000 Binary files a/content/engineering/lets-take-meme-break/17.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/17.webp b/content/engineering/lets-take-meme-break/17.webp new file mode 100644 index 000000000..4415498fe Binary files /dev/null and b/content/engineering/lets-take-meme-break/17.webp differ diff --git a/content/engineering/lets-take-meme-break/18.png b/content/engineering/lets-take-meme-break/18.png deleted file mode 100644 index 1c595c52d..000000000 Binary files a/content/engineering/lets-take-meme-break/18.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/18.webp b/content/engineering/lets-take-meme-break/18.webp new file mode 100644 index 000000000..06e0103f5 Binary files /dev/null and b/content/engineering/lets-take-meme-break/18.webp differ diff --git a/content/engineering/lets-take-meme-break/19.png b/content/engineering/lets-take-meme-break/19.png deleted file mode 100644 index 19e38f2ee..000000000 Binary files a/content/engineering/lets-take-meme-break/19.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/19.webp b/content/engineering/lets-take-meme-break/19.webp new file mode 100644 index 000000000..d0691e9e9 Binary files /dev/null and b/content/engineering/lets-take-meme-break/19.webp differ diff --git a/content/engineering/lets-take-meme-break/2.png b/content/engineering/lets-take-meme-break/2.png deleted file mode 100644 index a55e9ce48..000000000 Binary files a/content/engineering/lets-take-meme-break/2.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/2.webp b/content/engineering/lets-take-meme-break/2.webp new file mode 100644 index 000000000..ca5c0f20c Binary files /dev/null and b/content/engineering/lets-take-meme-break/2.webp differ diff --git a/content/engineering/lets-take-meme-break/20.png b/content/engineering/lets-take-meme-break/20.png deleted file mode 100644 index c7daa6038..000000000 Binary files a/content/engineering/lets-take-meme-break/20.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/20.webp b/content/engineering/lets-take-meme-break/20.webp new file mode 100644 index 000000000..bb855c6b5 Binary files /dev/null and b/content/engineering/lets-take-meme-break/20.webp differ diff --git a/content/engineering/lets-take-meme-break/21.png b/content/engineering/lets-take-meme-break/21.png deleted file mode 100644 index c1204c35a..000000000 Binary files a/content/engineering/lets-take-meme-break/21.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/21.webp b/content/engineering/lets-take-meme-break/21.webp new file mode 100644 index 000000000..885e3648d Binary files /dev/null and b/content/engineering/lets-take-meme-break/21.webp differ diff --git a/content/engineering/lets-take-meme-break/3.png b/content/engineering/lets-take-meme-break/3.png deleted file mode 100644 index 3ddc63f4d..000000000 Binary files a/content/engineering/lets-take-meme-break/3.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/3.webp b/content/engineering/lets-take-meme-break/3.webp new file mode 100644 index 000000000..2238e792f Binary files /dev/null and b/content/engineering/lets-take-meme-break/3.webp differ diff --git a/content/engineering/lets-take-meme-break/4.png b/content/engineering/lets-take-meme-break/4.png deleted file mode 100644 index 28e27a3bc..000000000 Binary files a/content/engineering/lets-take-meme-break/4.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/4.webp b/content/engineering/lets-take-meme-break/4.webp new file mode 100644 index 000000000..01b75c392 Binary files /dev/null and b/content/engineering/lets-take-meme-break/4.webp differ diff --git a/content/engineering/lets-take-meme-break/5.jpg b/content/engineering/lets-take-meme-break/5.jpg deleted file mode 100644 index 2ff12a001..000000000 Binary files a/content/engineering/lets-take-meme-break/5.jpg and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/5.webp b/content/engineering/lets-take-meme-break/5.webp new file mode 100644 index 000000000..2baf5bbc0 Binary files /dev/null and b/content/engineering/lets-take-meme-break/5.webp differ diff --git a/content/engineering/lets-take-meme-break/6.png b/content/engineering/lets-take-meme-break/6.png deleted file mode 100644 index 903fbbca8..000000000 Binary files a/content/engineering/lets-take-meme-break/6.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/6.webp b/content/engineering/lets-take-meme-break/6.webp new file mode 100644 index 000000000..50c56070a Binary files /dev/null and b/content/engineering/lets-take-meme-break/6.webp differ diff --git a/content/engineering/lets-take-meme-break/7.png b/content/engineering/lets-take-meme-break/7.png deleted file mode 100644 index 4e6ffea2f..000000000 Binary files a/content/engineering/lets-take-meme-break/7.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/7.webp b/content/engineering/lets-take-meme-break/7.webp new file mode 100644 index 000000000..809521fb5 Binary files /dev/null and b/content/engineering/lets-take-meme-break/7.webp differ diff --git a/content/engineering/lets-take-meme-break/8.png b/content/engineering/lets-take-meme-break/8.png deleted file mode 100644 index 22618c3cc..000000000 Binary files a/content/engineering/lets-take-meme-break/8.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/8.webp b/content/engineering/lets-take-meme-break/8.webp new file mode 100644 index 000000000..cfae7c7a1 Binary files /dev/null and b/content/engineering/lets-take-meme-break/8.webp differ diff --git a/content/engineering/lets-take-meme-break/9.png b/content/engineering/lets-take-meme-break/9.png deleted file mode 100644 index 333cbd7b9..000000000 Binary files a/content/engineering/lets-take-meme-break/9.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/9.webp b/content/engineering/lets-take-meme-break/9.webp new file mode 100644 index 000000000..be4d13878 Binary files /dev/null and b/content/engineering/lets-take-meme-break/9.webp differ diff --git a/content/engineering/lets-take-meme-break/cover.png b/content/engineering/lets-take-meme-break/cover.png deleted file mode 100644 index 3eebcf6c4..000000000 Binary files a/content/engineering/lets-take-meme-break/cover.png and /dev/null differ diff --git a/content/engineering/lets-take-meme-break/cover.webp b/content/engineering/lets-take-meme-break/cover.webp new file mode 100644 index 000000000..367b66219 Binary files /dev/null and b/content/engineering/lets-take-meme-break/cover.webp differ diff --git a/content/engineering/lets-take-meme-break/index.md b/content/engineering/lets-take-meme-break/index.md index 8e1eb9c01..83bde73c9 100644 --- a/content/engineering/lets-take-meme-break/index.md +++ b/content/engineering/lets-take-meme-break/index.md @@ -1,7 +1,7 @@ --- title: "Let’s Take A MEME Break!!!" date: "2020-09-04" -coverImage: "cover.png" +coverImage: "cover.webp" author: "Ashish Sharma" tags: ["MEME","Programming","Humor"] --- @@ -17,83 +17,83 @@ MEMEs can light the environment for every programmer in the world. On that note, ### 1. Always ready for new!!! - [Kunal](/author/kunal/) - + ### 2. Nothing Changes With Time - [Tanvi Jain](/author/tanvi-jain/) - + ### 3. Heaviest Object In The Universe - [Nitesh Jain](/author/nitesh-jain/) - + ### 4. Perception!! - [Vikram Jain](/author/vikram-jain/) - + ### 5. Maths Always A hurdle !! - [Mohammed Modi](/author/mohammed-modi/) - + ### 6. I had a problem so I thought to use Java - [Indrasen Kumar](/author/indrasen-kumar/) - + ### 7. Avoid Handshakes. - [Piyush Kumar](/author/piyush-kumar/) - + ### 8. I’m Really Unsure About My Own Creation - [Kheenvraj Lomror](/author/kheenvraj-lomror/) - + ### 9. That Missing Fact - [Priyadarshan Mohanty](/author/priyadarshan-mohanty/) - + ### 10. Every IT Administrator. - [Narendra Pareek](/author/narendra-pareek/) - + ### 11. Imma Genius! - [Abhimanyu Singh Rathore](/author/abhimanyu-singh-rathore/) - + ### 12. My Logical Thinking as Programmer. - [Ankit Singh](/author/ankit-singh/) - + ### 13. HTML is a Programming Language - [Hitesh Kumawat](/author/hitesh-kumawat/) - + ### 14. Programmers while Sleeping. - [Versha Gupta](/author/versha-gupta/) - + ### 15. Programmer Swag!! - [Gaurav Bewal](/author/gaurav-bewal/) - + ### 16. QA Life!! - [Rakesh Pareek](/author/rakesh-pareek/) - + ### 17. Infinite... - [Hridayesh Sharma](/author/hridayesh-sharma/) - + ### 18. Python Lover!! - [Aman Agrawal](/author/aman-agrawal/) - + ### 19. What's your address? - [Vijay Singh Shekhawat](/author/vijay-singh-shekhawat/) - + ### 20. Gamer and Programmer - [Chinmaya Pati](/author/chinmaya-pati/) - + If you have better ones, reply in the comments below and we’ll include them. diff --git a/content/engineering/linkedin-login-using-node-passport/app-credentials.png b/content/engineering/linkedin-login-using-node-passport/app-credentials.png deleted file mode 100644 index 22b8b817b..000000000 Binary files a/content/engineering/linkedin-login-using-node-passport/app-credentials.png and /dev/null differ diff --git a/content/engineering/linkedin-login-using-node-passport/app-credentials.webp b/content/engineering/linkedin-login-using-node-passport/app-credentials.webp new file mode 100644 index 000000000..6aa10d0ca Binary files /dev/null and b/content/engineering/linkedin-login-using-node-passport/app-credentials.webp differ diff --git a/content/engineering/linkedin-login-using-node-passport/create-app.png b/content/engineering/linkedin-login-using-node-passport/create-app.png deleted file mode 100644 index afed68c9c..000000000 Binary files a/content/engineering/linkedin-login-using-node-passport/create-app.png and /dev/null differ diff --git a/content/engineering/linkedin-login-using-node-passport/create-app.webp b/content/engineering/linkedin-login-using-node-passport/create-app.webp new file mode 100644 index 000000000..4baaf39fb Binary files /dev/null and b/content/engineering/linkedin-login-using-node-passport/create-app.webp differ diff --git a/content/engineering/linkedin-login-using-node-passport/index.md b/content/engineering/linkedin-login-using-node-passport/index.md index 70b4594c9..de25522fc 100644 --- a/content/engineering/linkedin-login-using-node-passport/index.md +++ b/content/engineering/linkedin-login-using-node-passport/index.md @@ -1,7 +1,7 @@ --- title: "LinkedIn Login using Node JS and passport" date: "2020-06-10" -coverImage: "linkedin_login_node.png" +coverImage: "linkedin_login_node.webp" author: "Aman Agrawal" tags: ["LinkedIn", "Login", "NodeJs", "PassportJS"] description: "Learn social login benefits and how we can implement LinkedIn Login on our website or mobile app." @@ -24,7 +24,7 @@ Passport is an authentication middleware for Node, which authenticates requests - Go to [Developer Linkedin](https://www.linkedin.com/developers/) and login with your Linkedin account. - Once you have registered, click on the `create app` link and add the required details to create an app - + Provide basic details about your app: - App name @@ -35,7 +35,7 @@ Provide basic details about your app: - After creating apps go to the `auth` tab in the navigation bar as shown below. You can now copy your secret and ID from here -  +  2. Now enough, let's move to code, First of all, create a directory named `Linkedin-node-authentication` @@ -320,10 +320,10 @@ npm start -  +  Click on the sign in button, and you will be asked to login through Linkedin. Once logged in you will be redirected to profile page as below: -  +  The complete sample code for the above tutorial can be found [here](https://github.com/LoginRadius/engineering-blog-samples/tree/master/NodeJs/LinkedinLoginPassport) \ No newline at end of file diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.png b/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.png deleted file mode 100644 index eac9b8b24..000000000 Binary files a/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.png and /dev/null differ diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.webp b/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.webp new file mode 100644 index 000000000..2e97db849 Binary files /dev/null and b/content/engineering/linkedin-login-using-node-passport/linkedin-login-page.webp differ diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.png b/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.png deleted file mode 100644 index 3a15d01e0..000000000 Binary files a/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.png and /dev/null differ diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.webp b/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.webp new file mode 100644 index 000000000..a1aa0dc5e Binary files /dev/null and b/content/engineering/linkedin-login-using-node-passport/linkedin-profile-page.webp differ diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.png b/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.png deleted file mode 100644 index 32da4b032..000000000 Binary files a/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.png and /dev/null differ diff --git a/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.webp b/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.webp new file mode 100644 index 000000000..f443dfbbd Binary files /dev/null and b/content/engineering/linkedin-login-using-node-passport/linkedin_login_node.webp differ diff --git a/content/engineering/list-csharp/coverimage.jpg b/content/engineering/list-csharp/coverimage.jpg deleted file mode 100644 index a0733a7b0..000000000 Binary files a/content/engineering/list-csharp/coverimage.jpg and /dev/null differ diff --git a/content/engineering/list-csharp/coverimage.webp b/content/engineering/list-csharp/coverimage.webp new file mode 100644 index 000000000..317728b16 Binary files /dev/null and b/content/engineering/list-csharp/coverimage.webp differ diff --git a/content/engineering/list-csharp/index.md b/content/engineering/list-csharp/index.md index 890826a7c..1e8931dac 100644 --- a/content/engineering/list-csharp/index.md +++ b/content/engineering/list-csharp/index.md @@ -1,7 +1,7 @@ --- title: "How to Create List in C#" date: "2021-02-25" -coverImage: "coverimage.jpg" +coverImage: "coverimage.webp" author: "Hemant Manwani" tags: ["C#", "List"] description: "In this article, we will learn how to create lists in C# also how to use the C# list class to add, remove, and search items in a collection of objects." diff --git a/content/engineering/live-data-migration-mongodb/index.md b/content/engineering/live-data-migration-mongodb/index.md index a14b337a3..369e7cc2a 100644 --- a/content/engineering/live-data-migration-mongodb/index.md +++ b/content/engineering/live-data-migration-mongodb/index.md @@ -1,7 +1,7 @@ --- title: "How to Migrate Data In MongoDB" date: "2020-12-14" -coverImage: "index.png" +coverImage: "index.webp" author: "Chinmaya Pati" tags: ["MongoDB"] description: "This article covers the guide to migrate data from offline or live MongoDB instance using oplog replay alongside mitigate connection switch latency with existing utilities." diff --git a/content/engineering/live-data-migration-mongodb/index.png b/content/engineering/live-data-migration-mongodb/index.png deleted file mode 100644 index 67caa5d98..000000000 Binary files a/content/engineering/live-data-migration-mongodb/index.png and /dev/null differ diff --git a/content/engineering/live-data-migration-mongodb/index.webp b/content/engineering/live-data-migration-mongodb/index.webp new file mode 100644 index 000000000..dfac39605 Binary files /dev/null and b/content/engineering/live-data-migration-mongodb/index.webp differ diff --git a/content/engineering/login-with-facebook/facebook-login-wow.png b/content/engineering/login-with-facebook/facebook-login-wow.png deleted file mode 100644 index 6323b95a1..000000000 Binary files a/content/engineering/login-with-facebook/facebook-login-wow.png and /dev/null differ diff --git a/content/engineering/login-with-facebook/facebook-login-wow.webp b/content/engineering/login-with-facebook/facebook-login-wow.webp new file mode 100644 index 000000000..dd845f22e Binary files /dev/null and b/content/engineering/login-with-facebook/facebook-login-wow.webp differ diff --git a/content/engineering/login-with-facebook/index.md b/content/engineering/login-with-facebook/index.md index c6fd19d27..88fb90a60 100644 --- a/content/engineering/login-with-facebook/index.md +++ b/content/engineering/login-with-facebook/index.md @@ -1,7 +1,7 @@ --- title: "How to implement Facebook Login" date: "2020-09-16" -coverImage: "index.png" +coverImage: "index.webp" author: "Vijay Singh Shekhawat" tags: ["Login With Facebook", "Facebook","Facebook Login", "Login", "Oauth"] description: "This article will explain about social login benefits and how we can implement Sign In using Facebook on our website or mobile app." @@ -11,7 +11,7 @@ There are more than 1 million websites or apps are using **"SignIn with Facebook According to multiple surveys, there are more than 3 billion users worldwide are using social media and it is around 50% of the world's population. - + The biggest challenge and most important things are to make user registration and login quick and easy while developing our application. The registration forms required a lot of data that need to be filled by users manually and it causes lost, potential users. Additionally, users need to enter their usernames/emails and passwords in the login forms to authenticate themselves and also need to remember more individual IDs and passwords. @@ -31,45 +31,45 @@ Go to [Facebook Developer](https://developers.facebook.com) and log in using you **NOTE**: Please do not log in using a business account as Facebook will not allow you to create an app if you do so. - + #### Step 2 Select the **My Apps** as displayed on the below screen. - + #### Step 3 Click on **Add a New App** as displayed in the below screen. - + #### Step 4 Input display name and contact email. Once you have done so, click on **Create App ID** - + #### Step 5 In the security check, Complete the security steps and click on the **submit** button. - + #### Step 6 Once you land on the App dashboard, Select Facebook Login, and click **Set Up**. - + #### Step 7 Click on Settings in the sidebar under Facebook Login. Turn on Client OAuth Login. Turn on Web OAuth Login. Put the valid redirect URL on **"Valid OAuth redirect URIs"**. Click on the Save button. - + #### Step 8 Click on Basic under settings in the sidebar. Under App, Domains include your website Url. Enter all the required details. Change the status of the app from Development to Live from the top-right corner. Click on the **Save Changes** button. Now your Facebook app is ready. You can start implementing Facebook login - + ### Data Selection diff --git a/content/engineering/login-with-facebook/index.png b/content/engineering/login-with-facebook/index.png deleted file mode 100644 index fc28df2c8..000000000 Binary files a/content/engineering/login-with-facebook/index.png and /dev/null differ diff --git a/content/engineering/login-with-facebook/index.webp b/content/engineering/login-with-facebook/index.webp new file mode 100644 index 000000000..40a9b4d62 Binary files /dev/null and b/content/engineering/login-with-facebook/index.webp differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img1.png b/content/engineering/login-with-facebook/loginadius-facebook-img1.png deleted file mode 100644 index 88d0b1497..000000000 Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img1.png and /dev/null differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img1.webp b/content/engineering/login-with-facebook/loginadius-facebook-img1.webp new file mode 100644 index 000000000..97d9b4599 Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img1.webp differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img2.png b/content/engineering/login-with-facebook/loginadius-facebook-img2.png deleted file mode 100644 index 9f1435258..000000000 Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img2.png and /dev/null differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img2.webp b/content/engineering/login-with-facebook/loginadius-facebook-img2.webp new file mode 100644 index 000000000..3fb0e46f1 Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img2.webp differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img3.png b/content/engineering/login-with-facebook/loginadius-facebook-img3.png deleted file mode 100644 index 53cfcb0ff..000000000 Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img3.png and /dev/null differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img3.webp b/content/engineering/login-with-facebook/loginadius-facebook-img3.webp new file mode 100644 index 000000000..bbd755003 Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img3.webp differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img4.png b/content/engineering/login-with-facebook/loginadius-facebook-img4.png deleted file mode 100644 index e77035ece..000000000 Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img4.png and /dev/null differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img4.webp b/content/engineering/login-with-facebook/loginadius-facebook-img4.webp new file mode 100644 index 000000000..ef6767da4 Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img4.webp differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img5.png b/content/engineering/login-with-facebook/loginadius-facebook-img5.png deleted file mode 100644 index 5292f038c..000000000 Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img5.png and /dev/null differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img5.webp b/content/engineering/login-with-facebook/loginadius-facebook-img5.webp new file mode 100644 index 000000000..d97982a0b Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img5.webp differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img6.png b/content/engineering/login-with-facebook/loginadius-facebook-img6.png deleted file mode 100644 index caccd16f9..000000000 Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img6.png and /dev/null differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img6.webp b/content/engineering/login-with-facebook/loginadius-facebook-img6.webp new file mode 100644 index 000000000..3d9ee634f Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img6.webp differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img7.png b/content/engineering/login-with-facebook/loginadius-facebook-img7.png deleted file mode 100644 index b57aa0aeb..000000000 Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img7.png and /dev/null differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img7.webp b/content/engineering/login-with-facebook/loginadius-facebook-img7.webp new file mode 100644 index 000000000..13bebd091 Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img7.webp differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img8.png b/content/engineering/login-with-facebook/loginadius-facebook-img8.png deleted file mode 100644 index 9a3f45163..000000000 Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img8.png and /dev/null differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img8.webp b/content/engineering/login-with-facebook/loginadius-facebook-img8.webp new file mode 100644 index 000000000..11419bae3 Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img8.webp differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img9.png b/content/engineering/login-with-facebook/loginadius-facebook-img9.png deleted file mode 100644 index f6e58a1c6..000000000 Binary files a/content/engineering/login-with-facebook/loginadius-facebook-img9.png and /dev/null differ diff --git a/content/engineering/login-with-facebook/loginadius-facebook-img9.webp b/content/engineering/login-with-facebook/loginadius-facebook-img9.webp new file mode 100644 index 000000000..1750b7201 Binary files /dev/null and b/content/engineering/login-with-facebook/loginadius-facebook-img9.webp differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.png deleted file mode 100644 index 7771f482e..000000000 Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.png and /dev/null differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.webp new file mode 100644 index 000000000..ef2546be7 Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/4.webp differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.png deleted file mode 100644 index 26efe0f88..000000000 Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.png and /dev/null differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.webp new file mode 100644 index 000000000..d2c1751df Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-1.webp differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.png deleted file mode 100644 index 094ccea5a..000000000 Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.png and /dev/null differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.webp new file mode 100644 index 000000000..55a33fb6f Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-2.webp differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.png deleted file mode 100644 index 794345aff..000000000 Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.png and /dev/null differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.webp new file mode 100644 index 000000000..185d19dec Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-3.webp differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.png deleted file mode 100644 index ac8d117e0..000000000 Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.png and /dev/null differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.webp new file mode 100644 index 000000000..d30eb1f45 Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cl-5.webp differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.png b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.png deleted file mode 100644 index 6f77eea8b..000000000 Binary files a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.png and /dev/null differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.webp b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.webp new file mode 100644 index 000000000..5101e3eff Binary files /dev/null and b/content/engineering/loginradius-launches-cli-enterprise-dashboard/cli-1.webp differ diff --git a/content/engineering/loginradius-launches-cli-enterprise-dashboard/index.md b/content/engineering/loginradius-launches-cli-enterprise-dashboard/index.md index fb5563d14..c0eeb5f1b 100644 --- a/content/engineering/loginradius-launches-cli-enterprise-dashboard/index.md +++ b/content/engineering/loginradius-launches-cli-enterprise-dashboard/index.md @@ -1,7 +1,7 @@ --- title: "LoginRadius Launches a CLI for Enterprise Dashboard" date: "2023-01-16" -coverImage: "cli-1.png" +coverImage: "cli-1.webp" author: "Kundan Singh" tags: ["enterprise", "admin console", "developers"] description: "We are happy to announce that we have launched LoginRadius CLI for enterprise dashboard." @@ -35,7 +35,7 @@ To add a domain through LoginRadius Admin Console, you need to: \ On the flip side, you can do this by running a single command: - + **Here are some more of LoginRadius CLI Enterprise's commands:** @@ -43,7 +43,7 @@ On the flip side, you can do this by running a single command: **1. Login/Logout to your LoginRadius Dashboard** - + This command (_lr login_) will help you to login to your LoginRadius Enterprise Dashboard. Once logged in, you can perform other operations and configure your LoginRadius Application through CLI. @@ -51,7 +51,7 @@ This command (_lr login_) will help you to login to your LoginRadius Enterprise **2. Manage Application Credentials** - + You can get our App Credentials, reset Secret key, update account password and generate SOTT through LoginRadius CLI. @@ -59,7 +59,7 @@ You can get our App Credentials, reset Secret key, update account password and g **Set Schema for Your LoginRadius Application** - + @@ -68,7 +68,7 @@ This command will help you set the schema for your application. We can get all t **Theme Management (LoginRadius Page)** - + You can update the LoginRadius IDX Page(Hosted Page) from the available themes through LoginRadius CLI commands. @@ -87,4 +87,4 @@ We hope you will love trying LoginRadius CLI for Enterprise Dashboard. We will a We are eager to know your feedback, test cases and also what we can bring up next in our CLI. If you have any suggestions, please create an issue on our [open source github repository](https://github.com/LoginRadius/lr-cli/issues). -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-launches-cli-enterprise-dashboard) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=loginradius-launches-cli-enterprise-dashboard) diff --git a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.png b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.png deleted file mode 100644 index 70406afa9..000000000 Binary files a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.png and /dev/null differ diff --git a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.webp b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.webp new file mode 100644 index 000000000..a05b6946a Binary files /dev/null and b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/hacktober-fest-banner.webp differ diff --git a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/index.md b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/index.md index 656b2d096..0ab4f6355 100644 --- a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/index.md +++ b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/index.md @@ -1,7 +1,7 @@ --- title: "LoginRadius Open Source For Hacktoberfest 2020" date: "2020-09-25" -coverImage: "hacktober-fest-banner.png" +coverImage: "hacktober-fest-banner.webp" author: "Hridayesh Sharma" description: "Checkout LoginRadius Open Source Repositories where you can contribute for hackotberfest 2020" tags: ["hacktoberfest", "open-source", "LoginRadius"] @@ -15,7 +15,7 @@ Just 1 week left in hacktoberfest 2020 and being part of it, we at LoginRadius a **Here is a list of our open source projects available on Github for hacktoberfest 2020** - + - [LoginRadius Engineering Portal](https://github.com/LoginRadius/engineering-portal) - Our Engineering Blog where you can contribute by writing a guest blog of fixing any issue you find with any of the available blogs. diff --git a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.png b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.png deleted file mode 100644 index 60a409a33..000000000 Binary files a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.png and /dev/null differ diff --git a/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.webp b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.webp new file mode 100644 index 000000000..e7547b6d0 Binary files /dev/null and b/content/engineering/loginradius-opensource-repos-for-hacktoberfest-2020/lr-open-source.webp differ diff --git a/content/engineering/loginradius-sponsorship-freecodecamp/cover.png b/content/engineering/loginradius-sponsorship-freecodecamp/cover.png deleted file mode 100644 index 6f8b4663f..000000000 Binary files a/content/engineering/loginradius-sponsorship-freecodecamp/cover.png and /dev/null differ diff --git a/content/engineering/loginradius-sponsorship-freecodecamp/cover.webp b/content/engineering/loginradius-sponsorship-freecodecamp/cover.webp new file mode 100644 index 000000000..1c4016f1d Binary files /dev/null and b/content/engineering/loginradius-sponsorship-freecodecamp/cover.webp differ diff --git a/content/engineering/loginradius-sponsorship-freecodecamp/index.md b/content/engineering/loginradius-sponsorship-freecodecamp/index.md index 91f154505..90af4fbd3 100644 --- a/content/engineering/loginradius-sponsorship-freecodecamp/index.md +++ b/content/engineering/loginradius-sponsorship-freecodecamp/index.md @@ -1,7 +1,7 @@ --- title: "One Vision, Many Paths: How We’re Supporting freeCodeCamp" date: "2021-07-16" -coverImage: "cover.png" +coverImage: "cover.webp" author: "Raghunath Reddy" tags: ["LoginRadius", "sponsorship", "freeCodeCamp"] description: "LoginRadius now supports the freeCodeCamp community through a sponsorship program. We also offer $200 credits to freeCodeCamp developers to help them rapidly implement world-class customer identity and access management in their applications." diff --git a/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.png b/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.png deleted file mode 100644 index 70406afa9..000000000 Binary files a/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.png and /dev/null differ diff --git a/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.webp b/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.webp new file mode 100644 index 000000000..a05b6946a Binary files /dev/null and b/content/engineering/loginradius-supports-hacktoberfest-2020/hacktober-fest-banner.webp differ diff --git a/content/engineering/loginradius-supports-hacktoberfest-2020/index.md b/content/engineering/loginradius-supports-hacktoberfest-2020/index.md index d4aba5242..197116dc9 100644 --- a/content/engineering/loginradius-supports-hacktoberfest-2020/index.md +++ b/content/engineering/loginradius-supports-hacktoberfest-2020/index.md @@ -1,7 +1,7 @@ --- title: "LoginRadius Supports Hacktoberfest 2020" date: "2020-09-18" -coverImage: "hacktober-fest-banner.png" +coverImage: "hacktober-fest-banner.webp" author: "Hridayesh Sharma" description: "Open Source is changing the world, One Pull Request at a time. Join LoginRadius this year in supporting hacktoerbest 2020 by contributing to open source and get cool swags from LoginRadius" tags: ["hacktoberfest", "open-source", "LoginRadius"] diff --git a/content/engineering/loginscreen-testing-tips/CoverImage.jpg b/content/engineering/loginscreen-testing-tips/CoverImage.jpg deleted file mode 100644 index 42d7d27a2..000000000 Binary files a/content/engineering/loginscreen-testing-tips/CoverImage.jpg and /dev/null differ diff --git a/content/engineering/loginscreen-testing-tips/CoverImage.webp b/content/engineering/loginscreen-testing-tips/CoverImage.webp new file mode 100644 index 000000000..b488b239c Binary files /dev/null and b/content/engineering/loginscreen-testing-tips/CoverImage.webp differ diff --git a/content/engineering/loginscreen-testing-tips/Login-Page.png b/content/engineering/loginscreen-testing-tips/Login-Page.png deleted file mode 100644 index cbc4ba713..000000000 Binary files a/content/engineering/loginscreen-testing-tips/Login-Page.png and /dev/null differ diff --git a/content/engineering/loginscreen-testing-tips/Login-Page.webp b/content/engineering/loginscreen-testing-tips/Login-Page.webp new file mode 100644 index 000000000..ef7be3907 Binary files /dev/null and b/content/engineering/loginscreen-testing-tips/Login-Page.webp differ diff --git a/content/engineering/loginscreen-testing-tips/index.md b/content/engineering/loginscreen-testing-tips/index.md index 6b59a35ee..ddcfcbbcb 100644 --- a/content/engineering/loginscreen-testing-tips/index.md +++ b/content/engineering/loginscreen-testing-tips/index.md @@ -2,7 +2,7 @@ title: "Login Screen - Tips and Ideas for Testing" date: "2020-10-30" author: "Sudhey Sharma" -coverImage: "CoverImage.jpg" +coverImage: "CoverImage.webp" tags: ["LoginScreen", "TestingTips"] description: "Login process is the most important feature for any system/application as it provides access to an entire web-site/application or part of it. This article is providing you with some important tips & ideas about login testing." --- @@ -10,7 +10,7 @@ description: "Login process is the most important feature for any system/applica A **login screen** is a web **page** or an entry **page** to a web/mobile application that requires user identification and authentication, regularly performed by entering a username and password combination. The login process is the most essential feature for any system/application as it provides access to an entire **web-site/application** or part of it. So, testing of the login screen needs complete coverage. - + Mentioned below are few tips that can be referred for testing the login screen of any system/application. diff --git a/content/engineering/memcach-memory-management/index.md b/content/engineering/memcach-memory-management/index.md index 753f00618..c73c605b4 100644 --- a/content/engineering/memcach-memory-management/index.md +++ b/content/engineering/memcach-memory-management/index.md @@ -1,7 +1,7 @@ --- title: "Memcached Memory Management" date: "2015-07-07" -coverImage: "memcached-memory-management.png" +coverImage: "memcached-memory-management.webp" author: "Mark Duan" tags: ["Memory Management"] --- @@ -10,7 +10,7 @@ The [memcached](https://github.com/memcached) is one of the most popular open ### Chunk and Slab - + ```cpp /* powers-of-N allocation structures */ @@ -37,7 +37,7 @@ This is the struct declaration of slabclass\_t. Each slab class contains the sam The content value factor is defined when memcached memory is deployed with -f, which can change the size between slab classes. For this loop, the size is multiplied by a specified factor. - + You can get this information by adding -vvv and you can use the command diff --git a/content/engineering/memcach-memory-management/memcached-1.png b/content/engineering/memcach-memory-management/memcached-1.png deleted file mode 100644 index f6ba61e2c..000000000 Binary files a/content/engineering/memcach-memory-management/memcached-1.png and /dev/null differ diff --git a/content/engineering/memcach-memory-management/memcached-1.webp b/content/engineering/memcach-memory-management/memcached-1.webp new file mode 100644 index 000000000..c20fb6cac Binary files /dev/null and b/content/engineering/memcach-memory-management/memcached-1.webp differ diff --git a/content/engineering/memcach-memory-management/memcached-2.png b/content/engineering/memcach-memory-management/memcached-2.png deleted file mode 100644 index f3ca4a704..000000000 Binary files a/content/engineering/memcach-memory-management/memcached-2.png and /dev/null differ diff --git a/content/engineering/memcach-memory-management/memcached-2.webp b/content/engineering/memcach-memory-management/memcached-2.webp new file mode 100644 index 000000000..030973aa5 Binary files /dev/null and b/content/engineering/memcach-memory-management/memcached-2.webp differ diff --git a/content/engineering/memcach-memory-management/memcached-memory-management.png b/content/engineering/memcach-memory-management/memcached-memory-management.png deleted file mode 100644 index cdcf46e1d..000000000 Binary files a/content/engineering/memcach-memory-management/memcached-memory-management.png and /dev/null differ diff --git a/content/engineering/memcach-memory-management/memcached-memory-management.webp b/content/engineering/memcach-memory-management/memcached-memory-management.webp new file mode 100644 index 000000000..0cf8ad335 Binary files /dev/null and b/content/engineering/memcach-memory-management/memcached-memory-management.webp differ diff --git a/content/engineering/memcach-memory-management/memcached1.png b/content/engineering/memcach-memory-management/memcached1.png deleted file mode 100644 index f6ba61e2c..000000000 Binary files a/content/engineering/memcach-memory-management/memcached1.png and /dev/null differ diff --git a/content/engineering/memcach-memory-management/memcached1.webp b/content/engineering/memcach-memory-management/memcached1.webp new file mode 100644 index 000000000..c20fb6cac Binary files /dev/null and b/content/engineering/memcach-memory-management/memcached1.webp differ diff --git a/content/engineering/mongodb-as-datasource-in-golang/gomongo.png b/content/engineering/mongodb-as-datasource-in-golang/gomongo.png deleted file mode 100644 index 3a25b8c59..000000000 Binary files a/content/engineering/mongodb-as-datasource-in-golang/gomongo.png and /dev/null differ diff --git a/content/engineering/mongodb-as-datasource-in-golang/gomongo.webp b/content/engineering/mongodb-as-datasource-in-golang/gomongo.webp new file mode 100644 index 000000000..a120a6a10 Binary files /dev/null and b/content/engineering/mongodb-as-datasource-in-golang/gomongo.webp differ diff --git a/content/engineering/mongodb-as-datasource-in-golang/index.md b/content/engineering/mongodb-as-datasource-in-golang/index.md index a2a5d76c2..25b87fba6 100644 --- a/content/engineering/mongodb-as-datasource-in-golang/index.md +++ b/content/engineering/mongodb-as-datasource-in-golang/index.md @@ -1,7 +1,7 @@ --- title: Using MongoDB as Datasource in GoLang date: "2020-09-21" -coverImage: "gomongo.png" +coverImage: "gomongo.webp" author: "Puneet Singh" tags: ["Go","MongoDB"] description: "Learn how to use MongoDB as a data source for your Go application using the mongo-go driver" diff --git a/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.png b/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.png deleted file mode 100644 index eb80e51fa..000000000 Binary files a/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.png and /dev/null differ diff --git a/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.webp b/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.webp new file mode 100644 index 000000000..e96a60e28 Binary files /dev/null and b/content/engineering/my-name-is-darryl-this-is-how-work/darryl-how-i-work-300x300.webp differ diff --git a/content/engineering/my-name-is-darryl-this-is-how-work/index.md b/content/engineering/my-name-is-darryl-this-is-how-work/index.md index 6f91cccd4..85c1d4f1b 100644 --- a/content/engineering/my-name-is-darryl-this-is-how-work/index.md +++ b/content/engineering/my-name-is-darryl-this-is-how-work/index.md @@ -1,7 +1,7 @@ --- title: "Hi, My Name is Darryl, and This is How I Work" date: "2015-09-22" -coverImage: "darryl-how-i-work-300x300.png" +coverImage: "darryl-how-i-work-300x300.webp" author: "Team LoginRadius" tags: ["Tools", "Engineering"] --- @@ -39,4 +39,4 @@ As a normal human being — and not an extraterrestrial or alien as you tiny hum ### Getting out of a sticky situation -Now that my brain is full of design food. How do I put it to work? There's this thing called a notebook. If you don't know what that is. It looks like this.  This is where I start sketching or wireframing all the things I need before moving on to the digital format. And there you have it. A sneak peek on how I work. I hope that this gave you an idea on how to improve your everyday design life. A word of advice. _There are a thousand ways to do 1 thing. If someone told you it can't be done; prove them wrong._ +Now that my brain is full of design food. How do I put it to work? There's this thing called a notebook. If you don't know what that is. It looks like this.  This is where I start sketching or wireframing all the things I need before moving on to the digital format. And there you have it. A sneak peek on how I work. I hope that this gave you an idea on how to improve your everyday design life. A word of advice. _There are a thousand ways to do 1 thing. If someone told you it can't be done; prove them wrong._ diff --git a/content/engineering/my-name-is-darryl-this-is-how-work/notebook.jpg b/content/engineering/my-name-is-darryl-this-is-how-work/notebook.jpg deleted file mode 100644 index 7f2a41f29..000000000 Binary files a/content/engineering/my-name-is-darryl-this-is-how-work/notebook.jpg and /dev/null differ diff --git a/content/engineering/my-name-is-darryl-this-is-how-work/notebook.webp b/content/engineering/my-name-is-darryl-this-is-how-work/notebook.webp new file mode 100644 index 000000000..33ffc6666 Binary files /dev/null and b/content/engineering/my-name-is-darryl-this-is-how-work/notebook.webp differ diff --git a/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/index.md b/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/index.md index 03c99602a..da96acc23 100644 --- a/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/index.md +++ b/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/index.md @@ -1,7 +1,7 @@ --- title: "Nim Game, Add Digits, Maximum Depth of Binary Tree" date: "2015-11-24" -coverImage: "nim-blog-150x150.png" +coverImage: "nim-blog-150x150.webp" author: "Lucius Yu" tags: ["Nim", "JavaScript"] --- diff --git a/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.png b/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.png deleted file mode 100644 index fda13ab89..000000000 Binary files a/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.png and /dev/null differ diff --git a/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.webp b/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.webp new file mode 100644 index 000000000..f1f389943 Binary files /dev/null and b/content/engineering/nim-game-add-digits-maximum-depth-of-binary-tree/nim-blog-150x150.webp differ diff --git a/content/engineering/node-http-module-server/coverImage.jpg b/content/engineering/node-http-module-server/coverImage.jpg deleted file mode 100644 index 811d5d360..000000000 Binary files a/content/engineering/node-http-module-server/coverImage.jpg and /dev/null differ diff --git a/content/engineering/node-http-module-server/coverImage.webp b/content/engineering/node-http-module-server/coverImage.webp new file mode 100644 index 000000000..d63acdaaa Binary files /dev/null and b/content/engineering/node-http-module-server/coverImage.webp differ diff --git a/content/engineering/node-http-module-server/index.md b/content/engineering/node-http-module-server/index.md index 6e4b3c0f6..ebfd7014c 100644 --- a/content/engineering/node-http-module-server/index.md +++ b/content/engineering/node-http-module-server/index.md @@ -1,7 +1,7 @@ --- title: "NodeJS Server using Core HTTP Module" date: "2020-11-27" -coverImage: "coverImage.jpg" +coverImage: "coverImage.webp" author: "Hridayesh Sharma" tags: ["NodeJs", "JavaScript"] description: "Let us understand the core http module in NodeJS, which is the basic building block of frameworks like ExpressJS etc." diff --git a/content/engineering/node-package-manager-npm/image1.png b/content/engineering/node-package-manager-npm/image1.png deleted file mode 100644 index f15704fc4..000000000 Binary files a/content/engineering/node-package-manager-npm/image1.png and /dev/null differ diff --git a/content/engineering/node-package-manager-npm/image1.webp b/content/engineering/node-package-manager-npm/image1.webp new file mode 100644 index 000000000..0c9b03b04 Binary files /dev/null and b/content/engineering/node-package-manager-npm/image1.webp differ diff --git a/content/engineering/node-package-manager-npm/index.md b/content/engineering/node-package-manager-npm/index.md index e619106dd..f34f129b0 100644 --- a/content/engineering/node-package-manager-npm/index.md +++ b/content/engineering/node-package-manager-npm/index.md @@ -1,12 +1,12 @@ --- title: "Node Package Manager (NPM)" date: "2017-08-04" -coverImage: "the-guide-to-NPM.png" +coverImage: "the-guide-to-NPM.webp" author: "Eric Chan" tags: ["NodeJs", "NPM"] --- -##### What is This, and Why Should I Care? +##### What is This, and Why Should I Care? NPM is a package manager for javascript. It is used to share and distribute code amongst the coding community. There are over half a million packages for free developed and shared to help your JavaScript development. @@ -32,7 +32,7 @@ Head over here to search for your package. Once you’ve found it, type in your Since NPM packages are open-source, be wary that some of the packages may not be built correctly. A good way to tell would be viewing the top of the page for any errors. - + ##### How Do I Keep My Packages Up-To-Date? diff --git a/content/engineering/node-package-manager-npm/the-guide-to-NPM.png b/content/engineering/node-package-manager-npm/the-guide-to-NPM.png deleted file mode 100644 index 3697a6b32..000000000 Binary files a/content/engineering/node-package-manager-npm/the-guide-to-NPM.png and /dev/null differ diff --git a/content/engineering/node-package-manager-npm/the-guide-to-NPM.webp b/content/engineering/node-package-manager-npm/the-guide-to-NPM.webp new file mode 100644 index 000000000..63167a85d Binary files /dev/null and b/content/engineering/node-package-manager-npm/the-guide-to-NPM.webp differ diff --git a/content/engineering/nullable-csharp/coverimage.jpg b/content/engineering/nullable-csharp/coverimage.jpg deleted file mode 100644 index b385d9396..000000000 Binary files a/content/engineering/nullable-csharp/coverimage.jpg and /dev/null differ diff --git a/content/engineering/nullable-csharp/coverimage.webp b/content/engineering/nullable-csharp/coverimage.webp new file mode 100644 index 000000000..fd08894e2 Binary files /dev/null and b/content/engineering/nullable-csharp/coverimage.webp differ diff --git a/content/engineering/nullable-csharp/index.md b/content/engineering/nullable-csharp/index.md index 2429b7f89..49fed967a 100644 --- a/content/engineering/nullable-csharp/index.md +++ b/content/engineering/nullable-csharp/index.md @@ -1,7 +1,7 @@ --- title: "How to Work with Nullable Types in C#" date: "2021-01-29" -coverImage: "coverimage.jpg" +coverImage: "coverimage.webp" author: "Hemant Manwani" tags: ["C#","Nullable"] description: "Nullable is a term in C# that allows an extra value null to be owned by a form. We will learn in this article how to work with Nullable types in C#." diff --git a/content/engineering/oAuth-implemenation-using-node/git_new_app.jpg b/content/engineering/oAuth-implemenation-using-node/git_new_app.jpg deleted file mode 100644 index 367d28e06..000000000 Binary files a/content/engineering/oAuth-implemenation-using-node/git_new_app.jpg and /dev/null differ diff --git a/content/engineering/oAuth-implemenation-using-node/git_new_app.webp b/content/engineering/oAuth-implemenation-using-node/git_new_app.webp new file mode 100644 index 000000000..658cbd709 Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/git_new_app.webp differ diff --git a/content/engineering/oAuth-implemenation-using-node/github_auth.jpg b/content/engineering/oAuth-implemenation-using-node/github_auth.jpg deleted file mode 100644 index 417fd40e7..000000000 Binary files a/content/engineering/oAuth-implemenation-using-node/github_auth.jpg and /dev/null differ diff --git a/content/engineering/oAuth-implemenation-using-node/github_auth.webp b/content/engineering/oAuth-implemenation-using-node/github_auth.webp new file mode 100644 index 000000000..c9bca4b3b Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/github_auth.webp differ diff --git a/content/engineering/oAuth-implemenation-using-node/github_cred.jpg b/content/engineering/oAuth-implemenation-using-node/github_cred.jpg deleted file mode 100644 index 1a5e56be6..000000000 Binary files a/content/engineering/oAuth-implemenation-using-node/github_cred.jpg and /dev/null differ diff --git a/content/engineering/oAuth-implemenation-using-node/github_cred.webp b/content/engineering/oAuth-implemenation-using-node/github_cred.webp new file mode 100644 index 000000000..d97be192b Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/github_cred.webp differ diff --git a/content/engineering/oAuth-implemenation-using-node/github_login.jpg b/content/engineering/oAuth-implemenation-using-node/github_login.jpg deleted file mode 100644 index 59f6e3ab1..000000000 Binary files a/content/engineering/oAuth-implemenation-using-node/github_login.jpg and /dev/null differ diff --git a/content/engineering/oAuth-implemenation-using-node/github_login.webp b/content/engineering/oAuth-implemenation-using-node/github_login.webp new file mode 100644 index 000000000..4d11a0801 Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/github_login.webp differ diff --git a/content/engineering/oAuth-implemenation-using-node/github_profile.jpg b/content/engineering/oAuth-implemenation-using-node/github_profile.jpg deleted file mode 100644 index a5014c67e..000000000 Binary files a/content/engineering/oAuth-implemenation-using-node/github_profile.jpg and /dev/null differ diff --git a/content/engineering/oAuth-implemenation-using-node/github_profile.webp b/content/engineering/oAuth-implemenation-using-node/github_profile.webp new file mode 100644 index 000000000..5ab785f14 Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/github_profile.webp differ diff --git a/content/engineering/oAuth-implemenation-using-node/index.md b/content/engineering/oAuth-implemenation-using-node/index.md index 094f8aece..227409ece 100644 --- a/content/engineering/oAuth-implemenation-using-node/index.md +++ b/content/engineering/oAuth-implemenation-using-node/index.md @@ -1,7 +1,7 @@ --- title: "OAuth implementation with Node.js and Github" date: "2020-03-22" -coverImage: "oauth.png" +coverImage: "oauth.webp" author: "Puneet Singh" tags: ["Oauth", "NodeJs"] canonical: https://www.loginradius.com/blog/engineering/google-authentication-with-nodejs-and-passportjs/ @@ -23,14 +23,14 @@ To implement Github Auth we need to register a new application in [Github OAuth Once you start the process you will get a form like this. - + You need to fill all the required details and put the Authorization callback URL as `http://localhost:2400/github/callback` (This will be the URL on which Github will send the authorization code once authorization is finished) Once you register the application you will get the App's Client Id and Secret which we will use in our code. - + @@ -200,15 +200,15 @@ node index.js Once our server is running, we can see our social login page on `http://localhost:2400/` - + We need to click on the **Github Login button**, which will redirect us to google login page. - + After login with our GitHub credentials, it will redirect back to our application and on the success page, we can see the details of users' GitHub profile and can save this detail in a database for future use also. - + You can implement the OAuth in Node.js by the above process, You can found the complete code used in this tutorial on out diff --git a/content/engineering/oAuth-implemenation-using-node/oauth.png b/content/engineering/oAuth-implemenation-using-node/oauth.png deleted file mode 100644 index 790e19a37..000000000 Binary files a/content/engineering/oAuth-implemenation-using-node/oauth.png and /dev/null differ diff --git a/content/engineering/oAuth-implemenation-using-node/oauth.webp b/content/engineering/oAuth-implemenation-using-node/oauth.webp new file mode 100644 index 000000000..7e9e91ff4 Binary files /dev/null and b/content/engineering/oAuth-implemenation-using-node/oauth.webp differ diff --git a/content/engineering/oauth2/image2.png b/content/engineering/oauth2/image2.png deleted file mode 100644 index d24853faf..000000000 Binary files a/content/engineering/oauth2/image2.png and /dev/null differ diff --git a/content/engineering/oauth2/image2.webp b/content/engineering/oauth2/image2.webp new file mode 100644 index 000000000..920c9987c Binary files /dev/null and b/content/engineering/oauth2/image2.webp differ diff --git a/content/engineering/oauth2/image3.png b/content/engineering/oauth2/image3.png deleted file mode 100644 index 8994b0ccb..000000000 Binary files a/content/engineering/oauth2/image3.png and /dev/null differ diff --git a/content/engineering/oauth2/image3.webp b/content/engineering/oauth2/image3.webp new file mode 100644 index 000000000..9c40253dc Binary files /dev/null and b/content/engineering/oauth2/image3.webp differ diff --git a/content/engineering/oauth2/image4.png b/content/engineering/oauth2/image4.png deleted file mode 100644 index 163cdd137..000000000 Binary files a/content/engineering/oauth2/image4.png and /dev/null differ diff --git a/content/engineering/oauth2/image4.webp b/content/engineering/oauth2/image4.webp new file mode 100644 index 000000000..2b7270832 Binary files /dev/null and b/content/engineering/oauth2/image4.webp differ diff --git a/content/engineering/oauth2/index.md b/content/engineering/oauth2/index.md index 6b91e8e28..a43fb9e20 100644 --- a/content/engineering/oauth2/index.md +++ b/content/engineering/oauth2/index.md @@ -1,7 +1,7 @@ --- title: Getting Started with OAuth 2.0 date: "2020-08-24" -coverImage: "oauth2.png" +coverImage: "oauth2.webp" author: "Indrasen Kumar" tags: ["Engineering", "Oauth", "Authentication"] description: "Using this blog one can easily understand the basic concept of Oauth 2.0" @@ -41,7 +41,7 @@ In total, there are five different grant type flows defined and described to per ### Authorization Code Grant The Authorization Code Grant Type is the most commonly used grant type. - + **The Story:** A user tries to log in on abc.com but he can’t remember his password and he discovers an option to sign in with google, by clicking on this, the user will easily get logged using google account. @@ -72,7 +72,7 @@ In the entire flow, the access token is never exposed to a web browser. ### Implicit Grant The Implicit flow was a simplified OAuth flow previously recommended for client-side applications like JavaScript apps where the access token was returned immediately without an extra authorization code exchange step. - + The Story: In this flow abc.com directly get access token without an extra authorization code exchange steps and able to access resources on a resource server @@ -108,7 +108,7 @@ The client then sends a POST request with following body parameters to the autho Using this flow the client can request an access token using only its client credentials (or other supported means of authentication). - + **The Story:** The client application presents its client credentials (client identifier and client secret) to the authorization server requesting approval to access the protected resource (owned by the client application) on the resource server. The authorization server authenticates the client credential and issues an access token. diff --git a/content/engineering/oauth2/oauth2.png b/content/engineering/oauth2/oauth2.png deleted file mode 100644 index c91932ab6..000000000 Binary files a/content/engineering/oauth2/oauth2.png and /dev/null differ diff --git a/content/engineering/oauth2/oauth2.webp b/content/engineering/oauth2/oauth2.webp new file mode 100644 index 000000000..6baa070f2 Binary files /dev/null and b/content/engineering/oauth2/oauth2.webp differ diff --git a/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.png b/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.png deleted file mode 100644 index f3774cd10..000000000 Binary files a/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.png and /dev/null differ diff --git a/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.webp b/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.webp new file mode 100644 index 000000000..18b7cc390 Binary files /dev/null and b/content/engineering/okta-and-the-lapsus-breach/how-lapsus-breached-okta.webp differ diff --git a/content/engineering/okta-and-the-lapsus-breach/index.md b/content/engineering/okta-and-the-lapsus-breach/index.md index 90173cd80..7da2586fa 100644 --- a/content/engineering/okta-and-the-lapsus-breach/index.md +++ b/content/engineering/okta-and-the-lapsus-breach/index.md @@ -1,7 +1,7 @@ --- title: "How Lapsus$ Breached Okta and What Organizations Should Learn" date: "2022-03-25" -coverImage: "how-lapsus-breached-okta.png" +coverImage: "how-lapsus-breached-okta.webp" author: "Kundan Singh" tags: ["Breach", "Cybersecurity"] description: "Businesses have to be extra vigilant in safeguarding customer data. Minor mistakes can cause a massive data breach, violating data privacy regulations and attracting penalties from regulatory authorities." @@ -87,4 +87,4 @@ In this specific example, the hackers accessed the laptop of one of Okta's custo However, it offers a valuable learning experience that business entities should not ignore the minutest of details regarding network security. It surfaces the adage that ' A chain is only as strong as its weakest link.' -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=okta-and-the-lapsus-breach) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=okta-and-the-lapsus-breach) \ No newline at end of file diff --git a/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.png b/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.png deleted file mode 100644 index ade48958e..000000000 Binary files a/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.png and /dev/null differ diff --git a/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.webp b/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.webp new file mode 100644 index 000000000..5dcf1865c Binary files /dev/null and b/content/engineering/open-source-business-email-validator-by-loginradius/Open-Source-Business-Validator-By-Loginradius.webp differ diff --git a/content/engineering/open-source-business-email-validator-by-loginradius/index.md b/content/engineering/open-source-business-email-validator-by-loginradius/index.md index b5437d80b..cad687a08 100644 --- a/content/engineering/open-source-business-email-validator-by-loginradius/index.md +++ b/content/engineering/open-source-business-email-validator-by-loginradius/index.md @@ -1,7 +1,7 @@ --- title: "Open Source Business Email Validator By Loginradius" date: "2017-04-25" -coverImage: "Open-Source-Business-Validator-By-Loginradius.png" +coverImage: "Open-Source-Business-Validator-By-Loginradius.webp" author: "Team LoginRadius" tags: ["Engineering"] --- diff --git a/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.png b/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.png deleted file mode 100644 index 52eff7be5..000000000 Binary files a/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.png and /dev/null differ diff --git a/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.webp b/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.webp new file mode 100644 index 000000000..18290289a Binary files /dev/null and b/content/engineering/opensource-Automation-for-identity-experience-framework/automation_ief.webp differ diff --git a/content/engineering/opensource-Automation-for-identity-experience-framework/index.md b/content/engineering/opensource-Automation-for-identity-experience-framework/index.md index c20529e2d..b19fc66db 100644 --- a/content/engineering/opensource-Automation-for-identity-experience-framework/index.md +++ b/content/engineering/opensource-Automation-for-identity-experience-framework/index.md @@ -1,7 +1,7 @@ --- title: "Automation for Identity Experience Framework is now open-source !!!" date: "2020-06-04" -coverImage: automation_ief.png +coverImage: automation_ief.webp author: Sudhey Sharma tags: ["OpenSource","Automation"] canonical: https://www.loginradius.com/blog/identity/loginradius-identity-experience-framework/ diff --git a/content/engineering/optimize-jquery-sizzle-element-selector/index.md b/content/engineering/optimize-jquery-sizzle-element-selector/index.md index f6e514036..65c256675 100644 --- a/content/engineering/optimize-jquery-sizzle-element-selector/index.md +++ b/content/engineering/optimize-jquery-sizzle-element-selector/index.md @@ -1,7 +1,7 @@ --- title: "Optimize jQuery & Sizzle Element Selector" date: "2015-11-05" -coverImage: "jquery-sizzle-element-selector-150x150.png" +coverImage: "jquery-sizzle-element-selector-150x150.webp" author: "Kundan Singh" tags: ["Engineering", "JQuery"] --- diff --git a/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.png b/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.png deleted file mode 100644 index 335e64012..000000000 Binary files a/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.png and /dev/null differ diff --git a/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.webp b/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.webp new file mode 100644 index 000000000..e59793c83 Binary files /dev/null and b/content/engineering/optimize-jquery-sizzle-element-selector/jquery-sizzle-element-selector-150x150.webp differ diff --git a/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.png b/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.png deleted file mode 100644 index a94d36663..000000000 Binary files a/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.png and /dev/null differ diff --git a/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.webp b/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.webp new file mode 100644 index 000000000..1e2555cbe Binary files /dev/null and b/content/engineering/part-2-creating-a-custom-login-form/cust-login-2-150x150.webp differ diff --git a/content/engineering/part-2-creating-a-custom-login-form/index.md b/content/engineering/part-2-creating-a-custom-login-form/index.md index d9c3d7eb8..45db03c04 100644 --- a/content/engineering/part-2-creating-a-custom-login-form/index.md +++ b/content/engineering/part-2-creating-a-custom-login-form/index.md @@ -1,7 +1,7 @@ --- title: "Part 2 - Creating a Custom Login Form" date: "2015-12-08" -coverImage: "cust-login-2-150x150.png" +coverImage: "cust-login-2-150x150.webp" author: "Zoie Carnegie" tags: ["Engineering", "Login"] --- @@ -10,7 +10,7 @@ In this tutorial I will demonstrate how to build a custom login form scratch. Th ## Building a Custom Login Form - + This is what WordPress gives us out of the box.. Boring, right? @@ -47,7 +47,7 @@ Remember me ``` - + Let's take a look at that custom form diff --git a/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.png b/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.png deleted file mode 100644 index 6f299ebdf..000000000 Binary files a/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.png and /dev/null differ diff --git a/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.webp b/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.webp new file mode 100644 index 000000000..45a3145aa Binary files /dev/null and b/content/engineering/part-2-creating-a-custom-login-form/login-2-custom.webp differ diff --git a/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.png b/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.png deleted file mode 100644 index 59ae3519c..000000000 Binary files a/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.png and /dev/null differ diff --git a/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.webp b/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.webp new file mode 100644 index 000000000..984450396 Binary files /dev/null and b/content/engineering/part-2-creating-a-custom-login-form/wp-login-boring.webp differ diff --git a/content/engineering/password-hashing-with-nodejs/cover.png b/content/engineering/password-hashing-with-nodejs/cover.png deleted file mode 100644 index 5d38968b6..000000000 Binary files a/content/engineering/password-hashing-with-nodejs/cover.png and /dev/null differ diff --git a/content/engineering/password-hashing-with-nodejs/cover.webp b/content/engineering/password-hashing-with-nodejs/cover.webp new file mode 100644 index 000000000..9a7ca0d78 Binary files /dev/null and b/content/engineering/password-hashing-with-nodejs/cover.webp differ diff --git a/content/engineering/password-hashing-with-nodejs/index.md b/content/engineering/password-hashing-with-nodejs/index.md index 36d41c9e6..a0bdff893 100644 --- a/content/engineering/password-hashing-with-nodejs/index.md +++ b/content/engineering/password-hashing-with-nodejs/index.md @@ -1,7 +1,7 @@ --- title: "Password hashing with NodeJS" date: "2020-06-25" -coverImage: "cover.png" +coverImage: "cover.webp" author: "Ashish Sharma" tags: ["Security", "NodeJs"] --- diff --git a/content/engineering/password-secure/index.md b/content/engineering/password-secure/index.md index 55d6cd708..cefec144d 100644 --- a/content/engineering/password-secure/index.md +++ b/content/engineering/password-secure/index.md @@ -1,7 +1,7 @@ --- title: "Password Security" date: "2015-05-14" -coverImage: "password-security.png" +coverImage: "password-security.webp" author: "Kundan Singh" tags: ["Security", "Password"] --- diff --git a/content/engineering/password-secure/password-security.png b/content/engineering/password-secure/password-security.png deleted file mode 100644 index 00ed50cdc..000000000 Binary files a/content/engineering/password-secure/password-security.png and /dev/null differ diff --git a/content/engineering/password-secure/password-security.webp b/content/engineering/password-secure/password-security.webp new file mode 100644 index 000000000..8c949da5c Binary files /dev/null and b/content/engineering/password-secure/password-security.webp differ diff --git a/content/engineering/password-security-best-practices-compliance/index.md b/content/engineering/password-security-best-practices-compliance/index.md index 603344b09..613d3f394 100644 --- a/content/engineering/password-security-best-practices-compliance/index.md +++ b/content/engineering/password-security-best-practices-compliance/index.md @@ -1,7 +1,7 @@ --- title: "Password Security Best Practices & Compliance" date: "2020-11-12" -coverImage: "password-security.jpg" +coverImage: "password-security.webp" author: "Vijay Singh Shekhawat" tags: ["Security", "Password","Compliance","Passowrd Policy"] --- diff --git a/content/engineering/password-security-best-practices-compliance/password-security.jpg b/content/engineering/password-security-best-practices-compliance/password-security.jpg deleted file mode 100644 index beb0419c4..000000000 Binary files a/content/engineering/password-security-best-practices-compliance/password-security.jpg and /dev/null differ diff --git a/content/engineering/password-security-best-practices-compliance/password-security.webp b/content/engineering/password-security-best-practices-compliance/password-security.webp new file mode 100644 index 000000000..31495200f Binary files /dev/null and b/content/engineering/password-security-best-practices-compliance/password-security.webp differ diff --git a/content/engineering/personal-branding-for-developers/Apple-logo-248x300.png b/content/engineering/personal-branding-for-developers/Apple-logo-248x300.png deleted file mode 100644 index 7c58bfb68..000000000 Binary files a/content/engineering/personal-branding-for-developers/Apple-logo-248x300.png and /dev/null differ diff --git a/content/engineering/personal-branding-for-developers/Apple-logo-248x300.webp b/content/engineering/personal-branding-for-developers/Apple-logo-248x300.webp new file mode 100644 index 000000000..6fa4c91af Binary files /dev/null and b/content/engineering/personal-branding-for-developers/Apple-logo-248x300.webp differ diff --git a/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.jpg b/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.jpg deleted file mode 100644 index 2f7f49b0e..000000000 Binary files a/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.jpg and /dev/null differ diff --git a/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.webp b/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.webp new file mode 100644 index 000000000..4a2b962c9 Binary files /dev/null and b/content/engineering/personal-branding-for-developers/Personal-Branding-For-Developers-150x150.webp differ diff --git a/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.jpg b/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.jpg deleted file mode 100644 index 1f93205a2..000000000 Binary files a/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.jpg and /dev/null differ diff --git a/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.webp b/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.webp new file mode 100644 index 000000000..fe4565ad9 Binary files /dev/null and b/content/engineering/personal-branding-for-developers/Social-media-for-personal-branding.webp differ diff --git a/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.jpg b/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.jpg deleted file mode 100644 index d49fd0add..000000000 Binary files a/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.jpg and /dev/null differ diff --git a/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.webp b/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.webp new file mode 100644 index 000000000..b0273cdf5 Binary files /dev/null and b/content/engineering/personal-branding-for-developers/blogging-for-personal-branding.webp differ diff --git a/content/engineering/personal-branding-for-developers/index.md b/content/engineering/personal-branding-for-developers/index.md index 743364b85..fa75049c3 100644 --- a/content/engineering/personal-branding-for-developers/index.md +++ b/content/engineering/personal-branding-for-developers/index.md @@ -1,7 +1,7 @@ --- title: "Personal Branding For Developers: Why and How?" date: "2016-09-23" -coverImage: "Personal-Branding-For-Developers-150x150.jpg" +coverImage: "Personal-Branding-For-Developers-150x150.webp" author: "Sreekant" tags: ["Branding"] --- @@ -12,7 +12,7 @@ In this article I am going to focus on why as a developer you should focus on pe **What is personal branding?** -Do you recognize this logo? Well, Of course you do! But have you ever wondered how come you recognized this logo without even a name? Well, you recognized it because the brand is so strong that without even a proper title, you are able to recognize it and that’s what branding do. +Do you recognize this logo? Well, Of course you do! But have you ever wondered how come you recognized this logo without even a name? Well, you recognized it because the brand is so strong that without even a proper title, you are able to recognize it and that’s what branding do. The concept of personal branding is quite similar to that of company branding. Personal branding is all about thinking yourself as a brand. It is about showing people who you are and what is your passion. When you think about some specific programming language, your mind goes back to some specific names associated with that language, who are either the father of that language or have done some amazing work in that field, right? @@ -55,11 +55,11 @@ You might have the best expertise in certain technology, you might have designed 1. **Try your hand at blogging :** Blogging is an amazing way to tell people who you are. Blog about anything you hold expertize in, whether it is a programming language or it is some kind of technology, let people understand who you actually are. There are many developers out there who have some awesome technical blogs where they share their knowledge and write about their specialities.For inspiration you can have a look at the blog of [John Resig](http://ejohn.org/), the creator and founder of jQuery. Another tech blog champion is Scott Hanselman. Make sure to have a look on his popular blogs [www.hanselman.com](http://www.hanselman.com), [hanselminutes](http://hanselminutes.com/), etc. - Stick to one topic, you are best at and select the blogging platform that suits you like Wordpress, Tumblr, Blogspot, etc. Post informative content on regular basis and soon you will have a huge audience waiting for your content and engaging with you. Posting two to three informative blog is enough to keep you in demand. Also there are some specific sites like[www.asp.net](http://www.asp.net) where you can submit articles to gain immense popularity. + Stick to one topic, you are best at and select the blogging platform that suits you like Wordpress, Tumblr, Blogspot, etc. Post informative content on regular basis and soon you will have a huge audience waiting for your content and engaging with you. Posting two to three informative blog is enough to keep you in demand. Also there are some specific sites like[www.asp.net](http://www.asp.net) where you can submit articles to gain immense popularity. 2. **Embrace Social Media :** You might have heard that Facebook and Twitter are all about wasting time, but let me tell you this is not at all true. Social media provides you a great opportunity to build networks. It is must to get visibility on various social media networks if you want to be found by people who share same niche as you. -  +  There are various ways how you can track your brand on social media. My personal favorite is Google Alert which notifies whenever people are talking about me or my projects. While some times they are talking about the work I have done, sometimes they also complaint which helps me understand where I am wrong. There are many others, like on Twitter, you can use [Tweetdeck](https://tweetdeck.twitter.com/) . Apart from that, create a strong persona on Linkedin, Facebook, Google+, etc. Interact with people, reply to their queries and become social media champion. Some popular developers who are social media champions as well include [Scott Hanselman](https://twitter.com/shanselman), [John Resig](https://www.linkedin.com/in/jeresig), etc diff --git a/content/engineering/pkce/index.md b/content/engineering/pkce/index.md index 98fc887d8..02d4ddc41 100644 --- a/content/engineering/pkce/index.md +++ b/content/engineering/pkce/index.md @@ -2,7 +2,7 @@ title: "PKCE: What it is and how to use it with OAuth 2.0" date: "2020-09-03" author: "Narendra Pareek" -coverImage: "pkce.png" +coverImage: "pkce.webp" tags: ["PKCE", "Oauth", "OIDC"] description: "If you are working with OAuth and OIDC authorization code flow and want to setup PKCE flow then this article will help you to understand everything about PKCE." --- diff --git a/content/engineering/pkce/pkce.png b/content/engineering/pkce/pkce.png deleted file mode 100644 index 32e0aa702..000000000 Binary files a/content/engineering/pkce/pkce.png and /dev/null differ diff --git a/content/engineering/pkce/pkce.webp b/content/engineering/pkce/pkce.webp new file mode 100644 index 000000000..44ade1d0e Binary files /dev/null and b/content/engineering/pkce/pkce.webp differ diff --git a/content/engineering/production-grade-development-using-docker-compose/UserToSystem.png b/content/engineering/production-grade-development-using-docker-compose/UserToSystem.png deleted file mode 100644 index 7cb968452..000000000 Binary files a/content/engineering/production-grade-development-using-docker-compose/UserToSystem.png and /dev/null differ diff --git a/content/engineering/production-grade-development-using-docker-compose/UserToSystem.webp b/content/engineering/production-grade-development-using-docker-compose/UserToSystem.webp new file mode 100644 index 000000000..612555e27 Binary files /dev/null and b/content/engineering/production-grade-development-using-docker-compose/UserToSystem.webp differ diff --git a/content/engineering/production-grade-development-using-docker-compose/example-arch.png b/content/engineering/production-grade-development-using-docker-compose/example-arch.png deleted file mode 100644 index 21551b94a..000000000 Binary files a/content/engineering/production-grade-development-using-docker-compose/example-arch.png and /dev/null differ diff --git a/content/engineering/production-grade-development-using-docker-compose/example-arch.webp b/content/engineering/production-grade-development-using-docker-compose/example-arch.webp new file mode 100644 index 000000000..e0a2f80df Binary files /dev/null and b/content/engineering/production-grade-development-using-docker-compose/example-arch.webp differ diff --git a/content/engineering/production-grade-development-using-docker-compose/index.md b/content/engineering/production-grade-development-using-docker-compose/index.md index 251ea79ff..6858a4461 100644 --- a/content/engineering/production-grade-development-using-docker-compose/index.md +++ b/content/engineering/production-grade-development-using-docker-compose/index.md @@ -1,7 +1,7 @@ --- title: "Production Grade Development using Docker-Compose" date: "2020-09-11" -coverImage: "index.png" +coverImage: "index.webp" author: "Anurag Choudhary" tags: ["Docker", "Docker-compose"] --- @@ -28,7 +28,7 @@ the developer has two choices, create a script in a scripting language of choice Here in this *kind of* practical example, we are going to demonstrate a similar situation, where multiple containers talk to each other. We are going to use docker-compose as our primary tool to build and deploy images. - + The picture above depicts the architecture of a hypothetical portal of flash sale. @@ -54,7 +54,7 @@ You may fork a copy from here. ``` git clone https://github.com/LoginRadius/engineering-blog-samples/tree/master/Docker/docker-compose-dev-sample ``` - + ### The use of docker-compose and why? @@ -232,7 +232,7 @@ upstream apiserver{ The Nginx container opens port 80 to an external port 5500. The Nginx container keeps configuration where the user can see just one port 5500 from out of the system, everything else is gray. - + And this is, how it happens in the real world as well! @@ -254,7 +254,7 @@ To stop This scratches the surface of using docker-compose for a production-grade development environment. - + Thanks for reading the blog. For detailed information and execution example of this blog, please refer to the video below: diff --git a/content/engineering/production-grade-development-using-docker-compose/index.png b/content/engineering/production-grade-development-using-docker-compose/index.png deleted file mode 100644 index a58184170..000000000 Binary files a/content/engineering/production-grade-development-using-docker-compose/index.png and /dev/null differ diff --git a/content/engineering/production-grade-development-using-docker-compose/index.webp b/content/engineering/production-grade-development-using-docker-compose/index.webp new file mode 100644 index 000000000..5cd8db50d Binary files /dev/null and b/content/engineering/production-grade-development-using-docker-compose/index.webp differ diff --git a/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.png b/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.png deleted file mode 100644 index b6d4b3c93..000000000 Binary files a/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.png and /dev/null differ diff --git a/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.webp b/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.webp new file mode 100644 index 000000000..0baff8079 Binary files /dev/null and b/content/engineering/production-grade-development-using-docker-compose/noanimalsharmed.webp differ diff --git a/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.jpg b/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.jpg deleted file mode 100644 index c45218a0e..000000000 Binary files a/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.jpg and /dev/null differ diff --git a/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.webp b/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.webp new file mode 100644 index 000000000..87d526362 Binary files /dev/null and b/content/engineering/production-grade-development-using-docker-compose/what-is-the-problem.webp differ diff --git a/content/engineering/progressive-app-vs-native-app/index.md b/content/engineering/progressive-app-vs-native-app/index.md index ccef57acd..388d7f094 100644 --- a/content/engineering/progressive-app-vs-native-app/index.md +++ b/content/engineering/progressive-app-vs-native-app/index.md @@ -1,7 +1,7 @@ --- title: "PWA vs Native App: Which one is Better for you?" date: "2021-02-04" -coverImage: "index.png" +coverImage: "index.webp" author: Nathan Nguyen tags: ["Progressive App", "PWA", "JavaScript"] description: "How do Native Apps compare to Progressive Web Apps, and which platform does your company use to communicate with your clients? read on!" diff --git a/content/engineering/progressive-app-vs-native-app/index.png b/content/engineering/progressive-app-vs-native-app/index.png deleted file mode 100644 index d969b8662..000000000 Binary files a/content/engineering/progressive-app-vs-native-app/index.png and /dev/null differ diff --git a/content/engineering/progressive-app-vs-native-app/index.webp b/content/engineering/progressive-app-vs-native-app/index.webp new file mode 100644 index 000000000..a7cdf1db5 Binary files /dev/null and b/content/engineering/progressive-app-vs-native-app/index.webp differ diff --git a/content/engineering/python-basics-in-minutes/index.md b/content/engineering/python-basics-in-minutes/index.md index e05c01279..6c6effa79 100644 --- a/content/engineering/python-basics-in-minutes/index.md +++ b/content/engineering/python-basics-in-minutes/index.md @@ -1,7 +1,7 @@ --- title: "Python basics in minutes" date: "2020-11-06" -coverImage: "python.png" +coverImage: "python.webp" author: "Sara Lins" description: "Learn the basics of Python programming lanuage (For Beginners)" tags: ["Python"] diff --git a/content/engineering/python-basics-in-minutes/python.png b/content/engineering/python-basics-in-minutes/python.png deleted file mode 100644 index dcc8db1fa..000000000 Binary files a/content/engineering/python-basics-in-minutes/python.png and /dev/null differ diff --git a/content/engineering/python-basics-in-minutes/python.webp b/content/engineering/python-basics-in-minutes/python.webp new file mode 100644 index 000000000..376f59b84 Binary files /dev/null and b/content/engineering/python-basics-in-minutes/python.webp differ diff --git a/content/engineering/python-virtual-environments/activate.png b/content/engineering/python-virtual-environments/activate.png deleted file mode 100644 index 4c428c881..000000000 Binary files a/content/engineering/python-virtual-environments/activate.png and /dev/null differ diff --git a/content/engineering/python-virtual-environments/activate.webp b/content/engineering/python-virtual-environments/activate.webp new file mode 100644 index 000000000..d56ffea29 Binary files /dev/null and b/content/engineering/python-virtual-environments/activate.webp differ diff --git a/content/engineering/python-virtual-environments/activated.png b/content/engineering/python-virtual-environments/activated.png deleted file mode 100644 index 3fd159656..000000000 Binary files a/content/engineering/python-virtual-environments/activated.png and /dev/null differ diff --git a/content/engineering/python-virtual-environments/activated.webp b/content/engineering/python-virtual-environments/activated.webp new file mode 100644 index 000000000..e3daeed68 Binary files /dev/null and b/content/engineering/python-virtual-environments/activated.webp differ diff --git a/content/engineering/python-virtual-environments/check.png b/content/engineering/python-virtual-environments/check.png deleted file mode 100644 index 7a0b60611..000000000 Binary files a/content/engineering/python-virtual-environments/check.png and /dev/null differ diff --git a/content/engineering/python-virtual-environments/check.webp b/content/engineering/python-virtual-environments/check.webp new file mode 100644 index 000000000..8f4ab3dc0 Binary files /dev/null and b/content/engineering/python-virtual-environments/check.webp differ diff --git a/content/engineering/python-virtual-environments/deactivate.png b/content/engineering/python-virtual-environments/deactivate.png deleted file mode 100644 index fc12d0cd8..000000000 Binary files a/content/engineering/python-virtual-environments/deactivate.png and /dev/null differ diff --git a/content/engineering/python-virtual-environments/deactivate.webp b/content/engineering/python-virtual-environments/deactivate.webp new file mode 100644 index 000000000..7963ce9c8 Binary files /dev/null and b/content/engineering/python-virtual-environments/deactivate.webp differ diff --git a/content/engineering/python-virtual-environments/index.md b/content/engineering/python-virtual-environments/index.md index 025a6275f..56baecb19 100644 --- a/content/engineering/python-virtual-environments/index.md +++ b/content/engineering/python-virtual-environments/index.md @@ -1,7 +1,7 @@ --- title: "Python Virtual Environment: What is it and how it works?" date: "2020-10-16" -coverImage: "python.jpg" +coverImage: "python.webp" author: "Ashish Maharjan" tags: ["Python"] description: "We'll cover the basics of virtual environments in this guide and how to use them. We will then take a closer look at how virtual environments actually work." @@ -30,49 +30,49 @@ If project1 uses Django-2.2 and project2 uses Django-3.2, they would be stored i To create a virtual environment, we need a [module named](https://pypi.org/project/virtualenv/) virtualenv. It creates a folder with all the necessary executables to run Python projects. Make sure **pip** is installed on your computer. If not, then use the following command: -
+

### Install virtualenv: Open the terminal and paste the following command to install a virtualenv: -

+

### Check your version of virtualenv: If you want to confirm whether it is installed or not, paste the command below in your terminal: -

+

### Create a virtual environment: After successful installation of virtualenv, now you can create a virtual environment with your desired name using following command: -

+

Here, I created `venv` as the name of my virtual environment. You can name it whatever you desire. The folder with the name `venv` is created that contains all the necessary executables to [run the Python project](/speed-up-python-code/). This is the folder where all your python packages will run. To specify the Python interpreter of your choice, you can do it easily by specifying Python{version-name}. Eg: To create python2.7 virtual environment, we use following command: -

+

After successfully creating the virtual environment, you need to activate it to enter into that particular isolated environment. Always remember to activate the required virtual environment before working on the project. To activate it, we move to the location where the name of your desired virtual environment is located and follow the command below: -

+

**Note:** Instead of `venv`, you write the name of your virtual environment you created.
#### In Windows, -

+

After activating the virtual environment, you can see your name on the virtual environment on the terminal's left side. It confirms the activation of your virtual environment and is currently active. -

+

Finally, you successfully created and activated your virtual environment. Now, you can install the dependencies and requirements your project asks for without interfering with other projects. Once you completed your work, then you can return to the system default environment by just using the **deactivate** command as shown below: -
 +
+ diff --git a/content/engineering/python-virtual-environments/install.png b/content/engineering/python-virtual-environments/install.png
deleted file mode 100644
index 3e8133321..000000000
Binary files a/content/engineering/python-virtual-environments/install.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/install.webp b/content/engineering/python-virtual-environments/install.webp
new file mode 100644
index 000000000..a61c396f4
Binary files /dev/null and b/content/engineering/python-virtual-environments/install.webp differ
diff --git a/content/engineering/python-virtual-environments/name.png b/content/engineering/python-virtual-environments/name.png
deleted file mode 100644
index 8543e362d..000000000
Binary files a/content/engineering/python-virtual-environments/name.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/name.webp b/content/engineering/python-virtual-environments/name.webp
new file mode 100644
index 000000000..59e30503d
Binary files /dev/null and b/content/engineering/python-virtual-environments/name.webp differ
diff --git a/content/engineering/python-virtual-environments/pip.png b/content/engineering/python-virtual-environments/pip.png
deleted file mode 100644
index 945ed1afa..000000000
Binary files a/content/engineering/python-virtual-environments/pip.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/pip.webp b/content/engineering/python-virtual-environments/pip.webp
new file mode 100644
index 000000000..b0b2279a1
Binary files /dev/null and b/content/engineering/python-virtual-environments/pip.webp differ
diff --git a/content/engineering/python-virtual-environments/python.jpg b/content/engineering/python-virtual-environments/python.jpg
deleted file mode 100644
index 4acb9db7a..000000000
Binary files a/content/engineering/python-virtual-environments/python.jpg and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/python.webp b/content/engineering/python-virtual-environments/python.webp
new file mode 100644
index 000000000..609ffa433
Binary files /dev/null and b/content/engineering/python-virtual-environments/python.webp differ
diff --git a/content/engineering/python-virtual-environments/version.png b/content/engineering/python-virtual-environments/version.png
deleted file mode 100644
index 30ddd8e47..000000000
Binary files a/content/engineering/python-virtual-environments/version.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/version.webp b/content/engineering/python-virtual-environments/version.webp
new file mode 100644
index 000000000..ce9e88498
Binary files /dev/null and b/content/engineering/python-virtual-environments/version.webp differ
diff --git a/content/engineering/python-virtual-environments/windows.png b/content/engineering/python-virtual-environments/windows.png
deleted file mode 100644
index 82e9d374a..000000000
Binary files a/content/engineering/python-virtual-environments/windows.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/windows.webp b/content/engineering/python-virtual-environments/windows.webp
new file mode 100644
index 000000000..9cb5d066a
Binary files /dev/null and b/content/engineering/python-virtual-environments/windows.webp differ
diff --git a/content/engineering/qa-teams-deliver-quality-software/index.md b/content/engineering/qa-teams-deliver-quality-software/index.md
index 62b160718..356e07852 100644
--- a/content/engineering/qa-teams-deliver-quality-software/index.md
+++ b/content/engineering/qa-teams-deliver-quality-software/index.md
@@ -1,7 +1,7 @@
---
title: "QA Testing Process: How to Deliver Quality Software"
date: "2021-03-01"
-coverImage: "software-testing.png"
+coverImage: "software-testing.webp"
author: "Neha Vyas"
description: "A comprehensive overview of the QA testing process is given. Learn what it takes to get top-notch testing facilities."
tags: ["QA", "Processes", "Testing"]
diff --git a/content/engineering/qa-teams-deliver-quality-software/software-testing.png b/content/engineering/qa-teams-deliver-quality-software/software-testing.png
deleted file mode 100644
index 179f9aa33..000000000
Binary files a/content/engineering/qa-teams-deliver-quality-software/software-testing.png and /dev/null differ
diff --git a/content/engineering/qa-teams-deliver-quality-software/software-testing.webp b/content/engineering/qa-teams-deliver-quality-software/software-testing.webp
new file mode 100644
index 000000000..ab46a211c
Binary files /dev/null and b/content/engineering/qa-teams-deliver-quality-software/software-testing.webp differ
diff --git a/content/engineering/quick-kafka-installation/index.md b/content/engineering/quick-kafka-installation/index.md
index 736f68096..8a35e8466 100644
--- a/content/engineering/quick-kafka-installation/index.md
+++ b/content/engineering/quick-kafka-installation/index.md
@@ -1,7 +1,7 @@
---
title: "Setting Up and Running Apache Kafka on Windows OS"
date: "2020-08-25"
-coverImage: "messagelog.png"
+coverImage: "messagelog.webp"
author: "Ashish Sharma"
tags: ["Kafka", "Windows"]
---
@@ -39,7 +39,7 @@ tar -xvzf kafka_2.12-2.4.1.tgz
**Step 3:** Copy the path of the Kafka folder. Now go to _config_ inside Kafka folder and open _zookeeper.properties_ file. Copy the path against the field _dataDir_ and add _/zookeeper-data_ to the path.
-
+
**Step 4:** we have to modify the config/server.properties file. Below is the change:
diff --git a/content/engineering/quick-kafka-installation/messagelog.png b/content/engineering/quick-kafka-installation/messagelog.png
deleted file mode 100644
index 47f716339..000000000
Binary files a/content/engineering/quick-kafka-installation/messagelog.png and /dev/null differ
diff --git a/content/engineering/quick-kafka-installation/messagelog.webp b/content/engineering/quick-kafka-installation/messagelog.webp
new file mode 100644
index 000000000..9b5f8e93b
Binary files /dev/null and b/content/engineering/quick-kafka-installation/messagelog.webp differ
diff --git a/content/engineering/quick-kafka-installation/zookeeper.png b/content/engineering/quick-kafka-installation/zookeeper.png
deleted file mode 100644
index fe9c5eb93..000000000
Binary files a/content/engineering/quick-kafka-installation/zookeeper.png and /dev/null differ
diff --git a/content/engineering/quick-kafka-installation/zookeeper.webp b/content/engineering/quick-kafka-installation/zookeeper.webp
new file mode 100644
index 000000000..debbd0f99
Binary files /dev/null and b/content/engineering/quick-kafka-installation/zookeeper.webp differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/index.md b/content/engineering/quick-look-at-react-speech-recognition/index.md
index 0544235c6..cd77b78c0 100644
--- a/content/engineering/quick-look-at-react-speech-recognition/index.md
+++ b/content/engineering/quick-look-at-react-speech-recognition/index.md
@@ -1,7 +1,7 @@
---
title: "A Quick Look at the React Speech Recognition Hook"
date: "2020-10-29"
-coverImage: "mic.jpg"
+coverImage: "mic.webp"
author: "Krista Singleton"
tags: ["React", "React Speech Recognition", "React Speech", "React Hook"]
description: "Learning and exploring the react-speech-recognition hook basics."
@@ -31,7 +31,7 @@ Note: This framework uses WebSpeech API. Browser support for this API is current
I will be making a simple voice memo app with basic voice commands that run in the browser. If you would like to follow this tutorial, please be ready to work with the create-react-app boilerplate.
-
+
## Let's Get Started
diff --git a/content/engineering/quick-look-at-react-speech-recognition/mic.jpg b/content/engineering/quick-look-at-react-speech-recognition/mic.jpg
deleted file mode 100644
index 71884632c..000000000
Binary files a/content/engineering/quick-look-at-react-speech-recognition/mic.jpg and /dev/null differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/mic.webp b/content/engineering/quick-look-at-react-speech-recognition/mic.webp
new file mode 100644
index 000000000..816a21698
Binary files /dev/null and b/content/engineering/quick-look-at-react-speech-recognition/mic.webp differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/styledExample.png b/content/engineering/quick-look-at-react-speech-recognition/styledExample.png
deleted file mode 100644
index cc35d7c45..000000000
Binary files a/content/engineering/quick-look-at-react-speech-recognition/styledExample.png and /dev/null differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp b/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp
new file mode 100644
index 000000000..ee46f472f
Binary files /dev/null and b/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp differ
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/index.md b/content/engineering/react-code-splitting-with-lazy-suspense/index.md
index 8db7ef374..c7b776ac0 100644
--- a/content/engineering/react-code-splitting-with-lazy-suspense/index.md
+++ b/content/engineering/react-code-splitting-with-lazy-suspense/index.md
@@ -1,7 +1,7 @@
---
title: Code spliting in React via lazy and suspense
date: "2021-05-13"
-coverImage: "react.png"
+coverImage: "react.webp"
author: "Abhimanyu Singh Rathore"
description: "Load Application faster with code spliting and dynamic loading"
tags: ["React"]
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/react.png b/content/engineering/react-code-splitting-with-lazy-suspense/react.png
deleted file mode 100644
index 5969c4dd3..000000000
Binary files a/content/engineering/react-code-splitting-with-lazy-suspense/react.png and /dev/null differ
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/react.webp b/content/engineering/react-code-splitting-with-lazy-suspense/react.webp
new file mode 100644
index 000000000..4f4f67d78
Binary files /dev/null and b/content/engineering/react-code-splitting-with-lazy-suspense/react.webp differ
diff --git a/content/engineering/react-constructor-get-initial-state/index.md b/content/engineering/react-constructor-get-initial-state/index.md
index a2dc65dd4..ab2ee63b1 100644
--- a/content/engineering/react-constructor-get-initial-state/index.md
+++ b/content/engineering/react-constructor-get-initial-state/index.md
@@ -1,7 +1,7 @@
---
title: "Constructor vs getInitialState in React"
date: "2021-01-05"
-coverImage: "index.png"
+coverImage: "index.webp"
author: Nathan Nguyen
tags: ["JavaScript", "React"]
description: "No ES6? No problem. getInitialState is the ES5 friendly method to define the initial state of a React component."
diff --git a/content/engineering/react-constructor-get-initial-state/index.png b/content/engineering/react-constructor-get-initial-state/index.png
deleted file mode 100644
index fd3825ea4..000000000
Binary files a/content/engineering/react-constructor-get-initial-state/index.png and /dev/null differ
diff --git a/content/engineering/react-constructor-get-initial-state/index.webp b/content/engineering/react-constructor-get-initial-state/index.webp
new file mode 100644
index 000000000..d72d1b5ec
Binary files /dev/null and b/content/engineering/react-constructor-get-initial-state/index.webp differ
diff --git a/content/engineering/react-context-api-guide-with-Example/index.md b/content/engineering/react-context-api-guide-with-Example/index.md
index 69e450eca..48cfe0797 100644
--- a/content/engineering/react-context-api-guide-with-Example/index.md
+++ b/content/engineering/react-context-api-guide-with-Example/index.md
@@ -1,7 +1,7 @@
---
title: "React's Context API Guide with Example"
date: "2021-06-09"
-coverImage: "title-image.png"
+coverImage: "title-image.webp"
author: "Versha Gupta"
tags: ["React", "Redux", "Hooks"]
description: "Deep Dive into React's Context API with example"
diff --git a/content/engineering/react-context-api-guide-with-Example/title-image.png b/content/engineering/react-context-api-guide-with-Example/title-image.png
deleted file mode 100644
index 1feb7118a..000000000
Binary files a/content/engineering/react-context-api-guide-with-Example/title-image.png and /dev/null differ
diff --git a/content/engineering/react-context-api-guide-with-Example/title-image.webp b/content/engineering/react-context-api-guide-with-Example/title-image.webp
new file mode 100644
index 000000000..e884d7a9d
Binary files /dev/null and b/content/engineering/react-context-api-guide-with-Example/title-image.webp differ
diff --git a/content/engineering/react-context-api/index.md b/content/engineering/react-context-api/index.md
index 5ee467147..f133b5272 100644
--- a/content/engineering/react-context-api/index.md
+++ b/content/engineering/react-context-api/index.md
@@ -1,7 +1,7 @@
---
title: "React Context API: What is it and How it works?"
date: "2020-10-07"
-coverImage: "react.jpg"
+coverImage: "react.webp"
author: "Eylon Ronen"
tags: ["React", "Redux", "Hooks"]
description: "Context API is a (kind of) new feature added in version 16.3 of React that allows one to share state across the entire app (or part of it) lightly and with ease. Let's see how to use it."
diff --git a/content/engineering/react-context-api/react.jpg b/content/engineering/react-context-api/react.jpg
deleted file mode 100644
index 2e22923df..000000000
Binary files a/content/engineering/react-context-api/react.jpg and /dev/null differ
diff --git a/content/engineering/react-context-api/react.webp b/content/engineering/react-context-api/react.webp
new file mode 100644
index 000000000..5b729e68d
Binary files /dev/null and b/content/engineering/react-context-api/react.webp differ
diff --git a/content/engineering/react-error-boundaries/error_boundary_cover.png b/content/engineering/react-error-boundaries/error_boundary_cover.png
deleted file mode 100644
index ef42fee87..000000000
Binary files a/content/engineering/react-error-boundaries/error_boundary_cover.png and /dev/null differ
diff --git a/content/engineering/react-error-boundaries/error_boundary_cover.webp b/content/engineering/react-error-boundaries/error_boundary_cover.webp
new file mode 100644
index 000000000..54cab35cc
Binary files /dev/null and b/content/engineering/react-error-boundaries/error_boundary_cover.webp differ
diff --git a/content/engineering/react-error-boundaries/index.md b/content/engineering/react-error-boundaries/index.md
index d5ea641e8..da317942f 100644
--- a/content/engineering/react-error-boundaries/index.md
+++ b/content/engineering/react-error-boundaries/index.md
@@ -1,7 +1,7 @@
---
title: "React Error Boundaries"
date: "2021-05-20"
-coverImage: "error_boundary_cover.png"
+coverImage: "error_boundary_cover.webp"
author: "Versha Gupta"
tags: ["React", "Error Handling", "JavaScript"]
description: "Error Handling in React using React Error Boundaries"
diff --git a/content/engineering/react-hooks-guide/index.md b/content/engineering/react-hooks-guide/index.md
index bc9d0952f..44d8a2683 100644
--- a/content/engineering/react-hooks-guide/index.md
+++ b/content/engineering/react-hooks-guide/index.md
@@ -2,7 +2,7 @@
title: "React Hooks: A Beginners Guide"
date: "2020-08-07"
author: "Mohammed Modi"
-coverImage: "react-hooks.png"
+coverImage: "react-hooks.webp"
tags: ["React", "Hooks"]
description: "A walkthrough guide on React Hooks, what is React Hooks, benefits of Hooks, and how to use Hooks in React and more."
---
diff --git a/content/engineering/react-hooks-guide/react-hooks.png b/content/engineering/react-hooks-guide/react-hooks.png
deleted file mode 100644
index b06e44fa2..000000000
Binary files a/content/engineering/react-hooks-guide/react-hooks.png and /dev/null differ
diff --git a/content/engineering/react-hooks-guide/react-hooks.webp b/content/engineering/react-hooks-guide/react-hooks.webp
new file mode 100644
index 000000000..5f712b755
Binary files /dev/null and b/content/engineering/react-hooks-guide/react-hooks.webp differ
diff --git a/content/engineering/react-renderer/index.md b/content/engineering/react-renderer/index.md
index 92819ae21..aa888f280 100644
--- a/content/engineering/react-renderer/index.md
+++ b/content/engineering/react-renderer/index.md
@@ -1,7 +1,7 @@
---
title: "React renderers, react everywhere?"
date: "2021-06-23"
-coverImage: "react.png"
+coverImage: "react.webp"
author: "Abhimanyu Singh Rathore"
description: "There is an advanced feature of React is that it can write renderers for multiple different env."
tags: ["JavaScript", "React", "Renderer"]
diff --git a/content/engineering/react-renderer/react.png b/content/engineering/react-renderer/react.png
deleted file mode 100644
index dfe1b03e1..000000000
Binary files a/content/engineering/react-renderer/react.png and /dev/null differ
diff --git a/content/engineering/react-renderer/react.webp b/content/engineering/react-renderer/react.webp
new file mode 100644
index 000000000..b53a41959
Binary files /dev/null and b/content/engineering/react-renderer/react.webp differ
diff --git a/content/engineering/react-router-basics/image1.png b/content/engineering/react-router-basics/image1.png
deleted file mode 100644
index 12c01b68e..000000000
Binary files a/content/engineering/react-router-basics/image1.png and /dev/null differ
diff --git a/content/engineering/react-router-basics/image1.webp b/content/engineering/react-router-basics/image1.webp
new file mode 100644
index 000000000..e414a9a97
Binary files /dev/null and b/content/engineering/react-router-basics/image1.webp differ
diff --git a/content/engineering/react-router-basics/index.md b/content/engineering/react-router-basics/index.md
index b31566425..462600279 100644
--- a/content/engineering/react-router-basics/index.md
+++ b/content/engineering/react-router-basics/index.md
@@ -1,7 +1,7 @@
---
title: "React Router Basics: Routing in a Single-page Application"
date: "2020-11-20"
-coverImage: "index.png"
+coverImage: "index.webp"
author: Nathan Nguyen
tags: ["JavaScript", "Node", "React", "React Router"]
description: "Everything essential you need to know about React Router."
@@ -105,7 +105,7 @@ If you are currently looking at the render of this structure from the CodePen, y
-
+
Clicking on the
diff --git a/content/engineering/python-virtual-environments/install.png b/content/engineering/python-virtual-environments/install.png
deleted file mode 100644
index 3e8133321..000000000
Binary files a/content/engineering/python-virtual-environments/install.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/install.webp b/content/engineering/python-virtual-environments/install.webp
new file mode 100644
index 000000000..a61c396f4
Binary files /dev/null and b/content/engineering/python-virtual-environments/install.webp differ
diff --git a/content/engineering/python-virtual-environments/name.png b/content/engineering/python-virtual-environments/name.png
deleted file mode 100644
index 8543e362d..000000000
Binary files a/content/engineering/python-virtual-environments/name.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/name.webp b/content/engineering/python-virtual-environments/name.webp
new file mode 100644
index 000000000..59e30503d
Binary files /dev/null and b/content/engineering/python-virtual-environments/name.webp differ
diff --git a/content/engineering/python-virtual-environments/pip.png b/content/engineering/python-virtual-environments/pip.png
deleted file mode 100644
index 945ed1afa..000000000
Binary files a/content/engineering/python-virtual-environments/pip.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/pip.webp b/content/engineering/python-virtual-environments/pip.webp
new file mode 100644
index 000000000..b0b2279a1
Binary files /dev/null and b/content/engineering/python-virtual-environments/pip.webp differ
diff --git a/content/engineering/python-virtual-environments/python.jpg b/content/engineering/python-virtual-environments/python.jpg
deleted file mode 100644
index 4acb9db7a..000000000
Binary files a/content/engineering/python-virtual-environments/python.jpg and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/python.webp b/content/engineering/python-virtual-environments/python.webp
new file mode 100644
index 000000000..609ffa433
Binary files /dev/null and b/content/engineering/python-virtual-environments/python.webp differ
diff --git a/content/engineering/python-virtual-environments/version.png b/content/engineering/python-virtual-environments/version.png
deleted file mode 100644
index 30ddd8e47..000000000
Binary files a/content/engineering/python-virtual-environments/version.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/version.webp b/content/engineering/python-virtual-environments/version.webp
new file mode 100644
index 000000000..ce9e88498
Binary files /dev/null and b/content/engineering/python-virtual-environments/version.webp differ
diff --git a/content/engineering/python-virtual-environments/windows.png b/content/engineering/python-virtual-environments/windows.png
deleted file mode 100644
index 82e9d374a..000000000
Binary files a/content/engineering/python-virtual-environments/windows.png and /dev/null differ
diff --git a/content/engineering/python-virtual-environments/windows.webp b/content/engineering/python-virtual-environments/windows.webp
new file mode 100644
index 000000000..9cb5d066a
Binary files /dev/null and b/content/engineering/python-virtual-environments/windows.webp differ
diff --git a/content/engineering/qa-teams-deliver-quality-software/index.md b/content/engineering/qa-teams-deliver-quality-software/index.md
index 62b160718..356e07852 100644
--- a/content/engineering/qa-teams-deliver-quality-software/index.md
+++ b/content/engineering/qa-teams-deliver-quality-software/index.md
@@ -1,7 +1,7 @@
---
title: "QA Testing Process: How to Deliver Quality Software"
date: "2021-03-01"
-coverImage: "software-testing.png"
+coverImage: "software-testing.webp"
author: "Neha Vyas"
description: "A comprehensive overview of the QA testing process is given. Learn what it takes to get top-notch testing facilities."
tags: ["QA", "Processes", "Testing"]
diff --git a/content/engineering/qa-teams-deliver-quality-software/software-testing.png b/content/engineering/qa-teams-deliver-quality-software/software-testing.png
deleted file mode 100644
index 179f9aa33..000000000
Binary files a/content/engineering/qa-teams-deliver-quality-software/software-testing.png and /dev/null differ
diff --git a/content/engineering/qa-teams-deliver-quality-software/software-testing.webp b/content/engineering/qa-teams-deliver-quality-software/software-testing.webp
new file mode 100644
index 000000000..ab46a211c
Binary files /dev/null and b/content/engineering/qa-teams-deliver-quality-software/software-testing.webp differ
diff --git a/content/engineering/quick-kafka-installation/index.md b/content/engineering/quick-kafka-installation/index.md
index 736f68096..8a35e8466 100644
--- a/content/engineering/quick-kafka-installation/index.md
+++ b/content/engineering/quick-kafka-installation/index.md
@@ -1,7 +1,7 @@
---
title: "Setting Up and Running Apache Kafka on Windows OS"
date: "2020-08-25"
-coverImage: "messagelog.png"
+coverImage: "messagelog.webp"
author: "Ashish Sharma"
tags: ["Kafka", "Windows"]
---
@@ -39,7 +39,7 @@ tar -xvzf kafka_2.12-2.4.1.tgz
**Step 3:** Copy the path of the Kafka folder. Now go to _config_ inside Kafka folder and open _zookeeper.properties_ file. Copy the path against the field _dataDir_ and add _/zookeeper-data_ to the path.
-
+
**Step 4:** we have to modify the config/server.properties file. Below is the change:
diff --git a/content/engineering/quick-kafka-installation/messagelog.png b/content/engineering/quick-kafka-installation/messagelog.png
deleted file mode 100644
index 47f716339..000000000
Binary files a/content/engineering/quick-kafka-installation/messagelog.png and /dev/null differ
diff --git a/content/engineering/quick-kafka-installation/messagelog.webp b/content/engineering/quick-kafka-installation/messagelog.webp
new file mode 100644
index 000000000..9b5f8e93b
Binary files /dev/null and b/content/engineering/quick-kafka-installation/messagelog.webp differ
diff --git a/content/engineering/quick-kafka-installation/zookeeper.png b/content/engineering/quick-kafka-installation/zookeeper.png
deleted file mode 100644
index fe9c5eb93..000000000
Binary files a/content/engineering/quick-kafka-installation/zookeeper.png and /dev/null differ
diff --git a/content/engineering/quick-kafka-installation/zookeeper.webp b/content/engineering/quick-kafka-installation/zookeeper.webp
new file mode 100644
index 000000000..debbd0f99
Binary files /dev/null and b/content/engineering/quick-kafka-installation/zookeeper.webp differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/index.md b/content/engineering/quick-look-at-react-speech-recognition/index.md
index 0544235c6..cd77b78c0 100644
--- a/content/engineering/quick-look-at-react-speech-recognition/index.md
+++ b/content/engineering/quick-look-at-react-speech-recognition/index.md
@@ -1,7 +1,7 @@
---
title: "A Quick Look at the React Speech Recognition Hook"
date: "2020-10-29"
-coverImage: "mic.jpg"
+coverImage: "mic.webp"
author: "Krista Singleton"
tags: ["React", "React Speech Recognition", "React Speech", "React Hook"]
description: "Learning and exploring the react-speech-recognition hook basics."
@@ -31,7 +31,7 @@ Note: This framework uses WebSpeech API. Browser support for this API is current
I will be making a simple voice memo app with basic voice commands that run in the browser. If you would like to follow this tutorial, please be ready to work with the create-react-app boilerplate.
-
+
## Let's Get Started
diff --git a/content/engineering/quick-look-at-react-speech-recognition/mic.jpg b/content/engineering/quick-look-at-react-speech-recognition/mic.jpg
deleted file mode 100644
index 71884632c..000000000
Binary files a/content/engineering/quick-look-at-react-speech-recognition/mic.jpg and /dev/null differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/mic.webp b/content/engineering/quick-look-at-react-speech-recognition/mic.webp
new file mode 100644
index 000000000..816a21698
Binary files /dev/null and b/content/engineering/quick-look-at-react-speech-recognition/mic.webp differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/styledExample.png b/content/engineering/quick-look-at-react-speech-recognition/styledExample.png
deleted file mode 100644
index cc35d7c45..000000000
Binary files a/content/engineering/quick-look-at-react-speech-recognition/styledExample.png and /dev/null differ
diff --git a/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp b/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp
new file mode 100644
index 000000000..ee46f472f
Binary files /dev/null and b/content/engineering/quick-look-at-react-speech-recognition/styledExample.webp differ
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/index.md b/content/engineering/react-code-splitting-with-lazy-suspense/index.md
index 8db7ef374..c7b776ac0 100644
--- a/content/engineering/react-code-splitting-with-lazy-suspense/index.md
+++ b/content/engineering/react-code-splitting-with-lazy-suspense/index.md
@@ -1,7 +1,7 @@
---
title: Code spliting in React via lazy and suspense
date: "2021-05-13"
-coverImage: "react.png"
+coverImage: "react.webp"
author: "Abhimanyu Singh Rathore"
description: "Load Application faster with code spliting and dynamic loading"
tags: ["React"]
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/react.png b/content/engineering/react-code-splitting-with-lazy-suspense/react.png
deleted file mode 100644
index 5969c4dd3..000000000
Binary files a/content/engineering/react-code-splitting-with-lazy-suspense/react.png and /dev/null differ
diff --git a/content/engineering/react-code-splitting-with-lazy-suspense/react.webp b/content/engineering/react-code-splitting-with-lazy-suspense/react.webp
new file mode 100644
index 000000000..4f4f67d78
Binary files /dev/null and b/content/engineering/react-code-splitting-with-lazy-suspense/react.webp differ
diff --git a/content/engineering/react-constructor-get-initial-state/index.md b/content/engineering/react-constructor-get-initial-state/index.md
index a2dc65dd4..ab2ee63b1 100644
--- a/content/engineering/react-constructor-get-initial-state/index.md
+++ b/content/engineering/react-constructor-get-initial-state/index.md
@@ -1,7 +1,7 @@
---
title: "Constructor vs getInitialState in React"
date: "2021-01-05"
-coverImage: "index.png"
+coverImage: "index.webp"
author: Nathan Nguyen
tags: ["JavaScript", "React"]
description: "No ES6? No problem. getInitialState is the ES5 friendly method to define the initial state of a React component."
diff --git a/content/engineering/react-constructor-get-initial-state/index.png b/content/engineering/react-constructor-get-initial-state/index.png
deleted file mode 100644
index fd3825ea4..000000000
Binary files a/content/engineering/react-constructor-get-initial-state/index.png and /dev/null differ
diff --git a/content/engineering/react-constructor-get-initial-state/index.webp b/content/engineering/react-constructor-get-initial-state/index.webp
new file mode 100644
index 000000000..d72d1b5ec
Binary files /dev/null and b/content/engineering/react-constructor-get-initial-state/index.webp differ
diff --git a/content/engineering/react-context-api-guide-with-Example/index.md b/content/engineering/react-context-api-guide-with-Example/index.md
index 69e450eca..48cfe0797 100644
--- a/content/engineering/react-context-api-guide-with-Example/index.md
+++ b/content/engineering/react-context-api-guide-with-Example/index.md
@@ -1,7 +1,7 @@
---
title: "React's Context API Guide with Example"
date: "2021-06-09"
-coverImage: "title-image.png"
+coverImage: "title-image.webp"
author: "Versha Gupta"
tags: ["React", "Redux", "Hooks"]
description: "Deep Dive into React's Context API with example"
diff --git a/content/engineering/react-context-api-guide-with-Example/title-image.png b/content/engineering/react-context-api-guide-with-Example/title-image.png
deleted file mode 100644
index 1feb7118a..000000000
Binary files a/content/engineering/react-context-api-guide-with-Example/title-image.png and /dev/null differ
diff --git a/content/engineering/react-context-api-guide-with-Example/title-image.webp b/content/engineering/react-context-api-guide-with-Example/title-image.webp
new file mode 100644
index 000000000..e884d7a9d
Binary files /dev/null and b/content/engineering/react-context-api-guide-with-Example/title-image.webp differ
diff --git a/content/engineering/react-context-api/index.md b/content/engineering/react-context-api/index.md
index 5ee467147..f133b5272 100644
--- a/content/engineering/react-context-api/index.md
+++ b/content/engineering/react-context-api/index.md
@@ -1,7 +1,7 @@
---
title: "React Context API: What is it and How it works?"
date: "2020-10-07"
-coverImage: "react.jpg"
+coverImage: "react.webp"
author: "Eylon Ronen"
tags: ["React", "Redux", "Hooks"]
description: "Context API is a (kind of) new feature added in version 16.3 of React that allows one to share state across the entire app (or part of it) lightly and with ease. Let's see how to use it."
diff --git a/content/engineering/react-context-api/react.jpg b/content/engineering/react-context-api/react.jpg
deleted file mode 100644
index 2e22923df..000000000
Binary files a/content/engineering/react-context-api/react.jpg and /dev/null differ
diff --git a/content/engineering/react-context-api/react.webp b/content/engineering/react-context-api/react.webp
new file mode 100644
index 000000000..5b729e68d
Binary files /dev/null and b/content/engineering/react-context-api/react.webp differ
diff --git a/content/engineering/react-error-boundaries/error_boundary_cover.png b/content/engineering/react-error-boundaries/error_boundary_cover.png
deleted file mode 100644
index ef42fee87..000000000
Binary files a/content/engineering/react-error-boundaries/error_boundary_cover.png and /dev/null differ
diff --git a/content/engineering/react-error-boundaries/error_boundary_cover.webp b/content/engineering/react-error-boundaries/error_boundary_cover.webp
new file mode 100644
index 000000000..54cab35cc
Binary files /dev/null and b/content/engineering/react-error-boundaries/error_boundary_cover.webp differ
diff --git a/content/engineering/react-error-boundaries/index.md b/content/engineering/react-error-boundaries/index.md
index d5ea641e8..da317942f 100644
--- a/content/engineering/react-error-boundaries/index.md
+++ b/content/engineering/react-error-boundaries/index.md
@@ -1,7 +1,7 @@
---
title: "React Error Boundaries"
date: "2021-05-20"
-coverImage: "error_boundary_cover.png"
+coverImage: "error_boundary_cover.webp"
author: "Versha Gupta"
tags: ["React", "Error Handling", "JavaScript"]
description: "Error Handling in React using React Error Boundaries"
diff --git a/content/engineering/react-hooks-guide/index.md b/content/engineering/react-hooks-guide/index.md
index bc9d0952f..44d8a2683 100644
--- a/content/engineering/react-hooks-guide/index.md
+++ b/content/engineering/react-hooks-guide/index.md
@@ -2,7 +2,7 @@
title: "React Hooks: A Beginners Guide"
date: "2020-08-07"
author: "Mohammed Modi"
-coverImage: "react-hooks.png"
+coverImage: "react-hooks.webp"
tags: ["React", "Hooks"]
description: "A walkthrough guide on React Hooks, what is React Hooks, benefits of Hooks, and how to use Hooks in React and more."
---
diff --git a/content/engineering/react-hooks-guide/react-hooks.png b/content/engineering/react-hooks-guide/react-hooks.png
deleted file mode 100644
index b06e44fa2..000000000
Binary files a/content/engineering/react-hooks-guide/react-hooks.png and /dev/null differ
diff --git a/content/engineering/react-hooks-guide/react-hooks.webp b/content/engineering/react-hooks-guide/react-hooks.webp
new file mode 100644
index 000000000..5f712b755
Binary files /dev/null and b/content/engineering/react-hooks-guide/react-hooks.webp differ
diff --git a/content/engineering/react-renderer/index.md b/content/engineering/react-renderer/index.md
index 92819ae21..aa888f280 100644
--- a/content/engineering/react-renderer/index.md
+++ b/content/engineering/react-renderer/index.md
@@ -1,7 +1,7 @@
---
title: "React renderers, react everywhere?"
date: "2021-06-23"
-coverImage: "react.png"
+coverImage: "react.webp"
author: "Abhimanyu Singh Rathore"
description: "There is an advanced feature of React is that it can write renderers for multiple different env."
tags: ["JavaScript", "React", "Renderer"]
diff --git a/content/engineering/react-renderer/react.png b/content/engineering/react-renderer/react.png
deleted file mode 100644
index dfe1b03e1..000000000
Binary files a/content/engineering/react-renderer/react.png and /dev/null differ
diff --git a/content/engineering/react-renderer/react.webp b/content/engineering/react-renderer/react.webp
new file mode 100644
index 000000000..b53a41959
Binary files /dev/null and b/content/engineering/react-renderer/react.webp differ
diff --git a/content/engineering/react-router-basics/image1.png b/content/engineering/react-router-basics/image1.png
deleted file mode 100644
index 12c01b68e..000000000
Binary files a/content/engineering/react-router-basics/image1.png and /dev/null differ
diff --git a/content/engineering/react-router-basics/image1.webp b/content/engineering/react-router-basics/image1.webp
new file mode 100644
index 000000000..e414a9a97
Binary files /dev/null and b/content/engineering/react-router-basics/image1.webp differ
diff --git a/content/engineering/react-router-basics/index.md b/content/engineering/react-router-basics/index.md
index b31566425..462600279 100644
--- a/content/engineering/react-router-basics/index.md
+++ b/content/engineering/react-router-basics/index.md
@@ -1,7 +1,7 @@
---
title: "React Router Basics: Routing in a Single-page Application"
date: "2020-11-20"
-coverImage: "index.png"
+coverImage: "index.webp"
author: Nathan Nguyen
tags: ["JavaScript", "Node", "React", "React Router"]
description: "Everything essential you need to know about React Router."
@@ -105,7 +105,7 @@ If you are currently looking at the render of this structure from the CodePen, y
-
+
Clicking on the <Link>’s in the navigation bar will “navigate” you to the corresponding paths. In effect, what this does is twofold:
diff --git a/content/engineering/react-router-basics/index.png b/content/engineering/react-router-basics/index.png
deleted file mode 100644
index 8e0750cc9..000000000
Binary files a/content/engineering/react-router-basics/index.png and /dev/null differ
diff --git a/content/engineering/react-router-basics/index.webp b/content/engineering/react-router-basics/index.webp
new file mode 100644
index 000000000..24503fe81
Binary files /dev/null and b/content/engineering/react-router-basics/index.webp differ
diff --git a/content/engineering/react-security-vulnerabilities/index.md b/content/engineering/react-security-vulnerabilities/index.md
index 1007dc410..508a2e6fd 100644
--- a/content/engineering/react-security-vulnerabilities/index.md
+++ b/content/engineering/react-security-vulnerabilities/index.md
@@ -1,7 +1,7 @@
---
title: "React Security Vulnerabilities and How to Fix/Prevent Them"
date: "2021-12-24"
-coverImage: "react-security.png"
+coverImage: "react-security.webp"
author: "Gaurav Kumar Roy"
tags: ["React", "Vulnerability"]
description: "React security vulnerabilities are hard to detect. However, this article talks about the top 7 vulnerabilities and how to fix them to enjoy all the benefits React caters to in developing Progressive Web Applications."
diff --git a/content/engineering/react-security-vulnerabilities/react-security.png b/content/engineering/react-security-vulnerabilities/react-security.png
deleted file mode 100644
index 6a4ada3c6..000000000
Binary files a/content/engineering/react-security-vulnerabilities/react-security.png and /dev/null differ
diff --git a/content/engineering/react-security-vulnerabilities/react-security.webp b/content/engineering/react-security-vulnerabilities/react-security.webp
new file mode 100644
index 000000000..d9ad352a9
Binary files /dev/null and b/content/engineering/react-security-vulnerabilities/react-security.webp differ
diff --git a/content/engineering/react-state-management/image1.png b/content/engineering/react-state-management/image1.png
deleted file mode 100644
index 38e7d0c3f..000000000
Binary files a/content/engineering/react-state-management/image1.png and /dev/null differ
diff --git a/content/engineering/react-state-management/image1.webp b/content/engineering/react-state-management/image1.webp
new file mode 100644
index 000000000..285314639
Binary files /dev/null and b/content/engineering/react-state-management/image1.webp differ
diff --git a/content/engineering/react-state-management/index.md b/content/engineering/react-state-management/index.md
index 3b7f0a5d2..31a6cd64a 100644
--- a/content/engineering/react-state-management/index.md
+++ b/content/engineering/react-state-management/index.md
@@ -1,7 +1,7 @@
---
title: "React state management: What is it and why to use it?"
date: "2020-07-17"
-coverImage: "title-image.png"
+coverImage: "title-image.webp"
author: "Versha Gupta"
tags: ["React","Redux","Hooks"]
description: "Learn about React state management and why we need state management and how to use it with React hooks and Redux in the best possible way."
@@ -39,7 +39,7 @@ Let’s discuss how to use react state management using react hooks and redux
Redux was created to resolve this particular issue. it provides a central store that holds all states of your application. Each component can access the stored state without sending it from one component to another. Here is a simple view of how Redux works.
-
+
There are three building parts: actions, store, and reducers. Let’s briefly discuss what each of them does.
diff --git a/content/engineering/react-state-management/title-image.png b/content/engineering/react-state-management/title-image.png
deleted file mode 100644
index 26d6ac7b8..000000000
Binary files a/content/engineering/react-state-management/title-image.png and /dev/null differ
diff --git a/content/engineering/react-state-management/title-image.webp b/content/engineering/react-state-management/title-image.webp
new file mode 100644
index 000000000..952ff5252
Binary files /dev/null and b/content/engineering/react-state-management/title-image.webp differ
diff --git a/content/engineering/react-with-refs/index.md b/content/engineering/react-with-refs/index.md
index 89d8bfb9b..9aad4d02b 100644
--- a/content/engineering/react-with-refs/index.md
+++ b/content/engineering/react-with-refs/index.md
@@ -1,7 +1,7 @@
---
title: "React with Ref"
date: "2021-04-16"
-coverImage: "title-image.png"
+coverImage: "title-image.webp"
author: "Versha Gupta"
tags: ["React","Refs","DOM"]
description: "Learn about manipulation of DOM elements with Ref directly with React"
diff --git a/content/engineering/react-with-refs/title-image.png b/content/engineering/react-with-refs/title-image.png
deleted file mode 100644
index 64bcc8204..000000000
Binary files a/content/engineering/react-with-refs/title-image.png and /dev/null differ
diff --git a/content/engineering/react-with-refs/title-image.webp b/content/engineering/react-with-refs/title-image.webp
new file mode 100644
index 000000000..1bda575f8
Binary files /dev/null and b/content/engineering/react-with-refs/title-image.webp differ
diff --git a/content/engineering/reacts-reconciliation-algorithm/Capture.png b/content/engineering/reacts-reconciliation-algorithm/Capture.png
deleted file mode 100644
index 7fad59a4b..000000000
Binary files a/content/engineering/reacts-reconciliation-algorithm/Capture.png and /dev/null differ
diff --git a/content/engineering/reacts-reconciliation-algorithm/Capture.webp b/content/engineering/reacts-reconciliation-algorithm/Capture.webp
new file mode 100644
index 000000000..063759fb2
Binary files /dev/null and b/content/engineering/reacts-reconciliation-algorithm/Capture.webp differ
diff --git a/content/engineering/reacts-reconciliation-algorithm/index.md b/content/engineering/reacts-reconciliation-algorithm/index.md
index 9c91bac7c..5722e2d60 100644
--- a/content/engineering/reacts-reconciliation-algorithm/index.md
+++ b/content/engineering/reacts-reconciliation-algorithm/index.md
@@ -1,7 +1,7 @@
---
title: "React's Reconciliation Algorithm"
date: "2019-12-03"
-coverImage: "react-fiber.png"
+coverImage: "react-fiber.webp"
author: "Team LoginRadius"
tags: ["React"]
---
diff --git a/content/engineering/reacts-reconciliation-algorithm/react-fiber.png b/content/engineering/reacts-reconciliation-algorithm/react-fiber.png
deleted file mode 100644
index 7052c9d32..000000000
Binary files a/content/engineering/reacts-reconciliation-algorithm/react-fiber.png and /dev/null differ
diff --git a/content/engineering/reacts-reconciliation-algorithm/react-fiber.webp b/content/engineering/reacts-reconciliation-algorithm/react-fiber.webp
new file mode 100644
index 000000000..54252e8c9
Binary files /dev/null and b/content/engineering/reacts-reconciliation-algorithm/react-fiber.webp differ
diff --git a/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.png b/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.png
deleted file mode 100644
index da91f8515..000000000
Binary files a/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.png and /dev/null differ
diff --git a/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.webp b/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.webp
new file mode 100644
index 000000000..f13aa9b56
Binary files /dev/null and b/content/engineering/read-and-write-in-a-local-file-with-deno/deno_file_system.webp differ
diff --git a/content/engineering/read-and-write-in-a-local-file-with-deno/index.md b/content/engineering/read-and-write-in-a-local-file-with-deno/index.md
index 25a982534..3dc9cff97 100644
--- a/content/engineering/read-and-write-in-a-local-file-with-deno/index.md
+++ b/content/engineering/read-and-write-in-a-local-file-with-deno/index.md
@@ -1,7 +1,7 @@
---
title: Read and Write in a local file with Deno
date: "2020-06-09"
-coverImage: "deno_file_system.png"
+coverImage: "deno_file_system.webp"
author: "Puneet Singh"
tags: ["Deno"]
---
diff --git a/content/engineering/recoiling-the-react/index.md b/content/engineering/recoiling-the-react/index.md
index 1dcfd850c..8617f4647 100644
--- a/content/engineering/recoiling-the-react/index.md
+++ b/content/engineering/recoiling-the-react/index.md
@@ -1,7 +1,7 @@
---
title: What is recoil.js and how it is managing in react?
date: "2021-04-30"
-coverImage: "react.png"
+coverImage: "react.webp"
author: "Abhimanyu Singh Rathore"
description: "Recoil is an experimental state management library and It provides several capabilities that are difficult to achieve with React alone.In this article we learn about the recoil.js, and how it is managing state in react."
tags: [JavaScript,React,Recoil]
diff --git a/content/engineering/recoiling-the-react/react.png b/content/engineering/recoiling-the-react/react.png
deleted file mode 100644
index 56a6acf20..000000000
Binary files a/content/engineering/recoiling-the-react/react.png and /dev/null differ
diff --git a/content/engineering/recoiling-the-react/react.webp b/content/engineering/recoiling-the-react/react.webp
new file mode 100644
index 000000000..9255c63cc
Binary files /dev/null and b/content/engineering/recoiling-the-react/react.webp differ
diff --git a/content/engineering/relational-database-management-system-rdbms-vs-nosql/index.md b/content/engineering/relational-database-management-system-rdbms-vs-nosql/index.md
index 2ed7c0fb8..10d15a3b8 100644
--- a/content/engineering/relational-database-management-system-rdbms-vs-nosql/index.md
+++ b/content/engineering/relational-database-management-system-rdbms-vs-nosql/index.md
@@ -1,7 +1,7 @@
---
title: "RDBMS vs NoSQL"
date: "2015-04-28"
-coverImage: "rdbms-vs-nosql.png"
+coverImage: "rdbms-vs-nosql.webp"
author: "Team LoginRadius"
tags: ["Database"]
description: "Learn about RDBMS and NoSQL Database systems, their differences, benefits and limitations"
diff --git a/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.png b/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.png
deleted file mode 100644
index 81bde6ccc..000000000
Binary files a/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.png and /dev/null differ
diff --git a/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.webp b/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.webp
new file mode 100644
index 000000000..1727b2ea2
Binary files /dev/null and b/content/engineering/relational-database-management-system-rdbms-vs-nosql/rdbms-vs-nosql.webp differ
diff --git a/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.png b/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.png
deleted file mode 100644
index 711d9912e..000000000
Binary files a/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.png and /dev/null differ
diff --git a/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.webp b/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.webp
new file mode 100644
index 000000000..f6a4e52b1
Binary files /dev/null and b/content/engineering/rest-api-cucumber-blog/cucumber_rest_assured.webp differ
diff --git a/content/engineering/rest-api-cucumber-blog/index.md b/content/engineering/rest-api-cucumber-blog/index.md
index b7c013d47..6eb2bcb8e 100644
--- a/content/engineering/rest-api-cucumber-blog/index.md
+++ b/content/engineering/rest-api-cucumber-blog/index.md
@@ -1,7 +1,7 @@
---
title: "Automating Rest API's using Cucumber and Java"
date: "2020-11-05"
-coverImage: "cucumber_rest_assured.png"
+coverImage: "cucumber_rest_assured.webp"
author: "Surendranath Reddy Birudala"
tags: ["Automation", "Cucumber", "Rest API", "Java"]
description: "This article is about basic overview of how to automate Rest API using Cucumber and JAVA."
diff --git a/content/engineering/rest-api-kubernetes/cover.png b/content/engineering/rest-api-kubernetes/cover.png
deleted file mode 100644
index d9133312c..000000000
Binary files a/content/engineering/rest-api-kubernetes/cover.png and /dev/null differ
diff --git a/content/engineering/rest-api-kubernetes/cover.webp b/content/engineering/rest-api-kubernetes/cover.webp
new file mode 100644
index 000000000..5f27cdcf8
Binary files /dev/null and b/content/engineering/rest-api-kubernetes/cover.webp differ
diff --git a/content/engineering/rest-api-kubernetes/index.md b/content/engineering/rest-api-kubernetes/index.md
index 0a8da52bc..8d35ec817 100644
--- a/content/engineering/rest-api-kubernetes/index.md
+++ b/content/engineering/rest-api-kubernetes/index.md
@@ -1,7 +1,7 @@
---
title: "How to Deploy a REST API in Kubernetes"
date: "2021-02-03"
-coverImage: "cover.png"
+coverImage: "cover.webp"
author: "Andy Yeung"
tags: ["Kubernetes"]
description: "Beginner guide on how to create and deploy a REST API in local Kubernetes."
diff --git a/content/engineering/risk-based-authentication/cover.jpg b/content/engineering/risk-based-authentication/cover.jpg
deleted file mode 100644
index 83d253ef9..000000000
Binary files a/content/engineering/risk-based-authentication/cover.jpg and /dev/null differ
diff --git a/content/engineering/risk-based-authentication/cover.webp b/content/engineering/risk-based-authentication/cover.webp
new file mode 100644
index 000000000..3f7dae913
Binary files /dev/null and b/content/engineering/risk-based-authentication/cover.webp differ
diff --git a/content/engineering/risk-based-authentication/incorrect.jpg b/content/engineering/risk-based-authentication/incorrect.jpg
deleted file mode 100644
index 9bb1c2645..000000000
Binary files a/content/engineering/risk-based-authentication/incorrect.jpg and /dev/null differ
diff --git a/content/engineering/risk-based-authentication/incorrect.webp b/content/engineering/risk-based-authentication/incorrect.webp
new file mode 100644
index 000000000..e744164fa
Binary files /dev/null and b/content/engineering/risk-based-authentication/incorrect.webp differ
diff --git a/content/engineering/risk-based-authentication/index.md b/content/engineering/risk-based-authentication/index.md
index 2eca3b1f4..53eab1f4c 100644
--- a/content/engineering/risk-based-authentication/index.md
+++ b/content/engineering/risk-based-authentication/index.md
@@ -1,7 +1,7 @@
---
title: "What is Risk-Based Authentication? And Why Should You Implement It?"
date: "2021-05-25"
-coverImage: "cover.jpg"
+coverImage: "cover.webp"
author: "Raghunath Reddy"
tags: ["RBA","Authentication"]
description: "RBA is a process of assessing the risk of an authentication request in real-time and requesting additional layers of authentication and identification based on the risk profile to validate that a user attempting to authenticate is who they claim to be."
@@ -11,7 +11,7 @@ While most of you — developers and architects — understand the need for stro
For years security researchers have been hollering about the risks of weak, repeated passwords. Still, average Joe seems to be complacent about it and reuses the same or similar passwords across multiple logins, despite the fact that even a strong password is secure only if used for a single login.
-
+
A good password manager can alleviate the problem of remembering tens of passwords, if not hundreds. However, in reality, the average Joe doesn't invest in a password manager and carries on with life.
diff --git a/content/engineering/roadmap-idx-autotester/index.md b/content/engineering/roadmap-idx-autotester/index.md
index 3b9d36039..77d3fe6ff 100644
--- a/content/engineering/roadmap-idx-autotester/index.md
+++ b/content/engineering/roadmap-idx-autotester/index.md
@@ -1,7 +1,7 @@
---
title: "Roadmap of idx-auto-tester"
date: "2020-06-30"
-coverImage: "roadmap_idx_auto_tester.png"
+coverImage: "roadmap_idx_auto_tester.webp"
author: "Rakesh Pareek"
tags: ["Automation", "idx", "roadmap"]
canonical: https://www.loginradius.com/blog/engineering/introduction-of-idx-auto-tester/
diff --git a/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.png b/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.png
deleted file mode 100644
index c1a4e8a89..000000000
Binary files a/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.png and /dev/null differ
diff --git a/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.webp b/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.webp
new file mode 100644
index 000000000..4f067d758
Binary files /dev/null and b/content/engineering/roadmap-idx-autotester/roadmap_idx_auto_tester.webp differ
diff --git a/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.png b/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.png
deleted file mode 100644
index be559cb7a..000000000
Binary files a/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.png and /dev/null differ
diff --git a/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.webp b/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.webp
new file mode 100644
index 000000000..bfc6256cb
Binary files /dev/null and b/content/engineering/saas-single-tenancy-vs-multi-tenancy/coverImage.webp differ
diff --git a/content/engineering/saas-single-tenancy-vs-multi-tenancy/index.md b/content/engineering/saas-single-tenancy-vs-multi-tenancy/index.md
index 12d82c979..66fa37d74 100644
--- a/content/engineering/saas-single-tenancy-vs-multi-tenancy/index.md
+++ b/content/engineering/saas-single-tenancy-vs-multi-tenancy/index.md
@@ -1,7 +1,7 @@
---
title: "Single-Tenant vs. Multi-Tenant: Which SaaS Architecture is better for Your Business? "
date: "2021-12-01"
-coverImage: "coverImage.png"
+coverImage: "coverImage.webp"
author: "Rakesh Soni"
tags: ["saas", "Architecture"]
description: "When choosing a SaaS architecture for your business, the decision between single-tenant and multi-tenant models can significantly impact performance, security, and cost. This blog explores the key differences, advantages, and potential drawbacks of each approach, helping you determine which solution best aligns with your business needs."
diff --git a/content/engineering/sdk-version-10-0-0/SDK.png b/content/engineering/sdk-version-10-0-0/SDK.png
deleted file mode 100644
index 95971dff2..000000000
Binary files a/content/engineering/sdk-version-10-0-0/SDK.png and /dev/null differ
diff --git a/content/engineering/sdk-version-10-0-0/SDK.webp b/content/engineering/sdk-version-10-0-0/SDK.webp
new file mode 100644
index 000000000..7a3830350
Binary files /dev/null and b/content/engineering/sdk-version-10-0-0/SDK.webp differ
diff --git a/content/engineering/sdk-version-10-0-0/index.md b/content/engineering/sdk-version-10-0-0/index.md
index b71911959..75d58e822 100644
--- a/content/engineering/sdk-version-10-0-0/index.md
+++ b/content/engineering/sdk-version-10-0-0/index.md
@@ -1,7 +1,7 @@
---
title: "SDK Version 10.0.0"
date: "2019-10-31"
-coverImage: "SDK.png"
+coverImage: "SDK.webp"
author: "Indrasen Kumar"
tags: ["Engineering", "SDK", "Version"]
---
diff --git a/content/engineering/self-hosted-mongo/atlas.png b/content/engineering/self-hosted-mongo/atlas.png
deleted file mode 100644
index 6cf420feb..000000000
Binary files a/content/engineering/self-hosted-mongo/atlas.png and /dev/null differ
diff --git a/content/engineering/self-hosted-mongo/atlas.webp b/content/engineering/self-hosted-mongo/atlas.webp
new file mode 100644
index 000000000..7643b9f1a
Binary files /dev/null and b/content/engineering/self-hosted-mongo/atlas.webp differ
diff --git a/content/engineering/self-hosted-mongo/aws.png b/content/engineering/self-hosted-mongo/aws.png
deleted file mode 100644
index 9b0980a56..000000000
Binary files a/content/engineering/self-hosted-mongo/aws.png and /dev/null differ
diff --git a/content/engineering/self-hosted-mongo/aws.webp b/content/engineering/self-hosted-mongo/aws.webp
new file mode 100644
index 000000000..6b89a7d19
Binary files /dev/null and b/content/engineering/self-hosted-mongo/aws.webp differ
diff --git a/content/engineering/self-hosted-mongo/blkid.png b/content/engineering/self-hosted-mongo/blkid.png
deleted file mode 100644
index c5f381f95..000000000
Binary files a/content/engineering/self-hosted-mongo/blkid.png and /dev/null differ
diff --git a/content/engineering/self-hosted-mongo/blkid.webp b/content/engineering/self-hosted-mongo/blkid.webp
new file mode 100644
index 000000000..0fced3f21
Binary files /dev/null and b/content/engineering/self-hosted-mongo/blkid.webp differ
diff --git a/content/engineering/self-hosted-mongo/cover.jpeg b/content/engineering/self-hosted-mongo/cover.jpeg
deleted file mode 100644
index 5a3aae58a..000000000
Binary files a/content/engineering/self-hosted-mongo/cover.jpeg and /dev/null differ
diff --git a/content/engineering/self-hosted-mongo/cover.webp b/content/engineering/self-hosted-mongo/cover.webp
new file mode 100644
index 000000000..8f52e5640
Binary files /dev/null and b/content/engineering/self-hosted-mongo/cover.webp differ
diff --git a/content/engineering/self-hosted-mongo/index.md b/content/engineering/self-hosted-mongo/index.md
index 6aa25d7cd..850085074 100644
--- a/content/engineering/self-hosted-mongo/index.md
+++ b/content/engineering/self-hosted-mongo/index.md
@@ -1,7 +1,7 @@
---
title: "Self-Hosted MongoDB"
date: "2020-06-30T12:00:00"
-coverImage: "cover.jpeg"
+coverImage: "cover.webp"
author: "Chinmaya Pati"
tags: ["MongoDB", "Mongo", "AWS", "Atlas"]
description: "Learn how to optimize your DB cost? This article will help you with the complete migration steps from a cloud to a self-hosted environment."
@@ -15,11 +15,11 @@ BTW, how much savings are we talking about? Let’s do a quick comparison betwee
**Atlas (~$166/month)**
-
+
$0.23/hour based on the above-selected requirements (~ [cloud.mongodb.com](https://cloud.mongodb.com))
**AWS (~$36/month)** - + $0.0416/hour for the instance and additional pricing based on the EBS type and storage (~ [calculator.aws](https://calculator.aws/)) @@ -65,7 +65,7 @@ $ sudo lsblk The additional volumes will be listed right after the root block (refer to the arrows) - + In the image above, you can see that the additional volumes are named 1. **xvdb** (30Gb space to store data) @@ -93,7 +93,7 @@ Before that let's copy the UUID of the above partitions(*because they are unique $ sudo blkid ``` - + Copy the UUIDs listed for **/dev/xvdb** and **/dev/xvdc**. Refer to the **“LABEL”** for block identification diff --git a/content/engineering/self-hosted-mongo/lsblk.png b/content/engineering/self-hosted-mongo/lsblk.png deleted file mode 100644 index 0396ca6eb..000000000 Binary files a/content/engineering/self-hosted-mongo/lsblk.png and /dev/null differ diff --git a/content/engineering/self-hosted-mongo/lsblk.webp b/content/engineering/self-hosted-mongo/lsblk.webp new file mode 100644 index 000000000..8fd9ddb88 Binary files /dev/null and b/content/engineering/self-hosted-mongo/lsblk.webp differ diff --git a/content/engineering/sending-emails-with-golang/email_cover.jpg b/content/engineering/sending-emails-with-golang/email_cover.jpg deleted file mode 100644 index 25569ede9..000000000 Binary files a/content/engineering/sending-emails-with-golang/email_cover.jpg and /dev/null differ diff --git a/content/engineering/sending-emails-with-golang/email_cover.webp b/content/engineering/sending-emails-with-golang/email_cover.webp new file mode 100644 index 000000000..f5b5b10a5 Binary files /dev/null and b/content/engineering/sending-emails-with-golang/email_cover.webp differ diff --git a/content/engineering/sending-emails-with-golang/index.md b/content/engineering/sending-emails-with-golang/index.md index 694eb1282..ed16e1841 100644 --- a/content/engineering/sending-emails-with-golang/index.md +++ b/content/engineering/sending-emails-with-golang/index.md @@ -1,7 +1,7 @@ --- title: Different ways to send an email with Golang date: "2020-08-03" -coverImage: "email_cover.jpg" +coverImage: "email_cover.webp" author: "Puneet Singh" tags: ["Go","Email"] description: "In this blog, we’ll look at different methods to send an email with Go, First we will explore inbuilt smtp package, then we will move to use a popular package Gomail and finally we will send HTML emails using custom templates." diff --git a/content/engineering/separate-login-page-for-admin-and-user/drupal.png b/content/engineering/separate-login-page-for-admin-and-user/drupal.png deleted file mode 100644 index 7ccb47873..000000000 Binary files a/content/engineering/separate-login-page-for-admin-and-user/drupal.png and /dev/null differ diff --git a/content/engineering/separate-login-page-for-admin-and-user/drupal.webp b/content/engineering/separate-login-page-for-admin-and-user/drupal.webp new file mode 100644 index 000000000..883abc12b Binary files /dev/null and b/content/engineering/separate-login-page-for-admin-and-user/drupal.webp differ diff --git a/content/engineering/separate-login-page-for-admin-and-user/index.md b/content/engineering/separate-login-page-for-admin-and-user/index.md index eca75a4aa..a4b9b4503 100644 --- a/content/engineering/separate-login-page-for-admin-and-user/index.md +++ b/content/engineering/separate-login-page-for-admin-and-user/index.md @@ -1,7 +1,7 @@ --- title: "Separate Drupal Login Page for Admin and User" date: "2015-10-29" -coverImage: "drupal.png" +coverImage: "drupal.webp" author: Versha Gupta tags: ["Drupal", "Admin Panel"] --- diff --git a/content/engineering/serverless-overview/cover.png b/content/engineering/serverless-overview/cover.png deleted file mode 100644 index e999a7383..000000000 Binary files a/content/engineering/serverless-overview/cover.png and /dev/null differ diff --git a/content/engineering/serverless-overview/cover.webp b/content/engineering/serverless-overview/cover.webp new file mode 100644 index 000000000..93b905d4f Binary files /dev/null and b/content/engineering/serverless-overview/cover.webp differ diff --git a/content/engineering/serverless-overview/index.md b/content/engineering/serverless-overview/index.md index 1fefff770..518447eb7 100644 --- a/content/engineering/serverless-overview/index.md +++ b/content/engineering/serverless-overview/index.md @@ -1,7 +1,7 @@ --- title: "Top 4 Serverless Computing Platforms in 2021" date: "2021-03-04" -coverImage: "cover.png" +coverImage: "cover.webp" author: "Andy Yeung" tags: ["Serverless"] description: "Traditional software development is being transformed by serverless computing. Check out the best serveless computing platforms that will assist you in getting started." diff --git a/content/engineering/service-mesh-with-envoy/front-image.jpeg b/content/engineering/service-mesh-with-envoy/front-image.jpeg deleted file mode 100644 index b9b6eea72..000000000 Binary files a/content/engineering/service-mesh-with-envoy/front-image.jpeg and /dev/null differ diff --git a/content/engineering/service-mesh-with-envoy/front-image.webp b/content/engineering/service-mesh-with-envoy/front-image.webp new file mode 100644 index 000000000..596ab1a58 Binary files /dev/null and b/content/engineering/service-mesh-with-envoy/front-image.webp differ diff --git a/content/engineering/service-mesh-with-envoy/index.md b/content/engineering/service-mesh-with-envoy/index.md index 9fa2a0fa6..eb291c81f 100644 --- a/content/engineering/service-mesh-with-envoy/index.md +++ b/content/engineering/service-mesh-with-envoy/index.md @@ -1,7 +1,7 @@ --- title: "Service Mesh with Envoy" date: "2020-07-06" -coverImage: "front-image.jpeg" +coverImage: "front-image.webp" author: "Piyush Kumar" tags: ["Service Mesh", "Envoy", "Microservices"] --- diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.png b/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.png deleted file mode 100644 index 08ca7e676..000000000 Binary files a/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.png and /dev/null differ diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.webp b/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.webp new file mode 100644 index 000000000..1d290ef07 Binary files /dev/null and b/content/engineering/setup-blog-in-minutes-with-jekyll/enable-github-pages.webp differ diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.png b/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.png deleted file mode 100644 index 6d5c3b63a..000000000 Binary files a/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.png and /dev/null differ diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.webp b/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.webp new file mode 100644 index 000000000..462c36053 Binary files /dev/null and b/content/engineering/setup-blog-in-minutes-with-jekyll/github-pages-action.webp differ diff --git a/content/engineering/setup-blog-in-minutes-with-jekyll/index.md b/content/engineering/setup-blog-in-minutes-with-jekyll/index.md index eff007cd1..c67540562 100644 --- a/content/engineering/setup-blog-in-minutes-with-jekyll/index.md +++ b/content/engineering/setup-blog-in-minutes-with-jekyll/index.md @@ -1,7 +1,7 @@ --- title: "Setup a blog in minutes with Jekyll & Github" date: "2020-10-26" -coverImage: "jekyll-github-pages.png" +coverImage: "jekyll-github-pages.webp" author: "Malathi T" tags: ["jekyll", "blogging", "blog", "github-pages"] description: Getting started with Jekyll & Github pages @@ -18,7 +18,7 @@ bundle exec jekyll serve ``` That's it. You can navigate to `http://localhost:8080` and see your blog up and running like this - + ## Customizing the blog As you see, the blog is a bare minimum, and the default values mentioned in the config file (`_config.yml`) are used. You can use the `_config.yml` file to add new plugins, provide metadata about the blog, add your social media profiles, modify themes, etc. @@ -46,11 +46,11 @@ Using your GitHub account, create a new repository. Push the contents of the jek `https://github.com/
-  +
+ 
 +
+ 
 +
+ 
 +
+ 
 +
+ 
 +
+ 
 +
+ 
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digitization-of-agile-marketing-principles) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digitization-of-agile-marketing-principles) diff --git a/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/index.md b/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/index.md index d3c047fe9..cc81748de 100644 --- a/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/index.md +++ b/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/index.md @@ -1,7 +1,7 @@ --- title: "Does Your Site’s Imagery Reflect Your Brand Identity" date: "2021-04-09" -coverImage: "website-branding-loginradius.jpg" +coverImage: "website-branding-loginradius.webp" category: ["loginradius"] featured: false author: "Vishal Sharma" @@ -105,4 +105,4 @@ The perfect intermingling of text and graphics with the right choice of colors i The aforementioned aspects help businesses in enhancing brand imagery that further improves brand identity in the long run. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=does-your-website-imagery-reflect-your-brand-identity) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=does-your-website-imagery-reflect-your-brand-identity) diff --git a/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.jpg b/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.jpg deleted file mode 100644 index 162126172..000000000 Binary files a/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.jpg and /dev/null differ diff --git a/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.webp b/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.webp new file mode 100644 index 000000000..45b1388e1 Binary files /dev/null and b/content/growth/Does-Your-website-Imagery-Reflect-Your-Brand-Identity/website-branding-loginradius.webp differ diff --git a/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.png b/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.png deleted file mode 100644 index e7cfcf9a0..000000000 Binary files a/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.png and /dev/null differ diff --git a/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.webp b/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.webp new file mode 100644 index 000000000..735ec1c8d Binary files /dev/null and b/content/growth/Duplicate-Content-and-SEO/book-a-demo-Consultation.webp differ diff --git a/content/growth/Duplicate-Content-and-SEO/content-writing-skills.jpg b/content/growth/Duplicate-Content-and-SEO/content-writing-skills.jpg deleted file mode 100644 index 427dd1ba7..000000000 Binary files a/content/growth/Duplicate-Content-and-SEO/content-writing-skills.jpg and /dev/null differ diff --git a/content/growth/Duplicate-Content-and-SEO/content-writing-skills.webp b/content/growth/Duplicate-Content-and-SEO/content-writing-skills.webp new file mode 100644 index 000000000..95468c223 Binary files /dev/null and b/content/growth/Duplicate-Content-and-SEO/content-writing-skills.webp differ diff --git a/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.jpg b/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.jpg deleted file mode 100644 index c7de5d0f9..000000000 Binary files a/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.jpg and /dev/null differ diff --git a/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.webp b/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.webp new file mode 100644 index 000000000..b97c19f28 Binary files /dev/null and b/content/growth/Duplicate-Content-and-SEO/duplicate-content-and-seo.webp differ diff --git a/content/growth/Duplicate-Content-and-SEO/duplicate-content.jpg b/content/growth/Duplicate-Content-and-SEO/duplicate-content.jpg deleted file mode 100644 index 1f3dd49fb..000000000 Binary files a/content/growth/Duplicate-Content-and-SEO/duplicate-content.jpg and /dev/null differ diff --git a/content/growth/Duplicate-Content-and-SEO/duplicate-content.webp b/content/growth/Duplicate-Content-and-SEO/duplicate-content.webp new file mode 100644 index 000000000..65435b478 Binary files /dev/null and b/content/growth/Duplicate-Content-and-SEO/duplicate-content.webp differ diff --git a/content/growth/Duplicate-Content-and-SEO/index.md b/content/growth/Duplicate-Content-and-SEO/index.md index 5c078fb7b..372113137 100644 --- a/content/growth/Duplicate-Content-and-SEO/index.md +++ b/content/growth/Duplicate-Content-and-SEO/index.md @@ -1,7 +1,7 @@ --- title: "Duplicate Content and SEO: What’s the Big Deal" date: "2021-05-06" -coverImage: "duplicate-content-and-seo.jpg" +coverImage: "duplicate-content-and-seo.webp" category: ["loginradius"] featured: false author: "Deependra Singh" @@ -25,7 +25,7 @@ Let’s have a quick look at some of the aspects associated with duplicate conte Every business seeks substantial growth by leveraging best-in-class **[content marketing](https://www.loginradius.com/blog/fuel/2021/03/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/)** and website optimization tactics that also build a brand reputation. But if the content on a website is duplicated, the owner may face traffic issues and dwindling website rankings.
- + Since search engines precisely crawl content on every website and won’t show multiple versions of content that is already published on different websites, there’s a huge chance that the duplicate one wouldn’t be listed in the search results. @@ -51,7 +51,7 @@ Businesses need to quickly analyze their website and figure out the actual cause Here are few effective ways to ensure your website contains any duplicate content pages, especially due to some technical glitches.
- + ### 1. Check your website’s indexed pages. @@ -87,4 +87,4 @@ Besides the fact that duplicate content leads to traffic and ranking issues, som It’s advised to consider auditing your website frequently to shun any chance of availability of duplicate content or pages. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=duplicate-content-and-seo) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=duplicate-content-and-seo) \ No newline at end of file diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.jpg b/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.jpg deleted file mode 100644 index 50f8cf210..000000000 Binary files a/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.jpg and /dev/null differ diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.webp b/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.webp new file mode 100644 index 000000000..12bdb78d9 Binary files /dev/null and b/content/growth/Future-Of-Social-Media-Video-Marketing/1500-0-.webp differ diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/index.md b/content/growth/Future-Of-Social-Media-Video-Marketing/index.md index 689f9260a..b882590cc 100644 --- a/content/growth/Future-Of-Social-Media-Video-Marketing/index.md +++ b/content/growth/Future-Of-Social-Media-Video-Marketing/index.md @@ -1,7 +1,7 @@ --- title: "Social Media Video Marketing: What Is In Store For Future Marketers" date: "2021-06-02" -coverImage: "social-videos.jpg" +coverImage: "social-videos.webp" category: ["loginradius"] featured: false author: "Deependra Singh" @@ -28,7 +28,7 @@ Fortunately, companies already know the reasons why using social media videos is Videos are one of the most profitable digital marketing tools. 91% of marketers believe video is crucial for business growth even during the coronavirus pandemic. Yet, if you are still not convinced, here are the reasons why marketers will love to use social media video marketing in 2021 and even in the years to come. - + ## Reasons Why the Future of Social Media Video Marketing is Bright @@ -74,7 +74,7 @@ Even though Facebook, YouTube, and Instagram are the giants in social media vide Twitter has also started using video with its newest feature, Fleets. With this feature, users can post videos to their timelines and promote their business creatively. Below is an example. -  +  Image Source: [Twitter](https://twitter.com/charts_k/status/1384136283547594757) @@ -94,4 +94,4 @@ So, it is not surprising when YouTube reports mobile video consumption rising ev Today, many brands are posting consumer testimonial videos on their website and hosting Q&A sessions to boost their social content marketing with a dash of digital decoration. Therefore, it will be wiser to start creating videos that matter to you and your audiences and be a part of the golden future of social media video marketing.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-of-social-media-video-marketing) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-of-social-media-video-marketing) \ No newline at end of file diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.jpg b/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.jpg deleted file mode 100644 index 2680c70df..000000000 Binary files a/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.jpg and /dev/null differ diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.webp b/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.webp new file mode 100644 index 000000000..cc8f49bac Binary files /dev/null and b/content/growth/Future-Of-Social-Media-Video-Marketing/scale-video-marketing-wordpress-social-media.webp differ diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.png b/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.png deleted file mode 100644 index 6d2bdaaf7..000000000 Binary files a/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.png and /dev/null differ diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.webp b/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.webp new file mode 100644 index 000000000..8b6c9c38c Binary files /dev/null and b/content/growth/Future-Of-Social-Media-Video-Marketing/social-brand-videos.webp differ diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.jpg b/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.jpg deleted file mode 100644 index e8e977db2..000000000 Binary files a/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.jpg and /dev/null differ diff --git a/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.webp b/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.webp new file mode 100644 index 000000000..bda056203 Binary files /dev/null and b/content/growth/Future-Of-Social-Media-Video-Marketing/social-videos.webp differ diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.jpg b/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.jpg deleted file mode 100644 index bf047630c..000000000 Binary files a/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.jpg and /dev/null differ diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.webp b/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.webp new file mode 100644 index 000000000..27eb11772 Binary files /dev/null and b/content/growth/Hotjar-vs-Microsoft-Clarity/Heatmap-Tools-loginradius.webp differ diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.png b/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.png deleted file mode 100644 index e7cfcf9a0..000000000 Binary files a/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.png and /dev/null differ diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.webp b/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.webp new file mode 100644 index 000000000..735ec1c8d Binary files /dev/null and b/content/growth/Hotjar-vs-Microsoft-Clarity/book-a-demo-Consultation.webp differ diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.jpg b/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.jpg deleted file mode 100644 index fd49cbafa..000000000 Binary files a/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.jpg and /dev/null differ diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.webp b/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.webp new file mode 100644 index 000000000..e878904c5 Binary files /dev/null and b/content/growth/Hotjar-vs-Microsoft-Clarity/hotjar-vs-ms-clarity.webp differ diff --git a/content/growth/Hotjar-vs-Microsoft-Clarity/index.md b/content/growth/Hotjar-vs-Microsoft-Clarity/index.md index ab46bbe58..1f0faebd3 100644 --- a/content/growth/Hotjar-vs-Microsoft-Clarity/index.md +++ b/content/growth/Hotjar-vs-Microsoft-Clarity/index.md @@ -1,7 +1,7 @@ --- title: "Website Heat Mapping with Hotjar vs. Microsoft Clarity" date: "2021-05-07" -coverImage: "hotjar-vs-ms-clarity.jpg" +coverImage: "hotjar-vs-ms-clarity.webp" category: ["loginradius"] featured: false author: "Deependra Singh" @@ -89,7 +89,7 @@ Several case studies reveal how heatmap tracking can help you improve your websi After understanding what heatmaps are and why they are essential, it’s time to compare Hotjar with Microsoft Clarity. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hotjar-vs-microsoft-clarity) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hotjar-vs-microsoft-clarity) ## Hotjar vs. Microsoft Clarity @@ -230,4 +230,4 @@ But it’s adding plenty of features at a fast pace. Putting all drawbacks aside ## Our Verdict Ideally, you must go with Hotjar if you are looking to access highly advanced [website tracking and Analytics features](https://www.loginradius.com/integrations/google-analytics/). But if you receive less traffic on your website and are looking for excellent free heat map software, then Clarity is your best bet. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hotjar-vs-microsoft-clarity) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hotjar-vs-microsoft-clarity) \ No newline at end of file diff --git a/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.jpg b/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.jpg deleted file mode 100644 index 81d15ecd6..000000000 Binary files a/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.jpg and /dev/null differ diff --git a/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.webp b/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.webp new file mode 100644 index 000000000..864059a33 Binary files /dev/null and b/content/growth/How-customer-retention-can-help-businesses-grow/consumer-audit-trail.webp differ diff --git a/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.jpg b/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.jpg deleted file mode 100644 index 47a56022b..000000000 Binary files a/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.jpg and /dev/null differ diff --git a/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.webp b/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.webp new file mode 100644 index 000000000..cc2a2ab33 Binary files /dev/null and b/content/growth/How-customer-retention-can-help-businesses-grow/customer-retention-LoginRadius-colorized.webp differ diff --git a/content/growth/How-customer-retention-can-help-businesses-grow/index.md b/content/growth/How-customer-retention-can-help-businesses-grow/index.md index dbfb9e31b..5a701895c 100644 --- a/content/growth/How-customer-retention-can-help-businesses-grow/index.md +++ b/content/growth/How-customer-retention-can-help-businesses-grow/index.md @@ -1,7 +1,7 @@ --- title: "How Customer Retention Can Help Businesses Grow" date: "2021-03-15" -coverImage: "customer-retention-LoginRadius-colorized.jpg" +coverImage: "customer-retention-LoginRadius-colorized.webp" category: ["loginradius"] featured: false author: "Yash Rathi" @@ -51,7 +51,7 @@ Customer retention strategies aim to maintain the existing customer base, which It is important to note that none of these strategies should be considered enough in isolation. They serve different purposes and goals to collectively increase the customer retention rate if implemented consistently and accurately. -[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail) +[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail) Some of the customer retention strategies are listed below: @@ -99,4 +99,4 @@ The training and development programs specifically designed to improve customer Customer acquisition and maintenance should not be seen as two mutually exclusive parts of the broader process of business growth. This is because the former can grow the business, while the latter is necessary for its expansion. Retaining the existing customers makes the business more recognizable as it focuses on creating brand loyalty and emotional bonding by prioritizing how the customers feel. Maintaining these customers becomes easy with customer loyalty programs, feedback, understanding customer churn patterns, and customer-oriented marketing. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-customer-retention-can-help-businesses-grow) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-customer-retention-can-help-businesses-grow) \ No newline at end of file diff --git a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.jpg b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.jpg deleted file mode 100644 index 7cde5f9fa..000000000 Binary files a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.jpg and /dev/null differ diff --git a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.webp b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.webp new file mode 100644 index 000000000..ce7c8f3ac Binary files /dev/null and b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/Effective-Communication-Strategies.webp differ diff --git a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/index.md b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/index.md index 156d0efff..5310ac62e 100644 --- a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/index.md +++ b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/index.md @@ -1,7 +1,7 @@ --- title: "How to Boost Your B2B Marketing Strategy with Hyper-Personalization" date: "2021-03-31" -coverImage: "Effective-Communication-Strategies.jpg" +coverImage: "Effective-Communication-Strategies.webp" category: ["loginradius"] featured: false author: "Vishal Sharma" @@ -109,4 +109,4 @@ The ones that will leverage hyper-personalization by understanding its impact on The aforementioned aspects depict the role of artificial intelligence coupled with content strategies that helps in winning consumer trust and getting chosen over competitors. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-boost-your-b2b-marketing-strategy-with-hyper-personalization) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-boost-your-b2b-marketing-strategy-with-hyper-personalization) \ No newline at end of file diff --git a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.png b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.png deleted file mode 100644 index 7602d120d..000000000 Binary files a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.png and /dev/null differ diff --git a/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.webp b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.webp new file mode 100644 index 000000000..9a00697f9 Binary files /dev/null and b/content/growth/How-to-Boost-Your-B2B-Marketing-Strategy-with-Hyper-Personalization/loginradius-book-a-demo.webp differ diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.png b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.png deleted file mode 100644 index bc0c2b3f3..000000000 Binary files a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.png and /dev/null differ diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.webp b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.webp new file mode 100644 index 000000000..b0f1ac055 Binary files /dev/null and b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/EB-Guide-to-Modern-Customer-Identity.webp differ diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.jpg b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.jpg deleted file mode 100644 index 9b807448a..000000000 Binary files a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.jpg and /dev/null differ diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.webp b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.webp new file mode 100644 index 000000000..fa200ed3a Binary files /dev/null and b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-marketing-loginradius.webp differ diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.jpg b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.jpg deleted file mode 100644 index 0ffe32b3f..000000000 Binary files a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.jpg and /dev/null differ diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.webp b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.webp new file mode 100644 index 000000000..e2e0f303d Binary files /dev/null and b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/content-seo-loginradius.webp differ diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/index.md b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/index.md index 87d11aaab..dd15a260e 100644 --- a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/index.md +++ b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/index.md @@ -1,7 +1,7 @@ --- title: "How to Drive in the Highest Quality Leads in 2021 with Content and SEO" date: "2021-03-23" -coverImage: "content-marketing-loginradius.jpg" +coverImage: "content-marketing-loginradius.webp" category: ["loginradius"] featured: false author: "Deependra Singh" @@ -42,7 +42,7 @@ As more businesses and consumers shift online for ease, the only way to stay con SEO helps your content to rank higher on Search Engine Result Pages (SERPs). Thus, driving in more traffic and, in turn, leading to more conversions. The major use of SEO is to generate more leads and conversions by diverting more traffic towards your webpage. [57% B2B marketers](https://blog.hubspot.com/marketing/the-future-of-content-marketing) swear by SEO for generating more leads and prefer the same more than other marketing forms. -[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) +[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) ## Important Questions to Ask When Using SEO for Lead Generation @@ -129,7 +129,7 @@ Content marketing through social media platforms or blog posts provides the user The basics of content marketing strategies are the same for all. To ensure that your content stands out amongst the thousands of web pages, implementing a winning content strategy is necessary. [69% of B2B marketers](https://www.smartinsights.com/content-management/content-marketing-strategy/essential-content-marketing-statistics/) have a sound content marketing strategy, and you need one, too. -  +  Here are some strategies you can employ for your business: @@ -193,4 +193,4 @@ The only constant when working with content marketing strategies is change. As l SEO lead generation is all about constant change. Understanding the market trends and keeping up with them is necessary. With the proper keywords and SEO strategy, business owners can successfully generate leads and conversions to sell their products and services. SEO leads have a [14.6% close rate](https://cdn2.hubspot.net/hub/212967/file-28030930-pdf/the_2012_state_of_inbound_marketing.pdf), more than any type. Therefore, effective SEO usage is necessary for businesses to stand apart from other competitors in the market. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-drive-in-the-highest-quality-leads-in-2021-with-content-and-seo) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-drive-in-the-highest-quality-leads-in-2021-with-content-and-seo) diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.png b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.png deleted file mode 100644 index 2fc6ddac9..000000000 Binary files a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.png and /dev/null differ diff --git a/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.webp b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.webp new file mode 100644 index 000000000..5522d721c Binary files /dev/null and b/content/growth/How-to-Drive-in-the-Highest-Quality-Leads-in-2021-with-Content-and-SEO/try-with-us-Partner.webp differ diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png deleted file mode 100644 index 9dc5bea48..000000000 Binary files a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png and /dev/null differ diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp new file mode 100644 index 000000000..7e0c48356 Binary files /dev/null and b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp differ diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.png b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.png deleted file mode 100644 index 7602d120d..000000000 Binary files a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.png and /dev/null differ diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.webp b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.webp new file mode 100644 index 000000000..9a00697f9 Binary files /dev/null and b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/Makeover-book-a-demo.webp differ diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.jpg b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.jpg deleted file mode 100644 index 9282aabce..000000000 Binary files a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.jpg and /dev/null differ diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.webp b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.webp new file mode 100644 index 000000000..161bfb0c7 Binary files /dev/null and b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/business-after-covid-loginradius.webp differ diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.jpg b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.jpg deleted file mode 100644 index 06c7975dc..000000000 Binary files a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.jpg and /dev/null differ diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.webp b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.webp new file mode 100644 index 000000000..5df733218 Binary files /dev/null and b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/covid-loginradius.webp differ diff --git a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/index.md b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/index.md index e0010d156..47abcc2fc 100644 --- a/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/index.md +++ b/content/growth/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/index.md @@ -1,7 +1,7 @@ --- title: "Thinking Beyond the Pandemic: How to Make Marketing Plans After Coronavirus" date: "2021-03-25" -coverImage: "business-after-covid-loginradius.jpg" +coverImage: "business-after-covid-loginradius.webp" category: ["loginradius"] featured: false author: "Rakesh Soni" @@ -41,7 +41,7 @@ Creative content strategy has now emerged as one of the most reliable B2B market Let's now explore some of the strategies employed by companies to survive in a post-pandemic world. - + ## 9 Successful B2B Marketing Strategies Post COVID @@ -101,7 +101,7 @@ From search engine optimization to email marketing, digital ad campaigns, and cr Companies are better served by taking advantage of the digital spectrum and remain omnipresent across various digital marketing platforms. -[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/) +[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/) ### 6. Employ data-driven storytelling. @@ -138,4 +138,4 @@ High-value B2B rarely deals closely with a conversation, and companies need thei While there is no way to tell which B2B marketing trends post COVID continue to remain in favor, consumer-centric offerings will always find relevance in a post-pandemic world. Incorporate any of the above suggestions in your B2B marketing strategies to reap the combined benefits of maximum consumer loyalty, satisfaction, and sustained profitability. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-make-businesses-marketing-plans-after-coronavirus) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-make-businesses-marketing-plans-after-coronavirus) \ No newline at end of file diff --git a/content/growth/How-to-add-Twitter-Blue-Checkmark/index.md b/content/growth/How-to-add-Twitter-Blue-Checkmark/index.md index 47ff8c62e..021ba116a 100644 --- a/content/growth/How-to-add-Twitter-Blue-Checkmark/index.md +++ b/content/growth/How-to-add-Twitter-Blue-Checkmark/index.md @@ -1,7 +1,7 @@ --- title: "Why Should You Have A Blue Checkmark In Front of Your Twitter Account" date: "2021-06-04" -coverImage: "twitter-verified-account.jpg" +coverImage: "twitter-verified-account.webp" category: ["loginradius"] featured: false author: "Rashmi Mathur" @@ -88,7 +88,7 @@ When you go through this process, Twitter will ask if the account name is the on Ideally, this is what the verification dialog box will look like: - + Once you submit this form, you just need to wait for the verification mark. And you are done. @@ -98,4 +98,4 @@ Twitter verification badge, commonly known as the blue checkmark, is super impor So, what are you waiting for? Get your Twitter account verified today! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-add-twitter-blue-checkmark) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-add-twitter-blue-checkmark) diff --git a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.png b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.png deleted file mode 100644 index 19f9aab8a..000000000 Binary files a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.png and /dev/null differ diff --git a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.webp b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.webp new file mode 100644 index 000000000..4d327df28 Binary files /dev/null and b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-bluemark-loginradius-readers-choice.webp differ diff --git a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.jpg b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.jpg deleted file mode 100644 index a4bde541e..000000000 Binary files a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.jpg and /dev/null differ diff --git a/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.webp b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.webp new file mode 100644 index 000000000..0d4e5f19e Binary files /dev/null and b/content/growth/How-to-add-Twitter-Blue-Checkmark/twitter-verified-account.webp differ diff --git a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.jpg b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.jpg deleted file mode 100644 index 4856545e2..000000000 Binary files a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.jpg and /dev/null differ diff --git a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.webp b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.webp new file mode 100644 index 000000000..4b9b2208f Binary files /dev/null and b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Facebook-Instagram.webp differ diff --git a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.png b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.png deleted file mode 100644 index 98e481315..000000000 Binary files a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.png and /dev/null differ diff --git a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.webp b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.webp new file mode 100644 index 000000000..5e3eaf627 Binary files /dev/null and b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/Product-Social-Login.webp differ diff --git a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/index.md b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/index.md index 8feead1eb..5d7a64d9c 100644 --- a/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/index.md +++ b/content/growth/Instagram-vs-Facebook-Which-One-is-Better-for-Your-Business-in-2021/index.md @@ -1,7 +1,7 @@ --- title: "Instagram vs Facebook – Which One is Better for Your Business in 2021?" date: "2021-04-28" -coverImage: "Facebook-Instagram.jpg" +coverImage: "Facebook-Instagram.webp" tags: ["social media","social login","cx"] author: "Vishal Sharma" description: "Even the most experienced video content creators use a system to make sure everything goes smoothly so they don't miss deadlines or lose track of what they need to do next. A transparent plan with checklists and milestones will help you adopt a more professional tone in your videos." @@ -21,7 +21,7 @@ Both of these platforms are powerful and influential with endless opportunities So, let’s take a quick look at both of these platforms and learn the differences and advantages so that you can understand where to focus attention. -[](https://www.loginradius.com/resource/loginradius-ciam-social-login/) +[](https://www.loginradius.com/resource/loginradius-ciam-social-login/) ## Instagram vs. Facebook: Audience Demographics @@ -77,4 +77,4 @@ When it comes to choosing between Facebook and Instagram, both platforms have th We can’t say Facebook > Instagram or vice-versa. It’s just the fact that as a marketer, one needs to understand its audience and their behavior. This will help in building a winning social media marketing strategy. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=instagram-vs-facebook-which-one-is-better-for-your-business-in-2021) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=instagram-vs-facebook-which-one-is-better-for-your-business-in-2021) diff --git a/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.jpg b/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.jpg deleted file mode 100644 index e6da87f70..000000000 Binary files a/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.jpg and /dev/null differ diff --git a/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.webp b/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.webp new file mode 100644 index 000000000..9a5705035 Binary files /dev/null and b/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/AI-Myth-True.webp differ diff --git a/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/index.md b/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/index.md index 528409389..2f6707abc 100644 --- a/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/index.md +++ b/content/growth/Is-AI-Really-Transforming-the-Digital-Marketing-Industry/index.md @@ -1,7 +1,7 @@ --- title: "Myth or True - Is AI Really Transforming the Digital Marketing Industry?" date: "2021-05-18" -coverImage: "AI-Myth-True.jpg" +coverImage: "AI-Myth-True.webp" category: ["loginradius"] featured: false author: "Ashley Lipman" @@ -62,4 +62,4 @@ While all artificially intelligent tools and software aren’t always cheap, the In conclusion, yes, AI is transforming the digital marketing industry. We hope the information in this [marketing growth blog](https://www.loginradius.com/blog/fuel/) has been able to show you how.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=is-ai-really-transforming-the-digital-marketing-industry) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=is-ai-really-transforming-the-digital-marketing-industry) diff --git a/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.jpg b/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.jpg deleted file mode 100644 index 0e2981a86..000000000 Binary files a/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.jpg and /dev/null differ diff --git a/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.webp b/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.webp new file mode 100644 index 000000000..b8b9bbd2b Binary files /dev/null and b/content/growth/Leverage-Website-for-More-Conversions/Leads-conversion-Loginradius.webp differ diff --git a/content/growth/Leverage-Website-for-More-Conversions/index.md b/content/growth/Leverage-Website-for-More-Conversions/index.md index a84fa986f..2a328d08a 100644 --- a/content/growth/Leverage-Website-for-More-Conversions/index.md +++ b/content/growth/Leverage-Website-for-More-Conversions/index.md @@ -1,7 +1,7 @@ --- title: "5 Quick Steps to Leverage your Website for More Conversions" date: "2021-04-21" -coverImage: "Leads-conversion-Loginradius.jpg" +coverImage: "Leads-conversion-Loginradius.webp" category: ["loginradius"] featured: false author: "Vishal Sharma" @@ -25,7 +25,7 @@ Though driving conversions isn’t a piece of cake, it largely depends on the wa Here we’ve clubbed some crucial aspects that will help your business enhance conversion rate through correct utilization of your website in this ever-increasing competitive world. - + 1. Mobile Optimization @@ -80,4 +80,4 @@ A business website holds a bunch of opportunities that can be fostered by utiliz Marketers need to put their best foot forward in understanding their targeted audience and what exactly they’re looking for in a business website. The aforementioned aspects can be quite fruitful for every business regardless of the industry to [enhance conversion rates](https://www.loginradius.com/blog/fuel/2021/03/how-to-drive-in-the-highest-quality-leads-in-2021-with-content-and-seo/) and improve overall traffic. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=leverage-website-for-more-conversions) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=leverage-website-for-more-conversions) \ No newline at end of file diff --git a/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.jpg b/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.jpg deleted file mode 100644 index 5b4a179d2..000000000 Binary files a/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.jpg and /dev/null differ diff --git a/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.webp b/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.webp new file mode 100644 index 000000000..d98e81357 Binary files /dev/null and b/content/growth/Leverage-Website-for-More-Conversions/website-optimization-conversion.webp differ diff --git a/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.jpg b/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.jpg deleted file mode 100644 index 2f59dd1a9..000000000 Binary files a/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.jpg and /dev/null differ diff --git a/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.webp b/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.webp new file mode 100644 index 000000000..5cbcc24fb Binary files /dev/null and b/content/growth/PR-Trends-to-Consider-in-2021/PR-Strategy-2021.webp differ diff --git a/content/growth/PR-Trends-to-Consider-in-2021/index.md b/content/growth/PR-Trends-to-Consider-in-2021/index.md index 7c9279b88..94ac6db12 100644 --- a/content/growth/PR-Trends-to-Consider-in-2021/index.md +++ b/content/growth/PR-Trends-to-Consider-in-2021/index.md @@ -1,7 +1,7 @@ --- title: "Three Unique PR Trends to Consider in 2021" date: "2021-04-22" -coverImage: "pr-trends-2021.jpg" +coverImage: "pr-trends-2021.webp" category: ["loginradius"] featured: false author: "Yash Rathi" @@ -27,7 +27,7 @@ Can companies continue to pursue the "traditional" form of PR and risk falling b Along with the masks and social distancing, here are 3 unique PR trends to consider in 2021 – they are here to stay over the next decade. Let us discuss each one of them in detail. - + ## PR Trends to Follow in 2021 @@ -122,4 +122,4 @@ As businesses adopt digital technologies, brand honesty is among the top concern ## Conclusion The evolving post-pandemic business world brings both challenges and opportunities to PR and communication teams. With more businesses going remote and to online platforms, it will be interesting to see how corporate PR responds to this change and devise their organizational strategy for the next decade. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pr-trends-to-consider-in-2021) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=pr-trends-to-consider-in-2021) diff --git a/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.jpg b/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.jpg deleted file mode 100644 index ffbfc7311..000000000 Binary files a/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.jpg and /dev/null differ diff --git a/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.webp b/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.webp new file mode 100644 index 000000000..2e9dff170 Binary files /dev/null and b/content/growth/PR-Trends-to-Consider-in-2021/pr-trends-2021.webp differ diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.png b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.png deleted file mode 100644 index e7cfcf9a0..000000000 Binary files a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.png and /dev/null differ diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.webp b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.webp new file mode 100644 index 000000000..735ec1c8d Binary files /dev/null and b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/book-a-demo-free-consultation.webp differ diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/index.md b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/index.md index 56228ffad..93b3d845c 100644 --- a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/index.md +++ b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/index.md @@ -1,7 +1,7 @@ --- title: "Top 10 Tips to Enhance Your Creativity While Working From Home" date: "2021-04-14" -coverImage: "work-from-home-loginradius.jpg" +coverImage: "work-from-home-loginradius.webp" category: ["loginradius"] featured: false author: "Deependra Singh" @@ -28,7 +28,7 @@ So, what does the picture look like now? According to statistics, [25-30% of the workforce will be working from home by the end of 2021.](https://globalworkplaceanalytics.com/work-at-home-after-covid-19-our-forecast) -  +  Living at home has its pros and cons. You can enjoy quality time with your family, save on travel expenses, and focus more on your kids. @@ -69,7 +69,7 @@ Deadlines play a significant role in developing a sense of accountability, wheth Strict timelines generate a sense of urgency in the employee and motivate them to find creative solutions to finish the task in a specified duration. Creativity allows them to judge their capabilities well, increase productivity and submit deliverables on time. -  +  ### 3. Consider multiple perspectives while having meetings @@ -99,7 +99,7 @@ For example, before you start discussing business issues, lighten your team's mo Share the recipe of your favorite cuisine or talk about the song your kid sang last night. You can gradually shift the focus towards more essential issues once you see people actively participating in the conversation. - + ### 5. Read, read, and read! @@ -168,4 +168,4 @@ But data alone doesn't lead anywhere. You need to have storytelling skills that ## Conclusion As the second wave of the coronavirus pandemic has spread across the world, work from home is here to stay, at least for a while. So, this is the best time to identify your strengths, polish your skills, and learn something new. Follow the ten tips given in this article to enhance your creativity while working from home and make the best use of your skills, time, and money during the pandemic. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-10-tips-to-enhance-your-creativity-while-working-from-home) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-10-tips-to-enhance-your-creativity-while-working-from-home) \ No newline at end of file diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.jpg b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.jpg deleted file mode 100644 index 3ece32e0f..000000000 Binary files a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.jpg and /dev/null differ diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.webp b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.webp new file mode 100644 index 000000000..067507538 Binary files /dev/null and b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/tips-for-work-from-home-creativity-loginradius.webp differ diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.jpg b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.jpg deleted file mode 100644 index 8c7a6d92d..000000000 Binary files a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.jpg and /dev/null differ diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.webp b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.webp new file mode 100644 index 000000000..ce2d97312 Binary files /dev/null and b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-1-loginradius.webp differ diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.jpg b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.jpg deleted file mode 100644 index a855bf456..000000000 Binary files a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.jpg and /dev/null differ diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.webp b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.webp new file mode 100644 index 000000000..995084c21 Binary files /dev/null and b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-creativity-loginradius.webp differ diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.jpg b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.jpg deleted file mode 100644 index afd0398c7..000000000 Binary files a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.jpg and /dev/null differ diff --git a/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.webp b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.webp new file mode 100644 index 000000000..77f6895ac Binary files /dev/null and b/content/growth/Top-10-Tips-to-Enhance-Your-Creativity-While-Working-From-Home/work-from-home-loginradius.webp differ diff --git a/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.jpg b/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.jpg deleted file mode 100644 index 1140d86f2..000000000 Binary files a/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.jpg and /dev/null differ diff --git a/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.webp b/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.webp new file mode 100644 index 000000000..128a5f7b2 Binary files /dev/null and b/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/Google-Local-Business.webp differ diff --git a/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/index.md b/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/index.md index 9e3ae0dc0..28a306bae 100644 --- a/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/index.md +++ b/content/growth/Top-5-Features-of-Google-My-Business-for-Marketers/index.md @@ -1,7 +1,7 @@ --- title: "5 Features of Google My Business You Should Be Using" date: "2021-05-18" -coverImage: "Google-Local-Business.jpg" +coverImage: "Google-Local-Business.webp" category: ["loginradius"] featured: false author: "Deependra Singh" @@ -61,4 +61,4 @@ When a subjective FAQ list is slowly generated, consumers can find answers to al There are over tens of Google Business features that you can use to build a targeted marketing campaign. And like the above five, they are created to ensure you get the highest SERP ranking. You can read our article on [Benefits of Google Tag Manager](https://www.loginradius.com/blog/fuel/2021/05/Benefits-of-Google-Tag-Manager/) to learn more marketing techniques. With Google My Business, you have an additional platform to get in touch with your consumers and generate more leads. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-features-of-google-my-business-for-marketers) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-features-of-google-my-business-for-marketers) diff --git a/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/index.md b/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/index.md index bcc08af7b..248dac6d6 100644 --- a/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/index.md +++ b/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/index.md @@ -1,7 +1,7 @@ --- title: "Top 5 Marketing Strategies to Power-up Your Business" date: "2021-04-15" -coverImage: "top-5-marketing-strategy.jpg" +coverImage: "top-5-marketing-strategy.webp" category: ["loginradius"] featured: false author: "Deependra Singh" @@ -99,4 +99,4 @@ These three practices can help gain your client’s trust and help build a long- Marketing strategies are dynamic, and you should never grow comfortable in a single marketing strategy. While this can help create a **[brand identity](https://www.loginradius.com/blog/fuel/2021/04/does-your-website-imagery-reflect-your-brand-identity/)**, consumers can quickly grow bored if they see the same content. This means, while you promise them data security best practices, you should also ensure to change and adapt your marketing strategies as the market grows. Digital Marketing evolves faster than any business can expect. The best way to ensure you’re on par with your competition is to keep track of all the trends, the data, the various data security best practices, and your campaign’s performance. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-marketing-strategies-to-power-up-your-business) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-marketing-strategies-to-power-up-your-business) diff --git a/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.jpg b/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.jpg deleted file mode 100644 index cf04664c0..000000000 Binary files a/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.jpg and /dev/null differ diff --git a/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.webp b/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.webp new file mode 100644 index 000000000..530082cda Binary files /dev/null and b/content/growth/Top-5-Marketing-Strategies-to-Power-up-Your-Business/top-5-marketing-strategy.webp differ diff --git a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.png b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.png deleted file mode 100644 index e7cfcf9a0..000000000 Binary files a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.png and /dev/null differ diff --git a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.webp b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.webp new file mode 100644 index 000000000..735ec1c8d Binary files /dev/null and b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/book-a-demo-Consultation.webp differ diff --git a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/index.md b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/index.md index 4de274c1d..24488d84b 100644 --- a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/index.md +++ b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/index.md @@ -1,7 +1,7 @@ --- title: "Top 5 tools to Audit Wordpress Website" date: "2021-05-06" -coverImage: "top-5-wp-seo-tools.jpg" +coverImage: "top-5-wp-seo-tools.webp" category: ["loginradius"] featured: false author: "Tanvi Soni" @@ -157,4 +157,4 @@ SEO tools help rank your website on the first page of Google and other search en It would be best if you begin by using free SEO tools available on the internet. If you notice any visible improvements on your website, you can purchase the paid version to get maximum benefits. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-seo-tools-for-auditing-wordpress-website) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-5-seo-tools-for-auditing-wordpress-website) diff --git a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.jpg b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.jpg deleted file mode 100644 index 4c92a3ba1..000000000 Binary files a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.jpg and /dev/null differ diff --git a/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.webp b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.webp new file mode 100644 index 000000000..8f4d559bc Binary files /dev/null and b/content/growth/Top-5-SEO-Tools-for-Auditing-WordPress-Website/top-5-wp-seo-tools.webp differ diff --git a/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.jpg b/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.jpg deleted file mode 100644 index d1d76248a..000000000 Binary files a/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.jpg and /dev/null differ diff --git a/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.webp b/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.webp new file mode 100644 index 000000000..5e7c17f38 Binary files /dev/null and b/content/growth/Top-UI-UX-Design-Tools-2021/best-ui-ux-design-loginradius.webp differ diff --git a/content/growth/Top-UI-UX-Design-Tools-2021/index.md b/content/growth/Top-UI-UX-Design-Tools-2021/index.md index a3ccdcec3..ab49ceb81 100644 --- a/content/growth/Top-UI-UX-Design-Tools-2021/index.md +++ b/content/growth/Top-UI-UX-Design-Tools-2021/index.md @@ -1,7 +1,7 @@ --- title: "Top UI/UX Design Tools 2021" date: "2021-04-19" -coverImage: "best-ui-ux-design-loginradius.jpg" +coverImage: "best-ui-ux-design-loginradius.webp" category: ["loginradius"] featured: false author: "Rakesh Soni" @@ -161,4 +161,4 @@ User behavior and expectations constantly evolve, so designers need to adapt and You can also work with a web design agency that provides comprehensive web design services to create an excellent user interface and user experience design. This also helps ensure your website retains or improves its current search rankings after the Google page experience update. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-ui-ux-design-tools-2021) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-ui-ux-design-tools-2021) diff --git a/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.jpg b/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.jpg deleted file mode 100644 index caf0d77a8..000000000 Binary files a/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.jpg and /dev/null differ diff --git a/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.webp b/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.webp new file mode 100644 index 000000000..720a3e0d1 Binary files /dev/null and b/content/growth/Twitter-for-B2B-Marketing-in-2021/Twitter-for-B2B-Marketing-in-2021.webp differ diff --git a/content/growth/Twitter-for-B2B-Marketing-in-2021/index.md b/content/growth/Twitter-for-B2B-Marketing-in-2021/index.md index 82316c245..394efc4f7 100644 --- a/content/growth/Twitter-for-B2B-Marketing-in-2021/index.md +++ b/content/growth/Twitter-for-B2B-Marketing-in-2021/index.md @@ -1,7 +1,7 @@ --- title: "How to Use Twitter for B2B Marketing in 2021" date: "2021-05-13" -coverImage: "Twitter-for-B2B-Marketing-in-2021.jpg" +coverImage: "Twitter-for-B2B-Marketing-in-2021.webp" category: ["loginradius"] featured: false author: "Navanita Devi" @@ -14,7 +14,7 @@ Twitter launched way back in 2006 and hasn't undergone any radical changes like -Research by the Content Marketing Institute tells that [82% of B2B content marketers](https://contentmarketinginstitute.com/wp-content/uploads/2020/09/b2b-2021-research-final.pdf) use Twitter for running marketing campaigns. +Research by the Content Marketing Institute tells that *82% of B2B content marketers* use Twitter for running marketing campaigns. @@ -86,7 +86,7 @@ Community building is emerging as an essential B2B online marketing strategy. Ma -A study found out that [32% of B2B marketers](https://contentmarketinginstitute.com/wp-content/uploads/2020/09/b2b-2021-research-final.pdf) work in organizations with established online communities, and 27% are looking forward to doing the same in the next 12 months. +A study found out that *32% of B2B marketers* work in organizations with established online communities, and 27% are looking forward to doing the same in the next 12 months. @@ -111,4 +111,4 @@ Each of the three marketing strategies explained in this article will help you g Firstly, you should check whether the Twitter B2B marketing strategies are aligned with your social media marketing strategy. Secondly, assess whether you have the resources and expertise to deal with businesses. And then, you are good to go!
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=twitter-for-b2b-marketing-in-2021) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=twitter-for-b2b-marketing-in-2021) diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.jpg b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.jpg deleted file mode 100644 index 097963e34..000000000 Binary files a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.jpg and /dev/null differ diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.webp b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.webp new file mode 100644 index 000000000..fbca27c87 Binary files /dev/null and b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/Types_of_Data_Analysis_Methods--colorized.webp differ diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.png b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.png deleted file mode 100644 index e7cfcf9a0..000000000 Binary files a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.png and /dev/null differ diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.webp b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.webp new file mode 100644 index 000000000..735ec1c8d Binary files /dev/null and b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/book-a-demo-Consultation.webp differ diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.jpg b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.jpg deleted file mode 100644 index 81d15ecd6..000000000 Binary files a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.jpg and /dev/null differ diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.webp b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.webp new file mode 100644 index 000000000..864059a33 Binary files /dev/null and b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/consumer-audit-trail.webp differ diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.jpg b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.jpg deleted file mode 100644 index 06aefad1f..000000000 Binary files a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.jpg and /dev/null differ diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.webp b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.webp new file mode 100644 index 000000000..055a2c748 Binary files /dev/null and b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/data-analysis-importance--colorized.webp differ diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.jpg b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.jpg deleted file mode 100644 index e6faba40c..000000000 Binary files a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.jpg and /dev/null differ diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.webp b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.webp new file mode 100644 index 000000000..bcef1714b Binary files /dev/null and b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/growth-hacking-2-colorized.webp differ diff --git a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/index.md b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/index.md index 61e0c3c4f..6a0c4bf18 100644 --- a/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/index.md +++ b/content/growth/Understanding-Growth-Hacking-and-How-SaaS-Businesses-Can-Use-It-to-Optimize-Growth/index.md @@ -1,7 +1,7 @@ --- title: "Growth Hacking: What it is and How SaaS Businesses Can Use it to Optimize Growth" date: "2021-03-30" -coverImage: "growth-hacking-2-colorized.jpg" +coverImage: "growth-hacking-2-colorized.webp" category: ["loginradius"] featured: false author: "Shachindra Saxena" @@ -116,7 +116,7 @@ Revenue is what remains after the cost that you invested in the acquisition of t -[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail) +[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail) ## Beginner's Guide to Start With Growth Hacking @@ -156,7 +156,7 @@ As you kickstart your business, set specific goals that you aim to achieve. For Growth hacking is based on analyzing data and implementing tasks based on the results. The data will dictate the prospect of the company. For example, if a SaaS company has a [retention rate of more than 35%](https://mixpanel.com/topics/whats-a-good-retention-rate/) then it is considered faring well. - + @@ -252,7 +252,7 @@ Another one of the case studies of growth hacking is Dropbox. It offered 16 GB Growth hacking is not a string of strategies that can be taught. It won't be wrong to call it a mindset one gains when their only focus is the business's growth. With affordable techniques suitable even for start-ups and analysis of the data, one can achieve millions of users in the least period. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=understanding-growth-hacking-and-how-saas-businesses-can-use-it-to-optimize-growth) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=understanding-growth-hacking-and-how-saas-businesses-can-use-it-to-optimize-growth) diff --git a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.jpg b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.jpg deleted file mode 100644 index 7f0b95783..000000000 Binary files a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.jpg and /dev/null differ diff --git a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.webp b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.webp new file mode 100644 index 000000000..a55aa085b Binary files /dev/null and b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/COVID-vaccines-for-remote-culture.webp differ diff --git a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/index.md b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/index.md index c55ace2cb..593a5918d 100644 --- a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/index.md +++ b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/index.md @@ -1,7 +1,7 @@ --- title: "COVID-19 Vaccine Success in USA and Remote Working – What’s The Connection" date: "2021-05-26" -coverImage: "COVID-vaccines-for-remote-culture.jpg" +coverImage: "COVID-vaccines-for-remote-culture.webp" category: ["loginradius"] featured: false author: "Navanita Devi" @@ -32,7 +32,7 @@ The study took a thorough look into the effectiveness of the mRNA vaccines among The findings clearly show that the USA has eventually got the better of the issue (or at least gotten very close to eliminating it) and is looking at a tomorrow that is safe and completely free from the pandemic that has claimed the lives of millions. - + ## Slowly but Steadily, Work from Home in the USA has Begun to Ease Even though work from home has by and large been quite productive, there is no substitute for the real-world interaction that professionals have in the office. It not only bolsters collaboration but also enhances the much-needed bonds among colleagues that eventually turn out to be the key aspects for overall growth. @@ -64,5 +64,5 @@ Considering that it would be apt to remain guarded against COVID-19 so that the The remarkable [COVID-19 business success](https://www.loginradius.com/blog/fuel/2021/03/how-to-make-businesses-marketing-plans-after-coronavirus/) in the USA is going to pave the way forward for other countries as well, especially the ones that are struggling to find the right answers to get rid of the pandemic. This success is all set to have a huge impact on the work from home culture and help people return to real-world interaction and teamwork, which are essential for long-term growth. The hybrid model will most likely lead the change. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=vaccine-success-can-impact-the-remote-working-culture) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=vaccine-success-can-impact-the-remote-working-culture) diff --git a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.jpg b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.jpg deleted file mode 100644 index 509ce9e96..000000000 Binary files a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.jpg and /dev/null differ diff --git a/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.webp b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.webp new file mode 100644 index 000000000..c22460970 Binary files /dev/null and b/content/growth/Vaccine-Success-can-Impact-the-Remote-Working-Culture/remot-working-in-covid.webp differ diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/index.md b/content/growth/Which-Marketing-Strategy-is-Best-for-You/index.md index 064120ef9..415f5d2fe 100644 --- a/content/growth/Which-Marketing-Strategy-is-Best-for-You/index.md +++ b/content/growth/Which-Marketing-Strategy-is-Best-for-You/index.md @@ -1,7 +1,7 @@ --- title: "Inbound Vs Outbound: Which Marketing Strategy is Best for You" date: "2021-03-31" -coverImage: "marketing-plan.jpg" +coverImage: "marketing-plan.webp" category: ["loginradius"] featured: false author: "Shachindra Saxena" @@ -37,7 +37,7 @@ Previously known just as simply ‘marketing,’ outbound marketing is an interr While once perhaps the only way to get people’s attention, outdoor marketing has steadily fallen out of favor with audiences. These days, audiences ignore these advances and do not feel obliged in the slightest. -[](https://www.loginradius.com/resource/digital-identity-future-whitepaper) +[](https://www.loginradius.com/resource/digital-identity-future-whitepaper) ## Inbound Marketing Methodology @@ -96,4 +96,4 @@ Marketing pixels allow companies to gather information about visitors and send t Companies would benefit from trying out new strategies while continuing to deploy those that work for them. Combining with regular data analysis to assess profitability will help companies stay on top of the game. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=which-marketing-strategy-is-best-for-you) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=which-marketing-strategy-is-best-for-you) \ No newline at end of file diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.png b/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.png deleted file mode 100644 index 7602d120d..000000000 Binary files a/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.png and /dev/null differ diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.webp b/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.webp new file mode 100644 index 000000000..9a00697f9 Binary files /dev/null and b/content/growth/Which-Marketing-Strategy-is-Best-for-You/loginradius-book-a-demo.webp differ diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.jpg b/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.jpg deleted file mode 100644 index b81dd8903..000000000 Binary files a/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.jpg and /dev/null differ diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.webp b/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.webp new file mode 100644 index 000000000..c7ff82441 Binary files /dev/null and b/content/growth/Which-Marketing-Strategy-is-Best-for-You/marketing-plan.webp differ diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.png b/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.png deleted file mode 100644 index 1338927e7..000000000 Binary files a/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.png and /dev/null differ diff --git a/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.webp b/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.webp new file mode 100644 index 000000000..468202b9e Binary files /dev/null and b/content/growth/Which-Marketing-Strategy-is-Best-for-You/the-Future-of-Digital-Identity.webp differ diff --git a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.png b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.png deleted file mode 100644 index e7cfcf9a0..000000000 Binary files a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.png and /dev/null differ diff --git a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.webp b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.webp new file mode 100644 index 000000000..735ec1c8d Binary files /dev/null and b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/book-a-demo-Consultation.webp differ diff --git a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/index.md b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/index.md index b8c9e744a..7eb13d27e 100644 --- a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/index.md +++ b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/index.md @@ -1,7 +1,7 @@ --- title: "Why Video Testimonials Are A Marketing Must" date: "2021-04-16" -coverImage: "video-testimonial-client-loginradius.jpg" +coverImage: "video-testimonial-client-loginradius.webp" category: ["loginradius"] featured: false author: "Navanita Devi" @@ -107,4 +107,4 @@ By now, it must be clear how important it is to develop video testimonials and t However, creating impactful video testimonials isn't a cakewalk. It requires a potent mixture of creativity, understanding of user needs, and digital marketing methods. So, start focusing more on video testimonials instead of investing resources for developing text-based marketing collaterals. With time, you will get better at it and create a massive impact on your audience. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-video-testimonials-are-a-marketing-must) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-video-testimonials-are-a-marketing-must) \ No newline at end of file diff --git a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.jpg b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.jpg deleted file mode 100644 index cc7e41739..000000000 Binary files a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.jpg and /dev/null differ diff --git a/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.webp b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.webp new file mode 100644 index 000000000..883ea53dd Binary files /dev/null and b/content/growth/Why-Video-Testimonials-Are-A-Marketing-Must/video-testimonial-client-loginradius.webp differ diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.jpg b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.jpg deleted file mode 100644 index dbbc9659f..000000000 Binary files a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.jpg and /dev/null differ diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.webp b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.webp new file mode 100644 index 000000000..8f262e4dd Binary files /dev/null and b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/client-onboard-loginradius-fuel-blog.webp differ diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.jpg b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.jpg deleted file mode 100644 index 4d47fc0b1..000000000 Binary files a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.jpg and /dev/null differ diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.webp b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.webp new file mode 100644 index 000000000..2e9888530 Binary files /dev/null and b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-churn--colorized.webp differ diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.jpg b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.jpg deleted file mode 100644 index 30badd2a4..000000000 Binary files a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.jpg and /dev/null differ diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.webp b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.webp new file mode 100644 index 000000000..eff3f719c Binary files /dev/null and b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/customer-onboarding-logiradius.webp differ diff --git a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/index.md b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/index.md index 978bda595..48aa7e86f 100644 --- a/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/index.md +++ b/content/growth/Why-is-Consumer-Onboarding-Critical-for-Startups/index.md @@ -1,7 +1,7 @@ --- title: "Why is Consumer Onboarding Critical for Startups" date: "2021-03-18" -coverImage: "client-onboard-loginradius-fuel-blog.jpg" +coverImage: "client-onboard-loginradius-fuel-blog.webp" category: ["loginradius"] featured: false author: "Rakesh Soni" @@ -30,7 +30,7 @@ It is imperative that consumers achieve desired results from your product or ser Approximately [52% of consumers abandon products](https://www.kickstartall.com/what-is-orchestrated-onboarding/) or services within 90 days due to a flawed onboarding process. 55% of people say they've [returned a product](https://www.wyzowl.com/customer-onboarding-statistics) because they didn't fully understand how to use it. -  +  A good consumer onboarding process ensures that your consumer is achieving the desired outcome of your product or services and as a result, it will help you reduce the churn rate. @@ -65,7 +65,7 @@ There is no single method of successful consumer onboarding as it depends on the This is the first touchpoint of your consumer onboarding. Therefore, the signup process should be simple and secure. Nowadays, consumers are concerned with the lengthy signup process and data security. Instead of building your signup form, you can opt for [**Best CIAM providers**](https://www.loginradius.com/resource/loginradius-ciam-developers-whitepaper) to ensure a good user experience, data security, and compliance. - + ### Welcome email @@ -91,4 +91,4 @@ Don't forget to take feedback from the consumer after onboarding. Ask them if th There are many free and paid tools available that help you set up a good consumer onboarding process. You can also [**refer to this article**](https://www.loginradius.com/blog/fuel/2021/01/user-onboarding-tools/) for the list of highly recommended consumer onboarding tools for businesses. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-is-consumer-onboarding-critical-for-startups) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-is-consumer-onboarding-critical-for-startups) diff --git a/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.png b/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.png deleted file mode 100644 index 4ea16b064..000000000 Binary files a/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.png and /dev/null differ diff --git a/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.webp b/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.webp new file mode 100644 index 000000000..7e6ca6673 Binary files /dev/null and b/content/growth/advantage-social-login-as-marketer/WP-social-login-rec.webp differ diff --git a/content/growth/advantage-social-login-as-marketer/index.md b/content/growth/advantage-social-login-as-marketer/index.md index ac3c3b4f1..ebaa07c89 100644 --- a/content/growth/advantage-social-login-as-marketer/index.md +++ b/content/growth/advantage-social-login-as-marketer/index.md @@ -1,7 +1,7 @@ --- title: "Can Social Login Boost Conversion Rates? 5 Things Marketers Should Know" date: "2021-11-12" -coverImage: "social-login-marketer.jpg" +coverImage: "social-login-marketer.webp" tags: ["social login","cx","data privacy"] author: "Navanita Devi" description: "Using social login to drive sign-ups usually makes sense because it increases user privacy. If users like the site, they're more likely to return, and you're more likely to convert them into paying customers. This blog explains how social login can boost conversion rates." @@ -28,7 +28,7 @@ The companies pull the user information to create a wholesome experience for the 2. **It enables the usage of social media functionalities.** Social login enables users to like, share, comment, subscribe, play online games, and much more without having to create an account or waste time by typing their login credentials over and over again. 3. **It doesn't force the users to create a new password:** The process utilizes the information of social media accounts of the users. Thus, they have one less password to remember. It is something they might appreciate and hence visit the website more frequently. -[](https://www.loginradius.com/resource/social-login-reconsidered/) +[](https://www.loginradius.com/resource/social-login-reconsidered/) 4. **It results in fewer unsuccessful logins:** The users only need to click on the social media account they want to log in with. Thus, they will not have the scope of making mistakes while entering their login credentials. @@ -58,4 +58,4 @@ Marketers can use personalized emails to [build relationships with customers](ht Thus, if used properly, **social logins** can boost conversion rates like no other authentication tool. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advantage-social-login-as-marketer) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advantage-social-login-as-marketer) diff --git a/content/growth/advantage-social-login-as-marketer/social-login-marketer.jpg b/content/growth/advantage-social-login-as-marketer/social-login-marketer.jpg deleted file mode 100644 index b39b73c77..000000000 Binary files a/content/growth/advantage-social-login-as-marketer/social-login-marketer.jpg and /dev/null differ diff --git a/content/growth/advantage-social-login-as-marketer/social-login-marketer.webp b/content/growth/advantage-social-login-as-marketer/social-login-marketer.webp new file mode 100644 index 000000000..208b41776 Binary files /dev/null and b/content/growth/advantage-social-login-as-marketer/social-login-marketer.webp differ diff --git a/content/growth/advantage-social-login-as-marketer/social-login-wp.png b/content/growth/advantage-social-login-as-marketer/social-login-wp.png deleted file mode 100644 index 412e2195c..000000000 Binary files a/content/growth/advantage-social-login-as-marketer/social-login-wp.png and /dev/null differ diff --git a/content/growth/advantage-social-login-as-marketer/social-login-wp.webp b/content/growth/advantage-social-login-as-marketer/social-login-wp.webp new file mode 100644 index 000000000..6e975bd35 Binary files /dev/null and b/content/growth/advantage-social-login-as-marketer/social-login-wp.webp differ diff --git a/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.png b/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.png deleted file mode 100644 index 1116bcde5..000000000 Binary files a/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.png and /dev/null differ diff --git a/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.webp b/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.webp new file mode 100644 index 000000000..8efa78c3e Binary files /dev/null and b/content/growth/ai-innovations-transforming-compliance/WP-ai-iam.webp differ diff --git a/content/growth/ai-innovations-transforming-compliance/ai-compliance.jpg b/content/growth/ai-innovations-transforming-compliance/ai-compliance.jpg deleted file mode 100644 index 1990c1172..000000000 Binary files a/content/growth/ai-innovations-transforming-compliance/ai-compliance.jpg and /dev/null differ diff --git a/content/growth/ai-innovations-transforming-compliance/ai-compliance.webp b/content/growth/ai-innovations-transforming-compliance/ai-compliance.webp new file mode 100644 index 000000000..24b5ec723 Binary files /dev/null and b/content/growth/ai-innovations-transforming-compliance/ai-compliance.webp differ diff --git a/content/growth/ai-innovations-transforming-compliance/index.md b/content/growth/ai-innovations-transforming-compliance/index.md index dcff36a65..4f2b548fd 100644 --- a/content/growth/ai-innovations-transforming-compliance/index.md +++ b/content/growth/ai-innovations-transforming-compliance/index.md @@ -1,7 +1,7 @@ --- title: "5 Breakthrough Innovations: How AI is Transforming Compliance" date: "2024-07-23" -coverImage: "ai-compliance.jpg" +coverImage: "ai-compliance.webp" tags: ["ai","consent management","compliance"] author: "Rakesh Soni" description: "Artificial Intelligence is reshaping the landscape of compliance with groundbreaking innovations. Here are five transformative ways AI is revolutionizing compliance, offering enhanced accuracy, efficiency, and risk management." @@ -50,7 +50,7 @@ AI can analyze patterns and behaviors to detect anomalies indicative of fraudule * Deploy AI-powered behavioral analytics tools to continuously monitor transactions and activities, flagging any suspicious behavior for further investigation. -[](https://www.loginradius.com/resource/whitepaper/how-ai-change-iam-initiatives/) +[](https://www.loginradius.com/resource/whitepaper/how-ai-change-iam-initiatives/) ### 5. Predictive Analytics for Compliance Trends @@ -68,4 +68,4 @@ As regulatory landscapes continue to evolve, leveraging AI will be crucial for b Embrace these AI-driven innovations and position your organization at the forefront of compliance efficiency and accuracy. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-innovations-transforming-compliance) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-innovations-transforming-compliance) \ No newline at end of file diff --git a/content/growth/attract-consumers-to-your-website/consumer-to-website.jpg b/content/growth/attract-consumers-to-your-website/consumer-to-website.jpg deleted file mode 100644 index 6de9cd7ec..000000000 Binary files a/content/growth/attract-consumers-to-your-website/consumer-to-website.jpg and /dev/null differ diff --git a/content/growth/attract-consumers-to-your-website/consumer-to-website.webp b/content/growth/attract-consumers-to-your-website/consumer-to-website.webp new file mode 100644 index 000000000..67610aa56 Binary files /dev/null and b/content/growth/attract-consumers-to-your-website/consumer-to-website.webp differ diff --git a/content/growth/attract-consumers-to-your-website/index.md b/content/growth/attract-consumers-to-your-website/index.md index edd2f9a60..b6726a47b 100644 --- a/content/growth/attract-consumers-to-your-website/index.md +++ b/content/growth/attract-consumers-to-your-website/index.md @@ -1,7 +1,7 @@ --- title: "5 Tricks to Attract MORE Consumers to Your Website" date: "2021-02-23" -coverImage: "consumer-to-website.jpg" +coverImage: "consumer-to-website.webp" category: ["all"] featured: false author: "Rakesh Soni" @@ -79,7 +79,7 @@ By considering these factors, you can get a hold of the social media channels ha Once you've identified and started concentrating on platforms, build a publishing plan for social media that allows you to keep to a schedule. You will find several resources that will help you plan social media posts in advance, giving you time to interact with your audience and checking out the competitors every day. Being disciplined about this will allow you to get more visitors to your site. -Many businesses today rely a lot on sharing and advertising their material on social media, with around [83% of marketers](https://contentmarketinginstitute.com/wp-content/uploads/2020/09/b2b-2021-research-final.pdf) using and viewing them as a lucrative marketing channel. They use social media to connect and share their content and that of others, and so should you. Through social media accounts, you can share your blog posts with your audience; doing so can increase traffic to your website. +Many businesses today rely a lot on sharing and advertising their material on social media, with around *83% of marketers* using and viewing them as a lucrative marketing channel. They use social media to connect and share their content and that of others, and so should you. Through social media accounts, you can share your blog posts with your audience; doing so can increase traffic to your website. Since not many brands reply to follower comments, if you do it, your audience is more likely to go through the funnel quickly, i.e., they convert into consumers of your products or services._ _ @@ -122,4 +122,4 @@ Don't forget to build growth strategies after creating content to draw users to By following these five tricks, you can make the most of your strategies to attract online consumers while also maintaining them and ensuring that they get converted into leads. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=attract-consumers-to-your-website) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=attract-consumers-to-your-website) diff --git a/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.png b/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.png deleted file mode 100644 index b6c1daad3..000000000 Binary files a/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.png and /dev/null differ diff --git a/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.webp b/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.webp new file mode 100644 index 000000000..3e81105a6 Binary files /dev/null and b/content/growth/authentication-challenges-retail-industry/DS-retail-consumer-goods.webp differ diff --git a/content/growth/authentication-challenges-retail-industry/index.md b/content/growth/authentication-challenges-retail-industry/index.md index 6abf935cd..21b7ecdcb 100644 --- a/content/growth/authentication-challenges-retail-industry/index.md +++ b/content/growth/authentication-challenges-retail-industry/index.md @@ -1,7 +1,7 @@ --- title: "What are the Authentication Challenges in the Retail Industry?" date: "2021-10-26" -coverImage: "retail-auth.jpg" +coverImage: "retail-auth.webp" tags: ["data security","retail authentication","cx"] author: "Rashmi Mathur" description: "Losing business means paying for remediation, business disruption, legal expenses, identity repair, regulatory penalties, and other clean-up costs. Although retail has some distinct differences from other industries regarding identity and authentication, it also faces many challenges." @@ -39,7 +39,7 @@ Along with providing authentication solutions, it is important to protect the di Cloud applications have made applications and data accessible from anywhere in the world. However, the local laws require several retailers to be tight over how and from where the employees can access the data. Additionally, various governments might have different regulations. Hence, complying with multiple rules at the same time might prove to be a challenge. -[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/) +[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/) ## Solving These Challenges @@ -73,4 +73,4 @@ Typical business-to-employee scenarios, like e-commerce portals, require a much The ability to authenticate customers in real time using multiple modalities is challenging. Understanding how solutions vary by use case, threat model and authentication technology used is crucial to choosing the right one for your unique requirements. [Contact us](https://www.loginradius.com/contact-sales) for better understanding. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-challenges-retail-industry) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-challenges-retail-industry) diff --git a/content/growth/authentication-challenges-retail-industry/retail-auth.jpg b/content/growth/authentication-challenges-retail-industry/retail-auth.jpg deleted file mode 100644 index 89347396a..000000000 Binary files a/content/growth/authentication-challenges-retail-industry/retail-auth.jpg and /dev/null differ diff --git a/content/growth/authentication-challenges-retail-industry/retail-auth.webp b/content/growth/authentication-challenges-retail-industry/retail-auth.webp new file mode 100644 index 000000000..4d4ebc759 Binary files /dev/null and b/content/growth/authentication-challenges-retail-industry/retail-auth.webp differ diff --git a/content/growth/authentication-challenges-retail-industry/retail-ciam.png b/content/growth/authentication-challenges-retail-industry/retail-ciam.png deleted file mode 100644 index 89245ae36..000000000 Binary files a/content/growth/authentication-challenges-retail-industry/retail-ciam.png and /dev/null differ diff --git a/content/growth/authentication-challenges-retail-industry/retail-ciam.webp b/content/growth/authentication-challenges-retail-industry/retail-ciam.webp new file mode 100644 index 000000000..929b7daff Binary files /dev/null and b/content/growth/authentication-challenges-retail-industry/retail-ciam.webp differ diff --git a/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.jpg b/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.jpg deleted file mode 100644 index 35564fe12..000000000 Binary files a/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.jpg and /dev/null differ diff --git a/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.webp b/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.webp new file mode 100644 index 000000000..38eaa2f02 Binary files /dev/null and b/content/growth/authentication-critical-customer-acquistion-tool/auth-marketers.webp differ diff --git a/content/growth/authentication-critical-customer-acquistion-tool/index.md b/content/growth/authentication-critical-customer-acquistion-tool/index.md index a9c0bfb34..1024b1b0d 100644 --- a/content/growth/authentication-critical-customer-acquistion-tool/index.md +++ b/content/growth/authentication-critical-customer-acquistion-tool/index.md @@ -1,7 +1,7 @@ --- title: "Authentication Has Gone Mainstream: Are Marketers Ready to Take the Responsibility?" date: "2022-07-29" -coverImage: "auth-marketers.jpg" +coverImage: "auth-marketers.webp" category: ["authentication", "authorization", "customer verification"] author: "Navanita Devi" description: "Authentication is the most important security feature any application can have because it's the gateway through which users interact with your data. This blog explains how marketers can leverage user authentication." @@ -77,4 +77,4 @@ As the world becomes more connected, users have become increasingly more aware o Marketers need to strike a balance between user security and experience when it comes to user privacy. That means providing security services that won't frustrate customers who want to get the most out of their devices and applications. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-critical-customer-acquistion-tool) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-critical-customer-acquistion-tool) \ No newline at end of file diff --git a/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.png b/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.png deleted file mode 100644 index 4ea16b064..000000000 Binary files a/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.png and /dev/null differ diff --git a/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.webp b/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.webp new file mode 100644 index 000000000..7e6ca6673 Binary files /dev/null and b/content/growth/authentication-evolution-to-passwordless/WP-social-login-rec.webp differ diff --git a/content/growth/authentication-evolution-to-passwordless/evolution-auth.jpg b/content/growth/authentication-evolution-to-passwordless/evolution-auth.jpg deleted file mode 100644 index e56a4dd78..000000000 Binary files a/content/growth/authentication-evolution-to-passwordless/evolution-auth.jpg and /dev/null differ diff --git a/content/growth/authentication-evolution-to-passwordless/evolution-auth.webp b/content/growth/authentication-evolution-to-passwordless/evolution-auth.webp new file mode 100644 index 000000000..8d1366811 Binary files /dev/null and b/content/growth/authentication-evolution-to-passwordless/evolution-auth.webp differ diff --git a/content/growth/authentication-evolution-to-passwordless/index.md b/content/growth/authentication-evolution-to-passwordless/index.md index b8bed1807..342cd1d09 100644 --- a/content/growth/authentication-evolution-to-passwordless/index.md +++ b/content/growth/authentication-evolution-to-passwordless/index.md @@ -1,7 +1,7 @@ --- title: "The Evolution of Authentication: From Passwords to Passwordless & More" date: "2022-05-27" -coverImage: "evolution-auth.jpg" +coverImage: "evolution-auth.webp" tags: ["passwordless authentication","new age authentication","cx"] author: "Navanita Devi" description: "Over the past years, the evolution of authentication portrays the risks associated with unauthorized access and the growing number of cybersecurity threats that leads to compromised user information and sensitive business data. Here’s an insightful read depicting authentication aspects and how it has evolved over a decade." @@ -48,7 +48,7 @@ It simplifies the sign-in and registration experiences, providing a convenient a For consumers, social login is a single-click login method for accessing the website and mobile application—one in which there is no need for excess credentials and allows consumers to skip traditional registration methods. -[](https://www.loginradius.com/resource/social-login-reconsidered/) +[](https://www.loginradius.com/resource/social-login-reconsidered/) ### #2. Passwordless Authentication @@ -86,4 +86,4 @@ And the crux of the matter is that businesses relying on old-school authenticati Businesses leveraging cutting-edge authentication technologies always stand ahead of their competitors since their customers enjoy a seamless user experience reinforced by robust security. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-evolution-to-passwordless) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-evolution-to-passwordless) \ No newline at end of file diff --git a/content/growth/authentication-evolution-to-passwordless/social-login-wp.png b/content/growth/authentication-evolution-to-passwordless/social-login-wp.png deleted file mode 100644 index 412e2195c..000000000 Binary files a/content/growth/authentication-evolution-to-passwordless/social-login-wp.png and /dev/null differ diff --git a/content/growth/authentication-evolution-to-passwordless/social-login-wp.webp b/content/growth/authentication-evolution-to-passwordless/social-login-wp.webp new file mode 100644 index 000000000..6e975bd35 Binary files /dev/null and b/content/growth/authentication-evolution-to-passwordless/social-login-wp.webp differ diff --git a/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.png b/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.png deleted file mode 100644 index c8e655587..000000000 Binary files a/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.png and /dev/null differ diff --git a/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.webp b/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.webp new file mode 100644 index 000000000..1082e7522 Binary files /dev/null and b/content/growth/authentication-mainstream-marketers-benefit/WP-sec-user-auth.webp differ diff --git a/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.jpg b/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.jpg deleted file mode 100644 index 114bb8c17..000000000 Binary files a/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.jpg and /dev/null differ diff --git a/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.webp b/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.webp new file mode 100644 index 000000000..b52380171 Binary files /dev/null and b/content/growth/authentication-mainstream-marketers-benefit/auth-benefit.webp differ diff --git a/content/growth/authentication-mainstream-marketers-benefit/index.md b/content/growth/authentication-mainstream-marketers-benefit/index.md index f5e754cc5..68ed19554 100644 --- a/content/growth/authentication-mainstream-marketers-benefit/index.md +++ b/content/growth/authentication-mainstream-marketers-benefit/index.md @@ -1,7 +1,7 @@ --- title: "How Authentication Leads The Way in Strategic Customer Acquisitions?" date: "2022-10-12" -coverImage: "auth-benefit.jpg" +coverImage: "auth-benefit.webp" tags: ["passwordless authentication","digital identity","sso","cx"] author: "Grigori Monaselidze" description: "With digital businesses taking over the entire industry, improving customer authentication and email communication with customers has never been more important to maintaining a successful business. This blog explains how authentication can help you increase your customer acquisition." @@ -41,7 +41,7 @@ KBA, or Knowledge-based Authentication is a common method for securely aiding a [Single sign-on](https://www.loginradius.com/single-sign-on/) or SSO, is mostly used by services using password as their main authentication method. SSO allows a customer to authenticate themselves once to use various accounts or systems. This provides comfort, as it eliminates the need to remember various passwords for various applications. -[](https://www.loginradius.com/resource/securing-user-authentication-understanding-the-basics-best-practices/) +[](https://www.loginradius.com/resource/securing-user-authentication-understanding-the-basics-best-practices/) All of the three above-mentioned customer authentication methods present a challenge, where a business must determine a common ground between comfort and security. @@ -96,4 +96,4 @@ Email campaigns certainly can be tricky, a lot of resources are invested in stra With digital businesses taking over the entire industry, improving customer authentication and email communication with customers has never been more important to maintaining a successful business. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-mainstream-marketers-benefit) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-mainstream-marketers-benefit) \ No newline at end of file diff --git a/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.png b/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.png deleted file mode 100644 index 2af543487..000000000 Binary files a/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.png and /dev/null differ diff --git a/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.webp b/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.webp new file mode 100644 index 000000000..2e2a4d5c2 Binary files /dev/null and b/content/growth/authentication-mainstream-marketers-benefit/user-auth-wp.webp differ diff --git a/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.png b/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.png deleted file mode 100644 index a3580f13e..000000000 Binary files a/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.png and /dev/null differ diff --git a/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.webp b/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.webp new file mode 100644 index 000000000..0257eff22 Binary files /dev/null and b/content/growth/authentication-tools-boost-sales/DS-Mob-Bio-Auth.webp differ diff --git a/content/growth/authentication-tools-boost-sales/auth-tools.jpg b/content/growth/authentication-tools-boost-sales/auth-tools.jpg deleted file mode 100644 index 64d56cb05..000000000 Binary files a/content/growth/authentication-tools-boost-sales/auth-tools.jpg and /dev/null differ diff --git a/content/growth/authentication-tools-boost-sales/auth-tools.webp b/content/growth/authentication-tools-boost-sales/auth-tools.webp new file mode 100644 index 000000000..ea6e40cdc Binary files /dev/null and b/content/growth/authentication-tools-boost-sales/auth-tools.webp differ diff --git a/content/growth/authentication-tools-boost-sales/bio-auth.png b/content/growth/authentication-tools-boost-sales/bio-auth.png deleted file mode 100644 index 69293181d..000000000 Binary files a/content/growth/authentication-tools-boost-sales/bio-auth.png and /dev/null differ diff --git a/content/growth/authentication-tools-boost-sales/bio-auth.webp b/content/growth/authentication-tools-boost-sales/bio-auth.webp new file mode 100644 index 000000000..b272f8563 Binary files /dev/null and b/content/growth/authentication-tools-boost-sales/bio-auth.webp differ diff --git a/content/growth/authentication-tools-boost-sales/index.md b/content/growth/authentication-tools-boost-sales/index.md index a91f0ebc3..c8765c359 100644 --- a/content/growth/authentication-tools-boost-sales/index.md +++ b/content/growth/authentication-tools-boost-sales/index.md @@ -1,7 +1,7 @@ --- title: "Can Authentication Convert Sales? 4 Authentication Tools for Every Retailer" date: "2021-11-08" -coverImage: "auth-tools.jpg" +coverImage: "auth-tools.webp" tags: ["biometric authentication","social login","passwordless authentication"] author: "Navanita Devi" description: "Authentication is a serious process that can help you convert sales. In many cases, it determines whether a customer will take the time to complete a purchase. Therefore, it is important for your store to have multiple layers of security throughout the checkout process." @@ -51,7 +51,7 @@ Additionally, it reduces the need to create digital contracts and also the waiti As a result of the above advantages, customers are more likely to engage with your brand and be loyal to you. Additionally, with more customers, you are more likely to get more data. Proper analysis of it can lead to a further high conversion rate. -[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet) +[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet) ### #3. Social Logins @@ -72,4 +72,4 @@ Moving away from traditional **authentication tools** such as standard authentic There is no doubt that using an authentication tool can improve your website's conversion rate. This is because you will protect your customers better while keeping out hackers, fraudsters and other malicious individuals. However, you should take the time to look for the best authentication solutions in the market today. [Contact us](https://www.loginradius.com/contact-sales) for more information on how we can help! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-tools-boost-sales) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-tools-boost-sales) diff --git a/content/growth/b2b-saas-security-management/WP-LR-resiliency.png b/content/growth/b2b-saas-security-management/WP-LR-resiliency.png deleted file mode 100644 index cbe459800..000000000 Binary files a/content/growth/b2b-saas-security-management/WP-LR-resiliency.png and /dev/null differ diff --git a/content/growth/b2b-saas-security-management/WP-LR-resiliency.webp b/content/growth/b2b-saas-security-management/WP-LR-resiliency.webp new file mode 100644 index 000000000..efb695fb3 Binary files /dev/null and b/content/growth/b2b-saas-security-management/WP-LR-resiliency.webp differ diff --git a/content/growth/b2b-saas-security-management/b2b-saas.jpg b/content/growth/b2b-saas-security-management/b2b-saas.jpg deleted file mode 100644 index 9747952f1..000000000 Binary files a/content/growth/b2b-saas-security-management/b2b-saas.jpg and /dev/null differ diff --git a/content/growth/b2b-saas-security-management/b2b-saas.webp b/content/growth/b2b-saas-security-management/b2b-saas.webp new file mode 100644 index 000000000..92d24630a Binary files /dev/null and b/content/growth/b2b-saas-security-management/b2b-saas.webp differ diff --git a/content/growth/b2b-saas-security-management/index.md b/content/growth/b2b-saas-security-management/index.md index 77b5c246c..569d3dd70 100644 --- a/content/growth/b2b-saas-security-management/index.md +++ b/content/growth/b2b-saas-security-management/index.md @@ -1,7 +1,7 @@ --- title: "Securing B2B SaaS: How Identity Management Leads the Charge Against Top 5 Security Challenges" date: "2024-04-12" -coverImage: "b2b-saas.jpg" +coverImage: "b2b-saas.webp" tags: ["saas","digital identity management","compliance"] author: "Alok Patidar" description: "Security is paramount in the dynamic B2B SaaS landscape. Explore how Identity Management addresses the top 5 security challenges, from data breaches to compliance, offering insights to fortify digital defenses. Discover proactive measures to safeguard systems and data, letting Identity Management lead the charge in securing the future of B2B SaaS." @@ -44,7 +44,7 @@ As B2B SaaS businesses scale, so do their security challenges. Identity Manageme Single Sign-On (SSO) solutions simplify user access management, ensuring seamless scalability without compromising security. -[](https://www.loginradius.com/resource/enterprise-scalability-and-performance) +[](https://www.loginradius.com/resource/enterprise-scalability-and-performance) ### 5. Password Woes @@ -58,4 +58,4 @@ In the face of evolving security challenges, B2B SaaS companies need proactive m By implementing robust authentication, access controls, and compliance measures, businesses can confidently navigate the security landscape. As the digital realm expands, let Identity Management lead the charge in securing the future of B2B SaaS. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2b-saas-security-management) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2b-saas-security-management) diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.png b/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.png deleted file mode 100644 index 4afe9c15b..000000000 Binary files a/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.png and /dev/null differ diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.webp b/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.webp new file mode 100644 index 000000000..982ab7a25 Binary files /dev/null and b/content/growth/b2c-enterprises-ciam-retail-supply-chain/DS-consumer-audit-trail.webp differ diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.jpg b/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.jpg deleted file mode 100644 index 81d15ecd6..000000000 Binary files a/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.jpg and /dev/null differ diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.webp b/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.webp new file mode 100644 index 000000000..864059a33 Binary files /dev/null and b/content/growth/b2c-enterprises-ciam-retail-supply-chain/cosumer-audit.webp differ diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/index.md b/content/growth/b2c-enterprises-ciam-retail-supply-chain/index.md index 7a5823652..e07e67d28 100644 --- a/content/growth/b2c-enterprises-ciam-retail-supply-chain/index.md +++ b/content/growth/b2c-enterprises-ciam-retail-supply-chain/index.md @@ -1,7 +1,7 @@ --- title: "How B2C Industries are Leveraging CIAM in the Retail Supply Chain Management" date: "2021-10-25" -coverImage: "retail-supply-chain-cover.jpg" +coverImage: "retail-supply-chain-cover.webp" tags: ["ciam solution","iot authentication","cx"] author: "Navanita Devi" description: "Retailers hold access to a comprehensive range of technologies. From today's current options, such as RFID tags, to stimulating creativity, such as self-driving trucks, businesses will largely depend on computers to manage their daily operations. Learn how they are incorporating CIAM in their environment." @@ -30,7 +30,7 @@ Currently, AI assembles and collects client information and consumer audit trail Retailers benefit from AI solutions that accumulate and analyze consumer data from social media, their purchasing habits, and other sources to render valuable business insights. Retailers who use this information make educated, data-driven decisions about when and ways to target consumers with the most definite promotion or deal. -[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail) +[](https://www.loginradius.com/resource/loginradius-consumer-audit-trail) @@ -75,4 +75,4 @@ Also, clients are now constantly anticipating deeper social connections supplied Customers likewise expect some control over how companies collect, store, manage, and share their personal information. With the competition just a click away, your company's misuse of customer data, whether intentional or unintentional, can severely harm brand equity. [Contact us](https://www.loginradius.com/contact-sales) to secure your operations with LoginRadius today! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2c-enterprises-ciam-retail-supply-chain) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=b2c-enterprises-ciam-retail-supply-chain) diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.jpg b/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.jpg deleted file mode 100644 index 3fb6d6fa8..000000000 Binary files a/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.jpg and /dev/null differ diff --git a/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.webp b/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.webp new file mode 100644 index 000000000..e59106c81 Binary files /dev/null and b/content/growth/b2c-enterprises-ciam-retail-supply-chain/retail-supply-chain-cover.webp differ diff --git a/content/growth/balance-between-personalization-data-privacy/index.md b/content/growth/balance-between-personalization-data-privacy/index.md index b1c26a92c..307595a3e 100644 --- a/content/growth/balance-between-personalization-data-privacy/index.md +++ b/content/growth/balance-between-personalization-data-privacy/index.md @@ -1,7 +1,7 @@ --- title: "Finding The Balance Between Personalization and Data Privacy" date: "2022-01-20" -coverImage: "personalize-cover.jpg" +coverImage: "personalize-cover.webp" category: ["all"] featured: false author: "Rashmi Mathur" @@ -56,4 +56,4 @@ Implementing personalization in an effective manner is challenging. Hence, you n -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=balance-between-personalization-data-privacy) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=balance-between-personalization-data-privacy) \ No newline at end of file diff --git a/content/growth/balance-between-personalization-data-privacy/personalize-cover.jpg b/content/growth/balance-between-personalization-data-privacy/personalize-cover.jpg deleted file mode 100644 index 43f709ffe..000000000 Binary files a/content/growth/balance-between-personalization-data-privacy/personalize-cover.jpg and /dev/null differ diff --git a/content/growth/balance-between-personalization-data-privacy/personalize-cover.webp b/content/growth/balance-between-personalization-data-privacy/personalize-cover.webp new file mode 100644 index 000000000..19ba4262e Binary files /dev/null and b/content/growth/balance-between-personalization-data-privacy/personalize-cover.webp differ diff --git a/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.jpg b/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.jpg deleted file mode 100644 index 2b1624009..000000000 Binary files a/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.jpg and /dev/null differ diff --git a/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.webp b/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.webp new file mode 100644 index 000000000..166cac22b Binary files /dev/null and b/content/growth/best-brainstorming-tools-and-techniques/best-brainstorming-tools-and-techniques.webp differ diff --git a/content/growth/best-brainstorming-tools-and-techniques/index.md b/content/growth/best-brainstorming-tools-and-techniques/index.md index 63ddb2039..ef6e3fec4 100644 --- a/content/growth/best-brainstorming-tools-and-techniques/index.md +++ b/content/growth/best-brainstorming-tools-and-techniques/index.md @@ -1,7 +1,7 @@ --- title: "Boost Creativity With The Best Brainstorming Tools And Techniques" date: "2021-06-09" -coverImage: "best-brainstorming-tools-and-techniques.jpg" +coverImage: "best-brainstorming-tools-and-techniques.webp" category: ["loginradius"] featured: false author: "Rashmi Mathur" @@ -12,20 +12,12 @@ metatitle: "How To Spark Creativity In Virtual Brainstorms With The Best Brainst Today a large number of professionals are working remotely from different locations due to the pandemic. Are you worried that your marketing team won't be able to generate profitable ideas from isolation? Don't worry! According to a [report by CoSo Cloud](https://www.cosocloud.com/press-releases/connectsolutions-survey-shows-working-remotely-benefits-employers-and-employees), 77% of work from home workers have become more productive during isolation. - - Wondering how? - - - -Research shows that [80% of remote workers](https://velocityglobal.com/blog/the-complete-guide-how-to-successfully-build-and-manage-a-remote-international-workforce/) say that their productivity has improved with real-time collaborative solutions. Virtual brainstorming tools can help you grow your ideas, rethink your marketing strategies, and collaborate theme for successful outcomes. - - + +Research shows that *80% of remote workers* say that their productivity has improved with real-time collaborative solutions. Virtual brainstorming tools can help you grow your ideas, rethink your marketing strategies, and collaborate theme for successful outcomes. A brainstorming tool is strategically designed to help organize and gather ideas. It helps in collaborative brainstorming online, making it easier to harness collective mentality to [create content strategies](https://www.loginradius.com/blog/fuel/20-content-ideas-for-most-engaging-b2b-linkedin-posts/). - - So, let's start your online brainstorming practice tips with the tools first. ## 5 Best Brainstorming Tools @@ -33,9 +25,7 @@ So, let's start your online brainstorming practice tips with the tools first. ### 1. IdeaBoardz IdeaBoardz is an easy-to-use collaborative brainstorming tool that can help your team members to combine their ideas in one location online. With the help of this tool, your teammates can post notes on a collaborative board and even export the board as a PDF or excel file. - - - + ### 2. Google Documents Google Documents is a popular tool to use for brainstorming as it has all the resources that your team may need during brainstorming. It supports multiple files, including TXT, PDF, DOCX, and HTML. Plus, it lets team members track changes in the docs too. @@ -43,9 +33,7 @@ Google Documents is a popular tool to use for brainstorming as it has all the re ### 3. Coggle Coggle is another result-oriented brainstorming tool that allows real-time collaboration. It helps share flow charts, complex algorithms, diagrams, mind maps effortlessly with other team members. Plus, Coggle allows unlimited image uploads, the addition of floating texts, etc. - - - + ### 4. WiseMapping WiseMapping is an effective tool for brainstorming and mind mapping. This tool is apt for small groups and individuals. Plus, one can install it on their devices or use it online. Moreover, WiseMapping is a free tool for even business users and allows a teammate to share his/her mind map online with other members. The most attractive features of this tool include customizable font, customizable colors, easy export of maps, etc. @@ -53,17 +41,11 @@ WiseMapping is an effective tool for brainstorming and mind mapping. This tool i ### 5. MindMup MindMup is a tremendous tool for collaboration planning and brainstorming with its advanced features. It allows you to convert maps easily to PowerPoint and PDF and lets you share and publish your maps online. Further, MindMup enables you to save your mind maps to Google Drive and allows you to access them later through any device. It has an in-built keyboard shortcuts feature too that lets you and your team members jot down ideas faster. - - So, once you've ensured that you have the people you need and the tools and resources they need, here is what you have to do next. - - - + Also Read: [Thinking Beyond the Pandemic: How to Make Marketing Plans After Coronavirus](https://www.loginradius.com/blog/fuel/How-to-Make-Businesses-Marketing-Plans-After-Coronavirus/) - - ## Virtual Brainstorming Tips/Tricks Here are some of the effective tips for running brainstorming sessions for your [marketing strategies](https://www.loginradius.com/blog/growth/top-5-marketing-strategies-to-power-up-your-business/). @@ -87,9 +69,7 @@ Moderators can help focus on the goals, clarify ideas, motivate introverts, and ### 5. Let everyone speak If only a few people talk in your meeting, you won't get as many business ideas as you need. Some of the introverts of your team may not come forward at all. Therefore, it is crucial to approach the session more supportively and positively. Press the Mute button whenever needed. Giving everyone a chance to speak by encouraging others to set themselves to mute will let others speak up, and everyone will listen and hear each other. - - ### 6. Experiment with different techniques and tools Each brainstorming session doesn't have to be the same. If you are thinking about how to boost creativity? You can use different mind mapping tools and an online brainstorming board to create a plan of opportunities, information, and issues. @@ -101,10 +81,7 @@ Want to motivate your team to participate in brainstorm sessions in the future? ## Wrapping Up You can also try the rapid virtual Ideation technique, where you give your participants a limited timescale to come up with ideas. You will be surprised that sometimes even time pressure can bring the best out of people. Finally, use the above tips and tools to spark your team's creativity now and [manage remote teams efficiently.](https://www.loginradius.com/blog/fuel/2021/02/tips-managing-remote-team/) - - Keep the ideas flowing! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-brainstorming-tools-and-techniques) - +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-brainstorming-tools-and-techniques) \ No newline at end of file diff --git a/content/growth/best-practices-verification-emails-effective/discord-example.jpg b/content/growth/best-practices-verification-emails-effective/discord-example.jpg deleted file mode 100644 index 9ccaa4721..000000000 Binary files a/content/growth/best-practices-verification-emails-effective/discord-example.jpg and /dev/null differ diff --git a/content/growth/best-practices-verification-emails-effective/discord-example.webp b/content/growth/best-practices-verification-emails-effective/discord-example.webp new file mode 100644 index 000000000..d9f3d3712 Binary files /dev/null and b/content/growth/best-practices-verification-emails-effective/discord-example.webp differ diff --git a/content/growth/best-practices-verification-emails-effective/harry-potter-example.jpg b/content/growth/best-practices-verification-emails-effective/harry-potter-example.jpg deleted file mode 100644 index f288d8953..000000000 Binary files a/content/growth/best-practices-verification-emails-effective/harry-potter-example.jpg and /dev/null differ diff --git a/content/growth/best-practices-verification-emails-effective/harry-potter-example.webp b/content/growth/best-practices-verification-emails-effective/harry-potter-example.webp new file mode 100644 index 000000000..6cf38cf0e Binary files /dev/null and b/content/growth/best-practices-verification-emails-effective/harry-potter-example.webp differ diff --git a/content/growth/best-practices-verification-emails-effective/index.md b/content/growth/best-practices-verification-emails-effective/index.md index 165a751c0..bbb7b2d25 100644 --- a/content/growth/best-practices-verification-emails-effective/index.md +++ b/content/growth/best-practices-verification-emails-effective/index.md @@ -1,7 +1,7 @@ --- title: "Tips to Make Verification Emails Effective: Best Practices & Examples" date: "2022-03-21" -coverImage: "verification-email.jpg" +coverImage: "verification-email.webp" category: ["all"] featured: false author: "Maxim Grigoryev" @@ -95,17 +95,17 @@ Besides, the examples of validation emails often have information regarding thei Here is an example of how Discord used fun facts in their [validation emails](https://reallygoodemails.com/emails/verify-email) in 2019: - + While these examples show the usage of call to action buttons and tone of voice to produce additional value when engaging with customers: - + The first case illustrates how the brand uses colors to create a space and underline non-intrusive elements. The particular template is pretty straightforward and suits its purpose. - + @@ -117,4 +117,4 @@ The second example has more to offer with regard to fonts, colors, and tone of v The goal of the particular article is to convince you that verification emails should not necessarily be basic and boring. They can add to the marketing strategy and be a starting point for your engagement with the customer. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-practices-verification-emails-effective) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=best-practices-verification-emails-effective) diff --git a/content/growth/best-practices-verification-emails-effective/typform-example.jpg b/content/growth/best-practices-verification-emails-effective/typform-example.jpg deleted file mode 100644 index 07a58632a..000000000 Binary files a/content/growth/best-practices-verification-emails-effective/typform-example.jpg and /dev/null differ diff --git a/content/growth/best-practices-verification-emails-effective/typform-example.webp b/content/growth/best-practices-verification-emails-effective/typform-example.webp new file mode 100644 index 000000000..9d3e09885 Binary files /dev/null and b/content/growth/best-practices-verification-emails-effective/typform-example.webp differ diff --git a/content/growth/best-practices-verification-emails-effective/verification-email.jpg b/content/growth/best-practices-verification-emails-effective/verification-email.jpg deleted file mode 100644 index 89b635cb7..000000000 Binary files a/content/growth/best-practices-verification-emails-effective/verification-email.jpg and /dev/null differ diff --git a/content/growth/best-practices-verification-emails-effective/verification-email.webp b/content/growth/best-practices-verification-emails-effective/verification-email.webp new file mode 100644 index 000000000..b984af087 Binary files /dev/null and b/content/growth/best-practices-verification-emails-effective/verification-email.webp differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.jpg b/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.jpg deleted file mode 100644 index 926fd6f3b..000000000 Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.jpg and /dev/null differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.webp new file mode 100644 index 000000000..c7462c375 Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/4975166968_793305a326_b.webp differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.png deleted file mode 100644 index 97820fd89..000000000 Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.png and /dev/null differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.webp new file mode 100644 index 000000000..562e594d2 Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/Hubspot.webp differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.png deleted file mode 100644 index f7ee3a134..000000000 Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.png and /dev/null differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.webp new file mode 100644 index 000000000..2c53e2c91 Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/Pro-Tip-2.webp differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.png deleted file mode 100644 index 1ea0a696c..000000000 Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.png and /dev/null differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.webp new file mode 100644 index 000000000..732bb450c Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/evernote.webp differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.png deleted file mode 100644 index cf9bfff24..000000000 Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.png and /dev/null differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.webp new file mode 100644 index 000000000..fd3d0aa8d Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/grammarly.webp differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.png deleted file mode 100644 index 430c5985b..000000000 Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.png and /dev/null differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.webp new file mode 100644 index 000000000..cade42b5e Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/hemignwayapp.webp differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/index.md b/content/growth/best-writing-tools-software-for-a-creative-blogger/index.md index a623b1c77..5103b09e9 100644 --- a/content/growth/best-writing-tools-software-for-a-creative-blogger/index.md +++ b/content/growth/best-writing-tools-software-for-a-creative-blogger/index.md @@ -1,7 +1,7 @@ --- title: "16 Best Writing Tools and Software For A Creative Blogger [ Free tools Inside]" date: "2017-02-17" -coverImage: "Pro-Tip-2.png" +coverImage: "Pro-Tip-2.webp" category: ["content", "marketing", "loginradius"] featured: false author: "Rakesh Soni" @@ -41,19 +41,19 @@ Now, here are some tools according to various categories every writer should use #### **1\. Hubspot’s blog topic generator** - + This blog title generator from Hubspot is very efficient. You just need to provide it with three keywords (even one keyword can work). The tool helps you to find topics you can write upon. Hence, if you are struggling for ideas, [Hubspot’s blog topic generator](https://www.hubspot.com/blog-topic-generator#/Tools%20for%20Writers) is the right tool for you. #### **2\. TweakYourBiz Title Generator** - + Just like the above line from the text box says “just enter your topic and go” using this tool is insanely easy. The title generator also breaks your given ideas into various categories such as ‘problems,' ‘motivation’ and ‘how to.' So, [Tweak Your Biz Title Generator](http://tweakyourbiz.com/tools/title-generator/index.php) is worth a try. #### **3\. Portent’s Content Idea Generator** - + This great tool on my favorite list is very easy to use. You just need to enter your idea and Portent’s Content Idea Generator will provide you with a great title for your post. And if you don’t like the title, refresh your subject, and it will give you a different title instantly. @@ -61,7 +61,7 @@ This great tool on my favorite list is very easy to use. You just need to enter #### **1\. Google keyword planner** - + Google keyword planner is a chunk from the Google AdWords program. The tool is completely free and is used to figure out and discuss keywords and develop a pay per click strategy. Type a keyword in the search bar, check the competition for your keywords and other related keyword phrases. Moreover, you can find out things like:- @@ -88,7 +88,7 @@ It is my most favorite tool for graphics generation. This easy to use tool helps #### **2\. Infogr.am** - + If you want to present your technical content in a fun way, use [Infogr.am](https://infogr.am/app/#/library). Infographics are a great way to attract more readers to your posts. So, sign in and get your data loaded in your favorite theme. Well, you may not be able to customize much with the tool like Canva, and you don’t get a blank option in Infogr.am but it may be a lifesaver tool when you want to create a detailed infographic. @@ -116,7 +116,7 @@ This user-friendly tool expertly examines your article for a perfect readability Readable.io is a free tool when you use it occasionally. To move to advanced features, you can select any of these plans. - + Plans are available for individual and business purpose. Features like Readable.io’s API is only for business plans. @@ -124,7 +124,7 @@ Plans are available for individual and business purpose. Features like Readable. #### **1\. Grammarly** - + Grammarly is an effective tool which can improve your language skills. It can find typo errors and grammatically incorrect sentences. Just enter your text in the [Grammarly](https://www.grammarly.com/) web app and the Grammarly editor will proofread your blog post. @@ -140,19 +140,19 @@ So, if you are more convenient using apps than browsers, here are some goodies f #### **1\. Hemingway App** - + Hemingway App work wonders when it comes to rectifying your content. It increases clarity in your writing. Thought, it was introduced as a web app, later it evolved as one of the best desktop apps for writers. The app edits your content, comes with distraction free mode feature, exports PDFs and does much more. If you want to buy the latest version which is Hemingway 3.0, it will come with a price tag of $19.99. Well, the web app continues to be free. #### **2\. Evernote** - + Evernote can be your best friend when you like to store media, information or ideas. Devices can easily integrate with the content stored in Evernote which make materials more accessible. You can share your content on LinkedIn, Facebook, Twitter or just your content’s URL to clipboard. #### **3\. Tomighty Pomodoro timer** - + It is my personal favorite Pomodoro timer. It is a small desktop app which can help you stay productive during your working hours. The free app uses Pomodoro technique to keep you focused throughout the day while allowing you to relax properly at regular intervals. diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.png deleted file mode 100644 index fa4fcd5df..000000000 Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.png and /dev/null differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.webp new file mode 100644 index 000000000..8ba013e0d Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/infogr.webp differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.png deleted file mode 100644 index e8a420260..000000000 Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.png and /dev/null differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.webp new file mode 100644 index 000000000..8055df39d Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/keywordplanner.webp differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.png deleted file mode 100644 index 82a0bc54d..000000000 Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.png and /dev/null differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.webp new file mode 100644 index 000000000..3bd167776 Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/plans.webp differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.png deleted file mode 100644 index 838fe11b4..000000000 Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.png and /dev/null differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.webp new file mode 100644 index 000000000..684afec71 Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/portent.webp differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.png b/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.png deleted file mode 100644 index 2103bf7bf..000000000 Binary files a/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.png and /dev/null differ diff --git a/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.webp b/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.webp new file mode 100644 index 000000000..101491c11 Binary files /dev/null and b/content/growth/best-writing-tools-software-for-a-creative-blogger/tweakyourbiz.webp differ diff --git a/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.png b/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.png deleted file mode 100644 index c8e655587..000000000 Binary files a/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.png and /dev/null differ diff --git a/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.webp b/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.webp new file mode 100644 index 000000000..1082e7522 Binary files /dev/null and b/content/growth/biometric-authentication-security-cx-balance/WP-user-auth.webp differ diff --git a/content/growth/biometric-authentication-security-cx-balance/biometric-auth.jpg b/content/growth/biometric-authentication-security-cx-balance/biometric-auth.jpg deleted file mode 100644 index cd250ebfc..000000000 Binary files a/content/growth/biometric-authentication-security-cx-balance/biometric-auth.jpg and /dev/null differ diff --git a/content/growth/biometric-authentication-security-cx-balance/biometric-auth.webp b/content/growth/biometric-authentication-security-cx-balance/biometric-auth.webp new file mode 100644 index 000000000..38c707e0e Binary files /dev/null and b/content/growth/biometric-authentication-security-cx-balance/biometric-auth.webp differ diff --git a/content/growth/biometric-authentication-security-cx-balance/index.md b/content/growth/biometric-authentication-security-cx-balance/index.md index 33392ec76..965951cc0 100644 --- a/content/growth/biometric-authentication-security-cx-balance/index.md +++ b/content/growth/biometric-authentication-security-cx-balance/index.md @@ -1,7 +1,7 @@ --- title: "The Power of Behavioral Biometric Authentication in Enhancing Security and CX Synergy" date: "2024-04-05" -coverImage: "biometric-auth.jpg" +coverImage: "biometric-auth.webp" tags: ["biometric authentication","data security","cx"] author: "Vishal Sharma" description: "Explore the innovative world of behavioral biometric authentication and its role in fortifying security and enhancing customer experience (CX). This cutting-edge method analyzes unique behavioral patterns to verify identities, offering a seamless user experience." @@ -48,7 +48,7 @@ Imagine a user simply picking up their smartphone and typing a message. Unbeknow This streamlined authentication process saves time and enhances the overall user experience. Customers feel more at ease knowing their interactions are secure yet effortless, increasing satisfaction and loyalty. -[](https://www.loginradius.com/resource/whitepaper/user-authentication-security/) +[](https://www.loginradius.com/resource/whitepaper/user-authentication-security/) ## Implementing Behavioral Biometrics: Best Practices @@ -70,4 +70,4 @@ Behavioral Biometric Authentication represents a significant step forward in sec As the digital landscape continues to evolve, embracing innovative solutions like behavioral biometrics is not just a choice but a necessity for staying ahead of the curve and earning customer trust. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=biometric-authentication-security-cx-balance) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=biometric-authentication-security-cx-balance) diff --git a/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.jpg b/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.jpg deleted file mode 100644 index 508d6206c..000000000 Binary files a/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.jpg and /dev/null differ diff --git a/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.webp b/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.webp new file mode 100644 index 000000000..1b7154259 Binary files /dev/null and b/content/growth/boost-your-business-sales-with-marketing-business/customer-relationship-for-business.webp differ diff --git a/content/growth/boost-your-business-sales-with-marketing-business/index.md b/content/growth/boost-your-business-sales-with-marketing-business/index.md index f8e917a42..2898fae3f 100644 --- a/content/growth/boost-your-business-sales-with-marketing-business/index.md +++ b/content/growth/boost-your-business-sales-with-marketing-business/index.md @@ -1,7 +1,7 @@ --- title: "Will Focusing on Relationship Marketing Boost Your Business Sales?" date: "2021-05-27" -coverImage: "customer-relationship-for-business.jpg" +coverImage: "customer-relationship-for-business.webp" category: ["loginradius"] featured: false author: "Deependra Singh" @@ -102,4 +102,4 @@ Businesses can employ a wide variety of tools to market their relationship. This Many businesses assume that relationship marketing is a method to retain consumers, and this often leads to huge financial investment. However, the core of relationship marketing is building long-term positive relationships with [clients](https://www.loginradius.com/customers/) and prospective clients to build mutual loyalty rather than changing their opinions for short-term gain. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=boost-your-business-sales-with-marketing-business) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=boost-your-business-sales-with-marketing-business) \ No newline at end of file diff --git a/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.jpg b/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.jpg deleted file mode 100644 index 6878e440d..000000000 Binary files a/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.jpg and /dev/null differ diff --git a/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.webp b/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.webp new file mode 100644 index 000000000..06e49b224 Binary files /dev/null and b/content/growth/boosting-ecommerce-marketing-social-login/ecommerce-mrktng.webp differ diff --git a/content/growth/boosting-ecommerce-marketing-social-login/index.md b/content/growth/boosting-ecommerce-marketing-social-login/index.md index fafc26a7c..ee7922608 100644 --- a/content/growth/boosting-ecommerce-marketing-social-login/index.md +++ b/content/growth/boosting-ecommerce-marketing-social-login/index.md @@ -1,7 +1,7 @@ --- title: "Why Should Social Login Be a Part of Your E-Commerce Marketing?" date: "2023-02-28" -coverImage: "ecommerce-mrktng.jpg" +coverImage: "ecommerce-mrktng.webp" tags: ["ecommerce", "social login","cx"] author: "Vishal Sharma" description: "Social login is a seamless authentication process that allows users to sign in to an e-commerce site using their existing social media credentials, such as Facebook, Google, Twitter, and LinkedIn. By offering social login options, e-commerce sites can offer customers a more personalized, streamlined, and engaging shopping experience." @@ -61,4 +61,4 @@ By incorporating social login into e-commerce sites, businesses can improve the With these benefits in mind, it's easy to see why social login has become a must-have for businesses in the digital age. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=boosting-ecommerce-marketing-social-login) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=boosting-ecommerce-marketing-social-login) \ No newline at end of file diff --git a/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.png b/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.png deleted file mode 100644 index f97184f2f..000000000 Binary files a/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.png and /dev/null differ diff --git a/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.webp b/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.webp new file mode 100644 index 000000000..88d19cbb8 Binary files /dev/null and b/content/growth/build-customer-journeys-data-transparency/EB-progressive-profiling.webp differ diff --git a/content/growth/build-customer-journeys-data-transparency/customer-journey.jpg b/content/growth/build-customer-journeys-data-transparency/customer-journey.jpg deleted file mode 100644 index 9dbef816c..000000000 Binary files a/content/growth/build-customer-journeys-data-transparency/customer-journey.jpg and /dev/null differ diff --git a/content/growth/build-customer-journeys-data-transparency/customer-journey.webp b/content/growth/build-customer-journeys-data-transparency/customer-journey.webp new file mode 100644 index 000000000..1f04c61e3 Binary files /dev/null and b/content/growth/build-customer-journeys-data-transparency/customer-journey.webp differ diff --git a/content/growth/build-customer-journeys-data-transparency/index.md b/content/growth/build-customer-journeys-data-transparency/index.md index 7731ae42f..f4ea49556 100644 --- a/content/growth/build-customer-journeys-data-transparency/index.md +++ b/content/growth/build-customer-journeys-data-transparency/index.md @@ -1,7 +1,7 @@ --- title: "Why is Data Transparency Critical To Building Connected Consumer Journeys?" date: "2022-08-18" -coverImage: "customer-journey.jpg" +coverImage: "customer-journey.webp" tags: ["progressive profiling", "cx", "data transparency"] author: "Lucy Manole" description: "Data is your most valuable resource when it comes to enhancing customer transparency. But how exactly can your company sort and apply all the data you collect from different customer touchpoints? This blog shares some actionable ideas." @@ -72,7 +72,7 @@ The last few years have seen a growth in the use of [progressive profiling](http This data can also help you come up with innovative ways to engage customers, such as immersive VR experiences that let them ‘try on’ a product or ‘walk through’ a showroom. Plus, the right data helps you be more transparent with your customers at the touchpoints where it’s needed the most. -[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) +[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) ### 3. Efficient decision-making @@ -100,4 +100,4 @@ In short, data transparency can boost your brand reputation and customer loyalty Remember, honesty is always the best policy — tell your customers the truth, even if that truth is not always the most pleasant. They will respect your integrity and like you the most for it in the long run. Rely on data transparency to deliver a complete end-to-end experience from the customer’s perspective. All the best! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=build-customer-journeys-data-transparency) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=build-customer-journeys-data-transparency) diff --git a/content/growth/build-customer-journeys-data-transparency/progressive-profiling.png b/content/growth/build-customer-journeys-data-transparency/progressive-profiling.png deleted file mode 100644 index c9ad88d9e..000000000 Binary files a/content/growth/build-customer-journeys-data-transparency/progressive-profiling.png and /dev/null differ diff --git a/content/growth/build-customer-journeys-data-transparency/progressive-profiling.webp b/content/growth/build-customer-journeys-data-transparency/progressive-profiling.webp new file mode 100644 index 000000000..2b537fe1a Binary files /dev/null and b/content/growth/build-customer-journeys-data-transparency/progressive-profiling.webp differ diff --git a/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.png b/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.png deleted file mode 100644 index cbe459800..000000000 Binary files a/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.png and /dev/null differ diff --git a/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.webp b/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.webp new file mode 100644 index 000000000..efb695fb3 Binary files /dev/null and b/content/growth/business-advantages-cloud-computing/WP-decoding-resiliency.webp differ diff --git a/content/growth/business-advantages-cloud-computing/cloud-marketg.jpg b/content/growth/business-advantages-cloud-computing/cloud-marketg.jpg deleted file mode 100644 index 4d528c09e..000000000 Binary files a/content/growth/business-advantages-cloud-computing/cloud-marketg.jpg and /dev/null differ diff --git a/content/growth/business-advantages-cloud-computing/cloud-marketg.webp b/content/growth/business-advantages-cloud-computing/cloud-marketg.webp new file mode 100644 index 000000000..d7190b2bb Binary files /dev/null and b/content/growth/business-advantages-cloud-computing/cloud-marketg.webp differ diff --git a/content/growth/business-advantages-cloud-computing/index.md b/content/growth/business-advantages-cloud-computing/index.md index 903ee2b01..616bb1567 100644 --- a/content/growth/business-advantages-cloud-computing/index.md +++ b/content/growth/business-advantages-cloud-computing/index.md @@ -1,7 +1,7 @@ --- title: "Reaping the Benefits of the Cloud Beyond Marketing" date: "2022-06-21" -coverImage: "cloud-marketg.jpg" +coverImage: "cloud-marketg.webp" category: ["cloud computing", "marketing", "ciam"] author: "Navanita Devi" description: "Cloud computing offers more than just helping marketers plan and execute effective marketing campaigns. Let’s look at some advantages of adopting cloud computing and why enterprises should consider relying on cloud computing to thrive overall business success." @@ -34,7 +34,7 @@ Cloud servers are made to support massive sign-ins and sudden, dramatic surges o The [LoginRadius Identity Platform](https://www.loginradius.com/) was designed with service provider-class scale in mind. The distributed CIAM network has regularly experienced peak transaction volumes of over 150,000 logins per second and typically handles 10,000 requests per second with less than 500 milliseconds latency. -[](https://www.loginradius.com/scalability/) +[](https://www.loginradius.com/scalability/) ### #2. Highly secure @@ -80,4 +80,4 @@ With the changing digital landscape, businesses relying on on-premise infrastruc Hence, to ensure they stay ahead of the curve, businesses should put their best efforts into adopting the cloud since it’s secure, scalable, cost-efficient, and maintenance-free. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=business-advantages-cloud-computing) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=business-advantages-cloud-computing) \ No newline at end of file diff --git a/content/growth/business-advantages-cloud-computing/wp-resilency.png b/content/growth/business-advantages-cloud-computing/wp-resilency.png deleted file mode 100644 index 8fb3d9233..000000000 Binary files a/content/growth/business-advantages-cloud-computing/wp-resilency.png and /dev/null differ diff --git a/content/growth/business-advantages-cloud-computing/wp-resilency.webp b/content/growth/business-advantages-cloud-computing/wp-resilency.webp new file mode 100644 index 000000000..eebe75dbe Binary files /dev/null and b/content/growth/business-advantages-cloud-computing/wp-resilency.webp differ diff --git a/content/growth/business-review-meeting-success/business-review.jpg b/content/growth/business-review-meeting-success/business-review.jpg deleted file mode 100644 index 272b0c2a7..000000000 Binary files a/content/growth/business-review-meeting-success/business-review.jpg and /dev/null differ diff --git a/content/growth/business-review-meeting-success/business-review.webp b/content/growth/business-review-meeting-success/business-review.webp new file mode 100644 index 000000000..def9886b7 Binary files /dev/null and b/content/growth/business-review-meeting-success/business-review.webp differ diff --git a/content/growth/business-review-meeting-success/index.md b/content/growth/business-review-meeting-success/index.md index 88f20756a..e594ba90a 100644 --- a/content/growth/business-review-meeting-success/index.md +++ b/content/growth/business-review-meeting-success/index.md @@ -1,7 +1,7 @@ --- title: "A Successful Business Review Meeting Paves the Path for Your Business Success" date: "2022-01-13" -coverImage: "business-review.jpg" +coverImage: "business-review.webp" category: ["all"] featured: false author: "Ritika Kapahi" @@ -103,4 +103,4 @@ Moreover, you can help cement the relationship since you get a lot of feedback f Enterprises that aren’t yet leveraging the true potential of QBRs must quickly put their best foot forward in conducting the same for ensuring better and lasting relationships with their clients. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=business-review-meeting-success) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=business-review-meeting-success) \ No newline at end of file diff --git a/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.png b/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.png deleted file mode 100644 index fb9e830ba..000000000 Binary files a/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.png and /dev/null differ diff --git a/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.webp b/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.webp new file mode 100644 index 000000000..4ea6dbcbf Binary files /dev/null and b/content/growth/cdp-ciam-cookieless-marketing/WP-privacy.webp differ diff --git a/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.jpg b/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.jpg deleted file mode 100644 index 3a5484fd4..000000000 Binary files a/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.jpg and /dev/null differ diff --git a/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.webp b/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.webp new file mode 100644 index 000000000..69b8d4d73 Binary files /dev/null and b/content/growth/cdp-ciam-cookieless-marketing/customer-data-platform.webp differ diff --git a/content/growth/cdp-ciam-cookieless-marketing/index.md b/content/growth/cdp-ciam-cookieless-marketing/index.md index db09a5a30..579c1e16a 100644 --- a/content/growth/cdp-ciam-cookieless-marketing/index.md +++ b/content/growth/cdp-ciam-cookieless-marketing/index.md @@ -1,7 +1,7 @@ --- title: "How do CDP and CIAM Help Marketers in Cookieless Marketing?" date: "2024-02-20" -coverImage: "customer-data-platform.jpg" +coverImage: "customer-data-platform.webp" tags: ["customer data platform","ciam solutions","cx"] author: "Navanita Devi" description: "Gone are the days when marketing strategy included collecting and using third-party cookies to target consumers. In today’s era, consumers are calling the shots to control their privacy, leading to a big change in how marketers manage customer data. While the concept evolved into reality, how can marketers move forward? Stay tuned as we explore how CDP and CIAM help marketers thrive in cookieless marketing." @@ -76,7 +76,7 @@ The identity graphs encompass information about a particular customer. With the Marketers can also integrate various information, including demographics, purchase data, lifestyle, and more, using CDP and CIAM solutions. The data can create a customer identity that enables targeted marketing campaigns for exclusive customers. -[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper) +[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper) ### 4. Remain compliant with regulations @@ -110,4 +110,4 @@ Complementing each other, CDP and CIAM help brands identify the customer across Simply put, the ban on third-party cookies will inevitably affect marketers. However, the changes don't have to be too drastic. The blended approach of CDP and CIAM will give you the power to bridge the gaps and boost your marketing strategies in the cookieless world. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cdp-ciam-cookieless-marketing) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cdp-ciam-cookieless-marketing) diff --git a/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.png b/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.png deleted file mode 100644 index 6df429ab7..000000000 Binary files a/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.png and /dev/null differ diff --git a/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.webp b/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.webp new file mode 100644 index 000000000..9684babf6 Binary files /dev/null and b/content/growth/change-management-consumer-security-tool/WP-dig-id-mngmnt.webp differ diff --git a/content/growth/change-management-consumer-security-tool/change-managmt.jpg b/content/growth/change-management-consumer-security-tool/change-managmt.jpg deleted file mode 100644 index ff670f2b3..000000000 Binary files a/content/growth/change-management-consumer-security-tool/change-managmt.jpg and /dev/null differ diff --git a/content/growth/change-management-consumer-security-tool/change-managmt.webp b/content/growth/change-management-consumer-security-tool/change-managmt.webp new file mode 100644 index 000000000..40c27b41f Binary files /dev/null and b/content/growth/change-management-consumer-security-tool/change-managmt.webp differ diff --git a/content/growth/change-management-consumer-security-tool/ciso-wp.png b/content/growth/change-management-consumer-security-tool/ciso-wp.png deleted file mode 100644 index d7768e095..000000000 Binary files a/content/growth/change-management-consumer-security-tool/ciso-wp.png and /dev/null differ diff --git a/content/growth/change-management-consumer-security-tool/ciso-wp.webp b/content/growth/change-management-consumer-security-tool/ciso-wp.webp new file mode 100644 index 000000000..c3af9b9a1 Binary files /dev/null and b/content/growth/change-management-consumer-security-tool/ciso-wp.webp differ diff --git a/content/growth/change-management-consumer-security-tool/index.md b/content/growth/change-management-consumer-security-tool/index.md index df1bfce38..8e76ff35d 100644 --- a/content/growth/change-management-consumer-security-tool/index.md +++ b/content/growth/change-management-consumer-security-tool/index.md @@ -1,7 +1,7 @@ --- title: "Unlock the Business Benefits of Change Management in Securing Consumer Identity" date: "2022-01-19" -coverImage: "change-managmt.jpg" +coverImage: "change-managmt.webp" tags: ["ciam solution","digital identity management","cx"] author: "Rakesh Soni" description: "If you are one of the many businesses that have not yet developed an effective change management strategy, this article is for you. With new data privacy regulations coming into effect, organizations face complex compliance issues. Ignoring these rules can turn out to be expensive." @@ -69,7 +69,7 @@ This plan should take into consideration every possible requirement, outcome, an Make a great plan, then manage it effectively. Choose the best leader to manage your plan, someone who can oversee the plan effectively. Effective oversight means following the change management procedure, from ensuring quality at each step to adequately resolving issues that arise. -[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper) +[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper) Someone who understands the day-to-day operations of customer identity and access management is essential to a firm's customer security efforts. This person should also be able to visualize the impact of security on the brand, so that they can effectively implement necessary change management strategies. @@ -93,4 +93,4 @@ Here are some of the tangible benefits of implementing change management strateg Change management is the need of the hour in this internet driver business market. Enterprises can benefit a lot from focusing on customer identity and access management. A key part of this is ensuring customer security. The implementation of such change management strategies can also be outsourced to firms that specialize in [CIAM solutions](https://www.loginradius.com/), like LoginRadius. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=change-management-consumer-security-tool) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=change-management-consumer-security-tool) \ No newline at end of file diff --git a/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.jpg b/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.jpg deleted file mode 100644 index 5ab02152a..000000000 Binary files a/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.jpg and /dev/null differ diff --git a/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.webp b/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.webp new file mode 100644 index 000000000..9f337475f Binary files /dev/null and b/content/growth/christmas-spirit-of-giving/christmas-spirit-of-giving.webp differ diff --git a/content/growth/christmas-spirit-of-giving/index.md b/content/growth/christmas-spirit-of-giving/index.md index 065c5178e..41d5ef1b5 100644 --- a/content/growth/christmas-spirit-of-giving/index.md +++ b/content/growth/christmas-spirit-of-giving/index.md @@ -1,7 +1,7 @@ --- title: "LoginRadius Gets into the Christmas Spirit (of Giving)" date: "2019-12-17" -coverImage: "christmas-spirit-of-giving.jpg" +coverImage: "christmas-spirit-of-giving.webp" category: ["media-and-publication"] featured: false author: "Rakesh Soni" diff --git a/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.png b/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.png deleted file mode 100644 index 404532996..000000000 Binary files a/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.png and /dev/null differ diff --git a/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.webp b/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.webp new file mode 100644 index 000000000..832cb0156 Binary files /dev/null and b/content/growth/ciam-budget-2023-recession/WP-zerotrust-1.webp differ diff --git a/content/growth/ciam-budget-2023-recession/budget.jpg b/content/growth/ciam-budget-2023-recession/budget.jpg deleted file mode 100644 index 8923bdf6d..000000000 Binary files a/content/growth/ciam-budget-2023-recession/budget.jpg and /dev/null differ diff --git a/content/growth/ciam-budget-2023-recession/budget.webp b/content/growth/ciam-budget-2023-recession/budget.webp new file mode 100644 index 000000000..a99fe2fd3 Binary files /dev/null and b/content/growth/ciam-budget-2023-recession/budget.webp differ diff --git a/content/growth/ciam-budget-2023-recession/index.md b/content/growth/ciam-budget-2023-recession/index.md index 7fa5c860d..45ced627f 100644 --- a/content/growth/ciam-budget-2023-recession/index.md +++ b/content/growth/ciam-budget-2023-recession/index.md @@ -1,7 +1,7 @@ --- title: "How To Plan Your CIAM Budget In A Recession As We Look Ahead Towards 2023?" date: "2022-12-21" -coverImage: "budget.jpg" +coverImage: "budget.webp" category: ["ciam", "cybersecurity", "budget"] author: "Rakesh Soni" description: "The key to optimizing and protecting your CIAM budget is to be clear and sure about everything that adds value to your organization. Here are some tips that can help you plan your CIAM budget smartly for 2023 on the declining global economy." @@ -54,7 +54,7 @@ Many organizations understand the importance of investing in cybersecurity tools * Enable risk-based authentication * Frequent employee training sessions -[](https://www.loginradius.com/resource/zero-trust-security/) +[](https://www.loginradius.com/resource/zero-trust-security/) ## Making the Most out of Your Current CIAM Budget @@ -77,4 +77,4 @@ As you plan your CIAM budget for 2023, consider which challenges pose the most s An intelligent approach to budget planning can make all the difference for your security team. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-budget-2023-recession) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-budget-2023-recession) diff --git a/content/growth/ciam-budget-2023-recession/zerotrust-wp.png b/content/growth/ciam-budget-2023-recession/zerotrust-wp.png deleted file mode 100644 index 3e6b81ee6..000000000 Binary files a/content/growth/ciam-budget-2023-recession/zerotrust-wp.png and /dev/null differ diff --git a/content/growth/ciam-budget-2023-recession/zerotrust-wp.webp b/content/growth/ciam-budget-2023-recession/zerotrust-wp.webp new file mode 100644 index 000000000..2f7c01062 Binary files /dev/null and b/content/growth/ciam-budget-2023-recession/zerotrust-wp.webp differ diff --git a/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.png b/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.png deleted file mode 100644 index 6bddf0db4..000000000 Binary files a/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.png and /dev/null differ diff --git a/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.webp b/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.webp new file mode 100644 index 000000000..2842c3bcc Binary files /dev/null and b/content/growth/ciam-challenges-saas-business-app/DS-customer-identity.webp differ diff --git a/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.png b/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.png deleted file mode 100644 index 8bad2f974..000000000 Binary files a/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.png and /dev/null differ diff --git a/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.webp b/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.webp new file mode 100644 index 000000000..903afa91e Binary files /dev/null and b/content/growth/ciam-challenges-saas-business-app/core-of-digital-transformation.webp differ diff --git a/content/growth/ciam-challenges-saas-business-app/index.md b/content/growth/ciam-challenges-saas-business-app/index.md index f7bc6b0bd..25cfebedf 100644 --- a/content/growth/ciam-challenges-saas-business-app/index.md +++ b/content/growth/ciam-challenges-saas-business-app/index.md @@ -1,7 +1,7 @@ --- title: "8 Common Challenges With Your SaaS Business that CIAM Can Solve" date: "2021-09-10" -coverImage: "saas-buisness.jpg" +coverImage: "saas-buisness.webp" tags: ["saas","customer identity management","ciam solution"] author: "Rashmi Mathur" description: "To be successful, your SaaS needs to use the right application performance management software. CIAM is the first step you need to take to avoid common challenges like lack of compliance, and incompetent onboarding." @@ -13,7 +13,7 @@ Digital communication between clients and a company is now a regular practice ac The data gathered in databases can be vulnerable to cyber attacks that result in stolen customer and business identities. Hence, businesses look to increase their cybersecurity with the help of SaaS-based CIAM business solutions. -[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/) +[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/) ## Top Challenges With SaaS Apps and How CIAM Overcomes Them @@ -61,4 +61,4 @@ One of the surpassing advantages of cloud applications is that admittance is obt To summarize, we can say that a cloud-based CIAM service should present accurate visibility of user access. Also, providing your customers with the required protection against identity theft is crucial in preserving your company prominence. This is why it is vital to overcome these challenges to better leverage the benefits of CIAM to protect your business and clients. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-challenges-saas-business-app) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-challenges-saas-business-app) \ No newline at end of file diff --git a/content/growth/ciam-challenges-saas-business-app/saas-buisness.jpg b/content/growth/ciam-challenges-saas-business-app/saas-buisness.jpg deleted file mode 100644 index 30fa6b6fb..000000000 Binary files a/content/growth/ciam-challenges-saas-business-app/saas-buisness.jpg and /dev/null differ diff --git a/content/growth/ciam-challenges-saas-business-app/saas-buisness.webp b/content/growth/ciam-challenges-saas-business-app/saas-buisness.webp new file mode 100644 index 000000000..1a5ff6795 Binary files /dev/null and b/content/growth/ciam-challenges-saas-business-app/saas-buisness.webp differ diff --git a/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.jpg b/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.jpg deleted file mode 100644 index b71009e0f..000000000 Binary files a/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.jpg and /dev/null differ diff --git a/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.webp b/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.webp new file mode 100644 index 000000000..f8b508c06 Binary files /dev/null and b/content/growth/ciam-challenges-saas-business-app/saas-business-app-2.webp differ diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.png b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.png deleted file mode 100644 index 93302c0ce..000000000 Binary files a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.png and /dev/null differ diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.webp b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.webp new file mode 100644 index 000000000..9d62b96b8 Binary files /dev/null and b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-comp.webp differ diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.png b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.png deleted file mode 100644 index 6784e19bd..000000000 Binary files a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.png and /dev/null differ diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.webp b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.webp new file mode 100644 index 000000000..c27d2fee5 Binary files /dev/null and b/content/growth/ciam-improves-customer-trust-and-loyalty/DS-CCPA-compliance.webp differ diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.jpg b/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.jpg deleted file mode 100644 index de44c8838..000000000 Binary files a/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.jpg and /dev/null differ diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.webp b/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.webp new file mode 100644 index 000000000..41d5677b8 Binary files /dev/null and b/content/growth/ciam-improves-customer-trust-and-loyalty/customer-trust.webp differ diff --git a/content/growth/ciam-improves-customer-trust-and-loyalty/index.md b/content/growth/ciam-improves-customer-trust-and-loyalty/index.md index d4ed162d3..5d8312023 100644 --- a/content/growth/ciam-improves-customer-trust-and-loyalty/index.md +++ b/content/growth/ciam-improves-customer-trust-and-loyalty/index.md @@ -1,7 +1,7 @@ --- title: "How Can CIAM Help Businesses Build Trust And Loyalty?" date: "2023-04-05" -coverImage: "customer-trust.jpg" +coverImage: "customer-trust.webp" tags: ["ciam solution","mfa","compliance","sso","cx"] author: "Vishal Sharma" description: "By implementing CIAM solutions, businesses can provide customers with a personalized and secure experience while improving operational efficiency. Let’s figure out how companies can leverage the true potential of a robust CIAM to build trust and loyalty." @@ -49,7 +49,7 @@ Many industries are subject to strict regulatory requirements around data privac By demonstrating a commitment to compliance, businesses can build trust and confidence among customers, who will feel reassured that their data is being handled responsibly. -[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance) +[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance) ### 4. Convenience Customers expect a seamless and hassle-free experience when interacting with businesses. CIAM solutions can help companies to deliver this by enabling [single sign-on](https://www.loginradius.com/single-sign-on/) (SSO) across multiple channels and applications. @@ -66,4 +66,4 @@ CIAM is undoubtedly the need of the hour for businesses looking to build trust a By providing a personalized, secure, compliant, convenient, and transparent experience, businesses can differentiate themselves from their competitors and build long-lasting customer relationships. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-improves-customer-trust-and-loyalty) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-improves-customer-trust-and-loyalty) diff --git a/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.png b/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.png deleted file mode 100644 index 0d7046172..000000000 Binary files a/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.png and /dev/null differ diff --git a/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.webp b/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.webp new file mode 100644 index 000000000..ea0737a8b Binary files /dev/null and b/content/growth/ciam-minimizes-expenses-access-management/GD-to-RBA.webp differ diff --git a/content/growth/ciam-minimizes-expenses-access-management/access-managemt.jpg b/content/growth/ciam-minimizes-expenses-access-management/access-managemt.jpg deleted file mode 100644 index 57a8ff437..000000000 Binary files a/content/growth/ciam-minimizes-expenses-access-management/access-managemt.jpg and /dev/null differ diff --git a/content/growth/ciam-minimizes-expenses-access-management/access-managemt.webp b/content/growth/ciam-minimizes-expenses-access-management/access-managemt.webp new file mode 100644 index 000000000..a9fe5ce89 Binary files /dev/null and b/content/growth/ciam-minimizes-expenses-access-management/access-managemt.webp differ diff --git a/content/growth/ciam-minimizes-expenses-access-management/index.md b/content/growth/ciam-minimizes-expenses-access-management/index.md index 1c179efa5..9183aa475 100644 --- a/content/growth/ciam-minimizes-expenses-access-management/index.md +++ b/content/growth/ciam-minimizes-expenses-access-management/index.md @@ -1,7 +1,7 @@ --- title: "An Exclusive CIAM Benefit: The Role of Access Management in Cost Optimization" date: "2023-01-13" -coverImage: "access-managemt.jpg" +coverImage: "access-managemt.webp" category: ["ciam", "access managment", "user onboarding"] author: "Rakesh Soni" description: "Whether we talk about delivering a seamless authentication experience or reinforcing the overall business and customer identity security, a CIAM solution leaves no stone unturned in scaling business growth. This blog explains the aspects of leveraging the role of a CIAM’s access management in cost optimization." @@ -58,7 +58,7 @@ CIAM is an integrated digital security platform combining advanced and user beha And if you're wondering how it all fits together, here's how: CIAM incorporates MFA and risk-based authentication that helps mitigate the risks of identity theft and prevents a breach by gathering data about user behavior patterns for each employee or user account based on their specific role within your organization. -[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) +[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) Risk assessments are performed based on this data to determine whether or not an unauthorized user should have access to sensitive information via an online portal or application portal. @@ -88,4 +88,4 @@ LoginRadius' extensive experience in the identity and access management market w -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-minimizes-expenses-access-management) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-minimizes-expenses-access-management) diff --git a/content/growth/ciam-minimizes-expenses-access-management/rba-gd.png b/content/growth/ciam-minimizes-expenses-access-management/rba-gd.png deleted file mode 100644 index c820cfc17..000000000 Binary files a/content/growth/ciam-minimizes-expenses-access-management/rba-gd.png and /dev/null differ diff --git a/content/growth/ciam-minimizes-expenses-access-management/rba-gd.webp b/content/growth/ciam-minimizes-expenses-access-management/rba-gd.webp new file mode 100644 index 000000000..9cfe7e407 Binary files /dev/null and b/content/growth/ciam-minimizes-expenses-access-management/rba-gd.webp differ diff --git a/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.png b/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.png deleted file mode 100644 index 61deb3295..000000000 Binary files a/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.png and /dev/null differ diff --git a/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.webp b/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.webp new file mode 100644 index 000000000..00c5933a4 Binary files /dev/null and b/content/growth/ciam-opportunity-for-cmos/EB-GD-to-MFA.webp differ diff --git a/content/growth/ciam-opportunity-for-cmos/cmo-ciam.jpg b/content/growth/ciam-opportunity-for-cmos/cmo-ciam.jpg deleted file mode 100644 index b85bccaec..000000000 Binary files a/content/growth/ciam-opportunity-for-cmos/cmo-ciam.jpg and /dev/null differ diff --git a/content/growth/ciam-opportunity-for-cmos/cmo-ciam.webp b/content/growth/ciam-opportunity-for-cmos/cmo-ciam.webp new file mode 100644 index 000000000..e82d5dc8a Binary files /dev/null and b/content/growth/ciam-opportunity-for-cmos/cmo-ciam.webp differ diff --git a/content/growth/ciam-opportunity-for-cmos/index.md b/content/growth/ciam-opportunity-for-cmos/index.md index 2d9c19f64..9d1e611c0 100644 --- a/content/growth/ciam-opportunity-for-cmos/index.md +++ b/content/growth/ciam-opportunity-for-cmos/index.md @@ -1,7 +1,7 @@ --- title: "Why CMOs should care about CIAM" date: "2021-11-22" -coverImage: "cmo-ciam.jpg" +coverImage: "cmo-ciam.webp" tags: ["data security","ciam solution","cx","mfa"] author: "Rakesh Soni" description: "CMOs can deliver more efficient, secure, and relevant services and goods if they have a detailed grasp of who their customers are and what they require. Learn how a CIAM solution may be a valuable strategic asset for CMOs to utilize in their department." @@ -54,7 +54,7 @@ It entails a legitimate registration procedure that can be conducted and finishe The advancement of 2FA/MFA (multi-factor authentication) with features like biometrics, geolocation, face recognition, and so on has resulted in higher degrees of protection. These characteristics make it simpler to spot abnormalities and strange actions in a less time-consuming manner. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) ### #4. Privacy and regulatory compliance @@ -86,4 +86,4 @@ The goal of digital transformation is to [improve the customer experience](https Consumer behavior and aspirations have never been static. A consumer identity management solution may be a valuable strategic asset for CMOs to utilize in their department. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-opportunity-for-cmos) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-opportunity-for-cmos) diff --git a/content/growth/ciam-opportunity-for-cmos/mfa-eb.png b/content/growth/ciam-opportunity-for-cmos/mfa-eb.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/growth/ciam-opportunity-for-cmos/mfa-eb.png and /dev/null differ diff --git a/content/growth/ciam-opportunity-for-cmos/mfa-eb.webp b/content/growth/ciam-opportunity-for-cmos/mfa-eb.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/growth/ciam-opportunity-for-cmos/mfa-eb.webp differ diff --git a/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.png b/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.png deleted file mode 100644 index f97184f2f..000000000 Binary files a/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.png and /dev/null differ diff --git a/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.webp b/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.webp new file mode 100644 index 000000000..88d19cbb8 Binary files /dev/null and b/content/growth/ciam-prevents-abandoned-carts/EB-progressive-profiling.webp differ diff --git a/content/growth/ciam-prevents-abandoned-carts/cart-abandon.jpg b/content/growth/ciam-prevents-abandoned-carts/cart-abandon.jpg deleted file mode 100644 index 81c3dffa4..000000000 Binary files a/content/growth/ciam-prevents-abandoned-carts/cart-abandon.jpg and /dev/null differ diff --git a/content/growth/ciam-prevents-abandoned-carts/cart-abandon.webp b/content/growth/ciam-prevents-abandoned-carts/cart-abandon.webp new file mode 100644 index 000000000..fd0900b95 Binary files /dev/null and b/content/growth/ciam-prevents-abandoned-carts/cart-abandon.webp differ diff --git a/content/growth/ciam-prevents-abandoned-carts/index.md b/content/growth/ciam-prevents-abandoned-carts/index.md index 6fa049b4f..5672dc082 100644 --- a/content/growth/ciam-prevents-abandoned-carts/index.md +++ b/content/growth/ciam-prevents-abandoned-carts/index.md @@ -1,7 +1,7 @@ --- title: "How CIAM can help in Preventing Abandoned Carts" date: "2021-11-16" -coverImage: "cart-abandon.jpg" +coverImage: "cart-abandon.webp" tags: ["progressive profiling","ciam solution","mfa","cx"] author: "Rashmi Mathur" description: "Shoppers leave their carts behind all the time. When this happens, it usually means that they're abandoning their purchase but also that they're possibly losing interest in your brand altogether. This blog takes a deeper look into how CIAM can stop the issue of abandoned carts." @@ -34,7 +34,7 @@ Customer identity and other credentials are sensitive information that hackers c Thankfully, CIAM helps you collect data as well as secure it. What makes it even better is that you can collect customers’ data that is beyond just registration! That’s right, through CIAM, you can even collect helpful information such as customers’ shopping patterns, buying choices, etc. And of course, you can use this information to boost your targeted marketing strategies and other ventures. -[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) +[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) Talking about security, CIAM solutions tokenize customer identities to detach them from sensitive data while it's in storage. Furthermore, these solutions also use robust [data encryption and hashing](https://www.loginradius.com/blog/engineering/encryption-and-hashing/) to ensure the privacy of sensitive information and credentials. @@ -65,4 +65,4 @@ It helps enable the organizations to have greater control of their information a Consumers expect simplicity and speed with new-age authentication like the use of biometrics that replace passwords for secure and seamless login. Likewise, CIAM helps streamline the data storage and authentication to secure your customer experience and provide you with a competitive edge. The combination of these factors makes CIAM a powerful platform for any eCommerce enterprise. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-prevents-abandoned-carts) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-prevents-abandoned-carts) diff --git a/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.png b/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.png deleted file mode 100644 index c9ad88d9e..000000000 Binary files a/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.png and /dev/null differ diff --git a/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.webp b/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.webp new file mode 100644 index 000000000..2b537fe1a Binary files /dev/null and b/content/growth/ciam-prevents-abandoned-carts/valuable-visitor-eb.webp differ diff --git a/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.png b/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.png deleted file mode 100644 index cbe459800..000000000 Binary files a/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.png and /dev/null differ diff --git a/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.webp b/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.webp new file mode 100644 index 000000000..efb695fb3 Binary files /dev/null and b/content/growth/ciam-solution-digital-native-business/WP-LR-resiliency.webp differ diff --git a/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.jpg b/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.jpg deleted file mode 100644 index 35b39f712..000000000 Binary files a/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.jpg and /dev/null differ diff --git a/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.webp b/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.webp new file mode 100644 index 000000000..f8d57c575 Binary files /dev/null and b/content/growth/ciam-solution-digital-native-business/ciam-dig-transformation.webp differ diff --git a/content/growth/ciam-solution-digital-native-business/index.md b/content/growth/ciam-solution-digital-native-business/index.md index 08a4578ba..77f67ff3b 100644 --- a/content/growth/ciam-solution-digital-native-business/index.md +++ b/content/growth/ciam-solution-digital-native-business/index.md @@ -1,7 +1,7 @@ --- title: "How is CIAM Solution a Critical Part of DNBs’ Digital Transformation Strategy?" date: "2024-02-16" -coverImage: "ciam-dig-transformation.jpg" +coverImage: "ciam-dig-transformation.webp" tags: ["digital transformation","ciam solutions","cx"] author: "Vishal Sharma" description: "Customer Identity and Access Management is about keeping customer data safe and giving them the proper access to things online. In today's interconnected era, digital native businesses must help them stay nimble and grow with evolving times. Let's explore the indispensable role of CIAM solutions in digital companies more!" @@ -52,7 +52,7 @@ With CIAM solution, MFA is employed broadly in every business, including financi A **CIAM solution** can handle millions of users across web and mobile channels to accommodate large volumes of users and spikes in registrations and access requests without affecting the high level of performance. -[](https://www.loginradius.com/resource/enterprise-scalability-and-performance) +[](https://www.loginradius.com/resource/enterprise-scalability-and-performance) ### 3. Privacy and Compliance @@ -98,4 +98,4 @@ Today, CIAM has become more than just an identity gateway for customers. It has At LoginRadius, we offer constructive CIAM solutions and add the factor of the outcome – a better performing, more scalable, flexible, and secure system that will scale your business to billions of customers. As a trustworthy **CIAM provider,** we help you earn their trust and set you up for long-term success in the digital age. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-solution-digital-native-business) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ciam-solution-digital-native-business) diff --git a/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.jpg b/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.jpg deleted file mode 100644 index 6476faf01..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.jpg and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.webp b/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.webp new file mode 100644 index 000000000..ef0a00d8d Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/A-Complete-Color-Scheme-Guide-For-Your-Website.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.png b/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.png deleted file mode 100644 index 76b1c7bae..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.webp b/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.webp new file mode 100644 index 000000000..265f4380c Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Coca-Cola.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.png deleted file mode 100644 index c49cb67a7..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.webp new file mode 100644 index 000000000..d9f323285 Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-emotion-guide.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.png deleted file mode 100644 index fd32e89f4..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.webp new file mode 100644 index 000000000..4583e99aa Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-naming-based-on-gender-2.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.png deleted file mode 100644 index e7dedd6b6..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.webp new file mode 100644 index 000000000..244d96f86 Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-based-on-gender.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.png deleted file mode 100644 index 596540f99..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.webp new file mode 100644 index 000000000..dded6d4ed Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-behind-Cadbury.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.png deleted file mode 100644 index e3ba2b701..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.webp new file mode 100644 index 000000000..6474361cc Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-for-E-commerce-or-Content-Driven-Websites.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.png b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.png deleted file mode 100644 index 28c7174df..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.webp new file mode 100644 index 000000000..18df8cb4f Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology-while-Promoting-a-Service-or-Product.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.jpg b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.jpg deleted file mode 100644 index 6b02e681e..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.jpg and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.webp b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.webp new file mode 100644 index 000000000..ee91429c5 Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Color-psychology.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.jpg b/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.jpg deleted file mode 100644 index 64aee97a5..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.jpg and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.webp b/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.webp new file mode 100644 index 000000000..4075a053e Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Colors-and-types-of-consumers.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Departika.png b/content/growth/complete-color-scheme-guide-for-your-website/Departika.png deleted file mode 100644 index e7489e714..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Departika.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Departika.webp b/content/growth/complete-color-scheme-guide-for-your-website/Departika.webp new file mode 100644 index 000000000..87a5dddd3 Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Departika.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.png b/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.png deleted file mode 100644 index 904dbdad3..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.webp b/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.webp new file mode 100644 index 000000000..a820766bd Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Enterprise-England.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Magoz.png b/content/growth/complete-color-scheme-guide-for-your-website/Magoz.png deleted file mode 100644 index 23884a37d..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Magoz.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Magoz.webp b/content/growth/complete-color-scheme-guide-for-your-website/Magoz.webp new file mode 100644 index 000000000..74f3451f3 Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Magoz.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.png b/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.png deleted file mode 100644 index e473ad3bb..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.webp b/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.webp new file mode 100644 index 000000000..5cb722a71 Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/SecretKey.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.png b/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.png deleted file mode 100644 index f8e8a9c56..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.webp b/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.webp new file mode 100644 index 000000000..c19026d55 Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Softwaremill.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.png b/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.png deleted file mode 100644 index 4fec530f2..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.webp b/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.webp new file mode 100644 index 000000000..c32a2d7f0 Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Spektrum.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.png b/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.png deleted file mode 100644 index 5e14abdd5..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.webp b/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.webp new file mode 100644 index 000000000..918ee89c3 Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Using-The-Prominent-Color-2.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.png b/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.png deleted file mode 100644 index 367d9c4b3..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.png and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.webp b/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.webp new file mode 100644 index 000000000..d5806bca1 Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/Using-accent-colors.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.jpg b/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.jpg deleted file mode 100644 index d59962368..000000000 Binary files a/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.jpg and /dev/null differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.webp b/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.webp new file mode 100644 index 000000000..8f1ed86b6 Binary files /dev/null and b/content/growth/complete-color-scheme-guide-for-your-website/color-psychology-for-creative-stylish-websites.webp differ diff --git a/content/growth/complete-color-scheme-guide-for-your-website/index.md b/content/growth/complete-color-scheme-guide-for-your-website/index.md index d10770ec2..ae1924130 100644 --- a/content/growth/complete-color-scheme-guide-for-your-website/index.md +++ b/content/growth/complete-color-scheme-guide-for-your-website/index.md @@ -1,7 +1,7 @@ --- title: "A Complete Color Scheme Guide For Your Website" date: "2017-05-19" -coverImage: "A-Complete-Color-Scheme-Guide-For-Your-Website.jpg" +coverImage: "A-Complete-Color-Scheme-Guide-For-Your-Website.webp" category: ["business", "Marketing", "technology"] featured: false author: "Rakesh Soni" @@ -32,15 +32,15 @@ Whether it is your brand image or your website, colors can work like magic on yo What are the things that come to your mind when I say the word Coca Cola? Obviously, a bottle of it. Then, the red logo of Coca-Cola. There was a reason why Coca-Cola chose the color “Red”. - + -**[Source](http://1.bp.blogspot.com/-feRUkS6z3uo/VIctsB0pI1I/AAAAAAAAAAo/nbmsMeSl_ls/s1600/india.png?ver=1553881376)** +**[Source](http://1.bp.blogspot.com/-feRUkS6z3uo/VIctsB0pI1I/AAAAAAAAAAo/nbmsMeSl_ls/s1600/india.webp?ver=1553881376)** Red shows excitement, passion and boldness and these were the emotions Coca-Cola wanted to convey with its product. Moreover, the color red makes it more visible on the shelves from its competitors. Well, here is an image showing reasons for different brands choosing respective colors in their logos. - + -**[Source](http://blog.dahmundfreunde.de/wp-content/uploads/2014/05/grafik.png?ver=1553881376)** +**[Source](http://blog.dahmundfreunde.de/wp-content/uploads/2014/05/grafik.webp?ver=1553881376)** Kissmetrics says that there is an [80% increase in brand recognition](https://blog.kissmetrics.com/color-psychology/) when colors are used. @@ -52,15 +52,15 @@ Create an awesome color scheme and here’s **how you can create a color scheme* Your customers will connect their emotions with your brand through your prominent color. Hence, choose a color that convey the emotions about your company (like the red color in Coca-Cola does). Your logo should contain your prominent color as the primary color. However, if you have no clue which color to cast as your prominent color, see this image to decide the color of your choice. - + -**[Source](https://mustafa12abdall.files.wordpress.com/2015/01/colors_customers_2.jpg?ver=1553881376)** +**[Source](https://mustafa12abdall.files.wordpress.com/2015/01/colors_customers_2.webp?ver=1553881376)** You can also see for this chart to decide which colors to pick from the slot:- - + -[**Source**](https://s-media-cache-ak0.pinimg.com/originals/25/93/1f/25931fe9980a8a2e06cd66df76a055ee.jpg?ver=1553881376) +[**Source**](https://s-media-cache-ak0.pinimg.com/originals/25/93/1f/25931fe9980a8a2e06cd66df76a055ee.webp?ver=1553881376) Other than these psychological facts, you can check whether you are going to serve a youthful and energetic audience or your product is targeting a female audience. Hence, you have to decide the color on the basis of your targeted audience. @@ -70,13 +70,13 @@ It is found out that most of the color blind patients are red-green color blinde _Some statistics that show what color do what men and women get attracted to while shopping_ - + [**Source**](https://blog.kissmetrics.com/how-colors-affect-conversions/) Also in another experiment, it was found that men preferred shades and bright colors while women preferred tints and soft colors. -**[Source](https://blog.kissmetrics.com/gender-and-color/)** +**[Source](https://blog.kissmetrics.com/gender-and-color/)** By these data, you can certainly improve your color marketing strategies through color scheme. @@ -88,7 +88,7 @@ Now, let’s discuss about the areas on your website where we can use the promin Only use prominent color on areas which you want to highlight to you customers like you logo, menu tabs, call to actions, and any important information. Here’s, how we do it at LoginRadius. - + **[Source](https://loginradius.com/)** @@ -100,7 +100,7 @@ For example, you can use accent colors on secondary information, current menu ta Also, do not use more than two accent colors on your webpages. It may confuse your prospects. Here’s a simple example to use accent colors on your website:- - **[Source](https://loginradius.com/)** + **[Source](https://loginradius.com/)** Now, there are two ways to select your color scheme. Pursue a Phd career in color psychology or use these color matching tools to create a color palette (well, hiring a good designer may cost you more). @@ -130,7 +130,7 @@ Thus, here I have divided the websites into three types on the basis of their in You will find that majority of the content driven or e-commerce websites have neutral or white background. The intent of such websites is to promote their products or ideas rather than flashing the background of the website. Hence, the prominent and accent colors provide focus and personality to your website whereas the neutral background keeps your customers focused on your products or content. - + #### **2\. Corporate Websites** @@ -142,7 +142,7 @@ While you are promoting a brand, use your prominent colors as a part of your bac In case, you have a bold prominent color, then you can use less intense shades of the prominent colors. Here’s an example of how [Cadbury](https://www.cadbury.co.uk/) does it:- - + You can use the above discussed tools to choose different shades of your prominent colors that will go well with your website’s background. @@ -150,7 +150,7 @@ You can use the above discussed tools to choose different shades of your promine Now, when you want your services to be the attention grabbers, use light colors for background as it will automatically highlight the content (product) on the page. Our web designers have done a good job highlighting our services. - + [**Source**](https://loginradius.com/) @@ -158,9 +158,9 @@ Now, when you want your services to be the attention grabbers, use light colors When it comes to creative or stylish websites (creative, beauty, restaurant, design and fashion industries), you can use any colors in the background of your website. You can design a black background to provide a luxurious look or you can inspire your visitors with a rainbow background. Don’t lose your content’s visibility for the sake of charm on your website. Here’s a great template you can use for your creative website. - + -[**Source**](https://blog.spoongraphics.co.uk/wp-content/uploads/2008/doodle-websites/24.jpg?ver=1553881376) +[**Source**](https://blog.spoongraphics.co.uk/wp-content/uploads/2008/doodle-websites/24.webp?ver=1553881376) In a nutshell, the best background for your website will make your content more visible and will render a good feeling to your visitors while browsing. And still if you are struggling with the background color, use a light color for your background. Don’t expect your website to look inspirational enough, however, your content will be noticed. @@ -178,37 +178,37 @@ Here are some websites you can take a look for some inspiration. #### **1.** [**Departika**](http://www.departika.com/) - + Specialty: Minimal yet effective #### **2\. [Magoz](https://magoz.is/)** - + Specialty: Vibrant #### **3. [SecretKey](https://www.secretkey.it/)** - + Specialty: Attractive combination of multiple colors #### **4. [Softwaremill](https://softwaremill.com/)** - + Specialty: Beautiful yet elegant #### **5. [Spektrum](http://spektrummedia.com/)** - + Specialty: Wise usage of neon colors to give it modern touch #### **6. [Enterprise England](http://enterpriseengland.org.uk/)** - + Specialty: Beautiful color combination diff --git a/content/growth/consent-management-business-advantages/DS-consent-mngmnt.png b/content/growth/consent-management-business-advantages/DS-consent-mngmnt.png deleted file mode 100644 index b2c0a4d84..000000000 Binary files a/content/growth/consent-management-business-advantages/DS-consent-mngmnt.png and /dev/null differ diff --git a/content/growth/consent-management-business-advantages/DS-consent-mngmnt.webp b/content/growth/consent-management-business-advantages/DS-consent-mngmnt.webp new file mode 100644 index 000000000..8dcbd7082 Binary files /dev/null and b/content/growth/consent-management-business-advantages/DS-consent-mngmnt.webp differ diff --git a/content/growth/consent-management-business-advantages/index.md b/content/growth/consent-management-business-advantages/index.md index d61b8ba27..5274d6a90 100644 --- a/content/growth/consent-management-business-advantages/index.md +++ b/content/growth/consent-management-business-advantages/index.md @@ -1,7 +1,7 @@ --- title: "The Power Of Consent Marketing- A Deep Dive Into Its Endless Advantages" date: "2024-04-16" -coverImage: "power-consent-mngmnt.jpg" +coverImage: "power-consent-mngmnt.webp" tags: ["consent management","data security","compliance"] author: "Navanita Devi" description: "Discover the pivotal role of consent marketing in today's digital landscape. Explore how it goes beyond legal compliance to build trust, enhance targeting, ensure legal compliance, and foster long-term customer relationships." @@ -38,7 +38,7 @@ Consent marketing allows for more targeted campaigns, ensuring that messages are This targeted approach improves engagement rates and enhances the overall [user experience](https://www.loginradius.com/blog/growth/4-tips-secure-frictionless-ux/). Users receive content that is meaningful to them, leading to higher conversion rates and customer satisfaction. -[](https://www.loginradius.com/resource/loginradius-consent-management) +[](https://www.loginradius.com/resource/loginradius-consent-management) ### Legal Compliance @@ -80,4 +80,4 @@ Consent marketing is not just a legal requirement; it's a strategic approach tha By respecting user preferences, businesses can create a more trustworthy and engaging brand image while fostering long-lasting customer relationships. With solutions like LoginRadius' consent management, businesses can navigate the complexities of consent marketing with ease, ensuring compliance and building customer trust every step of the way. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consent-management-business-advantages) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consent-management-business-advantages) diff --git a/content/growth/consent-management-business-advantages/power-consent-mngmnt.jpg b/content/growth/consent-management-business-advantages/power-consent-mngmnt.jpg deleted file mode 100644 index 751ebda5e..000000000 Binary files a/content/growth/consent-management-business-advantages/power-consent-mngmnt.jpg and /dev/null differ diff --git a/content/growth/consent-management-business-advantages/power-consent-mngmnt.webp b/content/growth/consent-management-business-advantages/power-consent-mngmnt.webp new file mode 100644 index 000000000..28b5a65d7 Binary files /dev/null and b/content/growth/consent-management-business-advantages/power-consent-mngmnt.webp differ diff --git a/content/growth/consent-management-online-retail/DS-ccpa-compliance.png b/content/growth/consent-management-online-retail/DS-ccpa-compliance.png deleted file mode 100644 index 93302c0ce..000000000 Binary files a/content/growth/consent-management-online-retail/DS-ccpa-compliance.png and /dev/null differ diff --git a/content/growth/consent-management-online-retail/DS-ccpa-compliance.webp b/content/growth/consent-management-online-retail/DS-ccpa-compliance.webp new file mode 100644 index 000000000..9d62b96b8 Binary files /dev/null and b/content/growth/consent-management-online-retail/DS-ccpa-compliance.webp differ diff --git a/content/growth/consent-management-online-retail/index.md b/content/growth/consent-management-online-retail/index.md index e497a2498..610356ee9 100644 --- a/content/growth/consent-management-online-retail/index.md +++ b/content/growth/consent-management-online-retail/index.md @@ -1,7 +1,7 @@ --- title: "Exploring the Vital Role of Consent Management for Your Online Store" date: "2023-09-08" -coverImage: "online-store-consent-mngmnt.jpg" +coverImage: "online-store-consent-mngmnt.webp" tags: ["consent management","data privacy","compliance","cx"] author: "Vishal Sharma" description: "In today’s modern digital world, online success hinges on more than just great products and user-friendly interfaces. It's about respecting privacy, complying with regulations, and fostering trust. Consent management plays a vital role in achieving these goals. By being transparent about data usage, respecting customer privacy, and complying with regulations like GDPR, you not only avoid legal troubles but also gain a competitive edge." @@ -55,7 +55,7 @@ Customers are often annoyed by relentless marketing emails and ads that seem irr Proper consent management includes safeguarding customer data. You reduce the risk of data breaches by implementing robust security measures, limiting data access to authorized personnel, and monitoring for suspicious activity. Customers appreciate the peace of mind that their data is protected. -[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance) +[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance) ### 2. Data Portability @@ -77,4 +77,4 @@ Consent management is a legal requirement and a strategic business practice. It' Implementing an effective consent management system should be a top priority for any online business looking to thrive in the digital era. Your commitment to data privacy can set you apart from competitors and create long-lasting customer relationships. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consent-management-online-retail) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consent-management-online-retail) diff --git a/content/growth/consent-management-online-retail/online-store-consent-mngmnt.jpg b/content/growth/consent-management-online-retail/online-store-consent-mngmnt.jpg deleted file mode 100644 index 4bc171ef9..000000000 Binary files a/content/growth/consent-management-online-retail/online-store-consent-mngmnt.jpg and /dev/null differ diff --git a/content/growth/consent-management-online-retail/online-store-consent-mngmnt.webp b/content/growth/consent-management-online-retail/online-store-consent-mngmnt.webp new file mode 100644 index 000000000..00bc7ce74 Binary files /dev/null and b/content/growth/consent-management-online-retail/online-store-consent-mngmnt.webp differ diff --git a/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.jpg b/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.jpg deleted file mode 100644 index f223fce72..000000000 Binary files a/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.jpg and /dev/null differ diff --git a/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.webp b/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.webp new file mode 100644 index 000000000..e810c34c2 Binary files /dev/null and b/content/growth/consumer-experience-and-privacy/consumer-experience-privacy.webp differ diff --git a/content/growth/consumer-experience-and-privacy/index.md b/content/growth/consumer-experience-and-privacy/index.md index 7f6b7c589..b997ee36c 100644 --- a/content/growth/consumer-experience-and-privacy/index.md +++ b/content/growth/consumer-experience-and-privacy/index.md @@ -1,7 +1,7 @@ --- title: "Walking the Fine Line Between Consumer Experience and Privacy" date: "2021-02-24" -coverImage: "consumer-experience-privacy.jpg" +coverImage: "consumer-experience-privacy.webp" category: ["all"] featured: false author: "Rakesh Soni" @@ -64,4 +64,4 @@ Unfortunately, the current consumer experience and [data security practices](htt Consent as well as robust security protocols play key roles in walking the fine line between data management and consumer privacy expectations. An organization that handles their consumers’ data ethically stands to gain a considerable edge against competitors through greater access to data, greater consumer trust, and potential to secure more privacy-conscious consumers. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-experience-and-privacy) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-experience-and-privacy) diff --git a/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.jpg b/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.jpg deleted file mode 100644 index 3425702c2..000000000 Binary files a/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.jpg and /dev/null differ diff --git a/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.webp b/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.webp new file mode 100644 index 000000000..6a7acacba Binary files /dev/null and b/content/growth/consumer-experience-b2b-saas/5-tips-consumer-experience-b2b-saas.webp differ diff --git a/content/growth/consumer-experience-b2b-saas/index.md b/content/growth/consumer-experience-b2b-saas/index.md index f49b09d48..287f32efb 100644 --- a/content/growth/consumer-experience-b2b-saas/index.md +++ b/content/growth/consumer-experience-b2b-saas/index.md @@ -1,7 +1,7 @@ --- title: "5 Tips to Enhance the Consumer Experience in B2B SaaS" date: "2021-01-15" -coverImage: "5-tips-consumer-experience-b2b-saas.jpg" +coverImage: "5-tips-consumer-experience-b2b-saas.webp" category: ["all"] featured: false author: "Rakesh Soni" @@ -43,7 +43,7 @@ Speak to them about the business principles they would anticipate from using you In reality, companies should organize their teams to facilitate and carry out substantive consumer discussions about adding value to their businesses. It includes pre-sales, post-sales, marketing, and consumer/technology support. -[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience) +[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience) ## #4. Omnichannel approach for B2B SaaS. @@ -71,4 +71,4 @@ To bring it all together, the basis of B2B SaaS consumer experience depends on h It is essential to make sure that anything your client comes across from your business should turn out to be an enjoyable experience. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-experience-b2b-saas) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-experience-b2b-saas) \ No newline at end of file diff --git a/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.jpg b/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.jpg deleted file mode 100644 index 17940ab41..000000000 Binary files a/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.jpg and /dev/null differ diff --git a/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.webp b/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.webp new file mode 100644 index 000000000..39f6da380 Binary files /dev/null and b/content/growth/consumer-experience-b2b-saas/omnichannel-retailer-whitepaper.webp differ diff --git a/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.jpg b/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.jpg deleted file mode 100644 index e59da3184..000000000 Binary files a/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.jpg and /dev/null differ diff --git a/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.webp b/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.webp new file mode 100644 index 000000000..086a5ed87 Binary files /dev/null and b/content/growth/consumer-identity-role-in-the-digital-banking/Digital-banking-platform-making-opt.webp differ diff --git a/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.png b/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.png deleted file mode 100644 index 69d26339f..000000000 Binary files a/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.png and /dev/null differ diff --git a/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.webp b/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.webp new file mode 100644 index 000000000..96ed92a38 Binary files /dev/null and b/content/growth/consumer-identity-role-in-the-digital-banking/Product-Passwordless-Login.webp differ diff --git a/content/growth/consumer-identity-role-in-the-digital-banking/index.md b/content/growth/consumer-identity-role-in-the-digital-banking/index.md index 86ecbf29b..0a0757330 100644 --- a/content/growth/consumer-identity-role-in-the-digital-banking/index.md +++ b/content/growth/consumer-identity-role-in-the-digital-banking/index.md @@ -1,7 +1,7 @@ --- title: "Role of Consumer Identity Authentication in Digital Banking" date: "2021-07-19" -coverImage: "Digital-banking-platform-making-opt.jpg" +coverImage: "Digital-banking-platform-making-opt.webp" category: ["loginradius"] featured: false author: "Navanita Devi" @@ -39,7 +39,7 @@ To put that in context, identity solutions for digital marketing and access mana The instruments that assure the legality of these distant movements are the electronic signature and systems for certified evidence retention. The main problem, however, is identity identification, which ensures the transaction's authenticity and intentionality. It is no longer sufficient to protect a basic user code and password. -[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/) +[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/) ## What To Do To Highlight Consumer Identity @@ -75,4 +75,4 @@ If identification is the real cash, then digital identity and banking authentica [LoginRadius](https://www.loginradius.com/) provides seamless, call or SMS-based Multi-Factor Authentication with a visible layer of security protection. You get to choose whether this security system is mandatory or optional for your consumers. The SMS and call systems hold zero lag with global coverage! [Contact the team](https://www.loginradius.com/contact-sales/) today! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-identity-role-in-the-digital-banking) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-identity-role-in-the-digital-banking) diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.png b/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.png deleted file mode 100644 index 74eef3e01..000000000 Binary files a/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.png and /dev/null differ diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.webp b/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.webp new file mode 100644 index 000000000..cae55baf0 Binary files /dev/null and b/content/growth/consumer-identity-rule-personalized-marketing-2022/EB-GD-to-Mod-Cust-ID.webp differ diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/index.md b/content/growth/consumer-identity-rule-personalized-marketing-2022/index.md index a35140c1b..6d77a6035 100644 --- a/content/growth/consumer-identity-rule-personalized-marketing-2022/index.md +++ b/content/growth/consumer-identity-rule-personalized-marketing-2022/index.md @@ -1,7 +1,7 @@ --- title: "Do Consumer Identity Programs Really Work for Personalized Marketing?" date: "2021-12-14" -coverImage: "personalized-marketing.jpg" +coverImage: "personalized-marketing.webp" tags: ["identity management","ciam solution","mfa","cx"] author: "Navanita Devi" description: "Consumer identity management is actually a great way to help companies grow. It is through high quality CIAM that a business can create better targeted, safer, more meaningful marketing experiences for their customers." @@ -49,7 +49,7 @@ When registering for an application the first time, you have to fill out details After this, the application observes your activities and keeps the interface evolving according to the user activities. -[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) +[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) * **_Multi-factor authentication_** @@ -73,4 +73,4 @@ Consumer data is precious for your business, and its safety is the number one co There are many benefits of consumer identity programs for marketing, the two most important benefits being safety and personalization. Both of these can be achieved by proper implementation of CIAM from the business leaders. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-identity-rule-personalized-marketing-2022) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-identity-rule-personalized-marketing-2022) diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.png b/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.png deleted file mode 100644 index bc0c2b3f3..000000000 Binary files a/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.png and /dev/null differ diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.webp b/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.webp new file mode 100644 index 000000000..b0f1ac055 Binary files /dev/null and b/content/growth/consumer-identity-rule-personalized-marketing-2022/modern-customer-id.webp differ diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.jpg b/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.jpg deleted file mode 100644 index f0d218a47..000000000 Binary files a/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.jpg and /dev/null differ diff --git a/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.webp b/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.webp new file mode 100644 index 000000000..6fabe031a Binary files /dev/null and b/content/growth/consumer-identity-rule-personalized-marketing-2022/personalized-marketing.webp differ diff --git a/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.jpg b/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.jpg deleted file mode 100644 index 731b4880c..000000000 Binary files a/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.jpg and /dev/null differ diff --git a/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.webp b/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.webp new file mode 100644 index 000000000..8939c20bc Binary files /dev/null and b/content/growth/consumer-journey-from-sign-up-to-purchase/consumer-signup-to-purchase.webp differ diff --git a/content/growth/consumer-journey-from-sign-up-to-purchase/index.md b/content/growth/consumer-journey-from-sign-up-to-purchase/index.md index 7989e801b..ef53f71ac 100644 --- a/content/growth/consumer-journey-from-sign-up-to-purchase/index.md +++ b/content/growth/consumer-journey-from-sign-up-to-purchase/index.md @@ -1,7 +1,7 @@ --- title: "From Sign-Up to Purchase – How LoginRadius Offers a Frictionless Consumer Journey" date: "2021-07-14" -coverImage: "consumer-signup-to-purchase.jpg" +coverImage: "consumer-signup-to-purchase.webp" tags: ["user onboarding","ciam solution","cx"] author: "Vishal Sharma" description: " Enterprises, today, must be aware of the fact that the secret to success lies in quickly identifying and eliminating any pain point that occurs when consumers interact with their brand. Here’s an insightful read depicting how LoginRadius helps enterprises navigate their business success through a frictionless consumer journey." @@ -124,4 +124,4 @@ LoginRadius understands the importance of consumer onboarding and has designed a Ready to leverage the next level of CIAM solution? Or have any doubts? [Schedule a Quick Personalized Call](https://www.loginradius.com/contact-sales/) and understand how LoginRadius can be a game-changer for your business success. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-journey-from-sign-up-to-purchase) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-journey-from-sign-up-to-purchase) diff --git a/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.jpg b/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.jpg deleted file mode 100644 index c1302a657..000000000 Binary files a/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.jpg and /dev/null differ diff --git a/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.webp b/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.webp new file mode 100644 index 000000000..32a9bee9d Binary files /dev/null and b/content/growth/consumer-management-to-consumer-engagement/consumer-engagement.webp differ diff --git a/content/growth/consumer-management-to-consumer-engagement/index.md b/content/growth/consumer-management-to-consumer-engagement/index.md index 9c63aa302..b1741ecca 100644 --- a/content/growth/consumer-management-to-consumer-engagement/index.md +++ b/content/growth/consumer-management-to-consumer-engagement/index.md @@ -1,7 +1,7 @@ --- title: "How to Shift Focus From Consumer Management to Consumer Engagement" date: "2021-02-12" -coverImage: "consumer-engagement.jpg" +coverImage: "consumer-engagement.webp" category: ["customer-engagement", "customer-experience"] author: "Yash Rathi" description: "Historically, organizations were more focused on managing and facilitating consumers' to be on top of everything. However, in the past couple of years, the paradigm has shifted from working as the facilitator to acting as a consultant and driving consumer engagement." @@ -72,4 +72,4 @@ Strategies that bring out the 'wow' factor are always the best ones. Be it via s I hope these consumer engagement strategies will induce you to get into action. Keep in touch for more strategies and possible outcomes. Keep reading :) -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-management-to-consumer-engagement) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-management-to-consumer-engagement) diff --git a/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.jpg b/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.jpg deleted file mode 100644 index 007557626..000000000 Binary files a/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.jpg and /dev/null differ diff --git a/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.webp b/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.webp new file mode 100644 index 000000000..39a554bb3 Binary files /dev/null and b/content/growth/consumer-onboarding-strategies-for-saas-businesses/customer-onboarding.webp differ diff --git a/content/growth/consumer-onboarding-strategies-for-saas-businesses/index.md b/content/growth/consumer-onboarding-strategies-for-saas-businesses/index.md index 26ca18684..1f4038f53 100644 --- a/content/growth/consumer-onboarding-strategies-for-saas-businesses/index.md +++ b/content/growth/consumer-onboarding-strategies-for-saas-businesses/index.md @@ -1,7 +1,7 @@ --- title: "Consumer Onboarding Strategies for SaaS Businesses" date: "2021-06-17" -coverImage: "customer-onboarding.jpg" +coverImage: "customer-onboarding.webp" category: ["loginradius"] featured: false author: "Vishal Sharma" @@ -96,4 +96,4 @@ As an enterprise, you may have a lot of information regarding your potential cli LoginRadius can be your best onboarding partner that can help increase conversions and also minimize consumer churn. With a long list of features to enhance your business growth, LoginRadius paves the path for a successful onboarding journey. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-onboarding-strategies-for-saas-businesses) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-onboarding-strategies-for-saas-businesses) diff --git a/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.png b/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.png deleted file mode 100644 index 74eef3e01..000000000 Binary files a/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.png and /dev/null differ diff --git a/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.webp b/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.webp new file mode 100644 index 000000000..cae55baf0 Binary files /dev/null and b/content/growth/consumer-sentiments-on-modern-identity/EB-GD-to-Mod-Cust-id.webp differ diff --git a/content/growth/consumer-sentiments-on-modern-identity/index.md b/content/growth/consumer-sentiments-on-modern-identity/index.md index 541667d58..8ad9d65ba 100644 --- a/content/growth/consumer-sentiments-on-modern-identity/index.md +++ b/content/growth/consumer-sentiments-on-modern-identity/index.md @@ -1,7 +1,7 @@ --- title: "Uncovering Consumer Sentiments on Modern Identity: A Deep Dive Into Their Behavior" date: "2023-06-26" -coverImage: "modern-identity.jpg" +coverImage: "modern-identity.webp" tags: ["customer identity","identity management","authentication","cx"] author: "Rakesh Soni" description: "Today, consumers' attitudes toward modern identity are evolving rapidly. This blog explains the complexities of consumer sentiments, exploring the impact of social media, privacy concerns, inclusivity, and authenticity. Learn how businesses can effectively engage with their target audiences in this ever-changing landscape." @@ -46,7 +46,7 @@ Modern identity is closely intertwined with the concepts of inclusivity and dive Brands that embrace and celebrate diversity resonate more with consumers as they align with their values and aspirations. Fostering inclusivity enhances brand perception and cultivates a sense of belonging and loyalty among consumers. -[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) +[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) ### 5. Authenticity and purpose-driven brands @@ -74,4 +74,4 @@ By recognizing and understanding the complexities of consumer perceptions, busin Brands that embrace inclusivity prioritize data security, and demonstrate authenticity will stand out in today's competitive landscape. Ultimately, brands can forge meaningful connections and build a loyal customer base by aligning their values with their consumers. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-sentiments-on-modern-identity) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=consumer-sentiments-on-modern-identity) \ No newline at end of file diff --git a/content/growth/consumer-sentiments-on-modern-identity/modern-identity.jpg b/content/growth/consumer-sentiments-on-modern-identity/modern-identity.jpg deleted file mode 100644 index 20229b861..000000000 Binary files a/content/growth/consumer-sentiments-on-modern-identity/modern-identity.jpg and /dev/null differ diff --git a/content/growth/consumer-sentiments-on-modern-identity/modern-identity.webp b/content/growth/consumer-sentiments-on-modern-identity/modern-identity.webp new file mode 100644 index 000000000..949d7bfd5 Binary files /dev/null and b/content/growth/consumer-sentiments-on-modern-identity/modern-identity.webp differ diff --git a/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.png b/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.png deleted file mode 100644 index 0d7046172..000000000 Binary files a/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.png and /dev/null differ diff --git a/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.webp b/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.webp new file mode 100644 index 000000000..ea0737a8b Binary files /dev/null and b/content/growth/continuous-adaptive-authentication-future-2024/GD-to-RBA.webp differ diff --git a/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.jpg b/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.jpg deleted file mode 100644 index a6ae8bb89..000000000 Binary files a/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.jpg and /dev/null differ diff --git a/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.webp b/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.webp new file mode 100644 index 000000000..6a9069d91 Binary files /dev/null and b/content/growth/continuous-adaptive-authentication-future-2024/continuous-adptive-auth.webp differ diff --git a/content/growth/continuous-adaptive-authentication-future-2024/index.md b/content/growth/continuous-adaptive-authentication-future-2024/index.md index 47eacfbc7..7e0cf22e9 100644 --- a/content/growth/continuous-adaptive-authentication-future-2024/index.md +++ b/content/growth/continuous-adaptive-authentication-future-2024/index.md @@ -1,7 +1,7 @@ --- title: "Continuous Adaptive Trust - Adaptive Authentication Future" date: "2023-11-23" -coverImage: "continuous-adptive-auth.jpg" +coverImage: "continuous-adptive-auth.webp" tags: ["continuous adaptive authentication","compliance","cx"] author: "Rakesh Soni" description: "Discover the game-changing evolution of authentication with Continuous Adaptive Trust (CAT) in 2024 & beyond. CAT ensures a secure, seamless digital experience by continuously assessing trust in real time, making it a pivotal shift in cybersecurity." @@ -32,7 +32,7 @@ This ongoing evaluation ensures that trust levels are dynamically adjusted, resp CAT enables organizations to assess risk continuously, allowing for immediate response to any suspicious activities. This real-time approach minimizes the window of opportunity for attackers, providing a proactive defense against emerging threats. -[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) +[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) ### Enhanced User Experience @@ -52,4 +52,4 @@ The continuous evaluation in CAT minimizes false positives by understanding the As we enter 2024, Continuous Adaptive Trust emerges as a beacon of innovation, promising a future where adaptive authentication secures digital interactions and does so with unparalleled precision and adaptability. This paradigm shift heralds a new era in cybersecurity, where trust is not a static state but an ever-evolving, continuous journey. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=continuous-adaptive-authentication-future-2024) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=continuous-adaptive-authentication-future-2024) diff --git a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.png b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.png deleted file mode 100644 index 97611c609..000000000 Binary files a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.png and /dev/null differ diff --git a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.webp b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.webp new file mode 100644 index 000000000..0db381c53 Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-02-1024x709.webp differ diff --git a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.png b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.png deleted file mode 100644 index cf28a6f97..000000000 Binary files a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.png and /dev/null differ diff --git a/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.webp b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.webp new file mode 100644 index 000000000..4cd58ff77 Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/Identity-blog-graphic-03-1024x709.webp differ diff --git a/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.jpg b/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.jpg deleted file mode 100644 index a18057b42..000000000 Binary files a/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.jpg and /dev/null differ diff --git a/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.webp b/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.webp new file mode 100644 index 000000000..4b00d26d8 Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/customer-experience-media-entertainment-industry.webp differ diff --git a/content/growth/customer-experience-media-entertainment-industry/image4.jpg b/content/growth/customer-experience-media-entertainment-industry/image4.jpg deleted file mode 100644 index dcde4a14c..000000000 Binary files a/content/growth/customer-experience-media-entertainment-industry/image4.jpg and /dev/null differ diff --git a/content/growth/customer-experience-media-entertainment-industry/image4.webp b/content/growth/customer-experience-media-entertainment-industry/image4.webp new file mode 100644 index 000000000..5cf995130 Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/image4.webp differ diff --git a/content/growth/customer-experience-media-entertainment-industry/image5.png b/content/growth/customer-experience-media-entertainment-industry/image5.png deleted file mode 100644 index 924fec52b..000000000 Binary files a/content/growth/customer-experience-media-entertainment-industry/image5.png and /dev/null differ diff --git a/content/growth/customer-experience-media-entertainment-industry/image5.webp b/content/growth/customer-experience-media-entertainment-industry/image5.webp new file mode 100644 index 000000000..97f0f4080 Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/image5.webp differ diff --git a/content/growth/customer-experience-media-entertainment-industry/index.md b/content/growth/customer-experience-media-entertainment-industry/index.md index 5fe67bf91..3661cce63 100644 --- a/content/growth/customer-experience-media-entertainment-industry/index.md +++ b/content/growth/customer-experience-media-entertainment-industry/index.md @@ -1,7 +1,7 @@ --- title: "Digital Trends Transforming the Media and Entertainment Industry in 2020" date: "2020-02-25" -coverImage: "media-industry.jpg" +coverImage: "media-industry.webp" tags: ["digital transformation","ciam solution","cx"] author: "Rakesh Soni" description: "The worldwide media and entertainment industry is going through a huge transformation at the moment. 2020 aims to be the year of digital change in the media and entertainment sector with a large-scale roll-out of technology." @@ -33,7 +33,7 @@ According to an estimation by Strategy Analytics, revenue from OTT video in the These figures grab attention and are hard to ignore. - + Data source: Strategy analytics OTT video forecast @@ -55,7 +55,7 @@ Following suit came the [California Consumer Privacy Act (CCPA)](https://www.log But will it hit the right chords among organizations and individuals? Only time will tell. - + ## 5 Technologies That Will Impact User Experience in Media and Entertainment Industry @@ -91,7 +91,7 @@ Facial Recognition is swiftly turning into one of the most common forms of biome For instance, it will identify individuals in-store and offer purchasing recommendations based on their demographic. - + ## How will CIAM solutions gain momentum in the media and entertainment industry? @@ -111,7 +111,7 @@ The digitization of media content has also changed the way companies earn revenu A [CIAM platform like LoginRadius](https://www.loginradius.com/blog/identity/perfect-ciam-platform/) can record the preferences of their audience in unified customer profiles and generate relevant content. -[](https://www.loginradius.com/resource/how-media-and-publication-companies-use-loginradius-identity-platform/) +[](https://www.loginradius.com/resource/how-media-and-publication-companies-use-loginradius-identity-platform/) ### **Frictionless customer interaction.** @@ -125,4 +125,4 @@ With a large scale roll-out of the technology, 2020 promises to be the year of d Amidst the ever-changing regulatory landscape, there are high chances that new opportunities are waiting to be capitalized. _Now_ is your chance to reap the benefits. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-experience-media-entertainment-industry) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-experience-media-entertainment-industry) diff --git a/content/growth/customer-experience-media-entertainment-industry/media-industry.jpg b/content/growth/customer-experience-media-entertainment-industry/media-industry.jpg deleted file mode 100644 index 092e63f46..000000000 Binary files a/content/growth/customer-experience-media-entertainment-industry/media-industry.jpg and /dev/null differ diff --git a/content/growth/customer-experience-media-entertainment-industry/media-industry.webp b/content/growth/customer-experience-media-entertainment-industry/media-industry.webp new file mode 100644 index 000000000..6153655ad Binary files /dev/null and b/content/growth/customer-experience-media-entertainment-industry/media-industry.webp differ diff --git a/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.png b/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.png deleted file mode 100644 index 6bbda92e9..000000000 Binary files a/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.png and /dev/null differ diff --git a/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.webp b/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.webp new file mode 100644 index 000000000..0aeacb9f7 Binary files /dev/null and b/content/growth/customer-experience-retail-industry/BD-Plexicon1-1024x310.webp differ diff --git a/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png b/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png deleted file mode 100644 index b53535020..000000000 Binary files a/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.png and /dev/null differ diff --git a/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp b/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp new file mode 100644 index 000000000..02dbccb4e Binary files /dev/null and b/content/growth/customer-experience-retail-industry/DS-How-Retail-Consumer-Goods-Companies-Use-the-LoginRadius.webp differ diff --git a/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.jpg b/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.jpg deleted file mode 100644 index 340570c91..000000000 Binary files a/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.jpg and /dev/null differ diff --git a/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.webp b/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.webp new file mode 100644 index 000000000..13131c015 Binary files /dev/null and b/content/growth/customer-experience-retail-industry/customer-exp-retail-industry-1.webp differ diff --git a/content/growth/customer-experience-retail-industry/customer-exp-retail.jpg b/content/growth/customer-experience-retail-industry/customer-exp-retail.jpg deleted file mode 100644 index 2fe697885..000000000 Binary files a/content/growth/customer-experience-retail-industry/customer-exp-retail.jpg and /dev/null differ diff --git a/content/growth/customer-experience-retail-industry/customer-exp-retail.webp b/content/growth/customer-experience-retail-industry/customer-exp-retail.webp new file mode 100644 index 000000000..fb8c52ff6 Binary files /dev/null and b/content/growth/customer-experience-retail-industry/customer-exp-retail.webp differ diff --git a/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.jpg b/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.jpg deleted file mode 100644 index f29a7d5f9..000000000 Binary files a/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.jpg and /dev/null differ diff --git a/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.webp b/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.webp new file mode 100644 index 000000000..2943d9a80 Binary files /dev/null and b/content/growth/customer-experience-retail-industry/customer-experience-retail-industry.webp differ diff --git a/content/growth/customer-experience-retail-industry/index.md b/content/growth/customer-experience-retail-industry/index.md index 72829bf89..b7f48b0e3 100644 --- a/content/growth/customer-experience-retail-industry/index.md +++ b/content/growth/customer-experience-retail-industry/index.md @@ -1,7 +1,7 @@ --- title: "Enhancing Customer Experience in Retail Industry" date: "2020-05-05" -coverImage: "retail-cx.jpg" +coverImage: "retail-cx.webp" tags: ["cx", "ciam solution","compliance"] author: "Rakesh Soni" description: "Not only does a perfect plan for customer experience rely on the product, store, and customers, but also on how companies smartly coordinate the entities listed. They need to integrate customer service through multiple genres of retail." @@ -62,7 +62,7 @@ Moving on, let's find out a few ways how [brands can enhance customer experience ## How Retail Companies Can Benefit From Customer Experience - + The retail industry is brutally competitive. It takes more than offering the right product at the right price to deliver amazing customer experiences. As already discussed, brands also need to treat customers with respect and trigger them on an emotional level. @@ -82,7 +82,7 @@ When it comes to customer experience in the retail industry, compared to [brick- There is one downside, though - and it is the inability to touch and feel the products before making a decision. Retailers need to break even to rebuild customer loyalty. They need to bring the convenience of online shopping to brick and mortar stores and make in-store experiences as smooth and easy as possible. -[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/) +[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/) The good news is that initiatives like smaller format stores, auto-checkout, online ordering (while inside the store), and mobile app offers are in action to lure shoppers back into physical stores. @@ -104,7 +104,7 @@ Furthermore, it will be easier for brands to consolidate all customer data (purc ## The role of LoginRadius to protect customer data for online retail business - + LoginRadius is a [customer identity and access management](https://www.loginradius.com/blog/2019/06/customer-identity-and-access-management/) tool that offers a seamless and secure way to access customer information - in your case, shoppers' data. @@ -128,4 +128,4 @@ Rivalry in the retail industry has always been a big deal. Amidst online players It is only a matter of time that customer experience in the retail industry will win the war, and nothing else will matter. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-experience-retail-industry) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-experience-retail-industry) diff --git a/content/growth/customer-experience-retail-industry/retail-cx.jpg b/content/growth/customer-experience-retail-industry/retail-cx.jpg deleted file mode 100644 index 1f4129d0f..000000000 Binary files a/content/growth/customer-experience-retail-industry/retail-cx.jpg and /dev/null differ diff --git a/content/growth/customer-experience-retail-industry/retail-cx.webp b/content/growth/customer-experience-retail-industry/retail-cx.webp new file mode 100644 index 000000000..b781f37d9 Binary files /dev/null and b/content/growth/customer-experience-retail-industry/retail-cx.webp differ diff --git a/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.png b/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.png deleted file mode 100644 index 9fd09f050..000000000 Binary files a/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.png and /dev/null differ diff --git a/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.webp b/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.webp new file mode 100644 index 000000000..e2c41fa9b Binary files /dev/null and b/content/growth/customer-identity-drives-business-growth/DS-LR-loyalty.webp differ diff --git a/content/growth/customer-identity-drives-business-growth/business-growth.jpg b/content/growth/customer-identity-drives-business-growth/business-growth.jpg deleted file mode 100644 index 93e291360..000000000 Binary files a/content/growth/customer-identity-drives-business-growth/business-growth.jpg and /dev/null differ diff --git a/content/growth/customer-identity-drives-business-growth/business-growth.webp b/content/growth/customer-identity-drives-business-growth/business-growth.webp new file mode 100644 index 000000000..7e111e53b Binary files /dev/null and b/content/growth/customer-identity-drives-business-growth/business-growth.webp differ diff --git a/content/growth/customer-identity-drives-business-growth/index.md b/content/growth/customer-identity-drives-business-growth/index.md index 141da462d..013a6609e 100644 --- a/content/growth/customer-identity-drives-business-growth/index.md +++ b/content/growth/customer-identity-drives-business-growth/index.md @@ -1,7 +1,7 @@ --- title: "The Strategic Impact of Customer Identity on Business Growth" date: "2024-07-03" -coverImage: "business-growth.jpg" +coverImage: "business-growth.webp" tags: ["customer identity management","cx"] author: "Cooper Matheson" description: "Understanding and leveraging customer identity is crucial for driving business growth in today's competitive market. By personalizing customer experiences and utilizing data effectively, businesses can meet customer expectations and achieve substantial growth." @@ -30,7 +30,7 @@ For example, a customer who frequently purchases eco-friendly products would app Loyal customers are invaluable to any business. They not only make repeat purchases but also act as brand advocates, spreading positive word-of-mouth and attracting new customers. Understanding customer identity helps businesses identify loyal customers and reward them appropriately. -[](https://www.loginradius.com/resource/datasheet/ciam-loyalty-programs/) +[](https://www.loginradius.com/resource/datasheet/ciam-loyalty-programs/) Loyalty programs tailored to individual customers' preferences and behaviors can significantly boost customer retention. Offering exclusive discounts, early access to sales, or personalized rewards based on past purchases can make customers feel valued and appreciated, strengthening their loyalty to the brand. @@ -66,4 +66,4 @@ Understanding and leveraging customer identity is a powerful strategy for drivin Embrace the power of customer identity to unlock new opportunities and pave the way for sustained success. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-drives-business-growth) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-drives-business-growth) diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.png b/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.png and /dev/null differ diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.webp b/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/growth/customer-identity-drives-digital-eCommerce-success/Buyers-Guide-to-Multi-Factor-Authentication.webp differ diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.png b/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.png deleted file mode 100644 index 61deb3295..000000000 Binary files a/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.png and /dev/null differ diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.webp b/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.webp new file mode 100644 index 000000000..00c5933a4 Binary files /dev/null and b/content/growth/customer-identity-drives-digital-eCommerce-success/EB-GD-to-MFA.webp differ diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.jpg b/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.jpg deleted file mode 100644 index 61fb95aa5..000000000 Binary files a/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.jpg and /dev/null differ diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.webp b/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.webp new file mode 100644 index 000000000..9a332ac6b Binary files /dev/null and b/content/growth/customer-identity-drives-digital-eCommerce-success/ecommerce-digital-identity-solutions.webp differ diff --git a/content/growth/customer-identity-drives-digital-eCommerce-success/index.md b/content/growth/customer-identity-drives-digital-eCommerce-success/index.md index d8e933bb0..c27d4a4df 100644 --- a/content/growth/customer-identity-drives-digital-eCommerce-success/index.md +++ b/content/growth/customer-identity-drives-digital-eCommerce-success/index.md @@ -1,7 +1,7 @@ --- title: "How Customer Identity Solution Drives Digital eCommerce Success" date: "2021-07-10" -coverImage: "ecommerce-digital-identity-solutions.jpg" +coverImage: "ecommerce-digital-identity-solutions.webp" tags: ["identity management","digital transformation","cx"] author: "Vishal Sharma" description: "Learn how a CIAM solution paves the path for an eCommerce business success and why enterprises thinking to step into the eCommerce world should leverage a cutting-edge CIAM solution." @@ -31,7 +31,7 @@ In a world when data and identity thefts lead to losses worth millions of dollar Adding more robust authentication layers, including multi-factor authentication (MFA) and [risk-based authentication](https://www.loginradius.com/blog/identity/risk-based-authentication/) (RBA) to log in and sign-up procedures, can help secure consumer data and prevent a breach. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) Also, these secure authentication practices help enterprises to verify the individuals quickly they say they are. @@ -78,4 +78,4 @@ Here's how this works. For example, you want some details from your customers to Ecommerce is the new normal in a pandemic era and beyond. Businesses that are swiftly adopting the new age of selling products and services must emphasize delivering a seamless and secure user experience. A consumer identity and access management solution is undoubtedly the key to win consumer success as enterprises can identify their visitors and [build personalized experiences](https://www.loginradius.com/customer-experience-solutions/) around foremost touchpoints, including research, purchase, discovery, and more.
-[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-drives-digital-ecommerce-success) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-drives-digital-ecommerce-success) diff --git a/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.png b/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.png deleted file mode 100644 index 99b5a25ea..000000000 Binary files a/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.png and /dev/null differ diff --git a/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.webp b/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.webp new file mode 100644 index 000000000..a8ae17db9 Binary files /dev/null and b/content/growth/customer-identity-resolution-marketing-success/GD-ciam-roi.webp differ diff --git a/content/growth/customer-identity-resolution-marketing-success/customer-id-res.jpg b/content/growth/customer-identity-resolution-marketing-success/customer-id-res.jpg deleted file mode 100644 index 780c59b7f..000000000 Binary files a/content/growth/customer-identity-resolution-marketing-success/customer-id-res.jpg and /dev/null differ diff --git a/content/growth/customer-identity-resolution-marketing-success/customer-id-res.webp b/content/growth/customer-identity-resolution-marketing-success/customer-id-res.webp new file mode 100644 index 000000000..5681405ab Binary files /dev/null and b/content/growth/customer-identity-resolution-marketing-success/customer-id-res.webp differ diff --git a/content/growth/customer-identity-resolution-marketing-success/index.md b/content/growth/customer-identity-resolution-marketing-success/index.md index 2d18547f5..738dce7c6 100644 --- a/content/growth/customer-identity-resolution-marketing-success/index.md +++ b/content/growth/customer-identity-resolution-marketing-success/index.md @@ -1,7 +1,7 @@ --- title: "How to Leverage Advanced Customer Identity Resolution for Better Marketing Outcomes" date: "2024-06-27" -coverImage: "customer-id-res.jpg" +coverImage: "customer-id-res.webp" tags: ["identity resolution","compliance","cx"] author: "Cooper Matheson" description: "In the digital marketing landscape, understanding your customers is crucial for driving exceptional results. Advanced customer identity resolution unifies disparate data points to create comprehensive customer profiles. This enables personalized experiences, precise targeting, and higher ROI. Explore the power and implementation of this technology to enhance your marketing strategy." @@ -28,7 +28,7 @@ This involves matching identifiers from different data sources, such as email ad 3. **Increased ROI**: Personalization and precise targeting lead to more efficient marketing spend. By focusing efforts on high-potential customers and reducing wasted ad spend on uninterested audiences, businesses can achieve a higher return on investment (ROI) for their marketing campaigns. -[](https://www.loginradius.com/resource/guide/ciam-increase-roi-for-enterprise/) +[](https://www.loginradius.com/resource/guide/ciam-increase-roi-for-enterprise/) 4. **Omnichannel Consistency**: Customers today interact with brands across multiple touchpoints, including social media, websites, mobile apps, and in-store visits. Advanced identity resolution ensures a consistent and seamless experience across all these channels, fostering brand loyalty and trust. @@ -62,4 +62,4 @@ Advanced customer identity resolution is a powerful tool for driving exceptional As the digital landscape continues to evolve, investing in advanced identity management solutions will be crucial for staying ahead of the competition and achieving long-term success in your marketing efforts. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-resolution-marketing-success) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-resolution-marketing-success) diff --git a/content/growth/customer-identity-use-case/EB-gd-mci.png b/content/growth/customer-identity-use-case/EB-gd-mci.png deleted file mode 100644 index 74eef3e01..000000000 Binary files a/content/growth/customer-identity-use-case/EB-gd-mci.png and /dev/null differ diff --git a/content/growth/customer-identity-use-case/EB-gd-mci.webp b/content/growth/customer-identity-use-case/EB-gd-mci.webp new file mode 100644 index 000000000..cae55baf0 Binary files /dev/null and b/content/growth/customer-identity-use-case/EB-gd-mci.webp differ diff --git a/content/growth/customer-identity-use-case/cust-identity.jpg b/content/growth/customer-identity-use-case/cust-identity.jpg deleted file mode 100644 index 1546ff7f9..000000000 Binary files a/content/growth/customer-identity-use-case/cust-identity.jpg and /dev/null differ diff --git a/content/growth/customer-identity-use-case/cust-identity.webp b/content/growth/customer-identity-use-case/cust-identity.webp new file mode 100644 index 000000000..c8a02c1c6 Binary files /dev/null and b/content/growth/customer-identity-use-case/cust-identity.webp differ diff --git a/content/growth/customer-identity-use-case/index.md b/content/growth/customer-identity-use-case/index.md index 52fabafc4..01ae2fea4 100644 --- a/content/growth/customer-identity-use-case/index.md +++ b/content/growth/customer-identity-use-case/index.md @@ -1,7 +1,7 @@ --- title: "Unveiling the Customer Identity Business Case: Strategies for Success" date: "2023-10-19" -coverImage: "cust-identity.jpg" +coverImage: "cust-identity.webp" tags: ["customer identity management","ciam solutions","cx"] author: "Rakesh Soni" description: "Dive into the world of the customer identity base case – your key to personalized success. Explore strategies for tailored experiences, fraud prevention, and ethical data practices. Stay ahead in the digital era with our expert insights." @@ -46,7 +46,7 @@ As we move into an era dominated by digital interactions, the importance of the Emerging technologies like the Internet of Things (IoT) and augmented reality are reshaping customer interactions, providing even more touchpoints for data collection. By embracing these technologies and integrating the insights gained into their customer identity base case, businesses can create seamless, omnichannel experiences that delight customers across various platforms. -[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) +[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) Moreover, the rise of ethical consumerism underscores the significance of transparent data practices. Companies that prioritize customer privacy and utilize data responsibly will not only comply with regulations but also earn the trust and loyalty of their customer base. @@ -90,4 +90,4 @@ The customer identity base case is the cornerstone of a successful business stra Embracing these strategies and understanding the value of the customer identity base case will undoubtedly pave the way for long-term success in the digital realm. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-use-case) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-identity-use-case) \ No newline at end of file diff --git a/content/growth/customer-relationship-business/customer-relations-management.jpg b/content/growth/customer-relationship-business/customer-relations-management.jpg deleted file mode 100644 index c321593ba..000000000 Binary files a/content/growth/customer-relationship-business/customer-relations-management.jpg and /dev/null differ diff --git a/content/growth/customer-relationship-business/customer-relations-management.webp b/content/growth/customer-relationship-business/customer-relations-management.webp new file mode 100644 index 000000000..f116a5acd Binary files /dev/null and b/content/growth/customer-relationship-business/customer-relations-management.webp differ diff --git a/content/growth/customer-relationship-business/index.md b/content/growth/customer-relationship-business/index.md index d76d6f889..392d1030e 100644 --- a/content/growth/customer-relationship-business/index.md +++ b/content/growth/customer-relationship-business/index.md @@ -1,7 +1,7 @@ --- title: "Why Is Customer Relationship Important for Every Business in 2021" date: "2021-02-26" -coverImage: "customer-relations-management.jpg" +coverImage: "customer-relations-management.webp" tags: ["customer relation management","ciam solution","cx"] author: "Rakesh Soni" description: "Positive customer relations help you connect with your customers on a much more personal level. When you connect with the target audience deeply, you are much more likely to understand their requirements, resolve their problems, and create a sense of mutual understanding." @@ -104,4 +104,4 @@ Some reasons as to why the CRM system(s) are so prevalent: So, having learned about customer relationship management, you would be able to decide hows of customer relationships approach it, and make the most of it! However, one thing that is sure to happen when you build profound customer relations is that you would witness an increasing customer base. Moreover, when you have a positive relationship with your customers, you are not very far from establishing some favourable B2B customer relationships! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-relationship-business) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-relationship-business) diff --git a/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.png b/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.png deleted file mode 100644 index f81b79a36..000000000 Binary files a/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.png and /dev/null differ diff --git a/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.webp b/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.webp new file mode 100644 index 000000000..33ac3b3da Binary files /dev/null and b/content/growth/customer-retention-magic-links/DS-passwordless-login-magic-link-otp.webp differ diff --git a/content/growth/customer-retention-magic-links/customer-retention.jpg b/content/growth/customer-retention-magic-links/customer-retention.jpg deleted file mode 100644 index 7c5be30e2..000000000 Binary files a/content/growth/customer-retention-magic-links/customer-retention.jpg and /dev/null differ diff --git a/content/growth/customer-retention-magic-links/customer-retention.webp b/content/growth/customer-retention-magic-links/customer-retention.webp new file mode 100644 index 000000000..be7b2e517 Binary files /dev/null and b/content/growth/customer-retention-magic-links/customer-retention.webp differ diff --git a/content/growth/customer-retention-magic-links/index.md b/content/growth/customer-retention-magic-links/index.md index 00648d69c..4403aa1da 100644 --- a/content/growth/customer-retention-magic-links/index.md +++ b/content/growth/customer-retention-magic-links/index.md @@ -1,7 +1,7 @@ --- title: "Enhancing Customer Retention with Magic Links: A User-Friendly Approach to Authentication" date: "2024-03-28" -coverImage: "customer-retention.jpg" +coverImage: "customer-retention.webp" tags: ["user authentication","customer retention","cx"] author: "Cooper Matheson" description: "Discover the magic of Magic Links, a frictionless authentication method that simplifies login. Easily enhance security and boost customer retention. Say goodbye to password woes and 2FA complexity. Learn how to implement Magic Links for a seamless user experience." @@ -74,7 +74,7 @@ Inform your users about this new feature and highlight its benefits. Clear commu As with any new feature, monitoring its performance is essential. Gather user feedback and analyze metrics such as login success rates and user satisfaction. Use this data to make improvements and further optimize the Magic Links experience. -[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet) +[](https://www.loginradius.com/resource/passwordless-login-magic-link-otp-datasheet) ## How LoginRadius's Passwordless Magic Link Thrives Business Success? @@ -104,4 +104,4 @@ User authentication for customer retention is not just a technical necessity; it By adopting innovative approaches like Magic Links, businesses can transform a potentially tedious process into a delightful user experience. Remember, the magic lies in simplicity, security, and the profound impact it can have on customer loyalty. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-retention-magic-links) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customer-retention-magic-links) \ No newline at end of file diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.png b/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.png deleted file mode 100644 index f5fa0b0f9..000000000 Binary files a/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.png and /dev/null differ diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.webp b/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.webp new file mode 100644 index 000000000..b0761321e Binary files /dev/null and b/content/growth/customize-marketing-programs-on-consumer-journey/EB-omnichannel.webp differ diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.jpg b/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.jpg deleted file mode 100644 index 5f0d20d7b..000000000 Binary files a/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.jpg and /dev/null differ diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.webp b/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.webp new file mode 100644 index 000000000..f7eeecdf4 Binary files /dev/null and b/content/growth/customize-marketing-programs-on-consumer-journey/customer-marketing.webp differ diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/index.md b/content/growth/customize-marketing-programs-on-consumer-journey/index.md index 21ef9fafd..e54452532 100644 --- a/content/growth/customize-marketing-programs-on-consumer-journey/index.md +++ b/content/growth/customize-marketing-programs-on-consumer-journey/index.md @@ -1,7 +1,7 @@ --- title: "Why You Should Customize Your Marketing Programs Based on Consumer Journey" date: "2021-11-10" -coverImage: "customer-marketing.jpg" +coverImage: "customer-marketing.webp" tags: ["ciam solution","cx","mfa"] author: "Vishal Sharma" description: "Personalized consumer experience is becoming the need of the hour. Let’s understand how a personalized consumer journey can help businesses stay ahead of the curve and how a CIAM solution like LoginRadius offers valuable insights for creating personalized user experiences." @@ -38,7 +38,7 @@ Well, consumers are already interacting with established brands, including Apple As a vendor, if you have the data regarding the buyer’s behavior, you can pitch exactly the same product or service for which they have landed. -[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) +[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) ## How LoginRadius Helps Build Personalized Consumer Journeys? @@ -70,4 +70,4 @@ Consumer data can help businesses craft personalized consumer journeys that not With a [consumer identity and access management (CIAM)](https://www.loginradius.com/blog/identity/customer-identity-and-access-management/#:~:text=Customer%20identity%20and%20access%20management%20(CIAM)%20is%20a%20digital%20identity,while%20securely%20managing%20customer%20identities.) solution in place, enterprises can yield better results by creating rich, personalized user experiences that help engage potential clients and increase the chances of conversions. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customize-marketing-programs-on-consumer-journey) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=customize-marketing-programs-on-consumer-journey) diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.png b/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.png deleted file mode 100644 index 86c15a159..000000000 Binary files a/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.png and /dev/null differ diff --git a/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.webp b/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.webp new file mode 100644 index 000000000..025782e92 Binary files /dev/null and b/content/growth/customize-marketing-programs-on-consumer-journey/omnichannel-eb.webp differ diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.png b/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.png deleted file mode 100644 index 61deb3295..000000000 Binary files a/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.png and /dev/null differ diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.webp b/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.webp new file mode 100644 index 000000000..00c5933a4 Binary files /dev/null and b/content/growth/cyberinsurance-2023-insurers-adapt-survive/EB-GD-to-MFA.webp differ diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.jpg b/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.jpg deleted file mode 100644 index 26b5cedbb..000000000 Binary files a/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.jpg and /dev/null differ diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.webp b/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.webp new file mode 100644 index 000000000..ed8cc4378 Binary files /dev/null and b/content/growth/cyberinsurance-2023-insurers-adapt-survive/cyber-insurance.webp differ diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/index.md b/content/growth/cyberinsurance-2023-insurers-adapt-survive/index.md index 6bd66bf78..ffad7d989 100644 --- a/content/growth/cyberinsurance-2023-insurers-adapt-survive/index.md +++ b/content/growth/cyberinsurance-2023-insurers-adapt-survive/index.md @@ -1,7 +1,7 @@ --- title: "Cyber Insurance in 2023: Takeaways For The Future And How To Prepare For It" date: "2023-01-06" -coverImage: "cyber-insurance.jpg" +coverImage: "cyber-insurance.webp" tags: ["cybersecurity", "cyberinsurance", "risk management"] author: "Alok Patidar" description: "As cyber risks continue to evolve and increase, it is no surprise that cyber insurance is becoming one of the fastest-growing insurance products in the market. Learn how it will shape the security space in 2023." @@ -70,7 +70,7 @@ When it comes to cyber insurance renewals, here are a few things insurers will w Multi-factor authentication protection on all remote access to your network, including any remote desktop protocol connections, email server, cloud services, and backup data solutions. Ensure that all network administrator accounts and any other user accounts with elevated permissions have multi-factor authentication protection. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) ### 2. Endpoint security @@ -103,6 +103,6 @@ As cyber security threats continue to grow and evolve into a full-blown crisis, In 2023, we will have many more concrete innovations, propelling the insurance industry into a better place than it ever has before. This will put them in a prime position to meet the challenges of tomorrow with agility, not uncertainty. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cyberinsurance-2023-insurers-adapt-survive) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=cyberinsurance-2023-insurers-adapt-survive) diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.png b/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.png and /dev/null differ diff --git a/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.webp b/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/growth/cyberinsurance-2023-insurers-adapt-survive/mfa-eb.webp differ diff --git a/content/growth/data-privacy-boost-marketing-success/WP-privacy.png b/content/growth/data-privacy-boost-marketing-success/WP-privacy.png deleted file mode 100644 index fb9e830ba..000000000 Binary files a/content/growth/data-privacy-boost-marketing-success/WP-privacy.png and /dev/null differ diff --git a/content/growth/data-privacy-boost-marketing-success/WP-privacy.webp b/content/growth/data-privacy-boost-marketing-success/WP-privacy.webp new file mode 100644 index 000000000..4ea6dbcbf Binary files /dev/null and b/content/growth/data-privacy-boost-marketing-success/WP-privacy.webp differ diff --git a/content/growth/data-privacy-boost-marketing-success/index.md b/content/growth/data-privacy-boost-marketing-success/index.md index 5a472cc23..6f47c62f9 100644 --- a/content/growth/data-privacy-boost-marketing-success/index.md +++ b/content/growth/data-privacy-boost-marketing-success/index.md @@ -1,7 +1,7 @@ --- title: "Strategic Insights: Leveraging Data Privacy for Marketers' Success" date: "2024-03-20" -coverImage: "marketing-success.jpg" +coverImage: "marketing-success.webp" tags: ["data privacy","compliance","cx"] author: "Rakesh Soni" description: "Data has become invaluable in digital marketing. However, amidst the quest for personalization, data privacy often takes a back seat. Explore how a strategic approach to data privacy can ensure compliance, build trust, and drive long-term success for marketers. Discover the importance of transparency and ethical data practices and how prioritizing privacy can set brands apart in a crowded marketplace." @@ -39,7 +39,7 @@ Beyond legal compliance, marketers should prioritize ethical considerations in t An example of ethical data use is implementing granular consent mechanisms. Instead of blanket opt-ins, give consumers control over what they share. Allow them to choose the types of communication they receive and the data they're comfortable sharing. This not only builds trust but also ensures that the data collected is more accurate and relevant. -[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper) +[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper) ## Data Privacy as a Competitive Advantage @@ -53,4 +53,4 @@ Data privacy is not just a legal requirement for marketers; it's a strategic imp Brands that prioritize privacy comply with regulations and build lasting relationships with customers. In an era where data is abundant but trust is scarce, cultivating a privacy-first mindset is not just good ethics—it's good business. As marketers navigate the evolving landscape of digital marketing, let data privacy be their guiding star toward success. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-boost-marketing-success) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-boost-marketing-success) diff --git a/content/growth/data-privacy-boost-marketing-success/marketing-success.jpg b/content/growth/data-privacy-boost-marketing-success/marketing-success.jpg deleted file mode 100644 index aafcea017..000000000 Binary files a/content/growth/data-privacy-boost-marketing-success/marketing-success.jpg and /dev/null differ diff --git a/content/growth/data-privacy-boost-marketing-success/marketing-success.webp b/content/growth/data-privacy-boost-marketing-success/marketing-success.webp new file mode 100644 index 000000000..fdc4a9804 Binary files /dev/null and b/content/growth/data-privacy-boost-marketing-success/marketing-success.webp differ diff --git a/content/growth/data-privacy-marketers-success/WP-building-privacy.png b/content/growth/data-privacy-marketers-success/WP-building-privacy.png deleted file mode 100644 index fb9e830ba..000000000 Binary files a/content/growth/data-privacy-marketers-success/WP-building-privacy.png and /dev/null differ diff --git a/content/growth/data-privacy-marketers-success/WP-building-privacy.webp b/content/growth/data-privacy-marketers-success/WP-building-privacy.webp new file mode 100644 index 000000000..4ea6dbcbf Binary files /dev/null and b/content/growth/data-privacy-marketers-success/WP-building-privacy.webp differ diff --git a/content/growth/data-privacy-marketers-success/data-privacy.jpg b/content/growth/data-privacy-marketers-success/data-privacy.jpg deleted file mode 100644 index 7f42a68c2..000000000 Binary files a/content/growth/data-privacy-marketers-success/data-privacy.jpg and /dev/null differ diff --git a/content/growth/data-privacy-marketers-success/data-privacy.webp b/content/growth/data-privacy-marketers-success/data-privacy.webp new file mode 100644 index 000000000..b1f5ecb66 Binary files /dev/null and b/content/growth/data-privacy-marketers-success/data-privacy.webp differ diff --git a/content/growth/data-privacy-marketers-success/index.md b/content/growth/data-privacy-marketers-success/index.md index 969c63715..9a7834d26 100644 --- a/content/growth/data-privacy-marketers-success/index.md +++ b/content/growth/data-privacy-marketers-success/index.md @@ -1,7 +1,7 @@ --- title: "Seizing Opportunities: How Can Marketers Leverage Data Privacy for Success" date: "2024-01-16" -coverImage: "data-privacy.jpg" +coverImage: "data-privacy.webp" tags: ["data privacy","compliance","cx"] author: "Rakesh Soni" description: "Data privacy is one of the most essential aspects of data security. With stringent data privacy laws all around the world, marketers are finding it challenging to navigate through this new framework. Let’s discuss how data privacy laws for marketers are actually beneficial." @@ -44,7 +44,7 @@ In this world with stringent data protection laws, it becomes the responsibility * Marketers are in a better position to explain what data will be required and where. So, while approaching the [customer for marketing consent](https://www.loginradius.com/consent-preference-management/), ensure to spell out clearly and specifically if an email address is required for daily mail-outs regarding specific product details. You can even give them options to narrow down how the customer wants to move forward with the relationship, like through emails, phones, or texts, SMS. * Marketers need to ensure data visibility is in accordance with the consent of the authority, like who has access to view and edit it. When it comes to data privacy for marketers, an identity access management tool can help define who can access it and change the data over time. -[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper) +[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper) * Email marketing is a boon, but as a marketer, it is best to clean and verify email lists. Like, perform regular sweeps for addresses that are no longer current. Most data regulations mention that storing obsolete data does not demonstrate a careful approach to the duty of data protection. * When the data comes from different sources, there is a chance of data disparity. A DRM (Data Relationship Management) can provide a way to keep on top of multiple data inputs and structuring them in a meaningful way. @@ -53,4 +53,4 @@ In this world with stringent data protection laws, it becomes the responsibility Data privacy necessitates the requirement to preview the processes that can improve the entire company’s operation, not only the marketing vertical. With the help of the right tools for compliance and privacy regulations, marketers can implement their data-driven marketing strategies while capturing customer trust and providing enhanced user experience. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-marketers-success) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-marketers-success) diff --git a/content/growth/data-privacy-marketing-regulations/DS-privacy.png b/content/growth/data-privacy-marketing-regulations/DS-privacy.png deleted file mode 100644 index 67c1c093f..000000000 Binary files a/content/growth/data-privacy-marketing-regulations/DS-privacy.png and /dev/null differ diff --git a/content/growth/data-privacy-marketing-regulations/DS-privacy.webp b/content/growth/data-privacy-marketing-regulations/DS-privacy.webp new file mode 100644 index 000000000..42c0492a7 Binary files /dev/null and b/content/growth/data-privacy-marketing-regulations/DS-privacy.webp differ diff --git a/content/growth/data-privacy-marketing-regulations/data-privacy.jpg b/content/growth/data-privacy-marketing-regulations/data-privacy.jpg deleted file mode 100644 index 6b34ed54b..000000000 Binary files a/content/growth/data-privacy-marketing-regulations/data-privacy.jpg and /dev/null differ diff --git a/content/growth/data-privacy-marketing-regulations/data-privacy.webp b/content/growth/data-privacy-marketing-regulations/data-privacy.webp new file mode 100644 index 000000000..7f92af196 Binary files /dev/null and b/content/growth/data-privacy-marketing-regulations/data-privacy.webp differ diff --git a/content/growth/data-privacy-marketing-regulations/index.md b/content/growth/data-privacy-marketing-regulations/index.md index e96b3b2e5..70de25081 100644 --- a/content/growth/data-privacy-marketing-regulations/index.md +++ b/content/growth/data-privacy-marketing-regulations/index.md @@ -1,7 +1,7 @@ --- title: "Navigating the Shifting Landscape of Data Privacy Regulations: Embracing Core Marketing Principles" date: "2024-04-30" -coverImage: "data-privacy.jpg" +coverImage: "data-privacy.webp" tags: ["data privacy","compliance","cx"] author: "Cooper Matheson" description: "In today's digital business landscape, navigating data privacy regulations is paramount. Discover how businesses worldwide are adapting to safeguard user data privacy while embracing transparency and responsible personalization. Explore the importance of empowering users through choice and accountability in the ever-evolving regulatory landscape." @@ -24,7 +24,7 @@ Users are increasingly aware of the value of their personal information and dema Central to effective marketing in this era is transparency. Honesty about data collection and usage builds trust and fosters stronger relationships with customers. -[](https://www.loginradius.com/resource/datasheet/privacy-policy-management/) +[](https://www.loginradius.com/resource/datasheet/privacy-policy-management/) It's essential to communicate clearly with users about what data is being collected, how it's being used, and how they can opt-in or opt-out. Transparency should permeate every aspect of marketing, from email campaigns to targeted advertising. @@ -60,4 +60,4 @@ This might mean providing easy-to-use privacy settings, allowing users to opt ou By putting users in the driver's seat, businesses not only comply with regulations but also foster a sense of empowerment and respect that can lead to long-term loyalty and advocacy. In the ever-evolving landscape of data privacy regulations, prioritizing user empowerment is not just good ethics—it's good business. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-marketing-regulations) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=data-privacy-marketing-regulations) \ No newline at end of file diff --git a/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.png b/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.png deleted file mode 100644 index 61deb3295..000000000 Binary files a/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.png and /dev/null differ diff --git a/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.webp b/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.webp new file mode 100644 index 000000000..00c5933a4 Binary files /dev/null and b/content/growth/digital-identity-key-to-economic-growth/EB-GD-to-MFA.webp differ diff --git a/content/growth/digital-identity-key-to-economic-growth/digital-id.jpg b/content/growth/digital-identity-key-to-economic-growth/digital-id.jpg deleted file mode 100644 index 547c2f197..000000000 Binary files a/content/growth/digital-identity-key-to-economic-growth/digital-id.jpg and /dev/null differ diff --git a/content/growth/digital-identity-key-to-economic-growth/digital-id.webp b/content/growth/digital-identity-key-to-economic-growth/digital-id.webp new file mode 100644 index 000000000..f2749e3e5 Binary files /dev/null and b/content/growth/digital-identity-key-to-economic-growth/digital-id.webp differ diff --git a/content/growth/digital-identity-key-to-economic-growth/index.md b/content/growth/digital-identity-key-to-economic-growth/index.md index 931d4354d..6fdded9c6 100644 --- a/content/growth/digital-identity-key-to-economic-growth/index.md +++ b/content/growth/digital-identity-key-to-economic-growth/index.md @@ -1,7 +1,7 @@ --- title: "How Digital Identification Could Be the Key to Inclusive and Economic Growth?" date: "2022-11-09" -coverImage: "digital-id.jpg" +coverImage: "digital-id.webp" tags: ["digital identity","mfa","cx","data security"] author: "Alex Williams" description: "A digital ID is a digitized representation of legal identity, and unlike traditional paper-based IDs, digital identification allows for remote verification via digital channels. In this article, we’ll look at how digital identification can help with growth on an economic level." @@ -59,7 +59,7 @@ At face value, these advantages appear to benefit institutions primarily. Howeve The fact that individuals are becoming savvier to the [benefits of digital ID](https://blog.loginradius.com/identity/pros-cons-reusable-digital-identity/) is seen with most consumers looking for banking accounts that come with essential security features such as Multi-Factor Authentication (MFA), among other digital identification features. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) ### 4. Financial inclusion @@ -84,4 +84,4 @@ Besides enabling social and civic empowerment, digital identification is critica Through sound design principles and policy enforcement, digital protects individual rights from abuse and creates economic benefits for states, institutions, and people. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-identity-key-to-economic-growth) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-identity-key-to-economic-growth) \ No newline at end of file diff --git a/content/growth/digital-identity-key-to-economic-growth/mfa-eb.png b/content/growth/digital-identity-key-to-economic-growth/mfa-eb.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/growth/digital-identity-key-to-economic-growth/mfa-eb.png and /dev/null differ diff --git a/content/growth/digital-identity-key-to-economic-growth/mfa-eb.webp b/content/growth/digital-identity-key-to-economic-growth/mfa-eb.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/growth/digital-identity-key-to-economic-growth/mfa-eb.webp differ diff --git a/content/growth/digital-trust-business-invest-2022/GD-to-RBA.png b/content/growth/digital-trust-business-invest-2022/GD-to-RBA.png deleted file mode 100644 index 0d7046172..000000000 Binary files a/content/growth/digital-trust-business-invest-2022/GD-to-RBA.png and /dev/null differ diff --git a/content/growth/digital-trust-business-invest-2022/GD-to-RBA.webp b/content/growth/digital-trust-business-invest-2022/GD-to-RBA.webp new file mode 100644 index 000000000..ea0737a8b Binary files /dev/null and b/content/growth/digital-trust-business-invest-2022/GD-to-RBA.webp differ diff --git a/content/growth/digital-trust-business-invest-2022/digital-trust.jpg b/content/growth/digital-trust-business-invest-2022/digital-trust.jpg deleted file mode 100644 index 0aeadd833..000000000 Binary files a/content/growth/digital-trust-business-invest-2022/digital-trust.jpg and /dev/null differ diff --git a/content/growth/digital-trust-business-invest-2022/digital-trust.webp b/content/growth/digital-trust-business-invest-2022/digital-trust.webp new file mode 100644 index 000000000..9605527ed Binary files /dev/null and b/content/growth/digital-trust-business-invest-2022/digital-trust.webp differ diff --git a/content/growth/digital-trust-business-invest-2022/index.md b/content/growth/digital-trust-business-invest-2022/index.md index bed46178c..22ebbeefb 100644 --- a/content/growth/digital-trust-business-invest-2022/index.md +++ b/content/growth/digital-trust-business-invest-2022/index.md @@ -1,7 +1,7 @@ --- title: "Earning Digital Trust in 2022: Where Should Businesses Invest?" date: "2022-06-28" -coverImage: "digital-trust.jpg" +coverImage: "digital-trust.webp" tags: ["digital transformation", "customer trust", "enterprises"] author: "Rakesh Soni" description: "Whether securing access control or rethinking privacy policies, businesses skipping a small step in protecting customer information could lead to losses worth millions of dollars and reputational damages since bad actors are already exploring new ways to exploit customer information. Here’s an insightful post that uncovers the aspects of digital trust and where businesses need to invest to earn digital trust in 2022 and beyond." @@ -81,7 +81,7 @@ The risk-based implementation allows your application to challenge the consumer It is a method of applying various levels of stringency to authentication processes based on the likelihood that access to a given system could result in compromise. As the level of risk increases, the authentication process becomes more complicated and restrictive. -[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) +[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) Risk-based authentication is an essential security feature because it works in real-time to prevent cyber frauds like accounts from getting compromised without causing an inconvenience for legitimate consumers. And thus building digital trust. @@ -96,6 +96,6 @@ Hence, businesses embarking on a digital transformation journey shouldn’t unde The aspects mentioned above could help businesses build digital trust that further fosters growth in the future. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-trust-business-invest-2022) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=digital-trust-business-invest-2022) diff --git a/content/growth/digital-trust-business-invest-2022/rba-gd.png b/content/growth/digital-trust-business-invest-2022/rba-gd.png deleted file mode 100644 index c820cfc17..000000000 Binary files a/content/growth/digital-trust-business-invest-2022/rba-gd.png and /dev/null differ diff --git a/content/growth/digital-trust-business-invest-2022/rba-gd.webp b/content/growth/digital-trust-business-invest-2022/rba-gd.webp new file mode 100644 index 000000000..9cfe7e407 Binary files /dev/null and b/content/growth/digital-trust-business-invest-2022/rba-gd.webp differ diff --git a/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.png b/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.png and /dev/null differ diff --git a/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.webp b/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/growth/driving-merchant-growth-robust-authentication/Buyers-Guide-MFA-EB.webp differ diff --git a/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.png b/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.png deleted file mode 100644 index 61deb3295..000000000 Binary files a/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.png and /dev/null differ diff --git a/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.webp b/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.webp new file mode 100644 index 000000000..00c5933a4 Binary files /dev/null and b/content/growth/driving-merchant-growth-robust-authentication/EB-GD-to-MFA.webp differ diff --git a/content/growth/driving-merchant-growth-robust-authentication/index.md b/content/growth/driving-merchant-growth-robust-authentication/index.md index 85d73e862..c328d184e 100644 --- a/content/growth/driving-merchant-growth-robust-authentication/index.md +++ b/content/growth/driving-merchant-growth-robust-authentication/index.md @@ -1,7 +1,7 @@ --- title: "The Crucial Role of Security and CX in Providing Robust Authentication for Merchants" date: "2023-03-09" -coverImage: "robust-authntcation.jpg" +coverImage: "robust-authntcation.webp" tags: ["online shopping","data security","cx"] author: "Vishal Sharma" description: "Customers expect great experiences backed with robust security while interacting with a brand online. Hence, businesses must cater to them with the appropriate services by leveraging a robust authentication mechanism. Let’s have a look at some of the authentication benefits for merchants." @@ -61,7 +61,7 @@ CIAM helps merchants to better manage risk by identifying potentially fraudulent Merchants can implement CIAM using two-factor authentication (2FA) or multi-factor authentication (MFA). 2FA requires customers to provide two forms of identification: a password and a code sent to their mobile device. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) MFA requires customers to provide three or more forms of identification, such as a password, a code sent to their mobile device, and a fingerprint scan. @@ -74,4 +74,4 @@ As e-commerce continues to grow, merchants must take measures to protect themsel By implementing CIAM, merchants can protect against fraud, comply with regulations, increase customer trust, improve the customer experience, and better manage risk. With the right tools and strategies, merchants can ensure the security of their online transactions and build a successful and profitable e-commerce business. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=driving-merchant-growth-robust-authentication) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=driving-merchant-growth-robust-authentication) diff --git a/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.jpg b/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.jpg deleted file mode 100644 index 30be39383..000000000 Binary files a/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.jpg and /dev/null differ diff --git a/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.webp b/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.webp new file mode 100644 index 000000000..4dc6475e6 Binary files /dev/null and b/content/growth/driving-merchant-growth-robust-authentication/robust-authntcation.webp differ diff --git a/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.png b/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.png deleted file mode 100644 index cf809b333..000000000 Binary files a/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.png and /dev/null differ diff --git a/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.webp b/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.webp new file mode 100644 index 000000000..dd88d73ba Binary files /dev/null and b/content/growth/driving-success-through-customer-onboarding/DS-Prod-Reg-Service.webp differ diff --git a/content/growth/driving-success-through-customer-onboarding/customer-onboarding.jpg b/content/growth/driving-success-through-customer-onboarding/customer-onboarding.jpg deleted file mode 100644 index 04cafa4d7..000000000 Binary files a/content/growth/driving-success-through-customer-onboarding/customer-onboarding.jpg and /dev/null differ diff --git a/content/growth/driving-success-through-customer-onboarding/customer-onboarding.webp b/content/growth/driving-success-through-customer-onboarding/customer-onboarding.webp new file mode 100644 index 000000000..d447d2feb Binary files /dev/null and b/content/growth/driving-success-through-customer-onboarding/customer-onboarding.webp differ diff --git a/content/growth/driving-success-through-customer-onboarding/index.md b/content/growth/driving-success-through-customer-onboarding/index.md index 91708ad13..c179fefbf 100644 --- a/content/growth/driving-success-through-customer-onboarding/index.md +++ b/content/growth/driving-success-through-customer-onboarding/index.md @@ -1,7 +1,7 @@ --- title: "Driving Success Through Customer Onboarding: The Role of Marketing Strategies" date: "2023-05-24" -coverImage: "customer-onboarding.jpg" +coverImage: "customer-onboarding.webp" tags: ["customer onboarding","customer experience"] author: "Yash Rathi" description: "Explore the role of marketing in enhancing customer onboarding. Learn practical strategies like personalized communication, clear materials, streamlined experience, and continuous support for successful onboarding." @@ -41,7 +41,7 @@ Marketing strategies contribute significantly to creating a streamlined user exp This can involve optimizing the user interface, refining the registration process, and incorporating intuitive navigation elements. A seamless user experience enhances customer satisfaction and reduces the likelihood of customers abandoning the onboarding process prematurely. -[](https://www.loginradius.com/resource/loginradius-ciam-registration-service/) +[](https://www.loginradius.com/resource/loginradius-ciam-registration-service/) ### 4. Continuous Support and Education @@ -75,4 +75,4 @@ By focusing on personalized communication, explicit onboarding materials, stream Investing in these strategies benefits the individual customer and contributes to business growth, increased customer retention, and a strong brand reputation. Businesses can pave the way for success in today's competitive landscape by optimizing the customer onboarding process. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=driving-success-through-customer-onboarding) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=driving-success-through-customer-onboarding) \ No newline at end of file diff --git a/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.png b/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.png deleted file mode 100644 index 4ea16b064..000000000 Binary files a/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.png and /dev/null differ diff --git a/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.webp b/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.webp new file mode 100644 index 000000000..7e6ca6673 Binary files /dev/null and b/content/growth/ecommerce-social-login-success/WP-social-login-reconsidered.webp differ diff --git a/content/growth/ecommerce-social-login-success/ecommerce-social-login.jpg b/content/growth/ecommerce-social-login-success/ecommerce-social-login.jpg deleted file mode 100644 index db1cd4715..000000000 Binary files a/content/growth/ecommerce-social-login-success/ecommerce-social-login.jpg and /dev/null differ diff --git a/content/growth/ecommerce-social-login-success/ecommerce-social-login.webp b/content/growth/ecommerce-social-login-success/ecommerce-social-login.webp new file mode 100644 index 000000000..8ec84aa16 Binary files /dev/null and b/content/growth/ecommerce-social-login-success/ecommerce-social-login.webp differ diff --git a/content/growth/ecommerce-social-login-success/index.md b/content/growth/ecommerce-social-login-success/index.md index 5bf64d76b..57d13fef4 100644 --- a/content/growth/ecommerce-social-login-success/index.md +++ b/content/growth/ecommerce-social-login-success/index.md @@ -1,7 +1,7 @@ --- title: "8 Essential Insights for Enabling E-Commerce Social Login" date: "2023-09-20" -coverImage: "ecommerce-social-login.jpg" +coverImage: "ecommerce-social-login.webp" tags: ["ecommerce","social login","data privacy","cx"] author: "Vishal Sharma" description: "E-commerce social login is the way forward for businesses looking to simplify user authentication and improve the overall user experience. However, success lies in the details, from offering multiple social login options to prioritizing data privacy and security. Explore these eight essential insights to ensure your e-commerce platform thrives in the age of social login." @@ -34,7 +34,7 @@ While convenience is paramount, it's crucial to [prioritize data privacy and sec Your privacy policy and terms of service clearly outline how user data obtained through social login will be utilized. Be transparent about data protection measures and assure users that their information will not be misused or shared without consent. This transparency builds trust and encourages users to embrace social login. -[](https://www.loginradius.com/resource/whitepaper/social-login-reconsidered/) +[](https://www.loginradius.com/resource/whitepaper/social-login-reconsidered/) ### #4. Streamline Checkout @@ -60,4 +60,4 @@ Leverage the user data obtained through social login to provide tailored product Enabling social media profile login for users can be a game-changer for your e-commerce application/platform, enhancing user convenience and providing valuable data. However, balancing this convenience with robust data privacy and security measures is essential. By implementing these eight aspects, you can create a seamless experience for your customers for your e-commerce store. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ecommerce-social-login-success) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ecommerce-social-login-success) \ No newline at end of file diff --git a/content/growth/emotional-intelligence/1.png b/content/growth/emotional-intelligence/1.png deleted file mode 100644 index 6ffed62c5..000000000 Binary files a/content/growth/emotional-intelligence/1.png and /dev/null differ diff --git a/content/growth/emotional-intelligence/1.webp b/content/growth/emotional-intelligence/1.webp new file mode 100644 index 000000000..61279c240 Binary files /dev/null and b/content/growth/emotional-intelligence/1.webp differ diff --git a/content/growth/emotional-intelligence/2.png b/content/growth/emotional-intelligence/2.png deleted file mode 100644 index f04b28d4e..000000000 Binary files a/content/growth/emotional-intelligence/2.png and /dev/null differ diff --git a/content/growth/emotional-intelligence/2.webp b/content/growth/emotional-intelligence/2.webp new file mode 100644 index 000000000..e6d97b6da Binary files /dev/null and b/content/growth/emotional-intelligence/2.webp differ diff --git a/content/growth/emotional-intelligence/emotional-intelligence-loginradius.jpg b/content/growth/emotional-intelligence/emotional-intelligence-loginradius.jpg deleted file mode 100644 index 67d7f84e2..000000000 Binary files a/content/growth/emotional-intelligence/emotional-intelligence-loginradius.jpg and /dev/null differ diff --git a/content/growth/emotional-intelligence/emotional-intelligence-loginradius.webp b/content/growth/emotional-intelligence/emotional-intelligence-loginradius.webp new file mode 100644 index 000000000..47ea009b2 Binary files /dev/null and b/content/growth/emotional-intelligence/emotional-intelligence-loginradius.webp differ diff --git a/content/growth/emotional-intelligence/index.md b/content/growth/emotional-intelligence/index.md index 65eadc190..eb611b1a5 100644 --- a/content/growth/emotional-intelligence/index.md +++ b/content/growth/emotional-intelligence/index.md @@ -1,7 +1,7 @@ --- title: "Steps to Grow Your Emotional Intelligence for Better Consumer Relations" date: "2021-03-31" -coverImage: "emotional-intelligence-loginradius.jpg" +coverImage: "emotional-intelligence-loginradius.webp" category: ["loginradius"] featured: false author: "Lesley Vos" @@ -48,7 +48,7 @@ Psychologist and science journalist, Goleman examined EI with application to lea It appeared that the [top five components of EI](https://www.cognitiveinstitute.org/get-smart-about-emotional-intelligence/) — self-awareness, self-regulation, motivation, empathy, and social skills — result in an influence on business communication. - + In plain English, emotional intelligence is "the ability to perceive, control and evaluate emotions – in oneself and others – and to use that information appropriately." ([Source](https://www.psychologytoday.com/intl/blog/your-mind-your-body/201201/10-ways-enhance-your-emotional-intelligence)) @@ -64,7 +64,7 @@ That's how Goleman explained the growing interest in emotional intelligence in t He described EI with four domains and [twelve competencies](https://hbr.org/2017/02/emotional-intelligence-has-12-elements-which-do-you-need-to-work-on) a person needed to develop to become emotionally intelligent: - + Today, experts agree on two statements: @@ -237,4 +237,4 @@ Emotional intelligence is the ability to control emotions and relate well to oth It takes commitment and time but yields loyalty. Grow the emotional intelligence of your agents, be emotionally intelligent yourself, and implement them across business communication systems for productive consumer relations. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=emotional-intelligence) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=emotional-intelligence) \ No newline at end of file diff --git a/content/growth/emotional-intelligence/loginradius-book-a-demo.png b/content/growth/emotional-intelligence/loginradius-book-a-demo.png deleted file mode 100644 index 7602d120d..000000000 Binary files a/content/growth/emotional-intelligence/loginradius-book-a-demo.png and /dev/null differ diff --git a/content/growth/emotional-intelligence/loginradius-book-a-demo.webp b/content/growth/emotional-intelligence/loginradius-book-a-demo.webp new file mode 100644 index 000000000..9a00697f9 Binary files /dev/null and b/content/growth/emotional-intelligence/loginradius-book-a-demo.webp differ diff --git a/content/growth/engineering-as-marketing/engineering-as-marketing.jpg b/content/growth/engineering-as-marketing/engineering-as-marketing.jpg deleted file mode 100644 index 25911e0d8..000000000 Binary files a/content/growth/engineering-as-marketing/engineering-as-marketing.jpg and /dev/null differ diff --git a/content/growth/engineering-as-marketing/engineering-as-marketing.webp b/content/growth/engineering-as-marketing/engineering-as-marketing.webp new file mode 100644 index 000000000..8767178f6 Binary files /dev/null and b/content/growth/engineering-as-marketing/engineering-as-marketing.webp differ diff --git a/content/growth/engineering-as-marketing/index.md b/content/growth/engineering-as-marketing/index.md index 882cb0d76..5b7b26de6 100644 --- a/content/growth/engineering-as-marketing/index.md +++ b/content/growth/engineering-as-marketing/index.md @@ -1,7 +1,7 @@ --- title: "Engineering As Marketing: 5 Growth Hack Strategies For Modern Businesses" date: "2021-01-05" -coverImage: "engineering-as-marketing.jpg" +coverImage: "engineering-as-marketing.webp" category: ["all"] featured: false author: "Rakesh Soni" @@ -73,4 +73,4 @@ If it blends into the overall story with goal and vision, the use of resources t If you build the lead magnets so that they deliver a quick win and do not give too many possibilities to the consumer, you lay the foundation stone for throwing out a net in which you can attract the long-term attention of prospective customers to yourself. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=engineering-as-marketing) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=engineering-as-marketing) diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.png b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.png deleted file mode 100644 index 3fad38dd7..000000000 Binary files a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.png and /dev/null differ diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.webp b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.webp new file mode 100644 index 000000000..3e1dc7d36 Binary files /dev/null and b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/DS-dig-trans-insurance.webp differ diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.png b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.png deleted file mode 100644 index b042ccc74..000000000 Binary files a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.png and /dev/null differ diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.webp b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.webp new file mode 100644 index 000000000..ad52fb6e1 Binary files /dev/null and b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/How-Customer-Identity-Drives-Digital-Transformation-for-Insurance-Companies.webp differ diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.jpg b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.jpg deleted file mode 100644 index c4547121e..000000000 Binary files a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.jpg and /dev/null differ diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.webp b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.webp new file mode 100644 index 000000000..591108cec Binary files /dev/null and b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/couple-meeting-with-insurance-agent.webp differ diff --git a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/index.md b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/index.md index c3acb39dc..57eed3b51 100644 --- a/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/index.md +++ b/content/growth/enhance-customer-experience-in-insurance-companies-with-ciam/index.md @@ -1,7 +1,7 @@ --- title: "Enhance Your Consumer Experience in Insurance Companies With CIAM" date: "2021-08-09" -coverImage: "couple-meeting-with-insurance-agent.jpg" +coverImage: "couple-meeting-with-insurance-agent.webp" tags: ["ciam solution","mfa","passwordless authentication"] author: "Deependra Singh" description: "Unaided consumer interactions are a lost opportunity. The main goal of an insurance company should be to reduce the time taken in all their consumer interactions and increase the consumer experience level. This can only happen by implementing excellent systems and processes, which is where a CIAM comes into play." @@ -21,7 +21,7 @@ A [consumer identity and access management](https://www.loginradius.com/blog/ide The seamless user onboarding of new consumers, the overall [consumer experience](https://www.loginradius.com/resource/how-customer-identity-drives-digital-transformation-for-insurance-companies-2/), and good authentication services and identification process when individuals use their online apps are some of the primary concerns. Other issues include managing multiple brands within a single organization and managing personal data both within and outside the company. -[](https://www.loginradius.com/resource/how-customer-identity-drives-digital-transformation-for-insurance-companies-2/) +[](https://www.loginradius.com/resource/how-customer-identity-drives-digital-transformation-for-insurance-companies-2/) ## What Businesses Use CIAM @@ -100,4 +100,4 @@ Insurance companies will have to make trade-offs between protection and the clie Insurance companies often operate in a fast-paced environment, serving both consumers and businesses. They also deal with a complex IT infrastructure resulting from the multiple acquisitions that make up a typical contemporary insurance company. [Implementing the right CIAM](https://www.loginradius.com/) solution is critical in the digital world of insurance firms in order to achieve their objectives and go above and beyond. This [CIAM digital strategy](https://www.loginradius.com/blog/identity/digital-transformation-consumer-iam/) can assist in the transformation of a conventional life insurance product into a more modern digital banking offering geared at wider consumer segments while still utilizing the traditional agent channel. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enhance-customer-experience-in-insurance-companies-with-ciam) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enhance-customer-experience-in-insurance-companies-with-ciam) \ No newline at end of file diff --git a/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.png b/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.png deleted file mode 100644 index f97184f2f..000000000 Binary files a/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.png and /dev/null differ diff --git a/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.webp b/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.webp new file mode 100644 index 000000000..88d19cbb8 Binary files /dev/null and b/content/growth/enhancing-ciam-customer-experience/EB-progressive-profiling.webp differ diff --git a/content/growth/enhancing-ciam-customer-experience/customer-experience.jpg b/content/growth/enhancing-ciam-customer-experience/customer-experience.jpg deleted file mode 100644 index 0700debe1..000000000 Binary files a/content/growth/enhancing-ciam-customer-experience/customer-experience.jpg and /dev/null differ diff --git a/content/growth/enhancing-ciam-customer-experience/customer-experience.webp b/content/growth/enhancing-ciam-customer-experience/customer-experience.webp new file mode 100644 index 000000000..4421f9531 Binary files /dev/null and b/content/growth/enhancing-ciam-customer-experience/customer-experience.webp differ diff --git a/content/growth/enhancing-ciam-customer-experience/index.md b/content/growth/enhancing-ciam-customer-experience/index.md index 98a8d579a..40ea0fd86 100644 --- a/content/growth/enhancing-ciam-customer-experience/index.md +++ b/content/growth/enhancing-ciam-customer-experience/index.md @@ -1,7 +1,7 @@ --- title: "Transforming Customer Experience: Enhancing CX through CIAM and Insights" date: "2024-04-25" -coverImage: "customer-experience.jpg" +coverImage: "customer-experience.webp" tags: ["ciam solutions","data security","cx"] author: "Vishal Sharma" description: "Learn how to elevate your CX strategies with CIAM and data-driven insights. From seamless digital experiences to proactive customer engagement, discover the key to driving growth and loyalty in a competitive market." @@ -40,7 +40,7 @@ These insights empower CMOs to personalize marketing campaigns, tailor product o One of the key advantages of CIAM is its integration capabilities with other business systems such as CRM platforms, marketing automation tools, and analytics solutions. By integrating CIAM with these systems, CMOs can gain a comprehensive view of the customer journey, from initial interaction to post-purchase engagement. -[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) +[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) This holistic understanding enables organizations to identify areas for improvement, optimize touchpoints, and deliver consistent and personalized experiences across all channels. @@ -66,4 +66,4 @@ By leveraging CIAM to create seamless digital experiences and harnessing data in As CX continues to evolve, CMOs must embrace innovative solutions like LoginRadius CIAM to stay ahead of the curve and deliver exceptional experiences that drive growth and loyalty. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enhancing-ciam-customer-experience) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enhancing-ciam-customer-experience) diff --git a/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.png b/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.png deleted file mode 100644 index a448013ef..000000000 Binary files a/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.png and /dev/null differ diff --git a/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.webp b/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.webp new file mode 100644 index 000000000..31886ad27 Binary files /dev/null and b/content/growth/enterprise-level-security-trends/GD-Enterprise-RP.webp differ diff --git a/content/growth/enterprise-level-security-trends/GD-Incident-RP.png b/content/growth/enterprise-level-security-trends/GD-Incident-RP.png deleted file mode 100644 index a7dbc3ac7..000000000 Binary files a/content/growth/enterprise-level-security-trends/GD-Incident-RP.png and /dev/null differ diff --git a/content/growth/enterprise-level-security-trends/GD-Incident-RP.webp b/content/growth/enterprise-level-security-trends/GD-Incident-RP.webp new file mode 100644 index 000000000..e57053baa Binary files /dev/null and b/content/growth/enterprise-level-security-trends/GD-Incident-RP.webp differ diff --git a/content/growth/enterprise-level-security-trends/ceo-enterprise-security.jpg b/content/growth/enterprise-level-security-trends/ceo-enterprise-security.jpg deleted file mode 100644 index eda598c2c..000000000 Binary files a/content/growth/enterprise-level-security-trends/ceo-enterprise-security.jpg and /dev/null differ diff --git a/content/growth/enterprise-level-security-trends/ceo-enterprise-security.webp b/content/growth/enterprise-level-security-trends/ceo-enterprise-security.webp new file mode 100644 index 000000000..cccd3343f Binary files /dev/null and b/content/growth/enterprise-level-security-trends/ceo-enterprise-security.webp differ diff --git a/content/growth/enterprise-level-security-trends/index.md b/content/growth/enterprise-level-security-trends/index.md index 19f225dc2..921d9c5e3 100644 --- a/content/growth/enterprise-level-security-trends/index.md +++ b/content/growth/enterprise-level-security-trends/index.md @@ -1,7 +1,7 @@ --- title: "Enterprise-Level Security Trends: 5 Things to Know As a CEO" date: "2023-05-17" -coverImage: "ceo-enterprise-security.jpg" +coverImage: "ceo-enterprise-security.webp" tags: ["enterprise level security","cybersecurity","cx"] author: "Lucy Manole" description: "A gradual transition towards a robust security culture signifies the importance of integrating cybersecurity awareness. As a result, many organizations are now building dedicated board-level cybersecurity committees under the CEO’s wing to better address this growing concern." @@ -55,7 +55,7 @@ CEOs should consider some key aspects when building a dedicated board-level cybe * **Top-down approach:** A security culture must be driven from the top down, with the CEO and executive team demonstrating a commitment to security. This helps set a strong example for the rest of the organization. * **Incident response plan:** A CEO must approve a comprehensive incident response plan that outlines steps to be taken in case of a security breach, including communication, containment, and recovery. -[](https://www.loginradius.com/resource/survive-a-cyber-apocalypse) +[](https://www.loginradius.com/resource/survive-a-cyber-apocalypse) * **Review and evaluation:** The committee periodically reviews and evaluates the organization's cybersecurity posture, including the effectiveness of its risk management strategies, incident response plans, and overall security controls. @@ -87,4 +87,4 @@ Cybersecurity is no longer just an IT concern but a top strategic priority for e Remember, a robust security posture prevents potential attacks and demonstrates to customers, investors, and stakeholders that your organization is committed to ensuring the highest levels of trust and confidence. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enterprise-level-security-trends) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=enterprise-level-security-trends) diff --git a/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.png b/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.png deleted file mode 100644 index b2c0a4d84..000000000 Binary files a/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.png and /dev/null differ diff --git a/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.webp b/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.webp new file mode 100644 index 000000000..8dcbd7082 Binary files /dev/null and b/content/growth/evolution-digital-identity-better-cx/DS-consent-mngmnt.webp differ diff --git a/content/growth/evolution-digital-identity-better-cx/consent-ds.png b/content/growth/evolution-digital-identity-better-cx/consent-ds.png deleted file mode 100644 index 51524f116..000000000 Binary files a/content/growth/evolution-digital-identity-better-cx/consent-ds.png and /dev/null differ diff --git a/content/growth/evolution-digital-identity-better-cx/consent-ds.webp b/content/growth/evolution-digital-identity-better-cx/consent-ds.webp new file mode 100644 index 000000000..ae3c4b53d Binary files /dev/null and b/content/growth/evolution-digital-identity-better-cx/consent-ds.webp differ diff --git a/content/growth/evolution-digital-identity-better-cx/digital.jpg b/content/growth/evolution-digital-identity-better-cx/digital.jpg deleted file mode 100644 index efb304bc4..000000000 Binary files a/content/growth/evolution-digital-identity-better-cx/digital.jpg and /dev/null differ diff --git a/content/growth/evolution-digital-identity-better-cx/digital.webp b/content/growth/evolution-digital-identity-better-cx/digital.webp new file mode 100644 index 000000000..3919c6d36 Binary files /dev/null and b/content/growth/evolution-digital-identity-better-cx/digital.webp differ diff --git a/content/growth/evolution-digital-identity-better-cx/index.md b/content/growth/evolution-digital-identity-better-cx/index.md index f5194ef06..1b91135c5 100644 --- a/content/growth/evolution-digital-identity-better-cx/index.md +++ b/content/growth/evolution-digital-identity-better-cx/index.md @@ -1,7 +1,7 @@ --- title: "Your Digital Identity Is Changing - So, What Does It Mean For Customer Experience?" date: "2022-12-16" -coverImage: "digital.jpg" +coverImage: "digital.webp" tags: ["digital id", "cx", "customer identity"] author: "Rakesh Soni" description: "Now, more than ever, customer experience is baked into every business. That means that as a business owner, you need to deliver great digital experiences and customer interactions every time. This blog covers some of the important aspects of an effective digital strategy." @@ -65,7 +65,7 @@ When it comes to customer data management, laws are changing fast. New regulatio While this may seem to be a lot of work, your business must comply with new laws and regulations. While collecting data from your website, you will need to know how to get consent from your visitors and store that information securely. -[](https://www.loginradius.com/resource/loginradius-consent-management) +[](https://www.loginradius.com/resource/loginradius-consent-management) ## How To Learn From Customer Behavior And Stay Ahead Of Evolving Needs? @@ -88,5 +88,5 @@ When you invest in proper training and technology, your team will be empowered t By looking at customer identity, both online and off, you should be able to create a connection with customers you could not have made before. This improves understanding between your brand and your audience and provides an insightful picture that can help build stronger relationships for more tremendous digital success. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=evolution-digital-identity-better-cx) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=evolution-digital-identity-better-cx) diff --git a/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.png b/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.png deleted file mode 100644 index e73f6428b..000000000 Binary files a/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.png and /dev/null differ diff --git a/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.webp b/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.webp new file mode 100644 index 000000000..2ceed6beb Binary files /dev/null and b/content/growth/fight-mediocrity-at-your-workplace/Fight-mediocrity-at-your-workplace-dare-to-be-awesome.webp differ diff --git a/content/growth/fight-mediocrity-at-your-workplace/index.md b/content/growth/fight-mediocrity-at-your-workplace/index.md index 2db5a850e..ec98f7276 100644 --- a/content/growth/fight-mediocrity-at-your-workplace/index.md +++ b/content/growth/fight-mediocrity-at-your-workplace/index.md @@ -1,7 +1,7 @@ --- title: "Fight Mediocrity at Your Workplace, Dare to be Awesome!" date: "2017-04-07" -coverImage: "Fight-mediocrity-at-your-workplace-dare-to-be-awesome.png" +coverImage: "Fight-mediocrity-at-your-workplace-dare-to-be-awesome.webp" category: ["business","General"] featured: false author: "Rakesh Soni" diff --git a/content/growth/finding-ideal-customer-user-profile-management/index.md b/content/growth/finding-ideal-customer-user-profile-management/index.md index e60dc17c3..64a8cf8be 100644 --- a/content/growth/finding-ideal-customer-user-profile-management/index.md +++ b/content/growth/finding-ideal-customer-user-profile-management/index.md @@ -1,7 +1,7 @@ --- title: "How to Target Your Ideal Customer with User Profile Management?" date: "2023-02-22" -coverImage: "profile-mangemnt.jpg" +coverImage: "profile-mangemnt.webp" category: ["user experience", "ciam", "user management"] author: "Rakesh Soni" description: "Targeting the right audience isn’t a piece of cake. It requires much effort, detailed user insights from user profiles, and research to develop a plan to increase engagement. This blog uncovers the aspects of user profile management with CIAM and how businesses can navigate their success journey by targeting the right audience." @@ -87,5 +87,5 @@ Targeting your ideal customer is essential for any business looking to grow and By following these steps, companies can build lasting relationships with their customers and drive long-term success. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=finding-ideal-customer-user-profile-management) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=finding-ideal-customer-user-profile-management) diff --git a/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.jpg b/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.jpg deleted file mode 100644 index 133bb34e1..000000000 Binary files a/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.jpg and /dev/null differ diff --git a/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.webp b/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.webp new file mode 100644 index 000000000..b3f9a80b8 Binary files /dev/null and b/content/growth/finding-ideal-customer-user-profile-management/profile-mangemnt.webp differ diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/cta.png b/content/growth/flexible-work-culture-game-changer-for-employees/cta.png deleted file mode 100644 index 600361d60..000000000 Binary files a/content/growth/flexible-work-culture-game-changer-for-employees/cta.png and /dev/null differ diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/cta.webp b/content/growth/flexible-work-culture-game-changer-for-employees/cta.webp new file mode 100644 index 000000000..bf117ad57 Binary files /dev/null and b/content/growth/flexible-work-culture-game-changer-for-employees/cta.webp differ diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.jpg b/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.jpg deleted file mode 100644 index 9c1430dca..000000000 Binary files a/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.jpg and /dev/null differ diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.webp b/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.webp new file mode 100644 index 000000000..8818ee363 Binary files /dev/null and b/content/growth/flexible-work-culture-game-changer-for-employees/flexible-work-culture.webp differ diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/index.md b/content/growth/flexible-work-culture-game-changer-for-employees/index.md index 007ffecdc..bdb458e49 100644 --- a/content/growth/flexible-work-culture-game-changer-for-employees/index.md +++ b/content/growth/flexible-work-culture-game-changer-for-employees/index.md @@ -1,7 +1,7 @@ --- title: "Flexible Work Culture: A Game-Changer for LoginRadius and its Employees" date: "2023-07-13" -coverImage: "flexible-work-culture.jpg" +coverImage: "flexible-work-culture.webp" tags: ["flexible work culture","work life balance","LoginRadius"] author: "Azharuddin Mohammad" description: "At LoginRadius, we believe that good work comes from a healthy work-life balance. That's why we've created a flexible working environment that allows our employees to make the most of their time and energy while they're at work. But what does it mean to have a flexible work culture, anyway? Let's dig in." @@ -28,7 +28,7 @@ The combination of in-office and remote work at LoginRadius has successfully fos ## Daily Virtual Zumba Sessions: Shake, Sweat, and Smile! - + In addition to providing flexibility and autonomy, LoginRadius has taken employee well-being to another level by organizing daily virtual Zumba sessions. These fitness sessions are a testament to the company's commitment to fostering a healthy and vibrant work environment. The virtual Zumba sessions offer a fun and energetic outlet for us to stay active, destress, and recharge our minds. It's an opportunity to connect with colleagues virtually, share positive energy, and build camaraderie. @@ -38,7 +38,7 @@ LoginRadius TT League is an interdepartmental table tennis league that brings ou ## Celebrate You: Let's Party! - + LoginRadius understands the importance of celebrating milestones, recognizing achievements, and fostering a sense of community among its employees. To honor our hard work and create memorable experiences, LoginRadius organizes Celebrate You: Month End celebrations. These celebrations encompass a range of activities, including team-building exercises, recognition ceremonies, and engaging games. It's a time to come together as a team, celebrate our collective achievements, and forge deeper connections. @@ -52,4 +52,4 @@ As an [employee at LoginRadius](https://www.loginradius.com/careers/), I am grat Together, we are embracing the exciting future of flexible work at LoginRadius, where collaboration, well-being, and celebration go hand in hand. -[](https://www.loginradius.com/careers/) \ No newline at end of file +[](https://www.loginradius.com/careers/) \ No newline at end of file diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.jpg b/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.jpg deleted file mode 100644 index 6b47dff91..000000000 Binary files a/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.jpg and /dev/null differ diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.webp b/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.webp new file mode 100644 index 000000000..d6ddbc8e2 Binary files /dev/null and b/content/growth/flexible-work-culture-game-changer-for-employees/party-mode.webp differ diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.jpg b/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.jpg deleted file mode 100644 index 1efb1717f..000000000 Binary files a/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.jpg and /dev/null differ diff --git a/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.webp b/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.webp new file mode 100644 index 000000000..bf4fd645c Binary files /dev/null and b/content/growth/flexible-work-culture-game-changer-for-employees/zumba-sessions.webp differ diff --git a/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.png b/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.png deleted file mode 100644 index d036bd814..000000000 Binary files a/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.png and /dev/null differ diff --git a/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.webp b/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.webp new file mode 100644 index 000000000..d11016a0f Binary files /dev/null and b/content/growth/free-resources-that-you-might-not-have-heard-of/free-resources-150x150.webp differ diff --git a/content/growth/free-resources-that-you-might-not-have-heard-of/index.md b/content/growth/free-resources-that-you-might-not-have-heard-of/index.md index 4c8989b02..413e76243 100644 --- a/content/growth/free-resources-that-you-might-not-have-heard-of/index.md +++ b/content/growth/free-resources-that-you-might-not-have-heard-of/index.md @@ -1,7 +1,7 @@ --- title: "Free Resources That You Might Not Have Heard Of" date: "2017-01-23" -coverImage: "free-resources-150x150.png" +coverImage: "free-resources-150x150.webp" tags: ["resources","article","cx"] author: "Rakesh Soni" description: "It is said that every good thing comes with a price tag attached. Well, looks like this is not applicable to all good things. The articles lists down some useful free resources you might not have heard of." @@ -31,4 +31,4 @@ Here are some things which are not that popular but are worth trying at least on So here are my favorite free resources that make my everyday life easier! Have you tried these? Or do you know about any other free resources that can make my job easier, would love to know in the comments below! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=free-resources-that-you-might-not-have-heard-of) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=free-resources-that-you-might-not-have-heard-of) \ No newline at end of file diff --git a/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.png b/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.png deleted file mode 100644 index a3580f13e..000000000 Binary files a/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.png and /dev/null differ diff --git a/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.webp b/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.webp new file mode 100644 index 000000000..0257eff22 Binary files /dev/null and b/content/growth/future-customer-authentication-market-needs/DS-Mob-Bio-Auth.webp differ diff --git a/content/growth/future-customer-authentication-market-needs/auth-future.jpg b/content/growth/future-customer-authentication-market-needs/auth-future.jpg deleted file mode 100644 index c16da3515..000000000 Binary files a/content/growth/future-customer-authentication-market-needs/auth-future.jpg and /dev/null differ diff --git a/content/growth/future-customer-authentication-market-needs/auth-future.webp b/content/growth/future-customer-authentication-market-needs/auth-future.webp new file mode 100644 index 000000000..c2cf5208f Binary files /dev/null and b/content/growth/future-customer-authentication-market-needs/auth-future.webp differ diff --git a/content/growth/future-customer-authentication-market-needs/bio-auth.png b/content/growth/future-customer-authentication-market-needs/bio-auth.png deleted file mode 100644 index 69293181d..000000000 Binary files a/content/growth/future-customer-authentication-market-needs/bio-auth.png and /dev/null differ diff --git a/content/growth/future-customer-authentication-market-needs/bio-auth.webp b/content/growth/future-customer-authentication-market-needs/bio-auth.webp new file mode 100644 index 000000000..b272f8563 Binary files /dev/null and b/content/growth/future-customer-authentication-market-needs/bio-auth.webp differ diff --git a/content/growth/future-customer-authentication-market-needs/index.md b/content/growth/future-customer-authentication-market-needs/index.md index 95fadb4de..6240a260a 100644 --- a/content/growth/future-customer-authentication-market-needs/index.md +++ b/content/growth/future-customer-authentication-market-needs/index.md @@ -1,7 +1,7 @@ --- title: "Customer Authentication: Unfolding The Market Needs Of The Future" date: "2022-01-06" -coverImage: "auth-future.jpg" +coverImage: "auth-future.webp" tags: ["data security","biometric authentication","mfa","cx"] author: "Navanita Devi" description: "Consumer authentication is getting more challenging than ever. Learn how the biggest brands in the world are innovating their way through the disruption that's already underway, and get the tactics you need to deliver a seamless experience to your customers." @@ -47,7 +47,7 @@ Here’s how you can implement biometric authentication into your system: * **Voice recognition:** The vocal input, analog data are taken in and converted into digital data. The comparator checks the stored patterns with the output of the A/D converter to confirm the authentication. * **Face recognition:** The captured face image details like alignment, size, and shape of the face are analysed and processed with deep learning techniques. -[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet) +[](https://www.loginradius.com/resource/mobile-biometric-authentication-datasheet) ### 3. Behavioural biometrics authentication @@ -78,5 +78,5 @@ As another customer authentication future trend, cloud-based authentication uses Organizations need to enlarge and modify their capabilities to take control of security more efficiently in this new environment. Identity platforms like [LoginRadius](https://www.loginradius.com/) provide customer registration, SSO, MFA, directory services, user management, and data access governance to help companies achieve top-notch for their consumers. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-customer-authentication-market-needs) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-customer-authentication-market-needs) diff --git a/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.png b/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.png and /dev/null differ diff --git a/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.webp b/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/growth/future-of-authentication-service-market/Buyers-Guide-to-Multi-Factor-Authentication.webp differ diff --git a/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.png b/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.png deleted file mode 100644 index 61deb3295..000000000 Binary files a/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.png and /dev/null differ diff --git a/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.webp b/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.webp new file mode 100644 index 000000000..00c5933a4 Binary files /dev/null and b/content/growth/future-of-authentication-service-market/EB-GD-to-MFA.webp differ diff --git a/content/growth/future-of-authentication-service-market/future-of-authentication-market.jpg b/content/growth/future-of-authentication-service-market/future-of-authentication-market.jpg deleted file mode 100644 index 22b49f0c6..000000000 Binary files a/content/growth/future-of-authentication-service-market/future-of-authentication-market.jpg and /dev/null differ diff --git a/content/growth/future-of-authentication-service-market/future-of-authentication-market.webp b/content/growth/future-of-authentication-service-market/future-of-authentication-market.webp new file mode 100644 index 000000000..1e3600801 Binary files /dev/null and b/content/growth/future-of-authentication-service-market/future-of-authentication-market.webp differ diff --git a/content/growth/future-of-authentication-service-market/index.md b/content/growth/future-of-authentication-service-market/index.md index e3fb0c201..b88d61d1e 100644 --- a/content/growth/future-of-authentication-service-market/index.md +++ b/content/growth/future-of-authentication-service-market/index.md @@ -1,7 +1,7 @@ --- title: "How Does the Future Look Like for the Authentication Services Market?" date: "2021-09-02" -coverImage: "future-of-authentication-market.jpg" +coverImage: "future-of-authentication-market.webp" tags: ["data security","authentication","mfa","cybersecurity"] author: "Rakesh Soni" description: "Authentication services have a lot to offer every sector possible, from healthcare to even defense. It is essentially the future of login security and will play an important role in reducing ransomware attacks." @@ -31,7 +31,7 @@ The analysis of the authentication services market takes place after segmenting - Geography: The analysis of the adoption and growth of the market from a geographical standpoint. For example, what does the market look like on different continents or a specific region? These include regions like North America, Europe, Asia-Pacific, Latin America, Middle East and Africa. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) By analysing the market through different segments, it becomes possible to obtain a better understanding of the digital identity trends. @@ -74,5 +74,5 @@ According to analysis, from a geographical standpoint, North America will be the Therefore, authentication services have a lot to offer every sector possible, from healthcare to even defense. It is essentially the future of login security and will play an important role in reducing ransomware attacks. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-of-authentication-service-market) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=future-of-authentication-service-market) diff --git a/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.png b/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.png and /dev/null differ diff --git a/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.webp b/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/growth/good-transaction-security/Buyers-Guide-to-Multi-Factor-Authentication.webp differ diff --git a/content/growth/good-transaction-security/EB-GD-to-MFA.png b/content/growth/good-transaction-security/EB-GD-to-MFA.png deleted file mode 100644 index 61deb3295..000000000 Binary files a/content/growth/good-transaction-security/EB-GD-to-MFA.png and /dev/null differ diff --git a/content/growth/good-transaction-security/EB-GD-to-MFA.webp b/content/growth/good-transaction-security/EB-GD-to-MFA.webp new file mode 100644 index 000000000..00c5933a4 Binary files /dev/null and b/content/growth/good-transaction-security/EB-GD-to-MFA.webp differ diff --git a/content/growth/good-transaction-security/index.md b/content/growth/good-transaction-security/index.md index d99cfcfc0..b138078db 100644 --- a/content/growth/good-transaction-security/index.md +++ b/content/growth/good-transaction-security/index.md @@ -1,7 +1,7 @@ --- title: "How Good Transaction Security Ensures Smooth Consumer Visits" date: "2021-09-07" -coverImage: "smooth-transaction-security-with-loginradius.jpg" +coverImage: "smooth-transaction-security-with-loginradius.webp" tags: ["ciam solution","compliance","data security"] author: "Vishal Sharma" description: "The sudden increase in the number of transaction-related security breaches is undeniably pointing towards the need for a robust security mechanism that can build consumer trust. This post uncovers the role of secure transactions and how businesses can ensure smooth consumer visits." @@ -118,7 +118,7 @@ Data security and privacy are ensured through a built-in web application firewal RBA goes beyond a static list of rules and adapts to ask consumers for the types of verification that best suit a user session. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) LoginRadius incorporates the following additional factors to its RBA solutions: @@ -154,4 +154,4 @@ Good transaction security coupled with a great user experience is the key to onl Businesses can leverage the true potential of a robust CIAM solution like LoginRadius to secure their transactions without hampering user experience to get a competitive advantage in terms of smooth consumer visits. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=good-transaction-security) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=good-transaction-security) \ No newline at end of file diff --git a/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.jpg b/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.jpg deleted file mode 100644 index 9fd09c60a..000000000 Binary files a/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.jpg and /dev/null differ diff --git a/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.webp b/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.webp new file mode 100644 index 000000000..9a0aa4878 Binary files /dev/null and b/content/growth/good-transaction-security/smooth-transaction-security-with-loginradius.webp differ diff --git a/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.jpg b/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.jpg deleted file mode 100644 index 19bedb4de..000000000 Binary files a/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.jpg and /dev/null differ diff --git a/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.webp b/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.webp new file mode 100644 index 000000000..ea592302d Binary files /dev/null and b/content/growth/google-keep-tips-for-productivity/How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.webp differ diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.png b/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.png deleted file mode 100644 index 1b5b130e1..000000000 Binary files a/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.png and /dev/null differ diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.webp b/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.webp new file mode 100644 index 000000000..f0f286c26 Binary files /dev/null and b/content/growth/google-keep-tips-for-productivity/Keep-Notes-in-Checklist.webp differ diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.png b/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.png deleted file mode 100644 index c6b0e25f6..000000000 Binary files a/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.png and /dev/null differ diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.webp b/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.webp new file mode 100644 index 000000000..f50f330d5 Binary files /dev/null and b/content/growth/google-keep-tips-for-productivity/Keep-Pinned-Note.webp differ diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.png b/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.png deleted file mode 100644 index d9dccd99b..000000000 Binary files a/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.png and /dev/null differ diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.webp b/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.webp new file mode 100644 index 000000000..0d5c02ead Binary files /dev/null and b/content/growth/google-keep-tips-for-productivity/Keep-Voice-Note.webp differ diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.png b/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.png deleted file mode 100644 index 4cf6bb13d..000000000 Binary files a/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.png and /dev/null differ diff --git a/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.webp b/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.webp new file mode 100644 index 000000000..7b4635aa7 Binary files /dev/null and b/content/growth/google-keep-tips-for-productivity/Keep-Widget-Android.webp differ diff --git a/content/growth/google-keep-tips-for-productivity/index.md b/content/growth/google-keep-tips-for-productivity/index.md index 08edde2f5..41a9a6ac7 100644 --- a/content/growth/google-keep-tips-for-productivity/index.md +++ b/content/growth/google-keep-tips-for-productivity/index.md @@ -1,7 +1,7 @@ --- title: "How To Insert Keep Notes in Doc Plus other Keep Tips For Better Productivity" date: "2017-03-06" -coverImage: "How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.jpg" +coverImage: "How-To-Insert-Keep-notes-in-Doc-Plus-other-Keep-tips-For-Better-Productivity.webp" category: ["general", "technology", "loginradius"] featured: false author: "Rakesh Soni" @@ -44,7 +44,7 @@ Using Keep for multiple things like homework or some event? Create Labels and ad ### **4\. Add Keep widget in your phone.** - + Add your desired keep note to the home screen of your Android using the Keep widget. You can choose which note you want to display. Using the widget you can also add a note or an image and view the existing notes. For me, the Keep widget is a great way to remind myself about the important tasks I have. @@ -56,7 +56,7 @@ Saw an awesome DIY bottle and want to make it too? Just save it to Keep by openi ### **6\. Voice Notes** - + You can also add voice notes if you don’t want to type the notes! @@ -76,13 +76,13 @@ Just like Google Docs, you can also share your keep notes with your team and fri ### **9\. Make a checklist!** - + Add checkpoints to your tasks and mark them check when you are done. The checked points move down to the list.. \[Though you can change that in settings\] ### **10\. Add a pinned note** - + Want to keep a note always at top? Pin it. diff --git a/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.png b/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.png deleted file mode 100644 index 404532996..000000000 Binary files a/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.png and /dev/null differ diff --git a/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.webp b/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.webp new file mode 100644 index 000000000..832cb0156 Binary files /dev/null and b/content/growth/grow-business-with-right-identity-strategy/WP-zero-trust-1.webp differ diff --git a/content/growth/grow-business-with-right-identity-strategy/id-strategy.jpg b/content/growth/grow-business-with-right-identity-strategy/id-strategy.jpg deleted file mode 100644 index a7f6977ec..000000000 Binary files a/content/growth/grow-business-with-right-identity-strategy/id-strategy.jpg and /dev/null differ diff --git a/content/growth/grow-business-with-right-identity-strategy/id-strategy.webp b/content/growth/grow-business-with-right-identity-strategy/id-strategy.webp new file mode 100644 index 000000000..51b1b315c Binary files /dev/null and b/content/growth/grow-business-with-right-identity-strategy/id-strategy.webp differ diff --git a/content/growth/grow-business-with-right-identity-strategy/index.md b/content/growth/grow-business-with-right-identity-strategy/index.md index b7a8a953e..b385992e3 100644 --- a/content/growth/grow-business-with-right-identity-strategy/index.md +++ b/content/growth/grow-business-with-right-identity-strategy/index.md @@ -1,7 +1,7 @@ --- title: "How Implementing the Right Identity Strategy Can Grow Your Business?" date: "2022-04-07" -coverImage: "id-strategy.jpg" +coverImage: "id-strategy.webp" tags: ["consumer iam solution","digital identity management","cx"] author: "Rakesh Soni" description: "The right identity strategy can help businesses stay up and running even in challenging situations since enterprises can rely on valuable consumer insights, including their preferences, behavior, and purchase trends. Let’s understand the role of identity management and how a good strategy for managing consumer identities can help businesses excel in growth." @@ -67,7 +67,7 @@ Here’s how LoginRadius manages security and usability: * **Safeguard sensitive data:** Our modern cloud infrastructure is protected to the highest industry standards. LoginRadius maintains all major security compliances for our application and data storage. * **Manage consumer consent:** Stay current on regulations for acquiring consumer consent, data collection and use, age verification, and site access. Give consumers transparency into the consent process to demonstrate good faith. -[](https://www.loginradius.com/resource/zero-trust-security/) +[](https://www.loginradius.com/resource/zero-trust-security/) Hence, businesses must understand the importance of a modern CIAM solution like LoginRadius and consider incorporating it into their identity strategy. @@ -79,4 +79,4 @@ By implementing the benefits of the LoginRadius CIAM as a unified solution, you Need more information about how [LoginRadius CIAM benefits](https://www.loginradius.com/blog/identity/loginradius-private-cloud-ciam-benefits/) your business? Reach us for a free personalized demo. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=grow-business-with-right-identity-strategy) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=grow-business-with-right-identity-strategy) \ No newline at end of file diff --git a/content/growth/grow-business-with-right-identity-strategy/zero-trust1.png b/content/growth/grow-business-with-right-identity-strategy/zero-trust1.png deleted file mode 100644 index 3e6b81ee6..000000000 Binary files a/content/growth/grow-business-with-right-identity-strategy/zero-trust1.png and /dev/null differ diff --git a/content/growth/grow-business-with-right-identity-strategy/zero-trust1.webp b/content/growth/grow-business-with-right-identity-strategy/zero-trust1.webp new file mode 100644 index 000000000..2f7c01062 Binary files /dev/null and b/content/growth/grow-business-with-right-identity-strategy/zero-trust1.webp differ diff --git a/content/growth/happy-12th-birthday-loginradius/WP-ai.png b/content/growth/happy-12th-birthday-loginradius/WP-ai.png deleted file mode 100644 index 1116bcde5..000000000 Binary files a/content/growth/happy-12th-birthday-loginradius/WP-ai.png and /dev/null differ diff --git a/content/growth/happy-12th-birthday-loginradius/WP-ai.webp b/content/growth/happy-12th-birthday-loginradius/WP-ai.webp new file mode 100644 index 000000000..8efa78c3e Binary files /dev/null and b/content/growth/happy-12th-birthday-loginradius/WP-ai.webp differ diff --git a/content/growth/happy-12th-birthday-loginradius/bday-cover.jpg b/content/growth/happy-12th-birthday-loginradius/bday-cover.jpg deleted file mode 100644 index 04224745f..000000000 Binary files a/content/growth/happy-12th-birthday-loginradius/bday-cover.jpg and /dev/null differ diff --git a/content/growth/happy-12th-birthday-loginradius/bday-cover.webp b/content/growth/happy-12th-birthday-loginradius/bday-cover.webp new file mode 100644 index 000000000..7dbcb01a6 Binary files /dev/null and b/content/growth/happy-12th-birthday-loginradius/bday-cover.webp differ diff --git a/content/growth/happy-12th-birthday-loginradius/cta.png b/content/growth/happy-12th-birthday-loginradius/cta.png deleted file mode 100644 index 600361d60..000000000 Binary files a/content/growth/happy-12th-birthday-loginradius/cta.png and /dev/null differ diff --git a/content/growth/happy-12th-birthday-loginradius/cta.webp b/content/growth/happy-12th-birthday-loginradius/cta.webp new file mode 100644 index 000000000..bf117ad57 Binary files /dev/null and b/content/growth/happy-12th-birthday-loginradius/cta.webp differ diff --git a/content/growth/happy-12th-birthday-loginradius/index.md b/content/growth/happy-12th-birthday-loginradius/index.md index 51893244a..81b5361dd 100644 --- a/content/growth/happy-12th-birthday-loginradius/index.md +++ b/content/growth/happy-12th-birthday-loginradius/index.md @@ -1,7 +1,7 @@ --- title: "Happy Birthday, LoginRadius: One Year Away from the Big Teen Milestone!" date: "2024-07-20" -coverImage: "bday-cover.jpg" +coverImage: "bday-cover.webp" tags: ["LoginRadius birthday"] author: "Rakesh Soni" description: "As LoginRadius celebrates its 12th anniversary, we reflect on a year filled with significant milestones and innovations. From groundbreaking features like Push Notification MFA and Passkeys to impactful CSR initiatives, we continue to set new standards in digital identity and social responsibility. Join us in celebrating our journey, and looking forward to an exciting future." @@ -76,7 +76,7 @@ We are committed to staying ahead of the curve, leveraging cutting-edge technolo Our goal is to make digital identities even more secure, user-friendly, and efficient, empowering businesses to thrive in the digital age through the advancement of AI. -[](https://www.loginradius.com/resource/whitepaper/how-ai-change-iam-initiatives/) +[](https://www.loginradius.com/resource/whitepaper/how-ai-change-iam-initiatives/) ## Gratitude and Reflection: A Heartfelt Thank You @@ -108,4 +108,4 @@ As we celebrate our 12th birthday, we not only look back at our achievements but Here’s to many more years of innovation, growth, and success. Happy Birthday, LoginRadius! -[](https://www.loginradius.com/careers/) \ No newline at end of file +[](https://www.loginradius.com/careers/) \ No newline at end of file diff --git a/content/growth/happy-birthday-loginradius/CEO-Rakesh.jpg b/content/growth/happy-birthday-loginradius/CEO-Rakesh.jpg deleted file mode 100644 index 12288c73e..000000000 Binary files a/content/growth/happy-birthday-loginradius/CEO-Rakesh.jpg and /dev/null differ diff --git a/content/growth/happy-birthday-loginradius/CEO-Rakesh.webp b/content/growth/happy-birthday-loginradius/CEO-Rakesh.webp new file mode 100644 index 000000000..b4c92de04 Binary files /dev/null and b/content/growth/happy-birthday-loginradius/CEO-Rakesh.webp differ diff --git a/content/growth/happy-birthday-loginradius/LR-birthday.jpg b/content/growth/happy-birthday-loginradius/LR-birthday.jpg deleted file mode 100644 index 704136e4a..000000000 Binary files a/content/growth/happy-birthday-loginradius/LR-birthday.jpg and /dev/null differ diff --git a/content/growth/happy-birthday-loginradius/LR-birthday.webp b/content/growth/happy-birthday-loginradius/LR-birthday.webp new file mode 100644 index 000000000..d509d0431 Binary files /dev/null and b/content/growth/happy-birthday-loginradius/LR-birthday.webp differ diff --git a/content/growth/happy-birthday-loginradius/cta.png b/content/growth/happy-birthday-loginradius/cta.png deleted file mode 100644 index 600361d60..000000000 Binary files a/content/growth/happy-birthday-loginradius/cta.png and /dev/null differ diff --git a/content/growth/happy-birthday-loginradius/cta.webp b/content/growth/happy-birthday-loginradius/cta.webp new file mode 100644 index 000000000..bf117ad57 Binary files /dev/null and b/content/growth/happy-birthday-loginradius/cta.webp differ diff --git a/content/growth/happy-birthday-loginradius/index.md b/content/growth/happy-birthday-loginradius/index.md index 200bb2a05..f3f085b04 100644 --- a/content/growth/happy-birthday-loginradius/index.md +++ b/content/growth/happy-birthday-loginradius/index.md @@ -1,7 +1,7 @@ --- title: "Happy Birthday, LoginRadius: Two Years Away From Becoming A Teenager" date: "2023-07-24" -coverImage: "LR-birthday.jpg" +coverImage: "LR-birthday.webp" tags: ["LoginRadius birthday"] author: "Rakesh Soni" description: "I still vividly remember the day when I incorporated the company on July 20, 2012. At that time, all we had was an idea—an idea to solve the login problem for billions of internet users. As we approach our 11th birthday, I can't help but feel a little nostalgic." @@ -12,7 +12,7 @@ metatitle: "LoginRadius Turns 11: 2 Years Away From Becoming A Teenager" I’m struck by the profound similarity between our journey as founders and the experience of raising a child. Just like parents nurture and care for their baby, we have poured our hearts and souls into building and nurturing LoginRadius. - + Throughout this incredible journey, I have experienced a whirlwind of emotions—pride, joy, worry, and excitement. We have celebrated together during moments of triumph, persevered through challenging times, and shared in the deep sense of pride that comes with witnessing the growth and accomplishments of LoginRadius. @@ -72,4 +72,4 @@ When all these pieces are tied together, I am filled with excitement about Login Have a great week! -[](https://www.loginradius.com/careers/) +[](https://www.loginradius.com/careers/) diff --git a/content/growth/high-performing-growth-team/growth-team.jpg b/content/growth/high-performing-growth-team/growth-team.jpg deleted file mode 100644 index 885e47bc4..000000000 Binary files a/content/growth/high-performing-growth-team/growth-team.jpg and /dev/null differ diff --git a/content/growth/high-performing-growth-team/growth-team.webp b/content/growth/high-performing-growth-team/growth-team.webp new file mode 100644 index 000000000..70da87f76 Binary files /dev/null and b/content/growth/high-performing-growth-team/growth-team.webp differ diff --git a/content/growth/high-performing-growth-team/index.md b/content/growth/high-performing-growth-team/index.md index 2afc48547..56c12e2b2 100644 --- a/content/growth/high-performing-growth-team/index.md +++ b/content/growth/high-performing-growth-team/index.md @@ -1,7 +1,7 @@ --- title: "5 Steps to Build a High Performing Growth Team in 2021" date: "2021-02-23" -coverImage: "growth-team.jpg" +coverImage: "growth-team.webp" category: ["all"] featured: false author: "Rakesh Soni" @@ -144,4 +144,4 @@ The importance of growth teams is more than the startup founders assume, and the Whether you are a business firm, one of many portfolio corporations, a startup, or a small enterprise, you need to concentrate on creating a professional growth team if your product has already hit the market. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=high-performing-growth-team) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=high-performing-growth-team) diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.png b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.png deleted file mode 100644 index 4926b2aaf..000000000 Binary files a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.png and /dev/null differ diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.webp b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.webp new file mode 100644 index 000000000..d4581b1bd Binary files /dev/null and b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/WP-Credential-stuffing.webp differ diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.jpg b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.jpg deleted file mode 100644 index 1d1476ae2..000000000 Binary files a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.jpg and /dev/null differ diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.webp b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.webp new file mode 100644 index 000000000..b696f8c3a Binary files /dev/null and b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/ciso-cover-image.webp differ diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.png b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.png deleted file mode 100644 index 904e3a28e..000000000 Binary files a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.png and /dev/null differ diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.webp b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.webp new file mode 100644 index 000000000..c2d6821c3 Binary files /dev/null and b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/credential-stuffing.webp differ diff --git a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/index.md b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/index.md index 63042621d..ead969a58 100644 --- a/content/growth/how-CISO-can-improve-collaboration-on-security-risks/index.md +++ b/content/growth/how-CISO-can-improve-collaboration-on-security-risks/index.md @@ -1,7 +1,7 @@ --- title: "How CISOs Can Improve Collaboration on Security Risks" date: "2021-09-27" -coverImage: "ciso-cover-image.jpg" +coverImage: "ciso-cover-image.webp" tags: ["data security","cybersecurity","cx"] author: "Shivangini Yadav" description: "It no longer makes sense to think of security as a single system, because there are so many different layers, and so many different points of entry. This blog explains how CISOs can respond to these multivalent threats across an organization." @@ -55,7 +55,7 @@ Effective CISOs are those that encourage their team to share their skills with t Finally, make sure you are using the technology available to you in order to share information and insight across all the teams in your organization. A comprehensive security incident and event management (SIEM) can greatly improve network visibility, but also allow you to share real-time, actionable insights with teams that may be opening themselves up to attack. -[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper) +[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper) And, over time, it’s possible to leverage the power of big data to pull the insights drawn from your SIEM into a holistic picture of cybersecurity across your organization. By tracking the types of threats that you are exposed to, and their relative success, you can begin to plan a cybersecurity strategy that reduces your future vulnerability. @@ -65,4 +65,4 @@ Ultimately, collaboration is a necessary part of the contemporary business envir Building collaborative ways of working is not a quick process, but it can be done. And just as we’ve seen the evolutionary development of cyber security over the past few years, now we are witnessing the evolution of the business environment itself. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciso-can-improve-collaboration-on-security-risks) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciso-can-improve-collaboration-on-security-risks) \ No newline at end of file diff --git a/content/growth/how-businesses-approach-customer-security/EB-omnichannel.png b/content/growth/how-businesses-approach-customer-security/EB-omnichannel.png deleted file mode 100644 index f5fa0b0f9..000000000 Binary files a/content/growth/how-businesses-approach-customer-security/EB-omnichannel.png and /dev/null differ diff --git a/content/growth/how-businesses-approach-customer-security/EB-omnichannel.webp b/content/growth/how-businesses-approach-customer-security/EB-omnichannel.webp new file mode 100644 index 000000000..b0761321e Binary files /dev/null and b/content/growth/how-businesses-approach-customer-security/EB-omnichannel.webp differ diff --git a/content/growth/how-businesses-approach-customer-security/growth-comp.jpg b/content/growth/how-businesses-approach-customer-security/growth-comp.jpg deleted file mode 100644 index 2f17dd28c..000000000 Binary files a/content/growth/how-businesses-approach-customer-security/growth-comp.jpg and /dev/null differ diff --git a/content/growth/how-businesses-approach-customer-security/growth-comp.webp b/content/growth/how-businesses-approach-customer-security/growth-comp.webp new file mode 100644 index 000000000..066bd3880 Binary files /dev/null and b/content/growth/how-businesses-approach-customer-security/growth-comp.webp differ diff --git a/content/growth/how-businesses-approach-customer-security/index.md b/content/growth/how-businesses-approach-customer-security/index.md index 062a84968..4dc906b5c 100644 --- a/content/growth/how-businesses-approach-customer-security/index.md +++ b/content/growth/how-businesses-approach-customer-security/index.md @@ -1,7 +1,7 @@ --- title: "How Should Growth-Minded Enterprises Approach Customer Security?" date: "2022-04-22" -coverImage: "growth-comp.jpg" +coverImage: "growth-comp.webp" tags: ["data security", "compliance", "ciam", "customer experience"] author: "Rakesh Soni" description: "Customer security is crucial for any business striving to stay ahead of the competition. However, balancing customer security with a rich consumer experience is what it all takes to propel growth. Learn the aspects of a robust CIAM solution and how it helps businesses stay ahead of their competitors." @@ -54,7 +54,7 @@ An omnichannel consumer experience refers to seamless interaction across multipl For example, it is omnichannel when marketing, sales, consumer support, and even in-store experiences are synced up so users can seamlessly switch channels and make the purchase. -[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) +[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) ### #2. Single consumer view @@ -92,4 +92,4 @@ Hence, the critical role of a CIAM solution in enhancing customer security and i Businesses need to invoke the potential of a reliable CIAM like LoginRadius to ensure they get perfect harmony of user experience and security. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-businesses-approach-customer-security) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-businesses-approach-customer-security) \ No newline at end of file diff --git a/content/growth/how-businesses-approach-customer-security/omnichannel-eb.png b/content/growth/how-businesses-approach-customer-security/omnichannel-eb.png deleted file mode 100644 index 86c15a159..000000000 Binary files a/content/growth/how-businesses-approach-customer-security/omnichannel-eb.png and /dev/null differ diff --git a/content/growth/how-businesses-approach-customer-security/omnichannel-eb.webp b/content/growth/how-businesses-approach-customer-security/omnichannel-eb.webp new file mode 100644 index 000000000..025782e92 Binary files /dev/null and b/content/growth/how-businesses-approach-customer-security/omnichannel-eb.webp differ diff --git a/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.png b/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.png deleted file mode 100644 index fc6f98c05..000000000 Binary files a/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.png and /dev/null differ diff --git a/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.webp b/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.webp new file mode 100644 index 000000000..c60f3551f Binary files /dev/null and b/content/growth/how-ciam-and-crm-integration-optimize-cx/DS-user-management.webp differ diff --git a/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.jpg b/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.jpg deleted file mode 100644 index 1a4bc9e0f..000000000 Binary files a/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.jpg and /dev/null differ diff --git a/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.webp b/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.webp new file mode 100644 index 000000000..a3cfef024 Binary files /dev/null and b/content/growth/how-ciam-and-crm-integration-optimize-cx/customer-experience.webp differ diff --git a/content/growth/how-ciam-and-crm-integration-optimize-cx/index.md b/content/growth/how-ciam-and-crm-integration-optimize-cx/index.md index b92d6dfee..0e4ed7c41 100644 --- a/content/growth/how-ciam-and-crm-integration-optimize-cx/index.md +++ b/content/growth/how-ciam-and-crm-integration-optimize-cx/index.md @@ -1,7 +1,7 @@ --- title: "Customer-Centric Strategies: How CIAM and CRM Integration Optimize Consumer Experience" date: "2023-08-28" -coverImage: "customer-experience.jpg" +coverImage: "customer-experience.webp" tags: ["ciam solutions","user management","cx"] author: "King Conrad Fanoga" description: "Any successful business knows that an excellent customer experience is essential; thus, a customer's needs and expectations are of utmost priority. Learn how to optimize your consumer experiences and boost customer-centric strategies." @@ -76,7 +76,7 @@ Facilitate collaborative synergy among IT, marketing, and customer service teams Utilize customer insights and feedback to adjust and optimize your CIAM and CRM strategies continuously. You should also be mindful of the evolving customer preferences and behaviors and be proactive in keeping your approach relative. -[](https://www.loginradius.com/resource/loginradius-ciam-user-management/) +[](https://www.loginradius.com/resource/loginradius-ciam-user-management/) ### 4. Harnessing Emerging Technologies for Elevated Experiences @@ -100,4 +100,4 @@ In conclusion, customer-centric strategies are essential for your business or an The future holds exciting potential for CIAM and CRM integration. As digital innovations continue to appear, your company should embrace them or, better else, pioneer them. Consistently deliver excellent value and exceptional customer service. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciam-and-crm-integration-optimize-cx) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciam-and-crm-integration-optimize-cx) diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.png b/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.png deleted file mode 100644 index a49793446..000000000 Binary files a/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.png and /dev/null differ diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.webp b/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.webp new file mode 100644 index 000000000..f5170c511 Binary files /dev/null and b/content/growth/how-ciam-can-resolve-retail-industry-challenges/WP-omnichannel-retail.webp differ diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/index.md b/content/growth/how-ciam-can-resolve-retail-industry-challenges/index.md index 5cd82098a..c4ba49808 100644 --- a/content/growth/how-ciam-can-resolve-retail-industry-challenges/index.md +++ b/content/growth/how-ciam-can-resolve-retail-industry-challenges/index.md @@ -1,7 +1,7 @@ --- title: "5 Key CIAM Benefits and Challenges in the Retail Industry" date: "2021-09-17" -coverImage: "retail-industry.jpg" +coverImage: "retail-industry.webp" tags: ["mfa","ciam provider","user experience","cx"] author: "Navanita Devi" description: "The modern retail industry has several challenges that can be solved by deploying a CIAM solution. Read this blog to learn how CIAM goes beyond just streamlining a platform to make it more intuitive, and how it boosts the marketing and sales efforts of a business in the retail industry." @@ -39,7 +39,7 @@ It has been established that an [effective marketing strategy](https://www.login Another challenging aspect that online platforms face is the problem of personalization. Personalization, if executed properly, can urge the customer to make several purchases at a time and keep them coming back for more. In other words, it can improve the loyalty of the customer. However, this requires the platform to get to know the customer and their wants and needs, which is difficult. -[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience) +[](https://www.loginradius.com/resource/omnichannel-retailer-customer-experience) ## 5 Benefits of Implementing CIAM for E-commerce Platforms @@ -119,4 +119,4 @@ The critical issues in retailing are fluid platform experience for seamless cust Retail marketing faces challenges such as reaching customers across multiple platforms, managing data silos, and the need for personalized strategies to enhance customer loyalty. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciam-can-resolve-retail-industry-challenges) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-ciam-can-resolve-retail-industry-challenges) diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.jpg b/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.jpg deleted file mode 100644 index 17940ab41..000000000 Binary files a/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.jpg and /dev/null differ diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.webp b/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.webp new file mode 100644 index 000000000..39f6da380 Binary files /dev/null and b/content/growth/how-ciam-can-resolve-retail-industry-challenges/omnichannel-retailer-whitepaper.webp differ diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.jpg b/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.jpg deleted file mode 100644 index 551d54c39..000000000 Binary files a/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.jpg and /dev/null differ diff --git a/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.webp b/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.webp new file mode 100644 index 000000000..5a140a73c Binary files /dev/null and b/content/growth/how-ciam-can-resolve-retail-industry-challenges/retail-industry.webp differ diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.jpg b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.jpg deleted file mode 100644 index 28a77df29..000000000 Binary files a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.jpg and /dev/null differ diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.webp b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.webp new file mode 100644 index 000000000..9548b267e Binary files /dev/null and b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-identity.webp differ diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.png b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.png deleted file mode 100644 index 4c933839b..000000000 Binary files a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.png and /dev/null differ diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.webp b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.webp new file mode 100644 index 000000000..bce6534de Binary files /dev/null and b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability.webp differ diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.png b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.png deleted file mode 100644 index bd559ec47..000000000 Binary files a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.png and /dev/null differ diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.webp b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.webp new file mode 100644 index 000000000..b3f1a625f Binary files /dev/null and b/content/growth/how-consumer-identity-influence-brand-recognizability/brand-recognizability2.webp differ diff --git a/content/growth/how-consumer-identity-influence-brand-recognizability/index.md b/content/growth/how-consumer-identity-influence-brand-recognizability/index.md index 4d0be0bff..86a97aa1c 100644 --- a/content/growth/how-consumer-identity-influence-brand-recognizability/index.md +++ b/content/growth/how-consumer-identity-influence-brand-recognizability/index.md @@ -1,7 +1,7 @@ --- title: "How Consumer Identity Influence Brand Recognizability" date: "2021-08-31" -coverImage: "brand-identity.jpg" +coverImage: "brand-identity.webp" category: ["loginradius"] featured: false author: "Conrad Sturdy" @@ -17,7 +17,7 @@ Brand recognizability depends on various aspects, and consumer identity is one o Let’s explore more about how people's self-perception influences brand choice and the types of consumer identities for you to consider. - + Image Source: Live Inspired Mag @@ -41,7 +41,7 @@ The things we buy help us to better express who we are. Sounds fantastic, isn’ Consumers try to express their internal feelings with external means such as brands. We can conclude that purchase is the form of self-expression, and brand is the symbol of our inner self. - + Image Source: XO @@ -83,4 +83,4 @@ Emotions mean a lot to many of us, but the emotion-oriented type of consumers fi Now you understand the concept of [brand recognizability](https://www.loginradius.com/blog/growth/does-your-website-imagery-reflect-your-brand-identity/) and its bounds with customer identity. We explored four types of consumer identities you should pay attention to and defined their main preferences. Brand recognizability is based on the self-perceptions of potential consumers, and you should target their self-concepts properly. These findings can help you build stronger connections with consumers and increase your brand's success. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-consumer-identity-influence-brand-recognizability) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-consumer-identity-influence-brand-recognizability) diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.png b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.png deleted file mode 100644 index 86c15a159..000000000 Binary files a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.png and /dev/null differ diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.webp b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.webp new file mode 100644 index 000000000..025782e92 Binary files /dev/null and b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel-cx.webp differ diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.png b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.png deleted file mode 100644 index f5fa0b0f9..000000000 Binary files a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.png and /dev/null differ diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.webp b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.webp new file mode 100644 index 000000000..b0761321e Binary files /dev/null and b/content/growth/how-digital-identity-unlock-success-in-retail/EB-omnichannel.webp differ diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.jpg b/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.jpg deleted file mode 100644 index 4d94cd8d8..000000000 Binary files a/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.jpg and /dev/null differ diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.webp b/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.webp new file mode 100644 index 000000000..d5d6f33b3 Binary files /dev/null and b/content/growth/how-digital-identity-unlock-success-in-retail/dig-identity-retail.webp differ diff --git a/content/growth/how-digital-identity-unlock-success-in-retail/index.md b/content/growth/how-digital-identity-unlock-success-in-retail/index.md index ac224c18e..d5f2d4cb4 100644 --- a/content/growth/how-digital-identity-unlock-success-in-retail/index.md +++ b/content/growth/how-digital-identity-unlock-success-in-retail/index.md @@ -1,7 +1,7 @@ --- title: "Digital Identity: The Future of Successful Retail Operations" date: "2023-04-19" -coverImage: "dig-identity-retail.jpg" +coverImage: "dig-identity-retail.webp" tags: ["digital identity management","ecommerce","cx"] author: "Vishal Sharma" description: "With the rise of e-commerce, mobile shopping, and social media, retailers can use digital identity to personalize the customer experience, optimize marketing efforts, and drive sales. Let’s uncover the aspects of digital identity and how it thrives overall retail success." @@ -45,7 +45,7 @@ Another key benefit of digital identity is the ability to create a seamless, omn By leveraging digital identity, retailers can create a unified view of each customer that spans all channels, allowing them to deliver a seamless experience whether browsing on a mobile device or shopping in-store. -[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) +[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) ### Privacy and Security Concerns @@ -73,4 +73,4 @@ However, retailers must also be mindful of the privacy and security implications As the retail industry continues evolving and increasingly digitizing, digital identity will become an essential tool for retailers looking to stay competitive. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-digital-identity-unlock-success-in-retail) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-digital-identity-unlock-success-in-retail) diff --git a/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.png b/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.png deleted file mode 100644 index f5fa0b0f9..000000000 Binary files a/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.png and /dev/null differ diff --git a/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.webp b/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.webp new file mode 100644 index 000000000..b0761321e Binary files /dev/null and b/content/growth/how-identity-management-help-mistaken-identity/EB-omnichannel.webp differ diff --git a/content/growth/how-identity-management-help-mistaken-identity/index.md b/content/growth/how-identity-management-help-mistaken-identity/index.md index 104448429..8a2646beb 100644 --- a/content/growth/how-identity-management-help-mistaken-identity/index.md +++ b/content/growth/how-identity-management-help-mistaken-identity/index.md @@ -1,7 +1,7 @@ --- title: "How Identity Management Can Help You Avoid Targeting The Wrong Customers?" date: "2022-06-14" -coverImage: "mistaken-id.jpg" +coverImage: "mistaken-id.webp" tags: ["identity security", "ciam", "customer experience"] author: "Yash Rathi" description: "Since businesses serve customers across various devices and channels, yielding multiple views of the same customer becomes tricky. And the result is a messed experience that hampers customer experience and expectations, leading to mistaken identity. Let’s dig deeper into the aspects of leveraging a CIAM solution that helps overcome the challenges of mistaken identity." @@ -56,7 +56,7 @@ An omnichannel customer experience refers to seamless interaction across multipl For example, it is omnichannel when marketing, sales, consumer support, and even in-store experiences are synced up so users can seamlessly switch channels and make the purchase. -[](https://www.loginradius.com/resource/cloud-streaming-for-omnichannel-experience) +[](https://www.loginradius.com/resource/cloud-streaming-for-omnichannel-experience) ### #2. Single consumer view @@ -87,4 +87,4 @@ CIAM ensures brands have a better understanding of consumers. Hence, they can qu Add to that the top-of-the-line shield against the prying eyes, and the new-age CIAM seems to be a must for modern enterprises. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-identity-management-help-mistaken-identity) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-identity-management-help-mistaken-identity) \ No newline at end of file diff --git a/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.jpg b/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.jpg deleted file mode 100644 index 30a223367..000000000 Binary files a/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.jpg and /dev/null differ diff --git a/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.webp b/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.webp new file mode 100644 index 000000000..d5f9adaa5 Binary files /dev/null and b/content/growth/how-identity-management-help-mistaken-identity/mistaken-id.webp differ diff --git a/content/growth/how-identity-management-help-mistaken-identity/omni-eb.png b/content/growth/how-identity-management-help-mistaken-identity/omni-eb.png deleted file mode 100644 index 86c15a159..000000000 Binary files a/content/growth/how-identity-management-help-mistaken-identity/omni-eb.png and /dev/null differ diff --git a/content/growth/how-identity-management-help-mistaken-identity/omni-eb.webp b/content/growth/how-identity-management-help-mistaken-identity/omni-eb.webp new file mode 100644 index 000000000..025782e92 Binary files /dev/null and b/content/growth/how-identity-management-help-mistaken-identity/omni-eb.webp differ diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.png b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.png and /dev/null differ diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.webp b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/Buyers-Guide-to-Multi-Factor-Authentication.webp differ diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.png b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.png deleted file mode 100644 index 61deb3295..000000000 Binary files a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.png and /dev/null differ diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.webp b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.webp new file mode 100644 index 000000000..00c5933a4 Binary files /dev/null and b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/EB-GD-to-MFA.webp differ diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/index.md b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/index.md index 80315efb0..3fcb17bbe 100644 --- a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/index.md +++ b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/index.md @@ -1,7 +1,7 @@ --- title: "How MFA Makes Quick Service Restaurants (QSR) Promotion Fraud-Free" date: "2021-09-01" -coverImage: "qsr-payment-ciam-loginradius.jpg" +coverImage: "qsr-payment-ciam-loginradius.webp" tags: ["mfa","digital transformation","biometric authentication"] author: "Navanita Devi" description: "Quick-Service Restaurants are seeing a boom in engagement, but so are the scammers. Read this blog to find out how to boost your restaurant’s confidence in its capacity to defend itself from hackers." @@ -41,7 +41,7 @@ The majority of MFA authentication methods rely on one of three sorts of extra d In an interview with PYMNTS, Vikram Dhawan, vice president and senior product leader at Kount, an Equifax business, warned that QSRs and other merchants must safeguard their promotions and customers' accounts to strengthen their defenses against an assault of faceless, digitally-mounted attackers. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) The news came as PYMNTS research revealed that 44 percent of respondents indicated they were more likely to order from restaurants that offered specials or discounts. According to Dhawan, this circumstance allows for marketing misuse and fraud. @@ -99,4 +99,4 @@ In an age where, even after the pandemic, [digital transformation](https://www.l Consumers may now eat these goods in a variety of ways. So it would be fascinating for merchants to react to that change and that dynamic nature.” -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-mfa-makes-qsr-promotions-fraud-free) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-mfa-makes-qsr-promotions-fraud-free) \ No newline at end of file diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.jpg b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.jpg deleted file mode 100644 index cb6ab92f5..000000000 Binary files a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.jpg and /dev/null differ diff --git a/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.webp b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.webp new file mode 100644 index 000000000..ce4f6335e Binary files /dev/null and b/content/growth/how-mfa-makes-qsr-promotions-fraud-free/qsr-payment-ciam-loginradius.webp differ diff --git a/content/growth/how-retailers-balance-security-ux/index.md b/content/growth/how-retailers-balance-security-ux/index.md index 184b125e1..914a23f5a 100644 --- a/content/growth/how-retailers-balance-security-ux/index.md +++ b/content/growth/how-retailers-balance-security-ux/index.md @@ -1,7 +1,7 @@ --- title: "How Can Retailers Lead The Experience Economy While Securing Consumer Identities?" date: "2022-02-23" -coverImage: "retailers-balance.jpg" +coverImage: "retailers-balance.webp" category: ["security"] featured: false author: "Rakesh Soni" @@ -49,7 +49,7 @@ When combined, these aspects could do wonders for retailers by improving user ex These are opportunities ready to be grabbed. But are retailers ready to incorporate identity management into their workflow? If not, it is high time that they should. -**[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)** +**[](https://www.loginradius.com/resource/how-retail-and-consumer-goods-companies-use-loginradius-identity-solution/)** ## How Does a Consumer Identity and Access Management (CIAM) Solution Help Retailers? @@ -94,4 +94,4 @@ Moreover, to meet the stringent [data regulations and compliances](https://www.l A consumer identity and access management (CIAM) solution can help retailers meet their security and user experience-related requirements like a breeze without compromising compliances and regulations. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-retailers-balance-security-ux) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-retailers-balance-security-ux) \ No newline at end of file diff --git a/content/growth/how-retailers-balance-security-ux/retailers-balance.jpg b/content/growth/how-retailers-balance-security-ux/retailers-balance.jpg deleted file mode 100644 index 889d1f607..000000000 Binary files a/content/growth/how-retailers-balance-security-ux/retailers-balance.jpg and /dev/null differ diff --git a/content/growth/how-retailers-balance-security-ux/retailers-balance.webp b/content/growth/how-retailers-balance-security-ux/retailers-balance.webp new file mode 100644 index 000000000..01a070fd8 Binary files /dev/null and b/content/growth/how-retailers-balance-security-ux/retailers-balance.webp differ diff --git a/content/growth/how-retailers-balance-security-ux/retailers-ds.png b/content/growth/how-retailers-balance-security-ux/retailers-ds.png deleted file mode 100644 index 89245ae36..000000000 Binary files a/content/growth/how-retailers-balance-security-ux/retailers-ds.png and /dev/null differ diff --git a/content/growth/how-retailers-balance-security-ux/retailers-ds.webp b/content/growth/how-retailers-balance-security-ux/retailers-ds.webp new file mode 100644 index 000000000..929b7daff Binary files /dev/null and b/content/growth/how-retailers-balance-security-ux/retailers-ds.webp differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.png deleted file mode 100644 index 7f6fe4f49..000000000 Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.png and /dev/null differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.webp new file mode 100644 index 000000000..3c8f991c0 Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.webp differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.png deleted file mode 100644 index 185001af7..000000000 Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.png and /dev/null differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.webp new file mode 100644 index 000000000..b07edb57d Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-slackbot-reminder-responds.webp differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.png deleted file mode 100644 index 0cce4e5e8..000000000 Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.png and /dev/null differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.webp new file mode 100644 index 000000000..780e44e42 Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-highlights-words-in-Slack.webp differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.png deleted file mode 100644 index 377aec73d..000000000 Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.png and /dev/null differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.webp new file mode 100644 index 000000000..d97b061aa Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-set-notification-preferences-in-Slack.webp differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.png deleted file mode 100644 index bbb625503..000000000 Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.png and /dev/null differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.webp new file mode 100644 index 000000000..5f1431e73 Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/How-to-use-emojis-in-Slack.webp differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.png deleted file mode 100644 index 8f2015baf..000000000 Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.png and /dev/null differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.webp new file mode 100644 index 000000000..c9f65ed5a Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-Shortcuts.webp differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.png deleted file mode 100644 index b44f651b5..000000000 Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.png and /dev/null differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.webp new file mode 100644 index 000000000..3e66e54d3 Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/Slack-on-browser-and-app.webp differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/index.md b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/index.md index 9d4ffd1f8..67ed11848 100644 --- a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/index.md +++ b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/index.md @@ -1,7 +1,7 @@ --- title: "How To Be A Pro At Slack In 6 Simple Steps" date: "2017-02-11" -coverImage: "How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.png" +coverImage: "How-To-Be-A-Pro-At-Slack-In-6-Simple-Steps.webp" category: ["general", "loginradius"] featured: false author: "Rakesh Soni" @@ -30,9 +30,9 @@ So, for people who are still struggling with Slack at their workplace, this arti Well, there are two ways to access Slack: via browser and via app. But, everything gets faster and automatic with Slack desktop app. - + -[**Source**](https://www.windowscentral.com/sites/wpcentral.com/files/styles/xlarge/public/field/image/2015/03/slack-windows.png?ver=1553881376?itok=aTD2os-J) +[**Source**](https://www.windowscentral.com/sites/wpcentral.com/files/styles/xlarge/public/field/image/2015/03/slack-windows.webp?ver=1553881376?itok=aTD2os-J) Slack app launches itself automatically by default every time you start your system. Thus, no need to open your browsers to use Slack from now. @@ -62,7 +62,7 @@ Well, now coming to joining/choosing channels, you can join any channel that see - **Step 1:** Go to your channel’s **_notification preferences_** through settings (gear icon on top right corner). - **Step 2:** Select “mention of my name or highlights” for getting notifications related to your name or highlighted words. - + **Note:** _You can mute a channel through “mute this channel” option. Moreover, you can clear all unread messages through **SHIFT + ESC.**_ @@ -77,7 +77,7 @@ Slack will notify you whenever your name is included in a message but if you wan - Click **_notifications_** tab. - Fill the **_highlight words_** box with your choice of highlighted phrases or words. - + ### **Make SlackBot your multi-tasking friend:** @@ -95,11 +95,11 @@ Neither you nor your team can forget a thing when Slackbot is here. Set reminder - Type ‘/remind \[#channel, a coworker, or yourself\] + \[the work\] + \[time\]. Press Enter. - + - Slackbot will respond to your message. - + _The response will be exclusively for you. So, your little secret about you ‘forgetting things’ will always remain a secret with Slackbot :D_ @@ -196,11 +196,11 @@ Join #CodeNewbie for hanging out with other coders who are mad about coding. You - **You can Search anything with Ctrl + F in Slack :** Now, don’t waste time by moving your pointer to find things. Just do Ctrl + F to open search dialogue and search your desired files and messages all over Slack. - You need to love and learn shortcuts at least when you work on Slack.You don’t need to learn all but even a handful of them can make working on Slack simpler.Check the list for shortcut keys through **Ctrl + /**. - + - Using emoji can be really fun and an art worth mastering. There are two ways to use emoji in Slack. You can type the name of emoji starting with “:”. It will raise a menu - + Or else just click on the smiley face in message box section to select your favorite emoji. diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.png b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.png deleted file mode 100644 index 785ac4ae3..000000000 Binary files a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.png and /dev/null differ diff --git a/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.webp b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.webp new file mode 100644 index 000000000..008b49028 Binary files /dev/null and b/content/growth/how-to-be-a-pro-at-slack-in-6-simple-steps/slackbot-reminder.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.jpg b/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.jpg deleted file mode 100644 index 323aad074..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.jpg and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.webp new file mode 100644 index 000000000..1cdf84741 Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp-cover-page.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp.png deleted file mode 100644 index cced7af22..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp.webp new file mode 100644 index 000000000..ba49903af Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.png deleted file mode 100644 index e334dd40a..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.webp new file mode 100644 index 000000000..7c5302298 Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp10.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.png deleted file mode 100644 index f3f7babca..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.webp new file mode 100644 index 000000000..fe8814e78 Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp11.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.png deleted file mode 100644 index 6948a23be..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.webp new file mode 100644 index 000000000..3502d0fea Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp12.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.png deleted file mode 100644 index 738109c4c..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.webp new file mode 100644 index 000000000..588976a04 Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp13.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.png deleted file mode 100644 index 880f75057..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.webp new file mode 100644 index 000000000..9d3407cb0 Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp14.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.png deleted file mode 100644 index 4250d4c4d..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.webp new file mode 100644 index 000000000..fc6f18327 Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp15.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.png deleted file mode 100644 index 4f75f5622..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.webp new file mode 100644 index 000000000..14f13078b Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp2.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.png deleted file mode 100644 index 5169e3bec..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.webp new file mode 100644 index 000000000..59d52edbf Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp3.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.png deleted file mode 100644 index 40a6dc588..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.webp new file mode 100644 index 000000000..240b4733a Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp4.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.png deleted file mode 100644 index 63c94c3fa..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.webp new file mode 100644 index 000000000..0cdf62c43 Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp5.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.png deleted file mode 100644 index 5613de6b8..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.webp new file mode 100644 index 000000000..86eb7eeae Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp6.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.png deleted file mode 100644 index 2bbfa4aa3..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.webp new file mode 100644 index 000000000..14d9a75b2 Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp7.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.png deleted file mode 100644 index 3d9901b8a..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.webp new file mode 100644 index 000000000..27b9191b3 Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp8.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.png b/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.png deleted file mode 100644 index 508b9641d..000000000 Binary files a/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.png and /dev/null differ diff --git a/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.webp b/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.webp new file mode 100644 index 000000000..93c51526e Binary files /dev/null and b/content/growth/how-to-improve-the-customer-xperience/consumer-exp9.webp differ diff --git a/content/growth/how-to-improve-the-customer-xperience/index.md b/content/growth/how-to-improve-the-customer-xperience/index.md index b95bf76a6..2c8ddb716 100644 --- a/content/growth/how-to-improve-the-customer-xperience/index.md +++ b/content/growth/how-to-improve-the-customer-xperience/index.md @@ -1,7 +1,7 @@ --- title: "7 Expert Tips on How to Improve the Customer Experience" date: "2021-09-22" -coverImage: "consumer-exp-cover-page.jpg" +coverImage: "consumer-exp-cover-page.webp" category: ["loginradius"] featured: false author: "Alyse Falk" @@ -12,7 +12,7 @@ metatitle: "Lets explore top 7 expert tips on how to improve the consumer experi Excellent customer experiences motivate people to become regular consumers. The main goal of any company is to put itself in the customer’s shoes. An improved user experience brings more leads that will convert into clients and the opportunity to increase your customer base. - + Note that your perfect customer experience depends on numerous factors. These are positive feedback, brand awareness, a good reputation, the SEO-friendliness of your website, and many more. @@ -27,7 +27,7 @@ According to a [Business2Community](https://www.business2community.com/customer- Additionally, your company will be able to generate more revenue via customer acquisition by renewing and upselling to your standing customers. - + ## Overview of the CX Evolution (2017-2020) @@ -66,7 +66,7 @@ If you are interested in the best practices that will come in handy for improvin If you still have not digitized your business, it is time to do it right now. Start with your website and social media network accounts. Your site should be mobile-friendly because about 70% of global traffic is generated via mobile device screens. - + Besides the technical aspects that affect user experience, seven others are described in the following expert tips. Having implemented these approaches into practice, your CX will become significantly improved according to 2021 trends. ### #1 Understand Who Are Your Customers @@ -83,7 +83,7 @@ For improved customer loyalty with a guaranteed individual approach, you can spl - For entrepreneurs. - + This way, first-time visitors are easily navigated to the information and features that best fit their segment. So, while being a single platform with many different SEO services, the company has improved the customer experience by providing their potential clients with a simple way to find the package designed for their needs. @@ -100,7 +100,7 @@ Omnichannel CX is a way to provide an integrated customer experience through syn Omnichannel CX implements many approaches simultaneously to convert CX into a seamless process. Many integration strategies bring higher conversion rates and more traffic. Additionally, it benefits customer retention. It is worth noting that omnichannel and multichannel user experiences are not the same. - + The main idea of the multichannel approach is to provide many customer service channels that are not linked to each other. It means that social media networks, websites, online shops, and call centers are not synchronized. But omnichannel CX infers that all these multiple channels are connected. @@ -119,7 +119,7 @@ To strengthen the omnichannel customer experience, tie in a CX-driven combinatio A good example of omnichannel CX is the pharmaceutical brand [Walgreens](https://www.walgreens.com/). Brand communication takes place via a mobile-friendly app. The shopping experience is improved with the help of convenient digital features such as refilling prescriptions virtually, setting up reminders and notifications. The app saves customers time because they do not need to visit the pharmacy to get medications. - + Simplified interactions and virtual communication is in high demand today and are highly appreciated by consumers and increases Walgreens’ customer retention. @@ -141,7 +141,7 @@ The customer journey is a full cycle that takes place from the first interaction 7. Loyalty – An utterly positive experience means that the client will likely repeat the purchase and recommend your product. Encourage loyal customers to submit thankful reviews that will improve your reputation, brand awareness, and search rankings. - + ## Tips for Customer Journey Optimization @@ -223,7 +223,7 @@ The rule of a great CX-driven online community is the desire for your loyal cust For example, [Inkbox](https://inkbox.com/) consists of a community with millions (2 million) of followers. This company makes it a priority of tattooing and shares all completed work on the Internet. The community was created around the popular Instagram hashtag #tattoosfornow. People throughout the world shared beautiful photos with tattoos and grew the community. - + ### #5 Take Advantage of Customer Reviews @@ -234,7 +234,7 @@ You can use reviews for your customer experience purposes. Additionally, you can - + @@ -242,8 +242,8 @@ You can use reviews for your customer experience purposes. Additionally, you can 2. Use reviews for your search ranking. Add a Sitemap with reviews to engage people to visit your site and help Google consider your website as trusted. - - + + 3. Use reviews to prove your reputation on other online communication channels (social media platforms, forums, blogs). @@ -253,13 +253,13 @@ You can use reviews for your customer experience purposes. Additionally, you can 4. Use client testimonials in newsletters and for other email marketing purposes. This way, you will increase the chances that your letter will be read and taken into consideration. - + 5. Add reviews to your video marketing materials. You can use screenshots of some eye-catching and detailed testimonials in your advertising videos. 6. Analyze your customer satisfaction rates with the help of the percentages that rank positive, neutral, and negative reviews. For example, you can offer short online surveys to get more reviews after any customer journey stage (especially at the last two) and measure them. Here is a set of survey templates by [NiceReply](https://www.nicereply.com/). - + ### #6 Personalize Your Content @@ -268,13 +268,13 @@ According to [Harvard Business Review](https://hbr.org/2018/01/ads-that-dont-ove [Spotify](https://www.spotify.com/us/) decided to launch the option “Discover Weekly” for this purpose. A personalized playlist is generated according to the listener’s preferences. Some users like this option, while some Spotify fans dislike it. Nevertheless, this is a way to promote a personalized approach and show each customer your meaningful marketing strategy. - + ### #7 Make the Customer Experience Safer A significant number of Internet users are still afraid of scammers and cyber hacks regarding the user experience on a website. Assure visitors that your ecommerce platform and corporate site are risk-free for them. For example, [LoginRadius](https://www.loginradius.com/customer-security/) provides businesses with adoptive safety tools to make their CX 100% secure. - + Having implemented tech solutions to protect client accounts, your company strengthens its brand awareness, improves reputation and loyalty. Usually, the most challenging aspects for customers are the security of personal data and online payments. Your task in the context of CX improvement is to maintain privacy and guarantee safe transactions. @@ -282,5 +282,5 @@ Having implemented tech solutions to protect client accounts, your company stren Your CX strategy should meet customer requirements and your business goals. Customer experience is a proven way to develop high retention, cross-sales, and up-sales. If people decide to come back and recommend your products, this is a good sign for your company. An improved user experience benefits SEO, brand awareness, and generally the online presence of your business. 2021 requires marketers, entrepreneurs, and SEO specialists to demonstrate an omnichannel CX approach with comprehensive security, reviews, and customer journey strategies. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-improve-the-customer-xperience) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-improve-the-customer-xperience) diff --git a/content/growth/how-to-learn-copywriting/index.md b/content/growth/how-to-learn-copywriting/index.md index d26f97f2d..51a07f3e0 100644 --- a/content/growth/how-to-learn-copywriting/index.md +++ b/content/growth/how-to-learn-copywriting/index.md @@ -1,7 +1,7 @@ --- title: "Want to Learn Copywriting? 3 Tips That Will Keep Readers Glued to Your Content" date: "2021-05-25" -coverImage: "learn-copywriting.jpg" +coverImage: "learn-copywriting.webp" category: ["loginradius"] featured: false author: "Navanita Devi" @@ -188,4 +188,4 @@ Remember that SEO-optimized content is essential to rank your blogs or website p To develop a unique [brand identity](https://www.loginradius.com/blog/fuel/2021/04/does-your-website-imagery-reflect-your-brand-identity/), you need to have a team of top-notch copywriters who can keep the readers glued to the content and eventually help increase your business. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-learn-copywriting) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-learn-copywriting) diff --git a/content/growth/how-to-learn-copywriting/learn-copywriting.jpg b/content/growth/how-to-learn-copywriting/learn-copywriting.jpg deleted file mode 100644 index 09b5dbad8..000000000 Binary files a/content/growth/how-to-learn-copywriting/learn-copywriting.jpg and /dev/null differ diff --git a/content/growth/how-to-learn-copywriting/learn-copywriting.webp b/content/growth/how-to-learn-copywriting/learn-copywriting.webp new file mode 100644 index 000000000..ea850919c Binary files /dev/null and b/content/growth/how-to-learn-copywriting/learn-copywriting.webp differ diff --git a/content/growth/how-to-leverage-email-automation-personalization/email-automation.jpg b/content/growth/how-to-leverage-email-automation-personalization/email-automation.jpg deleted file mode 100644 index 7f11984b2..000000000 Binary files a/content/growth/how-to-leverage-email-automation-personalization/email-automation.jpg and /dev/null differ diff --git a/content/growth/how-to-leverage-email-automation-personalization/email-automation.webp b/content/growth/how-to-leverage-email-automation-personalization/email-automation.webp new file mode 100644 index 000000000..37082ab01 Binary files /dev/null and b/content/growth/how-to-leverage-email-automation-personalization/email-automation.webp differ diff --git a/content/growth/how-to-leverage-email-automation-personalization/image1.png b/content/growth/how-to-leverage-email-automation-personalization/image1.png deleted file mode 100644 index ccf0c0210..000000000 Binary files a/content/growth/how-to-leverage-email-automation-personalization/image1.png and /dev/null differ diff --git a/content/growth/how-to-leverage-email-automation-personalization/image1.webp b/content/growth/how-to-leverage-email-automation-personalization/image1.webp new file mode 100644 index 000000000..f8e453304 Binary files /dev/null and b/content/growth/how-to-leverage-email-automation-personalization/image1.webp differ diff --git a/content/growth/how-to-leverage-email-automation-personalization/image2.png b/content/growth/how-to-leverage-email-automation-personalization/image2.png deleted file mode 100644 index d08f0c448..000000000 Binary files a/content/growth/how-to-leverage-email-automation-personalization/image2.png and /dev/null differ diff --git a/content/growth/how-to-leverage-email-automation-personalization/image2.webp b/content/growth/how-to-leverage-email-automation-personalization/image2.webp new file mode 100644 index 000000000..4b4bd1699 Binary files /dev/null and b/content/growth/how-to-leverage-email-automation-personalization/image2.webp differ diff --git a/content/growth/how-to-leverage-email-automation-personalization/index.md b/content/growth/how-to-leverage-email-automation-personalization/index.md index 8dfb1e07c..94d4dd0a9 100644 --- a/content/growth/how-to-leverage-email-automation-personalization/index.md +++ b/content/growth/how-to-leverage-email-automation-personalization/index.md @@ -1,7 +1,7 @@ --- title: "How to Make Your Automated Emails Sound Personal, Relevant, and Effective?" date: "2021-07-02" -coverImage: "email-automation.jpg" +coverImage: "email-automation.webp" tags: ["email marketing","customer experience","personalization"] author: "Akshay Deogiri" description: " The chances are that as a marketer, you’re already segmenting your audience and sending them targeted emails. But is that enough? Making your emails relevant is one thing, and making them interesting and engaging is something completely different. If implemented correctly, personalization is a powerful tool that can help you engage your audience and nurture your leads." @@ -85,7 +85,7 @@ All email automation solutions support triggers. You can choose a trigger that Here’s a great example from an automated welcome email from Healthline, a health information provider. - + Image Source: [Healthline](https://www.healthline.com/) @@ -93,7 +93,7 @@ Setting up triggers is great, but not enough. If you want to truly personalize y For example, Sephora, a cosmetics and personal care brand, sends an email providing a 20% discount to customers who shop for more than $200. - + Image Source: [Sephora](https://www.sephora.com/) @@ -158,4 +158,4 @@ Personalizing emails isn’t a choice anymore for brands. Customers expect you t This can help your brand in two ways. First, it can reduce your costs and increase your marketing efficiency. And second, it can make your marketing more personal, relevant, and effective, resulting in better engagement and more customers. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-leverage-email-automation-personalization) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-leverage-email-automation-personalization) diff --git a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/index.md b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/index.md index a35562d2b..d87846103 100644 --- a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/index.md +++ b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/index.md @@ -1,7 +1,7 @@ --- title: "Personalize Your Marketing With The Help Of A CIAM Platform" date: "2021-07-30" -coverImage: "personalized-marketing.jpg" +coverImage: "personalized-marketing.webp" tags: ["ciam solution","data security","cx","authentication"] author: "Navanita Devi" description: "Personalized marketing is a promotional strategy tailored to the individual at the precise moment they require it, and there's no other communication like it. The question is, how will you fulfill that promise? You may utilize tools to acquire and aggregate information about your clients' preferences. Read on to find out what these tools are and how they benefit your business." @@ -25,7 +25,7 @@ CIAM solutions also typically offer self-service capabilities for customers, suc ## Grow Your Business with CIAM - + Providing consumers with digital services is a delicate balancing act. You must provide an exceptional client experience while also establishing trust in the security of your services. If you get one of these things incorrect, the consequences can be devastating. @@ -81,4 +81,4 @@ By using a robust CIAM solution, organizations can build trust and loyalty with In a nutshell, CIAM enables organizations to deliver an exceptional and secure personalized experience that meets the needs of their customers, ultimately leading to increased customer satisfaction and brand loyalty. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-make-personalized-marketing-effective-with-consumer-identity) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-make-personalized-marketing-effective-with-consumer-identity) \ No newline at end of file diff --git a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.png b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.png deleted file mode 100644 index 83ffe682c..000000000 Binary files a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.png and /dev/null differ diff --git a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.webp b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.webp new file mode 100644 index 000000000..5527fbf0b Binary files /dev/null and b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing-experience.webp differ diff --git a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.jpg b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.jpg deleted file mode 100644 index 8e1713a97..000000000 Binary files a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.jpg and /dev/null differ diff --git a/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.webp b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.webp new file mode 100644 index 000000000..b0df12f9e Binary files /dev/null and b/content/growth/how-to-make-personalized-marketing-effective-with-consumer-identity/personalized-marketing.webp differ diff --git a/content/growth/how-to-protect-consumer-social-identity/index.md b/content/growth/how-to-protect-consumer-social-identity/index.md index 9b6663787..244deabe0 100644 --- a/content/growth/how-to-protect-consumer-social-identity/index.md +++ b/content/growth/how-to-protect-consumer-social-identity/index.md @@ -1,7 +1,7 @@ --- title: "Why Consumers’ Social Identities Matter & How You Can Protect It?" date: "2021-12-07" -coverImage: "social-id.jpg" +coverImage: "social-id.webp" category: ["security"] featured: false author: "Navanita Devi" @@ -82,5 +82,5 @@ Businesses can benefit from greater customer engagement and loyalty by providing Today, data is king. Sensitive information about the social identity of consumers is used by organisations for many reasons, but it's also organisations' responsibility to maintain privacy. This can only be achieved by investing in the best CIAM. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-protect-consumer-social-identity) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-protect-consumer-social-identity) diff --git a/content/growth/how-to-protect-consumer-social-identity/social-id.jpg b/content/growth/how-to-protect-consumer-social-identity/social-id.jpg deleted file mode 100644 index 841a3bab5..000000000 Binary files a/content/growth/how-to-protect-consumer-social-identity/social-id.jpg and /dev/null differ diff --git a/content/growth/how-to-protect-consumer-social-identity/social-id.webp b/content/growth/how-to-protect-consumer-social-identity/social-id.webp new file mode 100644 index 000000000..8e295c037 Binary files /dev/null and b/content/growth/how-to-protect-consumer-social-identity/social-id.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.jpg deleted file mode 100644 index cf5d7f92b..000000000 Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.jpg and /dev/null differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.webp new file mode 100644 index 000000000..dddde8839 Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1132a-1024x658.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.jpg deleted file mode 100644 index adf6e1415..000000000 Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.jpg and /dev/null differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.webp new file mode 100644 index 000000000..6640ebaa2 Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1149a-1024x658.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.jpg deleted file mode 100644 index 3f6c926b6..000000000 Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.jpg and /dev/null differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.webp new file mode 100644 index 000000000..17a881a21 Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1159a-1024x658.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.jpg deleted file mode 100644 index d77141fd3..000000000 Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.jpg and /dev/null differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.webp new file mode 100644 index 000000000..d91162fd0 Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1178a-1024x658.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.jpg deleted file mode 100644 index c72dfb1a9..000000000 Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.jpg and /dev/null differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.webp new file mode 100644 index 000000000..4926c866e Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1215a-1-1024x658.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.jpg deleted file mode 100644 index fee6d7dc3..000000000 Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.jpg and /dev/null differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.webp new file mode 100644 index 000000000..7e46c6ae6 Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1238-1a-1024x658.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.jpg deleted file mode 100644 index c8040898a..000000000 Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.jpg and /dev/null differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.webp new file mode 100644 index 000000000..1b5292b3b Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1244a-1024x658.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.jpg deleted file mode 100644 index a39d2d500..000000000 Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.jpg and /dev/null differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.webp new file mode 100644 index 000000000..f2612bd4e Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_1257a-1-1024x658.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.jpg b/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.jpg deleted file mode 100644 index ebb5fca2a..000000000 Binary files a/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.jpg and /dev/null differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.webp b/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.webp new file mode 100644 index 000000000..757cd74b2 Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/IMG_20190913_200408a-1024x659.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.png b/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.png deleted file mode 100644 index c4fa3a11c..000000000 Binary files a/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.png and /dev/null differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.webp b/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.webp new file mode 100644 index 000000000..b15b42635 Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/VWS-V01.03_LinkedIn-1-1200x627-1-1024x536.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.jpg b/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.jpg deleted file mode 100644 index c56bcb0e2..000000000 Binary files a/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.jpg and /dev/null differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.webp b/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.webp new file mode 100644 index 000000000..267cec516 Binary files /dev/null and b/content/growth/how-to-throw-a-tiki-tech-party/how-to-throw-a-tiki-tech-party.webp differ diff --git a/content/growth/how-to-throw-a-tiki-tech-party/index.md b/content/growth/how-to-throw-a-tiki-tech-party/index.md index 79e1539a5..0aa4522d8 100644 --- a/content/growth/how-to-throw-a-tiki-tech-party/index.md +++ b/content/growth/how-to-throw-a-tiki-tech-party/index.md @@ -1,7 +1,7 @@ --- title: "How To Throw A Tiki Tech Party" date: "2019-09-20" -coverImage: "how-to-throw-a-tiki-tech-party.jpg" +coverImage: "how-to-throw-a-tiki-tech-party.webp" category: ["media-and-publication", "LoginRadius"] featured: false author: "Karl Wittig" @@ -13,7 +13,7 @@ metadescription: "Learn more about how LoginRadius organized its first Tiki Tech Last week, we had a great time participating in Vancouver Startup Week's Community Crawl. - + The Community Crawl is like a pub crawl except you hop from startup offices to startup offices. It’s an engaging open house event where guests can check out different startups. Over a dozen startups opened their doors, so **thanks to everyone who took the time to check us out!** @@ -21,7 +21,7 @@ Those who attended immediately noticed our new spacious office space, complete w To celebrate our move and christen our new space and tiki bar, we hosted a tiki party, replete with festive Hawaiian leis and shirts. - + _LoginRadius founder & CEO, Rakesh Soni, enjoying our new custom-made tiki bar._ @@ -37,11 +37,11 @@ Being a startup with a modest budget, we had to be creative with the DIY decor. We painted colourful signs on cardboard and made little pineapple lanterns which we strung across the room. Then, to brighten the room, we added flamingo-pink dangling paper tissue balls from the ceiling. Hanging decorations from the ceiling are better than sticking them on walls. It makes a room look full and festive with very little material. - + _We bought yellow lanterns and turned them into pineapples._ - + _We placed hand-painted signs, including our drinks menu, all over the room._ @@ -49,7 +49,7 @@ _We placed hand-painted signs, including our drinks menu, all over the room._ Another easy way to add more tiki into a room is by playing music. We found a pre-made tiki playlist on a streaming app and let it loop throughout the night. There wasn’t any official dancing at our party, but we had lots of people bobbing their heads or tapping their feet to the beat. - + _Our team members and guests having fun at our tiki tech party._ @@ -59,7 +59,7 @@ The tiki bar was made by a local carpenter. He came by our office to look at the What he built was better than what we expected! The frame is made of durable wood and lined with the bamboo-like exterior. On the inside, we have a fridge for the keg and another fridge for other drinks. On the surface of the bar is the tap for the beer. The front was lined with LED lights that changed colours. Everything is covered by a thatched roof, completing the tiki look. - + _To the left is Mark from Torlay, our local carpenter, who designed and built our lovely tiki bar!_ @@ -73,7 +73,7 @@ To ensure a fun relaxing night for everyone, we hired a bartender. His lime marg The tap beer on the tiki bar was also a celebration on its own. Plus, right before the event, one of our team members whipped up some killer tropical sangria. - + _Our bartender, Sam, making amazing tropical drinks for us all night long._ @@ -84,7 +84,7 @@ Whether you do or don’t have a tiki bar, you can create the vibe around your c The first impression is everything. Each guest who came through our doors received a flower lei over their heads. It’s a great way to create that instant tiki environment. We went a step further and created little tags for each lei with our company logo and a QR code that took them to our [Careers page](https://www.loginradius.com/careers/) for those who are interested in joining us for more than just a tiki party. - + _Lovely volunteers from Vancouver Startup Week helped us give leis to our guests._ @@ -92,7 +92,7 @@ _Lovely volunteers from Vancouver Startup Week helped us give leis to our guests On our TV, we displayed a one-minute online survey that can be taken on mobile phones. Since LoginRadius secures digital identities, we asked our guests to check all the different digital identities they used in the past week. This included emails, online banking, various video games, social media, and more. - + _Individuals scanned the QR code on our TV to take our one-minute digital identity survey._ @@ -109,7 +109,7 @@ On a weekend night, what better way to end a party than with an after-party? We Planning fun parties can be exhausting. Allowing spontaneous after parties can help you feel free and serve as a reminder that an enjoyable event doesn’t always have to be stringently planned. - + _The after-party selfie—no party is complete without it!_ diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.png b/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.png deleted file mode 100644 index 802253f09..000000000 Binary files a/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.png and /dev/null differ diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.webp b/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.webp new file mode 100644 index 000000000..c98143e9e Binary files /dev/null and b/content/growth/how-to-use-identity-marketing-privacy-centric-world/WP-compliance.webp differ diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.png b/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.png deleted file mode 100644 index a2c9e2a07..000000000 Binary files a/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.png and /dev/null differ diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.webp b/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.webp new file mode 100644 index 000000000..1717fdcbb Binary files /dev/null and b/content/growth/how-to-use-identity-marketing-privacy-centric-world/complaince-wp.webp differ diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.jpg b/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.jpg deleted file mode 100644 index 797463755..000000000 Binary files a/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.jpg and /dev/null differ diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.webp b/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.webp new file mode 100644 index 000000000..27095170a Binary files /dev/null and b/content/growth/how-to-use-identity-marketing-privacy-centric-world/identity-marketing.webp differ diff --git a/content/growth/how-to-use-identity-marketing-privacy-centric-world/index.md b/content/growth/how-to-use-identity-marketing-privacy-centric-world/index.md index 6d8228d34..4ae72ed63 100644 --- a/content/growth/how-to-use-identity-marketing-privacy-centric-world/index.md +++ b/content/growth/how-to-use-identity-marketing-privacy-centric-world/index.md @@ -1,7 +1,7 @@ --- title: "The Right Way to Use Identity Marketing in a Privacy-Centric World" date: "2022-02-15" -coverImage: "identity-marketing.jpg" +coverImage: "identity-marketing.webp" tags: ["identity management","compliance","cx"] author: "Navanita Devi" description: "There are numerous ways that you can use identity marketing to strengthen your business reputation. With the right techniques, you can make this an extremely powerful strategy. The points mentioned in this blog will help you to understand how identity marketing has transformed the modern digital age." @@ -37,7 +37,7 @@ First, there's the issue of data protection. The GDPR requires businesses to giv Second, businesses need to rethink how they use their systems and communicate with their customers. The good news is that many of the issues can be resolved simply by taking an extra minute to verify if the legislations' conditions are met. -[](https://www.loginradius.com/resource/) +[](https://www.loginradius.com/resource/) ## Exploring the Concept of Incrementality @@ -73,4 +73,4 @@ As mentioned above, there are many things that you might want to do with your co Another important point is that you need to understand when you are asking questions and gathering information from your consumers as well. All these aspects should be discussed with [privacy policies](https://www.loginradius.com/blog/identity/privacy-policy-management/) so that consumers know what they are doing in regards to your brand identity. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-use-identity-marketing-privacy-centric-world) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=how-to-use-identity-marketing-privacy-centric-world) \ No newline at end of file diff --git a/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.png b/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.png deleted file mode 100644 index b18dabb9d..000000000 Binary files a/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.png and /dev/null differ diff --git a/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.webp b/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.webp new file mode 100644 index 000000000..86a87bf76 Binary files /dev/null and b/content/growth/how-to-write-professional-bio-with-examples/Quick-tips-to-learn-to-write-the-Best-Professional-Bio.webp differ diff --git a/content/growth/how-to-write-professional-bio-with-examples/index.md b/content/growth/how-to-write-professional-bio-with-examples/index.md index 64d992d9b..e0c8db9ca 100644 --- a/content/growth/how-to-write-professional-bio-with-examples/index.md +++ b/content/growth/how-to-write-professional-bio-with-examples/index.md @@ -1,7 +1,7 @@ --- title: "Don’t Waste Time! Facts to learn to write the Best Professional Bio" date: "2017-02-27" -coverImage: "Quick-tips-to-learn-to-write-the-Best-Professional-Bio.png" +coverImage: "Quick-tips-to-learn-to-write-the-Best-Professional-Bio.webp" category: ["general", "marketing", "loginradius"] featured: false author: "Rakesh Soni" @@ -113,15 +113,15 @@ Most importantly, do not forget to proofread your bio. Always invite some of you ### **Some real life examples of best professional bios that I found in my research:** - + [**Source**](https://twitter.com/adampopescu) - + [**Source**](https://twitter.com/alisoncrowewine) - + [**Source**](https://twitter.com/WaltHickey) diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.png b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.png deleted file mode 100644 index 51122125d..000000000 Binary files a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.png and /dev/null differ diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.webp b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.webp new file mode 100644 index 000000000..fb269bab7 Binary files /dev/null and b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-1.webp differ diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.png b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.png deleted file mode 100644 index 953880036..000000000 Binary files a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.png and /dev/null differ diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.webp b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.webp new file mode 100644 index 000000000..dc22adac0 Binary files /dev/null and b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-2.webp differ diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.png b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.png deleted file mode 100644 index 558f7d35f..000000000 Binary files a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.png and /dev/null differ diff --git a/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.webp b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.webp new file mode 100644 index 000000000..694249287 Binary files /dev/null and b/content/growth/how-to-write-professional-bio-with-examples/real-life-professional-bio-example-3.webp differ diff --git a/content/growth/hybrid-workforce/hybrid-workforce.jpg b/content/growth/hybrid-workforce/hybrid-workforce.jpg deleted file mode 100644 index c52dc4a21..000000000 Binary files a/content/growth/hybrid-workforce/hybrid-workforce.jpg and /dev/null differ diff --git a/content/growth/hybrid-workforce/hybrid-workforce.webp b/content/growth/hybrid-workforce/hybrid-workforce.webp new file mode 100644 index 000000000..2314dbfd9 Binary files /dev/null and b/content/growth/hybrid-workforce/hybrid-workforce.webp differ diff --git a/content/growth/hybrid-workforce/index.md b/content/growth/hybrid-workforce/index.md index bc9c356a7..410224b41 100644 --- a/content/growth/hybrid-workforce/index.md +++ b/content/growth/hybrid-workforce/index.md @@ -1,7 +1,7 @@ --- title: "Hybrid Workforce: Laying The Foundation of Remote Working" date: "2021-02-22" -coverImage: "hybrid-workforce.jpg" +coverImage: "hybrid-workforce.webp" category: ["all"] featured: false author: "Rakesh Soni" @@ -113,4 +113,4 @@ Companies also need to provide the [employees working remotely](https://www.logi A Hybrid workforce can prove to be beneficial both for companies and the employees who would work remotely. This change was forced into action due to the covid-19 pandemic, but it'll be the future of the work. It'll lead to a great many changes. It will not only help businesses build more money, but it'll also help them lessen the workload on the employees. In a nutshell, the hybrid workforce model is a win-win for both employers and employees. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hybrid-workforce) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=hybrid-workforce) diff --git a/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.png b/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.png deleted file mode 100644 index f5fa0b0f9..000000000 Binary files a/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.png and /dev/null differ diff --git a/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.webp b/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.webp new file mode 100644 index 000000000..b0761321e Binary files /dev/null and b/content/growth/identity-at-centre-of-your-customer-strategy/EB-omnichannel.webp differ diff --git a/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.jpg b/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.jpg deleted file mode 100644 index ab8c0477b..000000000 Binary files a/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.jpg and /dev/null differ diff --git a/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.webp b/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.webp new file mode 100644 index 000000000..abc23d05e Binary files /dev/null and b/content/growth/identity-at-centre-of-your-customer-strategy/identity-at-centre.webp differ diff --git a/content/growth/identity-at-centre-of-your-customer-strategy/index.md b/content/growth/identity-at-centre-of-your-customer-strategy/index.md index 8d84ebb8a..b32aa9e97 100644 --- a/content/growth/identity-at-centre-of-your-customer-strategy/index.md +++ b/content/growth/identity-at-centre-of-your-customer-strategy/index.md @@ -1,7 +1,7 @@ --- title: "Why Identity Should Be At The Centre of Your Customer Strategy" date: "2023-07-20" -coverImage: "identity-at-centre.jpg" +coverImage: "identity-at-centre.webp" tags: ["identity management","data security","cx"] author: "Vishal Sharma" description: "Dive into the vital role of identity in your customer strategy. Explore how leveraging identity data can revolutionize personalization, establish trust, ensure seamless experiences across channels, drive data-driven decision-making, and maximize customer lifetime value." @@ -35,7 +35,7 @@ Transparent privacy policies and clear communication regarding data usage also c Customers expect consistency and continuity as they interact with a brand across different channels. Integrating identity management across your various touchpoints allows you to provide a seamless omnichannel experience. -[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) +[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) For example, a customer who starts shopping on your website should be able to continue their journey seamlessly on a mobile app or even in-store without any disruptions. @@ -63,4 +63,4 @@ Incorporating identity into your customer strategy is a strategic imperative in By placing identity at the center of your customer strategy, you create a customer-centric approach that drives customer satisfaction, enhances brand reputation, and positions your business as a leader in your industry. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-at-centre-of-your-customer-strategy) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-at-centre-of-your-customer-strategy) diff --git a/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.png b/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.png deleted file mode 100644 index fb9e830ba..000000000 Binary files a/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.png and /dev/null differ diff --git a/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.webp b/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.webp new file mode 100644 index 000000000..4ea6dbcbf Binary files /dev/null and b/content/growth/identity-convergence-market-dominance/WP-fundamentals-privacy.webp differ diff --git a/content/growth/identity-convergence-market-dominance/identity-convergence.jpg b/content/growth/identity-convergence-market-dominance/identity-convergence.jpg deleted file mode 100644 index 6b33c773b..000000000 Binary files a/content/growth/identity-convergence-market-dominance/identity-convergence.jpg and /dev/null differ diff --git a/content/growth/identity-convergence-market-dominance/identity-convergence.webp b/content/growth/identity-convergence-market-dominance/identity-convergence.webp new file mode 100644 index 000000000..ef3fddf6d Binary files /dev/null and b/content/growth/identity-convergence-market-dominance/identity-convergence.webp differ diff --git a/content/growth/identity-convergence-market-dominance/index.md b/content/growth/identity-convergence-market-dominance/index.md index aecef03ad..1d4de3783 100644 --- a/content/growth/identity-convergence-market-dominance/index.md +++ b/content/growth/identity-convergence-market-dominance/index.md @@ -1,7 +1,7 @@ --- title: "Unlocking the Secret to Dominating the Market: How Can Give You a Competitive Edge" date: "2024-05-23" -coverImage: "identity-convergence.jpg" +coverImage: "identity-convergence.webp" tags: ["identity convergence","data privacy","cx"] author: "Cooper Matheson" description: "Identity convergence integrates diverse customer data into unified profiles, enabling unmatched personalization and efficiency. Learn how to leverage this strategy for superior business outcomes and gain a competitive edge in today's market." @@ -40,7 +40,7 @@ Identity convergence allows for the creation of highly targeted marketing campai * **Predictive Analytics:** By utilizing predictive analytics, businesses can anticipate customer needs and behaviors, enabling proactive marketing efforts that capture attention at the right moment. -[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper) +[](https://www.loginradius.com/resource/privacy-assured-marketing-whitepaper) ### 3. Improved Product Development @@ -103,4 +103,4 @@ By creating a unified view of the customer, companies can develop more effective Identity convergence is more than a buzzword; it's a strategic approach that can transform businesses' interactions with their customers and drive long-term growth. Embrace identity convergence today and watch your competitive edge soar. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-convergence-market-dominance) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-convergence-market-dominance) diff --git a/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.png b/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.png deleted file mode 100644 index 74eef3e01..000000000 Binary files a/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.png and /dev/null differ diff --git a/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.webp b/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.webp new file mode 100644 index 000000000..cae55baf0 Binary files /dev/null and b/content/growth/identity-management-critical-revenue-generation/EB-GD-to-Mod-Cust-Id.webp differ diff --git a/content/growth/identity-management-critical-revenue-generation/ciam-eb.png b/content/growth/identity-management-critical-revenue-generation/ciam-eb.png deleted file mode 100644 index bc0c2b3f3..000000000 Binary files a/content/growth/identity-management-critical-revenue-generation/ciam-eb.png and /dev/null differ diff --git a/content/growth/identity-management-critical-revenue-generation/ciam-eb.webp b/content/growth/identity-management-critical-revenue-generation/ciam-eb.webp new file mode 100644 index 000000000..b0f1ac055 Binary files /dev/null and b/content/growth/identity-management-critical-revenue-generation/ciam-eb.webp differ diff --git a/content/growth/identity-management-critical-revenue-generation/index.md b/content/growth/identity-management-critical-revenue-generation/index.md index be84cf865..8d6ee69c0 100644 --- a/content/growth/identity-management-critical-revenue-generation/index.md +++ b/content/growth/identity-management-critical-revenue-generation/index.md @@ -1,7 +1,7 @@ --- title: "Demystifying Identity Management For Revenue Generation - Going Beyond Compliance" date: "2022-10-17" -coverImage: "revenue-generation.jpg" +coverImage: "revenue-generation.webp" tags: ["digital identity management", "ciam", "compliance"] author: "Rakesh Soni" description: "Modern businesses quickly realize that leveraging digital identities as fuel for driving their organizational growth through personalization and robust identity security is becoming the need of the hour. This blog outlines the major depicting how identity management paves the way for organizational growth." @@ -40,7 +40,7 @@ Your users always expect personalization from the moment they interact with your With a customer identity and access management (CIAM) solution for identity management, organizations can ensure they remain ahead of their competitors by leveraging the true potential of personalization. -[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) +[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) As a brand, one could utilize customer-related details in a way that helps automatically generate suggestions based on a user’s interest and past behavior on your platform. This means you have a greater chance of lead generation and conversion. @@ -73,4 +73,4 @@ Identity management is a critical part of the revenue generation process. In tod A modern CIAM solution can help you manage your customers' information, enhance user experience, and ensures you build better-personalized experiences to convert your targetted audience into customers. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-critical-revenue-generation) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-critical-revenue-generation) diff --git a/content/growth/identity-management-critical-revenue-generation/revenue-generation.jpg b/content/growth/identity-management-critical-revenue-generation/revenue-generation.jpg deleted file mode 100644 index b104f996c..000000000 Binary files a/content/growth/identity-management-critical-revenue-generation/revenue-generation.jpg and /dev/null differ diff --git a/content/growth/identity-management-critical-revenue-generation/revenue-generation.webp b/content/growth/identity-management-critical-revenue-generation/revenue-generation.webp new file mode 100644 index 000000000..45eaea07c Binary files /dev/null and b/content/growth/identity-management-critical-revenue-generation/revenue-generation.webp differ diff --git a/content/growth/identity-management-for-better-cx/EB-omnichannel.png b/content/growth/identity-management-for-better-cx/EB-omnichannel.png deleted file mode 100644 index f5fa0b0f9..000000000 Binary files a/content/growth/identity-management-for-better-cx/EB-omnichannel.png and /dev/null differ diff --git a/content/growth/identity-management-for-better-cx/EB-omnichannel.webp b/content/growth/identity-management-for-better-cx/EB-omnichannel.webp new file mode 100644 index 000000000..b0761321e Binary files /dev/null and b/content/growth/identity-management-for-better-cx/EB-omnichannel.webp differ diff --git a/content/growth/identity-management-for-better-cx/id-cx.jpg b/content/growth/identity-management-for-better-cx/id-cx.jpg deleted file mode 100644 index f63f28934..000000000 Binary files a/content/growth/identity-management-for-better-cx/id-cx.jpg and /dev/null differ diff --git a/content/growth/identity-management-for-better-cx/id-cx.webp b/content/growth/identity-management-for-better-cx/id-cx.webp new file mode 100644 index 000000000..6896847e6 Binary files /dev/null and b/content/growth/identity-management-for-better-cx/id-cx.webp differ diff --git a/content/growth/identity-management-for-better-cx/index.md b/content/growth/identity-management-for-better-cx/index.md index ded3b7ed8..228150f41 100644 --- a/content/growth/identity-management-for-better-cx/index.md +++ b/content/growth/identity-management-for-better-cx/index.md @@ -1,7 +1,7 @@ --- title: "How To Use Identity To Make Your Customers Feel Safe And Empowered?" date: "2022-10-28" -coverImage: "id-cx.jpg" +coverImage: "id-cx.webp" category: ["identity management", "cx", "data security"] author: "Navanita Devi" description: "It goes without saying that excellent UX can improve conversion rates, reduce churn and increase adoption rates. In this blog post, we'll help you figure out how to use digital identity to improve your relationships with customers and make them feel more confident in their interactions with you." @@ -37,7 +37,7 @@ They want to be able to access their information from any device at any time, wh A CIAM improves the omnichannel experience for its customers by making them feel safe and empowered. All they need to do is provide them with one login that works across all their devices and channels. -[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) +[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) ### 3. Balancing between user experience and security @@ -75,4 +75,4 @@ In the end, CIAM is all about driving revenue. A good CIAM solution can deliver But if you don't consider all components of your CIAM, you'll miss out on valuable benefits for both businesses and consumers. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-for-better-cx) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-for-better-cx) diff --git a/content/growth/identity-management-for-better-cx/omni-eb.png b/content/growth/identity-management-for-better-cx/omni-eb.png deleted file mode 100644 index 86c15a159..000000000 Binary files a/content/growth/identity-management-for-better-cx/omni-eb.png and /dev/null differ diff --git a/content/growth/identity-management-for-better-cx/omni-eb.webp b/content/growth/identity-management-for-better-cx/omni-eb.webp new file mode 100644 index 000000000..025782e92 Binary files /dev/null and b/content/growth/identity-management-for-better-cx/omni-eb.webp differ diff --git a/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.png b/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.png deleted file mode 100644 index f97184f2f..000000000 Binary files a/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.png and /dev/null differ diff --git a/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.webp b/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.webp new file mode 100644 index 000000000..88d19cbb8 Binary files /dev/null and b/content/growth/identity-management-reduce-cpa-marketers/EB-Progressive-profiling.webp differ diff --git a/content/growth/identity-management-reduce-cpa-marketers/cpa-market.jpg b/content/growth/identity-management-reduce-cpa-marketers/cpa-market.jpg deleted file mode 100644 index 0c31a2593..000000000 Binary files a/content/growth/identity-management-reduce-cpa-marketers/cpa-market.jpg and /dev/null differ diff --git a/content/growth/identity-management-reduce-cpa-marketers/cpa-market.webp b/content/growth/identity-management-reduce-cpa-marketers/cpa-market.webp new file mode 100644 index 000000000..635df37b8 Binary files /dev/null and b/content/growth/identity-management-reduce-cpa-marketers/cpa-market.webp differ diff --git a/content/growth/identity-management-reduce-cpa-marketers/index.md b/content/growth/identity-management-reduce-cpa-marketers/index.md index 0fe9000d7..8b16c2a05 100644 --- a/content/growth/identity-management-reduce-cpa-marketers/index.md +++ b/content/growth/identity-management-reduce-cpa-marketers/index.md @@ -1,7 +1,7 @@ --- title: "Planning to Reduce Your CPA By 50%? You Need ID Management" date: "2022-07-06" -coverImage: "cpa-market.jpg" +coverImage: "cpa-market.webp" category: ["cost per acquisition", "identity management", "marketing"] author: "Navanita Devi" description: "An essential marketing requirement is to know your customers first and then learn about their preferences. With a reliable CIAM system, marketers need not worry about collecting valuable customer insights; CIAM does it all without burning a pocket! Let’s understand how." @@ -59,7 +59,7 @@ Collecting unnecessary data wastes resources and increases the risk of identity With a reliable CIAM, businesses can leverage the true potential of progressive profiling. -[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) +[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) Progressive profiling for customer registration allows you to split a potentially complicated registration process into multiple steps. You can capture a customer’s information upfront and then slowly build a holistic view of that customer through subsequent actions. @@ -75,4 +75,4 @@ Apart from reducing the cost per acquisition, businesses can ensure robust custo Hence, if a business wishes to succeed with minimum investment, it must leverage the true potential of a CIAM solution. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-reduce-cpa-marketers) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-management-reduce-cpa-marketers) diff --git a/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.png b/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.png deleted file mode 100644 index c9ad88d9e..000000000 Binary files a/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.png and /dev/null differ diff --git a/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.webp b/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.webp new file mode 100644 index 000000000..2b537fe1a Binary files /dev/null and b/content/growth/identity-management-reduce-cpa-marketers/progressive-eb.webp differ diff --git a/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.png b/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.png deleted file mode 100644 index ccf2bf5b2..000000000 Binary files a/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.png and /dev/null differ diff --git a/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.webp b/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.webp new file mode 100644 index 000000000..1c92d79a3 Binary files /dev/null and b/content/growth/identity-proofing-orchestration-security/DS-id-orchestration.webp differ diff --git a/content/growth/identity-proofing-orchestration-security/id-proofing.jpg b/content/growth/identity-proofing-orchestration-security/id-proofing.jpg deleted file mode 100644 index d199f04dd..000000000 Binary files a/content/growth/identity-proofing-orchestration-security/id-proofing.jpg and /dev/null differ diff --git a/content/growth/identity-proofing-orchestration-security/id-proofing.webp b/content/growth/identity-proofing-orchestration-security/id-proofing.webp new file mode 100644 index 000000000..a566fc9a8 Binary files /dev/null and b/content/growth/identity-proofing-orchestration-security/id-proofing.webp differ diff --git a/content/growth/identity-proofing-orchestration-security/index.md b/content/growth/identity-proofing-orchestration-security/index.md index 52522cb61..2f0e8569e 100644 --- a/content/growth/identity-proofing-orchestration-security/index.md +++ b/content/growth/identity-proofing-orchestration-security/index.md @@ -1,7 +1,7 @@ --- title: "Mastering Orchestration: The Business Case for End-to-End Identity Proofing Solutions" date: "2024-08-12" -coverImage: "id-proofing.jpg" +coverImage: "id-proofing.webp" tags: ["identity orchestration","identity proofing","cx"] author: "Cooper Matheson" description: "In the rapidly evolving digital landscape, businesses are turning to comprehensive identity-proofing solutions to bolster security, ensure compliance, and enhance customer experiences. By leveraging orchestration, companies can streamline identity verification processes, reduce fraud, and build trust with their users." @@ -52,7 +52,7 @@ A streamlined and efficient identity verification process is crucial for providi With orchestration, businesses can reduce the time and effort required for users to prove their identities, leading to higher satisfaction and loyalty. Automated processes also minimize the risk of false positives, ensuring unnecessary security hurdles do not inconvenience legitimate users. -[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/) +[](https://www.loginradius.com/resource/datasheet/identity-orchestration-workflow/) ### 4. Cost Efficiency @@ -70,4 +70,4 @@ In a world where digital interactions are becoming the norm, businesses must pri By embracing comprehensive identity proofing solutions through orchestration, companies can enhance security, ensure compliance, and deliver a superior customer experience. As cyber threats continue to evolve, the adoption of orchestration will be crucial for businesses looking to stay ahead of the curve. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-proofing-orchestration-security) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-proofing-orchestration-security) \ No newline at end of file diff --git a/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.png b/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.png deleted file mode 100644 index 9ecea83f3..000000000 Binary files a/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.png and /dev/null differ diff --git a/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.webp b/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.webp new file mode 100644 index 000000000..ec4419e57 Binary files /dev/null and b/content/growth/identity-resolution-data-accuracy/WP-digital-transformation-ecommerce.webp differ diff --git a/content/growth/identity-resolution-data-accuracy/identity-resolution.jpg b/content/growth/identity-resolution-data-accuracy/identity-resolution.jpg deleted file mode 100644 index 6a3543298..000000000 Binary files a/content/growth/identity-resolution-data-accuracy/identity-resolution.jpg and /dev/null differ diff --git a/content/growth/identity-resolution-data-accuracy/identity-resolution.webp b/content/growth/identity-resolution-data-accuracy/identity-resolution.webp new file mode 100644 index 000000000..e8329f3c8 Binary files /dev/null and b/content/growth/identity-resolution-data-accuracy/identity-resolution.webp differ diff --git a/content/growth/identity-resolution-data-accuracy/idntity-resolution.jpg b/content/growth/identity-resolution-data-accuracy/idntity-resolution.jpg deleted file mode 100644 index e9cddd843..000000000 Binary files a/content/growth/identity-resolution-data-accuracy/idntity-resolution.jpg and /dev/null differ diff --git a/content/growth/identity-resolution-data-accuracy/idntity-resolution.webp b/content/growth/identity-resolution-data-accuracy/idntity-resolution.webp new file mode 100644 index 000000000..689bcd98e Binary files /dev/null and b/content/growth/identity-resolution-data-accuracy/idntity-resolution.webp differ diff --git a/content/growth/identity-resolution-data-accuracy/index.md b/content/growth/identity-resolution-data-accuracy/index.md index b84a2bb80..dd8e80ec1 100644 --- a/content/growth/identity-resolution-data-accuracy/index.md +++ b/content/growth/identity-resolution-data-accuracy/index.md @@ -1,7 +1,7 @@ --- title: "Elevating Data Precision-Power of Identity Resolution" date: "2023-10-12" -coverImage: "identity-resolution.jpg" +coverImage: "identity-resolution.webp" tags: ["data governance","e-commerce","identity resolution"] author: "Vishal Sharma" description: "Dive into the world of identity resolution and learn how businesses connect data dots, ensuring precision in every interaction. Uncover real-life examples in healthcare and retail and understand the challenges organizations face. Embrace these techniques for unparalleled success in today's competitive landscape." @@ -38,7 +38,7 @@ Accurate data is the foundation of numerous business operations, and identity re 2. **Retail and Marketing:** In the retail industry, identity resolution can be a game-changer for understanding customer behavior. Let's say a customer shop online, subscribes to a newsletter, and makes in-store purchases. By accurately resolving the identity of this customer across different channels, the retailer can gain insights into their preferences and habits, allowing for targeted marketing campaigns that resonate with the customer's interests. -[](https://www.loginradius.com/resource/digital-transformation-retail-ecommerce-whitepaper) +[](https://www.loginradius.com/resource/digital-transformation-retail-ecommerce-whitepaper) ### Considerations in Identity Resolution @@ -54,4 +54,4 @@ From delivering personalized customer experiences to enhancing risk management, By embracing these techniques and addressing the associated challenges, organizations can unlock a new level of efficiency and effectiveness in their operations, ultimately leading to tremendous success in today's competitive landscape. As technology evolves, identity resolution will remain a cornerstone of data accuracy and a driving force behind data-driven innovation. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-resolution-data-accuracy) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-resolution-data-accuracy) diff --git a/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.png b/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.png deleted file mode 100644 index a7a656cfa..000000000 Binary files a/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.png and /dev/null differ diff --git a/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.webp b/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.webp new file mode 100644 index 000000000..44c9529c0 Binary files /dev/null and b/content/growth/identity-security-digital-trade/EB-LR-GDPR-Compliance.webp differ diff --git a/content/growth/identity-security-digital-trade/identity-security.jpg b/content/growth/identity-security-digital-trade/identity-security.jpg deleted file mode 100644 index 76c59a1fa..000000000 Binary files a/content/growth/identity-security-digital-trade/identity-security.jpg and /dev/null differ diff --git a/content/growth/identity-security-digital-trade/identity-security.webp b/content/growth/identity-security-digital-trade/identity-security.webp new file mode 100644 index 000000000..0b58e590e Binary files /dev/null and b/content/growth/identity-security-digital-trade/identity-security.webp differ diff --git a/content/growth/identity-security-digital-trade/index.md b/content/growth/identity-security-digital-trade/index.md index ccfad5738..96903c3c4 100644 --- a/content/growth/identity-security-digital-trade/index.md +++ b/content/growth/identity-security-digital-trade/index.md @@ -1,7 +1,7 @@ --- title: "Can Cybersecurity Be a Unifying Factor in Digital Trade Negotiations?" date: "2024-06-05" -coverImage: "identity-security.jpg" +coverImage: "identity-security.webp" tags: ["cybersecurity","data security","ciam solutions"] author: "Karl Wittig" description: "Cybersecurity is crucial for safeguarding digital trade in the interconnected digital economy. This article explores how identity security, supported by robust Customer Identity Management (CIAM) solutions, can unify global digital trade negotiations by building trust and establishing common security standards." @@ -46,7 +46,7 @@ A robust Customer Identity Management (CIAM) solution plays a pivotal role in ac 2. **Data Privacy and Compliance**: CIAM systems help businesses comply with [data governance](https://www.loginradius.com/data-governance/) regulations such as GDPR and CCPA. They ensure that customer data is collected, stored, and processed in accordance with legal requirements, thereby fostering trust and reducing the risk of regulatory penalties. -[](https://www.loginradius.com/resource/ebook/loginradius-gdpr-compliance/) +[](https://www.loginradius.com/resource/ebook/loginradius-gdpr-compliance/) 3. **User Experience**: A robust CIAM solution balances security with user experience. It provides a frictionless login process, personalized experiences, and consistent access across multiple channels, enhancing customer satisfaction and loyalty. @@ -60,4 +60,4 @@ A robust Customer Identity Management (CIAM) solution, like LoginRadius, is cri As digital trade grows, cybersecurity will undoubtedly play a central role in shaping its future, unifying diverse stakeholders in pursuing a safe and reliable digital world. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-security-digital-trade) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-security-digital-trade) diff --git a/content/growth/identity-verification-in-customer-journey/GD-to-RBA.png b/content/growth/identity-verification-in-customer-journey/GD-to-RBA.png deleted file mode 100644 index 0d7046172..000000000 Binary files a/content/growth/identity-verification-in-customer-journey/GD-to-RBA.png and /dev/null differ diff --git a/content/growth/identity-verification-in-customer-journey/GD-to-RBA.webp b/content/growth/identity-verification-in-customer-journey/GD-to-RBA.webp new file mode 100644 index 000000000..ea0737a8b Binary files /dev/null and b/content/growth/identity-verification-in-customer-journey/GD-to-RBA.webp differ diff --git a/content/growth/identity-verification-in-customer-journey/identity-verification.jpg b/content/growth/identity-verification-in-customer-journey/identity-verification.jpg deleted file mode 100644 index 6ee78d5bb..000000000 Binary files a/content/growth/identity-verification-in-customer-journey/identity-verification.jpg and /dev/null differ diff --git a/content/growth/identity-verification-in-customer-journey/identity-verification.webp b/content/growth/identity-verification-in-customer-journey/identity-verification.webp new file mode 100644 index 000000000..bbeac7a5a Binary files /dev/null and b/content/growth/identity-verification-in-customer-journey/identity-verification.webp differ diff --git a/content/growth/identity-verification-in-customer-journey/index.md b/content/growth/identity-verification-in-customer-journey/index.md index 1a0768124..1d9c5e683 100644 --- a/content/growth/identity-verification-in-customer-journey/index.md +++ b/content/growth/identity-verification-in-customer-journey/index.md @@ -1,7 +1,7 @@ --- title: "Achieving Harmony: Balancing Identity Verification in the Customer Journey" date: "2023-06-07" -coverImage: "identity-verification.jpg" +coverImage: "identity-verification.webp" tags: ["identity verification","ciam authentication","cx"] author: "Vishal Sharma" description: "In today's digital landscape, businesses face the challenge of balancing identity verification throughout the customer journey. This blog dives into the complexities and offers actionable strategies to achieve harmony. Find out how to balance security and user experience, fostering trust and driving long-term success." @@ -37,7 +37,7 @@ Here’s the list of actionable strategies that businesses can employ to achieve Adopting a risk-based approach allows businesses to calibrate the verification level according to the perceived risk associated with each interaction. By tailoring verification requirements based on factors such as transaction value, user behavior, and historical data, businesses can strike a balance between security and user experience. -[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) +[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) ### Leveraging advanced authentication technologies @@ -77,4 +77,4 @@ Organizations can foster trust, enhance customer satisfaction, and drive long-te Through the strategic implementation of technology, adaptive verification processes, and a customer-centric approach, businesses can navigate the complexities of identity verification while ensuring a pleasant customer journey in today's digital landscape. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-verification-in-customer-journey) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-verification-in-customer-journey) diff --git a/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.png b/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.png deleted file mode 100644 index dac7c2e34..000000000 Binary files a/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.png and /dev/null differ diff --git a/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.webp b/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.webp new file mode 100644 index 000000000..a6fdfd674 Binary files /dev/null and b/content/growth/identity-verification-retailers-benefits/GD-consumer-identity.webp differ diff --git a/content/growth/identity-verification-retailers-benefits/identity-verification.jpg b/content/growth/identity-verification-retailers-benefits/identity-verification.jpg deleted file mode 100644 index 2945a024c..000000000 Binary files a/content/growth/identity-verification-retailers-benefits/identity-verification.jpg and /dev/null differ diff --git a/content/growth/identity-verification-retailers-benefits/identity-verification.webp b/content/growth/identity-verification-retailers-benefits/identity-verification.webp new file mode 100644 index 000000000..c5a186c30 Binary files /dev/null and b/content/growth/identity-verification-retailers-benefits/identity-verification.webp differ diff --git a/content/growth/identity-verification-retailers-benefits/index.md b/content/growth/identity-verification-retailers-benefits/index.md index 705b2d86e..c5facb142 100644 --- a/content/growth/identity-verification-retailers-benefits/index.md +++ b/content/growth/identity-verification-retailers-benefits/index.md @@ -1,7 +1,7 @@ --- title: "Unveiling the Benefits of Identity Verification for Online Retailers " date: "2023-08-31" -coverImage: "identity-verification.jpg" +coverImage: "identity-verification.webp" tags: ["digital identity verification","compliance","cx"] author: "Vishal Sharma" description: "In the dynamic realm of online retail, establishing trust while countering cyber threats is paramount. Identity verification emerges as a game-changer, bolstering security, trust, compliance, and even personalization. Dive into the advantages it brings to businesses navigating the digital landscape." @@ -36,7 +36,7 @@ In an increasingly regulated digital landscape, businesses must adhere to strict Identity verification aids in complying with various data security and privacy regulations, ensuring that businesses operate within legal boundaries and avoid penalties. These regulations include the EU’s GDPR and California’s CCPA. -[](https://www.loginradius.com/resource/consumer-identity-in-challenges) +[](https://www.loginradius.com/resource/consumer-identity-in-challenges) ### 4. Reducing Chargebacks and False Positives @@ -86,4 +86,4 @@ Identity verification is a critical component of the online retail and financial Use cases encompass enhanced security, fraud prevention, regulatory compliance, personalized customer experiences, and operational efficiency. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-verification-retailers-benefits) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=identity-verification-retailers-benefits) \ No newline at end of file diff --git a/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.png b/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.png deleted file mode 100644 index 7cc78c915..000000000 Binary files a/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.png and /dev/null differ diff --git a/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.webp b/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.webp new file mode 100644 index 000000000..86276b545 Binary files /dev/null and b/content/growth/implement-continuous-authentication-business-value/WP-cont-auth.webp differ diff --git a/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.png b/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.png deleted file mode 100644 index 46e301e6d..000000000 Binary files a/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.png and /dev/null differ diff --git a/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.webp b/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.webp new file mode 100644 index 000000000..7a77e6d27 Binary files /dev/null and b/content/growth/implement-continuous-authentication-business-value/cont-auth-wp.webp differ diff --git a/content/growth/implement-continuous-authentication-business-value/cont-auth.jpg b/content/growth/implement-continuous-authentication-business-value/cont-auth.jpg deleted file mode 100644 index ff2f78591..000000000 Binary files a/content/growth/implement-continuous-authentication-business-value/cont-auth.jpg and /dev/null differ diff --git a/content/growth/implement-continuous-authentication-business-value/cont-auth.webp b/content/growth/implement-continuous-authentication-business-value/cont-auth.webp new file mode 100644 index 000000000..eb4f1c026 Binary files /dev/null and b/content/growth/implement-continuous-authentication-business-value/cont-auth.webp differ diff --git a/content/growth/implement-continuous-authentication-business-value/index.md b/content/growth/implement-continuous-authentication-business-value/index.md index bf4961f8f..0aafe2e57 100644 --- a/content/growth/implement-continuous-authentication-business-value/index.md +++ b/content/growth/implement-continuous-authentication-business-value/index.md @@ -1,7 +1,7 @@ --- title: "Implementing The Power Of Continuous Authentication for Boundless Business Value" date: "2022-01-04" -coverImage: "cont-auth.jpg" +coverImage: "cont-auth.webp" tags: ["continuous authentication","data security","cx"] author: "Rakesh Soni" description: "With advancements in technology and the increasing rate of cybercrimes, continuous authentication for business is gaining popularity in modern times. As a smarter and better authentication method, it can help in reducing the number of these attacks." @@ -42,7 +42,7 @@ Here's a list of the technologies used to implement continuous authentication: * **Behavioral biometrics** - Here, you can continuously [track a user's behavioral patterns](https://www.loginradius.com/blog/identity/biometric-authentication-mobile-apps/) like interactive gestures, typing style, finger pressure, how long a user holds a key on the keyboard, or how they swipe through the screen or hold the mouse. Variation from the normal behavioral patterns can then be marked. * **Voice Authentication** - You can monitor pitch and frequency variations in voice for continuous authentication. Also, deviations from ordinary qualities can be identified by constantly tracking input speech against a reference control conversation. -[](https://www.loginradius.com/resource/continuous-authentication-whitepaper) +[](https://www.loginradius.com/resource/continuous-authentication-whitepaper) ## Benefits and Drawbacks @@ -61,4 +61,4 @@ When executed the right way, it can massively enhance corporate security by decr After years of discussion and product development by security specialists, the concept of continuous authentication has emerged as a new wave in cybersecurity. And it is just the right time to embrace it! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=implement-continuous-authentication-business-value) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=implement-continuous-authentication-business-value) \ No newline at end of file diff --git a/content/growth/importance-customer-health-scoring-saas-businesses/index.md b/content/growth/importance-customer-health-scoring-saas-businesses/index.md index a35cc14cc..48d891ddb 100644 --- a/content/growth/importance-customer-health-scoring-saas-businesses/index.md +++ b/content/growth/importance-customer-health-scoring-saas-businesses/index.md @@ -1,7 +1,7 @@ --- title: "How Important is Customer Health Scoring for SaaS Business?" date: "2023-01-19" -coverImage: "saas-score.jpg" +coverImage: "saas-score.webp" tags: ["saas", "customer retention", "customer behavior"] author: "Yash Rathi" description: "A customer health score is an organization's metric to determine whether customers are healthy or at risk of churn. Based on the score of the individual customer, retention strategies are implemented." @@ -89,4 +89,4 @@ However, you can't simply add it as another feature and hope it'll work out magi You must understand that customer health scoring is a long-term investment with high returns. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=importance-customer-health-scoring-saas-businesses) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=importance-customer-health-scoring-saas-businesses) diff --git a/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.jpg b/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.jpg deleted file mode 100644 index 242f5950d..000000000 Binary files a/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.jpg and /dev/null differ diff --git a/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.webp b/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.webp new file mode 100644 index 000000000..cc1aa2d84 Binary files /dev/null and b/content/growth/importance-customer-health-scoring-saas-businesses/saas-score.webp differ diff --git a/content/growth/importance-customer-onboarding/customer-onboarding-importance.jpg b/content/growth/importance-customer-onboarding/customer-onboarding-importance.jpg deleted file mode 100644 index ba2a0f850..000000000 Binary files a/content/growth/importance-customer-onboarding/customer-onboarding-importance.jpg and /dev/null differ diff --git a/content/growth/importance-customer-onboarding/customer-onboarding-importance.webp b/content/growth/importance-customer-onboarding/customer-onboarding-importance.webp new file mode 100644 index 000000000..7f95f7302 Binary files /dev/null and b/content/growth/importance-customer-onboarding/customer-onboarding-importance.webp differ diff --git a/content/growth/importance-customer-onboarding/index.md b/content/growth/importance-customer-onboarding/index.md index efd525ac0..299ac32c3 100644 --- a/content/growth/importance-customer-onboarding/index.md +++ b/content/growth/importance-customer-onboarding/index.md @@ -1,7 +1,7 @@ --- title: "Customer Success: The Importance of Customer Onboarding" date: "2021-02-26" -coverImage: "customer-onboarding-importance.jpg" +coverImage: "customer-onboarding-importance.webp" tags: ["customer onboarding","authentication","cx"] author: "Karl Wittig" description: "Customer onboarding is one of the more delicate components of marketing. This process can make or break a business. In addition to increasing the revenue, it also allows businesses to create relationships with their customers." @@ -104,4 +104,4 @@ In addition to receiving free marketing, one will also understand their customer Customer onboarding is one of the more delicate components of marketing. This process can make or break a business. In addition to increasing the revenue, it also allows businesses to create relationships with their customers through surveys or even phone calls. The most significant benefits of customer onboarding are that an individual can have an unprecedented amount of faith in the company and product. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=importance-customer-onboarding) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=importance-customer-onboarding) diff --git a/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.png b/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.png deleted file mode 100644 index e794b3769..000000000 Binary files a/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.png and /dev/null differ diff --git a/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.webp b/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.webp new file mode 100644 index 000000000..371ef34ea Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/BD-Developers2-1024x310.webp differ diff --git a/content/growth/improve-customer-experience-ecommerce/customer-experience.jpg b/content/growth/improve-customer-experience-ecommerce/customer-experience.jpg deleted file mode 100644 index c7c694e0b..000000000 Binary files a/content/growth/improve-customer-experience-ecommerce/customer-experience.jpg and /dev/null differ diff --git a/content/growth/improve-customer-experience-ecommerce/customer-experience.webp b/content/growth/improve-customer-experience-ecommerce/customer-experience.webp new file mode 100644 index 000000000..23e7d7d9f Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/customer-experience.webp differ diff --git a/content/growth/improve-customer-experience-ecommerce/image-2.jpg b/content/growth/improve-customer-experience-ecommerce/image-2.jpg deleted file mode 100644 index ad3223120..000000000 Binary files a/content/growth/improve-customer-experience-ecommerce/image-2.jpg and /dev/null differ diff --git a/content/growth/improve-customer-experience-ecommerce/image-2.webp b/content/growth/improve-customer-experience-ecommerce/image-2.webp new file mode 100644 index 000000000..9b6043452 Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/image-2.webp differ diff --git a/content/growth/improve-customer-experience-ecommerce/image-3.jpg b/content/growth/improve-customer-experience-ecommerce/image-3.jpg deleted file mode 100644 index 2b22e710d..000000000 Binary files a/content/growth/improve-customer-experience-ecommerce/image-3.jpg and /dev/null differ diff --git a/content/growth/improve-customer-experience-ecommerce/image-3.webp b/content/growth/improve-customer-experience-ecommerce/image-3.webp new file mode 100644 index 000000000..c0d100f2a Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/image-3.webp differ diff --git a/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.jpg b/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.jpg deleted file mode 100644 index ce22930fc..000000000 Binary files a/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.jpg and /dev/null differ diff --git a/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.webp b/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.webp new file mode 100644 index 000000000..7448d2be5 Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/improve-customer-experience-ecommerce.webp differ diff --git a/content/growth/improve-customer-experience-ecommerce/index.md b/content/growth/improve-customer-experience-ecommerce/index.md index 636024c9f..d8a32a03b 100644 --- a/content/growth/improve-customer-experience-ecommerce/index.md +++ b/content/growth/improve-customer-experience-ecommerce/index.md @@ -1,7 +1,7 @@ --- title: "5 Ways to Enhance Customer Experience in E-commerce" date: "2019-11-28" -coverImage: "customer-experience.jpg" +coverImage: "customer-experience.webp" tags: ["cx", "ecommerce", "digital identity"] author: "Rakesh Soni" description: "A smart e-commerce customer service strategy is as critical as a marketing strategy when it comes to growing your business. You will get 360-degree customer profiling, with 100% customer consent, at all touchpoints, with a customer identity and access management solution." @@ -41,7 +41,7 @@ When it comes to providing a superior customer experience, "people" and "product Providing excellent mobile e-commerce (m-commerce) shopping [experience can benefit retailers](https://www.loginradius.com/blog/2020/05/customer-experience-retail-industry/) significantly. By 2021, m-commerce sales are expected to be responsible for 54% of overall e-commerce revenue, [predicts](https://www.bigcommerce.com/blog/mobile-commerce/#why-does-mobile-commerce-matter) Big Commerce. - + This is one of the reasons why your online retail store should be easily accessible on mobile devices, not just desktops and laptops. @@ -79,7 +79,7 @@ In short, integrating digital and traditional touchpoints using CIAM tools will **–** [**Rick Kenney**](https://twitter.com/rickkenney)**, Head of Consumer Insights, Salesforce** - + ### **3\. Emphasize the employee experience to boost customer retention.** @@ -113,7 +113,7 @@ No matter what e-commerce shopping experience you offer your customers, data sec What's worse is that most customers often don’t take the necessary steps to protect themselves. [CreditDonkey](https://www.creditdonkey.com/identity-theft-survey.html) reports that 68% of customers use the same password for multiple websites. That’s a good reason for you to be extra vigilant when building a secure e-commerce customer experience. Here’s how you can get started. - + ## Tips to protect e-commerce customer data @@ -134,4 +134,4 @@ What's worse is that most customers often don’t take the necessary steps to pr When it comes to growing your business, a smart e-commerce customer experience strategy is as important as a marketing strategy. With a customer identity and access management solution, you can get 360-degree customer profiling, with 100% customer consent, across all touchpoints. This allows you to personalize marketing and loyalty programs that engage your audience. And that’s a win-win for you and your customers. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=improve-customer-experience-ecommerce) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=improve-customer-experience-ecommerce) diff --git a/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.jpg b/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.jpg deleted file mode 100644 index 9ba0bbabe..000000000 Binary files a/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.jpg and /dev/null differ diff --git a/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.webp b/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.webp new file mode 100644 index 000000000..38ac2509a Binary files /dev/null and b/content/growth/improve-customer-experience-ecommerce/shopping-bags-XMAS_blog-300x150.webp differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/hospitality.jpg b/content/growth/improve-customer-experience-hospitality-industry/hospitality.jpg deleted file mode 100644 index e35eb8efd..000000000 Binary files a/content/growth/improve-customer-experience-hospitality-industry/hospitality.jpg and /dev/null differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/hospitality.webp b/content/growth/improve-customer-experience-hospitality-industry/hospitality.webp new file mode 100644 index 000000000..989ec4212 Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/hospitality.webp differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/image2-1.png b/content/growth/improve-customer-experience-hospitality-industry/image2-1.png deleted file mode 100644 index f17e3d6aa..000000000 Binary files a/content/growth/improve-customer-experience-hospitality-industry/image2-1.png and /dev/null differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/image2-1.webp b/content/growth/improve-customer-experience-hospitality-industry/image2-1.webp new file mode 100644 index 000000000..c1a39bba2 Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/image2-1.webp differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/image3-1.png b/content/growth/improve-customer-experience-hospitality-industry/image3-1.png deleted file mode 100644 index 5fd3cb530..000000000 Binary files a/content/growth/improve-customer-experience-hospitality-industry/image3-1.png and /dev/null differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/image3-1.webp b/content/growth/improve-customer-experience-hospitality-industry/image3-1.webp new file mode 100644 index 000000000..4a7ca7fef Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/image3-1.webp differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/image4-1.png b/content/growth/improve-customer-experience-hospitality-industry/image4-1.png deleted file mode 100644 index ca9006b5a..000000000 Binary files a/content/growth/improve-customer-experience-hospitality-industry/image4-1.png and /dev/null differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/image4-1.webp b/content/growth/improve-customer-experience-hospitality-industry/image4-1.webp new file mode 100644 index 000000000..011dbd014 Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/image4-1.webp differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/image5-1.png b/content/growth/improve-customer-experience-hospitality-industry/image5-1.png deleted file mode 100644 index 4922420fd..000000000 Binary files a/content/growth/improve-customer-experience-hospitality-industry/image5-1.png and /dev/null differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/image5-1.webp b/content/growth/improve-customer-experience-hospitality-industry/image5-1.webp new file mode 100644 index 000000000..437fd7a9c Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/image5-1.webp differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.png b/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.png deleted file mode 100644 index 155ded62b..000000000 Binary files a/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.png and /dev/null differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.webp b/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.webp new file mode 100644 index 000000000..9c97d4ed9 Binary files /dev/null and b/content/growth/improve-customer-experience-hospitality-industry/improve-customer-experience-hospitality-industry.webp differ diff --git a/content/growth/improve-customer-experience-hospitality-industry/index.md b/content/growth/improve-customer-experience-hospitality-industry/index.md index a745af9e9..745515f9e 100644 --- a/content/growth/improve-customer-experience-hospitality-industry/index.md +++ b/content/growth/improve-customer-experience-hospitality-industry/index.md @@ -1,7 +1,7 @@ --- title: "Improving Customer Experience in the Hospitality Industry" date: "2020-03-13" -coverImage: "hospitality.jpg" +coverImage: "hospitality.webp" tags: ["digital transformation","cx","ciam solution"] author: "Rakesh Soni" description: "It has always been about luxury, pleasure, and excellent customer service in the hospitality industry. Modern guests travel for both company and fun. They also want business owners to better connect and understand them well." @@ -50,7 +50,7 @@ IoT solutions for hotels will add extra oomph to customer experience in 2020. At the core of the hospitality industry lies the ultimate guest experience. People love to feel special – a reason why the concept of customization went mainstream. Blending hospitality with IoT will do [wonders for hotel operators](https://www.ezeeabsolute.com/blog/iot-in-hospitality-industry/). - + Wondering how? Let’s find out. @@ -85,7 +85,7 @@ Augmented Reality, on the other hand, simulates real-world surroundings with dig The hospitality industry can use it to its [advantage in a number of ways](https://www.revfine.com/augmented-reality-hospitality-industry/). Imagine the walls of your room are infused with AR-powered technology. At the tap of a button, it can transform into any surrounding (beach, forest, cloud, city heights) you like and let you enjoy the experience without actually being physically present. - + ### 5\. Digital registration forms will replace the use of pen and paper @@ -105,7 +105,7 @@ Simply put, data security is a crucial metric for hotel owners. Guests should ne Henceforth, advanced identity management policies, coupled with frictionless verification should make security seem effortless. -[](https://www.loginradius.com/resource/how-travel-and-leisure-companies-use-loginradius-identity-solution/) +[](https://www.loginradius.com/resource/how-travel-and-leisure-companies-use-loginradius-identity-solution/) When your business revolves around accommodating customer preferences, the need for identity verification becomes crucial. LoginRadius is a [customer identity and access management](https://www.loginradius.com/blog/2019/06/customer-identity-and-access-management/) (CIAM) platform that helps hotel owners to roll out strict security policies while offering excellent customer experiences. @@ -115,7 +115,7 @@ With LoginRadius, here’s what you can offer your customers: The hospitality industry is a booming market at the moment. With intense competition happening at the backdrop, taking charge of internal processes and increasing security within the hotel staff has become more crucial than ever. - + Looking ahead, LoginRadius’ biometric technology will help you: @@ -146,4 +146,4 @@ Most businesses in the hospitality sector offer complex ownership structures. He After all, the hospitality industry is all about customer experiences and keeping up with their changing expectations. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=improve-customer-experience-hospitality-industry) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=improve-customer-experience-hospitality-industry) diff --git a/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.png b/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.png deleted file mode 100644 index 74eef3e01..000000000 Binary files a/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.png and /dev/null differ diff --git a/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.webp b/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.webp new file mode 100644 index 000000000..cae55baf0 Binary files /dev/null and b/content/growth/improve-customer-relation-brand-identity/EB-GD-to-Mod-Cust-Id.webp differ diff --git a/content/growth/improve-customer-relation-brand-identity/brand-identity.jpg b/content/growth/improve-customer-relation-brand-identity/brand-identity.jpg deleted file mode 100644 index 5b4f56318..000000000 Binary files a/content/growth/improve-customer-relation-brand-identity/brand-identity.jpg and /dev/null differ diff --git a/content/growth/improve-customer-relation-brand-identity/brand-identity.webp b/content/growth/improve-customer-relation-brand-identity/brand-identity.webp new file mode 100644 index 000000000..d28d93001 Binary files /dev/null and b/content/growth/improve-customer-relation-brand-identity/brand-identity.webp differ diff --git a/content/growth/improve-customer-relation-brand-identity/index.md b/content/growth/improve-customer-relation-brand-identity/index.md index f6c7eac44..d2ce14cb4 100644 --- a/content/growth/improve-customer-relation-brand-identity/index.md +++ b/content/growth/improve-customer-relation-brand-identity/index.md @@ -1,7 +1,7 @@ --- title: "How to Create Brand Identity to Attract More Customers" date: "2022-02-04" -coverImage: "brand-identity.jpg" +coverImage: "brand-identity.webp" tags: ["identity management","customer identity","cx"] author: "Mike Abelson" description: "Branding is composed of so much more other than just your logo and chosen brand colors. Developing customer identity is also a must when it comes to getting your brand out for consumers. These tips will help you refine your branding to suit the goals of your business." @@ -39,7 +39,7 @@ Aside from that, don’t forget to develop who your -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=product-marketing-tips-for-b2c) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=product-marketing-tips-for-b2c) diff --git a/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.png b/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.png deleted file mode 100644 index f97184f2f..000000000 Binary files a/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.png and /dev/null differ diff --git a/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.webp b/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.webp new file mode 100644 index 000000000..88d19cbb8 Binary files /dev/null and b/content/growth/progressive-profiling-lead-generation-tool/EB-progressive-profiling.webp differ diff --git a/content/growth/progressive-profiling-lead-generation-tool/index.md b/content/growth/progressive-profiling-lead-generation-tool/index.md index 62bcb562d..8d6c0401e 100644 --- a/content/growth/progressive-profiling-lead-generation-tool/index.md +++ b/content/growth/progressive-profiling-lead-generation-tool/index.md @@ -1,7 +1,7 @@ --- title: "How Progressive Profiling Reduces Registration Fatigue and Improves Lead Quality?" date: "2022-07-15" -coverImage: "lead-gen.jpg" +coverImage: "lead-gen.webp" category: ["Progressive profiling", "lead generation", "marketing"] author: "Vishal Sharma" description: "Progressive profiling ensures valuable information about a user is gradually collected over time so that it doesn’t create friction while a user lands on a platform, which enhances the overall quality and number of leads. This blog explains the role of progressive profiling in improving overall lead quality and quantity." @@ -38,7 +38,7 @@ In this way, digital marketing teams obtain several data points about a lead wit Hence, if a business strives for quality leads, it must incorporate the true potential of progressive profiling that eventually helps generate quality leads. -[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) +[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) ## Why Your Business Needs Progressive Profiling in 2022 and Beyond @@ -90,4 +90,4 @@ And if customers are bombarded with registration forms when they land on your we Progressive profiling is undeniably the best way to nurture and improve the quality of leads, which helps businesses enhance their overall growth and revenues. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=progressive-profiling-lead-generation-tool) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=progressive-profiling-lead-generation-tool) diff --git a/content/growth/progressive-profiling-lead-generation-tool/lead-gen.jpg b/content/growth/progressive-profiling-lead-generation-tool/lead-gen.jpg deleted file mode 100644 index e41f93a37..000000000 Binary files a/content/growth/progressive-profiling-lead-generation-tool/lead-gen.jpg and /dev/null differ diff --git a/content/growth/progressive-profiling-lead-generation-tool/lead-gen.webp b/content/growth/progressive-profiling-lead-generation-tool/lead-gen.webp new file mode 100644 index 000000000..7060dfb70 Binary files /dev/null and b/content/growth/progressive-profiling-lead-generation-tool/lead-gen.webp differ diff --git a/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.png b/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.png deleted file mode 100644 index c9ad88d9e..000000000 Binary files a/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.png and /dev/null differ diff --git a/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.webp b/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.webp new file mode 100644 index 000000000..2b537fe1a Binary files /dev/null and b/content/growth/progressive-profiling-lead-generation-tool/progressive-profiling.webp differ diff --git a/content/growth/protect-digital-customer-onboarding-deepfakes/cta.png b/content/growth/protect-digital-customer-onboarding-deepfakes/cta.png deleted file mode 100644 index c1f47d8bc..000000000 Binary files a/content/growth/protect-digital-customer-onboarding-deepfakes/cta.png and /dev/null differ diff --git a/content/growth/protect-digital-customer-onboarding-deepfakes/cta.webp b/content/growth/protect-digital-customer-onboarding-deepfakes/cta.webp new file mode 100644 index 000000000..89e798f06 Binary files /dev/null and b/content/growth/protect-digital-customer-onboarding-deepfakes/cta.webp differ diff --git a/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.jpg b/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.jpg deleted file mode 100644 index 35a771ea3..000000000 Binary files a/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.jpg and /dev/null differ diff --git a/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.webp b/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.webp new file mode 100644 index 000000000..4008d695e Binary files /dev/null and b/content/growth/protect-digital-customer-onboarding-deepfakes/deepfake.webp differ diff --git a/content/growth/protect-digital-customer-onboarding-deepfakes/index.md b/content/growth/protect-digital-customer-onboarding-deepfakes/index.md index 8f34f544b..f2b7ed986 100644 --- a/content/growth/protect-digital-customer-onboarding-deepfakes/index.md +++ b/content/growth/protect-digital-customer-onboarding-deepfakes/index.md @@ -1,7 +1,7 @@ --- title: "Strengthening Digital Customer Onboarding to Combat Deep Fakes" date: "2024-07-15" -coverImage: "deepfake.jpg" +coverImage: "deepfake.webp" tags: ["customer onboarding", "cx", "deepfake", "authentication"] author: "Kundan Singh" description: "As deepfake technology advances, the risk of fraudulent activities in digital customer onboarding increases. This article explores how to safeguard your onboarding processes against deepfakes, ensuring a secure and trustworthy experience for your customers." @@ -82,7 +82,7 @@ In digital onboarding, deepfakes can be used to impersonate individuals, potenti - Allocate resources to acquire and integrate advanced identity verification and deepfake detection technologies. -[](https://www.loginradius.com/resource/whitepaper/identity-management-data-governance/) +[](https://www.loginradius.com/resource/whitepaper/identity-management-data-governance/) - Prioritize systems that offer scalability and adaptability to future advancements in deepfake techniques. diff --git a/content/growth/publishers-start-using-single-sign-on/DS-SSO.png b/content/growth/publishers-start-using-single-sign-on/DS-SSO.png deleted file mode 100644 index 8c6f3fcdd..000000000 Binary files a/content/growth/publishers-start-using-single-sign-on/DS-SSO.png and /dev/null differ diff --git a/content/growth/publishers-start-using-single-sign-on/DS-SSO.webp b/content/growth/publishers-start-using-single-sign-on/DS-SSO.webp new file mode 100644 index 000000000..465df5f3d Binary files /dev/null and b/content/growth/publishers-start-using-single-sign-on/DS-SSO.webp differ diff --git a/content/growth/publishers-start-using-single-sign-on/SSO-LR.png b/content/growth/publishers-start-using-single-sign-on/SSO-LR.png deleted file mode 100644 index 25ea42026..000000000 Binary files a/content/growth/publishers-start-using-single-sign-on/SSO-LR.png and /dev/null differ diff --git a/content/growth/publishers-start-using-single-sign-on/SSO-LR.webp b/content/growth/publishers-start-using-single-sign-on/SSO-LR.webp new file mode 100644 index 000000000..015f518c5 Binary files /dev/null and b/content/growth/publishers-start-using-single-sign-on/SSO-LR.webp differ diff --git a/content/growth/publishers-start-using-single-sign-on/index.md b/content/growth/publishers-start-using-single-sign-on/index.md index d79500e47..a188f08d4 100644 --- a/content/growth/publishers-start-using-single-sign-on/index.md +++ b/content/growth/publishers-start-using-single-sign-on/index.md @@ -1,7 +1,7 @@ --- title: "5 Reasons Why Publishers Should (Seriously) Consider Using SSO" date: "2022-09-20" -coverImage: "sso-publish.jpg" +coverImage: "sso-publish.webp" tags: ["sso","data privacy","cx"] author: "Navanita Devi" description: "Single sign-on allows publishers to seamlessly integrate their existing subscription services into one platform so they can collect first party data without having to worry about anything else." @@ -46,7 +46,7 @@ With single sign-on, there’s no need for third parties by design; everything h The ability to track user behavior across multiple platforms allows publishers to offer customized content and advertising that is relevant to each individual reader's interests. This helps publishers retain loyal readers who value having access to personalized content and ads. -[](https://www.loginradius.com/resource/loginradius-single-sign-on/) +[](https://www.loginradius.com/resource/loginradius-single-sign-on/) ### 5. Combine seamless digitization with data privacy for reader trust @@ -58,4 +58,4 @@ Publishers can benefit from SSO technology by ensuring data protection and provi So, there you have it. SSO is a great way to improve the user experience and boost conversions on your site. If you're looking to implement a solution that will benefit your users, improve your bottom line, and make life easier for your team—all while being easy to manage—SSO is definitely worth considering. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=publishers-start-using-single-sign-on) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=publishers-start-using-single-sign-on) diff --git a/content/growth/publishers-start-using-single-sign-on/sso-publish.jpg b/content/growth/publishers-start-using-single-sign-on/sso-publish.jpg deleted file mode 100644 index 90420fd3e..000000000 Binary files a/content/growth/publishers-start-using-single-sign-on/sso-publish.jpg and /dev/null differ diff --git a/content/growth/publishers-start-using-single-sign-on/sso-publish.webp b/content/growth/publishers-start-using-single-sign-on/sso-publish.webp new file mode 100644 index 000000000..53ee253b6 Binary files /dev/null and b/content/growth/publishers-start-using-single-sign-on/sso-publish.webp differ diff --git a/content/growth/qr-code-in-marketing/index.md b/content/growth/qr-code-in-marketing/index.md index 12bfd4464..dd9cececf 100644 --- a/content/growth/qr-code-in-marketing/index.md +++ b/content/growth/qr-code-in-marketing/index.md @@ -1,7 +1,7 @@ --- title: "How QR Codes are Shaping the Future of Marketing" date: "2021-06-28" -coverImage: "qr-codes-digital-contactless-payments.jpg" +coverImage: "qr-codes-digital-contactless-payments.webp" tags: ["brand identity","smart authentication","cx"] author: "Vishal Sharma" description: "From redirecting customers to social media pages to asking them to leave feedback and review, enterprises can do a lot through a QR Code. This insightful read covers all the aspects that depict the role of QR codes in enhancing marketing for enterprises during uncertain times." @@ -82,4 +82,4 @@ There’s no second thought to the fact that the market for QR Codes is helping With correct marketing strategies, including adequate content placement and website responsiveness, marketers must quickly understand that just adding a QR Code won’t speed up sales. Also, adequate analysis strategies must be in place to trace the user behavior that can be further utilized to build personalized experiences for enhanced business growth during the uncertain times of COVID-19. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=qr-code-in-marketing) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=qr-code-in-marketing) diff --git a/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.jpg b/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.jpg deleted file mode 100644 index 0e2e83118..000000000 Binary files a/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.jpg and /dev/null differ diff --git a/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.webp b/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.webp new file mode 100644 index 000000000..8263b92e3 Binary files /dev/null and b/content/growth/qr-code-in-marketing/qr-codes-digital-contactless-payments.webp differ diff --git a/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.jpg b/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.jpg deleted file mode 100644 index 3304adc84..000000000 Binary files a/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.jpg and /dev/null differ diff --git a/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.webp b/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.webp new file mode 100644 index 000000000..274e5c9d6 Binary files /dev/null and b/content/growth/questions-to-ask-your-identity-provider-2022/id-provider.webp differ diff --git a/content/growth/questions-to-ask-your-identity-provider-2022/index.md b/content/growth/questions-to-ask-your-identity-provider-2022/index.md index 96a687b36..004d05374 100644 --- a/content/growth/questions-to-ask-your-identity-provider-2022/index.md +++ b/content/growth/questions-to-ask-your-identity-provider-2022/index.md @@ -1,7 +1,7 @@ --- title: "What Should You Ask Your Identity Provider in 2022" date: "2021-12-21" -coverImage: "id-provider.jpg" +coverImage: "id-provider.webp" category: ["all"] featured: false author: "Yash Rathi" @@ -144,4 +144,4 @@ However, LoginRadius offers endless possibilities and provides all the features, You can choose LoginRadius as your CIAM to witness substantial business growth. Reach us for a free personalized demo today. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=questions-to-ask-your-identity-provider-2022) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=questions-to-ask-your-identity-provider-2022) diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.png b/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.png deleted file mode 100644 index 0d7046172..000000000 Binary files a/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.png and /dev/null differ diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.webp b/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.webp new file mode 100644 index 000000000..ea0737a8b Binary files /dev/null and b/content/growth/reasons-business-needs-customer-identity-strategy/GD-to-RBA.webp differ diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.png b/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.png deleted file mode 100644 index c820cfc17..000000000 Binary files a/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.png and /dev/null differ diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.webp b/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.webp new file mode 100644 index 000000000..9cfe7e407 Binary files /dev/null and b/content/growth/reasons-business-needs-customer-identity-strategy/RBA-GD.webp differ diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.jpg b/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.jpg deleted file mode 100644 index 0b6edf8fa..000000000 Binary files a/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.jpg and /dev/null differ diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.webp b/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.webp new file mode 100644 index 000000000..774e707e5 Binary files /dev/null and b/content/growth/reasons-business-needs-customer-identity-strategy/customer-identity.webp differ diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.jpg b/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.jpg deleted file mode 100644 index b3384ebe4..000000000 Binary files a/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.jpg and /dev/null differ diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.webp b/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.webp new file mode 100644 index 000000000..4b7191c98 Binary files /dev/null and b/content/growth/reasons-business-needs-customer-identity-strategy/customer-idntity.webp differ diff --git a/content/growth/reasons-business-needs-customer-identity-strategy/index.md b/content/growth/reasons-business-needs-customer-identity-strategy/index.md index abf8ad4ab..ca4f2e0f7 100644 --- a/content/growth/reasons-business-needs-customer-identity-strategy/index.md +++ b/content/growth/reasons-business-needs-customer-identity-strategy/index.md @@ -1,7 +1,7 @@ --- title: "5 Reasons Why a Strong Customer Identity Strategy Can Benefit Your Business" date: "2023-03-22" -coverImage: "customer-idntity.jpg" +coverImage: "customer-idntity.webp" tags: ["customer identity management","data security","cx"] author: "Yash Rathi" description: "Whether deep consumer insights or delivering seamless and secure customer experiences, an identity management solution could help businesses stay ahead of the curve. Let’s uncover some of the top reasons your business needs an identity strategy." @@ -39,7 +39,7 @@ In today's digital age, cybersecurity threats are a constant concern for busines Whether multi-factor or risk-based, an identity management solution can reinforce authentication security even in the highest-risk environments. -[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) +[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) Adding multiple layers of authentication not only protects customers' personal information and helps build trust and credibility with customers, which can lead to increased loyalty and referrals. @@ -61,4 +61,4 @@ A customer identity strategy is critical for businesses that want to grow and su By personalizing experiences, gaining better customer insights, enhancing security, improving marketing ROI, and increasing customer loyalty, businesses can create a strong foundation for growth and long-term success. If you haven't already implemented a customer identity strategy, now is the time to start. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=reasons-business-needs-customer-identity-strategy) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=reasons-business-needs-customer-identity-strategy) \ No newline at end of file diff --git a/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.png b/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.png deleted file mode 100644 index 1f39a27f3..000000000 Binary files a/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.png and /dev/null differ diff --git a/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.webp b/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.webp new file mode 100644 index 000000000..8a8067f56 Binary files /dev/null and b/content/growth/risk-based-authentication-gaming-industry/GD-Adaptive-MFA.webp differ diff --git a/content/growth/risk-based-authentication-gaming-industry/index.md b/content/growth/risk-based-authentication-gaming-industry/index.md index 3ab84330e..f36fc7d2d 100644 --- a/content/growth/risk-based-authentication-gaming-industry/index.md +++ b/content/growth/risk-based-authentication-gaming-industry/index.md @@ -1,7 +1,7 @@ --- title: "Embracing Risk-Based Authentication in the Gaming Industry" date: "2021-10-18" -coverImage: "rba-gaming-cover.jpg" +coverImage: "rba-gaming-cover.webp" category: ["security"] featured: false author: "Navanita Devi" @@ -40,7 +40,7 @@ If the system detects any risk, then it follows either of the following measures * The system blocks the user if any risk is observed. * The system uses [multi-factor authentication](https://www.loginradius.com/blog/identity/multi-factor-authentication-a-beginners-guide/) to authenticate the user identity, i.e., using SMS or Google authenticator. -[](https://www.loginradius.com/resource/fixing-broken-authentication-with-adaptive-mfa/) +[](https://www.loginradius.com/resource/fixing-broken-authentication-with-adaptive-mfa/) ## How to Use RBA in the Gaming Industry @@ -86,4 +86,4 @@ An effective RBA can make a huge difference between a safe and unsafe gaming exp The focus is to confide the users' personal information, and with LoginRadius, you will find more than just one solution to your digital predicaments. [Contact us](https://www.loginradius.com/contact-sales) to know more. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=risk-based-authentication-gaming-industry) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=risk-based-authentication-gaming-industry) \ No newline at end of file diff --git a/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.jpg b/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.jpg deleted file mode 100644 index 92bbcae18..000000000 Binary files a/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.jpg and /dev/null differ diff --git a/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.webp b/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.webp new file mode 100644 index 000000000..279886fd7 Binary files /dev/null and b/content/growth/risk-based-authentication-gaming-industry/rba-gaming-cover.webp differ diff --git a/content/growth/role-cookieless-authentication-marketers/cookieless-auth.jpg b/content/growth/role-cookieless-authentication-marketers/cookieless-auth.jpg deleted file mode 100644 index a992f8755..000000000 Binary files a/content/growth/role-cookieless-authentication-marketers/cookieless-auth.jpg and /dev/null differ diff --git a/content/growth/role-cookieless-authentication-marketers/cookieless-auth.webp b/content/growth/role-cookieless-authentication-marketers/cookieless-auth.webp new file mode 100644 index 000000000..5ad759cba Binary files /dev/null and b/content/growth/role-cookieless-authentication-marketers/cookieless-auth.webp differ diff --git a/content/growth/role-cookieless-authentication-marketers/index.md b/content/growth/role-cookieless-authentication-marketers/index.md index cf3c861f5..3a92a2160 100644 --- a/content/growth/role-cookieless-authentication-marketers/index.md +++ b/content/growth/role-cookieless-authentication-marketers/index.md @@ -1,7 +1,7 @@ --- title: "The Peerless Role of Cookieless Identity Solution for Marketers" date: "2022-06-09" -coverImage: "cookieless-auth.jpg" +coverImage: "cookieless-auth.webp" category: ["marketing", "authentication", "ciam"] author: "Vishal Sharma" description: "With cookieless authentication, enterprises can leverage the true potential of a CIAM solution in marketing their products and services without compromising user experience. This post explains why businesses quickly need to put their best foot forward in adopting a cookieless authentication platform." @@ -80,4 +80,4 @@ Businesses can choose [a reliable CIAM platform](https://www.loginradius.com/blo -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-cookieless-authentication-marketers) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-cookieless-authentication-marketers) \ No newline at end of file diff --git a/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.png b/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.png deleted file mode 100644 index f97184f2f..000000000 Binary files a/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.png and /dev/null differ diff --git a/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.webp b/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.webp new file mode 100644 index 000000000..88d19cbb8 Binary files /dev/null and b/content/growth/role-it-marketing-customer-identity-management/EB-progressive-profiling.webp differ diff --git a/content/growth/role-it-marketing-customer-identity-management/index.md b/content/growth/role-it-marketing-customer-identity-management/index.md index be6f6ffc5..93e3b9ca2 100644 --- a/content/growth/role-it-marketing-customer-identity-management/index.md +++ b/content/growth/role-it-marketing-customer-identity-management/index.md @@ -1,7 +1,7 @@ --- title: "How IT and Marketing Go Hand-in-Hand in the Business of Customer Identity Management?" date: "2022-05-31" -coverImage: "it-marketing.jpg" +coverImage: "it-marketing.webp" tags: ["marketing", "ciam", "IT"] author: "Rakesh Soni" description: "Promoting your brand and delivering out-of-the-box services reinforced with robust security is paramount for business success. However, delivering rich experiences remains the most underrated catalyst that can pave the path for exponential growth!" @@ -48,7 +48,7 @@ A [customer identity and access management](https://www.loginradius.com/blog/ide Through progressive profiling, users aren’t bombarded with big registration forms; instead, they are asked to share their details when they interact with the platform gradually. This ensures a seamless and rich user experience. -[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) +[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) ## What About Security? Should it be a Part of Preference Management and Digital Experience Strategy? @@ -105,4 +105,4 @@ Customer identity management is crucial for businesses striving for growth in a With a new-age CIAM like LoginRadius, businesses can ensure they deliver a rich consumer experience backed with robust security that can offer endless marketing opportunities. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-it-marketing-customer-identity-management) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-it-marketing-customer-identity-management) \ No newline at end of file diff --git a/content/growth/role-it-marketing-customer-identity-management/it-marketing.jpg b/content/growth/role-it-marketing-customer-identity-management/it-marketing.jpg deleted file mode 100644 index 64287bdd9..000000000 Binary files a/content/growth/role-it-marketing-customer-identity-management/it-marketing.jpg and /dev/null differ diff --git a/content/growth/role-it-marketing-customer-identity-management/it-marketing.webp b/content/growth/role-it-marketing-customer-identity-management/it-marketing.webp new file mode 100644 index 000000000..e59a0763d Binary files /dev/null and b/content/growth/role-it-marketing-customer-identity-management/it-marketing.webp differ diff --git a/content/growth/role-it-marketing-customer-identity-management/visitor-eb.png b/content/growth/role-it-marketing-customer-identity-management/visitor-eb.png deleted file mode 100644 index c9ad88d9e..000000000 Binary files a/content/growth/role-it-marketing-customer-identity-management/visitor-eb.png and /dev/null differ diff --git a/content/growth/role-it-marketing-customer-identity-management/visitor-eb.webp b/content/growth/role-it-marketing-customer-identity-management/visitor-eb.webp new file mode 100644 index 000000000..2b537fe1a Binary files /dev/null and b/content/growth/role-it-marketing-customer-identity-management/visitor-eb.webp differ diff --git a/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.png b/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.png deleted file mode 100644 index f5fa0b0f9..000000000 Binary files a/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.png and /dev/null differ diff --git a/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.webp b/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.webp new file mode 100644 index 000000000..b0761321e Binary files /dev/null and b/content/growth/role-of-frictionless-payments-for-businesses/EB-omnichannel.webp differ diff --git a/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.jpg b/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.jpg deleted file mode 100644 index 169a8f3c0..000000000 Binary files a/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.jpg and /dev/null differ diff --git a/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.webp b/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.webp new file mode 100644 index 000000000..db3327067 Binary files /dev/null and b/content/growth/role-of-frictionless-payments-for-businesses/frictionless-paymt.webp differ diff --git a/content/growth/role-of-frictionless-payments-for-businesses/index.md b/content/growth/role-of-frictionless-payments-for-businesses/index.md index 4b6603565..fc5561df8 100644 --- a/content/growth/role-of-frictionless-payments-for-businesses/index.md +++ b/content/growth/role-of-frictionless-payments-for-businesses/index.md @@ -1,7 +1,7 @@ --- title: "5 Reasons Why Frictionless Payments Matter To Marketers And Business Owners" date: "2022-03-11" -coverImage: "frictionless-paymt.jpg" +coverImage: "frictionless-paymt.webp" tags: ["omnichannel cx","authentication","user experience","ciam solution"] author: "Vishal Sharma" description: "When it comes to frictionless payments, most brands ignore that a bit of hustle in the overall payment process could encourage their users to switch. Let’s understand why frictionless payments matter today more than ever before, especially for business owners and marketers." @@ -52,7 +52,7 @@ Admit it; a great user experience is paramount for online business success in to Users need not enter their card details or provide pins every time they shop from the same platform. Instead, they can use different authentication methods, including a fingerprint that completes payment in a fraction of seconds. -[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) +[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) ### #3. Better payment security @@ -91,4 +91,4 @@ Adding frictionless payment methods to their branding strategy is the need of th Businesses can quickly adopt frictionless payments by leveraging [seamless authentication methods](https://www.loginradius.com/blog/identity/authentication-option-for-your-product/) that offer a great experience and eventually reinforce payment security. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-of-frictionless-payments-for-businesses) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-of-frictionless-payments-for-businesses) \ No newline at end of file diff --git a/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.png b/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.png deleted file mode 100644 index 86c15a159..000000000 Binary files a/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.png and /dev/null differ diff --git a/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.webp b/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.webp new file mode 100644 index 000000000..025782e92 Binary files /dev/null and b/content/growth/role-of-frictionless-payments-for-businesses/omnichannel-eb.webp differ diff --git a/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.png b/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.png deleted file mode 100644 index 1e4c62adb..000000000 Binary files a/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.png and /dev/null differ diff --git a/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.webp b/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.webp new file mode 100644 index 000000000..53e9a5b34 Binary files /dev/null and b/content/growth/role-sso-in-digital-marketing/DS-native-mob-app.webp differ diff --git a/content/growth/role-sso-in-digital-marketing/index.md b/content/growth/role-sso-in-digital-marketing/index.md index 2290b0223..ccdc739f6 100644 --- a/content/growth/role-sso-in-digital-marketing/index.md +++ b/content/growth/role-sso-in-digital-marketing/index.md @@ -1,7 +1,7 @@ --- title: "The Critical Role of SSO in Reshaping Digital Marketing Landscape" date: "2023-02-10" -coverImage: "sso.jpg" +coverImage: "sso.webp" tags: ["sso","ciam platform","customer retention"] author: "Vishal Sharma" description: "With SSO, enterprises can understand their target audience's needs, preferences, and behavior when they land on their platform for the first time. And this helps them in creating winning digital marketing campaigns to foster growth." @@ -61,7 +61,7 @@ Another thing SSO does is reduce barriers for users. By leveraging single sign-o That means one login, one set of credentials, and one consistent experience—and we all know how important consistency is when converting new users. -[](https://www.loginradius.com/resource/authentication-sso-native-mobile-apps-datasheet) +[](https://www.loginradius.com/resource/authentication-sso-native-mobile-apps-datasheet) ### 4. Helps Craft Personalized Experiences @@ -77,4 +77,4 @@ While SSO offers a convenient, secure, and efficient way for users to access mul Brands that are thinking about accelerating their digital marketing efforts shouldn’t wait, and just put their best foot forward in implementing SSO into their website/mobile applications. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-sso-in-digital-marketing) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=role-sso-in-digital-marketing) \ No newline at end of file diff --git a/content/growth/role-sso-in-digital-marketing/native-ds.png b/content/growth/role-sso-in-digital-marketing/native-ds.png deleted file mode 100644 index 9368b122c..000000000 Binary files a/content/growth/role-sso-in-digital-marketing/native-ds.png and /dev/null differ diff --git a/content/growth/role-sso-in-digital-marketing/native-ds.webp b/content/growth/role-sso-in-digital-marketing/native-ds.webp new file mode 100644 index 000000000..44fba692f Binary files /dev/null and b/content/growth/role-sso-in-digital-marketing/native-ds.webp differ diff --git a/content/growth/role-sso-in-digital-marketing/sso-role.jpg b/content/growth/role-sso-in-digital-marketing/sso-role.jpg deleted file mode 100644 index 4d0169064..000000000 Binary files a/content/growth/role-sso-in-digital-marketing/sso-role.jpg and /dev/null differ diff --git a/content/growth/role-sso-in-digital-marketing/sso-role.webp b/content/growth/role-sso-in-digital-marketing/sso-role.webp new file mode 100644 index 000000000..41941f421 Binary files /dev/null and b/content/growth/role-sso-in-digital-marketing/sso-role.webp differ diff --git a/content/growth/role-sso-in-digital-marketing/sso.jpg b/content/growth/role-sso-in-digital-marketing/sso.jpg deleted file mode 100644 index 329a2a2fa..000000000 Binary files a/content/growth/role-sso-in-digital-marketing/sso.jpg and /dev/null differ diff --git a/content/growth/role-sso-in-digital-marketing/sso.webp b/content/growth/role-sso-in-digital-marketing/sso.webp new file mode 100644 index 000000000..0d4ee682a Binary files /dev/null and b/content/growth/role-sso-in-digital-marketing/sso.webp differ diff --git a/content/growth/saas-consumer-support/index.md b/content/growth/saas-consumer-support/index.md index eb58f0027..20d99f9b4 100644 --- a/content/growth/saas-consumer-support/index.md +++ b/content/growth/saas-consumer-support/index.md @@ -1,7 +1,7 @@ --- title: "How to Deliver the Perfect Consumer Support System for SaaS Companies" date: "2021-02-12" -coverImage: "saas-consumer-support.jpg" +coverImage: "saas-consumer-support.webp" category: ["all"] featured: false author: "Rakesh Soni" @@ -232,4 +232,4 @@ They can help to define your organization and drive your organization's reputati Hopefully, the above insights into the LoginRadius support team and some of the things that have helped us to support our consumers enable you to drive efficiencies within your organization. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=saas-consumer-support) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=saas-consumer-support) diff --git a/content/growth/saas-consumer-support/saas-consumer-support.jpg b/content/growth/saas-consumer-support/saas-consumer-support.jpg deleted file mode 100644 index 0da446195..000000000 Binary files a/content/growth/saas-consumer-support/saas-consumer-support.jpg and /dev/null differ diff --git a/content/growth/saas-consumer-support/saas-consumer-support.webp b/content/growth/saas-consumer-support/saas-consumer-support.webp new file mode 100644 index 000000000..c77bc95aa Binary files /dev/null and b/content/growth/saas-consumer-support/saas-consumer-support.webp differ diff --git a/content/growth/sanitary-pad-donation-drive/LR-donation-drive.jpg b/content/growth/sanitary-pad-donation-drive/LR-donation-drive.jpg deleted file mode 100644 index 522d95f9e..000000000 Binary files a/content/growth/sanitary-pad-donation-drive/LR-donation-drive.jpg and /dev/null differ diff --git a/content/growth/sanitary-pad-donation-drive/LR-donation-drive.webp b/content/growth/sanitary-pad-donation-drive/LR-donation-drive.webp new file mode 100644 index 000000000..612cfc4d0 Binary files /dev/null and b/content/growth/sanitary-pad-donation-drive/LR-donation-drive.webp differ diff --git a/content/growth/sanitary-pad-donation-drive/cta-careers.png b/content/growth/sanitary-pad-donation-drive/cta-careers.png deleted file mode 100644 index 600361d60..000000000 Binary files a/content/growth/sanitary-pad-donation-drive/cta-careers.png and /dev/null differ diff --git a/content/growth/sanitary-pad-donation-drive/cta-careers.webp b/content/growth/sanitary-pad-donation-drive/cta-careers.webp new file mode 100644 index 000000000..bf117ad57 Binary files /dev/null and b/content/growth/sanitary-pad-donation-drive/cta-careers.webp differ diff --git a/content/growth/sanitary-pad-donation-drive/hope-basket.jpg b/content/growth/sanitary-pad-donation-drive/hope-basket.jpg deleted file mode 100644 index cd931234a..000000000 Binary files a/content/growth/sanitary-pad-donation-drive/hope-basket.jpg and /dev/null differ diff --git a/content/growth/sanitary-pad-donation-drive/hope-basket.webp b/content/growth/sanitary-pad-donation-drive/hope-basket.webp new file mode 100644 index 000000000..8e52dcd99 Binary files /dev/null and b/content/growth/sanitary-pad-donation-drive/hope-basket.webp differ diff --git a/content/growth/sanitary-pad-donation-drive/index.md b/content/growth/sanitary-pad-donation-drive/index.md index d9cc0765d..5d35f790a 100644 --- a/content/growth/sanitary-pad-donation-drive/index.md +++ b/content/growth/sanitary-pad-donation-drive/index.md @@ -1,7 +1,7 @@ --- title: "Making a Difference: LoginRadius' Sanitary Pad Donation Drive" date: "2023-09-27" -coverImage: "social-cause.jpg" +coverImage: "social-cause.webp" tags: ["LoginRadius donation drive","women empowerment","hope basket foundation"] author: "Azharuddin Mohammad" description: "Join LoginRadius in our mission to create a positive change in our community. Learn how we're providing sanitary pads, educating women, and making a difference in the lives of underprivileged girls. Together, we can ensure dignity, comfort, and safety for all during their menstrual cycles." @@ -24,7 +24,7 @@ Many women still prefer using clothes during their menstrual cycles due to conce The market prices of sanitary pads are often beyond the reach of underprivileged women and girls. The high cost of these essential hygiene products forces them to compromise their health and well-being. - + ### 3. Stigma and Shyness @@ -40,7 +40,7 @@ Our donation drive is being carried out in phases, targeting different underpriv None of this would have been possible without the dedication and commitment of our operations team and volunteers who stepped up to make a difference. We thank Naveen, Vikas, Shreya, Soniya, Sudhey, and Pankaj for their invaluable contributions to this noble cause. - + ## Conclusion: @@ -50,4 +50,4 @@ Join us in our mission to create a positive change in our community. We can empo Stay tuned for updates on our Sanitary Pad Donation Drive and the impact we're creating in the lives of underprivileged girls. Together, we can make a difference. -[](https://www.loginradius.com/careers/) \ No newline at end of file +[](https://www.loginradius.com/careers/) \ No newline at end of file diff --git a/content/growth/sanitary-pad-donation-drive/social-cause.jpg b/content/growth/sanitary-pad-donation-drive/social-cause.jpg deleted file mode 100644 index 81adcb03d..000000000 Binary files a/content/growth/sanitary-pad-donation-drive/social-cause.jpg and /dev/null differ diff --git a/content/growth/sanitary-pad-donation-drive/social-cause.webp b/content/growth/sanitary-pad-donation-drive/social-cause.webp new file mode 100644 index 000000000..876d04f1f Binary files /dev/null and b/content/growth/sanitary-pad-donation-drive/social-cause.webp differ diff --git a/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.jpg b/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.jpg deleted file mode 100644 index 3c4d54db0..000000000 Binary files a/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.jpg and /dev/null differ diff --git a/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.webp b/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.webp new file mode 100644 index 000000000..33ef68a75 Binary files /dev/null and b/content/growth/scale-business-with-loginradius-customer-segmentation/customer-segmt.webp differ diff --git a/content/growth/scale-business-with-loginradius-customer-segmentation/index.md b/content/growth/scale-business-with-loginradius-customer-segmentation/index.md index d888315d9..f2817ae76 100644 --- a/content/growth/scale-business-with-loginradius-customer-segmentation/index.md +++ b/content/growth/scale-business-with-loginradius-customer-segmentation/index.md @@ -1,7 +1,7 @@ --- title: "Driving Revenue Using LoginRadius' Customer Segmentation Insights" date: "2022-03-15" -coverImage: "customer-segmt.jpg" +coverImage: "customer-segmt.webp" category: ["business", "Marketing", "technology"] featured: false author: "Manish Tiwari" @@ -81,4 +81,4 @@ Businesses can’t ignore the importance of user insights that can help them und LoginRadius helps businesses transform the way they approach their marketing by taking the guesswork out of their efforts. One can quickly segment their customers and get specific about their population right from the LoginRadius Admin Console. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=scale-business-with-loginradius-customer-segmentation) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=scale-business-with-loginradius-customer-segmentation) diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.png b/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.png deleted file mode 100644 index 404532996..000000000 Binary files a/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.png and /dev/null differ diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.webp b/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.webp new file mode 100644 index 000000000..832cb0156 Binary files /dev/null and b/content/growth/secure-your-remote-workforce-with-identity-management/WP-zero-trust-1.webp differ diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.png b/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.png deleted file mode 100644 index 3e6b81ee6..000000000 Binary files a/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.png and /dev/null differ diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.webp b/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.webp new file mode 100644 index 000000000..2f7c01062 Binary files /dev/null and b/content/growth/secure-your-remote-workforce-with-identity-management/Zero-Trust-Security.webp differ diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/index.md b/content/growth/secure-your-remote-workforce-with-identity-management/index.md index 5882fc065..0529a8908 100644 --- a/content/growth/secure-your-remote-workforce-with-identity-management/index.md +++ b/content/growth/secure-your-remote-workforce-with-identity-management/index.md @@ -1,7 +1,7 @@ --- title: "7 Best Practices for Securing Your Remote Workforce with Identity Management" date: "2021-08-04" -coverImage: "remote-workforce.jpg" +coverImage: "remote-workforce.webp" tags: ["zero trust security","identity management","cybersecurity","cx"] author: "Vishal Sharma" description: "Learn about the best practices to ensure cybersecurity for remote workers using identity management" @@ -40,7 +40,7 @@ Businesses should be wary of everything on the internet. In fact, even on-premis Consider adopting this approach into your remote work policies and protocols so your remote employees will be guided accordingly. One great example would be implementing multi-factor authentication for each login. This will add an extra layer of protection and verification for your users. -[](https://www.loginradius.com/resource/zero-trust-security/) +[](https://www.loginradius.com/resource/zero-trust-security/) ## 3. Perform routine review of accounts @@ -79,5 +79,5 @@ As your business migrates to a virtual workplace, you must learn how to maintain Through identity management, you reduce password issues and enhance security for your remote teams. It streamlines the process of logging in, authenticating, and authorizing access to your organization’s data and resources. To find out more about the benefits of identity management, [contact our team](https://www.loginradius.com/contact-sales2/). -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-your-remote-workforce-with-identity-management) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-your-remote-workforce-with-identity-management) diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.png b/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.png deleted file mode 100644 index e7cfcf9a0..000000000 Binary files a/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.png and /dev/null differ diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.webp b/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.webp new file mode 100644 index 000000000..735ec1c8d Binary files /dev/null and b/content/growth/secure-your-remote-workforce-with-identity-management/loginradius-free-Consultation.webp differ diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.jpg b/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.jpg deleted file mode 100644 index b3648a108..000000000 Binary files a/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.jpg and /dev/null differ diff --git a/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.webp b/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.webp new file mode 100644 index 000000000..6b9660902 Binary files /dev/null and b/content/growth/secure-your-remote-workforce-with-identity-management/remote-workforce.webp differ diff --git a/content/growth/secure-your-wi-fi-against-hackers/index.md b/content/growth/secure-your-wi-fi-against-hackers/index.md index 10655abe3..12a297fac 100644 --- a/content/growth/secure-your-wi-fi-against-hackers/index.md +++ b/content/growth/secure-your-wi-fi-against-hackers/index.md @@ -1,7 +1,7 @@ --- title: "10 Tips to Ensure Your Wi-Fi is Private and Blocking Hackers" date: "2021-08-19" -coverImage: "secure-wi-fi-against-hackers.jpg" +coverImage: "secure-wi-fi-against-hackers.webp" category: ["loginradius"] featured: false author: "Rashmi Mathur" @@ -203,4 +203,4 @@ To maintain the system with firewalls and anti-malware software. Always keep the Many hackers are using different methods like [ransomware](https://www.loginradius.com/resource/with-ransomware-on-the-rise-how-safe-is-your-business/) and identity theft. To avoid all these issues, you can make some changes by practicing these tips. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-your-wi-fi-against-hackers) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=secure-your-wi-fi-against-hackers) \ No newline at end of file diff --git a/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.jpg b/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.jpg deleted file mode 100644 index b1600c310..000000000 Binary files a/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.jpg and /dev/null differ diff --git a/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.webp b/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.webp new file mode 100644 index 000000000..d1432879c Binary files /dev/null and b/content/growth/secure-your-wi-fi-against-hackers/secure-wi-fi-against-hackers.webp differ diff --git a/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.png b/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.png deleted file mode 100644 index f12e48c23..000000000 Binary files a/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.png and /dev/null differ diff --git a/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.webp b/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.webp new file mode 100644 index 000000000..56ca58866 Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Above-the-fold-registration-form.webp differ diff --git a/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.png b/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.png deleted file mode 100644 index a166c214e..000000000 Binary files a/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.png and /dev/null differ diff --git a/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.webp b/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.webp new file mode 100644 index 000000000..0d5102393 Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Add-User-Friendly-Features-to-Your-Forms.webp differ diff --git "a/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.jpg" "b/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.jpg" deleted file mode 100644 index 8adab10af..000000000 Binary files "a/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.jpg" and /dev/null differ diff --git "a/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.webp" "b/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.webp" new file mode 100644 index 000000000..ab9d2994c Binary files /dev/null and "b/content/growth/sign-up-forms-best-practices/Don\342\200\231t-use-Captchas.webp" differ diff --git a/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.jpg b/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.jpg deleted file mode 100644 index 0c86a73fc..000000000 Binary files a/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.jpg and /dev/null differ diff --git a/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.webp b/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.webp new file mode 100644 index 000000000..cbcff4ce9 Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Field-Width-Submit-Button-Width.webp differ diff --git a/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.png b/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.png deleted file mode 100644 index 22caf4e48..000000000 Binary files a/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.png and /dev/null differ diff --git a/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.webp b/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.webp new file mode 100644 index 000000000..b4dfdd332 Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Have-an-Effective-CTA-in-registration-form.webp differ diff --git a/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.png b/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.png deleted file mode 100644 index 817131a60..000000000 Binary files a/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.png and /dev/null differ diff --git a/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.webp b/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.webp new file mode 100644 index 000000000..176bb730c Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Test-Your-Forms-with-AB-testing.webp differ diff --git a/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.png b/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.png deleted file mode 100644 index af997195a..000000000 Binary files a/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.png and /dev/null differ diff --git a/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.webp b/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.webp new file mode 100644 index 000000000..4259974c8 Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Testimonial-on-registration-page.webp differ diff --git a/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.png b/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.png deleted file mode 100644 index 9e4619738..000000000 Binary files a/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.png and /dev/null differ diff --git a/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.webp b/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.webp new file mode 100644 index 000000000..171e1040a Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.webp differ diff --git a/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.png b/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.png deleted file mode 100644 index 98fb88c37..000000000 Binary files a/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.png and /dev/null differ diff --git a/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.webp b/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.webp new file mode 100644 index 000000000..6b0ac103f Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Trade-Your-Email-Signup-while-registration.webp differ diff --git a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.png b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.png deleted file mode 100644 index 72e5392e5..000000000 Binary files a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.png and /dev/null differ diff --git a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.webp b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.webp new file mode 100644 index 000000000..0010c4149 Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists-1.webp differ diff --git a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.jpg b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.jpg deleted file mode 100644 index 344e1896b..000000000 Binary files a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.jpg and /dev/null differ diff --git a/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.webp b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.webp new file mode 100644 index 000000000..56f44d40c Binary files /dev/null and b/content/growth/sign-up-forms-best-practices/Use-Auto-fill-Fields-instead-of-Drop-Down-Lists.webp differ diff --git a/content/growth/sign-up-forms-best-practices/index.md b/content/growth/sign-up-forms-best-practices/index.md index 823eb696e..be4bf5474 100644 --- a/content/growth/sign-up-forms-best-practices/index.md +++ b/content/growth/sign-up-forms-best-practices/index.md @@ -1,7 +1,7 @@ --- title: "The Ultimate Guide to Craft Sign-up Forms That Convert Like Crazy" date: "2017-04-28" -coverImage: "The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.png" +coverImage: "The-ultimate-guide-to-craft-sign-up-forms-that-covert-like-crazy.webp" category: ["technology"] featured: false author: "Rakesh Soni" @@ -32,7 +32,7 @@ _Your goal is to acquire leads!_ Engaged time generally declines till the time the prospect hits below the fold of your page. Hence, make it a practice to introduce them above the fold. Other than forms, you can also introduce CTAs and other important elements on your page. Thus, you can acquire utmost exposure to your business prospects that can help you to convert maximum leads. For example, if you are selling a software, just introduce your product with an eye-catching title, some images and a call -to-action button. This layout should crack a deal for you. Modifying the Unbounce’s page layout and placing plans with a call-to-action button [increased their conversion to 41%](https://econsultancy.com/blog/63139-six-useful-case-studies-on-where-to-place-your-cta-to-maximise-conversions). - + ### **Lessen your Number of Fields** @@ -52,23 +52,23 @@ In the previous image, Semrush does a great job by keeping just two fields in th There is a golden rule when you want your prospects to perform an email signup- “ ask less but provide as good as you can”. It means that you need to trade your idea of an email signup with a commodity or a service. For example, if your prospect is on your website to download a file, ask them to provide their email address and a couple of data in return. Now, that’s a successful transaction! - + -[Source](https://help.aweber.com/hc/en-us/article_attachments/211926128/227394387_step01.png?ver=1553881376) +[Source](https://help.aweber.com/hc/en-us/article_attachments/211926128/227394387_step01.webp?ver=1553881376) ### **Have an Effective CTA** I still wonder why [72% of B2B marketers](http://contentmarketinginstitute.com/2013/09/small-businesses-website-content-calls-to-action/) do not think of placing CTAs on their internal pages. Hence, while you are placing a CTA on your website, ensure to make it eye-catching. This will assist to change your bounce rates into conversion rates. Moreover, replace “Submit” buttons with some buttons that perform an action. For example, use “**Start your Free Trial**” or “**Start Bookmarking**” instead of “Submit”. - + -[Source](https://blog.aweber.com/wp-content/uploads/2016/08/marie-forleo-sign-up-form-cta.png?ver=1553881376) +[Source](https://blog.aweber.com/wp-content/uploads/2016/08/marie-forleo-sign-up-form-cta.webp?ver=1553881376) ### **Show Your User Base** Giving a proof for your social acceptance is a good technique to attract more customers. Look at the different companies who have endorsed themselves with this technique. You can also add some client testimonials to support your brand. - + [Source](https://signup.ballparkapp.com/) @@ -94,7 +94,7 @@ _Perform A/B testing._ Intuition, experience and expertise are certainly required for page positioning, nothing can replace testing. So, decide the appearance of your form with testing. - + ### **Try Out Templates like Mad Libs** @@ -111,9 +111,9 @@ Don’t be so choosy about the characteristics of your fields. For example, if t Many websites ask for passwords over again just for the sake that other websites have done it earlier. The sole purpose of asking passwords again is to prevent typo errors. Thus, a more user friendly method to do it is giving an option to view the password. - + -[Source](https://i.stack.imgur.com/pO6KD.png?ver=1553881376) +[Source](https://i.stack.imgur.com/pO6KD.webp?ver=1553881376) ### **Use Auto-fill Fields instead of Drop Down Lists** @@ -121,15 +121,15 @@ Drop down lists are not a good option when the list of choices are too long, eg: _Don’t do this_ - + -[Source](https://i1.wp.com/conversionxl.com/wp-content/uploads/2011/12/dropdown.jpg?ver=1553881376) +[Source](https://i1.wp.com/conversionxl.com/wp-content/uploads/2011/12/dropdown.webp?ver=1553881376) Instead, - + -[Source](https://www.smashingmagazine.com/wp-content/uploads/2011/03/signup4.png?ver=1553881376) +[Source](https://www.smashingmagazine.com/wp-content/uploads/2011/03/signup4.webp?ver=1553881376) @@ -137,9 +137,9 @@ Instead, Small CTA buttons are poor implementations and can look less effective from the users point of view. Hence, it is recommended to equal the width of submit button with the width of the adjacent input field. - + -[Source](https://codropspz-tympanus.netdna-ssl.com/codrops/wp-content/uploads/2012/10/CustomLoginForms_02.jpg?ver=1553881376) +[Source](https://codropspz-tympanus.netdna-ssl.com/codrops/wp-content/uploads/2012/10/CustomLoginForms_02.webp?ver=1553881376) ### **Please! Don’t use Captchas** @@ -147,9 +147,9 @@ Adding Captchas are new methods to put someone to eternal torture. I know that w ‘[Honeypot captcha technique](http://haacked.com/archive/2007/09/11/honeypot-captcha.aspx/)’ is an anti-spam technique which helps your website to identify spammers by hiding a field in your form that is only visible to spamming tools. Hence, if that field is checked or filled, you can easily confirm it as spam. Still, if you want captchas to be a part of your form, try out some fun questions that prove the user is a human. For example, ask simple math calculations like ‘2+7=’. - + -[Source](http://carlofontanos.com/wp-content/uploads/2014/04/Math_Captcha-300x202.jpg?ver=1553881376) +[Source](http://carlofontanos.com/wp-content/uploads/2014/04/Math_Captcha-300x202.webp?ver=1553881376) ### **It’s all about user comfort and trust** diff --git a/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.png b/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.png deleted file mode 100644 index 848826bd5..000000000 Binary files a/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.png and /dev/null differ diff --git a/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.webp b/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.webp new file mode 100644 index 000000000..b76ff5fdf Binary files /dev/null and b/content/growth/sign-up-tips-conversion-rate/forms-fewer-fields.webp differ diff --git a/content/growth/sign-up-tips-conversion-rate/index.md b/content/growth/sign-up-tips-conversion-rate/index.md index 1f82b04e8..6dc49baac 100644 --- a/content/growth/sign-up-tips-conversion-rate/index.md +++ b/content/growth/sign-up-tips-conversion-rate/index.md @@ -1,7 +1,7 @@ --- title: "9 Signup Tips To Skyrocket The Conversion Rate" date: "2021-01-05" -coverImage: "sign-up-rate.jpg" +coverImage: "sign-up-rate.webp" category: ["all"] featured: false author: "Rakesh Soni" @@ -51,7 +51,7 @@ Shorter forms are not only easier to fill out, but the visitor is also less intr Longer forms need more details. But the visitor to the website may be unwilling to provide you with any information about themselves. - + Source: wingify @@ -69,7 +69,7 @@ The key here is as much as possible to lower the barrier to entry. You don't wan To find the best balance between customer experience and protection, the LoginRadius Identity Platform provides a full range of [customer registration and authentication options](https://www.loginradius.com/authentication/). - + Source: moreconversion @@ -103,7 +103,7 @@ For users, [social login](https://www.loginradius.com/social-login/) is easy to Nevertheless, with social sign-up, the user's privacy is again in the spotlight. Most of them do not realize that, with this registration form, they agree to the use of their data by businesses. An opportunity that companies take to sell the product that best fits their preferences and desires to each customer, in a much more segmented and customized way. -[](https://www.loginradius.com/resource/social-login-reconsidered/) +[](https://www.loginradius.com/resource/social-login-reconsidered/) Few advantages of using social signups: @@ -157,4 +157,4 @@ Make sure it has a simple value proposition when writing a copy of your sign-up Following the tips and examples shown in this article is your next move. If you can get it right, you can build better sign-up forms for conversion and increase the number of quality leads created. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sign-up-tips-conversion-rate) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sign-up-tips-conversion-rate) \ No newline at end of file diff --git a/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.png b/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.png deleted file mode 100644 index 0f48687fa..000000000 Binary files a/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.png and /dev/null differ diff --git a/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.webp b/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.webp new file mode 100644 index 000000000..4f4683121 Binary files /dev/null and b/content/growth/sign-up-tips-conversion-rate/long-form-vs-short-form.webp differ diff --git a/content/growth/sign-up-tips-conversion-rate/sign-up-rate.jpg b/content/growth/sign-up-tips-conversion-rate/sign-up-rate.jpg deleted file mode 100644 index e440247c9..000000000 Binary files a/content/growth/sign-up-tips-conversion-rate/sign-up-rate.jpg and /dev/null differ diff --git a/content/growth/sign-up-tips-conversion-rate/sign-up-rate.webp b/content/growth/sign-up-tips-conversion-rate/sign-up-rate.webp new file mode 100644 index 000000000..bb06bce51 Binary files /dev/null and b/content/growth/sign-up-tips-conversion-rate/sign-up-rate.webp differ diff --git a/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.png b/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.png deleted file mode 100644 index 412e2195c..000000000 Binary files a/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.png and /dev/null differ diff --git a/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.webp b/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.webp new file mode 100644 index 000000000..6e975bd35 Binary files /dev/null and b/content/growth/sign-up-tips-conversion-rate/social-login-reconsidered.webp differ diff --git a/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.png b/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.png deleted file mode 100644 index 16ef5993b..000000000 Binary files a/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.png and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.webp b/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.webp new file mode 100644 index 000000000..4ebbfc00a Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/2000px-Logo_of_Google_Drive.svg.webp differ diff --git a/content/growth/slack-integrations-for-productivity/Asana_logo_new.png b/content/growth/slack-integrations-for-productivity/Asana_logo_new.png deleted file mode 100644 index 680f8b14f..000000000 Binary files a/content/growth/slack-integrations-for-productivity/Asana_logo_new.png and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/Asana_logo_new.webp b/content/growth/slack-integrations-for-productivity/Asana_logo_new.webp new file mode 100644 index 000000000..3538dd085 Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/Asana_logo_new.webp differ diff --git a/content/growth/slack-integrations-for-productivity/Hangouts_Icon.png b/content/growth/slack-integrations-for-productivity/Hangouts_Icon.png deleted file mode 100644 index f3c6f87ee..000000000 Binary files a/content/growth/slack-integrations-for-productivity/Hangouts_Icon.png and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/Hangouts_Icon.webp b/content/growth/slack-integrations-for-productivity/Hangouts_Icon.webp new file mode 100644 index 000000000..1c65150e2 Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/Hangouts_Icon.webp differ diff --git a/content/growth/slack-integrations-for-productivity/JIRA.png b/content/growth/slack-integrations-for-productivity/JIRA.png deleted file mode 100644 index 6427eb684..000000000 Binary files a/content/growth/slack-integrations-for-productivity/JIRA.png and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/JIRA.webp b/content/growth/slack-integrations-for-productivity/JIRA.webp new file mode 100644 index 000000000..f73cefe05 Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/JIRA.webp differ diff --git a/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.png b/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.png deleted file mode 100644 index 8e27f2eac..000000000 Binary files a/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.png and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.webp b/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.webp new file mode 100644 index 000000000..81908d4f6 Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/Stripe_logo_revised_2014.webp differ diff --git a/content/growth/slack-integrations-for-productivity/Untitled-design-6.png b/content/growth/slack-integrations-for-productivity/Untitled-design-6.png deleted file mode 100644 index 3ccc592e9..000000000 Binary files a/content/growth/slack-integrations-for-productivity/Untitled-design-6.png and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/Untitled-design-6.webp b/content/growth/slack-integrations-for-productivity/Untitled-design-6.webp new file mode 100644 index 000000000..e577f4924 Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/Untitled-design-6.webp differ diff --git a/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.png b/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.png deleted file mode 100644 index 2b641562b..000000000 Binary files a/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.png and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.webp b/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.webp new file mode 100644 index 000000000..1ccb5e3f4 Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/Wordpress-logo-hoz-rgb.webp differ diff --git a/content/growth/slack-integrations-for-productivity/github.jpg b/content/growth/slack-integrations-for-productivity/github.jpg deleted file mode 100644 index bceac6e3a..000000000 Binary files a/content/growth/slack-integrations-for-productivity/github.jpg and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/github.webp b/content/growth/slack-integrations-for-productivity/github.webp new file mode 100644 index 000000000..b8054ee7e Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/github.webp differ diff --git a/content/growth/slack-integrations-for-productivity/hubot.png b/content/growth/slack-integrations-for-productivity/hubot.png deleted file mode 100644 index 2df25bd95..000000000 Binary files a/content/growth/slack-integrations-for-productivity/hubot.png and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/hubot.webp b/content/growth/slack-integrations-for-productivity/hubot.webp new file mode 100644 index 000000000..9b788738d Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/hubot.webp differ diff --git a/content/growth/slack-integrations-for-productivity/index.md b/content/growth/slack-integrations-for-productivity/index.md index 068ca7499..23b27debd 100644 --- a/content/growth/slack-integrations-for-productivity/index.md +++ b/content/growth/slack-integrations-for-productivity/index.md @@ -1,7 +1,7 @@ --- title: "11 Slack App Integrations to Boost Productivity at Your Workplace" date: "2017-02-28" -coverImage: "Untitled-design-6.png" +coverImage: "Untitled-design-6.webp" category: ["business", "technology", "loginradius"] featured: false author: "Rakesh Soni" @@ -21,7 +21,7 @@ Slack is well known for its chatting environment. You can create various channel #### **Asana** - + As one of the best tools to manage projects in many organizations, [Asana](https://asana.com/customers/) is widely used. So, if your organization is one of them, you can highly benefit in terms of productivity with this app integration. @@ -33,7 +33,7 @@ As one of the best tools to manage projects in many organizations, [Asana](https #### **Mailchimp** - + As one of the best online platforms for email marketing, [Mailchimp-Slack integration](https://slack.com/apps/new/A0F82E726-mailchimp) can help you to get updates about the number of subscriptions and you can check a campaign’ sent status. The process includes authentication from your Mailchimp account. Afterwards, you can also select which lists to monitor through Slack. @@ -45,7 +45,7 @@ In a nutshell, you can [check the following events](https://connect.mailchimp.co #### **Github** - + With [Github](https://github.com/)\-Slack integration, you can have access to the repository of source codes for your Git projects. This integration provides you with the privilege to cooperate, analyze, and practice codes for your private projects. @@ -69,19 +69,19 @@ Process to [connect your Slack with Github](https://get.slack.help/hc/en-us/arti #### **Hubot** - + [Hubot](https://hubot.github.com/) is a popular chatbot which can be used for anything in your team. For example, you can have a poll of what your team is going to have for lunch or you can look for people who want to have a coffee. Well, this bot is fun and this is how you can [integrate](https://slack.com/apps/A0F7XDU93-hubot) it with Slack. #### **Google Hangouts** - + Integrating [Google Hangouts](https://hangouts.google.com/?hl=en&authuser=0) with Slack will help you to communicate with your team via voice calls and video conferencing. So, you can boost your communication in a certain channel and accelerate conversations through Hangout. People across different niche such as marketers, developers, and other professionals can benefit from [Google Hangouts-Slack](https://slack.com/apps/new/A0F7YS351-google-hangouts) integration. #### **Google Drive** - + [Google drive](https://drive.google.com/) is used to create, save and **corporate** documents online. Many people can work simultaneously on a document in Google drive. @@ -89,7 +89,7 @@ Well, it is one of the most popular integrations in Slack. You just simply need #### **Intercom** - + [Intercom](https://www.intercom.com/) is a great tool to interact with the users of your software. You can send in-app messages and targeted emails to your users through your app during special occurrences. @@ -102,7 +102,7 @@ Integrating Slack to Intercom will allow you to receive following notifications #### **WordPress** - + [WordPress](https://wordpress.com/), which is another highly customizable tool which creates and manages your blog or website. @@ -110,13 +110,13 @@ Integrating Slack to Intercom will allow you to receive following notifications #### **Stripe** - + [Stripe](https://stripe.com/) is an app for accepting payments online. You will be able to get updates about transfers, subscriptions, invoice payments, charges etc. through integrating [Stripe with Slack](https://slack.com/apps/new/A0F81FNVC-stripe). #### **Jira** - + [Jira](https://www.atlassian.com/software/jira) is a powerful project management tool which can help to keep track of issues related to a project, assign tasks, and check team’s activity. @@ -124,7 +124,7 @@ You can receive notifications about your new and existing [JIRA issues on Slack] #### **Zendesk** - + [Zendesk](https://www.zendesk.com/), which is another tool to support tickets against issues can be [integrated to Slack](https://slack.com/apps/new/A0F81FPJS-zendesk) to get notifications about your tickets. The following events are notified on Slack:- 1\. Open 2\. Pending 3\. Solved 4. Closed diff --git a/content/growth/slack-integrations-for-productivity/intercom.png b/content/growth/slack-integrations-for-productivity/intercom.png deleted file mode 100644 index aaf224e19..000000000 Binary files a/content/growth/slack-integrations-for-productivity/intercom.png and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/intercom.webp b/content/growth/slack-integrations-for-productivity/intercom.webp new file mode 100644 index 000000000..5c8702594 Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/intercom.webp differ diff --git a/content/growth/slack-integrations-for-productivity/mailchimp.jpg b/content/growth/slack-integrations-for-productivity/mailchimp.jpg deleted file mode 100644 index 408ce08bd..000000000 Binary files a/content/growth/slack-integrations-for-productivity/mailchimp.jpg and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/mailchimp.webp b/content/growth/slack-integrations-for-productivity/mailchimp.webp new file mode 100644 index 000000000..8c980b071 Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/mailchimp.webp differ diff --git a/content/growth/slack-integrations-for-productivity/zendesk-300x300.jpg b/content/growth/slack-integrations-for-productivity/zendesk-300x300.jpg deleted file mode 100644 index 6ce047f09..000000000 Binary files a/content/growth/slack-integrations-for-productivity/zendesk-300x300.jpg and /dev/null differ diff --git a/content/growth/slack-integrations-for-productivity/zendesk-300x300.webp b/content/growth/slack-integrations-for-productivity/zendesk-300x300.webp new file mode 100644 index 000000000..77cdb2fa4 Binary files /dev/null and b/content/growth/slack-integrations-for-productivity/zendesk-300x300.webp differ diff --git a/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.png b/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.png deleted file mode 100644 index f97184f2f..000000000 Binary files a/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.png and /dev/null differ diff --git a/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.webp b/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.webp new file mode 100644 index 000000000..88d19cbb8 Binary files /dev/null and b/content/growth/smooth-onboarding-positive-user-impression/EB-progressive-profiling.webp differ diff --git a/content/growth/smooth-onboarding-positive-user-impression/index.md b/content/growth/smooth-onboarding-positive-user-impression/index.md index d81737576..f5f15d2e5 100644 --- a/content/growth/smooth-onboarding-positive-user-impression/index.md +++ b/content/growth/smooth-onboarding-positive-user-impression/index.md @@ -1,7 +1,7 @@ --- title: "How to Make a Strong Impression With Your Onboarding Process?" date: "2022-02-02" -coverImage: "onboarding.jpg" +coverImage: "onboarding.webp" tags: ["user onboarding","progressive profiling","cx"] author: "Navanita Devi" description: "The key to a seamless onboarding experience is to make the process as simple and safe as possible – from the first moment a new customer accesses your site until the moment they are authenticated and logged in. This article explains how." @@ -67,7 +67,7 @@ How will this app aid them in fulfilling their needs? You can easily demonstrate In many ways, onboarding can provide the personalization every user is searching for. Progressive onboarding ensures you don't overwhelm the user with too many functions they aren't prepared to work with. Instead, as they gradually glide through the app, they require new information, so their experience isn’t monotonous. The instructions correspond to the unique page the user is on, allowing the user to learn as they get deeper into the app. As a result, the user can only grab what they need out of the app. -[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) +[](https://www.loginradius.com/resource/how-to-squeeze-every-drop-of-progressive-profiling/) ## Conclusion @@ -76,4 +76,4 @@ While including onboarding into your app strategy helps the overall UX, the onbo The end goal remains to provision your users with a positive experience from the beginning of the app to the end of the game when they achieve their main goal. Onboarding is just one cog in the wheel that can help you get a more positive experience. While the goal remains to make certain the user is satisfied with the product, your business also benefits from [providing a positive experience](https://www.loginradius.com/customer-experience-solutions/). -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=smooth-onboarding-positive-user-impression) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=smooth-onboarding-positive-user-impression) diff --git a/content/growth/smooth-onboarding-positive-user-impression/onboarding.jpg b/content/growth/smooth-onboarding-positive-user-impression/onboarding.jpg deleted file mode 100644 index 6ec170de5..000000000 Binary files a/content/growth/smooth-onboarding-positive-user-impression/onboarding.jpg and /dev/null differ diff --git a/content/growth/smooth-onboarding-positive-user-impression/onboarding.webp b/content/growth/smooth-onboarding-positive-user-impression/onboarding.webp new file mode 100644 index 000000000..f864fc3d0 Binary files /dev/null and b/content/growth/smooth-onboarding-positive-user-impression/onboarding.webp differ diff --git a/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.png b/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.png deleted file mode 100644 index c9ad88d9e..000000000 Binary files a/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.png and /dev/null differ diff --git a/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.webp b/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.webp new file mode 100644 index 000000000..2b537fe1a Binary files /dev/null and b/content/growth/smooth-onboarding-positive-user-impression/visitor-eb.webp differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.png b/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.png deleted file mode 100644 index ef9040a01..000000000 Binary files a/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.png and /dev/null differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.webp b/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.webp new file mode 100644 index 000000000..5c6b32599 Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Creating-virtual-resume-with-Canva.webp differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.jpg b/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.jpg deleted file mode 100644 index 9ee8bf8d6..000000000 Binary files a/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.jpg and /dev/null differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.webp b/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.webp new file mode 100644 index 000000000..177a76a7f Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Spice-up-your-resume-Create-a-virtual-one.webp differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.jpg b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.jpg deleted file mode 100644 index 13ba22de9..000000000 Binary files a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.jpg and /dev/null differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.webp b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.webp new file mode 100644 index 000000000..df6681469 Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-1.webp differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.png b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.png deleted file mode 100644 index 9cab71078..000000000 Binary files a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.png and /dev/null differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.webp b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.webp new file mode 100644 index 000000000..fed0bdd44 Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-2.webp differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.jpg b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.jpg deleted file mode 100644 index 0f11557f3..000000000 Binary files a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.jpg and /dev/null differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.webp b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.webp new file mode 100644 index 000000000..8305a2679 Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-3.webp differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.jpg b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.jpg deleted file mode 100644 index ec7a9ea28..000000000 Binary files a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.jpg and /dev/null differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.webp b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.webp new file mode 100644 index 000000000..1063b395c Binary files /dev/null and b/content/growth/spice-up-your-resume-create-visual-one/Virtual-resume-example-4.webp differ diff --git a/content/growth/spice-up-your-resume-create-visual-one/index.md b/content/growth/spice-up-your-resume-create-visual-one/index.md index 8d4053299..8481d9946 100644 --- a/content/growth/spice-up-your-resume-create-visual-one/index.md +++ b/content/growth/spice-up-your-resume-create-visual-one/index.md @@ -1,7 +1,7 @@ --- title: "Spice Up Your Resume: Create a Visual One" date: "2017-05-15" -coverImage: "Spice-up-your-resume-Create-a-virtual-one.jpg" +coverImage: "Spice-up-your-resume-Create-a-virtual-one.webp" category: ["General"] featured: false author: "Navanita Devi" @@ -25,17 +25,17 @@ Visual resumes are welcomed as the next thing in the recruitment world. Still ma ### **Some Examples** - + **[Source](https://www.behance.net/gallery/26611697/Curriculum-Vitae)** - + -**[Source](https://biginterview.com/wp-content/uploads/2013-6-18-infographic-resume-3.jpg?ver=1553881376)** +**[Source](https://biginterview.com/wp-content/uploads/2013-6-18-infographic-resume-3.webp?ver=1553881376)** - + -**[Source](https://staticblog.virtualvocations.com/2012/12/4_PERSONALITY.jpg?ver=1553881376)** +**[Source](https://staticblog.virtualvocations.com/2012/12/4_PERSONALITY.webp?ver=1553881376)** ### **How to Make a Visual Resume (using Adobe Photoshop)** @@ -50,7 +50,7 @@ _Note:- The steps are written according to Adobe Photoshop CS6._ You can also use Canva to create a stunning resume. There are many templates available in Canva which are well suited for visual resumes. Here’s an example which I carved out from my favorite tool Canva:- - + Well, you can also use these FREE tools to have a seamless resume creation experience:- diff --git a/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.png b/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.png deleted file mode 100644 index 99b5a25ea..000000000 Binary files a/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.png and /dev/null differ diff --git a/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.webp b/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.webp new file mode 100644 index 000000000..a8ae17db9 Binary files /dev/null and b/content/growth/sso-saas-business-sales/GD-ciam-increases-roi.webp differ diff --git a/content/growth/sso-saas-business-sales/business-sales.jpg b/content/growth/sso-saas-business-sales/business-sales.jpg deleted file mode 100644 index 0e5647637..000000000 Binary files a/content/growth/sso-saas-business-sales/business-sales.jpg and /dev/null differ diff --git a/content/growth/sso-saas-business-sales/business-sales.webp b/content/growth/sso-saas-business-sales/business-sales.webp new file mode 100644 index 000000000..366ef6657 Binary files /dev/null and b/content/growth/sso-saas-business-sales/business-sales.webp differ diff --git a/content/growth/sso-saas-business-sales/index.md b/content/growth/sso-saas-business-sales/index.md index ade74ec48..b067e7755 100644 --- a/content/growth/sso-saas-business-sales/index.md +++ b/content/growth/sso-saas-business-sales/index.md @@ -1,7 +1,7 @@ --- title: "SSO for SaaS Business: The Key to Boost Sales For Enterprises" date: "2024-03-07" -coverImage: "business-sales.jpg" +coverImage: "business-sales.webp" tags: ["saas","sso","cx"] author: "Vishal Sharma" description: "Explore the impact of Single Sign-On (SSO) on SaaS businesses, from enhancing user experiences to improving sales performance. Discover the benefits of SSO and how LoginRadius stands out as a reliable solution for enterprises seeking a competitive edge." @@ -51,7 +51,7 @@ The benefits of leveraging a reliable SSO solution for SaaS businesses are manif * **Cost Efficiency:** SSO reduces the burden on IT support teams, leading to lower operational costs. Additionally, the time saved by users in managing passwords translates into tangible cost savings for enterprises. -[](https://www.loginradius.com/resource/how-ciam-increases-roi-for-your-enterprise/) +[](https://www.loginradius.com/resource/how-ciam-increases-roi-for-your-enterprise/) ## How LoginRadius SSO Offers Competitive Advantage to SaaS Enterprises? @@ -75,4 +75,4 @@ For SaaS businesses looking to gain a competitive advantage and boost sales, inv In the evolving SaaS landscape, where user experience is the ultimate differentiator, SSO for SaaS businesses is not just a convenience—it's a necessity for success. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-saas-business-sales) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=sso-saas-business-sales) diff --git a/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.png b/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.png deleted file mode 100644 index 6df429ab7..000000000 Binary files a/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.png and /dev/null differ diff --git a/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.webp b/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.webp new file mode 100644 index 000000000..9684babf6 Binary files /dev/null and b/content/growth/stakeholder-engagement-modernize-ciam/WP-dig-id-mngmnt.webp differ diff --git a/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.png b/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.png deleted file mode 100644 index d7768e095..000000000 Binary files a/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.png and /dev/null differ diff --git a/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.webp b/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.webp new file mode 100644 index 000000000..c3af9b9a1 Binary files /dev/null and b/content/growth/stakeholder-engagement-modernize-ciam/cmo-cio-wp.webp differ diff --git a/content/growth/stakeholder-engagement-modernize-ciam/index.md b/content/growth/stakeholder-engagement-modernize-ciam/index.md index 1c183aeb8..07101e895 100644 --- a/content/growth/stakeholder-engagement-modernize-ciam/index.md +++ b/content/growth/stakeholder-engagement-modernize-ciam/index.md @@ -1,7 +1,7 @@ --- title: "How to Bring Stakeholders Together to Modernize CIAM Across Your Organization" date: "2022-01-18" -coverImage: "saas-modernize.jpg" +coverImage: "saas-modernize.webp" tags: ["ciam solution","compliance","convenience","cx"] author: "Rakesh Soni" description: "If you’re ready to modernize your CIAM but aren’t quite sure where to start, then this blog should get you on the right path with your stakeholders." @@ -49,7 +49,7 @@ The requirements and priorities of each department are different. Your Chief Mar Each stakeholder has a set of expectations. Stakeholders should be involved from the initial phase of the CIAM modernization process. Doing so will help boost participation and goal alignment, making the overall objectives easier to achieve. -[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper) +[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper) ### 4. Manage expectations Technology can do anything, but if we expect the impossible, we may end up empty-handed. If you listen carefully to each team’s needs and concerns, however, you’re more likely to build a system that works for everyone. It’s important to take many things into account when designing the CIAM solution—for instance, usability, customer experience, convenience, security, and maintainability. @@ -86,4 +86,4 @@ Cloud-based [CIAM gives better ROI](https://www.loginradius.com/blog/fuel/ciam-o Even though it may sound like a daunting task, modernizing your CIAM is not impossible if you are willing to put in the work. The key lies in communicating how and why modernization will be beneficial for all stakeholders, and eventually getting everyone onboard with the plan. The tips mentioned in this blog will help you make this process easier since stakeholder engagement will simplify things for you. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=stakeholder-engagement-modernize-ciam) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=stakeholder-engagement-modernize-ciam) diff --git a/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.jpg b/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.jpg deleted file mode 100644 index d6a3d2a48..000000000 Binary files a/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.jpg and /dev/null differ diff --git a/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.webp b/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.webp new file mode 100644 index 000000000..441750abb Binary files /dev/null and b/content/growth/stakeholder-engagement-modernize-ciam/saas-modernize.webp differ diff --git a/content/growth/striking-balance-with-identity-orchestration/WP-resilience.png b/content/growth/striking-balance-with-identity-orchestration/WP-resilience.png deleted file mode 100644 index cbe459800..000000000 Binary files a/content/growth/striking-balance-with-identity-orchestration/WP-resilience.png and /dev/null differ diff --git a/content/growth/striking-balance-with-identity-orchestration/WP-resilience.webp b/content/growth/striking-balance-with-identity-orchestration/WP-resilience.webp new file mode 100644 index 000000000..efb695fb3 Binary files /dev/null and b/content/growth/striking-balance-with-identity-orchestration/WP-resilience.webp differ diff --git a/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.jpg b/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.jpg deleted file mode 100644 index 02c9126eb..000000000 Binary files a/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.jpg and /dev/null differ diff --git a/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.webp b/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.webp new file mode 100644 index 000000000..d2a89dfab Binary files /dev/null and b/content/growth/striking-balance-with-identity-orchestration/identity-orchestration.webp differ diff --git a/content/growth/striking-balance-with-identity-orchestration/index.md b/content/growth/striking-balance-with-identity-orchestration/index.md index 63884f6bf..9d4ca155f 100644 --- a/content/growth/striking-balance-with-identity-orchestration/index.md +++ b/content/growth/striking-balance-with-identity-orchestration/index.md @@ -1,7 +1,7 @@ --- title: "Striking the Perfect Balance: Leveraging Identity Orchestration for Cost, Security, & Enhanced UX" date: "2023-06-20" -coverImage: "identity-orchestration.jpg" +coverImage: "identity-orchestration.webp" tags: ["identity orchestration","compliance","cx"] author: "Rakesh Soni" description: "Discover the power of identity orchestration in achieving a balanced approach to cost, security, and user experience. Explore the advantages of centralized user management and streamlined authentication for a seamless digital environment that optimizes resources and enhances security measures." @@ -58,7 +58,7 @@ As organizations expand their digital footprint or undergo mergers and acquisiti This scalability enables organizations to efficiently manage user identities and access controls across a dynamic and evolving technology landscape. -[](https://www.loginradius.com/resource/enterprise-scalability-and-performance) +[](https://www.loginradius.com/resource/enterprise-scalability-and-performance) ### 7. Seamless integration with existing infrastructure @@ -78,4 +78,4 @@ Achieving the perfect balance between cost, security, and user experience is a c By optimizing costs, strengthening security measures, and delivering an enhanced user experience, identity orchestration becomes a crucial component of a modern and successful digital strategy. Embracing this approach enables organizations to unlock the full potential of their digital ecosystems while maintaining a competitive edge in today's dynamic business landscape. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=striking-balance-with-identity-orchestration) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=striking-balance-with-identity-orchestration) \ No newline at end of file diff --git a/content/growth/successful-saas-onboarding-process/DS-User-management.png b/content/growth/successful-saas-onboarding-process/DS-User-management.png deleted file mode 100644 index fc6f98c05..000000000 Binary files a/content/growth/successful-saas-onboarding-process/DS-User-management.png and /dev/null differ diff --git a/content/growth/successful-saas-onboarding-process/DS-User-management.webp b/content/growth/successful-saas-onboarding-process/DS-User-management.webp new file mode 100644 index 000000000..c60f3551f Binary files /dev/null and b/content/growth/successful-saas-onboarding-process/DS-User-management.webp differ diff --git a/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.png b/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.png deleted file mode 100644 index 4da86607c..000000000 Binary files a/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.png and /dev/null differ diff --git a/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.webp b/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.webp new file mode 100644 index 000000000..32fb1890f Binary files /dev/null and b/content/growth/successful-saas-onboarding-process/LoginRadius-User-Management.webp differ diff --git a/content/growth/successful-saas-onboarding-process/index.md b/content/growth/successful-saas-onboarding-process/index.md index 8911e5231..3b24fd776 100644 --- a/content/growth/successful-saas-onboarding-process/index.md +++ b/content/growth/successful-saas-onboarding-process/index.md @@ -1,7 +1,7 @@ --- title: "The ABCs of a Successful Saas Onboarding Process" date: "2021-08-27" -coverImage: "user-onboarding.jpg" +coverImage: "user-onboarding.webp" tags: ["user onboarding","saas","login authentication"] author: "Navanita Devi" description: "The onboarding process is the lifeline for your customer, and it's one of the most valuable tools that you as a company can control. Here are a few tips for a stellar SaaS company onboarding process that will greatly improve your customer retention and overall satisfaction." @@ -25,7 +25,7 @@ Here are a few phases you should know about when it comes to [consumer onboardin The initial onboarding phase does not occur on your website or blog but typically occurs on social media, in a forum or remark, or on another person's blog. Your onboarding experience begins with a customer's first interaction with your brand. - + ### User Onboarding: Phase 2 @@ -55,7 +55,7 @@ The onboarding process should be done properly, it can take your business to new Now, below we will discuss some elements that you need to keep in mind while onboarding consumers for your SaaS business. -[](https://www.loginradius.com/resource/loginradius-ciam-user-management/) +[](https://www.loginradius.com/resource/loginradius-ciam-user-management/) ## 4 Important SaaS Onboarding Elements @@ -95,4 +95,4 @@ When it comes to [SaaS onboarding](https://www.loginradius.com/blog/fuel/why-is- Start working on fixing your weak points once you've recognized them. Begin by making one adjustment at a time and seeing how it affects your cohort analysis. Your onboarding strategy won't be built in a day, and it won't be modified in a day, either. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=successful-saas-onboarding-process) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=successful-saas-onboarding-process) \ No newline at end of file diff --git a/content/growth/successful-saas-onboarding-process/user-onboarding.jpg b/content/growth/successful-saas-onboarding-process/user-onboarding.jpg deleted file mode 100644 index a8b6dfa71..000000000 Binary files a/content/growth/successful-saas-onboarding-process/user-onboarding.jpg and /dev/null differ diff --git a/content/growth/successful-saas-onboarding-process/user-onboarding.webp b/content/growth/successful-saas-onboarding-process/user-onboarding.webp new file mode 100644 index 000000000..e6b004cdc Binary files /dev/null and b/content/growth/successful-saas-onboarding-process/user-onboarding.webp differ diff --git a/content/growth/successful-saas-onboarding-process/user-onboarding2.jpg b/content/growth/successful-saas-onboarding-process/user-onboarding2.jpg deleted file mode 100644 index 703824043..000000000 Binary files a/content/growth/successful-saas-onboarding-process/user-onboarding2.jpg and /dev/null differ diff --git a/content/growth/successful-saas-onboarding-process/user-onboarding2.webp b/content/growth/successful-saas-onboarding-process/user-onboarding2.webp new file mode 100644 index 000000000..ad97df2d4 Binary files /dev/null and b/content/growth/successful-saas-onboarding-process/user-onboarding2.webp differ diff --git a/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.png b/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.png deleted file mode 100644 index fb5784fcf..000000000 Binary files a/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.png and /dev/null differ diff --git a/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.webp b/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.webp new file mode 100644 index 000000000..987fca8c1 Binary files /dev/null and b/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.webp differ diff --git a/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/index.md b/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/index.md index 613d774d2..d2daf98c4 100644 --- a/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/index.md +++ b/content/growth/test-cases-for-your-e-commerce-payment-gateway-page/index.md @@ -1,7 +1,7 @@ --- title: "Test Cases For Your E-commerce Payment Gateway Page" date: "2017-07-21" -coverImage: "Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.png" +coverImage: "Test-Cases-for-your-Ecommerce-Payment-Gateway-Page.webp" tags: ["payment gateway", "technology", "ecommerce"] author: "Rakesh Soni" description: "Trying to make test cases to build a flawless payment gateway page for your ecommerce website? Here are some factors you need to take seriously before creating test cases for payment gateway page." diff --git a/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.png b/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.png deleted file mode 100644 index 98e481315..000000000 Binary files a/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.png and /dev/null differ diff --git a/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.webp b/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.webp new file mode 100644 index 000000000..5e3eaf627 Binary files /dev/null and b/content/growth/the-relative-importance-of-customer-identity/DS-Product-Social-Login.webp differ diff --git a/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.jpg b/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.jpg deleted file mode 100644 index aaf510e3f..000000000 Binary files a/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.jpg and /dev/null differ diff --git a/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.webp b/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.webp new file mode 100644 index 000000000..36d17120a Binary files /dev/null and b/content/growth/the-relative-importance-of-customer-identity/importance-of-customer-identity.webp differ diff --git a/content/growth/the-relative-importance-of-customer-identity/index.md b/content/growth/the-relative-importance-of-customer-identity/index.md index b19084e7d..da59d9c1b 100644 --- a/content/growth/the-relative-importance-of-customer-identity/index.md +++ b/content/growth/the-relative-importance-of-customer-identity/index.md @@ -1,7 +1,7 @@ --- title: "Exploring the Relative Importance of Identity in Today’s Digital Landscape" date: "2023-05-05" -coverImage: "importance-of-customer-identity.jpg" +coverImage: "importance-of-customer-identity.webp" tags: ["digital identity","authentication","identity management","cx"] author: "Vishal Sharma" description: "With the rapid growth of online platforms and digital communication, our identities are more important than ever. Let’s examine how our identities have evolved in the digital age and explore their relative role in shaping our online experiences." @@ -42,7 +42,7 @@ Social media platforms have become a primary way to express our identities and c Understanding the impact of identity on social media can help us navigate these platforms in a way that aligns with our values and goals. This includes being mindful of the information we share, the people we connect with, and the communities we participate in. -[](https://www.loginradius.com/resource/loginradius-ciam-social-login/) +[](https://www.loginradius.com/resource/loginradius-ciam-social-login/) ## Identity and the Development of a Digital Society @@ -64,4 +64,4 @@ Understanding the significance of identity in the digital world is crucial for n By taking steps to protect and leverage our identities, we can make the most of the benefits technology offers. As we continue integrating technology into our lives, the importance of identity will only continue to grow. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=the-relative-importance-of-customer-identity) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=the-relative-importance-of-customer-identity) \ No newline at end of file diff --git a/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.jpg b/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.jpg deleted file mode 100644 index 3abbe6d42..000000000 Binary files a/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.jpg and /dev/null differ diff --git a/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.webp b/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.webp new file mode 100644 index 000000000..8d5940153 Binary files /dev/null and b/content/growth/tips-and-tricks-b2b-consultant/b2b-consultant.webp differ diff --git a/content/growth/tips-and-tricks-b2b-consultant/index.md b/content/growth/tips-and-tricks-b2b-consultant/index.md index a30d4d4db..d299ea10e 100644 --- a/content/growth/tips-and-tricks-b2b-consultant/index.md +++ b/content/growth/tips-and-tricks-b2b-consultant/index.md @@ -1,7 +1,7 @@ --- title: "7 Tips and Tricks for B2B Consultant: How to Grow Your Client's Business" date: "2021-02-26" -coverImage: "b2b-consultant.jpg" +coverImage: "b2b-consultant.webp" category: ["all"] featured: false author: "Lidia Hovhannisyan" @@ -104,7 +104,7 @@ If you are speaking with someone resistant to pain, focus on cutting costs, mini While [FedEx](https://www.fedex.com/en-us/home.html) is currently available to individual customers, it has been approved and rated as one of the best B2B companies in the world. The company is placed as [the 2nd most trusted B2B company](https://smallbiztrends.com/2018/08/most-trusted-b2b-brands-2018.html) by SageFrog and appears in Sacunas’ Top 100 B2B brands list. This company hasn’t made to these lists by mistake, this is because it is mostly committed towards customer service, experience, and open communication. Unlike most of its competitors, FedEx has taken into consideration its customers’ pain points and presented itself as a customer-centric company. - + ## Be Your Client's Personal Trainer @@ -145,4 +145,4 @@ As a B2B consultant, you are selling more than just a product. You are selling s Don't forget to qualify each prospect to see if they fit with your company. Doing so allows you to optimize your limited resources. When you do your due diligence, it would be so much easier to convert your leads and prospects to actual clients. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-and-tricks-b2b-consultant) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-and-tricks-b2b-consultant) diff --git a/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.png b/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.png deleted file mode 100644 index c2022eecb..000000000 Binary files a/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.png and /dev/null differ diff --git a/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.webp b/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.webp new file mode 100644 index 000000000..7e3b032b0 Binary files /dev/null and b/content/growth/tips-and-tricks-b2b-consultant/tips-b2b.webp differ diff --git a/content/growth/tips-managing-remote-team/index.md b/content/growth/tips-managing-remote-team/index.md index b8671ae55..8a574f497 100644 --- a/content/growth/tips-managing-remote-team/index.md +++ b/content/growth/tips-managing-remote-team/index.md @@ -1,7 +1,7 @@ --- title: "13 Tips for Leading and Managing Remote Teams" date: "2021-02-12" -coverImage: "tips-managing-remote-team.jpg" +coverImage: "tips-managing-remote-team.webp" category: ["all"] featured: false author: "Vikas Soni" @@ -135,4 +135,4 @@ Educating employees about the purpose of remote working can help them understand Each of the tips mentioned above and advice requires patience, attention, flexibility, and consistency. Working out on these tips can lead to better results and help the management handle the remote teams more easily and comfortably. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-managing-remote-team) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-managing-remote-team) diff --git a/content/growth/tips-managing-remote-team/tips-managing-remote-team.jpg b/content/growth/tips-managing-remote-team/tips-managing-remote-team.jpg deleted file mode 100644 index 7301d8e51..000000000 Binary files a/content/growth/tips-managing-remote-team/tips-managing-remote-team.jpg and /dev/null differ diff --git a/content/growth/tips-managing-remote-team/tips-managing-remote-team.webp b/content/growth/tips-managing-remote-team/tips-managing-remote-team.webp new file mode 100644 index 000000000..79e1ea525 Binary files /dev/null and b/content/growth/tips-managing-remote-team/tips-managing-remote-team.webp differ diff --git a/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.png b/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.png deleted file mode 100644 index 6df429ab7..000000000 Binary files a/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.png and /dev/null differ diff --git a/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.webp b/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.webp new file mode 100644 index 000000000..9684babf6 Binary files /dev/null and b/content/growth/tips-on-how-cisos-convince-board-members/WP-cmo-ciso-cio.webp differ diff --git a/content/growth/tips-on-how-cisos-convince-board-members/board-members.jpg b/content/growth/tips-on-how-cisos-convince-board-members/board-members.jpg deleted file mode 100644 index 7deec3ad1..000000000 Binary files a/content/growth/tips-on-how-cisos-convince-board-members/board-members.jpg and /dev/null differ diff --git a/content/growth/tips-on-how-cisos-convince-board-members/board-members.webp b/content/growth/tips-on-how-cisos-convince-board-members/board-members.webp new file mode 100644 index 000000000..f25eee832 Binary files /dev/null and b/content/growth/tips-on-how-cisos-convince-board-members/board-members.webp differ diff --git a/content/growth/tips-on-how-cisos-convince-board-members/index.md b/content/growth/tips-on-how-cisos-convince-board-members/index.md index 03abe22b0..362e1bd1c 100644 --- a/content/growth/tips-on-how-cisos-convince-board-members/index.md +++ b/content/growth/tips-on-how-cisos-convince-board-members/index.md @@ -1,7 +1,7 @@ --- title: "7 Tips on How CISOs Should Present Identity Security to Board Members" date: "2023-08-04" -coverImage: "board-members.jpg" +coverImage: "board-members.webp" tags: ["customer identity security","compliance","cx"] author: "Rakesh Soni" description: "While most CISOs are now concerned about the risks associated with customer identity security and identity thefts, they’re struggling to create a strategy to convince the board members to prepare beforehand. And to help CISOs present a compelling identity security strategy to board members, we’ve compiled a list of some helpful tips." @@ -46,7 +46,7 @@ Hence, you must avoid using technical jargon and complex terms when presenting y You could translate technical concepts and terms into business terms that resonate with your C-level executives’ expertise. And it would be great if you could focus on tangible risks, potential financial and reputational implications, and regulatory compliance, as this will facilitate more productive and meaningful conversation. -[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper) +[](https://www.loginradius.com/resource/digital-identity-management-cio-ciso-cmo-whitepaper) ### 4. Provide Real-World Examples @@ -84,4 +84,4 @@ While cybercriminals are hunting new ways to exploit consumer identities, CISOs And with a reliable customer identity and access management (CIAM) solution in place, security heads can ensure their customers’ identities are safe, and their board members don’t need to worry about the consequences of identity thefts. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-on-how-cisos-convince-board-members) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=tips-on-how-cisos-convince-board-members) \ No newline at end of file diff --git a/content/growth/top-3-ciam-indicators/ciam-loginradius.jpg b/content/growth/top-3-ciam-indicators/ciam-loginradius.jpg deleted file mode 100644 index c9d858090..000000000 Binary files a/content/growth/top-3-ciam-indicators/ciam-loginradius.jpg and /dev/null differ diff --git a/content/growth/top-3-ciam-indicators/ciam-loginradius.webp b/content/growth/top-3-ciam-indicators/ciam-loginradius.webp new file mode 100644 index 000000000..4e0c409dd Binary files /dev/null and b/content/growth/top-3-ciam-indicators/ciam-loginradius.webp differ diff --git a/content/growth/top-3-ciam-indicators/index.md b/content/growth/top-3-ciam-indicators/index.md index fa3da9add..0d7f1aa09 100644 --- a/content/growth/top-3-ciam-indicators/index.md +++ b/content/growth/top-3-ciam-indicators/index.md @@ -1,7 +1,7 @@ --- title: "Top 3 CIAM Indicators That You’ll Get the Consumer Satisfaction You Deserve" date: "2021-07-06" -coverImage: "ciam-loginradius.jpg" +coverImage: "ciam-loginradius.webp" category: ["loginradius"] featured: false author: "Vishal Sharma" @@ -29,7 +29,7 @@ CIAM offers the luxury of a centralized consumer database that links all other a Moreover, a cutting-edge CIAM solution like LoginRadius offers a seamless login experience through Social Login, Single-Sign-On (SSO), and [Passwordless Login for customers](https://www.loginradius.com/passwordless-login/). -[](https://www.loginradius.com/resource/loginradius-ciam-social-login/) +[](https://www.loginradius.com/resource/loginradius-ciam-social-login/) ## CIAM Indicators that Describe Your Consumers Love Your Platform @@ -102,4 +102,4 @@ The aspects above depict the role and responsibilities of a robust CIAM that can If you wish to experience the ease of consumer onboarding that increases consumer satisfaction and boosts your business revenues, it’s time to [experience the LoginRadius CIAM](https://www.loginradius.com/contact-sales/). -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-3-ciam-indicators) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-3-ciam-indicators) diff --git a/content/growth/top-3-ciam-indicators/social-login-loginradius.png b/content/growth/top-3-ciam-indicators/social-login-loginradius.png deleted file mode 100644 index 98e481315..000000000 Binary files a/content/growth/top-3-ciam-indicators/social-login-loginradius.png and /dev/null differ diff --git a/content/growth/top-3-ciam-indicators/social-login-loginradius.webp b/content/growth/top-3-ciam-indicators/social-login-loginradius.webp new file mode 100644 index 000000000..5e3eaf627 Binary files /dev/null and b/content/growth/top-3-ciam-indicators/social-login-loginradius.webp differ diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.png b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.png deleted file mode 100644 index 6bddf0db4..000000000 Binary files a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.png and /dev/null differ diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.webp b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.webp new file mode 100644 index 000000000..2842c3bcc Binary files /dev/null and b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/DS-customer-identity.webp differ diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.png b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.png deleted file mode 100644 index 8bad2f974..000000000 Binary files a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.png and /dev/null differ diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.webp b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.webp new file mode 100644 index 000000000..903afa91e Binary files /dev/null and b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/core-of-digital-transformation.webp differ diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/index.md b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/index.md index b673bf8fb..303fbd170 100644 --- a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/index.md +++ b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/index.md @@ -1,7 +1,7 @@ --- title: "8 Common Challenges With Your SaaS Business that CIAM Can Solve" date: "2021-09-10" -coverImage: "saas-business-app.jpg" +coverImage: "saas-business-app.webp" tags: ["identity management","customer identity","ciam solution"] author: "Rashmi Mathur" description: "To be successful, your SaaS needs to use the right application performance management software. CIAM is the first step you need to take to avoid common challenges like lack of compliance, and incompetent onboarding." @@ -13,7 +13,7 @@ Digital communication between clients and a company is now a regular practice ac The data gathered in databases can be vulnerable to cyber attacks that result in stolen customer and business identities. Hence, businesses look to increase their cybersecurity with the help of SaaS-based CIAM business solutions. -[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/) +[](https://www.loginradius.com/resource/customer-identity-the-core-of-digital-transformation/) ## Top Challenges With SaaS Apps and How CIAM Overcomes Them @@ -60,4 +60,4 @@ One of the surpassing advantages of cloud applications is that admittance is obt ## Conclusion To summarize, we can say that a cloud-based CIAM service should present accurate visibility of user access. Also, providing your customers with the required protection against identity theft is crucial in preserving your company prominence. This is why it is vital to overcome these challenges to better leverage the benefits of CIAM to protect your business and clients. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-8-ciam-challenges-with-your-saas-business-app) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-8-ciam-challenges-with-your-saas-business-app) \ No newline at end of file diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.jpg b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.jpg deleted file mode 100644 index b71009e0f..000000000 Binary files a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.jpg and /dev/null differ diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.webp b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.webp new file mode 100644 index 000000000..f8b508c06 Binary files /dev/null and b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app-2.webp differ diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.jpg b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.jpg deleted file mode 100644 index 30fa6b6fb..000000000 Binary files a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.jpg and /dev/null differ diff --git a/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.webp b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.webp new file mode 100644 index 000000000..1a5ff6795 Binary files /dev/null and b/content/growth/top-8-ciam-challenges-with-your-saas-business-app/saas-business-app.webp differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.png deleted file mode 100644 index 4021a46fc..000000000 Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.png and /dev/null differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.webp new file mode 100644 index 000000000..0b5d48b48 Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Basic-Email-Signature.webp differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.png deleted file mode 100644 index 8b2d73783..000000000 Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.png and /dev/null differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.webp new file mode 100644 index 000000000..4ea14fb99 Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Htmlsig-tool-for-professional-email-signature.webp differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.jpg b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.jpg deleted file mode 100644 index 86b32af12..000000000 Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.jpg and /dev/null differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.webp new file mode 100644 index 000000000..21275632c Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Modern-Style-Professional-Email-Signature.webp differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.png deleted file mode 100644 index e41b6b375..000000000 Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.png and /dev/null differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.webp new file mode 100644 index 000000000..e3f53067e Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Newoldstamp-tool-for-professional-email-signature.webp differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.png deleted file mode 100644 index dddc5590e..000000000 Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.png and /dev/null differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.webp new file mode 100644 index 000000000..3b80a20d4 Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Normal-Email-Signature-Vs-Professional-Email-Signature.webp differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.png deleted file mode 100644 index 08f335433..000000000 Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.png and /dev/null differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.webp new file mode 100644 index 000000000..4b64b438d Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-With-Social-Icons.webp differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.png deleted file mode 100644 index 442778014..000000000 Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.png and /dev/null differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.webp new file mode 100644 index 000000000..e34e0a3e7 Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-CTA.webp differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.png deleted file mode 100644 index e09f1f376..000000000 Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.png and /dev/null differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.webp new file mode 100644 index 000000000..69a0baa5d Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/Professional-Email-Signature-with-real-image.webp differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.png deleted file mode 100644 index 0e6596130..000000000 Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.png and /dev/null differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.webp new file mode 100644 index 000000000..a49ee1cb5 Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.webp differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.png deleted file mode 100644 index 43fb50be5..000000000 Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.png and /dev/null differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.webp new file mode 100644 index 000000000..9d4d6f453 Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/WiseStamp-tool-for-professional-email-signature.webp differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/index.md b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/index.md index 0cb872c78..1eb757ed2 100644 --- a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/index.md +++ b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/index.md @@ -1,7 +1,7 @@ --- title: "The Ultimate Guide To Create Professional Email Signatures With Examples" date: "2017-01-27" -coverImage: "The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.png" +coverImage: "The-Ultimate-Guide-To-Create-Professional-Email-Signatures-With-Examples.webp" category: ["general", "loginradius"] featured: false author: "Rakesh Soni" @@ -26,7 +26,7 @@ There are many people out there who in the process of creating a professional em Now at this stage, many of you might be thinking why can’t we just drop the use of email signature**.** But then my friend, you will lose an excellent opportunity as well. What most of us still don’t know is that a right email signature can make a huge difference to your emails. So guys, please wear your marketing hats and dig into the art of creating a perfect signature. - + The email signature rides along with all the emails you send, whether personal or professional but contrast to the importance of right email signature, here are some facts that will blow up your mind @@ -43,7 +43,7 @@ This data is enough to prove the unawareness lying around signature and that’s While there are many who don’t have any email signature at all, there are some others as well who treat their email signature like the mini autobiographies, jamming all possible links, quotes, and tons of information. But what they don’t realize is that by adding excessive information, the signature loses its original charm and will seem bulky for readers to even look at it let alone clicking on the same. -In general, the basic information needed in email signature is as below :Therefore experts recommend to use only the information that best indicates your professional brand, generally the email signature of four lines is standard format. Once you are done with the basic format, the next step is to personalize it. +In general, the basic information needed in email signature is as below :Therefore experts recommend to use only the information that best indicates your professional brand, generally the email signature of four lines is standard format. Once you are done with the basic format, the next step is to personalize it. PS.. To condense email signature in fewer lines, make use of pipeline (|) or colons (::) to separate links. @@ -60,7 +60,7 @@ You must save this place for something more valuable like your social icons, CTA Ever seen an overstuffed email signature? Here is what it looks like : - + Imagine how difficult and irritating it will be for the reader especially if he or she uses a mobile device. @@ -76,13 +76,13 @@ But again, nobody is implying you to add links of all of your social media profi Check out this email signature example of our head marketing analyst, Prince Kapoor who is active on multiple profiles, so it makes sense that he has made social icons a part of his email signature as the points of contact. - + #### **5\. Add Image :** It is a widely known fact that people remember visuals more than the plain text. But with that, I don’t mean you can put any kind of image in your email signature. There is always a certain kind of image that can make a difference to your email signature. You are more likely to remember a signature like this, won’t you? - + Reason being as per research says, most memorable photos are those that contain people, also color images are often more memorable than the black and white ones. Here are some tips you need to follow : @@ -97,7 +97,7 @@ One of the smartest way of leveraging the power of email signature is by adding For more clear idea, check out this email signature that encourages the reader to visit his blog. - + #### **7\. Make sure the links are trackable :** @@ -118,7 +118,7 @@ Most of the brands these days are opting for the modern email signature approach - Large text with flat design (3-D looks are strict no) - Use small splash of the bold color. - + #### **10\. Test your email signature with more than one email clients to make sure it works fine :** @@ -148,19 +148,19 @@ Now if you don’t want to make email signature on your own, there are various t It is an awesome free email signature creator that integrates easily with your email client and benefits you with some beautiful and customized email signatures. Using WiseStamp, it is quite simple to add the picture or your blog RSS feed and much more. - + **2. [htmlSig](https://htmlsig.com/)****:** If a neat email signature with required information without unnecessary clutter is what defines you, htmlsig is the place you need to land. A free and simple way to create email signature for your email clients that can make a long-lasting impression. It also contains the paid option, if you want more creativity. - + **3. [Newoldstamp](https://newoldstamp.com/)** **:** World’s simplest email signatures creation tool- as they define it. If creativity and uniqueness are your traits, newoldstamp is the perfect place for you. The tool provides you the chance to choose among the 11 professional email signature templates that come in several design, color and formats. - + Other tools that you can opt for : diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.png b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.png deleted file mode 100644 index d408dce8e..000000000 Binary files a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.png and /dev/null differ diff --git a/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.webp b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.webp new file mode 100644 index 000000000..c6c97b41c Binary files /dev/null and b/content/growth/ultimate-guide-to-professional-email-signatures-with-examples/over-stuffed-email-signature.webp differ diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.png b/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.png deleted file mode 100644 index 0d7046172..000000000 Binary files a/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.png and /dev/null differ diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.webp b/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.webp new file mode 100644 index 000000000..ea0737a8b Binary files /dev/null and b/content/growth/unified-identity-ensures-great-customer-interactions/GD-to-RBA.webp differ diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.jpg b/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.jpg deleted file mode 100644 index e7af6ef4e..000000000 Binary files a/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.jpg and /dev/null differ diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.webp b/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.webp new file mode 100644 index 000000000..8fa1d62f2 Binary files /dev/null and b/content/growth/unified-identity-ensures-great-customer-interactions/customer-interactions.webp differ diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/index.md b/content/growth/unified-identity-ensures-great-customer-interactions/index.md index dbd843dec..b92687660 100644 --- a/content/growth/unified-identity-ensures-great-customer-interactions/index.md +++ b/content/growth/unified-identity-ensures-great-customer-interactions/index.md @@ -1,7 +1,7 @@ --- title: "How Can Enterprises Deliver Better Customer Experiences with Unified Identity?" date: "2022-05-18" -coverImage: "customer-interactions.jpg" +coverImage: "customer-interactions.webp" tags: ["customer experience","sso","identity management","mfa"] author: "Yash Rathi" description: "Unified identity can do wonders for a brand if a business leverages its true potential. Let’s uncover some aspects of unified identity and how brands leverage the same to engage users and foster business growth." @@ -76,7 +76,7 @@ Risk-based authentication is a non-static authentication system that considers t It is a method of applying various levels of stringency to authentication processes based on the likelihood that access to a given system could be compromised. As the level of risk increases, the authentication process becomes more complicated and restrictive. -[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) +[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) Hence, managing security doesn't necessarily mean compromising user experience with MFA and RBA. This further boosts engagement and trust in a brand. @@ -101,4 +101,4 @@ Enterprises that have incorporated a reliable consumer identity and access manag Hence, it’s the right time for enterprises to understand the importance of rethinking their identity management strategy around a cutting-edge CIAM solution. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=unified-identity-ensures-great-customer-interactions) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=unified-identity-ensures-great-customer-interactions) \ No newline at end of file diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.png b/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.png deleted file mode 100644 index c820cfc17..000000000 Binary files a/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.png and /dev/null differ diff --git a/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.webp b/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.webp new file mode 100644 index 000000000..9cfe7e407 Binary files /dev/null and b/content/growth/unified-identity-ensures-great-customer-interactions/risk-auth-gd.webp differ diff --git a/content/growth/user-access-management-business-security/GD-to-RBA.png b/content/growth/user-access-management-business-security/GD-to-RBA.png deleted file mode 100644 index 0d7046172..000000000 Binary files a/content/growth/user-access-management-business-security/GD-to-RBA.png and /dev/null differ diff --git a/content/growth/user-access-management-business-security/GD-to-RBA.webp b/content/growth/user-access-management-business-security/GD-to-RBA.webp new file mode 100644 index 000000000..ea0737a8b Binary files /dev/null and b/content/growth/user-access-management-business-security/GD-to-RBA.webp differ diff --git a/content/growth/user-access-management-business-security/index.md b/content/growth/user-access-management-business-security/index.md index f03776b33..dee02bf53 100644 --- a/content/growth/user-access-management-business-security/index.md +++ b/content/growth/user-access-management-business-security/index.md @@ -1,7 +1,7 @@ --- title: "Strengthening Your Business Security: 7 Key User Access Management Best Practices" date: "2024-05-14" -coverImage: "user-access-mngmnt.jpg" +coverImage: "user-access-mngmnt.webp" tags: ["user access management","data security","cx"] author: "Rakesh Soni" description: "Strengthen your business security with proven user access management strategies. Discover how role-based access control, regular permission reviews, and strong password policies can safeguard your sensitive data and ensure compliance with regulations." @@ -42,7 +42,7 @@ Additionally, consider implementing [multi-factor authentication](https://www.lo With risk-based authentication, businesses can define adaptive authentication policies that tailor authentication requirements based on the assessed risk level. -[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) +[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) For low-risk access attempts, users may only need to provide basic credentials, while high-risk attempts may trigger additional authentication factors, such as biometric verification or one-time passwords. @@ -70,4 +70,4 @@ Optimizing business security requires a proactive approach to user access manage Prioritize security and invest in comprehensive user access management strategies to protect your business from evolving cyber threats. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-access-management-business-security) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-access-management-business-security) diff --git a/content/growth/user-access-management-business-security/user-access-mngmnt.jpg b/content/growth/user-access-management-business-security/user-access-mngmnt.jpg deleted file mode 100644 index 104bb1d4c..000000000 Binary files a/content/growth/user-access-management-business-security/user-access-mngmnt.jpg and /dev/null differ diff --git a/content/growth/user-access-management-business-security/user-access-mngmnt.webp b/content/growth/user-access-management-business-security/user-access-mngmnt.webp new file mode 100644 index 000000000..962842fb0 Binary files /dev/null and b/content/growth/user-access-management-business-security/user-access-mngmnt.webp differ diff --git a/content/growth/user-onboarding-tools/amplitude.png b/content/growth/user-onboarding-tools/amplitude.png deleted file mode 100644 index dd8524cdb..000000000 Binary files a/content/growth/user-onboarding-tools/amplitude.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/amplitude.webp b/content/growth/user-onboarding-tools/amplitude.webp new file mode 100644 index 000000000..a4f48c388 Binary files /dev/null and b/content/growth/user-onboarding-tools/amplitude.webp differ diff --git a/content/growth/user-onboarding-tools/appcues.png b/content/growth/user-onboarding-tools/appcues.png deleted file mode 100644 index 1334d466f..000000000 Binary files a/content/growth/user-onboarding-tools/appcues.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/appcues.webp b/content/growth/user-onboarding-tools/appcues.webp new file mode 100644 index 000000000..6604334de Binary files /dev/null and b/content/growth/user-onboarding-tools/appcues.webp differ diff --git a/content/growth/user-onboarding-tools/customer-io.png b/content/growth/user-onboarding-tools/customer-io.png deleted file mode 100644 index 09d6086f0..000000000 Binary files a/content/growth/user-onboarding-tools/customer-io.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/customer-io.webp b/content/growth/user-onboarding-tools/customer-io.webp new file mode 100644 index 000000000..f74cc3e78 Binary files /dev/null and b/content/growth/user-onboarding-tools/customer-io.webp differ diff --git a/content/growth/user-onboarding-tools/diy-github.png b/content/growth/user-onboarding-tools/diy-github.png deleted file mode 100644 index c57f9bf5d..000000000 Binary files a/content/growth/user-onboarding-tools/diy-github.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/diy-github.webp b/content/growth/user-onboarding-tools/diy-github.webp new file mode 100644 index 000000000..4c2c008dc Binary files /dev/null and b/content/growth/user-onboarding-tools/diy-github.webp differ diff --git a/content/growth/user-onboarding-tools/drip.png b/content/growth/user-onboarding-tools/drip.png deleted file mode 100644 index e035499ca..000000000 Binary files a/content/growth/user-onboarding-tools/drip.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/drip.webp b/content/growth/user-onboarding-tools/drip.webp new file mode 100644 index 000000000..a33f95593 Binary files /dev/null and b/content/growth/user-onboarding-tools/drip.webp differ diff --git a/content/growth/user-onboarding-tools/feedier.png b/content/growth/user-onboarding-tools/feedier.png deleted file mode 100644 index 99d280830..000000000 Binary files a/content/growth/user-onboarding-tools/feedier.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/feedier.webp b/content/growth/user-onboarding-tools/feedier.webp new file mode 100644 index 000000000..89f6d99a9 Binary files /dev/null and b/content/growth/user-onboarding-tools/feedier.webp differ diff --git a/content/growth/user-onboarding-tools/freshdesk.png b/content/growth/user-onboarding-tools/freshdesk.png deleted file mode 100644 index 32f7f9ae1..000000000 Binary files a/content/growth/user-onboarding-tools/freshdesk.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/freshdesk.webp b/content/growth/user-onboarding-tools/freshdesk.webp new file mode 100644 index 000000000..f227c9598 Binary files /dev/null and b/content/growth/user-onboarding-tools/freshdesk.webp differ diff --git a/content/growth/user-onboarding-tools/fullstory.png b/content/growth/user-onboarding-tools/fullstory.png deleted file mode 100644 index 2771811e8..000000000 Binary files a/content/growth/user-onboarding-tools/fullstory.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/fullstory.webp b/content/growth/user-onboarding-tools/fullstory.webp new file mode 100644 index 000000000..e07e36846 Binary files /dev/null and b/content/growth/user-onboarding-tools/fullstory.webp differ diff --git a/content/growth/user-onboarding-tools/google-optimize.png b/content/growth/user-onboarding-tools/google-optimize.png deleted file mode 100644 index 67eaccf4b..000000000 Binary files a/content/growth/user-onboarding-tools/google-optimize.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/google-optimize.webp b/content/growth/user-onboarding-tools/google-optimize.webp new file mode 100644 index 000000000..3ff4b8424 Binary files /dev/null and b/content/growth/user-onboarding-tools/google-optimize.webp differ diff --git a/content/growth/user-onboarding-tools/helpscout.png b/content/growth/user-onboarding-tools/helpscout.png deleted file mode 100644 index ec0b0c7e2..000000000 Binary files a/content/growth/user-onboarding-tools/helpscout.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/helpscout.webp b/content/growth/user-onboarding-tools/helpscout.webp new file mode 100644 index 000000000..c02415c84 Binary files /dev/null and b/content/growth/user-onboarding-tools/helpscout.webp differ diff --git a/content/growth/user-onboarding-tools/helpshelf.png b/content/growth/user-onboarding-tools/helpshelf.png deleted file mode 100644 index 5bcd55c43..000000000 Binary files a/content/growth/user-onboarding-tools/helpshelf.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/helpshelf.webp b/content/growth/user-onboarding-tools/helpshelf.webp new file mode 100644 index 000000000..c1b3e541b Binary files /dev/null and b/content/growth/user-onboarding-tools/helpshelf.webp differ diff --git a/content/growth/user-onboarding-tools/hotjar.png b/content/growth/user-onboarding-tools/hotjar.png deleted file mode 100644 index ad706e662..000000000 Binary files a/content/growth/user-onboarding-tools/hotjar.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/hotjar.webp b/content/growth/user-onboarding-tools/hotjar.webp new file mode 100644 index 000000000..6c96a1e1c Binary files /dev/null and b/content/growth/user-onboarding-tools/hotjar.webp differ diff --git a/content/growth/user-onboarding-tools/index.md b/content/growth/user-onboarding-tools/index.md index d51e7d09f..5e465c687 100644 --- a/content/growth/user-onboarding-tools/index.md +++ b/content/growth/user-onboarding-tools/index.md @@ -1,7 +1,7 @@ --- title: "Top 27 User Onboarding Tools: Highly Recommended for Businesses" date: "2021-01-20" -coverImage: "user-onboarding.jpg" +coverImage: "user-onboarding.webp" category: ["all"] featured: false author: "Navanita Devi" @@ -84,7 +84,7 @@ Tool #27: Helpshelf ## 1. AppCues - + Without writing a single line of code, create customized user onboarding flows, and increase adoption and retention rates with [appcues](https://www.appcues.com/). Within one dashboard, you can design, publish, and manage your onboarding experience, enabling your users to delve deeper into your platform. Patterns and templates are available, including easy tooltips, full-screen takeovers, slide outs, and in-app alerts. @@ -93,7 +93,7 @@ Without writing a single line of code, create customized user onboarding flows, ## 2. DIY with JavaScript - + Onboarding helps to familiarise new users with an interface. There are several different styles of this, and there is no perfect way of doing it. But you can pick up ideas for your work if you study [how onboarding sites](https://speckyboy.com/onboarding-ui-css-javascript/) and apps do. @@ -110,7 +110,7 @@ Just include the CSS and JS files on your page to get started, and you can start ## 3. Seamless Sign-in Experience With Single Sign-On - + [Single sign-on](https://www.loginradius.com/blog/identity/2019/05/what-is-single-sign-on/) (SSO) is an access control property of several related but independent software systems. To gain access to a linked device, a user logs in with a single ID and password with this house. @@ -132,7 +132,7 @@ LoginRadius supports both programming languages, so it doesn't matter if you hav ## 4. Intercom - + [Intercom](https://www.intercom.com/) tells you who your clients are and what your product is doing. You can also interact with them using in-app and email messages in real-time. Using Intercom implies making educated decisions by asking for input with event-triggered notes at the right time. @@ -143,7 +143,7 @@ It is simple to embed and convert new users to become active customers, and you ## 5. MailJet - + [Mailjet](https://www.mailjet.com/) is an easy-to-use and all-in-one email-sending network. It's excellent for research and cooperation with A/B. @@ -154,7 +154,7 @@ It enables you to collaborate, target specific users, and create personalized em ## 6. Drip - + [Drip](https://www.drip.com/) is an onboarding email creation tool. Without going to the promotion channel (if the user uses Gmail), it will send trigger-based emails directly in the inbox. @@ -165,7 +165,7 @@ Drip helps you to go beyond simple emails and build multiple onboard processes f ## 7. Customer.io (Paid) - + The [Customer.io](https://customer.io/) tool for submitting drip campaigns is a little more costly. It's nice to start onboarding, converting, and keeping your audience for your needs. @@ -180,7 +180,7 @@ What separates Customer.io from Mailjet and Drip is its ability for every custom - + One of the best-known and most common experimentation platforms for SaaS companies is [Optimizely](https://www.optimizely.com/). @@ -192,7 +192,7 @@ It enables both product and marketing divisions to experiment with each other. Y - + [Omniconvert](https://www.omniconvert.com/) is a platform for optimizing conversion rates that provides an A/B testing tool and tools for surveying, personalization, overlay, and segmentation. You can run desktop, mobile, and tablet A/B tests using their A/B testing tool. To validate your tests, you can convert winning versions of an A / B test into the control for a future trial and leverage Frequentist or Bayesian statistics. @@ -202,7 +202,7 @@ It enables both product and marketing divisions to experiment with each other. Y - + [Google Optimize](https://support.google.com/analytics/answer/12979939) can be an excellent way for you to A / B test various things if you're at your company's early stage. It's free, and it will meet all your needs at the start. @@ -214,7 +214,7 @@ Currently, Google Optimize's most extensive feature is its in-depth integration - + Trusted by over 4,500 enterprise brands, [VWO](https://vwo.com/) is a platform designed specifically for enterprise brands for A/B testing and conversion rate optimization. In their suit, with a drop-and-drop editor, you can create A / B tests, Split URL tests, and multivariate tests. @@ -227,7 +227,7 @@ Trusted by over 4,500 enterprise brands, [VWO](https://vwo.com/) is a platform d - + With a simple-to-use analytics app and dashboard, [Amplitude](https://amplitude.com/) enables you to monitor your data and metrics. The real-time platform tracks the use of your product and statistics from second to second, letting you know when your app crashes, or checkout flows break down. @@ -237,7 +237,7 @@ With a simple-to-use analytics app and dashboard, [Amplitude](https://amplitude. - + A behavioral analytics framework such as [Mixpanel](https://mixpanel.com/) can be used to run tests, such as slideouts and tooltips, on the performance of individual UI elements in your user onboarding. @@ -252,7 +252,7 @@ You can gather accurate information about your product use with Mixpanel, recogn - + [Feedier](https://feedier.com/) is an all-in-one feedback collection platform for your application, product, in-app interactions, or even onboarding processes for a customer. @@ -266,7 +266,7 @@ Feedier has incorporated incentive management to make the survey enjoyable and s - + [Qualaroo](https://qualaroo.com/) user research and feedback tools promise the capacity to do precisely that. At each point of the onboarding process, you can segment your clients by attribute, plan the timing or action exactly when you want questions to pop up, and get the hot take. @@ -276,7 +276,7 @@ Feedier has incorporated incentive management to make the survey enjoyable and s - + [Wootric](https://www.wootric.com/) is one of the best onboarding methods for customer loyalty and happiness tracking. @@ -290,7 +290,7 @@ You can monitor the satisfaction of your customers in real time and even generat - + Use a simple form development tool like [Typeform](https://www.typeform.com/) if you're strapped for cash but still need to get the answers you need. Its conversational, collaborative survey style is one benefit of Typeform. The simplicity of producing a survey is another advantage; it is similar to typing in a notepad, with no coding necessary. @@ -303,7 +303,7 @@ Use a simple form development tool like [Typeform](https://www.typeform.com/) if - + Through heatmaps, session recordings, and conversion funnels, [Hotjar](https://www.hotjar.com/) offers invaluable insights into the behavior of your users. @@ -317,7 +317,7 @@ Knowing what your customers already do on your website will help you build smoot - + Another tool for analyzing heat maps and digital experiences is [FullStory](https://www.fullstory.com/). @@ -334,7 +334,7 @@ Almost every session made on your website or application can be looked at. Your - + Live chat is an excellent platform for onboarding your new users and gathering feedback for your product. @@ -350,7 +350,7 @@ It has a fantastic dashboard that supports all of your tickets on multiple platf - + A simple way to frustrate them and create unnecessary pressure is to disturb the users and sign in as they go through onboarding or complete vital tasks. With a live chat tool like Olark, you can do this. Using a chat box that suits your branding, [Olark](https://www.olark.com/) allows you to live chat with clients that run into an issue. @@ -360,7 +360,7 @@ A simple way to frustrate them and create unnecessary pressure is to disturb the - + [Helpscout](https://www.helpscout.com/) is another perfect solution to incorporate live chat support in your user onboarding. @@ -374,7 +374,7 @@ with this tool you can create more personalized ticket emails for every user. To - + Another great software tool for talking to clients and solving their problems in real-time is [LiveChat](https://www.livechat.com/). Use it to speak with your users and address their issues as they happen. LiveChat's rich analytics show you where your users face most roadblocks during their onboarding (or elsewhere in their journey). Using LiveChat to monitor the onboarding process and recognize the moments of friction that your clients encounter. @@ -384,7 +384,7 @@ Another great software tool for talking to clients and solving their problems in - + Knowledge base tools such as [Zendesk](https://www.zendesk.com/) allow you to build an online support center where customers can access FAQs, fixes for prevalent problems, step-by-step posts, and community-cured solutions. Before it's too late, help the clients help themselves. @@ -397,7 +397,7 @@ Knowledge base tools such as [Zendesk](https://www.zendesk.com/) allow you to bu - + One of the helpful onboarding video tools for customers is [Loom](https://www.loom.com/). Video user onboarding is the next best thing to offer you a competitive advantage if you do not have the time or the workers to hold in-person training or training seminars. @@ -411,7 +411,7 @@ By encouraging your future clients to watch a short video rather than read an en - + The [Inline Manual](https://inlinemanual.com/) is an advanced method for onboarding users, inline documentation, and quicker adoption of greater conversions applications. To engage and help your customers, you can quickly produce walkthroughs, onboarding guides, videos, and product documentation by presenting a new layer on top of your website or application that enables your customers to learn on the go. @@ -421,7 +421,7 @@ The [Inline Manual](https://inlinemanual.com/) is an advanced method for onboard - + [Helpshelf](https://helpshelf.co/) is a fantastic user-onboarding knowledge base application. @@ -438,4 +438,4 @@ Luckily, the market gives us an overwhelming range of different resources. We ha Customer Onboarding is a critical step that forms the entire lifecycle of the user. The best onboarding experiences help users quickly achieve their magic moment; they also set up new users for long-term success. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-onboarding-tools) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=user-onboarding-tools) diff --git a/content/growth/user-onboarding-tools/inline-manual.png b/content/growth/user-onboarding-tools/inline-manual.png deleted file mode 100644 index f2550553b..000000000 Binary files a/content/growth/user-onboarding-tools/inline-manual.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/inline-manual.webp b/content/growth/user-onboarding-tools/inline-manual.webp new file mode 100644 index 000000000..8193d5136 Binary files /dev/null and b/content/growth/user-onboarding-tools/inline-manual.webp differ diff --git a/content/growth/user-onboarding-tools/intercom.png b/content/growth/user-onboarding-tools/intercom.png deleted file mode 100644 index bb61a30f4..000000000 Binary files a/content/growth/user-onboarding-tools/intercom.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/intercom.webp b/content/growth/user-onboarding-tools/intercom.webp new file mode 100644 index 000000000..c4d46d106 Binary files /dev/null and b/content/growth/user-onboarding-tools/intercom.webp differ diff --git a/content/growth/user-onboarding-tools/livechat.png b/content/growth/user-onboarding-tools/livechat.png deleted file mode 100644 index 598981f49..000000000 Binary files a/content/growth/user-onboarding-tools/livechat.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/livechat.webp b/content/growth/user-onboarding-tools/livechat.webp new file mode 100644 index 000000000..4a148e67f Binary files /dev/null and b/content/growth/user-onboarding-tools/livechat.webp differ diff --git a/content/growth/user-onboarding-tools/loginradius-sso.png b/content/growth/user-onboarding-tools/loginradius-sso.png deleted file mode 100644 index d7ed9afa6..000000000 Binary files a/content/growth/user-onboarding-tools/loginradius-sso.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/loginradius-sso.webp b/content/growth/user-onboarding-tools/loginradius-sso.webp new file mode 100644 index 000000000..c9ad26bb8 Binary files /dev/null and b/content/growth/user-onboarding-tools/loginradius-sso.webp differ diff --git a/content/growth/user-onboarding-tools/loom.png b/content/growth/user-onboarding-tools/loom.png deleted file mode 100644 index c19d5d42d..000000000 Binary files a/content/growth/user-onboarding-tools/loom.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/loom.webp b/content/growth/user-onboarding-tools/loom.webp new file mode 100644 index 000000000..ac8ee5f35 Binary files /dev/null and b/content/growth/user-onboarding-tools/loom.webp differ diff --git a/content/growth/user-onboarding-tools/mailjet.png b/content/growth/user-onboarding-tools/mailjet.png deleted file mode 100644 index b8834113d..000000000 Binary files a/content/growth/user-onboarding-tools/mailjet.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/mailjet.webp b/content/growth/user-onboarding-tools/mailjet.webp new file mode 100644 index 000000000..dc096fe2b Binary files /dev/null and b/content/growth/user-onboarding-tools/mailjet.webp differ diff --git a/content/growth/user-onboarding-tools/mixpanel.png b/content/growth/user-onboarding-tools/mixpanel.png deleted file mode 100644 index f542d99d8..000000000 Binary files a/content/growth/user-onboarding-tools/mixpanel.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/mixpanel.webp b/content/growth/user-onboarding-tools/mixpanel.webp new file mode 100644 index 000000000..52d403b96 Binary files /dev/null and b/content/growth/user-onboarding-tools/mixpanel.webp differ diff --git a/content/growth/user-onboarding-tools/olark.png b/content/growth/user-onboarding-tools/olark.png deleted file mode 100644 index 4ead3ffc5..000000000 Binary files a/content/growth/user-onboarding-tools/olark.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/olark.webp b/content/growth/user-onboarding-tools/olark.webp new file mode 100644 index 000000000..76b121d75 Binary files /dev/null and b/content/growth/user-onboarding-tools/olark.webp differ diff --git a/content/growth/user-onboarding-tools/omniconvert.png b/content/growth/user-onboarding-tools/omniconvert.png deleted file mode 100644 index caa99bfb2..000000000 Binary files a/content/growth/user-onboarding-tools/omniconvert.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/omniconvert.webp b/content/growth/user-onboarding-tools/omniconvert.webp new file mode 100644 index 000000000..1792d365e Binary files /dev/null and b/content/growth/user-onboarding-tools/omniconvert.webp differ diff --git a/content/growth/user-onboarding-tools/optimizely.png b/content/growth/user-onboarding-tools/optimizely.png deleted file mode 100644 index 3b258f16c..000000000 Binary files a/content/growth/user-onboarding-tools/optimizely.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/optimizely.webp b/content/growth/user-onboarding-tools/optimizely.webp new file mode 100644 index 000000000..57766c978 Binary files /dev/null and b/content/growth/user-onboarding-tools/optimizely.webp differ diff --git a/content/growth/user-onboarding-tools/qualaroo.png b/content/growth/user-onboarding-tools/qualaroo.png deleted file mode 100644 index a8d83b917..000000000 Binary files a/content/growth/user-onboarding-tools/qualaroo.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/qualaroo.webp b/content/growth/user-onboarding-tools/qualaroo.webp new file mode 100644 index 000000000..95143c03b Binary files /dev/null and b/content/growth/user-onboarding-tools/qualaroo.webp differ diff --git a/content/growth/user-onboarding-tools/typeform.png b/content/growth/user-onboarding-tools/typeform.png deleted file mode 100644 index a028058d8..000000000 Binary files a/content/growth/user-onboarding-tools/typeform.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/typeform.webp b/content/growth/user-onboarding-tools/typeform.webp new file mode 100644 index 000000000..8c9c2012e Binary files /dev/null and b/content/growth/user-onboarding-tools/typeform.webp differ diff --git a/content/growth/user-onboarding-tools/user-onboarding.jpg b/content/growth/user-onboarding-tools/user-onboarding.jpg deleted file mode 100644 index 8609842c7..000000000 Binary files a/content/growth/user-onboarding-tools/user-onboarding.jpg and /dev/null differ diff --git a/content/growth/user-onboarding-tools/user-onboarding.webp b/content/growth/user-onboarding-tools/user-onboarding.webp new file mode 100644 index 000000000..5a765e211 Binary files /dev/null and b/content/growth/user-onboarding-tools/user-onboarding.webp differ diff --git a/content/growth/user-onboarding-tools/vwo.png b/content/growth/user-onboarding-tools/vwo.png deleted file mode 100644 index 9f8d3631c..000000000 Binary files a/content/growth/user-onboarding-tools/vwo.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/vwo.webp b/content/growth/user-onboarding-tools/vwo.webp new file mode 100644 index 000000000..f9672ed94 Binary files /dev/null and b/content/growth/user-onboarding-tools/vwo.webp differ diff --git a/content/growth/user-onboarding-tools/wootric.png b/content/growth/user-onboarding-tools/wootric.png deleted file mode 100644 index 057f82072..000000000 Binary files a/content/growth/user-onboarding-tools/wootric.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/wootric.webp b/content/growth/user-onboarding-tools/wootric.webp new file mode 100644 index 000000000..b73174728 Binary files /dev/null and b/content/growth/user-onboarding-tools/wootric.webp differ diff --git a/content/growth/user-onboarding-tools/zendesk.png b/content/growth/user-onboarding-tools/zendesk.png deleted file mode 100644 index 6d97d2aea..000000000 Binary files a/content/growth/user-onboarding-tools/zendesk.png and /dev/null differ diff --git a/content/growth/user-onboarding-tools/zendesk.webp b/content/growth/user-onboarding-tools/zendesk.webp new file mode 100644 index 000000000..77e017050 Binary files /dev/null and b/content/growth/user-onboarding-tools/zendesk.webp differ diff --git a/content/growth/what-advanced-identity-means-for-cx/cx-identity.jpg b/content/growth/what-advanced-identity-means-for-cx/cx-identity.jpg deleted file mode 100644 index 27d4d7e8b..000000000 Binary files a/content/growth/what-advanced-identity-means-for-cx/cx-identity.jpg and /dev/null differ diff --git a/content/growth/what-advanced-identity-means-for-cx/cx-identity.webp b/content/growth/what-advanced-identity-means-for-cx/cx-identity.webp new file mode 100644 index 000000000..bda4892ca Binary files /dev/null and b/content/growth/what-advanced-identity-means-for-cx/cx-identity.webp differ diff --git a/content/growth/what-advanced-identity-means-for-cx/index.md b/content/growth/what-advanced-identity-means-for-cx/index.md index cdedc8fdf..9d298251c 100644 --- a/content/growth/what-advanced-identity-means-for-cx/index.md +++ b/content/growth/what-advanced-identity-means-for-cx/index.md @@ -1,7 +1,7 @@ --- title: "The Future of Customer Experience is All About Advanced Identity" date: "2022-09-08" -coverImage: "cx-identity.jpg" +coverImage: "cx-identity.webp" category: ["customer experience", "identity management", "compliance"] author: "Vishal Sharma" description: "Since customer journeys are becoming increasingly complex, brands should focus more on improving their identity management infrastructure. This blog explains the aspects of identity management and how to deliver a rich and secure CX across multiple touchpoints." @@ -42,7 +42,7 @@ A rich customer experience begins when users interact with their platform for th Besides, global data privacy and security compliances, including the GDPR and CCPA, are more stringent than ever. Hence, to comply with these regulations, brands should adopt a robust identity management solution to continue delivering services to their customers. -[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance) +[](https://www.loginradius.com/resource/loginradius-and-ccpa-compliance) ## Your Customers Know What to Share What Not @@ -71,4 +71,4 @@ The power of identity management is helping brands navigate their digital transf With a reliable customer identity and access management solution, brands can ensure they stand ahead of the curve by delivering rich customer experiences backed with robust security. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-advanced-identity-means-for-cx) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-advanced-identity-means-for-cx) \ No newline at end of file diff --git a/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.png b/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.png deleted file mode 100644 index 6784e19bd..000000000 Binary files a/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.png and /dev/null differ diff --git a/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.webp b/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.webp new file mode 100644 index 000000000..c27d2fee5 Binary files /dev/null and b/content/growth/what-advanced-identity-means-for-cx/lr-ccpa.webp differ diff --git a/content/growth/what-is-digital-privacy/WP-compliance-retailers.png b/content/growth/what-is-digital-privacy/WP-compliance-retailers.png deleted file mode 100644 index 802253f09..000000000 Binary files a/content/growth/what-is-digital-privacy/WP-compliance-retailers.png and /dev/null differ diff --git a/content/growth/what-is-digital-privacy/WP-compliance-retailers.webp b/content/growth/what-is-digital-privacy/WP-compliance-retailers.webp new file mode 100644 index 000000000..c98143e9e Binary files /dev/null and b/content/growth/what-is-digital-privacy/WP-compliance-retailers.webp differ diff --git a/content/growth/what-is-digital-privacy/compliance-wp.png b/content/growth/what-is-digital-privacy/compliance-wp.png deleted file mode 100644 index a2c9e2a07..000000000 Binary files a/content/growth/what-is-digital-privacy/compliance-wp.png and /dev/null differ diff --git a/content/growth/what-is-digital-privacy/compliance-wp.webp b/content/growth/what-is-digital-privacy/compliance-wp.webp new file mode 100644 index 000000000..1717fdcbb Binary files /dev/null and b/content/growth/what-is-digital-privacy/compliance-wp.webp differ diff --git a/content/growth/what-is-digital-privacy/digi-privacy.jpg b/content/growth/what-is-digital-privacy/digi-privacy.jpg deleted file mode 100644 index a42c7c0f8..000000000 Binary files a/content/growth/what-is-digital-privacy/digi-privacy.jpg and /dev/null differ diff --git a/content/growth/what-is-digital-privacy/digi-privacy.webp b/content/growth/what-is-digital-privacy/digi-privacy.webp new file mode 100644 index 000000000..c23ff4abe Binary files /dev/null and b/content/growth/what-is-digital-privacy/digi-privacy.webp differ diff --git a/content/growth/what-is-digital-privacy/index.md b/content/growth/what-is-digital-privacy/index.md index d1c53bcac..b92a02815 100644 --- a/content/growth/what-is-digital-privacy/index.md +++ b/content/growth/what-is-digital-privacy/index.md @@ -1,7 +1,7 @@ --- title: "Decoding the Business Advantage of Digital Privacy for Customers" date: "2022-11-03" -coverImage: "digi-privacy.jpg" +coverImage: "digi-privacy.webp" category: ["digital privacy","compliance","passwordless authentication"] author: "Alok Patidar" description: "Investing in privacy isn’t just a matter of mitigating risks pertaining to data breaches; it’s also about navigating business success by building trust and offering value to customers through enhanced security and protections. Let’s understand how businesses can invoke the true potential of digital privacy." @@ -57,7 +57,7 @@ Businesses operating in different parts of the world couldn’t deny that meetin However, digital privacy has more to offer besides the security and privacy advantages; it navigates overall business success. -[](https://www.loginradius.com/resource/role-of-data-and-privacy-compliance-in-retail) +[](https://www.loginradius.com/resource/role-of-data-and-privacy-compliance-in-retail) According to a consumer data protection and privacy survey conducted by [McKinsey](https://www.mckinsey.com/business-functions/risk-and-resilience/our-insights/the-consumer-data-opportunity-and-the-privacy-imperative), half of the respondents agreed that they are most likely to trust a business/organization that asks for only information relevant to its products/services. @@ -83,4 +83,4 @@ In conclusion, we’ve found that building a foundation of strong digital privac Brands can’t afford to lose a single customer because of non-compliance issues. Hence, it won’t be a good decision for businesses to miss out on the chance to stay ahead of the competition. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-digital-privacy) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-digital-privacy) \ No newline at end of file diff --git a/content/growth/what-is-identity-resolution/DS-user-mngmnt.png b/content/growth/what-is-identity-resolution/DS-user-mngmnt.png deleted file mode 100644 index fc6f98c05..000000000 Binary files a/content/growth/what-is-identity-resolution/DS-user-mngmnt.png and /dev/null differ diff --git a/content/growth/what-is-identity-resolution/DS-user-mngmnt.webp b/content/growth/what-is-identity-resolution/DS-user-mngmnt.webp new file mode 100644 index 000000000..c60f3551f Binary files /dev/null and b/content/growth/what-is-identity-resolution/DS-user-mngmnt.webp differ diff --git a/content/growth/what-is-identity-resolution/identity-resolution.jpg b/content/growth/what-is-identity-resolution/identity-resolution.jpg deleted file mode 100644 index 5bb891709..000000000 Binary files a/content/growth/what-is-identity-resolution/identity-resolution.jpg and /dev/null differ diff --git a/content/growth/what-is-identity-resolution/identity-resolution.webp b/content/growth/what-is-identity-resolution/identity-resolution.webp new file mode 100644 index 000000000..c408d7c32 Binary files /dev/null and b/content/growth/what-is-identity-resolution/identity-resolution.webp differ diff --git a/content/growth/what-is-identity-resolution/index.md b/content/growth/what-is-identity-resolution/index.md index 01ee6a365..ba7b92c6b 100644 --- a/content/growth/what-is-identity-resolution/index.md +++ b/content/growth/what-is-identity-resolution/index.md @@ -1,7 +1,7 @@ --- title: "What Is Identity Resolution And How Can It Benefit Your Business?" date: "2023-08-09" -coverImage: "identity-resolution.jpg" +coverImage: "identity-resolution.webp" tags: ["identity resolution","user management","compliance","cx"] author: "Vishal Sharma" description: "Uncover the power of identity resolution to boost your business. Enhance customer experiences, optimize marketing efforts, and mitigate fraud risks with accurate, unified customer data." @@ -38,7 +38,7 @@ Identity resolution empowers marketers to segment and target their audience with These segmented profiles enable marketers to tailor their messages, promotions, and advertisements to specific customer segments, maximizing relevance and driving higher conversion rates. With identity resolution, businesses can optimize their marketing strategies and allocate resources more effectively. -[](https://www.loginradius.com/resource/loginradius-ciam-user-management/) +[](https://www.loginradius.com/resource/loginradius-ciam-user-management/) ### 3. Fraud Detection and Risk Mitigation @@ -76,4 +76,4 @@ By leveraging the power of identity resolution, businesses can unlock a wealth o Investing in identity resolution enables organizations to optimize their operations, deepen customer relationships, and stay ahead in a rapidly evolving marketplace. Embrace identity resolution as a core component of your business strategy and unlock its transformative potential. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-resolution) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-identity-resolution) \ No newline at end of file diff --git a/content/growth/what-is-omnichannel-cx/Omnichannel-CX.jpg b/content/growth/what-is-omnichannel-cx/Omnichannel-CX.jpg deleted file mode 100644 index 0039316f8..000000000 Binary files a/content/growth/what-is-omnichannel-cx/Omnichannel-CX.jpg and /dev/null differ diff --git a/content/growth/what-is-omnichannel-cx/Omnichannel-CX.webp b/content/growth/what-is-omnichannel-cx/Omnichannel-CX.webp new file mode 100644 index 000000000..5cd87f332 Binary files /dev/null and b/content/growth/what-is-omnichannel-cx/Omnichannel-CX.webp differ diff --git a/content/growth/what-is-omnichannel-cx/index.md b/content/growth/what-is-omnichannel-cx/index.md index 47b1ed6b9..d39bf116f 100644 --- a/content/growth/what-is-omnichannel-cx/index.md +++ b/content/growth/what-is-omnichannel-cx/index.md @@ -1,7 +1,7 @@ --- title: "Omnichannel CX : Your Key to Consumer Experience Success" date: "2021-06-30" -coverImage: "Omnichannel-CX.jpg" +coverImage: "Omnichannel-CX.webp" category: ["loginradius"] featured: false author: "Tanvi Soni" @@ -109,4 +109,4 @@ For seamless humanized omnichannel journeys and consumer experience, [consumer Continue the conversation effortlessly if consumers switch from one channel to another. Start with chat, move on to voice, and then interact through video seamlessly. [Contact LoginRadius](https://www.loginradius.com/contact-us/) to know more. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-omnichannel-cx) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-omnichannel-cx) \ No newline at end of file diff --git a/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.png b/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.png deleted file mode 100644 index bdd52a34c..000000000 Binary files a/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.png and /dev/null differ diff --git a/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.webp b/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.webp new file mode 100644 index 000000000..19580a6f8 Binary files /dev/null and b/content/growth/when-to-switch-your-security-vendor/WP-futureproof-security.webp differ diff --git a/content/growth/when-to-switch-your-security-vendor/index.md b/content/growth/when-to-switch-your-security-vendor/index.md index 8822f0ed1..1b0f454a4 100644 --- a/content/growth/when-to-switch-your-security-vendor/index.md +++ b/content/growth/when-to-switch-your-security-vendor/index.md @@ -1,7 +1,7 @@ --- title: "Renewing Your Security Vendor Contract? Know When It’s the Time to Switch" date: "2022-08-31" -coverImage: "sec-vendor.jpg" +coverImage: "sec-vendor.webp" tags: ["cybersecurity", "mfa", "digital identity","cloud security"] author: "Rakesh Soni" description: "Since cybercriminals are constantly exploring new ways to exploit sensitive business and customer information, companies must upgrade their security infrastructure to ensure they remain in a safe zone. Here are some aspects of upgrading your security practices and when businesses must rethink their cybersecurity posture." @@ -40,7 +40,7 @@ But besides endless security mechanisms working simultaneously to prevent a brea Hence, when organizations face violations, they must consider switching their security vendor or renewing the same with added security features. -[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper) +[](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper) ## Signs You Need to Switch/Renew Your Security Vendor Contract @@ -86,4 +86,4 @@ Technology has provided endless opportunities to enterprises. However, adopting Companies need to understand that they may need to change their cybersecurity policies or rely on third-party vendors to ensure the highest level of security. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=when-to-switch-your-security-vendor) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=when-to-switch-your-security-vendor) diff --git a/content/growth/when-to-switch-your-security-vendor/sec-vendor.jpg b/content/growth/when-to-switch-your-security-vendor/sec-vendor.jpg deleted file mode 100644 index 101c52a66..000000000 Binary files a/content/growth/when-to-switch-your-security-vendor/sec-vendor.jpg and /dev/null differ diff --git a/content/growth/when-to-switch-your-security-vendor/sec-vendor.webp b/content/growth/when-to-switch-your-security-vendor/sec-vendor.webp new file mode 100644 index 000000000..510894fbe Binary files /dev/null and b/content/growth/when-to-switch-your-security-vendor/sec-vendor.webp differ diff --git a/content/growth/when-to-switch-your-security-vendor/security-wp.png b/content/growth/when-to-switch-your-security-vendor/security-wp.png deleted file mode 100644 index 9b885caa8..000000000 Binary files a/content/growth/when-to-switch-your-security-vendor/security-wp.png and /dev/null differ diff --git a/content/growth/when-to-switch-your-security-vendor/security-wp.webp b/content/growth/when-to-switch-your-security-vendor/security-wp.webp new file mode 100644 index 000000000..62f54b93f Binary files /dev/null and b/content/growth/when-to-switch-your-security-vendor/security-wp.webp differ diff --git a/content/growth/why-brand-authenticity-is-important/brand-engagement.jpg b/content/growth/why-brand-authenticity-is-important/brand-engagement.jpg deleted file mode 100644 index dada5592c..000000000 Binary files a/content/growth/why-brand-authenticity-is-important/brand-engagement.jpg and /dev/null differ diff --git a/content/growth/why-brand-authenticity-is-important/brand-engagement.webp b/content/growth/why-brand-authenticity-is-important/brand-engagement.webp new file mode 100644 index 000000000..8b8362c51 Binary files /dev/null and b/content/growth/why-brand-authenticity-is-important/brand-engagement.webp differ diff --git a/content/growth/why-brand-authenticity-is-important/index.md b/content/growth/why-brand-authenticity-is-important/index.md index c1448a6c1..5c8095f6a 100644 --- a/content/growth/why-brand-authenticity-is-important/index.md +++ b/content/growth/why-brand-authenticity-is-important/index.md @@ -1,7 +1,7 @@ --- title: "Why Brand Authenticity is Important & How to Build it" date: "2021-06-24" -coverImage: "brand-engagement.jpg" +coverImage: "brand-engagement.webp" category: ["loginradius"] featured: false author: "Navanita Devi" @@ -126,4 +126,4 @@ The final step towards achieving brand authenticity is to showcase your [brand r Brand authenticity is not a one-time activity, but a constant process of discovering what your brand means for your consumers. No matter which industry you are in, brand identity is critical for business success in today’s times. As outlined in this article, an authentic brand can connect with consumers and establish a brand value that goes way beyond profits and revenues. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-brand-authenticity-is-important) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-brand-authenticity-is-important) diff --git a/content/growth/why-should-implement-social-login-authentication/Social-Login.png b/content/growth/why-should-implement-social-login-authentication/Social-Login.png deleted file mode 100644 index 98e481315..000000000 Binary files a/content/growth/why-should-implement-social-login-authentication/Social-Login.png and /dev/null differ diff --git a/content/growth/why-should-implement-social-login-authentication/Social-Login.webp b/content/growth/why-should-implement-social-login-authentication/Social-Login.webp new file mode 100644 index 000000000..5e3eaf627 Binary files /dev/null and b/content/growth/why-should-implement-social-login-authentication/Social-Login.webp differ diff --git a/content/growth/why-should-implement-social-login-authentication/index.md b/content/growth/why-should-implement-social-login-authentication/index.md index 3aecae763..085f8cbe9 100644 --- a/content/growth/why-should-implement-social-login-authentication/index.md +++ b/content/growth/why-should-implement-social-login-authentication/index.md @@ -1,7 +1,7 @@ --- title: "Why Should You Implement Social Login Authentication?" date: "2021-08-16" -coverImage: "social-login-1.jpg" +coverImage: "social-login-1.webp" tags: ["social login authentication","data security","cx"] author: "Navanita Devi" description: "If you're building a startup today, social login should be the default, not an afterthought. It will give you a huge competitive advantage, because your users won't have to register or even create an email address to use your site." @@ -28,7 +28,7 @@ Social logins is usually manifested using the following steps: 4. Finally, the social media provider will confirm the identity of the user, who will then obtain access to the application or site. -[](https://www.loginradius.com/resource/loginradius-ciam-social-login/) +[](https://www.loginradius.com/resource/loginradius-ciam-social-login/) Depending on the social network provider and their respective CIAM management practices, the process of social login authentication differs slightly. This is because each platform collects different user information and implements distinct consumer data security strategies. @@ -129,4 +129,4 @@ Organizations can implement social login by using a robust CIAM solution like Lo Single Sign-On (SSO) allows users to access multiple applications with one set of credentials. At the same time, social login is an authentication mechanism that specifically uses social media credentials for user authentication. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-should-implement-social-login-authentication) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=why-should-implement-social-login-authentication) \ No newline at end of file diff --git a/content/growth/why-should-implement-social-login-authentication/social-login-1.jpg b/content/growth/why-should-implement-social-login-authentication/social-login-1.jpg deleted file mode 100644 index 0e38b9458..000000000 Binary files a/content/growth/why-should-implement-social-login-authentication/social-login-1.jpg and /dev/null differ diff --git a/content/growth/why-should-implement-social-login-authentication/social-login-1.webp b/content/growth/why-should-implement-social-login-authentication/social-login-1.webp new file mode 100644 index 000000000..0d0559b38 Binary files /dev/null and b/content/growth/why-should-implement-social-login-authentication/social-login-1.webp differ diff --git a/content/growth/zero-party-data/DS-Progressive-Profiling.png b/content/growth/zero-party-data/DS-Progressive-Profiling.png deleted file mode 100644 index c98c144d4..000000000 Binary files a/content/growth/zero-party-data/DS-Progressive-Profiling.png and /dev/null differ diff --git a/content/growth/zero-party-data/DS-Progressive-Profiling.webp b/content/growth/zero-party-data/DS-Progressive-Profiling.webp new file mode 100644 index 000000000..b34c41174 Binary files /dev/null and b/content/growth/zero-party-data/DS-Progressive-Profiling.webp differ diff --git a/content/growth/zero-party-data/index.md b/content/growth/zero-party-data/index.md index 27a020955..efe5a32ce 100644 --- a/content/growth/zero-party-data/index.md +++ b/content/growth/zero-party-data/index.md @@ -1,7 +1,7 @@ --- title: "Unlocking Success: Marketing in a Cookieless World with Zero-Party Data" date: "2023-11-07" -coverImage: "zero-party-data.jpg" +coverImage: "zero-party-data.webp" tags: ["zero-party","progressive profiling","compliance","cx"] author: "Yash Rathi" description: "Discover the power of zero-party data in the cookieless era. Explore innovative strategies for personalized marketing and trust-building. Embrace ethical practices and human connection to unlock unprecedented success in the digital world." @@ -35,7 +35,7 @@ Zero-party data enables businesses to tailor their marketing messages to individ Progressive profiling helps businesses collect useful customer details gradually over time. When customers willingly share their data, it fosters a sense of trust and transparency between the brand and the consumer. By respecting user privacy and preferences, businesses can create lasting relationships with their audience. -[](https://www.loginradius.com/resource/progressive-profiling-by-loginradius-2/) +[](https://www.loginradius.com/resource/progressive-profiling-by-loginradius-2/) ### 3. Improved Customer Engagement @@ -85,4 +85,4 @@ By adopting innovative strategies to collect and utilize zero-party data effecti Embracing this paradigm shift not only meets the demands of the evolving digital ecosystem but also establishes a foundation for ethical and customer-centric marketing practices, leading to long-term brand loyalty and business growth. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=zero-party-data) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=zero-party-data) diff --git a/content/growth/zero-party-data/zero-party-data.jpg b/content/growth/zero-party-data/zero-party-data.jpg deleted file mode 100644 index 18dcedd24..000000000 Binary files a/content/growth/zero-party-data/zero-party-data.jpg and /dev/null differ diff --git a/content/growth/zero-party-data/zero-party-data.webp b/content/growth/zero-party-data/zero-party-data.webp new file mode 100644 index 000000000..f70a6321e Binary files /dev/null and b/content/growth/zero-party-data/zero-party-data.webp differ diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.png b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.png deleted file mode 100644 index 404532996..000000000 Binary files a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.png and /dev/null differ diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.webp b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.webp new file mode 100644 index 000000000..832cb0156 Binary files /dev/null and b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/WP-Zero-Trust-Security-1.webp differ diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.jpg b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.jpg deleted file mode 100644 index 3df9b3b8b..000000000 Binary files a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.jpg and /dev/null differ diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.webp b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.webp new file mode 100644 index 000000000..8b9a2bb63 Binary files /dev/null and b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/cyber-monday.webp differ diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/index.md b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/index.md index 25b847a6c..b57745410 100644 --- a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/index.md +++ b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/index.md @@ -1,7 +1,7 @@ --- title: "10 Ways To Keep Your Business Safe On Black Friday and Cyber Monday" date: "2022-11-23" -coverImage: "cyber-monday.jpg" +coverImage: "cyber-monday.webp" tags: ["online shopping", "online security", "cx"] author: "Navanita Devi" description: "Black Friday and Cyber Monday mean big deals, but they also mean big risks. Take control of your security and privacy with these tips to keep your business safe for cyber attacks." @@ -61,7 +61,7 @@ As a retailer, your organization will likely experience a significant increase i To avoid this, retailers need to shift to a more pragmatic and strategic security approach to ensure the organization can recover quickly from a cybersecurity event and get back to business with zero data loss. -[](https://www.loginradius.com/resource/zero-trust-security/) +[](https://www.loginradius.com/resource/zero-trust-security/) ### 6. Think of uptime as an opportunity to maximize efficiency. @@ -105,4 +105,4 @@ When you take some time to craft a post-purchase journey tailored to your custom -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=10-black-friday-cyber-monday-tips-for-businesses) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=10-black-friday-cyber-monday-tips-for-businesses) diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.png b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.png deleted file mode 100644 index 3e6b81ee6..000000000 Binary files a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.png and /dev/null differ diff --git a/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.webp b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.webp new file mode 100644 index 000000000..2f7c01062 Binary files /dev/null and b/content/identity/10-black-friday-cyber-monday-tips-for-businesses/zerotrust-wp.webp differ diff --git a/content/identity/1fa-vs-2fa-vs-mfa/index.md b/content/identity/1fa-vs-2fa-vs-mfa/index.md index 0db283527..1bdd3b80b 100644 --- a/content/identity/1fa-vs-2fa-vs-mfa/index.md +++ b/content/identity/1fa-vs-2fa-vs-mfa/index.md @@ -282,4 +282,4 @@ Yes, MFA is highly secure as it requires multiple factors, reducing the chances Yes, 2FA codes typically expire within 30–60 seconds, ensuring they can’t be reused by attackers. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=1fa-vs-2fa-vs-mfa) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=1fa-vs-2fa-vs-mfa) \ No newline at end of file diff --git a/content/identity/2fa-mfa-key-differences/2fa-vs-mfa.webp b/content/identity/2fa-mfa-key-differences/2fa-vs-mfa.webp new file mode 100644 index 000000000..4db479189 Binary files /dev/null and b/content/identity/2fa-mfa-key-differences/2fa-vs-mfa.webp differ diff --git a/content/identity/2fa-mfa-key-differences/EB-GD-to-MFA.webp b/content/identity/2fa-mfa-key-differences/EB-GD-to-MFA.webp new file mode 100644 index 000000000..00c5933a4 Binary files /dev/null and b/content/identity/2fa-mfa-key-differences/EB-GD-to-MFA.webp differ diff --git a/content/identity/2fa-mfa-key-differences/index.md b/content/identity/2fa-mfa-key-differences/index.md index e816a8206..2b2c02382 100644 --- a/content/identity/2fa-mfa-key-differences/index.md +++ b/content/identity/2fa-mfa-key-differences/index.md @@ -259,4 +259,4 @@ To incorporate MFA or advanced adaptive MFA from LoginRadius, you can [reach us **A:** Absolutely. Two-factor authentication significantly enhances security compared to just using passwords, effectively reducing common cyber threats. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=2fa-mfa-key-differences) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=2fa-mfa-key-differences) \ No newline at end of file diff --git a/content/identity/2fa-security-measures/2fa-security.jpg b/content/identity/2fa-security-measures/2fa-security.jpg deleted file mode 100644 index a01ce75fc..000000000 Binary files a/content/identity/2fa-security-measures/2fa-security.jpg and /dev/null differ diff --git a/content/identity/2fa-security-measures/2fa-security.webp b/content/identity/2fa-security-measures/2fa-security.webp new file mode 100644 index 000000000..d594388ac Binary files /dev/null and b/content/identity/2fa-security-measures/2fa-security.webp differ diff --git a/content/identity/2fa-security-measures/GD-to-RBA.png b/content/identity/2fa-security-measures/GD-to-RBA.png deleted file mode 100644 index 0d7046172..000000000 Binary files a/content/identity/2fa-security-measures/GD-to-RBA.png and /dev/null differ diff --git a/content/identity/2fa-security-measures/GD-to-RBA.webp b/content/identity/2fa-security-measures/GD-to-RBA.webp new file mode 100644 index 000000000..ea0737a8b Binary files /dev/null and b/content/identity/2fa-security-measures/GD-to-RBA.webp differ diff --git a/content/identity/2fa-security-measures/index.md b/content/identity/2fa-security-measures/index.md index 3ead8f8f5..2c00868c4 100644 --- a/content/identity/2fa-security-measures/index.md +++ b/content/identity/2fa-security-measures/index.md @@ -1,7 +1,7 @@ --- title: "Strengthening Security Measures: The Role of Two-Factor Authentication (2FA)" date: "2023-11-17" -coverImage: "2fa-security.jpg" +coverImage: "2fa-security.webp" tags: ["data security","2FA","MFA","cx"] author: "Rakesh Soni" description: "Dive into the world of Two-Factor Authentication (2FA) and its pivotal role in fortifying security. Discover the dual-layered defense, benefits against cyber threats, and insights on implementing MFA and RBA for a proactive defense strategy." @@ -46,7 +46,7 @@ Whether combining something you know (like a password) with something you have ( As the digital landscape evolves, so do the strategies employed by cybercriminals. In response to this ever-changing threat landscape, organizations increasingly turn to Risk-Based Authentication (RBA) to fortify their authentication security. -[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) +[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) RBA is a dynamic approach that assesses various risk factors in real-time to determine the level of authentication required for a particular user or transaction. By analyzing contextual data such as device information, location, user behavior, and the sensitivity of the requested action, RBA adapts the authentication process to match the perceived risk level. @@ -58,4 +58,4 @@ As we stand at the intersection of technological advancement and heightened cybe By comprehending its significance, embracing its implementation, and adapting to evolving technologies, individuals and organizations can proactively defend against the ever-shifting landscape of cyber threats. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=2fa-security-measures) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=2fa-security-measures) \ No newline at end of file diff --git a/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.png b/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.png deleted file mode 100644 index f5fa0b0f9..000000000 Binary files a/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.png and /dev/null differ diff --git a/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.webp b/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.webp new file mode 100644 index 000000000..b0761321e Binary files /dev/null and b/content/identity/3-digital-onboarding-trends-2023/EB-omnichannel.webp differ diff --git a/content/identity/3-digital-onboarding-trends-2023/digi-onboard.jpg b/content/identity/3-digital-onboarding-trends-2023/digi-onboard.jpg deleted file mode 100644 index 0150acead..000000000 Binary files a/content/identity/3-digital-onboarding-trends-2023/digi-onboard.jpg and /dev/null differ diff --git a/content/identity/3-digital-onboarding-trends-2023/digi-onboard.webp b/content/identity/3-digital-onboarding-trends-2023/digi-onboard.webp new file mode 100644 index 000000000..425dd6115 Binary files /dev/null and b/content/identity/3-digital-onboarding-trends-2023/digi-onboard.webp differ diff --git a/content/identity/3-digital-onboarding-trends-2023/index.md b/content/identity/3-digital-onboarding-trends-2023/index.md index b67103a98..b5d7a084b 100644 --- a/content/identity/3-digital-onboarding-trends-2023/index.md +++ b/content/identity/3-digital-onboarding-trends-2023/index.md @@ -1,7 +1,7 @@ --- title: "3 Digital Onboarding Trends To Watch In 2023 (And What You Can Do About It Now)" date: "2023-01-06" -coverImage: "digi-onboard.jpg" +coverImage: "digi-onboard.webp" tags: ["user onboarding", "digital transformation", "omnichannel"] author: "Rakesh Soni" description: "Digital onboarding plays a crucial role in enhancing user experience. This blog will help you understand what digital onboarding is, how it impacts conversions, and the trends in digital onboarding that will shape the future of identity verification." @@ -38,7 +38,7 @@ An omnichannel customer experience is a multifold approach to advertising, selli A digital omnichannel strategy adopts a multichannel approach for sales, consumer service, and marketing. It focuses on providing a united consumer experience regardless of the channel they contact your company. -[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) +[](https://www.loginradius.com/resource/making-customers-feel-seen-in-an-omnichannel-world/) The key to providing constant omnichannel engagement is to offer a smooth experience across all online and offline platforms. Every contact should be considered a single experience from the consumer's perspective. It implies it shouldn't be segregated or repetitious. @@ -81,4 +81,4 @@ Learn more about the LoginRadius Identity Platform, starting with a Quick Person -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=3-digital-onboarding-trends-2023) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=3-digital-onboarding-trends-2023) diff --git a/content/identity/3-digital-onboarding-trends-2023/omni-eb.png b/content/identity/3-digital-onboarding-trends-2023/omni-eb.png deleted file mode 100644 index 86c15a159..000000000 Binary files a/content/identity/3-digital-onboarding-trends-2023/omni-eb.png and /dev/null differ diff --git a/content/identity/3-digital-onboarding-trends-2023/omni-eb.webp b/content/identity/3-digital-onboarding-trends-2023/omni-eb.webp new file mode 100644 index 000000000..025782e92 Binary files /dev/null and b/content/identity/3-digital-onboarding-trends-2023/omni-eb.webp differ diff --git a/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.png b/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.png deleted file mode 100644 index 1b6f5ad00..000000000 Binary files a/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.png and /dev/null differ diff --git a/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.webp b/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.webp new file mode 100644 index 000000000..2e16ce904 Binary files /dev/null and b/content/identity/3-stages-gartner-carta-it-security/adaptive-auth-eb.webp differ diff --git a/content/identity/3-stages-gartner-carta-it-security/carta.jpg b/content/identity/3-stages-gartner-carta-it-security/carta.jpg deleted file mode 100644 index 5e4916d12..000000000 Binary files a/content/identity/3-stages-gartner-carta-it-security/carta.jpg and /dev/null differ diff --git a/content/identity/3-stages-gartner-carta-it-security/carta.webp b/content/identity/3-stages-gartner-carta-it-security/carta.webp new file mode 100644 index 000000000..2f9f457f8 Binary files /dev/null and b/content/identity/3-stages-gartner-carta-it-security/carta.webp differ diff --git a/content/identity/3-stages-gartner-carta-it-security/index.md b/content/identity/3-stages-gartner-carta-it-security/index.md index a111141db..4f4d94aef 100644 --- a/content/identity/3-stages-gartner-carta-it-security/index.md +++ b/content/identity/3-stages-gartner-carta-it-security/index.md @@ -1,7 +1,7 @@ --- title: "3 Best Stages of IT Security for Implementing Gartner's CARTA" date: "2021-11-10" -coverImage: "carta.jpg" +coverImage: "carta.webp" tags: ["security"] featured: false author: "Vishal Sharma" @@ -72,4 +72,4 @@ CARTA’s risk reduction model is [built on the premise](https://www.loginradius Hence, businesses striving to implement the best security practices must consider relying on CARTA for enhanced risk management for their organization. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=3-stages-gartner-carta-it-security) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=3-stages-gartner-carta-it-security) diff --git a/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.jpg b/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.jpg deleted file mode 100644 index ebbb1948f..000000000 Binary files a/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.jpg and /dev/null differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.webp b/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.webp new file mode 100644 index 000000000..f416611c0 Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/4-barriers-building-digital-business-overcome.webp differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.jpg b/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.jpg deleted file mode 100644 index 3d2fa2fd1..000000000 Binary files a/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.jpg and /dev/null differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.webp b/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.webp new file mode 100644 index 000000000..04194cb2c Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/glenn-carstens-peters-190592-unsplash-1024x681.webp differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.png b/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.png deleted file mode 100644 index dbb57ace9..000000000 Binary files a/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.png and /dev/null differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.webp b/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.webp new file mode 100644 index 000000000..98937f902 Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/guide-to-modern-cover.webp differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/image5.png b/content/identity/4-barriers-building-digital-business-overcome/image5.png deleted file mode 100644 index 6bbda92e9..000000000 Binary files a/content/identity/4-barriers-building-digital-business-overcome/image5.png and /dev/null differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/image5.webp b/content/identity/4-barriers-building-digital-business-overcome/image5.webp new file mode 100644 index 000000000..0aeacb9f7 Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/image5.webp differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/index.md b/content/identity/4-barriers-building-digital-business-overcome/index.md index 51944615f..c7f22acbd 100644 --- a/content/identity/4-barriers-building-digital-business-overcome/index.md +++ b/content/identity/4-barriers-building-digital-business-overcome/index.md @@ -1,7 +1,7 @@ --- title: "4 Barriers to Building a Digital Business and How to Overcome Them" date: "2018-08-02" -coverImage: "4-barriers-building-digital-business-overcome.jpg" +coverImage: "4-barriers-building-digital-business-overcome.webp" tags: ["customer-experience"] featured: false author: "Rakesh Soni" @@ -13,7 +13,7 @@ metadescription: "Thinking about starting a business online? Here are the most c The movement towards digitalization is occurring across all business sectors. Even industries that have always been solely focused on growing and expanding their existing business models are joining the movement. However, there are some roadblocks that these companies have to overcome in order to successfully build a digital business. But don't let these roadblocks stunt your digital growth! Here are some tips to help you along: ### 1\. Inability to work as a team - + Many companies across industries are actively working towards transforming their businesses to digital. This includes using technology to improve/optimize the existing business model, in order to pave the way towards building more efficient digital workflows. @@ -25,7 +25,7 @@ This team, comprised of different representations from within the company, will ### 2\. Lack of corporate vision - + While the majority of your company may have the same goal of moving towards digital, the motives and driving force behind achieving this goal can differ from one person or team to the other. Some may be looking to simply optimize the current workflows to enhance productivity and business outcomes, while others are seeing this as a move towards bigger innovations that will potentially disrupt the entire industry. In this case, there are conflicting ideas of why the company is undergoing a digital reform and how to proceed. @@ -35,7 +35,7 @@ In order to do this, however, you first need to consider and be certain to commu ### 3\. Gaps in organizational capabilities to deliver digital innovation - + Your goals are set and you've got everyone on board to work towards a common digital outcome. @@ -49,17 +49,17 @@ More often than not, it's not the team's incapabilities to deliver certain resul ### 4\. Inadequate leadership - + [Digital transformation is exciting](https://www.loginradius.com/blog/identity/what-is-digital-transformation/), but it is also a new concept that companies across industries are only experimenting with in the past few years. Excitement aside, new processes, especially one that affects entire business models and operations, can be daunting. Transforming existing processes and building new ones are dramatic changes that affect the entire company. Changes such as this can lead to discomfort and conflict. Therefore, strong leadership is essential at all levels to drive beneficial change without increasing risk or creating organizational chaos. Make sure you have the right leadership roles in place as the company moves towards its digital initiatives to ensure its success. - +
@@ -85,5 +85,5 @@ Successful digital transformation involves the full breadth of an enterprise – If you or your company are currently going through digital transformation, see how [LoginRadius can help you speed this up](https://www.loginradius.com/customer-identity-management-b2c-ciam/)! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=4-barriers-building-digital-business-overcome) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=4-barriers-building-digital-business-overcome) diff --git a/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.jpg b/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.jpg deleted file mode 100644 index 64b1e0ced..000000000 Binary files a/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.jpg and /dev/null differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.webp b/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.webp new file mode 100644 index 000000000..996bdb339 Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/james-pond-185593-unsplash-1024x683.webp differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.jpg b/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.jpg deleted file mode 100644 index 4b759fc7f..000000000 Binary files a/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.jpg and /dev/null differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.webp b/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.webp new file mode 100644 index 000000000..0fa935c27 Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/rawpixel-741662-unsplash-1024x684.webp differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.jpg b/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.jpg deleted file mode 100644 index 6e6196d67..000000000 Binary files a/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.jpg and /dev/null differ diff --git a/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.webp b/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.webp new file mode 100644 index 000000000..41eebfab3 Binary files /dev/null and b/content/identity/4-barriers-building-digital-business-overcome/steven-lelham-342930-unsplash-1024x540.webp differ diff --git a/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.png b/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.png deleted file mode 100644 index 61deb3295..000000000 Binary files a/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.png and /dev/null differ diff --git a/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.webp b/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.webp new file mode 100644 index 000000000..00c5933a4 Binary files /dev/null and b/content/identity/5-access-management-best-practices-enterprises/EB-GD-to-MFA.webp differ diff --git a/content/identity/5-access-management-best-practices-enterprises/access-mangmt.jpg b/content/identity/5-access-management-best-practices-enterprises/access-mangmt.jpg deleted file mode 100644 index c7fcf8cf8..000000000 Binary files a/content/identity/5-access-management-best-practices-enterprises/access-mangmt.jpg and /dev/null differ diff --git a/content/identity/5-access-management-best-practices-enterprises/access-mangmt.webp b/content/identity/5-access-management-best-practices-enterprises/access-mangmt.webp new file mode 100644 index 000000000..147bdbc4e Binary files /dev/null and b/content/identity/5-access-management-best-practices-enterprises/access-mangmt.webp differ diff --git a/content/identity/5-access-management-best-practices-enterprises/index.md b/content/identity/5-access-management-best-practices-enterprises/index.md index 748042e65..605b7c2d6 100644 --- a/content/identity/5-access-management-best-practices-enterprises/index.md +++ b/content/identity/5-access-management-best-practices-enterprises/index.md @@ -1,7 +1,7 @@ --- title: " 5 Access Management Best Practices and Benefits For Businesses" date: "2022-05-10" -coverImage: "access-mangmt.jpg" +coverImage: "access-mangmt.webp" tags: ["zero trust", "mfa", "enterprise security", "access control"] author: "Vikas Kalwani" description: "Access management is essential for modern businesses. This blog will walk you through the five access management best practices to help you keep your systems reserved for valid users only." @@ -61,7 +61,7 @@ One of the best ways to protect your company’s digital assets is to implement [Zero trust](https://www.loginradius.com/blog/identity/beginners-guide-zero-trust-security/) is exactly what it sounds like. Every member of your organization is forced to authenticate their identities before being able to access any resources. This includes employees who are already active inside a company network. - + ([Image Source](https://www.infusedinnovations.com/blog/secure-intelligent-workplace/pros-and-cons-of-the-zero-trust-model)) @@ -86,7 +86,7 @@ That’s why multi-factor authentication has become an essential access manageme When you use MFA, anyone logging in will be asked to provide an additional method of verification once they enter their password. This could be entering a code sent to their email or via text message. It could also be a biometric scan on a mobile device like a fingerprint or facial recognition. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) ### 4. Get rid of high-risk systems @@ -125,4 +125,4 @@ Use these best practices to manage access to your systems and ensure that all da -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-access-management-best-practices-enterprises) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-access-management-best-practices-enterprises) diff --git a/content/identity/5-access-management-best-practices-enterprises/mfa-eb.png b/content/identity/5-access-management-best-practices-enterprises/mfa-eb.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/identity/5-access-management-best-practices-enterprises/mfa-eb.png and /dev/null differ diff --git a/content/identity/5-access-management-best-practices-enterprises/mfa-eb.webp b/content/identity/5-access-management-best-practices-enterprises/mfa-eb.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/identity/5-access-management-best-practices-enterprises/mfa-eb.webp differ diff --git a/content/identity/5-access-management-best-practices-enterprises/zero-trust.png b/content/identity/5-access-management-best-practices-enterprises/zero-trust.png deleted file mode 100644 index 992596c7f..000000000 Binary files a/content/identity/5-access-management-best-practices-enterprises/zero-trust.png and /dev/null differ diff --git a/content/identity/5-access-management-best-practices-enterprises/zero-trust.webp b/content/identity/5-access-management-best-practices-enterprises/zero-trust.webp new file mode 100644 index 000000000..678c59027 Binary files /dev/null and b/content/identity/5-access-management-best-practices-enterprises/zero-trust.webp differ diff --git a/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.png b/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.png deleted file mode 100644 index 4926b2aaf..000000000 Binary files a/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.png and /dev/null differ diff --git a/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.webp b/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.webp new file mode 100644 index 000000000..d4581b1bd Binary files /dev/null and b/content/identity/5-myths-about-phishing-attack/WP-credential-stuffing.webp differ diff --git a/content/identity/5-myths-about-phishing-attack/cred-stuffing.png b/content/identity/5-myths-about-phishing-attack/cred-stuffing.png deleted file mode 100644 index 904e3a28e..000000000 Binary files a/content/identity/5-myths-about-phishing-attack/cred-stuffing.png and /dev/null differ diff --git a/content/identity/5-myths-about-phishing-attack/cred-stuffing.webp b/content/identity/5-myths-about-phishing-attack/cred-stuffing.webp new file mode 100644 index 000000000..c2d6821c3 Binary files /dev/null and b/content/identity/5-myths-about-phishing-attack/cred-stuffing.webp differ diff --git a/content/identity/5-myths-about-phishing-attack/index.md b/content/identity/5-myths-about-phishing-attack/index.md index d97d70bdd..441fb1f12 100644 --- a/content/identity/5-myths-about-phishing-attack/index.md +++ b/content/identity/5-myths-about-phishing-attack/index.md @@ -1,7 +1,7 @@ --- title: "5 Myths About Phishing You Should Know" date: "2022-03-28" -coverImage: "phish-email.jpg" +coverImage: "phish-email.webp" tags: ["data security","mfa","cx"] author: "Lucy Manole" description: "Most of us think we can spot a phishing email, but are we really safe against online fraud? Here are some truths about credential phishing." @@ -34,7 +34,7 @@ Credential phishing attacks are usually targeted attacks that are backed by exte The victims' credentials are then used to carry out secondary attacks like fraudulent funds transfer, stealing company data, identity fraud, and other fraudulent activities. -[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper) +[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper) ## Top 5 Myths About Credential Phishing You Should Know @@ -75,7 +75,7 @@ copying the same messaging format, logo, and signature. They project urgency in For example, this is a new email intercepted by MailGuard that seems like an auto-generated notification about password expiry. - + [Source](https://www.mailguard.com.au/blog/phishing-email-employing-cpanel-branding-claims-your-password-has-expired) @@ -126,4 +126,4 @@ Regardless of [how secure your email systems](https://www.loginradius.com/blog/i We are sure the information shared in this post will help keep your organization safe from such attacks. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-myths-about-phishing-attack) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-myths-about-phishing-attack) diff --git a/content/identity/5-myths-about-phishing-attack/phish-email.jpg b/content/identity/5-myths-about-phishing-attack/phish-email.jpg deleted file mode 100644 index 8e0d77ddf..000000000 Binary files a/content/identity/5-myths-about-phishing-attack/phish-email.jpg and /dev/null differ diff --git a/content/identity/5-myths-about-phishing-attack/phish-email.webp b/content/identity/5-myths-about-phishing-attack/phish-email.webp new file mode 100644 index 000000000..6718fd37f Binary files /dev/null and b/content/identity/5-myths-about-phishing-attack/phish-email.webp differ diff --git a/content/identity/5-myths-about-phishing-attack/ss-1.jpg b/content/identity/5-myths-about-phishing-attack/ss-1.jpg deleted file mode 100644 index 1407e55cc..000000000 Binary files a/content/identity/5-myths-about-phishing-attack/ss-1.jpg and /dev/null differ diff --git a/content/identity/5-myths-about-phishing-attack/ss-1.webp b/content/identity/5-myths-about-phishing-attack/ss-1.webp new file mode 100644 index 000000000..284f4d877 Binary files /dev/null and b/content/identity/5-myths-about-phishing-attack/ss-1.webp differ diff --git a/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.jpg b/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.jpg deleted file mode 100644 index 884181a12..000000000 Binary files a/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.jpg and /dev/null differ diff --git a/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.webp b/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.webp new file mode 100644 index 000000000..f34b7c0a6 Binary files /dev/null and b/content/identity/5-ways-to-handle-a-data-breach/5-ways-to-handle-a-data-breach-cover.webp differ diff --git a/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.png b/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.png deleted file mode 100644 index b32dcb27b..000000000 Binary files a/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.png and /dev/null differ diff --git a/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.webp b/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.webp new file mode 100644 index 000000000..6c250a4f7 Binary files /dev/null and b/content/identity/5-ways-to-handle-a-data-breach/RP-Data-Breaches.webp differ diff --git a/content/identity/5-ways-to-handle-a-data-breach/index.md b/content/identity/5-ways-to-handle-a-data-breach/index.md index c3c502c8d..300e6fe32 100644 --- a/content/identity/5-ways-to-handle-a-data-breach/index.md +++ b/content/identity/5-ways-to-handle-a-data-breach/index.md @@ -1,7 +1,7 @@ --- title: "How to Manage Situation After a Data Breach" date: "2021-07-27" -coverImage: "5-ways-to-handle-a-data-breach-cover.jpg" +coverImage: "5-ways-to-handle-a-data-breach-cover.webp" tags: ["data security","cybersecurity","cx"] author: "Rakesh Soni" description: "Data breaches are becoming the new normal and enterprises aren’t aware of the necessary steps that should be taken immediately after a breach. This post offers valuable insights that help organizations to quickly and effectively manage a situation after a data breach is detected." @@ -74,7 +74,7 @@ But many of you would wonder why we need to mention a breach if it isn’t causi Organizations must take adequate measures to maintain integrity and reputation since a data breach isn’t something that one can hide for an extended period. -[](https://www.loginradius.com/resource/pii-data-breach-report/) +[](https://www.loginradius.com/resource/pii-data-breach-report/) ### **4. Investigate- How did it Happen?** @@ -104,4 +104,4 @@ The aspects mentioned above can be quite helpful in managing the overall situati It’s recommended that enterprises should consider stringent security measures to avoid any chance of sneaking into the company’s network. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-ways-to-handle-a-data-breach) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=5-ways-to-handle-a-data-breach) \ No newline at end of file diff --git a/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.png b/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.png deleted file mode 100644 index 61deb3295..000000000 Binary files a/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.png and /dev/null differ diff --git a/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.webp b/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.webp new file mode 100644 index 000000000..00c5933a4 Binary files /dev/null and b/content/identity/6-reliable-authentication-methods-customers/EB-GD-to-MFA.webp differ diff --git a/content/identity/6-reliable-authentication-methods-customers/auth-method.png b/content/identity/6-reliable-authentication-methods-customers/auth-method.png deleted file mode 100644 index c37e9b0a2..000000000 Binary files a/content/identity/6-reliable-authentication-methods-customers/auth-method.png and /dev/null differ diff --git a/content/identity/6-reliable-authentication-methods-customers/auth-method.webp b/content/identity/6-reliable-authentication-methods-customers/auth-method.webp new file mode 100644 index 000000000..bf1da33a0 Binary files /dev/null and b/content/identity/6-reliable-authentication-methods-customers/auth-method.webp differ diff --git a/content/identity/6-reliable-authentication-methods-customers/index.md b/content/identity/6-reliable-authentication-methods-customers/index.md index 1019ab91c..e5b1a55ab 100644 --- a/content/identity/6-reliable-authentication-methods-customers/index.md +++ b/content/identity/6-reliable-authentication-methods-customers/index.md @@ -1,7 +1,7 @@ --- title: "6 Alternative Authentication Methods For Your Online Customers" date: "2022-08-26" -coverImage: "reliable-auth.jpg" +coverImage: "reliable-auth.webp" tags: ["authentication", "biometric authentication", "digital trust"] author: "Andre Oentoro" description: "Providing alternative authentication methods to your customers will not only make your site more secure but will also give them peace of mind knowing that their information is well-protected. This blog breaks down the popular authentication methods to consider for your customers." @@ -19,7 +19,7 @@ Providing alternative authentication methods will not only make your site more s This blog will break down popular authentication methods to consider. - + ## Alternative Authentications: Why Do You Need Them? @@ -67,7 +67,7 @@ MFA essentially adds an extra layer of security by requiring users to provide mo This could include a password, as well as a code that’s sent to the user’s mobile phone or email address. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) ### #2. SMS-based authentication @@ -115,4 +115,4 @@ Ultimately, the decision comes down to what you feel is best for your business. It’s also important to keep in mind that no single authentication method is perfect. The best way to keep your site secure is to use a combination of methods. This will make it more difficult for hackers to gain access to your site and ensure that your customers’ data is safe. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=6-reliable-authentication-methods-customers) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=6-reliable-authentication-methods-customers) diff --git a/content/identity/6-reliable-authentication-methods-customers/mfa-eb.png b/content/identity/6-reliable-authentication-methods-customers/mfa-eb.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/identity/6-reliable-authentication-methods-customers/mfa-eb.png and /dev/null differ diff --git a/content/identity/6-reliable-authentication-methods-customers/mfa-eb.webp b/content/identity/6-reliable-authentication-methods-customers/mfa-eb.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/identity/6-reliable-authentication-methods-customers/mfa-eb.webp differ diff --git a/content/identity/6-reliable-authentication-methods-customers/reliable-auth.jpg b/content/identity/6-reliable-authentication-methods-customers/reliable-auth.jpg deleted file mode 100644 index 611a87b0f..000000000 Binary files a/content/identity/6-reliable-authentication-methods-customers/reliable-auth.jpg and /dev/null differ diff --git a/content/identity/6-reliable-authentication-methods-customers/reliable-auth.webp b/content/identity/6-reliable-authentication-methods-customers/reliable-auth.webp new file mode 100644 index 000000000..ff281e80f Binary files /dev/null and b/content/identity/6-reliable-authentication-methods-customers/reliable-auth.webp differ diff --git a/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.png b/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.png deleted file mode 100644 index 31b7cc833..000000000 Binary files a/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.png and /dev/null differ diff --git a/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.webp b/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.webp new file mode 100644 index 000000000..61229103e Binary files /dev/null and b/content/identity/7-uncommon-cyberattacks-2023/WP-Trade-Zone.webp differ diff --git a/content/identity/7-uncommon-cyberattacks-2023/index.md b/content/identity/7-uncommon-cyberattacks-2023/index.md index 7ca59b2be..9a7801bdf 100644 --- a/content/identity/7-uncommon-cyberattacks-2023/index.md +++ b/content/identity/7-uncommon-cyberattacks-2023/index.md @@ -1,7 +1,7 @@ --- title: "7 Uncommon Cyber Attacks in 2023: Why Your Organization Needs To Be Ready For The Worst-Case Scenarios" date: "2023-01-27" -coverImage: "uncommon.jpg" +coverImage: "uncommon.webp" tags: ["cybersecurity", "identity management", "cyberattacks"] author: "Alok Patidar" description: "Cybercriminals are resourceful and innovative creatures who constantly develop new ways to exploit businesses and customer information to reap benefits. While every organization is aware of the potential threats, they are equally unaware of the uncommon attacks that could severely impact their overall cybersecurity posture." @@ -51,7 +51,7 @@ The Internet of Things is a growing industry; several intelligent, interconnecte IoT networks are mainly vulnerable to spoofing, denial-of-service attacks (DDoS), and phishing. And these kinds of attacks can be avoided by leveraging various network security measures, including encryption, identity management, robust authentication, and authorization. -[](https://www.loginradius.com/resource/digital-trade-zone-threats-cybersecurity-whitepaper) +[](https://www.loginradius.com/resource/digital-trade-zone-threats-cybersecurity-whitepaper) ### #5. Deepfake @@ -88,4 +88,4 @@ Cyberattacks are inevitable. As business teams continue to invest in securing th While organizations need to be wary of both, they should also gear up for complex commodity watering hole attacks and dark web compromises. These are some of the uncommon cyberattacks that all companies should keep an eye out for, especially in a digital transformation environment. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-uncommon-cyberattacks-2023) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-uncommon-cyberattacks-2023) diff --git a/content/identity/7-uncommon-cyberattacks-2023/trade-wp.png b/content/identity/7-uncommon-cyberattacks-2023/trade-wp.png deleted file mode 100644 index 24d5add74..000000000 Binary files a/content/identity/7-uncommon-cyberattacks-2023/trade-wp.png and /dev/null differ diff --git a/content/identity/7-uncommon-cyberattacks-2023/trade-wp.webp b/content/identity/7-uncommon-cyberattacks-2023/trade-wp.webp new file mode 100644 index 000000000..cce7d892c Binary files /dev/null and b/content/identity/7-uncommon-cyberattacks-2023/trade-wp.webp differ diff --git a/content/identity/7-uncommon-cyberattacks-2023/uncommon.jpg b/content/identity/7-uncommon-cyberattacks-2023/uncommon.jpg deleted file mode 100644 index bdde8cee6..000000000 Binary files a/content/identity/7-uncommon-cyberattacks-2023/uncommon.jpg and /dev/null differ diff --git a/content/identity/7-uncommon-cyberattacks-2023/uncommon.webp b/content/identity/7-uncommon-cyberattacks-2023/uncommon.webp new file mode 100644 index 000000000..56f8fab80 Binary files /dev/null and b/content/identity/7-uncommon-cyberattacks-2023/uncommon.webp differ diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.jpg b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.jpg deleted file mode 100644 index 2afea04eb..000000000 Binary files a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.jpg and /dev/null differ diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.webp b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.webp new file mode 100644 index 000000000..7df2b6150 Binary files /dev/null and b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-1.webp differ diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.png b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.png deleted file mode 100644 index 3e43eac92..000000000 Binary files a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.png and /dev/null differ diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.webp b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.webp new file mode 100644 index 000000000..8f2a0af16 Binary files /dev/null and b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-2.webp differ diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.png b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.png deleted file mode 100644 index 991f7c73b..000000000 Binary files a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.png and /dev/null differ diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.webp b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.webp new file mode 100644 index 000000000..d8afed4d0 Binary files /dev/null and b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-3.webp differ diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.jpg b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.jpg deleted file mode 100644 index 3925fedcd..000000000 Binary files a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.jpg and /dev/null differ diff --git a/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.webp b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.webp new file mode 100644 index 000000000..9dd29f119 Binary files /dev/null and b/content/identity/7-web-app-sec-threats/7-Common-Web-Application-Security-Threats-cover.webp differ diff --git a/content/identity/7-web-app-sec-threats/credential-stuffing.png b/content/identity/7-web-app-sec-threats/credential-stuffing.png deleted file mode 100644 index 904e3a28e..000000000 Binary files a/content/identity/7-web-app-sec-threats/credential-stuffing.png and /dev/null differ diff --git a/content/identity/7-web-app-sec-threats/credential-stuffing.webp b/content/identity/7-web-app-sec-threats/credential-stuffing.webp new file mode 100644 index 000000000..c2d6821c3 Binary files /dev/null and b/content/identity/7-web-app-sec-threats/credential-stuffing.webp differ diff --git a/content/identity/7-web-app-sec-threats/index.md b/content/identity/7-web-app-sec-threats/index.md index b5042ba58..4c61d28e9 100644 --- a/content/identity/7-web-app-sec-threats/index.md +++ b/content/identity/7-web-app-sec-threats/index.md @@ -1,7 +1,7 @@ --- title: "7 Common Web Application Security Threats" date: "2021-01-29" -coverImage: "7-Common-Web-Application-Security-Threats-cover.jpg" +coverImage: "7-Common-Web-Application-Security-Threats-cover.webp" tags: ["security"] featured: false author: "Rakesh Soni" @@ -10,7 +10,7 @@ metatitle: "7 Common Web Application Security Threats | LoginRadius" metadescription: "Use this list of the top 7 common web application threats and vulnerabilities to find a sound security base for your web apps. Also, learn how to prevent them." --- - + Malicious actors and security experts are in an endless battle over data. While the former wants to steal it, the latter seeks to protect it. Each year, attackers develop inventive web application security threats to compromise sensitive data and access their targets' database. Consequently, security experts build on the exploited vulnerabilities and strengthen their systems through their learnings every year. @@ -21,7 +21,7 @@ To ensure adequate safety against web application security threats, businesses s ## 7 Common Web Application Security Threats - + ### 1. Injection Attacks @@ -94,7 +94,7 @@ According to [OWASP top 10 2017](https://owasp.org/www-project-top-ten/), this i Given how easy it is to detect and exploit default settings that were initially placed to accommodate a simple [user experience](https://www.loginradius.com/customer-experience-solutions/), the implications of such a vulnerability can be vast once the website is live: from admin privileges to complete database access. -[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper) +[](https://www.loginradius.com/resource/understanding-credential-stuffing-attacks-whitepaper) **How to prevent:** @@ -138,7 +138,7 @@ Like, IDOR, access to these functions can be gained through URL manipulation as ## How Loginradius Helps in Securing Web Applications for Businesses While Providing a Seamless Experience - + \ Despite the multitude of solutions available to each vulnerability, it is hardly easy to produce your own code to secure a site against web application security threats. Managing an extensive portfolio can be unscalable. @@ -164,4 +164,4 @@ Among other features, LoginRadius offers: We recommend using this list of top 7 web application threats and vulnerabilities to find a sound security base for your web apps. Developers can build on these vulnerabilities and learn from previous exploits of other entities to create a more secure application. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-web-app-sec-threats) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=7-web-app-sec-threats) diff --git a/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.png b/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.png and /dev/null differ diff --git a/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.webp b/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/identity/Maintaining-Quality-Data-Security-Practices/Multi-Factor-Authentication.webp differ diff --git a/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.jpg b/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.jpg deleted file mode 100644 index e09cc99c1..000000000 Binary files a/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.jpg and /dev/null differ diff --git a/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.webp b/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.webp new file mode 100644 index 000000000..d26bfbce8 Binary files /dev/null and b/content/identity/Maintaining-Quality-Data-Security-Practices/data-security-loginradius.webp differ diff --git a/content/identity/Maintaining-Quality-Data-Security-Practices/index.md b/content/identity/Maintaining-Quality-Data-Security-Practices/index.md index 2c86c4c3b..cc16ea951 100644 --- a/content/identity/Maintaining-Quality-Data-Security-Practices/index.md +++ b/content/identity/Maintaining-Quality-Data-Security-Practices/index.md @@ -1,7 +1,7 @@ --- title: "Maintaining Quality Data Security Practices" date: "2021-04-30" -coverImage: "data-security-loginradius.jpg" +coverImage: "data-security-loginradius.webp" tags: ["data security","mfa","cx"] author: "Rakesh Soni" description: "Data security is important for businesses today, more than it ever was. By definition, data security is the practice of protecting digital information from unauthorised access, cyber corruption or theft." @@ -31,7 +31,7 @@ It's not uncommon for businesses to face security risks due to employee’s weak It's highly recommended to implement [multi-factor authentication](https://www.loginradius.com/blog/identity/2019/06/what-is-multi-factor-authentication/) because it can reduce the likelihood of being attacked by a cyber-criminal. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) **2. Strict Permissions** @@ -75,4 +75,4 @@ Therefore, educating and training employees is important as it ensures that ever To conclude, as technology advances and more activities are being processed in the digital space, it’s becoming more and more important to keep data private and secure. There are several ways organisations can do this; some of which are easy to implement while others may take more time, resources, and focus than others. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=maintaining-quality-data-security-practices) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=maintaining-quality-data-security-practices) \ No newline at end of file diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.png b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.png deleted file mode 100644 index 0059aade7..000000000 Binary files a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.png and /dev/null differ diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.webp b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.webp new file mode 100644 index 000000000..3b5872929 Binary files /dev/null and b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Book-a-free-demo-request-1024x310.webp differ diff --git "a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.png" "b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.png" deleted file mode 100644 index d63fdd4ac..000000000 Binary files "a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.png" and /dev/null differ diff --git "a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.webp" "b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.webp" new file mode 100644 index 000000000..4486d4d7d Binary files /dev/null and "b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/EB-Buyer\342\200\231s-Guide-to-Multi-Factor-Authentication.webp" differ diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.jpg b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.jpg deleted file mode 100644 index 93d151248..000000000 Binary files a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.jpg and /dev/null differ diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.webp b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.webp new file mode 100644 index 000000000..08abf7133 Binary files /dev/null and b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/MFA-Loginradius.webp differ diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.jpg b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.jpg deleted file mode 100644 index 59f4bb9db..000000000 Binary files a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.jpg and /dev/null differ diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.webp b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.webp new file mode 100644 index 000000000..613155ae1 Binary files /dev/null and b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/Type-of-mfa.webp differ diff --git a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/index.md b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/index.md index 85120d41a..555059b1c 100644 --- a/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/index.md +++ b/content/identity/Multi-Factor-Authentication-A-Beginners-Guide/index.md @@ -1,7 +1,7 @@ --- title: "Multi-Factor Authentication - A Beginner’s Guide" date: "2021-03-23" -coverImage: "MFA-Loginradius.jpg" +coverImage: "MFA-Loginradius.webp" tags: ["mfa","password security","compliance"] author: "Ashish Kumar Yadav" description: "MFA or multi-factor authentication is a feature widely used by businesses to ensure that the consumers coming on their website are actually who they say they are. There are multiple ways to implement multifactor authentication. We will get to them one by one in this blog." @@ -38,7 +38,7 @@ It is done by providing at least two pieces of proof or evidence to state their MFA works in this way because, let’s suppose one of the factors is hacked by the attackers or invalid user, the chances of another factor also getting compromised are pretty low. That is why **[MFA authentication](https://www.loginradius.com/multi-factor-authentication/)** requires multiple factors, and this is how it provides a higher level of API security to consumers’ identity data. - [](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) + [](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) ## Why MFA is So Important @@ -71,7 +71,7 @@ These are three main reasons which are most relevant to explain how and why **[I Now that you’ve learned why MFA is critical, you may be keen to know how this feature works and how you can implement it. - + ## How Does Multi-Factor Authentication Work @@ -115,5 +115,5 @@ In this article, we talked about applying a simple approach of using Multi-facto Cheers! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=multi-factor-authentication-a-beginners-guide) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=multi-factor-authentication-a-beginners-guide) diff --git a/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.jpg b/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.jpg deleted file mode 100644 index ec1570d08..000000000 Binary files a/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.jpg and /dev/null differ diff --git a/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.webp b/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.webp new file mode 100644 index 000000000..bd49597f2 Binary files /dev/null and b/content/identity/OAuth-authentication-vulnerabilities/OAuth-authentication-vulnerabilities-cover.webp differ diff --git a/content/identity/OAuth-authentication-vulnerabilities/index.md b/content/identity/OAuth-authentication-vulnerabilities/index.md index 72ef8604b..24088f89f 100644 --- a/content/identity/OAuth-authentication-vulnerabilities/index.md +++ b/content/identity/OAuth-authentication-vulnerabilities/index.md @@ -1,7 +1,7 @@ --- title: "5 Tips to Prevent OAuth Authentication Vulnerabilities" date: "2021-04-01" -coverImage: "OAuth-authentication-vulnerabilities-cover.jpg" +coverImage: "OAuth-authentication-vulnerabilities-cover.webp" tags: ["security"] featured: false author: "Vishal Sharma" @@ -102,4 +102,4 @@ Avoiding implementation mistakes is the only way to ensure maximum safety for co The aforementioned methods are proven to minimize security threats and ensure seamless interaction between the end-user and resource owner. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=oauth-authentication-vulnerabilities) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=oauth-authentication-vulnerabilities) diff --git a/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.jpg b/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.jpg deleted file mode 100644 index 29ddecb57..000000000 Binary files a/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.jpg and /dev/null differ diff --git a/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.webp b/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.webp new file mode 100644 index 000000000..d3ff3ea01 Binary files /dev/null and b/content/identity/OAuth2-0-guide/OAuth2.0-guide-cover.webp differ diff --git a/content/identity/OAuth2-0-guide/index.md b/content/identity/OAuth2-0-guide/index.md index 8de218d6a..c7f548be1 100644 --- a/content/identity/OAuth2-0-guide/index.md +++ b/content/identity/OAuth2-0-guide/index.md @@ -1,7 +1,7 @@ --- title: "Working With Industry Authorization: A Beginner's Guide to OAuth 2.0" date: "2021-06-08" -coverImage: "OAuth2.0-guide-cover.jpg" +coverImage: "OAuth2.0-guide-cover.webp" tags: ["data security","authorization","cx"] author: "Vishal Sharma" description: " OAuth 2.0 is an authorization protocol designed to control access within a web application or a mobile application. Here’s an interesting read showcasing the role of OAuth 2.0 for offering secure access to resources and why enterprises should get it in place." @@ -94,4 +94,4 @@ Businesses seeking the finest modes of authentication coupled with authorization The LoginRadius CIAM is designed to empower businesses by offering the finest user experience and maximum security through industry-standard protocols including OAuth 2.0. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=oauth2-0-guide) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=oauth2-0-guide) diff --git a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.png b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.png deleted file mode 100644 index 25ea42026..000000000 Binary files a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.png and /dev/null differ diff --git a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.webp b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.webp new file mode 100644 index 000000000..015f518c5 Binary files /dev/null and b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/LoginRadius-Single-Sign-on.webp differ diff --git a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/index.md b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/index.md index 3469bdc19..3cfe189e2 100644 --- a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/index.md +++ b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/index.md @@ -1,7 +1,7 @@ --- title: "How to Put Yourself In Control of Your Data by Leveraging LoginRadius' SSO" date: "2021-03-18" -coverImage: "sso-loginradius.jpg" +coverImage: "sso-loginradius.webp" tags: ["customer-experience"] featured: false author: "Rakesh Soni" @@ -38,7 +38,7 @@ With the advent of remote, mobile, and fluid workforces, several of whom may cho The costs of **[identity and access management](https://www.loginradius.com/blog/identity/2021/01/what-is-iam/)** often entail several components, including the technology platform, IT overheads, and any required physical infrastructure. The initial costs of establishing this system can be relatively high. It is easy to go overboard with it or make expensive choices that are not suitable for the company. -[](https://www.loginradius.com/single-sign-on/) +[](https://www.loginradius.com/single-sign-on/) Smart investment is essential here, and the right tools can have a massive impact on the ROI in terms of minimizing risk, securing identities, and better compliance. @@ -106,4 +106,4 @@ We have explained the importance of having an SSO strategy that fits the organiz If you would like to speak to an expert about developing an SSO strategy for your organization, please click to your Book A Demo Link. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=put-yourself-in-control-of-your-data-by-leveraging-loginradius-sso) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=put-yourself-in-control-of-your-data-by-leveraging-loginradius-sso) diff --git a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.jpg b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.jpg deleted file mode 100644 index c62ea2bed..000000000 Binary files a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.jpg and /dev/null differ diff --git a/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.webp b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.webp new file mode 100644 index 000000000..4d13319ea Binary files /dev/null and b/content/identity/Put-Yourself-In-Control-of-Your-Data-by-Leveraging-LoginRadius-SSO/sso-loginradius.webp differ diff --git a/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.png b/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.png deleted file mode 100644 index c5d330417..000000000 Binary files a/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.png and /dev/null differ diff --git a/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.webp b/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.webp new file mode 100644 index 000000000..82a4caffb Binary files /dev/null and b/content/identity/Single-Sign-On-A-Beginners-Guide/DS-LoginRadius-Single-Sign-on.webp differ diff --git a/content/identity/Single-Sign-On-A-Beginners-Guide/index.md b/content/identity/Single-Sign-On-A-Beginners-Guide/index.md index 13e48c21a..f22713b72 100644 --- a/content/identity/Single-Sign-On-A-Beginners-Guide/index.md +++ b/content/identity/Single-Sign-On-A-Beginners-Guide/index.md @@ -1,7 +1,7 @@ --- title: "Single Sign-On- A Beginner’s Guide" date: "2021-03-23" -coverImage: "sso-loginradius.jpg" +coverImage: "sso-loginradius.webp" tags: ["single sign on","data security","cx"] author: "Ashish Kumar Yadav" description: "The beauty of single sign-on lies in its simplicity. The feature authenticates you on a one-on-one designated platform, allowing you to utilize tons of available services without having to login and logout every time. Consumers can think of this as similar to the social sign-in via Google, Facebook, Twitter, etc." @@ -26,7 +26,7 @@ Today, a single consumer interacts with various apps/websites which require them Unfortunately, when it comes to the protection of such data, 100% prevention is never possible. However, there are various methods to reduce this breach possibility to a bare minimum. One such way is Single Sign-On. -[](https://www.loginradius.com/resource/loginradius-single-sign-on/) +[](https://www.loginradius.com/resource/loginradius-single-sign-on/) ## What is Single Sign-On @@ -72,4 +72,4 @@ In this article, we talked about applying a simple approach of using Single Sign Cheers! -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=single-sign-on-a-beginners-guide) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=single-sign-on-a-beginners-guide) \ No newline at end of file diff --git a/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.jpg b/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.jpg deleted file mode 100644 index a086d1101..000000000 Binary files a/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.jpg and /dev/null differ diff --git a/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.webp b/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.webp new file mode 100644 index 000000000..85d88b1f4 Binary files /dev/null and b/content/identity/Single-Sign-On-A-Beginners-Guide/sso-loginradius.webp differ diff --git a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.png b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.png deleted file mode 100644 index 9b885caa8..000000000 Binary files a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.png and /dev/null differ diff --git a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.webp b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.webp new file mode 100644 index 000000000..62f54b93f Binary files /dev/null and b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/Future-proof-your-security.webp differ diff --git a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.jpg b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.jpg deleted file mode 100644 index 6031ea088..000000000 Binary files a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.jpg and /dev/null differ diff --git a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.webp b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.webp new file mode 100644 index 000000000..429a0fc59 Binary files /dev/null and b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/cybersecurity-loginradius.webp differ diff --git a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/index.md b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/index.md index 50cbc65ae..1bd17c6f9 100644 --- a/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/index.md +++ b/content/identity/Top-10-Cybersecurity-Predictions-for-2021-That-SMBs-Must-Know/index.md @@ -1,7 +1,7 @@ --- title: "Top 10 Cybersecurity Predictions for 2021 That SMBs Must Know" date: "2021-03-19" -coverImage: "cybersecurity-loginradius.jpg" +coverImage: "cybersecurity-loginradius.webp" tags: ["security"] featured: false author: "Rakesh Soni" @@ -43,7 +43,7 @@ Targeted phishing attacks are one of the leading cybersecurity threats that SMBs Last year, despite the pandemic, hackers actively targeted **[healthcare](https://www.loginradius.com/industry-healthcare/)** and pharma companies and spread fake news about vaccine development. Data breaches in the healthcare sector peaked in 2020 and are expected to continue in the short-term future. - [](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper) + [](https://www.loginradius.com/resource/cloud-security-system-sase-whitepaper) [**McKinsey**](https://www.mckinsey.com/business-functions/risk/our-insights/covid-19-crisis-shifts-cybersecurity-priorities-and-budgets) predicts that the healthcare industry will be among the top four spenders in cybersecurity solutions in the coming decade. Apart from increasing their spending, SME players in the healthcare sector also need to evaluate their security infrastructure to counter these cyber threats. @@ -107,4 +107,4 @@ Some of the common threats faced by the financial services industry include phis For SMBs, the global market for cybersecurity solutions is expected to touch [$80 billion](https://www.infosecurity-magazine.com/news/attacks-on-banks-spike-238-during/) in the future. This article has highlighted ten of the biggest cybersecurity predictions for SMBs in the coming decade. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-10-cybersecurity-predictions-for-2021-that-smbs-must-know) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=top-10-cybersecurity-predictions-for-2021-that-smbs-must-know) diff --git a/content/identity/What-is-User-Management/DS-user-management.png b/content/identity/What-is-User-Management/DS-user-management.png deleted file mode 100644 index fc6f98c05..000000000 Binary files a/content/identity/What-is-User-Management/DS-user-management.png and /dev/null differ diff --git a/content/identity/What-is-User-Management/DS-user-management.webp b/content/identity/What-is-User-Management/DS-user-management.webp new file mode 100644 index 000000000..c60f3551f Binary files /dev/null and b/content/identity/What-is-User-Management/DS-user-management.webp differ diff --git a/content/identity/What-is-User-Management/LoginRadius-User-Management.png b/content/identity/What-is-User-Management/LoginRadius-User-Management.png deleted file mode 100644 index 4da86607c..000000000 Binary files a/content/identity/What-is-User-Management/LoginRadius-User-Management.png and /dev/null differ diff --git a/content/identity/What-is-User-Management/LoginRadius-User-Management.webp b/content/identity/What-is-User-Management/LoginRadius-User-Management.webp new file mode 100644 index 000000000..32fb1890f Binary files /dev/null and b/content/identity/What-is-User-Management/LoginRadius-User-Management.webp differ diff --git a/content/identity/What-is-User-Management/index.md b/content/identity/What-is-User-Management/index.md index 2622ac670..460121c51 100644 --- a/content/identity/What-is-User-Management/index.md +++ b/content/identity/What-is-User-Management/index.md @@ -1,7 +1,7 @@ --- title: "What Is User Management?" date: "2021-03-16" -coverImage: "user-mngmnt.jpg" +coverImage: "user-mngmnt.webp" tags: ["user management","identity access management","cx"] author: "Rakesh Soni" description: "Though user management has been around for a long time now, especially within the IAM and ITAM space, it has assumed new importance with introducing cloud-based subscriptions. Recent trends show that there is a sure shift to cloud-based IAM, granting administrators greater access and control over digital assets management." @@ -124,7 +124,7 @@ The third generation of user management solutions is designed for the cloud-firs These solutions support a wide range of authentication methods, including [social login](https://www.loginradius.com/social-login/) and multi-factor authentication, and can integrate with existing identity and access management systems. They also provide advanced analytics and monitoring capabilities to detect and prevent security threats. -[](https://www.loginradius.com/resource/loginradius-user-management-datasheet) +[](https://www.loginradius.com/resource/loginradius-user-management-datasheet) ## **Why Should Businesses Use LoginRadius’ Effective User Management?** @@ -160,4 +160,4 @@ Example: Granting specific employees access to financial data while restricting User access management includes assigning permissions, managing passwords, implementing multi-factor authentication, and monitoring login attempts. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-user-management) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=what-is-user-management) diff --git a/content/identity/What-is-User-Management/user-mngmnt.jpg b/content/identity/What-is-User-Management/user-mngmnt.jpg deleted file mode 100644 index 94a03628f..000000000 Binary files a/content/identity/What-is-User-Management/user-mngmnt.jpg and /dev/null differ diff --git a/content/identity/What-is-User-Management/user-mngmnt.webp b/content/identity/What-is-User-Management/user-mngmnt.webp new file mode 100644 index 000000000..b07c58595 Binary files /dev/null and b/content/identity/What-is-User-Management/user-mngmnt.webp differ diff --git a/content/identity/What-is-User-Management/what-is-user-management-loginradius.jpg b/content/identity/What-is-User-Management/what-is-user-management-loginradius.jpg deleted file mode 100644 index 1379ab046..000000000 Binary files a/content/identity/What-is-User-Management/what-is-user-management-loginradius.jpg and /dev/null differ diff --git a/content/identity/What-is-User-Management/what-is-user-management-loginradius.webp b/content/identity/What-is-User-Management/what-is-user-management-loginradius.webp new file mode 100644 index 000000000..c33fbd620 Binary files /dev/null and b/content/identity/What-is-User-Management/what-is-user-management-loginradius.webp differ diff --git a/content/identity/account-security-consumers/account-security-consumers-cover.jpg b/content/identity/account-security-consumers/account-security-consumers-cover.jpg deleted file mode 100644 index 7b754a1d2..000000000 Binary files a/content/identity/account-security-consumers/account-security-consumers-cover.jpg and /dev/null differ diff --git a/content/identity/account-security-consumers/account-security-consumers-cover.webp b/content/identity/account-security-consumers/account-security-consumers-cover.webp new file mode 100644 index 000000000..ffa70d5eb Binary files /dev/null and b/content/identity/account-security-consumers/account-security-consumers-cover.webp differ diff --git a/content/identity/account-security-consumers/index.md b/content/identity/account-security-consumers/index.md index c55cdc273..994d8fe76 100644 --- a/content/identity/account-security-consumers/index.md +++ b/content/identity/account-security-consumers/index.md @@ -1,7 +1,7 @@ --- title: "How Companies can Enable Account security for their Consumers" date: "2021-04-09" -coverImage: "account-security-consumers-cover.jpg" +coverImage: "account-security-consumers-cover.webp" tags: ["Security"] featured: false author: "Navanita Devi" @@ -68,7 +68,7 @@ Integrating a two-factor authentication process adds an extra layer of security Multi-factor authentication can easily be done by adding a verification code, personal security question, or biometrics. These can easily be integrated into any business or company to increase overall account security. This reduces the likelihood of fraud and identity theft. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) However, integration of the two-factor or multi-factor authentication process can take time, especially because consumers upgrade their account security at their own pace. In the meanwhile, companies can take other security measures to increase their data security. @@ -131,4 +131,4 @@ What else makes [LoginRadius' Single Sign-On](https://www.loginradius.com/protoc With data at more risk than ever, more users are demanding businesses streamline their user onboarding process while protecting the data at the same time. This usually results in compromising the account security in favor of user-friendliness. As technology advances rapidly, businesses should keep track of the emerging cybersecurity trends and upgrade their data security systems accordingly. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=account-security-consumers) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=account-security-consumers) diff --git a/content/identity/account-security-consumers/mfa.png b/content/identity/account-security-consumers/mfa.png deleted file mode 100644 index 9de9444df..000000000 Binary files a/content/identity/account-security-consumers/mfa.png and /dev/null differ diff --git a/content/identity/account-security-consumers/mfa.webp b/content/identity/account-security-consumers/mfa.webp new file mode 100644 index 000000000..3f25bb5dc Binary files /dev/null and b/content/identity/account-security-consumers/mfa.webp differ diff --git a/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.png b/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.png deleted file mode 100644 index 1f39a27f3..000000000 Binary files a/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.png and /dev/null differ diff --git a/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.webp b/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.webp new file mode 100644 index 000000000..8a8067f56 Binary files /dev/null and b/content/identity/adaptive-authentication/LoginRadius-Adaptive-MFA.webp differ diff --git a/content/identity/adaptive-authentication/adaptive-authentication.jpg b/content/identity/adaptive-authentication/adaptive-authentication.jpg deleted file mode 100644 index 528ea7bb0..000000000 Binary files a/content/identity/adaptive-authentication/adaptive-authentication.jpg and /dev/null differ diff --git a/content/identity/adaptive-authentication/adaptive-authentication.webp b/content/identity/adaptive-authentication/adaptive-authentication.webp new file mode 100644 index 000000000..bec684d35 Binary files /dev/null and b/content/identity/adaptive-authentication/adaptive-authentication.webp differ diff --git a/content/identity/adaptive-authentication/index.md b/content/identity/adaptive-authentication/index.md index be6136155..ea0b7312c 100644 --- a/content/identity/adaptive-authentication/index.md +++ b/content/identity/adaptive-authentication/index.md @@ -1,7 +1,7 @@ --- title: "Adaptive Authentication- Is it the Next Breakthrough in Customer Authentication?" date: "2021-07-15" -coverImage: "adaptive-authentication.jpg" +coverImage: "adaptive-authentication.webp" tags: ["adaptive authentication","mfa","ciam solution"] author: "Vishal Sharma" description: "Adaptive authentication is a game-changer for enterprises that require strong fencing to protect consumer and enterprise data. Here’s a quick read depicting the role and need for adaptive authentication instead of just multi-factor authentication." @@ -65,7 +65,7 @@ Apart from this, adaptive authentication is considered far smarter than multi-fa This means the mechanism automatically implements robust authentication controls whenever a login seems to be suspicious. -[](https://www.loginradius.com/resource/fixing-broken-authentication-with-adaptive-mfa/) +[](https://www.loginradius.com/resource/fixing-broken-authentication-with-adaptive-mfa/) ## Adaptive Authentication and Strong Customer Authentication @@ -118,4 +118,4 @@ Enterprises seeking the highest level of consumer and organization data security Need more help? [Reach us](https://www.loginradius.com/contact-sales2/) to know how LoginRadius’ “Adaptive Authentication” can help secure your consumer identities and business information. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=adaptive-authentication) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=adaptive-authentication) diff --git a/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.png b/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.png deleted file mode 100644 index 404532996..000000000 Binary files a/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.png and /dev/null differ diff --git a/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.webp b/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.webp new file mode 100644 index 000000000..832cb0156 Binary files /dev/null and b/content/identity/advanced-identity-security-based-attacks/WP-zero-trust-security.webp differ diff --git a/content/identity/advanced-identity-security-based-attacks/identity-attacks.jpg b/content/identity/advanced-identity-security-based-attacks/identity-attacks.jpg deleted file mode 100644 index 6d0396f2f..000000000 Binary files a/content/identity/advanced-identity-security-based-attacks/identity-attacks.jpg and /dev/null differ diff --git a/content/identity/advanced-identity-security-based-attacks/identity-attacks.webp b/content/identity/advanced-identity-security-based-attacks/identity-attacks.webp new file mode 100644 index 000000000..0b341036c Binary files /dev/null and b/content/identity/advanced-identity-security-based-attacks/identity-attacks.webp differ diff --git a/content/identity/advanced-identity-security-based-attacks/index.md b/content/identity/advanced-identity-security-based-attacks/index.md index 19094cabc..908d57f78 100644 --- a/content/identity/advanced-identity-security-based-attacks/index.md +++ b/content/identity/advanced-identity-security-based-attacks/index.md @@ -1,7 +1,7 @@ --- title: "The Growing Threat of Identity-Based Attacks and the Need for an Advanced Identity Security Approach" date: "2024-06-05" -coverImage: "identity-attacks.jpg" +coverImage: "identity-attacks.webp" tags: ["identity security","zero trust security","cx"] author: "Kundan Singh" description: "Identity-based attacks are escalating, targeting personal data and business secrets with unprecedented sophistication. Traditional security measures fall short; a new approach is essential. Explore advanced identity security strategies like Zero Trust, MFA, CIAM, and behavioral analytics to safeguard against these evolving threats." @@ -55,7 +55,7 @@ To address the growing threat of identity-based attacks, organizations must adop 1. **Zero Trust Architecture**: Zero Trust assumes that no entity, whether inside or outside the network, should be trusted by default. It requires continuous verification of identities and strict access controls based on the principle of least privilege. -[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-modern-business/) +[](https://www.loginradius.com/resource/whitepaper/zero-trust-security-modern-business/) 2. **Multi-Factor Authentication (MFA)**: MFA should be implemented with robust factors beyond SMS-based verification, such as biometrics, hardware tokens, and adaptive authentication that assesses risk based on user behavior and context. @@ -75,4 +75,4 @@ By adopting an advanced identity security approach that emphasizes Zero Trust, r As cybercriminals continue to evolve their tactics, staying ahead requires a proactive and comprehensive strategy that prioritizes identity security at every level. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advanced-identity-security-based-attacks) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advanced-identity-security-based-attacks) \ No newline at end of file diff --git a/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.png b/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.png deleted file mode 100644 index 0d7046172..000000000 Binary files a/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.png and /dev/null differ diff --git a/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.webp b/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.webp new file mode 100644 index 000000000..ea0737a8b Binary files /dev/null and b/content/identity/advanced-risk-based-authentication-2024/GD-to-RBA.webp differ diff --git a/content/identity/advanced-risk-based-authentication-2024/index.md b/content/identity/advanced-risk-based-authentication-2024/index.md index 1c956dec9..cac00238a 100644 --- a/content/identity/advanced-risk-based-authentication-2024/index.md +++ b/content/identity/advanced-risk-based-authentication-2024/index.md @@ -1,7 +1,7 @@ --- title: "Reinforcing Security with Advanced Risk-Based Authentication in 2024 & Beyond" date: "2024-02-08" -coverImage: "rba.jpg" +coverImage: "rba.webp" tags: ["risk based authentication","mfa","cx"] author: "Rakesh Soni" description: "Explore the significance of Risk-Based Authentication (RBA) in today's digital landscape, where robust security measures are essential. Learn how RBA adds an extra layer of defense against sophisticated cyber threats, shields against modern attack vectors, and enhances security in high-risk situations." @@ -42,7 +42,7 @@ Securing sensitive accounts and data against unauthorized access and fraudulent The Device Factor in Risk-Based Authentication (RBA) offers a vital layer of defense by validating user authenticity through device characteristics, significantly reducing the risk of unauthorized access and bolstering overall security posture. -[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) +[](https://www.loginradius.com/resource/an-enterprises-guide-to-risk-based-authentication/) LoginRadius’s Device Factor in RBA precisely considers factors such as device type, operating system, and security patches; RBA systems can make informed decisions about granting access, ensuring that only trusted devices are permitted. @@ -64,4 +64,4 @@ Advanced Risk-Based Authentication (RBA) is an indispensable component of modern By leveraging solutions like LoginRadius CIAM, businesses can harness the full potential of RBA to fortify their defenses, safeguard user accounts, and uphold trust in their digital ecosystems, both now and in the years to come. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advanced-risk-based-authentication-2024) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=advanced-risk-based-authentication-2024) \ No newline at end of file diff --git a/content/identity/advanced-risk-based-authentication-2024/rba.jpg b/content/identity/advanced-risk-based-authentication-2024/rba.jpg deleted file mode 100644 index 55cdf90ca..000000000 Binary files a/content/identity/advanced-risk-based-authentication-2024/rba.jpg and /dev/null differ diff --git a/content/identity/advanced-risk-based-authentication-2024/rba.webp b/content/identity/advanced-risk-based-authentication-2024/rba.webp new file mode 100644 index 000000000..6e6ed1b4d Binary files /dev/null and b/content/identity/advanced-risk-based-authentication-2024/rba.webp differ diff --git a/content/identity/ai-cybersecurity-online-security/cta.png b/content/identity/ai-cybersecurity-online-security/cta.png deleted file mode 100644 index 1116bcde5..000000000 Binary files a/content/identity/ai-cybersecurity-online-security/cta.png and /dev/null differ diff --git a/content/identity/ai-cybersecurity-online-security/cta.webp b/content/identity/ai-cybersecurity-online-security/cta.webp new file mode 100644 index 000000000..8efa78c3e Binary files /dev/null and b/content/identity/ai-cybersecurity-online-security/cta.webp differ diff --git a/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.jpg b/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.jpg deleted file mode 100644 index 925ad6dd8..000000000 Binary files a/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.jpg and /dev/null differ diff --git a/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.webp b/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.webp new file mode 100644 index 000000000..1e390e7db Binary files /dev/null and b/content/identity/ai-cybersecurity-online-security/cyber-security-technology-online-data-protection-by-ai-robot.webp differ diff --git a/content/identity/ai-cybersecurity-online-security/index.md b/content/identity/ai-cybersecurity-online-security/index.md index bf0c90e8a..9460a6da7 100644 --- a/content/identity/ai-cybersecurity-online-security/index.md +++ b/content/identity/ai-cybersecurity-online-security/index.md @@ -1,7 +1,7 @@ --- title: "How AI-Enabled Cybersecurity Solutions Are Strengthening Our Online Security" date: "2024-09-30" -coverImage: "cyber-security-technology-online-data-protection-by-ai-robot.jpg" +coverImage: "cyber-security-technology-online-data-protection-by-ai-robot.webp" tags: ["cybersecurity","AI","customer identity"] author: "Carl Torrence" description: "CIAM gets a major upgrade with AI, which secures customer identities, streamlines access, and ensures only the right people get in. But we can't just set it and forget it. Discover why AI is a game changer, key applications in the field, and what the future looks like with AI advancements." @@ -58,7 +58,7 @@ For example, the credit union knowledge base includes large volumes of sensitive This dual focus on security and efficiency helps credit unions maintain the trust of their members while navigating the complexities of modern digital threats. -[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) +[](https://www.loginradius.com/resource/ebook/buyers-guide-to-multi-factor-authentication/) ### 4. Fraud detection and prevention diff --git a/content/identity/ai-enterprise-security-threats/cta.png b/content/identity/ai-enterprise-security-threats/cta.png deleted file mode 100644 index c8e655587..000000000 Binary files a/content/identity/ai-enterprise-security-threats/cta.png and /dev/null differ diff --git a/content/identity/ai-enterprise-security-threats/cta.webp b/content/identity/ai-enterprise-security-threats/cta.webp new file mode 100644 index 000000000..1082e7522 Binary files /dev/null and b/content/identity/ai-enterprise-security-threats/cta.webp differ diff --git a/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.jpg b/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.jpg deleted file mode 100644 index 0fba23a25..000000000 Binary files a/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.jpg and /dev/null differ diff --git a/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.webp b/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.webp new file mode 100644 index 000000000..d2c164f1b Binary files /dev/null and b/content/identity/ai-enterprise-security-threats/future-artificial-intelligence-robot-cyborg.webp differ diff --git a/content/identity/ai-enterprise-security-threats/index.md b/content/identity/ai-enterprise-security-threats/index.md index cc682b23d..00f88b0dc 100644 --- a/content/identity/ai-enterprise-security-threats/index.md +++ b/content/identity/ai-enterprise-security-threats/index.md @@ -1,7 +1,7 @@ --- title: "AI and the Changing Face of Enterprise Security Threats" date: "2024-07-15" -coverImage: "future-artificial-intelligence-robot-cyborg.jpg" +coverImage: "future-artificial-intelligence-robot-cyborg.webp" tags: ["enterprise security", "ai", "cyberattacks"] author: "Rakesh Soni" description: "Explore how AI is revolutionizing enterprise security by improving threat detection, prevention, and response. Learn about the new challenges and opportunities that AI brings to the cybersecurity landscape." @@ -52,7 +52,7 @@ Cybercriminals are leveraging AI to develop more sophisticated and targeted atta AI-generated deepfakes pose a significant threat to enterprise security. These realistic fake videos and audio can be used for social engineering attacks, manipulating individuals into divulging sensitive information or performing unauthorized actions. -[](https://www.loginradius.com/resource/whitepaper/user-authentication-security/) +[](https://www.loginradius.com/resource/whitepaper/user-authentication-security/) ### 3. Automated Vulnerability Exploitation diff --git a/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.png b/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.png deleted file mode 100644 index 7cc78c915..000000000 Binary files a/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.png and /dev/null differ diff --git a/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.webp b/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.webp new file mode 100644 index 000000000..86276b545 Binary files /dev/null and b/content/identity/ai-revolutionizing-user-authentication/WP-continuous-auth.webp differ diff --git a/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.jpg b/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.jpg deleted file mode 100644 index 2c42544f5..000000000 Binary files a/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.jpg and /dev/null differ diff --git a/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.webp b/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.webp new file mode 100644 index 000000000..49f7df794 Binary files /dev/null and b/content/identity/ai-revolutionizing-user-authentication/artificial-intelligence.webp differ diff --git a/content/identity/ai-revolutionizing-user-authentication/index.md b/content/identity/ai-revolutionizing-user-authentication/index.md index 0741a53ea..da8c12c7b 100644 --- a/content/identity/ai-revolutionizing-user-authentication/index.md +++ b/content/identity/ai-revolutionizing-user-authentication/index.md @@ -1,7 +1,7 @@ --- title: "How AI Is Changing the Game in User Authentication" date: "2024-05-23" -coverImage: "artificial-intelligence.jpg" +coverImage: "artificial-intelligence.webp" tags: ["user authentication","data security","artificial intelligence"] author: "Maya Kirianova" description: "This blog explores how AI can revolutionize authentication, from addressing the limitations of traditional methods to utilizing innovative techniques that use machine learning algorithms." @@ -20,9 +20,9 @@ This blog explores how AI can revolutionize [authentication](https://www.loginra ## Traditional Methods of User Authentication - + -Source: [safety4sea.com](https://safety4sea.com/wp-content/uploads/2019/01/NCSC-Password-Security-1140x806.png) +Source: [safety4sea.com](https://safety4sea.com/wp-content/uploads/2019/01/NCSC-Password-Security-1140x806.webp) [Password-based authentication](https://www.loginradius.com/blog/identity/common-vulnerabilities-password-based-login/) is the oldest and most widely used method. A user is required to enter a username and password and nothing else. However, this way of accessing the account is pretty vulnerable to phishing and brute-force attacks. Hackers can use automated tools to try different password combinations until they find the correct one or just send fraudulent emails or website links to compromise security. If a user utilizes the same password across multiple accounts, the threat of a security breach grows. @@ -34,7 +34,7 @@ Source: [safety4sea.com](https://safety4sea.com/wp-content/uploads/2019/01/NCSC- AI-powered authentication involves the use of machine learning algorithms to analyze user behavior, detect anomalies, and verify identities in real-time. It can adapt to dynamic patterns and learn from user interactions. It means that AI provides continuous authentication. Such an approach can detect suspicious activities or authorized access attempts in real-time. -[](https://www.loginradius.com/resource/whitepaper/continuous-authentication/) +[](https://www.loginradius.com/resource/whitepaper/continuous-authentication/) AI algorithms can evaluate the risks related to each authentication attempt. They use device characteristics, location, and behavioral patterns to adjust authentication requirements. Moreover, AI-powered authentication systems can identify unusual or suspicious behavior that may indicate fraud or cyber-attacks. They can flag potential security threats before they escalate. @@ -94,4 +94,4 @@ The future for AI in user authentication is promising, though more potential cha Although AI is changing the game in user authentication, everyone must be aware of its potential benefits and drawbacks to protect sensitive information and reduce security risks. In this way, organizations and companies will be able to secure important data and build trust with users. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-revolutionizing-user-authentication) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-revolutionizing-user-authentication) \ No newline at end of file diff --git a/content/identity/ai-revolutionizing-user-authentication/password-security.png b/content/identity/ai-revolutionizing-user-authentication/password-security.png deleted file mode 100644 index 71146b196..000000000 Binary files a/content/identity/ai-revolutionizing-user-authentication/password-security.png and /dev/null differ diff --git a/content/identity/ai-revolutionizing-user-authentication/password-security.webp b/content/identity/ai-revolutionizing-user-authentication/password-security.webp new file mode 100644 index 000000000..19d2690fd Binary files /dev/null and b/content/identity/ai-revolutionizing-user-authentication/password-security.webp differ diff --git a/content/identity/ai-security-risk-management/ai-security.jpg b/content/identity/ai-security-risk-management/ai-security.jpg deleted file mode 100644 index 7ac37c071..000000000 Binary files a/content/identity/ai-security-risk-management/ai-security.jpg and /dev/null differ diff --git a/content/identity/ai-security-risk-management/ai-security.webp b/content/identity/ai-security-risk-management/ai-security.webp new file mode 100644 index 000000000..ed4d586bb Binary files /dev/null and b/content/identity/ai-security-risk-management/ai-security.webp differ diff --git a/content/identity/ai-security-risk-management/index.md b/content/identity/ai-security-risk-management/index.md index 88d102a05..a6c8bc2a9 100644 --- a/content/identity/ai-security-risk-management/index.md +++ b/content/identity/ai-security-risk-management/index.md @@ -1,7 +1,7 @@ --- title: "Managing Generative AI Security Risks in the Enterprise- A Quick Guide" date: "2023-10-25" -coverImage: "ai-security.jpg" +coverImage: "ai-security.webp" tags: ["data security","artificial intelligence","ciam solutions","cx"] author: "Rakesh Soni" description: "Navigate generative AI security with our concise guide for enterprises. From data encryption to countering adversarial attacks, discover essential strategies for safeguarding your digital assets. Embrace transparency and empower your team to stay ahead in the rapidly evolving landscape of AI innovation." @@ -44,7 +44,7 @@ Ethical Implications: AI systems can inadvertently generate biased or inappropri The field of AI security is ever-evolving, with security threats and defense mechanisms advancing rapidly. Enterprises must adopt a proactive stance by staying updated with the latest AI security research and practice developments. -[](https://www.loginradius.com/resource/how-ai-is-going-to-change-your-iam-initiatives/) +[](https://www.loginradius.com/resource/how-ai-is-going-to-change-your-iam-initiatives/) Regularly reassessing security protocols and investing in cutting-edge technologies can significantly enhance an organization's resilience against emerging threats. Moreover, fostering a culture of innovation within the organization can lead to the development of novel solutions and strategies. Encouraging research and development in AI security benefits the enterprise and contributes to the broader cybersecurity community. @@ -65,4 +65,4 @@ By understanding the unique threats, implementing robust security measures, and Staying informed and prepared is the key to success. As technologies continue advancing, enterprises must remain vigilant, adapt their security strategies, and explore innovative ways to protect their assets and stakeholders in the digital age. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-security-risk-management) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=ai-security-risk-management) diff --git a/content/identity/ai-security-risk-management/wp-ai.png b/content/identity/ai-security-risk-management/wp-ai.png deleted file mode 100644 index 1116bcde5..000000000 Binary files a/content/identity/ai-security-risk-management/wp-ai.png and /dev/null differ diff --git a/content/identity/ai-security-risk-management/wp-ai.webp b/content/identity/ai-security-risk-management/wp-ai.webp new file mode 100644 index 000000000..8efa78c3e Binary files /dev/null and b/content/identity/ai-security-risk-management/wp-ai.webp differ diff --git a/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.jpg b/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.jpg deleted file mode 100644 index ffbd5fdd9..000000000 Binary files a/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.jpg and /dev/null differ diff --git a/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.webp b/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.webp new file mode 100644 index 000000000..8acaba125 Binary files /dev/null and b/content/identity/alok-patidar-answers-cybersecurity-questions/cyber.webp differ diff --git a/content/identity/alok-patidar-answers-cybersecurity-questions/index.md b/content/identity/alok-patidar-answers-cybersecurity-questions/index.md index 7c0090cb7..d073c6840 100644 --- a/content/identity/alok-patidar-answers-cybersecurity-questions/index.md +++ b/content/identity/alok-patidar-answers-cybersecurity-questions/index.md @@ -1,7 +1,7 @@ --- title: "InfoSec Director, Alok Patidar Answers Your Most Difficult Questions on Cybersecurity" date: "2022-10-28" -coverImage: "cyber.jpg" +coverImage: "cyber.webp" tags: ["cybersecurity", "cyberattacks", "compliance"] author: "Vishal Sharma" description: "Every organization has unique needs, which means each one has to be protected in its own way. Therefore, we asked Alok Patidar to chip in. As the Director of Information Security at LoginRadius, he’s dedicated his career to helping businesses protect themselves from cyber criminals." @@ -107,4 +107,4 @@ Hence, the aforementioned questions can help clear their doubts regarding cybers -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=alok-patidar-answers-cybersecurity-questions) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=alok-patidar-answers-cybersecurity-questions) diff --git a/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.png b/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.png deleted file mode 100644 index f395fc87a..000000000 Binary files a/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.png and /dev/null differ diff --git a/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.webp b/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.webp new file mode 100644 index 000000000..9d7f96b4e Binary files /dev/null and b/content/identity/announcing-new-look-of-loginradius/Announcing-New-Look-of-LoginRadius.webp differ diff --git a/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.png b/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.png deleted file mode 100644 index a77a88ecc..000000000 Binary files a/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.png and /dev/null differ diff --git a/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.webp b/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.webp new file mode 100644 index 000000000..53eae8e39 Binary files /dev/null and b/content/identity/announcing-new-look-of-loginradius/CTA-Graphics-for-Blogs-V03.01-05-2-1024x310.webp differ diff --git a/content/identity/announcing-new-look-of-loginradius/index.md b/content/identity/announcing-new-look-of-loginradius/index.md index faf160996..90c7fd204 100644 --- a/content/identity/announcing-new-look-of-loginradius/index.md +++ b/content/identity/announcing-new-look-of-loginradius/index.md @@ -1,7 +1,7 @@ --- title: "Announcing New Look of LoginRadius" date: "2020-03-25" -coverImage: "Announcing-New-Look-of-LoginRadius.png" +coverImage: "Announcing-New-Look-of-LoginRadius.webp" tags: ["LoginRadius", "industry-news"] featured: false author: "Rakesh Soni" @@ -16,7 +16,7 @@ Yes! We loved the old one, but we decided to upgrade it as part of our ever-evol So, here’s our new look. - + As a leader in cloud-based Customer Identity and Access Management (CIAM) solution that the following two core principles are reflected in the branding: @@ -46,7 +46,7 @@ First, we would like to take a moment to highlight the retirement of our current Fast-forward to the present day, the new logo marks a crucial milestone towards representing our brand-building process. - + - **Brandmark**: It comprises two concentric circles. Most obvious is the negative space showing a keyhole which is also a literal radius from the centre to the outer edge. The keyhole represents robust security foundation of our platform. It can also be seen as a user icon, protected by white arms implied by the negative space and by the light blue circle. This demonstrates our philosophy of putting the user at the centre of everything. Both of these ideas speak to the concept of protecting identity. @@ -58,7 +58,7 @@ Letting go of our core designing heritage was never our objective. Our color pal ## Logo Color Combinations - + ## A Final Word @@ -66,4 +66,4 @@ The new logo is an attempt at modernizing our brand and helping it connect more Amidst the huge chunk of workload that rebranding brings along, we are super thrilled to share this news and would like to take a moment to thank our loyal customer base. Do share your comments about the change. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=announcing-new-look-of-loginradius) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=announcing-new-look-of-loginradius) diff --git a/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.png b/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.png deleted file mode 100644 index 2f2f14377..000000000 Binary files a/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.png and /dev/null differ diff --git a/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.webp b/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.webp new file mode 100644 index 000000000..af62cf468 Binary files /dev/null and b/content/identity/announcing-new-look-of-loginradius/loginradius-logo-horizontal-full-colour-on-white-1024x211.webp differ diff --git a/content/identity/announcing-new-look-of-loginradius/logo-1024x991.png b/content/identity/announcing-new-look-of-loginradius/logo-1024x991.png deleted file mode 100644 index 8bc117428..000000000 Binary files a/content/identity/announcing-new-look-of-loginradius/logo-1024x991.png and /dev/null differ diff --git a/content/identity/announcing-new-look-of-loginradius/logo-1024x991.webp b/content/identity/announcing-new-look-of-loginradius/logo-1024x991.webp new file mode 100644 index 000000000..05727e6d2 Binary files /dev/null and b/content/identity/announcing-new-look-of-loginradius/logo-1024x991.webp differ diff --git a/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.png b/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.png deleted file mode 100644 index faebe4a27..000000000 Binary files a/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.png and /dev/null differ diff --git a/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.webp b/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.webp new file mode 100644 index 000000000..db78ea1ea Binary files /dev/null and b/content/identity/announcing-new-look-of-loginradius/logo-2-1024x589.webp differ diff --git a/content/identity/api-authentication-analytics/api-authentication-analytics-cover.png b/content/identity/api-authentication-analytics/api-authentication-analytics-cover.png deleted file mode 100644 index dcb92dfe0..000000000 Binary files a/content/identity/api-authentication-analytics/api-authentication-analytics-cover.png and /dev/null differ diff --git a/content/identity/api-authentication-analytics/api-authentication-analytics-cover.webp b/content/identity/api-authentication-analytics/api-authentication-analytics-cover.webp new file mode 100644 index 000000000..43f7155a8 Binary files /dev/null and b/content/identity/api-authentication-analytics/api-authentication-analytics-cover.webp differ diff --git a/content/identity/api-authentication-analytics/index.md b/content/identity/api-authentication-analytics/index.md index e4dbdeadb..baa35de50 100644 --- a/content/identity/api-authentication-analytics/index.md +++ b/content/identity/api-authentication-analytics/index.md @@ -1,7 +1,7 @@ --- title: "Announcement - Authentication API Analytics to Evaluate the Performance of LoginRadius APIs for Your Applications" date: "2021-03-23" -coverImage: "api-authentication-analytics-cover.png" +coverImage: "api-authentication-analytics-cover.webp" tags: ["authentication","ciam solution","cx"] author: "Kundan Singh" description: "Recently, LoginRadius launched Authentication API Analytics to provide an analytics report to businesses and their developers for requests made to different LoginRadius APIs. The feature contains useful charts and analytic tools to view and measure an application's overall performance (where using LoginRadius)." @@ -25,7 +25,7 @@ The feature contains useful charts and analytic tools to view and measure an app -[](https://www.loginradius.com/resource/authentication-api-analytics/) +[](https://www.loginradius.com/resource/authentication-api-analytics/) @@ -44,7 +44,7 @@ The [Authentication API Analytics](https://www.loginradius.com/resource/authenti - + The API analytical and performance data are available in the following three categories: @@ -57,7 +57,7 @@ The API analytical and performance data are available in the following three cat -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=api-authentication-analytics) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=api-authentication-analytics) diff --git a/content/identity/api-authentication-analytics/lets-talk.png b/content/identity/api-authentication-analytics/lets-talk.png deleted file mode 100644 index 2fc6ddac9..000000000 Binary files a/content/identity/api-authentication-analytics/lets-talk.png and /dev/null differ diff --git a/content/identity/api-authentication-analytics/lets-talk.webp b/content/identity/api-authentication-analytics/lets-talk.webp new file mode 100644 index 000000000..5522d721c Binary files /dev/null and b/content/identity/api-authentication-analytics/lets-talk.webp differ diff --git a/content/identity/api-authentication-analytics/loginradius-api-authentication.png b/content/identity/api-authentication-analytics/loginradius-api-authentication.png deleted file mode 100644 index c1fdf0aa5..000000000 Binary files a/content/identity/api-authentication-analytics/loginradius-api-authentication.png and /dev/null differ diff --git a/content/identity/api-authentication-analytics/loginradius-api-authentication.webp b/content/identity/api-authentication-analytics/loginradius-api-authentication.webp new file mode 100644 index 000000000..af708e831 Binary files /dev/null and b/content/identity/api-authentication-analytics/loginradius-api-authentication.webp differ diff --git a/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.png b/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.png deleted file mode 100644 index 404532996..000000000 Binary files a/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.png and /dev/null differ diff --git a/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.webp b/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.webp new file mode 100644 index 000000000..832cb0156 Binary files /dev/null and b/content/identity/apple-lockdown-mode-robust-security/WP-Zerotrust-1.webp differ diff --git a/content/identity/apple-lockdown-mode-robust-security/apple-inc.jpg b/content/identity/apple-lockdown-mode-robust-security/apple-inc.jpg deleted file mode 100644 index fcdae6908..000000000 Binary files a/content/identity/apple-lockdown-mode-robust-security/apple-inc.jpg and /dev/null differ diff --git a/content/identity/apple-lockdown-mode-robust-security/apple-inc.webp b/content/identity/apple-lockdown-mode-robust-security/apple-inc.webp new file mode 100644 index 000000000..d937689cc Binary files /dev/null and b/content/identity/apple-lockdown-mode-robust-security/apple-inc.webp differ diff --git a/content/identity/apple-lockdown-mode-robust-security/index.md b/content/identity/apple-lockdown-mode-robust-security/index.md index 14457d27f..3555799a3 100644 --- a/content/identity/apple-lockdown-mode-robust-security/index.md +++ b/content/identity/apple-lockdown-mode-robust-security/index.md @@ -1,7 +1,7 @@ --- title: "Will Apple’s ‘Lockdown Mode’ Reduce State-Sponsored Attacks?" date: "2022-07-07" -coverImage: "apple-inc.jpg" +coverImage: "apple-inc.webp" tags: ["cyberattacks", "apple", "zero trust"] author: "Rakesh Soni" description: "The ‘lockdown mode’ is considered a giant leap as a part of their information security for protecting operating systems of iPhone, iPad, and Mac against various threats, including spyware. Let’s understand what a state-sponsored attack is and how this new feature in Apple devices would work to protect critical customer information." @@ -28,7 +28,7 @@ These attacks usually target a specific group of people that can be spied on to Various states employ hackers through their government authorities or militaries, making it easier to deny any state involvement even if an attack is detected. -[](https://www.loginradius.com/resource/zero-trust-security/) +[](https://www.loginradius.com/resource/zero-trust-security/) ## How Does Apple’s ‘Lockdown Mode’ Work? @@ -52,4 +52,4 @@ However, the underlying risks associated with state-sponsored attacks can’t be -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=apple-lockdown-mode-robust-security) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=apple-lockdown-mode-robust-security) diff --git a/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.png b/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.png deleted file mode 100644 index 3e6b81ee6..000000000 Binary files a/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.png and /dev/null differ diff --git a/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.webp b/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.webp new file mode 100644 index 000000000..2f7c01062 Binary files /dev/null and b/content/identity/apple-lockdown-mode-robust-security/zero-trust-wp.webp differ diff --git a/content/identity/assess-improve-your-authentication-system/WP-digitization.png b/content/identity/assess-improve-your-authentication-system/WP-digitization.png deleted file mode 100644 index 526ebf3e8..000000000 Binary files a/content/identity/assess-improve-your-authentication-system/WP-digitization.png and /dev/null differ diff --git a/content/identity/assess-improve-your-authentication-system/WP-digitization.webp b/content/identity/assess-improve-your-authentication-system/WP-digitization.webp new file mode 100644 index 000000000..6ed0d46f2 Binary files /dev/null and b/content/identity/assess-improve-your-authentication-system/WP-digitization.webp differ diff --git a/content/identity/assess-improve-your-authentication-system/api-wp.png b/content/identity/assess-improve-your-authentication-system/api-wp.png deleted file mode 100644 index a268e3d22..000000000 Binary files a/content/identity/assess-improve-your-authentication-system/api-wp.png and /dev/null differ diff --git a/content/identity/assess-improve-your-authentication-system/api-wp.webp b/content/identity/assess-improve-your-authentication-system/api-wp.webp new file mode 100644 index 000000000..234c6abdc Binary files /dev/null and b/content/identity/assess-improve-your-authentication-system/api-wp.webp differ diff --git a/content/identity/assess-improve-your-authentication-system/index.md b/content/identity/assess-improve-your-authentication-system/index.md index 937cfd4f1..167a4488c 100644 --- a/content/identity/assess-improve-your-authentication-system/index.md +++ b/content/identity/assess-improve-your-authentication-system/index.md @@ -1,7 +1,7 @@ --- title: "How to Evaluate the Quality of Your User Authentication System" date: "2021-11-18" -coverImage: "user-authentication.jpg" +coverImage: "user-authentication.webp" tags: ["user authentication","authorization","compliance"] author: "Arpita Garg" description: "Whether we talk about data leaks or identity thefts, businesses that become victims of security breaches compromise their brand reputation and lose millions of dollars every year. Hence, robust authentication and authorization mechanisms become a necessity and not just a luxury. Let’s understand how businesses can evaluate the quality of a user authentication system." @@ -68,7 +68,7 @@ A CIAM solution uses authentication and authorization technologies like JWT, SAM * **OpenID Authorization:** It verifies user identity based on an authorization server's authentication. * **OAuth:** It allows the API to authenticate and access the requested system or resource. -[](https://www.loginradius.com/resource/how-to-secure-api-using-oauth2) +[](https://www.loginradius.com/resource/how-to-secure-api-using-oauth2) Since we’ve got a fair understanding of the authentication and authorization system, let’s just quickly jump to the aspects that define the quality of the authentication system. @@ -141,4 +141,4 @@ The aspects mentioned above could help businesses choose the most exemplary auth Moreover, businesses can witness the world-class authentication system in action with LoginRadius CIAM that helps establish a secure and user-friendly authentication and authorization system. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=assess-improve-your-authentication-system) \ No newline at end of file +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=assess-improve-your-authentication-system) \ No newline at end of file diff --git a/content/identity/assess-improve-your-authentication-system/user-authentication.jpg b/content/identity/assess-improve-your-authentication-system/user-authentication.jpg deleted file mode 100644 index ffb087acd..000000000 Binary files a/content/identity/assess-improve-your-authentication-system/user-authentication.jpg and /dev/null differ diff --git a/content/identity/assess-improve-your-authentication-system/user-authentication.webp b/content/identity/assess-improve-your-authentication-system/user-authentication.webp new file mode 100644 index 000000000..5dfa71a09 Binary files /dev/null and b/content/identity/assess-improve-your-authentication-system/user-authentication.webp differ diff --git a/content/identity/assess-improve-your-authentication-system/verification.jpg b/content/identity/assess-improve-your-authentication-system/verification.jpg deleted file mode 100644 index cc5c00f79..000000000 Binary files a/content/identity/assess-improve-your-authentication-system/verification.jpg and /dev/null differ diff --git a/content/identity/assess-improve-your-authentication-system/verification.webp b/content/identity/assess-improve-your-authentication-system/verification.webp new file mode 100644 index 000000000..ba84d92d3 Binary files /dev/null and b/content/identity/assess-improve-your-authentication-system/verification.webp differ diff --git a/content/identity/attack-surface-vs-attack-vector/attack-vector.jpg b/content/identity/attack-surface-vs-attack-vector/attack-vector.jpg deleted file mode 100644 index f9bc74887..000000000 Binary files a/content/identity/attack-surface-vs-attack-vector/attack-vector.jpg and /dev/null differ diff --git a/content/identity/attack-surface-vs-attack-vector/attack-vector.webp b/content/identity/attack-surface-vs-attack-vector/attack-vector.webp new file mode 100644 index 000000000..8d7dd7b01 Binary files /dev/null and b/content/identity/attack-surface-vs-attack-vector/attack-vector.webp differ diff --git a/content/identity/attack-surface-vs-attack-vector/index.md b/content/identity/attack-surface-vs-attack-vector/index.md index a479b5563..9e110dc68 100644 --- a/content/identity/attack-surface-vs-attack-vector/index.md +++ b/content/identity/attack-surface-vs-attack-vector/index.md @@ -1,7 +1,7 @@ --- title: "What’s the Difference Between Attack Surface and Attack Vector?" date: "2022-11-11" -coverImage: "attack-vector.jpg" +coverImage: "attack-vector.webp" tags: ["surface attack", "attack vector", "login security"] author: "Vishal Sharma" description: "Vulnerability management is essential in security, but more is needed. Attack surface and attack vector are two terms that can help you understand where vulnerabilities are most likely to occur, so you can improve your security posture and reduce risk." @@ -88,4 +88,4 @@ Choosing a robust security mechanism is essential to overall security hygiene wi Once a business knows potential threat vectors, it can deploy stringent authentication security mechanisms to mitigate the risks. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=attack-surface-vs-attack-vector) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=attack-surface-vs-attack-vector) diff --git a/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.jpg b/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.jpg deleted file mode 100644 index 6c14d6e93..000000000 Binary files a/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.jpg and /dev/null differ diff --git a/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.webp b/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.webp new file mode 100644 index 000000000..3423afcbf Binary files /dev/null and b/content/identity/aurora-wdc-loginradius-customer-success-story/LR-Aurora-WDC.webp differ diff --git a/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.jpg b/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.jpg deleted file mode 100644 index 6c14d6e93..000000000 Binary files a/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.jpg and /dev/null differ diff --git a/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.webp b/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.webp new file mode 100644 index 000000000..3423afcbf Binary files /dev/null and b/content/identity/aurora-wdc-loginradius-customer-success-story/aurora-wdc-loginradius-customer-success-story.webp differ diff --git a/content/identity/aurora-wdc-loginradius-customer-success-story/index.md b/content/identity/aurora-wdc-loginradius-customer-success-story/index.md index 9fa4bf182..bde6686e6 100644 --- a/content/identity/aurora-wdc-loginradius-customer-success-story/index.md +++ b/content/identity/aurora-wdc-loginradius-customer-success-story/index.md @@ -1,7 +1,7 @@ --- title: "Aurora WDC, a LoginRadius Customer Success Story" date: "2017-05-26" -coverImage: "aurora-wdc-loginradius-customer-success-story.jpg" +coverImage: "aurora-wdc-loginradius-customer-success-story.webp" tags: ["media-and-publication"] featured: false author: "Karl Wittig" @@ -12,7 +12,7 @@ metadescription: "Aurora WDC is leading analytics & intelligence firm who, with --- - + Founded in 1995 by Arik Johnson, [Aurora Worldwide Development Corporation (WDC)](https://aurorawdc.com/) is a leading analytics and intelligence firm providing consultative services to corporate clients worldwide. We are grateful to be able to have such a long-standing relationship with Aurora WDC and glad that we have been able to help them in providing a better user experience and a well-rounded solution to better manage their client relationships. @@ -49,4 +49,4 @@ As Aurora WDC transitioned to Hubspot, we stepped up our game and re-integrated Aurora WDC - LoginRadius Customer Success Story -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=aurora-wdc-loginradius-customer-success-story) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=aurora-wdc-loginradius-customer-success-story) diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.png b/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.png deleted file mode 100644 index 79ef6d6fa..000000000 Binary files a/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.png and /dev/null differ diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.webp b/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.webp new file mode 100644 index 000000000..4ad020497 Binary files /dev/null and b/content/identity/authenticating-in-the-age-of-no-code-technology/CIAM-buyers-GD.webp differ diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.png b/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.png deleted file mode 100644 index bfcdef5af..000000000 Binary files a/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.png and /dev/null differ diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.webp b/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.webp new file mode 100644 index 000000000..785585d66 Binary files /dev/null and b/content/identity/authenticating-in-the-age-of-no-code-technology/ciam-roi-gd.webp differ diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/index.md b/content/identity/authenticating-in-the-age-of-no-code-technology/index.md index f84362b5a..b6ea5536f 100644 --- a/content/identity/authenticating-in-the-age-of-no-code-technology/index.md +++ b/content/identity/authenticating-in-the-age-of-no-code-technology/index.md @@ -1,7 +1,7 @@ --- title: "Age of No-Code Technologies: Identification and Authentication" date: "2022-06-03" -coverImage: "no-code.jpg" +coverImage: "no-code.webp" tags: ["no code", "identification", "authentication"] author: "Tim Ferguson" description: "No code is a process of developing applications through a graphical interface that requires zero coding. All you need to know is your requirements and you are ready to go. Let’s take a look at how it has improved the identification and authentication process for businesses." @@ -86,7 +86,7 @@ No-code development requires fewer engineers. This reduces all the auxiliaries t Updating processes and systems that were created using no-code technology is also easier. Often, it is taken care of by the platform. -[](https://www.loginradius.com/resource/ciam-buyers-guide-to-secure-your-roi) +[](https://www.loginradius.com/resource/ciam-buyers-guide-to-secure-your-roi) ### 4. Increased customer satisfaction. @@ -107,4 +107,4 @@ Identification and authentication are two major processes that secure customer d The good news is that no-code technologies are helping businesses secure their services by enabling the developers to create processes faster. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authenticating-in-the-age-of-no-code-technology) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authenticating-in-the-age-of-no-code-technology) diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.jpg b/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.jpg deleted file mode 100644 index 0b9c8570c..000000000 Binary files a/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.jpg and /dev/null differ diff --git a/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.webp b/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.webp new file mode 100644 index 000000000..762b432e2 Binary files /dev/null and b/content/identity/authenticating-in-the-age-of-no-code-technology/no-code.webp differ diff --git a/content/identity/authentication-authorization-encryption/index.md b/content/identity/authentication-authorization-encryption/index.md index 9e04bcce3..ac0c1a396 100644 --- a/content/identity/authentication-authorization-encryption/index.md +++ b/content/identity/authentication-authorization-encryption/index.md @@ -187,4 +187,4 @@ We’ve come a long way from passwords and PINs. In today’s zero-trust, cloud- ### 4. Is SSO authentication or authorization? **A.** SSO is an authentication method. It lets you log in once and access multiple systems without logging in again. Authorization still controls what you can do once inside. -[](https://www.loginradius.com/contact-us) \ No newline at end of file +[](https://www.loginradius.com/contact-us) \ No newline at end of file diff --git a/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.png b/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.png deleted file mode 100644 index 74eef3e01..000000000 Binary files a/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.png and /dev/null differ diff --git a/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.webp b/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.webp new file mode 100644 index 000000000..cae55baf0 Binary files /dev/null and b/content/identity/authentication-identity-verification-identification/EB-GD-to-Mod-Cust-ID.webp differ diff --git a/content/identity/authentication-identity-verification-identification/auth-identity.jpg b/content/identity/authentication-identity-verification-identification/auth-identity.jpg deleted file mode 100644 index 636e66817..000000000 Binary files a/content/identity/authentication-identity-verification-identification/auth-identity.jpg and /dev/null differ diff --git a/content/identity/authentication-identity-verification-identification/auth-identity.webp b/content/identity/authentication-identity-verification-identification/auth-identity.webp new file mode 100644 index 000000000..37909346e Binary files /dev/null and b/content/identity/authentication-identity-verification-identification/auth-identity.webp differ diff --git a/content/identity/authentication-identity-verification-identification/ciam-eb.png b/content/identity/authentication-identity-verification-identification/ciam-eb.png deleted file mode 100644 index bc0c2b3f3..000000000 Binary files a/content/identity/authentication-identity-verification-identification/ciam-eb.png and /dev/null differ diff --git a/content/identity/authentication-identity-verification-identification/ciam-eb.webp b/content/identity/authentication-identity-verification-identification/ciam-eb.webp new file mode 100644 index 000000000..b0f1ac055 Binary files /dev/null and b/content/identity/authentication-identity-verification-identification/ciam-eb.webp differ diff --git a/content/identity/authentication-identity-verification-identification/index.md b/content/identity/authentication-identity-verification-identification/index.md index 391b9fc9a..2c9c464c8 100644 --- a/content/identity/authentication-identity-verification-identification/index.md +++ b/content/identity/authentication-identity-verification-identification/index.md @@ -1,7 +1,7 @@ --- title: "Authentication, Identity Verification, and Identification: What's the Difference" date: "2022-07-06" -coverImage: "auth-identity.jpg" +coverImage: "auth-identity.webp" tags: ["authentication","identity verification","identity security"] author: "Rakesh Soni" description: "People usually consider authentication, id verification, and identification the same thing, but they are entirely different when we see stuff through the lens of information security experts. Learn the fundamental differences between the three and the importance of each from an information security perspective." @@ -55,7 +55,7 @@ Moreover, identity theft is swiftly becoming the new way of exploiting customer Adding stringent security layers in the form of multi-factor authentication (MFA) and risk-based authentication (RBA) could significantly decrease the chances of identity theft. -[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) +[](https://www.loginradius.com/resource/guide-to-modern-customer-identity/) ## What is the Purpose of Identity Security? @@ -95,4 +95,4 @@ What puts LoginRadius ahead of the curve are the three most fundamental aspects: If you wish to experience the next level of account security and authentication, reach the LoginRadius team to schedule a personalized demo. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-identity-verification-identification) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-identity-verification-identification) diff --git a/content/identity/authentication-option-for-your-product/DS-magic-link-pass.png b/content/identity/authentication-option-for-your-product/DS-magic-link-pass.png deleted file mode 100644 index f81b79a36..000000000 Binary files a/content/identity/authentication-option-for-your-product/DS-magic-link-pass.png and /dev/null differ diff --git a/content/identity/authentication-option-for-your-product/DS-magic-link-pass.webp b/content/identity/authentication-option-for-your-product/DS-magic-link-pass.webp new file mode 100644 index 000000000..33ac3b3da Binary files /dev/null and b/content/identity/authentication-option-for-your-product/DS-magic-link-pass.webp differ diff --git a/content/identity/authentication-option-for-your-product/index.md b/content/identity/authentication-option-for-your-product/index.md index d5298ef3c..20f5bbec1 100644 --- a/content/identity/authentication-option-for-your-product/index.md +++ b/content/identity/authentication-option-for-your-product/index.md @@ -2,7 +2,7 @@ title: "How to Choose the Right User Authentication Option for your Product" date: "2021-11-08" author: "Rakesh Soni" -coverImage: "user-authentication.jpg" +coverImage: "user-authentication.webp" tags: ["data security","passwordless login","authentication","mfa"] description: "When choosing the right authentication option for your product, there’s a lot of confusion and misconceptions that may eventually make it difficult to finalize one or even more." metatitle: "Here’s the Ideal Authentication Option for Your Product" @@ -80,7 +80,7 @@ Passwordless login eliminates the need to generate passwords altogether. There Since one needs not type passwords anymore, it leads to a better screen time experience. While for organizations, it will lead to fewer breaches and support costs. -[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/) +[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/) **#5. Social Authentication** @@ -128,6 +128,6 @@ LoginRadius understands the importance of frictionless authentication and helps With LoginRadius’ Passwordless Authentication and Social Authentication, businesses can ensure the highest level of security coupled with a flawless user experience while they prove their identity. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-option-for-your-product) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-option-for-your-product) diff --git a/content/identity/authentication-option-for-your-product/magiclink-ds.png b/content/identity/authentication-option-for-your-product/magiclink-ds.png deleted file mode 100644 index f0d635566..000000000 Binary files a/content/identity/authentication-option-for-your-product/magiclink-ds.png and /dev/null differ diff --git a/content/identity/authentication-option-for-your-product/magiclink-ds.webp b/content/identity/authentication-option-for-your-product/magiclink-ds.webp new file mode 100644 index 000000000..16c0455b4 Binary files /dev/null and b/content/identity/authentication-option-for-your-product/magiclink-ds.webp differ diff --git a/content/identity/authentication-option-for-your-product/user-authentication.jpg b/content/identity/authentication-option-for-your-product/user-authentication.jpg deleted file mode 100644 index 1853272f4..000000000 Binary files a/content/identity/authentication-option-for-your-product/user-authentication.jpg and /dev/null differ diff --git a/content/identity/authentication-option-for-your-product/user-authentication.webp b/content/identity/authentication-option-for-your-product/user-authentication.webp new file mode 100644 index 000000000..18ea3400b Binary files /dev/null and b/content/identity/authentication-option-for-your-product/user-authentication.webp differ diff --git a/content/identity/authentication-sso-native-mobile-apps/index.md b/content/identity/authentication-sso-native-mobile-apps/index.md index ccd26812c..ec586e298 100644 --- a/content/identity/authentication-sso-native-mobile-apps/index.md +++ b/content/identity/authentication-sso-native-mobile-apps/index.md @@ -2,7 +2,7 @@ title: "Announcement - LoginRadius Announces Authentication and SSO for Native Mobile Apps" date: "2020-11-25" author: "Rakesh Soni" -coverImage: "loginradius-mobile-native-app.png" +coverImage: "loginradius-mobile-native-app.webp" tags: ["authentication","SSO","data security","compliance"] description: "Both companies and their customers benefit from LoginRadius Native Mobile SDKs. It allows companies to build and deploy seamless authentication and SSO functionality, while stable, easy and improved customer experiences are on-the-go for later." metatitle: "LoginRadius Authentication and SSO for Native Mobile Apps" @@ -33,7 +33,7 @@ The recently launched LoginRadius Authentication and SSO for Native Mobile Apps -[](https://www.loginradius.com/resource/authentication-sso-native-mobile-apps-datasheet) +[](https://www.loginradius.com/resource/authentication-sso-native-mobile-apps-datasheet) ## Key Features Offered by LoginRadius Android and iOS SDKs @@ -53,6 +53,6 @@ The recently launched LoginRadius Authentication and SSO for Native Mobile Apps LoginRadius Native Mobile SDKs benefit both businesses and their consumers. It helps in developing and deploying seamless authentication and [SSO features for businesses](https://www.loginradius.com/single-sign-on/), while for the later, secure, simple, and enhanced consumer experiences are on-the-go. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-sso-native-mobile-apps) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-sso-native-mobile-apps) diff --git a/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.png b/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.png deleted file mode 100644 index 00d6adb36..000000000 Binary files a/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.png and /dev/null differ diff --git a/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.webp b/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.webp new file mode 100644 index 000000000..a2de2b338 Binary files /dev/null and b/content/identity/authentication-sso-native-mobile-apps/loginradius-mobile-native-app.webp differ diff --git a/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.png b/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.png deleted file mode 100644 index 9368b122c..000000000 Binary files a/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.png and /dev/null differ diff --git a/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.webp b/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.webp new file mode 100644 index 000000000..44fba692f Binary files /dev/null and b/content/identity/authentication-sso-native-mobile-apps/loginradius-native-mobile-apps-datasheet.webp differ diff --git a/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.png b/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.png deleted file mode 100644 index f21e58bc7..000000000 Binary files a/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.png and /dev/null differ diff --git a/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.webp b/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.webp new file mode 100644 index 000000000..c63b4b200 Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/Authentication-Vs-Authorization-1.webp differ diff --git a/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.png b/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.png deleted file mode 100644 index 87a04b8f9..000000000 Binary files a/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.png and /dev/null differ diff --git a/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.webp b/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.webp new file mode 100644 index 000000000..aa8921d95 Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/Authentication-vs.-Authorization.webp differ diff --git a/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.png b/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.png deleted file mode 100644 index 0059aade7..000000000 Binary files a/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.png and /dev/null differ diff --git a/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.webp b/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.webp new file mode 100644 index 000000000..3b5872929 Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/Book-a-free-demo-request.webp differ diff --git a/content/identity/authentication-vs-authorization-infographic/SASE-approach.png b/content/identity/authentication-vs-authorization-infographic/SASE-approach.png deleted file mode 100644 index 9b885caa8..000000000 Binary files a/content/identity/authentication-vs-authorization-infographic/SASE-approach.png and /dev/null differ diff --git a/content/identity/authentication-vs-authorization-infographic/SASE-approach.webp b/content/identity/authentication-vs-authorization-infographic/SASE-approach.webp new file mode 100644 index 000000000..62f54b93f Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/SASE-approach.webp differ diff --git a/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.jpg b/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.jpg deleted file mode 100644 index e5dffc2fb..000000000 Binary files a/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.jpg and /dev/null differ diff --git a/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.webp b/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.webp new file mode 100644 index 000000000..1efaf4b64 Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/authentication-vs-authorization.webp differ diff --git a/content/identity/authentication-vs-authorization-infographic/index.md b/content/identity/authentication-vs-authorization-infographic/index.md index 6f7f9f11d..2986b1a06 100644 --- a/content/identity/authentication-vs-authorization-infographic/index.md +++ b/content/identity/authentication-vs-authorization-infographic/index.md @@ -1,7 +1,7 @@ --- title: "Authentication and Authorization Defined: What's the Difference? [Infographic]" date: "2020-06-11" -coverImage: "authentication-vs-authorization.jpg" +coverImage: "authentication-vs-authorization.webp" tags: ["authentication","authorization","ciam solution"] author: "Rakesh Soni" description: "As companies progress towards digital maturity in times of robust cloud-based systems and stringent online security, authentication and authorization are used in conjunction with each other." @@ -163,7 +163,7 @@ Here is the common authentication vs authorization techniques used by CIAM solut - **Password-based authentication** is a simple [method of authentication](https://www.loginradius.com/blog/2019/06/what-is-multi-factor-authentication/) that requires a password to verify the user's identity. - **Passwordless authentication** is [where a user is verified](https://www.loginradius.com/blog/2019/10/passwordless-authentication-the-future-of-identity-and-security/) through OTP or a magic link delivered to the registered email or phone number. -[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/) +[](https://www.loginradius.com/resource/loginradius-ciam-passwordless-login/) - **2FA/MFA** requires [more than one security level](https://www.loginradius.com/blog/2019/06/what-is-multi-factor-authentication/), like an additional PIN or security question, to identify a user and grant access to a system. - **Single sign-on** (SSO) allows users to access multiple applications with a single set of credentials. @@ -179,7 +179,7 @@ Here is the common authentication vs authorization techniques used by CIAM solut To learn more about the authentication vs authorization - concept, differences, and techniques, check out the infographic created by LoginRadius. - + ## Implementing Identity and Access Management with LoginRadius @@ -217,4 +217,4 @@ Properly implemented authentication and authorization processes can ensure data The future likely involves more advanced biometrics, continuous authentication, and AI-driven security measures to combat evolving cyber threats and enhance user experience. -[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-vs-authorization-infographic) +[](https://www.loginradius.com/contact-us?utm_source=blog&utm_medium=web&utm_campaign=authentication-vs-authorization-infographic) diff --git a/content/identity/authentication-vs-authorization-infographic/passwordless-login.png b/content/identity/authentication-vs-authorization-infographic/passwordless-login.png deleted file mode 100644 index 69d26339f..000000000 Binary files a/content/identity/authentication-vs-authorization-infographic/passwordless-login.png and /dev/null differ diff --git a/content/identity/authentication-vs-authorization-infographic/passwordless-login.webp b/content/identity/authentication-vs-authorization-infographic/passwordless-login.webp new file mode 100644 index 000000000..96ed92a38 Binary files /dev/null and b/content/identity/authentication-vs-authorization-infographic/passwordless-login.webp differ diff --git a/content/identity/authentication-vs-authorization/authentication-vs-authorization.webp b/content/identity/authentication-vs-authorization/authentication-vs-authorization.webp new file mode 100644 index 000000000..eefe132c6 Binary files /dev/null and b/content/identity/authentication-vs-authorization/authentication-vs-authorization.webp differ diff --git a/content/identity/authentication-vs-authorization/index.md b/content/identity/authentication-vs-authorization/index.md new file mode 100644 index 000000000..3135bb5fa --- /dev/null +++ b/content/identity/authentication-vs-authorization/index.md @@ -0,0 +1,260 @@ +--- +title: "Authentication vs Authorization: What's the Difference?" +date: "2025-04-08" +coverImage: "authentication-vs-authorization.webp" +tags: ["Authentication","Authorization","Data Privacy","Identity Management"] +author: "Rakesh Soni" +description: "Authentication and authorization are often confused but play very different roles in cybersecurity. This blog breaks down what each term means, why authentication always comes first, and how both work together to keep systems secure. With relatable examples and real-world scenarios, you'll understand the key differences, best practices, and why mastering both is essential for protecting digital assets." +metatitle: "Authentication vs Authorization: Key Differences Explained" +metadescription: "Discover the core difference between authentication vs authorization. Learn how each secures access, their roles in cybersecurity, and real-world use cases." +--- + +## Introduction + +In a world where cyber threats like data breaches and identity theft are making headlines almost daily, securing digital systems isn’t just important — it’s essential. That’s where two commonly confused terms come in: authentication and authorization. You’ve probably heard them used together (or even interchangeably), but they serve very different purposes. + +Whether you're building secure apps, managing access for a team, or simply curious about how systems stay protected, understanding the difference between authentication and authorization is key. + +In this blog, we’ll unpack both concepts with relatable examples and clear insights — so you can confidently grasp how each one keeps your data and users safe. + +## What is Authentication? + +[Authentication ](https://www.loginradius.com/blog/identity/what-is-authentication/)is the process of verifying who a user is. It answers the question: Are you really who you say you are? + +For authentication, users typically provide credentials — such as a username and password, biometric data, or a one-time code — to prove their identity. It acts like a digital passport that validates a person before letting them into a system. + +Imagine you walk into a secured office building. At the entrance, a security guard checks your ID. If it matches the employee database, you’re allowed in. That’s authentication. + +In technical aspects, imagine a user logs into an online banking app with a password and receives a 2FA code on their phone. Only after both credentials are verified is the user granted access. This is a prime example of authentication in cyber security. + + + +## What is the Purpose of Authentication? + +The core goal of authentication is to ensure that only verified users can access a system. It prevents impersonation, data theft, and breaches by validating user identities before granting entry. + +In today’s digital landscape, where everything from cloud apps to enterprise databases is remotely accessible, robust authentication methods — like biometrics, OTPs, and social logins — are critical for security. + +Authentication lays the foundation. Without it, systems wouldn’t know *who* they are dealing with — making any additional security effort meaningless. + +## What is Authorization? + +Authorization, on the other hand, determines *what* an authenticated user is allowed to do. It answers: *Do you have permission to access this resource or perform this action?* + +If authentication is the security guard verifying your ID, authorization is the list showing what rooms or data you're allowed to access. + +In simple terms, authorization in cybersecurity is about assigning privileges and access levels to different users based on their role, location, or behavior. + +## Common Types of Authorization + +There are various ways to authorize users, depending on the system’s needs. Here are some of the most common: + +### 1. Role-Based Access Control (RBAC): + +In role-based access control, users are granted permissions based on roles (admin, editor, viewer). For example, in the [LoginRadius console](https://accounts.loginradius.com/auth.aspx?return_url=https://console.loginradius.com/login&action=register) below, the “Admin” has permission to broadcast, download, edit, and read. On the other hand, the “Customer” is only authorized to download and read. + + + +Explore how [Role-Based Access Control (RBAC)](https://www.loginradius.com/blog/identity/what-is-rbac/) simplifies permissions and strengthens security. +In a nutshell, RBAC simplifies access management by assigning permissions based on user roles, such as admin, editor, or viewer, rather than handling access at the individual level. + +In a B2C context, this often means differentiating capabilities between everyday users and internal staff. For instance, a streaming platform might allow viewers to consume content, while admins manage uploads and settings. + +In B2B scenarios, this concept scales to entire organizations. For example, a retail company which collaborates with suppliers, franchisees, and distributors, requires precise control over who can access what across partner ecosystems. + +Our Partner IAM feature enables role-based permissions at the organization level, such as Partner Admin or Franchise Manager with access defined down to specific resources or workflows. + +Discover how LoginRadius Partner IAM enables precise, organization-level [RBAC tailored for complex B2B environments](https://www.loginradius.com/docs/user-management/roles-and-permissions/). + +### 2. Attribute-Based Access Control (ABAC) + +Attribute-based access ensures that access is granted based on a combination of user attributes such as department, role, location, time of day, or device type. + +For example, an employee from the finance department can access payroll data only during working hours and only when using a company-issued device—ensuring granular and context-aware security controls. + +You can read our [RBAC vs ABAC guide](https://www.loginradius.com/blog/identity/rbac-vs-abac/)for a detailed comparison between RBAC and ABAC to ensure you make the right decision that meets your business requirements. + +### 3. JSON Web Token (JWT) Authorization + +JWT (JSON Web Token) authorization is a widely used method for securely transmitting user data between parties—particularly in modern web applications and services. It's especially popular in systems that use stateless authentication, such as RESTful APIs. For instance, after a user logs in, the server issues a JWT that the client includes in subsequent requests to authenticate without needing to re-enter credentials. + +If you’d like to dive deeper into how JWTs work and when to use them, check out our full guide on [JWT authorization best practices](https://www.loginradius.com/blog/engineering/guest-post/jwt-authentication-best-practices-and-when-to-use/). + +### 4. OAuth 2.0 + +OAuth 2.0 is a widely adopted protocol for delegating access without exposing user credentials. For example, when you log into Spotify using your Google account, Google handles the authentication, and Spotify receives limited, authorized access to your basic profile—without ever seeing your Google password. This secure delegation is ideal for third-party integrations and API-based systems. + +To understand how OAuth 2.0 works, its core flows, and when to use it, check out our in-depth breakdown on[ OAuth 2.0 and its role in modern identity management.](https://www.loginradius.com/blog/engineering/what-is-oauth2-0/) + +The aforementioned types show the depth of authorization in cybersecurity, shaping how users interact with systems securely. + +## Authentication vs Authorization + +To put it plainly, authentication and authorization are two sides of the same coin — often paired but serving different purposes. + +* *Authentication*: Confirms your identity. + +* *Authorization*: Grants or denies permissions based on that identity. + +Let’s go back to the real world: You check into a hotel (authentication), but your key card only grants you access to your room and the gym — not the penthouse suite (authorization). + +### Key Differences Between Authentication and Authorization + +| Feature + | +Authentication + | +Authorization + | +
| Definition + | +Verifies identity + | +Determines access rights + | +
| Function + | +"Who are you?" + | +"What are you allowed to do?" + | +
| Process + | +Done before authorization + | +Done after authentication + | +
| Data + | +Requires login credentials + | +Requires permission policies + | +
| Visibility to user + | +Visible (e.g., login form) + | +Often invisible to the user + | +
| Use case + | +Login portals, biometric scans + | +Accessing internal dashboards or APIs + | +
| Feature + | +Identification + | +Authentication + | +Authorization + | +
| Definition + | +Claiming an identity + | +Proving that identity + | +Granting access to resources + | +
| Example + | +Entering your username or email + | +Typing your password or scanning fingerprint + | +Accessing files based on user role + | +
| When it Occurs + | +First step of login + | +Second step—verification + | +After successful authentication + | +
| Used In + | +Login forms, registration, device pairing + | +MFA systems, biometrics, 2FA + | +Role-based access, permissions frameworks + | +
| Failure Risk + | +Misidentification + | +Credential theft, phishing + | +Privilege escalation + | +
 **Step 6:** Now edit the AntiXssMiddlewars.cs file and paste below code.
diff --git a/content/engineering/apache-beam/beam_architecture.png b/content/engineering/apache-beam/beam_architecture.png
deleted file mode 100644
index 943220a08..000000000
Binary files a/content/engineering/apache-beam/beam_architecture.png and /dev/null differ
diff --git a/content/engineering/apache-beam/beam_architecture.webp b/content/engineering/apache-beam/beam_architecture.webp
new file mode 100644
index 000000000..81a7cdbfd
Binary files /dev/null and b/content/engineering/apache-beam/beam_architecture.webp differ
diff --git a/content/engineering/apache-beam/index.md b/content/engineering/apache-beam/index.md
index 7d6e0486e..063ac6cb1 100644
--- a/content/engineering/apache-beam/index.md
+++ b/content/engineering/apache-beam/index.md
@@ -1,7 +1,7 @@
---
title: "Apache Beam: A Basic Guide"
date: "2020-10-16"
-coverImage: "main.png"
+coverImage: "main.webp"
author: "Abhilash K R"
tags: ["Engineering","Big Data","Streaming","Apache Beam","Java"]
description: "Apache Beam simplifies large-scale data processing dynamics. Let’s read more about the features, basic concepts, and the fundamentals of Apache beam."
@@ -15,7 +15,7 @@ Different technologies came into existence for different paradigms, solving vari
As a developer or a business, it's always challenging to maintain different tech stacks and technologies. Hence, Apache Beam to the rescue!
-
+
## What is Apache Beam?
@@ -24,7 +24,7 @@ Apache Beam is an open source, centralised model for describing parallel-process
The Apache Beam model offers helpful abstractions that insulate you from distributed processing information at low levels, such as managing individual staff, exchanging databases, and other activities. These low-level information are handled entirely by Dataflow.
-
+
## Features of Apache Beam
@@ -61,7 +61,7 @@ Apache Beam has three main abstractions. They are
2. PCollection
3. PTransform
-
+
### Pipeline:
diff --git a/content/engineering/apache-beam/main.png b/content/engineering/apache-beam/main.png
deleted file mode 100644
index aa981b7c9..000000000
Binary files a/content/engineering/apache-beam/main.png and /dev/null differ
diff --git a/content/engineering/apache-beam/main.webp b/content/engineering/apache-beam/main.webp
new file mode 100644
index 000000000..b6bc0bf6c
Binary files /dev/null and b/content/engineering/apache-beam/main.webp differ
diff --git a/content/engineering/apache-beam/pipeline-design.png b/content/engineering/apache-beam/pipeline-design.png
deleted file mode 100644
index b2f8ffe09..000000000
Binary files a/content/engineering/apache-beam/pipeline-design.png and /dev/null differ
diff --git a/content/engineering/apache-beam/pipeline-design.webp b/content/engineering/apache-beam/pipeline-design.webp
new file mode 100644
index 000000000..5212b3bcc
Binary files /dev/null and b/content/engineering/apache-beam/pipeline-design.webp differ
diff --git a/content/engineering/apache-beam/timeline-bigdata-frameworks.png b/content/engineering/apache-beam/timeline-bigdata-frameworks.png
deleted file mode 100644
index 50822ee94..000000000
Binary files a/content/engineering/apache-beam/timeline-bigdata-frameworks.png and /dev/null differ
diff --git a/content/engineering/apache-beam/timeline-bigdata-frameworks.webp b/content/engineering/apache-beam/timeline-bigdata-frameworks.webp
new file mode 100644
index 000000000..c35718f4d
Binary files /dev/null and b/content/engineering/apache-beam/timeline-bigdata-frameworks.webp differ
diff --git a/content/engineering/api-debugging-tools/api_debugging-tools-300x300.png b/content/engineering/api-debugging-tools/api_debugging-tools-300x300.png
deleted file mode 100644
index c58cc27ff..000000000
Binary files a/content/engineering/api-debugging-tools/api_debugging-tools-300x300.png and /dev/null differ
diff --git a/content/engineering/api-debugging-tools/api_debugging-tools-300x300.webp b/content/engineering/api-debugging-tools/api_debugging-tools-300x300.webp
new file mode 100644
index 000000000..d4cec35ed
Binary files /dev/null and b/content/engineering/api-debugging-tools/api_debugging-tools-300x300.webp differ
diff --git a/content/engineering/api-debugging-tools/index.md b/content/engineering/api-debugging-tools/index.md
index 4723ed991..6d084f414 100644
--- a/content/engineering/api-debugging-tools/index.md
+++ b/content/engineering/api-debugging-tools/index.md
@@ -1,7 +1,7 @@
---
title: "API Debugging Tools"
date: "2015-05-26"
-coverImage: "api_debugging-tools-300x300.png"
+coverImage: "api_debugging-tools-300x300.webp"
author: "Karl Wittig"
tags: ["Engineering","GoogleChorme","MozilaFirefox","SoupUI","RunScope"]
---
diff --git a/content/engineering/api-testing-and-benefits/api-testing.png b/content/engineering/api-testing-and-benefits/api-testing.png
deleted file mode 100644
index f1e9c5774..000000000
Binary files a/content/engineering/api-testing-and-benefits/api-testing.png and /dev/null differ
diff --git a/content/engineering/api-testing-and-benefits/api-testing.webp b/content/engineering/api-testing-and-benefits/api-testing.webp
new file mode 100644
index 000000000..9fae90d6d
Binary files /dev/null and b/content/engineering/api-testing-and-benefits/api-testing.webp differ
diff --git a/content/engineering/api-testing-and-benefits/index.md b/content/engineering/api-testing-and-benefits/index.md
index 716c7c52f..648e9926b 100644
--- a/content/engineering/api-testing-and-benefits/index.md
+++ b/content/engineering/api-testing-and-benefits/index.md
@@ -1,7 +1,7 @@
---
title: "What is API Testing? - Discover the Benefits"
date: "2021-02-12"
-coverImage: "api-testing.png"
+coverImage: "api-testing.webp"
author: "Surendranath Reddy Birudala"
tags: ["Automation", "API Testing", "Agile", "Benefits"]
description: "Communication between software components is handled by an API (Application Programming Interface). Discover the advantages of automated API testing."
diff --git a/content/engineering/authorization-code-flow-oauth/acf.png b/content/engineering/authorization-code-flow-oauth/acf.png
deleted file mode 100644
index 12776b849..000000000
Binary files a/content/engineering/authorization-code-flow-oauth/acf.png and /dev/null differ
diff --git a/content/engineering/authorization-code-flow-oauth/acf.webp b/content/engineering/authorization-code-flow-oauth/acf.webp
new file mode 100644
index 000000000..6bf20454e
Binary files /dev/null and b/content/engineering/authorization-code-flow-oauth/acf.webp differ
diff --git a/content/engineering/authorization-code-flow-oauth/index.md b/content/engineering/authorization-code-flow-oauth/index.md
index c7ce68d12..5b58b4d8f 100644
--- a/content/engineering/authorization-code-flow-oauth/index.md
+++ b/content/engineering/authorization-code-flow-oauth/index.md
@@ -1,7 +1,7 @@
---
title: "Guide to Authorization Code Flow for OAuth 2.0"
date: "2021-03-24"
-coverImage: "unsplash.jpg"
+coverImage: "unsplash.webp"
author: "Nick Chim"
tags: ["Oauth", "Authorization Code Flow"]
description: "This article will help you to understand the OAuth 2.0 authorization code flow."
@@ -13,7 +13,7 @@ In the Authorization Code flow, the server-side component of the web application
### Overview
-
+
The flow illustrated above aims to provide a rough overview of a typical Authorization Code workflow:
diff --git a/content/engineering/authorization-code-flow-oauth/unsplash.jpg b/content/engineering/authorization-code-flow-oauth/unsplash.jpg
deleted file mode 100644
index 8af73a4e7..000000000
Binary files a/content/engineering/authorization-code-flow-oauth/unsplash.jpg and /dev/null differ
diff --git a/content/engineering/authorization-code-flow-oauth/unsplash.webp b/content/engineering/authorization-code-flow-oauth/unsplash.webp
new file mode 100644
index 000000000..a135d68d0
Binary files /dev/null and b/content/engineering/authorization-code-flow-oauth/unsplash.webp differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/1.png b/content/engineering/azure-ad-as-an-identity-provider/1.png
deleted file mode 100644
index 4ed46d0df..000000000
Binary files a/content/engineering/azure-ad-as-an-identity-provider/1.png and /dev/null differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/1.webp b/content/engineering/azure-ad-as-an-identity-provider/1.webp
new file mode 100644
index 000000000..4c27a4edd
Binary files /dev/null and b/content/engineering/azure-ad-as-an-identity-provider/1.webp differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/2.png b/content/engineering/azure-ad-as-an-identity-provider/2.png
deleted file mode 100644
index f08b0363c..000000000
Binary files a/content/engineering/azure-ad-as-an-identity-provider/2.png and /dev/null differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/2.webp b/content/engineering/azure-ad-as-an-identity-provider/2.webp
new file mode 100644
index 000000000..5a3f9511e
Binary files /dev/null and b/content/engineering/azure-ad-as-an-identity-provider/2.webp differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/A-1.png b/content/engineering/azure-ad-as-an-identity-provider/A-1.png
deleted file mode 100644
index 52247393d..000000000
Binary files a/content/engineering/azure-ad-as-an-identity-provider/A-1.png and /dev/null differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/A-1.webp b/content/engineering/azure-ad-as-an-identity-provider/A-1.webp
new file mode 100644
index 000000000..ef8ddf280
Binary files /dev/null and b/content/engineering/azure-ad-as-an-identity-provider/A-1.webp differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.png b/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.png
deleted file mode 100644
index 4460d2ef6..000000000
Binary files a/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.png and /dev/null differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.webp b/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.webp
new file mode 100644
index 000000000..330c94a71
Binary files /dev/null and b/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.webp differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/index.md b/content/engineering/azure-ad-as-an-identity-provider/index.md
index a14054a15..ca256da25 100644
--- a/content/engineering/azure-ad-as-an-identity-provider/index.md
+++ b/content/engineering/azure-ad-as-an-identity-provider/index.md
@@ -1,7 +1,7 @@
---
title: "Azure AD as an Identity provider"
date: "2019-05-30"
-coverImage: "TN0lxUr0.png"
+coverImage: "TN0lxUr0.webp"
author: "Team LoginRadius"
tags: ["Engineering","Authentication","AzureAD"]
---
@@ -13,17 +13,17 @@ Windows Azure provides a number of identity-based technologies to support such k
- Log in to the Azure Portal.
- On the Azure active directory tab, click on the App registrations tab. From the top of the screen, create a new application by clicking on "New application registration".
-
+
- Give your SaaS/Web application a name (company name Demo). Using the drop-down, select the type of application i.e Web Application / Web API.
- For Sign-On URL fill in the Assertion Consumer Service (ACS) URL for the Service Provider
-
+
- Go to the App setting at the top of the page and fill in the required fields
- Go to the endpoints at the top of the application registration page and use these app endpoints to set up the azure ad with your saas application.
-
+
Here are the meanings of the terms, we have used above:
diff --git a/content/engineering/basic-query-operations-in-mongodb/coverImage.png b/content/engineering/basic-query-operations-in-mongodb/coverImage.png
deleted file mode 100644
index a333977de..000000000
Binary files a/content/engineering/basic-query-operations-in-mongodb/coverImage.png and /dev/null differ
diff --git a/content/engineering/basic-query-operations-in-mongodb/coverImage.webp b/content/engineering/basic-query-operations-in-mongodb/coverImage.webp
new file mode 100644
index 000000000..72aa80e83
Binary files /dev/null and b/content/engineering/basic-query-operations-in-mongodb/coverImage.webp differ
diff --git a/content/engineering/basic-query-operations-in-mongodb/index.md b/content/engineering/basic-query-operations-in-mongodb/index.md
index 862e2e006..1041a3b70 100644
--- a/content/engineering/basic-query-operations-in-mongodb/index.md
+++ b/content/engineering/basic-query-operations-in-mongodb/index.md
@@ -1,7 +1,7 @@
---
title: How to Perform Basic Query Operations in MongoDB
date: "2021-01-20"
-coverImage: "coverImage.png"
+coverImage: "coverImage.webp"
author: "Anil Gupta"
Description: In this blog, we will learn how query operations can be performed in MongoDB. Also, how we can perform fundamental query operations, as we do in RDBMS.
tags: ["MongoDB"]
diff --git a/content/engineering/be-more-manipulative-with-underscore-js/index.md b/content/engineering/be-more-manipulative-with-underscore-js/index.md
index 122c0924f..08cce7d6c 100644
--- a/content/engineering/be-more-manipulative-with-underscore-js/index.md
+++ b/content/engineering/be-more-manipulative-with-underscore-js/index.md
@@ -1,7 +1,7 @@
---
title: "Be More Manipulative with Underscore JS"
date: "2016-02-16"
-coverImage: "underscore.png"
+coverImage: "underscore.webp"
author: "Zakary Hughes"
tags: ["JavaScript", "UnderscoreJs"]
---
diff --git a/content/engineering/be-more-manipulative-with-underscore-js/underscore.png b/content/engineering/be-more-manipulative-with-underscore-js/underscore.png
deleted file mode 100644
index 0f4c8757f..000000000
Binary files a/content/engineering/be-more-manipulative-with-underscore-js/underscore.png and /dev/null differ
diff --git a/content/engineering/be-more-manipulative-with-underscore-js/underscore.webp b/content/engineering/be-more-manipulative-with-underscore-js/underscore.webp
new file mode 100644
index 000000000..971027c4f
Binary files /dev/null and b/content/engineering/be-more-manipulative-with-underscore-js/underscore.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.png
deleted file mode 100644
index 8a4233605..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.webp
new file mode 100644
index 000000000..6c9730ee1
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.png
deleted file mode 100644
index b00449d2b..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.webp
new file mode 100644
index 000000000..9dfada225
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/index.md b/content/engineering/beginners-guide-for-sublime-text-3-part-2/index.md
index 34a214728..3841b9146 100644
--- a/content/engineering/beginners-guide-for-sublime-text-3-part-2/index.md
+++ b/content/engineering/beginners-guide-for-sublime-text-3-part-2/index.md
@@ -1,7 +1,7 @@
---
title: "Beginner's Guide for Sublime Text 3 Plugins"
date: "2015-11-10"
-coverImage: "Beginner-Guide-Sublime-Text.png"
+coverImage: "Beginner-Guide-Sublime-Text.webp"
author: "Team LoginRadius"
tags: ["SublimeText", "CodeEditor"]
description: "Getting started with one of the lightweight Code Editor Sublime Text and introduction to Snippets, Project and Macros"
@@ -20,7 +20,7 @@ Back when i introduced Sublime editor to my friends,"Snippets" was among the fir
This is definitely the feature you will use the most! To start using snippets, you can either create your own snippets according to your needs or download some ready-made snippets created by others to fulfill some generic coding needs. Like the one I demonstrated, it is pre-made from a plugin called `Html Page Snippets`, and command `docjq` will create a boiler template for a Html page that contains bootstrap and jQuery.
-
+
To create your own snippet, go to "Tools" => "New Snippet", an interface to create your own snippet will pop up, it would look something like this:
@@ -37,7 +37,7 @@ Now save it, but keep in mind putting it in the correct location is important!
If you can not find it, go to "Sublime" - > "Preferences" -> "Browse Packages", and create a folder called "User" if there isn't one already, and save it there.
-
+
### Project
@@ -48,7 +48,7 @@ Saving and using your projects is very straightforward.
- First drag some folders and files that you want to open into Sublime
- Then go to the menu, click "Project" -> "Save Project As"
- 
+ 
- Note the extension is ".sublime-project" and you may want to put all your project files in one central location
@@ -62,7 +62,7 @@ Do you always feel frustrated by repeating the same tedious task again & again?
It takes about 8 shortcuts to finish each process, that's including the first paste action and then adding a space character after each comma. Imagine having to do this for each line of a table, and for every single spreadsheet you have to work on. It would be hundreds of shortcuts you need to press and each time you are just repeating the exact same sequence of keys.
-
+
Well you might think there must be a better way! You bet there is! "Macros" are designed to handle this kind of nasty situation and save you from all that boring work. Here I made a very quick and easy example, it converts a vertical line of data into an array:
@@ -70,7 +70,7 @@ Magic! Lots of time and lives will be saved by this little gadget. So now, how t
- Go to "Tools" -> "Record Mac
- 
+ 
- Do your operations
@@ -78,7 +78,7 @@ Usually you would have something copied in your clipboard, so it could start wit
- Stop your macro
- 
+ 
- Playback
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.png
deleted file mode 100644
index de0521927..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.webp
new file mode 100644
index 000000000..db3baa55a
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.png
deleted file mode 100644
index 7e2fd2948..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.webp
new file mode 100644
index 000000000..8f02a9964
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.png
deleted file mode 100644
index 227077bdd..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.webp
new file mode 100644
index 000000000..5205c313b
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.png
deleted file mode 100644
index 227077bdd..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.webp
new file mode 100644
index 000000000..5205c313b
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.png
deleted file mode 100644
index dbe8d9e37..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.webp
new file mode 100644
index 000000000..a9587639d
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.png b/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.png
deleted file mode 100644
index 8a4233605..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.webp b/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.webp
new file mode 100644
index 000000000..6c9730ee1
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/index.md b/content/engineering/beginners-guide-for-sublime-text/index.md
index 125ed4416..07614842c 100644
--- a/content/engineering/beginners-guide-for-sublime-text/index.md
+++ b/content/engineering/beginners-guide-for-sublime-text/index.md
@@ -1,7 +1,7 @@
---
title: "Beginner's Guide for Sublime Text 3"
date: "2015-09-15"
-coverImage: "Beginner-Guide-Sublime-Text.png"
+coverImage: "Beginner-Guide-Sublime-Text.webp"
author: "Team LoginRadius"
tags: ["SublimeText", "CodeEditor"]
description: "Getting started with one of the lightweight Code Editor Sublime Text and it's package control and shortcut commends"
@@ -33,7 +33,7 @@ Cmd + Shift + p
Then type "Install Package", you should see it now:
-
+
2\. Theme
@@ -48,7 +48,7 @@ After installing your preferred theme, the font and color scheme for sublime may
Navigate to:
-
+
What this file does is actually overwrite the settings in the default-setting JSON file, if you mess up with this user file, just delete them to recover back to the original settings. So feel free to play around with it, from here you can define the settings from your theme provider's guidance, here I will post mine as a sample
@@ -64,7 +64,7 @@ What this file does is actually overwrite the settings in the default-setting JS
Please note JSON format is significant to Sublime Settings, when you are not sure about it, check it with an online JSON validator. Now with this step done, you will have a delightful working environment to write your code in:
-
+
3\. Goto Everywhere
diff --git a/content/engineering/beginners-guide-for-sublime-text/install-package.png b/content/engineering/beginners-guide-for-sublime-text/install-package.png
deleted file mode 100644
index 7cf445a1a..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text/install-package.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/install-package.webp b/content/engineering/beginners-guide-for-sublime-text/install-package.webp
new file mode 100644
index 000000000..7527826cf
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text/install-package.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/sample-code.png b/content/engineering/beginners-guide-for-sublime-text/sample-code.png
deleted file mode 100644
index ee7be4876..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text/sample-code.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/sample-code.webp b/content/engineering/beginners-guide-for-sublime-text/sample-code.webp
new file mode 100644
index 000000000..3cb763997
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text/sample-code.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/user-preference.png b/content/engineering/beginners-guide-for-sublime-text/user-preference.png
deleted file mode 100644
index d0376faab..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text/user-preference.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/user-preference.webp b/content/engineering/beginners-guide-for-sublime-text/user-preference.webp
new file mode 100644
index 000000000..363e949c6
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text/user-preference.webp differ
diff --git a/content/engineering/beginners-guide-to-tweepy/coverimage.jpg b/content/engineering/beginners-guide-to-tweepy/coverimage.jpg
deleted file mode 100644
index be61218a6..000000000
Binary files a/content/engineering/beginners-guide-to-tweepy/coverimage.jpg and /dev/null differ
diff --git a/content/engineering/beginners-guide-to-tweepy/coverimage.webp b/content/engineering/beginners-guide-to-tweepy/coverimage.webp
new file mode 100644
index 000000000..14a9cbf21
Binary files /dev/null and b/content/engineering/beginners-guide-to-tweepy/coverimage.webp differ
diff --git a/content/engineering/beginners-guide-to-tweepy/index.md b/content/engineering/beginners-guide-to-tweepy/index.md
index 374fd0fa4..bafcb0bf3 100644
--- a/content/engineering/beginners-guide-to-tweepy/index.md
+++ b/content/engineering/beginners-guide-to-tweepy/index.md
@@ -1,7 +1,7 @@
---
title: "Beginners Guide to Tweepy "
date: "2020-11-02"
-coverImage: "coverimage.jpg"
+coverImage: "coverimage.webp"
author: "Sameer Mahajan"
tags: ["Twitter","Tweepy","Python"]
description: "Learn how to use Twitter APIs using Tweepy, a python package,"
@@ -14,18 +14,18 @@ In simple words, Tweepy is an open-source python package that provides a way for
### Installation
Tweepy can be installed by using Python package manager **pip**. A simple demonstration can be seen below:
-
+
Installation on Linux and macOS should follow similar steps as well.
Twitter API uses OAuth for authentication, so initially, you need to apply for authentication credentials from Twitter. These authentication credentials basically consists of 4 components namely : _consumer_key, consumer_secret_key, access_token, access_token_secret_ . These credentials from Twitter are used to instantiate the API. **Each account gets a unique key, so don't reuse someone else's keys.**
For getting those credentials from Twitter, apply for a developer account on the [Twitter Developers](https://developer.twitter.com/en) page.
-
+
This is what the account looks like. Here you will get detailed information about the total no. of requests made, your API credentials, and much more information. After creating an account, you need to create an app wherein you will be asked to name your app and a short description. You must be wondering what an app is?
The app is like a gateway that contains a set of permissions and keys used to access the Twitter API. An app is needed for accessing the Twitter API as a part of Twitter's OAuth authentication. After creating an app, generate new authentication tokens for authorization purposes.
-
+
### Getting Started: Tweepy
There are four common basic steps in any Tweepy application.
diff --git a/content/engineering/beginners-guide-to-tweepy/installation.PNG b/content/engineering/beginners-guide-to-tweepy/installation.PNG
deleted file mode 100644
index 0a3ba332e..000000000
Binary files a/content/engineering/beginners-guide-to-tweepy/installation.PNG and /dev/null differ
diff --git a/content/engineering/beginners-guide-to-tweepy/installation.webp b/content/engineering/beginners-guide-to-tweepy/installation.webp
new file mode 100644
index 000000000..9194b1615
Binary files /dev/null and b/content/engineering/beginners-guide-to-tweepy/installation.webp differ
diff --git a/content/engineering/beginners-guide-to-tweepy/keys.PNG b/content/engineering/beginners-guide-to-tweepy/keys.PNG
deleted file mode 100644
index efd4d14e1..000000000
Binary files a/content/engineering/beginners-guide-to-tweepy/keys.PNG and /dev/null differ
diff --git a/content/engineering/beginners-guide-to-tweepy/keys.webp b/content/engineering/beginners-guide-to-tweepy/keys.webp
new file mode 100644
index 000000000..b44866084
Binary files /dev/null and b/content/engineering/beginners-guide-to-tweepy/keys.webp differ
diff --git a/content/engineering/beginners-guide-to-tweepy/twitterdev.PNG b/content/engineering/beginners-guide-to-tweepy/twitterdev.PNG
deleted file mode 100644
index d84d45a44..000000000
Binary files a/content/engineering/beginners-guide-to-tweepy/twitterdev.PNG and /dev/null differ
diff --git a/content/engineering/beginners-guide-to-tweepy/twitterdev.webp b/content/engineering/beginners-guide-to-tweepy/twitterdev.webp
new file mode 100644
index 000000000..3bc033c32
Binary files /dev/null and b/content/engineering/beginners-guide-to-tweepy/twitterdev.webp differ
diff --git a/content/engineering/best-practice-guide-for-rest-api-security/index.jpg b/content/engineering/best-practice-guide-for-rest-api-security/index.jpg
deleted file mode 100644
index 4b82dcc8c..000000000
Binary files a/content/engineering/best-practice-guide-for-rest-api-security/index.jpg and /dev/null differ
diff --git a/content/engineering/best-practice-guide-for-rest-api-security/index.md b/content/engineering/best-practice-guide-for-rest-api-security/index.md
index 1a0506528..d91993944 100644
--- a/content/engineering/best-practice-guide-for-rest-api-security/index.md
+++ b/content/engineering/best-practice-guide-for-rest-api-security/index.md
@@ -1,7 +1,7 @@
---
title: "Best Practice Guide For Rest API Security | LoginRadius"
date: "2020-08-20"
-coverImage: "index.jpg"
+coverImage: "index.webp"
author: "Vijay Singh Shekhawat"
tags: ["RestAPI", "Rest API","Rest API Security", "Best Practice", "Rest API Developer Guide", "Security"]
---
diff --git a/content/engineering/best-practice-guide-for-rest-api-security/index.webp b/content/engineering/best-practice-guide-for-rest-api-security/index.webp
new file mode 100644
index 000000000..9c0af6f7c
Binary files /dev/null and b/content/engineering/best-practice-guide-for-rest-api-security/index.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/Homepage.png b/content/engineering/best-practice-reviewing-qq-app/Homepage.png
deleted file mode 100644
index 24d518083..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/Homepage.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/Homepage.webp b/content/engineering/best-practice-reviewing-qq-app/Homepage.webp
new file mode 100644
index 000000000..49ae3af56
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/Homepage.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/add_assets.png b/content/engineering/best-practice-reviewing-qq-app/add_assets.png
deleted file mode 100644
index c2d8f4139..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/add_assets.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/add_assets.webp b/content/engineering/best-practice-reviewing-qq-app/add_assets.webp
new file mode 100644
index 000000000..a17576b6d
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/add_assets.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/app_for_website.png b/content/engineering/best-practice-reviewing-qq-app/app_for_website.png
deleted file mode 100644
index 051c07958..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/app_for_website.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/app_for_website.webp b/content/engineering/best-practice-reviewing-qq-app/app_for_website.webp
new file mode 100644
index 000000000..54e7b6aa2
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/app_for_website.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/app_submit.png b/content/engineering/best-practice-reviewing-qq-app/app_submit.png
deleted file mode 100644
index 108f9e0bd..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/app_submit.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/app_submit.webp b/content/engineering/best-practice-reviewing-qq-app/app_submit.webp
new file mode 100644
index 000000000..5ebfb02c8
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/app_submit.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/confirm_submit.png b/content/engineering/best-practice-reviewing-qq-app/confirm_submit.png
deleted file mode 100644
index b2449e66d..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/confirm_submit.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/confirm_submit.webp b/content/engineering/best-practice-reviewing-qq-app/confirm_submit.webp
new file mode 100644
index 000000000..684322f0b
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/confirm_submit.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/create_app_button.png b/content/engineering/best-practice-reviewing-qq-app/create_app_button.png
deleted file mode 100644
index 56c204ed2..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/create_app_button.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/create_app_button.webp b/content/engineering/best-practice-reviewing-qq-app/create_app_button.webp
new file mode 100644
index 000000000..3eeded170
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/create_app_button.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.png b/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.png
deleted file mode 100644
index c59000837..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.webp b/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.webp
new file mode 100644
index 000000000..b5f351a48
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/index.md b/content/engineering/best-practice-reviewing-qq-app/index.md
index 52130ff29..8a947a377 100644
--- a/content/engineering/best-practice-reviewing-qq-app/index.md
+++ b/content/engineering/best-practice-reviewing-qq-app/index.md
@@ -1,7 +1,7 @@
---
title: "Best practice for reviewing QQ app"
date: "2015-08-04"
-coverImage: "qq-app-review-best-practices.png"
+coverImage: "qq-app-review-best-practices.webp"
author: "Kundan Singh"
tags: ["SocialLogin", "QQ"]
---
@@ -12,7 +12,7 @@ QQ is the most popular ID provider for Chinese people since the 90s, it is alway
And click the 4th tab (in orange box)
- 
+ 
2. ### Registration
@@ -21,7 +21,7 @@ QQ is the most popular ID provider for Chinese people since the 90s, it is alway
Click "register a new account", like shown:
- 
+ 
It will link you to [this page](http://zc.qq.com/en/index.html?from=pt), it is written in English, sweet! I am pretty sure you can register an account by yourself. After filling in the information, it will send a confirmation email to your email box. After your email is verified go back to the [login page](http://connect.qq.com/manage/login), and use the QQ number you just got to log in with.
@@ -30,33 +30,33 @@ QQ is the most popular ID provider for Chinese people since the 90s, it is alway
Click the big green button on the right side of your screen to create an app, and here we will create a website type app.
- 
+ 
- 
+ 
After choosing the type, you need to fill in some basic information for your website, in case if you do not use Google translate to translate the page, I did a little translations for you, there you go.
- 
+ 
Here is what I have filled in
- 
+ 
Please note, when you fill in your website address, it will ask you to verify your website, so you need to copy and paste the javascript code under your website page, and then click the button beside to verify it.
- 
+ 
Once all the information is filled, then move on to next step, click the blue text link, it asks you to upload different sizes of the images about your company.
- 
+ 
- 
+ 
Then, it is time to submit by clicking that big green button in the middle.
- 
+ 
Confirm it by clicking the right button again.
- 
+ 
If everything works well, you will get you app approved in a week, just remember to check it back periodically, good luck!
diff --git a/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.png b/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.png
deleted file mode 100644
index fe49d18f5..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.webp b/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.webp
new file mode 100644
index 000000000..941b78170
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.png b/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.png
deleted file mode 100644
index 2a7cb30b9..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.webp b/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.webp
new file mode 100644
index 000000000..51527cac8
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.png b/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.png
deleted file mode 100644
index c12fd7957..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.webp b/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.webp
new file mode 100644
index 000000000..fc8001794
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.png b/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.png
deleted file mode 100644
index 7a1ff32f3..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.webp b/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.webp
new file mode 100644
index 000000000..0c5a2bc6c
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/verify_successfully.png b/content/engineering/best-practice-reviewing-qq-app/verify_successfully.png
deleted file mode 100644
index 9adc2f797..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/verify_successfully.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/verify_successfully.webp b/content/engineering/best-practice-reviewing-qq-app/verify_successfully.webp
new file mode 100644
index 000000000..3d663b086
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/verify_successfully.webp differ
diff --git a/content/engineering/best-ui-ux-design-tools-2020/index.md b/content/engineering/best-ui-ux-design-tools-2020/index.md
index 71d8fb35c..268bf20dd 100644
--- a/content/engineering/best-ui-ux-design-tools-2020/index.md
+++ b/content/engineering/best-ui-ux-design-tools-2020/index.md
@@ -1,7 +1,7 @@
---
title: "Best Free UI/UX Design Tools/Resources 2020"
date: "2020-08-13"
-coverImage: "ux-ui.jpg"
+coverImage: "ux-ui.webp"
author: "Hitesh Kumawat"
tags: ["Design", "UX", "Tools"]
description: "As a designer, often wondered which new tools and utilities, other designers are using? So here is a list of all the tools and utilities famous around the world in designers."
diff --git a/content/engineering/best-ui-ux-design-tools-2020/ux-ui.jpg b/content/engineering/best-ui-ux-design-tools-2020/ux-ui.jpg
deleted file mode 100644
index 025faf3f3..000000000
Binary files a/content/engineering/best-ui-ux-design-tools-2020/ux-ui.jpg and /dev/null differ
diff --git a/content/engineering/best-ui-ux-design-tools-2020/ux-ui.webp b/content/engineering/best-ui-ux-design-tools-2020/ux-ui.webp
new file mode 100644
index 000000000..bd28b4a33
Binary files /dev/null and b/content/engineering/best-ui-ux-design-tools-2020/ux-ui.webp differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-1.png b/content/engineering/big-data-testing-strategy/BigDataTesting-1.png
deleted file mode 100644
index 4f9d958d8..000000000
Binary files a/content/engineering/big-data-testing-strategy/BigDataTesting-1.png and /dev/null differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-1.webp b/content/engineering/big-data-testing-strategy/BigDataTesting-1.webp
new file mode 100644
index 000000000..3fe8f3f3b
Binary files /dev/null and b/content/engineering/big-data-testing-strategy/BigDataTesting-1.webp differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-2.png b/content/engineering/big-data-testing-strategy/BigDataTesting-2.png
deleted file mode 100644
index 07c542c5f..000000000
Binary files a/content/engineering/big-data-testing-strategy/BigDataTesting-2.png and /dev/null differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-2.webp b/content/engineering/big-data-testing-strategy/BigDataTesting-2.webp
new file mode 100644
index 000000000..f6753fbd7
Binary files /dev/null and b/content/engineering/big-data-testing-strategy/BigDataTesting-2.webp differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-3.png b/content/engineering/big-data-testing-strategy/BigDataTesting-3.png
deleted file mode 100644
index 25df85c22..000000000
Binary files a/content/engineering/big-data-testing-strategy/BigDataTesting-3.png and /dev/null differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-3.webp b/content/engineering/big-data-testing-strategy/BigDataTesting-3.webp
new file mode 100644
index 000000000..e1c830625
Binary files /dev/null and b/content/engineering/big-data-testing-strategy/BigDataTesting-3.webp differ
diff --git a/content/engineering/big-data-testing-strategy/big-data.png b/content/engineering/big-data-testing-strategy/big-data.png
deleted file mode 100644
index a5cd9b219..000000000
Binary files a/content/engineering/big-data-testing-strategy/big-data.png and /dev/null differ
diff --git a/content/engineering/big-data-testing-strategy/big-data.webp b/content/engineering/big-data-testing-strategy/big-data.webp
new file mode 100644
index 000000000..17253b792
Binary files /dev/null and b/content/engineering/big-data-testing-strategy/big-data.webp differ
diff --git a/content/engineering/big-data-testing-strategy/index.md b/content/engineering/big-data-testing-strategy/index.md
index 0e5b7a0be..ed072e7db 100644
--- a/content/engineering/big-data-testing-strategy/index.md
+++ b/content/engineering/big-data-testing-strategy/index.md
@@ -1,7 +1,7 @@
---
title: "Big Data - Testing Strategy"
date: "2020-09-02"
-coverImage: "big-data.png"
+coverImage: "big-data.webp"
author: "Sudhey Sharma"
tags: ["Testing", "Big Data","Big Data Testing"]
description: "With the exponential growth in the number of big data applications in the world, Testing in big data applications is related to database, infrastructure and performance testing and functional testing. This blog guides what should be the strategy for testing Big Data applications."
@@ -23,7 +23,7 @@ Testing is an art of achieving quality in your software product, in terms of per
Processing may be of three types:–
-
+
And based on which, we need to integrate different components along with NoSQL data store as per the needs.
@@ -53,7 +53,7 @@ Scalability is also desired to be there in the test environment of big data test
**Big Data Testing can be categorized into three stages:**
-
+
@@ -87,7 +87,7 @@ The output validation process is the final or third stage involved in big data t
Big data applications are meant to process a large amount of data, and it is expected that it should take minimum time to process maximum data. Along with it, application jobs should consume a considerable amount of memory and CPU. In big data testing, performance parameter plays an important role and helps to define SLA's. It covers the performance of the base machine and cluster. Also, for example, In the case of Hadoop, map-reduce jobs should be written with proper coding guidelines, to perform better in the production environment. Profiling can also be done on map-reduce jobs before integration, to ensure their optimized execution.
## Tools used in Big Data Scenarios
-
+
## Big Data Testing - Challenges
diff --git a/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.jpg b/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.jpg
deleted file mode 100644
index c9a3785e8..000000000
Binary files a/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.jpg and /dev/null differ
diff --git a/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.webp b/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.webp
new file mode 100644
index 000000000..74aa0b20c
Binary files /dev/null and b/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.webp differ
diff --git a/content/engineering/blockchain-the-new-technology-of-security-trust/block.png b/content/engineering/blockchain-the-new-technology-of-security-trust/block.png
deleted file mode 100644
index 40adf3c8b..000000000
Binary files a/content/engineering/blockchain-the-new-technology-of-security-trust/block.png and /dev/null differ
diff --git a/content/engineering/blockchain-the-new-technology-of-security-trust/block.webp b/content/engineering/blockchain-the-new-technology-of-security-trust/block.webp
new file mode 100644
index 000000000..c5fadfff4
Binary files /dev/null and b/content/engineering/blockchain-the-new-technology-of-security-trust/block.webp differ
diff --git a/content/engineering/blockchain-the-new-technology-of-security-trust/index.md b/content/engineering/blockchain-the-new-technology-of-security-trust/index.md
index 3178ce212..cab6660d1 100644
--- a/content/engineering/blockchain-the-new-technology-of-security-trust/index.md
+++ b/content/engineering/blockchain-the-new-technology-of-security-trust/index.md
@@ -1,7 +1,7 @@
---
title: "Blockchain: The new technology of trust"
date: "2020-10-08"
-coverImage: "CoverPage.jpg"
+coverImage: "CoverPage.webp"
author: "Shraddha V Prasad"
tags: ["Blockchain", "Cyber Security"]
description: "Learn about Blockchain technology and how it works."
@@ -26,7 +26,7 @@ Hash: It is quite similar to human fingerprint and is unique to each block, once
- LOCKING THE BLOCKS DOWN
Hash of the previous block-the hash of one block gives the data for the next block, and this new block uses this hash function and traces of it is woven into the new hash this continues to build an enormous chain.
-
+
## Establishing the trust
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.PNG b/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.PNG
deleted file mode 100644
index 13055ce3b..000000000
Binary files a/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.PNG and /dev/null differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.webp b/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.webp
new file mode 100644
index 000000000..2e67b5525
Binary files /dev/null and b/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.webp differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.png b/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.png
deleted file mode 100644
index 01e115080..000000000
Binary files a/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.png and /dev/null differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.webp b/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.webp
new file mode 100644
index 000000000..c1434a5dd
Binary files /dev/null and b/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.webp differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.png b/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.png
deleted file mode 100644
index 87c18faf4..000000000
Binary files a/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.png and /dev/null differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.webp b/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.webp
new file mode 100644
index 000000000..3ce34db06
Binary files /dev/null and b/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.webp differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/index.md b/content/engineering/bluetooth-controlled-arduino-car-miniature/index.md
index b9b67c930..fbbe43c58 100644
--- a/content/engineering/bluetooth-controlled-arduino-car-miniature/index.md
+++ b/content/engineering/bluetooth-controlled-arduino-car-miniature/index.md
@@ -1,7 +1,7 @@
---
title: "Bluetooth Controlled Arduino Car Miniature"
date: "2020-11-04"
-coverImage: "Arduinocar.png"
+coverImage: "Arduinocar.webp"
author: "Abhishek Potekar"
tags: ["Arduino","Bluetooth"]
description: "In this blog, you will learn how to make a Bluetooth controlled Arduino Car."
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/global-context.PNG b/content/engineering/breaking-down-this-keyword-in-javascript/global-context.PNG
deleted file mode 100644
index d08ca1add..000000000
Binary files a/content/engineering/breaking-down-this-keyword-in-javascript/global-context.PNG and /dev/null differ
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/global-context.webp b/content/engineering/breaking-down-this-keyword-in-javascript/global-context.webp
new file mode 100644
index 000000000..9a2dd828f
Binary files /dev/null and b/content/engineering/breaking-down-this-keyword-in-javascript/global-context.webp differ
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/index.md b/content/engineering/breaking-down-this-keyword-in-javascript/index.md
index cca4a6bae..92878caa5 100644
--- a/content/engineering/breaking-down-this-keyword-in-javascript/index.md
+++ b/content/engineering/breaking-down-this-keyword-in-javascript/index.md
@@ -1,7 +1,7 @@
---
title : "Breaking down the 'this' keyword in Javascript"
date: "2020-10-06"
-coverImage: "this-image.png"
+coverImage: "this-image.webp"
author: "Efereyan Karen"
tags: ["JavaScript", "JSConcepts"]
description: "As one of the most popular programming languages currently being used all around the world, understanding the core of Javascript is essential. The 'this' keyword is one of the most difficult concepts to grasp. This blog post aims to break down the 'this' keyword into small and understandable bits."
@@ -60,13 +60,13 @@ The definition of [this](https://developer.mozilla.org/en-US/docs/Web/JavaScript
console.log(y)
```
- .
+ .
Since that is true, if you make a strict comparison between the value of this and the window object, we get the boolean value of true.
If you run this javascript file inside your computer using a tool like [node](https://www.w3schools.com/nodejs/), this keyword refers to an object of type of object, like so......
- 
+ 
- ### `this` in a function
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/system.PNG b/content/engineering/breaking-down-this-keyword-in-javascript/system.PNG
deleted file mode 100644
index f4836f724..000000000
Binary files a/content/engineering/breaking-down-this-keyword-in-javascript/system.PNG and /dev/null differ
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/system.webp b/content/engineering/breaking-down-this-keyword-in-javascript/system.webp
new file mode 100644
index 000000000..add947c2a
Binary files /dev/null and b/content/engineering/breaking-down-this-keyword-in-javascript/system.webp differ
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/this-image.png b/content/engineering/breaking-down-this-keyword-in-javascript/this-image.png
deleted file mode 100644
index 3d53eebbb..000000000
Binary files a/content/engineering/breaking-down-this-keyword-in-javascript/this-image.png and /dev/null differ
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/this-image.webp b/content/engineering/breaking-down-this-keyword-in-javascript/this-image.webp
new file mode 100644
index 000000000..d2d6c54cd
Binary files /dev/null and b/content/engineering/breaking-down-this-keyword-in-javascript/this-image.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.png b/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.png
deleted file mode 100644
index 2b7c23b74..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.png and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.webp b/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.webp
new file mode 100644
index 000000000..b3c8b6e7d
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.png b/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.png
deleted file mode 100644
index b801ed1e6..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.png and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.webp b/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.webp
new file mode 100644
index 000000000..dad4475b7
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.png b/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.png
deleted file mode 100644
index 8a5bef661..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.png and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.webp b/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.webp
new file mode 100644
index 000000000..65adecf30
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.png b/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.png
deleted file mode 100644
index b89223914..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.png and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.webp b/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.webp
new file mode 100644
index 000000000..69c085847
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.jpeg b/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.jpeg
deleted file mode 100644
index f68e07b43..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.jpeg and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.webp b/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.webp
new file mode 100644
index 000000000..8ddd26dc9
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.png b/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.png
deleted file mode 100644
index 1fa0c1dfc..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.png and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.webp b/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.webp
new file mode 100644
index 000000000..8456d2a62
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/index.md b/content/engineering/bruteforce-lock-and-unlock/index.md
index 9e5358993..46a078046 100644
--- a/content/engineering/bruteforce-lock-and-unlock/index.md
+++ b/content/engineering/bruteforce-lock-and-unlock/index.md
@@ -1,7 +1,7 @@
---
title: "Testing Brute-force Lockout with LoginRadius"
date: "2024-05-29"
-coverImage: implementing-brute-force-lockout.png
+coverImage: implementing-brute-force-lockout.webp
author: "Gayathri Suresh"
tags: ["Brute-force", "LoginRadius", "Authentication"]
description: "In this blog, you'll learn about brute-force lockout, the creation of a basic app using Identity Experience Framework, and how to unlock a user account using APIs."
@@ -44,21 +44,21 @@ Let's go through the API implementation of brute-force lockout and user unlock.
In LoginRadius, the brute-force lockout feature can be enabled from the _[Admin Console](https://admin-console.loginradius.com/platform-security/account-protection/auth-security/brute-force-lockout)_.
-
+
#### Testing
1. Register with a new user and log in with the correct email and password. It is observed that the user is redirected to the profile page after authentication.
-
+
**Step 6:** Now edit the AntiXssMiddlewars.cs file and paste below code.
diff --git a/content/engineering/apache-beam/beam_architecture.png b/content/engineering/apache-beam/beam_architecture.png
deleted file mode 100644
index 943220a08..000000000
Binary files a/content/engineering/apache-beam/beam_architecture.png and /dev/null differ
diff --git a/content/engineering/apache-beam/beam_architecture.webp b/content/engineering/apache-beam/beam_architecture.webp
new file mode 100644
index 000000000..81a7cdbfd
Binary files /dev/null and b/content/engineering/apache-beam/beam_architecture.webp differ
diff --git a/content/engineering/apache-beam/index.md b/content/engineering/apache-beam/index.md
index 7d6e0486e..063ac6cb1 100644
--- a/content/engineering/apache-beam/index.md
+++ b/content/engineering/apache-beam/index.md
@@ -1,7 +1,7 @@
---
title: "Apache Beam: A Basic Guide"
date: "2020-10-16"
-coverImage: "main.png"
+coverImage: "main.webp"
author: "Abhilash K R"
tags: ["Engineering","Big Data","Streaming","Apache Beam","Java"]
description: "Apache Beam simplifies large-scale data processing dynamics. Let’s read more about the features, basic concepts, and the fundamentals of Apache beam."
@@ -15,7 +15,7 @@ Different technologies came into existence for different paradigms, solving vari
As a developer or a business, it's always challenging to maintain different tech stacks and technologies. Hence, Apache Beam to the rescue!
-
+
## What is Apache Beam?
@@ -24,7 +24,7 @@ Apache Beam is an open source, centralised model for describing parallel-process
The Apache Beam model offers helpful abstractions that insulate you from distributed processing information at low levels, such as managing individual staff, exchanging databases, and other activities. These low-level information are handled entirely by Dataflow.
-
+
## Features of Apache Beam
@@ -61,7 +61,7 @@ Apache Beam has three main abstractions. They are
2. PCollection
3. PTransform
-
+
### Pipeline:
diff --git a/content/engineering/apache-beam/main.png b/content/engineering/apache-beam/main.png
deleted file mode 100644
index aa981b7c9..000000000
Binary files a/content/engineering/apache-beam/main.png and /dev/null differ
diff --git a/content/engineering/apache-beam/main.webp b/content/engineering/apache-beam/main.webp
new file mode 100644
index 000000000..b6bc0bf6c
Binary files /dev/null and b/content/engineering/apache-beam/main.webp differ
diff --git a/content/engineering/apache-beam/pipeline-design.png b/content/engineering/apache-beam/pipeline-design.png
deleted file mode 100644
index b2f8ffe09..000000000
Binary files a/content/engineering/apache-beam/pipeline-design.png and /dev/null differ
diff --git a/content/engineering/apache-beam/pipeline-design.webp b/content/engineering/apache-beam/pipeline-design.webp
new file mode 100644
index 000000000..5212b3bcc
Binary files /dev/null and b/content/engineering/apache-beam/pipeline-design.webp differ
diff --git a/content/engineering/apache-beam/timeline-bigdata-frameworks.png b/content/engineering/apache-beam/timeline-bigdata-frameworks.png
deleted file mode 100644
index 50822ee94..000000000
Binary files a/content/engineering/apache-beam/timeline-bigdata-frameworks.png and /dev/null differ
diff --git a/content/engineering/apache-beam/timeline-bigdata-frameworks.webp b/content/engineering/apache-beam/timeline-bigdata-frameworks.webp
new file mode 100644
index 000000000..c35718f4d
Binary files /dev/null and b/content/engineering/apache-beam/timeline-bigdata-frameworks.webp differ
diff --git a/content/engineering/api-debugging-tools/api_debugging-tools-300x300.png b/content/engineering/api-debugging-tools/api_debugging-tools-300x300.png
deleted file mode 100644
index c58cc27ff..000000000
Binary files a/content/engineering/api-debugging-tools/api_debugging-tools-300x300.png and /dev/null differ
diff --git a/content/engineering/api-debugging-tools/api_debugging-tools-300x300.webp b/content/engineering/api-debugging-tools/api_debugging-tools-300x300.webp
new file mode 100644
index 000000000..d4cec35ed
Binary files /dev/null and b/content/engineering/api-debugging-tools/api_debugging-tools-300x300.webp differ
diff --git a/content/engineering/api-debugging-tools/index.md b/content/engineering/api-debugging-tools/index.md
index 4723ed991..6d084f414 100644
--- a/content/engineering/api-debugging-tools/index.md
+++ b/content/engineering/api-debugging-tools/index.md
@@ -1,7 +1,7 @@
---
title: "API Debugging Tools"
date: "2015-05-26"
-coverImage: "api_debugging-tools-300x300.png"
+coverImage: "api_debugging-tools-300x300.webp"
author: "Karl Wittig"
tags: ["Engineering","GoogleChorme","MozilaFirefox","SoupUI","RunScope"]
---
diff --git a/content/engineering/api-testing-and-benefits/api-testing.png b/content/engineering/api-testing-and-benefits/api-testing.png
deleted file mode 100644
index f1e9c5774..000000000
Binary files a/content/engineering/api-testing-and-benefits/api-testing.png and /dev/null differ
diff --git a/content/engineering/api-testing-and-benefits/api-testing.webp b/content/engineering/api-testing-and-benefits/api-testing.webp
new file mode 100644
index 000000000..9fae90d6d
Binary files /dev/null and b/content/engineering/api-testing-and-benefits/api-testing.webp differ
diff --git a/content/engineering/api-testing-and-benefits/index.md b/content/engineering/api-testing-and-benefits/index.md
index 716c7c52f..648e9926b 100644
--- a/content/engineering/api-testing-and-benefits/index.md
+++ b/content/engineering/api-testing-and-benefits/index.md
@@ -1,7 +1,7 @@
---
title: "What is API Testing? - Discover the Benefits"
date: "2021-02-12"
-coverImage: "api-testing.png"
+coverImage: "api-testing.webp"
author: "Surendranath Reddy Birudala"
tags: ["Automation", "API Testing", "Agile", "Benefits"]
description: "Communication between software components is handled by an API (Application Programming Interface). Discover the advantages of automated API testing."
diff --git a/content/engineering/authorization-code-flow-oauth/acf.png b/content/engineering/authorization-code-flow-oauth/acf.png
deleted file mode 100644
index 12776b849..000000000
Binary files a/content/engineering/authorization-code-flow-oauth/acf.png and /dev/null differ
diff --git a/content/engineering/authorization-code-flow-oauth/acf.webp b/content/engineering/authorization-code-flow-oauth/acf.webp
new file mode 100644
index 000000000..6bf20454e
Binary files /dev/null and b/content/engineering/authorization-code-flow-oauth/acf.webp differ
diff --git a/content/engineering/authorization-code-flow-oauth/index.md b/content/engineering/authorization-code-flow-oauth/index.md
index c7ce68d12..5b58b4d8f 100644
--- a/content/engineering/authorization-code-flow-oauth/index.md
+++ b/content/engineering/authorization-code-flow-oauth/index.md
@@ -1,7 +1,7 @@
---
title: "Guide to Authorization Code Flow for OAuth 2.0"
date: "2021-03-24"
-coverImage: "unsplash.jpg"
+coverImage: "unsplash.webp"
author: "Nick Chim"
tags: ["Oauth", "Authorization Code Flow"]
description: "This article will help you to understand the OAuth 2.0 authorization code flow."
@@ -13,7 +13,7 @@ In the Authorization Code flow, the server-side component of the web application
### Overview
-
+
The flow illustrated above aims to provide a rough overview of a typical Authorization Code workflow:
diff --git a/content/engineering/authorization-code-flow-oauth/unsplash.jpg b/content/engineering/authorization-code-flow-oauth/unsplash.jpg
deleted file mode 100644
index 8af73a4e7..000000000
Binary files a/content/engineering/authorization-code-flow-oauth/unsplash.jpg and /dev/null differ
diff --git a/content/engineering/authorization-code-flow-oauth/unsplash.webp b/content/engineering/authorization-code-flow-oauth/unsplash.webp
new file mode 100644
index 000000000..a135d68d0
Binary files /dev/null and b/content/engineering/authorization-code-flow-oauth/unsplash.webp differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/1.png b/content/engineering/azure-ad-as-an-identity-provider/1.png
deleted file mode 100644
index 4ed46d0df..000000000
Binary files a/content/engineering/azure-ad-as-an-identity-provider/1.png and /dev/null differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/1.webp b/content/engineering/azure-ad-as-an-identity-provider/1.webp
new file mode 100644
index 000000000..4c27a4edd
Binary files /dev/null and b/content/engineering/azure-ad-as-an-identity-provider/1.webp differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/2.png b/content/engineering/azure-ad-as-an-identity-provider/2.png
deleted file mode 100644
index f08b0363c..000000000
Binary files a/content/engineering/azure-ad-as-an-identity-provider/2.png and /dev/null differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/2.webp b/content/engineering/azure-ad-as-an-identity-provider/2.webp
new file mode 100644
index 000000000..5a3f9511e
Binary files /dev/null and b/content/engineering/azure-ad-as-an-identity-provider/2.webp differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/A-1.png b/content/engineering/azure-ad-as-an-identity-provider/A-1.png
deleted file mode 100644
index 52247393d..000000000
Binary files a/content/engineering/azure-ad-as-an-identity-provider/A-1.png and /dev/null differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/A-1.webp b/content/engineering/azure-ad-as-an-identity-provider/A-1.webp
new file mode 100644
index 000000000..ef8ddf280
Binary files /dev/null and b/content/engineering/azure-ad-as-an-identity-provider/A-1.webp differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.png b/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.png
deleted file mode 100644
index 4460d2ef6..000000000
Binary files a/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.png and /dev/null differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.webp b/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.webp
new file mode 100644
index 000000000..330c94a71
Binary files /dev/null and b/content/engineering/azure-ad-as-an-identity-provider/TN0lxUr0.webp differ
diff --git a/content/engineering/azure-ad-as-an-identity-provider/index.md b/content/engineering/azure-ad-as-an-identity-provider/index.md
index a14054a15..ca256da25 100644
--- a/content/engineering/azure-ad-as-an-identity-provider/index.md
+++ b/content/engineering/azure-ad-as-an-identity-provider/index.md
@@ -1,7 +1,7 @@
---
title: "Azure AD as an Identity provider"
date: "2019-05-30"
-coverImage: "TN0lxUr0.png"
+coverImage: "TN0lxUr0.webp"
author: "Team LoginRadius"
tags: ["Engineering","Authentication","AzureAD"]
---
@@ -13,17 +13,17 @@ Windows Azure provides a number of identity-based technologies to support such k
- Log in to the Azure Portal.
- On the Azure active directory tab, click on the App registrations tab. From the top of the screen, create a new application by clicking on "New application registration".
-
+
- Give your SaaS/Web application a name (company name Demo). Using the drop-down, select the type of application i.e Web Application / Web API.
- For Sign-On URL fill in the Assertion Consumer Service (ACS) URL for the Service Provider
-
+
- Go to the App setting at the top of the page and fill in the required fields
- Go to the endpoints at the top of the application registration page and use these app endpoints to set up the azure ad with your saas application.
-
+
Here are the meanings of the terms, we have used above:
diff --git a/content/engineering/basic-query-operations-in-mongodb/coverImage.png b/content/engineering/basic-query-operations-in-mongodb/coverImage.png
deleted file mode 100644
index a333977de..000000000
Binary files a/content/engineering/basic-query-operations-in-mongodb/coverImage.png and /dev/null differ
diff --git a/content/engineering/basic-query-operations-in-mongodb/coverImage.webp b/content/engineering/basic-query-operations-in-mongodb/coverImage.webp
new file mode 100644
index 000000000..72aa80e83
Binary files /dev/null and b/content/engineering/basic-query-operations-in-mongodb/coverImage.webp differ
diff --git a/content/engineering/basic-query-operations-in-mongodb/index.md b/content/engineering/basic-query-operations-in-mongodb/index.md
index 862e2e006..1041a3b70 100644
--- a/content/engineering/basic-query-operations-in-mongodb/index.md
+++ b/content/engineering/basic-query-operations-in-mongodb/index.md
@@ -1,7 +1,7 @@
---
title: How to Perform Basic Query Operations in MongoDB
date: "2021-01-20"
-coverImage: "coverImage.png"
+coverImage: "coverImage.webp"
author: "Anil Gupta"
Description: In this blog, we will learn how query operations can be performed in MongoDB. Also, how we can perform fundamental query operations, as we do in RDBMS.
tags: ["MongoDB"]
diff --git a/content/engineering/be-more-manipulative-with-underscore-js/index.md b/content/engineering/be-more-manipulative-with-underscore-js/index.md
index 122c0924f..08cce7d6c 100644
--- a/content/engineering/be-more-manipulative-with-underscore-js/index.md
+++ b/content/engineering/be-more-manipulative-with-underscore-js/index.md
@@ -1,7 +1,7 @@
---
title: "Be More Manipulative with Underscore JS"
date: "2016-02-16"
-coverImage: "underscore.png"
+coverImage: "underscore.webp"
author: "Zakary Hughes"
tags: ["JavaScript", "UnderscoreJs"]
---
diff --git a/content/engineering/be-more-manipulative-with-underscore-js/underscore.png b/content/engineering/be-more-manipulative-with-underscore-js/underscore.png
deleted file mode 100644
index 0f4c8757f..000000000
Binary files a/content/engineering/be-more-manipulative-with-underscore-js/underscore.png and /dev/null differ
diff --git a/content/engineering/be-more-manipulative-with-underscore-js/underscore.webp b/content/engineering/be-more-manipulative-with-underscore-js/underscore.webp
new file mode 100644
index 000000000..971027c4f
Binary files /dev/null and b/content/engineering/be-more-manipulative-with-underscore-js/underscore.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.png
deleted file mode 100644
index 8a4233605..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.webp
new file mode 100644
index 000000000..6c9730ee1
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/Beginner-Guide-Sublime-Text.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.png
deleted file mode 100644
index b00449d2b..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.webp
new file mode 100644
index 000000000..9dfada225
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/browse-package.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/index.md b/content/engineering/beginners-guide-for-sublime-text-3-part-2/index.md
index 34a214728..3841b9146 100644
--- a/content/engineering/beginners-guide-for-sublime-text-3-part-2/index.md
+++ b/content/engineering/beginners-guide-for-sublime-text-3-part-2/index.md
@@ -1,7 +1,7 @@
---
title: "Beginner's Guide for Sublime Text 3 Plugins"
date: "2015-11-10"
-coverImage: "Beginner-Guide-Sublime-Text.png"
+coverImage: "Beginner-Guide-Sublime-Text.webp"
author: "Team LoginRadius"
tags: ["SublimeText", "CodeEditor"]
description: "Getting started with one of the lightweight Code Editor Sublime Text and introduction to Snippets, Project and Macros"
@@ -20,7 +20,7 @@ Back when i introduced Sublime editor to my friends,"Snippets" was among the fir
This is definitely the feature you will use the most! To start using snippets, you can either create your own snippets according to your needs or download some ready-made snippets created by others to fulfill some generic coding needs. Like the one I demonstrated, it is pre-made from a plugin called `Html Page Snippets`, and command `docjq` will create a boiler template for a Html page that contains bootstrap and jQuery.
-
+
To create your own snippet, go to "Tools" => "New Snippet", an interface to create your own snippet will pop up, it would look something like this:
@@ -37,7 +37,7 @@ Now save it, but keep in mind putting it in the correct location is important!
If you can not find it, go to "Sublime" - > "Preferences" -> "Browse Packages", and create a folder called "User" if there isn't one already, and save it there.
-
+
### Project
@@ -48,7 +48,7 @@ Saving and using your projects is very straightforward.
- First drag some folders and files that you want to open into Sublime
- Then go to the menu, click "Project" -> "Save Project As"
- 
+ 
- Note the extension is ".sublime-project" and you may want to put all your project files in one central location
@@ -62,7 +62,7 @@ Do you always feel frustrated by repeating the same tedious task again & again?
It takes about 8 shortcuts to finish each process, that's including the first paste action and then adding a space character after each comma. Imagine having to do this for each line of a table, and for every single spreadsheet you have to work on. It would be hundreds of shortcuts you need to press and each time you are just repeating the exact same sequence of keys.
-
+
Well you might think there must be a better way! You bet there is! "Macros" are designed to handle this kind of nasty situation and save you from all that boring work. Here I made a very quick and easy example, it converts a vertical line of data into an array:
@@ -70,7 +70,7 @@ Magic! Lots of time and lives will be saved by this little gadget. So now, how t
- Go to "Tools" -> "Record Mac
- 
+ 
- Do your operations
@@ -78,7 +78,7 @@ Usually you would have something copied in your clipboard, so it could start wit
- Stop your macro
- 
+ 
- Playback
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.png
deleted file mode 100644
index de0521927..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.webp
new file mode 100644
index 000000000..db3baa55a
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/new-snippet.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.png
deleted file mode 100644
index 7e2fd2948..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.webp
new file mode 100644
index 000000000..8f02a9964
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/save-proj.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.png
deleted file mode 100644
index 227077bdd..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.webp
new file mode 100644
index 000000000..5205c313b
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.png
deleted file mode 100644
index 227077bdd..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.webp
new file mode 100644
index 000000000..5205c313b
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/start-macro1.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.png b/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.png
deleted file mode 100644
index dbe8d9e37..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.webp b/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.webp
new file mode 100644
index 000000000..a9587639d
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text-3-part-2/stop-macro.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.png b/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.png
deleted file mode 100644
index 8a4233605..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.webp b/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.webp
new file mode 100644
index 000000000..6c9730ee1
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text/Beginner-Guide-Sublime-Text.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/index.md b/content/engineering/beginners-guide-for-sublime-text/index.md
index 125ed4416..07614842c 100644
--- a/content/engineering/beginners-guide-for-sublime-text/index.md
+++ b/content/engineering/beginners-guide-for-sublime-text/index.md
@@ -1,7 +1,7 @@
---
title: "Beginner's Guide for Sublime Text 3"
date: "2015-09-15"
-coverImage: "Beginner-Guide-Sublime-Text.png"
+coverImage: "Beginner-Guide-Sublime-Text.webp"
author: "Team LoginRadius"
tags: ["SublimeText", "CodeEditor"]
description: "Getting started with one of the lightweight Code Editor Sublime Text and it's package control and shortcut commends"
@@ -33,7 +33,7 @@ Cmd + Shift + p
Then type "Install Package", you should see it now:
-
+
2\. Theme
@@ -48,7 +48,7 @@ After installing your preferred theme, the font and color scheme for sublime may
Navigate to:
-
+
What this file does is actually overwrite the settings in the default-setting JSON file, if you mess up with this user file, just delete them to recover back to the original settings. So feel free to play around with it, from here you can define the settings from your theme provider's guidance, here I will post mine as a sample
@@ -64,7 +64,7 @@ What this file does is actually overwrite the settings in the default-setting JS
Please note JSON format is significant to Sublime Settings, when you are not sure about it, check it with an online JSON validator. Now with this step done, you will have a delightful working environment to write your code in:
-
+
3\. Goto Everywhere
diff --git a/content/engineering/beginners-guide-for-sublime-text/install-package.png b/content/engineering/beginners-guide-for-sublime-text/install-package.png
deleted file mode 100644
index 7cf445a1a..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text/install-package.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/install-package.webp b/content/engineering/beginners-guide-for-sublime-text/install-package.webp
new file mode 100644
index 000000000..7527826cf
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text/install-package.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/sample-code.png b/content/engineering/beginners-guide-for-sublime-text/sample-code.png
deleted file mode 100644
index ee7be4876..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text/sample-code.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/sample-code.webp b/content/engineering/beginners-guide-for-sublime-text/sample-code.webp
new file mode 100644
index 000000000..3cb763997
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text/sample-code.webp differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/user-preference.png b/content/engineering/beginners-guide-for-sublime-text/user-preference.png
deleted file mode 100644
index d0376faab..000000000
Binary files a/content/engineering/beginners-guide-for-sublime-text/user-preference.png and /dev/null differ
diff --git a/content/engineering/beginners-guide-for-sublime-text/user-preference.webp b/content/engineering/beginners-guide-for-sublime-text/user-preference.webp
new file mode 100644
index 000000000..363e949c6
Binary files /dev/null and b/content/engineering/beginners-guide-for-sublime-text/user-preference.webp differ
diff --git a/content/engineering/beginners-guide-to-tweepy/coverimage.jpg b/content/engineering/beginners-guide-to-tweepy/coverimage.jpg
deleted file mode 100644
index be61218a6..000000000
Binary files a/content/engineering/beginners-guide-to-tweepy/coverimage.jpg and /dev/null differ
diff --git a/content/engineering/beginners-guide-to-tweepy/coverimage.webp b/content/engineering/beginners-guide-to-tweepy/coverimage.webp
new file mode 100644
index 000000000..14a9cbf21
Binary files /dev/null and b/content/engineering/beginners-guide-to-tweepy/coverimage.webp differ
diff --git a/content/engineering/beginners-guide-to-tweepy/index.md b/content/engineering/beginners-guide-to-tweepy/index.md
index 374fd0fa4..bafcb0bf3 100644
--- a/content/engineering/beginners-guide-to-tweepy/index.md
+++ b/content/engineering/beginners-guide-to-tweepy/index.md
@@ -1,7 +1,7 @@
---
title: "Beginners Guide to Tweepy "
date: "2020-11-02"
-coverImage: "coverimage.jpg"
+coverImage: "coverimage.webp"
author: "Sameer Mahajan"
tags: ["Twitter","Tweepy","Python"]
description: "Learn how to use Twitter APIs using Tweepy, a python package,"
@@ -14,18 +14,18 @@ In simple words, Tweepy is an open-source python package that provides a way for
### Installation
Tweepy can be installed by using Python package manager **pip**. A simple demonstration can be seen below:
-
+
Installation on Linux and macOS should follow similar steps as well.
Twitter API uses OAuth for authentication, so initially, you need to apply for authentication credentials from Twitter. These authentication credentials basically consists of 4 components namely : _consumer_key, consumer_secret_key, access_token, access_token_secret_ . These credentials from Twitter are used to instantiate the API. **Each account gets a unique key, so don't reuse someone else's keys.**
For getting those credentials from Twitter, apply for a developer account on the [Twitter Developers](https://developer.twitter.com/en) page.
-
+
This is what the account looks like. Here you will get detailed information about the total no. of requests made, your API credentials, and much more information. After creating an account, you need to create an app wherein you will be asked to name your app and a short description. You must be wondering what an app is?
The app is like a gateway that contains a set of permissions and keys used to access the Twitter API. An app is needed for accessing the Twitter API as a part of Twitter's OAuth authentication. After creating an app, generate new authentication tokens for authorization purposes.
-
+
### Getting Started: Tweepy
There are four common basic steps in any Tweepy application.
diff --git a/content/engineering/beginners-guide-to-tweepy/installation.PNG b/content/engineering/beginners-guide-to-tweepy/installation.PNG
deleted file mode 100644
index 0a3ba332e..000000000
Binary files a/content/engineering/beginners-guide-to-tweepy/installation.PNG and /dev/null differ
diff --git a/content/engineering/beginners-guide-to-tweepy/installation.webp b/content/engineering/beginners-guide-to-tweepy/installation.webp
new file mode 100644
index 000000000..9194b1615
Binary files /dev/null and b/content/engineering/beginners-guide-to-tweepy/installation.webp differ
diff --git a/content/engineering/beginners-guide-to-tweepy/keys.PNG b/content/engineering/beginners-guide-to-tweepy/keys.PNG
deleted file mode 100644
index efd4d14e1..000000000
Binary files a/content/engineering/beginners-guide-to-tweepy/keys.PNG and /dev/null differ
diff --git a/content/engineering/beginners-guide-to-tweepy/keys.webp b/content/engineering/beginners-guide-to-tweepy/keys.webp
new file mode 100644
index 000000000..b44866084
Binary files /dev/null and b/content/engineering/beginners-guide-to-tweepy/keys.webp differ
diff --git a/content/engineering/beginners-guide-to-tweepy/twitterdev.PNG b/content/engineering/beginners-guide-to-tweepy/twitterdev.PNG
deleted file mode 100644
index d84d45a44..000000000
Binary files a/content/engineering/beginners-guide-to-tweepy/twitterdev.PNG and /dev/null differ
diff --git a/content/engineering/beginners-guide-to-tweepy/twitterdev.webp b/content/engineering/beginners-guide-to-tweepy/twitterdev.webp
new file mode 100644
index 000000000..3bc033c32
Binary files /dev/null and b/content/engineering/beginners-guide-to-tweepy/twitterdev.webp differ
diff --git a/content/engineering/best-practice-guide-for-rest-api-security/index.jpg b/content/engineering/best-practice-guide-for-rest-api-security/index.jpg
deleted file mode 100644
index 4b82dcc8c..000000000
Binary files a/content/engineering/best-practice-guide-for-rest-api-security/index.jpg and /dev/null differ
diff --git a/content/engineering/best-practice-guide-for-rest-api-security/index.md b/content/engineering/best-practice-guide-for-rest-api-security/index.md
index 1a0506528..d91993944 100644
--- a/content/engineering/best-practice-guide-for-rest-api-security/index.md
+++ b/content/engineering/best-practice-guide-for-rest-api-security/index.md
@@ -1,7 +1,7 @@
---
title: "Best Practice Guide For Rest API Security | LoginRadius"
date: "2020-08-20"
-coverImage: "index.jpg"
+coverImage: "index.webp"
author: "Vijay Singh Shekhawat"
tags: ["RestAPI", "Rest API","Rest API Security", "Best Practice", "Rest API Developer Guide", "Security"]
---
diff --git a/content/engineering/best-practice-guide-for-rest-api-security/index.webp b/content/engineering/best-practice-guide-for-rest-api-security/index.webp
new file mode 100644
index 000000000..9c0af6f7c
Binary files /dev/null and b/content/engineering/best-practice-guide-for-rest-api-security/index.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/Homepage.png b/content/engineering/best-practice-reviewing-qq-app/Homepage.png
deleted file mode 100644
index 24d518083..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/Homepage.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/Homepage.webp b/content/engineering/best-practice-reviewing-qq-app/Homepage.webp
new file mode 100644
index 000000000..49ae3af56
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/Homepage.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/add_assets.png b/content/engineering/best-practice-reviewing-qq-app/add_assets.png
deleted file mode 100644
index c2d8f4139..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/add_assets.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/add_assets.webp b/content/engineering/best-practice-reviewing-qq-app/add_assets.webp
new file mode 100644
index 000000000..a17576b6d
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/add_assets.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/app_for_website.png b/content/engineering/best-practice-reviewing-qq-app/app_for_website.png
deleted file mode 100644
index 051c07958..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/app_for_website.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/app_for_website.webp b/content/engineering/best-practice-reviewing-qq-app/app_for_website.webp
new file mode 100644
index 000000000..54e7b6aa2
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/app_for_website.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/app_submit.png b/content/engineering/best-practice-reviewing-qq-app/app_submit.png
deleted file mode 100644
index 108f9e0bd..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/app_submit.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/app_submit.webp b/content/engineering/best-practice-reviewing-qq-app/app_submit.webp
new file mode 100644
index 000000000..5ebfb02c8
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/app_submit.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/confirm_submit.png b/content/engineering/best-practice-reviewing-qq-app/confirm_submit.png
deleted file mode 100644
index b2449e66d..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/confirm_submit.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/confirm_submit.webp b/content/engineering/best-practice-reviewing-qq-app/confirm_submit.webp
new file mode 100644
index 000000000..684322f0b
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/confirm_submit.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/create_app_button.png b/content/engineering/best-practice-reviewing-qq-app/create_app_button.png
deleted file mode 100644
index 56c204ed2..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/create_app_button.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/create_app_button.webp b/content/engineering/best-practice-reviewing-qq-app/create_app_button.webp
new file mode 100644
index 000000000..3eeded170
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/create_app_button.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.png b/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.png
deleted file mode 100644
index c59000837..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.webp b/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.webp
new file mode 100644
index 000000000..b5f351a48
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/form_with_english_translations.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/index.md b/content/engineering/best-practice-reviewing-qq-app/index.md
index 52130ff29..8a947a377 100644
--- a/content/engineering/best-practice-reviewing-qq-app/index.md
+++ b/content/engineering/best-practice-reviewing-qq-app/index.md
@@ -1,7 +1,7 @@
---
title: "Best practice for reviewing QQ app"
date: "2015-08-04"
-coverImage: "qq-app-review-best-practices.png"
+coverImage: "qq-app-review-best-practices.webp"
author: "Kundan Singh"
tags: ["SocialLogin", "QQ"]
---
@@ -12,7 +12,7 @@ QQ is the most popular ID provider for Chinese people since the 90s, it is alway
And click the 4th tab (in orange box)
- 
+ 
2. ### Registration
@@ -21,7 +21,7 @@ QQ is the most popular ID provider for Chinese people since the 90s, it is alway
Click "register a new account", like shown:
- 
+ 
It will link you to [this page](http://zc.qq.com/en/index.html?from=pt), it is written in English, sweet! I am pretty sure you can register an account by yourself. After filling in the information, it will send a confirmation email to your email box. After your email is verified go back to the [login page](http://connect.qq.com/manage/login), and use the QQ number you just got to log in with.
@@ -30,33 +30,33 @@ QQ is the most popular ID provider for Chinese people since the 90s, it is alway
Click the big green button on the right side of your screen to create an app, and here we will create a website type app.
- 
+ 
- 
+ 
After choosing the type, you need to fill in some basic information for your website, in case if you do not use Google translate to translate the page, I did a little translations for you, there you go.
- 
+ 
Here is what I have filled in
- 
+ 
Please note, when you fill in your website address, it will ask you to verify your website, so you need to copy and paste the javascript code under your website page, and then click the button beside to verify it.
- 
+ 
Once all the information is filled, then move on to next step, click the blue text link, it asks you to upload different sizes of the images about your company.
- 
+ 
- 
+ 
Then, it is time to submit by clicking that big green button in the middle.
- 
+ 
Confirm it by clicking the right button again.
- 
+ 
If everything works well, you will get you app approved in a week, just remember to check it back periodically, good luck!
diff --git a/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.png b/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.png
deleted file mode 100644
index fe49d18f5..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.webp b/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.webp
new file mode 100644
index 000000000..941b78170
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/lucius_fillin_info.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.png b/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.png
deleted file mode 100644
index 2a7cb30b9..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.webp b/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.webp
new file mode 100644
index 000000000..51527cac8
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/qq-app-review-best-practices.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.png b/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.png
deleted file mode 100644
index c12fd7957..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.webp b/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.webp
new file mode 100644
index 000000000..fc8001794
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/qq-register-1024x630.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.png b/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.png
deleted file mode 100644
index 7a1ff32f3..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.webp b/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.webp
new file mode 100644
index 000000000..0c5a2bc6c
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/upload_different_assets.webp differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/verify_successfully.png b/content/engineering/best-practice-reviewing-qq-app/verify_successfully.png
deleted file mode 100644
index 9adc2f797..000000000
Binary files a/content/engineering/best-practice-reviewing-qq-app/verify_successfully.png and /dev/null differ
diff --git a/content/engineering/best-practice-reviewing-qq-app/verify_successfully.webp b/content/engineering/best-practice-reviewing-qq-app/verify_successfully.webp
new file mode 100644
index 000000000..3d663b086
Binary files /dev/null and b/content/engineering/best-practice-reviewing-qq-app/verify_successfully.webp differ
diff --git a/content/engineering/best-ui-ux-design-tools-2020/index.md b/content/engineering/best-ui-ux-design-tools-2020/index.md
index 71d8fb35c..268bf20dd 100644
--- a/content/engineering/best-ui-ux-design-tools-2020/index.md
+++ b/content/engineering/best-ui-ux-design-tools-2020/index.md
@@ -1,7 +1,7 @@
---
title: "Best Free UI/UX Design Tools/Resources 2020"
date: "2020-08-13"
-coverImage: "ux-ui.jpg"
+coverImage: "ux-ui.webp"
author: "Hitesh Kumawat"
tags: ["Design", "UX", "Tools"]
description: "As a designer, often wondered which new tools and utilities, other designers are using? So here is a list of all the tools and utilities famous around the world in designers."
diff --git a/content/engineering/best-ui-ux-design-tools-2020/ux-ui.jpg b/content/engineering/best-ui-ux-design-tools-2020/ux-ui.jpg
deleted file mode 100644
index 025faf3f3..000000000
Binary files a/content/engineering/best-ui-ux-design-tools-2020/ux-ui.jpg and /dev/null differ
diff --git a/content/engineering/best-ui-ux-design-tools-2020/ux-ui.webp b/content/engineering/best-ui-ux-design-tools-2020/ux-ui.webp
new file mode 100644
index 000000000..bd28b4a33
Binary files /dev/null and b/content/engineering/best-ui-ux-design-tools-2020/ux-ui.webp differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-1.png b/content/engineering/big-data-testing-strategy/BigDataTesting-1.png
deleted file mode 100644
index 4f9d958d8..000000000
Binary files a/content/engineering/big-data-testing-strategy/BigDataTesting-1.png and /dev/null differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-1.webp b/content/engineering/big-data-testing-strategy/BigDataTesting-1.webp
new file mode 100644
index 000000000..3fe8f3f3b
Binary files /dev/null and b/content/engineering/big-data-testing-strategy/BigDataTesting-1.webp differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-2.png b/content/engineering/big-data-testing-strategy/BigDataTesting-2.png
deleted file mode 100644
index 07c542c5f..000000000
Binary files a/content/engineering/big-data-testing-strategy/BigDataTesting-2.png and /dev/null differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-2.webp b/content/engineering/big-data-testing-strategy/BigDataTesting-2.webp
new file mode 100644
index 000000000..f6753fbd7
Binary files /dev/null and b/content/engineering/big-data-testing-strategy/BigDataTesting-2.webp differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-3.png b/content/engineering/big-data-testing-strategy/BigDataTesting-3.png
deleted file mode 100644
index 25df85c22..000000000
Binary files a/content/engineering/big-data-testing-strategy/BigDataTesting-3.png and /dev/null differ
diff --git a/content/engineering/big-data-testing-strategy/BigDataTesting-3.webp b/content/engineering/big-data-testing-strategy/BigDataTesting-3.webp
new file mode 100644
index 000000000..e1c830625
Binary files /dev/null and b/content/engineering/big-data-testing-strategy/BigDataTesting-3.webp differ
diff --git a/content/engineering/big-data-testing-strategy/big-data.png b/content/engineering/big-data-testing-strategy/big-data.png
deleted file mode 100644
index a5cd9b219..000000000
Binary files a/content/engineering/big-data-testing-strategy/big-data.png and /dev/null differ
diff --git a/content/engineering/big-data-testing-strategy/big-data.webp b/content/engineering/big-data-testing-strategy/big-data.webp
new file mode 100644
index 000000000..17253b792
Binary files /dev/null and b/content/engineering/big-data-testing-strategy/big-data.webp differ
diff --git a/content/engineering/big-data-testing-strategy/index.md b/content/engineering/big-data-testing-strategy/index.md
index 0e5b7a0be..ed072e7db 100644
--- a/content/engineering/big-data-testing-strategy/index.md
+++ b/content/engineering/big-data-testing-strategy/index.md
@@ -1,7 +1,7 @@
---
title: "Big Data - Testing Strategy"
date: "2020-09-02"
-coverImage: "big-data.png"
+coverImage: "big-data.webp"
author: "Sudhey Sharma"
tags: ["Testing", "Big Data","Big Data Testing"]
description: "With the exponential growth in the number of big data applications in the world, Testing in big data applications is related to database, infrastructure and performance testing and functional testing. This blog guides what should be the strategy for testing Big Data applications."
@@ -23,7 +23,7 @@ Testing is an art of achieving quality in your software product, in terms of per
Processing may be of three types:–
-
+
And based on which, we need to integrate different components along with NoSQL data store as per the needs.
@@ -53,7 +53,7 @@ Scalability is also desired to be there in the test environment of big data test
**Big Data Testing can be categorized into three stages:**
-
+
@@ -87,7 +87,7 @@ The output validation process is the final or third stage involved in big data t
Big data applications are meant to process a large amount of data, and it is expected that it should take minimum time to process maximum data. Along with it, application jobs should consume a considerable amount of memory and CPU. In big data testing, performance parameter plays an important role and helps to define SLA's. It covers the performance of the base machine and cluster. Also, for example, In the case of Hadoop, map-reduce jobs should be written with proper coding guidelines, to perform better in the production environment. Profiling can also be done on map-reduce jobs before integration, to ensure their optimized execution.
## Tools used in Big Data Scenarios
-
+
## Big Data Testing - Challenges
diff --git a/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.jpg b/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.jpg
deleted file mode 100644
index c9a3785e8..000000000
Binary files a/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.jpg and /dev/null differ
diff --git a/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.webp b/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.webp
new file mode 100644
index 000000000..74aa0b20c
Binary files /dev/null and b/content/engineering/blockchain-the-new-technology-of-security-trust/CoverPage.webp differ
diff --git a/content/engineering/blockchain-the-new-technology-of-security-trust/block.png b/content/engineering/blockchain-the-new-technology-of-security-trust/block.png
deleted file mode 100644
index 40adf3c8b..000000000
Binary files a/content/engineering/blockchain-the-new-technology-of-security-trust/block.png and /dev/null differ
diff --git a/content/engineering/blockchain-the-new-technology-of-security-trust/block.webp b/content/engineering/blockchain-the-new-technology-of-security-trust/block.webp
new file mode 100644
index 000000000..c5fadfff4
Binary files /dev/null and b/content/engineering/blockchain-the-new-technology-of-security-trust/block.webp differ
diff --git a/content/engineering/blockchain-the-new-technology-of-security-trust/index.md b/content/engineering/blockchain-the-new-technology-of-security-trust/index.md
index 3178ce212..cab6660d1 100644
--- a/content/engineering/blockchain-the-new-technology-of-security-trust/index.md
+++ b/content/engineering/blockchain-the-new-technology-of-security-trust/index.md
@@ -1,7 +1,7 @@
---
title: "Blockchain: The new technology of trust"
date: "2020-10-08"
-coverImage: "CoverPage.jpg"
+coverImage: "CoverPage.webp"
author: "Shraddha V Prasad"
tags: ["Blockchain", "Cyber Security"]
description: "Learn about Blockchain technology and how it works."
@@ -26,7 +26,7 @@ Hash: It is quite similar to human fingerprint and is unique to each block, once
- LOCKING THE BLOCKS DOWN
Hash of the previous block-the hash of one block gives the data for the next block, and this new block uses this hash function and traces of it is woven into the new hash this continues to build an enormous chain.
-
+
## Establishing the trust
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.PNG b/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.PNG
deleted file mode 100644
index 13055ce3b..000000000
Binary files a/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.PNG and /dev/null differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.webp b/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.webp
new file mode 100644
index 000000000..2e67b5525
Binary files /dev/null and b/content/engineering/bluetooth-controlled-arduino-car-miniature/AppInterface.webp differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.png b/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.png
deleted file mode 100644
index 01e115080..000000000
Binary files a/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.png and /dev/null differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.webp b/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.webp
new file mode 100644
index 000000000..c1434a5dd
Binary files /dev/null and b/content/engineering/bluetooth-controlled-arduino-car-miniature/Arduinocar.webp differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.png b/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.png
deleted file mode 100644
index 87c18faf4..000000000
Binary files a/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.png and /dev/null differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.webp b/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.webp
new file mode 100644
index 000000000..3ce34db06
Binary files /dev/null and b/content/engineering/bluetooth-controlled-arduino-car-miniature/Bluetooth Arduino car Circuit.webp differ
diff --git a/content/engineering/bluetooth-controlled-arduino-car-miniature/index.md b/content/engineering/bluetooth-controlled-arduino-car-miniature/index.md
index b9b67c930..fbbe43c58 100644
--- a/content/engineering/bluetooth-controlled-arduino-car-miniature/index.md
+++ b/content/engineering/bluetooth-controlled-arduino-car-miniature/index.md
@@ -1,7 +1,7 @@
---
title: "Bluetooth Controlled Arduino Car Miniature"
date: "2020-11-04"
-coverImage: "Arduinocar.png"
+coverImage: "Arduinocar.webp"
author: "Abhishek Potekar"
tags: ["Arduino","Bluetooth"]
description: "In this blog, you will learn how to make a Bluetooth controlled Arduino Car."
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/global-context.PNG b/content/engineering/breaking-down-this-keyword-in-javascript/global-context.PNG
deleted file mode 100644
index d08ca1add..000000000
Binary files a/content/engineering/breaking-down-this-keyword-in-javascript/global-context.PNG and /dev/null differ
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/global-context.webp b/content/engineering/breaking-down-this-keyword-in-javascript/global-context.webp
new file mode 100644
index 000000000..9a2dd828f
Binary files /dev/null and b/content/engineering/breaking-down-this-keyword-in-javascript/global-context.webp differ
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/index.md b/content/engineering/breaking-down-this-keyword-in-javascript/index.md
index cca4a6bae..92878caa5 100644
--- a/content/engineering/breaking-down-this-keyword-in-javascript/index.md
+++ b/content/engineering/breaking-down-this-keyword-in-javascript/index.md
@@ -1,7 +1,7 @@
---
title : "Breaking down the 'this' keyword in Javascript"
date: "2020-10-06"
-coverImage: "this-image.png"
+coverImage: "this-image.webp"
author: "Efereyan Karen"
tags: ["JavaScript", "JSConcepts"]
description: "As one of the most popular programming languages currently being used all around the world, understanding the core of Javascript is essential. The 'this' keyword is one of the most difficult concepts to grasp. This blog post aims to break down the 'this' keyword into small and understandable bits."
@@ -60,13 +60,13 @@ The definition of [this](https://developer.mozilla.org/en-US/docs/Web/JavaScript
console.log(y)
```
- .
+ .
Since that is true, if you make a strict comparison between the value of this and the window object, we get the boolean value of true.
If you run this javascript file inside your computer using a tool like [node](https://www.w3schools.com/nodejs/), this keyword refers to an object of type of object, like so......
- 
+ 
- ### `this` in a function
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/system.PNG b/content/engineering/breaking-down-this-keyword-in-javascript/system.PNG
deleted file mode 100644
index f4836f724..000000000
Binary files a/content/engineering/breaking-down-this-keyword-in-javascript/system.PNG and /dev/null differ
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/system.webp b/content/engineering/breaking-down-this-keyword-in-javascript/system.webp
new file mode 100644
index 000000000..add947c2a
Binary files /dev/null and b/content/engineering/breaking-down-this-keyword-in-javascript/system.webp differ
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/this-image.png b/content/engineering/breaking-down-this-keyword-in-javascript/this-image.png
deleted file mode 100644
index 3d53eebbb..000000000
Binary files a/content/engineering/breaking-down-this-keyword-in-javascript/this-image.png and /dev/null differ
diff --git a/content/engineering/breaking-down-this-keyword-in-javascript/this-image.webp b/content/engineering/breaking-down-this-keyword-in-javascript/this-image.webp
new file mode 100644
index 000000000..d2d6c54cd
Binary files /dev/null and b/content/engineering/breaking-down-this-keyword-in-javascript/this-image.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.png b/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.png
deleted file mode 100644
index 2b7c23b74..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.png and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.webp b/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.webp
new file mode 100644
index 000000000..b3c8b6e7d
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/assets/admin_bfl_page.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.png b/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.png
deleted file mode 100644
index b801ed1e6..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.png and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.webp b/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.webp
new file mode 100644
index 000000000..dad4475b7
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/assets/incorrect_pwd.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.png b/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.png
deleted file mode 100644
index 8a5bef661..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.png and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.webp b/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.webp
new file mode 100644
index 000000000..65adecf30
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/assets/loginpage_with_data.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.png b/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.png
deleted file mode 100644
index b89223914..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.png and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.webp b/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.webp
new file mode 100644
index 000000000..69c085847
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/assets/successful_login.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.jpeg b/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.jpeg
deleted file mode 100644
index f68e07b43..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.jpeg and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.webp b/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.webp
new file mode 100644
index 000000000..8ddd26dc9
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/assets/unlocked_account_update.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.png b/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.png
deleted file mode 100644
index 1fa0c1dfc..000000000
Binary files a/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.png and /dev/null differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.webp b/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.webp
new file mode 100644
index 000000000..8456d2a62
Binary files /dev/null and b/content/engineering/bruteforce-lock-and-unlock/implementing-brute-force-lockout.webp differ
diff --git a/content/engineering/bruteforce-lock-and-unlock/index.md b/content/engineering/bruteforce-lock-and-unlock/index.md
index 9e5358993..46a078046 100644
--- a/content/engineering/bruteforce-lock-and-unlock/index.md
+++ b/content/engineering/bruteforce-lock-and-unlock/index.md
@@ -1,7 +1,7 @@
---
title: "Testing Brute-force Lockout with LoginRadius"
date: "2024-05-29"
-coverImage: implementing-brute-force-lockout.png
+coverImage: implementing-brute-force-lockout.webp
author: "Gayathri Suresh"
tags: ["Brute-force", "LoginRadius", "Authentication"]
description: "In this blog, you'll learn about brute-force lockout, the creation of a basic app using Identity Experience Framework, and how to unlock a user account using APIs."
@@ -44,21 +44,21 @@ Let's go through the API implementation of brute-force lockout and user unlock.
In LoginRadius, the brute-force lockout feature can be enabled from the _[Admin Console](https://admin-console.loginradius.com/platform-security/account-protection/auth-security/brute-force-lockout)_.
-
+
#### Testing
1. Register with a new user and log in with the correct email and password. It is observed that the user is redirected to the profile page after authentication.
-
+
 +
+ 