Maintainers
+Maintainers
This module is maintained by the OCA.
 @@ -603,5 +608,6 @@
@@ -603,5 +608,6 @@ This module allows users to login through an OpenID Connect provider using the authorization code flow or implicit flow.
Note the implicit flow is not recommended because it exposes access @@ -408,15 +413,15 @@
This module depends on the python-jose library, not to be confused with jose which is also available on PyPI.
Example configuration with OpenID Connect authorization code flow.
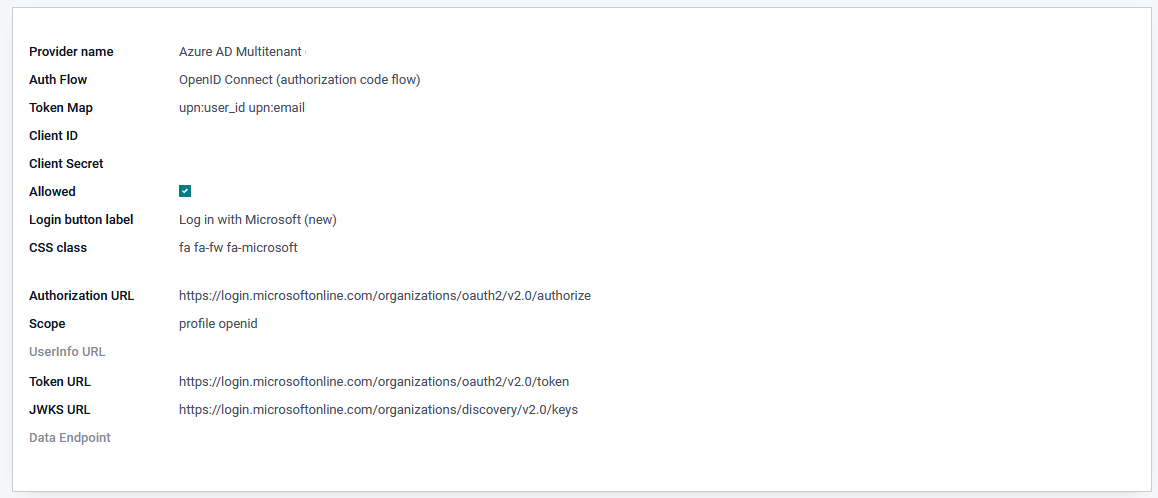
Example configuration with OpenID Connect authorization code flow.
In Keycloak:
Bugs are tracked on GitHub Issues. In case of trouble, please check there if your issue has already been reported. If you spotted it first, help us to smash it by providing a detailed and welcomed @@ -569,9 +574,9 @@
Do not contact contributors directly about support or help with technical issues.